id int64 5 1.93M | title stringlengths 0 128 | description stringlengths 0 25.5k | collection_id int64 0 28.1k | published_timestamp timestamp[s] | canonical_url stringlengths 14 581 | tag_list stringlengths 0 120 | body_markdown stringlengths 0 716k | user_username stringlengths 2 30 |
|---|---|---|---|---|---|---|---|---|
1,874,938 | Top 10 Construction Companies in UAE | *Introduction * The United Arab Emirates (UAE) is well-known for its impressive skyline and... | 0 | 2024-06-03T04:48:47 | https://dev.to/aiwa_ae_584cf1fdf9f50cb48/top-10-construction-companies-in-uae-5372 |
**Introduction **
The United Arab Emirates (UAE) is well-known for its impressive skyline and ground-breaking architectural achievements. This reputation is maintained by the efforts of some of the region's best construction businesses.
Here, we showcase the UAE's top ten construction businesses, each of which contributes to the country's dynamic infrastructure scene.
**1. Nael Gen Contracting Group**
[Nael Gen Contracting Group](https://aiwa.ae/company/naelgencontracting-group) is a key participant in the UAE construction business, noted for its dedication to quality and on-time project completion. The firm focuses on civil engineering and construction projects, with a portfolio that includes residential, commercial, and industrial developments.
**2. Fujairah National Group**
[Fujairah National Group](https://aiwa.ae/company/Fujairah-National-Group) stands out for its wide variety of construction services and significant presence in the Eastern Region. This business excels at producing high-quality construction projects, ranging from residential structures to large-scale infrastructure works, exhibiting flexibility and skill.
**3. Abraj Building Contracting Co. LLC**
[Abraj Building Contracting Co. LLC](https://aiwa.ae/company/Abraj-Building-Contracting-Co-LLC) is well-known for its exceptional work on residential, commercial, and industrial projects. The firm is known for its creative construction processes and sustainable building procedures, which ensure high standards in all projects.
**4. Smart Cities Building Contracting LLC**
[Smartcities Building Contracting LLC](https://aiwa.ae/company/Smartcities-Building-Contracting-LLC) specializes in the design and construction of smart, sustainable buildings using cutting-edge technology and environmental design. The company's forward-thinking strategy has established it as a market leader in contemporary building solutions in the UAE.
**5. Mabani Steel**
[Mabani Steel](https://aiwa.ae/company/Smartcities-Building-Contracting-LLC) is a major participant in the steel construction business, offering both pre-engineered steel buildings and structural steel services. Their projects cover several sectors, including industrial, commercial, and residential, demonstrating their adaptability and engineering expertise.
List your business on [Aiwa.ae](https://aiwa.ae/freelisting) to enhance your growth in Dubai, UAE, and connect with a wider audience.
**6. AB Building Contracting Co. LLC**
[AB Building Contracting Co. LLC](https://aiwa.ae/company/ab-building-contracting-co-llc) is well-known for providing full construction services, ranging from early planning and design to project execution and delivery. The firm prioritizes superior workmanship and client happiness, guaranteeing that all projects exceed stringent requirements.
**7. Aroma International Building Contracting, LLC**
[Aroma International Building Contracting LLC](https://aiwa.ae/company/aromainternationalbuildingcontracting-l-l-c) focuses on high-end residential and commercial projects. The firm is characterized by its attention to detail, luxury finishing, and devotion to exceeding customer expectations, making it a top choice for high-end developments.
**8. 3M Gulf Limited**
[3M Gulf Limited](https://aiwa.ae/company/3-M-Gulf-Limited) provides unique construction solutions and is well-known for incorporating cutting-edge technology and materials into its projects. The company's competence in a wide range of fields, from residential structures to huge infrastructure projects, guarantees that they consistently offer high-quality products.
**9. Nadia Steel Construction Contracting, L.L.C.**
[Nadia Steel Construction Contracting L.L.C.](https://aiwa.ae/company/nadia-steel-construction-contracting-llc) excels at providing durable steel construction solutions for a variety of industries. Their dedication to quality and safety, along with their significant expertise, make them a dependable partner for complicated steel construction projects.
**10. Al Aber Contracting Establishment**
[Al Aber Contracting Establishment](https://aiwa.ae/company/Al-Aber-Contracting-Establishment) has a long history of delivering great building projects in the UAE. The company's portfolio covers a diverse variety of projects, from residential developments to large-scale commercial endeavors, all distinguished by high quality and attention to detail.
**Conclusion**
The UAE construction sector is led by enterprises that prioritize innovation, quality, and sustainability. These top ten [construction companies in uae](https://aiwa.ae/category/construction-companies) represent the finest in the business, contributing to the country's progress and improving its architectural legacy. Whether it's a towering skyscraper or a large industrial complex, these enterprises help the UAE remain a worldwide leader in building and infrastructure development.
Explore more business categories at [Aiwa.ae.](https://aiwa.ae/) | aiwa_ae_584cf1fdf9f50cb48 | |
1,874,937 | Where to Find the Best Deals on Solar Garden Lights | looking for the Finest Offers on Solar Yard Illuminations Here is Where towards Discover All of... | 0 | 2024-06-03T04:47:43 | https://dev.to/alex_damianisi_f1cfe95e60/where-to-find-the-best-deals-on-solar-garden-lights-42ok | solar, garden | looking for the Finest Offers on Solar Yard Illuminations Here is Where towards Discover All of them
Have actually you ever before thought about setting up yard that is solar in your outside area? Solar yard illuminations are actually ingenious as well as environmentally friendly outside illumination choices that utilize solar power towards work. They are actually risk free, user-friendly, as well as include a variety of benefits. we will check out a few of the very best locations towards discover offers on solar yard illuminations, their benefits, as well as ways to utilize all of them
Benefits of Solar Garden Lights Illuminations
The complying with are actually a few of the considerable benefits of utilization yard that is solar:
1. Cost-Effective: Solar yard illuminations economical towards set up as well as run. They operate on solar power, which is actually cost-free as well as easily offered
2. Eco-Friendly: Solar yard illuminations utilize cleanse power, which decreases your carbon dioxide impact as well as assists safeguard the atmosphere
3. Risk-free: Solar yard illuminations don't need cable links as well as deal with reduced voltage. For that good reason, they are actually risk-free towards utilize, particularly if you have actually kids or even animals in your house
4. Reduced Upkeep: When set up, solar yard illuminations need very upkeep that is little. They have actually no components that are relocating which additional decreases the possibilities of damaging down
5. Simple towards Set up: Solar yard illuminations are actually simple towards set up as well as don't need any type of electrical circuitry or proficiency that is even technological
Development as well as Security
Solar Fence Lights illuminations are actually an ingenious as well as risk-free method towards illuminate your outside area. They utilize photo voltaic panels towards transform sunshine right in to power that is electrical which powers the illuminations. Consequently, you do not need to stress over the sets you back of electrical power. Furthermore, you will certainly certainly not need to manage any type of electric circuitry that is electrical creating it a much safer
choice particularly for kids as well as animals
Ways to Utilize Solar Yard Illuminations
Utilizing yard this is certainly solar is clearly simple:
1. Select a Warm Place: Select a accepted place that gets sunshine for at the least 6-8 hrs an occasion. This can certainly guarantee that the illuminations obtain sufficient power towards energy these with the evening
2. Set up the Solar Boards: Location the photo voltaic panels in a spot where they may be able easily get sunshine this is certainly optimum. Very most yard that is solar include integrated photo voltaic panels
3. Transform All of those On turn on the yard this is certainly solar in addition to take pleasure in the smooth radiance they feature your outside area
High premium this is certainly top well as Solution
When appearing when it comes to absolute best offers on Solar Post Lights illuminations, constantly think of high premium this is certainly top well as solution. You want to acquisition illuminations which can be actually resilient in addition to can very quickly endure weather this is certainly severe. Guarantee which you buy from a dependable provider which provides customer care this is certainly outstanding. It is possible to inspect the world-wide-web evaluations on and sometimes even request recommendations towards discover a dependable provider
Requests of Solar Yard Illuminations
Solar yard illuminations could possibly be utilized for different illumination this is certainly outside, consisting of:
1. Path Illumination: utilize yard this is certainly solar towards illuminate paths in addition to pathways in your yard
2. Yard Illumination: Solar yard illuminations could possibly be utilized towards emphasize different yard locations like blossom mattress, bushes, in addition to trees
3. Accent Illumination: utilize yard this is certainly solar towards highlight various functions in your outside area, like sculptures, water fountains, as well as private pools
4. Safety and safety Illumination: Solar yard illuminations could possibly be utilized towards improve safety and safety through illuminating dark areas regarding your house
Source: https://www.beslonsolarlight.com/solar-post-lights | alex_damianisi_f1cfe95e60 |
1,873,850 | Understanding the Factory Design Pattern with Node.js | Design patterns are a crucial part of software engineering, helping to create robust, scalable, and... | 0 | 2024-06-03T04:44:33 | https://dev.to/heisdinesh/understanding-the-factory-design-pattern-with-nodejs-1ihm | designpatterns, factorydesignpattern, factorymethod, node | Design patterns are a crucial part of software engineering, helping to create robust, scalable, and maintainable code. There are various design patterns, the Factory Design Pattern is particularly useful for managing object creation.
Factory design pattern helps create objects without having to specify the exact class of the object that will be created. This is particularly useful in scenarios where the exact type of object may not be known until runtime.
## Use cases of Factory Design Pattern
Whenever we create objects that have similar behavior or are closely related, we can use a factory design pattern.
- In Swiggy, when we are creating orders, orders can be of type dine-in, delivery, or take-out. We have to decide at runtime what type of order should be created.
- In Ola, when we are booking a ride, rides can be of type solo rides, share rides, or luxury rides. We have to decide at runtime what type of ride should be created.
In both examples, the creation process is encapsulated using the factory design pattern.
## Understanding with an example
Let's take an example of a notification system, there are different types of notifications including Email, SMS, and Push notifications. The type of notification required will be decided during runtime.
In Factory Pattern, the code will be split into 4 major parts.
- Interface (Notification interface)
- Concrete Classes (EmailNotification, SMSNotification, PushNotification)
- Factory (Notification Factory)
- Client
The interface acts as a blueprint for concrete classes. Each Concrete class extends the interface and provides its implementation of methods declared in the interface. Factory determines which concrete class to instantiate based on input parameters. The client utilizes the Factory to create instances of objects and Interacts with the created objects to perform actions.
## Code
**Notification Interface**
First, we'll define a common interface for all types of notifications. In Nodejs, we'll use a base class with an abstract method to achieve this.
```
class Notification {
send(message) {
throw new Error('Method "send()" must be implemented.');
}
}
module.exports = Notification;
```
**Concrete Classes**
Now, we'll create concrete classes for Email, SMS, and Push notifications that extend the base Notification class.
```
const Notification = require('./Notification');
class EmailNotification extends Notification {
send(message) {
console.log(`Sending email with message: ${message}`);
// Email sending logic here
}
}
class SMSNotification extends Notification {
send(message) {
console.log(`Sending SMS with message: ${message}`);
// SMS sending logic here
}
}
class PushNotification extends Notification {
send(message) {
console.log(`Sending push notification with message: ${message}`);
// Push notification sending logic here
}
}
module.exports = { EmailNotification, SMSNotification, PushNotification };
```
**Notification Factory**
Now, we'll create a factory class that will return the appropriate notification object based on the input.
```
const { EmailNotification, SMSNotification, PushNotification } = require('./notifications/Notifications');
class NotificationFactory {
static createNotification(type) {
switch (type) {
case 'email':
return new EmailNotification();
case 'sms':
return new SMSNotification();
case 'push':
return new PushNotification();
default:
throw new Error('Unknown notification type');
}
}
}
module.exports = NotificationFactory;
```
**Client**
Finally, we'll use the factory to create notification objects in our client code.
```
const NotificationFactory = require('./notifications/NotificationFactory');
const notificationType = process.argv[2]; // 'email', 'sms', or 'push'
const message = 'Hello, this is a test message!';
const notification = NotificationFactory.createNotification(notificationType);
notification.send(message);
```
## What benefit did we get by following this factory design pattern ?
- Encapsulation: It encapsulates the instantiation logic, making the code cleaner and more modular.
- Decoupling: It decouples the client code from the concrete classes, promoting flexibility and maintainability.
- Single Responsibility Principle: It adheres to the Single Responsibility Principle by delegating the creation logic to the factory class.
- Open/Closed Principle: It adheres to the Open/Closed Principle, allowing new types to be added without modifying the existing client code.
## Conclusions
The Factory Design Pattern is one of the best ways to manage object creation in a clean and decoupled manner. By incorporating design patterns like the Factory Design Pattern into development practices, we can write more robust, scalable, and maintainable code.
If you found this article helpful, connect with me on [LinkedIn ](https://www.linkedin.com/in/heisdinesh)and follow my posts on [DEV.to](https://dev.to/heisdinesh). Share your thoughts and questions in the comments below!
| heisdinesh |
1,874,936 | Building a Feature Proposal and Voting System with React, NodeJS, and DynamoDB | Building a Feature Proposal and Voting System with React, NodeJS, and DynamoDB | 0 | 2024-06-03T04:44:06 | https://radzion.com/blog/features | react, node, dynamodb, webdev | {% embed https://youtu.be/PXad8WzI0L0 %}
🐙 [GitHub](https://github.com/radzionc/radzionkit) | 🎮 [Demo](https://increaser.org)
In this article, we'll create a lightweight solution that enables users to propose new features for our web application and vote on them. We will utilize React for the front-end and construct a simple NodeJS API for the back-end, integrating DynamoDB as our database. Although the source code for this project is hosted in a private repository, all reusable components and utilities are accessible in the [RadzionKit](https://github.com/radzionc/radzionkit) repository.
### Introduction to Feature Proposal and Voting System
At [Increaser](https://increaser.org), our community page is the central hub for all social interactions within the application. Currently in its early stages, the page features a panel for users to edit their profiles, a leaderboard, the founder's contact information, and a widget for proposed features, which we'll explore further in this article. We have adopted a minimalist design for the features widget, using a single list with a toggle to switch between proposed ideas and those that have already been implemented. Although an alternative layout could include a "TO DO," "IN PROGRESS," and "DONE" board, our workflow typically involves focusing on one feature at a time, making the "IN PROGRESS" column redundant. Additionally, we aim to keep users focused on voting for new ideas rather than being distracted by completed features.

We use a dedicated DynamoDB table to store proposed features for [Increaser](https://increaser.org). Each item in this table includes several attributes:
- `id`: A unique identifier for the feature.
- `name`: The name of the feature.
- `description`: A brief description of the feature.
- `createdAt`: The timestamp marking when the feature was proposed.
- `proposedBy`: The ID of the user who proposed the feature.
- `upvotedBy`: An array of user IDs who have upvoted the feature.
- `isApproved`: A boolean indicating whether the feature has been approved by the founder.
- `status`: The current status of the feature, with possible values including "idea" or "done". If you prefer to display the features on a board, you might consider adding a status such as "in progress".
```tsx
export const productFeatureStatuses = ["idea", "done"] as const
export type ProductFeatureStatus = (typeof productFeatureStatuses)[number]
export type ProductFeature = {
id: string
name: string
description: string
createdAt: number
proposedBy: string
upvotedBy: string[]
isApproved: boolean
status: ProductFeatureStatus
}
```
### API Design and Feature Management Workflow
Our API includes just three endpoints dedicated to managing features. If you're interested in learning how to efficiently build backends within TypeScript monorepos, be sure to explore [this insightful article](https://radzion.com/blog/api).
```tsx
import { ApiMethod } from "./ApiMethod"
import { ProductFeature } from "@increaser/entities/ProductFeature"
import { ProductFeatureResponse } from "./ProductFeatureResponse"
export interface ApiInterface {
proposeFeature: ApiMethod<
Omit<ProductFeature, "isApproved" | "status" | "proposedBy" | "upvotedBy">,
undefined
>
voteForFeature: ApiMethod<{ id: string }, undefined>
features: ApiMethod<undefined, ProductFeatureResponse[]>
// other methods...
}
export type ApiMethodName = keyof ApiInterface
```
The `proposeFeature` method is crucial to our feature proposal process. It identifies the user's ID from a JWT token included in the request, which is used for user authentication. To stay informed about new proposals, I've set up a Telegram channel where the API sends notifications detailing the proposed features. Upon receiving a message on this channel, I access the DynamoDB explorer on AWS to verify the feature's validity and refine the name and description for easier comprehension by other users. Although we could monitor new features with a separate Lambda function that listens to the DynamoDB stream, the current setup of direct notifications from the API is effective, especially as this is the only method for proposing features.
```tsx
import { getUser } from "@increaser/db/user"
import { assertUserId } from "../../auth/assertUserId"
import { getEnvVar } from "../../getEnvVar"
import { getTelegramBot } from "../../notifications/telegram"
import { ApiResolver } from "../../resolvers/ApiResolver"
import { putFeature } from "@increaser/db/features"
import { getProductFeautureDefaultFields } from "@increaser/entities/ProductFeature"
export const proposeFeature: ApiResolver<"proposeFeature"> = async ({
input: feature,
context,
}) => {
const proposedBy = assertUserId(context)
const { email } = await getUser(proposedBy, ["email"])
await getTelegramBot().sendMessage(
getEnvVar("TELEGRAM_CHAT_ID"),
[
"New feature proposal",
feature.name,
feature.description,
`Proposed by ${email}`,
feature.id,
].join("\n\n")
)
await putFeature({
...feature,
...getProductFeautureDefaultFields({ proposedBy }),
})
}
```
Before adding a new feature to the DynamoDB table, we initialize default fields. The `isApproved` field is set to `false`, indicating that the feature has not yet been reviewed. The `status` is set to `idea`. The `proposedBy` field captures the user ID of the proposer. Additionally, the `upvotedBy` field starts with an array containing the proposer’s ID, ensuring that each new feature begins with one upvote.
```tsx
export const getProductFeautureDefaultFields = ({
proposedBy,
}: Pick<ProductFeature, "proposedBy">): Pick<
ProductFeature,
"isApproved" | "status" | "proposedBy" | "upvotedBy"
> => ({
isApproved: false,
status: "idea",
proposedBy,
upvotedBy: [proposedBy],
})
```
We organize all functions for interacting with the "features" table into a single file. Utilizing helpers from [RadzionKit](https://github.com/radzionc/radzionkit), such as `makeGetItem`, `updateItem`, and `totalScan`, makes it easy to add new tables to our application.
```tsx
import { PutCommand } from "@aws-sdk/lib-dynamodb"
import { ProductFeature } from "@increaser/entities/ProductFeature"
import { tableName } from "./tableName"
import { dbDocClient } from "@lib/dynamodb/client"
import { totalScan } from "@lib/dynamodb/totalScan"
import { getPickParams } from "@lib/dynamodb/getPickParams"
import { makeGetItem } from "@lib/dynamodb/makeGetItem"
import { updateItem } from "@lib/dynamodb/updateItem"
export const putFeature = (value: ProductFeature) => {
const command = new PutCommand({
TableName: tableName.features,
Item: value,
})
return dbDocClient.send(command)
}
export const getFeature = makeGetItem<string, ProductFeature>({
tableName: tableName.features,
getKey: (id: string) => ({ id }),
})
export const updateFeature = async (
id: string,
fields: Partial<ProductFeature>
) => {
return updateItem({
tableName: tableName.features,
key: { id },
fields,
})
}
export const getAllFeatures = async <T extends (keyof ProductFeature)[]>(
attributes?: T
) =>
totalScan<Pick<ProductFeature, T[number]>>({
TableName: tableName.features,
...getPickParams(attributes),
})
```
The `voteForFeature` method toggles the user's vote for a feature. If the user has already upvoted the feature, the method removes their vote; otherwise, it adds it. This approach ensures that users can only vote once for each feature.
```tsx
import { without } from "@lib/utils/array/without"
import { assertUserId } from "../../auth/assertUserId"
import { ApiResolver } from "../../resolvers/ApiResolver"
import { getFeature, updateFeature } from "@increaser/db/features"
export const voteForFeature: ApiResolver<"voteForFeature"> = async ({
input: { id },
context,
}) => {
const userId = assertUserId(context)
const { upvotedBy } = await getFeature(id, ["upvotedBy"])
await updateFeature(id, {
upvotedBy: upvotedBy.includes(userId)
? without(upvotedBy, userId)
: [...upvotedBy, userId],
})
}
```
The `features` method retrieves all features from the DynamoDB table but filters out unapproved features, ensuring that only the proposer can view their unapproved ideas. Additionally, this method calculates the number of upvotes for each feature and checks if the current user has upvoted the feature. Instead of returning the entire list of user IDs who have upvoted, it provides a more streamlined output.
```tsx
import { ApiResolver } from "../../resolvers/ApiResolver"
import { getAllFeatures } from "@increaser/db/features"
import { ProductFeatureResponse } from "@increaser/api-interface/ProductFeatureResponse"
import { pick } from "@lib/utils/record/pick"
export const features: ApiResolver<"features"> = async ({
context: { userId },
}) => {
const features = await getAllFeatures()
const result: ProductFeatureResponse[] = []
features.forEach((feature) => {
if (!feature.isApproved && feature.proposedBy !== userId) {
return
}
result.push({
...pick(feature, [
"id",
"name",
"description",
"isApproved",
"status",
"proposedBy",
"createdAt",
]),
upvotes: feature.upvotedBy.length,
upvotedByMe: Boolean(userId && feature.upvotedBy.includes(userId)),
})
})
return result
}
```
### Front-End Implementation: Building the Feature Voting Interface
With the server-side logic established, we can now turn our attention to the front-end implementation. The widget is displayed on the right side of the community page using the `ProductFeaturesBoard` component.
```tsx
import { Page } from "@lib/next-ui/Page"
import { FixedWidthContent } from "@increaser/app/components/reusable/fixed-width-content"
import { PageTitle } from "@increaser/app/ui/PageTitle"
import { VStack } from "@lib/ui/layout/Stack"
import { UserStateOnly } from "@increaser/app/user/state/UserStateOnly"
import { ClientOnly } from "@increaser/app/ui/ClientOnly"
import { ManageProfile } from "./ManageProfile"
import { Scoreboard } from "@increaser/ui/scoreboard/Scoreboard"
import { RequiresOnboarding } from "../../onboarding/RequiresOnboarding"
import { ProductFeaturesBoard } from "../../productFeatures/components/ProductFeaturesBoard"
import { FounderContacts } from "./FounderContacts"
import { UniformColumnGrid } from "@lib/ui/layout/UniformColumnGrid"
export const CommunityPage: Page = () => {
return (
<FixedWidthContent>
<ClientOnly>
<PageTitle documentTitle={`👋 Community`} title="Community" />
</ClientOnly>
<UserStateOnly>
<RequiresOnboarding>
<UniformColumnGrid minChildrenWidth={320} gap={40}>
<VStack style={{ width: "fit-content" }} gap={40}>
<ManageProfile />
<Scoreboard />
<FounderContacts />
</VStack>
<ProductFeaturesBoard />
</UniformColumnGrid>
</RequiresOnboarding>
</UserStateOnly>
</FixedWidthContent>
)
}
```
We render the content within a `Panel` component, which is set to have a minimum width of `320px` and occupies the remaining space in the parent container. The header displays the title "Product Features" and includes the `ProductFeaturesViewSelector` component, allowing users to toggle between the "idea" and "done" views. The `RenderProductFeaturesView` component is used to conditionally display a prompt for proposing new features, ensuring it is visible only when the "idea" view is selected. The `ProductFeatureList` component is then used to display the list of features.
```tsx
import { HStack, VStack } from "@lib/ui/layout/Stack"
import { Panel } from "@lib/ui/panel/Panel"
import { Text } from "@lib/ui/text"
import styled from "styled-components"
import {
ProductFeaturesViewProvider,
ProductFeaturesViewSelector,
RenderProductFeaturesView,
} from "./ProductFeaturesView"
import { ProposeFeaturePrompt } from "./ProposeFeaturePrompt"
import { ProductFeatureList } from "./ProductFeatureList"
const Container = styled(Panel)`
min-width: 320px;
flex: 1;
`
export const ProductFeaturesBoard = () => {
return (
<ProductFeaturesViewProvider>
<Container>
<VStack gap={20}>
<HStack
alignItems="center"
gap={20}
justifyContent="space-between"
wrap="wrap"
fullWidth
>
<Text size={18} weight="bold">
Product Features
</Text>
<ProductFeaturesViewSelector />
</HStack>
<RenderProductFeaturesView
idea={() => <ProposeFeaturePrompt />}
done={() => null}
/>
<VStack gap={8}>
<ProductFeatureList />
</VStack>
</VStack>
</Container>
</ProductFeaturesViewProvider>
)
}
```
It's a common scenario to need a filter or selector for switching between different views. To facilitate this, we utilize the `getViewSetup` utility from [RadzionKit](https://github.com/radzionc/radzionkit). This utility accepts a default view and a setup name, returning a provider, hook, and renderer that enable convenient conditional rendering based on the current view. For the selector component, we use the `TabNavigation` component from [RadzionKit](https://github.com/radzionc/radzionkit), which takes an array of views, a function to get the view name, the active view, and a callback to set the view.
```tsx
import { getViewSetup } from "@lib/ui/view/getViewSetup"
import { TabNavigation } from "@lib/ui/navigation/TabNavigation"
import {
ProductFeatureStatus,
productFeatureStatuses,
} from "@increaser/entities/ProductFeature"
export const {
ViewProvider: ProductFeaturesViewProvider,
useView: useProductFeaturesView,
RenderView: RenderProductFeaturesView,
} = getViewSetup<ProductFeatureStatus>({
defaultView: "idea",
name: "productFeatures",
})
const taskViewName: Record<ProductFeatureStatus, string> = {
idea: "Ideas",
done: "Done",
}
export const ProductFeaturesViewSelector = () => {
const { view, setView } = useProductFeaturesView()
return (
<TabNavigation
views={productFeatureStatuses}
getViewName={(view) => taskViewName[view]}
activeView={view}
onSelect={setView}
/>
)
}
```
### Enhancing User Interaction: Feature Proposal Components
The `ProposeFeaturePrompt` component displays a call-to-action using the `PanelPrompt` component. When activated, it reveals the `ProposeFeatureForm` component. Additionally, we employ the `Opener` component from [RadzionKit](https://github.com/radzionc/radzionkit), which acts as a wrapper around `useState` for conditional rendering. While I prefer using the `Opener` for its streamlined syntax, you might find using a simple `useState` hook more to your liking.
```tsx
import { Opener } from "@lib/ui/base/Opener"
import { ProposeFeatureForm } from "./ProposeFeatureForm"
import { PanelPrompt } from "@lib/ui/panel/PanelPrompt"
export const ProposeFeaturePrompt = () => {
return (
<Opener
renderOpener={({ onOpen, isOpen }) =>
!isOpen && (
<PanelPrompt onClick={onOpen} title="Make Increaser Yours">
Tell us what feature you want to see next
</PanelPrompt>
)
}
renderContent={({ onClose }) => <ProposeFeatureForm onFinish={onClose} />}
/>
)
}
```
In the `ProposeFeatureForm` component, users input a `name` and `description` for their feature idea. We keep validation simple, only ensuring that these fields are not empty, as I manually approve and edit each feature later. The form's `onSubmit` function checks if the submit button is disabled and, if not, it calls the `mutate` function from the `useProposeFeatureMutation` hook with the new feature details. Once the mutation is initiated, the `onFinish` callback is invoked to notify the parent component that the submission process is complete, prompting the `ProposeFeaturePrompt` to display the `PanelPrompt` again.
```tsx
import { Button } from "@lib/ui/buttons/Button"
import { Form } from "@lib/ui/form/components/Form"
import { UniformColumnGrid } from "@lib/ui/layout/UniformColumnGrid"
import { Panel } from "@lib/ui/panel/Panel"
import { FinishableComponentProps } from "@lib/ui/props"
import styled from "styled-components"
import { useProposeFeatureMutation } from "../hooks/useProposeFeatureMutation"
import { useState } from "react"
import { Fields } from "@lib/ui/inputs/Fields"
import { Field } from "@lib/ui/inputs/Field"
import { TextInput } from "@lib/ui/inputs/TextInput"
import { TextArea } from "@lib/ui/inputs/TextArea"
import { Validators } from "@lib/ui/form/utils/Validators"
import { validate } from "@lib/ui/form/utils/validate"
import { getId } from "@increaser/entities-utils/shared/getId"
const Container = styled(Panel)``
type FeatureFormShape = {
name: string
description: string
}
const featureFormValidator: Validators<FeatureFormShape> = {
name: (name) => {
if (!name) {
return "Name is required"
}
},
description: (description) => {
if (!description) {
return "Description is required"
}
},
}
export const ProposeFeatureForm = ({ onFinish }: FinishableComponentProps) => {
const { mutate } = useProposeFeatureMutation()
const [value, setValue] = useState<FeatureFormShape>({
name: "",
description: "",
})
const errors = validate(value, featureFormValidator)
const [isDisabled] = Object.values(errors)
return (
<Container kind="secondary">
<Form
onSubmit={() => {
if (isDisabled) return
mutate({
name: value.name,
description: value.description,
id: getId(),
createdAt: Date.now(),
})
onFinish()
}}
content={
<Fields>
<Field>
<TextInput
value={value.name}
onValueChange={(name) => setValue({ ...value, name })}
label="Title"
placeholder="Give your feature a clear name"
/>
</Field>
<Field>
<TextArea
rows={4}
value={value.description}
onValueChange={(description) =>
setValue({ ...value, description })
}
label="Description"
placeholder="Detail your feature for easy understanding"
/>
</Field>
</Fields>
}
actions={
<UniformColumnGrid gap={20}>
<Button size="l" type="button" kind="secondary" onClick={onFinish}>
Cancel
</Button>
<Button
isDisabled={isDisabled}
size="l"
type="submit"
kind="primary"
>
Submit
</Button>
</UniformColumnGrid>
}
/>
</Container>
)
}
```
### Dynamic Feature Listing and User Interaction Components
To display the list of features, we first retrieve the query result from the API using the `useApiQuery` hook, which requires the name of the method and the input parameters. The `QueryDependant` component from [RadzionKit](https://github.com/radzionc/radzionkit) is utilized to manage the query state effectively. During the loading state, we display a spinner; in the error state, an error message is shown; and in the success state, we render the list of features. The retrieved features are then divided into two arrays: `myUnapprovedFeatures`, which contains features proposed by the current user but not yet approved, and `otherFeatures`, which includes all other features sorted by the number of upvotes in descending order. Each feature is rendered using the `ProductFeatureItem` component.
```tsx
import { useApiQuery } from "@increaser/api-ui/hooks/useApiQuery"
import { QueryDependant } from "@lib/ui/query/components/QueryDependant"
import { getQueryDependantDefaultProps } from "@lib/ui/query/utils/getQueryDependantDefaultProps"
import { splitBy } from "@lib/utils/array/splitBy"
import { order } from "@lib/utils/array/order"
import { ProductFeatureItem } from "./ProductFeatureItem"
import { useProductFeaturesView } from "./ProductFeaturesView"
import { useAssertUserState } from "@increaser/ui/user/UserStateContext"
import { CurrentProductFeatureProvider } from "./CurrentProductFeatureProvider"
export const ProductFeatureList = () => {
const featuresQuery = useApiQuery("features", undefined)
const { view } = useProductFeaturesView()
const { id } = useAssertUserState()
return (
<QueryDependant
query={featuresQuery}
{...getQueryDependantDefaultProps("features")}
success={(features) => {
const [myUnapprovedFeatures, otherFeatures] = splitBy(
features.filter((feature) => view === feature.status),
(feature) =>
feature.proposedBy === id && !feature.isApproved ? 0 : 1
)
return (
<>
{[
...myUnapprovedFeatures,
...order(otherFeatures, (f) => f.upvotes, "desc"),
].map((feature) => (
<CurrentProductFeatureProvider key={feature.id} value={feature}>
<ProductFeatureItem />
</CurrentProductFeatureProvider>
))}
</>
)
}}
/>
)
}
```
To minimize prop drilling, the `ProductFeatureItem` component is provided with the current feature using the `CurrentProductFeatureProvider` component. Recognizing the frequent need to pass a single value through a component tree, I created the utility function `getValueProviderSetup` in [RadzionKit](https://github.com/radzionc/radzionkit). This generic function accepts the name of the entity and returns both a provider and a hook for that entity, streamlining the process of passing contextual data to nested components.
```tsx
import { ProductFeatureResponse } from "@increaser/api-interface/ProductFeatureResponse"
import { getValueProviderSetup } from "@lib/ui/state/getValueProviderSetup"
export const {
useValue: useCurrentProductFeature,
provider: CurrentProductFeatureProvider,
} = getValueProviderSetup<ProductFeatureResponse>("ProductFeature")
```
The `ProductFeatureItem` component displays the feature's name, a cropped description, and includes a voting button. To facilitate two actions within a single card, the component uses a specific layout pattern. Users can click on the card to open the feature details in a modal, while the "Vote" button allows them to vote for the feature separately. Due to HTML constraints that prevent nesting buttons, we utilize a relatively positioned container for the card, with the "Vote" button absolutely positioned within it. This layout pattern is common enough that [RadzionKit](https://github.com/radzionc/radzionkit) provides an abstraction for it, known as `ActionInsideInteractiveElement`, which simplifies the implementation of multiple interactive elements in a single component.
```tsx
import { HStack, VStack } from "@lib/ui/layout/Stack"
import { Panel, panelDefaultPadding } from "@lib/ui/panel/Panel"
import { Text } from "@lib/ui/text"
import { ShyInfoBlock } from "@lib/ui/info/ShyInfoBlock"
import styled from "styled-components"
import { maxTextLines } from "@lib/ui/css/maxTextLines"
import { ActionInsideInteractiveElement } from "@lib/ui/base/ActionInsideInteractiveElement"
import { Spacer } from "@lib/ui/layout/Spacer"
import { Opener } from "@lib/ui/base/Opener"
import { Modal } from "@lib/ui/modal"
import { interactive } from "@lib/ui/css/interactive"
import { getColor } from "@lib/ui/theme/getters"
import { transition } from "@lib/ui/css/transition"
import { useCurrentProductFeature } from "./CurrentProductFeatureProvider"
import { ProductFeatureDetails } from "./ProductFeatureDetails"
import { VoteForFeature } from "./VoteForFeature"
const Description = styled(Text)`
${maxTextLines(2)}
`
const Container = styled(Panel)`
${interactive};
${transition};
&:hover {
background: ${getColor("foreground")};
}
`
export const ProductFeatureItem = () => {
const { name, description, isApproved } = useCurrentProductFeature()
return (
<ActionInsideInteractiveElement
render={({ actionSize }) => (
<Opener
renderOpener={({ onOpen }) => (
<Container onClick={onOpen} kind="secondary">
<VStack gap={8}>
<HStack
justifyContent="space-between"
alignItems="start"
fullWidth
gap={20}
>
<VStack gap={8}>
<Text weight="semibold" style={{ flex: 1 }} height="large">
{name}
</Text>
<Description height="large" color="supporting" size={14}>
{description}
</Description>
</VStack>
<Spacer {...actionSize} />
</HStack>
{!isApproved && (
<ShyInfoBlock>
Thank you! Your feature is awaiting approval and will be
open for voting soon."
</ShyInfoBlock>
)}
</VStack>
</Container>
)}
renderContent={({ onClose }) => (
<Modal width={480} onClose={onClose} title={name}>
<ProductFeatureDetails />
</Modal>
)}
/>
)}
action={<VoteForFeature />}
actionPlacerStyles={{
top: panelDefaultPadding,
right: panelDefaultPadding,
}}
/>
)
}
```
We utilize the `Opener` component again to manage the modal state for displaying feature details. To ensure that the title does not overlap with the absolutely positioned "Vote" button, we insert a "Spacer" component with the same dimensions as the "Vote" button, as determined by `ActionInsideInteractiveElement`. To keep the card's appearance concise, we crop the description using the `maxTextLines` CSS utility from [RadzionKit](https://github.com/radzionc/radzionkit). Additionally, if the feature has not been approved yet, we display a `ShyInfoBlock` component to inform the user that their feature is awaiting approval.
```tsx
import { UpvoteButton } from "@lib/ui/buttons/UpvoteButton"
import { useVoteForFeatureMutation } from "../hooks/useVoteForFeatureMutation"
import { useCurrentProductFeature } from "./CurrentProductFeatureProvider"
export const VoteForFeature = () => {
const { id, upvotedByMe, upvotes } = useCurrentProductFeature()
const { mutate } = useVoteForFeatureMutation()
return (
<UpvoteButton
onClick={() => {
mutate({
id,
})
}}
value={upvotedByMe}
upvotes={upvotes}
/>
)
}
```
The `VoteForFeature` component utilizes the `UpvoteButton` to provide a straightforward and intuitive voting interface. When clicked, the component triggers the `mutate` function from the `useVoteForFeatureMutation` hook, with the feature ID passed as an input parameter. The `UpvoteButton` features a chevron icon and displays the count of upvotes. It dynamically changes color based on the `value` prop to visually indicate whether the user has already voted for the feature.
```tsx
import styled from "styled-components"
import { UnstyledButton } from "./UnstyledButton"
import { borderRadius } from "../css/borderRadius"
import { interactive } from "../css/interactive"
import { getColor, matchColor } from "../theme/getters"
import { transition } from "../css/transition"
import { getHoverVariant } from "../theme/getHoverVariant"
import { VStack } from "../layout/Stack"
import { IconWrapper } from "../icons/IconWrapper"
import { Text } from "../text"
import { CaretUpIcon } from "../icons/CaretUpIcon"
import { ClickableComponentProps } from "../props"
type UpvoteButtonProps = ClickableComponentProps & {
value: boolean
upvotes: number
}
const Cotainer = styled(UnstyledButton)<{ value: boolean }>`
padding: 8px;
min-width: 48px;
${borderRadius.s};
border: 1px solid;
${interactive};
color: ${matchColor("value", {
true: "primary",
false: "text",
})};
${transition};
&:hover {
background: ${getColor("mist")};
color: ${(value) =>
value ? getHoverVariant("primary") : getColor("contrast")};
}
`
export const UpvoteButton = ({
value,
upvotes,
...rest
}: UpvoteButtonProps) => (
<Cotainer {...rest} value={value}>
<VStack alignItems="center">
<IconWrapper style={{ fontSize: 20 }}>
<CaretUpIcon />
</IconWrapper>
<Text size={14} weight="bold">
{upvotes}
</Text>
</VStack>
</Cotainer>
)
```
The `ProductFeatureDetails` component displays the feature's creation date, the user who proposed the feature alongside the voting button, and the full feature description. To fetch the proposer's profile details, we use the `UserProfileQueryDependant` component. This component determines if the user has a public profile, displaying their name and country, or labels them as "Anonymous" if they maintain an anonymous account. The `UserProfileQueryDependant` is an enhancement of the `QueryDependant` component, providing a more streamlined approach to accessing user profile information.
```tsx
import { HStack, VStack } from "@lib/ui/layout/Stack"
import { Text } from "@lib/ui/text"
import { LabeledValue } from "@lib/ui/text/LabeledValue"
import { format } from "date-fns"
import { UserProfileQueryDependant } from "../../community/components/UserProfileQueryDependant"
import { ScoreboardDisplayName } from "@increaser/ui/scoreboard/ScoreboardDisplayName"
import { VoteForFeature } from "./VoteForFeature"
import { useCurrentProductFeature } from "./CurrentProductFeatureProvider"
export const ProductFeatureDetails = () => {
const { createdAt, proposedBy, description } = useCurrentProductFeature()
return (
<VStack gap={18}>
<HStack fullWidth alignItems="center" justifyContent="space-between">
<VStack style={{ fontSize: 14 }} gap={8}>
<LabeledValue name="Proposed at">
{format(createdAt, "dd MMM yyyy")}
</LabeledValue>
<LabeledValue name="Proposed by">
<UserProfileQueryDependant
id={proposedBy}
success={(profile) => {
return (
<ScoreboardDisplayName
name={profile?.name || "Anonymous"}
country={profile?.country}
/>
)
}}
/>
</LabeledValue>
</VStack>
<VoteForFeature />
</HStack>
<Text height="large">{description}</Text>
</VStack>
)
}
```
| radzion |
1,873,957 | Mozilla Firefox Politikası | Liman MYS'de Mozilla Firefox Politikası Nasıl Uygulanır Mozilla Firefox politikaları,... | 0 | 2024-06-03T04:42:14 | https://dev.to/aciklab/mozilla-firefox-politikasi-proxy-ayarlari-4op5 | # Liman MYS'de Mozilla Firefox Politikası Nasıl Uygulanır
Mozilla Firefox politikaları, kullanıcıların ve sistem yöneticilerinin tarayıcı davranışlarını yönetmelerine olanak tanır. Bu politikalar sayesinde çeşitli tarayıcı ayarları merkezi olarak yapılandırılabilir ve yönetilebilir.
Öncelikle nasıl politika oluşturacağımıza bakalım:
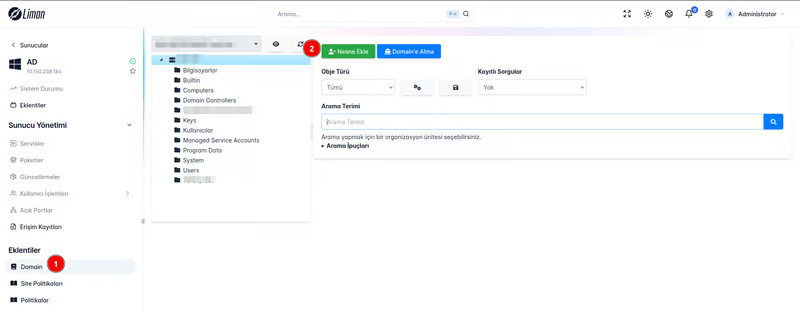
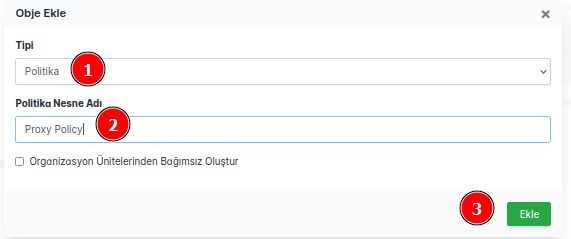
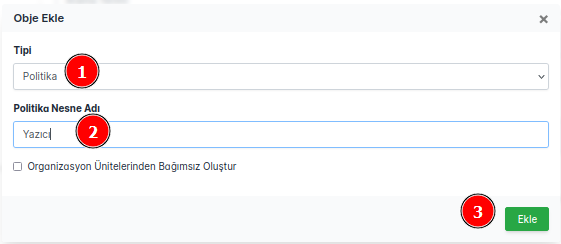
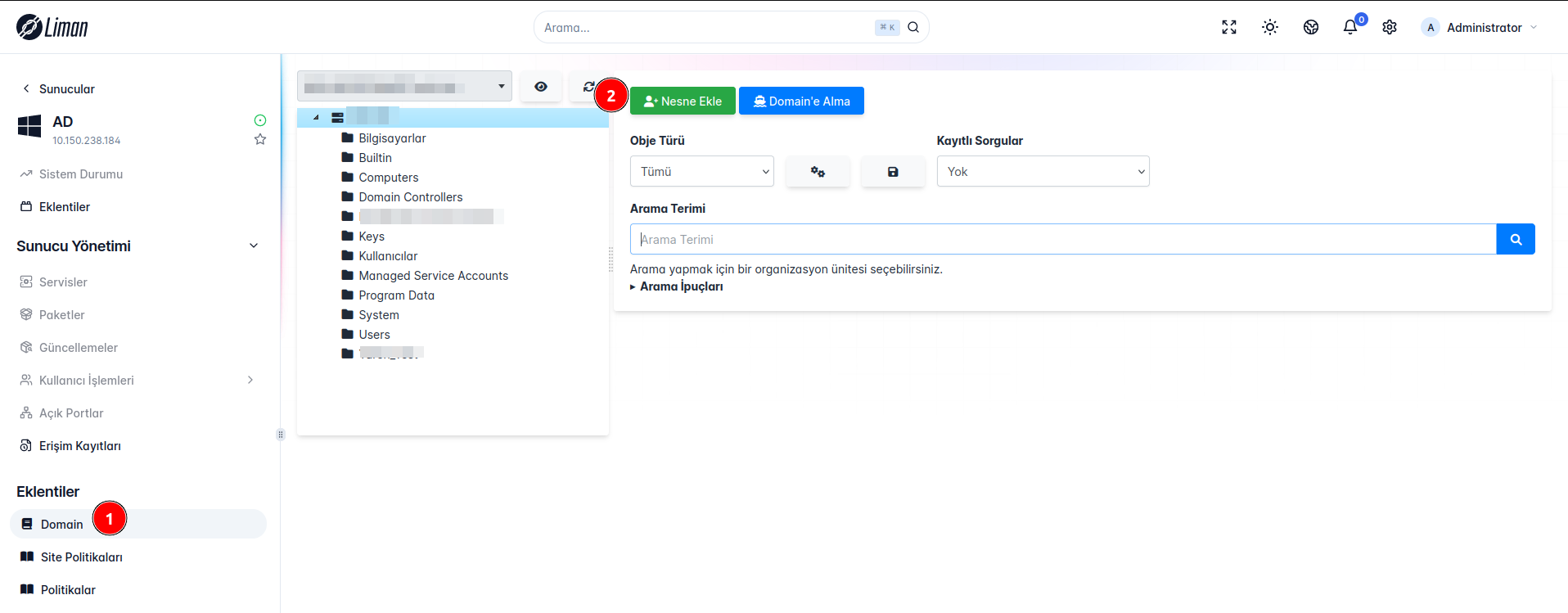
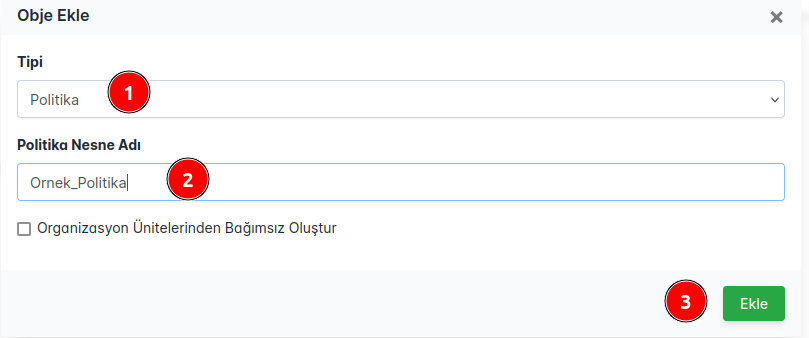
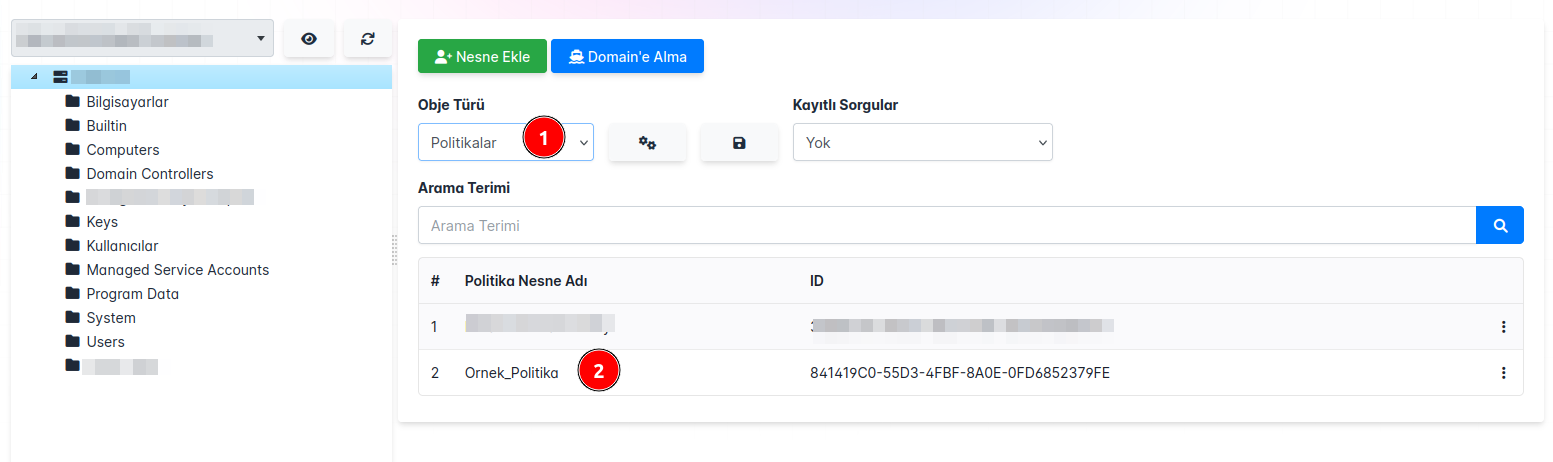
**Domain** Eklentimiz ile karşımıza çıkan ekrandan **Nesne Ekle** butonuna tıkladığımızda bizi karşılayan seçim ekranından tip bölümünü **Politika** seçerek politikamıza isim vererek **Ekle** butonuna bastığımızda politikamız eklenmiş olacaktır.
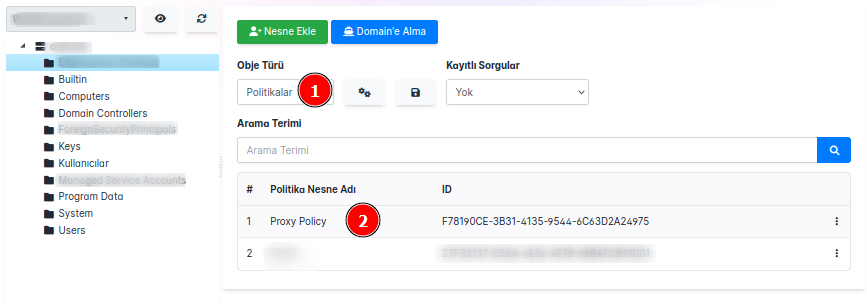
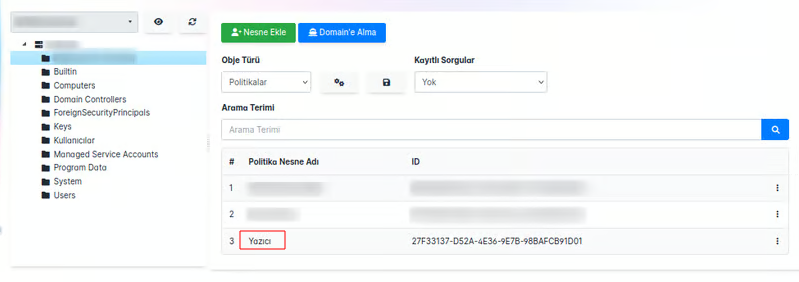
Politikaları görüntülediğimizde eklediğimiz politikayı görebiliriz.
**NOT:** Politikanızı nerede oluşturmak istiyorsanız o bölümün üstüne tıkladıktan sonra nesne oluşturma işleminizi yapınız.
# Politika Ayarları
## Politika Değerleri
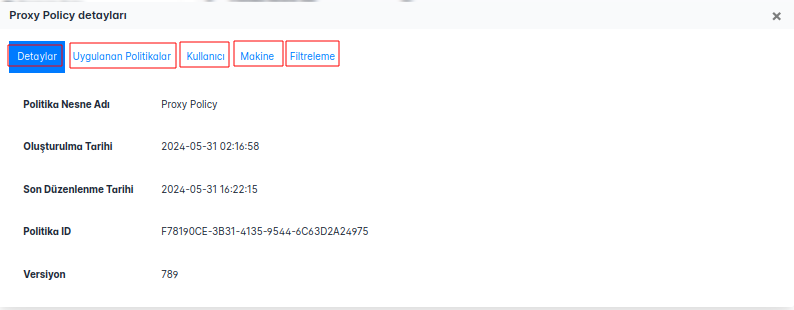
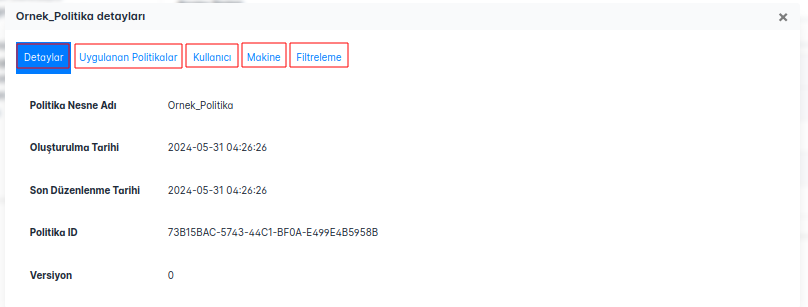
Oluşturduğumuz politikayı açtığımızda karşılaştığımız başlıklar:
**Detaylar:** Politikamızın adı, oluşturma tarihi, versiyonu, ID bilgisi gibi temel bilgiler bizi karşılamaktadır.
**Uygulanan Politikalar:** Makine ve Kullanıcı bazında uygulanan politikalar sergilenmektedir.
**Kullanıcı:** Kullanıcı bazında politikaları yönetebileceğimiz alan bu kısımda yer almaktadır.
**Makine:** Makine bazında politikaları yönetebileceğimiz alan bu kısımda yer almaktadır.
**Filtreleme:** Oluşturduğumuz politikamızın hangi kullanıcılarda veya gruplar uygulanmasını ya da uygulanmamasını seçebildiğimiz alandır.
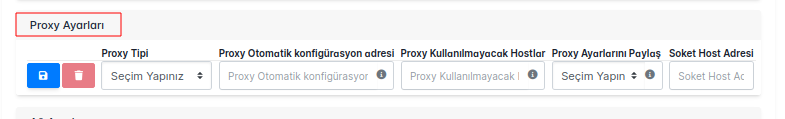
**Proxy** politikası oluşturmak için de şu adımları izleyebiliriz:
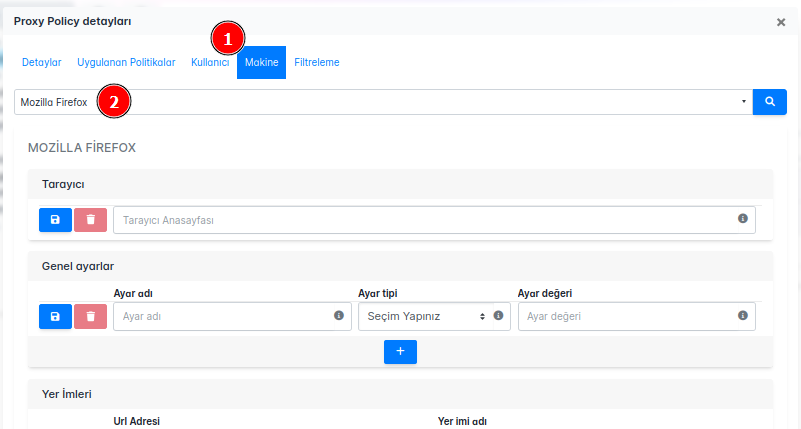
**Proxy** politika ekranı şu şekildedir:
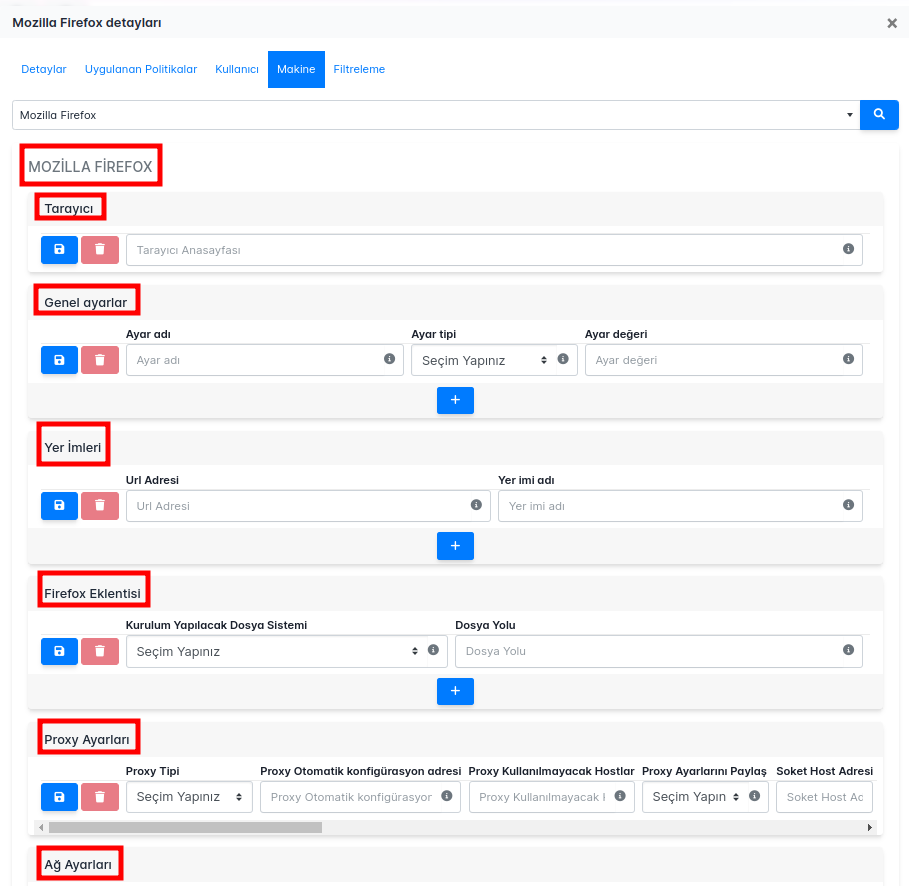
# Genel Ayarlar
Mozilla Firefox'ta genel ayarları yönetmek için **about:config** sayfasını kullanabilirsiniz. Bu sayfa, tarayıcının gelişmiş ayarlarına erişim sağlar ve kullanıcıların belirli ayarları ince ayar yaparak özelleştirmesine olanak tanır. Aşağıdaki adımları izleyerek about:config sayfasına erişebilir ve genel ayarları yönetebilirsiniz:
1. Firefox tarayıcısını açın.
2. Adres çubuğuna **_about:config_** yazın ve **_Enter_** tuşuna basın.
3. Uyarı mesajını onaylayarak devam edin.
4. Arama çubuğunu kullanarak ihtiyacınıza yönelik ayar adlarını arayın ve gerekli değişiklikleri yapın.
### Genel Ayarlar Politikası Çalışması ve Kontrolü
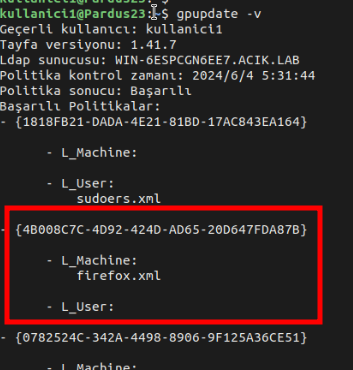
**Genel Ayarlar** politikası ile oluşturacağımız senaryolar Pardus 23 üzerinde test edilmiştir.
#### Örnek Konfigürasyon
Kerberos kimlik doğrulaması için tarayıcı ayarlarının yapılandırması örneği ele alınacaktır.
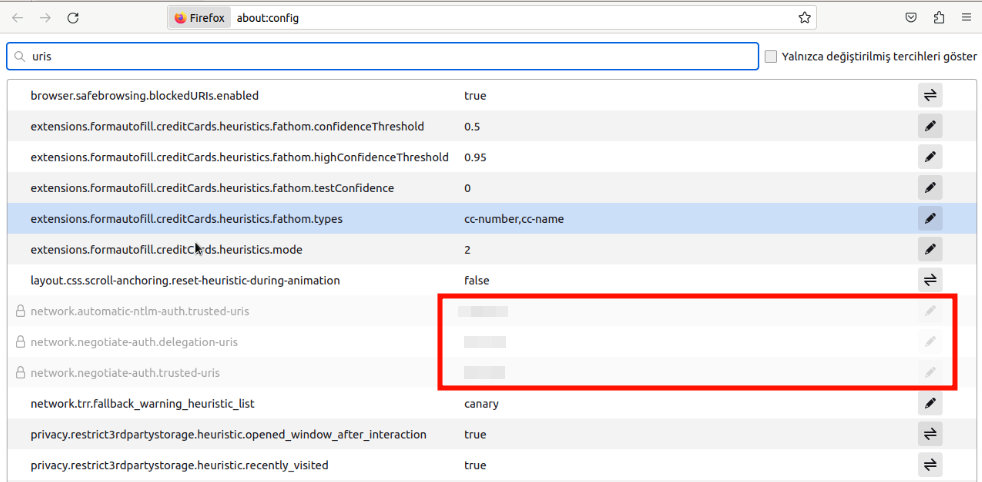
- Tarayıcı penceresine şu URL'yi girelim: **about:config.**
- Riski Kabul Et ve Devam Et'e tıklayalım.
- Arama tercihi adı alanına _uris_ yazalım ve aşağıdakileri Ayar Adı olarak ekleyelim.
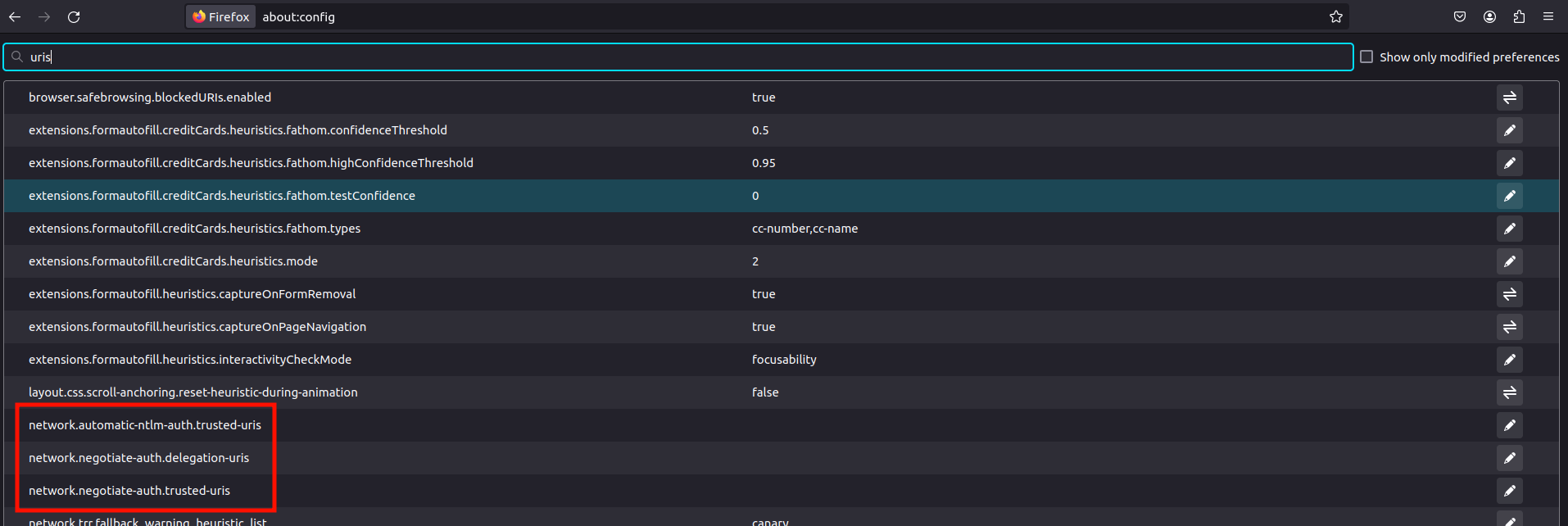
| | | |
|------------------------------------------|-------|--------------|
| network.automatic-ntlm-auth.trusted-uris | Metin | _DomainName_ |
| network.negotiate-auth.delegation-uris | Metin | _DomainName_ |
| network.negotiate-auth.trusted-uris | Metin | _DomainName_ |
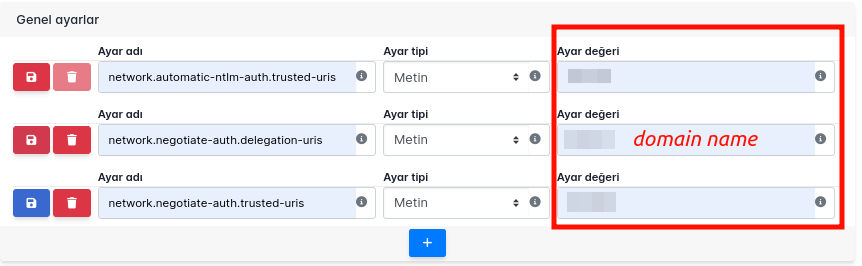
*!* Tayfa kurulumu esnasında aldığımız ticket belirli bir süre boyunca geçerlidir. Politikamız sayesinde belirttiğimiz ayarlar, tarayıcıya Kerberos kimlik doğrulama bilgilerini kullanarak otomatik oturum açmamızı sağlar. Bu sayede kullanıcılar sık sık kimlik bilgilerini girmek zorunda kalmaz.
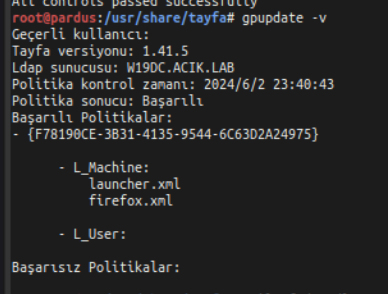
Politikamızı uygulayıp Pardus makinamız üzerinde **gpupdate -v** komutu ile politikamızı tetikliyoruz.
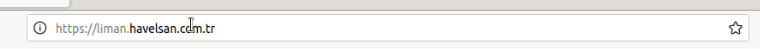
Sonrasında domaindeki bilgisayarımız üzerinde yine **about:config** üzerinde kontrol sağladığımızda girdiğimiz FQDN'i görebiliriz.
[Kerberos authentication - Documentation for BMC Helix Single ](https://docs.bmc.com/docs/hsso/241/configuring-browser-settings-for-kerberos-authentication-1284942260.html)
# Tarayıcı
Bu politika ile Firefox tarayıcısı açıldığında belirlediğiniz URL **anasayfa** olarak yüklenecektir.
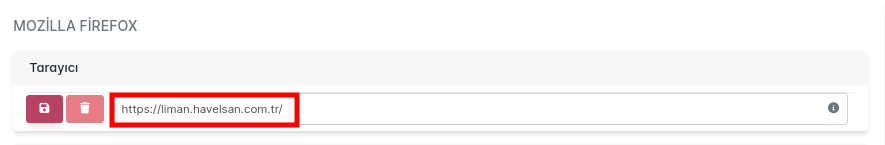
Tarayıcı kısmına url olarak veri girmemiz gerekmektir.
### Tarayıcı Politikası Çalışması ve Kontrolü
**Tarayıcı** politikası ile oluşturacağımız senaryolar Pardus 23 üzerinde test edilmiştir.
Firefox'u açtığımızda girdiğimiz url bizi karşıladığında politikamızın çalıştığını doğrulamış oluruz.
# Yer İmleri
Bu alan, belirli URL'leri tarayıcı yer imlerine eklemek için kullanılır. Örneğin, _https://www.example.com_ URL adresi _Example_ adıyla yer imlerine eklenebilir.
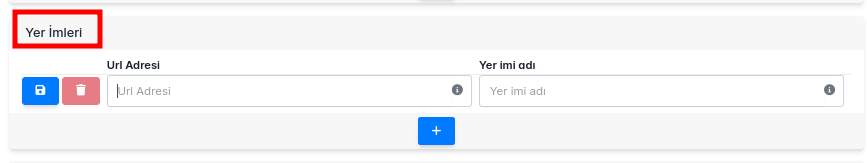
| | |
|-----------------|------------------------------------------------------------------------|
| **Url Adresi** | Yer imlerine eklenmek istenen url'dir |
| **Yer İmi Adı** | Yer imlerinde eklenen url adrseinin hangi ad ile ekleneceği bilgisidir |
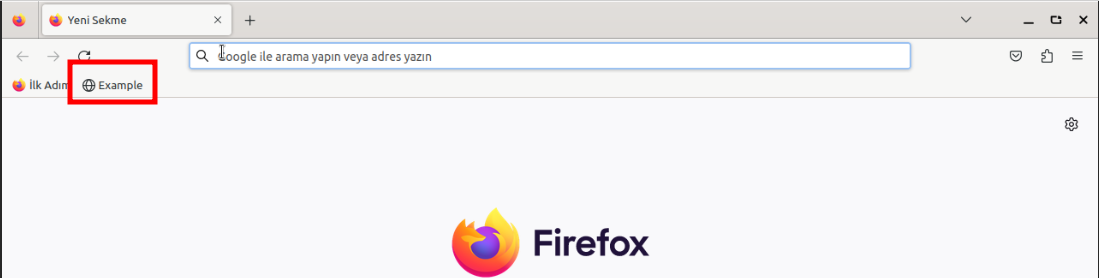
### Yer İmleri Çalışması ve Kontrolü
**Yer İmleri **politikası ile oluşturacağımız senaryolar Pardus 23 üzerinde test edilmiştir
#### Örnek Konfigürasyon:
**Url Adresi**: https://www.example.com
**Yer İmi Adı**: Example
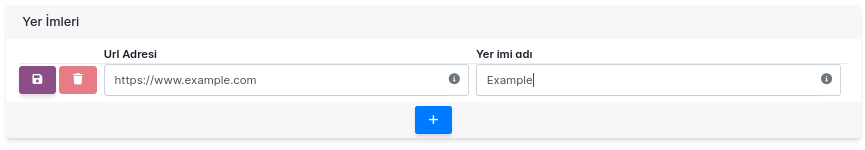
Politikamızı uygulayıp Pardus makinamız üzerinde **gpupdate -v** komutu ile politikamızı tetikliyoruz.
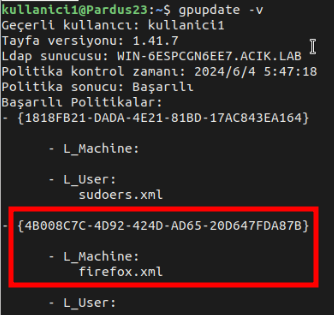
Firefox üzerinde **Yer İmleri**ni kontrol ettiğinizde url adresimizin verdiğimiz isim ile eklendiğini ayarlandığını görebilirsiniz.
# Proxy Ayarları
Bu politika ile internet tarayıcısının Proxy ayarlarını değiştirebilir, **HTTPS vekil sunucusu** kısmını politika aracılığı ile yönetebilirsiniz.
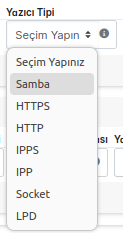
#### Proxy Tipi Seçenekleri
**Doğrudan Bağlantı (Proxy Yok):**
Proxy kullanmak istemiyorsanız bu seçeneği seçin.
**Proxy'yi Manuel Ayarla:**
Proxy sunucusunun IP adresini ve port numarasını elle girmeniz gerektiğinde bu seçeneği kullanın.
**Proxy'yi Otomatik Ayarla (PAC):**
Proxy ayarlarını otomatik olarak bir PAC dosyasından almak için bu seçeneği kullanın. PAC dosyasının URL'sini girmeniz gerekecek.
**Proxy'yi Ayarlarını Otomatik Algıla:**
Proxy ayarlarını otomatik olarak algılamak için bu seçeneği kullanın.
**Sistem Proxy Ayarlarını Kullan:**
İşletim sisteminin proxy ayarlarını kullanmak için bu seçeneği seçin.
| Alan Adı | Açıklama |
|:-----------------------------------:|:---------------------------------------------------------------------------------------------------------:|
| Proxy Tipi | Kullanılacak proxy türünü seçin. Örneğin: "Proxy'yi Manuel Ayarla" veya "Proxy'yi Otomatik Ayarla (PAC)". |
| Proxy Otomatik Konfigürasyon Adresi | Proxy ayarlarını otomatik olarak çekecek PAC dosyasının URL'si. Örneğin: http://192.168.1.110/proxy.pac. |
| Proxy Kullanılmayacak Hostlar | Proxy sunucusunu atlayacak ve doğrudan erişilecek hostların listesi. Örneğin: localhost, 127.0.0.1. |
| Proxy Ayarlarını Paylaş | Proxy ayarlarını diğer kullanıcılarla veya istemcilerle paylaşma seçeneği. |
| Soket Host Adresi | SOCKS proxy sunucusunun IP adresi veya hostname'i. SOCKS proxy kullanmıyorsanız boş bırakın. |
| Soket Port Numarası | SOCKS proxy sunucusunun port numarası. SOCKS proxy kullanmıyorsanız boş bırakın. |
| SSL Host Adresi | HTTPS (SSL) trafiği için kullanılacak proxy sunucusunun IP adresi veya hostname'i. |
| SSL Port Numarası | HTTPS (SSL) trafiği için proxy sunucusunun port numarası. |
| HTTP Host Adresi | HTTP trafiği için kullanılacak proxy sunucusunun IP adresi veya hostname'i. |
| HTTP Port Numarası | HTTP trafiği için proxy sunucusunun port numarası. |
| FTP Host Adresi | FTP trafiği için kullanılacak proxy sunucusunun IP adresi veya hostname'i. |
| FTP Port Numarası | FTP trafiği için proxy sunucusunun port numarası. |
### Proxy Ayarları Çalışması ve Kontrolü
**Proxy** politikası ile oluşturacağımız senaryolar Pardus 23 üzerinde test edilmiştir.
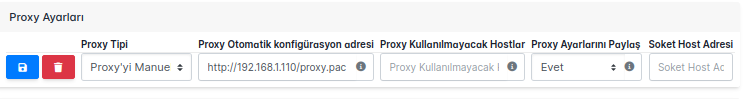
#### Örnek Konfigürasyon:
| Proxy Tipi | Proxy Otomatik konfigürasyon adresi | Proxy Kullanılmayacak Hostlar | Proxy Ayarlarını Paylaş | Soket Host Adresi | Soket Port Numarası | SSL Host Adresi | SSL Port Numarası | HTTP Host Adresi | HTTP Port Numarası | FTP Host Adresi | FTP Port Numarası |
|------------|-------------------------------------|-------------------------------|-------------------------|-------------------|---------------------|-----------------|-------------------|------------------|--------------------|-----------------|-------------------|
| HTTP | http://192.168.1.110/proxy.pac | localhost, 127.0.0.1 | Seçim Yapın | (boş bırakın) | (boş bırakın) | 192.168.1.110 | 3128 | 192.168.1.110 | 3128 | (boş bırakın) | (boş bırakın) |
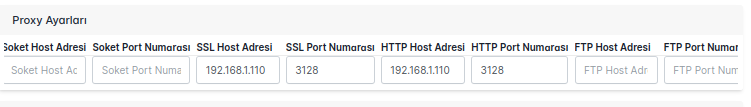
Politikamızı uygulayıp Pardus makinamız üzerinde gpupdate -v komutu ile politikamızı tetikliyoruz.
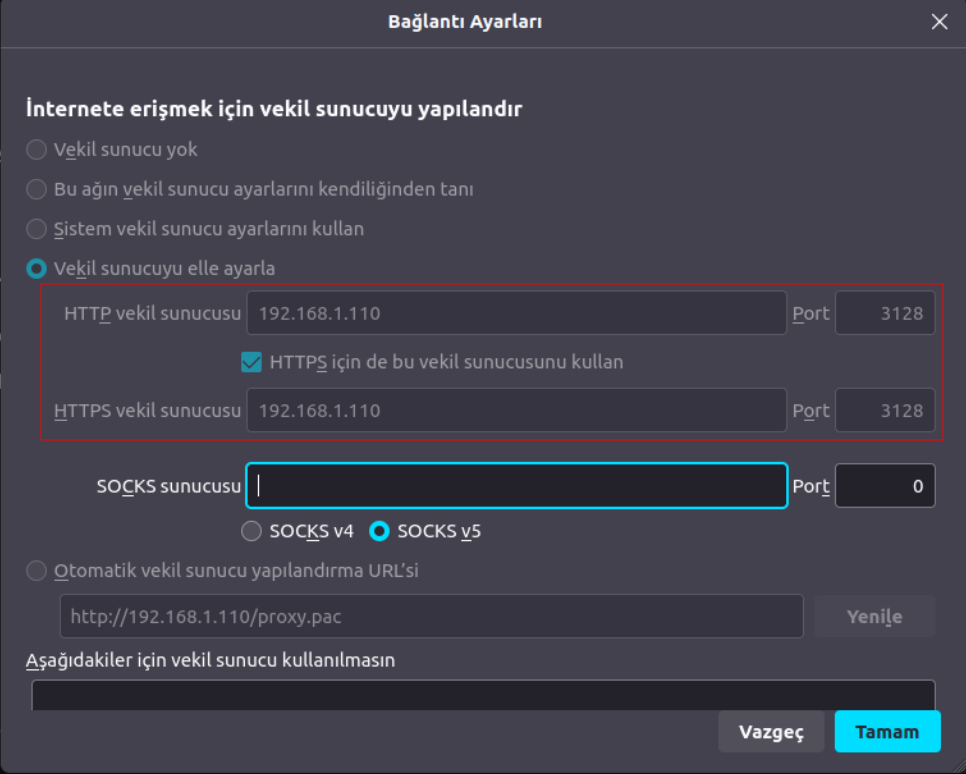
Firefox üzerinde **Vekil Sunucu** ayarlarınızı kontrol ettiğinizde proxy sunucunuzun vekil sunucu olarak ayarlandığını görebilirsiniz.
Aynı zamanda proxy sunucunuzun log kayıtlarından kontrol edebilirsiniz.
| yarensari | |
1,874,935 | Buy Negative Google Reviews | Buy Negative Google Reviews Negative reviews on Google are detrimental critiques that expose... | 0 | 2024-06-03T04:42:05 | https://dev.to/annewalkere23/buy-negative-google-reviews-ee7 | Buy Negative Google Reviews
Negative reviews on Google are detrimental critiques that expose customers’ unfavorable experiences with a business. These reviews can significantly damage a company’s reputation, presenting challenges in both attracting new customers and retaining current ones. If you are considering purchasing negative Google reviews from dmhelpshop.com, we encourage you to reconsider and instead focus on providing exceptional products and services to ensure positive feedback and sustainable success.
Buy Negative Google Reviews
Why Buy Negative Google Reviews from dmhelpshop
We take pride in our fully qualified, hardworking, and experienced team, who are committed to providing quality and safe services that meet all your needs. Our professional team ensures that you can trust us completely, knowing that your satisfaction is our top priority. With us, you can rest assured that you’re in good hands.
Is Buy Negative Google Reviews safe?
At dmhelpshop, we understand the concern many business persons have about the safety of purchasing Buy negative Google reviews. We are here to guide you through a process that sheds light on the importance of these reviews and how we ensure they appear realistic and safe for your business. Our team of qualified and experienced computer experts has successfully handled similar cases before, and we are committed to providing a solution tailored to your specific needs. Contact us today to learn more about how we can help your business thrive.
Buy Google 5 Star Reviews
Reviews represent the opinions of experienced customers who have utilized services or purchased products from various online or offline markets. These reviews convey customer demands and opinions, and ratings are assigned based on the quality of the products or services and the overall user experience. Google serves as an excellent platform for customers to leave reviews since the majority of users engage with it organically. When you purchase Buy Google 5 Star Reviews, you have the potential to influence a large number of people either positively or negatively. Positive reviews can attract customers to purchase your products, while negative reviews can deter potential customers.
If you choose to Buy Google 5 Star Reviews, people will be more inclined to consider your products. However, it is important to recognize that reviews can have both positive and negative impacts on your business. Therefore, take the time to determine which type of reviews you wish to acquire. Our experience indicates that purchasing Buy Google 5 Star Reviews can engage and connect you with a wide audience. By purchasing positive reviews, you can enhance your business profile and attract online traffic. Additionally, it is advisable to seek reviews from reputable platforms, including social media, to maintain a positive flow. We are an experienced and reliable service provider, highly knowledgeable about the impacts of reviews. Hence, we recommend purchasing verified Google reviews and ensuring their stability and non-gropability.
https://dmhelpshop.com/product/buy-negative-google-reviews/
Let us now briefly examine the direct and indirect benefits of reviews:
Reviews have the power to enhance your business profile, influencing users at an affordable cost.
To attract customers, consider purchasing only positive reviews, while negative reviews can be acquired to undermine your competitors. Collect negative reports on your opponents and present them as evidence.
If you receive negative reviews, view them as an opportunity to understand user reactions, make improvements to your products and services, and keep up with current trends.
By earning the trust and loyalty of customers, you can control the market value of your products. Therefore, it is essential to buy online reviews, including Buy Google 5 Star Reviews.
Reviews serve as the captivating fragrance that entices previous customers to return repeatedly.
Positive customer opinions expressed through reviews can help you expand your business globally and achieve profitability and credibility.
When you purchase positive Buy Google 5 Star Reviews, they effectively communicate the history of your company or the quality of your individual products.
https://dmhelpshop.com/product/buy-negative-google-reviews/
as a collective voice representing potential customers, boosting your business to amazing heights.
Now, let’s delve into a comprehensive understanding of reviews and how they function:
Google, with its significant organic user base, stands out as the premier platform for customers to leave reviews. When you purchase Buy Google 5 Star Reviews , you have the power to positively influence a vast number of individuals. Reviews are essentially written submissions by users that provide detailed insights into a company, its products, services, and other relevant aspects based on their personal experiences. In today’s business landscape, it is crucial for every business owner to consider buying verified Buy Google 5 Star Reviews, both positive and negative, in order to reap various benefits.
https://dmhelpshop.com/product/buy-negative-google-reviews/
Why are Google reviews considered the best tool to attract customers?
Google, being the leading search engine and the largest source of potential and organic customers, is highly valued by business owners. Many business owners choose to purchase Google reviews to enhance their business profiles and also sell them to third parties. Without reviews, it is challenging to reach a large customer base globally or locally. Therefore, it is crucial to consider buying positive Buy Google 5 Star Reviews from reliable sources. When you invest in Buy Google 5 Star Reviews for your business, you can expect a significant influx of potential customers, as these reviews act as a pheromone, attracting audiences towards your products and services. Every business owner aims to maximize sales and attract a substantial customer base, and purchasing Buy Google 5 Star Reviews is a strategic move.
According to online business analysts and economists, trust and affection are the essential factors that determine whether people will work with you or do business with you. However, there are additional crucial factors to consider, such as establishing effective communication systems, providing 24/7 customer support, and maintaining product quality to engage online audiences. If any of these rules are broken, it can lead to a negative impact on your business. Therefore, obtaining positive reviews is vital for the success of an online business
What are the benefits of purchasing reviews online?
In today’s fast-paced world, the impact of new technologies and IT sectors is remarkable. Compared to the past, conducting business has become significantly easier, but it is also highly competitive. To reach a global customer base, businesses must increase their presence on social media platforms as they provide the easiest way to generate organic traffic. Numerous surveys have shown that the majority of online buyers carefully read customer opinions and reviews before making purchase decisions. In fact, the percentage of customers who rely on these reviews is close to 97%. Considering these statistics, it becomes evident why we recommend buying reviews online. In an increasingly rule-based world, it is essential to take effective steps to ensure a smooth online business journey.
Buy Google 5 Star Reviews
Many people purchase reviews online from various sources and witness unique progress. Reviews serve as powerful tools to instill customer trust, influence their decision-making, and bring positive vibes to your business. Making a single mistake in this regard can lead to a significant collapse of your business. Therefore, it is crucial to focus on improving product quality, quantity, communication networks, facilities, and providing the utmost support to your customers.
Reviews reflect customer demands, opinions, and ratings based on their experiences with your products or services. If you purchase Buy Google 5-star reviews, it will undoubtedly attract more people to consider your offerings. Google is the ideal platform for customers to leave reviews due to its extensive organic user involvement. Therefore, investing in Buy Google 5 Star Reviews can significantly influence a large number of people in a positive way.
How to generate google reviews on my business profile?
Focus on delivering high-quality customer service in every interaction with your customers. By creating positive experiences for them, you increase the likelihood of receiving reviews. These reviews will not only help to build loyalty among your customers but also encourage them to spread the word about your exceptional service. It is crucial to strive to meet customer needs and exceed their expectations in order to elicit positive feedback. If you are interested in purchasing affordable Google reviews, we offer that service.
https://dmhelpshop.com/product/buy-negative-google-reviews/
Contact Us / 24 Hours Reply
Telegram:dmhelpshop
WhatsApp: +1 (980) 277-2786
Skype:dmhelpshop
Email:dmhelpshop@gmail.com | annewalkere23 | |
1,873,354 | Yazıcı Politikası | Liman MYS'de Yazıcı Politikası Nasıl Uygulanır Bu politika ile, yazıcıların güvenli ve... | 0 | 2024-06-03T04:40:40 | https://dev.to/aciklab/yazici-politikasi-10fb | pointer, liman, linux, debian | # Liman MYS'de Yazıcı Politikası Nasıl Uygulanır
Bu politika ile, yazıcıların güvenli ve verimli bir şekilde kullanılmasını sağlamak amacıyla çeşitli kurallar belirlenmiştir.
Öncelikle nasıl politika oluşturacağımıza bakalım:
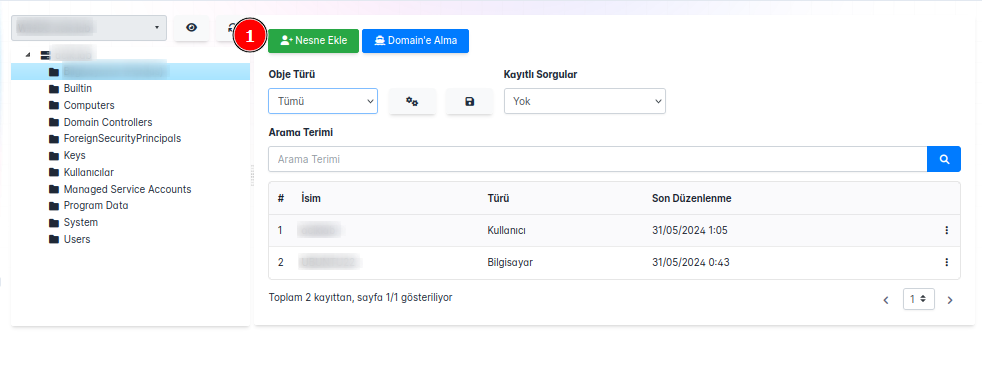
Domain Eklentimiz ile karşımıza çıkan ekrandan **Nesne Ekle** butonuna tıkladığımızda bizi karşılayan seçim ekranından tip bölümünü **Politika** seçerek politikamıza isim vererek **Ekle** butonuna bastığımızda politikamız eklenmiş olacaktır.
Politikaları görüntülediğimizde eklediğimiz politikayı görebiliriz.
## Politika Ayarları
### Politika Değerleri
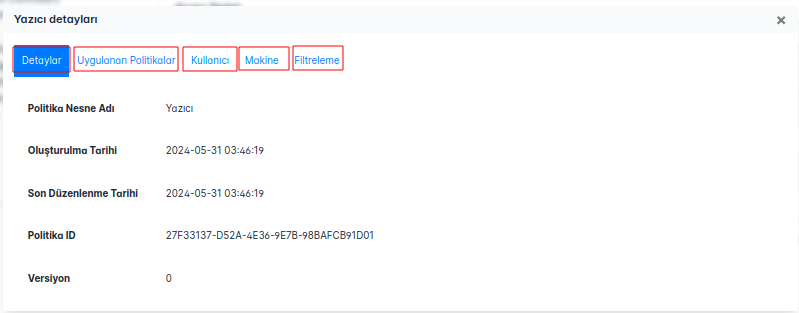
Oluşturduğumuz politikayı açtığımızda karşılaştığımız başlıklar:
**Detaylar:** Politikamızın adı, oluşturma tarihi, versiyonu, ID bilgisi gibi temel bilgiler bizi karşılamaktadır.
**Uygulanan Politikalar:** Makine ve Kullanıcı bazında uygulanan politikalar sergilenmektedir.
**Kullanıcı:** Kullanıcı bazında politikaları yönetebileceğimiz alan bu kısımda yer almaktadır.
**Makine:** Makine bazında politikaları yönetebileceğimiz alan bu kısımda yer almaktadır.
**Filtreleme:** Oluşturduğumuz politikamızın hangi kullanıcılarda veya gruplar uygulanmasını ya da uygulanmamasını seçebildiğimiz alandır.
**Yazıcı** politikası oluşturmak için de şu adımları izleyebiliriz:
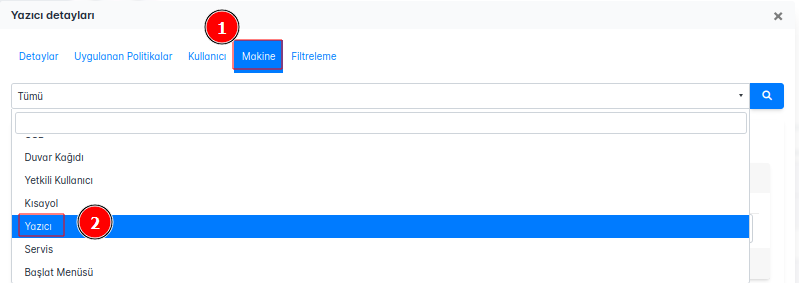
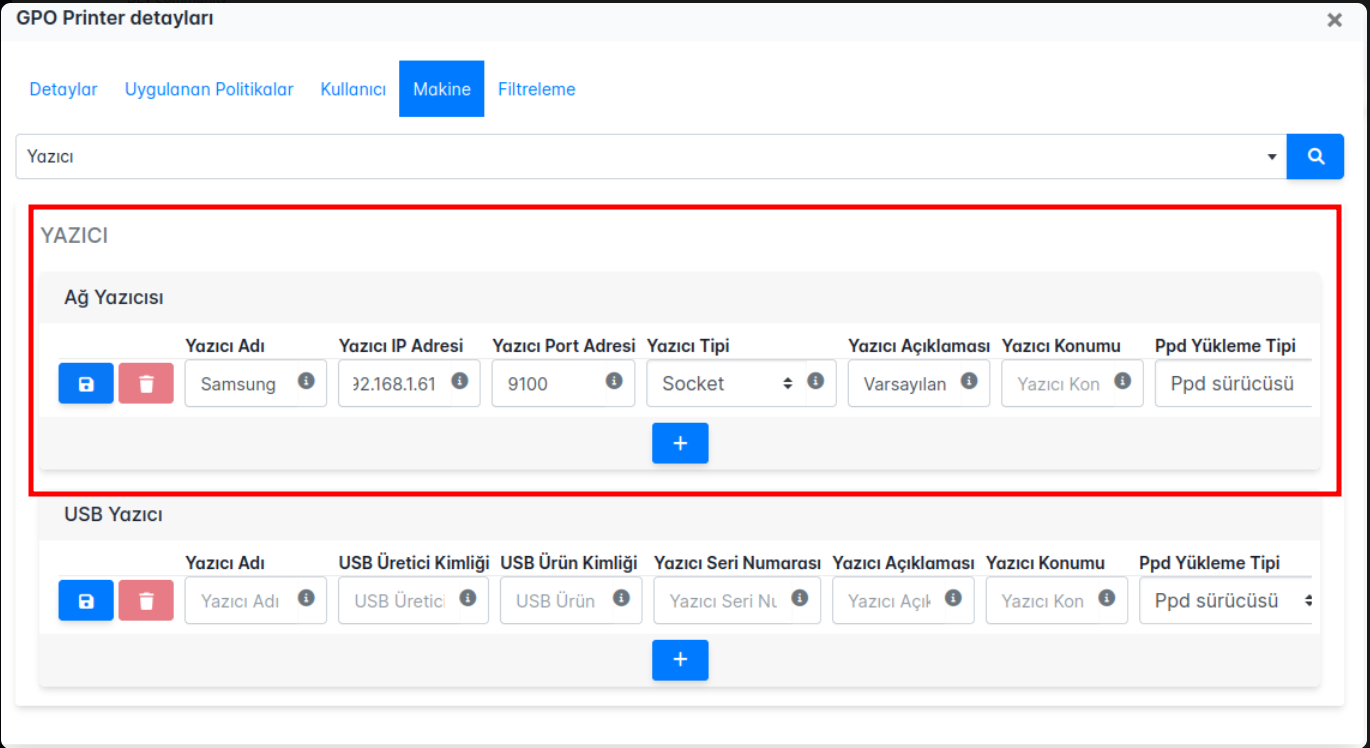
**Yazıcı** politika ekranı şu şekildedir:
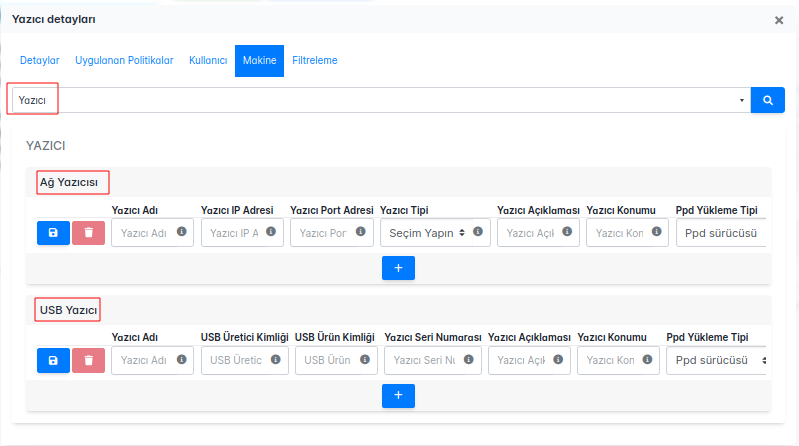
Hem ağ yazıcıları hem de USB yazıcılar için geçerli olan bu politika, yazıcıların doğru yapılandırılması ve yetkisiz erişimlerin önlenmesi için aşağıdaki kuralları içerir:
**Yazıcı Adı:** Her yazıcıya benzersiz ve anlamlı bir isim verilmelidir. Bu, kullanıcıların yazıcıları kolayca tanımasını sağlar.
**Yazıcı IP Adresi:** Ağ yazıcılarının IP adresleri doğru bir şekilde yapılandırılmalıdır. Bu adresler, ağ üzerinde yazıcıların doğru şekilde iletişim kurabilmesi için gereklidir.
**Yazıcı Port Adresi:** Yazıcıya erişim için kullanılan port numarası belirlenmelidir. Yaygın portlar arasında 9100 (RAW), 515 (LPD) veya 631 (IPP) bulunur.
**Yazıcı Tipi:** Yazıcının türü (ağ yazıcısı, USB yazıcısı vb.) doğru bir şekilde belirtilmelidir.
**Yazıcı Açıklaması:** Yazıcı hakkında açıklayıcı bilgiler sağlanmalıdır. Bu bilgiler, yazıcının nerede kullanıldığı veya hangi özelliklere sahip olduğu gibi detayları içermelidir.
**Yazıcı Konumu:** Yazıcının fiziksel olarak bulunduğu yer açıkça belirtilmelidir. Bu, kullanıcıların yazıcıyı fiziksel olarak bulmalarını kolaylaştırır.
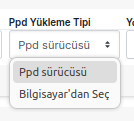
**Ppd Yükleme Tipi:** Yazıcı için kullanılan PPD dosyasının yükleme tipi belirlenmelidir. PPD dosyaları, yazıcının özelliklerini ve yeteneklerini tanımlar.
**NOT:** Bizim yapacağımız örnekte _Varsayılan_ olarak ayarlama yapıldığında konumumuz şu şekilde olmaktadır:
**usr/share/ppd/**cupsfilters/HP-Color_LaserJet_CM3530_MFP-PDF.ppd
- Driver'ın yüklü olması gerekmektedir, 3. parti driveları betikler veya paketler ile yüklenebilir, bu durum da konumda değişikliğe sebep olabilmektedir. Politikanızı oluştururken bu durumlara dikkat ediniz.
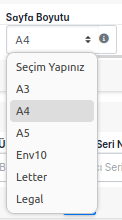
**Sayfa Boyutu:** Yazıcının desteklediği varsayılan sayfa boyutu doğru bir şekilde yapılandırılmalıdır. Örneğin, A4, Letter gibi boyutlar seçilebilir.
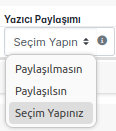
**Yazıcı Paylaşımı:** Yazıcının ağ üzerindeki diğer kullanıcılarla paylaşılıp paylaşılmayacağı belirlenmelidir. Paylaşılmayan yazıcılar sadece belirli kullanıcılar tarafından kullanılabilir.
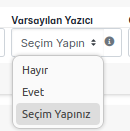
**Varsayılan Yazıcı:** Bu yazıcının varsayılan yazıcı olarak ayarlanıp ayarlanmadığı belirtilmelidir. Varsayılan yazıcı, kullanıcıların herhangi bir yazıcı seçmeden doğrudan çıktı alacakları yazıcıdır.
**Cups Opsiyonları**: Common Unix Printing System (CUPS) ile ilgili ek seçenekler ve ayarlar yapılandırılmalıdır. Bu ayarlar, yazıcının davranışını ve özelliklerini daha ayrıntılı olarak belirlemek için kullanılır.
# Politika Çalışması ve Kontrolü
Yaptığımız örnek politikamız ve durumu şu şekildedir:
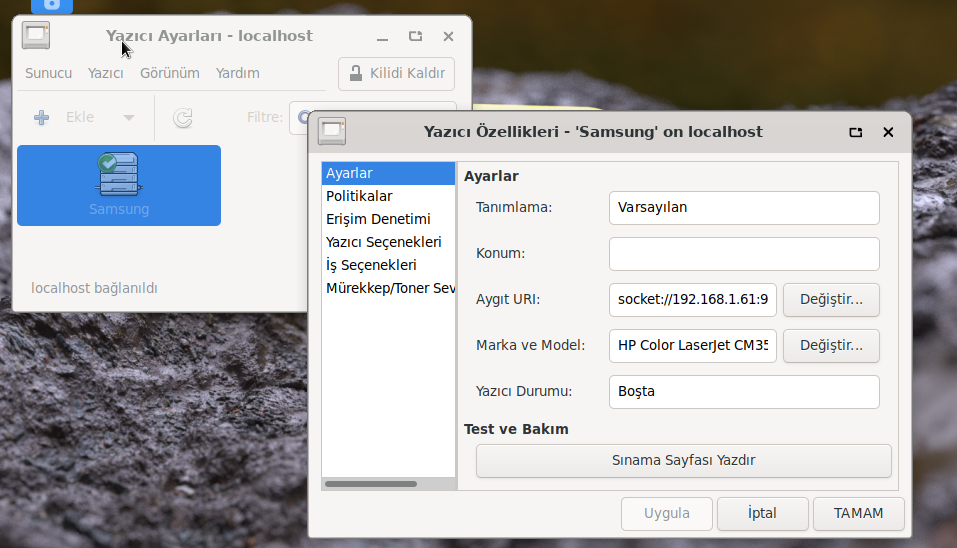
| yarensari |
1,871,820 | Yetkili Kullanıcı Politikası | Liman MYS'de Yetkili Kullanıcı Politikası Nasıl Uygulanır Bu politika ile var olan domain... | 0 | 2024-06-03T04:40:11 | https://dev.to/aciklab/yetkili-kullanici-politikasi-21hb | linux, debian, pardus, liman | # Liman MYS'de Yetkili Kullanıcı Politikası Nasıl Uygulanır
Bu politika ile var olan domain yapısında domaine alınmış istemciler üzerinde lokal admin dışında domain kullanıcılara ve lokalde açılmış/oluşturulmuş yetkisiz kullanıcılara admin yetkisi verilebilmektedir.
Öncelikle nasıl politika oluşturacağımıza bakalım:
Domain Eklentimiz ile karşımıza çıkan ekrandan **Nesne Ekle** butonuna tıkladığımızda bizi karşılayan seçim ekranından tip bölümünü **Politika** seçerek politikamıza isim vererek **Ekle** butonuna bastığımızda politikamız eklenmiş olacaktır.
Politikaları görüntülediğimizde eklediğimiz politikayı görebiliriz.
**NOT:** Politikanızı nerede oluşturmak istiyorsanız o bölümün üstüne tıkladıktan sonra nesne oluşturma işleminizi yapınız.
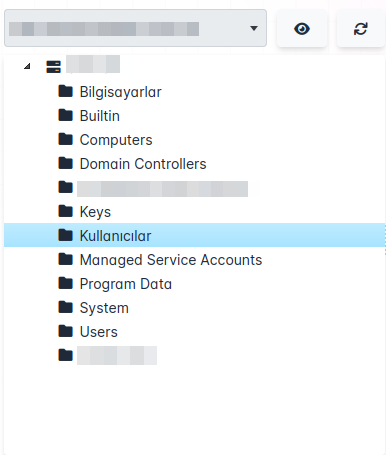
Örneğin bu örnekte politikanız _Kullanıcılar_ altında oluşacaktır.
# Politika Ayarları
## Politika Değerleri
Oluşturduğumuz politikayı açtığımızda karşılaştığımız başlıklar:
**Detaylar:** Politikamızın adı, oluşturma tarihi, versiyonu, ID bilgisi gibi temel bilgiler bizi karşılamaktadır.
**Uygulanan Politikalar:** Makine ve Kullanıcı bazında uygulanan politikalar sergilenmektedir.
**Kullanıcı:** Kullanıcı bazında politikaları yönetebileceğimiz alan bu kısımda yer almaktadır.
**Makine:** Makine bazında politikaları yönetebileceğimiz alan bu kısımda yer almaktadır.
**Filtreleme:** Oluşturduğumuz politikamızın hangi kullanıcılarda veya gruplar uygulanmasını ya da uygulanmamasını seçebildiğimiz alandır.
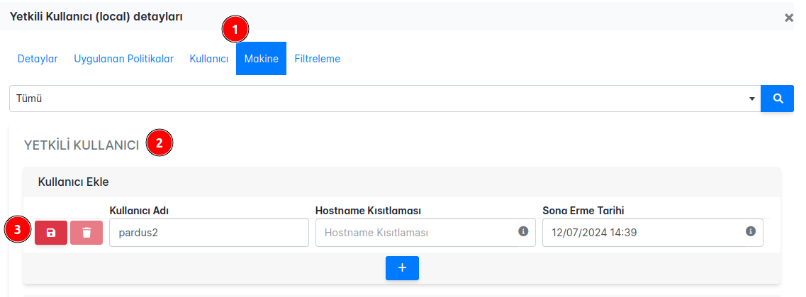
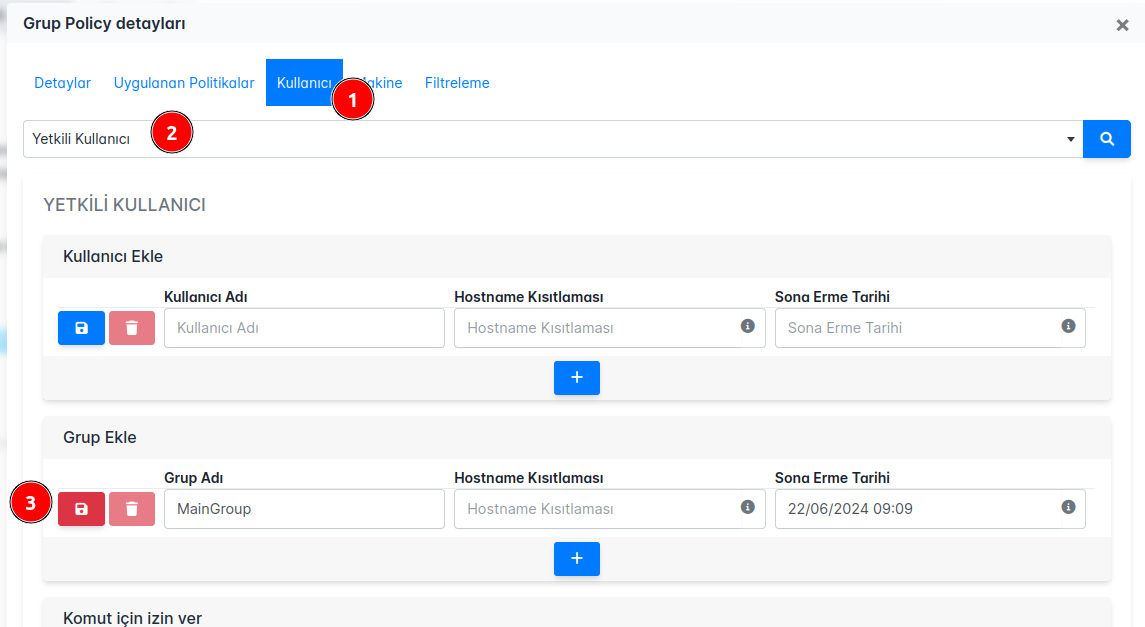
**Yetkili Kullanıcı** politikası oluşturmak için de şu adımları izleyebiliriz:
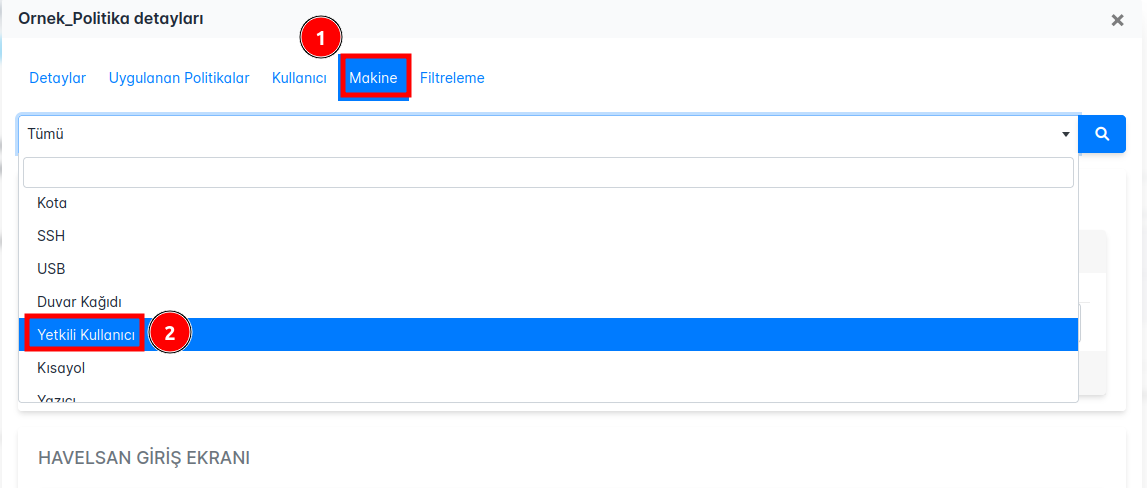
**Yetkili Kullanıcı** politika ekranı şu şekildedir:
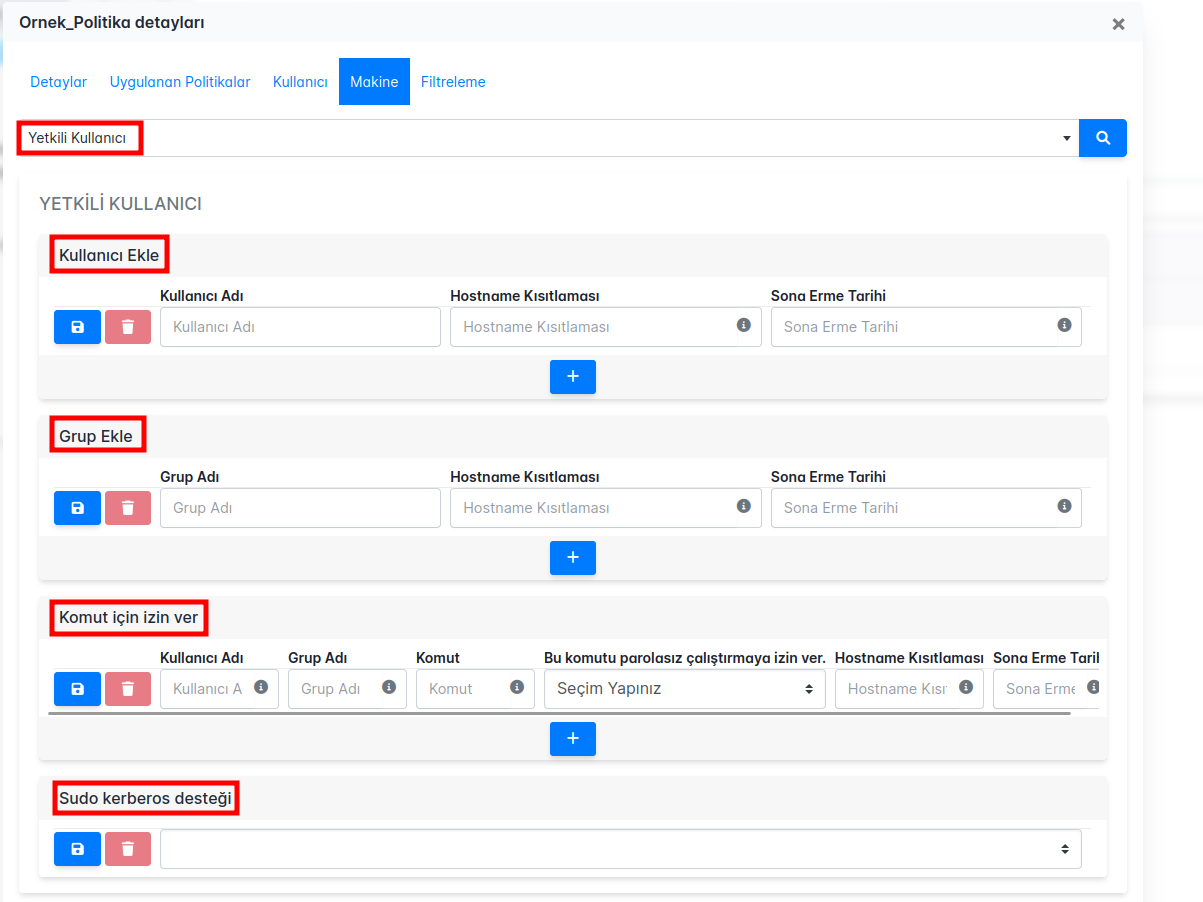
**1. Kullanıcı Ekleme Bölümü:**
**Kullanıcı Adı:** Domain veya lokal ortamda oluşturulmuş kullanıcı adı girilir.
**Hostname Kısıtlaması:** Kullanıcının sudo yetkisine sahip olacağı cihazların hostname listesini belirleyin. Birden fazla hostname için virgülle ayırma yöntemi kullanılabilir. Bu alan boş bırakıldığında, kısıtlama uygulanmaz.
**Sona Erme Tarihi:** Kullanıcının sudo yetkisinin sona ereceği tarih. Bu tarih belirtilmezse, politika süresiz olarak geçerli olur.
**2. Grup Ekleme Bölümü:**
**Grup Adı:** Domain veya lokal ortamda oluşturulmuş güvenlik grubunun adı girilir.
**Hostname Kısıtlaması:** Grubun sudo yetkisine sahip olacağı cihazların hostname listesini belirleyin. Birden fazla hostname için virgülle ayırma yöntemi kullanılabilir. Bu alan boş bırakıldığında, kısıtlama uygulanmaz.
**3. Komut İçin İzin Verme Bölümü:**
**Kullanıcı Adı:** Domain veya lokal ortamda oluşturulmuş kullanıcı adı girilir. Birden fazla kullanıcı için virgülle ayırma yöntemi kullanılabilir, tüm kullanıcılar için 'all' yazılabilir.
**Grup Adı:** Domain veya lokal ortamda oluşturulmuş güvenlik grubu adı girilir. Birden fazla grup için virgülle ayırma yöntemi kullanılabilir, tüm gruplar için 'all' yazılabilir.
**Komut:** İzin verilecek komut girilir.
**Parola Kullanımı:** Bu komutun parolasız çalıştırılıp çalıştırılmayacağını belirtin (Evet/Hayır).
## Politika Çalışması ve Kontrolü
**Yetkili Kullanıcı** politikası ile oluşturacağımız senaryolar Pardus 23 üzerinde test edilmiştir.
### 1. Domain Kullanıcısına Admin Yetkisi Vermek
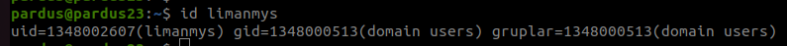
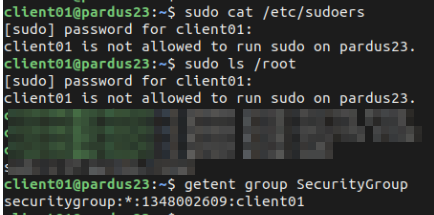
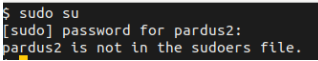
Öncelikle kullancımızın **sudo** yetkisine sahip olmadığını doğrulayalım:
- _limanmys_ bu örneğimizde kullanıcı olarak oluşturulmuştur.
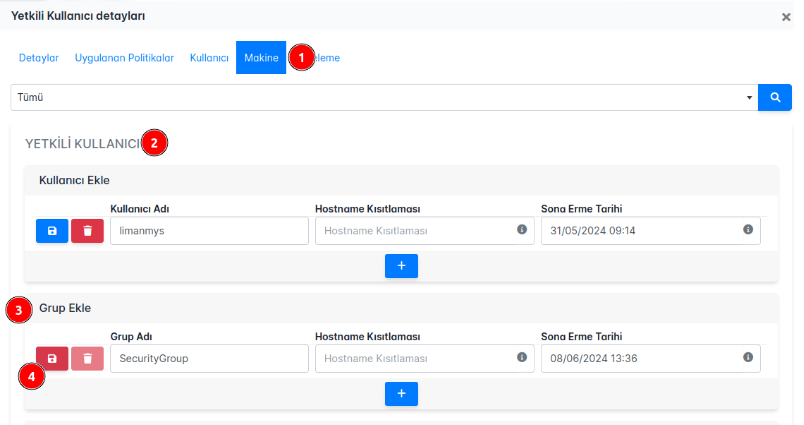
Şimdi politikamızı **Yetkili Kullanıcı** seçeneğini seçerek admin yetkisi vermek istediğimiz domain kullanıcının kullanıcı adını, isteğe göre hostname bilgisini ve isteğe göre sona erme tarihini belirtebiliriz.
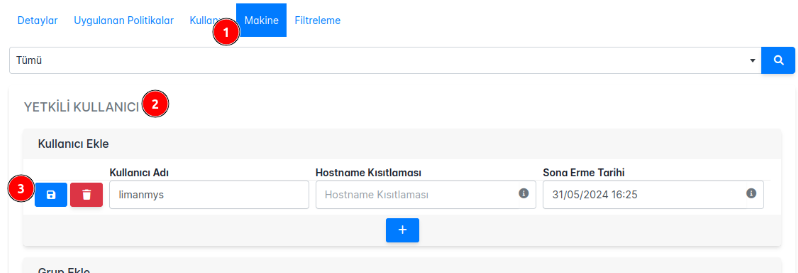
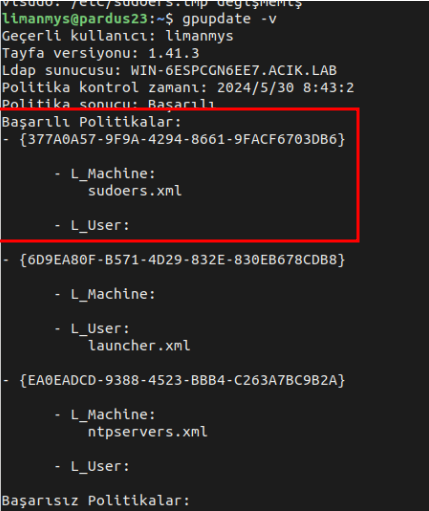
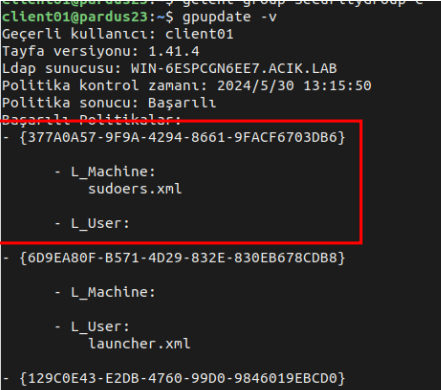
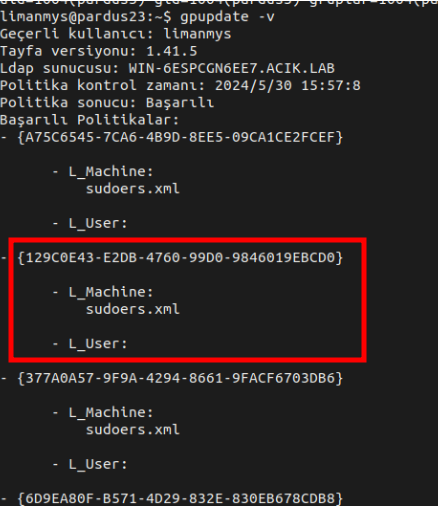
Sonrasında _limanmys_ kullancısı ile giriş yaptığımız Pardus makinamız üzerinde **gpupdate -v** komutu ile politikamızı tetikliyoruz.
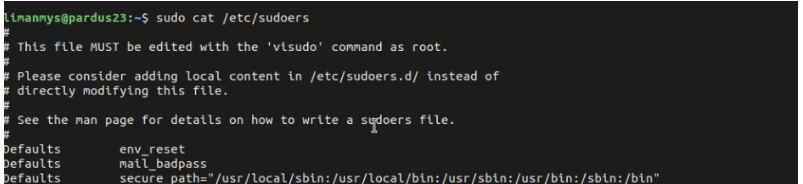
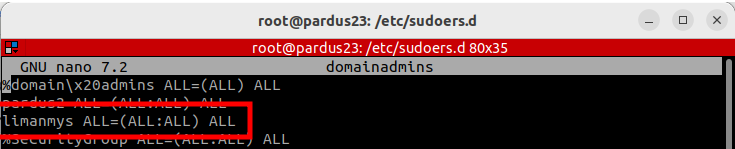
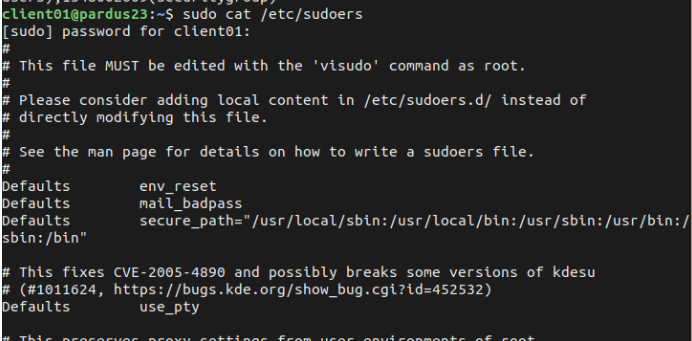
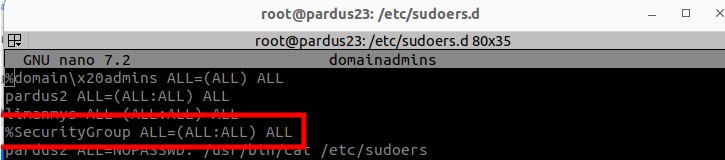
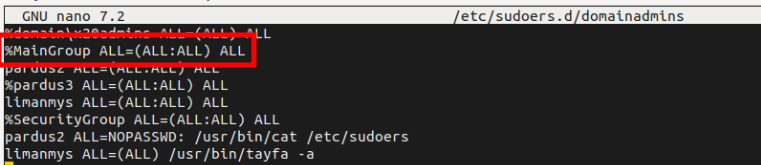
Hem kullancının sudo yetkisini test ederek hem de **/etc/sudoers.d/domainadmins** da gördüğümüzde politikamızın çalıştığından emin olabiliriz.
### 2. Domain Yapısında Bulunan Gruba Admin Yetkisi Vermek
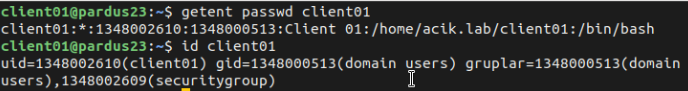
Security grubumuza yetki vermeden önce bu grubun altında olan kullancımızın **sudo** yetkisi olmadığını doğrulayalım:
- _client01_ bu örneğimizde kullanıcı olarak oluşturulmuştur.
Şimdi politikamızı **Yetkili Kullanıcı** seçeneğini seçerek admin yetkisi vermek istediğimiz domain grubunun adını, isteğe göre hostname bilgisini ve isteğe göre sona erme tarihini belirtebiliriz.
Sonrasında grubumuzun üyesi olan kullanıcı ile giriş yaptığımız Pardus makinamız üzerinde **gpupdate -v** komutu ile politikamızı tetikliyoruz.
Hem kullancının sudo yetkisini test ederek hem de **/etc/sudoers.d/domainadmins** da gördüğümüzde politikamızın çalıştığından emin olabiliriz.
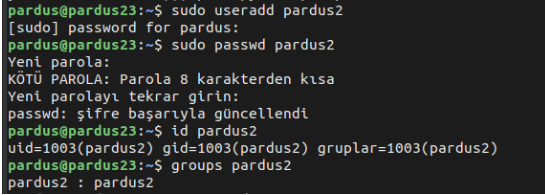
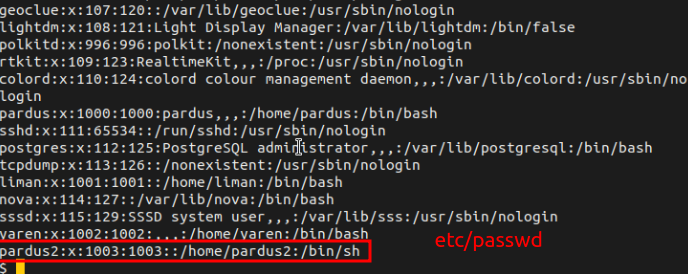
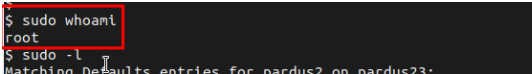
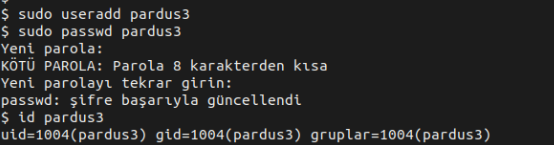
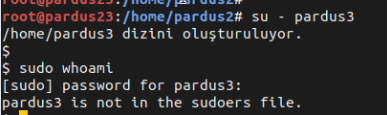
### 3. Lokalde Oluşturulmuş Kullanıcıya Admin Yetkisi Vermek
Öncelikle kullancımızı oluşturup **sudo** yetkisine sahip olmadığını doğrulayalım:
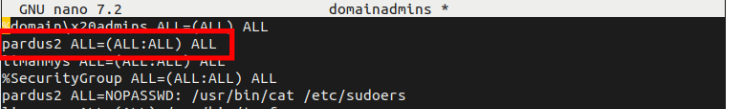
- _pardus2_ bu örneğimizde local kullanıcı olarak oluşturulmuştur.
Şimdi politikamızı **Yetkili Kullanıcı** seçeneğini seçerek admin yetkisi vermek istediğimiz domain grubunun adını, isteğe göre hostname bilgisini ve isteğe göre sona erme tarihini belirtebiliriz.
Sonrasında grubumuzun üyesi olan kullanıcı ile giriş yaptığımız Pardus makinamız üzerinde **gpupdate -v** komutu ile politikamızı tetikliyoruz.
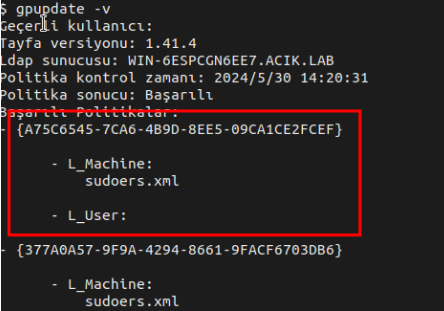
Hem kullancının sudo yetkisini test ederek hem de **/etc/sudoers.d/domainadmins** da gördüğümüzde politikamızın çalıştığından emin olabiliriz.
### 4. Lokalde Oluşturulan Gruba Admin Yetkisi Vermek
Kullanıcımızı ve grubumuzu oluşturup lokaldeki grubumuza yetki vermeden önce bu grubun altında olan kullancımızın **sudo** yetkisi olmadığını doğrulayalım:
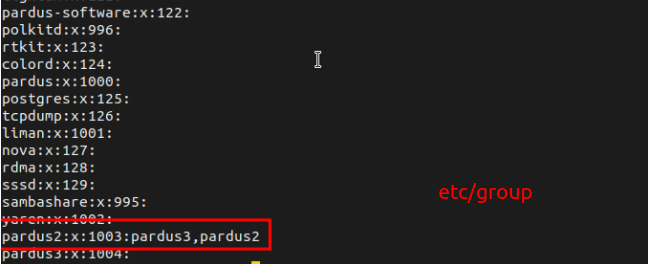
Şimdi politikamızı **Yetkili Kullanıcı** seçeneğini seçerek admin yetkisi vermek istediğimiz grubun adını, isteğe göre hostname bilgisini ve isteğe göre sona erme tarihini belirtebiliriz.
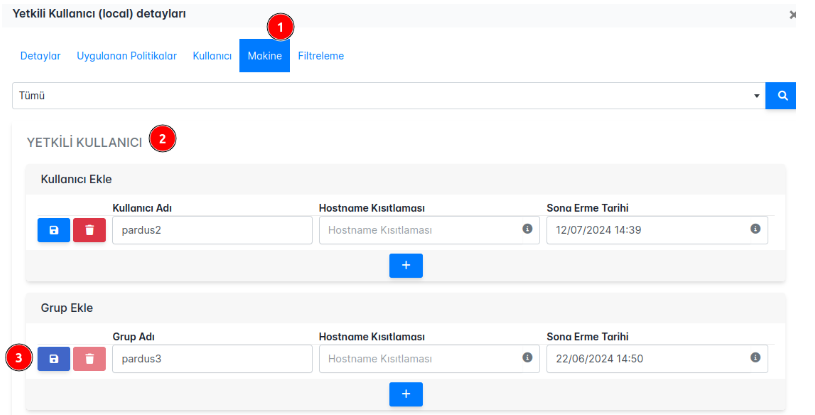
Bu kısımda **pardus3** grubu pardus3 kullanıcısı oluştuğunda oluşmuş olan grup adıdır.
Pardus makinamız üzerinde **gpupdate -v** komutu ile politikamızı tetikliyoruz.
### 5. Domain Yapısında Grup Yetkilendirmesi
İç içe olan grupların yetkilendirme aşamasıdır. Örnek yapı şu şekildedir:
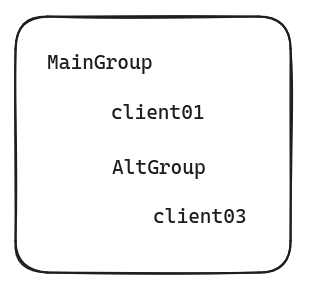
client01 ve cleint03 = kullanıcı
MainGroup ve AltGroup = Security Group
Gruplar ve kullanıcılar için şu şekilde çıktılar elde ederiz:
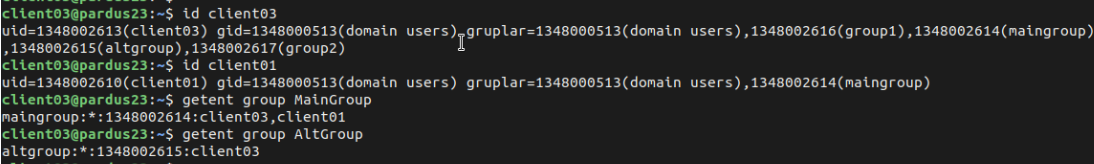
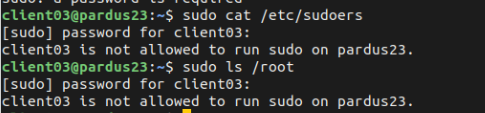
Alt grubumuzdaki kullanıcının politika oluşturmadan önce yetkisi olmadığını doğrulayalım:
Politikamızı üst gruba yetki vererek gerçekleştiririz.
Sonrasında grubumuzun üyesi olan kullanıcı ile giriş yaptığımız Pardus makinamız üzerinde **gpupdate -v** komutu ile politikamızı tetikliyoruz.
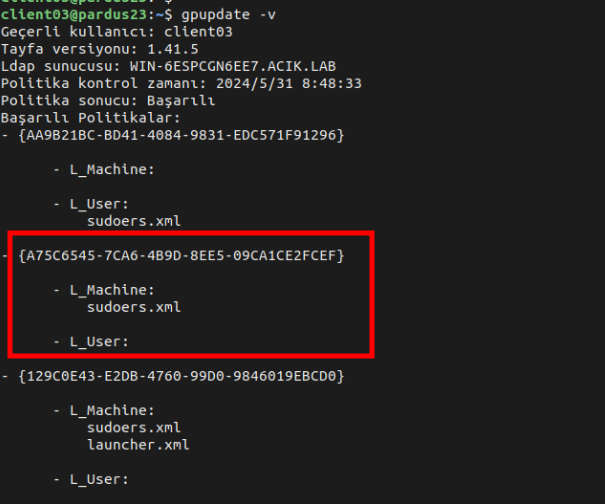
**/etc/sudoers.d/domainadmins** da gördüğümüzde politikamızın çalıştığından emin olabiliriz.
**NOT:**Politikamızı test etmek için yani alt gruptaki kullanıcımızın yetkilendiğinin kontrol edilmesi için lütfen login/logout işleminizi gerçekleştiriniz.
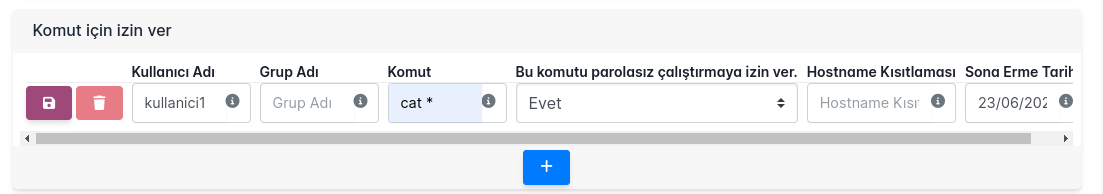
### 6. Komut İçin İzin Verilmesi
Belirli bir komut bazında yetkilendirme yapabilirsiniz.
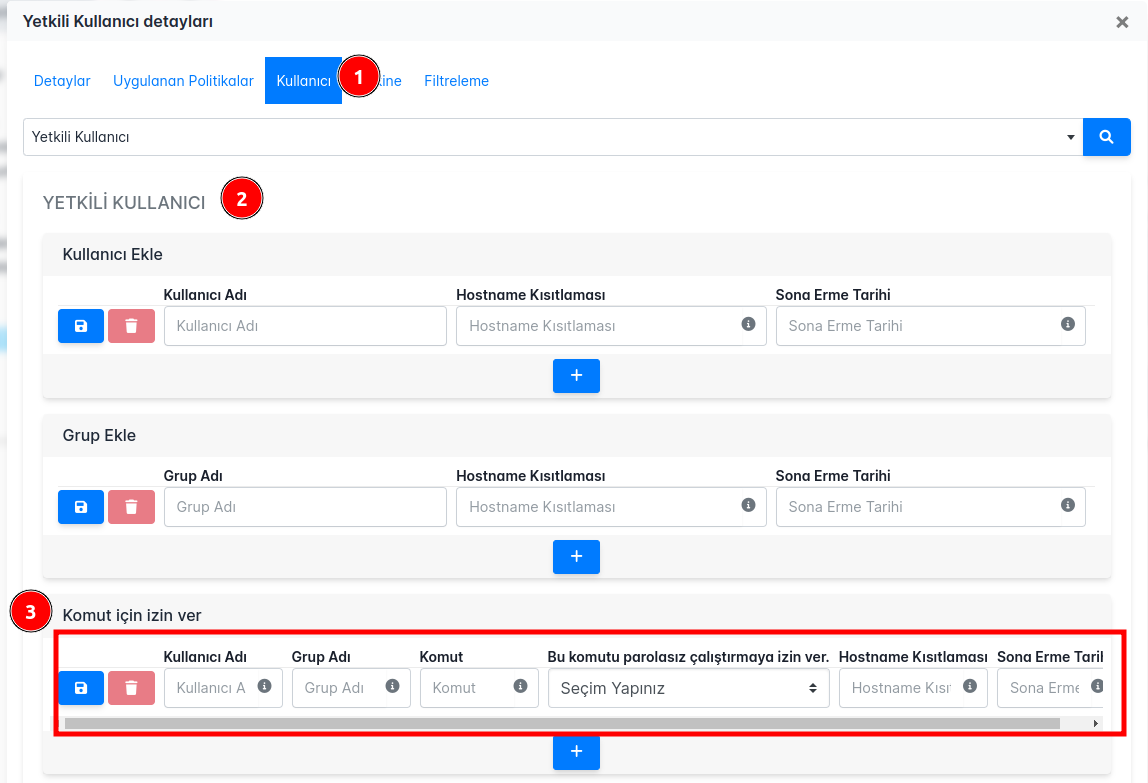
**Kullanıcı Adı:** Domainde oluşturulmuş kullanıcı adı girilir.
**Grup Adı:** Domainde oluşturulmuş grup adı girilir.
Komut: İzin verilecek komut girilir,
**Bu Komutu Parolasız Çalıştırmaya İzin Ver**: İsteğe göre komutu parolasız çalıştırma izni verilir.
**Hostname Kısıtlaması**: İzin verilen komutun hangi makine/makinelerde uygulanacağı seçilir.
**Sona Erme Tarihi**: Yetkinin sona erme tarihi girilir. Boş bırakıldığında politikanın etkisi hiçbir zaman bitmez.
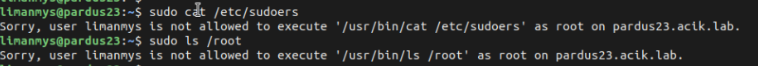
Öncesinde _kullanici1_ kullanıcısının _cat_ komutu yetkisi test edilir:
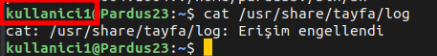
Şimdi politikamızı oluşturup uygulayalım:
Sonrasında _kullanici1_ üyesi olan kullanıcı ile giriş yaptığımız Pardus makinamız üzerinde **gpupdate -v** komutu ile politikamızı tetikliyoruz.
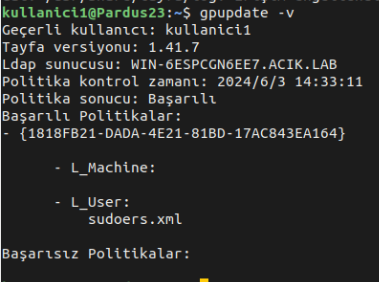
_cat_ komutumuzun çalıştığnı da gördüğümüzde politikamızın çalıştığından emin olabiliriz.
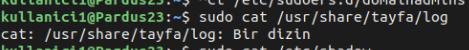
**NOT:** '*' olmadığında komutun birebir aynı yazılması gerekir. Aynı işlem kullanıcı yerine gruba vermek istenilirse aynı bölümündeki _Kullanıcı Adı_ yerine _Grup Adı_ kısmına domainde oluşturulmuş grup adı girilir.
### Sudo Kerberos Desteği
Evet/Hayır seçenekleri ile Kerberos sudo desteğini yönetebilirsiniz.
| yarensari |
1,874,933 | Everything About JSX Syntax And Its Basics: A Quick Guide | When diving into the world of ReactJS, one of the first things you encounter is JSX. JSX, or... | 0 | 2024-06-03T04:37:07 | https://dev.to/mroman7/everything-about-jsx-syntax-and-its-basics-a-quick-guide-4a76 | react, jsx, jsxsyntax, reactsyntax | When [diving into the world of ReactJS](https://dev.to/mroman7/the-fundamentals-of-reactjs-a-rich-understanding-of-its-basics-118l), one of the first things you encounter is JSX. JSX, or JavaScript XML, is a syntax extension that enables you to write HTML-like code within JavaScript. Despite its initial appearance, JSX is a powerful tool that enhances the way we build user interfaces in React. In this blog post, we’ll take a deep dive into JSX syntax, exploring its intricacies, capabilities, and best practices.
JSX was introduced by Facebook as part of the React library. It was designed to make the process of writing user interfaces in JavaScript easier and more intuitive. Facebook’s development team recognized that traditional JavaScript was not well-suited for describing UIs, which led to the creation of JSX.
## Understanding JSX
JSX allows developers to write UI components using a syntax that closely resembles HTML. It’s important to note that JSX is not valid JavaScript or HTML on its own. Instead, JSX code gets transpiled into regular JavaScript code before being executed in the browser. This transpilation process is handled by tools like Babel, which convert JSX syntax into React.createElement calls.
Let’s start with a basic example of JSX:
```
const element = <h1>Hello, world!</h1>;
```
In this example, <h1>Hello, world!</h1> looks like HTML, but it’s actually JSX. When transpiled, it becomes:
```
const element = React.createElement('h1', null, 'Hello, world!');
```
This React.createElement function creates a React element, which is used to render content to the DOM.
## How Does JSX Work?
JSX is not valid JavaScript or HTML on its own. Under the hood, JSX is transpiled to regular JavaScript by a tool like Babel before the code runs in the browser. This transpilation process converts JSX into [React.createElement](https://react.dev/reference/react/createElement) calls.
For example, the JSX:
```
const element = <h1>Hello, world!</h1>;
```
gets transpiled to:
```
const element = React.createElement('h1', null, 'Hello, world!');
```
The React.createElement function is what actually creates the React element used to update the UI.
## How JSX Syntax benefits us?
- **Improved Readability**: JSX’s HTML-like syntax makes the code more readable and easier to understand, especially for those who are already familiar with HTML.
- **Component-based Structure**: JSX fits naturally with React’s component-based architecture, making it easy to see the structure and hierarchy of components.
- **Enhanced Developer Experience**: With JSX, you get better error messages and warnings during development, which helps in debugging and maintaining the code.
- **Problem JSX Solved**: JSX simplifies this process by allowing developers to write HTML-like code directly within JavaScript, which is then seamlessly transformed into React elements.
- **Is JSX Mandatory in React**: No, JSX is not mandatory in React, but it is highly recommended. You can write React code using plain JavaScript by calling React.createElement directly.
## JSX Features and Syntax
### Embedding Expressions
One of the powerful features of JSX is the ability to embed JavaScript expressions within curly braces {}. This allows you to include dynamic content within your JSX code:
```
const name = 'Alice';
const element = <h1>Hello, {name}!</h1>;
```
### Attributes
JSX supports HTML-like attributes for elements. However, there are some differences. For example, the class attribute in HTML becomes className in JSX:
```
const element = <div className="container">Content here</div>;
```
### Self-Closing Tags
Similar to HTML, elements with no children must be self-closed in JSX:
```
const element = <img src="image.jpg" alt="A description" />;
```
### Conditional Rendering
JSX allows you to render elements conditionally using JavaScript conditions:
```
const isLoggedIn = true;
const element = isLoggedIn ? <h1>Welcome back!</h1> : <h1>Please sign up.</h1>;
```
### Looping
You can use JavaScript loops like map to render lists of elements:
```
const numbers = [1, 2, 3, 4, 5];
const listItems = numbers.map((number) =>
<li key={number.toString()}>
{number}
</li>
);
const element = <ul>{listItems}</ul>;
```
### Fragments
JSX supports fragments, which allow you to group multiple elements without adding extra nodes to the DOM:
```
const element = (
<>
<h1>Hello, world!</h1>
<h2>Welcome to learning JSX.</h2>
</>
);
```
### Inline Styles
You can style JSX elements using inline styles by passing a JavaScript object to the style attribute:
```
const element = <h1 style={{ color: 'blue', fontSize: '24px' }}>Hello, world!</h1>;
```
## Best Practices for JSX
- **Keep Components Small and Focused**: Each component should do one thing and do it well, promoting reusability and readability.
Use Descriptive Names: Clearly name your components and props to make your code more understandable.
- **Consistent Formatting**: Follow a consistent code style to improve maintainability.
- **Avoid Inline Styles**: For better maintainability and consistency, use CSS classes or styled-components instead of inline styles.
## Conclusion
JSX is a powerful syntax extension for JavaScript that enhances the React development experience. It makes it easier to write and understand UI components by allowing developers to use an HTML-like syntax directly within JavaScript. By solving the verbosity and complexity issues of traditional JavaScript UI creation, JSX has become an essential tool for React developers. Whether you’re new to React or looking to deepen your understanding, mastering JSX is a key step towards becoming a proficient React developer. Happy coding!
| mroman7 |
1,874,932 | Empowering Independence with Digital Assistance in Ted Home Care | In today's rapidly advancing world of healthcare, Ted Home Care emerges as a guiding light, offering... | 0 | 2024-06-03T04:35:59 | https://dev.to/georgermerriman/empowering-independence-with-digital-assistance-in-ted-home-care-53f8 | home, ted, career |

