Unnamed: 0
int64 0
832k
| id
float64 2.49B
32.1B
| type
stringclasses 1
value | created_at
stringlengths 19
19
| repo
stringlengths 4
112
| repo_url
stringlengths 33
141
| action
stringclasses 3
values | title
stringlengths 1
1.02k
| labels
stringlengths 4
1.54k
| body
stringlengths 1
262k
| index
stringclasses 17
values | text_combine
stringlengths 95
262k
| label
stringclasses 2
values | text
stringlengths 96
252k
| binary_label
int64 0
1
|
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
415,762
| 12,133,958,461
|
IssuesEvent
|
2020-04-23 09:54:06
|
comic/grand-challenge.org
|
https://api.github.com/repos/comic/grand-challenge.org
|
opened
|
Replace lesion type item list with new lesion types
|
area/api area/ophthalmology-workstation area/workstations estimate/week priority/p0
|
A new lesion item list has been supplied. I need to:
- Replace the old list, both in CIRRUS Ophthalmology and the legacy workstation
- Split up the lists for 2d (enface) images and 3d (OCT) images
- Create a data migration to change all the old values to the new ones according to the list I received
Only support the following features in CIRRUS Ophthalmology:
- Freetext/ICD9 lesion annotation option
- Checkbox (boolean) lesion specific annotations
- OCT Retinal layer segmentation/annotation
|
1.0
|
Replace lesion type item list with new lesion types - A new lesion item list has been supplied. I need to:
- Replace the old list, both in CIRRUS Ophthalmology and the legacy workstation
- Split up the lists for 2d (enface) images and 3d (OCT) images
- Create a data migration to change all the old values to the new ones according to the list I received
Only support the following features in CIRRUS Ophthalmology:
- Freetext/ICD9 lesion annotation option
- Checkbox (boolean) lesion specific annotations
- OCT Retinal layer segmentation/annotation
|
non_test
|
replace lesion type item list with new lesion types a new lesion item list has been supplied i need to replace the old list both in cirrus ophthalmology and the legacy workstation split up the lists for enface images and oct images create a data migration to change all the old values to the new ones according to the list i received only support the following features in cirrus ophthalmology freetext lesion annotation option checkbox boolean lesion specific annotations oct retinal layer segmentation annotation
| 0
|
148,868
| 23,392,529,691
|
IssuesEvent
|
2022-08-11 19:20:18
|
department-of-veterans-affairs/va.gov-team
|
https://api.github.com/repos/department-of-veterans-affairs/va.gov-team
|
closed
|
Accordion design inconsistency (Vet Centers)
|
design vsa Facilities vet-center
|
## Issue Description
As result of the work to standardize accordions (#24636), the accordions are visually inconsistent on Vet Center pages.
- The FAQs at the bottom of the page _do not_ have a border around the content when open.
- Service accordions _do_ have a border around the content when open.
This is likely occurring in other locations across VA.gov but is immediately evident on Vet Center pages due to the proximity of the two accordion types.
---
## Tasks
- [ ] Determine expected style, based on design system and other factors
## Acceptance Criteria
- [ ] _What will be created or happen as a result of this story?_
|
1.0
|
Accordion design inconsistency (Vet Centers) - ## Issue Description
As result of the work to standardize accordions (#24636), the accordions are visually inconsistent on Vet Center pages.
- The FAQs at the bottom of the page _do not_ have a border around the content when open.
- Service accordions _do_ have a border around the content when open.
This is likely occurring in other locations across VA.gov but is immediately evident on Vet Center pages due to the proximity of the two accordion types.
---
## Tasks
- [ ] Determine expected style, based on design system and other factors
## Acceptance Criteria
- [ ] _What will be created or happen as a result of this story?_
|
non_test
|
accordion design inconsistency vet centers issue description as result of the work to standardize accordions the accordions are visually inconsistent on vet center pages the faqs at the bottom of the page do not have a border around the content when open service accordions do have a border around the content when open this is likely occurring in other locations across va gov but is immediately evident on vet center pages due to the proximity of the two accordion types tasks determine expected style based on design system and other factors acceptance criteria what will be created or happen as a result of this story
| 0
|
622,006
| 19,603,865,771
|
IssuesEvent
|
2022-01-06 06:33:12
|
oam-dev/kubevela
|
https://api.github.com/repos/oam-dev/kubevela
|
closed
|
[Chore] Deprecate AppRollout and remove the CRD and controller in v1.2
|
priority/important-longterm effort/medium
|
AppRollout has become a rollout trait in v1.1, we should deprecate the usage of AppRollout and remove the legacy code.
|
1.0
|
[Chore] Deprecate AppRollout and remove the CRD and controller in v1.2 - AppRollout has become a rollout trait in v1.1, we should deprecate the usage of AppRollout and remove the legacy code.
|
non_test
|
deprecate approllout and remove the crd and controller in approllout has become a rollout trait in we should deprecate the usage of approllout and remove the legacy code
| 0
|
280,872
| 24,339,819,498
|
IssuesEvent
|
2022-10-01 15:03:50
|
moodlebox/moodlebox
|
https://api.github.com/repos/moodlebox/moodlebox
|
closed
|
Make H5P libraries available out of the box
|
Type: enhancement Status: testing in progress
|
This needs semi-manual downloading H5P libraries after MoodleBox automatic building, using `Run now` link on scheduled task "Download available H5P content types from h5p.org".
URL: http://moodlebox.home/h5p/overview.php
See [this forum discussion](https://discuss.moodlebox.net/d/340-bibliotheques-h5p-manquantes-pour-faire-tourner-activites-h5p).
|
1.0
|
Make H5P libraries available out of the box - This needs semi-manual downloading H5P libraries after MoodleBox automatic building, using `Run now` link on scheduled task "Download available H5P content types from h5p.org".
URL: http://moodlebox.home/h5p/overview.php
See [this forum discussion](https://discuss.moodlebox.net/d/340-bibliotheques-h5p-manquantes-pour-faire-tourner-activites-h5p).
|
test
|
make libraries available out of the box this needs semi manual downloading libraries after moodlebox automatic building using run now link on scheduled task download available content types from org url see
| 1
|
213,593
| 16,526,000,823
|
IssuesEvent
|
2021-05-26 20:12:18
|
pytorch/pytorch
|
https://api.github.com/repos/pytorch/pytorch
|
closed
|
NcclErrorHandlingTest.test_nccl_errors_blocking_abort frequently fails
|
module: flaky-tests module: nccl oncall: distributed triaged
|
See
https://app.circleci.com/pipelines/github/pytorch/pytorch/327201/workflows/9dbba324-6d2e-4839-bcb5-3eeb2ba466cc/jobs/13707781
https://app.circleci.com/pipelines/github/pytorch/pytorch/327199/workflows/f260c6cf-6d4f-46a8-ad5d-fe1f08be9614/jobs/13707707
https://app.circleci.com/pipelines/github/pytorch/pytorch/327174/workflows/75c37a70-c7b3-42cc-a2f4-e4a4e2c22387/jobs/13706979
for example
cc @pietern @mrshenli @pritamdamania87 @zhaojuanmao @satgera @rohan-varma @gqchen @aazzolini @osalpekar @jiayisuse @agolynski @SciPioneer @H-Huang @mrzzd @cbalioglu @gcramer23
|
1.0
|
NcclErrorHandlingTest.test_nccl_errors_blocking_abort frequently fails - See
https://app.circleci.com/pipelines/github/pytorch/pytorch/327201/workflows/9dbba324-6d2e-4839-bcb5-3eeb2ba466cc/jobs/13707781
https://app.circleci.com/pipelines/github/pytorch/pytorch/327199/workflows/f260c6cf-6d4f-46a8-ad5d-fe1f08be9614/jobs/13707707
https://app.circleci.com/pipelines/github/pytorch/pytorch/327174/workflows/75c37a70-c7b3-42cc-a2f4-e4a4e2c22387/jobs/13706979
for example
cc @pietern @mrshenli @pritamdamania87 @zhaojuanmao @satgera @rohan-varma @gqchen @aazzolini @osalpekar @jiayisuse @agolynski @SciPioneer @H-Huang @mrzzd @cbalioglu @gcramer23
|
test
|
ncclerrorhandlingtest test nccl errors blocking abort frequently fails see for example cc pietern mrshenli zhaojuanmao satgera rohan varma gqchen aazzolini osalpekar jiayisuse agolynski scipioneer h huang mrzzd cbalioglu
| 1
|
315,623
| 27,090,990,456
|
IssuesEvent
|
2023-02-14 21:02:57
|
acikkaynak/deprem-yardim-frontend
|
https://api.github.com/repos/acikkaynak/deprem-yardim-frontend
|
opened
|
bug: Safe places and hotels button is not visible
|
bug discussion unchecked test-failed
|
## Bug Definition
Safe places and hotels button is not visible. When left drawer menu is open, there is an extra icon button that can't be seen in viewport.
-- Please add discord contact information
** discord username: `notDepresseDeveloper#0919` **
## Bug environment
For pr #985
https://deprem-yardim-frontend-6wyrwo0i7-afet.vercel.app/
## Describe how you are producing the bug step by step
1. Go to ['...'](https://deprem-yardim-frontend-6wyrwo0i7-afet.vercel.app/)
2. Click layer button
3. Bug appears
## Expected Behaviour
Safe places and hotels button should be seen
## Screen shots

## Desktop Information
- Operating System: [for example iOS]
- Browser [for example, safari]
- Version [for example 22]
## Mobile Phone Information
- Devıce: [for example iPhone6]
- Operating System (with the version): [for example iOS8.1]
- Version [for example default browser, safari]
- Browser Version [for example 22]
## Additional Context
Add any other context about the bug here
|
1.0
|
bug: Safe places and hotels button is not visible - ## Bug Definition
Safe places and hotels button is not visible. When left drawer menu is open, there is an extra icon button that can't be seen in viewport.
-- Please add discord contact information
** discord username: `notDepresseDeveloper#0919` **
## Bug environment
For pr #985
https://deprem-yardim-frontend-6wyrwo0i7-afet.vercel.app/
## Describe how you are producing the bug step by step
1. Go to ['...'](https://deprem-yardim-frontend-6wyrwo0i7-afet.vercel.app/)
2. Click layer button
3. Bug appears
## Expected Behaviour
Safe places and hotels button should be seen
## Screen shots

## Desktop Information
- Operating System: [for example iOS]
- Browser [for example, safari]
- Version [for example 22]
## Mobile Phone Information
- Devıce: [for example iPhone6]
- Operating System (with the version): [for example iOS8.1]
- Version [for example default browser, safari]
- Browser Version [for example 22]
## Additional Context
Add any other context about the bug here
|
test
|
bug safe places and hotels button is not visible bug definition safe places and hotels button is not visible when left drawer menu is open there is an extra icon button that can t be seen in viewport please add discord contact information discord username notdepressedeveloper bug environment for pr describe how you are producing the bug step by step go to click layer button bug appears expected behaviour safe places and hotels button should be seen screen shots desktop information operating system browser version mobile phone information devıce operating system with the version version browser version additional context add any other context about the bug here
| 1
|
63,852
| 12,392,553,224
|
IssuesEvent
|
2020-05-20 14:10:29
|
dotnet/interactive
|
https://api.github.com/repos/dotnet/interactive
|
opened
|
Display output is not correct in VS Code
|
Area-VS Code Extension bug
|
### Describe the bug
Display a string and then an object the outputs overlap.
### Please complete the following:
**Which version of .NET Interactive are you using?**
1.0.126905
- OS
- [ ] Windows 10
- [ ] macOS
- [ ] Linux (Please specify distro)
- [ ] iOS
- [ ] Android
- Browser
- [ ] Chrome
- [ ] Edge
- [ ] Firefox
- [ ] Safari
- Frontend
- [ ] Jupyter Notebook
- [ ] Jupyter Lab
- [ ] nteract
- [x] Visual Studio Code
- [ ] Other (please specify)
### Screenshots
|
1.0
|
Display output is not correct in VS Code - ### Describe the bug
Display a string and then an object the outputs overlap.
### Please complete the following:
**Which version of .NET Interactive are you using?**
1.0.126905
- OS
- [ ] Windows 10
- [ ] macOS
- [ ] Linux (Please specify distro)
- [ ] iOS
- [ ] Android
- Browser
- [ ] Chrome
- [ ] Edge
- [ ] Firefox
- [ ] Safari
- Frontend
- [ ] Jupyter Notebook
- [ ] Jupyter Lab
- [ ] nteract
- [x] Visual Studio Code
- [ ] Other (please specify)
### Screenshots
|
non_test
|
display output is not correct in vs code describe the bug display a string and then an object the outputs overlap please complete the following which version of net interactive are you using os windows macos linux please specify distro ios android browser chrome edge firefox safari frontend jupyter notebook jupyter lab nteract visual studio code other please specify screenshots
| 0
|
61,883
| 25,767,419,738
|
IssuesEvent
|
2022-12-09 03:51:48
|
wso2/apk
|
https://api.github.com/repos/wso2/apk
|
closed
|
[Internal Backoffice] API definition comes from data plane should be able to persist into database via back office API
|
backoffice-internal-domain-service
|
Management server should be able to call /apis/api-id/definition PUT operation and update API definition.
|
1.0
|
[Internal Backoffice] API definition comes from data plane should be able to persist into database via back office API - Management server should be able to call /apis/api-id/definition PUT operation and update API definition.
|
non_test
|
api definition comes from data plane should be able to persist into database via back office api management server should be able to call apis api id definition put operation and update api definition
| 0
|
208,361
| 16,111,789,847
|
IssuesEvent
|
2021-04-27 22:33:23
|
webaverse/app
|
https://api.github.com/repos/webaverse/app
|
closed
|
DOCS: refresh
|
documentation
|
The docs need a whole passover/updating, some things are simpler to do now (baking physics, building xrpks, website minting), some things need more content / images, and the different classes of items like pets/mount/wearables/etc. need to be documented.
|
1.0
|
DOCS: refresh - The docs need a whole passover/updating, some things are simpler to do now (baking physics, building xrpks, website minting), some things need more content / images, and the different classes of items like pets/mount/wearables/etc. need to be documented.
|
non_test
|
docs refresh the docs need a whole passover updating some things are simpler to do now baking physics building xrpks website minting some things need more content images and the different classes of items like pets mount wearables etc need to be documented
| 0
|
281,390
| 24,389,285,054
|
IssuesEvent
|
2022-10-04 14:07:18
|
elastic/kibana
|
https://api.github.com/repos/elastic/kibana
|
reopened
|
Failing test: Jest Tests.x-pack/plugins/security_solution/public/management/components/artifact_list_page/components - When displaying the Delete artifact modal in the Artifact List Page should prevent modal from being closed while deletion is in flight
|
failed-test Team: SecuritySolution Team:Onboarding and Lifecycle Mgt OLM Sprint
|
A test failed on a tracked branch
```
Error: thrown: "Exceeded timeout of 10000 ms for a hook.
Use jest.setTimeout(newTimeout) to increase the timeout value, if this is a long-running test."
at /var/lib/buildkite-agent/builds/kb-n2-4-spot-16522228d99ea90c/elastic/kibana-on-merge/kibana/x-pack/plugins/security_solution/public/management/components/artifact_list_page/components/artifact_delete_modal.test.ts:40:3
at _dispatchDescribe (/var/lib/buildkite-agent/builds/kb-n2-4-spot-16522228d99ea90c/elastic/kibana-on-merge/kibana/node_modules/jest-circus/build/index.js:67:26)
at describe (/var/lib/buildkite-agent/builds/kb-n2-4-spot-16522228d99ea90c/elastic/kibana-on-merge/kibana/node_modules/jest-circus/build/index.js:30:5)
at Object.<anonymous> (/var/lib/buildkite-agent/builds/kb-n2-4-spot-16522228d99ea90c/elastic/kibana-on-merge/kibana/x-pack/plugins/security_solution/public/management/components/artifact_list_page/components/artifact_delete_modal.test.ts:16:1)
at Runtime._execModule (/var/lib/buildkite-agent/builds/kb-n2-4-spot-16522228d99ea90c/elastic/kibana-on-merge/kibana/node_modules/jest-runtime/build/index.js:1299:24)
at Runtime._loadModule (/var/lib/buildkite-agent/builds/kb-n2-4-spot-16522228d99ea90c/elastic/kibana-on-merge/kibana/node_modules/jest-runtime/build/index.js:898:12)
at Runtime.requireModule (/var/lib/buildkite-agent/builds/kb-n2-4-spot-16522228d99ea90c/elastic/kibana-on-merge/kibana/node_modules/jest-runtime/build/index.js:746:10)
at jestAdapter (/var/lib/buildkite-agent/builds/kb-n2-4-spot-16522228d99ea90c/elastic/kibana-on-merge/kibana/node_modules/jest-circus/build/legacy-code-todo-rewrite/jestAdapter.js:106:13)
at processTicksAndRejections (node:internal/process/task_queues:96:5)
at runTestInternal (/var/lib/buildkite-agent/builds/kb-n2-4-spot-16522228d99ea90c/elastic/kibana-on-merge/kibana/node_modules/jest-runner/build/runTest.js:380:16)
at runTest (/var/lib/buildkite-agent/builds/kb-n2-4-spot-16522228d99ea90c/elastic/kibana-on-merge/kibana/node_modules/jest-runner/build/runTest.js:472:34)
at Object.worker (/var/lib/buildkite-agent/builds/kb-n2-4-spot-16522228d99ea90c/elastic/kibana-on-merge/kibana/node_modules/jest-runner/build/testWorker.js:133:12)
```
First failure: [CI Build - main](https://buildkite.com/elastic/kibana-on-merge/builds/21289#018365a0-dfc0-4da5-9b47-532ebd4eba56)
<!-- kibanaCiData = {"failed-test":{"test.class":"Jest Tests.x-pack/plugins/security_solution/public/management/components/artifact_list_page/components","test.name":"When displaying the Delete artifact modal in the Artifact List Page should prevent modal from being closed while deletion is in flight","test.failCount":3}} -->
|
1.0
|
Failing test: Jest Tests.x-pack/plugins/security_solution/public/management/components/artifact_list_page/components - When displaying the Delete artifact modal in the Artifact List Page should prevent modal from being closed while deletion is in flight - A test failed on a tracked branch
```
Error: thrown: "Exceeded timeout of 10000 ms for a hook.
Use jest.setTimeout(newTimeout) to increase the timeout value, if this is a long-running test."
at /var/lib/buildkite-agent/builds/kb-n2-4-spot-16522228d99ea90c/elastic/kibana-on-merge/kibana/x-pack/plugins/security_solution/public/management/components/artifact_list_page/components/artifact_delete_modal.test.ts:40:3
at _dispatchDescribe (/var/lib/buildkite-agent/builds/kb-n2-4-spot-16522228d99ea90c/elastic/kibana-on-merge/kibana/node_modules/jest-circus/build/index.js:67:26)
at describe (/var/lib/buildkite-agent/builds/kb-n2-4-spot-16522228d99ea90c/elastic/kibana-on-merge/kibana/node_modules/jest-circus/build/index.js:30:5)
at Object.<anonymous> (/var/lib/buildkite-agent/builds/kb-n2-4-spot-16522228d99ea90c/elastic/kibana-on-merge/kibana/x-pack/plugins/security_solution/public/management/components/artifact_list_page/components/artifact_delete_modal.test.ts:16:1)
at Runtime._execModule (/var/lib/buildkite-agent/builds/kb-n2-4-spot-16522228d99ea90c/elastic/kibana-on-merge/kibana/node_modules/jest-runtime/build/index.js:1299:24)
at Runtime._loadModule (/var/lib/buildkite-agent/builds/kb-n2-4-spot-16522228d99ea90c/elastic/kibana-on-merge/kibana/node_modules/jest-runtime/build/index.js:898:12)
at Runtime.requireModule (/var/lib/buildkite-agent/builds/kb-n2-4-spot-16522228d99ea90c/elastic/kibana-on-merge/kibana/node_modules/jest-runtime/build/index.js:746:10)
at jestAdapter (/var/lib/buildkite-agent/builds/kb-n2-4-spot-16522228d99ea90c/elastic/kibana-on-merge/kibana/node_modules/jest-circus/build/legacy-code-todo-rewrite/jestAdapter.js:106:13)
at processTicksAndRejections (node:internal/process/task_queues:96:5)
at runTestInternal (/var/lib/buildkite-agent/builds/kb-n2-4-spot-16522228d99ea90c/elastic/kibana-on-merge/kibana/node_modules/jest-runner/build/runTest.js:380:16)
at runTest (/var/lib/buildkite-agent/builds/kb-n2-4-spot-16522228d99ea90c/elastic/kibana-on-merge/kibana/node_modules/jest-runner/build/runTest.js:472:34)
at Object.worker (/var/lib/buildkite-agent/builds/kb-n2-4-spot-16522228d99ea90c/elastic/kibana-on-merge/kibana/node_modules/jest-runner/build/testWorker.js:133:12)
```
First failure: [CI Build - main](https://buildkite.com/elastic/kibana-on-merge/builds/21289#018365a0-dfc0-4da5-9b47-532ebd4eba56)
<!-- kibanaCiData = {"failed-test":{"test.class":"Jest Tests.x-pack/plugins/security_solution/public/management/components/artifact_list_page/components","test.name":"When displaying the Delete artifact modal in the Artifact List Page should prevent modal from being closed while deletion is in flight","test.failCount":3}} -->
|
test
|
failing test jest tests x pack plugins security solution public management components artifact list page components when displaying the delete artifact modal in the artifact list page should prevent modal from being closed while deletion is in flight a test failed on a tracked branch error thrown exceeded timeout of ms for a hook use jest settimeout newtimeout to increase the timeout value if this is a long running test at var lib buildkite agent builds kb spot elastic kibana on merge kibana x pack plugins security solution public management components artifact list page components artifact delete modal test ts at dispatchdescribe var lib buildkite agent builds kb spot elastic kibana on merge kibana node modules jest circus build index js at describe var lib buildkite agent builds kb spot elastic kibana on merge kibana node modules jest circus build index js at object var lib buildkite agent builds kb spot elastic kibana on merge kibana x pack plugins security solution public management components artifact list page components artifact delete modal test ts at runtime execmodule var lib buildkite agent builds kb spot elastic kibana on merge kibana node modules jest runtime build index js at runtime loadmodule var lib buildkite agent builds kb spot elastic kibana on merge kibana node modules jest runtime build index js at runtime requiremodule var lib buildkite agent builds kb spot elastic kibana on merge kibana node modules jest runtime build index js at jestadapter var lib buildkite agent builds kb spot elastic kibana on merge kibana node modules jest circus build legacy code todo rewrite jestadapter js at processticksandrejections node internal process task queues at runtestinternal var lib buildkite agent builds kb spot elastic kibana on merge kibana node modules jest runner build runtest js at runtest var lib buildkite agent builds kb spot elastic kibana on merge kibana node modules jest runner build runtest js at object worker var lib buildkite agent builds kb spot elastic kibana on merge kibana node modules jest runner build testworker js first failure
| 1
|
261,278
| 22,714,795,645
|
IssuesEvent
|
2022-07-06 00:15:30
|
microsoft/playwright
|
https://api.github.com/repos/microsoft/playwright
|
closed
|
[BUG] Inconsistencies when test is skipped during fixture setup
|
feature-test-runner v1.24
|
**Context:**
- Playwright Version: 1.22.2
**Code Snippet**
```typescript
import { test as baseTest } from '@playwright/test'
const test = baseTest.extend<{ foo: string }>({
foo: [
async ({}, use, testInfo) => {
testInfo.skip() // or throw new Error()
await use('bar')
},
{ auto: true },
]
})
test.beforeEach(({ foo }) => {
console.log('first beforeEach', foo) // does not log
})
test.beforeEach(({ foo }) => {
console.log('second beforeEach', foo) // logs "second beforeEach null"
})
test.afterEach(({ foo }) => {
console.log('afterEach', foo) // logs "afterEach null"
})
test('should not run', async ({ foo }) => {
console.log('test', foo) // does not log
})
```
**Describe the bug**
If you call `testInfo.skip()` (or throw an Error) during fixture setup:
1. The first `beforeEach` hook is skipped, while all other hooks are executed. (After a brief debugging I came to a conclusion that this is due to the fact that playwright initializes the fixtures during first hook execution. So whatever error is thrown by the fixture is considered to be thrown by the hook itself);
2. Fixture value is `null` which violates TS typings.
|
1.0
|
[BUG] Inconsistencies when test is skipped during fixture setup - **Context:**
- Playwright Version: 1.22.2
**Code Snippet**
```typescript
import { test as baseTest } from '@playwright/test'
const test = baseTest.extend<{ foo: string }>({
foo: [
async ({}, use, testInfo) => {
testInfo.skip() // or throw new Error()
await use('bar')
},
{ auto: true },
]
})
test.beforeEach(({ foo }) => {
console.log('first beforeEach', foo) // does not log
})
test.beforeEach(({ foo }) => {
console.log('second beforeEach', foo) // logs "second beforeEach null"
})
test.afterEach(({ foo }) => {
console.log('afterEach', foo) // logs "afterEach null"
})
test('should not run', async ({ foo }) => {
console.log('test', foo) // does not log
})
```
**Describe the bug**
If you call `testInfo.skip()` (or throw an Error) during fixture setup:
1. The first `beforeEach` hook is skipped, while all other hooks are executed. (After a brief debugging I came to a conclusion that this is due to the fact that playwright initializes the fixtures during first hook execution. So whatever error is thrown by the fixture is considered to be thrown by the hook itself);
2. Fixture value is `null` which violates TS typings.
|
test
|
inconsistencies when test is skipped during fixture setup context playwright version code snippet typescript import test as basetest from playwright test const test basetest extend foo async use testinfo testinfo skip or throw new error await use bar auto true test beforeeach foo console log first beforeeach foo does not log test beforeeach foo console log second beforeeach foo logs second beforeeach null test aftereach foo console log aftereach foo logs aftereach null test should not run async foo console log test foo does not log describe the bug if you call testinfo skip or throw an error during fixture setup the first beforeeach hook is skipped while all other hooks are executed after a brief debugging i came to a conclusion that this is due to the fact that playwright initializes the fixtures during first hook execution so whatever error is thrown by the fixture is considered to be thrown by the hook itself fixture value is null which violates ts typings
| 1
|
78,766
| 7,667,792,502
|
IssuesEvent
|
2018-05-14 00:42:32
|
threatgrid/ctia
|
https://api.github.com/repos/threatgrid/ctia
|
closed
|
HTTP 500 error when deleting nonexistant relationship
|
QATest QAVerified bug
|
If you delete a relationship object that no longer exists, you will receive an HTTP 500 error, instead of a 404, due to an unhandled NPE.
|
1.0
|
HTTP 500 error when deleting nonexistant relationship - If you delete a relationship object that no longer exists, you will receive an HTTP 500 error, instead of a 404, due to an unhandled NPE.
|
test
|
http error when deleting nonexistant relationship if you delete a relationship object that no longer exists you will receive an http error instead of a due to an unhandled npe
| 1
|
29,200
| 11,726,282,463
|
IssuesEvent
|
2020-03-10 14:17:47
|
metodiobetsanov/eb
|
https://api.github.com/repos/metodiobetsanov/eb
|
closed
|
WS-2020-0042 (Medium) detected in acorn-5.7.3.tgz, acorn-6.4.0.tgz
|
security vulnerability
|
## WS-2020-0042 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>acorn-5.7.3.tgz</b>, <b>acorn-6.4.0.tgz</b></p></summary>
<p>
<details><summary><b>acorn-5.7.3.tgz</b></p></summary>
<p>ECMAScript parser</p>
<p>Library home page: <a href="https://registry.npmjs.org/acorn/-/acorn-5.7.3.tgz">https://registry.npmjs.org/acorn/-/acorn-5.7.3.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/eb/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/eb/node_modules/jsdom/node_modules/acorn/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-3.4.0.tgz (Root Library)
- jest-24.9.0.tgz
- jest-cli-24.9.0.tgz
- jest-config-24.9.0.tgz
- jest-environment-jsdom-24.9.0.tgz
- jsdom-11.12.0.tgz
- :x: **acorn-5.7.3.tgz** (Vulnerable Library)
</details>
<details><summary><b>acorn-6.4.0.tgz</b></p></summary>
<p>ECMAScript parser</p>
<p>Library home page: <a href="https://registry.npmjs.org/acorn/-/acorn-6.4.0.tgz">https://registry.npmjs.org/acorn/-/acorn-6.4.0.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/eb/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/eb/node_modules/jest-environment-jsdom-fourteen/node_modules/acorn/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-3.4.0.tgz (Root Library)
- webpack-4.41.5.tgz
- :x: **acorn-6.4.0.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/metodiobetsanov/eb/commit/f0378d20f2e3e1cf95b0cc53acb84306ac23560e">f0378d20f2e3e1cf95b0cc53acb84306ac23560e</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
acorn is vulnerable to REGEX DoS. A regex of the form /[x-\ud800]/u causes the parser to enter an infinite loop. attackers may leverage the vulnerability leading to a Denial of Service since the string is not valid UTF16 and it results in it being sanitized before reaching the parser.
<p>Publish Date: 2020-03-08
<p>URL: <a href=https://github.com/acornjs/acorn/commit/b5c17877ac0511e31579ea31e7650ba1a5871e51>WS-2020-0042</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: N/A
- Attack Complexity: N/A
- Privileges Required: N/A
- User Interaction: N/A
- Scope: N/A
- Impact Metrics:
- Confidentiality Impact: N/A
- Integrity Impact: N/A
- Availability Impact: N/A
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1488">https://www.npmjs.com/advisories/1488</a></p>
<p>Release Date: 2020-03-08</p>
<p>Fix Resolution: 7.1.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
WS-2020-0042 (Medium) detected in acorn-5.7.3.tgz, acorn-6.4.0.tgz - ## WS-2020-0042 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>acorn-5.7.3.tgz</b>, <b>acorn-6.4.0.tgz</b></p></summary>
<p>
<details><summary><b>acorn-5.7.3.tgz</b></p></summary>
<p>ECMAScript parser</p>
<p>Library home page: <a href="https://registry.npmjs.org/acorn/-/acorn-5.7.3.tgz">https://registry.npmjs.org/acorn/-/acorn-5.7.3.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/eb/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/eb/node_modules/jsdom/node_modules/acorn/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-3.4.0.tgz (Root Library)
- jest-24.9.0.tgz
- jest-cli-24.9.0.tgz
- jest-config-24.9.0.tgz
- jest-environment-jsdom-24.9.0.tgz
- jsdom-11.12.0.tgz
- :x: **acorn-5.7.3.tgz** (Vulnerable Library)
</details>
<details><summary><b>acorn-6.4.0.tgz</b></p></summary>
<p>ECMAScript parser</p>
<p>Library home page: <a href="https://registry.npmjs.org/acorn/-/acorn-6.4.0.tgz">https://registry.npmjs.org/acorn/-/acorn-6.4.0.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/eb/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/eb/node_modules/jest-environment-jsdom-fourteen/node_modules/acorn/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-3.4.0.tgz (Root Library)
- webpack-4.41.5.tgz
- :x: **acorn-6.4.0.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/metodiobetsanov/eb/commit/f0378d20f2e3e1cf95b0cc53acb84306ac23560e">f0378d20f2e3e1cf95b0cc53acb84306ac23560e</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
acorn is vulnerable to REGEX DoS. A regex of the form /[x-\ud800]/u causes the parser to enter an infinite loop. attackers may leverage the vulnerability leading to a Denial of Service since the string is not valid UTF16 and it results in it being sanitized before reaching the parser.
<p>Publish Date: 2020-03-08
<p>URL: <a href=https://github.com/acornjs/acorn/commit/b5c17877ac0511e31579ea31e7650ba1a5871e51>WS-2020-0042</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: N/A
- Attack Complexity: N/A
- Privileges Required: N/A
- User Interaction: N/A
- Scope: N/A
- Impact Metrics:
- Confidentiality Impact: N/A
- Integrity Impact: N/A
- Availability Impact: N/A
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1488">https://www.npmjs.com/advisories/1488</a></p>
<p>Release Date: 2020-03-08</p>
<p>Fix Resolution: 7.1.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_test
|
ws medium detected in acorn tgz acorn tgz ws medium severity vulnerability vulnerable libraries acorn tgz acorn tgz acorn tgz ecmascript parser library home page a href path to dependency file tmp ws scm eb package json path to vulnerable library tmp ws scm eb node modules jsdom node modules acorn package json dependency hierarchy react scripts tgz root library jest tgz jest cli tgz jest config tgz jest environment jsdom tgz jsdom tgz x acorn tgz vulnerable library acorn tgz ecmascript parser library home page a href path to dependency file tmp ws scm eb package json path to vulnerable library tmp ws scm eb node modules jest environment jsdom fourteen node modules acorn package json dependency hierarchy react scripts tgz root library webpack tgz x acorn tgz vulnerable library found in head commit a href vulnerability details acorn is vulnerable to regex dos a regex of the form u causes the parser to enter an infinite loop attackers may leverage the vulnerability leading to a denial of service since the string is not valid and it results in it being sanitized before reaching the parser publish date url a href cvss score details base score metrics exploitability metrics attack vector n a attack complexity n a privileges required n a user interaction n a scope n a impact metrics confidentiality impact n a integrity impact n a availability impact n a for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource
| 0
|
4,623
| 2,734,131,673
|
IssuesEvent
|
2015-04-17 17:58:48
|
mozilla/marketplace-tests
|
https://api.github.com/repos/mozilla/marketplace-tests
|
opened
|
Developer_hub tests are failing because of 403 errors from the API that is used to add apps
|
priority high Test Failure
|
Example failure: https://webqa-ci.mozilla.com/job/marketplace.dev.developer_hub/82/testReport/tests.desktop.developer_hub.test_api_submit/TestAPI/test_assert_that_a_app_can_be_added_and_deleted_via_the_api/
@krupa is going to reinstate access for our test user. This issue can be closed once that is done.
|
1.0
|
Developer_hub tests are failing because of 403 errors from the API that is used to add apps - Example failure: https://webqa-ci.mozilla.com/job/marketplace.dev.developer_hub/82/testReport/tests.desktop.developer_hub.test_api_submit/TestAPI/test_assert_that_a_app_can_be_added_and_deleted_via_the_api/
@krupa is going to reinstate access for our test user. This issue can be closed once that is done.
|
test
|
developer hub tests are failing because of errors from the api that is used to add apps example failure krupa is going to reinstate access for our test user this issue can be closed once that is done
| 1
|
189,572
| 14,514,636,642
|
IssuesEvent
|
2020-12-13 09:11:45
|
kalexmills/github-vet-tests-dec2020
|
https://api.github.com/repos/kalexmills/github-vet-tests-dec2020
|
closed
|
hyperhq/kubernetes: pkg/controller/node/nodecontroller_test.go; 3 LoC
|
fresh test tiny
|
Found a possible issue in [hyperhq/kubernetes](https://www.github.com/hyperhq/kubernetes) at [pkg/controller/node/nodecontroller_test.go](https://github.com/hyperhq/kubernetes/blob/49f8b6a0fee8b81244231da99411e7d585d106de/pkg/controller/node/nodecontroller_test.go#L618-L620)
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first
issue it finds, so please do not limit your consideration to the contents of the below message.
> function call which takes a reference to ds at line 619 may start a goroutine
[Click here to see the code in its original context.](https://github.com/hyperhq/kubernetes/blob/49f8b6a0fee8b81244231da99411e7d585d106de/pkg/controller/node/nodecontroller_test.go#L618-L620)
<details>
<summary>Click here to show the 3 line(s) of Go which triggered the analyzer.</summary>
```go
for _, ds := range item.daemonSets {
nodeController.daemonSetInformer.Informer().GetStore().Add(&ds)
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: 49f8b6a0fee8b81244231da99411e7d585d106de
|
1.0
|
hyperhq/kubernetes: pkg/controller/node/nodecontroller_test.go; 3 LoC -
Found a possible issue in [hyperhq/kubernetes](https://www.github.com/hyperhq/kubernetes) at [pkg/controller/node/nodecontroller_test.go](https://github.com/hyperhq/kubernetes/blob/49f8b6a0fee8b81244231da99411e7d585d106de/pkg/controller/node/nodecontroller_test.go#L618-L620)
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first
issue it finds, so please do not limit your consideration to the contents of the below message.
> function call which takes a reference to ds at line 619 may start a goroutine
[Click here to see the code in its original context.](https://github.com/hyperhq/kubernetes/blob/49f8b6a0fee8b81244231da99411e7d585d106de/pkg/controller/node/nodecontroller_test.go#L618-L620)
<details>
<summary>Click here to show the 3 line(s) of Go which triggered the analyzer.</summary>
```go
for _, ds := range item.daemonSets {
nodeController.daemonSetInformer.Informer().GetStore().Add(&ds)
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: 49f8b6a0fee8b81244231da99411e7d585d106de
|
test
|
hyperhq kubernetes pkg controller node nodecontroller test go loc found a possible issue in at below is the message reported by the analyzer for this snippet of code beware that the analyzer only reports the first issue it finds so please do not limit your consideration to the contents of the below message function call which takes a reference to ds at line may start a goroutine click here to show the line s of go which triggered the analyzer go for ds range item daemonsets nodecontroller daemonsetinformer informer getstore add ds leave a reaction on this issue to contribute to the project by classifying this instance as a bug mitigated or desirable behavior rocket see the descriptions of the classifications for more information commit id
| 1
|
752,989
| 26,336,577,534
|
IssuesEvent
|
2023-01-10 14:45:32
|
vaticle/docs
|
https://api.github.com/repos/vaticle/docs
|
closed
|
English to TypeQL: guidelines
|
type: feature priority: low
|
_Migrated from https://github.com/vaticle/typedb-studio/issues/153_
## Problem to Solve
TypeQL is a good language but it still can be a bit foreign with a bit of learning curve to non-programmers or programmers turned management personnel. It's easier for us to express what we want in English, hence a translator or a helper module could be beneficial to new and existing clients.
## Current Workaround
Using TypeQL and manually translating the English requirements to TypeQL.
## Proposed Solution
The translator is a helper and does not have to successful 100% in translating English sentences into TypeQL spec. The least it should do is present a template filling in most if not all of the entities from the English query into its TypeQL equivalent.
If presented via GUI, it can be further enhanced to help map the sentences and components of it into the TypeDB entities and TypeQL language constructs. Two-Way reverse engineering would be an awesome topping on the cake.
Saving a template of such mappings between English queries and TypeDB and then making them available to end-users can improve productivity massively.
## Additional Information
@tomassabat tells me mauna.ai is busy working with something similar, although we do not know if they will publish an open source version of this work.
Looking at TypeQL its not far away from English hence the mapping and translations can be done fluently.
|
1.0
|
English to TypeQL: guidelines - _Migrated from https://github.com/vaticle/typedb-studio/issues/153_
## Problem to Solve
TypeQL is a good language but it still can be a bit foreign with a bit of learning curve to non-programmers or programmers turned management personnel. It's easier for us to express what we want in English, hence a translator or a helper module could be beneficial to new and existing clients.
## Current Workaround
Using TypeQL and manually translating the English requirements to TypeQL.
## Proposed Solution
The translator is a helper and does not have to successful 100% in translating English sentences into TypeQL spec. The least it should do is present a template filling in most if not all of the entities from the English query into its TypeQL equivalent.
If presented via GUI, it can be further enhanced to help map the sentences and components of it into the TypeDB entities and TypeQL language constructs. Two-Way reverse engineering would be an awesome topping on the cake.
Saving a template of such mappings between English queries and TypeDB and then making them available to end-users can improve productivity massively.
## Additional Information
@tomassabat tells me mauna.ai is busy working with something similar, although we do not know if they will publish an open source version of this work.
Looking at TypeQL its not far away from English hence the mapping and translations can be done fluently.
|
non_test
|
english to typeql guidelines migrated from problem to solve typeql is a good language but it still can be a bit foreign with a bit of learning curve to non programmers or programmers turned management personnel it s easier for us to express what we want in english hence a translator or a helper module could be beneficial to new and existing clients current workaround using typeql and manually translating the english requirements to typeql proposed solution the translator is a helper and does not have to successful in translating english sentences into typeql spec the least it should do is present a template filling in most if not all of the entities from the english query into its typeql equivalent if presented via gui it can be further enhanced to help map the sentences and components of it into the typedb entities and typeql language constructs two way reverse engineering would be an awesome topping on the cake saving a template of such mappings between english queries and typedb and then making them available to end users can improve productivity massively additional information tomassabat tells me mauna ai is busy working with something similar although we do not know if they will publish an open source version of this work looking at typeql its not far away from english hence the mapping and translations can be done fluently
| 0
|
47,298
| 19,595,371,708
|
IssuesEvent
|
2022-01-05 17:12:53
|
bcgov/devhub-app-web
|
https://api.github.com/repos/bcgov/devhub-app-web
|
closed
|
[Pipeline Templates] Develop a Tekton pipeline template to perform a SAST scan using SonarQube
|
ops and shared services automation Arctiq Team
|
DoD:
[ ] template has been reviewed by BC Gov
[ ] template has been tested and is working
[ ] template has been demoed to BC Gov community during Meetup
[ ] template is available to BC Gov community, in the appropriate repo folder
|
1.0
|
[Pipeline Templates] Develop a Tekton pipeline template to perform a SAST scan using SonarQube - DoD:
[ ] template has been reviewed by BC Gov
[ ] template has been tested and is working
[ ] template has been demoed to BC Gov community during Meetup
[ ] template is available to BC Gov community, in the appropriate repo folder
|
non_test
|
develop a tekton pipeline template to perform a sast scan using sonarqube dod template has been reviewed by bc gov template has been tested and is working template has been demoed to bc gov community during meetup template is available to bc gov community in the appropriate repo folder
| 0
|
239,633
| 26,231,990,639
|
IssuesEvent
|
2023-01-05 01:36:56
|
vdekercd/MyJobSearches
|
https://api.github.com/repos/vdekercd/MyJobSearches
|
closed
|
MyJobSearches.Common.Test-1.0.0: 1 vulnerabilities (highest severity is: 9.8) - autoclosed
|
security vulnerability
|
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>MyJobSearches.Common.Test-1.0.0</b></p></summary>
<p></p>
<p>Path to vulnerable library: /home/wss-scanner/.nuget/packages/system.drawing.common/4.7.0/system.drawing.common.4.7.0.nupkg</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/vdekercd/MyJobSearches/commit/5c2bc7236cb1efea61cd0dce64d7808ebc76449e">5c2bc7236cb1efea61cd0dce64d7808ebc76449e</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (MyJobSearches.Common.Test version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2021-24112](https://www.mend.io/vulnerability-database/CVE-2021-24112) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | system.drawing.common.4.7.0.nupkg | Transitive | N/A* | ❌ |
<p>*For some transitive vulnerabilities, there is no version of direct dependency with a fix. Check the section "Details" below to see if there is a version of transitive dependency where vulnerability is fixed.</p>
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-24112</summary>
### Vulnerable Library - <b>system.drawing.common.4.7.0.nupkg</b></p>
<p>Provides access to GDI+ graphics functionality.
Commonly Used Types:
System.Drawing.Bitmap
System.D...</p>
<p>Library home page: <a href="https://api.nuget.org/packages/system.drawing.common.4.7.0.nupkg">https://api.nuget.org/packages/system.drawing.common.4.7.0.nupkg</a></p>
<p>Path to dependency file: /test/MyJobSearches.DataAccess.IntegrationTests/MyJobSearches.DataAccess.IntegrationTest.csproj</p>
<p>Path to vulnerable library: /home/wss-scanner/.nuget/packages/system.drawing.common/4.7.0/system.drawing.common.4.7.0.nupkg</p>
<p>
Dependency Hierarchy:
- MyJobSearches.Common.Test-1.0.0 (Root Library)
- fluentassertions.6.2.0.nupkg
- system.configuration.configurationmanager.4.7.0.nupkg
- system.security.permissions.4.7.0.nupkg
- system.windows.extensions.4.7.0.nupkg
- :x: **system.drawing.common.4.7.0.nupkg** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vdekercd/MyJobSearches/commit/5c2bc7236cb1efea61cd0dce64d7808ebc76449e">5c2bc7236cb1efea61cd0dce64d7808ebc76449e</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
.NET Core Remote Code Execution Vulnerability This CVE ID is unique from CVE-2021-26701.
<p>Publish Date: 2021-02-25
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-24112>CVE-2021-24112</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-rxg9-xrhp-64gj">https://github.com/advisories/GHSA-rxg9-xrhp-64gj</a></p>
<p>Release Date: 2021-02-25</p>
<p>Fix Resolution: System.Drawing.Common - 4.7.2,5.0.3</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details>
|
True
|
MyJobSearches.Common.Test-1.0.0: 1 vulnerabilities (highest severity is: 9.8) - autoclosed - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>MyJobSearches.Common.Test-1.0.0</b></p></summary>
<p></p>
<p>Path to vulnerable library: /home/wss-scanner/.nuget/packages/system.drawing.common/4.7.0/system.drawing.common.4.7.0.nupkg</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/vdekercd/MyJobSearches/commit/5c2bc7236cb1efea61cd0dce64d7808ebc76449e">5c2bc7236cb1efea61cd0dce64d7808ebc76449e</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (MyJobSearches.Common.Test version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2021-24112](https://www.mend.io/vulnerability-database/CVE-2021-24112) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | system.drawing.common.4.7.0.nupkg | Transitive | N/A* | ❌ |
<p>*For some transitive vulnerabilities, there is no version of direct dependency with a fix. Check the section "Details" below to see if there is a version of transitive dependency where vulnerability is fixed.</p>
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-24112</summary>
### Vulnerable Library - <b>system.drawing.common.4.7.0.nupkg</b></p>
<p>Provides access to GDI+ graphics functionality.
Commonly Used Types:
System.Drawing.Bitmap
System.D...</p>
<p>Library home page: <a href="https://api.nuget.org/packages/system.drawing.common.4.7.0.nupkg">https://api.nuget.org/packages/system.drawing.common.4.7.0.nupkg</a></p>
<p>Path to dependency file: /test/MyJobSearches.DataAccess.IntegrationTests/MyJobSearches.DataAccess.IntegrationTest.csproj</p>
<p>Path to vulnerable library: /home/wss-scanner/.nuget/packages/system.drawing.common/4.7.0/system.drawing.common.4.7.0.nupkg</p>
<p>
Dependency Hierarchy:
- MyJobSearches.Common.Test-1.0.0 (Root Library)
- fluentassertions.6.2.0.nupkg
- system.configuration.configurationmanager.4.7.0.nupkg
- system.security.permissions.4.7.0.nupkg
- system.windows.extensions.4.7.0.nupkg
- :x: **system.drawing.common.4.7.0.nupkg** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vdekercd/MyJobSearches/commit/5c2bc7236cb1efea61cd0dce64d7808ebc76449e">5c2bc7236cb1efea61cd0dce64d7808ebc76449e</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
.NET Core Remote Code Execution Vulnerability This CVE ID is unique from CVE-2021-26701.
<p>Publish Date: 2021-02-25
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-24112>CVE-2021-24112</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-rxg9-xrhp-64gj">https://github.com/advisories/GHSA-rxg9-xrhp-64gj</a></p>
<p>Release Date: 2021-02-25</p>
<p>Fix Resolution: System.Drawing.Common - 4.7.2,5.0.3</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details>
|
non_test
|
myjobsearches common test vulnerabilities highest severity is autoclosed vulnerable library myjobsearches common test path to vulnerable library home wss scanner nuget packages system drawing common system drawing common nupkg found in head commit a href vulnerabilities cve severity cvss dependency type fixed in myjobsearches common test version remediation available high system drawing common nupkg transitive n a for some transitive vulnerabilities there is no version of direct dependency with a fix check the section details below to see if there is a version of transitive dependency where vulnerability is fixed details cve vulnerable library system drawing common nupkg provides access to gdi graphics functionality commonly used types system drawing bitmap system d library home page a href path to dependency file test myjobsearches dataaccess integrationtests myjobsearches dataaccess integrationtest csproj path to vulnerable library home wss scanner nuget packages system drawing common system drawing common nupkg dependency hierarchy myjobsearches common test root library fluentassertions nupkg system configuration configurationmanager nupkg system security permissions nupkg system windows extensions nupkg x system drawing common nupkg vulnerable library found in head commit a href found in base branch main vulnerability details net core remote code execution vulnerability this cve id is unique from cve publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution system drawing common step up your open source security game with mend
| 0
|
76,927
| 9,529,636,421
|
IssuesEvent
|
2019-04-29 11:54:13
|
researchstudio-sat/webofneeds
|
https://api.github.com/repos/researchstudio-sat/webofneeds
|
closed
|
Uncomfortable handling of What's New view
|
UX design issue testing
|
The What's New view behaves unintuitively:
* no indication that the What's New button opens a new view instead of creating a post/opening an edit interface like all other buttons
* no obvious way back to the default view
* no obvious way back to the What's New interface after viewing a need
* no obvious way back to the What's New view from the default interface
* do discernible method of sorting (see #2759 )
* invisible needs are shown
* personas are shown as new needs
* own needs are shown but there is no indication that they are own needs
requires #2876 (for preloading timestamps and types so we can sort before fetching the actual needs)
|
1.0
|
Uncomfortable handling of What's New view - The What's New view behaves unintuitively:
* no indication that the What's New button opens a new view instead of creating a post/opening an edit interface like all other buttons
* no obvious way back to the default view
* no obvious way back to the What's New interface after viewing a need
* no obvious way back to the What's New view from the default interface
* do discernible method of sorting (see #2759 )
* invisible needs are shown
* personas are shown as new needs
* own needs are shown but there is no indication that they are own needs
requires #2876 (for preloading timestamps and types so we can sort before fetching the actual needs)
|
non_test
|
uncomfortable handling of what s new view the what s new view behaves unintuitively no indication that the what s new button opens a new view instead of creating a post opening an edit interface like all other buttons no obvious way back to the default view no obvious way back to the what s new interface after viewing a need no obvious way back to the what s new view from the default interface do discernible method of sorting see invisible needs are shown personas are shown as new needs own needs are shown but there is no indication that they are own needs requires for preloading timestamps and types so we can sort before fetching the actual needs
| 0
|
180,800
| 21,625,826,560
|
IssuesEvent
|
2022-05-05 01:54:51
|
meroflash132/inventory
|
https://api.github.com/repos/meroflash132/inventory
|
opened
|
CVE-2022-27777 (Medium) detected in actionview-6.0.3.2.gem
|
security vulnerability
|
## CVE-2022-27777 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>actionview-6.0.3.2.gem</b></p></summary>
<p>Simple, battle-tested conventions and helpers for building web pages.</p>
<p>Library home page: <a href="https://rubygems.org/gems/actionview-6.0.3.2.gem">https://rubygems.org/gems/actionview-6.0.3.2.gem</a></p>
<p>
Dependency Hierarchy:
- rails-6.0.3.2.gem (Root Library)
- :x: **actionview-6.0.3.2.gem** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
There is a possible XSS vulnerability in Action View tag helpers. Passing
untrusted input as hash keys can lead to a possible XSS vulnerability.
Fixed Versions: 7.0.2.4, 6.1.5.1, 6.0.4.8, 5.2.7.1
<p>Publish Date: 2022-03-24
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-27777>CVE-2022-27777</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-ch3h-j2vf-95pv">https://github.com/advisories/GHSA-ch3h-j2vf-95pv</a></p>
<p>Release Date: 2022-03-24</p>
<p>Fix Resolution: actionview - 5.2.7.1,6.0.4.8,6.1.5.1,7.0.2.4</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2022-27777 (Medium) detected in actionview-6.0.3.2.gem - ## CVE-2022-27777 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>actionview-6.0.3.2.gem</b></p></summary>
<p>Simple, battle-tested conventions and helpers for building web pages.</p>
<p>Library home page: <a href="https://rubygems.org/gems/actionview-6.0.3.2.gem">https://rubygems.org/gems/actionview-6.0.3.2.gem</a></p>
<p>
Dependency Hierarchy:
- rails-6.0.3.2.gem (Root Library)
- :x: **actionview-6.0.3.2.gem** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
There is a possible XSS vulnerability in Action View tag helpers. Passing
untrusted input as hash keys can lead to a possible XSS vulnerability.
