id int64 5 1.93M | title stringlengths 0 128 | description stringlengths 0 25.5k | collection_id int64 0 28.1k | published_timestamp timestamp[s] | canonical_url stringlengths 14 581 | tag_list stringlengths 0 120 | body_markdown stringlengths 0 716k | user_username stringlengths 2 30 |
|---|---|---|---|---|---|---|---|---|
1,875,785 | Data Field Encapsulation | Making data fields private protects data and makes the class easy to maintain. The data fields radius... | 0 | 2024-06-03T19:14:18 | https://dev.to/paulike/data-field-encapsulation-4i7b | java, programming, learning, beginners | Making data fields private protects data and makes the class easy to maintain. The data fields **radius** and **numberOfObjects** in the **CircleWithStaticMembers** class in **CircleWithStaticMembers.java** can be modified directly (e.g., **c1.radius = 5** or **CircleWithStaticMembers.numberOfObjects = 10**). This is n... | paulike |
1,875,784 | I'am would like to start a startup | A post by Granger Aj | 0 | 2024-06-03T19:12:14 | https://dev.to/granger_aj_1109fd18d64004/iam-would-like-to-start-a-startup-2ca5 | granger_aj_1109fd18d64004 | ||
1,858,904 | 99okuk | 99ok cung cấp một loạt các trò chơi cá cược, bao gồm Tài Xỉu, Baccarat, Slot, và nhiều trò chơi khác.... | 0 | 2024-05-20T06:27:13 | https://dev.to/99okuk/99okuk-4dbm | 99ok cung cấp một loạt các trò chơi cá cược, bao gồm Tài Xỉu, Baccarat, Slot, và nhiều trò chơi khác. Với sự đa dạng này, người chơi có thể tận hưởng nhiều trải nghiệm giải trí khác nhau trên cùng một nền tảng....
Địa Chỉ: 83/2N ấp Xuân Thới Đông 3, Xuân Thới Đông, Hóc Môn, Thành phố Hồ Chí Minh, Việt Nam
Email: vasili... | 99okuk | |
1,875,783 | Cloud SecOps: Enhancing Security and Operations in the Cloud | Introduction: The Evolution of Cloud Security and Operations In the age of digital transformation,... | 0 | 2024-06-03T19:12:05 | https://dev.to/unicloud/cloud-secops-enhancing-security-and-operations-in-the-cloud-4ol9 | **Introduction: The Evolution of Cloud Security and Operations**
In the age of digital transformation, cloud computing has become a cornerstone of modern IT infrastructure. However, with the increased reliance on cloud services comes the growing need for robust security measures. Cloud Security Operations, or Cloud Se... | unicloud | |
1,875,782 | AWS Blog | Hi All, is there any way to publish Technical blog in AWS? | 0 | 2024-06-03T19:01:42 | https://dev.to/taha_yabali_4015ec5bff54/aws-blog-ijo | Hi All, is there any way to publish Technical blog in AWS? | taha_yabali_4015ec5bff54 | |
1,875,781 | Lifetime access for Limited Users! | Lifetime access for Limited Users! PortfolioBee Home Contact Login Sign up Cart 1 1 item Everything... | 0 | 2024-06-03T19:00:48 | https://dev.to/akashjas1996/lifetime-access-for-limited-users-2ikb | webdev, beginners, javascript, productivity |
Lifetime access for Limited Users!
PortfolioBee
Home
Contact
Login
Sign up
Cart
1
1 item
Everything at a Glance
In today’s competitive job market, standing out is crucial. PortfolioBee lets you present all your skills, achievements, and projects in one visually appealing space. Transform your journey and make a great... | akashjas1996 |
1,875,777 | PUT it at REST | Introduction Understanding REST and Its Rise to Prominence REST (Representational State... | 0 | 2024-06-03T18:57:15 | https://dev.to/jwtiller_c47bdfa134adf302/put-it-at-rest-395a | rest, grpc, signalr, dotnet | ## Introduction
Understanding REST and Its Rise to Prominence
REST (Representational State Transfer) has been the cornerstone of web API design for decades, renowned for its simplicity and effectiveness in integrating various systems over the internet. Initially conceptualized by Roy Fielding in his doctoral dissertati... | jwtiller_c47bdfa134adf302 |
1,875,779 | Visibility Modifiers | Visibility modifiers can be used to specify the visibility of a class and its members. You can use... | 0 | 2024-06-03T18:56:32 | https://dev.to/paulike/visibility-modifiers-1jf4 | java, programming, learning, beginners | Visibility modifiers can be used to specify the visibility of a class and its members. You can use the **public** visibility modifier for classes, methods, and data fields to denote that they can be accessed from any other classes. If no visibility modifier is used, then by default the classes, methods, and data fields... | paulike |
1,875,538 | Declaring Variables in Golang | In Golang (Go) programming, variables are the fundamental building blocks for data storage and... | 0 | 2024-06-03T14:40:11 | https://dev.to/thelady_bella/declaring-variables-in-golang-3kj0 | go | In Golang (Go) programming, variables are the fundamental building blocks for data storage and manipulation. They are containers that hold the values that your code can access and modify, serving as the driving force of any program's functionality. Mastering variable declaration techniques is paramount for writing clea... | thelady_bella |
1,875,778 | Returning HTML With fetch() | You can use the hmpl-js package to load HTML from the server. It works on fetch, so it can help you... | 0 | 2024-06-03T18:55:36 | https://dev.to/antonmak1/returning-html-with-fetch-m1k | webdev, javascript, programming, tutorial | You can use the hmpl-js package to load HTML from the server. It works on `fetch`, so it can help you avoid writing a bunch of code:
```html
<div id="wrapper"></div>
<script src="https://unpkg.com/hmpl-js"></script>
<script>
const templateFn = hmpl.compile(
`<div>
<button class="getHTML">Get HTML!</button>
<... | antonmak1 |
1,875,775 | Insertion Sort Algorithm | Insertion Sort is a straightforward and efficient comparison-based sorting algorithm. The algorithm... | 27,581 | 2024-06-03T18:51:53 | https://blog.masum.dev/insertion-sort-algorithm | algorithms, computerscience, cpp, tutorial | Insertion Sort is a straightforward and efficient comparison-based sorting algorithm. The algorithm works similarly to how you might sort playing cards in your hands. It builds the sorted array one item at a time by taking each element from the unsorted portion and inserting it into its correct position in the sorted p... | masum-dev |
1,875,776 | Understanding the differences between JavaScript, Node.js, and Express.js | What is JavaScript? JavaScript is a popular programming language primarily used to make... | 0 | 2024-06-03T18:48:52 | https://dev.to/richardshaju/understanding-the-differences-between-javascript-nodejs-and-expressjs-5cb9 | javascript, node, express, web | ## What is JavaScript?
JavaScript is a popular programming language primarily used to make websites interactive. When you click a button and something happens on a webpage, it's likely thanks to JavaScript. It's like the magic behind the scenes that makes web pages dynamic and engaging.
- Where is it used? JavaScript... | richardshaju |
1,875,774 | Static Variables, Constants, and Methods | A static variable is shared by all objects of the class. A static method cannot access instance... | 0 | 2024-06-03T18:44:57 | https://dev.to/paulike/static-variables-constants-and-methods-mok | java, programming, learning, beginners | A static variable is shared by all objects of the class. A static method cannot access instance members of the class. The data field **radius** in the circle class is known as an _instance variable_. An instance variable is tied to a specific instance of the class; it is not shared among objects of the same class. For ... | paulike |
1,873,150 | Building in Public | Building in Public is rather quite self-explanatory: Building. In. Public, need I say more?... | 0 | 2024-06-03T17:52:51 | https://dev.to/aws-builders/building-in-public-4e91 | aws, buildinginpublic, cloud, webdev | **Building in Public** is rather quite self-explanatory:
Building. In. Public, need I say more?
Building in Public basically emphasizes and hopes to encourage you to develop the habit of documenting and sharing your journey, as it happens _in near real time_, which is why I have decided to document the development o... | ntombizakhona |
1,875,773 | 🔥🔥🔥 NOTCOIN NEW LISTINGS🔥🔥🔥 | 🚀Notcoin is a rapidly emerging cryptocurrency that has gained significant traction in recent months,... | 0 | 2024-06-03T18:44:26 | https://dev.to/irmakork/notcoin-new-listings-46h4 |
🚀Notcoin is a rapidly emerging cryptocurrency that has gained significant traction in recent months, propelled by social media interest. Its price surged over 300% in the past week alone, reaching a new all-time high. With a growing user base of over 30 million on Telegram, Notcoin is poised to continue its upward tr... | irmakork | |
1,873,950 | Pure SVG color change animation | A first SVG animation, using the animate tag to change between several different colors. 1.... | 0 | 2024-06-03T18:41:57 | https://dev.to/anonymouser/pure-svg-color-change-animation-25id | svg, animation, color, codepen | A first SVG animation, using the animate tag to change between several different colors.
## 1. Create the SVG shape.
This one is just a square `<rect>` 100 pixels long, with a color fill of blue `#0000ff` and a stroke color black `#000000`.
```<svg width="100" height="100" xmlns="http://www.w3.org/2000/svg">
<rect ... | anonymouser |
1,872,386 | The Future of Bug Logging and Internet Security | by Donnie Brown As we navigate through an increasingly digital world, the landscape of internet... | 0 | 2024-06-03T18:39:45 | https://dev.to/owasp/the-future-of-bug-logging-and-internet-security-2fp4 | security, ai | **by Donnie Brown**
As we navigate through an increasingly digital world, the landscape of internet security continues to evolve at a rapid pace. Emerging trends in bug logging and security highlight the critical need for robust, adaptive, and community-driven approaches to safeguard our digital environment. This post... | donnieblt |
1,875,770 | Buy verified cash app account | https://dmhelpshop.com/product/buy-verified-cash-app-account/ Buy verified cash app account Cash app... | 0 | 2024-06-03T18:30:40 | https://dev.to/aawqaa225/buy-verified-cash-app-account-516o | javascript, beginners, programming, tutorial | ERROR: type should be string, got "https://dmhelpshop.com/product/buy-verified-cash-app-account/\n\nBuy verified cash app account\nCash app has emerged as a dominant force in the realm of mobile banking within the USA, offering unparalleled convenience for digital money transfers, deposits, and trading. As the foremost provider of fully verified cash app accounts, we take pride in our ability to deliver accounts with substantial limits. Bitcoin enablement, and an unmatched level of security.\n\nOur commitment to facilitating seamless transactions and enabling digital currency trades has garnered significant acclaim, as evidenced by the overwhelming response from our satisfied clientele. Those seeking buy verified cash app account with 100% legitimate documentation and unrestricted access need look no further. Get in touch with us promptly to acquire your verified cash app account and take advantage of all the benefits it has to offer.\n\nWhy dmhelpshop is the best place to buy USA cash app accounts?\nIt’s crucial to stay informed about any updates to the platform you’re using. If an update has been released, it’s important to explore alternative options. Contact the platform’s support team to inquire about the status of the cash app service.\n\nClearly communicate your requirements and inquire whether they can meet your needs and provide the buy verified cash app account promptly. If they assure you that they can fulfill your requirements within the specified timeframe, proceed with the verification process using the required documents.\n\nOur account verification process includes the submission of the following documents: [List of specific documents required for verification].\n\nGenuine and activated email verified\nRegistered phone number (USA)\nSelfie verified\nSSN (social security number) verified\nDriving license\nBTC enable or not enable (BTC enable best)\n100% replacement guaranteed\n100% customer satisfaction\nWhen it comes to staying on top of the latest platform updates, it’s crucial to act fast and ensure you’re positioned in the best possible place. If you’re considering a switch, reaching out to the right contacts and inquiring about the status of the buy verified cash app account service update is essential.\n\nClearly communicate your requirements and gauge their commitment to fulfilling them promptly. Once you’ve confirmed their capability, proceed with the verification process using genuine and activated email verification, a registered USA phone number, selfie verification, social security number (SSN) verification, and a valid driving license.\n\nAdditionally, assessing whether BTC enablement is available is advisable, buy verified cash app account, with a preference for this feature. It’s important to note that a 100% replacement guarantee and ensuring 100% customer satisfaction are essential benchmarks in this process.\n\nHow to use the Cash Card to make purchases?\nTo activate your Cash Card, open the Cash App on your compatible device, locate the Cash Card icon at the bottom of the screen, and tap on it. Then select “Activate Cash Card” and proceed to scan the QR code on your card. Alternatively, you can manually enter the CVV and expiration date. How To Buy Verified Cash App Accounts.\n\nAfter submitting your information, including your registered number, expiration date, and CVV code, you can start making payments by conveniently tapping your card on a contactless-enabled payment terminal. Consider obtaining a buy verified Cash App account for seamless transactions, especially for business purposes. Buy verified cash app account.\n\nWhy we suggest to unchanged the Cash App account username?\nTo activate your Cash Card, open the Cash App on your compatible device, locate the Cash Card icon at the bottom of the screen, and tap on it. Then select “Activate Cash Card” and proceed to scan the QR code on your card.\n\nAlternatively, you can manually enter the CVV and expiration date. After submitting your information, including your registered number, expiration date, and CVV code, you can start making payments by conveniently tapping your card on a contactless-enabled payment terminal. Consider obtaining a verified Cash App account for seamless transactions, especially for business purposes. Buy verified cash app account. Purchase Verified Cash App Accounts.\n\nSelecting a username in an app usually comes with the understanding that it cannot be easily changed within the app’s settings or options. This deliberate control is in place to uphold consistency and minimize potential user confusion, especially for those who have added you as a contact using your username. In addition, purchasing a Cash App account with verified genuine documents already linked to the account ensures a reliable and secure transaction experience.\n\n \n\nBuy verified cash app accounts quickly and easily for all your financial needs.\nAs the user base of our platform continues to grow, the significance of verified accounts cannot be overstated for both businesses and individuals seeking to leverage its full range of features. How To Buy Verified Cash App Accounts.\n\nFor entrepreneurs, freelancers, and investors alike, a verified cash app account opens the door to sending, receiving, and withdrawing substantial amounts of money, offering unparalleled convenience and flexibility. Whether you’re conducting business or managing personal finances, the benefits of a verified account are clear, providing a secure and efficient means to transact and manage funds at scale.