In today's rapidly advancing world of healthcare, Ted Home Care emerges as a guiding light, offering comprehensive solutions that foster independence and well-being for individuals in need of care. Central to the ethos of **[Ted Home Care](https://www.tedhomecare.com/)** is the integration of digital assistance technologies, empowering individuals to maintain autonomy and live life on their terms while receiving the support they require in the comfort of their own homes.
## Understanding Digital Assistance in Ted Home Care
Digital assistance encompasses an array of innovative technologies designed to enhance the lives of individuals receiving Ted Home Care. From smart home devices to wearable health monitors and virtual caregiver assistants, these technologies serve as invaluable tools in promoting independence and improving quality of life.
## Promoting Safety and Security
One of the primary objectives of digital assistance in Ted Home Care is to promote safety and security for individuals receiving care. Smart home devices, such as motion sensors, smart locks, and video surveillance cameras, provide peace of mind by detecting potential hazards and alerting caregivers or emergency services as needed. These devices create a secure environment that allows individuals to feel safe and confident in their homes.
## Enhancing Communication and Connectivity
Digital assistance also facilitates communication and connectivity, enabling individuals to stay connected with loved ones and healthcare providers. Virtual caregiver assistants, powered by artificial intelligence and natural language processing, offer companionship, answer questions, and provide reminders for medications or appointments. These virtual companions foster social engagement and emotional well-being, reducing feelings of loneliness and isolation.
## Empowering Self-Care and Independence
Perhaps most importantly, digital assistance empowers individuals to take an active role in their own care and maintain independence. Wearable health monitors, such as smartwatches or fitness trackers, track vital signs, monitor activity levels, and provide personalized health insights. By keeping individuals informed about their health status and encouraging healthy behaviors, these devices promote self-care and autonomy, empowering individuals to live life to the fullest.
## The Transformative Impact of Ted Home Care
Ted Home Care, with its focus on digital assistance, is revolutionizing the way individuals receive care and support. By harnessing the power of technology, Ted Home Care empowers individuals to age in place gracefully while also easing the burden on caregivers and healthcare providers. With the integration of digital assistance, Ted Home Care offers a holistic and person-centered approach to care, prioritizing independence, dignity, and quality of life.
## Conclusion
digital assistance plays a pivotal role in Ted Home Care, empowering individuals to embrace independence and live life on their own terms. By promoting safety, enhancing communication, and empowering self-care, digital assistance technologies are transforming the landscape of healthcare, offering new possibilities for individuals in need of care. In the journey towards independence and well-being, Ted Home Care stands as a beacon of hope, offering innovative solutions that empower individuals to live life to the fullest. | georgermerriman |
1,874,931 | The Advantages of Purchasing Solar Outdoor Lights | The Advantages of Purchasing Solar Outdoor Lights Advantages Of Solar Outdoor... | 0 | 2024-06-03T04:35:29 | https://dev.to/alex_damianisi_f1cfe95e60/the-advantages-of-purchasing-solar-outdoor-lights-2pbg | lights | The Advantages of Purchasing Solar Outdoor Lights
2. Advantages Of Solar Outdoor Illumination
3. Innovation of Solar Outdoor Lights
4. How to work with Solar Outdoor Lights
5. Quality Service plus Applications of Solar Outdoor lights
Exactly what are Solar Outdoor Lights
Solar Outdoor lights that are outside fixtures and this can be place to offer lighting outside, which might be operating on solar power which are driven. It catches the sunshine's energy plus utilizes it to power the light. These illumination are present in gardens, walkways, plus areas being outside. They've been available a real range that is wide of and forms, and they are often battery-powered.
Options that come with Solar Outdoor Illumination
Solar Wall Lights illumination which are outside massive amount value which create them an excellent investment for anyone whom calls for lights which was outside. A number of the importance contain:
1. Economical: because Solar Outdoor Lights running on solar technologies, they do not actually need electricity to exert effort. This means they are often place to illuminate areas that are outside adding to their energy bills.
2. Eco-Friendly: solar energy is a renewable website, meaning utilizing solar outside illumination had been green. For the good reason that these illumination never build any co2 because most toxins.
3. Easy Maintenance: Solar Outdoor Lights which are outside actually fix that are little. They do not must be associated with an company which are electric and also they will have no area that are going can breakdown. This may make sure they are many dependable plus durable.
4. Automatic Operation: Solar Outdoor Lights which may be outdoors immediately. They beginning at plus turn fully off at night dawn. Meaning them on and off manually you do not need certainly to concern yourself with turning.
5. Versatile: Solar Outdoor Lights which was outside are presented in a variety of sizes and shapes, meaning they might be employed in a number that was wide of. They truly are generally speaking employed to illuminate gardens, paths, plus areas that are outside.
Innovation of Solar Outdoor Lights
Solar Garden Lights which was outside a better way that are much longer present times. Innovations in solar technology is creating these light best plus dependable. Many of the innovations include:
1. better Panels that are solar effectiveness of solar power panels has improved significantly within the last ages that are few can be few. Which means that lighting being solar is outdoor now capture most power through the sunshine, creating them dramatically dependable.
2. LED Lights: light-emitting lights which was diode become better than traditional lights that are incandescent. Meaning lighting that is solar outside offer brighter lighting now with all the less energy.
3. Motion Sensors: some illumination which is solar outside have movement sensors which turn the lights on whenever somebody attracts near. This can cause them to perfect for providing security lighting.
4. Smart Controls: some illumination which are Solar Outdoor Lights come plus smart settings that allow clients to ad the brightness plus duration connected with illumination. This may cause them to become more customizable plus versatile.
How exactly to Render Use Of Solar Outdoor Lighting
Using lights that are Solar Outdoor Lights a breeze. Right here your shall get the actions to check out:
1. select the location that is correct lighting that is solar can be outdoor be placed in stores which bring sunshine. This means they should maybe not be situated in shaded areas.
2. Install the lights: Solar Outdoor Lights which are often outside quite simple to create. Additional illumination include stakes and this can be forced in towards the smashed. Somebody could be attached with walls because fences.
3. Turn the lights on: Most solar lights which are outside an changes that was on/off the thing that is important ought to be pressed to exhibit them in.
four. Await the illumination to charge the illumination as soon as was thrilled, they shall commence to charge. Ordinarily it requires hours being fully a few the illumination to charge completely.
five. Enjoy their lighting: if the lights is wholly charged, they will turn on automatically at plus turn off at night dawn. Get pleasure from the lighting which is stunning they provide.
Quality Service plus Applications of Solar Outdoor Lights
When selecting Solar Outdoor Lights or Solar Post Lights which are outside it is important to obtain a top-quality product through the manufacturer that are reputable. This could make sure the illumination are dependable plus durable. Additionally, it is critical to choose a manufacturer that provides consumer which was near if you would like any assistance with their lights.
Solar Outdoor Lights which are outdoor be properly used in an assortment that are wide of. Consider of the very most applications being typical
1. Garden Lighting: solar illumination that are outside perfect for smoking cigarettes gardens plus vegetation. They invest a feeling that was stunning any garden, and so they will help keep insects from increasing.
2. Pathway Lighting: solar lights that can be outside well fitted to cigarette smoking paths plus walkways. It truly is produced you stay going, that grows safeguards by them better to see where.
3. Security Lighting: solar illumination which are often outside motion sensors are suitable for providing safeguards lighting. They begin immediately an approaches which can be specific which may deter intruders.
3. Patio Lighting: solar lights which was outside you to definitely illuminate patios plus areas that are outside. They devote the hot plus radiance that has been inviting assisting to cause them to perfect for outside gatherings.
5. Holiday Lighting: solar illumination that are outdoor be used to improve for the vacation period. They might be useful to produce shows that are breathtaking Christmas, Halloween, as well as other vacation breaks.
Solar Outdoor Lights which was outdoors an absolute affordable, eco-friendly, plus lighting solution which was easy-to-use. They truly are ideal for a variety that has been wide of, and also they include a choice of revolutionary properties. By choosing the product that take to top-quality the manufacturer which are expert you are able to take delight in the benefits of solar outside lights for quite some time in the foreseeable future.
Source: https://www.beslonsolarlight.com/Solar-wall-lights | alex_damianisi_f1cfe95e60 |
1,874,930 | Functional Programming vs Object Oriented Progamming: Mana yang Lebih Keren? | Halo, temen-temen! Kali ini kita bakal bahas dua cara keren buat ngoding: Pemrograman Fungsional /... | 0 | 2024-06-03T04:34:40 | https://dev.to/yogameleniawan/functional-programming-vs-object-oriented-progamming-mana-yang-lebih-keren-389i | programming |
Halo, temen-temen! Kali ini kita bakal bahas dua cara keren buat ngoding: Pemrograman Fungsional / _Functional Programming_ (FP) dan Pemrograman Berorientasi Objek / _Object Oriented Programming_ (OOP). Yuk, kita lihat mana yang lebih cocok buat temen-temen!
## _Functional Programming_ (FP)
### Apa Itu FP?
- FP itu kayak bikin rumus matematika, bro. Nggak ada perubahan data mendadak, semua data tuh kayak patung, nggak bisa diubah.
- Di FP, fungsi tuh kayak raja. Lo bisa simpen fungsi di variabel, kirim sebagai argumen, atau balikin dari fungsi lain. Asik, kan?
### Ciri-Ciri Utama FP:
1. **Immutability:**
- Data nggak bisa diubah-ubah. Jadi lebih aman dari bug yang bikin pusing.
2. **Pure Functions:**
- Fungsi murni nggak punya efek samping. Jadi outputnya cuma tergantung input.
3. **Higher-Order Functions:**
- Fungsi bisa nerima fungsi lain atau balikin fungsi. Misalnya `map`, `filter`, `reduce`.
4. **Recursion:**
- Lebih sering pake rekursi daripada loop.
5. **Lazy Evaluation:**
- Hitung cuma kalo bener-bener butuh. Hemat tenaga, bro.
### Contoh Bahasa FP:
- Go, Elixir
### Kelebihan FP:
- Kode lebih gampang dites dan di-debug.
- Lebih gampang buat paralel dan concurrent programming.
- Mengurangi risiko kesalahan karena data nggak bisa diubah.
### Kekurangan FP:
- Agak susah dipelajari buat yang baru mulai.
- Nggak semua masalah cocok diselesaikan dengan FP.
- Performanya bisa lambat kalo nggak dioptimalkan.
## _Object Oriented Programming_ (OOP)
### Apa Itu OOP?
- OOP itu fokus ke objek yang gabungin data dan aksi. Kayak bikin dunia mini di dalam program temen-temen.
- Kode diatur dalam _object_ dan _class_. Mirip kayak bikin blueprint rumah.
### Ciri-Ciri Utama OOP:
1. **Encapsulation:**
- Data dalam _object_ disembunyiin, cuma bisa diakses lewat _method/function_. Bikin lebih aman dan rapi.
2. **Inheritance:**
- Kelas bisa nurunin sifat ke _class_ lain. Mirip kayak warisan keluarga, bro.
3. **Polymorphism:**
- Metode yang sama bisa punya implementasi beda. Bikin kode lebih fleksibel.
4. **Abstraction:**
- Fokus ke yang penting aja, detail nggak perlu ditunjukin. Bikin lebih gampang diatur.
### Contoh Bahasa OOP:
- Java, C++, Python, Ruby, C#.
### Kelebihan OOP:
- Mudah dimengerti dan diimplementasiin karena mirip dunia nyata.
- Kode lebih modular dan bisa dipake ulang.
- Gampang dikembangin dan dipelihara lewat _inheritance_ dan _polymorphism_.
### Kekurangan OOP:
- Bisa berlebihan buat masalah kecil.
- Struktur warisan yang dalam bisa bikin kode susah diubah.
- Banyak kode template yang harus ditulis.
## Perbandingan FP dan OOP
| Aspek | Pemrograman Fungsional (FP) | Pemrograman Berorientasi Objek (OOP) |
|-------|------------------------------|--------------------------------------|
| **Fokus Utama** | Fungsi dan komposisi fungsi | Objek dan interaksi antar objek |
| **Data** | Nggak bisa diubah | Bisa diubah |
| **Efek Samping** | Dihindari | Boleh |
| **Pendekatan** | Deklaratif | Imperatif |
| **Penggunaan Ulang Kode** | Fungsi murni dan higher-order functions | Inheritance dan polymorphism |
| **Kesederhanaan Pengujian** | Lebih mudah | Butuh pengaturan state yang tepat |
## Mana yang Lebih Keren?
Nggak ada jawaban pasti, bro. Semua tergantung:
- **Jenis proyek:** Kalo banyak state dan interaksi antar objek, OOP lebih cocok. Tapi kalo transformasi data, FP lebih mantap.
- **Tim dan skill:** Tim yang udah biasa pake salah satu cara bakal lebih produktif pake cara itu.
- **Performa:** Tergantung kebutuhan proyek temen-temen.
## Kesimpulan
Masing-masing punya kelebihan dan kekurangan. Kadang, temen-temen perlu gabungin prinsip dari kedua paradigma buat bikin solusi yang fleksibel dan scalable. Jadi, pilih yang paling cocok buat proyek temen-temen dan tim temen-temen!
---
Semoga penjelasan ini bisa bikin temen-temen lebih paham dan bisa milih yang paling cocok buat temen-temen! Jangan lupa ngoding itu diketik jangan dipikir! Sampai jumpa di artikel yang lainnya!!
| yogameleniawan |
1,874,929 | Day 3 of 30 | This is what I did on the previous day and just forgot to post. But so far it has been good and I am... | 0 | 2024-06-03T04:29:37 | https://dev.to/francis_ngugi/day-3-of-30-gkf | webdev, beginners, react | This is what I did on the previous day and just forgot to post.
But so far it has been good and I am slowly picking up on React nicely
**So for Yesterday, this is what I did:**
>Event Handling in React: https://github.com/FrancisNgigi05/react-hooks-event-handling-lab
>React State and Events: https://github.com/FrancisNgigi05/react-hooks-state-and-events-codealong
>React State and Arrays: https://github.com/FrancisNgigi05/react-hooks-state-arrays
>A small project covering the above topics:
(i)Source Code: https://github.com/FrancisNgigi05/react-hooks-state-and-events-lab
(ii)Vercel Deployment link: https://react-hooks-state-and-events-lab-eight.vercel.app/
| francis_ngugi |
1,875,157 | Conquering Your System Design Interview: A Book Guide | System design interviews are nerve-wracking but essential to the software engineering interview... | 0 | 2024-06-03T21:11:17 | https://deniskisina.dev/conquering-your-system-design-interview-a-book-guide/ | article, systemdesign | ---
title: Conquering Your System Design Interview: A Book Guide
published: true
date: 2024-06-03 04:27:16 UTC
tags: article,systemdesign
canonical_url: https://deniskisina.dev/conquering-your-system-design-interview-a-book-guide/
---
System design interviews are nerve-wracking but essential to the software engineering interview process. These interviews assess your ability to design scalable, reliable, and maintainable software systems. But fear not! With the right study materials, you can confidently approach your next system design interview. This guide highlights various resources, from foundational texts to interview prep guides, to help you ace your interview.
**Building Your Foundation**
- **Designing Data-Intensive Applications by Martin Kleppmann:** This classic text explores data management challenges in large-scale systems. Kleppmann dives deep into data storage solutions, scalability considerations, and how to design data pipelines. While not strictly an interview prep guide, this book provides a strong foundation for understanding the core principles of system design.
- **Designing Distributed Systems by Brendan Burns:** If you’re looking for a more theoretical approach, Designing Distributed Systems offers a comprehensive overview of distributed system concepts. This book covers consistency models, fault tolerance, and distributed transactions. Grasping these fundamental concepts will equip you to tackle various system design problems.
**Sharpening Your Interview Skills**
- **System Design Interview – An Insider’s Guide (Volume 1 & 2) by Alex Xu:** This two-volume set provides a comprehensive approach to system design interviewing. Author Alex Xu, a former Facebook engineer, shares practical advice on approaching common system design problems and presents detailed explanations for various systems, from photo-sharing applications to news feeds.
- **Grokking the System Design Interview:** This popular online course offers a structured approach to preparing for system design interviews. It includes lectures, practice problems, and mock interviews to help you hone your problem-solving and communication skills.
- **Grokking Microservice Design Patterns** and **Grokking the Advanced System Design Interview:** If you’re looking to take your preparation a step further, consider these Grokking companion courses. These resources delve deeper into specific design patterns and advanced system design concepts.
**For Those Getting Hands-On**
- **Hands-On System Design: Learn System Design, Scaling Applications, Software Development Design Patterns with Real Use-Cases by Harsh Kumar Ramchandani:** This resource offers a practical approach to system design, focusing on real-world use cases. Through this book, you’ll gain experience designing systems for common applications like social media platforms and e-commerce sites.
**Beyond the Technical**
- **The Design of the Design: Essays of a Computer Scientist by Frederick P. Brooks Jr.:** This thought-provoking book explores the art and philosophy of system design from a broader perspective. While not directly focused on technical details, Brooks’ insights on design principles and decision-making can be invaluable for any aspiring system designer.
**For the Truly Enthusiastic**
- **Synchronization Algorithms and Concurrent Programming by Gadi Taubenfield:** This text dives into the complexities of concurrent programming, a critical skill for designing scalable and reliable distributed systems. This book is a deep dive and is recommended for those with a strong foundation in programming concepts.
This list provides a starting point for your system design interview preparation journey. The best resources for you will depend on your current knowledge base and learning style. So, grab a book, explore some online courses, and get ready to impress your interviewers with your system design prowess! | deniskisina |
1,874,927 | Preparing for Hurricane Season: How to Protect Your Home and Mortgage in Florida | Living in Florida offers many perks, from sunny beaches to vibrant communities. However, it also... | 0 | 2024-06-03T04:24:39 | https://dev.to/georgermerriman/preparing-for-hurricane-season-how-to-protect-your-home-and-mortgage-in-florida-4lm6 | florida, morgage, warre, webdev |

Living in Florida offers many perks, from sunny beaches to vibrant communities. However, it also comes with the annual threat of hurricane season. As a homeowner in the Sunshine State, preparing for hurricanes is not just about stocking up on supplies; it's also about protecting your most significant investment—your home and mortgage. Here are some essential tips from Warren F Herman to help you safeguard your home and mortgage during hurricane season.
## Review Your Insurance Coverage:
One of the most crucial steps in hurricane preparedness is ensuring that you have adequate insurance coverage for your home. Review your homeowner's insurance policy to understand what is covered and what is not, especially regarding wind and flood damage. Consider purchasing additional coverage if necessary, such as flood insurance, to protect your home and belongings from potential storm-related losses.
## Fortify Your Home:
Warren F Herman recommends taking proactive measures to strengthen your home's defenses against hurricanes. This may include installing hurricane shutters or impact-resistant windows, reinforcing garage doors, securing outdoor furniture and objects, and trimming trees and shrubs. By fortifying your home, you can minimize the risk of damage and increase its resilience to strong winds and flying debris.
Create a Disaster Preparedness Plan:
Develop a comprehensive disaster preparedness plan for your family that includes evacuation routes, emergency contacts, and a designated meeting place. Stock up on essential supplies, such as non-perishable food, water, flashlights, batteries, and first aid kits. Keep important documents, including insurance policies and mortgage documents, in a waterproof and easily accessible container.
## Stay Informed:
Warren F Herman emphasizes staying informed about weather updates and evacuation orders issued by local authorities. Monitor the progress of hurricanes and tropical storms using reliable sources of information, such as the National Hurricane Center and local news outlets. Being aware of potential threats and taking prompt action can help keep you and your family safe during hurricane season.
## Communicate with Your Mortgage Lender:
In the event of a hurricane or natural disaster, it is essential to communicate with your mortgage lender as soon as possible. If you anticipate difficulties making mortgage payments due to storm-related damage or financial hardship, notify your lender promptly. **[Warren F Herman](https://warrenfherman.com/)** advises that many lenders offer assistance programs, such as forbearance or loan modifications, to help homeowners facing temporary financial challenges.
## Document Damage and Losses:
If your home sustains damage during a hurricane, document the extent of the damage and losses for insurance purposes. Take photographs or videos of the damage, make a list of damaged items, and keep records of repair estimates and receipts. Providing thorough documentation can streamline the insurance claims process and ensure you receive fair compensation for your losses.
Hurricane season in Florida can be a challenging time for homeowners, but by taking proactive steps to prepare, you can minimize the impact of storms on your home and mortgage. From reviewing your insurance coverage to fortifying your home and creating a disaster preparedness plan, there are many measures you can take to protect your most significant investment. Remember, being prepared is key to weathering the storm and ensuring your home and mortgage remain secure. | georgermerriman |
1,874,926 | Innovative Solar Post Lights for Modern Gardens | Illumination Up Your Yard in a Method that is contemporary Message Illuminations Are actually you... | 0 | 2024-06-03T04:24:30 | https://dev.to/alex_damianisi_f1cfe95e60/innovative-solar-post-lights-for-modern-gardens-2b9j | lights |
Illumination Up Your Yard in a Method that is contemporary Message Illuminations
Are actually you sick of the conventional outside illuminations that take in much a lot power that is extra well as enhance your regular month-to-month expenses? After that, it is opportunity to think about the ingenious message that is solar that are actually taking the marketplace through tornado. These illuminations are actually certainly not just environmentally friendly, however likewise include a contact of course as well as modernity for your yard
Benefits of Solar Message Illuminations
Among the primary benefits of Solar Wall Lanterns message illuminations is actually their power effectiveness. They harness the energy of the sunlight throughout the as well as utilize it towards illuminate your yard in the evening day. This implies you back or even enhanced carbon dioxide impact that you do not need to stress over electrical power sets. Furthermore, solar message illuminations are actually low-maintenance as well as need very little interest because they are actually self-powering. They likewise final for a very time that is long offering brilliant as well as background illumination for many years with no require for substitute
Development in Solar Message Illuminations
Solar Garden Lights message illuminations have actually happened a very way that is long their creation. Today, they flaunt ingenious functions that create all of them much more practical as well as dependable. For example, they include integrated illumination units that are sensing immediately transform all of them on/off when the sunlight decreases or even happens up, specifically. They likewise have actually movement sensing units that spot motion as well as switch on the illuminations when individuals or even pets stroll through. Furthermore, some message that is solar have actually lowering abilities that assist towards save power when complete illumination is actually certainly not required
Security as well as Use of Solar Message Illuminations
Solar message illuminations are actually risk-free towards utilize because they do not produce any type of hazardous radiation or even chemicals that can hurt individuals or easily even the atmosphere. They are actually likewise user-friendly as well as need no proficiency that is technological set up or even run. All of you need to perform is actually location all of them in the area that is appropriate they can easily get guide sunshine, as well as they'll perform the remainder. Furthermore, solar message illuminations are available in various styles as well as dimensions, enabling you towards select the ones that suit your garden's style as well as design
Ways to Utilize Solar Message Illuminations
Utilizing message that is solar is actually rather easy as well as simple. Very initial, identify the locations in your yard that require illumination as well as select the kind that is appropriate of message illuminations that fit all of them. Following, set up the illuminations through complying with the manufacturer's directions, guaranteeing that they are actually safely repaired in position. The illuminations throughout the day as well as delight in their cozy radiance in the evening after that, wait on the sunlight towards fee. Lastly, keep in mind towards cleanse the photo voltaic panels routinely towards guarantee efficiency that is ideal
Solution as well as High premium that is top of Message Illuminations
When it concerns solution as well as high premium that is top Solar Wall Lamp message illuminations offer outstanding worth for cash. They are actually developed utilizing quality that is top that are actually weather-resistant as well as resilient, guaranteeing that they can easily endure severe outside problems such as sunlight, rainfall, as well as wind. Furthermore, very most solar message illuminations include guarantees that deal with problems as well as problems, providing you assurance as well as guarantee that you are buying a quality item that is high
Request of Solar Message Illuminations
Solar message illuminations have actually a variety that is wide of in contemporary yards. For example, you can easily utilize all of them towards illuminate your paths, driveways, outdoor patio areas, as well as blossom mattress. You can easily likewise utilize all of them as spotlights towards emphasize your garden's centerpieces such as sculptures, water fountains, as well as home varieties. Furthermore, solar message illuminations could be utilized for safety and safety functions, assisting towards discourage burglars as well as intruders through illuminating dark locations
Souce: https://www.beslonsolarlight.com/product-solar-wall-lamp-waterproof-solar-garden-lamp-outdoor-led-solar-wall-light-modern
| alex_damianisi_f1cfe95e60 |
1,874,900 | What is the best, flutter or react native? | Flutter and React Native are both used for cross-platform development. Both frameworks are used to... | 0 | 2024-06-03T04:20:15 | https://dev.to/joyanderson1702/what-is-the-best-flutter-or-react-native-4b45 | reactnative, flutter, programming, framework | Flutter and React Native are both used for cross-platform development. Both frameworks are used to build applications for Android and iOS. Since both provide the same purpose, it is crucial to understand which one is the best flutter or react native.
According to a [StackOverflow survey](https://survey.stackoverflow.co/2023/#other-frameworks-and-libraries), Flutter is used 9.12% for developing projects, while React native is used 8.43% for projects. If we compare in terms of GitHub popularity, Flutter has [162k](https://github.com/flutter/flutter), and React native has [116k](https://github.com/facebook/react-native).
Let’s understand which one is best for app development,
**Flutter : **
- Flutter was introduced by Google in 2017. It is written in Dart programming language and allows developers to build and deploy attractive Android, iOS, web, and desktop apps based on a single code.
- Flutter widgets like structural, platform, and proprietary visual are built-in UI components used for creating user interfaces.
- Flutter owns a rendering engine and uses dart language. That’s why it gives high performance and fast load times.
- Flutter provides hot reload features that boost development productivity, allowing you to see changes instantly by restarting it.
- Flutter provides streamlined and straightforward documentation that helps developers make it easy to read.
- Dart is a new language, so the adoption rate is low, and the community is smaller.
**React Native : **
- React Native was introduced by Facebook in 2015. It uses the most popular programming language, JavaScript, so web developers can also move to mobile app development.
- It is based on native components and a collection of external UI kits that help you to make creative user interfaces.
- React native uses JavaScript to connect native components, so the development and running time speed is slower than Flutter.
- React native has no straightforward documentation; it depends on the external developer community.
- React native is the most popular and adopted for app development compared to Flutter.
- React Native has limited choices, does not provide out-of-the-box components, and sometimes abandons libraries and packages.
Ultimately, both frameworks are used for cross-platform [app development](https://www.green-apex.com/mobile-app-development) with different functionalities. Flutter is the best option if you have a smaller budget, fast growth, and a great UI. Alternatively, if you have a website and want to reuse its components for a mobile app and have a team of developers who have experience in JavasScript and can use many plugins, modules, and widgets, then choose React Native.
| joyanderson1702 |
1,874,897 | Guide to Building Credit Risk Models with Machine Learning | In the financial sector, assessing credit risk is crucial for making informed lending decisions.... | 0 | 2024-06-03T04:20:00 | https://dev.to/laxita01/guide-to-building-credit-risk-models-with-machine-learning-39n4 | model, machinelearning, ai | In the financial sector, assessing credit risk is crucial for making informed lending decisions. Traditional methods of evaluating creditworthiness are increasingly being complemented—and in some cases, replaced—by machine learning models. These models offer superior accuracy, scalability, and adaptability, helping financial institutions manage risk more effectively. This guide delves into the process of building [credit risk models using machine learning,](https://www.solulab.com/guide-to-building-credit-risk-models-with-machine-learning/) highlighting key steps, benefits, and practical considerations.
**Understanding Credit Risk Models**
Credit risk models are designed to predict the likelihood of a borrower defaulting on a loan. By leveraging historical data and advanced algorithms, machine learning models can identify patterns and correlations that traditional statistical methods might miss. This leads to more accurate risk assessments and better decision-making.
**Steps to Build a Credit Risk Model with Machine Learning**
**Data Collection and Preprocessing:**
Gather historical data, including borrower information, loan details, repayment history, and macroeconomic indicators.
Clean the data to handle missing values, outliers, and inconsistencies.
Feature engineering: Create new features that may enhance the predictive power of the model, such as debt-to-income ratio or recent credit inquiries.
**Data Splitting:**
Divide the data into training and test sets. The training set is used to build the model, while the test set evaluates its performance.
Use techniques like cross-validation to ensure the model's robustness and avoid overfitting.
**Model Selection:**
Choose the appropriate machine learning algorithms based on the data characteristics and business requirements. Common choices include logistic regression, decision trees, random forests, and gradient boosting machines.
Collaborate with a machine learning development company to access expertise and advanced tools for model selection and tuning.
**Model Training:**
Train the model using the training data. Adjust hyperparameters to optimize performance.
Evaluate the model using metrics such as accuracy, precision, recall, and the area under the ROC curve (AUC-ROC).
**Model Evaluation:**
Test the model on the test data to assess its generalizability.
Conduct backtesting using historical data to ensure the model performs well under different market conditions.
**Model Deployment and Monitoring:**
Deploy the model into production to start making predictions on new loan applications.
Continuously monitor the model's performance and retrain it as necessary to maintain accuracy and relevance.
Benefits of Using Machine Learning for Credit Risk Modeling
**Improved Accuracy:**
Machine learning models can analyze vast amounts of data and identify complex patterns, leading to more accurate risk assessments.
**Scalability:**
These models can handle large datasets and can be scaled to accommodate growing amounts of data and new variables.
**Adaptability:**
Machine learning models can be continuously updated and refined as new data becomes available, ensuring they remain relevant and accurate over time.
**Efficiency:**
Automated processes reduce the time and effort required for risk assessment, enabling faster decision-making.
Practical Considerations
**Data Quality:**
High-quality, relevant data is the foundation of any effective machine learning model. Ensure that data collection processes are robust and reliable.
**Regulatory Compliance:**
Adhere to regulatory requirements and ensure that the model's decisions are transparent and explainable. Partnering with an [AI consulting company](https://www.solulab.com/ai-consulting-company/) can help navigate these complexities.
**Expertise:**
Building and maintaining machine learning models require specialized skills. [Hire AI developers](https://www.solulab.com/hire-ai-developers/) with experience in credit risk modeling to ensure the success of your project.
**Conclusion**
Machine learning offers a powerful toolset for building sophisticated credit risk models that can significantly enhance the accuracy and efficiency of risk assessment in the financial sector. By following a structured approach and leveraging expert resources, financial institutions can harness the full potential of machine learning to drive better lending decisions. Whether working with a [machine learning development company](https://www.solulab.com/machine-learning-development-company/) or seeking guidance from an AI consulting company, the key to success lies in combining high-quality data, robust algorithms, and specialized expertise to build and maintain effective credit risk models. | laxita01 |
1,874,896 | Buy Verified Paxful Account | Buy Verified Paxful Account There are several compelling reasons to consider purchasing a... | 0 | 2024-06-03T04:18:26 | https://dev.to/annewalkere23/buy-verified-paxful-account-3eg0 | Buy Verified Paxful Account
There are several compelling reasons to consider purchasing a verified Paxful account. Firstly, a verified account offers enhanced security, providing peace of mind to all users. Additionally, it opens up a wider range of trading opportunities, allowing individuals to partake in various transactions, ultimately expanding their financial horizons.
Moreover, Buy verified Paxful account ensures faster and more streamlined transactions, minimizing any potential delays or inconveniences. Furthermore, by opting for a verified account, users gain access to a trusted and reputable platform, fostering a sense of reliability and confidence.
Lastly, Paxful’s verification process is thorough and meticulous, ensuring that only genuine individuals are granted verified status, thereby creating a safer trading environment for all users. Overall, the decision to Buy Verified Paxful account can greatly enhance one’s overall trading experience, offering increased security, access to more opportunities, and a reliable platform to engage with. Buy Verified Paxful Account.
Buy US verified paxful account from the best place dmhelpshop
Why we declared this website as the best place to buy US verified paxful account? Because, our company is established for providing the all account services in the USA (our main target) and even in the whole world. With this in mind we create paxful account and customize our accounts as professional with the real documents. Buy Verified Paxful Account.
If you want to buy US verified paxful account you should have to contact fast with us. Because our accounts are-
Email verified
Phone number verified
Selfie and KYC verified
SSN (social security no.) verified
Tax ID and passport verified
Sometimes driving license verified
MasterCard attached and verified
Used only genuine and real documents
100% access of the account
All documents provided for customer security
What is Verified Paxful Account?
In today’s expanding landscape of online transactions, ensuring security and reliability has become paramount. Given this context, Paxful has quickly risen as a prominent peer-to-peer Bitcoin marketplace, catering to individuals and businesses seeking trusted platforms for cryptocurrency trading.
In light of the prevalent digital scams and frauds, it is only natural for people to exercise caution when partaking in online transactions. As a result, the concept of a verified account has gained immense significance, serving as a critical feature for numerous online platforms. Paxful recognizes this need and provides a safe haven for users, streamlining their cryptocurrency buying and selling experience.
For individuals and businesses alike, Buy verified Paxful account emerges as an appealing choice, offering a secure and reliable environment in the ever-expanding world of digital transactions. Buy Verified Paxful Account.
Verified Paxful Accounts are essential for establishing credibility and trust among users who want to transact securely on the platform. They serve as evidence that a user is a reliable seller or buyer, verifying their legitimacy.
But what constitutes a verified account, and how can one obtain this status on Paxful? In this exploration of verified Paxful accounts, we will unravel the significance they hold, why they are crucial, and shed light on the process behind their activation, providing a comprehensive understanding of how they function. Buy verified Paxful account.
Why should to Buy Verified Paxful Account?
There are several compelling reasons to consider purchasing a verified Paxful account. Firstly, a verified account offers enhanced security, providing peace of mind to all users. Additionally, it opens up a wider range of trading opportunities, allowing individuals to partake in various transactions, ultimately expanding their financial horizons.
Moreover, a verified Paxful account ensures faster and more streamlined transactions, minimizing any potential delays or inconveniences. Furthermore, by opting for a verified account, users gain access to a trusted and reputable platform, fostering a sense of reliability and confidence. Buy Verified Paxful Account.
Lastly, Paxful’s verification process is thorough and meticulous, ensuring that only genuine individuals are granted verified status, thereby creating a safer trading environment for all users. Overall, the decision to buy a verified Paxful account can greatly enhance one’s overall trading experience, offering increased security, access to more opportunities, and a reliable platform to engage with.
What is a Paxful Account
Paxful and various other platforms consistently release updates that not only address security vulnerabilities but also enhance usability by introducing new features. Buy Verified Paxful Account.
In line with this, our old accounts have recently undergone upgrades, ensuring that if you purchase an old buy Verified Paxful account from dmhelpshop.com, you will gain access to an account with an impressive history and advanced features. This ensures a seamless and enhanced experience for all users, making it a worthwhile option for everyone.
Is it safe to buy Paxful Verified Accounts?
Buying on Paxful is a secure choice for everyone. However, the level of trust amplifies when purchasing from Paxful verified accounts. These accounts belong to sellers who have undergone rigorous scrutiny by Paxful. Buy verified Paxful account, you are automatically designated as a verified account. Hence, purchasing from a Paxful verified account ensures a high level of credibility and utmost reliability. Buy Verified Paxful Account.
PAXFUL, a widely known peer-to-peer cryptocurrency trading platform, has gained significant popularity as a go-to website for purchasing Bitcoin and other cryptocurrencies. It is important to note, however, that while Paxful may not be the most secure option available, its reputation is considerably less problematic compared to many other marketplaces. Buy Verified Paxful Account.
This brings us to the question: is it safe to purchase Paxful Verified Accounts? Top Paxful reviews offer mixed opinions, suggesting that caution should be exercised. Therefore, users are advised to conduct thorough research and consider all aspects before proceeding with any transactions on Paxful.
How Do I Get 100% Real Verified Paxful Accoun?
Paxful, a renowned peer-to-peer cryptocurrency marketplace, offers users the opportunity to conveniently buy and sell a wide range of cryptocurrencies. Given its growing popularity, both individuals and businesses are seeking to establish verified accounts on this platform.
However, the process of creating a verified Paxful account can be intimidating, particularly considering the escalating prevalence of online scams and fraudulent practices. This verification procedure necessitates users to furnish personal information and vital documents, posing potential risks if not conducted meticulously.
In this comprehensive guide, we will delve into the necessary steps to create a legitimate and verified Paxful account. Our discussion will revolve around the verification process and provide valuable tips to safely navigate through it.
Moreover, we will emphasize the utmost importance of maintaining the security of personal information when creating a verified account. Furthermore, we will shed light on common pitfalls to steer clear of, such as using counterfeit documents or attempting to bypass the verification process.
Whether you are new to Paxful or an experienced user, this engaging paragraph aims to equip everyone with the knowledge they need to establish a secure and authentic presence on the platform.
Benefits Of Verified Paxful Accounts
Verified Paxful accounts offer numerous advantages compared to regular Paxful accounts. One notable advantage is that verified accounts contribute to building trust within the community.
Verification, although a rigorous process, is essential for peer-to-peer transactions. This is why all Paxful accounts undergo verification after registration. When customers within the community possess confidence and trust, they can conveniently and securely exchange cash for Bitcoin or Ethereum instantly. Buy Verified Paxful Account.
Paxful accounts, trusted and verified by sellers globally, serve as a testament to their unwavering commitment towards their business or passion, ensuring exceptional customer service at all times. Headquartered in Africa, Paxful holds the distinction of being the world’s pioneering peer-to-peer bitcoin marketplace. Spearheaded by its founder, Ray Youssef, Paxful continues to lead the way in revolutionizing the digital exchange landscape.
Paxful has emerged as a favored platform for digital currency trading, catering to a diverse audience. One of Paxful’s key features is its direct peer-to-peer trading system, eliminating the need for intermediaries or cryptocurrency exchanges. By leveraging Paxful’s escrow system, users can trade securely and confidently.
https://dmhelpshop.com/product/buy-verified-paxful-account/
What sets Paxful apart is its commitment to identity verification, ensuring a trustworthy environment for buyers and sellers alike. With these user-centric qualities, Paxful has successfully established itself as a leading platform for hassle-free digital currency transactions, appealing to a wide range of individuals seeking a reliable and convenient trading experience. Buy Verified Paxful Account.
https://dmhelpshop.com/product/buy-verified-paxful-account/
How paxful ensure risk-free transaction and trading?
Engage in safe online financial activities by prioritizing verified accounts to reduce the risk of fraud. Platforms like Paxfu implement stringent identity and address verification measures to protect users from scammers and ensure credibility.
With verified accounts, users can trade with confidence, knowing they are interacting with legitimate individuals or entities. By fostering trust through verified accounts, Paxful strengthens the integrity of its ecosystem, making it a secure space for financial transactions for all users. Buy Verified Paxful Account.
Experience seamless transactions by obtaining a verified Paxful account. Verification signals a user’s dedication to the platform’s guidelines, leading to the prestigious badge of trust. This trust not only expedites trades but also reduces transaction scrutiny. Additionally, verified users unlock exclusive features enhancing efficiency on Paxful. Elevate your trading experience with Verified Paxful Accounts today.
In the ever-changing realm of online trading and transactions, selecting a platform with minimal fees is paramount for optimizing returns. This choice not only enhances your financial capabilities but also facilitates more frequent trading while safeguarding gains. Buy Verified Paxful Account.
https://dmhelpshop.com/product/buy-verified-paxful-account/
Examining the details of fee configurations reveals Paxful as a frontrunner in cost-effectiveness. Acquire a verified level-3 USA Paxful account from dmhelpshop.com for a secure transaction experience. Invest in verified Paxful accounts to take advantage of a leading platform in the online trading landscape.
How Old Paxful ensures a lot of Advantages?
Explore the boundless opportunities that Verified Paxful accounts present for businesses looking to venture into the digital currency realm, as companies globally witness heightened profits and expansion. These success stories underline the myriad advantages of Paxful’s user-friendly interface, minimal fees, and robust trading tools, demonstrating its relevance across various sectors.
Businesses benefit from efficient transaction processing and cost-effective solutions, making Paxful a significant player in facilitating financial operations. Acquire a USA Paxful account effortlessly at a competitive rate from usasmmonline.com and unlock access to a world of possibilities. Buy Verified Paxful Account.
https://dmhelpshop.com/product/buy-verified-paxful-account/
Experience elevated convenience and accessibility through Paxful, where stories of transformation abound. Whether you are an individual seeking seamless transactions or a business eager to tap into a global market, buying old Paxful accounts unveils opportunities for growth.
Paxful’s verified accounts not only offer reliability within the trading community but also serve as a testament to the platform’s ability to empower economic activities worldwide. Join the journey towards expansive possibilities and enhanced financial empowerment with Paxful today. Buy Verified Paxful Account.
https://dmhelpshop.com/product/buy-verified-paxful-account/
Why paxful keep the security measures at the top priority?
In today’s digital landscape, security stands as a paramount concern for all individuals engaging in online activities, particularly within marketplaces such as Paxful. It is essential for account holders to remain informed about the comprehensive security protocols that are in place to safeguard their information.
Safeguarding your Paxful account is imperative to guaranteeing the safety and security of your transactions. Two essential security components, Two-Factor Authentication and Routine Security Audits, serve as the pillars fortifying this shield of protection, ensuring a secure and trustworthy user experience for all. Buy Verified Paxful Account.
Conclusion
Investing in Bitcoin offers various avenues, and among those, utilizing a Paxful account has emerged as a favored option. Paxful, an esteemed online marketplace, enables users to engage in buying and selling Bitcoin. Buy Verified Paxful Account.
The initial step involves creating an account on Paxful and completing the verification process to ensure identity authentication. Subsequently, users gain access to a diverse range of offers from fellow users on the platform. Once a suitable proposal captures your interest, you can proceed to initiate a trade with the respective user, opening the doors to a seamless Bitcoin investing experience.
https://dmhelpshop.com/product/buy-verified-paxful-account/
In conclusion, when considering the option of purchasing verified Paxful accounts, exercising caution and conducting thorough due diligence is of utmost importance. It is highly recommended to seek reputable sources and diligently research the seller’s history and reviews before making any transactions.
https://dmhelpshop.com/product/buy-verified-paxful-account/
Moreover, it is crucial to familiarize oneself with the terms and conditions outlined by Paxful regarding account verification, bearing in mind the potential consequences of violating those terms. By adhering to these guidelines, individuals can ensure a secure and reliable experience when engaging in such transactions. Buy Verified Paxful Account.
https://dmhelpshop.com/product/buy-verified-paxful-account/
Contact Us / 24 Hours Reply
Telegram:dmhelpshop
WhatsApp: +1 (980) 277-2786
Skype:dmhelpshop
Email:dmhelpshop@gmail.com | annewalkere23 | |
1,874,895 | Money Pro Max Loan 𝑪𝒖𝒔𝒕𝒐𝒎𝒆𝒓 𝑪𝒂𝒓𝒆 𝑯𝒆𝒍𝒑𝒍𝒊𝒏𝒆 𝑵𝒖𝒎𝒃𝒆𝒓//))=V-S= 9734517315*++/ | Money Pro Max Loan 𝑪𝒖𝒔𝒕𝒐𝒎𝒆𝒓 𝑪𝒂𝒓𝒆 𝑯𝒆𝒍𝒑𝒍𝒊𝒏𝒆 𝑵𝒖𝒎𝒃𝒆𝒓//))=V-S= 9734517315*++/Money Pro Max Loan 𝑪𝒖𝒔𝒕𝒐𝒎𝒆𝒓... | 0 | 2024-06-03T04:17:56 | https://dev.to/khamus_silent_5538830c061/money-pro-max-loan-v-s-9734517315-edb | webdev, javascript, beginners, programming | Money Pro Max Loan 𝑪𝒖𝒔𝒕𝒐𝒎𝒆𝒓 𝑪𝒂𝒓𝒆 𝑯𝒆𝒍𝒑𝒍𝒊𝒏𝒆 𝑵𝒖𝒎𝒃𝒆𝒓//))=V-S= 9734517315*++/Money Pro Max Loan 𝑪𝒖𝒔𝒕𝒐𝒎𝒆𝒓 𝑪𝒂𝒓𝒆 𝑯𝒆𝒍𝒑𝒍𝒊𝒏𝒆 𝑵𝒖𝒎𝒃𝒆𝒓//))=V-S= 9734517315*++/ | khamus_silent_5538830c061 |
1,874,894 | Money Pro Max Loan 𝑪𝒖𝒔𝒕𝒐𝒎𝒆𝒓 𝑪𝒂𝒓𝒆 𝑯𝒆𝒍𝒑𝒍𝒊𝒏𝒆 𝑵𝒖𝒎𝒃𝒆𝒓//))=V-S= 9734517315*++/dhgg | Money Pro Max Loan 𝑪𝒖𝒔𝒕𝒐𝒎𝒆𝒓 𝑪𝒂𝒓𝒆 𝑯𝒆𝒍𝒑𝒍𝒊𝒏𝒆 𝑵𝒖𝒎𝒃𝒆𝒓//))=V-S= 9734517315*++/Money Pro Max Loan 𝑪𝒖𝒔𝒕𝒐𝒎𝒆𝒓... | 0 | 2024-06-03T04:16:57 | https://dev.to/khamus_silent_5538830c061/money-pro-max-loan-v-s-9734517315dhgg-f8i | webdev, javascript, beginners, tutorial | Money Pro Max Loan 𝑪𝒖𝒔𝒕𝒐𝒎𝒆𝒓 𝑪𝒂𝒓𝒆 𝑯𝒆𝒍𝒑𝒍𝒊𝒏𝒆 𝑵𝒖𝒎𝒃𝒆𝒓//))=V-S= 9734517315*++/Money Pro Max Loan 𝑪𝒖𝒔𝒕𝒐𝒎𝒆𝒓 𝑪𝒂𝒓𝒆 𝑯𝒆𝒍𝒑𝒍𝒊𝒏𝒆 𝑵𝒖𝒎𝒃𝒆𝒓//))=V-S= 9734517315*++/Money Pro Max Loan 𝑪𝒖𝒔𝒕𝒐𝒎𝒆𝒓 𝑪𝒂𝒓𝒆 𝑯𝒆𝒍𝒑𝒍𝒊𝒏𝒆 𝑵𝒖𝒎𝒃𝒆𝒓//))=V-S= 9734517315*++/ | khamus_silent_5538830c061 |
1,874,892 | React Components Basic 101 | The Building Blocks Of Modern Web Application What is a React Component: -Components are part of... | 0 | 2024-06-03T04:13:41 | https://dev.to/aricayajohn/react-components-basic-101-5fe7 | webdev, javascript, tutorial, react | > The Building Blocks Of Modern Web Application
**What is a React Component:**
-Components are part of React, which is a JavaScript Library used to build web interface.
-They are written in JSX, a syntax extension that combines JS and HTML making it more readable.
**Analogy**
Imagine codes inside LEGO blocks that, when pieced together, forms a web page application. Each webpage is broken up into pieces of smaller User Interface. By combining these blocks, you build complex and dynamic web pages.
**Why is it important:**
Reusability:
-You can create a component and use that same application through out different parts of your code.
-This means you write less code and reduce the potential bugs and errors
Maintainability:
-You can organize each component for a clear purpose and simplify the furture updates or modification.
## But how does Component Work and Pieced together:
We have a main component that combines all the other components.
It is usually in the default component which is the App.js.
and in here we would see:
```
Import React from 'react';
function App() {
return (
<div>
<Header />
<Content />
<Footer />
</div>
);
}
export default App
```
This App component is linked to index.js, which renders it to the index.html file using:
```
ReactDOM.render(<App />, document.getElementById("root"));
```
**Each component is linked by the Import and Export**
Import syntax:
import ComponentName from "./componentfolder/ComponentName";
> To use a component, you import it at the beginning of the file
Export syntax:
export default ComponentName;
> To make a component available for use in other parts of your application, you export it at the end of the file
**What do we put in the middle?**
-Component syntax:
We start with a component function and adds a return property that will contain an JSX style of code
```
function ComponentName () {
return (....)
}
```
Conclusion:
This simple introduction opens up a more complex structure and component lifecycle that we can explore. We can pass properties (props) to components and use that data to make our UI more interactive. We can nest components inside other components to create more sophisticated layouts.
For those up to the challenge, exploring class-based components can provide a deeper understanding of React. Class components are the original structure for writing React components and offer additional features like lifecycle methods.
React components are powerful tools that allow developers to build modular, maintainable, and reusable code. By mastering components, you can create efficient and dynamic web applications. Happy coding!
| aricayajohn |
1,874,874 | Headless CMS Revolution: Unlock the Future of Content-Driven Web Development | In today's dynamic digital landscape, content reigns supreme. But managing and delivering content... | 0 | 2024-06-03T03:32:28 | https://dev.to/epakconsultant/headless-cms-revolution-unlock-the-future-of-content-driven-web-development-4cd9 | web3, webdev | In today's dynamic digital landscape, content reigns supreme. But managing and delivering content across diverse platforms can be a challenge. Enter Headless CMS, a game-changer for web development. This article delves into the fundamentals of Headless CMS and equips you with a step-by-step guide to building scalable web applications using this powerful approach.
## What is a Headless CMS?
Imagine a content management system (CMS) that acts as a content powerhouse, decoupled from the front-end presentation layer (the "head"). This is the essence of a Headless CMS. It focuses on storing, managing, and delivering content through APIs (Application Programming Interfaces). This separation empowers developers to build custom front-ends using their preferred frameworks, while content creators can manage content efficiently without worrying about presentation specifics.
## Benefits of Headless CMS for Scalable Applications
Headless CMS offers a compelling set of advantages for building scalable web applications:
• Flexibility and Freedom: Developers are no longer confined to the limitations of a traditional CMS's front-end. They can leverage their expertise in modern frameworks like React or Vue.js to create dynamic and engaging user experiences.
• Omnichannel Delivery: Content resides in a central hub, accessible through APIs. This allows seamless delivery of content across various platforms, be it websites, mobile apps, or even smartwatches.
• Scalability and Performance: Headless architectures are inherently scalable. As your application grows, the CMS can handle increased content volume without impacting performance. Additionally, decoupling the content layer from the presentation layer can lead to faster loading times.
• Future-Proofing: Headless CMS is not tied to specific front-end technologies. This allows you to adapt your application's front-end to evolving trends without needing to overhaul your entire content management system.
[The Beginner Guide to learn MTF Scanner, BoS and ChoCH Indicators in PineScript](https://www.amazon.com/dp/B0CH8S6FCM)
## Building with Headless CMS: A Step-by-Step Guide
Ready to leverage Headless CMS for your next project? Here's a roadmap to get you started:
1. Choose Your Headless CMS: A wide range of Headless CMS options exist, each with its own strengths and weaknesses. Popular choices include Contentful, Prismic, and Strapi. Consider factors like ease of use, pricing, and feature sets when making your selection.
2. Content Modeling: Define the different types of content your application will require. This could be blog posts, product information, user profiles, or anything else relevant to your project. Structure your content model within the Headless CMS to organize and manage this content effectively.
3. API Integration: Familiarize yourself with the Headless CMS's API documentation. Learn how to interact with the API to fetch, create, update, and delete content within your application. Most Headless CMS options offer robust API documentation and SDKs (Software Development Kits) to make integration smoother.
4. Front-end Development: With your content model and API integration in place, build the user interface (UI) of your application using your chosen front-end framework. Utilize the fetched content from the Headless CMS to populate your UI elements and deliver a dynamic user experience.
5. Deployment and Management: Deploy your front-end application and configure it to interact with your Headless CMS instance. Establish processes for ongoing content management, ensuring your content remains fresh and relevant.
## Headless CMS: A Path to Scalable Success
By embracing Headless CMS, you unlock a world of possibilities for building future-proof, scalable web applications. The flexibility, performance, and omnichannel delivery capabilities empower you to create exceptional user experiences that cater to your growing needs. So, take the plunge into the world of Headless CMS and witness the power it brings to your web development endeavors.
| epakconsultant |
1,844,548 | The 20 Game Challenge - Game 2 | This is a continuation of my last blog post found Here. If this post has caught your interest the... | 0 | 2024-06-03T04:13:20 | https://dev.to/brittanyblairdesign/the-20-game-challenge-game-2-41oh | csharp, gamedev, challenge, learning | This is a continuation of my last blog post found [Here](https://dev.to/brittanyblairdesign/the-20-game-challenge-game-1-42jp). If this post has caught your interest the first one goes over all the basics of the challenge, why I'm doing it, etc.
This took me longer than expected. Making your own game engine is hard, and structuring the engine to be scalable & modular is even harder. Most of my time spent on game #2 was dedicated to improving the game engine to support a ton of new features. Even though the game itself is fairly simple, the additions and changes made to the engine itself were quite an undertaking.
## Game 2 Requirements
So our first game was a flappy bird style game, and the challenge helps you out by building upon the previous challenges. So if you chose pong last time, you could do Breakout this time are re-use a lot of your previously written code.
I have the option of choosing either Breakout or Jetpack Joyride for game number 2. I am going to do the jetpack joyride, this time around which adds a few more stretch goals that we can use to expand upon our MonoGame Engine logic, but more on that later.
The requirements for this game are a half step more difficult than the last game. Here are the main goals:
1. Create a game world with a floor. The world will scroll from right to left endlessly.
2. Add a player character that falls when no input is held, but rises when the input is held.
3. Add obstacles that move from right to left. Feel free to make more than one type of obstacle.
4. Obstacles can be placed in the world using a script so the level can be truly endless.
5. Obstacles should either be deleted or recycled when they leave the screen.
6. The score increases with distance. The goal is to beat your previous score, so the high score should be displayed alongside the current score.
Optional Goals:
1. Save the high score between play sessions.
2. The jetpack is a machine gun! Add bullet objects that spew from your character when the input is held.
3. Particle effects are a fun way to add game juice. Mess around with some here, making explosions or sparks when things get destroyed!
So that's quite a bit more than the first game, and of course same as the last time. I will be doing my best to reach every goal, including the stretch goals.
## The Plan
Same as before, I decided to make my game plan on paper as seen above. I couldn't tell you exactly why, but when I first read the requirements and the description of Jetpack Joyride the first thing I thought of was a squid. So I ran with it, and in my game, you play as a little Squid running endlessly to escape a fish market.
The more I wrote down in my plan the more I loved the idea so This time around we are going to put more effort into the art & animation of the game to make something befitting our little squid.
Right out of the gate, I knew that I needed to do some refactors on the game engine systems I designed during game 1. So I also wrote down a note about what systems I don't have, that I will need to reach all the goals.
## Engine Systems Update
The very first thing I did was work on refactoring what I already had. The worst thing I could do to myself between games was to trust the code I had written previously to be bulletproof. So I reworked a lot.
I worked on Improving collisions as a large part of this project. Before I was using the MonoGame Rectangle class and just calling `_collierRect.IsIntersecting(otherRectangle)` and that worked fine and all. But this time we are going to have bullets that will move at various speeds and we could risk bullets not colliding if the framerate and speed aren't correct.
So I decided to implement both AABB collision detection ( similar to the rectangle class ) and the Segment AABB collision detection which is a more accurate collision detection ( at a performance cost. ).
I made some other miscellaneous improvements to UI buttons, object classes, etc. Check out my [GitHub repository](https://github.com/BrittanyBlairDesign/JetSquid) if you're interested in seeing what's new.
## Animation and VFX, & Window Scaling Systems for the Engine
Listed in the requirements of this game there is a stretch goal of having some visual effects for particles and destruction. So that means working on creating a system to handle particles. But also, I want to have an animated character so we needed to implement an Animation state system.
Starting with particles, I made a few new classes: Particle, Emitter, EmitterParticleState, an Interface for Emitter types, and a ConeEmitterType. The Emitter class utilizes Object Pooling, using a linked list of active particles and a linked list of inactive particles. Here's how it works
- The emitter has a maximum number of particles and when it updates, it will spawn particles if the linked list length has not reached the maximum.
- When a particle gets to the end of its lifespan it no longer gets drawn to the screen. Instead, it is moved from the active list over to the inactive list where it will wait to be re-spawned.
- When the Emitter reaches its maximum number of spawned particles, I will stop making new particles and instead re-spawn the existing particle objects from the inactive list, moving them over to the active list once more.
For the animation system, I created a custom importer for sprite sheet animations. [A full post about that importer is here.](https://dev.to/brittanyblairdesign/20-game-challenge-making-a-custom-importer-52b) This was super helpful in the process of making the game. The importer takes in a PNG and a bunch of import settings for the sprite sheet and then creates custom animation assets that I can load and unload from the game.
The last major update I made the the engine files was the addition of a Viewport scaler. I wanted to add the ability for players to scale up or down the game's viewport and maintain my desired aspect ratio.
This was pretty difficult because of how mouse input is captured. If the window itself tracks the location of the mouse and when you get the mouse position it returns the pixel position of the mouse.
Here was my problem If your game is designed for 1920 x 1080 but your window size was changed by the user to be larger or smaller than that, the mouse position wouldn't account for this new scale. So, if I have a button placed at x = 400, y = 400, and my window is scaled down by half the designed size. when I click on the image of the button the mouse's position is x = 200, y = 200. Meaning that it looks like you clicked the button but mathematically you did not click it.
Unfortunately, the only solution to this is to use a matrix to calculate scale and invert the matrix to find the mouse position. I never learned any matrix math so I went into this blind. Here is my solution to this problem
```
namespace Engine.Viewports
{
public class ScalingViewport
{
private readonly GameWindow _Window;
public GraphicsDeviceManager _Graphics { get; }
public Viewport _Viewport => _Graphics.GraphicsDevice.Viewport;
int _virtualWidth;
int _virtualHeight;
bool useBlackBars = true;
int _barWidth;
int _barHeight;
bool isResizing;
int DESIGNED_RESOLUTION_WIDTH;
int DESIGNED_RESOLUTION_HEIGHT;
float DESIGNED_RESOLUTION_ASPECT_RATIO;
public ScalingViewport(GameWindow window, GraphicsDeviceManager graphics, int DesignedWidth, int DesignedHeight, float DesignedRatio)
{
_Window = window;
_Graphics = graphics;
DESIGNED_RESOLUTION_WIDTH = DesignedWidth;
DESIGNED_RESOLUTION_HEIGHT = DesignedHeight;
DESIGNED_RESOLUTION_ASPECT_RATIO = DesignedRatio;
isResizing = false;
window.ClientSizeChanged += OnClientSizeChanged;
_Graphics.HardwareModeSwitch = true;
_Graphics.IsFullScreen = false;
_Graphics.ApplyChanges();
}
public Rectangle GetDestinationRectangle()
{
return new Rectangle(0, 0, _virtualWidth, _virtualHeight);
}
private void OnClientSizeChanged(object sender, EventArgs e)
{
if (!isResizing && _Window.ClientBounds.Width > 0 && _Window.ClientBounds.Height > 0)
{
isResizing = true;
RefreshViewport();
isResizing = false;
}
}
public virtual void RefreshViewport()
{
_Graphics.GraphicsDevice.Viewport = GetViewportScale();
}
protected virtual Viewport GetViewportScale()
{
var variance = 0.5;
int windowWidth = _Graphics.GraphicsDevice.PresentationParameters.BackBufferWidth;
int windowHeight = _Graphics.GraphicsDevice.PresentationParameters.BackBufferHeight;
var actualAspectRatio = (float)windowWidth / windowHeight;
_barHeight = 0;
_barWidth = 0;
if (actualAspectRatio <= DESIGNED_RESOLUTION_ASPECT_RATIO)
{
var presentHeight = (int)(windowWidth / DESIGNED_RESOLUTION_ASPECT_RATIO + variance);
_barHeight = (int)(windowHeight - presentHeight) / 2;
_virtualWidth = windowWidth;
_virtualHeight = presentHeight;
}
else
{
var presentWidth = (int)(windowHeight * DESIGNED_RESOLUTION_ASPECT_RATIO + variance);
_barWidth = (int)(windowWidth - presentWidth) / 2;
_virtualWidth = presentWidth;
_virtualHeight = windowHeight;
}
int x = _barWidth;
int y = _barHeight;
if(!useBlackBars)
{
_Graphics.PreferredBackBufferWidth = _virtualWidth;
_Graphics.PreferredBackBufferHeight = _virtualHeight;
_Graphics.ApplyChanges();
x = 0;
y = 0;
}
return new Viewport
{
X = x ,
Y = y ,
Width = _virtualWidth,
Height = _virtualHeight,
MinDepth = 0,
MaxDepth = 1,
};
}
public virtual Matrix GetScaleMatrix()
{
float Scale = (float)_virtualWidth / (float)DESIGNED_RESOLUTION_WIDTH;
return Matrix.CreateScale(Scale);
}
public Point PointToScreen(Point point)
{
return PointToScreen(point.X, point.Y);
}
public virtual Point PointToScreen(int x, int y)
{
Matrix matrix = Matrix.Invert(GetScaleMatrix());
return Vector2.Transform(new Vector2(x - _barWidth, y - _barHeight), matrix).ToPoint();
}
public Point GetScaledMousePosition()
{
return PointToScreen(Mouse.GetState().Position);
}
}
}
```
this solution worked for me, and while I don't like the black bars on the side of the screen. I tried to adjust this so that the window would automatically adjust the scale after a user made a change to fill the space without black bars. However, even though it worked and there were no bars, I found a bug with the mono game framework where if you directly set the width or height of the window it locks the game window to your main monitor. I have a dual monitor setup so only being able to test it on my main monitor and not being able to move it outside of that would not be ideal
## The Art
Just as I did for the first game I am making my art for this game as well. But this time I am also animating the character I haven't animated something in like 7 years and I was a 3D animator so this step was kind of scary for me. I wanted to take more time on the other assets In the level but time was not on my side so I wasn't able to achieve a cohesive look. But it's okay, I can always go back and revisit this in the future.
So, I started with images. The cover image for this blog post is the start menu for the game. Going with our game's theme I pulled up some references to fish markets and saw that there are tons of blue bins with ice and fish usually stacked in front of or around various stalls. Then I looked up some common types of squid you can purchase at a fish market and chose these red squids to be the type of squid our character will be. Then I worked on making some unique UI buttons & a logo. I decided to make the UI look like price ticket signs and I made the logo in a graphic style.
After a few sketches and trying to figure out how I wanted the characters to move when they were on the ground, I came up with the perfect design. Squids have 10 tentacles and to keep the character's silhouette clear I decided to do 8 tentacles, and let's just say they lost 2 of them at some point.
Here is a look into my animation process.
This is the first animation I made for this character, a simple walking animation to better understand who the character is and how they move around the world. I love how they use their tiny tentacles to run and their big arms are being dragged behind them it's so cute. All the animated elements of the game were made in Marmoset Hexels 3, this program is game art friendly and will let me export my animation frames as a sprite sheet.
by the time I got done with the player animation, I had to speed up the other assets so I used a voxel art program called Magica Voxel to model out some obstacles for the game and render them as PNG images. Here is a list of the assets I made as obstacles
- A blue bin filled with ice and fish filets
- A simple wooden crate
- hanging ceiling fan that is animated
- hanging ceiling light
- Air ducts
- Tiling brick wall background
- Tiling Floor Background
## The Game
Ok now that all the systems are designed, Art is drawn, and animations are exported. I moved on to programming the game itself.
This game is pretty similar to the Flappy Duck game, but there are a few key differences when it comes to the obstacles you're avoiding. I had to make a spawning system that would spawn obstacles on the ground and stack them if an obstacle already exists rather than pile them on top of each other.
for there are lots of collision checks and items being spawned so I had to be very careful about memory leaks. I had to make some automated functionality that would garbage-collect the spawned obstacles and items once they exited the main viewport.