Fixed Versions: 7.0.2.4, 6.1.5.1, 6.0.4.8, 5.2.7.1
<p>Publish Date: 2022-03-24
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-27777>CVE-2022-27777</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-ch3h-j2vf-95pv">https://github.com/advisories/GHSA-ch3h-j2vf-95pv</a></p>
<p>Release Date: 2022-03-24</p>
<p>Fix Resolution: actionview - 5.2.7.1,6.0.4.8,6.1.5.1,7.0.2.4</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_test
|
cve medium detected in actionview gem cve medium severity vulnerability vulnerable library actionview gem simple battle tested conventions and helpers for building web pages library home page a href dependency hierarchy rails gem root library x actionview gem vulnerable library found in base branch master vulnerability details there is a possible xss vulnerability in action view tag helpers passing untrusted input as hash keys can lead to a possible xss vulnerability fixed versions publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution actionview step up your open source security game with whitesource
| 0
|
648,366
| 21,184,104,686
|
IssuesEvent
|
2022-04-08 10:52:13
|
pika-org/pika
|
https://api.github.com/repos/pika-org/pika
|
closed
|
User-provided lambdas with auto parameters are instantiated with receiver types
|
effort: 2 effort: 3 priority: medium type: senders/receivers
|
The following currently fails to compile with `auto` in the lambda because the lambda gets instantiated with a receiver type. An explicit type `int` compiles correctly.
```
sync_wait(transfer_just(thread_pool_scheduler{}, 3) | then([](auto x) { return x + 1; }));
```
Find out if this is "user error" and the lambda must be correctly constrained, or if the instantiation can be avoided in pika. Does the P2300 reference implementation compile correctly with `auto`?
|
1.0
|
User-provided lambdas with auto parameters are instantiated with receiver types - The following currently fails to compile with `auto` in the lambda because the lambda gets instantiated with a receiver type. An explicit type `int` compiles correctly.
```
sync_wait(transfer_just(thread_pool_scheduler{}, 3) | then([](auto x) { return x + 1; }));
```
Find out if this is "user error" and the lambda must be correctly constrained, or if the instantiation can be avoided in pika. Does the P2300 reference implementation compile correctly with `auto`?
|
non_test
|
user provided lambdas with auto parameters are instantiated with receiver types the following currently fails to compile with auto in the lambda because the lambda gets instantiated with a receiver type an explicit type int compiles correctly sync wait transfer just thread pool scheduler then auto x return x find out if this is user error and the lambda must be correctly constrained or if the instantiation can be avoided in pika does the reference implementation compile correctly with auto
| 0
|
367,009
| 25,714,279,081
|
IssuesEvent
|
2022-12-07 09:14:50
|
themesberg/flowbite-react
|
https://api.github.com/repos/themesberg/flowbite-react
|
opened
|
WARNING: The last 0.3.7 includes a non documented breaking changed
|
documentation
|
Folks, my bad...
I didn't notice that this breaking change wasn't documented by the script that automatically generates our release notes. So, I want to ensure that this one is here.
We are working at #443 which will bring a log of flexibility to the library, and by achieving this goal we are doing a lot of refactoring and reorganizing some things, one of those things is that we basically reorganized our [FlowbiteTheme](https://github.com/themesberg/flowbite-react/blob/491e2f6dd476978bd25b5ce4cb7c58f0d23fee1f/src/lib/components/Flowbite/FlowbiteTheme.ts#L38) to get the components theming from their own interfaces. At the same time, we moved (#463) all the old `FormControls` components to their own folders, of course, with their own interfaces (theming, props, etc).
These breaking changes will break any custom theme that applies some themes for the old `FormControls` components in your custom theme.
|
1.0
|
WARNING: The last 0.3.7 includes a non documented breaking changed - Folks, my bad...
I didn't notice that this breaking change wasn't documented by the script that automatically generates our release notes. So, I want to ensure that this one is here.
We are working at #443 which will bring a log of flexibility to the library, and by achieving this goal we are doing a lot of refactoring and reorganizing some things, one of those things is that we basically reorganized our [FlowbiteTheme](https://github.com/themesberg/flowbite-react/blob/491e2f6dd476978bd25b5ce4cb7c58f0d23fee1f/src/lib/components/Flowbite/FlowbiteTheme.ts#L38) to get the components theming from their own interfaces. At the same time, we moved (#463) all the old `FormControls` components to their own folders, of course, with their own interfaces (theming, props, etc).
These breaking changes will break any custom theme that applies some themes for the old `FormControls` components in your custom theme.
|
non_test
|
warning the last includes a non documented breaking changed folks my bad i didn t notice that this breaking change wasn t documented by the script that automatically generates our release notes so i want to ensure that this one is here we are working at which will bring a log of flexibility to the library and by achieving this goal we are doing a lot of refactoring and reorganizing some things one of those things is that we basically reorganized our to get the components theming from their own interfaces at the same time we moved all the old formcontrols components to their own folders of course with their own interfaces theming props etc these breaking changes will break any custom theme that applies some themes for the old formcontrols components in your custom theme
| 0
|
75,692
| 20,959,326,188
|
IssuesEvent
|
2022-03-27 15:06:08
|
microsoft/azure-pipelines-tasks
|
https://api.github.com/repos/microsoft/azure-pipelines-tasks
|
closed
|
Publish Build Artifact from Linux Agent
|
enhancement stale Task: PublishBuildArtifacts
|
**Question, Bug, or Feature?**
*Type*: Feature
**Enter Task Name**: Publish build artifacts
Hi team,
at the time of this writing the Publish build artifacts task only supports Windows agents when used in the file share mode. Is there any plan to support the scenario also for Linux agents?
|
1.0
|
Publish Build Artifact from Linux Agent - **Question, Bug, or Feature?**
*Type*: Feature
**Enter Task Name**: Publish build artifacts
Hi team,
at the time of this writing the Publish build artifacts task only supports Windows agents when used in the file share mode. Is there any plan to support the scenario also for Linux agents?
|
non_test
|
publish build artifact from linux agent question bug or feature type feature enter task name publish build artifacts hi team at the time of this writing the publish build artifacts task only supports windows agents when used in the file share mode is there any plan to support the scenario also for linux agents
| 0
|
126,483
| 10,424,816,453
|
IssuesEvent
|
2019-09-16 14:19:02
|
GetTerminus/terminus-ui
|
https://api.github.com/repos/GetTerminus/terminus-ui
|
closed
|
Integration Testing Import Paths
|
Goal: Library Stabilization Target: latest Type: chore
|
After moving to INT tests, imports should be updated to `@terminus/ui/[component-name]/testing`. When creating these files in initial transition to INT, the paths have to be relative, but once they are published/committed, we can update them.
|
1.0
|
Integration Testing Import Paths - After moving to INT tests, imports should be updated to `@terminus/ui/[component-name]/testing`. When creating these files in initial transition to INT, the paths have to be relative, but once they are published/committed, we can update them.
|
test
|
integration testing import paths after moving to int tests imports should be updated to terminus ui testing when creating these files in initial transition to int the paths have to be relative but once they are published committed we can update them
| 1
|
678,961
| 23,217,417,763
|
IssuesEvent
|
2022-08-02 15:06:56
|
rpitv/glimpse-api
|
https://api.github.com/repos/rpitv/glimpse-api
|
opened
|
Two-factor authentication
|
enhancement Priority: MED
|
Users should be able to enable two-factor authentication for their account. Additionally, groups/users should have an additional property specifying whether 2FA is required for that user/members of that group.
Possible 2FA methods:
- Duo
- Webauthn (password alternative instead?)
- TOTP
- Authy
- Backup codes
- Email
- SMS
|
1.0
|
Two-factor authentication - Users should be able to enable two-factor authentication for their account. Additionally, groups/users should have an additional property specifying whether 2FA is required for that user/members of that group.
Possible 2FA methods:
- Duo
- Webauthn (password alternative instead?)
- TOTP
- Authy
- Backup codes
- Email
- SMS
|
non_test
|
two factor authentication users should be able to enable two factor authentication for their account additionally groups users should have an additional property specifying whether is required for that user members of that group possible methods duo webauthn password alternative instead totp authy backup codes email sms
| 0
|
253,496
| 21,685,818,710
|
IssuesEvent
|
2022-05-09 11:10:13
|
mmastro31/talking-oscilloscope
|
https://api.github.com/repos/mmastro31/talking-oscilloscope
|
closed
|
ST7735R Project Specific Tests
|
Medium Individual Software Testing
|
Describe and justify tests performed and what the outcomes/results stand for; were those the expected outcomes?
|
1.0
|
ST7735R Project Specific Tests - Describe and justify tests performed and what the outcomes/results stand for; were those the expected outcomes?
|
test
|
project specific tests describe and justify tests performed and what the outcomes results stand for were those the expected outcomes
| 1
|
252,138
| 27,229,866,939
|
IssuesEvent
|
2023-02-21 12:26:43
|
uriel-naor/HOTFIX
|
https://api.github.com/repos/uriel-naor/HOTFIX
|
closed
|
tap-5.8.0.tgz: 32 vulnerabilities (highest severity is: 9.8) - autoclosed
|
security vulnerability
|
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tap-5.8.0.tgz</b></p></summary>
<p></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/nyc/node_modules/istanbul/node_modules/handlebars/package.json</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/HOTFIX/commit/3bc753a65c01eab39a0bf5cf3aed58995c79c72a">3bc753a65c01eab39a0bf5cf3aed58995c79c72a</a></p></details>
#### <img src='https://whitesource-resources.whitesourcesoftware.com/suggestedVersion.png' width=19 height=20> Mend has checked all newer package trees, and you are on the least vulnerable package!
#### Please note: There might be a version that explicitly solves one or more of the vulnerabilities listed below, but we do not recommend it. For more info about the optional fixes, check the section “Details” below.
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (tap version) | Fix PR available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2021-23369](https://www.mend.io/vulnerability-database/CVE-2021-23369) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | handlebars-4.0.5.tgz | Transitive | N/A* | ❌ |
| [CVE-2019-19919](https://www.mend.io/vulnerability-database/CVE-2019-19919) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | handlebars-4.0.5.tgz | Transitive | N/A* | ❌ |
| [CVE-2020-7774](https://www.mend.io/vulnerability-database/CVE-2020-7774) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | y18n-3.2.1.tgz | Transitive | N/A* | ❌ |
| [CVE-2018-1000620](https://www.mend.io/vulnerability-database/CVE-2018-1000620) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2021-44906](https://www.mend.io/vulnerability-database/CVE-2021-44906) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2021-23383](https://www.mend.io/vulnerability-database/CVE-2021-23383) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | handlebars-4.0.5.tgz | Transitive | N/A* | ❌ |
| [CVE-2018-3728](https://www.mend.io/vulnerability-database/CVE-2018-3728) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2019-20920](https://www.mend.io/vulnerability-database/CVE-2019-20920) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | handlebars-4.0.5.tgz | Transitive | N/A* | ❌ |
| [WS-2019-0063](https://github.com/nodeca/js-yaml/pull/480) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | js-yaml-3.6.1.tgz | Transitive | N/A* | ❌ |
| [CVE-2019-20922](https://www.mend.io/vulnerability-database/CVE-2019-20922) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | handlebars-4.0.5.tgz | Transitive | N/A* | ❌ |
| [CVE-2020-28469](https://www.mend.io/vulnerability-database/CVE-2020-28469) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | glob-parent-2.0.0.tgz | Transitive | N/A* | ❌ |
| [CVE-2016-10540](https://www.mend.io/vulnerability-database/CVE-2016-10540) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2016-2515](https://www.mend.io/vulnerability-database/CVE-2016-2515) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | hawk-1.1.1.tgz | Transitive | N/A* | ❌ |
| [CVE-2017-1000048](https://www.mend.io/vulnerability-database/CVE-2017-1000048) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | qs-1.2.2.tgz | Transitive | N/A* | ❌ |
| [CVE-2022-29167](https://www.mend.io/vulnerability-database/CVE-2022-29167) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | hawk-3.1.3.tgz | Transitive | N/A* | ❌ |
| [WS-2019-0032](https://github.com/nodeca/js-yaml/commit/a567ef3c6e61eb319f0bfc2671d91061afb01235) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | js-yaml-3.6.1.tgz | Transitive | N/A* | ❌ |
| [CVE-2017-18077](https://www.mend.io/vulnerability-database/CVE-2017-18077) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | brace-expansion-1.1.4.tgz | Transitive | N/A* | ❌ |
| [CVE-2022-24999](https://www.mend.io/vulnerability-database/CVE-2022-24999) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | qs-1.2.2.tgz | Transitive | N/A* | ❌ |
| [WS-2020-0450](https://github.com/handlebars-lang/handlebars.js/commit/33a3b46bc205f768f8edbc67241c68591fe3472c) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | handlebars-4.0.5.tgz | Transitive | N/A* | ❌ |
| [CVE-2022-3517](https://www.mend.io/vulnerability-database/CVE-2022-3517) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [WS-2019-0064](https://github.com/wycats/handlebars.js/compare/v4.1.1...v4.1.2) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | handlebars-4.0.5.tgz | Transitive | N/A* | ❌ |
| [WS-2018-0590](https://bugzilla.redhat.com/show_bug.cgi?id=1552148) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.1 | diff-1.4.0.tgz | Transitive | N/A* | ❌ |
| [CVE-2020-8244](https://www.mend.io/vulnerability-database/CVE-2020-8244) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | bl-0.9.5.tgz | Transitive | N/A* | ❌ |
| [CVE-2017-16026](https://www.mend.io/vulnerability-database/CVE-2017-16026) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.9 | request-2.42.0.tgz | Transitive | N/A* | ❌ |
| [CVE-2020-7598](https://www.mend.io/vulnerability-database/CVE-2020-7598) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.6 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [WS-2019-0103](https://github.com/wycats/handlebars.js/issues/1267#issue-187151586) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.6 | handlebars-4.0.5.tgz | Transitive | N/A* | ❌ |
| [CVE-2017-16032](https://www.mend.io/vulnerability-database/CVE-2017-16032) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.5 | brace-expansion-1.1.4.tgz | Transitive | N/A* | ❌ |
| [CVE-2020-7608](https://www.mend.io/vulnerability-database/CVE-2020-7608) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | yargs-parser-2.4.0.tgz | Transitive | N/A* | ❌ |
| [CVE-2021-23362](https://www.mend.io/vulnerability-database/CVE-2021-23362) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | hosted-git-info-2.1.5.tgz | Transitive | N/A* | ❌ |
| [CVE-2017-16028](https://www.mend.io/vulnerability-database/CVE-2017-16028) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | randomatic-1.1.5.tgz | Transitive | N/A* | ❌ |
| [WS-2018-0076](https://github.com/request/tunnel-agent/commit/9ca95ec7219daface8a6fc2674000653de0922c0) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.1 | tunnel-agent-0.4.3.tgz | Transitive | N/A* | ❌ |
| [WS-2017-0266](https://github.com/joyent/node-http-signature/commit/78ab1da232f31f695f5c362d863593a143aa8b56) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 3.5 | http-signature-0.10.1.tgz | Transitive | N/A* | ❌ |
<p>*For some transitive vulnerabilities, there is no version of direct dependency with a fix. Check the section "Details" below to see if there is a version of transitive dependency where vulnerability is fixed.</p>
## Details
> Partial details (23 vulnerabilities) are displayed below due to a content size limitation in GitHub. To view information on the remaining vulnerabilities, navigate to the Mend Application.<br>
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-23369</summary>
### Vulnerable Library - <b>handlebars-4.0.5.tgz</b></p>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://registry.npmjs.org/handlebars/-/handlebars-4.0.5.tgz">https://registry.npmjs.org/handlebars/-/handlebars-4.0.5.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/nyc/node_modules/istanbul/node_modules/handlebars/package.json</p>
<p>
Dependency Hierarchy:
- tap-5.8.0.tgz (Root Library)
- nyc-6.6.1.tgz
- istanbul-0.4.3.tgz
- :x: **handlebars-4.0.5.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/HOTFIX/commit/3bc753a65c01eab39a0bf5cf3aed58995c79c72a">3bc753a65c01eab39a0bf5cf3aed58995c79c72a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The package handlebars before 4.7.7 are vulnerable to Remote Code Execution (RCE) when selecting certain compiling options to compile templates coming from an untrusted source.
<p>Publish Date: 2021-04-12
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-23369>CVE-2021-23369</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23369">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23369</a></p>
<p>Release Date: 2021-04-12</p>
<p>Fix Resolution: com.github.jknack:handlebars:4.2.0, handlebars - 4.7.7</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-19919</summary>
### Vulnerable Library - <b>handlebars-4.0.5.tgz</b></p>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://registry.npmjs.org/handlebars/-/handlebars-4.0.5.tgz">https://registry.npmjs.org/handlebars/-/handlebars-4.0.5.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/nyc/node_modules/istanbul/node_modules/handlebars/package.json</p>
<p>
Dependency Hierarchy:
- tap-5.8.0.tgz (Root Library)
- nyc-6.6.1.tgz
- istanbul-0.4.3.tgz
- :x: **handlebars-4.0.5.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/HOTFIX/commit/3bc753a65c01eab39a0bf5cf3aed58995c79c72a">3bc753a65c01eab39a0bf5cf3aed58995c79c72a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Versions of handlebars prior to 4.3.0 are vulnerable to Prototype Pollution leading to Remote Code Execution. Templates may alter an Object's __proto__ and __defineGetter__ properties, which may allow an attacker to execute arbitrary code through crafted payloads.
<p>Publish Date: 2019-12-20
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-19919>CVE-2019-19919</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-19919">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-19919</a></p>
<p>Release Date: 2019-12-20</p>
<p>Fix Resolution: handlebars - 4.3.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-7774</summary>
### Vulnerable Library - <b>y18n-3.2.1.tgz</b></p>
<p>the bare-bones internationalization library used by yargs</p>
<p>Library home page: <a href="https://registry.npmjs.org/y18n/-/y18n-3.2.1.tgz">https://registry.npmjs.org/y18n/-/y18n-3.2.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/nyc/node_modules/yargs/node_modules/y18n/package.json</p>
<p>
Dependency Hierarchy:
- tap-5.8.0.tgz (Root Library)
- nyc-6.6.1.tgz
- yargs-4.7.1.tgz
- :x: **y18n-3.2.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/HOTFIX/commit/3bc753a65c01eab39a0bf5cf3aed58995c79c72a">3bc753a65c01eab39a0bf5cf3aed58995c79c72a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The package y18n before 3.2.2, 4.0.1 and 5.0.5, is vulnerable to Prototype Pollution.
<p>Publish Date: 2020-11-17
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-7774>CVE-2020-7774</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1654">https://www.npmjs.com/advisories/1654</a></p>
<p>Release Date: 2020-11-17</p>
<p>Fix Resolution: 3.2.2, 4.0.1, 5.0.5</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2018-1000620</summary>
### Vulnerable Libraries - <b>cryptiles-0.2.2.tgz</b>, <b>cryptiles-2.0.5.tgz</b></p>
<p>
### <b>cryptiles-0.2.2.tgz</b></p>
<p>General purpose crypto utilities</p>
<p>Library home page: <a href="https://registry.npmjs.org/cryptiles/-/cryptiles-0.2.2.tgz">https://registry.npmjs.org/cryptiles/-/cryptiles-0.2.2.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/cryptiles/package.json</p>
<p>
Dependency Hierarchy:
- tap-5.8.0.tgz (Root Library)
- codecov.io-0.1.6.tgz
- request-2.42.0.tgz
- hawk-1.1.1.tgz
- :x: **cryptiles-0.2.2.tgz** (Vulnerable Library)
### <b>cryptiles-2.0.5.tgz</b></p>
<p>General purpose crypto utilities</p>
<p>Library home page: <a href="https://registry.npmjs.org/cryptiles/-/cryptiles-2.0.5.tgz">https://registry.npmjs.org/cryptiles/-/cryptiles-2.0.5.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/coveralls/node_modules/cryptiles/package.json</p>
<p>
Dependency Hierarchy:
- tap-5.8.0.tgz (Root Library)
- coveralls-2.13.3.tgz
- request-2.79.0.tgz
- hawk-3.1.3.tgz
- :x: **cryptiles-2.0.5.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/HOTFIX/commit/3bc753a65c01eab39a0bf5cf3aed58995c79c72a">3bc753a65c01eab39a0bf5cf3aed58995c79c72a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Eran Hammer cryptiles version 4.1.1 earlier contains a CWE-331: Insufficient Entropy vulnerability in randomDigits() method that can result in An attacker is more likely to be able to brute force something that was supposed to be random.. This attack appear to be exploitable via Depends upon the calling application.. This vulnerability appears to have been fixed in 4.1.2.
<p>Publish Date: 2018-07-09
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-1000620>CVE-2018-1000620</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2018-1000620">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2018-1000620</a></p>
<p>Release Date: 2018-07-09</p>
<p>Fix Resolution: v4.1.2</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-44906</summary>
### Vulnerable Libraries - <b>minimist-1.2.0.tgz</b>, <b>minimist-0.0.8.tgz</b>, <b>minimist-0.0.10.tgz</b></p>
<p>
### <b>minimist-1.2.0.tgz</b></p>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-1.2.0.tgz">https://registry.npmjs.org/minimist/-/minimist-1.2.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/coveralls/node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- tap-5.8.0.tgz (Root Library)
- coveralls-2.13.3.tgz
- :x: **minimist-1.2.0.tgz** (Vulnerable Library)
### <b>minimist-0.0.8.tgz</b></p>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-0.0.8.tgz">https://registry.npmjs.org/minimist/-/minimist-0.0.8.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/nyc/node_modules/mkdirp/node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- tap-5.8.0.tgz (Root Library)
- nyc-6.6.1.tgz
- mkdirp-0.5.1.tgz
- :x: **minimist-0.0.8.tgz** (Vulnerable Library)
### <b>minimist-0.0.10.tgz</b></p>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-0.0.10.tgz">https://registry.npmjs.org/minimist/-/minimist-0.0.10.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/nyc/node_modules/istanbul/node_modules/handlebars/node_modules/optimist/node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- tap-5.8.0.tgz (Root Library)
- nyc-6.6.1.tgz
- istanbul-0.4.3.tgz
- handlebars-4.0.5.tgz
- optimist-0.6.1.tgz
- :x: **minimist-0.0.10.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/HOTFIX/commit/3bc753a65c01eab39a0bf5cf3aed58995c79c72a">3bc753a65c01eab39a0bf5cf3aed58995c79c72a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Minimist <=1.2.5 is vulnerable to Prototype Pollution via file index.js, function setKey() (lines 69-95).
<p>Publish Date: 2022-03-17
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-44906>CVE-2021-44906</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-03-17</p>
<p>Fix Resolution: minimist - 1.2.6</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-23383</summary>
### Vulnerable Library - <b>handlebars-4.0.5.tgz</b></p>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://registry.npmjs.org/handlebars/-/handlebars-4.0.5.tgz">https://registry.npmjs.org/handlebars/-/handlebars-4.0.5.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/nyc/node_modules/istanbul/node_modules/handlebars/package.json</p>
<p>
Dependency Hierarchy:
- tap-5.8.0.tgz (Root Library)
- nyc-6.6.1.tgz
- istanbul-0.4.3.tgz
- :x: **handlebars-4.0.5.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/HOTFIX/commit/3bc753a65c01eab39a0bf5cf3aed58995c79c72a">3bc753a65c01eab39a0bf5cf3aed58995c79c72a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The package handlebars before 4.7.7 are vulnerable to Prototype Pollution when selecting certain compiling options to compile templates coming from an untrusted source.
<p>Publish Date: 2021-05-04
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-23383>CVE-2021-23383</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23383">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23383</a></p>
<p>Release Date: 2021-05-04</p>
<p>Fix Resolution: handlebars - 4.7.7</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2018-3728</summary>
### Vulnerable Libraries - <b>hoek-2.16.3.tgz</b>, <b>hoek-0.9.1.tgz</b></p>
<p>
### <b>hoek-2.16.3.tgz</b></p>
<p>General purpose node utilities</p>
<p>Library home page: <a href="https://registry.npmjs.org/hoek/-/hoek-2.16.3.tgz">https://registry.npmjs.org/hoek/-/hoek-2.16.3.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/coveralls/node_modules/hoek/package.json</p>
<p>
Dependency Hierarchy:
- tap-5.8.0.tgz (Root Library)
- coveralls-2.13.3.tgz
- request-2.79.0.tgz
- hawk-3.1.3.tgz
- :x: **hoek-2.16.3.tgz** (Vulnerable Library)
### <b>hoek-0.9.1.tgz</b></p>
<p>General purpose node utilities</p>
<p>Library home page: <a href="https://registry.npmjs.org/hoek/-/hoek-0.9.1.tgz">https://registry.npmjs.org/hoek/-/hoek-0.9.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/hoek/package.json</p>
<p>
Dependency Hierarchy:
- tap-5.8.0.tgz (Root Library)
- codecov.io-0.1.6.tgz
- request-2.42.0.tgz
- hawk-1.1.1.tgz
- :x: **hoek-0.9.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/HOTFIX/commit/3bc753a65c01eab39a0bf5cf3aed58995c79c72a">3bc753a65c01eab39a0bf5cf3aed58995c79c72a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
hoek node module before 4.2.0 and 5.0.x before 5.0.3 suffers from a Modification of Assumed-Immutable Data (MAID) vulnerability via 'merge' and 'applyToDefaults' functions, which allows a malicious user to modify the prototype of "Object" via __proto__, causing the addition or modification of an existing property that will exist on all objects.
<p>Publish Date: 2018-03-30
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-3728>CVE-2018-3728</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-16082">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-16082</a></p>
<p>Release Date: 2018-03-30</p>
<p>Fix Resolution: 4.2.0,5.0.3</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-20920</summary>
### Vulnerable Library - <b>handlebars-4.0.5.tgz</b></p>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://registry.npmjs.org/handlebars/-/handlebars-4.0.5.tgz">https://registry.npmjs.org/handlebars/-/handlebars-4.0.5.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/nyc/node_modules/istanbul/node_modules/handlebars/package.json</p>
<p>
Dependency Hierarchy:
- tap-5.8.0.tgz (Root Library)
- nyc-6.6.1.tgz
- istanbul-0.4.3.tgz
- :x: **handlebars-4.0.5.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/HOTFIX/commit/3bc753a65c01eab39a0bf5cf3aed58995c79c72a">3bc753a65c01eab39a0bf5cf3aed58995c79c72a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Handlebars before 3.0.8 and 4.x before 4.5.3 is vulnerable to Arbitrary Code Execution. The lookup helper fails to properly validate templates, allowing attackers to submit templates that execute arbitrary JavaScript. This can be used to run arbitrary code on a server processing Handlebars templates or in a victim's browser (effectively serving as XSS).
<p>Publish Date: 2020-09-30
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-20920>CVE-2019-20920</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1324">https://www.npmjs.com/advisories/1324</a></p>
<p>Release Date: 2020-10-15</p>
<p>Fix Resolution: handlebars - 4.5.3</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> WS-2019-0063</summary>
### Vulnerable Library - <b>js-yaml-3.6.1.tgz</b></p>
<p>YAML 1.2 parser and serializer</p>
<p>Library home page: <a href="https://registry.npmjs.org/js-yaml/-/js-yaml-3.6.1.tgz">https://registry.npmjs.org/js-yaml/-/js-yaml-3.6.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/nyc/node_modules/istanbul/node_modules/js-yaml/package.json,/node_modules/coveralls/node_modules/js-yaml/package.json</p>
<p>
Dependency Hierarchy:
- tap-5.8.0.tgz (Root Library)
- nyc-6.6.1.tgz
- istanbul-0.4.3.tgz
- :x: **js-yaml-3.6.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/HOTFIX/commit/3bc753a65c01eab39a0bf5cf3aed58995c79c72a">3bc753a65c01eab39a0bf5cf3aed58995c79c72a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Js-yaml prior to 3.13.1 are vulnerable to Code Injection. The load() function may execute arbitrary code injected through a malicious YAML file.
<p>Publish Date: 2019-04-05
<p>URL: <a href=https://github.com/nodeca/js-yaml/pull/480>WS-2019-0063</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/813">https://www.npmjs.com/advisories/813</a></p>
<p>Release Date: 2019-04-05</p>
<p>Fix Resolution: js-yaml - 3.13.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-20922</summary>
### Vulnerable Library - <b>handlebars-4.0.5.tgz</b></p>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://registry.npmjs.org/handlebars/-/handlebars-4.0.5.tgz">https://registry.npmjs.org/handlebars/-/handlebars-4.0.5.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/nyc/node_modules/istanbul/node_modules/handlebars/package.json</p>
<p>
Dependency Hierarchy:
- tap-5.8.0.tgz (Root Library)
- nyc-6.6.1.tgz
- istanbul-0.4.3.tgz
- :x: **handlebars-4.0.5.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/HOTFIX/commit/3bc753a65c01eab39a0bf5cf3aed58995c79c72a">3bc753a65c01eab39a0bf5cf3aed58995c79c72a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Handlebars before 4.4.5 allows Regular Expression Denial of Service (ReDoS) because of eager matching. The parser may be forced into an endless loop while processing crafted templates. This may allow attackers to exhaust system resources.
<p>Publish Date: 2020-09-30
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-20922>CVE-2019-20922</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1300">https://www.npmjs.com/advisories/1300</a></p>
<p>Release Date: 2020-09-30</p>
<p>Fix Resolution: handlebars - 4.4.5</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-28469</summary>
### Vulnerable Library - <b>glob-parent-2.0.0.tgz</b></p>
<p>Strips glob magic from a string to provide the parent path</p>
<p>Library home page: <a href="https://registry.npmjs.org/glob-parent/-/glob-parent-2.0.0.tgz">https://registry.npmjs.org/glob-parent/-/glob-parent-2.0.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/nyc/node_modules/micromatch/node_modules/parse-glob/node_modules/glob-base/node_modules/glob-parent/package.json</p>
<p>
Dependency Hierarchy:
- tap-5.8.0.tgz (Root Library)
- nyc-6.6.1.tgz
- micromatch-2.3.8.tgz
- parse-glob-3.0.4.tgz
- glob-base-0.3.0.tgz
- :x: **glob-parent-2.0.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/HOTFIX/commit/3bc753a65c01eab39a0bf5cf3aed58995c79c72a">3bc753a65c01eab39a0bf5cf3aed58995c79c72a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
This affects the package glob-parent before 5.1.2. The enclosure regex used to check for strings ending in enclosure containing path separator.
<p>Publish Date: 2021-06-03
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-28469>CVE-2020-28469</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28469">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28469</a></p>
<p>Release Date: 2021-06-03</p>
<p>Fix Resolution: glob-parent - 5.1.2</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2016-10540</summary>
### Vulnerable Libraries - <b>minimatch-3.0.0.tgz</b>, <b>minimatch-2.0.10.tgz</b></p>
<p>
### <b>minimatch-3.0.0.tgz</b></p>
<p>a glob matcher in javascript</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimatch/-/minimatch-3.0.0.tgz">https://registry.npmjs.org/minimatch/-/minimatch-3.0.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/nyc/node_modules/glob/node_modules/minimatch/package.json</p>
<p>
Dependency Hierarchy:
- tap-5.8.0.tgz (Root Library)
- nyc-6.6.1.tgz
- glob-7.0.3.tgz
- :x: **minimatch-3.0.0.tgz** (Vulnerable Library)
### <b>minimatch-2.0.10.tgz</b></p>
<p>a glob matcher in javascript</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimatch/-/minimatch-2.0.10.tgz">https://registry.npmjs.org/minimatch/-/minimatch-2.0.10.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/nyc/node_modules/istanbul/node_modules/fileset/node_modules/minimatch/package.json</p>
<p>
Dependency Hierarchy:
- tap-5.8.0.tgz (Root Library)
- nyc-6.6.1.tgz
- istanbul-0.4.3.tgz
- fileset-0.2.1.tgz
- :x: **minimatch-2.0.10.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/HOTFIX/commit/3bc753a65c01eab39a0bf5cf3aed58995c79c72a">3bc753a65c01eab39a0bf5cf3aed58995c79c72a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Minimatch is a minimal matching utility that works by converting glob expressions into JavaScript `RegExp` objects. The primary function, `minimatch(path, pattern)` in Minimatch 3.0.1 and earlier is vulnerable to ReDoS in the `pattern` parameter.
<p>Publish Date: 2018-05-31
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-10540>CVE-2016-10540</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2016-10540">https://nvd.nist.gov/vuln/detail/CVE-2016-10540</a></p>
<p>Release Date: 2018-04-26</p>
<p>Fix Resolution: Pvc.Browserify - 0.0.1.1;JetBrains.Rider.Frontend4 - 203.0.20201014.202610-eap04;JetBrains.Rider.Frontend5 - 203.0.20201006.200056-eap03,213.0.20211008.154703-eap03;Bridge.AWS - 0.3.30.36;tslint - 3.11.0;MIDIator.WebClient - 1.0.105;BumperLane.Public.Service.Contracts - 0.23.35.214-prerelease;ng-grid - 2.0.4;minimatch - 3.0.2;Virteom.Tenant.Mobile.Bluetooth - 0.21.29.159-prerelease;ShowingVault.DotNet.Sdk - 0.13.41.190-prerelease;Triarc.Web.Build - 1.3.0;Virteom.Tenant.Mobile.Framework.UWP - 0.20.41.103-prerelease;Virteom.Tenant.Mobile.Framework.iOS - 0.20.41.103-prerelease;BumperLane.Public.Api.V2.ClientModule - 0.23.35.214-prerelease;Virteom.Tenant.Mobile.Bluetooth.iOS - 0.20.41.103-prerelease;Virteom.Public.Utilities - 0.23.37.212-prerelease;Mustache.Reports.Data - 1.2.2;Virteom.Tenant.Mobile.Framework - 0.21.29.159-prerelease;Virteom.Tenant.Mobile.Bluetooth.Android - 0.20.41.103-prerelease;z4a-dotnet-scaffold - 1.0.0.2;Raml.Parser - 2.0.0,1.0.2;AntData.ORM - 1.2.9;ApiExplorer.HelpPage - 1.0.0-alpha3;SitecoreMaster.TrueDynamicPlaceholders - 1.0.3;Virteom.Tenant.Mobile.Framework.Android - 0.20.41.103-prerelease;BumperLane.Public.Api.Client - 0.23.35.214-prerelease</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2016-2515</summary>
### Vulnerable Library - <b>hawk-1.1.1.tgz</b></p>
<p>HTTP Hawk Authentication Scheme</p>
<p>Library home page: <a href="https://registry.npmjs.org/hawk/-/hawk-1.1.1.tgz">https://registry.npmjs.org/hawk/-/hawk-1.1.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/hawk/package.json</p>
<p>
Dependency Hierarchy:
- tap-5.8.0.tgz (Root Library)
- codecov.io-0.1.6.tgz
- request-2.42.0.tgz
- :x: **hawk-1.1.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/HOTFIX/commit/3bc753a65c01eab39a0bf5cf3aed58995c79c72a">3bc753a65c01eab39a0bf5cf3aed58995c79c72a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Hawk before 3.1.3 and 4.x before 4.1.1 allow remote attackers to cause a denial of service (CPU consumption or partial outage) via a long (1) header or (2) URI that is matched against an improper regular expression.
<p>Publish Date: 2016-04-13
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-2515>CVE-2016-2515</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2016-2515">https://nvd.nist.gov/vuln/detail/CVE-2016-2515</a></p>
<p>Release Date: 2016-04-13</p>
<p>Fix Resolution: 3.1.3,4.1.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2017-1000048</summary>
### Vulnerable Library - <b>qs-1.2.2.tgz</b></p>
<p>A querystring parser that supports nesting and arrays, with a depth limit</p>
<p>Library home page: <a href="https://registry.npmjs.org/qs/-/qs-1.2.2.tgz">https://registry.npmjs.org/qs/-/qs-1.2.2.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/request/node_modules/qs/package.json</p>
<p>
Dependency Hierarchy:
- tap-5.8.0.tgz (Root Library)
- codecov.io-0.1.6.tgz
- request-2.42.0.tgz
- :x: **qs-1.2.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/HOTFIX/commit/3bc753a65c01eab39a0bf5cf3aed58995c79c72a">3bc753a65c01eab39a0bf5cf3aed58995c79c72a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
the web framework using ljharb's qs module older than v6.3.2, v6.2.3, v6.1.2, and v6.0.4 is vulnerable to a DoS. A malicious user can send a evil request to cause the web framework crash.
<p>Publish Date: 2017-07-17
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2017-1000048>CVE-2017-1000048</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-1000048">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-1000048</a></p>
<p>Release Date: 2017-07-17</p>
<p>Fix Resolution: qs - 6.0.4,6.1.2,6.2.3,6.3.2</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-29167</summary>
### Vulnerable Library - <b>hawk-3.1.3.tgz</b></p>
<p>HTTP Hawk Authentication Scheme</p>
<p>Library home page: <a href="https://registry.npmjs.org/hawk/-/hawk-3.1.3.tgz">https://registry.npmjs.org/hawk/-/hawk-3.1.3.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/coveralls/node_modules/hawk/package.json</p>
<p>
Dependency Hierarchy:
- tap-5.8.0.tgz (Root Library)
- coveralls-2.13.3.tgz
- request-2.79.0.tgz
- :x: **hawk-3.1.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/HOTFIX/commit/3bc753a65c01eab39a0bf5cf3aed58995c79c72a">3bc753a65c01eab39a0bf5cf3aed58995c79c72a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Hawk is an HTTP authentication scheme providing mechanisms for making authenticated HTTP requests with partial cryptographic verification of the request and response, covering the HTTP method, request URI, host, and optionally the request payload. Hawk used a regular expression to parse `Host` HTTP header (`Hawk.utils.parseHost()`), which was subject to regular expression DoS attack - meaning each added character in the attacker's input increases the computation time exponentially. `parseHost()` was patched in `9.0.1` to use built-in `URL` class to parse hostname instead. `Hawk.authenticate()` accepts `options` argument. If that contains `host` and `port`, those would be used instead of a call to `utils.parseHost()`.
<p>Publish Date: 2022-05-05
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-29167>CVE-2022-29167</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/mozilla/hawk/security/advisories/GHSA-44pw-h2cw-w3vq">https://github.com/mozilla/hawk/security/advisories/GHSA-44pw-h2cw-w3vq</a></p>
<p>Release Date: 2022-05-05</p>
<p>Fix Resolution: hawk - 9.0.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> WS-2019-0032</summary>
### Vulnerable Library - <b>js-yaml-3.6.1.tgz</b></p>
<p>YAML 1.2 parser and serializer</p>
<p>Library home page: <a href="https://registry.npmjs.org/js-yaml/-/js-yaml-3.6.1.tgz">https://registry.npmjs.org/js-yaml/-/js-yaml-3.6.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/nyc/node_modules/istanbul/node_modules/js-yaml/package.json,/node_modules/coveralls/node_modules/js-yaml/package.json</p>
<p>
Dependency Hierarchy:
- tap-5.8.0.tgz (Root Library)
- nyc-6.6.1.tgz
- istanbul-0.4.3.tgz
- :x: **js-yaml-3.6.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/HOTFIX/commit/3bc753a65c01eab39a0bf5cf3aed58995c79c72a">3bc753a65c01eab39a0bf5cf3aed58995c79c72a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Versions js-yaml prior to 3.13.0 are vulnerable to Denial of Service. By parsing a carefully-crafted YAML file, the node process stalls and may exhaust system resources leading to a Denial of Service.
<p>Publish Date: 2019-03-20
<p>URL: <a href=https://github.com/nodeca/js-yaml/commit/a567ef3c6e61eb319f0bfc2671d91061afb01235>WS-2019-0032</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/788/versions">https://www.npmjs.com/advisories/788/versions</a></p>
<p>Release Date: 2019-03-20</p>
<p>Fix Resolution: js-yaml - 3.13.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2017-18077</summary>
### Vulnerable Library - <b>brace-expansion-1.1.4.tgz</b></p>
<p>Brace expansion as known from sh/bash</p>
<p>Library home page: <a href="https://registry.npmjs.org/brace-expansion/-/brace-expansion-1.1.4.tgz">https://registry.npmjs.org/brace-expansion/-/brace-expansion-1.1.4.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/nyc/node_modules/istanbul/node_modules/fileset/node_modules/minimatch/node_modules/brace-expansion/package.json,/node_modules/nyc/node_modules/glob/node_modules/minimatch/node_modules/brace-expansion/package.json</p>
<p>
Dependency Hierarchy:
- tap-5.8.0.tgz (Root Library)
- nyc-6.6.1.tgz
- istanbul-0.4.3.tgz
- fileset-0.2.1.tgz
- minimatch-2.0.10.tgz
- :x: **brace-expansion-1.1.4.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/HOTFIX/commit/3bc753a65c01eab39a0bf5cf3aed58995c79c72a">3bc753a65c01eab39a0bf5cf3aed58995c79c72a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
index.js in brace-expansion before 1.1.7 is vulnerable to Regular Expression Denial of Service (ReDoS) attacks, as demonstrated by an expand argument containing many comma characters.
<p>Publish Date: 2018-01-27
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2017-18077>CVE-2017-18077</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2017-18077">https://nvd.nist.gov/vuln/detail/CVE-2017-18077</a></p>
<p>Release Date: 2018-01-27</p>
<p>Fix Resolution: 1.1.7</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-24999</summary>
### Vulnerable Library - <b>qs-1.2.2.tgz</b></p>
<p>A querystring parser that supports nesting and arrays, with a depth limit</p>
<p>Library home page: <a href="https://registry.npmjs.org/qs/-/qs-1.2.2.tgz">https://registry.npmjs.org/qs/-/qs-1.2.2.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/request/node_modules/qs/package.json</p>
<p>
Dependency Hierarchy:
- tap-5.8.0.tgz (Root Library)
- codecov.io-0.1.6.tgz
- request-2.42.0.tgz
- :x: **qs-1.2.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/HOTFIX/commit/3bc753a65c01eab39a0bf5cf3aed58995c79c72a">3bc753a65c01eab39a0bf5cf3aed58995c79c72a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
qs before 6.10.3, as used in Express before 4.17.3 and other products, allows attackers to cause a Node process hang for an Express application because an __ proto__ key can be used. In many typical Express use cases, an unauthenticated remote attacker can place the attack payload in the query string of the URL that is used to visit the application, such as a[__proto__]=b&a[__proto__]&a[length]=100000000. The fix was backported to qs 6.9.7, 6.8.3, 6.7.3, 6.6.1, 6.5.3, 6.4.1, 6.3.3, and 6.2.4 (and therefore Express 4.17.3, which has "deps: qs@6.9.7" in its release description, is not vulnerable).
<p>Publish Date: 2022-11-26
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-24999>CVE-2022-24999</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.cve.org/CVERecord?id=CVE-2022-24999">https://www.cve.org/CVERecord?id=CVE-2022-24999</a></p>
<p>Release Date: 2022-11-26</p>
<p>Fix Resolution: qs - 6.2.4,6.3.3,6.4.1,6.5.3,6.6.1,6.7.3,6.8.3,6.9.7,6.10.3</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> WS-2020-0450</summary>
### Vulnerable Library - <b>handlebars-4.0.5.tgz</b></p>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://registry.npmjs.org/handlebars/-/handlebars-4.0.5.tgz">https://registry.npmjs.org/handlebars/-/handlebars-4.0.5.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/nyc/node_modules/istanbul/node_modules/handlebars/package.json</p>
<p>
Dependency Hierarchy:
- tap-5.8.0.tgz (Root Library)
- nyc-6.6.1.tgz
- istanbul-0.4.3.tgz
- :x: **handlebars-4.0.5.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/HOTFIX/commit/3bc753a65c01eab39a0bf5cf3aed58995c79c72a">3bc753a65c01eab39a0bf5cf3aed58995c79c72a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Handlebars before 4.6.0 vulnerable to Prototype Pollution. Prototype access to the template engine allows for potential code execution, which may lead to Denial Of Service (DoS).
<p>Publish Date: 2020-01-09
<p>URL: <a href=https://github.com/handlebars-lang/handlebars.js/commit/33a3b46bc205f768f8edbc67241c68591fe3472c>WS-2020-0450</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2020-01-09</p>
<p>Fix Resolution: handlebars - 4.6.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-3517</summary>
### Vulnerable Libraries - <b>minimatch-2.0.10.tgz</b>, <b>minimatch-3.0.0.tgz</b></p>
<p>
### <b>minimatch-2.0.10.tgz</b></p>
<p>a glob matcher in javascript</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimatch/-/minimatch-2.0.10.tgz">https://registry.npmjs.org/minimatch/-/minimatch-2.0.10.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/nyc/node_modules/istanbul/node_modules/fileset/node_modules/minimatch/package.json</p>
<p>
Dependency Hierarchy:
- tap-5.8.0.tgz (Root Library)
- nyc-6.6.1.tgz
- istanbul-0.4.3.tgz
- fileset-0.2.1.tgz
- :x: **minimatch-2.0.10.tgz** (Vulnerable Library)
### <b>minimatch-3.0.0.tgz</b></p>
<p>a glob matcher in javascript</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimatch/-/minimatch-3.0.0.tgz">https://registry.npmjs.org/minimatch/-/minimatch-3.0.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/nyc/node_modules/glob/node_modules/minimatch/package.json</p>
<p>
Dependency Hierarchy:
- tap-5.8.0.tgz (Root Library)
- nyc-6.6.1.tgz
- glob-7.0.3.tgz
- :x: **minimatch-3.0.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/HOTFIX/commit/3bc753a65c01eab39a0bf5cf3aed58995c79c72a">3bc753a65c01eab39a0bf5cf3aed58995c79c72a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A vulnerability was found in the minimatch package. This flaw allows a Regular Expression Denial of Service (ReDoS) when calling the braceExpand function with specific arguments, resulting in a Denial of Service.
<p>Publish Date: 2022-10-17
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-3517>CVE-2022-3517</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-10-17</p>
<p>Fix Resolution: minimatch - 3.0.5</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> WS-2019-0064</summary>
### Vulnerable Library - <b>handlebars-4.0.5.tgz</b></p>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://registry.npmjs.org/handlebars/-/handlebars-4.0.5.tgz">https://registry.npmjs.org/handlebars/-/handlebars-4.0.5.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/nyc/node_modules/istanbul/node_modules/handlebars/package.json</p>
<p>
Dependency Hierarchy:
- tap-5.8.0.tgz (Root Library)
- nyc-6.6.1.tgz
- istanbul-0.4.3.tgz
- :x: **handlebars-4.0.5.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/HOTFIX/commit/3bc753a65c01eab39a0bf5cf3aed58995c79c72a">3bc753a65c01eab39a0bf5cf3aed58995c79c72a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Versions of handlebars prior to 4.0.14 are vulnerable to Prototype Pollution. Templates may alter an Objects' prototype, thus allowing an attacker to execute arbitrary code on the server.
<p>Publish Date: 2019-01-30
<p>URL: <a href=https://github.com/wycats/handlebars.js/compare/v4.1.1...v4.1.2>WS-2019-0064</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/755/">https://www.npmjs.com/advisories/755/</a></p>
<p>Release Date: 2019-01-30</p>
<p>Fix Resolution: 3.0.7,4.0.14,4.1.2</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> WS-2018-0590</summary>
### Vulnerable Library - <b>diff-1.4.0.tgz</b></p>
<p>A javascript text diff implementation.</p>
<p>Library home page: <a href="https://registry.npmjs.org/diff/-/diff-1.4.0.tgz">https://registry.npmjs.org/diff/-/diff-1.4.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/diff/package.json</p>
<p>
Dependency Hierarchy:
- tap-5.8.0.tgz (Root Library)
- tap-mocha-reporter-0.0.27.tgz
- :x: **diff-1.4.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/HOTFIX/commit/3bc753a65c01eab39a0bf5cf3aed58995c79c72a">3bc753a65c01eab39a0bf5cf3aed58995c79c72a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A vulnerability was found in diff before v3.5.0, the affected versions of this package are vulnerable to Regular Expression Denial of Service (ReDoS) attacks.
<p>Publish Date: 2018-03-05
<p>URL: <a href=https://bugzilla.redhat.com/show_bug.cgi?id=1552148>WS-2018-0590</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2018-03-05</p>
<p>Fix Resolution: 3.5.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2020-8244</summary>
### Vulnerable Library - <b>bl-0.9.5.tgz</b></p>
<p>Buffer List: collect buffers and access with a standard readable Buffer interface, streamable too!</p>
<p>Library home page: <a href="https://registry.npmjs.org/bl/-/bl-0.9.5.tgz">https://registry.npmjs.org/bl/-/bl-0.9.5.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/bl/package.json</p>
<p>
Dependency Hierarchy:
- tap-5.8.0.tgz (Root Library)
- codecov.io-0.1.6.tgz
- request-2.42.0.tgz
- :x: **bl-0.9.5.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/HOTFIX/commit/3bc753a65c01eab39a0bf5cf3aed58995c79c72a">3bc753a65c01eab39a0bf5cf3aed58995c79c72a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A buffer over-read vulnerability exists in bl <4.0.3, <3.0.1, <2.2.1, and <1.2.3 which could allow an attacker to supply user input (even typed) that if it ends up in consume() argument and can become negative, the BufferList state can be corrupted, tricking it into exposing uninitialized memory via regular .slice() calls.
<p>Publish Date: 2020-08-30
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-8244>CVE-2020-8244</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-pp7h-53gx-mx7r">https://github.com/advisories/GHSA-pp7h-53gx-mx7r</a></p>
<p>Release Date: 2020-08-30</p>
<p>Fix Resolution: bl - 1.2.3,2.2.1,3.0.1,4.0.3</p>
</p>
<p></p>
</details>
|
True
|
tap-5.8.0.tgz: 32 vulnerabilities (highest severity is: 9.8) - autoclosed - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tap-5.8.0.tgz</b></p></summary>
<p></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/nyc/node_modules/istanbul/node_modules/handlebars/package.json</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/HOTFIX/commit/3bc753a65c01eab39a0bf5cf3aed58995c79c72a">3bc753a65c01eab39a0bf5cf3aed58995c79c72a</a></p></details>
#### <img src='https://whitesource-resources.whitesourcesoftware.com/suggestedVersion.png' width=19 height=20> Mend has checked all newer package trees, and you are on the least vulnerable package!
#### Please note: There might be a version that explicitly solves one or more of the vulnerabilities listed below, but we do not recommend it. For more info about the optional fixes, check the section “Details” below.
