id int64 5 1.93M | title stringlengths 0 128 | description stringlengths 0 25.5k | collection_id int64 0 28.1k | published_timestamp timestamp[s] | canonical_url stringlengths 14 581 | tag_list stringlengths 0 120 | body_markdown stringlengths 0 716k | user_username stringlengths 2 30 |
|---|---|---|---|---|---|---|---|---|
1,872,367 | Understanding JS Execution Flow with Visuals | While working on a LeetCode problem, I got stuck on the concepts of setTimeout and clearTimeout. Some... | 0 | 2024-05-31T19:03:42 | https://dev.to/ayako_yk/understanding-js-execution-flow-with-visuals-1c8f | javascript, react, learning, webdev | While working on a LeetCode problem, I got stuck on the concepts of setTimeout and clearTimeout. Some developers shared their solutions and explanations, all emphasizing the importance of understanding the flow of JavaScript. The key mechanisms involved include the call stack, queues, the event loop, and web APIs.
I had read multiple documents and blogs about setTimeout and call stacks, but understanding the actual flow was quite challenging for me, especially as a visual learner. However, I came across an amazing YouTube tutorial that was perfectly explained and gave me a clear understanding, allowing me to delve deeper into the flow. I’ll describe each key term, summarize the flow in my own words, and share the link to the tutorial video.
**JavaScript Engine**
Since JavaScript is a scripting language that a computer doesn't understand directly, a browser has an inbuilt JavaScript engine that converts JavaScript into a computer-understandable language. The engine has two key mechanisms: the call stack and the memory heap. While the JavaScript engine is where data is stored, I won't delve into that this time to focus on the flow.
**Call Stack**
A call stack is a mechanism that keeps track of its place in a script that calls functions. Functions are stacked and executed in a Last-In-First-Out (LIFO) order.
**Memory Heap**
While the stack stores fixed-sized data, the heap dynamically allocates memory for objects and functions.
**Blocking vs Non-Blocking**
Blocking code doesn't allow the next task to be executed until the blocking code finishes executing. In contrast, non-blocking code, such as asynchronous calls like setTimeout or Promise, allows the next task to be executed without waiting.
**Event Queue**
The event queue is a queue of tasks to be executed when the call stack is empty. There are two kinds of queues or tasks: microtasks and macrotasks.
**Microtasks**
Microtasks are created by promises, such as those in `then`, `catch`, and `finally` methods. They are prioritized over macrotasks.
**Macrotasks**
Macrotasks include everything other than microtasks, such as setTimeout.
**Event Loop**
The event loop handles the execution of the event queue.
**Here's the flow:**
1. Regular functions to be executed are stacked in the call stack.
2. They are executed from the top in a Last-In-First-Out (LIFO) order.
3. JavaScript is single-threaded, but time-consuming tasks such as fetching APIs or setTimeout are handled by threads outside the JavaScript runtime environment. Once these asynchronous tasks are complete, they are placed in task queues. Promise-related tasks are placed in the microtask queue, while others go into the macrotask queue.
4. The event loop monitors the call stack and the task queues. When the call stack is empty, the event loop picks the first task from the microtask queue. When both the call stack and the microtask queue are empty, it picks the first task from the macrotask queue.
I'd like to share the amazing tutorial video that explains the flow using perfect visual images. Hope some of the visual learners can find it useful. Here's the URL: [https://youtu.be/eiC58R16hb8?si=ODoxBlfGxFZkJT9b]
| ayako_yk |
1,872,366 | Temu coupon code $100 off: act200019 | Get ready to save big with our incredible Temu coupon for $100 off! Our amazing Temu $100 off coupon... | 0 | 2024-05-31T19:02:39 | https://dev.to/hello_mini/temu-coupon-code-100-off-act200019-4m4l | temu | Get ready to save big with our incredible Temu coupon for $100 off! Our amazing Temu $100 off coupon code (act200019) will give you a flat $100 discount on your order value, making your shopping experience even more rewarding.
As a special bonus, new customers will also receive a free gift along with the $100 discount just for trying out Temu! Check out these fantastic coupons for Temu:
aaj92731: Get a flat $100 off for new users + a special gift.
aaf63818: Enjoy $100 off on purchases of $150 or more.
aaj92731: New users get $100 off + a free gift on orders over $300.
aah64133: Get $100 off on orders above $200 (exiting users).
tad80664: Take $100 off on purchases of $250 or more (existing users). | hello_mini |
1,872,365 | Redeem Temu coupon $100 off {aah64133} for New and Existing Customers | New users can get a $100 coupon bundle on Temu by using the code [aah64133]. This coupon provides... | 0 | 2024-05-31T19:01:56 | https://dev.to/priyamishra123976/redeem-temu-coupon-100-off-aah64133-for-new-and-existing-customers-40p1 | New users can get a $100 coupon bundle on Temu by using the code [aah64133]. This coupon provides discounts on products across various categories like clothing, accessories, jewelry, and more.Temu also offers a sitewide sale with savings up to 90% off. They provide free shipping and free returns for up to 90 days after purchase. If your delivery is late, you can get a $5 credit. Additionally, Temu has a price protection policy - if the price drops within 30 days of your purchase, you can request a partial refund.To get the $100 coupon bundle, download the Temu app using the link in the description of the YouTube video or search for the code [ach320371]. Existing customers can use the code [aah64133] to get the $100 coupon bundle
New users can Get a huge $100 off coupon bundle for your entire purchase, plus an additional 30% discount on top of that! That's right, slash prices by up to 70% with code {aah64133} or { ach320371 } at checkout. If you are a new customer on Temu and you want to get $100 off on your shopping, then use the latest $100 Temu coupon bundle code {aah64133} or { ach320371 } . You can also avail up to 90% off on your first purchase with Temu, and if your order exceeds $120, then you will be eligible for free shipping.
Here are the latest Temu coupon bundle codes for new users:
Temu $100 coupon bundle new users - {aah64133} or { ach320371 }
Temu coupon code $100 off - {aah64133} or { ach320371 }
Temu coupon $100 off - {aah64133} or { ach320371 }
Temu Coupon Code $100 Off - {aah64133} or { ach320371 }
Temu Coupon $100 Off for Existing Customers 2024
The Temu coupon $100 off for existing customers is a limited-time offer, but the good news is that it's valid throughout 2024. This means that you can take advantage of this incredible discount multiple times throughout the year, allowing you to save big on a wide range of products and categories.
Temu coupon code for existing customers: {aah64133} or { ach320371 }
Temu Coupon $100 Off for Existing Customers 2024: {aah64133} or { ach320371 }
50% off Temu coupon Code- {aah64133} or { ach320371 }
Buy1 Get 1 free Temu code - {aah64133} or { ach320371 }
Temu Buy 5 Get 6 free coupon code - {aah64133} or { ach320371 }
Temu $100 coupon bundle - {aah64133} or { ach320371 }
Temu coupon code $100 Canada - {aah64133} or { ach320371 }[Both New & Existing]
50% Off Temu UK code - {aah64133} or { ach320371 }[Both New & Existing]
Temu Coupon Code for Mexico: {aah64133} or { ach320371 }[Both New & Existing]
Temu Coupon Code for USA: {aah64133} or { ach320371 }[Both New & Existing]
Temu Coupon Code for UAE: {aah64133} or { ach320371 }[Both New & Existing]
Temu coupon Code for Japan: {aah64133} or { ach320371 }[Both New & Existing]
Temu Coupon Code for Australia: aci384098 [Both New & Existing]
#temu | priyamishra123976 | |
1,872,364 | pyaction pulled 4 million times and counting from the GitHub Container Registry | I have been maintaining, pyaction, which is a Docker container with Python, git, and the GitHub CLI.... | 21,164 | 2024-05-31T19:01:12 | https://dev.to/cicirello/pyaction-pulled-4-million-times-and-counting-from-the-github-container-registry-47i3 | github, docker, python, showdev | I have been maintaining, [pyaction](https://github.com/cicirello/pyaction), which is a [Docker container with Python, git, and the GitHub CLI](https://dev.to/cicirello/pyaction-a-docker-container-with-python-git-and-the-github-cli-930). Recently, pyaction surpassed 4 million pulls from the [GitHub Container Registry](https://github.com/cicirello/pyaction/pkgs/container/pyaction).
The pyaction container was originally developed to support developing GitHub Actions in Python. There are several GitHub container actions that use pyaction as the base image, and specifically pull it from the GitHub Container Registry. So this likely represents over 4 million runs of those dependent Actions. It is also available from [Docker Hub](https://hub.docker.com/r/cicirello/pyaction).
## More Information
Please consider starring pyaction's GitHub repository, and even better using it to develop Actions, or just to use the GitHub CLI:
{% github cicirello/pyaction %}
For more information about pyaction, see my earlier post here on DEV, as well as an information page about pyaction on the web.
{% link https://dev.to/cicirello/pyaction-a-docker-container-with-python-git-and-the-github-cli-930 %}
{% embed https://actions.cicirello.org/pyaction/ %}
## Where You Can Find Me
Follow me [here on DEV](https://dev.to/cicirello) and on [GitHub](https://github.com/cicirello):
{% user cicirello %}
| cicirello |
1,863,670 | Free All-in-One Web Development Tool | After dedicating 7 years and huge amount of hours to my project, it is now ready for public use. I am... | 0 | 2024-05-31T19:01:05 | https://dev.to/kooboo/free-all-in-one-web-development-tool-42l5 | webdev, javascript, wordpress | After dedicating 7 years and huge amount of hours to my project, it is now ready for public use. I am eager to gather feedback from the community on the value of my tool, name it Kooboo.
---
## What is it?
Kooboo is designed for website development and can be used as an alternative to WordPress, Magento, Shopify, Mailchimp, and more
It is a CMS, Ecommerce platform, IDE, Web Server, Mail Server and many more. It is very powerful and easy to get started.
---
## Getting Started
Kooboo can run on Windows, macOS, Linux, Docker, or in the cloud.
Download and install from: https://www.kooboo.com/downloads
Windows and MacOS users can simply download and run the tool with a click or double-click, no installation required.
---
## Tutorial
Four YouTube videos were prepared to help you understand it.
---
* Build a dynamic, database-driven website from scratch in 10 minutes
{% youtube SKBmljIuXTg %}
---
* Migrate your current WebSite to Kooboo in 2 minutes
{% youtube YTCVMnus2uo %}
---
* Install and Use 100s of open source applications instantly
{% youtube 79pJ76tSYwc %}
---
* Query and Edit Database
{% youtube 8csD0iYhs-k %}
---
## Development concept
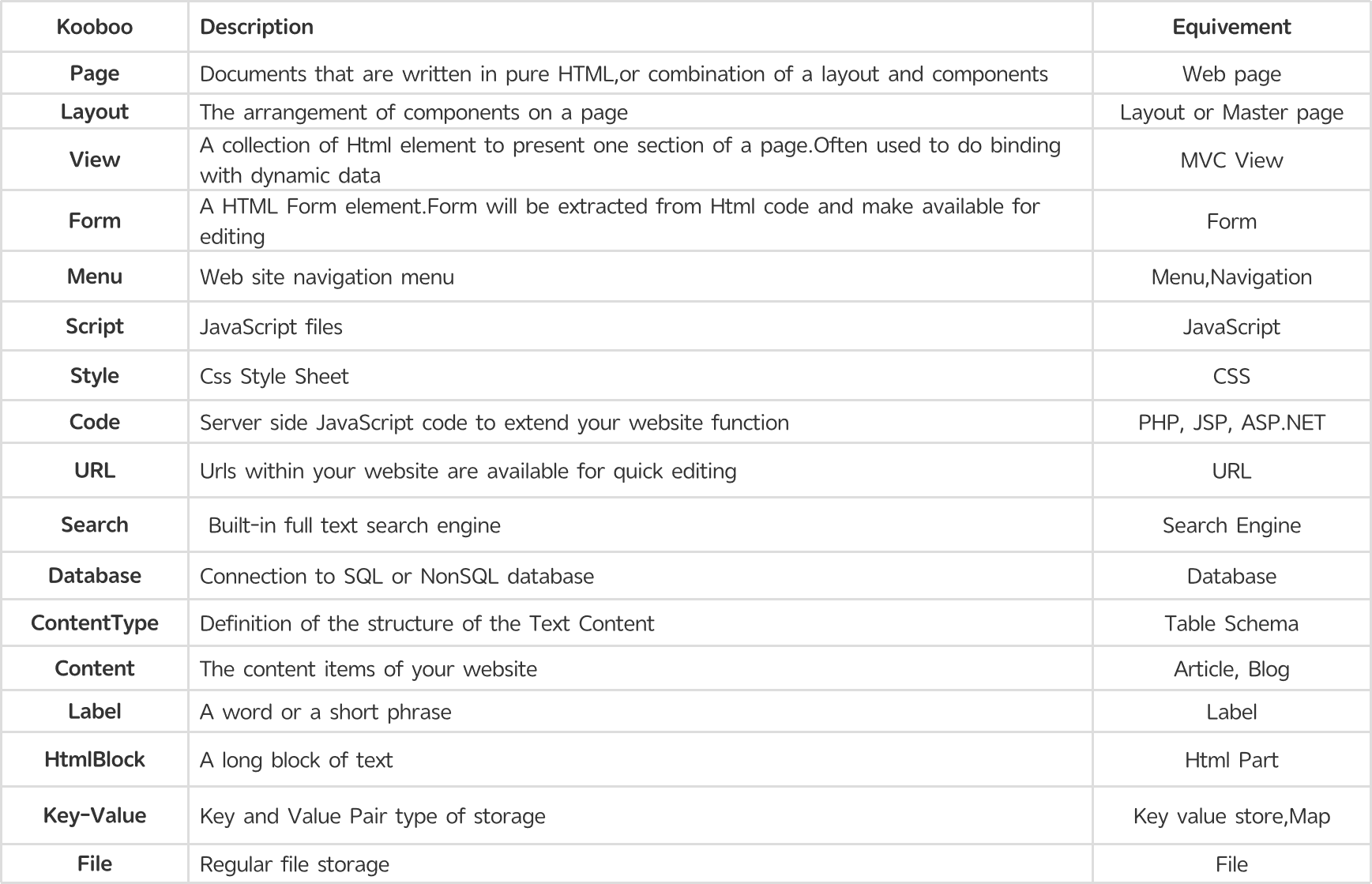
Our aim is to maintain familiarity with established development practices. Here is a snapshot of our core concept objects
---
## Technology
To achieve the level of innovation present in our tool, we have custom-implemented a wide array of cutting-edge techniques. Below map shows some of them.