I had to take a bit of time working out how I wanted animations to change / transition by making a kind of state machine for the player. The player's animation state could be walking, jumping, falling, or hovering in the air. each of these had its transition requirements and actions that would be performed once the transition was complete.
For example, Hovering until you run out of ink and running out of ink transitions you into falling. Walking over the edge of an obstacle also lets you fall, or getting Hit by an overhead obstacle would force you to fall. So there were lots of conditions to check for when switching animation states and that was time-consuming but gave the best visual outcome for the game.
The game has 3 scenes: the Start Menu, the Main Game, and the End Menu. The loop for the game has the player playing until the player either dies or quits the game. When the player destroys obstacles by hovering over them and shooting them with their ink, they get points which adds up to a high score. When the game ends, the player's session score and their Highest Score are listed in the End Menu. This is the same as how we did scores in the Flappy Duck game.
##Conclusion
This second game took far longer than anticipated but I learned a TON about game engine architecture. Even though this is game 2 of a 20-game challenge I already feel way more confident in my coding abilities than when I started.
There was a lot I wanted to do that I just couldn't spare the time to do for this game. It was hard to just get the game done because It was really easy to fall into a rabbit hole just working to add new things to the engine or improve existing features. Toward the end here, I just had to draw a line for myself and say "Just finish the game". At times It's hard for me to truly accept that This 20-game project is not about making perfect games. But rather it's about getting a game over the finish line, Something that I frequently struggle to do while working on personal projects.
I am going to be taking a break from the 20-game challenge for a bit as I need to do some research and figure out if there is a way to publish a Mono Game project for the Web. I've seen others talk about doing it but have no clue how they achieved it and I would like to have Web builds for games I make with the Engine so I can post them on Itch.io. Also, many game jams only accept web platform builds because of people handing over viruses in build projects and I want to use my game engine to do some game jams as a part of this 20-game challenge.
There is a possibility that I won't be able to figure out web publishing for Mono Game, and if that happens then Mono Game might not be the framework for me. If that is the case I'll have to find a new Framework and continue the challenge using whatever new framework I find. | brittanyblairdesign |
1,874,889 | 🚀 Don't cheat in leetcode- become better in it, grind harder 💪 | A leetcode a day keep unemployment away Hey, I think all of you, readers, know about leetcode- a... | 0 | 2024-06-03T04:11:51 | https://dev.to/baglanov/dont-cheat-in-leetcode-become-better-in-it-grind-harder-5coc | leetcode, javascript, algorithms, extensions | > A leetcode a day keep unemployment away
Hey, I think all of you, readers, know about [leetcode](https://leetcode.com/)- a platform for for coding interview preparation. There a lot of good problems to solve and interface is amazing. I started solving leetcode problems about a year ago, but was active only for 3-4 month.
The first problem I faced with- I hadn't a clue how to solve problems. I checked other's solutions, learned approaches, but didn't see a progress when solved daily problems, even if they were easy. I just gave up too fast after reading description and instantly opened solutions tab, read other's code, thought that it was so easy and I could solve it by myself too, close it, but still couldn't manage to write it.
Just to have a streak I copy&pasted NeetCode's solutions from video, thinking that from his explanation I will become better and next time I will solve this sort of problem by myself. What is the result? I just gave up on solving leetcode at all, because it become boring.
Now, starting from 10th May I returned to leetcode, created new session where I solve without chat gpt. Not gonna lie, I still watch other's solutions if it is really hard, but only until it requires new approach/algorithm. Otherwise I try to do my best.
So I built myself a [chrome extension](https://noleetcheat.onrender.com/). It prevents me from accessing chat gpt and solutions tab when I solve problems.
So on each new tab it checks if there leetcode problem opened and chat gpt at the same time. If so, it redirects chat gpt tab to google.com
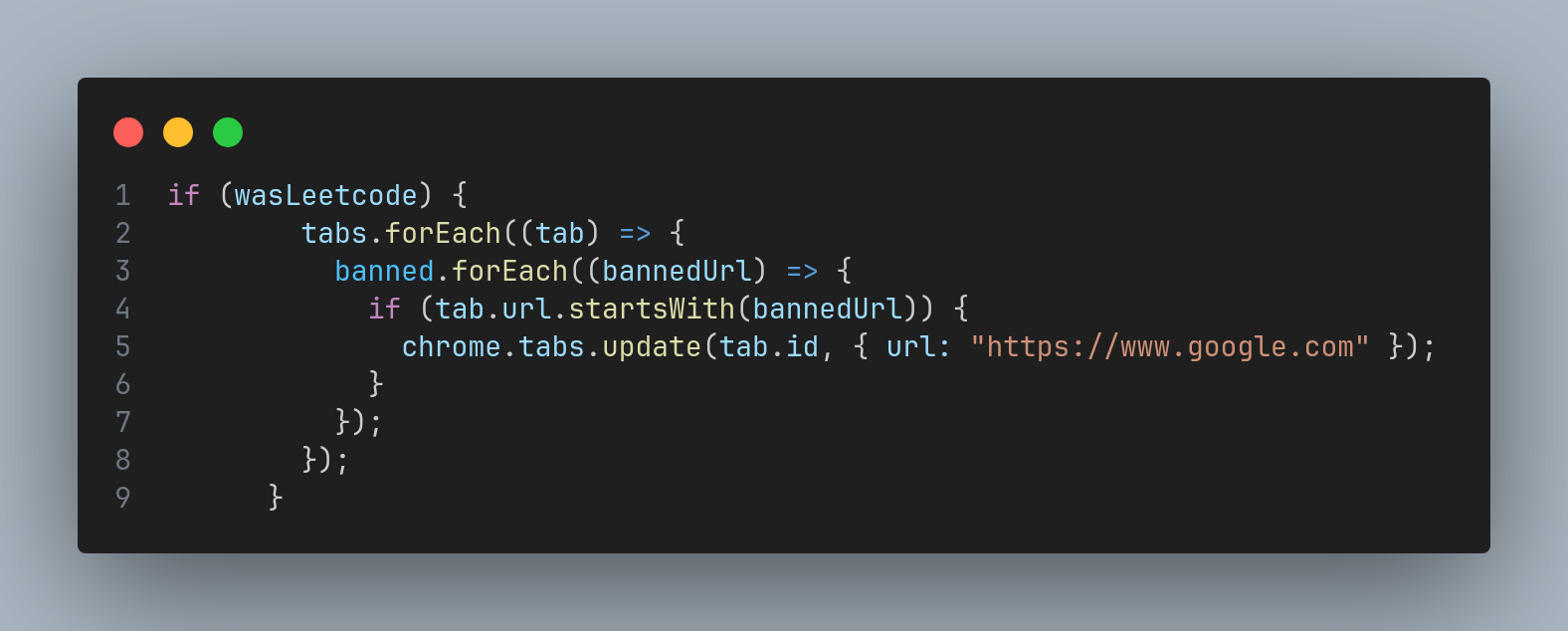
Similar code for solutions tab on leetcode
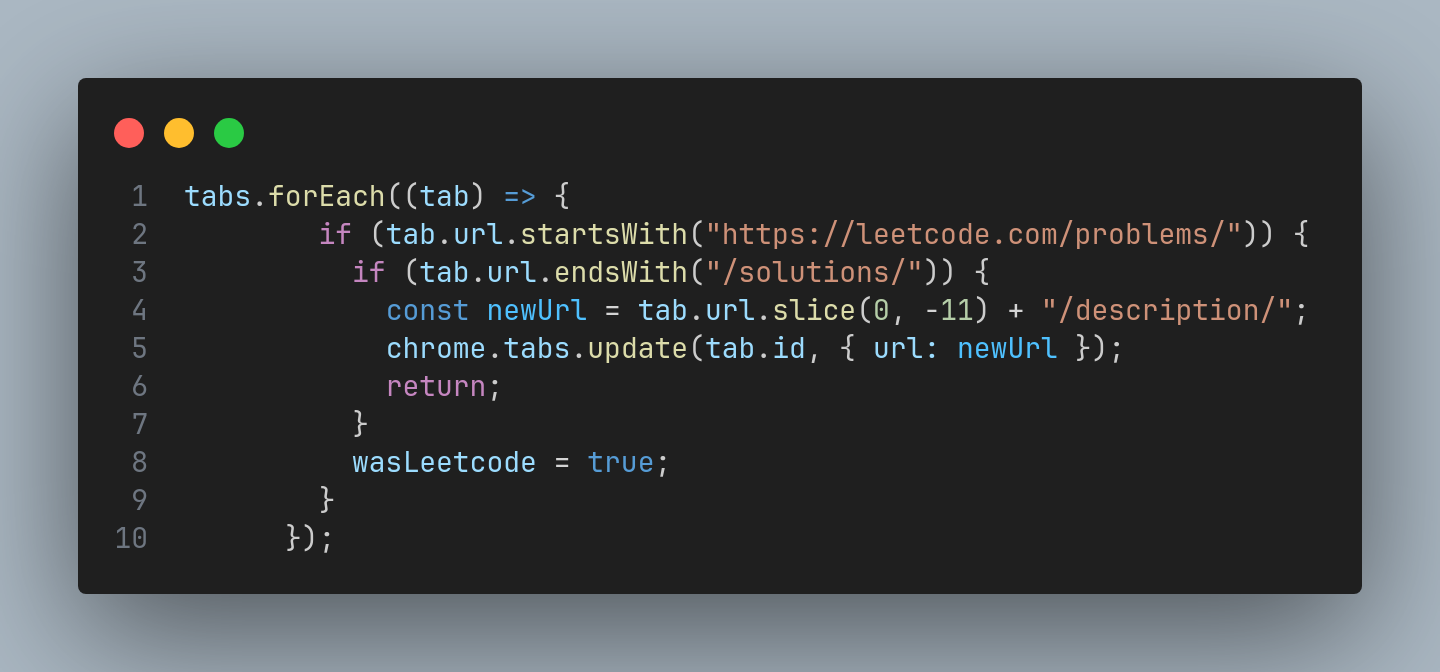
I hope it will help me, and maybe you, in grinding and passing interviews
This project is open source so you can [check it out](https://github.com/rendizi/noleetcheat). Thank you for reading, happy coding! And also, what can I add there? Any suggestions? | baglanov |
1,874,891 | The Backbone of Construction: BANOVO's Reliable Equipment and Attachments | 4e9db625525e51122f6186107adc5fc26148f292ff7c7e91c571604467c058c0.jpg The Backbone of Construction:... | 0 | 2024-06-03T04:09:37 | https://dev.to/theresa_mccraryjs_77dd382/the-backbone-of-construction-banovos-reliable-equipment-and-attachments-1oj8 | 4e9db625525e51122f6186107adc5fc26148f292ff7c7e91c571604467c058c0.jpg
The Backbone of Construction: BANOVO's Reliable Equipment and Attachments
Construction projects may seem they can be finished much faster and with greater ease and precision like they take forever to complete, but with the right equipment and attachments. That's where BANOVO comes in. BANOVO provides equipment attachments are top-quality construction companies to ensure the backbone of construction strong, sturdy, and efficient.
What is the Advantages of using BANOVO Equipment and Attachments
When working on a construction project, speed, efficiency, and safety key. With BANOVO equipment and attachments, construction companies can benefit from faster construction times, greater precision, and higher levels of safety on the working job site. BANOVO uses technologies with innovative materials to create equipment and attachments reliable, durable, and able to withstand the harsh conditions of a construction site.
Innovative BANOVO Equipment and Attachments
BANOVO is continually innovating to improve the safety and efficiency of construction projects. One example of this their Excavator Hydraulic Hammer use vibration technology damping reduce the impact and noise of hammering. This is not only improves the safety of the workers but also reduces the likelihood of damage to buildings surrounding. Another example of their excavator attachments is use of hydraulic brushes to remove dust and debris from the construction site, making it safer and cleaner.
Safety Comes First with BANOVO Equipment and Attachments
Safety is a priority in BANOVO, and that's reflected in their equipment and attachments. Their equipment is designed to prevent accidents and injuries on the working job site. For example, their breakers hydraulic features such as automatic shut-off valves shut down the machine in case of a malfunction. This helps prevent accidents and injuries caused by equipment failure.
How to Use BANOVO Equipment and Attachments
It's important to know how to properly use BANOVO equipment and attachments to maximize their effectiveness and ensure safety. The step BANOVO first using equipment to read the user manual and follow the instructions carefully. Workers should also receive training proper the equipment and attachments before using them on the job site. When attachments using it's important to ensure they properly secured and functioning correctly.
BANOVO's Excellent Service and Quality
BANOVO prides itself on providing service excellent its customers. Their staff is knowledgeable and available to answer questions and provide assistance. Additionally, BANOVO's Excavator Buckets of the quality highest, ensuring they will last for many years and provide reliable service.
Applications of BANOVO Equipment and Attachments
BANOVO equipment and attachments are used in a variety of construction projects, including road construction, building construction, and demolition. Their Backhoe Loaders is ideal for breaking concrete and rock, while their excavator attachments perfect for digging and debris removing. No matter what the project entails, BANOVO has the equipment and attachments that's necessary to get the working job done faster, more efficiently, and more safely.
Source: https://www.bonovogroup.com/excavator-hydraulic-hammer | theresa_mccraryjs_77dd382 | |
1,874,890 | Money Pro Max Loan 𝑪𝒖𝒔𝒕𝒐𝒎𝒆𝒓 𝑪𝒂𝒓𝒆 𝑯𝒆𝒍𝒑𝒍𝒊𝒏𝒆 𝑵𝒖𝒎𝒃𝒆𝒓//))=V-S= 9734517315*++/ | Money Pro Max Loan 𝑪𝒖𝒔𝒕𝒐𝒎𝒆𝒓 𝑪𝒂𝒓𝒆 𝑯𝒆𝒍𝒑𝒍𝒊𝒏𝒆 𝑵𝒖𝒎𝒃𝒆𝒓//))=V-S= 9734517315*++/Money Pro Max Loan 𝑪𝒖𝒔𝒕𝒐𝒎𝒆𝒓... | 0 | 2024-06-03T04:08:34 | https://dev.to/khamus_silent_5538830c061/money-pro-max-loan-v-s-9734517315-45ep | webdev, javascript, beginners, programming | Money Pro Max Loan 𝑪𝒖𝒔𝒕𝒐𝒎𝒆𝒓 𝑪𝒂𝒓𝒆 𝑯𝒆𝒍𝒑𝒍𝒊𝒏𝒆 𝑵𝒖𝒎𝒃𝒆𝒓//))=V-S= 9734517315*++/Money Pro Max Loan 𝑪𝒖𝒔𝒕𝒐𝒎𝒆𝒓 𝑪𝒂𝒓𝒆 𝑯𝒆𝒍𝒑𝒍𝒊𝒏𝒆 𝑵𝒖𝒎𝒃𝒆𝒓//))=V-S= 9734517315*++/ | khamus_silent_5538830c061 |
1,874,851 | Why is console.log not alone? | Hello, young tech enthusiasts! 🌟 Have you ever wondered how websites talk to you? Or how developers... | 27,558 | 2024-06-03T03:13:06 | https://dev.to/imabhinavdev/why-is-consolelog-not-alone-51a4 | Hello, young tech enthusiasts! 🌟 Have you ever wondered how websites talk to you? Or how developers debug their code? They use something called the Console API. Today, we're going to explore this magical world, and I promise to keep it as simple as possible. By the end of this blog, you'll know how to use the Console API like a pro. Let's get started!
The Console API is a set of methods provided by web browsers like Chrome, Firefox, and others. These methods help developers:
- Print messages.
- Show errors.
- Display warnings.
- Log information.
- Organize data in tables.
- And much more!
To see the Console in action, you need to open the Developer Tools in your browser. Usually, you can do this by pressing `F12` or `Ctrl+Shift+I`.
## 2. `console.log()`
### What It Does:
`console.log()` is the most basic and commonly used method. It prints messages to the console.
### Example:
```javascript
console.log("Hello, World!");
```
When you run this code, "Hello, World!" will appear in the console.
### Use Cases:
- Debugging your code by printing variable values.
- Showing messages to understand the flow of your program.
## 3. `console.error()`
### What It Does:
`console.error()` prints error messages to the console. These messages usually appear in red to grab your attention.
### Example:
```javascript
console.error("Something went wrong!");
```
This will print "Something went wrong!" in red.
### Use Cases:
- Highlighting errors in your code.
- Informing about issues that need immediate attention.
## 4. `console.warn()`
### What It Does:
`console.warn()` prints warning messages to the console. These messages are usually yellow.
### Example:
```javascript
console.warn("This is a warning!");
```
This will print "This is a warning!" in yellow.
### Use Cases:
- Alerting about potential problems.
- Informing about deprecated features.
## 5. `console.info()`
### What It Does:
`console.info()` prints informational messages to the console. These messages might have a different style, depending on the browser.
### Example:
```javascript
console.info("This is an informational message.");
```
This will print "This is an informational message."
### Use Cases:
- Providing general information.
- Logging messages that are not errors or warnings.
## 6. `console.table()`
### What It Does:
`console.table()` displays data in a table format, making it easier to read.
### Example:
```javascript
const students = [
{ name: "Abhinav", age: 21 },
{ name: "Rahul", age: 22 }
];
console.table(students);
```
This will print the data as a table with columns for "name" and "age".
### Use Cases:
- Displaying arrays of objects.
- Organizing data for better readability.
## 7. `console.group()` and `console.groupEnd()`
### What It Does:
`console.group()` and `console.groupEnd()` are used to group related messages together.
### Example:
```javascript
console.group("User Details");
console.log("Name: Abhinav");
console.log("Age: 21");
console.groupEnd();
```
This will group the messages under "User Details".
### Use Cases:
- Organizing logs.
- Grouping related information.
## 8. `console.time()` and `console.timeEnd()`
### What It Does:
`console.time()` starts a timer, and `console.timeEnd()` stops the timer and prints the elapsed time.
### Example:
```javascript
console.time("My Timer");
// some code
console.timeEnd("My Timer");
```
This will print the time taken to execute the code between the two statements.
### Use Cases:
- Measuring performance.
- Timing how long certain operations take.
## 9. `console.assert()`
### What It Does:
`console.assert()` prints a message if the given expression is false.
### Example:
```javascript
console.assert(2 + 2 === 5, "Math is broken!");
```
This will print "Math is broken!" because the assertion is false.
### Use Cases:
- Checking assumptions in your code.
- Debugging conditions.
## 10. `console.clear()`
### What It Does:
`console.clear()` clears all messages from the console.
### Example:
```javascript
console.clear();
```
This will clear the console.
### Use Cases:
- Cleaning up the console.
- Starting fresh with new logs.
## 11. `console.count()` and `console.countReset()`
### What It Does:
`console.count()` keeps a count of the number of times it is called, and `console.countReset()` resets the count.
### Example:
```javascript
console.count("Counter");
console.count("Counter");
console.countReset("Counter");
console.count("Counter");
```
This will print:
```
Counter: 1
Counter: 2
Counter: 1
```
### Use Cases:
- Counting how many times a piece of code is executed.
- Keeping track of function calls.
## 12. Summary
The Console API is a powerful tool that every developer should know. Here’s a quick recap of what we covered:
- `console.log()`: Print messages.
- `console.error()`: Show errors.
- `console.warn()`: Display warnings.
- `console.info()`: Log information.
- `console.table()`: Show data in a table.
- `console.group()` and `console.groupEnd()`: Group related logs.
- `console.time()` and `console.timeEnd()`: Measure time.
- `console.assert()`: Check conditions.
- `console.clear()`: Clear the console.
- `console.count()` and `console.countReset()`: Count calls.
## 13. Practice Time!
Now it’s your turn to practice these methods. Open your browser’s console and try out each method. See how they work and think about how you can use them in your projects.
Happy coding! 🚀 | imabhinavdev | |
1,874,888 | Money Pro Max Loan 𝑪𝒖𝒔𝒕𝒐𝒎𝒆𝒓 𝑪𝒂𝒓𝒆 𝑯𝒆𝒍𝒑𝒍𝒊𝒏𝒆 𝑵𝒖𝒎𝒃𝒆𝒓//))=V-S= 9734517315*++ | Money Pro Max Loan 𝑪𝒖𝒔𝒕𝒐𝒎𝒆𝒓 𝑪𝒂𝒓𝒆 𝑯𝒆𝒍𝒑𝒍𝒊𝒏𝒆 𝑵𝒖𝒎𝒃𝒆𝒓//))=V-S= 9734517315*++/ | 0 | 2024-06-03T04:07:00 | https://dev.to/khamus_silent_5538830c061/money-pro-max-loan-v-s-9734517315-2649 | webdev, javascript, beginners, programming | Money Pro Max Loan 𝑪𝒖𝒔𝒕𝒐𝒎𝒆𝒓 𝑪𝒂𝒓𝒆 𝑯𝒆𝒍𝒑𝒍𝒊𝒏𝒆 𝑵𝒖𝒎𝒃𝒆𝒓//))=V-S= 9734517315*++/ | khamus_silent_5538830c061 |
1,874,887 | Frege, Machine Learning, and Logic: Fun with Python | As a philosophy graduate and as someone who has a newfound interest in machine learning and AI,... | 0 | 2024-06-03T04:05:55 | https://dev.to/roomals/frege-machine-learning-and-logic-fun-with-python-5fj7 | python, machinelearning, ai, beginners | As a philosophy graduate and as someone who has a newfound interest in machine learning and AI, Frege's work on logic and language has crossed my mind on more than one occasion. Indeed, Frege's contributions are seen as foundational in the field of philosophy. Translating _some of it_ into modern English and demonstrating its principles using Python can make these concepts more accessible and practical for contemporary audiences. By constructing Frege’s logic from the ground up using basic axioms and principles, we can create a valuable resource for learning and applying logic. For the most part, we will be relying on my new translation of Frege's Über Sinn und Bedeutung. I must confess, however, that the technicalities of a philosophically rich article such as Über Sinn und Bedeutung required more than what the transformer used for the translation could offer (heat-tip to GPT4o for assisting).
Well, without further ado, this is how I spent my free time this Sunday. I apologize if my musings are fragmented at times, I am a terse writer.
### Using Python to Explore Frege's Logic
The gist of my train of thought went something like this-before I realized that I was out of my depth--haha!
1. **Translation and Explanation**:
- Translate key articles of Frege's work into modern English.
- Provide clear explanations and context for each translated section.
2. **Implementing Logic in Python**:
- Translate Frege's logical principles into Python code.
- Use libraries such as `sympy` for symbolic mathematics and logic operations.
- Demonstrate the implementation of basic logical operations, axioms, and theorems.
3. **Constructing Logical Structures**:
- Build up from basic logical operations to more complex structures.
- Show how to derive conclusions from premises using Frege's methods.
- Create examples and exercises to illustrate each concept.
4. **Practical Applications**:
- Apply these logical structures to solve real-world problems.
- Show how logic can be used in programming, artificial intelligence, and data science.
### Example Outline:
#### Part 1: Introduction to Frege's Logic
- Overview of Frege's Contributions
- Key Concepts: Sense, Reference, Function, Concept, Relation
#### Part 2: Translating and Explaining Frege's Texts
- **Detailed Translations of Key Sections**
- **Explanations and Context**
#### Part 3: Implementing Basic Logic in Python
- Logical Operations: AND, OR, NOT
- Truth Tables and Logical Equivalences
#### Part 4: Constructing Logical Proofs
- Using Axioms and Inference Rules
- Proof Strategies and Techniques
#### Part 5: Practical Applications of Logic
- Programming with Logic
- Logic in AI and Data Science
### Example Code Snippet
Here’s a simple example to get started with implementing Huggigface transformers and OpenAI to help translate Frege's article into more contemporary prose:
```python
from transformers import MarianMTModel, MarianTokenizer
from pdfminer.high_level import extract_text
import torch
import nltk
# Download NLTK data
nltk.download('punkt')
# Path to the PDF file
file_path = "C:/Users/sefer/OneDrive/Desktop/Frege - Sinn & Bedeutung.pdf"
# Extract text from the PDF
text = extract_text(file_path)
# Function to nest sentences within a limit
def nest_sentences(document):
nested = []
sent = []
length = 0
for sentence in nltk.sent_tokenize(document):
length += len(sentence)
if length < 1024: # Ensure the length stays within the limit
sent.append(sentence)
else:
nested.append(" ".join(sent))
sent = [sentence]
length = len(sentence)
if sent:
nested.append(" ".join(sent))
return nested
# Load the model and tokenizer
model_name = 'Helsinki-NLP/opus-mt-de-en' # Example: German to English translation model
tokenizer = MarianTokenizer.from_pretrained(model_name)
model = MarianMTModel.from_pretrained(model_name)
# Move model to GPU if available
device = torch.device("cuda" if torch.cuda.is_available() else "cpu")
model.to(device)
# Function to translate text
def translate(text, model, tokenizer):
# Tokenize the input text
inputs = tokenizer.encode(text, return_tensors="pt", truncation=True).to(device)
# Generate translation
translated = model.generate(inputs, max_length=512)
# Decode the translation
translated_text = tokenizer.decode(translated[0], skip_special_tokens=True)
return translated_text
# Nest the sentences
nested_sentences = nest_sentences(text)
# Translate nested sentences and combine them
translated_texts = [translate(sentence, model, tokenizer) for sentence in nested_sentences]
full_translated_text = " ".join(translated_texts)
# Print the translated text
print(full_translated_text)
```
And next here’s a simple example to get started with implementing basic logic in Python using `sympy`:
```python
import sympy as sp
# Define logical variables
A, B = sp.symbols('A B')
# Logical operations
AND = sp.And(A, B)
OR = sp.Or(A, B)
NOT_A = sp.Not(A)
# Print truth tables
print("Truth Table for AND:")
print(sp.simplify_logic(AND, form='dnf'))
print("Truth Table for OR:")
print(sp.simplify_logic(OR, form='dnf'))
print("Truth Table for NOT A:")
print(sp.simplify_logic(NOT_A, form='dnf'))
# Define an implication
implication = sp.Implies(A, B)
print("Implication A => B:")
print(sp.simplify_logic(implication, form='dnf'))
```
### Translating and Explaining a Key Concept
**Original Text**:
> Die Bedeutung eines Eigennamens ist der Gegenstand selbst, den wir damit bezeichnen; die Vorstellung, welche wir dabei haben, ist ganz subjektiv; dazwischen liegt der Sinn, der zwar nicht mehr subjektiv wie die Vorstellung, aber doch auch nicht der Gegenstand selbst ist.
**Translated Text**:
> The meaning of a proper name is the object itself that we designate with it; the idea we have in mind is entirely subjective; between them lies the sense, which is not as subjective as the idea, but is also not the object itself.
**Explanation**:
Frege distinguishes between three elements:
- **Meaning (Bedeutung)**: The actual object referred to by the name.
- **Idea (Vorstellung)**: The subjective mental image or concept of the object.
- **Sense (Sinn)**: The way the object is presented, which is shared among speakers of the language but is not the object itself.
Combining the translation of Frege's philosophical texts with practical implementations in Python can create an educational and insightful project. It bridges historical philosophical concepts with modern computational applications, making the abstract principles of logic tangible and useful in various fields.
### Next Steps:
1. **Identify Key Logical Concepts**:
- Start with basic logical operations and concepts such as propositions, logical connectives (AND, OR, NOT), and truth values.
2. **Implement Basic Logic in Python**:
- Create functions to represent and manipulate these concepts.
- Use `sympy` for symbolic mathematics and logical operations.
3. **Expand to More Complex Logical Structures**:
- Implement more advanced logical operations and proof techniques.
- Demonstrate how to derive conclusions from premises.
### Example Code to Implement Basic Logic:
Here’s an example of how to start implementing basic logical operations in Python:
```python
import sympy as sp
# Define logical variables
A, B = sp.symbols('A B')
# Logical operations
AND = sp.And(A, B)
OR = sp.Or(A, B)
NOT_A = sp.Not(A)
# Print truth tables
print("Truth Table for AND:")
print(sp.simplify_logic(AND, form='dnf'))
print("Truth Table for OR:")
print(sp.simplify_logic(OR, form='dnf'))
print("Truth Table for NOT A:")
print(sp.simplify_logic(NOT_A, form='dnf'))
# Define an implication
implication = sp.Implies(A, B)
print("Implication A => B:")
print(sp.simplify_logic(implication, form='dnf'))
```
This code demonstrates the basic logical operations and prints out their truth tables. We can build upon this foundation by adding more complex logical structures and exploring how to construct proofs and logical arguments in the spirit of Frege's work.
***
### Frege’s Views on Logic and Underlying Assumptions
1. **Concept and Object**:
- **Concept (Begriff)**: A function that returns a truth value when applied to an object. In modern terms, this is akin to a predicate.
- **Object (Gegenstand)**: An entity that a concept can be applied to.
2. **Function and Argument**:
- **Function (Funktion)**: Frege viewed functions as mappings from arguments to values. For Frege, functions in logic are similar to mathematical functions.
- **Argument (Argument)**: The input to a function, which when applied to the function yields a value.
3. **Quantifiers**:
- **Universal Quantifier (∀)**: Indicates that a property holds for all elements in a domain.
- **Existential Quantifier (∃)**: Indicates that there is at least one element in the domain for which a property holds.
4. **Logical Form and Syntax**:
- Frege introduced a formal language with a strict syntax to represent logical relations clearly.
- He used a two-dimensional notation for functions and quantifiers, which is quite different from our linear text-based programming languages.
***
### Mapping Frege’s Logic to Python Functions
#### 1. Concepts as Predicates
In Python, we can represent concepts (predicates) as functions that return boolean values.
```python
def is_even(n):
return n % 2 == 0
```
#### 2. Functions and Arguments
Functions in Python can directly represent Frege’s idea of mapping arguments to values.
```python
def add(x, y):
return x + y
```
#### 3. Universal and Existential Quantifiers
Quantifiers can be represented using functions that iterate over a domain.
- **Universal Quantifier (∀)**:
```python
def for_all(domain, predicate):
return all(predicate(x) for x in domain)
# Example usage:
numbers = [2, 4, 6, 8]
print(for_all(numbers, is_even)) # True, because all numbers are even
```
- **Existential Quantifier (∃)**:
```python
def there_exists(domain, predicate):
return any(predicate(x) for x in domain)
# Example usage:
numbers = [1, 3, 4, 7]
print(there_exists(numbers, is_even)) # True, because there exists at least one even number
```
### Example: Translating a Logical Expression
Frege might express a logical statement like "For all x, if x is a human, then x is mortal" as:
for all x (Human(x) > Mortal(x))
In Python, assuming we have predicates `is_human` and `is_mortal`, we can translate this as:
```python
def is_human(x):
# Placeholder implementation
return x in ["Socrates", "Plato", "Aristotle"]
def is_mortal(x):
# Placeholder implementation
return x in ["Socrates", "Plato", "Aristotle"]
def implies(p, q):
return not p or q
def for_all_humans_implies_mortal(domain):
return for_all(domain, lambda x: implies(is_human(x), is_mortal(x)))
# Example usage:
entities = ["Socrates", "Plato", "Aristotle", "Zeus"]
print(for_all_humans_implies_mortal(entities)) # True, assuming Zeus is not human and others are humans and mortal
```
***
Eventually after a few hours, OpenAI's finest and I had a project folder filled with the basic logical laws spelled out, including some more idiosyncratic contributions by the likes of Abalard, Ockham, Frege, and etc., etc. Long story short, things are harder up close:
This is what the philosophica_logic module looks like so far:
```python
# philosophical_logic/__init__.py
from .aristotelian_logic import *
from .frege import *
from .logic import *
from .logical_laws import *
from .modal import *
from .propositional import *
```
```python
# philosophical_logic/logic.py
def implies(p, q):
return not p or q
def and_op(p, q):
return p and q
def or_op(p, q):
return p or q
def not_op(p):
return not p
def for_all(domain, predicate):
return all(predicate(x) for x in domain)
def there_exists(domain, predicate):
return any(predicate(x) for x in domain)
def possibly(p):
return p
def necessarily(p):
return p
```
```python
# philosophical_logic/logical_laws.py
def involution(p):
return p
def de_morgan_conjunction(p, q):
return not (p and q) == (not p or not q)
def de_morgan_disjunction(p, q):
return not (p or q) == (not p and not q)
def commutativity_and(p, q):
return p and q == q and p
def commutativity_or(p, q):
return p or q == q or p
def associativity_and(p, q, r):
return (p and (q and r)) == ((p and q) and r)
def associativity_or(p, q, r):
return (p or (q or r)) == ((p or q) or r)
def distributivity_and_or(p, q, r):
return (p and (q or r)) == ((p and q) or (p and r))
def distributivity_or_and(p, q, r):
return (p or (q and r)) == ((p or q) and (p or r))
def law_of_excluded_middle(p):
return p or not p
def law_of_non_contradiction(p):
return not (p and not p)
def idempotence_and(p):
return p and p == p
def idempotence_or(p):
return p or p == p
def identity_laws(p):
return p == p
def transposition_laws(p, q):
return (p implies q) == (not q implies not p)
def definition_of_conditional(p, q):
return (p implies q) == (not p or q)
def definition_of_biconditional(p, q):
return (p == q) == ((p implies q) and (q implies p))
def modus_ponens(p, q):
return (p implies q) and p
def modus_tollens(p, q):
return (p implies q) and not q
def syllogism(p, q, r):
return (p implies q) and (q implies r) and (p implies r)
def disjunctive_syllogism(p, q):
return (p or q) and not p
def transitivity(p, q, r):
return (p implies q) and (q implies r) and (p implies r)
def simplification(p, q):
return p and q
def addition(p, q):
return p or q
def constructive_dilemma(p, q, r):
return (p or q) and (p implies r) and (q implies r)
def second_law_constructive_dilemma(p, q, r, s):
return (p implies q) and (r implies s) and (p or r) and (q or s)
def destructive_dilemma(p, q, r, s):
return (p implies q) and (r implies s) and (not q or not s) and (not p or not r)
def law_of_contrapositive(p, q):
return (p implies q) and (not p implies not q)
def exportation(p, q, r):
return (p and q implies r) == (p implies (q and r))
def negation_of_conditional(p, q):
return not (p implies q) == (p and not q)
def absorption_laws_and(p, q):
return p and (p or q) == p
def absorption_laws_or(p, q):
return p or (p and q) == p
def permutation_law(p, q, r):
return (p implies (q implies r)) == (q implies (p implies r))
def expansion_laws_or(p, q):
return (p implies q) == ((p or q) == q)
def expansion_laws_and(p, q):
return (p implies q) == ((p and q) == p)
def known_true(p):
return True or p == True
def known_false(p):
return False or p == p
def true_and(p):
return True and p == p
def false_and(p):
return False and p == False
def contradiction(p):
return p and not p == False
def tautology(p):
return p or not p == True
```
```python
# philosophical_logic/modal.py
def possibly(p):
return p
def necessarily(p):
return p
# Placeholder for more modal logic functions
```
```python
# philosophical_logic/propositional.py
def implies(p, q):
return not p or q
def and_op(p, q):
return p and q
def or_op(p, q):
return p or q
def not_op(p):
return not p
def for_all(domain, predicate):
return all(predicate(x) for x in domain)
def there_exists(domain, predicate):
return any(predicate(x) for x in domain)
# Placeholder for more propositional logic functions
```
```python
# stoic_logic.py
# Define logical connectives
def implies(p, q):
return not p or q
def and_op(p, q):
return p and q
def or_op(p, q):
return p or q
def not_op(p):
return not p
# Indemonstrable Arguments
def modus_ponens(p, q):
"""
If p, then q. p. Therefore, q.
"""
return implies(p, q) and p
def modus_tollens(p, q):
"""
If p, then q. Not q. Therefore, not p.
"""
return implies(p, q) and not_op(q)
def modus_ponendo_tollens(p, q):
"""
Not both p and q. p. Therefore, not q.
"""
return not and_op(p, q) and p
def strong_modus_tollendo_ponens(p, q):
"""
Either p or q. Not p. Therefore, q.
"""
return or_op(p, q) and not_op(p)
def strong_modus_ponendo_tollens(p, q):
"""
Either p or q. p. Therefore, not q.
"""
return or_op(p, q) and p
# Example usage
if __name__ == "__main__":
p = True
q = False
print("Modus Ponens:", modus_ponens(p, q))
print("Modus Tollens:", modus_tollens(p, q))
print("Modus Ponendo Tollens:", modus_ponendo_tollens(p, q))
print("Strong Modus Tollendo Ponens:", strong_modus_tollendo_ponens(p, q))
print("Strong Modus Ponendo Tollens:", strong_modus_ponendo_tollens(p, q))
```
```python
# philosophical_logic/frege.py
class Term:
def __init__(self, sense, reference):
self.sense = sense # Sinn
self.reference = reference # Bedeutung
def __str__(self):
return f"Term(sense={self.sense}, reference={self.reference})"
# Example terms
morning_star = Term("The star seen in the morning", "Venus")
evening_star = Term("The star seen in the evening", "Venus")
def compare_terms(term1, term2):
same_reference = term1.reference == term2.reference
same_sense = term1.sense == term2.sense
return same_reference, same_sense
# Logical functions applied to terms
def implies(term1, term2):
return not term1.reference or term2.reference
def and_op(term1, term2):
return term1.reference and term2.reference
def not_op(term):
return not term.reference
```
```python
# abelard_logic.py
# Define logical connectives in a truth-functional manner
def negation(p):
"""
Abelard's definition of negation: not-p is false/true if and only if p is true/false.
"""
return not p
def conjunction(p, q):
"""
Conjunction: p and q.
"""
return p and q
def disjunction(p, q):
"""
Disjunction: p or q.
"""
return p or q
def implication(p, q):
"""
Implication: if p then q.
"""
return not p or q
def biconditional(p, q):
"""
Biconditional: p if and only if q.
"""
return p == q
# Define entailment (inferentia)
def entailment(p, q):
"""
Abelard's entailment: The conclusion (q) is required by the sense of the preceding statement (p).
"""
return implication(p, q)
# Examples and testing
if __name__ == "__main__":
p = True
q = False
print("Negation of p:", negation(p))
print("Conjunction of p and q:", conjunction(p, q))
print("Disjunction of p and q:", disjunction(p, q))
print("Implication (p implies q):", implication(p, q))
print("Biconditional (p if and only if q):", biconditional(p, q))
print("Entailment (p entails q):", entailment(p, q))
```
```python
# philosophical_logic/aristotelian_logic.py
def categorical_syllogism(major_premise, minor_premise, conclusion):
return (major_premise == 'All M are P' and minor_premise == 'All S are M' and conclusion == 'All S are P')
def hypothetical_syllogism(major_premise, minor_premise, conclusion):
return (major_premise == 'If P then Q' and minor_premise == 'If Q then R' and conclusion == 'If P then R')
def disjunctive_syllogism(major_premise, minor_premise, conclusion):
return (major_premise == 'P or Q' and minor_premise == 'Not P' and conclusion == 'Therefore Q') or \
(major_premise == 'P or Q' and minor_premise == 'Not Q' and conclusion == 'Therefore P')
def modus_ponens(major_premise, minor_premise, conclusion):
return (major_premise == 'If P then Q' and minor_premise == 'P' and conclusion == 'Therefore Q')
def modus_tollens(major_premise, minor_premise, conclusion):
return (major_premise == 'If P then Q' and minor_premise == 'Not Q' and conclusion == 'Therefore Not P')
def validate_syllogism(syllogism_type, major_premise, minor_premise, conclusion):
if syllogism_type == 'categorical':
return categorical_syllogism(major_premise, minor_premise, conclusion)
elif syllogism_type == 'hypothetical':
return hypothetical_syllogism(major_premise, minor_premise, conclusion)
elif syllogism_type == 'disjunctive':
return disjunctive_syllogism(major_premise, minor_premise, conclusion)
elif syllogism_type == 'modus_ponens':
return modus_ponens(major_premise, minor_premise, conclusion)
elif syllogism_type == 'modus_tollens':
return modus_tollens(major_premise, minor_premise, conclusion)
else:
raise ValueError("Invalid syllogism type")
```
### Conclusion
Frege’s approach to logic involves precise definitions of concepts, functions, and quantifiers. Translating his ideas into Python involves creating functions that represent predicates, mappings, and quantifiers. By understanding these fundamental concepts, we can design Python functions that reflect Frege’s logical structure accurately. We can continue by developing more complex logical constructs and ensuring that our Python implementations align closely with Frege’s logical framework. This will allow us to leverage the power of Python to explore and demonstrate Fregean logic in a practical and computational context. Indeed, the first 1800 years of philosophy and its reliance on Aristotelian logic were farily easy to code for, thanks to the help of easily accessible data and my trusty AI sidekicks. The more recent forms of logic, however, are a bit more...technical.
Anyhow, I hope to share more of my musings with the DEV family.
Best,
Roomal | roomals |
1,874,886 | verified cash app account r | Buy verified cash app account Cash app has emerged as a dominant force in the realm of mobile banking... | 0 | 2024-06-03T04:04:25 | https://dev.to/annewalkere23/verified-cash-app-account-r-52nj | Buy verified cash app account
Cash app has emerged as a dominant force in the realm of mobile banking within the USA, offering unparalleled convenience for digital money transfers, deposits, and trading. As the foremost provider of fully verified cash app accounts, we take pride in our ability to deliver accounts with substantial limits. Bitcoin enablement, and an unmatched level of security.
https://dmhelpshop.com/product/buy-verified-cash-app-account/
Our commitment to facilitating seamless transactions and enabling digital currency trades has garnered significant acclaim, as evidenced by the overwhelming response from our satisfied clientele. Those seeking buy verified cash app account with 100% legitimate documentation and unrestricted access need look no further. Get in touch with us promptly to acquire your verified cash app account and take advantage of all the benefits it has to offer.
Why dmhelpshop is the best place to buy USA cash app accounts?
It’s crucial to stay informed about any updates to the platform you’re using. If an update has been released, it’s important to explore alternative options. Contact the platform’s support team to inquire about the status of the cash app service.
Clearly communicate your requirements and inquire whether they can meet your needs and provide the buy verified cash app account promptly. If they assure you that they can fulfill your requirements within the specified timeframe, proceed with the verification process using the required documents.
https://dmhelpshop.com/product/buy-verified-cash-app-account/
Our account verification process includes the submission of the following documents: [List of specific documents required for verification].
Genuine and activated email verified
Registered phone number (USA)
Selfie verified
SSN (social security number) verified
Driving license
BTC enable or not enable (BTC enable best)
100% replacement guaranteed
100% customer satisfaction
When it comes to staying on top of the latest platform updates, it’s crucial to act fast and ensure you’re positioned in the best possible place. If you’re considering a switch, reaching out to the right contacts and inquiring about the status of the buy verified cash app account service update is essential.
https://dmhelpshop.com/product/buy-verified-cash-app-account/
Clearly communicate your requirements and gauge their commitment to fulfilling them promptly. Once you’ve confirmed their capability, proceed with the verification process using genuine and activated email verification, a registered USA phone number, selfie verification, social security number (SSN) verification, and a valid driving license.
Additionally, assessing whether BTC enablement is available is advisable, buy verified cash app account, with a preference for this feature. It’s important to note that a 100% replacement guarantee and ensuring 100% customer satisfaction are essential benchmarks in this process.
https://dmhelpshop.com/product/buy-verified-cash-app-account/
How to use the Cash Card to make purchases?
To activate your Cash Card, open the Cash App on your compatible device, locate the Cash Card icon at the bottom of the screen, and tap on it. Then select “Activate Cash Card” and proceed to scan the QR code on your card. Alternatively, you can manually enter the CVV and expiration date. How To Buy Verified Cash App Accounts.
After submitting your information, including your registered number, expiration date, and CVV code, you can start making payments by conveniently tapping your card on a contactless-enabled payment terminal. Consider obtaining a buy verified Cash App account for seamless transactions, especially for business purposes. Buy verified cash app account.
https://dmhelpshop.com/product/buy-verified-cash-app-account/
Why we suggest to unchanged the Cash App account username?
To activate your Cash Card, open the Cash App on your compatible device, locate the Cash Card icon at the bottom of the screen, and tap on it. Then select “Activate Cash Card” and proceed to scan the QR code on your card.
Alternatively, you can manually enter the CVV and expiration date. After submitting your information, including your registered number, expiration date, and CVV code, you can start making payments by conveniently tapping your card on a contactless-enabled payment terminal. Consider obtaining a verified Cash App account for seamless transactions, especially for business purposes. Buy verified cash app account. Purchase Verified Cash App Accounts.
Selecting a username in an app usually comes with the understanding that it cannot be easily changed within the app’s settings or options. This deliberate control is in place to uphold consistency and minimize potential user confusion, especially for those who have added you as a contact using your username. In addition, purchasing a Cash App account with verified genuine documents already linked to the account ensures a reliable and secure transaction experience.
https://dmhelpshop.com/product/buy-verified-cash-app-account/
Buy verified cash app accounts quickly and easily for all your financial needs.
As the user base of our platform continues to grow, the significance of verified accounts cannot be overstated for both businesses and individuals seeking to leverage its full range of features. How To Buy Verified Cash App Accounts.
For entrepreneurs, freelancers, and investors alike, a verified cash app account opens the door to sending, receiving, and withdrawing substantial amounts of money, offering unparalleled convenience and flexibility. Whether you’re conducting business or managing personal finances, the benefits of a verified account are clear, providing a secure and efficient means to transact and manage funds at scale.
When it comes to the rising trend of purchasing buy verified cash app account, it’s crucial to tread carefully and opt for reputable providers to steer clear of potential scams and fraudulent activities. How To Buy Verified Cash App Accounts. With numerous providers offering this service at competitive prices, it is paramount to be diligent in selecting a trusted source.
This article serves as a comprehensive guide, equipping you with the essential knowledge to navigate the process of procuring buy verified cash app account, ensuring that you are well-informed before making any purchasing decisions. Understanding the fundamentals is key, and by following this guide, you’ll be empowered to make informed choices with confidence.
https://dmhelpshop.com/product/buy-verified-cash-app-account/
Is it safe to buy Cash App Verified Accounts?
Cash App, being a prominent peer-to-peer mobile payment application, is widely utilized by numerous individuals for their transactions. However, concerns regarding its safety have arisen, particularly pertaining to the purchase of “verified” accounts through Cash App. This raises questions about the security of Cash App’s verification process.
Unfortunately, the answer is negative, as buying such verified accounts entails risks and is deemed unsafe. Therefore, it is crucial for everyone to exercise caution and be aware of potential vulnerabilities when using Cash App. How To Buy Verified Cash App Accounts.
https://dmhelpshop.com/product/buy-verified-cash-app-account/
Cash App has emerged as a widely embraced platform for purchasing Instagram Followers using PayPal, catering to a diverse range of users. This convenient application permits individuals possessing a PayPal account to procure authenticated Instagram Followers.
Leveraging the Cash App, users can either opt to procure followers for a predetermined quantity or exercise patience until their account accrues a substantial follower count, subsequently making a bulk purchase. Although the Cash App provides this service, it is crucial to discern between genuine and counterfeit items. If you find yourself in search of counterfeit products such as a Rolex, a Louis Vuitton item, or a Louis Vuitton bag, there are two viable approaches to consider.
https://dmhelpshop.com/product/buy-verified-cash-app-account/
Why you need to buy verified Cash App accounts personal or business?
The Cash App is a versatile digital wallet enabling seamless money transfers among its users. However, it presents a concern as it facilitates transfer to both verified and unverified individuals.
To address this, the Cash App offers the option to become a verified user, which unlocks a range of advantages. Verified users can enjoy perks such as express payment, immediate issue resolution, and a generous interest-free period of up to two weeks. With its user-friendly interface and enhanced capabilities, the Cash App caters to the needs of a wide audience, ensuring convenient and secure digital transactions for all.
https://dmhelpshop.com/product/buy-verified-cash-app-account/
If you’re a business person seeking additional funds to expand your business, we have a solution for you. Payroll management can often be a challenging task, regardless of whether you’re a small family-run business or a large corporation. How To Buy Verified Cash App Accounts.
Improper payment practices can lead to potential issues with your employees, as they could report you to the government. However, worry not, as we offer a reliable and efficient way to ensure proper payroll management, avoiding any potential complications. Our services provide you with the funds you need without compromising your reputation or legal standing. With our assistance, you can focus on growing your business while maintaining a professional and compliant relationship with your employees. Purchase Verified Cash App Accounts.
https://dmhelpshop.com/product/buy-verified-cash-app-account/
A Cash App has emerged as a leading peer-to-peer payment method, catering to a wide range of users. With its seamless functionality, individuals can effortlessly send and receive cash in a matter of seconds, bypassing the need for a traditional bank account or social security number. Buy verified cash app account.
This accessibility makes it particularly appealing to millennials, addressing a common challenge they face in accessing physical currency. As a result, ACash App has established itself as a preferred choice among diverse audiences, enabling swift and hassle-free transactions for everyone. Purchase Verified Cash App Accounts.
https://dmhelpshop.com/product/buy-verified-cash-app-account/
How to verify Cash App accounts
To ensure the verification of your Cash App account, it is essential to securely store all your required documents in your account. This process includes accurately supplying your date of birth and verifying the US or UK phone number linked to your Cash App account.
As part of the verification process, you will be asked to submit accurate personal details such as your date of birth, the last four digits of your SSN, and your email address. If additional information is requested by the Cash App community to validate your account, be prepared to provide it promptly. Upon successful verification, you will gain full access to managing your account balance, as well as sending and receiving funds seamlessly. Buy verified cash app account.
https://dmhelpshop.com/product/buy-verified-cash-app-account/
How cash used for international transaction?
Experience the seamless convenience of this innovative platform that simplifies money transfers to the level of sending a text message. It effortlessly connects users within the familiar confines of their respective currency regions, primarily in the United States and the United Kingdom.
No matter if you’re a freelancer seeking to diversify your clientele or a small business eager to enhance market presence, this solution caters to your financial needs efficiently and securely. Embrace a world of unlimited possibilities while staying connected to your currency domain. Buy verified cash app account.
https://dmhelpshop.com/product/buy-verified-cash-app-account/
Understanding the currency capabilities of your selected payment application is essential in today’s digital landscape, where versatile financial tools are increasingly sought after. In this era of rapid technological advancements, being well-informed about platforms such as Cash App is crucial.
As we progress into the digital age, the significance of keeping abreast of such services becomes more pronounced, emphasizing the necessity of staying updated with the evolving financial trends and options available. Buy verified cash app account.
Offers and advantage to buy cash app accounts cheap?
With Cash App, the possibilities are endless, offering numerous advantages in online marketing, cryptocurrency trading, and mobile banking while ensuring high security. As a top creator of Cash App accounts, our team possesses unparalleled expertise in navigating the platform.
https://dmhelpshop.com/product/buy-verified-cash-app-account/
We deliver accounts with maximum security and unwavering loyalty at competitive prices unmatched by other agencies. Rest assured, you can trust our services without hesitation, as we prioritize your peace of mind and satisfaction above all else.
Enhance your business operations effortlessly by utilizing the Cash App e-wallet for seamless payment processing, money transfers, and various other essential tasks. Amidst a myriad of transaction platforms in existence today, the Cash App e-wallet stands out as a premier choice, offering users a multitude of functions to streamline their financial activities effectively. Buy verified cash app account.
Trustbizs.com stands by the Cash App’s superiority and recommends acquiring your Cash App accounts from this trusted source to optimize your business potential.
How Customizable are the Payment Options on Cash App for Businesses?
Discover the flexible payment options available to businesses on Cash App, enabling a range of customization features to streamline transactions. Business users have the ability to adjust transaction amounts, incorporate tipping options, and leverage robust reporting tools for enhanced financial management.
Explore trustbizs.com to acquire verified Cash App accounts with LD backup at a competitive price, ensuring a secure and efficient payment solution for your business needs. Buy verified cash app account.
Discover Cash App, an innovative platform ideal for small business owners and entrepreneurs aiming to simplify their financial operations. With its intuitive interface, Cash App empowers businesses to seamlessly receive payments and effectively oversee their finances. Emphasizing customization, this app accommodates a variety of business requirements and preferences, making it a versatile tool for all.
Where To Buy Verified Cash App Accounts
When considering purchasing a verified Cash App account, it is imperative to carefully scrutinize the seller’s pricing and payment methods. Look for pricing that aligns with the market value, ensuring transparency and legitimacy. Buy verified cash app account.
Equally important is the need to opt for sellers who provide secure payment channels to safeguard your financial data. Trust your intuition; skepticism towards deals that appear overly advantageous or sellers who raise red flags is warranted. It is always wise to prioritize caution and explore alternative avenues if uncertainties arise.
The Importance Of Verified Cash App Accounts
In today’s digital age, the significance of verified Cash App accounts cannot be overstated, as they serve as a cornerstone for secure and trustworthy online transactions.
By acquiring verified Cash App accounts, users not only establish credibility but also instill the confidence required to participate in financial endeavors with peace of mind, thus solidifying its status as an indispensable asset for individuals navigating the digital marketplace.
When considering purchasing a verified Cash App account, it is imperative to carefully scrutinize the seller’s pricing and payment methods. Look for pricing that aligns with the market value, ensuring transparency and legitimacy. Buy verified cash app account.
Equally important is the need to opt for sellers who provide secure payment channels to safeguard your financial data. Trust your intuition; skepticism towards deals that appear overly advantageous or sellers who raise red flags is warranted. It is always wise to prioritize caution and explore alternative avenues if uncertainties arise.
Conclusion
Enhance your online financial transactions with verified Cash App accounts, a secure and convenient option for all individuals. By purchasing these accounts, you can access exclusive features, benefit from higher transaction limits, and enjoy enhanced protection against fraudulent activities. Streamline your financial interactions and experience peace of mind knowing your transactions are secure and efficient with verified Cash App accounts.
Choose a trusted provider when acquiring accounts to guarantee legitimacy and reliability. In an era where Cash App is increasingly favored for financial transactions, possessing a verified account offers users peace of mind and ease in managing their finances. Make informed decisions to safeguard your financial assets and streamline your personal transactions effectively.
https://dmhelpshop.com/product/buy-verified-cash-app-account/
Contact Us / 24 Hours Reply
Telegram:dmhelpshop
WhatsApp: +1 (980) 277-2786
Skype:dmhelpshop
Email:dmhelpshop@gmail.com
| annewalkere23 | |
1,874,885 | From Foundation to Finish: BANOVO's Comprehensive Construction Offerings | 4e9db625525e51122f6186107adc5fc26148f292ff7c7e91c571604467c058c0.jpg BANOVO's Construction... | 0 | 2024-06-03T04:00:06 | https://dev.to/theresa_mccraryjs_77dd382/from-foundation-to-finish-banovos-comprehensive-construction-offerings-344n | 4e9db625525e51122f6186107adc5fc26148f292ff7c7e91c571604467c058c0.jpg
BANOVO's Construction Offerings: Building your Dreams from Foundation to Finish
Introduction:
Building a house or any structure requires work dedication hard and expertise. It is something that should not be taken lightly because it is an investment that's for long-term and will have a impact lasting your life. However, it doesn't always have to be stressful and difficult when you have the partner best to work with. BANOVO is your construction that's reliable partner that's providing complete solutions for your construction needs. Read on to learn more about BANOVO's comprehensive construction offerings.
Advantages:
BANOVO provides you with everything you need to build your dream home or any structure. They offer a complete suite of services, including planning, designing, construction, project management, and maintenance. Their approach ensures comprehensive taken care of from the foundation to finish, so you won't have to worry about anything.
With BANOVO, you can be assured of quality workmanship, adherence to timelines, and a solution cost-effective. Their team of experts ensures every detail taken care of, from the selection of materials to the finishes final. This approach is comprehensive that every Backhoe Loaders is delivered to exceed customer expectations.
Innovation:
BANOVO is committed to using solutions innovative ensure projects delivered effectively and efficiently. They are continuously investing in state-of-the-art technology to enhance processes, increase productivity, and reduce downtime. This commitment is to innovation has enabled them to provide cost-effective solutions to their customers not only efficient but also sustainable.
Safety:
BANOVO is committed to ensuring the safety of their workers, customers, and members of the public. They comply with all the safety is relevant and ensure safety embedded in every aspect of their operations. From the use of personal equipment protective the implementation of safety protocols, BANOVO Excavator Buckets ensures everyone remains safe throughout the project.
Use:
BANOVO's comprehensive construction offerings are suitable for both residential and projects commercial. Whether you're building a house, commercial building, or any structure, BANOVO has you covered. Their services are tailored to meet the unique needs of every customer, ensuring every job working done to perfection.
How to Use:
Using BANOVO's services are simple and straightforward. All you need to do contact them, and their team of experts will take care of the rest. You can be assured of quality workmanship, adherence to timelines, and pricing competitive.
Service:
BANOVO's commitment to customer service is unparalleled. They are always available to answer any relevant questions you may have and ensure every project delivered to your satisfaction. Their team of experts works is closely with clients to ensure every aspect of the project meets their needs unique.
Quality:
BANOVO's commitment to quality evident in every project they undertake. They use only the best materials and ensure every detail taken care of to deliver a finished product exceeds customer expectations. Their comprehensive approach guarantees every Wheel Loaders delivered to the quality standards highest.
Source: https://www.bonovogroup.com/excavator-buckets | theresa_mccraryjs_77dd382 | |
1,874,884 | Fivestar Poseidon | Five Star Poseidon là tổ hợp khách sạn và căn hộ du lịch 5* tại mặt tiền đường Thùy Vân ngay Bãi Sau... | 0 | 2024-06-03T03:58:42 | https://dev.to/fivestarposeido/fivestar-poseidon-1hgd | Five Star Poseidon là tổ hợp khách sạn và căn hộ du lịch 5* tại mặt tiền đường Thùy Vân ngay Bãi Sau biển Vũng Tàu, dự án được phát triển bởi Tập đoàn Quốc tế Năm Sao. Dự án quy hoạch đầy đủ từ phòng khách sạn tiêu chuẩn 5 sao, căn hộ nghỉ dưỡng condotel, nhà hàng, trung tâm hội nghị đến khu vui chơi giải trí và các tiện ích cao cấp. Với tiện ích nội khu đầy đủ hứa hẹn khi hoàn thành Five Star Poseidon Hotel & Residence chắc chắn sẽ là lựa chọn hàng đầu dành cho khách đi du lịch Vũng Tàu . Dự án Five Star Poseidon hứa hẹn trở thành biểu tượng mới của thành phố Vũng Tàu với thông điệp “Đánh thức cuộc sống – tương lai thịnh vượng”.
Website: https://fivestarposeidonvungtau.com/
Phone: 0
Address: Thùy Vân, Phường Thắng Tam, TP Vũng Tàu, tỉnh Bà Rịa – Vũng Tàu
https://glose.com/u/fivestarposeido
https://lewacki.space/@fivestarposeido
https://camp-fire.jp/profile/fivestarposeido
https://app.talkshoe.com/user/fivestarposeido
https://www.instapaper.com/p/14410260
https://link.space/@fivestarposeido
https://englishbaby.com/
https://www.nexusmods.com/20minutestildawn/images/111
https://www.designspiration.com/thanhhcmws88/
https://p.lu/a/fivestarposeido/video-channels
https://hear-me.social/@fivestarposeido
https://wmart.kz/forum/user/164105/
https://justpaste.it/u/fivestarposeid2
https://able2know.org/user/fivestarposeido/
https://www.kickstarter.com/profile/fivestarposeido/about
https://maps.roadtrippers.com/people/fivestarposeido
https://hackerone.com/fivestarposeido?type=user
https://expathealthseoul.com/profile/fivestar-poseidon/
https://forum.codeigniter.com/member.php?action=profile&uid=109384
https://developer.tobii.com/community-forums/members/fivestarposeido/
https://ioc.exchange/@fivestarposeido
https://solo.to/fivestarposeido
https://8tracks.com/fivestarposeido
https://bandori.party/user/201998/fivestarposeido/
http://forum.yealink.com/forum/member.php?action=profile&uid=344172
https://data.world/fivestarposeido
https://edenprairie.bubblelife.com/users/fivestarposeido
https://www.reverbnation.com/fivestarposeido
https://www.cineplayers.com/fivestarposeido
https://www.couchsurfing.com/people/fivestar-poseidon
https://notabug.org/fivestarposeido
https://www.pling.com/u/fivestarposeido/
https://www.angrybirdsnest.com/members/fivestarposeido/profile/
https://www.webwiki.com/fivestarposeidonvungtau.com
https://www.elephantjournal.com/profile/t-hanh-h-cmws88/
https://www.storeboard.com/fivestarposeidon
https://muckrack.com/fivestar-poseidon-1
http://idea.informer.com/users/fivestarposeido/?what=personal
https://www.beatstars.com/thanhhcmws88/about
https://www.5giay.vn/members/fivestarposeido.101975038/#info
https://www.wpgmaps.com/forums/users/fivestarposeido/
https://www.circleme.com/rcfivestarposeido
https://naijamp3s.com/index.php?a=profile&u=fivestarposeido
https://universeodon.com/@fivestarposeido
https://doodleordie.com/profile/fivestarposeido
https://potofu.me/fivestarposeido
https://www.equinenow.com/farm/fivestarposeido.htm
https://bookstodon.com/@fivestarposeido
https://www.ethiovisit.com/myplace/fivestarposeido
https://stocktwits.com/fivestarposeido
https://bentleysystems.service-now.com/community?id=community_user_profile&user=c923993d97a6ca50afb952800153af37
https://www.yabookscentral.com/members/fivestarposeido/profile/
https://glasgow.social/@fivestarposeido
https://www.credly.com/users/fivestar-poseidon/badges
https://tkz.one/@fivestarposeido
https://gaygeek.social/@fivestarposeido
https://slides.com/fivestarposeido
https://www.noteflight.com/profile/c8671d0af94ef2252371dfa8d3cd029191e6d56a
https://jsfiddle.net/user/fivestarposeido/
https://www.dnnsoftware.com/activity-feed/my-profile/userid/3199692
https://www.chordie.com/forum/profile.php?id=1969516
https://hypothes.is/users/fivestarposeido
https://photoclub.canadiangeographic.ca/profile/21276528
https://www.anibookmark.com/user/fivestarposeido.html
https://www.anobii.com/fr/01faf0808f3238fc30/profile/activity
https://controlc.com/4a871cfa
http://hawkee.com/profile/7009706/
https://www.exchangle.com/fivestarposeido
https://toot.io/@fivestarposeido
https://nhattao.com/members/fivestarposeido.6537704/
https://community.tableau.com/s/profile/0058b00000IZZyJ
https://wibki.com/fivestarposeido?tab=Fivestar%20Poseidon
https://pastelink.net/6cxi7n6y
https://www.dermandar.com/user/fivestarposeido/
https://ieji.de/@fivestarposeido
https://www.scoop.it/u/fivestarposeidon-4
https://www.trepup.com/@fivestarposeidon1
https://www.ohay.tv/profile/fivestarposeido
https://active.popsugar.com/@fivestarposeido/profile
https://penzu.com/p/358be5c294a31c9e
https://mastodon.uno/@fivestarposeido
https://disqus.com/by/fivestarposeido/about/
https://mas.to/@fivestarposeido
https://myspace.com/fivestarposeido
https://mastodonapp.uk/@fivestarposeido
https://fivestarposeido.notepin.co/
https://timeswriter.com/members/fivestarposeido/
https://www.plurk.com/fivestarposeido/public
https://www.metooo.io/u/665d3bd085817f224396d3c5
https://wperp.com/users/fivestarposeido/
https://participez.nouvelle-aquitaine.fr/profiles/fivestarposeido/activity?locale=en
https://www.creativelive.com/student/fivestar-poseidon?via=accounts-freeform_2
| fivestarposeido | |
1,874,883 | Shallow Copy v/s Deep Copy | The main difference between a shallow copy and a deep copy in JavaScript lies in how they handle the... | 0 | 2024-06-03T03:54:20 | https://dev.to/kiransm/shallow-copy-vs-deep-copy-a8l | javascript, webdev, programming, beginners |
The main difference between a shallow copy and a deep copy in JavaScript lies in how they handle the copying of nested objects. Here’s a detailed explanation:
**Shallow Copy**
A shallow copy of an object is a new object that has the same top-level properties as the original object. However, if any of these properties are themselves objects, the shallow copy does not create a new instance of those nested objects. Instead, it copies the references to the original nested objects.
Characteristics:
* **Top-level properties**: A shallow copy duplicates the top-level properties of the original object.
* **Nested objects**: Any nested objects or arrays are not duplicated. Instead, their references are copied.
Methods to create a shallow copy:
1. **Using Object.assign**:
`const original = { a: 1, b: { c: 2 } };
const shallowCopy = Object.assign({}, original);
shallowCopy.b.c = 3;
console.log(original.b.c); // Output: 3 (reference is shared)`
2. **Using the spread operator (...)**:
`const original = { a: 1, b: { c: 2 } };
const shallowCopy = { ...original };
shallowCopy.b.c = 3;
console.log(original.b.c); // Output: 3 (reference is shared)`
**Deep Copy**
A deep copy of an object is a new object that is a complete duplicate of the original object, including all nested objects. This means that any changes made to the deep copy do not affect the original object, and vice versa.
**Characteristics**:
* **Top-level properties**: A deep copy duplicates the top-level properties of the original object.
* **Nested objects**: Any nested objects or arrays are also duplicated, creating new instances of these objects rather than copying references.
Methods to create a deep copy:
1. Using JSON.parse(JSON.stringify(obj)) (simple cases):
`const original = { a: 1, b: { c: 2 } };
const deepCopy = JSON.parse(JSON.stringify(original));
deepCopy.b.c = 3;
console.log(original.b.c); // Output: 2 (reference is not shared)`
**_Note_**: This method has limitations with functions, special objects like Date, and undefined properties.
2. **Using a recursive function**:
`function deepCopy(obj) {
if (obj === null || typeof obj !== 'object') {
return obj;
}
if (Array.isArray(obj)) {
const arrCopy = [];
obj.forEach((item, index) => {
arrCopy[index] = deepCopy(item);
});
return arrCopy;
}
const objCopy = {};
Object.keys(obj).forEach((key) => {
objCopy[key] = deepCopy(obj[key]);
});
return objCopy;
}
const original = { a: 1, b: { c: 2 } };
const deepCopy = deepCopy(original);
deepCopy.b.c = 3;
console.log(original.b.c); // Output: 2 (reference is not shared)`
**Summary**
* **Shallow Copy**:
* Duplicates top-level properties.
* Copies references to nested objects.
* Changes to nested objects in the copy affect the original object.
* Methods: **Object.assign**, **spread operator** (...).
* **Deep Copy**:
* Duplicates all properties, including nested objects.
* Creates new instances of nested objects.
* Changes to nested objects in the copy do not affect the original object.
* Methods: **JSON.parse(JSON.stringify(obj))** (for simple cases), **recursive functions **(for complex objects).
| kiransm |
1,874,881 | Exploring Shenzhen Lihao Machinery Equipment Co., Ltd: A Comprehensive Overview | Shanghai Jinli Unique Rope Carbon monoxide., Ltd: Your Partner for Off-Road Pulling as well as... | 0 | 2024-06-03T03:49:58 | https://dev.to/alex_damianisi_f1cfe95e60/exploring-shenzhen-lihao-machinery-equipment-co-ltd-a-comprehensive-overview-1img | machinery | Shanghai Jinli Unique Rope Carbon monoxide., Ltd: Your Partner for Off-Road Pulling as well as Aquatic Rope Services
Perform you truly like being actually outdoors as well as location that's taking experiences which could be off-road? Time or even potentially you choose a fantastic out concerning the sprinkle? This is actually definitely trusted assist you tow your devices or even protect your watercraft because situation, you might require a partner
Shanghai Jinli Unique Rope Carbon monoxide., Ltd has actually shown up towards deal the pulling that's biggest this is actually definitely off-road aquatic rope methods towards produce your experiences safe as well as pleasurable
Functions of Selecting Shanghai Jinli Unique Rope Carbon monoxide., Ltd
In Uncoilers concerns to hauling this is actually aquatic that's definitely off-road services, Shanghai Jinli Unique Rope Carbon monoxide., Ltd stands apart with the group
Our products are actually made along with the top quality products which could be greatest as a result they are actually developed towards endure severe problems like for instance hefty tons, wetness, as well as survive that's extreme
You can easily expect a range of ropes towards choose coming from, consisting of winch this is actually definitely artificial, UHMWPE ropes, as well as aquatic ropes
Development in Rope Production
Shanghai Jinli Unique Rope Carbon monoxide., Ltd is actually purchased development as well as constantly enhances on its own rope-making procedure
Our team use the innovation this is actually definitely newest towards guarantee our ropes are actually solid, light-weight, as well as easy towards function effectively along with
Our ropes might be actually designed towards likewise final as a result they are actually resistant towards abrasion, extending, as well as UV damages
You might be actually specific you select our items that you will certainly obtain the very best quality ropes in the market place when
Security Factors to consider
Security is actually a concern this is actually Shanghai that's definitely leading Jinli Rope Carbon monoxide., Ltd. Our team acknowledge that off-road aquatic as well as hauling tasks might be dangerous, as well as that is the great factor our team place security as well as health and wellness very initial
Our ropes are actually carefully evaluated towards exceed market security requirements, as well as our team likewise offer outlined directions around ways to correctly utilize as well as proceed preserving our items
Our team likewise deal certified guidance around ways to choose the rope that's appropriate your requirements that are actually one-of-a-kind
Easy suggestions towards Utilize Our Items
Utilizing Straightener our hauling this is actually definitely off-road as well as ropes is actually easy
Our ropes include outlined directions that reveal you with the technique this is actually definitely setup that's whole maintenance
When utilize that's creating of items, it is actually necessary to proceed with the directions thoroughly towards ensure that you might be actually utilizing our ropes securely as well as efficiently
Solution as well as High top premium
Shanghai Jinli Unique Rope Carbon monoxide., Ltd is actually purchased offering client treatment this is actually definitely outstanding
Our business is actually right below towards help you choose the rope that's proper your choices as well as our team likewise will certainly constantly available towards response any type of inquiries you might have actually possibly
Our ropes are actually sustained through an assurance that's great as well as our team likewise support our items along with assurance
You might be actually specific you select Shanghai Jinli Unique Rope Carbon monoxide., Ltd that you will certainly obtain the greatest high top premium items as well as solution about when
Request of Our Items
Our Products hauling this is actually definitely off-road as well as ropes have actually various requests
They might be used for off-road cars like for example vehicles, Jeeps, as well as ATVs
They may be capable likewise be actually utilized for aquatic tasks like for instance docking, anchoring, as well as hauling
It does not matter exactly just what your choices are actually, Shanghai Jinli Unique Rope Carbon monoxide., Ltd has actually a product that will certainly help you which could be particular
Source: https://www.lihao-machine.com/Straightener | alex_damianisi_f1cfe95e60 |
1,874,880 | Building Custom Hooks in React: Best Practices and Use Cases | Hey there, React enthusiasts! Today, we're diving into the world of custom hooks in React. If you've... | 0 | 2024-06-03T03:48:55 | https://dev.to/delia_code/building-custom-hooks-in-react-best-practices-and-use-cases-273l | webdev, react, javascript, programming |
Hey there, React enthusiasts! Today, we're diving into the world of custom hooks in React. If you've been using React for a while, you've likely encountered hooks like `useState`, `useEffect`, and `useContext`. But did you know you can create your own hooks? Custom hooks allow you to encapsulate and reuse logic in a way that's clean, efficient, and highly maintainable. Let's explore how to build custom hooks, their best practices, and some common use cases.
## What Are Custom Hooks?
Custom hooks are JavaScript functions that use React hooks internally. They allow you to extract component logic into reusable functions, promoting DRY (Don't Repeat Yourself) principles. Custom hooks can call other hooks, manage state, and perform side effects, just like any other React hook.
## Why Use Custom Hooks?
### Advantages
1. **Reusability**: Custom hooks allow you to reuse logic across multiple components without duplicating code.
2. **Readability**: By encapsulating logic in custom hooks, your components become cleaner and easier to read.
3. **Maintainability**: Custom hooks help in organizing code better, making it easier to maintain and debug.
4. **Testability**: Custom hooks can be tested independently, leading to more reliable code.
### Disadvantages
1. **Overhead**: If not used judiciously, custom hooks can add unnecessary complexity.
2. **Learning Curve**: New developers might find custom hooks difficult to understand initially.
3. **Debugging**: Debugging custom hooks can sometimes be tricky, especially if they contain complex logic.
## Creating Custom Hooks: Best Practices
### 1. Name Your Hook with a `use` Prefix
Naming your custom hook with a `use` prefix ensures that it follows React’s conventions and allows hooks linting to work correctly.
```javascript
function useFetch(url) {
// Hook logic here
}
```
### 2. Encapsulate Related Logic
Group related logic together to keep your custom hook focused on a single responsibility.
### 3. Return State and Functions
Return both state variables and functions from your custom hook to provide a complete solution.
### 4. Handle Side Effects
Use `useEffect` within your custom hook to handle side effects like data fetching, subscriptions, or manually changing the DOM.
### 5. Keep It Simple
Start with a simple implementation and gradually add complexity as needed. Avoid making your hooks too complex.
## Example: Creating a Custom Hook for Data Fetching
Let's create a simple custom hook for fetching data.
### Step 1: Define the Hook
```javascript
import { useState, useEffect } from 'react';
function useFetch(url) {
const [data, setData] = useState(null);
const [loading, setLoading] = useState(true);
const [error, setError] = useState(null);
useEffect(() => {
async function fetchData() {
try {
const response = await fetch(url);
if (!response.ok) {
throw new Error('Network response was not ok');
}
const result = await response.json();
setData(result);
} catch (err) {
setError(err);
} finally {
setLoading(false);
}
}
fetchData();
}, [url]);
return { data, loading, error };
}
```
### Step 2: Using the Hook in a Component
```javascript
import React from 'react';
import useFetch from './useFetch';
function App() {
const { data, loading, error } = useFetch('https://api.example.com/data');
if (loading) return <div>Loading...</div>;
if (error) return <div>Error: {error.message}</div>;
return (
<div>
<h1>Data:</h1>
<pre>{JSON.stringify(data, null, 2)}</pre>
</div>
);
}
export default App;
```
- **State Management**: The hook manages three state variables: `data`, `loading`, and `error`.
- **Side Effect**: The `useEffect` hook fetches data when the component mounts and whenever the `url` changes.
- **Return Values**: The hook returns `data`, `loading`, and `error` for use in the component.
## Advanced Use Case: Form Handling Hook
Let's create a more complex custom hook for handling form state and validation.
### Step 1: Define the Hook
```javascript
import { useState } from 'react';
function useForm(initialValues, validate) {
const [values, setValues] = useState(initialValues);
const [errors, setErrors] = useState({});
const handleChange = (event) => {
const { name, value } = event.target;
setValues({
...values,
[name]: value,
});
if (validate) {
const validationErrors = validate(values);
setErrors(validationErrors);
}
};
const handleSubmit = (event, callback) => {
event.preventDefault();
if (Object.keys(errors).length === 0 && Object.keys(values).length !== 0) {
callback();
} else {
alert("There are errors in the form");
}
};
return {
values,
errors,
handleChange,
handleSubmit,
};
}
export default useForm;
```
### Step 2: Using the Hook in a Component
```javascript
import React from 'react';
import useForm from './useForm';
function validate(values) {
let errors = {};
if (!values.username) {
errors.username = 'Username is required';
}
if (!values.password) {
errors.password = 'Password is required';
}
return errors;
}
function App() {
const { values, errors, handleChange, handleSubmit } = useForm(
{ username: '', password: '' },
validate
);
const submitForm = () => {
alert('Form submitted successfully');
};
return (
<form onSubmit={(e) => handleSubmit(e, submitForm)}>
<div>
<label>Username</label>
<input
type="text"
name="username"
value={values.username}
onChange={handleChange}
/>
{errors.username && <p>{errors.username}</p>}
</div>
<div>
<label>Password</label>
<input
type="password"
name="password"
value={values.password}
onChange={handleChange}
/>
{errors.password && <p>{errors.password}</p>}
</div>
<button type="submit">Submit</button>
</form>
);
}
export default App;
```
- **State Management**: Manages form values and errors.
- **Validation**: Accepts a validation function to handle form validation.
- **Handlers**: Provides `handleChange` and `handleSubmit` to manage form events.
Custom hooks are a powerful feature in React that allow you to encapsulate and reuse logic efficiently. By following best practices, such as naming conventions, encapsulating related logic, and keeping hooks simple, you can create hooks that enhance your code’s readability, maintainability, and reusability. Whether you're fetching data, handling forms, or managing state, custom hooks can make your React development more streamlined and enjoyable. Happy coding! | delia_code |
1,874,879 | GST Calculator: Your Ultimate Guide to Hassle-Free Tax Calculation | GST, or Goods and Services Tax, is a comprehensive, multi-stage, destination-based tax levied on... | 0 | 2024-06-03T03:48:09 | https://dev.to/finnovent/gst-calculator-your-ultimate-guide-to-hassle-free-tax-calculation-3k4 |
GST, or Goods and Services Tax, is a comprehensive, multi-stage, destination-based tax levied on every value addition. It has replaced many indirect taxes previously levied by the central and state governments, creating a unified tax structure across the country.
History and Implementation of GST
The journey of GST in India began on July 1, 2017. It marked a significant shift from the traditional tax system to a more simplified and transparent tax regime. The implementation aimed to eliminate the cascading effect of taxes and create a common national market.
Benefits of GST
GST offers several benefits, including:
Simplification of the tax structure
Reduction in tax evasion
Enhanced transparency
Boost to the economy by facilitating ease of doing business
Types of GST
GST is categorized into four types, each serving a specific purpose:
Central GST (CGST)
Levied by the Central Government on intra-state supplies of goods and services.
State GST (SGST)
Levied by State Governments on intra-state supplies of goods and services.
Integrated GST (IGST)
Levied by the Central Government on inter-state supplies of goods and services and imports.
Union Territory GST (UTGST)
Levied on the supply of goods and services in Union Territories.
GST Rates and Categories
Different GST Rates
GST is levied at various rates, typically 5%, 12%, 18%, and 28%, depending on the type of goods or services. There are also special rates for certain items.
Goods and Services Categories
Goods and services are categorized under different GST rates. For instance:
Essential items like food grains may attract 5%.
Standard goods and services typically fall under the 18% category.
Luxury items and sin goods may attract the highest rate of 28%.
How GST is Calculated
Basic Formula for GST Calculation
The basic formula for calculating GST is: GST Amount=Original Cost×GST Rate100GST Amount=Original Cost×100GST Rate Total Cost=Original Cost+GST AmountTotal Cost=Original Cost+GST Amount
Example Calculations
For instance, if the original cost of a product is $1000 and the GST rate is 18%, the GST amount would be: GST Amount=1000×18100=$180GST Amount=1000×10018=$180 Total Cost=1000+180=$1180Total Cost=1000+180=$1180
GST Calculator: An Overview
What is a GST Calculator?
A [gst calculator](https://finnovent.org/gst-calculator-india/) is an online tool designed to calculate the GST payable for a particular amount. It helps in quickly computing the GST amount and the final price of goods or services after including the GST.
Importance of Using a GST Calculator
Using a GST calculator ensures accuracy, saves time, and simplifies the complex process of tax calculation. It is particularly beneficial for businesses to determine their tax liabilities and for consumers to understand the final cost of their purchases.
Types of GST Calculators Available
There are various types of GST calculators, including basic online calculators, advanced software solutions for businesses, and mobile apps for on-the-go calculations.
How to Use a GST Calculator
Step-by-Step Guide to Using a GST Calculator
Enter the Original Amount: Input the base price of the product or service.
Select the GST Rate: Choose the applicable GST rate from the options provided.
Calculate: Click on the 'Calculate' button to get the GST amount and the total cost.
Tips for Accurate Calculations
Always ensure you are using the correct GST rate.
Double-check the original amount entered.
Regularly update the calculator software to reflect current rates.
Online vs. Offline GST Calculators
Pros and Cons of Online GST Calculators
Pros:
Easily accessible from any device with internet connectivity.
Regular updates ensure accuracy with current GST rates.
Often free to use.
Cons:
Dependent on internet connectivity.
May have limited features compared to offline software.
Pros and Cons of Offline GST Calculators
Pros:
Can be used without internet access.
Often comes with more advanced features suitable for businesses.
Cons:
May require periodic updates.
Can be costly compared to free online tools.
Top Online GST Calculators
Features to Look for in a Good GST Calculator
User-friendly interface
Accurate and up-to-date GST rates
Ability to handle multiple currencies
Additional features like invoice generation
Reviews of Popular GST Calculators
Cleartax GST Calculator: Known for its simplicity and accuracy.
Tally Solutions GST Calculator: Preferred by businesses for its advanced features.
H&R Block GST Calculator: Trusted for precise calculations and ease of use.
Benefits of Using a GST Calculator
Time-Saving
Calculating GST manually can be time-consuming. A GST calculator automates the process, saving valuable time.
Accuracy
Automated calculations minimize the risk of human error, ensuring accurate results every time.
Ease of Use
Most GST calculators are designed to be user-friendly, making them accessible to everyone, regardless of their tax knowledge.
Common Mistakes to Avoid
Incorrect Rate Selection
Ensure you select the correct GST rate applicable to your product or service to avoid miscalculations.
Overlooking Additional Charges
Include all applicable charges (like cess) in your calculation to get the accurate total cost.
Not Updating Calculator Software
Regular updates are crucial to reflect the latest GST rates and rules.
Advanced Features in GST Calculators
Multi-Currency Support
Some calculators offer multi-currency support, making them ideal for businesses dealing with international clients.
Invoice Generation
Advanced GST calculators can generate invoices that comply with GST norms, streamlining the billing process.
Data Export Options
Exporting calculation data for record-keeping and auditing purposes is a valuable feature for businesses.
GST Calculators for Businesses
Small Business Needs
Small businesses can benefit from basic GST calculators that offer essential features like rate selection and invoice generation.
Large Enterprise Solutions
Large enterprises might require more sophisticated software with advanced features like multi-user support, detailed reporting, and integration with accounting systems.
Future of GST Calculation
Automation and AI in GST Calculation
The future of GST calculation lies in automation and artificial intelligence, which can further simplify tax management by predicting tax liabilities and ensuring compliance.
Potential Changes in GST Laws and Rates
As GST laws and rates evolve, GST calculators will need to adapt to these changes to remain accurate and reliable tools for tax calculation.
In summary, a GST calculator is an invaluable tool for both consumers and businesses. It simplifies the complex process of tax calculation, saves time, ensures accuracy, and offers advanced features for better financial management. Staying updated with the latest GST rates and using reliable calculators can make managing taxes a breeze.
Contact Us:
Email: info@finnovent.org
Visit Here: https://finnovent.org/gst-calculator-india/ | finnovent | |
1,871,739 | What is DevSecOps? A Comprehensive Look at DevSecOps | Welcome Aboard Week 1 of DevSecOps in 5: Your Ticket to Secure Development Superpowers! _Hey there,... | 27,560 | 2024-06-03T03:48:00 | https://dev.to/gauri1504/what-is-devsecops-a-comprehensive-look-at-devsecops-4892 | devops, cloud, security, devsecops | _Welcome Aboard Week 1 of DevSecOps in 5: Your Ticket to Secure Development Superpowers!_
_Hey there, security champions and coding warriors!
Are you itching to level up your DevSecOps game and become an architect of rock-solid software? Well, you've landed in the right place! This 5-_week blog series is your fast track to mastering secure development and deployment._
This week, we're setting the foundation for your success. We'll be diving into:
**The DevSecOps Revolution
Cloud-Native Applications Demystified
Zero Trust Takes the Stage**
Get ready to ditch the development drama and build unshakeable confidence in your security practices. We're in this together, so buckle up, and let's embark on this epic journey!_
---
## DevSecOps: A Deep Dive into Secure and Agile Development
-The software development landscape has undergone a dramatic transformation.
-Gone are the days of waterfall methodologies, siloed teams, and slow, insecure deployments.
-DevSecOps, a methodology that seamlessly integrates security into the development lifecycle, has emerged as the new standard for building robust and agile software.
-This comprehensive message dives deep into the history, applications, and future of DevSecOps, equipping you with the knowledge to navigate this transformative approach.
## 1. History and Evolution of DevSecOps: A Long Road to Collaboration
The Siloed Struggle: Development vs. Operations in the Trenches
-Traditional software development, often following a waterfall methodology, was a breeding ground for inefficiency and insecurity. Development teams, under pressure to deliver features quickly, might prioritize functionality over secure coding practices.
-Imagine a scenario where a development team implements a new login feature but neglects to properly sanitize user input, leaving the application vulnerable to SQL injection attacks.
Meanwhile, operations teams, responsible for keeping applications running smoothly in production, often inherited code riddled with vulnerabilities. Imagine operations scrambling to patch a critical vulnerability after it was exploited by attackers, leading to a data breach and reputational damage for the organization. This siloed approach resulted in several problems:
#### Slow Deployments:
The hand-off between development and operations was a cumbersome process, often involving manual configuration changes and lengthy testing cycles. New features could take weeks or even months to reach users.
#### Finger-Pointing and Blame Games:
When security issues arose in production, both Dev and Ops often resorted to finger-pointing, hindering productive problem-solving. "It wasn't our fault, the devs wrote insecure code!" or "Ops didn't patch the vulnerability in time!" were typical refrains.
#### Insecure Applications:
The lack of communication and collaboration between Dev and Ops resulted in applications with critical vulnerabilities that attackers could easily exploit. A data breach at a major retailer due to a simple SQL injection vulnerability is a stark example of the consequences of siloed development.
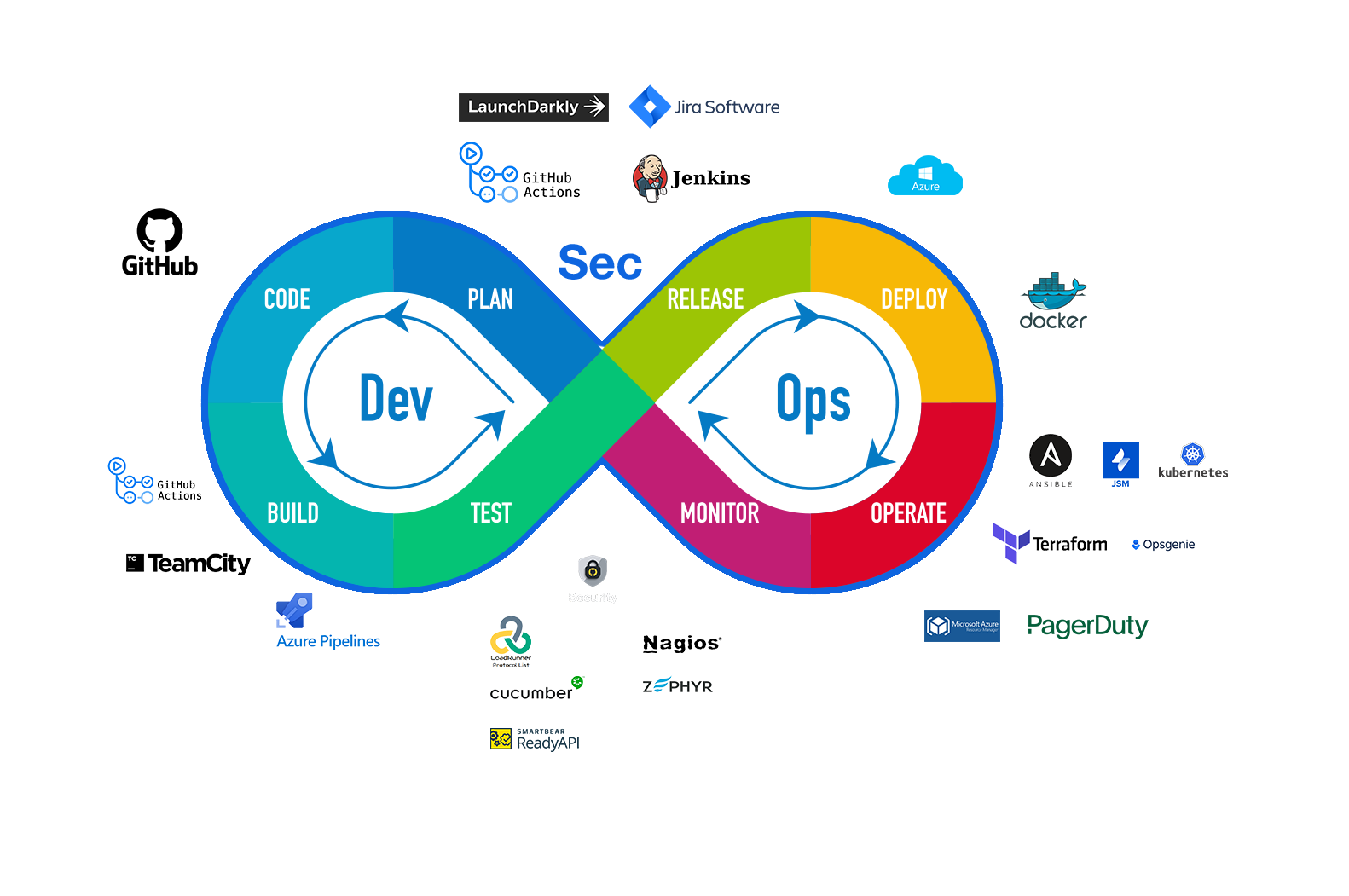
### The DevOps Dawn: Breaking Down the Walls
-The early 2000s witnessed the birth of DevOps, a philosophy that aimed to bridge the gap between development and operations. DevOps emphasizes several key principles:
#### Collaboration and Communication:
DevOps fosters a culture of collaboration where Dev and Ops teams work together throughout the entire development lifecycle. Regular communication channels are established to ensure everyone is on the same page and potential issues are identified early.
#### Shared Responsibility:
Both Dev and Ops share responsibility for the security, performance, and overall quality of the application. This fosters a sense of ownership and accountability within both teams.
#### Automation:
DevOps encourages automating repetitive tasks such as testing and deployment, freeing up developers and operators to focus on higher-value activities. Imagine automating security testing within the development pipeline, allowing developers to receive immediate feedback on potential vulnerabilities.
By breaking down the silos between Dev and Ops and promoting a culture of shared ownership, DevOps paved the way for faster deployments, improved application quality, and a more agile development process.
### Shifting Left Security: Baking Security In, Not Bolting It On
-Historically, security was often an afterthought, bolted onto applications during the final stages of development, like a security audit. This approach had several drawbacks:
#### Late Detection of Vulnerabilities:
Security vulnerabilities often went undetected until late in the development cycle, leading to costly rework and delays. Imagine a critical vulnerability discovered during a pre-production security audit, forcing developers to scramble and rewrite significant portions of code.
#### Security Bottlenecks:
Security audits could create bottlenecks in the development process, slowing down deployments. Security testers might be overwhelmed with a backlog of applications, delaying the release of new features.
#### Insecure Applications:
By the time vulnerabilities were discovered, the application might already be in production, exposing users to security risks. A data breach at a social media company due to a known but unpatched vulnerability highlights the dangers of this approach.
-DevSecOps flips the script entirely with the concept of "shifting left security." This means integrating security practices throughout the entire SDLC, including:
#### Security Training for Developers:
Equipping developers with the knowledge to write secure code from the get-go. Training programs can cover topics like secure coding practices, common vulnerabilities, and how to avoid them. For instance, training developers on how to properly sanitize user input can prevent SQL injection attacks.
#### Static Code Analysis (SCA) Tools:
Using automated tools to scan code for vulnerabilities early in the development process. These tools can identify common coding mistakes that might lead to security vulnerabilities, allowing developers to fix them before they become a problem. For instance, an SCA tool might detect a potential SQL injection vulnerability in a login form, prompting the developer to sanitize user input.
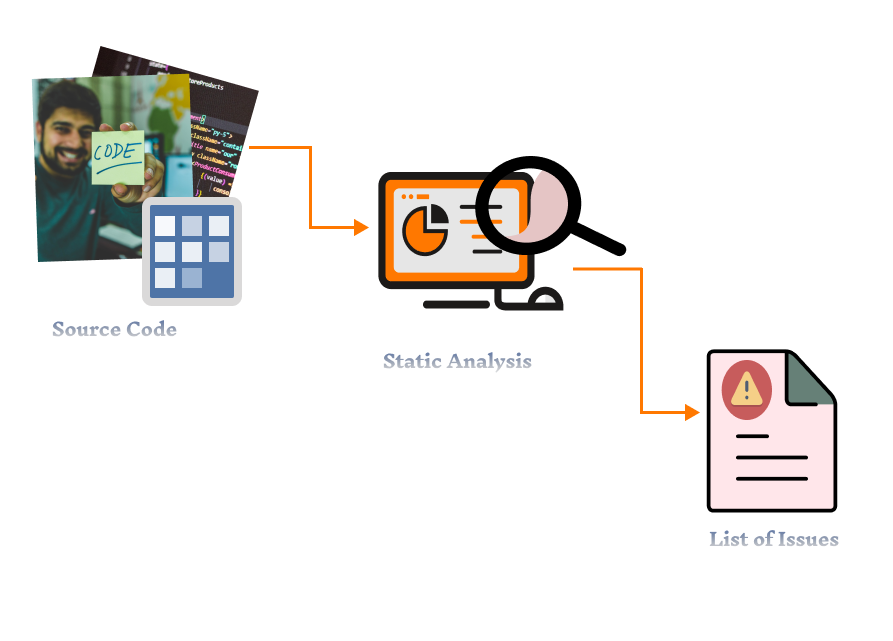
#### Dynamic Application Security Testing (DAST) Tools:
- Complementing SCA tools, DAST tools scan a running application to identify vulnerabilities that exploit runtime behavior.
These tools can detect vulnerabilities that SCA might miss, such as cross-site scripting (XSS) vulnerabilities that rely on dynamic user input.
Imagine a DAST tool identifying a potential XSS vulnerability in a product search function, where a malicious user could inject a script to steal user cookies.
By integrating SCA and DAST tools throughout the development pipeline, DevSecOps ensures that a wider range of vulnerabilities are caught early in the development process.
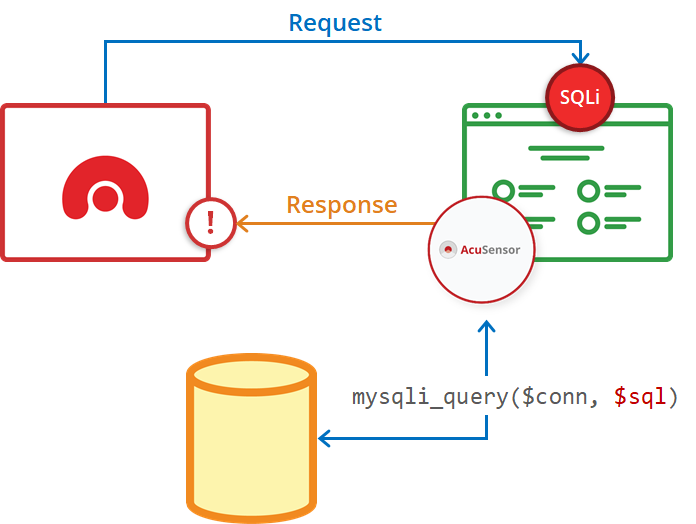
#### Infrastructure Security as Code (IAc as Code):
Following the principles of Infrastructure as Code (IaC) where infrastructure configurations are managed as code, ISec as Code applies the same concept to security configurations.
This allows for security controls like firewalls and access controls to be defined and deployed alongside the application code.
ISec as Code ensures that security is built into the infrastructure from the very beginning, not as an afterthought. For instance, ISec as Code can be used to automatically configure a web server to block common attack vectors like SQL injection attempts.
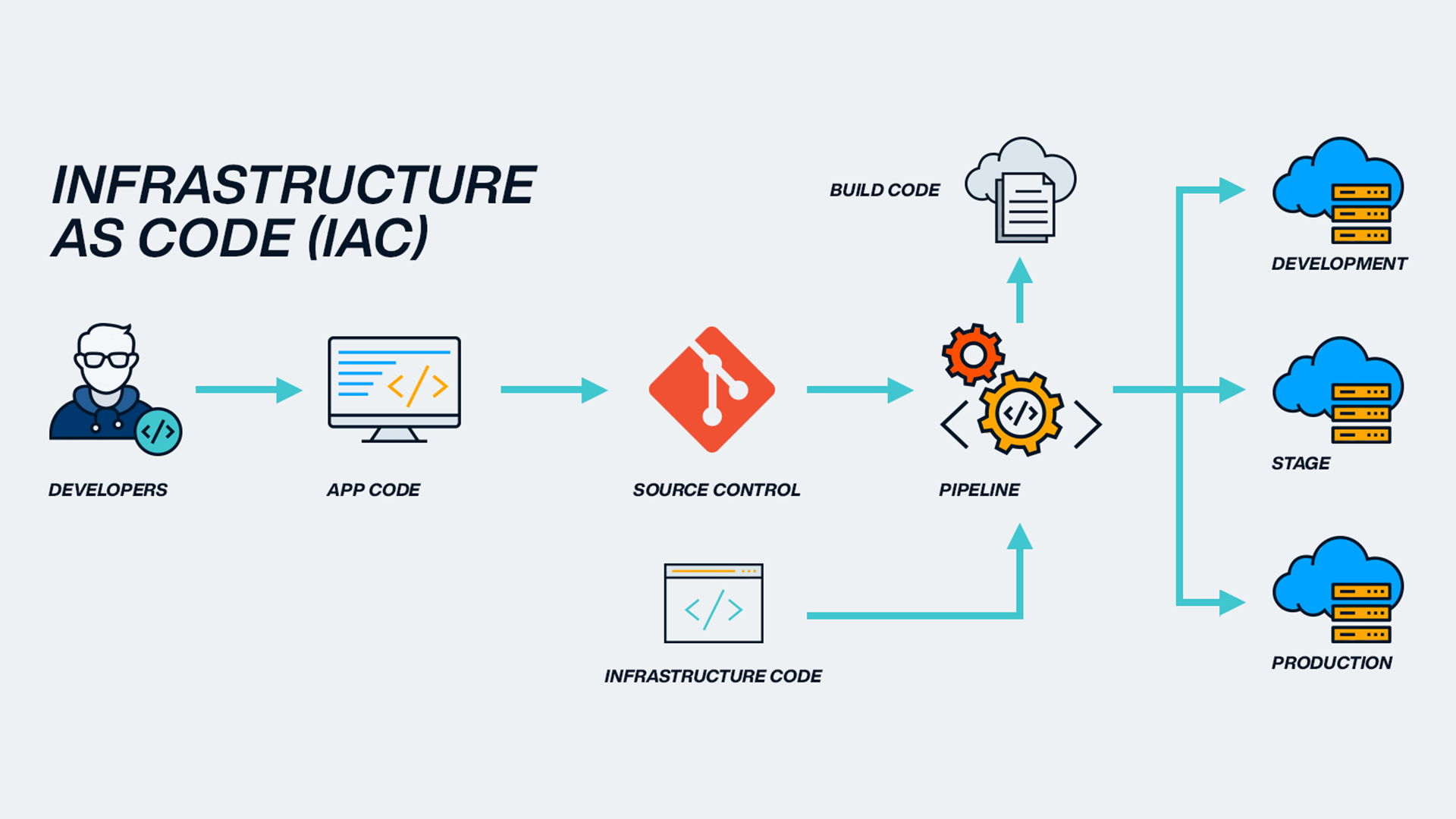
### The DevSecOps Adoption Storm: Perfect Timing Breeds Progress
Several key advancements fueled the rapid adoption of DevSecOps methodologies:
#### The Rise of Cloud Computing:
The late 2000s saw the rise of cloud computing, providing a scalable and flexible platform for application development. Cloud platforms offered features like automated infrastructure provisioning and self-service deployment, which streamlined the development process. Imagine a scenario where a development team working on a new social networking application needs to scale up their infrastructure to accommodate a surge in user registrations. Traditionally, this might involve lengthy back-and-forth communication with the operations team to provision new servers. However, with a cloud platform like Amazon Web Services (AWS), the development team can leverage tools like AWS Auto Scaling to automatically provision additional resources based on pre-defined parameters. This empowers developers to focus on building features and reduces reliance on the operations team for infrastructure management tasks.
#### Containerization Technologies:
Containerization technologies like Docker, popularized around 2013, further streamlined deployments and enabled the adoption of microservices architectures. Microservices architectures break down applications into smaller, independent services, making them easier to develop, deploy, and manage. This modularity also enhances security, as a vulnerability in one microservice is less likely to impact the entire application. For instance, a large financial institution might leverage containerization to build its online banking application as a collection of microservices. One microservice might handle user authentication, another might handle account balance inquiries, and another might handle money transfers. If a vulnerability is discovered in the authentication microservice, it can be isolated and patched without affecting the functionality of the other microservices. This modularity allows for faster deployments and easier remediation of security issues.
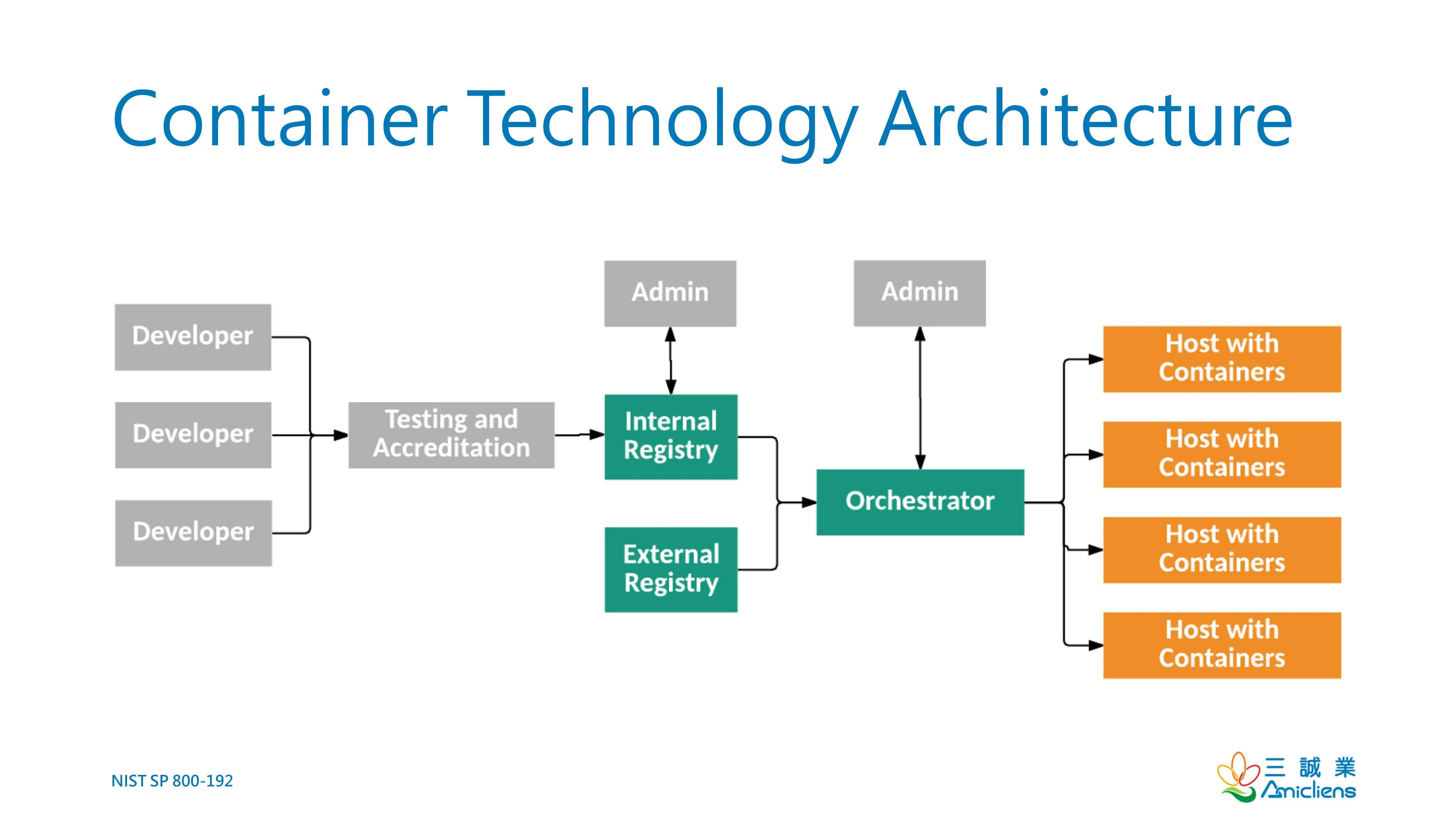
#### Growing Awareness of Cyber Threats:
As cyber threats became more sophisticated and frequent, organizations realized the need to prioritize application security. DevSecOps offered a way to integrate security into the development process without sacrificing speed or agility. High-profile breaches at major companies like Equifax, where a vulnerability in a web application compromised the personal data of millions of customers, served as a wake-up call. These breaches demonstrated the devastating consequences of insecure software and the urgent need for a more proactive approach to application security. DevSecOps emerged as a response to this growing need, offering a methodology for building secure software while maintaining development agility.

These advancements, coupled with a growing demand for faster time-to-market, created the perfect storm for DevSecOps adoption. Organizations across industries began to recognize the benefits of DevSecOps, not just for security but also for improved development efficiency, agility, and a reduction in security vulnerabilities.
## 2. DevSecOps in Regulated Industries: Aligning Security with Compliance
Regulated industries like finance and healthcare face a unique set of challenges. They must navigate a complex web of security regulations and compliance requirements. For instance, the Payment Card Industry Data Security Standard (PCI-DSS) in finance mandates specific security measures for protecting sensitive cardholder data. Similarly, the Health Insurance Portability and Accountability Act (HIPAA) in healthcare safeguards patient privacy. Failure to comply with these regulations can result in hefty fines, reputational damage, and even criminal charges.
### DevSecOps as a Compliance Streamliner
DevSecOps practices can be powerful tools for navigating the complexities of compliance. Techniques like automated security testing and vulnerability management can significantly streamline compliance efforts. Here's how:
#### Automated Security Testing:
DevSecOps integrates automated security testing tools throughout the development pipeline. These tools can continuously scan code for vulnerabilities known to be exploited by attackers. Early detection of vulnerabilities allows for timely remediation, reducing the risk of non-compliance. For instance, a DAST tool integrated into the development pipeline might identify a potential XSS vulnerability in a healthcare application's online appointment booking form. This early warning allows developers to fix the vulnerability before the application goes live, ensuring compliance with HIPAA regulations concerning the protection of patient data.
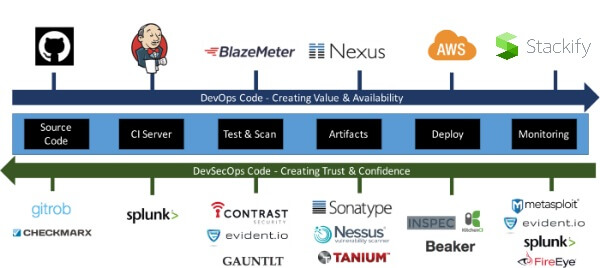
#### Vulnerability Management:
DevSecOps fosters a culture of continuous vulnerability management. Identified vulnerabilities are prioritized based on severity and risk, and developers are notified to fix them promptly. Vulnerability management tools can also track the progress of remediation efforts and ensure that all vulnerabilities are addressed before deployment. This proactive approach helps regulated organizations maintain a secure development environment and reduces the likelihood of non-compliance incidents.
#### Compliance Automation:
DevSecOps principles can be extended to automate compliance checks. Compliance automation tools can be integrated into the development pipeline to verify that code adheres to specific regulatory requirements. For instance, in the finance industry, a compliance automation tool might scan code to ensure it meets PCI-DSS standards for handling sensitive cardholder data. This automation reduces the manual effort required for compliance audits and streamlines the development process.