\n\nWhen it comes to the rising trend of purchasing buy verified cash app account, it’s crucial to tread carefully and opt for reputable providers to steer clear of potential scams and fraudulent activities. How To Buy Verified Cash App Accounts. With numerous providers offering this service at competitive prices, it is paramount to be diligent in selecting a trusted source.\n\nThis article serves as a comprehensive guide, equipping you with the essential knowledge to navigate the process of procuring buy verified cash app account, ensuring that you are well-informed before making any purchasing decisions. Understanding the fundamentals is key, and by following this guide, you’ll be empowered to make informed choices with confidence.\n\n \n\nIs it safe to buy Cash App Verified Accounts?\nCash App, being a prominent peer-to-peer mobile payment application, is widely utilized by numerous individuals for their transactions. However, concerns regarding its safety have arisen, particularly pertaining to the purchase of “verified” accounts through Cash App. This raises questions about the security of Cash App’s verification process.\n\nUnfortunately, the answer is negative, as buying such verified accounts entails risks and is deemed unsafe. Therefore, it is crucial for everyone to exercise caution and be aware of potential vulnerabilities when using Cash App. How To Buy Verified Cash App Accounts.\n\nCash App has emerged as a widely embraced platform for purchasing Instagram Followers using PayPal, catering to a diverse range of users. This convenient application permits individuals possessing a PayPal account to procure authenticated Instagram Followers.\n\nLeveraging the Cash App, users can either opt to procure followers for a predetermined quantity or exercise patience until their account accrues a substantial follower count, subsequently making a bulk purchase. Although the Cash App provides this service, it is crucial to discern between genuine and counterfeit items. If you find yourself in search of counterfeit products such as a Rolex, a Louis Vuitton item, or a Louis Vuitton bag, there are two viable approaches to consider.\n\n \n\nWhy you need to buy verified Cash App accounts personal or business?\nThe Cash App is a versatile digital wallet enabling seamless money transfers among its users. However, it presents a concern as it facilitates transfer to both verified and unverified individuals.\n\nTo address this, the Cash App offers the option to become a verified user, which unlocks a range of advantages. Verified users can enjoy perks such as express payment, immediate issue resolution, and a generous interest-free period of up to two weeks. With its user-friendly interface and enhanced capabilities, the Cash App caters to the needs of a wide audience, ensuring convenient and secure digital transactions for all.\n\nIf you’re a business person seeking additional funds to expand your business, we have a solution for you. Payroll management can often be a challenging task, regardless of whether you’re a small family-run business or a large corporation. How To Buy Verified Cash App Accounts.\n\nImproper payment practices can lead to potential issues with your employees, as they could report you to the government. However, worry not, as we offer a reliable and efficient way to ensure proper payroll management, avoiding any potential complications. Our services provide you with the funds you need without compromising your reputation or legal standing. With our assistance, you can focus on growing your business while maintaining a professional and compliant relationship with your employees. Purchase Verified Cash App Accounts.\n\nA Cash App has emerged as a leading peer-to-peer payment method, catering to a wide range of users. With its seamless functionality, individuals can effortlessly send and receive cash in a matter of seconds, bypassing the need for a traditional bank account or social security number. Buy verified cash app account.\n\nThis accessibility makes it particularly appealing to millennials, addressing a common challenge they face in accessing physical currency. As a result, ACash App has established itself as a preferred choice among diverse audiences, enabling swift and hassle-free transactions for everyone. Purchase Verified Cash App Accounts.\n\n \n\nHow to verify Cash App accounts\nTo ensure the verification of your Cash App account, it is essential to securely store all your required documents in your account. This process includes accurately supplying your date of birth and verifying the US or UK phone number linked to your Cash App account.\n\nAs part of the verification process, you will be asked to submit accurate personal details such as your date of birth, the last four digits of your SSN, and your email address. If additional information is requested by the Cash App community to validate your account, be prepared to provide it promptly. Upon successful verification, you will gain full access to managing your account balance, as well as sending and receiving funds seamlessly. Buy verified cash app account.\n\n \n\nHow cash used for international transaction?\nExperience the seamless convenience of this innovative platform that simplifies money transfers to the level of sending a text message. It effortlessly connects users within the familiar confines of their respective currency regions, primarily in the United States and the United Kingdom.\n\nNo matter if you’re a freelancer seeking to diversify your clientele or a small business eager to enhance market presence, this solution caters to your financial needs efficiently and securely. Embrace a world of unlimited possibilities while staying connected to your currency domain. Buy verified cash app account.\n\nUnderstanding the currency capabilities of your selected payment application is essential in today’s digital landscape, where versatile financial tools are increasingly sought after. In this era of rapid technological advancements, being well-informed about platforms such as Cash App is crucial.\n\nAs we progress into the digital age, the significance of keeping abreast of such services becomes more pronounced, emphasizing the necessity of staying updated with the evolving financial trends and options available. Buy verified cash app account.\n\nOffers and advantage to buy cash app accounts cheap?\nWith Cash App, the possibilities are endless, offering numerous advantages in online marketing, cryptocurrency trading, and mobile banking while ensuring high security. As a top creator of Cash App accounts, our team possesses unparalleled expertise in navigating the platform.\n\nWe deliver accounts with maximum security and unwavering loyalty at competitive prices unmatched by other agencies. Rest assured, you can trust our services without hesitation, as we prioritize your peace of mind and satisfaction above all else.\n\nEnhance your business operations effortlessly by utilizing the Cash App e-wallet for seamless payment processing, money transfers, and various other essential tasks. Amidst a myriad of transaction platforms in existence today, the Cash App e-wallet stands out as a premier choice, offering users a multitude of functions to streamline their financial activities effectively. Buy verified cash app account.\n\nTrustbizs.com stands by the Cash App’s superiority and recommends acquiring your Cash App accounts from this trusted source to optimize your business potential.\n\nHow Customizable are the Payment Options on Cash App for Businesses?\nDiscover the flexible payment options available to businesses on Cash App, enabling a range of customization features to streamline transactions. Business users have the ability to adjust transaction amounts, incorporate tipping options, and leverage robust reporting tools for enhanced financial management.\n\nExplore trustbizs.com to acquire verified Cash App accounts with LD backup at a competitive price, ensuring a secure and efficient payment solution for your business needs. Buy verified cash app account.\n\nDiscover Cash App, an innovative platform ideal for small business owners and entrepreneurs aiming to simplify their financial operations. With its intuitive interface, Cash App empowers businesses to seamlessly receive payments and effectively oversee their finances. Emphasizing customization, this app accommodates a variety of business requirements and preferences, making it a versatile tool for all.\n\nWhere To Buy Verified Cash App Accounts\nWhen considering purchasing a verified Cash App account, it is imperative to carefully scrutinize the seller’s pricing and payment methods. Look for pricing that aligns with the market value, ensuring transparency and legitimacy. Buy verified cash app account.\n\nEqually important is the need to opt for sellers who provide secure payment channels to safeguard your financial data. Trust your intuition; skepticism towards deals that appear overly advantageous or sellers who raise red flags is warranted. It is always wise to prioritize caution and explore alternative avenues if uncertainties arise.\n\nThe Importance Of Verified Cash App Accounts\nIn today’s digital age, the significance of verified Cash App accounts cannot be overstated, as they serve as a cornerstone for secure and trustworthy online transactions.\n\nBy acquiring verified Cash App accounts, users not only establish credibility but also instill the confidence required to participate in financial endeavors with peace of mind, thus solidifying its status as an indispensable asset for individuals navigating the digital marketplace.\n\nWhen considering purchasing a verified Cash App account, it is imperative to carefully scrutinize the seller’s pricing and payment methods. Look for pricing that aligns with the market value, ensuring transparency and legitimacy. Buy verified cash app account.\n\nEqually important is the need to opt for sellers who provide secure payment channels to safeguard your financial data. Trust your intuition; skepticism towards deals that appear overly advantageous or sellers who raise red flags is warranted. It is always wise to prioritize caution and explore alternative avenues if uncertainties arise.\n\nConclusion\nEnhance your online financial transactions with verified Cash App accounts, a secure and convenient option for all individuals. By purchasing these accounts, you can access exclusive features, benefit from higher transaction limits, and enjoy enhanced protection against fraudulent activities. Streamline your financial interactions and experience peace of mind knowing your transactions are secure and efficient with verified Cash App accounts.\n\nChoose a trusted provider when acquiring accounts to guarantee legitimacy and reliability. In an era where Cash App is increasingly favored for financial transactions, possessing a verified account offers users peace of mind and ease in managing their finances. Make informed decisions to safeguard your financial assets and streamline your personal transactions effectively.\n\nContact Us / 24 Hours Reply\nTelegram:dmhelpshop\nWhatsApp: +1 (980) 277-2786\nSkype:dmhelpshop\nEmail:dmhelpshop@gmail.com" | aawqaa225 |
1,875,768 | How to link your Blob file storage to Azure SQL database | Step 1: Login to Azure portal and search for storage accounts **First we need to create a... | 0 | 2024-06-03T18:27:23 | https://dev.to/busybrain/how-to-link-your-blob-file-storage-to-azure-sql-database-2d91 | **[Step 1: Login to Azure portal and search for storage accounts](url)**
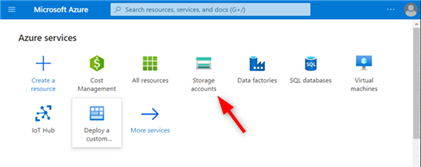
## **First we need to create a Blob file storage before we link it to our SQL database.
Step 2 : Create a file storage **
The first method involves appointing a dedicated architect. This approach centralizes decision-maki... | raphael-dumhart |
1,875,735 | Bubble Sort Algorithm | Bubble Sort is a simple comparison-based sorting algorithm. It repeatedly steps through the list,... | 27,581 | 2024-06-03T18:20:59 | https://blog.masum.dev/bubble-sort-algorithm | algorithms, computerscience, cpp, tutorial | Bubble Sort is a simple comparison-based sorting algorithm. It repeatedly steps through the list, **compares adjacent** elements and **swaps** them if they are in the wrong order. The process is repeated until the list is sorted. This algorithm gets its name because larger elements "bubble" to the top (end) of the list... | masum-dev |
1,875,742 | Output Laravel SQL Query log | You’ve likely encountered many query issues while developing software with Laravel. You might be... | 0 | 2024-06-03T18:19:33 | https://dev.to/bri4n0/output-laravel-sql-query-log-285b | You’ve likely encountered many query issues while developing software with Laravel. You might be wondering why your features are slow or how many queries your function is making to the database. You may not know if you’re experiencing N+1 problems or how to optimize your queries. This package is here to support you wit... | bri4n0 | |
1,875,741 | Key Factors to Consider for Effective Database Design (Constraints, Indexes) | Constraints: Using constraints in database design is essential to enforce data integrity,... | 0 | 2024-06-03T18:17:59 | https://dev.to/_akajuthi_/key-factors-to-consider-for-effective-database-design-constraints-30he | database, sql | ## Constraints:
Using constraints in database design is essential to enforce data integrity, ensure data consistency, and prevent invalid data entry. Here’s when and how to use various constraints effectively:
**1. PRIMARY KEY Constraint**
- **Purpose:** Uniquely identifies each record in a table.
- **When to Use:** ... | _akajuthi_ |
1,875,740 | New Moon This Week! Astrologer Reveals Who Jupiter is Protecting and Who Will Have the Most Luck in Love | Detailed Astrological Forecast for the Week of June 3 to June 9, 2024 The new moon this week marks... | 0 | 2024-06-03T18:16:38 | https://dev.to/press_horoscope/new-moon-this-week-astrologer-reveals-who-jupiter-is-protecting-and-who-will-have-the-most-luck-in-love-1p8b | horoscope, astrology, astro, zodiac | Detailed [Astrological Forecast](https://presshoroskop.com/new-moon-this-week-astrologer-reveals-who-jupiter-is-protecting-and-who-will-have-the-most-luck-in-love/) for the Week of June 3 to June 9, 2024
The new moon this week marks the beginning of a new cycle, a time to plant seeds for our goals and desires. Astrolo... | press_horoscope |
1,875,739 | How to Install MongoDB with OpenSSL 3 Support on Fedora 39 | If you're still having troubles running MongoDB + OpenSSL3 on Fedora, learn how to install it... | 0 | 2024-06-03T18:14:52 | https://dev.to/matheus4lves/how-to-install-mongodb-with-openssl-3-support-on-fedora-39-4nii | mongodb, fedora, linux | If you're still having troubles running MongoDB + OpenSSL3 on Fedora, learn how to install it properly by checking my first article as a freeCodeCamp Publication Contributor: [How to Install MongoDB with OpenSSL 3 Support on Fedora 39](https://www.freecodecamp.org/news/how-to-install-mongodb-with-openssl-3-support-on-f... | matheus4lves |
1,875,738 | Using Classes from the Java Library | The Java API contains a rich set of classes for developing Java programs. This section gives some... | 0 | 2024-06-03T18:14:05 | https://dev.to/paulike/using-classes-from-the-java-library-2jna | java, programming, learning, beginners | The Java API contains a rich set of classes for developing Java programs. This section gives some examples of the classes in the Java library.