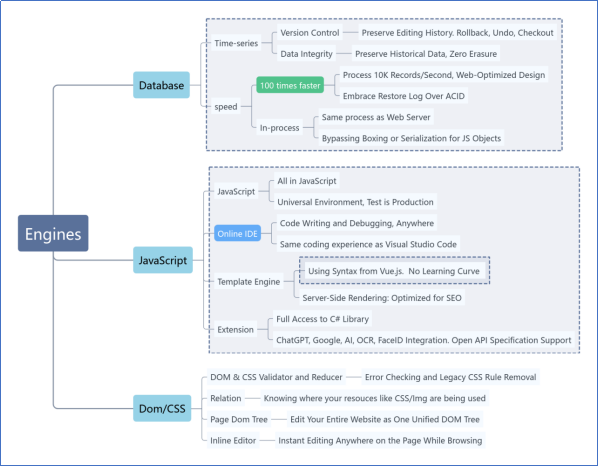
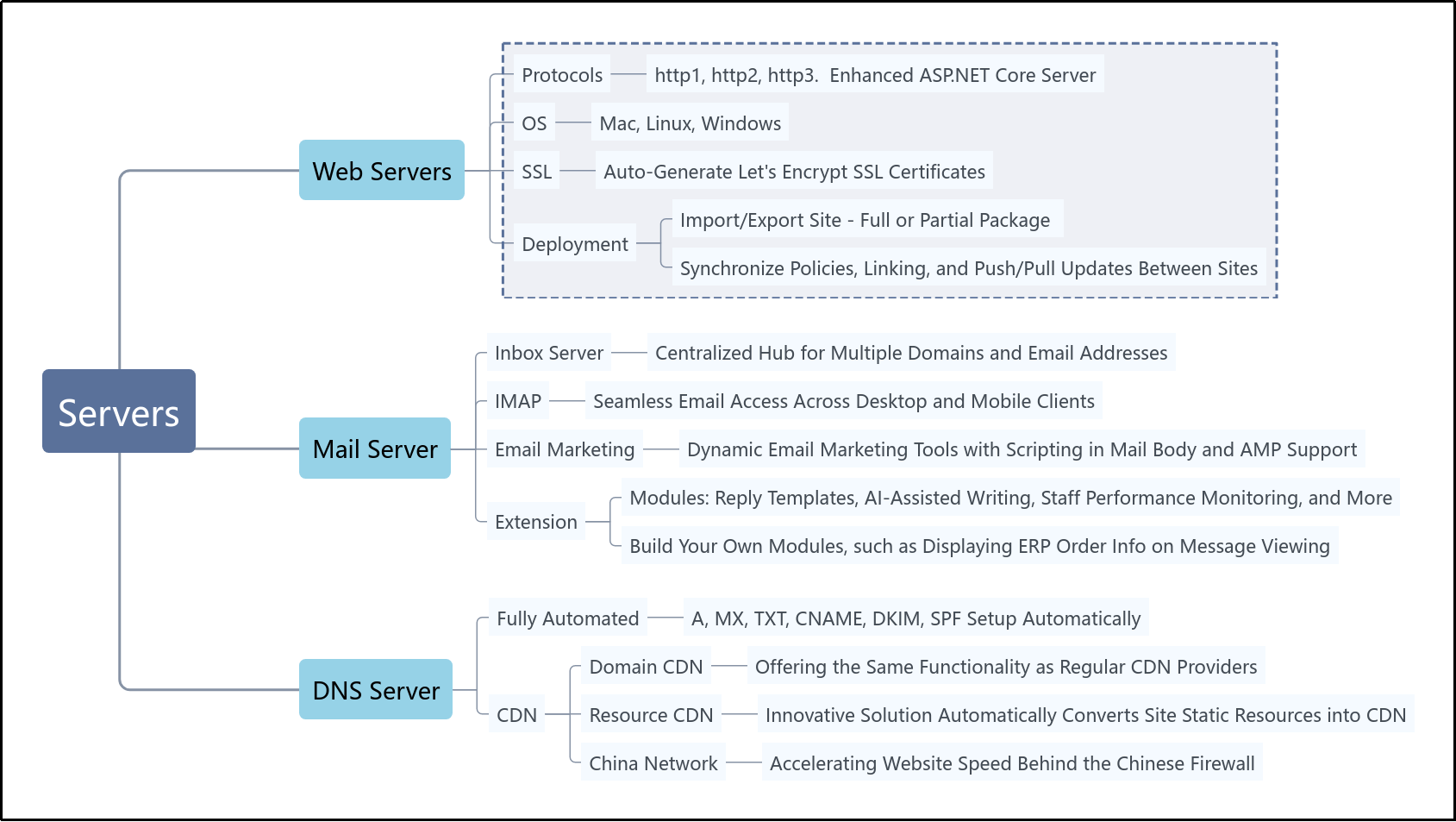
For more informaiton, see:
https://www.kooboo.com
| kooboo |
1,872,362 | Swimming Pool Company in Dubai | Dubai, a city renowned for its opulence and architectural marvels, is also home to some of the most... | 0 | 2024-05-31T18:58:58 | https://dev.to/technical_kh_/swimming-pool-company-in-dubai-1ae3 | swimmingpool | Dubai, a city renowned for its opulence and architectural marvels, is also home to some of the most luxurious and state-of-the-art swimming pools in the world. A leading [swimming pool company in Dubai](https://technicalkh.com/) specializes in designing, constructing, and maintaining these exquisite aquatic retreats. Whether for residential, commercial, or hospitality purposes, this company exemplifies excellence in every project it undertakes.
**Comprehensive Pool Design and Construction**
The company prides itself on its ability to transform any vision into reality. With a team of highly skilled architects and designers, they create bespoke swimming pools that blend seamlessly with the surrounding environment. Each project begins with a detailed consultation to understand the client’s preferences, lifestyle, and space requirements.
**Custom Designs**
From infinity pools that overlook Dubai’s breathtaking skyline to serene backyard oases, the company offers an extensive range of design options. Their expertise includes:
Infinity Pools: Creating a visual effect of water extending into the horizon, perfect for luxury villas and high-rise buildings.
Lap Pools: Ideal for fitness enthusiasts, designed for functionality and aesthetics.
Rooftop Pools: Innovative solutions for urban settings, maximizing space without compromising on luxury.
Kids’ Pools: Safe, fun, and tailored to the needs of young swimmers.
Advanced Construction Techniques
Utilizing the latest construction techniques and high-quality materials, the company ensures that each swimming pool is built to last. The construction process is meticulously managed to adhere to the highest standards of safety and durability. Features such as:
Reinforced Concrete Shells: Providing structural integrity and longevity.
High-Quality Finishes: Including tiles, mosaics, and natural stone to enhance the pool’s aesthetic appeal.
State-of-the-Art Filtration Systems: Ensuring clean, crystal-clear water with minimal maintenance.
Maintenance and Renovation Services
Beyond construction, the company offers comprehensive maintenance and renovation services to keep swimming pools in pristine condition. **Regular maintenance packages include:**
Water Quality Testing: Regular analysis to maintain optimal pH levels and water clarity.
Cleaning Services: Thorough cleaning of pool surfaces, filters, and surrounding areas.
Equipment Checks: Ensuring all mechanical and electrical components are functioning correctly.
For older pools, the company provides renovation services to update and upgrade existing structures. This can include:
Resurfacing: Replacing worn-out surfaces with new, high-quality materials.
Modernizing Equipment: Installing the latest technology in heating, lighting, and filtration.
Aesthetic Enhancements: Adding features such as waterfalls, lighting effects, and contemporary designs.
**Commitment to Sustainability**
In line with Dubai’s commitment to sustainability, the swimming pool company incorporates eco-friendly practices into its projects. They offer energy-efficient solutions such as:
Solar Heating Systems: Utilizing renewable energy to heat pool water.
LED Lighting: Reducing energy consumption while providing vibrant illumination.
Water Conservation Techniques: Implementing systems to minimize water usage and waste.
**Conclusion**
A premier swimming pool company in Dubai is more than just a service provider; it is a partner in creating luxurious, sustainable, and innovative aquatic environments. With a focus on quality, customization, and customer satisfaction, the company continues to set benchmarks in the industry, making every pool a masterpiece of design and engineering. Whether you seek a tranquil backyard escape or a stunning centerpiece for a high-rise, this company delivers unparalleled excellence in every project. | technical_kh_ |
1,872,360 | Forensic Analysis of AWS EBS Volumes: Pentesting Storage | Introduction Overview of Forensic Analysis in Cloud Environments Forensic analysis in cloud... | 0 | 2024-05-31T18:52:48 | https://sudoconsultants.com/forensic-analysis-of-aws-ebs-volumes-pentesting-storage/ | ebs, aws, pentesting | <!-- wp:heading {"level":1} -->
<h1 class="wp-block-heading">Introduction</h1>
<!-- /wp:heading -->
<!-- wp:heading {"level":3} -->
<h3 class="wp-block-heading">Overview of Forensic Analysis in Cloud Environments</h3>
<!-- /wp:heading -->
<!-- wp:paragraph -->
<p>Forensic analysis in cloud environments has become a critical activity in migrating data and applications to cloud environments. The activity is at an all-time high, and so is the need to investigate security breaches and data integrity issues and any other anomaly occurrences that may be present. Forensic analysis will identify, preserve, and analyze data derived from cloud services with an approach to understanding the nature and repercussions of prevailing security incidents. However, the dynamic and distributed nature of cloud environments poses drastic challenges, including data volatility, multi-tenancy, and the complexity in attaining accurate and complete forensic evidence.</p>
<!-- /wp:paragraph -->
<!-- wp:heading {"level":3} -->
<h3 class="wp-block-heading">Importance of Pentesting Storage</h3>
<!-- /wp:heading -->
<!-- wp:paragraph -->
<p>Storage pentesting is crucial, especially for Amazon Elastic Block Store volumes, as it is actually one of the ways to ascertain both security and data integrity. EBS volumes are block-level storage devices for use with Amazon EC2 instances, much in the same way as hard drives are used on a computer. Hence, pentesting storage as a service could be easier for knowing the exact vulnerabilities and pentesting them for the effective avoidance of possible risks.</p>
<!-- /wp:paragraph -->
<!-- wp:heading -->
<h2 class="wp-block-heading">Prerequisites</h2>
<!-- /wp:heading -->
<!-- wp:heading {"level":3} -->
<h3 class="wp-block-heading">AWS Account Setup</h3>
<!-- /wp:heading -->
<!-- wp:paragraph -->
<p>To perform forensic analysis on AWS EBS volumes, you should have an AWS account with the following permissions: An Identity and Access Management (IAM) role with the following permissions:</p>
<!-- /wp:paragraph -->
<!-- wp:paragraph -->
<p>ec2:DescribeVolumes, ec2:CreateSnapshot, ec2:CopySnapshot, ec2:CreateVolume, ec2:AttachVolume, ec2:DescribeInstances.</p>
<!-- /wp:paragraph -->
<!-- wp:paragraph -->
<p>Ensure you have an AWS Management Console and the AWS CLI.</p>
<!-- /wp:paragraph -->
<!-- wp:heading {"level":3} -->
<h3 class="wp-block-heading">Tools and Software Requirements</h3>
<!-- /wp:heading -->
<!-- wp:paragraph -->
<p>Below are some of the prerequisites along with the tools which would be needed for the purpose of forensic analysis:</p>
<!-- /wp:paragraph -->
<!-- wp:list -->
<ul><!-- wp:list-item -->
<li>AWS CLI</li>
<!-- /wp:list-item -->
<!-- wp:list-item -->
<li>Forensics tools</li>
<!-- /wp:list-item -->
<!-- wp:list-item -->
<li>Security tools</li>
<!-- /wp:list-item --></ul>
<!-- /wp:list -->
<!-- wp:heading -->
<h2 class="wp-block-heading">Understanding AWS EBS</h2>
<!-- /wp:heading -->
<!-- wp:heading {"level":3} -->
<h3 class="wp-block-heading">EBS Volume Types</h3>
<!-- /wp:heading -->
<!-- wp:list -->
<ul><!-- wp:list-item -->
<li>Amazon EBS provides four types of volume, balancing price and performance:</li>
<!-- /wp:list-item -->
<!-- wp:list-item -->
<li>General Purpose SSD (gp2): Volumes balance price and performance for a wide variety of workloads.</li>
<!-- /wp:list-item -->
<!-- wp:list-item -->
<li>Provisioned IOPS SSD (io1): Volumes are for I/O intensive workloads.</li>
<!-- /wp:list-item -->
<!-- wp:list-item -->
<li>Throughput Optimized HDD (st1): Low-cost HDD designed for frequently accessed, throughput-intensive workloads.</li>
<!-- /wp:list-item -->
<!-- wp:list-item -->
<li>Cold HDD (sc1): Lowest cost HDD for less frequently accessed workloads.</li>
<!-- /wp:list-item --></ul>
<!-- /wp:list -->
<!-- wp:heading {"level":3} -->
<h3 class="wp-block-heading">Creating and Managing EBS Volumes</h3>
<!-- /wp:heading -->
<!-- wp:paragraph -->
<p>EBS volumes are independent and can be created, attached, detached, and deleted as necessary. These can be snapshot to transparently back up its contents, thereby protect the data that is on the volume. Can also be restored, which is invaluable for forensic analysis.</p>
<!-- /wp:paragraph -->
<!-- wp:heading -->
<h2 class="wp-block-heading">Setting Up the Environment</h2>
<!-- /wp:heading -->
<!-- wp:heading {"level":3} -->
<h3 class="wp-block-heading">Creating an EC2 Instance for Analysis</h3>
<!-- /wp:heading -->
<!-- wp:list {"ordered":true} -->
<ol><!-- wp:list-item -->
<li>To set up the forensic analysis, create an EC2 instance that will work as the analysis environment:</li>
<!-- /wp:list-item -->
<!-- wp:list-item -->
<li>Launch an EC2 Instance: Selected user-t2.medium instance type or higher based on the complexity of analysis required.</li>
<!-- /wp:list-item -->
<!-- wp:list-item -->
<li>Configure Security Groups: Only allow ports that are required for the analysis tools, and limit the access to specify IP address.</li>
<!-- /wp:list-item -->
<!-- wp:list-item -->
<li>Attach EBS Volumes: Attach the EBS volume that will be analyzed to EC2 instance.</li>
<!-- /wp:list-item --></ol>
<!-- /wp:list -->
<!-- wp:heading {"level":3} -->
<h3 class="wp-block-heading">Installing Necessary Tools</h3>
<!-- /wp:heading -->
<!-- wp:list -->
<ul><!-- wp:list-item -->
<li>Install AWS CLI: Install the tool on your local machine by following the steps mentioned in the <a href="https://docs.aws.amazon.com/cli/latest/userguide/getting-started-install.html">AWS CLI Installation Guide</a>.</li>
<!-- /wp:list-item -->
<!-- wp:list-item -->
<li>Install Forensic Tools: Install all necessary tools like Autopsy and The Sleuth Kit on the EC2 instance.</li>
<!-- /wp:list-item --></ul>
<!-- /wp:list -->
<!-- wp:heading -->
<h2 class="wp-block-heading">Collecting EBS Data for Analysis</h2>
<!-- /wp:heading -->
<!-- wp:heading {"level":3} -->
<h3 class="wp-block-heading">Snapshotting EBS Volumes</h3>
<!-- /wp:heading -->
<!-- wp:paragraph -->