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (tap version) | Fix PR available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2021-23369](https://www.mend.io/vulnerability-database/CVE-2021-23369) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | handlebars-4.0.5.tgz | Transitive | N/A* | ❌ |
| [CVE-2019-19919](https://www.mend.io/vulnerability-database/CVE-2019-19919) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | handlebars-4.0.5.tgz | Transitive | N/A* | ❌ |
| [CVE-2020-7774](https://www.mend.io/vulnerability-database/CVE-2020-7774) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | y18n-3.2.1.tgz | Transitive | N/A* | ❌ |
| [CVE-2018-1000620](https://www.mend.io/vulnerability-database/CVE-2018-1000620) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2021-44906](https://www.mend.io/vulnerability-database/CVE-2021-44906) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2021-23383](https://www.mend.io/vulnerability-database/CVE-2021-23383) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | handlebars-4.0.5.tgz | Transitive | N/A* | ❌ |
| [CVE-2018-3728](https://www.mend.io/vulnerability-database/CVE-2018-3728) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2019-20920](https://www.mend.io/vulnerability-database/CVE-2019-20920) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | handlebars-4.0.5.tgz | Transitive | N/A* | ❌ |
| [WS-2019-0063](https://github.com/nodeca/js-yaml/pull/480) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | js-yaml-3.6.1.tgz | Transitive | N/A* | ❌ |
| [CVE-2019-20922](https://www.mend.io/vulnerability-database/CVE-2019-20922) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | handlebars-4.0.5.tgz | Transitive | N/A* | ❌ |
| [CVE-2020-28469](https://www.mend.io/vulnerability-database/CVE-2020-28469) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | glob-parent-2.0.0.tgz | Transitive | N/A* | ❌ |
| [CVE-2016-10540](https://www.mend.io/vulnerability-database/CVE-2016-10540) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2016-2515](https://www.mend.io/vulnerability-database/CVE-2016-2515) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | hawk-1.1.1.tgz | Transitive | N/A* | ❌ |
| [CVE-2017-1000048](https://www.mend.io/vulnerability-database/CVE-2017-1000048) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | qs-1.2.2.tgz | Transitive | N/A* | ❌ |
| [CVE-2022-29167](https://www.mend.io/vulnerability-database/CVE-2022-29167) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | hawk-3.1.3.tgz | Transitive | N/A* | ❌ |
| [WS-2019-0032](https://github.com/nodeca/js-yaml/commit/a567ef3c6e61eb319f0bfc2671d91061afb01235) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | js-yaml-3.6.1.tgz | Transitive | N/A* | ❌ |
| [CVE-2017-18077](https://www.mend.io/vulnerability-database/CVE-2017-18077) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | brace-expansion-1.1.4.tgz | Transitive | N/A* | ❌ |
| [CVE-2022-24999](https://www.mend.io/vulnerability-database/CVE-2022-24999) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | qs-1.2.2.tgz | Transitive | N/A* | ❌ |
| [WS-2020-0450](https://github.com/handlebars-lang/handlebars.js/commit/33a3b46bc205f768f8edbc67241c68591fe3472c) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | handlebars-4.0.5.tgz | Transitive | N/A* | ❌ |
| [CVE-2022-3517](https://www.mend.io/vulnerability-database/CVE-2022-3517) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [WS-2019-0064](https://github.com/wycats/handlebars.js/compare/v4.1.1...v4.1.2) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | handlebars-4.0.5.tgz | Transitive | N/A* | ❌ |
| [WS-2018-0590](https://bugzilla.redhat.com/show_bug.cgi?id=1552148) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.1 | diff-1.4.0.tgz | Transitive | N/A* | ❌ |
| [CVE-2020-8244](https://www.mend.io/vulnerability-database/CVE-2020-8244) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | bl-0.9.5.tgz | Transitive | N/A* | ❌ |
| [CVE-2017-16026](https://www.mend.io/vulnerability-database/CVE-2017-16026) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.9 | request-2.42.0.tgz | Transitive | N/A* | ❌ |
| [CVE-2020-7598](https://www.mend.io/vulnerability-database/CVE-2020-7598) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.6 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [WS-2019-0103](https://github.com/wycats/handlebars.js/issues/1267#issue-187151586) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.6 | handlebars-4.0.5.tgz | Transitive | N/A* | ❌ |
| [CVE-2017-16032](https://www.mend.io/vulnerability-database/CVE-2017-16032) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.5 | brace-expansion-1.1.4.tgz | Transitive | N/A* | ❌ |
| [CVE-2020-7608](https://www.mend.io/vulnerability-database/CVE-2020-7608) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | yargs-parser-2.4.0.tgz | Transitive | N/A* | ❌ |
| [CVE-2021-23362](https://www.mend.io/vulnerability-database/CVE-2021-23362) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | hosted-git-info-2.1.5.tgz | Transitive | N/A* | ❌ |
| [CVE-2017-16028](https://www.mend.io/vulnerability-database/CVE-2017-16028) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | randomatic-1.1.5.tgz | Transitive | N/A* | ❌ |
| [WS-2018-0076](https://github.com/request/tunnel-agent/commit/9ca95ec7219daface8a6fc2674000653de0922c0) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.1 | tunnel-agent-0.4.3.tgz | Transitive | N/A* | ❌ |
| [WS-2017-0266](https://github.com/joyent/node-http-signature/commit/78ab1da232f31f695f5c362d863593a143aa8b56) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 3.5 | http-signature-0.10.1.tgz | Transitive | N/A* | ❌ |
<p>*For some transitive vulnerabilities, there is no version of direct dependency with a fix. Check the section "Details" below to see if there is a version of transitive dependency where vulnerability is fixed.</p>
## Details
> Partial details (23 vulnerabilities) are displayed below due to a content size limitation in GitHub. To view information on the remaining vulnerabilities, navigate to the Mend Application.<br>
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-23369</summary>
### Vulnerable Library - <b>handlebars-4.0.5.tgz</b></p>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://registry.npmjs.org/handlebars/-/handlebars-4.0.5.tgz">https://registry.npmjs.org/handlebars/-/handlebars-4.0.5.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/nyc/node_modules/istanbul/node_modules/handlebars/package.json</p>
<p>
Dependency Hierarchy:
- tap-5.8.0.tgz (Root Library)
- nyc-6.6.1.tgz
- istanbul-0.4.3.tgz
- :x: **handlebars-4.0.5.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/HOTFIX/commit/3bc753a65c01eab39a0bf5cf3aed58995c79c72a">3bc753a65c01eab39a0bf5cf3aed58995c79c72a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The package handlebars before 4.7.7 are vulnerable to Remote Code Execution (RCE) when selecting certain compiling options to compile templates coming from an untrusted source.
<p>Publish Date: 2021-04-12
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-23369>CVE-2021-23369</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23369">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23369</a></p>
<p>Release Date: 2021-04-12</p>
<p>Fix Resolution: com.github.jknack:handlebars:4.2.0, handlebars - 4.7.7</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-19919</summary>
### Vulnerable Library - <b>handlebars-4.0.5.tgz</b></p>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://registry.npmjs.org/handlebars/-/handlebars-4.0.5.tgz">https://registry.npmjs.org/handlebars/-/handlebars-4.0.5.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/nyc/node_modules/istanbul/node_modules/handlebars/package.json</p>
<p>
Dependency Hierarchy:
- tap-5.8.0.tgz (Root Library)
- nyc-6.6.1.tgz
- istanbul-0.4.3.tgz
- :x: **handlebars-4.0.5.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/HOTFIX/commit/3bc753a65c01eab39a0bf5cf3aed58995c79c72a">3bc753a65c01eab39a0bf5cf3aed58995c79c72a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Versions of handlebars prior to 4.3.0 are vulnerable to Prototype Pollution leading to Remote Code Execution. Templates may alter an Object's __proto__ and __defineGetter__ properties, which may allow an attacker to execute arbitrary code through crafted payloads.
<p>Publish Date: 2019-12-20
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-19919>CVE-2019-19919</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-19919">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-19919</a></p>
<p>Release Date: 2019-12-20</p>
<p>Fix Resolution: handlebars - 4.3.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-7774</summary>
### Vulnerable Library - <b>y18n-3.2.1.tgz</b></p>
<p>the bare-bones internationalization library used by yargs</p>
<p>Library home page: <a href="https://registry.npmjs.org/y18n/-/y18n-3.2.1.tgz">https://registry.npmjs.org/y18n/-/y18n-3.2.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/nyc/node_modules/yargs/node_modules/y18n/package.json</p>
<p>
Dependency Hierarchy:
- tap-5.8.0.tgz (Root Library)
- nyc-6.6.1.tgz
- yargs-4.7.1.tgz
- :x: **y18n-3.2.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/HOTFIX/commit/3bc753a65c01eab39a0bf5cf3aed58995c79c72a">3bc753a65c01eab39a0bf5cf3aed58995c79c72a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The package y18n before 3.2.2, 4.0.1 and 5.0.5, is vulnerable to Prototype Pollution.
<p>Publish Date: 2020-11-17
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-7774>CVE-2020-7774</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1654">https://www.npmjs.com/advisories/1654</a></p>
<p>Release Date: 2020-11-17</p>
<p>Fix Resolution: 3.2.2, 4.0.1, 5.0.5</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2018-1000620</summary>
### Vulnerable Libraries - <b>cryptiles-0.2.2.tgz</b>, <b>cryptiles-2.0.5.tgz</b></p>
<p>
### <b>cryptiles-0.2.2.tgz</b></p>
<p>General purpose crypto utilities</p>
<p>Library home page: <a href="https://registry.npmjs.org/cryptiles/-/cryptiles-0.2.2.tgz">https://registry.npmjs.org/cryptiles/-/cryptiles-0.2.2.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/cryptiles/package.json</p>
<p>
Dependency Hierarchy:
- tap-5.8.0.tgz (Root Library)
- codecov.io-0.1.6.tgz
- request-2.42.0.tgz
- hawk-1.1.1.tgz
- :x: **cryptiles-0.2.2.tgz** (Vulnerable Library)
### <b>cryptiles-2.0.5.tgz</b></p>
<p>General purpose crypto utilities</p>
<p>Library home page: <a href="https://registry.npmjs.org/cryptiles/-/cryptiles-2.0.5.tgz">https://registry.npmjs.org/cryptiles/-/cryptiles-2.0.5.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/coveralls/node_modules/cryptiles/package.json</p>
<p>
Dependency Hierarchy:
- tap-5.8.0.tgz (Root Library)
- coveralls-2.13.3.tgz
- request-2.79.0.tgz
- hawk-3.1.3.tgz
- :x: **cryptiles-2.0.5.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/HOTFIX/commit/3bc753a65c01eab39a0bf5cf3aed58995c79c72a">3bc753a65c01eab39a0bf5cf3aed58995c79c72a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Eran Hammer cryptiles version 4.1.1 earlier contains a CWE-331: Insufficient Entropy vulnerability in randomDigits() method that can result in An attacker is more likely to be able to brute force something that was supposed to be random.. This attack appear to be exploitable via Depends upon the calling application.. This vulnerability appears to have been fixed in 4.1.2.
<p>Publish Date: 2018-07-09
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-1000620>CVE-2018-1000620</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2018-1000620">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2018-1000620</a></p>
<p>Release Date: 2018-07-09</p>
<p>Fix Resolution: v4.1.2</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-44906</summary>
### Vulnerable Libraries - <b>minimist-1.2.0.tgz</b>, <b>minimist-0.0.8.tgz</b>, <b>minimist-0.0.10.tgz</b></p>
<p>
### <b>minimist-1.2.0.tgz</b></p>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-1.2.0.tgz">https://registry.npmjs.org/minimist/-/minimist-1.2.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/coveralls/node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- tap-5.8.0.tgz (Root Library)
- coveralls-2.13.3.tgz
- :x: **minimist-1.2.0.tgz** (Vulnerable Library)
### <b>minimist-0.0.8.tgz</b></p>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-0.0.8.tgz">https://registry.npmjs.org/minimist/-/minimist-0.0.8.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/nyc/node_modules/mkdirp/node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- tap-5.8.0.tgz (Root Library)
- nyc-6.6.1.tgz
- mkdirp-0.5.1.tgz
- :x: **minimist-0.0.8.tgz** (Vulnerable Library)
### <b>minimist-0.0.10.tgz</b></p>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-0.0.10.tgz">https://registry.npmjs.org/minimist/-/minimist-0.0.10.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/nyc/node_modules/istanbul/node_modules/handlebars/node_modules/optimist/node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- tap-5.8.0.tgz (Root Library)
- nyc-6.6.1.tgz
- istanbul-0.4.3.tgz
- handlebars-4.0.5.tgz
- optimist-0.6.1.tgz
- :x: **minimist-0.0.10.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/HOTFIX/commit/3bc753a65c01eab39a0bf5cf3aed58995c79c72a">3bc753a65c01eab39a0bf5cf3aed58995c79c72a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Minimist <=1.2.5 is vulnerable to Prototype Pollution via file index.js, function setKey() (lines 69-95).
<p>Publish Date: 2022-03-17
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-44906>CVE-2021-44906</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-03-17</p>
<p>Fix Resolution: minimist - 1.2.6</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-23383</summary>
### Vulnerable Library - <b>handlebars-4.0.5.tgz</b></p>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://registry.npmjs.org/handlebars/-/handlebars-4.0.5.tgz">https://registry.npmjs.org/handlebars/-/handlebars-4.0.5.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/nyc/node_modules/istanbul/node_modules/handlebars/package.json</p>
<p>
Dependency Hierarchy:
- tap-5.8.0.tgz (Root Library)
- nyc-6.6.1.tgz
- istanbul-0.4.3.tgz
- :x: **handlebars-4.0.5.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/HOTFIX/commit/3bc753a65c01eab39a0bf5cf3aed58995c79c72a">3bc753a65c01eab39a0bf5cf3aed58995c79c72a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The package handlebars before 4.7.7 are vulnerable to Prototype Pollution when selecting certain compiling options to compile templates coming from an untrusted source.
<p>Publish Date: 2021-05-04
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-23383>CVE-2021-23383</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23383">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23383</a></p>
<p>Release Date: 2021-05-04</p>
<p>Fix Resolution: handlebars - 4.7.7</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2018-3728</summary>
### Vulnerable Libraries - <b>hoek-2.16.3.tgz</b>, <b>hoek-0.9.1.tgz</b></p>
<p>
### <b>hoek-2.16.3.tgz</b></p>
<p>General purpose node utilities</p>
<p>Library home page: <a href="https://registry.npmjs.org/hoek/-/hoek-2.16.3.tgz">https://registry.npmjs.org/hoek/-/hoek-2.16.3.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/coveralls/node_modules/hoek/package.json</p>
<p>
Dependency Hierarchy:
- tap-5.8.0.tgz (Root Library)
- coveralls-2.13.3.tgz
- request-2.79.0.tgz
- hawk-3.1.3.tgz
- :x: **hoek-2.16.3.tgz** (Vulnerable Library)
### <b>hoek-0.9.1.tgz</b></p>
<p>General purpose node utilities</p>
<p>Library home page: <a href="https://registry.npmjs.org/hoek/-/hoek-0.9.1.tgz">https://registry.npmjs.org/hoek/-/hoek-0.9.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/hoek/package.json</p>
<p>
Dependency Hierarchy:
- tap-5.8.0.tgz (Root Library)
- codecov.io-0.1.6.tgz
- request-2.42.0.tgz
- hawk-1.1.1.tgz
- :x: **hoek-0.9.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/HOTFIX/commit/3bc753a65c01eab39a0bf5cf3aed58995c79c72a">3bc753a65c01eab39a0bf5cf3aed58995c79c72a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
hoek node module before 4.2.0 and 5.0.x before 5.0.3 suffers from a Modification of Assumed-Immutable Data (MAID) vulnerability via 'merge' and 'applyToDefaults' functions, which allows a malicious user to modify the prototype of "Object" via __proto__, causing the addition or modification of an existing property that will exist on all objects.
<p>Publish Date: 2018-03-30
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-3728>CVE-2018-3728</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-16082">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-16082</a></p>
<p>Release Date: 2018-03-30</p>
<p>Fix Resolution: 4.2.0,5.0.3</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-20920</summary>
### Vulnerable Library - <b>handlebars-4.0.5.tgz</b></p>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://registry.npmjs.org/handlebars/-/handlebars-4.0.5.tgz">https://registry.npmjs.org/handlebars/-/handlebars-4.0.5.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/nyc/node_modules/istanbul/node_modules/handlebars/package.json</p>
<p>
Dependency Hierarchy:
- tap-5.8.0.tgz (Root Library)
- nyc-6.6.1.tgz
- istanbul-0.4.3.tgz
- :x: **handlebars-4.0.5.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/HOTFIX/commit/3bc753a65c01eab39a0bf5cf3aed58995c79c72a">3bc753a65c01eab39a0bf5cf3aed58995c79c72a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Handlebars before 3.0.8 and 4.x before 4.5.3 is vulnerable to Arbitrary Code Execution. The lookup helper fails to properly validate templates, allowing attackers to submit templates that execute arbitrary JavaScript. This can be used to run arbitrary code on a server processing Handlebars templates or in a victim's browser (effectively serving as XSS).
<p>Publish Date: 2020-09-30
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-20920>CVE-2019-20920</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1324">https://www.npmjs.com/advisories/1324</a></p>
<p>Release Date: 2020-10-15</p>
<p>Fix Resolution: handlebars - 4.5.3</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> WS-2019-0063</summary>
### Vulnerable Library - <b>js-yaml-3.6.1.tgz</b></p>
<p>YAML 1.2 parser and serializer</p>
<p>Library home page: <a href="https://registry.npmjs.org/js-yaml/-/js-yaml-3.6.1.tgz">https://registry.npmjs.org/js-yaml/-/js-yaml-3.6.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/nyc/node_modules/istanbul/node_modules/js-yaml/package.json,/node_modules/coveralls/node_modules/js-yaml/package.json</p>
<p>
Dependency Hierarchy:
- tap-5.8.0.tgz (Root Library)
- nyc-6.6.1.tgz
- istanbul-0.4.3.tgz
- :x: **js-yaml-3.6.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/HOTFIX/commit/3bc753a65c01eab39a0bf5cf3aed58995c79c72a">3bc753a65c01eab39a0bf5cf3aed58995c79c72a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Js-yaml prior to 3.13.1 are vulnerable to Code Injection. The load() function may execute arbitrary code injected through a malicious YAML file.
<p>Publish Date: 2019-04-05
<p>URL: <a href=https://github.com/nodeca/js-yaml/pull/480>WS-2019-0063</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/813">https://www.npmjs.com/advisories/813</a></p>
<p>Release Date: 2019-04-05</p>
<p>Fix Resolution: js-yaml - 3.13.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-20922</summary>
### Vulnerable Library - <b>handlebars-4.0.5.tgz</b></p>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://registry.npmjs.org/handlebars/-/handlebars-4.0.5.tgz">https://registry.npmjs.org/handlebars/-/handlebars-4.0.5.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/nyc/node_modules/istanbul/node_modules/handlebars/package.json</p>
<p>
Dependency Hierarchy:
- tap-5.8.0.tgz (Root Library)
- nyc-6.6.1.tgz
- istanbul-0.4.3.tgz
- :x: **handlebars-4.0.5.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/HOTFIX/commit/3bc753a65c01eab39a0bf5cf3aed58995c79c72a">3bc753a65c01eab39a0bf5cf3aed58995c79c72a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Handlebars before 4.4.5 allows Regular Expression Denial of Service (ReDoS) because of eager matching. The parser may be forced into an endless loop while processing crafted templates. This may allow attackers to exhaust system resources.
<p>Publish Date: 2020-09-30
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-20922>CVE-2019-20922</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1300">https://www.npmjs.com/advisories/1300</a></p>
<p>Release Date: 2020-09-30</p>
<p>Fix Resolution: handlebars - 4.4.5</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-28469</summary>
### Vulnerable Library - <b>glob-parent-2.0.0.tgz</b></p>
<p>Strips glob magic from a string to provide the parent path</p>
<p>Library home page: <a href="https://registry.npmjs.org/glob-parent/-/glob-parent-2.0.0.tgz">https://registry.npmjs.org/glob-parent/-/glob-parent-2.0.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/nyc/node_modules/micromatch/node_modules/parse-glob/node_modules/glob-base/node_modules/glob-parent/package.json</p>
<p>
Dependency Hierarchy:
- tap-5.8.0.tgz (Root Library)
- nyc-6.6.1.tgz
- micromatch-2.3.8.tgz
- parse-glob-3.0.4.tgz
- glob-base-0.3.0.tgz
- :x: **glob-parent-2.0.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/HOTFIX/commit/3bc753a65c01eab39a0bf5cf3aed58995c79c72a">3bc753a65c01eab39a0bf5cf3aed58995c79c72a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
This affects the package glob-parent before 5.1.2. The enclosure regex used to check for strings ending in enclosure containing path separator.
<p>Publish Date: 2021-06-03
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-28469>CVE-2020-28469</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28469">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28469</a></p>
<p>Release Date: 2021-06-03</p>
<p>Fix Resolution: glob-parent - 5.1.2</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2016-10540</summary>
### Vulnerable Libraries - <b>minimatch-3.0.0.tgz</b>, <b>minimatch-2.0.10.tgz</b></p>
<p>
### <b>minimatch-3.0.0.tgz</b></p>
<p>a glob matcher in javascript</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimatch/-/minimatch-3.0.0.tgz">https://registry.npmjs.org/minimatch/-/minimatch-3.0.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/nyc/node_modules/glob/node_modules/minimatch/package.json</p>
<p>
Dependency Hierarchy:
- tap-5.8.0.tgz (Root Library)
- nyc-6.6.1.tgz
- glob-7.0.3.tgz
- :x: **minimatch-3.0.0.tgz** (Vulnerable Library)
### <b>minimatch-2.0.10.tgz</b></p>
<p>a glob matcher in javascript</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimatch/-/minimatch-2.0.10.tgz">https://registry.npmjs.org/minimatch/-/minimatch-2.0.10.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/nyc/node_modules/istanbul/node_modules/fileset/node_modules/minimatch/package.json</p>
<p>
Dependency Hierarchy:
- tap-5.8.0.tgz (Root Library)
- nyc-6.6.1.tgz
- istanbul-0.4.3.tgz
- fileset-0.2.1.tgz
- :x: **minimatch-2.0.10.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/HOTFIX/commit/3bc753a65c01eab39a0bf5cf3aed58995c79c72a">3bc753a65c01eab39a0bf5cf3aed58995c79c72a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Minimatch is a minimal matching utility that works by converting glob expressions into JavaScript `RegExp` objects. The primary function, `minimatch(path, pattern)` in Minimatch 3.0.1 and earlier is vulnerable to ReDoS in the `pattern` parameter.
<p>Publish Date: 2018-05-31
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-10540>CVE-2016-10540</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2016-10540">https://nvd.nist.gov/vuln/detail/CVE-2016-10540</a></p>
<p>Release Date: 2018-04-26</p>
<p>Fix Resolution: Pvc.Browserify - 0.0.1.1;JetBrains.Rider.Frontend4 - 203.0.20201014.202610-eap04;JetBrains.Rider.Frontend5 - 203.0.20201006.200056-eap03,213.0.20211008.154703-eap03;Bridge.AWS - 0.3.30.36;tslint - 3.11.0;MIDIator.WebClient - 1.0.105;BumperLane.Public.Service.Contracts - 0.23.35.214-prerelease;ng-grid - 2.0.4;minimatch - 3.0.2;Virteom.Tenant.Mobile.Bluetooth - 0.21.29.159-prerelease;ShowingVault.DotNet.Sdk - 0.13.41.190-prerelease;Triarc.Web.Build - 1.3.0;Virteom.Tenant.Mobile.Framework.UWP - 0.20.41.103-prerelease;Virteom.Tenant.Mobile.Framework.iOS - 0.20.41.103-prerelease;BumperLane.Public.Api.V2.ClientModule - 0.23.35.214-prerelease;Virteom.Tenant.Mobile.Bluetooth.iOS - 0.20.41.103-prerelease;Virteom.Public.Utilities - 0.23.37.212-prerelease;Mustache.Reports.Data - 1.2.2;Virteom.Tenant.Mobile.Framework - 0.21.29.159-prerelease;Virteom.Tenant.Mobile.Bluetooth.Android - 0.20.41.103-prerelease;z4a-dotnet-scaffold - 1.0.0.2;Raml.Parser - 2.0.0,1.0.2;AntData.ORM - 1.2.9;ApiExplorer.HelpPage - 1.0.0-alpha3;SitecoreMaster.TrueDynamicPlaceholders - 1.0.3;Virteom.Tenant.Mobile.Framework.Android - 0.20.41.103-prerelease;BumperLane.Public.Api.Client - 0.23.35.214-prerelease</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2016-2515</summary>
### Vulnerable Library - <b>hawk-1.1.1.tgz</b></p>
<p>HTTP Hawk Authentication Scheme</p>
<p>Library home page: <a href="https://registry.npmjs.org/hawk/-/hawk-1.1.1.tgz">https://registry.npmjs.org/hawk/-/hawk-1.1.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/hawk/package.json</p>
<p>
Dependency Hierarchy:
- tap-5.8.0.tgz (Root Library)
- codecov.io-0.1.6.tgz
- request-2.42.0.tgz
- :x: **hawk-1.1.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/HOTFIX/commit/3bc753a65c01eab39a0bf5cf3aed58995c79c72a">3bc753a65c01eab39a0bf5cf3aed58995c79c72a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Hawk before 3.1.3 and 4.x before 4.1.1 allow remote attackers to cause a denial of service (CPU consumption or partial outage) via a long (1) header or (2) URI that is matched against an improper regular expression.
<p>Publish Date: 2016-04-13
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-2515>CVE-2016-2515</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2016-2515">https://nvd.nist.gov/vuln/detail/CVE-2016-2515</a></p>
<p>Release Date: 2016-04-13</p>
<p>Fix Resolution: 3.1.3,4.1.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2017-1000048</summary>
### Vulnerable Library - <b>qs-1.2.2.tgz</b></p>
<p>A querystring parser that supports nesting and arrays, with a depth limit</p>
<p>Library home page: <a href="https://registry.npmjs.org/qs/-/qs-1.2.2.tgz">https://registry.npmjs.org/qs/-/qs-1.2.2.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/request/node_modules/qs/package.json</p>
<p>
Dependency Hierarchy:
- tap-5.8.0.tgz (Root Library)
- codecov.io-0.1.6.tgz
- request-2.42.0.tgz
- :x: **qs-1.2.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/HOTFIX/commit/3bc753a65c01eab39a0bf5cf3aed58995c79c72a">3bc753a65c01eab39a0bf5cf3aed58995c79c72a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
the web framework using ljharb's qs module older than v6.3.2, v6.2.3, v6.1.2, and v6.0.4 is vulnerable to a DoS. A malicious user can send a evil request to cause the web framework crash.
<p>Publish Date: 2017-07-17
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2017-1000048>CVE-2017-1000048</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-1000048">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-1000048</a></p>
<p>Release Date: 2017-07-17</p>
<p>Fix Resolution: qs - 6.0.4,6.1.2,6.2.3,6.3.2</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-29167</summary>
### Vulnerable Library - <b>hawk-3.1.3.tgz</b></p>
<p>HTTP Hawk Authentication Scheme</p>
<p>Library home page: <a href="https://registry.npmjs.org/hawk/-/hawk-3.1.3.tgz">https://registry.npmjs.org/hawk/-/hawk-3.1.3.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/coveralls/node_modules/hawk/package.json</p>
<p>
Dependency Hierarchy:
- tap-5.8.0.tgz (Root Library)
- coveralls-2.13.3.tgz
- request-2.79.0.tgz
- :x: **hawk-3.1.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/HOTFIX/commit/3bc753a65c01eab39a0bf5cf3aed58995c79c72a">3bc753a65c01eab39a0bf5cf3aed58995c79c72a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Hawk is an HTTP authentication scheme providing mechanisms for making authenticated HTTP requests with partial cryptographic verification of the request and response, covering the HTTP method, request URI, host, and optionally the request payload. Hawk used a regular expression to parse `Host` HTTP header (`Hawk.utils.parseHost()`), which was subject to regular expression DoS attack - meaning each added character in the attacker's input increases the computation time exponentially. `parseHost()` was patched in `9.0.1` to use built-in `URL` class to parse hostname instead. `Hawk.authenticate()` accepts `options` argument. If that contains `host` and `port`, those would be used instead of a call to `utils.parseHost()`.
<p>Publish Date: 2022-05-05
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-29167>CVE-2022-29167</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/mozilla/hawk/security/advisories/GHSA-44pw-h2cw-w3vq">https://github.com/mozilla/hawk/security/advisories/GHSA-44pw-h2cw-w3vq</a></p>
<p>Release Date: 2022-05-05</p>
<p>Fix Resolution: hawk - 9.0.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> WS-2019-0032</summary>
### Vulnerable Library - <b>js-yaml-3.6.1.tgz</b></p>
<p>YAML 1.2 parser and serializer</p>
<p>Library home page: <a href="https://registry.npmjs.org/js-yaml/-/js-yaml-3.6.1.tgz">https://registry.npmjs.org/js-yaml/-/js-yaml-3.6.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/nyc/node_modules/istanbul/node_modules/js-yaml/package.json,/node_modules/coveralls/node_modules/js-yaml/package.json</p>
<p>
Dependency Hierarchy:
- tap-5.8.0.tgz (Root Library)
- nyc-6.6.1.tgz
- istanbul-0.4.3.tgz
- :x: **js-yaml-3.6.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/HOTFIX/commit/3bc753a65c01eab39a0bf5cf3aed58995c79c72a">3bc753a65c01eab39a0bf5cf3aed58995c79c72a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Versions js-yaml prior to 3.13.0 are vulnerable to Denial of Service. By parsing a carefully-crafted YAML file, the node process stalls and may exhaust system resources leading to a Denial of Service.
<p>Publish Date: 2019-03-20
<p>URL: <a href=https://github.com/nodeca/js-yaml/commit/a567ef3c6e61eb319f0bfc2671d91061afb01235>WS-2019-0032</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/788/versions">https://www.npmjs.com/advisories/788/versions</a></p>
<p>Release Date: 2019-03-20</p>
<p>Fix Resolution: js-yaml - 3.13.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2017-18077</summary>
### Vulnerable Library - <b>brace-expansion-1.1.4.tgz</b></p>
<p>Brace expansion as known from sh/bash</p>
<p>Library home page: <a href="https://registry.npmjs.org/brace-expansion/-/brace-expansion-1.1.4.tgz">https://registry.npmjs.org/brace-expansion/-/brace-expansion-1.1.4.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/nyc/node_modules/istanbul/node_modules/fileset/node_modules/minimatch/node_modules/brace-expansion/package.json,/node_modules/nyc/node_modules/glob/node_modules/minimatch/node_modules/brace-expansion/package.json</p>
<p>
Dependency Hierarchy:
- tap-5.8.0.tgz (Root Library)
- nyc-6.6.1.tgz
- istanbul-0.4.3.tgz
- fileset-0.2.1.tgz
- minimatch-2.0.10.tgz
- :x: **brace-expansion-1.1.4.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/HOTFIX/commit/3bc753a65c01eab39a0bf5cf3aed58995c79c72a">3bc753a65c01eab39a0bf5cf3aed58995c79c72a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
index.js in brace-expansion before 1.1.7 is vulnerable to Regular Expression Denial of Service (ReDoS) attacks, as demonstrated by an expand argument containing many comma characters.
<p>Publish Date: 2018-01-27
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2017-18077>CVE-2017-18077</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2017-18077">https://nvd.nist.gov/vuln/detail/CVE-2017-18077</a></p>
<p>Release Date: 2018-01-27</p>
<p>Fix Resolution: 1.1.7</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-24999</summary>
### Vulnerable Library - <b>qs-1.2.2.tgz</b></p>
<p>A querystring parser that supports nesting and arrays, with a depth limit</p>
<p>Library home page: <a href="https://registry.npmjs.org/qs/-/qs-1.2.2.tgz">https://registry.npmjs.org/qs/-/qs-1.2.2.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/request/node_modules/qs/package.json</p>
<p>
Dependency Hierarchy:
- tap-5.8.0.tgz (Root Library)
- codecov.io-0.1.6.tgz
- request-2.42.0.tgz
- :x: **qs-1.2.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/HOTFIX/commit/3bc753a65c01eab39a0bf5cf3aed58995c79c72a">3bc753a65c01eab39a0bf5cf3aed58995c79c72a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
qs before 6.10.3, as used in Express before 4.17.3 and other products, allows attackers to cause a Node process hang for an Express application because an __ proto__ key can be used. In many typical Express use cases, an unauthenticated remote attacker can place the attack payload in the query string of the URL that is used to visit the application, such as a[__proto__]=b&a[__proto__]&a[length]=100000000. The fix was backported to qs 6.9.7, 6.8.3, 6.7.3, 6.6.1, 6.5.3, 6.4.1, 6.3.3, and 6.2.4 (and therefore Express 4.17.3, which has "deps: qs@6.9.7" in its release description, is not vulnerable).
<p>Publish Date: 2022-11-26
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-24999>CVE-2022-24999</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.cve.org/CVERecord?id=CVE-2022-24999">https://www.cve.org/CVERecord?id=CVE-2022-24999</a></p>
<p>Release Date: 2022-11-26</p>
<p>Fix Resolution: qs - 6.2.4,6.3.3,6.4.1,6.5.3,6.6.1,6.7.3,6.8.3,6.9.7,6.10.3</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> WS-2020-0450</summary>
### Vulnerable Library - <b>handlebars-4.0.5.tgz</b></p>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://registry.npmjs.org/handlebars/-/handlebars-4.0.5.tgz">https://registry.npmjs.org/handlebars/-/handlebars-4.0.5.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/nyc/node_modules/istanbul/node_modules/handlebars/package.json</p>
<p>
Dependency Hierarchy:
- tap-5.8.0.tgz (Root Library)
- nyc-6.6.1.tgz
- istanbul-0.4.3.tgz
- :x: **handlebars-4.0.5.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/HOTFIX/commit/3bc753a65c01eab39a0bf5cf3aed58995c79c72a">3bc753a65c01eab39a0bf5cf3aed58995c79c72a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Handlebars before 4.6.0 vulnerable to Prototype Pollution. Prototype access to the template engine allows for potential code execution, which may lead to Denial Of Service (DoS).
<p>Publish Date: 2020-01-09
<p>URL: <a href=https://github.com/handlebars-lang/handlebars.js/commit/33a3b46bc205f768f8edbc67241c68591fe3472c>WS-2020-0450</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2020-01-09</p>
<p>Fix Resolution: handlebars - 4.6.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-3517</summary>
### Vulnerable Libraries - <b>minimatch-2.0.10.tgz</b>, <b>minimatch-3.0.0.tgz</b></p>
<p>
### <b>minimatch-2.0.10.tgz</b></p>
<p>a glob matcher in javascript</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimatch/-/minimatch-2.0.10.tgz">https://registry.npmjs.org/minimatch/-/minimatch-2.0.10.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/nyc/node_modules/istanbul/node_modules/fileset/node_modules/minimatch/package.json</p>
<p>
Dependency Hierarchy:
- tap-5.8.0.tgz (Root Library)
- nyc-6.6.1.tgz
- istanbul-0.4.3.tgz
- fileset-0.2.1.tgz
- :x: **minimatch-2.0.10.tgz** (Vulnerable Library)
### <b>minimatch-3.0.0.tgz</b></p>
<p>a glob matcher in javascript</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimatch/-/minimatch-3.0.0.tgz">https://registry.npmjs.org/minimatch/-/minimatch-3.0.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/nyc/node_modules/glob/node_modules/minimatch/package.json</p>
<p>
Dependency Hierarchy:
- tap-5.8.0.tgz (Root Library)
- nyc-6.6.1.tgz
- glob-7.0.3.tgz
- :x: **minimatch-3.0.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/HOTFIX/commit/3bc753a65c01eab39a0bf5cf3aed58995c79c72a">3bc753a65c01eab39a0bf5cf3aed58995c79c72a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A vulnerability was found in the minimatch package. This flaw allows a Regular Expression Denial of Service (ReDoS) when calling the braceExpand function with specific arguments, resulting in a Denial of Service.
<p>Publish Date: 2022-10-17
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-3517>CVE-2022-3517</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-10-17</p>
<p>Fix Resolution: minimatch - 3.0.5</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> WS-2019-0064</summary>
### Vulnerable Library - <b>handlebars-4.0.5.tgz</b></p>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://registry.npmjs.org/handlebars/-/handlebars-4.0.5.tgz">https://registry.npmjs.org/handlebars/-/handlebars-4.0.5.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/nyc/node_modules/istanbul/node_modules/handlebars/package.json</p>
<p>
Dependency Hierarchy:
- tap-5.8.0.tgz (Root Library)
- nyc-6.6.1.tgz
- istanbul-0.4.3.tgz
- :x: **handlebars-4.0.5.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/HOTFIX/commit/3bc753a65c01eab39a0bf5cf3aed58995c79c72a">3bc753a65c01eab39a0bf5cf3aed58995c79c72a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Versions of handlebars prior to 4.0.14 are vulnerable to Prototype Pollution. Templates may alter an Objects' prototype, thus allowing an attacker to execute arbitrary code on the server.
<p>Publish Date: 2019-01-30
<p>URL: <a href=https://github.com/wycats/handlebars.js/compare/v4.1.1...v4.1.2>WS-2019-0064</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/755/">https://www.npmjs.com/advisories/755/</a></p>
<p>Release Date: 2019-01-30</p>
<p>Fix Resolution: 3.0.7,4.0.14,4.1.2</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> WS-2018-0590</summary>
### Vulnerable Library - <b>diff-1.4.0.tgz</b></p>
<p>A javascript text diff implementation.</p>
<p>Library home page: <a href="https://registry.npmjs.org/diff/-/diff-1.4.0.tgz">https://registry.npmjs.org/diff/-/diff-1.4.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/diff/package.json</p>
<p>
Dependency Hierarchy:
- tap-5.8.0.tgz (Root Library)
- tap-mocha-reporter-0.0.27.tgz
- :x: **diff-1.4.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/HOTFIX/commit/3bc753a65c01eab39a0bf5cf3aed58995c79c72a">3bc753a65c01eab39a0bf5cf3aed58995c79c72a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A vulnerability was found in diff before v3.5.0, the affected versions of this package are vulnerable to Regular Expression Denial of Service (ReDoS) attacks.
<p>Publish Date: 2018-03-05
<p>URL: <a href=https://bugzilla.redhat.com/show_bug.cgi?id=1552148>WS-2018-0590</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2018-03-05</p>
<p>Fix Resolution: 3.5.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2020-8244</summary>
### Vulnerable Library - <b>bl-0.9.5.tgz</b></p>
<p>Buffer List: collect buffers and access with a standard readable Buffer interface, streamable too!</p>
<p>Library home page: <a href="https://registry.npmjs.org/bl/-/bl-0.9.5.tgz">https://registry.npmjs.org/bl/-/bl-0.9.5.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/bl/package.json</p>
<p>
Dependency Hierarchy:
- tap-5.8.0.tgz (Root Library)
- codecov.io-0.1.6.tgz
- request-2.42.0.tgz
- :x: **bl-0.9.5.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/HOTFIX/commit/3bc753a65c01eab39a0bf5cf3aed58995c79c72a">3bc753a65c01eab39a0bf5cf3aed58995c79c72a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A buffer over-read vulnerability exists in bl <4.0.3, <3.0.1, <2.2.1, and <1.2.3 which could allow an attacker to supply user input (even typed) that if it ends up in consume() argument and can become negative, the BufferList state can be corrupted, tricking it into exposing uninitialized memory via regular .slice() calls.
<p>Publish Date: 2020-08-30
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-8244>CVE-2020-8244</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-pp7h-53gx-mx7r">https://github.com/advisories/GHSA-pp7h-53gx-mx7r</a></p>
<p>Release Date: 2020-08-30</p>
<p>Fix Resolution: bl - 1.2.3,2.2.1,3.0.1,4.0.3</p>
</p>
<p></p>
</details>
|
non_test
|
tap tgz vulnerabilities highest severity is autoclosed vulnerable library tap tgz path to dependency file package json path to vulnerable library node modules nyc node modules istanbul node modules handlebars package json found in head commit a href mend has checked all newer package trees and you are on the least vulnerable package please note there might be a version that explicitly solves one or more of the vulnerabilities listed below but we do not recommend it for more info about the optional fixes check the section “details” below vulnerabilities cve severity cvss dependency type fixed in tap version fix pr available high handlebars tgz transitive n a high handlebars tgz transitive n a high tgz transitive n a high detected in multiple dependencies transitive n a high detected in multiple dependencies transitive n a high handlebars tgz transitive n a high detected in multiple dependencies transitive n a high handlebars tgz transitive n a high js yaml tgz transitive n a high handlebars tgz transitive n a high glob parent tgz transitive n a high detected in multiple dependencies transitive n a high hawk tgz transitive n a high qs tgz transitive n a high hawk tgz transitive n a high js yaml tgz transitive n a high brace expansion tgz transitive n a high qs tgz transitive n a high handlebars tgz transitive n a high detected in multiple dependencies transitive n a high handlebars tgz transitive n a high diff tgz transitive n a medium bl tgz transitive n a medium request tgz transitive n a medium detected in multiple dependencies transitive n a medium handlebars tgz transitive n a medium brace expansion tgz transitive n a medium yargs parser tgz transitive n a medium hosted git info tgz transitive n a medium randomatic tgz transitive n a medium tunnel agent tgz transitive n a low http signature tgz transitive n a for some transitive vulnerabilities there is no version of direct dependency with a fix check the section details below to see if there is a version of transitive dependency where vulnerability is fixed details partial details vulnerabilities are displayed below due to a content size limitation in github to view information on the remaining vulnerabilities navigate to the mend application cve vulnerable library handlebars tgz handlebars provides the power necessary to let you build semantic templates effectively with no frustration library home page a href path to dependency file package json path to vulnerable library node modules nyc node modules istanbul node modules handlebars package json dependency hierarchy tap tgz root library nyc tgz istanbul tgz x handlebars tgz vulnerable library found in head commit a href found in base branch main vulnerability details the package handlebars before are vulnerable to remote code execution rce when selecting certain compiling options to compile templates coming from an untrusted source publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com github jknack handlebars handlebars cve vulnerable library handlebars tgz handlebars provides the power necessary to let you build semantic templates effectively with no frustration library home page a href path to dependency file package json path to vulnerable library node modules nyc node modules istanbul node modules handlebars package json dependency hierarchy tap tgz root library nyc tgz istanbul tgz x handlebars tgz vulnerable library found in head commit a href found in base branch main vulnerability details versions of handlebars prior to are vulnerable to prototype pollution leading to remote code execution templates may alter an object s proto and definegetter properties which may allow an attacker to execute arbitrary code through crafted payloads publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution handlebars cve vulnerable library tgz the bare bones internationalization library used by yargs library home page a href path to dependency file package json path to vulnerable library node modules nyc node modules yargs node modules package json dependency hierarchy tap tgz root library nyc tgz yargs tgz x tgz vulnerable library found in head commit a href found in base branch main vulnerability details the package before and is vulnerable to prototype pollution publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution cve vulnerable libraries cryptiles tgz cryptiles tgz cryptiles tgz general purpose crypto utilities library home page a href path to dependency file package json path to vulnerable library node modules cryptiles package json dependency hierarchy tap tgz root library codecov io tgz request tgz hawk tgz x cryptiles tgz vulnerable library cryptiles tgz general purpose crypto utilities library home page a href path to dependency file package json path to vulnerable library node modules coveralls node modules cryptiles package json dependency hierarchy tap tgz root library coveralls tgz request tgz hawk tgz x cryptiles tgz vulnerable library found in head commit a href found in base branch main vulnerability details eran hammer cryptiles version earlier contains a cwe insufficient entropy vulnerability in randomdigits method that can result in an attacker is more likely to be able to brute force something that was supposed to be random this attack appear to be exploitable via depends upon the calling application this vulnerability appears to have been fixed in publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution cve vulnerable libraries minimist tgz minimist tgz minimist tgz minimist tgz parse argument options library home page a href path to dependency file package json path to vulnerable library node modules coveralls node modules minimist package json dependency hierarchy tap tgz root library coveralls tgz x minimist tgz vulnerable library minimist tgz parse argument options library home page a href path to dependency file package json path to vulnerable library node modules nyc node modules mkdirp node modules minimist package json dependency hierarchy tap tgz root library nyc tgz mkdirp tgz x minimist tgz vulnerable library minimist tgz parse argument options library home page a href path to dependency file package json path to vulnerable library node modules nyc node modules istanbul node modules handlebars node modules optimist node modules minimist package json dependency hierarchy tap tgz root library nyc tgz istanbul tgz handlebars tgz optimist tgz x minimist tgz vulnerable library found in head commit a href found in base branch main vulnerability details minimist is vulnerable to prototype pollution via file index js function setkey lines publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution minimist cve vulnerable library handlebars tgz handlebars provides the power necessary to let you build semantic templates effectively with no frustration library home page a href path to dependency file package json path to vulnerable library node modules nyc node modules istanbul node modules handlebars package json dependency hierarchy tap tgz root library nyc tgz istanbul tgz x handlebars tgz vulnerable library found in head commit a href found in base branch main vulnerability details the package handlebars before are vulnerable to prototype pollution when selecting certain compiling options to compile templates coming from an untrusted source publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution handlebars cve vulnerable libraries hoek tgz hoek tgz hoek tgz general purpose node utilities library home page a href path to dependency file package json path to vulnerable library node modules coveralls node modules hoek package json dependency hierarchy tap tgz root library coveralls tgz request tgz hawk tgz x hoek tgz vulnerable library hoek tgz general purpose node utilities library home page a href path to dependency file package json path to vulnerable library node modules hoek package json dependency hierarchy tap tgz root library codecov io tgz request tgz hawk tgz x hoek tgz vulnerable library found in head commit a href found in base branch main vulnerability details hoek node module before and x before suffers from a modification of assumed immutable data maid vulnerability via merge and applytodefaults functions which allows a malicious user to modify the prototype of object via proto causing the addition or modification of an existing property that will exist on all objects publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution cve vulnerable library handlebars tgz handlebars provides the power necessary to let you build semantic templates effectively with no frustration library home page a href path to dependency file package json path to vulnerable library node modules nyc node modules istanbul node modules handlebars package json dependency hierarchy tap tgz root library nyc tgz istanbul tgz x handlebars tgz vulnerable library found in head commit a href found in base branch main vulnerability details handlebars before and x before is vulnerable to arbitrary code execution the lookup helper fails to properly validate templates allowing attackers to submit templates that execute arbitrary javascript this can be used to run arbitrary code on a server processing handlebars templates or in a victim s browser effectively serving as xss publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope changed impact metrics confidentiality impact high integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution handlebars ws vulnerable library js yaml tgz yaml parser and serializer library home page a href path to dependency file package json path to vulnerable library node modules nyc node modules istanbul node modules js yaml package json node modules coveralls node modules js yaml package json dependency hierarchy tap tgz root library nyc tgz istanbul tgz x js yaml tgz vulnerable library found in head commit a href found in base branch main vulnerability details js yaml prior to are vulnerable to code injection the load function may execute arbitrary code injected through a malicious yaml file publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution js yaml cve vulnerable library handlebars tgz handlebars provides the power necessary to let you build semantic templates effectively with no frustration library home page a href path to dependency file package json path to vulnerable library node modules nyc node modules istanbul node modules handlebars package json dependency hierarchy tap tgz root library nyc tgz istanbul tgz x handlebars tgz vulnerable library found in head commit a href found in base branch main vulnerability details handlebars before allows regular expression denial of service redos because of eager matching the parser may be forced into an endless loop while processing crafted templates this may allow attackers to exhaust system resources publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution handlebars cve vulnerable library glob parent tgz strips glob magic from a string to provide the parent path library home page a href path to dependency file package json path to vulnerable library node modules nyc node modules micromatch node modules parse glob node modules glob base node modules glob parent package json dependency hierarchy tap tgz root library nyc tgz micromatch tgz parse glob tgz glob base tgz x glob parent tgz vulnerable library found in head commit a href found in base branch main vulnerability details this affects the package glob parent before the enclosure regex used to check for strings ending in enclosure containing path separator publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution glob parent cve vulnerable libraries minimatch tgz minimatch tgz minimatch tgz a glob matcher in javascript library home page a href path to dependency file package json path to vulnerable library node modules nyc node modules glob node modules minimatch package json dependency hierarchy tap tgz root library nyc tgz glob tgz x minimatch tgz vulnerable library minimatch tgz a glob matcher in javascript library home page a href path to dependency file package json path to vulnerable library node modules nyc node modules istanbul node modules fileset node modules minimatch package json dependency hierarchy tap tgz root library nyc tgz istanbul tgz fileset tgz x minimatch tgz vulnerable library found in head commit a href found in base branch main vulnerability details minimatch is a minimal matching utility that works by converting glob expressions into javascript regexp objects the primary function minimatch path pattern in minimatch and earlier is vulnerable to redos in the pattern parameter publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution pvc browserify jetbrains rider jetbrains rider bridge aws tslint midiator webclient bumperlane public service contracts prerelease ng grid minimatch virteom tenant mobile bluetooth prerelease showingvault dotnet sdk prerelease triarc web build virteom tenant mobile framework uwp prerelease virteom tenant mobile framework ios prerelease bumperlane public api clientmodule prerelease virteom tenant mobile bluetooth ios prerelease virteom public utilities prerelease mustache reports data virteom tenant mobile framework prerelease virteom tenant mobile bluetooth android prerelease dotnet scaffold raml parser antdata orm apiexplorer helppage sitecoremaster truedynamicplaceholders virteom tenant mobile framework android prerelease bumperlane public api client prerelease cve vulnerable library hawk tgz http hawk authentication scheme library home page a href path to dependency file package json path to vulnerable library node modules hawk package json dependency hierarchy tap tgz root library codecov io tgz request tgz x hawk tgz vulnerable library found in head commit a href found in base branch main vulnerability details hawk before and x before allow remote attackers to cause a denial of service cpu consumption or partial outage via a long header or uri that is matched against an improper regular expression publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution cve vulnerable library qs tgz a querystring parser that supports nesting and arrays with a depth limit library home page a href path to dependency file package json path to vulnerable library node modules request node modules qs package json dependency hierarchy tap tgz root library codecov io tgz request tgz x qs tgz vulnerable library found in head commit a href found in base branch main vulnerability details the web framework using ljharb s qs module older than and is vulnerable to a dos a malicious user can send a evil request to cause the web framework crash publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution qs cve vulnerable library hawk tgz http hawk authentication scheme library home page a href path to dependency file package json path to vulnerable library node modules coveralls node modules hawk package json dependency hierarchy tap tgz root library coveralls tgz request tgz x hawk tgz vulnerable library found in head commit a href found in base branch main vulnerability details hawk is an http authentication scheme providing mechanisms for making authenticated http requests with partial cryptographic verification of the request and response covering the http method request uri host and optionally the request payload hawk used a regular expression to parse host http header hawk utils parsehost which was subject to regular expression dos attack meaning each added character in the attacker s input increases the computation time exponentially parsehost was patched in to use built in url class to parse hostname instead hawk authenticate accepts options argument if that contains host and port those would be used instead of a call to utils parsehost publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution hawk ws vulnerable library js yaml tgz yaml parser and serializer library home page a href path to dependency file package json path to vulnerable library node modules nyc node modules istanbul node modules js yaml package json node modules coveralls node modules js yaml package json dependency hierarchy tap tgz root library nyc tgz istanbul tgz x js yaml tgz vulnerable library found in head commit a href found in base branch main vulnerability details versions js yaml prior to are vulnerable to denial of service by parsing a carefully crafted yaml file the node process stalls and may exhaust system resources leading to a denial of service publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution js yaml cve vulnerable library brace expansion tgz brace expansion as known from sh bash library home page a href path to dependency file package json path to vulnerable library node modules nyc node modules istanbul node modules fileset node modules minimatch node modules brace expansion package json node modules nyc node modules glob node modules minimatch node modules brace expansion package json dependency hierarchy tap tgz root library nyc tgz istanbul tgz fileset tgz minimatch tgz x brace expansion tgz vulnerable library found in head commit a href found in base branch main vulnerability details index js in brace expansion before is vulnerable to regular expression denial of service redos attacks as demonstrated by an expand argument containing many comma characters publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution cve vulnerable library qs tgz a querystring parser that supports nesting and arrays with a depth limit library home page a href path to dependency file package json path to vulnerable library node modules request node modules qs package json dependency hierarchy tap tgz root library codecov io tgz request tgz x qs tgz vulnerable library found in head commit a href found in base branch main vulnerability details qs before as used in express before and other products allows attackers to cause a node process hang for an express application because an proto key can be used in many typical express use cases an unauthenticated remote attacker can place the attack payload in the query string of the url that is used to visit the application such as a b a a the fix was backported to qs and and therefore express which has deps qs in its release description is not vulnerable publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution qs ws vulnerable library handlebars tgz handlebars provides the power necessary to let you build semantic templates effectively with no frustration library home page a href path to dependency file package json path to vulnerable library node modules nyc node modules istanbul node modules handlebars package json dependency hierarchy tap tgz root library nyc tgz istanbul tgz x handlebars tgz vulnerable library found in head commit a href found in base branch main vulnerability details handlebars before vulnerable to prototype pollution prototype access to the template engine allows for potential code execution which may lead to denial of service dos publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution handlebars cve vulnerable libraries minimatch tgz minimatch tgz minimatch tgz a glob matcher in javascript library home page a href path to dependency file package json path to vulnerable library node modules nyc node modules istanbul node modules fileset node modules minimatch package json dependency hierarchy tap tgz root library nyc tgz istanbul tgz fileset tgz x minimatch tgz vulnerable library minimatch tgz a glob matcher in javascript library home page a href path to dependency file package json path to vulnerable library node modules nyc node modules glob node modules minimatch package json dependency hierarchy tap tgz root library nyc tgz glob tgz x minimatch tgz vulnerable library found in head commit a href found in base branch main vulnerability details a vulnerability was found in the minimatch package this flaw allows a regular expression denial of service redos when calling the braceexpand function with specific arguments resulting in a denial of service publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution minimatch ws vulnerable library handlebars tgz handlebars provides the power necessary to let you build semantic templates effectively with no frustration library home page a href path to dependency file package json path to vulnerable library node modules nyc node modules istanbul node modules handlebars package json dependency hierarchy tap tgz root library nyc tgz istanbul tgz x handlebars tgz vulnerable library found in head commit a href found in base branch main vulnerability details versions of handlebars prior to are vulnerable to prototype pollution templates may alter an objects prototype thus allowing an attacker to execute arbitrary code on the server publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution ws vulnerable library diff tgz a javascript text diff implementation library home page a href path to dependency file package json path to vulnerable library node modules diff package json dependency hierarchy tap tgz root library tap mocha reporter tgz x diff tgz vulnerable library found in head commit a href found in base branch main vulnerability details a vulnerability was found in diff before the affected versions of this package are vulnerable to regular expression denial of service redos attacks publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction required scope unchanged impact metrics confidentiality impact high integrity impact high availability impact low for more information on scores click a href suggested fix type upgrade version release date fix resolution cve vulnerable library bl tgz buffer list collect buffers and access with a standard readable buffer interface streamable too library home page a href path to dependency file package json path to vulnerable library node modules bl package json dependency hierarchy tap tgz root library codecov io tgz request tgz x bl tgz vulnerable library found in head commit a href found in base branch main vulnerability details a buffer over read vulnerability exists in bl and which could allow an attacker to supply user input even typed that if it ends up in consume argument and can become negative the bufferlist state can be corrupted tricking it into exposing uninitialized memory via regular slice calls publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact none availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution bl
| 0
|
186,665
| 14,403,693,372
|
IssuesEvent
|
2020-12-03 16:21:50
|
haskell/haskell-language-server
|
https://api.github.com/repos/haskell/haskell-language-server
|
closed
|
Flaky test "code actions -> hlint suggestions -> falls back to pre 3.8 code actions"
|
can-workaround status: needs confirmation type: bug type: testing
|
I am trying to enable hls tests in nixpkgs. This test seems to fail only sometimes on my local system (a thinkpad notebook with nixos). This is with hls 0.6.0 and ghcide 0.5.0.