## The Date Class
Java provides a system-independent encapsulation of date and time in the **java.util.Date** class, as shown in Figure below.
 container in ASP.NET Core. ASP.NET Core 8 introduces the concept of keyed services to solve this probl... | moh_moh701 |
1,875,733 | testing python code | def test_user_names(first, last): """" a function that prompts for user names """ full_name =... | 0 | 2024-06-03T18:09:24 | https://dev.to/mw_nz_3025915caf4a61ed7/testing-python-code-40ib | programming, beginners, python, learning | def test_user_names(first, last):
"""" a function that prompts for user names """
full_name = first + " " + last
return full_name.title()
guys above is my basic python code which is supposed to prompt for user input, first and last names.
note*.. i have written my file name containing the function above... | mw_nz_3025915caf4a61ed7 |
1,875,731 | Buy Verified Paxful Account | https://dmhelpshop.com/product/buy-verified-paxful-account/ Buy Verified Paxful Account There are... | 0 | 2024-06-03T18:05:23 | https://dev.to/yyrwasti22/buy-verified-paxful-account-4bdf | react, python, ai, devops | ERROR: type should be string, got "https://dmhelpshop.com/product/buy-verified-paxful-account/\n\n\n\n\nBuy Verified Paxful Account\nThere are several compelling reasons to consider purchasing a verified Paxful account. Firstly, a verified account offers enhanced security, providing peace of mind to all users. Additionally, it opens up a wider range of trading opportunities, allowing individuals to partake in various transactions, ultimately expanding their financial horizons.\n\nMoreover, Buy verified Paxful account ensures faster and more streamlined transactions, minimizing any potential delays or inconveniences. Furthermore, by opting for a verified account, users gain access to a trusted and reputable platform, fostering a sense of reliability and confidence.\n\nLastly, Paxful’s verification process is thorough and meticulous, ensuring that only genuine individuals are granted verified status, thereby creating a safer trading environment for all users. Overall, the decision to Buy Verified Paxful account can greatly enhance one’s overall trading experience, offering increased security, access to more opportunities, and a reliable platform to engage with. Buy Verified Paxful Account.\n\nBuy US verified paxful account from the best place dmhelpshop\nWhy we declared this website as the best place to buy US verified paxful account? Because, our company is established for providing the all account services in the USA (our main target) and even in the whole world. With this in mind we create paxful account and customize our accounts as professional with the real documents. Buy Verified Paxful Account.\n\nIf you want to buy US verified paxful account you should have to contact fast with us. Because our accounts are-\n\nEmail verified\nPhone number verified\nSelfie and KYC verified\nSSN (social security no.) verified\nTax ID and passport verified\nSometimes driving license verified\nMasterCard attached and verified\nUsed only genuine and real documents\n100% access of the account\nAll documents provided for customer security\nWhat is Verified Paxful Account?\nIn today’s expanding landscape of online transactions, ensuring security and reliability has become paramount. Given this context, Paxful has quickly risen as a prominent peer-to-peer Bitcoin marketplace, catering to individuals and businesses seeking trusted platforms for cryptocurrency trading.\n\nIn light of the prevalent digital scams and frauds, it is only natural for people to exercise caution when partaking in online transactions. As a result, the concept of a verified account has gained immense significance, serving as a critical feature for numerous online platforms. Paxful recognizes this need and provides a safe haven for users, streamlining their cryptocurrency buying and selling experience.\n\nFor individuals and businesses alike, Buy verified Paxful account emerges as an appealing choice, offering a secure and reliable environment in the ever-expanding world of digital transactions. Buy Verified Paxful Account.\n\nVerified Paxful Accounts are essential for establishing credibility and trust among users who want to transact securely on the platform. They serve as evidence that a user is a reliable seller or buyer, verifying their legitimacy.\n\nBut what constitutes a verified account, and how can one obtain this status on Paxful? In this exploration of verified Paxful accounts, we will unravel the significance they hold, why they are crucial, and shed light on the process behind their activation, providing a comprehensive understanding of how they function. Buy verified Paxful account.\n\n \n\nWhy should to Buy Verified Paxful Account?\nThere are several compelling reasons to consider purchasing a verified Paxful account. Firstly, a verified account offers enhanced security, providing peace of mind to all users. Additionally, it opens up a wider range of trading opportunities, allowing individuals to partake in various transactions, ultimately expanding their financial horizons.\n\nMoreover, a verified Paxful account ensures faster and more streamlined transactions, minimizing any potential delays or inconveniences. Furthermore, by opting for a verified account, users gain access to a trusted and reputable platform, fostering a sense of reliability and confidence. Buy Verified Paxful Account.\n\nLastly, Paxful’s verification process is thorough and meticulous, ensuring that only genuine individuals are granted verified status, thereby creating a safer trading environment for all users. Overall, the decision to buy a verified Paxful account can greatly enhance one’s overall trading experience, offering increased security, access to more opportunities, and a reliable platform to engage with.\n\n \n\nWhat is a Paxful Account\nPaxful and various other platforms consistently release updates that not only address security vulnerabilities but also enhance usability by introducing new features. Buy Verified Paxful Account.\n\nIn line with this, our old accounts have recently undergone upgrades, ensuring that if you purchase an old buy Verified Paxful account from dmhelpshop.com, you will gain access to an account with an impressive history and advanced features. This ensures a seamless and enhanced experience for all users, making it a worthwhile option for everyone.\n\n \n\nIs it safe to buy Paxful Verified Accounts?\nBuying on Paxful is a secure choice for everyone. However, the level of trust amplifies when purchasing from Paxful verified accounts. These accounts belong to sellers who have undergone rigorous scrutiny by Paxful. Buy verified Paxful account, you are automatically designated as a verified account. Hence, purchasing from a Paxful verified account ensures a high level of credibility and utmost reliability. Buy Verified Paxful Account.\n\nPAXFUL, a widely known peer-to-peer cryptocurrency trading platform, has gained significant popularity as a go-to website for purchasing Bitcoin and other cryptocurrencies. It is important to note, however, that while Paxful may not be the most secure option available, its reputation is considerably less problematic compared to many other marketplaces. Buy Verified Paxful Account.\n\nThis brings us to the question: is it safe to purchase Paxful Verified Accounts? Top Paxful reviews offer mixed opinions, suggesting that caution should be exercised. Therefore, users are advised to conduct thorough research and consider all aspects before proceeding with any transactions on Paxful.\n\n \n\nHow Do I Get 100% Real Verified Paxful Accoun?\nPaxful, a renowned peer-to-peer cryptocurrency marketplace, offers users the opportunity to conveniently buy and sell a wide range of cryptocurrencies. Given its growing popularity, both individuals and businesses are seeking to establish verified accounts on this platform.\n\nHowever, the process of creating a verified Paxful account can be intimidating, particularly considering the escalating prevalence of online scams and fraudulent practices. This verification procedure necessitates users to furnish personal information and vital documents, posing potential risks if not conducted meticulously.\n\nIn this comprehensive guide, we will delve into the necessary steps to create a legitimate and verified Paxful account. Our discussion will revolve around the verification process and provide valuable tips to safely navigate through it.\n\nMoreover, we will emphasize the utmost importance of maintaining the security of personal information when creating a verified account. Furthermore, we will shed light on common pitfalls to steer clear of, such as using counterfeit documents or attempting to bypass the verification process.\n\nWhether you are new to Paxful or an experienced user, this engaging paragraph aims to equip everyone with the knowledge they need to establish a secure and authentic presence on the platform.\n\nBenefits Of Verified Paxful Accounts\nVerified Paxful accounts offer numerous advantages compared to regular Paxful accounts. One notable advantage is that verified accounts contribute to building trust within the community.\n\nVerification, although a rigorous process, is essential for peer-to-peer transactions. This is why all Paxful accounts undergo verification after registration. When customers within the community possess confidence and trust, they can conveniently and securely exchange cash for Bitcoin or Ethereum instantly. Buy Verified Paxful Account.\n\nPaxful accounts, trusted and verified by sellers globally, serve as a testament to their unwavering commitment towards their business or passion, ensuring exceptional customer service at all times. Headquartered in Africa, Paxful holds the distinction of being the world’s pioneering peer-to-peer bitcoin marketplace. Spearheaded by its founder, Ray Youssef, Paxful continues to lead the way in revolutionizing the digital exchange landscape.\n\nPaxful has emerged as a favored platform for digital currency trading, catering to a diverse audience. One of Paxful’s key features is its direct peer-to-peer trading system, eliminating the need for intermediaries or cryptocurrency exchanges. By leveraging Paxful’s escrow system, users can trade securely and confidently.\n\nWhat sets Paxful apart is its commitment to identity verification, ensuring a trustworthy environment for buyers and sellers alike. With these user-centric qualities, Paxful has successfully established itself as a leading platform for hassle-free digital currency transactions, appealing to a wide range of individuals seeking a reliable and convenient trading experience. Buy Verified Paxful Account.\n\n \n\nHow paxful ensure risk-free transaction and trading?\nEngage in safe online financial activities by prioritizing verified accounts to reduce the risk of fraud. Platforms like Paxfu implement stringent identity and address verification measures to protect users from scammers and ensure credibility.\n\nWith verified accounts, users can trade with confidence, knowing they are interacting with legitimate individuals or entities. By fostering trust through verified accounts, Paxful strengthens the integrity of its ecosystem, making it a secure space for financial transactions for all users. Buy Verified Paxful Account.\n\nExperience seamless transactions by obtaining a verified Paxful account. Verification signals a user’s dedication to the platform’s guidelines, leading to the prestigious badge of trust. This trust not only expedites trades but also reduces transaction scrutiny. Additionally, verified users unlock exclusive features enhancing efficiency on Paxful. Elevate your trading experience with Verified Paxful Accounts today.\n\nIn the ever-changing realm of online trading and transactions, selecting a platform with minimal fees is paramount for optimizing returns. This choice not only enhances your financial capabilities but also facilitates more frequent trading while safeguarding gains. Buy Verified Paxful Account.\n\nExamining the details of fee configurations reveals Paxful as a frontrunner in cost-effectiveness. Acquire a verified level-3 USA Paxful account from usasmmonline.com for a secure transaction experience. Invest in verified Paxful accounts to take advantage of a leading platform in the online trading landscape.\n\n \n\nHow Old Paxful ensures a lot of Advantages?\n\nExplore the boundless opportunities that Verified Paxful accounts present for businesses looking to venture into the digital currency realm, as companies globally witness heightened profits and expansion. These success stories underline the myriad advantages of Paxful’s user-friendly interface, minimal fees, and robust trading tools, demonstrating its relevance across various sectors.\n\nBusinesses benefit from efficient transaction processing and cost-effective solutions, making Paxful a significant player in facilitating financial operations. Acquire a USA Paxful account effortlessly at a competitive rate from usasmmonline.com and unlock access to a world of possibilities. Buy Verified Paxful Account.\n\nExperience elevated convenience and accessibility through Paxful, where stories of transformation abound. Whether you are an individual seeking seamless transactions or a business eager to tap into a global market, buying old Paxful accounts unveils opportunities for growth.\n\nPaxful’s verified accounts not only offer reliability within the trading community but also serve as a testament to the platform’s ability to empower economic activities worldwide. Join the journey towards expansive possibilities and enhanced financial empowerment with Paxful today. Buy Verified Paxful Account.\n\n \n\nWhy paxful keep the security measures at the top priority?\nIn today’s digital landscape, security stands as a paramount concern for all individuals engaging in online activities, particularly within marketplaces such as Paxful. It is essential for account holders to remain informed about the comprehensive security protocols that are in place to safeguard their information.\n\nSafeguarding your Paxful account is imperative to guaranteeing the safety and security of your transactions. Two essential security components, Two-Factor Authentication and Routine Security Audits, serve as the pillars fortifying this shield of protection, ensuring a secure and trustworthy user experience for all. Buy Verified Paxful Account.\n\nConclusion\nInvesting in Bitcoin offers various avenues, and among those, utilizing a Paxful account has emerged as a favored option. Paxful, an esteemed online marketplace, enables users to engage in buying and selling Bitcoin. Buy Verified Paxful Account.\n\nThe initial step involves creating an account on Paxful and completing the verification process to ensure identity authentication. Subsequently, users gain access to a diverse range of offers from fellow users on the platform. Once a suitable proposal captures your interest, you can proceed to initiate a trade with the respective user, opening the doors to a seamless Bitcoin investing experience.\n\nIn conclusion, when considering the option of purchasing verified Paxful accounts, exercising caution and conducting thorough due diligence is of utmost importance. It is highly recommended to seek reputable sources and diligently research the seller’s history and reviews before making any transactions.\n\nMoreover, it is crucial to familiarize oneself with the terms and conditions outlined by Paxful regarding account verification, bearing in mind the potential consequences of violating those terms. By adhering to these guidelines, individuals can ensure a secure and reliable experience when engaging in such transactions. Buy Verified Paxful Account.\n\n \n\nContact Us / 24 Hours Reply\nTelegram:dmhelpshop\nWhatsApp: +1 (980) 277-2786\nSkype:dmhelpshop\nEmail:dmhelpshop@gmail.com" | yyrwasti22 |
1,875,676 | Combining Inheritance and Polymorphism in Real-World Applications | Introduction Welcome to the final part of our series, "Mastering OOP Concepts: Inheritance... | 27,582 | 2024-06-03T18:02:11 | https://dev.to/techtobe101/combining-inheritance-and-polymorphism-in-real-world-applications-384 | oop, programming, techtobe101, beginners | ### Introduction
Welcome to the final part of our series, "Mastering OOP Concepts: Inheritance and Polymorphism." Today, we’ll look at how inheritance and polymorphism work together in real-world applications.
### Combining Inheritance and Polymorphism
In complex systems, inheritance and polymorphism are often used ... | techtobe101 |
1,875,675 | Diving Deeper into Polymorphism | Introduction Welcome to the second part of our series, "Mastering OOP Concepts:... | 27,582 | 2024-06-03T18:01:53 | https://dev.to/techtobe101/diving-deeper-into-polymorphism-3i0i | oop, programming, techtobe101, beginners | ### Introduction
Welcome to the second part of our series, "Mastering OOP Concepts: Inheritance and Polymorphism." Today, we’ll explore polymorphism, which allows methods to do different things based on the object they are called on.
### What is Polymorphism?
Polymorphism means "many forms." In OOP, it allows you to... | techtobe101 |
1,875,674 | Introduction to Inheritance in Object-Oriented Programming | Introduction Welcome to the first part of our series, "Mastering OOP Concepts: Inheritance... | 27,582 | 2024-06-03T18:00:04 | https://dev.to/techtobe101/introduction-to-inheritance-in-object-oriented-programming-1cg2 | oop, programming, techtobe101, beginners | ### Introduction
Welcome to the first part of our series, "Mastering OOP Concepts: Inheritance and Polymorphism." Today, we’re focusing on inheritance, a key concept in object-oriented programming (OOP) that allows for code reusability and logical organization of classes.
### What is Inheritance?
Inheritance allows ... | techtobe101 |
1,875,727 | Accessing Objects via Reference Variables | An object’s data and methods can be accessed through the dot (.) operator via the object’s reference... | 0 | 2024-06-03T17:57:30 | https://dev.to/paulike/accessing-objects-via-reference-variables-44p7 | java, programming, learning, beginners | An object’s data and methods can be accessed through the dot (**.**) operator via the object’s reference variable. Newly created objects are allocated in the memory. They can be accessed via reference variables.
## Reference Variables and Reference Types
Objects are accessed via the object’s _reference variables_, wh... | paulike |
1,875,725 | Controlled & Uncontrolled Component | Uncontrolled 🔽 In the example, each accordion has its own state(isOpen). By default, it is... | 26,254 | 2024-06-03T17:55:59 | https://dev.to/jorjishasan/controlled-uncontrolled-component-3h3h | webdev, javascript, react, discuss | ## Uncontrolled 🔽
In the example, each accordion has its own state(`isOpen`). By default, it is set to `false`. On click, it flips the value of the state variable(`isOpen`) to `true or false`. Based on the `isOpen` value, it expands and collapses.