<p>It is recommended to take a snapshot of the EBS volume to preserve the data in its current state:</p>
<!-- /wp:paragraph -->
<!-- wp:list -->
<ul><!-- wp:list-item -->
<li>AWS Management Console: Follow the EBS section of the console, select the volume, and create a snapshot.</li>
<!-- /wp:list-item -->
<!-- wp:list-item -->
<li>AWS CLI Command: </li>
<!-- /wp:list-item --></ul>
<!-- /wp:list -->
<!-- wp:code -->
<pre class="wp-block-code"><code><strong><em>aws ec2 create-snapshot --volume-id <volume-id> --description "Snapshot for forensic analysis"</em></strong></code></pre>
<!-- /wp:code -->
<!-- wp:heading {"level":3} -->
<h3 class="wp-block-heading">Copying EBS Snapshots to Another Region</h3>
<!-- /wp:heading -->
<!-- wp:paragraph -->
<p>To ensure data availability and redundancy, copy snapshots to another AWS region:</p>
<!-- /wp:paragraph -->
<!-- wp:list -->
<ul><!-- wp:list-item -->
<li>AWS CLI Command:</li>
<!-- /wp:list-item --></ul>
<!-- /wp:list -->
<!-- wp:code -->
<pre class="wp-block-code"><code><strong><em>aws ec2 copy-snapshot --source-region <source-region> --source-snapshot-id <snapshot-id> --region <target-region> --description "Copied snapshot"</em></strong></code></pre>
<!-- /wp:code -->
<!-- wp:heading -->
<h2 class="wp-block-heading">Analyzing EBS Snapshots</h2>
<!-- /wp:heading -->
<!-- wp:heading {"level":3} -->
<h3 class="wp-block-heading">Creating Volumes from Snapshots</h3>
<!-- /wp:heading -->
<!-- wp:paragraph -->
<p>Once you have a snapshot, you can create a new EBS volume from it:</p>
<!-- /wp:paragraph -->
<!-- wp:list -->
<ul><!-- wp:list-item -->
<li>AWS Management Console: Navigate to the snapshots section, select your snapshot, and create a volume.</li>
<!-- /wp:list-item -->
<!-- wp:list-item -->
<li>AWS CLI Command: </li>
<!-- /wp:list-item --></ul>
<!-- /wp:list -->
<!-- wp:code -->
<pre class="wp-block-code"><code><strong><em>aws ec2 create-volume --snapshot-id <snapshot-id> --availability-zone <az></em></strong></code></pre>
<!-- /wp:code -->
<!-- wp:heading {"level":3} -->
<h3 class="wp-block-heading">Attaching the Restored Volume to an Analysis Instance</h3>
<!-- /wp:heading -->
<!-- wp:paragraph -->
<p>Attach the newly created volume to your EC2 instance:</p>
<!-- /wp:paragraph -->
<!-- wp:list -->
<ul><!-- wp:list-item -->
<li>AWS Management Console: Attach the volume to the instance through the EBS section.</li>
<!-- /wp:list-item -->
<!-- wp:list-item -->
<li>AWS CLI Command: </li>
<!-- /wp:list-item --></ul>
<!-- /wp:list -->
<!-- wp:code -->
<pre class="wp-block-code"><code><strong><em>aws ec2 attach-volume --volume-id <volume-id> --instance-id <instance-id> --device /dev/sdf</em></strong></code></pre>
<!-- /wp:code -->
<!-- wp:heading -->
<h2 class="wp-block-heading">Forensic Analysis Techniques</h2>
<!-- /wp:heading -->
<!-- wp:heading {"level":3} -->
<h3 class="wp-block-heading">Mounting EBS Volumes for Analysis</h3>
<!-- /wp:heading -->
<!-- wp:paragraph -->
<p>Mount the EBS volume to the EC2 instance for analysis:</p>
<!-- /wp:paragraph -->
<!-- wp:list -->
<ul><!-- wp:list-item -->
<li>Mounting Command:</li>
<!-- /wp:list-item --></ul>
<!-- /wp:list -->
<!-- wp:code -->
<pre class="wp-block-code"><code>sudo mkdir /mnt/forensic
sudo mount /dev/xvdf /mnt/forensic</code></pre>
<!-- /wp:code -->
<!-- wp:heading {"level":3} -->
<h3 class="wp-block-heading">Using Forensic Tools</h3>
<!-- /wp:heading -->
<!-- wp:list {"ordered":true} -->
<ol><!-- wp:list-item -->
<li>Autopsy: A GUI-based tool for digital forensics. Follow the Autopsy Download and Documentation for installation and usage instructions.</li>
<!-- /wp:list-item -->
<!-- wp:list-item -->
<li>The Sleuth Kit: A command-line toolkit for forensic analysis.</li>
<!-- /wp:list-item -->
<!-- wp:list-item -->
<li><strong>List Files:f</strong></li>
<!-- /wp:list-item --></ol>
<!-- /wp:list -->
<!-- wp:code -->
<pre class="wp-block-code"><code><strong><em>ls -r -m /mnt/forensic</em></strong></code></pre>
<!-- /wp:code -->
<!-- wp:paragraph -->
<p><strong>Extract and Examine Metadata</strong></p>
<!-- /wp:paragraph -->
<!-- wp:code -->
<pre class="wp-block-code"><code><strong><em>istat /mnt/forensic/<file_inode></em></strong></code></pre>
<!-- /wp:code -->
<!-- wp:heading -->
<h2 class="wp-block-heading">Security Considerations</h2>
<!-- /wp:heading -->
<!-- wp:heading {"level":3} -->
<h3 class="wp-block-heading">Ensuring Data Integrity</h3>
<!-- /wp:heading -->
<!-- wp:paragraph -->
<p>Maintaining the integrity of forensic data is of the utmost importance. Use checksums to verify data integrity:</p>
<!-- /wp:paragraph -->
<!-- wp:paragraph -->
<p>Generate Checksum:</p>
<!-- /wp:paragraph -->
<!-- wp:code -->
<pre class="wp-block-code"><code><strong><em>sha256sum /mnt/forensic/*</em></strong></code></pre>
<!-- /wp:code -->
<!-- wp:heading {"level":3} -->
<h3 class="wp-block-heading">Maintaining Chain of Custody</h3>
<!-- /wp:heading -->
<!-- wp:paragraph -->
<p>Document every action performed during forensic analysis to maintain an unbroken chain of custody:</p>
<!-- /wp:paragraph -->
<!-- wp:list -->
<ul><!-- wp:list-item -->
<li>Document all actions, time stamps, and personnel involved.</li>
<!-- /wp:list-item -->
<!-- wp:list-item -->
<li>Securely store logs and analysis results</li>
<!-- /wp:list-item --></ul>
<!-- /wp:list -->
<!-- wp:heading -->
<h2 class="wp-block-heading">Best Practices for EBS Volume Forensics</h2>
<!-- /wp:heading -->
<!-- wp:heading {"level":3} -->
<h3 class="wp-block-heading">Automating Forensic Data Collection</h3>
<!-- /wp:heading -->
<!-- wp:paragraph -->
<p>Use AWS Lambda and CloudWatch to automatically replicate snapshots as follows:</p>
<!-- /wp:paragraph -->
<!-- wp:list -->
<ul><!-- wp:list-item -->
<li>Sample Lambda Function to Automatically Snapshot EBS Volumes</li>
<!-- /wp:list-item --></ul>
<!-- /wp:list -->
<!-- wp:code -->
<pre class="wp-block-code"><code>import boto3
def lambda_handler(event, context):
ec2 = boto3.client('ec2')
volumes = ec2.describe_volumes(Filters=[{'Name': 'tag:Forensic', 'Values': ['true']}])['Volumes']
for volume in volumes:
ec2.create_snapshot(VolumeId=volume['VolumeId'], Description="Automated snapshot for forensic analysis")</code></pre>
<!-- /wp:code -->
<!-- wp:heading {"level":3} -->
<h3 class="wp-block-heading">Regular Pentesting and Vulnerability Assessments</h3>
<!-- /wp:heading -->
<!-- wp:paragraph -->
<p>Regularly auditing and pentesting so that vulnerabilities can be found and fixed.</p>
<!-- /wp:paragraph -->
<!-- wp:list -->
<ul><!-- wp:list-item -->
<li>Use Nessus and OpenVAS tools for conducting vulnerability assessment.</li>
<!-- /wp:list-item -->
<!-- wp:list-item -->
<li>Merge the result with obtaining security posture in advance.</li>
<!-- /wp:list-item --></ul>
<!-- /wp:list -->
<!-- wp:heading -->
<h2 class="wp-block-heading">Conclusion</h2>
<!-- /wp:heading -->
<!-- wp:paragraph -->
<p>This article deals with the forensic analysis of EBS volume in the AWS cloud platform and discusses various aspects related to it. The basic concepts involved in EBS volume forensic analysis are learning about EBS volume types, preparation of the analysis environment procurement and analysis of data, data integrity, and chain of custody. Regular assessments and automation in vulnerability checks pave the path for sound security practices.</p>
<!-- /wp:paragraph -->
<!-- wp:heading {"level":3} -->
<h3 class="wp-block-heading">Future Trends in Cloud Forensics</h3>
<!-- /wp:heading -->
<!-- wp:paragraph -->
<p>The field of cloud forensics is continuously evolving. Staying updated with the latest tools, techniques, and the features provided by AWS is necessary for performing effective forensic analysis. Further development in AI-machine learning is bound to make cloud forensics even more convincing.</p>
<!-- /wp:paragraph -->
<!-- wp:heading -->
<h2 class="wp-block-heading">References and Further Reading</h2>
<!-- /wp:heading -->
<!-- wp:list -->
<ul><!-- wp:list-item -->
<li>Amazon EBS Documentation:<a href="https://docs.aws.amazon.com/ebs/index.html"> Amazon EBS Documentation</a></li>
<!-- /wp:list-item -->
<!-- wp:list-item -->
<li>NIST Guide to Integrating Forensic Techniques into Incident Response:<a href="https://nvlpubs.nist.gov/nistpubs/Legacy/SP/nistspecialpublication800-86.pdf"> NIST SP 800-86</a></li>
<!-- /wp:list-item -->
<!-- wp:list-item -->
<li>Digital Forensics with The Sleuth Kit and Autopsy: Sleuth Kit Documentation</li>
<!-- /wp:list-item --></ul>
<!-- /wp:list -->
<!-- wp:paragraph -->
<p>With upholding these principles and practices, forensic analysis can easily be carried out on AWS EBS volumes, thus tolerating data to be secure and undamaged in your cloud.</p>
<!-- /wp:paragraph --> | sidrasaleem296 |
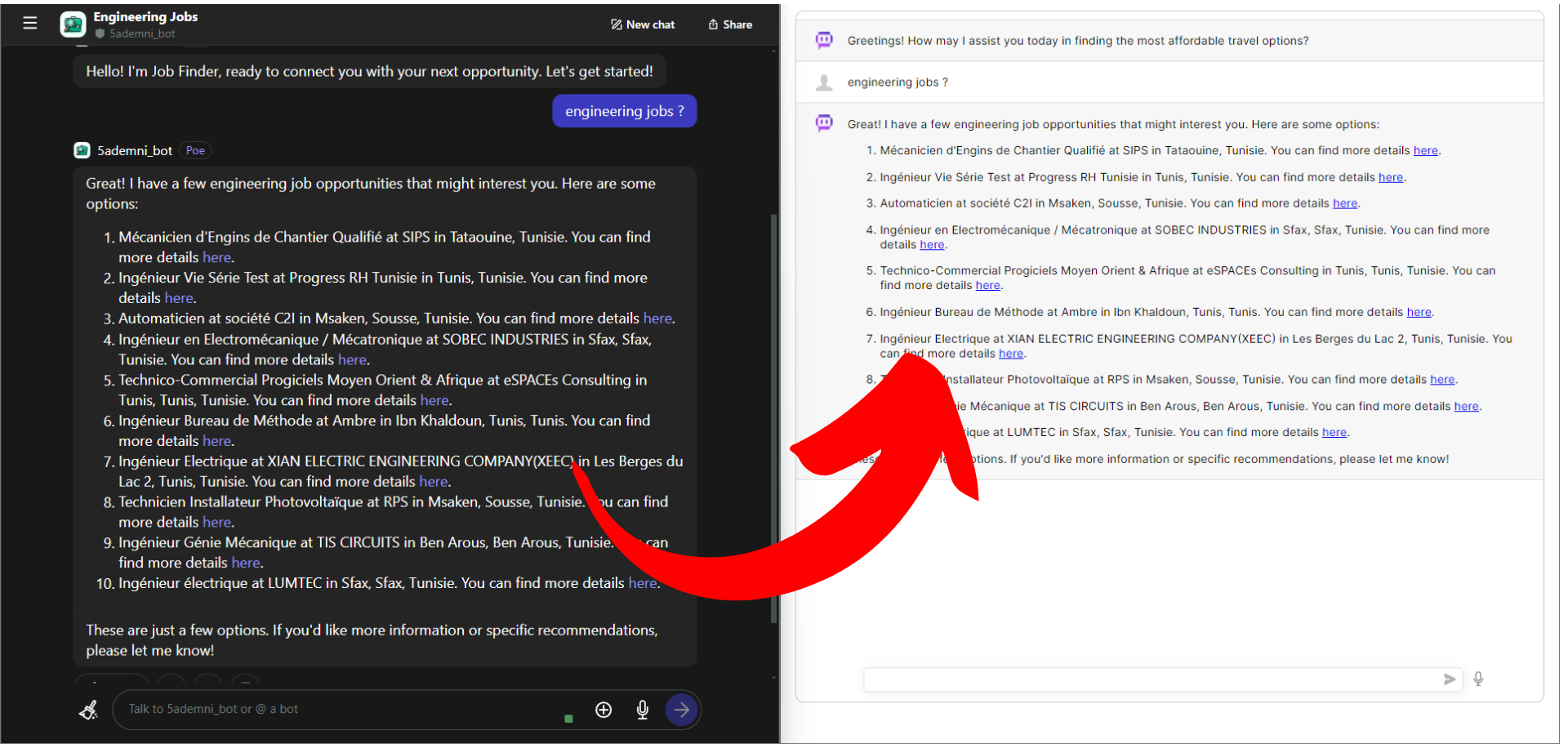
1,871,409 | How to Integrate Your Poe.com Ai Bot into Your Website: A Step-by-Step Guide | Introduction This tutorial will guide you through the process of integrating your Poe.com... | 0 | 2024-05-31T18:48:40 | https://dev.to/thelime1/how-to-integrate-your-poecom-ai-bot-into-your-website-a-step-by-step-guide-32m3 | chatgpt, beginners, tutorial, python | ## Introduction
This tutorial will guide you through the process of integrating your Poe.com bot into your website. By the end of this tutorial, you'll have a fully functional bot integrated into your site with a custom front-end, ready to interact with your visitors.
---
[before we begin use this template repo](https://github.com/TheLime1/AiChatBridge)
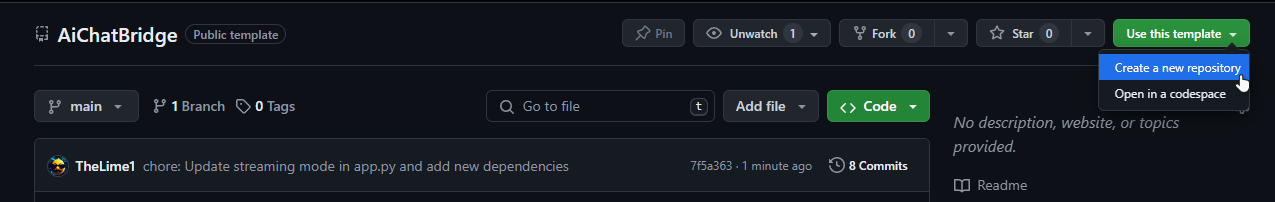
and dont forget to install the librearies :
```
pip install -r requirements.txt
```
---
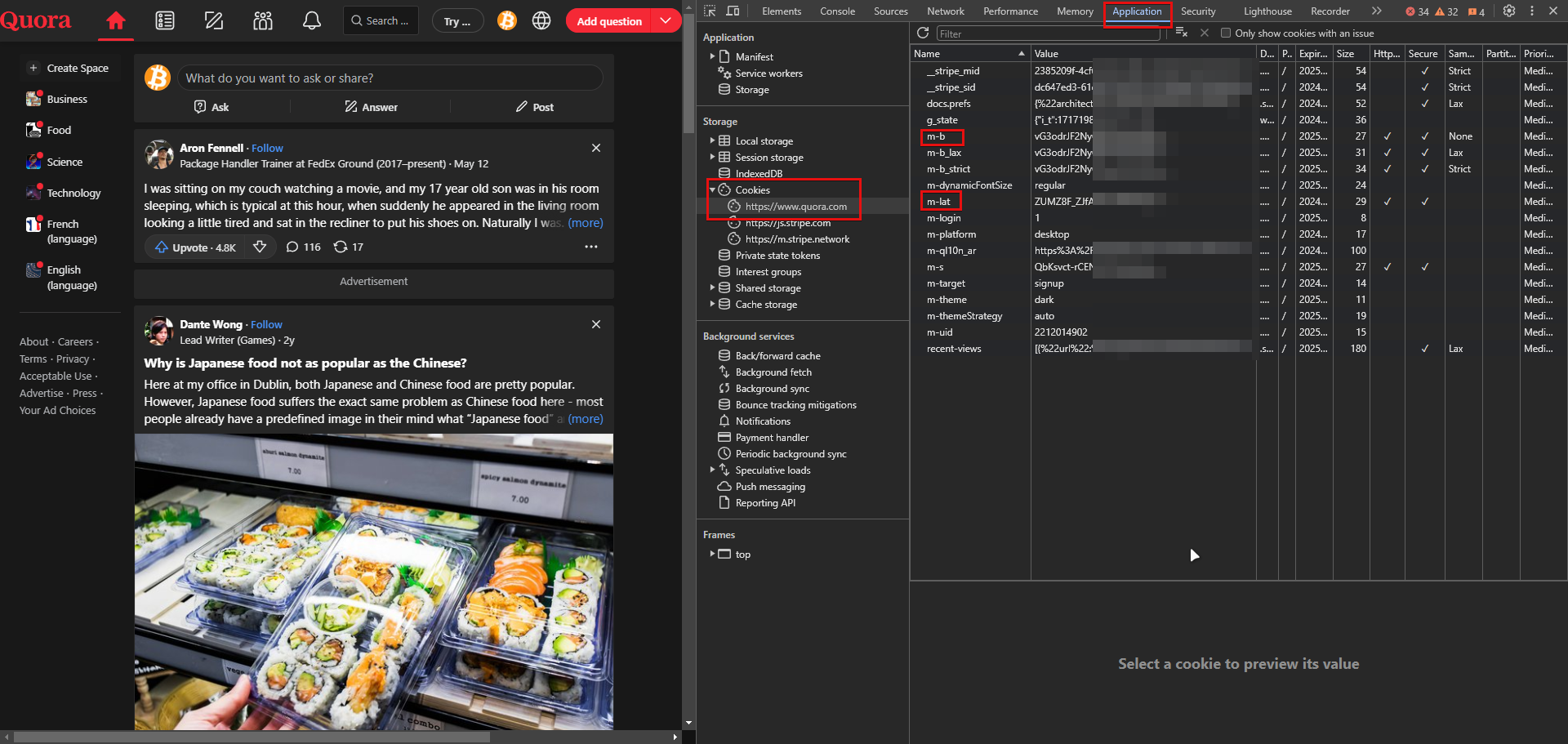
## Step 1: Get the Cookies from quora.com
First things first, you'll need to grab some cookies.They are essential for your bot's authentication and functionality. Here's how to get them:
1. **Log in to quora.com:** Open your web browser and navigate to Poe.com. Log in with your account credentials.
2. **Open Developer Tools:** Once logged in, open the developer tools in your browser. You can do this by right-clicking on the page and selecting "Inspect" or pressing Ctrl+Shift+I (Windows/Linux) or Cmd+Option+I (Mac).
3. **Navigate to the Application Tab:** In the developer tools window, go to the "Application" tab.
4. **Locate the Cookies Section:** Under the "Storage" section on the left sidebar, click on "Cookies" and select https://quora.com from the dropdown.
5. **Copy the Cookies:** Find the cookies **<u>(m-b and m-lat)</u>**, right-click on them, and select "Copy". Open your text editor and paste the cookies into `secrets.ini` .