#### Continuous Audit Logging:
DevSecOps emphasizes maintaining detailed audit logs of system activity. These logs can be used to demonstrate compliance with regulations that mandate the monitoring of user activity and access controls. For instance, HIPAA requires healthcare organizations to maintain audit logs of who accessed patient data and when. DevSecOps practices ensure that such audit logs are captured and readily available for compliance audits. By automating the collection and storage of audit logs, DevSecOps reduces the burden on IT teams and simplifies compliance audits.
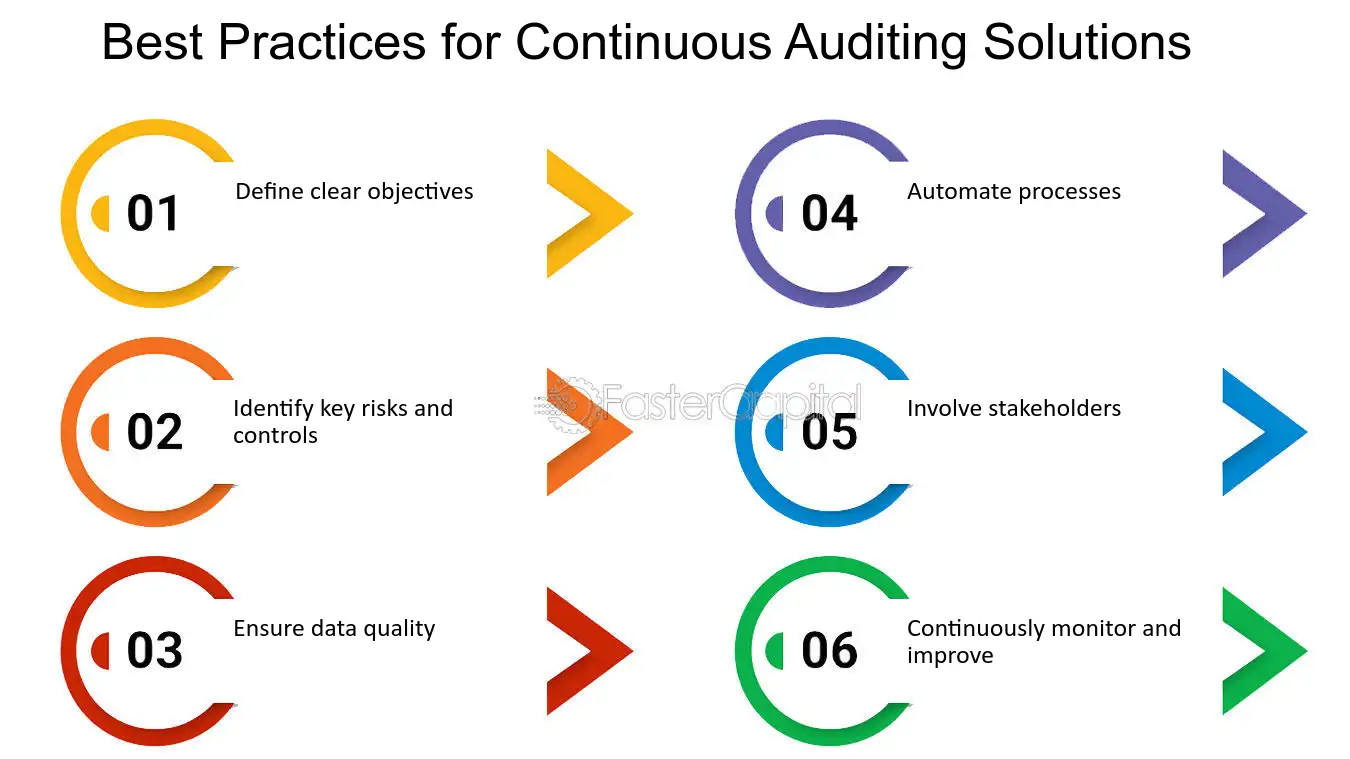
By automating these security practices and fostering a culture of continuous monitoring, DevSecOps empowers regulated industries to achieve compliance with greater efficiency and confidence.
### Real-World Success: Case Studies in Action
Leading financial institutions like Bank of America have adopted DevSecOps to automate security testing and infrastructure provisioning. This has resulted in faster deployments, improved security posture, and a demonstrably stronger compliance posture. Bank of America can now confidently assert that their development processes adhere to the stringent security requirements of PCI-DSS.
In the healthcare sector, Kaiser Permanente has leveraged DevSecOps principles to streamline HIPAA compliance and enhance patient data security. By integrating automated security testing into their development pipeline, Kaiser Permanente can identify and address potential HIPAA violations early in the development process. This proactive approach minimizes the risk of patient data breaches and ensures compliance with healthcare privacy regulations.
These real-world examples showcase the effectiveness of DevSecOps in enabling regulated industries to achieve both agility and compliance. By embracing DevSecOps methodologies, organizations can navigate the complexities of security regulations while delivering innovative software solutions to their users.
## 3. Key Influencers and Thought Leaders in the DevSecOps Community: Shaping the Future
Several prominent figures have significantly shaped the DevSecOps landscape. Here are a few key influencers:
#### The Four Keys of DevOps:
**Gene Kim, Jez Humble, Patrick Debois,** and **John Willis** authored the influential book _"The Phoenix Project."_ This fictionalized account of a company's successful DevOps transformation has become a cornerstone text for DevSecOps practitioners. The book outlines the principles and practices of DevOps, providing a valuable roadmap for organizations embarking on their DevSecOps journey. While the book focuses on DevOps, its core principles of collaboration, automation, and shared responsibility are fundamental to DevSecOps as well.
#### Genevieve Bell:
A renowned security researcher, Genevieve Bell advocates for integrating security considerations throughout the design process. She argues that security shouldn't be an afterthought but a fundamental principle from the very beginning. By fostering a security-conscious design culture, organizations can build applications that are inherently more secure. Her work emphasizes the importance of shifting security left, a core tenet of DevSecOps.
### Building the Community: Knowledge is Power
The DevSecOps community thrives on collaboration and knowledge sharing. Here are some key resources to stay up-to-date on the latest DevSecOps trends:
#### DevSecOpsDays conferences:
These international conferences bring together DevSecOps practitioners from around the world to share best practices, learn from industry leaders, and network with peers. Attending DevSecOpsDays conferences is a fantastic way to stay on the cutting edge of DevSecOps methodologies. These conferences offer workshops, presentations, and opportunities to connect with experts who can provide valuable guidance on implementing DevSecOps within your organization.
#### Online Resources:
Numerous online resources offer valuable insights into the world of DevSecOps. Websites like DevSecOps.com and DOJO (The DevSecOps Learning Network) provide articles, tutorials, and webinars on various DevSecOps topics. Leveraging these online resources allows you to continuously learn and refine your DevSecOps skills. These websites are constantly updated with the latest trends and best practices, making them a valuable resource for anyone interested in staying ahead of the curve in DevSecOps.
#### Open-Source Security Tools:
The DevSecOps community is a strong proponent of open-source software. Many powerful security testing tools are available as open-source projects, allowing organizations to integrate security into their development pipelines without a significant financial investment. Popular open-source security tools include OWASP ZAP (Zed Attack Proxy) for web application security testing and OpenVAS for vulnerability scanning. These tools can be seamlessly integrated into the development pipeline to automate security testing and identify vulnerabilities early in the development process.
### The Future of DevSecOps: A Journey of Continuous Improvement
The DevSecOps landscape is constantly evolving. Here are some key trends shaping the future of DevSecOps:
#### Security by Design:
The concept of security by design goes beyond integrating security into the development pipeline. It emphasizes building security considerations directly into the software architecture from the very beginning. This proactive approach can significantly reduce the number of vulnerabilities introduced during development.
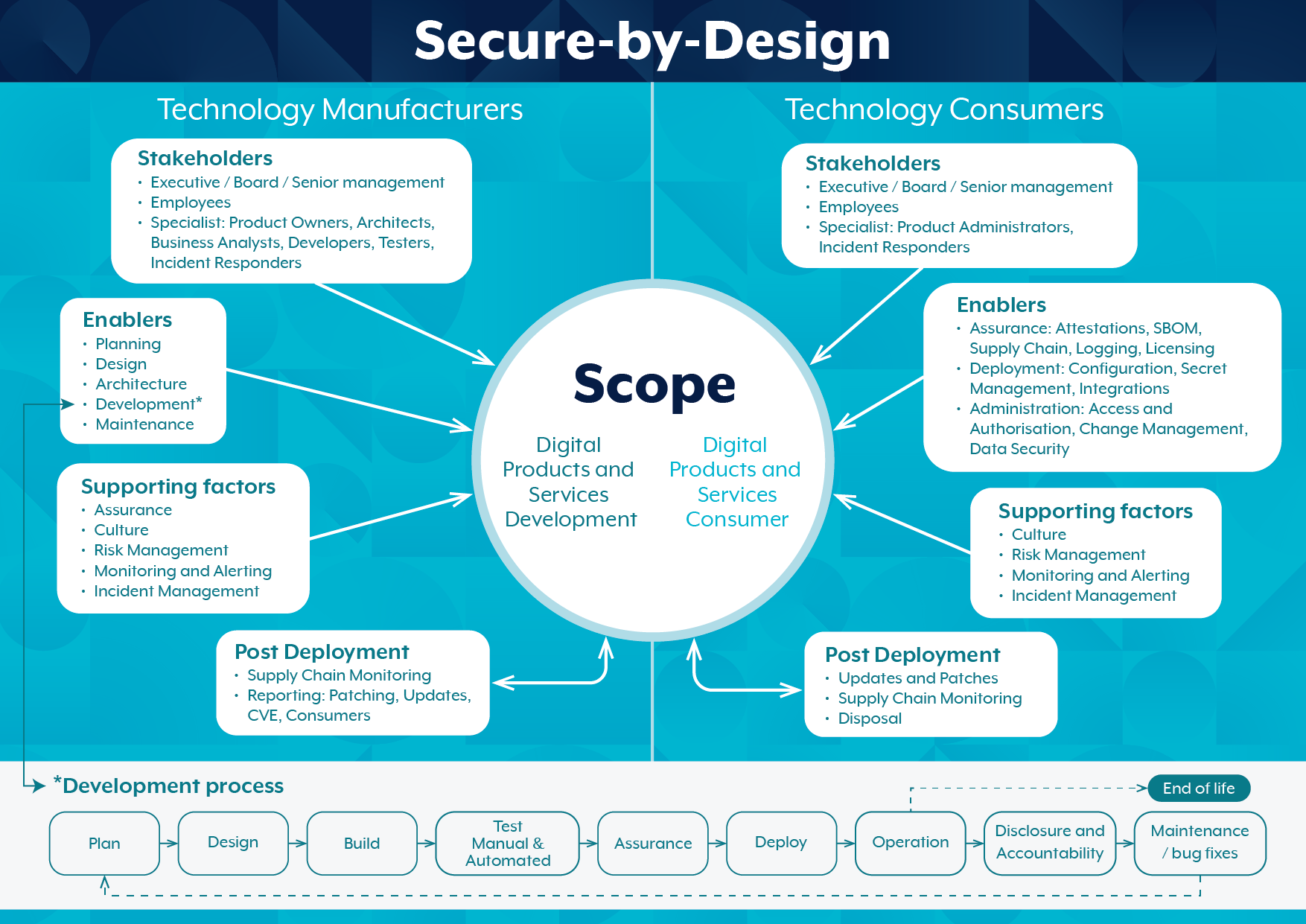
#### Artificial Intelligence (AI) and Machine Learning (ML):
AI and ML are poised to play a transformative role in DevSecOps. These technologies can be used to automate security tasks, identify emerging threats, and predict vulnerabilities. For instance, AI-powered tools can analyze code commits to identify potential security risks and recommend remediation strategies.
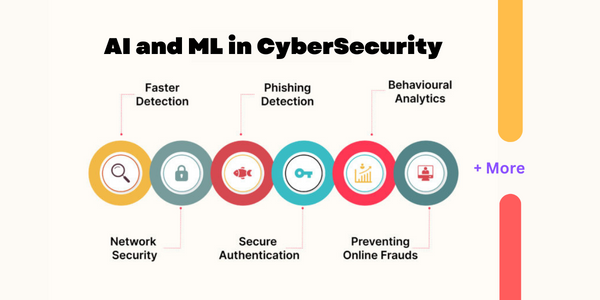
#### Cloud-Native Security:
As cloud adoption continues to grow, DevSecOps practices must adapt to secure cloud-native applications. This involves integrating security considerations into cloud infrastructure and leveraging cloud-based security services. For instance, cloud platforms like AWS offer a suite of security services that can be used to secure applications running in the cloud.
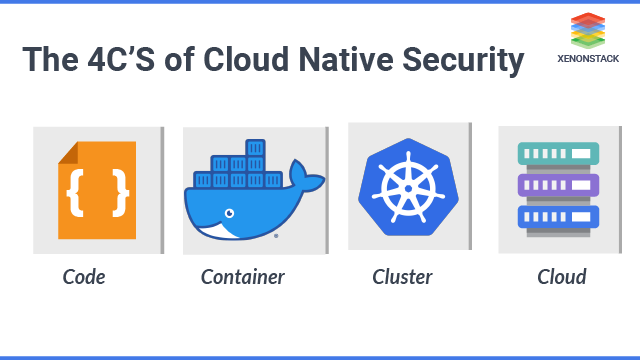
By embracing these trends and fostering a culture of continuous improvement, DevSecOps can empower organizations to deliver secure and innovative software solutions at an ever-increasing pace.
## Conclusion
DevSecOps has emerged as a transformative approach to software development. By integrating security throughout the development lifecycle, DevSecOps empowers organizations to achieve:
Faster deployments: Streamlined development pipelines and automated processes lead to quicker deployments and faster time-to-market.
Improved application quality: DevSecOps practices identify and address vulnerabilities early in the development process, resulting in more robust and secure applications.
Enhanced agility: DevSecOps fosters a culture of collaboration and continuous improvement, allowing organizations to adapt to changing business needs and security threats.
Streamlined compliance: Automated security testing and vulnerability management simplify compliance audits and help organizations meet regulatory requirements.
As the DevSecOps landscape continues to evolve, organizations that embrace this methodology will be well-positioned to thrive in the ever-changing world of software development. By prioritizing security throughout the development process, DevSecOps paves the way for a future where secure and innovative software is the norm.
---
I'm grateful for the opportunity to delve into **What is DevSecOps? A Comprehensive Look at DevSecOps** with you today. It's a fascinating area with so much potential to improve the security landscape.
Thanks for joining me on this exploration of What is DevSecOps? A Comprehensive Look at DevSecOps. Your continued interest and engagement fuel this journey!
If you found this discussion on What is DevSecOps? A Comprehensive Look at DevSecOps helpful, consider sharing it with your network! Knowledge is power, especially when it comes to security.
Let's keep the conversation going! Share your thoughts, questions, or experiences What is DevSecOps? A Comprehensive Look at DevSecOps in the comments below.
Eager to learn more about DevSecOps best practices? Stay tuned for the next post!
By working together and adopting secure development practices, we can build a more resilient and trustworthy software ecosystem.
Remember, the journey to secure development is a continuous learning process. Here's to continuous improvement!🥂
| gauri1504 |
1,874,878 | Maximizing Productivity: BANOVO's Advanced Construction Equipment | 4e9db625525e51122f6186107adc5fc26148f292ff7c7e91c571604467c058c0.jpg Title: Get More Done with... | 0 | 2024-06-03T03:46:09 | https://dev.to/theresa_mccraryjs_77dd382/maximizing-productivity-banovos-advanced-construction-equipment-583n | construction | 4e9db625525e51122f6186107adc5fc26148f292ff7c7e91c571604467c058c0.jpg
Title: Get More Done with BANOVO's Advanced Construction Equipment
Are you sick of being stuck in the place work same do you want a better way to obtain points done much faster and more efficiently? Look no more compared to BANOVO's advanced construction equipment. With its advantages lots of innovations, and safety top-notch, BANOVO's equipment the key to maximizing your efficiency at work website. We will explore how to use the equipment, its service and quality, and some of the applications lots of this gear top-of-the-line.
Advantages of BANOVO's Advanced Construction Equipment
Among the greatest advantages of BANOVO's equipment is its advanced technology. This equipment is designed to make your job easier and more efficient. With features like automatic progressing systems and procedure remote you can obtain your work done much faster and with greater accuracy compared to before ever. By you done quickly and properly whether you excavating, grading, or paving, BANOVO's equipment can help it obtained.
Innovation at Its Finest
BANOVO's progressed construction tools is anything but regular, it's truly innovative. The company invests significantly in advancement and research study to create new and much far better methods to acquire points done. A few of the most recent innovations include smart sensing units offer info real-time soil issues and different various other elements, along with self-governing devices can kept up bit to no intervention human. With BANOVO's Excavator Buckets, you can remainder ensured you utilizing among one of the most tools that are progressed.
Safety First
Safety is a concern that's top of BANOVO, and their equipment reflects. With features like backup video cams, distance sensing units, and shutoffs automated you can feel great you using equipment designed to always keep you and your coworkers safe. Plus, with advanced warning systems that alert you to hazards potential you shall have an layer extra of at work site. When safety is your top priority equipment your the choice obvious.
How to Use BANOVO's Advanced Construction Equipment
Using BANOVO's equipment is er compared to you might think. Lots of the machines come with user-friendly user interfaces touchscreen make it easy to control the equipment. On the other hand, indicate processing formulas and control complex handle the lifting hefty so you can concentrate on obtaining your work done. And with remote operation, you can also control the Excavator Grapples from a range safe getting rid of the need for physical contact with the machine while it being used.
Service and Quality You Can Depend On
BANOVO's advanced construction equipment is backed by a group of dedicated experts who dedicated to service providing expert top-notch. With a network of service centers worldwide global you can rest guaranteed you shall constantly have access to the help you need when you need it. Plus, with a dedication to using just components quality top, you can feel great your equipment will last for many years to come.
Applications for BANOVO's Equipment
BANOVO's advanced construction equipment has a range wide of throughout lots of markets. You need to obtain the job done whether you building roadways and bridges, digging foundations, or planet mining moving, BANOVO has the equipment. And with its technology advanced and features, you can be certain you using one of the most equipment and efficient effective.
Source: https://www.bonovogroup.com/excavator-buckets | theresa_mccraryjs_77dd382 |
1,874,877 | How new Builders Tame Mode Network | Configuring Hardhat for Development on Mode Network In this article, we'll explore how new... | 0 | 2024-06-03T03:40:54 | https://dev.to/wolfcito/how-new-builders-tame-mode-network-b1l | viem1, modenetwork, blockchain, development |

**Configuring Hardhat for Development on Mode Network**
In this article, we'll explore how new builders, even those who feel like baby dinosaurs handling slightly older technologies, can configure their development environment using Hardhat to integrate with Mode Network. We'll break down the configuration file, covering network setup, Solidity compiler settings, gas usage reporting, Sourcify integration, and Etherscan integration. Each step is designed to allow any developer, regardless of their level of experience, to optimize their environment and work efficiently on Mode Network-specific projects.
Configuration Code Example
To get started, you need to install Hardhat locally in your project. Make sure you have Node.js and npm installed. Then, follow these steps:
Install Hardhat:
```bash
npm install --save-dev hardhat
```
Create a Hardhat Project:
```bash
npx hardhat
```
Update the hardhat.config.js File:
Here's an example configuration for Mode Network Mainnet:
```ts
import { HardhatUserConfig } from 'hardhat/config'
import '@nomicfoundation/hardhat-toolbox'
require('hardhat-deploy')
import * as dotenv from 'dotenv'
dotenv.config()
// Load environment variables
const { DEPLOYER_PRIVATE_KEY, ETHERSCAN_API_KEY } = process.env
const providerApiKey = process.env.ALCHEMY_API_KEY
// Configuration object for Hardhat
const config: HardhatUserConfig = {
networks: {
// Configuration for local development network
hardhat: {
forking: {
// URL for forking mainnet
url: `https://eth-mainnet.alchemyapi.io/v2/${providerApiKey}`,
// Enable forking if MAINNET_FORKING_ENABLED is 'true'
enabled: process.env.MAINNET_FORKING_ENABLED === 'true',
},
},
// Configuration for ModeTest network
modetest: {
// URL for ModeTest network
url: 'https://sepolia.mode.network',
// Chain ID for ModeTest network
chainId: 919,
// Account(s) to use for deployments on ModeTest network
accounts: [DEPLOYER_PRIVATE_KEY as string],
// Gas price for transactions on ModeTest network
gasPrice: 10000,
},
// Configuration for Mode network
mode: {
// URL for Mode network
url: 'https://mainnet.mode.network',
// Chain ID for Mode network
chainId: 34443,
// Account(s) to use for deployments on Mode network
accounts: [DEPLOYER_PRIVATE_KEY as string],
},
},
// Solidity compiler configuration
solidity: {
// Version of Solidity compiler to use
version: '0.8.20',
settings: {
// EVM version
evmVersion: 'london',
},
},
// Configuration for gas reporting
gasReporter: {
// Enable gas reporting if REPORT_GAS is defined
enabled: process.env.REPORT_GAS !== undefined,
// Set currency for gas reporting
currency: 'USD',
},
// Configuration for Sourcify
sourcify: {
// Enable Sourcify
enabled: true,
},
// Configuration for Etherscan integration
etherscan: {
// API key for Etherscan
apiKey: {
mode: ETHERSCAN_API_KEY as string,
},
// Custom chains configuration for Etherscan
customChains: [
// Configuration for ModeTest network in Etherscan
{
network: 'modetest',
chainId: 919,
urls: {
// API URL for ModeTest network explorer
apiURL: 'https://sepolia.explorer.mode.network/api',
// Browser URL for ModeTest network explorer
browserURL: 'https://sepolia.explorer.mode.network/',
},
},
// Configuration for Mode network in Etherscan
{
network: 'mode',
chainId: 34443,
urls: {
// API URL for Mode network explorer
apiURL: 'https://explorer.mode.network/api',
// Browser URL for Mode network explorer
browserURL: 'https://explorer.mode.network/',
},
},
],
},
}
export default config
```
Environment Variables:
Make sure to have your environment variables configured in a .env file:
```makefile
PRIVATE_KEY=your_private_key
INFURA_PROJECT_ID=your_infura_project_id
ETHERSCAN_API_KEY=your_etherscan_api_key
```
| Property | Description |
| ----------- | --------------------------------------------------------------------------------- |
| networks | Configuration for different Ethereum networks. |
| - hardhat | Configuration for local Hardhat network for development and testing. |
| - modetest | Configuration for ModeTest network. |
| - mode | Configuration for Mode network. |
| solidity | Configuration for Solidity compiler. |
| gasReporter | Configuration for gas usage reporting during tests. |
| sourcify | Configuration for Sourcify to verify contract source. |
| etherscan | Configuration for Etherscan integration, including API key and custom chain URLs. |
**Conclusion**
With this setup, new builders, even those who consider themselves ""Very new to the ecosystem", can seamlessly integrate and contribute to development on Mode Network. The detailed configuration and provided examples ensure a straightforward and accessible process for everyone.
Let's tame Mode Network together, step by step, like true builders in this "new" era! 🦖💻 | wolfcito |
1,874,876 | What is Google auth(Oauth 2.0) | Whenever you play a game or go to some site, 100% of the time you will have to log in to your account... | 0 | 2024-06-03T03:40:22 | https://dev.to/gagecantrelle/what-is-google-authoauth-20-n5g |
Whenever you play a game or go to some site, 100% of the time you will have to log in to your account before moving on, handing out your account name and password to confirm your identity. Unaware that someone may be spying on you for your account information, this can lead to accounts being stolen with your personal information being deleted, sold online, or posted on social media, making you hesitate whenever you make an account. Luckly Google released an authentication application to calm your fear. Google Auth, or Oauth 2.0, will allow you to log in and create an account without having to put in your password or email account. This is done by having Google create an access token that will be sent to the account you’re trying to login to, and say, “Hey this this is the account created by this use so let her/him in”.
**Fun facts**
Oauth began development in November 2006, when later in 2007 a small group of implementers was created. The Group discussed ideas and proposed drafts for the Oauth application. Soon in July of the same year, google heard about Oauth and showed an interest in supporting the project. In April 2010 the Ouath 1.0 was released, with Oauth 2.0 being released two
years later in October. This application is free to use, but you need to have a Google account to use it. So let’s look at where to get started.
**Creating a Google Auth project**
To use Oauth 2.0 you will need to create a project on Google Cloud.
1. Go to this site https://console.cloud.google.com/ Then, if you don’t have any project created, you should see a new/create project. If not, then next to the Google Cloud symbol you should see a button with three circles. Click it and you should see a new/create project button.
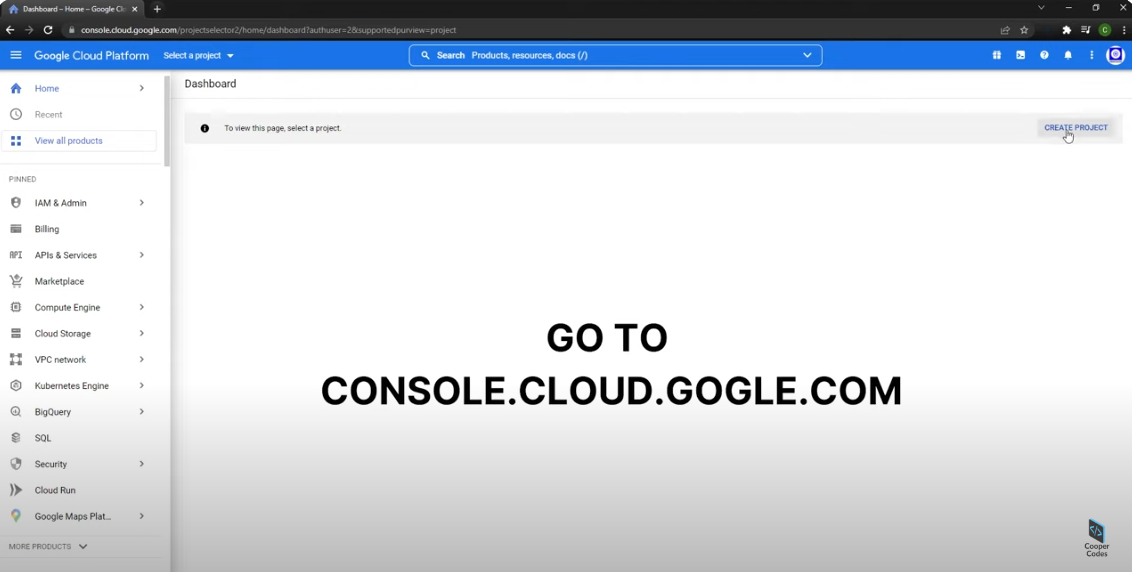
2. After you click it, it will ask for a project name and organization name. You can skip the organization name.
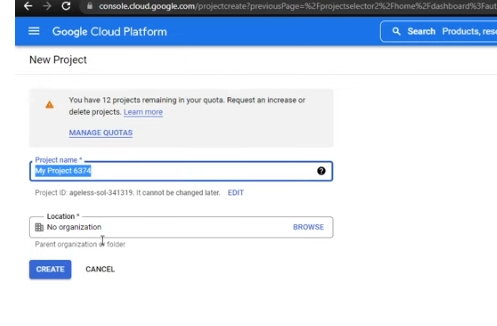
3. When your project gets created, you should be sent to your project folder. Go to the search bar and search for Oauth consent screen. It should be under API and services.
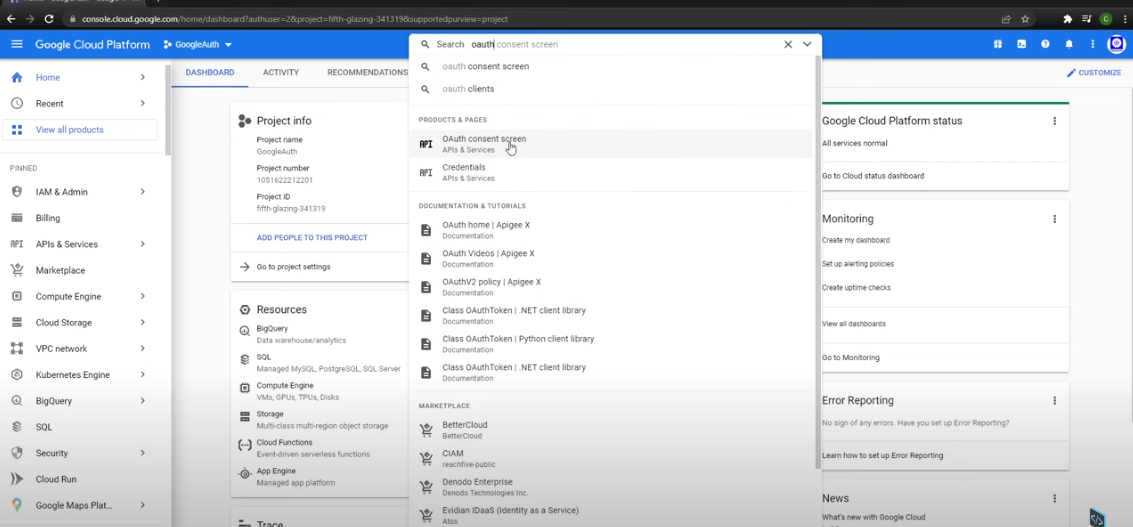
4. After clicking you should see a screen asking how you want to configure your app, elect external (allow you to use test user with any account), then click create it.
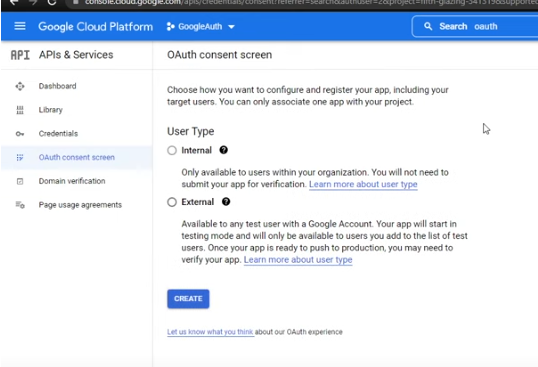
5. You will then see another screen. It will ask you to name your app, user support email, and developer contact email. Then click save and continue.
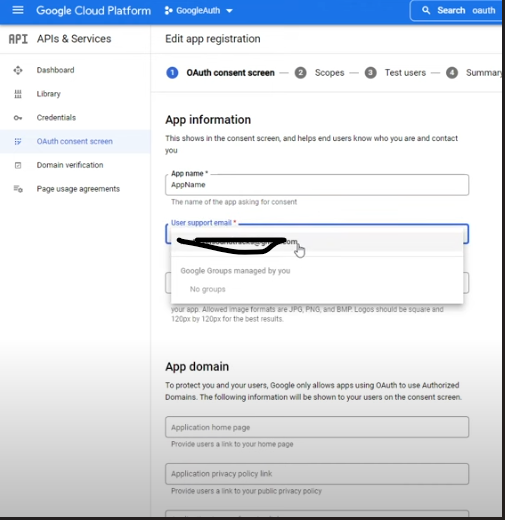
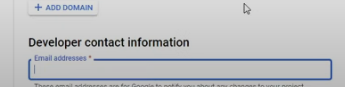
6. Next you will see a button called add or remove scopes. Click it and another screen will appear with checkboxes. Check the boxes that say auth/user/email and auth/user/profile. Press update then click save and continue.
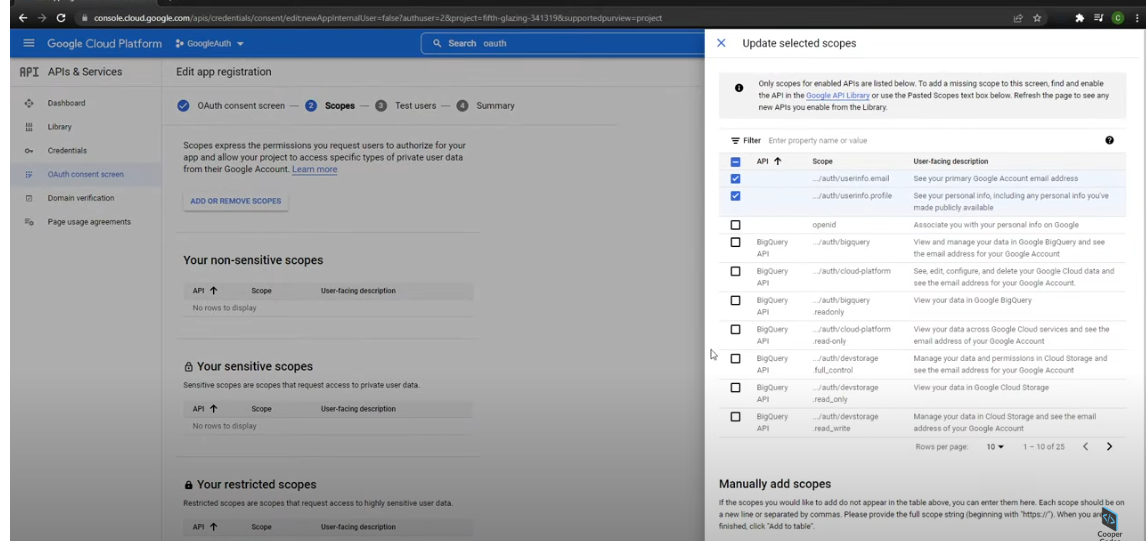
7. Next it will ask you to add a test account. This could be any Google regular account. But if you don’t want your project to mess with something on one of your Google accounts, just create a new Google account for testing. But be careful because the account you added will be the only one able to log in. Then click save and continue.
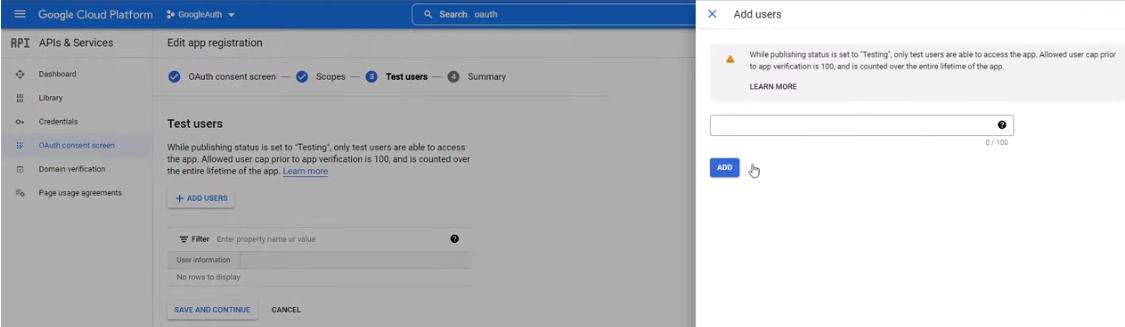
8. Next you will see a summary screen which you can skip and then you just need to click back to dashboard.
9. When you get to the dashboard screen, under API & service, click credential. Then click Create credentials. Finally, click Oauth client ID.
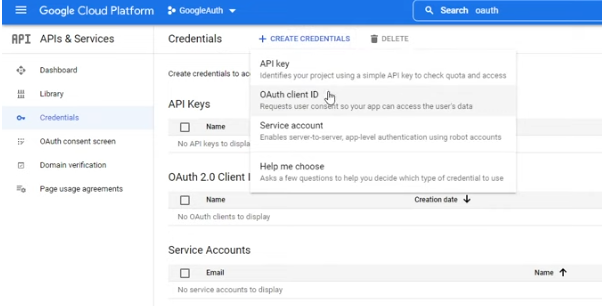
10. It will then ask for a link to where your web application is being hosted (example: http://localhost:3000). Pass it in the authorized JavaScript origins and authorized uris, then click Create.
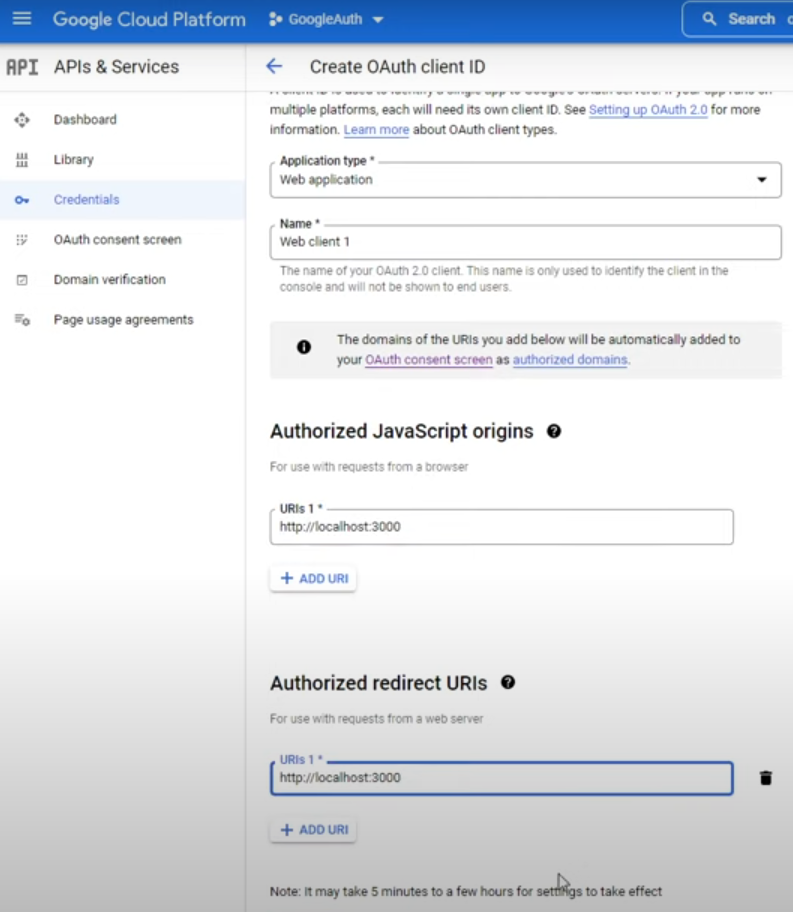
11. You should then get a client ID and secret. Save them somewhen like a Google Doc file or text file.
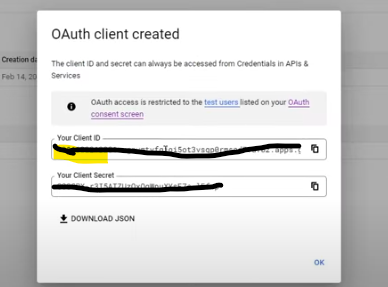
**Now it’s coding time.**
If you’ve never used react before, here is a link to a blog I did that talks about the basics of react https://dev.to/gagecantrelle/the-basics-of-react-57a1 . If you don’t feel like making a react application from scratch, run this command in an empty folder in the terminal npx create-react-app. Then add the name of the file you will create npx create-react-app client. Npx should be installed when you install node same as npm. If you’re not sure, run the command npx –v, this will show what version of npx you have. Then after all that cd into the folder you create (client) run npm install gapi-script then npm install react-google-login. Next, create a component folder that holds two js files login and logout. Then create a function for login and logout with a const holding your ClientID you got when making your Google project.
```
//file name login
Import { GoogleLogin } from ‘react-google-login’;
Const clientId = ‘your client id’;
Function login(){
Return();
};
Export default loging;
```
```
//file name logout
Import { GoogleLogout } from ‘react-google-login’;
Const clientId = ‘your client id’;
Function logout(){
Return();
};
Export default logout;
```
Next for your login and logout function pass these in return, this code will go and try to log in you Google account
```
//for login
(
<div id=”signInButton>
<GoogleLogin
clientId={clientId}
buttonText=”login”
onSuccess={onSuccess}
onFailure={onFailure}
cookiePolicy={‘single_host_origin’}
isSignIn={true}
/>
</div>
)
```
```
// for logout
(
<div id=”signInButton>
<GoogleLogout
clientId={clientId}
buttonText=”login”
onSuccess={onSuccess}
/>
</div>
)
```
Now that we have that setup, we then need to create an onScuccess and onFailure function. These functions will take in a parameter, For onSuccess it takes in an object that holds a profileObj key. which like the name implies it an object that holds some information from your google account. for onFailure it takes in the same object as onSuccess.
```
onSuccess(res){
console.log(‘hey it worked”, res.profileObj);
};
onFailure(res){
console.log(‘error: cant log in’, res);
};
```
Finally, let’s add our login and logout function to the app.js/app.jsx file or the main file you’re using for your React project. In your app file, you’ll import both login and logout functions, useEffect from react, and gapi from the gapi-script we installed. Along with your client ID. The useEffect hook allows you to fetch data, directly updating the dom, and used it as a timer for side effects in your component. Then inside of your app call the useEffect and pass it a function called start that runs gapi.clent.int function. That takes in an object that holds the clientId and scope, the scope is empty unless you're using some API’s alongside Google auth. Then run the start function with gapi.load function. After that, put the imported login and logout functions inside the return div.
```
// file app.js
Import login from ‘./components/Login’;
Import logout from ‘./components/Logout’;
Import { useEffect } from ‘react’;
Import { gapi } from ‘gapi-script’;
Const clientId = ‘your client id’;
Function App(){
useEffect(() =>{
function start(){
gapi.client.init({
clientId: clientId,
scope: “”
});
};
Gapi.loade(‘client:auth2’, start)
});
Return(<div className=”app”>
<login />
<logout />
</div>)
}
```
After that run your react application and test it out. You should see a login and logout button. Click login then you should see a Google select account screen pop up. Select the test account you pick when setting up your project in Google Cloud, and that it’s. Click the inspect button to check your console log for the login function and you should see a console log with an object containing the information about that account minus the password. Then when you click the logout button you’ll be logged out.
Also, like I said in the beginning google auth creates an access token for other sites to use, instead giving them your password and email account. To get that generated token, use this command in the code block. Remember this token is not permanent, it has a time limit before it goes bad.
```
Var accessToken =gapi.auth.getToken().access_token;
```
So now that you know about Google auth and how to use it, you probably see how useful it is. Allowing you to create accounts connected to a Google account, without taking in personal information like a password. also Allowing users to see that the account they are trying to make, won’t ask for a password or email account. Making the user feel safe knowing that their personal information is safe. Another good thing about Google auths is that it is fast to log in with it, removing the time it takes to put in a password and account name. In conclusion, using Google auth will be a great start for making your website.
links used for this blog:
https://www.youtube.com/watch?v=bOd4eFqIg00&t=323s
https://en.wikipedia.org/wiki/OAuth
https://developers.google.com/identity/protocols/oauth2
https://www.youtube.com/watch?v=ZDuRmhLSLOY
https://www.youtube.com/watch?v=HtJKUQXmtok
| gagecantrelle | |
1,874,875 | Material UI Mastery: Elevate Your Web Design with Google's Premium UI Framework | The world of web development thrives on efficiency and aesthetics. Material UI swoops in, offering a... | 0 | 2024-06-03T03:35:53 | https://dev.to/epakconsultant/material-ui-mastery-elevate-your-web-design-with-googles-premium-ui-framework-2edf | webdev | The world of web development thrives on efficiency and aesthetics. Material UI swoops in, offering a powerful solution for both. This beginner-friendly guide equips you to leverage Material UI and craft stunning, user-friendly web applications.
## What is Material UI?
Material UI is a React component library based on Google's Material Design guidelines. Material Design emphasizes clean layouts, bold colors, and intuitive interactions. Material UI provides a rich set of pre-built, customizable components that adhere to these principles. Think buttons, text fields, cards, menus – the list goes on. By incorporating these components into your React applications, you can achieve a modern, consistent, and visually appealing user experience.
[Write Your First Break and Trial Strategy In Pine Script: Guide to Crypto Trading With Pine Script](https://www.amazon.com/dp/B0CHBYYT8T)
## Why Choose Material UI?
Here's what makes Material UI an attractive option for building modern web applications:
• Rapid Prototyping: Material UI's extensive library of pre-built components allows you to quickly assemble prototypes and user interfaces. This streamlines the development process and lets you focus on core functionalities.
• Consistent Design Language: Enforcing Material Design principles through Material UI components ensures a unified and polished user experience throughout your application.
• Customization Power: While Material UI offers pre-built components, it doesn't restrict customization. You can tailor the look and feel of components to match your specific design needs using themes, props, and overrides.
• Performance Optimization: Material UI components are built with performance in mind. This translates to a faster and more responsive user experience for your web application.
• Active Community and Resources: Material UI boasts a large and active community of developers. This translates to an abundance of resources, tutorials, and support readily available online.
## Taking Your First Steps with Material UI
Ready to embark on your Material UI journey? Here's a breakdown to get you started:
1.Installation: Material UI offers multiple installation methods. You can use npm or yarn to install the library and its dependencies within your React project.
2.Hello World with Material UI: Start with a simple example. Import a basic component like a button (Button from '@mui/material/Button) and render it in your React application. Experiment with different button variants (contained, outlined, text) to witness the styling capabilities.
3.Exploring Components: Material UI provides a vast array of components. Dive into the official documentation to explore the different categories – buttons, forms, navigation, layouts, and more. Familiarize yourself with the available components and their functionalities.
4.Customization Magic: While Material UI components come pre-styled, customization is key. Explore theming options to create a custom look and feel for your application. You can also leverage props and overrides to fine-tune the appearance and behavior of individual components.
## Beyond the Basics
As you gain confidence with Material UI, delve deeper into its potential:
• Advanced Interactions: Material UI supports complex interactions like animations, drag-and-drop functionalities, and more. This allows you to create dynamic and engaging user experiences.
• Form Handling: Building forms with Material UI is a breeze. Utilize components like TextField, Select, and Checkbox to create user-friendly forms for data collection and interaction.
• Integration with Other Libraries: Material UI plays well with other popular React libraries like Redux and React Router. This enables seamless integration for complex application functionalities.
## Building Beautiful and Functional Web Applications
Material UI empowers you to streamline the development process while crafting beautiful and functional web applications. With its extensive component library, adherence to Material Design principles, and customization options, Material UI stands as a valuable asset for both beginners and experienced React developers. So, dive into the world of Material UI and witness the transformation it brings to your web development endeavors.
| epakconsultant |
1,873,823 | Step-by-Step Guide to Building Your Own Notes App | Project:- 2/500 Notes App Project Description The Notes App is a simple, user-friendly... | 27,575 | 2024-06-03T03:35:00 | https://dev.to/raajaryan/notes-app-project-3dp6 | javascript, beginners, opensource, tutorial | > Project:- 2/500 Notes App Project
## Description
The Notes App is a simple, user-friendly application designed to help users create, edit, and manage their personal notes. This app allows users to quickly jot down thoughts, reminders, and important information in a clean and organized interface. With the Notes App, users can easily access and manage their notes from any device with a web browser.
## Features
- **Create Notes**: Add new notes with a title and content.
- **Edit Notes**: Modify existing notes to update information.
- **Delete Notes**: Remove notes that are no longer needed.
- **Search Notes**: Quickly find notes by searching through titles and content.
- **Responsive Design**: Access the app on various devices with a seamless experience.
## Technologies Used
- **JavaScript**: Provides the functionality for creating, editing, and managing notes.
- **HTML**: Structures the web pages of the app.
- **CSS**: Styles the app for a clean and modern look.
## Setup
To set up and run the project, follow these steps:
1. **Clone the Repository**
```bash
git clone https://github.com/deepakkumar55/ULTIMATE-JAVASCRIPT-PROJECT.git
cd Intermediate Projects/1-notes_app
```
2. **Open the Project**
- Open the `index.html` file in your preferred web browser to view the app.
3. **Development Setup**
- If you want to make changes to the app, you can use a code editor like Visual Studio Code.
- Open the project folder in your code editor.
- Edit the HTML, CSS, and JavaScript files as needed.
4. **Hosting the App**
- For local development, you can use a simple HTTP server like `http-server`:
```bash
npm install -g http-server
http-server
```
## Contribution
Contributions are welcome! If you'd like to improve the Notes App, please follow these steps:
1. **Fork the Repository**
- Click the "Fork" button at the top right corner of the repository page on GitHub.
2. **Clone Your Fork**
```bash
git clone https://github.com/deepakkumar55/ULTIMATE-JAVASCRIPT-PROJECT.git
cd Intermediate Projects/1-notes_app
```
3. **Create a Branch**
```bash
git checkout -b feature/your-feature-name
```
4. **Make Your Changes**
- Implement your changes in the codebase using your preferred code editor.
- Ensure your changes adhere to the coding standards and style of the project.
5. **Commit Your Changes**
```bash
git add .
git commit -m "Add your feature description"
```
6. **Push to Your Fork**
```bash
git push origin feature/your-feature-name
```
7. **Submit a Pull Request**
- Go to the original repository on GitHub.
- Click on "Pull Requests" and then click the "New Pull Request" button.
- Select your feature branch from the head fork and the main branch from the base fork.
- Submit the pull request with a descriptive title and detailed description of your changes.
## Get in Touch
If you have any questions or need further assistance, feel free to open an issue on GitHub or contact us directly. Your contributions and feedback are highly appreciated!
---
Thank you for your interest in Notes app project. Together, we can build a more robust and feature-rich application. Happy coding!
| raajaryan |
1,874,873 | Multi-Agent System | All of us have heard about the Mixture-of-Experts (MoE) architecture for LLMs. MoE divides models... | 0 | 2024-06-03T03:28:55 | https://dev.to/akkiprime/multi-agent-system-4d95 | ai, agents, autonomous, superagi | All of us have heard about the Mixture-of-Experts (MoE) architecture for LLMs. MoE divides models into separate sub-networks (or “experts”), each specializing in a subset of the input data, to jointly perform a task. A mixture of Expert architectures enables large-scale models, even those comprising many billions of parameters, to greatly reduce computation costs during pre-training and achieve faster performance during inference time. Broadly speaking, it achieves this efficiency through selectively activating only the specific experts needed for a given task, rather than activating the entire neural network for every task.
What if we adopt the principles of MoE on the agent level? Agents, like LLMs, become hard to scale as we add multiple responsibilities to them. This simple yet ground-breaking insight led us to develop the world’s first Multi-Agent System (MAS) which is also deployed in production. But we dive deeper, let’s start with the basics of Single-Agent Architecture and how it can be extended to MAS.
## Agent – The fundamental building block
An agent, in the context of Large Language Models (LLMs), is a system that uses an LLM as the fundamental computational component to construct a plan with appropriate reasoning to tackle any challenge using the tools and resources at its disposal. It is similar to a human, who, given a problem, will devise a strategy and solve the problem utilizing the tools required to tackle the problem. The LLM acts similarly to the human brain in the Agent. For any given task, one will not solve it as such. The ideal way is to break it down into one or more smaller tasks that can be done sequentially or independently to solve the task. An agent will also do the same thing. The LLM will plan out the way it intends to solve the task. To accomplish any of the intermediate steps, the plan usually calls for the use of one or more tools available to the agent. Apart from the LLM and the tools the agent will also have other components for its proper intended functioning.
Broadly, there are three main components of an agent:
- A prompt
- Memory for the Agent
- The Tools
The prompt will define the way the system is going to behave and work. It will define the set of goals the agent must achieve, while also having the constraints it must follow to achieve these goals. Think of the prompt as the blueprint for our multi-agent system. It’s like the master plan that outlines what each agent needs to achieve and how they should go about doing it. Without this guidance, agents would lack direction and might wander aimlessly. So, the prompt essentially serves as the compass that keeps our system on course, ensuring that all agents are working towards common objectives within a defined framework. This prompt is also the major bottleneck in increasing the complexity of a single agent. To build complex systems, we divide the responsibilities between multiple agents so that the prompt of every agent remains simple.
Memory is the backbone of our LLM agents. It acts like their personal archive of knowledge and experiences. Similar to how humans draw from past experiences to make decisions, LLM agents utilize their memory to understand context, learn from past interactions, and make informed choices. Memory can simply be just passing the conversation history back to the LLM, or it can even be passing the extracted semantic information from the conversation and giving it to the LLM.
Tools are the Swiss Army knives of our agents, providing them with specialized capabilities to tackle various tasks effectively. These tools can be APIs, executable functions, or other services that help agents finish their tasks.
Now that we have understood the basic components of an Agent, let’s see how these components work together in a single-agent system.
## Single-Agent System
A single-agent system consists of one particular AI agent that is equipped with multiple tools at its disposal to achieve any given problem. These systems are designed to handle tasks autonomously, leveraging the combined capabilities of the tools along with the reasoning capability of the LLM. The agent will devise a step-by-step plan that is to be followed to achieve the user goal. Once the plan is formulated, the agent will use the required tools to complete each of the available steps. Once each steps are completed, the outputs that were achieved at each stage can be clubbed together to get the final output.
There are different ways a particular user goal can be achieved. The plan that the LLMs will come up with depends on the availability of tools, its overall goal, and the constraints that it has to follow. The prompt, that controls the behavior of the agent should be therefore crafted in such a way that it works in the way we want it to work, and will be utilizing the resources efficiently to achieve the goals.
Architecture:

## Why are Single-Agent Systems still relevant?
There are a few advantages to going with a Single-Agent system architecture. Firstly, simplicity, with just one agent handling all tasks, the system becomes easier to design, implement, and manage. The overhead of organizing communication between multiple agents will not be there.
Single-agent systems often boast greater coherence and consistency in decision-making. With a single agent in control, there’s no possibility of conflicting goals or actions among multiple agents. This can result in more predictable and stable behavior, making it easier to understand and debug the system.
Single-agent systems are typically more suitable for tasks that don’t require complex coordination. In fields and areas where centralized decision-making is required, a single-agent system will be quite efficient and will perform well in achieving the user goal.
## Limitations of Single-Agent System
Single agents are often designed with a narrow focus, which can limit their ability to handle tasks outside their immediate domain. This limitation can pose challenges in environments where tasks are diverse or rapidly changing. Their narrow focus can hinder their ability to handle tasks beyond their immediate domain.
Scaling a single agent for more extensive or varied tasks often requires substantial redesign. When faced with the need to handle a broader range of tasks or increased complexity, simply adding more capabilities to a single agent may not be sufficient. Furthermore, scaling a single agent may introduce performance bottlenecks or efficiency issues.
Single-agent systems are also limited by memory constraints and processing capabilities. Since all tasks and responsibilities are concentrated within a single agent, it must contend with the finite resources available to it, including memory and processing power.
## The shift towards Multi-Agent System Architecture
The exploration of Single-Agent Systems has highlighted significant limitations, particularly in handling complex, dynamic tasks and scalability issues. This sets the stage for the introduction of Multi-Agent Systems (MAS), which offer a robust framework capable of overcoming these challenges. In MAS, architecture, there are multiple independent agents who all work together to solve complex tasks.
In MAS, individual agents have their own responsibilities, characterized by their prompts and tools. Unlike single-agent systems, where one agent is responsible for all tasks, MAS allows for specialization and collaboration among several agents. This approach not only enhances efficiency but also improves the system’s ability to handle more complex and varied tasks.
Adding more agents to the system can extend its capabilities without the need for significant redesign. When faced with increasing demands or expanding task domains, incorporating additional agents offers a scalable solution that can accommodate growth seamlessly. Unlike single-agent systems, where scaling often requires substantial modifications to the existing architecture, multi-agent systems can adapt more readily to changing requirements by simply adding new agents with specialized capabilities. The redundancy inherent in multi-agent systems provides built-in fault tolerance and resilience. If one or more agents malfunction, the system can still perform the right intended work as the rest of the agents would come to a mutual agreement.
Architecture:

## Concept and Structure of Multi-Agent Systems
Multi-Agent system consist of multiple intelligent agents, each capable of performing tasks autonomously but designed to work collaboratively toward a common goal. The structure of MAS allows for distributed problem-solving and decision-making, which significantly enhances the system’s overall efficiency and effectiveness. Each agent in a MAS can specialize in different tasks or aspects of a problem, bringing a diverse set of skills and perspectives to the table. Unlike single-agent systems, control in MAS is distributed among multiple agents, which reduces bottlenecks and single points of failure. Agents in a MAS can communicate and coordinate with each other, sharing information and decisions to optimize outcomes. The system is inherently modular, allowing for the addition, removal, or modification of agents without disrupting the entire system.
## Agent to Agent Communication Protocol (AACP)
In a Multi-Agent system, the Agent-to-Agent Communication Protocol (AACP) is designed to facilitate structured and efficient communication among agents, pivotal for achieving consensus and addressing complex problems collaboratively. This protocol is instrumental in enhancing the overall system performance by leveraging the diverse insights and capabilities of individual agents, each characterized by a unique persona responding to system prompts.
The AACP adopts a dual-faceted communication architecture:
1. Hierarchical Communication Flow: This structure allows for the dissemination of information across different levels of the system hierarchy, enabling superior agents to coordinate and direct the actions of subordinate agents efficiently.
2. Lateral Communication: Agents situated at the same hierarchical level possess the capability to engage in direct communication. This feature is essential for collaborative problem-solving and task execution, facilitating rapid information exchange and coordination among peers.
The reconfigurability of the communication flow, tailored to the specific requirements of the task at hand, underscores the flexibility and adaptiveness of the AACP.
## Analysis of single and multi-agent systems
When comparing single-agent and multi-agent systems, several key differences emerge:
- Scalability: MAS are inherently more scalable than single-agent systems due to their distributed nature. They can handle more complex tasks by dividing the workload among multiple agents.
- Robustness and Reliability: Multi-agent systems are generally more robust and reliable. The failure of one agent does not cripple the system, and others can take over or redistribute the tasks.
- Flexibility and Adaptability: MAS can adapt to changes in the environment or task requirements more effectively. They can reconfigure themselves, with agents taking on new roles as needed.
## Two Design Choices for MAS
In this section, we will highlight two possible design patterns for MAS. But before we delve into the differences between these two patterns, let’s highlight their commonalities. The core premise of MAS is that the observation from the environment will be passed to multiple experts and different experts will recommend different actions. Then there will be an aggregation layer where these recommendations will analyzed and some of them will be approved. Now the two flavors discussed below differ on just one parameter – do we consult all the experts or do we selectively invoke relevant experts only?
## Routing-Based Multi-Agent System
In a routing-based MAS, the orchestration acts as a routing layer. Depending on the message sent by the user, it will decide the agents it needs to invoke. The invoked agents will interact among themselves regarding the message and will decide on what is the best action to take and communicate it effectively to the user. By routing, the orchestrator will be solely responsible for identifying the right agents and communicating the same to the user. The main drawback of this is that the routing layer will tend to become the single point of failure. If the router decides not to invoke an agent that is required, or if it invokes some other agent that is not needed, there might be discrepancies in the communication to the user.
## Broadcast-Based Multi-Agent System
The Broadcast-Based MAS architecture represents a generalized evolution of the Routing-Based MAS, effectively eliminating the Routing Layer that acts as a potential single point of failure. In instances where the Routing Layer mismanages the user query, the system’s integrity may be compromised. To enhance robustness and circumvent this vulnerability, the Routing Layer is omitted, permitting the free dissemination of information to all corresponding agents in unison. This way all the agents will get the input, and they will decide whether or not to give their output for the aggregation. This way it will ensure that there is no communication mishap between any of the agents.
## Why do we believe the Multi-Agent System is a fundamental breakthrough?
The collaborative nature of multi-agent systems brings several benefits, especially in complex and dynamic environments
- Enhanced Problem-Solving Capabilities: By leveraging the diverse capabilities of various agents, MAS can tackle complex problems more effectively than single-agent systems.
- Increased Efficiency: Collaboration among agents often leads to more efficient use of resources, as tasks are allocated based on the specialization of each agent.
- Resilience to Uncertainty and Change: Multi-agent systems are better equipped to handle uncertainty and changes in the environment, as they can quickly reorganize and adapt.
Besides, the above-mentioned benefits, Multi-Agents systems have a strong resemblance to systems that have stood the test of time. For example, the hierarchal organizational structure that powers some of the largest organizations in the world is a lot similar to multi-agent systems. Even the human body is a composition of multiple organ systems. These resemblances instill our confidence in that MAS is going to be an enduring concept in the evolution journey of agents. | akkiprime |
1,874,872 | Next.js Mastery: Unlock the Power of React for Seamless Web Development | The web development landscape is constantly evolving, demanding frameworks that can keep pace. Enter... | 0 | 2024-06-03T03:28:51 | https://dev.to/epakconsultant/nextjs-mastery-unlock-the-power-of-react-for-seamless-web-development-5fln | web3, webdev | The web development landscape is constantly evolving, demanding frameworks that can keep pace. Enter Next.js, a powerful React framework designed to simplify the creation of fast, SEO-friendly, and scalable web applications. Whether you're a React enthusiast or a curious newcomer, Next.js offers a compelling set of tools to elevate your development experience.
## What is Next.js?
Next.js sits on top of React, providing a collection of features and conventions specifically tailored for building modern web applications. It offers several key advantages over vanilla React:
• Pre-rendering for SEO and Performance: Next.js allows you to choose between Static Site Generation (SSG) and Server-side Rendering (SSR) for your pages. SSG pre-renders your content at build time, resulting in blazing-fast load times and excellent SEO. SSR generates content on the server for each request, ideal for dynamic applications that require frequent data updates.
• Automatic Code Splitting: Next.js automatically splits your codebase into smaller bundles, ensuring only the necessary code is loaded for each page. This significantly improves initial page load speeds and user experience.
• Built-in Routing: Next.js offers an intuitive file-based routing system. Simply create React components within designated folders, and Next.js automatically maps them to corresponding routes in your application.
• API Routes: Next.js allows you to create serverless functions directly within your application using API routes. This lets you handle data fetching, authentication, and other server-side logic without the need for a separate backend server.
## Getting Started with Next.js
Building your first Next.js application is surprisingly simple. Here's a quick guide to get you started:
1. Create a New Project: Utilize the npx create-next-app command to set up a new Next.js project. This command will create a project directory with the necessary files and dependencies pre-configured.
2. Explore the Project Structure: Next.js projects follow a well-defined structure. The pages directory houses your React components representing individual pages of your application. The components directory holds reusable UI components, promoting code organization and maintainability.
3. Build and Run: Once you've familiarized yourself with the project structure, run npm run dev in your terminal to start the development server. This will launch your application in a local environment, allowing you to see your changes reflected instantly as you code.
## Next.js Essentials for Beginners
As you embark on your Next.js journey, here are some fundamental concepts to grasp:
• Understanding Components: Next.js leverages React components to build your application. Each component represents a reusable UI element, making it easy to create complex user interfaces.
• Data Fetching: Next.js offers various ways to fetch data for your application. You can use getStaticProps for SSG or getServerSideProps for SSR to retrieve data at build time or on each request, respectively.
• Styling Your Application: Next.js provides flexibility when it comes to styling. You can use CSS modules for scoped styles, global CSS files for application-wide styles, or even integrate with popular CSS-in-JS libraries like Styled Components.
• Routing and Navigation: The file-based routing system in Next.js makes navigation a breeze. Simply create new pages within the pages directory, and Next.js handles the routing automatically. You can also leverage the built-in Link component for smooth navigation between pages.
[Pinescript: multi-timeframe indicators in trading view: Learn Pinescript and Muti-timeframe analysis](https://www.amazon.com/dp/B0CGXXCCHD)
## Building on Your Foundation
Once you've mastered the basics, Next.js offers a wealth of features to explore further:
• Image Optimization: Next.js offers built-in image optimization techniques, ensuring your images load quickly and efficiently without sacrificing quality.
• Automatic Code Splitting: As mentioned earlier, Next.js automatically splits your code into smaller bundles, improving initial load times. You can further customize this behavior for granular control.
• Headless CMS Integration: Next.js integrates seamlessly with popular headless CMS solutions like Contentful and Prismic, allowing you to manage your website content efficiently.
## Why Choose Next.js?
With its focus on performance, SEO, and developer experience, Next.js stands out as a powerful framework for building modern web applications. Here's why you might consider Next.js for your next project:
• Faster Development Time: Next.js streamlines the development process by providing a pre-configured environment and features like automatic code splitting and routing.
• Improved User Experience: The focus on performance and SEO in Next.js translates to a faster, more responsive, and search-engine-friendly user experience.
•Scalability: Next.js applications are inherently scalable.
| epakconsultant |
1,874,871 | Mastering Framer: Elevate Your Web Design with Advanced Techniques | In the ever-evolving landscape of web development, innovative tools emerge to streamline the creation... | 0 | 2024-06-03T03:23:35 | https://dev.to/epakconsultant/mastering-framer-elevate-your-web-design-with-advanced-techniques-70 | In the ever-evolving landscape of web development, innovative tools emerge to streamline the creation process. Framer stands out as a powerful contender, offering a unique blend of design and prototyping functionalities. Whether you're a seasoned designer or a curious beginner, Framer can elevate your website building experience.
## What is Framer?
Framer is more than just a design tool. It's a comprehensive platform that allows you to design, prototype, and animate user interfaces (UIs) – all within a single workspace. Framer uses code (specifically, JavaScript) to build interfaces, giving you greater control and flexibility compared to traditional design software. This code-based approach might seem intimidating at first, but fear not – Framer offers a gentle learning curve with a beginner-friendly interface and ample resources.
## Why Choose Framer?
Here are some compelling reasons to consider Framer for your next website project:
• Prototyping Magic: Framer excels at creating interactive prototypes. Imagine crafting a website where users can click buttons, navigate through pages, and experience real-time interactions – all within the design phase itself. This allows for superior user testing and iteration before any code is written.
[A Beginners Guide to Integrating ChatGPT into Your Chatbot](https://www.amazon.com/dp/B0CNZ1T4WX)
• Seamless Design-to-Development Workflow: Framer bridges the gap between design and development. The code you use to design your UI elements can often be directly exported for use in the final website. This eliminates the need for lengthy handoff processes and ensures a consistent look and feel from design to development.
• Component-Based Design: Framer promotes a component-based design approach, where reusable UI elements are built and stored in libraries. This fosters consistency, efficiency, and easier maintenance of your website.
• Thriving Community and Resources: Framer boasts a vibrant community of designers and developers. There's a wealth of tutorials, documentation, and plugins readily available to help you on your Framer journey.
Getting Started with Framer
Embarking on your Framer exploration is a breeze. Here's a quick roadmap:
1. Sign Up and Explore: Head over to [Framer] to create a free account. Framer offers a generous free plan with enough features to get you started. Once you're in, take some time to explore the interface and familiarize yourself with the basic tools.
2. Learn the Basics: Framer provides excellent learning resources, including interactive tutorials and workshops. These resources will teach you the fundamentals of building interfaces with Framer, including working with components, animations, and interactions.
3. Practice Makes Perfect: The best way to learn Framer is by diving in and practicing. Start with a simple website design and gradually build upon your skills. There are plenty of online challenges and community projects you can participate in to hone your craft.
## Beyond the Basics
As you become comfortable with Framer, you can unlock its true potential:
• Advanced Animations: Framer allows you to create complex and engaging animations, breathing life into your website.
• Custom Interactions: Go beyond basic clicks and taps. Craft unique interactions that respond to user behavior, creating a more dynamic and immersive website experience.
• Collaboration Features: Framer facilitates seamless collaboration between designers and developers. Team members can work on the same project simultaneously, ensuring everyone stays on the same page.
## Crafting Stunning Websites with Framer
Framer empowers you to create not just functional websites, but truly stunning ones. With its intuitive interface, powerful features, and collaborative nature, Framer streamlines the design and development process, allowing you to focus on crafting exceptional user experiences.
So, are you ready to explore the world of Framer? With its combination of design muscle and development prowess, Framer can be your secret weapon to crafting captivating websites that leave a lasting impression.
| epakconsultant | |
1,874,870 | Top Trends in Solar Garden Lights Manufacturing | highly recommend Patterns in Solar Yard Illuminations Production Carrying Illumination towards Your... | 0 | 2024-06-03T03:20:43 | https://dev.to/theresa_mccraryjs_77dd382/top-trends-in-solar-garden-lights-manufacturing-3ok | solarlights, solarledlights | highly recommend Patterns in Solar Yard Illuminations Production Carrying Illumination towards Your Yard
Are now actually you trying to find an method this is certainly affordable illuminate your yard later in the day Solar yard illuminations are now actually an excellent
choice
for people who want to conserve cash on electrical energy expenses as well as add to sustainability this is certainly ecological. we are going to speak about the trends which can be top garden this is certainly manufacturing this is certainly solar well as precisely how they are able to easily profit you plus your yard
Advantages of Solar Yard Illuminations
The power that is certainly main of yard illuminations is clearly which they have no need for power this is certainly work this is certainly electrical. They function through taking in sunshine for the in addition to keeping it within their batteries which can be electric which energy the illuminations when you look at the day. This suggests that these are generally actually most certainly not just affordable, however likewise environmentally friendly while they did not add to skin tightening and discharges
Development in Solar Yard Illuminations
The pattern that is most this is certainly recent yard this is certainly Solar Post Lights production is clearly using ingenious innovations, like movement sensing units, that could easily spot motion along with turn on the illuminations immediately. This include most certainly not just conserves power, however likewise improves safety and safety through deterring intruders. Furthermore, some producers are now actually yard this is certainly currently providing is solar along side internet providers, enabling individuals towards command the illuminations from another location through a phone application this is certainly mobile
Security of Solar Yard Illuminations
Solar yard illuminations are now actually towards which can be risk-free while they did not produce gases which can be hazardous even radiation. Furthermore, these are generally actually developed towards endure weather this is certainly rainfall that is warm this is certainly severe in addition to chilly. Nevertheless, it is vital towards guarantee that the illuminations are now actually put up safely when you look at the ground towards prevent mishaps. Some producers currently deal solar yard illuminations along side surge styles that creates each of them simple towards set up along with Solar Garden Lights
Techniques to Utilize Solar Yard Illuminations
Utilizing yard that is solar is actually easy as well as simple. All of you require to perform is actually location the illuminations in an area where they can easily take in sunshine throughout the day. Preferably, you ought to select a place that gets guide sunshine for a minimum of 6 hrs each day. After that, turn on the illuminations at sunset as well as delight in the background lighting in your yard
Solution in addition to High premium this is certainly top of Yard Illuminations
When yard this is certainly purchasing is solar, it is in reality essential to select a producer that is dependable delivers supreme quality items in addition to customer care that is outstanding. To locate producers that deal guarantees in addition to solution that is guarantee that is after-sales the illuminations are now actually constantly in leading problem. Furthermore, inspect the evaluations in addition to scores regarding the producer in addition to items ahead of purchasing Outdoor Solar Lights
Request of Solar Yard Illuminations
Solar yard illuminations could possibly be employed in an array of setups, composed of domestic yards, parks, in addition to community areas. These are generally actually ideal for illuminating paths, driveways, in addition to decks, in addition to can very quickly likewise be actually utilized towards produce a atmosphere this is certainly charming outside suppers in addition to events. Furthermore, they are often utilized for security in addition to safety and safety functions, as discussed previously
Source: https://www.beslonsolarlight.com/solar-post-lights
| theresa_mccraryjs_77dd382 |
1,874,852 | Why Choose Quantitative Trading | Summary Many people think complex trading strategies as a starting point when discussing... | 0 | 2024-06-03T03:19:47 | https://dev.to/fmzquant/why-choose-quantitative-trading-3oi1 | trading, cryptocurrency, fmzquant, market | ## Summary
Many people think complex trading strategies as a starting point when discussing quantitative trading, and inadvertently put a layer of mystery on quantitative trading. In this section, we will try to make a simple "sketch" for quantitative trading in an easy-to-understand language, revealing his mystery, and I believe that even a beginner can easily understand.
## The difference between quantitative trading and subjective trading
Subjective trading pay more attention to artificial analysis and sense of market price. Even if there is a trading signal, they will selectively place orders, preferring to miss the trading chances and not doing anything wrong. The human feeling is complex and unreliable, and most traders often switch to another method in the event of a continuous loss, which comes with strong randomness, easy to be plagued by profit and loss, making it difficult to stabilize profits.
Quantitative trading develop a consistent trading strategy through an understanding of the trading. In the trading, all the trends are treated equally, and all the open positions are systematically processed. It is better to do something wrong than to miss it. It also has a complete evaluation system, through historical data backtesting, to determine which type of market and variety is more suitable for the strategy, and to achieve profitability with a variety of strategies and varieties.
In short, subjective trading are the basis for quantitative trading and quantitative trading are the refinement of subjective trading. Subjective trading are more like martial arts. In the end, success or not, talents account for the majority, some people spend their whole life still can't success. Quantitative trading is more like fitness. As long as you work hard, you can train your muscles even if you don't have the talent.
## Is quantitative trading better than subjective trading?
A successful subjective trader, in some way, is also a quantitative trader. Because a successful subjective trader, there must be a set of rules and methods of its own, that is, the trading system. Successful subjective trading must be based on trading discipline and trading rules, and the execution of trading rules is actually a quantitative part of subjective trading.
On the contrary, a successful quantitative trader must also be an excellent subjective trader, because the development of quantitative trading strategies is actually the crystallization of one's trading philosophy. If a cognition and understanding of the market is wrong from the beginning, then the developed trading strategy has long been difficult to profit.
Therefore, from a profit perspective, the key factor in determining whether a trader will ultimately succeed is the trading philosophy, not whether it is a subjective trading or a quantitative trading. Quantitative trading seem to be superficial on the surface, and the essence of their profits is not essentially different from subjective trading They are like the two-sided opposition and unity of one thing.
But there is no denying that quantitative trading does have many advantages from trading instruments.
• Backtesting is faster. To test a trading strategy, you need to calculate a large amount of historical data, and the quantitative trading can calculate the result within a few minutes. This speed is many times faster than subjective trading
• It is more scientific, evaluating whether a strategy is excellent, relying on data (eg, Sharpe ratio, maximum retracement rate, annualized income) rather than self-explanatory talks.
• More opportunities, there are thousands of trading varieties around the world, subjective trading can not focus on them all at the same time, but quantitative trading can be market-wide focusing all time, never miss any trading opportunities, increase profitability.
## Does quantitative trading 100% works?
It depends, it is a very difficult thing to stick to it for a long time. Making money or not does not depend on the quantitative trading itself. It is only a tool. Quantitative trading only implements the trading ideas in a programmatic, regular, and quantitative manner. The procedure replaces only the execution power. The hard part is to make money in a long-term and stable way, because the market is game-changing and dynamic, and the trading ideas must follow the market transformation.
## Quantitative Trading Risk
Quantitative trading is also risky, why? Because quantitative trading is to mine the rules in historical data, form a trading strategy. But the financial market is an ecological system. Its law and humanity are an interactive dynamic process. In the final analysis, it is the human market. The laws of the market will be affected by human nature, and the greed and fear between human beings will change with the changes of the market. There are few unchanging laws in the market, and even the most powerful trading strategies are difficult to cope with such sudden changes.
## To sum up
Through the above explanation, we can see that quantitative trading is not a unique trading method, it is just a trading tool that helps us analyze trading logic and improve trading strategies. Whether you are a value believer or a technical analysis believer, whether you are doing stocks, bonds, commodities or options, you can actually quantitative them. Quantitative trading's weapons in the hands of traders are market evidence and rationality. It has a hugh advantage compared to traders who make decisions based on personal experience.
## Next section notice
Quantitative trading is only a trading method. The trading strategy is only the carrier of trading ideas, and the program executes each trading process. The next section will take you through the complete life cycle of quantitative trading, which will include: strategy design, model building, backtesting tuning, simulation trading, real market trading, strategy running monitoring, etc.
After-school exercises
1. What is the most important difference between quantitative trading and subjective trading?
2. What are the advantages of quantitative trading compared to subjective trading?
From: https://blog.mathquant.com/2019/04/10/1-2-why-choose-quantitative-trading.html | fmzquant |
1,874,850 | Domain Name Magic: Demystifying AWS Route 53 | Domain Name Magic: Demystifying AWS Route 53 Domain names are the foundation of web... | 0 | 2024-06-03T03:07:16 | https://dev.to/virajlakshitha/domain-name-magic-demystifying-aws-route-53-256n | # Domain Name Magic: Demystifying AWS Route 53
Domain names are the foundation of web presence. They are what users type into their browsers to reach your websites and applications. AWS Route 53, a fully managed Domain Name System (DNS) service, plays a crucial role in routing internet traffic to your resources.
This blog post delves into the world of AWS Route 53, exploring its core functionalities and how it empowers developers, businesses, and organizations to build robust, scalable, and reliable internet-facing applications.
### What is AWS Route 53?
AWS Route 53 is a highly available and scalable DNS service that provides a range of features, including:
- **Domain registration:** Register your domain names directly through Route 53, simplifying domain management.
- **DNS hosting:** Host your DNS records, enabling name resolution for your websites and applications.
- **Health checks:** Monitor the health of your resources and automatically route traffic away from unhealthy endpoints.
- **Traffic routing:** Distribute traffic across multiple endpoints, ensuring high availability and resilience.
- **Geolocation routing:** Direct traffic to specific locations based on user geography.
- **Latency-based routing:** Route traffic to the endpoint with the lowest latency for the user.
- **Failover routing:** Automatically switch traffic to a backup endpoint if the primary endpoint fails.
- **Weighted routing:** Allocate different percentages of traffic to multiple endpoints, enabling gradual rollout of new features or applications.
- **Alias records:** Point your domain names to other AWS services, such as Amazon S3 buckets or Elastic Load Balancers.
### Unlocking the Power of Route 53: Use Cases
Route 53's versatility makes it a core component for various web-facing applications and services. Let's explore five illustrative use cases:
**1. High Availability for E-Commerce Applications:**
Imagine an online store experiencing a sudden surge in traffic during a major holiday sale. This could overwhelm your website's servers, causing downtime and lost revenue. Route 53's health checks and failover routing come to the rescue.
You can configure health checks to monitor the availability of your web servers. If a server becomes unresponsive, Route 53 automatically routes traffic to a healthy backup server, ensuring uninterrupted service for your customers. This minimizes downtime and protects your online store from outages.
**2. Global Content Delivery with Latency-Based Routing:**
Serving static content, such as images and videos, from different regions across the globe can significantly reduce latency for your users. Route 53's latency-based routing allows you to distribute traffic across multiple CloudFront edge locations.
The service automatically directs users to the closest edge location, resulting in faster loading times and enhanced user experience. This approach is especially beneficial for applications with global user bases, optimizing content delivery and improving user satisfaction.
**3. Secure Access with Geolocation Routing:**
Certain regions may have legal or regulatory constraints that restrict access to specific content. Route 53's geolocation routing feature enables you to route traffic based on the user's geographical location.
For example, you can block access to specific content in a particular country while allowing it in others. This ensures compliance with regional regulations while providing tailored content experiences for different user groups.
**4. Gradual Feature Rollout with Weighted Routing:**
Introducing new features or functionality to your application can be risky. A sudden rollout to all users might cause unexpected issues. Route 53's weighted routing provides a solution.
You can allocate a small percentage of traffic to the new feature, gradually increasing the weight as you gain confidence. This allows you to test the feature in production, monitor user feedback, and identify any potential problems before fully deploying it to all users.
**5. DNS-Based Authentication for Secure APIs:**
Securely authenticating API requests is crucial for protecting sensitive data. Route 53's DNS-based authentication, combined with AWS Certificate Manager (ACM), offers a robust and scalable solution.
You can leverage Route 53 to host DNS records that validate requests originating from authorized clients. ACM issues certificates that validate your domain ownership. This combination ensures that only trusted clients can access your APIs, enhancing security and data integrity.
### Route 53 Alternatives
While Route 53 stands out as a powerful DNS solution, other cloud providers offer similar services:
- **Google Cloud DNS:** Google Cloud's DNS service offers features comparable to Route 53, including health checks, load balancing, and DNSSEC support.
- **Azure DNS:** Microsoft Azure provides DNS hosting and management services with features like custom DNS zones, advanced DNS analytics, and integration with other Azure services.
It's worth noting that Route 53's integration with other AWS services, like CloudFront, S3, and Elastic Load Balancers, offers unique advantages for AWS users.
### Advanced Use Case: Global Load Balancing with Route 53 and AWS Application Load Balancer
Here's a scenario where Route 53, combined with other AWS resources, delivers high-performance and highly available web applications:
**The Scenario:**
An online gaming platform with a global user base needs to handle massive traffic spikes during game releases and events. The platform relies on a distributed architecture with servers in multiple AWS regions.
**The Solution:**
- **Route 53:** Acts as the central DNS entry point, handling requests from users across the globe.
- **AWS Application Load Balancer (ALB):** Distributes traffic across multiple Amazon EC2 instances within each region, ensuring load balancing and high availability.
- **Amazon EC2 instances:** Run the gaming application and handle user requests.
- **Amazon CloudFront:** Caches static content (game assets) at edge locations, minimizing latency for users.
- **Amazon S3:** Stores the game assets and serves as a backend for CloudFront.
**How it Works:**
1. A user accesses the game's website using its domain name, which resolves through Route 53.
2. Route 53 directs traffic to the closest ALB based on the user's location or latency.
3. The ALB distributes the traffic across the healthy EC2 instances within that region.
4. If an EC2 instance becomes unhealthy, the ALB automatically routes traffic away from it.
5. For static content, the ALB directs requests to CloudFront, which serves the content from the closest edge location.
6. CloudFront retrieves the content from S3.
This setup ensures high availability, scalability, and performance for the gaming platform, regardless of user location or traffic volume. Route 53, along with other AWS services, orchestrates traffic flow, load balancing, and content delivery, providing a seamless and reliable experience for the platform's users.
### Conclusion
AWS Route 53 is an indispensable service for any organization seeking to establish and manage a robust online presence. Its comprehensive DNS features, integration with other AWS services, and scalability make it a powerful tool for building reliable, high-performance web applications. Whether you're a small business or a large enterprise, Route 53 empowers you to effectively manage your domain names, route traffic intelligently, and enhance the user experience for your web-facing applications.
**References:**
- [AWS Route 53](https://aws.amazon.com/route53/)
- [AWS Application Load Balancer](https://aws.amazon.com/elasticloadbalancing/application/)
- [Amazon CloudFront](https://aws.amazon.com/cloudfront/)
- [Amazon S3](https://aws.amazon.com/s3/)
- [Google Cloud DNS](https://cloud.google.com/dns/)
- [Azure DNS](https://azure.microsoft.com/en-us/services/dns/)
| virajlakshitha | |
1,874,849 | fcyftyrdytrtes5eses5es | https://gitlab.com/-/snippets/3715468 https://gitlab.com/-/snippets/3715469 https://gitlab.com/-/snip... | 0 | 2024-06-03T03:01:13 | https://dev.to/edi_sadiri_5c7f32732ec930/fcyftyrdytrtes5eses5es-50k0 | https://gitlab.com/-/snippets/3715468
https://gitlab.com/-/snippets/3715469
https://gitlab.com/-/snippets/3715470
https://gitlab.com/-/snippets/3715471
https://gitlab.com/-/snippets/3715473
https://gitlab.com/-/snippets/3715474
https://gitlab.com/-/snippets/3715475
https://gitlab.com/-/snippets/3715476
https://gitlab.com/-/snippets/3715477
https://gitlab.com/-/snippets/3715478
https://www.lesswrong.com/posts/MdoButW7FqTuepwXT/fyftydftgfdtdtdtdtrdtdrt | edi_sadiri_5c7f32732ec930 | |
1,874,847 | Quality Plate Bending Machines for Diverse Metalworking Needs | screenshot-1717035556607.png Quality Plate Bending Machines for Diverse Metalworking... | 0 | 2024-06-03T02:54:15 | https://dev.to/theresa_mccraryjs_77dd382/quality-plate-bending-machines-for-diverse-metalworking-needs-3fj |
screenshot-1717035556607.png
Quality Plate Bending Machines for Diverse Metalworking Needs
Introduction
Do you need to bend metal plates for your school projects or home DIYs? Or are you a professional metalworker looking for a reliable machine? If yes, then you should consider using a quality plate bending machine. This article will explain the advantages, innovation, safety, use, and service of these machines.
Benefits of Plate Bending Machines
Plate bending devices are essential tools for metal operations that are bending
They offer several benefits over handbook methods that are bending such as precision, speed, and consistency
These devices use hydraulic or power like mechanical fold steel dishes towards the needed angle and form
They're able to manage material like different and types, including stainless steel, aluminum, copper, and brass
Innovation in Plate Bending Machines
The growth of dish that are bending evolved in the long run to meet the needs of modern metalworking industries
Today, there is advanced with features such as cnc bending machine controls, automatic measuring systems, and programmable bending sequences
These innovations are making plate machines being bending effective, accurate, and user-friendly
Safety Methods For Plate Bending Machines
Using plate devices that are bending some dangers, especially if you're not really acquainted with their operation
But, following some safety like fundamental can reduce the likelihood of accidents and accidents
A few of these safety guidelines consist of wearing gear like appropriate is protective keeping the task area clean and organized, and avoiding overloading the equipment beyond its capability
Quality Plate Bending Machines for Different Applications
Plate bending machines are versatile tools that can provide metalworking like different
They have been useful in manufacturing industries, construction websites, and metal fabrication workshops
A number of the common applications of plate bending devices consist of making pipelines, ducts, tanks, cylinders, and facades which are architectural
Therefore, you time, price, and energy if you'd like to flex steel plates for almost any project, a great dish bending device can conserve
Repair and Service of plate bending machine
Like most other machine, dish devices which are bending regular maintenance and servicing to function optimally
A number of the tasks that are upkeep cleansing, lubricating, and changing parts being worn-out
It's also advisable to proceed with the recommended servicing schedule or seek assistance like professional you see any noises that are unusual leakages, or malfunctions
By keeping constantly your dish device like bending good condition, it is possible to prolong its lifespan and prevent costly repairs or replacements
Conclusion:
In summary, a quality plate bending machine is a valuable investment for anyone who needs to bend metal plates. These machines offer several advantages over manual bending methods, such as precision, speed, and consistency. They are also safe, user-friendly, and versatile. By following some basic safety tips, learning how to use them effectively, and maintaining them regularly, you can enhance your metalworking skills and productivity.
Source: https://www.liweicnc.com/application/cnc-bending-machine | theresa_mccraryjs_77dd382 | |
1,874,846 | Phòng khám phụ khoa ở Hưng Yên | Việc thực hiện khám phụ khoa tổng quát giúp phụ nữ phát hiện sớm các vấn đề về sức khỏe ở vùng kín và... | 0 | 2024-06-03T02:52:55 | https://dev.to/phongkhamdakhoahungyen/phong-kham-phu-khoa-o-hung-yen-1j5m | Việc thực hiện khám phụ khoa tổng quát giúp phụ nữ phát hiện sớm các vấn đề về sức khỏe ở vùng kín và bảo vệ khả năng sinh sản. Tuy nhiên, việc quan trọng nhất là lựa chọn một cơ sở y tế đáng tin cậy và đảm bảo an toàn, chính xác. Nếu bạn đang phân vân về việc chọn địa chỉ khám phụ khoa tổng quát tại Hưng Yên, hãy đến phòng khám đa khoa Hưng Yên có địa chỉ tại Số 84, KĐT Lạc Hồng Phúc, Phường Nhân Hòa, Thị xã Mỹ Hào, Tỉnh Hưng Yên. Hotline: 1900 638 889 - 0923 638 889. Đây là địa chỉ khám chữa bệnh phụ khoa được nhiều chị em tin tưởng lựa chọn.
https://www.abruzzoairport.com/web/bacsituvan24h/home/-/blogs/dia-chi-kham-phu-khoa-o-hung-yen | phongkhamdakhoahungyen | |
1,874,844 | How to Build a Custom Client Portal In Five Steps | Learn How to Develop a Custom Client Portal Rapidly Effective interactions with clients are critical... | 0 | 2024-06-03T02:50:05 | https://five.co/blog/how-to-build-a-custom-client-portal/ | portal, sql, tutorial, database | <!-- wp:heading -->
<h2 class="wp-block-heading" id="learn-how-to-develop-a-custom-client-portal-rapidly">Learn How to Develop a Custom Client Portal Rapidly</h2>
<!-- /wp:heading -->
<!-- wp:paragraph -->
<p>Effective interactions with clients are critical for every business. In today's world, clients want access to the right information if and when needed, at any time and from anywhere. This is where software can help: by building a <strong>custom client portal</strong>, businesses can streamline client interactions, provide information, and share documents. Designed to be <strong>self-service portals</strong>, these custom portals give clients access to information, provide resources, or visualize important performance data that clients can access on-demand. </p>
<!-- /wp:paragraph -->
<!-- wp:paragraph -->
<p>In this blog post, you will learn how to rapidly develop dedicated portals and business apps for customers, clients, vendors, and partners. </p>
<!-- /wp:paragraph -->
<!-- wp:essential-blocks/table-of-contents {"blockId":"eb-toc-yoixq","blockMeta":{"desktop":".eb-toc-yoixq.eb-toc-container { max-width:610px; background-color:var(\u002d\u002deb-global-background-color); padding:30px; border-radius:4px; transition:all 0.5s, border 0.5s, border-radius 0.5s, box-shadow 0.5s }.eb-toc-yoixq.eb-toc-container .eb-toc-title { text-align:center; cursor:default; color:rgba(255,255,255,1); background-color:rgba(69,136,216,1); font-size:22px; font-weight:normal }.eb-toc-yoixq.eb-toc-container .eb-toc-wrapper { background-color:rgba(241,235,218,1); text-align:left }.eb-toc-yoixq.eb-toc-container .eb-toc-wrapper li { color:rgba(0,21,36,1); font-size:14px; line-height:1.4em; font-weight:normal }.eb-toc-yoixq.eb-toc-container .eb-toc-wrapper li:hover,.eb-toc-yoixq.eb-toc-container .eb-toc-wrapper li.eb-toc-active \u003e a { color:var(\u002d\u002deb-global-link-color) }.eb-toc-yoixq.eb-toc-container .eb-toc-wrapper li a { color:inherit }.eb-toc-yoixq.eb-toc-container .eb-toc-wrapper li svg path { stroke:rgba(0,21,36,1) }.eb-toc-yoixq.eb-toc-container .eb-toc-wrapper li:hover svg path { stroke:var(\u002d\u002deb-global-link-color) }.eb-toc-yoixq.eb-toc-container .eb-toc-wrapper li a,.eb-toc-yoixq.eb-toc-container .eb-toc-wrapper li a:focus { text-decoration:none; background:none }.eb-toc-yoixq.eb-toc-container .eb-toc-wrapper li { padding-top:4px }.eb-toc-yoixq.eb-toc-container .eb-toc-wrapper .eb-toc__list li:not(:last-child) { padding-bottom:4px }.eb-toc-yoixq.eb-toc-container.style-1 .eb-toc__list-wrap \u003e .eb-toc__list li .eb-toc__list { background:#fff; border-radius:4px }","tab":"","mobile":"","editorDesktop":"\n\t\t \n\t\t \n\n\t\t .eb-toc-yoixq.eb-toc-container{\n\t\t\t max-width:610px;\n\n\t\t\t background-color:var(\u002d\u002deb-global-background-color);\n\n\t\t\t \n \n\n \n\t\t\t \n padding: 30px;\n\n \n\t\t\t \n \n \n \n\n \n \n border-radius: 4px;\n\n \n \n\n \n\n\n \n\t\t\t transition:all 0.5s, \n border 0.5s, border-radius 0.5s, box-shadow 0.5s\n ;\n\t\t }\n\n\t\t .eb-toc-yoixq.eb-toc-container:hover{\n\t\t\t \n \n \n\n\n \n\n \n \n \n\n \n \n\n \n\n \n\t\t }\n\n\t\t .eb-toc-yoixq.eb-toc-container .eb-toc-title{\n\t\t\t text-align: center;\n\t\t\t cursor:default;\n\t\t\t color: rgba(255,255,255,1);\n\t\t\t background-color:rgba(69,136,216,1);\n\t\t\t \n\t\t\t \n \n\n \n\t\t\t \n \n font-size: 22px;\n \n font-weight: normal;\n \n \n \n \n \n\n\t\t }\n\n\t\t .eb-toc-yoixq.eb-toc-container .eb-toc-wrapper{\n\t\t\t background-color:rgba(241,235,218,1);\n\t\t\t text-align: left;\n\t\t\t \n \n\n \n\t\t }\n\n\t\t .eb-toc-yoixq.eb-toc-container .eb-toc-wrapper ul,\n\t\t .eb-toc-yoixq.eb-toc-container .eb-toc-wrapper ol\n\t\t {\n\t\t\t \n\t\t\t \n\t\t }\n\n\t\t .eb-toc-yoixq.eb-toc-container .eb-toc-wrapper li {\n\t\t\t color:rgba(0,21,36,1);\n\t\t\t \n \n font-size: 14px;\n line-height: 1.4em;\n font-weight: normal;\n \n \n \n \n \n\t\t }\n\n\t\t .eb-toc-yoixq.eb-toc-container .eb-toc-wrapper li:hover,\n .eb-toc-yoixq.eb-toc-container .eb-toc-wrapper li.eb-toc-active \u003e a{\n\t\t\t color:var(\u002d\u002deb-global-link-color);\n\t\t }\n\n\t\t .eb-toc-yoixq.eb-toc-container .eb-toc-wrapper li a {\n\t\t\t color:inherit;\n\t\t }\n\n .eb-toc-yoixq.eb-toc-container .eb-toc-wrapper li svg path{\n stroke:rgba(0,21,36,1);\n }\n .eb-toc-yoixq.eb-toc-container .eb-toc-wrapper li:hover svg path{\n stroke:var(\u002d\u002deb-global-link-color);\n }\n\n\n\t\t .eb-toc-yoixq.eb-toc-container .eb-toc-wrapper li a,\n\t\t .eb-toc-yoixq.eb-toc-container .eb-toc-wrapper li a:focus{\n\t\t\t text-decoration:none;\n\t\t\t background:none;\n\t\t }\n\n\t\t \n\n .eb-toc-yoixq.eb-toc-container .eb-toc-wrapper li {\n padding-top: 4px;\n }\n\n .eb-toc-yoixq.eb-toc-container .eb-toc-wrapper .eb-toc__list li:not(:last-child) {\n padding-bottom: 4px;\n }\n\n \n .eb-toc-yoixq.eb-toc-container.style-1 .eb-toc__list-wrap \u003e .eb-toc__list li .eb-toc__list{\n background: #fff;\n \n \n \n \n\n \n \n border-radius: 4px;\n\n \n \n\n \n\n\n \n }\n\n\n\t \n\n\n\t\t .eb-toc-yoixq.eb-toc-container .eb-toc-wrapper{\n\t\t\t display:block;\n\t\t }\n\t\t ","editorTab":"\n\t\t \n\t\t .eb-toc-yoixq.eb-toc-container{\n\t\t\t \n\n\t\t\t \n \n\n \n\t\t\t \n \n\n \n\t\t\t \n \n \n\n \n\n \n \n \n\n \n \n\n \n\t\t }\n\t\t .eb-toc-yoixq.eb-toc-container:hover{\n\t\t\t \n \n \n \n \n \n \n\n \n \n \n\t\t }\n\n\t\t .eb-toc-yoixq.eb-toc-container .eb-toc-title{\n\t\t\t \n \n\n \n\t\t\t \n \n \n \n \n\t\t }\n\n\t\t .eb-toc-yoixq.eb-toc-container .eb-toc-wrapper{\n\t\t\t \n \n\n \n\t\t }\n\n\t\t .eb-toc-yoixq.eb-toc-container .eb-toc-wrapper li{\n\t\t\t \n \n \n \n \n\t\t }\n\n .eb-toc-yoixq.eb-toc-container.style-1 .eb-toc__list-wrap \u003e .eb-toc__list li .eb-toc__list{\n \n \n \n\n \n\n \n \n \n\n \n \n\n \n }\n\n\t \n\t\t ","editorMobile":"\n\t\t \n\t\t .eb-toc-yoixq.eb-toc-container{\n\t\t\t \n\n\n\t\t\t \n \n\n \n\t\t\t \n \n\n \n\t\t\t \n \n \n\n \n\n \n \n \n\n \n \n \n\t\t }\n\n\t\t .eb-toc-yoixq.eb-toc-container:hover{\n\t\t\t \n \n \n\n \n \n \n \n\n \n \n\n \n\t\t }\n\n\t\t .eb-toc-yoixq.eb-toc-container .eb-toc-title{\n\t\t\t \n \n\n \n\t\t\t \n \n \n \n \n\t\t }\n\n\t\t .eb-toc-yoixq.eb-toc-container .eb-toc-wrapper{\n\t\t\t \n \n\n \n\t\t }\n\n\t\t .eb-toc-yoixq.eb-toc-container .eb-toc-wrapper li{\n\t\t\t \n \n \n \n \n\t\t }\n\n .eb-toc-yoixq.eb-toc-container.style-1 .eb-toc__list-wrap \u003e .eb-toc__list li .eb-toc__list{\n \n \n \n\n \n\n \n \n \n\n \n \n \n }\n\n\t \n\t "},"headers":[{"level":2,"content":"Learn How to Develop a Custom Client Portal Rapidly","text":"Learn How to Develop a Custom Client Portal Rapidly","link":"learn-how-to-develop-a-custom-client-portal-rapidly"},{"level":3,"content":"Building a Custom Client Portal","text":"Building a Custom Client Portal","link":"building-a-custom-client-portal"},{"level":4,"content":"What are the Typical Features of Custom Client Portals?","text":"What are the Typical Features of Custom Client Portals?","link":"what-are-the-typical-features-of-custom-client-portals"},{"level":4,"content":"Developing a Custom Client Portal","text":"Developing a Custom Client Portal","link":"developing-a-custom-client-portal"},{"level":4,"content":"What Does a Custom Client Portal Do?","text":"What Does a Custom Client Portal Do?","link":"what-does-a-custom-client-portal-do"},{"level":2,"content":"Using Five to Develop a Client Portal","text":"Using Five to Develop a Client Portal","link":"using-five-to-develop-a-client-portal"}],"deleteHeaderList":[{"label":"Learn How to Develop a Custom Client Portal Rapidly","value":"learn-how-to-develop-a-custom-client-portal-rapidly","isDelete":true},{"label":"Building a Custom Client Portal","value":"building-a-custom-client-portal","isDelete":false},{"label":"What are the Typical Features of Custom Client Portals?","value":"what-are-the-typical-features-of-custom-client-portals","isDelete":false},{"label":"Developing a Custom Client Portal","value":"developing-a-custom-client-portal","isDelete":false},{"label":"What Does a Custom Client Portal Do?","value":"what-does-a-custom-client-portal-do","isDelete":false},{"label":"Using Five to Develop a Client Portal","value":"using-five-to-develop-a-client-portal","isDelete":false}],"isMigrated":true,"titleBg":"rgba(69,136,216,1)","titleColor":"rgba(255,255,255,1)","contentBg":"rgba(241,235,218,1)","contentColor":"rgba(0,21,36,1)","contentGap":8,"titleAlign":"center","titleFontSize":22,"titleFontWeight":"normal","titleLineHeightUnit":"px","contentFontWeight":"normal","contentLineHeight":1.4,"ttlP_isLinked":true,"commonStyles":{"desktop":".wp-admin .eb-parent-eb-toc-yoixq { display:block }.wp-admin .eb-parent-eb-toc-yoixq { filter:unset }.wp-admin .eb-parent-eb-toc-yoixq::before { content:none }.eb-parent-eb-toc-yoixq { display:block }.root-eb-toc-yoixq { position:relative }","tab":".editor-styles-wrapper.wp-embed-responsive .eb-parent-eb-toc-yoixq { display:block }.editor-styles-wrapper.wp-embed-responsive .eb-parent-eb-toc-yoixq { filter:none }.editor-styles-wrapper.wp-embed-responsive .eb-parent-eb-toc-yoixq::before { content:none }.eb-parent-eb-toc-yoixq { display:block }","mobile":".editor-styles-wrapper.wp-embed-responsive .eb-parent-eb-toc-yoixq { display:block }.editor-styles-wrapper.wp-embed-responsive .eb-parent-eb-toc-yoixq { filter:none }.editor-styles-wrapper.wp-embed-responsive .eb-parent-eb-toc-yoixq::before { content:none }.eb-parent-eb-toc-yoixq { display:block }"}} /-->
<!-- wp:separator -->
<hr class="wp-block-separator has-alpha-channel-opacity"/>
<!-- /wp:separator -->
<!-- wp:tadv/classic-paragraph -->
<div style="background-color: #001524;"><hr style="height: 5px;">
<pre style="text-align: center; overflow: hidden; white-space: pre-line;"><span style="color: #f1ebda; background-color: #4588d8; font-size: calc(18px + 0.390625vw);"><strong>Develop and Deploy a Custom Client Portal</strong>
<span style="font-size: 14pt;">Build dedicated portals for vendors, partners and clients</span></span></pre>
<p style="text-align: center;"><a href="https://five.co/get-started" target="_blank" rel="noopener"><button style="background-color: #f8b92b; border: none; color: black; padding: 20px; text-align: center; text-decoration: none; display: inline-block; font-size: 18px; cursor: pointer; margin: 4px 2px; border-radius: 5px;"><strong>Get Started</strong></button><br></a></p>
<hr style="height: 5px;"></div>
<!-- /wp:tadv/classic-paragraph -->
<!-- wp:separator -->
<hr class="wp-block-separator has-alpha-channel-opacity"/>
<!-- /wp:separator -->
<!-- wp:heading {"level":3} -->
<h3 class="wp-block-heading" id="building-a-custom-client-portal">Building a Custom Client Portal</h3>
<!-- /wp:heading -->
<!-- wp:heading {"level":4} -->
<h4 class="wp-block-heading" id="what-are-typical-features-of-custom-client-portals">What are the Typical Features of Custom Client Portals?</h4>
<!-- /wp:heading -->
<!-- wp:paragraph -->
<p>Custom client portals provide clients with access to important information regarding the business relationship, such as a history of past orders, open and paid invoices, upcoming campaigns, or available services. They also have important self-service capabilities, such as updating or maintaining contact information or sharing documents, which help reduce the manual work involved in maintaining client relationships.</p>
<!-- /wp:paragraph -->
<!-- wp:paragraph -->
<p>Client portals are an important part of effective account management and can help ease the burden on team members, as they reduce the need for client interactions by email, on the phone, or through face-to-face meetings. </p>
<!-- /wp:paragraph -->
<!-- wp:paragraph -->
<p>Custom client portals are a great tool for small- and medium-sized businesses that don't have the human resources to follow up on every client request ("Could you re-send last month's invoice please?"), but would rather enable clients to request and maintain information through a self-service web application.</p>
<!-- /wp:paragraph -->
<!-- wp:heading {"level":4} -->
<h4 class="wp-block-heading" id="developing-a-custom-client-portal">Developing a Custom Client Portal</h4>
<!-- /wp:heading -->
<!-- wp:paragraph -->
<p>Luckily, modern rapid application development environments, such as Five, make it easy to go from idea to production-ready and secure client portals. These customer portal builders give access to the right features to create a web interface for customers in just a few days.</p>
<!-- /wp:paragraph -->
<!-- wp:paragraph -->
<p>To develop a custom client portal, follow these five steps:</p>
<!-- /wp:paragraph -->
<!-- wp:list {"ordered":true} -->
<ol><!-- wp:list-item -->
<li><strong>Collect Relevant Information, Data, and Documents: </strong>first, ask what information and documents clients need to access on a regular and recurring basis. <br>Compile a list of the top 5 pieces of information and documents. If you are unsure what these information and documents are, ask your account managers: they will be able to tell you what consumes most of their time when dealing with clients.</li>
<!-- /wp:list-item -->
<!-- wp:list-item -->
<li><strong>List Out Manual Client Interactions:</strong> it is also helpful to ask your account managers (or even your clients) what other manual interactions are suitable for automation or self-service. List out these interactions and draw up ways to automate them through a self-service client portal.</li>
<!-- /wp:list-item -->
<!-- wp:list-item -->
<li><strong>Choose an Effective User Interface</strong>: client portals, especially for B2B businesses, frequently use an <a href="https://five.co/blog/the-admin-panel-the-best-web-app-template/" data-type="post" data-id="995">admin panel </a>as their layout and user interface. Through its clean and professional design, the admin panel lets your clients easily navigate the portal. This is important, as there is no need to reinvent the wheel: the admin panel provides a tried-and-tested user interface suitable for custom client portals. </li>
<!-- /wp:list-item -->
<!-- wp:list-item -->
<li><strong>Develop the Client Portal: </strong>once the scope of your custom client portal is well-defined and the mock-ups are ready, it's time to start developing. Client portal builders, such as Five, turn the process of translating your requirements into working software easy, fast, and efficient. </li>
<!-- /wp:list-item -->
<!-- wp:list-item -->
<li><strong>Customize the Client Portal and Apply Your Branding: </strong>well-designed client portals are an important part of doing business. A custom client portal can be branded by applying your corporate colors, and logos or through a custom domain, theme, and branded signup and login pages.</li>
<!-- /wp:list-item --></ol>
<!-- /wp:list -->
<!-- wp:heading {"level":4} -->
<h4 class="wp-block-heading" id="what-does-a-custom-client-portal-do">What Does a Custom Client Portal Do?</h4>
<!-- /wp:heading -->
<!-- wp:paragraph -->
<p>Typical interactions and features that are suitable for inclusion in a client portal are:</p>
<!-- /wp:paragraph -->
<!-- wp:list {"ordered":true} -->
<ol><!-- wp:list-item -->
<li><em>Billing and payments:</em> automatically create invoices, and let clients access invoices online through the portal.</li>
<!-- /wp:list-item -->
<!-- wp:list-item -->
<li><em>Project management: </em>update clients about timelines, deliverables, and tasks online to facilitate project management and progress reporting.</li>
<!-- /wp:list-item -->
<!-- wp:list-item -->
<li><em>Document management: </em>collect and give access to important business documents through a login-protected, secure client portal to minimize time spent on searching, sharing or accessing important documents.</li>
<!-- /wp:list-item -->
<!-- wp:list-item -->
<li><em>Account management: </em>give clients the ability to update and maintain important contact information through a self-service portal. </li>
<!-- /wp:list-item -->
<!-- wp:list-item -->
<li><em>Client onboarding: </em>invite new clients to your business through a well-designed and smooth onboarding process with a clearly defined onboarding process that takes place online.</li>
<!-- /wp:list-item -->
<!-- wp:list-item -->
<li><em>Support & Resources:</em> furnish important information about your business and how you can support your clients online in a resource hub.</li>
<!-- /wp:list-item -->
<!-- wp:list-item -->
<li><em>Client Communication: </em>communicate with clients through your portal and keep a secure audit trail of all communication between you and your clients.</li>
<!-- /wp:list-item -->
<!-- wp:list-item -->
<li><em>Purchasing: </em>collect client orders online and provide live updates about available products, delivery times, and order fulfillment. </li>
<!-- /wp:list-item --></ol>
<!-- /wp:list -->
<!-- wp:separator -->
<hr class="wp-block-separator has-alpha-channel-opacity"/>
<!-- /wp:separator -->
<!-- wp:heading -->
<h2 class="wp-block-heading">Using Five to Develop a Client Portal</h2>
<!-- /wp:heading -->
<!-- wp:paragraph -->
<p>Five is a rapid application development environment suitable for building custom client portals. </p>
<!-- /wp:paragraph -->
<!-- wp:paragraph -->
<p>Five can securely manage your data by providing out-of-the-box user management and provide a clean, auto-generated user interface for your client's data. It also provides the ability to setup automatic notifications, manage documents, or brand your custom client portal. To learn more, <a href="https://five.co/get-started">sign up for a free trial.</a></p>
<!-- /wp:paragraph --> | domfive |
1,874,842 | How to export and import data in SQLynx | In this article, I'll to teach how to export and import data using the DBweaver, its very simple. In... | 0 | 2024-06-03T02:45:12 | https://dev.to/concerate/how-to-export-and-import-data-in-sqlynx-bja | In this article, I'll to teach how to export and import data using the DBweaver, its very simple.
In yours SQLynx select database and table that you want to export data.
Right mouse button and select option Export data.
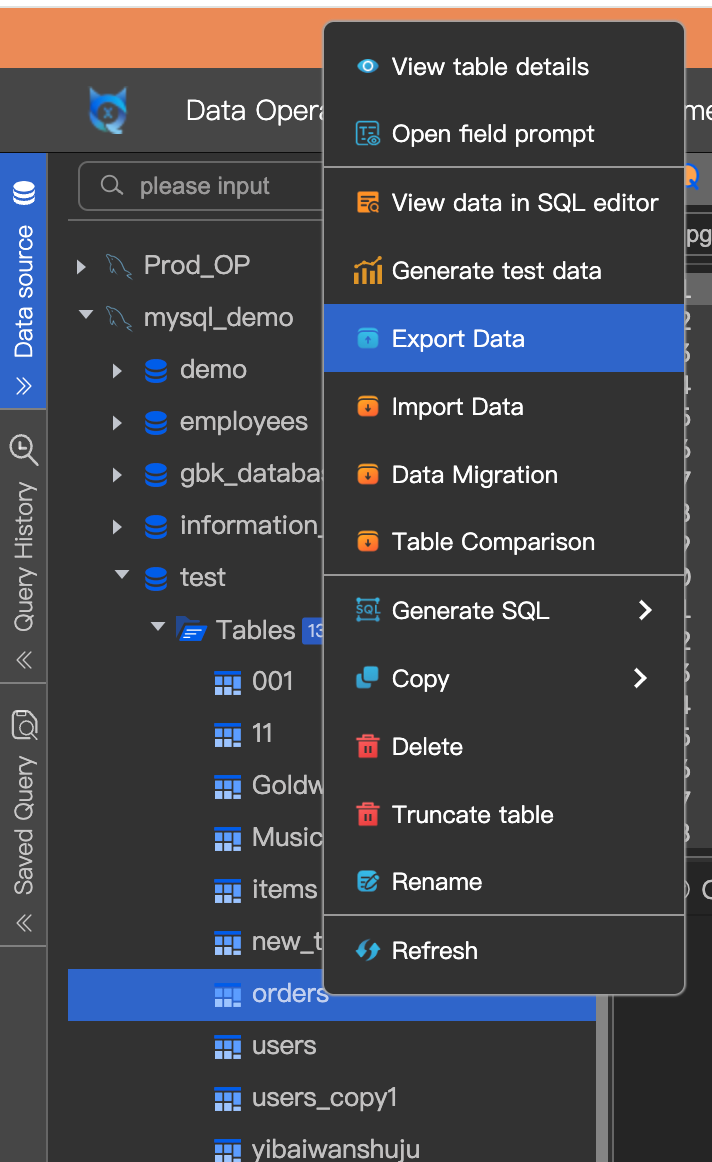
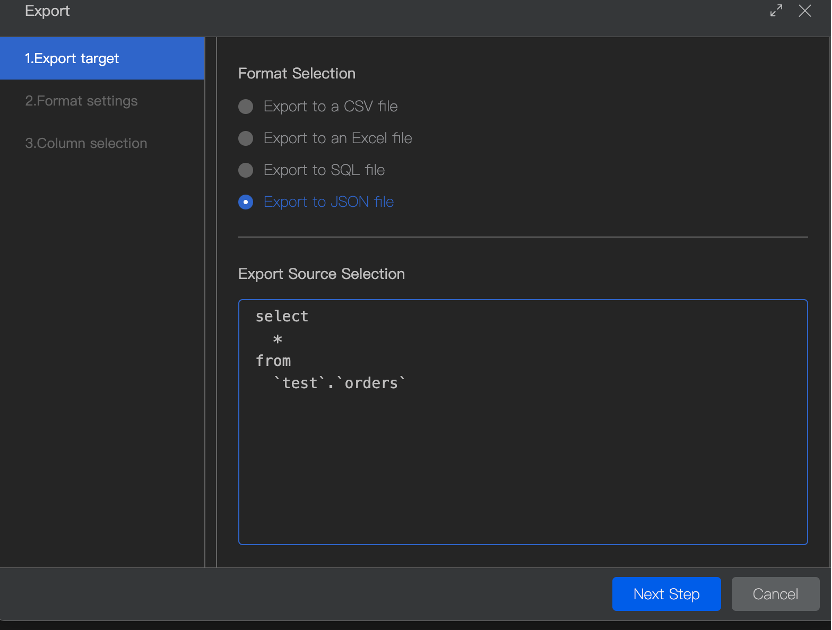
In SQL query result, you can also export data.
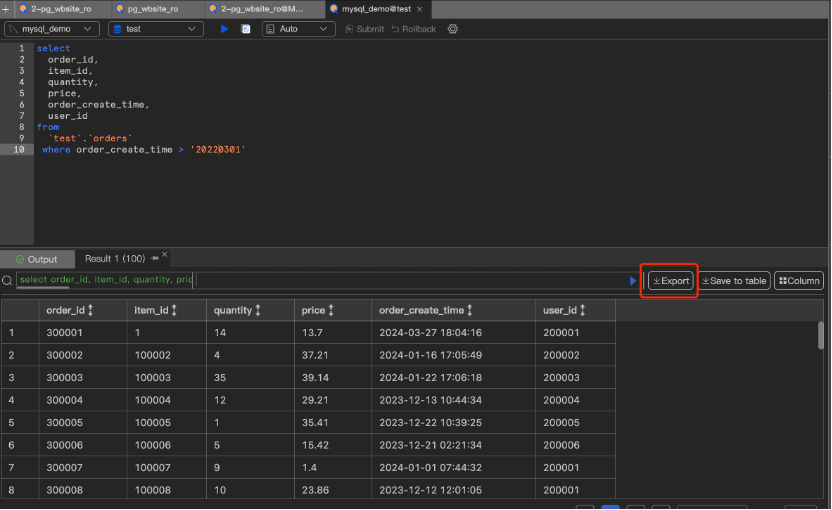
| concerate | |
1,874,840 | State-of-the-Art Sheet Rolling Machines for Enhanced Productivity | screenshot-1717035556607.png State-of-the-art Sheet Rolling Machines for Enhanced... | 0 | 2024-06-03T02:43:35 | https://dev.to/theresa_mccraryjs_77dd382/state-of-the-art-sheet-rolling-machines-for-enhanced-productivity-2ik2 | screenshot-1717035556607.png
State-of-the-art Sheet Rolling Machines for Enhanced Productivity
Sheet rolling machines are some of the most useful tools in the industry. They save time and reduce manual workload by enabling workers to achieve a variety of complex shapes and forms in materials like metal, plastics, and composite materials. Their importance is recognized by hundreds of industries worldwide, from construction to modern aviation. While traditional sheet rolling machines still perform the task, the latest state-of-the-art machines have numerous advantages over them. This article aims to explain and simplify the technological intricacies of state-of-the-art sheet rolling machines, highlighting innovational features, safety protocols, how to use them, the impact of their application, quality, and their serviceability.
Great things about State-of-the-art Sheet Rolling Machines
State-of-the-art sheet which can be rolling advantages that are numerous old-fashioned bending roll machine
The most benefit like prominent that they'll achieve accurate and precise perspectives that are bending and curved forms, also at tight radii
They function dependable repeatability in production, assuring increased effectiveness, better yield loss reduction, and profitability
With your devices, organizations can notably reduce the amount of manual procedures associated with their production, leading to more constant and products that are standardized higher quality control
State-of-the-art sheet machines which can be rolling additionally more versatile because they are designed for a wider choice of materials which might be difficult to shape with conventional gear
Innovation in State-of-the-art sheet rolling machine
The sheet like latest that are rolling introduced several new and revolutionary features to pay attention to the ever-evolving needs associated with the users
One of the more features that are notable be the usage of programmable logic controllers and display software like touchscreen
These access like supply like unique with the ability to adjust a massive array of machine settings accurately and rapidly
Additionally they provide for easy upgrade change, making the devices more adaptable to forthcoming advancements being technological
State-of-the-art sheet machines that are rolling have electronically driven roller leveling, which assists in creating more consistent, flat sheets present in busbars and enclosures
This feature like innovative you to expel wrinkles and creases, that will result in an item defect
Security precautions in State-of-the-art Sheet Rolling Machines
The safety of both the buyer and also the device is of utmost importance with regards to sheet devices that are rolling
State-of-the-art machines have actually a safety like few such as for example electronic overload security, crisis stop switches, and shut-off like automatic operating outside of prescribed limits
They also have safety light obstacles that prevent operators from entering the machine or the location like working machine components have been in motion
Furthermore, they have security guards, protective covers, and interlocking systems that prevent unauthorized utilization of the moving areas of the unit
Advanced sheet devices which are rolling prioritize operator and device security most importantly of all
Utilizing State-of-the-art Sheet Rolling Machines
Using sheet like devices that are state-of-the-art hassle-free
Due to programmable logic controllers set up during the devices, operators makes settings that quickly match their preferred manufacturing requirements
The setup like result like electronic the machine user-friendly, that will be possible to regulate its features on the basis of the product getting used
An operator should make sure that the materials is free and neat of defects as blemishes together with the product used can cause ripples and wrinkles if the device starts its work before setting within the machine
The material should be flat, have actually a straight depth, and possess the most suitable width based on the machine's requirements for the flawless sheet
The apparatus will begin the process like rolling as well as the finished sheet will materialize within minutes following the operator has loaded the sheet, programmed the device, and pressed the beginning switch
Impact of Application of State-of-the-art Sheet Rolling Machines
The use of state-of-the-art machines that are rolling affected industries that are various
For example, the construction industry has utilized these devices to create roofing sheets, insulated panels, as well as other building components
With all the current versatility of state-of-the-art machines, companies is with the capacity of their design goals, producing both customized and products which are traditional ease
Sheet devices that are rolling also create top-notch products which may have a area finish like beautiful
Organizations could use these devices to produce furniture, airplane components, automobiles, and applications that are architectural producing a safer, efficient, and much more procedure like lucrative
Quality and Provider of State-of-the-art Sheet Rolling Machines
State-of-the-art sheet machines that are rolling made to last through years of heavy solution like commercial
They're produced from top-notch materials and undergo strict quality checks before leaving the factory
To help keep the machine operating smoothly, operators should carry out maintenance like typical, including maintaining the equipment clean, lubricated and replacing the worn-out parts as required
The product may encounter if operators have any questions or issues, they ought to contact the equipment's provider who is able to offer advice like professional the procedure or any dilemmas
Advanced manufacturers provide regular service checks to guarantee the machines keep on and operate at optimal efficiency, increasing the expected life of this device
Conclusion
In conclusion, state-of-the-art sheet rolling machines are essential to a wide range of industries, offering numerous advantages over traditional machines while providing unparalleled safety, innovation, and service. It is possible to achieve a higher level of productivity, quality, and profitability with state-of-the-art machinery. Businesses should invest in these machines to increase efficiency and profitability.
Source:
| theresa_mccraryjs_77dd382 | |
1,874,838 | A Comprehensive Guide to Udyam Aadhaar Registration: Empowering Small Businesses in India | The Micro, Small, and Medium Enterprises (MSME) sector is a crucial pillar of the Indian economy,... | 0 | 2024-06-03T02:34:08 | https://dev.to/vartynews/a-comprehensive-guide-to-udyam-aadhaar-registration-empowering-small-businesses-in-india-d8p | webdev | The Micro, Small, and Medium Enterprises (MSME) sector is a crucial pillar of the Indian economy, contributing significantly to employment, GDP, and export. Recognizing its importance, the Government of India introduced the Udyam Aadhaar registration, a simplified process to facilitate the registration of MSMEs. This article delves into the significance, benefits, and step-by-step process of **[Udyam Aadhaar registration](https://www.udyam-registration.com/)**.
**What is Udyam Aadhaar?**
[Udyam Aadhaar](https://www.udyam-registration.com/), also known as Udyam Registration, is a unique identification number provided to MSMEs to streamline the registration process. This initiative replaces the earlier system of filing for an MSME registration with a simplified, single-window process. The objective is to make it easier for small businesses to avail of various government schemes, incentives, and benefits.
**Benefits of Udyam Aadhaar Registration**
Access to Government Schemes and Subsidies: Registered MSMEs can avail themselves of numerous government schemes and subsidies, including credit facilities, low-interest loans, and financial support for market development.
Ease of Doing Business: With Udyam Aadhaar registration, businesses gain recognition, making it easier to obtain licenses, approvals, and registrations from different government authorities.
Credit and Financing Benefits: Registered MSMEs are eligible for priority sector lending by banks and financial institutions, ensuring better access to funds.
Protection against Delayed Payments: The registration provides a mechanism to address delayed payments from buyers, ensuring smoother cash flow and operational stability.
Tax Benefits and Concessions: Registered MSMEs can benefit from various tax exemptions and concessions, reducing their financial burden.
Step-by-Step Guide to Udyam Aadhaar Registration
Visit the Official Udyam Registration Portal: Go to the official Udyam Registration website (https://udyamregistration.gov.in).
**Enter Aadhaar Number:** The applicant's Aadhaar number is mandatory for the registration process. For proprietorship firms, the Aadhaar number of the proprietor is required; for partnership firms, the managing partner's Aadhaar number; and for Hindu Undivided Family (HUF), the Karta's Aadhaar number.
**Validate Aadhaar:** After entering the Aadhaar number, the applicant needs to validate it through an OTP sent to the registered mobile number linked with the Aadhaar.
**Fill in Business Details:** Provide essential business details, including the name of the enterprise, type of organization, address, bank details, and the major activity of the enterprise (manufacturing or service).
**Enter Additional Information:** Fill in additional information like the number of employees, investment in plant and machinery or equipment, and National Industry Classification (NIC) Code.
Submit and Receive [Udyam Registration](https://www.udyam-registration.com/) Certificate: After filling in all the necessary details, submit the form. Upon successful registration, an e-certificate, known as the Udyam Registration Certificate, is issued. This certificate contains a unique Udyam Registration Number (URN).
**Important Points to Note**
**No Fees for Registration: **The Udyam Aadhaar registration process is entirely free of cost.
Validity: The Udyam Registration is valid for a lifetime and does not require renewal.
**Self-Declaration:** The entire registration process is based on self-declaration, and no supporting documents or proof is required, except the Aadhaar number.
**Linking with PAN and GST:** From April 1, 2021, it is mandatory to link PAN and GST with Udyam Registration for businesses liable to obtain these.
Conclusion
Udyam Aadhaar registration is a significant step towards simplifying the process for MSMEs to avail themselves of various benefits and support from the government. By registering under Udyam, small businesses can unlock a plethora of opportunities and resources, fostering growth and sustainability. If you are an MSME, it is highly recommended to get your Udyam Aadhaar registration done and take advantage of the benefits it offers. | vartynews |
1,874,835 | What Is Quantitative Trading? | Summary As a product of the combination of science and machine, quantitative trading is... | 0 | 2024-06-03T02:22:07 | https://dev.to/fmzquant/what-is-quantitative-trading-2p2j | trading, cryptocurrency, fmzquant, strategy | ## Summary
As a product of the combination of science and machine, quantitative trading is changing the pattern of modern financial markets. Many investors have turned their attention to this field. How to minimize risk and achieve the best possible return? It is also the purpose of this series of courses. As the first part of the opening ceremony, we will briefly explain "What is quantitative trading".
## Overview
Many retail investors get the feeling of "high-level" and "getting rich overnight" when they hear the words "quantitative trading." In the era of artificial intelligence, with the rise of advanced technologies such as deep learning, big data, and cloud computing, it has given it a mysterious color. It seems that as long as you use quantitative trading, you can build a "perfect" trading strategy.
In fact, to a certain extent, quantitative trading has been overrated. Putting aside the trading part, "quantitative" is actually using a computer, statistical methods, mathematics and other tools, through a scientific investment system, to find a set of positive expected trading signal system. This signal system tells us when to buy and sell.
## Quantitative trading history and development
Tracing back to its source, the first to use quantitative methods to analyze data changes, and find out the market price rise and fall laws, not the origin of the stock of the Dutch, nor the British who carry forward modern finance, nor the symbiosis with the financial development of the country American, but a Frenchman.
As early as the 18th century, French stockbroker assistant Jules Regnault proposed a modern theory of stock price changes, followed by the book <<Probability Computing and Stock Trading Philosophy>>, and elaborated on the market ups and downs that he discovered. (Normal distribution): “The deviation of price is proportional to the square root of time”, and finally the trading success is obtained by rational quantitative investment decision.
Nowadays, in the era of Internet + big data + cloud computing + artificial intelligence, quantitative tradings have also developed rapidly. Once in the global financial hinterland, London Canary Wharf has long since become a distribution center for IT companies. The world's top investment banks are also cultivating their own quantitative teams, trying to get into the financial battle of “mathematic models are everything”. These IT teams that develop trading models are also called Quant Team. In terms of scale, the United States, which started earlier, already has a large number of powerful quantitative hedge funds.
## Quantitative trading characteristics
• Scientific verification: Imagine that when you have a trading system, if you use an simulated trading to test its effectiveness, you may have to pay a huge time cost. If you take the test in the real market directly, you may lose real money. However, the backtesting function in the quantitative trading can be utilized to verify the trading system in a scientific way through a large amount of historical data. What works, what doesn't work, let the data speak, not people.
• Objective and accurate: In the trading, our real enemy is ourselves. Mentality management is easier said than done. Greedy, fear, luck and other human weaknesses will multiply in the trading market. Quantitative trading can help us overcome these weaknesses and make better decisions in trading.
• Timely and efficient: Subjective tradings, people's speed of response can not be faster than the computer, and people's physical strength and energy can not run 24 hours, in the high speed running trading market, quantitative trading can completely replace subjective tradings, looking for tradings Opportunity to track market changes in a timely and fast manner.
• Risk control: Quantitative tradings can not only extract historical rules that may be repeated in the future from historical data, but these historical laws are strategies for winning with greater probability. You can also build a variety of different portfolios to reduce systemic risk and smooth the capital profit curve.
## What are the classic trading strategies for quantitative trading?
### Opening price breakthrough strategy
Opening for half an hour can often determine the trend of the day. This strategy's logic is determined by half an hour after the opening of the market, weather the first 30-minutes candle graphic is positive line or negative line, as a criterion for judging the trend of the day. If it is a positive line, open a position to buy, if it is a negative line, vice versa. closing all position within a few minutes before the market close. This is a very simple trading strategy.
### Donchian Channel Strategy