Since it controls its own state and doesn't rely on its parents, the... | jorjishasan |
1,875,722 | A Guide to Successful Infotainment System Testing | Mastering infotainment testing becomes pivotal in automotive embedded systems’ intricate and highly... | 0 | 2024-06-03T17:50:14 | https://nyweekly.com/tech/a-guide-to-successful-infotainment-system-testing/ | testing, webdev, mobile, automotives | Mastering infotainment testing becomes pivotal in automotive embedded systems’ intricate and highly technical world. With the advent and progression of intelligent vehicle technology, a seamless user experience has traversed beyond being merely desirable, etching itself as an absolute necessity. Focusing on automotive ... | abhayit2000 |
1,875,721 | Buy verified cash app account | https://dmhelpshop.com/product/buy-verified-cash-app-account/ Buy verified cash app account Cash... | 0 | 2024-06-03T17:48:04 | https://dev.to/yyrwasti22/buy-verified-cash-app-account-k9i | webdev, javascript, beginners, programming | ERROR: type should be string, got "https://dmhelpshop.com/product/buy-verified-cash-app-account/\n\n\n\nBuy verified cash app account\nCash app has emerged as a dominant force in the realm of mobile banking within the USA, offering unparalleled convenience for digital money transfers, deposits, and trading. As the foremost provider of fully verified cash app accounts, we take pride in our ability to deliver accounts with substantial limits. Bitcoin enablement, and an unmatched level of security.\n\nOur commitment to facilitating seamless transactions and enabling digital currency trades has garnered significant acclaim, as evidenced by the overwhelming response from our satisfied clientele. Those seeking buy verified cash app account with 100% legitimate documentation and unrestricted access need look no further. Get in touch with us promptly to acquire your verified cash app account and take advantage of all the benefits it has to offer.\n\nWhy dmhelpshop is the best place to buy USA cash app accounts?\nIt’s crucial to stay informed about any updates to the platform you’re using. If an update has been released, it’s important to explore alternative options. Contact the platform’s support team to inquire about the status of the cash app service.\n\nClearly communicate your requirements and inquire whether they can meet your needs and provide the buy verified cash app account promptly. If they assure you that they can fulfill your requirements within the specified timeframe, proceed with the verification process using the required documents.\n\nOur account verification process includes the submission of the following documents: [List of specific documents required for verification].\n\nGenuine and activated email verified\nRegistered phone number (USA)\nSelfie verified\nSSN (social security number) verified\nDriving license\nBTC enable or not enable (BTC enable best)\n100% replacement guaranteed\n100% customer satisfaction\nWhen it comes to staying on top of the latest platform updates, it’s crucial to act fast and ensure you’re positioned in the best possible place. If you’re considering a switch, reaching out to the right contacts and inquiring about the status of the buy verified cash app account service update is essential.\n\nClearly communicate your requirements and gauge their commitment to fulfilling them promptly. Once you’ve confirmed their capability, proceed with the verification process using genuine and activated email verification, a registered USA phone number, selfie verification, social security number (SSN) verification, and a valid driving license.\n\nAdditionally, assessing whether BTC enablement is available is advisable, buy verified cash app account, with a preference for this feature. It’s important to note that a 100% replacement guarantee and ensuring 100% customer satisfaction are essential benchmarks in this process.\n\nHow to use the Cash Card to make purchases?\nTo activate your Cash Card, open the Cash App on your compatible device, locate the Cash Card icon at the bottom of the screen, and tap on it. Then select “Activate Cash Card” and proceed to scan the QR code on your card. Alternatively, you can manually enter the CVV and expiration date. How To Buy Verified Cash App Accounts.\n\nAfter submitting your information, including your registered number, expiration date, and CVV code, you can start making payments by conveniently tapping your card on a contactless-enabled payment terminal. Consider obtaining a buy verified Cash App account for seamless transactions, especially for business purposes. Buy verified cash app account.\n\nWhy we suggest to unchanged the Cash App account username?\nTo activate your Cash Card, open the Cash App on your compatible device, locate the Cash Card icon at the bottom of the screen, and tap on it. Then select “Activate Cash Card” and proceed to scan the QR code on your card.\n\nAlternatively, you can manually enter the CVV and expiration date. After submitting your information, including your registered number, expiration date, and CVV code, you can start making payments by conveniently tapping your card on a contactless-enabled payment terminal. Consider obtaining a verified Cash App account for seamless transactions, especially for business purposes. Buy verified cash app account. Purchase Verified Cash App Accounts.\n\nSelecting a username in an app usually comes with the understanding that it cannot be easily changed within the app’s settings or options. This deliberate control is in place to uphold consistency and minimize potential user confusion, especially for those who have added you as a contact using your username. In addition, purchasing a Cash App account with verified genuine documents already linked to the account ensures a reliable and secure transaction experience.\n\n \n\nBuy verified cash app accounts quickly and easily for all your financial needs.\nAs the user base of our platform continues to grow, the significance of verified accounts cannot be overstated for both businesses and individuals seeking to leverage its full range of features. How To Buy Verified Cash App Accounts.\n\nFor entrepreneurs, freelancers, and investors alike, a verified cash app account opens the door to sending, receiving, and withdrawing substantial amounts of money, offering unparalleled convenience and flexibility. Whether you’re conducting business or managing personal finances, the benefits of a verified account are clear, providing a secure and efficient means to transact and manage funds at scale.\n\nWhen it comes to the rising trend of purchasing buy verified cash app account, it’s crucial to tread carefully and opt for reputable providers to steer clear of potential scams and fraudulent activities. How To Buy Verified Cash App Accounts. With numerous providers offering this service at competitive prices, it is paramount to be diligent in selecting a trusted source.\n\nThis article serves as a comprehensive guide, equipping you with the essential knowledge to navigate the process of procuring buy verified cash app account, ensuring that you are well-informed before making any purchasing decisions. Understanding the fundamentals is key, and by following this guide, you’ll be empowered to make informed choices with confidence.\n\n \n\nIs it safe to buy Cash App Verified Accounts?\nCash App, being a prominent peer-to-peer mobile payment application, is widely utilized by numerous individuals for their transactions. However, concerns regarding its safety have arisen, particularly pertaining to the purchase of “verified” accounts through Cash App. This raises questions about the security of Cash App’s verification process.\n\nUnfortunately, the answer is negative, as buying such verified accounts entails risks and is deemed unsafe. Therefore, it is crucial for everyone to exercise caution and be aware of potential vulnerabilities when using Cash App. How To Buy Verified Cash App Accounts.\n\nCash App has emerged as a widely embraced platform for purchasing Instagram Followers using PayPal, catering to a diverse range of users. This convenient application permits individuals possessing a PayPal account to procure authenticated Instagram Followers.\n\nLeveraging the Cash App, users can either opt to procure followers for a predetermined quantity or exercise patience until their account accrues a substantial follower count, subsequently making a bulk purchase. Although the Cash App provides this service, it is crucial to discern between genuine and counterfeit items. If you find yourself in search of counterfeit products such as a Rolex, a Louis Vuitton item, or a Louis Vuitton bag, there are two viable approaches to consider.\n\n \n\nWhy you need to buy verified Cash App accounts personal or business?\nThe Cash App is a versatile digital wallet enabling seamless money transfers among its users. However, it presents a concern as it facilitates transfer to both verified and unverified individuals.\n\nTo address this, the Cash App offers the option to become a verified user, which unlocks a range of advantages. Verified users can enjoy perks such as express payment, immediate issue resolution, and a generous interest-free period of up to two weeks. With its user-friendly interface and enhanced capabilities, the Cash App caters to the needs of a wide audience, ensuring convenient and secure digital transactions for all.\n\nIf you’re a business person seeking additional funds to expand your business, we have a solution for you. Payroll management can often be a challenging task, regardless of whether you’re a small family-run business or a large corporation. How To Buy Verified Cash App Accounts.\n\nImproper payment practices can lead to potential issues with your employees, as they could report you to the government. However, worry not, as we offer a reliable and efficient way to ensure proper payroll management, avoiding any potential complications. Our services provide you with the funds you need without compromising your reputation or legal standing. With our assistance, you can focus on growing your business while maintaining a professional and compliant relationship with your employees. Purchase Verified Cash App Accounts.\n\nA Cash App has emerged as a leading peer-to-peer payment method, catering to a wide range of users. With its seamless functionality, individuals can effortlessly send and receive cash in a matter of seconds, bypassing the need for a traditional bank account or social security number. Buy verified cash app account.\n\nThis accessibility makes it particularly appealing to millennials, addressing a common challenge they face in accessing physical currency. As a result, ACash App has established itself as a preferred choice among diverse audiences, enabling swift and hassle-free transactions for everyone. Purchase Verified Cash App Accounts.\n\n \n\nHow to verify Cash App accounts\nTo ensure the verification of your Cash App account, it is essential to securely store all your required documents in your account. This process includes accurately supplying your date of birth and verifying the US or UK phone number linked to your Cash App account.\n\nAs part of the verification process, you will be asked to submit accurate personal details such as your date of birth, the last four digits of your SSN, and your email address. If additional information is requested by the Cash App community to validate your account, be prepared to provide it promptly. Upon successful verification, you will gain full access to managing your account balance, as well as sending and receiving funds seamlessly. Buy verified cash app account.\n\n \n\nHow cash used for international transaction?\nExperience the seamless convenience of this innovative platform that simplifies money transfers to the level of sending a text message. It effortlessly connects users within the familiar confines of their respective currency regions, primarily in the United States and the United Kingdom.\n\nNo matter if you’re a freelancer seeking to diversify your clientele or a small business eager to enhance market presence, this solution caters to your financial needs efficiently and securely. Embrace a world of unlimited possibilities while staying connected to your currency domain. Buy verified cash app account.\n\nUnderstanding the currency capabilities of your selected payment application is essential in today’s digital landscape, where versatile financial tools are increasingly sought after. In this era of rapid technological advancements, being well-informed about platforms such as Cash App is crucial.\n\nAs we progress into the digital age, the significance of keeping abreast of such services becomes more pronounced, emphasizing the necessity of staying updated with the evolving financial trends and options available. Buy verified cash app account.\n\nOffers and advantage to buy cash app accounts cheap?\nWith Cash App, the possibilities are endless, offering numerous advantages in online marketing, cryptocurrency trading, and mobile banking while ensuring high security. As a top creator of Cash App accounts, our team possesses unparalleled expertise in navigating the platform.\n\nWe deliver accounts with maximum security and unwavering loyalty at competitive prices unmatched by other agencies. Rest assured, you can trust our services without hesitation, as we prioritize your peace of mind and satisfaction above all else.\n\nEnhance your business operations effortlessly by utilizing the Cash App e-wallet for seamless payment processing, money transfers, and various other essential tasks. Amidst a myriad of transaction platforms in existence today, the Cash App e-wallet stands out as a premier choice, offering users a multitude of functions to streamline their financial activities effectively. Buy verified cash app account.\n\nTrustbizs.com stands by the Cash App’s superiority and recommends acquiring your Cash App accounts from this trusted source to optimize your business potential.\n\nHow Customizable are the Payment Options on Cash App for Businesses?\nDiscover the flexible payment options available to businesses on Cash App, enabling a range of customization features to streamline transactions. Business users have the ability to adjust transaction amounts, incorporate tipping options, and leverage robust reporting tools for enhanced financial management.\n\nExplore trustbizs.com to acquire verified Cash App accounts with LD backup at a competitive price, ensuring a secure and efficient payment solution for your business needs. Buy verified cash app account.\n\nDiscover Cash App, an innovative platform ideal for small business owners and entrepreneurs aiming to simplify their financial operations. With its intuitive interface, Cash App empowers businesses to seamlessly receive payments and effectively oversee their finances. Emphasizing customization, this app accommodates a variety of business requirements and preferences, making it a versatile tool for all.\n\nWhere To Buy Verified Cash App Accounts\nWhen considering purchasing a verified Cash App account, it is imperative to carefully scrutinize the seller’s pricing and payment methods. Look for pricing that aligns with the market value, ensuring transparency and legitimacy. Buy verified cash app account.\n\nEqually important is the need to opt for sellers who provide secure payment channels to safeguard your financial data. Trust your intuition; skepticism towards deals that appear overly advantageous or sellers who raise red flags is warranted. It is always wise to prioritize caution and explore alternative avenues if uncertainties arise.\n\nThe Importance Of Verified Cash App Accounts\nIn today’s digital age, the significance of verified Cash App accounts cannot be overstated, as they serve as a cornerstone for secure and trustworthy online transactions.\n\nBy acquiring verified Cash App accounts, users not only establish credibility but also instill the confidence required to participate in financial endeavors with peace of mind, thus solidifying its status as an indispensable asset for individuals navigating the digital marketplace.\n\nWhen considering purchasing a verified Cash App account, it is imperative to carefully scrutinize the seller’s pricing and payment methods. Look for pricing that aligns with the market value, ensuring transparency and legitimacy. Buy verified cash app account.\n\nEqually important is the need to opt for sellers who provide secure payment channels to safeguard your financial data. Trust your intuition; skepticism towards deals that appear overly advantageous or sellers who raise red flags is warranted. It is always wise to prioritize caution and explore alternative avenues if uncertainties arise.\n\nConclusion\nEnhance your online financial transactions with verified Cash App accounts, a secure and convenient option for all individuals. By purchasing these accounts, you can access exclusive features, benefit from higher transaction limits, and enjoy enhanced protection against fraudulent activities. Streamline your financial interactions and experience peace of mind knowing your transactions are secure and efficient with verified Cash App accounts.\n\nChoose a trusted provider when acquiring accounts to guarantee legitimacy and reliability. In an era where Cash App is increasingly favored for financial transactions, possessing a verified account offers users peace of mind and ease in managing their finances. Make informed decisions to safeguard your financial assets and streamline your personal transactions effectively.\n\nContact Us / 24 Hours Reply\nTelegram:dmhelpshop\nWhatsApp: +1 (980) 277-2786\nSkype:dmhelpshop\nEmail:dmhelpshop@gmail.com" | yyrwasti22 |
1,875,720 | The Best Habit Tracking Apps on iPhone | In the pursuit of personal growth, forming good habits is indisputably beneficial. For those seeking... | 0 | 2024-06-03T17:47:39 | https://blog.productivity.directory/the-best-habit-tracking-apps-on-iphone-397414e89a57 | habittrackerapps, productivity, habittracking, iphoneapps | In the pursuit of personal growth, forming good habits is indisputably beneficial. For those seeking a little digital assistance in tracking their daily routines and goals, iPhone apps have become invaluable tools. These applications not only help in building and maintaining good habits but also offer insights into one... | stan8086 |
1,875,719 | How to Read A Barcode in C# | How to Read Barcodes in C Download Barcode Reader for C# Project Create a Visual Studio... | 0 | 2024-06-03T17:46:19 | https://dev.to/mhamzap10/how-to-read-a-barcode-in-c-21hk | barcode, csharp, dotnet, aspdotnet | ##How to Read Barcodes in C#
1. Download [Barcode Reader](https://ironsoftware.com/csharp/barcode/tutorials/csharp-barcode-image-generator/) for C# Project
2. Create a Visual Studio Project:
3. Install Barcode Library
4. Write a Code to Read a Barcode
5. Write Code to read multiple barcode images
This tutorial provid... | mhamzap10 |
1,875,716 | My First Post!!! | I am a CS Graduate Student at Illinois Tech. As I didn't land any internships for the summer, I have... | 0 | 2024-06-03T17:43:26 | https://dev.to/gopi_ravady_64fee83fc400d/my-first-post-324e | mongodb, flutter, dart, socketio | I am a CS Graduate Student at Illinois Tech. As I didn't land any internships for the summer, I have developed a hobby project.
