id int64 5 1.93M | title stringlengths 0 128 | description stringlengths 0 25.5k | collection_id int64 0 28.1k | published_timestamp timestamp[s] | canonical_url stringlengths 14 581 | tag_list stringlengths 0 120 | body_markdown stringlengths 0 716k | user_username stringlengths 2 30 |
|---|---|---|---|---|---|---|---|---|
1,875,035 | Deploying a NestJS Application on Vercel with a PostgreSQL Database | Deploying a NestJS Application on Vercel with a PostgreSQL Database Prerequisites:- This article is... | 0 | 2024-06-03T07:56:38 | https://dev.to/bilalurrehman27/deploying-a-nestjs-application-on-vercel-with-a-postgresql-database-2be0 | nestjs, vercel, typescript, helmet | Deploying a NestJS Application on Vercel with a PostgreSQL Database
**Prerequisites:-**
This article is for someone who already knows the nest.js.
**Familiarity with Nest.js**
Nest.js application connected and working locally with PostgreSQL
Vercel account to deploy your application
Vercel and Supabase accounts
**Database Setup:-**
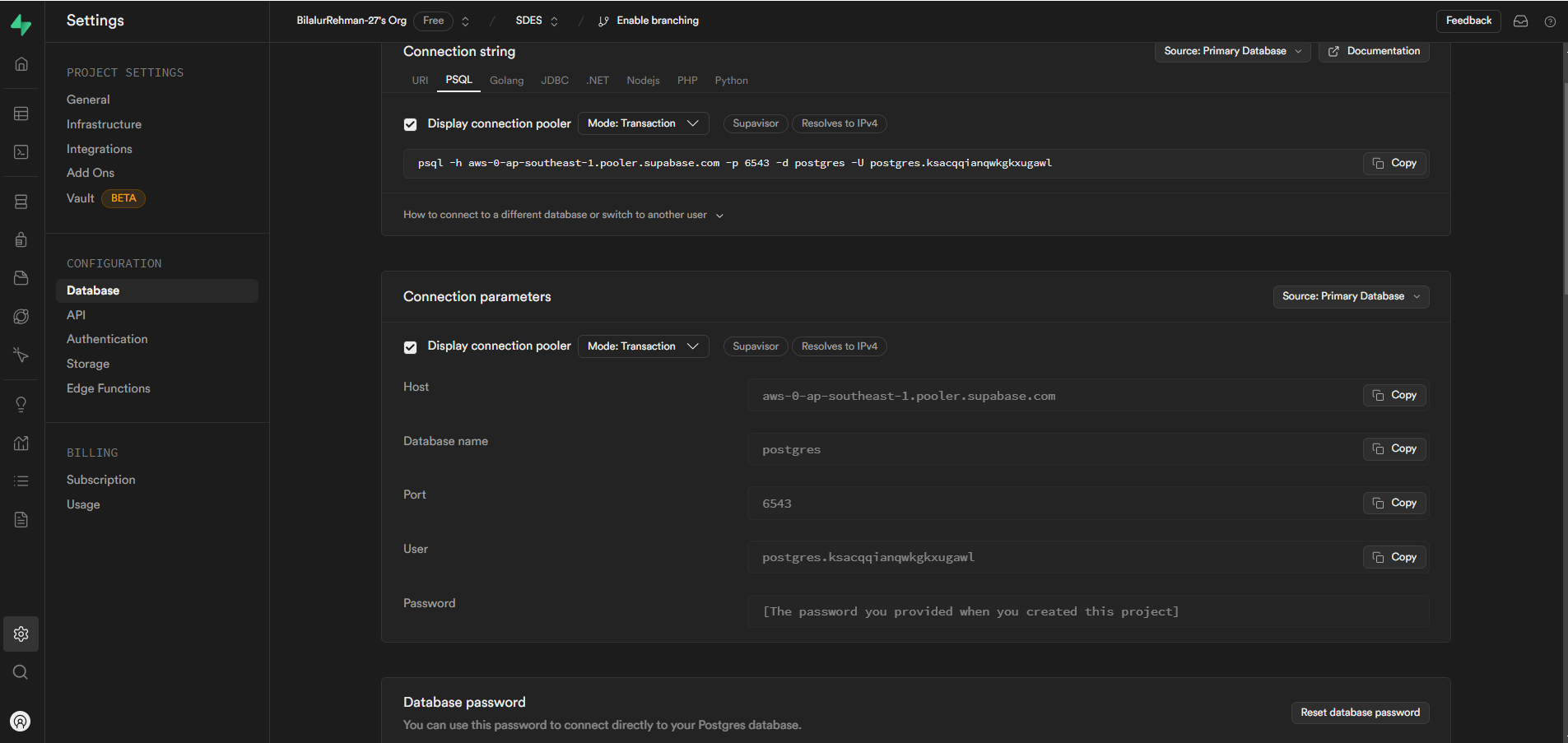
Login to Supabase to obtain database credentials: Hostname, Database Name, Username, and Password.
Try to connect your application with the credentials locally to make sure everything is working fine.
You will get this under the settings under
/settings/database section
**Prepping for Vercel Deployment:-**
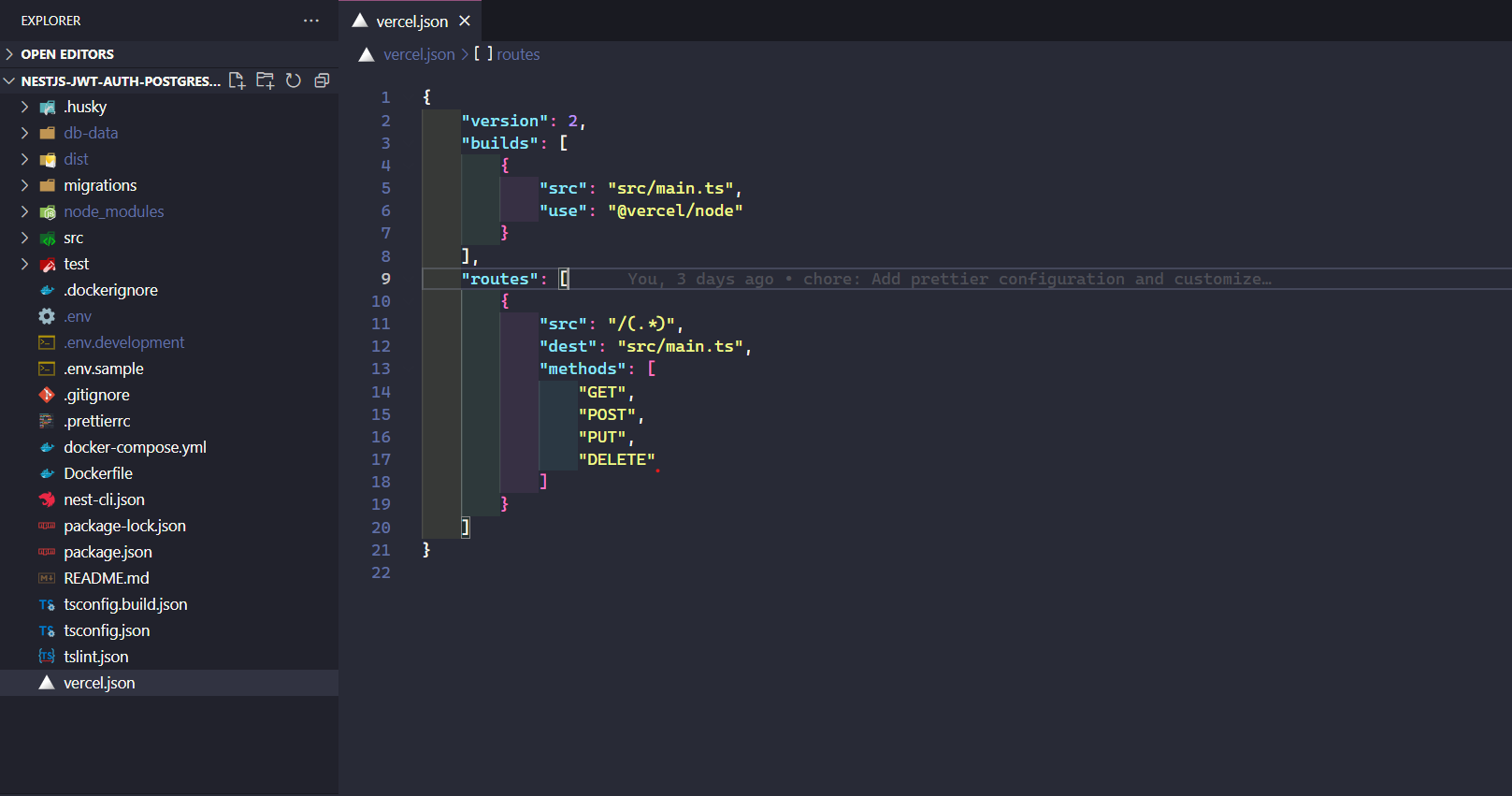
Now create vercel.json file in the root of your application and add the following configuration in to it.
```
{
"version": 2,
"builds": [
{
"src": "src/main.ts",
"use": "@vercel/node"
}
],
"routes": [
{
"src": "/(.*)",
"dest": "src/main.ts",
"methods": ["GET", "POST", "PUT", "PATCH" , "DELETE"]
}
]
}
```
It should look like something like this
**Project Setup on Vercel:-**
Now login/signup to your vercel account and create a new project there
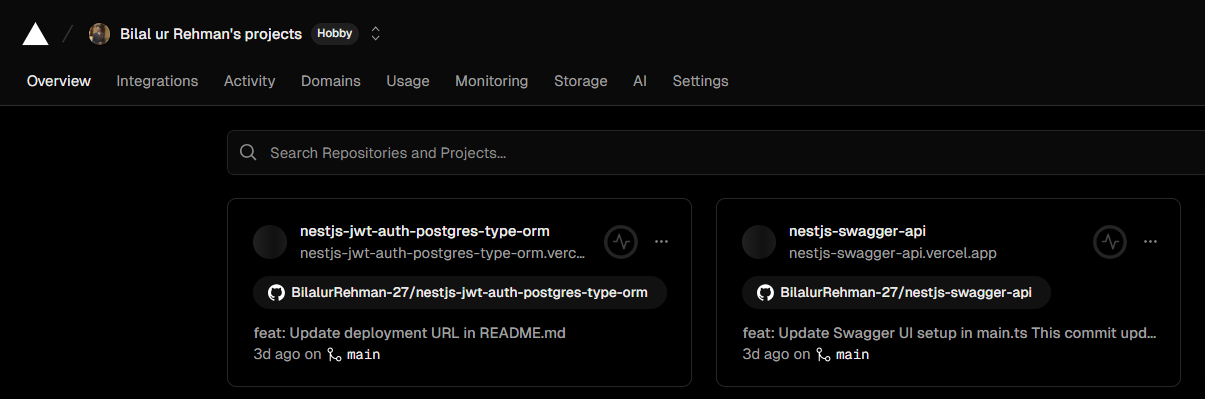
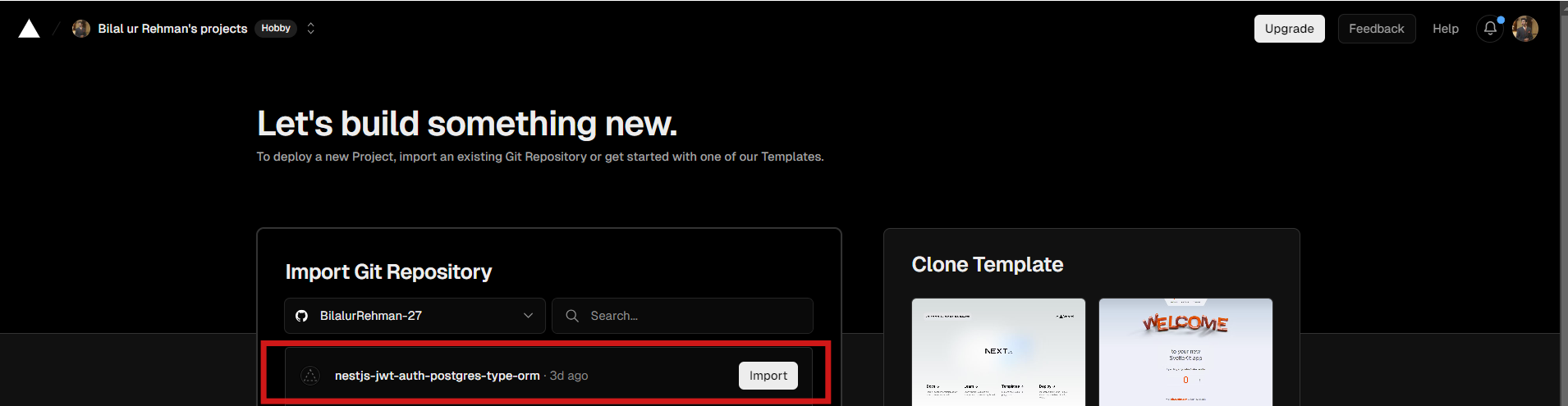
Import your git repository and connect your github repository
**Configure your project:-**
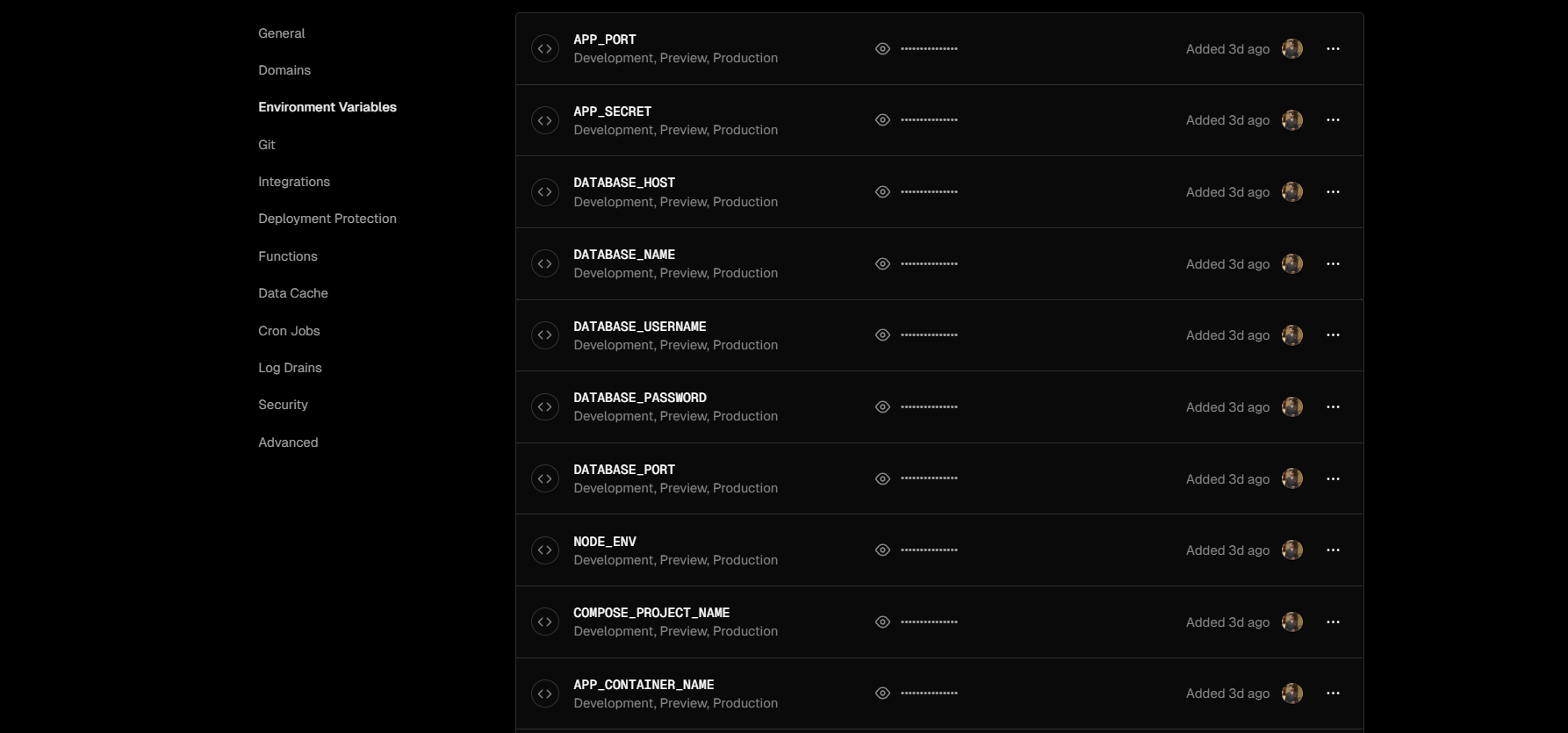
Now configure your project i.e. name, enter the environment variables if any and then hit deploy.
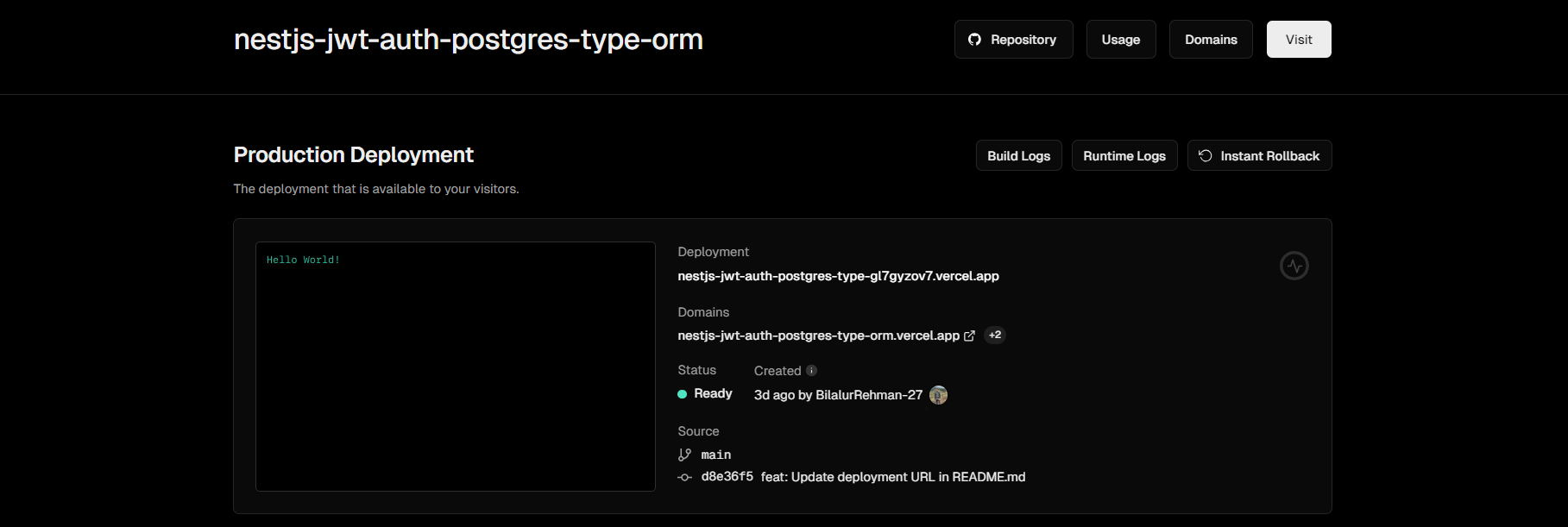
And that’s it. Wait for deployment and test using the provided link.
**Swagger UI Loading Issue Fix:-**
You might not be able to see your swagger docs on your deployed nest.js app, as vercel was unable to load the swagger css. For that you need to load the swagger css with external css,
Here is the sample code which shoes, how to do it.
```
SwaggerModule.setup("docs", app, document, {
customSiteTitle: "Api Docs",
customfavIcon: "https://avatars.githubusercontent.com/u/6936373?s=200&v=4",
customJs: [
"https://cdnjs.cloudflare.com/ajax/libs/swagger-ui/4.15.5/swagger-ui-bundle.min.js",
"https://cdnjs.cloudflare.com/ajax/libs/swagger-ui/4.15.5/swagger-ui-standalone-preset.min.js",
],
customCssUrl: [
"https://cdnjs.cloudflare.com/ajax/libs/swagger-ui/4.15.5/swagger-ui.min.css",
"https://cdnjs.cloudflare.com/ajax/libs/swagger-ui/4.15.5/swagger-ui-standalone-preset.min.css",
"https://cdnjs.cloudflare.com/ajax/libs/swagger-ui/4.15.5/swagger-ui.css",
],
});
```
And that’s it.
Now you can access your nest.js application on vercel.
**Issue With Helmet:-**
For all those who are using helmet might not be able to see the swagger page as helmet blocks the request.
Now the hack is just initialize the helmet after the swagger is initilized, as in node file is read from top to bottom then the request won’t get’s blocked and you will got to see segger docs.
This is how your main file will look like.
```
SwaggerModule.setup("docs", app, document, {
customSiteTitle: "Api Docs",
customfavIcon: "https://avatars.githubusercontent.com/u/6936373?s=200&v=4",
customJs: [
"https://cdnjs.cloudflare.com/ajax/libs/swagger-ui/4.15.5/swagger-ui-bundle.min.js",
"https://cdnjs.cloudflare.com/ajax/libs/swagger-ui/4.15.5/swagger-ui-standalone-preset.min.js",
],
customCssUrl: [
"https://cdnjs.cloudflare.com/ajax/libs/swagger-ui/4.15.5/swagger-ui.min.css",
"https://cdnjs.cloudflare.com/ajax/libs/swagger-ui/4.15.5/swagger-ui-standalone-preset.min.css",
"https://cdnjs.cloudflare.com/ajax/libs/swagger-ui/4.15.5/swagger-ui.css",
],
});
app.use(helmet()); //here
```
**Follow Me on GitHub**
If you found this article helpful or interesting, consider following me on [GitHub ](https://github.com/BilalurRehman-27
)for more updates, projects, and resources related to NestJS and other technologies. You can find my GitHub profile [here](https://github.com/BilalurRehman-27/nestjs-jwt-auth-postgres-type-orm).
That’s it.
Happy Coding !
| bilalurrehman27 |
1,875,034 | How to Make Limoncello | solution Step 1 step 2 peel the lemons Step 3 distill | 0 | 2024-06-03T07:52:05 | https://dev.to/bobbyliunardo/how-to-make-limoncello-32d3 | # solution Step 1
## step 2
peel the lemons
### Step 3
distill
| bobbyliunardo | |
1,875,030 | Responsive vs Mobile-First Design: What’s the Difference? | When it comes to web design, two prominent approaches often come into play: responsive design and... | 0 | 2024-06-03T07:46:53 | https://dev.to/ajmal_kp/responsive-vs-mobile-first-design-whats-the-difference-4p9m | <p> <span face="source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif" style="background-color: white; color: #242424; font-size: 20px; letter-spacing: -0.003em;">When it comes to web design, two prominent approaches often come into play: responsive design and mobile-first design. Both strategies aim to ensure websites look and function well on a variety of devices, but they differ in their methodologies and priorities. Understanding these differences can help businesses choose the best approach for their needs.</span></p><h1 class="mt mu gg be mv mw mx my mz na nb nc nd ne nf ng nh ni nj nk nl nm nn no np nq bj" data-selectable-paragraph="" id="d877" style="background-color: white; box-sizing: inherit; color: #242424; font-family: sohne, "Helvetica Neue", Helvetica, Arial, sans-serif; font-size: 24px; letter-spacing: -0.016em; line-height: 30px; margin: 1.95em 0px -0.28em;">Responsive Design</h1><p class="pw-post-body-paragraph lv lw gg lx b ly nr ma mb mc ns me mf mg nt mi mj mk nu mm mn mo nv mq mr ms fk bj" data-selectable-paragraph="" id="1a37" style="background-color: white; box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; margin: 0.94em 0px -0.46em; word-break: break-word;">Responsive design is an approach where the layout and content of a website adjust seamlessly based on the screen size and orientation of the device being used. This technique uses flexible grids, fluid images, and CSS media queries to ensure the website provides an optimal viewing experience across all devices, from desktops to smartphones.</p><h1 class="mt mu gg be mv mw mx my mz na nb nc nd ne nf ng nh ni nj nk nl nm nn no np nq bj" data-selectable-paragraph="" id="a6ab" style="background-color: white; box-sizing: inherit; color: #242424; font-family: sohne, "Helvetica Neue", Helvetica, Arial, sans-serif; font-size: 24px; letter-spacing: -0.016em; line-height: 30px; margin: 1.95em 0px -0.28em;">Key Features of Responsive Design:</h1><ol style="background-color: white; box-sizing: inherit; color: rgba(0, 0, 0, 0.8); font-family: medium-content-sans-serif-font, -apple-system, "system-ui", "Segoe UI", Roboto, Oxygen, Ubuntu, Cantarell, "Open Sans", "Helvetica Neue", sans-serif; list-style: none none; margin: 0px; padding: 0px;"><li class="lv lw gg lx b ly nr ma mb mc ns me mf mg nt mi mj mk nu mm mn mo nv mq mr ms aib op oq bj" data-selectable-paragraph="" id="3677" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; list-style-type: decimal; margin-bottom: -0.46em; margin-left: 30px; margin-top: 0.94em; padding-left: 0px;">Flexibility: The website layout automatically adjusts to fit any screen size.</li><li class="lv lw gg lx b ly or ma mb mc os me mf mg ot mi mj mk ou mm mn mo ov mq mr ms aib op oq bj" data-selectable-paragraph="" id="5d40" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; list-style-type: decimal; margin-bottom: -0.46em; margin-left: 30px; margin-top: 1.14em; padding-left: 0px;">Efficiency: A single codebase serves all devices, reducing the need for separate mobile and desktop sites.</li><li class="lv lw gg lx b ly or ma mb mc os me mf mg ot mi mj mk ou mm mn mo ov mq mr ms aib op oq bj" data-selectable-paragraph="" id="44a3" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; list-style-type: decimal; margin-bottom: -0.46em; margin-left: 30px; margin-top: 1.14em; padding-left: 0px;">User Experience: Ensures consistency in design and functionality across various devices.</li></ol><h1 class="mt mu gg be mv mw mx my mz na nb nc nd ne nf ng nh ni nj nk nl nm nn no np nq bj" data-selectable-paragraph="" id="14c3" style="background-color: white; box-sizing: inherit; color: #242424; font-family: sohne, "Helvetica Neue", Helvetica, Arial, sans-serif; font-size: 24px; letter-spacing: -0.016em; line-height: 30px; margin: 1.95em 0px -0.28em;">Mobile-First Design</h1><p class="pw-post-body-paragraph lv lw gg lx b ly nr ma mb mc ns me mf mg nt mi mj mk nu mm mn mo nv mq mr ms fk bj" data-selectable-paragraph="" id="c740" style="background-color: white; box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; margin: 0.94em 0px -0.46em; word-break: break-word;">Mobile-first design is a strategy where the design process starts with the mobile version of the website, considering the constraints and usability on smaller screens first. Once the mobile design is solidified, it is progressively enhanced to create a more complex and content-rich version for larger screens such as tablets and desktops.</p><h1 class="mt mu gg be mv mw mx my mz na nb nc nd ne nf ng nh ni nj nk nl nm nn no np nq bj" data-selectable-paragraph="" id="6a31" style="background-color: white; box-sizing: inherit; color: #242424; font-family: sohne, "Helvetica Neue", Helvetica, Arial, sans-serif; font-size: 24px; letter-spacing: -0.016em; line-height: 30px; margin: 1.95em 0px -0.28em;">Key Features of Mobile-First Design:</h1><ol style="background-color: white; box-sizing: inherit; color: rgba(0, 0, 0, 0.8); font-family: medium-content-sans-serif-font, -apple-system, "system-ui", "Segoe UI", Roboto, Oxygen, Ubuntu, Cantarell, "Open Sans", "Helvetica Neue", sans-serif; list-style: none none; margin: 0px; padding: 0px;"><li class="lv lw gg lx b ly nr ma mb mc ns me mf mg nt mi mj mk nu mm mn mo nv mq mr ms aib op oq bj" data-selectable-paragraph="" id="d3e9" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; list-style-type: decimal; margin-bottom: -0.46em; margin-left: 30px; margin-top: 0.94em; padding-left: 0px;">Prioritization: Focuses on the most critical content and features for mobile users, ensuring essential functionality is available on smaller screens.</li><li class="lv lw gg lx b ly or ma mb mc os me mf mg ot mi mj mk ou mm mn mo ov mq mr ms aib op oq bj" data-selectable-paragraph="" id="6d27" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; list-style-type: decimal; margin-bottom: -0.46em; margin-left: 30px; margin-top: 1.14em; padding-left: 0px;">Performance: Often leads to faster load times and better performance on mobile devices due to the streamlined initial design.</li><li class="lv lw gg lx b ly or ma mb mc os me mf mg ot mi mj mk ou mm mn mo ov mq mr ms aib op oq bj" data-selectable-paragraph="" id="c80b" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; list-style-type: decimal; margin-bottom: -0.46em; margin-left: 30px; margin-top: 1.14em; padding-left: 0px;">Progressive Enhancement: Builds on the mobile design to add more features and content for larger screens, ensuring a robust experience for all users.</li></ol><h1 class="mt mu gg be mv mw mx my mz na nb nc nd ne nf ng nh ni nj nk nl nm nn no np nq bj" data-selectable-paragraph="" id="3a43" style="background-color: white; box-sizing: inherit; color: #242424; font-family: sohne, "Helvetica Neue", Helvetica, Arial, sans-serif; font-size: 24px; letter-spacing: -0.016em; line-height: 30px; margin: 1.95em 0px -0.28em;">Which Approach to Choose?</h1><p class="pw-post-body-paragraph lv lw gg lx b ly nr ma mb mc ns me mf mg nt mi mj mk nu mm mn mo nv mq mr ms fk bj" data-selectable-paragraph="" id="8d4e" style="background-color: white; box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; margin: 0.94em 0px -0.46em; word-break: break-word;">The choice between responsive and mobile-first design depends on your audience and business goals. If your primary audience accesses your site from mobile devices, starting with a mobile-first design can ensure a better user experience for the majority of your users. Conversely, if your audience predominantly uses desktops, a responsive design might be more appropriate, offering a consistent experience across all devices.</p><h1 class="mt mu gg be mv mw mx my mz na nb nc nd ne nf ng nh ni nj nk nl nm nn no np nq bj" data-selectable-paragraph="" id="eed0" style="background-color: white; box-sizing: inherit; color: #242424; font-family: sohne, "Helvetica Neue", Helvetica, Arial, sans-serif; font-size: 24px; letter-spacing: -0.016em; line-height: 30px; margin: 1.95em 0px -0.28em;">5ine: Your Partner in Web Development</h1><p class="pw-post-body-paragraph lv lw gg lx b ly nr ma mb mc ns me mf mg nt mi mj mk nu mm mn mo nv mq mr ms fk bj" data-selectable-paragraph="" id="2d63" style="background-color: white; box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; margin: 0.94em 0px -0.46em; word-break: break-word;">Choosing the right web design approach is crucial, and partnering with an experienced <a class="af nw" href="https://www.5ines.com/web-development-service-bangalore.php" rel="noopener ugc nofollow" style="-webkit-tap-highlight-color: transparent; box-sizing: inherit;" target="_blank">web development</a> company like <a class="af nw" href="https://www.5ines.com/" rel="noopener ugc nofollow" style="-webkit-tap-highlight-color: transparent; box-sizing: inherit;" target="_blank">5ine</a> can make all the difference. 5ine specializes in creating custom websites that are not only visually appealing but also highly functional and user-friendly.</p><h1 class="mt mu gg be mv mw mx my mz na nb nc nd ne nf ng nh ni nj nk nl nm nn no np nq bj" data-selectable-paragraph="" id="837c" style="background-color: white; box-sizing: inherit; color: #242424; font-family: sohne, "Helvetica Neue", Helvetica, Arial, sans-serif; font-size: 24px; letter-spacing: -0.016em; line-height: 30px; margin: 1.95em 0px -0.28em;">Services Offered by 5ine:</h1><ol style="background-color: white; box-sizing: inherit; color: rgba(0, 0, 0, 0.8); font-family: medium-content-sans-serif-font, -apple-system, "system-ui", "Segoe UI", Roboto, Oxygen, Ubuntu, Cantarell, "Open Sans", "Helvetica Neue", sans-serif; list-style: none none; margin: 0px; padding: 0px;"><li class="lv lw gg lx b ly nr ma mb mc ns me mf mg nt mi mj mk nu mm mn mo nv mq mr ms aib op oq bj" data-selectable-paragraph="" id="3a09" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; list-style-type: decimal; margin-bottom: -0.46em; margin-left: 30px; margin-top: 0.94em; padding-left: 0px;">Responsive Web Design: Ensuring your website looks great and functions well on all devices.</li><li class="lv lw gg lx b ly or ma mb mc os me mf mg ot mi mj mk ou mm mn mo ov mq mr ms aib op oq bj" data-selectable-paragraph="" id="1a79" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; list-style-type: decimal; margin-bottom: -0.46em; margin-left: 30px; margin-top: 1.14em; padding-left: 0px;">Mobile-First Design: Prioritizing mobile users to deliver a superior browsing experience.</li><li class="lv lw gg lx b ly or ma mb mc os me mf mg ot mi mj mk ou mm mn mo ov mq mr ms aib op oq bj" data-selectable-paragraph="" id="11bd" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; list-style-type: decimal; margin-bottom: -0.46em; margin-left: 30px; margin-top: 1.14em; padding-left: 0px;">Custom Web Development: Tailoring solutions to meet your specific business needs.</li><li class="lv lw gg lx b ly or ma mb mc os me mf mg ot mi mj mk ou mm mn mo ov mq mr ms aib op oq bj" data-selectable-paragraph="" id="d498" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; list-style-type: decimal; margin-bottom: -0.46em; margin-left: 30px; margin-top: 1.14em; padding-left: 0px;">Performance Optimization: Enhancing site speed and performance for better user experience.</li><li class="lv lw gg lx b ly or ma mb mc os me mf mg ot mi mj mk ou mm mn mo ov mq mr ms aib op oq bj" data-selectable-paragraph="" id="52e3" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; list-style-type: decimal; margin-bottom: -0.46em; margin-left: 30px; margin-top: 1.14em; padding-left: 0px;">SEO-Friendly Design: Building websites that rank well in search engines, driving more traffic to your site.</li></ol><p class="pw-post-body-paragraph lv lw gg lx b ly lz ma mb mc md me mf mg mh mi mj mk ml mm mn mo mp mq mr ms fk bj" data-selectable-paragraph="" id="c809" style="background-color: white; box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; margin: 2.14em 0px -0.46em; word-break: break-word;">By leveraging the expertise of 5ine, you can create a website that not only meets the demands of today’s diverse digital landscape but also sets you apart from the competition. Whether you prefer a responsive or mobile-first approach, 5ine is equipped to deliver a solution that aligns with your business objectives.</p> | ajmal_kp | |
1,874,998 | Flutter: Best Practices for API Key Security ✅ | Securing API keys in Flutter is crucial to prevent unauthorized access to your app's functionalities.... | 0 | 2024-06-03T07:51:57 | https://dev.to/harsh8088/flutter-best-practices-for-api-key-security-145m | flutter, security | ---
title: Flutter: Best Practices for API Key Security ✅
published: true
description:
tags: flutter, security,
cover_image: https://dev-to-uploads.s3.amazonaws.com/uploads/articles/enua8kyxgm57orhzvwt3.png
# Use a ratio of 100:42 for best results.
# published_at: 2024-06-03 05:38 +0000
---
Securing API keys in Flutter is crucial to prevent unauthorized access to your app's functionalities. Here are some common methods with increasing security:
###**1. Least Secure (Not Recommended): Hardcoding API Keys**###
This involves storing the API key directly in a Dart file. While simple, it exposes the key to anyone with access to your code.
```dart
// This is a VULNERABLE approach! Never use it in production.
import 'package:http/http.dart' as http;
final String apiUrl = 'https://api.sample.com/data';
final String apiKey = 'YOUR_ACTUAL_API_KEY';
Future<http.Response> fetchData() async {
final url = Uri.parse('$apiUrl?key=$apiKey');
final response = await http.get(url);
return response;
}
```
**Important:** Never hardcode API keys in your Flutter code, as it exposes them to anyone with access to your codebase. Here's why it's not recommended:
**Version Control Exposure:** If you commit the code containing the API key to a version control system (e.g., Git), anyone with access to the repository can see it.
**App Vulnerability:** Hackers can potentially decompile your app and extract the API key, compromising your app's security.
###**2. Using `--dart-define` Flag**###
Pass the API key at compile time using the `--dart-define` flag. This keeps the key out of your codebase but requires remembering the flag during development and deployment.
The `--dart-define` flag in Flutter allows you to define compile-time constants that you can access in your code. This can be useful for storing environment-specific configurations, such as API keys, without hardcoding them directly in your source code. Here's an example of how to use it:
* **Define the Flag:**
```
flutter run --dart-define=API_KEY=YOUR_API_KEY
```
* **Access the Constant in Your Code:**
```dart
import 'package:flutter/foundation.dart';
void main() {
final apiKey = String.fromEnvironment('API_KEY');
// Use the apiKey variable for your API calls
}
```
Here we use `String.fromEnvironment('API_KEY')` to retrieve the value of the constant defined with the `--dart-define` flag.
**Limitations:**
* The `--dart-define` flag defines constants only during compilation. You cannot dynamically change them at runtime.
* It's less secure than other methods as someone can potentially see the flag arguments in your terminal history.
###**3. Using a .env File with ENVied Package**###
This method is more secure. Here's how it works:
* **Install Dependencies:**
```dart
flutter pub add envied
flutter pub add --dev envied_generator
flutter pub add --dev build_runner
```
* **Create the `.env` File:**
Create a file named `.env` at the root of your Flutter project. This file will store your environment variables in the format `KEY=VALUE`. Here's an example:
```dart
API_KEY=your_actual_api_key (Replace with your actual API key)
BASE_URL=https://api.sample.com
```
**Important:** Never commit the .env file to version control (e.g., Git). Add it to your .gitignore file to prevent accidental exposure.
* **Create the `env.dart` File:**
Create a new Dart file named `env.dart` in your project's lib directory. This file will define a class to access the environment variables.
```dart
import 'package:envied/envied.dart';
part 'env.g.dart';
@Envied(path: '.env') // Specify the path to your .env file
abstract class Env {
@EnviedField(varName: 'API_KEY')
static final String apiKey = _Env.apiKey; // Use obfuscate: true for extra security (optional)
@EnviedField(varName: 'BASE_URL')
static final String baseUrl = _Env.baseUrl;
}
```
* **Generate Code (Run Once):**
Run the following command in your terminal to generate the necessary code for accessing environment variables:
```
flutter pub run build_runner build
```
This will create a new file named env.g.dart next to your env.dart file.
* **Access Environment Variables:**
Now you can access your environment variables defined in the `.env` file using the Env class. Import `env.dart` in your code where you need to use the API key or base URL:
```dart
import 'package:samples/env.dart'; // Replace with your project path
void main() async {
final url = Uri.parse('$Env.baseUrl/data');
final response = await http.get(url);
// ... process the response using your API key if needed
}
```
**Benefits:**
* **Security:** `.env` files are excluded from version control, keeping your API keys safe.
* **Flexibility:** You can easily change environment variables (e.g., dev vs. production) without modifying your codebase.
* **Maintainability:** Keeps sensitive information separate from your application code.
> Remember, this is a recommended approach for securing API keys. Consider using `obfuscate: true` in the `@EnviedField` annotation for an extra layer of protection (though it's not a foolproof method).
```dart
import 'package:envied/envied.dart';
part 'env.g.dart';
@Envied(path: '.env')
abstract class Env {
@EnviedField(varName: 'API_KEY', obfuscate: true)
static final String apiKey = _Env.apiKey;
@EnviedField(varName: 'BASE_URL')
static final String baseUrl = _Env.baseUrl;
}
```
###**4. Using Firebase Functions**###
Implement a backend layer with Firebase Functions to manage API calls. Store keys securely in Firebase project environment variables and access them within the function
Here's how to leverage Firebase Functions to securely manage API keys in your Flutter application:
* **Firebase Project Setup:**
Ensure you have a Firebase project set up and connected to your Flutter app.
* **Enable Firebase Secrets Manager:**
In the Firebase console, navigate to "Project Settings" -> "Your apps" and select your Flutter app.
Under "Secrets Manager," enable the service.
* **Set Up Your Firebase Function:**
In your Firebase project directory, create a new function using the Firebase CLI:
```
firebase functions:create function fetchUserData
```
* **Write the Function Code (index.js):**
```javascript
const functions = require('firebase-functions');
const admin = require('firebase-admin');
admin.initializeApp();
exports.fetchUserData = functions.https.onCall((data, context) => {
// Retrieve API key from Firebase Secrets Manager
const apiKey = admin.secretManager().secretVersion('api-key-secret/versions/latest').accessSync();
// Use the API key to fetch data (replace with your actual API call)
const url = `https://api.sample.com/data?key=${apiKey}`;
const response = await fetch(url);
const userData = await response.json();
return userData;
});
```
**Explanation:**
> We import necessary libraries: firebase-functions and firebase-admin.
We initialize the Firebase Admin SDK.
The `fetchUserData` function is triggered on call from your Flutter app.
It retrieves the API key from a Firebase Secret Manager named `api-key-secret`.
The key is accessed securely using `accessSync()` within a protected environment.
Replace the example API call (fetch) with your actual API interaction using the retrieved key.
The function returns the fetched user data.
* **Create the Firebase Secret:**
> Go to "Secrets Manager" in the Firebase console.
Create a new secret named your-api-key-secret.
Add a version with your actual API key as the value.
* **Call the Function from Flutter:**
```dart
import 'package:cloud_functions/cloud_functions.dart';
Future<dynamic> getUserData() async {
final functions = FirebaseFunctions.instance;
final callable = functions.httpsCallable('fetchUserData');
final result = await callable();
return result.data;
}
```
**Conclusion:**
This guide explored various approaches to securing API keys in your Flutter application. We learned that:
* Hardcoding API keys is highly discouraged due to exposure in your codebase.
* The `--dart-define` flag offers some protection but has limitations.
* Using a `.env` file with the ENVied package provides a more secure solution by storing keys outside your code.
* Firebase Functions are the most secure option, keeping keys entirely out of the app and leveraging Firebase's secret management features.
Remember, choose the method that best suits your security needs and project complexity. Prioritize keeping API keys confidential and avoid version control exposure.
**Security is an Ongoing Process**
Securing your Flutter app goes beyond API keys. Consider additional measures like user authentication, data encryption, and secure communication protocols. Stay updated on best practices as security threats evolve.
**Thank you for reading!**🧑🏻💻
| harsh8088 |
1,875,033 | hello every one! | A post by Adithyan Adhi | 0 | 2024-06-03T07:51:15 | https://dev.to/adithyan_adhi_2281fe7cc96/hello-every-one-21f3 |
| adithyan_adhi_2281fe7cc96 | |
1,875,032 | Setting Up a CI/CD Pipeline with Jenkins, GitHub Actions, or CircleCI | Continuous Integration and Continuous Deployment (CI/CD) pipelines have become essential for modern... | 0 | 2024-06-03T07:49:51 | https://dev.to/markwilliams21/setting-up-a-cicd-pipeline-with-jenkins-github-actions-or-circleci-2bfi | cicd, github, jenkins, circleci | Continuous Integration and Continuous Deployment (CI/CD) pipelines have become essential for modern software development, allowing teams to automate the testing, integration, and deployment of code. In this blog post, we'll explore how to set up a [CI/CD pipeline](https://www.redhat.com/en/topics/devops/what-cicd-pipeline) using three popular tools: [Jenkins](https://www.janbasktraining.com/blog/jenkins-tutorial/), GitHub Actions, and CircleCI. Each tool has its unique features and strengths, so let's dive in to see how they can be leveraged for efficient and effective CI/CD processes.
## 1. Setting Up a CI/CD Pipeline with Jenkins
Jenkins is one of the most popular open-source automation servers. It offers a robust and flexible way to set up CI/CD pipelines.
**Step-by-Step Guide:**
**1. Install Jenkins:**
- Download and install Jenkins from the official site.
- Follow the setup wizard to complete the installation.
**2. Configure Jenkins:**
- Install necessary plugins, such as Git, GitHub, and Pipeline plugins.
- Go to "Manage Jenkins" > "Manage Plugins" and search for these plugins to install them.
**3. Create a New Pipeline Job:**
- Navigate to "New Item" and select "Pipeline" to create a new job.
- Name your job and click "OK".
**4. Set Up Pipeline Script:**
- In the pipeline configuration, choose "Pipeline script" and enter your Jenkinsfile script. A basic example:
```
pipeline {
agent any
stages {
stage('Build') {
steps {
echo 'Building...'
sh 'make build'
}
}
stage('Test') {
steps {
echo 'Testing...'
sh 'make test'
}
}
stage('Deploy') {
steps {
echo 'Deploying...'
sh 'make deploy'
}
}
}
}
```
- Save the configuration.
**5. Run the Pipeline:**
- Click "Build Now" to trigger the pipeline. Jenkins will execute the defined stages.
## 2. Setting Up a CI/CD Pipeline with GitHub Actions
GitHub Actions is a powerful CI/CD tool integrated directly into GitHub, making it easy to automate workflows from within your repositories.
**Step-by-Step Guide:**
**1. Create a GitHub Repository:**
- If you don't have a repository, create one on GitHub.
**2. Create a Workflow File:**
- In your repository, create a .github/workflows directory.
- Add a new file named ci-cd.yml in this directory.
**3. Define the Workflow:**
- Add the following YAML configuration to ci-cd.yml:
```
name: CI/CD Pipeline
on:
push:
branches:
- main
jobs:
build:
runs-on: ubuntu-latest
steps:
- name: Checkout code
uses: actions/checkout@v2
- name: Set up Node.js
uses: actions/setup-node@v2
with:
node-version: '14'
- name: Install dependencies
run: npm install
- name: Run tests
run: npm test
- name: Deploy
run: npm run deploy
```
- This configuration triggers the pipeline on every push to the main branch, checks out the code, sets up Node.js, installs dependencies, runs tests, and deploys the application.
**4. Commit and Push:**
- Commit and push the .github/workflows/ci-cd.yml file to your repository.
**5. View Workflow Runs:**
Go to the "Actions" tab in your GitHub repository to see the workflow runs and their statuses.
## 3. Setting Up a CI/CD Pipeline with CircleCI
CircleCI is another popular CI/CD tool that provides powerful automation capabilities.
**Step-by-Step Guide:**
**1. Sign Up and Link Your Repository:**
- Sign up for CircleCI and link your GitHub repository.
**2. Add Configuration File:**
- In your repository, create a .circleci/config.yml file.
**3. Define the Pipeline:**
- Add the following YAML configuration to config.yml:
```
version: 2.1
jobs:
build:
docker:
- image: circleci/node:14
steps:
- checkout
- run: npm install
- run: npm test
- run: npm run deploy
workflows:
version: 2
build_and_deploy:
jobs:
- build
```
- This configuration defines a job that uses a Node.js Docker image, checks out the code, installs dependencies, runs tests, and deploys the application.
**4. Commit and Push:**
- Commit and push the.circleci/config.yml file to your repository.
**5. Monitor the Pipeline:**
- Go to the CircleCI dashboard to monitor the pipeline execution and view detailed logs.
## Conclusion
Setting up a CI/CD pipeline is crucial for automating your software development process, ensuring high-quality code, and accelerating deployment cycles. Jenkins, GitHub Actions, and CircleCI are all powerful tools that can help you achieve these goals. Each has its unique strengths: Jenkins offers extensive customization and plugin support, GitHub Actions provides seamless integration with GitHub repositories, and CircleCI excels in ease of setup and use with Docker.
By following the steps outlined above, you can set up a robust CI/CD pipeline with any of these tools, tailored to your specific needs and workflows. Happy coding and automating! | markwilliams21 |
1,875,031 | Comfort Redefined: The Story of Hotel Slippersa | Title: Comfort Redefined: the complete story of Hotel Slippers Introduction Have you ever stayed in... | 0 | 2024-06-03T07:48:35 | https://dev.to/theresa_mccraryjs_77dd382/comfort-redefined-the-story-of-hotel-slippersa-4hm1 | Title: Comfort Redefined: the complete story of Hotel Slippers
Introduction
Have you ever stayed in a hotel and seen those fluffy and slippers which can be comfy next to your bed? Those are known as hotel slippers, and are not merely any slippers which can be ordinary. Hotel slippers are specially built to provide safety and comfort to hotel guests. we're going to talk about the advantages, innovation, safety, use, simple tips to use, service, quality, and application of hotel slippers
Features of Hotel Slippers
Hotel slippers will be the epitome of comfort. These are generally made of soft and materials which can be durable cause them to become perfect for indoor use. One of several key features of hotel slippers would be that they often helps lower the chance of falling and slipping on slippery floors. It is particularly essential in hotels where guests is almost certainly not knowledgeable about the layout regarding the hotel and will slip and fall accidentally
Innovation in Hotel Slippers
Over time, hotel slippers have undergone innovation this is certainly significant meet with the changing needs of hotel guests. Initially, hotel slippers disposable were made of basic materials such as for example leather and cotton. Today, hotel slippers can be bought in a multitude of materials, including polyester, terry cloth, and microfiber. These materials provide additional benefits such as for instance breath ability, moisture-wicking, and properties which can be anti-microbial
Safety of Hotel Slippers
Hotel slippers were created with safety in your mind. They feature slip-resistant soles that offer traction on slippery surfaces. It will help lower the chance of falling and slipping while walking on hotel floors. Additionally, hotel slippers are available with non-toxic materials which can be safe for usage by hotel guests
Utilization of Hotel Slippers
Hotel slippers provide guests with a comfy and method in which is convenient move about the college accommodation. These are generally ideal for guests who prefer to not ever walk barefoot on hotel floors. Hotel slippers also help in keeping hotel floors clean by preventing debris and dirt from being tracked in to the room
Simple tips to Use Hotel Slippers
Using hotel slippers is not difficult. Simply slip them on the feet and relish the comfort they give you. Hotel slippers should simply be used indoors to avoid problems for the soles. Additionally, guests should remove their hotel room slippers before walking on wet surfaces, such as for example when you look at the bathroom or close to the pool
Service and Quality of Hotel Slippers
Hotel slippers are an essential part regarding the guest experience this is certainly overall. Hotel managers comprehend the significance of providing hotel that is high-quality that are comfortable, safe, and sturdy. This is the reason hotels which can be many in luxury hotel slipperswhich can be made of high-quality materials and offer superior comfort
Application of Hotel Slippers
Hotel slippers are not restricted to utilize in hotels. Also they are found in spas, salons, as well as other hospitality industries. Additionally, many individuals purchase hotel slippers for personal use in the home. Hotel slippers provide a comfy and solution this is certainly practical anybody who loves the experience of walking on soft and fluffy surfaces.
Source: https://www.kailai-amenity.com/application/hotel-slippers-disposable
| theresa_mccraryjs_77dd382 | |
1,875,024 | How to Read a Traceroute | How to Run the Traceroute Command Running a traceroute is very simple. The first step is... | 0 | 2024-06-03T07:47:01 | https://dev.to/enginpiril/how-to-read-a-traceroute-586h | ## How to Run the Traceroute Command
Running a traceroute is very simple. The first step is to bring up a command prompt on your computer. The specific method will depend on your operating system. For Windows 10, for example, you can simply click on the start button and type CMD to bring up the options below.
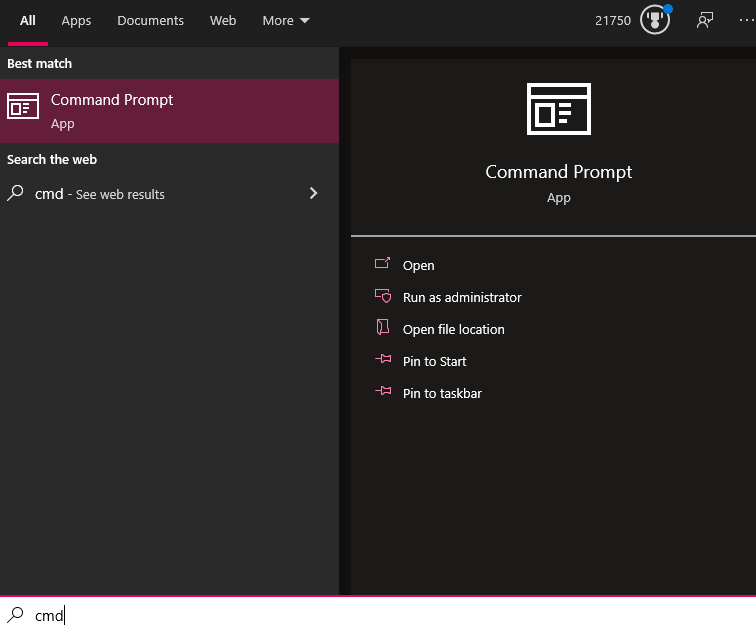
Figure 1: Command Prompt options in Windows 10.
From here, simply click on the Command Prompt app to open it. When your command prompt has loaded, just type the command **tracert** followed by the destination you want to use to run the test. For example, to run a test to catchpoint.com, you would type **tracert catchpoint.com** and hit enter. (For Linux and macOS devices, you would type **traceroute catchpoint.com** instead.)
### Available Options for the Traceroute Command
In most cases, the default traceroute command will give you the information you need. However, there are some additional options that you can use to get more details or change how the command runs. Accessing these options is done by adding one or more option flags after the traceroute command and before the destination.
## How to Read the Results from a Traceroute
One of the best things about the traceroute tool is that once you learn how to read the results, you can understand the information it provides with just a quick glance. When you look at the example results of the traceroute listed above, you will see several key pieces of information.
The following table breaks down the key information you will see:
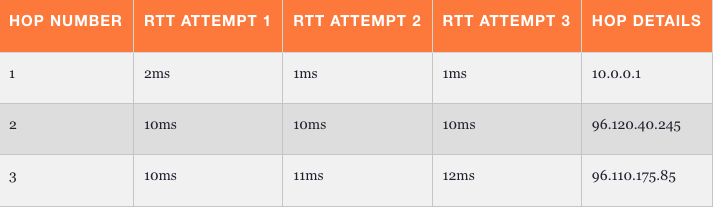
### Hop Number
The first column just tells you which hop the trace is on. Whenever you access the Internet (or even data on an internal network), the data travels from one piece of hardware to another. These will typically be routers, but could also be switches, servers, or even computers. Each of these pieces of hardware that the data goes through is considered a hop.
### Round Trip Time (RTT) Results
The next three columns show the amount of time it took data to go from the source (typically your computer) to that hop and back. This is measured in milliseconds.
## Common Problems Discovered with Traceroute
You can use this command to look for various network issues and, based on the results displayed, determine what types of problems may be present.
### Asterisks (Timeouts) at Various Points
The most common issue you will see with a traceroute is a timeout response, which is represented by an asterisk (*). These happen quite frequently and for a variety of different reasons. In the following example, you can see multiple hops have asterisks when attempting to run a traceroute to google.com.
```
C:\Users>tracert google.com
Tracing route to google.com [2607:f8b0:4009:819::200e]
Over a maximum of 30 hops:
1 1ms 1ms 1ms 2601:404:cf00:75c0:e2db:d1ff:fe1d:23ad
2 8ms * * 2001:558:4020:30::1
3 9ms 11ms 13ms 2001:558:112:3c0a::1
4 12ms 9ms 10ms 2001:558:110:b02c::1
5 * 20ms * 2001:558:110:f1::1
6 34ms 20ms 27ms 2001:558:110:71::2
7 * 21ms 21ms be-32131-cs03.350cermak.il.ibone.comcast.net [2001:558:3:2ae::1]
8 21ms * * be-2311-pe11.350cermak.il.ibone.comcast.net [2001:558:3:72::2]
9 20ms 20ms 21ms 2001:559::11b2
10 19ms 20ms 20ms 2607:f8b0:831d::1
11 22ms 23ms 23ms ord38s30-in-x0e.1e100.net [2607:f8b0:4009:819::200e]
Trace Complete
C:\Users>
```
Figure 2: Example output of traceroute to Google.
When you see an asterisk, it will mean one of the following things:
- Single Asterisk on a Hop: This means that the request timed out on just one of the three attempts. This can be a sign that there is an intermittent problem at that hop.
- Three Asterisks, Then Failure: If you see all three attempts at a hop have asterisks and then the traceroute errors out, it means that the hop is completely down.
### Elevated Latency After One Hop
If everything looks fine for several hops, but then the response times jump up significantly at one point, and each hop after that remains high, it likely means a problem either at that hop or on the connection between it and the previous one.
## Conclusion
The traceroute command is an essential tool for understanding the path your data takes across a network and for identifying connectivity issues along that path. By running traceroute tests to various destinations and analyzing the output, you can gain visibility into latency, loss, and other problems that may exist.
Key things to look for when interpreting traceroute results include asterisks indicating timed-out requests, sudden spikes in round-trip latency, and missing or unresponsive hops. These can help narrow down where an issue lies.
While traceroute has some limitations in very large or complex networks, it remains one of the simplest first steps in network troubleshooting. Understanding how to properly run the command, configure options like setting the maximum hops, and read the output is critical for anyone working with networks.
With a bit of practice reading traceroute results, the information it provides can save you substantial time getting to the root cause of connectivity and performance issues. It is a tool that should be in every network engineer's toolbox.
Read more at https://www.catchpoint.com/network-admin-guide/how-to-read-a-traceroute. | enginpiril | |
1,874,977 | React Native: Using KeyboardAvoidingView for Multiline TextInput | When using KeyboardAvoidingView with a single line TextInput, it looks like this: Issue with... | 0 | 2024-06-03T07:46:51 | https://dev.to/saiful__bashar/react-native-using-keyboardavoidingview-for-multiline-textinput-g4m | reactnative, react, programming, learning | When using `KeyboardAvoidingView` with a single line `TextInput`, it looks like this:
<img width="100%" style="width:100%" src="https://media.giphy.com/media/v1.Y2lkPTc5MGI3NjExenJxanZrdDF2YjFzaG1vNzdxNmVlYTN4dTgycXRqczZ2aXBsYzJmZyZlcD12MV9pbnRlcm5hbF9naWZfYnlfaWQmY3Q9Zw/cxVJqeg7MomCaRWyJi/giphy.gif">
**Issue with Multiline TextInput**
The issue arises when the multiline prop is added to TextInput:
<img width="100%" style="width:100%" src="https://media.giphy.com/media/v1.Y2lkPTc5MGI3NjExb3llMnVwMzh4dGNrbG9hM2FmcXNhZHRmaWJhbGEzbWU3cnU3ZDl3aSZlcD12MV9pbnRlcm5hbF9naWZfYnlfaWQmY3Q9Zw/tZB1tt8KDcCvWvbgcN/giphy.gif">
**Solution**
The solution is to toggle the `scrollEnabled` property on focus using setTimeout and disable it on blur. Here is a code snippet demonstrating this:
[github link](https://github.com/SaifulBashar/keyboardavoidingview-for-multiline-textInput.?tab=readme-ov-file)
```javascript
import React from "react";
import { StyleProp, Text, TextInput, View, ViewStyle } from "react-native";
export default function InputField({
label,
inputProps,
containerStyle
}: {
label: string;
inputProps?: React.ComponentProps<typeof TextInput>;
containerStyle?: StyleProp<ViewStyle>
}) {
const [focused, setFocused] = React.useState(false);
const [scrolled, setScrolled] = React.useState(true);
return (
<View style={containerStyle}>
<Text style={{ marginBottom: 8 }}>{label}</Text>
<View
style={{
borderWidth: focused ? 2 : 1,
borderColor: focused ? "white" : "grey",
borderRadius: 8,
maxHeight: 200,
flexDirection: "row",
alignItems: "center",
}}
>
<TextInput
{...inputProps}
scrollEnabled={scrolled}
onFocus={(e) => {
if (inputProps && inputProps.onFocus) {
inputProps.onFocus(e);
}
setFocused(true);
setScrolled(false);
setTimeout(() => {
setScrolled(true);
}, 1000);
}}
onBlur={(e) => {
if (inputProps && inputProps.onBlur) {
inputProps.onBlur(e);
}
setFocused(false);
setScrolled(true);
}}
style={{
padding: 16,
flex: 1,
margin: 0,
minHeight: inputProps?.multiline ? 100 : "auto",
}}
placeholderTextColor="grey"
/>
</View>
</View>
);
}
```
**Result**
After implementing the solution, the behavior is as expected:
<img width="100%" style="width:100%" src="https://media.giphy.com/media/v1.Y2lkPTc5MGI3NjExeDNscmIzcnRtMGd6cW9mbnBjYWs4aTBpZTY1aTVlaGVyaHRkNGQ0aSZlcD12MV9pbnRlcm5hbF9naWZfYnlfaWQmY3Q9Zw/9mr2qD1ufBHpk0uDKS/giphy.gif">
| saiful__bashar |
1,875,028 | 9 Ways Cloud Computing Solutions Improve Collaboration | Have you ever felt like your team's collaboration could be more efficient? Are you wasting time... | 0 | 2024-06-03T07:45:58 | https://dev.to/adelenoble/9-ways-cloud-computing-solutions-improve-collaboration-2c1o | Have you ever felt like your team's collaboration could be more efficient? Are you wasting time switching between too many tools or waiting for others to finish tasks before you can start your own work?
What if there was a way to streamline workflows, share resources seamlessly, and give everyone the tools they need to work together simultaneously? That's where adopting a client-server model can help. A [**cloud computing solutio**n](https://www.lenovo.com/ca/en/servers-storage/solutions/cloud-computing/) architecture allows you to centralize resources on a server while distributing user interfaces to clients.
This simple but powerful approach can radically improve how your team collaborates in 9 key ways.
### 1. Get Everyone Access to Shared Files and Resources from Any Device
When you store all your team's central files and resources on a centralized server, anyone on your team can access what they need from any device, whether they're in the office, working remotely, or on the go. No more waiting for large files to be emailed or sent through other channels. Everyone has near-instant access to the same up-to-date resources.
### 2. Distribute Work Balancing for Maximum Efficiency
With a cloud computing solutions model, your centralized server has a bird's-eye view of all workloads and tasks across clients.
- It can intelligently distribute pieces of large projects to balance the utilization of your team's combined skills and availability. For example, if you have a new product launch that involves parallel work in design, development, and marketing, the server can dynamically assign specific design assets, code modules, or campaign elements to team members. It ensures the right resources are always working while avoiding bottlenecks from dependencies.
- The server also tracks individual progress and status in real-time. This allows it to automatically rebalance work as needed. If someone finishes ahead of schedule, they can redistribute their following tasks to others to maintain an even pace. Or if someone is overwhelmed, it identifies top-priority pieces to offload first. All without manual scheduling or coordination between team members.
- With this level of optimization, work that used to be done sequentially can now overlap. For instance, your designers can start wireframing before developers finish the last feature, allowing projects to be completed weeks faster. Team members have full visibility into overall workflow of their clients too, so no more waiting around without understanding where help is needed. Productivity skyrockets as your highly coordinated team works as a well-oiled machine across all time zones.
### 3. Simplify Application Deployment and Management
Rather than deploying and configuring each application instance individually on dozens or hundreds of cloud computing solutions machines, you only need to manage your server software stack.
- Updating to a new version or installing a new tool is as simple as executing a single command on the server. It then pushes the changes out seamlessly to all connected clients in the background. No more tedious manual software distribution or troubleshooting installation issues on client machines.
- With a centralized management console, you have full control and visibility over your entire application infrastructure from one place. You can monitor usage, perform backups, push security patches, run maintenance tasks, and more without touching individual clients. Access and permission controls are also applied uniformly to all interfaces, from the server down.
- This unified deployment approach future-proofs your systems as your team and tools evolve over time. New hire onboarding becomes a breeze; their cloud computing device is pre-configured automatically on first use. And scaling to accommodate growth merely requires adding more clients that pull configurations from the server.
Best of all, your applications run with a consistent experience across any device. Team members gain flexibility to use the clients that suit them best without compatibility or configuration issues. The transition to remote work becomes seamless when everyone accesses the same familiar work tools from anywhere.
### 4. Collaborate in Real-Time from Anywhere with Synchronized Tools
With a client-server model, your team's collaborative tools like documents, spreadsheets, and code repositories are automatically synced across all clients in real-time. This lets you all work together seamlessly on the same files from anywhere without delay. Your team will feel like you're in one room, even when you're half a world apart.
### 5. Tap into Infinite Server Power for Heavy Tasks
Don't let limiting cloud computing-side hardware or browsers slow you down. Offload resource-intensive processes like large data analysis, video rendering, or model training to your powerful centralized server. This frees up client devices and lets you tackle much heavier tasks at incredible speeds.
### 6. Give Customized Interfaces for Each Team Member's Role
Not everyone on your team needs the same tools for their role. With an edge computing model, you can build customized interfaces for each client, tailored precisely to each person's workflow and needs. This simplifies their experience while maximizing their productivity in their unique function.
### 7. Scale Effortlessly to Accommodate Growth
As your team and workloads grow, scaling becomes a breeze with a client-server model. You can simply add more clients by installing your application interface on new devices. Or add more servers behind the scenes for additional processing power and storage. Your infrastructure grows with you without disruption.
### 8. Boost Security with a Single Fortress to Protect
Rather than securing countless endpoints, you now only need to protect a single centralized server. This minimizes your attack surface area while allowing you to enforce uniform access controls and policies across all clients. Remote access becomes far more secure too, with encryption of all data in transit.
### 9. Analyze Usage Patterns and Optimize Workflows
With an [edge computing](https://www.lenovo.com/ca/en/servers-storage/solutions/edge-computing/) model, your server can collect rich analytics on tool usage, task durations, bottlenecks, and more. This provides invaluable insights to continuously improve processes, balance workloads smarter, streamline workflows and take productivity to new heights.
**Final Words**
As you can see, adopting a client-server architecture is a game-changing way to supercharge your team's level of collaboration. It removes friction, simplifies deployment and management, and unleashes the full power of distributed yet synchronized work. Why not start leveraging this approach today to improve how your team works together radically? | adelenoble | |
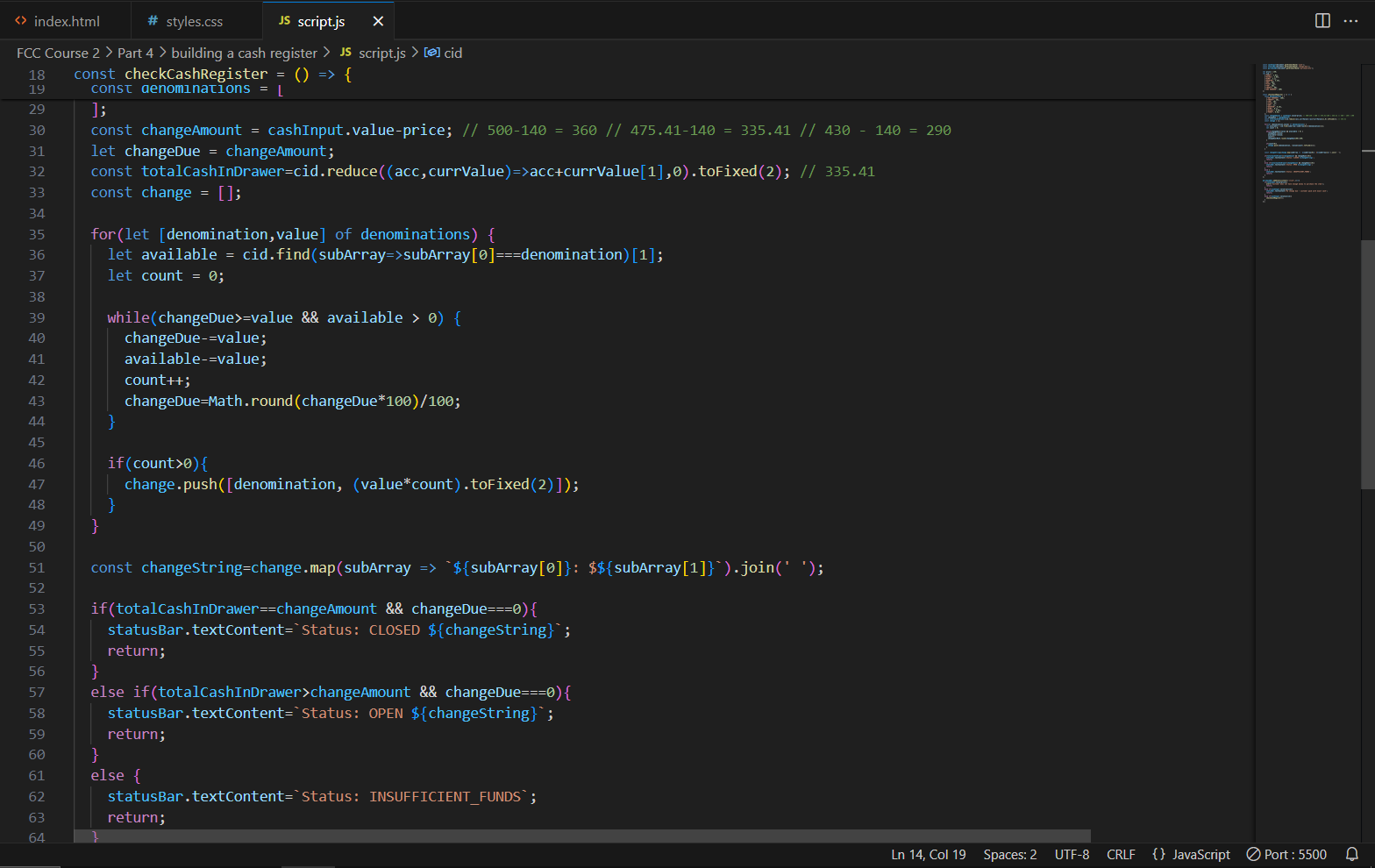
1,875,027 | [DAY 42-47] I Built A Cash Register App | Hi everyone! Welcome back to another blog where I document the things I learned in web development. I... | 27,380 | 2024-06-03T07:45:35 | https://dev.to/thomascansino/day-42-47-i-built-a-cash-register-app-1hn0 | beginners, learning, javascript, webdev | Hi everyone! Welcome back to another blog where I document the things I learned in web development. I do this because it helps retain the information and concepts as it is some sort of an active recall.
On days 42-47, I built a cash register app to complete part 4 of the data structures & algorithms certification project in freecodecamp.
In this app, you will need to input the cash from the customer and the program will output the total change in the form of each available denomination.
For example, the declared price of the object is $140, and the customer’s cash is $455.41, the program will output a total change of $315.41 as well as the customer’s change in the form of each available denomination. In this case, it’s: `ONE-HUNDRED: $100.00, TWENTY: $60.00, TEN: $20.00, FIVE: $55.00, ONE: $80.00, QUARTER: $0.25, DIME: $0.10, NICKEL: $0.05, PENNY: $0.01`
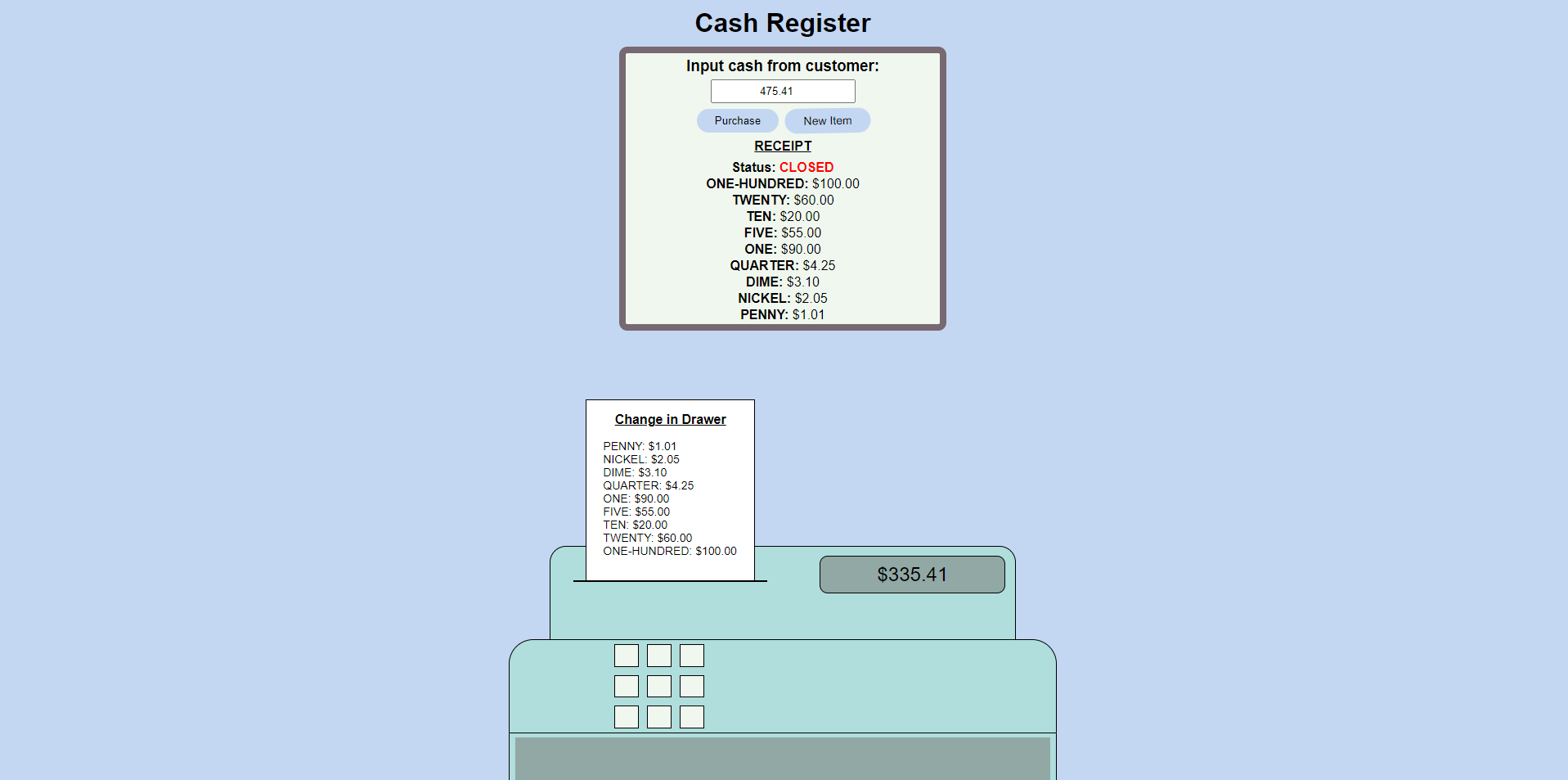
While building this project, I got stuck in a certain problem for a few days.
These are the reasons why:
1. In Javascript, floating-point numbers have limited precision due to the way they are represented internally. This can lead to unexpected results when performing arithmetic operations, especially with decimals (e.g., 0.01 might be read as 0.009999998321).
2. I did not take into account that denominations cannot be physically divided into cents (e.g., a $1 bill cannot be physically divided, nor can a $100 bill or any other bills). Therefore, I need to create a function that will loop through every denomination and check if their respective values can be used as a change.
3. At this point, my entire code was a complete mess. My if-else statements were redundant, and some of them were not even making sense. Additionally, the conditions of my if-else statements were not properly specified, leading to unexpected results. Because of this, it took me a while to figure out the solution to my problem, as I needed to deal with other issues first since I was entangled in a series of them.
After some time, I finally finished the program and was able to solve the problems mentioned earlier.
Here’s what I did:
1. First, I realized that to solve my main problem, which was to satisfy the conditions of the specified user stories to complete the project, I needed to clean up my code. I started by reworking the entire logic from top to bottom and reorganized everything because it was in complete chaos. Next, I rearranged the logic of my functions and loops and removed unnecessary if-else statements. After that, I properly specified the conditions of the remaining if-else statements.
2. Second, I debugged my code to identify which variables were returning unexpected results (e.g., what was meant to be 0.01 is returned as 0.009999998321). This was crucial since it disrupted the flow of calculations and prevented the conditions of my if-else statements from being satisfied.
3. Lastly, I created a function that will loop through every denomination and check if their respective values can be used as a change.
Overall, this was my first time, _and definitely not the last_, of being stuck in a project for days.
I realized that we learn much more in this phase compared to smoothly completing a project.
As I continue on my path to web development, the projects I take on are gradually becoming more difficult for me. Therefore, I must prepare myself to debug the problems that I will potentially encounter in order to gain experience and be okay with the fact that it’s normal to be stuck on a project for a long time. What matters most is the continuous search for answers until the problem is eventually solved. After all, it’s what most job descriptions require: the attitude to persistently seek answers to your questions while knowing the right questions to ask.
Anyways, that’s all for now, more updates in my next blog! See you there! | thomascansino |
1,874,837 | How to Create Your Own Memes Generator Project | Project:- 3/500 Meme Generator Project Description The Meme Generator project... | 27,575 | 2024-06-03T07:44:00 | https://raajaryan.tech/meme-generator-project | javascript, opensource, beginners, learning | > ### Project:- 3/500 Meme Generator Project
## Description
The Meme Generator project is a web-based application that allows users to create their own memes. Users can upload images or provide image URLs, add custom text to the top and bottom of the image, adjust text size, and export the final meme as a PNG file.
## Features
- **Image Upload**: Upload an image from your local system.
- **Image URL**: Use an image from the web by providing its URL.
- **Custom Text**: Add and edit custom text at the top and bottom of the image.
- **Text Styling**: Adjust the font size of the text.
- **Export Meme**: Export the created meme as a PNG file.
## Technologies Used
- **JavaScript**: Core logic for handling image upload, text rendering, and exporting the meme.
- **HTML**: Structure of the application.
- **CSS**: Styling for the application.

## Setup
Follow these steps to set up and run the project locally:
1. **Clone the repository**:
```sh
git clone https://github.com/deepakkumar55/ULTIMATE-JAVASCRIPT-PROJECT.git
cd Fun%20and%20Creative%20Projects/2-meme_generator/
```
2. **Open the project**:
Open the `index.html` file in your preferred web browser.
3. **Start Creating Memes**:
- Upload an image or provide an image URL.
- Add custom text to the top and bottom of the image.
- Adjust the text size as needed.
- Export your meme as a PNG file.
## Contribution
Contributions are welcome! If you have any ideas for improvements or new features, please follow these steps:
1. **Fork the repository**:
Click the "Fork" button on the top right of the repository page.
2. **Clone your forked repository**:
```sh
git clone https://github.com/deepakkumar55/ULTIMATE-JAVASCRIPT-PROJECT.git
cd Fun%20and%20Creative%20Projects/2-meme_generator/
```
3. **Create a new branch**:
```sh
git checkout -b feature-or-bugfix-name
```
4. **Make your changes**:
Implement your feature or fix the bug.
5. **Commit your changes**:
```sh
git add .
git commit -m "Description of your changes"
```
6. **Push to your forked repository**:
```sh
git push origin feature-or-bugfix-name
```
7. **Create a pull request**:
Go to the original repository and click on the "New Pull Request" button. Provide a detailed description of your changes and submit the pull request.
---
## Get in Touch
If you have any questions or need further assistance, feel free to open an issue on GitHub or contact us directly. Your contributions and feedback are highly appreciated!
---
Thank you for your interest in Meme Generator Project. Together, we can build a more robust and feature-rich application. Happy coding!
| raajaryan |
1,875,026 | XTAPBIT buy now before it listed on the market | A post by Gift oyibo | 0 | 2024-06-03T07:41:21 | https://dev.to/gift_dollar/xtapbit-buy-now-before-it-listed-on-the-market-21e1 |
 | gift_dollar | |
1,875,023 | Introduction to the quantitative trading tool | Summary In the previous chapter, we learned about the concepts of quantitative trading,... | 0 | 2024-06-03T07:33:21 | https://dev.to/fmzquant/introduction-to-the-quantitative-trading-tool-5ckj | trading, cryptocurrency, fmzquant, backtest | ## Summary
In the previous chapter, we learned about the concepts of quantitative trading, have a basic understanding of quantitative trading. So what tools are available on the market that can do quantitative trading? How can we choose according to our own needs?
## Open source software and commercial software
Most quantitative trading tools can be broadly divided into two categories: open source software and commercial software. The so-called open source software can be understood as the source code of the software is open, you can directly download the source code; commercial software generally refers to closed source software maintained and operated by commercial companies, users usually need to pay to use it.
## Open source quantitative software
First of all, open source software has great flexibility and is completely free. Users can basically use this software to implement any function. Whether it is a low-frequency trading strategy, an arbitrage strategy or an option strategy, it can be realized through a customized module. The user controls the source code of the software, and can understand every corner of the software, so it is more reliable and safe.
Although open source software has many advantages, it is not very user-friendly to beginners in quantitative trading. You need to systematically learn a standard programming language such as Python, Java or C++. From entry to give up, the difficulty can be imagined, sometimes the bug can be transferred to your doubts about life. And unlike commercial software, there is a dedicated technical customer service to answer questions instantly. At this time, not only does it have no sense of accomplishment, but it also dispels the motivation for your continued learning.
Therefore, from a learning perspective, it is recommended to start a quantitative trading beginner step by step, starting with the simplest commercial software, although it is paid, but if the strategy is profitable, the software cost is only a fraction of the profit, and further, the commercial software was maintained by a mature team, and its maturity is definitely much stronger than open source software.
## Commercial quantitative trading software
There are dozens of commercial software that can do quantitative trading worldwide, such as: Interactive Broker with professional and comprehensive products, capable of handling massive concurrent data; APAMA for high-frequency trading, C++-supported interface; and MultiCharts for individual traders. Users can choose according to their actual situation.