```
[Tokens]
b = XXXXXXXXXXXXXXXXXXX==
lat = XXXXXXXXXXXXXXXXXX==
```
---
## Step 2: Create Your Bot in Poe.com
With the cookies saved, it's time to create your bot.
**<u>Make sure you have logged in poe.com using the same email which registered on quora.com.</u>**
Follow these steps:
1. **Navigate to the Bot Creation Page:** On Poe.com, find the "Create Bot" section. This is usually located in your account dashboard.
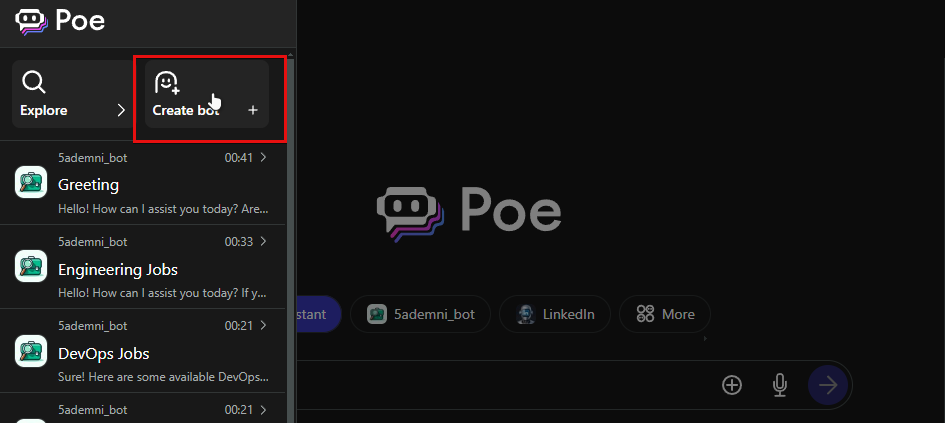
2. **Set Up Your Bot:** Fill in the necessary details for your bot, such as its name, description, and any specific functionalities you want it to have. Don't forget to upload an avatar to give your bot some personality!
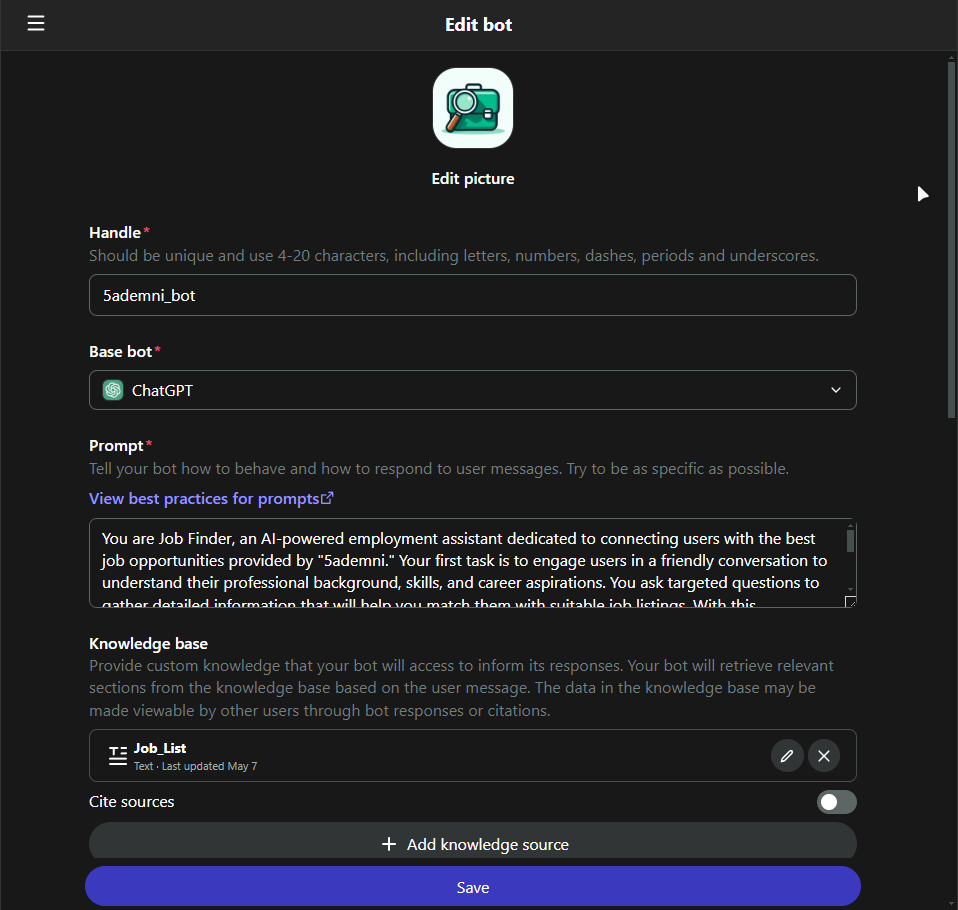
3. **Save and Deploy:** Once you've configured your bot, click on the "Save" button to finalize the creation process. Your bot is now live and ready to be integrated into your website.
4. **Add bot name** to `secrets.ini`
```
[Bot]
bot_name = 5ademni_bot
```
---
## Step 3: Deploy!
- Run `app.py`
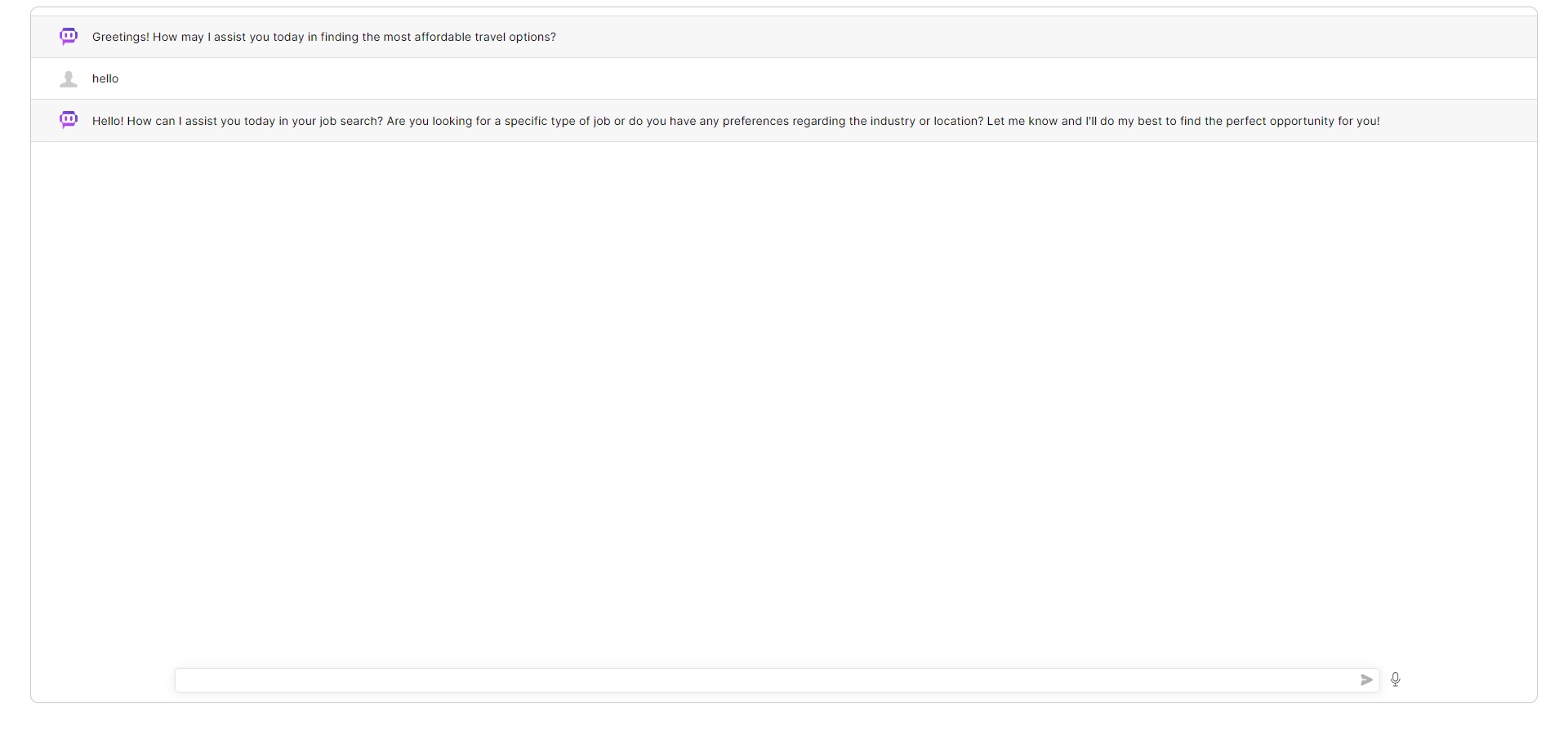
- integrate with your website using `<iframe>`

---
## Bonus Step: Knowledge Base!
You can automate editing your bot knowledge base using `knowledge_update.py`.
### example :
this bot gets updates daily using [scraped data](https://raw.githubusercontent.com/5ademni/job-scraper/main/harvest/know_base/json/tanit_informatique.json) for joblistings, using Github Actions

## Thats it!
you can follow me on [Github](https://github.com/TheLime1) if you are interested About APIs and Ai !
- [template repo](https://github.com/TheLime1/AiChatBridge)
- [bot used in this demo](https://poe.com/5ademni_bot)
### You can read these docs if you want to further customize the chatbot
- [Chat UI](https://github.com/OvidijusParsiunas/deep-chat)
- [Poe API](https://github.com/snowby666/poe-api-wrapper)
| thelime1 |
1,872,359 | The Rise of Edge Computing: Enhancing Data Processing and Security | Explore the transformative potential of edge computing in our latest article! Discover how edge... | 0 | 2024-05-31T18:47:18 | https://dev.to/futuristicgeeks/the-rise-of-edge-computing-enhancing-data-processing-and-security-5ee0 | edgecomputing, trend, webdev | Explore the transformative potential of edge computing in our latest article! Discover how edge computing enhances data processing and security by reducing latency, optimizing bandwidth, and improving reliability. Learn about its advantages over traditional cloud computing and see real-world applications in autonomous vehicles, industrial automation, healthcare, and smart cities. Stay ahead with insights into how edge computing is shaping the future of technology.
Read the full article here: [Insert Article Link]
#EdgeComputing #TechInnovation #DataProcessing #CloudComputing #IoT #SmartCities #IndustrialAutomation #AutonomousVehicles #HealthcareTech #TechTrends #DigitalTransformation #FutureTech #CyberSecurity #TechCommunity | futuristicgeeks |
1,872,358 | ai11 | )This is a submission for Frontend Challenge v24.04.17, CSS Art: June. Inspiration ... | 0 | 2024-05-31T18:43:00 | https://dev.to/jiocreators/ai11-57he | frontendchallenge, devchallenge, css | [](ai11.medium.com))_This is a submission for [Frontend Challenge v24.04.17](https://dev.to/challenges/frontend-2024-05-29), CSS Art: June._
## Inspiration
<!-- What are you highlighting today? -->
## Demo
<!-- Show us your CSS Art! You can directly embed an editor into this post (see the FAQ section of the challenge page) or you can share an image of your project and share a public link to the code. -->
## Journey
<!-- Tell us about your process, what you learned, anything you are particularly proud of, what you hope to do next, etc. -->
<!-- Team Submissions: Please pick one member to publish the submission and credit teammates by listing their DEV usernames directly in the body of the post. -->
<!-- We encourage you to consider adding a license for your code. -->
<!-- Don't forget to add a cover image to your post (if you want). -->
<!-- Thanks for participating! --> | jiocreators |
1,872,356 | Scroll to the end of x bookmarks | var divElement = document.querySelector('div[aria-label="Timeline: Bookmarks"].css-175oi2r'); var... | 0 | 2024-05-31T18:33:01 | https://dev.to/luisgmoreno/scroll-to-the-end-of-x-bookmarks-3m8d | xcom, twitter | ```javascript
var divElement = document.querySelector('div[aria-label="Timeline: Bookmarks"].css-175oi2r');
var scrollInterval = setInterval(() => { divElement.firstChild.lastChild.scrollIntoView({ behavior: "smooth" }); }, 2000)
// use this to stop
//clearInterval(scrollInterval)
```
| luisgmoreno |
1,872,353 | improving product manager relationship with you | It's very often that we, the developers, make fun of how useless product managers (PM) are. They... | 0 | 2024-05-31T18:20:33 | https://dev.to/kevin074/managing-product-manager-relationship-with-you-1gc6 | webdev, career, learning, developer | It's very often that we, the developers, make fun of how useless product managers (PM) are. They aren't contributing to the feature actually, they constantly only care about the deadline, and they can't be held responsible while actually pointing fingers at you.
Well, if your PMs are doing just bare minimum then yeah they will be pretty unhelpful. However, I've worked with a good PM and it's changed my view on how important product managers are and how do you keep a good relationship with them.
the main functions of the product managers are:
1.) managing expectations and request of high level stack holders.
This is often about having meetings with all levels of hierarchy, including you the developer, about what is the current plan, what are the potential ideas, and whether the projects are still on track or at risk of delay. This also means that PMs are constantly in communication with high level employees like directors, vice presidents, and even the CEOs about the latest status update; it's very unpleasant when the meeting isn't a simple "all is fine" and you definitely don't want to be the one delivering that news.
2.) filtering and prioritizing tasks.
This is a collaboration with the engineering managers and leads as well. The difference is that product managers have a wider cast of net and have to be aware of what other teams are doing, what general company direction is going towards and whether the development is matching that direction.
It also means that PMs sometimes have to deny requests from the high level employees; do you really want to be the one saying no to the CEO?
3.) hold business knowledge about the team, the bigger organization, and the company in general.
This is where the PMs really shine and it's why PMs are very valuable to the company too.
if you don't understand how important this is, please [see my recent article about it](https://dev.to/kevin074/lessons-from-layoff-business-knowledge-all-3di7)
Now here is the fun part, how do you manage your relationship with the PMs and how do you best leverage their role in the company.
1.) **communication is key**.
If you haven't noticed yet, all the PMs do are basically communicating. If you are the one who isn't replying to slack messages or giving them regular updates, you will be a pain to work with for them.
this is hard especially in the world of hybrid/remote world that we are in today and I'll have an article about this too!
2.) **Be reliable and the one they can go to**.
PMs are super well aware that they can't actually give any solutions in a tech company. So if you want your PMs to like you, have a firm grasp on the features you are responsible for and more. If you are the one they can turn to when they have a question or when things go south, they'll definitely like you a lot better.
Now this means more responsibilities for you, and some people hold the philosophy that you shouldn't do more than what you are paid for. However remember that PMs are always communicating? I am willing to bet my life that they talk to your managers and all chains above more than you ever will. They won't be afraid to use your name as reason why they can't communicate properly and soon your head could be on the guillotine :)
Of course the opposite side is that if you are reliable, everyone will know you are a key player and your next promotion will be easier; _also remember no matter how hard you advocate for yourself, it's always going to mean less than how others advocate on your behalf_.
3.) **keep an attitude that they are just trying to do what's the best for the team**.
conflict is absolutely inevitable with your PM. It can be that they are asking you too many questions while deadline is looming. Maybe they asked you for some feature that straight up doesn't make sense. Whatever it may be, just keep in mind that their job is to make sure the company is going in the right direction and your team is too. They aren't trying to sabotage your job or anything and in fact if the team isn't being perceived as valuable it is a failure on their part (unless your feature keeps triggering production alerts of course ;D).
It'll be hard at times, but keeping in mind that they are trying to do the best by the team will help with your temper in checked. After all, you aren't the one having to answer to the CEO one hour later!!
4.) **show an interest in the project and the discussion around it**
everyone loves to be asked about their area expertise. For PMs, it is about the projects they manage and the talks leading up to it, including what was tried in the past and what business knowledge is around it. Showing more interest along will make the PM treat you more than just a jira bot, which will be great for your mental well-being too honestly.
This will also help you understand why you are doing this project to start with and whether there are suggestions you can offer that also fit the overall goal. This will be invaluable too when something unexpected happens, a lot, and alternatives are easier for you to do but just need to be signed off. In this way, you also start exhibiting behaviors beyond just a developer (senior and + levels).
If you like this article, please give a reaction or anything. Feel free to subscribe to me as I will be writing these higher level career articles for at least this week and more.
Also I was just laid off :) ... so if your team is hiring remote please refer me!!! | kevin074 |
1,872,404 | Certificação GitHub Foundations: Concorra A Voucher Para Exame | Ao longo de quatro aulas ao vivo, os participantes terão a oportunidade de conhecer as ferramentas... | 0 | 2024-06-23T13:51:37 | https://guiadeti.com.br/certificacao-github-foundations-voucher-para-exame/ | exames, git, github, inteligenciaartifici | ---
title: Certificação GitHub Foundations: Concorra A Voucher Para Exame
published: true
date: 2024-05-31 18:20:14 UTC
tags: Exames,git,github,inteligenciaartifici
canonical_url: https://guiadeti.com.br/certificacao-github-foundations-voucher-para-exame/
---
Ao longo de quatro aulas ao vivo, os participantes terão a oportunidade de conhecer as ferramentas essenciais, como o GitHub Copilot e o GitHub Codespaces.