```
falls back to pre 3.8 code actions: FAIL
Exception: Timed out waiting to receive a message from the server.
Last message received:
{
"tag": "RspExecuteCommand",
"contents": {
"result": null,
"jsonrpc": "2.0",
"id": 4
}
}
```
|
1.0
|
Flaky test "code actions -> hlint suggestions -> falls back to pre 3.8 code actions" - I am trying to enable hls tests in nixpkgs. This test seems to fail only sometimes on my local system (a thinkpad notebook with nixos). This is with hls 0.6.0 and ghcide 0.5.0.
```
falls back to pre 3.8 code actions: FAIL
Exception: Timed out waiting to receive a message from the server.
Last message received:
{
"tag": "RspExecuteCommand",
"contents": {
"result": null,
"jsonrpc": "2.0",
"id": 4
}
}
```
|
test
|
flaky test code actions hlint suggestions falls back to pre code actions i am trying to enable hls tests in nixpkgs this test seems to fail only sometimes on my local system a thinkpad notebook with nixos this is with hls and ghcide falls back to pre code actions fail exception timed out waiting to receive a message from the server last message received tag rspexecutecommand contents result null jsonrpc id
| 1
|
282,981
| 24,510,189,261
|
IssuesEvent
|
2022-10-10 20:32:37
|
nosovk/upptime-test
|
https://api.github.com/repos/nosovk/upptime-test
|
opened
|
🛑 test-api is down
|
status test-api
|
In [`dc038f1`](https://github.com/nosovk/upptime-test/commit/dc038f13892eb554dd1a564ad3165834ac1572f7
), test-api (http://$GEOAU:$GEO_PASSWORD@$GEONODE_DNS http://ip-api.com/json) was **down**:
- HTTP code: 0
- Response time: 0 ms
|
1.0
|
🛑 test-api is down - In [`dc038f1`](https://github.com/nosovk/upptime-test/commit/dc038f13892eb554dd1a564ad3165834ac1572f7
), test-api (http://$GEOAU:$GEO_PASSWORD@$GEONODE_DNS http://ip-api.com/json) was **down**:
- HTTP code: 0
- Response time: 0 ms
|
test
|
🛑 test api is down in test api was down http code response time ms
| 1
|
381,078
| 26,439,027,799
|
IssuesEvent
|
2023-01-15 18:53:33
|
KaterynaHerasymiva/homepage
|
https://api.github.com/repos/KaterynaHerasymiva/homepage
|
closed
|
Update repository description with website link
|
documentation good first issue
|
Update repository description with website link to GitHub Pages
|
1.0
|
Update repository description with website link - Update repository description with website link to GitHub Pages
|
non_test
|
update repository description with website link update repository description with website link to github pages
| 0
|
208,631
| 23,627,535,594
|
IssuesEvent
|
2022-08-25 06:16:09
|
sast-automation-dev/soundcloud-redux-15
|
https://api.github.com/repos/sast-automation-dev/soundcloud-redux-15
|
opened
|
express-4.15.3.tgz: 4 vulnerabilities (highest severity is: 7.5)
|
security vulnerability
|
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>express-4.15.3.tgz</b></p></summary>
<p></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/forwarded/package.json</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/soundcloud-redux-15/commit/435bcff28cc7f6cf1ca2c79909872f3fb8a20cd9">435bcff28cc7f6cf1ca2c79909872f3fb8a20cd9</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2017-16138](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16138) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | mime-1.3.4.tgz | Transitive | 4.16.0 | ✅ |
| [CVE-2017-16118](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16118) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | forwarded-0.1.0.tgz | Transitive | 4.15.4 | ✅ |
| [CVE-2017-16119](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16119) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | fresh-0.5.0.tgz | Transitive | 4.15.5 | ✅ |
| [CVE-2017-16137](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16137) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | debug-2.6.7.tgz | Transitive | 4.15.5 | ✅ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2017-16138</summary>
### Vulnerable Library - <b>mime-1.3.4.tgz</b></p>
<p>A comprehensive library for mime-type mapping</p>
<p>Library home page: <a href="https://registry.npmjs.org/mime/-/mime-1.3.4.tgz">https://registry.npmjs.org/mime/-/mime-1.3.4.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/mime/package.json</p>
<p>
Dependency Hierarchy:
- express-4.15.3.tgz (Root Library)
- send-0.15.3.tgz
- :x: **mime-1.3.4.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/soundcloud-redux-15/commit/435bcff28cc7f6cf1ca2c79909872f3fb8a20cd9">435bcff28cc7f6cf1ca2c79909872f3fb8a20cd9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The mime module < 1.4.1, 2.0.1, 2.0.2 is vulnerable to regular expression denial of service when a mime lookup is performed on untrusted user input.
<p>Publish Date: 2018-06-07
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16138>CVE-2017-16138</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-16138">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-16138</a></p>
<p>Release Date: 2018-06-07</p>
<p>Fix Resolution (mime): 1.4.1</p>
<p>Direct dependency fix Resolution (express): 4.16.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2017-16118</summary>
### Vulnerable Library - <b>forwarded-0.1.0.tgz</b></p>
<p>Parse HTTP X-Forwarded-For header</p>
<p>Library home page: <a href="https://registry.npmjs.org/forwarded/-/forwarded-0.1.0.tgz">https://registry.npmjs.org/forwarded/-/forwarded-0.1.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/forwarded/package.json</p>
<p>
Dependency Hierarchy:
- express-4.15.3.tgz (Root Library)
- proxy-addr-1.1.5.tgz
- :x: **forwarded-0.1.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/soundcloud-redux-15/commit/435bcff28cc7f6cf1ca2c79909872f3fb8a20cd9">435bcff28cc7f6cf1ca2c79909872f3fb8a20cd9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The forwarded module is used by the Express.js framework to handle the X-Forwarded-For header. It is vulnerable to a regular expression denial of service when it's passed specially crafted input to parse. This causes the event loop to be blocked causing a denial of service condition.
<p>Publish Date: 2018-06-07
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16118>CVE-2017-16118</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/527/versions">https://www.npmjs.com/advisories/527/versions</a></p>
<p>Release Date: 2018-06-07</p>
<p>Fix Resolution (forwarded): 0.1.2</p>
<p>Direct dependency fix Resolution (express): 4.15.4</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2017-16119</summary>
### Vulnerable Library - <b>fresh-0.5.0.tgz</b></p>
<p>HTTP response freshness testing</p>
<p>Library home page: <a href="https://registry.npmjs.org/fresh/-/fresh-0.5.0.tgz">https://registry.npmjs.org/fresh/-/fresh-0.5.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/fresh/package.json</p>
<p>
Dependency Hierarchy:
- express-4.15.3.tgz (Root Library)
- :x: **fresh-0.5.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/soundcloud-redux-15/commit/435bcff28cc7f6cf1ca2c79909872f3fb8a20cd9">435bcff28cc7f6cf1ca2c79909872f3fb8a20cd9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Fresh is a module used by the Express.js framework for HTTP response freshness testing. It is vulnerable to a regular expression denial of service when it is passed specially crafted input to parse. This causes the event loop to be blocked causing a denial of service condition.
<p>Publish Date: 2018-06-07
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16119>CVE-2017-16119</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/526">https://www.npmjs.com/advisories/526</a></p>
<p>Release Date: 2018-06-07</p>
<p>Fix Resolution (fresh): 0.5.2</p>
<p>Direct dependency fix Resolution (express): 4.15.5</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2017-16137</summary>
### Vulnerable Library - <b>debug-2.6.7.tgz</b></p>
<p>small debugging utility</p>
<p>Library home page: <a href="https://registry.npmjs.org/debug/-/debug-2.6.7.tgz">https://registry.npmjs.org/debug/-/debug-2.6.7.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/send/node_modules/debug/package.json,/node_modules/express/node_modules/debug/package.json,/node_modules/finalhandler/node_modules/debug/package.json,/node_modules/connect/node_modules/debug/package.json</p>
<p>
Dependency Hierarchy:
- express-4.15.3.tgz (Root Library)
- :x: **debug-2.6.7.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/soundcloud-redux-15/commit/435bcff28cc7f6cf1ca2c79909872f3fb8a20cd9">435bcff28cc7f6cf1ca2c79909872f3fb8a20cd9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The debug module is vulnerable to regular expression denial of service when untrusted user input is passed into the o formatter. It takes around 50k characters to block for 2 seconds making this a low severity issue.
<p>Publish Date: 2018-06-07
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16137>CVE-2017-16137</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/view/vuln/detail?vulnId=CVE-2017-16137">https://nvd.nist.gov/view/vuln/detail?vulnId=CVE-2017-16137</a></p>
<p>Release Date: 2018-06-07</p>
<p>Fix Resolution (debug): 2.6.9</p>
<p>Direct dependency fix Resolution (express): 4.15.5</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p>
|
True
|
express-4.15.3.tgz: 4 vulnerabilities (highest severity is: 7.5) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>express-4.15.3.tgz</b></p></summary>
<p></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/forwarded/package.json</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/soundcloud-redux-15/commit/435bcff28cc7f6cf1ca2c79909872f3fb8a20cd9">435bcff28cc7f6cf1ca2c79909872f3fb8a20cd9</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2017-16138](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16138) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | mime-1.3.4.tgz | Transitive | 4.16.0 | ✅ |
| [CVE-2017-16118](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16118) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | forwarded-0.1.0.tgz | Transitive | 4.15.4 | ✅ |
| [CVE-2017-16119](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16119) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | fresh-0.5.0.tgz | Transitive | 4.15.5 | ✅ |
| [CVE-2017-16137](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16137) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | debug-2.6.7.tgz | Transitive | 4.15.5 | ✅ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2017-16138</summary>
### Vulnerable Library - <b>mime-1.3.4.tgz</b></p>
<p>A comprehensive library for mime-type mapping</p>
<p>Library home page: <a href="https://registry.npmjs.org/mime/-/mime-1.3.4.tgz">https://registry.npmjs.org/mime/-/mime-1.3.4.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/mime/package.json</p>
<p>
Dependency Hierarchy:
- express-4.15.3.tgz (Root Library)
- send-0.15.3.tgz
- :x: **mime-1.3.4.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/soundcloud-redux-15/commit/435bcff28cc7f6cf1ca2c79909872f3fb8a20cd9">435bcff28cc7f6cf1ca2c79909872f3fb8a20cd9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The mime module < 1.4.1, 2.0.1, 2.0.2 is vulnerable to regular expression denial of service when a mime lookup is performed on untrusted user input.
<p>Publish Date: 2018-06-07
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16138>CVE-2017-16138</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-16138">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-16138</a></p>
<p>Release Date: 2018-06-07</p>
<p>Fix Resolution (mime): 1.4.1</p>
<p>Direct dependency fix Resolution (express): 4.16.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2017-16118</summary>
### Vulnerable Library - <b>forwarded-0.1.0.tgz</b></p>
<p>Parse HTTP X-Forwarded-For header</p>
<p>Library home page: <a href="https://registry.npmjs.org/forwarded/-/forwarded-0.1.0.tgz">https://registry.npmjs.org/forwarded/-/forwarded-0.1.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/forwarded/package.json</p>
<p>
Dependency Hierarchy:
- express-4.15.3.tgz (Root Library)
- proxy-addr-1.1.5.tgz
- :x: **forwarded-0.1.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/soundcloud-redux-15/commit/435bcff28cc7f6cf1ca2c79909872f3fb8a20cd9">435bcff28cc7f6cf1ca2c79909872f3fb8a20cd9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The forwarded module is used by the Express.js framework to handle the X-Forwarded-For header. It is vulnerable to a regular expression denial of service when it's passed specially crafted input to parse. This causes the event loop to be blocked causing a denial of service condition.
<p>Publish Date: 2018-06-07
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16118>CVE-2017-16118</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/527/versions">https://www.npmjs.com/advisories/527/versions</a></p>
<p>Release Date: 2018-06-07</p>
<p>Fix Resolution (forwarded): 0.1.2</p>
<p>Direct dependency fix Resolution (express): 4.15.4</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2017-16119</summary>
### Vulnerable Library - <b>fresh-0.5.0.tgz</b></p>
<p>HTTP response freshness testing</p>
<p>Library home page: <a href="https://registry.npmjs.org/fresh/-/fresh-0.5.0.tgz">https://registry.npmjs.org/fresh/-/fresh-0.5.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/fresh/package.json</p>
<p>
Dependency Hierarchy:
- express-4.15.3.tgz (Root Library)
- :x: **fresh-0.5.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/soundcloud-redux-15/commit/435bcff28cc7f6cf1ca2c79909872f3fb8a20cd9">435bcff28cc7f6cf1ca2c79909872f3fb8a20cd9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Fresh is a module used by the Express.js framework for HTTP response freshness testing. It is vulnerable to a regular expression denial of service when it is passed specially crafted input to parse. This causes the event loop to be blocked causing a denial of service condition.
<p>Publish Date: 2018-06-07
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16119>CVE-2017-16119</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/526">https://www.npmjs.com/advisories/526</a></p>
<p>Release Date: 2018-06-07</p>
<p>Fix Resolution (fresh): 0.5.2</p>
<p>Direct dependency fix Resolution (express): 4.15.5</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2017-16137</summary>
### Vulnerable Library - <b>debug-2.6.7.tgz</b></p>
<p>small debugging utility</p>
<p>Library home page: <a href="https://registry.npmjs.org/debug/-/debug-2.6.7.tgz">https://registry.npmjs.org/debug/-/debug-2.6.7.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/send/node_modules/debug/package.json,/node_modules/express/node_modules/debug/package.json,/node_modules/finalhandler/node_modules/debug/package.json,/node_modules/connect/node_modules/debug/package.json</p>
<p>
Dependency Hierarchy:
- express-4.15.3.tgz (Root Library)
- :x: **debug-2.6.7.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/soundcloud-redux-15/commit/435bcff28cc7f6cf1ca2c79909872f3fb8a20cd9">435bcff28cc7f6cf1ca2c79909872f3fb8a20cd9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The debug module is vulnerable to regular expression denial of service when untrusted user input is passed into the o formatter. It takes around 50k characters to block for 2 seconds making this a low severity issue.
<p>Publish Date: 2018-06-07
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16137>CVE-2017-16137</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/view/vuln/detail?vulnId=CVE-2017-16137">https://nvd.nist.gov/view/vuln/detail?vulnId=CVE-2017-16137</a></p>
<p>Release Date: 2018-06-07</p>
<p>Fix Resolution (debug): 2.6.9</p>
<p>Direct dependency fix Resolution (express): 4.15.5</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p>
|
non_test
|
express tgz vulnerabilities highest severity is vulnerable library express tgz path to dependency file package json path to vulnerable library node modules forwarded package json found in head commit a href vulnerabilities cve severity cvss dependency type fixed in remediation available high mime tgz transitive high forwarded tgz transitive high fresh tgz transitive medium debug tgz transitive details cve vulnerable library mime tgz a comprehensive library for mime type mapping library home page a href path to dependency file package json path to vulnerable library node modules mime package json dependency hierarchy express tgz root library send tgz x mime tgz vulnerable library found in head commit a href found in base branch master vulnerability details the mime module is vulnerable to regular expression denial of service when a mime lookup is performed on untrusted user input publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution mime direct dependency fix resolution express rescue worker helmet automatic remediation is available for this issue cve vulnerable library forwarded tgz parse http x forwarded for header library home page a href path to dependency file package json path to vulnerable library node modules forwarded package json dependency hierarchy express tgz root library proxy addr tgz x forwarded tgz vulnerable library found in head commit a href found in base branch master vulnerability details the forwarded module is used by the express js framework to handle the x forwarded for header it is vulnerable to a regular expression denial of service when it s passed specially crafted input to parse this causes the event loop to be blocked causing a denial of service condition publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution forwarded direct dependency fix resolution express rescue worker helmet automatic remediation is available for this issue cve vulnerable library fresh tgz http response freshness testing library home page a href path to dependency file package json path to vulnerable library node modules fresh package json dependency hierarchy express tgz root library x fresh tgz vulnerable library found in head commit a href found in base branch master vulnerability details fresh is a module used by the express js framework for http response freshness testing it is vulnerable to a regular expression denial of service when it is passed specially crafted input to parse this causes the event loop to be blocked causing a denial of service condition publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution fresh direct dependency fix resolution express rescue worker helmet automatic remediation is available for this issue cve vulnerable library debug tgz small debugging utility library home page a href path to dependency file package json path to vulnerable library node modules send node modules debug package json node modules express node modules debug package json node modules finalhandler node modules debug package json node modules connect node modules debug package json dependency hierarchy express tgz root library x debug tgz vulnerable library found in head commit a href found in base branch master vulnerability details the debug module is vulnerable to regular expression denial of service when untrusted user input is passed into the o formatter it takes around characters to block for seconds making this a low severity issue publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution debug direct dependency fix resolution express rescue worker helmet automatic remediation is available for this issue rescue worker helmet automatic remediation is available for this issue
| 0
|
128,750
| 5,074,891,148
|
IssuesEvent
|
2016-12-27 16:39:01
|
gitomator/gitomator-classroom
|
https://api.github.com/repos/gitomator/gitomator-classroom
|
closed
|
Specify default_repo_properties in context config
|
Feature Priority-Low
|
These will be the default properties that will be used when creating new repositories.
|
1.0
|
Specify default_repo_properties in context config - These will be the default properties that will be used when creating new repositories.
|
non_test
|
specify default repo properties in context config these will be the default properties that will be used when creating new repositories
| 0
|
209,151
| 16,176,799,147
|
IssuesEvent
|
2021-05-03 08:15:16
|
Arquisoft/radarin_en1a
|
https://api.github.com/repos/Arquisoft/radarin_en1a
|
reopened
|
Discuss and write conclusions related to Admin role
|
documentation
|
So far an admin role is not implemented, even though it is in the requirements. We should discuss this matter and write and argument our conclusions
|
1.0
|
Discuss and write conclusions related to Admin role - So far an admin role is not implemented, even though it is in the requirements. We should discuss this matter and write and argument our conclusions
|
non_test
|
discuss and write conclusions related to admin role so far an admin role is not implemented even though it is in the requirements we should discuss this matter and write and argument our conclusions
| 0
|
145,456
| 11,695,225,039
|
IssuesEvent
|
2020-03-06 06:55:08
|
GlobalMediaBridge/cosmetic-app
|
https://api.github.com/repos/GlobalMediaBridge/cosmetic-app
|
closed
|
supernova 변환된 코드 테스팅 및 renaming
|
test
|
모든 스크린에 대해서 테스팅 작업
모든 위젯의 이름을 적절하게 변경
```
lib/
├── screens/
├── common/
├── utils/
└── main.dart
```
|
1.0
|
supernova 변환된 코드 테스팅 및 renaming - 모든 스크린에 대해서 테스팅 작업
모든 위젯의 이름을 적절하게 변경
```
lib/
├── screens/
├── common/
├── utils/
└── main.dart
```
|
test
|
supernova 변환된 코드 테스팅 및 renaming 모든 스크린에 대해서 테스팅 작업 모든 위젯의 이름을 적절하게 변경 lib ├── screens ├── common ├── utils └── main dart
| 1
|
163,385
| 25,803,810,144
|
IssuesEvent
|
2022-12-11 08:01:33
|
xyntechx/NexLiber
|
https://api.github.com/repos/xyntechx/NexLiber
|
closed
|
Redesign Library
|
design
|
- [x] list & grid views
- [x] project cards resemble books in grid view
- [x] search button (magnifying glass) launches popup search bar
|
1.0
|
Redesign Library - - [x] list & grid views
- [x] project cards resemble books in grid view
- [x] search button (magnifying glass) launches popup search bar
|
non_test
|
redesign library list grid views project cards resemble books in grid view search button magnifying glass launches popup search bar
| 0
|
169,046
| 20,828,012,072
|
IssuesEvent
|
2022-03-19 01:17:46
|
rsoreq/kjua
|
https://api.github.com/repos/rsoreq/kjua
|
opened
|
CVE-2021-44906 (Medium) detected in minimist-1.2.5.tgz
|
security vulnerability
|
## CVE-2021-44906 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>minimist-1.2.5.tgz</b></p></summary>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-1.2.5.tgz">https://registry.npmjs.org/minimist/-/minimist-1.2.5.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- ghu-0.26.0.tgz (Root Library)
- :x: **minimist-1.2.5.tgz** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Minimist <=1.2.5 is vulnerable to Prototype Pollution via file index.js, function setKey() (lines 69-95).
<p>Publish Date: 2022-03-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-44906>CVE-2021-44906</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2021-44906">https://nvd.nist.gov/vuln/detail/CVE-2021-44906</a></p>
<p>Release Date: 2022-03-17</p>
<p>Fix Resolution: BumperLane.Public.Service.Contracts - 0.23.35.214-prerelease;cloudscribe.templates - 5.2.0;Virteom.Tenant.Mobile.Bluetooth - 0.21.29.159-prerelease;ShowingVault.DotNet.Sdk - 0.13.41.190-prerelease;Envisia.DotNet.Templates - 3.0.1;Yarnpkg.Yarn - 0.26.1;Virteom.Tenant.Mobile.Framework.UWP - 0.20.41.103-prerelease;Virteom.Tenant.Mobile.Framework.iOS - 0.20.41.103-prerelease;BumperLane.Public.Api.V2.ClientModule - 0.23.35.214-prerelease;VueJS.NetCore - 1.1.1;Dianoga - 4.0.0,3.0.0-RC02;Virteom.Tenant.Mobile.Bluetooth.iOS - 0.20.41.103-prerelease;Virteom.Public.Utilities - 0.23.37.212-prerelease;Indianadavy.VueJsWebAPITemplate.CSharp - 1.0.1;NorDroN.AngularTemplate - 0.1.6;Virteom.Tenant.Mobile.Framework - 0.21.29.159-prerelease;Virteom.Tenant.Mobile.Bluetooth.Android - 0.20.41.103-prerelease;z4a-dotnet-scaffold - 1.0.0.2;Raml.Parser - 1.0.7;CoreVueWebTest - 3.0.101;dotnetng.template - 1.0.0.4;SitecoreMaster.TrueDynamicPlaceholders - 1.0.3;Virteom.Tenant.Mobile.Framework.Android - 0.20.41.103-prerelease;Fable.Template.Elmish.React - 0.1.6;BlazorPolyfill.Build - 6.0.100.2;Fable.Snowpack.Template - 2.1.0;BumperLane.Public.Api.Client - 0.23.35.214-prerelease;Yarn.MSBuild - 0.22.0,0.24.6;Blazor.TailwindCSS.BUnit - 1.0.2;Bridge.AWS - 0.3.30.36;tslint - 5.6.0;SAFE.Template - 3.0.1;GR.PageRender.Razor - 1.8.0;MIDIator.WebClient - 1.0.105</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"minimist","packageVersion":"1.2.5","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"ghu:0.26.0;minimist:1.2.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"BumperLane.Public.Service.Contracts - 0.23.35.214-prerelease;cloudscribe.templates - 5.2.0;Virteom.Tenant.Mobile.Bluetooth - 0.21.29.159-prerelease;ShowingVault.DotNet.Sdk - 0.13.41.190-prerelease;Envisia.DotNet.Templates - 3.0.1;Yarnpkg.Yarn - 0.26.1;Virteom.Tenant.Mobile.Framework.UWP - 0.20.41.103-prerelease;Virteom.Tenant.Mobile.Framework.iOS - 0.20.41.103-prerelease;BumperLane.Public.Api.V2.ClientModule - 0.23.35.214-prerelease;VueJS.NetCore - 1.1.1;Dianoga - 4.0.0,3.0.0-RC02;Virteom.Tenant.Mobile.Bluetooth.iOS - 0.20.41.103-prerelease;Virteom.Public.Utilities - 0.23.37.212-prerelease;Indianadavy.VueJsWebAPITemplate.CSharp - 1.0.1;NorDroN.AngularTemplate - 0.1.6;Virteom.Tenant.Mobile.Framework - 0.21.29.159-prerelease;Virteom.Tenant.Mobile.Bluetooth.Android - 0.20.41.103-prerelease;z4a-dotnet-scaffold - 1.0.0.2;Raml.Parser - 1.0.7;CoreVueWebTest - 3.0.101;dotnetng.template - 1.0.0.4;SitecoreMaster.TrueDynamicPlaceholders - 1.0.3;Virteom.Tenant.Mobile.Framework.Android - 0.20.41.103-prerelease;Fable.Template.Elmish.React - 0.1.6;BlazorPolyfill.Build - 6.0.100.2;Fable.Snowpack.Template - 2.1.0;BumperLane.Public.Api.Client - 0.23.35.214-prerelease;Yarn.MSBuild - 0.22.0,0.24.6;Blazor.TailwindCSS.BUnit - 1.0.2;Bridge.AWS - 0.3.30.36;tslint - 5.6.0;SAFE.Template - 3.0.1;GR.PageRender.Razor - 1.8.0;MIDIator.WebClient - 1.0.105","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-44906","vulnerabilityDetails":"Minimist \u003c\u003d1.2.5 is vulnerable to Prototype Pollution via file index.js, function setKey() (lines 69-95).","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-44906","cvss3Severity":"medium","cvss3Score":"5.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"Required","AV":"Local","I":"None"},"extraData":{}}</REMEDIATE> -->
|
True
|
CVE-2021-44906 (Medium) detected in minimist-1.2.5.tgz - ## CVE-2021-44906 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>minimist-1.2.5.tgz</b></p></summary>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-1.2.5.tgz">https://registry.npmjs.org/minimist/-/minimist-1.2.5.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- ghu-0.26.0.tgz (Root Library)
- :x: **minimist-1.2.5.tgz** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Minimist <=1.2.5 is vulnerable to Prototype Pollution via file index.js, function setKey() (lines 69-95).
<p>Publish Date: 2022-03-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-44906>CVE-2021-44906</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2021-44906">https://nvd.nist.gov/vuln/detail/CVE-2021-44906</a></p>
<p>Release Date: 2022-03-17</p>
<p>Fix Resolution: BumperLane.Public.Service.Contracts - 0.23.35.214-prerelease;cloudscribe.templates - 5.2.0;Virteom.Tenant.Mobile.Bluetooth - 0.21.29.159-prerelease;ShowingVault.DotNet.Sdk - 0.13.41.190-prerelease;Envisia.DotNet.Templates - 3.0.1;Yarnpkg.Yarn - 0.26.1;Virteom.Tenant.Mobile.Framework.UWP - 0.20.41.103-prerelease;Virteom.Tenant.Mobile.Framework.iOS - 0.20.41.103-prerelease;BumperLane.Public.Api.V2.ClientModule - 0.23.35.214-prerelease;VueJS.NetCore - 1.1.1;Dianoga - 4.0.0,3.0.0-RC02;Virteom.Tenant.Mobile.Bluetooth.iOS - 0.20.41.103-prerelease;Virteom.Public.Utilities - 0.23.37.212-prerelease;Indianadavy.VueJsWebAPITemplate.CSharp - 1.0.1;NorDroN.AngularTemplate - 0.1.6;Virteom.Tenant.Mobile.Framework - 0.21.29.159-prerelease;Virteom.Tenant.Mobile.Bluetooth.Android - 0.20.41.103-prerelease;z4a-dotnet-scaffold - 1.0.0.2;Raml.Parser - 1.0.7;CoreVueWebTest - 3.0.101;dotnetng.template - 1.0.0.4;SitecoreMaster.TrueDynamicPlaceholders - 1.0.3;Virteom.Tenant.Mobile.Framework.Android - 0.20.41.103-prerelease;Fable.Template.Elmish.React - 0.1.6;BlazorPolyfill.Build - 6.0.100.2;Fable.Snowpack.Template - 2.1.0;BumperLane.Public.Api.Client - 0.23.35.214-prerelease;Yarn.MSBuild - 0.22.0,0.24.6;Blazor.TailwindCSS.BUnit - 1.0.2;Bridge.AWS - 0.3.30.36;tslint - 5.6.0;SAFE.Template - 3.0.1;GR.PageRender.Razor - 1.8.0;MIDIator.WebClient - 1.0.105</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"minimist","packageVersion":"1.2.5","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"ghu:0.26.0;minimist:1.2.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"BumperLane.Public.Service.Contracts - 0.23.35.214-prerelease;cloudscribe.templates - 5.2.0;Virteom.Tenant.Mobile.Bluetooth - 0.21.29.159-prerelease;ShowingVault.DotNet.Sdk - 0.13.41.190-prerelease;Envisia.DotNet.Templates - 3.0.1;Yarnpkg.Yarn - 0.26.1;Virteom.Tenant.Mobile.Framework.UWP - 0.20.41.103-prerelease;Virteom.Tenant.Mobile.Framework.iOS - 0.20.41.103-prerelease;BumperLane.Public.Api.V2.ClientModule - 0.23.35.214-prerelease;VueJS.NetCore - 1.1.1;Dianoga - 4.0.0,3.0.0-RC02;Virteom.Tenant.Mobile.Bluetooth.iOS - 0.20.41.103-prerelease;Virteom.Public.Utilities - 0.23.37.212-prerelease;Indianadavy.VueJsWebAPITemplate.CSharp - 1.0.1;NorDroN.AngularTemplate - 0.1.6;Virteom.Tenant.Mobile.Framework - 0.21.29.159-prerelease;Virteom.Tenant.Mobile.Bluetooth.Android - 0.20.41.103-prerelease;z4a-dotnet-scaffold - 1.0.0.2;Raml.Parser - 1.0.7;CoreVueWebTest - 3.0.101;dotnetng.template - 1.0.0.4;SitecoreMaster.TrueDynamicPlaceholders - 1.0.3;Virteom.Tenant.Mobile.Framework.Android - 0.20.41.103-prerelease;Fable.Template.Elmish.React - 0.1.6;BlazorPolyfill.Build - 6.0.100.2;Fable.Snowpack.Template - 2.1.0;BumperLane.Public.Api.Client - 0.23.35.214-prerelease;Yarn.MSBuild - 0.22.0,0.24.6;Blazor.TailwindCSS.BUnit - 1.0.2;Bridge.AWS - 0.3.30.36;tslint - 5.6.0;SAFE.Template - 3.0.1;GR.PageRender.Razor - 1.8.0;MIDIator.WebClient - 1.0.105","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-44906","vulnerabilityDetails":"Minimist \u003c\u003d1.2.5 is vulnerable to Prototype Pollution via file index.js, function setKey() (lines 69-95).","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-44906","cvss3Severity":"medium","cvss3Score":"5.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"Required","AV":"Local","I":"None"},"extraData":{}}</REMEDIATE> -->
|
non_test
|
cve medium detected in minimist tgz cve medium severity vulnerability vulnerable library minimist tgz parse argument options library home page a href path to dependency file package json path to vulnerable library node modules minimist package json dependency hierarchy ghu tgz root library x minimist tgz vulnerable library found in base branch master vulnerability details minimist is vulnerable to prototype pollution via file index js function setkey lines publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution bumperlane public service contracts prerelease cloudscribe templates virteom tenant mobile bluetooth prerelease showingvault dotnet sdk prerelease envisia dotnet templates yarnpkg yarn virteom tenant mobile framework uwp prerelease virteom tenant mobile framework ios prerelease bumperlane public api clientmodule prerelease vuejs netcore dianoga virteom tenant mobile bluetooth ios prerelease virteom public utilities prerelease indianadavy vuejswebapitemplate csharp nordron angulartemplate virteom tenant mobile framework prerelease virteom tenant mobile bluetooth android prerelease dotnet scaffold raml parser corevuewebtest dotnetng template sitecoremaster truedynamicplaceholders virteom tenant mobile framework android prerelease fable template elmish react blazorpolyfill build fable snowpack template bumperlane public api client prerelease yarn msbuild blazor tailwindcss bunit bridge aws tslint safe template gr pagerender razor midiator webclient isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree ghu minimist isminimumfixversionavailable true minimumfixversion bumperlane public service contracts prerelease cloudscribe templates virteom tenant mobile bluetooth prerelease showingvault dotnet sdk prerelease envisia dotnet templates yarnpkg yarn virteom tenant mobile framework uwp prerelease virteom tenant mobile framework ios prerelease bumperlane public api clientmodule prerelease vuejs netcore dianoga virteom tenant mobile bluetooth ios prerelease virteom public utilities prerelease indianadavy vuejswebapitemplate csharp nordron angulartemplate virteom tenant mobile framework prerelease virteom tenant mobile bluetooth android prerelease dotnet scaffold raml parser corevuewebtest dotnetng template sitecoremaster truedynamicplaceholders virteom tenant mobile framework android prerelease fable template elmish react blazorpolyfill build fable snowpack template bumperlane public api client prerelease yarn msbuild blazor tailwindcss bunit bridge aws tslint safe template gr pagerender razor midiator webclient isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails minimist is vulnerable to prototype pollution via file index js function setkey lines vulnerabilityurl
| 0
|
78,689
| 27,715,514,227
|
IssuesEvent
|
2023-03-14 16:41:08
|
vector-im/element-web
|
https://api.github.com/repos/vector-im/element-web
|
opened
|
Extremely low fps (about 5-10 seconds per frame) on secondary monitor while running fine on primary monitor
|
T-Defect
|
### Steps to reproduce
1. Have 2 monitors (Dell UP2718Q 3840x2160 @ 60Hz and Siemens P17-2 @ 75Hz) in a layout where the Dell is at 150% scale in landscape and the Siemens at 100% scale in portrait. Use fractional scaling under X11 with Budgie for this.
2. Move the window to the primary monitor. Everything is smooth and fluid.
3. Move the window to the secondary monitor.
### Outcome
#### What did you expect?
Element Desktop should be just as fluid as on the secondary monitor as other apps (e.g., Quassel) are, or as Element Web in Firefox is.
#### What happened instead?
Element was hanging, stuttering, even taking minutes to act on user input. Only electron apps like Element or Discord are affected, it does not affect Quassel or Telegram. It does not occur in element in Chromium or Firefox, only the desktop app.
### Operating system
Ubuntu Budgie 22.04.2 LTS
### Application version
Element version: 1.11.24 Olm version: 3.2.12
### How did you install the app?
Element DEB repo
### Homeserver
matrix.org
### Will you send logs?
Yes
|
1.0
|
Extremely low fps (about 5-10 seconds per frame) on secondary monitor while running fine on primary monitor - ### Steps to reproduce
1. Have 2 monitors (Dell UP2718Q 3840x2160 @ 60Hz and Siemens P17-2 @ 75Hz) in a layout where the Dell is at 150% scale in landscape and the Siemens at 100% scale in portrait. Use fractional scaling under X11 with Budgie for this.
2. Move the window to the primary monitor. Everything is smooth and fluid.
3. Move the window to the secondary monitor.
### Outcome
#### What did you expect?
Element Desktop should be just as fluid as on the secondary monitor as other apps (e.g., Quassel) are, or as Element Web in Firefox is.
#### What happened instead?
Element was hanging, stuttering, even taking minutes to act on user input. Only electron apps like Element or Discord are affected, it does not affect Quassel or Telegram. It does not occur in element in Chromium or Firefox, only the desktop app.
### Operating system
Ubuntu Budgie 22.04.2 LTS
### Application version
Element version: 1.11.24 Olm version: 3.2.12
### How did you install the app?
Element DEB repo
### Homeserver
matrix.org
### Will you send logs?
Yes
|
non_test
|
extremely low fps about seconds per frame on secondary monitor while running fine on primary monitor steps to reproduce have monitors dell and siemens in a layout where the dell is at scale in landscape and the siemens at scale in portrait use fractional scaling under with budgie for this move the window to the primary monitor everything is smooth and fluid move the window to the secondary monitor outcome what did you expect element desktop should be just as fluid as on the secondary monitor as other apps e g quassel are or as element web in firefox is what happened instead element was hanging stuttering even taking minutes to act on user input only electron apps like element or discord are affected it does not affect quassel or telegram it does not occur in element in chromium or firefox only the desktop app operating system ubuntu budgie lts application version element version olm version how did you install the app element deb repo homeserver matrix org will you send logs yes
| 0
|
270,152
| 23,494,400,159
|
IssuesEvent
|
2022-08-17 22:35:16
|
microsoft/AzureStorageExplorer
|
https://api.github.com/repos/microsoft/AzureStorageExplorer
|
closed
|
Officially support raw svg contents in IconBinding
|
:heavy_check_mark: merged :test_tube: engineering
|
We don't need to log in console when loading raw SVGs in IconBinding
|
1.0
|
Officially support raw svg contents in IconBinding - We don't need to log in console when loading raw SVGs in IconBinding
|
test
|
officially support raw svg contents in iconbinding we don t need to log in console when loading raw svgs in iconbinding
| 1
|
243,429
| 20,386,647,752
|
IssuesEvent
|
2022-02-22 07:47:11
|
tendermint/fundraising
|
https://api.github.com/repos/tendermint/fundraising
|
closed
|
test: add test cases for `MsgCreateBatchAuction` and `MsgModifyBid`
|
tests
|
<!-- < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < ☺
v ✰ Thanks for opening an issue! ✰
v Before smashing the submit button please review the template.
v Word of caution: poorly thought-out proposals may be rejected
v without deliberation
☺ > > > > > > > > > > > > > > > > > > > > > > > > > > > > > > > > > -->
## Summary
This issue requests to add test cases for `MsgCreateBatchAuction` and `MsgModifyBid`. It must start after https://github.com/tendermint/fundraising/issues/87 is implemented and merged.
## References
Reference codes can be found [here](https://github.com/tendermint/fundraising/blob/main/x/fundraising/types/msgs_test.go#L15)
____
#### For Admin Use
- [ ] Not duplicate issue
- [ ] Appropriate labels applied
- [ ] Appropriate contributors tagged
- [ ] Contributor assigned/self-assigned
|
1.0
|
test: add test cases for `MsgCreateBatchAuction` and `MsgModifyBid` - <!-- < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < ☺
v ✰ Thanks for opening an issue! ✰
v Before smashing the submit button please review the template.
v Word of caution: poorly thought-out proposals may be rejected
v without deliberation
☺ > > > > > > > > > > > > > > > > > > > > > > > > > > > > > > > > > -->
## Summary
This issue requests to add test cases for `MsgCreateBatchAuction` and `MsgModifyBid`. It must start after https://github.com/tendermint/fundraising/issues/87 is implemented and merged.
## References
Reference codes can be found [here](https://github.com/tendermint/fundraising/blob/main/x/fundraising/types/msgs_test.go#L15)
____
#### For Admin Use
- [ ] Not duplicate issue
- [ ] Appropriate labels applied
- [ ] Appropriate contributors tagged
- [ ] Contributor assigned/self-assigned
|
test
|
test add test cases for msgcreatebatchauction and msgmodifybid ☺ v ✰ thanks for opening an issue ✰ v before smashing the submit button please review the template v word of caution poorly thought out proposals may be rejected v without deliberation ☺ summary this issue requests to add test cases for msgcreatebatchauction and msgmodifybid it must start after is implemented and merged references reference codes can be found for admin use not duplicate issue appropriate labels applied appropriate contributors tagged contributor assigned self assigned
| 1
|
107,066
| 9,201,475,878
|
IssuesEvent
|
2019-03-07 19:44:03
|
cockroachdb/cockroach
|
https://api.github.com/repos/cockroachdb/cockroach
|
closed
|
roachtest: backupTPCC failed
|
C-test-failure O-roachtest O-robot
|
SHA: https://github.com/cockroachdb/cockroach/commits/b80d241d5693d6ba2bde01ae9167b49b04b47226
Parameters:
To repro, try:
```
# Don't forget to check out a clean suitable branch and experiment with the
# stress invocation until the desired results present themselves. For example,
# using stress instead of stressrace and passing the '-p' stressflag which
# controls concurrency.
./scripts/gceworker.sh start && ./scripts/gceworker.sh mosh
cd ~/go/src/github.com/cockroachdb/cockroach && \
stdbuf -oL -eL \
make stressrace TESTS=backupTPCC PKG=roachtest TESTTIMEOUT=5m STRESSFLAGS='-maxtime 20m -timeout 10m' 2>&1 | tee /tmp/stress.log
```
Failed test: https://teamcity.cockroachdb.com/viewLog.html?buildId=1133193&tab=buildLog
```
The test failed on master:
cluster.go:1585,backup.go:127,test.go:1206: pq: AS OF SYSTEM TIME: cannot specify timestamp in the future
```
|
2.0
|
roachtest: backupTPCC failed - SHA: https://github.com/cockroachdb/cockroach/commits/b80d241d5693d6ba2bde01ae9167b49b04b47226
Parameters:
To repro, try:
```
# Don't forget to check out a clean suitable branch and experiment with the
# stress invocation until the desired results present themselves. For example,
# using stress instead of stressrace and passing the '-p' stressflag which
# controls concurrency.
./scripts/gceworker.sh start && ./scripts/gceworker.sh mosh
cd ~/go/src/github.com/cockroachdb/cockroach && \
stdbuf -oL -eL \
make stressrace TESTS=backupTPCC PKG=roachtest TESTTIMEOUT=5m STRESSFLAGS='-maxtime 20m -timeout 10m' 2>&1 | tee /tmp/stress.log
```
Failed test: https://teamcity.cockroachdb.com/viewLog.html?buildId=1133193&tab=buildLog
```
The test failed on master:
cluster.go:1585,backup.go:127,test.go:1206: pq: AS OF SYSTEM TIME: cannot specify timestamp in the future
```
|
test
|
roachtest backuptpcc failed sha parameters to repro try don t forget to check out a clean suitable branch and experiment with the stress invocation until the desired results present themselves for example using stress instead of stressrace and passing the p stressflag which controls concurrency scripts gceworker sh start scripts gceworker sh mosh cd go src github com cockroachdb cockroach stdbuf ol el make stressrace tests backuptpcc pkg roachtest testtimeout stressflags maxtime timeout tee tmp stress log failed test the test failed on master cluster go backup go test go pq as of system time cannot specify timestamp in the future
| 1
|
81,170
| 7,769,974,829
|
IssuesEvent
|
2018-06-04 07:10:52
|
kubernetes/kubernetes
|
https://api.github.com/repos/kubernetes/kubernetes
|
closed
|
[Failing Test] : gke-ingress-1.11 job failing to checkout Boskos project 1.11-release-blocking
|
kind/bug milestone/needs-attention priority/critical-urgent priority/failing-test sig/network sig/testing status/approved-for-milestone
|
## Failing Job
* [sig-release-1.11-blocking#gke-ingress-1.11](https://k8s-testgrid.appspot.com/sig-release-1.11-blocking#gke-ingress-1.11)
## Error
https://k8s-gubernator.appspot.com/build/kubernetes-jenkins/logs/ci-kubernetes-e2e-gke-cos-k8sbeta-ingress/2836
Something went wrong: failed to prepare test environment: --provider=gke boskos failed to acquire project: resource not found
/kind bug
/priority failing-test
/priority critical-urgent
/sig testing
/milestone v1.11
@kubernetes/sig-testing-bugs
cc @jberkus @tpepper
/assign @BenTheElder to investigate
|
2.0
|
[Failing Test] : gke-ingress-1.11 job failing to checkout Boskos project 1.11-release-blocking - ## Failing Job
* [sig-release-1.11-blocking#gke-ingress-1.11](https://k8s-testgrid.appspot.com/sig-release-1.11-blocking#gke-ingress-1.11)
## Error
https://k8s-gubernator.appspot.com/build/kubernetes-jenkins/logs/ci-kubernetes-e2e-gke-cos-k8sbeta-ingress/2836
Something went wrong: failed to prepare test environment: --provider=gke boskos failed to acquire project: resource not found
/kind bug
/priority failing-test
/priority critical-urgent
/sig testing
/milestone v1.11
@kubernetes/sig-testing-bugs
cc @jberkus @tpepper
/assign @BenTheElder to investigate
|
test
|
gke ingress job failing to checkout boskos project release blocking failing job error something went wrong failed to prepare test environment provider gke boskos failed to acquire project resource not found kind bug priority failing test priority critical urgent sig testing milestone kubernetes sig testing bugs cc jberkus tpepper assign bentheelder to investigate
| 1
|
408,773
| 11,951,791,070
|
IssuesEvent
|
2020-04-03 17:32:25
|
googleapis/google-cloud-dotnet
|
https://api.github.com/repos/googleapis/google-cloud-dotnet
|
closed
|
Synthesis failed for Google.Cloud.Dialogflow.V2
|
autosynth failure priority: p2 type: bug
|
Hello! Autosynth couldn't regenerate Google.Cloud.Dialogflow.V2. :broken_heart:
Here's the output from running `synth.py`:
```
Cloning into 'working_repo'...
Switched to a new branch 'autosynth-Google.Cloud.Dialogflow.V2'
Running synthtool
['/tmpfs/src/git/autosynth/env/bin/python3', '-m', 'synthtool', '--metadata', 'synth.metadata', 'synth.py', '--']
2020-03-20 22:38:53,528 synthtool > Executing /tmpfs/src/git/autosynth/working_repo/apis/Google.Cloud.Dialogflow.V2/synth.py.
Skipping microgenerator fetch/build: already built, and running on Kokoro
Building existing version of Google.Cloud.Dialogflow.V2 for compatibility checking
Generating Google.Cloud.Dialogflow.V2
--gapic_out: System.InvalidOperationException: Not all patterns can be matched to a parent resource for field CreateContextRequest.parent
at Google.Api.Generator.ProtoUtils.ResourceDetails.LoadResourceReference(MessageDescriptor msgDesc, FieldDescriptor fieldDesc, IReadOnlyDictionary`2 resourcesByUrt, IReadOnlyDictionary`2 resourcesByPattern)+MoveNext()
at System.Collections.Generic.List`1..ctor(IEnumerable`1 collection)
at System.Linq.Enumerable.ToList[TSource](IEnumerable`1 source)
at Google.Api.Generator.ProtoUtils.ProtoCatalog.<>c__DisplayClass0_2.<.ctor>b__20(FieldDescriptor field) in /home/kbuilder/.cache/synthtool/gapic-generator-csharp/Google.Api.Generator/ProtoUtils/ProtoCatalog.cs:line 43
at System.Linq.Enumerable.SelectIListIterator`2.MoveNext()
at System.Linq.Enumerable.WhereEnumerableIterator`1.MoveNext()
at System.Linq.Enumerable.SelectManySingleSelectorIterator`2.MoveNext()
at System.Linq.Enumerable.ToDictionary[TSource,TKey,TElement](IEnumerable`1 source, Func`2 keySelector, Func`2 elementSelector, IEqualityComparer`1 comparer)
at System.Linq.Enumerable.ToDictionary[TSource,TKey,TElement](IEnumerable`1 source, Func`2 keySelector, Func`2 elementSelector)
at Google.Api.Generator.ProtoUtils.ProtoCatalog..ctor(String defaultPackage, IEnumerable`1 descs, IEnumerable`1 commonResourcesConfigs) in /home/kbuilder/.cache/synthtool/gapic-generator-csharp/Google.Api.Generator/ProtoUtils/ProtoCatalog.cs:line 39
at Google.Api.Generator.CodeGenerator.Generate(IReadOnlyList`1 descriptors, IEnumerable`1 filesToGenerate, IClock clock, String grpcServiceConfigPath, IEnumerable`1 commonResourcesConfigPaths)+MoveNext() in /home/kbuilder/.cache/synthtool/gapic-generator-csharp/Google.Api.Generator/CodeGenerator.cs:line 71
at System.Linq.Enumerable.SelectEnumerableIterator`2.MoveNext()
at Google.Protobuf.Collections.RepeatedField`1.AddRange(IEnumerable`1 values)
at Google.Protobuf.Collections.RepeatedField`1.Add(IEnumerable`1 values)
at Google.Api.Generator.Program.GenerateFromProtoc(Stream stdin, Stream stdout) in /home/kbuilder/.cache/synthtool/gapic-generator-csharp/Google.Api.Generator/Program.cs:line 157
rm: missing operand
Try 'rm --help' for more information.
2020-03-20 22:39:01,934 synthtool > Failed executing /bin/bash generateapis.sh --check_compatibility Google.Cloud.Dialogflow.V2:
None
2020-03-20 22:39:01,935 synthtool > Wrote metadata to synth.metadata.
Traceback (most recent call last):
File "/home/kbuilder/.pyenv/versions/3.6.9/lib/python3.6/runpy.py", line 193, in _run_module_as_main
"__main__", mod_spec)
File "/home/kbuilder/.pyenv/versions/3.6.9/lib/python3.6/runpy.py", line 85, in _run_code
exec(code, run_globals)
File "/tmpfs/src/git/autosynth/env/lib/python3.6/site-packages/synthtool/__main__.py", line 102, in <module>
main()
File "/tmpfs/src/git/autosynth/env/lib/python3.6/site-packages/click/core.py", line 829, in __call__
return self.main(*args, **kwargs)
File "/tmpfs/src/git/autosynth/env/lib/python3.6/site-packages/click/core.py", line 782, in main
rv = self.invoke(ctx)
File "/tmpfs/src/git/autosynth/env/lib/python3.6/site-packages/click/core.py", line 1066, in invoke
return ctx.invoke(self.callback, **ctx.params)
File "/tmpfs/src/git/autosynth/env/lib/python3.6/site-packages/click/core.py", line 610, in invoke
return callback(*args, **kwargs)
File "/tmpfs/src/git/autosynth/env/lib/python3.6/site-packages/synthtool/__main__.py", line 94, in main
spec.loader.exec_module(synth_module) # type: ignore
File "<frozen importlib._bootstrap_external>", line 678, in exec_module
File "<frozen importlib._bootstrap>", line 219, in _call_with_frames_removed
File "/tmpfs/src/git/autosynth/working_repo/apis/Google.Cloud.Dialogflow.V2/synth.py", line 20, in <module>
hide_output = False)
File "/tmpfs/src/git/autosynth/env/lib/python3.6/site-packages/synthtool/shell.py", line 39, in run
raise exc
File "/tmpfs/src/git/autosynth/env/lib/python3.6/site-packages/synthtool/shell.py", line 33, in run
encoding="utf-8",
File "/home/kbuilder/.pyenv/versions/3.6.9/lib/python3.6/subprocess.py", line 438, in run
output=stdout, stderr=stderr)
subprocess.CalledProcessError: Command '('/bin/bash', 'generateapis.sh', '--check_compatibility', 'Google.Cloud.Dialogflow.V2')' returned non-zero exit status 1.