I have developed a user-friendly chat application using my primary mobile applications development framework: Flutter. I have also utilized socket.io for bidirectional communication from my F... | gopi_ravady_64fee83fc400d |
1,875,715 | From Solopreneur to Scalable Success: Building a Sustainable SaaS Business Model | The tech world is full of solopreneurs – tech-savvy individuals who run their own businesses. This... | 0 | 2024-06-03T17:43:21 | https://dev.to/marufhossain/from-solopreneur-to-scalable-success-building-a-sustainable-saas-business-model-4i64 | The tech world is full of solopreneurs – tech-savvy individuals who run their own businesses. This approach is especially attractive for building a [SaaS application](https://www.clickittech.com/saas/saas-application/?utm_source=backlinks&utm_medium=referral
) (software delivered online with a subscription fee). SaaS... | marufhossain | |
1,875,714 | Mastering the GMAT: The Power of Expert GMAT Coaching | Introduction: Are you looking for Expert GMAT Coaching? Preparing for the Graduate Management... | 0 | 2024-06-03T17:42:38 | https://dev.to/alijutt_seo_a59e5d5e3087f/mastering-the-gmat-the-power-of-expert-gmat-coaching-435j | Introduction:
Are you looking for Expert GMAT Coaching? Preparing for the Graduate Management Admission Test (GMAT) is a crucial step for many individuals aspiring to pursue graduate business education. However, navigating the complexities of the GMAT exam can be daunting without proper guidance and support. This is w... | alijutt_seo_a59e5d5e3087f | |
1,873,752 | I built an open-source multi-platforms Note-taking app using Reactjs and Tauri | Hi everyone, It's Hudy again. Almost a month ago, I shared my open-source project manager with you... | 0 | 2024-06-03T17:40:55 | https://dev.to/hudy9x/i-built-a-note-taking-app-for-2-years-ago-and-released-it-open-source-2m0j | react, tauri | Hi everyone, It's Hudy again.
Almost a month ago, I shared [my open-source project manager](https://dev.to/hudy9x/i-built-a-free-open-source-project-manager-that-helps-teams-keep-costs-under-15month-3pmk) with you guys. And it got a lot of attention from community. Besides, I received valuable comments from you all wh... | hudy9x |
1,875,626 | Manual de uso Immigrant - Jira | Visão geral O Immigrant - Jira é uma abordagem baseada em ontologia que auxilia na... | 0 | 2024-06-03T17:40:28 | https://dev.to/dadecoelho/manual-de-uso-immigrant-jira-4m86 | ledscommunity | ## Visão geral
O Immigrant - Jira é uma abordagem baseada em ontologia que auxilia na identificação das necessidades de informação da organização, recuperando dados do Jira e fornecendo dados integrados que atendam às necessidades de informação.
### Pré-requisitos
1- Python
2- Docker
3- Java 17
## Infraestrutura
Fo... | dadecoelho |
1,872,956 | Deletes and MVCC in YugabyteDB | An application pattern that could cause issues with Multi-Version Concurrent Control (MVCC) databases... | 27,563 | 2024-06-03T17:40:27 | https://dev.to/yugabyte/deletes-and-mvcc-in-yugabytedb-12ip | yugabytedb, distributed, sql, postgres | An application pattern that could cause issues with Multi-Version Concurrent Control (MVCC) databases is a queuing table with frequent insertions and deletions. Since all reads are based on a consistent snapshot, rows are not physically deleted, allowing the system to retrieve the state at any point since the start of ... | franckpachot |
1,857,858 | CDI scope | Java'da CDI (Contexts and Dependency Injection) scope, bir bean'in yaşam süresini ve hangi durumlarda... | 0 | 2024-05-18T20:15:45 | https://dev.to/mustafacam/cdi-scope-3m2d | Java'da CDI (Contexts and Dependency Injection) scope, bir bean'in yaşam süresini ve hangi durumlarda yeni bir instance'ın oluşturulacağını belirleyen bir mekanizmadır. CDI scope'lar, bean'lerin uygulama içindeki farklı kullanım senaryolarına göre nasıl yönetileceğini tanımlar¹.
CDI'de kullanılan bazı yaygın scope'lar... | mustafacam | |
1,875,713 | Understanding Web Hosting: A Comprehensive Guide | Web hosting is a fundamental component of the internet, serving as the backbone for websites and... | 0 | 2024-06-03T17:40:13 | https://dev.to/harry_jack_5bec57012370cf/understanding-web-hosting-a-comprehensive-guide-obo | webhosting, webhostingservices | Web hosting is a fundamental component of the internet, serving as the backbone for websites and online applications. For anyone looking to establish an online presence, understanding web hosting is crucial. This guide will delve into what web hosting is, the types of web hosting available, and how to choose the right ... | harry_jack_5bec57012370cf |
1,872,201 | Routing in Umbraco Part 2: Content Finders | The previous article in this series demoed how to adjust segments for your Umbraco nodes using an... | 27,570 | 2024-06-03T17:39:42 | https://dev.to/hartviglarsen/routing-in-umbraco-part-2-content-finders-4j0i | umbraco, dotnet, routing, cms | The [previous article](https://dev.to/hartviglarsen/routing-in-umbraco-part-1-url-segments-4lmj) in this series demoed how to adjust segments for your Umbraco nodes using an `IUrlSegmentProvider`. When an altered segment is returned in an `IUrlSegmentProvider` it becomes a _native_ segment that Umbraco can handle out o... | hartviglarsen |
1,875,712 | What sets this gaming platform apart from other free online Android games that require no download? | This gaming platform have revolutionized the world of free online Android games by offering a unique... | 0 | 2024-06-03T17:36:38 | https://dev.to/claywinston/what-sets-this-gaming-platform-apart-from-other-free-online-android-games-that-require-no-download-l16 | game, mobilegame, androidgames, gamedev | This [**gaming platform**](https://medium.com/@adreeshelk/how-to-play-hundreds-of-games-on-your-lock-screen-without-downloading-anything-4f03e0173441?utm_source=referral&utm_medium=Medium&utm_campaign=Nostra) have revolutionized the world of free online Android games by offering a unique and unparalleled gaming experie... | claywinston |
1,875,711 | packagemain.tech - Newsletter about Backend, Cloud, DevOps, APIs... | The Backend is the backbone of any modern application. It handles data storage, user interactions,... | 0 | 2024-06-03T17:31:19 | https://dev.to/plutov/packagemaintech-newsletter-about-backend-cloud-devops-apis-3bh9 | backend, cloud, devops, api | ---
title: packagemain.tech - Newsletter about Backend, Cloud, DevOps, APIs...
published: true
description:
tags: backend, cloud, devops, api
cover_image: https://dev-to-uploads.s3.amazonaws.com/uploads/articles/mkf7uembk3lz1p1pugpc.png
# Use a ratio of 100:42 for best results.
# published_at: 2024-06-03 17:30 +0000
-... | plutov |
1,869,509 | Manual de Uso R2D2 | Este manual descreve o uso da extensão de Visual Studio Code geradora de código e documentação R2D2.... | 0 | 2024-06-03T16:44:23 | https://dev.to/joaomrpimentel/manual-de-uso-r2d2-3aog | ledscommunity, langium, codegenerator, csharp | Este manual descreve o uso da extensão de Visual Studio Code geradora de código e documentação R2D2.
### Instalação:
1- Abra o Visual Studio Code
2- Clique em extensões
3- Pesquise R2D2
4- Clique para instalar a extensão R2D2 do LEDS IFES
. Notion style Avatar generator,... | 0 | 2024-06-03T17:13:14 | https://dev.to/mddanishyusuf/free-notion-style-avatar-generator-2a4l | notion, avatar | I built a free tool this weekend for Notion lovers[(Notion Avatar)](https://iconbuddy.com/notion-style-avatar-generator).
[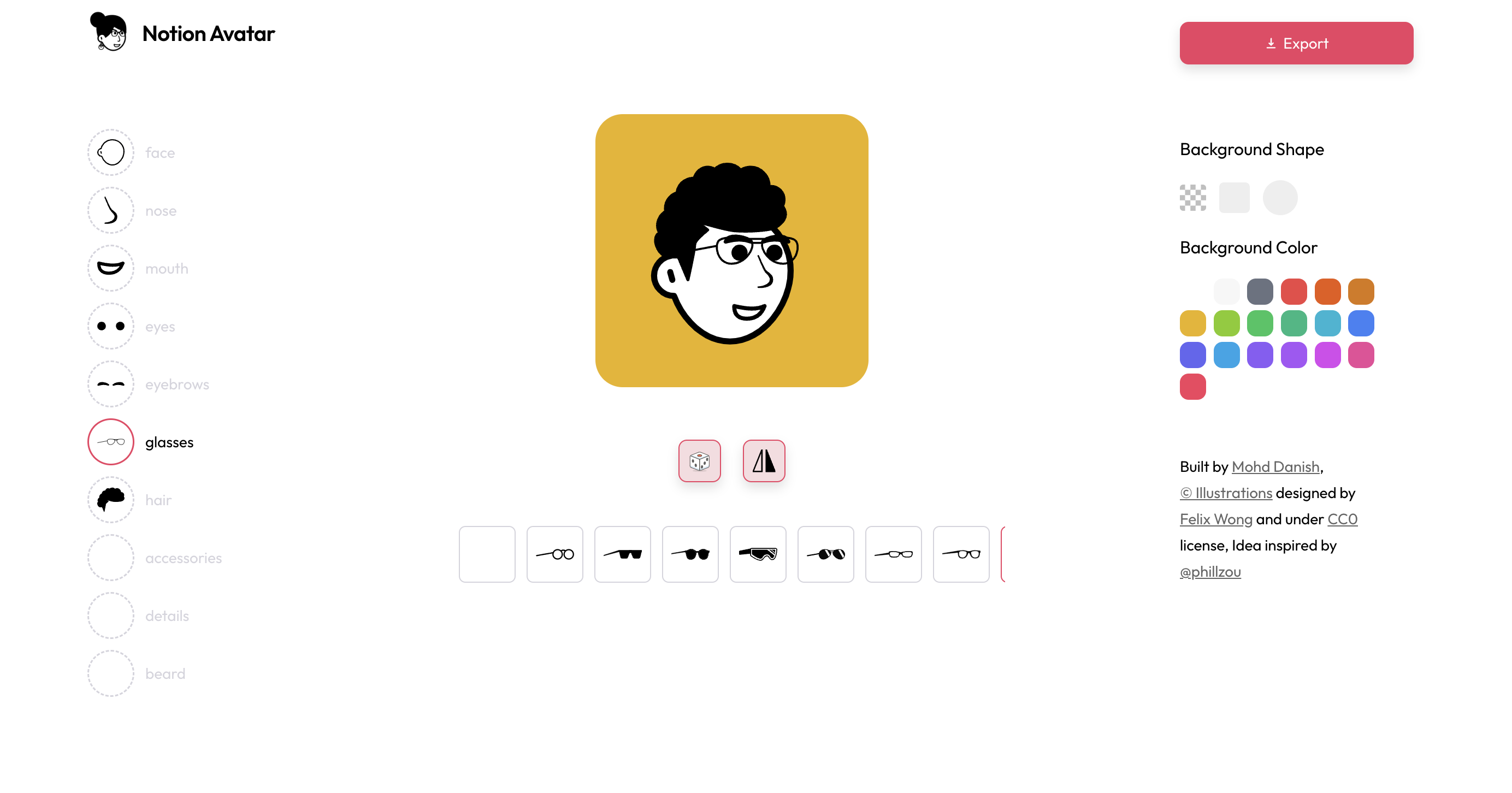](https://iconbuddy.com/notion-style-avatar-generator)
Notion style Avatar generator, A onl... | mddanishyusuf |
1,875,560 | Selection Sort Algorithm | Selection Sort is a simple and intuitive sorting algorithm. It divides the input list into two parts:... | 27,581 | 2024-06-03T17:10:09 | https://blog.masum.dev/selection-sort-algorithm | algorithms, computerscience, cpp, tutorial | Selection Sort is a simple and intuitive sorting algorithm. It divides the input list into two parts: a sorted sublist of items which is built up from left to right at the front (left) of the list and a sublist of the remaining unsorted items. The algorithm proceeds by **finding the smallest** (or largest, depending on... | masum-dev |
1,875,694 | 5 Reasons Why Every Business Needs Professional Commercial Cleaning Services | As a business owner, maintaining a clean and well-organized workspace should be a top priority. A... | 0 | 2024-06-03T17:09:49 | https://dev.to/sparklymaids/5-reasons-why-every-business-needs-professional-commercial-cleaning-services-21pk | cleaningservices | As a business owner, maintaining a clean and well-organized workspace should be a top priority. A tidy environment not only creates a positive first impression for customers and clients but also contributes to employee productivity and overall profitability.