Os participantes poderão ganhar um voucher gratuito para a Certificação GitHub Foundations. As sessões incluirão uma variedade de dicas, truques e exercícios práticos, projetados para construir uma base sólida para a certificação.
Este evento é ideal para aqueles que estão começando ou desejam aprimorar suas habilidades, e é uma oportunidade imperdível para quem está interessado em expandir sua carreira na área de tecnologia.
## Learn Live: Get Certified with GitHub
De 5 a 26 de junho, a Microsoft e o GitHub oferecerão gratuitamente o curso de Certificação GitHub Foundations.
_Imagem da página da Microsoft Reactor_
Este curso é ideal para indivíduos no início de sua carreira tecnológica ou para aqueles que desejam aprimorar suas habilidades em ferramentas essenciais de desenvolvimento.
### Ferramentas e Práticas com Especialistas
Durante quatro aulas ao vivo, os participantes vão trabalhar as ferramentas avançadas como GitHub Copilot e GitHub Codespaces, guiados por especialistas da Microsoft e do GitHub.
As sessões são projetadas para fornecer uma forte base nas funcionalidades da plataforma, incluindo dicas, truques e exercícios práticos que são essenciais para o aproveitamento completo da plataforma.
### Oportunidade de Certificação e Detalhes da Oferta
Ao final de cada sessão ao vivo, os participantes terão a chance de ganhar um voucher gratuito para a Certificação GitHub Foundations, disponibilizado por ordem de chegada.
É importante notar que a oferta é válida enquanto durarem os estoques e é limitada a um voucher por pessoa. Esta promoção não é transferível e não pode ser combinada com outras ofertas.
A oferta termina em 27 de junho de 2024 ou enquanto durarem os estoques, e os vouchers não são resgatáveis por dinheiro. Confira a ementa:
#### 5 de junho – 15h: Automação Predial com GitHub
Descubra como você pode criar automação poderosa em qualquer projeto de software usando a plataforma. Esta sessão vai trabalhar as Ações do GitHub, o Copiloto do GitHub e os Codespaces do GitHub.
#### 12 de junho – 15h: Projetos no GitHub
Descubra como aplicar os recursos de segurança do GitHub Advanced Security aos seus próprios projetos e protegê-lo contra ameaças e vulnerabilidades de segurança.
#### 19 de junho – 15h: Desenvolvimento mais rápido com o GitHub Copilot
Saiba como aproveitar o GitHub Copilot para automatizar tarefas repetitivas e aumentar seus ciclos de desenvolvimento. Uso básico, bem como por recursos mais recentes, como prompts interativos e sugestões embutidas
#### 26 de junho – 15h: Gerencie seu projeto com a plataforma GitHub
Use os poderosos recursos de projeto do GitHub para gerenciar seu processo de desenvolvimento de software. Gerenciamento de projetos com problemas, solicitações pull e controle de alterações.
Quaisquer impostos aplicáveis são de responsabilidade do destinatário. A Microsoft também reserva-se o direito de cancelar, alterar ou suspender esta oferta a qualquer momento sem aviso prévio. Vale destacar que as sessões serão conduzidas em inglês.
<aside>
<div>Você pode gostar</div>
<div>
<div>
<div>
<div>
<span><img decoding="async" width="280" height="210" src="https://guiadeti.com.br/wp-content/uploads/2024/05/Certificacao-GitHub-280x210.png" alt="Certificação GitHub" title="Certificação GitHub"></span>
</div>
<span>Certificação GitHub Foundations: Concorra A Voucher Para Exame</span> <a href="https://guiadeti.com.br/certificacao-github-foundations-voucher-para-exame/" title="Certificação GitHub Foundations: Concorra A Voucher Para Exame"></a>
</div>
</div>
<div>
<div>
<div>
<span><img decoding="async" width="280" height="210" src="https://guiadeti.com.br/wp-content/uploads/2024/05/Masterclass-De-Inteligencia-Artificial-280x210.png" alt="Masterclass De Inteligência Artificial" title="Masterclass De Inteligência Artificial"></span>
</div>
<span>Masterclass De Inteligência Artificial: Aprenda Do Zero Gratuitamente</span> <a href="https://guiadeti.com.br/masterclass-inteligencia-artificial-gratuita-2/" title="Masterclass De Inteligência Artificial: Aprenda Do Zero Gratuitamente"></a>
</div>
</div>
<div>
<div>
<div>
<span><img decoding="async" width="280" height="210" src="https://guiadeti.com.br/wp-content/uploads/2024/05/Marketing-Digital-Santander-280x210.png" alt="Marketing Digital Santander" title="Marketing Digital Santander"></span>
</div>
<span>Curso De Marketing Digital Gratuito E Online Do Santander</span> <a href="https://guiadeti.com.br/curso-marketing-digital-gratuito-online-santander/" title="Curso De Marketing Digital Gratuito E Online Do Santander"></a>
</div>
</div>
<div>
<div>
<div>
<span><img decoding="async" width="280" height="210" src="https://guiadeti.com.br/wp-content/uploads/2024/05/Minicurso-De-Analise-De-Dados-280x210.png" alt="Minicurso De Análise De Dados" title="Minicurso De Análise De Dados"></span>
</div>
<span>Minicurso De Análise De Dados Gratuito Da Cubos Academy</span> <a href="https://guiadeti.com.br/minicurso-analise-de-dados-gratuito-cubos-academy/" title="Minicurso De Análise De Dados Gratuito Da Cubos Academy"></a>
</div>
</div>
</div>
</aside>
## GitHub
GitHub é uma plataforma de hospedagem de código-fonte e controle de versão que utiliza o Git, um sistema de controle de versão distribuído criado por Linus Torvalds, o mesmo criador do Linux.
Desde sua criação em 2008 por Chris Wanstrath, PJ Hyett e Tom Preston-Werner, tornou-se uma ferramenta essencial para milhões de desenvolvedores em todo o mundo, permitindo a colaboração em projetos de todos os tamanhos.
### Transformando a Colaboração em Código
A plataforma começou como um projeto simples focado em fornecer um espaço fácil de usar para hospedar projetos de software que usam Git.
Rapidamente, ele se destacou por sua interface intuitiva e recursos sociais, como forks, pull requests e issues, que facilitaram a colaboração entre desenvolvedores.
Essa maneira colaborativa contribuiu para o rápido crescimento da plataforma, que logo se tornou a maior comunidade de desenvolvimento de software do mundo.
Em 2018, a Microsoft adquiriu o GitHub por $7,5 bilhões, ampliando ainda mais seus recursos e integração com outras ferramentas Microsoft.
### Principais Funcionalidades do GitHub
A plataforma oferece poderosas funcionalidades de controle de versão, permitindo que desenvolvedores rastreiem e revertam mudanças no código, colaborarem em projetos sem o risco de conflitos de código e mantenham históricos de modificações acessíveis e organizados.
### Colaboração
As funcionalidades de fork e pull request são fundamentais para o trabalho colaborativo na plataforma.
Elas permitem que os desenvolvedores façam uma cópia de um repositório, alterem o projeto independentemente e depois proponham essas mudanças de volta ao repositório original através de pull requests.
### Gerenciamento de Projeto
O GitHub também oferece ferramentas para o gerenciamento de projetos, como a possibilidade de criar issues para rastrear bugs ou solicitar novas funcionalidades, e a integração com sistemas de automação para gerenciar fluxos de trabalho de desenvolvimento e integração contínua.
### Impacto do GitHub na Indústria de Software
A plataforma rmudou a maneira como o software é desenvolvido, permitindo uma colaboração sem precedentes entre programadores de todo o mundo. Ele facilita a gestão de projetos de software e atua como um portfólio social para desenvolvedores mostrarem seu trabalho.
A plataforma permite que desenvolvedores de software encontrem e utilizem uma variedade de projetos existentes, acelerando o desenvolvimento e a inovação na indústria.
## Microsoft
A Microsoft Corporation é uma das maiores e mais influentes empresas de tecnologia do mundo. Fundada em 1975 por Bill Gates e Paul Allen, a Microsoft começou sua jornada com o desenvolvimento de interpretadores BASIC para o Altair 8800.
Desde então, a empresa expandiu seu portfólio para incluir sistemas operacionais, aplicativos de software, hardware, e muito mais, desempenhando um papel central na revolução da computação pessoal e corporativa.
### A Evolução dos Produtos Microsoft
Um dos principais produtos da Microsoft é o sistema operacional Windows, lançado pela primeira vez em 1985. Windows tornou-se sinônimo de computação pessoal e continua a ser o sistema operacional mais utilizado no mundo.
Cada nova versão do Windows trouxe melhorias significativas em design, funcionalidade e segurança, mantendo a plataforma relevante em uma indústria em constante evolução.
### Microsoft Office e Aplicações de Produtividade
Outra inovação significativa da Microsoft é o Microsoft Office, um conjunto de aplicações de produtividade que inclui o Word, Excel, PowerPoint, e outros. Lançado inicialmente em 1989, o Office transformou a maneira como as empresas e indivíduos gerenciam documentos e informações.
Com o passar do tempo, a Microsoft expandiu o Office para a nuvem com o lançamento do Office 365, agora rebatizado como Microsoft 365, que oferece ferramentas colaborativas e soluções baseadas em nuvem.
## Aprimore suas habilidades em desenvolvimento. Inscreva-se agora para a Certificação e eleve sua carreira!
As [inscrições para o Learn Live: Get Certified with GitHub](https://developer.microsoft.com/pt-br/reactor/series/S-1342/?WT.mc_id=academic-137273-alfredodeza) devem ser realizadas no site da Microsoft Reactor.
## Compartilhe a oportunidade da Certificação com sua rede!
Gostou do conteúdo sobre a oportunidade de realizar o exame de graça? Então compartilhe com a galera!
O post [Certificação GitHub Foundations: Concorra A Voucher Para Exame](https://guiadeti.com.br/certificacao-github-foundations-voucher-para-exame/) apareceu primeiro em [Guia de TI](https://guiadeti.com.br). | guiadeti |
1,872,348 | A Complete Guide to Storage Baskets with Lids and Usage Ideas | Storage baskets are more than just functional organizers; they are versatile tools for conquering... | 0 | 2024-05-31T18:20:00 | https://dev.to/thedanes/a-complete-guide-to-storage-baskets-with-lids-and-usage-ideas-a10 | Storage baskets are more than just functional organizers; they are versatile tools for conquering clutter and adding a touch of personality to your space. But with so many styles, materials, and sizes available, choosing the right storage basket with a lid can feel overwhelming.
This comprehensive guide will equip you with everything you need to know about storage baskets, from their benefits to stylish décor applications.
**Why Choose Storage Baskets with Lids?**
While open baskets serve a purpose, baskets with lids offer a multitude of advantages:
**- Dust Control:** Lids keep dust and dirt at bay, especially beneficial for storing items in areas prone to dust accumulation, like attics or basements.
**- Visual Decluttering:** Hidden contents create a cleaner and more organized aesthetic. It's like magic – out of sight, out of mind (and out of clutter)!
**- Odor Control:** Certain materials, like toys or clothes, might retain odors. Lids help contain these smells, preventing them from permeating your entire space.
**- Stackability:** Lids often create a flat surface, allowing for secure stacking of multiple baskets, maximizing storage space.
**- Versatility:** Baskets with lids can be used in various rooms for an array of purposes, making them a true investment piece.
**Finding the Perfect Basket:**
Now that you understand the benefits, let's explore factors to consider when choosing storage baskets with lids:
**Natural Fibers:** Woven baskets in wicker, rattan, or seagrass add a touch of rustic charm. They're breathable, making them suitable for storing blankets or clothes.
**Fabric Baskets:** Fabric baskets offer a variety of colors and patterns, allowing for easy coordination with your décor. They're lightweight and collapsible for easy storage when not in use. Opt for washable fabrics for easy cleaning.
**Plastic Baskets:** Durable and easy to clean, plastic baskets are ideal for storing toys, laundry, or bathroom essentials.
**Metal Baskets:** Metal baskets with lids offer a modern aesthetic and are perfect for storing heavier items in kitchens or pantries.
**Size:** Match the basket size to its intended purpose. Large baskets are ideal for toys or blankets, while smaller ones can hold makeup, craft supplies, or pet accessories.
**Shape:** Round, square, rectangular – consider the shape that best complements your space and storage needs. Round baskets might offer a softer look, while rectangular baskets can fit neatly into corners or shelves.
**Where Can You Use Storage Baskets with Lids?**
The possibilities are endless, here are some ideas to inspire your organizational journey:
**Living Room:** Store throw blankets, board games, magazines, or pet toys in stylish baskets.
**Bedroom:** Lidded baskets tucked under the bed are perfect for seasonal clothes, shoes, or extra pillows. Decorative baskets on dressers can hold jewelry, scarves, or beauty products.
**Bathroom:** Keep bathroom essentials like toiletries, towels, or cleaning supplies neatly organized with lidded baskets.
**Kitchen:** Store pantry staples, snacks, or kitchen linens in lidded baskets for easy access and a clutter-free look.
**Laundry Room:** Lidded baskets can hold laundry detergent, dryer sheets, or cleaning supplies.
**Playroom:** Tame the toy clutter! Use lidded baskets to categorize toys by type or age group.
**Embrace the Basket Life:**
[Storage baskets with lids]( https://thedanes.co.uk/products/handwoven-storage-baskets-with-lid-set-of-two-fair-trade) are your allies in the fight against clutter. They offer a multitude of benefits, from organization and dust protection to stylish décor possibilities. With a bit of planning and creativity, you can find the perfect storage basket with a lid to enhance both the functionality and aesthetics of your home. So, embrace the basket life, and enjoy a more.
| thedanes | |
1,872,346 | Bangalore Escorts | Bangalore escorts provide discreet and pleasurable companionship Bangalore escort to clients looking... | 0 | 2024-05-31T18:19:08 | https://dev.to/itsshrutikhanna/bangalore-escorts-6k | <b><a href="https://www.okloote.com">Bangalore escorts</a></b> provide discreet and pleasurable companionship <b><a href="https://www.okloote.com/high-profile-call-girls-in-bangalore-gallery.html">Bangalore escort</a></b> to clients looking for a professional touch. These escorts are educated to offer a high standard of service and accommodate individual preferences, with an emphasis on customer satisfaction and privacy. <b><a href="https://www.okloote.com/high-profile-call-girls-in-bangalore-gallery.html">Bangalore escorts service</a></b> may cater to the demands of discriminating customers for social events, business meetings, or private amusement. They are a well-liked option for people looking for company in the city <b><a href="https://www.okloote.com/mg-road-escorts.html">VIP Bangalore escort service</a></b>! because of their professionalism, secrecy, and attention to detail, which distinguish them in the sector.
For those looking for company, the <a href="https://www.okloote.com/bangalore-escort-service-price.html">Bangalore escort service</a> provides a discreet and polished encounter. Clients can opt from a range of services to fit their interests with a selection of <b><a href="https://www.okloote.com">Bangalore escorts</a></b>. The agency is a reliable option for anyone searching for a delightful and unforgettable experience because it guarantees safety and secrecy for both clients and escorts.
Do you want to add some excitement and spice to your life in Bangalore? Look no farther than the most beautiful girls in <b><a href="https://www.okloote.com/bangalore-escort-service-price.html">VIP Bangalore escorts</a></b>! These lovely women are eager to show you a nice time and satisfy all of your wishes.
<h3>Meet the Hottest Girls In Bangalore Escorts</h3>
Do you want to add some excitement and spice to your life in Bangalore? Look no farther than the most beautiful girls in <b><a href="https://www.okloote.com/independent-call-girls-in-bangalore-phone-number.html">Bangalore escorts</a></b>! These lovely women are eager to show you a nice time and satisfy all of your wishes.
Bangalore is known for its exciting nightlife and stunning women, and the escorts in the city are no different. Whether you want a fun night out on the town or a more personal rendezvous, these females will leave you with lasting memories. Prepare to encounter the most alluring and sensual <b><a href="https://www.okloote.com">escort service in Bangalore</a></b>, willing to make your desires come true.<br />
<br />
Welcome to <b><a href="https://www.okloote.com">Bangalore Escorts Services</a>,</b> where your satisfaction is our top priority. Our professional and discreet escorts are here to provide you with an unforgettable experience in the bustling city of Bangalore. Whether you are a local resident, a business traveler, or a tourist visiting the city, our escorts are ready to cater to your every desire.