Donchian channel strategy can be called the originator of intraday trading. The rule is: if the current price is higher than the highest price of the previous number of N K-line, buying long; if the current price is lower than the lowest price of the previous number of N K-line, selling short. The famous "Turtle Trading Strategy" was using the revised version of it.
### Intertemporal arbitrage strategy
Intertemporal arbitrage is the most common type of arbitrage trading. It is based on the same trading variety and the price of different delivery month contracts. If there is a large price difference between the two prices, you can buy and sell futures contracts at the same time. Assume that the spread between the main contract and the sub-primary contract is maintained at around -50~50 for a long time. If the spread reaches 70 on a certain day, we expect the spread to return to 50 at some time in the future. Then you can sell the main contract and buy the sub-primary contract at the same time to short the spread. vice versa.
## To sum up
Above, we briefly introduced the related concepts of quantitative trading from the definition, development, characteristics and some classic trading strategies for quantitative trading.
Understanding quantitative trading is an important stepping stone on the road to Quant. Finally, I wish you all enrich yourself in the bear market and realize cognitive increment as soon as possible! Remember, you are only one bull market away from financial freedom ^_^
Next section notice
What is the difference between quantitative trading and traditional trading? In real market trading, do you choose traditional trading or quantitative trading? In the next section, we will take with these two questions to learn more about quantitative trading.
After-school exercises
1. In one sentence, what is quantitative trading?
2. What are the characteristics of quantitative trading?
From: https://blog.mathquant.com/2019/04/09/1-1-what-is-quantitative-trading.html | fmzquant |
1,874,834 | Styling in ReactJS: Exploring the Best Libraries | Styling is an essential aspect of building appealing and user-friendly web applications. In the React... | 0 | 2024-06-03T02:16:09 | https://dev.to/vyan/styling-in-reactjs-exploring-the-best-libraries-j42 | webdev, react, css, javascript | Styling is an essential aspect of building appealing and user-friendly web applications. In the React ecosystem, several libraries have emerged to help developers manage and implement styles effectively. This blog explores some of the most popular libraries for styling in ReactJS, including their features, benefits, and use cases.
## 1. Styled-components
### Overview
Styled-components is a popular library that allows you to write CSS-in-JS. It leverages tagged template literals to style your components, making your styling dynamic and scoped to individual components.
### Features
- **Component-Based Styling**: Styles are tied directly to components, promoting modular and reusable code.
- **Dynamic Styling**: Supports props and themes to dynamically change styles.
- **Automatic Vendor Prefixing**: Ensures compatibility across different browsers.
- **Theming**: Provides an easy way to manage themes across your application.
### Example
```jsx
import styled from 'styled-components';
const Button = styled.button`
background: ${props => props.primary ? 'blue' : 'gray'};
color: white;
font-size: 1em;
padding: 0.5em 1em;
border: none;
border-radius: 3px;
`;
function App() {
return (
<div>
<Button primary>Primary Button</Button>
<Button>Secondary Button</Button>
</div>
);
}
```
### Use Cases
- Ideal for projects requiring modular and reusable components.
- Great for applications where dynamic theming and styling based on props are essential.
## 2. CSS Modules
### Overview
CSS Modules allow you to write CSS that is scoped locally to the component. This prevents global namespace pollution, a common issue with traditional CSS.
### Features
- **Local Scope**: Automatically generates unique class names to avoid conflicts.
- **Simple Integration**: Works seamlessly with Create React App and other build setups.
- **CSS Composition**: Allows composition of class names and styles.
### Example
```css
/* Button.module.css */
.button {
background: gray;
color: white;
font-size: 1em;
padding: 0.5em 1em;
border: none;
border-radius: 3px;
}
.buttonPrimary {
background: blue;
}
```
```jsx
import styles from './Button.module.css';
function Button({ primary, children }) {
return (
<button className={`${styles.button} ${primary ? styles.buttonPrimary : ''}`}>
{children}
</button>
);
}
function App() {
return (
<div>
<Button primary>Primary Button</Button>
<Button>Secondary Button</Button>
</div>
);
}
```
### Use Cases
- Suitable for projects where you want to avoid style conflicts and maintain clean, local scope styles.
- Ideal for teams familiar with traditional CSS but looking for better modularity.
## 3. Emotion
### Overview
Emotion is a library designed for writing CSS styles with JavaScript. It provides powerful and flexible ways to style applications, supporting both styled components and CSS-in-JS.
### Features
- **High Performance**: Optimized for performance with minimal runtime overhead.
- **Flexibility**: Offers both styled component API and low-level CSS-in-JS capabilities.
- **Theming**: Supports theming with a context-based API.
### Example
```jsx
/** @jsxImportSource @emotion/react */
import { css } from '@emotion/react';
const buttonStyle = css`
background: gray;
color: white;
font-size: 1em;
padding: 0.5em 1em;
border: none;
border-radius: 3px;
`;
const primaryStyle = css`
background: blue;
`;
function Button({ primary, children }) {
return (
<button css={[buttonStyle, primary && primaryStyle]}>
{children}
</button>
);
}
function App() {
return (
<div>
<Button primary>Primary Button</Button>
<Button>Secondary Button</Button>
</div>
);
}
```
### Use Cases
- Excellent for developers who need both flexibility and performance.
- Suitable for applications requiring dynamic theming and advanced styling capabilities.
## 4. Tailwind CSS
### Overview
Tailwind CSS is a utility-first CSS framework that provides low-level utility classes to build custom designs without writing custom CSS. It can be integrated with React to create highly customizable and responsive components.
### Features
- **Utility-First**: Offers a wide range of utility classes for building custom designs.
- **Responsive Design**: Built-in support for responsive design with utility classes.
- **Customization**: Highly customizable through configuration files.
### Example
```jsx
function Button({ primary, children }) {
const buttonClass = primary
? 'bg-blue-500 text-white font-bold py-2 px-4 rounded'
: 'bg-gray-500 text-white font-bold py-2 px-4 rounded';
return (
<button className={buttonClass}>
{children}
</button>
);
}
function App() {
return (
<div>
<Button primary>Primary Button</Button>
<Button>Secondary Button</Button>
</div>
);
}
```
### Use Cases
- Ideal for projects requiring rapid prototyping and highly customizable design systems.
- Great for developers who prefer utility-first CSS and want to avoid writing custom CSS.
## Conclusion
Choosing the right styling library for your ReactJS project depends on your specific needs and preferences.
- **Styled-components** and **Emotion** are great for component-based and dynamic styling.
- **CSS Modules** provide a way to write traditional CSS with local scope.
- **Tailwind CSS** is perfect for utility-first, highly customizable designs.
Each of these libraries offers unique advantages, and understanding their features and use cases will help you make the best decision for your project. Happy styling! | vyan |
1,874,833 | Web Dev Day 5: Bootstrap Guide | What is Bootstrap? Bootstrap is a popular open-source front-end framework used for... | 0 | 2024-06-03T02:12:14 | https://dev.to/_bhupeshk_/web-dev-day-5-bootstrap-guide-359p | webdev, bootstrap, programming, css | ## What is Bootstrap?
Bootstrap is a popular open-source front-end framework used for developing responsive and mobile-first websites quickly and efficiently. It was originally developed by Twitter and released in 2011.
### Key Features
1. **Responsive Grid System**: A flexible 12-column layout system for creating responsive designs.
2. **Pre-styled Components**: Includes a wide range of UI components like buttons, forms, navbars, modals, and more.
3. **CSS and JavaScript**: Provides CSS styles and JavaScript plugins for enhanced functionality.
4. **Customization**: Easily customizable using Sass variables and built-in themes.
5. **Cross-browser Compatibility**: Ensures consistency across modern browsers.
6. **Extensive Documentation and Community Support**: Large community and comprehensive documentation available.
### Basic Example
A simple Bootstrap layout:
```html
<!DOCTYPE html>
<html lang="en">
<head>
<meta charset="UTF-8">
<meta name="viewport" content="width=device-width, initial-scale=1.0">
<title>Bootstrap Example</title>
<link href="https://maxcdn.bootstrapcdn.com/bootstrap/4.5.2/css/bootstrap.min.css" rel="stylesheet">
</head>
<body>
<div class="container">
<div class="row">
<div class="col-md-4">Column 1</div>
<div class="col-md-4">Column 2</div>
<div class="col-md-4">Column 3</div>
</div>
</div>
<script src="https://ajax.googleapis.com/ajax/libs/jquery/3.5.1/jquery.min.js"></script>
<script src="https://cdnjs.cloudflare.com/ajax/libs/popper.js/1.16.0/umd/popper.min.js"></script>
<script src="https://maxcdn.bootstrapcdn.com/bootstrap/4.5.2/js/bootstrap.min.js"></script>
</body>
</html>
```
Bootstrap simplifies the process of designing responsive, visually appealing web pages with its ready-to-use components and customization options.
## Benefits of Bootstrap
1. **Responsive Design**
- Mobile-first approach ensures websites look great on all devices.
- 12-column grid system for flexible layouts.
2. **Pre-styled Components**
- Consistent design with buttons, forms, navbars, and more.
- Saves time on custom styling.
3. **Customizable**
- Easily modify default styles with Sass variables.
- Supports custom themes.
4. **Cross-browser Compatibility**
- Ensures uniform appearance across all major browsers.
5. **Comprehensive Documentation**
- Detailed documentation with examples and code snippets.
- Large community support.
6. **Built-in JavaScript Plugins**
- Enhances functionality with interactive components like modals and carousels.
7. **Consistency**
- Standardized UI elements for a uniform look and feel.
8. **Speed of Development**
- Rapid prototyping with ready-to-use components.
- Reusable components across projects.
9. **Integration with Other Tools**
- Compatible with modern frameworks (React, Angular, Vue.js).
- Works with build tools like Webpack and Gulp.
10. **Accessibility**
- Supports ARIA attributes for better accessibility.
Bootstrap helps developers build responsive, consistent, and visually appealing websites quickly and efficiently.
## Using Bootstrap
### 1. **Include Bootstrap in Your Project**
**Using a CDN:**
- Quick and easy way to get started.
- Add Bootstrap CSS and JS files via a CDN link in your HTML.
**Using NPM:**
- Install Bootstrap for projects using Node.js.
- Import Bootstrap CSS and JS in your project files.
### 2. **Create a Basic Layout**
- Utilize Bootstrap's responsive grid system.
- Structure your layout using containers, rows, and columns to create a responsive design.
### 3. **Use Bootstrap Components**
- **Buttons:** Pre-styled button classes for various styles (e.g., `btn-primary`, `btn-secondary`).
- **Forms:** Form controls with built-in validation styles.
- **Navbar:** Responsive navigation bar components.
### 4. **Customize Bootstrap**
**Using Sass:**
- Modify Bootstrap's default styles with Sass variables.
- Create a custom Sass file to override Bootstrap variables and compile it into custom CSS.
Bootstrap simplifies web development with its responsive grid system, pre-styled components, and extensive customization options. It allows for rapid development of consistent and visually appealing websites while ensuring responsiveness and cross-browser compatibility.
## Container
In Bootstrap, a container is a layout element used to contain and organize content within a web page. There are two types: `.container` for fixed-width content and `.container-fluid` for full-width content.
- **`.container`**: Provides a fixed-width container for content. Ideal for standard layouts.
- **`.container-fluid`**: Creates a full-width container that spans the entire viewport. Suitable for wide layouts or sections.
**Usage**:
- **Structuring Content**: Wraps content to ensure consistent spacing and alignment.
- **Responsive Design**: Adapts to different screen sizes for readability and aesthetics.
- **Grid System Alignment**: Works seamlessly with Bootstrap's grid system for responsive layouts.
**Example**:
```html
<div class="container">
<!-- Fixed-width content -->
</div>
<div class="container-fluid">
<!-- Full-width content -->
</div>
```
Bootstrap's container classes provide a framework for creating structured, responsive web layouts with ease.
## Buttons
Bootstrap buttons come in various styles and sizes, making it easy to add interactive elements to your website. Here’s a quick rundown:
- **Styles**: Bootstrap provides styles for primary, secondary, success, warning, danger, info, light, and dark buttons. There are also outline buttons for a different look.
- **Sizes**: Buttons can be large, medium, small, or block-level (full-width).
- **Usage**: Use primary buttons for main actions, secondary buttons for alternate actions, and other styles for specific contexts or emphasis.
Example:
```html
<button type="button" class="btn btn-primary">Primary</button>
<button type="button" class="btn btn-secondary">Secondary</button>
<button type="button" class="btn btn-success">Success</button>
<button type="button" class="btn btn-outline-danger">Danger</button>
```
Bootstrap buttons provide consistency and responsiveness, making them a convenient choice for web development.
## Badges
Bootstrap badges are small components used to highlight information or provide visual feedback. Here's a quick summary with examples:
**Features**: Badges offer visual indicators, flexible usage, and customization options.
**Example**:
```html
<button type="button" class="btn btn-primary">
Notifications <span class="badge badge-light">5</span>
</button>
<a href="#" class="btn btn-success">
Inbox <span class="badge badge-pill badge-danger">10</span>
</a>
<h4>Important <span class="badge badge-warning">!</span></h4>
```
Bootstrap badges are versatile and can be added to buttons, links, or headings to display counts, statuses, or other relevant information in a visually appealing manner.
## Alert
Bootstrap alerts provide contextual feedback messages to users. Here's a brief summary with examples:
**Features**: Alerts offer contextual styles, dismissible options, and flexible usage.
**Example**:
```html
<div class="alert alert-success" role="alert">
Success alert!
</div>
<div class="alert alert-warning" role="alert">
Warning alert!
</div>
<div class="alert alert-danger" role="alert">
Error alert!
</div>
<div class="alert alert-info" role="alert">
Info alert!
</div>
```
Bootstrap alerts are versatile and can be easily integrated into any part of a webpage to provide feedback or notifications to users.
## Button Group
Bootstrap button groups allow you to group buttons together for better organization and appearance. Here's a quick summary with an example:
**Features**: Button groups organize multiple buttons, ensuring visual consistency and responsive behavior.
**Example**:
```html
<div class="btn-group" role="group" aria-label="Basic example">
<button type="button" class="btn btn-primary">Left</button>
<button type="button" class="btn btn-primary">Middle</button>
<button type="button" class="btn btn-primary">Right</button>
</div>
```
Bootstrap button groups help improve user interfaces by grouping related buttons together in a visually consistent manner.
## Navbar
Bootstrap navbar is a responsive navigation component that's easy to customize. Here's a quick overview with an example:
**Features**: Navbar adjusts for different screen sizes, supports various styles, and accommodates flexible content.
**Example**:
```html
<nav class="navbar navbar-expand-lg navbar-light bg-light">
<a class="navbar-brand" href="#">Navbar</a>
<button class="navbar-toggler" type="button" data-toggle="collapse" data-target="#navbarNav" aria-controls="navbarNav" aria-expanded="false" aria-label="Toggle navigation">
<span class="navbar-toggler-icon"></span>
</button>
<div class="collapse navbar-collapse" id="navbarNav">
<ul class="navbar-nav">
<li class="nav-item active">
<a class="nav-link" href="#">Home <span class="sr-only">(current)</span></a>
</li>
<li class="nav-item">
<a class="nav-link" href="#">Features</a>
</li>
<li class="nav-item">
<a class="nav-link" href="#">Pricing</a>
</li>
</ul>
</div>
</nav>
```
Bootstrap navbar simplifies navigation setup with its responsive design and easy-to-use components.
## Card
Bootstrap cards are versatile containers for displaying content. Here's a concise summary with an example:
**Features**: Cards offer flexibility, responsiveness, and customization options.
**Example**:
```html
<div class="card" style="width: 18rem;">
<img src="..." class="card-img-top" alt="...">
<div class="card-body">
<h5 class="card-title">Card title</h5>
<p class="card-text">Some quick example text to build on the card title and make up the bulk of the card's content.</p>
<a href="#" class="btn btn-primary">Go somewhere</a>
</div>
</div>
```
Bootstrap cards simplify content presentation with their adaptable design and numerous customization possibilities.
## Grid
Bootstrap's grid system is a flexible way to create responsive layouts. Here's a quick summary with an example:
**Features**: Responsive, based on a 12-column layout, and easy to use.
**Example**:
```html
<div class="container">
<div class="row">
<div class="col-sm-4">Column 1</div>
<div class="col-sm-4">Column 2</div>
<div class="col-sm-4">Column 3</div>
</div>
</div>
```
Bootstrap's grid system simplifies layout creation, providing flexibility and responsiveness across devices.
## Form Controls
Bootstrap's form controls offer pre-styled elements for easy form creation. Here's a quick summary with examples:
**Features**: Pre-styled form inputs, selects, textareas, and more for consistent appearance and validation states.
**Example**:
```html
<form>
<div class="form-group">
<label for="exampleInputUsername">Username</label>
<input type="text" class="form-control" id="exampleInputUsername" placeholder="Enter username">
</div>
<div class="form-group">
<label for="exampleInputEmail">Email address</label>
<input type="email" class="form-control" id="exampleInputEmail" placeholder="Enter email">
</div>
<div class="form-group">
<label for="exampleTextarea">Example textarea</label>
<textarea class="form-control" id="exampleTextarea" rows="3"></textarea>
</div>
<button type="submit" class="btn btn-primary">Submit</button>
</form>
```
Bootstrap's form controls simplify form creation and enhance user experience with consistent styling and validation states.
## Select in Forms
Bootstrap's select dropdowns offer pre-styled options for form selections. Here's a brief summary with an example:
**Features**: Styled select dropdowns for consistent appearance and responsiveness.
**Example**:
```html
<select class="form-select" aria-label="Default select example">
<option selected>Open this select menu</option>
<option value="1">Option 1</option>
<option value="2">Option 2</option>
<option value="3">Option 3</option>
</select>
```
Bootstrap select dropdowns enhance form elements with consistent styling and usability.
## Checkbox and Radio in Form
Bootstrap's pre-styled checkboxes and radio buttons enhance form inputs with consistent styling and functionality. Here's a brief summary with examples:
### Checkbox Example:
```html
<div class="form-check">
<input class="form-check-input" type="checkbox" value="" id="defaultCheck1">
<label class="form-check-label" for="defaultCheck1">
Default checkbox
</label>
</div>
```
### Radio Button Example:
```html
<div class="form-check">
<input class="form-check-input" type="radio" name="exampleRadios" id="exampleRadios1" value="option1" checked>
<label class="form-check-label" for="exampleRadios1">
Default radio
</label>
</div>
```
Bootstrap's styled checkboxes and radio buttons improve the appearance and usability of form inputs.
## Form Layout
Bootstrap's form layout system enables the creation of structured and responsive forms with ease. Here's a concise overview with an example:
```html
<form>
<div class="row mb-3">
<div class="col-md-6">
<label for="inputEmail" class="form-label">Email</label>
<input type="email" class="form-control" id="inputEmail">
</div>
<div class="col-md-6">
<label for="inputPassword" class="form-label">Password</label>
<input type="password" class="form-control" id="inputPassword">
</div>
</div>
<div class="mb-3">
<label for="exampleTextarea" class="form-label">Textarea</label>
<textarea class="form-control" id="exampleTextarea" rows="3"></textarea>
</div>
<button type="submit" class="btn btn-primary">Submit</button>
</form>
```
Bootstrap's form layout system simplifies the creation of responsive and structured forms, ensuring consistency and usability across different screen sizes.
Bootstrap Website: https://getbootstrap.com/docs/5.3/getting-started/introduction/ | _bhupeshk_ |
1,874,832 | Which reCAPTCHA Solver is Best? Best reCAPTCHA Solver 2024 | Introduction Navigating the digital landscape often brings us face-to-face with various... | 0 | 2024-06-03T02:11:26 | https://dev.to/gurakuqienrik6/which-recaptcha-solver-is-best-best-recaptcha-solver-2024-5cem | recaptcha, captchasolvers, aitools |
## Introduction
Navigating the digital landscape often brings us face-to-face with various obstacles designed to protect websites from malicious activities. One of the most common defenses employed by websites is reCAPTCHA. But what if you're an avid user needing a reCAPTCHA solver? The year 2024 brings advanced solutions in reCAPTCHA solvers, making it crucial to identify the best one for your needs. Let's dive into the world of reCAPTCHA solvers and uncover the top contenders of 2024.
## Understanding reCAPTCHA
### What is reCAPTCHA?
reCAPTCHA is a service developed by Google to protect websites from spam and abuse. It uses advanced risk analysis techniques to differentiate between human users and bots. While it's a fantastic tool for website security, it can sometimes be a hurdle for legitimate users trying to access information quickly.
## Why Do We Need reCAPTCHA Solvers?
While reCAPTCHA is beneficial for website owners, it can be a nuisance for users who frequently encounter it. This is where reCAPTCHA solvers come into play. These tools help users bypass the verification process smoothly, saving time and effort, especially in scenarios requiring bulk operations or automated tasks.
## Types of reCAPTCHA Solvers
### Manual reCAPTCHA Solvers
Manual solvers involve human intervention to solve the CAPTCHA challenges. They are generally more accurate but can be slower and less practical for large-scale operations due to the time required for manual input.
### Automated reCAPTCHA Solvers
Automated solvers use algorithms and machine learning to decode and bypass CAPTCHA challenges without human intervention. They are faster and more suitable for bulk tasks, although their accuracy can vary depending on the complexity of the CAPTCHA.
## Criteria for Evaluating reCAPTCHA Solvers
### Accuracy
The primary criterion for any reCAPTCHA solver is its accuracy. An ideal solver should have a high success rate in bypassing CAPTCHA challenges without error.
### Speed
Speed is crucial, especially for users needing to solve multiple CAPTCHAs in a short period. The faster the solver, the more efficient your workflow.
### User-Friendliness
A user-friendly interface ensures that even non-technical users can navigate and use the solver without difficulty.
### Cost
Affordability is another important factor. The best reCAPTCHA solver should offer a balance between cost and functionality, providing value for money.
## Top reCAPTCHA Solvers of 2024
**[NextCaptcha](https://nextcaptcha.com/)**
### Features
- Uses AI to solve reCAPTCHA challenges.
- Supports various CAPTCHA types, including image and text-based.
- Offers API integration for automated solving.
- Pros and Cons
### Pros:
- High accuracy rate.
- Efficient API integration.
- Good customer support.
- cheapest CAPTCHA solver services.
- pay as you go CAPTCHA solver services.
- pay every success request
### Cons:
- Not many supported types
**[2Captcha](https://2captcha.com)**
### Features
- Human-powered solving system.
- API support for automation.
- Supports a wide range of CAPTCHA types.
Pros and Cons
### Pros:
- Cost-effective for low-volume users.
- High accuracy due to human solvers.
- Extensive CAPTCHA type support.
Cons:
- Slower due to manual solving.
- Not ideal for large-scale operations.
**[XEvil](https://xevil.net/)**
### Features
- Advanced AI algorithms for solving.
- Supports multiple CAPTCHA forms.
- High-speed performance.
Pros and Cons
### Pros:
- Extremely fast solving speed.
- High accuracy with advanced AI.
- Versatile CAPTCHA support.
### Cons:
- Higher cost for premium features.
- Requires technical knowledge for setup.
**[CapMonster](https://capmonster.cloud/)**
### Features
- Automated solving with machine learning.
- API available for integration.
- Supports multiple CAPTCHA types.
Pros and Cons
### Pros:
- Good balance of speed and accuracy.
- Cost-effective for bulk operations.
- Easy to integrate with various platforms.
### Cons:
- Initial setup can be complex.
- Limited customer support options.
## Performance
When it comes to performance, NextCaptcha and CapMonster lead the pack with their advanced AI and machine learning capabilities, ensuring high-speed and accurate solving. Anti-Captcha also performs well but may experience occasional delays.
## Cost Efficiency
For cost-conscious users, NextCaptcha and Death By Captcha offer competitive pricing models that are ideal for low to medium volumes. CapMonster provides a balanced approach with cost-effective bulk solutions.
## User Experience
In terms of user experience, NextCaptcha and Death By Captcha stand out due to their user-friendly interfaces and reliable customer support. XEvil and CapMonster, while powerful, may require more technical know-how, which could be a barrier for some users.
## Conclusion
Choosing the best reCAPTCHA solver in 2024 depends largely on your specific needs and circumstances. For those prioritizing speed and advanced features, XEvil and CapMonster are excellent choices. If accuracy and cost-effectiveness are your main concerns, 2Captcha and Death By Captcha are worth considering. Anti-Captcha strikes a good balance between performance and usability, making it a versatile option for various needs.
## FAQs
Which reCAPTCHA solver is the fastest?
XEvil is widely regarded as the fastest reCAPTCHA solver, thanks to its advanced AI algorithms that enable rapid and accurate solving of CAPTCHA challenges.
Are reCAPTCHA solvers legal?
The legality of using reCAPTCHA solvers depends on the context and jurisdiction. While they are technically legal, using them to bypass security measures on websites without permission can lead to ethical and legal issues. | gurakuqienrik6 |
1,871,837 | Top 4 Reasons Why I Learnt JavaScript | Popularity JavaScript is one of the most widely used programming languages, with millions... | 0 | 2024-06-03T02:11:00 | https://dev.to/thekarlesi/top-4-reasons-to-learn-javascript-7m3 | webdev, javascript, beginners, html | ## Popularity
JavaScript is one of the most widely used programming languages, with millions of developers using it to develop websites, web applications, browser-based games, server-side APIs and more.
So, it makes it a very valuable skill to have and it opens up many job opportunities, and it allows for collaboration with other developers.
## Versatility
So, it is also very versatile.
It is used both on the frontend and backend of web development, making it a full stack language.
This versatility allows developers to build complete web applications using only JavaScript.
Not only that, but there are technologies like React Native, which allows you to build complex mobile applications, and technologies like Electrons that allow you to create desktop applications.
Some of the most popular desktop applications are actually built on JavaScript and Electron, including VS Code, which is the text editor that we will be using, as well as Postman which is the HTTP client that we will be using.
Before we continue, please [subscribe to my free weekly newsletter](https://karlgusta.substack.com) where I help you get a high paying developer job.
## Relatively Easy To Learn
So, I would say that JavaScript is relatively easy, relative being the key term.
So, if you compare it to other languages especially more low-level compile languages like C and C++, it is much easier to get into.
Anyone who has a passion for coding, can learn JavaScript.
You don't have to be some genius, you don't have to be great in Maths or anything like that.
You just have to have some drive and the willingness to learn and to put the effort in.
## Community
So JavaScript also has a very very large and active community, which provides a wealth of resources, support, tutorials, and tools for learning and improving your skills.
From websites like Stack Overflow to social media, JavaScript has a huge reach.
And when it comes to tools like actual development tools, there is just so much open-source software.
So, you have NPM which is the Node Package Manager, with like 1.3 million packages that you can just download and install and use.
So, there is no shortage of resources or tools when it comes to JavaScript.
Happy Coding!
Karl | thekarlesi |
1,874,831 | Comparison of synchronous and asynchronous control of LED display screens | In modern display technology, LED display screens are widely used in advertising, information... | 0 | 2024-06-03T02:07:31 | https://dev.to/sostrondylan/comparison-of-synchronous-and-asynchronous-control-of-led-display-screens-3opo | led, display, screens | In modern display technology, [LED display screens](https://www.sostron.com/product?category=2) are widely used in advertising, information release, stage background and other fields with their advantages of high brightness, low power consumption and long life. The control system of LED display screens is mainly divided into synchronous control and asynchronous control, each of which has unique characteristics and application scenarios. This article will compare and analyze these two control systems to help users make a more reasonable choice according to their needs.

1. Characteristics and application of synchronous control system
Synchronous control system, as the name suggests, is a control method for synchronous display of LED display screen and computer monitor. This system is usually used for indoor or outdoor full-color large-screen display screens, which can display videos, pictures, texts, notifications and other content in real time. [What is the difference between indoor LED display screens and outdoor LED display screens? ](https://www.sostron.com/service/faq/3020)
Features:
Real-time: The synchronous control system can map the image on the computer monitor in real time at an update rate of at least 60 frames per second, meeting the application scenarios with high real-time requirements.
Rich expression: Due to synchronous control, the display can display multi-grayscale colors to achieve multimedia advertising effects.
Complex operation: The operation of the synchronous control system is relatively complex and requires professional technicians to set up and maintain.
High price: Due to high technical requirements, the cost of the synchronous control system is relatively high. [Here is the price range of commercial LED display screens. ](https://www.sostron.com/service/faq/7183)
Dependence on the computer: The content of the display screen is completely synchronized with the computer monitor. Once the computer is turned off, the display screen will also stop displaying.
Application scenario: The synchronous control system is mainly suitable for places where dynamic video or graphic information needs to be displayed in real time, such as TV stations, large-scale event sites, shopping malls, etc.
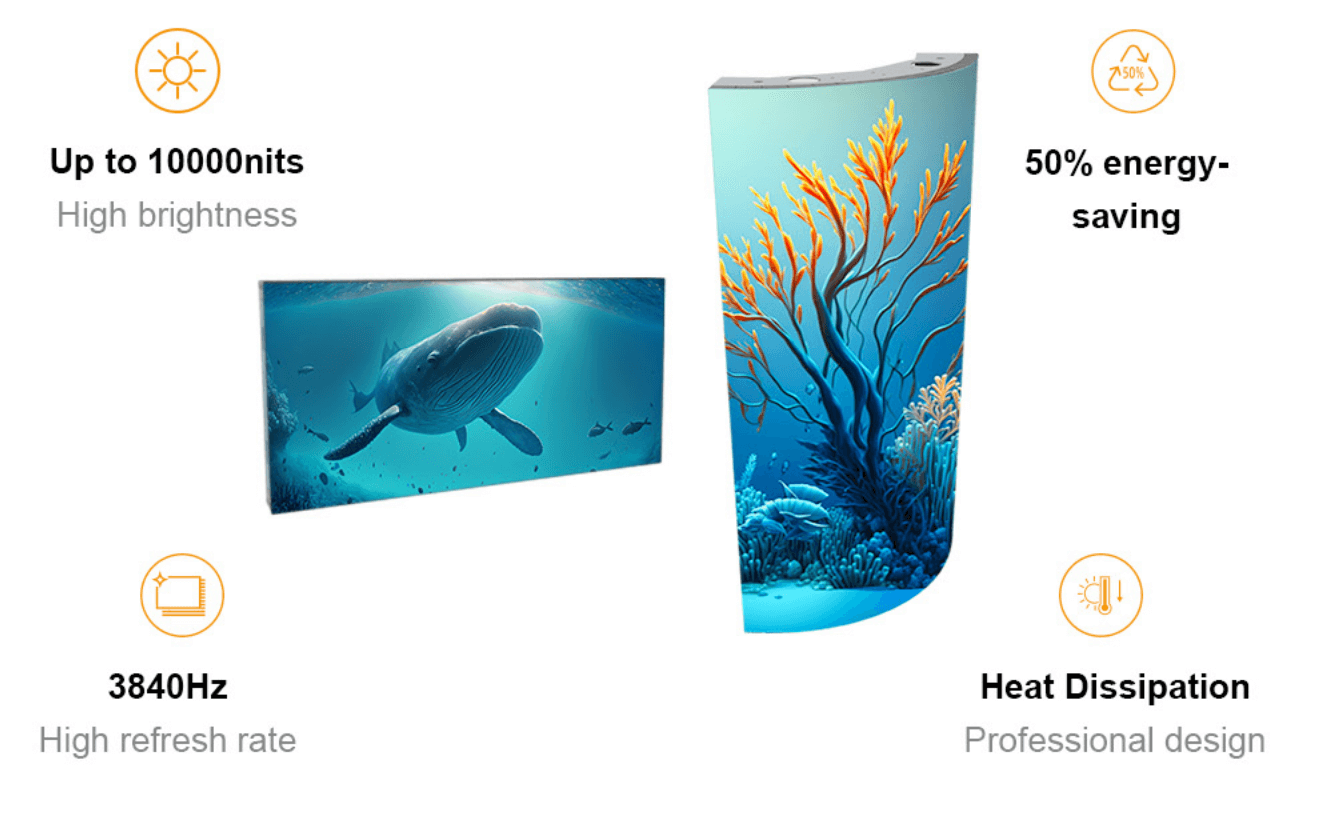
2. Characteristics and application of asynchronous control system
Asynchronous control system, also known as offline control system or offline card, is mainly used to display text, symbols, graphics or animation. Unlike synchronous control system, after the asynchronous control system edits the content on the computer, it is pre-placed into the frame memory of the LED screen through the RS232/485 serial port, and then played independently. [Take you to understand the LED display control system in 5 minutes. ](https://www.sostron.com/service/faq/4384)
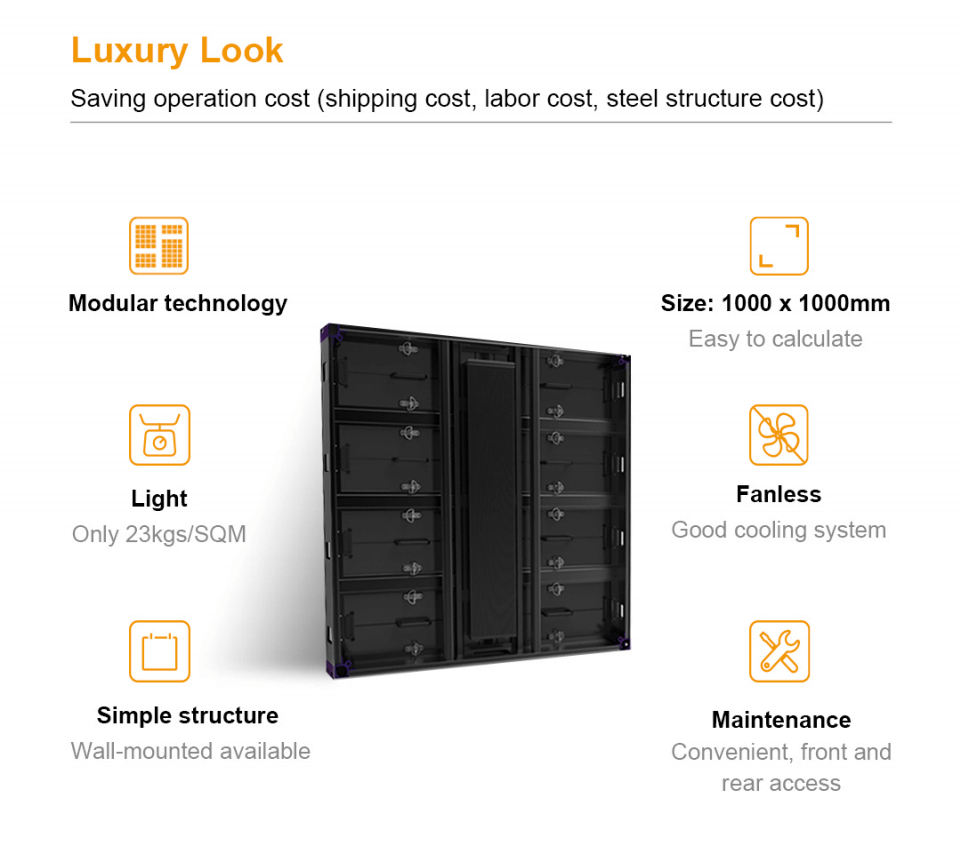
Features:
Simple operation: The operation of the asynchronous control system is relatively simple, and users can easily edit and update the display content.
Low price: Due to the low technical requirements, the cost of the asynchronous control system is relatively low.
Wide range of use: The asynchronous control system is suitable for a variety of application scenarios, including outdoor billboards, information display screens, etc.
Regional control: It can realize regional control of the display screen content, with high flexibility.
Independent playback: Even if the computer is turned off, the LED display can be displayed independently, but the amount of playback information is limited by the storage capacity of the control card.
Application scenario: The asynchronous control system is suitable for places that do not require high real-time performance, but need to flexibly display static or simple dynamic content, such as bus stops, shopping mall signs, etc. [Provide you with a guide to the application of LED display screens in shopping malls. ](https://sostron.com/news/3144)
Conclusion
Synchronous control systems and asynchronous control systems each have their own advantages and limitations. Synchronous control systems are suitable for occasions that require high real-time display of dynamic content, while asynchronous control systems are more suitable for cost-sensitive applications that do not require high real-time performance. When choosing an LED display control system, users should weigh the pros and cons of the two systems based on their specific needs and budget and make the most appropriate choice. By understanding the differences between the two control systems, users can more wisely choose an LED display product that suits their needs.
Thank you for watching. I hope we can solve your problems. Sostron is a professional [LED display manufacturer](https://sostron.com/about). We provide all kinds of displays, display leasing and display solutions around the world. If you want to know: [LED display technology analysis and advantages.](https://dev.to/sostrondylan/led-display-technology-analysis-and-advantages-4pa6) Please click read.
Follow me! Take you to know more about led display knowledge.
Contact us on WhatsApp:https://api.whatsapp.com/send/?phone=8613570218702&text&type=phone_number&app_absent=0 | sostrondylan |
1,874,830 | Unmatched Performance: BANOVO's Construction Equipment Portfolio | Unmatched Performance: BANOVO's Construction Equipment Portfolio Construction is a tremendously... | 0 | 2024-06-03T02:05:44 | https://dev.to/jennifer_garciakd_7c34d57/unmatched-performance-banovos-construction-equipment-portfolio-53m6 | performance | Unmatched Performance: BANOVO's Construction Equipment Portfolio
Construction is a tremendously challenging job that will require the usage strong, sturdy, and efficient machines. BANOVO is a high manufacturer of construction equipment that delivers unmatched performance. we're going to talk about the advantages, innovation, safety, use, simple tips to use, service, quality, and application associated with the BANOVO construction equipment portfolio
Advantages
BANOVO Backhoe Loaders construction equipment has advantages that are numerous other brands. First off is its performance that is unmatched with to productivity, efficiency, and durability. The apparatus is designed with cutting-edge technology that means it is an task that is easy operate, maintain, and repair. Additionally, BANOVO equipment is exclusive and customized to generally meet your needs that are unique requirements
Innovation
BANOVO is well known if you are a manufacturer that is forward thinking of equipment. The organization invests heavily in development and research to boost the grade of their products or services. Their equipment is made to provide performance that is maximum low-to-zero maintenance and operational costs. The business uses technology that is state-of-the-art create equipment this is certainly energy-efficient, environmentally friendly, and simple to utilize
Safety
Safety is a vital facet of construction work, and BANOVO Wheel Loaders equipment is made to provide safety that is maximum. The organization meets all safety that is international, making their equipment safe to use on any construction site. Furthermore, their equipment features safety that is innovative that ensure operator safety with all the machine
Use
BANOVO construction equipment is versatile and certainly will be properly used for assorted construction jobs, such as for example excavation, grading, paving, and demolition. The apparatus is made to make the work easier and quicker, thereby reducing labor costs and project completion time that is minimizing
Simple tips to Use
Using BANOVO Excavator Buckets construction equipment is not at all hard, especially using its user-friendly design. Operators can quickly operate and control the apparatus with just training that is minimal. BANOVO provides user that is comprehensive and guidelines to ensure operators may use the apparatus effectively
Service
BANOVO understands the necessity of good services that are after-sale. The organization provides customer that is exceptional through their knowledgeable technical team and prompt service centers. A trusted service that is after-sale to ensure that any difficulties with the apparatus get resolved quickly, minimizing downtime from the construction site
Quality
The grade of BANOVO construction equipment is unmatched. The organization is focused on producing equipment this is certainly reliable as well as the quality that is best. They use premium-grade materials to produce their equipment, making sure the apparatus has a lifespan that is lengthy certainly will withstand harsh conditions
Application
BANOVO construction equipment is perfect for construction projects of every size, which range from small-scale to projects that are large-scale. The apparatus would work for used in different terrains, including regions that are mountainous deserts, and oceans. BANOVO offers an array of equipment, including excavators, bulldozers, cranes, loaders, and road construction equipment.
Source: https://www.bonovogroup.com/backhoe-loaders | jennifer_garciakd_7c34d57 |
1,874,828 | Use Gemini to Understand Errors with Google Chrome Dev Tools | requirement Google Chrome version 125+ Settings Check Understand console... | 0 | 2024-06-03T01:58:33 | https://dev.to/0xkoji/use-gemini-to-understand-errors-with-google-chrome-dev-tools-4b54 | gemini, google, chrome | ## requirement
Google Chrome version 125+
## Settings
Check **Understand console messages with AI**
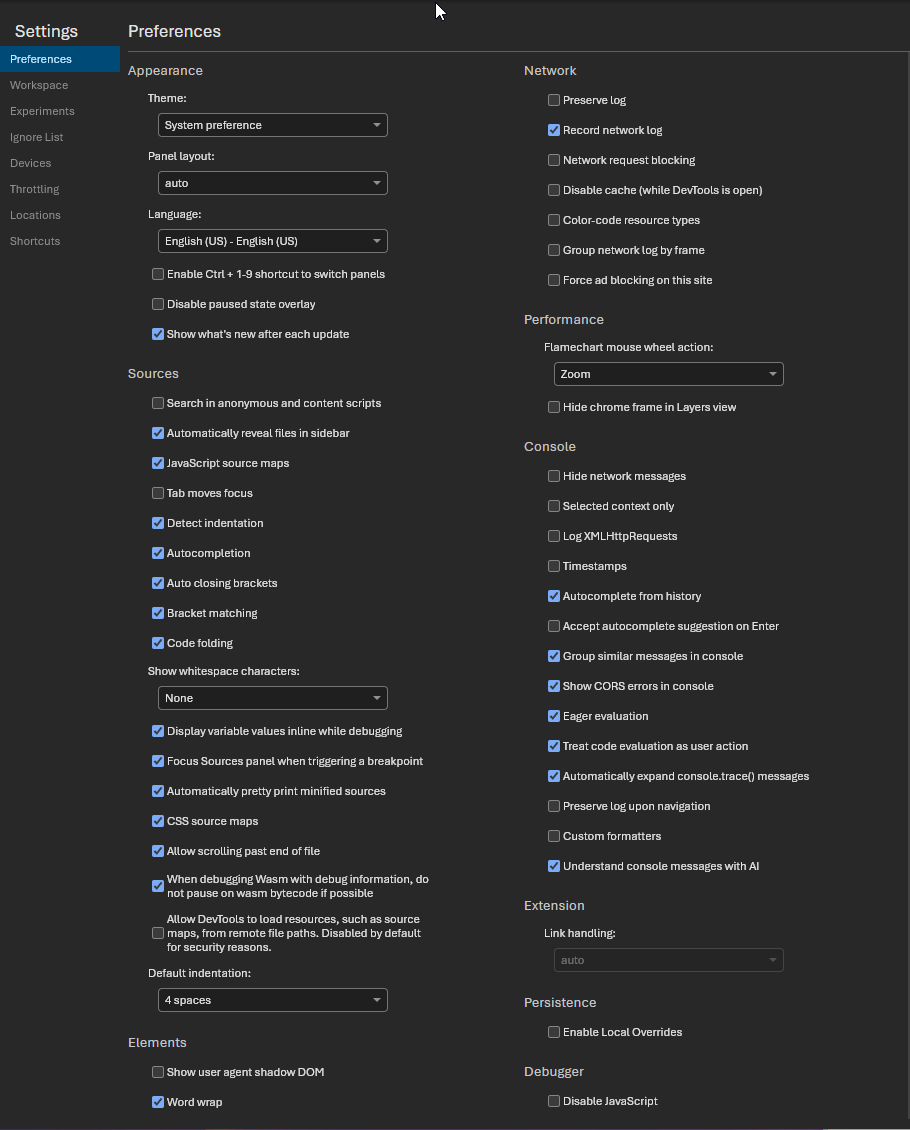
## Try Gemini
https://bubble-jingle.web.app/search
1. open Devtools-console
2. click text input
3. click the light icon
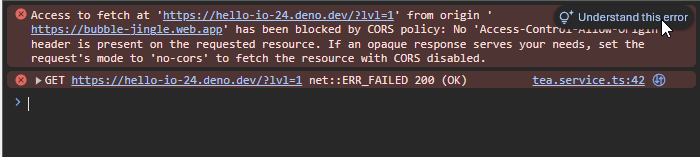
In the first time, you will see the following messages
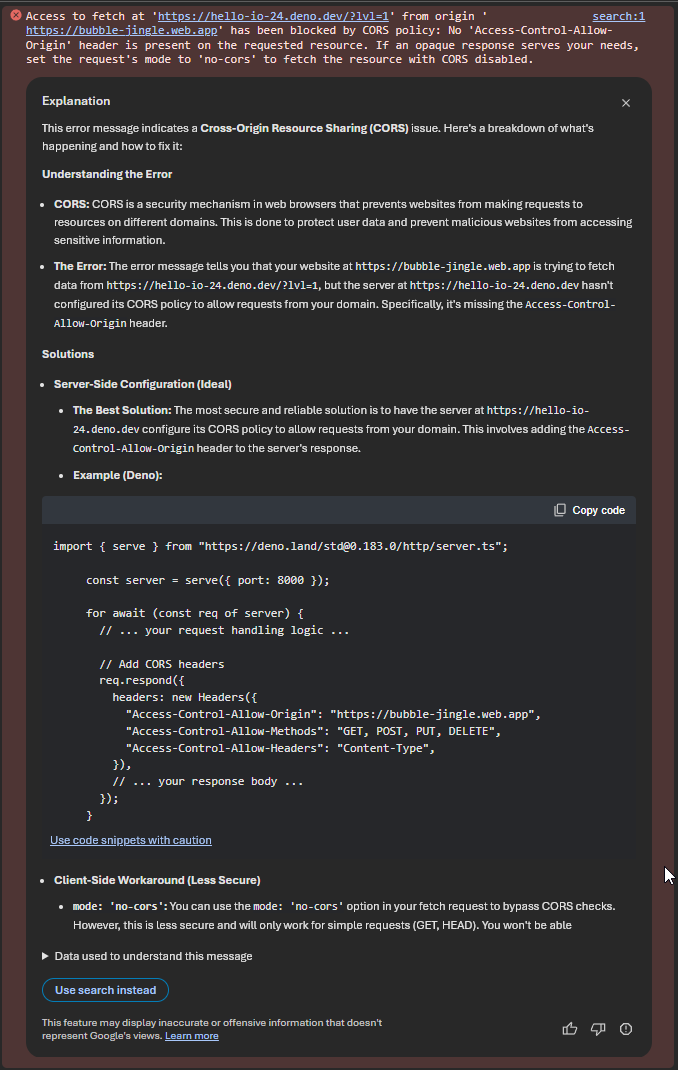
| 0xkoji |
1,874,827 | HIRE A CRYPTO EXPERT FROM RESILIENT SHIELD RECOVERY | At just 17 , I became a trader, venturing into the world of cryptocurrency trading early on in my... | 0 | 2024-06-03T01:55:44 | https://dev.to/bassy_troy_636c84ae17a654/hire-a-crypto-expert-from-resilient-shield-recovery-2a0n | At just 17 , I became a trader, venturing into the world of cryptocurrency trading early on in my teenage years. Through countless hours of research, strategy, and diligent effort, I was able to amass a substantial fortune of over $600,000 worth of Bitcoin assets. My success was both thrilling and empowering, but little did I know that a devastating turn of events was just around the corner.My troubles started when I shared my achievements with a few friends, unaware of the potential risks. Shortly after, I began receiving suspicious emails. One day, I made the mistake of opening one of these emails, which led to my Bitcoin wallet being hacked. In a matter of moments, all my hard-earned assets disappeared, leaving me in a state of shock and despair.Desperate to find a solution, I turned to the internet for help and came across RESILIENT SHIELD RECOVERY . Despite my initial skepticism, I decided to reach out to them, clinging to the hope that they could help me reclaim my lost assets. From the very beginning, the team at RESILIENT SHIELD RECOVERY provided exceptional support and reassurance. Their constant communication and encouragement helped me stay hopeful during this trying time.Within just 12 hours, the dedicated team at RESILIENT SHIELD RECOVERY managed to recover my compromised email account and secure it against further attacks. Unfortunately, my Bitcoin assets had already been transferred out. However, the team didn't stop there. Through their meticulous investigation, they were able to track down the perpetrators behind the scam.To my utter shock, the investigation revealed that the scammers were individuals I had considered close friends. It was a painful revelation, but RESILIENT SHIELD RECOVERY unwavering support helped me navigate through the betrayal. With their assistance, I took legal action against those responsible. The legal process culminated in a court settlement, which compensated me for the stolen assets and provided a sense of justice.This harrowing experience taught me invaluable lessons about cybersecurity and the importance of being cautious with whom I share sensitive information. It also reinforced the significance of having trustworthy allies in the digital age. The expertise and dedication of RESILIENT SHIELD RECOVERY were instrumental in helping me regain control over my financial future and restoring my peace of mind.In conclusion, my encounter with RESILIENT SHIELD RECOVERY was nothing short of life-changing. Their exceptional service and commitment to helping victims of digital fraud are truly commendable. For anyone facing similar challenges, I highly recommend ( resilientshieldrecovery@contractor.net ) as a reliable partner in navigating the complex world of cryptocurrency and digital security. WhatsApp Number : +1 (936) 244‑3264 | bassy_troy_636c84ae17a654 | |
1,874,826 | Introducing Idyllic Apps AI Dictionary: Redefining the Way You Understand Words | We're thrilled to announce the launch of the Idyllic Apps AI Dictionary, a revolutionary tool... | 0 | 2024-06-03T01:55:23 | https://dev.to/tonux-jan/introducing-idyllic-apps-ai-dictionary-redefining-the-way-you-understand-words-2dpb | We're thrilled to announce the launch of the Idyllic Apps AI Dictionary, a revolutionary tool designed to elevate your language learning and comprehension experience. Imagine having a personal linguistic assistant that's always ready to help you understand, pronounce, and use words accurately—Idyllic Apps AI Dictionary makes this a reality.
**Watch Our Launch Video**
To get a sneak peek at the AI Dictionary in action, check out our launch video here. See firsthand how this innovative app can transform your interaction with words.
{% embed https://www.youtube.com/watch?v=bxkt3KCdQvI %}
**What Makes Idyllic Apps AI Dictionary Unique?**
AI-Powered Definitions
Our AI Dictionary leverages cutting-edge artificial intelligence to provide precise and contextually relevant definitions. No more wading through archaic or overly technical explanations; our AI ensures you get the most accurate and understandable meanings.
**Pronunciation Guides (Coming Soon)**
Struggling with pronunciation? Our app offers audio guides for every entry, voiced by native speakers. Improve your pronunciation with ease and confidence, knowing you're learning from the best.
**Example Sentences**
Understanding a word is more than just knowing its definition. That's why we include example sentences for every entry, helping you see how words are used in real-life contexts.
**Multilingual Support (Coming Soon)**
Whether you're a polyglot or just learning a new language, our AI Dictionary supports multiple languages, making it a versatile tool for learners worldwide. Switch between languages effortlessly and expand your vocabulary across different tongues.
**User-Friendly Interface**
Our sleek, intuitive design ensures a seamless user experience. Quickly search for words, save your favorites, and explore new vocabulary with ease.
**Why Choose [Idyllic Apps AI Dictionary?]**(https://us.idyllic.app/dictionary)
In today’s fast-paced world, clarity and precision in language are more important than ever. Whether you're a student, professional, or language enthusiast, Idyllic Apps AI Dictionary is designed to meet your needs. Our AI technology continually learns and evolves, ensuring you always have access to the most up-to-date and accurate information.
**Join the Revolution**
Don't miss out on this game-changing tool. Visit [Idyllic Apps AI Dictionary](https://us.idyllic.app/dictionary) today and start your journey toward mastering any language with ease and confidence.
Stay tuned for more updates and features as we continue to enhance your language learning experience. Together, let's redefine the way we understand and use words.
For more information, visit our [website](https://idyllic.app/) or contact our support team. We're here to help you every step of the way.
Happy learning! | tonux-jan | |
1,874,825 | Stay Updated with Python/FastAPI/Django: Weekly News Summary (27/05/2024 - 02/06/2024) | Dive into the latest tech buzz with this weekly news summary, focusing on Python, FastAPI, and Django... | 0 | 2024-06-03T01:55:01 | https://poovarasu.dev/python-fastapi-django-weekly-news-summary-27-05-2024-to-02-06-2024/ | python, django, flask, fastapi | Dive into the latest tech buzz with this weekly news summary, focusing on Python, FastAPI, and Django updates from May 20th to May 26th, 2024. Stay ahead in the tech game with insights curated just for you!
This summary offers a concise overview of recent advancements in the Python/FastAPI/Django framework, providing valuable insights for developers and enthusiasts alike. Explore the full post for more in-depth coverage and stay updated on the latest in Python/FastAPI/Django development.
Check out the complete article here [https://poovarasu.dev/python-fastapi-django-weekly-news-summary-27-05-2024-to-02-06-2024/](https://poovarasu.dev/python-fastapi-django-weekly-news-summary-27-05-2024-to-02-06-2024/) | poovarasu |
1,874,822 | DIY Dog Diapers: A Practical Guide | Managing a dog’s hygiene, especially during their heat cycle or when they have incontinence issues,... | 0 | 2024-06-03T01:52:39 | https://dev.to/fayre_fan_55056404018ea3b/diy-dog-diapers-a-practical-guide-de3 | Managing a dog’s hygiene, especially during their heat cycle or when they have incontinence issues, can be challenging. While commercial [dog diapers](https://wegreeco.com/collections/dog-diapers) are available, making your own DIY dog diapers can be a cost-effective and customizable solution. This article provides a step-by-step guide on how to create your own dog diapers at home.
Why DIY Dog Diapers?
Creating your own dog diapers offers several benefits:
• Cost Savings: DIY diapers are often cheaper than store-bought options.
• Custom Fit: You can tailor the diaper to fit your dog’s specific size and needs.
• Eco-Friendly: Reusable materials reduce waste compared to disposable diapers.
Materials Needed
To make a DIY dog diaper, you will need the following materials:
• Old T-shirts or Fabric: Soft and absorbent materials work best.
• Scissors: For cutting the fabric.
• Velcro Strips or Safety Pins: For securing the diaper.
• Sanitary Pads or Absorbent Liners: For added absorbency.
• Measuring Tape: To ensure a good fit.
Step-by-Step Instructions
Step 1: Measure Your Dog
• Use the measuring tape to measure your dog’s waist circumference, around the widest part.
• Measure the length from the waist to the base of the tail.
Step 2: Cut the Fabric
• Cut a rectangular piece of fabric based on the measurements. The width should be the waist measurement plus a few extra inches for overlap. The length should be from the waist to the tail base, plus a few inches.
Step 3: Add Tail Hole
• Fold the fabric in half and cut a small hole in the center for the tail. Make sure it’s not too large, to prevent leaks.
Step 4: Attach Absorbent Liner
• Place a sanitary pad or absorbent liner in the center of the fabric. This will help absorb urine and keep your dog dry.
Step 5: Secure the Diaper
• Wrap the fabric around your dog’s waist, ensuring the tail goes through the hole.
• Use Velcro strips or safety pins to secure the diaper snugly but comfortably around the waist.
Step 6: Test and Adjust
• Put the diaper on your dog and check for fit. Ensure it’s not too tight to cause discomfort or too loose to prevent leaks. Adjust as needed.
Tips for Using DIY Dog Diapers
• Frequent Changes: Change the diaper regularly to maintain hygiene and prevent skin irritation.
• Washing: Use washable materials and clean the diapers after each use to ensure they are fresh and odor-free.
• Comfort: Ensure the diaper does not restrict movement. Your dog should be able to walk, sit, and lie down comfortably.
• Materials: Consider using breathable fabrics to prevent rashes and irritation.
Additional Ideas for DIY Dog Diapers
Reusable Baby Diapers:
• Modify reusable baby diapers by adding a tail hole and securing them with Velcro strips.
Old Underwear:
• Repurpose old underwear by cutting a tail hole and adding an absorbent liner. Secure it with a safety pin or Velcro strip.
Sock Diapers:
• For small dogs, you can use a large sock. Cut a tail hole, insert an absorbent pad, and secure it with Velcro.
Conclusion
DIY dog diapers are a practical and customizable solution for managing your dog’s hygiene needs. By following these simple steps and using materials you likely already have at home, you can create comfortable and effective diapers for your dog. This not only helps you save money but also ensures your furry friend stays clean and happy. | fayre_fan_55056404018ea3b | |
1,874,821 | BANOVO: Pioneering Solutions for the Construction Industry | BANOVO :A Solution For The Construction Business. Will you be sick and tired of coping with the... | 0 | 2024-06-03T01:52:36 | https://dev.to/jennifer_garciakd_7c34d57/banovo-pioneering-solutions-for-the-construction-industry-42d6 | constructions | BANOVO :A Solution For The Construction Business.
Will you be sick and tired of coping with the complexity of building projects? Or are you worried about the safety of your employees? Don't worry because BANOVO will be here to revolutionize the construction industry along with its solutions which are pioneering promise to help make your job much easier and safer. So let's dive right into it as we discussed it further.
Benefits of BANOVO
BANOVO Backhoe Loaders is just a business technology-driven provides several solutions when it comes to building business. The business's solutions aim to make construction jobs more efficient, cost-effective, and safe. BANOVO's offerings tend to be innovative and provide advantages which can be many technicians and builders. For example, BANOVO's solutions help you save money and time by streamlining processes and construction this is certainly making more cost-effective. Additionally, BANOVO's solutions supply unrivaled security, and therefore the potential risks are decreased by it of work-related accidents.
Innovation at its Most Useful
BANOVO's technology-driven solutions allow it to be the pinnacle of development into the construction business. The company's offerings, such as for example drones, 3D printing, and AR/VR technology, ensure that building projects tend to be completed on some time within budget. Drones are incredibly helpful when building examining, using pictures, and measuring distances. Having said that, AR/VR technology provides project managers with important insights as a project. Meanwhile, 3D printing technology makes it easier to create building this is certainly complex and prototypes. These innovations have made BANOVO an industry-leader in construction solutions.
Safety And Health First
BANOVO's Skid Steer Loaders solutions prioritizes the security of construction workers. A number of its items are designed with protection at heart. For instance, drones may be used to check construction internet sites, which can be safer than having a worker rise up a building to carry out an inspection. BANOVO's Augmented truth (AR) technology can simulate situations that are dangerous enabling workers to prepare better for potential hazards. Additionally, BANOVO makes use of information that are real-time analytics to improve safety treatments and minimize the risk of accidents.
Using BANOVO
BANOVO's solutions tend to be user-friendly, making them accessible to everyone in the building industry. Although some solutions may need some training, BANOVO's customer service group provides assistance to make users which are certain the most from their products or services. Drones, for-instance, are simple to operate, and AR/VR technology only requires a phone mobile a tablet to run. Nearly all BANOVO's solutions come with training manuals, therefore the organization provides tutorials which can be online rendering it possible for anybody who would like to utilize it.
High Quality Is Fully Guaranteed
BANOVO ensures that its items are of the quality highest. The organization uses cutting-edge technology additionally the analysis latest to deliver exemplary solutions. BANOVO's quality management methods happen certified to meet standards being international which means that people can be certain they've been purchasing high-quality products. BANOVO's objective is always to offer items that are top-notch help to make building projects safer, more effective, and economical.
Application of BANOVO
BANOVO's Excavator Ripper solutions may be used in lot of applications. For-instance, drones can be used to inspect buildings, survey land, and take aerial pictures. Having said that, AR/VR technology can simulate a building design, leading to better problem-solving and decision-making. BANOVO's 3D publishing technology could be used to create prototypes and develop styles that are complex. Each one of these programs make BANOVO's solutions invaluable when you look at the building industry.
Source: https://www.bonovogroup.com/backhoe-loaders | jennifer_garciakd_7c34d57 |
1,874,820 | Stay Updated with PHP/Laravel: Weekly News Summary (27/05/2024 - 02/06/2024) | Dive into the latest tech buzz with this weekly news summary, focusing on PHP and Laravel updates... | 0 | 2024-06-03T01:52:36 | https://poovarasu.dev/php-laravel-weekly-news-summary-27-05-2024-to-02-06-2024/ | php, laravel | Dive into the latest tech buzz with this weekly news summary, focusing on PHP and Laravel updates from May 27th to June 2nd, 2024. Stay ahead in the tech game with insights curated just for you!
This summary offers a concise overview of recent advancements in the PHP/Laravel framework, providing valuable insights for developers and enthusiasts alike. Explore the full post for more in-depth coverage and stay updated on the latest PHP/Laravel development.
Check out the complete article here [https://poovarasu.dev/php-laravel-weekly-news-summary-27-05-2024-to-02-06-2024/](https://poovarasu.dev/php-laravel-weekly-news-summary-27-05-2024-to-02-06-2024/) | poovarasu |
1,874,819 | Precision and Performance: BANOVO Construction Equipment Unleashed | BANOVO Construction Equipment: Precision and Performance Unleashed BANOVO Construction Equipment is... | 0 | 2024-06-03T01:44:56 | https://dev.to/jennifer_garciakd_7c34d57/precision-and-performance-banovo-construction-equipment-unleashed-4dd7 | equipments | BANOVO Construction Equipment: Precision and Performance Unleashed
BANOVO Construction Equipment is a manufacturer that's leading in equipment that provides the ultimate combination of precision, performance, and safety. Our cutting-edge dedication and innovation to quality make our equipment ideal for a range wide of. Whether you're a contractor, landscaper, or DIY enthusiast, our equipment is designed to meet all your needs. So, let's take a closer look at the advantages of using BANOVO Construction Equipment.
Advantages
BANOVO Construction Equipment offers a wide range of benefits make it a top choice for construction. Our equipment is designed to Wheel Loaders provide precision and accuracy, which essential when structures building require high levels of detail and accuracy. Our construction equipment is also designed to be durable, reliable, and to withstand the toughest conditions. This makes it an investment that's good that anyone who needs equipment can last for years.
Innovation
At BANOVO Construction Equipment, we are committed to improvement and innovation continuous. We invest heavily in research and development to ensure our equipment stays ahead of the competition. Our innovative design features include precise controls allow for accurate movement and positioning, intuitive interfaces make our equipment easy to use, and advanced safety features provide protection for operators and workers.
Safety
Safety is essential in construction, and it one of our priorities top BANOVO Construction Equipment. We have incorporated advanced safety features into our equipment to ensure operators and workers protected at all times. Our equipment includes safety switches, emergency stops, protective covers, and other safety features help reduce accidents and injuries.
Use and How to Use
BANOVO Construction Equipment Mini Excavators is easy to use, even for those who have little experience construction equipment operating. Our equipment has interfaces intuitive make it easy to understand and use. We provide detailed instructions and training materials to help operators get up to speed quickly. This ensures our equipment used safely and effectively.
Service and Quality
At BANOVO Construction Equipment, we believe quality and service go hand in hand. We provide outstanding customer service to ensure our customers satisfied with their equipment. We provide fast and repair efficient maintenance services to ensure our equipment stays in good condition and performs at its best. Our commitment is to quality reflected in our equipment, which built to last and provide performance years reliable.
Application
BANOVO Construction Equipment Excavator Buckets is ideal for a wide of range. Our equipment is suitable for construction projects of all sizes, from small home renovations to projects large-scale commercial. Our equipment also is ideal for landscaping, agriculture, and other applications require precise positioning and movement. Our equipment is versatile, reliable, and easy to use, making it an investment that's excellent to any construction or project industrial.
Source: https://www.bonovogroup.com/Wheel-loaders | jennifer_garciakd_7c34d57 |
1,874,817 | Heavy Duty Towing Services: Baltimore's Reliable Rescue | In the bustling streets of Baltimore, where vehicles of all sizes navigate through daily challenges,... | 0 | 2024-06-03T01:40:04 | https://dev.to/towingmaryland/heavy-duty-towing-services-baltimores-reliable-rescue-5g5o | towingservices | In the bustling streets of Baltimore, where vehicles of all sizes navigate through daily challenges, the need for reliable heavy-duty towing services stands paramount. Amidst the city's rhythm, where every minute counts, having a dependable rescue team can make all the difference. Enter Baltimore's trusted ally in vehicular emergencies: Heavy Duty Towing Services.
With a fleet equipped to handle the most demanding situations, they epitomize efficiency and reliability in heavy-duty towing. Whether a large truck stranded on a busy highway or a commercial vehicle facing mechanical woes, their adept team ensures swift and safe resolution.
In the heart of Baltimore's automotive landscape, Heavy Duty Towing Services stands tall as the go-to solution for those seeking prompt and professional assistance. When breakdowns or accidents strike, count on Heavy Duty Towing Services to be the steadfast beacon of rescue.
The Backbone of Baltimore's Transportation Network
Heavy-duty towing services form the robust backbone of Baltimore's transportation network, ensuring the seamless flow of goods and services across the city. From clearing accidents on major highways to relocating oversized industrial equipment, these services are the unsung heroes keeping Baltimore moving. With their timely intervention, gridlocks could bypass commerce and emergency response efforts.
Their strategic positioning throughout the city allows for rapid deployment, minimizing disruptions and maximizing efficiency. Beyond just towing disabled vehicles, they facilitate the restoration of normalcy on Baltimore's roads, contributing to the city's economic vitality.
Essentially, they are not just service providers but essential components of Baltimore's infrastructure, supporting its growth and development.
Specialized Equipment for Heavy-Duty Challenges
Specialized equipment is the cornerstone of heavy-duty towing services, enabling them to tackle the most challenging situations precisely and efficiently.
Powerful winches: These winches are capable of pulling tons of cargo and are essential for recovering stranded vehicles and equipment.
Hydraulic lifting systems: Used for uprighting overturned vehicles safely and efficiently.
Heavy-duty wreckers: Specifically designed to handle the weight and size of industrial machinery and oversized vehicles.
Air cushions: Utilized for lifting and moving heavy loads in tight spaces or on unstable terrain.
Specialized rigging equipment: Allows for the secure attachment and maneuvering of heavy loads during recovery operations.
The specialized equipment utilized by heavy-duty towing services is essential for navigating the challenges posed by large-scale accidents and breakdowns.
24/7 Availability: Answering the Call Day or Night
Heavy-duty towing services in Baltimore understand that emergencies don't adhere to regular business hours. That's why they offer around-the-clock availability, ready to answer distress calls anytime, day or night.
Whether it's the middle of rush hour or the dead of night, these dedicated professionals are on standby, prepared to spring into action at a moment's notice.
This commitment to 24/7 availability ensures that motorists and businesses alike can have peace of mind knowing that help is just a phone call away, regardless of the time or circumstances. Baltimore's heavy-duty towing services' unwavering dedication to serving the community sets them apart as reliable rescue partners.
Trained Professionals: The Heart of Reliable Rescue
Trained professionals are the cornerstone of reliable rescue operations in the heavy-duty towing industry. Equipped with specialized skills and knowledge, these professionals are the heartbeat of dependable assistance in times of crisis.
Rigorous Training: Extensive programs prepare professionals for the complexities of heavy-duty towing.
Mastery of Techniques: Advanced driving skills and recovery procedures are honed to perfection.
Adaptable Expertise: Professionals can confidently assess and respond to evolving situations.
Commitment to Excellence: Ongoing skill development ensures they stay at the forefront of their field.
Trusted by the Community: Their professionalism and reliability make them the go-to choice for reliable rescue.
Trained professionals are the backbone of reliable rescue in the heavy-duty towing industry. They ensure the safety and efficiency of operations on Baltimore's roads. With their expertise and dedication, they uphold the highest service standards, earning the trust and gratitude of the community they serve.
Handling High-Stakes Situations with Precision
Precision and expertise are paramount in the high-stakes world of heavy-duty towing in Baltimore. Professionals tackle challenges like navigating narrow urban streets and executing delicate recoveries with meticulous planning. Each move is calculated to minimize risks and ensure safety, even in hazardous terrain.
Their experience allows them to adapt swiftly to evolving circumstances, making split-second decisions confidently. In heavy-duty towing, where errors can have severe consequences, the ability to handle such situations with precision distinguishes the best from the rest.
Ensuring Safety First: Protocols and Procedures
Safety is the cornerstone of heavy-duty towing services in Maryland. From the moment a call comes to the completion of a rescue operation, strict protocols and procedures are followed to mitigate risks and ensure the well-being of everyone involved.
Thorough Risk Assessments: Before any operation begins, comprehensive risk assessments are conducted to identify potential hazards and develop strategies to address them proactively.
Stringent Safety Measures: Throughout the operation, strict safety measures are implemented to protect personnel and bystanders, including personal protective equipment and traffic control measures.
Ongoing Safety Training: Personnel undergo regular safety training to stay updated on the latest protocols and best practices, equipping them with the knowledge and skills to respond effectively in emergencies.
Communication Protocols: Clear communication protocols are established to ensure seamless coordination between team members and other stakeholders, minimizing the risk of misunderstandings or errors.
Continuous Improvement: Heavy-duty towing services prioritize continuous improvement, regularly reviewing and updating their protocols and procedures to incorporate lessons learned and emerging best practices.
Ensuring safety through rigorous protocols and procedures is a priority and a commitment for heavy-duty towing services in Maryland.
Beyond Towing: Comprehensive Recovery Services
Heavy-duty towing services in Baltimore go beyond simply towing disabled vehicles; they offer comprehensive recovery services to minimize the impact of accidents and breakdowns on businesses and communities.
From roadside assistance and vehicle extrication to cargo recovery and hazardous materials spill cleanup, these companies ensure they can handle any situation, no matter how complex. Their swift response and efficient execution minimize disruptions to traffic flow and restore normalcy as quickly as possible. Essentially, they provide essential support to keep Baltimore's roads safe and accessible for all.
Navigating Baltimore's Unique Terrain and Traffic
Navigating Baltimore's unique terrain and traffic presents a formidable challenge for heavy-duty towing services. The city's narrow streets, tight turns, and congested traffic patterns demand precision and skill from operators.
Advanced GPS Navigation: Plotting efficient routes to avoid congestion.
Local Knowledge: Leveraging familiarity with Baltimore's streets to anticipate hazards.
Experience: Applying years of expertise to navigate complex towing operations.
Adaptability: Adjusting approaches in real-time to minimize delays.
Determination: Tackling challenges with unwavering dedication to ensure prompt and safe assistance.
Navigating Baltimore's unique terrain and traffic requires technology, knowledge, and determination from heavy-duty towing services. Despite the challenges posed by the city's layout, operators leverage their skills and experience to provide efficient and reliable assistance to motorists in need.
Partnerships with Industry Leaders: Strengthening the Safety Net
To bolster community safety, heavy-duty towing services in Baltimore collaborate closely with industry leaders, such as insurance companies, transportation agencies, and law enforcement agencies. These strategic partnerships facilitate seamless coordination and communication during emergencies, ensuring swift responses to incidents on Baltimore's roads.
By combining resources and expertise, they develop innovative solutions to emerging challenges and elevate safety standards. Ultimately, these partnerships serve as force multipliers, enabling heavy-duty towing services to offer enhanced support and assistance to the community when needed.
The Unsung Heroes: Recognizing the Contributions of Heavy-Duty Tow Operators
While heavy-duty towing services play a critical role in keeping Baltimore's roads safe and accessible, it's the operators behind the scenes who truly deserve recognition as unsung heroes. These dedicated professionals work tirelessly, often in challenging conditions and under immense pressure, to ensure that help is always available for motorists in need.
They brave all hazards, from inclement weather to hazardous materials, to execute their duties with professionalism and integrity. Despite the risks and challenges they face, they remain committed to their mission of reliable rescue, day in and day out. It's their unwavering dedication and selflessness that make them true heroes in the eyes of the community, deserving of our utmost respect and gratitude.
The heavy-duty towing services in Maryland, particularly in Baltimore, stand as pillars of reliability and resilience within the transportation landscape. From being the backbone of Baltimore's transportation network to handling high-stakes situations with precision, these services epitomize professionalism and dedication.
Their commitment to 24/7 availability ensures that help is always within reach, day or night, safeguarding the well-being of motorists and businesses alike. Moreover, their emphasis on safety-first protocols and comprehensive recovery services underscores their unwavering commitment to excellence.
As we recognize the contributions of heavy-duty tow operators, it's evident that they are the unsung heroes who ensure the smooth functioning of Baltimore's roads and the safety of its residents. To ensure continued support for these vital services, let's advocate for partnerships and resources that strengthen their capabilities and enhance road safety for all. Together, we can ensure that heavy-duty towing services remain the reliable rescue partners that Baltimore relies on in times of need.
[Heavy Duty Towing Maryland](https://heavydutytowingmaryland.com/
) | towingmaryland |
1,871,412 | Load Testing Solium Infernum with Docker, Kubernetes and Enemy AI | Load testing a video game is a critical part of the development process if you have any intention of... | 0 | 2024-06-03T01:38:40 | https://dev.to/romesh_dev/load-testing-solium-infernum-with-docker-kubernetes-and-enemy-ai-9pl | gamedev, kubernetes, testing, docker | Load testing a video game is a critical part of the development process if you have any intention of building online systems into your game. As we’ve seen many times before, it's important that you plan for both critical success as well as critical failure when it comes to online multiplayer systems. The results of being over or under prepared can have devastating effects on your players, or your bank account.
For Solium Infernum, we had a 4-6 player, turn-based, _asynchronous_ multiplayer game. That last part is important because it means that a game of Solium Infernum can last for hours, weeks, even months. Even with the fastest game configurations in place, a single game of Solium Infernum can last an hour or two, so it was critical for us to have a way to load test the game that didn't consume hours and hours of human time for every change.
#What Options Do We Have?
##Load Testing Services

When it comes to load testing, one option that often comes to mind is beta testing or third party load testing services. This is where either you or a third-party, organise hundreds, or thousands of players around the world to load test your game. This is pretty much the closest you can get to a real-world scenario testing. The main issue here is that people are expensive, and at a certain scale, it is no longer feasible to get _enough_ humans involved to properly load test.
##Automated testing

Another option for load testing is, of course, automation. Automation has the potential to save us huge amounts of time in testing scenarios, and you are able to run tests at a much higher volume and frequency. The trade-off here is that, generally, it's less 'exhaustive' solution than manual testing.
I’d like to clarify that I’m not talking about Unit Testing here, although I do think that Unit Testing is an incredibly useful tool for development. Specifically, in this instance, I'm talking about load testing, which means creating automation tools that can attempt to saturate live backend systems, preferably in some kind of ‘non-live’ load testing environment. If I were to give this kind of testing a label, it would probably fit more broadly into the 'integration test' bucket.
##The Challenges
Load testing systems like this is about more than just finding the maximum throughput of a given endpoint, it's also about finding hot and cold paths in your system and working out what kind of reasonable 'soft limits' can be set to protect you from cloud overspend. In most cloud environments, there is a level of fine-grained control over metered endpoints/databases, so we want to be able to fairly reliably imitate player behavior if we can so that we can confidently configure our backend so scale nicely with player growth.
The other challenge we faced is that video games are resource intensive to run. With more traditional software, you may be able to more easily run a few hundred or thousand instances of your application on not very much hardware, but video games have a minimum spec, and unless you happen to have access to a huge number of GPUs that you're not already using to build LLMs and mine bitcoin, you're going to need to find another way to scale up your game for automation.
##The Goal
So, back to Solium Infernum, we need a test solution that is lightweight enough to scale meaningfully for load testing, and we also need to find a way to simulate the actions of real players sending multiplayer traffic to our online systems without using actual people. One thing that came to mind when looking into this problem is that there is another key area of game development that aims to simulate player behavior very closely, the enemy AI.
_Now, I want to be super clear here that when I’m talking about 'enemy AI' in this article, I’m not talking about LLMs or Generative AI. Though I imagine you could achieve similar outcomes using those tools, what I’m talking about in our case is more traditional game AI._
#Building The Load Testers
##The Core Game Package
To understand how we achieved the next step, you will need to understand our core packaging systems. The core architecture of Solium Infernum was designed in a way that allowed us to package the core systems of the game in a library that was not dependent on any specific engine libraries. What this meant is that at build time, we were able to create a separate [NuGet](https://www.nuget.org/) package that contained the core game libraries for that version of the game and ship that package to the upstream server project to be consumed server-side for turn processing.
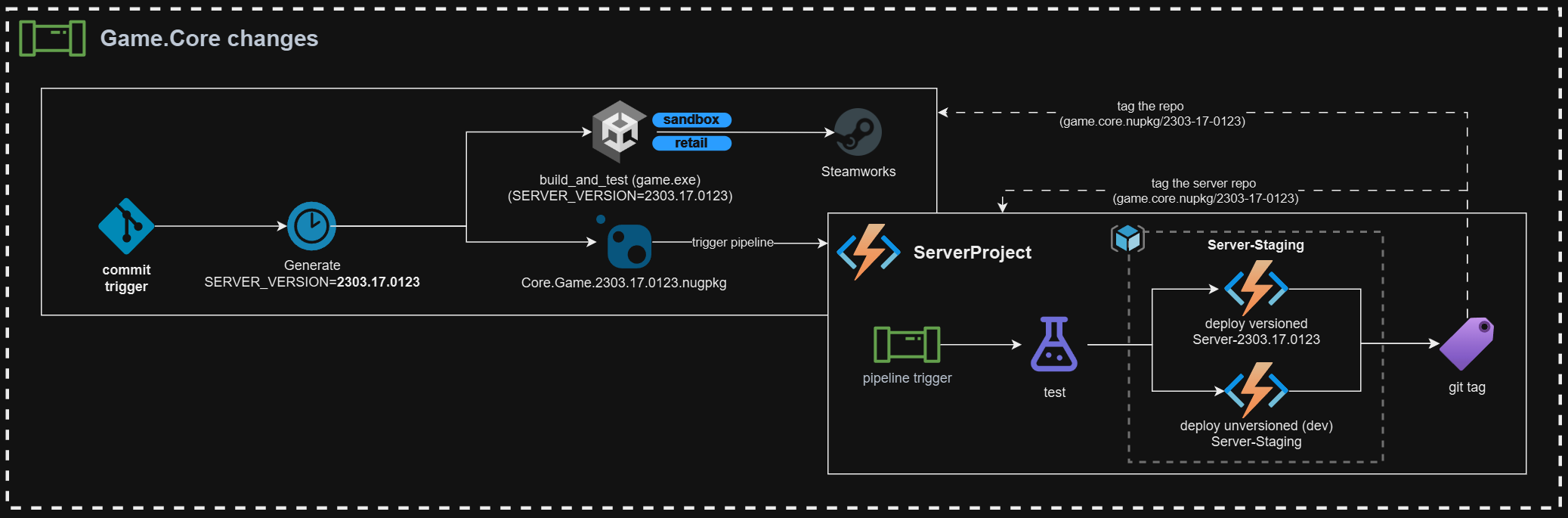
The most important part of the above is that NuGet package. Using this package, we were able to solve both of our biggest challenges. We can use this package to build a lightweight load testing application that has access to the core game systems like turn processing, validation, and most importantly for us, the enemy AI.
##The Dummy Client