However, keeping a commercial space spotless can take time ... | sparklymaids |
1,875,688 | Making a Totally Free Uptime Monitor using a Worker Runtime and OpenTelemetry | Table of Contents What is an Uptime Monitor and When to Use One? Traditional... | 0 | 2024-06-03T17:09:33 | https://dev.to/grunet/making-a-totally-free-uptime-monitor-using-a-worker-runtime-and-opentelemetry-1bha | devops, monitoring | ## Table of Contents
- [What is an Uptime Monitor and When to Use One?](#what-is-an-uptime-monitor-and-when-to-use-one)
- [Traditional Options](#traditional-options)
- [Using a Worker Runtime and OpenTelemetry](#using-a-worker-runtime-and-opentelemetry)
* [The High-Level Solution](#the-highlevel-solution)
* [The... | grunet |
1,875,692 | Example: Defining Classes and Creating Objects | Classes are definitions for objects and objects are created from classes. This section gives two... | 0 | 2024-06-03T17:09:32 | https://dev.to/paulike/example-defining-classes-and-creating-objects-2nni | java, programming, learning, beginners | Classes are definitions for objects and objects are created from classes. This section gives two examples of defining classes and uses the classes to create objects. Below is a program that defines the **Circle** class and uses it to create objects. The program constructs three circle objects with radius **1**, **25**,... | paulike |
1,875,691 | Senior Growth is Brutal | Hello everyone, better that I get this out in the open, being a senior dev still involves a hell of a... | 0 | 2024-06-03T17:02:55 | https://dev.to/adam_cyclones/senior-growth-is-brutal-nnk | watercooler | Hello everyone, better that I get this out in the open, being a senior dev still involves a hell of a lot of personal growth, contrary to my initial belief that the great seniors I see are PERFECT, they probably (and i say that with a heavy question mark) go through the same journey of learning, and apparently I am doi... | adam_cyclones |
1,875,690 | How to Use CompanionLink to Manage Contacts, Calendars, and Tasks? | Ever feel overwhelmed by the chaos of managing contacts, calendars, and tasks? CompanionLink might be... | 0 | 2024-06-03T17:02:14 | https://dev.to/companionlink-1/how-to-use-companionlink-to-manage-contacts-calendars-and-tasks-4mm9 | companionlink | Ever feel overwhelmed by the chaos of managing contacts, calendars, and tasks? CompanionLink might be the solution you need. This powerful tool streamlines your data management and helps you stay organized and efficient.
 may be obstructing the functionality of your... | 0 | 2024-06-03T16:53:58 | https://dev.to/aws-builders/step-by-step-troubleshooting-wafv2-with-pictures-4hnp | aws, cloud, waf, security |
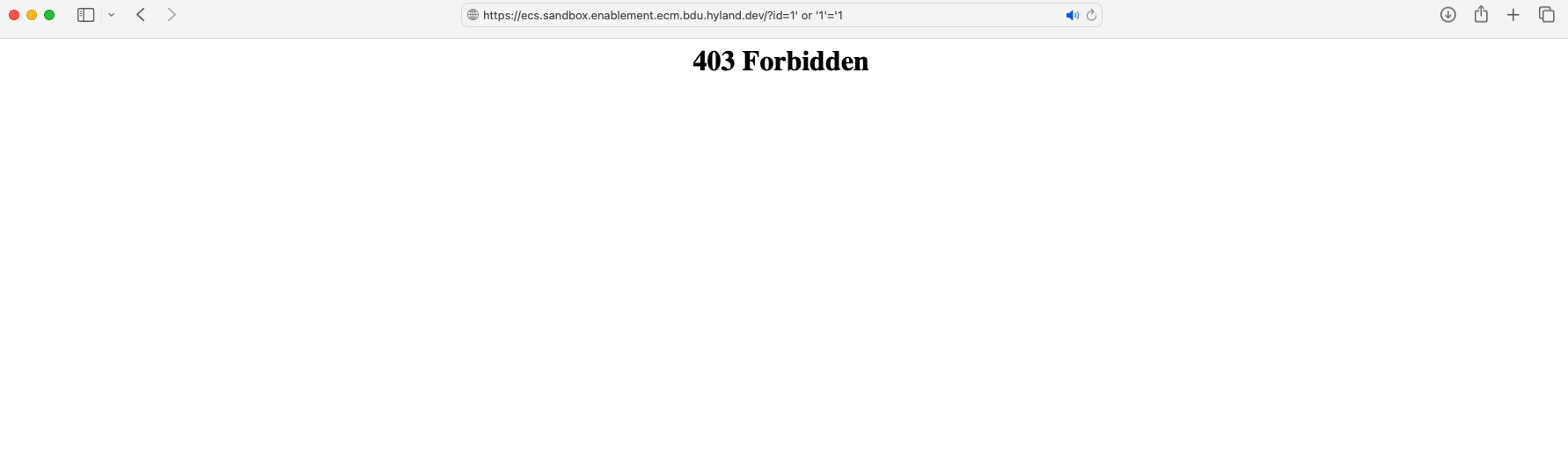
You suspect that the Web Application Firewall (WAF) may be obstructing the functionality of your application. This article provides guidance on diagnosing the issue and adjusting/removing WAF rules as necessary.
!... | ayogun |
1,875,683 | Start and Stop Timer | const App = () => { const [count, setCount] = React.useState(0); const [isCount0,... | 0 | 2024-06-03T16:53:57 | https://dev.to/alamfatima1999/start-and-stop-timer-5487 | ```JS
const App = () => {
const [count, setCount] = React.useState(0);
const [isCount0, setIsCount0] =
React.useState(true);
const [id, setId] =
React.useState(true);
React.useEffect(() => {
console.log("Inside useEffect");
// setIsCount0(false);
setCount(0);
const newId = setInterv... | alamfatima1999 | |
1,875,682 | 🧠 Part 1 - Memory Management in JavaScript: 10+ Data Structures & Garbage Collection Techniques | JS Deep Dive | Memory management is a fundamental aspect of programming that varies significantly between... | 0 | 2024-06-03T16:53:48 | https://dev.to/nikhilgupta946/part-1-memory-management-in-javascript-10-data-structures-garbage-collection-techniques-js-deep-dive-4c5b | javascript, programming, webdev, react | - Memory management is a fundamental aspect of programming that varies significantly between languages.
- Low-level languages like C require manual memory management through functions like malloc() and free(), whereas high-level languages like JavaScript automate this process through garbage collection.
> This article... | nikhilgupta946 |
1,875,680 | A course on Automating boring staff | I was navigating the confines of Udemy when I came across a Python course that powerfully caught my... | 0 | 2024-06-03T16:53:08 | https://dev.to/maxwellnewage/a-course-on-automating-boring-staff-26g7 | python, programming, beginners | I was navigating the confines of Udemy when I came across a Python course that powerfully caught my curiosity: [Automate the Boring Stuff with Python Programming](https://www.udemy.com/course/automate/). It lasts about nine and a half hours, it's somewhat old, but it captivated me from the first minute.
strategy is content that catches attention and builds up genuine connections. Quality content is not just facts and figures; it is storytelling—something that pulsates with life and speaks directly to the hearts ... | urmila_1b8eb242ff335f2045 | |
1,875,678 | Mastering React Component Lifecycle: The Foundation for React Concepts | React, with its component-based architecture and declarative syntax, has become a staple in modern... | 0 | 2024-06-03T16:52:06 | https://dev.to/harshitt1617/mastering-react-component-lifecycle-the-foundation-for-react-concepts-b9a | react, javascript, webdev, reactnative | React, with its component-based architecture and declarative syntax, has become a staple in modern web development. However, to truly harness the power of React, understanding its lifecycle methods is essential. These methods form the foundation for advanced concepts like re-rendering, caching, and performance optimisa... | harshitt1617 |
1,875,677 | Support My YouTube Channel - devDive with Dipak! | Hey Dev Community! 👋 I hope you're all doing well and enjoying your coding journey. As some of you... | 0 | 2024-06-03T16:51:40 | https://dev.to/dipakahirav/support-my-youtube-channel-devdive-with-dipak-1pb7 | coding, javascript, webdev, learning | Hey Dev Community! 👋
I hope you're all doing well and enjoying your coding journey. As some of you might know, I've recently started a YouTube channel called **devDive with Dipak** where I share my knowledge and passion for full-stack development, coding problem-solving, and much more!
🔗 **[Check out my YouTube cha... | dipakahirav |
1,875,672 | Website Design: A Powerful Tool for Lead Generation and Startups | In today's digital age, having a well-designed website is not just a luxury but a necessity for... | 0 | 2024-06-03T16:47:56 | https://dev.to/mdarafath/website-design-a-powerful-tool-for-lead-generation-and-startups-2pg1 | In today's digital age, having a well-designed website is not just a luxury but a necessity for businesses aiming to thrive and grow. For startups, especially, a compelling online presence can make the difference between success and obscurity.
The Role of Website Design in Lead Generation
Website design plays a pivota... | mdarafath | |
1,875,671 | Blockchain Beyond Bitcoin: Innovative Uses in Various Industries | Supply Chain Management: Blockchain enhances transparency and traceability, allowing real-time... | 0 | 2024-06-03T16:39:48 | https://dev.to/bingecoder89/blockchain-beyond-bitcoin-innovative-uses-in-various-industries-5boo | webdev, javascript, devops, ai | - **Supply Chain Management**: Blockchain enhances transparency and traceability, allowing real-time tracking of goods from origin to consumer, reducing fraud and errors.
- **Healthcare**: Securing patient data on a blockchain ensures privacy and data integrity, while also enabling efficient sharing of medical records... | bingecoder89 |
1,875,669 | Top 10 SaaS Applications To Help Businesses Grow | In today's competitive business world, staying ahead of the curve requires using the right tools.... | 0 | 2024-06-03T16:35:21 | https://dev.to/marufhossain/top-10-saas-applications-to-help-businesses-grow-259k | In today's competitive business world, staying ahead of the curve requires using the right tools. Enter SaaS (Software as a Service) applications – game-changers that deliver software on demand over the internet. No expensive installations, no complex maintenance – just powerful features accessible from any device. But... | marufhossain | |
1,875,667 | Buy Verified Paxful Account | https://dmhelpshop.com/product/buy-verified-paxful-account/ Buy Verified Paxful Account There are... | 0 | 2024-06-03T16:33:55 | https://dev.to/uiueqay3/buy-verified-paxful-account-2g6d | python, ai, devops, productivity | ERROR: type should be string, got "https://dmhelpshop.com/product/buy-verified-paxful-account/\n\n\n\n\nBuy Verified Paxful Account\nThere are several compelling reasons to consider purchasing a verified Paxful account. Firstly, a verified account offers enhanced security, providing peace of mind to all users. Additionally, it opens up a wider range of trading opportunities, allowing individuals to partake in various transactions, ultimately expanding their financial horizons.\n\nMoreover, Buy verified Paxful account ensures faster and more streamlined transactions, minimizing any potential delays or inconveniences. Furthermore, by opting for a verified account, users gain access to a trusted and reputable platform, fostering a sense of reliability and confidence.\n\nLastly, Paxful’s verification process is thorough and meticulous, ensuring that only genuine individuals are granted verified status, thereby creating a safer trading environment for all users. Overall, the decision to Buy Verified Paxful account can greatly enhance one’s overall trading experience, offering increased security, access to more opportunities, and a reliable platform to engage with. Buy Verified Paxful Account.\n\nBuy US verified paxful account from the best place dmhelpshop\nWhy we declared this website as the best place to buy US verified paxful account? Because, our company is established for providing the all account services in the USA (our main target) and even in the whole world. With this in mind we create paxful account and customize our accounts as professional with the real documents. Buy Verified Paxful Account.\n\nIf you want to buy US verified paxful account you should have to contact fast with us. Because our accounts are-\n\nEmail verified\nPhone number verified\nSelfie and KYC verified\nSSN (social security no.) verified\nTax ID and passport verified\nSometimes driving license verified\nMasterCard attached and verified\nUsed only genuine and real documents\n100% access of the account\nAll documents provided for customer security\nWhat is Verified Paxful Account?\nIn today’s expanding landscape of online transactions, ensuring security and reliability has become paramount. Given this context, Paxful has quickly risen as a prominent peer-to-peer Bitcoin marketplace, catering to individuals and businesses seeking trusted platforms for cryptocurrency trading.\n\nIn light of the prevalent digital scams and frauds, it is only natural for people to exercise caution when partaking in online transactions. As a result, the concept of a verified account has gained immense significance, serving as a critical feature for numerous online platforms. Paxful recognizes this need and provides a safe haven for users, streamlining their cryptocurrency buying and selling experience.\n\nFor individuals and businesses alike, Buy verified Paxful account emerges as an appealing choice, offering a secure and reliable environment in the ever-expanding world of digital transactions. Buy Verified Paxful Account.\n\nVerified Paxful Accounts are essential for establishing credibility and trust among users who want to transact securely on the platform. They serve as evidence that a user is a reliable seller or buyer, verifying their legitimacy.\n\nBut what constitutes a verified account, and how can one obtain this status on Paxful? In this exploration of verified Paxful accounts, we will unravel the significance they hold, why they are crucial, and shed light on the process behind their activation, providing a comprehensive understanding of how they function. Buy verified Paxful account.\n\n \n\nWhy should to Buy Verified Paxful Account?\nThere are several compelling reasons to consider purchasing a verified Paxful account. Firstly, a verified account offers enhanced security, providing peace of mind to all users. Additionally, it opens up a wider range of trading opportunities, allowing individuals to partake in various transactions, ultimately expanding their financial horizons.\n\nMoreover, a verified Paxful account ensures faster and more streamlined transactions, minimizing any potential delays or inconveniences. Furthermore, by opting for a verified account, users gain access to a trusted and reputable platform, fostering a sense of reliability and confidence. Buy Verified Paxful Account.\n\nLastly, Paxful’s verification process is thorough and meticulous, ensuring that only genuine individuals are granted verified status, thereby creating a safer trading environment for all users. Overall, the decision to buy a verified Paxful account can greatly enhance one’s overall trading experience, offering increased security, access to more opportunities, and a reliable platform to engage with.\n\n \n\nWhat is a Paxful Account\nPaxful and various other platforms consistently release updates that not only address security vulnerabilities but also enhance usability by introducing new features. Buy Verified Paxful Account.\n\nIn line with this, our old accounts have recently undergone upgrades, ensuring that if you purchase an old buy Verified Paxful account from dmhelpshop.com, you will gain access to an account with an impressive history and advanced features. This ensures a seamless and enhanced experience for all users, making it a worthwhile option for everyone.\n\n \n\nIs it safe to buy Paxful Verified Accounts?\nBuying on Paxful is a secure choice for everyone. However, the level of trust amplifies when purchasing from Paxful verified accounts. These accounts belong to sellers who have undergone rigorous scrutiny by Paxful. Buy verified Paxful account, you are automatically designated as a verified account. Hence, purchasing from a Paxful verified account ensures a high level of credibility and utmost reliability. Buy Verified Paxful Account.\n\nPAXFUL, a widely known peer-to-peer cryptocurrency trading platform, has gained significant popularity as a go-to website for purchasing Bitcoin and other cryptocurrencies. It is important to note, however, that while Paxful may not be the most secure option available, its reputation is considerably less problematic compared to many other marketplaces. Buy Verified Paxful Account.\n\nThis brings us to the question: is it safe to purchase Paxful Verified Accounts? Top Paxful reviews offer mixed opinions, suggesting that caution should be exercised. Therefore, users are advised to conduct thorough research and consider all aspects before proceeding with any transactions on Paxful.\n\n \n\nHow Do I Get 100% Real Verified Paxful Accoun?\nPaxful, a renowned peer-to-peer cryptocurrency marketplace, offers users the opportunity to conveniently buy and sell a wide range of cryptocurrencies. Given its growing popularity, both individuals and businesses are seeking to establish verified accounts on this platform.\n\nHowever, the process of creating a verified Paxful account can be intimidating, particularly considering the escalating prevalence of online scams and fraudulent practices. This verification procedure necessitates users to furnish personal information and vital documents, posing potential risks if not conducted meticulously.\n\nIn this comprehensive guide, we will delve into the necessary steps to create a legitimate and verified Paxful account. Our discussion will revolve around the verification process and provide valuable tips to safely navigate through it.\n\nMoreover, we will emphasize the utmost importance of maintaining the security of personal information when creating a verified account. Furthermore, we will shed light on common pitfalls to steer clear of, such as using counterfeit documents or attempting to bypass the verification process.