Although the above is commercial software, it is also a standard programming language or scripting language. It is not as good as directly using free and secure open source software. beginners here are recommended using the FMZ Quant directly as a stepping stone to quantitative trading learning.
### Knowing the FMZ Quant trading tools

The FMZ Quant trading tool is very user-friendly to beginners, and even if you are zero-based, you can experience the quantitative charm based on the tools inside. The tool is designed for high-frequency trading and has stringent requirements for performance and safety. Support high frequency strategy, arbitrage strategy, trend strategy. And it integrates the complete process of strategy development, testing, optimization, simulation, and real trading. In addition, it supports both simple and easy-to-use M languages, as well as advanced quantitative trading languages such as Python and C++ with the costs only 0.125 yuan / hour, reducing the cost of software in your learning and exploration phase, and can simulate simulation trading for free.
## Take the first step in quantitative trading : using quantitative tools
Quantitative tools are very simple to use and you only need to go to the website to design your own quantitative strategy. You can log in to the official website of the FMZ Quant platform, click on the "dashboard" to use it (as shown below).
The FMZ Quant platform programming will have a centralized function area. (as shown in the figure below). you can write the trading strategy and performing backtesting; Create the unique "docker" system and a specific trading robot. As for the specific usage of the function, we will introduce it in detail in the follow-up article. Currently we only do the preliminary.
1.Your main control page
2.Manage all your bots (start,stop,delete,open,etc)
3.Manage all your strategies' code
4.Deploy and manage your docker
5.Add new exchanges
6.Manual trading on the exchanges you added
7.Pay your bill
8.Ask any question here
9.FMZ's simulated exchange
10.Debug tool where you can run a block of code without start a bot.
11.All kinds of message
12.Strategy square where open-source and charging strategies are listed
13.Live Robots where all live-running bots are listed.
14.Forums where you can post a post to discuss any question related.
15.Ask for someone to write code for you or provide this service for others.
16.Products for exchanges and agencies.
17.API documentation.
18.Some usefull tools, check fo yourself.
19.Your account information.
People who first reaches quantitative trading don't have to be discouraged if they don't understand programming. In order to reduce the user's usage threshold, the FMZ Quant community has produced a number of video tutorials to help beginners for a quick start. At the same time, thousands of official and third-party free and open trading strategies are aggregated in the Strategy square to facilitate copying and learning.
Before jump in the real market, the simulation trading is also an indispensable stage. The simulation tool is in line with the real exchange, and it is completely free, which is highly consistent. Greatly improve the efficiency of strategy verification.
## To sum up
No matter whether it is open source software or commercial software, there is no good or bad at all, and there is no perfect quantitative trading tool. Each tool has its own focus, and the most important one is to choose the tool that suits you according to your own needs. Commercial software needs to pay, it is better in terms of services, etc. It may be more suitable for beginners who have just entered the Quants industry. If you have been in the industry for a long time, have accumulated a lot of experience, or need to implement more complex trading strategies, open source software is a better choice.
## Next section notice
How to use the tool? when we bought a new phone, the first time we need to do a simple boot settings, the quantification tool also needs to do the basic configuration, in the next section we will take you to configure the FMZ Quant trading tools. Including: adding exchanges, adding dockers, creating trading strategies, creating robots, and more. After completing the basic configuration, we can formally write our first quantitative trading strategy.
After-school exercises
1. What are the two major categories of quantitative trading tools?
2. What are the commonly used quantitative trading programming languages?
From: https://blog.mathquant.com/2019/04/13/2-1-introduction-to-the-quantitative-trading-tool.html | fmzquant |
1,875,022 | Top Fraud Detection Solutions 2024 | Imagine a scenario where a rapidly growing e-commerce company is experiencing an increase in... | 0 | 2024-06-03T07:32:55 | https://dev.to/luxandcloud/top-fraud-detection-solutions-2024-417l | news, productivity, tutorial, ai | Imagine a scenario where a rapidly growing e-commerce company is experiencing an increase in fraudulent transactions. Despite having basic security measures in place, they are facing sophisticated scams that are not only affecting their bottom line but also damaging their reputation. The CEO realizes the need for a robust fraud detection system that can adapt to evolving threats and protect their customers’ data.
The company’s CTO (chief technology officer) starts researching the latest advancements in fraud detection technology. The goal is to find the most suitable options that align with the company’s specific needs and budget.
This blog will provide the CTO (or any other stakeholders) with an in-depth analysis of the most effective solutions available, highlighting features like real-time transaction monitoring, AI-driven anomaly detection, and multi-layered authentication processes.
Learn more here: [Top Fraud Detection Solutions 2024](https://luxand.cloud/face-recognition-blog/top-fraud-detection-solutions-2024/?utm_source=devto&utm_medium=police-facial-recognition-safe-or-scary-what-you-need-to-know-2024) | luxandcloud |
1,875,021 | How Do Users Benefit from Decentralized Governance in Metaverse NFT Marketplaces? | The digital world is rapidly evolving, and terms like "metaverse," "NFTs," and "decentralized... | 0 | 2024-06-03T07:32:54 | https://dev.to/elena_marie_dad5c9d5d5706/how-do-users-benefit-from-decentralized-governance-in-metaverse-nft-marketplaces-50an | metaversenftmarketplace, metaversedevelopment | The digital world is rapidly evolving, and terms like "metaverse," "NFTs," and "decentralized governance" are becoming part of our daily vocabulary. But what do they mean, and more importantly, how do they impact us? This article dives into the fascinating intersection of these concepts, focusing on how users benefit from decentralized governance in metaverse NFT marketplaces.
What is Decentralized Governance?
Core Concept
Decentralized governance is a system where control and decision-making are spread out across a network instead of being concentrated in one central authority. This is often done using blockchain technology, which provides transparency and security.
How It Works
In a decentralized governance model, stakeholders like users, developers, and investors participate in the decision-making process. They can vote on platform upgrades, fee structures, and more. This is very different from traditional centralized models, where a few people make all the decisions.
Benefits of Decentralized Governance in NFT Marketplaces
Enhanced Security
Reduced Risk of Fraud
Decentralized Metaverse NFT marketplaces which are developed by Metaverse NFT Marketplace development company use blockchain technology, making it hard for fraudsters to alter records or engage in malicious activities. Every transaction is permanent and traceable.
Ownership Verification
NFTs are stored on a blockchain, providing undeniable proof of ownership. This minimizes disputes and ensures the rightful owner is recognized.
Greater Transparency
Open Ledgers
All transactions in decentralized NFT marketplaces are recorded on an open ledger. This visibility ensures everyone can see what is happening, reducing unethical behavior.
Fair Trading Practices
With every transaction being visible, users can trust they are engaging in fair trades. This transparency fosters a trustworthy environment, which is crucial for marketplace growth.
User Empowerment
Decision-Making Power
Users in decentralized NFT marketplaces can vote on key decisions, such as platform changes or new features. This democratization aligns the platform's development with the community's needs.
Community Building
Decentralized governance encourages community building. Users feel more connected to the platform and each other, fostering a supportive and engaged user base.
Economic Advantages
Fair Revenue Distribution
Revenue is often distributed more fairly among creators, users, and developers in decentralized NFT marketplaces. This equitable distribution sustains the ecosystem and encourages participation.
Lower Transaction Fees
Traditional marketplaces can have high transaction fees, but decentralized platforms often have lower fees due to the absence of intermediaries. This makes trading more accessible and cost-effective for users.
Conclusion:
Decentralized governance in metaverse NFT marketplaces which is developed by **[Metaverse development company](https://www.clarisco.com/metaverse-development-company)** offers numerous benefits, from enhanced security and transparency to user empowerment and economic advantages. As technology continues to evolve, these platforms are set to play an increasingly significant role in the digital economy. Embracing decentralized governance can provide users with greater control, more opportunities, and a more inclusive digital environment. | elena_marie_dad5c9d5d5706 |
1,875,020 | One Year of DevOps at Idus: Reflections and Learnings | From Work Experience to Development Community Activities One Year... | 0 | 2024-06-03T07:32:15 | https://dev.to/paikend/one-year-of-devops-at-idus-reflections-and-learnings-5ehb | devops, cicd, sre, idus |

### From Work Experience to Development Community Activities
#### One Year Already…
Although my previous company was a fast-growing firm with much to learn, I needed to change my environment for my personal growth. Among several companies, I chose Idus because it made me reflect on my career direction.
After presenting at the Django Lightning Talk in June 2020, I met a senior developer from Idus (now my leader) during the networking session. I was introduced to DevOps and became interested in the DevOps culture.
#### SRE (Site Reliability Engineering)
Curious about DevOps culture, I began an SRE study. Although there were many aspects not suitable for application in an early startup, the philosophy of DevOps was clear.
One of the most impressive phrases from SRE is:
> “Culture eats strategy for breakfast.”
Simply liking coding does not create a good development culture. The principles I believe are essential for creating a good development culture are:
1. Acknowledge failures without deceiving oneself or others.
2. Be tolerant of others' failures and encourage challenges.
3. Improve the environment based on failures.
This DevOps philosophy was captivating, and I wanted to embody the inspiration it gave me into my experiences.
Just in time, a DevOps position opened up at Idus, the company that had sparked my curiosity about DevOps, and in May 2021, I joined Idus.
#### Work Experience at Idus
##### Idus DevOps Team
My work at Idus can be categorized into three main perspectives:
1. **Incident Response**: The highest priority task to ensure stable service delivery.
- **Process**:
- Incident occurs → Incident acknowledgment (reporter or alert) → Incident communication (relevant stakeholders) → Incident resolution → Post-mortem review
- **Post-mortem**:
- Post-mortem involves analyzing the cause of an incident and systematizing measures to prevent the same mistake from recurring. Originating from the medical/aviation industry, if there are casualties due to an accident, the responsible party is held accountable. To avoid blame, the responsible party might hide the cause, but if the cause is concealed, repeated problems can lead to further harm. This is the worst scenario, and everyone would flee if accountability is enforced.
- To prevent this, post-mortems do not blame individuals. Instead, companies often reward well-identified and improved structural issues (Google is a notable example).
Idus’s incident response embraces the post-mortem culture:
- **Short term**: Share warnings about the issue with team members.
- **Long term**: Prepare tasks to systematize measures preventing recurrence.
2. **Technical Research**: Introducing new technologies & repaying technical debt.
- To enhance team productivity, I explore tools suitable for the team and review the benefits.
- Projects I participated in include:
- Improving DEV/QA separation
- Refactoring EKS Helm & deployment pipeline
- Adopting Terraform Cloud
- Adopting Datadog
- Preparing for global services
- Detailed project information will be covered in future posts.
3. **Operational Tasks**: Facilitating the smooth growth of Idus.
- Infrastructure setup for Idus
- Legacy system performance improvement
- Cost optimization
- ISMS response
The advent of IaC (Infrastructure as Code) significantly contributed to the popularity of DevOps. Managing infrastructure with code and automating it became possible. I worked on writing basic modules for infrastructure setup and constructing Terraform code to inject variables and create infrastructure. I provided infrastructure setup guides to developers, and resources are created through reviews.
- **Global Resource Creation Guide**:
- **Positives**:
- Contribution to infrastructure structure unification.
- Previously, the infrastructure was complex with PROD and STAGE environments combined for development, testing, and QA, leading to discrepancies over time and unreliable QA.
- We removed the STAGE environment and restructured QA and DEV environments, focusing on unifying infrastructure structure across environments and specializing each environment.
- **Resolving bottlenecks in the infrastructure creation process**:
- Before I joined, every step from A to Z in infrastructure setup had to go through DevOps.
- Now, developers can refer to guides and directly involve themselves in infrastructure creation, reducing the wait time for DevOps to proceed with tasks.
#### Areas for Improvement
1. **Data-Driven Tasks**:
- One advantage of working in an IT company is the ease of data-driven tasks. Data-driven tasks clearly communicate the contribution of work.
- For example:
- AS-IS: Improved API latency of the XX endpoint in OO service.
- TO-BE: Improved API latency (p99) of the XX endpoint in OO service by 50% (from 500ms to 250ms) in 5 hours of work.
- Though it takes effort to data-driven tasks, it reduces communication costs significantly and is a more effective way of working. Initially, I spoke generally about the benefits, but working at Idus has increased data-driven communication.
2. **Sharing Small Tasks**:
- When recently adding Datadog Integration to the DEV environment, I mistakenly removed the EC2 host filter, significantly increasing costs. Though notified of ticket completions, it's challenging to monitor all notifications. If shared simply on a messenger before proceeding, issues could be identified quicker.
3. **Developing a Habit of Double-Checking**:
- Most incidents result from human error. Though guaranteed systems would prevent issues, initial tasks may require handmade (manual) processes. In such cases, developing a habit of reviewing 2-3 times and double-checking with team members before proceeding can reduce incident frequency.
#### Additionally: (People + Development) = Good Development Community Activities
CTO Sungil always shares good news. Participating in the development community provides much inspiration. It also helps build great relationships with fellow developers who share similar concerns and relieve stress. Idus supports and encourages growth and happiness.
#### In Conclusion
I write retrospectives each year to make the current year better than the last. This year's retrospective was meaningful. Writing this made me think of each team member at Idus, and I want to express my gratitude.
| paikend |
1,875,019 | Police Facial Recognition: Safe or Scary? What You Need to Know (2024) | As we know, police forces around the world are increasingly adopting facial recognition technology... | 0 | 2024-06-03T07:31:36 | https://dev.to/luxandcloud/police-facial-recognition-safe-or-scary-what-you-need-to-know-2024-5fjc | news, discuss, ai, machinelearning | As we know, police forces around the world are increasingly adopting facial recognition technology for various purposes. Here are some real-world examples.
For example, New Zealand's police force is introducing an advanced facial recognition system, which represents a significant upgrade in their law enforcement technology. This "state of the art" system is expected to enhance their capabilities in identifying suspects, locating missing persons, and improving overall public safety. The introduction of this technology marks a major step forward in modernizing the country's policing efforts.
How is face recognition used by police? What are the benefits and concerts? We’ll explain everything in this blog post.
## What is Face Recognition Technology?
Face recognition is a technology used to identify or confirm a person's identity based solely on their face. These systems can analyze photos, videos, or even live footage.
Many are familiar with face recognition through features like Apple's FaceID for unlocking phones. But that's just one example.
Beyond phone security, face recognition often works by comparing faces captured by special cameras to a database of individuals. These databases, also known as "watch lists," can include anyone, even those without criminal records. The images used for comparison can come from various sources, including social media.
Learn more here: [Police Facial Recognition: Safe or Scary? What You Need to Know (2024)](https://luxand.cloud/face-recognition-blog/police-facial-recognition-safe-or-scary-what-you-need-to-know-2024/?utm_source=devto&utm_medium=police-facial-recognition-safe-or-scary-what-you-need-to-know-2024) | luxandcloud |
1,873,625 | Introduction to React Fiber | React Fiber is a complete rewrite of the React core algorithm, introduced in React 16. It's designed... | 0 | 2024-06-03T07:30:00 | https://dev.to/jehnz/introduction-to-react-fiber-48c4 | react, reactfiber, architecture, reactfibertree | **React Fiber** is a complete rewrite of the React core algorithm, introduced in React 16. It's designed to improve the rendering performance of applications and provide a more seamless user experience. This deep dive into React Fiber will cover its architecture, the reconciliation process, and how it enhances rendering performance.
### Deep Dive into React Fiber Architecture
#### What is React Fiber?
React Fiber is a reimplementation of the React reconciliation algorithm. The primary goal of Fiber is to enable incremental rendering of the virtual DOM. This allows React to split the rendering work into chunks and spread it out over multiple frames, making updates more efficient and interactive experiences smoother.
**Key Concepts of Fiber**
1. **Fiber Node**: The basic unit of work in React Fiber. Each element in the component tree corresponds to a fiber node. These nodes are linked together to form a fiber tree, mirroring the structure of the component tree.
2. **Work Loop**: Fiber introduces a work loop that processes units of work in a cooperative scheduling manner. This means React can pause and resume work, prioritizing more urgent updates to maintain a responsive user interface.
3. **Priority Levels**: Fiber assigns priority levels to different types of updates. High-priority updates (like user interactions) are processed before lower-priority updates (like network responses).
4. **Phases:**
* _Render Phase_: This phase is responsible for creating fiber trees and computing the changes that need to be made to the DOM.
* _Commit Phase_: This phase applies the changes computed in the render phase to the DOM.
**Fiber Tree**
The fiber tree is a data structure that React uses to hold information about the components. Each node in the tree is an instance of the Fiber class, containing properties such as:
* `type`: The component type (e.g., div, MyComponent).
* `stateNode`: The local state of the component.
* `return`: A link to the parent fiber node.
* `child`: The first child fiber node.
* `sibling`: The next sibling fiber node.
### Understanding How Reconciliation Works Under the Hood
**What is Reconciliation?**
Reconciliation is the process of updating the DOM to match the React elements. React compares the previous and current virtual DOM trees to determine the minimal set of changes required.
**The Reconciliation Algorithm**
1. **Diffing Algorithm**: React's diffing algorithm is optimized for performance. It makes assumptions to reduce the complexity from O(n^3) to O(n):
* _Elements of different types produce different trees_.
* _Keyed elements are tracked and updated efficiently_.
2. **Fiber Reconciliation**: Fiber enhances the reconciliation process by breaking down the update process into smaller units of work. This allows React to pause and resume work, handle high-priority updates first, and avoid blocking the main thread.
3. **Double Buffering**: React Fiber uses a double buffering approach where the current tree represents the UI shown to the user, and the work-in-progress tree is used to calculate the next update. Once the work-in-progress tree is complete, it becomes the current tree.
**Steps of Reconciliation in Fiber**
1. Begin Work: _React traverses the fiber tree, starting from the root, and begins work on each fiber node_.
2. Complete Work: _After processing a node, React moves to its children and continues this process until it completes the entire tree_.
3. Commit Changes: _Once the work-in-progress tree is complete, React commits the changes to the DOM in the commit phase_.
### How Fiber Improves Rendering Performance
**Incremental Rendering**
Fiber's ability to break down rendering work into smaller chunks allows for incremental rendering. This means React can pause rendering to handle higher-priority updates, like user interactions, ensuring the UI remains responsive.
**Cooperative Scheduling**
Fiber's cooperative scheduling allows React to prioritize and manage different tasks effectively. By yielding control back to the browser, React ensures that animations and interactions are not blocked, improving the overall user experience.
**Better Error Handling**
Fiber introduces improved error boundaries, enabling components to catch errors during rendering and lifecycle methods. This enhances the stability of applications by preventing errors from crashing the entire app.
**Improved Memory Usage**
Fiber optimizes memory usage by reusing fiber nodes and reducing the overhead associated with maintaining multiple versions of the virtual DOM. This results in more efficient memory management, especially in large applications.
### Conclusion
React Fiber is a significant advancement in the React ecosystem, bringing improvements in performance, responsiveness, and user experience. By understanding its architecture, reconciliation process, and performance enhancements, developers can leverage Fiber's capabilities to build high-performance, scalable React applications.
>As React continues to evolve, Fiber lays the foundation for future innovations, ensuring that React remains a leading choice for modern web development. **Happy coding!** 😉
| jehnz |
1,875,018 | Construction Made Easy: BONOVO's Range of Equipment and Attachments | screenshot-1717175075894.png Construction Made Easy with BONOVO's Range of Equipment and... | 0 | 2024-06-03T07:29:23 | https://dev.to/theresa_mccraryjs_77dd382/construction-made-easy-bonovos-range-of-equipment-and-attachments-1p6b | screenshot-1717175075894.png
Construction Made Easy with BONOVO's Range of Equipment and Attachments
Are you looking for powerful and innovative equipment to make your construction job easy and safe? Look no further! BONOVO has got you covered with its range of quality construction equipment
Features of making use of BONOVO gear:
BONOVO equipment is made to produce construction work easier and quicker
The apparatus is manufactured with quality materials to withstand construction like harsh
The device and accessories are often an easy task to utilize and require upkeep like little downtime like reducing the likelihood of accidents
Innovation in gear design:
BONOVO is specialized in innovation and tools which are developing produce work easier
The equipment is manufactured with technology that increases precision and decreases work like handbook work like making and much better
Safety first:
Security is really a concern like top BONOVO
These devices and accessories had been created with security features that protect the operator furthermore the people round the construction site
The equipment additionally fits security demands, ensuring you shall get quality gear like safe to work well with Excavator Buckets
Utilizing BONOVO gear:
Utilizing BONOVO gear is simple and easy
Each bit like little of features a person manual providing you with step-by-step guidelines how to run the gear
The machine could be constructed from user-friendly controls, rendering it possible for operators to utilize
Utilizing BONOVO add-ons:
BONOVO attachments are now easy to use and might additionally get in contact towards kit rapidly and safely
The accessories have actually directions on the way like best to utilize them and simply precisely how to install Excavator Quick Coupler towards the device
Operators must always follow the instructions supplied in order to avoid accidents
Provider which assist:
At BONOVO, we pride ourselves on providing help like great
You are able to expect help for the equipment and accessories, including upkeep, fix, and replacement components
We also provide training for operators to ensure they are properly able to make use of the equipment and effortlessly
Quality it is possible to trust:
BONOVO equipment and accessories are manufactured with quality materials and are generally built to endure
Our equipment undergoes testing like ensure like rigorous it fulfills the utmost requirements of quality
You can expect to trust which you shall get quality tools that may endure for many years after you get BONOVO gear
Applications of BONOVO gear:
BONOVO equipment and add-ons are used inside a large amount of different construction jobs, including road construction, building construction, and gardening
The product is versatile that may even be utilized for various tasks, including digging, increasing, and grading
In conclusion, BONOVO's range of equipment and attachments provides an excellent solution for construction work. The equipment is powerful, innovative, safe, and easy to use, making it an excellent choice for construction professionals. With BONOVO, you can be assured of quality Backhoe Loaders equipment that will make your construction job easy and efficient.
Source: https://www.bonovogroup.com/excavator-buckets
| theresa_mccraryjs_77dd382 | |
1,875,017 | Turso Driver for Laravel | Hello Punk! 👋 Yes, I am again. Sorry for wasting your time reading this pretty... | 0 | 2024-06-03T07:27:55 | https://dev.to/darkterminal/libsql-driver-for-laravel-2g62 | webdev, laravel, php, sql | Hello Punk! 👋 Yes, I am again. Sorry for wasting your time reading this pretty blog/article/whatever.
---
## It's re-write?
{% embed https://dev.to/darkterminal/turso-libsql-driver-laravel-131k %}
Yes! But, the first blog is just copy-paste from `README.md` file. Here the actual story what I've done with Laravel.
PHP Community it's huge! But when Turso/LibSQL Database came, they did not support PHP, because they doesn't have developer that really into in PHP and LibSQL build using Rust, so they have Rust only binary.
For the first launch, They have Rust, Go, Python and TypeScript/JS Official SDKs.
However, Turso provides the HTTP SDK as a creation tool for developers who want to create an SDK that is not yet supported by the official SDK.
From there, several Community SDKs emerged, most of which use the HTTP SDK. When using HTTP SDK so database interact with Remote Database and the developer still use SQLite for In-Memory or Local Interaction. Is it wrong? Of course not, I also did the same thing at first. **This is an art, so people can have their own interpretation**.
Here is my first Turso/LibSQL Library that support Turso HTTP SDK and Platform API.
{% embed https://dev.to/darkterminal/the-php-library-for-turso-http-1p47 %}
But, Turso also have a Embedded Replica that sync local database with remote database on the edge, how do sync then?
Don't worry I am also create a Stupid Worker which will make you poor when using it with the number of interactions reading and writing databases from local to remote via HTTP Protocol.
{% embed https://github.com/darkterminal/turso-syncd %}
---
## Back to This!
> When using HTTP SDK so database interact with Remote Database and the developer still use SQLite for In-Memory or Local Interaction. Is it wrong? Of course not, I also did the same thing at first.
But if we use SQLite to create an In-Memory or Local File Connection, it will reduce the artistic value of LibSQL, because with Binary LibSQL, we can create 4 different types of database connections.
- In-Memory Connection
- Local Connection
- Remote Connection
- Remote Replica (Embedded Replica) Connection
That's why I was challenged to create a Native Extension/Driver/Whatever to get the full power of what Turso/LibSQL has to offer.
You can read the `README.md` when you landed at my Laravel Driver repository in GitHub
{% embed https://github.com/tursodatabase/turso-driver-laravel %}
I just want to bring some joy out of the mess I've made writing code while dancing to the music I hate the most.
You can read [Turso Documentation](https://docs.turso.tech/sdk/php/guides/laravel)
If you like this project and want to support my activities, you can [sponsor me on GitHub](https://github.com/sponsors/darkterminal). Sorry and thank you for taking the time to read. | darkterminal |
1,875,016 | Construction Made Easy: BONOVO's Range of Equipment and Attachments | screenshot-1717175075894.png Construction Made Easy with BONOVO's Range of Equipment and... | 0 | 2024-06-03T07:27:51 | https://dev.to/theresa_mccraryjs_77dd382/construction-made-easy-bonovos-range-of-equipment-and-attachments-560h | screenshot-1717175075894.png
Construction Made Easy with BONOVO's Range of Equipment and Attachments
Are you looking for powerful and innovative equipment to make your construction job easy and safe? Look no further! BONOVO has got you covered with its range of quality construction equipment
Features of making use of BONOVO gear:
BONOVO equipment is made to produce construction work easier and quicker
The apparatus is manufactured with quality materials to withstand construction like harsh
The device and accessories are often an easy task to utilize and require upkeep like little downtime like reducing the likelihood of accidents
Innovation in gear design:
BONOVO is specialized in innovation and tools which are developing produce work easier
The equipment is manufactured with technology that increases precision and decreases work like handbook work like making and much better
Safety first:
Security is really a concern like top BONOVO
These devices and accessories had been created with security features that protect the operator furthermore the people round the construction site
The equipment additionally fits security demands, ensuring you shall get quality gear like safe to work well with Excavator Buckets
Utilizing BONOVO gear:
Utilizing BONOVO gear is simple and easy
Each bit like little of features a person manual providing you with step-by-step guidelines how to run the gear
The machine could be constructed from user-friendly controls, rendering it possible for operators to utilize
Utilizing BONOVO add-ons:
BONOVO attachments are now easy to use and might additionally get in contact towards kit rapidly and safely
The accessories have actually directions on the way like best to utilize them and simply precisely how to install Excavator Quick Coupler towards the device
Operators must always follow the instructions supplied in order to avoid accidents
Provider which assist:
At BONOVO, we pride ourselves on providing help like great
You are able to expect help for the equipment and accessories, including upkeep, fix, and replacement components
We also provide training for operators to ensure they are properly able to make use of the equipment and effortlessly
Quality it is possible to trust:
BONOVO equipment and accessories are manufactured with quality materials and are generally built to endure
Our equipment undergoes testing like ensure like rigorous it fulfills the utmost requirements of quality
You can expect to trust which you shall get quality tools that may endure for many years after you get BONOVO gear
Applications of BONOVO gear:
BONOVO equipment and add-ons are used inside a large amount of different construction jobs, including road construction, building construction, and gardening
The product is versatile that may even be utilized for various tasks, including digging, increasing, and grading
In conclusion, BONOVO's range of equipment and attachments provides an excellent solution for construction work. The equipment is powerful, innovative, safe, and easy to use, making it an excellent choice for construction professionals. With BONOVO, you can be assured of quality Backhoe Loaders equipment that will make your construction job easy and efficient.
| theresa_mccraryjs_77dd382 | |
1,875,014 | How Does AI Shape NFT Art Creation in the Digital Era? | rapidinnovation#AIArt #NFTRevolution #DigitalCreativity #BlockchainArt #GenerativeArt | 27,548 | 2024-06-03T07:27:11 | https://dev.to/aishikl/how-does-ai-shape-nft-art-creation-in-the-digital-era-9p7 | #rapidinnovation#AIArt #NFTRevolution #DigitalCreativity #BlockchainArt #GenerativeArt | aishikl | |
1,875,013 | Can Crypto-Friendly Neobanks Help Businesses Reach New Customers? | rapidinnovation#NeobankingRevolution #CryptoFriendly #FintechInnovation #DigitalBanking... | 27,548 | 2024-06-03T07:27:00 | https://dev.to/aishikl/can-crypto-friendly-neobanks-help-businesses-reach-new-customers-1hcn | #rapidinnovation#NeobankingRevolution #CryptoFriendly #FintechInnovation #DigitalBanking #CryptoIntegration | aishikl | |
1,875,012 | Streamline Your AWS Asset Inventory with Automated Discovery and Reporting | Managing resources across multiple AWS accounts and regions can be a daunting task, especially as... | 0 | 2024-06-03T07:23:41 | https://dev.to/praveenha/streamline-your-aws-asset-inventory-with-automated-discovery-and-reporting-4c29 | aws, inventory, report, awschallenge | Managing resources across multiple AWS accounts and regions can be a daunting task, especially as your cloud infrastructure grows. To simplify this process, I have developed an AWS Inventory Discovery tool that scans all your AWS accounts across all regions and compiles a comprehensive, searchable HTML report. In this blog, I'll walk you through the features, benefits, and technical details of this solution.
Introduction
As organizations scale their use of AWS, keeping track of resources scattered across various accounts and regions becomes increasingly challenging. Manual inventory management is not only time-consuming but also prone to errors. This is where the AWS Inventory Discovery tool comes in.
Features
Comprehensive Scanning: The tool scans all your AWS accounts across all regions, ensuring no resource is left unaccounted for.
Detailed Reporting: Generates a detailed HTML report that lists all discovered resources, including their ARNs and regions.
Searchable Interface: The HTML report includes a search functionality, making it easy to find specific resources quickly.
Visual Representation: Includes pie charts to provide a visual summary of your resources, helping you quickly understand the distribution of resources across various dimensions.
User-Friendly: The generated report is easy to navigate, allowing users to drill down into resource details with just a few clicks.
Benefits
Improved Visibility: Gain a clear overview of all your AWS resources across accounts and regions.
Time Savings: Automate the discovery process, freeing up time for your team to focus on more critical tasks.
Error Reduction: Minimize the risk of overlooking resources or making mistakes in manual inventories.
Enhanced Security: Quickly identify and manage resources to ensure compliance with security policies and best practices.
How It Works
Prerequisites
Before you begin, ensure you have the following set up:
AWS CLI: Install the AWS Command Line Interface (CLI).
```
pip install awscli
AWS Credentials: Export your AWS profile or access keys and secrets, and specify the region.
export AWS_PROFILE=your-aws-profile
export AWS_ACCESS_KEY_ID=your-access-key-id
export AWS_SECRET_ACCESS_KEY=your-secret-access-key
export AWS_DEFAULT_REGION=your-default-region`
```
```
#!/bin/bash
AccountID="<YOUR_AWS_ACCOUNT>"
regions=$(aws ec2 describe-regions --query "Regions[].RegionName" --output text)
#regions=(ap-south-1 eu-north-1 eu-west-3 eu-west-1 ap-northeast-3 ap-northeast-2 ap-northeast-1 ca-central-1 sa-east-1 ap-southeast-1 ap-southeast-2 eu-central-1 us-east-1 us-east-2 us-west-1 us-west-2 )
# Initialize arrays to store data
declare -a summary_data=()
declare -a detailed_data=()
# Fetch resources from all regions
for region in $regions; do
# Fetch resource ARNs and process them
data=$(aws --region $region resourcegroupstaggingapi get-resources | jq -r '.ResourceTagMappingList[].ResourceARN' | \
awk -v region=$region -F '[:/]' '
{
resourceType = "unknown"
if ($3 == "s3") {
resourceType = "bucket"
} else if ($3 == "sns") {
resourceType = "topic"
} else {
resourceType = $6
}
# Construct a unique key for each service-resource pair
pair = $3 ":" resourceType
count[pair]++
}
END {
for (pair in count) {
split(pair, s, ":") # Split the pair back into service and resource
service = s[1]
resource = s[2]
print "{\"service\":\"" service "\", \"resource\":\"" resource "\", \"count\":" count[pair] "}"
}
}
')
# Append to summary_data
summary_data+=($data)
# Fetch detailed resource information
detailed_info=$(aws resourcegroupstaggingapi get-resources --region $region | jq -r --arg region $region '.ResourceTagMappingList[] | {Resource_Arn: .ResourceARN, Region: ($region // "Global"), Detailed_Service: (.ResourceARN | split(":")[2])}')
# Append to detailed_data
detailed_data+=($detailed_info)
done
# Process summary data
summary_json=$(printf "%s\n" "${summary_data[@]}" | jq -s 'group_by(.service, .resource) | map({service: .[0].service, resource: .[0].resource, count: map(.count) | add})')
total_resources=$(echo "$summary_json" | jq 'map(.count) | add')
# Process detailed data
detailed_json=$(printf "%s\n" "${detailed_data[@]}" | jq -s .)
# Generate HTML
cat <<EOF > index.html
<!DOCTYPE html>
<html lang="en">
<head>
<meta charset="UTF-8">
<meta name="viewport" content="width=device-width, initial-scale=1.0">
<title>AWS Resources</title>
<style>
body {
font-family: Arial, sans-serif;
background-color: #f4f4f9;
margin: 0;
padding: 20px;
}
h1 {
color: #333;
}
#searchBox, #searchBox2 {
width: 100%;
padding: 10px;
margin-bottom: 20px;
box-sizing: border-box;
font-size: 16px;
}
table {
width: 100%;
border-collapse: collapse;
}
th, td {
border: 1px solid #ddd;
padding: 8px;
text-align: left;
}
th {
background-color: #4CAF50;
color: white;
}
tr:nth-child(even) {
background-color: #f2f2f2;
}
tr:hover {
background-color: #ddd;
}
.total-count {
font-size: 18px;
margin: 20px 0;
}
#chartContainer {
width: 50%;
margin: 0 auto;
}
</style>
</head>
<body>
<h1>AWS Resources for Account ID: $AccountID</h1>
<div class="total-count">Total Resources: $total_resources</div>
<input type="text" id="searchBox" onkeyup="filterTable()" placeholder="Search for services..">
<table id="resourcesTable">
<thead>
<tr>
<th>Service</th>
<th>Resource</th>
<th>Count</th>
</tr>
</thead>
<tbody>
</tbody>
</table>
<h1>Detailed AWS Resources</h1>
<input type="text" id="searchBox2" onkeyup="filterTable2()" placeholder="Search for resources..">
<table id="detailedResourcesTable">
<thead>
<tr>
<th>Resource ARN</th>
<th>Region</th>
<th>Detailed Service</th>
</tr>
</thead>
<tbody>
</tbody>
</table>
<div id="chartContainer">
<canvas id="resourceChart"></canvas>
</div>
<script src="https://cdn.jsdelivr.net/npm/chart.js"></script>
<script>
const data = $summary_json;
const resourceData = $detailed_json;
function loadTableData(data) {
const tableBody = document.getElementById('resourcesTable').getElementsByTagName('tbody')[0];
tableBody.innerHTML = "";
data.forEach(item => {
let row = tableBody.insertRow();
let cellService = row.insertCell(0);
let cellResource = row.insertCell(1);
let cellCount = row.insertCell(2);
cellService.innerHTML = item.service;
cellResource.innerHTML = item.resource;
cellCount.innerHTML = item.count;
});
updateChart(data);
}
function loadDetailedTableData(resourceData) {
const tableBody = document.getElementById('detailedResourcesTable').getElementsByTagName('tbody')[0];
tableBody.innerHTML = "";
resourceData.forEach(item => {
let row = tableBody.insertRow();
let cellArn = row.insertCell(0);
let cellRegion = row.insertCell(1);
let cellService = row.insertCell(2);
cellArn.innerHTML = item.Resource_Arn;
cellRegion.innerHTML = item.Region;
cellService.innerHTML = item.Detailed_Service;
});
}
function filterTable() {
const searchValue = document.getElementById('searchBox').value.toLowerCase();
const filteredData = data.filter(item => item.service && item.service.toLowerCase().includes(searchValue));
loadTableData(filteredData);
}
function filterTable2() {
const searchValue = document.getElementById('searchBox2').value.toLowerCase();
const filteredResourceData = resourceData.filter(item =>
item.Resource_Arn.toLowerCase().includes(searchValue) ||
item.Region.toLowerCase().includes(searchValue) ||
item.Detailed_Service.toLowerCase().includes(searchValue)
);
loadDetailedTableData(filteredResourceData);
}
function updateChart(data) {
const services = data.reduce((acc, item) => {
acc[item.service] = (acc[item.service] || 0) + item.count;
return acc;
}, {});
const labels = Object.keys(services);
const counts = Object.values(services);
const ctx = document.getElementById('resourceChart').getContext('2d');
new Chart(ctx, {
type: 'pie',
data: {
labels: labels,
datasets: [{
data: counts,
backgroundColor: [
'#FF6384', '#36A2EB', '#FFCE56', '#4CAF50', '#FF9800', '#9C27B0', '#00BCD4'
]
}]
},
options: {
responsive: true,
plugins: {
legend: {
position: 'top',
},
title: {
display: true,
text: 'Resource Distribution by Service'
}
}
}
});
}
document.addEventListener('DOMContentLoaded', () => {
loadTableData(data);
loadDetailedTableData(resourceData);
});
</script>
</body>
</html>
EOF
```
| praveenha |
1,875,011 | Drum Spill Pallets: Safeguarding Workplaces and the Environment | In industries where hazardous substances are handled, drum spill pallet serve as crucial elements in... | 0 | 2024-06-03T07:21:09 | https://dev.to/wendellgriffith/drum-spill-pallets-safeguarding-workplaces-and-the-environment-15ph | drumspillpallet | In industries where hazardous substances are handled, **[drum spill pallet](https://oceansafetysupplies.com/product-category/spill-pallet/)** serve as crucial elements in maintaining safety protocols and preventing environmental damage. These specialized containment units are designed to capture spills, leaks, and drips from drums or other containers, thereby reducing the risk of workplace accidents and environmental contamination. Whether you're considering a 1 drum spill pallet or 4 drum spill pallets, integrating these solutions into your facility is essential for promoting safety and regulatory compliance.

**Environmental Protection**
A primary function of drum spill pallets is to protect the environment from the harmful effects of spills. Hazardous substances, if released into the environment, can contaminate soil, water bodies, and ecosystems, posing significant risks to both human health and wildlife. By confining spills on a pallet, businesses can prevent these substances from spreading and causing long-term environmental damage, demonstrating a commitment to sustainable practices.
**Ensuring Workplace Safety**
Aside from environmental concerns, drum spill pallets also play a vital role in maintaining workplace safety. Spills present immediate hazards to employees, including slip and fall risks and exposure to toxic substances. By containing spills on a **[1 drum spill pallet](https://oceansafetysupplies.com/product/1-drum-spill-pallet/)** or 4 drum spill pallets, these risks are effectively managed, creating a safer working environment and reducing the likelihood of accidents and injuries among personnel.
**Factors to Consider in Selection**
**Choosing the appropriate drum spill pallet involves considering various factors:**
Capacity and Size: Assess your storage needs to determine whether a 1 drum spill pallet or **[4 drum spill pallet](https://oceansafetysupplies.com/product/4-drum-spill-pallet/)** are more suitable for your requirements. Consider factors such as the volume of drums stored and available space in your facility.
Material Compatibility: Select a pallet constructed from materials compatible with the substances it will encounter, ensuring durability and resistance to corrosion. This ensures the longevity and effectiveness of the pallet in containing spills.
Regulatory Compliance: Ensure that the selected pallet meets relevant regulations and standards governing spill containment in your industry or region. Compliance with these requirements is crucial for avoiding fines and penalties and maintaining a safe workplace environment.
**Conclusion**
In conclusion, drum spill pallets are essential tools for promoting safety and environmental responsibility in industries handling hazardous materials. Whether you're a small-scale operation or a large industrial facility, investing in 1 drum spill pallet or 4 drum spill pallets is vital for ensuring safety, protecting the environment, and complying with regulations. By containing spills and minimizing environmental impact, these pallets contribute to a safer, more sustainable future for businesses and communities alike.
| wendellgriffith |
1,875,008 | Five Challenges to Effective Cost Controls | Cost management is the most critical portion of managing any project and any change in cost... | 0 | 2024-06-03T07:18:34 | https://dev.to/bidkon_quantitysurveyors/five-challenges-to-effective-cost-controls-41mg | cost, project, consultats | Cost management is the most critical portion of managing any project and any change in cost estimation directly impacts on the project schedule and scope. The accurate practice of project cost control is very important in any project in order to successfully attain the project goal. Advancement in technology has made a mind-set of stakeholders to complete the entire project within tight schedules and low project cost. There are a number of challenges that occur while practicing project cost control in any project.
Following are the top five challenges that comes across for effective cost controls:
Controlling Scope Variation
For any project, a budget is prepared beforehand and it is very common to have an inevitable variation in the scope, which leads to variation in the budget. In this scenario, it is very important for the project manager to control the changes in scope. It can be identified that only controlling the variation in scope would help the project manager to make the budget manageable. Therefore, controlling this variation in cost is due to scope variation, which is very difficult and is one of the major challenges faced for effective cost controls.
Accurate Cost Analysis
Every project requires appropriate analysis of costs for the resources within the project. Project professionals are frustrated due to the difficulty they face in managing and maintaining cost accounting for the project. It is very important for the project professionals to implement effective cost analytical tools in order to monitor the cash flow within the project. Hiring an appropriate accountant for cost analysis is the common challenge that project professionals come across while attaining the required target.
Integrating Schedule and Cost
Aligning the schedule and budget of the project is another difficult task that project professionals come across in cost control management. In every project, managers of Controlling and monitoring activities and managers for managing cost codes, fiscal periods, and transactions are typically different. Managers responsible for managing WBS (Work Breakdown Structure) and task activities are least aware about the cost analysts who monitors the flow of cash for each activity and so, it becomes very difficult for the cost analysts or accountants to control costs for each task. Therefore, it accounts as a major challenge for project managers to control cost.
Accurate Reporting
In every project, customers are involved in the project where customers might include stakeholders, the IT business unit, funding authorities, and many more. These customers demand regularly for accurate reports for each activity in order to check its proceedings. Sometimes, it becomes very difficult for a project manager to provide error free reports of all departments associated with the project to its customers.
Adapting Advanced Technology
There are numerous advancement in project cost management but only an appropriate usage of this technology can lead in attaining the project’s goal. Despite all major advancements in technology, project managers are afraid of adapting it correctly. This is also a common challenge to cost control management faced by many project professionals.
Cost management is the most critical portion of managing any project and any change in cost estimation directly impacts on the project schedule and scope. The accurate practice of project cost control is very important in any project in order to successfully attain the project goal. Advancement in technology has made a mind-set of stakeholders to complete the entire project within tight schedules and low project cost. There are a number of challenges that occur while practicing project cost control in any project.
Contact Info
Address
Unit 3, Dynon Road,
West Melbourne, VIC 3003.
AUSTRALIA.
info@bidkon.com.au
+61 430 194 637 | bidkon_quantitysurveyors |
1,875,007 | Enhance Your Campaigns with a Detailed Nephrologists Email List | Introduction In the competitive field of healthcare marketing, reaching the right audience with... | 0 | 2024-06-03T07:17:16 | https://dev.to/axton_jameson_5f69fdf0732/enhance-your-campaigns-with-a-detailed-nephrologists-email-list-5c26 | Introduction
In the competitive field of healthcare marketing, reaching the right audience with tailored messages is crucial. Nephrologists, as specialists in kidney care, are key targets for pharmaceutical companies, medical device manufacturers, and healthcare service providers. To connect with these professionals effectively, a detailed [[nephrologists email list](

)]is indispensable. Let's delve into why this tool is so essential and how you can leverage it to enhance your campaigns.

What is a Nephrologists Email List?
Definition and Components
A nephrologists email list is a curated database containing the contact information of nephrology specialists. This list includes:
• Full Names: For personalized communication.
• Email Addresses: Primary mode of contact.
• Phone Numbers: For direct communication and follow-ups.
• Workplace Information: Hospitals, clinics, research centers, or private practices.
• Specialization Details: Specific areas within nephrology, such as dialysis, transplantation, etc.
Purpose and Benefits
The main purpose of a nephrologists email list is to facilitate direct and efficient communication with kidney care specialists. This targeted approach helps in delivering relevant information, promoting products or services, and building professional relationships.
Building a High-Quality Nephrologists Email List
Data Collection Strategies
To build a high-quality email list, employ various data collection strategies:
• Website Sign-Ups: Offer valuable content in exchange for email addresses.
• Industry Events: Collect contacts during conferences, seminars, and workshops.
• Professional Networks: Leverage existing networks and partnerships.
Segmenting Your Nephrologists Email List
Importance of Segmentation
Segmentation is critical for delivering targeted and relevant messages. By dividing your email list into smaller groups based on specific criteria, you can tailor your content more effectively, leading to better engagement.
Common Segmentation Criteria
You can segment your nephrologists email list based on:
• Specialization: Focus areas within nephrology.
• Geographic Location: Country, state, or city.
• Workplace Type: Hospitals, private practices, academic institutions.
Compliance and Best Practices
Understanding Relevant Regulations
Compliance with email marketing laws such as the CAN-SPAM Act in the United States and GDPR in Europe is essential. These regulations require you to obtain consent before sending emails and to provide an easy way for recipients to unsubscribe.
Obtaining Consent and Respecting Privacy
Always obtain explicit consent from individuals before adding them to your email list. This can be done through opt-in forms on your website or during events. Respect your recipients' privacy by protecting their data and never sharing it without permission.
Ethical Email Marketing Practices
Ethical email marketing involves sending relevant, valuable content to your recipients and respecting their preferences. Avoid spamming, honor unsubscribe requests promptly, and always provide an option for recipients to manage their email preferences.
Analyzing and Optimizing Campaigns
Key Performance Indicators (KPIs) to Monitor
Track essential metrics to gauge the success of your email campaigns:
• Open Rates: Percentage of recipients who open your emails.
• Click-Through Rates: Percentage of recipients who click on links within your emails.
• Conversion Rates: Percentage of recipients who take a desired action after clicking a link.
A/B Testing for Continuous Improvement
A/B testing involves sending two versions of an email to a small segment of your list to see which performs better. This helps you optimize various elements like subject lines, content, and send times for maximum impact.
Strategies for Optimizing Campaigns
Email marketing is an ongoing process. Continuously analyze your results and make adjustments to improve your campaigns. Stay updated with the latest trends and best practices to keep your strategies fresh and effective.
Case Studies and Success Stories
Examples of Successful Campaigns
Learning from real-life examples can provide valuable insights. Study case studies of companies that have effectively used nephrologists email lists to achieve their goals. Analyze their strategies and results to apply similar approaches to your campaigns.
Lessons Learned from Less Successful Efforts
Understanding what went wrong in failed campaigns can be just as important. Identify common pitfalls and learn how to avoid them in your email marketing efforts.
Overcoming Common Challenges
Typical Issues in Email Marketing
Email marketing comes with its own set of challenges, such as:
• Low Open Rates: Recipients may ignore your emails.
• High Unsubscribe Rates: Your content may not be resonating with your audience.
• Deliverability Issues: Emails may end up in spam folders.
Solutions and Strategies to Overcome These Challenges
To overcome these challenges:
• Improve Subject Lines: Make them more engaging and relevant.
• Enhance Content Quality: Ensure your emails provide value to recipients.
• Monitor Deliverability: Use tools to check if your emails are being delivered properly.
Cost-Benefit Analysis
Evaluating the Investment in Email Marketing
Investing in a high-quality nephrologists email list can be costly, but the potential returns are significant. By reaching a targeted audience, you can achieve better engagement and higher conversion rates, making the investment worthwhile.
Long-Term Benefits of a Well-Maintained Email List
A well-maintained email list is a valuable asset. It allows you to build long-term relationships with nephrologists, leading to sustained engagement and ongoing business opportunities.
Future Trends in Email Marketing for Healthcare
Emerging Technologies and Innovations
Stay ahead of the curve by keeping an eye on emerging technologies in email marketing. AI-driven personalization, advanced analytics, and interactive emails are some trends to watch.
Predicted Changes in Marketing Strategies
As the digital landscape evolves, so do marketing strategies. Expect a shift towards more personalized, data-driven approaches that focus on delivering value to recipients.
Conclusion
Enhancing your campaigns with a detailed nephrologists email list requires a strategic approach. From building and maintaining a quality list to crafting effective campaigns and analyzing results, every step is crucial. By understanding the needs of nephrologists and adhering to best practices, you can create impactful email marketing campaigns that drive engagement and conversions.
| axton_jameson_5f69fdf0732 | |
1,874,966 | Queues, Data Structures | Queues Queues are a fundamental data structure in computer science that follow a specific... | 0 | 2024-06-03T07:12:25 | https://dev.to/harshm03/queues-data-structures-1dd1 | dsa, datastructures | ## Queues
Queues are a fundamental data structure in computer science that follow a specific order for insertion and deletion of elements, adhering to the First-In-First-Out (FIFO) principle. This means that the first element added to the queue will be the first one to be removed, akin to a line of people waiting for service where the person at the front is served first. Queues are widely used in various applications such as scheduling tasks, handling requests in web servers, and breadth-first search algorithms in graphs.
### Basic Concepts of Queues
- **Enqueue**: This operation adds an element to the end of the queue. If the queue is full, an overflow condition is encountered.
- **Dequeue**: This operation removes an element from the front of the queue. If the queue is empty, an underflow condition is encountered.
- **Front/Peek**: This operation returns the front element of the queue without removing it. It allows us to inspect the element that will be dequeued next.
- **IsEmpty**: This operation checks whether the queue is empty. It returns true if there are no elements in the queue and false otherwise.
### Characteristics of Queues
1. **FIFO Structure**:
Queues operate on a First-In-First-Out basis, meaning the first element added is the first to be removed. This ensures that elements are processed in the order they were added, which is crucial for tasks that require sequential processing.
2. **Linear Data Structure**:
Queues are a linear data structure, where elements are arranged in a sequential manner. Each element in the queue is connected to its predecessor and successor, forming a linear sequence of elements.
3. **Dynamic Size**:
The size of a queue can change dynamically with the addition and removal of elements. This flexibility allows queues to adapt to varying workloads, making them suitable for scenarios with fluctuating demands.
4. **Multiple Types**:
There are several variations of queues tailored for specific needs, such as circular queues, double-ended queues (deques), and priority queues. Each type of queue offers unique features and advantages, expanding the range of applications where queues can be effectively utilized.
Understanding these characteristics and basic operations of queues provides a solid foundation for exploring more advanced implementations and applications of this essential data structure.
### Implementing Queues
Implementing queues involves creating a data structure that supports the fundamental operations of enqueue (insertion) and dequeue (removal) while maintaining the FIFO order. There are various ways to implement queues, each with its own advantages and trade-offs. The two most common implementations are using arrays and linked lists. Understanding these implementations is crucial for applying queues effectively in different scenarios and optimizing performance.
### Array-Based Implementation
In an array-based implementation, a fixed-size array is used to store the queue elements. This approach is straightforward but can lead to inefficiencies such as wasted space or the need for dynamic resizing.
- **Static Array**: A static array has a fixed size. Enqueue operations are straightforward until the array is full, leading to an overflow condition. Dequeue operations can cause elements to shift, which may be inefficient.
- **Circular Array**: A circular array improves efficiency by treating the array as a loop, so the end of the array wraps around to the beginning. This eliminates the need to shift elements after dequeue operations and makes better use of available space.
### Linked List-Based Implementation
A linked list-based implementation uses nodes to store queue elements, with each node pointing to the next element in the sequence. This approach offers dynamic sizing and eliminates the need for shifting elements.
- **Singly Linked List**: In a singly linked list, each node contains data and a reference to the next node. The queue maintains pointers to the front and rear nodes for efficient enqueue and dequeue operations.
- **Doubly Linked List**: A doubly linked list, where each node has references to both the next and previous nodes, can be used to implement a double-ended queue (deque) efficiently. This allows for insertion and deletion at both ends of the queue.
By understanding and implementing these different types of queues, you can tailor the data structure to fit specific use cases, optimizing performance and functionality for various applications.
## Queue Implementation Using Arrays in C++
Queue implementation using arrays in C++ is a straightforward and efficient way to manage elements in a First-In-First-Out (FIFO) manner. By using arrays, we can leverage their fast access times and simple structure to create a queue that supports basic operations like enqueue, dequeue, and peek.
### Creation of the Queue
To create a queue using arrays in C++, we define a class that contains the basic attributes and methods required to manage the queue. Below is the initial part of the class definition, including the basic attributes and the constructor.
```cpp
#include <iostream>
using namespace std;
class Queue {
private:
int front;
int rear;
int size;
int *arr;
public:
Queue(int s) {
front = -1;
rear = -1;
size = s;
arr = new int[size];
}
~Queue() {
delete[] arr;
}
};
```
### Attributes Explanation
1. **front**: This integer variable keeps track of the front position of the queue. It indicates the position from where elements will be dequeued. Initially set to -1, indicating the queue is empty.
2. **rear**: This integer variable tracks the rear position of the queue. It indicates the position where new elements will be enqueued. Initially set to -1, indicating the queue is empty.
3. **size**: This integer variable defines the maximum size of the queue. It is set through the constructor when a queue object is created.
4. **arr**: This is a pointer to an array that will store the queue elements. The array is dynamically allocated based on the specified size.
### Constructor Explanation
The constructor `Queue(int s)` initializes the queue with a specified size:
- **front = -1**: Initializes the front index to -1, indicating that the queue is currently empty.
- **rear = -1**: Initializes the rear index to -1, indicating that the queue is currently empty.
- **size = s**: Sets the size of the queue.
- **arr = new int[size]**: Allocates memory for the queue's array based on the given size.
This setup provides the basic framework for the queue, allowing us to build upon it with the necessary operations such as enqueue, dequeue, and peek. The constructor ensures that the queue is properly initialized with the specified size and is ready for use.
## Operations on Queue (Array Implementation)
Queue operations in array implementation involve adding elements to the rear (enqueue) and removing elements from the front (dequeue). Additionally, we can check if the queue is empty and if it's full.
### Enqueue Operation
The enqueue operation adds an element to the rear of the queue. In array implementation, this involves incrementing the rear pointer and assigning the element to the corresponding index in the array.
```cpp
void enqueue(int value) {
if (rear == size - 1) {
cout << "Queue is full. Cannot enqueue." << endl;
return;
}
else {
rear++;
arr[rear] = value;
}
}
```
`Time Complexity: O(1)`
### Dequeue Operation
The dequeue operation removes an element from the front of the queue. In array implementation, this involves incrementing the front pointer to remove the element at the front position.
```cpp
void dequeue() {
if (front == rear) {
cout << "Queue is empty. Cannot dequeue." << endl;
return;
}
else {
front++;
}
}
```
`Time Complexity: O(1)`
#### Problem with the Dequeue Operation
The above dequeue implementation is simple and efficient, with a time complexity of O(1). However, it has a significant drawback: as the `front` pointer keeps incrementing with each dequeue operation, it moves towards the end of the array. Eventually, the `front` pointer reaches the end of the array, and no further enqueues can be performed, even if there is available space at the beginning of the array. This leads to inefficient use of the array space.
#### Solution: Shifting Elements
To solve this issue, we can shift the elements of the array to the left whenever a dequeue operation is performed. This way, the `front` pointer always points to the first valid element in the queue, and the `rear` pointer correctly reflects the position of the last valid element. Shifting elements ensures that we can reuse the space at the beginning of the array and maintain the efficient functionality of the queue.
#### Updated Dequeue Operation
Here is the updated `dequeue` function that includes shifting elements to the left:
```cpp
void dequeue() {
if (front == rear) {
cout << "Queue is empty. Cannot dequeue." << endl;
return;
}
else {
cout << "Removing " << arr[front + 1] << endl;
for (int i = front + 1; i < rear; i++) {
arr[i] = arr[i + 1];
}
rear--;
}
}
```
`Time Complexity: O(n)`
The time complexity of the updated dequeue operation is O(n), where n is the number of elements in the queue. This is because, in the worst case, we may need to shift all elements to the left.
### IsEmpty Operation
The isEmpty operation checks if the queue is empty by comparing the front and rear pointers.
```cpp
bool isEmpty() {
return front == rear;
}
```
`Time Complexity: O(1)`
### IsFull Operation
The isFull operation checks if the queue is full by comparing the rear pointer with the size of the array.
```cpp
bool isFull() {
return rear == size - 1;
}
```
`Time Complexity: O(1)`
These operations provide the basic functionality to manage a queue using array implementation. Each operation has constant time complexity, ensuring efficient performance for typical queue operations.
### Full Code Implementation of Queues Using Arrays
Implementing queues using arrays in C++ involves creating a class that encapsulates the necessary attributes and methods to manage the queue efficiently. The class will include operations such as enqueue, dequeue, isEmpty, and isFull.
Below is the complete implementation of the Queue class in C++, including all the required operations.
```cpp
#include <iostream>
using namespace std;
class Queue {
private:
int front;
int rear;
int size;
int *arr;
public:
Queue(int s) {
size = s;
front = -1;
rear = -1;
arr = new int[size];
}
~Queue() {
delete[] arr;
}
void enqueue(int value) {
if (isFull()) {
cout << "Queue is full. Cannot enqueue." << endl;
return;
}
else {
rear++;
arr[rear] = value;
}
}
void dequeue() {
if (isEmpty()) {
cout << "Queue is empty. Cannot dequeue." << endl;
return;
}
else {
cout << "Removing " << arr[front + 1] << endl;
for (int i = front + 1; i < rear; i++) {
arr[i] = arr[i + 1];
}
rear--;
}
}
bool isEmpty() {
return front == rear;
}
bool isFull() {
return rear == size - 1;
}
void display() {
if (isEmpty()) {
cout << "Queue is empty." << endl;
return;
}
cout << "Queue elements: ";
for (int i = front + 1; i <= rear; i++) {
cout << arr[i] << " ";
}
cout << endl;
}
};
int main() {
Queue q(5); // Create a queue of size 5
q.enqueue(1); // Enqueue elements
q.enqueue(2);
q.enqueue(3);
q.enqueue(4);
q.enqueue(5);
q.display(); // Display queue elements
q.dequeue(); // Dequeue an element
q.display(); // Display queue elements after dequeue
return 0;
}
```
This complete code demonstrates the implementation of a queue using arrays in C++. It includes all the necessary operations such as enqueue, dequeue, isEmpty, and isFull. The main function demonstrates how to create a queue object, enqueue and dequeue elements, and display the queue contents.
## Queue Implementation Using Linked List in C++
Queue implementation using a linked list in C++ offers flexibility and dynamic sizing, making it suitable for scenarios where the size of the queue may change dynamically. Linked list-based implementation eliminates the need for a fixed-size array and allows for efficient insertion and deletion of elements at both ends of the queue.
### Creation of the Queue
To create a queue using a linked list in C++, we define a class that encapsulates the necessary attributes and methods required to manage the queue. Below is the initial part of the class definition, including the basic attributes and the constructor.
```cpp
#include <iostream>
using namespace std;
class Queue {
private:
struct Node {
int data;
Node* next;
Node(int val) : data(val), next(nullptr) {}
};
Node* front;
Node* rear;
public:
Queue() : front(nullptr), rear(nullptr) {}
~Queue() {
// Destructor code to deallocate memory
}
};
```
### Attributes Explanation
1. **front**: This pointer points to the front node of the queue, indicating the position from where elements will be dequeued. Initially set to nullptr, indicating the queue is empty.
2. **rear**: This pointer points to the rear node of the queue, indicating the position where new elements will be enqueued. Initially set to nullptr, indicating the queue is empty.
### Constructor Explanation
The constructor initializes the queue:
**Queue()**: Initializes the front and rear pointers to nullptr.
- **front**: Points to the front node of the queue. Initially set to nullptr to indicate an empty queue.
- **rear**: Points to the rear node of the queue. Initially set to nullptr to indicate an empty queue.
This setup provides the basic framework for the queue, allowing us to build upon it with the necessary operations such as enqueue, dequeue, and isEmpty. The constructor ensures that the queue is properly initialized with empty pointers and is ready for use.
### Operations on Queues (Linked List Implementation)
Queue operations in linked list implementation involve adding elements to the rear (enqueue) and removing elements from the front (dequeue). Additionally, we can check if the queue is empty.
### Enqueue Operation
The enqueue operation adds an element to the rear of the queue. In linked list implementation, this involves creating a new node and updating the rear pointer to point to this new node.
```cpp
void enqueue(int value) {
Node* newNode = new Node(value);
if (isEmpty()) {
front = rear = newNode;
} else {
rear->next = newNode;
rear = newNode;
}
}
```
`Time Complexity: O(1)`
### Dequeue Operation
The dequeue operation removes an element from the front of the queue. In linked list implementation, this involves updating the front pointer to point to the next node.
```cpp
void dequeue() {
if (isEmpty()) {
cout << "Queue is empty. Cannot dequeue." << endl;
return;
}
Node* temp = front;
front = front->next;
delete temp;
}
```
`Time Complexity: O(1)`
### IsEmpty Operation
The isEmpty operation checks if the queue is empty by checking if the front pointer is nullptr.
```cpp
bool isEmpty() {
return front == nullptr;
}
```
`Time Complexity: O(1)`
These operations provide the basic functionality to manage a queue using linked list implementation. Each operation has constant time complexity, ensuring efficient performance for typical queue operations.
### Full Code Implementation of Queues Using Linked List
Queue implementation using a linked list in C++ provides flexibility and dynamic sizing, making it suitable for scenarios where the size of the queue may change dynamically. This implementation eliminates the need for a fixed-size array and allows for efficient insertion and deletion of elements.
Below is the complete implementation of the Queue class using linked lists in C++, including all the required operations.
```cpp
#include <iostream>
using namespace std;
class Queue {
private:
struct Node {
int data;
Node* next;
Node(int val) : data(val), next(nullptr) {}
};
Node* front;
Node* rear;
public:
Queue() : front(nullptr), rear(nullptr) {}
~Queue() {
while (!isEmpty()) {
dequeue();
}
}
void enqueue(int value) {
Node* newNode = new Node(value);
if (isEmpty()) {
front = rear = newNode;
} else {
rear->next = newNode;
rear = newNode;
}
}
void dequeue() {
if (isEmpty()) {
cout << "Queue is empty. Cannot dequeue." << endl;
return;
}
Node* temp = front;
front = front->next;
delete temp;
}
bool isEmpty() {
return front == nullptr;
}
void display() {
if (isEmpty()) {
cout << "Queue is empty." << endl;
return;
}
cout << "Queue elements: ";
Node* current = front;
while (current != nullptr) {
cout << current->data << " ";
current = current->next;
}
cout << endl;
}
};
int main() {
Queue q;
q.enqueue(1);
q.enqueue(2);
q.enqueue(3);
q.display();
q.dequeue();
q.display();
return 0;
}
```
This complete code demonstrates the implementation of a queue using linked lists in C++. It includes all the necessary operations such as enqueue, dequeue, isEmpty, and display. The main function demonstrates how to create a queue object, enqueue and dequeue elements, and display the queue contents.
## Circular Queue Using Arrays
A circular queue is a data structure that extends the functionality of a regular queue by allowing efficient use of space and avoiding the need to shift elements when dequeuing. It achieves this by treating the underlying array as circular, so when the rear pointer reaches the end of the array, it wraps around to the beginning. This circular behavior enables efficient memory utilization and constant-time enqueue and dequeue operations.
**Differences with Simple Queue in Array Implementation:**
- In a simple queue, when the rear pointer reaches the end of the array, further enqueue operations are not possible even if there are empty spaces at the beginning of the array. However, in a circular queue, the rear pointer wraps around to the beginning to utilize any available empty spaces.
- Similarly, in a simple queue, when the front pointer reaches the end of the array, further dequeue operations are not possible even if there are elements at the beginning of the array. In contrast, in a circular queue, the front pointer wraps around to the beginning to access elements.
### Full Code Implementation of Circular Queues Using Arrays
Implementing a circular queue using arrays in C++ allows for efficient memory utilization and constant-time enqueue and dequeue operations. Below is the complete implementation of the Queue class for a circular queue using arrays.
```cpp
#include <iostream>
using namespace std;
class CircularQueue {
private:
int *arr;
int front;
int rear;
int capacity;
public:
CircularQueue(int size) {
capacity = size;
arr = new int[capacity];
front = -1;
rear = -1;
}
~CircularQueue() {
delete[] arr;
}
void enqueue(int value) {
if (isFull()) {
cout << "Queue is full. Cannot enqueue." << endl;
return;
}
if (isEmpty())
front = 0;
rear = (rear + 1) % capacity;
arr[rear] = value;
}
void dequeue() {
if (isEmpty()) {
cout << "Queue is empty. Cannot dequeue." << endl;
return;
}
if (front == rear)
front = rear = -1;
else
front = (front + 1) % capacity;
}
bool isEmpty() {
return front == -1;
}
bool isFull() {
return (rear + 1) % capacity == front;
}
void display() {
if (isEmpty()) {
cout << "Queue is empty." << endl;
return;
}
cout << "Queue elements: ";
int i = front;
while (i != rear) {
cout << arr[i] << " ";
i = (i + 1) % capacity;
}
cout << arr[rear] << endl;
}
};
int main() {
CircularQueue cq(5); // Create a circular queue of size 5
cq.enqueue(1); // Enqueue elements
cq.enqueue(2);
cq.enqueue(3);
cq.enqueue(4);
cq.enqueue(5);
cq.display(); // Display queue elements
cq.dequeue(); // Dequeue an element
cq.display(); // Display queue elements after dequeue
return 0;
}
```
This complete code demonstrates the implementation of a circular queue using arrays in C++. It includes all the necessary operations such as enqueue, dequeue, isEmpty, and isFull. The main function demonstrates how to create a circular queue object, enqueue and dequeue elements, and display the queue contents.
## Queue Implementation Using Doubly Linked List
A queue implemented using a doubly linked list offers efficient insertion and deletion operations at both ends of the queue. Each node in the linked list contains pointers to both the next and previous nodes, allowing for easy traversal and manipulation.
### Full Code Implementation of Queue Using Doubly Linked List
Implementing a queue using a doubly linked list in C++ provides flexibility and efficient operations. Below is the complete implementation of the Queue class for a doubly linked list-based queue.
```cpp
#include <iostream>
using namespace std;
class Queue {
private:
struct Node {
int data;
Node* next;
Node* prev;
Node(int val) : data(val), next(nullptr), prev(nullptr) {}
};
Node* front;
Node* rear;
public:
Queue() : front(nullptr), rear(nullptr) {}
~Queue() {
while (!isEmpty()) {
dequeue();
}
}
void enqueue(int value) {
Node* newNode = new Node(value);
if (isEmpty()) {
front = rear = newNode;
} else {
rear->next = newNode;
newNode->prev = rear;
rear = newNode;
}
}
void dequeue() {
if (isEmpty()) {
cout << "Queue is empty. Cannot dequeue." << endl;
return;
}
Node* temp = front;
if (front == rear) {
front = rear = nullptr;
} else {
front = front->next;
front->prev = nullptr;
}
delete temp;
}
bool isEmpty() {
return front == nullptr;
}
void display() {
if (isEmpty()) {
cout << "Queue is empty." << endl;
return;
}
cout << "Queue elements: ";
Node* current = front;
while (current != nullptr) {
cout << current->data << " ";
current = current->next;
}
cout << endl;
}
};
int main() {
Queue q;
q.enqueue(1);
q.enqueue(2);
q.enqueue(3);
q.display();
q.dequeue();
q.display();
return 0;
}
```
This complete code demonstrates the implementation of a queue using a doubly linked list in C++. It includes all the necessary operations such as enqueue, dequeue, isEmpty, and display. The main function demonstrates how to create a queue object, enqueue and dequeue elements, and display the queue contents.
## Deque (Doubly Ended Queue)
A Deque, short for "Double-ended Queue," is an abstract data type that allows insertion and deletion of elements from both ends (front and rear). It combines the properties of both stacks and queues, providing more flexibility for adding and removing elements.
**Key Features of Deque:**
- **Insertion/Deletion at Both Ends**: Elements can be added or removed from both the front and the rear of the deque.
- **Dynamic Size**: The size of the deque can grow or shrink dynamically as elements are added or removed.
- **Bidirectional Traversal**: Allows traversal from both ends, making it useful for certain algorithms.
### Full Code Implementation of Deque Using Doubly Linked List
Below is the implementation of a Deque using a doubly linked list in C++:
```cpp
#include <iostream>
using namespace std;
class Deque {
private:
struct Node {
int data;
Node* next;
Node* prev;
Node(int val) : data(val), next(nullptr), prev(nullptr) {}
};
Node* front;
Node* rear;
public:
Deque() : front(nullptr), rear(nullptr) {}
~Deque() {
while (!isEmpty()) {
removeFront();
}
}
// Insert at the front
void insertFront(int value) {
Node* newNode = new Node(value);
if (isEmpty()) {
front = rear = newNode;
} else {
newNode->next = front;
front->prev = newNode;
front = newNode;
}
}
// Insert at the rear
void insertRear(int value) {
Node* newNode = new Node(value);
if (isEmpty()) {
front = rear = newNode;
} else {
rear->next = newNode;
newNode->prev = rear;
rear = newNode;
}
}
// Remove from the front
void removeFront() {
if (isEmpty()) {
cout << "Deque is empty. Cannot remove from front." << endl;
return;
}
Node* temp = front;
if (front == rear) {
front = rear = nullptr;
} else {
front = front->next;
front->prev = nullptr;
}
delete temp;
}
// Remove from the rear
void removeRear() {
if (isEmpty()) {
cout << "Deque is empty. Cannot remove from rear." << endl;
return;
}
Node* temp = rear;
if (front == rear) {
front = rear = nullptr;
} else {
rear = rear->prev;
rear->next = nullptr;
}
delete temp;
}
// Check if the deque is empty
bool isEmpty() {
return front == nullptr;
}
// Display the deque from front to rear
void display() {
if (isEmpty()) {
cout << "Deque is empty." << endl;
return;
}
Node* temp = front;
while (temp != nullptr) {
cout << temp->data << " ";
temp = temp->next;
}
cout << endl;
}
};
int main() {
Deque dq;
dq.insertFront(10);
dq.insertRear(20);
dq.insertFront(5);
dq.insertRear(25);
cout << "Deque after insertions: ";
dq.display();
dq.removeFront();
cout << "Deque after removing from front: ";
dq.display();
dq.removeRear();
cout << "Deque after removing from rear: ";
dq.display();
return 0;
}
```
This implementation ensures that the Deque provides efficient operations for insertion and removal from both ends, leveraging the properties of a doubly linked list.
## Priority Queue Using Linked List
A priority queue using a linked list is an implementation where each element is associated with a priority and elements are dequeued in order of their priority. In a linked list implementation, elements are inserted in such a way that the list remains sorted based on priority.
**Key Features of Priority Queue with Linked List:**
- **Ordered Insertion**: Elements are inserted in the correct position to maintain the order based on priority.
- **Dynamic Size**: The size of the priority queue can grow or shrink dynamically as elements are added or removed.
- **Efficient Deletion**: Deleting the highest-priority element (at the front) is efficient.
### Full Code Implementation of Priority Queue Using Linked List
Below is the implementation of a priority queue using a singly linked list in C++:
```cpp
#include <iostream>
using namespace std;
class PriorityQueue {
private:
struct Node {
int data;
int priority;
Node* next;
Node(int val, int pri) : data(val), priority(pri), next(nullptr) {}
};
Node* front;
public:
PriorityQueue() : front(nullptr) {}
~PriorityQueue() {
while (!isEmpty()) {
dequeue();
}
}
// Insert with priority
void enqueue(int value, int priority) {
Node* newNode = new Node(value, priority);
if (isEmpty() || front->priority > priority) {
newNode->next = front;
front = newNode;
} else {
Node* temp = front;
while (temp->next != nullptr && temp->next->priority <= priority) {
temp = temp->next;
}
newNode->next = temp->next;
temp->next = newNode;
}
}
// Remove the highest priority element
int dequeue() {
if (isEmpty()) {
cout << "Priority Queue is empty. Cannot dequeue." << endl;
return -1; // or throw an exception
}
Node* temp = front;
int value = temp->data;
front = front->next;
delete temp;
return value;
}
// Peek at the highest priority element
int peek() {
if (isEmpty()) {
cout << "Priority Queue is empty." << endl;
return -1;
}
return front->data;
}
// Check if the priority queue is empty
bool isEmpty() {
return front == nullptr;
}
// Display the priority queue
void display() {
if (isEmpty()) {
cout << "Priority Queue is empty." << endl;
return;
}
Node* temp = front;
while (temp != nullptr) {
cout << "(" << temp->data << ", " << temp->priority << ") ";
temp = temp->next;
}
cout << endl;
}
};
int main() {
PriorityQueue pq;
pq.enqueue(10, 2);
pq.enqueue(20, 1);
pq.enqueue(30, 3);
pq.enqueue(15, 1);
cout << "Priority Queue: ";
pq.display();
cout << "Dequeued element: " << pq.dequeue() << endl;
cout << "Priority Queue after dequeue: ";
pq.display();
cout << "Peek element: " << pq.peek() << endl;
return 0;
}
```
This implementation ensures that the priority queue maintains the correct order of elements based on their priority, providing efficient insertion and removal operations. The use of a linked list allows the priority queue to dynamically grow and shrink as elements are added or removed. | harshm03 |
1,875,006 | S2V Infotech: Your Go-To Source for Digital Marketing, Design, and Web Development | S2V Infotech provides the best website development, website design, and digital marketing services... | 0 | 2024-06-03T07:11:35 | https://dev.to/s2v_infotech_50/s2v-infotech-your-go-to-source-for-digital-marketing-design-and-web-development-2m | education, webdev, learning |
S2V Infotech provides the best website development, website design, and digital marketing services with over 9500 clients globally. Our 24/7 help expedites the website support procedure for their clients.
Here's how:
Reaching New Heights in Website Development:
• Working with S2vinfotech, one of the Best Website Development Services, you may create an educational and user-friendly website.
• Professional website developers will guarantee that your website is easy to use and has all the information required by teachers, staff, and prospective students.
• By looking for website development firms near me or top website development businesses, you can locate qualified developers who understand the particular needs of the educational sector.
Using Website Design to Make a Statement:
• An eye-catching and captivating website created by a Top Website Design firm will capture the attention of visitors and leave a lasting impact.
• Seek for businesses that specialize in the best website design so they can make a website that accurately captures the essence of your organization and its core principles.
• Taking into account a nearby website design firm can help with simple communication and comprehension of regional design trends.
Using Digital Marketing to Amplify Your Voice:
• Working with a top digital marketing agency, such as S2vinfotech, can assist you in creating a data-driven plan for your online presence.
• The most effective digital marketing initiatives will raise brand awareness, draw in quality leads, and eventually boost enrollment.
• Finding a company with experience in the education industry can be ensured by searching for a top digital marketing company or a company near you.
Expanding the Horizons in Website Development
• By working with S2vinfotech, one of the Best Website Development Services, you can create an educational and user-friendly website.
• Skilled web developers will guarantee that your website is easy to navigate and has all the information teachers, staff, and prospective students might ever require.
• By looking for website development firms near me or top website development businesses, you can locate qualified developers that are aware of the particular requirements of the educational sector.
The following are some advantages that your educational institution can gain by investing in a well-designed website and a smart digital marketing strategy:
• Increased brand awareness and visibility
• Improved communication with prospective students, faculty, and staff
• Enhanced recruitment efforts
• Stronger community engagement
• A more efficient and streamlined admissions process
In conclusion
Invest in the resources your educational institution needs to succeed in the digital era. Invest in digital marketing solutions, website development, and design with S2vinfotech, a top supplier of these services. Our area of expertise is creating engaging web content that will appeal to your target audience and advance your educational objectives.
Contact us to discuss your unique needs and explore how we can help you achieve your goals.
Contact us: +1 8442964279
For more information visit here
https://www.s2vinfotech.com/best-digital-marketing-institute/
| s2v_infotech_50 |
1,875,005 | Superior to Classic: How Salesforce Lightning Services Make Your CRM Better | A decade has passed since the release of the Salesforce Lightning Platform. Some businesses are still... | 0 | 2024-06-03T07:10:35 | https://dev.to/edgar_joes/superior-to-classic-how-salesforce-lightning-services-make-your-crm-better-30nc | salesforce, development, lightningservices | A decade has passed since the release of the Salesforce Lightning Platform. Some businesses are still skeptical about switching from Salesforce Classic to Lightning. The reason behind this hesitation is making a significant change that could affect the operations of their organization. Switching to a new platform can be challenging and might result in a work gap in between. However, with the help of Salesforce Lightning services, businesses can make this switch with ease, eliminating the hassles that an organization might encounter. Businesses that have already made their switch to Salesforce Lightning from Classic have experienced numerous benefits of this transition.
## Salesforce Lightning Services: How They Make Your CRM Better
Salesforce Lightning is a framework based on components that help develop applications on the Salesforce CRM. Even for businesses that are not experts in coding, maintaining a digital presence through applications and websites is crucial. These businesses utilize component-based frameworks. The Lightning framework can be considered as a means of designing your application without requiring in-depth technical skills.
Salesforce Lightning services comprise multiple components that function together to offer a quality user experience, drive productivity, and promote high levels of customization. These services include the Lightning App Builder, Lightning Component Framework, Lightning Process Builder, Lightning Experience, and more.
Here are important ways in which Salesforce Lightning services can improve the usability and performance of your CRM:
### Automation of Sales Workflows
You cannot maintain 100% efficiency while converting leads into sales. These days, organizations build unique strategies to boost their conversion rates. Nevertheless, the outcome does not come what’s anticipated. Salesforce Lightning implementation equips businesses with updated features to help automate the process of sales, hence enhancing the efficiency of their CRM. You can design your sales pipeline by leveraging the feature called ‘Sales Path’. Using this feature, you can also know about the next steps in case things don’t go according to your plan. This helps you react efficiently and quickly, convincing the leads and gaining their confidence.
### Improved Einstein AI Integration
While AI is a revolution in itself, Einstein integration has introduced entirely new features in Salesforce Lightning. Einstein Forecasting and Einstein Opportunity Insights are the two most notable features in the Salesforce Lightning version. Einstein Account Insights is another feature that deserves due consideration.
These features help improve the process of analytics generation, lead generation, and building the profile of customers. You can save time during customer research by leveraging the visual reports of all the analytics.
Einstein recommends objects, people, and groups to you in the Chatter Component in Salesforce Lightning. The Chatter Component helps you know your most visited pages so that you can easily access your desired page. By allowing you to see the most utilized streams, Einstein AI integration helps improve your overall CRM experience.
### Quick App Development
Salesforce Lightning services make way for the easier designing and developing of applications. One of the key benefits of Salesforce Lightning is its component-based platform. This allows you to easily integrate components pre-built by the Salesforce partners and utilize them in your application. All you need to do is drag and drop the components for their use. The process helps you in designing high-quality applications for your organization without having to invest additional time. Also, there are multiple built-in components to select from depending on your needs. You just need to incorporate the most appropriate ones in the Salesforce Lightning framework for your application to be ready.
### Third-Party Integrations
Salesforce Lightning includes multiple components, more and more of which are being developed and made available on the AppExchange platform of Salesforce. Hence, you can always ensure that your needs will be met. Nevertheless, you can still integrate tailored components from third-party apps. Considering the evolving needs of modern businesses, Salesforce Lightning services guarantee you easy integration of third-party components. This way you don’t have to compensate for your business requirements. You can effortlessly integrate anything you need, from any source, and create your custom application.
### Good-Quality Leads
Now that you have sufficient time saved up from creating applications and streamlining sales processes, you can devote more time to Einstein AI technology. This will help you understand your goals and needs effectively while tracking down a potential lead. Einstein AI tracks down the data of all potential leads including their behavior, interactions, and sales choices. Using this data, Einstein filters the leads before you approach them individually. The end result of this activity is you receive access to high-quality leads that have a higher potential of turning into sales.
### Privacy of Information
The most crucial component of any framework needs to always be privacy. It helps ensure that no one can breach the policies and sneak into your company information. Salesforce understands the significance of privacy and with new updates in Lightning, the CRM has made significant privacy improvements. The separate components present in the Salesforce Lightning framework can’t interact with each other. This feature offers you a clean interface, removing the probability of any malicious activity.
### Enhance User Experience
One of the most important advantages of Salesforce Lightning services is improved user experience. Compared to Classic, Salesforce has improved the user interface of the Lightning framework. Though the changes may not be directly visible to users, the overall experience has become seamless and swift. There are new and improved fonts, icons, graphics, and text patterns. An updated dashboard offers a checklist for your partners, employees, and customers. You can make your CRM more efficient and user-friendly by leveraging features such as activity timelines, Kanban view, and customizable homepages.
## Conclusion
Salesforce Lightning services provide a revolutionary approach to customer relationship management. This helps improve user experience and productivity and makes way for advanced analytics and better customization. [Salesforce Classic to Lightning migration](https://www.damcogroup.com/salesforce/salesforce-classic-to-lightning-migration) helps you unravel the advantages of an improved CRM, putting your organization in a better position to manage customer relationships. Leveraging Salesforce Lightning services from organizations like Damco Solutions, you can take the first step towards an effective and dynamic CRM.
| edgar_joes |
1,875,004 | 5 Mistakes to Avoid While Going for Regression Test Automation | In the changing world of software development, regression testing is crucial to ensuring that new... | 0 | 2024-06-03T07:09:19 | https://etruesports.com/2024/04/15/5-mistakes-to-avoid-while-going-for-regression-test-automation/ | regression, test, automation | 
In the changing world of software development, regression testing is crucial to ensuring that new code updates or changes do not break existing functionalities or result in inadvertent errors. The intricacy of systems and the rapidity of release cycles lead to increased mistake and time consumption in regression test automation. To get the most out of a regression test automation and stay out of trouble, it is essential to be aware of common mistakes and take proactive measures to avoid them.
**Lack of a Clear Test Automation Strategy**
One of the most common mistakes companies make when trying regression test automation is not developing a comprehensive test automation strategy. Without a defined plan in place, teams may end themselves automating tests haphazardly, which could lead to inconsistencies and redundancies with ineffective test coverage. To avoid this pitfall, it is imperative to have a well-defined test automation strategy that aligns with your organization’s overall software development goals as well as processes.
**Overlooking Test Case Design and Maintainability**
Regression test execution can be greatly accelerated by automation, but it’s important to keep in mind that poorly thought out or unmaintainable test cases can compromise the effectiveness of the automation process as a whole. Test scripts that are weak and brittle that break easily with small application changes might result from neglecting test case design and maintainability. This can cause frequent rework and reduce the overall effectiveness of the automation process. Organizations can use best practices for test case design, such as reusable and modular test scripts, consistent naming conventions, and comprehensive documentation, to reduce this risk.
**Inadequate Test Data Management**
Regression testing effectiveness is largely dependent on the availability of precise and thorough test data. Inadequate test data management procedures can result in uneven or insufficient test coverage, which can miss faults and lower the quality of the product.
Organizations should put in place a centralized test data management strategy that guarantees data confidentiality, consistency, and accessibility across many testing environments in order to avoid this trap.
**Neglecting Test Environment Management**
Automated tests for regression testing are frequently run in several settings, including development, staging, and production. The efficacy of the automation initiatives can be undermined by inconsistent or misconfigured test results resulting from these test environments. Organizations should give test environment management a priority in order to reduce this risk by putting procedures and instruments in place for providing, setting up, and keeping up-to-date test environments.
**Insufficient Collaboration and Knowledge Sharing**
Automation of regression tests is a team endeavor involving developers, testers, and operations teams, among other stakeholders. Ineffective communication and knowledge sharing between these teams might result in isolated efforts, redundant tasks, and a misalignment of testing priorities and procedures. Organizations should encourage a collaborative and knowledge-sharing culture in order to meet this problem. Regular meetings, code reviews, pair programming, and the creation of shared repositories for the best practices, documentation, and test scripts can all help achieve this.
**Conclusion**
Automation of regression tests is a potent technique for improving software quality, quickening release cycles, and making the best use of available resources. Opkey revolutionizes regression testing with its AI-powered automation platform. You can effortlessly transform manual tests into automated ones with a single click through its intuitive no-code interface. The teams can leverage an extensive library of over 30,000 pre-built test cases for 12+ ERPs to rapidly expand test coverage.
Their change impact analysis pinpoints how updates impact processes, recommending prioritized regression tests. Self-healing capabilities diagnose and fix broken tests automatically, reducing maintenance by 80%. Comprehensive end-to-end testing ensures seamless ERP integrations and customizations post-update. Companies like Just Group reduced regression cycles by 68% while achieving optimal coverage with Opkey.
Continue Reading | rohitbhandari102 |
1,875,003 | Day 1: Introduction to Data Science | What is Data Science? Data Science is an interdisciplinary field that combines statistical analysis,... | 0 | 2024-06-03T07:05:10 | https://dev.to/harshpatel080503/day-1-introduction-to-data-science-3614 | **What is Data Science?**
Data Science is an interdisciplinary field that combines statistical analysis, data engineering, machine learning, and domain expertise to extract meaningful insights and knowledge from structured and unstructured data. It involves collecting, processing, analyzing, and interpreting vast amounts of data to aid decision-making, solve complex problems, and uncover hidden patterns.
**Importance of Data Science**
In today’s data-driven world, data science plays a crucial role in various industries. Here are a few reasons why data science is important:
1. **Informed Decision-Making**: Organizations leverage data science to make data-driven decisions, leading to more accurate and effective outcomes.
2. **Predictive Analytics**: By analyzing past data, businesses can predict future trends, behaviors, and events, allowing for proactive strategies.
3. **Improved Efficiency**: Data science helps optimize operations, reduce costs, and increase efficiency through automation and process improvements.
4. **Enhanced Customer Experience**: Personalized recommendations and targeted marketing campaigns are possible through data science, improving customer satisfaction and loyalty.
5. **Innovative Solutions**: Data science fosters innovation by providing insights that lead to new products, services, and business models.
**Applications of Data Science**
Data science has a wide range of applications across various domains:
**Healthcare**: Predictive analytics for disease outbreak prediction, personalized treatment plans, and drug discovery.

**Finance**: Fraud detection, risk management, and algorithmic trading.

**Retail**: Inventory management, customer segmentation, and personalized recommendations.

**Transportation**: Route optimization, predictive maintenance, and self-driving cars.
**Marketing**: Customer sentiment analysis, targeted advertising, and campaign optimization.

**Sports**: Performance analysis, injury prediction, and game strategy optimization.

### **Key Components of Data Science**
1. **Data Collection**: Gathering data from various sources such as databases, APIs, web scraping, and sensors.
2. **Data Cleaning and Preprocessing**: Handling missing values, outliers, and inconsistencies to ensure data quality.
3. **Exploratory Data Analysis (EDA)**: Visualizing and summarizing data to understand its main characteristics and uncover patterns.
4. **Statistical Analysis**: Applying statistical methods to test hypotheses and infer conclusions from data.
5. **Machine Learning**: Building predictive models using algorithms like regression, classification, clustering, and deep learning.
6. **Data Visualization**: Creating charts, graphs, and dashboards to present insights in an understandable and actionable manner.
7. **Model Deployment**: Integrating models into production systems for real-time decision-making.
8. **Model Monitoring and Maintenance**: Continuously evaluating model performance and making necessary adjustments.
### **Tools and Technologies**
Data scientists use a variety of tools and technologies, including:
1. **Programming Languages**: Python, R, SQL.
2. **Data Manipulation Libraries**: Pandas, NumPy.
3. **Data Visualization Tools**: Matplotlib, Seaborn, Tableau, Power BI.
4. **Machine Learning Libraries**: Scikit-learn, TensorFlow, PyTorch.
5. **Big Data Technologies**: Hadoop, Spark.
6. **Databases**: MySQL, PostgreSQL, MongoDB.
7. **Cloud Platforms**: AWS, Google Cloud, Microsoft Azure.
### **Data Science Workflow**
1. **Define the Problem**: Clearly articulate the problem you are trying to solve.
2. **Collect Data**: Gather relevant data from various sources.
3. **Clean and Preprocess Data**: Prepare the data for analysis by cleaning and transforming it.
4. **Explore and Visualize Data**: Conduct exploratory data analysis to understand the data.
5. **Build and Evaluate Models**: Develop machine learning models and evaluate their performance.
6. **Deploy and Monitor Models**: Deploy models into production and continuously monitor their performance.
### **Learning Path for Aspiring Data Scientists**
1. **Mathematics and Statistics**: Build a strong foundation in statistics, probability, linear algebra, and calculus.
2. **Programming**: Learn Python or R, focusing on data manipulation and analysis libraries.
3. **Data Manipulation and Analysis**: Master data cleaning, preprocessing, and exploratory data analysis.
4. **Machine Learning**: Study supervised and unsupervised learning algorithms and practice building models.
5. **Data Visualization**: Learn how to create effective visualizations and dashboards.
6. **Big Data Technologies**: Get familiar with big data tools and platforms.
7. **Projects and Portfolio**: Work on real-world projects and build a portfolio to showcase your skills.
8. **Networking and Community**: Engage with the data science community through blogs, forums, and social media.
### **Conclusion**
Data science is a dynamic and rapidly evolving field with immense potential. By understanding its core concepts, applications, and tools, you can embark on a rewarding journey to become a proficient data scientist. Stay curious, keep learning, and leverage the power of data to drive innovation and make a meaningful impact.
---
**Author**: Patel Harsh Satishkumar
**Date**: 03-06-2024
**Follow Me**: [Linkedin](https://www.linkedin.com/in/harsh-patel-57540922a)
[Github](https://github.com/harshpatel080503)
[Portfolio](https://www.datascienceportfol.io/harshpatel080503)
[Twitter](https://x.com/Harshpatel8503)
[Reddit](https://www.reddit.com/user/harshpatel080503/?utm_source=share&utm_medium=web3x&utm_name=web3xcss&utm_term=1&utm_content=share_button) | harshpatel080503 | |
1,875,002 | Avianca Airlines at Boston Airport | Avianca Boston Terminal is located at Logan International Airport's Terminal E. This terminal,... | 0 | 2024-06-03T07:04:40 | https://dev.to/kellyohn/avianca-airlines-at-boston-airport-2hfl | [Avianca Boston Terminal](https://www.airlinesterminals.com/avianca-airlines/avianca-airlines-terminal-bos-airport/) is located at Logan International Airport's Terminal E. This terminal, dedicated to international flights, provides various amenities including dining options, duty-free shops, and comfortable waiting areas.
| kellyohn | |
1,870,081 | Weasel !! I Didn’t Know You Could Do This - Copilot EDI Adventure | Intro: In my job of designing and checking systems, I often look at the data-sharing... | 26,301 | 2024-06-03T07:04:28 | https://dev.to/balagmadhu/weasel-i-didnt-know-you-could-do-this-copilot-edi-adventure-304n | powerfuldevs, powerautomate, githubcopilot, edi | ## Intro:
In my job of designing and checking systems, I often look at the data-sharing agreements between them. Sometimes, when updating to newer systems, I need to understand how data is shared with older systems and even outside companies. A common challenge is that this data sharing is done using a business-to-business format known as EDI (Electronic Data Interchange). In EDI, the companies exchanging documents are called “trading partners.” They decide together what data will be sent and how it will be used, following guidelines that are written in a way people can understand. These guidelines are like blueprints, while the EDI standards they follow are like building codes. To make sense of a message, you need to know these standards and guidelines. As we work on modernizing, one idea is to make the way we exchange messages simpler. Analyzing these messages would require an EDI interpreter to quickly figure out how complex the data is. This led me to wonder if there’s a faster way to interpret these messages, which would help with planning and estimating the work needed before we look into it more deeply. Out of curiosity, I decided to see what Copilot could do in this new area, and I was happy with what I found.
## Open Mic / Curiousity Experiment:
So my little experiment was to post a EDI 96A invoice message and wanted the basic meta data pulled out of message into readable text. To extract the basic metadata from an EDI 96A invoice message and convert it into readable text, you would typically use an EDI parser or translator that understands the EDI standards and can map the segments and elements of the message to human-readable form.
**Input Data**:
```
UNA:+.? '
UNB+UNOA:1+5056013218685:14+1111111111111:14+220802:0737+8++ORDERS'
UNH+1+ORDERS:D:96A:UN'
BGM+220+PO000224267'
DTM+63:20220719:102'
DTM+64:20220719:102'
DTM+137:20220719:102'
NAD+BY+5056013218685::9++FENWICK'
NAD+SU+1111111111111::9++BUSINESS'
NAD+DP+KLW-DC::92++Killingworth+Fenwick Warehouse, 16 Mylord Cres+Newcastle upon Tyne++NE12 5SP+GBR'
LIN+1+1+018084851050:EN'
PIA+1+A220332:BP+A3W0010000:SA'
IMD+F++:::Item Description'
IMD+C+98+NS::91'
QTY+21:5:EA'
PRI+AAA:12.31'
LIN+2+1+018084891650:EN'
PIA+1+A221143:BP+A8AL010000:SA'
IMD+F++:::Item Description'
IMD+C+98+NS::91'
QTY+21:5:EA'
PRI+AAA:12.048'
LIN+3+1+018084020906:EN'
PIA+1+A221232:BP+AX62010000:SA'
IMD+F++:::Item Description'
IMD+C+98+NS::91'
QTY+21:5:EA'
PRI+AAA:18.334'
LIN+4+1+018084012864:EN'
PIA+1+A221435:BP+AW41014000:SA'
IMD+F++:::Item Description'
IMD+C+98+NS::91'
QTY+21:5:EA'
PRI+AAA:17.286'
LIN+5+1+018084922439:EN'
PIA+1+A221491:BP+AEAJ010000:SA'
IMD+F++:::Item Description'
IMD+C+98+NS::91'
QTY+21:5:EA'
PRI+AAA:38.5'
LIN+6+1+018084811108:EN'
PIA+1+A222367:BP+A1K8010000:SA'
IMD+F++:::Item Description'
IMD+C+98+NS::91'
QTY+21:5:EA'
PRI+AAA:53.428'
LIN+7+1+018084950104:EN'
PIA+1+A222369:BP+AHWY010000:SA'
IMD+F++:::Item Description'
IMD+C+98+NS::91'
QTY+21:5:EA'
PRI+AAA:4.714'
LIN+8+1+018084977323:EN'
PIA+1+A221818:BP+AMFT010000:SA'
IMD+F++:::Item Description'
IMD+C+98+OS::91'
QTY+21:5:EA'
PRI+AAA:61.808'
UNS+S'
UNT+58+1'
UNZ+1+8'
```
So what leveraging the GPT connector to decode the message
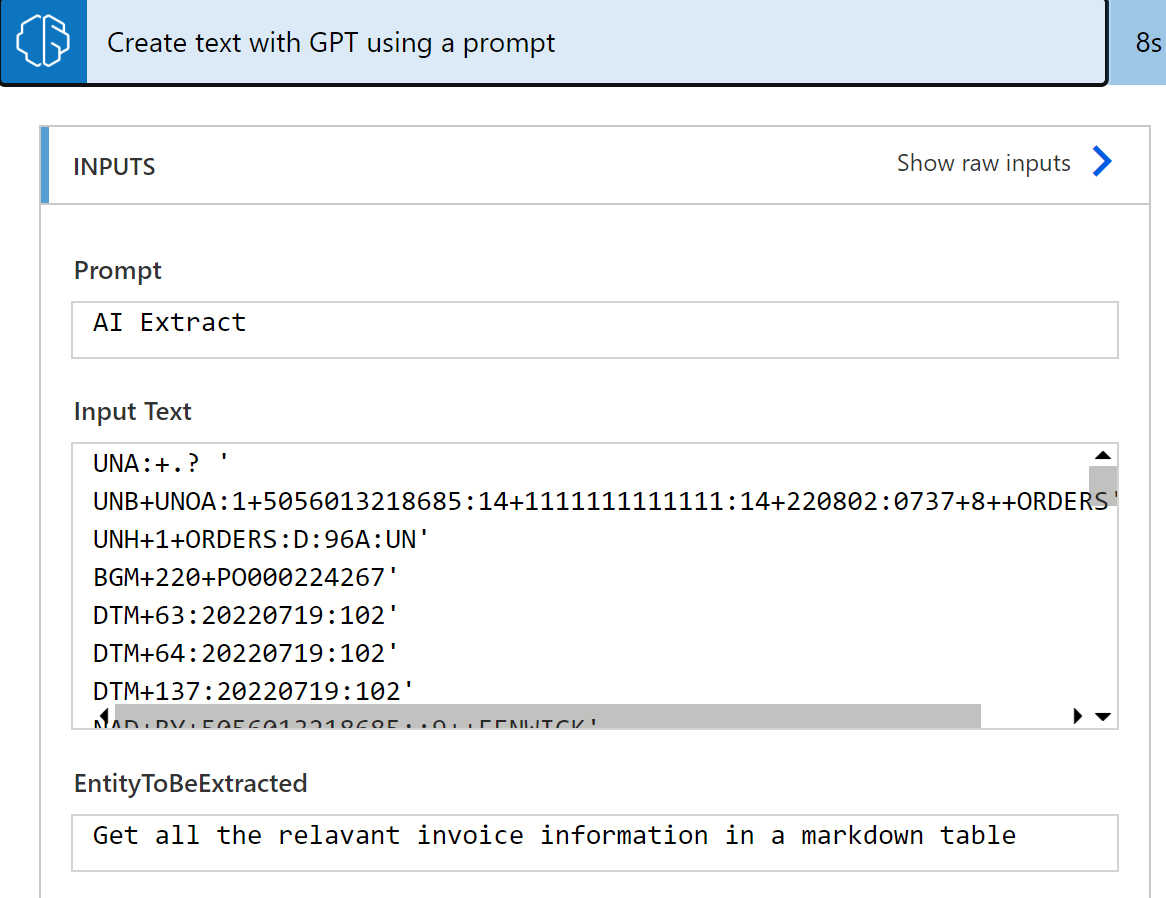
The flow looks something like this.