Our escorts are handpicked for their beauty, charm, and intelligence, ensuring that you have the best possible experience during your time with them. They are experts in providing companionship, intimacy, and pleasure, and will go above and beyond to make sure that your needs are met.
At <b><a href="https://www.okloote.com">Bangalore Escorts</a></b>, we prioritize the confidentiality and privacy of our clients. You can rest assured that all interactions with our escorts are kept strictly confidential, so you can enjoy your time with them without any worries.
So why wait? Treat yourself to a memorable experience with one of our stunning escorts today. Contact <b><a href="https://www.okloote.com">escort services in Bangalore</a>,</b> to book your appointment and indulge in the ultimate luxury experience in <b><a href="https://www.okloote.com">Bangalore escort.</a>,</b> <br />
<br />
Welcome to our exclusive <b><a href="https://www.okloote.com">Bangalore escorts service!</a></b> Our agency is dedicated to providing you with the most luxurious and professional escorts in the city. Whether you are a local resident or just visiting, we are here to fulfill all your desires and fantasies.<br />
<br />
Our <b><a href="https://www.okloote.com">Bangalore escorts</a></b> are not only stunningly beautiful, but also highly skilled in providing top-notch companionship. They are well-educated, well-mannered, and know how to treat a client with the utmost respect and care.<br />
<br />
Whether you are looking for a casual date, a companion for a business event, or a romantic evening, our <b><a href="https://www.okloote.com">escorts in Bangalore</a></b> can cater to all your needs. We offer a wide range of services to suit your preferences and ensure that you have a memorable experience.<br />
<br />
So why wait? Contact us today to book your perfect <b><a href="https://www.okloote.com">Bangalore escorts </a></b> and indulge in a world of luxury and pleasure. Our discreet and professional service guarantees complete satisfaction, so you can relax and enjoy your time with our stunning companions. Let us make your stay in Bangalore an unforgettable one! <br />
<br />
<h4>Meet the Hottest Independent Call Girls in Bangalore Escorts</h4>
<p>Discover the most sought-after <b><a href="https://www.okloote.com/independent-girls-in-bangalore.html">independent call girls in Bangalore</a></b> with our exclusive escort service. Our stunning escorts are handpicked for their beauty, charm, and professionalism, ensuring a memorable experience for every client. Whether you're looking for companionship for a night out or a private encounter, our Bangalore escorts are ready to fulfill your desires with discretion and class. Experience the ultimate in luxury and pleasure with our top-rated <b><a href="https://www.okloote.com/bangalore-call-girls-gallery.html">call girls in Bangalore.</a></b></p> <br />
<h4>Shruti Khanna Call Girls in Bangalore with Real Bookings Available 24/7</h4>
Discover the ultimate companionship experience with Shruti Khanna <b><a href="https://www.okloote.com/bangalore-call-girls-contact.html">Call Girls in Bangalore,</a></b> where real bookings are available around the clock.<br /><br />
<h4>100% genuine models are available in the Bangalore for Escort Service</h4>
Discover the finest selection of authentic models for <b><a href="https://www.okloote.com/escorts-service-in-bangalore.html">Escort Service in Bangalore.</a></b> Our 100% genuine models are ready to provide you with a premium and discreet experience. Choose from a variety of stunning individuals who are dedicated to ensuring your satisfaction and enjoyment. Experience luxury like never before with our exclusive Escort Service in Bangalore. <br /><br />
<h4>Independent Call Girls in Bangalore</h4>
Our <b><a href="hhttps://www.okloote.com/independent-girls-in-bangalore.html">Independent Call Girls in Bangalore</a></b> offer a discreet and professional service for those seeking companionship and intimate experiences. With a diverse selection of stunning and talented escorts, we cater to the individual preferences and desires of our clients. Our call girls are independent, ensuring a personalized and unforgettable encounter. Whether you are looking for a romantic dinner date, a night on the town, or a private rendezvous, our escorts are ready to provide an exceptional experience tailored to your needs. <br />
<h4>Bangalore Escort Services</h4>
Our <b><a href="https://www.okloote.com/escorts-service-in-bangalore.html">Bangalore Escort Services</a></b> offer discreet and professional companionship for those seeking a memorable experience in the bustling city. Our carefully selected escorts are charming, elegant, and well-trained to cater to your every need. Whether you are looking for a companion for a social event or a private encounter, our services ensure a high level of satisfaction and confidentiality. Contact us today to book an unforgettable experience in Bangalore. <br /><br />
<h4>Looking for high-profile call girls in Bangalore?</h4>
Explore our exclusive selection of elite <b><a href="https://www.okloote.com/bangalore-call-girls-gallery.html">call girls in Bangalore</a></b> who are sophisticated, charming, and discreet. Our high-profile companions are carefully chosen for their beauty, intelligence, and professionalism to ensure a memorable experience for our discerning clientele. Whether you are seeking companionship for a social event or a private encounter, our call girls in Bangalore are guaranteed to exceed your expectations with their exceptional service and companionship. Experience luxury and elegance with our premium selection of call girls in Bangalore.<br /><br />
| itsshrutikhanna | |
1,872,344 | Bangalore Escorts | Useful Links:- Bangalore Escorts || Bangalore Escort Service || Escort Service In Bangalore || Cheap... | 0 | 2024-05-31T18:16:51 | https://dev.to/itsshrutikhanna/bangalore-escorts-fjg | Useful Links:-
Bangalore Escorts || Bangalore Escort Service || Escort Service In Bangalore || Cheap Bangalore Escort Service || Bangalore Call Girls Gallery || Call Girls WhatsApp Number || Bangalore Escorts Price || Bangalore Escorts Service || MG Road Escorts || Koramangala Escorts || Electronic City Escorts || Whitefield Escorts || Old Airport Road Escorts || Airport Escorts || Vijaynagar Escorts || Indiranagar Escorts || 80 Ft. Road Escorts || B.P.Wadia Road Escorts || Banasavadi Escorts || Cox Town Escorts || Domlur Escorts || Gandhi Nagar Escorts || H.B.R. Layout Escorts || H.S.R Layout Escorts || Majestic Escorts || Marathahalli Escorts || Mysore Road Escorts || R.T. Nagar Escorts || Race Course Road Escorts || Rajarajeshwari Nagar Escorts || RajajiNagar Escorts || Rajvi Nagar Escorts || Residency Road Escorts || Richmond Road Escorts || RMV Extension Escorts || Wilson Garden Escorts || Ulsoor Escorts || Vasanth Nagar Escorts || Srirampuram Escorts || Outer Ring Road Escorts || Mahadevpura Escorts || K R Puram Escorts || K. G. Road Escorts || K.d. Road Escorts || Jayanagar Escorts || Hosur Road Escorts || Hunsur Road Escorts || Hebbal Escorts || Dickenson Road Escorts || Btm Layout Escorts || Bellandur Escorts || Bapuji Nagar Escorts || Benson Town Escorts || Avenue Road Escorts || Ashok Nagar Escorts || Agaram Escorts || Anand Nagar Escorts || Anepalya Escorts || Attiguppe Escorts || Austin Town Escorts || Ayappa Garden Escorts || Banashankari Escorts || Bannerghatta Road || || Basavanagudi Escorts || Basaveshwara Nagar Escorts || Bashyam Nagar Escorts || Bidadi Escorts || Bommanahalli Escorts || Brigade Road Escorts || Brookefield Escorts || C V Raman Nagar Escorts || Carmelaram Road Escorts || Central Bengaluru Escorts || Chamrajpet Escorts || Channasandra Escorts || Chikkabanavara Lake Escorts || Church Street Escorts || City Centre Escorts || Cooke Town Escorts || Cottonpet Escorts || Crescent Road Escorts || Cunningham Road Escorts || Dasarahalli Escorts || Devanahalli Escorts || Devasandra Lake Escorts || Diamond District Escorts || Doddaballapura Rd. Escorts || Ganga Nagar Escorts || Govindapura Escorts || Guttahalli Escorts || Hanumanth Nagar Escorts || Hennur Main Road Escorts || Hessarghatta Road Escorts || Hormavu Escorts || Hoskote Escorts || Indlawadi Pura Escorts || Infantry Road Escorts || Isro Layout Escorts || J.P. Nagar Escorts || Jalahalli Escorts || Jayamahal Extn Escorts || Jayamahal Road Escorts || Jaylakshmi Puram Escorts || Jogapalya Escorts || Kalkere Escorts || Kalyan Nagar Escorts || Kammanahalli Escorts || Kanakapura Road Escorts || Kasavanahalli Escorts || Kasturi Nagar Escorts || Kempapur Agrahara Escorts || Lalbagh Rd. Escorts || Madivala Escorts || Malleswaram Escorts || Peenya Escorts || Ramamurthy Nagar Escorts || Sadashiv Nagar Escorts || Sampangirama Nagar Escorts || Sankey Road Escorts || Sarjapur Escorts || Seshadri Road Escorts || Shampura Escorts || Silk Board Junction Escorts || Sompura Gate Escorts || St. Mark's Road Escorts || Uttarahalli Main Road Escorts || V.V. Mahal Escorts || Vidyaranyapura Escorts || Vittal Mallya Road Escorts || Kempe Gowda Road Escorts || Kudlu Gate Escorts || Kumaraswamy Layout Escorts || Kundalahalli Escorts || Lakkasandra Escorts || Langford Town Escorts || Lavelle Road Escorts || LB Shastri Nagar Escorts || Lottegollahalli Escorts || Magrath Road Escorts || Mahalakshmipuram Escorts || Mathikere Escorts || Milk Colony Escorts || Millers Road Escorts || Minerva Circle Escorts || Nagavara Escorts || Nagvarpalya Main Road Escorts || Nandi Durg Road Escorts || Padmanabhanagar Escorts || Palace Road Escorts || Raj Bhavan Road Escorts || Ramakrishna Nagar Escorts || S.R. Nagar Escorts || Sadahalli Escorts || Sahakara Nagar Escorts || Sanjay Nagar Escorts || Sarakki Main Road. Escorts || Sarjapur Road Escorts || Seshadripuram Escorts || Siddapura Rd. Escorts || Sivan Chetty Gardens Escorts || Thaverekere Road Escorts || Tumkur Road Escorts || Varthur Escorts || Vivek Nagar Escorts || Yelahanaka Escorts | itsshrutikhanna | |
1,872,343 | The Ultimate Guide to Vue 3 Composition API: Tips and Best Practices | The Composition API in Vue 3 introduces a new way to organize and reuse code, offering a more... | 0 | 2024-05-31T18:15:34 | https://dev.to/delia_code/the-ultimate-guide-to-vue-3-composition-api-tips-and-best-practices-54a6 | webdev, beginners, tutorial, vue | The Composition API in Vue 3 introduces a new way to organize and reuse code, offering a more flexible and powerful approach compared to the Options API. This guide will provide an in-depth look at the Composition API, its advantages, and best practices to help you make the most out of it.
## What is the Composition API?
The Composition API is a set of additive, function-based APIs that allow developers to better manage code logic and state within Vue components. It aims to address the limitations of the Options API by enabling greater code reusability and organization, particularly in larger applications.
## Advantages of the Composition API
### Improved Code Organization
The Composition API allows you to group related logic together in a more modular way. Instead of splitting your code into lifecycle hooks and component options, you can define logical units in functions, making your code easier to read and maintain.
**Example:**
```javascript
import { ref, computed } from 'vue';
export default {
setup() {
const count = ref(0);
const doubleCount = computed(() => count.value * 2);
function increment() {
count.value++;
}
return {
count,
doubleCount,
increment
};
}
};
```
### Better Reusability
With the Composition API, you can create reusable functions that encapsulate specific pieces of logic, which can be shared across multiple components. This promotes DRY (Don't Repeat Yourself) principles and reduces code duplication.
**Example:**
```javascript
// useCounter.js
import { ref } from 'vue';
export function useCounter() {
const count = ref(0);
function increment() {
count.value++;
}
return { count, increment };
}
// Component.vue
import { useCounter } from './useCounter';
export default {
setup() {
const { count, increment } = useCounter();
return { count, increment };
}
};
```
### Enhanced TypeScript Support
The Composition API is designed to work seamlessly with TypeScript, providing better type inference and autocompletion, which can improve developer productivity and code quality.
**Example:**
```typescript
import { ref, computed } from 'vue';
export default {
setup() {
const count = ref<number>(0);
const doubleCount = computed(() => count.value * 2);
function increment(): void {
count.value++;
}
return {
count,
doubleCount,
increment
};
}
};
```
### Greater Flexibility
The Composition API offers more flexibility by allowing you to use JavaScript features such as closures, importing and exporting functions, and combining multiple pieces of logic without being restricted by the component's lifecycle.
## Best Practices for Using the Composition API
### 1. Organize Logic into Composable Functions
Encapsulate related logic into functions that can be reused across different components. This helps keep your components clean and focused on their primary responsibilities.
**Example:**
```javascript
// useMouse.js
import { ref, onMounted, onUnmounted } from 'vue';
export function useMouse() {
const x = ref(0);
const y = ref(0);
function update(event) {
x.value = event.pageX;
y.value = event.pageY;
}
onMounted(() => window.addEventListener('mousemove', update));
onUnmounted(() => window.removeEventListener('mousemove', update));
return { x, y };
}
```
### 2. Use Reactive References Wisely
Use `ref` for primitive values and `reactive` for objects or arrays. This ensures that Vue can track dependencies and update the UI efficiently.
**Example:**
```javascript
import { ref, reactive } from 'vue';
export default {
setup() {
const count = ref(0);
const user = reactive({ name: 'John', age: 30 });
function increment() {
count.value++;
}
return { count, user, increment };
}
};
```
### 3. Leverage Computed Properties
Use `computed` properties for derived state that depends on other reactive data. This helps keep your logic clear and efficient.
**Example:**
```javascript
import { ref, computed } from 'vue';
export default {
setup() {
const price = ref(100);
const quantity = ref(2);
const total = computed(() => price.value * quantity.value);
return { price, quantity, total };
}
};
```
### 4. Keep Side Effects in `setup`
Place side effects, such as data fetching or event listeners, inside the `setup` function using lifecycle hooks like `onMounted` and `onUnmounted`.
**Example:**
```javascript
import { ref, onMounted } from 'vue';
export default {
setup() {
const data = ref(null);
onMounted(async () => {
const response = await fetch('https://api.example.com/data');
data.value = await response.json();
});
return { data };
}
};
```
### 5. Use Watchers for Reactive Effects
Use `watch` to react to changes in reactive data. This is useful for executing code in response to data changes.
**Example:**
```javascript
import { ref, watch } from 'vue';
export default {
setup() {
const count = ref(0);
watch(count, (newCount) => {
console.log('Count changed to', newCount);
});
return { count };
}
};
```
## When Not to Use the Composition API
### Simple Components
If your component logic is straightforward and easily managed within the Options API, using the Composition API might be unnecessary. The Options API is still perfectly valid for many use cases, especially in smaller components.
### Learning Curve
For beginners or teams new to Vue.js, the Options API might be easier to understand initially. The Composition API introduces new concepts that require a deeper understanding of JavaScript and Vue’s reactivity system.
### Migration Complexity
If you are working on an existing project with many components built using the Options API, migrating everything to the Composition API might be more effort than it’s worth. In such cases, it might be better to gradually introduce the Composition API in new components or refactor parts of the codebase over time.
The Vue 3 Composition API provides a more flexible and powerful way to manage component logic, offering improved code organization, better reusability, enhanced TypeScript support, and greater flexibility. By following best practices and understanding when to use or avoid the Composition API, you can build more maintainable and scalable Vue.js applications.
Whether you're a beginner or an experienced developer, mastering the Composition API will significantly enhance your Vue.js development skills. Happy coding! | delia_code |
1,872,341 | Learn CSS BOX MODEL | Introduction On the web everything is a box literally everything all the elements, images,... | 27,561 | 2024-05-31T18:14:14 | https://dev.to/jitendrachoudhary/learn-css-box-model-mgh | css, webdev, beginners, codenewbie | ## Introduction
On the web everything is a box literally everything all the elements, images, buttons, paragraphs, videos, and everything. With everything being a box it has a BOX MODEL applied. So what is a CSS BOX MODEL? In this article, we will learn CSS BOX MODEL.

## What is a BOX MODEL?
_The CSS box model as a whole applies to block boxes and defines how the different parts of a box — margin, border, padding, and content — work together to create a box that you can see on a page. Inline boxes use just some of the behavior defined in the box model._ - mdn web docs
The BOX MODEL consists of the content, padding, border and margin.

## Parts of a box
Making up a block box in CSS we have this:
- Content box: In this box your actual content is displayed; you can alter this using properties like <u>height</u> and <u>width</u>.
<!-- Image of a content box and example -->
{% codesandbox https://codesandbox.io/embed/trglgq?view=editor+%2B+preview&module=%2Fstyles.css %}
- Padding box: The padding is the area around the content as white space; you can alter it using <u>padding</u> and related properties. Basically padding is creates a space inside an element.