Synthesis failed
Traceback (most recent call last):
File "/home/kbuilder/.pyenv/versions/3.6.9/lib/python3.6/runpy.py", line 193, in _run_module_as_main
"__main__", mod_spec)
File "/home/kbuilder/.pyenv/versions/3.6.9/lib/python3.6/runpy.py", line 85, in _run_code
exec(code, run_globals)
File "/tmpfs/src/git/autosynth/autosynth/synth.py", line 509, in <module>
main()
File "/tmpfs/src/git/autosynth/autosynth/synth.py", line 356, in main
return _inner_main(temp_dir)
File "/tmpfs/src/git/autosynth/autosynth/synth.py", line 421, in _inner_main
deprecated_execution=args.deprecated_execution,
File "/tmpfs/src/git/autosynth/autosynth/synth.py", line 300, in synthesize
synth_proc.check_returncode() # Raise an exception.
File "/home/kbuilder/.pyenv/versions/3.6.9/lib/python3.6/subprocess.py", line 389, in check_returncode
self.stderr)
subprocess.CalledProcessError: Command '['/tmpfs/src/git/autosynth/env/bin/python3', '-m', 'synthtool', '--metadata', 'synth.metadata', 'synth.py', '--']' returned non-zero exit status 1.
```
Google internal developers can see the full log [here](https://sponge/b6efb4f2-22e9-4503-b75b-dbc0a65c36a1).
|
1.0
|
Synthesis failed for Google.Cloud.Dialogflow.V2 - Hello! Autosynth couldn't regenerate Google.Cloud.Dialogflow.V2. :broken_heart:
Here's the output from running `synth.py`:
```
Cloning into 'working_repo'...
Switched to a new branch 'autosynth-Google.Cloud.Dialogflow.V2'
Running synthtool
['/tmpfs/src/git/autosynth/env/bin/python3', '-m', 'synthtool', '--metadata', 'synth.metadata', 'synth.py', '--']
2020-03-20 22:38:53,528 synthtool > Executing /tmpfs/src/git/autosynth/working_repo/apis/Google.Cloud.Dialogflow.V2/synth.py.
Skipping microgenerator fetch/build: already built, and running on Kokoro
Building existing version of Google.Cloud.Dialogflow.V2 for compatibility checking
Generating Google.Cloud.Dialogflow.V2
--gapic_out: System.InvalidOperationException: Not all patterns can be matched to a parent resource for field CreateContextRequest.parent
at Google.Api.Generator.ProtoUtils.ResourceDetails.LoadResourceReference(MessageDescriptor msgDesc, FieldDescriptor fieldDesc, IReadOnlyDictionary`2 resourcesByUrt, IReadOnlyDictionary`2 resourcesByPattern)+MoveNext()
at System.Collections.Generic.List`1..ctor(IEnumerable`1 collection)
at System.Linq.Enumerable.ToList[TSource](IEnumerable`1 source)
at Google.Api.Generator.ProtoUtils.ProtoCatalog.<>c__DisplayClass0_2.<.ctor>b__20(FieldDescriptor field) in /home/kbuilder/.cache/synthtool/gapic-generator-csharp/Google.Api.Generator/ProtoUtils/ProtoCatalog.cs:line 43
at System.Linq.Enumerable.SelectIListIterator`2.MoveNext()
at System.Linq.Enumerable.WhereEnumerableIterator`1.MoveNext()
at System.Linq.Enumerable.SelectManySingleSelectorIterator`2.MoveNext()
at System.Linq.Enumerable.ToDictionary[TSource,TKey,TElement](IEnumerable`1 source, Func`2 keySelector, Func`2 elementSelector, IEqualityComparer`1 comparer)
at System.Linq.Enumerable.ToDictionary[TSource,TKey,TElement](IEnumerable`1 source, Func`2 keySelector, Func`2 elementSelector)
at Google.Api.Generator.ProtoUtils.ProtoCatalog..ctor(String defaultPackage, IEnumerable`1 descs, IEnumerable`1 commonResourcesConfigs) in /home/kbuilder/.cache/synthtool/gapic-generator-csharp/Google.Api.Generator/ProtoUtils/ProtoCatalog.cs:line 39
at Google.Api.Generator.CodeGenerator.Generate(IReadOnlyList`1 descriptors, IEnumerable`1 filesToGenerate, IClock clock, String grpcServiceConfigPath, IEnumerable`1 commonResourcesConfigPaths)+MoveNext() in /home/kbuilder/.cache/synthtool/gapic-generator-csharp/Google.Api.Generator/CodeGenerator.cs:line 71
at System.Linq.Enumerable.SelectEnumerableIterator`2.MoveNext()
at Google.Protobuf.Collections.RepeatedField`1.AddRange(IEnumerable`1 values)
at Google.Protobuf.Collections.RepeatedField`1.Add(IEnumerable`1 values)
at Google.Api.Generator.Program.GenerateFromProtoc(Stream stdin, Stream stdout) in /home/kbuilder/.cache/synthtool/gapic-generator-csharp/Google.Api.Generator/Program.cs:line 157
rm: missing operand
Try 'rm --help' for more information.
2020-03-20 22:39:01,934 synthtool > Failed executing /bin/bash generateapis.sh --check_compatibility Google.Cloud.Dialogflow.V2:
None
2020-03-20 22:39:01,935 synthtool > Wrote metadata to synth.metadata.
Traceback (most recent call last):
File "/home/kbuilder/.pyenv/versions/3.6.9/lib/python3.6/runpy.py", line 193, in _run_module_as_main
"__main__", mod_spec)
File "/home/kbuilder/.pyenv/versions/3.6.9/lib/python3.6/runpy.py", line 85, in _run_code
exec(code, run_globals)
File "/tmpfs/src/git/autosynth/env/lib/python3.6/site-packages/synthtool/__main__.py", line 102, in <module>
main()
File "/tmpfs/src/git/autosynth/env/lib/python3.6/site-packages/click/core.py", line 829, in __call__
return self.main(*args, **kwargs)
File "/tmpfs/src/git/autosynth/env/lib/python3.6/site-packages/click/core.py", line 782, in main
rv = self.invoke(ctx)
File "/tmpfs/src/git/autosynth/env/lib/python3.6/site-packages/click/core.py", line 1066, in invoke
return ctx.invoke(self.callback, **ctx.params)
File "/tmpfs/src/git/autosynth/env/lib/python3.6/site-packages/click/core.py", line 610, in invoke
return callback(*args, **kwargs)
File "/tmpfs/src/git/autosynth/env/lib/python3.6/site-packages/synthtool/__main__.py", line 94, in main
spec.loader.exec_module(synth_module) # type: ignore
File "<frozen importlib._bootstrap_external>", line 678, in exec_module
File "<frozen importlib._bootstrap>", line 219, in _call_with_frames_removed
File "/tmpfs/src/git/autosynth/working_repo/apis/Google.Cloud.Dialogflow.V2/synth.py", line 20, in <module>
hide_output = False)
File "/tmpfs/src/git/autosynth/env/lib/python3.6/site-packages/synthtool/shell.py", line 39, in run
raise exc
File "/tmpfs/src/git/autosynth/env/lib/python3.6/site-packages/synthtool/shell.py", line 33, in run
encoding="utf-8",
File "/home/kbuilder/.pyenv/versions/3.6.9/lib/python3.6/subprocess.py", line 438, in run
output=stdout, stderr=stderr)
subprocess.CalledProcessError: Command '('/bin/bash', 'generateapis.sh', '--check_compatibility', 'Google.Cloud.Dialogflow.V2')' returned non-zero exit status 1.
Synthesis failed
Traceback (most recent call last):
File "/home/kbuilder/.pyenv/versions/3.6.9/lib/python3.6/runpy.py", line 193, in _run_module_as_main
"__main__", mod_spec)
File "/home/kbuilder/.pyenv/versions/3.6.9/lib/python3.6/runpy.py", line 85, in _run_code
exec(code, run_globals)
File "/tmpfs/src/git/autosynth/autosynth/synth.py", line 509, in <module>
main()
File "/tmpfs/src/git/autosynth/autosynth/synth.py", line 356, in main
return _inner_main(temp_dir)
File "/tmpfs/src/git/autosynth/autosynth/synth.py", line 421, in _inner_main
deprecated_execution=args.deprecated_execution,
File "/tmpfs/src/git/autosynth/autosynth/synth.py", line 300, in synthesize
synth_proc.check_returncode() # Raise an exception.
File "/home/kbuilder/.pyenv/versions/3.6.9/lib/python3.6/subprocess.py", line 389, in check_returncode
self.stderr)
subprocess.CalledProcessError: Command '['/tmpfs/src/git/autosynth/env/bin/python3', '-m', 'synthtool', '--metadata', 'synth.metadata', 'synth.py', '--']' returned non-zero exit status 1.
```
Google internal developers can see the full log [here](https://sponge/b6efb4f2-22e9-4503-b75b-dbc0a65c36a1).
|
non_test
|
synthesis failed for google cloud dialogflow hello autosynth couldn t regenerate google cloud dialogflow broken heart here s the output from running synth py cloning into working repo switched to a new branch autosynth google cloud dialogflow running synthtool synthtool executing tmpfs src git autosynth working repo apis google cloud dialogflow synth py skipping microgenerator fetch build already built and running on kokoro building existing version of google cloud dialogflow for compatibility checking generating google cloud dialogflow gapic out system invalidoperationexception not all patterns can be matched to a parent resource for field createcontextrequest parent at google api generator protoutils resourcedetails loadresourcereference messagedescriptor msgdesc fielddescriptor fielddesc ireadonlydictionary resourcesbyurt ireadonlydictionary resourcesbypattern movenext at system collections generic list ctor ienumerable collection at system linq enumerable tolist ienumerable source at google api generator protoutils protocatalog c b fielddescriptor field in home kbuilder cache synthtool gapic generator csharp google api generator protoutils protocatalog cs line at system linq enumerable selectilistiterator movenext at system linq enumerable whereenumerableiterator movenext at system linq enumerable selectmanysingleselectoriterator movenext at system linq enumerable todictionary ienumerable source func keyselector func elementselector iequalitycomparer comparer at system linq enumerable todictionary ienumerable source func keyselector func elementselector at google api generator protoutils protocatalog ctor string defaultpackage ienumerable descs ienumerable commonresourcesconfigs in home kbuilder cache synthtool gapic generator csharp google api generator protoutils protocatalog cs line at google api generator codegenerator generate ireadonlylist descriptors ienumerable filestogenerate iclock clock string grpcserviceconfigpath ienumerable commonresourcesconfigpaths movenext in home kbuilder cache synthtool gapic generator csharp google api generator codegenerator cs line at system linq enumerable selectenumerableiterator movenext at google protobuf collections repeatedfield addrange ienumerable values at google protobuf collections repeatedfield add ienumerable values at google api generator program generatefromprotoc stream stdin stream stdout in home kbuilder cache synthtool gapic generator csharp google api generator program cs line rm missing operand try rm help for more information synthtool failed executing bin bash generateapis sh check compatibility google cloud dialogflow none synthtool wrote metadata to synth metadata traceback most recent call last file home kbuilder pyenv versions lib runpy py line in run module as main main mod spec file home kbuilder pyenv versions lib runpy py line in run code exec code run globals file tmpfs src git autosynth env lib site packages synthtool main py line in main file tmpfs src git autosynth env lib site packages click core py line in call return self main args kwargs file tmpfs src git autosynth env lib site packages click core py line in main rv self invoke ctx file tmpfs src git autosynth env lib site packages click core py line in invoke return ctx invoke self callback ctx params file tmpfs src git autosynth env lib site packages click core py line in invoke return callback args kwargs file tmpfs src git autosynth env lib site packages synthtool main py line in main spec loader exec module synth module type ignore file line in exec module file line in call with frames removed file tmpfs src git autosynth working repo apis google cloud dialogflow synth py line in hide output false file tmpfs src git autosynth env lib site packages synthtool shell py line in run raise exc file tmpfs src git autosynth env lib site packages synthtool shell py line in run encoding utf file home kbuilder pyenv versions lib subprocess py line in run output stdout stderr stderr subprocess calledprocesserror command bin bash generateapis sh check compatibility google cloud dialogflow returned non zero exit status synthesis failed traceback most recent call last file home kbuilder pyenv versions lib runpy py line in run module as main main mod spec file home kbuilder pyenv versions lib runpy py line in run code exec code run globals file tmpfs src git autosynth autosynth synth py line in main file tmpfs src git autosynth autosynth synth py line in main return inner main temp dir file tmpfs src git autosynth autosynth synth py line in inner main deprecated execution args deprecated execution file tmpfs src git autosynth autosynth synth py line in synthesize synth proc check returncode raise an exception file home kbuilder pyenv versions lib subprocess py line in check returncode self stderr subprocess calledprocesserror command returned non zero exit status google internal developers can see the full log
| 0
|
264,558
| 23,124,803,860
|
IssuesEvent
|
2022-07-28 03:46:19
|
w3c/epub-tests
|
https://api.github.com/repos/w3c/epub-tests
|
closed
|
Test publication resource internationalization
|
good first issue tests needed
|
This whole section needs tests:
https://w3c.github.io/epub-specs/epub33/rs/#sec-epub-rs-i18n
There are some similar tests in https://w3c.github.io/epub-tests/#sec-internationalization-data, but more are needed to satisfy this section.
|
1.0
|
Test publication resource internationalization - This whole section needs tests:
https://w3c.github.io/epub-specs/epub33/rs/#sec-epub-rs-i18n
There are some similar tests in https://w3c.github.io/epub-tests/#sec-internationalization-data, but more are needed to satisfy this section.
|
test
|
test publication resource internationalization this whole section needs tests there are some similar tests in but more are needed to satisfy this section
| 1
|
129,244
| 10,567,527,008
|
IssuesEvent
|
2019-10-06 05:13:23
|
QubesOS/updates-status
|
https://api.github.com/repos/QubesOS/updates-status
|
closed
|
app-thunderbird v2.0.1 (r4.0)
|
r4.0-centos7-cur-test r4.0-fc29-cur-test r4.0-fc30-cur-test r4.0-fc31-cur-test
|
Update of app-thunderbird to v2.0.1 for Qubes r4.0, see comments below for details.
Built from: https://github.com/QubesOS/qubes-app-thunderbird/commit/9180bf72f3c3dd559589ed9df0075c0ef96af16f
[Changes since previous version](https://github.com/QubesOS/qubes-app-thunderbird/compare/v2.0.0...v2.0.1):
QubesOS/qubes-app-thunderbird@9180bf7 version 2.0.1
QubesOS/qubes-app-thunderbird@44a7aa5 Fix preference window for Thunderbird 68
Referenced issues:
If you're release manager, you can issue GPG-inline signed command:
* `Upload app-thunderbird 9180bf72f3c3dd559589ed9df0075c0ef96af16f r4.0 current repo` (available 7 days from now)
* `Upload app-thunderbird 9180bf72f3c3dd559589ed9df0075c0ef96af16f r4.0 current (dists) repo`, you can choose subset of distributions, like `vm-fc24 vm-fc25` (available 7 days from now)
* `Upload app-thunderbird 9180bf72f3c3dd559589ed9df0075c0ef96af16f r4.0 security-testing repo`
Above commands will work only if packages in current-testing repository were built from given commit (i.e. no new version superseded it).
|
4.0
|
app-thunderbird v2.0.1 (r4.0) - Update of app-thunderbird to v2.0.1 for Qubes r4.0, see comments below for details.
Built from: https://github.com/QubesOS/qubes-app-thunderbird/commit/9180bf72f3c3dd559589ed9df0075c0ef96af16f
[Changes since previous version](https://github.com/QubesOS/qubes-app-thunderbird/compare/v2.0.0...v2.0.1):
QubesOS/qubes-app-thunderbird@9180bf7 version 2.0.1
QubesOS/qubes-app-thunderbird@44a7aa5 Fix preference window for Thunderbird 68
Referenced issues:
If you're release manager, you can issue GPG-inline signed command:
* `Upload app-thunderbird 9180bf72f3c3dd559589ed9df0075c0ef96af16f r4.0 current repo` (available 7 days from now)
* `Upload app-thunderbird 9180bf72f3c3dd559589ed9df0075c0ef96af16f r4.0 current (dists) repo`, you can choose subset of distributions, like `vm-fc24 vm-fc25` (available 7 days from now)
* `Upload app-thunderbird 9180bf72f3c3dd559589ed9df0075c0ef96af16f r4.0 security-testing repo`
Above commands will work only if packages in current-testing repository were built from given commit (i.e. no new version superseded it).
|
test
|
app thunderbird update of app thunderbird to for qubes see comments below for details built from qubesos qubes app thunderbird version qubesos qubes app thunderbird fix preference window for thunderbird referenced issues if you re release manager you can issue gpg inline signed command upload app thunderbird current repo available days from now upload app thunderbird current dists repo you can choose subset of distributions like vm vm available days from now upload app thunderbird security testing repo above commands will work only if packages in current testing repository were built from given commit i e no new version superseded it
| 1
|
170,147
| 14,242,333,268
|
IssuesEvent
|
2020-11-19 01:32:09
|
Hioptom/Daily-Record
|
https://api.github.com/repos/Hioptom/Daily-Record
|
opened
|
鸿蒙拿什么与安卓一战?
|
documentation
|
本文来自 “新智元”(ID:AI_era) ,作者 新智元
9月5日消息,在9月10日即将举行的2020 HDC开发者大会上,华为将发布鸿蒙新版。报道称,余承东最近在接受采访时表示,鸿蒙系统手机最快会在明年推出。同时,有业界分析师称,华为麒麟9000备货在1000万片左右,有望支撑半年。
2020华为开发者大会将于9月10日至9月12日在东莞松山湖举办。据了解,此次会议包含三大重点主题:鸿蒙系统、HMS Core 5.0及EMUI 11。
鸿蒙2.0将搭载大波新品,手机尚「难产」中明年见
据悉,本次发布的鸿蒙新系统可以称之为鸿蒙2.0,相较于鸿蒙1.0来说(此前只是用在了智慧屏上),其后会应用在华为的国产PC、手表/手环、车机产品上。
当然,万众瞩目的焦点的还是,鸿蒙系统何时用在手机上。根据硅谷分析狮报道,针对外界传闻多时的鸿蒙系统手机,余承东在最新接受采访时承认了它的存在,并表示最快会在2021年推出。
在去年发布会上展示的鸿蒙历程及路标上还没有提到鸿蒙手机。面对「明年复明年、明年何其多」的质疑,俗称大嘴的余承东说话留了半分,只是说鸿蒙手机「最快明年」推出,证明开发和适配确实还需要假以时日。
时隔一年,「不世出」的鸿蒙怎么样了?
在2019年的华为开发者大会上,华为消费者业务CEO余承东正式对外发布了基于微内核面向全场景的分布式操作系统HarmonyOS。
时隔一年后,这个被寄予厚望的操作系统将迎来新的升级。
余承东在介绍鸿蒙OS开发初衷时曾表示:「鸿蒙OS的出发点和Android、IOS都不一样,它是一款全新的基于微内核的面向全场景的分布式操作系统,能够同时满足全场景流畅体验、架构级可信安全、跨终端无缝协同以及一次开发多终端部署的要求。」
很多网友都喜欢说「鸿蒙基于安卓」,实际上,这个概念很重要,鸿蒙和安卓都是基于Linux内核的,但是安卓已经经过十几年的完善,其执行的效率、安全性,还有可靠性都趋于完美。
对此,余承东有过这样两个介绍:一是鸿蒙兼容全部安卓应用,二是鸿蒙比安卓快60%。
来源:网络
安卓是在Java虚拟机上运行,鸿蒙是不经过虚拟机直接运行,所以速度更快。
那问题来了,既然能兼容安卓,那能否兼容IOS呢?很遗憾,鉴于IOS的授权,暂时不支持IOS应用!
那么根据现有的信息,鸿蒙究竟有没有优势?
很多人都认为,优势还是有的。
首先,鸿蒙与安卓不是一个时代的产物。鸿蒙是基于5G万物互联的操作系统,优势应该是建立在物联网的基础上,一是适用性广,二是速度快,三是耗电小,可以提高设备续航能力。
类似地,谷歌也有一个不同于安卓的下一代系统。有网友表示,不论鸿蒙是否能成功,华为的勇气值得赞赏。
另外,同样是得益于时代,鸿蒙具有后发优势。因为前有安卓「试水」,很多错误的路已经不会再走了。至少,鸿蒙可以「避坑」。
但是,口说无凭,鸿蒙是否能真正出世,出世后能否经得住市场的考验,还都是未知。
去年在鸿蒙系统发布的第二天,华为发布了首款搭载鸿蒙系统的设备荣耀智慧屏。当时有媒体曾向余承东提问,「鸿蒙系统的首发是搭载在智慧屏上,鸿蒙系统是否可以应用到手机上?」对此,余承东给予了非常肯定的回答:可以,并表示随时可以用。
可以说,华为智慧屏,是鸿蒙系统的初体验。虽然有人直呼这款设备功能超乎想象;但也有人提出质疑:
问题的核心还是在于,「真正的」鸿蒙,是怎样的?
余承东透露,今年华为的智能手表产品也会搭载鸿蒙 OS。而未来华为所有的 IoT 产品,包括 PC、平板、手机都可能采用鸿蒙 OS。
按照余承东的说法,鸿蒙OS未来会成为全球都可以使用的操作系统。与其说这是技术问题,不如说「这是商业问题」。
有网友指出在官网里,暂时还没有鸿蒙的一席之地。
而有人认为,「真金不怕火炼」,鸿蒙此前受过太多的质疑,但质疑声也非空穴来风,想要彰显实力,必须拿出实实在在可用的系统。毕竟有太多PPT系统。
的确,技术是否过硬,不光是给用户看的,还要给美国看到。「当围追堵截不能扼杀你的时候,对方很可能就松口与你寻求合作了。」这次鸿蒙系统能否让人眼前一亮,甚至都可能扭转美国封杀的风向标。
鸿蒙难过「生态关」,但做好这件事可与安卓一战
早在去年年底,余承东给全体员工的新年信中就提出,要坚定打造「自研芯片+鸿蒙OS」新体系。
就在今天,最新消息,针对华为麒麟9000处理器或成「芯片绝唱」,以后将无法生产一事,有业内人士表示,目前华为麒麟9000备货量在1000万片左右,有1000万台华为Mate40/Pro手机可以用上这一芯片,有望支撑半年时间。
通信行业独立分析师黄海峰表示,当备货用完后,华为手机业务,尤其是高端手机业务很快会遇到巨大挑战。
未来,全面自研之路必将布满坎坷。
而鸿蒙OS亟待解决的还有应用生态的问题。从来,自研操作系统难过「生态关」。
目前,全球最主流的两大手机操作系统,苹果iOS与谷歌安卓,二者相加几乎占据了智能手机操作系统市场100%的份额。
华为也远非第一家开发独立操作系统的行业巨头。还记得诺基亚的塞班吗?三星的Bada和Tizen、微软的Windows Phone、黑莓的BlackBerry OS等系统都曾昙花一现,但最终都未能打破生态壁垒。
用通俗的话讲,就是有操作系统但没有足够的应用程序。
对此,网友表示「(鸿蒙)另类系统应用少,应用也不稳,难难难,肯定要兼容安卓或苹果的App才更容易兴起来。」
支持者却对鸿蒙生态信心满满,诺基亚时代他们也是这么说安卓的。「买的人多了,生态自然就出来了。」
2010年左右,安卓刚刚兴起的时候,塞班的市场占有率还是第一名,但已经开始走下坡路了。当时Android系统的生态环境还十分落后,连个官方的QQ都没有。生态的繁荣还需要一个过程。
随着华为鸿蒙整体战略发布和鸿蒙系统的成熟,有望打破国外巨头所垄断,为中国提供自己的安全可靠的操作系统。想必这一次,鸿蒙不会是雷声大雨点小。未来有了生态的积累,走出一条坚定的全面自研之路也未可知。
有了底层的操作系统,到上层的应用还远吗?不太远,但还需要一个核心部分HMS。HMS Core连接鸿蒙和app的中间能力,没有HMS Core,应用开发难度会大幅增加。
华为手机架构中的 HMS 生态,重点包括 HMS Apps 和 HMS Core。
HMS Core 主要为开发者提供服务支持,从开发、增长到盈利,全方位为其赋能。借助华为帐号一次接入,支持用户在手机、平板、PC、手表、大屏和车机等多终端登录,PUSH 服务为开发者提供可靠的消息推送通道,可按不同场景进行推送,支持文本、角标、铃声、大图片多种形式,到达率 99%。
HMS 应用已累计在全球 170 多个国家和地区上线,月活用户数已超过 4 亿,汇聚了 130 万全球开发者和合作伙伴。
马上,鸿蒙OS即将发布2.0,中间件HMS Core5.0也已初具规模,上层app又能无缝迁移。
多一点点信心,鸿蒙也许可以打破「生态关」,与安卓一战。
|
1.0
|
鸿蒙拿什么与安卓一战? - 本文来自 “新智元”(ID:AI_era) ,作者 新智元
9月5日消息,在9月10日即将举行的2020 HDC开发者大会上,华为将发布鸿蒙新版。报道称,余承东最近在接受采访时表示,鸿蒙系统手机最快会在明年推出。同时,有业界分析师称,华为麒麟9000备货在1000万片左右,有望支撑半年。
2020华为开发者大会将于9月10日至9月12日在东莞松山湖举办。据了解,此次会议包含三大重点主题:鸿蒙系统、HMS Core 5.0及EMUI 11。
鸿蒙2.0将搭载大波新品,手机尚「难产」中明年见
据悉,本次发布的鸿蒙新系统可以称之为鸿蒙2.0,相较于鸿蒙1.0来说(此前只是用在了智慧屏上),其后会应用在华为的国产PC、手表/手环、车机产品上。
当然,万众瞩目的焦点的还是,鸿蒙系统何时用在手机上。根据硅谷分析狮报道,针对外界传闻多时的鸿蒙系统手机,余承东在最新接受采访时承认了它的存在,并表示最快会在2021年推出。
在去年发布会上展示的鸿蒙历程及路标上还没有提到鸿蒙手机。面对「明年复明年、明年何其多」的质疑,俗称大嘴的余承东说话留了半分,只是说鸿蒙手机「最快明年」推出,证明开发和适配确实还需要假以时日。
时隔一年,「不世出」的鸿蒙怎么样了?
在2019年的华为开发者大会上,华为消费者业务CEO余承东正式对外发布了基于微内核面向全场景的分布式操作系统HarmonyOS。
时隔一年后,这个被寄予厚望的操作系统将迎来新的升级。
余承东在介绍鸿蒙OS开发初衷时曾表示:「鸿蒙OS的出发点和Android、IOS都不一样,它是一款全新的基于微内核的面向全场景的分布式操作系统,能够同时满足全场景流畅体验、架构级可信安全、跨终端无缝协同以及一次开发多终端部署的要求。」
很多网友都喜欢说「鸿蒙基于安卓」,实际上,这个概念很重要,鸿蒙和安卓都是基于Linux内核的,但是安卓已经经过十几年的完善,其执行的效率、安全性,还有可靠性都趋于完美。
对此,余承东有过这样两个介绍:一是鸿蒙兼容全部安卓应用,二是鸿蒙比安卓快60%。
来源:网络
安卓是在Java虚拟机上运行,鸿蒙是不经过虚拟机直接运行,所以速度更快。
那问题来了,既然能兼容安卓,那能否兼容IOS呢?很遗憾,鉴于IOS的授权,暂时不支持IOS应用!
那么根据现有的信息,鸿蒙究竟有没有优势?
很多人都认为,优势还是有的。
首先,鸿蒙与安卓不是一个时代的产物。鸿蒙是基于5G万物互联的操作系统,优势应该是建立在物联网的基础上,一是适用性广,二是速度快,三是耗电小,可以提高设备续航能力。
类似地,谷歌也有一个不同于安卓的下一代系统。有网友表示,不论鸿蒙是否能成功,华为的勇气值得赞赏。
另外,同样是得益于时代,鸿蒙具有后发优势。因为前有安卓「试水」,很多错误的路已经不会再走了。至少,鸿蒙可以「避坑」。
但是,口说无凭,鸿蒙是否能真正出世,出世后能否经得住市场的考验,还都是未知。
去年在鸿蒙系统发布的第二天,华为发布了首款搭载鸿蒙系统的设备荣耀智慧屏。当时有媒体曾向余承东提问,「鸿蒙系统的首发是搭载在智慧屏上,鸿蒙系统是否可以应用到手机上?」对此,余承东给予了非常肯定的回答:可以,并表示随时可以用。
可以说,华为智慧屏,是鸿蒙系统的初体验。虽然有人直呼这款设备功能超乎想象;但也有人提出质疑:
问题的核心还是在于,「真正的」鸿蒙,是怎样的?
余承东透露,今年华为的智能手表产品也会搭载鸿蒙 OS。而未来华为所有的 IoT 产品,包括 PC、平板、手机都可能采用鸿蒙 OS。
按照余承东的说法,鸿蒙OS未来会成为全球都可以使用的操作系统。与其说这是技术问题,不如说「这是商业问题」。
有网友指出在官网里,暂时还没有鸿蒙的一席之地。
而有人认为,「真金不怕火炼」,鸿蒙此前受过太多的质疑,但质疑声也非空穴来风,想要彰显实力,必须拿出实实在在可用的系统。毕竟有太多PPT系统。
的确,技术是否过硬,不光是给用户看的,还要给美国看到。「当围追堵截不能扼杀你的时候,对方很可能就松口与你寻求合作了。」这次鸿蒙系统能否让人眼前一亮,甚至都可能扭转美国封杀的风向标。
鸿蒙难过「生态关」,但做好这件事可与安卓一战
早在去年年底,余承东给全体员工的新年信中就提出,要坚定打造「自研芯片+鸿蒙OS」新体系。
就在今天,最新消息,针对华为麒麟9000处理器或成「芯片绝唱」,以后将无法生产一事,有业内人士表示,目前华为麒麟9000备货量在1000万片左右,有1000万台华为Mate40/Pro手机可以用上这一芯片,有望支撑半年时间。
通信行业独立分析师黄海峰表示,当备货用完后,华为手机业务,尤其是高端手机业务很快会遇到巨大挑战。
未来,全面自研之路必将布满坎坷。
而鸿蒙OS亟待解决的还有应用生态的问题。从来,自研操作系统难过「生态关」。
目前,全球最主流的两大手机操作系统,苹果iOS与谷歌安卓,二者相加几乎占据了智能手机操作系统市场100%的份额。
华为也远非第一家开发独立操作系统的行业巨头。还记得诺基亚的塞班吗?三星的Bada和Tizen、微软的Windows Phone、黑莓的BlackBerry OS等系统都曾昙花一现,但最终都未能打破生态壁垒。
用通俗的话讲,就是有操作系统但没有足够的应用程序。
对此,网友表示「(鸿蒙)另类系统应用少,应用也不稳,难难难,肯定要兼容安卓或苹果的App才更容易兴起来。」
支持者却对鸿蒙生态信心满满,诺基亚时代他们也是这么说安卓的。「买的人多了,生态自然就出来了。」
2010年左右,安卓刚刚兴起的时候,塞班的市场占有率还是第一名,但已经开始走下坡路了。当时Android系统的生态环境还十分落后,连个官方的QQ都没有。生态的繁荣还需要一个过程。
随着华为鸿蒙整体战略发布和鸿蒙系统的成熟,有望打破国外巨头所垄断,为中国提供自己的安全可靠的操作系统。想必这一次,鸿蒙不会是雷声大雨点小。未来有了生态的积累,走出一条坚定的全面自研之路也未可知。
有了底层的操作系统,到上层的应用还远吗?不太远,但还需要一个核心部分HMS。HMS Core连接鸿蒙和app的中间能力,没有HMS Core,应用开发难度会大幅增加。
华为手机架构中的 HMS 生态,重点包括 HMS Apps 和 HMS Core。
HMS Core 主要为开发者提供服务支持,从开发、增长到盈利,全方位为其赋能。借助华为帐号一次接入,支持用户在手机、平板、PC、手表、大屏和车机等多终端登录,PUSH 服务为开发者提供可靠的消息推送通道,可按不同场景进行推送,支持文本、角标、铃声、大图片多种形式,到达率 99%。
HMS 应用已累计在全球 170 多个国家和地区上线,月活用户数已超过 4 亿,汇聚了 130 万全球开发者和合作伙伴。
马上,鸿蒙OS即将发布2.0,中间件HMS Core5.0也已初具规模,上层app又能无缝迁移。
多一点点信心,鸿蒙也许可以打破「生态关」,与安卓一战。
|
non_test
|
鸿蒙拿什么与安卓一战? 本文来自 “新智元”(id ai era) ,作者 新智元 , hdc开发者大会上,华为将发布鸿蒙新版。报道称,余承东最近在接受采访时表示,鸿蒙系统手机最快会在明年推出。同时,有业界分析师称, ,有望支撑半年。 。据了解,此次会议包含三大重点主题:鸿蒙系统、hms core 。 ,手机尚「难产」中明年见 据悉, , (此前只是用在了智慧屏上),其后会应用在华为的国产pc、手表 手环、车机产品上。 当然,万众瞩目的焦点的还是,鸿蒙系统何时用在手机上。根据硅谷分析狮报道,针对外界传闻多时的鸿蒙系统手机,余承东在最新接受采访时承认了它的存在, 。 在去年发布会上展示的鸿蒙历程及路标上还没有提到鸿蒙手机。面对「明年复明年、明年何其多」的质疑,俗称大嘴的余承东说话留了半分,只是说鸿蒙手机「最快明年」推出,证明开发和适配确实还需要假以时日。 时隔一年,「不世出」的鸿蒙怎么样了? ,华为消费者业务ceo余承东正式对外发布了基于微内核面向全场景的分布式操作系统harmonyos。 时隔一年后,这个被寄予厚望的操作系统将迎来新的升级。 余承东在介绍鸿蒙os开发初衷时曾表示:「鸿蒙os的出发点和android、ios都不一样,它是一款全新的基于微内核的面向全场景的分布式操作系统,能够同时满足全场景流畅体验、架构级可信安全、跨终端无缝协同以及一次开发多终端部署的要求。」 很多网友都喜欢说「鸿蒙基于安卓」,实际上,这个概念很重要,鸿蒙和安卓都是基于linux内核的,但是安卓已经经过十几年的完善,其执行的效率、安全性,还有可靠性都趋于完美。 对此,余承东有过这样两个介绍:一是鸿蒙兼容全部安卓应用, 。 来源:网络 安卓是在java虚拟机上运行,鸿蒙是不经过虚拟机直接运行,所以速度更快。 那问题来了,既然能兼容安卓,那能否兼容ios呢?很遗憾,鉴于ios的授权,暂时不支持ios应用! 那么根据现有的信息,鸿蒙究竟有没有优势? 很多人都认为,优势还是有的。 首先,鸿蒙与安卓不是一个时代的产物。 ,优势应该是建立在物联网的基础上,一是适用性广,二是速度快,三是耗电小,可以提高设备续航能力。 类似地,谷歌也有一个不同于安卓的下一代系统。有网友表示,不论鸿蒙是否能成功,华为的勇气值得赞赏。 另外,同样是得益于时代,鸿蒙具有后发优势。因为前有安卓「试水」,很多错误的路已经不会再走了。至少,鸿蒙可以「避坑」。 但是,口说无凭,鸿蒙是否能真正出世,出世后能否经得住市场的考验,还都是未知。 去年在鸿蒙系统发布的第二天,华为发布了首款搭载鸿蒙系统的设备荣耀智慧屏。当时有媒体曾向余承东提问,「鸿蒙系统的首发是搭载在智慧屏上,鸿蒙系统是否可以应用到手机上?」对此,余承东给予了非常肯定的回答:可以,并表示随时可以用。 可以说,华为智慧屏,是鸿蒙系统的初体验。虽然有人直呼这款设备功能超乎想象;但也有人提出质疑: 问题的核心还是在于,「真正的」鸿蒙,是怎样的? 余承东透露,今年华为的智能手表产品也会搭载鸿蒙 os。而未来华为所有的 iot 产品,包括 pc、平板、手机都可能采用鸿蒙 os。 按照余承东的说法,鸿蒙os未来会成为全球都可以使用的操作系统。与其说这是技术问题,不如说「这是商业问题」。 有网友指出在官网里,暂时还没有鸿蒙的一席之地。 而有人认为,「真金不怕火炼」,鸿蒙此前受过太多的质疑,但质疑声也非空穴来风,想要彰显实力,必须拿出实实在在可用的系统。毕竟有太多ppt系统。 的确,技术是否过硬,不光是给用户看的,还要给美国看到。「当围追堵截不能扼杀你的时候,对方很可能就松口与你寻求合作了。」这次鸿蒙系统能否让人眼前一亮,甚至都可能扭转美国封杀的风向标。 鸿蒙难过「生态关」,但做好这件事可与安卓一战 早在去年年底,余承东给全体员工的新年信中就提出,要坚定打造「自研芯片 鸿蒙os」新体系。 就在今天,最新消息, 「芯片绝唱」,以后将无法生产一事,有业内人士表示, , pro手机可以用上这一芯片,有望支撑半年时间。 通信行业独立分析师黄海峰表示,当备货用完后,华为手机业务,尤其是高端手机业务很快会遇到巨大挑战。 未来,全面自研之路必将布满坎坷。 而鸿蒙os亟待解决的还有应用生态的问题。从来,自研操作系统难过「生态关」。 目前,全球最主流的两大手机操作系统,苹果ios与谷歌安卓, 的份额。 华为也远非第一家开发独立操作系统的行业巨头。还记得诺基亚的塞班吗?三星的bada和tizen、微软的windows phone、黑莓的blackberry os等系统都曾昙花一现,但最终都未能打破生态壁垒。 用通俗的话讲,就是有操作系统但没有足够的应用程序。 对此,网友表示「(鸿蒙)另类系统应用少,应用也不稳,难难难,肯定要兼容安卓或苹果的app才更容易兴起来。」 支持者却对鸿蒙生态信心满满,诺基亚时代他们也是这么说安卓的。「买的人多了,生态自然就出来了。」 ,安卓刚刚兴起的时候,塞班的市场占有率还是第一名,但已经开始走下坡路了。当时android系统的生态环境还十分落后,连个官方的qq都没有。生态的繁荣还需要一个过程。 随着华为鸿蒙整体战略发布和鸿蒙系统的成熟,有望打破国外巨头所垄断,为中国提供自己的安全可靠的操作系统。想必这一次,鸿蒙不会是雷声大雨点小。未来有了生态的积累,走出一条坚定的全面自研之路也未可知。 有了底层的操作系统,到上层的应用还远吗?不太远,但还需要一个核心部分hms。hms core连接鸿蒙和app的中间能力,没有hms core,应用开发难度会大幅增加。 华为手机架构中的 hms 生态,重点包括 hms apps 和 hms core。 hms core 主要为开发者提供服务支持,从开发、增长到盈利,全方位为其赋能。借助华为帐号一次接入,支持用户在手机、平板、pc、手表、大屏和车机等多终端登录,push 服务为开发者提供可靠的消息推送通道,可按不同场景进行推送,支持文本、角标、铃声、大图片多种形式,到达率 。 hms 应用已累计在全球 多个国家和地区上线,月活用户数已超过 亿,汇聚了 万全球开发者和合作伙伴。 马上, ,中间件hms ,上层app又能无缝迁移。 多一点点信心,鸿蒙也许可以打破「生态关」,与安卓一战。
| 0
|
167,567
| 13,035,327,296
|
IssuesEvent
|
2020-07-28 10:10:44
|
urapadmin/kiosk
|
https://api.github.com/repos/urapadmin/kiosk
|
closed
|
a feature can be linked twice by the same survey / feature recording excavation
|
bug filemaker test-stage
|
just using the new link button (see #679) twice with the same feature leads to a second, third etc. entry of the same feature.
That should not be possible.
|
1.0
|
a feature can be linked twice by the same survey / feature recording excavation - just using the new link button (see #679) twice with the same feature leads to a second, third etc. entry of the same feature.
That should not be possible.
|
test
|
a feature can be linked twice by the same survey feature recording excavation just using the new link button see twice with the same feature leads to a second third etc entry of the same feature that should not be possible
| 1
|
28,418
| 4,396,698,728
|
IssuesEvent
|
2016-08-10 03:54:30
|
statsmodels/statsmodels
|
https://api.github.com/repos/statsmodels/statsmodels
|
closed
|
TST: new test failures with scipy 0.8
|
backport-0.8.0 maintenance type-bug type-test
|
The first test run that uses newly released scipy 0.8 has two new test failures in old code
https://travis-ci.org/statsmodels/statsmodels/jobs/147587982
```
======================================================================
FAIL: statsmodels.miscmodels.tests.test_tmodel.TestTModel.test_basic
----------------------------------------------------------------------
Traceback (most recent call last):
File "/home/travis/miniconda2/envs/statsmodels-test/lib/python2.7/site-packages/nose/case.py", line 197, in runTest
self.test(*self.arg)
File "/home/travis/miniconda2/envs/statsmodels-test/lib/python2.7/site-packages/statsmodels-0.8.0-py2.7-linux-x86_64.egg/statsmodels/miscmodels/tests/test_tmodel.py", line 86, in test_basic
assert_allclose(res1.params[-2], res2.dof, rtol=1e-5)
File "/home/travis/miniconda2/envs/statsmodels-test/lib/python2.7/site-packages/numpy/testing/utils.py", line 1395, in assert_allclose
verbose=verbose, header=header)
File "/home/travis/miniconda2/envs/statsmodels-test/lib/python2.7/site-packages/numpy/testing/utils.py", line 737, in assert_array_compare
raise AssertionError(msg)
AssertionError:
Not equal to tolerance rtol=1e-05, atol=0
(mismatch 100.0%)
x: array(2.837219360564396)
y: array(2.837183)
======================================================================
FAIL: statsmodels.tools.tests.test_rootfinding.test_brentq_expanding
----------------------------------------------------------------------
Traceback (most recent call last):
File "/home/travis/miniconda2/envs/statsmodels-test/lib/python2.7/site-packages/nose/case.py", line 197, in runTest
self.test(*self.arg)
File "/home/travis/miniconda2/envs/statsmodels-test/lib/python2.7/site-packages/statsmodels-0.8.0-py2.7-linux-x86_64.egg/statsmodels/tools/tests/test_rootfinding.py", line 84, in test_brentq_expanding
assert_equal(info1[k], info.__dict__[k])
File "/home/travis/miniconda2/envs/statsmodels-test/lib/python2.7/site-packages/numpy/testing/utils.py", line 379, in assert_equal
raise AssertionError(msg)
AssertionError:
Items are not equal:
ACTUAL: 63
DESIRED: 66
```
|
1.0
|
TST: new test failures with scipy 0.8 - The first test run that uses newly released scipy 0.8 has two new test failures in old code
https://travis-ci.org/statsmodels/statsmodels/jobs/147587982
```
======================================================================
FAIL: statsmodels.miscmodels.tests.test_tmodel.TestTModel.test_basic
----------------------------------------------------------------------
Traceback (most recent call last):
File "/home/travis/miniconda2/envs/statsmodels-test/lib/python2.7/site-packages/nose/case.py", line 197, in runTest
self.test(*self.arg)
File "/home/travis/miniconda2/envs/statsmodels-test/lib/python2.7/site-packages/statsmodels-0.8.0-py2.7-linux-x86_64.egg/statsmodels/miscmodels/tests/test_tmodel.py", line 86, in test_basic
assert_allclose(res1.params[-2], res2.dof, rtol=1e-5)
File "/home/travis/miniconda2/envs/statsmodels-test/lib/python2.7/site-packages/numpy/testing/utils.py", line 1395, in assert_allclose
verbose=verbose, header=header)
File "/home/travis/miniconda2/envs/statsmodels-test/lib/python2.7/site-packages/numpy/testing/utils.py", line 737, in assert_array_compare
raise AssertionError(msg)
AssertionError:
Not equal to tolerance rtol=1e-05, atol=0
(mismatch 100.0%)
x: array(2.837219360564396)
y: array(2.837183)
======================================================================
FAIL: statsmodels.tools.tests.test_rootfinding.test_brentq_expanding
----------------------------------------------------------------------
Traceback (most recent call last):
File "/home/travis/miniconda2/envs/statsmodels-test/lib/python2.7/site-packages/nose/case.py", line 197, in runTest
self.test(*self.arg)
File "/home/travis/miniconda2/envs/statsmodels-test/lib/python2.7/site-packages/statsmodels-0.8.0-py2.7-linux-x86_64.egg/statsmodels/tools/tests/test_rootfinding.py", line 84, in test_brentq_expanding
assert_equal(info1[k], info.__dict__[k])
File "/home/travis/miniconda2/envs/statsmodels-test/lib/python2.7/site-packages/numpy/testing/utils.py", line 379, in assert_equal
raise AssertionError(msg)
AssertionError:
Items are not equal:
ACTUAL: 63
DESIRED: 66
```
|
test
|
tst new test failures with scipy the first test run that uses newly released scipy has two new test failures in old code fail statsmodels miscmodels tests test tmodel testtmodel test basic traceback most recent call last file home travis envs statsmodels test lib site packages nose case py line in runtest self test self arg file home travis envs statsmodels test lib site packages statsmodels linux egg statsmodels miscmodels tests test tmodel py line in test basic assert allclose params dof rtol file home travis envs statsmodels test lib site packages numpy testing utils py line in assert allclose verbose verbose header header file home travis envs statsmodels test lib site packages numpy testing utils py line in assert array compare raise assertionerror msg assertionerror not equal to tolerance rtol atol mismatch x array y array fail statsmodels tools tests test rootfinding test brentq expanding traceback most recent call last file home travis envs statsmodels test lib site packages nose case py line in runtest self test self arg file home travis envs statsmodels test lib site packages statsmodels linux egg statsmodels tools tests test rootfinding py line in test brentq expanding assert equal info dict file home travis envs statsmodels test lib site packages numpy testing utils py line in assert equal raise assertionerror msg assertionerror items are not equal actual desired
| 1
|
2,464
| 2,607,903,862
|
IssuesEvent
|
2015-02-26 00:14:47
|
chrsmithdemos/zen-coding
|
https://api.github.com/repos/chrsmithdemos/zen-coding
|
closed
|
Typo on Context Menu
|
auto-migrated Priority-Medium Type-Defect
|
```
Plug-Ins > TEA for Coda > Zen Coding > "Previuos" Edit Point
Previous ;)
```
-----
Original issue reported on code.google.com by `bobmajda...@gmail.com` on 3 May 2010 at 2:42
|
1.0
|
Typo on Context Menu - ```
Plug-Ins > TEA for Coda > Zen Coding > "Previuos" Edit Point
Previous ;)
```
-----
Original issue reported on code.google.com by `bobmajda...@gmail.com` on 3 May 2010 at 2:42
|
non_test
|
typo on context menu plug ins tea for coda zen coding previuos edit point previous original issue reported on code google com by bobmajda gmail com on may at
| 0
|
240,048
| 19,988,565,128
|
IssuesEvent
|
2022-01-31 01:12:01
|
Airbenders-490/AirbendersFE
|
https://api.github.com/repos/Airbenders-490/AirbendersFE
|
closed
|
[STUD-63] As a student, I want to be navigate through the important sections on the application.
|
acceptance test RELEASE 1
|
**Acceptance Criteria:**
- The icon for the current page is displayed with a visible cue
**Conditions of Success:**
- Selecting the different icons on the navigation bar redirects the user to the desired page
**User Acceptance Flow:**
- User clicks on graduation cap icon
- User is redirected to Classes screen
------------------------
- User clicks on enveloppe icon
- User is redirected to Messages screen
------------
- User clicks on calendar icon
- User is redirected to Schedule screen
------------
- User clicks on the user icon
- User is redirected to Profile screen
------------
- User clicks on the icon with 3 lines
- User is redirected to their Feed
|
1.0
|
[STUD-63] As a student, I want to be navigate through the important sections on the application. - **Acceptance Criteria:**
- The icon for the current page is displayed with a visible cue
**Conditions of Success:**
- Selecting the different icons on the navigation bar redirects the user to the desired page
**User Acceptance Flow:**
- User clicks on graduation cap icon
- User is redirected to Classes screen
------------------------
- User clicks on enveloppe icon
- User is redirected to Messages screen
------------
- User clicks on calendar icon
- User is redirected to Schedule screen
------------
- User clicks on the user icon
- User is redirected to Profile screen
------------
- User clicks on the icon with 3 lines
- User is redirected to their Feed
|
test
|
as a student i want to be navigate through the important sections on the application acceptance criteria the icon for the current page is displayed with a visible cue conditions of success selecting the different icons on the navigation bar redirects the user to the desired page user acceptance flow user clicks on graduation cap icon user is redirected to classes screen user clicks on enveloppe icon user is redirected to messages screen user clicks on calendar icon user is redirected to schedule screen user clicks on the user icon user is redirected to profile screen user clicks on the icon with lines user is redirected to their feed
| 1
|
643,424
| 20,957,149,759
|
IssuesEvent
|
2022-03-27 08:47:37
|
bitfoundation/bitframework
|
https://api.github.com/repos/bitfoundation/bitframework
|
closed
|
BitToggle of 'show preview box' in BitColorPicker demo does not work properly
|
bug area / components high priority
|
In [demo example 1](https://bitcomponents.azurewebsites.net/components/color-picker#example1) of `BitColorPicker` component demos, the corresponding `BitToggle` for showing/hiding preview box does not work properly
|
1.0
|
BitToggle of 'show preview box' in BitColorPicker demo does not work properly - In [demo example 1](https://bitcomponents.azurewebsites.net/components/color-picker#example1) of `BitColorPicker` component demos, the corresponding `BitToggle` for showing/hiding preview box does not work properly
|
non_test
|
bittoggle of show preview box in bitcolorpicker demo does not work properly in of bitcolorpicker component demos the corresponding bittoggle for showing hiding preview box does not work properly
| 0
|
42,627
| 2,872,562,218
|
IssuesEvent
|
2015-06-08 12:46:03
|
jackjonesfashion/wiz
|
https://api.github.com/repos/jackjonesfashion/wiz
|
closed
|
Source Ark: Refactor code and bring up to standard
|
Priority: High
|
Old code, poor performance, hard to update, hard to deploy
|
1.0
|
Source Ark: Refactor code and bring up to standard - Old code, poor performance, hard to update, hard to deploy
|
non_test
|
source ark refactor code and bring up to standard old code poor performance hard to update hard to deploy
| 0
|
147,239
| 5,635,884,453
|
IssuesEvent
|
2017-04-06 02:47:56
|
victorhahn/SCIM
|
https://api.github.com/repos/victorhahn/SCIM
|
closed
|
Pseudo Delete
|
high priority
|
1. Add column to each main table that corresponds to a page on the site, add an isArchived boolean (1 if true, 0 if false) - Events, Event Types, Clients, Vendors, Vendor Types, Vendor Documents, Inventory, Reminders
2. Add dropdown or buttons to show either All Records, Archived Records, or Current Records
3. Add back a delete icon, on button click update that row of the db's isArchived bool
4. Change all select statements of app
5. Change all input statements of app, default to isArchived=0
|
1.0
|
Pseudo Delete - 1. Add column to each main table that corresponds to a page on the site, add an isArchived boolean (1 if true, 0 if false) - Events, Event Types, Clients, Vendors, Vendor Types, Vendor Documents, Inventory, Reminders
2. Add dropdown or buttons to show either All Records, Archived Records, or Current Records
3. Add back a delete icon, on button click update that row of the db's isArchived bool
4. Change all select statements of app
5. Change all input statements of app, default to isArchived=0
|
non_test
|
pseudo delete add column to each main table that corresponds to a page on the site add an isarchived boolean if true if false events event types clients vendors vendor types vendor documents inventory reminders add dropdown or buttons to show either all records archived records or current records add back a delete icon on button click update that row of the db s isarchived bool change all select statements of app change all input statements of app default to isarchived
| 0
|
133,156
| 10,798,076,020
|
IssuesEvent
|
2019-11-06 09:19:36
|
SenseNet/sensenet
|
https://api.github.com/repos/SenseNet/sensenet
|
closed
|
[Test] local test web application for Services
|
test
|
I'd like to be able to **test a feature in the Services solution** without switching context and installing a whole new application and overriding dlls etc.
### Acceptance
- In the main Services solution there is a web application with the Services component integrated. When I hit **F5** in Visual Studio, a new application starts with the latest local dlls.
- This should work with the **in-memory data providers**, without having to install a full SQL database.
### TODO
- [x] decouple in-memory data providers from the *SenseNet.Tests* project to a standalone, regular (non-test) library.