TADA !!! the human readable output
```
The given text is an invoice information that includes details about a purchase order. The invoice contains the following information:
- The invoice number is PO000224267.
- The order was placed on July 19, 2022.
- The buyer is FENWICK, with the identification number 5056013218685.
- The supplier is BUSINESS, with the identification number 1111111111111.
- The delivery address is Killingworth Fenwick Warehouse, 16 Mylord Cres, Newcastle upon Tyne, NE12 5SP, GBR.
- The invoice includes multiple line items with their respective details:
- Item 1: Description, quantity of 5, and price of 12.31.
- Item 2: Description, quantity of 5, and price of 12.048.
- Item 3: Description, quantity of 5, and price of 18.334.
- Item 4: Description, quantity of 5, and price of 17.286.
- Item 5: Description, quantity of 5, and price of 38.5.
- Item 6: Description, quantity of 5, and price of 53.428.
- Item 7: Description, quantity of 5, and price of 4.714.
- Item 8: Description, quantity of 5, and price of 61.808.
This summary provides an overview of the invoice information, including the order details, buyer and supplier information, delivery address, and the line items with their respective quantities and prices.
```
**Consideration**:
- Custom trading partner mapping is not extracted
- Some of the terms and condition of the invoice were not extracted and the way to capture would be improving the prompt.
- This is just for initial analysis of the EDI interface and not the complete mapping. The costing to leverage a Co-Pilot service would expensive
- More compute and not sustainable, as AI service is a generic model where as the EDI translating software are built specific to this job
| balagmadhu |
1,875,001 | Adept Clipping Path Announces Lower Prices and Free Trial for Photo Editing Services | In today's fast-paced digital world, high-quality photo editing is essential for businesses and... | 0 | 2024-06-03T07:03:06 | https://dev.to/tawkirislam/adept-clipping-path-announces-lower-prices-and-free-trial-for-photo-editing-services-26l2 | photoshop, retouching, editing, services | In today's fast-paced digital world, high-quality photo editing is essential for businesses and individuals alike. Whether you're an e-commerce entrepreneur looking to enhance product images, a photographer perfecting your portfolio, or a marketing professional crafting compelling visuals, top-notch photo editing services can make all the difference. Understanding this need, Adept Clipping Path is thrilled to announce a significant reduction in prices for their comprehensive photo editing services, along with an exciting new offer: a free trial for all new customers.
## Why Choose Adept Clipping Path?
Adept Clipping Path has established itself as a leader in the photo editing industry, known for its meticulous attention to detail, quick turnaround times, and customer-centric approach. Here are a few reasons why they stand out:
## Expertise and Precision
With a team of highly skilled professionals, Adept Clipping Path guarantees precision in every project. From clipping paths and background removal to color correction and retouching, their expertise ensures your photos meet the highest standards of quality.
## Competitive Pricing
In a move that sets them apart from competitors, Adept Clipping Path has lowered their prices, making premium photo editing services more accessible than ever. This new pricing strategy aims to provide exceptional value without compromising on quality.
## Free Trial Offer
To showcase their commitment to excellence and customer satisfaction, Adept Clipping Path now offers a free trial for all new customers. This trial allows potential clients to experience firsthand the exceptional quality and service that have become synonymous with Adept Clipping Path.
## Comprehensive Photo Editing Services
Adept Clipping Path offers a wide range of photo editing services tailored to meet diverse needs:
## Clipping Path Services
Accurate [clipping paths](https://www.adeptclippingpath.com/clipping-path-service) are crucial for isolating subjects and ensuring clean, professional images. Adept Clipping Path uses advanced techniques to deliver flawless results, enhancing the visual appeal of your photos.
## Background Removal
Unwanted backgrounds can detract from the main subject of an image. Adept Clipping Path excels in [background removal](https://www.adeptclippingpath.com/image-background-removal-service), providing crisp, clear images that focus on the essential elements.
## Image Retouching
From minor touch-ups to extensive retouching, Adept Clipping Path's retouching services bring out the best in your photos. Their skilled editors enhance details, correct imperfections, and ensure your images look polished and professional.
## Color Correction
Achieving the perfect color balance is vital for impactful images. Adept Clipping Path's [color correction services](https://www.adeptclippingpath.com/photo-color-correction-service) adjust hues, saturation, and brightness to create visually stunning photos that capture attention.
## E-commerce Image Editing
For online retailers, high-quality product images are crucial for attracting customers and driving sales. Adept Clipping Path specializes in e-commerce image editing, providing optimized photos that enhance your product listings and boost conversions.
## How to Get Started
Taking advantage of Adept Clipping Path's new pricing and free trial offer is easy. Simply visit their website, fill out the contact form, and upload your images for the free trial. Their team will quickly get to work, delivering high-quality edited photos that meet your exact specifications.
## Customer Testimonials
## Here's what some of Adept Clipping Path's satisfied customers have to say:
"Adept Clipping Path has transformed our product images. The quality and attention to detail are unmatched." - Sarah M., E-commerce Business Owner
"The free trial convinced me of their expertise. I've been a loyal customer ever since." - James T., Professional Photographer
"Their color correction services made my marketing materials stand out. Highly recommended!" - Lisa R., Marketing Manager
## Conclusion
Adept Clipping Path's commitment to quality, affordability, and customer satisfaction sets them apart in the photo editing industry. With their new lower prices and free trial offer, there's never been a better time to experience their exceptional services. Visit their website today to get started and elevate your photos to the next level. | tawkirislam |
1,884,528 | Fast and Compact Structured Logging in C# Using String Interpolation | If you want to easily filter your application logs, structured logging is the way to go. However,... | 27,554 | 2024-06-11T15:07:37 | https://blog.postsharp.net/structured-logging-with-string-interpolation.html | dotnet, dotnetcore, csharp | ---
title: Fast and Compact Structured Logging in C# Using String Interpolation
published: true
date: 2024-06-03 07:00:01 UTC
tags: dotnet, dotnetcore, csharp
canonical_url: https://blog.postsharp.net/structured-logging-with-string-interpolation.html
series: The Timeless .NET Engineer
---

If you want to easily filter your application logs, structured logging is the way to go. However, using just the standard .NET libraries, structured logging in C# can be both cumbersome and inefficient. In this article, we will explore how to make structured logging efficient and simple.
In this article, you will learn:
- [What is structured logging](#what-it-is)
- [What’s wrong with using the vanilla LogInformation method for structured logging?](#logging-problems)
- [Why not use the standard C# string interpolation for logging?](#string-interpolation-problems)
- [What are custom string interpolation handlers?](#custom-string-interpolation-handler)
- [How to make structured logging efficient?](#efficient)
- [How to make structured logging clean and compact?](#compact)
- [How to automatically add structured logging to your code?](#metalama)
## What is structured logging?
Structured logging involves reporting errors, warnings, and messages in a consistent and organized format, making it straightforward to read, search, and analyze by applications or individuals. A common format for structured logging is JSON because it is both compact and readable. By contrast, unstructured logging reports unstructured text that can only be searched by substrings or regular expressions.
In C#, the most common logging API is the [Microsoft.Extensions.Logging](https://learn.microsoft.com/en-us/dotnet/core/extensions/logging) namespace. Typically, your structured logging code might look something like this:
```cs
_logger.LogInformation("Product {product} sold for {price}.", product, price);
```
Here, we specify the names of the arguments, `product` and `price`, allowing a [structured logging](https://stackify.com/what-is-structured-logging-and-why-developers-need-it/) backend to recognize them. The server might receive and index a JSON message like this:
```json
{
"EventId": 0,
"LogLevel": "Information",
"Category": "LoggingWithInterpolation.Shop",
"Message": "Product llama T-shirt sold for 10.0.",
"State": {
"Message": "Product llama T-shirt sold for 10.0.",
"product": "llama T-shirt",
"productPrice": 10.0,
"{OriginalFormat}": "Product {product} sold for {productPrice}."
}
}
```
As you can see, the message parameters are stored and indexed separately from the formatted message text, making it easier to filter messages.
## What’s wrong with using the vanilla LogInformation method for structured logging?
From a server point of view, structured logging looks great. However, there are two problems with the C# code above:
- There is some redundancy between the argument names in the formatting string and the argument list, i.e. `product` and `price` are duplicated. Not only does it require additional work, but it may also lead to inconsistencies if the formatting string is not synchronized with its argument list.
- This code isn’t efficient. It allocates an array for the arguments and boxes value type arguments every time, even when logging for this log level isn’t enabled. The inefficiency escalates if the computation of one of the arguments is expensive.
If you’re familiar with the `string.Format` method, you know that string interpolation was invented specifically to address these two issues. So, why not use string interpolation here?
## Why not use the standard C# string interpolation for logging?
You might think of the following code:
```cs
_logger.LogInformation($"Product {product} sold for {price}.");
```
But you’ll quickly realize that this approach is actually worse!
1. It doesn’t resolve the performance issue.
2. It loses argument names for structured logging.
This is why using string interpolation for logging is generally not recommended.
## What are custom string interpolation handlers?
Both problems of the default C# string interpolation can be solved thanks to the [improvements to string interpolation brought by C# 10](https://devblogs.microsoft.com/dotnet/string-interpolation-in-c-10-and-net-6/). Unfortunately, the necessary supporting classes and extension methods have not been implemented in the system libraries, so we need to implement them ourselves.
We must implement two artifacts ourselves:
1. a [custom string interpolation handler](https://learn.microsoft.com/en-us/dotnet/csharp/whats-new/tutorials/interpolated-string-handler) that gathers all the information and then calls the `ILogger.Log` method, and
2. a custom extension method of the `ILogger` extension, called `LogInformation`, but accepting our custom string interpolation handler instead of the formatting string.
Let’s start with a basic implementation. It will not address any of the two issues above, but at least we can learn the API.
```cs
public static class LoggingExtensions
{
public static void LogInformation(
this ILogger logger,
[InterpolatedStringHandlerArgument( nameof(logger) )]
LogInformationInterpolatedStringHandler handler )
=> handler.Log();
}
[InterpolatedStringHandler]
public ref struct LogInformationInterpolatedStringHandler
{
private readonly StringBuilder messageBuilder;
private readonly ILogger logger;
public LogInformationInterpolatedStringHandler(
int literalLength, int formattedCount, ILogger logger )
{
this.messageBuilder = new StringBuilder( literalLength + (formattedCount * 10) );
this.logger = logger;
}
public void AppendLiteral( string literal )
=> this.messageBuilder.Append( literal );
public void AppendFormatted<T>( T value )
=> this.messageBuilder.Append( value?.ToString() );
public void Log()
=> this.logger.Log(
LogLevel.Information, this.messageBuilder.ToString() );
}
```
> To get the full source code of the article, please refer to the [original article](https://blog.postsharp.net/structured-logging-with-string-interpolation).
What does this do? When the C# compiler encounters a call to a method like `LogInformation`, where an interpolated string is passed to a parameter whose type is marked with the `[InterpolatedStringHandler]` attribute, it first calls the constructor of that type. The constructor is passed basic information about the interpolated string, which can be used to guess an initial size of a buffer (here, `StringBuilder`). The constructor also receives the values of other arguments, as specified by the `[InterpolatedStringHandlerArgument]` attribute. Next, the compiler calls the `AppendLiteral` and `AppendFormatted` methods for each part of the interpolated string. Finally, the method is called with the newly constructed handler.
When applied to the earlier logging code, this process results in the following code:
```cs
var handler = new LogInformationInterpolatedStringHandler(19, 2, _logger);
handler.AppendLiteral("Product ");
handler.AppendFormatted(product);
handler.AppendLiteral(" sold for ");
handler.AppendFormatted(price);
handler.AppendLiteral(".");
_logger.LogInformation(handler);
```
This works, but, as announced, it neither addresses the issue of parameter names nor of efficiency.
Let’s address the performance problem first.
## How to make structured logging efficient?
Let’s first make sure that we don’t do too much work when logging is disabled. This is relatively straightforward: a custom string interpolation handler can have an `out bool` parameter on its constructor. When this parameter is set to `false`, it signifies that the handler is not enabled, so no further processing is done. This avoids all performance costs associated with that:
```cs
public LogInformationInterpolatedStringHandler(
int literalLength,
int formattedCount,
ILogger logger,
out bool isEnabled )
{
isEnabled = logger.IsEnabled( LogLevel.Information );
if ( isEnabled )
{
this.messageBuilder = new StringBuilder(
literalLength + (formattedCount * 10) );
this.logger = logger;
}
this.isEnabled = isEnabled;
}
```
For this modified handler, the C# compiler generates the following code:
```cs
var handler = new LogInformationInterpolatedStringHandler(
19, 2, _logger, out var isEnabled);
if (isEnabled)
{
handler.AppendLiteral("Product ");
handler.AppendFormatted(product);
handler.AppendLiteral(" sold for ");
handler.AppendFormatted(price);
handler.AppendLiteral(".");
}
_logger.LogInformation(handler);
```
This is a significant improvement: most of the code is executed only when logging is enabled, which is exactly what we wanted.
## How to make structured logging more compact?
So, what about argument names? For this, we’ll leverage another C# feature: [caller argument expression](https://learn.microsoft.com/en-us/dotnet/csharp/language-reference/proposals/csharp-10.0/caller-argument-expression). This feature allows us to obtain the C# code for an argument passed to a method. In the case of the `AppendFormatted` method, that would be the interpolated value, which is precisely what we’re looking for.
To ensure we don’t lose the ability to have a custom name for a logged argument, we can (ab)use the format string component of an interpolated value, i.e. the substring after the `:` character:
```cs
_logger.LogInformation($"Product {product} sold for {price:productPrice}.");
```
In the example above, the name of the `product` argument would be left to its default value (`product`), while the name of the second argument would be overridden to `productPrice`. Fortunately, this can be combined with a caller argument expression, provided we name the parameter to `AppendFormatted` as `format`.
When we combine these elements, we get:
```cs
[InterpolatedStringHandler]
public ref struct LogInformationInterpolatedStringHandler
{
private readonly StringBuilder messageBuilder;
private readonly object?[] arguments;
private readonly ILogger logger;
private readonly bool isEnabled;
private int argumentsIndex;
public LogInformationInterpolatedStringHandler(
int literalLength,
int formattedCount,
ILogger logger,
out bool isEnabled )
{
isEnabled = logger.IsEnabled( LogLevel.Information );
if ( isEnabled )
{
this.messageBuilder = new StringBuilder(
literalLength + (formattedCount * 10) );
this.arguments = new object?[formattedCount];
this.logger = logger;
}
this.isEnabled = isEnabled;
}
public readonly void AppendLiteral( string literal )
=> this.messageBuilder.Append( literal.Replace( "{", "{{", StringComparison.Ordinal ).Replace( "}", "}}", StringComparison.Ordinal ) );
public void AppendFormatted<T>( T value,
[CallerArgumentExpression( nameof(value) )] string format = null! )
{
this.messageBuilder.Append( $"{{{format}}}" );
this.arguments[this.argumentsIndex] = value;
this.argumentsIndex++;
}
public readonly void Log()
{
if ( this.isEnabled )
{
this.logger.Log( LogLevel.Information, this.messageBuilder.ToString(), this.arguments );
}
}
}
```
This time, the C# compiler generates the following code:
```cs
var handler = new LogInformationInterpolatedStringHandler(19, 2, _logger, out var isEnabled);
if (isEnabled)
{
handler.AppendLiteral("Product ");
handler.AppendFormatted(product, "product");
handler.AppendLiteral(" sold for ");
handler.AppendFormatted(price, "productPrice");
handler.AppendLiteral(".");
}
_logger.LogInformation(handler);
```
Note how the `format` argument for `product` is set by the caller argument expression to `"product"` and for `price` to `"productPrice"` from the format string.
When logging with the simple console logger, this produces output like:
```
info: LoggingWithInterpolation.Shop[0]
Product llama T-shirt sold for 10.0.
```
And with JSON logger (to see the structured logging in action):
```json
{
"EventId": 0,
"LogLevel": "Information",
"Category": "LoggingWithInterpolation.Shop",
"Message": "Product llama T-shirt sold for 10.0.",
"State": {
"Message": "Product llama T-shirt sold for 10.0.",
"product": "llama T-shirt",
"productPrice": 10.0,
"{OriginalFormat}": "Product {product} sold for {productPrice}."
}
}
```
## How to automatically add structured logging to your code?
We’ve seen how to achieve compact and efficient logging with clean code. However, there are situations where you want to log all method executions and their parameter values. This can lead to code repetition! Traditional code generators like T4 or source generators don’t help because they can only generate new files - they cannot add code into our hand-written code.
Enter [Metalama](https://www.postsharp.net/metalama), a code generation toolkit that can mix generated code with user-written code, all at build time.
Let’s see how we can use it to automate the logging of method calls.
First, we need to create an aspect, which is like a template describing how the code should be transformed.
```cs
public class LogAttribute : OverrideMethodAspect
{
[IntroduceDependency]
private readonly ILogger _logger;
public override dynamic? OverrideMethod()
{
// LogInformation can't be called as an extension method here,
// because Metalama uses the dynamic type to represent
// run-time values
// and dynamic is not compatible with extension methods.
LoggingExtensions.LogInformation( this._logger,
BuildInterpolatedString().ToValue() );
return meta.Proceed();
}
[CompileTime]
private static InterpolatedStringBuilder BuildInterpolatedString()
{
var stringBuilder = new InterpolatedStringBuilder();
// Include the type and method name.
stringBuilder.AddText(
$"{meta.Target.Type}.{meta.Target.Method.Name}(" );
var first = true;
// Include each parameter.
foreach ( var parameter in meta.Target.Parameters )
{
if ( !first )
{
stringBuilder.AddText( ", " );
}
stringBuilder.AddText( $"{parameter.Name}: " );
stringBuilder.AddExpression( parameter.Value );
first = false;
}
stringBuilder.AddText( ") started." );
return stringBuilder;
}
}
```
Most of the above code executes at compile time.
You can add the logging aspect to methods one at a time using the `[Log]` attribute. This feature is completely free. Another option is to use [a Metalama fabric](https://doc.postsharp.net/metalama/conceptual/using/fabrics) to add logging more widely using a single piece of code, but this is a commercial feature:
```cs
internal class Fabric : ProjectFabric
{
public override void AmendProject( IProjectAmender amender )
{
amender.Outbound
.SelectMany( c => c.Types )
.Where( t => t.TypeKind is not TypeKind.RecordClass
or TypeKind.RecordStruct )
.Where( t => t.Accessibility == Accessibility.Public )
.SelectMany( c => c.Methods )
.Where( m => m.Accessibility == Accessibility.Public )
.AddAspectIfEligible<LogAttribute>();
}
}
```
When applied to the `void Sell(Product product, decimal price)` method (whether using an attribute or using a fabric), the aspect generates the following code at the start of the method:
```cs
LoggingExtensions.LogInformation(_logger,
$"Shop.Sell(product: {product}, price: {price}) started.");
```
This code produces the following output from the simple console logger:
```cs
info: LoggingWithInterpolation.Metalama.Shop[0]
Shop.Sell(product: llama T-shirt, price: 10.0) started.
```
And with JSON:
```
{
"EventId": 0,
"LogLevel": "Information",
"Category": "LoggingWithInterpolation.Metalama.Shop",
"Message": "Shop.Sell(product: llama T-shirt, price: 10.0) started.",
"State": {
"Message": "Shop.Sell(product: llama T-shirt, price: 10.0) started.",
"product": "llama T-shirt",
"price": 10.0,
"{OriginalFormat}": "Shop.Sell(product: {product}, price: {price}) started."
}
}
```
Of course, you can also customize what is logged to suit your needs, such as logging exceptions or return values.
## Summary
Structured logging can be incredibly useful in production, and with just a couple of additional files in your project, you can use it easily and efficiently with familiar interpolated string builders. As a bonus, to automatically add structured logging to your code, you can create a Metalama aspect.
This article was first published on a [https://blog.postsharp.net](https://blog.postsharp.net) under the title [Fast and Compact Structured Logging in C# Using String Interpolation](https://blog.postsharp.net/structured-logging-with-string-interpolation.html). | gfraiteur |
1,874,934 | Perl Weekly #671 - In-person and online events | Originally published at Perl Weekly 671 Hi there! Last week I included an entry about the Getting... | 20,640 | 2024-06-03T04:39:52 | https://perlweekly.com/archive/671.html | perl, news, programming | ---
title: Perl Weekly #671 - In-person and online events
published: true
description:
tags: perl, news, programming
canonical_url: https://perlweekly.com/archive/671.html
series: perl-weekly
---
Originally published at [Perl Weekly 671](https://perlweekly.com/archive/671.html)
Hi there!
Last week I included an entry about the <a href="https://www.meetup.com/code-mavens/events/301268306/">Getting started with Docker for Perl developers</a> workshop I am going to run on June 13. This is part of a series of free virtual workshops I started to offer via the <a href="https://www.meetup.com/code-mavens/">Code Mavens</a> Meetup group. If things go well I'll run workshops for 3 languages: Perl, Python, and Rust and several related technologies. I've already schedule 3 events for Rust, 2 for Python, and 1 for Perl. Now, to plan ahead, I scheduled another Perl event:
<a href="https://www.meetup.com/code-mavens/events/301413566/">Continuous Integration (CI): GitHub Actions for Perl Projects</a> on July 14.
Even it these events are not relevant to you or they are not scheduled at a time when you can be available I'd like to invite you to register to the <a href="https://www.meetup.com/code-mavens/">Code Mavens</a> Meetup-group to get notified about other events. I am also going to send out (again) a survey to understand better what topics are more interesting to the members of that group, and at what time would it be most convenient for them. So by registering and voting for Perl you could get more Perl-related events.
Last Week Mohammad mentioned both the <a href="https://tprc.us/tprc-2024-las/">The Perl and Raku conference</a> to take place in Las Vegas between June 24-28 and the <a href="http://act.yapc.eu/lpw2024/">London Perl and Raku Workshop</a> that will take place, surprisingly, in London on October 26. Are there other in-person or virtual Perl conferences, workshops, or meeting planned? Let us know so we can include them in the Perl Weekly! At the bottom of each edition and on the <a href="https://perlweekly.com/events">events</a> page.
The last thing I would like to highlight this week is a link Wendy shared a few days ago of <a href="https://www.flickr.com/groups/yapc/pool/">lots of pictures from YAPCs since 2003</a>. I even found several pictures of myself and became a bit nostalgic.
Enjoy your week!
--
Your editor: Gabor Szabo.
## Articles
### [De-accentifying characters?](https://www.reddit.com/r/perl/comments/1d5k4cm/deaccentifying_characters/)
Is there a way to replace accented characters by their plain version, something like <b>tr/ûšḥ/ush/</b>?
### [Time is dwindling to book your trip to TPRC!](https://news.perlfoundation.org/post/trpc2024lv)
amber_krawczyk
### [Get CPU usage of PID](https://www.reddit.com/r/perl/comments/1d4m5cy/get_cpu_usage_of_pid/)
'I am making a script with multiple threads...' isn't that in itself a problem in Perl?
### [Paella. An interactive calendar application for the terminal](https://www.reddit.com/r/perl/comments/1d552hj/paella_an_interactive_calendar_application_for/)
### [MariaDB 10 and SQL::Translator::Producer](https://blogs.perl.org/users/usna78/2024/05/mariadb-10-and-sqltranslatorproducer.html)
---
## CPAN
### [List of new CPAN distributions – May 2024](https://perlancar.wordpress.com/2024/06/01/list-of-new-cpan-distributions-may-2024/)
---
## Grants
### [Maintaining Perl (Tony Cook) March 2024](https://news.perlfoundation.org/post/maintaining_perl_tonyc_march_2024)
---
## Perl
### [This week in PSC (149) | 2024-05-30](https://blogs.perl.org/users/psc/2024/05/this-week-in-psc-149-2024-05-30.html)
---
## The Weekly Challenge
<a href="https://theweeklychallenge.org">The Weekly Challenge</a> by <a href="https://manwar.org">Mohammad Sajid Anwar</a> will help you step out of your comfort-zone. We pick one champion at the end of the month from among all of the contributors during the month.
### [The Weekly Challenge - 272](https://theweeklychallenge.org/blog/perl-weekly-challenge-272)
Welcome to a new week with a couple of fun tasks "Defrang IP Address" and "String Score". If you are new to the weekly challenge then why not join us and have fun every week. For more information, please read the <a href="https://theweeklychallenge.org/faq">FAQ</a>.
### [RECAP - The Weekly Challenge - 271](https://theweeklychallenge.org/blog/recap-challenge-271)
Enjoy a quick recap of last week's contributions by Team PWC dealing with the "Maximum Ones" and "Sort by 1 bits" tasks in Perl and Raku. You will find plenty of solutions to keep you busy.
### [TWC271](https://deadmarshal.blogspot.com/2024/05/twc271.html)
Impressive compact and elegant Perl solutions. You are going to love it. Thanks for sharing.
### [Ones by 1](https://raku-musings.com/ones-by-1.html)
What I like about Raku is the ability to create compact solutions. I wish we could do similar things in Perl. Thanks for sharing.
### [Rows Without A Paddle](https://jacoby-lpwk.onrender.com/2024/05/28/rows-without-a-paddle-weekly-challenge-271.html)
Use of CPAN module makes the end result short and sweet. Keep it up great work.
### [Perl Weekly Challenge: Week 271](https://www.braincells.com/perl/2024/06/perl_weekly_challenge_week_271.html)
Unique style of narration is my favourite, line-by-line analysis is very handy. Thanks for sharing.
### [Counting Ones](https://github.sommrey.de/the-bears-den/2024/05/31/ch-271.html)
Being master of PDL, we got another classic solutions. You must check it out.
### [Perl Weekly Challenge 271: Maximum Ones](https://blogs.perl.org/users/laurent_r/2024/05/perl-weekly-challenge-271-maximum-ones.html)
Classic show of Raku and Perl power in one place. It is near identical, true talent. Well done.
### [Perl Weekly Challenge 271: Sort by 1 Bits](https://blogs.perl.org/users/laurent_r/2024/05/perl-weekly-challenge-271-sort-by-1-bits.html)
Playing with bits in Perl and Raku is a child play. You have to see it yourself to believe it.
### [Perl Weekly Challenge 271](https://wlmb.github.io/2024/05/28/PWC271/)
Are you PDL fan? If yes then you must checkout this post. Well done and thanks for sharing.
### [Riff Raff](https://fluca1978.github.io/2024/05/27/PerlWeeklyChallenge271.html)
Raku one-liner is showing off once again. Thanks for sharing the knowledge with us.
### [You are my only ones...](https://github.com/manwar/perlweeklychallenge-club/tree/master/challenge-271/matthias-muth#readme)
Breaking down task into smaller actions makes it easy to follow through. Keep it up great work.
### [Only Ones](https://packy.dardan.com/b/MC)
Like always, we got Perl, Raku, Python and Elixir. Even if you are new to language, you can easily follow through as they all follow the same login. Thanks for sharing.
### [All about ones](http://ccgi.campbellsmiths.force9.co.uk/pwc/challenge/271)
Using just grep to solve the binary matrix task is incredible. Don't forget to try it out the solutions.
### [The Weekly Challenge - 271](https://reiniermaliepaard.nl/perl/pwc/index.php?id=pwc271)
Smart move to get the help of CPAN module. Thanks for promoting the use of CPAN modules. Keep it up great work.
### [The Weekly Challenge #271](https://hatley-software.blogspot.com/2024/05/robbie-hatleys-solutions-to-weekly_29.html)
Loved the hack used to get the job done. It is very impressive. Highly recommended.
### [Sort the Maximum One](https://blog.firedrake.org/archive/2024/06/The_Weekly_Challenge_271__Sort_the_Maximum_One.html)
Happy to see PostScript is the chosen language for the blog post. It is not like any other programming languages but very special. Keep it up great work.
### [Maximizing the 1 bits](https://dev.to/simongreennet/maximizing-the-1-bits-m8a)
Thanks for sharing your encounter with GitHub Copilot. I have used it when it was FREE and enjoyed the magic. I must admit it did good job.
---
## Weekly collections
### [NICEPERL's lists](http://niceperl.blogspot.com/)
<a href="https://niceperl.blogspot.com/2024/06/cdxcviii-7-great-cpan-modules-released.html">Great CPAN modules released last week</a>
---
## Events
### [Getting sarted with Docker for Perl developers](https://www.meetup.com/code-mavens/events/301268306/)
June 13, 2024, in Zoom
### [The Perl and Raku conference](https://tprc.us/tprc-2024-las/)
June 24-28, 2024, in Las Vegas, NV, USA
### [Continuous Integration (CI): GitHub Actions for Perl Projects](https://www.meetup.com/code-mavens/events/301413566/)
July 14, 2024, in Zoom
### [London Perl and Raku Workshop](http://act.yapc.eu/lpw2024/)
October 26, 2024, in Las Vegas, NV, USA
---
You joined the Perl Weekly to get weekly e-mails about the Perl programming language and related topics.
Want to see more? See the [archives](https://perlweekly.com/archive/) of all the issues.
Not yet subscribed to the newsletter? [Join us free of charge](https://perlweekly.com/subscribe.html)!
(C) Copyright [Gabor Szabo](https://szabgab.com/)
The articles are copyright the respective authors.
| szabgab |
1,862,977 | Efficiently Managing Unstructured Data with PostgreSQL hstore | PostgreSQL’s hstore data type offers an efficient way to store key-value pairs in a single column,... | 21,681 | 2024-06-03T07:00:00 | https://dev.to/dbvismarketing/efficiently-managing-unstructured-data-with-postgresql-hstore-377f | PostgreSQL’s `hstore` data type offers an efficient way to store key-value pairs in a single column, ideal for semi-structured and unstructured data. This article outlines the basics of **`hstore`**, how to enable it, and practical usage examples.
## What Is hstore in PostgreSQL?
**`hstore`** allows storing key-value pairs in a single column, making it suitable for user preferences, settings, or metadata.
```sql
ALTER TABLE users ADD COLUMN metadata hstore;
```
Enable `hstore` with this command:
```sql
CREATE EXTENSION hstore;
```
Below are some code examples of how to create a table with hstore, insert data and querying data.
```sql
CREATE TABLE users(
id serial PRIMARY KEY,
username VARCHAR (255) NOT NULL,
password VARCHAR (255) NOT NULL,
config hstore
);
```
```sql
INSERT INTO users (username, password, config)
VALUES ('ThunderStrike', '$2y$10$Y8X1QL4q1MxKPKbUK05iB...',
'"points"=>"879", "language"=>"Danish", "bg-color"=>"#FF5733", "theme"=>"dark"');
```
```sql
SELECT config FROM users;
```
## Key `hstore` operators
- `>` , extracts a key-value pair.
- `||` , concatenates **`hstores`**.
- `@>`, checks for key-value pairs.
- `?`, checks for a key.
Below is an example of how to retrieve `language` key values:
```sql
SELECT config->'language' AS language FROM users;
```
## FAQs About the hstore Data Type
### Can an hstore column contain duplicated keys?
No, each key must be unique within an `hstore` column. If a duplicate key is inserted, the new value will overwrite the old one.
### What is the difference between hstore and JSONB?
`hstore` stores flat key-value pairs and supports basic data types, while `JSONB` supports complex nested structures and a broader range of data types.
### What databases support hstore?
`hstore` is native to PostgreSQL. Other databases might offer similar functionalities but not natively.
### What types of data can be stored in an hstore?
`hstore` stores strings and `NULL` values as key-value pairs. Complex data must be converted to string format.
### Can hstore be considered NoSQL?
While PostgreSQL is not a NoSQL database, **`hstore`** provides NoSQL-like capabilities by allowing unstructured data storage.
## Conclusion
PostgreSQL’s **`hstore`** is a versatile option for storing unstructured data. Its ease of use and powerful features make it a valuable tool for database management. For more information, read the article [Storing Unstructured Data With Hstore in PostgreSQL.](https://www.dbvis.com/thetable/storing-unstructured-data-with-hstore-in-postgresql/) | dbvismarketing | |
1,866,754 | ✨🧱 JavaScript Data Types: 27 Quick Questions You Need To Master | 1. What is a data type? Every value in JavaScript has a specific type. This type... | 0 | 2024-06-03T07:00:00 | https://dev.to/_ndeyefatoudiop/javascript-data-types-27-quick-questions-you-need-to-master-1828 | javascript, webdev, beginners, programming | # 1. What is a data type?
Every value in JavaScript has a specific type.
This type determines what operations can be performed on the value and how it's stored 🗳️.
This is known as the **data type**.
---
# 2. How many data types?
There are **8** data types in JavaScript: **number**, **string**, **boolean**, **null**, **undefined**, **bigint**, **symbol** and **object**.
<figure>
<img src="https://dev-to-uploads.s3.amazonaws.com/uploads/articles/ykizq6i9i6wmfvxz8oo8.png">
<figcaption>JavaScript data types with examples</figcaption>
</figure>
---
# 3. What is a primitive data type?
Every type except the **object** type 😅.
So, there are **7** primitive data types: **string**, **number**, **boolean**, **undefined**, **null**, **symbol**, **bigint**.
Primitive values have the following characteristics:
- They don't have methods or properties.
- They are **immutable**: you cannot modify the value once it is created.
- They are directly stored in the memory stack.
```javascript
let sample = 'immutable'
console.log(sample) // "immutable"
sample[0] = 'V' // changing the first letter to V
console.log(sample) //"immutable" (since the string cannot change)
```
### What the heck is the memory stack?
A JavaScript program has a memory where it stores variables/values for later access.
That memory consists of the **stack** and the **heap**.
- **Stack**: Stores static data (data with a fixed size). Since primitive values are immutable and won't change, they will be stored here.
- **Heap**: Stores object values. The heap's size can change during the code execution to accommodate object value changes.
---
# 4. What is a non-primitive data type?
The `object` type is the only non-primitive data type.
This includes: object literals (`{ name: "Fatou" }`), functions (`function sayHi(){}`), arrays (`[1, 2, 3]`), etc.
**There is a crucial difference between primitive and non-primitive data types.**
👉 When a variable contains a non-primitive data type, it doesn't hold the actual object value.
Instead, it contains a reference to that object in memory (i.e., in the heap).
Think of a reference like an address.
**House != Address**
However, if I do things like:
- Send a gift to `{fillInYourAdress}`.
- Paint the house at address `{fillInYourAdress}`.
It will affect your house.
In the JavaScript world, this is equivalent to the following code:
```javascript
const house = {
floors: 2,
gifts: [],
color: "blue"
}
house.gifts.push("Red dress")
house.color = "red"
```
**Keep this distinction in mind when passing objects to functions.**
In the following example, the code modifies the original array since it is passed to the function as an address:
```javascript
function addUser(arr){
const randomId = "123"
arr.push({ id: randomId } );
return arr;
}
const users = [];
console.log(users); // []
const newUsers = addUser(users);
console.log(newUsers); // [{ id: ... }]
console.log(users); // [{ id: ... }] (since users was modified)
```
---
# 5. How do you get the type of a value?
You can use `typeof` to get the type of a value.
```javascript
const name = "Ndeye Fatou Diop";
console.log(typeof "Hello") // "string"
console.log(typeof("Hi")) // "string"
console.log(typeof name) // "string"
```
> 💡 Note: This method doesn't work for `null` because `typeof null` returns `object` 😅. To safely check if `value` is an object, you need to do `value != null && typeof value === "object"`
---
# 6. What does `typeof (() => {})` return?
This is the other exception with `typeof`.
`typeof fn` returns `function` instead of `object` 🤦♀️.
```javascript
const sayHi = (name) => console.log(`Hi, ${name}`)
console.log(typeof sayHi); // "function"
```
---
# 7. How do you check if a `value` is an array in JavaScript?
`typeof arr` returns `object` since arrays are objects.
Instead, you can use `Array.isArray(value)`.
```javascript
const nums = [1, 2, 3];
console.log(Array.isArray(nums)); // true
console.log(Array.isArray({})); // false
```
---
# 8. What is the difference between number and bigint?
Only integers within the range `[-9007199254740991, 9007199254740991]` are safe to manipulate in JavaScript.
Integers outside this range can give incorrect mathematical results.
For example, `9007199254740993 - 9007199254740992` will return `0` instead of `1`.
**BigInt** was introduced for integers outside this range. Any integer can be converted to a **bigint** by appending `n` to it or using `BigInt(...)`
`9007199254740993n - 9007199254740992n` will correctly return `1n`.
> 💡 Tip: You can get the min/max safe integers with `Number.MIN_SAFE_INTEGER` and `Number.MAX_SAFE_INTEGER`.
---
# 9. What is the difference between `null` and `undefined`?
There is a slight difference.
- `undefined` conveys a value that hasn't been defined yet. It's like you just bought a new house, and someone asks about the swimming pool 🏊♂️. You haven't even thought about it yet — it's undefined!
- `null` conveys a value that has been set to "empty". It's like you bought the house and decided there wouldn't be a swimming pool (since you're too broke for it 😅).
> 💡 Note: Don't rely on that distinction in your code. Just consider any value `null` or `undefined` as empty.
---
# 10. What is a property?
Objects have properties.
Each property associates a _key_ with a _value_.
For example, the object `me` has the properties `name`, `age`, etc.
```javascript
const me = {
name: "Fatou",
age: 30,
job: "Software Engineer"
}
```
### Three things to know about keys
1. Only `string` or `symbol` values are allowed as keys. Any other value will be converted to `string` through coercion (see Question #12)
2. They are case-sensitive
3. You need `[]` to access keys with space separation
```javascript
const obj = {
"first name": "Fatou"
};
console.log(obj.first name); // Doesn't work
console.log(obj["first name"]); // "Fatou"
```
---
# 11. What is a method?
Methods are special properties that associate a _key_ with a _function_.
That function can only be accessed through the object like this:
```javascript
const me = {
name: "Ndeye Fatou Diop",
sayHi(){
console.log(`Hi, my name is ${this.name}`)
},
sayHelloWorld(){
console.log("Hello World")
}
}
me.sayHi(); // Hi, my name is Ndeye Fatou Diop
const sayHelloFn = me.sayHelloWorld;
sayHelloFn();
```
> 💡 Note: Be careful with the `this` object in the `sayHi` function. If the function was called like this, `const fn = me.sayHi; fn();`, `this != me`. You can learn more about `this` rule [here](https://developer.mozilla.org/en-US/docs/Web/JavaScript/Reference/Operators/this).
---
# 12. What is coercion?
Remember question #1?
_A data type only supports certain operations._
For example, we can add numbers like this `1 + 2`.
What happens when we try "invalid" operations like `"8" + 9`?
👉 **Coercion happens**.
It is when JavaScript implicitly converts values from one data type to another.
In the example above, JavaScript will convert `9` to the string `"9"` and return `"8" + "9" => "89"`.
More examples of coercion:
```javascript
const result = "9" - 5; // returns 4 since "9" is coerced into the number `9`
const sum = true + false; // returns 1 since true is coerced into 1 and false into 0
```
> 💡 Notes: There are [coercion rules](https://www.scaler.com/topics/javascript/type-coercion-javascript/), but you don't need to remember them all. Instead, avoid comparing apples and oranges and invalid operations 😅.
---
# 13. What is a falsy value? What is the opposite of it? Can you name all falsy values?
**The simplest answer**: If `Boolean(value)` returns **false**, `value` is falsy.
So, every **falsy** value will be coerced to `false` when JavaScript expects a boolean value (see Question #12).
**Examples:**
```javascript
// value is falsy
if(value) {
// Not reachable since `value` will be coerced into `false`
}
const name = value && "myValueHere"; // `name` will be equal to `value` since `value` will be coerced to false
```
There are only **10** falsy values:
- `false`
- `0`, `+0`, `-0`, `0n`, `NaN`
- empty string: `""`, `''`, etc.
- `null`
- `undefined`
- `document.all`: the only falsy object
If a value is not **falsy** (i.e., not present in this list), it is **truthy**.
---
# 14. How do you convert a value to its boolean representation?
You have two options:
- Option #1: `Boolean(value)`
- Option #2 (better): `!!value`
```javascript
console.log(Boolean(1)); // true
console.log(Boolean(0)); // false
console.log(!!1); // true
console.log(!!0); // false
```
---
# 15. What is the difference between `==` and `===`?
`===` is like `==` except no **coercion** happens, and the types need to be the same.
In fact, `==` will return **true** if the two values are equal after JavaScript coercion kicks in.
For example, `1 == true` returns **true** because JavaScript will coerce `1` into a boolean. Since `1` is truthy (see Question #13), it will be equivalent to **true**.
Conversely, `1 === true` will return **false** since the types differ.
> 💡 Tip: Never use `==` unless for checking if a value is null/undefined. Otherwise, coercion may kick in, resulting in unexpected results. For example `[] == ![]` returns `true` since both sides are coerced into numbers (`[] => 0`, `![] => false => 0` since `[]` is truthy)
---
# 16. Why does `0.1 + 0.2 === 0.3` return false?
_0.1_ and _0.2_ are floating point numbers.
In JavaScript (and many other languages), floating-point numbers are represented using the [IEEE 754](https://en.wikipedia.org/wiki/IEEE_754) standard.
Unfortunately, numbers like _0.1_ and _0.2_ cannot be represented precisely in this standard, leading to a loss of precision.
As a result, `0.1 + 0.2` is equivalent to `approximate(0.1) + approximate(0.2)`, which results in something slightly different from _0.3_.
---
# 17. Why is `{} === {}` returning false?
This question is easy if you understand Question #4.
`{}` are objects. As a result, each one stores a different reference pointing to a different value in memory (heap).
Since those references (i.e., addresses) are different, the comparison returns false.
---
# 18. What are the different ways to access an object property?
There are two options (using **dot notation** or **bracket notation**).
Let's say we have the following object, and we want to access the `name` property:
```javascript
const me = {
name: "Ndeye Fatou Diop",
job: "Software Engineer",
"way of life": "Coding"
}
```
We can do:
- `me.name`
- `me["name"]`
> 💡 Note: For properties with spaces like `"way of life"`, we can only use `me["way of life"]`.
---
# 19. How do you safely do `obj.value` when `obj` can be undefined or null?
We have two options:
- Option #1: `obj != null ? obj.value : undefined`
- Option #2 (better): Use the **optional chaining operator** like this `obj?.value`
---
# 20. How do you loop through the values of an array or object?
### For an array
```javascript
const arr = [1, 2, 3]
// Option 1: Use for...of
for(let x of arr) {
console.log(x)
}
// Option 2: Use for with indices
for(let i = 0; i < arr.length; i++) {
console.log(arr[i])
}
// Option 3: Use forEach
arr.forEach(x => {
console.log(x)
})
```
### For an object
```javascript
const obj = {
name: "Fatou",
age: 30
}
// Option 1: Use `Object.keys`
Object.keys(obj).forEach(k => {
console.log(obj[k])
})
// Option 2: Use `Object.values`
Object.values(obj).forEach(x => {
console.log(x)
})
// Option 3: Use `Object.entries`
Object.entries(obj).forEach(([k, x]) => {
console.log(x)
})
```
> 💡 Important: Avoid `for...in` since it may produce unexpected results.
---
# 21. What is prototypal inheritance?
Every object in JavaScript has a hidden property `[[Prototype]]` called the **prototype** that is either an object or _undefined_.
This property can be accessed via `obj.__proto__`.
### Where does the prototype come from?
There are **multiple** ways to set an object prototype:
**Option #1: Just create the object**
Every object will have a default prototype when set.
For example,
- The prototype of `array` objects is `Array.prototype`
- the prototype of objects like `{ name: "Fatou"}` is `Object.prototype`
- etc.
**Option #2: Explicitly set the prototype**
```javascript
const car = {
wheels: 4
};
const bmw = {
brand: "BMW"
};
bmw.__proto__ = car; // bmw.[[Prototype]] is equal to car
```
**Option #3: Create the object with a given function**
```javascript
function Car(brand){
this.brand = brand
}
const bmw = new Car("BMW"); // bmw.[[Prototype]] has the following shape: { constructor: Car, … }
```
**Option #4: Create the object with Object.create**
```javascript
const car = {
wheels: 4
};
const bmw = Object.create(car); // bmw.[[Prototype]] is equal to car
bmw.brand = "BMW";
```
### What is the prototype used for?
So, every object has a prototype. Now what? 😅
When you try to access a method or property on an object, JavaScript will first examine the object.
When no property/method can be found, JavaScript will look into the _prototype_ object.
Three things can happen:
1. The property/method exists on the _prototype_ object => JavaScript will return it
2. The prototype method is _undefined_ => JavaScript will return _undefined_
3. The prototype method is not _undefined_ => **Inheritance kicks in**. Since the prototype is an object, it has its own _prototype_. So JavaScript will look into the _prototype_ of the _prototype_. It will continue doing so until it finds the property/method or the prototype becomes undefined.
This is prototypal inheritance 😀. We inherit the properties/methods of the _prototype_. The ultimate prototype is `Object.prototype` and `Object.prototype.__proto__ === undefined`.
In the example below, `bmw` object does not have the `wheels` property, so the one on `car` will be returned.
```javascript
const car = {
wheels: 4
};
const bmw = {
brand: "BMW",
print(){
console.log(`My brand is ${this.brand} and I have ${this.wheels} wheels`);
}
};
bmw.__proto__ = car; // Sets bmw.[[Prototype]] to car
bmw.print(); //"My brand is BMW and I have 4 wheels"
```
> 💡 Note: If you want to learn more about prototypal inheritance? Check this great [post](https://dev.to/lydiahallie/javascript-visualized-prototypal-inheritance-47co) from @lydiahallie.
---
# 22. How do you check whether a property exists in an object?
Your first instinct may be to use `obj.value !== undefined`, but this can go wrong in these cases:
- `obj` is undefined
- `obj.value` is present by _undefined_
- `value` is present in the prototype chain (see Question #21)
We can try `value in obj`, but this breaks when `obj` is undefined or null.
The safest way to achieve this? 👉 `obj?.hasOwnProperty(value)`
---
# 23. Why can we call methods like `.trim()` on string values?
Primitive values like strings have no methods.
So, how the heck does this work? 😅
Well, it is through a neat feature called **auto-boxing** ✨
### What is auto-boxing in JavaScript?
Every primitive type except `null` and `undefined` has an associated object wrapper class (see table below).
| Data Type | Object wrapper |
|-------------|----------------|
| null | N/A |
| undefined | N/A |
| number | Number |
| string | String |
| boolean | Boolean |
| bigint | BigInt |
| symbol | Symbol |
**Auto-boxing** is when JavaScript temporarily converts a primitive type to its corresponding object wrapper when certain methods or properties are accessed.
Let's look at an example:
```javascript
const name = "Ndeye Fatou Diop ";
const cleanName = name.trim(); // cleanName = "Ndeye Fatou Diop"
```
When we do `name.trim()`, `name` is a primitive value and doesn't have methods. JavaScript will then:
1. Convert `name` to `new String(name)`, which is an object.
2. Access the `trim` method on the String object, returning "Ndeye Fatou Diop"
3. Return the result
---
# 24. Can you give 3 ways to create an `undefined` value?
- Option #1: Explicitly set the value to undefined
```javascript
let age = undefined;
```
- Option #2: Declare a variable without an initial value
```javascript
let age;
var name;
```
- Option #3: Access a property/method that doesn't exist
```javascript
const me = {
name: "Ndeye Fatou Diop"
}
let age = me.age; // `age` is undefined because it doesn't exist in the object
```
---
# 25. What is the difference between shallow copy and deep copy?
First, what is a copy?
Let's say I have an array `arr1`, and I want to create a copy of that array `arr2`.
I can't do `const arr2 = arr1` since the arrays will point to the same object, and any modification to `arr2` will affect `arr1` (see Question #3).
So what is the solution?
👉 `const arr2 = [...arr1];`
This will make sure the two arrays point to different objects in memory.
**But there is a catch 😅.**
This works fine when the arrays contain primitive values like `const arr1 = [1, 2, 3]`, but what if the arrays contain objects like `const arr1 = [ { name: "Fatou"}]`?
What happens when I do `arr2[0].name = "Thomas"`?
**Will `arr1[0]` be affected?** 👉 Yes.
Because `arr2` still contains a list of references that are the same as in `arr1`. So, any modification will affect the objects these references point to.
The copy we did was a **shallow copy**.
**A deep copy is when we create new references for every object, so any modification does not affect the original objects.**
In the example above, we can do a deep copy this way:
```javascript
const arr1 = [ { name: "Fatou"}]
// Option #1: This will only work when every value can be serialized
const arr2 = JSON.parse(JSON.stringify(arr1))
// Option #2: Use `structuredClone`
const arr2 = structuredClone(arr1)
```
> 💡 Important: `Deep copy` is more expensive than `shallow copy`. Make sure you actually need it before reaching for it.
---
# 26. What is the result of `Symbol("name") === Symbol("name")`
👉 **False**.
Every call to `Symbol` returns a different value, even if the descriptions are the same.
---
# 27. Can you change the data type of a variable?
Variables don't have a type; values have 😅.
In fact, when we have the following code, `typeof name` is equivalent to `typeof "Ndeye Fatou Diop"` which returns "string".
```javascript
const name = "Ndeye Fatou Diop"
const type = typeof name; // returns "string"
```
As a result, since variables declared with `var` and `let` can have their values changed, their types can also change.
```javascript
let x = "Ndeye Fatou Diop"
console.log(typeof x); // logs "string"
x = 45;
console.log(typeof x); // logs "number"
```
---
Thank you for reading this post 🙏.
If you liked this article, join my **FREE** newsletter, **[FrontendJoy](https://frontendjoy.substack.com/)**.
If you want daily tips, find me on [X/Twitter](https://twitter.com/_ndeyefatoudiop).
| _ndeyefatoudiop |
1,873,827 | Danger: keep order in your PRs | Good morning everyone and good MonDEV! I hope you had a good first weekend of June! Recently, I... | 25,147 | 2024-06-03T07:00:00 | https://dev.to/giuliano1993/danger-keep-order-in-your-prs-281d | opensource, cicd, ci |
Good morning everyone and good MonDEV!
I hope you had a good first weekend of June!
Recently, I found myself gathering all the various knowledge I had about the open-source world to prepare a small talk, and this led me to discover or come across some interesting tools that can help in managing our open-source projects. We have already seen in the past how to create specific bots to manage our repos, but we have never focused on tools built specifically for optimal management of the PRs we receive.
That's why today I thought of introducing you to Danger, a very interesting tool also among those directly recommended by GitHub for managing your projects.
What is it about? First of all, let's start by saying that this library exists in 5 languages, so you can use the version you prefer to manage your project: JS, Swift, Ruby, Kotlin, and Python.
That said, what does such a pompous name aim for?
[Danger](https://danger.systems/) helps you in managing your CI. Specifically, it allows you to perform a series of checks throughout the contribution flow.
For example, you can request the presence of a changelog change in a PR, require that a certain PR be assigned to someone before being merged, show some information about it, in order to have an overview of the new additions. In short, it's a bit like a Swiss army knife that allows you to work on all those aspects that are more difficult to control manually but essential as a project grows.
So, whether you already have it, or if you aim to have a growing Open Source project, I hope you will be willing to try this tool on one of your projects.
As always, let me know if you use it and how you find it.
Before I leave you, I remind you of [the event next week in Cesena](https://www.eventbrite.it/e/biglietti-4-dev-e-un-meetup-903009635127), to meet, talk a bit about development, and have some fun. I and the others will already be there from Friday so if anyone wants to join us, there are still a few spots available!
Meanwhile, have a great start to the week! As always...
Happy Coding 0_1 | giuliano1993 |
1,842,397 | AWS Security Best Practices: Leveraging IAM for Service-to-Service Authentication and Authorization | A critical aspect of cloud services is service-to-service communication, and it’s essential to do... | 0 | 2024-06-03T06:59:42 | https://www.ranthebuilder.cloud/post/aws-security-best-practices-leveraging-iam-for-service-to-service-authentication-and-authorization | aws, security, restapi, serverless |
](https://cdn-images-1.medium.com/max/3656/1*kIDRnddYyLIyD0Tsz8KWIA.png)
A critical aspect of cloud services is service-to-service communication, and it’s essential to do it securely. As an architect who designed centralized authentication and authorization services in [CyberArk](https://www.cyberark.com/), a cyber security SaaS provider, I will share my take on developing a secure authorization mechanism between AWS cloud-based services, whether serverless or containers.
**By the time you finish reading this post, you will not only understand the importance of service authentication and authorization, but also be equipped with the practical knowledge to implement it. This includes securely enabling cross-account access to resources for both synchronous and asynchronous communication patterns using AWS IAM.**
**This post includes JSON IAM policies and Python code examples.**
This post is the first of many security topics in an upcoming series.
](https://cdn-images-1.medium.com/max/2624/0*lrHYLOizEg3p81m0.png)
**This blog post was originally published on my website, [“Ran The Builder.”](https://www.ranthebuilder.cloud/)**
## Table of Contents
1. **Authentication and Authorization Concepts**
2. **Service-to-Service Communication Patterns**
3. **IAM Based Authentication & Authorization**
4. **Synchronous Communication IAM Solution**
5. **Asynchronous Communication Solution**
6. **Choosing Between Assume Role and Resource Based Policies**
7. **Summary**
8. **Appendix: Private and Public API Gateways**
## Authentication and Authorization Concepts
Authentication is:
> *Authentication is the act of proving an [assertion](https://en.wikipedia.org/wiki/Logical_assertion), such as the [identity](https://en.wikipedia.org/wiki/Digital_identity) of a computer system user — [Wikipedia](https://en.wikipedia.org/wiki/Authentication)*
and authorization on the other hand is:
> *is the function of specifying access rights/privileges to resources — [Wikipedia](https://en.wikipedia.org/wiki/Authorization)*
**In a secure service, authentication and authorization go hand in hand.**
As a service developer who exposes a REST API, it’s crucial to understand that leaving your API open to the world without proper authentication and authorization measures can lead to unauthorized access and data manipulation.
You want your service first to accept communication requests from authenticated services ([principals](https://docs.aws.amazon.com/IAM/latest/UserGuide/reference_policies_elements_principal.html)), those whose identities are proven to be trusted and known. Once identified, you want to ensure that only authorized services can trigger your API or communicate with your service.
Or in other words:
1. Authentication aims to validate and identify that a principal is who it claims to be.
2. Authorization aims to define the relationship between [principals](https://docs.aws.amazon.com/IAM/latest/UserGuide/reference_policies_elements_principal.html), [actions](https://docs.aws.amazon.com/IAM/latest/UserGuide/reference_policies_elements_action.html), and [resources](https://docs.aws.amazon.com/IAM/latest/UserGuide/reference_policies_elements_resource.html).
We can visualize authorization as the relationship between the principals (services), the actions they wish to take (e.g., execute an API), and the resources (the actual REST API endpoint and HTTP action type) on which their actions are called.

**So, service-to-service communication security comes in two parts:**
* **First, make sure the caller service is who it claims to be.**
* **Then, assert that it has permission to take action on the resource.**
To better understand the importance of authentication and authorization, let’s consider some real-world examples of service-to-service communication. These examples will highlight the critical role these measures play in ensuring the security and integrity of your REST API services.
## Service-to-Service Communication Patterns
Developers spend a lot of time designing customer-facing REST APIs. These APIs introduce the concept of users to the system (human or non-human). AWS offers several user and service authentication options such as Amazon Cognito (Cognito) and AWS Identity and Access Management (IAM), with IAM being the main option for internal user management, while Cognito can connect to external identity providers such as CyberArk and others.
In this post, I’d like to focus on AWS IAM and its role in an important aspect of cloud services: service-to-service authentication and authorization.
### Synchronous Communication Pattern
In this use case, there are three services: A, B, and C, each in its own AWS account.

Service A is serverless, B is EC2-based, and C serves a REST API with API Gateway. Both services A and B use service C’s API.
*This part discusses public API Gateways. For private API Gateway, visit the [appendix](#yt57p57106) below.
However, service C wants to ensure that only these specific services can call its API and perhaps even fine-tune it to be least privileged so that only a particular Lambda function or an EC2 machine can trigger it.
Let’s continue to the second pattern.
### Asynchronous Communication Pattern
In this use case, we have our three services as before:
* A, B and C each in its own AWS account as before.
* C holds an SNS topic used as a centralized publisher-subscriber asynchronous communication service in the organization.