\n\nWhether you are new to Paxful or an experienced user, this engaging paragraph aims to equip everyone with the knowledge they need to establish a secure and authentic presence on the platform.\n\nBenefits Of Verified Paxful Accounts\nVerified Paxful accounts offer numerous advantages compared to regular Paxful accounts. One notable advantage is that verified accounts contribute to building trust within the community.\n\nVerification, although a rigorous process, is essential for peer-to-peer transactions. This is why all Paxful accounts undergo verification after registration. When customers within the community possess confidence and trust, they can conveniently and securely exchange cash for Bitcoin or Ethereum instantly. Buy Verified Paxful Account.\n\nPaxful accounts, trusted and verified by sellers globally, serve as a testament to their unwavering commitment towards their business or passion, ensuring exceptional customer service at all times. Headquartered in Africa, Paxful holds the distinction of being the world’s pioneering peer-to-peer bitcoin marketplace. Spearheaded by its founder, Ray Youssef, Paxful continues to lead the way in revolutionizing the digital exchange landscape.\n\nPaxful has emerged as a favored platform for digital currency trading, catering to a diverse audience. One of Paxful’s key features is its direct peer-to-peer trading system, eliminating the need for intermediaries or cryptocurrency exchanges. By leveraging Paxful’s escrow system, users can trade securely and confidently.\n\nWhat sets Paxful apart is its commitment to identity verification, ensuring a trustworthy environment for buyers and sellers alike. With these user-centric qualities, Paxful has successfully established itself as a leading platform for hassle-free digital currency transactions, appealing to a wide range of individuals seeking a reliable and convenient trading experience. Buy Verified Paxful Account.\n\n \n\nHow paxful ensure risk-free transaction and trading?\nEngage in safe online financial activities by prioritizing verified accounts to reduce the risk of fraud. Platforms like Paxfu implement stringent identity and address verification measures to protect users from scammers and ensure credibility.\n\nWith verified accounts, users can trade with confidence, knowing they are interacting with legitimate individuals or entities. By fostering trust through verified accounts, Paxful strengthens the integrity of its ecosystem, making it a secure space for financial transactions for all users. Buy Verified Paxful Account.\n\nExperience seamless transactions by obtaining a verified Paxful account. Verification signals a user’s dedication to the platform’s guidelines, leading to the prestigious badge of trust. This trust not only expedites trades but also reduces transaction scrutiny. Additionally, verified users unlock exclusive features enhancing efficiency on Paxful. Elevate your trading experience with Verified Paxful Accounts today.\n\nIn the ever-changing realm of online trading and transactions, selecting a platform with minimal fees is paramount for optimizing returns. This choice not only enhances your financial capabilities but also facilitates more frequent trading while safeguarding gains. Buy Verified Paxful Account.\n\nExamining the details of fee configurations reveals Paxful as a frontrunner in cost-effectiveness. Acquire a verified level-3 USA Paxful account from usasmmonline.com for a secure transaction experience. Invest in verified Paxful accounts to take advantage of a leading platform in the online trading landscape.\n\n \n\nHow Old Paxful ensures a lot of Advantages?\n\nExplore the boundless opportunities that Verified Paxful accounts present for businesses looking to venture into the digital currency realm, as companies globally witness heightened profits and expansion. These success stories underline the myriad advantages of Paxful’s user-friendly interface, minimal fees, and robust trading tools, demonstrating its relevance across various sectors.\n\nBusinesses benefit from efficient transaction processing and cost-effective solutions, making Paxful a significant player in facilitating financial operations. Acquire a USA Paxful account effortlessly at a competitive rate from usasmmonline.com and unlock access to a world of possibilities. Buy Verified Paxful Account.\n\nExperience elevated convenience and accessibility through Paxful, where stories of transformation abound. Whether you are an individual seeking seamless transactions or a business eager to tap into a global market, buying old Paxful accounts unveils opportunities for growth.\n\nPaxful’s verified accounts not only offer reliability within the trading community but also serve as a testament to the platform’s ability to empower economic activities worldwide. Join the journey towards expansive possibilities and enhanced financial empowerment with Paxful today. Buy Verified Paxful Account.\n\n \n\nWhy paxful keep the security measures at the top priority?\nIn today’s digital landscape, security stands as a paramount concern for all individuals engaging in online activities, particularly within marketplaces such as Paxful. It is essential for account holders to remain informed about the comprehensive security protocols that are in place to safeguard their information.\n\nSafeguarding your Paxful account is imperative to guaranteeing the safety and security of your transactions. Two essential security components, Two-Factor Authentication and Routine Security Audits, serve as the pillars fortifying this shield of protection, ensuring a secure and trustworthy user experience for all. Buy Verified Paxful Account.\n\nConclusion\nInvesting in Bitcoin offers various avenues, and among those, utilizing a Paxful account has emerged as a favored option. Paxful, an esteemed online marketplace, enables users to engage in buying and selling Bitcoin. Buy Verified Paxful Account.\n\nThe initial step involves creating an account on Paxful and completing the verification process to ensure identity authentication. Subsequently, users gain access to a diverse range of offers from fellow users on the platform. Once a suitable proposal captures your interest, you can proceed to initiate a trade with the respective user, opening the doors to a seamless Bitcoin investing experience.\n\nIn conclusion, when considering the option of purchasing verified Paxful accounts, exercising caution and conducting thorough due diligence is of utmost importance. It is highly recommended to seek reputable sources and diligently research the seller’s history and reviews before making any transactions.\n\nMoreover, it is crucial to familiarize oneself with the terms and conditions outlined by Paxful regarding account verification, bearing in mind the potential consequences of violating those terms. By adhering to these guidelines, individuals can ensure a secure and reliable experience when engaging in such transactions. Buy Verified Paxful Account.\n\n \n\nContact Us / 24 Hours Reply\nTelegram:dmhelpshop\nWhatsApp: +1 (980) 277-2786\nSkype:dmhelpshop\nEmail:dmhelpshop@gmail.com" | uiueqay3 |
1,875,666 | Implementing API Rate Limiting with a Token Bucket 🪣 | In this article, We will try to explore Token Bucket algorithm and its implementation in NodeJS for... | 0 | 2024-06-03T16:30:00 | https://keploy.io/blog/community/create-api-rate-limiting-with-token-bucket | webdev, programming, news, api |
In this article, We will try to explore Token Bucket algorithm and its implementation in NodeJS for API Rate Limiting in very simple terms.
**What is Token Bucket ?**
Token Bucket is an algorithm which is used to ... | keploy |
1,875,665 | System Design Resources that are Not ByteByteGo | System design is a core engineering skill and everyone on your team should have some degree of... | 0 | 2024-06-03T16:29:47 | https://dev.to/vladi-stevanovic/system-design-resources-that-are-not-bytebytego-1h2j | systemdesign, softwaredevelopment, architecture, productivity | System design is a core engineering skill and everyone on your team should have [some degree of understanding of their system’s architecture](https://www.multiplayer.app/blog/why-everyone-in-your-team-should-understand-the-system-architecture-even-a-little/).
In addition to that, with the rise in the adoption of AI c... | vladi-stevanovic |
1,857,678 | cdi ==> bean | @data @AllArgsConstructor @NoArgsConstructor @builder //cdi ==> bean @Named(value =... | 0 | 2024-05-18T14:56:01 | https://dev.to/mustafacam/cdi-bean-30p9 | @Data
@AllArgsConstructor
@NoArgsConstructor
@Builder
//cdi ==> bean
@Named(value = "namedtuto")
@ApplicationScoped
public class _01_Named {
private Long namedId;
private String namedData="Merhabalar Named Cdi Bean";
}
Bu Java kodu, **CDI (Contexts and Dependency Injection)** ve **Lombok** kütüphanesini k... | mustafacam | |
1,875,664 | Hands-on Basic Linux Commands: #Day3 of 90DaysofDevOps | Task: What is the Linux command to: 1. To view what's written in a file. Viewing the Contents of a... | 0 | 2024-06-03T16:29:07 | https://dev.to/oncloud7/hands-on-basic-linux-commands-day3-of-90daysofdevops-49ma | devops, linux, awschallenge, 90daysofdevops | **Task: What is the Linux command to:**
**1. To view what's written in a file.**
Viewing the Contents of a File: You can use the cat command to see what's written in a file. For example:

\n\n\n\nBuy verified cash app account\nCash app has emerged as a dominant force in the realm of mobile banking within the USA, offering unparalleled convenience for digital money transfers, deposits, and trading. As the foremost provider of fully verified cash app accounts, we take pride in our ability to deliver accounts with substantial limits. Bitcoin enablement, and an unmatched level of security.\n\nOur commitment to facilitating seamless transactions and enabling digital currency trades has garnered significant acclaim, as evidenced by the overwhelming response from our satisfied clientele. Those seeking buy verified cash app account with 100% legitimate documentation and unrestricted access need look no further. Get in touch with us promptly to acquire your verified cash app account and take advantage of all the benefits it has to offer.\n\nWhy dmhelpshop is the best place to buy USA cash app accounts?\nIt’s crucial to stay informed about any updates to the platform you’re using. If an update has been released, it’s important to explore alternative options. Contact the platform’s support team to inquire about the status of the cash app service.\n\nClearly communicate your requirements and inquire whether they can meet your needs and provide the buy verified cash app account promptly. If they assure you that they can fulfill your requirements within the specified timeframe, proceed with the verification process using the required documents.\n\nOur account verification process includes the submission of the following documents: [List of specific documents required for verification].\n\nGenuine and activated email verified\nRegistered phone number (USA)\nSelfie verified\nSSN (social security number) verified\nDriving license\nBTC enable or not enable (BTC enable best)\n100% replacement guaranteed\n100% customer satisfaction\nWhen it comes to staying on top of the latest platform updates, it’s crucial to act fast and ensure you’re positioned in the best possible place. If you’re considering a switch, reaching out to the right contacts and inquiring about the status of the buy verified cash app account service update is essential.\n\nClearly communicate your requirements and gauge their commitment to fulfilling them promptly. Once you’ve confirmed their capability, proceed with the verification process using genuine and activated email verification, a registered USA phone number, selfie verification, social security number (SSN) verification, and a valid driving license.\n\nAdditionally, assessing whether BTC enablement is available is advisable, buy verified cash app account, with a preference for this feature. It’s important to note that a 100% replacement guarantee and ensuring 100% customer satisfaction are essential benchmarks in this process.\n\nHow to use the Cash Card to make purchases?\nTo activate your Cash Card, open the Cash App on your compatible device, locate the Cash Card icon at the bottom of the screen, and tap on it. Then select “Activate Cash Card” and proceed to scan the QR code on your card. Alternatively, you can manually enter the CVV and expiration date. How To Buy Verified Cash App Accounts.\n\nAfter submitting your information, including your registered number, expiration date, and CVV code, you can start making payments by conveniently tapping your card on a contactless-enabled payment terminal. Consider obtaining a buy verified Cash App account for seamless transactions, especially for business purposes. Buy verified cash app account.\n\nWhy we suggest to unchanged the Cash App account username?\nTo activate your Cash Card, open the Cash App on your compatible device, locate the Cash Card icon at the bottom of the screen, and tap on it. Then select “Activate Cash Card” and proceed to scan the QR code on your card.\n\nAlternatively, you can manually enter the CVV and expiration date. After submitting your information, including your registered number, expiration date, and CVV code, you can start making payments by conveniently tapping your card on a contactless-enabled payment terminal. Consider obtaining a verified Cash App account for seamless transactions, especially for business purposes. Buy verified cash app account. Purchase Verified Cash App Accounts.\n\nSelecting a username in an app usually comes with the understanding that it cannot be easily changed within the app’s settings or options. This deliberate control is in place to uphold consistency and minimize potential user confusion, especially for those who have added you as a contact using your username. In addition, purchasing a Cash App account with verified genuine documents already linked to the account ensures a reliable and secure transaction experience.\n\n \n\nBuy verified cash app accounts quickly and easily for all your financial needs.\nAs the user base of our platform continues to grow, the significance of verified accounts cannot be overstated for both businesses and individuals seeking to leverage its full range of features. How To Buy Verified Cash App Accounts.\n\nFor entrepreneurs, freelancers, and investors alike, a verified cash app account opens the door to sending, receiving, and withdrawing substantial amounts of money, offering unparalleled convenience and flexibility. Whether you’re conducting business or managing personal finances, the benefits of a verified account are clear, providing a secure and efficient means to transact and manage funds at scale.\n\nWhen it comes to the rising trend of purchasing buy verified cash app account, it’s crucial to tread carefully and opt for reputable providers to steer clear of potential scams and fraudulent activities. How To Buy Verified Cash App Accounts. With numerous providers offering this service at competitive prices, it is paramount to be diligent in selecting a trusted source.\n\nThis article serves as a comprehensive guide, equipping you with the essential knowledge to navigate the process of procuring buy verified cash app account, ensuring that you are well-informed before making any purchasing decisions. Understanding the fundamentals is key, and by following this guide, you’ll be empowered to make informed choices with confidence.\n\n \n\nIs it safe to buy Cash App Verified Accounts?\nCash App, being a prominent peer-to-peer mobile payment application, is widely utilized by numerous individuals for their transactions. However, concerns regarding its safety have arisen, particularly pertaining to the purchase of “verified” accounts through Cash App. This raises questions about the security of Cash App’s verification process.