The next stage of this process is to take that core game package and use it to build a more lightweight or 'dummy' version of our game client. This 'dummy client' will have no graphics, no UI, and not even have any user interaction. The purpose of this client is simply to use the enemy AI systems to simulate player turns and then submit them to our backend infrastructure, effectively masquerading as real players for the purpose of testing our backend systems.
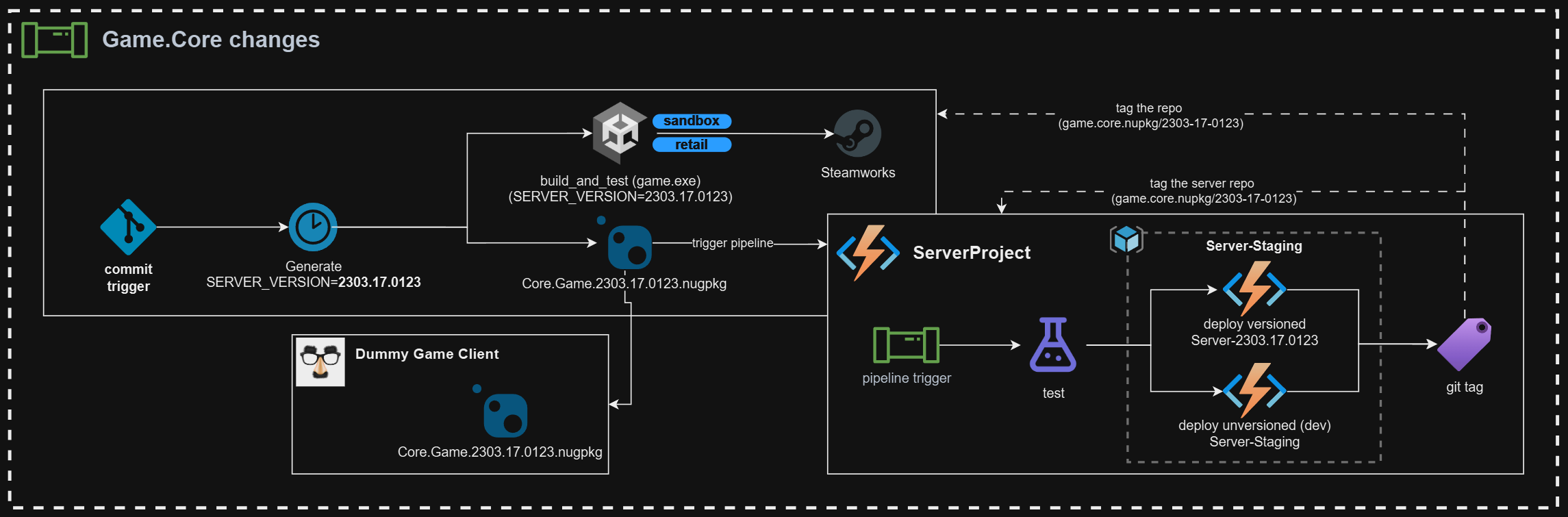
The specifics of how the dummy client is implemented are going to depend on the project and also personal preference for a load testing scenario. For Solium Infernum, the dummy client was set up as a .NET Core console application which simulated an entire multiplayer game start to finish, including several AI players running from a single dummy client.
It would also be possible to set up each client as an individual player, but that would require a bit more cross-client orchestration when it comes to hosting and joining lobbies, and we wanted to keep things as simple as possible. So, for us, each dummy client represents a single 'match' of between 4-6 players.
The core loop of the dummy client was as follows:
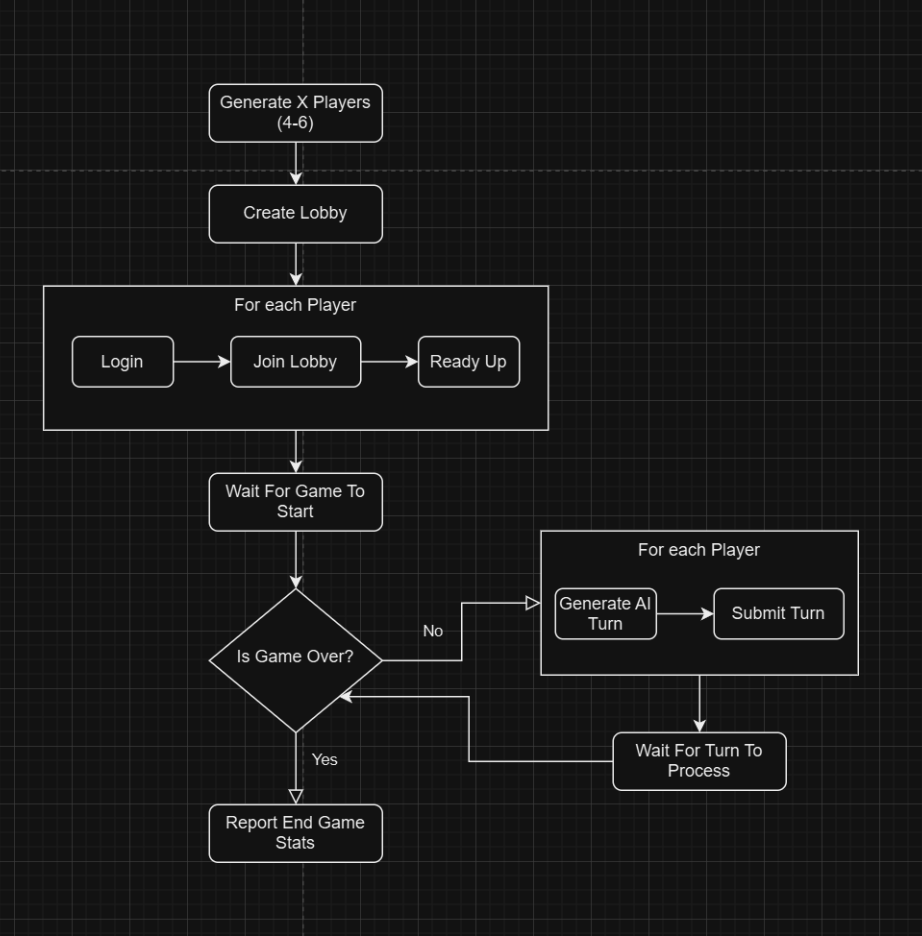
The end result here is a console application that can be run to simulate an entire game of Solium Infernum using real online infrastructure. The next part of this puzzle is being able to scale this application up to run as many concurrent games as we have the hardware to support.
##Packaging the Dummy Client
One of the simplest and most effective ways to package and distribute an application today is with a Docker image.
From docker.com:
> A Docker container image is a lightweight, standalone, executable package of software that includes everything needed to run an application: code, runtime, system tools, system libraries and settings
Bundling our dummy client up into a Docker image allows us to deploy it onto any kind of hardware and be confident that the client still has everything it needs to run, and that running multiple clients together won't create concurrency issues between them.
All you will need to containerise your Dummy Client is a copy of Docker Desktop and a Dockerfile in the root of your project. For us, something like this was enough to bundle up our Dummy Client console app for use with Docker.
```Dockerfile
FROM mcr.microsoft.com/dotnet/runtime:6.0 AS base
WORKDIR /app
FROM mcr.microsoft.com/dotnet/sdk:6.0 AS build
WORKDIR /src
COPY ["nuget.config", "DummyClient/"]
COPY ["DummyClient.csproj", "DummyClient/"]
RUN dotnet restore "DummyClient/DummyClient.csproj"
COPY . .
WORKDIR "/src/DummyClient"
RUN dotnet build "DummyClient.csproj" -c Release -o /app/build
FROM build AS publish
RUN dotnet publish "DummyClient.csproj" -c Release -o /app/publish
FROM base AS final
WORKDIR /app
COPY --from=publish /app/publish/ ./
ENTRYPOINT ["dotnet", "DummyClient.dll"]
```
Once you have your Dockerfile defined, you can build your image with:
```bash
docker build -t <image-name> .
```
Then the image can be run locally with:
```bash
docker rum -it -rm <image-name> sh
```
Now we have a packaged dummy client image that we can deploy just about anywhere. The next step is deploying _lots_ of them.
##Scale it up!
Now there are a few options when it comes to scaling up a number of container deployments. How frequently or easily you want to run your load tests will determine what solution might work for you.
### Docker compose
Probably the most straight forward way to quickly scale up a lot of containers for an image is with docker-compose. With a relatively simple `docker-compose.yml` file you can define the environment variables and resource limitations you want for the dummy clients.
```yaml
# Version of docker-compose
version: "3"
services:
loadtester.gamerunner:
image: dummy-client:dev
build:
context: .
dockerfile: DummyClient/Dockerfile
deploy:
replicas: <number-of-replicas>
resources:
limits:
cpus: '3'
memory: 1000M
reservations:
cpus: '1.50'
memory: 800M
environment:
OTHER_CONFIG: "..."
SOME_CONNECTION_STRING: "URL=...;KEY=...."
```
You can configure the number of replicas you want to run by setting the `deploy:replicas` value. Then you can run your load test with:
```bash
docker-compose up -d
```
The main thing to note here is that you are limited to the resources on the machine you are running on, so you can only run as many clients as your machine can handle. What happens if you want more? How do we spread our dummy clients across multiple machines?
### Kubernetes
Our next option for scaling up our load testing instances is Kubernetes. From kubernetes.io:
> Kubernetes is a portable, extensible, open source platform for managing containerized workloads and services, that facilitates both declarative configuration and automation.
Essentially, Kubernetes can be deployed across a series of machines and used to orchestrate application deployments and lifecycles. To learn more about setting up a Kubernetes cluster, you can find more information here: [Kubernetes Getting Started](https://kubernetes.io/docs/setup/)
####Deployments
Very briefly, a deployment is a resource that tells Kubernetes how a containerised application should be run, and how many instances should be maintained at any given time. The example below shows a deployment file for our dummy client, where we define what Docker image we will be using, any environment variables that are needed and importantly how many replicas to deploy across the cluster.
A possible `dummy-client-deployment.yaml` file might be:
```yaml
apiVersion: apps/v1
kind: Deployment
metadata:
name: dummy-client
labels:
app: dummy-client
spec:
replicas: <number-of-replicas>
selector:
matchLabels:
app: dummy-client
template:
metadata:
labels:
app: dummy-client
spec:
containers:
- name: dummy-client
image: dummy-client:dev
imagePullPolicy: Always
env:
- name: OTHER_CONFIG
value: "..."
- name: SOME_CONNECTION_STRING
value: "URL=...;KEY=...."
```
With this deployment file, Kubernetes will handle the provisioning and resource management for us.
You can apply it to your cluster manually with:
```bash
kubectl apply -f ./dummy-client-deployment.yaml
```
Once you have your deployment in place, you are able to manually tweak the number of instances with `kubectl` and then use that to spin down and spin up tests as needed. eg:
```bash
# Spin down the load testers
kubectl rollout restart deployment/dummy-client --replicas=0
# Spin up the load testers
kubectl rollout restart deployment/dummy-client --replicas=<num-replicas>
```
With this method, you can have your load test application deployed across any number of machines. If your Kubernetes cluster is cloud-based, like GKE or AKS, you only limitation on instances is how much you can afford to spend on nodes.
####Gitlab Kubernetes Executor
I'm adding this in for completeness, since this option will depend very heavily on your CI/CD setup, but in our case, we had available to us an on-prem Kubernetes cluster that was already connected to our GitLab CI system. I can talk about the GitLab and Kubernetes system in more detail in another post, but because of this setup we were able to trigger our load tests from our CI system.
We hooked up the dummy clients to the CI system in a way that allowed us to run a pipeline from GitLab that would trigger X jobs for the run, and each job was an instance of the load tester that ran in our cluster.
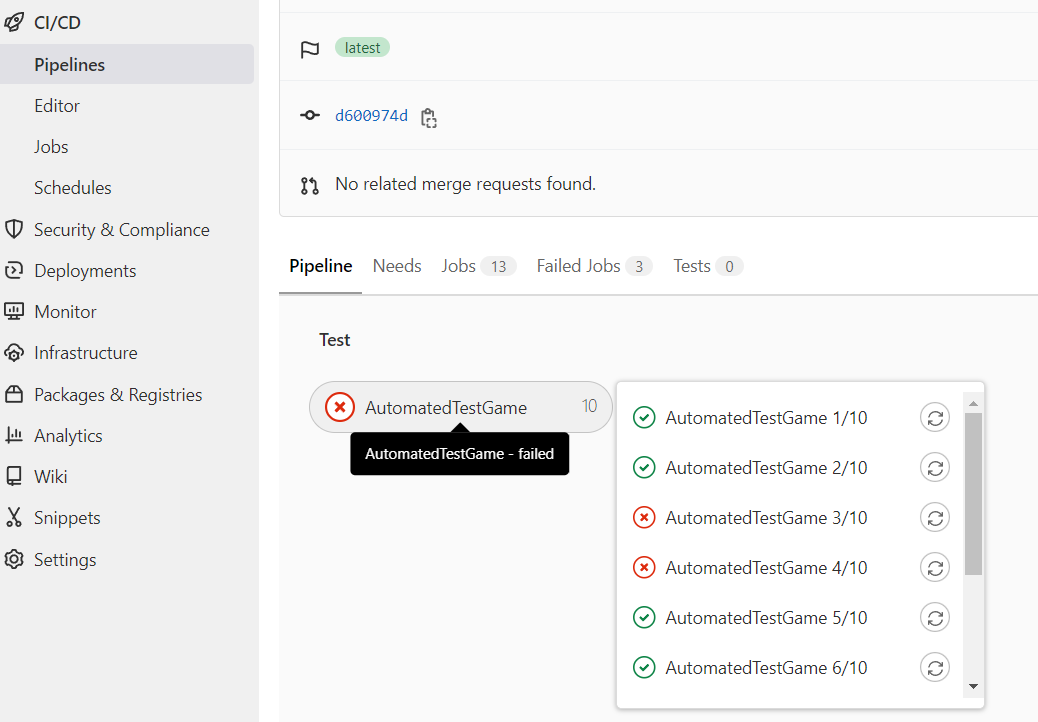
If you want to learn more about the GitLab Kubernetes Executor you can do so here: [GitLab Kubernetes Executor](https://docs.gitlab.com/runner/executors/kubernetes/)
##Reporting
The last, but most important, step in this whole process is reporting. If I can encourage you to do anything from this article when performing any kind of load testing, it would be to measure twice, measure twice again and then twice more for good luck. In order to properly assess your load test results you need to make sure that you have as much good information available to you as you can manage.
There are a lot of different kinds of monitoring and metrics tools available, and in our case, we built our own bespoke tools that were catered specifically for our needs. First, in the form of a simple console monitoring app.
Soon moving on to a full web-based front end that allowed us to interact with the load testing systems directly from the UI.
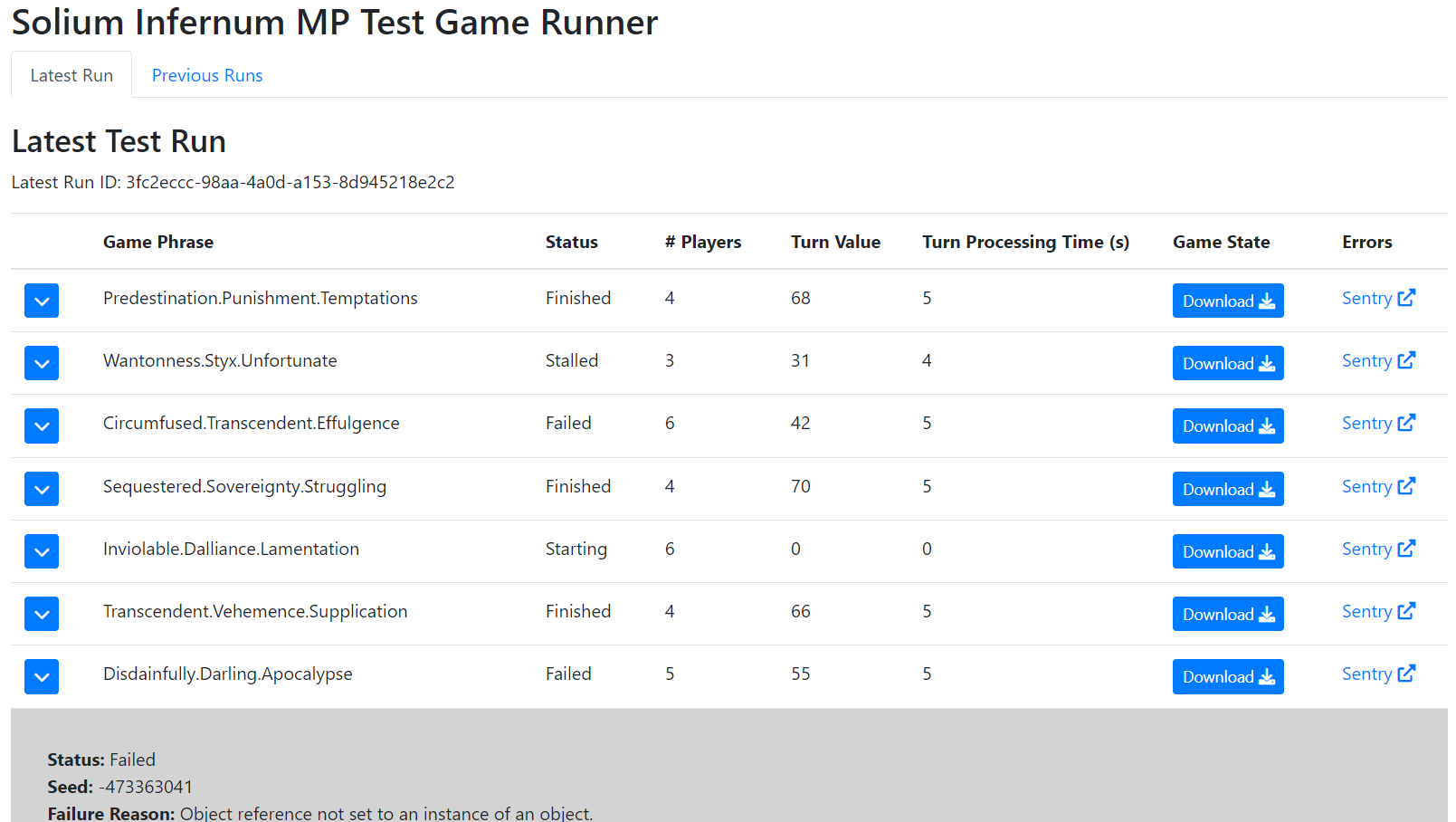
With the dummy client we made sure that every step of the way we were sending out metrics on what we were doing. We took records of load test timings, endpoint saturation, as well as stats on individual AI games and exception reports. Since we were running real games with AI, we ended up with a testing system that went beyond just load testing and into bug finding and stability testing.
#Finishing thoughts
Using our game AI to test our online infrastructure ended up giving us so much more than just a backend load tester. We definitely succeeded in our initial goal of testing our load limits in the backend, but we also had the ability to simulate hundreds of games every day, and using the AI to generate fake user actions we were able to get huge amounts of coverage on internal game system. This ultimately led us to finding bugs that we weren't even aware of at the time.
Load testing is absolutely critical in understanding the capabilities of the systems you are building, and sometimes simply saturating the network with bad traffic won't tell you enough about the real bottlenecks in your system.
Being able to package and reuse systems like AI and core gameplay loops allows you to be creative with your testing and get close to real life simulations on your backend. You get a double win out of doing this because you can test your server load, whilst also finding genuine game bugs because your bots are running real games against each other.
Tools like Docker and Kubernetes are still finding their way into the game development space, but there is some powerful tech here that can be leveraged in creative ways to see some incredible results. | romesh_dev |
1,874,816 | Hello dev,Check out my new tools | Check out my new tool, JSON Viewer! It's designed to make JSON Visualization easy and intuitive. Give... | 0 | 2024-06-03T01:37:05 | https://dev.to/bugblitz98/hello-devcheck-out-my-new-tools-1592 | webdev, javascript, beginners, showdev | Check out my new tool, JSON Viewer! It's designed to make JSON Visualization easy and intuitive. Give it a try at [[jsonviewer.tools](url)](url) and let me know what you think!
 | bugblitz98 |
1,874,812 | EMI Calculator | Overview of the Responsive EMI Calculator Purpose: The purpose of this EMI (Equated Monthly... | 0 | 2024-06-03T01:32:45 | https://dev.to/vinkalprajapati/emi-calculator-b2b | emicalculator, vinkal041, vinkalprajapati, emicalculatorbyvinkalprajapati |
{% codepen https://codepen.io/vinkalPrajapati/pen/WNBpBoB %}
Overview of the Responsive EMI Calculator
Purpose:
The purpose of this EMI (Equated Monthly Installment) Calculator is to help users easily calculate their monthly EMI payments for a loan based on the loan amount, annual interest rate, and loan tenure. This tool is particularly useful for individuals who are planning to take a loan and want to understand their monthly repayment obligations.
Features:
Responsive Design: The calculator is designed to be fully responsive, ensuring it looks good and functions well on devices of all sizes, including phones, tablets, and laptops.
User-Friendly Interface: The interface is clean and easy to navigate, with clear labels and input fields.
Default Values: Default loan amounts are provided for quick selection, making it easier for users to input common values without typing.
Dynamic Chart: A pie chart dynamically displays the breakdown of the principal loan amount and the total interest, helping users visualize their payment structure.
Real-Time Calculation: Calculations are updated in real-time whenever the user changes input values or presses the "Enter" key.
Detailed Results: Detailed breakdown of the EMI calculation, including total payment and total interest, is provided.
How It Works:
Input Fields: Users enter the loan amount, annual interest rate, and loan tenure in the respective input fields. Default values are provided below the loan amount input for quick selection.
Calculation Trigger:
Users can click the "Calculate" button to trigger the calculation.
Alternatively, pressing the "Enter" key will also trigger the calculation.
EMI Calculation: The calculator uses the standard EMI formula:
𝐸
𝑀
𝐼
=
𝑃
×
𝑟
×
(
1
+
𝑟
)
𝑛
(
1
+
𝑟
)
𝑛
−
1
EMI=
(1+r)
n
−1
P×r×(1+r)
n
where
𝑃
P is the loan amount,
𝑟
r is the monthly interest rate, and
𝑛
n is the total number of monthly installments.
Result Display: The calculated EMI amount is displayed prominently. Detailed information including the total payment, total interest, loan amount, annual interest rate, and loan tenure is shown below.
Dynamic Chart: A pie chart is generated to visually represent the proportion of the principal loan amount to the total interest. The chart is refreshed dynamically whenever the calculation is triggered.
Responsive Layout:
On larger screens (e.g., laptops), the calculator and the result (including the chart) are displayed side by side.
On smaller screens (e.g., phones), the calculator is displayed on top, followed by the detailed results and the chart below.
Code Explanation:
HTML Structure: The HTML structure includes input fields for loan amount, annual interest rate, and loan tenure. Default values are provided as clickable options. The calculation button and result display area are also included.
CSS Styling: The CSS ensures a clean and responsive layout, adjusting the display based on screen size.
JavaScript Functionality:
The calculateEMI function performs the EMI calculation, updates the result display, and refreshes the chart.
The setDefaultValue function allows users to quickly set the loan amount using the default values.
The formatRupee function formats numbers as Indian Rupees.
An event listener is added to trigger the calculation when the "Enter" key is pressed.
Conclusion:
This EMI Calculator is a robust, user-friendly tool designed to help users quickly and accurately calculate their monthly loan payments. Its responsive design, real-time calculations, and visual representation of data make it an invaluable resource for anyone considering a loan. | vinkalprajapati |
1,874,811 | BONOVO: Innovations in Construction Equipment and Attachments | BONOVO: Innovations in Construction Equipment and Attachments Introduction: BONOVO is a company... | 0 | 2024-06-03T01:32:23 | https://dev.to/jennifer_garciakd_7c34d57/bonovo-innovations-in-construction-equipment-and-attachments-1kg5 | equipments | BONOVO: Innovations in Construction Equipment and Attachments
Introduction:
BONOVO is a company that produces construction equipment and attachments that make work in the construction industry easier and more efficient. Their innovations have made them stand out among other companies in the industry, and they have several advantages that make their the best choice for construction workers.
Advantages:
BONOVO's equipment has advantages which can be several make it be noticed
One of these simple is its durability
BONOVO uses top-quality materials that may withstand possibly the construction jobs which are toughest
Another advantage is its affordability
BONOVO's equipment is competitively priced, rendering it an option like organizations that are great a budget
Furthermore, BONOVO's equipment is not hard to make use of, making this accessible also to those with very experience like little
Innovation:
BONOVO is celebrated for its way like revolutionary of equipment and accessories such as Excavator Attachments
One among their possibly many demonstrably innovations may be the use of hydraulic systems
This gives their equipment to become lighter and much more efficient, while still to be able to handle loads that are hefty perform jobs being tough
Another innovation could be the utilization of remote-controlled equipment
This permits employees to operate gear from a distance like safe decreasing the risk of accidents
Safety:
Safety is really a concern like BONOVO like high
Their equipment is made to be since safe as you can, with features such as for instance shut-off like automated and emergency end buttons
Also, BONOVO provides training to make sure that workers are using gear safely and properly
It will help to cut the possibility straight back of accidents and injuries at the working office website
Simple suggestions to Make Use Of:
Using BONOVO's Wheel Loaders equipment is straightforward, even for many with really experience like little
First, workers should cause them to become safety like wearing is suitable, such as hard caps and steel-toed shoes
Next, they should familiarize themselves utilizing the equipment's settings and procedure
Finally, they need to follow all safety protocols and recommendations when using the gear
Provider:
BONOVO provides service like great its customers
They offer fix and maintenance services using their equipment, making sure it continues to work optimally
Also, they function training and support for workers, assisting them to work well with the apparatus safely and efficiently
BONOVO's dedication to service helps ensure that customers are happy with their products or services as well as the company like ongoing speaking
Quality:
BONOVO's equipment is recognized for its construction like top-notch and
They ordinarily use only top materials and components, making sure their equipment gets up to probably the most challenging conditions
Also, BONOVO rigorously tests their products or services or services to make sure they meet the quality criteria that are best
This ensures that clients can trust BONOVO's equipment to execute at its most useful, every time
Application:
BONOVO's equipment and attachments can be employed inside a real amount of construction applications
For instance, their hydraulic hammers are well suited to breaking aside rock and concrete, while their grapples are ideal for going things which are hefty
Furthermore, BONOVO's excavator accessories works extremely well for digging, grading, and materials which are distributing
With many applications, BONOVO's gear is just a option like versatile any construction work
Conclusion:
BONOVO's Backhoe Loaders commitment to innovation, safety, and quality make their equipment and attachments the best choice for construction workers. Their products are durable, reliable, and easy to use, making them a great choice for companies and individuals in the industry. With BONOVO's excellent service and support, customers can trust that their equipment will perform at its best, every time.
Source: https://www.bonovogroup.com/attachments | jennifer_garciakd_7c34d57 |
1,874,809 | The flow of creating digital signatures and verification in Python | This flow demonstrates how to create and verify a digital signature using the cryptography library in... | 0 | 2024-06-03T01:27:46 | https://dev.to/u2633/the-flow-of-creating-digital-signature-and-verification-in-python-37ng | python, certification | This flow demonstrates how to create and verify a digital signature using the `cryptography` library in Python. This process ensures the authenticity and integrity of the message, confirming that it was signed by the holder of the private key and has not been altered.
There are main 3 steps.
1. **Generate Key Pair:**
- **Private Key**: Created using RSA, with a public exponent of 65537 and a key size of 2048 bits.
- **Public Key**: Derived from the private key.
- **Storage**: Both keys are saved to files in PEM format.
2. **Sign the Message:**
- **Message**: The data to be signed.
- **Hash Function**: SHA-256 is used to hash the message.
- **Padding**: PSS (Probabilistic Signature Scheme) with MGF1 (Mask Generation Function) and a maximum salt length is used for padding.
- **Signature**: The message is signed using the private key, and the signature is saved to a file.
3. **Verify the Signature:**
- **Public Key**: Loaded from the PEM file.
- **Signature**: Loaded from the file.
- **Message**: The original message that was signed.
- **Verification**: The public key, along with the message and the signature, is used to verify the authenticity of the signature. If the signature is valid, it means the message was signed by the corresponding private key.
### Step 1: Install the Required Library
First, ensure you have the `cryptography` library installed. You can install it using pip:
```sh
pip install cryptography
```
### Step 2: Generate a Key Pair
A key pair consists of a private key (used for signing) and a public key (used for verification).
```python
from cryptography.hazmat.primitives.asymmetric import rsa
from cryptography.hazmat.primitives import serialization
# Generate private key
private_key = rsa.generate_private_key(
public_exponent=65537,
key_size=2048,
)
# Generate public key from the private key
public_key = private_key.public_key()
# Save the private key to a file
with open("private_key.pem", "wb") as f:
f.write(private_key.private_bytes(
encoding=serialization.Encoding.PEM,
format=serialization.PrivateFormat.PKCS8,
encryption_algorithm=serialization.NoEncryption()
))
# Save the public key to a file
with open("public_key.pem", "wb") as f:
f.write(public_key.public_bytes(
encoding=serialization.Encoding.PEM,
format=serialization.PublicFormat.SubjectPublicKeyInfo
))
```
### Step 3: Sign a Message
To create a digital signature, you'll use the private key to sign a message.
```python
from cryptography.hazmat.primitives import hashes
from cryptography.hazmat.primitives.asymmetric import padding
# Message to be signed
message = b"Hello, this is a secret message!"
# Sign the message
signature = private_key.sign(
message,
padding.PSS(
mgf=padding.MGF1(hashes.SHA256()),
salt_length=padding.PSS.MAX_LENGTH
),
hashes.SHA256()
)
# Save the signature to a file
with open("signature.bin", "wb") as f:
f.write(signature)
```
### Step 4: Verify the Signature
To verify the signature, use the public key to check if it matches the message.
```python
# Load the public key
with open("public_key.pem", "rb") as f:
public_key = serialization.load_pem_public_key(f.read())
# Load the signature
with open("signature.bin", "rb") as f:
signature = f.read()
# Message to be verified
message = b"Hello, this is a secret message!"
# Verify the signature
try:
public_key.verify(
signature,
message,
padding.PSS(
mgf=padding.MGF1(hashes.SHA256()),
salt_length=padding.PSS.MAX_LENGTH
),
hashes.SHA256()
)
print("The signature is valid.")
except:
print("The signature is invalid.")
``` | u2633 |
1,874,808 | The Best Image Generator: Midjourney, DALL-E 3 or Idyllic? | AI Image generators can produce stunning images in seconds using simple language descriptions. While... | 0 | 2024-06-03T01:26:55 | https://dev.to/tonux-jan/the-best-image-generator-midjourney-dall-e-3-or-idyllic-dam | AI Image generators can produce stunning images in seconds using simple language descriptions. While well known projects like Midjourney and DALL-E 3 have dominated the consciousness of AI consumers due to their early arrival, lesser known, powerful models have emerged with a greater degree of specialisation and grunt. I[dyllic](https://idyllic.app/) is one such platform.
In a image quality head to head, our experts tested twenty prompts across Midjourney, DALL-E 3 and [Idyllic](https://idyllic.app/) platforms and presented the images to an unbiased control group of people aged between 18-55. The twenty test images covered popular use-cases for image generation technology and included book covers, movie posters, character concepts, pamphlets, digital art and more. One winner was selected based on each image prompt.
Our Results:

1. [Idyllic App](https://idyllic.app/) was preferred in 12/20 Images. MidJourney was preferred in 7/20 images and DALL-E 3 was preferred in 1/20 images.
2. 15/20 preferred Idyllic's user interface and described it as intuitive and simple when compared to DALL-E 3 or Midjourney.
3. All 3 apps struggled with text adherence when exceeding 80 Characters. Idyllic was preferred for text-reliant movie posters and book covers with 9/20 total votes. Midjourney received 8, DALL-E 3 received 3.
Winners Gallery:

**Pricing Comparison:**
[Idyllic](https://idyllic.app/) offers several subscription plans for image generation:
Starter Plan:
Price: $9.99 per month
Features:
100 images per month
Standard resolution
Personal use
Professional Plan:
Price: $29.99 per month
Features:
500 images per month
High resolution
Commercial usage rights
Business Plan:
Price: $49.99 per month
Features:
1000 images per month
Highest resolution
Advanced tools and features
Priority support
Enterprise Plan:
Price: Custom pricing
Features:
Unlimited images
Full resolution
Dedicated support
Custom integrations
Midjourney Pricing
Midjourney offers several subscription tiers for users, each providing different levels of access and usage limits. As of the most recent update, the pricing is as follows:
Basic Plan:
Price: $10 per month
Features:
Limited number of image generations per month
Access to the community feed and basic support
Personal use only
Standard Plan:
Price: $30 per month
Features:
Higher number of image generations
Commercial usage rights
Priority in image generation queues
Access to advanced features and tools
Pro Plan:
Price: $60 per month
Features:
Unlimited image generations
Enhanced commercial usage rights
Dedicated support and faster image generation
Access to exclusive features and early access to new tools
Enterprise Plan:
Price: Custom pricing
Features:
Tailored to business needs
Includes all Pro Plan features plus additional customization, dedicated support, and integration options
DALL-E 3 Pricing
OpenAI's DALL-E 3 also offers tiered pricing based on the usage, with both free and paid options. The details as of the latest update are:
Free Tier:
Price: Free
Features:
Limited number of image generations per month
Access to basic tools and features
Personal use only
Pay-As-You-Go:
Price: Variable, typically around $0.02 to $0.05 per image generation
Features:
No monthly commitment
Pay for each image generated
Suitable for occasional users or those with fluctuating needs
Subscription Plans:
Starter Plan:
Price: $15 per month
Features:
Fixed number of image generations included
Additional generations available at discounted rates
Commercial usage rights for generated images
Professional Plan:
Price: $45 per month
Features:
Higher number of image generations included
Additional generations at further discounted rates
Priority access and faster generation times
Enhanced commercial usage rights and support
Enterprise Solutions:
Price: Custom pricing
Features:
Tailored to business needs
Includes all Professional Plan features plus additional customization, dedicated support, and integration options
Choosing between Midjourney, DALL-E 3, and [Idyllic](https://idyllic.app/) depends on specific needs such as cost efficiency, feature requirements, and usage patterns. Midjourney offers predictability with flat-rate plans, DALL-E 3 provides flexibility with a pay-as-you-go model, and Idyllic balances limited and scalable options with competitive pricing. All platforms cater to both personal and commercial use, with advanced tools and dedicated support available at higher tiers.
Feature Spotlight:
Midjourney
Image Generation: Unlimited (Pro Plan), higher limits on lower plans.
Resolution: High-quality images.
Tools and Features:
Advanced image customization tools.
Early access to new tools.
Community and Support:
Community support for lower tiers.
Dedicated support for higher tiers.
Commercial Use: Available with higher-tier plans.
DALL-E 3
Image Generation: Pay-as-you-go or fixed with subscription plans.
Resolution: Variable based on subscription.
Tools and Features:
Integration with other OpenAI tools.
Priority generation times.
Community and Support:
Enhanced support for higher-tier plans.
Commercial Use: Available with subscription plans and pay-as-you-go.
[Idyllic](https://idyllic.app/)
Image Generation: Limited per month, scalable with higher plans.
Resolution: Standard to highest resolution depending on the plan.
Tools and Features:
In-Thread Editing: Allows users to edit images within the creation process.
Image-Remixing: Supports uploading reference images as part of the prompt for better customization.
Content Hub: More than just an image generation tool, Idyllic offers a vast repository of AI art, blogs, tutorials, and other content.
AI Dictionary: Comprehensive resource for users to explore AI-related terms and concepts.
Community and Support:
Priority support for business plans.
Dedicated support for enterprise plans.
Commercial Use: Available with Professional and higher plans.
Summary
Midjourney focuses on extensive customization and unlimited generation with predictable costs at higher tiers. DALL-E 3 provides flexible, scalable options and integration with other OpenAI tools. [Idyllic](https://idyllic.app/) stands out with its in-thread editing, image-remixing capabilities, and a comprehensive content hub, making it a versatile platform beyond just image generation.
| tonux-jan | |
1,874,805 | Simplified Version of Multi-Platform Hedging Stabilization Arbitrage Strategy | The original version of this strategy, you can find it at: https://www.fmz.com/bbs-topic/2279 it... | 0 | 2024-06-03T01:19:15 | https://dev.to/fmzquant/simplified-version-of-multi-platform-hedging-stabilization-arbitrage-strategy-4c1i | strategy, arbitrage, trading, fmzquant | The original version of this strategy, you can find it at: https://www.fmz.com/bbs-topic/2279
it contains a very specific comments about the code.
This shorter version is for study purpose only, due to our website’s tech improvement, most of your complicated strategies can be tremendously saving time on coding part. We are currently rebuilding our API function, we will make them easier to read and more effective to execute, besides the basic function, we will gather more method in some particular function than once you called the function, it will perform a serious great action.
Here is the simplified version:
```
var preSumBalance = 0
var initSumBalance = 0
function UpdateAccount(isFirst){
var msg = ""
var sumStocks = 0
var sumBalance = 0
for(var i = 0; i < exchanges.length; i++){
if(exchanges[i].needUpdate == true || isFirst == true){
exchanges[i].account = _C(exchanges[i].GetAccount)
exchanges[i].needUpdate = false
if(isFirst == true){
initSumBalance += (exchanges[i].account.Balance + exchanges[i].account.FrozenBalance)
exchanges[i].SetPrecision(_CurrencyPrecision, _BaseCurrencyPrecision)
}
}
sumStocks += (exchanges[i].account.Stocks + exchanges[i].account.FrozenStocks)
sumBalance += (exchanges[i].account.Balance + exchanges[i].account.FrozenBalance)
msg += exchanges[i].GetName() + "coin:" + exchanges[i].account.Stocks + "Frozen coin:" + exchanges[i].account.FrozenStocks + "money:" + exchanges[i].account.Balance + "Frozen money:" + exchanges[i].account.FrozenBalance + "\n"
}
LogStatus(_D(), "Total Coins:" + sumStocks, "Total Money:" + sumBalance, "\n", msg)
if(preSumBalance != sumBalance){
LogProfit(sumBalance - initSumBalance, preSumBalance = sumBalance)
}
}
function main(){
UpdateAccount(true)
while(1){
for(var i = 0; i < exchanges.length; i++){
for(var j = 0; j < exchanges.length; j++){
if(i == 0 && j == 0){
for(var m = 0; m < exchanges.length; m++){
exchanges[m].thread = exchanges[m].Go("GetTicker")
}
for(var n = 0; n < exchanges.length; n++){
exchanges[n].ticker = exchanges[n].thread.wait()
}
}
if(exchanges[i].GetName() != exchanges[j].GetName() && exchanges[i].ticker && exchanges[j].ticker && exchanges[i].ticker.Buy - exchanges[j].ticker.Sell > _HedgePrice){
if(exchanges[i].account.Stocks > _HedgeAmount && exchanges[j].account.Balance / ((exchanges[i].ticker.Buy + exchanges[j].ticker.Sell) / 2) > _HedgeAmount){
var sellId_I = exchanges[i].Sell((exchanges[i].ticker.Buy + exchanges[j].ticker.Sell) / 2, _HedgeAmount, exchanges[i].GetName())
var buyId_J = exchanges[j].Buy((exchanges[i].ticker.Buy + exchanges[j].ticker.Sell) / 2, _HedgeAmount, exchanges[i].GetName())
exchanges[i].needUpdate = exchanges[j].needUpdate = true
}
}
}
}
UpdateAccount(false)
Sleep(300) // test
}
}
```
From: https://blog.mathquant.com/2018/12/11/simplified-version-of-multi-platform-hedging-stabilization-arbitrage-strategy-study-purpose-only.html | fmzquant |
1,874,804 | Trusted Plate Bending Machines for Heavy-Duty Performance | Looking for a machine that can bend heavy-duty plates with ease? Look no further than the trusted... | 0 | 2024-06-03T01:14:11 | https://dev.to/jennifer_garciakd_7c34d57/trusted-plate-bending-machines-for-heavy-duty-performance-41d8 | machines | Looking for a machine that can bend heavy-duty plates with ease? Look no further than the trusted plate bending. These powerful machines are designed to provide reliable performance, innovative features, and safe operation that you can count on.
Benefits of Reliable Plate Bending Machines
One of the most significant features of utilizing a trusted plate device like bending be the capacity to flex dense and materials that are hefty ease, assisting you to save yourself time and effort
These Machine contain powerful motors and rollers which can be robust will handle tough materials and deliver accurate results every time
Additionally, these are typically designed with top-notch materials that can withstand the demands of heavy-duty applications, giving you several years of reliable service and satisfaction
Innovation in Plate Bending Machines
Trusted plate machines which can be bending created with revolutionary features that produce them even more efficient and user-friendly
Each and each time for instance, many models come with digital settings that allow you to certainly adjust the angle like bending speed with ease, ensuring that you will get the most perfect flex
Some machines even include automatic systems that are bending can lessen operator errors and enhance efficiency
Safety Top Options That Come With Plate Bending Machines
Safety can be a concern like top working together with heavy equipment, and trusted dish bending devices aren't any exclusion
These devices come with a array of safety features that protect operators from potential hazards and accidents
As an example, most models have crisis stop buttons that instantly turn the equipment down in the eventuality of an emergency
Also, these are typically equipped with safety guards that counter usage associated with metal sheet rolling machine as well as other parts which can be going the equipment is in use
Making Use Of Plate Bending Machines
Employing a dish like dependable machine is easy and simple
First, you are going to need to load the dish in the rollers and adjust the angle like rate like bending of the electronic controls
Next, you need to activate the rollers to start bending the plate
You need to keep a eye like close the process then make any corrections that are necessary make sure that the dish is bending precisely
When the plate is fully bent, it is simple to launch it through the rollers and repeat the process as needed
Provider and Quality of Trusted Plate Bending Machines
Whenever purchasing a plate bending machine, you want to make certain that you're getting a reliable and product like top-quality
For this reason trusted plate device like bending offer exceptional customer service and support, making sure your machine is frequently running well
Additionally, they use just the most materials that are useful elements to create their machines, making certain they truly are durable, lasting, plus in a posture to withstand the needs of heavy-duty applications
Applications of Plate Bending Machines
Trusted plate bending devices are utilized inside an selection of companies, including construction, shipbuilding, and manufacturing
They are tools being crucial bending and shaping dense and heavy materials such as for example steel dishes, aluminum sheets, and also other metals
A dependable dish bending device may be the perfect solution to your account whether you will need to fold just one dish or create thousands of components
In conclusion, trusted plate bending roll machine are powerful, reliable, and easy-to-use machines that can handle the demands of heavy-duty applications. With their innovative features, safety features, and high-quality construction, they are the go-to choice for professionals in a wide range of industries. When investing in a plate bending machine, be sure to choose a trusted brand that offers excellent customer support and quality products.
Source: https://www.liweicnc.com/application/bending-roll-machine | jennifer_garciakd_7c34d57 |
1,874,803 | Menjelajahi Dunia Domain, Entities, dan Value Objects di Golang: Panduan Asik Buat Ngoding Lebih Rapi dan Efektif | Halo temen-temen! Kali ini kita mau ngobrol nih soal konsep yang keren banget di dunia pemrograman,... | 0 | 2024-06-03T01:11:39 | https://dev.to/yogameleniawan/menjelajahi-dunia-domain-entities-dan-value-objects-di-golang-panduan-asik-buat-ngoding-lebih-rapi-dan-efektif-42db | go |
Halo temen-temen! Kali ini kita mau ngobrol nih soal konsep yang keren banget di dunia pemrograman, khususnya buat kalian yang suka atau mau belajar Golang. Kita bakal bahas tentang **Domain**, **Value Objects**, dan **Entities**. Tenang aja, saya bakal kasih contoh kode plus penjelasan yang asik supaya kalian makin paham. Gas kita mulai!
### Apa itu Domain?
Domain adalah area spesifik dari aplikasi yang berhubungan dengan masalah dunia nyata yang sedang diselesaikan. Dalam konteks Domain-Driven Design (DDD), domain adalah pusat dari model bisnis kita. Domain ini menggambarkan aturan, logika, dan proses yang ada di dalam bisnis atau aplikasi kita.
**Contoh Domain dalam Aplikasi E-commerce**
Misalkan kita punya aplikasi e-commerce. Domain kita mencakup:
- Produk (Product)
- Pelanggan (Customer)
- Pesanan (Order)
- Pembayaran (Payment)
Setiap bagian ini memiliki logika bisnis dan aturan yang spesifik.
### Apa itu Entities?
Entities adalah objek yang memiliki identitas unik yang konstan sepanjang _lifecycle_ dari sebuah aplikasi. Identitas ini biasanya berupa sebuah ID yang membedakan satu entity dengan entity lainnya.
**Karakteristik Entities:**
- Identitas Unik (Unique Identity): Memiliki satu atau lebih atribut yang berfungsi sebagai identitas yang unik (Unique Identity).
- Mutability: Entity dapat berubah sepanjang lifecycle aplikasi, tetapi identitasnya tetap sama.
**Contoh Kode Entities di Golang**
Misalkan kita punya `Product` sebagai entity dalam domain e-commerce:
```go
package main
import (
"fmt"
)
type Product struct {
ID string
Name string
Price float64
}
func NewProduct(id, name string, price float64) Product {
return Product{
ID: id,
Name: name,
Price: price,
}
}
func (p Product) Display() {
fmt.Printf("Product ID: %s, Name: %s, Price: %.2f\n", p.ID, p.Name, p.Price)
}
func main() {
product := NewProduct("123", "Smartphone", 999.99)
product.Display()
}
```
Penjelasan:
Struct `Product` di sini adalah entity karena memiliki ID unik (`ID`).
Kita punya fungsi `NewProduct` untuk membuat produk baru.
Fungsi `Display` untuk menampilkan informasi produk.
### Apa itu Value Objects?
Value Objects adalah objek yang dinilai berdasarkan atribut atau nilainya, bukan identitasnya. Mereka biasanya _immutable_, artinya nilai mereka tidak berubah setelah dibuat.
**Karakteristik Value Objects:**
- Equality: Dua value objects dianggap sama jika semua atributnya sama.
- Immutability: Setelah dibuat, nilainya tidak bisa diubah.
Contoh Kode Value Objects di Golang
Misalkan kita punya `Money` sebagai value object dalam domain e-commerce:
```go
package main
import (
"fmt"
)
type Money struct {
Amount float64
Currency string
}
func NewMoney(amount float64, currency string) Money {
return Money{
Amount: amount,
Currency: currency,
}
}
func (m Money) Display() {
fmt.Printf("Amount: %.2f, Currency: %s\n", m.Amount, m.Currency)
}
func main() {
money1 := NewMoney(100, "USD")
money2 := NewMoney(100, "USD")
money1.Display()
money2.Display()
if money1 == money2 {
fmt.Println("Money1 and Money2 are equal")
} else {
fmt.Println("Money1 and Money2 are not equal")
}
}
```
Penjelasan:
- Struct `Money` di sini adalah value object karena dinilai berdasarkan atribut `Amount` dan `Currency`.
- Fungsi `NewMoney` untuk membuat instance `Money` baru.
- Fungsi `Display` untuk menampilkan informasi Money.
- Kita membandingkan dua instance `Money` untuk melihat apakah mereka sama berdasarkan nilai atributnya.
---
### Kenapa Harus Menggunakan Domain, Value Objects, dan Entities?
**_Code Organization_ yang Lebih Baik:**
- Memisahkan domain, entities, dan value objects membuat kode lebih terstruktur dan mudah di-maintain. Setiap bagian kode memiliki tanggung jawab yang jelas.
- Contoh: Jika ada perubahan dalam aturan bisnis untuk produk, kita hanya perlu mengubah bagian Product entity, tanpa mempengaruhi bagian lain.
**Skalabilitas (_Scalability_)**:
- Dengan kode yang terstruktur, menambahkan fitur baru atau memperluas aplikasi jadi lebih mudah. Kita bisa fokus pada domain tertentu tanpa harus mengubah keseluruhan sistem.
- Contoh: Menambahkan fitur diskon hanya perlu menambahkan value object atau entity baru tanpa mengganggu struktur yang ada.
**Pemahaman yang Jelas:**
- Memudahkan tim untuk memahami dan bekerja sama karena setiap bagian kode menggambarkan aspek spesifik dari domain bisnis.
- Contoh: Tim bisa fokus pada pengembangan fitur pelanggan (Customer) tanpa harus memikirkan detail produk atau pesanan.
**Menghindari Duplikasi:**
- Dengan memisahkan domain, entities, dan value objects, kita bisa menghindari duplikasi kode yang bisa menyebabkan bug dan kesulitan dalam maintenance.
- Contoh: Atribut `Price` dari `Product` bisa menggunakan value object `Money`, sehingga logika terkait harga selalu konsisten di seluruh aplikasi.
---
### Kesimpulan
Oke teman-teman, kita sudah bahas banyak banget tentang **Domain**, **Entities**, dan **Value Objects** dalam konteks pemrograman Golang. Yuk, kita rangkum semuanya dengan gaya yang asik biar makin paham!
**Domain**
Domain itu kayak “dunia kecil” di dalam aplikasi kita yang mencerminkan area spesifik dari masalah yang kita coba selesaikan. Misalnya, dalam aplikasi e-commerce, domain kita meliputi produk, pelanggan, pesanan, dan pembayaran. Dengan memahami domain, kita bisa fokus menyelesaikan masalah-masalah spesifik yang ada di dunia nyata, dan menerapkannya ke dalam kode kita.
**Entities**
Entities itu ibarat karakter utama dalam cerita aplikasi kita. Mereka punya identitas unik yang nggak akan berubah, kayak nomor KTP yang kita punya. Contohnya, `Product` dalam aplikasi e-commerce punya ID unik yang memudahkan kita melacaknya. Entities bisa berubah-ubah sifatnya seiring waktu, tapi identitas mereka tetap sama. Ini membantu kita mengelola data yang terus bergerak dan berubah dalam aplikasi.
**Value Objects**
Value objects itu kayak properti dari karakter kita yang dinilai berdasarkan atributnya, bukan identitasnya. Misalnya, `Money` dalam aplikasi kita dinilai berdasarkan jumlah dan mata uangnya. Dua objek `Money` dianggap sama jika jumlah dan mata uangnya sama, nggak peduli kapan dan di mana mereka dibuat. Value objects biasanya immutable, artinya nggak bisa diubah setelah dibuat, sehingga kita bisa memastikan konsistensi nilai mereka di seluruh aplikasi.
---
### Penutup
Nah, itulah teman-teman, sedikit _deep dive_ kita ke dunia Domain, Entities, dan Value Objects di Golang. Dengan memahami dan mengimplementasikan konsep-konsep ini, kita bisa bikin aplikasi yang lebih solid, scalable, dan mudah di-maintain. Ingat, setiap bagian kode punya tanggung jawabnya sendiri, dan memisahkan mereka dengan baik bisa bikin kita lebih fokus dan produktif. Jadi, nggak ada lagi tuh drama-drama bug yang bikin kepala pusink tujuh kelilink wkwkwk
Semoga penjelasan ini bisa membantu kalian jadi lebih jago ngoding dan paham konsep-konsep penting dalam pemrograman. Jangan lupa ngoding itu diketik jangan dipikir! Sampai jumpa di artikel lainnya🚀
| yogameleniawan |
1,874,802 | Web-based SQL Editor. | Web-based SQL editors are online tools that allow users to write, execute, and manage SQL queries... | 0 | 2024-06-03T01:09:06 | https://dev.to/concerate/web-based-sql-editor-5a00 | Web-based SQL editors are online tools that allow users to write, execute, and manage SQL queries directly from their web browsers. These editors provide a user-friendly interface for interacting with databases and can be accessed from any device with an internet connection.
Web-based SQL editors typically offer features such as syntax highlighting, auto-completion, query history, and result visualization. They support various database management systems (DBMS) like MySQL, PostgreSQL, SQL Server, Oracle, and more. Users can connect to their databases by providing the necessary connection details such as hostname, port number, username, and password.
These editors make it convenient for developers, data analysts, and database administrators to work with databases without the need for installing any software or client-side tools. They can be used for tasks like querying and retrieving data, creating and modifying database structures, and performing database administration tasks.
Some popular web-based SQL editors include phpMyAdmin, Adminer, SQL Fiddle, and DBeaver (which also has a web-based version). Additionally, many cloud-based database providers offer their own web-based SQL editors as part of their services.
I recommend SQLynx as a reliable and user-friendly web-based SQL editor. SQLynx allows users to write and execute SQL queries directly from a web browser. It offers a clean and intuitive interface with features like syntax highlighting, auto-completion, query history, and result visualization.
SQLynx supports various popular databases, including MySQL, PostgreSQL, SQLite, SQL Server, and Oracle. It also provides database connection management and allows users to save and organize their queries for future use.
With SQLynx, you can easily connect to your databases, write complex SQL queries, and analyze the query results, all within a web-based environment. It is a great choice for developers, data analysts, and database administrators who prefer a web-based solution for their SQL editing needs.
Download:http://www.sqlynx.com/en/#/home/probation/SQLynx
| concerate | |
1,874,800 | VERSE.DB with a CLI commands ? | hi dev community, we just added a new update for the database and we are testing the CLI to see if... | 27,741 | 2024-06-03T01:08:20 | https://versedb.jedi-studio.com/blog/ | versedb, database, node, cli | hi dev community,
we just added a new update for the database and we are testing the **CLI** to see if you guys needs it for the database, so we made a simple **CLI** for the database that can create a new connection for you for the database and set it up for you so you don't need to code the connection and also can install the database since we are working on supporting other languages so this will help in case you want to install it for any other language like python soon, java, c#, ...etc and this staff.
you can **install the cli** with npm for now using this command:
```bash
npm install -g create-verse.db
```
then you can run it using the command:
```bash
verse.db
```
like in the image:

we wish you guys like and and tell us in the comments if you like the ideas and what suggestions you want us to add
### OUR IDEAD
we also have an idea but we need your help to decide if we should do it or not
we are going to make something like a **database server** it will be running on a **localhost** with a port of your choosin and i will be like an **API** for the data we will make an adapter for it also and everything will be on this localhost, something like that it will remain on the path you want and also will be made with the command **nothing of the usage will change**
```bash
npm create verse.db@latest
```
or
```bash
verse.db create
```
after that you can run the server if you wanted to use the server adapter
and this will help it for those who wants to make there own database api and hosting it on a host with api instead of coding a new api with express.js this will be faster with out api management
i wish you guys type in the comments what do you think about it we really are so existed for your opinion ✨
JEDI Studio.ص | marco5dev |
1,874,799 | AWS Resume Challenge using Pulumi, Golang, AWS S3 and AWS CloudFront | 1. Introduction I recently undertook the AWS resume challenge, which was quite... | 0 | 2024-06-03T01:07:34 | https://dev.to/audu97/aws-resume-challenge-using-pulumi-golang-aws-s3-and-aws-cloudfront-3005 | go, awschallenge, cloud, devops | ### 1. Introduction
I recently undertook the AWS resume challenge, which was quite interesting, so I decided to write about it.
The primary goal of the AWS resume challenge is for participants to build a static personal website using cloud services.
it encourages hands-on experience with various cloud technologies including infrastructure as code(IaC), serverless computing and storage devices.
For this challenge, I utilised the following:
Amazon Web Service(AWS): Served as my cloud provider.
AWS S3: Acted as a storage unit to host my static files.
AWS Cloudfront: as a content delivery network, to serve the static webpage. A content delivery network(CDN) is a geographically distributed group of servers that caches content close to users.
Pulumi: Used as my infrastructure as code(IaC) tool. Pulumi is an IaC that lets you describe and provision your cloud infrastructure using various programming languages.
### 2. Setting Up the Environment
The first steps were to install the necessary tools and software including Golang, an IDE(Goland) or any IDE of your choice and pulumi.
Next was to configure pulumi to work with my AWS account using the AWS CLI
Made sure I had the necessary permission to create and manage AWS resources in my AWS account.
Created a directory to initialise the Pulumi project. To do this I opened my terminal and ran the following command `mkdir aws-resume-challenge && cd aws-resume-challenge` This creates a new folder and navigates into it.
Then I ran `pulumi new aws-go` This creates a new pulumi aws project and downloads the go sdk. This also generates some files that are necessary for the program to execute successfully.
### 3.Creating the infrastructure
I copied my static website folder which contains some HTML, CSS, JavaScript, and jQuery code and my index.html file into the root of my project.
Because I have a folder containing about 6 different folders with different files I need an object for each file(each file is a separate resource). I need a program to crawl the directory and add a resource (Bucket object) for each file. I’ll use a component that will handle the folder, to do this I created another go file and called it s3folder.go which contains the following code:
```golang
type Folder struct {
pulumi.ResourceState
bucketName pulumi.IDOutput `pulumi:"bucketName"`
websiteUrl pulumi.StringOutput `pulumi:"websiteUrl"`
}
func NewS3Folder(ctx *pulumi.Context, bucketName string, siteDir string, args *FolderArgs) (*Folder, error) {
var resource Folder
// Stack exports
err := ctx.RegisterComponentResource("pulumi:example:S3Folder", bucketName, &resource)
if err != nil {
return nil, err
}
// Create a bucket and expose a website index document
siteBucket, err := s3.NewBucket(ctx, bucketName, &s3.BucketArgs{
Website: s3.BucketWebsiteArgs{
IndexDocument: pulumi.String("index.html"),
},
}, pulumi.Parent(&resource))
if err != nil {
return nil, err
}
// For each file in the directory, create an S3 object stored in `siteBucket`
err = filepath.Walk(siteDir, func(name string, info fs.FileInfo, err error) error {
if err != nil {
return err
}
if !info.IsDir() {
rel, err := filepath.Rel(siteDir, name)
if err != nil {
return err
}
if _, err := s3.NewBucketObject(ctx, rel, &s3.BucketObjectArgs{
Bucket: siteBucket.ID(),
Source: pulumi.NewFileAsset(name),
ContentType: pulumi.String(mime.TypeByExtension(path.Ext(name))),
}, pulumi.Parent(&resource)); err != nil {
return err
}
}
return nil
})
if err != nil {
return nil, err
}
return &resource, nil
}
type folderArgs struct {
}
type FolderArgs struct {
}
func (FolderArgs) ElementType() reflect.Type {
return reflect.TypeOf((*folderArgs)(nil)).Elem()
}
```
* FolderStruct: is a custom pulumi resource that has two properties, bucket name and website name. These are populated after the resource is created.
* newS3folder function: this function creates a new instance of the folder resource. The function takes in a pulumi context, a bucket name, a directory path and arguments for the folder resource.
It first creates a new component resource of type `pulumi:example:s3folder`
The s3 bucket is created with a website configuration that sets the index.html file as the index of the document
It goes through the provided directory for each file, it creates a new s3 bucket object. `BucketobjectArgs` specifies the bucket, using the bucket id, it also specifies the source file and the content type of the file which is determined by the file extension.
In `main.go`:
```golang
func main() {
pulumi.Run(func(ctx *pulumi.Context) error {
// Create a bucket and expose a website index document
f, err := NewS3Folder(ctx, "resume-bucket", "./website", &FolderArgs{})
if err != nil {
return err
}
ctx.Export("bucketName", f.bucketName)
ctx.Export("websiteUrl", f.websiteUrl)
return nil
})
}
```
This is the entry point of a pulumi program, using the pulumi.Run func. This is where the infrastructure is defined. Firstly
It calls the newS3Folder function to create a new bucker called “resume bucket” and uploads the contents of the `/website` directory to this bucket. It returns a folder resource
When the folder resource is created successfully it exports two outputs bucketname and websiteurl in the pulumi CLI
To deploy this infrastructure, I ran `pulumi up` command which creates these resources.
### 4. Configuring AWS Cloudfront for the s3Bucket:
I created a new Cloudfront distribution to properly serve this web page with low latency
* Chose the resume bucket as the origin domain
* Under origin access, I selected Origin access control settings and created a new AoC, which will be provided when the distribution is created
* Under the viewer protocol policy, I selected “https only” which means CloudFront will only accept HTTPS requests
Created the distribution and copied the policy
* Navigated to the bucket, then to the permission tab I edited the bucket policy, which says only traffic from Cloudfront should be allowed
### 5. Conclusion
In conclusion, participating in the AWS resume challenge has been rewarding, it allowed me to use my skills in Golang especially in crawling through the website folder and creating a bucket object for every one of the files, also My AWS skills were sharpened.
I intend to extend this and add further features to this static website like ci/cd. To automatically update the website when I make and push changes to it. Bye for now!🤗
the github link to the full project can be found [here](https://github.com/audu97/aws-resume-challenge)
| audu97 |
1,874,793 | Transforming Fullstack Development with Remix: A React Comparison | In my recent livestream, I discussed the crucial concept of Fullstack Data Flow in the Remix... | 0 | 2024-06-03T01:07:04 | https://dev.to/adriannavaldivia/transforming-fullstack-development-with-remix-a-react-comparison-480 | remix, javascript, react, beginners | In my recent livestream, I discussed the crucial concept of [Fullstack Data Flow](https://remix.run/docs/en/main/discussion/data-flow) in the Remix Framework. I mistakenly referred to it as the Remix Full stack cycle, so I want to clarify. This overarching flow within Remix is essential to grasp as you dive into this framework.
I aim to compare the new approach to building with React in Remix with our traditional way of using React alone, often with multiple libraries. This comparison should be particularly beneficial for React developers who are still undecided about adopting full stack frameworks like Remix.
Currently, Remix is built around React Router to enhance Server Side Rendering capabilities. It offers built-in support for nested routes, providing a more manageable structure through a single directory: `app/routes`.
The intricacies of building routes in Remix warrant their own blog post, so I won't dive into that here. I appreciate the variety of options available though, and many engineers have strong opinions about their preferred approach.
## Table of Contents
1. [Let’s talk about the flow of data](#lets-talk-about-the-flow-of-data)
- [Loaders](#loaders)
- [Components](#components)
- [Actions](#actions)
2. [React alone in comparison](#react-alone-in-comparison)
## Let’s talk about the flow of data
The flow is split into three phases:
**Loaders → Components → Action**
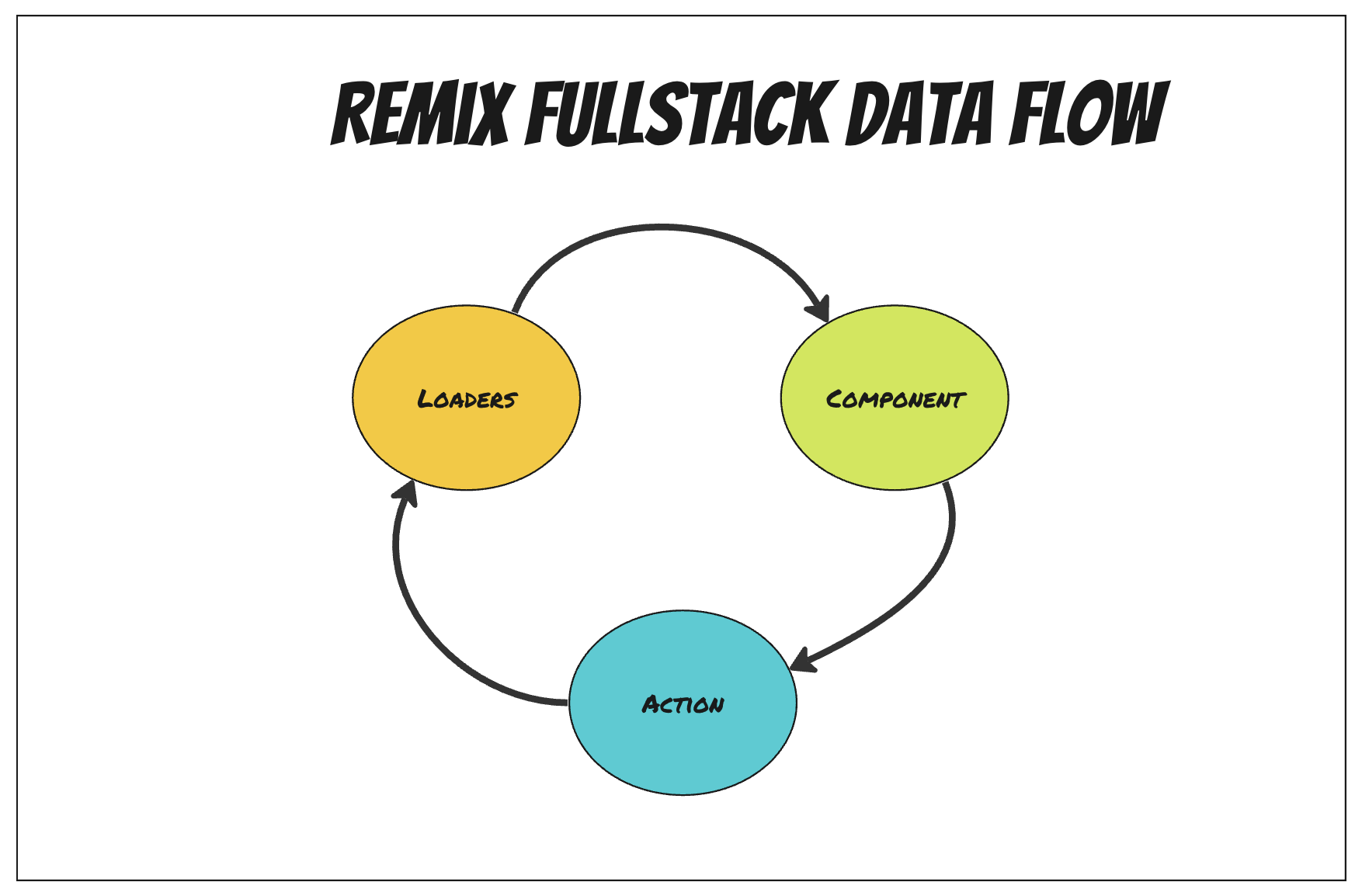
### Loaders
In Remix, `loader` functions are used to fetch data on the server-side. They should always be defined in route files.
Keep in mind by default in Remix we are rendering our data from the server or also known as Server Side Rendering (SSR)
**Example:**
```jsx
export const loader = async ({ params }) => {
const data = await fetchData(params.id);
return json(data);
};
```
### Components
In Remix, components receive the data fetched from loader functions to be rendered. Components access this data with `useLoaderData` hook.
**Example:**
```jsx
import { useLoaderData } from "@remix-run/react";
export const loader = async ({ params }) => {
const data = await fetchData(params.id);
return json(data);
};
export default function Post() {
const data = useLoaderData();
return (
<div>
<h1>{data.title}</h1>
<p>{data.content}</p>
</div>
);
}
```
### Actions
Action functions handle form submissions, validations, and other mutations. They are called when a form is being submitted, allow the server to process the data, update if successful or return validation errors that indicate to the user what failed.
**Example:**
```jsx
export default function NewPost() {
const actionData = useActionData();
return (
<div>
<h1>Create a New Post</h1>
{actionData?.error && <p style={{ color: "red" }}>{actionData.error}</p>}
<Form method="post">
<div>
<label>
Title: <input type="text" name="title" />
</label>
</div>
<div>
<label>
Content: <textarea name="content" />
</label>
</div>
<button type="submit">Create Post</button>
</Form>
</div>
);
}
export const action = async ({ request }) => {
const formData = await request.formData();
const newPost = await createPost(formData);
return redirect(`/posts/${newPost.id}`);
};
```
As we’ve seen in Remix how we fetch data, render that data in our components, and handle data mutations through form handling, the overall pattern is not that different from when we used React alone but as you can see we are are rarely using our regular hooks `useState` or `useEffect`.
## React alone in comparison
This would compare to Remix’s `loader` function and `useLoaderData` hook.
```jsx
import React, { useEffect, useState } from 'react';
import axios from 'axios';
const Post = ({ postId }) => {
const [post, setPost] = useState(null);
useEffect(() => {
axios.get(`/api/posts/${postId}`)
.then(response => {
setPost(response.data);
})
.catch(error => {
console.error("There was an error fetching the post!", error);
});
}, [postId]);
if (!post) return <div>Loading...</div>;
return (
<div>
<h1>{post.title}</h1>
<p>{post.content}</p>
</div>
);
};
export default Post;
```
That’s not bad but now there is less separation between the data and how we go about fetching that data. We’ve been used to that pattern for a while and got used to it.
Now let’s compare Remix’s `action` function and `useActionData` to using React standalone
```jsx
const PostForm = () => {
const [formData, setFormData] = useState({ title: '', content: '' });
const [errors, setErrors] = useState({});
const validate = () => {
const newErrors = {};
if (!formData.title.trim()) {
newErrors.title = 'Title is required';
}
if (!formData.content.trim()) {
newErrors.content = 'Content is required';
}
setErrors(newErrors);
return Object.keys(newErrors).length === 0;
};
const handleChange = (e) => {
const { name, value } = e.target;
setFormData({
...formData,
[name]: value,
});
};
const handleSubmit = async (event) => {
event.preventDefault();
if (!validate()) {
return;
}
try {
const response = await axios.post('/api/posts', formData);
console.log('Post created', response.data);
} catch (error) {
console.error('There was an error creating the post!', error);
}
};
return (
<form onSubmit={handleSubmit}>
<div>
<input
type="text"
name="title"
value={formData.title}
onChange={handleChange}
placeholder="Title"
/>
{errors.title && <p style={{ color: 'red' }}>{errors.title}</p>}
</div>
<div>
<textarea
name="content"
value={formData.content}
onChange={handleChange}
placeholder="Content"
/>
{errors.content && <p style={{ color: 'red' }}>{errors.content}</p>}
</div>
<button type="submit">Submit</button>
</form>
);
};
export default PostForm;
```
Yes, we can definitely find ways to consolidate this and use third party libraries that help with forms like [react-final-form](https://final-form.org/react) or [Formkik](https://formik.org/docs/overview) but can we be honest that following Remix’s pattern helps us write cleaner code from the beginning? There’s a lot you don’t need to do in Remix because of it’s intuitive nature to rely on not only React Router but on the browser’s natural flow as well.
If you made it this far, thanks for reading. I talk more about Remix than I write about it. I host a livestream titled [Astrology & JavaScript Series](https://astrology-javascript-series.vercel.app/) on Wednesdays at 1pm ET on X and Twitch. I’m building a tool that helps you understand astrology more by learning the foundational blocks first.
I use Typescript within Remix and good ole Tailwind. I pull all the required data from [DivineAPI](https://divineapi.com/) (Astrology & JavaScript Series Sponsor!). They provide me all the information I need, working with their Western Astrology API. I talk often about my process, go through the code and do some live-coding as well. | adriannavaldivia |
1,874,798 | Penjelasan Lengkap tentang Fungsi Midtrans Payment Gateway dan Integrasinya dengan Laravel | Apa Itu Payment Gateway? Payment gateway itu kayak jembatan antara situs web atau... | 0 | 2024-06-03T01:04:53 | https://dev.to/yogameleniawan/penjelasan-lengkap-tentang-fungsi-midtrans-payment-gateway-dan-integrasinya-dengan-laravel-1327 | laravel, php, programming |