Service A is the publisher, and Service B subscribes to the SNS topic via an SQS queue.
Service C wants to ensure that only Service A can publish messages to the SNS topic and that only Service B’s SQS can subscribe to the topic as the topic contains data that you should keep private.
This is a standard pattern. You can swap the SNS topic to the EventBridge bus or any messaging service you may have, such as Amazon MSK.
### Single or Multiple Accounts
As a side note, services A, B, and C may share the same account, simplifying the IAM solution. However, following the IAM practices in this post is essential, **even if all services share the same account** do not take shortcuts. You might find yourself moving them to different accounts in the future. In that case, if you don’t follow the best practices, you will have a hard time and many breaking changes ahead of you (from experience!). It’s best always to follow best practices, especially when security is involved.
## IAM Based Authentication & Authorization
Now that we’ve covered the basics of service to service authentication and authorization issues let’s discuss the solution and start using AWS IAM.
This solution will cover both cross-account and same-account authentication and authorization.
IAM authentication means that a principal, for instance, service A, must be authenticated (signed in to AWS) using their credentials to send a request to other AWS services and resources, or service C in our example. Once authenticated, we can leverage IAM again to ensure service A is authorized to access service C.
We will combine two aspects of IAM, [identity-based](https://docs.aws.amazon.com/IAM/latest/UserGuide/access_policies.html#policies_id-based) and [resource-based policies](https://docs.aws.amazon.com/IAM/latest/UserGuide/access_policies.html#policies_resource-based), and provide authorization solutions for both synchronous and asynchronous communications. We will also provide cross-account access, i.e., authorization services from different AWS accounts using the “assume role” or [delegation](https://docs.aws.amazon.com/IAM/latest/UserGuide/tutorial_cross-account-with-roles.html) mechanism.
### Resource Based Policies
According to AWS [documentation](https://docs.aws.amazon.com/IAM/latest/UserGuide/access_policies.html#policies_resource-based):
> *Resource-based policies grant the specified principal permission to perform specific actions on that resource and defines under what conditions this applies*
Resource-based policies are JSON policy documents that you attach to a resource, such as API Gateway, SNS, S3, or another resource. With resource-based policies, you can specify who has access to the resource and what actions they can perform on it. In addition, they can be used to allow cross-account access. Sounds perfect, right? Well, it has limitations, and not all resource types support it.
Let’s review the pros and cons of this IAM mechanism.
**Pros:**
1. Simple to define
2. Enable cross-account access.
**Cons:**
1. Not all AWS resources support resource-based policies.
2. Resource-based policies have a size limit like all IAM policies. When you define more resources and reach the maximum size, there’s no way to overcome it other than provisioning a new resource (duplicating part of service C, basically).
### Assume Role Mechanism
The IAM access delegation mechanism, or “assume role,” as I call it, is crucial in cross-account communication. However, it can also be used in a single AWS account scenario.
The IAM access delegation mechanism is underpinned by **identity-based policies** attached to an IAM role. In our example, role C is located in service C’s account and grants access to the resource in question, which could be service C’s API Gateway or SNS topic.
Whoever has permission to [assume role](https://docs.aws.amazon.com/STS/latest/APIReference/API_AssumeRole.html) C can get a set of temporary IAM security credentials that can be used for authentication and authorization to communicate with service C, whether to execute a REST API call or publish a message to an SNS topic.
Assuming a role involves making an [AWS SDK call](https://docs.aws.amazon.com/code-library/latest/ug/sts_example_sts_AssumeRole_section.html) to Amazon STS (AWS Security Token Service) and utilizing the temporary credentials from the SDK response to initiate a communication session with the service you intend to communicate with, we will explore code examples later in this post to ensure you have a comprehensive understanding of the process.
However, we need to define who can assume this role and gain access to service C. We will need resource policies and define that only the roles of services A and B can assume role C and gain access to service C.
Let’s review the pros and cons of this IAM mechanism.
**Pros:**
1. Supports all resource types as long as you can define an IAM policy.
2. Abstracts the resource and its ARN. You get a role that provides you access. The resource can change tomorrow, but all you know is the role of ARN and what API call to use. Suppose the call is abstracted in an organizational SDK that encapsulates the resource. In that case, you can change resources — SNS topic to EventBridge bus — and keep the changes in the role policies and SDK implementation levels, but the role ARNs remain the same.
3. Role C’s resource-based policy, which defines who can assume the role, has a size limit. However, if we want to add more services, we can provision a new role for new services to assume. Unlike the previous mechanism, it’s okay to provision a new resource as the protected resource remains unchanged (API Gateway or SNS topic).
**Cons:**
1. It is more complicated to define and requires an extra role in service C.
2. Assuming a role is another AWS SDK call that extends the overall runtime of services A and B and more error-prone code to maintain.
Let’s see how we can solve our authentication and authorization issues in synchronous and asynchronous communication patterns with concrete IAM policies and Python code examples.
## Synchronous Communication IAM Solution
Let’s start by boosting the security of service C, the API Gateway. First, we will add an IAM [authorizer](https://docs.aws.amazon.com/apigateway/latest/developerguide/http-api-access-control-iam.html) to all its API endpoints. By doing so, by default, all unauthenticated and unauthorized requests are denied.
> *When IAM authorization is enabled, clients must use [Signature Version 4](https://docs.aws.amazon.com/general/latest/gr/signature-version-4.html) to sign their requests with AWS credentials. API Gateway invokes your API route only if the client has execute-api permission for the route. — AWS [documentation](https://docs.aws.amazon.com/apigateway/latest/developerguide/http-api-access-control-iam.html)*
AWS IAM ensures that only requests with **authenticated** and valid IAM credentials which are **authorized** will execute the service’s C API. All that remains is for service C to define which services (identities) and AWS accounts can execute its APIs.
There are two ways to achieve that:
1. Resource-based policy
2. Identity-based policies assume role mechanisms.
Let’s start with a resource-based policy.
### Resource Based Policy
In this use case, we need to alter service C’s API Gateway resource based-policy to allow services A and B (their Lambda function role, for instance, or their entire account or VPC endpoint etc.) to execute the API and its endpoints. We can define a fine-grained definition and decide exactly what endpoint each service can communicate with.
Here’s an example of such a resource policy for service C API Gateway:
{% gist https://gist.github.com/ran-isenberg/bc4ed8a0f1d87a8eca56436c314df76b.js %}
In lines 8–9, we can allow an entire account (principal) such as the account of service A or B’s account or a specific role ARN in a different account (a better option, least privileged), the action (line 12) of executing an API endpoint. We can set the exact endpoint and HTTP command in line 14.
Be advised that at the moment, you cannot use this mechanism on an HTTP API Gateway, just the REST variant.
On services A and B side, they must define their roles (Lambda function role for service A) with identity permissions for the same action specified in the resource policy. For cross-account access, you **must** define the policy in this two-sided manner. Service A defines its Lambda function’s role with permissions to to call service C API Gateway, and service C allows service A to call it from the other account.
In addition, services A and B must send their IAM credentials ([Sig v4](https://docs.aws.amazon.com/AmazonS3/latest/API/sig-v4-authenticating-requests.html)) in the HTTP authorization header when calling service C’s API Gateway.
Here’s a Python example for this process:
{% gist https://gist.github.com/ran-isenberg/1457d12a7e1d35df85122c0c48e291f2.js %}
In this example, we use our service’s role to authenticate with IAM, create the auth headers in line 7, and send them in line 15.
### Assume Role
In this use case, we need to create a role in service C’s account with permissions to execute the API Gateway and let a principal in services A and B assume it.
We can start by defining the role’s trust policy — in this policy, the resource, is the role itself.
We let specific roles (principals) from services A and B assume this role (action). We can give a broader scope for services A or B, either to the entire account or to a role with a predefined prefix. However, it’s usually best to minimize the scope, so a role prefix or a specific role is better and more secure.
{% gist https://gist.github.com/ran-isenberg/7b89eb0de5e322f4f06859fc197e06e5.js %}
Next, we need to add the role’s permissions to execute service C’s API to the role :
{% gist https://gist.github.com/ran-isenberg/216c022278db971c1ccc272f1144e15a.js %}
Lastly, the code on service A is very similar to before, with the addition of the assumed role code.
You can find code examples for multiple services [here](https://docs.aws.amazon.com/code-library/latest/ug/sts_example_sts_AssumeRole_section.html) or refer to the code below.
For ‘RoleArn,’ you need to provide the role that service C creates and shares its ARN with you. Typically, service teams exchange ARNs manually. I’d recommend saving that ARN as an environment variable in the Lambda function. Also, ensure that your Lambda role has the necessary permissions to assume roles.
As you see below, the code is very similar to code example before, just with the addition of the STS API call in lines 5–10 and using the response values in lines 11–18.
{% gist https://gist.github.com/ran-isenberg/d4d6bdfe729c7a6f90a61b502abfef20.js %}
**If you wish to learn about private API Gateway use cases, refer to the [appendix](#yt57p57106).**
## Asynchronous Communication Solution
Our goal is to allow service A to publish SNS messages to service C’s SNS topic and to let service B subscribe via SQS to the SNS messages.
Let’s review the two IAM implementation options we have.
### Resource Based Policy
In this case, we will define an SNS access policy that allows service A (principal) to publish messages (action) to the SNS topic of service C (resource) and service B to subscribe to the messages. Be advised it’s best to fine-tune these permissions to the role that can publish and to the specific SQS that can subscribe.
{% gist https://gist.github.com/ran-isenberg/ad9238ce83afd2db845e065eec0a4b8d.js %}
On the service A side, the Lambda role will define its permissions to publish to the SNS topic. Having the two sides define the permissions allows them to work when dealing with cross-account access.
When publishing a message to the topic, service A’s Lambda function will utilize the AWS SDK to make the API call. The SDK uses the function role’s credentials to take care of the IAM authentication and authorization side.
{% gist https://gist.github.com/ran-isenberg/904c6f716eddcab2ff7b29678ca1be44.js %}
On the service B side, we need to define an SQS subscription to the SNS topic by following the documentation [here](https://docs.aws.amazon.com/AWSSimpleQueueService/latest/SQSDeveloperGuide/sqs-configure-subscribe-queue-sns-topic.html).
### Assume Role
In this case, we need to create a role in service C’s account with permission to publish messages to the SNS topic. Then, we let a specific role of service A assume this role.
We can do this by defining the role’s trust policy.
{% gist https://gist.github.com/ran-isenberg/e1f6a09be74c8c779aff10c513d8d08e.js %}
We can give a broader scope for service A to the entire account or a role with a predefined prefix. However, it’s usually best to minimize the scope. Hence, a role prefix or a specific role is better and more secure.
Next, we need to add to the role the permissions to publish messages to service C’s SNS topic:
{% gist https://gist.github.com/ran-isenberg/02f7b84ee7dbfb7e9ff2a12402c393f1.js %}
Now, on service A’s side, we need to assume the role and use AWS SDK to send SNS messages. It’s also important to ensure the Lambda function role has permissions ‘sns:Publish’ and ‘sts:AssumeRole’; otherwise, the AWS SDK calls will not work.
The service teams need to exchange the resource ARNs and account numbers for the policies to work.
Service A assumes the role of SDK call and uses the temporary IAM credentials to create a boto client for the SNS publish message SDK call.
{% gist https://gist.github.com/ran-isenberg/79ad98015341dae7d071bd326f9e0618.js %}
Service B remains as in the resource-based policy example; it can work only as a resource policy that allows its SQS to subscribe. However, service A requires some code changes.
## Choosing Between Assume Role and Resource Based Policies
Your service communication will be secure with authentication and authorization, whether you chose resource-based policies or assumed role solution. However, each implementation has its pros and cons that can make your life harder in the future if you ignore them.
I’ll divide my recommendation by different parameters.
Suppose I had to choose just one implementation. In that case, I’d go with the ‘assume role’ path, as it allows my service to support multiple services in the future easily. I can create more roles to support more services that assume them and I’m not limited by IAM policy size.
However, resource-based policies are better if you only care about performance, so don’t add another SDK call to assume the role. Keep in mind that these policies have a maximum size. Suppose you expect to connect many services and different AWS accounts (think of a central pub-sub account or central API). In that case, you will encounter these limitations at some point in the future. As it doesn’t make sense to duplicate the SNS topic or API gateway for integration with new services, you are better off choosing the ‘assume role’ path. It’s easier to provide new roles than to duplicate an SNS topic or an API Gateway, which doesn’t make sense.
Another deciding factor is whether the services are in the same account and who maintains them — the same team or not. The resource-based policy is excellent for internal service or micro-service communication when the same team maintains them, as it introduces some degree of coupling. Still, it is acceptable as it “stays” in the family. However, suppose different accounts and teams are involved. In that case, the ‘assume role’ route is better as it decouples the resources and teams in question and supports endless future extensions.
**Lastly, you can always change the implementation, so don’t be afraid to choose; just make sure you select one of these two options.**
## Summary
In this post, we have learned about authentication and authorization. We have also learned about two service-to-service communication patterns: asynchronous and synchronous.
We have implemented both authentication and authorization for those patterns using AWS IAM. We saw four different implementations and discussed their pros and cons, whether the resource-based policies route or the ‘assume role’ one.
In the following posts, we will discuss the challenges these patterns bring, how to solve them, and how to take authorization another step forward into the fine-grained domain.
## Appendix: Private and Public API Gateways
AWS recommends building private API Gateways for service-to-service communication to enhance performance, reduce network costs (you don’t leave the AWS network), and improve security.
> *…traffic to your private API uses secure connections and does not leave the Amazon network — it is isolated from the public internet — AWS [documentation](https://docs.aws.amazon.com/apigateway/latest/developerguide/apigateway-private-apis.html)*
In reality, it’s possible and easier to build APIs as public API Gateways. In that case, authentication and authorization become more critical and you must follow the guidelines in this post.
Private API Gateways require VPCs. They bring extra complexity as connecting services also need to use VPC and VPC endpoints.
AWS recommends connecting the services’ VPC networks via [resource policies](https://docs.aws.amazon.com/apigateway/latest/developerguide/apigateway-private-apis.html#apigateway-private-api-set-up-resource-policy) for VPC endpoints or [VPC peering](https://docs.aws.amazon.com/vpc/latest/peering/what-is-vpc-peering.html). You can read more about it [here](https://aws.amazon.com/blogs/compute/architecting-for-scale-with-amazon-api-gateway-private-integrations/).
](https://cdn-images-1.medium.com/max/3844/1*KGK59njG-_HjxQfZbV6ceQ.png)
When you use serverless and Lambda functions and wish to communicate with a private API Gateway, you need to put your Lambda functions inside VPCs. This is not ideal, as VPCs have unwanted effects on the Lambda functions, such as longer cold starts and increased costs.
### VPCs Don’t Replace Authentication and Authorization
I want to set this point straight.
Setting up a network connection between different VPC endpoints does not mean you implemented service authentication or authorization or that you are 100% secure.
Yes, it brings up an extra layer of security, but it does not replace IAM-based authentication and authorization.
First, it’s not the least privilege; any service inside those VPC networks can access your service. It’s an extra layer of security but does not replace authorization. In addition, it does not scale. The more services you add, the more “breached” your service becomes, with more VPCs and services that gain access.
In addition, if attackers gain access to one of the VPCs, they can communicate freely with your service because your service accepts any incoming calls.
However, combining IAM authentication and authorization with VPC provides the best and most comprehensive security for your API Gateway.
You can learn more about such patterns with API Gateways and VPC in this video: [https://www.youtube.com/watch?v=H4hCygngTrU](https://www.youtube.com/watch?v=H4hCygngTrU)
| ranisenberg |
1,875,000 | Buy verified cash app account | Buy verified cash app account Cash app has emerged as a dominant force in the realm of mobile banking... | 0 | 2024-06-03T06:58:19 | https://dev.to/whitemartin0549/buy-verified-cash-app-account-1ieb | Buy verified cash app account
Cash app has emerged as a dominant force in the realm of mobile banking within the USA, offering unparalleled convenience for digital money transfers, deposits, and trading. As the foremost provider of fully verified cash app accounts, we take pride in our ability to deliver accounts with substantial limits. Bitcoin enablement, and an unmatched level of security.
https://dmhelpshop.com/product/buy-verified-cash-app-account/
Our commitment to facilitating seamless transactions and enabling digital currency trades has garnered significant acclaim, as evidenced by the overwhelming response from our satisfied clientele. Those seeking buy verified cash app account with 100% legitimate documentation and unrestricted access need look no further. Get in touch with us promptly to acquire your verified cash app account and take advantage of all the benefits it has to offer.
Why dmhelpshop is the best place to buy USA cash app accounts?
It’s crucial to stay informed about any updates to the platform you’re using. If an update has been released, it’s important to explore alternative options. Contact the platform’s support team to inquire about the status of the cash app service.
Clearly communicate your requirements and inquire whether they can meet your needs and provide the buy verified cash app account promptly. If they assure you that they can fulfill your requirements within the specified timeframe, proceed with the verification process using the required documents.
https://dmhelpshop.com/product/buy-verified-cash-app-account/
Our account verification process includes the submission of the following documents: [List of specific documents required for verification].
Genuine and activated email verified
Registered phone number (USA)
Selfie verified
SSN (social security number) verified
Driving license
BTC enable or not enable (BTC enable best)
100% replacement guaranteed
100% customer satisfaction
When it comes to staying on top of the latest platform updates, it’s crucial to act fast and ensure you’re positioned in the best possible place. If you’re considering a switch, reaching out to the right contacts and inquiring about the status of the buy verified cash app account service update is essential.
https://dmhelpshop.com/product/buy-verified-cash-app-account/
Clearly communicate your requirements and gauge their commitment to fulfilling them promptly. Once you’ve confirmed their capability, proceed with the verification process using genuine and activated email verification, a registered USA phone number, selfie verification, social security number (SSN) verification, and a valid driving license.
Additionally, assessing whether BTC enablement is available is advisable, buy verified cash app account, with a preference for this feature. It’s important to note that a 100% replacement guarantee and ensuring 100% customer satisfaction are essential benchmarks in this process.
How to use the Cash Card to make purchases?
To activate your Cash Card, open the Cash App on your compatible device, locate the Cash Card icon at the bottom of the screen, and tap on it. Then select “Activate Cash Card” and proceed to scan the QR code on your card. Alternatively, you can manually enter the CVV and expiration date. How To Buy Verified Cash App Accounts.
After submitting your information, including your registered number, expiration date, and CVV code, you can start making payments by conveniently tapping your card on a contactless-enabled payment terminal. Consider obtaining a buy verified Cash App account for seamless transactions, especially for business purposes. Buy verified cash app account.
Why we suggest to unchanged the Cash App account username?
To activate your Cash Card, open the Cash App on your compatible device, locate the Cash Card icon at the bottom of the screen, and tap on it. Then select “Activate Cash Card” and proceed to scan the QR code on your card.
Alternatively, you can manually enter the CVV and expiration date. After submitting your information, including your registered number, expiration date, and CVV code, you can start making payments by conveniently tapping your card on a contactless-enabled payment terminal. Consider obtaining a verified Cash App account for seamless transactions, especially for business purposes. Buy verified cash app account. Purchase Verified Cash App Accounts.
Selecting a username in an app usually comes with the understanding that it cannot be easily changed within the app’s settings or options. This deliberate control is in place to uphold consistency and minimize potential user confusion, especially for those who have added you as a contact using your username. In addition, purchasing a Cash App account with verified genuine documents already linked to the account ensures a reliable and secure transaction experience.
https://dmhelpshop.com/product/buy-verified-cash-app-account/
Buy verified cash app accounts quickly and easily for all your financial needs.
As the user base of our platform continues to grow, the significance of verified accounts cannot be overstated for both businesses and individuals seeking to leverage its full range of features. How To Buy Verified Cash App Accounts.
For entrepreneurs, freelancers, and investors alike, a verified cash app account opens the door to sending, receiving, and withdrawing substantial amounts of money, offering unparalleled convenience and flexibility. Whether you’re conducting business or managing personal finances, the benefits of a verified account are clear, providing a secure and efficient means to transact and manage funds at scale.
When it comes to the rising trend of purchasing buy verified cash app account, it’s crucial to tread carefully and opt for reputable providers to steer clear of potential scams and fraudulent activities. How To Buy Verified Cash App Accounts. With numerous providers offering this service at competitive prices, it is paramount to be diligent in selecting a trusted source.
This article serves as a comprehensive guide, equipping you with the essential knowledge to navigate the process of procuring buy verified cash app account, ensuring that you are well-informed before making any purchasing decisions. Understanding the fundamentals is key, and by following this guide, you’ll be empowered to make informed choices with confidence.
https://dmhelpshop.com/product/buy-verified-cash-app-account/
Is it safe to buy Cash App Verified Accounts?
Cash App, being a prominent peer-to-peer mobile payment application, is widely utilized by numerous individuals for their transactions. However, concerns regarding its safety have arisen, particularly pertaining to the purchase of “verified” accounts through Cash App. This raises questions about the security of Cash App’s verification process.
Unfortunately, the answer is negative, as buying such verified accounts entails risks and is deemed unsafe. Therefore, it is crucial for everyone to exercise caution and be aware of potential vulnerabilities when using Cash App. How To Buy Verified Cash App Accounts.
Cash App has emerged as a widely embraced platform for purchasing Instagram Followers using PayPal, catering to a diverse range of users. This convenient application permits individuals possessing a PayPal account to procure authenticated Instagram Followers.
Leveraging the Cash App, users can either opt to procure followers for a predetermined quantity or exercise patience until their account accrues a substantial follower count, subsequently making a bulk purchase. Although the Cash App provides this service, it is crucial to discern between genuine and counterfeit items. If you find yourself in search of counterfeit products such as a Rolex, a Louis Vuitton item, or a Louis Vuitton bag, there are two viable approaches to consider.
https://dmhelpshop.com/product/buy-verified-cash-app-account/
Why you need to buy verified Cash App accounts personal or business?
The Cash App is a versatile digital wallet enabling seamless money transfers among its users. However, it presents a concern as it facilitates transfer to both verified and unverified individuals.
To address this, the Cash App offers the option to become a verified user, which unlocks a range of advantages. Verified users can enjoy perks such as express payment, immediate issue resolution, and a generous interest-free period of up to two weeks. With its user-friendly interface and enhanced capabilities, the Cash App caters to the needs of a wide audience, ensuring convenient and secure digital transactions for all.
If you’re a business person seeking additional funds to expand your business, we have a solution for you. Payroll management can often be a challenging task, regardless of whether you’re a small family-run business or a large corporation. How To Buy Verified Cash App Accounts.
Improper payment practices can lead to potential issues with your employees, as they could report you to the government. However, worry not, as we offer a reliable and efficient way to ensure proper payroll management, avoiding any potential complications. Our services provide you with the funds you need without compromising your reputation or legal standing. With our assistance, you can focus on growing your business while maintaining a professional and compliant relationship with your employees. Purchase Verified Cash App Accounts.
A Cash App has emerged as a leading peer-to-peer payment method, catering to a wide range of users. With its seamless functionality, individuals can effortlessly send and receive cash in a matter of seconds, bypassing the need for a traditional bank account or social security number. Buy verified cash app account.
This accessibility makes it particularly appealing to millennials, addressing a common challenge they face in accessing physical currency. As a result, ACash App has established itself as a preferred choice among diverse audiences, enabling swift and hassle-free transactions for everyone. Purchase Verified Cash App Accounts.
How to verify Cash App accounts
To ensure the verification of your Cash App account, it is essential to securely store all your required documents in your account. This process includes accurately supplying your date of birth and verifying the US or UK phone number linked to your Cash App account.
As part of the verification process, you will be asked to submit accurate personal details such as your date of birth, the last four digits of your SSN, and your email address. If additional information is requested by the Cash App community to validate your account, be prepared to provide it promptly. Upon successful verification, you will gain full access to managing your account balance, as well as sending and receiving funds seamlessly. Buy verified cash app account.
How cash used for international transaction?
Experience the seamless convenience of this innovative platform that simplifies money transfers to the level of sending a text message. It effortlessly connects users within the familiar confines of their respective currency regions, primarily in the United States and the United Kingdom.
No matter if you’re a freelancer seeking to diversify your clientele or a small business eager to enhance market presence, this solution caters to your financial needs efficiently and securely. Embrace a world of unlimited possibilities while staying connected to your currency domain. Buy verified cash app account.
Understanding the currency capabilities of your selected payment application is essential in today’s digital landscape, where versatile financial tools are increasingly sought after. In this era of rapid technological advancements, being well-informed about platforms such as Cash App is crucial.
As we progress into the digital age, the significance of keeping abreast of such services becomes more pronounced, emphasizing the necessity of staying updated with the evolving financial trends and options available. Buy verified cash app account.
Offers and advantage to buy cash app accounts cheap?
With Cash App, the possibilities are endless, offering numerous advantages in online marketing, cryptocurrency trading, and mobile banking while ensuring high security. As a top creator of Cash App accounts, our team possesses unparalleled expertise in navigating the platform.
We deliver accounts with maximum security and unwavering loyalty at competitive prices unmatched by other agencies. Rest assured, you can trust our services without hesitation, as we prioritize your peace of mind and satisfaction above all else.
Enhance your business operations effortlessly by utilizing the Cash App e-wallet for seamless payment processing, money transfers, and various other essential tasks. Amidst a myriad of transaction platforms in existence today, the Cash App e-wallet stands out as a premier choice, offering users a multitude of functions to streamline their financial activities effectively. Buy verified cash app account.
Trustbizs.com stands by the Cash App’s superiority and recommends acquiring your Cash App accounts from this trusted source to optimize your business potential.
How Customizable are the Payment Options on Cash App for Businesses?
Discover the flexible payment options available to businesses on Cash App, enabling a range of customization features to streamline transactions. Business users have the ability to adjust transaction amounts, incorporate tipping options, and leverage robust reporting tools for enhanced financial management.
Explore trustbizs.com to acquire verified Cash App accounts with LD backup at a competitive price, ensuring a secure and efficient payment solution for your business needs. Buy verified cash app account.
Discover Cash App, an innovative platform ideal for small business owners and entrepreneurs aiming to simplify their financial operations. With its intuitive interface, Cash App empowers businesses to seamlessly receive payments and effectively oversee their finances. Emphasizing customization, this app accommodates a variety of business requirements and preferences, making it a versatile tool for all.
Where To Buy Verified Cash App Accounts
When considering purchasing a verified Cash App account, it is imperative to carefully scrutinize the seller’s pricing and payment methods. Look for pricing that aligns with the market value, ensuring transparency and legitimacy. Buy verified cash app account.
Equally important is the need to opt for sellers who provide secure payment channels to safeguard your financial data. Trust your intuition; skepticism towards deals that appear overly advantageous or sellers who raise red flags is warranted. It is always wise to prioritize caution and explore alternative avenues if uncertainties arise.
The Importance Of Verified Cash App Accounts
In today’s digital age, the significance of verified Cash App accounts cannot be overstated, as they serve as a cornerstone for secure and trustworthy online transactions.
By acquiring verified Cash App accounts, users not only establish credibility but also instill the confidence required to participate in financial endeavors with peace of mind, thus solidifying its status as an indispensable asset for individuals navigating the digital marketplace.
When considering purchasing a verified Cash App account, it is imperative to carefully scrutinize the seller’s pricing and payment methods. Look for pricing that aligns with the market value, ensuring transparency and legitimacy. Buy verified cash app account.
Equally important is the need to opt for sellers who provide secure payment channels to safeguard your financial data. Trust your intuition; skepticism towards deals that appear overly advantageous or sellers who raise red flags is warranted. It is always wise to prioritize caution and explore alternative avenues if uncertainties arise.
https://dmhelpshop.com/product/buy-verified-cash-app-account/
Conclusion
Enhance your online financial transactions with verified Cash App accounts, a secure and convenient option for all individuals. By purchasing these accounts, you can access exclusive features, benefit from higher transaction limits, and enjoy enhanced protection against fraudulent activities. Streamline your financial interactions and experience peace of mind knowing your transactions are secure and efficient with verified Cash App accounts.
https://dmhelpshop.com/product/buy-verified-cash-app-account/
Choose a trusted provider when acquiring accounts to guarantee legitimacy and reliability. In an era where Cash App is increasingly favored for financial transactions, possessing a verified account offers users peace of mind and ease in managing their finances. Make informed decisions to safeguard your financial assets and streamline your personal transactions effectively.
Contact Us / 24 Hours Reply
Telegram:dmhelpshop
WhatsApp: +1 (980) 277-2786
Skype:dmhelpshop
Email:dmhelpshop@gmail.com
| whitemartin0549 | |
1,874,999 | Day 1: What is Node.js? | Let's start with Day 1: What is Node.js? Imagine you have a magic box called Node.js. This box lets... | 0 | 2024-06-03T06:57:25 | https://dev.to/learn_with_santosh/day-1-what-is-nodejs-436p | 30daysofnodejs, node, tutorial, learning | Let's start with Day **1: What is Node.js?**
Imagine you have a magic box called Node.js. This box lets you run special instructions written in a language called JavaScript, but it's not just for making websites like you do in your browser. With Node.js, you can make your computer do all sorts of cool things!
Here's a simple way to understand it:
1. **JavaScript Everywhere:** Normally, when you write JavaScript, it runs inside your web browser. But Node.js lets you run JavaScript code on your computer outside of the browser. It's like having a mini-browser right on your computer!
2. **Superpowers for JavaScript:** Node.js gives JavaScript special powers, like the ability to talk to your computer's file system, create web servers, and even interact with databases. This means you can build all kinds of programs, not just websites.
So, think of Node.js as your magic box that brings JavaScript to life beyond the web browser, letting you build all sorts of cool stuff on your computer!
Ready for Day 2? Let me know when you're set! | learn_with_santosh |
1,874,997 | Apartment Cleaning Costs in Zurich: What You Need to Know | Zurich, a city known for its high standard of living and pristine environment, offers its residents a... | 0 | 2024-06-03T06:56:21 | https://dev.to/servicefinders/apartment-cleaning-costs-in-zurich-what-you-need-to-know-4akn | Zurich, a city known for its high standard of living and pristine environment, offers its residents a vibrant lifestyle and numerous amenities. However, maintaining a clean and organized apartment amidst a busy schedule can be challenging. Hiring professional cleaning services can be an excellent solution, but understanding the associated costs is crucial. This blog post provides a comprehensive overview of [apartment cleaning costs in Zurich](https://servicefinders.ch/en/apartment-cleaning-in-zurich), the factors that influence these costs, and tips for finding the best value for your money.
Factors Influencing Apartment Cleaning Costs1. Frequency of Service
One-Time Cleaning: A single, thorough cleaning session, which is typically more expensive per visit due to the intensive work required.
Regular Cleaning: More cost-effective on a per-visit basis if you schedule weekly, bi-weekly, or monthly cleanings.
Custom Schedules: Prices can vary depending on the specific frequency and type of cleaning service needed.
2. Size and Condition of Your Apartment
Size: Larger apartments require more time and effort to clean, resulting in higher costs.
Condition: Apartments that need deep cleaning or have been neglected for a while will cost more due to the additional work involved.
3. Type of Cleaning Services
Basic Cleaning: Includes tasks like dusting, vacuuming, mopping, and cleaning bathrooms and kitchens.
Deep Cleaning: More intensive cleaning tasks such as scrubbing tiles, cleaning behind appliances, and addressing hard-to-reach areas.
Specialized Services: Additional services like window cleaning, carpet cleaning, or upholstery cleaning typically come at an extra cost.
4. Additional Services
Laundry and Ironing: Including laundry and ironing services will increase the overall cost.
Pet Hair Removal: Homes with pets may incur extra charges for pet hair removal and cleaning related to pet dander.
5. Experience and Reputation
Experienced Cleaners: More experienced and reputable cleaners or cleaning agencies often charge higher rates due to their expertise and reliability.
New Cleaners: Less experienced cleaners might offer lower rates, but the quality of service may vary.
6. Geographical Location
While Zurich is generally known for its high cost of living, prices can vary slightly depending on the specific area or neighborhood within the city.
Typical Pricing StructuresHourly Rates
Hourly rates are a common pricing structure for cleaning services. In Zurich, these rates typically range from CHF 30 to CHF 50 per hour. Factors influencing the rate include the complexity of the job and the cleaner’s experience. For instance, a basic cleaning might cost CHF 30 per hour, whereas deep cleaning or specialized services could be closer to CHF 50 per hour.
Flat Rates
Some cleaning services offer flat rates for specific tasks or packages. This can be beneficial if you have a clear idea of the services you need. For example:
End-of-Tenancy Cleaning: Ranges from CHF 500 to CHF 1,000, depending on the size and condition of the property.
Spring Cleaning: A comprehensive deep cleaning service might have a flat rate of CHF 300 to CHF 700.
Subscription Services
For regular cleaning, some agencies offer subscription services with discounted rates for weekly, bi-weekly, or monthly visits. This can be a cost-effective option for ongoing maintenance, often providing a reduced rate per visit compared to one-time cleanings.
Understanding What’s IncludedBasic Cleaning Tasks
Dusting: Dusting of all surfaces, including furniture, shelves, and electronics.
Vacuuming: Vacuuming carpets, rugs, and upholstered furniture.
Mopping: Mopping hard floors, including wood, tile, and laminate.
Bathroom Cleaning: Cleaning sinks, toilets, showers, and mirrors.
Kitchen Cleaning: Cleaning countertops, sinks, and wiping down appliances.
Deep Cleaning Tasks
Scrubbing Tiles and Grout: Thorough cleaning of bathroom and kitchen tiles.
Cleaning Behind Appliances: Moving and cleaning behind heavy appliances like refrigerators and stoves.
Interior Window Cleaning: Cleaning the inside of all windows.
Baseboards and Trim: Detailed cleaning of baseboards and trim around doors and windows.
Specialized Services
Carpet Cleaning: Professional steam cleaning of carpets.
Upholstery Cleaning: Cleaning and sanitizing upholstered furniture.
Window Cleaning: Cleaning both interior and exterior windows.
Tips for Getting the Best Value1. Get Multiple Quotes
Contact several cleaning services to get quotes for their services. This will give you a better idea of the going rates and help you identify any outliers. Be sure to compare what each quote includes to ensure you're comparing like-for-like services.
2. Check Reviews and References
Ensure the cleaning service has a good reputation. Check online reviews on platforms like Trustpilot, Yelp, and Google Reviews, and ask for references from previous clients. Reliable feedback can help you choose a trustworthy and efficient service.
3. Clarify What’s Included
Make sure you understand what tasks are included in the quoted price and what might cost extra. This will help you avoid unexpected charges and ensure the cleaning service meets your needs.
4. Negotiate a Trial Period
If you’re unsure about committing to a long-term arrangement, negotiate a trial period to assess the quality of the cleaning service before making a longer-term commitment.
5. Discuss Payment Terms
Clarify payment terms in advance, including accepted payment methods and any discounts available for long-term contracts or upfront payments.
6. Ensure Insurance Coverage
Make sure the cleaning service has liability insurance to cover any potential damages or accidents. This provides peace of mind and protects both parties.
7. Consider Local Recommendations
Personal recommendations from friends, family, or colleagues can be invaluable in finding a trustworthy and effective cleaning service. Local recommendations often come with firsthand experiences and honest feedback.
Conclusion
Hiring a professional cleaning service in Zurich is a great way to maintain a clean and organized apartment, but it’s essential to understand the costs involved. By considering the factors that influence cleaning costs, typical pricing structures, and tips for getting the best value, you can make an informed decision that suits your budget and needs. Whether you opt for a one-time deep clean or regular maintenance, investing in a professional cleaning service can greatly enhance your quality of life in Zurich, allowing you to enjoy more of what this beautiful city has to offer. | servicefinders | |
1,874,996 | Histogram: Your first statistical Analysis | The first step in any machine learning project is to analyze the data before building a model. This... | 0 | 2024-06-03T06:51:27 | https://dev.to/madhuripatil/histogram-your-first-statistical-analysis-1af2 | histogram, datascience, python, seaborn | The first step in any machine learning project is to analyze the data before building a model. This includes understanding of data, where we primarily use distribution visualization to perform some early analysis.
This visual representation can reveal a lot about the underlying distribution, such as its normality, whether it is skewed, has a single peak or multiple peaks, and their central tendencies and potential outliers, which are crucial for understanding the underlying structure of the data.
There are several methods that you can use to visualize distribution, and each has its own set of advantage and disadvantages.
The most common method to visualizing a distribution is the histogram.
In this article, let's study histogram and learn how to use them effectively to reveal valuable information from the data and their significance to avoid the common pitfalls such as inappropriate selection of bin sizes.
## What is Histogram
Histogram is a graphical representation of the distribution of numerical data. They divide the data into bins or intervals and display the frequency of occurrences within each bin using bars of varying heights.
You must use data that is continuous in nature, as histograms are best suited for continuous data because they can effectively represent the distribution of data points within continuous intervals.
Discrete numeric data, on the other hand, often contains a finite number of fixed values, which may result in a misleading representation if forced into a histogram.
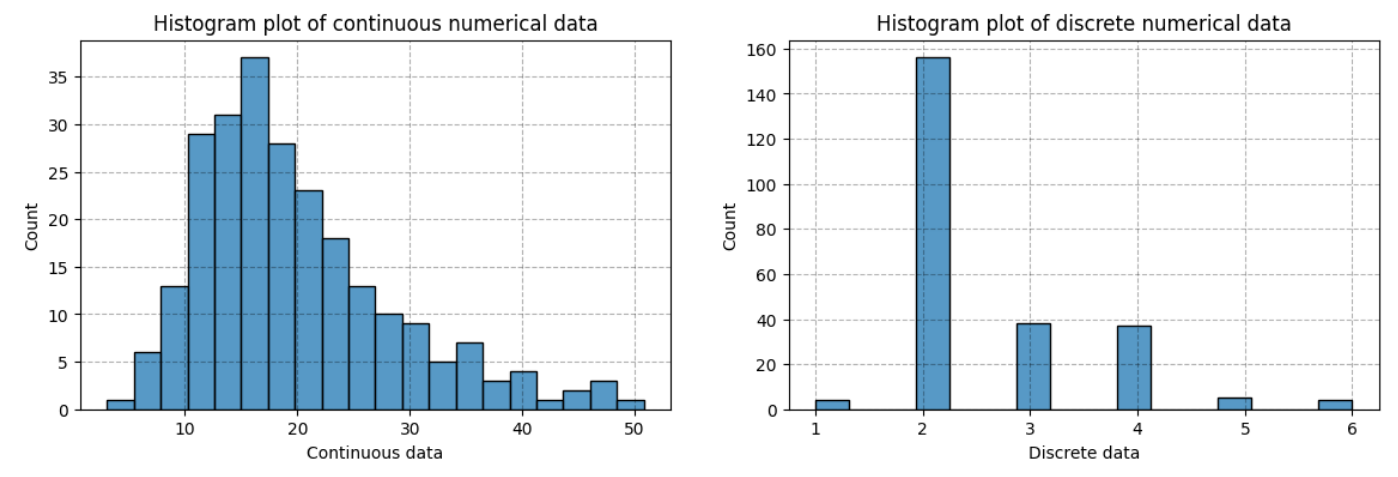
Above figure shows the histogram plots for both continuous and discrete data values.
Histogram is a type of bar plot that represents the counts of number of data points that fall within a range of values, known as bins.
The bins are typically of equal in width size which we can observe in both graphs, and there should be no gaps between the bars of the histogram like in plot for continuous data (left figure). However, there is huge gap can observe between the bars of histogram for discrete data (right figure).
You can specify `discrete=True` parameter if you are using seaborn for plotting, but it does not work all the time. So alternative visualizations like bar charts or frequency tables are typically more appropriate, as they accurately display the count or frequency of each unique value.
## Histogram plot using Seaborn library of python for data visualization
You can use _histplot_ method of seaborn library to plot histogram. It offers a range of functionalities to visualize data effectively.
```python
# import seaborn library
import seaborn as sns
import matplotlib.pyplot as plt
# load dataset
tips = sns.load_dataset('tips')
# Univariate plotting of histogram
sns.histplot(tips, x='total_bill', bins=20)
plt.grid(ls="--", c='#000', alpha=0.3)
plt.show()
```
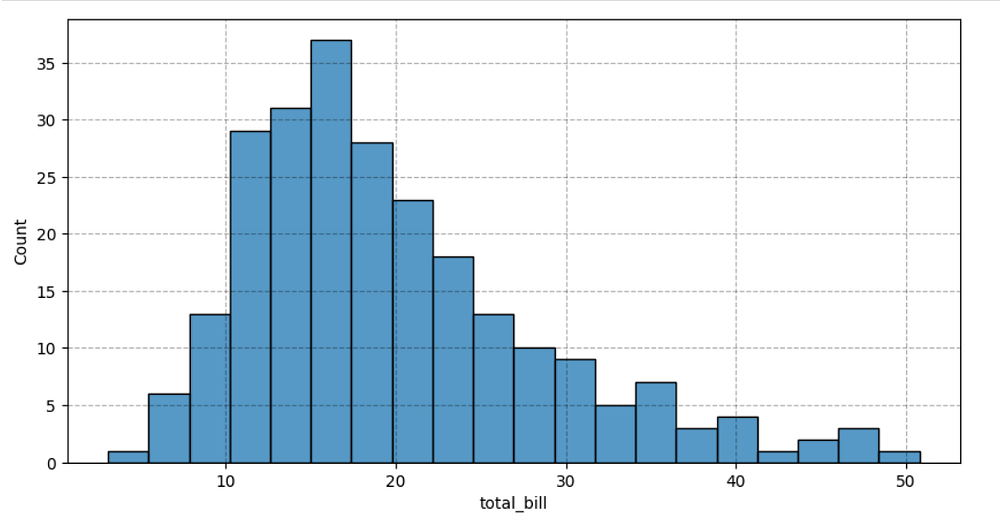
The above plot reveals the few insights about total bill of the customer's meal. For instance -
- We can see that the distribution has single peak, with most common total bill is between $14–$16.
- Distribution appeared to have positive tail which indicates the right skewness with some potential outliers.
You can evaluate the normality of data further, by observing the mean and median values of the data.
## Selection of Bin Size
The choice of the size of bins is very important, as wrong bin size can mislead the conclusion draw form the visualization.
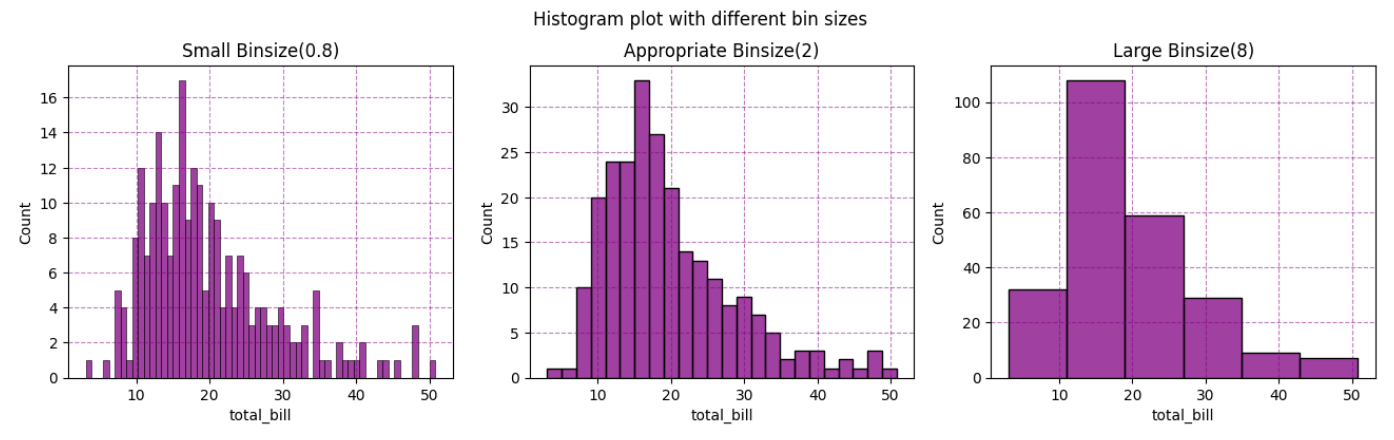
Too small bin size can lead to a histogram with many bins (plot 1), each bins containing a small number of observations, which can result in an overly complex and noisy distribution.
This granularity can distort the underlying trends and make it difficult to identify the true distribution pattern.
On the other hand, choosing an overly large bin size for a histogram (plot 3) can significantly affect its ability to accurately represent the underlying data distribution.
Large bins may lead to oversimplified distribution - as the multiple values are grouped in a single bin, the variations in the data points may lost, making it difficult to identify trends or anomalies.
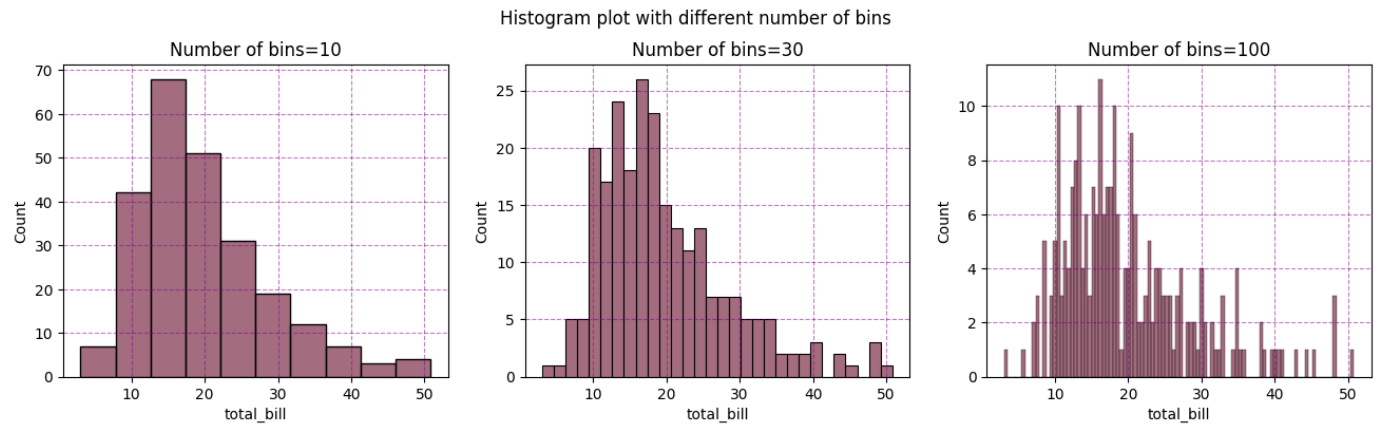
Conversely, a well-chosen bin size which is shown in second plot, can help in highlighting the true distribution of the data, allowing for better insights and decisions based on the visualized information.
Sometimes it is more appropriate to use number of bins instead of their size.
There are several methods to select the right size of the bins, each method has its advantages and is suitable for different types of data sets. You can learn about different methods for selection of the bin size here.
Seaborn uses the default bin size, which is determined using a reference rule that depends on the sample size and variance. This works well in many cases, (i.e., with "well-behaved" data) but it fails in others.
It is always a good to try different bin sizes to be sure that you are not missing something important.
Seaborn offers various functionality to specify bins in several different ways, such as by setting the total number of bins to use, the width of each bin, or the specific locations where the bins should break.
## hue
After univariate analysis of a particular feature, you must analyze their distribution further across the different set of groups of the variable.
For instance, here we must analyze the distribution of _total_bills_ across the different group of people such as male and female.
```python
sns.histplot(tips, x='total_bill', hue='sex', bins=20);
```
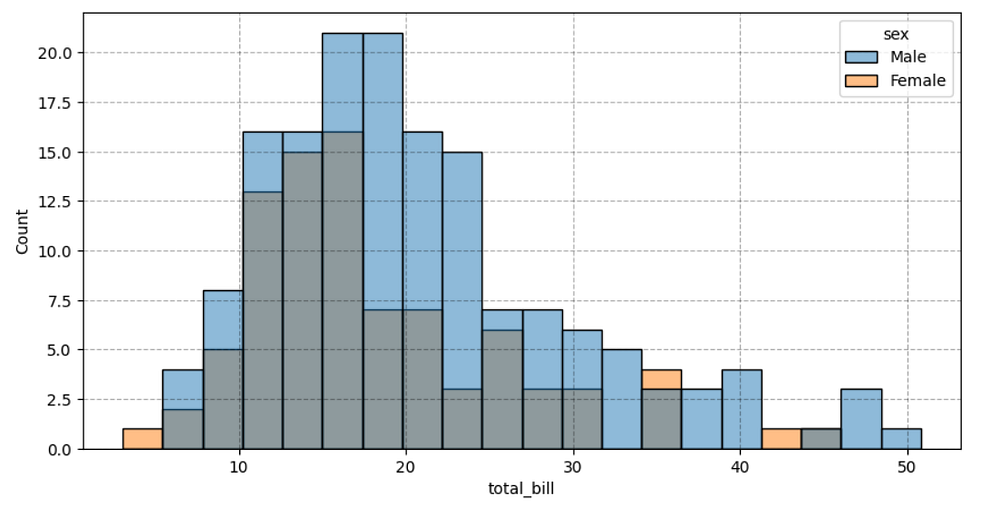
## element
In the above figure, it is little difficult to visualize the shape of the distributions for the groups as the histogram overlap by default on top of each other.
You can use step function instead of bars by setting up element parameter.
```python
sns.histplot(tips, x='total_bill', hue='sex', bins=20, element='stop');
```
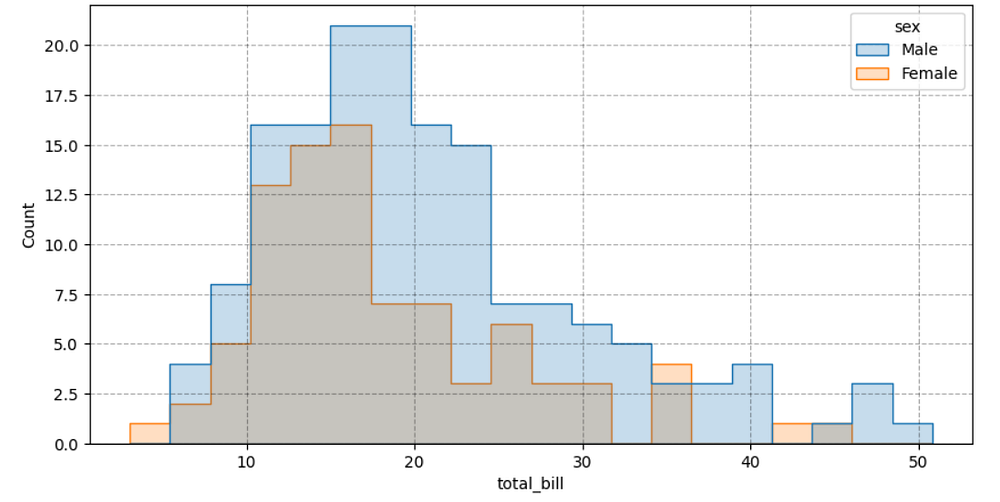
## kde
You can also visualize the smooth distribution of observations to understand the shape of the data, by producing continuous density estimate by setting _kde=True_.
```python
sns.histplot(tips, x='total_bill', kde=True, bins=20);
```
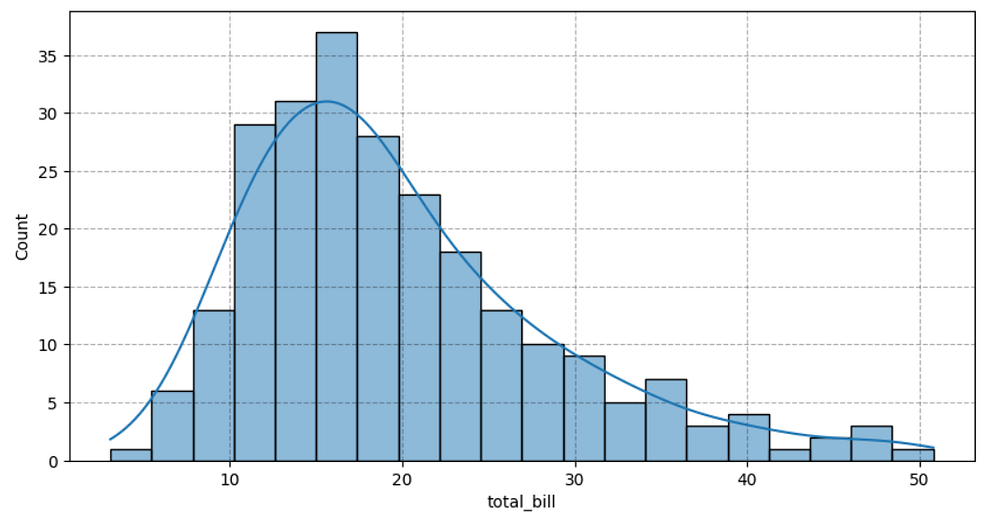
As data changes, so does the shape of the histograms. There are various types of histograms, each with different meanings. Understanding the implications of a histogram's shape can guide further analysis and algorithm selection. This understanding is crucial in interpreting data correctly and making informed decisions based on statistical information.
For instance, a normal distribution might suggest different data preprocessing steps or model assumptions than a bimodal distribution.
Let's explore these types and learn how to transform them into normally distributed data in upcoming tutorials. For now, let's conclude this article.
I hope this article helps you understand histograms using Seaborn. Don't forget to visit the Seaborn documentation to learn more details.
## Reference
Seaborn offers many more functionality to effectively analyze data distribution. You can learn about them here in - [seaborn histogram plot doc](https://seaborn.pydata.org/generated/seaborn.histplot.html)
## 🔗 Affiliate link
If you're interested in learning machine learning and are searching for a course, you should consider checking out this [Master machine learning with scikit-learn](https://courses.dataschool.io/master-machine-learning-with-scikit-learn/rxysi) offered by Kevin at Data School.
This course is designed to provide comprehensive knowledge and practical skills in machine learning using the Scikit-Learn library.
| madhuripatil |
1,874,995 | Sửa Airpods Thành Trung Mobile | Thông tin giới thiệu: Dịch vụ sửa AirPods tại Thành Trung Mobile là lựa chọn đáng tin cậy... | 0 | 2024-06-03T06:48:00 | https://dev.to/suaairrpodsthanhtrungmobile/sua-airpods-thanh-trung-mobile-2kk2 | ## Thông tin giới thiệu:
Dịch vụ [sửa AirPods](https://thanhtrungmobile.vn/sua-chua-tai-nghe/airpods) tại Thành Trung Mobile là lựa chọn đáng tin cậy cho những ai đang gặp vấn đề với tai nghe AirPods. Với đội ngũ kỹ thuật viên giàu kinh nghiệm, chúng tôi cam kết cung cấp các giải pháp toàn diện cho mọi sự cố kỹ thuật. Dịch vụ bao gồm thay thế pin, loa, mic, sửa chữa hỏng hóc do nước, phụ kiện thay thế và khắc phục sự cố kết nối. Bạn có thể yên tâm khi đến với Thành Trung Mobile, vì tai nghe của bạn sẽ được khôi phục hoạt động trơn tru như mới. Ngoài ra, họ cũng cung cấp dịch vụ sửa AirPods với giá cả hợp lý và thời gian nhanh chóng. Nếu bạn đang sở hữu tai nghe đẳng cấp này và gặp vấn đề, hãy đến với Thành Trung Mobile để trải nghiệm dịch vụ sửa chữa hàng đầu tại TP HCM!
#suaairpods #suachuaairrpods #suaairpodsthanhtrungmobile #suachuaaipodsthanhtrungmobile
## Thông tin liên hệ:
Website: [https://thanhtrungmobile.vn/sua-chua-tai-nghe/airpods](https://thanhtrungmobile.vn/sua-chua-tai-nghe/airpods)
Địa chỉ: 24 Trần Văn Kiểu, P.10, Quận 6, TP.HCM
Mail: suaairpods.thanhtrungmobile@gmail.com
Phone: 0909.650.650
Maps: https://goo.gl/maps/dybCPk55j2wG1Sc2A
## My socail:
[https://www.facebook.com/suaairrpodsthanhtrung](https://www.facebook.com/suaairrpodsthanhtrung)
[https://x.com/suaairpodsttmb](https://x.com/suaairpodsttmb)
[https://www.tumblr.com/suaairpodsthanhtrung](https://www.tumblr.com/suaairpodsthanhtrung)
[https://www.pinterest.com/suaairpodsthanhtrung](https://www.pinterest.com/suaairpodsthanhtrung)
[https://www.instagram.com/suaaipodsthanhtrung](https://www.instagram.com/suaaipodsthanhtrung)
[https://www.twitch.tv/suaairpodsthanhtrung/about](https://www.twitch.tv/suaairpodsthanhtrung/about)
[https://sites.google.com/view/danh-muc-sua-chua-airpods](https://sites.google.com/view/danh-muc-sua-chua-airpods)
[https://www.behance.net/suaairpodsthanhtrung](https://www.behance.net/suaairpodsthanhtrung)
[https://www.deviantart.com/suaairrpodsthanhtrun](https://www.deviantart.com/suaairrpodsthanhtrun)
[https://about.me/suaairpodsthanhtrung](https://about.me/suaairpodsthanhtrung)
[https://qiita.com/suaairpodsthanhtrung](https://qiita.com/suaairpodsthanhtrung)
[https://band.us/@suaairpodsthanhtrung](https://band.us/@suaairpodsthanhtrung)
[https://www.scoop.it/topic/suaairrpodsthanhtrung](https://www.scoop.it/topic/suaairrpodsthanhtrung)
[https://www.bark.com/en/gb/company/sua-airpods-thanh-trung/KOaaG/](https://www.bark.com/en/gb/company/sua-airpods-thanh-trung/KOaaG/)
[https://www.youtube.com/@SuaAirpodsThanhTrungMobile/about](https://www.youtube.com/@SuaAirpodsThanhTrungMobile/about)
[https://www.jigsawplanet.com/suaairrpodsthanhtrung](https://www.jigsawplanet.com/suaairrpodsthanhtrung)
[https://sketchfab.com/suaairpodsthanhtrung](https://sketchfab.com/suaairpodsthanhtrung)
[https://www.provenexpert.com/suaairpodsthanhtrung](https://www.provenexpert.com/suaairpodsthanhtrung)
[https://ko-fi.com/suaairrpodsthanhtrung](https://ko-fi.com/suaairrpodsthanhtrung)
[https://mastodon.social/@suaairpodsthanhtrung](https://mastodon.social/@suaairpodsthanhtrung)
[https://www.linkedin.com/company/sua-airpods-thanh-trung-mobile](https://www.linkedin.com/company/sua-airpods-thanh-trung-mobile)
[https://www.reddit.com/user/suaairpodsthanhtrung](https://www.reddit.com/user/suaairpodsthanhtrung)
[https://suaairpodsthanhtrung.quora.com](https://suaairpodsthanhtrung.quora.com)
| suaairrpodsthanhtrungmobile | |
1,874,993 | How to implement authorization with role based accessibility in Next js? | To implement authorization and role-based protected routes in Next.js, you can follow these... | 0 | 2024-06-03T06:45:07 | https://dev.to/nadim_ch0wdhury/how-to-implement-authorization-with-role-based-accessibility-in-next-js-21li | To implement authorization and role-based protected routes in Next.js, you can follow these steps:
1. **Set Up Authentication:**
Use an authentication library like `next-auth` for user authentication. This will handle user sign-in, sign-out, and session management.
2. **Create Roles:**
Define user roles (e.g., admin, user, editor) and assign them to users upon registration or within your user database.
3. **Protect Routes Based on Roles:**
Use a higher-order component (HOC) or middleware to protect your routes based on user roles.
### Step-by-Step Implementation
#### 1. Install NextAuth.js
First, install `next-auth`:
```bash
npm install next-auth
```
#### 2. Configure NextAuth.js
Create a file named `[...nextauth].js` in the `pages/api/auth` directory:
```javascript
import NextAuth from 'next-auth';
import Providers from 'next-auth/providers';
export default NextAuth({
providers: [
Providers.Credentials({
name: 'Credentials',
credentials: {
email: { label: 'Email', type: 'email' },
password: { label: 'Password', type: 'password' },
},
authorize: async (credentials) => {
const user = await fetchUserFromDatabase(credentials.email, credentials.password);
if (user) {
return user;
} else {
return null;
}
},
}),
],
callbacks: {
async session(session, user) {
session.user.role = user.role; // Add role to session
return session;
},
async jwt(token, user) {
if (user) {
token.role = user.role;
}
return token;
},
},
});
async function fetchUserFromDatabase(email, password) {
// Implement user fetching logic here
return { id: 1, name: 'John Doe', email, role: 'admin' }; // Example user
}
```
#### 3. Create Protected Route HOC
Create a higher-order component (HOC) to protect your routes based on user roles:
```javascript
import { useSession, getSession } from 'next-auth/client';
import { useRouter } from 'next/router';
import { useEffect } from 'react';
const withAuth = (Component, allowedRoles) => {
return (props) => {
const [session, loading] = useSession();
const router = useRouter();
useEffect(() => {
if (!loading) {
if (!session) {
router.push('/api/auth/signin');
} else if (!allowedRoles.includes(session.user.role)) {
router.push('/unauthorized');
}
}
}, [loading, session, router]);
if (loading || !session) {
return <p>Loading...</p>;
}
return <Component {...props} />;
};
};
export default withAuth;
```
#### 4. Protect Your Pages
Wrap your pages with the `withAuth` HOC to protect them based on user roles:
```javascript
import withAuth from '../hoc/withAuth';
const AdminPage = () => {
return <div>Admin Content</div>;
};
export default withAuth(AdminPage, ['admin']);
```
#### 5. Create an Unauthorized Page
Create a page to show when the user is unauthorized:
```javascript
// pages/unauthorized.js
const Unauthorized = () => {
return <h1>Unauthorized - You do not have access to this page</h1>;
};
export default Unauthorized;
```
### Summary
1. **Install and configure `next-auth`** for authentication.
2. **Define user roles** and include them in the session.
3. **Create a higher-order component (HOC)** to protect routes based on roles.
4. **Wrap your pages** with the HOC to enforce role-based access control.
5. **Create an unauthorized page** to handle access denial.
This setup provides a robust way to manage authentication and authorization in a Next.js application, allowing you to protect routes based on user roles effectively.
Disclaimer: This content is generated by AI. | nadim_ch0wdhury | |
1,874,992 | Loading | Check out this Pen I made! | 0 | 2024-06-03T06:41:26 | https://dev.to/vry/loading-33e0 | codepen, webdev, javascript, beginners | Check out this Pen I made!
{% codepen https://codepen.io/Vraj247/pen/YzbZxWG %} | vry |
1,874,991 | Zeeve Partners with LightHouse to Bring Low Cost Perpetual Cloud Storage Services for Rollups and AppChains | We are excited to announce that LightHouse, a file storage protocol, has partnered with Zeeve to... | 0 | 2024-06-03T06:38:02 | https://www.zeeve.io/blog/zeeve-partners-with-lighthouse-to-bring-low-cost-perpetual-cloud-storage-services-for-rollups-and-appchains/ | announcement, zeeve, lighthouse | <p>We are excited to announce that <a href="https://www.lighthouse.storage/">LightHouse</a>, a file storage protocol, has partnered with <a href="https://www.zeeve.io/">Zeeve</a> to bring low-cost perpetual cloud storage services to rollups and appchains. This partnership is all set to help the Zeeve RaaS ecosystem to get this integration on-demand, store all the valuable data on-chain under the model, pay once for your file and store them for eternity. </p>
<p>At the moment, developers prefer to store valuable data over the cloud so that it is easily accessible and readily available whenever needed. However, this practice, though it is very convenient, is expensive nonetheless; because organizations are spending around $0.30/GB/Mo.</p>
<p>Even the alternative option, which is Cloud NAS, becomes ineffective if they wish to shift to a different model because a mere 1 TB extension,demands developers/corporations to buy the entire package, which might be 200 TB to 300 TB, making it a costly proposition. LightHouse abstracts the older models of cloud storage and allows corporations to switch from a rent-based model to a perpetual file storage model, which is 1000X less expensive than Cloud NAS. </p>
<p>After this integration, builders on Zeeve will be getting LightHouse as an easily pluggable component. So, they can easily connect their Dapp to LightHouse and store all the data that they wish to use for ensuring that the dApp remains operative. Since Zeeve launchpad supports all the leading rollups and appchains frameworks namely OP Stack, Arbitrium Orbit, Polygon CDK, zkSync ZK Stack, Cosmos SDK, Substrate, and Avalanche Subnets, they can easily integrate LightHouse and move their data on-chain for perpetual storage without breaking the bank. </p>
<p><em>“Data is the new oil and everyone wants to tap into the data for numerous purposes like extracting actionable intelligence from them or using them as a multiple source of truth for consensus and validation. However, the practice should be made economical and scalable at the same time</em>. <em>Now, when Zeeve R-a-a-S services are bundled with LightHouse, businesses will have a high performance infrastructure to launch their dApps using LightHouse as a cloud storage partner, which is economical and easily deployable under our integration model.</em>"</p>
<p>Dr. Ravi Chamria</p>
<p>Co-founder and CEO of Zeeve</p>
<p><em>"Partnering with Zeeve brings our low-cost, perpetual storage to rollups and appchains, making data storage more accessible and affordable. Developers can now integrate Lighthouse with Zeeve's RaaS ecosystem, ensuring secure, on-chain data storage with a pay-once model.</em></p>
<p><em>This collaboration transforms how data is stored, shifting from expensive rent-based models to a cost-effective, perpetual solution. Builders on Zeeve can easily connect their dApps to Lighthouse, benefiting from scalable and economical data storage</em>."</p>
<p>Nandit</p>
<p>Founder of Lighthouse</p>
<p>Presently, Zeeve has partnered with more than 40+ partners spanning across alt data availability layers, sequencer networks, interoperability protocols, decentralized oracles, account abstraction SDKs, data indexers, and other developer tools and protocols that can be easily integrated on-demand with your rollup or app-chain. As we head further in our journey from 30,000 Web3 startups, 40+ institutional partners to more and counting, there would be more integration partnerships that would help develop fully customized and highly performant appchains and rollups. </p>
<p>For additional information or to discuss launching a rollup chain, please visit our <a href="https://www.zeeve.io/rollups/">Rollups-as-a-Service page</a> or <a href="https://www.zeeve.io/talk-to-an-expert/">contact our expert team</a> to find the ideal infrastructure for your needs. </p> | zeeve |
1,874,990 | Annotations in Java Spring | For decades as of today, Java is undoubtedly one of the most popular programming languages used at... | 0 | 2024-06-03T06:37:29 | https://dev.to/akritikeswani/annotations-in-java-spring-1d0h | programming, learning, java, backenddevelopment | For decades as of today, Java is undoubtedly one of the most popular programming languages used at companies with massive codebases. You would think that now with languages such as Kotlin and Scala, companies probably want to pivot and entirely modernize their codebases, but there must be something so special about Java that makes people want to stay and revert to it. I wonder what that is…
Well, one could argue that it is the mere fact of Java being such a popular choice for object-oriented programming and that the JVM makes it so dynamic to run and deploy across complex operating systems. One must also consider though, the sheer flexibility of Java, especially with frameworks such as Spring that leverage containerizing objects and method calls, which essentially make applications easier to scale, which is quite necessary in enterprise software environments.
Let’s get into why Spring is so awesome as a framework, especially when you are dealing with huge codebases that require you to sift through hundreds of services in several interconnected repositories - we have all been there!
So in most normal applications, you definitely need a lot of boilerplate code to get started, especially if you are running a client on top of a server, and Spring makes this seamless with the abstraction and layering of classes, as well as annotations classifying objects, services, and the lines of code actually executing the other lines of code. All that sort of may seem confusing, but here’s the thing, annotations can really enhance the way your code looks, operates, and performs after more code has been written.
So, in Java Spring, it is a known concept to use annotations, which can get pretty tricky fast, because it abstracts away so much code that you would otherwise have to write. Annotations such as `@Slf4j` (used for logging) can be super confusing to someone who is just starting to write classes in a Spring application. I'm here to tell you that it all gets easier, and makes sense eventually, like all things in life!
Typically, in these Java Spring applications, you usually have a main file that is like the runner, the one that calls the entire application, often denoted with a `@SpringBootApplication` annotation. In its bare form, this file looks like:
```java
@SpringBootApplication
public class MyApplication {
public static void main(String[] args) {
SpringApplication.run(MyApplication.class, args);
}
}
```
In reality `@SpringBootApplication` is actually a combination of `@SpringBootConfiguration` (specialized version of `@Configuration`) `@EnableAutoConfiguration,` and `@ComponentScan.` The reason for this is that we need to reduce the boilerplate code and make the code more readable. We can see this in the way that `@EnableAutoConfiguration` minimizes the need to write configuration code manually. Lastly, `@ComponentScan` can do the work of registering beans in the application context for the build to work without explicitly declaring each component.
---
As you can see, each annotation serves a specific purpose, and together they enable the entire application to function. Let's dive deeper into `@Repository`, another useful annotation that supports storage, retrieval, update, and delete operations on objects. This annotation is a specialization of `@Component`, which allows Spring to detect and manage repository classes.
Here's an example:
```java
@Repository
public interface UserRepository extends JpaRepository<User, Long> {
// Custom query methods can be defined here
}
```
In the comment area, you can include custom query logic using the `@Query` annotation or take advantage of Spring Data JPA's query method conventions. For example, methods like `IsStartingWith` or `Containing` can be used to filter data.
A practical example would be:
```java
List<User> findByFirstnameContaining(String fragment);
```
This method filters users whose first names contain the specified fragment. Using these conventions makes the code more readable and easier to maintain.
All this is great, but in order to do some action on the code and perform operations on how we are using all this data, understanding the `@Service` annotation is quite necessary. The `@Service` annotation is used to define a service class in the service layer of the application. This layer contains the business logic and acts on data passed between the controller and repository layers. Services often operate on models or **POJO** (Plain Old Java Object) objects, which represent the data in your application.
Here's an example of how a service can be structured:
```java
@Service
public class UserService {
@Autowired
private UserRepository userRepository;
// Logic on finding a user by ID
public User findUserById(Long id) {
return userRepository.findById(id).orElse(null);
}
// Logic on how to create or update a user
public User saveUser(User user) {
return userRepository.save(user);
}
}
```
Here we see that the `@Autowired` annotation is simply ensuring that the service uses the `UserRepository` to interface with the database. These methods are simply performing CRUD-like operations on the `User` objects which are just POJOs.
Now, we mentioned POJOs but how do they even represent the data we are using? Most of it is simply having a getter, setter, and maybe a few methods here to represent unique use cases of manipulating the data. An example of a User model associated with the above would look something like:
```java
@Entity
public class User {
@Id
@GeneratedValue(strategy = GenerationType.IDENTITY)
private Long id;
private String firstname;
private String lastname;
private String email;
// Getters and setters
public Long getId() {
return id;
}
public void setId(Long id) {
this.id = id;
}
public String getEmail() {
return email;
}
public void setEmail(String email) {
this.email = email;
}
}
```
Now we see that we also have the `@Entity` annotation here, but not to worry, it is simply ensuring that this can be mapped to a table in a database - this lets use the JPA (Java Persistance API) as mentioned earlier! `@Id` is also included in this class to mark a primary key of the entity and this is just a unique identifier as the name implies.
The service class ensures that these POJOs transfer data between the repository and the controller, which we have not touched upon much, but essentially allows us to separate the presentation later from the application logic. Services are special in the sense that we can make sure the core logic of the application is applied properly before any data is saved, retrieved, or manipulated.
After going through all of this, it is crucial to understand how a typical Spring application flows together, and some key parts as mentioned are the **controller (handling requests), service (business logic), and the repository (for CRUD operations)**. To leverage Java Spring’s full potential, these annotations are super useful to know and adapt, as they make the code more readable as well as maintainable!
**Looking Ahead**
In order to take full advantage of Spring and really understand what a brilliant architecture of an application may look like, it is vital to explore the **microservices architecture,** which I plan to delve into within the next article! Microservices are nice in that they offer more scalability and flexibility, since we can break down the application into smaller, deployable services. | akritikeswani |
1,874,989 | 5 Reasons to Go for System Integration Testing | For complicated software systems to integrate and perform seamlessly, System Integration Testing... | 0 | 2024-06-03T06:37:14 | https://2sistersgarlic.com/5-reasons-to-go-for-system-integration-testing/ | system, integration, testing | 
For complicated software systems to integrate and perform seamlessly, System Integration Testing (SIT) is essential. Adopting a SIT is becoming more of a must than a choice for companies looking to offer dependable, high-quality products. This article examines five strong arguments for why adopting SIT Testing ought to be the first priority for every project involving software development.
1. **Verify End-to-End System Functionality**
Verifying the whole functionality of the system under development is one of the main goals of SIT. Modern software systems frequently have a number of interconnected modules, components, and interfaces that need to function well together. SIT offers a thorough testing methodology that assesses how the system behaves when all these parts are combined and communicating with one another. SIT can find errors, incompatibilities, and performance snags that could have gone missed in component-by-component testing by modeling real-world situations.
2. **Identify and Resolve Integration Defects Early**
When various components don’t function as intended, it can lead to integration problems, which can be difficult to find and fix if ignored until much later in the development process. SIT is essential for spotting these flaws early on, when fixing them is usually simpler and less expensive. Before a system moves on to latter phases of testing and deployment, SIT enables development teams to make necessary corrections, address bugs, and optimize a system’s architecture.
3. **Ensure Compliance and Regulatory Standards**
A few sectors such as the government, finance and healthcare are among those that must follow regulatory compliance standards. SIT offers a chance to confirm that the integrated system complies with these laws and industry norms. Through comprehensive testing in the integration stage, companies can spot possible non-compliance problems early in the development cycle and fix them. An organization’s reputation may suffer, along with harsh fines and legal ramifications, if regulatory criteria are not met.
4. **Improve System Performance and Scalability**
In addition to confirming functional correctness, SIT evaluates the system’s scalability and performance. When separate components are tested separately, their interactions may not be able to identify scalability constraints, resource consumption problems, or performance bottlenecks until the components are merged. Organizations can detect and resolve these issues prior to the system going into production by incorporating load, stress, and performance testing into the SIT process.
5. **Facilitate Effective Communication and Association**
Those who are involved in SIT are mostly subject matter experts, business analysts, testers, and developers, along with other team members. Planning, carrying out, and evaluating SIT outcomes promote efficient communication and teamwork between these many groups. Teams can exchange knowledge, set expectations, and develop a shared understanding of the requirements and behavior of the system by cooperating to achieve a common goal, which is to ensure the system’s effective integration.
**Conclusion**
In the digital age, businesses thrive on interconnected systems and applications. Ensuring seamless integration between these components is crucial for operational efficiency and exceptional customer experiences. Opkey emerges as a game-changer, offering a robust solution for System Integration Testing (SIT). Opkey’s innovative platform empowers organizations to rigorously test and validate the interoperability of their software ecosystems. With advanced testing capabilities and automation frameworks, Opkey streamlines the SIT process, identifying and resolving integration issues before they impact business operations. By leveraging Opkey, companies can accelerate time-to-market, minimize disruptions and deliver seamless user experiences across their digital landscapes. | rohitbhandari102 |
1,874,988 | Which Scenarios Does ClickHouse Applies to? | ClickHouse has been popular in recent years as an analytic database. It is noted for the high speed... | 0 | 2024-06-03T06:36:26 | https://dev.to/esproc_spl/which-scenarios-does-clickhouse-applies-to-3mp5 | clickhouse, development, lauguage, beginners | ClickHouse has been popular in recent years as an analytic database. It is noted for the high speed and is often used as the benchmark by vendors of many other analytic databases whose selling points are high performance. Many users will consider turning to ClickHouse when they encounter database performance problems.
ClickHouse has an outstanding feature. Its column-oriented wide table runs fast, thanks to the excellent compression probably. However, it does not have any other merits. Users who hope to use it to solve database performance problems will likely feel disappointed.
We compare the TPC-H 100G performance of ClickHouse with that of Oracle in the same hardware environment. Below only lists the test results (Time unit: second). Find complete test report [HERE]
(http://c.raqsoft.com/article/1684805351312).
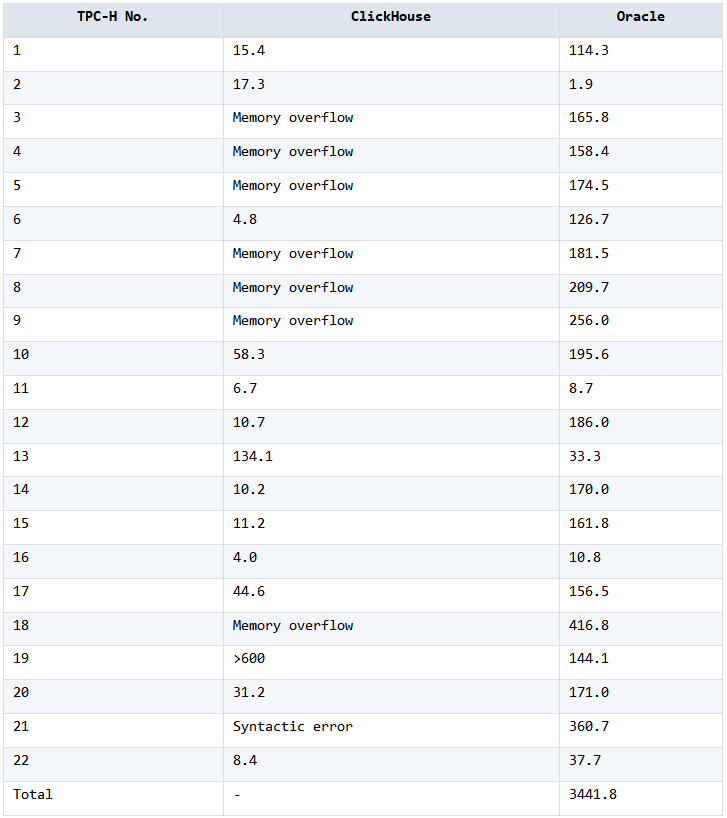
TPC-H database performance test is relatively basic and – generally speaking, not complicated. But not all tests are simple single table traversal, there are also JOINs and subqueries. In those cases, ClickHouse’s performance is very poor. There are quite a few computing tasks that can’t be finished at all; SQL statements of a few tasks are even considered too complicated to be executed. ClickHouse is not even as good as Oracle in handling them. Oracle is not a specialized analytic database and is much slower, but it can complete all tasks.
The specific reason is probably as mentioned above. ClickHouse only does a good job in data storage compression, which makes simple traversal very fast; but for slightly more complex computations, it has rather limited optimization capabilities and just cannot finish the execution.
So, users who want to use ClickHouse to solve performance problems should first examine the complexity of their computing tasks by comparing them with TPC-H.
Now we still use the TPC-H data to generate a table having a lot of columns and perform the multi-dimensional analysis ClickHouse is best at. Results are listed below (Time unit: second). Find complete test report [HERE.](http://c.raqsoft.com/article/1690170794600)
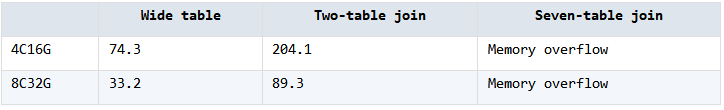
ClickHouse is good at handling scenarios involving wide table traversal and has the highest performance. Its performance, however, drops sharply once a join is involved. More complicated joins will cause memory overflow, which once again verifies the above cause analysis.
It seems that ClickHouse is fast only when it handles the simple single table traversals that do not involve any associations. But such “fast speed” ClickHouse can achieve applies too narrow application scenarios. Is it worthwhile to introduce a database specifically to do just such a simple job?
Unlike ClickHouse that has an exaggerated fame, esProc SPL mentioned in the above test report is the real performance champion.
esProc SPL is also open-source. It is developed in Java, but it can far outperform the C++ developed ClickHouse in many performance optimization scenarios.
Strictly speaking, esProc isn’t an analytic database. But it offers high-performance storage schemas (column-oriented storage, compression, etc.) and corresponding algorithm libraries, which enables it to completely replace the analytic database’s computing functionality.
Unlike ClickHouse’s other database competitors, esProc does not adopt the SQL syntax, but uses the more concise SPL (Structured Process Language) instead. The design can overcome SQL’s defects and help achieve high-performance algorithms SQL finds it difficult to or cannot implement. Find easy to understand illustrations [HERE](http://c.raqsoft.com/article/1644827578670). If the database based on the SQL system is still used, the product will still have the SQL limits and cannot make the most use of the hardware resources to obtain the best performance possible, even if it can surpass ClickHouse in certain aspects.
Let’s compare the esProc performances in the above test report with those of ClickHouse:
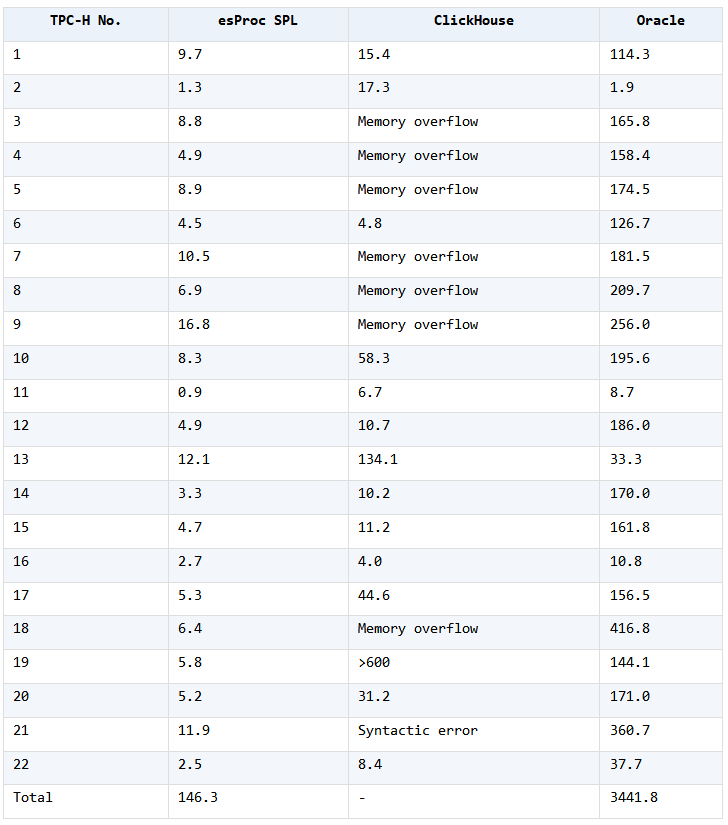
esProc SPL noticeably outstrips ClickHouse in performance as it executes all tasks very fast. It has comprehensive, overwhelming advantages over ClickHouse.
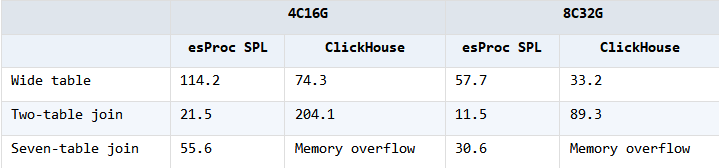
When data volume grows, ClickHouse is indeed better and faster than esProc SPL in handling traversal of a single wide table it is good at. Yet, as wide tables are used in most cases to avoid low-speed join operations (by increasing data volume and performing more complicated data preparations), they become unnecessary when esProc SPL’s unique join optimization strategy enables higher speed than ClickHouse wide tables. Wide tables do not have any merits any longer and become useless once they lose the performance advantages.
Though ClickHouse is faster in handling simple, non-association summarization on single tables, it isn’t orders of magnitude faster than esProc (after all, CPU and hard disk merely have this speed). In this case, even if task characteristics can be used to perform optimization, we will still find it difficult to work it out based on ClickHouse. Many optimization logics cannot be achieved in SQL and C++ programming is needed in the higher level to complete the goal. This is complicated and difficult. SPL, however, has much more powerful programming ability and can make good use of the task characteristics to write optimization code.
For example, contemporary multi-dimensional analyses almost always involve multi-index summarization. We can write multi-purpose traversal algorithm in SPL to compute multiple aggregate values during one traversal. Even if SPL is slightly slower than ClickHouse in handling the single-index computation, it can significantly surpass it when dealing with the multi-index summarization:
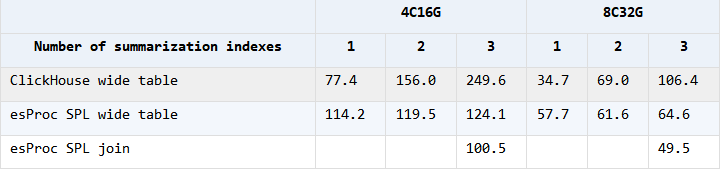
(Find the complete test report [HERE](http://c.raqsoft.com/article/1690190890595))
For more complicated computations, such as funnel analysis, they are too complex to be tested using the ClickHouse. But esProc SPL can test them. Find related information [HERE](http://c.raqsoft.com/article/1691043285347).
In a nutshell, esProc SPL has complete and comprehensive performance advantages, but ClickHouse’s performance advantages only apply in a very narrow range of applications.
Here is one real-world use case. A space-time collision problem involves about 25 billion rows of data. It seems that the SQL statement is not complicated:
```
WITH DT AS ( SELECT DISTINCT id, ROUND(tm/900)+1 as tn, loc FROM T WHERE tm<3*86400)
SELECT * FROM (
SELECT B.id id, COUNT( DISINCT B.tn ) cnt
FROM DT AS A JOIN DT AS B ON A.loc=B.loc AND A.tn=B.tn
WHERE A.id=a AND B.id<>a
GROUP BY id )
ORDER BY cnt DESC
LIMIT 20
```
Traditional databases run too slow and users turn to ClickHouse to solve the problem. ClickHouse runs over 30 minutes under a 5-node cluster environment and falls short of expectation. With the same amount of data, it takes SPL code one node and less than 6 minutes to complete the computation, which exceeds users’ expectations. Taking account of the gap between hardware resources, SPL is over 25 times faster than ClickHouse.
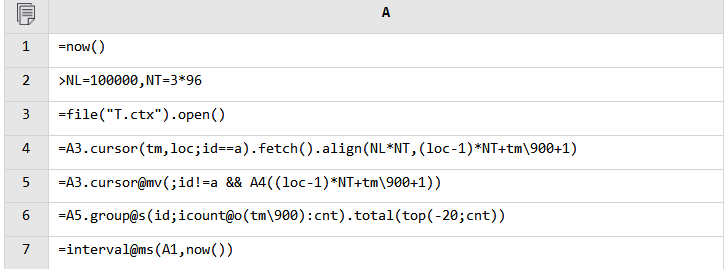
(Unlike the code produced by other programming languages, SPL code is written in a grid. Find related information [HERE](http://c.raqsoft.com/article/1681713093064)).
The SQL DISTINCT computation involves HASH values and their comparison. It becomes computation-intensive when data volume is huge. The self-join and the further COUNT(DISTINCT) will also seriously slow down the performance. SPL can make the most use of ordered grouping and ordinal-number-based location that SQL does not have to effectively avoid the high complexity self-joins and DISTINCT operations. Though SPL does not have the advantage over ClickHouse in the aspect of storage efficiency and Java is a little slower than C++, it still boosts the performance by orders of magnitude.
| esproc_spl |
1,874,987 | Streamlining Software Development with Efficient Email Archiving Solutions | Managing the massive flood of daily emails may become a difficult undertaking in the fast-paced world... | 0 | 2024-06-03T06:36:08 | https://dev.to/elainecbennet/streamlining-software-development-with-efficient-email-archiving-solutions-29c5 | emailarchiving, softwaredevelopment, development | Managing the massive flood of daily emails may become a difficult undertaking in the fast-paced world of software development. The sheer number creates compliance issues, slows down production, and clogs inboxes.
This is where efficient email archiving solutions come into play. Automated archiving systems can quicken the communication process and assure regulatory compliance while boosting productivity to the highest level.
For software development teams, where rapid and accurate information exchange is critical, effective email archiving solutions provide a reliable method to manage and retrieve important communications. This leads to better decision-making, improved knowledge management, and a more organized development process.
Let's explore how email archiving can transform the software development landscape, making it more efficient, compliant, and productive.
## Meeting Regulatory Compliance
An essential requirement for email archiving is industry regulations. The financial services, healthcare, and government industries are generally required to [save emails](https://dev.to/koossaayy/effortless-email-archiving-saving-sent-emails-on-server-with-laravel-imap-3he7) for several years, and failure to fulfill these obligations can result in heavy fines, legal action, and even malpractice exposure.
Email archiving can automatically classify and encrypt email, ensuring that it is stored correctly by pre-defined retention policies that enable your organization to stay compliant. [Archiving policies](https://www.hipaajournal.com/best-practices-for-creating-an-email-archiving-policy/) need to be in place to ensure that all your emails are automatically retained by company policy and that this is managed centrally — without the need for staff to move emails back and forth manually.
## Boosting Productivity
Effective email archiving can also rationalize software development by automating much of the storage and retrieval process. More productive time is spent doing the work when the relevant information is automatically retrieved. Developers can focus on the work at hand because they know they have all the information they need to get the job done.
This automation not only saves time but also decreases the likelihood of losing important emails due to human error. Automating the process of archiving emails to an appropriate email archiving solution rids your IT staff members of concern about managing and retrieving old emails and allows them to do something more productive instead, which, in turn, can result in quicker project completions and a more productive development cycle.
And, of course, automated archiving also means that the emails are stored in a safe, tamper-proof environment, and that means an increased level of data integrity and reliability as well.
## Improving Knowledge Management
[Cloud email archiving solutions](https://jatheon.com/products/cloud-email-archiving-solutions/) also serve as a valuable repository of knowledge. For software development teams, this means that past communications, project discussions, and decisions are all stored in an easily retrievable manner.
This historical information can be of great value to new team members to gain familiarity, for disputes, and to preserve knowledge even as some of the older members leave the team and new team members join.
Archiving tools also provide advanced search capabilities so developers can easily and quickly find relevant emails based on keywords, dates, or specific project names. This ready access to historical information can result in better decision-making and increased knowledge transfer within the team.
Additionally, email archiving can also be helpful in documenting the development process. Thus it is easier to monitor progress, review past decisions, and understand the context of current projects.
## Enhancing Data Security
Security is a big concern for any software development company. Email archives contain sensitive information that has to be protected from unauthorized access and breaches.
Email archiving solutions come with robust security capabilities, including encryption and secure access controls, ensuring that only authorized personnel can view sensitive data.
In the case of a data breach, a good email archiving solution will ensure that your email data is securely stored and easily retrievable, minimizing downtime and any lost time that may be incurred. The added layer of security ensures that the integrity of critical, sensitive data is kept up and that critical communications are not easily lost or subject to cyber attacks.
## Supportive of Legal Discovery
Disputes and audits are a fact of life in running a business, and a good email archiving solution makes the process much more straightforward. A good solution for archiving makes it possible to call up any necessary email correspondence promptly, ensuring that you can respond quickly to requests for legal proceedings or audits.
This is an essential part of proving your organization in court or under audit scrutiny, where the timing in acquiring the appropriate information can be an essential factor.
Additionally, a good email archiving solution offers well-maintained email archives that make transparency and accountability easy and straightforward. This can be extremely important for industries where regulatory oversight is close, as detailed records are essential in proving that you comply.
## Enabling Remote Work
With remote work on the rise, it has never been more critical to have good communication and data management practices in place.
Email archiving solutions offer all team members, no matter where they may be, an easy way to access the necessary email records. This centralizing process makes keeping consistent communication and collaborative practices in place a possibility, even for remote software development teams.
Email archiving solutions offer a reliable place to store and retrieve emails, helping remote teams stay in touch, stay informed, and easily reference past communications, details on projects, and other important information without needing to rely on others to dig out old emails or hunt and peck through email chaos.
## Streamlining Software Development
Email communication proliferates rapidly as software development projects advance, and an inability to effectively facilitate this communication can quickly erode into available storage capacity, bogging down overall system performance while driving costs higher.
Email archiving solutions enhance storage management by moving old, irrelevant emails from primary servers to exceptional archives. Not only do these solutions free up scarce storage space, but they make it much easier to manage and organize email data.
Through tiered storage schemes, organizations can ensure that only the most current and relevant emails are readily available. In contrast, older, more rarely accessed emails are filed away but still readily available for access when necessary.
## Conclusion
Email archiving solutions offer a host of benefits for software development streamlining. They ensure regulatory compliance, enhance productivity, enhance knowledge management, improve data security, streamline legal discovery, facilitate remote work, and optimize storage management.
Implementing a robust email archiving solution allows software development teams to focus more on the business of what they do best: conceiving creative software solutions that help drive business and deliver value to customers and stakeholders.
In a data-driven environment, where email remains a critical part of business communication, optimized email archiving is not simply a competitive imperative: it's a strategic one as well. The right archiving solution in place can revolutionize the way that your development team manages data, advances projects, and remains compliant with industry standards and regulations.
| elainecbennet |
1,874,983 | VFX Myths Busted! Separating Fact from Fiction in the World of Visual Effects | The world of Visual Effects (VFX) is a captivating blend of art, science, and technology. It's the... | 0 | 2024-06-03T06:33:49 | https://dev.to/skilzlearn/vfx-myths-busted-separating-fact-from-fiction-in-the-world-of-visual-effects-6d | vfxcourse, vfx, digitalcompusting, cgi | The world of [Visual Effects (VFX)](https://skilzlearn.com/) is a captivating blend of art, science, and technology. It's the invisible hand that brings fantastical creatures to life, creates mind-bending landscapes, and seamlessly integrates fantastical elements into our filmed reality. But along with the awe-inspiring creations come a plethora of myths and misconceptions.
In this blog post, we'll debunk some of the most common VFX myths, separating fact from fiction and offering a clearer picture of this fascinating field.

**Myth #1: VFX is Just About Making Things Explode**
Busted! While explosions are certainly a part of the VFX repertoire, they're just one piece of the puzzle. VFX encompasses a vast array of techniques, from creating realistic environments and characters to subtle enhancements like weather effects or rotoscoping (removing unwanted elements from a scene).
Fact:
VFX artists are skilled in a variety of areas, including compositing (layering visual elements), 3D animation, modeling, simulation, and even green screen technology.
**Myth #2: You Need a Hollywood Budget to Create Good VFX**
Busted! While blockbuster films undoubtedly have hefty budgets for VFX, advancements in technology have made creating compelling visual effects more accessible than ever.
Fact:
Open-source software and affordable tools empower even independent filmmakers and hobbyists to create impressive VFX. The key lies in resourcefulness, creative problem-solving, and utilizing free or low-cost alternatives.
**Myth #3: VFX Artists Are Just Tech Geeks with No Artistic Flair**
Busted! VFX artistry is a beautiful blend of technical expertise and artistic vision. A good VFX artist not only understands the intricacies of software and hardware but also possesses a strong understanding of composition, lighting, and storytelling.
Fact:
VFX artists collaborate closely with filmmakers, directors, and concept artists to translate their creative vision into stunning visuals. Their ability to understand the emotional weight of a scene and translate it visually is crucial.
**Myth #4: VFX is a One-Person Show**
Busted! VFX is a highly collaborative field. Creating stunning visuals involves the combined efforts of numerous talented individuals.
Fact:
A typical VFX project involves a team of artists, including modelers, animators, texture artists, lighting specialists, compositors, and technical directors. Each person contributes their skillset to bring the final vision to life.
**Myth # 5: VFX is All About Fancy Software**
Busted! While software plays a vital role in the VFX workflow, it's not the sole factor. Traditional artistic skills and a solid understanding of visual storytelling remain essential.
Fact:
Even the most advanced software relies on human input. VFX artists need to have a strong grasp of traditional art principles like color theory, perspective, and composition to create believable and visually appealing effects.
**Myth #6: Anyone Can Learn VFX with Online Tutorials**
Busted! Online tutorials are a fantastic resource for learning the basics of VFX, but they're not a replacement for dedicated training.
Fact:
VFX is a complex field with a steep learning curve. Mastering the required software, developing a strong artistic foundation, and understanding industry workflows all take time and dedication. Consider pursuing a structured VFX course or mentorship program for a comprehensive learning experience.
**Myth #7: The VFX Industry is Only for Big Studios in Hollywood**
Busted! The VFX industry has exploded in recent years, with opportunities available across the globe. Studios of all sizes, independent filmmakers, and even advertising agencies rely on VFX talent.
Fact:
The rise of streaming services and the increasing demand for visually stunning content have created a growing demand for VFX artists worldwide. With the ability to collaborate remotely, geographical location is less of a barrier than ever before.
**Myth #8: VFX Artists are Always Stuck Behind Computers**
Busted! While VFX work often involves computer software, the job isn't entirely isolated. Depending on the project, VFX artists might be involved in location scouting, set design, or even working with physical models or miniatures.
Fact:
Collaboration with other production teams is essential to ensure the VFX seamlessly integrates with the live-action footage. VFX artists might be required to visit sets, provide technical guidance, or even operate specialized equipment.
**Myth #9: A VFX Career is All About Glamorous Red Carpets**
Busted! While the end product might grace the silver screen, the VFX industry itself is fast-paced and often involves tight deadlines. VFX artists need to be dedicated, hardworking, and adept at managing time effectively.
Fact:
The VFX industry demands a high level of commitment and passion. | skilzlearn |
1,842,578 | LLM Fine-Tuning Workshop: Improve Question-Answering Skills | Large Language Models are a fascinating technology that becomes embedded into several applications... | 0 | 2024-06-03T06:30:29 | https://dev.to/admantium/llm-fine-tuning-workshop-improve-question-answering-skills-1h18 | llm | Large Language Models are a fascinating technology that becomes embedded into several applications and products. In my blog series about LLMs, I stated the goal to design a closed-book question answering systems with LLMs as the core or sole components. Following my overview to [question answer system architecture](https://admantium.com/blog/llm13_question_answer_system_architectures/), this is the second article, and its focus is to add question-answering skills to a Gen1 LLM.
This article shows how to finetune the GPT2 LLM with the SQAUD question answering dataset. You will learn about the SQUAD dataset: Its origin, its structure, and how to preprocess it for training. You will then see how to fine-tune GPT2 with this dataset using the transformers library, and how to use the model with custom questions from any context.
_The technical context of this article is `Python v3.11` and `transformers v4.37.2`. All instructions should work with newer versions of the tools as well._
_This article originally appeared at my blog [admantium.com](https://admantium.com/blog/llm16_qa_fine_tuning/)_.
## Question Answering Datasets
In classical NLP, question answering capabilities are considered as an advanced task. Models trained for this task are provided with a context section and a question, and then need to find the relevant spans in the context that best matches the question. Earlier, non LLM models were often trained to just identify the starting and ending position of the answer, and this still is the dominant form of available datasets.
SQUAD (Stanford Question Answer Dataset) is a well-known and often used dataset. It consists of a context, a question, and the expected answer in the form of a starting and ending token that identifies the relevant parts from the context. Here is an example of a question about the free working days in the European union.
```txt
Context
While the Treaties and Regulations will have direct effect (if clear, unconditional, and immediate), Directives do not generally give citizens (as opposed to the member state) standing to sue other citizens. In theory, this is because TFEU article 288 says Directives are addressed to the member states and usually "leave to the national authorities the choice of form and methods" to implement. In part this reflects that directives often create minimum standards, leaving member states to apply higher standards. For example, the Working Time Directive requires that every worker has at least 4 weeks paid holidays each year, but most member states require more than 28 days in national law. However, on the current position adopted by the Court of Justice, citizens have standing to make claims based on national laws that implement Directives, but not from Directives themselves. Directives do not have so called "horizontal" direct effect (i.e. between non-state parties). This view was instantly controversial, and in the early 1990s three Advocate Generals persuasively argued that Directives should create rights and duties for all citizens. The Court of Justice refused, but there are five large exceptions.
Question
How many paid holiday days does the Working Time directive require workers to have each year?
Answers:
start position: 594
start position: 595
text: 4 weeks
```
How the SQUAD dataset is used for fine-tuning should be put into a historic perspective. Essentially, training add a new fully-connected layer on top that outputs the two numbers of input and output tokens. This is a technique specifically used for gen 1 models, but newer models do not merely identify relevant spans, but can also summarize and synthesize answers. And therefore, this specific dataset and the training goal are applicable to Gen1 models but became obsolete with late Gen2 models.
## Step 1: Goal Definition
This project fine-tunes a GPT2 LLM with the SQUAD dataset to add question-answering behavior in which the LLM outputs the start and end position of tokens inside the context which is relevant to a given answer.
## Step 2: Data Selection & Exploration
The HuggingFace [dataset browser](https://huggingface.co/models) facilitates loading pre-processed datasets. You only need two lines of code for using the [squad dataset](https://huggingface.co/datasets/squad):
```py
from datasets import load_dataset
data = load_dataset('squad')
# Downloading readme: 100%
# 7.83k/7.83k [00:00<00:00, 434kB/s]
# Downloading data: 100%
# 14.5M/14.5M [00:00<00:00, 20.1MB/s]
# Downloading data: 100%
# 1.82M/1.82M [00:00<00:00, 7.13MB/s]
# Generating train split: 100%
# 87599/87599 [00:00<00:00, 350495.77 examples/s]
# Generating validation split: 100%
# 10570/10570 [00:00<00:00, 421873.03 examples/s]
```
The first time when a new dataset is loaded, source and configuration files will be downloaded and stored on your computer at a default (or configurable) cache directory.
Inspect the dataset's data structure with a simple `print`.
```py
print(data)
# DatasetDict({
# train: Dataset({
# features: ['id', 'title', 'context', 'question', 'answers'],
# num_rows: 87599
# })
# validation: Dataset({
# features: ['id', 'title', 'context', 'question', 'answers'],
# num_rows: 10570
# })
# })
```
Only a train and validation set exist. Let’s consider an individual example from the training dataset.
```py
print(data['train'][42])
# {
# 'id': '5733ae924776f41900661016',
# 'title': 'University_of_Notre_Dame',
# 'context': 'Notre Dame is known for its competitive admissions, with the incoming class enrolling in fall 2015 admitting 3,577 from a pool of 18,156 (19.7%). The academic profile of the enrolled class continues to rate among the top 10 to 15 in the nation for national research universities. The university practices a non-restrictive early action policy that allows admitted students to consider admission to Notre Dame as well as any other colleges to which they were accepted. 1,400 of the 3,577 (39.1%) were admitted under the early action plan. Admitted students came from 1,311 high schools and the average student traveled more than 750 miles to Notre Dame, making it arguably the most representative university in the United States. While all entering students begin in the College of the First Year of Studies, 25% have indicated they plan to study in the liberal arts or social sciences, 24% in engineering, 24% in business, 24% in science, and 3% in architecture.',
# 'question': 'What percentage of students at Notre Dame participated in the Early Action program?',
# 'answers': {'text': ['39.1%'],
# 'answer_start': [488]}
# }
```
## Step 3: Data Preprocessing
In the preprocessing step, the training data needs to be tokenized with the same model-specific tokenizer. To simplify this task, the convenient `AutoTokenizer` wrapper is used. Here is how:
```py
from transformers import AutoTokenizer
model_name = 'openai-community/gpt2'
tokenizer=AutoTokenizer.from_pretrained(model_name)
print(tokenizer.special_tokens_map)
# {'bos_token': '<|endoftext|>',
# 'eos_token': '<|endoftext|>',
# 'unk_token': '<|endoftext|>'}
```
In my previous article, these default tokens were used, and I suspect that it worsened the results. Instead, we will use the special tokens from the BERT model.
```py
from transformers import AutoTokenizer
bert_special_tokens = AutoTokenizer.from_pretrained('bert-base-uncased').special_tokens_map
model_name = 'openai-community/gpt2'
tokenizer=AutoTokenizer.from_pretrained(model_name)
tokenizer.add_special_tokens(tokens)
print(tokenizer.special_tokens_map)
# {'bos_token': '[BEG]',
# 'eos_token': '[END]',
# 'unk_token': '[UNK]',
# 'sep_token': '[SEP]',
# 'pad_token': '[PAD]',
# 'cls_token': '[CLS]',
# 'mask_token': '[MASK]'}
```
With this, we can define a tokenizer function and tokenize the datasets. This is a bit more complicated. The input data is a combination of the context and its question, which needs to be concatenated and tokenized. The labels, the expected values for a question, are numerical values for the start and end token. Given that the SQUAD dataset contains multiple answers in some examples, only the very first one will be used.
The following code is a refined version of the preprocessing method in [HuggingFace question answer tutorial](https://huggingface.co/docs/transformers/tasks/question_answering). I needed to add exception handling because the training data contains tokens unknown to the GPT2 tokenizer.
```py
# Source: HuggingFace, Question Answering, https://huggingface.co/docs/transformers/tasks/question_answering#preprocess
def preprocess(examples):
inputs = tokenizer(
examples["question"],
examples["context"],
truncation=True,
padding="max_length",
return_offsets_mapping=True,
max_length = 512,
stride = 128
)
offset_mapping = inputs.pop("offset_mapping")
answers = examples["answers"]
start_positions = []
end_positions = []
for i, offset in enumerate(offset_mapping):
answer = answers[i]
start_char = answer["answer_start"][0]
end_char = answer["answer_start"][0] + len(answer["text"][0])
sequence_ids = inputs.sequence_ids(i)
idx = 0
context_start = idx
context_end = idx
try:
while sequence_ids[idx] != 1:
idx += 1
context_start = idx
while sequence_ids[idx] == 1:
idx += 1
context_end = idx - 1
except:
pass
# If the answer is not fully inside the context, label it (0, 0)
if offset[context_start][0] > end_char or offset[context_end][1] < start_char:
start_positions.append(0)
end_positions.append(0)
else:
# Otherwise it's the start and end token positions
idx = context_start
while idx <= context_end and offset[idx][0] <= start_char:
idx += 1
start_positions.append(idx - 1)
idx = context_end
while idx >= context_start and offset[idx][1] >= end_char:
idx -= 1
end_positions.append(idx + 1)
inputs["start_positions"] = start_positions
inputs["end_positions"] = end_positions
return inputs
```
Let’s apply this function and see how it provides the input data and output data sets.
```py
gpt2_squad = data.map(preprocess, batched=True, remove_columns=data["train"].column_names)
gpt2_squad
# DatasetDict({
# train: Dataset({
# features: ['input_ids', 'attention_mask', 'start_posit <...> ut_ids', 'attention_mask', 'start_positions', 'end_positions'],
# num_rows: 10570
# })
# })
gpt2_squad["train"][42]
# {'input_ids': [2061, 5873, 286, 2444, 1, ..],
# 'attention_mask': [1, 1, 1, ...],
# 'start_positions': 116,
# 'end_positions': 119}
```
## Step 4: Training Parameter Definition
With the tokenization in place and using the `start` and `stop` values as the labels, we can continue the training setup.
For the training arguments, default values are suitable. We don't need to define a special metric.
```py
from transformers import TrainingArguments
training_args = TrainingArguments(output_dir="gpt2_qa", logging_steps=1)
```
## Step 5: Training Execution
The training uses a `DataCollator` object to handle batch input and tokenization. And for the model type, we will use the `AutoModelForQuestionAnswering`. The complete setup is as follows.
```py
from transformers import DataCollatorWithPadding
data_collator = DataCollatorWithPadding(tokenizer=tokenizer)
from transformers import AutoModelForQuestionAnswering
model = AutoModelForQuestionAnswering.from_pretrained(model_name)
model.config.max_length = 512
```
Finally, all pieces to create the trainer object are completed, and the training can start.
```py
from transformers import Trainer
trainer = Trainer(
model=model,
args=training_args,
train_dataset=gpt2_squad["train"],
eval_dataset=gpt2_squad["validation"],
data_collator=data_collator,
tokenizer=tokenizer
)
trainer.train()
```
## Step 6: Model Usage
The trained model is saved in the configured output directory, and from there, it can be loaded.
Let’s use the model with an example from the validation dataset.
```py
val1_id="57269cc3dd62a815002e8b13"
example = squad["validation"].filter(lambda x: x['id']==val1_id)[0]
# {'id': '57269cc3dd62a815002e8b13',
# 'title': 'European_Union_law',
# 'context': 'While the Treaties and Regulations will have direct effect (if clear, unconditional, and immediate), Directives do not generally give citizens (as opposed to the member state) standing to sue other citizens. In theory, this is because TFEU article 288 says Directives are addressed to the member states and usually "leave to the national authorities the choice of form and methods" to implement. In part this reflects that directives often create minimum standards, leaving member states to apply higher standards. For example, the Working Time Directive requires that every worker has at least 4 weeks paid holidays each year, but most member states require more than 28 days in national law. However, on the current position adopted by the Court of Justice, citizens have standing to make claims based on national laws that implement Directives, but not from Directives themselves. Directives do not have so called "horizontal" direct effect (i.e. between non-state parties). This view was instantly controversial, and in the early 1990s three Advocate Generals persuasively argued that Directives should create rights and duties for all citizens. The Court of Justice refused, but there are five large exceptions.',
# 'question': 'How many paid holiday days does the Working Time directive require workers to have each year?',
# 'answers': {'text': ['4 weeks',
# '4 weeks paid holidays each year',
# '4 weeks paid'],
# 'answer_start': [594, 594, 594]}}
```
To use the model, we create a question-answering pipeline, specify the tokenizer and local model. And then we transform an example dataset into a dictionary object with `question` and `context` keys.
```py
local_model = 'gpt2_qa'
qa = pipeline(
"question-answering",
tokenizer=tokenizer,
model=AutoModelForQuestionAnswering.from_pretrained(model_name)
)
d = qa({"question": example["question"], "context": example["context"]})
# {'score': 0.0003682523383758962,
# 'start': 662,
# 'end': 692,
# 'answer': ' than 28 days in national law.'}
```
However, this answer is only partially correct, it misses the first part.
## Question Answering with Fine-Tuned Model
Finally, lets apply the fine-tuned model to a context that it was not trained on - an excerpt from Wikipedia, and the question "What is NASA".
```py
query = {
"question": "What is NASA?",
"context": '''
The National Aeronautics and Space Administration (NASA) is an independent
agency of the U.S. federal government responsible for the civil space
program, aeronautics research, and space research. Established in 1958, it
succeeded the National Advisory Committee for Aeronautics (NACA) to give
the U.S. space development effort a distinctly civilian orientation,
emphasizing peaceful applications in space science. It has since
led most American space exploration, including Project Mercury, Project
Gemini, the 1968–1972 Apollo Moon landing missions, the Skylab space
station, and the Space Shuttle. It currently supports the International
Space Station and oversees the development of the Orion spacecraft and the
Space Launch System for the crewed lunar Artemis program, the Commercial
Crew spacecraft, and the planned Lunar Gateway space station.
NASA's science is focused on better understanding Earth through the Earth
Observing System; advancing heliophysics through the efforts of the
Science Mission Directorate's Heliophysics Research Program; exploring
bodies throughout the Solar System with advanced robotic spacecraft such as
New Horizons and planetary rovers such as Perseverance; and researching
astrophysics topics, such as the Big Bang, through the James Webb Space
Telescope, the Great Observatories and associated programs. The Launch
Services Program oversees launch operations and countdown management for
its uncrewed launches.
'''
}
qa(query)
# {'score': 0.008794573135674,
# 'start': 305,
# 'end': 369,
# 'answer': 'S. space development effort a distinctly civilian orientation,\n\t'}
```
However, this answer is dissatisfying. Also, trying other questions like "When was NASA founded?" led to similar results. Although the model is finetuned, it clearly shows that mere span-highlighting does not give precise answers, let alone reflective answers that work on a given text. And with this result, the second approach to building question-answering system, the limitations become clear.
## Conclusion
Early Gen1 LLMs are capable text generators but lack support for advanced NLP tasks. This article showed a practical approach to fine-tune GPT2 with a question-answering dataset. You learned the dataset structure and saw the necessary preprocessing step. You also saw how to define training hyperparameter and start the training process with the help of the transformers library. The fine-tuned model was then manually tested with questions about the Wikipedia article for NASA. However, the models answers were inaccurate, a mere span detection inside a context is clearly a non-reflective answer. The next article explored domain embeddings with GPT3.
| admantium |
1,874,982 | Converged Network Adapter and LWL Patchkabel at GBIC Shop | Discover the power of seamless connectivity with the converged network adapter and LWL Patchkabel... | 0 | 2024-06-03T06:28:21 | https://dev.to/gbicshop/converged-network-adapter-and-lwl-patchkabel-at-gbic-shop-h46 | convergednetworkadapter, lwlpatchkabel | Discover the power of seamless connectivity with the **[converged network adapter](https://www.gbic-shop.de/ethernet-2x-rj45-converged-network-adapter-karte-i350-t4)** and LWL Patchkabel from GBIC Shop. Our high-performance Converged Network Adapters integrate storage and networking functionalities, ensuring efficient data transfer and reduced latency. Paired with our top-tier **[lwl patchkabel](https://www.gbic-shop.de/lwl-patchkabel_1)**, these adapters provide robust and reliable fiber optic connections, ideal for high-speed data environments. Whether upgrading your data center or enhancing network performance, GBIC Shop offers unparalleled solutions to meet your needs. Shop with us for cutting-edge technology, expert support, and exceptional value.
**LWL Patchkabel**

**Converged network adapter**
 | gbicshop |
1,874,981 | Step-by-step guide to Build an OP Stack Rollup DevNet with Zeeve RaaS | OP Stack is one of the oldest and matured rollup frameworks, which is developed by OP Labs to focus... | 0 | 2024-06-03T06:27:02 | https://www.zeeve.io/blog/step-by-step-guide-to-build-an-op-stack-rollup-devnet-with-zeeve-raas/ | optimisticrollups, rollups | <p>OP Stack is one of the oldest and matured rollup frameworks, which is developed by OP Labs to focus on offering a high-quality, shared, and completely open-source system. If you are launching an OP Stack chain or superchain, you will need to set up a DevNet environment for troubleshooting purposes, such as testing the configurations, nodes, functionalities, and network connectivity to ensure the chain functions as expected. </p>
<p>Through this step-by-step guide, we will continue our DIY rollup deployment series by making today’s article focused on the step-by-step process to deploy your OP Stack devNet launch within minutes via a simple, low-code approach facilitated by Zeeve RaaS. </p>
<p>Similar guides we’ve done for <a href="https://www.zeeve.io/blog/a-comprehensive-guide-on-polygon-cdk-and-its-deployment/">Polygon CDK</a>, <a href="https://www.zeeve.io/blog/launch-your-first-zksync-hyperchain-test-rigorously-deploy-to-publicnet/">Zk Stack Hyperchain</a>, and <a href="https://www.zeeve.io/blog/deploy-an-arbitrum-orbit-devnet-with-zeeve-raas-your-diy-guide/">Arbitrum Orbit</a>. </p>
<h2 class="wp-block-heading" id="h-why-op-stack-is-a-preferred-option-for-top-web3-projects">Why OP Stack is a preferred option for top web3 projects?</h2>
<p>Since launch, <a href="https://www.zeeve.io/appchains/optimistic-rollups/">OP Stack</a> has been recognized as a high quality, comprehensive framework for building production-quality Optimistic rollup L2 and L3 chains. Now after the Bedrock upgrade, OP Stack supports creation of even powerful OP Stack chains that will leverage the following features:</p>
<ul><!-- wp:list-item -->
<li>Bedrock implements a unique data compression technique to reduce the network fees significantly– by 10% and meanwhile removing the execution gas from Layer1.</li>
<!-- /wp:list-item -->
<!-- wp:list-item -->
<li>After Bedrock, the deposit time has been reduced from 10 minutes to merely 3 minutes, contributing to better user experience and performance.</li>
<!-- /wp:list-item -->
<!-- wp:list-item -->
<li>OP Stack now enables rollup chains to maintain as high Ethereum equivalency as possible. Also, Bedrock supports EIP-1559, chain-reorgs along with all the important Ethereum features available for Layer1.</li>
<!-- /wp:list-item -->
<!-- wp:list-item -->
<li>With Bedrock, rollups have the ease to either use fraud or validity proof for correct execution of rollup inputs. This approach enables implementation of innovative systems like cannon for fault proving.</li>
<!-- /wp:list-item -->
<!-- wp:list-item -->
<li>Node performance is improved significantly after Bedrock as technical debt such as the need for an independent ‘data transport layer’ has been eliminated.</li>
<!-- /wp:list-item --></ul>
<p>There are a lot more on Bedrock that are worth mentioning for OP Stack rollups, such as enhanced modularity of chains, code reuse, quick withdrawals, revamped batch processing, block derivation, etc that you can read in-depth from more things <a href="https://community.optimism.io/docs/developers/bedrock/">here</a>.</p>
<figure class="wp-block-image aligncenter size-large"><a href="https://www.zeeve.io/rollups/"><img src="https://www.zeeve.io/wp-content/uploads/2024/05/Get-faster-time-to-market-for-your-production-grade-L2L3s-1-1024x213.jpg" alt="Guide to deploy OP Stack DevNet" class="wp-image-68128"/></a></figure>
<p>With such next-gen features, OP Stack keeps adding a range of innovative, top-grade L2/L3 projects to its ecosystem, such as Base, Blast L2, Mantle Network, Metic L2, Zircuit L2, Mode Network, Aevo, BNB Chain, etc. For a comprehensive view into industry-wise leading OP Stack projects, check out the detailed guide linked below: <a href="https://www.zeeve.io/blog/inside-op-stack-universe-latest-greatest-projects-to-watch-in-2024/">Inside OP Stack Universe: Latest & Greatest Projects to Watch in 2024</a></p>
<h2 class="wp-block-heading" id="h-quick-walkthrough-of-zeeve-s-op-stack-raas-stack">Quick walkthrough of Zeeve’s OP Stack RaaS Stack</h2>
<p>Zeeve offers a comprehensive RaaS stack for all the leading rollup frameworks, including OP stack. </p>
<ol><!-- wp:list-item -->
<li><strong>Production-grade infrastructure: </strong>Deploy your OP Stack rollups on Zeeve’s production-grade, highly optimized infrastructure to deploy, manage, and scale OP Stack rollups. Your rollups will benefit from powerful APIs, load-balancers, and security best practices with Enterprise SLAs.</li>
<!-- /wp:list-item -->
<!-- wp:list-item -->
<li><strong>One-click deployment sandbox: </strong>Use low-code OP Stack sandbox tool to setup your own DevNet before launching a fully-functional public testnet or mainnet. Access to sandbox is free for limited launches and it’s optimized for low-code deployment. We will learn more about the sandbox later in this guide.</li>
<!-- /wp:list-item -->
<!-- wp:list-item -->
<li><strong>40+ third-party rollup service integrations: </strong>If you want modularity in your OP Stack rollups, Zeeve RaaS allows you do so with its wide range of <a href="https://www.zeeve.io/integrations/">3rd party rollup integration list</a> comprising of decentralized sequencers, Alt DA layer, account abstraction, prover, custom block explorers, and a lot more. </li>
<!-- /wp:list-item -->
<!-- wp:list-item -->
<li><strong>24/7 monitoring with Enterprise SLA: </strong>All your OP stack rollups deployed through Zeeve RaaS will be monitored on critical parameters, such as node performance, resource consumption, block height, etc to ensure 99.9% uptime with Enterprise SLAs. </li>
<!-- /wp:list-item -->
<!-- wp:list-item -->
<li><strong>Ready-to-use, pluggable components: </strong>Free up significant development time by leveraging the ready-to-use rollup chain components offered at Zeeve RaaS. From custom data indexers to cross-chain bridges, MPC/AA-backed wallet, and testnet faucets– you will get everything in the form of pluggable components.</li>
<!-- /wp:list-item --></ol>
<h2 class="wp-block-heading" id="h-deploy-your-own-op-stack-rollup-devnet-with-zeeve-raas-step-by-step-guide-nbsp">Deploy your own OP Stack Rollup DevNet with Zeeve RaaS: Step-by-step guide </h2>
<p>Now that we understand the basics of OP Stack and Zeeve’s OP Stack RaaS, let’s time to move to DevNet setup with Zeeve RaaS platform. Below is a step-by-step process for the same:</p>
<p><strong>Step:1</strong> Login or signup to the Zeeve RaaS platform. From the dashboard, navigate to the ‘Appchains & Rollups’ section and click on ‘OP Stack’. </p>

<p><strong>Step:2</strong> A new dashboard will appear with the option to deploy OP Stack DevNet as well as a pre-deployed demo account. The purpose of this demo is to provide you hands-on access to a full-powered DevNet where you can interact with the setup, perform a range of activities such as sending/receiving tokens via bridges, using RPCs to fetch data, check transactions on explorer, and much more. Basically, the demo account gives you the confidence you need to set up your own DevNet. Check out this <a href="https://www.zeeve.io/blog/test-drive-zksync-hyperchain-on-zeeves-fully-powered-demo-network/">guide</a> for an in depth overview of the Zeeve demo account offerings on Zeeve RaaS. </p>

<p><strong>Step:3</strong> From the above dashboard, click on the ‘Deploy DevNet’ button and continue deploying your first OP Stack DevNet. However, Zeeve also gives you the flexibility to setup public testnet and mainnet through the same portal in a few clicks. As you can see, the OP Stack DevNet comes with 1-1 nodes for OP, Ethereum RPC, OP-Geth, OP-batcher, and OP-proposer. Also, you will get default smart contracts deployed on L1& L2, asset bridge, L1 & L2 supported explorer, 24/7 monitoring & analytics dashboard. All these offerings you can access for free in the Zeeve’s 30-days trial period.</p>
<p><strong>Step:4 </strong>Now to set up your OP Stack DevNet, provide the basic network details required on the dashboard, such as The name for your OP Stack DevNet, workspace, account address in where you would like to permit some tokens, and also the Ether account balance for this address so that you can get started with the transactions and thereby engage/interact with the network.</p>
<p>As you can see, we have picked ‘MyOPRollup’ name for our OP DevNet, workspace is set to default, and we’ve pulled the preminted account address and its account balance. The option for settlement layer is Ethereum as of now. </p>

<p><strong>Step:5</strong> Also, there’s the settlement layer which is provided as ‘Ethereum’ on Zeeve RaaS as of now. That means, you can deploy Layer2 OP stack rollup with Zeeve using Ethereum as your main chain for transaction settlement.</p>
<p><strong>Step:6</strong> For DA layer and sequencer, Zeeve Raas supports modularity, allowing you to choose Layer1 like Ethereum for on-chain data availability or move to off-chain data availability with alternative DA providers such as Celestia, NEAR DA, Avail, and Eigen DA. Depending on the level of modularity you expect from your OP Chain, you can configure the setup.</p>
<p><strong>Step:7</strong> The another important aspect of your OP Stack DevNet is ‘Integrations’. Zeeve’s RaaS stack is optimized to Zeeve-Managed cross-chain bridges, RPCs, and customizable block explorers. Also, it supports a bunch of 3rd party rollup service integrations, including decentralized oracles, block explorers, decentralized storage, MPC wallets, and a range of powerful developer tools to simplify development on various EVM chains. </p>

<p><strong>Step:8. </strong>Cross-verify all the configurations you’ve done so far and click on ‘Deploy’ to launch your OP Stack DevNet. Go back to the dashboard and it will show your DevNet with its environment (DevNet) and status (ready or syncing). The status will change to ‘Ready’ once the network is fully synched.</p>

<h2 class="wp-block-heading" id="h-24-7-monitoring-amp-analytics-for-your-op-stack-devnet">24/7 Monitoring & Analytics for your OP Stack DevNet</h2>
<p>Once your DevNet is ready, you can start monitoring its network to get vital 24/7 analytics and real-time alerts. For that, click ‘view’ as shown in the above image. A new page will appear showing the comprehensive details of your OP Stack DevNet.</p>
<li>Here’s what analytics you will get from the <strong>overview </strong>option.</li>

<li><strong>My nodes</strong>–Get details about nodes that underpins your DevNet network, such as Node ID, Name, Status, and creation info.</li>

<li><strong>Smart contracts</strong>– Check out the contract deployed on the Layer1 and Layer2 ecosystem. Dive deeper into the transactions by analyzing them on explorer. Click on the explorer icon under ‘Actions’ and explore further details.</li>

<li><strong>Bridge</strong>– Analytics for bridge operations will appear once you integrate a native bridge on your OP Stack chain. Contact Zeeve team for an effortless bridge integration. However, for TestNet and mainnet, you will automatically get a native bridge integrated already in your chain. </li>

<p>Further, the ‘Explorer’ and ‘Analytics’ options on the Zeeve RaaS platform will allow you to get transactional activities for Layer1/Layer2 through their explorers and analytics will appear for node, OP Node, Log, and real-time alerts (if any). Note that alerts are produced and get solved immediately to ensure a seamless performance of your network. </p>

<h2 class="wp-block-heading" id="h-ready-to-launch-testnet-or-mainnet">Ready to launch Testnet or Mainnet?</h2><p>That’s how easily you can set up your own OP Stack DevNet and test drive all the broad configurations and OP Stack-specific functionalities. Similar instructions can follow for launching your testnet or mainnet on Zeeve RaaS; only the options for integrations will expand to enable the highest degree of modularity. While Zeeve’s RaaS platform is standardized, we understand that your project’s requirements may differ. Hence, you can <a href="https://www.zeeve.io/talk-to-an-expert/">set up a call with our web3 experts</a> or send all your queries via email to us. We will handle all your queries diligently and provide you a solution as quickly as possible.</p> | zeeve |
1,874,980 | Transform Your Health with the Physicians Weight Loss Diet Menu | Discover the transformative power of the Physicians Weight Loss Diet Menu, designed to help you... | 0 | 2024-06-03T06:26:30 | https://dev.to/slim4life/transform-your-health-with-the-physicians-weight-loss-diet-menu-d44 | Discover the transformative power of the **[Physicians Weight Loss Diet Menu](https://www.slim4life.com/)**, designed to help you achieve your health and weight loss goals. Our physician-approved meal plans offer balanced nutrition and delicious options, making it easier than ever to stay on track. Start your journey today and experience the benefits of a medically-backed diet program tailored just for you! | slim4life | |
1,874,979 | Why I Switched from GitHub Pages to Netlify for Deploying Static Websites | If you're looking for the optimal platform to host your static site for free, this article will help... | 0 | 2024-06-03T06:25:39 | https://dev.to/ryoichihomma/why-i-switched-from-github-pages-to-netlify-for-deploying-static-websites-2lnn | netlify, deployment, staticwebapps, github | If you're looking for the optimal platform to host your static site for free, this article will help you make a better decision.
As a web developer, choosing the right platform to deploy and host static websites is crucial for seamless workflow and efficient project management. GitHub Pages was my favorite due to its integration with GitHub repositories and ease of use. However, I recently made the switch to Netlify, and I wanted to share the reasons behind this decision.
## 1. Simpler Deployment and Continuous Deployment (CD)
One of the standout features of Netlify is its continuous deployment capability. With GitHub Pages, while the initial setup is simple, continuous deployment often requires additional configuration through third-party CI/CD tools like GitHub Actions.
Netlify, on the other hand, automates the process. By connecting a GitHub repository to Netlify, every push to the repository automatically triggers a new build and auto-deployment. This seamless integration saves my time and reduces the complexity of maintaining deployment scripts.
## 2. Custom Domains and HTTPS
Both GitHub Pages and Netlify offer custom domains and HTTPS though, Netlify makes the process of setting up custom domains and obtaining SSL certificates incredibly easy. With a few clicks, you can link a custom domain and automatically get an SSL certificate via Let’s Encrypt, ensuring your site is secure without any hassle.
## 3. Superior Performance and CDN
Netlify’s infrastructure includes a globally distributed Content Delivery Network (CDN), ensuring that your website loads quickly from anywhere in the world. While GitHub Pages also serves content via a CDN, Netlify's performance optimizations and edge network capabilities are often superior, resulting in faster load times and better overall performance.
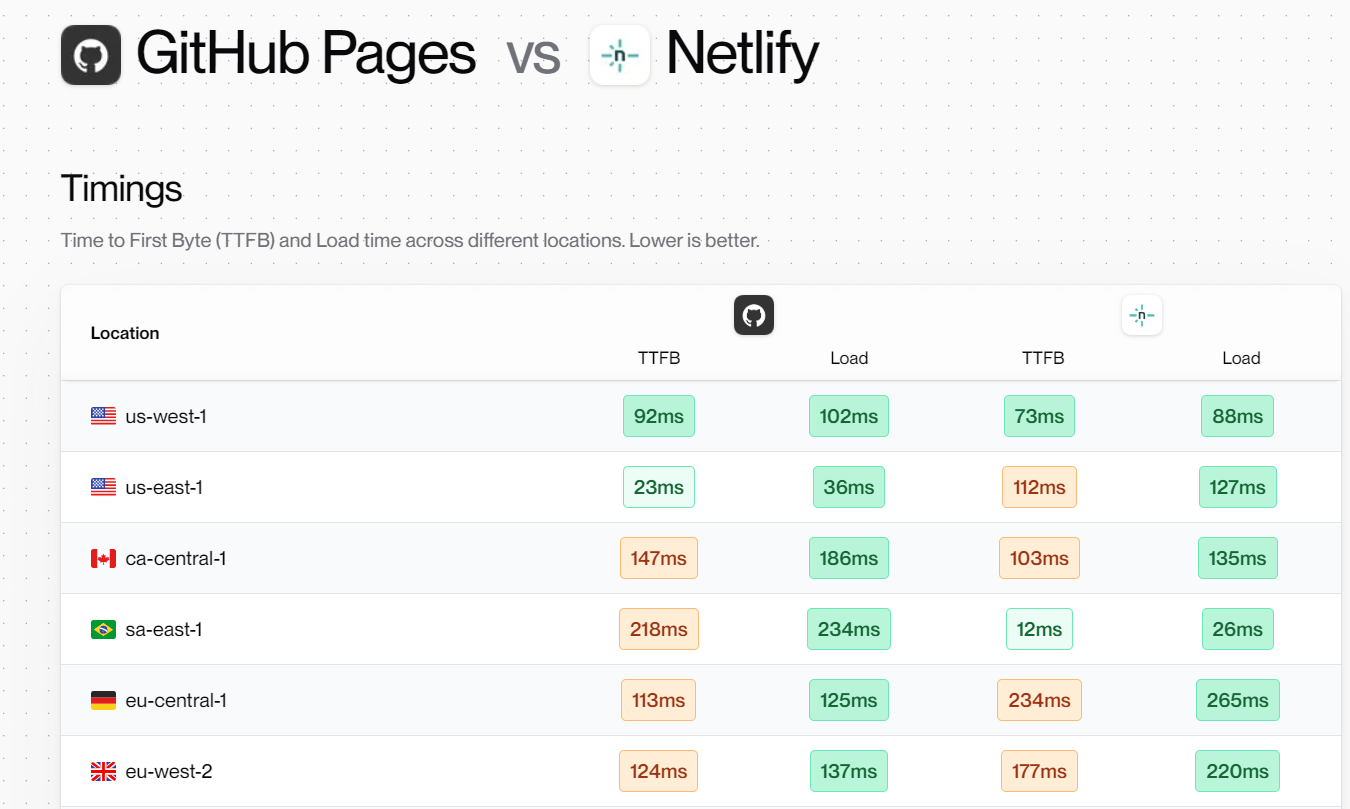
## 4. Detailed Analytics
Netlify provides detailed site analytics out of the box. Even on the free plan, you get access to essential metrics that help you understand the site's performance and user engagement. While GitHub Pages can be integrated with external analytics services like Google Analytics, having built-in analytics simplifies tracking and monitoring site metrics.
## Easy Rollbacks and Versioning
Netlify's deployment process keeps a history of all your deploys, enabling easy rollbacks to previous versions of your site if something goes wrong. This versioning capability is not as straightforward with GitHub Pages, where you probably need to manually manage branches or tags to achieve similar functionality.
## Conclusion
Switching from GitHub Pages to Netlify has significantly streamlined my workflow and provided additional features that enhance the development and deployment of static websites. The simplicity of continuous deployment, flexibility in build processes, built-in form handling, superior performance, and easy rollbacks make Netlify an excellent choice, even with the constraints of the free plan.
If you're looking for a robust, feature-rich platform to host your static sites, I highly recommend giving Netlify a try. The benefits it offers can greatly improve your development experience and site performance.
Here's a useful tool, [Compare Center](https://bejamas.io/compare/github-pages-vs-netlify), to compare multiple hosting platforms based on various aspects and features. | ryoichihomma |
1,874,978 | What are the elements of a complete strategy? | Summary A complete strategy is actually a set of rules that traders give themselves. It... | 0 | 2024-06-03T06:22:11 | https://dev.to/fmzquant/what-are-the-elements-of-a-complete-strategy-fel | strategy, cryptocurrency, trading, fmzquant | ## Summary
A complete strategy is actually a set of rules that traders give themselves. It includes all aspects of the trading, and does not leave a little room for subjective imagination. Every choices of buying and selling, the strategy will give an answer. It includes at least strategy selection, variety selection, fund management, order placing, extreme market situation response and so on.
## Strategy choosing
From the perspective of hedge funds, mainstream trading strategies can be divided into trend trading, paired trading, basket trading, event-driven, high-frequency trading, option strategy, etc., as shown below.
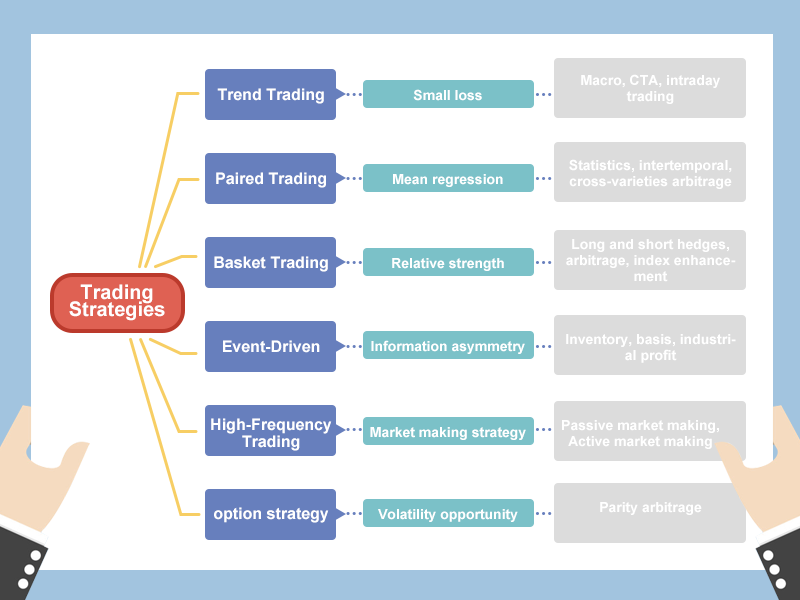
Of course, the way of strategy classification is not fixed. For the beginners, don't worry about so many noun concepts, let's start from the simplest. If only one type of quantitative trading strategy is recommended, it will be the trend trading, which is the most simple and effective. I believe that even if you don't have a systematic knowledge of financial learning, you can still use it. And this strategy has been around for a long time. Among the early public-published trading strategies, it is still effective in many markets today, because human nature is difficult to change.
## What to buy and sell
Those who have done trading should know that each variety has its own personality. Some varieties are very popular, with good liquidity, large fluctuations, and high volatility; some varieties are very "docile", and they are oscillating within a certain range all year round, with low volatility.
Therefore, when choosing a trading variety, there must be a concept of volatility. Varieties with high volatility are often easy to get out of a good trend. For commodity futures, if it is a trend-tracking strategy, try to choose industrial products. In terms of variety attributes, industrial products tend to be more volatile than agricultural products. For crypto trading, choose those major coins, such as bitcoin, eth, eos and so on.
Different strategies adapt to different market conditions. Choosing a good trading variety, which is a very crucial beginning for the future trading project. In absolute terms, there are no absolutely good varieties and no absolutely bad varieties. Depending on the investment style and the risk tolerance, you need to adjust accordingly to your own standards.
## How much to buy and sell
It is easy to loss money when trading. When the account fund loses 50%, the loss will require 100% profit to recover it. Even if you can earn 100% many times, you only need to lose 100% once, which will lose it all. So mature trading strategies should include money management.
In order to facilitate everyone's understanding, here also use the average line strategy of the previous section to explain. In fact, many trading strategies built with traditional technical indicators have a maximum retracement rate of more than 50% or more. But is a risky strategy completely unusable?
Obviously not, the maximum retracement rate can be completely controlled by money management. If you cut the position by half, the overall risk will be reduced by half, and the maximum retracement rate will be 30%. If you reduce the position by half again, the maximum retracement rate will become 15%. Finally, we get a maximum retracement rate at around 15%. This is a simple and easy method of money management. Many people know that they can't go all in, but they don't know why. The answer is here.
## When to buy and sell
A good jump in point is very important, and it allows you to get out of the cost zone quickly. But there will never be anyone who can tell you that it is right at this point, and it is wrong at that point. Opening a position is not the core of the trading. The core of the trading is how to optimize the position after opening the position.
Whether it is a short-term strategy or a long-term strategy, it doesn't matter how long the position will be holding, the important is the risk-to-profit ratio. In other words, the final result that affects the performance of the strategy is how to play and when to cash out. The cash out method can be divided into two types: stop loss and take profit. Both of these parts are necessary for any trading system and are an important watershed for the success or failure of trading strategies.
## How to buy
1. Type and method of order placement:
There are many types and methods of placing orders, such as: queuing limit orders, opponent price, latest price, over price, daily limit price, buying one price, buying two price, selling one price, selling two price. or use the queue price first, then use the over-price, sending batch order, or split the big order into small orders, or simply place the order directly.
2. Withdraw order
If there are unexecuted orders, whether continue waiting or withdraw the order. The condition for the withdrawal is based on the time. For example, there is no transaction within 10 seconds. The price has been 10 units away from the order price, whether to continue waiting, withdrawing or chasing the new price.
3. chase the price
When the order is unexecuted, whether to chase the price. If chasing the price, it is to chase according to the latest price, or the opponent price, or the limit price? If the order is still not executed, whether continue to pursue the latest price.
4. the price limit
When the order signal appears, it happens to be the limit price. Whether should to queue up the price.
5. set bidding
Do we need to participate in the market opening stage, how to participate.
6. night-time market
Some commodity futures varieties are from 21:00 to 02:30 the next day and all crypto trading are 27/7. Do we need participate these time period. Manually or automatically?
7. Major holidays
Before a long holiday, do we need clear all position or reduce some of them.
## Extreme market situation
1. Short-term price fluctuations
The price of the price suddenly huge rises and falls (black swan situation) etc., how to deal with these situations (as shown in the figure, the Swiss franc black swan event).