\n\nUnfortunately, the answer is negative, as buying such verified accounts entails risks and is deemed unsafe. Therefore, it is crucial for everyone to exercise caution and be aware of potential vulnerabilities when using Cash App. How To Buy Verified Cash App Accounts.\n\nCash App has emerged as a widely embraced platform for purchasing Instagram Followers using PayPal, catering to a diverse range of users. This convenient application permits individuals possessing a PayPal account to procure authenticated Instagram Followers.\n\nLeveraging the Cash App, users can either opt to procure followers for a predetermined quantity or exercise patience until their account accrues a substantial follower count, subsequently making a bulk purchase. Although the Cash App provides this service, it is crucial to discern between genuine and counterfeit items. If you find yourself in search of counterfeit products such as a Rolex, a Louis Vuitton item, or a Louis Vuitton bag, there are two viable approaches to consider.\n\n \n\nWhy you need to buy verified Cash App accounts personal or business?\nThe Cash App is a versatile digital wallet enabling seamless money transfers among its users. However, it presents a concern as it facilitates transfer to both verified and unverified individuals.\n\nTo address this, the Cash App offers the option to become a verified user, which unlocks a range of advantages. Verified users can enjoy perks such as express payment, immediate issue resolution, and a generous interest-free period of up to two weeks. With its user-friendly interface and enhanced capabilities, the Cash App caters to the needs of a wide audience, ensuring convenient and secure digital transactions for all.\n\nIf you’re a business person seeking additional funds to expand your business, we have a solution for you. Payroll management can often be a challenging task, regardless of whether you’re a small family-run business or a large corporation. How To Buy Verified Cash App Accounts.\n\nImproper payment practices can lead to potential issues with your employees, as they could report you to the government. However, worry not, as we offer a reliable and efficient way to ensure proper payroll management, avoiding any potential complications. Our services provide you with the funds you need without compromising your reputation or legal standing. With our assistance, you can focus on growing your business while maintaining a professional and compliant relationship with your employees. Purchase Verified Cash App Accounts.\n\nA Cash App has emerged as a leading peer-to-peer payment method, catering to a wide range of users. With its seamless functionality, individuals can effortlessly send and receive cash in a matter of seconds, bypassing the need for a traditional bank account or social security number. Buy verified cash app account.\n\nThis accessibility makes it particularly appealing to millennials, addressing a common challenge they face in accessing physical currency. As a result, ACash App has established itself as a preferred choice among diverse audiences, enabling swift and hassle-free transactions for everyone. Purchase Verified Cash App Accounts.\n\n \n\nHow to verify Cash App accounts\nTo ensure the verification of your Cash App account, it is essential to securely store all your required documents in your account. This process includes accurately supplying your date of birth and verifying the US or UK phone number linked to your Cash App account.\n\nAs part of the verification process, you will be asked to submit accurate personal details such as your date of birth, the last four digits of your SSN, and your email address. If additional information is requested by the Cash App community to validate your account, be prepared to provide it promptly. Upon successful verification, you will gain full access to managing your account balance, as well as sending and receiving funds seamlessly. Buy verified cash app account.\n\n \n\nHow cash used for international transaction?\nExperience the seamless convenience of this innovative platform that simplifies money transfers to the level of sending a text message. It effortlessly connects users within the familiar confines of their respective currency regions, primarily in the United States and the United Kingdom.\n\nNo matter if you’re a freelancer seeking to diversify your clientele or a small business eager to enhance market presence, this solution caters to your financial needs efficiently and securely. Embrace a world of unlimited possibilities while staying connected to your currency domain. Buy verified cash app account.\n\nUnderstanding the currency capabilities of your selected payment application is essential in today’s digital landscape, where versatile financial tools are increasingly sought after. In this era of rapid technological advancements, being well-informed about platforms such as Cash App is crucial.\n\nAs we progress into the digital age, the significance of keeping abreast of such services becomes more pronounced, emphasizing the necessity of staying updated with the evolving financial trends and options available. Buy verified cash app account.\n\nOffers and advantage to buy cash app accounts cheap?\nWith Cash App, the possibilities are endless, offering numerous advantages in online marketing, cryptocurrency trading, and mobile banking while ensuring high security. As a top creator of Cash App accounts, our team possesses unparalleled expertise in navigating the platform.\n\nWe deliver accounts with maximum security and unwavering loyalty at competitive prices unmatched by other agencies. Rest assured, you can trust our services without hesitation, as we prioritize your peace of mind and satisfaction above all else.\n\nEnhance your business operations effortlessly by utilizing the Cash App e-wallet for seamless payment processing, money transfers, and various other essential tasks. Amidst a myriad of transaction platforms in existence today, the Cash App e-wallet stands out as a premier choice, offering users a multitude of functions to streamline their financial activities effectively. Buy verified cash app account.\n\nTrustbizs.com stands by the Cash App’s superiority and recommends acquiring your Cash App accounts from this trusted source to optimize your business potential.\n\nHow Customizable are the Payment Options on Cash App for Businesses?\nDiscover the flexible payment options available to businesses on Cash App, enabling a range of customization features to streamline transactions. Business users have the ability to adjust transaction amounts, incorporate tipping options, and leverage robust reporting tools for enhanced financial management.\n\nExplore trustbizs.com to acquire verified Cash App accounts with LD backup at a competitive price, ensuring a secure and efficient payment solution for your business needs. Buy verified cash app account.\n\nDiscover Cash App, an innovative platform ideal for small business owners and entrepreneurs aiming to simplify their financial operations. With its intuitive interface, Cash App empowers businesses to seamlessly receive payments and effectively oversee their finances. Emphasizing customization, this app accommodates a variety of business requirements and preferences, making it a versatile tool for all.\n\nWhere To Buy Verified Cash App Accounts\nWhen considering purchasing a verified Cash App account, it is imperative to carefully scrutinize the seller’s pricing and payment methods. Look for pricing that aligns with the market value, ensuring transparency and legitimacy. Buy verified cash app account.\n\nEqually important is the need to opt for sellers who provide secure payment channels to safeguard your financial data. Trust your intuition; skepticism towards deals that appear overly advantageous or sellers who raise red flags is warranted. It is always wise to prioritize caution and explore alternative avenues if uncertainties arise.\n\nThe Importance Of Verified Cash App Accounts\nIn today’s digital age, the significance of verified Cash App accounts cannot be overstated, as they serve as a cornerstone for secure and trustworthy online transactions.\n\nBy acquiring verified Cash App accounts, users not only establish credibility but also instill the confidence required to participate in financial endeavors with peace of mind, thus solidifying its status as an indispensable asset for individuals navigating the digital marketplace.\n\nWhen considering purchasing a verified Cash App account, it is imperative to carefully scrutinize the seller’s pricing and payment methods. Look for pricing that aligns with the market value, ensuring transparency and legitimacy. Buy verified cash app account.\n\nEqually important is the need to opt for sellers who provide secure payment channels to safeguard your financial data. Trust your intuition; skepticism towards deals that appear overly advantageous or sellers who raise red flags is warranted. It is always wise to prioritize caution and explore alternative avenues if uncertainties arise.\n\nConclusion\nEnhance your online financial transactions with verified Cash App accounts, a secure and convenient option for all individuals. By purchasing these accounts, you can access exclusive features, benefit from higher transaction limits, and enjoy enhanced protection against fraudulent activities. Streamline your financial interactions and experience peace of mind knowing your transactions are secure and efficient with verified Cash App accounts.\n\nChoose a trusted provider when acquiring accounts to guarantee legitimacy and reliability. In an era where Cash App is increasingly favored for financial transactions, possessing a verified account offers users peace of mind and ease in managing their finances. Make informed decisions to safeguard your financial assets and streamline your personal transactions effectively.\n\nContact Us / 24 Hours Reply\nTelegram:dmhelpshop\nWhatsApp: +1 (980) 277-2786\nSkype:dmhelpshop\nEmail:dmhelpshop@gmail.com\n\n" | uiueqay3 |
1,875,662 | How can I modify the logo and footnote from a WP theme | I created a website and built it from a theme that comes with logo and footnote design. I want to... | 0 | 2024-06-03T16:21:57 | https://dev.to/bitiqa/how-can-i-modify-the-logo-and-footnote-from-a-wp-theme-32eb | I created a website and built it from a theme that comes with logo and footnote design. I want to change the logo to my own logo and the structure of the footnote section, and tried to do this by going to the Widgets section (under Appearance) but I don't seem to be able to do this. Any suggestions on how I can do this... | bitiqa | |
1,875,661 | Why Use Time Tracking Software? | Introduction: Maintaining team productivity and meeting project deadlines can be a... | 0 | 2024-06-03T16:21:48 | https://dev.to/goseoservices/why-use-time-tracking-software-550a | productivity, monitoring | ## Introduction:
Maintaining team productivity and meeting project deadlines can be a never-ending race against the clock in today's fast-paced business environment. It makes sense that managers would want a magic solution to make time management easier—juggling tasks, allocating resources, and monitoring employee hou... | goseoservices |
1,875,660 | Building great things | Ah, the journey of building a software house - an adventure that many developers face at the end of... | 0 | 2024-06-03T16:20:23 | https://dev.to/damnpedrini/building-great-things-41hi | buildinpublic, webdev, beginners, ai | Ah, the journey of building a software house - an adventure that many developers face at the end of college. It's like stepping into a parallel universe, where we can not only do what we love, but also breathe life into ideas that we believe will make a difference, all with a beautiful aesthetic, of course.
But like i... | damnpedrini |
1,875,658 | Defining Classes for Objects | Object-oriented programming enables you to develop large-scale software and GUIs effectively. A class... | 0 | 2024-06-03T16:20:05 | https://dev.to/paulike/defining-classes-for-objects-15o5 | java, programming, learning, beginners | Object-oriented programming enables you to develop large-scale software and GUIs effectively. A class defines the properties and behaviors for objects. Object-oriented programming (OOP) involves programming using objects. An _object_ represents an entity in the real world that can be distinctly identified. For example,... | paulike |
1,875,657 | easiest way to get ahead in tech quick. | Go Here Free tool to optimize yourself for the current landscape of jobs. Resume optimized for... | 0 | 2024-06-03T16:18:53 | https://dev.to/alexdonn/easiest-way-to-get-ahead-in-tech-quick-59ch | workplace, productivity, career | [Go Here
](https://sourceco.io/success)
Free tool to optimize yourself for the current landscape of jobs. Resume optimized for current ai resume filtering.
Free tools to make yourself standout amongst everyone else. To get picked for the top jobs, be at the top, look like #1.
| alexdonn |
1,875,655 | What is GitOps? | What is GitOps? GitOps is a set of practices that centers around using Git as a single... | 0 | 2024-06-03T16:15:14 | https://dev.to/oussamalakhdar/what-is-gitops-5al2 | devops, gitops, git, cloud | ## What is GitOps?
GitOps is a set of practices that centers around using Git as a single source of truth for declarative infrastructure and applications. It emphasizes using Git pull requests as the primary way to manage infrastructure and application configurations. This methodology is closely associated with `Kubern... | oussamalakhdar |
1,875,654 | Authenticate to multiple git based source accounts in single system | Generate SSH keys using the below two commands in gitbash terminal. ssh-keygen -t ed25519 -C... | 0 | 2024-06-03T16:11:52 | https://dev.to/mohan023/authenticate-to-multiple-git-based-source-accounts-in-single-system-4imb | 1. Generate SSH keys using the below two commands in gitbash terminal.
`ssh-keygen -t ed25519 -C "abc@gmail.com" -f ~/.ssh/P`
`ssh-keygen -t ed25519 -C "xyz@c.com" -f ~/.ssh/C`
2. Add public keys to respective accounts
3. Configure multiple host in **config** file under ~/.ssh directory

[Why are they needed](#chapter-2)
[Encapsulation & State Management](#chapter-3)
[Higher Order Functions](#chapter-4)
[Function Currying & Composition](#chapter-5)
[How Javascript libraries leverage closures](#chapter-6)
---
In the vast world of JavaScript, cl... | dev_diaries_by_varun |
1,875,647 | http://wpu.me | The website http://wpu.me appears to be related to WordPress tutorials and tips. It is designed to... | 0 | 2024-06-03T15:54:34 | https://dev.to/bebopalulasheismybaby/httpwpume-2fnc | The website [http://wpu.me](http://wpu.me) appears to be related to WordPress tutorials and tips. It is designed to assist users with basic WordPress requests, offering tutorials, tips, and tricks to enhance their WordPress skills. | bebopalulasheismybaby | |
1,875,656 | Une autre manière de faire fonctionner OpenStack au-dessus de Kubernetes avec Atmosphere … | Plusieurs projets de déploiement d’OpenStack qui reposent sur un cluster Kubernetes existent à... | 0 | 2024-06-03T16:18:41 | https://deep75.medium.com/une-autre-mani%C3%A8re-de-faire-fonctionner-openstack-au-dessus-de-kubernetes-avec-atmosphere-9ac8c46b4232 | kubernetes, openstack, docker, phoenixnap | ---
title: Une autre manière de faire fonctionner OpenStack au-dessus de Kubernetes avec Atmosphere …
published: true
date: 2024-06-03 15:53:30 UTC
tags: kubernetes,openstack,docker,phoenixnap
canonical_url: https://deep75.medium.com/une-autre-mani%C3%A8re-de-faire-fonctionner-openstack-au-dessus-de-kubernetes-avec-atm... | deep75 |
1,875,643 | Ai Will Live and Die By Trust it | AI will live and die by trust. The potential of AI is unmatched, but we have to be able to trust... | 0 | 2024-06-03T15:48:25 | https://dev.to/stealc/ai-will-live-and-die-by-trust-it-2l63 | ai, news, machinelearning, webdev | >_AI will live and die by trust._
The potential of AI is unmatched, but we have to be able to trust it. Once we trust it, we can address various use cases, ideally one at a time, to avoid confusion or overwhelm IT ... | stealc |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.