- [x] add a web application project with the necessary project references, code and config integrations
|
1.0
|
[Test] local test web application for Services - I'd like to be able to **test a feature in the Services solution** without switching context and installing a whole new application and overriding dlls etc.
### Acceptance
- In the main Services solution there is a web application with the Services component integrated. When I hit **F5** in Visual Studio, a new application starts with the latest local dlls.
- This should work with the **in-memory data providers**, without having to install a full SQL database.
### TODO
- [x] decouple in-memory data providers from the *SenseNet.Tests* project to a standalone, regular (non-test) library.
- [x] add a web application project with the necessary project references, code and config integrations
|
test
|
local test web application for services i d like to be able to test a feature in the services solution without switching context and installing a whole new application and overriding dlls etc acceptance in the main services solution there is a web application with the services component integrated when i hit in visual studio a new application starts with the latest local dlls this should work with the in memory data providers without having to install a full sql database todo decouple in memory data providers from the sensenet tests project to a standalone regular non test library add a web application project with the necessary project references code and config integrations
| 1
|
260,161
| 22,596,685,148
|
IssuesEvent
|
2022-06-29 04:20:56
|
trustbloc/wallet
|
https://api.github.com/repos/trustbloc/wallet
|
opened
|
Finish GNAP flow integration in wallet and auth
|
type: enhancement area: backend area: UI area: integration tests
|
- [ ] debug issue with agent wasm: unexpected failure while adding storage: failed to create storage: failed to create EDV provider: failed to create EDV provider: failed to prepare formatted provider: failed to prepare JWE encrypter: prepreRemoteJWEKey: keyURL not well well formatted: when vaults page is loaded (in wallet)
- [ ] wallet router should do /gnap logic on / (no sub-path) instead (in wallet)
- [ ] remove wallet signin/signup pages, provider popup (in wallet)
- [ ] update automation tests to cover the new gnap auth flow (in wallet)
- [ ] remove /oidc/userinfo calls from options.js/user.js (in wallet)
- [ ] remove mockbank provider (zcap-oidc) from auth login (in auth)
- [ ] test and debug wallet’s dev mode (make wallet-web-dev-start) to make sure it’s working with GNAP path (in wallet)
|
1.0
|
Finish GNAP flow integration in wallet and auth - - [ ] debug issue with agent wasm: unexpected failure while adding storage: failed to create storage: failed to create EDV provider: failed to create EDV provider: failed to prepare formatted provider: failed to prepare JWE encrypter: prepreRemoteJWEKey: keyURL not well well formatted: when vaults page is loaded (in wallet)
- [ ] wallet router should do /gnap logic on / (no sub-path) instead (in wallet)
- [ ] remove wallet signin/signup pages, provider popup (in wallet)
- [ ] update automation tests to cover the new gnap auth flow (in wallet)
- [ ] remove /oidc/userinfo calls from options.js/user.js (in wallet)
- [ ] remove mockbank provider (zcap-oidc) from auth login (in auth)
- [ ] test and debug wallet’s dev mode (make wallet-web-dev-start) to make sure it’s working with GNAP path (in wallet)
|
test
|
finish gnap flow integration in wallet and auth debug issue with agent wasm unexpected failure while adding storage failed to create storage failed to create edv provider failed to create edv provider failed to prepare formatted provider failed to prepare jwe encrypter prepreremotejwekey keyurl not well well formatted when vaults page is loaded in wallet wallet router should do gnap logic on no sub path instead in wallet remove wallet signin signup pages provider popup in wallet update automation tests to cover the new gnap auth flow in wallet remove oidc userinfo calls from options js user js in wallet remove mockbank provider zcap oidc from auth login in auth test and debug wallet’s dev mode make wallet web dev start to make sure it’s working with gnap path in wallet
| 1
|
384,176
| 26,576,846,236
|
IssuesEvent
|
2023-01-21 23:14:47
|
seg491X-team36/virtual-spatial-navigation
|
https://api.github.com/repos/seg491X-team36/virtual-spatial-navigation
|
closed
|
Add a conventions.md file
|
documentation
|
- decide branch naming conventions
- maybe find a C# linter for CI/CD or reasonable C# conventions
|
1.0
|
Add a conventions.md file - - decide branch naming conventions
- maybe find a C# linter for CI/CD or reasonable C# conventions
|
non_test
|
add a conventions md file decide branch naming conventions maybe find a c linter for ci cd or reasonable c conventions
| 0
|
177,920
| 14,654,827,061
|
IssuesEvent
|
2020-12-28 09:35:54
|
signal18/replication-manager
|
https://api.github.com/repos/signal18/replication-manager
|
closed
|
MySQL 8.0 issue
|
documentation
|
Hi,
I can see the following errors in the log for Percona MySQL 8.0.16,as GLOBAL_VARIABLES has been changed in MySQL 8.0
Could you please take a look?
Could not get variables Error 1109: Unknown table 'GLOBAL_VARIABLES' in information_schema
thanks
|
1.0
|
MySQL 8.0 issue - Hi,
I can see the following errors in the log for Percona MySQL 8.0.16,as GLOBAL_VARIABLES has been changed in MySQL 8.0
Could you please take a look?
Could not get variables Error 1109: Unknown table 'GLOBAL_VARIABLES' in information_schema
thanks
|
non_test
|
mysql issue hi i can see the following errors in the log for percona mysql as global variables has been changed in mysql could you please take a look could not get variables error unknown table global variables in information schema thanks
| 0
|
150,248
| 19,603,573,127
|
IssuesEvent
|
2022-01-06 06:03:21
|
snykiotcubedev/xstream-XSTREAM_1_4_14
|
https://api.github.com/repos/snykiotcubedev/xstream-XSTREAM_1_4_14
|
opened
|
CVE-2021-21349 (High) detected in xstream-1.4.14.jar
|
security vulnerability
|
## CVE-2021-21349 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>xstream-1.4.14.jar</b></p></summary>
<p></p>
<p>Library home page: <a href="http://x-stream.github.io">http://x-stream.github.io</a></p>
<p>Path to dependency file: /xstream-benchmark/pom.xml</p>
<p>Path to vulnerable library: /om/thoughtworks/xstream/xstream/1.4.14/xstream-1.4.14.jar,/om/thoughtworks/xstream/xstream/1.4.14/xstream-1.4.14.jar,/om/thoughtworks/xstream/xstream/1.4.14/xstream-1.4.14.jar</p>
<p>
Dependency Hierarchy:
- :x: **xstream-1.4.14.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/snykiotcubedev/xstream-XSTREAM_1_4_14/commit/6fcdcfd518f84918a0c4382ccbf2c1788cdfcdba">6fcdcfd518f84918a0c4382ccbf2c1788cdfcdba</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.16, there is a vulnerability which may allow a remote attacker to request data from internal resources that are not publicly available only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream's security framework with a whitelist limited to the minimal required types. If you rely on XStream's default blacklist of the Security Framework, you will have to use at least version 1.4.16.
<p>Publish Date: 2021-03-23
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21349>CVE-2021-21349</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.6</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/x-stream/xstream/security/advisories/GHSA-f6hm-88x3-mfjv">https://github.com/x-stream/xstream/security/advisories/GHSA-f6hm-88x3-mfjv</a></p>
<p>Release Date: 2021-03-23</p>
<p>Fix Resolution: com.thoughtworks.xstream:xstream:1.4.16</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2021-21349 (High) detected in xstream-1.4.14.jar - ## CVE-2021-21349 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>xstream-1.4.14.jar</b></p></summary>
<p></p>
<p>Library home page: <a href="http://x-stream.github.io">http://x-stream.github.io</a></p>
<p>Path to dependency file: /xstream-benchmark/pom.xml</p>
<p>Path to vulnerable library: /om/thoughtworks/xstream/xstream/1.4.14/xstream-1.4.14.jar,/om/thoughtworks/xstream/xstream/1.4.14/xstream-1.4.14.jar,/om/thoughtworks/xstream/xstream/1.4.14/xstream-1.4.14.jar</p>
<p>
Dependency Hierarchy:
- :x: **xstream-1.4.14.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/snykiotcubedev/xstream-XSTREAM_1_4_14/commit/6fcdcfd518f84918a0c4382ccbf2c1788cdfcdba">6fcdcfd518f84918a0c4382ccbf2c1788cdfcdba</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
XStream is a Java library to serialize objects to XML and back again. In XStream before version 1.4.16, there is a vulnerability which may allow a remote attacker to request data from internal resources that are not publicly available only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream's security framework with a whitelist limited to the minimal required types. If you rely on XStream's default blacklist of the Security Framework, you will have to use at least version 1.4.16.
<p>Publish Date: 2021-03-23
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21349>CVE-2021-21349</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.6</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/x-stream/xstream/security/advisories/GHSA-f6hm-88x3-mfjv">https://github.com/x-stream/xstream/security/advisories/GHSA-f6hm-88x3-mfjv</a></p>
<p>Release Date: 2021-03-23</p>
<p>Fix Resolution: com.thoughtworks.xstream:xstream:1.4.16</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_test
|
cve high detected in xstream jar cve high severity vulnerability vulnerable library xstream jar library home page a href path to dependency file xstream benchmark pom xml path to vulnerable library om thoughtworks xstream xstream xstream jar om thoughtworks xstream xstream xstream jar om thoughtworks xstream xstream xstream jar dependency hierarchy x xstream jar vulnerable library found in head commit a href found in base branch main vulnerability details xstream is a java library to serialize objects to xml and back again in xstream before version there is a vulnerability which may allow a remote attacker to request data from internal resources that are not publicly available only by manipulating the processed input stream no user is affected who followed the recommendation to setup xstream s security framework with a whitelist limited to the minimal required types if you rely on xstream s default blacklist of the security framework you will have to use at least version publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope changed impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com thoughtworks xstream xstream step up your open source security game with whitesource
| 0
|
290,904
| 25,104,942,731
|
IssuesEvent
|
2022-11-08 16:00:12
|
opentibiabr/canary
|
https://api.github.com/repos/opentibiabr/canary
|
closed
|
Error Source: Query: INSERT INTO `players_online` VALUES (22)
|
Type: Bug Priority: Medium Status: Pending Test source map
|
### Priority
Medium
### Area
- [ ] Datapack
- [X] Source
- [ ] Map
- [ ] Other
### What happened?
Query: INSERT INTO `players_online` VALUES (22)
2022-11-08 11:44:30 - [2022-08-11 11:44:30.016] [error] Message: Duplicate entry '22' for key 'PRIMARY'
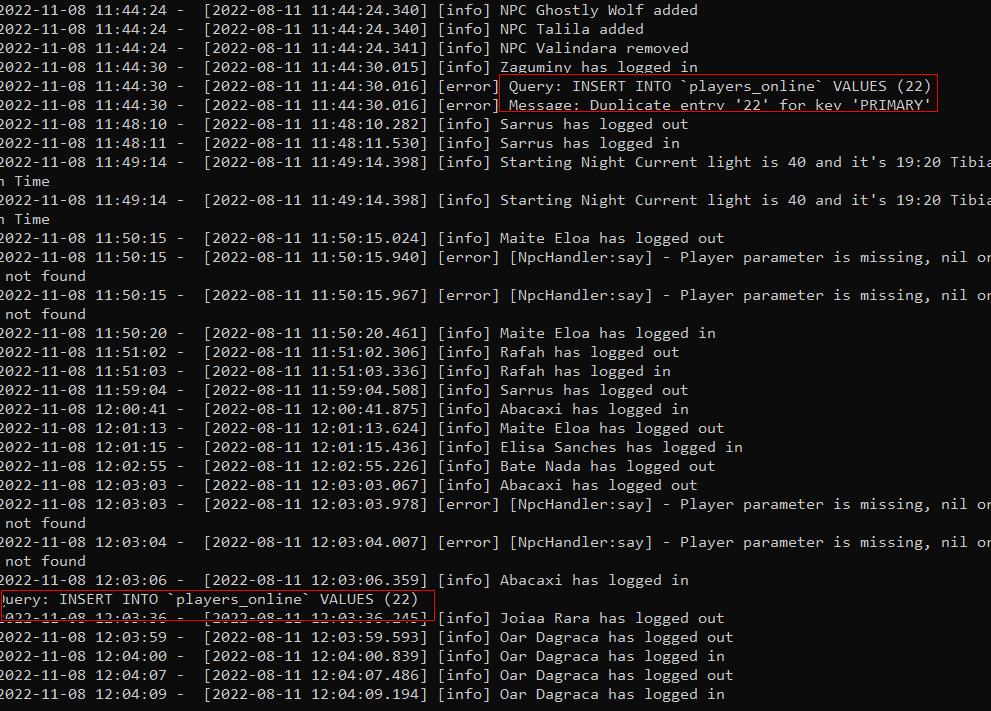
### What OS are you seeing the problem on?
Linux
### Code of Conduct
- [X] I agree to follow this project's Code of Conduct
|
1.0
|
Error Source: Query: INSERT INTO `players_online` VALUES (22) - ### Priority
Medium
### Area
- [ ] Datapack
- [X] Source
- [ ] Map
- [ ] Other
### What happened?
Query: INSERT INTO `players_online` VALUES (22)
2022-11-08 11:44:30 - [2022-08-11 11:44:30.016] [error] Message: Duplicate entry '22' for key 'PRIMARY'
### What OS are you seeing the problem on?
Linux
### Code of Conduct
- [X] I agree to follow this project's Code of Conduct
|
test
|
error source query insert into players online values priority medium area datapack source map other what happened query insert into players online values message duplicate entry for key primary what os are you seeing the problem on linux code of conduct i agree to follow this project s code of conduct
| 1
|
456,857
| 13,151,016,994
|
IssuesEvent
|
2020-08-09 14:40:57
|
chrisjsewell/docutils
|
https://api.github.com/repos/chrisjsewell/docutils
|
closed
|
Add :align: option to the table directives (table, csv-table and list-table) [SF:feature-requests:48]
|
closed-fixed feature-requests priority-5
|
author: tk0miya
created: 2016-02-22 03:41:45.318000
assigned: None
SF_url: https://sourceforge.net/p/docutils/feature-requests/48
attachments:
- https://sourceforge.net/p/docutils/feature-requests/48/attachment/align.patch
The rst2html command puts the tables to left of pages.
It would be nice if we are able to align these to arbitrary position.
Here's patch for the table directives take :align: option like figure directive.
---
commenter: milde
posted: 2016-02-26 20:19:24.456000
title: #48 Add :align: option to the table directives (table, csv-table and list-table)
You can pass the align-... class value to any object via the "class" directive. Styling with CSS should then be easy.
---
commenter: tk0miya
posted: 2016-03-04 02:38:23.385000
title: #48 Add :align: option to the table directives (table, csv-table and list-table)
Using CSS is fine, but we have to prepare CSS to align tables to center always.
I think aligning tables are common feature (mainly centering).
At the same time, it is useful for LaTeX and other writers too.
My patch including the fix for LaTeX's.
The class directive does not effect these writers I believe.
Are there any chance to add the option?
---
commenter: andreacassioli
posted: 2016-03-07 11:22:17.534000
title: #48 Add :align: option to the table directives (table, csv-table and list-table)
Hi,
just to elaborate a bit on the issue:
1. Despite using CSS is an easy fix, for more general uses it might be not that simple. As Takeshi said, if the target format is Latex one may need to have some information to decide the table alignement.
2. In terms of readability an explicit mention to the table alignement is a plus.
3. Such an option would also make figure and table behave in a more similar way.
---
commenter: milde
posted: 2016-05-27 10:36:00.667000
title: #48 Add :align: option to the table directives (table, csv-table and list-table)
I agree that this as an addition that nicely fits in.
For a complete patch, we would need test cases and a documentation update.
---
commenter: tk0miya
posted: 2016-05-28 03:16:08.516000
title: #48 Add :align: option to the table directives (table, csv-table and list-table)
attachments:
- https://sourceforge.net/p/docutils/feature-requests/_discuss/thread/e21f906b/31c6/attachment/align-20160528.patch
I'm grad to hear that. I updated the patch including testcases and documentation.
Could you review this please?
---
commenter: milde
posted: 2016-07-26 18:17:02.269000
title: #48 Add :align: option to the table directives (table, csv-table and list-table)
- **status**: open --> pending
---
commenter: milde
posted: 2016-07-26 18:17:02.458000
title: #48 Add :align: option to the table directives (table, csv-table and list-table)
Thanks for the update. I completed support for list tables, added some more tests and adapted the documentation.
Committed in 7952. Please test.
Still missing is an update of the Docutils DTD http://docutils.sourceforge.net/docs/ref/docutils.dtd adding the align option to tables.
---
commenter: milde
posted: 2017-02-04 20:39:48.972000
title: #48 Add :align: option to the table directives (table, csv-table and list-table)
- **status**: pending --> closed-fixed
---
commenter: milde
posted: 2017-02-04 20:39:49.299000
title: #48 Add :align: option to the table directives (table, csv-table and list-table)
The change is now complete. Please reopen if there are problems.
Thank you for the suggestion and patch.
|
1.0
|
Add :align: option to the table directives (table, csv-table and list-table) [SF:feature-requests:48] -
author: tk0miya
created: 2016-02-22 03:41:45.318000
assigned: None
SF_url: https://sourceforge.net/p/docutils/feature-requests/48
attachments:
- https://sourceforge.net/p/docutils/feature-requests/48/attachment/align.patch
The rst2html command puts the tables to left of pages.
It would be nice if we are able to align these to arbitrary position.
Here's patch for the table directives take :align: option like figure directive.
---
commenter: milde
posted: 2016-02-26 20:19:24.456000
title: #48 Add :align: option to the table directives (table, csv-table and list-table)
You can pass the align-... class value to any object via the "class" directive. Styling with CSS should then be easy.
---
commenter: tk0miya
posted: 2016-03-04 02:38:23.385000
title: #48 Add :align: option to the table directives (table, csv-table and list-table)
Using CSS is fine, but we have to prepare CSS to align tables to center always.
I think aligning tables are common feature (mainly centering).
At the same time, it is useful for LaTeX and other writers too.
My patch including the fix for LaTeX's.
The class directive does not effect these writers I believe.
Are there any chance to add the option?
---
commenter: andreacassioli
posted: 2016-03-07 11:22:17.534000
title: #48 Add :align: option to the table directives (table, csv-table and list-table)
Hi,
just to elaborate a bit on the issue:
1. Despite using CSS is an easy fix, for more general uses it might be not that simple. As Takeshi said, if the target format is Latex one may need to have some information to decide the table alignement.
2. In terms of readability an explicit mention to the table alignement is a plus.
3. Such an option would also make figure and table behave in a more similar way.
---
commenter: milde
posted: 2016-05-27 10:36:00.667000
title: #48 Add :align: option to the table directives (table, csv-table and list-table)
I agree that this as an addition that nicely fits in.
For a complete patch, we would need test cases and a documentation update.
---
commenter: tk0miya
posted: 2016-05-28 03:16:08.516000
title: #48 Add :align: option to the table directives (table, csv-table and list-table)
attachments:
- https://sourceforge.net/p/docutils/feature-requests/_discuss/thread/e21f906b/31c6/attachment/align-20160528.patch
I'm grad to hear that. I updated the patch including testcases and documentation.
Could you review this please?
---
commenter: milde
posted: 2016-07-26 18:17:02.269000
title: #48 Add :align: option to the table directives (table, csv-table and list-table)
- **status**: open --> pending
---
commenter: milde
posted: 2016-07-26 18:17:02.458000
title: #48 Add :align: option to the table directives (table, csv-table and list-table)
Thanks for the update. I completed support for list tables, added some more tests and adapted the documentation.
Committed in 7952. Please test.
Still missing is an update of the Docutils DTD http://docutils.sourceforge.net/docs/ref/docutils.dtd adding the align option to tables.
---
commenter: milde
posted: 2017-02-04 20:39:48.972000
title: #48 Add :align: option to the table directives (table, csv-table and list-table)
- **status**: pending --> closed-fixed
---
commenter: milde
posted: 2017-02-04 20:39:49.299000
title: #48 Add :align: option to the table directives (table, csv-table and list-table)
The change is now complete. Please reopen if there are problems.
Thank you for the suggestion and patch.
|
non_test
|
add align option to the table directives table csv table and list table author created assigned none sf url attachments the command puts the tables to left of pages it would be nice if we are able to align these to arbitrary position here s patch for the table directives take align option like figure directive commenter milde posted title add align option to the table directives table csv table and list table you can pass the align class value to any object via the class directive styling with css should then be easy commenter posted title add align option to the table directives table csv table and list table using css is fine but we have to prepare css to align tables to center always i think aligning tables are common feature mainly centering at the same time it is useful for latex and other writers too my patch including the fix for latex s the class directive does not effect these writers i believe are there any chance to add the option commenter andreacassioli posted title add align option to the table directives table csv table and list table hi just to elaborate a bit on the issue despite using css is an easy fix for more general uses it might be not that simple as takeshi said if the target format is latex one may need to have some information to decide the table alignement in terms of readability an explicit mention to the table alignement is a plus such an option would also make figure and table behave in a more similar way commenter milde posted title add align option to the table directives table csv table and list table i agree that this as an addition that nicely fits in for a complete patch we would need test cases and a documentation update commenter posted title add align option to the table directives table csv table and list table attachments i m grad to hear that i updated the patch including testcases and documentation could you review this please commenter milde posted title add align option to the table directives table csv table and list table status open pending commenter milde posted title add align option to the table directives table csv table and list table thanks for the update i completed support for list tables added some more tests and adapted the documentation committed in please test still missing is an update of the docutils dtd adding the align option to tables commenter milde posted title add align option to the table directives table csv table and list table status pending closed fixed commenter milde posted title add align option to the table directives table csv table and list table the change is now complete please reopen if there are problems thank you for the suggestion and patch
| 0
|
579,373
| 17,189,966,495
|
IssuesEvent
|
2021-07-16 09:30:37
|
status-im/StatusQ
|
https://api.github.com/repos/status-im/StatusQ
|
closed
|
Consider `StatusRoundButton` variation with solid colors
|
module: controls priority 2: required type: discuss type: feature
|
Most of the buttons provided by StatusQ use colors with alpha channels so they can be composed and mixed on various background, removing transparency as they are layered.
There is however cases where a transparent color isn't desired. Below is an example:
<img width="193" alt="Screenshot 2021-07-16 at 10 21 10" src="https://user-images.githubusercontent.com/445106/125916499-d9b1c485-86ce-4b0b-bf71-31a89827f5eb.png">
I think we have two way to go about this:
1. Provide a variant of this component that has solid colors (this might be overengineered, given that there's probably not many more places where this is needed)
2. Introduce a `StatusProfileImageUpdateButton` component that uses `StatusRoundButton` and hacks a solid color into it.
I'm slightly in favour of 2)
|
1.0
|
Consider `StatusRoundButton` variation with solid colors - Most of the buttons provided by StatusQ use colors with alpha channels so they can be composed and mixed on various background, removing transparency as they are layered.
There is however cases where a transparent color isn't desired. Below is an example:
<img width="193" alt="Screenshot 2021-07-16 at 10 21 10" src="https://user-images.githubusercontent.com/445106/125916499-d9b1c485-86ce-4b0b-bf71-31a89827f5eb.png">
I think we have two way to go about this:
1. Provide a variant of this component that has solid colors (this might be overengineered, given that there's probably not many more places where this is needed)
2. Introduce a `StatusProfileImageUpdateButton` component that uses `StatusRoundButton` and hacks a solid color into it.
I'm slightly in favour of 2)
|
non_test
|
consider statusroundbutton variation with solid colors most of the buttons provided by statusq use colors with alpha channels so they can be composed and mixed on various background removing transparency as they are layered there is however cases where a transparent color isn t desired below is an example img width alt screenshot at src i think we have two way to go about this provide a variant of this component that has solid colors this might be overengineered given that there s probably not many more places where this is needed introduce a statusprofileimageupdatebutton component that uses statusroundbutton and hacks a solid color into it i m slightly in favour of
| 0
|
617,656
| 19,402,098,572
|
IssuesEvent
|
2021-12-19 11:18:05
|
alexcoder04/rfap-go-server
|
https://api.github.com/repos/alexcoder04/rfap-go-server
|
opened
|
Server console
|
enhancement priority:low
|
Some kind of way to control the server: restart it, reload the configuration, shut down, ...
Original issue on the main repo:
> What should we use for the console?
> Stdin is not an option, because we don't have a window with the server running open all the time; moreover the server would print messages while you are typing your command, so it wouldn't really work.
> A Unix domain socket would be much better, but it's not supported on Windows (does Windows have something like that?).
Another socket listening on localhost? Seems complicated to me.
|
1.0
|
Server console - Some kind of way to control the server: restart it, reload the configuration, shut down, ...
Original issue on the main repo:
> What should we use for the console?
> Stdin is not an option, because we don't have a window with the server running open all the time; moreover the server would print messages while you are typing your command, so it wouldn't really work.
> A Unix domain socket would be much better, but it's not supported on Windows (does Windows have something like that?).
Another socket listening on localhost? Seems complicated to me.
|
non_test
|
server console some kind of way to control the server restart it reload the configuration shut down original issue on the main repo what should we use for the console stdin is not an option because we don t have a window with the server running open all the time moreover the server would print messages while you are typing your command so it wouldn t really work a unix domain socket would be much better but it s not supported on windows does windows have something like that another socket listening on localhost seems complicated to me
| 0
|
164,543
| 12,809,070,769
|
IssuesEvent
|
2020-07-03 14:51:52
|
aliasrobotics/RVD
|
https://api.github.com/repos/aliasrobotics/RVD
|
closed
|
RVD#3221: CWE-134 (format), If format strings can be influenced by an attacker, they can be exploi... @ xphlite-v3/nxphlite_spi.c:70
|
CWE-134 bug components software flawfinder flawfinder_level_4 mitigated robot component: PX4 static analysis testing triage version: v1.7.0
|
```yaml
id: 3221
title: 'RVD#3221: CWE-134 (format), If format strings can be influenced by an attacker,
they can be exploi... @ xphlite-v3/nxphlite_spi.c:70'
type: bug
description: If format strings can be influenced by an attacker, they can be exploited
(CWE-134). Use a constant for the format specification. . Happening @ ...xphlite-v3/nxphlite_spi.c:70
cwe:
- CWE-134
cve: None
keywords:
- flawfinder
- flawfinder_level_4
- static analysis
- testing
- triage
- CWE-134
- bug
- 'version: v1.7.0'
- 'robot component: PX4'
- components software
system: ./Firmware/src/drivers/boards/nxphlite-v3/nxphlite_spi.c:70:21
vendor: null
severity:
rvss-score: 0
rvss-vector: ''
severity-description: ''
cvss-score: 0
cvss-vector: ''
links:
- https://github.com/aliasrobotics/RVD/issues/3221
flaw:
phase: testing
specificity: subject-specific
architectural-location: application-specific
application: N/A
subsystem: N/A
package: N/A
languages: None
date-detected: 2020-06-29 (20:34)
detected-by: Alias Robotics
detected-by-method: testing static
date-reported: 2020-06-29 (20:34)
reported-by: Alias Robotics
reported-by-relationship: automatic
issue: https://github.com/aliasrobotics/RVD/issues/3221
reproducibility: always
trace: '(context) # define message printf'
reproduction: See artifacts below (if available)
reproduction-image: gitlab.com/aliasrobotics/offensive/alurity/pipelines/active/pipeline_px4/-/jobs/616402716/artifacts/download
exploitation:
description: ''
exploitation-image: ''
exploitation-vector: ''
exploitation-recipe: ''
mitigation:
description: Use a constant for the format specification
pull-request: ''
date-mitigation: ''
```
|
1.0
|
RVD#3221: CWE-134 (format), If format strings can be influenced by an attacker, they can be exploi... @ xphlite-v3/nxphlite_spi.c:70 - ```yaml
id: 3221
title: 'RVD#3221: CWE-134 (format), If format strings can be influenced by an attacker,
they can be exploi... @ xphlite-v3/nxphlite_spi.c:70'
type: bug
description: If format strings can be influenced by an attacker, they can be exploited
(CWE-134). Use a constant for the format specification. . Happening @ ...xphlite-v3/nxphlite_spi.c:70
cwe:
- CWE-134
cve: None
keywords:
- flawfinder
- flawfinder_level_4
- static analysis
- testing
- triage
- CWE-134
- bug
- 'version: v1.7.0'
- 'robot component: PX4'
- components software
system: ./Firmware/src/drivers/boards/nxphlite-v3/nxphlite_spi.c:70:21
vendor: null
severity:
rvss-score: 0
rvss-vector: ''
severity-description: ''
cvss-score: 0
cvss-vector: ''
links:
- https://github.com/aliasrobotics/RVD/issues/3221
flaw:
phase: testing
specificity: subject-specific
architectural-location: application-specific
application: N/A
subsystem: N/A
package: N/A
languages: None
date-detected: 2020-06-29 (20:34)
detected-by: Alias Robotics
detected-by-method: testing static
date-reported: 2020-06-29 (20:34)
reported-by: Alias Robotics
reported-by-relationship: automatic
issue: https://github.com/aliasrobotics/RVD/issues/3221
reproducibility: always
trace: '(context) # define message printf'
reproduction: See artifacts below (if available)
reproduction-image: gitlab.com/aliasrobotics/offensive/alurity/pipelines/active/pipeline_px4/-/jobs/616402716/artifacts/download
exploitation:
description: ''
exploitation-image: ''
exploitation-vector: ''
exploitation-recipe: ''
mitigation:
description: Use a constant for the format specification
pull-request: ''
date-mitigation: ''
```
|
test
|
rvd cwe format if format strings can be influenced by an attacker they can be exploi xphlite nxphlite spi c yaml id title rvd cwe format if format strings can be influenced by an attacker they can be exploi xphlite nxphlite spi c type bug description if format strings can be influenced by an attacker they can be exploited cwe use a constant for the format specification happening xphlite nxphlite spi c cwe cwe cve none keywords flawfinder flawfinder level static analysis testing triage cwe bug version robot component components software system firmware src drivers boards nxphlite nxphlite spi c vendor null severity rvss score rvss vector severity description cvss score cvss vector links flaw phase testing specificity subject specific architectural location application specific application n a subsystem n a package n a languages none date detected detected by alias robotics detected by method testing static date reported reported by alias robotics reported by relationship automatic issue reproducibility always trace context define message printf reproduction see artifacts below if available reproduction image gitlab com aliasrobotics offensive alurity pipelines active pipeline jobs artifacts download exploitation description exploitation image exploitation vector exploitation recipe mitigation description use a constant for the format specification pull request date mitigation
| 1
|
134,338
| 18,457,910,361
|
IssuesEvent
|
2021-10-15 19:11:13
|
bgoonz/Bgoonz-Bookmarks
|
https://api.github.com/repos/bgoonz/Bgoonz-Bookmarks
|
closed
|
CVE-2019-18797 (Medium) detected in opennmsopennms-source-26.0.0-1
|
security vulnerability
|
## CVE-2019-18797 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>opennmsopennms-source-26.0.0-1</b></p></summary>
<p>
<p>A Java based fault and performance management system</p>
<p>Library home page: <a href=https://sourceforge.net/projects/opennms/>https://sourceforge.net/projects/opennms/</a></p>
<p>Found in HEAD commit: <a href="https://github.com/bgoonz/Bgoonz-Bookmarks/commit/425fdc43f5a9970719d0d1ad15b5d28aadd965aa">425fdc43f5a9970719d0d1ad15b5d28aadd965aa</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/node_modules/node-sass/src/libsass/src/eval.cpp</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
LibSass 3.6.1 has uncontrolled recursion in Sass::Eval::operator()(Sass::Binary_Expression*) in eval.cpp.
<p>Publish Date: 2019-11-06
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-18797>CVE-2019-18797</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2019-18797 (Medium) detected in opennmsopennms-source-26.0.0-1 - ## CVE-2019-18797 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>opennmsopennms-source-26.0.0-1</b></p></summary>
<p>
<p>A Java based fault and performance management system</p>
<p>Library home page: <a href=https://sourceforge.net/projects/opennms/>https://sourceforge.net/projects/opennms/</a></p>
<p>Found in HEAD commit: <a href="https://github.com/bgoonz/Bgoonz-Bookmarks/commit/425fdc43f5a9970719d0d1ad15b5d28aadd965aa">425fdc43f5a9970719d0d1ad15b5d28aadd965aa</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/node_modules/node-sass/src/libsass/src/eval.cpp</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
LibSass 3.6.1 has uncontrolled recursion in Sass::Eval::operator()(Sass::Binary_Expression*) in eval.cpp.
<p>Publish Date: 2019-11-06
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-18797>CVE-2019-18797</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_test
|
cve medium detected in opennmsopennms source cve medium severity vulnerability vulnerable library opennmsopennms source a java based fault and performance management system library home page a href found in head commit a href found in base branch master vulnerable source files node modules node sass src libsass src eval cpp vulnerability details libsass has uncontrolled recursion in sass eval operator sass binary expression in eval cpp publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href step up your open source security game with whitesource
| 0
|
128,187
| 10,519,455,724
|
IssuesEvent
|
2019-09-29 18:07:00
|
commercialhaskell/stackage
|
https://api.github.com/repos/commercialhaskell/stackage
|
closed
|
asif test suite compilation failure
|
failure: test-suite
|
Pinging @newhoggy
```
[7 of 9] Compiling Gen.Feed ( test/Gen/Feed.hs, dist/build/asif-test/asif-test-tmp/Gen/Feed.o )
test/Gen/Feed.hs:16:43: error:
Not in scope: type constructor or class ‘Ipv4Address’
|
16 | ipv4 :: MonadGen m => Word8 -> Word8 -> m Ipv4Address
|
```
|
1.0
|
asif test suite compilation failure - Pinging @newhoggy
```
[7 of 9] Compiling Gen.Feed ( test/Gen/Feed.hs, dist/build/asif-test/asif-test-tmp/Gen/Feed.o )
test/Gen/Feed.hs:16:43: error:
Not in scope: type constructor or class ‘Ipv4Address’
|
16 | ipv4 :: MonadGen m => Word8 -> Word8 -> m Ipv4Address
|
```
|
test
|
asif test suite compilation failure pinging newhoggy compiling gen feed test gen feed hs dist build asif test asif test tmp gen feed o test gen feed hs error not in scope type constructor or class ‘ ’ monadgen m m
| 1
|
76,132
| 7,519,054,034
|
IssuesEvent
|
2018-04-12 10:18:16
|
ices-taf/doc
|
https://api.github.com/repos/ices-taf/doc
|
reopened
|
North Sea herring data prep
|
Test TAF stocks
|
### Summary
Data preparation scripts for North Sea herring
### Tasks required
- [ ] Explore how data were gathered and preprocessed
- [ ] Script the data gathering and preprocessing
### Links to other issues?
North Sea herring as first TAF assmt #153
|
1.0
|
North Sea herring data prep - ### Summary
Data preparation scripts for North Sea herring
### Tasks required
- [ ] Explore how data were gathered and preprocessed
- [ ] Script the data gathering and preprocessing
### Links to other issues?
North Sea herring as first TAF assmt #153
|
test
|
north sea herring data prep summary data preparation scripts for north sea herring tasks required explore how data were gathered and preprocessed script the data gathering and preprocessing links to other issues north sea herring as first taf assmt
| 1
|
28,984
| 4,154,843,231
|
IssuesEvent
|
2016-06-16 13:10:42
|
geetsisbac/P43RG5EXRRYODWDBFW23DQ45
|
https://api.github.com/repos/geetsisbac/P43RG5EXRRYODWDBFW23DQ45
|
closed
|
PtUFnkKnht0A9Io0HXxBsjFYq29x8lMHlN+EiPZeQ2de9jaiyE1OryYr1q8eVmQL8u3oFeNSI0OD6tHL4J33Tq1R3B0nZQfpryQ60r7kziJUBdM9LVun/9KF1rqoW+Svhy/n160x1m0hr0lwJYf6EAYQom7mtijCsZRXUA6j6M8=
|
design
|
1ncrfB5+1LLyF4yTDu0/JBOHRVFBVsgkj2lISJRATi5oTo0rBRm8q2bzeunNBy9/+rnP6UYIVImYITFKn3tekuIl7Tu4oCfAetMM9rGDmuWqi036F9k40sgUcQ2oBH5bkC+twwCZdNRw1RtPHrK9gQHQbgLix3rL4LeJg0kDCFyUl3PSDj+G70KBmsoWE0wuRsuCNcl7PvQLohRyRcSpSOj9GXxhU81jyPgLIrNIOKuGrczi7XAqZK3JhngvejHCq+LuMUdxw/yWc35PelsG4qruCnD4QlH8LrFG0EA+JM/HwoaEtRCVTv7fT7pyPV3rgTdg3PeBhCItKSNo0NmfpSVfZ3Jx4p2XujH+ASyEhyjpNkPXV1PJ4DtM0Ei4UzBBsRTV5AR4yl4VAqNlfh+wDAXVhdwUR7IKVIsFCEwFDpVLU2B/yD6jN6XSEdoEuptpESLCu+LVjeUFVGOryftaBG+2tw3z9idIZ5RaR1a6koMuIC98RZpiokRsnhR5MlaesUNL/roa6+pMf7WP9Zxm81seQRBH2qYR4t/yqFSG0bCF7SRuyqSPU+PD3rNhX2ZHhe0kbsqkj1Pjw96zYV9mRx+QxZuCq4MUQHTsmKC/89EokpLklAU6pEgridP31CRTFpuaKJ3zpEwoBc3f0yvc1yKjBWdjWhmUWJlZ6xNy9bKlnmvNgOFgLnMQ7kAAQQUortNKjUBWifNlsa/Oy5UjJaYElo7Lr3fRAcmuD6d++4UB08Vs7NrZTyFLgdztMndF+SaSEPfcgSl2QDJxQpK0V98r094EwbteAejMYV4oP45fukcjenEhmsI86B4WtFt5v20EMMf7Md9TEafbjg6jheKsUtPbOCZYJvib9C109O34C5E8CRICX/aHyq5Iee3Z7NFG37gkj0iWp11il/ypb20yK23OPaz6HZqJRMeEVvavFitfaEIvxvBV99vFbhv8QB3/S6LCBQ6+db3EY/b92uqXVTSZw5o9doDDRlk3JBTRrMTZKGvPrhJJt6w4Qc9sJz/aAdGdXiS1bRuKV9Vzf7IOs2ZopVNXD06WB+k5BAJS0WjxM/hILJhsNFVe2NqdtCdXA4EMJWQotxRWqp4eUI5rAwKhNvM+Id6nZYY4mOKpEbSAZIdJ1lR394la9ApAI7ynnqLembmObe/jElAkI0gzQdndCgFpfNMDCE8H3x2tBcgQW5oxgrlIOq4Rq5oHuaEivEZ0GqTtHZGS3kCcmgwCGDf1ppCXEIuI27jMzc8=
|
1.0
|
PtUFnkKnht0A9Io0HXxBsjFYq29x8lMHlN+EiPZeQ2de9jaiyE1OryYr1q8eVmQL8u3oFeNSI0OD6tHL4J33Tq1R3B0nZQfpryQ60r7kziJUBdM9LVun/9KF1rqoW+Svhy/n160x1m0hr0lwJYf6EAYQom7mtijCsZRXUA6j6M8= - 1ncrfB5+1LLyF4yTDu0/JBOHRVFBVsgkj2lISJRATi5oTo0rBRm8q2bzeunNBy9/+rnP6UYIVImYITFKn3tekuIl7Tu4oCfAetMM9rGDmuWqi036F9k40sgUcQ2oBH5bkC+twwCZdNRw1RtPHrK9gQHQbgLix3rL4LeJg0kDCFyUl3PSDj+G70KBmsoWE0wuRsuCNcl7PvQLohRyRcSpSOj9GXxhU81jyPgLIrNIOKuGrczi7XAqZK3JhngvejHCq+LuMUdxw/yWc35PelsG4qruCnD4QlH8LrFG0EA+JM/HwoaEtRCVTv7fT7pyPV3rgTdg3PeBhCItKSNo0NmfpSVfZ3Jx4p2XujH+ASyEhyjpNkPXV1PJ4DtM0Ei4UzBBsRTV5AR4yl4VAqNlfh+wDAXVhdwUR7IKVIsFCEwFDpVLU2B/yD6jN6XSEdoEuptpESLCu+LVjeUFVGOryftaBG+2tw3z9idIZ5RaR1a6koMuIC98RZpiokRsnhR5MlaesUNL/roa6+pMf7WP9Zxm81seQRBH2qYR4t/yqFSG0bCF7SRuyqSPU+PD3rNhX2ZHhe0kbsqkj1Pjw96zYV9mRx+QxZuCq4MUQHTsmKC/89EokpLklAU6pEgridP31CRTFpuaKJ3zpEwoBc3f0yvc1yKjBWdjWhmUWJlZ6xNy9bKlnmvNgOFgLnMQ7kAAQQUortNKjUBWifNlsa/Oy5UjJaYElo7Lr3fRAcmuD6d++4UB08Vs7NrZTyFLgdztMndF+SaSEPfcgSl2QDJxQpK0V98r094EwbteAejMYV4oP45fukcjenEhmsI86B4WtFt5v20EMMf7Md9TEafbjg6jheKsUtPbOCZYJvib9C109O34C5E8CRICX/aHyq5Iee3Z7NFG37gkj0iWp11il/ypb20yK23OPaz6HZqJRMeEVvavFitfaEIvxvBV99vFbhv8QB3/S6LCBQ6+db3EY/b92uqXVTSZw5o9doDDRlk3JBTRrMTZKGvPrhJJt6w4Qc9sJz/aAdGdXiS1bRuKV9Vzf7IOs2ZopVNXD06WB+k5BAJS0WjxM/hILJhsNFVe2NqdtCdXA4EMJWQotxRWqp4eUI5rAwKhNvM+Id6nZYY4mOKpEbSAZIdJ1lR394la9ApAI7ynnqLembmObe/jElAkI0gzQdndCgFpfNMDCE8H3x2tBcgQW5oxgrlIOq4Rq5oHuaEivEZ0GqTtHZGS3kCcmgwCGDf1ppCXEIuI27jMzc8=
|
non_test
|
svhy lumudxw jm lvjeufvgoryftabg
| 0
|
90,390
| 10,680,427,974
|
IssuesEvent
|
2019-10-21 21:23:48
|
python-discord/seasonalbot
|
https://api.github.com/repos/python-discord/seasonalbot
|
closed
|
Wikify Seasonalbot's README
|
area: documentation help wanted level: beginner status: work in progress
|
[Seasonalbot's README](https://github.com/python-discord/seasonalbot/blob/master/README.md) is a bit dense, and will only get moreso as we add guidance on getting the database up and running for local dev along with any other editor-specific guidance we work on adding.
This will be a great addition to our upcoming Django-wiki, but this can live in this project's GH wiki for now since both will accept markdown.
The README has been copy/pasted into the GH wiki: https://github.com/python-discord/seasonalbot/wiki
A couple TODOs that I can think of right now:
- [x] Rework the PyCharm specific guide to utilize the separate pages for generic tasks
- [ ] Add guides for other editors (e.g. VSCode)
- [x] Add a generic "getting started" page that outlines the general flow for getting set up to run the bot & contribute code to the project
- [x] Rework formatting & add some more to the pages where appropriate
- [ ] Add sidebar/footer
- [x] Rework the repo's README.md & point the specifics to the wiki
- [ ] Add steps for getting the bot running w/Docker
|
1.0
|
Wikify Seasonalbot's README - [Seasonalbot's README](https://github.com/python-discord/seasonalbot/blob/master/README.md) is a bit dense, and will only get moreso as we add guidance on getting the database up and running for local dev along with any other editor-specific guidance we work on adding.
This will be a great addition to our upcoming Django-wiki, but this can live in this project's GH wiki for now since both will accept markdown.
The README has been copy/pasted into the GH wiki: https://github.com/python-discord/seasonalbot/wiki
A couple TODOs that I can think of right now:
- [x] Rework the PyCharm specific guide to utilize the separate pages for generic tasks
- [ ] Add guides for other editors (e.g. VSCode)
- [x] Add a generic "getting started" page that outlines the general flow for getting set up to run the bot & contribute code to the project
- [x] Rework formatting & add some more to the pages where appropriate
- [ ] Add sidebar/footer
- [x] Rework the repo's README.md & point the specifics to the wiki
- [ ] Add steps for getting the bot running w/Docker
|
non_test
|
wikify seasonalbot s readme is a bit dense and will only get moreso as we add guidance on getting the database up and running for local dev along with any other editor specific guidance we work on adding this will be a great addition to our upcoming django wiki but this can live in this project s gh wiki for now since both will accept markdown the readme has been copy pasted into the gh wiki a couple todos that i can think of right now rework the pycharm specific guide to utilize the separate pages for generic tasks add guides for other editors e g vscode add a generic getting started page that outlines the general flow for getting set up to run the bot contribute code to the project rework formatting add some more to the pages where appropriate add sidebar footer rework the repo s readme md point the specifics to the wiki add steps for getting the bot running w docker
| 0
|
40,283
| 5,284,547,225
|
IssuesEvent
|
2017-02-08 00:44:51
|
expressjs/express
|
https://api.github.com/repos/expressjs/express
|
closed
|
Misplaced tests ?
|
4.x tests
|
some tests in app.router.js seems to be misplaced
looking at the code of tests in section "decode query string"
they seem to me dealing with named params and not with query
Shell they be moved to descrive("params") instead ?
decode querystring
✓ should decode correct params
✓ should not accept params in malformed paths
✓ should not decode spaces
✓ should work with unicode
|
1.0
|
Misplaced tests ? - some tests in app.router.js seems to be misplaced
looking at the code of tests in section "decode query string"
they seem to me dealing with named params and not with query
Shell they be moved to descrive("params") instead ?
decode querystring
✓ should decode correct params
✓ should not accept params in malformed paths
✓ should not decode spaces
✓ should work with unicode
|
test
|
misplaced tests some tests in app router js seems to be misplaced looking at the code of tests in section decode query string they seem to me dealing with named params and not with query shell they be moved to descrive params instead decode querystring ✓ should decode correct params ✓ should not accept params in malformed paths ✓ should not decode spaces ✓ should work with unicode
| 1
|
233,220
| 18,955,275,580
|
IssuesEvent
|
2021-11-18 19:28:38
|
EmmyMorris/product_tracker
|
https://api.github.com/repos/EmmyMorris/product_tracker
|
opened
|
Test for Model Relationships and Validations
|
Models Test
|
Create a model test to test model relationships and validations
|
1.0
|
Test for Model Relationships and Validations - Create a model test to test model relationships and validations
|
test
|
test for model relationships and validations create a model test to test model relationships and validations
| 1
|
649,712
| 21,317,907,072
|
IssuesEvent
|
2022-04-16 16:00:15
|
OpenNebula/one
|
https://api.github.com/repos/OpenNebula/one
|
closed
|
Optimize Logging for Security-Actions (eg. fail2ban)
|
Type: Backlog Category: Sunstone Type: Feature Status: Abandoned Priority: Low
|
https://github.com/OpenNebula/one/blob/bce8f9f40f33304516a4779d0d7f606ef2866e14/src/sunstone/sunstone-server.rb#L375
Optimize this logging-line with:
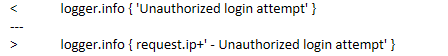
Then it is usable with fail2ban like:
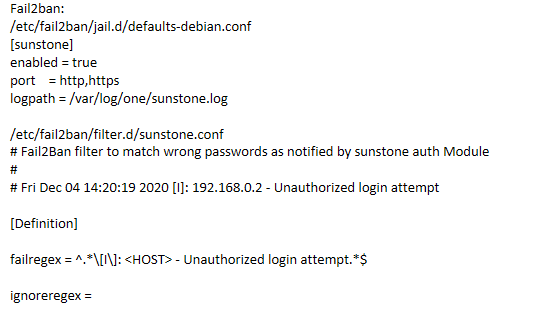
|
1.0
|
Optimize Logging for Security-Actions (eg. fail2ban) - https://github.com/OpenNebula/one/blob/bce8f9f40f33304516a4779d0d7f606ef2866e14/src/sunstone/sunstone-server.rb#L375
Optimize this logging-line with:
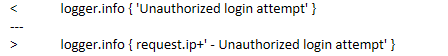
Then it is usable with fail2ban like:
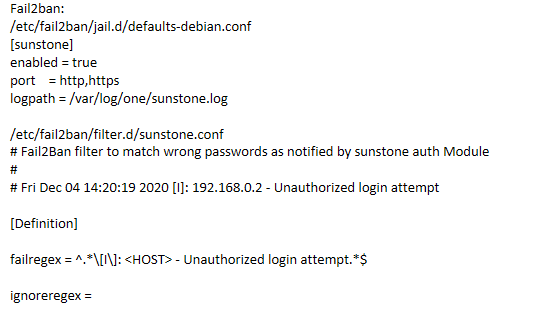
|
non_test
|
optimize logging for security actions eg optimize this logging line with then it is usable with like
| 0
|
3,759
| 3,238,355,049
|
IssuesEvent
|
2015-10-14 15:51:28
|
foam-framework/foam
|
https://api.github.com/repos/foam-framework/foam
|
closed
|
Builder BrowserView: After creating an app, scroll to it and show editor
|
app-builder enhancement
|
FABLE's main browser should scroll to show a new app in the list, and open the editor after the "create new" wizard is done. Highlight or flash the new entry if desirable.
|
1.0
|
Builder BrowserView: After creating an app, scroll to it and show editor - FABLE's main browser should scroll to show a new app in the list, and open the editor after the "create new" wizard is done. Highlight or flash the new entry if desirable.
|
non_test
|
builder browserview after creating an app scroll to it and show editor fable s main browser should scroll to show a new app in the list and open the editor after the create new wizard is done highlight or flash the new entry if desirable
| 0
|
177,681
| 13,736,057,425
|
IssuesEvent
|
2020-10-05 11:08:40
|
ajfisher/node-pixel
|
https://api.github.com/repos/ajfisher/node-pixel
|
closed
|
Update library to use github actions to run tests
|
Test enhancement
|
Travis is good but will be good to have everything native to GH and remove external dependencies.
|
1.0
|
Update library to use github actions to run tests - Travis is good but will be good to have everything native to GH and remove external dependencies.
|
test
|
update library to use github actions to run tests travis is good but will be good to have everything native to gh and remove external dependencies
| 1
|
89,920
| 8,221,208,184
|
IssuesEvent
|
2018-09-06 00:36:32
|
besongsamuel/eapp
|
https://api.github.com/repos/besongsamuel/eapp
|
closed
|
The product grid view
|
Pending Acceptance Test
|
Hello chef,
you please could you check the product grid view there is a bug sometime this is intermitent look the capture
|
1.0
|
The product grid view - Hello chef,
you please could you check the product grid view there is a bug sometime this is intermitent look the capture
|
test
|
the product grid view hello chef you please could you check the product grid view there is a bug sometime this is intermitent look the capture
| 1
|
84,564
| 7,926,558,647
|
IssuesEvent
|
2018-07-06 02:54:54
|
netblue30/firejail
|
https://api.github.com/repos/netblue30/firejail
|
closed
|
invalid whitelist path if /var/tmp is symlink to /tmp
|
in testing
|
Hi there!
I've faced sad issue on git HEAD:
if /var/tmp is symlink to /tmp, firejail refuses to start (because it includes `/etc/firejail/whitelist-var-common.inc`), and says:
```
...
Error: invalid whitelist path /var/tmp
Error: proc 1110 cannot sync with peer: unexpected EOF
Peer 1111 unexpectedly exited with status 1
```
Although, there is some checks for `/var/tmp` being a symlink in `fs.c`, it still fails in `whitelist.c`.
Can you fix it, please?
|
1.0
|
invalid whitelist path if /var/tmp is symlink to /tmp - Hi there!
I've faced sad issue on git HEAD:
if /var/tmp is symlink to /tmp, firejail refuses to start (because it includes `/etc/firejail/whitelist-var-common.inc`), and says:
```
...
Error: invalid whitelist path /var/tmp
Error: proc 1110 cannot sync with peer: unexpected EOF
Peer 1111 unexpectedly exited with status 1
```
Although, there is some checks for `/var/tmp` being a symlink in `fs.c`, it still fails in `whitelist.c`.