### Apa Itu Payment Gateway?
Payment gateway itu kayak jembatan antara situs web atau aplikasi e-commerce sama bank atau penyedia layanan keuangan lainnya buat memproses pembayaran. Jadi, setiap kali temen-temen belanja online dan bayar pake kartu kredit atau debit, payment gateway ini yang ngurusin. Mereka nge-enkripsi data sensitif biar aman dan cuma pihak berwenang yang bisa akses.
### Kenapa Payment Gateway Penting?
Payment gateway itu penting banget buat bisnis online karena:
1. **Keamanan Transaksi**: Payment gateway pake enkripsi yang kuat buat lindungi data kartu kredit/debit dari penipuan dan pencurian.
2. **Kemudahan Penggunaan**: Mempermudah pelanggan buat bayar langsung di situs web atau aplikasi tanpa harus pindah platform.
3. **Otomatisasi Proses Pembayaran**: Mengurangi kesalahan manusia dengan ngotomatiskan proses verifikasi dan konfirmasi pembayaran.
4. **Beragam Metode Pembayaran**: Mendukung berbagai metode pembayaran termasuk kartu kredit, debit, e-wallet, dan transfer bank.
### Midtrans sebagai Payment Gateway
Midtrans adalah salah satu payment gateway yang populer di Indonesia. Mereka punya fitur-fitur keren kayak:
- **Snap**: Solusi pembayaran yang gampang diintegrasikan cuma pake beberapa baris kode.
- **Core API**: API pembayaran yang fleksibel buat integrasi yang lebih kompleks.
- **Mobile SDK**: Buat integrasi pembayaran di aplikasi mobile.
- **Fraud Detection System**: Sistem deteksi penipuan buat cegah transaksi yang mencurigakan.
### Mengapa Mengintegrasikan Midtrans dengan Laravel?
Laravel itu salah satu framework PHP yang paling populer karena gampang dipake dan punya banyak fitur. Mengintegrasikan Midtrans dengan Laravel bikin temen-temen bisa:
- Menyediakan Opsi Pembayaran yang Beragam: Temen-temen bisa nerima pembayaran dari berbagai sumber kayak kartu kredit, e-wallet, dan bank transfer.
- Keamanan yang Lebih Baik: Pake layanan payment gateway yang udah teruji keamanannya.
- User Experience (UX) yang Lebih Baik: Proses pembayaran jadi lebih lancar dan cepat.
### Langkah-langkah Mengintegrasikan Midtrans dengan Laravel Menggunakan Snap.js
**Langkah 1: Setup Paket Midtrans**
Install Paket Midtrans Buka terminal temen-temen, masuk ke folder project Laravel, terus ketik ini:
```bash
composer require midtrans/midtrans-php
```
Tambahin API Key ke File **.env** Login ke Midtrans Dashboard buat dapetin kunci API, terus tambahin ke file **.env**:
```yaml
MIDTRANS_SERVER_KEY=your-server-key
MIDTRANS_CLIENT_KEY=your-client-key
MIDTRANS_IS_PRODUCTION=false
```
Sesuaikan credential server key dan client key berdasarkan key yang ada pada dashboard Midtrans temen-temen
Berhubung kita masih dalam tahap development silahkan pakai yang Environment Sandbox ya.
Sandbox Access Keys:
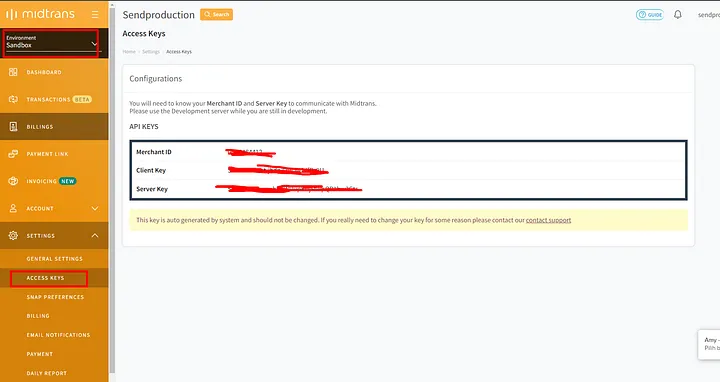
Nah, nanti kalau sudah siap bisa pakai **Production**.
Production Access Keys:
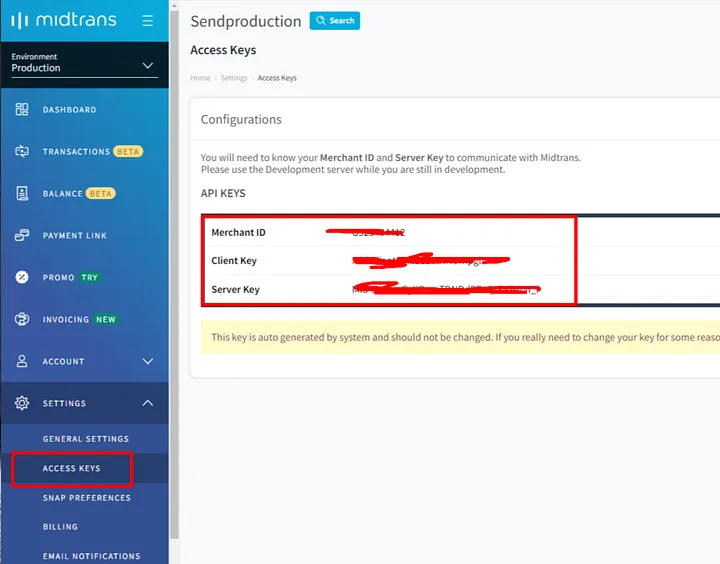
Update Config Midtrans di **config/services.php** Tambahin konfigurasi Midtrans di file **config/services.php**:
```php
return [
...
'midtrans' => [
'serverKey' => env('MIDTRANS_SERVER_KEY'),
'clientKey' => env('MIDTRANS_CLIENT_KEY'),
'isProduction' => env('MIDTRANS_IS_PRODUCTION', false),
'isSanitized' => true,
'is3ds' => true,
],
];
```
Bikin Middleware buat Midtrans Buat middleware baru buat konfigurasi Midtrans dengan perintah ini:
```bash
php artisan make:middleware MidtransConfig
```
Update file **MidtransConfig.php** jadi kaya gini:
```php
<?php
namespace App\Http\Middleware;
use Closure;
use Illuminate\Http\Request;
class MidtransConfig
{
public function handle(Request $request, Closure $next)
{
\Midtrans\Config::$serverKey = config('services.midtrans.serverKey');
\Midtrans\Config::$isProduction = config('services.midtrans.isProduction');
\Midtrans\Config::$isSanitized = config('services.midtrans.isSanitized');
\Midtrans\Config::$is3ds = config('services.midtrans.is3ds');
return $next($request);
}
}
```
Khusus **Laravel 10** kebawah
Daftarin middleware ini di `app/Http/Kernel.php`:
```php
protected $middlewareGroups = [
'web' => [
...
\App\Http\Middleware\MidtransConfig::class, // tambahkan ini
],
'api' => [
...
\App\Http\Middleware\MidtransConfig::class, // tambahkan ini
],
];
```
Untuk **Laravel 11** temen-temen bisa buka file `bootstrap/app.php` dan tambahkan `$middleware->append(MidtransConfig::class);` seperti berikut:
```php
<?php
use App\Http\Middleware\MidtransConfig;
use Illuminate\Foundation\Application;
use Illuminate\Foundation\Configuration\Exceptions;
use Illuminate\Foundation\Configuration\Middleware;
return Application::configure(basePath: dirname(__DIR__))
->withRouting(
web: __DIR__ . '/../routes/web.php',
commands: __DIR__ . '/../routes/console.php',
channels: __DIR__ . '/../routes/channels.php',
health: '/up',
)
->withMiddleware(function (Middleware $middleware) {
$middleware->append(MidtransConfig::class); // tambahkan ini
})
->withExceptions(function (Exceptions $exceptions) {
//
})->create();
```
**Langkah 2: Bikin Endpoint buat Dapetin Snap Token**
Bikin Controller buat Pembayaran
```bash
php artisan make:controller PaymentController
```
Tambahin Fungsi buat Bikin Snap Token di `PaymentController `Update file `PaymentController.php` jadi kaya gini:
```php
<?php
namespace App\Http\Controllers;
use Illuminate\Http\Request;
class PaymentController extends Controller
{
public function getSnapToken(Request $request)
{
$params = [
'transaction_details' => [
'order_id' => uniqid(),
'gross_amount' => 10000,
],
'customer_details' => [
'first_name' => 'Yoga',
'last_name' => 'Meleniawan',
'email' => 'yogameleniawan@example.com',
'phone' => '08111222333',
],
];
try {
$snapToken = \Midtrans\Snap::getSnapToken($params);
return response()->json(['snap_token' => $snapToken]);
} catch (\Exception $e) {
return response()->json(['error' => $e->getMessage()], 500);
}
}
}
```
Tambahin Route buat Dapetin Snap Token di `routes/web.php`
```bash
Route::post('/get-snap-token', [PaymentController::class, 'getSnapToken']);
```
**Langkah 3: Integrasi Snap.js di Frontend**
Bikin atau Update View dengan Form Pembayaran Bikin file `resources/views/payment.blade.php` kaya gini:
```html
<!DOCTYPE html>
<html>
<head>
<title>Payment Page</title>
<script type="text/javascript"
src="https://app.sandbox.midtrans.com/snap/snap.js"
data-client-key="{{ config('services.midtrans.clientKey') }}"></script>
</head>
<body>
<button id="pay-button">Pay!</button>
<script type="text/javascript">
document.getElementById('pay-button').onclick = function () {
fetch('/get-snap-token', {
method: 'POST',
headers: {
'Content-Type': 'application/json',
'X-CSRF-TOKEN': '{{ csrf_token() }}',
},
body: JSON.stringify({})
})
.then(response => response.json())
.then(data => {
if (data.snap_token) {
snap.pay(data.snap_token);
} else {
alert('Error getting Snap token');
}
});
};
</script>
</body>
</html>
```
Tambahin Route buat Nampilin View di `routes/web.php`
```php
Route::get('/pay', function () {
return view('payment');
});
```
**Langkah 4: Waktunya Uji Coba**
Jalankan Server Laravel
```bash
php artisan serve
```
Akses halaman pembayaran lewat browser
```
http://127.0.0.1:8000/pay
```
Klik Tombol **“Pay!”** buat mulai proses pembayaran pake Snap.js.
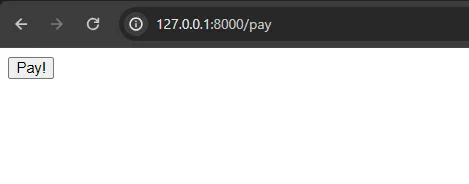
Nah nanti bakal muncul seperti ini, artinya integrasinya sudah berhasil temen-temen! Mantappp!
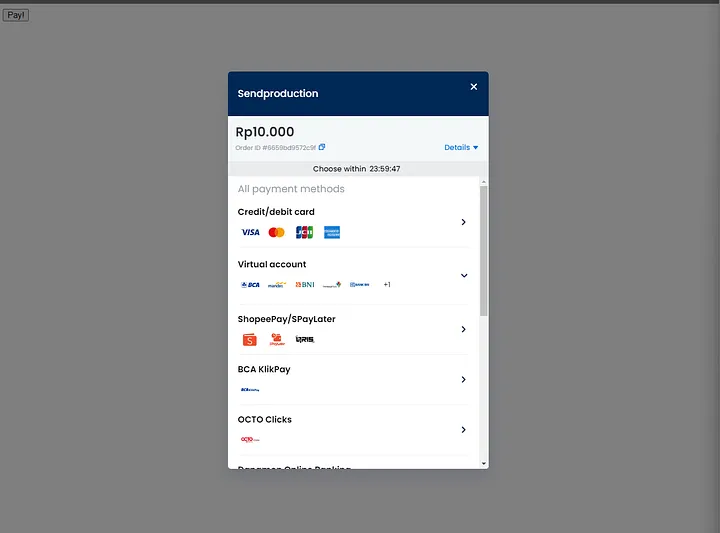
Nah, kalau kita lihat di dashboard Midtransnya juga bakal muncul seperti ini:
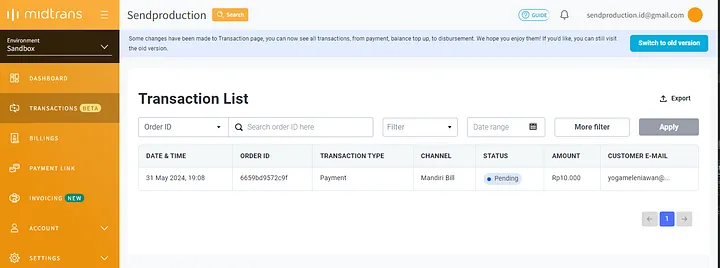
### Kesimpulan
Dengan ngikutin langkah-langkah di atas, temen-temen bisa dengan gampang ngintegrasiin Midtrans dengan aplikasi Laravel temen-temen pake Snap.js. Payment gateway kayak Midtrans penting banget buat pastiin transaksi online aman, mudah, dan cepat. Integrasi ini bakal ningkatin pengalaman pengguna di situs web atau aplikasi temen-temen dan ngasih berbagai pilihan metode pembayaran yang aman. Dengan setup ini, temen-temen siap nerima pembayaran dari pelanggan dengan cara yang efisien dan aman. Selamat mencoba temen-temen! sampai bertemu di artikel yang lainnya!
| yogameleniawan |
1,874,797 | Efficient Sheet Rolling Machines for Accurate Metal Shaping | Efficient Sheet Rolling Machines for Accurate Metal Shaping Sheet rolling machines are tools that... | 0 | 2024-06-03T01:03:59 | https://dev.to/jennifer_garciakd_7c34d57/efficient-sheet-rolling-machines-for-accurate-metal-shaping-k4e | metal, shaping | Efficient Sheet Rolling Machines for Accurate Metal Shaping
Sheet rolling machines are tools that help to bend, shape and cut metal sheets into various shapes. These machines are crucial to metalworkers, machinists, and artisans who need to make precise and accurate metal components for various projects. With the advancement of technology, have evolved to become more efficient, safer and easy to use.
Features of Effective Sheet Rolling Machines
Efficient sheet devices which can be rolling numerous advantages over traditional devices
First, they're built to be accurate and accurate, which guarantees creation like consistent of elements
Second, they're robust and durable, featuring materials which are high-quality make sure they are resistant to put on and tear
Third, the devices include higher level software that permits operators to generate parameters that are exact plus the machines adjust properly to produce the outcome which can be needed
Last but not least, efficient sheet rolling devices are time-saving and economical, making them great for both small and big companies
Innovation in Sheet Rolling Machines
Innovation in sheet devices being rolling resulted in the development of far better and safer devices
One innovation like particular be the incorporation of sensors and higher level software which makes it easier for operators to change parameters, monitor the machine, and identify any malfunctions
Furthermore, contemporary sheet rolling machines also have automatic lubrication systems that minimize friction and minimize deterioration
Safety First
With regards to sheet like devices that are utilizing safety is essential
Manufacturers have actually taken measures to make sure that their devices meet with the safety requirements that are greatest
Several of the security options that come with efficient sheet devices that are rolling of emergency stop buttons, security guards, and protection like overload
More over, operators have to be trained on how to handle the devices to avoid accidents and accidents
Provider and Quality
Efficient sheet rolling machine which are rolling upkeep like regular use smoothly and last longer
Manufacturers provide maintenance directions, and operators need certainly to follow them strictly
Additionally, efficient sheet rolling machines have warranties that cover defects and malfunctions
Therefore, operators should invest in top-quality machines offering a warranty like ensure like comprehensive have value with regards to their cash
Applications of Efficient Sheet Rolling Machines
Efficient sheet devices that are rolling a range of applications in various companies
They might be present in construction, manufacturing, engineering, and a complete lot of other companies where components which can be metal essential
Furthermore, they might be ideal for both small-scale and manufacturing like large-scale leaving them perfect for both tiny and businesses that are big
In conclusion, efficient steel sheet rolling machine are vital tools for metalworkers, machinists, and artisans who need to make precise and accurate metal components. These machines are the product of innovation and technology, and they come with numerous advantages over traditional machines. With their advanced software, safety features, and versatility, efficient sheet rolling machines are a must-have for anyone who is serious about metalworking.
Source: https://www.liweicnc.com/application/sheet-rolling-machine | jennifer_garciakd_7c34d57 |
1,869,815 | Implementing Role-Based Access Control, Managed Identities, and Protected Immutable Storage | Create the storage account and managed identity Provide a storage account for the web app. In the... | 0 | 2024-06-03T01:02:17 | https://dev.to/opsyog/provide-storage-for-a-new-company-app-4hce | cloudcomputing, identity, azure, storage | **Create the storage account and managed identity**
**Provide a storage account for the web app.**
**In the portal, search for and select Storage accounts.**
**Select + Create.**
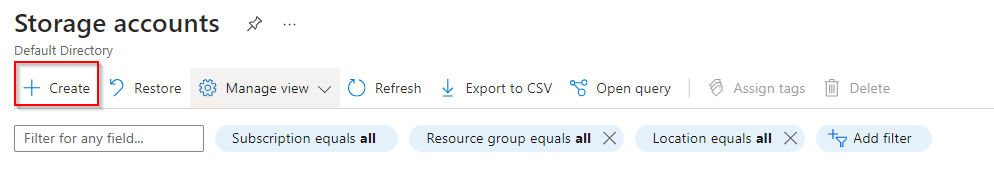
**For Resource group select Create new. Give your resource group a name and select OK to save your changes.**
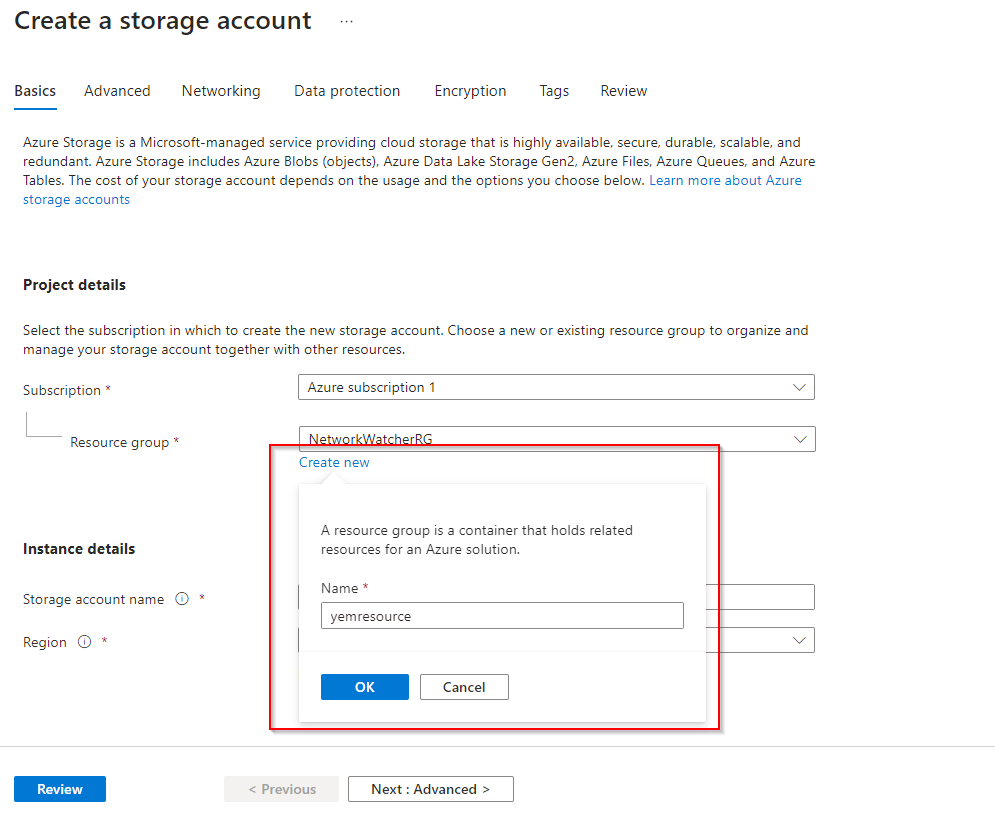
**Provide a Storage account name. Ensure the name is unique and meets the naming requirements.**
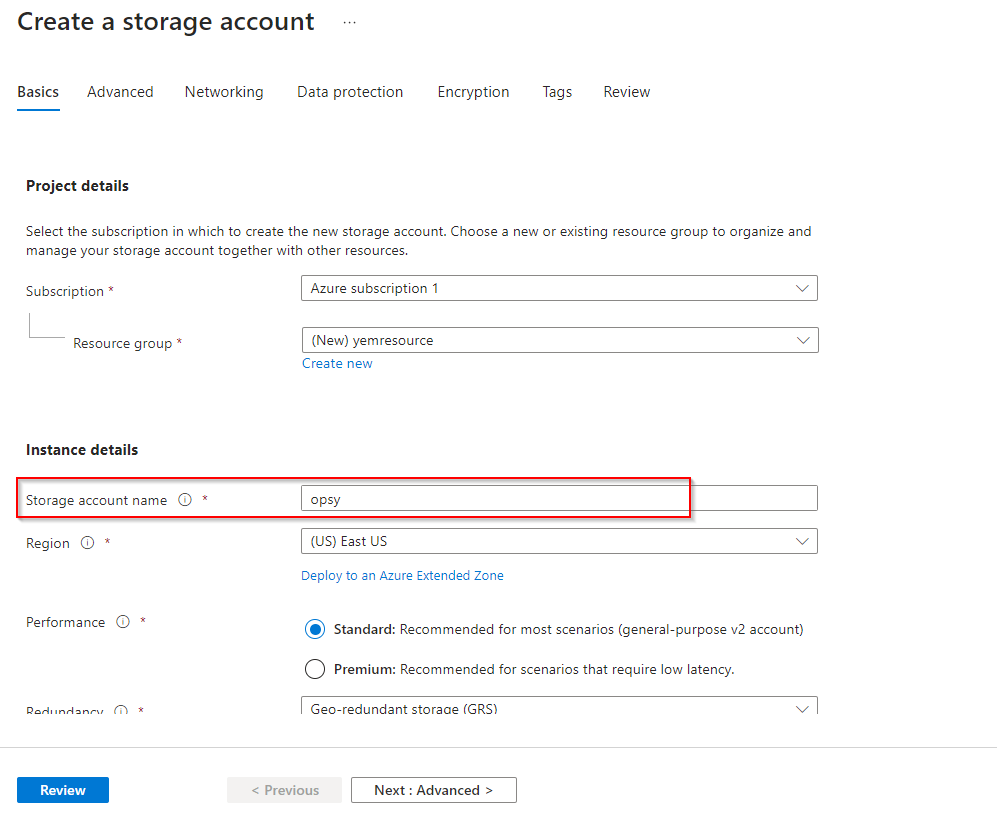
**Move to the Encryption tab.**
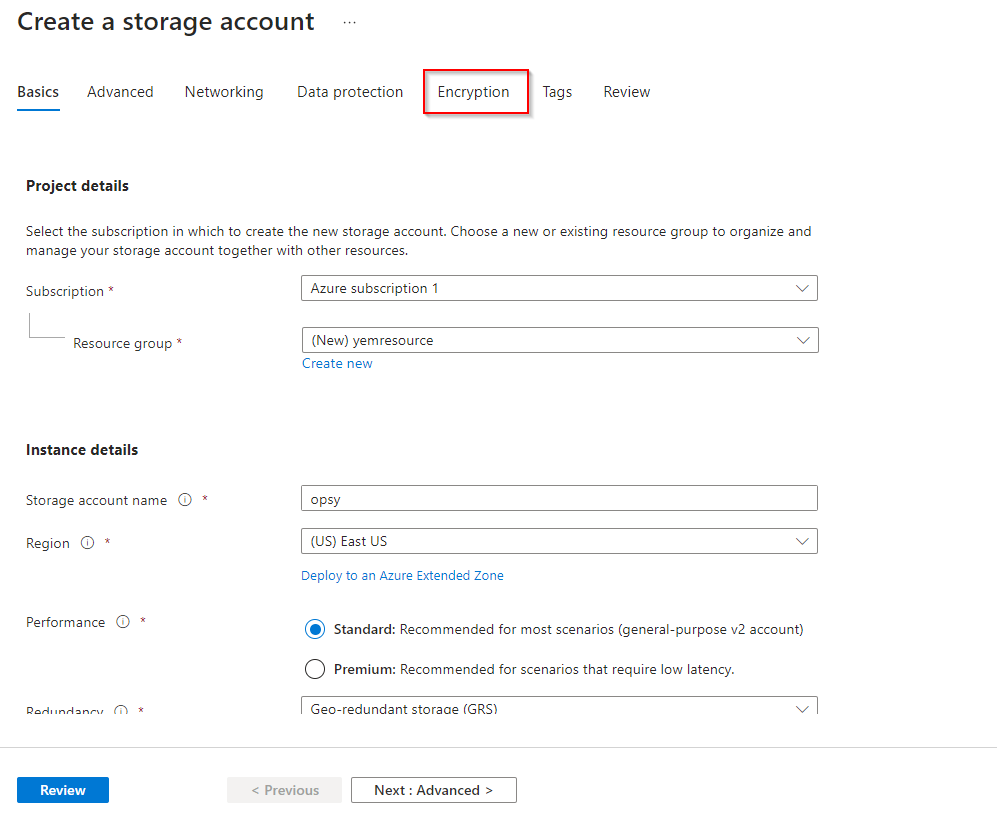
**Check the box for Enable infrastructure encryption.**
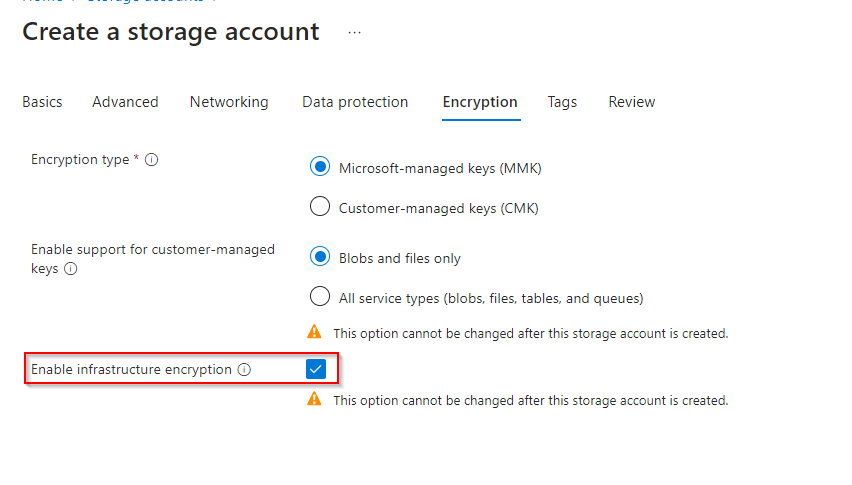
**Notice the warning, This option cannot be changed after this storage account is created.**
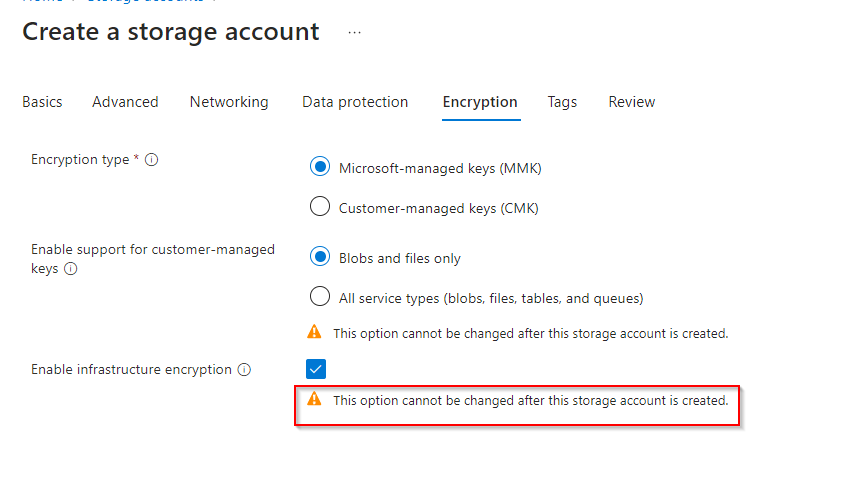
**Select Review + Create.**
**Wait for the resource to deploy.**
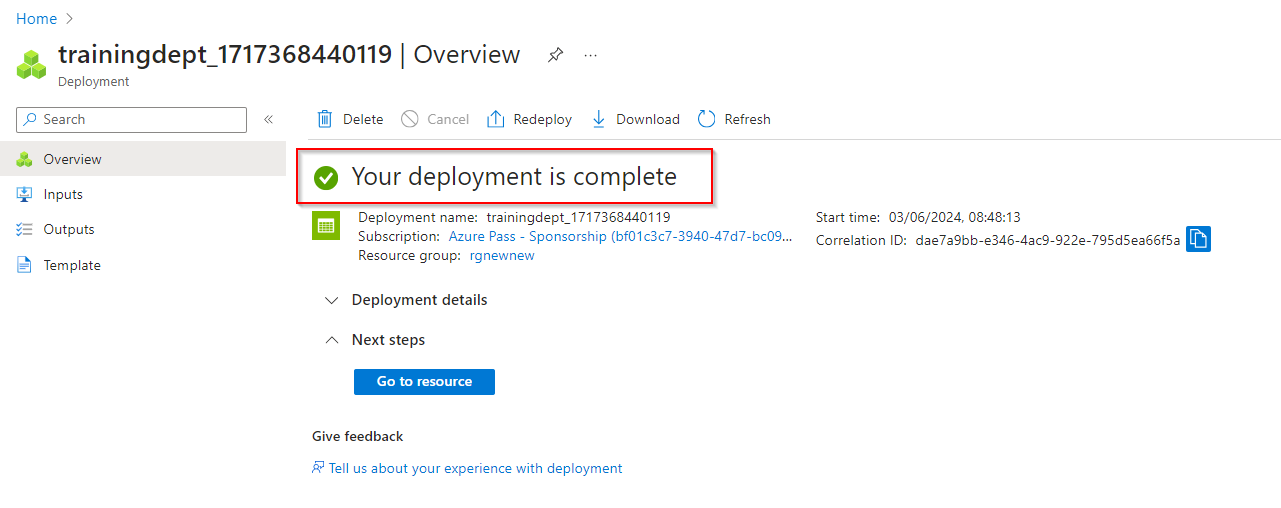
2.** Provide a managed identity for the web app to use. **
**Search for and select Managed identities.**
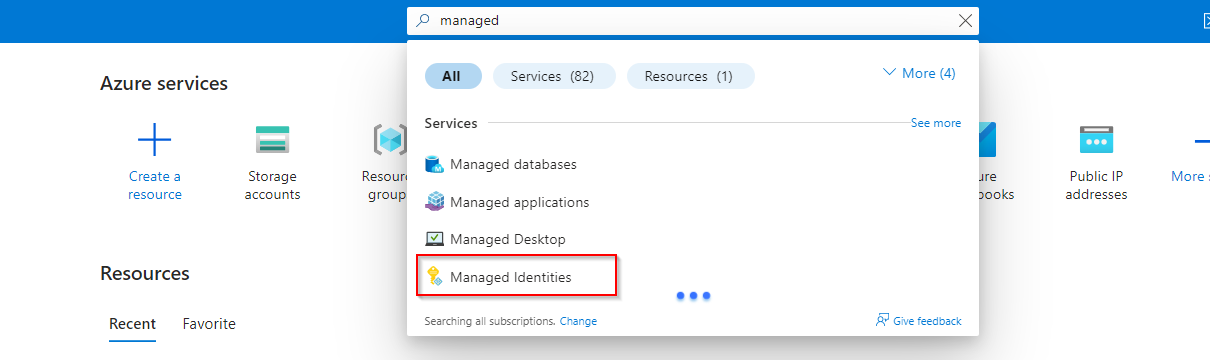
**Select Create.**
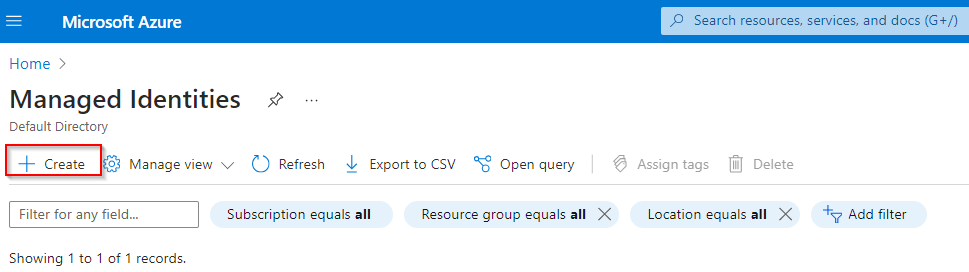
**Select your resource group.**
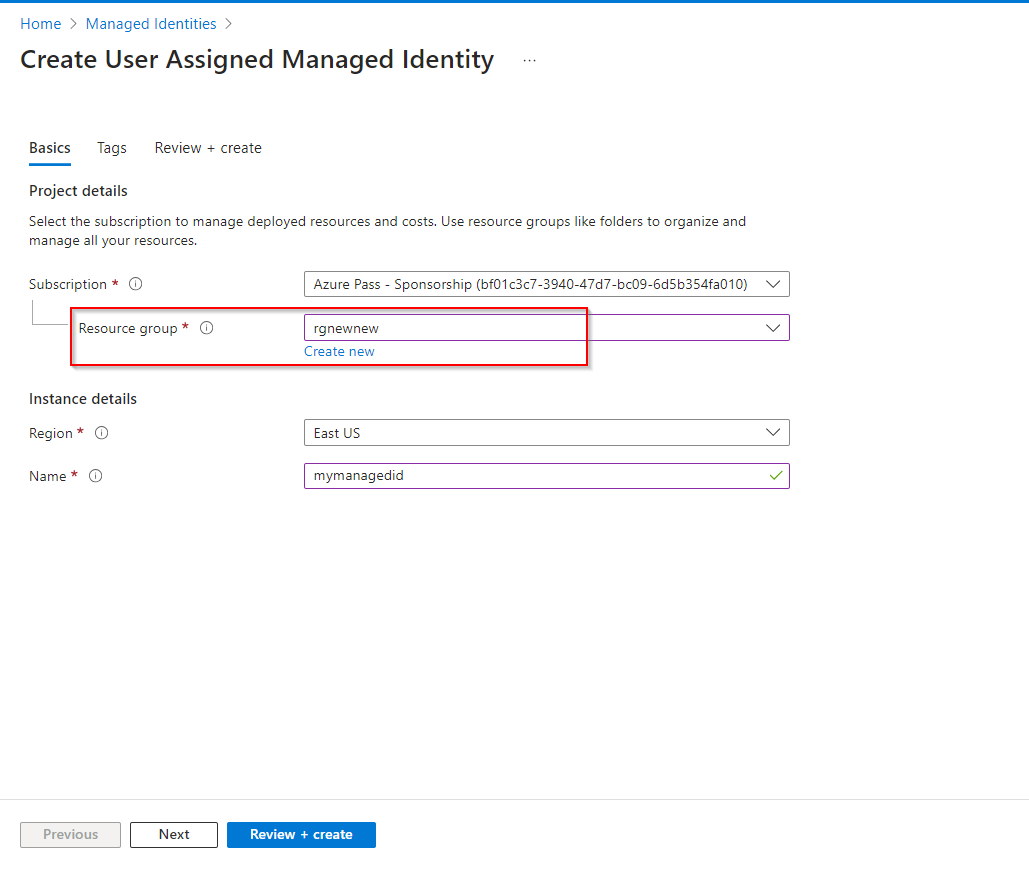
**Give your managed identity a name.**
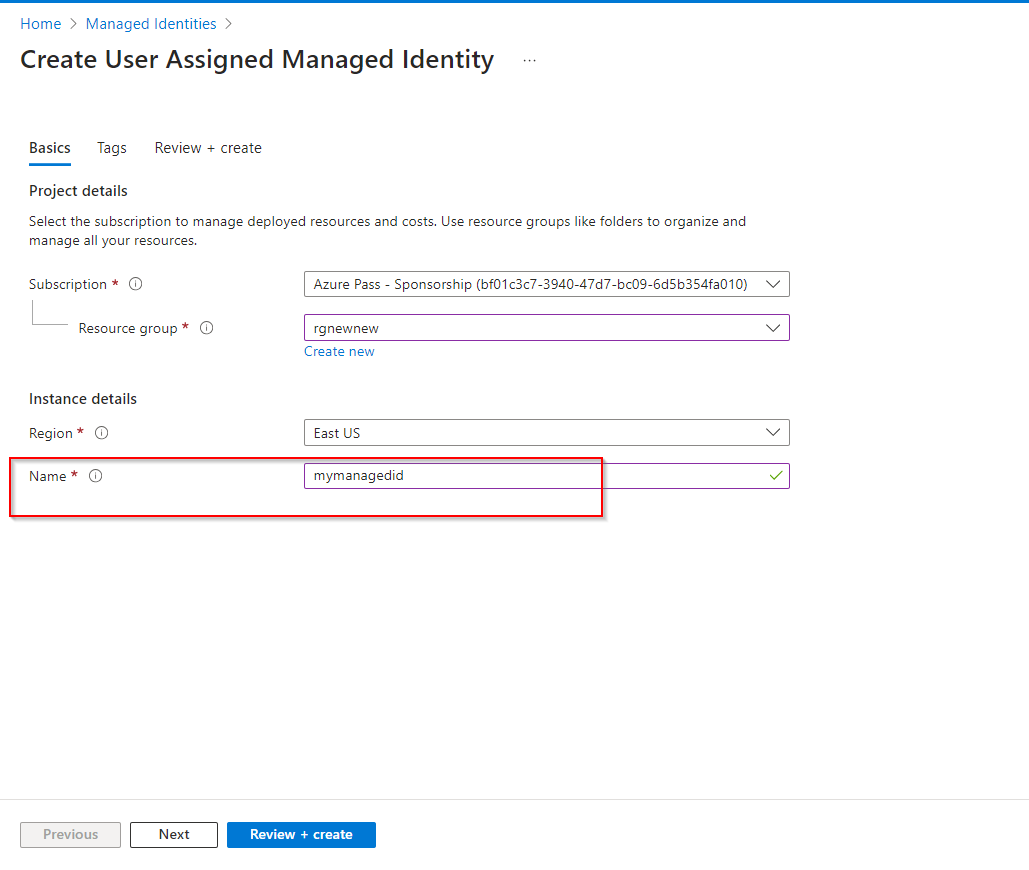
**Select Review and create, and then Create.**
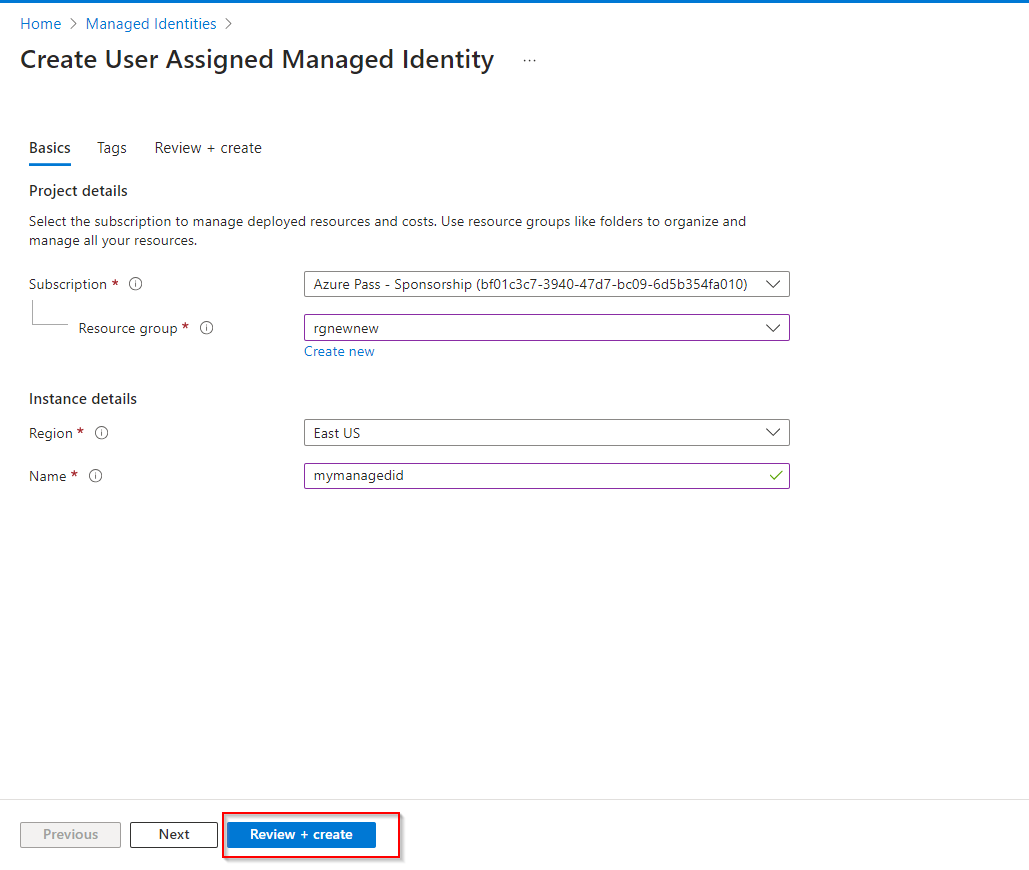
3. **Assign the correct permissions to the managed identity. The identity only needs to read and list containers and blobs. **
**Search for and select your storage account.**
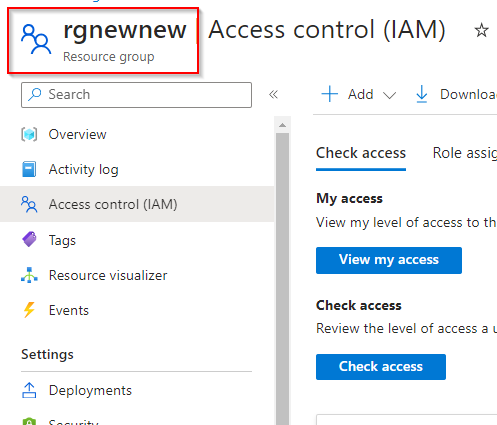
**Select the Access Control (IAM) blade.**
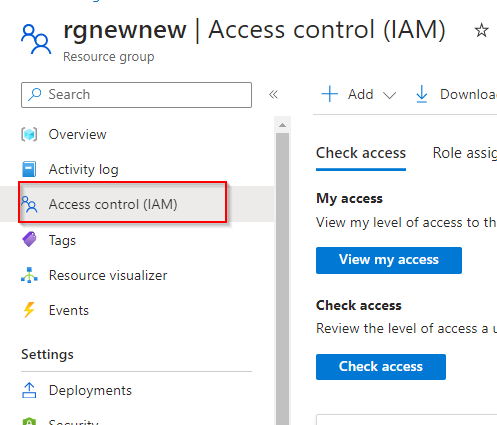
**Select Add role assignment (center of the page).**
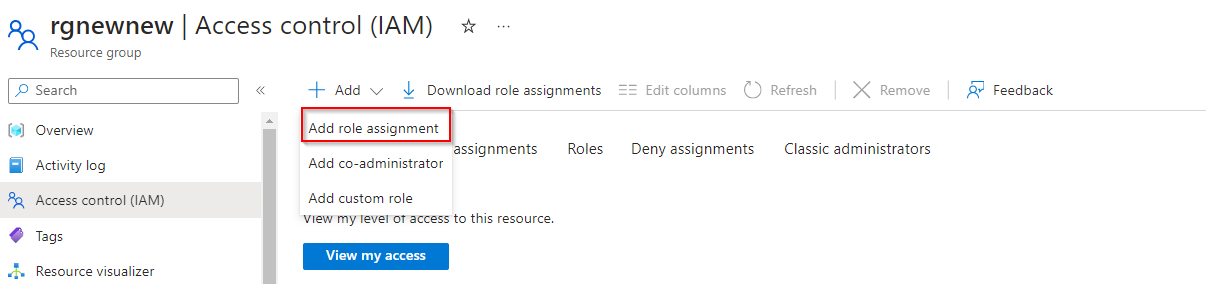
**On the Job functions roles page, search for and select the Storage Blob Data Reader role.**
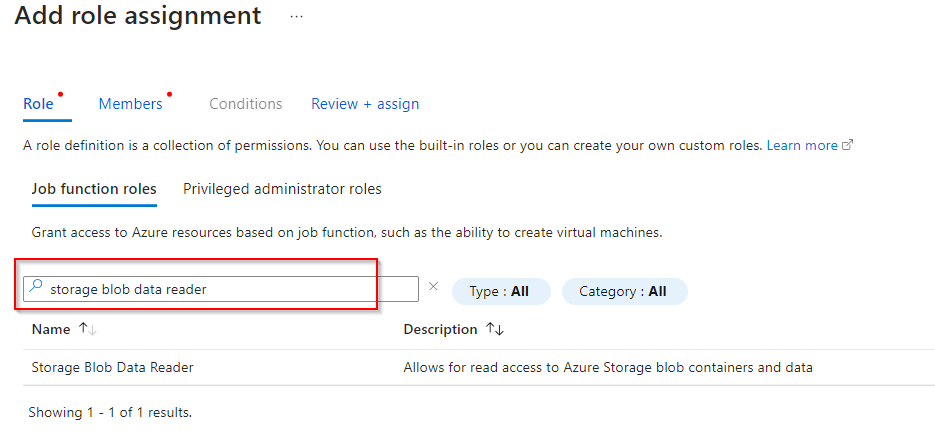
**On the Members page, select Managed identity.**
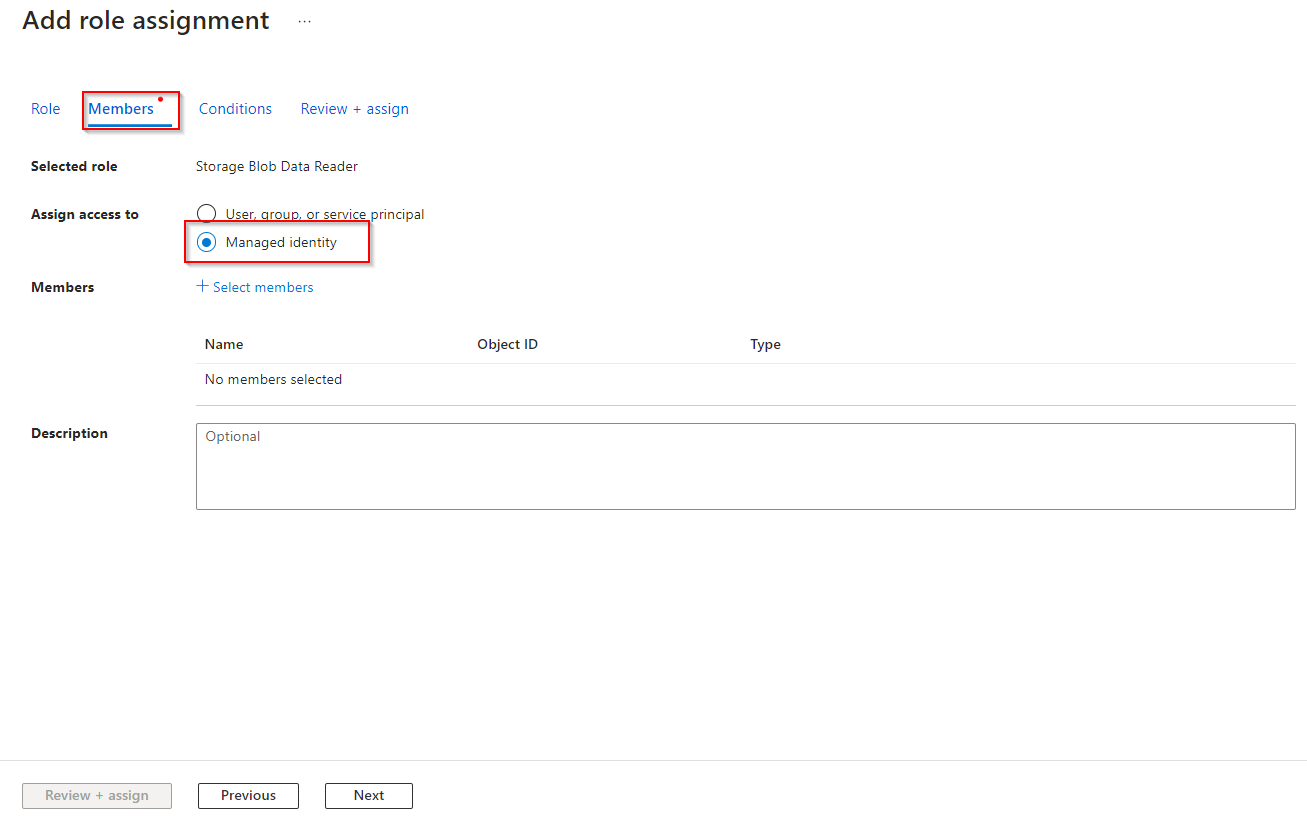
**Select Select members, in the Managed identity drop-down select User-assigned managed identity.**
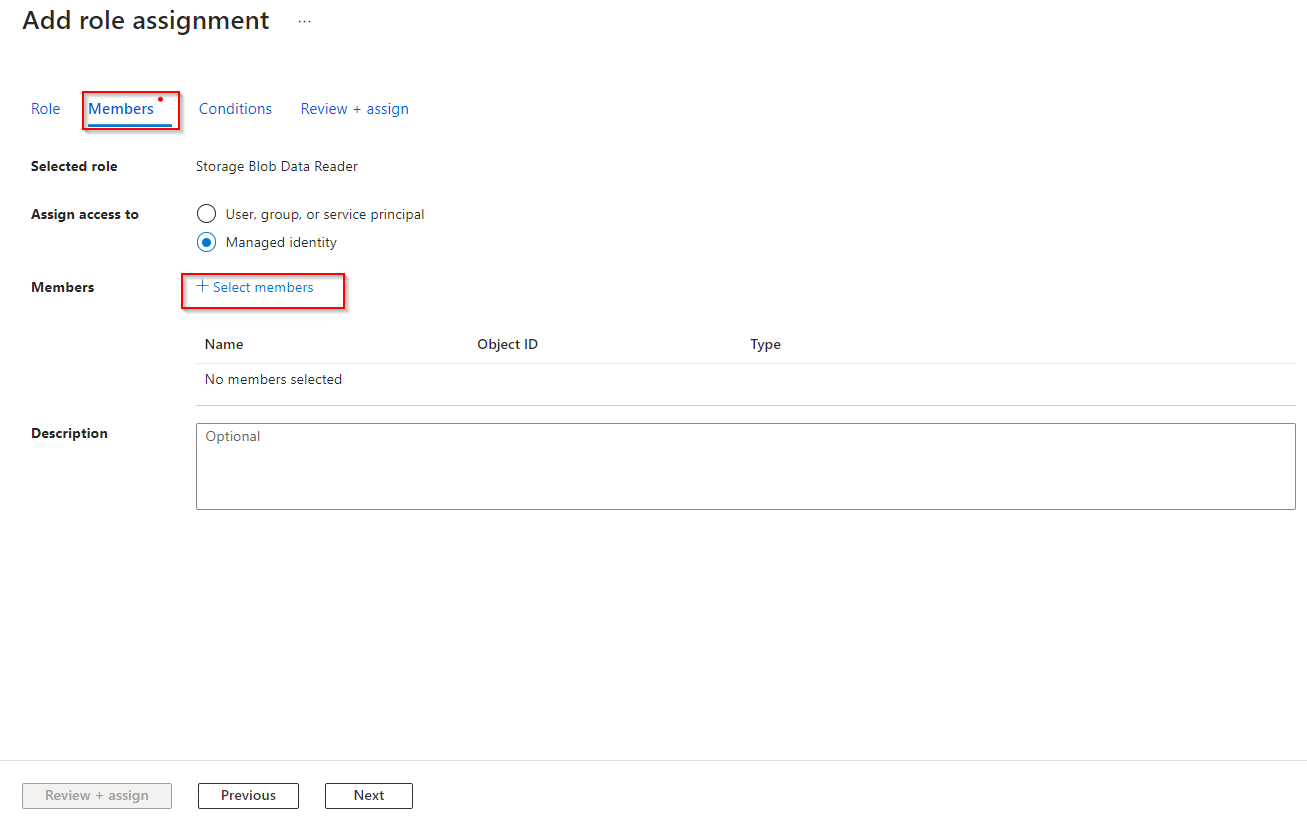
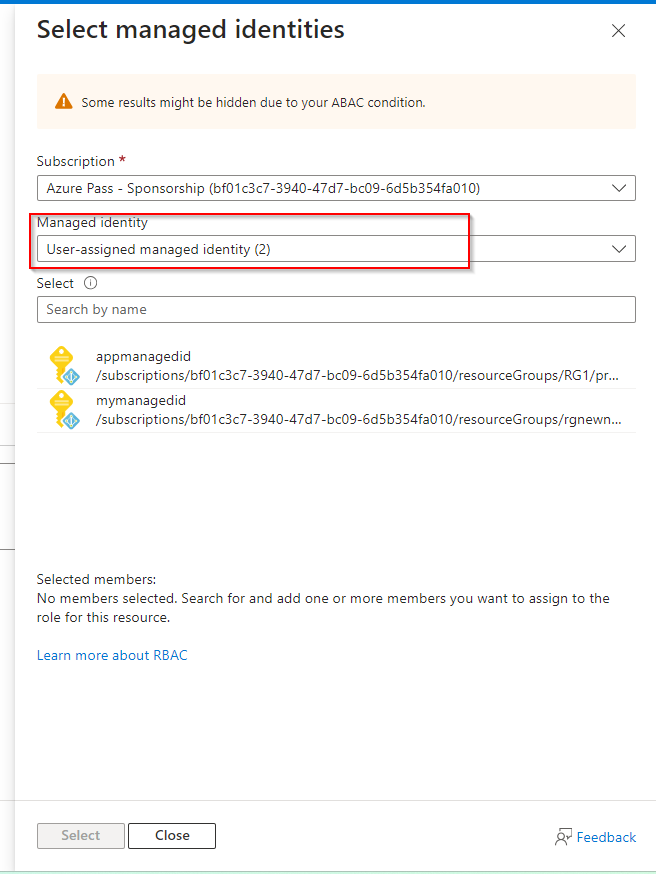
**Select the managed identity you created in the previous step.**
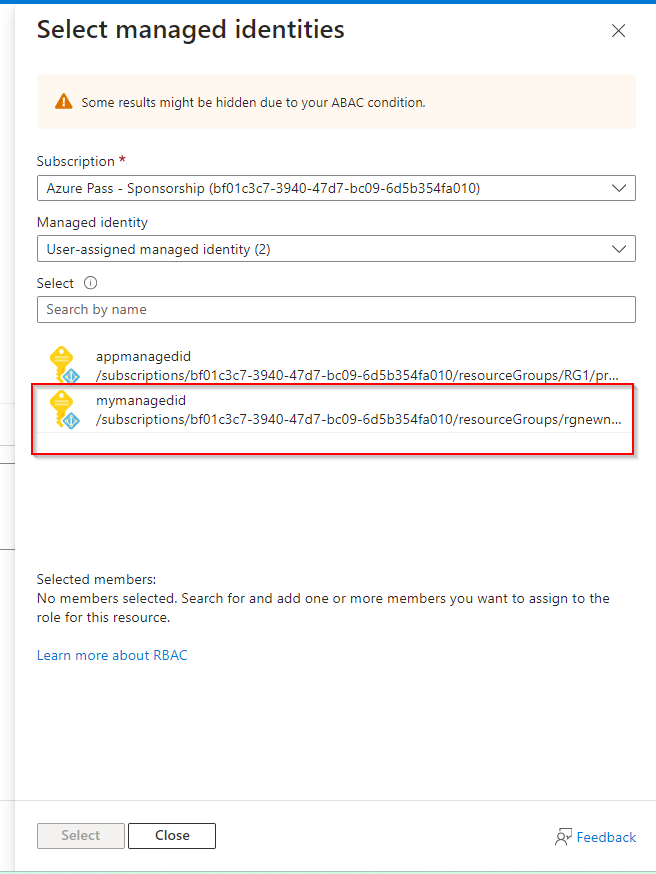
**Click Select and then Review + assign the role.**
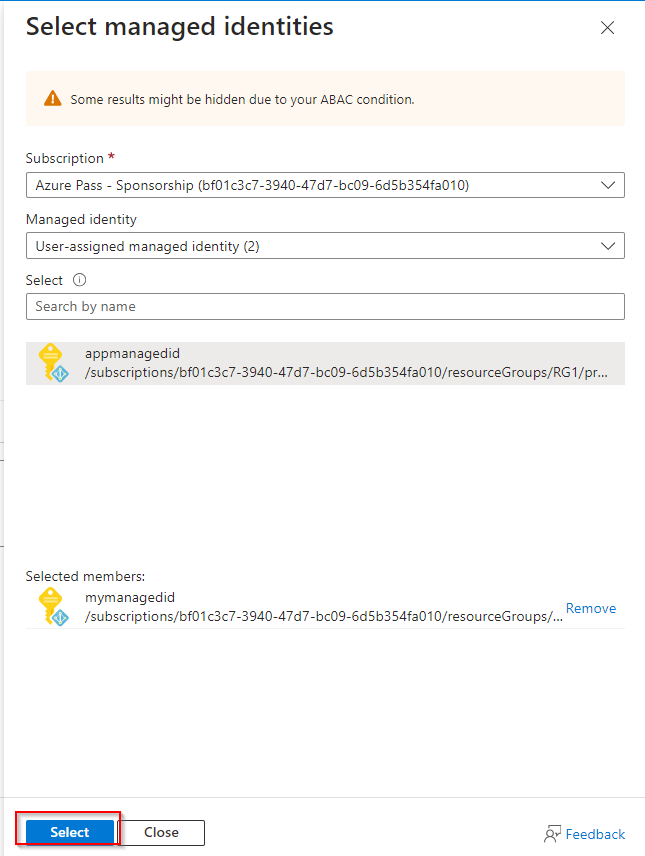
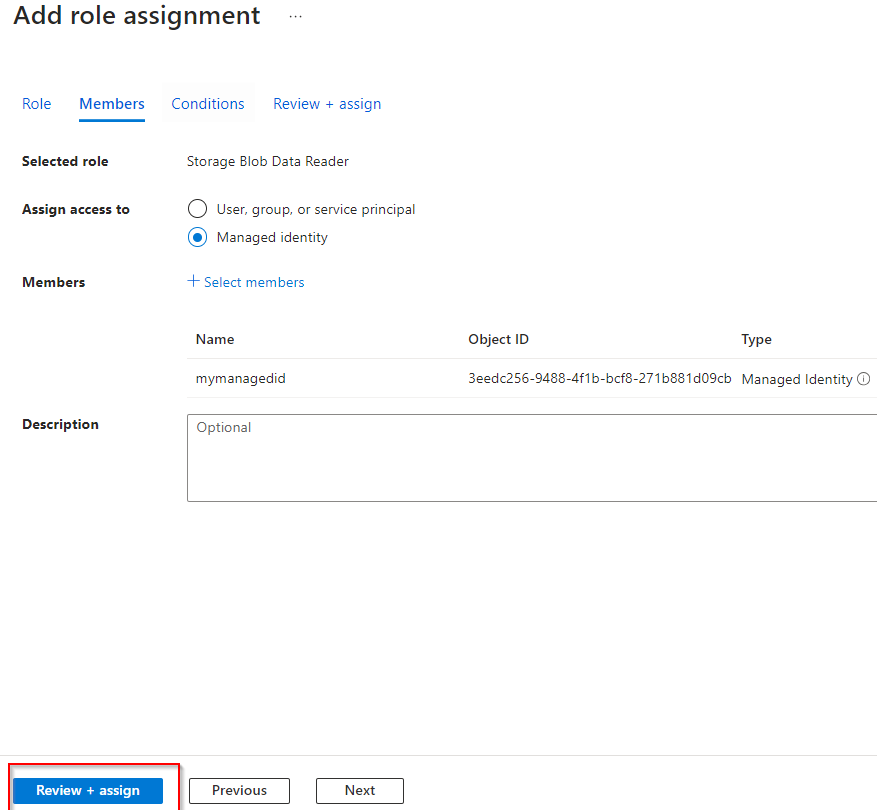
**Select Review + assign a second time to add the role assignment.**
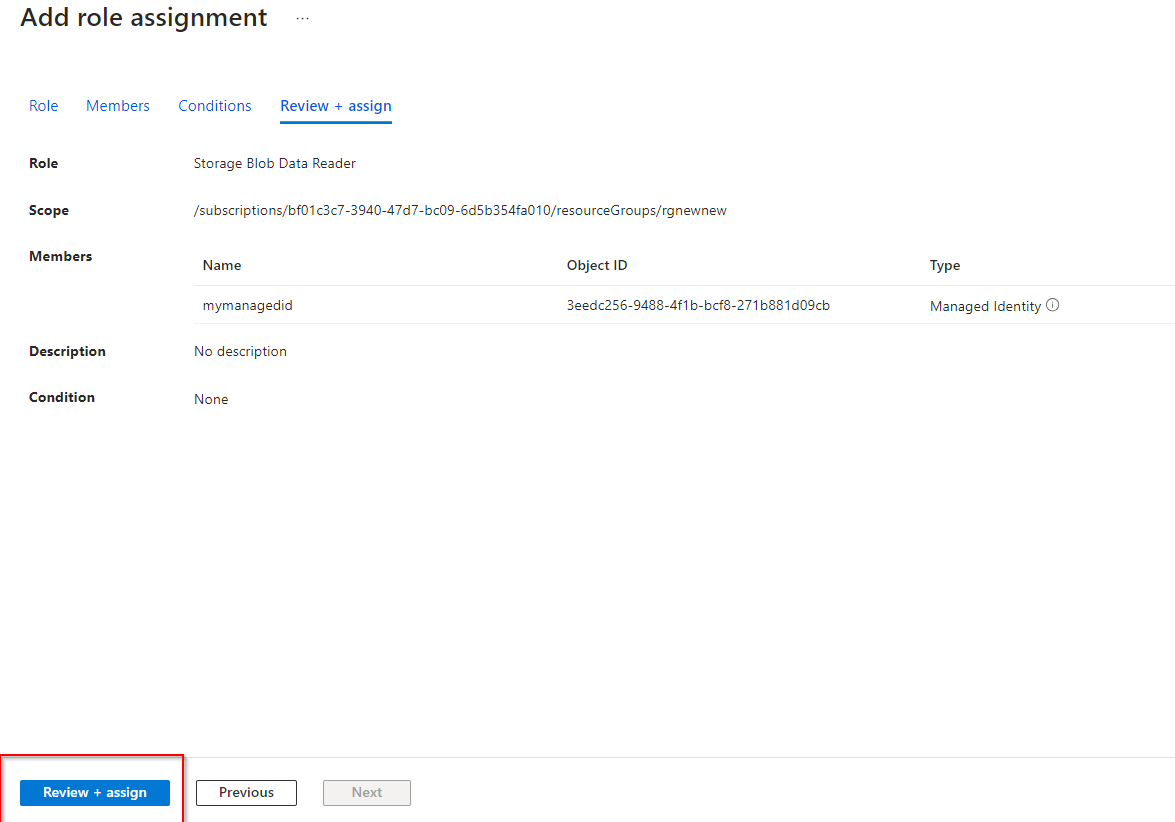
**Your storage account can now be accessed by a managed identity with the Storage Data Blob Reader permissions.**
**Secure access to the storage account with a key vault and key**
1. **To create the key vault and key needed for this part of the lab, your user account must have Key Vault Administrator permissions. **
**In the portal, search for and select Resource groups.**
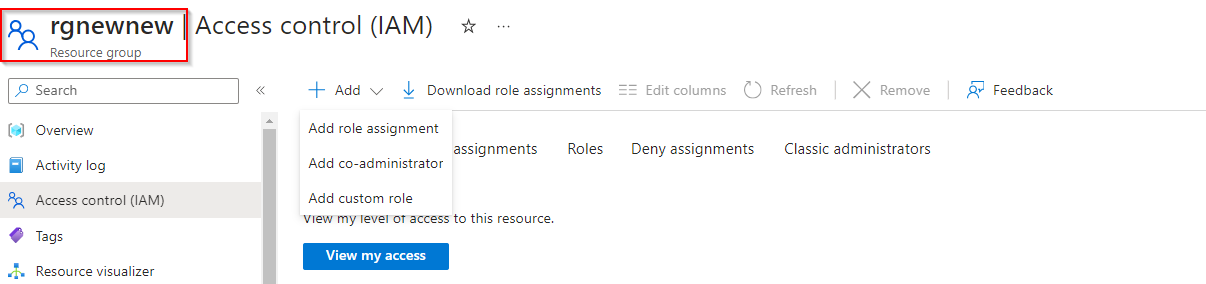
**Select your resource group, and then the Access Control (IAM) blade.**
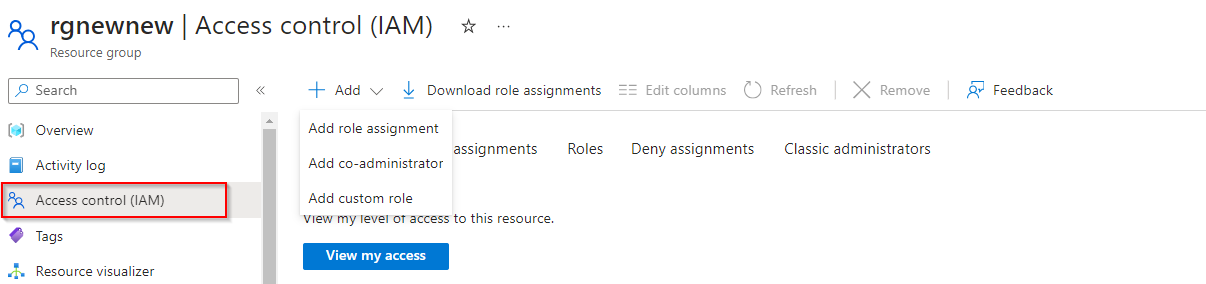
**Select Add role assignment (center of the page).**
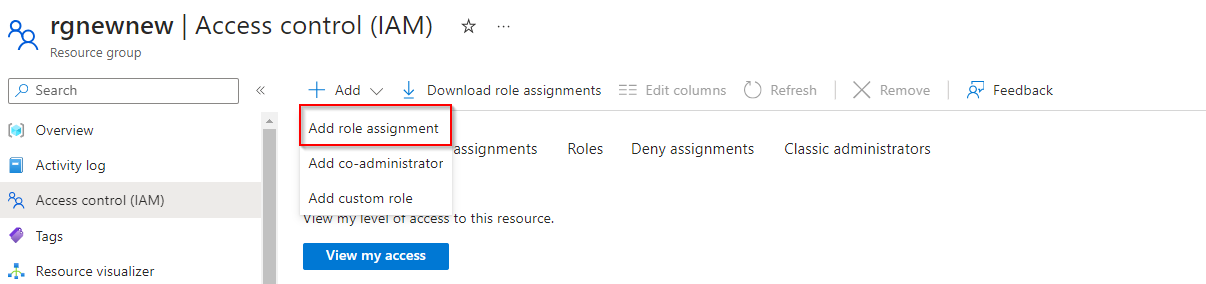
**On the Job functions roles page, search for and select the Key Vault Administrator role.**
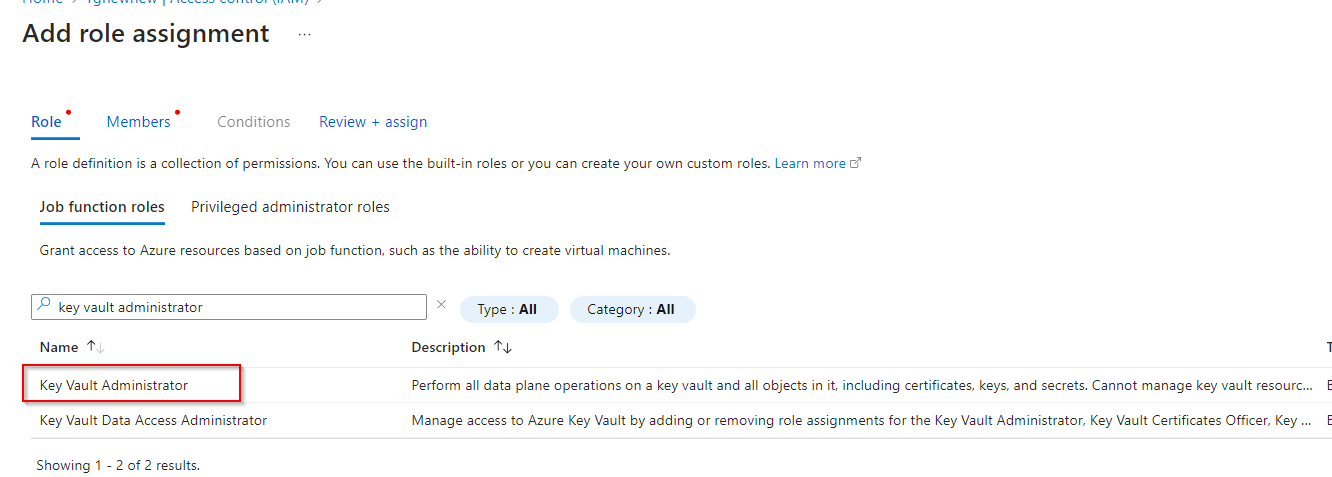
**On the Members page, select User, group, or service principal.**
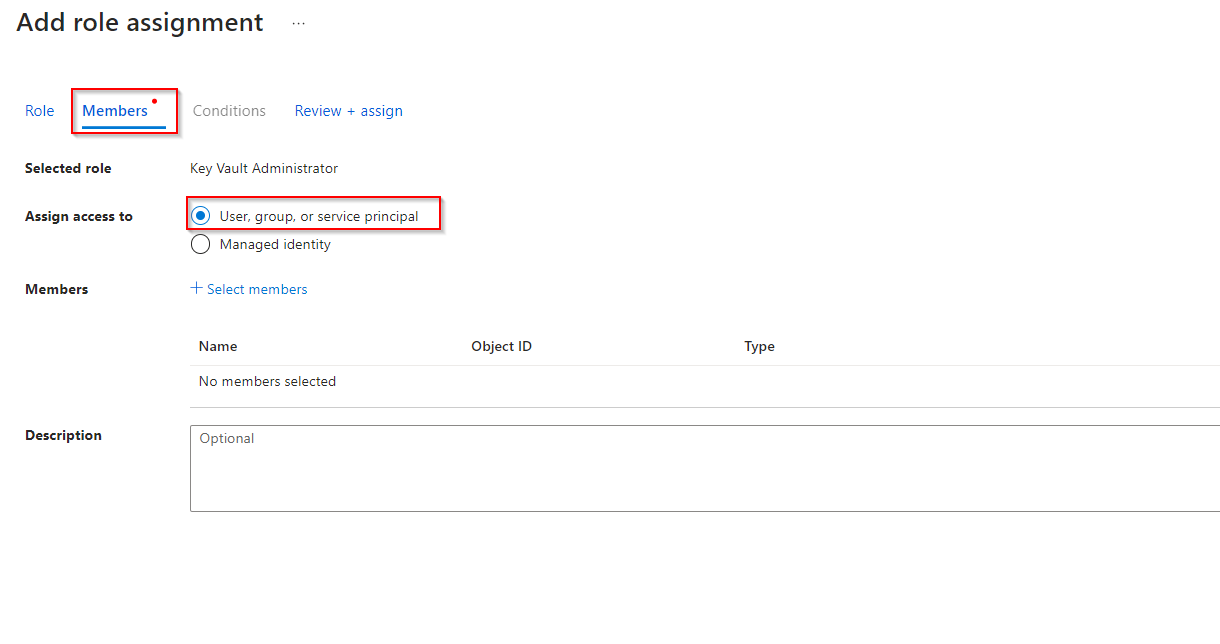
**Select Select members.**
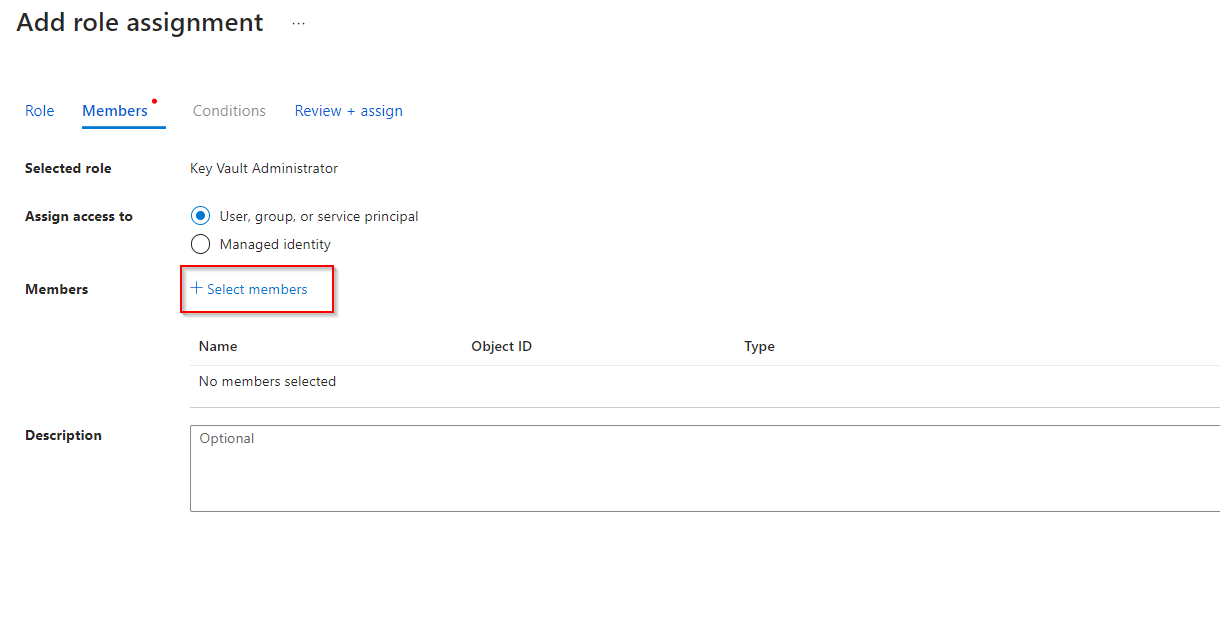
**Search for and select your user account. Your user account is shown in the top right of the portal.**
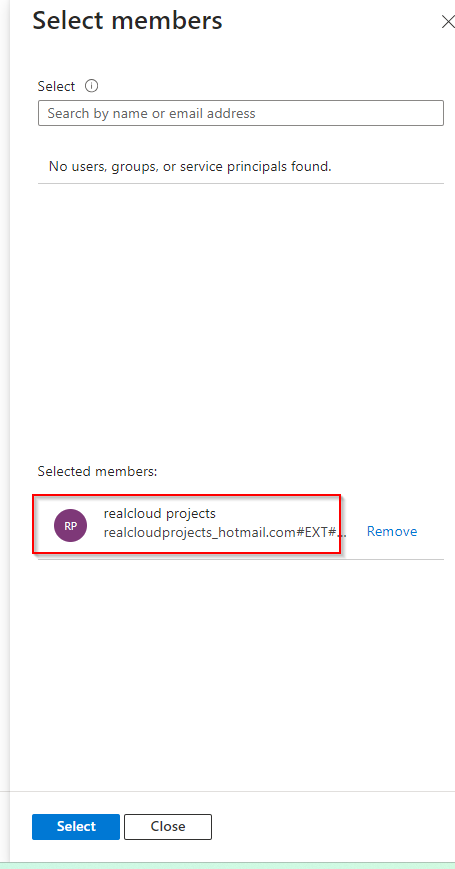
**Click Select and then Review + assign.**
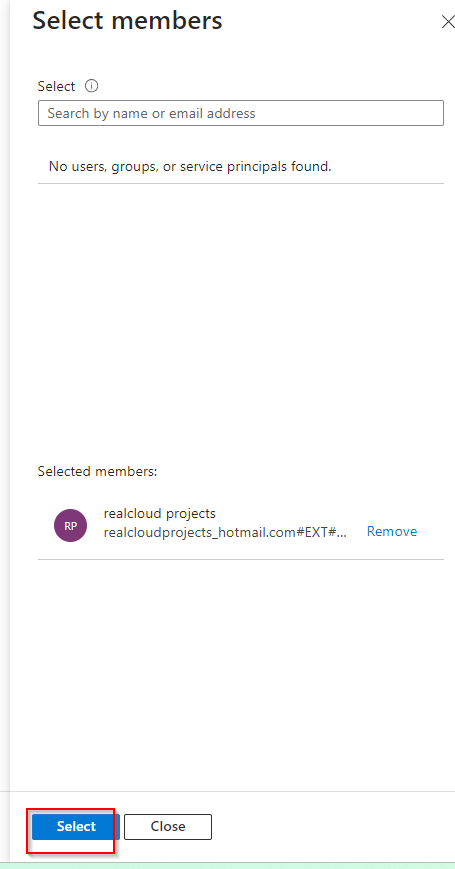
**Select Review + assign a second time to add the role assignment.**
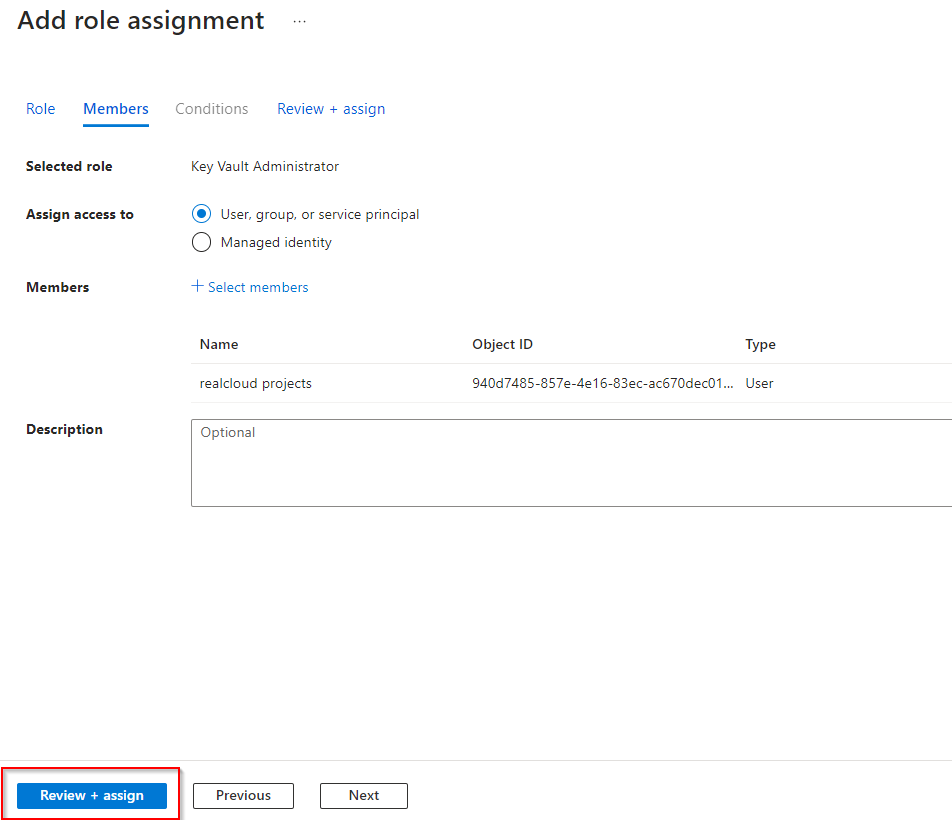
**You are now ready to continue with the lab.**
2. **Create a key vault to store the access keys.**
**In the portal, search for and select Key vaults.**
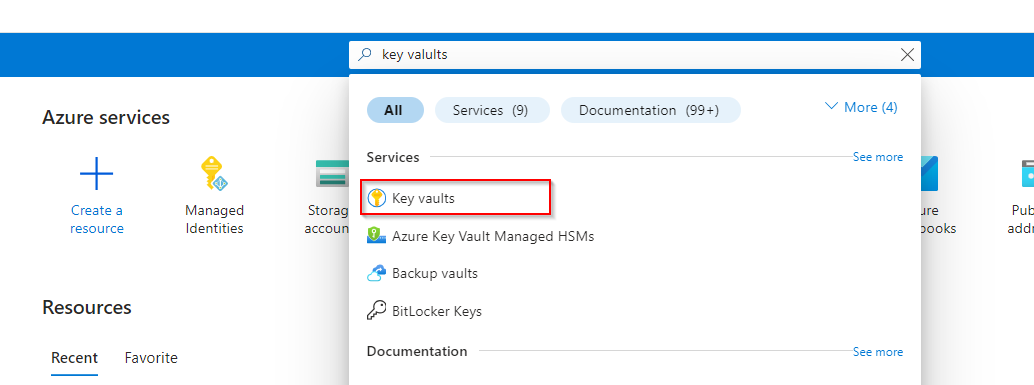
**Select Create.**
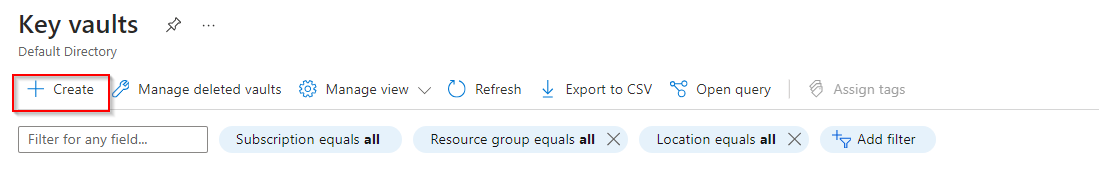
**Select your resource group.**
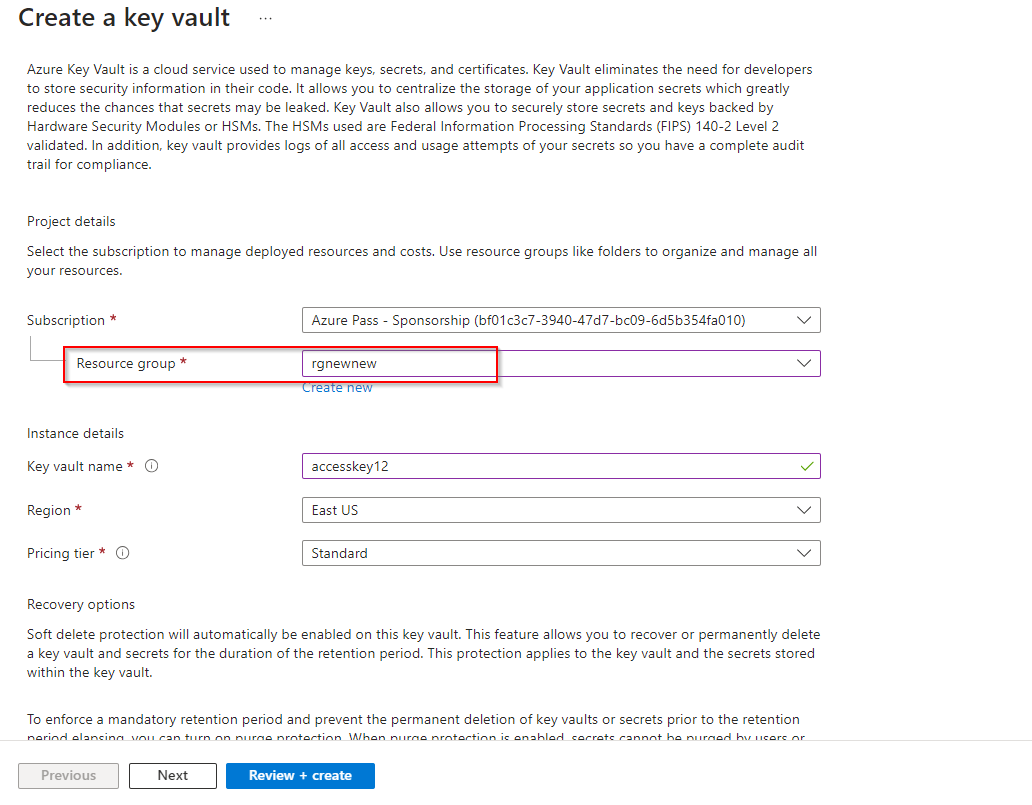
**Provide the name for the key vault. The name must be unique.**
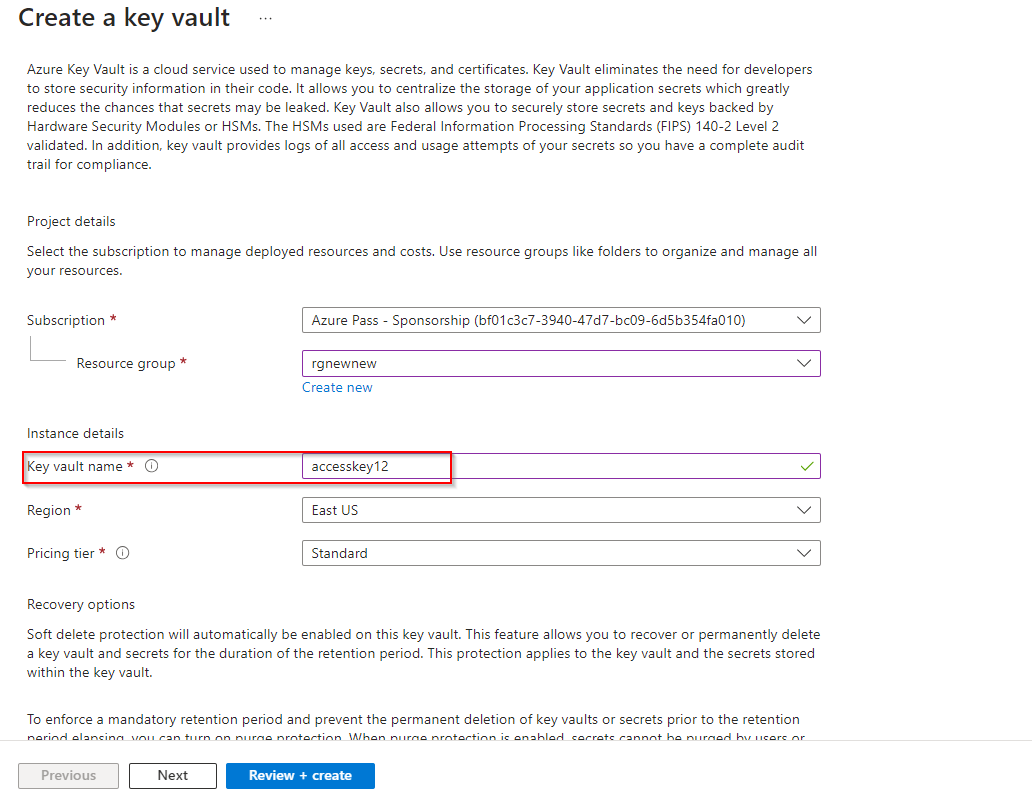
**Ensure on the Access configuration tab that Azure role-based access control (recommended) is selected.**
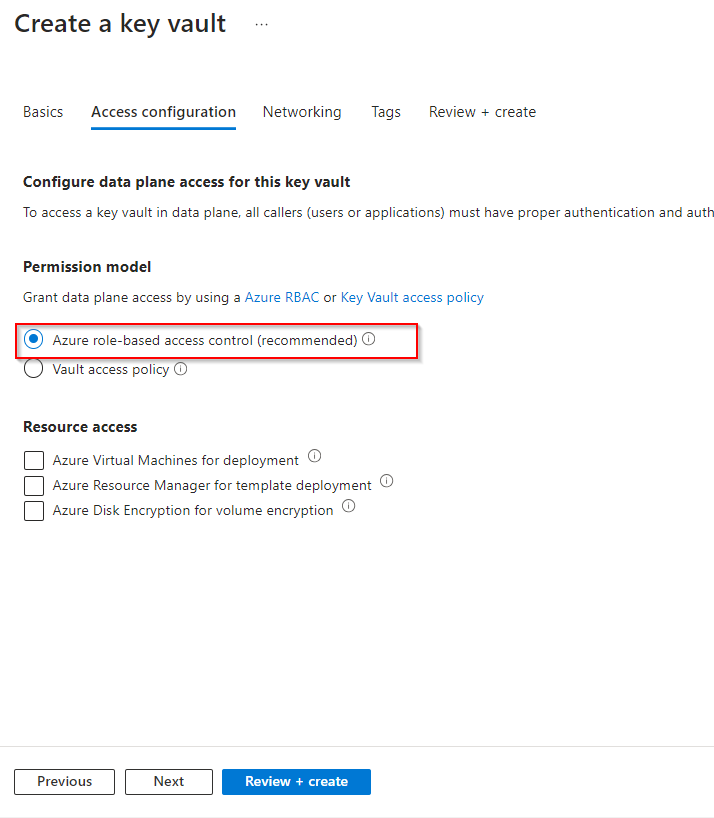
**Select Review + create.**
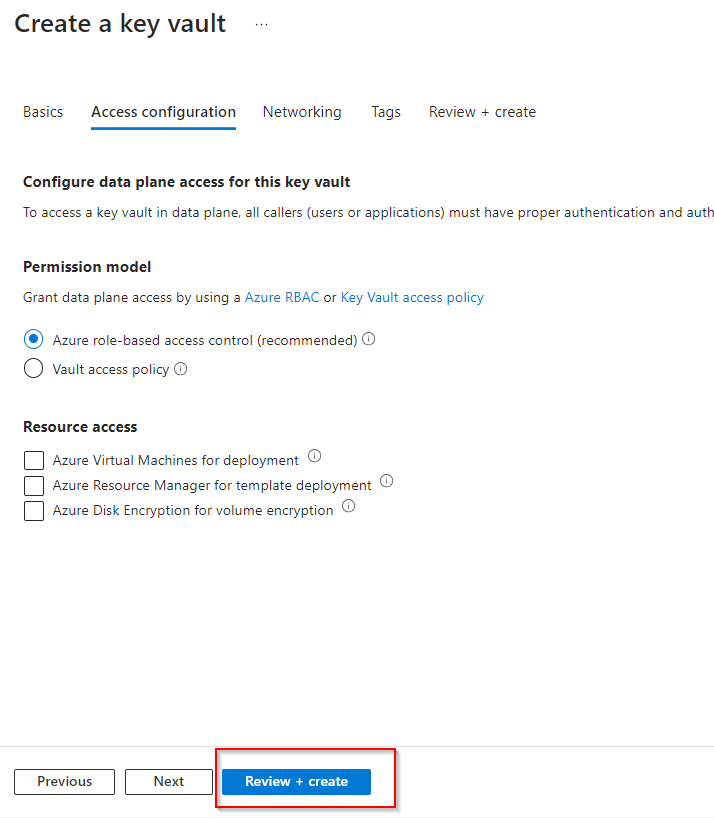
**Wait for the validation checks to complete and then select Create.**
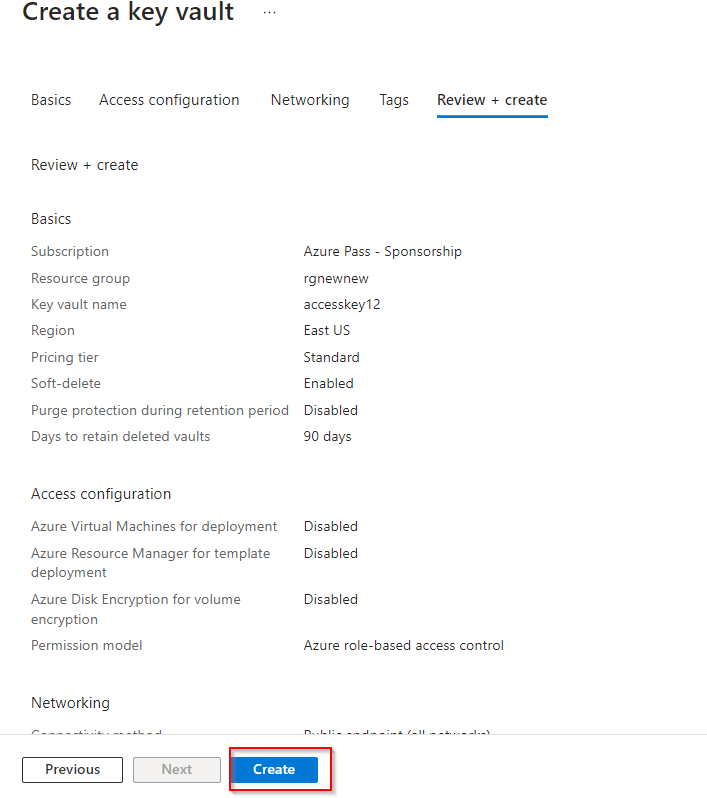
**After the deployment, select Go to resource.**
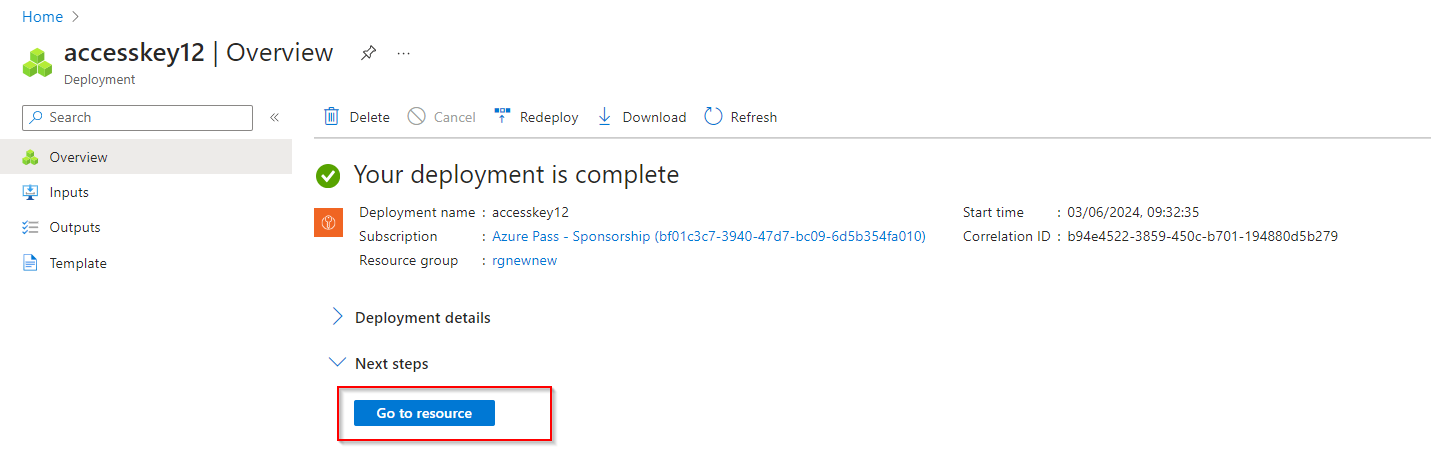
**On the Overview blade ensure both Soft-delete and Purge protection are enabled.**
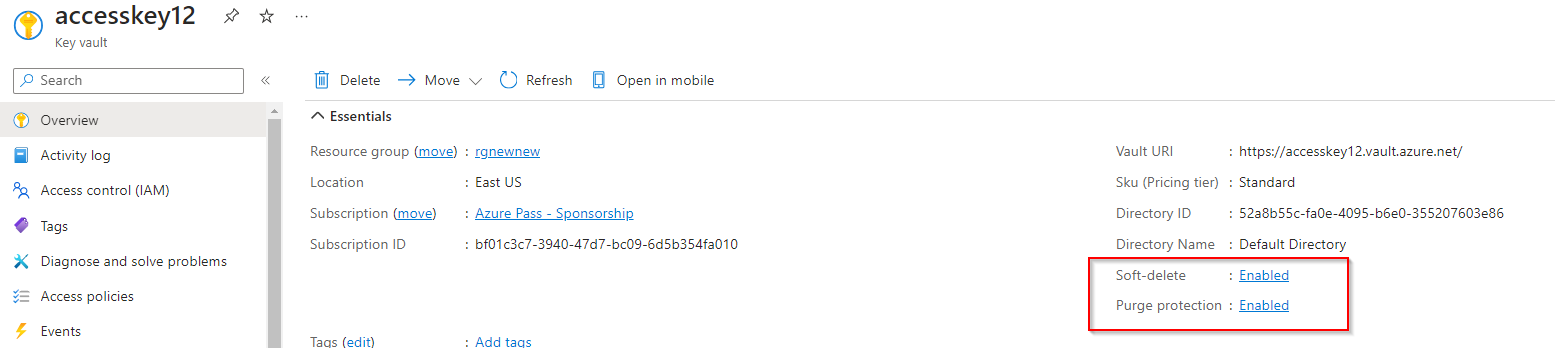
3. **Create a customer-managed key in the key vault.**
**In your key vault, in the Objects section, select the Keys blade.**
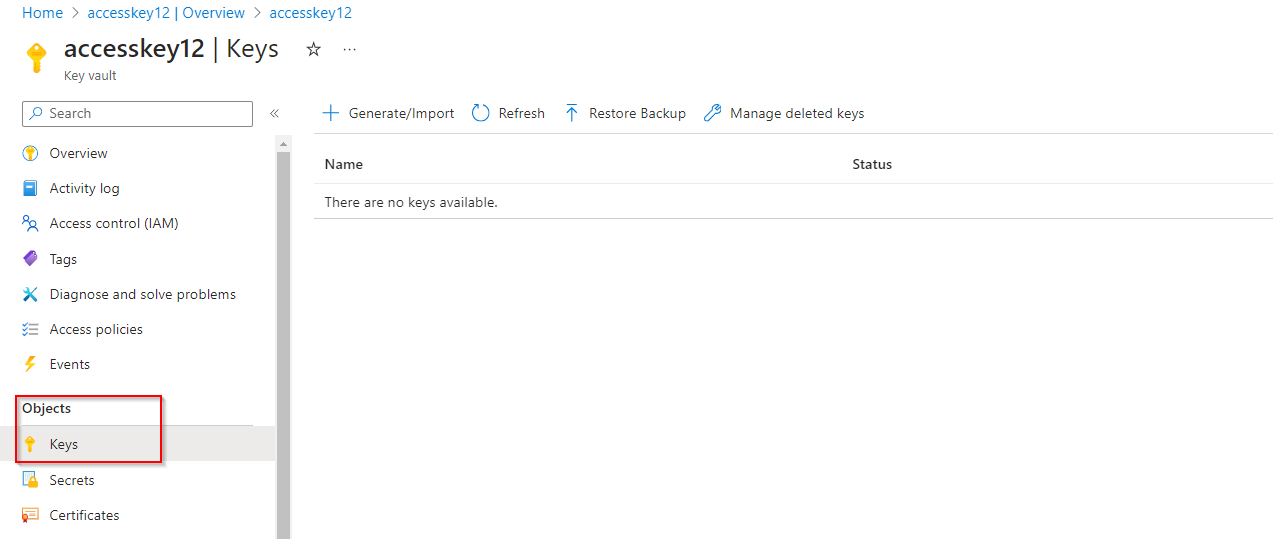
**Select Generate/Import and Name the key.**
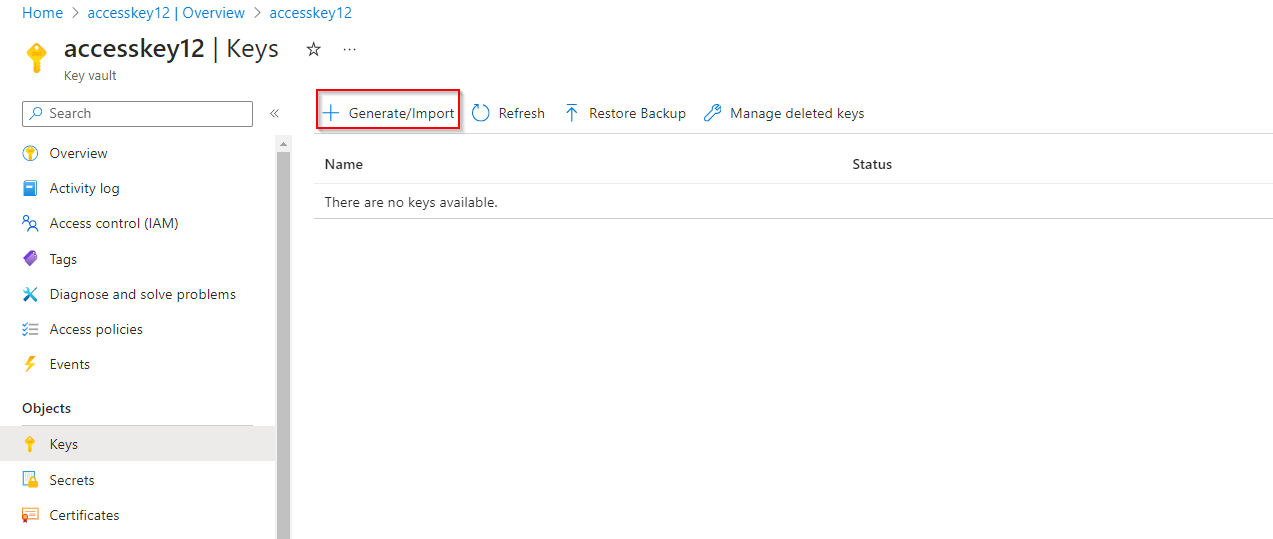
**Take the defaults for the rest of the parameters, and Create the key.**
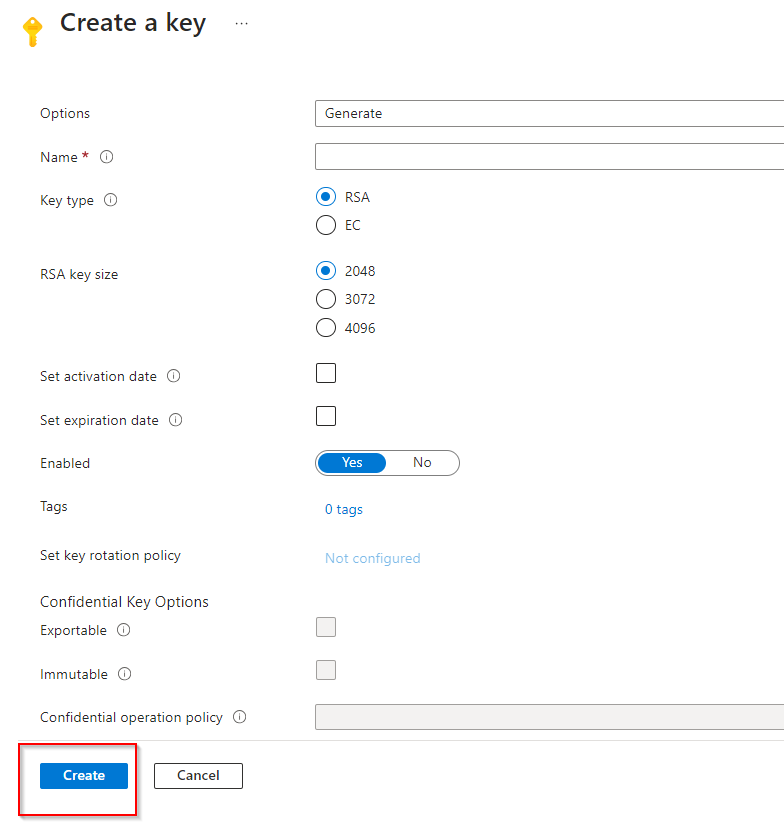
**Configure the storage account to use the customer managed key in the key vault**
1. **Before you can complete the next steps, you must assign the Key Vault Crypto Service Encryption User role to the managed identity.**
**In the portal, search for and select Resource groups.**
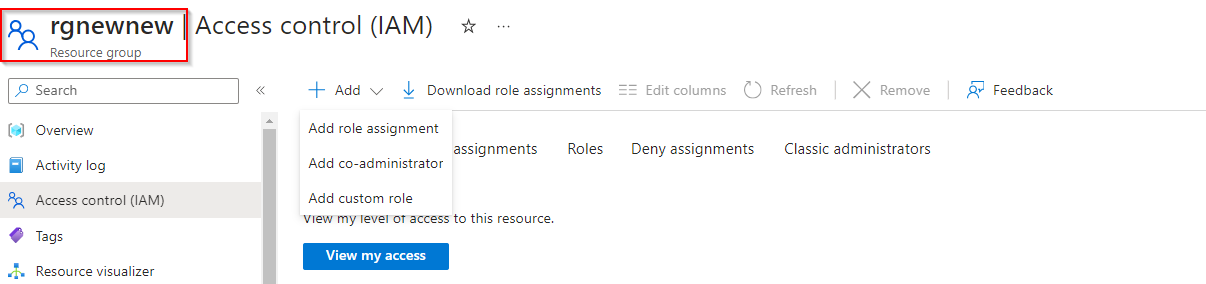
**Select your resource group, and then the Access Control (IAM) blade.**
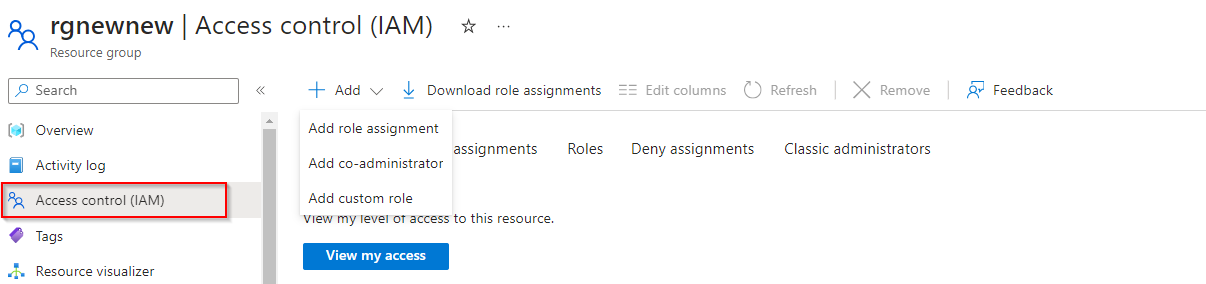
**Select Add role assignment (center of the page).**
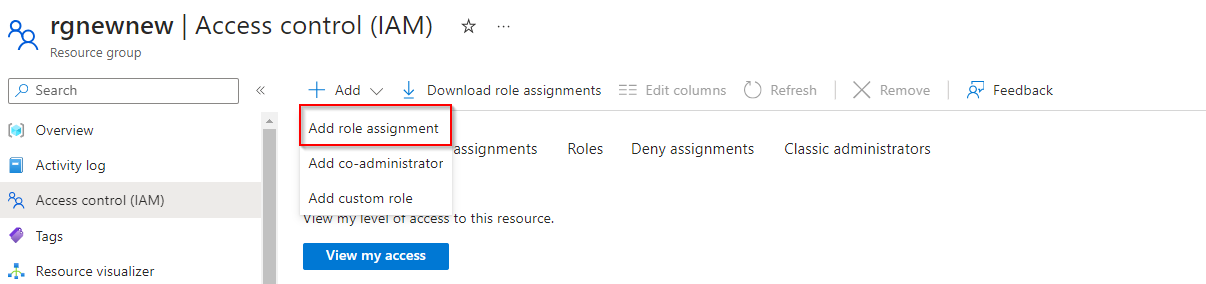
**On the Job functions roles page, search for and select the Key Vault Crypto Service Encryption User role.**
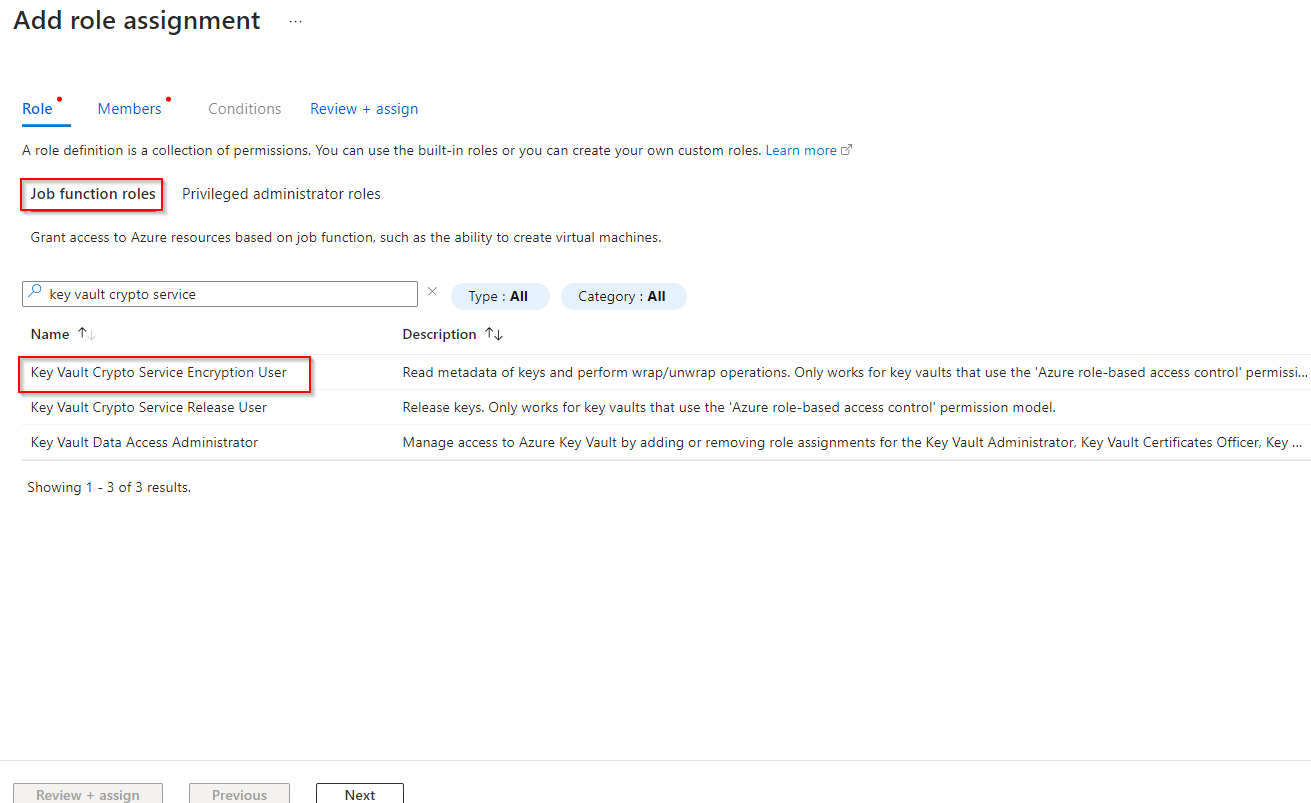
**On the Members page, select Managed identity.**
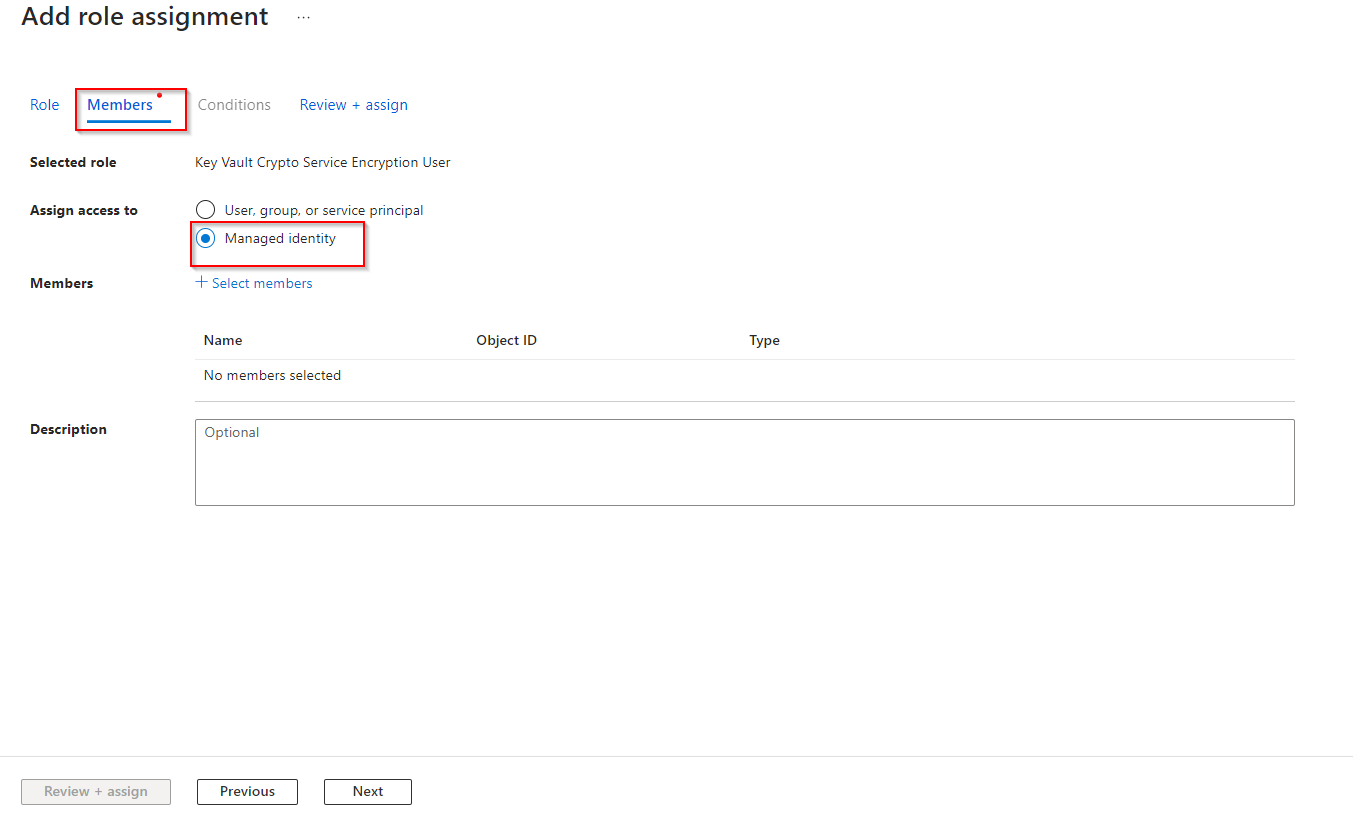
**Select Select members, in the Managed identity drop-down select User-assigned managed identity.**
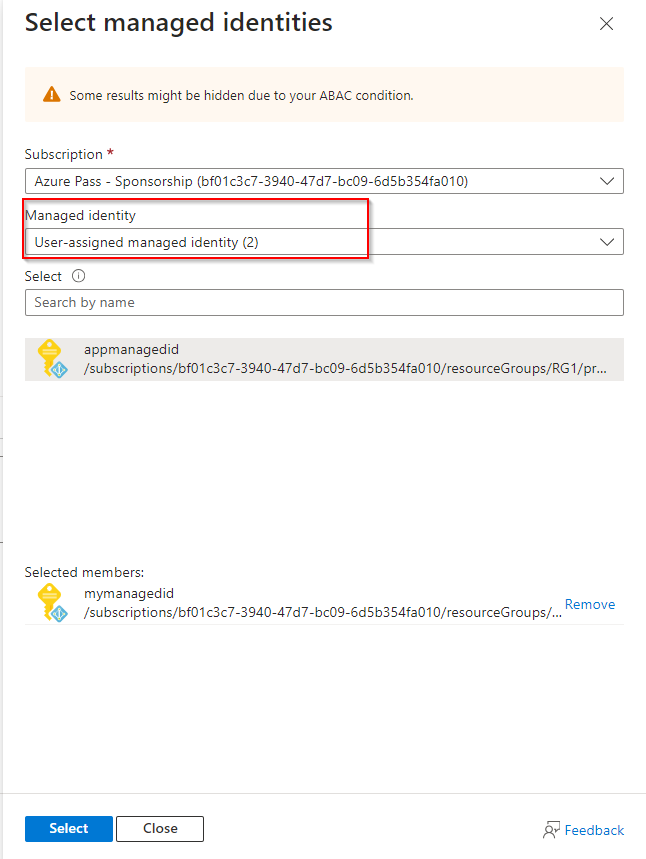
**Select your managed identity.**
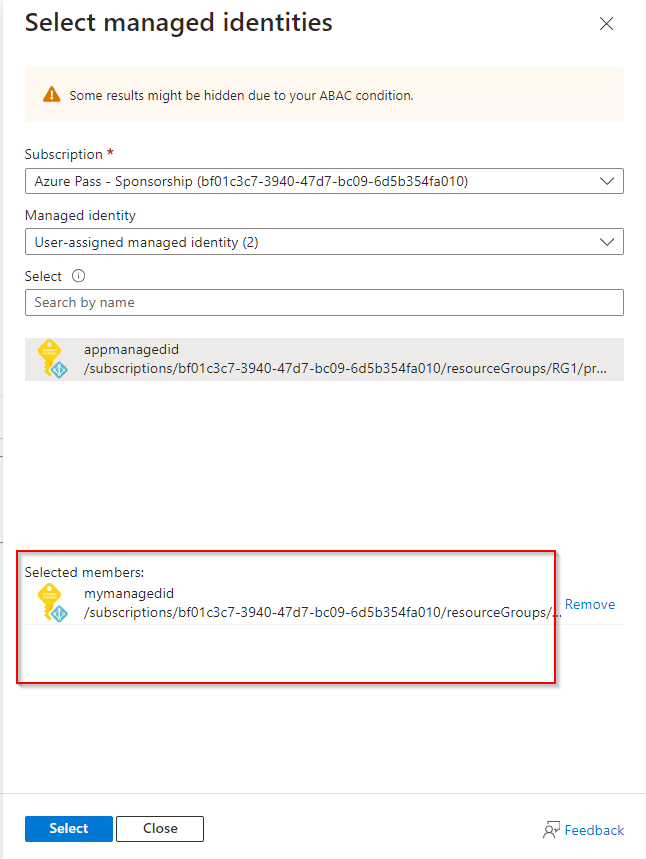
**Click Select and then Review + assign.**
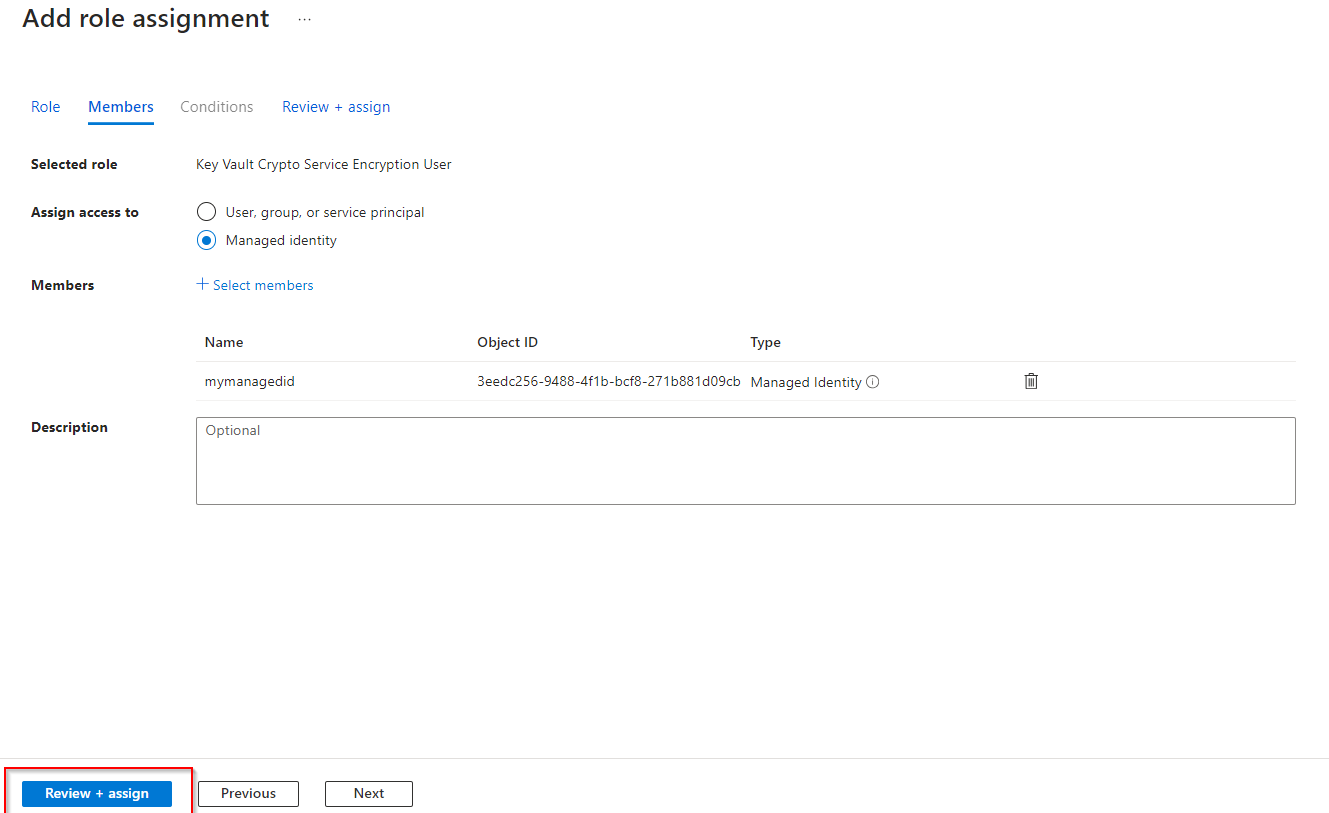
**Select Review + assign a second time to add the role assignment.**
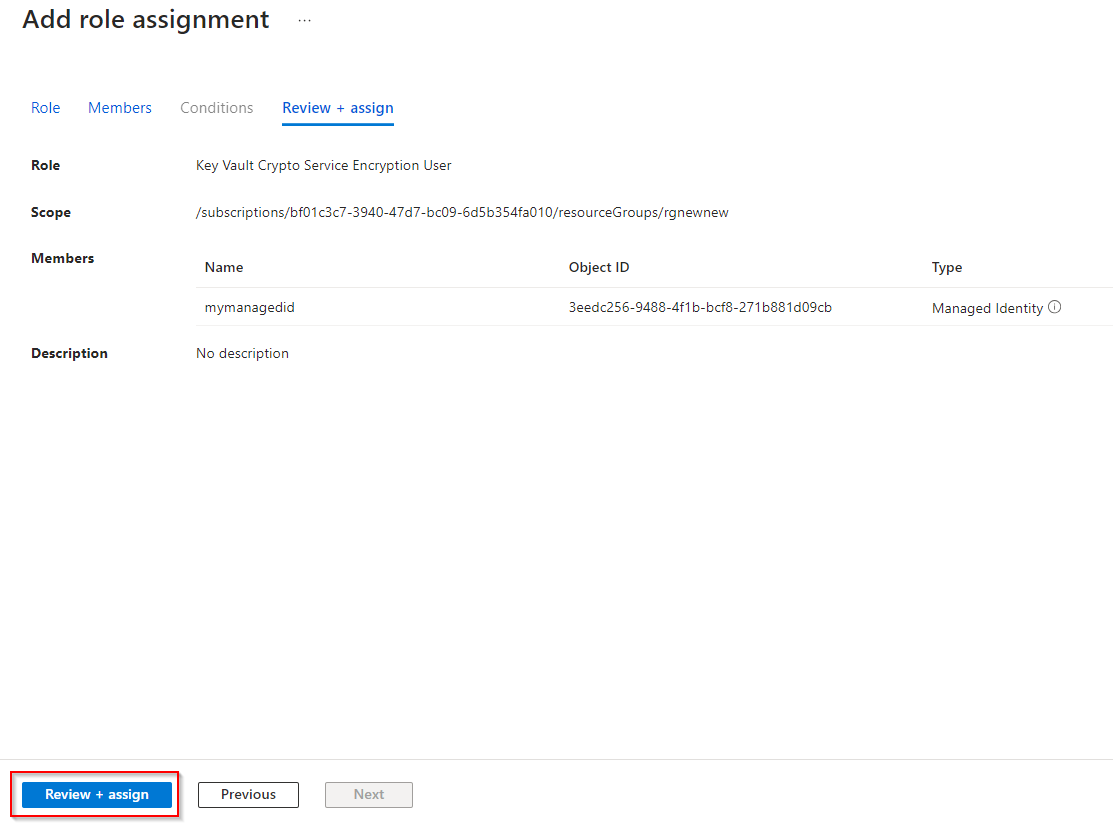
2. **Configure the storage account to use the customer managed key in your key vault. **
**Return to your the storage account.**
**In the Security + networking section, select the Encryption blade.**
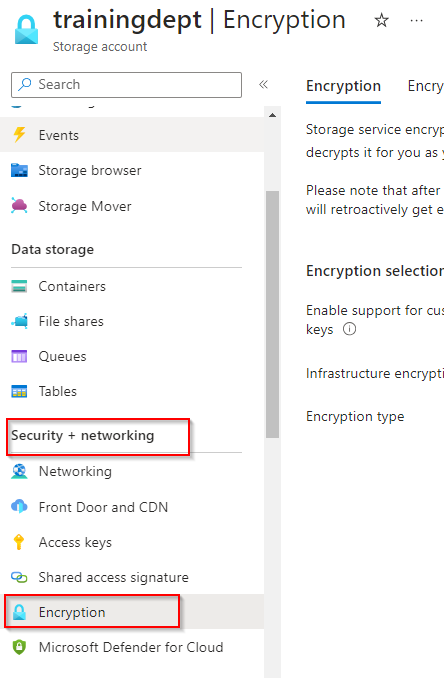
**Select Customer-managed keys.**
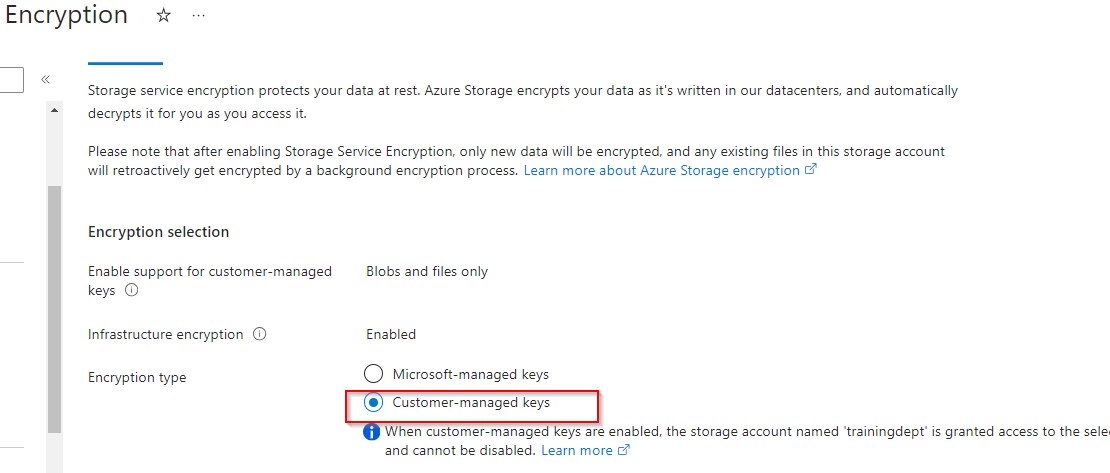
**Select a key vault and key. Select your key vault and key.**
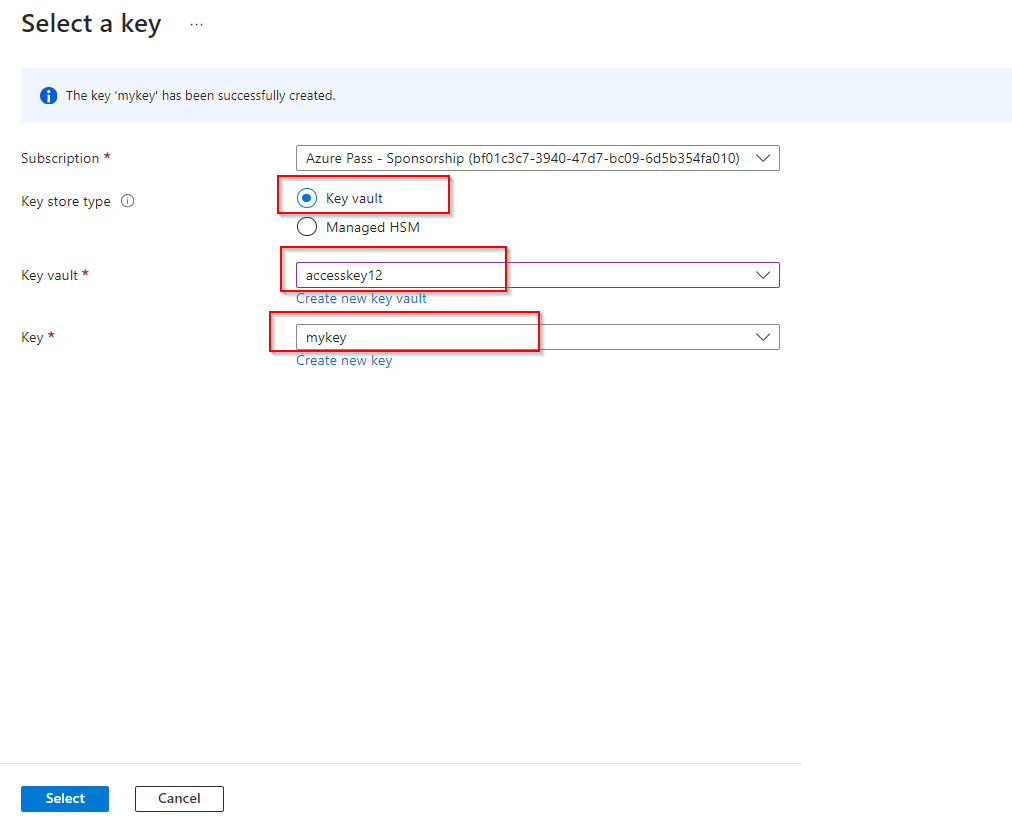
**Select to confirm your choices.**
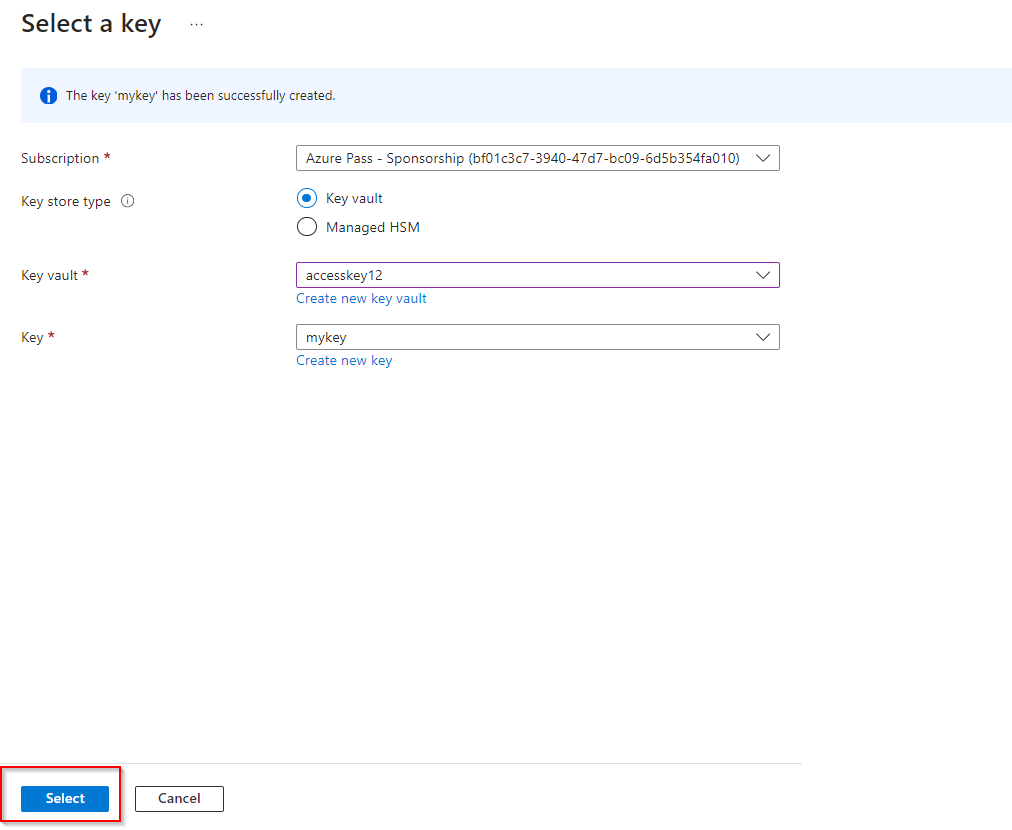
**Ensure the Identity type is User-assigned.**
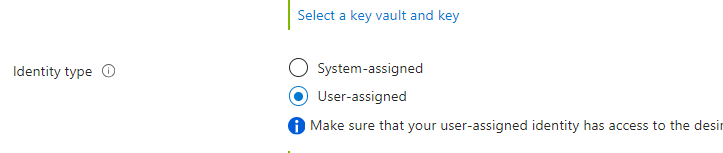
**Select an identity.**
**Select your managed identity then select Add.**
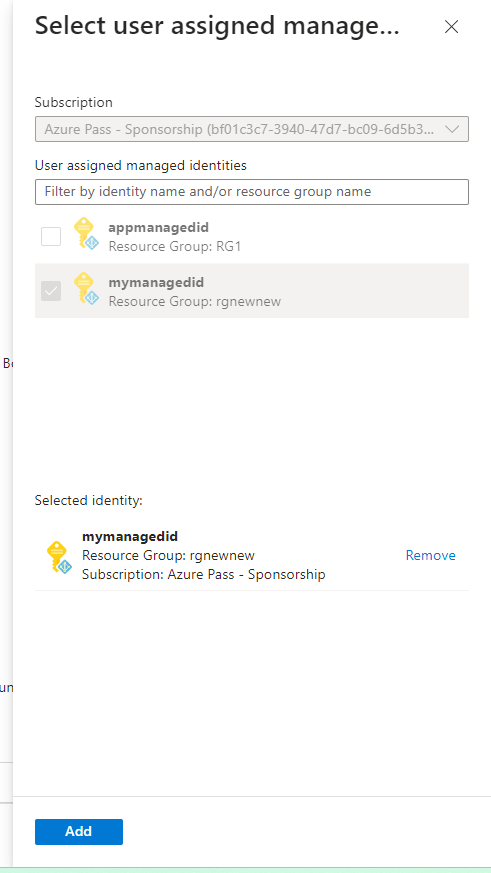
**Save your changes.**
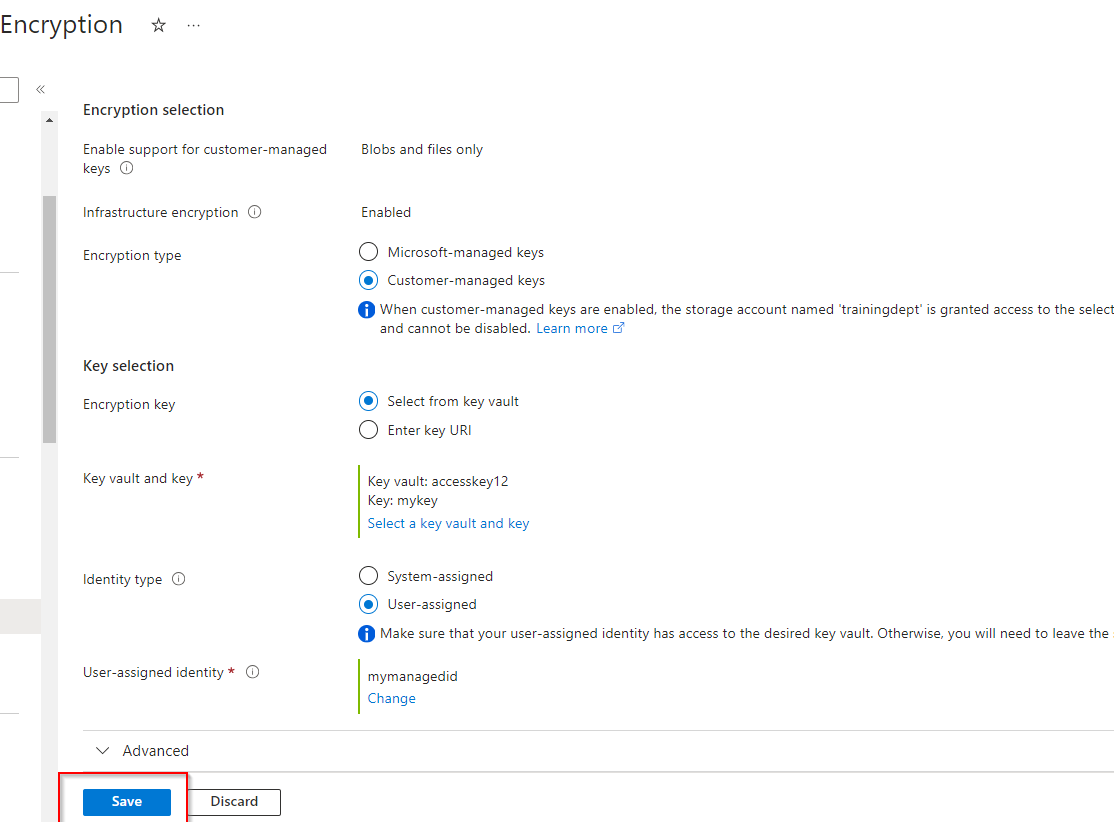
**Configure an time-based retention policy and an encryption scope.**
1. **The developers require a storage container where files can’t be modified, even by the administrator. **
**Navigate to your storage account.**
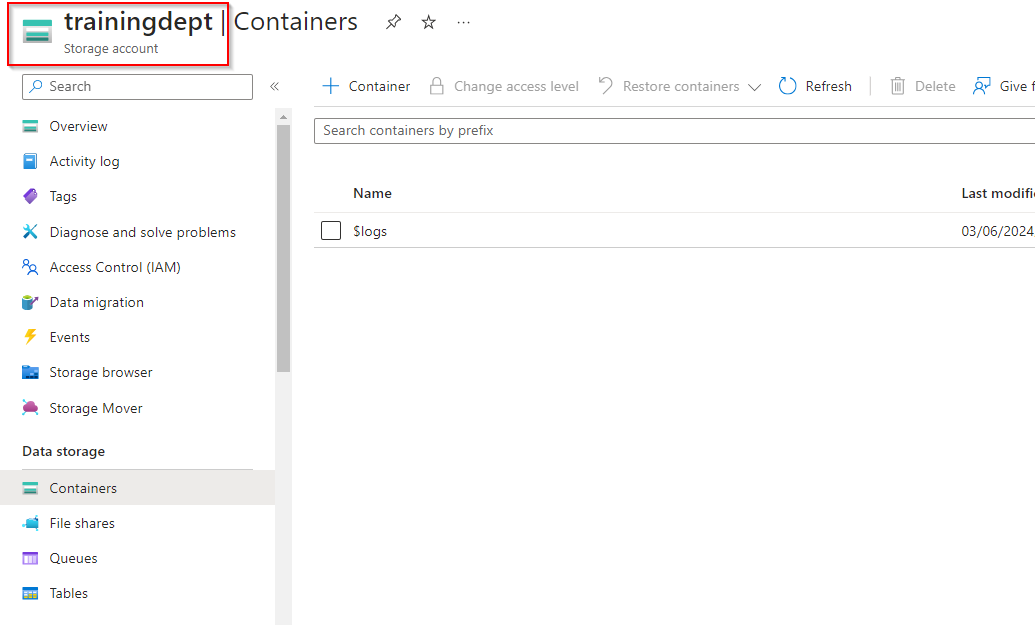
**In the Data storage section, select the Containers blade.**
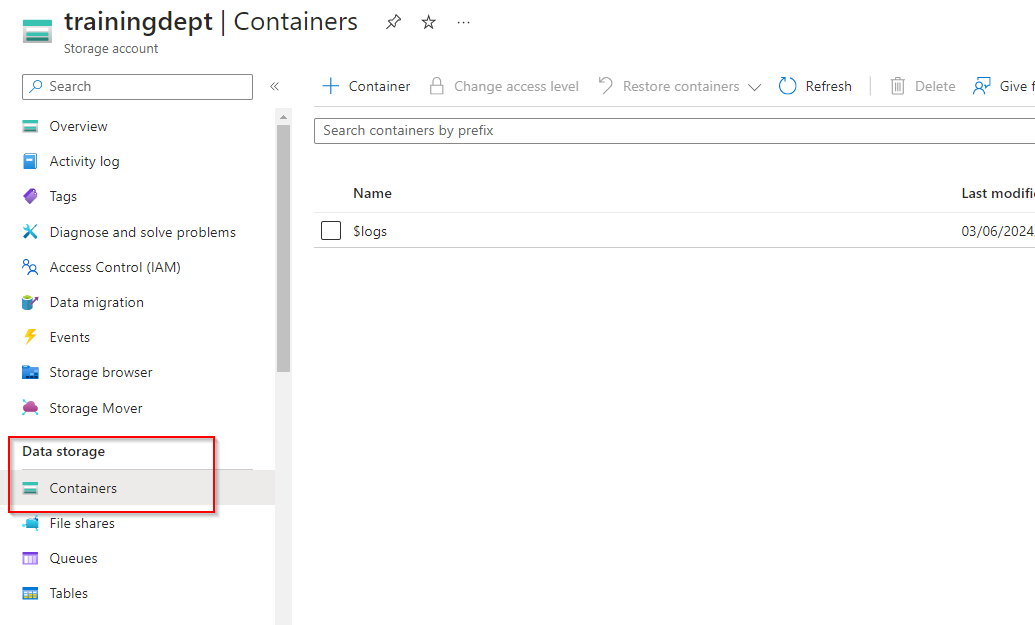
**Create a container called hold. Take the defaults. Be sure to Create the container.**
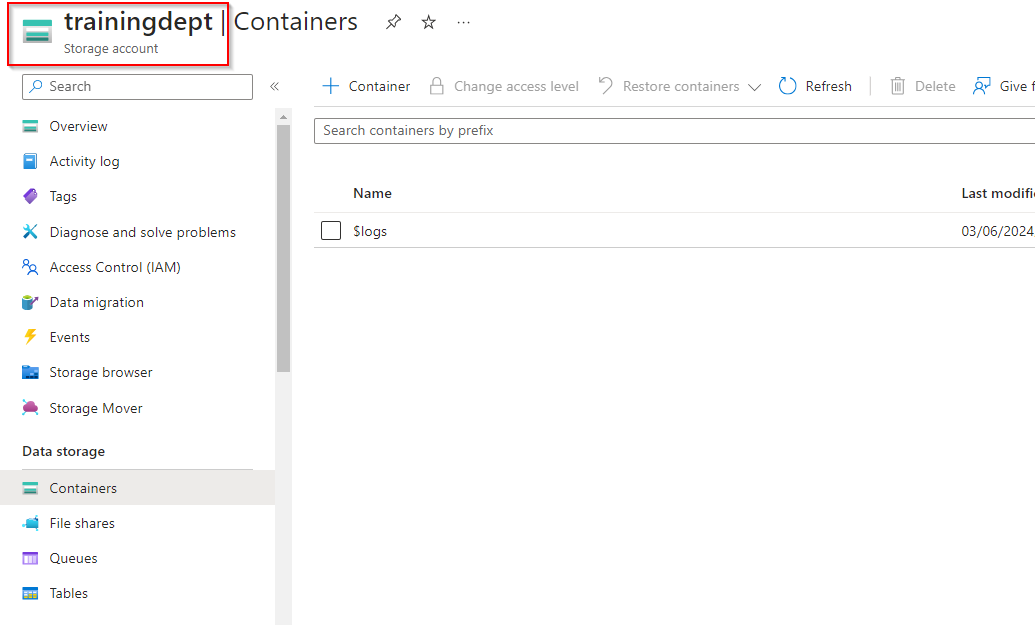
**Upload a file to the container.**
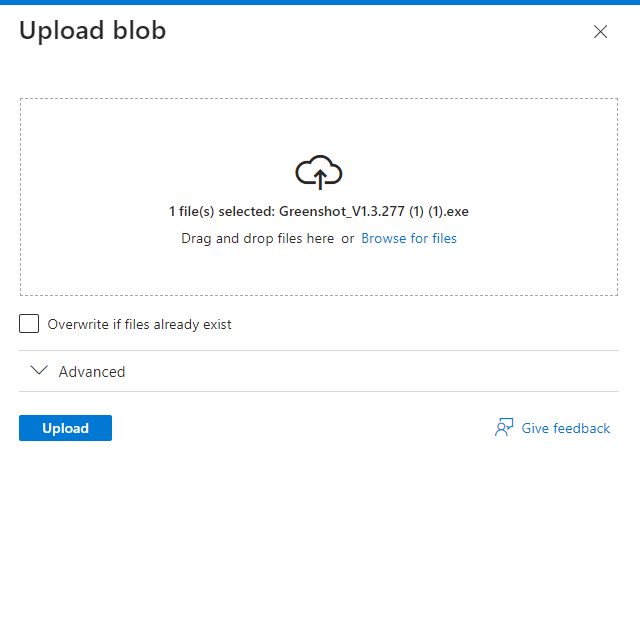
**In the Settings section, select the Access policy blade.**
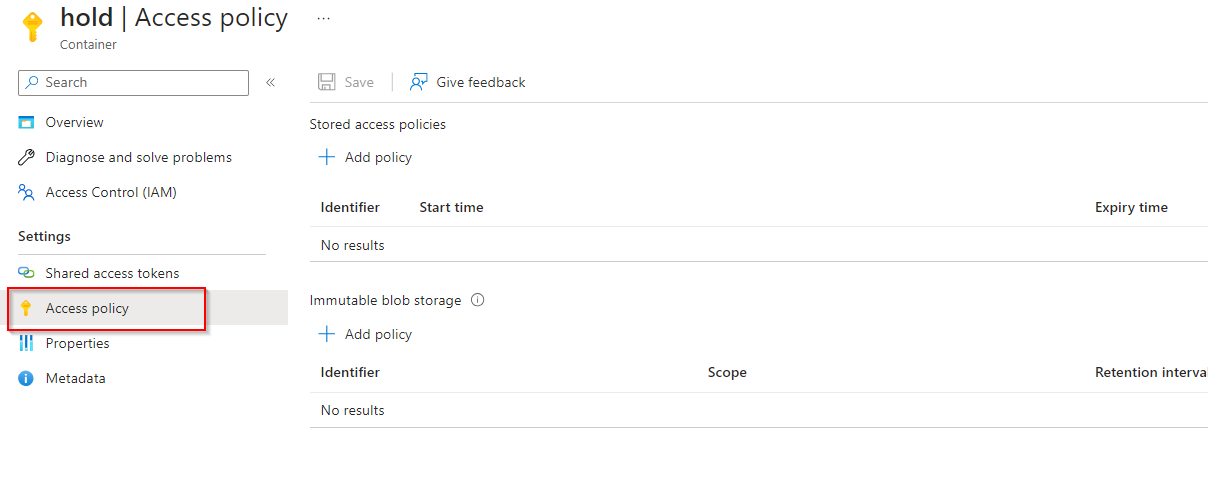
**In the Immutable blob storage section, select + Add policy.**
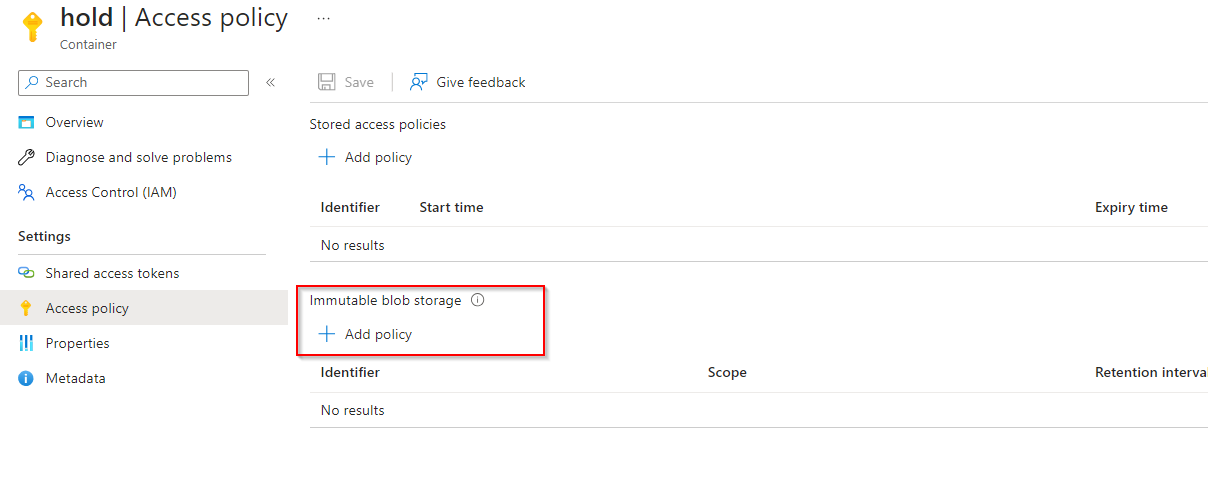
**For the Policy type, select time-based retention.**
**Set the Retention period to 5 days.**
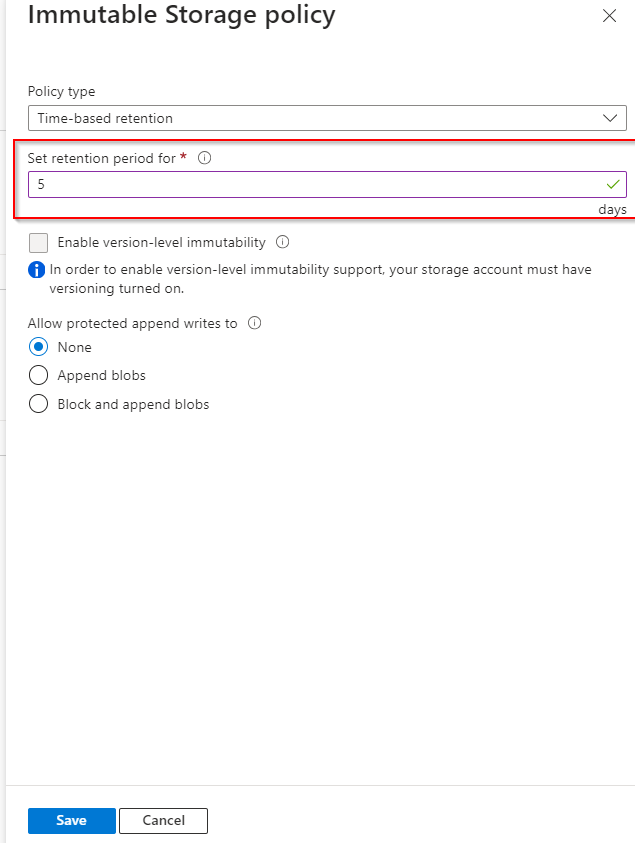
**Be sure to Save your changes.**
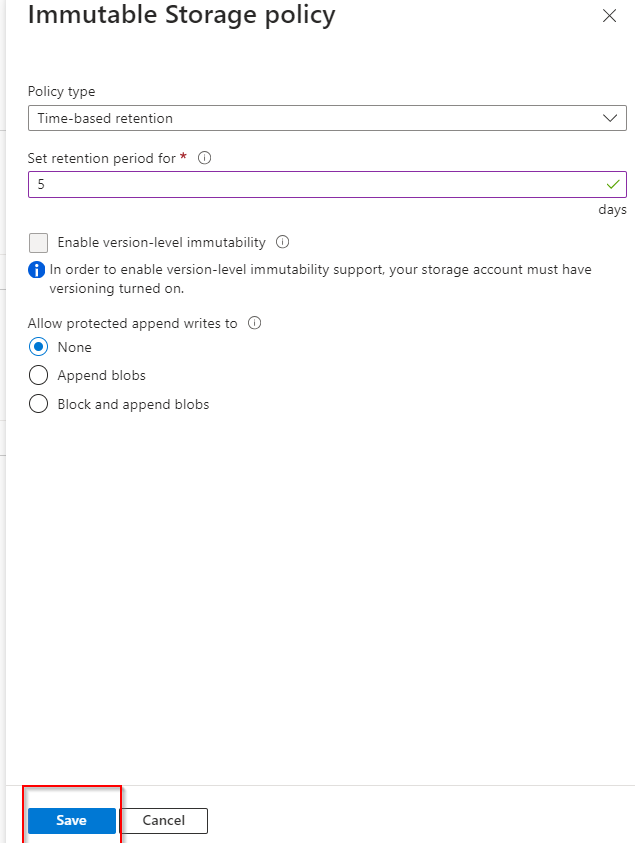
**Try to delete the file in the container.**
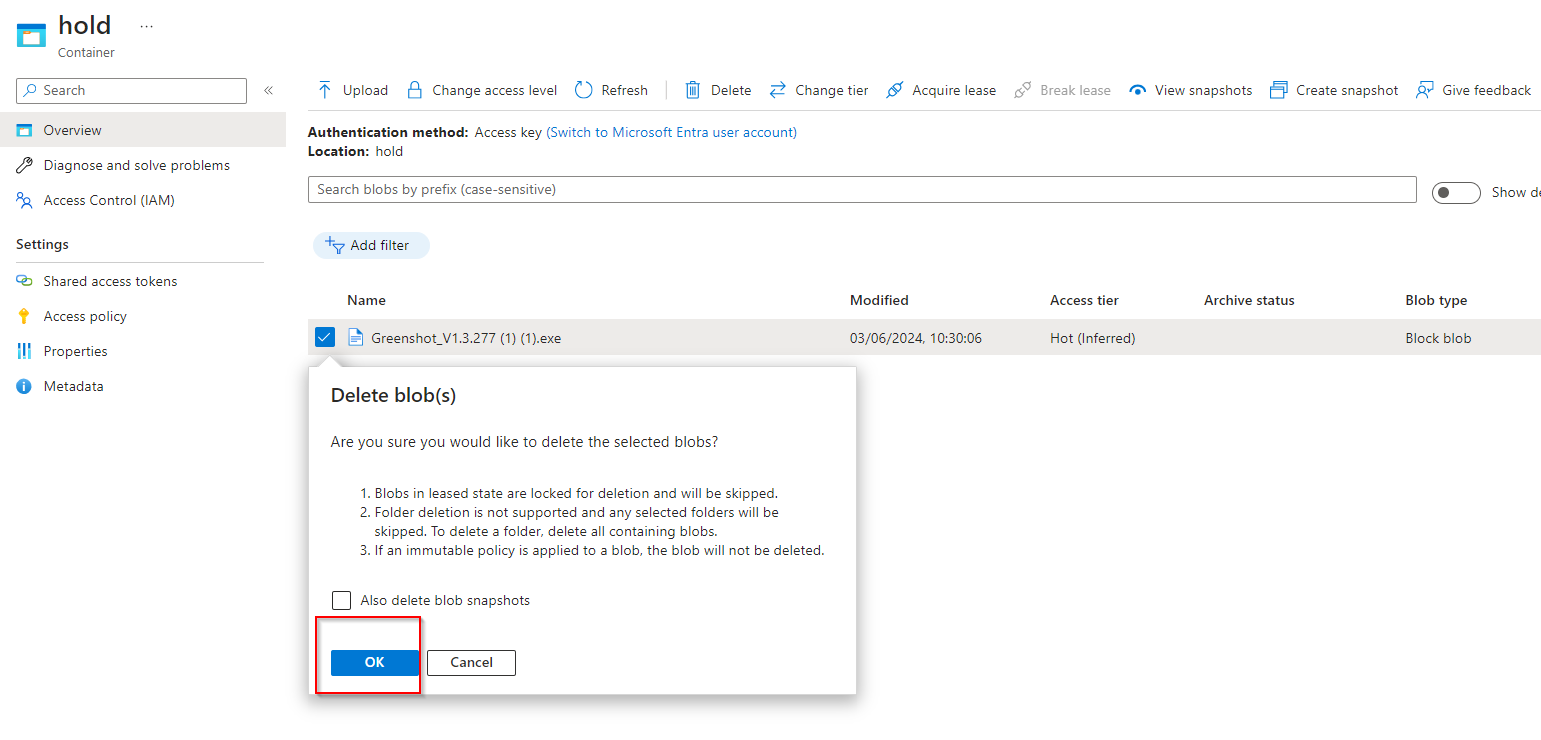
**Verify you are notified failed to delete blobs due to policy.**
2. **The developers require an encryption scope that enables infrastructure encryption. **
**Navigate back to your storage account.**
**In the Security + networking blade, select Encryption.**
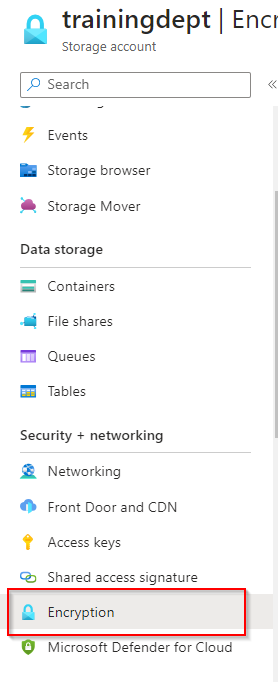
**In the Encryption scopes tab, select Add.**
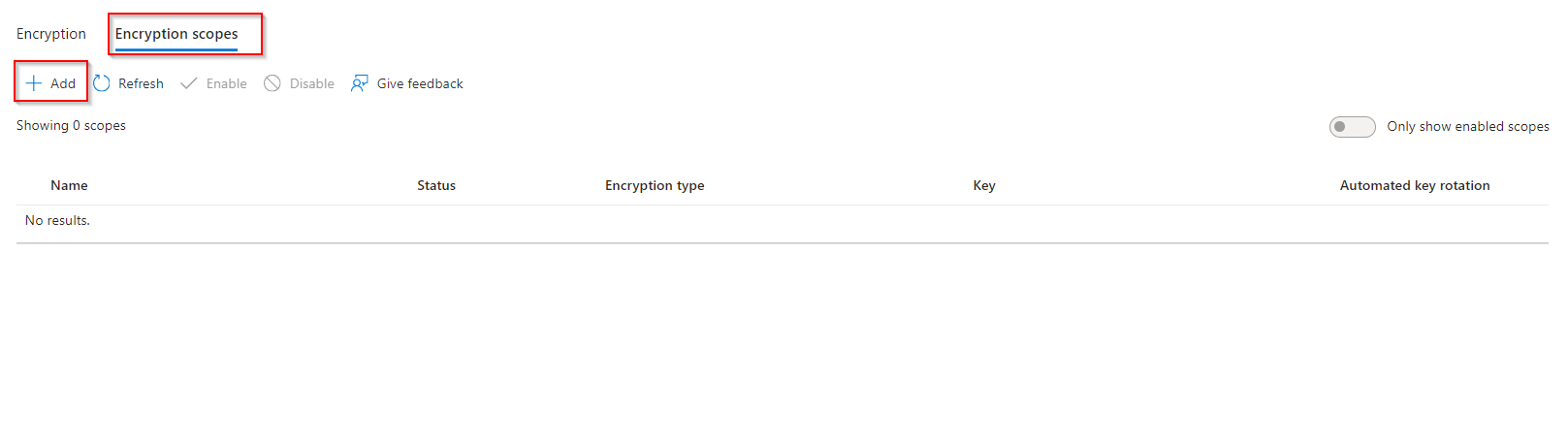
**Give your encryption scope a name.**
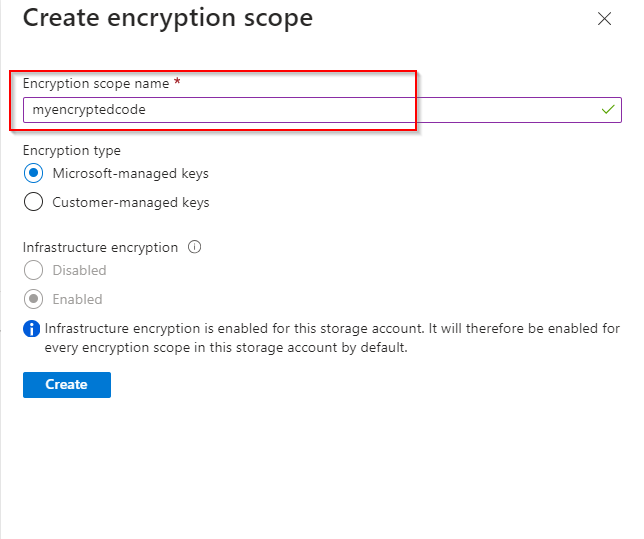
**The Encryption type is Microsoft-managed key.**
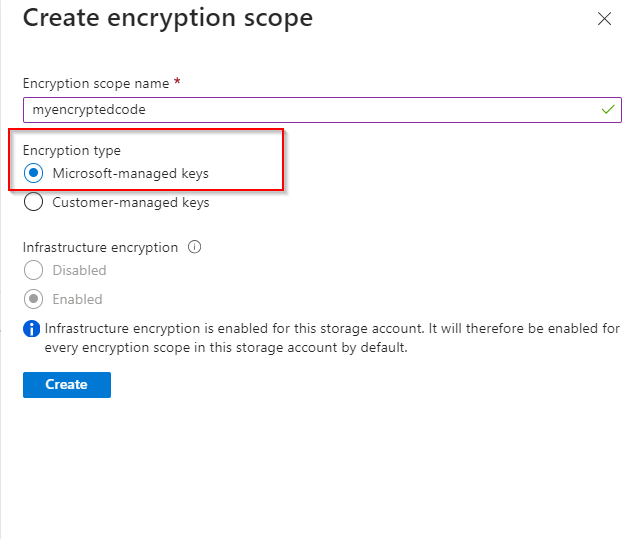
**Set Infrastructure encryption to Enable.**
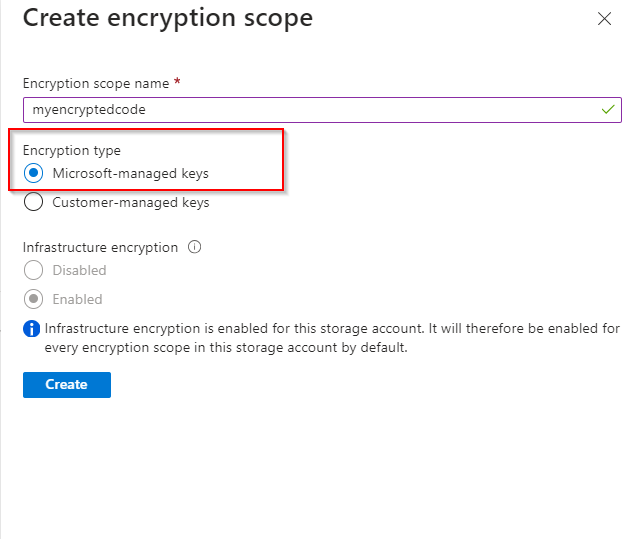
**Create the encryption scope.**
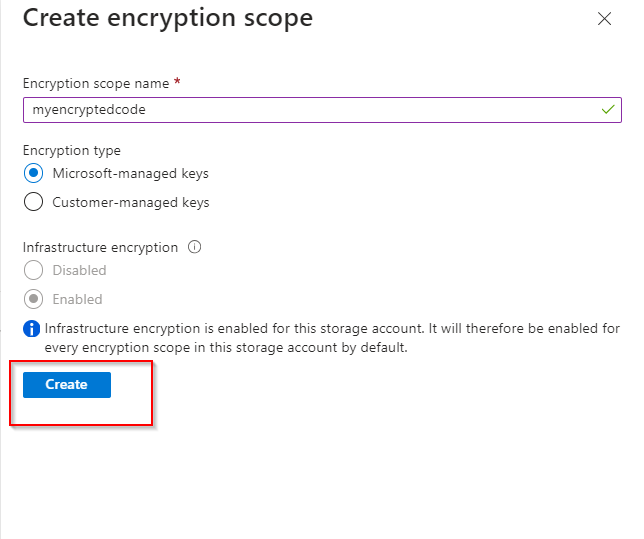
**Return to your storage account and create a new container.**
**Notice on the New container page, there is the Name and Public access level.
Notice in the Advanced section you can select the Encryption scope you created and apply it to all blobs in the container.**
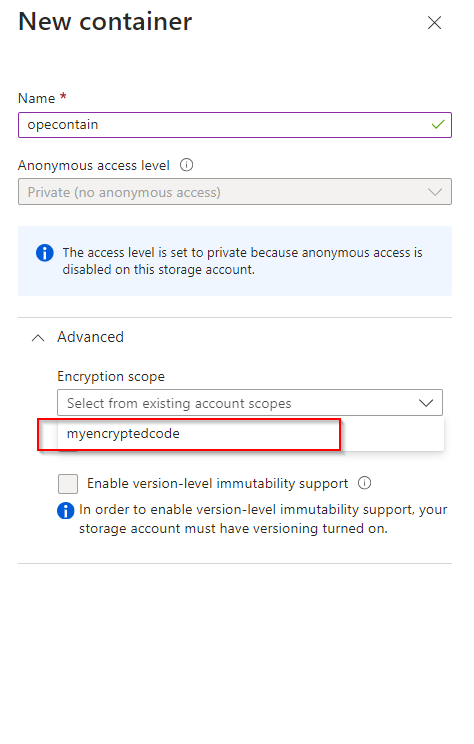
| opsyog |
1,874,796 | Mengenal Konsep MVC di Laravel: Panduan Lengkap untuk Pemula | Oke, teman-teman, kita akan membahas konsep MVC (Model-View-Controller) di Laravel secara lebih... | 0 | 2024-06-03T00:56:50 | https://dev.to/yogameleniawan/mengenal-konsep-mvc-di-laravel-panduan-lengkap-untuk-pemula-1h5o | laravel, programming |
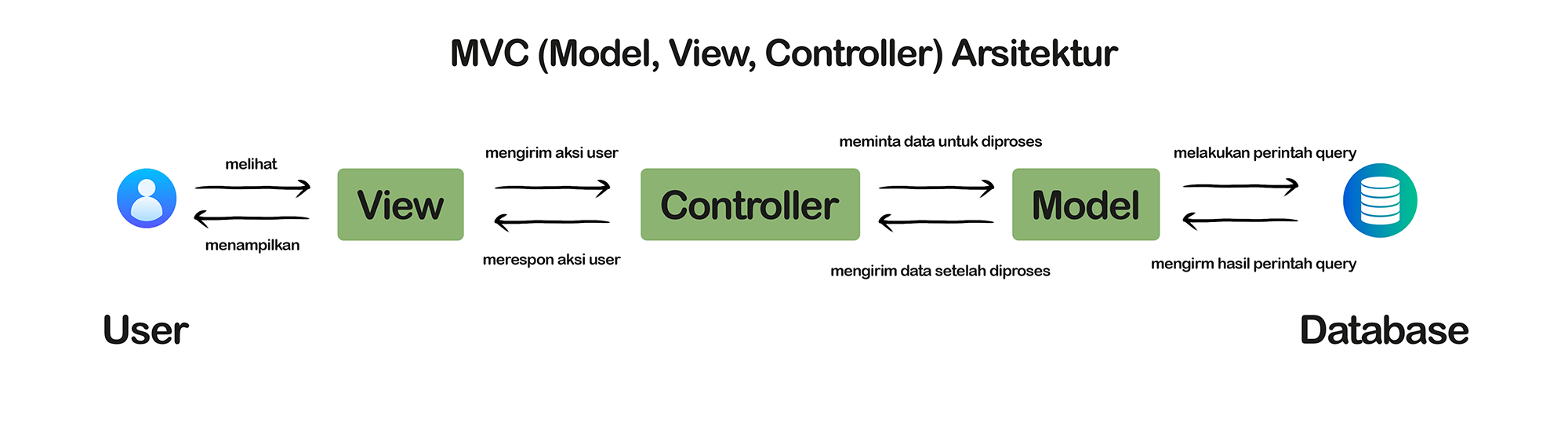
Oke, teman-teman, kita akan membahas konsep MVC (Model-View-Controller) di Laravel secara lebih detail dan panjang. MVC adalah pola desain arsitektur yang memisahkan aplikasi menjadi tiga komponen utama: Model, View, dan Controller. Ini membantu dalam menjaga kode tetap terorganisir dan memudahkan pengembangan, pemeliharaan, dan skalabilitas aplikasi. Mari kita lihat masing-masing komponen secara mendalam:
### 1. Model (M)
Model adalah bagian dari aplikasi yang mengelola data dan logika bisnis. Di Laravel, Model biasanya adalah kelas Eloquent yang berinteraksi dengan database. Model bertanggung jawab untuk mengambil, menyimpan, memperbarui, dan menghapus data dari database. Selain itu, Model juga mengatur relasi antar tabel dalam database.
**Contoh Implementasi Model:**
```php
<?php
namespace App\Models;
use Illuminate\Database\Eloquent\Model;
class User extends Model
{
// Nama tabel di database, jika berbeda dengan nama model
protected $table = 'users';
// Primary key dari tabel
protected $primaryKey = 'id';
// Kolom yang bisa diisi secara massal
protected $fillable = ['name', 'email', 'password'];
// Hidden attributes (biasanya untuk keamanan)
protected $hidden = ['password'];
// Relasi one-to-many dengan model Post
public function posts()
{
return $this->hasMany('App\Models\Post');
}
}
?>
```
### 2. View (V)
View adalah bagian dari aplikasi yang bertanggung jawab untuk menampilkan data kepada pengguna. Di Laravel, View biasanya ditulis menggunakan Blade, templating engine yang kuat dan mudah digunakan. Blade memungkinkan kita untuk menggunakan kontrol struktur seperti loops dan kondisi, serta menampilkan data yang dikirim dari Controller.
**Contoh Implementasi View:**
```html
<!-- resources/views/users/index.blade.php -->
<!DOCTYPE html>
<html>
<head>
<title>Daftar User</title>
</head>
<body>
<h1>Daftar User</h1>
<ul>
@foreach ($users as $user)
<li>{{ $user->name }} - {{ $user->email }}</li>
@endforeach
</ul>
</body>
</html>
```
### 3. Controller ©
Controller adalah bagian dari aplikasi yang menangani permintaan HTTP dari pengguna, berinteraksi dengan Model untuk mendapatkan data, dan mengirimkan data tersebut ke View. Controller bertindak sebagai penghubung antara Model dan View. Di Laravel, Controller biasanya ditempatkan di folder app/Http/Controllers.
**Contoh Implementasi Controller:**
```php
<?php
namespace App\Http\Controllers;
use App\Models\User;
use Illuminate\Http\Request;
class UserController extends Controller
{
// Method untuk menampilkan daftar pengguna
public function index()
{
// Mengambil semua data pengguna dari model
$users = User::all();
// Mengirim data pengguna ke view
return view('users.index', ['users' => $users]);
}
// Method untuk menampilkan form pendaftaran pengguna baru
public function create()
{
return view('users.create');
}
// Method untuk menyimpan pengguna baru ke database
public function store(Request $request)
{
// Validasi data yang dikirim dari form
$validatedData = $request->validate([
'name' => 'required|max:255',
'email' => 'required|email|unique:users',
'password' => 'required|min:6',
]);
// Membuat pengguna baru
User::create($validatedData);
// Redirect ke halaman daftar pengguna
return redirect('/users');
}
}
?>
```
### Alur Kerja MVC
Mari kita lihat bagaimana MVC bekerja dalam sebuah skenario umum, seperti menampilkan daftar pengguna:
1. **Request**: Pengguna mengunjungi URL yang ditentukan, misalnya /users.
2. **Routing**: Laravel mengarahkan request tersebut ke Controller yang sesuai berdasarkan definisi routing di routes/web.php.
3. **Controller**: Controller menerima request, memprosesnya, dan mungkin meminta data dari Model.
4. **Model**: Jika data diperlukan, Controller meminta Model untuk mengambil data dari database.
5. **View**: Controller mengirim data yang diperoleh dari Model ke View. View ini kemudian di-render menjadi HTML dan dikirim kembali ke pengguna sebagai response.
**Contoh Routing:**
```php
// routes/web.php
use App\Http\Controllers\UserController;
// Route untuk menampilkan daftar pengguna
Route::get('/users', [UserController::class, 'index']);
// Route untuk menampilkan form pendaftaran pengguna baru
Route::get('/users/create', [UserController::class, 'create']);
// Route untuk menyimpan pengguna baru
Route::post('/users', [UserController::class, 'store']);
```
### Keuntungan Menggunakan MVC
1. **Separation of Concerns**: Membagi aplikasi menjadi tiga komponen utama (Model, View, Controller) membuat kode lebih terorganisir dan memisahkan logika bisnis dari tampilan.
2. **Reusability**: Komponen dalam MVC bisa digunakan kembali di berbagai bagian aplikasi, mengurangi duplikasi kode.
3. **Maintainability**: Kode yang terorganisir memudahkan pemeliharaan dan pembaruan aplikasi.
4. **Scalability**: Memisahkan komponen membuat aplikasi lebih mudah dikembangkan dan diskalakan.
### Penutup
Dengan memahami konsep MVC di Laravel, teman-teman bisa mengembangkan aplikasi web yang lebih terstruktur, efisien, dan mudah dikelola. Meskipun pada awalnya mungkin terlihat kompleks, dengan latihan dan pemahaman yang mendalam, MVC akan sangat membantu dalam mengembangkan aplikasi yang lebih profesional dan berkualitas tinggi. Selamat berkoding, dan semoga aplikasi teman-teman semakin keren! | yogameleniawan |
1,874,792 | Developers Need Practical Kubernetes Experience | In today’s swiftly evolving tech landscape, programmers must constantly stay abreast of the latest... | 0 | 2024-06-03T00:50:06 | https://dev.to/coddicat/developers-need-practical-kubernetes-experience-24oh | kubernates, devops, programming, microservices | In today’s swiftly evolving tech landscape, programmers must constantly stay abreast of the latest technological advancements and methodologies. Mastery in developing and deploying distributed systems is no longer optional; it’s essential. Understanding the entire lifecycle — from development and CI/CD to Kubernetes cluster configuration, deployment, monitoring, and alerting — is critical for any developer aiming to thrive in this environment.
## The Importance of Kubernetes in Distributed Systems
Distributed systems, by nature, require robust management of multiple interdependent components across different servers. Kubernetes excels in this environment by automating deployment, scaling, and operations of application containers across clusters of hosts. This makes it an invaluable tool for developers looking to streamline their applications’ operations and ensure reliability and scalability.
## The Gap Between DevOps and Developers
Large organizations often have dedicated DevOps teams tasked with fine-tuning Kubernetes environments, which inadvertently might limit direct involvement from developers in these processes. This segregation can create a gap in understanding and hands-on experience for many developers who are otherwise involved in the broader development lifecycle.
## The Power of Practical Application
While theoretical knowledge gained from courses and books is invaluable, it pales in comparison to the insights and understanding developed through practical application. This belief drives me to initiate personal projects to explore new technologies and tools actively. For instance, to deepen my Kubernetes knowledge, I developed [CicadaKillerWasp.com](https://cicadakillerwasp.com), a simple interactive quest that leads users through a series of steps culminating in a reward.
## Kubernetes: More Than Just Tooling
Understanding Kubernetes involves more than just learning how to use its tools. It requires a deep understanding of the principles behind containerization, orchestration, and microservices architectures. Here are some deeper insights into the components and tools that every Kubernetes practitioner should know:
- **Containerization with Docker:** Before diving into Kubernetes, one must understand containerization with Docker. Containers package up the code and all its dependencies so the application runs quickly and reliably from one computing environment to another.
- **Microservices Architecture:** Kubernetes is particularly effective in a microservices architecture where small, independent services communicate over well-defined APIs. Understanding this architecture is crucial as it affects how applications are developed and deployed within Kubernetes.
- **Stateful vs Stateless Applications:** Kubernetes handles stateless applications — those not saving data to a server or disk — differently from stateful ones, which maintain a continuous state. Learning to manage these different types of applications within Kubernetes is essential for effective orchestration.
- **Monitoring and Logging:** Tools like Prometheus and Grafana are crucial for monitoring the health of applications running on Kubernetes. They provide insights into applications and infrastructure which can be vital for troubleshooting and optimizing performance.
- **Security Practices:** Security within Kubernetes involves more than just managing permissions. It includes securing container images, managing sensitive data through secrets, and protecting traffic with network policies.
## Choosing the Right Deployment Environment
For deploying this project, I opted for DigitalOcean over AWS due to its cost-effectiveness and simplicity. Unlike AWS, which often involves complex permissions settings, DigitalOcean offers a straightforward setup process that allowed me to focus more on the project’s specifics without getting bogged down by infrastructural complexities.
## Juggling Time: Project and Personal Life
The development of CicadaKillerWasp.com took about two months, fitting around my full-time job. Nights and weekends became my primary working times — thankfully, my supportive wife made this possible.
## Deep Dive into Essential Kubernetes Tools and Components
Kubernetes is not only a platform for managing containerized applications but also an ecosystem rich with tools that enhance and simplify various aspects of application and infrastructure management. Here’s an in-depth look at some of the key tools and components essential for anyone working with Kubernetes:
**1. Lens and K9s**
- **Lens:** Often described as the Kubernetes IDE, Lens provides a comprehensive, user-friendly GUI that allows developers to manage Kubernetes clusters. It integrates with other essential tools like Prometheus for real-time monitoring and has capabilities for viewing logs, managing resources, and accessing a terminal within Kubernetes pods.
- **K9s:** This tool offers a terminal-based UI to interact with your Kubernetes clusters. It focuses on simplicity and productivity, providing a real-time view of cluster activity and resource usage. It is ideal for those who prefer a command-line approach.
**2. Helm Charts**
Helm is the package manager for Kubernetes. It allows users to define, install, and upgrade even the most complex Kubernetes application. Charts, Helm’s packaging format, provide a set of files that describe a related set of Kubernetes resources. Helm simplifies the deployment and management of applications on Kubernetes and is indispensable for managing releases and rollbacks.
**3. Redis**
Redis, a powerful in-memory data structure store, is used as a database, cache, and message broker. In Kubernetes, Redis can be used to handle sessions, cache data, and perform real-time analysis. Its performance is critical in distributed systems where quick data access and high availability are required.
**4. Prometheus and the Kube-Prometheus Stack**
Prometheus is an open-source monitoring system with a dimensional data model, flexible query language, and real-time alerting. The Kube-Prometheus stack leverages Prometheus’s capabilities and adds a collection of resources to provide easy to operate end-to-end Kubernetes cluster monitoring. It includes Grafana dashboards for a rich visualization of the metrics collected.
**5. Ingress-Nginx**
Ingress-Nginx is an Ingress controller for Kubernetes using NGINX as a reverse proxy and load balancer. It provides an external access point to your services, routing traffic to internal Kubernetes endpoints, and is crucial for managing access to applications running within a cluster.
**6. Grafana/Loki Stack**
Grafana is an open-source platform for monitoring and observability. It is often paired with Loki, a log aggregation system inspired by Prometheus. Together, they provide capabilities to query, visualize, alert on, and understand your metrics and log data from Kubernetes.
**7. Cert-Manager**
Cert-Manager is a native Kubernetes certificate management controller. It can help automate certificate management in cloud-native environments, providing a way to acquire certificates from a variety of issuing sources and ensuring certificates are valid and up to date.
**8. Messaging Systems (NATS, Kafka, RabbitMQ)**
- **NATS:** A lightweight, high-performance messaging system for microservices architectures, ideal for scenarios requiring high speed and scalability.
- **Kafka:** A distributed streaming platform that can handle trillions of events a day. Initially conceived as a messaging queue, Kafka is based on an abstraction of a distributed commit log.
- **RabbitMQ:** Widely used open-source message broker software that supports multiple messaging protocols.
**9. GitHub Workflow Actions**
GitHub Actions make it easy to automate all your software workflows with CI/CD. Build, test, and deploy your code right from GitHub. They are particularly useful in Kubernetes environments for automating deployment and management tasks directly from a GitHub repository.
**10. ConfigMaps and Secrets**
- **ConfigMaps:** Allow you to decouple configuration artifacts from image content to keep containerized applications portable. They store non-confidential data in key-value pairs and can be consumed by pods or provide configuration data for system components.
- **Secrets:** Manage the storage and handling of sensitive information, such as passwords, OAuth tokens, and SSH keys. Using Kubernetes secrets is essential for maintaining the security of your applications.
Setting up the entire Kubernetes infrastructure from scratch — defining the deployment pipelines, setting up services, and ensuring proper load balancing and fault tolerance. This practical experience was invaluable, proving that real-world application is the best teacher. The project also incorporated essential Kubernetes tools and practices such as:
- **Using Cron Jobs for Automation:** Automation within Kubernetes, such as scheduling backups or maintenance jobs, can be managed through Cron Jobs, which execute tasks at scheduled times.
- **Managing Data with Persistent Volumes:** Understanding how Kubernetes handles data storage through Persistent Volume Claims (PVCs) is crucial for applications that require data persistence.
These tools and components are fundamental for effectively managing and operating Kubernetes environments. They not only enhance productivity and efficiency but also ensure robust, scalable, and secure application deployments. For developers and DevOps professionals alike, familiarity with these tools will provide a strong foundation in modern cloud-native technology landscapes.
## Concluding Thoughts
My experience with [CicadaKillerWasp.com](https://cicadakillerwasp.com) reinforced the idea that mastering Kubernetes is not just about handling its complexity but also about leveraging its full potential to build better, more resilient applications. For developers willing to dive deep and embrace the hands-on experience, Kubernetes offers a path to significantly enhance their capabilities and contribute more effectively to their projects and teams. In the realm of software development, where change is the only constant, embracing technologies like Kubernetes is not just an option — it’s a necessity. | coddicat |
1,874,791 | Ten Things I’ve Learned After Ten Years at Vets Who Code | Reflecting on a decade of leading Vets Who Code, here are ten valuable lessons learned about coding, mentorship, and personal growth. | 0 | 2024-06-03T00:49:39 | https://dev.to/vetswhocode/ten-things-ive-learned-after-ten-years-at-vets-who-code-37dp | veterans, coding, mentorship | ---
title: "Ten Things I’ve Learned After Ten Years at Vets Who Code"
published: true
description: "Reflecting on a decade of leading Vets Who Code, here are ten valuable lessons learned about coding, mentorship, and personal growth."
tags: Veterans, Coding, Mentorship
cover_image: https://res.cloudinary.com/vetswhocode/image/upload/v1717373882/ten-years_v9cvdv.jpg
# published_at: 2024-06-03 00:46 +0000
---
*Originally posted [here](https://vetswhocode.io/blogs/ten-things-learned-after-10-years-at-vets-who-code).*
## Introduction
As I reflect on a decade of leading Vets Who Code, the journey from a 27-year-old founder to a seasoned executive director has been nothing short of extraordinary. Over the years, I have accumulated a wealth of knowledge through my own career and by helping countless veterans and military spouses transition into software engineering. Here are ten valuable lessons I've learned during this time.
## Document Your Journey
One of the most powerful tools for growth is documenting your journey. Whether you're self-taught, boot camp trained, or college-educated, sharing your learning process publicly can accelerate your career. By doing so, you not only track your progress but also inspire and educate others. This transparency builds a robust community around you.
## Pair Programming
Engage in pair programming as much as possible. This collaborative approach accelerates your learning curve and prepares you for real-world job scenarios. The shared experience of problem-solving and code review enhances your skills and fosters a deeper understanding of coding practices.
## Network Early and Often
Start networking from day one, regardless of your current expertise. Building relationships within the industry is crucial for long-term success. Attend meetups, join online communities, and stay connected with peers even after landing a job. Networking opens doors to opportunities and keeps you informed about industry trends.
## The Value of Mentorship
Mentorship often outweighs formal education in today’s world of democratized learning resources. Finding a mentor who can guide you through the complexities of the tech industry can provide invaluable insights and accelerate your professional development.
## Build Solutions, Not Just Projects
Focus on creating solutions that address real-world problems rather than merely completing projects. This mindset shift helps you gain practical, impactful experience and demonstrates your ability to apply knowledge in meaningful ways. Solutions-oriented thinking also makes you more attractive to potential employers.
## Depth Over Breadth
When starting out, it's more beneficial to dive deep into a specific area rather than spreading yourself too thin. Mastering a particular skill set or technology can make you a subject matter expert, which is more advantageous than having superficial knowledge across many topics.
## Understand Language Ecosystems
Delve into the ecosystems of the programming languages you use. Knowing the tools, libraries, and best practices within these ecosystems allows you to work more efficiently and solve problems more effectively. This comprehensive understanding can distinguish you from other developers.
## Cultivate Adaptability
The tech industry is in a constant state of flux. Being adaptable is crucial to staying relevant and resilient amidst these changes. Embrace new technologies, methodologies, and perspectives to continually evolve with the industry.
## Commit to Continuous Learning
Never stop learning. The rapid pace of technological advancements means there’s always something new to master. Commit to ongoing education through courses, certifications, and staying updated with the latest industry developments.
## Focus on Personal Growth
Prioritize your growth by leveraging the best tools and practices within your field. Understand your strengths and weaknesses, and continually work on improving your skill set. Personal growth fuels professional success and ensures you remain at the top of your game.
## Conclusion
My journey with Vets Who Code has been a blend of challenges, triumphs, and continuous learning. These ten lessons encapsulate the essence of what I've discovered over the past decade. Whether you're a budding software engineer or a seasoned veteran, I hope these insights will guide and inspire you on your path to success.
**Join Us in Making a Difference**
If you believe in the power of coding to transform lives and want to support veterans and military spouses in their journey into tech, consider making a donation to Vets Who Code. Your contribution can help us provide the resources, mentorship, and training necessary to bridge the gap between military service and successful tech careers. [Donate Now](https://vetswhocode.io/donate)
Together, we can continue to empower those who have served our country to achieve their full potential in the tech industry. | jeromehardaway |
1,874,790 | Building a Personal Finance Application with Python | Introduction In this digital era, managing one's personal finances has become more... | 0 | 2024-06-03T00:33:02 | https://dev.to/kartikmehta8/building-a-personal-finance-application-with-python-525e | webdev, javascript, beginners, programming | ## Introduction
In this digital era, managing one's personal finances has become more important than ever. With the rapid growth of technology, building a personal finance application using Python has become an efficient and popular choice for many. Python, a widely-used high-level programming language, offers a variety of libraries and tools that make the development process easier and faster. In this article, we will explore the advantages, disadvantages, and features of building a personal finance application with Python.
## Advantages
1. **Flexibility and scalability:** Python's built-in data structures, flexibility, and object-oriented programming make it easy to handle large amounts of financial data and adapt the application as needed.
2. **User-friendly interface:** Python's syntax is simple and easy to understand, making it more user-friendly for both developers and users.
3. **Integration with third-party tools:** Python's vast library of modules and packages allows easy integration with different financial tools and services, making it a convenient choice for developers.
## Disadvantages
1. **Performance issues:** Python is an interpreted language, which can lead to slower performance compared to compiled languages like C++ and Java.
2. **Security concerns:** As with any digital financial application, security measures need to be carefully implemented to protect sensitive user data from cyber threats.
## Features
1. **Budget tracking and management:** The application can help users track their expenses and create personalized budgets to manage their finances better.
2. **Bill reminders and payment scheduling:** The application can send notifications for upcoming bills and allow users to schedule payments directly through the app.
3. **Investment tracking:** Users can track their investments, view performance charts, and receive alerts for changes in the market.
### Example Code for Budget Tracking
```python
import pandas as pd
# Sample data representing user expenses
data = {
'Date': ['2023-01-01', '2023-01-02', '2023-01-03'],
'Category': ['Groceries', 'Rent', 'Utilities'],
'Amount': [25.50, 1200, 175.75]
}
# Create a DataFrame
expenses = pd.DataFrame(data)
# Calculate total expenses
total_expenses = expenses['Amount'].sum()
print(f"Total Expenses: ${total_expenses:.2f}")
```
This simple Python script uses the pandas library to manage and calculate expenses, demonstrating how easily financial data can be handled.
## Conclusion
In conclusion, building a personal finance application with Python offers a combination of simplicity, flexibility, and features that make it a strong contender in the world of financial technology. However, it is essential to consider the potential drawbacks and ensure proper security measures are in place to protect user data. With proper planning and development, a well-built personal finance application with Python can provide users with a powerful tool for managing their finances effectively. | kartikmehta8 |
1,874,787 | #DataScience #Python #Analytic | S | 0 | 2024-06-03T00:23:30 | https://dev.to/eric_pimentel/datascience-python-analytic-4p2e | S | eric_pimentel | |
1,874,785 | Opus App Review -A Passive $529/day In 60 Seconds! | Opus App Review : Features Auto-Promote Any WarriorPlus Affiliate Link in 60 Seconds… Enjoy The... | 0 | 2024-06-03T00:15:41 | https://dev.to/alauddin10/opus-app-review-a-passive-529day-in-60-seconds-25f8 | opus, opusreview, opusfeatures, opusapp | Opus App Review : Features
Auto-Promote Any WarriorPlus Affiliate Link in 60 Seconds…
Enjoy The Power Of Human-Like A.I…
Built-On The Latest ChatGPT-4O…
Install In 1-Click & You’re Good To Go…
Auto Promote Any WarriorPlus Offer…
Works On All Devices…
Newbie Friendly Interface…
Analytics & Tracking Built-In…
Created For Beginners…
Automatic Traffic Generation…
Biz-In-A-Box Commercial Licence Included…
No Tech Skills Or Experience Needed…
Click Here : https://alauddinreview.com/opus-app-review/
| alauddin10 |
1,873,152 | Building with Supra: Powering Decentralized Applications with Better Data | Introduction The Challenge of Data in Blockchain Supra: Bridging the Data Gap Key Features of... | 0 | 2024-06-03T00:11:54 | https://dev.to/tosynthegeek/building-with-supra-powering-decentralized-applications-with-better-data-5d3c | web3, javascript, blockchain, data | - [Introduction](#a)
- [The Challenge of Data in Blockchain](#b)
- [Supra: Bridging the Data Gap](#c)
- [Key Features of Supra's Data Feeds](#d)
- [Consuming Supra Oracle Price Data Feeds with Ethers and Hardhat](#e)
- [Prerequisites](#f)
- [Setting Up the Environment](#g)
- [Build and Compile your Contract](#h)
- [Deploying and Interacting with the Supra Contract](#i)
- [What's Next?](#j)
# <a id = "a">Introduction </a>
Supra stands as a prominent player in the realm of decentralized oracles, providing a critical service for DeFi applications: secure and reliable data feeds for blockchain environments. This guide delves into Supra's functionalities and explores how it empowers developers to build trust-worthy DeFi applications. Let's dive in.
## <a id = "b">The Challenge of Data in Blockchain </a>
Blockchains, while revolutionary for security and immutability, are isolated ecosystems. This strength becomes a weakness when smart contracts, the engines of DeFi applications, require real-world data to function. External data is crucial for various DeFi use cases:
- **Decentralized Exchanges (DEXs):** Accurate and timely price feeds are essential for DEXs to facilitate fair and efficient token swaps.
- **Lending Protocols:** Reliable data on asset values is necessary for collateralization calculations and risk management in lending and borrowing platforms.