2. Liquidity risk
If the other side of trading direction order depth does not have the amount you want to execute, but you need to execute immediately. especially if the non-main commodity future contract is very rare, it is easy to make a price jump to the market. How to deal with it when the price slippage is large.
3. Variety trading rules change
Commodity futures varieties are added to the night-time market and the crypto trading is 24/7. the margin ratio is raised, and the commission fee is raised, especially the short-term trading strategy, which is very sensitive to these changes.
4. Trading environment risk
For example: sudden power failure, network disconnection, computer failure, software downtime, suspension of bank transfer, natural disasters, etc., how to deal with it when it occurs.
In the above case, the probability of occurrence is small, or almost impossible. But if things can happen, it will happen. It is very necessary to make these assumptions and prevent them.
## Psychological construction
The three main psychological emotions commonly in trading are greed, fear and lucky. Investors need a strong trading psychology system to control and even use the above three emotions at different stages.
There must be an overall expectation for the future before you placing an order, including market expectations and variety psychological expectations. Market expectations have a clearer target for the location and future direction of the market. Variety expectations refer to the trading opportunities and risk profiles of the variety at its current location. Without the above psychological foundation, nothing can be done.
The whole process of real market trading is the process of continuous analysis, correction and execution. During the trading period, there are not many transactions, and more is tracking and endurance. This is a process of comprehensively examining the state of mind and testing human nature. The various habits of traders will be revealed and enlarged during the transaction process. Only by continuously learning and summarizing lessons after lessons, can we overcome the commonalities and psychological weaknesses of human nature.
## To sum up
In summary, the so-called trading strategy is actually like this. When it has its perfect side and when it is incomplete, we can measure whether a trading strategy is reasonable. We can’t just look at his perfect side, and can’t just look at his broken side. On the one hand, it is more important to analyze the integrity of the strategy.
Finally, according to the characteristics of the strategy, combined with trader's own personality and financial situation to measure whether the strategy is suitable for themselves, if it is suitable for themselves, it is necessary to fully assess how likely it is to persist, the worst results must be planned in advance, if the most You have thought about the miserable side happens, you still can take it, then the possibility of implementation is relatively large.
Remember, in trading, confidence comes from your inner recognition, and confidence comes from the right trading philosophy!
## Next section notice
This article is the last one of the first chapter. In the next chapter, we will focus on quantitative trading tools for further explanation, including: a comprehensive introduction to quantitative tools, how to configure quantitative trading systems, common API explanations, and how to quantify a trading systems. Write a strategy on it.
After-school exercises
1. Should a trend-based trading strategy choose a high volatility or a low volatility?
2. What are the types of trading orders?
From: https://blog.mathquant.com/2019/04/12/1-4-what-are-the-elements-of-a-complete-strategy.html | fmzquant |
1,874,975 | Elevate Your Celebrations with Wholesale Carnations Flower | From weddings and church events to Valentine’s Day and Easter celebrations, flowers play a central... | 0 | 2024-06-03T06:19:37 | https://dev.to/merlinmcelroy/elevate-your-celebrations-with-wholesale-carnations-flower-2lo | From weddings and church events to Valentine’s Day and Easter celebrations, flowers play a central role in enhancing the ambiance and beauty of any occasion. Among the myriad floral options available, **[Carnations flower](https://wholesalecarnations.com/)** stands out for its timeless elegance and versatility. In this article, we explore the enchanting world of wholesale **[flowers carnation](https://wholesalecarnations.com/)** and the myriad ways they can elevate your celebrations.
The Charm of Carnations Flower
Carnations have long been cherished for their delicate petals, sweet fragrance, and enduring beauty. Wholesale suppliers offer a diverse range of carnations flower, including classic red, white, and pink varieties, as well as novelty blooms in an array of vibrant hues. Whether used as standalone bouquets or incorporated into larger floral arrangements, carnations add a touch of sophistication to any celebration.
Versatility for Every Occasion
One of the key advantages of wholesale carnations flower is their versatility. They are equally at home in formal settings like weddings and banquets as they are in more casual gatherings like Fourth of July parties and Mother’s Day brunches. Their ability to complement a wide range of themes and color schemes makes them a favorite choice for event planners and individuals alike.
Affordable Elegance
Despite their undeniable beauty, **[flowers wholesale](https://wholesalecarnations.com/)** are remarkably affordable, making them accessible to event planners with varying budgets. Buying in bulk allows for significant cost savings without compromising on quality, ensuring that every celebration is adorned with fresh, vibrant blooms. Whether you need a few stems for a small gathering or hundreds for a grand event, wholesale carnations flower offer an elegant solution at an affordable price.
Conclusion
Wholesale carnations flower offer a perfect blend of beauty, versatility, and affordability, making them an ideal choice for elevating any celebration. Whether you’re planning a lavish wedding or a simple gathering with loved ones, carnations add a touch of elegance and charm to the occasion. With their timeless appeal and wide range of options, wholesale carnations flower are sure to delight guests and create lasting memories for years to come.
| merlinmcelroy | |
1,874,974 | Finding the Perfect Path: Comparing Graphic Designers and UX Designers | Introduction: Graphic Designers vs UX Designers In the ever-evolving landscape of digital design, two... | 0 | 2024-06-03T06:19:18 | https://dev.to/apptagsolution/finding-the-perfect-path-comparing-graphic-designers-and-ux-designers-3f0d | graphic, designers, ux, designer | Introduction: Graphic Designers vs UX Designers
In the ever-evolving landscape of digital design, two roles have emerged as pivotal players: graphic designers and UX (user experience) designers. While these professions share some similarities, they possess distinct responsibilities, skillsets, and approaches to design. As an experienced writer in the field of design, I aim to provide a comprehensive comparison between these two disciplines, shedding light on their unique characteristics and guiding you toward the path that aligns best with your aspirations.
Understanding Graphic Designers
Graphic designers are the visual storytellers, crafting compelling narratives through the artful combination of typography, imagery, and layout. Their primary focus lies in creating visually striking designs that effectively communicate messages, evoke emotions, and captivate audiences.
Roles and Responsibilities of Graphic Designers
Branding and Identity Design: Graphic designers play a crucial role in developing and maintaining brand identities. They create logos, color palettes, typography styles, and other visual elements that establish a brand's unique personality and ensure consistent representation across various platforms.you have also to know [**graphic and product design**](https://apptagsolution.com/blog/product-design-graphic-design/)
Print and Digital Design: From printed materials like brochures, magazines, and packaging to digital assets like websites, social media graphics, and advertisements, graphic designers are responsible for conceptualizing and executing visually appealing designs that effectively convey information and engage viewers.
Typography and Layout: Mastering the art of typography and layout is a fundamental aspect of a graphic designer's skillset. They carefully select and arrange typefaces, sizes, and spacing to create harmonious and legible designs that enhance readability and visual appeal.
Skillset Required for Graphic Designers
Creativity and Artistic Ability: Graphic designers must possess a keen eye for aesthetics, color theory, and composition, as well as the ability to think creatively and conceptualize visually compelling designs.
Technical Skills: Proficiency in industry-standard design software, such as Adobe Creative Cloud (Photoshop, Illustrator, InDesign), is essential for graphic designers to bring their ideas to life.
Communication and Collaboration: Effective communication skills are crucial for understanding client requirements, presenting design concepts, and collaborating with teams to ensure successful project execution.
Understanding UX Designers
UX designers are the advocates for the end-user, focusing on creating intuitive and seamless digital experiences that meet user needs and expectations. Their primary objective is to bridge the gap between design and functionality, ensuring that products and services are not only visually appealing but also highly usable and accessible.
Roles and Responsibilities of UX Designers
User Research and Analysis: UX designers conduct extensive user research to gain insights into user behaviors, preferences, and pain points. This research informs the design process and ensures that solutions are tailored to meet the specific needs of the target audience.
Information Architecture and User Flows: UX designers are responsible for organizing and structuring information in a logical and intuitive manner. They create user flows, wireframes, and prototypes to map out the user journey and ensure a smooth and efficient experience.
Usability Testing and Iteration: Continuous testing and iteration are integral to the UX design process. UX designers gather feedback from users, analyze data, and refine designs to optimize usability, accessibility, and overall user satisfaction.
Skillset Required for UX Designers
User-Centric Mindset: UX designers must possess a deep understanding of user behavior, psychology, and design principles to create experiences that resonate with users and meet their needs.
Analytical and Problem-Solving Skills: UX designers must be adept at identifying and solving complex user problems through data-driven analysis, critical thinking, and creative problem-solving.
Prototyping and Testing: Proficiency in prototyping tools, such as Figma, Adobe XD, or InVision, is essential for UX designers to create interactive mockups and conduct usability testing.
Key Differences between Graphic Designers and UX Designers
While both graphic designers and UX designers contribute to the overall design process, their focus areas and priorities differ significantly:
Design Approach: Graphic designers prioritize visual aesthetics, branding, and communication, while UX designers concentrate on creating user-centric experiences that prioritize functionality and usability.
Design Process: Graphic designers typically follow a more linear process, starting with conceptualization and moving towards execution. UX designers, on the other hand, employ an iterative process involving user research, prototyping, testing, and refinement.
Skillset Emphasis: Graphic designers excel in artistic and creative skills, such as typography, layout, and visual communication. UX designers, while appreciating visual appeal, place greater emphasis on user research, information architecture, and usability principles.
Deliverables: Graphic designers produce visual assets like logos, brochures, advertisements, and marketing materials. UX designers create user flows, wireframes, prototypes, and design systems that guide the development of digital products and services.
Which Career Path is Right for You?
Choosing between a career as a graphic designer or a UX designer ultimately depends on your interests, strengths, and career aspirations. Here are some considerations to help you determine the right path:
Passion for Visual Storytelling: If you have a deep fascination with visual communication, branding, and creating visually captivating designs, a career as a graphic designer might be the perfect fit.
User-Centric Approach: If you are driven by a desire to understand user needs and create intuitive, user-friendly experiences, a career as a UX designer could be the ideal choice.
Iterative Process: If you thrive in an environment that encourages continuous iteration, testing, and refinement based on user feedback, the UX design path may align with your preferences.
Creative Freedom: If you value artistic expression and the ability to explore creative concepts without being constrained by usability guidelines, graphic design may offer you greater creative freedom.
It's important to note that these two disciplines often intersect and collaborate within the design process. Many professionals possess skills in both areas, and some roles may require a combination of graphic design and UX design expertise. you might also like[ **product design graphic design**](https://apptagsolution.com/blog/product-design-graphic-design/)
Conclusion
In the dynamic world of design, both graphic designers and UX designers play vital roles in shaping experiences that captivate and engage users. While graphic designers focus on visual storytelling and branding, UX designers prioritize user-centric design and seamless functionality.
Ultimately, the path you choose should align with your passions, skillset, and career aspirations. Whether you opt for the visually compelling world of graphic design or the user-focused realm of UX design, both paths offer rewarding opportunities to create impactful and meaningful experiences.
If you're passionate about design and seeking to embark on a fulfilling career journey, consider exploring our comprehensive design courses. Our expert instructors will guide you through the intricacies of graphic design, UX design, or a combination of both, equipping you with the skills and knowledge to thrive in your chosen field. Enroll today and unlock your creative potential! | apptagsolution |
1,875,160 | 5 Free Open Source Tools Every Developer Should Know | Do not start your next project without knowing those 5 free open source tools. They will save you... | 0 | 2024-06-10T08:03:04 | https://blog.elest.io/5-free-open-source-tools-every-developer-should-know/ | elestio, opensource | ---
title: 5 Free Open Source Tools Every Developer Should Know
published: true
date: 2024-06-03 06:16:59 UTC
tags: Elestio, OpenSource
cover_image: https://blog.elest.io/content/images/2024/06/5-free-open-source-tools.jpg
canonical_url: https://blog.elest.io/5-free-open-source-tools-every-developer-should-know/
---
Do not start your next project without knowing those 5 free open source tools.
They will save you time and effort by preventing you from redeveloping common features.
With these tools, you can have robust, efficient solutions ready in no time, often performing even better than what you could create from scratch.
<iframe width="200" height="113" src="https://www.youtube.com/embed/jpECO-gRCVQ?feature=oembed" frameborder="0" allow="accelerometer; autoplay; clipboard-write; encrypted-media; gyroscope; picture-in-picture; web-share" referrerpolicy="strict-origin-when-cross-origin" allowfullscreen title="5 Free Open Source Tools Every Developer Should Know"></iframe>
_Watch our video on YouTube_
### [**Logto**](https://elest.io/open-source/logto?ref=blog.elest.io)
If like me you’re tired of setting up login, signup, and forgotten password functionality for every new project, you will love LogTo. It simplifies the entire authentication process, allowing you to integrate: user management, email and sms passwordless, social sign-in from many providers with minimal effort.
It’s easy to implement and customize, freeing you up to focus on the core features of your application.
### [**Directus**](https://elest.io/open-source/directus?ref=blog.elest.io)
Why spend time developing a backend with a custom administration dashboard when you can have one up and ready in no time?
Directus offers a dynamic data platform that connects your database with a powerful, user-friendly interface. It allows you to manage your content effortlessly, with features like role-based access control, dynamic content types, and custom endpoints.
By using a low code solution, any member of the team can create the views and forms they need without the help of the development team.
With Directus, you can accelerate your backend development without losing total control of your project.
### [**FlagSmith**](https://elest.io/open-source/flagsmith?ref=blog.elest.io)
Project development is rarely linear. There are features you want to test and release to a subset of users, and others that you need to hide until they're production-ready. Flagsmith helps you manage feature flags with ease, offering functionalities such as:
- A/B testing to experiment with different features
- Canary deployments for phased rollouts
- User traits to target specific user groups
- A remote config server to update environment variables and keys on the fly
Flagsmith empowers you to handle these complexities seamlessly, making your development process more agile and controlled.
### [**SonarQube**](https://elest.io/open-source/sonarqube?ref=blog.elest.io)
Ensure your code remains clean, secure, and maintainable throughout your project's lifecycle with SonarQube. This comprehensive code quality and security solution helps you consistently deploy high-quality code.
SonarQube integrates seamlessly into your CI/CD pipeline, automatically analyzing your code with every build. If any issues are detected, you'll be notified immediately, and the deployment can be configured to fail, ensuring that only clean code makes it to production.
By integrating SonarQube into your development workflow, you can enhance your code's reliability and security, ultimately delivering a better product.
### [**Gotenberg**](https://elest.io/open-source/gotenberg?ref=blog.elest.io)
Turn any document or URL into a PDF file with this developer-friendly API.
Gotenberg provides endpoints to easily convert web pages, Markdown, Word and Excel files into PDF. But also allows you to merge multiple PDFs into one.
With the different parameters, you have full control of the output like landscape/portrait mode or margin/padding. Based on your project workflow requirements, you can choose to run it synchronously or asynchronously and get notified on a webhook when the process is finished. | kaiwalyakoparkar |
1,872,819 | Build OAuth 2.0 Server & API Server with Authlete + Spring Boot | This article explains how to build OAuth 2.0 server and API server with Authlete + Spring Boot. | 0 | 2024-06-03T06:13:28 | https://dev.to/authlete/build-oauth-20-server-api-server-with-authlete-spring-boot-5aj4 | oauth, security, java, spring | ---
title: "Build OAuth 2.0 Server & API Server with Authlete + Spring Boot"
published: true
description: This article explains how to build OAuth 2.0 server and API server with Authlete + Spring Boot.
tags: OAuth, Security, Java, Spring
---

# Overview
This article explains how to build OAuth 2.0 server and API server with [Authlete](https://www.authlete.com/) + [Spring Boot](https://spring.io/projects/spring-boot/).
# Architecture
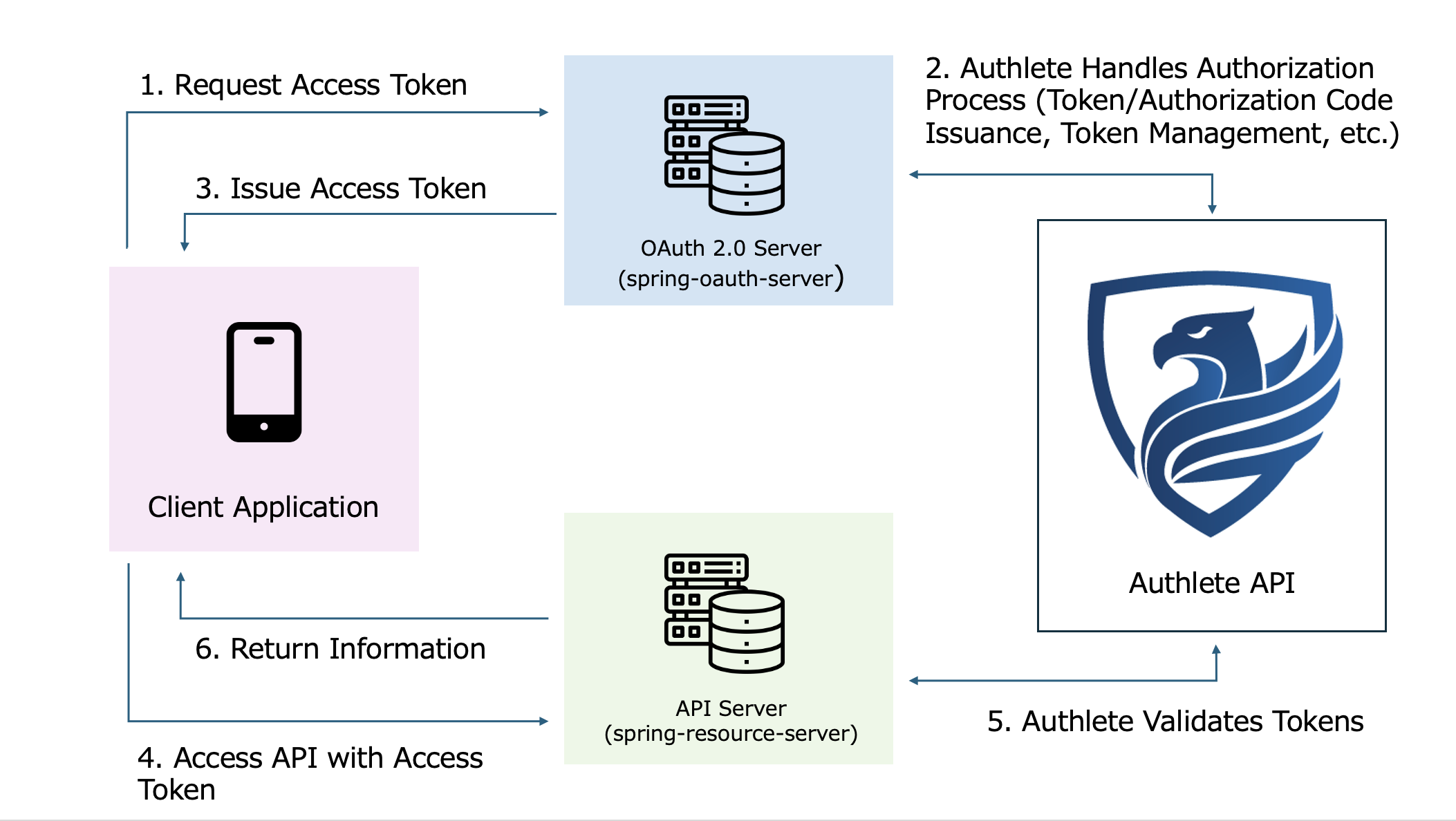
# How-to-Do
## 1. Create an Account at Authlete.
Create an Authlete account on the sign up page.
Upon successful signup, you will automatically login to the service owner console.
## 2. Create & Configure Service
Click **Create Service** tab at the service owner console. This redirects you to the service creation page.
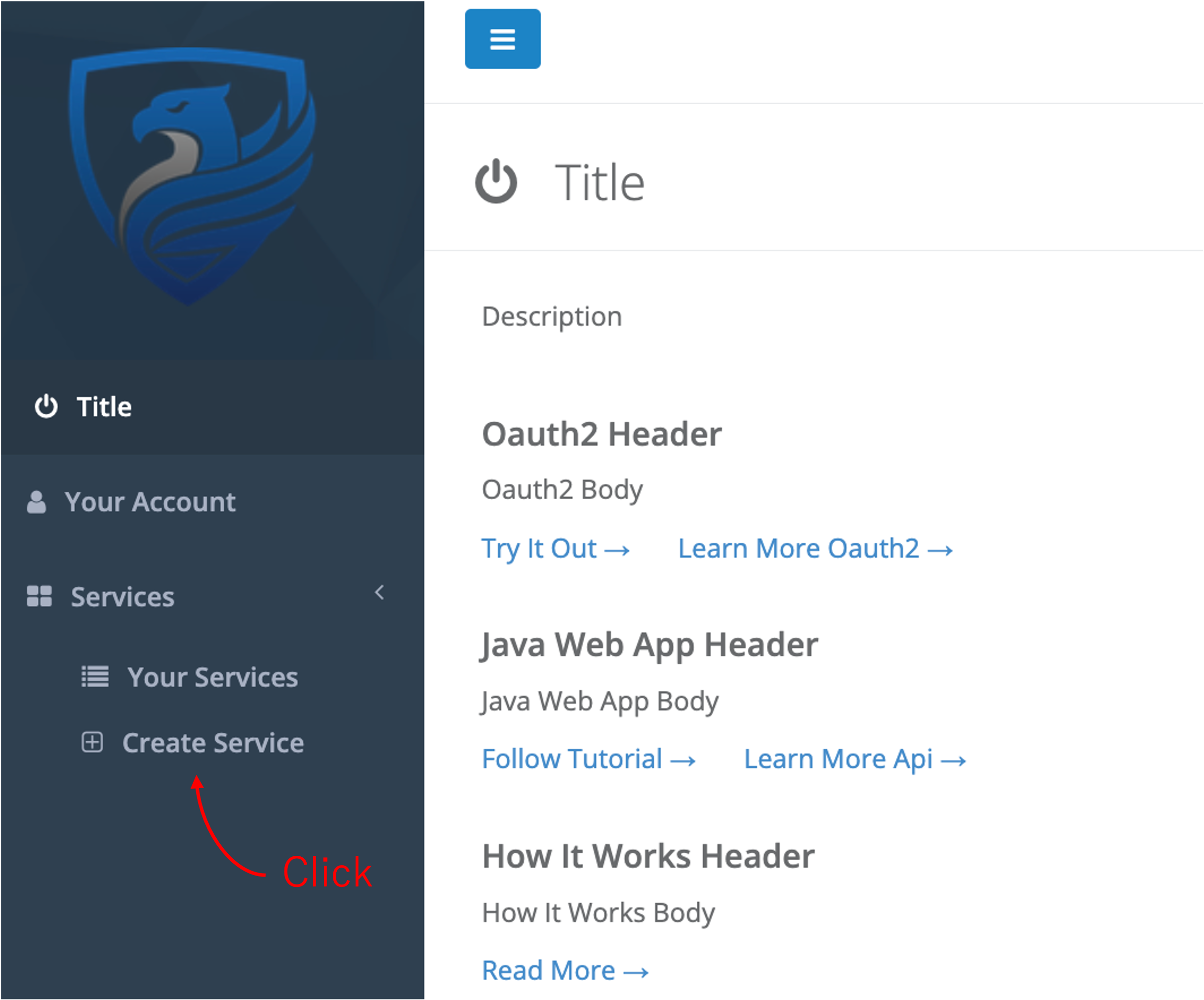
Input your service name and click **Create** button. Upon successful service creation, you will be redirected to the the service detail page,
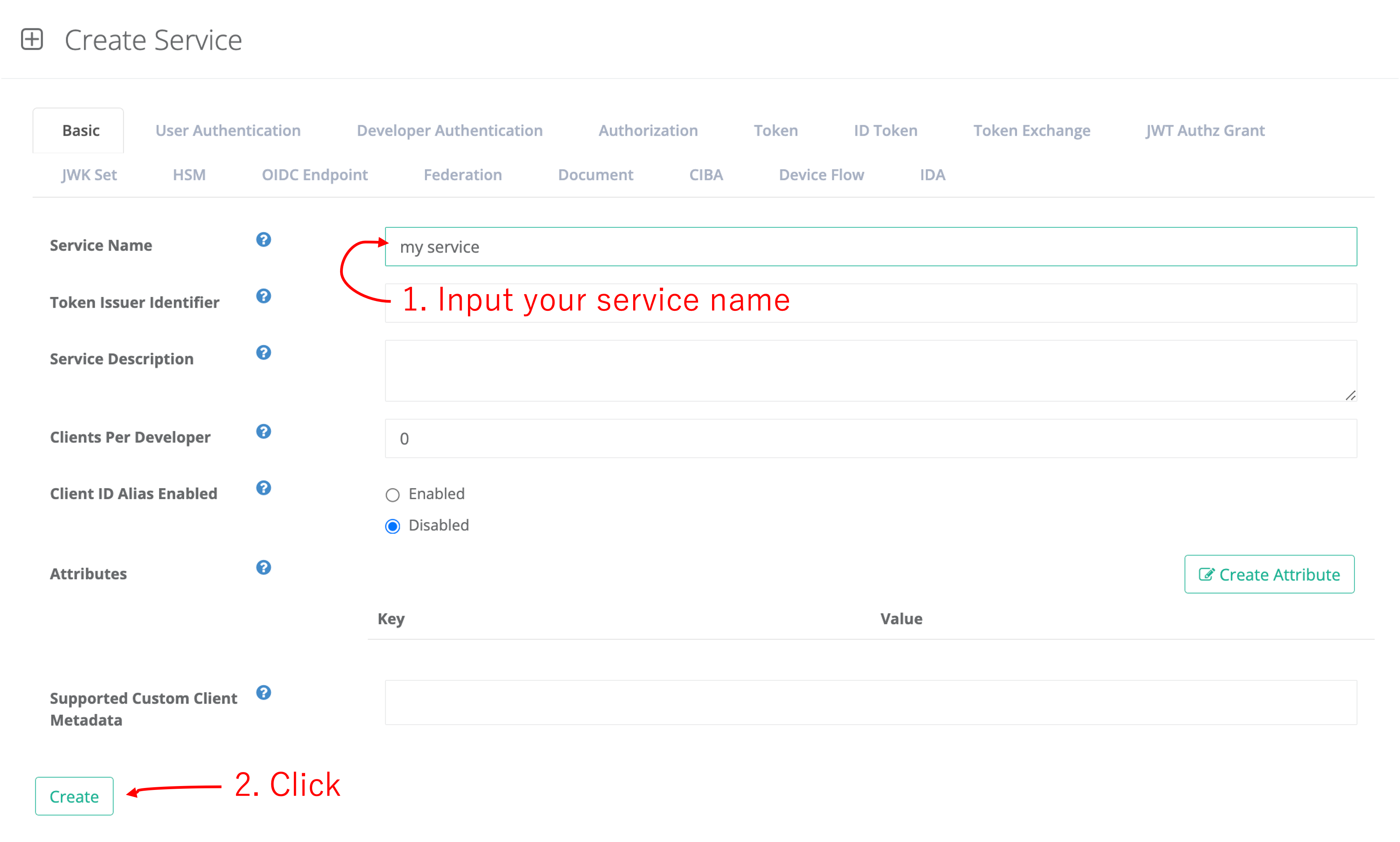
which shows the detailed information about your service as below. Write down the API key & secret value from the service detail page.
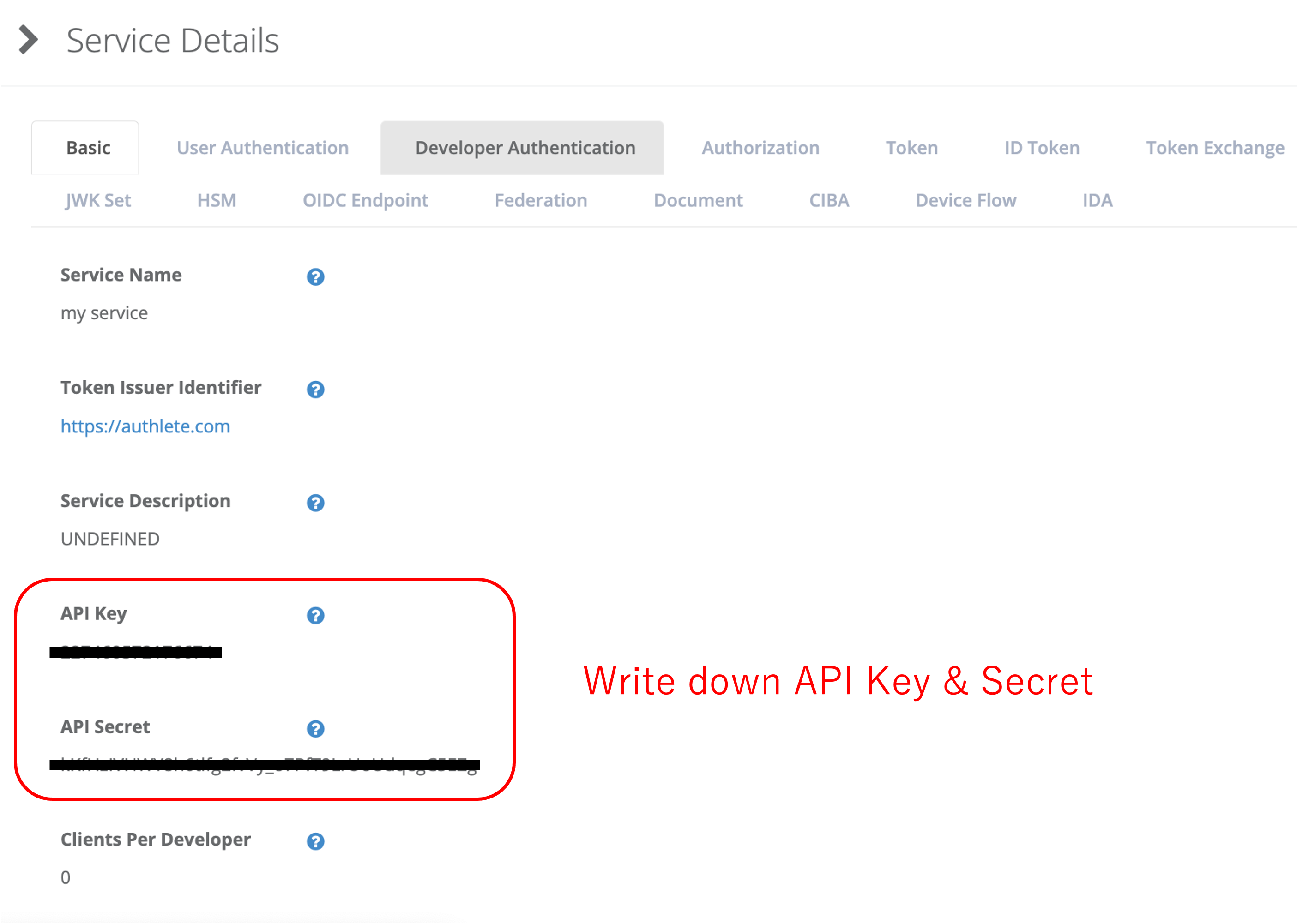
## 3. Create & Configure Client
Access the client application console at the following URL in your browser:
```
https://cd.authlete.com/{YOUR-SERVICE-API-KEY}
```
Then, login to the console with your service API key and secret.
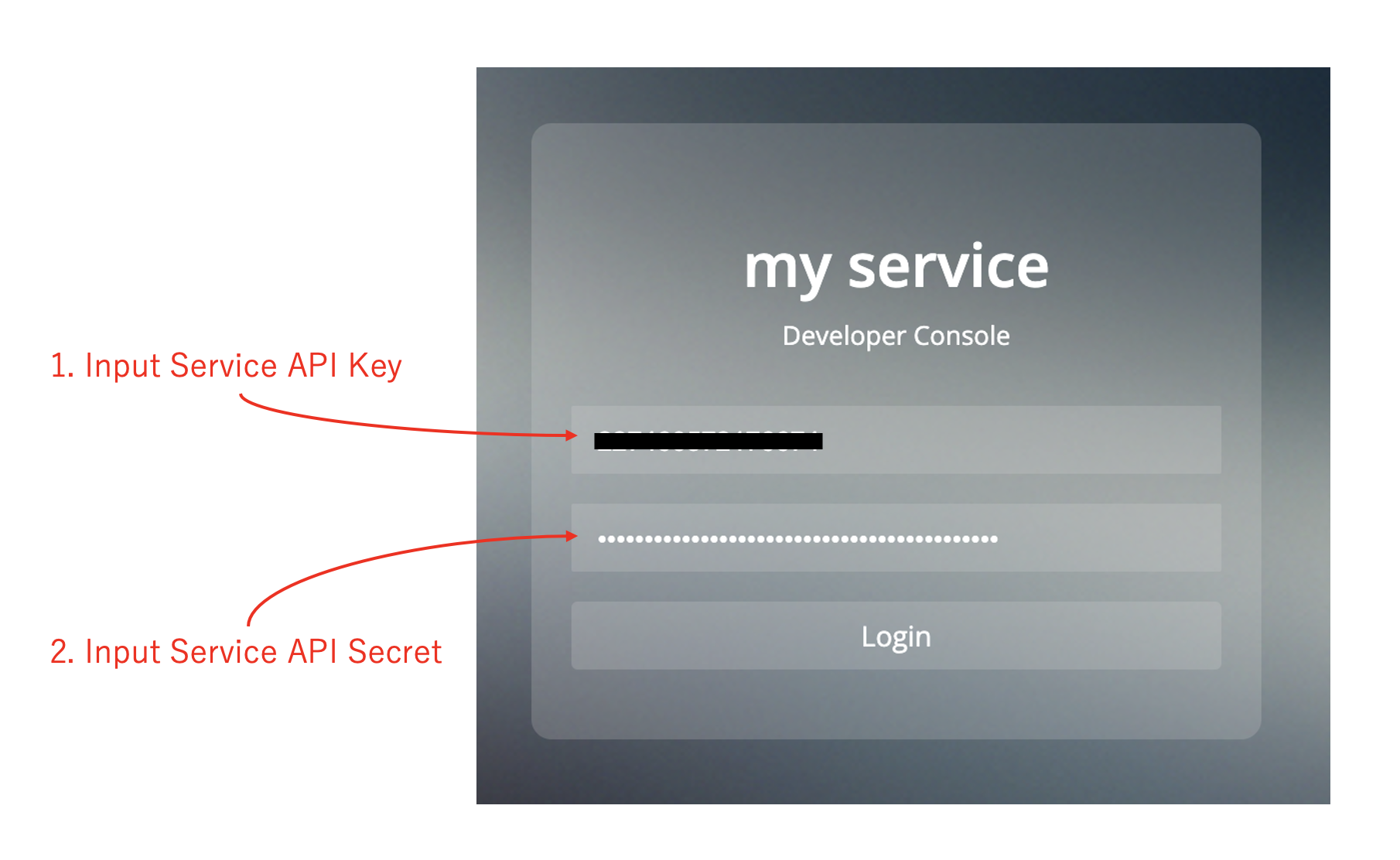
Input your client name and click **Create** button.
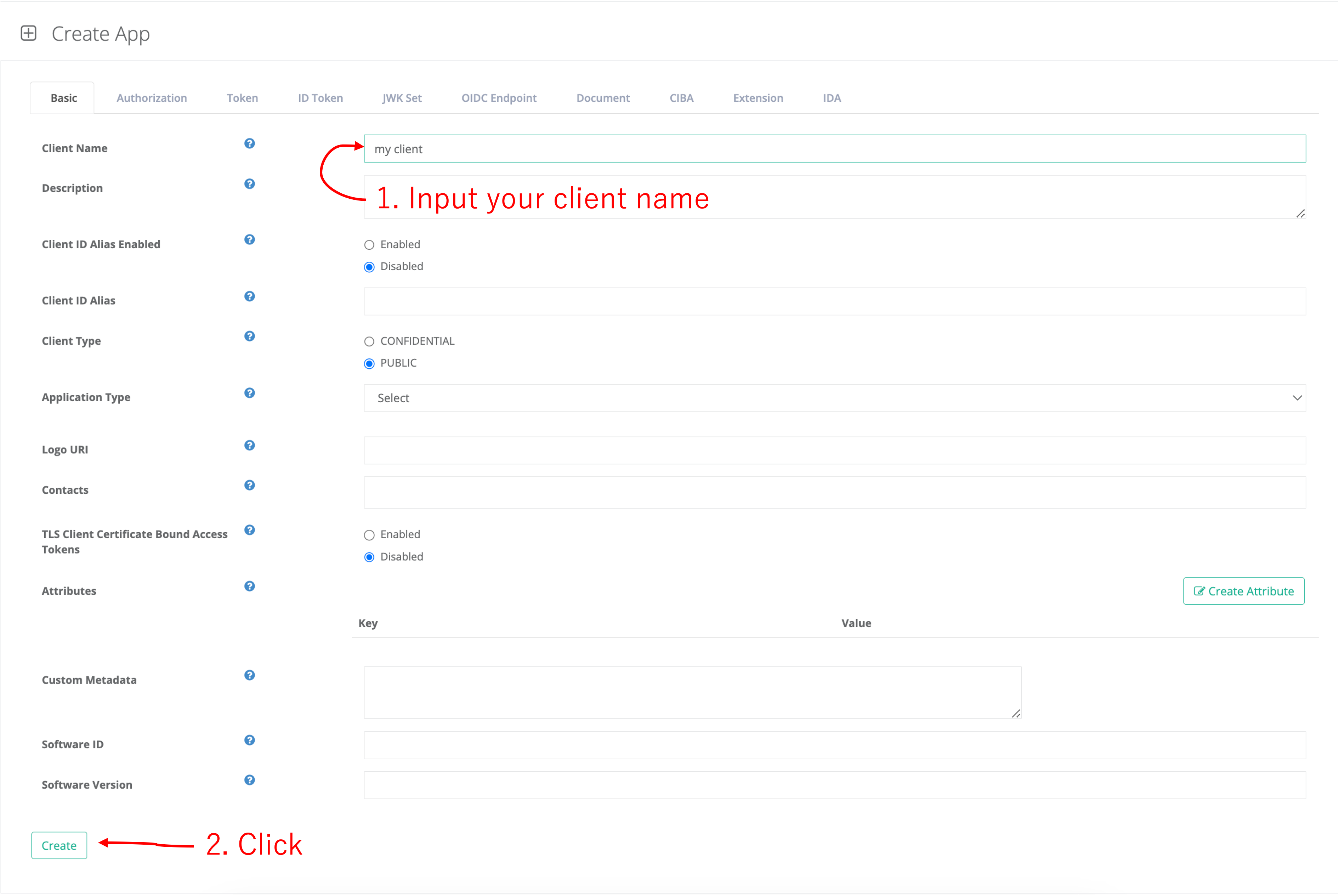
Write down **Client ID** and **Client Secret**.
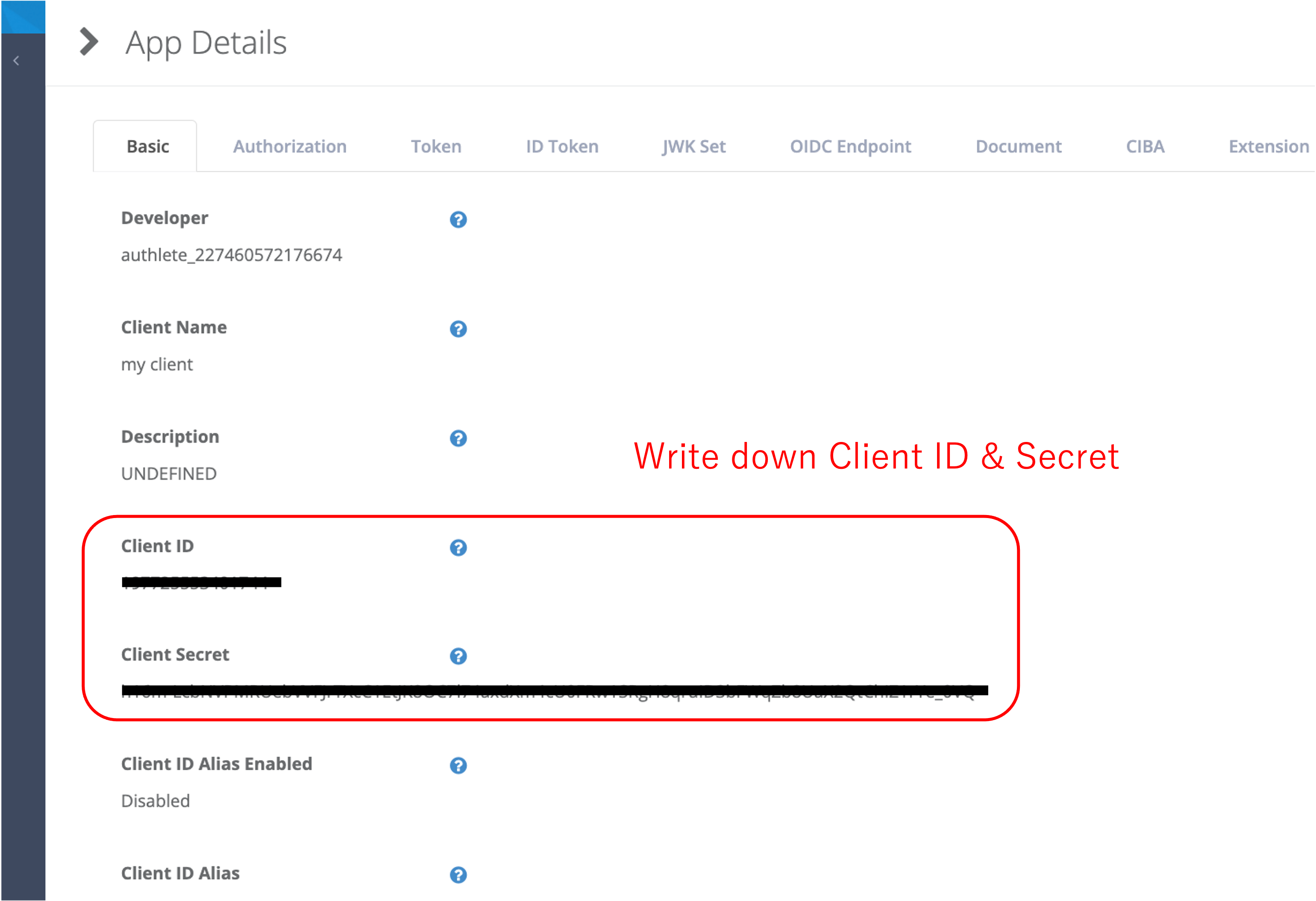
## 4. Configure & Run OAuth 2.0 Server
Run the following command to download the OAuth 2.0 server.
```bash
$ git clone https://github.com/authlete/spring-oauth-server.git
```
Navigate to spring-oauth-server directory and edit authlete.properties as below.
```
service.api_key = {YOUR-SERVICE-API-KEY}
service.api_secret = {YOUR-SERVICE-API-SECRET}
```
Start the OAuth 2.0 server by the following command. (It uses port 8080.)
```bash
$ docker-compose up
```
## 5. Configure & Run API Server
Run the following command to download the API server.
```bash
$ git clone https://github.com/authlete/spring-resource-server.git
```
Navigate to spring-resource-server directory and edit authlete.properties as below.
```
service.api_key = {YOUR-SERVICE-API-KEY}
service.api_secret = {YOUR-SERVICE-API-SECRET}
```
Start the API server by the following command. (It uses port 8081.)
```bash
$ docker-compose up
```
## 6. Test
### 6.1. Issue Access Token
Let’s check that the OAuth 2.0 server can issue an access token using Authorization Flow ([RFC6749](https://datatracker.ietf.org/doc/html/rfc6749)).
### 6.1.1. Authorization Request
First, access the authorization endpoint (of the OAuth 2.0 server) at the following URL in your browser.
```
http://localhost:8080/api/authorization?client_id={CLIENT-ID}&response_type=code
```
Then, an authorization page will appear.
Enter the following dummy user information and click Authorize button.
```
User ID = john
Password = john
```
Dummy user info is defined in `/src/main/java/com/authlete/spring/server/db/UserDao.java`. Modify it as needed.
Then, you will be redirected to the redirect URL like below. Write down the value of the code parameter.
```
https://api.authlete.com/api/mock/redirection/{YOUR-SERVICE-API-KEY}?code=xxxxx...
```
### 6.1.2. Token Request
Make a token request using the authorization code as follows.
```bash
$ curl -v -X POST -d 'code={AUTHORIZATION-CODE}' -d 'client_id={CLIENT-ID}' -d 'grant_type=authorization_code' http://localhost:8080/api/token
```
A successful response is like below.
```json
{
"access_token": "xxxxx",
"refresh_token": "xxxxx",
"scope": null,
"token_type": "Bearer",
"expires_in": 86400
}
```
## 6.2. Access API
Let’s access Country API (/api/country/{country-code}) on the API server using the access token.
```bash
$ curl -v -H "Authorization: Bearer {access-token}" http://localhost:8081/api/country/JP
```
A successful response will be like below.
```json
{
"name": "Japan",
"alpha2": "JP",
"alpha3": "JPN"
"numeric": 392
"currency": "JPY"
}
```
If you access the API without an access token like below,
```bash
$ curl -v http://localhost:8081/api/country/JP
```
it will return an appropriate error:
```
< HTTP/1.1 400
< Cache-Control: no-store, no-transform
< Pragma: no-cache
< WWW-Authenticate: Bearer error="invalid_token",error_description="An access token is missing."
< Content-Length: 0
...
```
# More Info
See the following information for more details.
- [README.md](https://github.com/authlete/spring-oauth-server/blob/master/README.md) & [CUSTOMIZATION.md](https://github.com/authlete/spring-oauth-server/blob/master/doc/CUSTOMIZATION.md) of spring-oauth-server
- [README.md](https://github.com/authlete/spring-resource-server/blob/master/README.md) & [CUSTOMIZATION.md](https://github.com/authlete/spring-resource-server/blob/master/doc/CUSTOMIZATION.md) of spring-resource-server
- [Authlete Website](https://www.authlete.com/)
- [Authlete API Document](https://api.authlete.com/)
- [Spring Boot Website](https://spring.io/projects/spring-boot) | hidebike712 |
1,874,973 | Dive into India: Explore with a Tailor-Made Holiday Package | India beckons you with a kaleidoscope of colors, a tapestry woven with vibrant cultures, ancient... | 0 | 2024-06-03T06:09:11 | https://dev.to/indiatourismpackages/dive-into-india-explore-with-a-tailor-made-holiday-package-3k91 |

India beckons you with a kaleidoscope of colors, a tapestry woven with vibrant cultures, ancient traditions, and breathtaking landscapes. India Holiday Packages and India Tourism Packages offer a gateway to explore this incredible country, whether you're a seasoned traveler or a curious first-timer. Here, amidst the majestic Himalayas, serene beaches, bustling cities, and tranquil backwaters, you'll discover an unforgettable journey that caters to your every whim.
What Kind of Traveler Are You?
India's diversity ensures there's something for everyone. Are you a history buff, enthralled by bygone eras? India Holiday Packages can whisk you away on a historical tour of the magnificent Taj Mahal, the majestic forts of Rajasthan, and the spiritual aura of Varanasi. Perhaps you're a nature enthusiast, yearning for fresh mountain air and emerald valleys. [India Tourism Packages](https://tailormadejourney.com/destination/india-tour-packages/) can take you trekking in the Himalayas, cruising through the serene backwaters of Kerala, or spotting tigers in the jungles of Ranthambore National Park. Do you crave adventure? India offers white-water rafting on the Ganges, paragliding in Himachal Pradesh, and scuba diving in the pristine waters of the Andamans. For those seeking relaxation, pristine beaches in Goa and Kerala promise golden sands and turquoise waters. Traveling with family? India Holiday Packages can be customized to include wildlife safaris, amusement parks, and cultural experiences that will leave lasting memories for everyone.
Explore by Region: Unveiling the Gems of India
The Golden Triangle: Delhi, Agra, and Jaipur form the quintessential India experience. Witness the architectural marvel of the Taj Mahal at sunrise, delve into the rich Mughal history of Agra Fort, and wander through the bustling bazaars of Delhi. Jaipur, the Pink City, awaits with its majestic forts, Hawa Mahal (Palace of Winds), and vibrant culture.
South India: Immerse yourself in the serene beauty of Kerala's backwaters, fringed by coconut palms and teeming with birdlife. Explore the beaches of Goa, famed for its laid-back charm and Portuguese influence. Venture into the heart of Karnataka, where ancient temples like Hampi stand as testaments to bygone eras.
The Himalayas: Trek through breathtaking mountain ranges, encounter snow-capped peaks, and experience the serenity of hill stations like Darjeeling and Munnar. For the truly adventurous, Ladakh offers challenging treks and mesmerizing landscapes.
Rajasthan: Step back in time and explore the majestic forts of Mehrangarh and Jaisalmer, witness the grandeur of the City Palace in Udaipur, and lose yourself in the vibrant culture of Rajasthan.
Beyond the Regions: Must-See Experiences in India
India Holiday Packages and India Tourism Packages go beyond sightseeing. Here are some unique experiences that will enrich your journey:
Witness the ethereal beauty of the Taj Mahal bathed in the golden light of sunrise.
Glide through the emerald backwaters of Kerala on a traditional houseboat, savoring the tranquility of the waterways.
Push your limits with a thrilling trek in the Himalayas, surrounded by snow-capped peaks and crisp mountain air.
Immerse yourself in the vibrant colors and joyous celebrations of a Hindu festival like Holi or Diwali.
Seek inner peace and learn the ancient practice of Yoga in Rishikesh, the birthplace of Yoga.
Planning Your Indian Adventure
To ensure a smooth and enriching experience, here are some essential aspects to consider:
Visas: A visa is mandatory for most nationalities. India Holiday Packages can often help you navigate the application process.
Currency: The Indian Rupee (INR) is the national currency. India Tourism Packages can provide you with an approximate cost breakdown based on your chosen experiences.
Best Time to Visit: India experiences diverse weather patterns. The ideal time to visit depends on the region. India Holiday Packages can advise you on the best season for your chosen destinations, keeping in mind the monsoon season.
Packing Essentials: Pack comfortable clothing suitable for the climate of your chosen destinations. Consult your India Holiday Package for specific recommendations.
Next Steps: Craft Your Dream Indian Holiday
Ready to embark on your Indian adventure? Browse our curated selection of India Holiday Packages or contact us to create a personalized itinerary that reflects your interests, budget, and travel style. India Tourism Packages offer a seamless way to explore this incredible land, ensuring memories that will last a lifetime. Let us be your guide as you discover the magic of India! | indiatourismpackages | |
1,874,972 | Microsoft team login not calling saml idp java script ajax call. | Can anyone help me on below... | 0 | 2024-06-03T06:06:52 | https://dev.to/dalip_choudhary_5c02424a3/microsoft-team-login-not-calling-saml-idp-java-script-ajax-call-2hn3 | microsoft, javascript | Can anyone help me on below question
https://stackoverflow.com/questions/78561111/ajax-call-not-happening-in-microsoft-team-login-popup-using-external-saml-identi
| dalip_choudhary_5c02424a3 |
1,874,971 | Understanding the Importance of Code Plagiarism Checkers | With our growing dependency on technology, preserving the authenticity of original code has become... | 0 | 2024-06-03T06:05:44 | https://dev.to/codequiry/understanding-the-importance-of-code-plagiarism-checkers-ebm | webdev, codeplagiarismchecker, codeplagiarism, codequiry | With our growing dependency on technology, preserving the authenticity of original code has become critical. As the number of programmers and coding projects grows, so does the frequency of code plagiarism. Plagiarism in code is more than just copying; it reduces the value of original work, jeopardizes academic integrity, and can result in serious legal and professional consequences.
A [Code Plagiarism Checker](https://codequiry.com/), such as Codequiry, is an indispensable tool for educators, students, and developers. It ensures that the submitted code is unique and that any similarities to existing codebases are identified and analyzed. This process promotes academic integrity and encourages genuine learning and innovation.
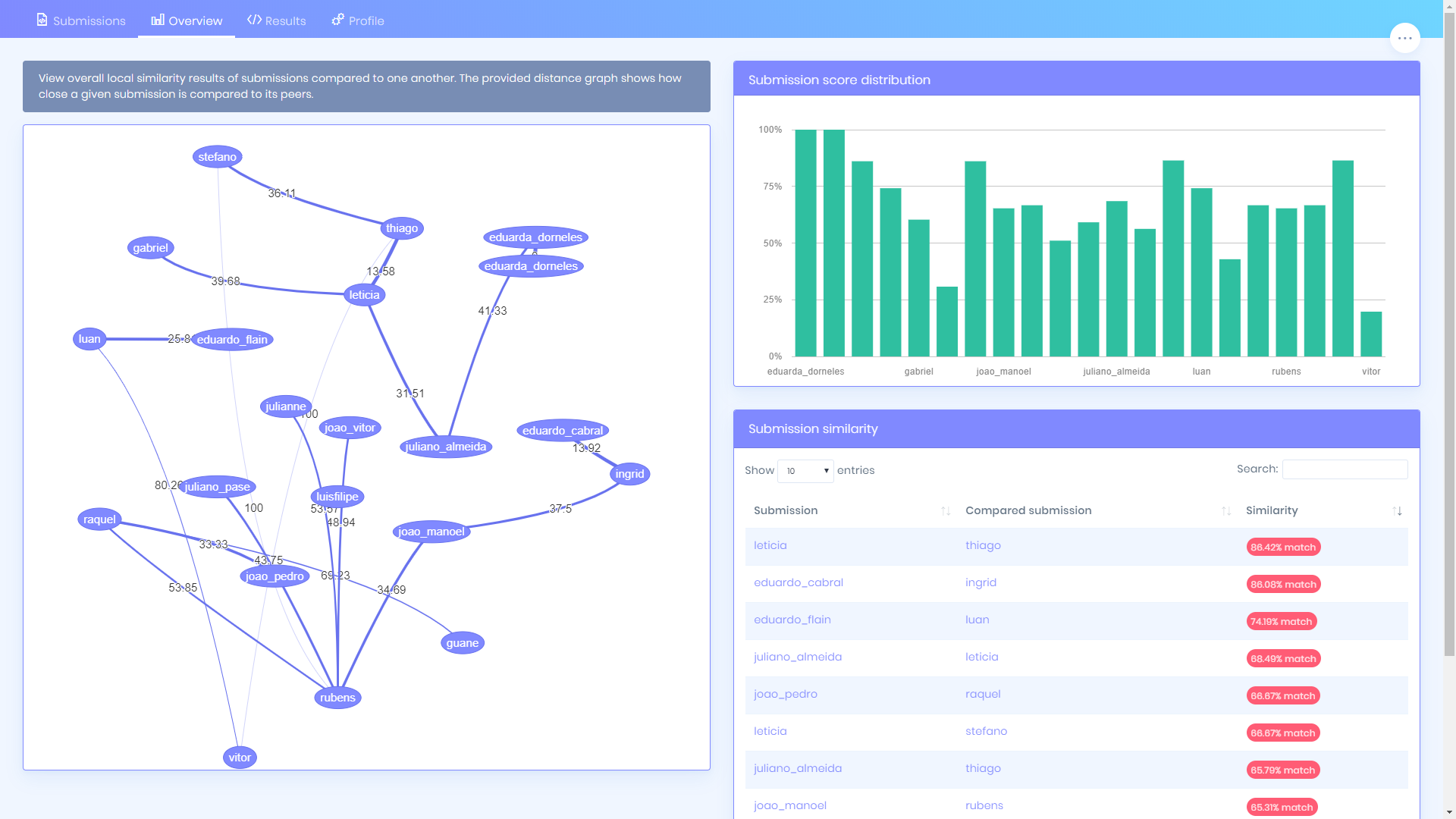
Modern code plagiarism checkers use sophisticated algorithms that go beyond basic text matching. They examine code structure, logical flow, and programming patterns from multiple languages. These tools can detect nuanced similarities even if the code has been superficially altered.
For educators, this means improved monitoring of student submissions. It encourages students to develop original solutions. For professionals, it protects intellectual property and fosters trust in collaborative settings.
Incorporating a tool like Codequiry, similar to the [Stanford Code Plagiarism Checker](https://codequiry.com/moss/measure-of-software-similarity), into your workflow can significantly improve code quality and originality while promoting a culture of integrity and respect for intellectual property in the programming community.
| codequiry |
1,859,584 | What's Your Power Platform Strategy | The Power Platform is a Citizen Developer platform, designed to be accessed by everyone, just like... | 20,311 | 2024-06-03T06:05:27 | https://dev.to/wyattdave/whats-your-power-platform-strategy-2a17 | powerplatform, lowcode, powerautomate, powerapps | The Power Platform is a Citizen Developer platform, designed to be accessed by everyone, just like Excel. But it is not just like Excel, it's built on Dynamics, a powerful fully featured CRM tool, so it can be much more like a standard IT solution. This means as a platform owner you have a choice, Excel or CRM, so what is your Power Platform strategy?
But there is not just your strategy, there is also your model. If the strategy is your direction, the model is how you get there. It's the practical implementation of the strategy, the rules and processes setup.
---
There are 4 main strategies/philosophy's when setting up the Power Platform, and they are:
1. Personal Owned
2. Scaled
3. Federated
4. IT Owned

## 1. Business Owned
Spun up by IT but then delegated to the users with little to no oversight. This is the "I trust you" approach, you empower the citizen developers to make any solution in their own way. Kind of like the Excel model but on purpose instead of by accident.
## 2. Scaled
Different controls depending on the solution, with low no IT involvement and high fully IT owned. This is the "I trust you but it depends", with different indicators/thresholds setting the level of independence for the developer. If it breaches the threshold there is less trust with IT getting more involved.
## 3. Federated
Business teams are up-skilled to own their own environments, with IT governance enforced but the process not managed by IT. This is the "I trust you but only if you do it my way" approach, building out the processes and tools for citizen developers to create their own IT setup.
## 4. IT Owned
IT owned, managed and used by IT professionals only. No mistaking this one, it's the "I don't trust you". The low code capability is only to improve the productivity of IT professionals, no citizen developers allowed as the risks of something going wrong are too high.
---
The most common models I see that represent the 4 strategies are:
1. Full Citizen Developer
2. Managed Risk
3. Business Managed
4. IT Integration Tool
## 1. Full Citizen Developer
The full Citizen Developer approach encompasses what I think the original vision of the Power Platform was. Just like Excel, anyone can build and share. The developer owns everything, from design to build to test to deployment to support.
There is no Dev/Test/Prod, everything is prod.
The organisation setups up with a 'Default' first approach. DLP policy is all or nothing, once approved anyone can use it. Dataverse is not used as tracking ownership of the space is difficult, so all the developers use SharePoint or Excel/OneDrive.
Pros
- Lowest barrier to entry so high users with high implied value
- Little platform administration
Cons
- Little visibility actual value generated
- Data/security risks
- High orphaned rate
- Low skilled solution as developer often have minimal dev time
_Orphaned are flows/apps that have no real owner as they have either left or switched teams with no handover_
## 2. Staged
The staged approach looks at business criticality and then positions the solution sliding governance process.
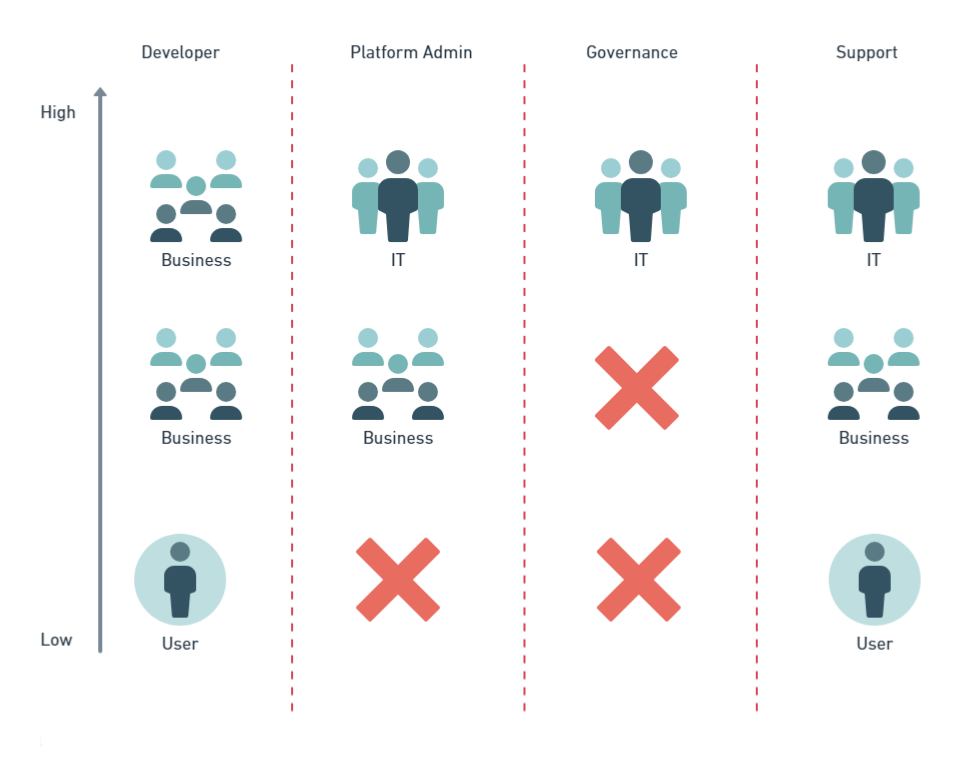
- Low user low criticality - Default environment (Personal)
- Medium user low criticality - Team environment (Teams)
- High user or Medium+ criticality - Managed environments (Enterprise)
**Personal**
Owned and maintained by the user (very much like Full Citizen Developer), only with limited DLP and sharing limits.
**Teams**
Approved business teams own their own environment each with its own DLP policy. Still owned and maintained by a user but with a process to share/switch owners
**Enterprise**
Developed by the business but supported by IT, Dev/Test/Prod environments, security, architecture & security review, enforced with seperation of duty through Service Account ownership and change management.
Pros
- Lowest barrier to entry so high users with high implied value
- Majority owned by business so low platform administration
- Focused dev teams generate skilled developer
- IT governance for high risk solutions
- Developer knowledge of solution/requirements
Cons
- Little visibility actual value generated
- Data/security risks as policy focus on criticality not security
## 3. Business Managed
Business owned environments but follow IT governance. Environments follow Dev/Test/Prod, security, architecture review and change management. Teams are responsible for administering their environments and work with central team for DLP updates.
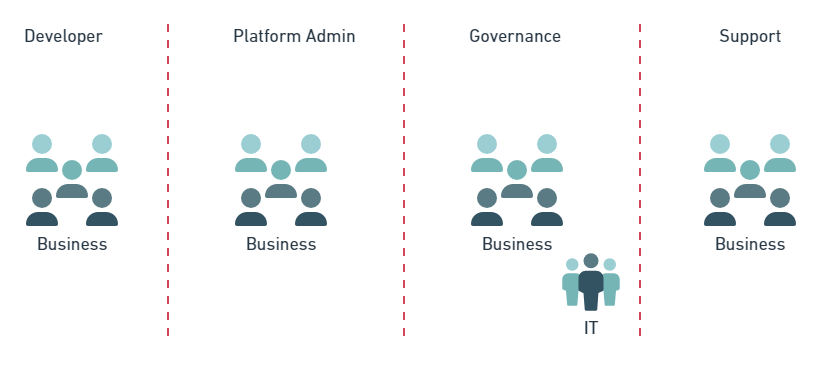
Pros
- Majority owned by business so low platform administration
- Focused dev teams generate skilled developer
- IT governance for all solutions
- Zero orphan rate
- Developer knowledge of solution/requirements
Cons
- Minimum visibility actual value generated
- Barrier to entry as business need to be upskilled to IT standards
- Teams have to replicate functionality (platform support, architects, user admin, etc)
## 4. IT Integration Tool
IT treats the platform like any other IT software. Enforcing IT governance on all aspects. Development only to be completed by certified developers in the IT team. Deliveries prioritised by ROI (Return On Investment) and delivered for all of the business.
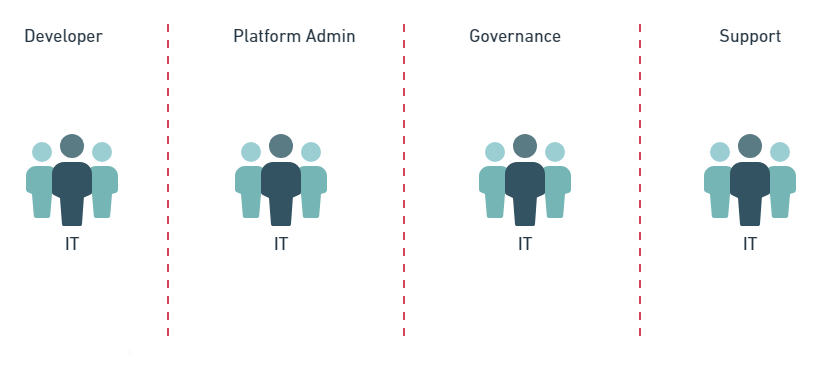
Pros
- Professional dev teams generating high value/quality solutions
- Improved productivity through certified developers
- IT governance for all solutions
- Zero orphan rate
- Accurate platform metrics
Cons
- Barrier to entry as business need to be upskilled to IT standards
- No developer knowledge of solution/requirements
- Consolidated backlog limits low value solutions
---
As you can see there is no right strategy, they all have their pros and cons, and right for certain organisations.
Additionally the models are not rigid, and can be mix and matched, with many shades of grey.
The key is to ensure your model aligns with your strategy, and you understand the practical impacts of the model.
| wyattdave |
1,874,970 | A dive into hacking and its evolution | Hacking is such a interesting topic, that I’ve always found completely fascinated. Hacking explained... | 0 | 2024-06-03T06:00:24 | https://dev.to/cougarred1/a-dive-into-hacking-and-its-evolution-3iop | hacking | Hacking is such a interesting topic, that I’ve always found completely fascinated. Hacking explained in one of it’s outer most layers simply refers to the act of manipulating or modifying systems and or devices to achieve objectives aside from it’s original goal. Now trust me I know when you hear that you may picture some under the radar geek in a dark room, with dramatic motions and random characters floating across a computer screen like exaggerated in movies, but I can assure you it’s one of those situations where the phrase “everything is not what it seems” fits perfectly here. Even though hacking is often looked at in a negative spotlight, understandably due to it’s relationship with illegal acts ranging from all sizes, it also can be used for many positive things also. Understanding hacking becomes easier to grasp once the individual allow themselves to be open minded, and consider the evolution of it, and the possible impacts its able to have within society.
The early days of where hacking was first becoming in the computer world can easily be tracked all the way back to the 1950s, where hacking was first used a cool nerdy term, meaning how creative could one get inside of the programming world. Passionate programmers wanted to see how far could they achieve modifying code, letting their imaginations roam wherever it possibly could. This was nothing more than curiosity of a specific niche, just like any other lane of focus. When people become so comfortable and experienced with something, it’s natural for their minds to roam and wonder exactly how far they can go. In some cases it’s even possible for some individuals to not just wonder how far they could go, but just repeatedly push their limits.
At the prestigious Massachusetts Institute of Technology (MIT) there was even a club called the Tech Model Railroad Club, which was affiliated with early computer hackers, having originated many different hacking styles and traditions. The tech savvy individuals within the Tech Model Railroad Club, would go on to create the blueprint that would go on to become known as the hacker culture, which stood on the values of keen problem solving, adventuring, and attacking curiosity. These students primarily focused on exploring ways to manipulate and modify complex systems.
As time went on in the years and technology became more advanced and popularity increased throughout society, the presence of hacking gained an even larger amount of individuals. With the personal computer making a uproar in the 1980s, this was the perfect opportunity for individuals all throughout society who had curiosity for technology to finally get a taste and see what they can do when it came to modifying these complex systems. It allowed innocent individuals to see how far they could let their creative minds roam within the computer world, and make their ideas come to life. However, with this being possible, as all things we know comes a dark side too. As one side allowed the harmless developers to let their creative brains roam free, it also birthed a generation of hackers seeing exactly how far they can go when it came to damaging systems taking actions with bad intentions.
There’s three different types of hacking which has to do with ones intentions and lawfulness. There’s white hat hacking, black hat hacking and gray hat hacking. They all independently stand for their own sole reason for existing, each being different than the other.
White Hat Hacking is also known as ethical hacking, and this primarily focuses on attempts to attack systems and identify vulnerabilities and improve security with given permission. These type of hackers play a very important role within cybersecurity, commonly assisting organizations in protecting their content or data from different type of attacks. These individuals are very useful for increasing protection from potential hits.
Next, there is Black Hat Hacking, which is hacking done without permission, usually for the most part involving illegal activitity being done without good intentions. These type of hackers find weaknesses within systems, and utilize them for their own use, which can include stealing information, or simply just attaking a system and making it not work properly. These powerful hacks can cause corporations or individuals to lose money, or lose data.
Finally there is Gray Hat Hacking, which is not so much Black Hat Hacking, but also not so much White Hat Hacking either. These type of hackers fall in between. They do things like gain access to weaknesses within systems without permission, but there isn’t any bad intentions behind them doing it. If they are seeking weaknesses within a system, and successfully get through their protection, even though their intentions aren’t bad, they still want a reward for doing it. Which isn’t so bad at all, and is honestly expected.
sources:
http://tmrc.mit.edu/hackers-ref.html
https://www.proofpoint.com/us/threat-reference/hacking
https://www.techtarget.com/searchsecurity/definition/white-hat
https://www.cybersmile.org/what-we-do/advice-help/online-security/hacking
https://digitalskills.ce.ucf.edu/cybersecurity/black-or-white-into-the-mind-of-the-hacker/
https://onlinedegrees.sandiego.edu/black-vs-gray-vs-white-hat-hackers/ | cougarred1 |
1,874,969 | Getting ImagePullBackOff in K8s? How to Fix and 4 Ways to Prevent It | What Is ImagePullBackOff in K8s? ImagePullBackOff is a status message in Kubernetes that... | 0 | 2024-06-03T05:56:47 | https://dev.to/giladmaayan/getting-imagepullbackoff-in-k8s-how-to-fix-and-4-ways-to-prevent-it-31g0 | imagepullbackoff, k8 | ## What Is ImagePullBackOff in K8s?
`ImagePullBackOff` is a status message in Kubernetes that indicates a failure in pulling a container image from its registry. When Kubernetes attempts to start a pod but cannot retrieve the specified image, the pod transitions to [the ImagePullBackOff status](https://komodor.com/learn/how-to-fix-errimagepull-and-imagepullbackoff/). This serves as an alert that the container engine was unable to access or download the desired image due to one or more issues.
This status is typically accompanied by a back-off delay before Kubernetes retries the image pull operation. The delay increases with each unsuccessful attempt, aiming to prevent overloading the container registry with repeated requests.
Understanding this message is crucial for troubleshooting deployment issues and ensuring that your applications run smoothly in a Kubernetes environment.
## Common Reasons for Encountering ImagePullBackOff
There are several underlying causes for the ImagePullBackOff error.
### Non-Existent Image
This error arises when Kubernetes is directed to pull an image that is not available in the specified container registry. This situation can occur due to a typo in the image name or tag, or if the image has been deleted or moved without updating the Kubernetes deployment configuration. To resolve this issue, verify the existence of the image and its correct path in the registry.
Ensuring that the specified tag matches the intended version of the image is also important. Tags are mutable and can lead to confusion if not used carefully. For example, using a ‘latest’ tag might not always retrieve the expected version of an image, leading to inconsistencies in deployments. Always double-check the image name, tag, and registry path to prevent this.
### Authentication Errors
Authentication errors occur when Kubernetes lacks the correct credentials to access a private container registry. This issue can arise if the secret containing the registry credentials is not correctly created or attached to the pod’s specification. To resolve this, verify that the secret exists and contains valid authentication information for the registry.
Ensure also that the pod specification correctly references this secret under `imagePullSecrets`. A missing or incorrect reference prevents Kubernetes from using the provided credentials, leading to `ImagePullBackOff` errors. Properly configuring these elements is essential for accessing private images securely.
### Network or Repository Issues
These issues can arise due to connectivity problems between the Kubernetes cluster and the container registry. This could be caused by network policies restricting access, DNS resolution failures, or the registry being temporarily unavailable. Verify network connectivity and ensure that the registry’s URL is reachable from within the cluster to troubleshoot this problem.
If a repository requires specific network configurations such as a proxy, these settings must be correctly configured in the Kubernetes nodes or within the container runtime environment. Misconfigurations here can prevent successful image pulls, leading to ImagePullBackOff errors. Ensure proper network setup and repository accessibility to resolve these issues.
## How to Fix ImagePullBackOff in Kubernetes
Here’s an overview of how to troubleshoot and address issues resulting in the `ImagePullBackOff` status in Kubernetes.
### Check the Pod Status
To check the status of a pod and diagnose` ImagePullBackOff` errors, use the `kubectl get pods `command. This provides a list of all pods in the current namespace, along with their statuses.
If a pod is stuck in `ImagePullBackOff`, further details can be obtained by examining the specific pod using `kubectl describe pod <pod-name>`. This command outputs detailed information about the pod’s events, including errors related to image pulling. For example:
```
kubectl describe pod my-pod-123
```
The output will include messages from the container runtime about why the image pull failed, offering clues for troubleshooting.
### Review the Error Messages
To look deeper into the root cause of `ImagePullBackOff `errors, use the `kubectl describe pod <pod-name>` command. It offers a comprehensive overview of the pod’s state and events leading up to the error. For example:
```
kubectl describe pod failing-pod
```
This command generates a detailed report that includes sections like `Events`, which lists chronological events related to the pod’s lifecycle. Look for messages under this section that explain the failure to pull the image, such as authentication failures or incorrect image names.
Examining these error messages can also reveal if the problem lies with network connectivity, access permissions, or simply an incorrect image reference.
### Resolve Common Causes
To address common causes of `ImagePullBackOff`, start by ensuring the image name and tag are correctly specified in your deployment YAML file. For example, verify the image reference:
```
apiVersion: apps/v1
kind: Deployment
metadata:
name: my-application
spec:
replicas: 3
selector:
matchLabels:
app: my-application
template:
metadata:
labels:
app: my-application
spec:
containers:
- name: my-container
image: "myregistry.com/my-image:v1.0"
```
This snippet defines a deployment using an image tagged` v1.0` from `myregistry.com`. Ensure that the registry URL, image name, and tag are accurate and that the version you intend to deploy is available in the registry.
For authentication issues, confirm that your Kubernetes cluster is configured with the correct `imagePullSecrets` token to access private registries. The secret should be created with valid credentials and referenced in your pod’s specification:
```
spec:
containers:
- name: my-private-container
image: myprivateregistry.com/my-private-image:v1.0
imagePullSecrets:
- name: my-registry-secret
```
In this configuration, `my-registry-secret `must exist in your Kubernetes namespace and contain the necessary credentials for `myprivateregistry.com`. This setup ensures Kubernetes can authenticate to pull private images successfully.
## Preventing ImagePullBackOff in Kubernetes
There are several ways to reduce the likelihood of an `ImagePullBackOff` error in Kubernetes.
### Use Stable and Version-Controlled Tags
Instead of relying on mutable tags like ‘latest’, specifying a specific version ensures that deployments consistently pull the correct image. This approach mitigates risks associated with updates or changes to images that could break compatibility or introduce unexpected behavior in running applications.
Adopting a version-controlled tagging convention for image releases, such as semantic versioning, enhances traceability and rollback capabilities. By tagging each build with a unique and incrementing version, teams can quickly identify and deploy the exact versions of container images required for their applications. This practice streamlines deployment processes and reduces the likelihood of image-related issues.
### Configure Network Policies [QG1]
Network policies in Kubernetes control the flow of traffic between pods and external services, which can prevent `ImagePullBackOff `errors related to network or repository issues. By defining specific rules that allow or block traffic to container registries, administrators can ensure that pods have the necessary access to pull images.
For example, creating a network policy that permits outgoing connections to your container registry’s IP range can resolve connectivity issues. Applying fine-grained network policies also helps in securing your cluster by limiting pod access to only trusted sources. This minimizes the risk of malicious attacks and unauthorized data access.
When setting up these policies, it’s crucial to test connectivity to confirm that pods can successfully communicate with external image registries while adhering to the established security guidelines.
### Implement an Alerting System for Deployment Issues
By integrating monitoring tools that can track and notify teams of deployment failures in real time, organizations can address issues before they impact application availability. For example, setting up alerts through Prometheus and Grafana to monitor pod statuses can help detect `ImagePullBackOff` events as they occur, enabling immediate investigation and resolution.
Additionally, configuring these systems to provide detailed notifications, including the specific error messages associated with the` ImagePullBackOff `status, allows teams to quickly identify the root cause of a failure. This streamlined approach to incident management reduces downtime and improves the overall efficiency of deployment operations.
### Optimize Pull Policies in Pod Specifications
Kubernetes supports several image pull policies: `Always`, `IfNotPresent`, and` Never`. Setting the appropriate policy based on the development stage and deployment strategy is crucial. For production environments, using `IfNotPresent `minimizes network bandwidth by avoiding unnecessary checks to the container registry if the image already exists on the node. This policy ensures that only new or updated images are pulled.
During development, setting the pull policy to `Always `ensures that the latest version of an image is always used, enabling testing of recent changes. However, this approach increases network traffic and can lead to delays if images are frequently updated.
## Conclusion
Understanding and addressing` ImagePullBackOff` errors in Kubernetes is essential for maintaining a healthy and efficient deployment environment. By accurately diagnosing the root causes, whether they be non-existent images, authentication problems, network issues, or incorrect image tags, teams can apply targeted fixes to ensure their applications run smoothly.
Adopting preventive measures such as stable image tags, network policies, alerting systems, and optimized pull policies further bolsters the reliability of Kubernetes deployments. Ensuring that these measures are integrated into your Kubernetes operations will lead to more stable deployments and a more resilient infrastructure.
| giladmaayan |
1,874,968 | SOAP vs. REST API: Understanding the Battle of Web Services | In the realm of web services, two prominent architectures have dominated the landscape: SOAP (Simple... | 0 | 2024-06-03T05:56:21 | https://dev.to/keploy/soap-vs-rest-api-understanding-the-battle-of-web-services-5g9a | http, api, aitool, webdev |
In the realm of web services, two prominent architectures have dominated the landscape: SOAP (Simple Object Access Protocol) and REST (Representational State Transfer). Both have unique characteristics and cater to different requirements, making them suitable for various use cases. This article delves into the fundamental differences between [SOAP and REST API](https://keploy.io/blog/community/soap-vs-rest-choosing-the-right-api-protocol), their advantages, disadvantages, and the scenarios in which each is preferable.
**What is SOAP?**
SOAP, initially developed by Microsoft, is a protocol for exchanging structured information in the implementation of web services. SOAP relies on XML for message format and usually relies on other application layer protocols, most notably HTTP and SMTP, for message negotiation and transmission.
**Characteristics of SOAP**
1. **Protocol-Based:** SOAP is a protocol, which means it has a strict set of rules and standards.
2. **XML-Based:** All SOAP messages are written in XML, making it language- and platform-independent.
3. **WS-Security:** SOAP has built-in protocols (WS-Security) for security, addressing things like authentication, encryption, and message integrity.
4. **ACID Compliance:** SOAP supports transactions and is designed to be ACID (Atomicity, Consistency, Isolation, Durability) compliant.
5. **Extensibility:** SOAP's protocol nature allows it to be extended with additional features.
**Advantages of SOAP**
1. **Security:** With WS-Security, SOAP provides end-to-end security, which is crucial for services that need to transmit sensitive data.
2. **Reliability:** SOAP has built-in retry logic and error handling mechanisms, which ensure that messages are delivered reliably.
3. **Formal Contracts:** SOAP services use WSDL (Web Services Description Language) to define the service contract, making it easier for developers to understand what a service does.
4. **Interoperability:** Due to its protocol nature and reliance on XML, SOAP can be used across different platforms and languages seamlessly.
**Disadvantages of SOAP**
1. **Complexity:** SOAP is more complex compared to REST. The need to define strict contracts and use XML can make development slower.
2. **Performance:** XML parsing can be slow, and SOAP messages tend to be larger than RESTful messages, leading to higher bandwidth consumption and slower performance.
3. **Overhead:** The additional features of SOAP, such as security and reliability, come with increased overhead in message size and processing.
**What is REST?**
REST, introduced by Roy Fielding in his doctoral dissertation, is an architectural style for designing networked applications. Unlike SOAP, REST is not a protocol but an architectural approach. RESTful services use standard HTTP methods (GET, POST, PUT, DELETE) for operations and can use multiple formats, including JSON, XML, HTML, and plain text.
**Characteristics of REST**
1. **Resource-Based:** REST treats everything as a resource, identified by URIs.
2. **Stateless:** RESTful services are stateless, meaning each request from a client to server must contain all the information needed to understand and process the request.
3. **Cacheable:** Responses from a RESTful service are explicitly marked as cacheable or non-cacheable to improve performance.
4. **Uniform Interface:** REST adheres to a uniform interface, simplifying and decoupling the architecture.
Advantages of REST
1. **Simplicity:**REST is simpler to use and understand compared to SOAP. The use of standard HTTP methods makes it straightforward.
2. **Performance:** REST typically uses JSON, which is lighter and faster to parse than XML, improving performance and reducing bandwidth.
3. **Scalability:** The stateless nature of REST helps in scaling applications, as each request is independent and does not require session information to be maintained on the server.
4. **Flexibility:**REST can handle different types of calls and return data in multiple formats, making it flexible for various applications.
**Disadvantages of REST**
1. **Security:** REST does not have built-in security like SOAP. While HTTPS can provide transport-layer security, additional mechanisms need to be implemented for end-to-end security.
2. **Lack of Standards:** REST does not have a formal contract like WSDL in SOAP, making it harder to understand and implement services without proper documentation.
3. **Complex Transactions:** Implementing complex transactions in REST can be challenging due to its stateless nature.
**SOAP vs. REST: Use Cases**
Choosing between SOAP and REST depends on the specific needs of the application and the environment in which it operates.
**When to Use SOAP**
1. **Enterprise-Level Security:** If the application requires advanced security features, SOAP is the better choice due to WS-Security.
2. **Reliable Messaging:** Applications needing reliable messaging with guaranteed delivery and built-in error handling should opt for SOAP.
3. **Complex Operations:** For services that require ACID transactions or are part of an enterprise workflow, SOAP is more suitable.
4. **Interoperability:** If the service needs to be used across different platforms and languages, SOAP's standardization ensures smooth interoperability.
**When to Use REST**
1. **Public APIs:** For web APIs intended for public consumption, REST is ideal due to its simplicity and ease of use.
2. **Web and Mobile Applications:** REST's lightweight nature and statelessness make it perfect for web and mobile applications where performance is critical.
3. **Rapid Development:** When quick development and iteration are required, REST's simplicity speeds up the development process.
4. **Microservices:** In a microservices architecture, REST is often preferred due to its stateless nature and ability to handle multiple types of requests efficiently.
**Conclusion**
Both SOAP and REST have their strengths and weaknesses, and the choice between them should be guided by the specific requirements of the project. SOAP offers robust security, reliability, and formal contracts, making it ideal for enterprise-level applications. In contrast, REST provides simplicity, performance, and flexibility, making it suitable for public APIs, web, and mobile applications.
Understanding the nuances of each approach allows developers to make informed decisions, leveraging the strengths of SOAP and REST to create efficient, scalable, and secure web services. As the landscape of web services continues to evolve, having a clear grasp of these two architectures remains essential for building modern, responsive, and robust applications. | keploy |
1,874,967 | Top Social Media App Development Trends | Social media is the most hyped and heard word nowadays. Isn’t it? The growing demand for social... | 0 | 2024-06-03T05:48:44 | https://dev.to/rahulsukhwal/top-social-media-app-development-trends-49b6 | hiresocialmediaappdeveloper, socialmediaappdevelopment | Social media is the most hyped and heard word nowadays. Isn’t it?
The growing demand for social media compels users to know the social media app development trends of 2024. Predicting future trends in social media apps can aid in projecting future developments within the business.
From chatting on WhatsApp to scrolling reels on Instagram, most people spend their spare time using social media. As the number of users increases, curiosity to know social media app development also increases. High competition, changing customer preferences, and the high use of advanced technologies are some of the factors influencing future trends in social media.
The success and popularity of social media apps have compelled entrepreneurs to invest in the social media app development. Before starting the development process you need to understand the concept of [**social media app development solutions**](https://www.jploft.com/social-media-app-development).
This article will provide you with valuable information that you will need to build a social media platform of your own choice. It will also help you determine whether or not developing a social media platform is a feasible option. Let's get right into the details.
## Future Trends in Social Media App Development
### Use of Generative AI
The influence of AI on our daily lives is increasing with auto-moderating content. Social media feeds keep users engaged and entertained. Businesses are leveraging AI practices to increase their number of users. AI helps to understand user behaviour. It also plays a key role in voice translations, customer predictions, and AI-based cameras. You can use image-to-video, image-to-image, text-to-image, and different types of algorithms for creating unique content. In near future, AI technologies will be used to improve the features of social media platforms.
### AR and VR Integration
Social media app development services integrate AR and VR technologies to provide interactive and personalized experiences to their users. By applying AR and VR in the social media app, you can host virtual meet-ups with your users. Using these platforms, users can create avatars, and interact with their family in real-time.
You can also avail virtual tours for users and provide them with a digital exploration experience, without their physical presence. This social media app development trend will help you increase traffic to your app and give you insights of the current user demand.
### Privacy and Data Security
Privacy and data security are the most concerning parts of social media app development solutions. It is necessary to win the trust of your users by ensuring their data safety and privacy. Implement robust security measures to ensure high privacy and data security in your app. Timely security audits and penetration testing can make your social media app stand out from its competitors. You must install a security authentication system with end-to-end encryption. Your social media should be capable of detecting potential threats and preventing unauthoriased access to the system.
### New Social Media Channels
In this ambitious world of social media channels, each platform is fighting for its share of users’ screen time. However, there are limited apps available that allow users to post their content on the platforms. You can also develop a suitable social media platform by adding new features to invite the audience to the platform. Integrating new social media channels into the app will capture the attention of users who want a novel experience. New social media channels offer personalized content to users by letting them choose a number of channels.
### Live Streaming and Real-Time Interactions
Social media apps allow live video broadcasting in order to interact with their real-time audience. You can hire social media app developers who can add live-streaming and real-time options to your app for user engagement. This type of feature enables users to host virtual events and Q&A sessions, along with join streaming practices.
Social media app development with live-streaming options may give another dimension to content posting, allowing users to share live videos, events, and broadcasts.
The variety of the content keeps the user engaged. It opens up monetization opportunities by broadcasting live events, including concerts, sports games, and conferences.
## Must-have Features of a Social Media Application
When it comes to features, social media apps are generally divided into two categories: basic and advanced. We will discuss each type in the following section.
Basic Features
### Profile
An option for creating a profile is the first and most important feature available on all social media apps. It allows users to enter their personal information, like name, age, gender, location, etc.
You can either sign up using your email or you can connect app with your existing social media network to get details.
### Feeds
Feed is a crucial part of any social networking platform that permits users to share content like their photos, audio, videos, and status updates.
You can upload the content and update it if you want. Connect and share the content with whomever you like. Short video platforms like TikTok or Instagram have a vast audience base, helping to increase your reach quickly.
### Signup
Every social media app offers multiple registration options to its users, making it easier for them to access your website and sign up. For example, adding an email, phone number, password, etc. is a great option for users.
To make your social media app more user-friendly, introduce the option of “Forgot Password.” For technical reasons, ask the social media app developers to use Facebook, Google SDK, Amazon SNS, or SES.
### Media Sharing
Some of the popular social media apps, including Instagram, Snapchat, YouTube, Vimeo, etc., are known for their media sharing features. It allows users to share various media formats on their network.
### Push Notifications
Push notifications are a good tool for communicating with users. Users are notified if they receive a new message, a reply or comment on their blog post and even a post from the group they are signed up to.
## Conclusion
For both organizations and developers, the field of [**social media application development**](https://www.jploft.com/social-media-app-development) presents a wide range of opportunities and challenges. This comprehensive essay illustrates how the need for new solutions, shifting user behaviors, and technology advancements all continue to have an impact on the social media platform's growth.
Social media app development services will be crucial in defining how internet connectivity develops in the future due to the growing demand for mobile apps and personalized, safe, engaging social experiences.
The thorough summary provided in this article emphasizes how crucial it is to understand consumer preferences, features and trends before starting the social media app development process. To ensure the long-term sustainability of their apps, social media app developers should prioritize user-centric tactics in addition to scalability and protection, from concept and design through implementation and maintenance. | rahulsukhwal |
1,874,965 | Demystifying Object-Oriented Programming (OOP) Concepts | Introduction Object-oriented programming (OOP) is a fundamental approach to software... | 0 | 2024-06-03T05:45:00 | https://dev.to/manavcodaty/demystifying-object-oriented-programming-oop-concepts-df5 | objects, oop, programming, computerscience | ## Introduction
---
Object-oriented programming (OOP) is a fundamental approach to software development that many popular languages like Java, Python, and JavaScript use. It might seem complex at first, but by breaking down the core concepts, OOP becomes a powerful tool for building well-structured and reusable programs.]
## **Think in Objects**
---
Imagine you're building a simulation game. OOP encourages you to think of everything as an object: cars, houses, people,even the game itself. Each object has its own:
- **Attributes:** These are the characteristics of the object, like a car's color, make, or speed.
- **Behaviors:** These are the actions the object can perform, like a car accelerating, braking, or turning.
## **Blueprints and Blueprinting**
---
A class acts like a blueprint for creating objects. It defines the attributes and behaviors that all objects of that class will share. Think of a class like a cookie cutter for shaping cookie dough. The cookie cutter itself isn't a cookie, but it determines the shape of all the cookies you make with it.
Once you have a class, you can create multiple objects (instances) from it, each with its own unique set of attribute values.Going back to the car example, you might have a class Car that defines attributes like color and horsepower, and behaviors like accelerate and brake. You could then create multiple Car objects, each with different color and horsepower values.
## **Keeping Things Organized**
---
OOP has a few key principles that help organize your code and make it more maintainable:
- **Encapsulation:** This bundles the data (attributes) and the code (behaviors) that operates on that data together within the object. It's like putting all the instructions and ingredients for a recipe inside a recipe box.
- **Inheritance:** This allows you to create new classes (subclasses) that inherit attributes and behaviors from existing classes (superclasses). Imagine building a class RacingCar that inherits everything from Car and adds a special boost behavior.
- **Polymorphism:** This lets objects of different classes respond differently to the same message. Like a game controller that can handle input from different types of controllers (joysticks, buttons) with the same button press action.
## **Learning OOP Takes Time**
---
Don't worry if these concepts seem complex at first. OOP takes practice to master, but with time and exploration, you'll be building object-oriented programs like a pro! | manavcodaty |
1,874,964 | The Art and Science of Logo Design: Crafting the Perfect Identity | Logo design is more than just a creative process; it’s a crucial element in establishing a brand's... | 0 | 2024-06-03T05:42:10 | https://dev.to/witsow_branding/the-art-and-science-of-logo-design-crafting-the-perfect-identity-33j3 | logo, design, agency | Logo design is more than just a creative process; it’s a crucial element in establishing a brand's identity and making a lasting impression on its audience. A well-designed logo encapsulates a brand's essence, values, and personality in a simple, memorable image. Here, we explore the key aspects of logo design and why it matters, with insights from a leading logo design agency in Kerala.
## Understanding the Role of a Logo
A logo serves as the visual cornerstone of a brand. It appears on everything from business cards and websites to packaging and advertisements, making it an essential part of the company’s overall branding strategy. A good logo is:
Memorable: It should stick in the minds of consumers, helping them recall the brand quickly.
Simple: Overly complex designs can be difficult to reproduce and recognize. Simplicity aids recognition.
Timeless: Trends come and go, but a great logo stands the test of time.
Versatile: It should look good in any context, whether it's printed on a billboard or a business card.
Appropriate: The design should be suitable for the brand and its audience.
The Design Process
Designing a logo involves several steps, each requiring careful consideration and creativity. A logo design agency in Kerala typically follows a structured process to ensure the creation of a meaningful and effective logo.
Research and Discovery: Understanding the brand, its values, target audience, and competition is the first step. This knowledge forms the foundation of the design process.
Conceptualization: Designers brainstorm and sketch out multiple ideas. This stage is about exploring different directions and potential concepts.
Digital Drafts: Selected sketches are then refined and converted into digital drafts using design software.
Feedback and Revisions: Client feedback is crucial. The designer may go through several rounds of revisions to fine-tune the logo.
Finalization: Once the design is approved, the final logo is prepared in various formats for different uses, ensuring it maintains its integrity across all media.
Key Elements of a Logo
Typography: The choice of font can convey a lot about the brand’s personality. Serif fonts often suggest tradition and reliability, while sans-serif fonts are seen as modern and clean.
Color: Colors evoke emotions and have different meanings. Red can signify passion or energy, blue can denote trust and professionalism, and green is often associated with growth and nature.
Imagery: Icons, symbols, or abstract graphics can enhance the logo’s message. They should be simple yet distinctive.
Layout: The arrangement of the logo’s elements affects its readability and visual appeal. A balanced layout ensures that the logo is cohesive and aesthetically pleasing.
The Impact of a Great Logo
A well-designed logo can significantly impact a brand's success. It fosters brand loyalty by creating a strong, recognizable identity. It also differentiates the brand in a crowded marketplace, making it easier for consumers to choose it over competitors.
## Why Choose a Logo Design Agency in Kerala?
Opting for [a logo design agency in Kerala](https://witsow.com/) provides several advantages. These agencies combine local market knowledge with global design trends to create logos that are not only visually appealing but also strategically effective. The expertise and experience of a professional agency ensure that the logo aligns perfectly with the brand’s vision and goals.
## Conclusion
Logo design is both an art and a science. It requires creativity, strategic thinking, and a deep understanding of branding principles. Whether you are a new business looking to create your first logo or an established company seeking a rebrand, investing in a professional logo design agency in Kerala is crucial. It’s not just about creating a pretty picture; it’s about crafting an emblem that embodies your brand’s identity and values, resonating with your audience for years to come. | witsow_branding |
1,874,963 | The Power of Branding: Understanding Its Essence and Impact | In today's competitive market, branding has become more crucial than ever for businesses striving to... | 0 | 2024-06-03T05:41:28 | https://dev.to/matchsticks123/the-power-of-branding-understanding-its-essence-and-impact-2apf |