Can you fix it, please?
|
test
|
invalid whitelist path if var tmp is symlink to tmp hi there i ve faced sad issue on git head if var tmp is symlink to tmp firejail refuses to start because it includes etc firejail whitelist var common inc and says error invalid whitelist path var tmp error proc cannot sync with peer unexpected eof peer unexpectedly exited with status although there is some checks for var tmp being a symlink in fs c it still fails in whitelist c can you fix it please
| 1
|
6,140
| 2,813,904,278
|
IssuesEvent
|
2015-05-18 17:02:42
|
easydigitaldownloads/Easy-Digital-Downloads
|
https://api.github.com/repos/easydigitaldownloads/Easy-Digital-Downloads
|
closed
|
We should not be flush_rewrite_rules using default hard flush
|
Bug Has PR Needs Testing
|
flush_rewrite_rules (unintuitively) defaults the only parameter ($hard) to true. This clears and rewrites the .htaccess file as well as clearing the rewrite rules. We should never call flush_rewrite_rules using the default, and instead call flush_rewrite_rules( false ). The effect of a network activation of EDD that flushes the rewrite rules using the default has the affect of writing the .htaccess file for a multisite instance for each subsite individually.
|
1.0
|
We should not be flush_rewrite_rules using default hard flush - flush_rewrite_rules (unintuitively) defaults the only parameter ($hard) to true. This clears and rewrites the .htaccess file as well as clearing the rewrite rules. We should never call flush_rewrite_rules using the default, and instead call flush_rewrite_rules( false ). The effect of a network activation of EDD that flushes the rewrite rules using the default has the affect of writing the .htaccess file for a multisite instance for each subsite individually.
|
test
|
we should not be flush rewrite rules using default hard flush flush rewrite rules unintuitively defaults the only parameter hard to true this clears and rewrites the htaccess file as well as clearing the rewrite rules we should never call flush rewrite rules using the default and instead call flush rewrite rules false the effect of a network activation of edd that flushes the rewrite rules using the default has the affect of writing the htaccess file for a multisite instance for each subsite individually
| 1
|
263,751
| 23,080,167,950
|
IssuesEvent
|
2022-07-26 06:18:49
|
WordPress/gutenberg
|
https://api.github.com/repos/WordPress/gutenberg
|
closed
|
[Block] Comment Template -> Columns -> change parent and inner blocks text colors
|
[Type] Bug Needs Testing [Block] Comment Template
|
### Description
1. Comment Template -> Columns. Change the text color to white.
2. Click Comment Date/Comment Author. Change the text color to green.
Which should decide the color of the Comment Date/Comment Author?
Parent or the inner block itself?
### Step-by-step reproduction instructions
See above.
### Screenshots, screen recording, code snippet
Backend Columns selected.
Notice Color:
Text is white
Background has a gradient.
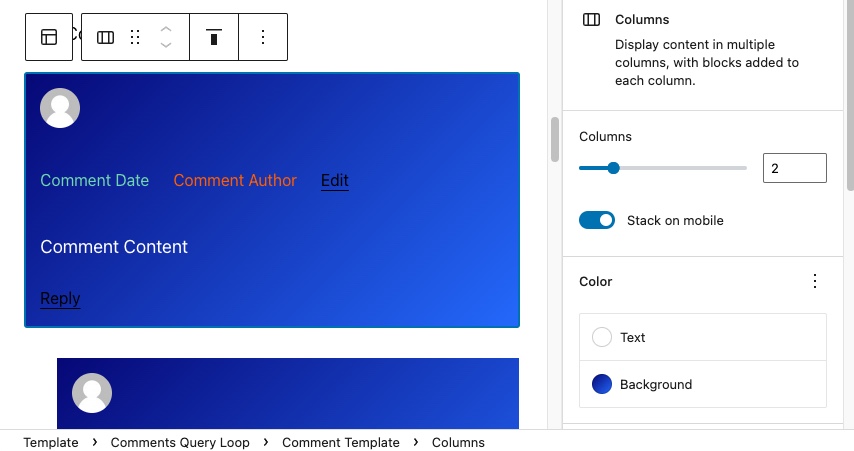
Selecting Comment Author.
Notice Color:
Text changed to orange.
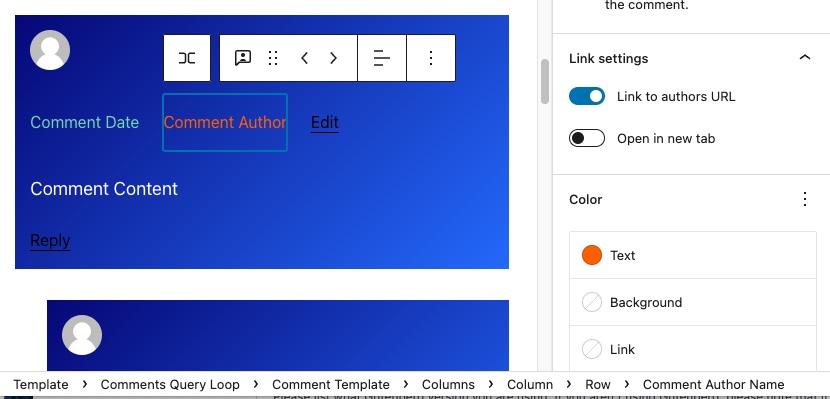
Frontend (no change to Comment Author color is seen)

### Environment info
WP 5.9.3
Gutenberg plugin 13.0RC2
Twenty Twenty Two
### Please confirm that you have searched existing issues in the repo.
Yes
### Please confirm that you have tested with all plugins deactivated except Gutenberg.
Yes
Associated issue:
[Block] Comment Template -> Columns - change text colors does not affect Edit and Reply text
https://github.com/WordPress/gutenberg/issues/40255
|
1.0
|
[Block] Comment Template -> Columns -> change parent and inner blocks text colors - ### Description
1. Comment Template -> Columns. Change the text color to white.
2. Click Comment Date/Comment Author. Change the text color to green.
Which should decide the color of the Comment Date/Comment Author?
Parent or the inner block itself?
### Step-by-step reproduction instructions
See above.
### Screenshots, screen recording, code snippet
Backend Columns selected.
Notice Color:
Text is white
Background has a gradient.
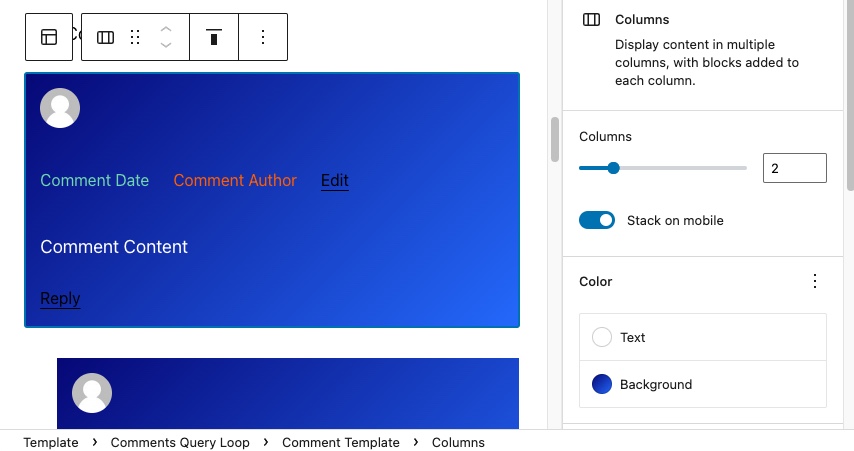
Selecting Comment Author.
Notice Color:
Text changed to orange.
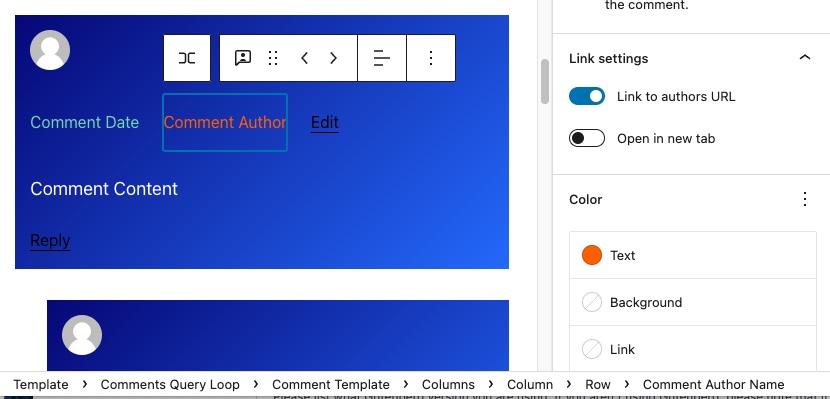
Frontend (no change to Comment Author color is seen)

### Environment info
WP 5.9.3
Gutenberg plugin 13.0RC2
Twenty Twenty Two
### Please confirm that you have searched existing issues in the repo.
Yes
### Please confirm that you have tested with all plugins deactivated except Gutenberg.
Yes
Associated issue:
[Block] Comment Template -> Columns - change text colors does not affect Edit and Reply text
https://github.com/WordPress/gutenberg/issues/40255
|
test
|
comment template columns change parent and inner blocks text colors description comment template columns change the text color to white click comment date comment author change the text color to green which should decide the color of the comment date comment author parent or the inner block itself step by step reproduction instructions see above screenshots screen recording code snippet backend columns selected notice color text is white background has a gradient selecting comment author notice color text changed to orange frontend no change to comment author color is seen environment info wp gutenberg plugin twenty twenty two please confirm that you have searched existing issues in the repo yes please confirm that you have tested with all plugins deactivated except gutenberg yes associated issue comment template columns change text colors does not affect edit and reply text
| 1
|
41,915
| 5,409,215,389
|
IssuesEvent
|
2017-03-01 03:01:55
|
openbmc/openbmc-test-automation
|
https://api.github.com/repos/openbmc/openbmc-test-automation
|
closed
|
[FFDC] Close SSH/Telnnet connection post FFDC
|
Test
|
We hit the SSH paramiko related issue each run as report by DVT.
```
No handlers could be found for logger "paramiko.transport"
#(CST) 2017/02/24 12:06:16.985204 - 2948.112677 - Executing: obmc_boot::exit_function "EXIT" "1"
#(CST) 2017/02/24 12:06:17.010056 - 0.024852 - Issuing: kill_autoend autoend_pid
```
On debugging we found that the SSH/Telnet sessions were not getting cleanup and increasing per FFDC call. Since the DVT auto boot calls FFDC every test cycle, it end up opening many connections and leaving stale sessions forcing parmaiko to error out now and then.
A simple fix was made in FFDC code to do the cleanup by calling `Close All Connections`
```
Call FFDC Methods
[Documentation] Calls into FFDC Keyword index list
@{entries}= Get ffdc method index
:FOR ${index} IN @{entries}
\ Method Call Keyword List ${index}
Close All Connections
```
|
1.0
|
[FFDC] Close SSH/Telnnet connection post FFDC - We hit the SSH paramiko related issue each run as report by DVT.
```
No handlers could be found for logger "paramiko.transport"
#(CST) 2017/02/24 12:06:16.985204 - 2948.112677 - Executing: obmc_boot::exit_function "EXIT" "1"
#(CST) 2017/02/24 12:06:17.010056 - 0.024852 - Issuing: kill_autoend autoend_pid
```
On debugging we found that the SSH/Telnet sessions were not getting cleanup and increasing per FFDC call. Since the DVT auto boot calls FFDC every test cycle, it end up opening many connections and leaving stale sessions forcing parmaiko to error out now and then.
A simple fix was made in FFDC code to do the cleanup by calling `Close All Connections`
```
Call FFDC Methods
[Documentation] Calls into FFDC Keyword index list
@{entries}= Get ffdc method index
:FOR ${index} IN @{entries}
\ Method Call Keyword List ${index}
Close All Connections
```
|
test
|
close ssh telnnet connection post ffdc we hit the ssh paramiko related issue each run as report by dvt no handlers could be found for logger paramiko transport cst executing obmc boot exit function exit cst issuing kill autoend autoend pid on debugging we found that the ssh telnet sessions were not getting cleanup and increasing per ffdc call since the dvt auto boot calls ffdc every test cycle it end up opening many connections and leaving stale sessions forcing parmaiko to error out now and then a simple fix was made in ffdc code to do the cleanup by calling close all connections call ffdc methods calls into ffdc keyword index list entries get ffdc method index for index in entries method call keyword list index close all connections
| 1
|
144,937
| 22,586,553,093
|
IssuesEvent
|
2022-06-28 15:42:10
|
blockframes/blockframes
|
https://api.github.com/repos/blockframes/blockframes
|
closed
|
Difference in font weight on notification action
|
Design - UI July clean up
|
Different font weights on same button
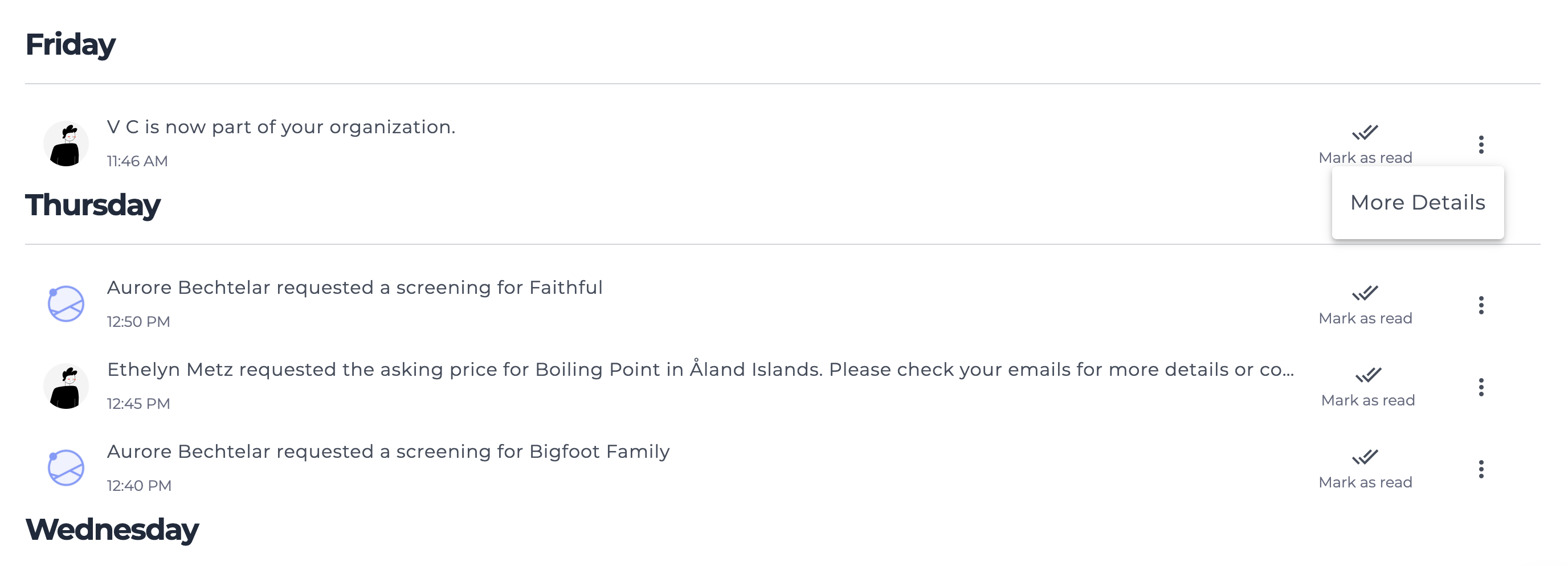
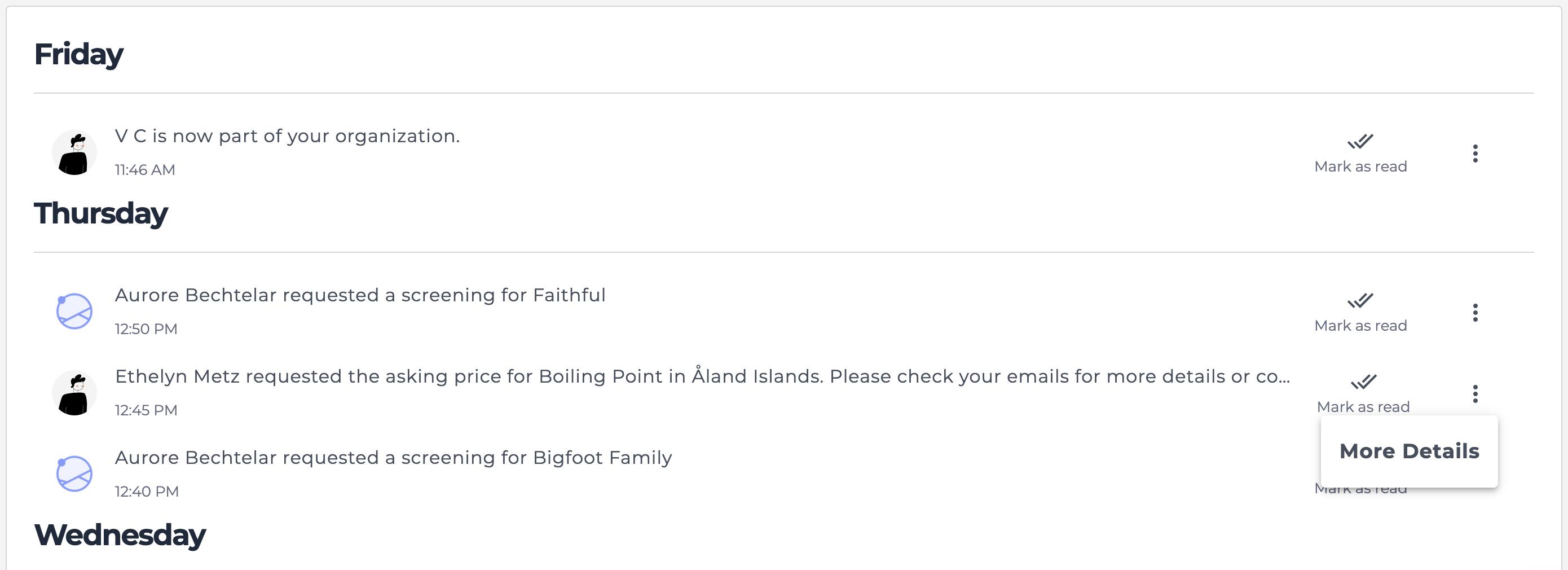
|
1.0
|
Difference in font weight on notification action - Different font weights on same button
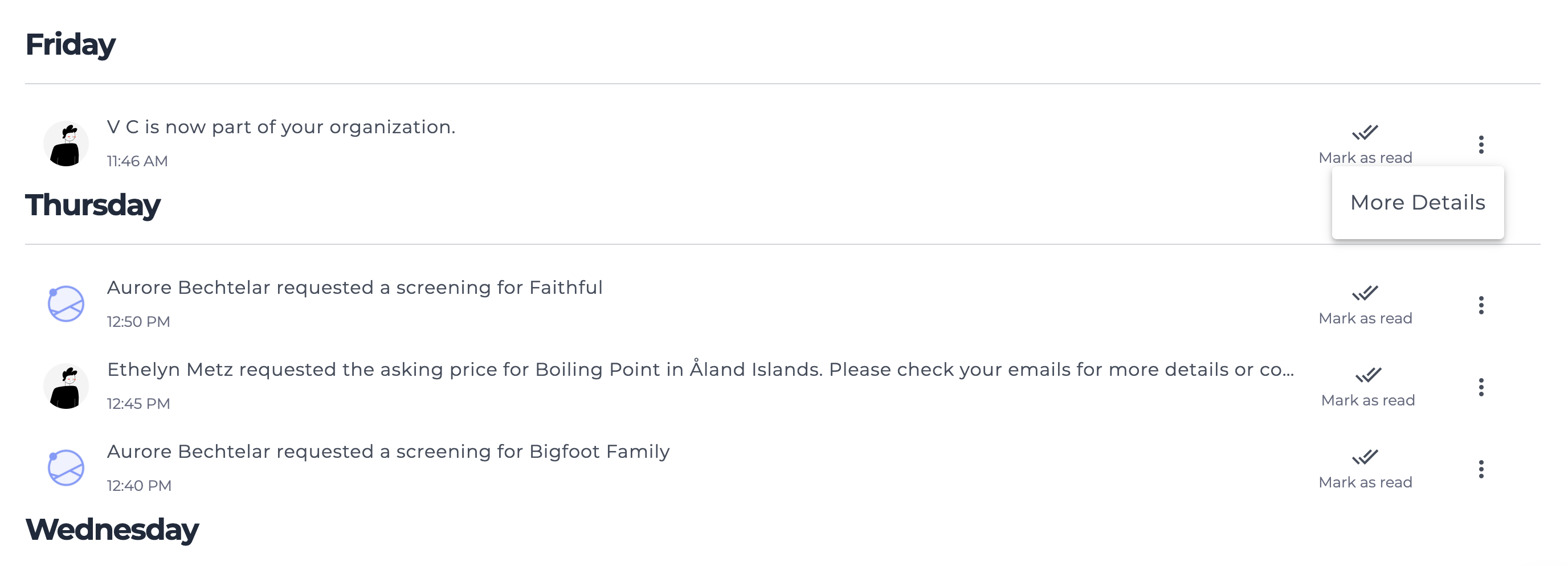
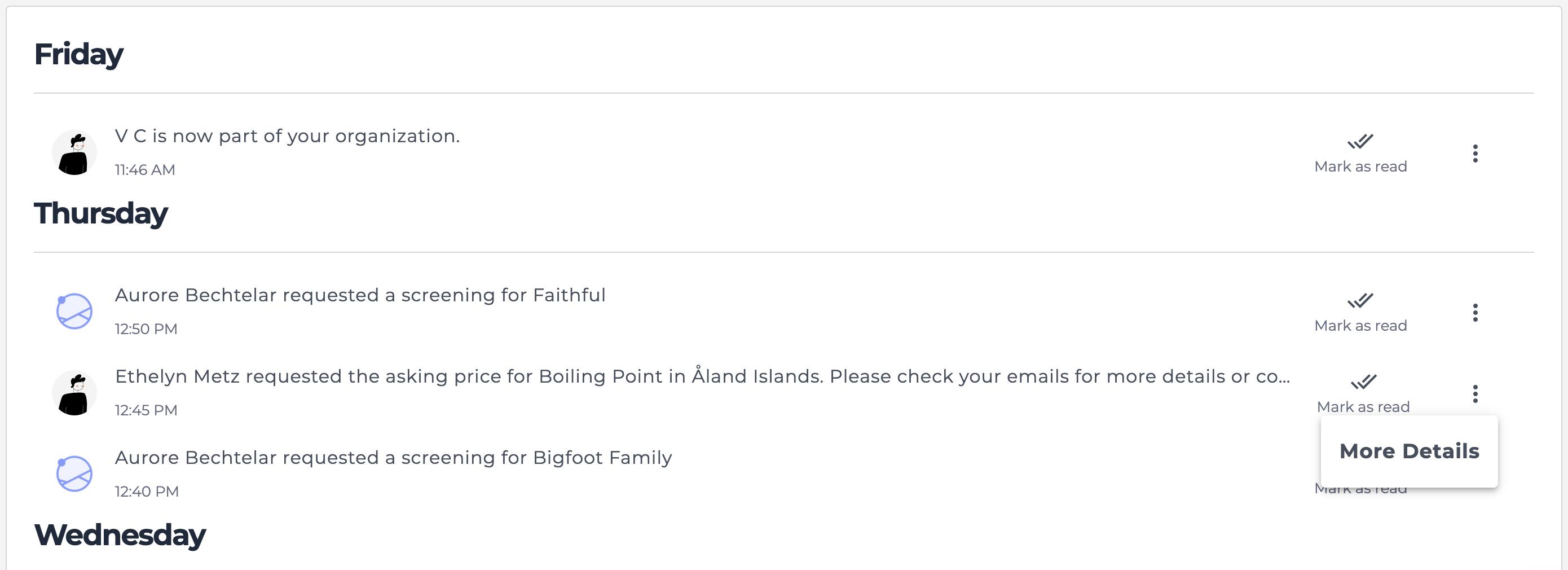
|
non_test
|
difference in font weight on notification action different font weights on same button
| 0
|
84,001
| 7,887,074,363
|
IssuesEvent
|
2018-06-27 17:15:20
|
golang/go
|
https://api.github.com/repos/golang/go
|
closed
|
x/net/http2: TestServer_Rejects_TooSmall test flake
|
NeedsFix Testing help wanted
|
```
linux-amd64 at c6295e72bf9536d75d3528ad17bdd49f2856b58d building net at 6fcffe453537651f4aa3d93714bc764543ec5978
ok golang.org/x/net/bpf 0.482s
ok golang.org/x/net/context 0.135s
ok golang.org/x/net/context/ctxhttp 0.146s
? golang.org/x/net/dict [no test files]
ok golang.org/x/net/dns/dnsmessage 0.085s
ok golang.org/x/net/html 0.167s
ok golang.org/x/net/html/atom 0.046s
ok golang.org/x/net/html/charset 0.040s
ok golang.org/x/net/http/httpguts 0.046s
ok golang.org/x/net/http/httpproxy 0.037s
--- FAIL: TestServer_Rejects_TooSmall (0.01s)
server_test.go:561: got a *http2.HeadersFrame; want *RSTStreamFrame
server_test.go:235: Framer read log:
2018-05-30 09:10:04.021264382 Framer 0xc0004e67e0: read SETTINGS len=24, settings: MAX_FRAME_SIZE=1048576, MAX_CONCURRENT_STREAMS=250, MAX_HEADER_LIST_SIZE=1048896, INITIAL_WINDOW_SIZE=1048576
2018-05-30 09:10:04.021454998 Framer 0xc0004e67e0: read WINDOW_UPDATE len=4 (conn) incr=983041
2018-05-30 09:10:04.021470353 Framer 0xc0004e67e0: read SETTINGS flags=ACK len=0
2018-05-30 09:10:04.02349049 Framer 0xc0004e67e0: read HEADERS flags=END_STREAM|END_HEADERS stream=1 len=28
server_test.go:241: Framer write log:
2018-05-30 09:10:04.020810306 Framer 0xc0004e67e0: wrote SETTINGS len=0
2018-05-30 09:10:04.021278064 Framer 0xc0004e67e0: wrote SETTINGS flags=ACK len=0
2018-05-30 09:10:04.021522082 Framer 0xc0004e67e0: wrote HEADERS flags=END_HEADERS stream=1 len=19
2018-05-30 09:10:04.022606786 Framer 0xc0004e67e0: wrote DATA flags=END_STREAM stream=1 len=5 data="12345"
FAIL
FAIL golang.org/x/net/http2 9.339s
? golang.org/x/net/http2/h2i [no test files]
```
|
1.0
|
x/net/http2: TestServer_Rejects_TooSmall test flake - ```
linux-amd64 at c6295e72bf9536d75d3528ad17bdd49f2856b58d building net at 6fcffe453537651f4aa3d93714bc764543ec5978
ok golang.org/x/net/bpf 0.482s
ok golang.org/x/net/context 0.135s
ok golang.org/x/net/context/ctxhttp 0.146s
? golang.org/x/net/dict [no test files]
ok golang.org/x/net/dns/dnsmessage 0.085s
ok golang.org/x/net/html 0.167s
ok golang.org/x/net/html/atom 0.046s
ok golang.org/x/net/html/charset 0.040s
ok golang.org/x/net/http/httpguts 0.046s
ok golang.org/x/net/http/httpproxy 0.037s
--- FAIL: TestServer_Rejects_TooSmall (0.01s)
server_test.go:561: got a *http2.HeadersFrame; want *RSTStreamFrame
server_test.go:235: Framer read log:
2018-05-30 09:10:04.021264382 Framer 0xc0004e67e0: read SETTINGS len=24, settings: MAX_FRAME_SIZE=1048576, MAX_CONCURRENT_STREAMS=250, MAX_HEADER_LIST_SIZE=1048896, INITIAL_WINDOW_SIZE=1048576
2018-05-30 09:10:04.021454998 Framer 0xc0004e67e0: read WINDOW_UPDATE len=4 (conn) incr=983041
2018-05-30 09:10:04.021470353 Framer 0xc0004e67e0: read SETTINGS flags=ACK len=0
2018-05-30 09:10:04.02349049 Framer 0xc0004e67e0: read HEADERS flags=END_STREAM|END_HEADERS stream=1 len=28
server_test.go:241: Framer write log:
2018-05-30 09:10:04.020810306 Framer 0xc0004e67e0: wrote SETTINGS len=0
2018-05-30 09:10:04.021278064 Framer 0xc0004e67e0: wrote SETTINGS flags=ACK len=0
2018-05-30 09:10:04.021522082 Framer 0xc0004e67e0: wrote HEADERS flags=END_HEADERS stream=1 len=19
2018-05-30 09:10:04.022606786 Framer 0xc0004e67e0: wrote DATA flags=END_STREAM stream=1 len=5 data="12345"
FAIL
FAIL golang.org/x/net/http2 9.339s
? golang.org/x/net/http2/h2i [no test files]
```
|
test
|
x net testserver rejects toosmall test flake linux at building net at ok golang org x net bpf ok golang org x net context ok golang org x net context ctxhttp golang org x net dict ok golang org x net dns dnsmessage ok golang org x net html ok golang org x net html atom ok golang org x net html charset ok golang org x net http httpguts ok golang org x net http httpproxy fail testserver rejects toosmall server test go got a headersframe want rststreamframe server test go framer read log framer read settings len settings max frame size max concurrent streams max header list size initial window size framer read window update len conn incr framer read settings flags ack len framer read headers flags end stream end headers stream len server test go framer write log framer wrote settings len framer wrote settings flags ack len framer wrote headers flags end headers stream len framer wrote data flags end stream stream len data fail fail golang org x net golang org x net
| 1
|
43,800
| 17,659,111,304
|
IssuesEvent
|
2021-08-21 05:47:19
|
misskey-dev/misskey
|
https://api.github.com/repos/misskey-dev/misskey
|
closed
|
(API) /api/sw/unregister
|
🧩API ✨Feature 🤖Service Worker
|
プッシュ通知が不要になったら購読を解除したいですが、それに相当するAPIがまだありません
<bountysource-plugin>
---
Want to back this issue? **[Post a bounty on it!](https://www.bountysource.com/issues/62789132-api-api-sw-unregister?utm_campaign=plugin&utm_content=tracker%2F51027576&utm_medium=issues&utm_source=github)** We accept bounties via [Bountysource](https://www.bountysource.com/?utm_campaign=plugin&utm_content=tracker%2F51027576&utm_medium=issues&utm_source=github).
</bountysource-plugin>
|
1.0
|
(API) /api/sw/unregister - プッシュ通知が不要になったら購読を解除したいですが、それに相当するAPIがまだありません
<bountysource-plugin>
---
Want to back this issue? **[Post a bounty on it!](https://www.bountysource.com/issues/62789132-api-api-sw-unregister?utm_campaign=plugin&utm_content=tracker%2F51027576&utm_medium=issues&utm_source=github)** We accept bounties via [Bountysource](https://www.bountysource.com/?utm_campaign=plugin&utm_content=tracker%2F51027576&utm_medium=issues&utm_source=github).
</bountysource-plugin>
|
non_test
|
api api sw unregister プッシュ通知が不要になったら購読を解除したいですが、それに相当するapiがまだありません want to back this issue we accept bounties via
| 0
|
137,169
| 12,747,077,138
|
IssuesEvent
|
2020-06-26 17:10:32
|
streamnative/pulsar
|
https://api.github.com/repos/streamnative/pulsar
|
closed
|
ISSUE-6927: Add C# client documentation
|
area/documentation component/documentation component/website size: 1 triage/week-19 type/feature workflow::in-review
|
Original Issue: apache/pulsar#6927
---
**Is your feature request related to a problem? Please describe.**
Since we have official c# client https://github.com/apache/pulsar-dotpulsar, we'd better add the C# client documentation in the client documentation.

|
2.0
|
ISSUE-6927: Add C# client documentation - Original Issue: apache/pulsar#6927
---
**Is your feature request related to a problem? Please describe.**
Since we have official c# client https://github.com/apache/pulsar-dotpulsar, we'd better add the C# client documentation in the client documentation.

|
non_test
|
issue add c client documentation original issue apache pulsar is your feature request related to a problem please describe since we have official c client we d better add the c client documentation in the client documentation
| 0
|
22,017
| 11,457,099,890
|
IssuesEvent
|
2020-02-06 22:46:35
|
PowerShell/vscode-powershell
|
https://api.github.com/repos/PowerShell/vscode-powershell
|
closed
|
IntelliSense slow or unresponsive forced to kill powershell to force it to work.
|
Area-Script Analysis Issue-Performance
|
<!--
BEFORE SUBMITTING A NEW ISSUE, PLEASE READ THE FAQ!!
https://github.com/PowerShell/vscode-powershell/wiki/FAQ
If your issue is not addressed by the FAQ, please
fill in the following details so that we can help you!
The more repro details you can provide, along with a zip
of the log files from your session, the better the chances
are for a quick resolution.
-->
### System Details
- Operating system name and version:
```
Platform ServicePack Version VersionString
-------- ----------- ------- -------------
Win32NT 10.0.16299.0 Microsoft Windows NT 10.0.16299.0
```
- VS Code version: 1.21.1
- PowerShell extension version: 1.6.0
- Output from `$PSVersionTable`:
```
Name Value
---- -----
PSVersion 5.1.16299.251
PSEdition Desktop
PSCompatibleVersions {1.0, 2.0, 3.0, 4.0...}
BuildVersion 10.0.16299.251
CLRVersion 4.0.30319.42000
WSManStackVersion 3.0
PSRemotingProtocolVersion 2.3
SerializationVersion 1.1.0.1
```
Copy / paste the following commands into the PowerShell Integrated Console, and paste the output here:
code -v
```
1.21.1
79b44aa704ce542d8ca4a3cc44cfca566e7720f1
x64
```
$pseditor.EditorServicesVersion
```
Major Minor Build Revision
----- ----- ----- --------
1 6 0 0
```
code --list-extensions --show-versions
```
codezombiech.gitignore@0.5.0
donjayamanne.githistory@0.4.0
DotJoshJohnson.xml@1.9.2
eamodio.gitlens@8.2.0
formulahendry.docker-explorer@0.1.6
mohsen1.prettify-json@0.0.3
ms-python.python@2018.3.1
ms-vscode.PowerShell@1.6.0
ms-vsliveshare.vsliveshare@0.2.307
njpwerner.autodocstring@0.2.0
PeterJausovec.vscode-docker@0.0.26
ryu1kn.partial-diff@0.5.1
tushortz.python-extended-snippets@0.0.1
vscoss.vscode-ansible@0.1.5
wholroyd.jinja@0.0.8
```
$PSVersionTable
```
Name Value
---- -----
PSVersion 5.1.16299.251
PSEdition Desktop
PSCompatibleVersions {1.0, 2.0, 3.0, 4.0...}
BuildVersion 10.0.16299.251
CLRVersion 4.0.30319.42000
WSManStackVersion 3.0
PSRemotingProtocolVersion 2.3
SerializationVersion 1.1.0.1
### Issue Description
IntelliSense is slow or unresponsive when using powershell in the editor.
To get it to work correctly again, I have to kill and restart powershell in Vscode to force it to work again.
### Attached Logs
```
[logs.zip](https://github.com/PowerShell/vscode-powershell/files/1872741/logs.zip)
|
True
|
IntelliSense slow or unresponsive forced to kill powershell to force it to work. - <!--
BEFORE SUBMITTING A NEW ISSUE, PLEASE READ THE FAQ!!
https://github.com/PowerShell/vscode-powershell/wiki/FAQ
If your issue is not addressed by the FAQ, please
fill in the following details so that we can help you!
The more repro details you can provide, along with a zip
of the log files from your session, the better the chances
are for a quick resolution.
-->
### System Details
- Operating system name and version:
```
Platform ServicePack Version VersionString
-------- ----------- ------- -------------
Win32NT 10.0.16299.0 Microsoft Windows NT 10.0.16299.0
```
- VS Code version: 1.21.1
- PowerShell extension version: 1.6.0
- Output from `$PSVersionTable`:
```
Name Value
---- -----
PSVersion 5.1.16299.251
PSEdition Desktop
PSCompatibleVersions {1.0, 2.0, 3.0, 4.0...}
BuildVersion 10.0.16299.251
CLRVersion 4.0.30319.42000
WSManStackVersion 3.0
PSRemotingProtocolVersion 2.3
SerializationVersion 1.1.0.1
```
Copy / paste the following commands into the PowerShell Integrated Console, and paste the output here:
code -v
```
1.21.1
79b44aa704ce542d8ca4a3cc44cfca566e7720f1
x64
```
$pseditor.EditorServicesVersion
```
Major Minor Build Revision
----- ----- ----- --------
1 6 0 0
```
code --list-extensions --show-versions
```
codezombiech.gitignore@0.5.0
donjayamanne.githistory@0.4.0
DotJoshJohnson.xml@1.9.2
eamodio.gitlens@8.2.0
formulahendry.docker-explorer@0.1.6
mohsen1.prettify-json@0.0.3
ms-python.python@2018.3.1
ms-vscode.PowerShell@1.6.0
ms-vsliveshare.vsliveshare@0.2.307
njpwerner.autodocstring@0.2.0
PeterJausovec.vscode-docker@0.0.26
ryu1kn.partial-diff@0.5.1
tushortz.python-extended-snippets@0.0.1
vscoss.vscode-ansible@0.1.5
wholroyd.jinja@0.0.8
```
$PSVersionTable
```
Name Value
---- -----
PSVersion 5.1.16299.251
PSEdition Desktop
PSCompatibleVersions {1.0, 2.0, 3.0, 4.0...}
BuildVersion 10.0.16299.251
CLRVersion 4.0.30319.42000
WSManStackVersion 3.0
PSRemotingProtocolVersion 2.3
SerializationVersion 1.1.0.1
### Issue Description
IntelliSense is slow or unresponsive when using powershell in the editor.
To get it to work correctly again, I have to kill and restart powershell in Vscode to force it to work again.
### Attached Logs
```
[logs.zip](https://github.com/PowerShell/vscode-powershell/files/1872741/logs.zip)
|
non_test
|
intellisense slow or unresponsive forced to kill powershell to force it to work before submitting a new issue please read the faq if your issue is not addressed by the faq please fill in the following details so that we can help you the more repro details you can provide along with a zip of the log files from your session the better the chances are for a quick resolution system details operating system name and version platform servicepack version versionstring microsoft windows nt vs code version powershell extension version output from psversiontable name value psversion psedition desktop pscompatibleversions buildversion clrversion wsmanstackversion psremotingprotocolversion serializationversion copy paste the following commands into the powershell integrated console and paste the output here code v pseditor editorservicesversion major minor build revision code list extensions show versions codezombiech gitignore donjayamanne githistory dotjoshjohnson xml eamodio gitlens formulahendry docker explorer prettify json ms python python ms vscode powershell ms vsliveshare vsliveshare njpwerner autodocstring peterjausovec vscode docker partial diff tushortz python extended snippets vscoss vscode ansible wholroyd jinja psversiontable name value psversion psedition desktop pscompatibleversions buildversion clrversion wsmanstackversion psremotingprotocolversion serializationversion issue description intellisense is slow or unresponsive when using powershell in the editor to get it to work correctly again i have to kill and restart powershell in vscode to force it to work again attached logs
| 0
|
276,047
| 20,966,321,842
|
IssuesEvent
|
2022-03-28 07:08:34
|
trixi-framework/Trixi.jl
|
https://api.github.com/repos/trixi-framework/Trixi.jl
|
closed
|
Discuss order of tutorials
|
documentation discussion
|
We should discuss the order of our new tutorials. When merge conflicts in #1084 are solved, we have something like
```
"Introduction to DG methods"
"DGSEM with flux differencing"
"Shock capturing with flux differencing and stage limiter"
"Non-periodic boundaries"
"Structured mesh with curvilinear mapping"
"Adding a new equation"
"Scalar conservation law"
"Nonconservative equation"
"Differentiable programming"
"Unstructured meshes with HOHQMesh.jl"
```
Some possibilities could be
- chronological (like DealII)
- based on the "complexity" or "difficulty"
- based on the topic
- something else
I would prefer a sorting based at first on the topic, then on the complexity. We should also make sure to have some links to other sections (like "further reading" sections). Such a sorting might look like
```
# Topic: DG semidiscretizations
"Introduction to DG methods"
"DGSEM with flux differencing"
"Shock capturing with flux differencing and stage limiter"
"Non-periodic boundaries"
# Topic: equations
"Adding a new equation"
"Scalar conservation law"
"Nonconservative equation"
# Topic: meshes
"Structured mesh with curvilinear mapping"
"Unstructured meshes with HOHQMesh.jl"
# Topic: other stuff
"Differentiable programming"
```
What do you think?
CC @bennibolm @trixi-framework/principal-developers
|
1.0
|
Discuss order of tutorials - We should discuss the order of our new tutorials. When merge conflicts in #1084 are solved, we have something like
```
"Introduction to DG methods"
"DGSEM with flux differencing"
"Shock capturing with flux differencing and stage limiter"
"Non-periodic boundaries"
"Structured mesh with curvilinear mapping"
"Adding a new equation"
"Scalar conservation law"
"Nonconservative equation"
"Differentiable programming"
"Unstructured meshes with HOHQMesh.jl"
```
Some possibilities could be
- chronological (like DealII)
- based on the "complexity" or "difficulty"
- based on the topic
- something else
I would prefer a sorting based at first on the topic, then on the complexity. We should also make sure to have some links to other sections (like "further reading" sections). Such a sorting might look like
```
# Topic: DG semidiscretizations
"Introduction to DG methods"
"DGSEM with flux differencing"
"Shock capturing with flux differencing and stage limiter"
"Non-periodic boundaries"
# Topic: equations
"Adding a new equation"
"Scalar conservation law"
"Nonconservative equation"
# Topic: meshes
"Structured mesh with curvilinear mapping"
"Unstructured meshes with HOHQMesh.jl"
# Topic: other stuff
"Differentiable programming"
```
What do you think?
CC @bennibolm @trixi-framework/principal-developers
|
non_test
|
discuss order of tutorials we should discuss the order of our new tutorials when merge conflicts in are solved we have something like introduction to dg methods dgsem with flux differencing shock capturing with flux differencing and stage limiter non periodic boundaries structured mesh with curvilinear mapping adding a new equation scalar conservation law nonconservative equation differentiable programming unstructured meshes with hohqmesh jl some possibilities could be chronological like dealii based on the complexity or difficulty based on the topic something else i would prefer a sorting based at first on the topic then on the complexity we should also make sure to have some links to other sections like further reading sections such a sorting might look like topic dg semidiscretizations introduction to dg methods dgsem with flux differencing shock capturing with flux differencing and stage limiter non periodic boundaries topic equations adding a new equation scalar conservation law nonconservative equation topic meshes structured mesh with curvilinear mapping unstructured meshes with hohqmesh jl topic other stuff differentiable programming what do you think cc bennibolm trixi framework principal developers
| 0
|
95,605
| 8,564,721,292
|
IssuesEvent
|
2018-11-09 17:33:25
|
magento-engcom/msi
|
https://api.github.com/repos/magento-engcom/msi
|
closed
|
[Configuration-Catalog-Products-Configurable product] Configurable Product created with text swatch attribute configuration and assigned to Test stock by Admin user
|
MFTF (Functional Test Coverage)
|
1. Login to backend as admin
2. Go to Catalog -> Categories
3. Select Default Category on Categories Tree
4. Click button "Add Subcategory"
5. set "Enable Category" to "Yes"
6. set "Include in Menu" to "Yes"
7. Fill in "Category Name" = "Category 1"
8. Click button "Save"
9. Success message "You saved the category." appears
10. Verify that Category 1 appeared in Categories tree as subcategory of Default category
11. Login to backend as admin
12. Go to Stores -> Manage Sources
13. Click button "Add New Source"
14. fill New Source data in General tab - Name, Code etc:
* name = Test Source 1
* code = test_source_1
15. Set your New Source "Is Enabled" = Yes
16. Fill all fields with data of your New Source in Contact Info tab
17. Fill in address data of your New Source in Address Data tab:
* Country: United States
* State/Province: California (CA)
* City: Culver City
* Street: 6161 West Centinela Avenue
* Postсode: 90230
18. Set In "Carriers" tab "Use global Shipping configuration" to Yes
19. Click button "Save & close"
20. Confirmation message "The Source has been saved" appears
21. verify that data in all tabs is correct
22. Login to backend as admin
23. Go to Stores -> Manage Stocks
24. Click button "Add New Stock"
25. Fill in field "Name" = "Test Stock 1"
26. In "Sales Channels" Tab select website "Test Website 1"
27. Click button "Assign Sources" In "Sources" Tab
28. modal window "Assign Sources" opened
29. Select "Test Source 1" in sources list
30. Click button "Done"
31. Click button "Save & close"
32. Success message "The Stock have been saved" appeared
33. Login to backend as admin
34. Go to Catalog -> Products
35. Click button "Add Configurable Product"
36. set "Enable Product" to "Yes"
37. fill Name = "Configurable Product 1"
38. set Price = "10"
39. set Weight = "1"
40. select Category = "Category 1"
41. in "Product in Websites" tab select "Main Website"
42. click button 'Create Configuration"
43. On page "Step 1" - click button 'Create New Attribute"
44. Fill in "Default label" - "Text swatch attribute"
45. Select in "Catalog Input Type for Store Owner" = Visual Swatch
46. Add two text swatches with labels - "Text 1" and "Text 2"
47. click button "Save attribute"
48. Select "Visual swatch attribute" from Attributes grid
49. click button "Next"
50. On page "Step 2" click on "Select all"
51. click button "Next"
52. On page "Step 3" select "Apply single quantity to each SKUs"
53. click button "Assign Sources"
54. In Assign Sources grid select "Test Source 1" and click "Done"
55. Set Quantity for source = 100
56. click button "Next"
57. On page "Step 4" click button "Generate Products"
58. click button "Save"
59. Success message "You saved the product." appears
60. Verify that created variation products are present on "Configuration" tab
61. Go to "Home page"
62. Open "Category 1" page
63. verify "Configurable Product 1" is present
64. verify that "Name" and "Price" are correct
65. Open "Configurable Product 1" page
66. verify that "Name" and "SKU" are correct
67. verify that text swatch options "Text 1" and "Text 2" are present
----
HipTest Original ID: 1695806
|
1.0
|
[Configuration-Catalog-Products-Configurable product] Configurable Product created with text swatch attribute configuration and assigned to Test stock by Admin user - 1. Login to backend as admin
2. Go to Catalog -> Categories
3. Select Default Category on Categories Tree
4. Click button "Add Subcategory"
5. set "Enable Category" to "Yes"
6. set "Include in Menu" to "Yes"
7. Fill in "Category Name" = "Category 1"
8. Click button "Save"
9. Success message "You saved the category." appears
10. Verify that Category 1 appeared in Categories tree as subcategory of Default category
11. Login to backend as admin
12. Go to Stores -> Manage Sources
13. Click button "Add New Source"
14. fill New Source data in General tab - Name, Code etc:
* name = Test Source 1
* code = test_source_1
15. Set your New Source "Is Enabled" = Yes
16. Fill all fields with data of your New Source in Contact Info tab
17. Fill in address data of your New Source in Address Data tab:
* Country: United States
* State/Province: California (CA)
* City: Culver City
* Street: 6161 West Centinela Avenue
* Postсode: 90230
18. Set In "Carriers" tab "Use global Shipping configuration" to Yes
19. Click button "Save & close"
20. Confirmation message "The Source has been saved" appears
21. verify that data in all tabs is correct
22. Login to backend as admin
23. Go to Stores -> Manage Stocks
24. Click button "Add New Stock"
25. Fill in field "Name" = "Test Stock 1"
26. In "Sales Channels" Tab select website "Test Website 1"
27. Click button "Assign Sources" In "Sources" Tab
28. modal window "Assign Sources" opened
29. Select "Test Source 1" in sources list
30. Click button "Done"
31. Click button "Save & close"
32. Success message "The Stock have been saved" appeared
33. Login to backend as admin
34. Go to Catalog -> Products
35. Click button "Add Configurable Product"
36. set "Enable Product" to "Yes"
37. fill Name = "Configurable Product 1"
38. set Price = "10"
39. set Weight = "1"
40. select Category = "Category 1"
41. in "Product in Websites" tab select "Main Website"
42. click button 'Create Configuration"
43. On page "Step 1" - click button 'Create New Attribute"
44. Fill in "Default label" - "Text swatch attribute"
45. Select in "Catalog Input Type for Store Owner" = Visual Swatch
46. Add two text swatches with labels - "Text 1" and "Text 2"
47. click button "Save attribute"
48. Select "Visual swatch attribute" from Attributes grid
49. click button "Next"
50. On page "Step 2" click on "Select all"
51. click button "Next"
52. On page "Step 3" select "Apply single quantity to each SKUs"
53. click button "Assign Sources"
54. In Assign Sources grid select "Test Source 1" and click "Done"
55. Set Quantity for source = 100
56. click button "Next"
57. On page "Step 4" click button "Generate Products"
58. click button "Save"
59. Success message "You saved the product." appears
60. Verify that created variation products are present on "Configuration" tab
61. Go to "Home page"
62. Open "Category 1" page
63. verify "Configurable Product 1" is present
64. verify that "Name" and "Price" are correct
65. Open "Configurable Product 1" page
66. verify that "Name" and "SKU" are correct
67. verify that text swatch options "Text 1" and "Text 2" are present
----
HipTest Original ID: 1695806
|
test
|
configurable product created with text swatch attribute configuration and assigned to test stock by admin user login to backend as admin go to catalog categories select default category on categories tree click button add subcategory set enable category to yes set include in menu to yes fill in category name category click button save success message you saved the category appears verify that category appeared in categories tree as subcategory of default category login to backend as admin go to stores manage sources click button add new source fill new source data in general tab name code etc name test source code test source set your new source is enabled yes fill all fields with data of your new source in contact info tab fill in address data of your new source in address data tab country united states state province california ca city culver city street west centinela avenue postсode set in carriers tab use global shipping configuration to yes click button save close confirmation message the source has been saved appears verify that data in all tabs is correct login to backend as admin go to stores manage stocks click button add new stock fill in field name test stock in sales channels tab select website test website click button assign sources in sources tab modal window assign sources opened select test source in sources list click button done click button save close success message the stock have been saved appeared login to backend as admin go to catalog products click button add configurable product set enable product to yes fill name configurable product set price set weight select category category in product in websites tab select main website click button create configuration on page step click button create new attribute fill in default label text swatch attribute select in catalog input type for store owner visual swatch add two text swatches with labels text and text click button save attribute select visual swatch attribute from attributes grid click button next on page step click on select all click button next on page step select apply single quantity to each skus click button assign sources in assign sources grid select test source and click done set quantity for source click button next on page step click button generate products click button save success message you saved the product appears verify that created variation products are present on configuration tab go to home page open category page verify configurable product is present verify that name and price are correct open configurable product page verify that name and sku are correct verify that text swatch options text and text are present hiptest original id
| 1
|
20,325
| 3,808,035,961
|
IssuesEvent
|
2016-03-25 12:49:36
|
magicmychal/Fiszki
|
https://api.github.com/repos/magicmychal/Fiszki
|
closed
|
Use of Algorithm in LM and "test yourself"
|
idea in testing
|
"test yourself" should use our algorithm, if user answer correct, a word goes up to the next box.
"learning mode" should show words user know at least but do not move words either up or down.
Why?
Because our mission is to help people in learning new languages, we should in every case predict which word he knows not so well and help him to remember it.
|
1.0
|
Use of Algorithm in LM and "test yourself" - "test yourself" should use our algorithm, if user answer correct, a word goes up to the next box.
"learning mode" should show words user know at least but do not move words either up or down.
Why?
Because our mission is to help people in learning new languages, we should in every case predict which word he knows not so well and help him to remember it.
|
test
|
use of algorithm in lm and test yourself test yourself should use our algorithm if user answer correct a word goes up to the next box learning mode should show words user know at least but do not move words either up or down why because our mission is to help people in learning new languages we should in every case predict which word he knows not so well and help him to remember it
| 1
|
566,762
| 16,829,029,062
|
IssuesEvent
|
2021-06-17 23:43:31
|
cjquines/qboard
|
https://api.github.com/repos/cjquines/qboard
|
opened
|
Store source TeX in `Image` object, serialize
|
enhancement priority: high
|
This is a baby version of #187 and should be rushed so that new files have the data
|
1.0
|
Store source TeX in `Image` object, serialize - This is a baby version of #187 and should be rushed so that new files have the data
|
non_test
|
store source tex in image object serialize this is a baby version of and should be rushed so that new files have the data
| 0
|
61,723
| 8,553,154,532
|
IssuesEvent
|
2018-11-07 23:33:08
|
MicrosoftDocs/VBA-Docs
|
https://api.github.com/repos/MicrosoftDocs/VBA-Docs
|
closed
|
HKCU
|
bug: documentation not actionable
|
I presume HKCU is the same as HKEY_CURRENT_USER. If so, the article should use them consistently.