- **Prediction Markets:** External data like sports scores or election results are crucial for settling prediction market contracts.
Existing oracle solutions often face challenges in terms of scalability and security, leaving developers with a gap to bridge when it comes to reliable data access for their DeFi applications.
## <a id = "c">Supra: Bridging the Data Gap </a>
Enter Supra, a next-generation oracle solution, addresses these limitations. Unlike traditional oracles that rely heavily on adding more nodes (horizontal scaling), Supra prioritizes **vertical scaling**. This means Supra focuses on packing more processing power and resources into each individual node within its network. This approach offers several potential advantages for DeFi data delivery:
- **Faster Speeds:** With more powerful nodes, Supra can potentially retrieve and process data significantly faster. This is crucial for real-time needs in DeFi, such as constantly fluctuating cryptocurrency prices or dynamic interest rates.
- **Reduced Latency:** By minimizing the number of communication needed between nodes, vertical scaling can lead to lower latency in data delivery. This translates to less time between when data is requested and when it reaches the smart contract, ensuring applications operate with the most real-time data.
- **Potential Cost Efficiency:** A smaller network of more powerful nodes could translate to lower operating costs for Supra and this would benefit developers by potentially leading to more competitive pricing for data feeds compared to oracles with a larger, horizontally scaled network.
Supra's core strength lies in its **decentralized oracle price feeds**. These oracles act as secure bridges, delivering real-world data to DeFi applications across various on-chain and off-chain scenarios. This ensures the data powering DeFi is accurate and verifiable, a critical requirement for applications relying on real-time information like cryptocurrency prices or market movements.
### <a id = "d">Key Features of Supra's Data Feeds </a>
- **Pull Oracles**: Pull Oracles function like a just-in-time data delivery system for smart contracts. Instead of receiving a constant stream of updates, smart contracts can actively request specific data points from the Supra network whenever they need them, minimizing unnecessary network congestion and lowering gas fees.
- **V1**: Initial version, providing basic on-demand data services.
- **V2**: Enhanced version with improved performance and additional features.
- **Push Oracles**: Not all data needs to be constantly refreshed. Some DeFi applications, like lending protocols that peg interest rates to established benchmarks, can function perfectly with regular data updates. Push Oracles handles this by proactively pushing data updates from the Supra network to smart contracts at predetermined intervals. This is a more efficient approach for situations where real-time data isn't crucial, saving resources and reducing network congestion.
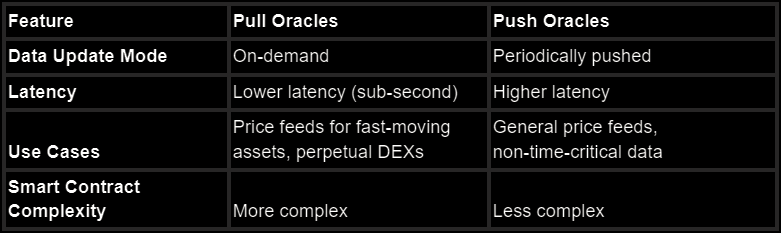
- **Decentralized VRF**
Supra's dVRF is designed to deliver secure, verifiable, and decentralized random number generation, offering DeFi applications a secure and reliable source of random numbers. Smart contracts can leverage this randomness for various purposes, ensuring fairness and transparency in a decentralized ecosystem.
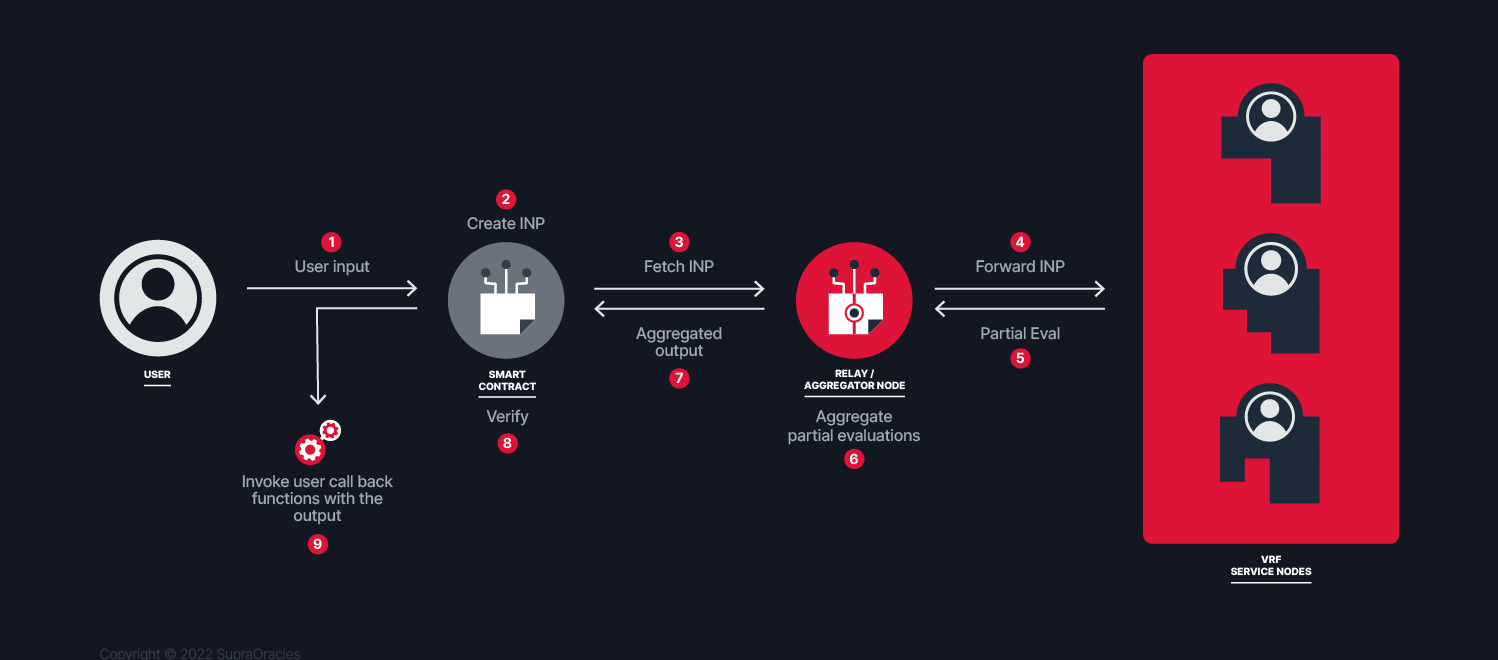
## <a id = "e">Consuming Supra Oracle Price Data Feeds with Ethers and Hardhat </a>
We would be building a smart contract that fetches price data feeds and emits an event if it meets a specific threshold using Hardhat and ethers. Code with me!
### <a id = "f">Prerequisites </a>
Before we dive in, ensure you have the following tools and prerequisites in place:
- Node.js
- Hardhat
- Metamask wallet: Configure metamask to connect to [Sepolia](https://www.alchemy.com/overviews/how-to-add-sepolia-to-metamask) network
- Alchemy or Infura: Get your HTTP endpoint for the Sepolia testnet. [Guide here](https://docs.alchemy.com/docs/how-to-add-alchemy-rpc-endpoint-for-local-development#step-2-add-http-url-to-local-project)
- Test tokens: Request for [Sepolia test](https://sepoliafaucet.com/)
- [gRPC Server address](https://supra.com/docs/data-feeds/pull-model/#configuration) for testnet
- Pull Contract Address from the [Avaialble networks](https://supra.com/docs/data-feeds/pull-model/networks/) on the Supra Docs. You can check for other available networks.
### <a id = "g">Setting Up the Environment </a>
Now that we've gathered our tools, it's time to set up our development environment. Here's a step-by-step guide:
- Start by running the following commands:
```bash
mkdir auction
cd auction
npm init -y
npm install --save-dev hardhat
npx hardhat init
npm install --save-dev @nomicfoundation/hardhat-toolbox
npm i dotenv
code .
```
- Next step would be to clone the Oracle pull example code from GitHub and install the necessary dependencies.
```bash
git clone https://github.com/Entropy-Foundation/oracle-pull-example
cd oracle-pull-example/javascript/evm_client
npm install
```
- To keep sensitive information like your Metamask private key and RPC URL secure, create a .env file in your project directory and store your keys there in the format below:
```javascript
PRIVATE_KEY=""
RPC_URL=""
```
- Modify your Hardhat configuration file (hardhat.config.js) to recognize the keys from your .env file. Also, add sepolia as a network.
```javascript
require("@nomicfoundation/hardhat-toolbox");
require("dotenv").config();
module.exports = {
solidity: "0.8.19",
networks: {
sepolia: {
url: process.env.RPC_URL,
accounts: [process.env.PRIVATE_KEY],
},
},
};
```
## <a id = "h">Build and Compile your Contract </a>
The next section will delve into building a smart contract that interacts with Supra Oracles using Hardhat. We'll walk you through the code, step-by-step, and demonstrate how to fetch price data feeds and emit events based on specific thresholds. I've added some comments to give more details of what's going on.
- First, we will add the `ISupraOraclePull` which contains the `verifyOracleProof` function which performs verification and returns a `PriceData` struct containing the extracted price data.
```javascript
interface ISupraOraclePull {
/**
* @dev Verified price data structure.
* @param pairs List of pairs.
* @param prices List of prices corresponding to the pairs.
* @param decimals List of decimals corresponding to the pairs.
*/
struct PriceData {
uint256[] pairs;
uint256[] prices;
uint256[] decimals;
}
/**
* @dev Verifies oracle proof and returns price data.
* @param _bytesproof The proof data in bytes.
* @return PriceData Verified price data.
*/
function verifyOracleProof(
bytes calldata _bytesproof
) external returns (PriceData memory);
}
```
- For our contract, we would create an internal variable `oracle` to represent the interface. With this we can call the oracle's `verifyOracleProof` function to validate the proofs accompanying price data (delivered as byte strings). Once verified, the contract extracts the price information (including pair IDs, prices, and decimals) and stores it in internal mappings `latestPrices` and `latestDecimal`.
```javascript
contract Supra {
// The oracle contract
ISupraOraclePull internal oracle;
// Stores the latest price data for a specific pair
mapping(uint256 => uint256) public latestPrices;
mapping(uint256 => uint256) public latestDecimals;
// Event to notify when a price threshold is met
event PriceThresholdMet(uint256 pairId, uint256 price);
/**
* @dev Sets the oracle contract address.
* @param oracle_ The address of the oracle contract.
*/
constructor(address oracle_) {
oracle = ISupraOraclePull(oracle_);
}
/**
* @dev Extracts price data from the bytes proof data.
* @param _bytesProof The proof data in bytes.
*/
function deliverPriceData(bytes calldata _bytesProof) external {
ISupraOraclePull.PriceData memory prices = oracle.verifyOracleProof(
_bytesProof
);
// Iterate over all the extracted prices and store them
for (uint256 i = 0; i < prices.pairs.length; i++) {
uint256 pairId = prices.pairs[i];
uint256 price = prices.prices[i];
uint256 decimals = prices.decimals[i];
// Update the latest price and decimals for the pair
latestPrices[pairId] = price;
latestDecimals[pairId] = decimals;
// Example utility: Trigger an event if the price meets a certain threshold
if (price > 1000 * (10 ** decimals)) {
// Example threshold
emit PriceThresholdMet(pairId, price);
}
}
}
/**
* @dev Updates the oracle contract address.
* @param oracle_ The new address of the oracle contract.
*/
function updatePullAddress(address oracle_) external {
oracle = ISupraOraclePull(oracle_);
}
/**
* @dev Returns the latest price and decimals for a given pair ID.
* @param pairId The ID of the pair.
* @return price The latest price of the pair.
* @return decimals The decimals of the pair.
*/
function getLatestPrice(
uint256 pairId
) external view returns (uint256 price, uint256 decimals) {
price = latestPrices[pairId];
decimals = latestDecimals[pairId];
}
}
```
The `getLatestPrice` function woula allow us to retrieve the most recent price and its corresponding decimals for a specific pair ID.
Compile your contract by running this command: `npx hardhat compile`
```bash
npx hardhat compile
Compiled 1 Solidity file successfully
```
## <a id = "i">Deploying and Interacting with the Supra Contract </a>
- Now that you have your contract compiled, we would import necessary libraries and set up the configuration for our script.
```javascript
const { ethers } = require("hardhat");
const PullServiceClient = require("../oracle-pull-example/javascript/evm_client/pullServiceClient");
require("dotenv").config();
const address = "testnet-dora.supraoracles.com";
const pairIndexes = [0, 21, 61, 49];
const sepoliaPullContractAdress = "0x6Cd59830AAD978446e6cc7f6cc173aF7656Fb917"; //Update for V1 or V2
const privateKey = process.env.PRIVATE_KEY;
```
- In our `main` function, we create a `PullServiceClient` instance (`client`) to communicate with the Supra Oracle service. We use this `client` to call the `getProof` method on the `client` object, passing the request (which contains the indexes and the chain type) and a callback function which also acepts two arguments and `err` and `response` . Now we can call the `calContract` function, passing the retrieved proof data (`response.evm`) as an argument.
```javascript
async function main() {
const client = new PullServiceClient(address);
const request = {
pair_indexes: pairIndexes,
chain_type: "evm",
};
console.log("Getting proof....");
const proof = client.getProof(request, (err, response) => {
if (err) {
console.error("Error getting proof:", err.details);
return;
}
console.log("Calling contract to verify the proofs.. ");
callContract(response.evm);
});
}
```
- The `callContract` function, takes retrieved price data proof (`response`) and prepares a transaction to interact with the deployed `Supra` contract.
```javascript
async function callContract(response) {
const Supra = await ethers.getContractFactory("Supra");
const supra = await Supra.deploy(sepoliaPullContractAdress);
const contractAddress = await supra.getAddress();
console.log("Supra deployed to: ", contractAdress);
const hex = ethers.hexlify(response);
const txData = await supra.deliverPriceData(hex);
const gasEstimate = await supra.estimateGas.deliverPriceData(hex);
const gasPrice = await ethers.provider.getGasPrice();
console.log("Estimated gas for deliverPriceData:", gasEstimate.toString());
console.log("Estimated gas price:", gasPrice.toString());
const tx = {
from: "0xDA01D79Ca36b493C7906F3C032D2365Fb3470aEC",
to: contractAddress,
data: txData,
gas: gasEstimate,
gasPrice: gasPrice,
};
const wallet = new ethers.Wallet(privateKey);
const signedTransaction = await wallet.signTransaction(tx);
const txResponse = await wallet.sendTransaction(tx);
console.log("Transaction sent! Hash:", txResponse.hash);
// (Optional) Wait for transaction confirmation (e.g., 1 block confirmation)
const receipt = await txResponse.wait(1);
console.log("Transaction receipt:", receipt);
}
```
### Deploying to Sepolia
To deploy to sepolia, run the following command:
```
npx hardhat run scripts/run-supra.js --network sepolia
```
With this, you should be able to use Supra price data feeds with Hardhat in building decentralized applications. You can find the full code for this tutorial [here](https://github.com/tosynthegeek/supraoracle-implementation).
## <a id = "j">What's Next? </a>
By leveraging Supra Oracles, developers can build secure and reliable DeFi applications with access to trustworthy and timely data feeds. To continue building with Supra and exploring other services, I recommend the following resources:
- [The Supra Docs](https://supra.com/docs/): for access to solution, repos, smart contract addresses, and other essential information
- [The Supra Research Page](https://supra.com/research/): for technical deep dives and researchs.
- [The Supra Academy](https://supra.com/academy/): # Explore topics. Dive in. Level up. | tosynthegeek |
1,874,784 | Merkle Proofs: A Simple Guide | You have millions of unique images in your gallery, each representing a piece of private or personal... | 0 | 2024-06-03T00:10:51 | https://blog.idrisolubisi.com/how-merkle-proofs-work | webdev, javascript, beginners, web3 | You have millions of unique images in your gallery, each representing a piece of private or personal data stored on your phone. After an incident, you lost your device, but it was returned to you after many months, with claims that the images hadn't been tampered with.
Verifying the authenticity of each image in this gallery could be difficult, right? How can they prove the images haven't been manipulated, or how can you confirm everything is as it should be? That's where **Merkle's proofs** come into play, as they offer a solution to verify the integrity of large datasets without the need to inspect each item individually.
In this tutorial, you will learn about Merkle proofs, how to create them using a [Merkle Tree](https://en.wikipedia.org/wiki/Merkle_tree), and how to implement Merkle proofs for whitelisting email addresses using JavaScript.
To understand how Merkle proofs help verify the authenticity and integrity of your data without the need to check each piece individually, such as your image gallery, as discussed earlier, you first need to understand the structure that underpins them: the **Merkle Tree**.
## What is a Merkle Tree?
A [Merkle Tree](https://en.wikipedia.org/wiki/Merkle_tree), [also known](https://en.wikipedia.org/wiki/Merkle_tree) as a hash tree, is a binary tree structure used to verify a data set's integrity effectively. It was a concept named after the computer scientist [Ralph Merkle](https://en.wikipedia.org/wiki/Ralph_Merkle), [who patented](https://en.wikipedia.org/wiki/Ralph_Merkle) it in 1979.
This binary [tree structure](https://en.wikipedia.org/wiki/Merkle_tree) has each leaf node representing a block of data or a piece of information. Instead of containing the data directly, the internal nodes hold a cryptographic h[ash of their](https://en.wikipedia.org/wiki/Ralph_Merkle) child nodes. The tree is built by repeatedly hashing pairs of child nodes until a single root hash is achieved.
## Components of Merkle Tree
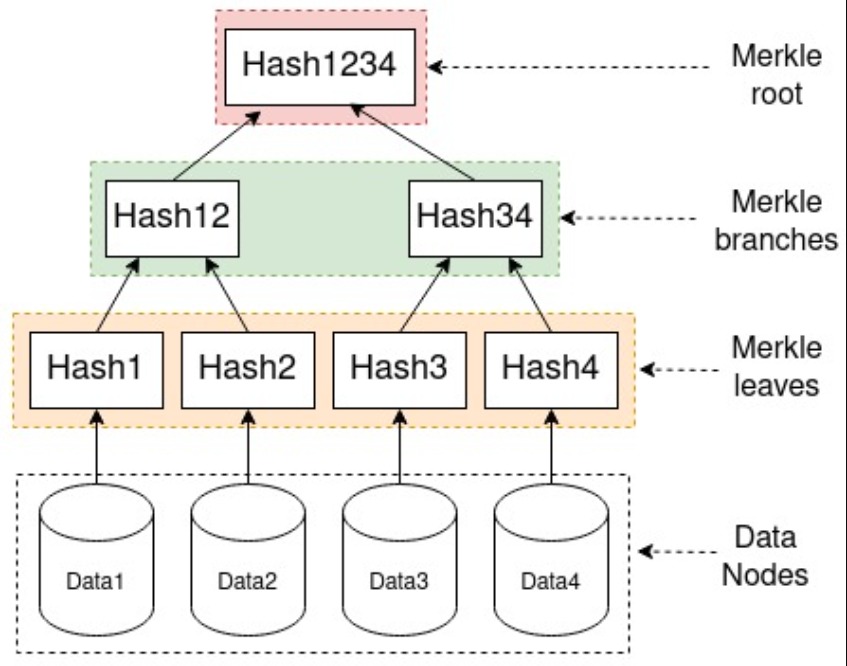
*Merkle Tree image by Teemu Kanstrén*
A Merkle tree has three different components, as shown in the image above Merkle root, Merkle branches, and Merkle leaves. Let's take a look at what they are.
* **Merkle root** is derived from hashing together the child hashes beneath it and down to the leaves. It is a single hash on its own that represents the top of the Merkle tree, as shown in the image above and is often used to store block headers in [blockchain](https://en.wikipedia.org/wiki/Blockchain) content without downloading the entire block.
* In a Merkle tree, we have **Merkle branches**, intermediate nodes between Merkle roots and Merkle leaves. Each branch node is created by hashing together the hashes of its child nodes. These branches form the connections between the leaves (where the data resides) and the Merkle root, making it easier to ensure that the Merkle tree can be efficiently tra[versed and](https://en.wikipedia.org/wiki/Blockchain) verified.
* **Merkle leaves** are the nodes at the bottom layer of the Merkle tree. They contain hashes of the actual data stored. The leaves are the foundation of the Merkle tree, as their hashes are combined and rehashed to produce the hashes of the nodes above them, ultimately leading to the Merkle root.
Additionally, we have the **Data nodes**, a layer representing how data is supplied to start the process before it hashed in the next layer(Merkle leaves), which is the Merkle leaves, as shown in the image.
## What is a Merkle Proof?
A Merkle proof is a method used to verify the presence and integrity of specific data within a dataset using a Merkle tree. It comprises a single data block (leaf), a series of hashes from the tree (branches), and the Merkle root.
While Merkle proof is used to verify the presence of specific data within a dataset using a Merkle tree, here are some areas where Merkle proof can be applied.
* In a distributed system for data verification
* Secure communication protocols
* Data storage solution
* Cryptocurrencies and blockchain
## Implementing a Merkle Proof for Whitelisting Email Addresses
Let's implement a Merkle proof for whitelisting email addresses in this section.
### Prerequisite
* [Node.js](https://nodejs.org/en/) and its package manager NPM, version 18. Verify Node.js is installed by running the followi[ng term](https://nodejs.org/en/)inal command: `node -v && npm -v`
* A basic understanding of [JavaScript](https://www.w3schools.com/js/default.asp)
### Project Setup and Installation
Navigate to any directory of [your c](https://nodejs.org/en/)hoice, and then r[un the fol](https://www.w3schools.com/js/default.asp)lowing commands to create a new folder and change the directory into the folder:
```bash
mkdir merkle-proof-tutorial
cd merkle-proof-tutorial
```
[Next,](https://www.w3schools.com/js/default.asp) you need to install the `merkletreejs` and `crypto-js` libraries, which will be needed to create a Merkle tree and hash data using the following command:
```bash
npm i merkletreejs crypto-js
```
Create a new file `proof.js` feel free to name it whatever you want, but for this tutorial, you will name it `proof.js`.
### Import Libraries
You will be using the `merkletreejs` and `crypto-js` libraries in this example to create a Merkle tree and hash the data, respectively.
Navigate into the `proof.js` file and add the following code snippet:
```javascript
const { MerkleTree } = require('merkletreejs')
const SHA256 = require('crypto-js/sha256')
```
### Create a List of Emails to Be Whitelisted
You need to create a list of emails to be whitelisted. In this example, you will add three emails, but it could be millions of emails, depending on the data you want to test with. Add the following code snippet to create an array of three email addresses:
```javascript
//...
// List of email addresses to be whitelisted
const emails = ["example1@mail.com", "example2@mail.com", "example3@mail.com"];
```
### Convert Emails to Hashes and Build the Merkle Tree
Next, you need to convert each email into a hash and create the Merkle tree using the hashed emails with the following code snippet:
```javascript
//...
// Convert each email into a hash
const leaves = emails.map(email => SHA256(email));
// Create the Merkle Tree using the hashed emails
const tree = new MerkleTree(leaves, SHA256);
// Get the root and convert it to a hexadecimal string
const root = tree.getRoot().toString('hex');
```
### Add Function to Verify Whitelisted Emails
In the previous step, you created a tree for the addresses; next, you must create a function to prove if an email is part of the whitelisted emails.
Create a function `verifyEmail`:
```javascript
//...
// Function to verify if an email is whitelisted
const verifyEmail = (email) => {
// Hash the email to be verified
const hashedEmail = SHA256(email);
// Get the proof for the hashed email from the tree
const proof = tree.getProof(hashedEmail);
// Verify the proof against the root of the tree; returns true if valid, false otherwise
const verified = tree.verify(proof, hashedEmail, root);
// Log the result to the console
console.log(`${email} is ${verified ? "whitelisted" : "not whitelisted"}.`);
};
```
In the code snippet, you created a function verifying whether an email is whitelisted. To do this, you:
* Hashed the email to be verified using SHA256
* Got the proof for the hashed email using the `getProof` method
* Verified the proof against the root of the tree
Here is what the complete code looks like:
```javascript
const { MerkleTree } = require("merkletreejs");
const SHA256 = require("crypto-js/sha256");
// List of email addresses to be whitelisted
const emails = ["example1@mail.com", "example2@mail.com", "example3@mail.com"];
// Convert each email into a hash
const leaves = emails.map((email) => SHA256(email));
// Create the Merkle Tree using the hashed emails
const tree = new MerkleTree(leaves, SHA256);
// Get the root and convert it to a hexadecimal string
const root = tree.getRoot().toString("hex");
// Function to verify if an email is whitelisted
const verifyEmail = (email) => {
// Hash the email to be verified
const hashedEmail = SHA256(email);
// Get the proof for the hashed email from the tree
const proof = tree.getProof(hashedEmail);
// Verify the proof against the root of the tree; returns true if valid, false otherwise
const verified = tree.verify(proof, hashedEmail, root);
// Log the result to the console
console.log(`${email} is ${verified ? "whitelisted" : "not whitelisted"}.`);
};
```
### Test the Verification Function
In this section, you will test the verification function with a whitelisted and non-whitelisted email.
Test with a whitelisted email address by calling the `verifyEmail` function inside the script file.
```javascript
//...
verifyEmail("example2@mail.com"); // Expected output: "example2@mail.com is whitelisted."
```
To run the script, use the following command:
```bash
node proof.js
```
The result printed on the console will return a response as shown below, indicating the email address is whitelisted because it is part of the emails we added to the email array.
Next, test with an email that is not whitelisted.
```javascript
//...
verifyEmail("x@mail.com");
// Expected output: "x@mail.com is not whitelisted."
```
You should see a response indicating the email is not whitelisted, as shown below. This is because it wasn't part of the emails whitelisted, meaning there is no proof for the email address to indicate it was part of the tree.
## Conclusion
In this tutorial, you learned about Merkle proofs, how they can be used to ensure the integrity of datasets in applications, how to create them using a Merkle Tree, and how to implement Merkle proofs for whitelisting email addresses using JavaScript.
## References
* [Merkle Tree](https://en.wikipedia.org/wiki/Merkle_tree)
* [Merkletreejs SDK](https://www.npmjs.com/package/merkletreejs) | olanetsoft |
1,874,789 | Azure PostgreSQL, Entra ID Authentication and .NET | I’m currently working on a project in which we are using Entra ID rather than a traditional Postgre... | 0 | 2024-06-03T00:34:02 | https://www.aaron-powell.com/posts/2024-06-03-azure-postgresql-and-entra-id-dotnet/ | dotnet, security, azure | ---
title: Azure PostgreSQL, Entra ID Authentication and .NET
published: true
date: 2024-06-03 00:08:47 UTC
tags: dotnet,security,azure
canonical_url: https://www.aaron-powell.com/posts/2024-06-03-azure-postgresql-and-entra-id-dotnet/
---
I’m currently working on a project in which we are using [Entra ID](https://learn.microsoft.com/azure/postgresql/single-server/how-to-configure-sign-in-azure-ad-authentication?WT.mc_id=dotnet-139180-aapowell) rather than a traditional Postgre username and password. This is a great way to secure your database and ensure that only the right people have access to it.
_Note: For the purpose of this article, I’m going to use Entra ID to refer to a user identity, as well as a managed identity such as a service principal, as the approach is the same in this context here._
The above linked documentation covers how you would setup the Azure resource with Entra ID as the authentication mode, so I won’t go over that here (also, you can configure that when you initial create the database, or using a Bicep script), instead I want to look at how we use that in a .NET application, because when you’re connecting using Entra ID you don’t have a password to use, or at least not in the traditional sense.
For this, I’m going to use the [Npgql](https://www.npgsql.org/) library, which is the most popular PostgreSQL driver for .NET. It’s a great library and has a lot of features, and integrates nicely with Entity Framework Core and .NET Aspire.
## What makes connecting different [<svg height="22px" viewbox="0 0 24 24" width="22px" xmlns="http://www.w3.org/2000/svg"><path d="M0 0h24v24H0z" fill="none"></path><path d="M3.9 12c0-1.71 1.39-3.1 3.1-3.1h4V7H7c-2.76 0-5 2.24-5 5s2.24 5 5 5h4v-1.9H7c-1.71 0-3.1-1.39-3.1-3.1zM8 13h8v-2H8v2zm9-6h-4v1.9h4c1.71 0 3.1 1.39 3.1 3.1s-1.39 3.1-3.1 3.1h-4V17h4c2.76 0 5-2.24 5-5s-2.24-5-5-5z"></path></svg>](#what-makes-connecting-different)
Before we look at the _how_ of connecting, we need to understand why this is a little different to using a username/password approach. When working with a PostgreSQL database that uses a username/password, you would have a connection string that looks like this:
```
Server=myServerAddress;Port=5432;Database=myDataBase;User Id=myUsername;Password=myPassword;
```
But when connecting using Entra ID, it looks like this:
```
Server=server-name.postgres.database.azure.com;Database=postgres;Port=5432;Username=<Entra ID>;Ssl Mode=Require;
```
Notice how there is no `Password` field in the connection string. This is because when you connect using Entra ID, you don’t have a password to use. Instead, you need to use a token that is generated by Entra.
## Generating a token [<svg height="22px" viewbox="0 0 24 24" width="22px" xmlns="http://www.w3.org/2000/svg"><path d="M0 0h24v24H0z" fill="none"></path><path d="M3.9 12c0-1.71 1.39-3.1 3.1-3.1h4V7H7c-2.76 0-5 2.24-5 5s2.24 5 5 5h4v-1.9H7c-1.71 0-3.1-1.39-3.1-3.1zM8 13h8v-2H8v2zm9-6h-4v1.9h4c1.71 0 3.1 1.39 3.1 3.1s-1.39 3.1-3.1 3.1h-4V17h4c2.76 0 5-2.24 5-5s-2.24-5-5-5z"></path></svg>](#generating-a-token)
When you connect to the database using Entra ID, you need to request an access token from Entra that you can use to authenticate. You can see this in action using the Azure CLI:
```bash
az account get-access-token --resource-type oss-rdbms
```
Which returns something like this:
```json
{
"accessToken": "<nope!>",
"expiresOn": "2024-05-31 17:52:59.000000",
"expires_on": 1717141979,
"subscription": "<nope!>",
"tenant": "<nope!>",
"tokenType": "Bearer"
}
```
If you extract the `accessToken` from the JSON you can then plug that into the connection string for PostgreSQL in the `Password` argument and you’re good to go.
But it’s not really practical to be running the Azure CLI every time you want to connect to the database, especially since this token is only short lived (you can see the expiry date in the JSON above). Instead, we’re going to want to do this in .NET, and for that we’ll use the [`Azure.Identity` NuGet package](https://www.nuget.org/packages/Azure.Identity/).
## Using Azure.Identity [<svg height="22px" viewbox="0 0 24 24" width="22px" xmlns="http://www.w3.org/2000/svg"><path d="M0 0h24v24H0z" fill="none"></path><path d="M3.9 12c0-1.71 1.39-3.1 3.1-3.1h4V7H7c-2.76 0-5 2.24-5 5s2.24 5 5 5h4v-1.9H7c-1.71 0-3.1-1.39-3.1-3.1zM8 13h8v-2H8v2zm9-6h-4v1.9h4c1.71 0 3.1 1.39 3.1 3.1s-1.39 3.1-3.1 3.1h-4V17h4c2.76 0 5-2.24 5-5s-2.24-5-5-5z"></path></svg>](#using-azureidentity)
`Azure.Identity` is a library that provides a way to authenticate with Azure services using the Azure SDK, and it contains a class called [`DefaultAzureCredential`](https://learn.microsoft.com/dotnet/api/azure.identity.defaultazurecredential?view=azure-dotnet&WT.mc_id=dotnet-139180-aapowell) that can be used to authenticate. This class is actually a roll-up of a number of different authentication sources, such as Managed Identity, as well as the Azure CLI, Visual Studio, and a bunch of other sources (check out [the docs](https://learn.microsoft.com/dotnet/api/azure.identity.defaultazurecredential?view=azure-dotnet&WT.mc_id=dotnet-139180-aapowell) to see all the sources).
To use `DefaultAzureCredential` you need to install the `Azure.Identity` NuGet package:
```bash
dotnet add package Azure.Identity
```
Then you can use it in your code like this:
```csharp
using Azure.Identity;
var credential = new DefaultAzureCredential();
var ctx = new TokenRequestContext(["https://ossrdbms-aad.database.windows.net/.default"]);
var tokenResponse = await credential.GetTokenAsync(ctx);
Console.WriteLine(tokenResponse.Token);
```
The important part here is that we’re providing a specific scope to the `TokenRequestContext` of `https://ossrdbms-aad.database.windows.net/.default`, which grants access to the Azure PostgreSQL Flexible Server. It’s what is being done with the `az account get-access-token` call and the `--resource-type oss-rdbms` argument. With this in C# though, we’re able to get the token and then use that to connect to the database.
## Handling Token Expiry [<svg height="22px" viewbox="0 0 24 24" width="22px" xmlns="http://www.w3.org/2000/svg"><path d="M0 0h24v24H0z" fill="none"></path><path d="M3.9 12c0-1.71 1.39-3.1 3.1-3.1h4V7H7c-2.76 0-5 2.24-5 5s2.24 5 5 5h4v-1.9H7c-1.71 0-3.1-1.39-3.1-3.1zM8 13h8v-2H8v2zm9-6h-4v1.9h4c1.71 0 3.1 1.39 3.1 3.1s-1.39 3.1-3.1 3.1h-4V17h4c2.76 0 5-2.24 5-5s-2.24-5-5-5z"></path></svg>](#handling-token-expiry)
One thing to note is that the token that is returned by `DefaultAzureCredential` is short lived, and will expire after a certain amount of time (24 hours service principal, 4 hours for a user token). This is fine for, say, a console app that is only running for a short period of time, but this becomes a problem if you’re using the connection string in something that is long running, like a web app, since the `NpgsqlDataSourceBuilder`, the type that is used to build the connection string, should be a singleton.
Thankfully, the authors of Npgsql have given us an approach to handling token refreshes in the box using a Periodic Password Provider. With this feature, we can provide a callback function to be run that will retrieve the password when a connection is opened, and then cache that password for a certain amount of time. This means that we can use the `DefaultAzureCredential` to get the token, and then use that token to connect to the database.
```csharp
NpgsqlDataSourceBuilder dataSourceBuilder = new(builder.Configuration.GetConnectionString("Database"));
dataSourceBuilder.UsePeriodicPasswordProvider(async (_, ct) =>
{
DefaultAzureCredential credential = new();
TokenRequestContext ctx = new(["https://ossrdbms-aad.database.windows.net/.default"]);
AccessToken tokenResponse = await credential.GetTokenAsync(ctx, ct);
return tokenResponse.Token;
}, TimeSpan.FromHours(4), TimeSpan.FromSeconds(10));
```
On the `dataSourceBuilder` we call the `UsePeriodicPasswordProvider` method, passing in a callback function that will get the token, and then two `TimeSpan` objects that represent the refresh period and the failure refresh period. The refresh period is how often the token will be refreshed, and the failure refresh period is how long to wait before trying to refresh the token again if the token retrieval fails.
## Connecting it all up [<svg height="22px" viewbox="0 0 24 24" width="22px" xmlns="http://www.w3.org/2000/svg"><path d="M0 0h24v24H0z" fill="none"></path><path d="M3.9 12c0-1.71 1.39-3.1 3.1-3.1h4V7H7c-2.76 0-5 2.24-5 5s2.24 5 5 5h4v-1.9H7c-1.71 0-3.1-1.39-3.1-3.1zM8 13h8v-2H8v2zm9-6h-4v1.9h4c1.71 0 3.1 1.39 3.1 3.1s-1.39 3.1-3.1 3.1h-4V17h4c2.76 0 5-2.24 5-5s-2.24-5-5-5z"></path></svg>](#connecting-it-all-up)
Now that we know how we can retrieve a token to act as the password for our connections, let’s look at how to connect it all up for a local dev or Azure deployed app:
```csharp
WebApplicationBuilder builder = WebApplication.CreateBuilder(args);
var connStr = builder.Configuration.GetConnectionString("db");
NpgsqlConnectionStringBuilder csb = new(connStr);
if (!string.IsNullOrEmpty(csb.Password))
{
builder.AddNpgsqlDataSource("db");
}
else
{
builder.AddNpgsqlDataSource("db", dataSourceBuilder =>
{
dataSourceBuilder.UsePeriodicPasswordProvider(async (_, ct) =>
{
DefaultAzureCredential credential = new();
TokenRequestContext ctx = new(["https://ossrdbms-aad.database.windows.net/.default"]);
AccessToken tokenResponse = await credential.GetTokenAsync(ctx, ct);
return tokenResponse.Token;
}, TimeSpan.FromHours(4), TimeSpan.FromSeconds(10));
});
}
// and the rest of your app code
```
Here we’re getting the connection string and creating a `NpgsqlConnectionStringBuilder` from it so that it gets parsed for us. If the connection string we have has a password, then we can just use that as normal, but if it doesn’t have a password, then we can use the `UsePeriodicPasswordProvider` method to get the token and use that as the password.
This means we can run locally against a database that uses username/password style access (since we don’t have Entra ID locally), and then deploy to Azure and use Entra ID without having to change the code.
## Conclusion [<svg height="22px" viewbox="0 0 24 24" width="22px" xmlns="http://www.w3.org/2000/svg"><path d="M0 0h24v24H0z" fill="none"></path><path d="M3.9 12c0-1.71 1.39-3.1 3.1-3.1h4V7H7c-2.76 0-5 2.24-5 5s2.24 5 5 5h4v-1.9H7c-1.71 0-3.1-1.39-3.1-3.1zM8 13h8v-2H8v2zm9-6h-4v1.9h4c1.71 0 3.1 1.39 3.1 3.1s-1.39 3.1-3.1 3.1h-4V17h4c2.76 0 5-2.24 5-5s-2.24-5-5-5z"></path></svg>](#conclusion)
When porting an app that uses PostgreSQL to using Managed Identity I was expecting that it would be quite a lot of work to manage the token retrieval and expiry, initially I thought that it’d require doing a bunch of work to discard the singleton for the `NpgsqlDataSourceBuilder` and then recreate it when the token expired. But thanks to the `UsePeriodicPasswordProvider` method, it’s actually quite easy to manage the token retrieval and expiry, and it’s all handled for you. | aaronpowell |
1,876,145 | I am not renewing my GitHub Copilot Subscription | I honestly tried to ironically have Microsoft Copilot make the hero image for this post. But they... | 0 | 2024-06-07T10:55:28 | https://www.jakehayes.net/blog/engineering/2024/not-renewing-copilot/ | ai, githubcopilot, engineering | ---
title: I am not renewing my GitHub Copilot Subscription
published: true
date: 2024-06-03 00:00:00 UTC
tags: ai, copilot, engineering
cover_image: https://www.jakehayes.net/blog-images/tech/2024/copilot.jpg
canonical_url: https://www.jakehayes.net/blog/engineering/2024/not-renewing-copilot/
---
_I honestly tried to ironically have Microsoft Copilot make the hero image for this post. But they were all terrible so I gave up. Credit [Gerard Siderius on Unsplash](https://unsplash.com/@siderius_creativ)_
I paid for an entire year of personal access to GitHub Copilot. About a month before my subscription ended, I asked myself if I was getting the value from it that I was hoping for. The answer, obviously, was no. So I wanted to explain some of my reasons, some of my hope, and why I am just using free LLM's and old-fashioned Googling again.
## It's good at the basics, mostly
All the marketing videos are not complete lies. If you are looking for a more advanced auto-complete, this is perfect. The problem is that I don't want to pay $100 per year for auto-complete. But when I'm trying to make a simple button in React or typing in some obvious lists with a key/value of an object, it does a good job of recognizing that and saving me the keystrokes.
### Bad at specific questions
I'm not the world's most advanced engineer. But I can handle pretty much all of the basic stuff. Especially if it's something in my technical wheelhouse like React or TypeScript. So I am not asking Copilot a lot of questions about the basics. If I am asking Copilot a question using its chat feature, it's usually a more advanced topic. Something that is tricky for me. The problem I have run into is that, more often than not, Copilot does not have a clue on how to answer me. And what I consider an even bigger problem is that it doesn't tell me that it doesn't know; it gives me the most ridiculous answer with as much confidence as it can muster.
Over the last year, though, I have become so pessimistic about using it that I just stopped asking Copilot questions. I would instead try to brute force it myself or _cringe_ read the documentation. 😱😱
Both of those methods turned out to be faster than Copilot because of...
### Rabbit holes
I don't want to add a bunch of packages to my already bloated React project. But Copilot is absolutely insistent on add more packages first. Then I have to actually find out what the package it's recommending is, are there better packages that do the same thing, down down down...
> Absolutely! All you need to do is install [package A], [package B], and [package C]. Then, adjust your dev server (and, of course, your build pipeline 🤭) and then add the following block of code:
>
> `js
> // ….
> `
Except Copilot didn't tell me the package I had mentioned by name could do what I asked without any other changes. Read the docs, kids.
### Code Churn
[I'm apparently not the only person who noticed this.](https://www.gitclear.com/coding_on_copilot_data_shows_ais_downward_pressure_on_code_quality) But I have had to update a lot more of my own code after starting to use Copilot.
#### Deleting so much code
I would also, especially at the beginning before becoming disillusioned, blindly trust Copilot and just press <Tab> any time a suggestion popped up without reading it. After painfully learning the lesson of not blindly tabbing, I got to experience a new pain in my coding workflow:
- Write some code, get in the groove, and a Copilot suggestion pops up ->
- Stop my coding flow; switch my brain to reading mode while slamming on the brakes, effectively killing my flow ->
- Realize the Copilot suggestion is kind of irrelevant to what I am trying to do; it's the most mid-engineer I've ever met in my life (which is kind of the point) ->
- Try my best to get back into the flow as quickly as possible ->
- Repeat ->
That workflow was not ideal for me or my ADHD, as every time I blast through my flow state barriers, who knows what I'll be doing 20 minutes later when I realize my office is clean but my code is still unwritten.
## The Dreaded Switch to NeoVim
But don't worry, I use [AstroNvim](https://astronvim.com) just so I can piss everyone off. It was a mistake to turn on Vim bindings in VSCode, because then I got good at them. And when I got the muscle memory, I felt like VSCode was just a touch too slow. And then I tried it in NeoVim and realized how slow VSCode is. Then I had to choose between Copilot Chat and the Copilot NVim extension, which is just glorified autocomplete. And I realized I would rather have NVim than Copilot chat.
This was actually one of the catalysts for me doing the self reflection on if I should renew Copilot at all. It turns out I didn't really miss it. I was faster; I got into a flow state more frequently. My code was more understandable to me and to other people.
## I'm Googling again
This feels weird to say, but is this considered "old school" now? I am searching for things on Google again instead of copying and pasting errors into an LLM. And you know what? I think I'm faster at it. A big part of the problem is that error messages usually stink or are irrelevant, so LLM's try to rely heavily on what the error message says is wrong. And usually it's something unrelated, but the Stack Overflow answer for that error message knows that and can point you in the right direction a lot faster.
Don't get me wrong, I'll check with an LLM sometimes, especially if the first few search results are not what I need. But for all the reasons outlined above, there are a lot of times when it is just as unhelpful.
## I hope it doesn't stay like this
I have hope for our AI overlord's future. When Copilot originally came out, and for the first few months I started using it, I thought I wouldn't have a job soon. But then there weren't really great improvements. And I started to realize how bad most of its suggestions are, and the AI sheen started to wear off. Then I had the feeling that it was actually getting worse. Then I saw other people [talk about it getting worse too](https://youtu.be/dDUC-LqVrPU?si=vfxXQXTYAWBBs0BG).
All of that made me really pessimistic about AI, and I thought it would turn out to be like Web3, crypto, NFT's, and GameStop stock, just another hype thing that has VCs throwing money at it, bankrupting any software engineer foolish enough to try to make an AI-based startup that overpromises the world. (Have you seen the first episode of Silicon Valley?) But now I don't feel that is right either.
At this point, I have swung so hard each way that I have pretty much just mellowed out. AI will be an impressive tool for anyone to use. Creating AI is tough, but you can build on the shoulders of giants and make impressive strides. It might fade just due to the costs of training; it might explode again; I'm not an oracle. But I personally am just so burned out on it that I'm just checking out for a little while. I will let it improve at whatever rate it does, and then check back in later.
Thanks for reading. | thejayhaykid |
1,874,780 | Implementing Progressive Web Apps (PWAs) with React | Introduction Progressive Web Apps (PWAs) have revolutionized the way we develop and... | 0 | 2024-06-02T23:54:49 | https://dev.to/emmanuelj/implementing-progressive-web-apps-pwas-with-react-oem | javascript, webdev, authjs, programming | #### Introduction
Progressive Web Apps (PWAs) have revolutionized the way we develop and deliver web applications by combining the best features of web and mobile apps. They offer offline capabilities, fast load times, and a native app-like experience, all from within a browser. React, a popular JavaScript library for building user interfaces, provides robust support for creating PWAs. This article will guide you through the process of implementing a PWA using React.
#### What is a Progressive Web App?
A PWA is a type of application software delivered through the web, built using standard web technologies including HTML, CSS, and JavaScript, intended to work on any platform that uses a standards-compliant browser. Key features of PWAs include:
- **Responsiveness**: Adapts to various screen sizes and orientations.
- **Offline Capabilities**: Functions without an internet connection using service workers.
- **App-like Experience**: Provides an experience similar to native apps.
- **Fast Loading**: Utilizes caching and other techniques to load quickly.
- **Push Notifications**: Engages users with real-time notifications.
#### Setting Up a React PWA
Creating a PWA with React is straightforward, thanks to Create React App (CRA), which provides a pre-configured environment for developing React applications, including PWA functionality.
##### Step 1: Create a React App
First, ensure you have Node.js and npm installed. Then, create a new React application using CRA:
```bash
npx create-react-app my-pwa-app
cd my-pwa-app
```
CRA automatically sets up a service worker and other configurations needed for a PWA.
##### Step 2: Understand the Project Structure
The key files and directories for PWA functionality include:
- **`public/manifest.json`**: Defines the app's metadata like name, icons, start URL, and theme color.
- **`src/service-worker.js`**: Manages caching and offline functionality.
- **`public/index.html`**: Contains the root HTML file, which links to the manifest and includes meta tags for PWA features.
##### Step 3: Configure `manifest.json`
The `manifest.json` file configures how your app will behave and appear when installed on a user's device. Customize it as follows:
```json
{
"short_name": "MyPWA",
"name": "My Progressive Web App",
"icons": [
{
"src": "icon-192x192.png",
"type": "image/png",
"sizes": "192x192"
},
{
"src": "icon-512x512.png",
"type": "image/png",
"sizes": "512x512"
}
],
"start_url": ".",
"display": "standalone",
"theme_color": "#000000",
"background_color": "#ffffff"
}
```
##### Step 4: Register the Service Worker
In `src/index.js`, ensure the service worker is registered. By default, CRA's service worker is commented out. Uncomment it to enable:
```javascript
import React from 'react';
import ReactDOM from 'react-dom';
import './index.css';
import App from './App';
import * as serviceWorker from './serviceWorker';
ReactDOM.render(<React.StrictMode><App /></React.StrictMode>, document.getElementById('root'));
// Register the service worker for offline capabilities
serviceWorker.register();
```
##### Step 5: Customize the Service Worker
The default service worker provided by CRA is sufficient for basic caching and offline functionality. However, you can customize it in `src/service-worker.js` if you need more advanced features like caching strategies or background sync.
```javascript
// Example: Custom cache strategy
self.addEventListener('fetch', (event) => {
event.respondWith(
caches.match(event.request)
.then((response) => {
return response || fetch(event.request);
})
);
});
```
##### Step 6: Test Your PWA
To test your PWA, run your React application in development mode:
```bash
npm start
```
Then, build the project for production:
```bash
npm run build
```
Serve the production build using a static server like `serve`:
```bash
npm install -g serve
serve -s build
```
Open your application in a browser and use the browser's developer tools to test PWA features. Check if it can be installed, runs offline, and responds to network changes.
#### Enhancing Your PWA
To fully leverage PWA capabilities, consider the following enhancements:
- **Push Notifications**: Integrate push notifications using the Web Push API.
- **Background Sync**: Use the Background Sync API to defer actions until the user has connectivity.
- **Performance Optimization**: Utilize lazy loading and code splitting to improve performance.
#### Conclusion
Implementing a Progressive Web App with React is a powerful way to deliver a seamless, app-like experience to your users directly through the web. With tools like Create React App, setting up a PWA is straightforward, enabling you to focus on building a responsive, fast, and reliable application. By following the steps outlined in this article, you'll be well on your way to creating a robust PWA with React. | emmanuelj |
1,874,778 | El principio | Fácil. Estuve dándole un poco la brasa a ChatGPT 4o sobre como girar desde las finanzas y la banca, a... | 0 | 2024-06-02T23:37:50 | https://dev.to/carlos_ruiz/el-principio-5kb | beginners, python, spanish, learning | Fácil.
Estuve dándole un poco la brasa a ChatGPT 4o sobre como girar desde las finanzas y la banca, a la programación. Le hablé de mis inquietudes sobre el machine learning y la investigación sobre escenarios y proyecciones con modelos montecarlo y teoría de opciones reales.
Me recomendó dos cosas:
- Comenzar a estudiar python en Coursera, con un curso concreto Python for everybody.
- Documentar mi aprendizaje. Me nombró GitHub para los proyectos, y me nombró algunas plataformas donde ir dejando mis avances, porque decía literalmente, que podría ser motivador para otros a la vez que me daría visibilidad para buscar alguna actividad que desarrollar en este mundo.
Y aquí estoy dando constancia de la segunda, en la que contaré de la primera.
Comencé el curso de iniciación el pasado 25 de mayo. Ya tenía conocimientos de alguna cosilla, por lo que no me fue demasiado difícil avanzar por él. Hasta me han dado un certificado y todo.
https://coursera.org/share/b6043ab6b07cd7ea55466c0464e94539
Lo mas interesante del curso es la cantidad de recursos que tiene por los que puedes volver a pasar y que además muchos de ellos están abiertos, sin tener que realizar el curso. Esta es la página https://www.py4e.com/ que mantiene vivo todo el material y videos donde Charles Severance imparte el curso en varias plataformas.
Ahora he pasado al segundo curso dentro de un programa de 5, de la misma universidad y también impartido por Severance, donde ya entramos en las Estructura de Datos.
La verdad que no se que mas poner por aquí por ahora, es tan incipiente el aprendizaje que todavía no veo lógico destacar ninguna parte.
Bueno, pues ya arranqué.
| carlos_ruiz |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.