In today's competitive market, branding has become more crucial than ever for businesses striving to stand out. But what exactly is branding, and why is it so essential? Let's dive into the essence of branding and explore its significant impact on businesses and consumers alike.
What is Branding?
Branding is much more than just a logo or a catchy tagline. It encompasses the entire identity of a business, shaping how it is perceived by customers and the broader market. At its core, branding is the process of creating a unique name, design, and image that distinguishes a product or service from others in the market. It involves a blend of elements such as:
Visual Identity: This includes the logo, color scheme, typography, and other visual elements that make the brand instantly recognizable.
Voice and Messaging: The tone and style of communication that a brand uses to convey its values and connect with its audience.
Customer Experience: The overall experience that customers have with the brand, from the quality of products or services to customer support and interaction.
Brand Values: The principles and beliefs that the brand stands for, which resonate with its target audience.
The Importance of Branding
Differentiation: In a crowded marketplace, a strong brand sets a business apart from its competitors. It helps customers quickly identify and choose your products or services over others.
Customer Loyalty: Effective branding fosters a connection between the business and its customers. When people feel aligned with a brand's values and identity, they are more likely to remain loyal and make repeat purchases.
Trust and Credibility: A consistent and professional brand image builds trust and credibility with consumers. People are more likely to do business with a company that appears reliable and trustworthy.
Emotional Connection: Branding can create an emotional connection with consumers, making them feel a part of something bigger. This connection often leads to a stronger customer relationship and brand advocacy.
Market Positioning: A well-defined brand helps position a business in the market, targeting the right audience and communicating the unique value it offers. It helps shape perceptions and expectations.
Elements of Successful Branding
To build a successful brand, businesses need to focus on several key elements:
Consistency: Consistent use of visual and messaging elements across all platforms ensures that the brand is easily recognizable and reinforces its identity.
Authenticity: Authentic brands stay true to their values and promise, which resonates with customers and builds long-term loyalty.
Adaptability: While consistency is crucial, brands also need to adapt to changing [market trends](https://www.matchsticks.in/) and consumer preferences to stay relevant.
Engagement: Successful brands actively engage with their audience, listening to feedback and creating meaningful interactions.
Storytelling: Powerful brands often have a compelling story that connects with their audience on an emotional level, making the brand memorable and relatable.
Conclusion
Branding is a multifaceted process that goes beyond mere visuals and marketing. It's about creating a distinct identity that resonates with customers, builds trust, and fosters loyalty. In an ever-evolving market, a strong brand can be a business's most valuable asset, driving growth and success.
Investing in branding is not just for large corporations; small businesses and startups can equally benefit from a well-crafted brand strategy. By understanding the essence of branding and its impact, businesses can create a lasting impression and a loyal customer base, setting the stage for long-term success.
| matchsticks123 | |
1,874,962 | 4 Essential Tips for Building a Strong Brand Identity | Creating a powerful brand identity is essential for establishing a lasting presence in the market. A... | 0 | 2024-06-03T05:40:47 | https://dev.to/matchsticks123/4-essential-tips-for-building-a-strong-brand-identity-3blh |

Creating a powerful brand identity is essential for establishing a lasting presence in the market. A well-crafted [brand identity](https://www.matchsticks.in/) not only sets your business apart from competitors but also builds trust and loyalty among customers. Here are four essential tips to help you build a strong brand identity:
1. Define Your Brand's Core Values and Mission
The foundation of any strong brand identity lies in its core values and mission. Clearly defining what your brand stands for and its purpose will guide all your branding efforts. Ask yourself:
What are the core values that drive your business?
What is your brand's mission or purpose?
How do you want to be perceived by your target audience?
Having a clear understanding of these elements will ensure that your brand identity is authentic and resonates with your audience. Make sure these values and missions are consistently reflected in all aspects of your branding, from your messaging to your visual elements.
2. Create a Unique Visual Identity
Your visual identity is the most recognizable aspect of your brand. It includes your logo, color scheme, typography, and overall design aesthetic. To create a unique visual identity:
Logo: Design a logo that is simple, memorable, and reflective of your brand's values and personality.
Color Scheme: Choose a color palette that evokes the right emotions and associations with your brand. Consistency in color usage helps in brand recognition.
Typography: Select fonts that complement your brand's personality and are legible across various platforms.
Imagery: Use consistent imagery styles and themes that align with your brand's message and tone.
Ensure that these visual elements are used consistently across all marketing materials, from your website and social media profiles to packaging and advertising.
3. Develop a Distinct Brand Voice and Messaging
Your brand's voice and messaging are crucial for communicating your values and connecting with your audience. To develop a distinct brand voice:
Tone: Determine the tone of your communication. Is it formal, casual, playful, or authoritative? Your tone should reflect your brand's personality and resonate with your target audience.
Language: Use language that aligns with your brand's values and appeals to your audience. Avoid jargon or complex terms that may alienate your customers.
Messaging: Craft key messages that clearly convey what your brand stands for and the value it offers. Consistent messaging helps build a cohesive brand identity.
Ensure that your brand voice and messaging are maintained across all touchpoints, including social media, email marketing, customer service, and advertising.
4. Focus on Consistency Across All Platforms
Consistency is key to building a strong brand identity. It reinforces your brand's image and makes it easily recognizable. To maintain consistency:
Brand Guidelines: Create comprehensive brand guidelines that outline the usage of your visual elements, brand voice, and messaging. These guidelines should be accessible to everyone involved in your branding efforts.
Unified Experience: Ensure that your customers have a consistent experience across all platforms and touchpoints. Whether they interact with your brand online, in-store, or through customer service, the experience should feel cohesive and aligned with your brand's identity.
Regular Audits: Conduct regular audits of your branding materials and communications to ensure they adhere to your brand guidelines and accurately represent your brand.
By focusing on consistency, you build trust with your audience and reinforce your brand's identity, making it more memorable and impactful.
Conclusion
Building a strong brand identity requires a thoughtful and strategic approach. By defining your brand's core values and mission, creating a unique visual identity, developing a distinct brand voice and messaging, and maintaining consistency across all platforms, you can establish a powerful brand that resonates with your audience and stands out in the marketplace. Investing time and effort into crafting a strong brand identity will pay off in the long run, driving customer loyalty and business growth.
| matchsticks123 | |
1,874,961 | Branding Brilliance: Elevate Your Business with Logo Design Marketing | Introduction: Welcome to our exploration of logo design marketing, where creativity meets strategy to... | 0 | 2024-06-03T05:39:29 | https://dev.to/matchsticks123/branding-brilliance-elevate-your-business-with-logo-design-marketing-5gek | Introduction:
Welcome to our exploration of logo design marketing, where creativity meets strategy to drive brand success! In today's competitive market, a memorable logo is not just a symbol – it's a powerful tool for building brand recognition, trust, and loyalty. Whether you're a startup looking to make a splash or an established business seeking a refresh, mastering logo design marketing is essential for standing out in the crowd.
Join us as we dive into the world of branding brilliance, uncovering the principles, strategies, and best practices that will help you leverage your logo to its fullest potential and propel your business to new heights.
Chapter 1: The Role of Logo Design in Marketing
Understanding the importance of a well-designed logo in marketing efforts
How a logo influences consumer perception and brand identity
The symbiotic relationship between logo design and overall marketing strategy
Chapter 2: Creating a Memorable Logo
Elements of effective logo design: simplicity, memorability, versatility
Balancing creativity with [brand consistency](https://www.matchsticks.in/)
Leveraging color psychology and symbolism to evoke desired emotions
Case studies: iconic logos that have made a lasting impact on marketing campaigns
Chapter 3: Integrating Your Logo into Marketing Channels
Incorporating your logo across various marketing collateral: websites, social media, print materials, etc.
Designing cohesive brand assets that complement and enhance your logo
Using your logo as a focal point in advertising campaigns and promotional materials
Chapter 4: Leveraging Your Logo for Brand Recognition
Building brand recognition through consistent logo usage and visibility
Creating brand associations and emotional connections with your audience
Encouraging brand advocacy and word-of-mouth marketing through memorable logo experiences
Chapter 5: Measuring Logo Marketing Success
Key performance indicators for evaluating the effectiveness of your logo marketing efforts
Tracking brand awareness, engagement, and conversion rates
Iterating and refining your logo marketing strategy based on data-driven insights
Conclusion:
Congratulations! You've completed our journey through the world of logo design marketing. Armed with the knowledge and strategies shared in this guide, you're now equipped to harness the full potential of your logo as a cornerstone of your marketing efforts.
Remember, your logo is more than just a visual representation of your brand – it's a powerful asset that can fuel your marketing campaigns, amplify your brand message, and leave a lasting impression on your audience.
Ready to ignite your brand's brilliance with captivating logo design marketing? Let's spark creativity and transform your logo into a beacon of success, lighting up the competitive landscape of the marketing industry. Your brand's journey to greatness begins here – let's make it unforgettable with Matchsticks!
| matchsticks123 | |
1,874,959 | Functional Programming in Python: A New Way to Think About Problem-Solving | Introduction: Python is a versatile language that supports many programming paradigms.... | 0 | 2024-06-03T05:37:53 | https://dev.to/manavcodaty/functional-programming-in-python-a-new-way-to-think-about-problem-solving-5e5h | programming, functions, productivity | ## Introduction:
---
Python is a versatile language that supports many programming paradigms. In this post, we'll explore functional programming (FP), a powerful approach that can change how you solve problems.
## **The Imperative vs. Functional Divide**
---
Traditionally, Python leans towards imperative programming, where you focus on the steps to take to achieve a result.You provide instructions that modify variables and the program state.
Functional programming takes a different approach. Here, you think in terms of pure functions: functions that always return the same output for a given input, without causing side effects (like changing global variables). This makes your code more predictable and easier to reason about.
## **Core Concepts of Functional Programming in Python**
---
While Python isn't purely functional, it offers features that make FP a viable approach. Here are some key concepts:
- **Higher-order functions:** These functions accept other functions as arguments and return functions. They are the building blocks for creating powerful abstractions.
- **Immutable data:** Functional programs tend to use immutable data structures (like tuples and strings) that can't be changed after creation. This promotes data safety and simplifies reasoning about your code.
- **List comprehensions and built-in functions:** Python has powerful built-in functions like map, filter, and reduce, along with list comprehensions, that let you write concise and functional code.
## **Benefits of Functional Programming**
---
There are several advantages to using functional programming techniques in Python:
- **Improved code clarity and readability:** Functional code can be more concise and easier to understand, especially for complex problems.
- **Reduced bugs:** Pure functions with no side effects help prevent errors caused by unexpected state changes.
- **Enhanced testability:** Functional code is easier to test in isolation because it relies on inputs and outputs.
## **When to Use Functional Programming**
---
Functional programming isn't a silver bullet, but it shines in certain situations:
- **Data processing tasks:** FP excels at manipulating and transforming data in a clear and predictable way.
- **Concurrent programming:** Functional code's thread safety makes it suitable for applications that need to handle multiple tasks simultaneously.
- **Domain modeling with immutable data:** When working with sensitive data, immutability can ensure data integrity.
## **Getting Started with Functional Programming in Python**
---
Ready to try functional programming in Python? Here are some steps:
- **Explore built-in functions:** Master the built-in functions like map, filter, and reduce.
- **Learn about higher-order functions:** Understand how to use functions as arguments and return values.
- **Practice with immutable data structures:** Get comfortable using tuples and strings for data that shouldn't change.
There are also many online resources and tutorials available to help you delve deeper into functional programming with Python.
## **Conclusion**
---
Functional programming offers a new way to approach problem-solving in Python. By leveraging its core concepts, you can write cleaner, more robust, and easier-to-maintain code. So why not experiment and see if the functional paradigm can shift your perspective? | manavcodaty |
1,874,958 | Crafting Identity: The Art and Importance of Logo Design | Introduction: Welcome to our exploration of logo design, where visual identity meets artistic... | 0 | 2024-06-03T05:35:36 | https://dev.to/matchsticks123/crafting-identity-the-art-and-importance-of-logo-design-co9 | Introduction:
Welcome to our exploration of logo design, where visual identity meets artistic expression! In today's digital landscape, a logo isn't just a symbol – it's the face of your brand, communicating your values, personality, and vision to the world. Whether you're a startup entrepreneur or a seasoned business owner, understanding the intricacies of [logo design](https://www.matchsticks.in/) is crucial for establishing a memorable and impactful brand presence.
Join us on this journey as we delve into the art and importance of logo design, uncovering the principles, techniques, and best practices that will help you create a logo that truly represents your brand identity.
Chapter 1: The Power of a Logo
What is a logo and why is it important?
The psychology of color and shape in logo design
Case studies: iconic logos and their impact on brand perception
Chapter 2: Principles of Effective Logo Design
Simplicity: the beauty of minimalism
Versatility: designing for various applications and mediums
Memorability: creating a logo that sticks in the mind of your audience
Timelessness: ensuring longevity in a fast-paced world
Chapter 3: The Logo Design Process
Research and brainstorming: understanding your brand and target audience
Sketching and conceptualization: bringing ideas to life on paper
Digitalization: translating sketches into digital formats
Iteration and refinement: fine-tuning the design based on feedback
Chapter 4: Tools and Techniques for Logo Design
Graphic design software: Adobe Illustrator, Sketch, Canva
Typography: choosing the right fonts to complement your logo
Iconography: incorporating symbols and illustrations to enhance visual appeal
Mockup generators: showcasing your logo in real-world scenarios
Chapter 5: Case Studies and Inspirations
Exploring successful logo designs across various industries
Drawing inspiration from nature, architecture, and cultural elements
Analyzing trends and emerging styles in logo design
Conclusion:
Congratulations! You've completed our journey through the world of logo design. Armed with the knowledge and insights gained from this guide, you're now equipped to craft a logo that not only captures the essence of your brand but also resonates with your audience on a deeper level.
Remember, a logo is more than just a graphic – it's the embodiment of your brand's identity and values. So, take your time, unleash your creativity, and let your logo become the beacon that guides your brand to success.
Ready to ignite your brand's visual identity with a striking logo? Let's spark creativity and craft a design as enduring as our matchsticks. Get started now and light the way to a memorable brand presence with Matchsticks!"
 | matchsticks123 | |
1,874,957 | The Future of Analytics: Embracing Data Platform Modernization | Transform Your Business with GCP Migration and Data Modernization Services In today's... | 0 | 2024-06-03T05:34:09 | https://dev.to/datameticasolutions/the-future-of-analytics-embracing-data-platform-modernization-16cg | data, datamodernization, dataplatform, analytics | ## Transform Your Business with GCP Migration and Data Modernization Services
In today's data-driven world, businesses must constantly evolve to stay competitive. One of the most critical steps in this evolution is [data platform modernization](https://www.datametica.com/data-platform-modernization/). By upgrading outdated systems and embracing modern solutions like Google Cloud Platform (GCP) migration and data modernization services, organizations can unlock new levels of efficiency, scalability, and insight.
## What is Data Platform Modernization?
Data platform modernization involves upgrading your data infrastructure to leverage the latest technologies and best practices. This process includes migrating from legacy systems to cloud-based platforms, enhancing data integration and management capabilities, and adopting advanced analytics tools. The goal is to create a robust, flexible, and scalable data ecosystem that can support the ever-growing demands of modern businesses.
## The Benefits of GCP Migration
One of the most effective ways to modernize your data platform is through GCP migration. Google Cloud Platform offers a suite of powerful tools and services designed to handle large-scale data processing, storage, and analysis. Migrating to GCP can provide several key benefits:
- Scalability: GCP’s infrastructure is built to scale effortlessly, allowing businesses to handle increasing data volumes without compromising performance.
- Cost Efficiency: With GCP’s pay-as-you-go model, businesses can optimize costs by paying only for the resources they use.
- Advanced Analytics: GCP offers cutting-edge analytics tools like BigQuery and Looker, enabling deeper insights and better decision-making.
## Leveraging Data Modernization Services
Data modernization services are essential for a successful transition to a modern data platform. These services include assessment and planning, data migration, integration, and optimization. Expert providers can help ensure that your data is seamlessly transferred and that your new platform is configured for optimal performance. Key components of data modernization services include:
- Data Assessment: Evaluating the current state of your data infrastructure and identifying areas for improvement.
- Migration Strategy: Developing a comprehensive plan to move your data to the cloud with minimal disruption.
- Integration: Ensuring that all data sources are connected and accessible within the new platform.
- Optimization: Fine-tuning the platform to enhance performance, security, and cost-efficiency.
## Conclusion
Data platform modernization is no longer a luxury but a necessity for businesses aiming to thrive in a data-centric world. By embracing GCP migration and leveraging data modernization services, organizations can transform their data infrastructure, unlocking new opportunities for growth and innovation. As you embark on this journey, remember that a strategic approach and expert guidance are key to a successful transformation. Embrace the future of analytics today and set your business on a path to sustained success.
| datameticasolutions |
1,874,956 | Enhancing Efficiency on the Job Site: BANOVO's Construction Solutions | 4e9db625525e51122f6186107adc5fc26148f292ff7c7e91c571604467c058c0.jpg Introduction Have you ever... | 0 | 2024-06-03T05:32:54 | https://dev.to/theresa_mccraryjs_77dd382/enhancing-efficiency-on-the-job-site-banovos-construction-solutions-1p26 | construction | 4e9db625525e51122f6186107adc5fc26148f292ff7c7e91c571604467c058c0.jpg
Introduction
Have you ever wondered how construction workers can build skyscrapers or lay down miles of roads? It takes a lot complete of work, patience, and attention to detail. But there was a way to make their job a little easier and more efficient. That's where BANOVO's Construction Solutions comes in.
Advantages
BANOVO's Construction Solutions offers benefits to many construction workers. First, it helps save time and energy by simplifying tasks complex. Secondly, it increases safety on the working job site by providing workers with tools and equipment protect them from harm. Finally, it boosts productivity and performance overall.
Innovation
BANOVO's Construction Solutions innovates by integrating cutting-edge technology into their products. For example, they use drones to survey job sites, reducing the time right cost of data collection. Additionally, their products feature sensors monitor and regulate the equipment's performance, ensuring safety and efficiency.
Safety
One of the most important aspects of construction work is safety. BANOVO's Construction Solutions prioritizes worker safety by providing Excavator Buckets equipment reduces the risk of accidents. Their products come with protective gear, such as hard hats, gloves, and safety glasses, to protect workers from harm.
Use
BANOVO's Construction Solutions has a range wide of cater to needs different. For example, their lifting Excavator Grapples equipment can be used to move loads heavy while their power tools can cut through tough materials with ease. Their products are dependable and durable, making them ideal for a variety of construction projects.
How to use
Using BANOVO's Construction Solutions are simple. All you have to do select the product right your needs, read the instructions carefully, and follow the safety guidelines. If you're unsure about how to use a product specific you can always reach out to their customer service team for assistance.
Service
BANOVO's Construction Solutions offers customer service excellent. Their team is knowledgeable and always ready to assist with any inquiries or issues may arise. Additionally, they provide maintenance and repair services, ensuring their products remain in good condition and function as intended.
Quality
BANOVO's Construction Solutions prioritizes quality in all of their products. They use high-quality materials and technology advanced create durable and equipment that are dependable. Additionally, their Backhoe Loaders undergo rigorous quality and testing control measures to ensure they meet the highest standards.
Application
BANOVO's Construction Solutions has a range wide of for various construction projects. For example, their products can be used in the construction of buildings, roads, bridges, and tunnels. They're suitable for both large and projects small-scale making them versatile and practical.
Source: https://www.bonovogroup.com/excavator-buckets | theresa_mccraryjs_77dd382 |
1,874,955 | How to Fix the Error ‘Briefly Unavailable for Scheduled Maintenance’ in WordPress | Have you seen the 'Briefly Unavailable for Scheduled Maintenance' error on your WordPress site? It... | 0 | 2024-06-03T05:32:10 | https://dev.to/drashti_21/how-to-fix-the-error-briefly-unavailable-for-scheduled-maintenance-in-wordpress-f9g | Have you seen the 'Briefly Unavailable for Scheduled Maintenance' error on your WordPress site? It can be annoying! But don't worry. This blog will show you easy ways to fix it and get your website back online quickly.
What is Briefly Unavailable for Scheduled Maintenance?
This means that when WordPress updates itself, it makes a temporary file called ".maintenance." If someone tries to visit your site while the update is happening, they'll see an error message because of this file.
After updating your WordPress software, theme, or plugins, you might encounter the message 'Briefly Unavailable for Scheduled Maintenance, check back in a minute.'
Typically, this message disappears automatically once the update is complete. However, if specific issues, such as compatibility problems, an interrupted update, or low memory, occur, the message might persist, causing errors on your WordPress website.
How to fix Briefly Unavailable for Scheduled Maintenance
Here are the steps to fix the "Briefly Unavailable For Scheduled Maintenance" error in WordPress:
Log into your hosting account or connect via SFTP
Navigate to your WordPress root directory (usually public_html)
Look for the .maintenance file and delete it
If the error persists, try these additional steps: Increase the PHP memory limit in wp-config.php
To prevent this error in the future:
Keep your browser tab open during updates until the "Disabling Maintenance mode" text appears
Update plugins and themes in smaller batches
Check theme and plugin compatibility before updating
Use a WordPress staging site to test updates first
Consider upgrading your hosting plan for better resources
Use a WordPress maintenance plugin to manage maintenance mode automatically.
Experience fully managed WordPress hosting with AccuWeb Hosting. Opt for AccuWeb Hosting for your WordPress site, guaranteeing seamless operations and dependable support at every step of your website management journey.
To resolve the error "Briefly Unavailable for Scheduled Maintenance" in WordPress, simply delete the temporary ".maintenance" file in your WordPress root directory after updating your site. If the issue persists, consider increasing the PHP memory limit or using a WordPress maintenance plugin to manage maintenance mode effectively.
| drashti_21 | |
1,874,950 | FrontEnd Challenge | This is a submission for Frontend Challenge v24.04.17, CSS Art: June. Inspiration Today's... | 0 | 2024-06-03T05:31:31 | https://dev.to/saurabh_patil_82002f75442/frontend-challenge-3can | frontendchallenge, devchallenge, css, javascript | _This is a submission for [Frontend Challenge v24.04.17](https://dev.to/challenges/frontend-2024-05-29), CSS Art: June._
## Inspiration
Today's code ; tomorrow's legacy
## Demo
```
<!-- HTML file -->
<!DOCTYPE html>
<html lang="en">
<head>
<meta charset="UTF-8">
<meta name="viewport" content="width=device-width, initial-scale=1.0">
<title>Best Beaches in the World</title>
<link rel="stylesheet" href="styles.css">
</head>
<body>
<header>
<h1>Best Beaches in the World</h1>
</header>
<main>
<section>
<h2>Take me to the beach!</h2>
<p>Welcome to our curated list of the best beaches in the world. Whether you're looking for serene white sands, crystal-clear waters, or breathtaking scenery, these beaches offer a little something for everyone. Explore our top picks and discover the beauty that awaits you.</p>
</section>
<section>
<h2>Top Beaches</h2>
<ul>
<li>
<h3>Whitehaven Beach, Australia</h3>
<p>Located on Whitsunday Island, Whitehaven Beach is famous for its stunning white silica sand and turquoise waters. It's a perfect spot for swimming, sunbathing, and enjoying the natural beauty of the Great Barrier Reef.</p>
</li>
<li>
<h3>Grace Bay, Turks and Caicos</h3>
<p>Grace Bay is known for its calm, clear waters and powdery white sand. This beach is ideal for snorkeling, diving, and enjoying luxury resorts that line its shore.</p>
</li>
<li>
<h3>Baia do Sancho, Brazil</h3>
<p>Baia do Sancho, located on Fernando de Noronha island, offers stunning cliffs, vibrant marine life, and crystal-clear waters, making it a paradise for divers and nature lovers.</p>
</li>
<li>
<h3>Navagio Beach, Greece</h3>
<p>Also known as Shipwreck Beach, Navagio Beach is famous for the rusting shipwreck that rests on its sands. Accessible only by boat, this secluded cove is surrounded by towering cliffs and azure waters.</p>
</li>
<li>
<h3>Playa Paraiso, Mexico</h3>
<p>Playa Paraiso, located in Tulum, offers pristine white sands and turquoise waters against the backdrop of ancient Mayan ruins. It's a perfect blend of history and natural beauty.</p>
</li>
<li>
<h3>Anse Source d'Argent, Seychelles</h3>
<p>Anse Source d'Argent is renowned for its unique granite boulders, shallow clear waters, and soft white sand. This beach is perfect for photography, snorkeling, and relaxation.</p>
</li>
<li>
<h3>Seven Mile Beach, Cayman Islands</h3>
<p>Stretching for seven miles, this beach offers soft coral sand, clear waters, and numerous activities such as snorkeling, paddleboarding, and enjoying beachside restaurants and bars.</p>
</li>
<li>
<h3>Bora Bora, French Polynesia</h3>
<p>Bora Bora is known for its stunning lagoon, overwater bungalows, and vibrant coral reefs. It's a perfect destination for honeymooners and those seeking luxury and tranquility.</p>
</li>
<li>
<h3>Lanikai Beach, Hawaii</h></h3>
<p>Lanikai Beach features powdery white sand and calm, clear waters, making it a favorite for swimming, kayaking, and enjoying the scenic views of the Mokulua Islands.</p>
</li>
<li>
<h3>Pink Sands Beach, Bahamas</h3>
<p>Pink Sands Beach is
```
```
<!-- CSS file -->
/* Basic Reset */
* {
margin: 0;
padding: 0;
box-sizing: border-box;
}
body {
font-family: 'Arial', sans-serif;
background: #f0f8ff;
color: #333;
line-height: 1.6;
/* max-width:1200px;
align-items: center; */
}
header {
background: #0073e6;
color: #fff;
padding: 20px 0;
text-align: center;
box-shadow: 0 2px 4px rgba(0, 0, 0, 0.1);
}
header h1 {
margin-bottom: 10px;
}
main {
padding: 20px;
}
section {
margin-bottom: 40px;
}
h2 {
color: #005bb5;
margin-bottom: 10px;
}
ul {
list-style-type: none;
}
ul li {
background: #fff;
border: 1px solid #ddd;
margin-bottom: 15px;
padding: 15px;
border-radius: 8px;
box-shadow: 0 2px 4px rgba(0, 0, 0, 0.1);
transition: transform 0.2s;
}
ul li:hover {
transform: translateY(-5px);
}
ul li h3 {
color: #0073e6;
margin-bottom: 8px;
}
/* Button Styling */
button {
background-color: #0073e6;
color: #fff;
border: none;
padding: 10px 20px;
border-radius: 5px;
cursor: pointer;
font-size: 16px;
transition: background-color 0.3s;
}
button:hover {
background-color: #005bb5;
}
.lightbox {
display: none;
position: fixed;
top: 0;
left: 0;
width: 100%;
height: 100%;
background: rgba(0, 0, 0, 0.8);
justify-content: center;
align-items: center;
z-index: 1000;
}
.lightbox img {
max-width: 90%;
max-height: 80%;
border: 5px solid #fff;
border-radius: 8px;
}
.lightbox:target {
display: flex;
}
.close {
position: absolute;
top: 20px;
right: 20px;
background: #fff;
color: #333;
border: none;
padding: 5px 10px;
border-radius: 50%;
cursor: pointer;
font-size: 20px;
}
```
```
<!-- JS file -->
document.addEventListener('DOMContentLoaded', function () {
// Adding images to each beach item
const beachData = [
{name: "Whitehaven Beach", img: "data:image/jpeg;base64,/9j/4AAQSkZJRgABAQAAAQABAAD/2wCEAAkGBwgHBgkIBwgKCgkLDRYPDQwMDRsUFRAWIB0iIiAdHx8kKDQsJCYxJx8fLT0tMTU3Ojo6Iys/RD84QzQ5OjcBCgoKDQwNGg8PGjclHyU3Nzc3Nzc3Nzc3Nzc3Nzc3Nzc3Nzc3Nzc3Nzc3Nzc3Nzc3Nzc3Nzc3Nzc3Nzc3Nzc3N//AABEIAJQA0gMBIgACEQEDEQH/xAAbAAACAwEBAQAAAAAAAAAAAAACAwABBAUGB//EAD0QAAIBAwIEAwUCDAcBAAAAAAECAwAEERIhBTFBURMiYQYycYGRFKEHFSMzQlJikrHB0fBDU3KCk+HxFv/EABsBAAIDAQEBAAAAAAAAAAAAAAECAAMEBQYH/8QAKhEAAgIBAwQBAwQDAAAAAAAAAAECEQMSITEEE0FRFCIygQVSYXEjodH/2gAMAwEAAhEDEQA/AOhZTrcMUjJtZ492imwUdc9D6bUxLeGRZGjt/BmCnVGORAri2zrdjRcrrUbh+oPTftXoXne0kjSYZzvrO+c7k1zP1LE+nax51afEkZ+mccq1w29o9Bw9FeFNA5AAjOcbVv0YUVyOD3Osto6MQwIwc13Y8OB612cUrxxd2M+TFJBsTjasqTSW8wa3U6+Q2rqzZU7U23uLZpE1hFYbDbfNW6tgUa7KCZ7dZJ5G8Q74G2PSvE8f4dNa37PImI3JKvnn8a9/bHmdWaRxbxHtXSKFJNQwfE90UmHK8cwzgpRPnkY8tEq5qSRyQSlJV0n05UxOVdqL2sw+aJkKN6uMg1GGauJCTgCiQJmwwzypioGGaiwNISMVojWKAgytt0ApGxkvYuK2Z12Bx3o1gAPnIwPSpcX5J0xDSg6nrWMzMT7xNCMZMNxRqmljTZTms0ru64GAooNQJ3oJZFXYDFPGFCynYDkYwRvWaTGCMYomck0mV81fGJRKRmlGNs5rM5p0pNZ3JrRFGKcgCM1nlXScU5uW5xSnDuxJHwqxIzTdozMKAintDJz0mhEMh5KTT2iimZ8VK0fZZv8ALNSpqQ2mXodwG2uLYRW8ziTyksTnykdP77V6qFhLCsc41afdPb+9qwwL4sryLzLENnbOK69pCNuleal0mPL0/bmrj4Xo9FCTjPUuTfZKPII8gDrXbh2AxXLgIXGkZrp2x1471m7axrTHg2J3uNkHkJxmuFd/kptek7GvRSqFiwTvXAv1zIQMGrcCtiz2QmLj8sBKlTjoM0//AOonMTJFEuSc5PSuTLb5JIxSViYNy+lbl0+N7tGZ5Zp1ZpnmmvZfEnGW9ABUERxtVxgijM6Ly94VYlWyB/LKjiPNtsUzxY4wQq+buaSLhm3O/wAqvZjuKlPyS/RfjsRjOkenWlFTkkb5700xqehoGZk2xTJIVt+RZXvQ4Gdqt2J7Cs7Mx6j41akVuSQx305rK83fc0TYHvNmgJXtVkY0VSnYHidhQlS/IGjLge6BSmlc/wDVWUVOSXJTW/67YoBBEvXNXqY8xUAkz7lEW0+EQJCu+M/KjEkYH5vPyq08QHzRbelNMflyYpAD16UjasdIT4it/h4FUs0Ee/gH4k0uV9PJiR2xQCSAjEuUPrvU0C9yjV9stf1KlY8W/wDnL9DV1O3/AGJ35fwdzh6xTQ6ot8EhgVIIPzrYiY5fcK8vw72kkt1dbhVM8kfibJsFzgAj/dzrp8W48U4YWsA7yspOsgAqAATtnseh6c687H9QxaDsaHyektkbIxmulDJHCMysBnua+P8ADvai+huRN9rlnRyZTDIwQEdwwP03xvXoU9r7e+jfwj5kJDBNyFzhTvzJwKSHVYsrep6f7G1OKPc33FbRY/yjjT6V565vbd5NUTnB671yYtNyglRvEVuR3rfBbxqMuoUdycV18eHFjjqsySzzm6SCDqerb+taLdXc4RS3qelYjfWrXCRW1xEzocugIO3r/XpW8Xahfybjc+Xrms/zIXpssjjlyzVFwueY76VBbDFmxinS8BlQkxTxugGdQPOuU9xKN9ROTsSefyplrxCSAkAhT3UmrXDK90yKePhkmgMa6gdQ7Dn9KQdeO2Kd4pd2ZV3JyTypExkZsNjHc71fC+GJJrwWJpG2329atpF0jUxJqord5CAZEQd2q3ssOy+Krjoycqa42J9TRkkfJOljStMjcsmupHZRjzHJx1JqPIsYOBgUyyLhCPG6ts5ohYjcGo0SgbnFMlk18yTQrHGSMqx+AqzU/JXt4FeHEdvExWi34as7AJOo+dare0t5FJOlCOjnBqjHawNsxPcK1JLLey5LI40t2bBwNIkDLPGzdcsKxz27QnYwD4HNFPNZrauI0Jk6Ekk1wyZj1cD1pMUZy+5hy5IQ2SNU9zcRnaZc+gFZWuruQEG4cjttU8Nm55PxqjGyjNa1GKMMpyYh4bhxqJZhSY7ZpXPIY6k1qMkoBAbArO5Oc5JJ7Vak6KJ6RRtXyfN99Sp5uzVKbcqtHk+HXETx+NZxNKEU6EY4c/vZ3xtkHqOXV9vcvC0rQylomCtIurO5GSG/vnmuBDdxsPFs7MtKQxbIICAblsDlv9/LtTZ7eSFki8ONJmZcxHzZLDYk88Yr57LHE9k0kent7nh98/gqzQmRMZ1b5JAGM5+G331VpacDhvVhbiEttfKV1agTGXx1Y52O23qK5XBrR5bjROCiKuSUUF48EEHBPLf+FdeXhcltctOzR3Kuqo6qmiQt02ztyByO9UxksbdqyiSXg+hWlqscI1PG53IaIYGCcjl6U2ZlK6QqjHUgGvEcA4qYrwRjXojOJkLNgKeZ36g9/X5e1hWG/kCcHWTiAzhpl8kKfFzz+ABru4Oqw5sf+TYz9ud/Sjg8TsWFpLcG5ihYJlpMY09Sf+6Ph1vLaGCZVikt3XzyPJ5s9cL616mP2RScqeKXbSAMD9ngXTGcHIz+k3zOPSt83B4re2ZbHUsm5ycHPcViy4dOTXgf4f8A00Qi9NT5PLyvrkwkJb0ArVBw64uGUQ2kkWeZY6q9BYXkggZVs4kkQ4bcbHGRVT8RvF/StkHzz/GuzDqZyitK/wBmZ9PFO5MzW3s8yqTcS79l6VBZWNoSZZEJ7E5rPcX0khzLdx/BVNZBcxxsSolkb/SBTqOWX3MjyY48I13NxCARBG7jlhFxXLmmlY7QlMftVpd7u9IjhRYyeQZ9zXXtfZWExBr+8ZJWHuow/iedO8mPCvr5K2p5fs4PM5uJGALY9M1vt+Ey3ELMbmFP1Vd92NduT2b4ZAC0d8wb9vDfcMVxLr8izRQz+Ii7BioBNNHOsu2Pb8CPE8f37/kQvDLgyMqhWx2YU48Nkij1SXEMR6An+dZneR92difjVF5SMFyV7E1c+4/JVqxrwMECt5ZL1MD76o2tkpGu5PypQRQjKUOo8mzgCriZEB1RI/qc1KfsGuPlDCvD0OVMoI7DnWeW41jC6setVIFYjQmn0zml6TjHX6VZGK8lU8j8AFQx8zED0FUVg6yOflR6PXFEyxmMDwQG/X1Hf5VY2VWI02ucFpB8qMfi4LgpLq/WNC0Yb3VxUjtvEkCurYz8KLryxVJt0ki8WH7X0qVt/EkB/wAaH/lH9KlVd7F+5lvay/tR8qs+GQ3drqh8C2kXYeJnGrGcKc/HbpXQs+BzwzwzBjPIjZQRyDSVPQnlnntmt68OtrOY8Quylsjx6fs9uv53n0/SJ6DYDuegp7WxhzbQ2hhTBCaG0uB2JHu57Dl614OWrls7+l1uzZ+L3hcT8R0ROdJR0YCRxpwdj0z9NquOeyiIzbB392LytKxHrnp8jgkV5izkiMsbSXN1OYmZyjMAGGc+/nOc7/0rrhIh4sovlt4m0PDrm1Mu24Ppv8aqk0nsJxwK4jNOqExo3hK2lmMZCK22AN8E7EfKvTexPtHc8Jt5pfB+0xMoEihiWLgeUgnkOmNzyrkrNPANN2LWdd1dEyCwxgfM8/lTLa2AJeOPw/Pq8PuvPnvvn47CqvkSW/kilJnsE/CQnn+32ktmqISz51jIXO3fOPrtXatOJycWs0u7CR3gkHvZA+Ir4txB78cXvIh4S+ModYWcsNI/Syd+ZJ5fdW32e9qOI8CHhROkPiSKVhQalkII1em4AGeldjB1jivqpglFvln1deH30ruQunU2WLPgHYAfwoJOF3kb4dVIPUbgVXDfay04lD4jsltMhOYn3I9RjmK2nj9npJe4B7kKf6V1MfVNq41RU8MHyznSWEofCFm9QuM0J4dPqwVYHs1dGPjfDnjytyoX9oEGqHG+GBwDdx6uxOavXUz9CPp8fsbwvhl9bqzxukSsct5d603F8LYKl4I7tseZg4OD8MVkbjlocgXqkE+7nakHivDHy5mi54JKms7euVzRclojUGL4jNFfYWC1WMAZIGKyRQINnUseYwfurp2vE+GSsUjuIckY93H8RWtOIcPXUizQ4A3TUtXxzaVUUUvCpO5SOGtmW3AG/I52qTWjwPpYAnsN8V2GvLBsESxAZz+cFC99YIAyPAXPLLg0/wAifoTsQ9nKPjMAhPqBiqexVFUuzajvgDO1MuuL8OtSTNcRKRuQGBpo4lZTxh4JoSpHvCUGn7kr2QjhGt2VDY28iqQXRgd99zTJLGwXzEySkdDnep+MwI1RZodK7jdaVLfrIctcx/JhS3kb3Y14qF/Z7WWRVWGRMnHLNMn4WtucvbSuP1lORSTeQ53u49v2xQtfRHzG8T/kFO3PwxE8dO0N02sYylqCfUGhebG6xgD0j/7pDX9ud/tcX/IKFpoufjJ++KNAc64O4nFbdEVSWyBj80alcHxIv85P3hV0nYgHvzOFH+Cnj6RyCX2ks2kkORM0Tlx3xvt/KgtPwLzwREN7SW4Zjuy2LMT8/EHx+lfS4rG/lJZrnR+rpPL54zThw2bCg3OCNhpBI+BrzdLfY7ulHyi5/AvOsQA9oEmbOQTZ6G+OdZ++uDN+DH2vtWZ7W2tLhV3GZ1y3qV/7r7qsEyOVWQkqM5EZC/Dr/ChluDaur3CMc7bb9PUD+NHZ8oDjE+K2nsD7UPpW5tbrV4mpmeRcAemGJr1Nv+DG+nhSBuIy2sY8ssbRaxIuOYbUCD8q9dP7VxQ3ASLhF7OoPmeHRnJ66c7inW/tdwaYZmjmt5Rn8lLC2vHoMYqdqN3QmmNnzvin4IeNvcy3Nt7QW9xI6hSZtaMABy2yMfSkxfgt40pha9vLSRozqBW6k05HLbw9q+rxcWguT+Qt5wvVmQDPrWjBZstkjsaahqR5HgXsZbWKJJMmu4C6S2rY/cM/OujLwO3/AMlMV3woU5FUyg9K0Yp9tVEzZMMZ/cjzEnBYM5MP0pJ4Lak+4fpXqWQdqBolznArQupl7M0ujxvwefh4LaA8uf7IrV+KrfYAgAfsiuqsS9qswr0FB55PlhXTxitjg3PCIGz5vqK554BAQcFP3K9PLbqRuD9azG09cfOrYdTJLkoydLGTPNt7Ow52EZ/20L+z6DksWP8ATXpBBoPmzjvzoXU9n9MirV1UjO+jieb/ABCvRE+lC3A0H+Cn7or0fhk9CPlUMeDyNN8plb6Je2ebHBYtIzAmf9Ipc3Boh/gqP9lepCg0MiZHWj8oj6NVyePPCYs/mYv3at+H26LvDEPgteqES53FR7dSPdH0qz5RT8J+zyH2KDGRDGfXRV/i+DI/IRfuV6hrWPHuj6Uo2cefdpvkoT4bXk4w4dbYH5GP92pXb+yj1+tVS99FnYZ7CWLVujhDyyEBoo4nUZM7ufhj7uVcu1m4zpkM4t3Odggx8+dbo5bryhgh2y2o4wa85Z62hrpcF0MckWkZ1awx+najDZGiaPV3IGVrI/DoZ38WYyBx+isrY3xtjPpWpIFRcDXpA/WNGwUMDKPdAVTsCBikzRJM5LIj6RhdSA00HUuoYxtQhTgj+dEFAhEQEMqR+ood9tOkqeua0FcqcYJxjeg05UBwARUIAV2OKCnkfIUBAztT2K0LI2oKcQflVFB0B3qahHETirzR6O1Dg43ajqFoAjPSlt6c+lNKnnzJoSMbnnmipCuIorQGPIp5B6jfnQsMfDrTqRW4ozGKhKY6Vqxn+W1Dozyx9abWK4IyFPMMquOhxzNRkzsBWgpnlVaOuPpyoqQugxyIA2RvjpnagGrONdazGdx1pZiGcNGc9x0ptQmgUVJJxgj40DxHG31p2gaSBnPcjehZMq25OD3xR1C6BYj9RV0zDDbxcVKOoGk9AhVMl2X5nFLe6tgpLOpUHGQCRn41wprFTMiS8STLZ/ItIAc9u/8A5Wuw4WFVmEzDfIJfOPQDGMfLNczVfB2qNjvaE61ZxpH6BwP6UIktclipUkbnJqJw0LkGRiOx3piWMYypyR+ljapuTYfG6GPMZyvTapFKHjD6WXPRhgirjQJ5QmkDkBV4Pu74x15GnsVokkqRDLhzyyFUnHxo2HY1WRjSMgnqOlEcYokBNBypm560DjehZKICGz6VCKADBqy29SxWgTpz61MCr6407d6moDnv8KlitCnHq39KDT2Oa0YyKApt3prFaFY0g9j6UJ8g1FgANzk8qY3LAznrtmqZQQCMb89tvp1o2LQBUcxz60JKglWH/lG5bI3DY2yOgqpMSKwyFOQSe1GxaAYDO2Mcx1qOHGjyrt72TRe5Jlt1Azn1qnDA6hgdsDJ+lGwULOcZBB7DuKGTKZGDzAOMY+dNGGGMAPzxUYEEroOQRnIx/wC01i6RBIVmDYGP7zQ6cKCF2A5dKfgDIXTvvgkUHlVy5yNXLJ2+6jYriJ+zMdwu3wqUfhxdUmJ9DV0dQNJqjsLVZGn+yxeK5ySFALGtqYC40hfSsiXKsM4Yqf2aaJtWrKlQNge9ZTojm5bECqYjkMEjmKFiBGWbJCjOBzpFlDCitNFb+A051OCAGP8AqI51CGojO+N6sagNlGarO2edKuZ/BAYI5PIBRnHrQboNDxq3yAO3XNISSdolLRrqzg8126nFHCCVSQO2CM4O38aNwCNDb6h8OdMKWKjbihjUKgUbAbCoscYkDqgDAYyO1AYHvmhO526f3yprLn40r40CFjS3T51DgKdBH1pbLv5d/uosMQRkURGTzDGAu43ovhkHs3WhbKLjO5IoTryCSo9edQUIpls6SpAOw60OGI8+PlTFDeISTscY9KjDygtsRtgVBaFEaB7wC4wSRvQ6dQ0uwORsBgYFNbYAkbUMoZXURjy8jnmKNgoTpWIq5PM96toyJAVPMbk5zmmHLMoyAQdy3WgkCrtjHPJHI0bFoBwBk75XmaoElCz7N26mjwcaiMkcjihK6Y85IZuZJJOaNgaE4ARVI1YbYHotNMS76mAC+5nrVkjSke2nVtnrQTs4HhqNkO4/Vo2AWzMGI8JzvzwalaQ0GBlt6qpYKJpCR5HOn4AJPpV1KqNhcfmVSeh/nVqSN8887VKlQIqORjePEcaVUEffWkDIJPMVKlQgMQZo2kaRyVb0xV6iXZT0qVKIPJdSpUoBLHOktzNSpUIASd6JWO3rUqURWFk6CeuKBVG47VdSgAVqbx0Go4KkkfOtBG2OlSpRFBC4yATilKxIqqlQBbMSADuAatdkIHQVKlRcCsB90Uk7k0J2ikbGSgyKlSigAMcmM98GjKjWCd9XMHlUqUwooxqCQBUqVKhD/9k="},
{name: "Grace Bay", img: "data:image/jpeg;base64,/9j/4AAQSkZJRgABAQAAAQABAAD/2wCEAAkGBwgHBgkIBwgKCgkLDRYPDQwMDRsUFRAWIB0iIiAdHx8kKDQsJCYxJx8fLT0tMTU3Ojo6Iys/RD84QzQ5OjcBCgoKDQwNGg8PGjclHyU3Nzc3Nzc3Nzc3Nzc3Nzc3Nzc3Nzc3Nzc3Nzc3Nzc3Nzc3Nzc3Nzc3Nzc3Nzc3Nzc3N//AABEIAJQA0QMBIgACEQEDEQH/xAAaAAACAwEBAAAAAAAAAAAAAAADBAABAgUG/8QAQBAAAgECBAMEBwUGBAcAAAAAAQIAAxEEEiExQVFhEyJxkQUUMlKBobFCYnKS4QYjU6LB0RUz8PEWNENzgpPS/8QAGgEAAwEBAQEAAAAAAAAAAAAAAAECAwQFBv/EACgRAAICAQMDAgcBAAAAAAAAAAABAhESAyFREzFBFGEEIkJSYnGRMv/aAAwDAQACEQMRAD8A9f6PqUa6AgXNtRHBhmzXINj1nMwlBqFtCDO9hnzIOduM81N+GenJLyI1qWR7QeWNVw2cl/aPKCC34T04v5UeVJfMwWWXlhcsrLKFQLLJlhssmWAUBKzJWMZZnLAKAFZkrGCsrJHZLQuUmCkayzJSVZm0KlJhkjZSYKR2ZOIoacwaccKTBSUmZuAmacwaccanBtR0tHZk9MVsBuZsLJ6mC+YsfCHFIR2T0xe0WxGKSkCB3mnT7MW1nNxGHBc5EGsVlw015OXXrmpc20ivZ1KugvedtcCzLta8ZwXo8U11UX5xI0btUeb9Tr9ZJ7D1USR5GeB1gbjUS1uDcEwddKiUwVOs1hagtatvzE859OL7HvrqSXcIbsbmFplQuo1lNkWxJNvCECq9mXQ8FluUXSM0pK2CK3lZYfIZYSaWZ0Ay9JMvSM9nK7OFhQvl6SssZ7OZKR2FC5TXTWUy2jWWyEaQGUHbYzPOWVIvCONsASt7Xl5dIY0xygzm4LNjmaBlZkrD5TaUVjshoXKTBSMlZRSOyGhXJMlIyUlFI7JxFikgWHKSZI7FiByX3mfV0OtoyFlhYWGIBaQA0E2Fhcsu0VhiCyyQtpIWGITFGzBW4zdChmFwAehjFTDJV1JMNRpCmLCeZKLbtHtqaUTNKioNyITKL8pu0qoSiZgLmapJf6MpNt7FZekvJAJVqFhddPCNpqt5ammRKDRkJLCQigGbyyrJAFJnJpGcswy7xDE3SDyw+YPfLwgyNzcaRxkiZRYMiUVmyDMlCdrzSzPExaZIhByttIY7IcQWWZKw0zpCxYgisorC6TMdixBZZWWENucwWA1vCxYlWkFopiscKDZQAZeHx6VOFjGKho90Xiz4kAWQXMZNQFdRoZAE3AHlEUqFPWKnuyRyw5CXHYbHRBCrcEAdTMmsU3Qzxa/tr6NxFIJiVq+yL5bWv8DA4j9slq+kKfq65qAFspOp1Gth0nnty4PSShye/SqjbGFWxtrPHYT9sfRzY1KAputMi+dp6iljKLgMpBU7EGRbb3Q3BLsOALymwottAJWQ8YVaqc5opoycWbyWNxNqNJSup2m5vCnujJtlEXgayMVIU2h4N2tvFqUkON2IOgpIQoueMUFVVJLcY9Xa4NjacXEo4Y2N5zKW51qOSHhiaZ1zAngBvEKuNVagdS2YnYf1ibmopuCbwVOrVWr2mUXGlp0xnZhPSaPRU3FRc4I1lVCFt1nKONquBlpZT4kQbvUrENUZsw5HSVkZ4M6we4vlNou+JRXysQD4wNGqtOmFCsTvcxY0lqVi7hutyI8kLBjjYumrBddeM16xTbRSSYFEprqFBPWVVYkjKQvhDNB02Frd5L5mWI1DR+1VLa8NI0xBp2LNFWw6k6ufKNSE4MWqBargICT1jmFphQO6Q3hN0glK3E9QIYVgNo8hYGyCRqDfwkC20AMz233pXb34wyYYIJkbrJB9r9+SGTDBHkx+yWDzXyAHnYSf8I4MHuhAeF6f6z1vYg7FvjLFAndh5TjbZ2qKPKL+y+FB7zKT0W06GD9GNgrDDYrEIBsvaXXyIM7gw9uN5rsdLFAflBFCtCtigbNVDnqoH0jlPEYjc5fKYFAm5ygE9ZoYaoAftH6R0iG2N0sW4PDyMbTGMfdM4wFZCFNJLdTYmO0FffsteN+PxhWPYVJ9x2pi3A2iVfG1Rc3+UuotZnIFBVW3F/0iOIStw0B0uWiavuCS8Aq+OrEkA68rTnVsbiP4gHS0NXRxdhUsfp8NIhVFSxtnY8CFtaXCEb7CnKSWxh8ZX3z/AMogvWsQftN+UTFZ66r/AMuTl01F7wZL1Ae6ACdeY+F51xhHg8/U1Z8jPrOKIAV3H/iJQxWKH2zrxyiAp06xBItptoQRM1u2Cnu3Kb3U2+GsvCPBzy1tTljJxGLze2QfwiQ4rFBrdqdfuiDDVXphiALDhrbx1i5qBARYBhbY5L+eseC4IerPvkx5cTiydKv8okOIxoP+YfIRBsa2XPTph7HhUAB+sw2PykMiGx1PfGg+krprgh67X1M6JxOK4sflMNiMbf2vMCK08a1fWmlXIAbk6/QzBr1AMz5yPsgIRKUFwZvWk/qY12/pHN/mL4ZIUV8ba7VNRySc6njTrfPtuUYWmfX87FQwudLFr2+Fo8PYjrP7mdP1rFDcuT+ACbGJxVtXP5BOScZWzHJme/2UF5KuJqMb9hWuOJB0+Yhh7B6h8s63rOI/ifyiVON2re7U/K//ANS4YexPqfyZ7VMQAfa+ULTxAO+0PUwlGof3lGm/41BlD0fhQLDC0AP+2P7Tym1wfU7kWuANxCCsLcz0lDA0BtTC/hJH0kOBpHg469o394riPc32yj21A+MycZSuF7amCdlJieLwuHS3aVKqXHHVfneCp0KQTuvSbra/0mkYxaM5OSOpTxFMP7SN0Uax+iVIBt5zk0KFJO8L3Pu30jSdkL/vG05gRSigt0N1rKbkqunHhE6xQkWu19iNhM1Ln/qNlPMgfSJV1c2sxy9Gv8yIummCk0bxNgO8b366Tms/tG+l+MYqUnZw7FyBsGcm3wgTTvnLVH1422mkdKPJM9WXAF7kMfnbSCWmSbMe6eEOaKkZg7MeGa1z5QTvTonvkIeOtzNaow2fcs4OjYEJf8Wv1lHCpltaxtbTT6Q1OuhUFdQdpecFiHFjC2iXpxFHwSZe6LH3tbxF/R1R3N6pKHfvGdosLZVIMwKYG/leUptGc9CEjif4HQLX7NCORBIkq+ighDUmVDbZUOvwvadwJyuPjKZCeMvqMyfwsfB52tha9IA06KsRuSbEfOxi1XE41HISkptrvfTw/WemdXUHKVa+4MA6ndqd7cbbS1qcnPqfCPwzzXr+MNRiq2PusAP6mb9dqEB8RhgtvtBbj9J6NUUnRQJr1OizZmXvc7S84mPpZ8nnaPpOmjAthVqEcaVQX+dow3pDAuQHWup4nUCdWr6IwlTVqS5veAsflIPRSD2GOTiDrFlET0NVHL9a9G/xcT+b9ZJ1/wDCsP8Awaf/AKhLjuJPR1fb+Hqg4vtNdoIpmN+6DCKKjchPHPqqD9p92ZbEKOIB6ShSuLsSfEyZAOCwxsLM9sX0Wm5+NpFwtJ2zNh6WY7lhcwizYjpibRqnhaAOlKn+WN06SAWQKOmURdCLxmm0StMiQDEU82jUqbDkR+k5mJ7CmL1MOFPM7fITsVWiWI1vDNoqMbORWqUFtZUYH7+nzgg4sSlHIvQAfSM4qhTqi1SmjjkVEDhsNQw9XtKaJTBNnIFhbrNo6hMoMV9cw6nSrTv5xauquS7Yh1PLU/SdWph6dYK1A07cwBLXCMik2ubbjedC2OaW5yGVSEZq1RVXgqkBhyN9TNYYKq9pTRwpOpZreQ1hXemH1ALcrXm+1De0jHlYAR5E4GGqr3n7N8q+0SNPheaLL2iogAA1Y257WhKbmxthzf3i/tSqq1rgrQS52Oa8NhVRvKde7pwIEhp2XYzFaucKouMi6sxvptz2i6Y6o9Y6sARdSLZWv12jSsLoLU/dC7ju9dZmmiupZGUjoL2hVak9PtKjjPzPGWMo9lMwtc24eNoB+zApgfZm1QHh5wopZqXaJcg7WF5dNb2sRfiLxD2Bsqjf5SC+ym/wh8inVdDNW6A+BiTE4oXyv7vykh8re8fzSR2LBDoAhVIECZYM4aPSD5plmmA0haWkQyw00Ggpq8qiA6NrGFaJqYRW11mckWgzvFKrQjmL1D0iSKQBzAE2MK3GBYzSJMgFTC4eoxZqS5uY0+kPgwmFBBeo1M+8S2XwmC0yXmtmLibNOhUJOGqo6k3sGGki4ZmOihvAiK1adKobvTQnnaDXDopvTLp+ByJVk0/B0ewqIbdmx+EMKb5dKYuOonLAqAWFet+eXetawxNb80doTjIdrUUZT2lPTclok60qZUI11voqre3yhFr4lQM1fMBwdQbwoxJOr0U8VYiGSFiznYjC020ylVbdg1h5Tp0qPZkEKthvMM2GY3NCqPBswhadPDtcU6g13ViQZSkJxCUkoZm9XsGXdAbDyhFokrdQLnfjFD6P7J8+GWxtwNv942M4s1NgpO9N+EVsHFeARpkErlN/G0LRp3GoYeImRUe+WoAoPx+cI1UCxpMG6E2jFRrsRzbyklesVeX0kgI1aXaUJDOQ7iEyrySjGIu8sGZvKzWjEFDWmw0AGkYm36SRhWYtxMA/jLJte5BY6a8P7wbHqb8zvEUgbGAc/wCuMJUcA6jxA4wLtb2jKQmZPx634TPGa116fKZ0Jva3SVZDRVpJqT+kdhRnWXaWRK4xWFEtaQy5ImxpGbyw2luEsiQLJLN06rL7LMPAwwxFQ6MVccmEXCzQ0MamyHCJ0FqpVUDMEI4Nt5yAOj60nT79gQYkDD0qrU/ZYr4GaR1OSJaXA5lf3h+WSB9cre//ACiSXmiOmzcoySTnOhlXlE6ySRiMsdJguV5HxkkjAKPYvYDwlUx2mjE7ySSGUgYYlrHpM1GIawkkggF3OZh0MwTeqy8ALySSySlJsDzlbH5SSQEX9oeUpdVPjJJEMs7yxv5ySQAg2WTn4ySQGWNpcuSSMsCWAJJIAbAEuSSMGSSSSAj/2Q=="},
{name: "Baia do Sancho", img: "data:image/jpeg;base64,/9j/4AAQSkZJRgABAQAAAQABAAD/2wCEAAkGBwgHBgkIBwgKCgkLDRYPDQwMDRsUFRAWIB0iIiAdHx8kKDQsJCYxJx8fLT0tMTU3Ojo6Iys/RD84QzQ5OjcBCgoKDQwNGg8PGjclHyU3Nzc3Nzc3Nzc3Nzc3Nzc3Nzc3Nzc3Nzc3Nzc3Nzc3Nzc3Nzc3Nzc3Nzc3Nzc3Nzc3N//AABEIAJQA9AMBIgACEQEDEQH/xAAbAAADAAMBAQAAAAAAAAAAAAADBAUAAgYBB//EAD4QAAIBAwIDBgMFBwMEAwEAAAECAwAEERIhBTFBEyJRYXGBBjKhFEJikbEVIzNScsHRgpLhQ1Pw8SRjohb/xAAaAQADAQEBAQAAAAAAAAAAAAABAgMEAAUG/8QAKREAAgIBBAMAAgIBBQAAAAAAAAECAxEEEiExE0FRFDIiQpEFI1Jhcf/aAAwDAQACEQMRAD8A4hRRAKxVoqrXtGFGoFb6c1sEoqpXYHTBCOtgmKYVRW/Zg1w+1ehXTW3Z0yIhXojpkSlFoXEdbiLyo6x70ZY8iiCMd3Al2ZztRlR5BjnTHYeVerGQdq7A8U4PkF9hYKWZT64oHY4qnGCWBbOKK4j6RZ9d6CyuCsq4SWUSBD5Vv2dUTGDyXFeGIEbLRyKqsdMltHvyrUxVTaDyrQ2/lRJuuROMdeGOqBg8q1MPlXHKDEdG1alKdMPlWvZZOMb0B1F+hIx1kAWKUPKMgbinGixzFbWdukl0gk+TPezU54SLUwfkX0KdUkQk0FQ242pCZeddNdQR9kCmNJG2K5+6XTnavH3pt4Pp7KnGOWS5sAUjKaavJNCncZqckhkOlhuOtHck8HmTmt2Dx6ERRmXxrQiqZEYPFZXpFZXCnQrEfDNbqnhR0hdSMAimFU/9SLPmNq9bJ5EYZFFXoaKqZp5Le1de47xH/wCwZH5itzZFR3ZI3/pNBSTKeKa6EhHRAlMrA3hRBCfCm4Aoy+CojoixA9KZEJ8KKkJNdwFRkKiDaiJFjpTiRY6UZYM9KGS8aRNIgelbfZ/Kn1tz0o8cPQil3FvDnhkxYAOlEFvnpVUWw5itltvKhuHWnwSha+Qoi2flVUW5/loiQN1pXMvDTrJHNoD0pd7bflXRGAAcqA9sC3SlVhWelWOCEbbblQGgydhXQSW/d2G9J9h39ximjMz2afHBLSxaQ4GxrBahc6huKu2kK6mznlQbqJV2AzUnY8llpIqO4gvb7jNeG3Iz3dqriNpz8vLrXktqUGa52Ajp/aAuyGBdfcVRsK5vi82QwjIA6ZqvxORz3QK567s+3bL6tI6CvPlVhto236huG1EO4ZixLNq86FaSM0xVsY8aoXNskbaARjw60i6hHKqu3Ws27bLk8ra85CFlZs6hjoDXjAGsaYaghjGPHNMRQRyqCq8/GtMZOXQ24V0VlUBagDAGKyq7WDJ10Lx/ft1z+DIqjFb2kiAqSGPTwqXChpyJDWpwT6eB43Sj3HI+OFRORlh6rtWr8HIOY2yPDFewI2MK2Keg7cbdqMedScpw6mXSps4cMf8AhPWzuE+4cUeFHU9+LI8OdVFkbkyAnxBoyjtPuhPEmp2apxhumuB4aeCf8WTo44HPei0+ooh4dAx7jYp+aKIPpJ6c8bGtTbBR3WFdGW6KlGWMlHFPhpCf7N5kOMedJ3U0FlII5jljvhd9qQ+IOK3ds5gQlPfJNTIL9NOuVS8mMb0fJYveRHGrPCOutDDcIHicYx1FNi1J3GPak+A3NqbdFDqrN91tq6JIIiOW/iKV6qUfQ04xRMFuVPI+4oyRZ5inuw37p1eR516sJU95CKMdbGXHsVNREuyNYsJHWnzF4ChOQhxpp/Omuh4vPQo8ediKF2QBJpyeSOOPW5CjzpFLuKZXKhgFPOh5Y5wVjzyaOPIUvL2Z5rv41C4xxqdbgpA+mMdFGKDZcfwGFzvyC4G/nTqZKVnODoA4HdTYUCVWclts5oTX9q8eYZlZugzvmonGOIXKAKF0nyPOi2lyTdnGGWCFXBQ6WzgjO1ezt2ihRkY8udc3ZcVmih0Oqvnlk8qscKuWeBmmOrJ2z0oZTFjPHGT2WIEZdak8TRkXRDHl2G3gPM1dkmB2CZ9TRYLVZV7S4AVcHGObUJtRXIOJvCPnl7bm0jy2WmfkTU0wsUcqu4wN/E12F5ai84nO8seiNO5Go8PGpCW6YvEJCLr7mepG/wDavPlU5PPohJ7eGTLOzjulIbIddwfKrFnY9lCFlxkHnQodrtprcKe6CVPUHp61veXcc8ZSKTQR84cYPpWmlQhFyl2RnJ54XAZ4olOMk/lXtQywP38eQNZUvzV8F5O/jhTlpYe1OQ2qHZXwfxCj3djx+QERNYoCMdzb9akSfD3HNPemUgHOBNyrPG5vnej1HOHwrmEwIXaSMKB8xOKGL+HfS4dcblTyqE3COMMpiYMFznDPtSs3DL+AEMpP9JzWmN6xzPIu1vpHSy8WQAC0cM+dwRkV6eITSW5RyEcnZsYxXN2kFxq+VximJC7OocNnzqFjhJ9mmuMsdF3hrtJcRpNMXXOFroby0VoTiV4jyDA1H4DEqR6pFxv83hTVzeuhYnvhW2Gdqzx1DU2ojuDbwiTc/CU0jGY3HaHnuMk0fhXw5EGYXMZ22GqqQ4+I411xgeY3oMHFmubvUBhANgelapXvbkmqZfDZ7W0iYoIMMmwPLNXeGgSWyE7YztmotxcrNP8Aw1JzzqvZyRrAIge8F6Vgnq5p7mddHEFwURFjlWMCB3uVa2JZoQXz70WRNa6SNjUp6+KWV2YG8PDF5HCqzH5QOdL9pHKmvIUee1MSxSRLhV1JjGKh3EsgLDszg/Slp18s4aNFMN/s24mqNDq16lzsOlc9eTXEcTRoCqHqOtHvp5RCw7NyPwgn9K4S++ILz7Xpk7SJEfOhcYI8CCK212py3ZNVk41Q2yHLwsxLO/LmT4UO3tDMwCsBmoXE+Ly3g20xR/yjmfWlF4rexqAkh0jYEDcVsjc2ujzZXQyd6OFSQFFVjqYbEdKTvbaZDody3nipb/GN/e2scAmFpOpAMqYAk9c8q7G24pw2SzV2uY7idFwwiTVuB5f2qiuXsO6MujnIrKRyO6dvKrFtZuqA6iPLFT+EfE63ENyt0qi5DkRlVwpXO3uBVbh/EGaOR5woGNup9qP5EY5bGjX5MbRgsLQBpoy556OVO3nEIBZ9s0fNcKOVc5xK+keXVFrAA5kYqZc3VzMQCzHblUpYteWzQmqlhId4rxaJImeJcFhpwOhrkL2fUSQxyd8k7D2p++zEUWdcBjnvUnKcaVWIliebcqjqbFuUUzDPMpZZpZzv9mfRszYDnwHjRYuyuA0TS6XHyu36Hy/ShS9pBJFIuAOTDG2eox4YNNRwwLGsiKRG5z6H+U/+eFQna3EVR54BG2iDFZdSODgjnWVi8SZMr2MUgBOC65/tyrKliQ2In2pjMSMXKgde4KKrKF77hvOuNF3xrr2OP6f+aPHPxc/9j8v+ahPQ3P8AsjYtRU/T/wAHUyhWXCFQfOhRW65y75HhmoSz8V6m3/2/80ZJ+J/zQj0U/wCahLRXr+yKK5Y4TLrW0OMqi6qF+zlkYFhEPapouuIL80kX+0/5rdOI3gIGuI/6P+al+Jev7L/IVbL0XYOHQbFtz5cq8m4PaSyKzlzp5AHA/SlLS5upMamjH+mmjJKObr/tpVVfF/sSc7M5yBuOAWcmCrSJ5DelouARRrnLk55A4qgZGHNh/trxZwxxqP5UH+T/AMx422pdgo+DQjvBpMjxIo9vYfebOr2oqygdaKplYgxsgHXUM0v+8+5CTtn7Y5bW5CaWdiDzpzSgGMVOVLskFJ4APAxk/wB6Q4hwi+uF34kwz0UHH600EorlZMe1Sl/KWC48kfIY8KTmePP3a5ZfhniUE3bWvF9MoBALx5Azz2JI+lL8U4F8QX8fZz8YgSPqsUbLn16/WllByfDKxrinxIQ+OviQWk0VvwudRKhzKybgeAr5bfztNK8jy5c7sTzNdL8Q/DF1wpl7S5EgbkVB/vXL3ERVirSZxzHKvY0mnSjlPIl1iSwwCKJEJwNupPOhSIRuBv5GjmIaRhtvMmhmE/zD8zXpxi8GR2R+i+GG5B968WZ03RmU8u6cCmDbsV3Y/WsFoug/vmQ+S5ouAqmvoBXdTjtdug3p0cWvkQILyUBeS55VpFw+3f8AiXsg9I6oQ8G4U3z8Rudxv+4FK4J9jRnjpiq8fvw5Y3UuonJzgg0xJ8RcTmXH2koPwIq/UDNUYOAcBYd66u2/0gf2plPhjg7thby6X1x/iput+kHdJ+zmRdyPIHnkZ9JyNRySarQGMoDMwLlSNj4iqT/DnBYiBLxCdD0yQCf/AM0/B8IcLvWEyXUrDAHcIC7egqFtfsvVGWfpzF5cL9oYLjSCGCgegocVy0YVM6lXIeNhsyk/2ruF+B+Hgj97PtuNx/iiR/A/DUKntLjb8S/4rPujA0eGT5OBFpLL37MpJET/ANQjUp6g71ld9/8AxXCySS9wDn+Yb/Sso+ePwb8d/SmCKLG4A3IqeJl5Ag+4oizKNtOT61rcWzIrUigZABkV4tyANxmk2nOnaM0Ltz0Vfeg6dy5HWoS9j73oHJce9Aa9yw7mfRjml2u3XYLH7f8AqgTTvJzwPc0q0y+BeqX06PhsxfkpA/ESKcd5OijFQuC3SrkPIFx6n+9UpLqJvlk+gH1qDoxL9Qu+LWdw1kspL90UCJohLjUufXNavPAE2Yv477UrHcoz9zGn+nAo/jSafAn5UI+yv2gB2B9hVG0Y6NwfyrnXvG2GIgPxSAUROMxQLiS5RR10IWqb0cmugS1dbOsic42zXssh6udulcqPiW1X+E9zKfwx4+ten4jkk3itrhj01ybflSPRySwS80G8nQtcIu5KgebYoLzxP8rqfRgagtxm/cfwFQe5/Q0rLxW5c4ZCT4CVh+uaC/09SCtQl0e/FlktxGrCRtugmx9N6+eX/CjrJHaHfq+RXZ3qSzIJJEAX8YGfoKiXVvJnCugXw7PBr1NPRGtYyZ7pztfCOWfhrAnDEeRrZOEM2NTE+a1bPDyWwZJcnoFx/aiGyePGt23+VTzPtzrasGfxWfCSeEKQAJsf1Y/xTQ4ZEI/4zH0p4KgOGZifDSaMkalCRGxHmMUy2g8NpIh4XAPvu1Mx8OgTku/t/iq8NlJJvoOOefKtpYbWBC0t0gYHBRW1n6bUycR1RMlrYxoclGPoascOsophoRFSXHdIXJ+tBgvbWDvJG83TJUD9aV+2XOt+zldFbONIwQPUVznFF4VP2K8UkupxJBJM2gHBX5eXiBTnBeOWthCsL2ejozoc6vM1NkUljqyT5ilSuDkDFYbsSRrrW1n0Sy4lZXg/+PMpPVScEUyWGa+bAEYOdxVXg3EriKdYXZnRjjc8q86UEbIT+nYlhWUsJM1lQL4ORXib4OhD7Ctf2jdMcKrfSp37SA3BU/6c1r+15OhGfJa+j2R+HyTtf0rrcXzchj2rB9rJ7zHfpsKitxec7ayPehNfO/Pve9HCEdn/AGdCToHfl38F3NDM6eDe7CoIum6KB6Vus0rjYqPPFHhCOUmXo7mJfmjLepop4iqrhYxH57f81AVJW+aQkfhoi2m+SH9xQbiMoTfBWfioB3kdvLXgfStRxWRW1JhfMc/rSa2qaclJMeOa9S2j1YCu3pvSuxDR0s88jD8SkkYlzKxPUvRIcMctCfVnNaRKFOFXSPMYpmNXIGFdieWQQPzqUrF6NUNK/YWKdIv4cDMfNzgU2l9dNspQeQpeOGaZu6gB5ZPSqUPCLmRAZx2aZwSxAx71B5Zsr0wjLO0h/fyZ9CBQpZzHFiGWcnHysQT+VWE4bDlktmE747rAZTPm1Fi4DIQGlIGDkBDjHvUZXV1/s+TQtKcw10Yu9NqY9FYYoX2+4MwMcCR+fjXUzcJijJxs341zn3qXcWzxt/Cxg7Y5U0dSn0OtNg1tOJXWMyatXh0NCvLwyOSAY2I7zLgMffFaNqOcrQ+yLNnRn0pvOxvChYJCXL97UfOmEDEYjmdRRktweakUzHAoGy1yskDxomvbStzm1f1GsWxcNlgCTzIOapvEOoz614qBRsMU6mwSgLLAoXcURI1wds0Q16CMHanciajyLNCuTtSVzbou42qizAchQJCp+ddvHNSsl/HA6jyTStP8JglM6yKAAvPI51poi1dcHxqzbaBCAhGBWCfCNNcU2Naq9oOaysuTZtPmIr0Kx2xTccGdhTCW6r87D0FfTnxqpEFhJo6QA86aJjGyZJO1N28VmgDXc+W/7cQ3/M/2FApGgRjgVTsMmm0SQj+Ef9tMfaYw5+zxm3ToWXvGtokupXDyvcCL+fsyRXYyVVaRpDau5y7xxjpkb1WtLezMXZpHrk6yFt/ypaLhpuWVUZyAd+6QP02pt+FpbNHmUl33CwnOPc06qyOmkB4jwu61p9jTtI3G+ehFCj4Perh5EdI221LGaozfbLeLTDJKM76soR9DRba24nc2+u7l+zrpz2sjFNvHNJKuC9l45b6AQ8KhtTi5M3aEZXSozj3NGD8LhYL9pRiPuhDI2fM8vaiRyW9vE0FszXbsN7lx3R4hc7n1pjhVnDB3kQKfrWG/UQh1ybK6ZPkPYvNMezsrN9PMSztoHsoq5YcAacrJfM1zp5KThVPpW1iwBXOT610do2IwV9xXkz1Vls9vSDc9iwiZNZrbKAsaoBypZjiqXEH1as7VFlkA61iUMzwh6G5LkFd95SRp9G5VFuECsQwKN/Ln/wAzVG4nG+9TpJ1HckAMZO/l5ivUqjhFmIyxgnb60ExgHlTl3btCcq4kjY92TOx8uXOl3jmyAInJPgpIrSkKaju7bV6Xoz2NxHGGl7KIHl2koU/WhyW6ImqS9tFPh2hP6CqJCMCXrRpK3jSDUDNcwlAdwpYk+2KJPNC8mIbKIRgbF2OTRQGKl6NatHMwjdCGPJs8vasZ1A2tYB+dCMrjOnSn9C0cinsyGORkbYil2G9bE9ep5k1oaVsGDwpqpqyDp6UsDTEb1G3otVjI3rr2ltVZWDBsycoBIw/dJj1r1bVmP76ZU8iasRcKmiQyTGG3jHN5G1EjyFEhHC5cKQ87DkzHAz5gV9HuPnfF9JJgih3VhIx+7ECWI8ycYpi0tby9J7CDRGnzFVyfTPjTn2S1TL3U2pCe7HENIzVC2hubgssUZgtFI3kYjO3Qc6MJJsZ1NdCy8K7CNFaSGN2PeeSQEr+tWoOHyG2R47o3gUd+KNm28PDP5VNzwqyl1PC1zMTpAIwAfIeNEufiW7tEeO1tYV0DcNuf/flVJNx6DFR9j/7Rt5T2PEuGNiPclcqF9aVvm4FJdd647USACOGHU0mfA8hURJeJccuY/wBo3P7ssP3UY0qBV3inBrOxtorrh0WhxlWZRv65rNZqVFcFq6ZP1wL8Ue74bNHb8NiisEZQ7SbSStnxPIe1LGOR5O0u55rlzyMrkj8q1JklkDu7McY7xphF2xWKy+cjVCqKDQrywPrVa1OKmRjGKbjlC4rJJZNKL1rMEYeFWre+UIBkfnXIJcb7ZpuG6K97IA8WrFZW85RKypSLN9dZOGOM1DuLjzrLu4LjUzDywamzSk8jT0QxyNXDajaefzpKWbmPGsdmY90E+QrZOHXs26xaAesgwK2wkhnEywvikyxSaXiY6SCOWaucTurbhahJdRLbrGvWo8ZsOEzCW5kFxcJusUY7oNT7u8mv7o3NwAD91R0FWrbTyyTz6DXl21/IrvEsca8lxk0EKi/KMUPUa8107sbO2fQ+vyrzVQdVZqpchwFLUM14WrXNDcdg9NaVtmtTQ3HbTw5r0ORWpNeGlbClgL21ZS+aypcDbmI8ERuL3Zhu5pOzUZwhxmt5I1t7h4IhhFfHnWVlexHs8qXR2HwtYW9xaJNOmtiTjVyX0qrLKy8UWzQBYypyQN6yspH7NMOiXxi0g4ZE9zaxr23JXYZ0+Y865ZIwtuHyWeUl3Zjkk1lZSXN4BFLcOcMOLtcV0PEZnPDmjGAp8KysrHL9TRAhIBRxyrKylY6CJRMnIr2sqbKINGTimgMRBgTvtisrKz2HM0u4ViYKpJBAJzTfC+GwXI7WYu2T8urasrKSXEQP9QvEGFgjC1jRMDw51xlxxO8vZ2SadgvgpxXlZW3S8xISbNUUJq09Otb1lZVZdlI9GVleVlAJle15WVxx6a8NeVlA4yvDXtZQONTWprKylYTSsrKykOP/2Q=="},
{name: "Navagio Beach", img: "data:image/jpeg;base64,/9j/4AAQSkZJRgABAQAAAQABAAD/2wCEAAkGBwgHBgkIBwgKCgkLDRYPDQwMDRsUFRAWIB0iIiAdHx8kKDQsJCYxJx8fLT0tMTU3Ojo6Iys/RD84QzQ5OjcBCgoKDQwNGg8PGjclHyU3Nzc3Nzc3Nzc3Nzc3Nzc3Nzc3Nzc3Nzc3Nzc3Nzc3Nzc3Nzc3Nzc3Nzc3Nzc3Nzc3N//AABEIAJQBCQMBIgACEQEDEQH/xAAbAAACAwEBAQAAAAAAAAAAAAADBAECBQAGB//EAEoQAAIBAwIDBAUJBAcGBgMAAAECAwAEERIhBTFBEyJRYTJxgZGhBhQVI0JSscHRYpLh8BYkVHKT0vEzU1VklKI0RYKDwuIHJUP/xAAbAQACAwEBAQAAAAAAAAAAAAACAwEEBQAGB//EACoRAAICAQQBAwQCAwEAAAAAAAABAgMRBBIhMVETIkEFFDJhgdEzcbEG/9oADAMBAAIRAxEAPwD0WmuAp1YQRVTAAM16NTMtxFCtVIppoxVQg3zU7gcC5TI5UEofA04RUJGWPLep34OcUxCRuyUaVYknGBXTWavGr3cfaxpl1iYgLGB9puntNarQuIyVUZ29LlS3EEeZuyRu85BEZUNpI66ep5c9htnpWV9Slu28ZLenjjJ5Pi9/NfKYbRZYo2GNSbSuvURj/wDmvi7YJ6eWdbJDw+TSyIRHhjBHsiHpkndmO/PfnsBmvT8SSHhXD5lkcLJO4yIjqmlYYwNR5nx6DI8qzLfh8UUWp1EZGSoIzpzz0g9OWT1PurAlKPKfZYUGhXicry2OWYgO5fQNtPIAjx2BGfKvJXwOVZQVnjIZWxyHMN7P0r196oMSpIQdS5J552z+fwrzVxC8c2ZBqaHbf7Uf87e6uctqSAk/cF4fHG90bqJCqTgllH2Gz3h7CRXpLBjJOZmXVbllt4BzBQYDH/1OT7MV5iwL2U7whiUcGSPI9Lbb4Ej117F1MPBIMKBowzsNicYPxwDSLp+7Pkcl7cmbfx9tHePEmPmkyOoUY2yQdvPNOyRJHcEaQY43DHH3MkfhUdkIDxEN3A8elcb97Kn8KXnmWe2gP21VQ+evdUVofTdNK6LSK9s1BpsqpkgzG472nDHzGzfhSjOcyaicljlh186tLLpOAMAkk+snNCtYzc3UcJOFZ8MfAcyfdmvY1aeNFfqS+EZtmo3S2oBxT6t1i7ytoCs6Y2Lc9jzxlaybDvQtG+frVDKPuN4++iccuGk4ko7kblDqXnhiAf401Kg7BJI0IJAZT4g749+a8xpErJ738l257YpBriVZIbWVmGsasoeTD0QfZmsWHvL2Y2j3CgjcA16b5TRDh9rwtplQHsh3AObc9/bWEkIXcDrRfR6o32OxLpkXy2VpAol7uMUXJiOVO45Gp0kdKtpHjXrFBRjtM1yy8jfypftrGz4ur5mu4zHcE9JV6fj7q8kQxRsjb7R/KvTcOifiUN1YjJbQ0sC4zlgQCAPE4Xl90Dwrzt+MyLCgIJ57cq8pOOyUofC6/k208pS8jnBGDW91IylkRF2zgEahRgEM75ZU7QDQpB0s2fQbwPgfOl+GsYY7tEkI7gBA67+NGtnV4GLKmuJxu3Mjw8/UfWORqpFPewnytppGNHjkWODsp4ziS2Oe0Q7cm+144rEljbX2va5ywLKzfEeG1emItlhSO4tj9YNdpeRnvLtuM9Qcj8+hORfQPHdImEd2kCs/jvv+GPZVeUfTntJfSFePQMJnVe8AcjbGx3+GatwwW97ZxFkZrmJwjYHNOlbPynsoZIUmBQ3GNSjTjtU2BU/tDBx1I8djWVwSARXDKsuRJjSAfSRhkH1jkfOok8VnXLHKPRW2i1s8qpLoQpcbHHPPhy8fCq/O2/3V3+8KZkiEkTWtrOMRhdbK2zHIByeR6nesrUfFf8U/rVCPPbE1aeqa3SPsQYfZqRJvgihqgAqdJavdcFU50VjkGhtHjkasVK9KqCc71KB7IEWdzVgqpjG5ooCkbipCagMDaucggbLIfRfR47ZI9VWh0R61TC4TLk9RvjPxqWwnM0hO+l5G7PtI5AFKgcz/AKVW1Vcp1NR7GVySlyY99p7Rr2UxxBYyYzIdKRRg7ysegJOw5k+0jBtZxxO5ke37QcOLE65hiS5blkjGy7bD9NjfKGyveL8WSCY/UyMJGjDYUquwLeQ3A88+ArTayWykSMLpOB5bfw/P3+XajGWwt7vBm8cGofVA6oe8RjmP4fz0rJng+riukj1Rtvt7mX9PUa2eIBlmR+RZvq8nYnqvt2rPuWe1L2MOlre70yR+KHO6nwPL3edDN88i0m5GPLEReQxWwM6xHtI3B3K+l+Y9ua9RInaWmjDFAu2rwyNvcVFZlnaC3vRbvkFE1qFweZGoe6txNSwvk51R95efipx7VU0qcXPCRYWFwwfESJ1gAUK0kIkc/tEA1myLpGB4U6BI5LORqxjA6c6WnTHXNfQvpejWnoUWuTB1t7nN7ehJ9zuRmj8NZYe2uZEJ0JoU4zgtsfhke2hOgBzv7qNfobbh/Ypq7UIXfybGR7hSfr+qVOk2LuXH9iNDW53ZfweRKCbiMrgBdBUMcdT3W/P3V6TgFv8AP5rO1ZWaOL/aY6IuCfeRj21jW8AmmkfSVTSpJ/a2z8c16vhVxFwvg9xJFGGurrA1E7Kvh79/ZXn3XZDSOVaeXwv54NebjKzDfAj8p7huJGKdWHYiZguob4wcVlnFaEOG4fLBJuxkDJkYx/O9KPEB5+qtT/zlEqqJKS+Spr5OTTXgDpLcjXGDHWmI4yfRU03Fbufs+2vQSZVhDPJlwSvZXMVwuxRuQPPYgjPqJ99J8ctfo66l1AASYlQcsK3LHmd8eQJrcms1LDtADjfT+H8+ANec+UN0LySCBTkwAhnP2iep92B4AAV5v6jHZYrP4Nah+1oBYx6rebLlHYqWfGw5/gelNIHXN7oWRUxHcwMcDB/AHGx6EEHlROFwm2RpJFVjldUZOMDB29e+aizvBbXjpHh4n7oyu0in7J+A9g9tGuKS93yNb8HpLKa1iEttITPaTDtrZsb5zuh8GB6fqK8/OBLxBAjMY4CQu+ck8/wA9nnWvY26wWzsqsbaQ6oSW8dtLeBBGx8vVQrW2RbgySNpiB1b9Tk55VSd0d+2TzgZ3FNEPPdzxGPQW0ZaGVuQPLH5Ut8m4RccR7N0bs2iIdBzQjfPnvk+2nLjiD9skWAqIf8AZrsG8/dsfbTTcMeyuVuLWN3jmXUqBc4Hh5/yDyNV9RYpJuPGSVF2RaRntPc2V4UkilVHPdVl9L1dPdQMzf2GX90VbiVwJX14brjK90ezpSnzs+MfxpKhldFOO6PB900VIGKOYm+6aoYmHMGvYbhYFk1dagQ70Uxnzqulh40WTiwjAxqIoc8wj7q4rnEhIxmq9iz7kGuSXyTl/ApM7PtjalLpH7PKsdjnA61tiFQnexmlZOx3BXnTFLKwDjDyKWUUWrUxJldtTbZzsefhz2pG8VGukiXvFT3zkHPgB/P501KY4JkJPdJOSB7ce7NTEM3Gs4bXuPDf+TXnNZoXG7dEu12KSwzE4vai4t5V3To2OYPTFK2tq81vIt1EGk1EFgcFX23GfEaT6/VXpJY0PZSBPrCNBGNgOufZS0Ni1veN9YGi1KwyceOD7sD2Vm2VWKXKHRjHk8zeL2XG0Z2HejChh552Hxp/shhIySZA+x6Y6/EfGp43EZYYbiHJaJnc45lSf/r8aYhJLKygK+ncnpjb8hWvodJKdsZNdFayai28i0ltg5pZovUa0Jsv6Ui0GQIPtJXsoyZjSghZIwsjSCLWIhqwTsSBkD30nMkzy3MU7k9TqGSd8n8cV6CKSG24P2swVkLF333IXkBWDIWjv+1Lg9oQ+eoJ3rxf1Gy3W6mUlH2x4X78mtp6YVVrnlinDuHXAsi3YOxTuOQvIg4r0Vv8m3a27Yyq2oZZT9nz+JrLjvJoomVCwDnLKDtmgtf3PJWYe2vWU0WuiMesGdO+qNjCXViI5iA2VHXlml5RHnvAbeFCd5XyWZjmh6WNW4V7VgrT1Sb4GVmjT0VrjcHpt6qW0NUiM8qLYhb1MscAr+4KwvgnOk7g755fwrM+TNpA/Ee3vVXSwZF1MFGvGQSeijqf1rQurdpCE8etBmt3VVWLCgb+HI7D8CfYKwfqmn3yyzU0l3C/YpDG8c8wZgzGTBZ/t+flnPsogigEjwCJmmVC4P8Av06jHiNxT1xGrhbjaSOQ6cDoQPz/ACpfhWXnYykLLEMC4bI0MfQbz1Y0kePrrGslGem57RelDE/0bFlbSpI9rdzAI2hmj1DMobcSc8Z2UEeIzTVzwe3gcsHaUAanLHCgZwo8c7HbzFK2NzDLHoy6NAHxq6g5z8fzq00d9JG0aO6rkykn7x3+GaxJRty5vhDt0FhIVmuOE2lw4js5SiKGCmQjKk50k8xn3U/Y/KnhMIMaQyKhYOHaTOg4GPy9ufCszh3yXuL64a4v5jHG0hyHb6xwCOXgPDzrbs7awsZ2FhawYjcZyMl9QBG58PhtSrPSaxy3+iINxe5GdxWDhfEJZLqyvWtWbLFWCsh9Q239tYvzWX/iY/wR/mr130+tvIyw4Op85iAOrbPt8R5EUl/TVPv8P/6cfrXVu+McRjwDKKk8s+vfWeAri+Oa0UIxo6WiEapJPZXrXNLsRtYmHXqoqwMR5gU2thG42LgfeNQba0jPed2I6DrUepE7axVlhP2QaFJ2ajKr8abWG1LksrAf3qKnDrd/tMB6xtXeol5J2tmHLGzqTsAfOkZI69gnCbRWDFNXkxyKtc2VpNHoESA9NIxRR1iT6OdDaPCTQlxyyPCqd6JQAg8APL+RXpn4FOWPeRUHLPOsy4s5IM5MZyfssDVtXQsEbJRFY4muiFCjbpnntj9aLdcMuplIit3YKBqblyx40MvKm0bFT5UCWSd1KtNJpJ5Z50FlCm88BxswsMXk4FfSI5Fq3dDjJwNic1nm3+bL2ckb6gMHO1ew4JAFhS6u71ueEhznIG1I8XlS/vZmSFgVGwA59MmmU3OM9rXAE61JZPLSA/doLRk862okEgCNGuxyTjeq3VpGNomBUVeWoWcFd0vGTEulkntzC2cHZcD2fhQjCDoOnSBvhhvWo0JxWhwLgcPEu3nuJjFbQ+kVGSSfZS5SprW59BqFklhHmTCoGBQXh8BXsJeA2HZs0V+y420Sx5YnryNZ/EODPYQRzPJCwkJChTvjxIp9euhJ4TEWaOXyeaMJ8M13YHwrVaHw+FDMNW1cvkqS07XRmmLTzFSI6fa38alIMb0fqrGUK9GXgQe3bGSAMDbV9qlL2PsYSoiaTG+x69B58zW8sK5BrO4lFlW7KFmKnGc8ic7/AI1l/UJZqbXZoaOHu2mVZoXsJ7KQECViwIPosP8AQe6qmBmt1mZMyxSaZkx7M+3n7KftrJokD7hoyoz6x/r76iZ1t7vXCpGtQrqd9fUbeW4z515W+P2vNkcxl/02li2HtfKGkjtY3jkVOzLLhlGcbdT8RT9nJD2c8rASLar2jBe8A2dhn8vKs51mRTFK2h2ZWGx7vl4Yp8f1fgPzaMZmmdpHCnOF5cx15+zFUNV9VtsrVUUlHrBVq0qVm/LHOK3j3KTxW6lblgGBQ7jJ06j54XNJ3UMTvOIyUit49EWBu0jc29/wAoDXMHDyFtnSfKBdSnORk9ep3NDkuIJLeWEzDtZVDEr09EY9mk1lQg4/iizJSfJycFk7J3D6zHEIs7jDk99hn1c/V4V30Q/+8X4frRY+KLGJVVwULEqV+1k5HwPwoHbwffb900Ttuz2Dhn21Vq2D0rDX5Tg/+V337qf5qv8A0jzy4Ze/9n617B1z8Ab0bBDEb0NkJ6Vl/wBID/wy896f5qn6eJ5cNux7U/zVOyXg7cjQKeVQEPTas48dfpw27PtT/NUfTcx2Xhl17XjH/wAqnEjsxNJu0AwXyPI1ZJp9GFIA8etZv0pcEZ+jLj/Ej/zUGXjM6f8Altx+8n6121snKH5lZz9ZJkeul3gj++vxrPfjj9eHT/vr+tLtx/8A5CYet1pka5fCBc4mi8EY5unuNDZExgMvqK86zTx3ws5P31qDx4qp/qLEH9sUzbNEboDTwAnHj50KTh8o72/voL8aaWMf1IhfJxS0vGxHs1mT/wC4KJbyG4ds0DYz9lq+r2HINv7aVa1lcgKpLHy50t/SEgEC0IB2/wBoKr/SCRcYs3wOnabUS9RA+pX5GF4ZctOkCp32bb116m1tY+CcIljkdZJpmIKqdq8bF8pLqKQtHbyDVz+sHWpm4hxOeyllsexjuVyFeaQsE88daVdGySw+goTr+BtLCaaUO6PGGOFB+1Rb7hZMzJLdxtoTOCcb+FfNuIWfHL4f1z5RawDkd8qB7BRuENe8IRk+lbW6VuUcz50nyJOalSsz4B3wXZ9G4XwKC4nYXdwAqqG7hzWtALDh0TLbWccsa7l3UfEtXhbP5QsFMbR24fr2cwx8aueLm47p0er5wu1TOuyx+6XBMbao9HpL++4Vfgia3UGL0Qi9PMisG9n4dJNFBE1tblV+3IE1eZyfGsDiIvJZD/XYoozyRZAPf41iz8KtFdEF3bCWRRq+s3J60iV1tL9kM/yRY4yjlf8AD3acNmKdoIhImcBs932Glr2wkt3BlRkBG2nlv/oK8rFwue0YIL9oY8Z7PtGUevGaYNtfPEFj4jO6jbd3amfd6mT99fH+0Ki68cZz/pm9BD9dMmhW7RMcs75O9J3PDZ2lZYGVXVslm5Fdhv8Ad68/Kl0j4kvdS41jAGTEc+2noLfikpCvcFeWG7POnBzy61W+o1S1deV7cZ7x/Y7TXOFmF8i0/FLRpJYoXjyo9KQFmlyMcuhGD8KBakyWsMSXDIwjZNGSVAzg5PsJ8MMKDJwyOWd9YZ1DB2ldQpB5jAHtNYfyh4nLZ6ITP/WUQKkQGsquScbbDpvvzNefqpivbE17KMLg9MeHW8sVwvzhOzXAbspdWGxkDHLNXt7CWO30SJ/WigAkdSSwOwPrPsryNjxKGAoL+F0kYhhIVYkeA2G9ejbinBJrjXdzTwXEz91njZAg26cxipvnbF8LKEU0zWVJncJil4dKqG7gRmONPZmRk8NvEU123/O3P+GP1pyW2d1WO0jabsxmO5BUiXzz/GmdF5/wyP4frWe3Y+cESotk8rB61Jl+43ltzozSBV3Q7+I/jWQOKNjA3HkhrjxOcY0En4Y+Fe3cWZu5GwkysuVQkf3as0mF9D3jFecPGrnJBl28AuasOJ3Tjz59wHP4Vzg0cpI3iTneL4irxatQAiPwrzUl3xAnV9YB4t0oBuuKM+lXJJ6M6qP412z9k7j2uZCgxFjHPvAUrcGQ8o1NeaK8aYlg7YxjAI295oE9lxSfAuJnX+9L+lCq1n8iXP8AR6CWM82EY9tJMqhirNEM/tCstuEzFBqu5D/dbP40P6EY79u+fMUxbV2xTy/g1sRA41x/vCqyJC2AXTfzpOLhJUbySH1UT6LTOWkc+2gd0FxklJ+BpLa10bzINvvYNZ09havKfrS3q3/KnoLBFUgM489qqLMqxIbOfGg+4SfDDcZNdCJ4XbDcyEddyaD9FW5GQ0hHrxWwluQSdK7joeVcbc430nHgaU9Zz2cqrH8GOeGWasO8zb+ZrWtbbhqWjL2a7n7h2q6RBTkYHiadtkJibZR5sgIpF2r3LsdXp7GYzWVq4Y9muGO2FzVJLGyOxhGf7grWZQowVXPjUMoIAxv5GgWqfBL0czE+hLCU9+Hcb7DaifQnDcKqwKGPINWuirq3ouI897DY5b8qa9XIJaWS7MJ+B2Kt/wCEU48KgcIsgNrSL3Vts8ecCOUDxK7VRTGQP0x+ND9w32iftn5M2Phtqo2tYgfHTmm4kWBcQxKg8FHOm49DHAHuq+nwWu9WMuWMjTOIqJmHNR7RVnYTRPHIA0bDBUbZpns+WRip7INt5eFLtvrhHI6uqblg+fNwW8jublUZ5YNX1TSMVOPA+qlz8n5jJJMtqvbn0W1KT+NfRRaxRhmdolPPDHG1Cu5+GWSq8zq5ONokLn3CvOeva3lGp6cUsNnzQ/IXidzITLKE33lkzn2AfqKJc/8A454jPKJReB5gPTmkbv45dGx0r6jbNHImuHCKu2ZAd/UMVoCS2Rdnc930wSDmmw1V/kCVUPB8L4l8h+PcHia8RTG++RBIwOCdsEc+h3xWV2Pyj8bj/qWr75eTQyd542kcLpDk9PVWd2Nr/ZR8P0qz97x1kFabPOSUhg6At6hUzdhCmTE4A8X5+6ivLAi99Vz0zQdQkOxIX9kbfz7a9Osvlnn3BC6T2zejbMu/Mr/GtNBCyqMMxx1H6VFrYq/eOl/7wIPxNNdgAO8FA8VFJttx0FGpsEsUbbiJSPA86ILbG6afUWxip0Y3GjHjn8hVVXBOHBHmun44qtK5j1RkJ2MpXUZHXBxhRqzQZFYb9oSf2gBRV7PkS2cZxk6RVJHUHOnJ8WwoHs3NL9XyH9uLaXzksD/PjXdn1Y4o2uXmvLyGkfGql2zuM+ZO1Q7w1pkR2e2eYqCo67eyiBhzwBXE+IIH41XlaOjp0img6crnPligurDdwR7aOHIyoH8++qklhuF99Jc8/I1VLwLkKNyGx5VOD1onIct6lgTzQUlz/Y2NaBqD4mrx5J3bA9VcqEbk4Hqq+kr1Knypbsx0GqyjAas5A9YqC69AT51YISd1z66v6AyUyPCuV8kwnWikQDknkemaIwhHpzxrt9psCh9rHuTCWwPCsu9vYFUK1tjvfdbNWqZ2TfQqcIRRqLNaEY+cxexqlXsxuJ4yPWK8/Lf2QYZgRSOa7gn4bUa3veHzSBGtsDGdSzDANWnVN/DE7oG8r2eCe2QeDahiqyXNsNAjuEAY8ypb8K88WtiW7rsuThlZcn3kZo8ps4rRGga6Zifs9mNO3LTuT6wa56dKLymR6vPA9dcTuIpVituxlY8xgjFRFf30wPbWgGnmUbelOFXFre3LATaCBnLqdz16CtCaWNHUQSCVM8ywHwG/wqt9vCxflwN9SUfgC902QZbfLAYDeVQ3ElHpWozjGdWPyq8qpKmpoAAd8iRcD1/6ClRDaTApGkbFRk9mx2/KlP6fF9Mn7hhTxsDlaH/EH6VVuMRMMm3I8g9Ul4bZrbieaQIh5DGomkZorGKLtIpj/dKHPupb0LXZ33DfQzLxW2I79vL7GoP0pZ/2af31ngpIuoQS5PLCD9ajSP7Pcfuj9aW6YJ4J9aT+TUjlw2pIyx6OSRWlw/DNqkZNXtLfnWHb2rzSay5cZrftoTCAFXYjnXqdRbtWEZNdWR7WxXOeXjttXLMpUMoA9ZyKXwC4yzyP1omGB7wCjwHOsyVnJcjWksBSC3eBz+yDtUlScEKSfANyqqOQMKuPAtUjLbYDDr4UqVsV2xirfg4v3SNZJ/ZXNBBY8s+pTijCJRsiIpPgSaq8RRdIG/7P50h2J9MaoNfBQ6Tz05HmSasu/Pn4Ac6ns2jGp+75VbR3e1PI7LS5WyXQcYIqrZ3xgeyuwpBwDt1NWVeaAc6uEbAQDIHOkuyQxQQPYAFVCnHuqMZGQ246UVkwQcYxUFQRqXnQObYShgGyghTnfNTo25VbGQCBv1oqpy1csULbC4ABM88+2rKpB7uB66YEf7W1WCqdwOVSlJ9HZQBYnzn0s9KJGm5LDJHTHKrGQHltUM+nmffRYeeWQXGOgqOwWX7GrHOg/OU3xlT4kbGh/PtHM7+Gk4Pwp0WA0HlSGPJaJAR4qO9S7WVjP3ns07x6rUvPFIupiyldzq6ZosVxGoIRlYDorZp0ZTx2Lai+xe34Bw7vKtuqEcnUcqlvk7bZ1RKhxjOgAgeY2yKc+dwIhJQYPPbNSlxE0Za3uQr45aSKs1XT6Yida7MO/wDk1w/WDC7xufTDk7+3akm+TLRBmR0Zc7A52+Jrb+fm5YJOoLDbPT2CpmvWgGBbu6+KEfnQu+WXgJVrBgy8Hn0ABLYeLDV3vhQ/oGSVCQ6KygsVVj3/ACAxWw3GUC/WWVwMfsg/gTQF4/ZGVV7KVDnmVIP4VHq2eDnXHyYZsJ+x0Ksmj7vaD8CNqhbe5VMKwXHUyL+temvuJ8IkuY1IALIQQ2xJ28vXSry8HY40D4Vmaqy6Nm2zkOEISjlGEvzvBBnHsdf1rs3n+/8A+9a1ZDwTP+xYHxFU/wD0n3JPcar78/Bzq/Y9awiJAqBVx9o9aMWQek2o+HSloo5nPeGPzplbbAyx38Aa3rdQ2KhUgizaR4DyFWLE8tvOoijTngbeNXLgbpnbrVCdtknhMsxhFckpGfWTyJ5UVVyAHJA8F2oQd3GXJVfE9aMqO8Bde7EDjUaXt5/YfRGuNCQBkiuWX0suDn0dsYq3YIkWpixPntmr9mme+cDGdhqo9sn0RuihRzrYEktR4ifQIG52qmoKzaUwB96iWxaQMxx3aS4vIzPBPZsrHUceVcO6eec0V2Zj6Oc0Nkw3nUemyEwc0ZkZDnSF3zRkCFtsZ8RQ2LZxVgQmPE+FTsJCacSZHUYoZUqxZTnxzRE0tkFtPiT+Qqxx3sbnng0W3gDJXtMqMeqp1BBsaARoIYMCxPo4ozoGi9Eh88xviu2+DngqyIzA8j4+dcYCx72DvsR0qqllGDs3nR5F7RVKn19KJJ4IbwLvHKrdomrAOynFdIhd17rFuoyMmmWmeNFRcY8xmoSRRNqZGUn2imRePkF5YpLCpOpC8eRgZOc1YWsZCmDSr8iR18jTLpCSXDE4bOCeVAmMcEckkcR7mNWOgJ5++mqST4BfKFzFCshHYJkc161cLaoHZYyhXcgjNdFLMw1nvbYGsDNSnayTqjRMqk5ONqlWNvEUQ4ce4Q+bRT5V1BwxJaPIJqG4fHkmMyrk7DJwK3btorHsClvHmVsE6sdM0tc8RcsOySFAPLUTRSio/lLkiLculwYy2TtIscU82pjjBanYuHi0kLXN3GdO+hhlj7Kt89vWcmGMgnmcAUo1rdyFmcqC3M5JJpVdkU3jsOUJP9IW4rPb3NyA1oBAm+TGNRPkeYFZs8HD/SjhIB9f5mtX6Glb0pNP944oEljw+1P9au9/urVW+fqvdLsKNaisJGO0dp0U+onFV7O0+7/3GtCS6tIv/AWBlP3pFJqn0pff2CH/AA6q5OcEemUbEjb1UJhq3JOa6urTbARcjC4ycUMHPd5Dyqa6lhnOAADz360+Tpt8j/SurqKPZ0ui08a6iSM4XO5oFnM88gt2OmNjg6Rg1FdUrtEP8RmO1jlvpISWCIvTrRUsoleIAthyQR6hXV1NjFCZSYeRFQJEB3T16ihcQjW1mRYxnK5JbcmurqiSW1kp+5C8OGkPdA2ztVHOpccu9japrqrMsIJKohZFTO45moVR2pHTNdXVL7ZC6BuASCfGojc62brqIrq6hQTGZAGQhgDS0crIOhOeorq6iXYOBq3fWm6rufCouZWOBge6prqbJ+wFL3AbaMTSvrzt4Vb5SotvbWkEKhUuJ1SQjmV54+FdXUWnS2NirW96K81Gd8cs03YD6wH+eddXVNf+RB2/gxLjcEZ49CpGVFuzhc7BtSjPxqwhTAwoHqrq6p1P+Rkaf8EVc9kp0gZ86VeeRh6WPVXV1VI/kyw+gJt0cEuzt62pf5vCZNokHmBua6uqLCYnXKLb47JQM0v2z+NTXVXaQWD/2Q=="},
{name: "Playa Paraiso", img: "data:image/jpeg;base64,/9j/4AAQSkZJRgABAQAAAQABAAD/2wCEAAkGBwgHBgkIBwgKCgkLDRYPDQwMDRsUFRAWIB0iIiAdHx8kKDQsJCYxJx8fLT0tMTU3Ojo6Iys/RD84QzQ5OjcBCgoKDQwNGg8PGjclHyU3Nzc3Nzc3Nzc3Nzc3Nzc3Nzc3Nzc3Nzc3Nzc3Nzc3Nzc3Nzc3Nzc3Nzc3Nzc3Nzc3N//AABEIAJQA4gMBIgACEQEDEQH/xAAcAAACAgMBAQAAAAAAAAAAAAAEBQIDAAEGBwj/xABAEAACAQMCAwUECAQEBgMAAAABAgMABBESIQUxQRMiUWFxFDKBkQYjQlKhscHRYnKS8BUzU/EHFiRDY+FUgqL/xAAaAQACAwEBAAAAAAAAAAAAAAADBAECBQYA/8QALhEAAgIBAwMDAwQBBQAAAAAAAQIAAxEEITESE0EUIlEyUmEFI0KhkRVDcYGx/9oADAMBAAIRAxEAPwDzHBqQzVwStiOnw0zTWZWKmoyasWPyq6OLffaiqcwLgiQSLNRePSdxTe0ii+1U73h22qLvCj9s42iffw2DE6rttU17p3qzsmjfDDFXgK64615QZZmmQSqNqbQKjaSDk9aTi3OdqLtzLEvXFMVsfMVuUNwY5EO3KsMPlVli5miGd6KMfiKaBmWzlTgxcYfKoGGmOlaiYs1OZPdMXGHyqPY0wMflUTFXpYXReYqiYqYGKoGKvYlxbAOyqJjo8xVAx+VRiXFsB7PyqLRnGAMk7ADqaOMdbjxGCVA1+J6Cg39XbITmMUMpsHWcCIeKxyWyiJBmQjLeXlSF7PiDyKEkcMegruMe0XISRgXYZOByHiaXfSJ0WeJLcDs/sge8ema4y5G07hCQWPOPE7fTWpqE61BCj+5zM0D2kDNcxCR+QOeR8cUKIu3kYSx6VVO4NWwHSmZZZLpDLqz7oyOtV8QhMCO6sdB2dOfx9d6sj4ODzDWV5XIgsV/cWgCezRADqetFLxqYgGS2XHkaVQSSW/NTJbtzz+Yp6vD47m1jltSGXGQfOtGu28D9szJtrpJ/cHMmvEgVB7Ftx4itVsWjY3tlJ6941qp9dq/j+pX0em+f7lwSpCOrglSC1AeNNVNQxgthjimkdhC1uX7ZNXRc7ml6jFWocGm67F8xO7Ts3EvWzkz3VNMrS0lKaCMZHWo8PuTykPz2o97pITk4Y42INPoVAzMbUVPnpxFfEOHMmO6fWgxw58ZwR8K6FOKwSjFyp25FRyqb31quMIXGPSpwh3gP3l2InN9g8XPPxFELLrTRMu464plcXdvKp0w6T86BZ1bbAqc44lhUX5Ets5lgOzbGmgmRk7rBj68qQttURIy8mIqRbiBt0Bc5EcEgOCfzogYYZXlSATOTuSaKhvHUacjHhRBYItZorBwI1IFRIFDf4hFpzzrcUrSd8HI8BVw0W7LjkS4qKEu51tkDMO71PhVlzdoq6Vyp6nwpTxKeQQMe2Z11Du6RkfvSWu1bUVkqJqfpn6f6i0BzgfEK/wAQgZVlyohMYcktuPUVQvF7R3CRszEnoOVcZc3UskksW6CRgCAOXp60fws2NtKJr2c9oPciQFj8cVmaP9QvICuf+5u639J065dAf+J2ZUEA1VMyxLqbxwAOpqi14taXRCIzK55B1IzRLshCsen4VtWv3a8I258/E56lO1b+8vHj5iqCNoXeeZ2j1k58f73pbdSnE13rV5RHiNV30DkKL4nN2dvJPJc60lcCNRsFA/v8KUW+YuFy3Mh3mOkZ2yAK5C9q1sPbHG2fmd3pUseod3zvgeIJaLJHdWxl3Zs4zzOaa3lsdD2+Psdpn13pOty13cwTBTiEgYFPGne5uyzAjtAEHp0FUtB6xGqWHaIMCsuGJc2bKVKsh7oxzBq+zgl4dKuvPYO2hx0z0I/vrTi3VLdSueW3riq52huYXiLjA54O61temKItqHDTnW1Ysselx7fmb0noBWULFf4iTCEjSN8c6ym/9RpiX+nXwgRCt9lincHAOIzkdnbNgjILEAVfcfRfiEEBlYRsRzRWya5ka2rOOoTtDpzxic6ExWad6KMRBIKkY55rOz8qeWyLtTKAcVPXnarOyqS2zNsBTK2mLNpxKRnpV8asRzqfsrLuRW8adqKLSOYFtMDING3jVbKR0q1n3qtmNX7sGdMJWc1GpHPhUSRyZgPU1DXYGZUabJ2kO0UA94bUN7aGRWBBGogjyHOqLuFhKrRr3Rv2nnSj2poZkUDuqST8Tmsr1lrWR46Opa+J1AY4zVkcjLkqcdDSnhc8t5KzdsAyn3PKnqxrvgb+NbNN5cZEx7tKgOCJAKzgso1Hpq23pJetdySvGHQKm76Nwvq1dCULLuByxVN3b67aK0tIhqkkAcDYf2BvWb+oWuoyx2PiaGgprJwq7zku0RpzFnSOkijHe/agY1ks7tmYOME5MR3X4cqZrABFLcTDEXblR16ECioxHG8NywBQgrIPz/SklboYfmO2J1qfxGVjKbm2jldkkJGzryP7VHidzFDbss8xUMPdHNvKhuHFba7eLWoWbvrGu+k/CgeKws1674Ekq7hTuFXHWtWzVHs4G3iZNekAuyRmAX1813HHbxowijXCjNG8Yu1XhVtadmukIMaT7uP/AHS5Tk6nXOpSA3UnyrbxjsHE0mWTbB8fCsjpG011dsGB2brHJqKqd/t8xXYcFiM1rrOGV86g35Vx6wSPMscXvNuvnT3gV57NE8FwzRMCSVf8xWnpOg2ZcbTI1fcFeKzg8xjeSizQrLJuQdDke+PPHUda5qSaS3vC6uxRjlt+eaePd8Nuv+kWQgyNlWZTpVvH48j/ALVz9+hs5WjIPgVI3U+FBsvsY9DeIavToo618/8AsHNxv7xrVDa2+7W6p0iEz+J9BWXF2QAzgKD1ptJxK0kh/wA5CSPGkp4VI53cYrT8ClzlJUx5jeuQOnrJ32nWWLWTmV3lvwy4laRioY88HGfOkc0KJKyowYZ2NNvYjBKyyxiQeIq22MEUymaBSq8tuVa1NjVDY5kPUrLOfKYbBGDWwWHWu3nm4XfRaJQgONjjBFc1e8O7AsUlSRc7DrTum13WcEYMRbT5ECXLe81RaMfeFS0kHBWpBAeYrUW0HmJtRiU6I+vOq2QeFGCFfD8a2bVumKKDAFDF/Z4OaX3ylSWZQPXenjQSLuQcClHE1eMa5DkucBB1NJ67Pb2hKFHVOeJKSl9RON8KcCgneKSVi6ED7TLzJ9K6C9sljtAzuNQAB0/ePT4Vz6RFVlOk5JwBSFTA7xixCNo24TBNMuq04iCF2KiMZX1GK6G3MyoRO6tg7Moxn4Vy/C4p7WVp0XBAGtejL4UZeTS3CSCN27mJFXHQU4NZ29gN4idN1bmPLm9itY9crZGRsOtW2lzFNIzRP3SGAPqCNvnXJ3V6slqVl1Bc6VIb3h5VfwGaeS6Cqy6EGCrfdqWc6jKvwZAXsgFZbxKO8trXsQiGPXqBx553pJKzsqi3DaQcSZbZWp3xF24hcMFb/podmPQnwHiaQ3sJgYud0J0sPA0H2dWF8QmGK5PmPeBR2KEGKeKe6+0QdzV5u44bySOWIKZA2lyMgnGKTwSuJFjjhWdT9lx3h6HwqmSWQEu3eOoh0H2fKrWv3ECiURehuqG2cfbz9oExHFkxgjYmgkijk9shc/WlS6t949autb/UZF7UIM5C45VWTEvEInGPDOeh6YpdQwJzD5DCAqCqkF8SROGjajbuWGZRdSyabgDODyOPCgRpMzLKpO5wQcb1boQJvuRsdQ5U4tnSCDEXr6jkTGu2kVJVhRX+0MbGr5XN9w8TH/Ogwkv8S/ZP6fAUtnbAwr5+FOeDxxCASs2UZezmz1B6D02PwoTtgdRhalyekREXjycN+FZTaXgciyuqqWAYgEdayp7ifMntP8T2sFl5Mw9DU/aZxtrYjzq82x+6agYCDy+dcfXf+Z1HUhmkudx2qq69QVokDg06fWwSRP4pvQ7w5x3MelVNbk8sin69WODBsiP5xCW4Zwl/dumHky7/ADqScFs5G7jgrjkH3NAtBIOpqJSYbkmmg6uecQZrYD6pTd8EkinZdwhOzEUvm4fLGd9LDOAVNORLcINnz5YzUGu5MHVCrHpgU9XaRwYMpt7orewu4oO1Kd3OPOh9EvhTu4uneLuiTV1DDagDLL/p/hTlVx8xeytfEEZXAJK4x40h4gzzSyMrbINmz+FPL8Sywt3xEgGXfrXM8QhnsomKTSd8j3+ZpTW3M7BQdpWtAu8XXOueUqzlYtmyTtvV1hw57jQCvuuVY8sb86TSyTfbc6c6d/Cu1+i6NfgxwsryNhsN3SSNjsf/AK1eisdQBlLHyDiBcVtGR9cOcMu4XxpJd28kKPpkJKjvEDGM+dddxOWC0vWspwwmxsAM5PQDzzS67t1MKRHGRsc+OcD86FqXVLMrxPVJ1rgzjlfsGRGjwG3D8yPKnH0ft2M4cOAuGJJ8D4H5ihZ4gt3KCgcKcYPLI9KZ8PuuzijicGIZ73XUP7xRltVfcYs9RPtEYXaRxQIBoCBtWhduVIL1EaQZI7KYkM3QHPP50fxWeVGdmVmVx3dPImuejnZ0ZWyUibBB8/8AahIWdjZLsQihIVZPNBcLbyJgKCmthjRg4O9XzRB1eXQqx+6vmPEeVU3qNNBb3QbGxBGcnK7Zx5j8qlPftgRPGiIVC9zkNtz8ulXK54g8gbHiEWvDuzjE0i90+759fyoOSJQ0cznJl3GfnT57yO54ZHpj0EREac8ttxSi6MclhG0eNUEhVvPH+1CrZiSTDlVA2gq28cj96QKdXI+P6VXMpRTI6FVO2cbVKKMy32qMA698HlnwoziySC1EUgB0yZAHILjyoxbDARbp2iSWLtItWO6DgU3UpbcLREP1jkk+Qxt+tV3ls/skE0SkrIe8oG49flVNyo9hQnIds56YFST1gSi+zeFRfSC8hiSJXyqKFBIznFapHlxtpb5Vur9pPie77/M+u5G4W3NUJ8OVDrHwmeQR4KMeW9XtYwH/ALI/Ohn4TBzCkHyFci2qfq9yD/EYUp9xhQ4Hbc0d/mDWm4Hbscszn5Cp2Si0jChpCPBt6vaUuNmI+FPpbpiueneDL2g7NBTwOxVcsGx/MaivBbBxlGf4PRavgjLkjwqRmTpgUZLqviR3bR/IwFuAWXjJ/VW14Pbx+5v/ADKp/SjPaF8ag1yvjRhqUHE912nkykcPQc1hI8DCK09hbNzgj/pFbebJBEjDyBqhruVW95StMV69fIkdp24MpvOFWcqoZIkEURLsioMNgda8747wG6mElzJCQMMcdF1b4+ANejm98hQt/MlxbPCFUh9iDttQtSVuPUDG9N3KtjvPn6e2XtmVM7OB65/3rv8A6P2r2V5DYX9ukhty8KS4P2k1KCfhjPnQl99HyOM3LjAhjmyWH2VbvA48AdvhXV31x7Zwi4cQhL6FkZkU764yGAz4EDY+DCrJY22IexBnaeY/SaXs+KdphCY3PZ9mrBcA74BOefnzpxc2krWMF8EgMTDuPFq0t1zvyzyxvypL9I1Es63FoFRWzJGqLsBnujHjzPxruLDitrwngEC8XZFY74ZtYY4zt4Zx1qSpdPzKD2PPPL2KW0vgkqae0zq8QeYzVnsy3Mi/WscEHslOWz+gqXEL2xnvGkgLFHLFVbHLlzBPLb5VlrerZrraIaJd8A7nflnwNebqC4xvPe1jmXcREkNpGSoDPkqi74x1zSN8Gxu4VjPaaBIrbb4YZ/M05kup72xkl2HvFduQ6fr8qTwqy31xEGypgf8ABf3q1AIBzKWrngQWxuDKksLZDuupB5r3vxGofGsdmnTtWbYHTgdT/e1VwRt2yMnMNketXS2DyORDIsaHcA+B6U3sTtE+lumUNczMkbLqCs8m3Pbu8qImYQ2MpBUgyRnY9cNW4rOWOJUE0R0sSDjxq64tu0tJO1MWZJua7DIU/vUkDMkA4JkLSSaS3e4tiS8ZxpIzkUZEwukJ0GJh78TnZvMVdaWjWfDViQKXI7xAyWPlQdxjulgVlRs55b0qXDE4lsECELcdncpCrEZXTik3FpC0zxHUVU6R5Y50c0kM03aSKyFSD3d6FuIk1+0KDIGJJBGMUSsAHMG4JEtjmxGo9nj2A6VuoC6AAHYrt5VlXyfiUn0BN9Kr9FJXh8ZI6CTnSaf/AIltC5jksGVhzBR8/lTm7ZSCFZc+RpQeE2M8mudC79Sck1y9Jr/3Bma/aqIyBiDn/ieCO7Zt8I3/AGqdr/xGlu51hjssM3Vw6j4kiiv8G4Wq6uwQeq4/OrLKxsIJe0hiCt0YLTGNORsh/wAyvbT8S8/SHi+M+w24Hm7VX/zBxk8rCD5t+1HvcAJjJz4aTg/IVH2nfln44/OoVVP8ZX2/bAG4/wAa/wDg2/zf9qHn+kPG1xiwhOf5/wBqaG6GNsfDehZrteWtWP8AMMj8aaSpPtkZWKH+kvH84HD7fflkyb//AJrf/MPHiMHh9uB6v+1GzTfbG/hQ0lwCCdYX1GP1pyuhD/GUa0LxBLj6ScaXY2cK+YLUsuPpRxaE/XdkmTtludGXjQ3Hdm0v4cj+RpHfcFtpzlZJ09Hz+dM9lANlg11OTJXHH+ISydtG8RkClGReTjz/AL60DLfcVK79uAFCHs5GBYdMkeFDjhns031dwxb/AMmDVwjug+YrsAnnhMDPLlVOn4jHcXkxfcRXgu4kj1oXwxBGQB4Z6VK64ZxO6m7zqY1PcUyDbxq173iNvJpN0H9UFWrxLiqqGURMP5BVgHHAlS1Z5MBP0fukQqAAWG31owK2eH3j4WURuoUL764AzTSLjs6kC5hUeap/7oiT6Q2yRkiIsw6BOdUZn8iXC1+DE0KXvYezyRoseSAoPTJJz8TtQwGiS7l7NgChWPunJLHf8AfnTn/mgfasZAP4TVsP0ihmYA2jg8ySRUb5zieIXGMzkJYp4QwFvIwB0hvPFFJaytZzLI2HRdQyeWTy867SC+gnXXoCb8n2q7tIjzSMj1qe7+JApG+88xjsLqdu4kh1HGd8etF3VmzQx20TkrFl5JSDgsfAcz4V6CBbON4V26YzWCKBWJ9nUfKrnUb8QfpBjGZwLDiBhht0dsR40SKh2GOtGxGd4W9st9bKNmVc6vTzrssW4/7IHwrai0PKNdv4aE1oPiWXTAb5nCTDA0kNq0Zx4VQIZBa9uI9WX09njceor0ApZsdkQkfwisEFt91BnfOkVItAHE8aJ5uzz6jiyfGfA1lej9hafw/0Csq3fH2wfpj907O5lwp3kGBy0YA+ZodLlSCFJY+WP0rc1nNnvdmuOeef61WptYh9dcw7dACTn41gog8RktgS72ghMO5UeBcD9KrS6AyVYOBz31fgK01/FoIgDuRyyQo/eh1vLhzkdguPDU2PngUytRMH1wtrltIaKGU5/wBJB+WTUQbqQjET+jkg/ICh5p7lwM3WgDfcBf3/ADpfNLauCt7xJ5B9wOW/cU3XTF3txGs8qwt9dLCjjmrDf8WoCbiOpsRyJj+bP5Uve74VbjTBHLKB1MhX8qr/AMWBP1FrGg/i1NTyUfiKvqIzNwWICKXJ/gcih5ZJUzr7NFHoPwzS+W8vpVOFOk9QAooMyXhO2dvGSm66opZfmM3mGcmVd+mMULcygIe+GPhjlQEguWzrcAHmATQ1xGRGdUi/E1W727Qun928pmuczYyBRUU4O2pj6YpELns5wNatvyFNYbkMBlR8RQakjV1kqvMmati5MceBHk+OavfSfKhJnC7YA8zR7UKrtAU3dTQS4uHkBCoRQjSSKd6OJRjv+db9mV8HYDxND6AVl+6eqQQgxA9fSh1ZtbBFz86Okt4kj2nAPkaXvqR/q5g3rzpRBvGC+0rEl0GP1bY9a210cYkaQEeGaoSW5LkRgN5mru0uE/zYiw8QKc6BiK91geZal3KfcuZvTJoy34heKO7PJ86VNdxE/wCUc/xCtwXILjGoY86oUWXW5weY0fjF7gjtW2PPb9qivGrw51XDAjlstAPINRwPXetFARkEHyxV+yvTB+qsDkZjROKTnVrmeQH7OrH5VWb913UTA+KzHb50pcqDhwy1iui+65xQxUIX1LfMZ/4nP9+4/rFbpd2kX3j/AH8a3Vu0JX1Jnps/FLiR/rFtEz9lYyzfiRWPeLGBqlOv7qRBT+VIVnvrgd19IPhGSTViQwRDN7cyM33E6+vKk1oUcQxtOIyl4rMw0rKy5+/kk/A/tVSXc7n/ADl1eAIj/Kh+5MPq1RVH3yAfkMn8arbsY2y13GB1WIHajhBjiANhzCZwJDquLiNf4RIzH5AVNIrfuhI5ZBjfuHH4gCg/a0TeBC3/AJJCF/ah5+KSL7sikeA7340ZFMC7rGbCANlgq4PLIGPXGaqe8UZ+2M7aVwPntSd+IOSdUYcnck5P4ViXYc4LKPIACmFQxZ7Iyl4iic41HyNBycULElfwSoMRjbb1oSaMn3Hx5AYphUEWZ8neTlvJ2Oc4HmKHnuGK9562tvKxwcAeOqsaziI77b+RpfUKsc0zEcQaKCJnDczz50yjVRuooNYo49kY5+FEW5ce5VKhvL2vscmFGMkAiqZIhjbn5gVd2pCjvADzqqTfJ17daPqEZl2i2luUMZUqL4jNW9krc9OPMUDKzA5Rsjp0qCvcPsGOKGtW28K93u2h8iWUMZwiO9LZJISxIgZT4jailmW3RdceSefjUWv7bqrY675pRa8MY2bcgYgUSRythdSnxxipG1uFJMc5YfdJojs4Z3LxMVHgtR03GSInbb7y02F2ihf3SrtnjAFxAT5jetx3NiT3o9HwqXb3EJKzKj5+7zrTXFtIcTwYP8v60EiGVzK5ktJTmJyo8KEaMqcKzEeIJomSa31dzHquams1uANcmPDK4plFBXBitjsHJEBMLvsNVVvAybbfGmwkt2H1cgNTWNGG+9eNXxKjUEciJOyP3U/qFZTr2ZP9M/0isr3aMn1InVT3Mwt43ZtbMcHUP2pZNckSYEUQAH3KysrNqAxNK0nOJtNUtm0rOwOfdU4FCiVlbugD4VlZTi/TM9vqEvhHbKWfn5UvvQFLAAbVlZRE4nn5gDSOdidvCooxU5U49KysosG0Y2sjOmWOSKKB69a3WUVYs/MomlYA4xQwXtFZnZj8aysoVsYoltuiqo0jBPWj4owFUhmBJ3waysoVXMJeYHdk5oZcluZrKymrOIpVNlFMuDv60XZqM8vwrVZUrxIs5jCWGOSPvrnFBzwxBQoRd/Kt1lKn6o0v0RfdW6pKFVnxz50F7RJHKYwe7jkaysq3iWWRBw2obHyNQmZlOQx36E1lZS55jA4kmbs1yACSOtVrKzbkKfhWVlFWBfiUv75q5XdFGl2HxrVZVpSWdvN/rP8AOt1lZUZMnpHxP//Z"},
{name: "Anse Source d'Argent", img: "https://encrypted-tbn0.gstatic.com/images?q=tbn:ANd9GcSEz7gsVYG6vB09H-xWEP-Ik1zqRJ9YqciFxhY2sCPLaUj_I7xZ2f8jOP2Hug&s"},
{name: "Seven Mile Beach", img: "https://encrypted-tbn0.gstatic.com/images?q=tbn:ANd9GcQGQ1xnjMSpomh7AMhkjD-3D__ZL9FQdoYDi8Qt65I30M7b9i9_WF6GhrgEuw&s"},
{name: "Bora Bora", img: "https://encrypted-tbn0.gstatic.com/images?q=tbn:ANd9GcRewsMBu7zcxcYxuGdGrYA0VDSoN6pUXTbSTA7VewTFhllOYSa44wkq_Hs21w&s"},
{name: "Lanikai Beach", img: "https://encrypted-tbn0.gstatic.com/images?q=tbn:ANd9GcQYTn3ms33h98I_hGc8j-hJGW8V_pkI00Uvco0pjT2is6uOxoi7u8DYeOu6Jg&s"},
{name: "Pink Sands Beach", img: "https://encrypted-tbn0.gstatic.com/images?q=tbn:ANd9GcTqbKPTx0Y6ibIZwbA2gX_AYShIDc6r57Tzw-Yp0j4F8uv86ogw1q5mPS7Wmw&s"}
];
const ul = document.querySelector('ul');
ul.querySelectorAll('li').forEach((li, index) => {
const img = document.createElement('img');
img.src = beachData[index].img;
img.alt = beachData[index].name;
img.style.width = '100%';
img.style.borderRadius = '8px';
img.style.marginBottom = '10px';
img.addEventListener('click', () => {
openLightbox(img.src);
});
li.prepend(img);
});
// Lightbox functionality
const lightbox = document.createElement('div');
lightbox.classList.add('lightbox');
lightbox.id = 'lightbox';
const lightboxImg = document.createElement('img');
lightbox.appendChild(lightboxImg);
const closeBtn = document.createElement('button');
closeBtn.textContent = '×';
closeBtn.classList.add('close');
closeBtn.addEventListener('click', closeLightbox);
lightbox.appendChild(closeBtn);
document.body.appendChild(lightbox);
function openLightbox(src) {
lightboxImg.src = src;
lightbox.style.display = 'flex';
}
function closeLightbox() {
lightbox.style.display = 'none';
}
});
```
## Journey
<!-- Having a fun while implementating styling to this code -->
<!-- Team Submissions: saurabh_patil_82002f75442 -->
<!-- Thanks for participating! --> | saurabh_patil_82002f75442 |
1,874,954 | Debugging 101: Conquering Code Critters | Introduction: Ever written code that seems to have a mind of its own? You put it... | 0 | 2024-06-03T05:29:45 | https://dev.to/manavcodaty/debugging-101-conquering-code-critters-3ebl | debugging, programming | ## Introduction:
---
Ever written code that seems to have a mind of its own? You put it together carefully, but it just won't run the way you expect. Don't worry, even the best programmers face these challenges. That's where debugging comes in!
Debugging is the process of finding and fixing errors, or bugs, in your code. It's a skill that takes time and practice, but anyone can learn the basics. Here's a look at some common mistakes to watch out for and how to track down those pesky bugs:
## **Common Mistakes:**
---
- **Syntax Errors:** These are typos or mistakes in the grammar of your code. They're often the easiest to fix, but they can be frustrating because they can prevent your code from even running.
- **Logic Errors:** These errors happen when your code runs without crashing, but it produces the wrong result. These can be trickier to find because the code might look fine at first glance.
- **Off-by-one Errors:** These are mistakes where you accidentally use one more (or one less) than the intended value.They can be tricky to spot because they can lead to subtle bugs.
## **How to Find the Bugs:**
---
- **Read the Error Messages:** Error messages aren't always perfect, but they can often give you a good clue about what's going wrong and where to look in your code.
- **Test Early and Often:** The sooner you can find a bug, the easier it will be to fix. Break your code down into smaller pieces and test them individually as you go.
- **Print Statements:** These are temporary lines of code that you can use to output the values of variables at different points in your program. This can help you see if the values are what you expect them to be.
- **Rubber Duck Debugging:** Sometimes just explaining your code to someone else, even if it's an inanimate object like a rubber duck, can help you spot the problem.
- **Take a Break:** If you're stuck, take a break and come back to the problem later with fresh eyes. You might see something you missed before.
## **Remember:**
---
Debugging is a skill that takes practice. Don't get discouraged if you don't find the bug right away. Just keep at it, and you'll eventually track it down. There are also many online resources and communities where you can get help from other programmers.
With a little perseverance, you'll be a debugging pro in no time! Happy coding! | manavcodaty |
1,874,953 | Why Hiring Laravel Developers Can Help Scale Your Business | Introduction In today's digitally driven world, businesses face the constant challenge of staying... | 0 | 2024-06-03T05:29:33 | https://dev.to/hirelaraveldevelopers/why-hiring-laravel-developers-can-help-scale-your-business-a3j | webdev, beginners, programming, opensource | <h2>Introduction</h2>
<p>In today's digitally driven world, businesses face the constant challenge of staying ahead of the competition. One effective strategy for achieving this is by leveraging the power of technology to streamline operations and enhance efficiency. Laravel, a popular PHP framework, has emerged as a valuable tool for businesses looking to scale their operations and stay competitive in the market. In this article, we'll explore why hiring Laravel developers can be a game-changer for your business and how they can help you achieve your growth objectives.</p>
<h3>What is Laravel?</h3>
<p>Laravel is an open-source PHP framework known for its elegant syntax and powerful features. It was created by Taylor Otwell in 2011 with the goal of providing a more advanced alternative to existing PHP frameworks. Since its inception, Laravel has gained widespread popularity among developers due to its simplicity, flexibility, and robust set of tools and libraries.</p>
<h3>Importance of Laravel in Business</h3>
<p>In today's fast-paced business environment, having a reliable and efficient web application is essential for success. Laravel offers several key advantages that make it an attractive choice for businesses:</p>
<ul>
<li><strong>Rapid Development</strong>: Laravel's intuitive syntax and built-in tools enable developers to build feature-rich web applications quickly and efficiently.</li>
<li><strong>Scalability</strong>: As businesses grow, their software needs evolve. Laravel's modular architecture and scalability features make it easy to adapt and expand applications as needed.</li>
<li><strong>Security</strong>: Security is a top priority for businesses, especially when dealing with sensitive data. Laravel provides built-in security features such as encryption, authentication, and authorization, helping businesses protect their valuable information.</li>
<li><strong>Community Support</strong>: Laravel has a large and active community of developers who contribute to its ongoing development and provide support through forums, tutorials, and documentation.</li>
</ul>
<h2>Types and Categories</h2>
<p>When it comes to hiring Laravel developers, businesses have several options to choose from depending on their specific needs and requirements. Here are some common types and categories of Laravel developers:</p>
<h3>Full-Stack Laravel Developers</h3>
<p>Full-stack Laravel developers have expertise in both front-end and back-end development. They are proficient in HTML, CSS, JavaScript, and other front-end technologies, as well as PHP and Laravel for back-end development. Full-stack developers are capable of handling all aspects of web application development, from designing user interfaces to implementing complex business logic.</p>
<h3>Back-End Laravel Developers</h3>
<p>Back-end Laravel developers specialize in server-side development using PHP and the Laravel framework. They are responsible for designing and implementing the core functionality of web applications, such as data processing, database management, and server integration. Back-end developers work closely with front-end developers to ensure seamless communication between the client and server sides of the application.</p>
<h3>Front-End Laravel Developers</h3>
<p>Front-end Laravel developers focus on designing and implementing the user interface of web applications using HTML, CSS, JavaScript, and other front-end technologies. They work closely with designers to translate mockups and wireframes into interactive and responsive web pages. Front-end developers collaborate with back-end developers to integrate front-end components with back-end functionality.</p>
<h2>Symptoms and Signs</h2>
<p>Identifying the need for Laravel developers is the first step towards addressing the scalability challenges faced by businesses. Here are some common symptoms and signs that indicate the need for hiring Laravel developers:</p>
<h3>Slow Performance</h3>
<p>If your web application is experiencing slow performance or frequent downtime, it may be a sign that your current development team lacks the expertise to optimize and maintain the codebase effectively. Hiring experienced Laravel developers can help identify and address performance bottlenecks, ensuring smooth and uninterrupted operation of your application.</p>
<h3>Limited Features and Functionality</h3>
<p>As your business grows, you may find that your current web application lacks the features and functionality needed to meet the evolving needs of your users. Laravel developers can help extend and enhance your application by implementing new features, integrating third-party services, and optimizing existing functionality for better performance and usability.</p>
<h3>Security Vulnerabilities</h3>
<p>Security is a major concern for businesses operating in the digital realm. If your web application is vulnerable to security threats such as SQL injection, cross-site scripting, or data breaches, it can have serious consequences for your business, including loss of sensitive data and damage to your reputation. Laravel developers can help identify and patch security vulnerabilities, implement best practices for secure coding, and fortify your application against cyber threats.</p>
<h2>Causes and Risk Factors</h2>
<p>Several factors can contribute to the need for hiring Laravel developers to scale your business effectively. Here are some common causes and risk factors:</p>
<h3>Lack of In-House Expertise</h3>
<p>Many businesses lack the in-house expertise required to develop and maintain complex web applications using Laravel. Outsourcing the development to experienced Laravel developers can help bridge this gap and ensure the successful implementation of your project.</p>
<h3>Growing User Base</h3>
<p>As your business attracts more users and customers, your web application needs to scale to accommodate the increased traffic and demand. Laravel developers can help optimize your application's performance, scalability, and reliability to handle growing user loads without sacrificing speed or stability.</p>
<h3>Technological Obsolescence</h3>
<p>Technological advancements and innovations are constantly reshaping the digital landscape. If your web application is built on outdated or unsupported technologies, it may struggle to keep pace with changing market trends and user expectations. Hiring Laravel developers can help modernize your application and future-proof it against obsolescence.</p>
<h2>Diagnosis and Tests</h2>
<p>Once you've identified the need for hiring Laravel developers, the next step is to diagnose the specific areas where their expertise is required. Here are some diagnostic tests and assessments to consider:</p>
<h3>Code Review</h3>
<p>Conduct a comprehensive review of your web application's codebase to identify areas of inefficiency, redundancy, or poor performance. Laravel developers can help optimize and refactor the code to improve maintainability, scalability, and performance.</p>
<h3>Performance Testing</h3>
<p>Perform rigorous performance testing on your web application to identify any bottlenecks or performance issues under different load conditions. Laravel developers can analyze the test results and implement optimizations to improve the application's speed and responsiveness.</p>
<h3>Security Audit</h3>
<p>Conduct a thorough security audit of your web application to identify and address any vulnerabilities or weaknesses that could compromise the integrity and confidentiality of your data. Laravel developers can implement best practices for secure coding and deploy security measures to protect against common threats and attacks.</p>
<h2>Treatment Options</h2>
<p>Once the diagnosis is complete, it's time to explore treatment options for addressing the scalability challenges faced by your business. Here are some effective treatment options:</p>
<h3>Custom Development</h3>
<p>Hire experienced Laravel developers to build custom solutions tailored to the unique needs and requirements of your business. Custom development allows you to leverage the full power and flexibility of the Laravel framework to create scalable, robust, and feature-rich web applications that drive business growth and success.</p>
<h3>Third-Party Integration</h3>
<p>Integrate third-party services, APIs, and plugins into your web application to extend its functionality and streamline business processes. Laravel developers can help identify and integrate the most suitable third-party solutions that align with your business objectives and requirements.</p>
<h3>Performance Optimization</h3>
<p>Optimize your web application's performance by implementing caching mechanisms, database optimizations, code refactoring, and other performance tuning techniques. Laravel developers can analyze your application's performance metrics and implement optimizations to improve speed, reliability, and scalability.</p>
<h2>Preventive Measures</h2>
<p>In addition to treating scalability issues as they arise, it's important to implement preventive measures to mitigate future challenges and </p>
<p>ensure the long-term scalability of your business. Here are some preventive measures to consider:</p>
<h3>Continuous Monitoring</h3>
<p>Implement a robust monitoring and alerting system to track key performance metrics, detect anomalies, and proactively address potential issues before they escalate. Laravel developers can set up monitoring tools and dashboards to provide real-time insights into the health and performance of your web application.</p>
<h3>Regular Maintenance</h3>
<p>Schedule regular maintenance and updates for your web application to keep it running smoothly and securely. Laravel developers can perform routine tasks such as software updates, security patches, and performance optimizations to ensure that your application remains up-to-date and resilient against emerging threats and vulnerabilities.</p>
<h3>Scalable Architecture</h3>
<p>Design your web application with scalability in mind from the outset. Adopt a modular architecture that allows components to scale independently and horizontally as demand increases. Laravel developers can help architect and implement scalable solutions that accommodate future growth and expansion without requiring major rewrites or redesigns.</p>
<h2>Personal Stories or Case Studies</h2>
<p>To illustrate the real-world impact of hiring Laravel developers, let's explore some personal stories and case studies of businesses that have successfully scaled their operations with the help of Laravel expertise.</p>
<h3> </h3>
<h2>Expert Insights</h2>
<p>To gain further insights into the benefits of hiring Laravel developers, let's hear from industry experts and professionals who have firsthand experience with Laravel development.</p>
<h3>Expert Quote: John Smith, CTO of TechCo</h3>
<p>"Laravel has been a game-changer for our company. By hiring Laravel developers, we were able to accelerate our development process, improve the quality and performance of our applications, and stay ahead of the competition. The expertise and dedication of our Laravel developers have been instrumental in helping us achieve our business goals and drive innovation in our industry."</p>
<h2>Conclusion</h2>
<p>In conclusion, <a href="https://www.aistechnolabs.com/hire-laravel-developers/">hiring Laravel developers</a> can be a strategic investment for businesses looking to scale their operations and achieve long-term success. With their expertise in Laravel development, these professionals can help businesses build scalable, robust, and high-performing web applications that drive growth, innovation, and competitive advantage. Whether you're a startup looking to disrupt the market or an established enterprise seeking to modernize your technology stack, hiring Laravel developers can help you achieve your objectives and thrive in today's digital economy.</p> | hirelaraveldevelopers |
1,874,951 | What are needed for quantitative trading? | Summary A complete quantitative trading life cycle is more than just the trading strategy... | 0 | 2024-06-03T05:25:19 | https://dev.to/fmzquant/what-are-needed-for-quantitative-trading-197k | trading, fmzquant, cryptocurrency, strategy | ## Summary
A complete quantitative trading life cycle is more than just the trading strategy itself. It consists of at least six parts, including: strategy design, model building, backtesting tuning, simulation trading, real market trading, strategy monitoring, etc.
## Strategy Concept
First of all, to do quantitative trading must first return to the trading market, to observe the price in the market, understand the law of market volatility, and try to infer each trading logic, and finally summarize the trading strategy. There are no shortcuts here, you may need to read classic investment books, or continue to insist on trading, summing up experience in failure.
For beginners of quantitative trading, the best way to start trading strategies is to imitate. Directly use the off-the-shelf technical analysis indicators to build the strategy logic and write the rules of trading, so that you can get a simple strategy. For example: If the price is higher than the average price of the last 10 days, buy long. If the price is lower than the average price of the last 10 days, sell short. Its architecture is like this (as shown below):
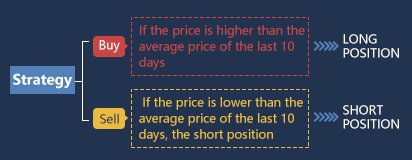
Of course, with the accumulation of strategic experience, after the formation of your own trading methods, the choice of logic will be more and more diversified, and then advanced to more systematic quantitative methods. If you can be a trader with quantitative thinking, whether in the stock or futures market, people with such ability will have a stable profitability regardless of which trading market.
## Modeling
Second, you need to master a quantitative trading tool to write trading strategies and implement your trading ideas. Commonly used software on the market is fine. But if you want to be a high-end quantitative trader, you need to learn a computer programming language. It is recommended to use Python, because it is the authoritative language of scientific computing, and provides a variety of open source analysis packages, file processing, network, Database, etc.
If your programming ability is weak, I believe this is the weakness of most beginners. It is recommended to use a relatively simple visual programming language or the M language, which can improve the interest of learning quantitative trading, and let you focus on strategy and complete strategy efficiently. As shown below: Using the M language, develop a trading strategy as described above.
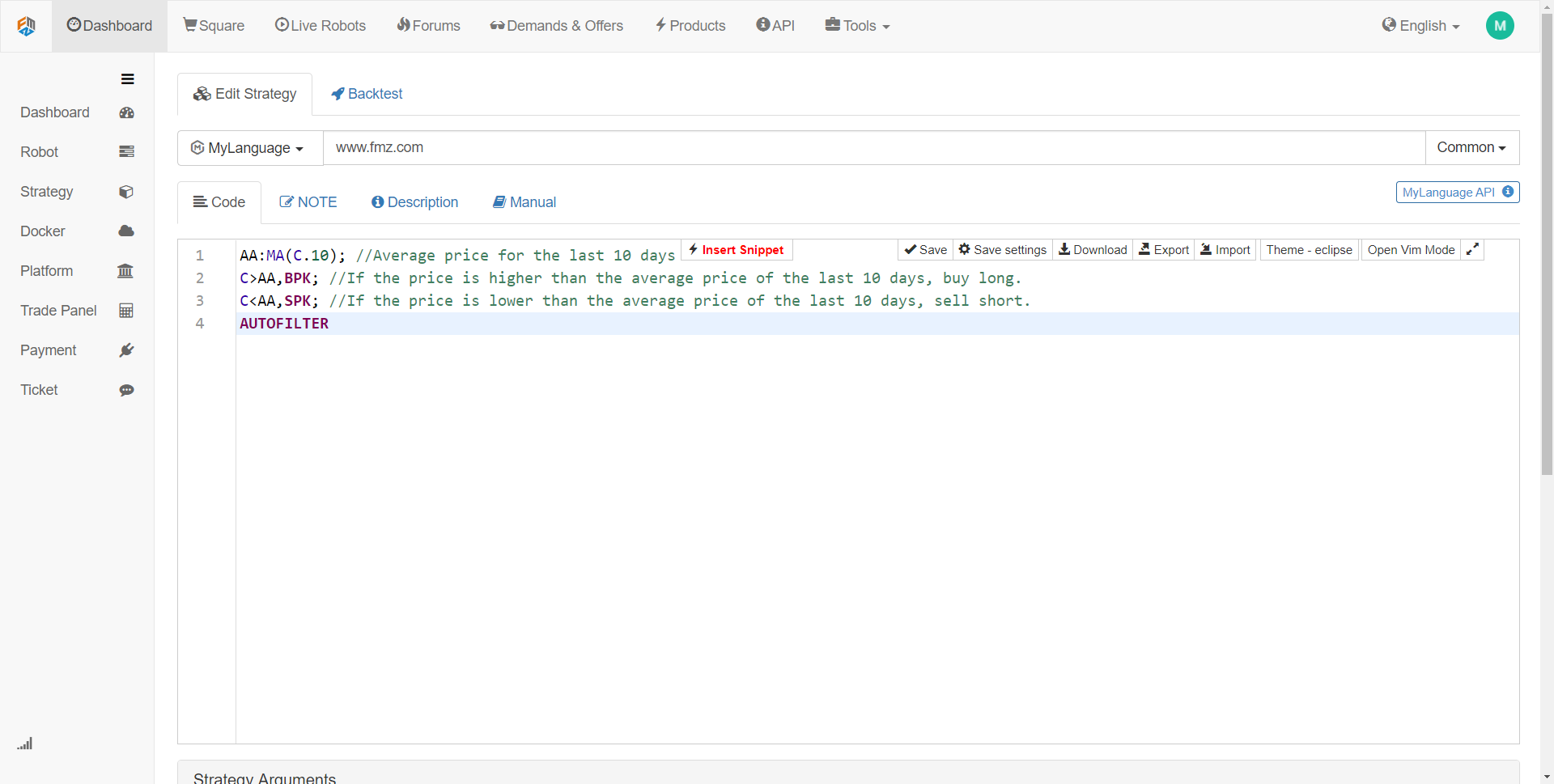
The strategy code in the above figure is a Mylanguage demonstration using the FMZ Quant tool. It integrates many function modules that can be used directly, and supports backtesting and real-time trading functions. It is a good quick start method.
## Backtesting and tuning
Then, when the strategy model is written, the next step is to backtest the strategy and filter and optimize the parameters. The strategy can be backtested with different parameters, and the Sharpe ratio, maximum retracement, and annualized income of the strategy can be observed. Through continuous debugging and modification of the strategy, a perfect quantitative trading strategy is finally obtained.
For example, we use 2017 historical data as sample data and 2018 historical data as off-sample data. First use the 2017 data to optimize several sets of well-behaved parameters, and then use these parameters to backtest the data in 2018. Under normal circumstances, the backtest results outside the sample are not as good as the backtest results in the sample. However, if the sample is very different from the results in the sample, then this strategy is almost ineffective. It is necessary to observe and analyze the reason for the strategy failure.
Assume that the strategy failure is due to off-sample data, a large loss caused by a few extreme market price movement, then you can add a fixed stop loss condition to avoid this risk; if the strategy is found to be invalid due to too many transactions, then we can Tightening the trading logic a bit and reducing the frequency of trading.
It should be noted that if the trading logic itself is wrong at the beginning, it is difficult to get a profitable strategy no matter how you modify it. At this time, you need to re-examine your own strategic thinking. In addition, in the parameter optimization, the more parameter groups available, the better, indicating that the applicability of the strategy is extensive. In the backtest, the strategy of too few transactions may be a survivor bias. If the result of the backtest is a super-profit curve, in many cases your logic is wrong.
## Simulation Trading
Next, when you get a strategy that makes the trading logic correct and makes money both inside and outside the sample, don't rush to trade on the real account. Especially for beginners, you must first run the simulation account for at least 3 months. If it is a mid-low frequency overnight strategy, you need even longer simulation trading time.
In a completely unknown simulation market in the future, the observation of strategy will behave in the simulation environment, and carefully check whether the backtest signal is consistent with the simulated trading signal, and whether the price at the time of placing the order is different from the price at the time of the transaction, if the performance is in line with the expectation, then the strategy is effective.
## Real Market Trading
Finally, after a long period of time to test the strategy, you can put the strategy into actual combat and trade. Of course, we must always be vigilant in the process of quantitative trading to guard against extreme market conditions. In the real market, the expectations of the strategy are generally discounted, and the expected 50% is qualified.
## Strategy Running Monitoring
Finally, we need to remind everyone that with the trading running, we must also observe the effectiveness of the strategy. When we find that the strategy exceeds the expected loss, we must re-evaluate the strategy. Because market characteristics are subject to change, our current strategy is primarily aimed at past market characteristics. Once the market characteristics change, the strategy model should be adjusted in time, or the strategy should be temporarily suspended.
## To sum up
In this article we describe the complete process of quantitative trading. All in all, if you are an investor with market experience, what will block you will be the computer programming language foundation, you can start with the visual programming language or the M language, exercise yourself on this platform, build a strategy, and then gradually turn to Python high-end quantitative trading.
If you are a science and engineering student or IT practitioner with strong programming skills, it will be market investment experience to block you, and don't underestimate this. As a qualified quantitative investor, two types of knowledge are indispensable.
## Next section notice
The core of the entire quantitative trading life cycle is the trading strategy. In the next section, we will elaborate on the elements of a complete trading strategy from the perspective of trading strategy structure. This will help you build your trading strategy more comprehensively and take the quantitative trading to a new level!
After-school exercises
1. Try to write the trading strategy in this section by M language.
2. What is the most important performance indicator in the quantitative trade backtest?
From: https://blog.mathquant.com/2019/04/11/1-3-what-are-needed-for-quantitative-trading.html | fmzquant |
1,874,949 | How Mobile Push Notifications Can Transform Your Business | Have you tried using mobile push notifications for your business? Like web push notifications, mobile... | 0 | 2024-06-03T05:24:26 | https://dev.to/syedbalkhi/how-mobile-push-notifications-can-transform-your-business-29mf | Have you tried using mobile push notifications for your business? Like web push notifications, mobile push notifications can help you re-engage your visitors, [increase sales](https://www.seedprod.com/best-woocommerce-plugins/), grow your followers, and boost overall conversions.
Did you know that out of 4.33 billion internet users globally, 3.7 billion were mobile users as of July 2019? This number has only grown since then. This means a significant portion of your website visitors comes from mobile devices.
Imagine the impact of [using mobile push notifications](https://www.pushengage.com/how-to-send-push-notifications/) to re-engage these visitors. Much like web app push notifications, mobile push notifications are messages sent to your customers' mobiles from your app installed on their devices.
You can use these notifications to alert users about your latest collection, upcoming sales, product updates, offers, and discounts. Users receive these notifications instantly, making message delivery more efficient and smooth.
If you're unsure how to create mobile push notifications, try using PushEngage. It lets you create engaging push notifications with just a few clicks; no coding is needed.
## Benefits of Mobile Push Notifications
Let's explore some powerful ways mobile push notifications can benefit your business.
### 1. Better Outreach
Marketing is about effectively reaching your [target audience](https://www.wpbeginner.com/beginners-guide/how-to-choose-a-target-audience-for-blogs/) and convincing them to convert. Mobile push notifications help you do this by sending the right message to the right audience in real-time.
Targeting a more specific audience makes it easier to convince them to take the desired action. This targeted approach makes achieving your [marketing goals](https://formidableforms.com/5-steps-to-set-goals-and-achieve-them/) much simpler.
### 2. Boost Engagement
Push notifications are hard to ignore. When you send out a push notification, some recipients will click on it to learn more. This action [boosts engagement](https://optinmonster.com/9-unique-popups-you-can-make-with-optinmonster-canvas-to-boost-engagement/) on your site.
Once visitors land on your site, they will likely explore more products and deals, increasing overall engagement. However, it's crucial to strike a balance. People may find notifications annoying if overused.
Be strategic and creative with your notifications. Ensure your content is engaging enough to avoid being dismissed. Limit your notifications to 3-4 per day to keep them effective.
### 3. Increase Conversions
[Conversions increase](https://funnelkit.com/woocommerce-facebook-pixel/) when people know about your business, products, and offers. Mobile push notifications allow you to promote your business and inform people about important updates.
You can notify users about [new product launches](https://wholesalesuiteplugin.com/how-to-promote-your-e-commerce-products-with-hauldrop/), limited-time offers, big sales, new collections, or anything else they need to know. When users are informed, they become interested and are more likely to convert.
By boosting conversions, mobile push notifications help you achieve your business goals, leading to more profit and [faster growth](https://trustpulse.com/growth-hacking-strategies/).
## Conclusion
Mobile push notifications are a [powerful tool](https://www.isitwp.com/headline-analyzer/) for your business. They enhance outreach, boost engagement, and increase conversions. Start using them today to see how they can transform your business.
We hope you found this article helpful. If you did, let us know in the comments below. We would love to hear from you. | syedbalkhi | |
1,874,947 | my refine project is deployed but still showing template page | Hello everyon! Anyone know how we can fix this issue. this issue is this my refine project is... | 0 | 2024-06-03T05:17:17 | https://dev.to/tectic_rg_3233e84c61e48ec/my-refine-project-is-deployed-but-still-showing-template-page-2322 | refine, netlify, render, help | Hello everyon!
Anyone know how we can fix this issue. this issue is this my refine project is deployed successfully without any trouble but when i visit that page it will show refine template which i used to create my own webApp. so how we can solve this problem. | tectic_rg_3233e84c61e48ec |
1,670,561 | Boost User Experience with HTML autocomplete Attribute for Form Inputs | Applications developed for the web will eventually run on the web and the browser vendor will always... | 0 | 2024-06-03T05:15:27 | https://dev.to/kipyegonline/boost-user-experience-with-html-autocomplete-attribute-for-form-inputs-2bkb | javascript, html, react, beginners |
Applications developed for the web will eventually run on the web and the browser vendor will always enforce its default user agent settings for HTML and CSS before being overridden by developer settings.
Have you ever tried filling out a form on a website only to have the fields instantly filled in for you by the browser? Most browser vendors have capability to save user input such as password,email and address for later use. The browser will automatically fill in saved details in form inputs the next time a user tries to fill out a form.
For example, for email addresses, the browser detects type="email" and prefills it with a saved email address. Fortunately HTML has a less known handy autofill feature to assist users auto-fill HTML forms with saved values.
**Autofill** is a form feature attribute that lets the browser suggest and automatically form fields with previously saved values as a user fills out a form. It can also disable the auto filling process.
It is the most overlooked yet versatile HTML feature that has been around for several years . When the user puts text into HTML input elements, the browser can easily save form information and attempt to autocomplete or suggest input the next time.
The autocomplete keyword can be used to add to the autofill keyword to HTML elements `<form>` and HTML input elements (`<input/>, <textarea> <select/>`).
Autocomplete can take one or more possible values referred to as tokens. There is a wide range of possible values for autocomplete attribute depending data type the user is expected to enter. It is supported by all browser vendors. It initially emanated from the Safari browser.
**Importance of autofill**
1. **Enhances websites/web app user experience** - A user avoids repetitions and simplifies filling of form fields. When a user types input, the form automatically fills in the input fields making data entry easier and faster.
2. **Formatting** - Autofill ensures a form field always hints at the intended input type. An email field ,for example, will always hint an email address while a telephone field will always hint digit values.
3. **It complements the type attribute** – If the type is not present on the HTML input, the browser will infer input type by using the value of autocomplete attribute. It will format digits where autofill is telephone or one-time-code.
On Visual studio code editor, you can see available autofill values by pressing ctrl/cmd + space bar on the autocomplete value field.
**NB:** React , JavaScript UI library, uses the camel case as autoComplete (and not autocomplete) attribute when rendering in react elements.
Let's examine some frequently used autofill values.
**1. on/off**
The autofill feature initially started with two values: on and off. By default, the autocomplete attribute is set to on which means that the browser is free to retain values submitted and to autofill them for the user.
The autofill feature initially started with two values: on and off. By default, the autocomplete attribute is set to on which means that the browser is free to retain values submitted and to autofill them for the user.
```html
<section>
<!-- Autocomplete off, will not autofill values to form fields-->
<form autocomplete="off">
<div>
<label for="username">Username</label>
<input type="" id="username" />
</div>
<!-- new password-->
<div>
<label for="password">Password</label>
<input type="password" id="password" />
</div>
<button>Login</button>
</form>
</section>
```
**2. Email**
The email value instructs the browser that an input field expects a valid email address. A browser will detect the type="email" and suggest stored email addresses. Additionally, if the required attribute is present on the type="email", the browser will require a valid email.
```html
<div>
<label for="email">Email</label>
<input type="email" id="email" autocomplete="email" />
</div>
```
**3. Password: new-password and current-password**
The password value provides a formatted password with asterisks to indicate the password entry field. There are two possible values; **new-password** when a user wants to enter a new password and **current-password** for existing password.
The browser will recommend saved passwords when the value is current-password and it will generate a new password when the value is new-password.
```html
<!-- current password-->
<div>
<label for="current-password">Password</label>
<input type="password" id="current-password" autocomplete="current-password" />
</div>
<!-- new password-->
<div>
<label for="new-password">Password</label>
<input type="password" id="new-password" autocomplete="new-password" />
</div>
```
**4. Name**
The following possible values are supported by the autofill when entering name variations.
a.) name for full name,
b.) given-name for first name,
c.) username,
d.) additional-name for middle name,
e.) nickname
f. family name for last name.
```html
<div>
<label for="username">Username</label>
<input type="text" id="username" autocomplete="username" />
</div>
```
**5. one-time-code**
Majority of web apps use one-time password codes (OTPs) sent by email or SMS to validate user account registration, sign-ins, and online transactions.
Using autocomplete value one-time-code provides a clue to the useragent to accept OTP , which consists of 4 to 6 letters and numbers. Note that one-time codes are helpful for suggesting fields like phone numbers, but they should not be used in situations where there is a constant supply of fresh one-time codes.
```html
<div>
<label for="otp">Verification code</label>
<input type="text" id="otp" autocomplete="one-time-code" />
</div>
```
**6. Date of birth**
The date of birth value has multiple possibilities and lets the user agent hint to the date of birth field.
a.) bday for day,month and year of birth
b.) bday-day for day of the month of birth
c.) bday-month for month of birth
d.) bday-year for year of birth
```html
<div>
<label for="dob">Date of birth</label>
<input type="date" id="dob" autocomplete="bday" />
</div>
```
**7. Telephone**
The user can enter a phone number in the input field of type "tel". You can indicate to the browser which phone number components the user needs to enter. There are multiple token values associated with the telephone value. Here are a few of these.
a.) tel for telephone
b.) tel-area-code
c.) tel-country-code
d. tel-extension
e.) tel-local
```html
<div>
<label for="telephone"> Telephone</label>
<input type="tel" autocomplete="tel" id="telephone"/>
</div>
```
**8. Organization**
The organization autofill value has 2 values for representing the organization name and organization title as **organization** and **organization-title**.
```html
<div>
<label for="org">Organization name</label>
<input type="text" id="org" autocomplete="organization"/>
</div>
```
**9. Country**
The country autofill value takes two possible values **country** and **country-name**.
```html
<div>
<label for="country">Country</label>
<input type="text" id="country" autocomplete="country-name"/>
</div>
```
**10. Address and postal code**
The user agent can determine the address value of an input field by using autofill address value . There are multiple versions available for address levels that begin with **address-level-***.
a.) address-level1,address-level2,address-level3 ,address-level4 for representing administrative addresses based on province,county,city, town or village levels.
b.) address-line1,address-line2,address-line3 ,for representing physical street address.
```html
<div>
<label for="address">Address</label>
<input type="text" id="address" autocomplete="address-level1"/>
</div>
```
**11. Credit card**
Autofill shines in credit card payment transactions because it makes it simple for the browser to submit credit card information. It contains multiple values that correspond to credit card information prefixed “cc-*”.
a.) **cc-exp** for card month and year of expiry.
b.) **cc-exp**-month for card expiry month.
c.) **cc-exp**-year for card expiry year.
d.) **cc-name** for the full name as it appears on the credit card
e.) **cc-number** for the credit card number.
f.) **cc-type** for type of card; visa or master card.
g.) **cc-family-name** for first name on the card.
h.) **cc-given-name** for last name on the card.
I.) **cc-additional-name** for middle name on the card.
j.) **cc-csc** for the security code on the credit card.
```html
<div>
<label for="card-number">Card number</label>
<input type="text" id="card-number" autocomplete="cc-number"/>
</div>
```
**12. Sex**
Sex value is used to suggest gender identity and gender expressions in the select field and the expected value is **sex**.
```html
<select autocomplete="sex">
<option>Male</option>
<option>Female</option>
</select>
```
In conclusion, you should consider the wide list of autocomplete fields on MDN to be your daily cheat sheet. You should always consider autofill when developing your form input as it is an essential feature that improves user experience. In my opinion, forms and their input fields can be enhanced by autofill.
**Further references**
1. [MDN](https://developer.mozilla.org/en-US/docs/Web/HTML/Attributes/autocomplete )
2. [Web dev](https://web.dev/leilarn/forms/autofl?hl=en )
3. [What web devs don’t know : ](https://cloudfour.com/thinks/autofill-what-web-devs-should-know-but-dont/ )
4. [Help users avoid re-entering forms](https://web.dev/learn/forms/auto )
| kipyegonline |
1,855,067 | 7 Differences Between Arrow Functions and Traditional Functions | The arrow function that appeared in ES6 has brought us great convenience, but it is still different... | 0 | 2024-06-03T05:12:49 | https://webdeveloper.beehiiv.com/p/7-differences-arrow-functions-traditional-functions | webdev, javascript, programming, frontend | The arrow function that appeared in ES6 has brought us great convenience, but it is still different from the traditional function. A little carelessness in development may cause problems, so follow me to see the 7 differences between arrow function and traditional function!
# 1. No arguments
In a traditional function, there is an `arguments` local variable. If the number of arguments to our function is dynamic, using `arguments` allows us to easily do things like calculating the maximum number of passed arguments:
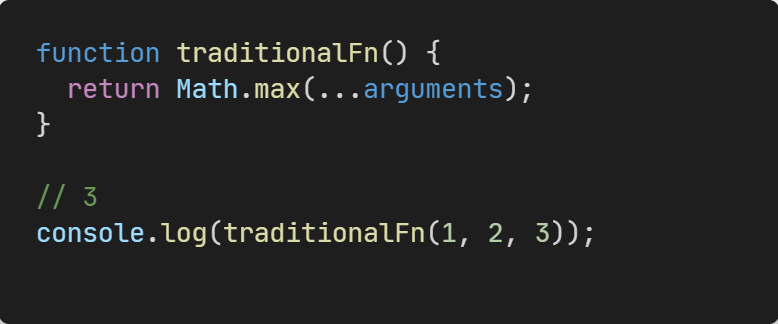
`arguments` is an array-like object. The similarities between array-like objects and array objects are that they can both use subscripts to access corresponding elements and have a length property. The difference is that array-like objects do not have built-in methods on arrays, but we can use `Array.from` converts an array-like object into an array object.
In the arrow function, there are no `arguments`, if we access arguments in the arrow function will return the arguments of the closest non-arrow parent function.
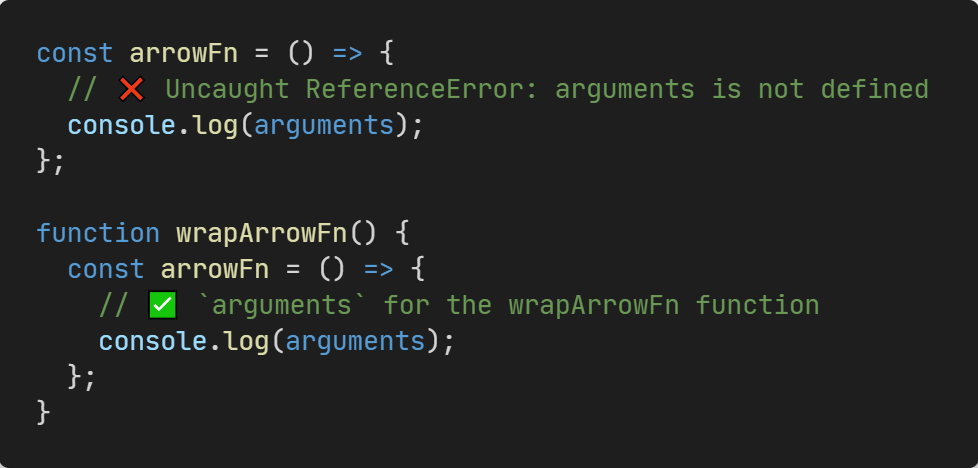
But we can use **[rest parameters](https://developer.mozilla.org/en-US/docs/Web/JavaScript/Reference/Functions/rest_parameters?utm_source=webdeveloper.beehiiv.com&utm_medium=newsletter&utm_campaign=7-differences-between-arrow-functions-and-traditional-functions)** instead, which get a normal array object.