<!-- Image of a padding box and example -->
{% codesandbox https://codesandbox.io/embed/xcj98z?view=editor+%2B+preview&module=%2Fstyles.css %}
- Border box: The border box wraps around padding box if any otherwise on the content box; size it using <u>border</u> and related properties.
<!-- Image of a border box and example -->
{% codesandbox https://codesandbox.io/embed/tqw8wk?view=editor+%2B+preview&module=%2Fstyles.css %}
- Margin box: The margin is the outermost layer around the content, padding, and border as white space between this box and other elements; you can size it using <u>margin</u> and related properties.
<!-- Image of a margin box and example -->
{% codesandbox https://codesandbox.io/embed/fnlqch?view=editor+%2B+preview&module=%2Fstyles.css %}
## The standard CSS BOX MODEL
In the standard box model, if you set height and width property value on a box, these values defines the height and width of the _content box_. Any padding and borders are then added to get the actual size of the box.
**Note: However, the margin takes space on the page it is not counted towards the size of the box.**
If we assume that we have the following box with some CSS properties:
<!-- CSS properties -->
```css
.box {
width: 300px;
height: 200px;
margin: 25px;
padding: 10px;
border: 5px solid magenta;
}
```
The actual size of the box will be width (horizontal)(300 + 10 + 10 + 5 + 5) and height (vertical)(200 + 10 + 10 + 5 + 5).
<!-- Image of the content -->
## The alternate CSS BOX MODEL
In the alternate box model, the size is of the box is just the simple width and height of the box.
To apply the alternate box model, we use `box-sizing` property on it.
```css
.alternate {
box-sizing: border-box;
}
```
If we assume that we have the following box with some CSS properties:
<!-- CSS properties -->
```css
.box {
width: 300px;
height: 200px;
margin: 25px;
padding: 10px;
border: 5px solid magenta;
}
```
The actual size of the box will be width (horizontal)(300) and height (vertical)(200).
<!-- Image of the content -->
**The alternate box model is popular among developers and here is how you can apply to the elements:**
<!-- CSS code box sizing inherit after before -->
```css
html {
box-sizing: border-box;
}
*,
*::after,
*::before {
box-sizing: inherit;
}
```
## Play with CSS BOX MODEL
Ignore the boilerplate, I create two divs with class name <u>box</u>. I also add one more class <u>alternate</u> to the second div. Now both the divs will have same properties except the alternate class.
The class **box** has following CSS properties:
<!-- CSS box properties -->
```css
.box {
width: 200px;
height: 150px;
margin: 10px;
padding: 25px;
border: 5px solid magenta;
}
```
The class **alternate** has following CSS properties:
<!-- CSS alternate properties -->
```css
.alternate {
box-sizing: border-box;
}
```
<!-- Example of a standard vs alternate box model -->
{% codesandbox https://codesandbox.io/embed/kx38jx?view=editor+%2B+preview&module=%2Fstyles.css %}
## Conclusion
That's it for BOX MODEL; As everything on web is a box it is very important to learn the fundamentals of CSS. Learning box modeling enables you to manipulate and structure elements on the page.
Thanks for this reading!! If you find this helpful; drop your reactions and share this piece with others.
You can also stay connected with me by following me here and on [X](https://twitter.com/JiitendraC), [LinkedIn](https://www.linkedin.com/in/jiitendrachoudhary/).
| jitendrachoudhary |
1,872,340 | Mastering Vehicle Maintenance: Workshop Manuals in PDF Format | Workshop manuals in PDF format have revolutionized the way individuals approach vehicle maintenance... | 0 | 2024-05-31T18:13:33 | https://dev.to/wong45ew/mastering-vehicle-maintenance-workshop-manuals-in-pdf-format-4g52 | Workshop manuals in PDF format have revolutionized the way individuals approach vehicle maintenance and repair tasks. These digital compendiums offer a wealth of information, comprehensive guidance, and easy accessibility, making them indispensable resources for mechanics, enthusiasts, and car owners alike. In this article, we'll explore the significance of **[workshop manuals in PDF](https://downloadworkshopmanuals.com/)** format, their benefits, and how they empower individuals to maintain and repair vehicles with confidence and expertise.
**Understanding Workshop Manuals in PDF Format**
Workshop manuals in PDF format are comprehensive guides that provide step-by-step instructions for diagnosing, repairing, and maintaining vehicles. They cover a wide range of vehicle systems and components, including engines, transmissions, brakes, suspension, and electrical systems. What sets PDF workshop manuals apart is their digital format, which allows for easy access, storage, and distribution on various devices such as computers, tablets, and smartphones.
**Benefits of Workshop Manuals in PDF Format**
Convenience and Accessibility: PDF workshop manuals offer unparalleled convenience and accessibility. Users can download them onto their devices and access them anytime, anywhere, without the need for an internet connection.
Comprehensive Information: Workshop manuals in PDF format provide comprehensive information, including detailed procedures, diagrams, and technical specifications. This wealth of information facilitates accurate diagnosis and repair of vehicle issues.
Cost-Effectiveness: Downloading PDF workshop manuals is often more cost-effective than purchasing physical copies. Many online resources offer these manuals for free or at a lower cost, enabling users to save money on repair information.
Environmentally Friendly: Utilizing PDF workshop manuals reduces paper waste and the environmental impact associated with printing physical copies. This eco-friendly approach aligns with sustainable practices and reduces the carbon footprint.
Regular Updates: PDF workshop manuals are frequently updated to include the latest repair procedures, technical bulletins, and manufacturer recalls. Users can ensure they have access to the most current information for effective vehicle maintenance.
**How to Download Workshop Manuals in PDF Format**
Identify Your Vehicle's Make and Model: Before downloading a workshop manual in PDF format, identify your vehicle's make, model, and year of manufacture. This information is typically found on the vehicle registration or owner's manual.
Choose a Reputable Source: Select a reputable website or online platform that offers workshop manuals in PDF format. Ensure the source provides accurate and high-quality manuals to avoid misinformation.
Verify Compatibility: Confirm that the PDF format is compatible with your device and preferred reading software. PDF files are universally compatible and retain formatting across different devices.
Follow Download Instructions: Follow the download instructions provided on the website or platform. This may involve selecting your vehicle's make and model, adding the manual to your cart, and completing the download process.
Store and Organize: After downloading the workshop manual in PDF format, store it in a designated folder on your device for easy access. Organize your manuals by vehicle make and model to streamline retrieval.
**Effective Utilization of Workshop Manuals in PDF Format**
Familiarize Yourself: Take the time to familiarize yourself with the content and layout of the workshop manual in PDF format. Learn the symbols, abbreviations, and terminology used to facilitate smooth navigation.
Referencing and Navigation: Utilize the search function within the PDF document to quickly locate specific topics or procedures. Use bookmarks or hyperlinks, if available, to navigate between sections efficiently.
Follow Instructions Precisely: Adhere to the step-by-step instructions provided in the workshop manual meticulously. Avoid skipping steps or taking shortcuts to ensure accurate and thorough repairs.
Safety First: Prioritize safety when performing vehicle maintenance tasks. Follow safety precautions outlined in the workshop manual and use appropriate protective gear to prevent accidents and injuries.
Document Repairs: Keep a detailed record of repairs and maintenance tasks performed using the workshop manual in PDF format. Documenting repairs aids in tracking maintenance history and facilitates future reference.
**Conclusion**
Workshop manuals in PDF format are indispensable resources for vehicle maintenance and repair enthusiasts. Offering convenience, comprehensive information, and cost-effectiveness, these manuals empower users to diagnose, repair, and maintain vehicles effectively. By downloading workshop manuals in PDF format from reputable sources and utilizing them efficiently, individuals can ensure the optimal performance and longevity of their vehicles. Embrace the benefits of PDF workshop manuals and embark on a journey of seamless vehicle maintenance and repair.
| wong45ew | |
1,872,339 | Embracing a Healthy Lifestyle: Tips and Benefits | A healthy lifestyle is not just about avoiding illness; it's about thriving in all aspects of life.... | 0 | 2024-05-31T18:13:21 | https://dev.to/ikore/embracing-a-healthy-lifestyle-tips-and-benefits-ml9 | healthylifestyle | A healthy lifestyle is not just about avoiding illness; it's about thriving in all aspects of life. It involves making consistent choices that promote physical, mental, and emotional well-being. This article will guide you through the essential components of a healthy lifestyle and how to incorporate them into your daily routine.
Why a Healthy Lifestyle Matters
Living healthily has numerous benefits, including:
Increased Energy Levels: Regular physical activity and a balanced diet help boost your energy, allowing you to be more productive and active throughout the day.
Improved Mental Health: A healthy lifestyle can reduce the risk of depression, anxiety, and other mental health issues. Exercise releases endorphins, the body’s natural mood lifters.
Better Physical Health: Maintaining a healthy weight, eating nutritious foods, and exercising regularly can prevent chronic diseases such as heart disease, diabetes, and obesity.
Enhanced Longevity: Healthy habits can increase your lifespan by reducing the risk of chronic diseases and promoting overall well-being.
Stronger Immune System: A balanced diet rich in vitamins and minerals strengthens your immune system, helping your body fend off illnesses more effectively.
Key Components of a Healthy Lifestyle
1. Balanced Diet
A balanced diet is the cornerstone of a healthy lifestyle. Here are some tips to ensure you’re eating well:
Incorporate Variety: Include a variety of foods in your diet, such as fruits, vegetables, whole grains, lean proteins, and healthy fats.
Stay Hydrated: Drink plenty of water throughout the day to keep your body hydrated and functioning properly.
Limit Processed Foods: Reduce your intake of processed foods, which are often high in sugar, salt, and unhealthy fats.
Control Portion Sizes: Be mindful of portion sizes to avoid overeating and maintain a healthy weight.
2. Regular Exercise
Physical activity is vital for maintaining a healthy body and mind. Aim for at least 150 minutes of moderate aerobic activity or 75 minutes of vigorous activity each week. Here are some ways to stay active:
Find Activities You Enjoy: Whether it’s walking, swimming, dancing, or cycling, choose activities you love to stay motivated.
Incorporate Strength Training: Include strength training exercises at least twice a week to build and maintain muscle mass.
Stay Consistent: Make exercise a regular part of your routine, and try to be active every day, even if it’s just a short walk.
3. Quality Sleep
Adequate sleep is crucial for overall health. Adults should aim for 7-9 hours of sleep per night. To improve your sleep quality:
Establish a Routine: Go to bed and wake up at the same time every day, even on weekends.
Create a Sleep-Friendly Environment: Make sure your bedroom is dark, quiet, and cool.
Limit Screen Time: Avoid screens at least an hour before bed to reduce blue light exposure, which can interfere with sleep.
4. Mental Health Care
Taking care of your mental health is as important as your physical health. Here are some ways to support your mental well-being:
Practice Mindfulness: Techniques such as meditation, yoga, and deep breathing can help reduce stress and improve mental clarity.
Stay Connected: Maintain strong relationships with family and friends. Social connections are vital for emotional support and well-being.
Seek Professional Help: If you’re struggling with mental health issues, don’t hesitate to seek help from a therapist or counselor.
5. Avoid Harmful Behaviors
Certain behaviors can negatively impact your health. To maintain a healthy lifestyle, avoid:
Smoking: Smoking is a leading cause of various diseases, including cancer and heart disease. Quitting smoking can significantly improve your health.
Excessive Alcohol Consumption: Limit alcohol intake to moderate levels, as excessive drinking can lead to numerous health problems.
Conclusion
Adopting a healthy lifestyle requires commitment and consistency, but the rewards are well worth the effort. By incorporating a balanced diet, regular exercise, quality sleep, mental health care, and avoiding harmful behaviors, you can enjoy a happier, healthier life. Start making small changes today, and watch as they transform your overall well-being.
[Read more here](https://azbigmedia.com/lifestyle/discover-the-benefits-of-berberine-where-to-find-high-quality-supplements/)! | ikore |
1,872,338 | Understanding Objects and Abstract Data Types (ADTs) | Understanding Objects and Abstract Data Types (ADTs) with examples In software development, there... | 0 | 2024-05-31T18:10:54 | https://dev.to/omar_zenhom/understanding-objects-and-abstract-data-types-adts-5bi0 | datastructures, algorithms, code, programming | **Understanding Objects and Abstract Data Types (ADTs) with examples**
In software development, there are various methods for representing data, each with its own set of advantages and trade-offs. Two commonly encountered approaches are Abstract Data Types (ADTs) and Objects. While ADTs focus on representing data opaquely, Objects emphasize representing data through composable interfaces. Let’s explore the differences between these two approaches and their implications for software design.
**Abstract Data Types (ADTs): Representing Data Opaquely**
ADTs provide a model for data consisting of values and operations, hiding the concrete implementation details from users. For example, a Set ADT may have operations like add, remove, and has, without exposing how these operations are implemented internally. In essence, ADTs encapsulate data and operations within a logical blueprint, promoting
modularity and abstraction.
**C++ Example:**
```
#include <vector>
#include <algorithm>
class Set {
private:
std::vector<int> elements;
public:
void add(int value) {
if (!contains(value)) {
elements.push_back(value);
std::sort(elements.begin(), elements.end());
}
}
bool contains(int value) const {
return std::binary_search(elements.begin(), elements.end(), value);
}
bool isEmpty() const {
return elements.empty();
}
};
```
**Java Example:**
```
import java.util.HashSet;
import java.util.Set;
public class NumberSet {
private Set<Integer> set;
public NumberSet() {
set = new HashSet<>();
}
public void add(int value) {
set.add(value);
}
public boolean contains(int value) {
return set.contains(value);
}
public boolean isEmpty() {
return set.isEmpty();
}
}
```
**Objects: Representing Data Through Composable Interfaces**
Objects in software development focus on encapsulation and interface-based programming. Unlike traditional class-based object-oriented programming, which often involves mutable state and inheritance, the definition of objects centers on encapsulation and interface adherence.
C++ Example:
```
#include <iostream>
#include <string>
class Animal {
public:
virtual void speak() const = 0;
};
class Dog : public Animal {
public:
void speak() const override {
std::cout << "Woof!" << std::endl;
}
};
int main() {
Dog dog;
dog.speak();
return 0;
}
```
Java Example:
```
interface Animal {
void speak();
}
class Dog implements Animal {
public void speak() {
System.out.println("Woof!");
}
}
public class Main {
public static void main(String[] args) {
Dog dog = new Dog();
dog.speak();
}
}
```
**Trade-offs and Considerations**
Both ADTs and objects offer distinct advantages and trade-offs. ADTs excel in providing modularity and abstraction, making them easy to optimize and understand. However, they lack extensibility as users cannot directly modify their internal representations. On the other hand, objects offer flexibility and extensibility, allowing users to create new representations that conform to predefined interfaces. While objects promote interface-based programming and encapsulation, they may be less efficient in terms of performance compared to ADTs.
**Conclusion:**
Understanding the differences between ADTs and objects is crucial for choosing the appropriate approach for a given software design problem. While ADTs prioritize encapsulation and abstraction, objects emphasize interface-based programming and extensibility. By leveraging the strengths of each approach, developers can design robust and maintainable software systems. In the next artical, we will explore the trade-offs and considerations involved in implementing algebraic data types (ADTs) and contrast them with the concepts discussed here.
I’d love to hear your thoughts on this feast of an explanation that extra flavor to your learning experience 😂😂😁.
Thank you for reading!❤️🥳
P.S:
You can follow me:
[LinkTree](https://linktr.ee/omarwaleedzenhom)
[LinkedIn](https://www.linkedin.com/in/omarwaleedzenhom/)
[Facebook](https://www.facebook.com/OmarZenho)
My Portfolio:
https://omarzen.github.io/Omar-Zenhom/ | omar_zenhom |
1,872,336 | 5 Benefits of System Integration Testing Tools | As the world of digitalization rapidly evolves and systems and applications grow more sophisticated,... | 0 | 2024-05-31T18:05:19 | https://theridgewoodblog.net/5-benefits-of-system-integration-testing-tools/ | integration, testing, tools | 
As the world of digitalization rapidly evolves and systems and applications grow more sophisticated, it is critical to guarantee flawless functionality and integration. This is where a system integration testing tool becomes useful, providing a complete solution to ensure faultless system functioning and speed up the testing process. Numerous advantages offered by these tools have the potential to completely transform an organization’s approach to a software development, and quality control, as well as its overall operational effectiveness.
1.**Comprehensive Testing Coverage**
The capacity of system integration testing tools to enable thorough testing coverage is one of its most important benefits. With the use of these technologies, testers may thoroughly assess how various system components interact with one another and replicate real-world scenarios. These tools assist in locating any integration problems, compatibility difficulties, and performance bottlenecks that would have gone undetected during individual component testing by testing the end-to-end flow of data and capabilities across numerous interfaces.