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 29565b93-a15a-c761-f3b2-315028b995d1
* Version Independent ID: f54fdbc6-93b8-d62a-7d69-e08a6b030428
* Content: [Support for Keeping Add-ins Enabled](https://docs.microsoft.com/en-us/office/vba/outlook/concepts/getting-started/support-for-keeping-add-ins-enabled)
* Content Source: [outlook/Concepts/Getting-Started/support-for-keeping-add-ins-enabled.md](https://github.com/MicrosoftDocs/VBA-Docs/blob/master/outlook/Concepts/Getting-Started/support-for-keeping-add-ins-enabled.md)
* Product: **outlook**
* GitHub Login: @o365devx
* Microsoft Alias: **o365devx**
|
1.0
|
HKCU - I presume HKCU is the same as HKEY_CURRENT_USER. If so, the article should use them consistently.
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 29565b93-a15a-c761-f3b2-315028b995d1
* Version Independent ID: f54fdbc6-93b8-d62a-7d69-e08a6b030428
* Content: [Support for Keeping Add-ins Enabled](https://docs.microsoft.com/en-us/office/vba/outlook/concepts/getting-started/support-for-keeping-add-ins-enabled)
* Content Source: [outlook/Concepts/Getting-Started/support-for-keeping-add-ins-enabled.md](https://github.com/MicrosoftDocs/VBA-Docs/blob/master/outlook/Concepts/Getting-Started/support-for-keeping-add-ins-enabled.md)
* Product: **outlook**
* GitHub Login: @o365devx
* Microsoft Alias: **o365devx**
|
non_test
|
hkcu i presume hkcu is the same as hkey current user if so the article should use them consistently document details ⚠ do not edit this section it is required for docs microsoft com ➟ github issue linking id version independent id content content source product outlook github login microsoft alias
| 0
|
91,108
| 3,837,871,779
|
IssuesEvent
|
2016-04-02 01:38:06
|
Glavin001/atom-beautify
|
https://api.github.com/repos/Glavin001/atom-beautify
|
closed
|
Beautify settings UX
|
enhancement high priority in-progress
|
Hello,
I like this plugin and find it really useful!
But as for me, the current state of settings is really messy. First, at the top you have a list of settings for every language. Not really categorized, "Language-Name - " prefixes are used instead of nice, clean sections:

But then goes the worst part of UX: when you scroll down, you find another list of settings for every language again:

Again, prefixes are used instead of sectioning.
Here are some ideas how to improve UX:
* make clean sections for every language, divided by headers with its name
* do either of:
* merge all settings concerning one language into one section
* make two main sections from what we have now
Please, tell me what you think about it. I really think that this nice plugin deserves a nicer look of settings.
I'm new to Atom plugins development, but I think I could create a pull request some time if nobody else would do that.
|
1.0
|
Beautify settings UX - Hello,
I like this plugin and find it really useful!
But as for me, the current state of settings is really messy. First, at the top you have a list of settings for every language. Not really categorized, "Language-Name - " prefixes are used instead of nice, clean sections:

But then goes the worst part of UX: when you scroll down, you find another list of settings for every language again:

Again, prefixes are used instead of sectioning.
Here are some ideas how to improve UX:
* make clean sections for every language, divided by headers with its name
* do either of:
* merge all settings concerning one language into one section
* make two main sections from what we have now
Please, tell me what you think about it. I really think that this nice plugin deserves a nicer look of settings.
I'm new to Atom plugins development, but I think I could create a pull request some time if nobody else would do that.
|
non_test
|
beautify settings ux hello i like this plugin and find it really useful but as for me the current state of settings is really messy first at the top you have a list of settings for every language not really categorized language name prefixes are used instead of nice clean sections but then goes the worst part of ux when you scroll down you find another list of settings for every language again again prefixes are used instead of sectioning here are some ideas how to improve ux make clean sections for every language divided by headers with its name do either of merge all settings concerning one language into one section make two main sections from what we have now please tell me what you think about it i really think that this nice plugin deserves a nicer look of settings i m new to atom plugins development but i think i could create a pull request some time if nobody else would do that
| 0
|
121,453
| 10,168,838,588
|
IssuesEvent
|
2019-08-07 21:59:32
|
rancher/rancher
|
https://api.github.com/repos/rancher/rancher
|
closed
|
[UI] Cluster Templates - Creating azure template with cloud provider config without providing all the credentials should be allowed
|
[zube]: To Test kind/bug-qa team/ui
|
Version: Master-head
Steps:
1. Create a cluster template/revision with azure cloud provider set and do not provide the credentials .
The credentials are made required currently. Users may not want to provide all the credentials during template creation. They will want to provide them during cluster creations.
Making them required will not allow us to create a template where credentials can be questions.
|
1.0
|
[UI] Cluster Templates - Creating azure template with cloud provider config without providing all the credentials should be allowed - Version: Master-head
Steps:
1. Create a cluster template/revision with azure cloud provider set and do not provide the credentials .
The credentials are made required currently. Users may not want to provide all the credentials during template creation. They will want to provide them during cluster creations.
Making them required will not allow us to create a template where credentials can be questions.
|
test
|
cluster templates creating azure template with cloud provider config without providing all the credentials should be allowed version master head steps create a cluster template revision with azure cloud provider set and do not provide the credentials the credentials are made required currently users may not want to provide all the credentials during template creation they will want to provide them during cluster creations making them required will not allow us to create a template where credentials can be questions
| 1
|
104,098
| 8,961,486,602
|
IssuesEvent
|
2019-01-28 09:47:42
|
muqeed11/FXTesting
|
https://api.github.com/repos/muqeed11/FXTesting
|
opened
|
DemoBankingTest2 : ApiV1OrgsIdPutOrgUsercDisallowAbac
|
DemoBankingTest2
|
Project : DemoBankingTest2
Job : Default
Env : Default
Category : null
Tags : null
Severity : null
Region : FXLabs/US_WEST_1
Result : fail
Status Code : 401
Headers : {WWW-Authenticate=[Basic realm="Realm", Basic realm="Realm"], X-Content-Type-Options=[nosniff], X-XSS-Protection=[1; mode=block], Cache-Control=[no-cache, no-store, max-age=0, must-revalidate], Pragma=[no-cache], Expires=[0], X-Frame-Options=[DENY], Content-Length=[0], Date=[Mon, 28 Jan 2019 09:47:37 GMT]}
Endpoint : http://54.215.136.217/api/v1/orgs/
Request :
{
"billingEmail" : "jackeline.rosenbaum@gmail.com",
"company" : "Dibbert and Sons",
"createdBy" : "",
"createdDate" : "",
"description" : "vUopaQdb",
"id" : "",
"inactive" : false,
"location" : "vUopaQdb",
"modifiedBy" : "",
"modifiedDate" : "",
"name" : "vUopaQdb",
"orgPlan" : "BUSINESS",
"orgType" : "ENTERPRISE",
"version" : ""
}
Response :
Logs :
Assertion [@StatusCode == 401 OR @StatusCode == 403 OR @Response.errors == true] resolved-to [401 == 401 OR 401 == 403 OR == true] result [Passed]
--- FX Bot ---
|
1.0
|
DemoBankingTest2 : ApiV1OrgsIdPutOrgUsercDisallowAbac - Project : DemoBankingTest2
Job : Default
Env : Default
Category : null
Tags : null
Severity : null
Region : FXLabs/US_WEST_1
Result : fail
Status Code : 401
Headers : {WWW-Authenticate=[Basic realm="Realm", Basic realm="Realm"], X-Content-Type-Options=[nosniff], X-XSS-Protection=[1; mode=block], Cache-Control=[no-cache, no-store, max-age=0, must-revalidate], Pragma=[no-cache], Expires=[0], X-Frame-Options=[DENY], Content-Length=[0], Date=[Mon, 28 Jan 2019 09:47:37 GMT]}
Endpoint : http://54.215.136.217/api/v1/orgs/
Request :
{
"billingEmail" : "jackeline.rosenbaum@gmail.com",
"company" : "Dibbert and Sons",
"createdBy" : "",
"createdDate" : "",
"description" : "vUopaQdb",
"id" : "",
"inactive" : false,
"location" : "vUopaQdb",
"modifiedBy" : "",
"modifiedDate" : "",
"name" : "vUopaQdb",
"orgPlan" : "BUSINESS",
"orgType" : "ENTERPRISE",
"version" : ""
}
Response :
Logs :
Assertion [@StatusCode == 401 OR @StatusCode == 403 OR @Response.errors == true] resolved-to [401 == 401 OR 401 == 403 OR == true] result [Passed]
--- FX Bot ---
|
test
|
project job default env default category null tags null severity null region fxlabs us west result fail status code headers www authenticate x content type options x xss protection cache control pragma expires x frame options content length date endpoint request billingemail jackeline rosenbaum gmail com company dibbert and sons createdby createddate description vuopaqdb id inactive false location vuopaqdb modifiedby modifieddate name vuopaqdb orgplan business orgtype enterprise version response logs assertion resolved to result fx bot
| 1
|
40,488
| 5,294,366,160
|
IssuesEvent
|
2017-02-09 10:35:04
|
khartec/waltz
|
https://api.github.com/repos/khartec/waltz
|
closed
|
Source Data Rating call error
|
bug fixed (test & close)
|
/api/source-data-rating
Exception: No enum constant com.khartec.waltz.model.EntityKind.CAPABILITY / java.lang.IllegalArgumentException
|
1.0
|
Source Data Rating call error - /api/source-data-rating
Exception: No enum constant com.khartec.waltz.model.EntityKind.CAPABILITY / java.lang.IllegalArgumentException
|
test
|
source data rating call error api source data rating exception no enum constant com khartec waltz model entitykind capability java lang illegalargumentexception
| 1
|
826,000
| 31,495,183,845
|
IssuesEvent
|
2023-08-31 01:21:13
|
carbynestack/carbynestack
|
https://api.github.com/repos/carbynestack/carbynestack
|
closed
|
Add support for edaBits
|
kind/feature priority/important-soon lifecycle/rotten lifecycle/stale triage/accepted
|
_Extended doubly-authenticated bits_ (edaBits) [EGK+20] are CR tuples composed of a secret shared integer in the arithmetic domain combined with its bit decomposition shared in the binary domain. They are used for MPC circuits that need to switch between arithmetic and binary representation.
Implementing edaBit support requires
- [ ] Providing support for storing and retrieving the new tuple type in Castor
- [ ] Fetching and feeding the new tuple type in Ephemeral
- [ ] Adding the new tuple type to the Klyshko Integration Interface (KII) and to the existing CRG implementations
[EGK+20] Daniel Escudero, Satrajit Ghosh, Marcel Keller, Rahul Rachuri, and Peter Scholl. Improved primitives for MPC over mixed arithmetic-binary circuits. In Daniele Micciancio and Thomas Ristenpart, editors, CRYPTO 2020, Part II, volume 12171 of LNCS, pages 823–852. Springer, Heidelberg, August 2020 ([PDF](https://eprint.iacr.org/2020/338.pdf))
|
1.0
|
Add support for edaBits - _Extended doubly-authenticated bits_ (edaBits) [EGK+20] are CR tuples composed of a secret shared integer in the arithmetic domain combined with its bit decomposition shared in the binary domain. They are used for MPC circuits that need to switch between arithmetic and binary representation.
Implementing edaBit support requires
- [ ] Providing support for storing and retrieving the new tuple type in Castor
- [ ] Fetching and feeding the new tuple type in Ephemeral
- [ ] Adding the new tuple type to the Klyshko Integration Interface (KII) and to the existing CRG implementations
[EGK+20] Daniel Escudero, Satrajit Ghosh, Marcel Keller, Rahul Rachuri, and Peter Scholl. Improved primitives for MPC over mixed arithmetic-binary circuits. In Daniele Micciancio and Thomas Ristenpart, editors, CRYPTO 2020, Part II, volume 12171 of LNCS, pages 823–852. Springer, Heidelberg, August 2020 ([PDF](https://eprint.iacr.org/2020/338.pdf))
|
non_test
|
add support for edabits extended doubly authenticated bits edabits are cr tuples composed of a secret shared integer in the arithmetic domain combined with its bit decomposition shared in the binary domain they are used for mpc circuits that need to switch between arithmetic and binary representation implementing edabit support requires providing support for storing and retrieving the new tuple type in castor fetching and feeding the new tuple type in ephemeral adding the new tuple type to the klyshko integration interface kii and to the existing crg implementations daniel escudero satrajit ghosh marcel keller rahul rachuri and peter scholl improved primitives for mpc over mixed arithmetic binary circuits in daniele micciancio and thomas ristenpart editors crypto part ii volume of lncs pages – springer heidelberg august
| 0
|
24,247
| 7,470,696,283
|
IssuesEvent
|
2018-04-03 06:31:51
|
openshiftio/openshift.io
|
https://api.github.com/repos/openshiftio/openshift.io
|
reopened
|
Lots of config errors on jenkins startup
|
SEV3-medium area/jenkins team/build-cd type/bug
|
Yesterday an update to OpenShift went in to the the latest CVEs [1]. That update made secrets and configmaps mounts go read-only.
Presumably on startup jenkins tries to update the files mounted from configmap before it copies it to /var/lib/jenkins. That doesn't work anymore. The file from the configmap mount should be copied elsewhere and updated there.
[1] kubernetes/kubernetes#60814
```
OPENSHIFT_JENKINS_JVM_ARCH is set to i686 so using 32 bit Java
mkdir: cannot create directory '/var/lib/jenkins/logs': File exists
No resources found.
No resources found.
Generating kubernetes-plugin configuration (/opt/openshift/configuration/config.xml.tpl) ...
/usr/libexec/s2i/run: line 111: /opt/openshift/configuration/config.xml: Read-only file system
Generating kubernetes-plugin credentials (/var/lib/jenkins/credentials.xml.tpl) ...
/usr/libexec/s2i/run: line 123: /opt/openshift/configuration/credentials.xml: Read-only file system
Copying Jenkins configuration to /var/lib/jenkins ...
rm: cannot remove '/opt/openshift/configuration/config.xml.tpl': Read-only file system
rm: cannot remove '/opt/openshift/configuration/credentials.xml.tpl': Read-only file system
rm: cannot remove '/opt/openshift/configuration/hudson.tasks.Maven.xml': Read-only file system
rm: cannot remove '/opt/openshift/configuration/io.fabric8.jenkins.openshiftsync.GlobalPluginConfiguration.xml': Read-only file system
rm: cannot remove '/opt/openshift/configuration/jenkins.plugins.nodejs.tools.NodeJSInstallation.xml': Read-only file system
rm: cannot remove '/opt/openshift/configuration/org.jenkinsci.main.modules.sshd.SSHD.xml': Read-only file system
rm: cannot remove '/opt/openshift/configuration/org.jenkinsci.plugins.updatebot.GlobalPluginConfiguration.xml': Read-only file system
rm: cannot remove '/opt/openshift/configuration/scriptApproval.xml': Read-only file system
Copying 143 Jenkins plugins to /var/lib/jenkins ...
Creating initial Jenkins 'admin' user ...
sed: can't read /var/lib/jenkins/users/admin/config.xml: No such file or directory
Running from: /usr/lib/jenkins/jenkins.war
webroot: EnvVars.masterEnvVars.get("JENKINS_HOME")
Mar 15, 2018 12:01:05 AM Main deleteWinstoneTempContents
WARNING: Failed to delete the temporary Winstone file /tmp/winstone/jenkins.war
Mar 15, 2018 12:01:05 AM org.eclipse.jetty.util.log.Log initialized
INFO: Logging initialized @1221ms to org.eclipse.jetty.util.log.JavaUtilLog
Mar 15, 2018 12:01:06 AM winstone.Logger logInternal
INFO: Beginning extraction from war file
Mar 15, 2018 12:01:06 AM org.eclipse.jetty.server.handler.ContextHandler setContextPath
WARNING: Empty contextPath
Mar 15, 2018 12:01:06 AM org.eclipse.jetty.server.Server doStart
INFO: jetty-9.4.z-SNAPSHOT
Mar 15, 2018 12:01:07 AM org.eclipse.jetty.webapp.StandardDescriptorProcessor visitServlet
INFO: NO JSP Support for /, did not find org.eclipse.jetty.jsp.JettyJspServlet
Mar 15, 2018 12:01:08 AM org.eclipse.jetty.server.session.DefaultSessionIdManager doStart
INFO: DefaultSessionIdManager workerName=node0
Mar 15, 2018 12:01:08 AM org.eclipse.jetty.server.session.DefaultSessionIdManager doStart
INFO: No SessionScavenger set, using defaults
Mar 15, 2018 12:01:08 AM org.eclipse.jetty.server.session.HouseKeeper startScavenging
INFO: Scavenging every 660000ms
Jenkins home directory: /var/lib/jenkins found at: EnvVars.masterEnvVars.get("JENKINS_HOME")
Mar 15, 2018 12:01:09 AM org.eclipse.jetty.server.handler.ContextHandler doStart
INFO: Started w.@112aa7c{/,file:///var/lib/jenkins/war/,AVAILABLE}{/var/lib/jenkins/war}
Mar 15, 2018 12:01:09 AM org.eclipse.jetty.server.AbstractConnector doStart
INFO: Started ServerConnector@1cb6996{HTTP/1.1,[http/1.1]}{0.0.0.0:8080}
Mar 15, 2018 12:01:09 AM org.eclipse.jetty.server.Server doStart
INFO: Started @5077ms
Mar 15, 2018 12:01:09 AM winstone.Logger logInternal
INFO: Winstone Servlet Engine v4.0 running: controlPort=disabled
Mar 15, 2018 12:01:11 AM jenkins.InitReactorRunner$1 onAttained
INFO: Started initialization
```
|
1.0
|
Lots of config errors on jenkins startup - Yesterday an update to OpenShift went in to the the latest CVEs [1]. That update made secrets and configmaps mounts go read-only.
Presumably on startup jenkins tries to update the files mounted from configmap before it copies it to /var/lib/jenkins. That doesn't work anymore. The file from the configmap mount should be copied elsewhere and updated there.
[1] kubernetes/kubernetes#60814
```
OPENSHIFT_JENKINS_JVM_ARCH is set to i686 so using 32 bit Java
mkdir: cannot create directory '/var/lib/jenkins/logs': File exists
No resources found.
No resources found.
Generating kubernetes-plugin configuration (/opt/openshift/configuration/config.xml.tpl) ...
/usr/libexec/s2i/run: line 111: /opt/openshift/configuration/config.xml: Read-only file system
Generating kubernetes-plugin credentials (/var/lib/jenkins/credentials.xml.tpl) ...
/usr/libexec/s2i/run: line 123: /opt/openshift/configuration/credentials.xml: Read-only file system
Copying Jenkins configuration to /var/lib/jenkins ...
rm: cannot remove '/opt/openshift/configuration/config.xml.tpl': Read-only file system
rm: cannot remove '/opt/openshift/configuration/credentials.xml.tpl': Read-only file system
rm: cannot remove '/opt/openshift/configuration/hudson.tasks.Maven.xml': Read-only file system
rm: cannot remove '/opt/openshift/configuration/io.fabric8.jenkins.openshiftsync.GlobalPluginConfiguration.xml': Read-only file system
rm: cannot remove '/opt/openshift/configuration/jenkins.plugins.nodejs.tools.NodeJSInstallation.xml': Read-only file system
rm: cannot remove '/opt/openshift/configuration/org.jenkinsci.main.modules.sshd.SSHD.xml': Read-only file system
rm: cannot remove '/opt/openshift/configuration/org.jenkinsci.plugins.updatebot.GlobalPluginConfiguration.xml': Read-only file system
rm: cannot remove '/opt/openshift/configuration/scriptApproval.xml': Read-only file system
Copying 143 Jenkins plugins to /var/lib/jenkins ...
Creating initial Jenkins 'admin' user ...
sed: can't read /var/lib/jenkins/users/admin/config.xml: No such file or directory
Running from: /usr/lib/jenkins/jenkins.war
webroot: EnvVars.masterEnvVars.get("JENKINS_HOME")
Mar 15, 2018 12:01:05 AM Main deleteWinstoneTempContents
WARNING: Failed to delete the temporary Winstone file /tmp/winstone/jenkins.war
Mar 15, 2018 12:01:05 AM org.eclipse.jetty.util.log.Log initialized
INFO: Logging initialized @1221ms to org.eclipse.jetty.util.log.JavaUtilLog
Mar 15, 2018 12:01:06 AM winstone.Logger logInternal
INFO: Beginning extraction from war file
Mar 15, 2018 12:01:06 AM org.eclipse.jetty.server.handler.ContextHandler setContextPath
WARNING: Empty contextPath
Mar 15, 2018 12:01:06 AM org.eclipse.jetty.server.Server doStart
INFO: jetty-9.4.z-SNAPSHOT
Mar 15, 2018 12:01:07 AM org.eclipse.jetty.webapp.StandardDescriptorProcessor visitServlet
INFO: NO JSP Support for /, did not find org.eclipse.jetty.jsp.JettyJspServlet
Mar 15, 2018 12:01:08 AM org.eclipse.jetty.server.session.DefaultSessionIdManager doStart
INFO: DefaultSessionIdManager workerName=node0
Mar 15, 2018 12:01:08 AM org.eclipse.jetty.server.session.DefaultSessionIdManager doStart
INFO: No SessionScavenger set, using defaults
Mar 15, 2018 12:01:08 AM org.eclipse.jetty.server.session.HouseKeeper startScavenging
INFO: Scavenging every 660000ms
Jenkins home directory: /var/lib/jenkins found at: EnvVars.masterEnvVars.get("JENKINS_HOME")
Mar 15, 2018 12:01:09 AM org.eclipse.jetty.server.handler.ContextHandler doStart
INFO: Started w.@112aa7c{/,file:///var/lib/jenkins/war/,AVAILABLE}{/var/lib/jenkins/war}
Mar 15, 2018 12:01:09 AM org.eclipse.jetty.server.AbstractConnector doStart
INFO: Started ServerConnector@1cb6996{HTTP/1.1,[http/1.1]}{0.0.0.0:8080}
Mar 15, 2018 12:01:09 AM org.eclipse.jetty.server.Server doStart
INFO: Started @5077ms
Mar 15, 2018 12:01:09 AM winstone.Logger logInternal
INFO: Winstone Servlet Engine v4.0 running: controlPort=disabled
Mar 15, 2018 12:01:11 AM jenkins.InitReactorRunner$1 onAttained
INFO: Started initialization
```
|
non_test
|
lots of config errors on jenkins startup yesterday an update to openshift went in to the the latest cves that update made secrets and configmaps mounts go read only presumably on startup jenkins tries to update the files mounted from configmap before it copies it to var lib jenkins that doesn t work anymore the file from the configmap mount should be copied elsewhere and updated there kubernetes kubernetes openshift jenkins jvm arch is set to so using bit java mkdir cannot create directory var lib jenkins logs file exists no resources found no resources found generating kubernetes plugin configuration opt openshift configuration config xml tpl usr libexec run line opt openshift configuration config xml read only file system generating kubernetes plugin credentials var lib jenkins credentials xml tpl usr libexec run line opt openshift configuration credentials xml read only file system copying jenkins configuration to var lib jenkins rm cannot remove opt openshift configuration config xml tpl read only file system rm cannot remove opt openshift configuration credentials xml tpl read only file system rm cannot remove opt openshift configuration hudson tasks maven xml read only file system rm cannot remove opt openshift configuration io jenkins openshiftsync globalpluginconfiguration xml read only file system rm cannot remove opt openshift configuration jenkins plugins nodejs tools nodejsinstallation xml read only file system rm cannot remove opt openshift configuration org jenkinsci main modules sshd sshd xml read only file system rm cannot remove opt openshift configuration org jenkinsci plugins updatebot globalpluginconfiguration xml read only file system rm cannot remove opt openshift configuration scriptapproval xml read only file system copying jenkins plugins to var lib jenkins creating initial jenkins admin user sed can t read var lib jenkins users admin config xml no such file or directory running from usr lib jenkins jenkins war webroot envvars masterenvvars get jenkins home mar am main deletewinstonetempcontents warning failed to delete the temporary winstone file tmp winstone jenkins war mar am org eclipse jetty util log log initialized info logging initialized to org eclipse jetty util log javautillog mar am winstone logger loginternal info beginning extraction from war file mar am org eclipse jetty server handler contexthandler setcontextpath warning empty contextpath mar am org eclipse jetty server server dostart info jetty z snapshot mar am org eclipse jetty webapp standarddescriptorprocessor visitservlet info no jsp support for did not find org eclipse jetty jsp jettyjspservlet mar am org eclipse jetty server session defaultsessionidmanager dostart info defaultsessionidmanager workername mar am org eclipse jetty server session defaultsessionidmanager dostart info no sessionscavenger set using defaults mar am org eclipse jetty server session housekeeper startscavenging info scavenging every jenkins home directory var lib jenkins found at envvars masterenvvars get jenkins home mar am org eclipse jetty server handler contexthandler dostart info started w file var lib jenkins war available var lib jenkins war mar am org eclipse jetty server abstractconnector dostart info started serverconnector http mar am org eclipse jetty server server dostart info started mar am winstone logger loginternal info winstone servlet engine running controlport disabled mar am jenkins initreactorrunner onattained info started initialization
| 0
|
216,718
| 16,812,546,681
|
IssuesEvent
|
2021-06-17 01:00:01
|
timberio/vector
|
https://api.github.com/repos/timberio/vector
|
closed
|
Flakey `simple_checkpoint` test in kubernetes e2e tests
|
domain: tests platform: kubernetes source: kubernetes_logs type: bug
|
This seems to occur more often in CI than locally, and I can't regularly reproduce the problem.
We fail on this line: https://github.com/timberio/vector/blob/bc3baa9863b5dba8faa2d00e515246e4b7127009/lib/k8s-e2e-tests/tests/vector-agent.rs#L1924
|
1.0
|
Flakey `simple_checkpoint` test in kubernetes e2e tests - This seems to occur more often in CI than locally, and I can't regularly reproduce the problem.
We fail on this line: https://github.com/timberio/vector/blob/bc3baa9863b5dba8faa2d00e515246e4b7127009/lib/k8s-e2e-tests/tests/vector-agent.rs#L1924
|
test
|
flakey simple checkpoint test in kubernetes tests this seems to occur more often in ci than locally and i can t regularly reproduce the problem we fail on this line
| 1
|
201,369
| 15,191,731,859
|
IssuesEvent
|
2021-02-15 20:30:19
|
tmiland/Invidious-Updater
|
https://api.github.com/repos/tmiland/Invidious-Updater
|
closed
|
Let's Encrypt integration if domain is configured
|
enhancement needs testing
|
**Is your feature request related to a problem? Please describe.**
Issuing Let's Encrypt certificates is easy and certbot (or alternative tools) are widely available to automatically sign certificates.
it would be nice if certificates could be issued using Invidious Updater (the script would call certbot as it does with Nginx auto installer), and if the certificate were installed automatically, either by configuring Invidious directly, or using the VHost (which already uses Let's Encrypt certificate in its default configuration).
**Describe the solution you'd like**
During the install process, if a domain is provided, the user should have the possibility to install a certificate for the domain.
If the user decides to install Nginx Vhost, the configuration set in Invidious should be updated to transfer the certificate handling to Nginx (remove SSL configuration ? I am not knowledgeable enough to be sure about this).
**Describe alternatives you've considered**
Installing the certificate manually might be a bit confusing for new users or people without high tech skills.
|
1.0
|
Let's Encrypt integration if domain is configured - **Is your feature request related to a problem? Please describe.**
Issuing Let's Encrypt certificates is easy and certbot (or alternative tools) are widely available to automatically sign certificates.
it would be nice if certificates could be issued using Invidious Updater (the script would call certbot as it does with Nginx auto installer), and if the certificate were installed automatically, either by configuring Invidious directly, or using the VHost (which already uses Let's Encrypt certificate in its default configuration).
**Describe the solution you'd like**
During the install process, if a domain is provided, the user should have the possibility to install a certificate for the domain.
If the user decides to install Nginx Vhost, the configuration set in Invidious should be updated to transfer the certificate handling to Nginx (remove SSL configuration ? I am not knowledgeable enough to be sure about this).
**Describe alternatives you've considered**
Installing the certificate manually might be a bit confusing for new users or people without high tech skills.
|
test
|
let s encrypt integration if domain is configured is your feature request related to a problem please describe issuing let s encrypt certificates is easy and certbot or alternative tools are widely available to automatically sign certificates it would be nice if certificates could be issued using invidious updater the script would call certbot as it does with nginx auto installer and if the certificate were installed automatically either by configuring invidious directly or using the vhost which already uses let s encrypt certificate in its default configuration describe the solution you d like during the install process if a domain is provided the user should have the possibility to install a certificate for the domain if the user decides to install nginx vhost the configuration set in invidious should be updated to transfer the certificate handling to nginx remove ssl configuration i am not knowledgeable enough to be sure about this describe alternatives you ve considered installing the certificate manually might be a bit confusing for new users or people without high tech skills
| 1
|
275,678
| 23,930,014,361
|
IssuesEvent
|
2022-09-10 11:54:56
|
pmgbergen/porepy
|
https://api.github.com/repos/pmgbergen/porepy
|
opened
|
Unit test from `test_interpolation(dim, factory)` failing
|
bug - test
|
Build Test caught the raised the following error when running scheduled tests:
FAILED tests/unit/test_interpolation_tables.py::test_interpolation[_QuadraticFunc-4]
This mostly indicates an issue when randomly generated values are used in the test.
|
1.0
|
Unit test from `test_interpolation(dim, factory)` failing - Build Test caught the raised the following error when running scheduled tests:
FAILED tests/unit/test_interpolation_tables.py::test_interpolation[_QuadraticFunc-4]
This mostly indicates an issue when randomly generated values are used in the test.
|
test
|
unit test from test interpolation dim factory failing build test caught the raised the following error when running scheduled tests failed tests unit test interpolation tables py test interpolation this mostly indicates an issue when randomly generated values are used in the test
| 1
|
645,452
| 21,004,985,015
|
IssuesEvent
|
2022-03-29 21:31:37
|
popovs/OPPtools
|
https://api.github.com/repos/popovs/OPPtools
|
closed
|
For low sample size reports, add option to save raw tracks/points
|
high priority
|
Reports with a high enough sample size provide the option to save the shapefile output of `opp_sites`. However, we need to add functionality to save either raw data points/tracks (pending Megan's input) for reports with low sample sizes.
|
1.0
|
For low sample size reports, add option to save raw tracks/points - Reports with a high enough sample size provide the option to save the shapefile output of `opp_sites`. However, we need to add functionality to save either raw data points/tracks (pending Megan's input) for reports with low sample sizes.
|
non_test
|
for low sample size reports add option to save raw tracks points reports with a high enough sample size provide the option to save the shapefile output of opp sites however we need to add functionality to save either raw data points tracks pending megan s input for reports with low sample sizes
| 0
|
18,917
| 10,266,522,281
|
IssuesEvent
|
2019-08-22 21:42:03
|
inspec/inspec-vault
|
https://api.github.com/repos/inspec/inspec-vault
|
opened
|
Cache input values
|
Aspect/Performance Triage/Feature Request
|
<!--- Provide a general summary of the requested feature in the Title above. -->
<!--- Also, please be aware of our [Code of Conduct](https://www.chef.io/code-of-conduct/). -->
## Detailed Description
<!--- Provide a detailed description of the change or addition you are proposing -->
Assuming that a profile is stored as a document, and inputs are stored as key-values on a document, fetching a single key is expensive - you have to fetch all keys / inputs.
Might as well cache them.
## Context
<!--- Why is this change important to you? How would you use it? -->
It would be faster, less network traffic, not hammer the Vault server.
## Possible Implementation
<!--- Not obligatory, but suggest an idea for implementing addition or change -->
|
True
|
Cache input values - <!--- Provide a general summary of the requested feature in the Title above. -->
<!--- Also, please be aware of our [Code of Conduct](https://www.chef.io/code-of-conduct/). -->
## Detailed Description
<!--- Provide a detailed description of the change or addition you are proposing -->
Assuming that a profile is stored as a document, and inputs are stored as key-values on a document, fetching a single key is expensive - you have to fetch all keys / inputs.
Might as well cache them.
## Context
<!--- Why is this change important to you? How would you use it? -->
It would be faster, less network traffic, not hammer the Vault server.
## Possible Implementation
<!--- Not obligatory, but suggest an idea for implementing addition or change -->
|
non_test
|
cache input values detailed description assuming that a profile is stored as a document and inputs are stored as key values on a document fetching a single key is expensive you have to fetch all keys inputs might as well cache them context it would be faster less network traffic not hammer the vault server possible implementation
| 0
|
122,589
| 26,147,260,587
|
IssuesEvent
|
2022-12-30 07:43:00
|
KLG-Software-Development/klbot
|
https://api.github.com/repos/KLG-Software-Development/klbot
|
closed
|
删除`/klbotlib/MessageServer/Mirai/MiraiMessageServer.cs`中无用的`_networkTask`历史遗留字段
|
optimization code improvement
|
另外,需要将`IMessageServer`中返回`Task<Exception?>`的API改为`Task`,并删除相应的历史遗留代码。
|
1.0
|
删除`/klbotlib/MessageServer/Mirai/MiraiMessageServer.cs`中无用的`_networkTask`历史遗留字段 - 另外,需要将`IMessageServer`中返回`Task<Exception?>`的API改为`Task`,并删除相应的历史遗留代码。
|
non_test
|
删除 klbotlib messageserver mirai miraimessageserver cs 中无用的 networktask 历史遗留字段 另外,需要将 imessageserver 中返回 task 的api改为 task ,并删除相应的历史遗留代码。
| 0
|
260,798
| 22,648,438,315
|
IssuesEvent
|
2022-07-01 11:03:10
|
wazuh/wazuh-qa
|
https://api.github.com/repos/wazuh/wazuh-qa
|
opened
|
Tests development - Test for new FIM DB sync options
|
team/qa type/tests-development status/not-tracked
|
| Target version | Related issue | Related PR/dev branch |
|--------------------|--------------------|-----------------|
| 4.5 | https://github.com/wazuh/wazuh/issues/14069 | TBD |
<!-- Important: No section may be left blank. If not, delete it directly (in principle only "Configurations" and "Considerations" could be left blank in case of not proceeding). -->
## Description
In https://github.com/wazuh/wazuh/issues/14069 we have been developing a new option for the FIM synchronization mechanism in order to avoid overlapping two syncrhoniations.
The options are:
- response_timeout
- max_interval
While the agent is performing the synchronization process and it has sent or receive a message from the manager, that syncrhonization is marked as failed and the interval is doubled until max_interval is reached.
Then, if there has been `response_timout` since the last sent or received message, the synchronization is marked as completed and the synchronization interval is set to the original value.
```
l message: {"component":"fim_file","data":{"attributes":{"attributes":"","checksum":"1ba6799a1a04442ae2a5e21d91a1e88b7c8c6e19","gid":"0","group_name":"root","hash_md5":"d41d8cd98f00b204e9800998ecf8427e","hash_sha1":"da39a3ee5e6b4b0d3255bfef95601890afd80709","hash_sha256":"e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855","inode":281519,"mtime":1656663120,"perm":"rw-r--r--","size":0,"type":"file","uid":"0","user_name":"root"},"index":"/home/vagrant/test/Test_753","timestamp":1656663666},"type":"state"}
2022/07/01 08:22:18 2022/07/01 08:22:18 wazuh-syscheckd[10801] logging_helper.c:65 at loggingFunction(): wazuh-syscheckd[10801] run_check.c:113 at fim_send_sync_state(): DEBUG: (6317): Sending integrity control message: {"component":"fim_file","data":{"attributes":{"attributes":"","checksum":"3bc290ceda08d9531f85cea22d35714c198fe3b5","gid":"0","group_name":"root","hash_md5":"d41d8cd98f00b204e9800998ecf8427e","hash_sha1":"da39a3ee5e6b4b0d3255bfef95601890afd80709","hash_sha256":"e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855","inode":281540,"mtime":1656663120,"perm":"rw-r--r--","size":0,"type":"file","uid":"0","user_name":"root"},"index":"/home/vagrant/test/Test_774","timestamp":1656663666},"type":"state"}
DEBUG: Synchronization has failed, sync interval will be doubled, current interval: 80
2022/07/01 08:22:19 wazuh-syscheckd[10801] run_check.c:113 at fim_send_sync_state(): DEBUG: (6317): Sending integrity control message: {"component":"fim_file","data":{"attributes":{"attributes":"","checksum":"674c3953777a0ef3e7d63edfb4eb7fb8bf88b602","gid":"0","group_name":"root","hash_md5":"d41d8cd98f00b204e9800998ecf8427e","hash_sha1":"da39a3ee5e6b4b0d3255bfef95601890afd80709","hash_sha256":"e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855","inode":281553,"mtime":1656663120,"perm":"rw-r--r--","size":0,"type":"file","uid":"0","user_name":"root"},"index":"/home/vagrant/test/Test_787","timestamp":1656663666},"type":"state"}
2022/07/01 08:22:20 wazuh-syscheckd[10801] run_check.c:113 at fim_send_sync_state(): DEBUG: (6317): Sending integrity control message: {"component":"fim_file","data":{"attributes":{"attributes":"","checksum":"fc1e8c0f67a56184a75d62d80221b74b9f4271d0","gid":"0","group_name":"root","hash_md5":"d41d8cd98f00b204e9800998ecf8427e","hash_sha1":"da39a3ee5e6b4b0d3255bfef95601890afd80709","hash_sha256":"e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855","inode":281564,"mtime":1656663120,"perm":"rw-r--r--","size":0,"type":"file","uid":"0","user_name":"root"},"index":"/home/vagrant/test/Test_798","timestamp":1656663666},"type":"state"}
2022/07/01 08:22:21 wazuh-syscheckd[10801] run_check.c:113 at fim_send_sync_state(): DEBUG: (6317): Sending integrity control message: {"component":"fim_file","data":{"attributes":{"attributes":"","checksum":"ee50658c312b55e69fc1271aa8a8b91a5ede5d48","gid":"0","group_name":"root","hash_md5":"d41d8cd98f00b204e9800998ecf8427e","hash_sha1":"da39a3ee5e6b4b0d3255bfef95601890afd80709","hash_sha256":"e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855","inode":281585,"mtime":1656663120,"perm":"rw-r--r--","size":0,"type":"file","uid":"0","user_name":"root"},"index":"/home/vagrant/test/Test_819","timestamp":1656663666},"type":"state"}
2022/07/01 08:22:22 wazuh-syscheckd[10801] run_check.c:113 at fim_send_sync_state(): DEBUG: (6317): Sending integrity control message: {"component":"fim_file","data":{"attributes":{"attributes":"","checksum":"c2da4687fbc668b726a3b01b7c3ce39cf0393dfc","gid":"0","group_name":"root","hash_md5":"d41d8cd98f00b204e9800998ecf8427e","hash_sha1":"da39a3ee5e6b4b0d3255bfef95601890afd80709","hash_sha256":"e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855","inode":280848,"mtime":1656663119,"perm":"rw-r--r--","size":0,"type":"file","uid":"0","user_name":"root"},"index":"/home/vagrant/test/Test_82","timestamp":1656663666},"type":"state"}
2022/07/01 08:22:23 wazuh-syscheckd[10801] run_check.c:113 at fim_send_sync_state(): DEBUG: (6317): Sending integrity control message: {"component":"fim_file","data":{"attributes":{"attributes":"","checksum":"7e0fa808583df389f68c221e4236c56b2bd66936","gid":"0","group_name":"root","hash_md5":"d41d8cd98f00b204e9800998ecf8427e","hash_sha1":"da39a3ee5e6b4b0d3255bfef95601890afd80709","hash_sha256":"e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855","inode":281636,"mtime":1656663120,"perm":"rw-r--r--","size":0,"type":"file","uid":"0","user_name":"root"},"index":"/home/vagrant/test/Test_870","timestamp":1656663666},"type":"state"}
2022/07/01 08:23:38 wazuh-syscheckd[10801] logging_helper.c:62 at loggingFunction(): DEBUG: Executing FIM sync.
2022/07/01 08:23:38 wazuh-syscheckd[10801] run_check.c:113 at fim_send_sync_state(): DEBUG: (6317): Sending integrity control message: {"component":"fim_file","data":{"begin":"/home/vagrant/test/Test_117","checksum":"bdb6ec241635e087bfaf1ced5df049337a207e3e","end":"/home/vagrant/test/Test_870","id":1656663818},"type":"integrity_check_global"}
2022/07/01 08:23:39 wazuh-syscheckd[10801] logging_helper.c:62 at loggingFunction(): DEBUG: Finished FIM sync.
2022/07/01 08:24:59 wazuh-syscheckd[10801] logging_helper.c:65 at loggingFunction(): DEBUG: Interval synchronization has been reset to its original configured value: 10
2022/07/01 08:24:59 wazuh-syscheckd[10801] logging_helper.c:62 at loggingFunction(): DEBUG: Executing FIM sync.
```
## Configurations
<!-- If any configuration has to be applied, it should be indicated as far as possible. -->
```xml
<syscheck>
<synchronization>
<enabled>yes</enabled>
<interval>10</interval>
<max_eps>1</max_eps>
<response_timeout>30s</response_timeout>
<max_interval>1h</max_interval>
</synchronization>
</syscheck>
```
## Proposed test cases
<!-- Indicate the minimum test cases proposed by the developer. -->
We want to check the behavior of the following cases:
- Check when the interval is doubled if the synchronization is marked as unsuccessfull
- Check that the interval won't be bigger than `max_interval`
- Check that when the synchronization is successfull, the interval is restored
|
1.0
|
Tests development - Test for new FIM DB sync options - | Target version | Related issue | Related PR/dev branch |
|--------------------|--------------------|-----------------|
| 4.5 | https://github.com/wazuh/wazuh/issues/14069 | TBD |
<!-- Important: No section may be left blank. If not, delete it directly (in principle only "Configurations" and "Considerations" could be left blank in case of not proceeding). -->
## Description
In https://github.com/wazuh/wazuh/issues/14069 we have been developing a new option for the FIM synchronization mechanism in order to avoid overlapping two syncrhoniations.
The options are:
- response_timeout
- max_interval
While the agent is performing the synchronization process and it has sent or receive a message from the manager, that syncrhonization is marked as failed and the interval is doubled until max_interval is reached.
Then, if there has been `response_timout` since the last sent or received message, the synchronization is marked as completed and the synchronization interval is set to the original value.
```
l message: {"component":"fim_file","data":{"attributes":{"attributes":"","checksum":"1ba6799a1a04442ae2a5e21d91a1e88b7c8c6e19","gid":"0","group_name":"root","hash_md5":"d41d8cd98f00b204e9800998ecf8427e","hash_sha1":"da39a3ee5e6b4b0d3255bfef95601890afd80709","hash_sha256":"e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855","inode":281519,"mtime":1656663120,"perm":"rw-r--r--","size":0,"type":"file","uid":"0","user_name":"root"},"index":"/home/vagrant/test/Test_753","timestamp":1656663666},"type":"state"}
2022/07/01 08:22:18 2022/07/01 08:22:18 wazuh-syscheckd[10801] logging_helper.c:65 at loggingFunction(): wazuh-syscheckd[10801] run_check.c:113 at fim_send_sync_state(): DEBUG: (6317): Sending integrity control message: {"component":"fim_file","data":{"attributes":{"attributes":"","checksum":"3bc290ceda08d9531f85cea22d35714c198fe3b5","gid":"0","group_name":"root","hash_md5":"d41d8cd98f00b204e9800998ecf8427e","hash_sha1":"da39a3ee5e6b4b0d3255bfef95601890afd80709","hash_sha256":"e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855","inode":281540,"mtime":1656663120,"perm":"rw-r--r--","size":0,"type":"file","uid":"0","user_name":"root"},"index":"/home/vagrant/test/Test_774","timestamp":1656663666},"type":"state"}
DEBUG: Synchronization has failed, sync interval will be doubled, current interval: 80
2022/07/01 08:22:19 wazuh-syscheckd[10801] run_check.c:113 at fim_send_sync_state(): DEBUG: (6317): Sending integrity control message: {"component":"fim_file","data":{"attributes":{"attributes":"","checksum":"674c3953777a0ef3e7d63edfb4eb7fb8bf88b602","gid":"0","group_name":"root","hash_md5":"d41d8cd98f00b204e9800998ecf8427e","hash_sha1":"da39a3ee5e6b4b0d3255bfef95601890afd80709","hash_sha256":"e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855","inode":281553,"mtime":1656663120,"perm":"rw-r--r--","size":0,"type":"file","uid":"0","user_name":"root"},"index":"/home/vagrant/test/Test_787","timestamp":1656663666},"type":"state"}
2022/07/01 08:22:20 wazuh-syscheckd[10801] run_check.c:113 at fim_send_sync_state(): DEBUG: (6317): Sending integrity control message: {"component":"fim_file","data":{"attributes":{"attributes":"","checksum":"fc1e8c0f67a56184a75d62d80221b74b9f4271d0","gid":"0","group_name":"root","hash_md5":"d41d8cd98f00b204e9800998ecf8427e","hash_sha1":"da39a3ee5e6b4b0d3255bfef95601890afd80709","hash_sha256":"e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855","inode":281564,"mtime":1656663120,"perm":"rw-r--r--","size":0,"type":"file","uid":"0","user_name":"root"},"index":"/home/vagrant/test/Test_798","timestamp":1656663666},"type":"state"}
2022/07/01 08:22:21 wazuh-syscheckd[10801] run_check.c:113 at fim_send_sync_state(): DEBUG: (6317): Sending integrity control message: {"component":"fim_file","data":{"attributes":{"attributes":"","checksum":"ee50658c312b55e69fc1271aa8a8b91a5ede5d48","gid":"0","group_name":"root","hash_md5":"d41d8cd98f00b204e9800998ecf8427e","hash_sha1":"da39a3ee5e6b4b0d3255bfef95601890afd80709","hash_sha256":"e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855","inode":281585,"mtime":1656663120,"perm":"rw-r--r--","size":0,"type":"file","uid":"0","user_name":"root"},"index":"/home/vagrant/test/Test_819","timestamp":1656663666},"type":"state"}
2022/07/01 08:22:22 wazuh-syscheckd[10801] run_check.c:113 at fim_send_sync_state(): DEBUG: (6317): Sending integrity control message: {"component":"fim_file","data":{"attributes":{"attributes":"","checksum":"c2da4687fbc668b726a3b01b7c3ce39cf0393dfc","gid":"0","group_name":"root","hash_md5":"d41d8cd98f00b204e9800998ecf8427e","hash_sha1":"da39a3ee5e6b4b0d3255bfef95601890afd80709","hash_sha256":"e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855","inode":280848,"mtime":1656663119,"perm":"rw-r--r--","size":0,"type":"file","uid":"0","user_name":"root"},"index":"/home/vagrant/test/Test_82","timestamp":1656663666},"type":"state"}
2022/07/01 08:22:23 wazuh-syscheckd[10801] run_check.c:113 at fim_send_sync_state(): DEBUG: (6317): Sending integrity control message: {"component":"fim_file","data":{"attributes":{"attributes":"","checksum":"7e0fa808583df389f68c221e4236c56b2bd66936","gid":"0","group_name":"root","hash_md5":"d41d8cd98f00b204e9800998ecf8427e","hash_sha1":"da39a3ee5e6b4b0d3255bfef95601890afd80709","hash_sha256":"e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855","inode":281636,"mtime":1656663120,"perm":"rw-r--r--","size":0,"type":"file","uid":"0","user_name":"root"},"index":"/home/vagrant/test/Test_870","timestamp":1656663666},"type":"state"}
2022/07/01 08:23:38 wazuh-syscheckd[10801] logging_helper.c:62 at loggingFunction(): DEBUG: Executing FIM sync.
2022/07/01 08:23:38 wazuh-syscheckd[10801] run_check.c:113 at fim_send_sync_state(): DEBUG: (6317): Sending integrity control message: {"component":"fim_file","data":{"begin":"/home/vagrant/test/Test_117","checksum":"bdb6ec241635e087bfaf1ced5df049337a207e3e","end":"/home/vagrant/test/Test_870","id":1656663818},"type":"integrity_check_global"}
2022/07/01 08:23:39 wazuh-syscheckd[10801] logging_helper.c:62 at loggingFunction(): DEBUG: Finished FIM sync.
2022/07/01 08:24:59 wazuh-syscheckd[10801] logging_helper.c:65 at loggingFunction(): DEBUG: Interval synchronization has been reset to its original configured value: 10
2022/07/01 08:24:59 wazuh-syscheckd[10801] logging_helper.c:62 at loggingFunction(): DEBUG: Executing FIM sync.
```
## Configurations
<!-- If any configuration has to be applied, it should be indicated as far as possible. -->
```xml
<syscheck>
<synchronization>
<enabled>yes</enabled>
<interval>10</interval>
<max_eps>1</max_eps>
<response_timeout>30s</response_timeout>
<max_interval>1h</max_interval>
</synchronization>
</syscheck>
```
## Proposed test cases
<!-- Indicate the minimum test cases proposed by the developer. -->
We want to check the behavior of the following cases:
- Check when the interval is doubled if the synchronization is marked as unsuccessfull
- Check that the interval won't be bigger than `max_interval`
- Check that when the synchronization is successfull, the interval is restored
|
test
|
tests development test for new fim db sync options target version related issue related pr dev branch tbd description in we have been developing a new option for the fim synchronization mechanism in order to avoid overlapping two syncrhoniations the options are response timeout max interval while the agent is performing the synchronization process and it has sent or receive a message from the manager that syncrhonization is marked as failed and the interval is doubled until max interval is reached then if there has been response timout since the last sent or received message the synchronization is marked as completed and the synchronization interval is set to the original value l message component fim file data attributes attributes checksum gid group name root hash hash hash inode mtime perm rw r r size type file uid user name root index home vagrant test test timestamp type state wazuh syscheckd logging helper c at loggingfunction wazuh syscheckd run check c at fim send sync state debug sending integrity control message component fim file data attributes attributes checksum gid group name root hash hash hash inode mtime perm rw r r size type file uid user name root index home vagrant test test timestamp type state debug synchronization has failed sync interval will be doubled current interval wazuh syscheckd run check c at fim send sync state debug sending integrity control message component fim file data attributes attributes checksum gid group name root hash hash hash inode mtime perm rw r r size type file uid user name root index home vagrant test test timestamp type state wazuh syscheckd run check c at fim send sync state debug sending integrity control message component fim file data attributes attributes checksum gid group name root hash hash hash inode mtime perm rw r r size type file uid user name root index home vagrant test test timestamp type state wazuh syscheckd run check c at fim send sync state debug sending integrity control message component fim file data attributes attributes checksum gid group name root hash hash hash inode mtime perm rw r r size type file uid user name root index home vagrant test test timestamp type state wazuh syscheckd run check c at fim send sync state debug sending integrity control message component fim file data attributes attributes checksum gid group name root hash hash hash inode mtime perm rw r r size type file uid user name root index home vagrant test test timestamp type state wazuh syscheckd run check c at fim send sync state debug sending integrity control message component fim file data attributes attributes checksum gid group name root hash hash hash inode mtime perm rw r r size type file uid user name root index home vagrant test test timestamp type state wazuh syscheckd logging helper c at loggingfunction debug executing fim sync wazuh syscheckd run check c at fim send sync state debug sending integrity control message component fim file data begin home vagrant test test checksum end home vagrant test test id type integrity check global wazuh syscheckd logging helper c at loggingfunction debug finished fim sync wazuh syscheckd logging helper c at loggingfunction debug interval synchronization has been reset to its original configured value wazuh syscheckd logging helper c at loggingfunction debug executing fim sync configurations xml yes proposed test cases we want to check the behavior of the following cases check when the interval is doubled if the synchronization is marked as unsuccessfull check that the interval won t be bigger than max interval check that when the synchronization is successfull the interval is restored
| 1
|
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.