# 2. Return value can omit the curly brackets

You can see that in an inline arrow function that contains only one expression, we can omit the curly braces to return the value, which makes the code clearer.
# 3. Duplicate named parameters are not allowed
In non-restrict mode, traditional functions allow us to use duplicate named parameters. But in strict mode, it is not allowed.
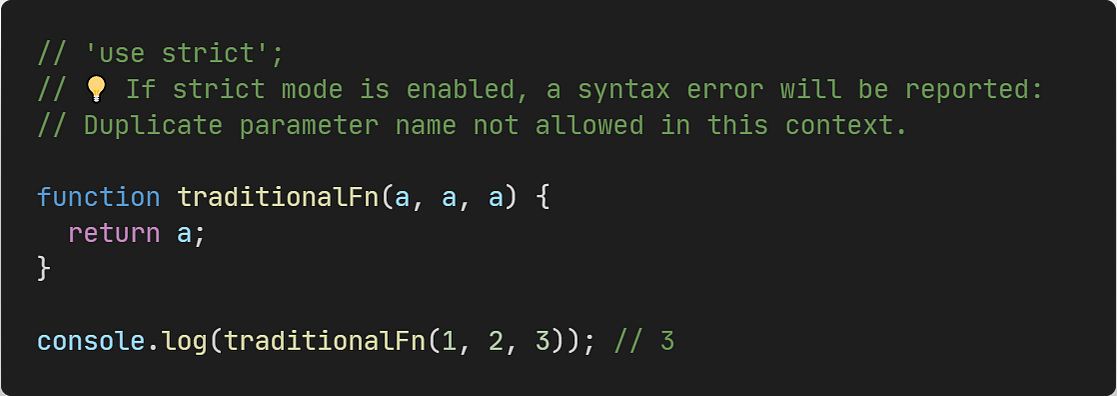
In arrow functions, parameters with the same name are not allowed whether the strict mode is enabled or not.
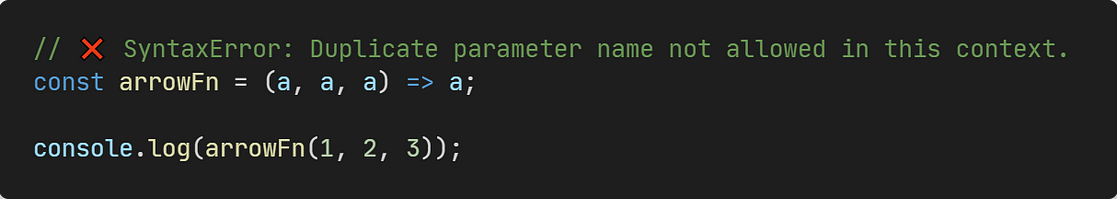
# 4. No prototype
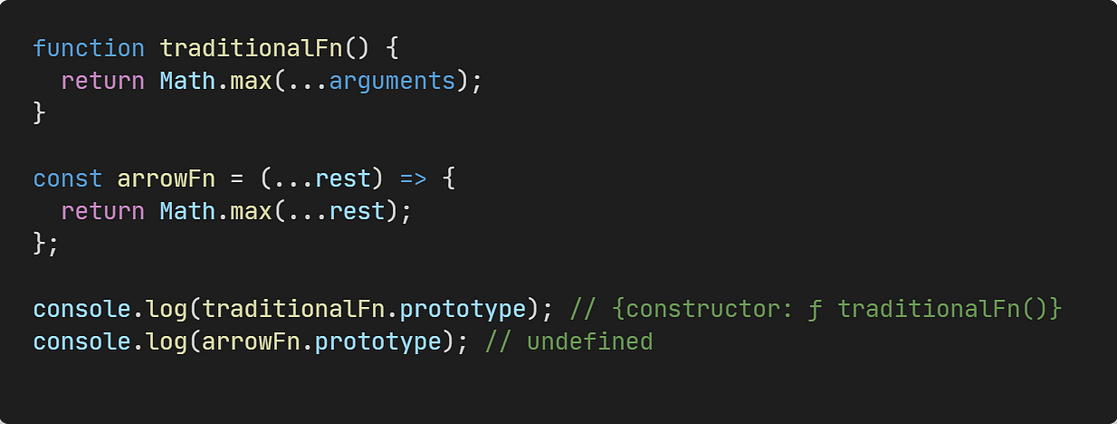
We can get `prototype` for traditional function, but the arrow function does not have `prototype` .
# 5. No this
In a traditional function, its internal `this` value is **dynamic** , it depends on how the function is invoked. For example:
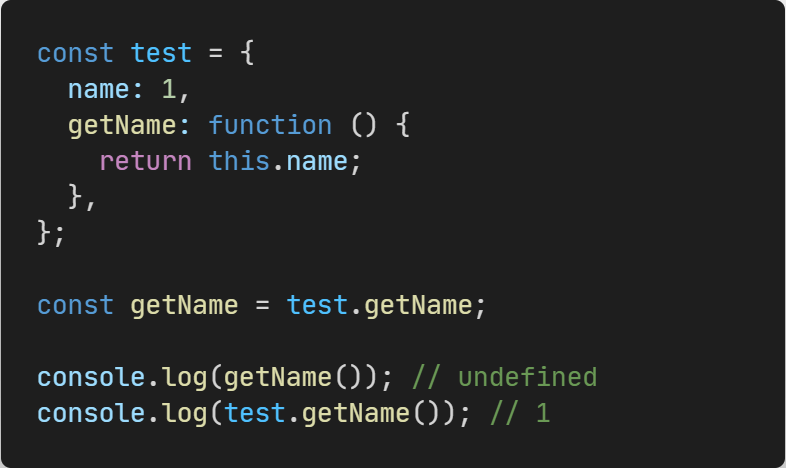
In the arrow function, there are no `this`, if we access this in the arrow function it will return the `this` of the closest non-arrow parent function.
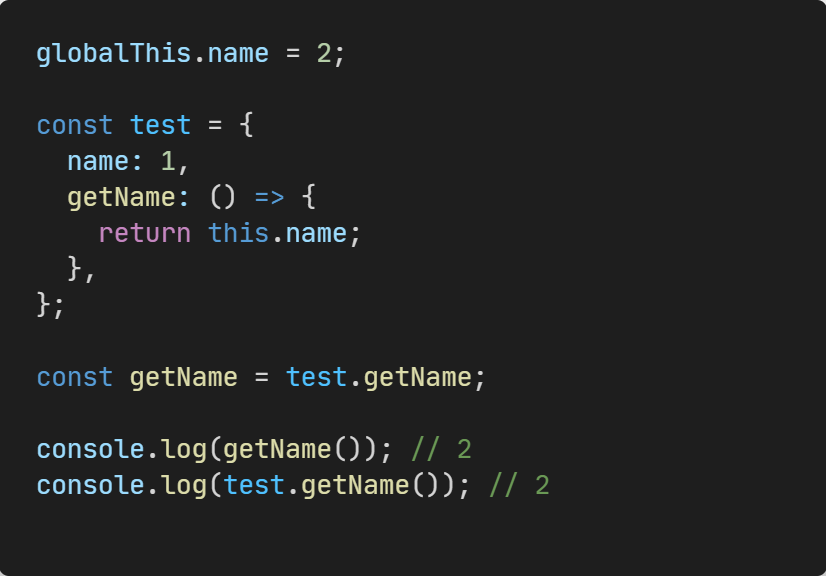
Note that the `this` of an arrow function is determined at the time of declaration and never changes. So `call`, `apply`, `bind` cannot change the value of arrow function `this`.
# 6. Cannot be invoked with new
We can use the `new` keyword on the traditional function to create a new object.
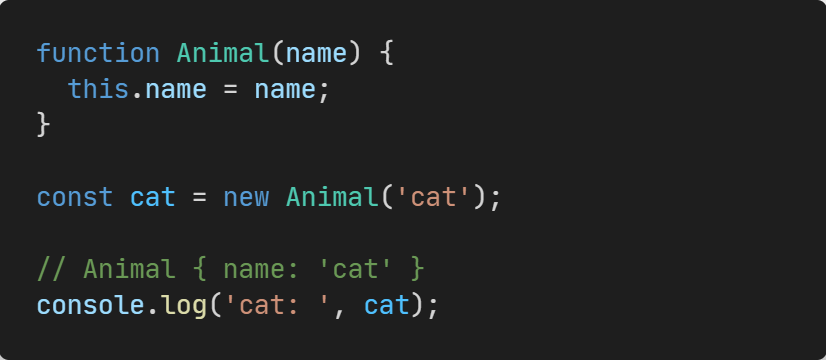
But arrow functions cannot be called with `new`.
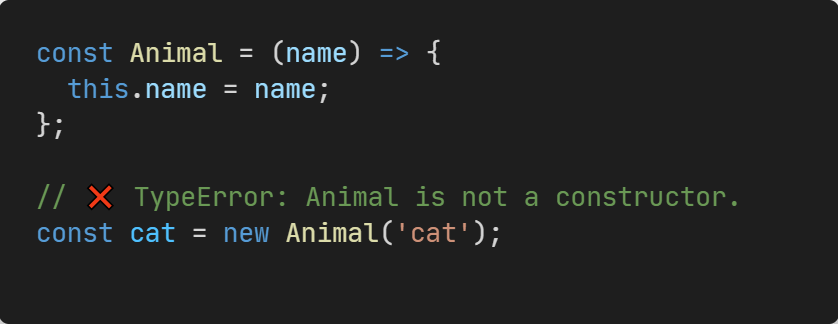
This is because when calling `new`, we go through the following four steps:
1. Create a new object
2. Point the ` __proto__ ` of the new object to the `prototype` of the constructor
3. Call the constructor with the new object as `this`
4. If the result of the call is an object, return the object, if not, return the new object created in the first step.
We can implement a mock new function:
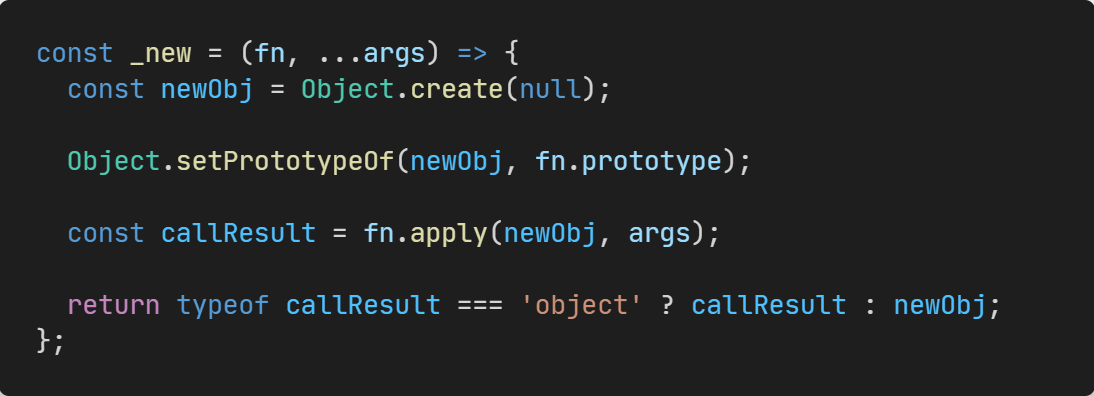
So you can see that the arrow function cannot be called by the new keyword because it has **no prototype** and **no this**.
# 7. Cannot be used as a Generator function
For historical reasons, the specification does not allow the use of the **yield** command in the arrow function, so the arrow function cannot be used as a Generator function.
To sum up, arrow functions avoid a lot of code scenarios that can lead to misunderstandings, it makes our code clearer and more controllable.
*If you find this helpful, [**please consider subscribing**](https://webdeveloper.beehiiv.com/) to my newsletter for more insights on web development. Thank you for reading!*
| zacharylee |
1,874,945 | Introducing FizzBee: Simplifying Formal Methods for All | Building a complex distributed system? How do you verify your design doesn't have issues with consistency, performance or fault tolerance? | 0 | 2024-06-03T05:09:00 | https://fizzbee.io/posts/formal-methods-wire-transfer/ | architecture, systemdesign, formalmethods, distributedsystems | ---
title: 'Introducing FizzBee: Simplifying Formal Methods for All'
published: true
description: "Building a complex distributed system? How do you verify your design doesn't have issues with consistency, performance or fault tolerance?"
canonical_url: "https://fizzbee.io/posts/formal-methods-wire-transfer/"
tags: architecture, systemdesign, formalmethods, distributedsystems
cover_image: https://dev-to-uploads.s3.amazonaws.com/uploads/articles/tmiv1dryltl25rhhb6ob.png
# Use a ratio of 100:42 for best results.
published_at: 2024-06-03 05:09 +0000
---
Building a complex distributed system? How do you verify your design doesn't have issues with consistency, performance or fault tolerance?
Amazon has been using formal methods to verify its distributed systems since 2012. Now, major players like Amazon, Microsoft, MongoDB, Confluent, Oracle, Elastic, CockroachDB, and many more are all embracing formal methods for their systems. Despite the immense benefits and relevance of this technique in modern software development, its widespread adoption has been hindered by the complexity of existing tools.
In this article, we’ll introduce you to [FizzBee](https://fizzbee.io), a new formal methods system that you can grasp in just a weekend.
Originally published at [The New Stack](https://thenewstack.io/introducing-fizzbee-simplifying-formal-methods-for-all/)
## What Are Formal Methods?
Formal methods encompass rigorous techniques employed to specify, model, design, and verify complex systems using mathematical logic. Particularly relevant to software engineers working on cloud-based SaaS or distributed systems, concurrent programming, and similar domains, these methods offer a systematic approach to guarantee correctness and reliability in both software and hardware systems.
> Formal methods find bugs in system designs that cannot be found through any other technique we know of.
— Chris Newcombe, AWS
## How Do We Find System Design Bugs Today?
Today, we rely on drafting design documents and team reviews to uncover system design bugs. However, this approach falls short due to its inefficiency and limited effectiveness. We rely on pattern matching based on past experiences and known anti-patterns to identify design flaws because we lack the mental capacity and time to explore every possible outcome. This is where computers excel: effortlessly exploring billions of states in minutes.
## FizzBee: Formal Methods for All
FizzBee, a recent addition to formal methods systems, closes the accessibility gap with its user-friendly interface and Python-like syntax. This makes it easy for developers of all levels to express complex algorithms and system designs.
1. **Easy to learn**: If you’ve written a few Python scripts, you can grasp FizzBee code in just 10 minutes. Then, you can learn model-checking principles in a few hours.
1. **Enhanced Readability**: FizzBee specifications are designed for easy comprehension by both reviewers and developers. Unlike other tools like TLA+, FizzBee’s familiar syntax ensures that even non-authors can understand the specifications, facilitating smoother review processes and implementation.
1. **Multi-Paradigm Flexibility**: FizzBee offers versatile programming options, including functional, imperative, structured, procedural, and object-oriented styles. This allows developers to choose the best approach for each problem, leading to concise and adaptable solutions.
1. **Visualization**: FizzBee’s state transition graph aids in debugging by providing a visual representation. This also improves understanding of the model-checking process and helps users identify and resolve issues more effectively.
1. **Online Playground**: FizzBee provides an online playground for practicing, experimenting, and exploring examples, making it accessible for both learning and exploration.
## Modeling a Wire Transfer System
Let’s model a simple money transfer between two accounts, a classic example showcasing database transaction consistency. The aim is to ensure that no money is lost or gained unexpectedly, maintaining the total amount across all users in the system at the end of the day.
### First Implementation
Let’s keep it simple, we have two users: Alice and Bob. Only Alice is permitted to initiate wire transfers to Bob.
```
action Init:
balances = {'Alice': 3, 'Bob': 2}
action FundTransfer:
any amount in range(0,100):
if balances['Alice'] >= amount:
balances['Alice'] -= amount
balances['Bob'] += amount
```
#### Actions:
*Actions* are building blocks of the system’s behavior specification, representing various behaviors, operations, or events like user interactions or timer events. The model checker calls these actions repeatedly in different sequences to explore the system’s potential states.
In our model, we define two actions using the `action` keyword. The first is `Init`, a special action called first and only once. The second action is `FundTransfer`, which is the sole action in our model and called repeatedly.
#### State:
The variables defined in the `Init` action become the system’s state variables, which later actions can modify. In our example, a single state variable is represented by a Python dictionary containing two accounts with balances of 3 and 2.
#### Non-determinism:
When testing an implementation, we often test with a single value. However, with FizzBee, you specify the possible values, and the model checker explores all combinations.
In this example, you select an amount to transfer from the range 0 to 100. `any` is one of two keywords used to specify non-determinism. Syntactically, this is equivalent to a Python `for` statement, allowing you to rerun the same test with different amounts.
The remaining code is straightforward: if Alice has the funds to transfer, the amount is deducted from her account and added to Bob’s.
#### Invariants:
In system modeling, it’s crucial to ensure certain properties hold true. One essential property is that the sum of balances in all accounts must equal 5.
There are three types of invariants: *safety* (conditions that must always be true), *liveness* (conditions that must eventually become true), and *stability* (conditions that must eventually become true and remain true).
Let’s start with an assertion that balances should always match, similar to transfers between accounts in the same bank.
Invariants are specified using the `assertion` keyword.
```
always assertion BalanceMatchTotal:
total = 0
for balance in balances.values():
total += balance
return total == 5
```
An `assertion` is akin to a Python function but expects a `Boolean` return value. `True` implies the condition is true in that state.
The `always` keyword implies that this condition must hold true in every state.
### Run the model checker.
The model checker will indicate a failure, showing a trace where a context switch occurs after deducting from Alice’s account but before crediting Bob’s account.

Fix: Put these two steps in a transaction.
#### atomic keyword:
Using `atomic` ensures that both intermediate steps happen together or not at all, shielding them from the rest of the system. During development, this translates to a transaction or lock. By default, the behavior is serial, but you can explicitly specify otherwise.
```
atomic action FundTransfer:
any amount in range(0,100):
if balances['Alice'] >= amount:
balances['Alice'] -= amount
balances['Bob'] += amount
```
After applying `atomic`, running the model checker succeeds. You can also review the full state graph to observe the system’s behavior.

#### Wire transfer — non atomic money transfer
Let us change the requirement to say once a wire transfer request is received, Alice’s account will be deducted immediately, but Bob’s account may not be credited immediately. We just want to ensure it will be credited eventually.
Let us start with the assertion. Instead of saying always, change from `always` to `always eventually`. From any state it will *eventually* reach a state where the predicates become true. This is called liveness expectation. (The stability expectation is specified with eventually always, this is less used and not covered here).
```
always eventually assertion BalanceMatchTotal:
total = 0
for balance in balances.values():
total += balance
return total == 5
```
Now, as a first attempt, remove the atomic keyword (or replace it with the serial keyword). So, the debiting and crediting happens in two separate steps
Now, when you run the command, you will see it failed with this trace.

This indicates, after deducting, the system could crash and if it did, it loses the next steps and stutter Stutter indicates, the system may not make any more progress.
Actions indicate what may happen in the system, not what must happen. We need to specify what must happen. This is done by adding keyword `fair` to an action.
Note: in this case, if we mark the FundTransfer action as fair, it just implies Alice would be able to keep sending the money, but it will be possible, the money will never reach Bob.
### Implementing wire transfer
It happens in two actions. In the first action, atomically, record the wire request and deduct from Alice’s account. On a second action, again atomically mark the transfer as complete and credit Bob’s account.
```
always eventually assertion BalanceMatchTotal:
total = 0
for balance in balances.values():
total += balance
return total == 5
action Init:
balances = {‘Alice’: 3, ‘Bob’: 2}
wire_requests = []
atomic action Wire:
any amount in range(1,10):
if balances[‘Alice’] >= amount:
balances[‘Alice’] -= amount
wire_requests.append((‘Alice’, ‘Bob’, amount))
atomic fair action DepositWireTransfer:
any req in wire_requests:
balances[req[1]] += req[2]
wire_requests.remove(req)
```
Here, we are keeping a list of wire requests indicating the pending requests for wire transfers that need to be completed. And the Action DepositWireTransfer completes the step by crediting Alice’s account.
Run this model, you will notice an error — Deadlock.

That is because, as the system starts transferring funds from Alice to Bob, Alice runs out of money and the system cannot make any progress. This is an issue with our problem statement, rather than the model or implementation. We can easily fix it by allowing Bob to transfer money back to Alice. We will make that change later. For now, to keep things simple, let us do a tiny trick — add an action that does nothing. Real code would never need this.
```
# Add this temporarily until we fix Bob to transfer money to Alice
atomic action NoOp:
pass
```
Now run this model checker, you will notice the model checker passes. This implies this design is correct.
Note: The model will not be directly transferable to code because wire_requests cannot be implemented in the current form. Is it a database in the same bank as the sender? Then, the receiver’s bank will not be able to atomically update along with crediting the sender. We will address it in a later post.
You can read more about [FizzBee](https://fizzbee.io/tutorials) and try other examples(https://fizzbee.io/examples).
#### Formal Verification Is Testing Your Design Before Coding
Formal verification allows you to test your design before coding. As demonstrated above, it helps you concentrate on the essentials and abstract away the details, similar to explaining a design using a basic example on a whiteboard.
By using formal verification, you can make sure your design is clear and correct before you start coding. However, it’s essential to remember that while formal verification tests the design well, it doesn’t replace the need for regular testing. Bugs can still crop up during implementation, but they’re usually easier to fix.
## Final Thoughts:
Formal methods stand out as the premier choice for design validation. Practitioners consistently highlight significant design simplification and faster implementation. For instance, in a recent project where I redesigned a buggy v1 system, specifying the v2 system’s design with TLA+ led to a 4x reduction in code size while incorporating additional features. However, it’s important to note that tools like TLA+ are notoriously challenging to use.
As shown in the example above, FizzBee code is easy to read and write, unlike TLA+, making it a compelling alternative for experienced software engineers to start formal methods for the first time. With FizzBee’s model checker, design correctness is ensured, while its concise and clear specifications communicate and document the design.
Originally published at [The New Stack](https://thenewstack.io/introducing-fizzbee-simplifying-formal-methods-for-all/) | jayaprabhakar |
1,874,939 | Intro to Deep Learning... | Introduction to Deep Learning: A Beginner's Guide Today's Agenda What is deep... | 0 | 2024-06-03T05:08:04 | https://dev.to/pranjal_ml/intro-to-deep-learning-31p6 | ai, python, datascience, machinelearning | # Introduction to Deep Learning: A Beginner's Guide
## Today's Agenda
* [What is deep learning?](#what-is-deep-learning)
* [AI vs ML vs DL](#ai-vs-ml-vs-dl)
* [Why DL is popular?](#why-deep-learning-is-popular)
* [Perceptron](#perceptron-building-block-of-neural-network)
---
Let's begin it -
## What is Deep Learning?
Deep learning is a subset of machine learning, which itself is a subset of artificial intelligence (AI). At its core, deep learning involves using neural networks with many layers (hence "deep") to model and understand complex patterns in data. These neural networks are inspired by the human brain's structure and function, aiming to simulate the way humans learn and make decisions. The most basic building block of DL is Perceptron (seen in detail below).
## AI vs ML vs DL
In the realm of technology and data science, terms like Artificial Intelligence (AI), Machine Learning (ML), and Deep Learning (DL) are often used interchangeably. While they are related, they are not the same. Understanding the distinctions between these concepts is crucial for anyone venturing into the world of advanced computing.
### What is Artificial Intelligence (AI)?
Artificial Intelligence is a broad field of computer science focused on creating systems capable of performing tasks that typically require human intelligence. These tasks include reasoning, learning, problem-solving, perception, and language understanding.
### Key Points:
- **Scope**: AI is an umbrella term that encompasses various technologies aimed at imitating human intelligence.
- **Techniques**: AI includes techniques like expert systems, natural language processing, robotics, and more.
- **Applications**: AI is used in diverse areas such as healthcare (diagnostic systems), finance (fraud detection), customer service (chatbots), and many more.
## What is Machine Learning (ML)?
Machine Learning is a subset of AI that involves the development of algorithms that allow computers to learn from and make decisions based on data. Instead of being explicitly programmed to perform a task, ML models identify patterns in data to make predictions or decisions. It is more about statistical methods.
### Key Points:
- **Scope**: ML is a narrower field within AI focused on building systems that learn from data.
- **Techniques**: It includes supervised learning, unsupervised learning, semi-supervised learning, and reinforcement learning.
- **Applications**: ML powers recommendation systems (like those used by Netflix and Amazon), spam detection, image recognition, and more.
## What is Deep Learning (DL)?
Deep Learning is a specialized subset of machine learning that uses neural networks with many layers (hence "deep"). These networks are capable of learning from large amounts of data, identifying intricate patterns, and making sophisticated decisions. It is more about the logical structure.
### Key Points:
- **Scope**: DL is a subset of ML that deals with deep neural networks.
- **Techniques**: It includes convolutional neural networks (CNNs) for image data, recurrent neural networks (RNNs) for sequential data, and various architectures like transformers for natural language processing.
- **Applications**: DL excels in tasks such as image and speech recognition, language translation, and playing complex games like Go and chess.
## Comparing AI, ML, and DL
### Hierarchical Relationship
To visualize the relationship between these fields, you can think of them as concentric circles:
- **AI** is the broadest, encompassing the overall goal of creating intelligent systems.
- **ML** is a subset of AI, focusing on algorithms that learn from data.
- **DL** is a further subset of ML, using deep neural networks to model complex patterns.
### Complexity and Data Requirements
- **AI** can range from simple rule-based systems to complex learning algorithms.
- **ML** requires a substantial amount of data for training but can be relatively simpler in terms of algorithm complexity compared to DL.
- **DL** demands vast amounts of data and computational power but achieves remarkable accuracy and performance on complex tasks.
### Practical Examples
- **AI**: A rule-based chatbot that answers customer queries using predefined rules.
- **ML**: A spam filter that learns to classify emails based on features extracted from the text.
- **DL**: An image recognition system that identifies objects in pictures with high accuracy using a deep neural network.
## DL vs ML (More technical terms)
### 1. Data Dependency
#### Machine Learning (ML)
- **Data Requirements**: Traditional ML algorithms can perform well with smaller datasets. Techniques like decision trees, SVMs (Support Vector Machines), and logistic regression do not require vast amounts of data to achieve reasonable accuracy.
- **Performance**: ML models often reach a plateau in performance with increasing data. Beyond a certain point, adding more data does not significantly improve accuracy.
#### Deep Learning (DL)
- **Data Requirements**: DL models, particularly deep neural networks, thrive on large datasets. They require extensive amounts of labeled data to perform effectively.
- **Performance**: The performance of DL models continues to improve with increasing data. They can capture complex patterns and nuances in large datasets that traditional ML models might miss.
### 2. Training
#### Machine Learning (ML)
- **Training Time**: Training ML models is generally faster and less computationally intensive. Algorithms like linear regression or k-nearest neighbors (k-NN) can be trained relatively quickly.
- **Optimization**: Training involves optimizing objective functions (like minimizing a loss function) using techniques such as gradient descent. The complexity of this optimization is usually lower compared to DL.
#### Deep Learning (DL)
- **Training Time**: DL models, particularly those with many layers (deep neural networks), require significantly more time and computational resources for training. Training can take from hours to weeks depending on the model size and data volume.
- **Optimization**: Training involves backpropagation and gradient descent optimization. The process is more complex due to the depth and non-linearity of the networks.
### 3. Feature Selection
#### Machine Learning (ML)
- **Manual Feature Engineering**: ML relies heavily on manual feature engineering. Data scientists need to identify and create relevant features that can improve model performance.
- **Domain Expertise**: Effective feature engineering often requires domain-specific knowledge to transform raw data into meaningful inputs for the model.
#### Deep Learning (DL)
- **Automatic Feature Extraction**: One of the key advantages of DL is its ability to automatically extract features from raw data. Convolutional Neural Networks (CNNs) for image data and Recurrent Neural Networks (RNNs) for sequential data are examples where DL models learn hierarchical feature representations.
- **Less Manual Effort**: While some preprocessing is still needed, DL significantly reduces the manual effort involved in feature engineering.
### 4. Hardware
#### Machine Learning (ML)
- **Hardware Requirements**: ML models can often be trained on standard CPUs without the need for specialized hardware. The computational requirements are generally lower.
- **Cost Efficiency**: Given the lower computational demands, training ML models is typically more cost-efficient.
#### Deep Learning (DL)
- **Hardware Requirements**: DL models, especially deep neural networks, require specialized hardware such as GPUs (Graphics Processing Units) or TPUs (Tensor Processing Units) to handle the extensive computations involved.
- **Cost and Infrastructure**: The need for powerful hardware increases the cost and complexity of deploying DL solutions. Cloud-based services like AWS, Google Cloud, and Azure offer scalable resources for DL training.
### 5. Interpretation
#### Machine Learning (ML)
- **Model Interpretability**: ML models like decision trees, linear regression, and logistic regression are generally more interpretable. It is easier to understand how input features affect the output predictions.
- **Transparency**: The simpler structures of many ML models allow for greater transparency and easier debugging.
#### Deep Learning (DL)
- **Model Interpretability**: DL models are often considered "black boxes" due to their complexity and the large number of parameters. Understanding how specific features impact the final prediction is challenging.
- **Explainability Techniques**: Techniques such as SHAP (SHapley Additive exPlanations) and LIME (Local Interpretable Model-agnostic Explanations) are used to interpret DL models, but they add an extra layer of complexity.
## Why Deep Learning is Popular
In recent years, deep learning has emerged as a leading approach in the field of artificial intelligence (AI), revolutionizing various industries and enabling remarkable advancements in technology. The popularity of deep learning can be attributed to several key factors:
### 1. **Impressive Performance**
Deep learning models, particularly neural networks with multiple layers, have demonstrated exceptional performance in a variety of tasks. These include image and speech recognition, natural language processing, game playing, and more. The ability of deep learning to outperform traditional machine learning algorithms in complex tasks has been a significant driver of its popularity.
### 2. **Availability of Large Datasets**
The success of deep learning is closely tied to the availability of large datasets. In the age of big data, we have access to vast amounts of information from diverse sources such as social media, medical records, and e-commerce. Deep learning algorithms thrive on data, and the abundance of data has allowed these models to be trained effectively, leading to improved performance.
### 3. **Advancements in Hardware**
The development of powerful hardware, particularly Graphics Processing Units (GPUs), has been crucial for the growth of deep learning. GPUs are well-suited for the parallel processing required by deep learning algorithms, enabling faster training times and the handling of larger models. Additionally, advancements in specialized hardware such as Tensor Processing Units (TP
Us) have further accelerated deep learning research and applications.
### 4. **Open-Source Frameworks and Tools**
The proliferation of open-source deep learning frameworks, such as TensorFlow, PyTorch, Keras, and others, has made it easier for researchers and developers to build, train, and deploy deep learning models. These tools provide accessible interfaces, extensive documentation, and pre-trained models, lowering the barrier to entry for those interested in deep learning.
### 5. **Breakthroughs in Research**
Continuous breakthroughs in deep learning research have contributed to its popularity. Innovations such as convolutional neural networks (CNNs) for image processing, recurrent neural networks (RNNs) for sequence data, and transformers for natural language processing have expanded the capabilities of deep learning models. These advancements have enabled deep learning to tackle a wider range of problems with increasing accuracy and efficiency.
### 6. **Real-World Applications**
Deep learning has proven to be highly effective in real-world applications, driving its adoption across various industries. Some notable applications include:
- **Healthcare:** Deep learning is used for medical image analysis, drug discovery, and personalized treatment recommendations.
- **Automotive:** It powers autonomous driving systems and advanced driver-assistance systems (ADAS).
- **Finance:** Deep learning models are used for fraud detection, algorithmic trading, and risk management.
- **Entertainment:** It enhances recommendation systems for streaming services, improves video game AI, and enables realistic computer-generated imagery (CGI).
- **Retail:** Deep learning optimizes inventory management, customer service, and personalized marketing strategies.
### 7. **Community and Industry Support**
The deep learning community is vibrant and collaborative, with researchers, developers, and organizations actively contributing to the field. Conferences, workshops, and online platforms facilitate the sharing of knowledge, fostering innovation and the rapid dissemination of new ideas. Industry giants like Google, Facebook, and Microsoft heavily invest in deep learning research and development, further propelling its growth and adoption.
## Perceptron (Building Block of Neural Network)
The perceptron is a fundamental unit in neural networks and serves as a basic building block for more complex architectures. Understanding the perceptron is essential for grasping how neural networks function.
### 1. **Introduction to Perceptrons**
A perceptron is a simple model of a biological neuron. It was introduced by Frank Rosenblatt in 1958 and is one of the earliest models of artificial neural networks. The perceptron takes several input signals, processes them, and produces an output signal.
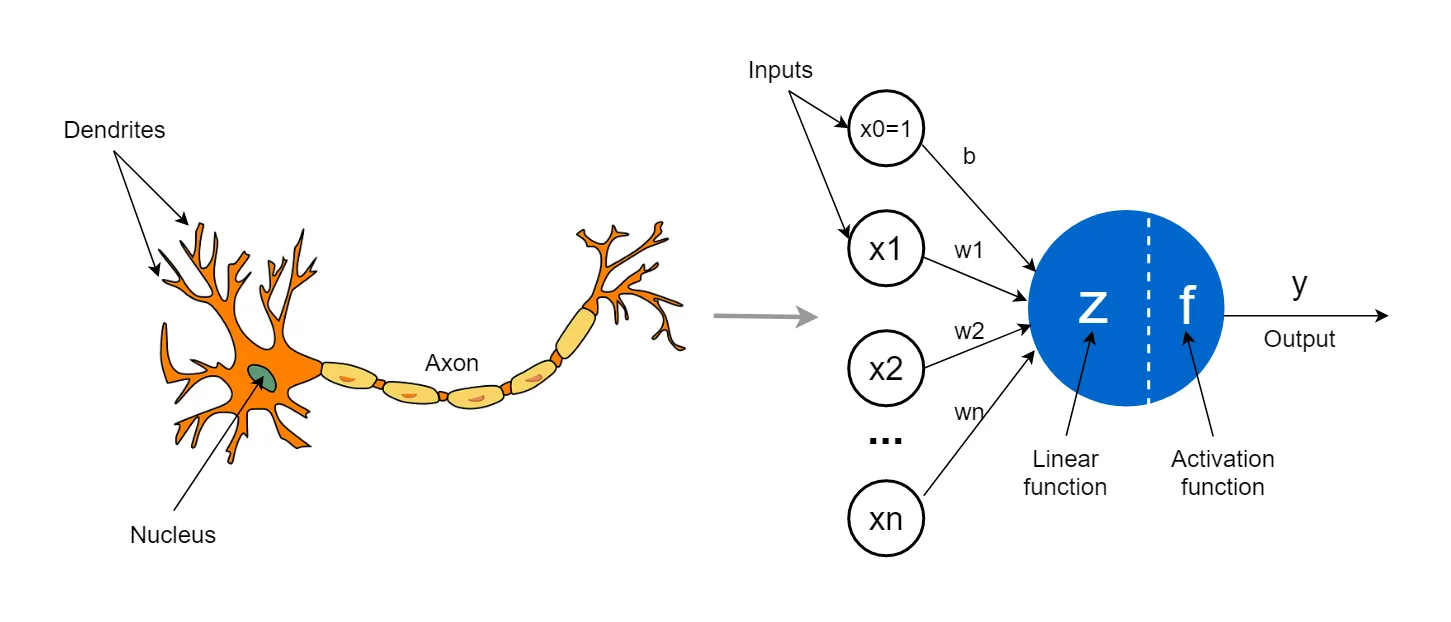
### 2. **Structure of a Perceptron**
A perceptron consists of:
- **Input Nodes:** These represent the input features. Each input node corresponds to a feature in the dataset.
- **Weights:** Each input node is associated with a weight. These weights determine the importance of each input in making the decision.
- **Bias:** A bias term is added to the weighted sum of the inputs to allow the activation function to shift.
- **Activation Function:** The activation function processes the weighted sum of the inputs and the bias. Common activation functions include the step function, sigmoid, and ReLU (Rectified Linear Unit).
### 3. **Mathematical Representation**
Mathematically, a perceptron can be represented as follows:
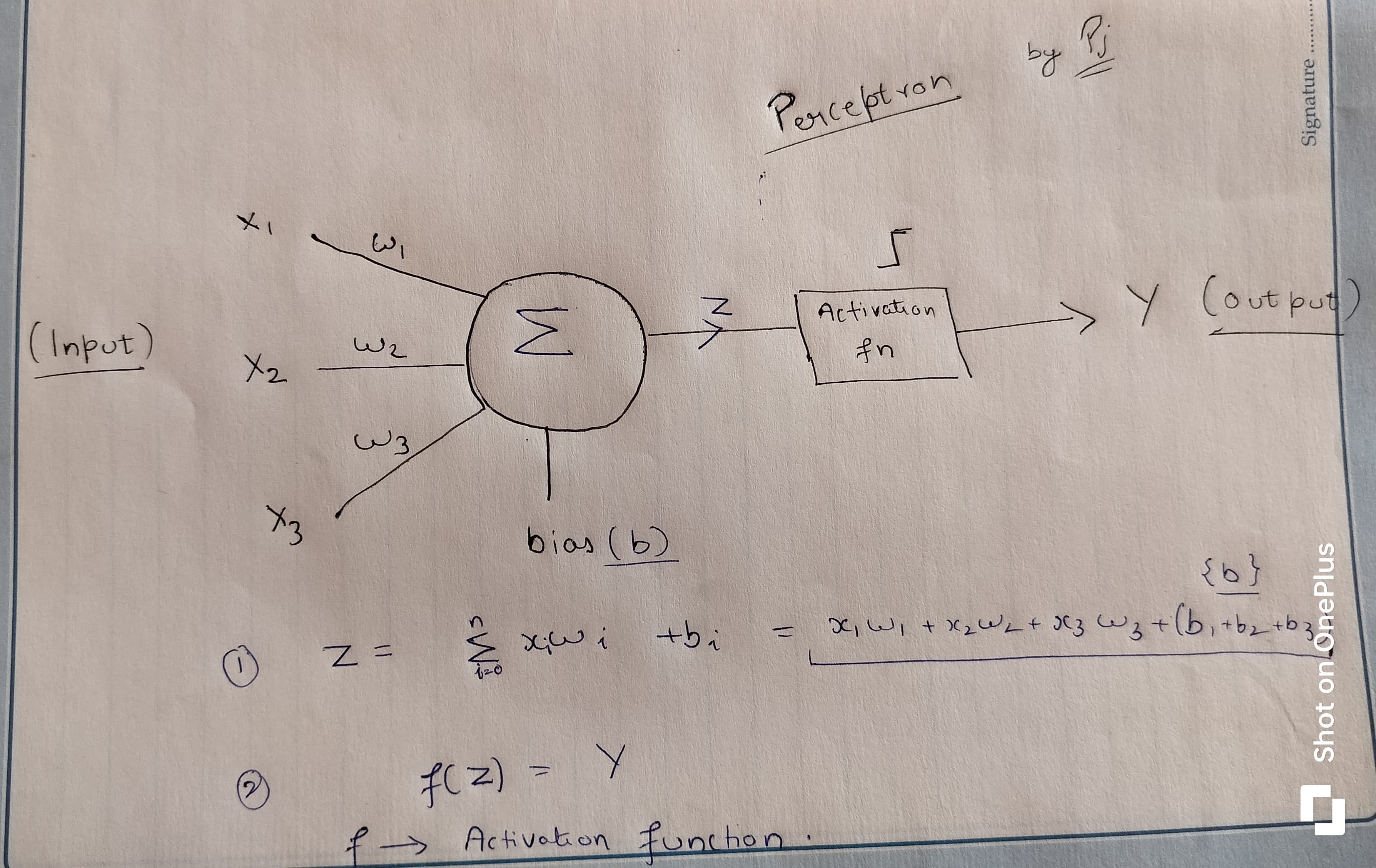
Where:
- \( y \) is the output of the perceptron.
- \( x_i \) are the input features.
- \( w_i \) are the weights associated with the inputs.
- \( b \) is the bias term.
- \( f \) is the activation function.
### 4. **Learning in Perceptrons**
The perceptron learning algorithm involves adjusting the weights and bias to minimize the error in the predictions. The process can be described in the following steps:
1. **Initialization:** Initialize the weights and bias randomly.
2. **Forward Pass:** Compute the output for a given input using the current weights and bias.
3. **Error Calculation:** Calculate the error by comparing the predicted output with the actual target value.
4. **Weight Update:** Adjust the weights and bias to reduce the error.
### 5. **Limitations of Perceptrons**
While perceptrons can solve linearly separable problems, they have limitations:
- **Linear Separability:** Perceptrons can only solve problems where the data is linearly separable. For instance, they cannot solve the XOR problem.
- **Single Layer:** A single-layer perceptron (single-layer neural network) has limited capacity and cannot model complex functions.
### 6. **Perceptrons in Neural Networks**
To overcome the limitations of single-layer perceptrons, multi-layer perceptrons (MLPs) were developed. MLPs consist of multiple layers of perceptrons (neurons) with non-linear activation functions, enabling them to learn and model complex, non-linear relationships.
## Conclusion
Deep learning is a powerful and transformative technology with the potential to solve complex problems across various domains. By understanding its core concepts and applications, you can start leveraging deep learning in your projects and contribute to this exciting field.
---
| pranjal_ml |
1,874,944 | Roadmap for learning HTML that can help you navigate the various concepts and technologies associated with it. | Beginner Level: Introduction to HTML: Understand what HTML is and its role in web... | 0 | 2024-06-03T05:01:07 | https://dev.to/sudeepmshetty/roadmap-for-learning-html-can-help-you-navigate-the-various-concepts-and-technologies-associated-with-it-14jp | html, beginners, roadmap, programming | ## Beginner Level:
1. **Introduction to HTML:**
- Understand what HTML is and its role in web development.
- Learn about basic HTML syntax, elements, and attributes.
2. **Document Structure:**
- Study the structure of an HTML document (DOCTYPE declaration, `<html>`, `<head>`, `<title>`, `<body>`).
- Learn about meta tags, character encoding, and document language.
3. **Text Formatting:**
- Explore text formatting elements like headings (`<h1>` to `<h6>`), paragraphs (`<p>`), emphasis (`<em>`, `<strong>`), etc.
- Understand how to create lists (`<ul>`, `<ol>`, `<li>`).
4. **Links and Images:**
- Learn how to create hyperlinks (`<a>`), including linking to other pages and external sites.
- Understand the `<img>` tag for embedding images.
5. **Tables:**
- Study how to create tables (`<table>`), table rows (`<tr>`), table headers (`<th>`), and table data (`<td>`).
6. **Forms:**
- Learn about form elements (`<form>`, `<input>`, `<textarea>`, `<select>`, `<button>`).
- Understand how to handle form submissions.
### Intermediate Level:
1. **Semantic HTML:**
- Dive deeper into semantic HTML elements (`<header>`, `<footer>`, `<nav>`, `<article>`, `<section>`, `<aside>`, `<main>`).
- Understand their importance for accessibility and SEO.
2. **CSS Fundamentals:**
- Start learning CSS alongside HTML to style your web pages.
- Understand selectors, properties, values, and basic styling techniques.
3. **Multimedia:**
- Explore embedding multimedia content like audio (`<audio>`) and video (`<video>`).
- Learn about the `<canvas>` element for dynamic graphics and animations.
4. **Responsive Design:**
- Study responsive design principles using media queries and flexible layouts.
- Understand how to make your web pages adapt to different screen sizes.
### Advanced Level:
1. **HTML5 Features:**
- Explore advanced HTML5 features like local storage, geolocation, web workers, etc.
- Understand the `<canvas>` element for drawing graphics and animations.
2. **Web Components:**
- Learn about web components and how to create custom reusable HTML elements.
- Understand shadow DOM, templates, custom elements, and HTML imports.
3. **Accessibility:**
- Dive deeper into accessibility principles and learn how to make your websites more accessible to all users.
- Understand ARIA roles and attributes.
4. **Performance Optimization:**
- Study techniques for optimizing HTML for performance, including minimizing HTTP requests, optimizing images, and using browser caching.
5. **Security:**
- Learn about HTML security best practices, including preventing XSS attacks and content security policies.
6. **Frameworks and Libraries:**
- Explore popular HTML frameworks like Bootstrap or Foundation.
- Understand how to integrate HTML with JavaScript frameworks like React, Angular, or Vue.js.
### Practice Projects:
- Create a personal portfolio website.
- Build a blog site with HTML and CSS.
- Develop a simple web application with forms and user interaction.
- Experiment with responsive design by creating a mobile-friendly version of a website.
Remember, consistent practice and building projects are crucial for mastering HTML. As you progress, don't hesitate to explore new technologies and experiment with different techniques to enhance your skills further. | sudeepmshetty |
1,838,291 | Beyond Utility: Bringing Delight to Everyday Apps | Our phones are crammed with apps. From banking and news to fitness trackers and social media, these... | 27,354 | 2024-06-03T05:00:00 | https://dev.to/shieldstring/beyond-utility-bringing-delight-to-everyday-apps-53b0 | startup, design, ux, learning | Our phones are crammed with apps. From banking and news to fitness trackers and social media, these tools have become an undeniable part of our daily lives. But let's face it, many essential apps can feel like a chore to use. So, how can we design everyday apps that go beyond utility and spark a sense of delight?
**The Power of Delightful Design**
Delightful design isn't just about aesthetics; it's about creating a positive emotional response in users. It's the unexpected surprise, the seamless interaction, or the touch of humor that elevates an app from functional to truly enjoyable. Here's why delight matters:
* **Boosts Engagement:** Delighted users are more likely to use an app frequently and recommend it to others.
* **Enhances Brand Loyalty:** Positive user experiences foster brand loyalty and create a stronger emotional connection.
* **Reduces Friction:** Delightful design can streamline complex tasks and make using the app feel effortless.
**Strategies for Designing Delight**
Here are some ways to inject delight into your everyday apps:
* **Microinteractions:** Small, well-designed animations and sound effects can add a touch of whimsy and satisfaction to even the most mundane tasks.
* **Personalized Touches:** Cater to individual user preferences with customizable themes, greetings, or recommendations.
* **Gamification:** Integrate game mechanics like points, badges, and leaderboards to motivate users and make completing tasks feel rewarding.
* **Easter Eggs:** Hide unexpected surprises or delightful interactions within the app to spark user curiosity and discovery.
* **Positive Reinforcement:** Celebrate user achievements with encouraging messages and animations, fostering a sense of accomplishment.
* **Humor and Playfulness:** A touch of humor can go a long way in making an app feel more approachable and engaging. (But be mindful of cultural sensitivities!)
* **User Onboarding:** Make the first interaction with your app delightful. Offer clear instructions, helpful tips, and a smooth setup process.
**Examples of Delightful Apps**
Several everyday apps excel at creating delightful user experiences:
* **Duolingo:** This language learning app uses gamification and a friendly mascot to make learning a new language feel fun and engaging.
* **Google Search:** The occasional "fun fact" displayed alongside search results adds a touch of whimsy and unexpected delight.
* **Forest:** This productivity app uses a gamified approach where users grow a virtual tree by staying focused on their tasks.
**The Road to Delightful Design**
Designing delightful apps requires a user-centric approach and a willingness to experiment. Here are some additional tips:
* **Focus on User Emotions:** Understand the emotions users experience while using your app. What frustrations can you alleviate? What moments of joy can you create?
* **Prioritize User Research:** Gather user feedback throughout the design process. What elements of existing apps do users find delightful? What could be improved?
* **Embrace Iteration:** Delightful design is not a one-time achievement. Continuously iterate and refine your app based on user feedback and data.
**Conclusion**
In today's competitive landscape, everyday apps need to do more than just function. By prioritizing delightful design, you can create apps that users genuinely enjoy using, fostering loyalty and building a thriving user base. Let's transform our essential apps from digital tools into experiences that bring a smile to our faces and a spark of joy to our daily routines. | shieldstring |
1,873,264 | Why Do Some Software Projects Fail? | It's not because of the tech stack, programming languages, or libraries. Choosing the right tech... | 27,567 | 2024-06-03T05:00:00 | https://dev.to/canro91/why-do-some-software-projects-fail-n16 | career, careerdevelopment, beginners | It's not because of the tech stack, programming languages, or libraries.
Choosing the right tech stack and libraries is a critical decision for the success of a software project.
But, in my experience, **software projects fail due to unclear expectations and communication issues**. Interestingly enough, I've heard the same thing about marriages.
Even, I'd dare to say that unclear expectations are a communication issue too.
I've been in software projects that use Domain-Driven Design, Test-Driven Development, and Kubernetes and sometimes end up late and going off the rails. It's not a tech problem. It's always a people problem.
Software projects fail when:
* Stakeholders fail to communicate their expectations.
* Leaders fail to communicate changes in project goals and scope.
* Leaders fail to communicate action plans.
* Team members fail to communicate technical issues on time.
One of the most common communication issues is waiting until the day before a deadline to say you've been dealing with a coding issue for weeks. But, in the meantime, you kept saying everything was fine. That would piss off any leader or project manager.
The lesson here is always to ask ourselves: **Who else should I communicate this to?**
From my recent software projects, I've learned more about leadership, communication, and hiring than about any specific programming language or library.
***
_Hey, there! I'm Cesar, a software engineer and lifelong learner. Visit my [Gumroad page](https://imcsarag.gumroad.com) to download my ebooks and check my courses._ | canro91 |
1,873,863 | Até os ventos te sopram experiências 🍃 | Logo pela manhã você já está navegando pela tela do seu whatsapp procurando a mensagem de bom dia da... | 0 | 2024-06-03T04:59:12 | https://dev.to/milenaemmert/ate-os-ventos-te-sopram-experiencias-c9l | ux, uxdesign, webdev | Logo pela manhã você já está navegando pela tela do seu whatsapp procurando a mensagem de bom dia da sua mãe (a única que você quer responder logo em meio a tantas outras), ao tempo que está mexendo no layout do seu micro-ondas para aquecer por 15 segundos aquele café que sobrou de ontem, e pedindo para a Alexa falar quais são os seus compromissos do dia. Veja bem, você realizou diversas interações com **produtos**, **dispositivos** e **serviços** e nem se deu conta disso.
— Com quantos produtos ou coisas você interagiu?
— Três! O zap, o micro, e a Alexa!
Pois é...
- E o sistema operacional do seu celular?
- E a notificação do aplicativo de clima que você limpou da tela em meio a esse caos todo e nem percebeu?
- E o botão de ligar do micro-ondas que você tem que apertar com mais força que os outros porque ele já está mais gasto?
- Ah, e a porta do micro-ondas que você abriu, foi fácil de abrir ou respingou um café por aí?
Aliás, por que será que a porta do micro-ondas abre para o lado e não como a de um forno de fogão?
Todas as coisas que você usou, a tela, o aplicativo, os botões, são interfaces projetadas para gerar a interação entre você e o produto, ou seja, estão no contexto de interface do usuário (_user interface, UI_). Cada toque na tela, cada botão pressionado, cada comando de voz, cada momento de raiva que você passou, contribuem para a sua experiência num geral, e é isso que chamamos de experiência do usuário (_user experience, UX_).
A UX vai além da funcionalidade básica do produto. É necessário que os conceitos de facilidade de uso (usabilidade), intuitividade e eficiência sejam explorados nesse universo. Necessitamos de uma tela bonita? Na maioria das vezes sim! A estética sempre nos atraiu e não é diferente agora, mas uma tela bonita que não consegue fazer com que o usuário atinja o objetivo final de uso não serve para nada. Uma UI bonita não é garantia de nada e agora me pego procurando um porquê para estar lembrando da Amazon...
---
Quantas vezes você, usuário de Android, já abriu a Play Store quando na verdade queria abrir o Google Maps? É a nossa **intuitividade** nos pregando uma peça. Mas o fato de deixarmos esses apps distantes um dos outros ou categorizá-los de forma diferente já ajuda, e isso está incluso na **arquitetura da informação**, algo que também é muito importante para uma boa UX.
---
Apesar de eu trabalhar com tecnologia e estar imersa nesse contexto praticamente o tempo inteiro, o que me motivou a escrever esse texto foi a disposição de objetos num laboratório de exames e vacinação.
→ A maioria dos exames de sangue exigem um tempo em jejum (e se você for esfomeado igual a mim, já sai quase desmaiando de fome). Muitos laboratórios têm colocado uma máquina de café com bolachinhas e frutas na saída, onde você pode desfrutar um cafezinho e um lanchinho.
É claro que um cafezinho "de graça" não se nega, e eu fui lá na salinha. Apesar do dia frio, a sala estava um forno, e quando vi a situação das pessoas tomando um café atrás do outro e fazendo um rancho de bolacha eu logo entendi o motivo de tornar a sala uma experiência de sauna.
Mas outra coisa me chamou mais atenção: a máquina tinha letras miúdas dizendo _"Não é necessário colocar copos. A máquina já contém."_. E ao lado da máquina estava um porta-copos gigante (que era pra ser utilizado no bebedouro de água) e todos que chegavam lá automaticamente tiravam um copo do porta-copos e enfiavam na máquina no lugar de onde saía o café, a máquina lançava outro copo entortando o copo que estava embaixo, derrubava o café, atrasava a fila... 🙃

Experiências mundanas um tanto divertidas e nada sustentáveis.
Como sou uma pessoa empática e um tanto metida, avisei uma pessoa responsável sobre a questão dos copos. Ah, sei lá, vai que eles nunca perceberam a situação.
Se vão tomar alguma providência, eu não sei.
Se de fato acontece aquilo todos os dias, também não sei. E aí entra a importância da coleta e análise de dados para direcionar nossas ações e soluções com o foco em problemas reais, e não desperdiçar nosso tempo porque uma garota com fome viu coisas que talvez foram só coincidências que acontecerem num sábado aleatório de uma manhã fria e cinzenta na capital do Paraná.
---
Agora eu deixo um questionamento: será que deixar a sala numa temperatura de sauna é um **dark pattern** que o laboratório utiliza para as pessoas tomarem menos café?
Afinal é um laboratório bem conceituado que pertence a uma rede de diagnósticos gigante, e que com certeza entende muito bem de UX. 😊
Será que deixar um aviso para as pessoas tomarem apenas um café e pegar apenas uma bolachinha não resolveria o problema? Ok, sempre tem aqueles que adoram bancar os espertinhos, mas eu ainda quero acreditar que a maioria das pessoas são boas e honestas e respeitariam o pedido.
E deixar o porta-copos onde estava, poderia ser relacionado com um site enfrentando problemas de arquitetura da informação?
> Ou talvez seja só eu matutando coisas sem sentido, mas que quando vou observando a vida em diversos lugares, aparecem coisas tão sem sentido que eu só quero acreditar que devem ser propositais. 😬
Falando em dark patterns, estou com um alerta de uma configuração desnecessária no onedrive, porque por _algum motivo_ a Microsoft quer que eu configure do jeito deles.

---
Bom, quis deixar esse registro por aqui apenas para lembrar que UX e UI não estão apenas em dispositivos virtuais. É legal observar a vida como ela é para podermos levar essas vivências para dentro do mundo virtual e aprimorar a experiência do usuário.
Inclusive, nessa situação entra em jogo várias **heurísticas de Nielsen**, como a _Compatibilidade entre o sistema e o mundo real_, quando nos tornamos mais empáticos ao realizar observações e conseguimos trazer boas perspectivas para dentro do virtual, e uma análise criteriosa para a _Prevenção de erros_, afinal enfiar um copo em uma máquina que não precisa copo parte do erro de alguém, pois a primeira informação que notei na máquina foi o contato para conserto, ou seja, observo o **princípio da hierarquia** do design visual sendo mal utilizado.
---
Experiência, experiência. Não sei se tu que leu essa viagem até aqui é mais rico em paciência ou se te falta consciência. (~~inspirado~~ roubado do Eduardo Bueno)
Até um dia, quem sabe, talvez! ⋆.˚🦋༘⋆ | milenaemmert |
1,874,943 | Factory Spotlight: Leading Producers of Solar Garden Lights | Factory Spotlight: Leading Providers of Solar Garden Lighting Introduction: Did you ever listen of... | 0 | 2024-06-03T04:58:49 | https://dev.to/alex_damianisi_f1cfe95e60/factory-spotlight-leading-producers-of-solar-garden-lights-524p | spotlight | Factory Spotlight: Leading Providers of Solar Garden Lighting
Introduction:
Did you ever listen of solar garden lights? They truly are outside lights which use solar technology in the accepted place of electricity to work. We’ll introduce the producer that has been leading of garden talk plus lighting about their value, innovation, safeguards, use, company, quality, plus application.
Value:
Solar Garden Lights have actually pros that are many old-fashioned garden that has been electric. They've been dramatically eco-friendly, affordable, plus efficient. They have reduced run costs plus require minimal fix since they use solar power which are driven. Furthermore easy to install and will also be correctly put anywhere, even in remote areas minus use of electricity.
Innovation:
The producer that was leading of Solar Garden Lights try constantly improving plus innovating their products or services as service. They ordinarily utilize the technology that are latest to develop panel which was solar which will absorb sunlight that is many change it into energy. Their lights can also be made out of smart sensors that immediately activate at plus pull the plug on at dawn night.
Protection:
Solar Post Lights is safer to work with plus produce no threat of fire because electrocution. And tripping dangers because cables which are often unveiled simply because they don’t require any wiring, you don't need to concern your self. Furthermore, they're weather-resistant and might withstand circumstances being extreme harsh circumstances being outside.
Use:
Solar garden lights is versatile plus which can be correctly utilized in a quantity that is genuine of settings. They are perfect for illuminating pathways, gardens, patios, as well as other areas being outside. Their radiance which is soft creates pleasant plus environment that was inviting producing them ideal for outside gatherings plus strategies.
How to integrate:
Utilizing Solar Garden Lights or Fence Decoration which can be solar isn't difficult plus easy. Firstly, make sure the panel that is solar afflicted by sunshine for at the minimum 6-8 hours every single to charge the battery power time. Then, turn the light on utilising the noticeable modification provided. The light could instantly begin at plus switch off at dawn night.
Service:
The producer which is better of Solar Garden Lights creates customer which will be great plus services. They offer the guarantee regarding the products and services and they are often available to answer any conditions that is dilemmas that is appropriate people might have. In addition they build installation guides plus videos that are instructional be sure that their products or services as service are setup properly plus work optimally.
Quality:
The grade of the Solar Garden Lights produced by the producer which was key top-notch. They usually make use of top-notch goods that is durable plus durable. Their illumination are designed to be sustainable plus energy-efficient, reducing their impact on the environment.
Application:
Solar Garden Lights have actually quantity that are wide of and can be utilized in a total large amount of outside settings. They're suitable for domiciles, areas, leisure areas, plus faculties that are commercial. They may be able also be properly used in developing countries plus areas that are remote they don’t want electricity to exert effort.
Solar Garden Lights Products certainly are a great substitute for antique garden lights which was electric. They truly are eco-friendly, affordable, efficient, plus safer to utilize. The thing that is important of solar garden lights is dedicated to innovation, quality, plus client which was excellent, making certain their products or services as solutions try of the standard that are best. With their versatile applications, solar garden illumination is an excellent investment for almost any area that was outside.
Source: https://www.beslonsolarlight.com/Solar-Garden-lights | alex_damianisi_f1cfe95e60 |
1,874,942 | Hello world, I'm newbie | A post by Anh Tuan | 0 | 2024-06-03T04:57:05 | https://dev.to/ngao_pug/hello-world-im-newbie-3f6f | ngao_pug | ||
1,874,940 | Stay ahead in web development: latest news, tools, and insights #35 | weeklyfoo #35 is here: your weekly digest of all webdev news you need to know! This time you'll find 54 valuable links in 7 categories! Enjoy! | 0 | 2024-06-03T04:56:14 | https://weeklyfoo.com/foos/foo-035/ | webdev, weeklyfoo, javascript, node |
weeklyfoo #35 is here: your weekly digest of all webdev news you need to know! This time you'll find 54 valuable links in 7 categories! Enjoy!
## 🚀 Read it!
- <a href="https://newsletter.posthog.com/p/hiring-and-managing-cracked-engineers?utm_source=weeklyfoo&utm_medium=web&utm_campaign=weeklyfoo-35&ref=weeklyfoo" target="_blank" rel="noopener" ping="https://api.weeklyfoo.com/api/foo/bar?foo=eyJldmVudCI6InVybC1jbGljayIsInByb3BzIjp7InVybCI6Imh0dHBzOi8vbmV3c2xldHRlci5wb3N0aG9nLmNvbS9wL2hpcmluZy1hbmQtbWFuYWdpbmctY3JhY2tlZC1lbmdpbmVlcnMiLCJwcm9qZWN0Ijoid2Vla2x5Zm9vIiwiaW5kZXgiOjM1LCJzZWN0aW9uIjoicmVhZEl0Iiwic291cmNlIjoid2ViIn19">Hiring (and managing) cracked engineers</a>: Cracked - Term used for people who are insanely good at something<small> / </small><small>*career*, *productivity*</small><small> / </small><small>8 min read</small>
- <a href="https://maheshba.bitbucket.io/blog/2024/05/08/2024-ThreeLaws.html?utm_source=weeklyfoo&utm_medium=web&utm_campaign=weeklyfoo-35&ref=weeklyfoo" target="_blank" rel="noopener" ping="https://api.weeklyfoo.com/api/foo/bar?foo=eyJldmVudCI6InVybC1jbGljayIsInByb3BzIjp7InVybCI6Imh0dHBzOi8vbWFoZXNoYmEuYml0YnVja2V0LmlvL2Jsb2cvMjAyNC8wNS8wOC8yMDI0LVRocmVlTGF3cy5odG1sIiwicHJvamVjdCI6IndlZWtseWZvbyIsImluZGV4IjozNSwic2VjdGlvbiI6InJlYWRJdCIsInNvdXJjZSI6IndlYiJ9fQ%3D%3D">Three Laws of Software Complexity (or: why software engineers are always grumpy)</a>: Nah, we're not always grumpy ;)<small> / </small><small>*engineering*</small><small> / </small><small>4 min read</small>
<Hr />
## 📰 Good to know
- <a href="https://www.benkuhn.net/progessays/?utm_source=weeklyfoo&utm_medium=web&utm_campaign=weeklyfoo-35&ref=weeklyfoo" target="_blank" rel="noopener" ping="https://api.weeklyfoo.com/api/foo/bar?foo=eyJldmVudCI6InVybC1jbGljayIsInByb3BzIjp7InVybCI6Imh0dHBzOi8vd3d3LmJlbmt1aG4ubmV0L3Byb2dlc3NheXMvIiwicHJvamVjdCI6IndlZWtseWZvbyIsImluZGV4IjozNSwic2VjdGlvbiI6Imdvb2RUb0tub3ciLCJzb3VyY2UiOiJ3ZWIifX0%3D">Essays on programming I think about a lot</a>: Great list of articles for software development.<small> / </small><small>*productivity*</small><small> / </small><small>18 min read</small>
- <a href="https://stern.bearblog.dev/raw-hours/?utm_source=weeklyfoo&utm_medium=web&utm_campaign=weeklyfoo-35&ref=weeklyfoo" target="_blank" rel="noopener" ping="https://api.weeklyfoo.com/api/foo/bar?foo=eyJldmVudCI6InVybC1jbGljayIsInByb3BzIjp7InVybCI6Imh0dHBzOi8vc3Rlcm4uYmVhcmJsb2cuZGV2L3Jhdy1ob3Vycy8iLCJwcm9qZWN0Ijoid2Vla2x5Zm9vIiwiaW5kZXgiOjM1LCJzZWN0aW9uIjoiZ29vZFRvS25vdyIsInNvdXJjZSI6IndlYiJ9fQ%3D%3D">Raw hours</a>: Pretty quick read, but so much truth in it.<small> / </small><small>*productivity*</small><small> / </small><small>2 min read</small>
- <a href="https://www.pcloadletter.dev/blog/clever-code/?utm_source=weeklyfoo&utm_medium=web&utm_campaign=weeklyfoo-35&ref=weeklyfoo" target="_blank" rel="noopener" ping="https://api.weeklyfoo.com/api/foo/bar?foo=eyJldmVudCI6InVybC1jbGljayIsInByb3BzIjp7InVybCI6Imh0dHBzOi8vd3d3LnBjbG9hZGxldHRlci5kZXYvYmxvZy9jbGV2ZXItY29kZS8iLCJwcm9qZWN0Ijoid2Vla2x5Zm9vIiwiaW5kZXgiOjM1LCJzZWN0aW9uIjoiZ29vZFRvS25vdyIsInNvdXJjZSI6IndlYiJ9fQ%3D%3D">Write code that you can understand when you get paged at 2am</a>: A hymn to writing understandable code.<small> / </small><small>*coding*</small><small> / </small><small>6 min read</small>
- <a href="https://robindev.substack.com/p/cloudflare-took-down-our-website?utm_source=weeklyfoo&utm_medium=web&utm_campaign=weeklyfoo-35&ref=weeklyfoo" target="_blank" rel="noopener" ping="https://api.weeklyfoo.com/api/foo/bar?foo=eyJldmVudCI6InVybC1jbGljayIsInByb3BzIjp7InVybCI6Imh0dHBzOi8vcm9iaW5kZXYuc3Vic3RhY2suY29tL3AvY2xvdWRmbGFyZS10b29rLWRvd24tb3VyLXdlYnNpdGUiLCJwcm9qZWN0Ijoid2Vla2x5Zm9vIiwiaW5kZXgiOjM1LCJzZWN0aW9uIjoiZ29vZFRvS25vdyIsInNvdXJjZSI6IndlYiJ9fQ%3D%3D">Cloudflare took down our website after trying to force us to pay 120k$ within 24h</a>: Crazy story.<small> / </small><small>*cloudflare*</small><small> / </small><small>12 min read</small>
- <a href="https://www.approachwithalacrity.com/what-are-you-getting-paid-in/?utm_source=weeklyfoo&utm_medium=web&utm_campaign=weeklyfoo-35&ref=weeklyfoo" target="_blank" rel="noopener" ping="https://api.weeklyfoo.com/api/foo/bar?foo=eyJldmVudCI6InVybC1jbGljayIsInByb3BzIjp7InVybCI6Imh0dHBzOi8vd3d3LmFwcHJvYWNod2l0aGFsYWNyaXR5LmNvbS93aGF0LWFyZS15b3UtZ2V0dGluZy1wYWlkLWluLyIsInByb2plY3QiOiJ3ZWVrbHlmb28iLCJpbmRleCI6MzUsInNlY3Rpb24iOiJnb29kVG9Lbm93Iiwic291cmNlIjoid2ViIn19">What are you getting paid in?</a>: Interesting view on salary and other things you are paid in.<small> / </small><small>*career*</small><small> / </small><small>7 min read</small>
- <a href="https://chasem.co/2024/05/css-animations?utm_source=weeklyfoo&utm_medium=web&utm_campaign=weeklyfoo-35&ref=weeklyfoo" target="_blank" rel="noopener" ping="https://api.weeklyfoo.com/api/foo/bar?foo=eyJldmVudCI6InVybC1jbGljayIsInByb3BzIjp7InVybCI6Imh0dHBzOi8vY2hhc2VtLmNvLzIwMjQvMDUvY3NzLWFuaW1hdGlvbnMiLCJwcm9qZWN0Ijoid2Vla2x5Zm9vIiwiaW5kZXgiOjM1LCJzZWN0aW9uIjoiZ29vZFRvS25vdyIsInNvdXJjZSI6IndlYiJ9fQ%3D%3D">New Magic For Animations in CSS</a>: Some simplifications for animations<small> / </small><small>*css*</small><small> / </small><small>5 min read</small>
- <a href="https://blog.ploetzli.ch/2024/should-i-use-jwt-for-authentication/?utm_source=weeklyfoo&utm_medium=web&utm_campaign=weeklyfoo-35&ref=weeklyfoo" target="_blank" rel="noopener" ping="https://api.weeklyfoo.com/api/foo/bar?foo=eyJldmVudCI6InVybC1jbGljayIsInByb3BzIjp7InVybCI6Imh0dHBzOi8vYmxvZy5wbG9ldHpsaS5jaC8yMDI0L3Nob3VsZC1pLXVzZS1qd3QtZm9yLWF1dGhlbnRpY2F0aW9uLyIsInByb2plY3QiOiJ3ZWVrbHlmb28iLCJpbmRleCI6MzUsInNlY3Rpb24iOiJnb29kVG9Lbm93Iiwic291cmNlIjoid2ViIn19">Should I Use jwts For Authentication Tokens?</a>: Short answer: No - but there's also a long answer ;)<small> / </small><small>*auth*</small><small> / </small><small>16 min read</small>
- <a href="https://www.ntietz.com/blog/lets-say-instead-of-auth/?utm_source=weeklyfoo&utm_medium=web&utm_campaign=weeklyfoo-35&ref=weeklyfoo" target="_blank" rel="noopener" ping="https://api.weeklyfoo.com/api/foo/bar?foo=eyJldmVudCI6InVybC1jbGljayIsInByb3BzIjp7InVybCI6Imh0dHBzOi8vd3d3Lm50aWV0ei5jb20vYmxvZy9sZXRzLXNheS1pbnN0ZWFkLW9mLWF1dGgvIiwicHJvamVjdCI6IndlZWtseWZvbyIsImluZGV4IjozNSwic2VjdGlvbiI6Imdvb2RUb0tub3ciLCJzb3VyY2UiOiJ3ZWIifX0%3D">Instead of 'auth', we should say 'permissions' and 'login'</a>: Good idea!<small> / </small><small>*auth*</small><small> / </small><small>4 min read</small>
- <a href="https://theengineeringmanager.substack.com/p/the-disappointment-frontier?utm_source=weeklyfoo&utm_medium=web&utm_campaign=weeklyfoo-35&ref=weeklyfoo" target="_blank" rel="noopener" ping="https://api.weeklyfoo.com/api/foo/bar?foo=eyJldmVudCI6InVybC1jbGljayIsInByb3BzIjp7InVybCI6Imh0dHBzOi8vdGhlZW5naW5lZXJpbmdtYW5hZ2VyLnN1YnN0YWNrLmNvbS9wL3RoZS1kaXNhcHBvaW50bWVudC1mcm9udGllciIsInByb2plY3QiOiJ3ZWVrbHlmb28iLCJpbmRleCI6MzUsInNlY3Rpb24iOiJnb29kVG9Lbm93Iiwic291cmNlIjoid2ViIn19">The Disappointment Frontier</a>: Keeping your team far from reality can cause a big fat mess.<small> / </small><small>*performance*, *management*</small><small> / </small><small>12 min read</small>
- <a href="https://react.dev/blog/2024/05/22/react-conf-2024-recap?utm_source=weeklyfoo&utm_medium=web&utm_campaign=weeklyfoo-35&ref=weeklyfoo" target="_blank" rel="noopener" ping="https://api.weeklyfoo.com/api/foo/bar?foo=eyJldmVudCI6InVybC1jbGljayIsInByb3BzIjp7InVybCI6Imh0dHBzOi8vcmVhY3QuZGV2L2Jsb2cvMjAyNC8wNS8yMi9yZWFjdC1jb25mLTIwMjQtcmVjYXAiLCJwcm9qZWN0Ijoid2Vla2x5Zm9vIiwiaW5kZXgiOjM1LCJzZWN0aW9uIjoiZ29vZFRvS25vdyIsInNvdXJjZSI6IndlYiJ9fQ%3D%3D">React Conf 2024 Recap</a>: All you need to know from React Conf<small> / </small><small>*react*</small><small> / </small><small>7 min read</small>
- <a href="https://slashpages.net/?utm_source=weeklyfoo&utm_medium=web&utm_campaign=weeklyfoo-35&ref=weeklyfoo" target="_blank" rel="noopener" ping="https://api.weeklyfoo.com/api/foo/bar?foo=eyJldmVudCI6InVybC1jbGljayIsInByb3BzIjp7InVybCI6Imh0dHBzOi8vc2xhc2hwYWdlcy5uZXQvIiwicHJvamVjdCI6IndlZWtseWZvbyIsImluZGV4IjozNSwic2VjdGlvbiI6Imdvb2RUb0tub3ciLCJzb3VyY2UiOiJ3ZWIifX0%3D">Slash Pages</a>: A guide to common pages you can add to your website<small> / </small><small>*pages*</small><small> / </small><small>4 min read</small>
- <a href="https://email.ml/?utm_source=weeklyfoo&utm_medium=web&utm_campaign=weeklyfoo-35&ref=weeklyfoo" target="_blank" rel="noopener" ping="https://api.weeklyfoo.com/api/foo/bar?foo=eyJldmVudCI6InVybC1jbGljayIsInByb3BzIjp7InVybCI6Imh0dHBzOi8vZW1haWwubWwvIiwicHJvamVjdCI6IndlZWtseWZvbyIsImluZGV4IjozNSwic2VjdGlvbiI6Imdvb2RUb0tub3ciLCJzb3VyY2UiOiJ3ZWIifX0%3D">Email.ML</a>: Minimalist temporary Email<small> / </small><small>*email*</small><small> / </small><small>1 min read</small>
- <a href="https://hiandrewquinn.github.io/til-site/posts/doing-is-normally-distributed-learning-is-log-normal/?utm_source=weeklyfoo&utm_medium=web&utm_campaign=weeklyfoo-35&ref=weeklyfoo" target="_blank" rel="noopener" ping="https://api.weeklyfoo.com/api/foo/bar?foo=eyJldmVudCI6InVybC1jbGljayIsInByb3BzIjp7InVybCI6Imh0dHBzOi8vaGlhbmRyZXdxdWlubi5naXRodWIuaW8vdGlsLXNpdGUvcG9zdHMvZG9pbmctaXMtbm9ybWFsbHktZGlzdHJpYnV0ZWQtbGVhcm5pbmctaXMtbG9nLW5vcm1hbC8iLCJwcm9qZWN0Ijoid2Vla2x5Zm9vIiwiaW5kZXgiOjM1LCJzZWN0aW9uIjoiZ29vZFRvS25vdyIsInNvdXJjZSI6IndlYiJ9fQ%3D%3D">Doing is normally distributed, learning is log-normal</a>: My conspiracy theory on why software estimation is such garbage<small> / </small><small>*productivity*</small><small> / </small><small>5 min read</small>
- <a href="https://rachelbythebay.com/w/2024/05/27/feed/?utm_source=weeklyfoo&utm_medium=web&utm_campaign=weeklyfoo-35&ref=weeklyfoo" target="_blank" rel="noopener" ping="https://api.weeklyfoo.com/api/foo/bar?foo=eyJldmVudCI6InVybC1jbGljayIsInByb3BzIjp7InVybCI6Imh0dHBzOi8vcmFjaGVsYnl0aGViYXkuY29tL3cvMjAyNC8wNS8yNy9mZWVkLyIsInByb2plY3QiOiJ3ZWVrbHlmb28iLCJpbmRleCI6MzUsInNlY3Rpb24iOiJnb29kVG9Lbm93Iiwic291cmNlIjoid2ViIn19">So many feed readers, so many bizarre behaviors</a>: Implications after introducing 429s for too many requests.<small> / </small><small>*api*, *rss*</small><small> / </small><small>7 min read</small>
- <a href="https://developer.chrome.com/blog/anchor-positioning-api?utm_source=weeklyfoo&utm_medium=web&utm_campaign=weeklyfoo-35&ref=weeklyfoo" target="_blank" rel="noopener" ping="https://api.weeklyfoo.com/api/foo/bar?foo=eyJldmVudCI6InVybC1jbGljayIsInByb3BzIjp7InVybCI6Imh0dHBzOi8vZGV2ZWxvcGVyLmNocm9tZS5jb20vYmxvZy9hbmNob3ItcG9zaXRpb25pbmctYXBpIiwicHJvamVjdCI6IndlZWtseWZvbyIsImluZGV4IjozNSwic2VjdGlvbiI6Imdvb2RUb0tub3ciLCJzb3VyY2UiOiJ3ZWIifX0%3D">Introducing the CSS anchor positioning API</a>: That could solve a lot of issues.<small> / </small><small>*css*</small><small> / </small><small>15 min read</small>
- <a href="https://www.dolthub.com/blog/2024-05-28-160-bits/?utm_source=weeklyfoo&utm_medium=web&utm_campaign=weeklyfoo-35&ref=weeklyfoo" target="_blank" rel="noopener" ping="https://api.weeklyfoo.com/api/foo/bar?foo=eyJldmVudCI6InVybC1jbGljayIsInByb3BzIjp7InVybCI6Imh0dHBzOi8vd3d3LmRvbHRodWIuY29tL2Jsb2cvMjAyNC0wNS0yOC0xNjAtYml0cy8iLCJwcm9qZWN0Ijoid2Vla2x5Zm9vIiwiaW5kZXgiOjM1LCJzZWN0aW9uIjoiZ29vZFRvS25vdyIsInNvdXJjZSI6IndlYiJ9fQ%3D%3D">How Large is a 160 Bit Number?</a>: What an enjoyable read!<small> / </small><small>*numbers*</small><small> / </small><small>12 min read</small>
- <a href="https://www.amitmerchant.com/little-devtools-snippet-to-check-broken-links-on-a-webpage/?utm_source=weeklyfoo&utm_medium=web&utm_campaign=weeklyfoo-35&ref=weeklyfoo" target="_blank" rel="noopener" ping="https://api.weeklyfoo.com/api/foo/bar?foo=eyJldmVudCI6InVybC1jbGljayIsInByb3BzIjp7InVybCI6Imh0dHBzOi8vd3d3LmFtaXRtZXJjaGFudC5jb20vbGl0dGxlLWRldnRvb2xzLXNuaXBwZXQtdG8tY2hlY2stYnJva2VuLWxpbmtzLW9uLWEtd2VicGFnZS8iLCJwcm9qZWN0Ijoid2Vla2x5Zm9vIiwiaW5kZXgiOjM1LCJzZWN0aW9uIjoiZ29vZFRvS25vdyIsInNvdXJjZSI6IndlYiJ9fQ%3D%3D">A little DevTools snippet to check broken links on a webpage</a>: Handy snippet to check all links on a web page.<small> / </small><small>*snippet*, *href*</small><small> / </small><small>4 min read</small>
- <a href="https://read.engineerscodex.com/p/4-software-design-principles-i-learned?utm_source=weeklyfoo&utm_medium=web&utm_campaign=weeklyfoo-35&ref=weeklyfoo" target="_blank" rel="noopener" ping="https://api.weeklyfoo.com/api/foo/bar?foo=eyJldmVudCI6InVybC1jbGljayIsInByb3BzIjp7InVybCI6Imh0dHBzOi8vcmVhZC5lbmdpbmVlcnNjb2RleC5jb20vcC80LXNvZnR3YXJlLWRlc2lnbi1wcmluY2lwbGVzLWktbGVhcm5lZCIsInByb2plY3QiOiJ3ZWVrbHlmb28iLCJpbmRleCI6MzUsInNlY3Rpb24iOiJnb29kVG9Lbm93Iiwic291cmNlIjoid2ViIn19">4 Software Design Principles I Learned the Hard Way</a>: If there’s two sources of truth, one is probably wrong. And yes, please repeat yourself.<small> / </small><small>*engineering*</small><small> / </small><small>8 min read</small>
- <a href="https://mtlynch.io/i-sold-tinypilot/?utm_source=weeklyfoo&utm_medium=web&utm_campaign=weeklyfoo-35&ref=weeklyfoo" target="_blank" rel="noopener" ping="https://api.weeklyfoo.com/api/foo/bar?foo=eyJldmVudCI6InVybC1jbGljayIsInByb3BzIjp7InVybCI6Imh0dHBzOi8vbXRseW5jaC5pby9pLXNvbGQtdGlueXBpbG90LyIsInByb2plY3QiOiJ3ZWVrbHlmb28iLCJpbmRleCI6MzUsInNlY3Rpb24iOiJnb29kVG9Lbm93Iiwic291cmNlIjoid2ViIn19">I Sold TinyPilot, My First Successful Business</a>: About an ex-Googler that started his own business and sold it.<small> / </small><small>*startups*</small><small> / </small><small>18 min read</small>
- <a href="https://blog.1password.com/new-extension-build-system/?utm_source=weeklyfoo&utm_medium=web&utm_campaign=weeklyfoo-35&ref=weeklyfoo" target="_blank" rel="noopener" ping="https://api.weeklyfoo.com/api/foo/bar?foo=eyJldmVudCI6InVybC1jbGljayIsInByb3BzIjp7InVybCI6Imh0dHBzOi8vYmxvZy4xcGFzc3dvcmQuY29tL25ldy1leHRlbnNpb24tYnVpbGQtc3lzdGVtLyIsInByb2plY3QiOiJ3ZWVrbHlmb28iLCJpbmRleCI6MzUsInNlY3Rpb24iOiJnb29kVG9Lbm93Iiwic291cmNlIjoid2ViIn19">How we used esbuild to reduce our browser extension build times by 90%</a>: Including type checks!<small> / </small><small>*ci*</small><small> / </small><small>22 min read</small>
- <a href="https://astro.build/blog/astro-490/?utm_source=weeklyfoo&utm_medium=web&utm_campaign=weeklyfoo-35&ref=weeklyfoo" target="_blank" rel="noopener" ping="https://api.weeklyfoo.com/api/foo/bar?foo=eyJldmVudCI6InVybC1jbGljayIsInByb3BzIjp7InVybCI6Imh0dHBzOi8vYXN0cm8uYnVpbGQvYmxvZy9hc3Ryby00OTAvIiwicHJvamVjdCI6IndlZWtseWZvbyIsImluZGV4IjozNSwic2VjdGlvbiI6Imdvb2RUb0tub3ciLCJzb3VyY2UiOiJ3ZWIifX0%3D">Astro 4.9</a>: Next minor release of Astro<small> / </small><small>*astro*</small><small> / </small><small>6 min read</small>
- <a href="https://github.com/theninthsky/client-side-rendering?utm_source=weeklyfoo&utm_medium=web&utm_campaign=weeklyfoo-35&ref=weeklyfoo" target="_blank" rel="noopener" ping="https://api.weeklyfoo.com/api/foo/bar?foo=eyJldmVudCI6InVybC1jbGljayIsInByb3BzIjp7InVybCI6Imh0dHBzOi8vZ2l0aHViLmNvbS90aGVuaW50aHNreS9jbGllbnQtc2lkZS1yZW5kZXJpbmciLCJwcm9qZWN0Ijoid2Vla2x5Zm9vIiwiaW5kZXgiOjM1LCJzZWN0aW9uIjoiZ29vZFRvS25vdyIsInNvdXJjZSI6IndlYiJ9fQ%3D%3D">Client-side rendering</a>: A case study of CSR.<small> / </small><small>*csr*</small><small> / </small><small>42 min read</small>
- <a href="https://bessey.dev/blog/2024/05/24/why-im-over-graphql/?utm_source=weeklyfoo&utm_medium=web&utm_campaign=weeklyfoo-35&ref=weeklyfoo" target="_blank" rel="noopener" ping="https://api.weeklyfoo.com/api/foo/bar?foo=eyJldmVudCI6InVybC1jbGljayIsInByb3BzIjp7InVybCI6Imh0dHBzOi8vYmVzc2V5LmRldi9ibG9nLzIwMjQvMDUvMjQvd2h5LWltLW92ZXItZ3JhcGhxbC8iLCJwcm9qZWN0Ijoid2Vla2x5Zm9vIiwiaW5kZXgiOjM1LCJzZWN0aW9uIjoiZ29vZFRvS25vdyIsInNvdXJjZSI6IndlYiJ9fQ%3D%3D">Why, after 6 years, I’m over GraphQL</a>: Prior GraphQL advocate does not recommend GraphQL anymore.<small> / </small><small>*graphql*</small><small> / </small><small>13 min read</small>
- <a href="https://boz.com/articles/inbox-ten?utm_source=weeklyfoo&utm_medium=web&utm_campaign=weeklyfoo-35&ref=weeklyfoo" target="_blank" rel="noopener" ping="https://api.weeklyfoo.com/api/foo/bar?foo=eyJldmVudCI6InVybC1jbGljayIsInByb3BzIjp7InVybCI6Imh0dHBzOi8vYm96LmNvbS9hcnRpY2xlcy9pbmJveC10ZW4iLCJwcm9qZWN0Ijoid2Vla2x5Zm9vIiwiaW5kZXgiOjM1LCJzZWN0aW9uIjoiZ29vZFRvS25vdyIsInNvdXJjZSI6IndlYiJ9fQ%3D%3D">Inbox ten</a>: Useful adjustment to Inbox Zero<small> / </small><small>*productivity*</small><small> / </small><small>8 min read</small>
<Hr />
## 🧰 Tools
- <a href="https://github.com/glebbash/LO?utm_source=weeklyfoo&utm_medium=web&utm_campaign=weeklyfoo-35&ref=weeklyfoo" target="_blank" rel="noopener" ping="https://api.weeklyfoo.com/api/foo/bar?foo=eyJldmVudCI6InVybC1jbGljayIsInByb3BzIjp7InVybCI6Imh0dHBzOi8vZ2l0aHViLmNvbS9nbGViYmFzaC9MTyIsInByb2plY3QiOiJ3ZWVrbHlmb28iLCJpbmRleCI6MzUsInNlY3Rpb24iOiJ0b29scyIsInNvdXJjZSI6IndlYiJ9fQ%3D%3D">LO</a>: small programming language targeting WASM that aims to be as simple as possible<small> / </small><small>*wasm*</small>
- <a href="https://www.visiwig.com/patterns/?utm_source=weeklyfoo&utm_medium=web&utm_campaign=weeklyfoo-35&ref=weeklyfoo" target="_blank" rel="noopener" ping="https://api.weeklyfoo.com/api/foo/bar?foo=eyJldmVudCI6InVybC1jbGljayIsInByb3BzIjp7InVybCI6Imh0dHBzOi8vd3d3LnZpc2l3aWcuY29tL3BhdHRlcm5zLyIsInByb2plY3QiOiJ3ZWVrbHlmb28iLCJpbmRleCI6MzUsInNlY3Rpb24iOiJ0b29scyIsInNvdXJjZSI6IndlYiJ9fQ%3D%3D">Vector Pattern Generator</a>: Create vector patterns.<small> / </small><small>*vector*, *patterns*</small>
- <a href="https://github.com/ynqa/sig?utm_source=weeklyfoo&utm_medium=web&utm_campaign=weeklyfoo-35&ref=weeklyfoo" target="_blank" rel="noopener" ping="https://api.weeklyfoo.com/api/foo/bar?foo=eyJldmVudCI6InVybC1jbGljayIsInByb3BzIjp7InVybCI6Imh0dHBzOi8vZ2l0aHViLmNvbS95bnFhL3NpZyIsInByb2plY3QiOiJ3ZWVrbHlmb28iLCJpbmRleCI6MzUsInNlY3Rpb24iOiJ0b29scyIsInNvdXJjZSI6IndlYiJ9fQ%3D%3D">sig</a>: Interactive grep (for streaming)<small> / </small><small>*cli*</small>
- <a href="https://github.com/chakra-ui/ark?utm_source=weeklyfoo&utm_medium=web&utm_campaign=weeklyfoo-35&ref=weeklyfoo" target="_blank" rel="noopener" ping="https://api.weeklyfoo.com/api/foo/bar?foo=eyJldmVudCI6InVybC1jbGljayIsInByb3BzIjp7InVybCI6Imh0dHBzOi8vZ2l0aHViLmNvbS9jaGFrcmEtdWkvYXJrIiwicHJvamVjdCI6IndlZWtseWZvbyIsImluZGV4IjozNSwic2VjdGlvbiI6InRvb2xzIiwic291cmNlIjoid2ViIn19">Ark</a>: A headless library for building reusable, scalable design systems that works for a wide range of JS frameworks.<small> / </small><small>*react*, *web-components*</small>
- <a href="https://github.com/dream-num/univer?utm_source=weeklyfoo&utm_medium=web&utm_campaign=weeklyfoo-35&ref=weeklyfoo" target="_blank" rel="noopener" ping="https://api.weeklyfoo.com/api/foo/bar?foo=eyJldmVudCI6InVybC1jbGljayIsInByb3BzIjp7InVybCI6Imh0dHBzOi8vZ2l0aHViLmNvbS9kcmVhbS1udW0vdW5pdmVyIiwicHJvamVjdCI6IndlZWtseWZvbyIsImluZGV4IjozNSwic2VjdGlvbiI6InRvb2xzIiwic291cmNlIjoid2ViIn19">Univer</a>: Univer is an open-source alternative to Google Sheets, Slides, and Docs<small> / </small><small>*office*</small>
- <a href="https://superdesigner.co/tools/patterns?utm_source=weeklyfoo&utm_medium=web&utm_campaign=weeklyfoo-35&ref=weeklyfoo" target="_blank" rel="noopener" ping="https://api.weeklyfoo.com/api/foo/bar?foo=eyJldmVudCI6InVybC1jbGljayIsInByb3BzIjp7InVybCI6Imh0dHBzOi8vc3VwZXJkZXNpZ25lci5jby90b29scy9wYXR0ZXJucyIsInByb2plY3QiOiJ3ZWVrbHlmb28iLCJpbmRleCI6MzUsInNlY3Rpb24iOiJ0b29scyIsInNvdXJjZSI6IndlYiJ9fQ%3D%3D">Pattern generator</a>: Another pattern generator<small> / </small><small>*shapes*, *patterns*</small>
- <a href="https://features.vote/?utm_source=weeklyfoo&utm_medium=web&utm_campaign=weeklyfoo-35&ref=weeklyfoo" target="_blank" rel="noopener" ping="https://api.weeklyfoo.com/api/foo/bar?foo=eyJldmVudCI6InVybC1jbGljayIsInByb3BzIjp7InVybCI6Imh0dHBzOi8vZmVhdHVyZXMudm90ZS8iLCJwcm9qZWN0Ijoid2Vla2x5Zm9vIiwiaW5kZXgiOjM1LCJzZWN0aW9uIjoidG9vbHMiLCJzb3VyY2UiOiJ3ZWIifX0%3D">Features.Vote</a>: Drive your product's growth with clarity by letting users post and vote on the features they want.<small> / </small><small>*features*</small>
- <a href="https://github.com/joye61/pic-smaller?utm_source=weeklyfoo&utm_medium=web&utm_campaign=weeklyfoo-35&ref=weeklyfoo" target="_blank" rel="noopener" ping="https://api.weeklyfoo.com/api/foo/bar?foo=eyJldmVudCI6InVybC1jbGljayIsInByb3BzIjp7InVybCI6Imh0dHBzOi8vZ2l0aHViLmNvbS9qb3llNjEvcGljLXNtYWxsZXIiLCJwcm9qZWN0Ijoid2Vla2x5Zm9vIiwiaW5kZXgiOjM1LCJzZWN0aW9uIjoidG9vbHMiLCJzb3VyY2UiOiJ3ZWIifX0%3D">pic-smaller</a>: Pic Smaller – Compress JPEG, PNG, WEBP, AVIF, SVG and GIF images intelligently<small> / </small><small>*images*, *compression*</small>
- <a href="https://typehints.org/?utm_source=weeklyfoo&utm_medium=web&utm_campaign=weeklyfoo-35&ref=weeklyfoo" target="_blank" rel="noopener" ping="https://api.weeklyfoo.com/api/foo/bar?foo=eyJldmVudCI6InVybC1jbGljayIsInByb3BzIjp7InVybCI6Imh0dHBzOi8vdHlwZWhpbnRzLm9yZy8iLCJwcm9qZWN0Ijoid2Vla2x5Zm9vIiwiaW5kZXgiOjM1LCJzZWN0aW9uIjoidG9vbHMiLCJzb3VyY2UiOiJ3ZWIifX0%3D">TypeHints</a>: These are answers to all the questions I had as a beginner in TypeScript.<small> / </small><small>*typescript*, *learning*</small>
- <a href="https://github.com/dolthub/dolt?utm_source=weeklyfoo&utm_medium=web&utm_campaign=weeklyfoo-35&ref=weeklyfoo" target="_blank" rel="noopener" ping="https://api.weeklyfoo.com/api/foo/bar?foo=eyJldmVudCI6InVybC1jbGljayIsInByb3BzIjp7InVybCI6Imh0dHBzOi8vZ2l0aHViLmNvbS9kb2x0aHViL2RvbHQiLCJwcm9qZWN0Ijoid2Vla2x5Zm9vIiwiaW5kZXgiOjM1LCJzZWN0aW9uIjoidG9vbHMiLCJzb3VyY2UiOiJ3ZWIifX0%3D">dolt</a>: Git for Data<small> / </small><small>*data*, *database*</small>
- <a href="https://github.com/ragapp/ragapp?utm_source=weeklyfoo&utm_medium=web&utm_campaign=weeklyfoo-35&ref=weeklyfoo" target="_blank" rel="noopener" ping="https://api.weeklyfoo.com/api/foo/bar?foo=eyJldmVudCI6InVybC1jbGljayIsInByb3BzIjp7InVybCI6Imh0dHBzOi8vZ2l0aHViLmNvbS9yYWdhcHAvcmFnYXBwIiwicHJvamVjdCI6IndlZWtseWZvbyIsImluZGV4IjozNSwic2VjdGlvbiI6InRvb2xzIiwic291cmNlIjoid2ViIn19">RAGapp</a>: The easiest way to use Agentic RAG in any enterprise<small> / </small><small>*ai*, *rag*</small>
- <a href="https://github.com/fontsource/fontsource?utm_source=weeklyfoo&utm_medium=web&utm_campaign=weeklyfoo-35&ref=weeklyfoo" target="_blank" rel="noopener" ping="https://api.weeklyfoo.com/api/foo/bar?foo=eyJldmVudCI6InVybC1jbGljayIsInByb3BzIjp7InVybCI6Imh0dHBzOi8vZ2l0aHViLmNvbS9mb250c291cmNlL2ZvbnRzb3VyY2UiLCJwcm9qZWN0Ijoid2Vla2x5Zm9vIiwiaW5kZXgiOjM1LCJzZWN0aW9uIjoidG9vbHMiLCJzb3VyY2UiOiJ3ZWIifX0%3D">Fontsource</a>: Self-host Open Source fonts in neatly bundled NPM packages.<small> / </small><small>*fonts*</small>
- <a href="https://github.com/grucloud/bau?utm_source=weeklyfoo&utm_medium=web&utm_campaign=weeklyfoo-35&ref=weeklyfoo" target="_blank" rel="noopener" ping="https://api.weeklyfoo.com/api/foo/bar?foo=eyJldmVudCI6InVybC1jbGljayIsInByb3BzIjp7InVybCI6Imh0dHBzOi8vZ2l0aHViLmNvbS9ncnVjbG91ZC9iYXUiLCJwcm9qZWN0Ijoid2Vla2x5Zm9vIiwiaW5kZXgiOjM1LCJzZWN0aW9uIjoidG9vbHMiLCJzb3VyY2UiOiJ3ZWIifX0%3D">bau.js</a>: Reactive library and components for building web user interface<small> / </small><small>*ui*</small>
- <a href="https://encore.dev/?utm_source=weeklyfoo&utm_medium=web&utm_campaign=weeklyfoo-35&ref=weeklyfoo" target="_blank" rel="noopener" ping="https://api.weeklyfoo.com/api/foo/bar?foo=eyJldmVudCI6InVybC1jbGljayIsInByb3BzIjp7InVybCI6Imh0dHBzOi8vZW5jb3JlLmRldi8iLCJwcm9qZWN0Ijoid2Vla2x5Zm9vIiwiaW5kZXgiOjM1LCJzZWN0aW9uIjoidG9vbHMiLCJzb3VyY2UiOiJ3ZWIifX0%3D">encore</a>: Encore is the Development Platform for startups building event-driven and distributed systems.<small> / </small><small>*infra*</small>
- <a href="https://earthly.dev/?utm_source=weeklyfoo&utm_medium=web&utm_campaign=weeklyfoo-35&ref=weeklyfoo" target="_blank" rel="noopener" ping="https://api.weeklyfoo.com/api/foo/bar?foo=eyJldmVudCI6InVybC1jbGljayIsInByb3BzIjp7InVybCI6Imh0dHBzOi8vZWFydGhseS5kZXYvIiwicHJvamVjdCI6IndlZWtseWZvbyIsImluZGV4IjozNSwic2VjdGlvbiI6InRvb2xzIiwic291cmNlIjoid2ViIn19">earthly</a>: Fast, consistent builds with an instantly familiar syntax – like Dockerfile and Makefile had a baby.<small> / </small><small>*ci*</small>
- <a href="https://github.com/dlvhdr/gh-dash?utm_source=weeklyfoo&utm_medium=web&utm_campaign=weeklyfoo-35&ref=weeklyfoo" target="_blank" rel="noopener" ping="https://api.weeklyfoo.com/api/foo/bar?foo=eyJldmVudCI6InVybC1jbGljayIsInByb3BzIjp7InVybCI6Imh0dHBzOi8vZ2l0aHViLmNvbS9kbHZoZHIvZ2gtZGFzaCIsInByb2plY3QiOiJ3ZWVrbHlmb28iLCJpbmRleCI6MzUsInNlY3Rpb24iOiJ0b29scyIsInNvdXJjZSI6IndlYiJ9fQ%3D%3D">gh-dash</a>: A beautiful CLI dashboard for GitHub<small> / </small><small>*github*, *cli*</small>
- <a href="https://css-pattern.com/?utm_source=weeklyfoo&utm_medium=web&utm_campaign=weeklyfoo-35&ref=weeklyfoo" target="_blank" rel="noopener" ping="https://api.weeklyfoo.com/api/foo/bar?foo=eyJldmVudCI6InVybC1jbGljayIsInByb3BzIjp7InVybCI6Imh0dHBzOi8vY3NzLXBhdHRlcm4uY29tLyIsInByb2plY3QiOiJ3ZWVrbHlmb28iLCJpbmRleCI6MzUsInNlY3Rpb24iOiJ0b29scyIsInNvdXJjZSI6IndlYiJ9fQ%3D%3D">CSS Pattern</a>: Explore 144 CSS-only patterns made with CSS gradients and optimized with CSS variables.<small> / </small><small>*css*, *gradients*</small>
- <a href="https://airtable.com/appGc7YdwCFVYwTK8/shrY4CRFRaIhLjiBe/tbldCHol3ABwHG9ex?utm_source=weeklyfoo&utm_medium=web&utm_campaign=weeklyfoo-35&ref=weeklyfoo" target="_blank" rel="noopener" ping="https://api.weeklyfoo.com/api/foo/bar?foo=eyJldmVudCI6InVybC1jbGljayIsInByb3BzIjp7InVybCI6Imh0dHBzOi8vYWlydGFibGUuY29tL2FwcEdjN1lkd0NGVll3VEs4L3Noclk0Q1JGUmFJaExqaUJlL3RibGRDSG9sM0FCd0hHOWV4IiwicHJvamVjdCI6IndlZWtseWZvbyIsImluZGV4IjozNSwic2VjdGlvbiI6InRvb2xzIiwic291cmNlIjoid2ViIn19">Art Style Gallery</a>: AI prompts<small> / </small><small>*ai*, *prompts*</small>
- <a href="https://aem1k.com/?utm_source=weeklyfoo&utm_medium=web&utm_campaign=weeklyfoo-35&ref=weeklyfoo" target="_blank" rel="noopener" ping="https://api.weeklyfoo.com/api/foo/bar?foo=eyJldmVudCI6InVybC1jbGljayIsInByb3BzIjp7InVybCI6Imh0dHBzOi8vYWVtMWsuY29tLyIsInByb2plY3QiOiJ3ZWVrbHlmb28iLCJpbmRleCI6MzUsInNlY3Rpb24iOiJ0b29scyIsInNvdXJjZSI6IndlYiJ9fQ%3D%3D">JS Hacks & Creativity</a>: This is awesome!<small> / </small><small>*javascript*</small>
- <a href="https://github.com/rossmoody/svg-gobbler?utm_source=weeklyfoo&utm_medium=web&utm_campaign=weeklyfoo-35&ref=weeklyfoo" target="_blank" rel="noopener" ping="https://api.weeklyfoo.com/api/foo/bar?foo=eyJldmVudCI6InVybC1jbGljayIsInByb3BzIjp7InVybCI6Imh0dHBzOi8vZ2l0aHViLmNvbS9yb3NzbW9vZHkvc3ZnLWdvYmJsZXIiLCJwcm9qZWN0Ijoid2Vla2x5Zm9vIiwiaW5kZXgiOjM1LCJzZWN0aW9uIjoidG9vbHMiLCJzb3VyY2UiOiJ3ZWIifX0%3D">SVG Gobbler</a>: Open source browser extension for finding, editing, exporting, optimizing, and managing SVG content.<small> / </small><small>*svg*, *extension*</small>
- <a href="https://github.com/wojtekmaj/react-pdf?utm_source=weeklyfoo&utm_medium=web&utm_campaign=weeklyfoo-35&ref=weeklyfoo" target="_blank" rel="noopener" ping="https://api.weeklyfoo.com/api/foo/bar?foo=eyJldmVudCI6InVybC1jbGljayIsInByb3BzIjp7InVybCI6Imh0dHBzOi8vZ2l0aHViLmNvbS93b2p0ZWttYWovcmVhY3QtcGRmIiwicHJvamVjdCI6IndlZWtseWZvbyIsImluZGV4IjozNSwic2VjdGlvbiI6InRvb2xzIiwic291cmNlIjoid2ViIn19">React PDF</a>: Display PDFs in your React app as easily as if they were images.<small> / </small><small>*react*, *pdf*</small>
- <a href="https://delve.a9.io/?utm_source=weeklyfoo&utm_medium=web&utm_campaign=weeklyfoo-35&ref=weeklyfoo" target="_blank" rel="noopener" ping="https://api.weeklyfoo.com/api/foo/bar?foo=eyJldmVudCI6InVybC1jbGljayIsInByb3BzIjp7InVybCI6Imh0dHBzOi8vZGVsdmUuYTkuaW8vIiwicHJvamVjdCI6IndlZWtseWZvbyIsImluZGV4IjozNSwic2VjdGlvbiI6InRvb2xzIiwic291cmNlIjoid2ViIn19">delve</a>: AI to chat<small> / </small><small>*ai*</small>
<Hr />
## 🎨 Design
- <a href="https://www.smashingmagazine.com/2024/05/naming-best-practices/?utm_source=weeklyfoo&utm_medium=web&utm_campaign=weeklyfoo-35&ref=weeklyfoo" target="_blank" rel="noopener" ping="https://api.weeklyfoo.com/api/foo/bar?foo=eyJldmVudCI6InVybC1jbGljayIsInByb3BzIjp7InVybCI6Imh0dHBzOi8vd3d3LnNtYXNoaW5nbWFnYXppbmUuY29tLzIwMjQvMDUvbmFtaW5nLWJlc3QtcHJhY3RpY2VzLyIsInByb2plY3QiOiJ3ZWVrbHlmb28iLCJpbmRleCI6MzUsInNlY3Rpb24iOiJkZXNpZ24iLCJzb3VyY2UiOiJ3ZWIifX0%3D">Best Practices For Naming Design Tokens, Components And Variables</a>: This post is dedicated to naming conventions, tips, and real-world examples that help you name things in a robust and flexible way.<small> / </small><small>*design-tokens*</small><small> / </small><small>10 min read</small>
- <a href="https://www.useronboard.com/how-canva-activates-users/?utm_source=weeklyfoo&utm_medium=web&utm_campaign=weeklyfoo-35&ref=weeklyfoo" target="_blank" rel="noopener" ping="https://api.weeklyfoo.com/api/foo/bar?foo=eyJldmVudCI6InVybC1jbGljayIsInByb3BzIjp7InVybCI6Imh0dHBzOi8vd3d3LnVzZXJvbmJvYXJkLmNvbS9ob3ctY2FudmEtYWN0aXZhdGVzLXVzZXJzLyIsInByb2plY3QiOiJ3ZWVrbHlmb28iLCJpbmRleCI6MzUsInNlY3Rpb24iOiJkZXNpZ24iLCJzb3VyY2UiOiJ3ZWIifX0%3D">How Canva Activates Users</a>: See the user onboarding flow of Canvas<small> / </small><small>*onboarding*</small><small> / </small><small>2 min read</small>
<Hr />
## 🤪 Fun
- <a href="https://aem1k.com/qlock/?utm_source=weeklyfoo&utm_medium=web&utm_campaign=weeklyfoo-35&ref=weeklyfoo" target="_blank" rel="noopener" ping="https://api.weeklyfoo.com/api/foo/bar?foo=eyJldmVudCI6InVybC1jbGljayIsInByb3BzIjp7InVybCI6Imh0dHBzOi8vYWVtMWsuY29tL3Fsb2NrLyIsInByb2plY3QiOiJ3ZWVrbHlmb28iLCJpbmRleCI6MzUsInNlY3Rpb24iOiJmdW4iLCJzb3VyY2UiOiJ3ZWIifX0%3D">qlock</a>: A JavaScript Quine Clock - loving it!<small> / </small><small>*quine*</small><small> / </small><small>1 min read</small>
<Hr />
## 📚 Tutorials
- <a href="https://github.com/kiwicopple/serverless-postgres?utm_source=weeklyfoo&utm_medium=web&utm_campaign=weeklyfoo-35&ref=weeklyfoo" target="_blank" rel="noopener" ping="https://api.weeklyfoo.com/api/foo/bar?foo=eyJldmVudCI6InVybC1jbGljayIsInByb3BzIjp7InVybCI6Imh0dHBzOi8vZ2l0aHViLmNvbS9raXdpY29wcGxlL3NlcnZlcmxlc3MtcG9zdGdyZXMiLCJwcm9qZWN0Ijoid2Vla2x5Zm9vIiwiaW5kZXgiOjM1LCJzZWN0aW9uIjoidHV0Iiwic291cmNlIjoid2ViIn19">serverless-postgres</a>: MVP for a Serverless Postgres using Oriole, Fly Machines, and Tigris for S3 Storage.<small> / </small><small>*postgres*, *serverless*</small><small> / </small><small>6 min read</small>
<Hr />
## 📺 Videos
- <a href="https://www.youtube.com/watch?v=yaMGtiPckAQ?utm_source=weeklyfoo&utm_medium=web&utm_campaign=weeklyfoo-35&ref=weeklyfoo" target="_blank" rel="noopener" ping="https://api.weeklyfoo.com/api/foo/bar?foo=eyJldmVudCI6InVybC1jbGljayIsInByb3BzIjp7InVybCI6Imh0dHBzOi8vd3d3LnlvdXR1YmUuY29tL3dhdGNoP3Y9eWFNR3RpUGNrQVEiLCJwcm9qZWN0Ijoid2Vla2x5Zm9vIiwiaW5kZXgiOjM1LCJzZWN0aW9uIjoidmlkcyIsInNvdXJjZSI6IndlYiJ9fQ%3D%3D">Act On Press</a>: John Carmack's Hot Take On UI<small> / </small><small>*ui*</small>
- <a href="https://www.youtube.com/watch?v=WPCrGYjrJ1Y?utm_source=weeklyfoo&utm_medium=web&utm_campaign=weeklyfoo-35&ref=weeklyfoo" target="_blank" rel="noopener" ping="https://api.weeklyfoo.com/api/foo/bar?foo=eyJldmVudCI6InVybC1jbGljayIsInByb3BzIjp7InVybCI6Imh0dHBzOi8vd3d3LnlvdXR1YmUuY29tL3dhdGNoP3Y9V1BDckdZanJKMVkiLCJwcm9qZWN0Ijoid2Vla2x5Zm9vIiwiaW5kZXgiOjM1LCJzZWN0aW9uIjoidmlkcyIsInNvdXJjZSI6IndlYiJ9fQ%3D%3D">The Most Dangerous Phrase</a>: This presentation was recorded at GOTO Copenhagen 2023.<small> / </small><small>*solid*, *scrum*</small>
Want to read more? Check out the full article [here](https://weeklyfoo.com/foos/foo-035/).
To sign up for the weekly newsletter, visit [weeklyfoo.com](https://weeklyfoo.com). | urbanisierung |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.