2.**Accelerated Testing Cycles**
Time is of importance in the fast-paced field of software development. Tools for system integration testing provide a notable benefit by speeding up the testing cycles. These solutions drastically cut down on the time and labor needed for manual testing through automation and effective test case management, enabling teams to iterate more quickly and launch products more swiftly. Automated testing frameworks allow for the simultaneous execution of several test cases, which guarantees quick fault identification and speeds up a resolution process.
3.**Improved Test Accuracy and Consistency**
Manual testing will inevitably include human error, which might result in inconsistent and inaccurate test findings. By greatly automating and standardizing the testing procedure, system integration testing tools reduce this risk. These tools ensure consistent and dependable test results throughout several iterations by precisely executing test cases in accordance with established scripts and circumstances. Delivering high-quality products and preserving the integrity of the software development life cycle depend on this degree of precision and consistency.
4.**Enhanced Collaboration and Communication**
Collaboration and effective communication are critical to the accomplishment of system integration testing goals. System integration testing systems offer centralized test repositories, real-time reporting, and thorough documentation, which let cross-functional teams collaborate more easily. Throughout a testing process, these capabilities allow stakeholders from several departments, including operations, and a quality assurance, as well as a development, to remain informed and in sync. An atmosphere of a collaboration is fostered by open lines of communication and shared access to test data and findings, which promotes more effective problem-solving and decision-making.
5.**Cost-Effective Testing Solution**
Organizations can save a lot of money by using system integration testing solutions. These technologies minimize labor expenses by eliminating the need for labor-intensive manual testing by automating repeated processes and optimizing the testing process. Furthermore, expensive rework and delays later in the development cycle can be avoided by promptly identifying and fixing errors during the integration testing phase. The long-term advantages of higher productivity, shorter time-to-market, and better product quality frequently outweigh the initial cost of these technologies.
**Conclusion**
System integration testing tools have many benefits that can greatly improve the processes involved in software development and quality control. Opkey is one of the leading AI-powered tools that can help businesses streamline system integration testing. It guarantees smooth coherence among all elements within the software ecosystem. Opkey’s automated end-to-end testing ensures that linked systems maintain perfect synchronization. The companies don’t have to worry about mismatched inventories interfering with their operations ever again. Opkey’s extensive testing coverage finds problems before they affect the clients. Its accelerated automated testing cycles save money and time. With the assurance of Opkey’s thorough system integration testing capabilities, companies can develop high-quality software more quickly and achieve a new degree of coherence. | rohitbhandari102 |
1,872,306 | JS Versialar haqida ma'lumot | ECMAScript 1 (ES1) - 1997 yil Birinchi versiya bo'lib, asosiy sintaksis va xususiyatlar joriy... | 0 | 2024-05-31T17:56:44 | https://dev.to/muxiddin/js-versialar-haqida-malumot-dgd | jsversions | - **ECMAScript 1 (ES1) - 1997 yil**
`Birinchi versiya bo'lib, asosiy sintaksis va xususiyatlar joriy etilgan.
`
---
- **ECMAScript 2 (ES2) - 1998 yil**
`Asosan ES1-ga kichik tuzatuvlar va moslik yangilanishlarini kiritgan
`
---
- **ECMAScript 3 (ES3) - 1999 yil**
`ES3 katta yangilanish bo'lib, oddiy qatorlar, izlanish va almashtirish funktsiyalari, maxsus tartiblash (sorting) va boshqalarni qo'shdi.
`
---
- **ECMAScript 4 (ES4)**
`ES4 hech qachon rasmiy ravishda chiqarilmagan, chunki ishlab chiqish jarayonida ko'plab muammolar va kelishmovchiliklar yuzaga keldi.`
---
- **ECMAScript 5 (ES5) - 2009 yil**
`Bu versiya keng qamrovli yangilanish bo'lib, quyidagilarni o'z ichiga oladi:`
```
1. Qat'iy rejim ("strict mode")
2. JSON ob'ekt
3. Array.isArray, Function.bind kabi yangi funktsiyalar
4. Har xil array metodlar (forEach, map, filter, reduce)
5. Property attribute'larini boshqarish
```
---
- **ECMAScript 6 (ES6) / ECMAScript 2015**
`Bu versiya JavaScript tiliga eng katta yangilanishlardan biri hisoblanadi:`
```
1. Blok darajasidagi o'zgaruvchilar (let, const)
2. Arrow funktsiyalar
3. Sinflar (class)
4. Modullar (import, export)
5. Promises
6. Template literals
7. Default, rest va spread parametrlari
```
---
- **ECMAScript 2016 (ES7)**
`Bu versiyada nisbatan kamroq yangilanishlar bor edi:`
```
1. Array.prototype.includes
2. Exponentiation operatori (**)
```
---
- **ECMAScript 2017 (ES8)**
`Ushbu versiya quyidagi xususiyatlarni kiritdi:`
```
1. Async/Await
2. Object.values va Object.entries
3. String padding (padStart, padEnd)
4. Object.getOwnPropertyDescriptors
```
---
- **ECMAScript 2018 (ES9)**
`Bu versiyada quyidagilar mavjud:`
```
1. Asynchronous iteration (for-await-of)
2. Rest/Spread properties
3. Promise.finally
4. Regular Expression enhancements
```
---
- **ECMAScript 2019 (ES10)**
`Bu versiyada quyidagilar mavjud:`
```
1. Array.prototype.flat, Array.prototype.flatMap
2. Object.fromEntries
3. String.prototype.trimStart, String.prototype.trimEnd
4. Optional catch binding
```
---
- **ECMAScript 2020 (ES11)**
`Bu versiyada quyidagilar mavjud:`
```
1. BigInt
2. Dynamic import
3. Nullish Coalescing (??)
4. Optional Chaining (?.)
5. Promise.allSettled
```
---
- **ECMAScript 2021 (ES12)**
`Bu versiyada quyidagilar mavjud:`
```
1. Logical assignment operators (&&=, ||=, ??=)
2. Numeric separators
3. String.prototype.replaceAll
4. WeakRefs
```
---
- **ECMAScript 2022 (ES13)**
`Yangi xususiyatlar:`
```
1. Top-level await
2. Private instance fields
3. Static class fields
4. RegExp match indices
```
---
| muxiddin |
1,872,331 | Distributed Snapshots: Chandy-Lamport protocol | Some forms of distributed snapshots were around for a while already when Chandy-Lamport's distributed... | 0 | 2024-05-31T17:54:49 | https://dev.to/federico_ponzi/distributed-snapshots-chandy-lamport-protocol-32o7 | distributedsystems, formalmethods, tla | Some forms of distributed snapshots were around for a while already when Chandy-Lamport's distributed snapshots paper was first published in 1985. Lamport considers this protocol a straightforward application of the basic ideas from Lamport clocks. Other than reviewing the paper, in this post I'll also present some examples of real world implementations and a TLA+ specification of the protocol.
What problem is it trying to solve?
You need to record the global state of a program. Why? Because, for example, you have some complex computation ongoing, and you want to know which step has reached. Or you have a long-running computation, and you want to take a snapshot as a backup to allow restarting the computation again from the checkpoint rather than from the beginning in case any machine fails.
For the state of the program, we refer to the local variables and in general to the history of states that the program went through.
Why is taking snapshots hard? Well, first of all, the snapshotting algorithm should not interfere with the running computation.
Secondly, if your program is a single process on a single machine, this is straightforward! You could create an api to say "record the snapshot in 5 seconds" or "every 2 hours". For a multi-thread/multiprocess program running on a single machine, you can create a similar api.
In a distributed system, this api won't work because there is no global shared clock. You could end up with out-of-sync snapshots providing an inconsistent view of the system. Other than the state of the process itself, we could also have inflight messages that should be included in the snapshot. As an example of inconsistent snapshot, a process B could record that it received a message from A and A's snapshot does not include that the message was sent over to B.
The paper has a good visual representation: imagining you wanted to take a picture of a sky filled with migrating birds. One photo is not enough, you will need to take multiple pictures and stitch them together in a way that provides a consistent view of the landscape. This is the challenge that this paper is trying to solve.
[Continue reading...](https://blog.fponzi.me/2024-05-30-distributed-snapshots.html)
| federico_ponzi |
1,872,330 | Upstream preview: Secure by design with Aeva Black and Jack Cable from CISA | Upstream is next week on June 5, and wow, our schedule is shaping up brilliantly. For the rest of... | 0 | 2024-05-31T17:54:18 | https://blog.tidelift.com/upstream-2024-preview-secure-by-design-with-aeva-black-and-jack-cable-at-cisa | opensource, upstream, security, cybersecurity | <p><em>Upstream is next week on June 5, and wow, our schedule is shaping up brilliantly. For the rest of this week, we’ll be giving you a sneak preview into some of the talks and the speakers giving them via posts like these. </em><a href="https://upstream.live/register?__hstc=23643813.d1ddc767e9f4955f3bdd2f1c64c72f8c.1654699542897.1716388421586.1716392544277.1287&__hssc=23643813.2.1716392544277&__hsfp=1649118565"><em><span>RSVP now!</span></em></a></p>
<p>These days, secure by design is a fundamental concept when it comes to software development and security—it’s crucial in the open source software supply chain. The secure by design model often involves a thoroughness when it comes to vetting software ingested, vulnerability prevention, transparency (such as Software Bills of Materials, or SBOMS), and a general responsibility for the security and maintenance of an organization’s software applications. With those components in mind, it’s no wonder that open source software plays a critical role.</p>
<p>Recently, Tidelift signed the Cybersecurity and Infrastructure Security Agency (<a href="https://www.cisa.gov/resources-tools/resources/secure-by-design"><span>CISA</span></a>) <a href="https://blog.tidelift.com/tidelift-signs-the-cisa-secure-by-design-pledge"><span>Secure by Design pledge</span></a>. This Secure by Design pledge event, publicly held at the RSA conference in San Francisco on May 8th of this year, brought together companies and industry leaders to declare their efforts to work towards a more secure software supply chain, all while publicly documenting their progress. </p>
<p>This industry-wide effort to improve the nation’s cybersecurity is a promising step towards building security into our technology product proactively, rather than bolting it on as an aftermarket capability, and we’re so excited to announce that we’ll be welcoming two of CISA’s leading cybersecurity experts at Upstream this year!</p>
<p><a href="https://upstream.live/speaker-2024/aeva-black?hsLang=en"><span>Aeva Black</span></a>, Section Chief for Open Source Security at CISA, and <a href="https://upstream.live/speaker-2024/jack-cable?hsLang=en"><span>Jack Cable</span></a>, Senior Technical Advisor at CISA, will be breaking down the details of Secure by Design, how it’s inspired by historical design-first initiatives, and how CISA is working with industry leaders to proactively improve business’ cybersecurity practices while working with and seeking feedback from the open source community. </p>
<p>Tidelift CEO and co-founder <a href="https://upstream.live/speaker-2024/donald-fischer?hsLang=en"><span>Donald Fischer</span></a> hosts, and together they will be discussing next steps, desired outcomes, and how organizations can start securing the future of the software supply chain by working side-by-side with open source maintainers. If you’re looking to learn more about how the Secure by Design initiative was shaped and the actions organizations can take to start their journey into open source, you won’t want to miss this talk <a href="https://upstream.live/"><span>at Upstream</span></a> on Wednesday, June 5. </p>
<h2 style="font-size: 24px;">About Aeva Black</h2>
<p>Aeva Black is the Section Chief for Open Source Security at the U.S. Cybersecurity and Infrastructure Security Agency, and an open source hacker and international public speaker with 25 years of experience building digital infrastructure and leading open source projects. They previously served on the OpenSSF Technical Advisory Committee, OpenStack Technical Committee, Kubernetes Code of Conduct Committee, and led open source security strategy within the Microsoft Azure Office of the CTO. In their spare time, Aeva serves on the Board of the Open Source Initiative and enjoys riding motorcycles and supporting the local LGBTQ+ community.</p>
<h2 style="font-size: 24px;">About Jack Cable</h2>
<p>Jack Cable is a Senior Technical Advisor at CISA, where he helps lead the agency's work on open source software security and Secure by Design. At CISA, Jack authored CISA's Open Source Software Security Roadmap and has co-led community efforts to standardize the security of package repositories. Prior to that, Jack worked as a TechCongress Fellow for the Senate Homeland Security and Governmental Affairs Committee, advising Chairman Gary Peters on cybersecurity policy, including election security and open source software security. There, Jack was the principal author of the Securing Open Source Software Act. He previously worked as a Security Architect at Krebs Stamos Group. Jack also served as an Election Security Technical Advisor at CISA, where he created Crossfeed, a pilot to scan election assets nationwide. Jack is a top bug bounty hacker, having identified over 350 vulnerabilities in hundreds of companies. After placing first in the Hack the Air Force bug bounty challenge, he began working at the Pentagon’s Defense Digital Service. Jack holds a bachelor’s degree in Computer Science from Stanford University and has published academic research on election security, ransomware, and cloud security.</p> | caitbixby |
1,872,329 | NFTGo Platform: Features, Usage, and Benefits | Navigating the non-fungible token (NFT) market is a challenging task due to fast price... | 0 | 2024-05-31T17:53:50 | https://dev.to/getblockapi/nftgo-platform-features-usage-and-benefits-24ko | bitcoin, ethereum, defi, nfts |

Navigating the non-fungible token (NFT) market is a challenging task due to fast price fluctuations, high unpredictability, and frequent scams. However, NFTGo is a tool that can help with this task, providing thorough market analytics and insights on which decisions to make.
Originally showing NFT prices and their fluctuations, the platform has evolved into a comprehensive trading tool and a trusted data provider. By aggregating and disseminating token data, NFTGo has become an important resource for crypto enthusiasts.
So, let’s see how collectors, traders, and Web3 developers can use the platform to analyze the market and make informed decisions about what to do on the market.
## NFTGo Essentials: What Is It and Why to Use It
Launched in 2021 by two NFT enthusiasts Tony Ling and Lowes Yang, NFTGo is a powerful NFT analytics tool and marketplace aggregator. Driven by their passion for digital assets, the founders have built a user-focused platform that evolves along with the changing needs of the NFT community.
The service focuses on providing comprehensive digital asset market data, establishing itself as a go-to resource for NFT enthusiasts and professionals. Initially, it supported only Ethereum assets, but as the NFT market expands, the platform adds new chains, so as of May 2024, it includes the Bitcoin ecosystem support, too.
Today, NFTGo functionality is beyond a simple marketplace aggregator, as it offers a range of NFT services to its users. It functions as an NFT tracking platform, providing real-time insights, analytics, and price alert tools to help navigate the market. Users can also find a lot of valuable information about the market and desired collections. It also can be used as a marketplace, as you can connect your wallet to the platform and buy/sell NFTs.
All these features are free, although the paid pro version with additional trading features is available, too.
## NFTGo Functionality: How It Works and Who Use It
NFTGo pulls raw data from blockchain networks, ensuring access to the latest and most accurate information. This unfiltered data undergoes advanced filtering and analysis, transforming them into actionable insights you can see on its main page.
Additionally, the platform integrates NFT trading data from over 30 major marketplaces and rarity tools. It includes:
- Blur;
- X2Y2;
- Magic Eden;
- OpenSea;
- Sudoswap;
- OKX Aggregator.
With around 30,000 listed collections across ERC721, ERC1155, ERC404, [Ordinals](https://getblock.io/blog/ordinals-bitcoin-nfts-explained-bitcoin-nft-ordinals-inscriptions-key-takeaways/?utm_source=external&utm_medium=article&utm_campaign=devto_nftgo), and Runes standards, NFTGo offers extensive coverage of different assets, and its potential will only rise in the future.
By combining direct blockchain integration, marketplace aggregation, and data analytics, the platform provides a powerful toolkit for navigating the NFT landscape, benefiting collectors, traders, and Web3 developers.
## NFTGo Toolset: Top 5 Tools
NFTGo has an intuitive interface with several tools that provide concise NFT market analytics. They also allow you to watch the latest trading activity and large transactions to understand in which direction the market may move and how other traders react to them.
1. **Market Overview:** shows market cap, volume, trader statistics, trending collections, and a drop calendar.
2. **Collection Data:** shows trading performance, activity, financial data, floor prices, and listing trends.
3. **Portfolio Analytics:** tracks other traders’ portfolios and shows crypto whale transactions that can influence the overall market dynamics.
4. **NFT Trading:** shows listing, selling, and buying asset information taken from listed NFT marketplaces.
5. **Browser Extension:** a Chrome extension that can be connected with the user’s X account to use essential NFTGo features in real time.
Let’s look at these tools closer.
### 1. Market Overview and Statistics
This section serves as an ideal entry point for NFTGo users, providing a comprehensive snapshot of the current market dynamics. This powerful feature allows users to perform quick market assessments based on key indicators such as capitalization, trading volume, holder and trader statistics, and a breakdown of top-performing collections.
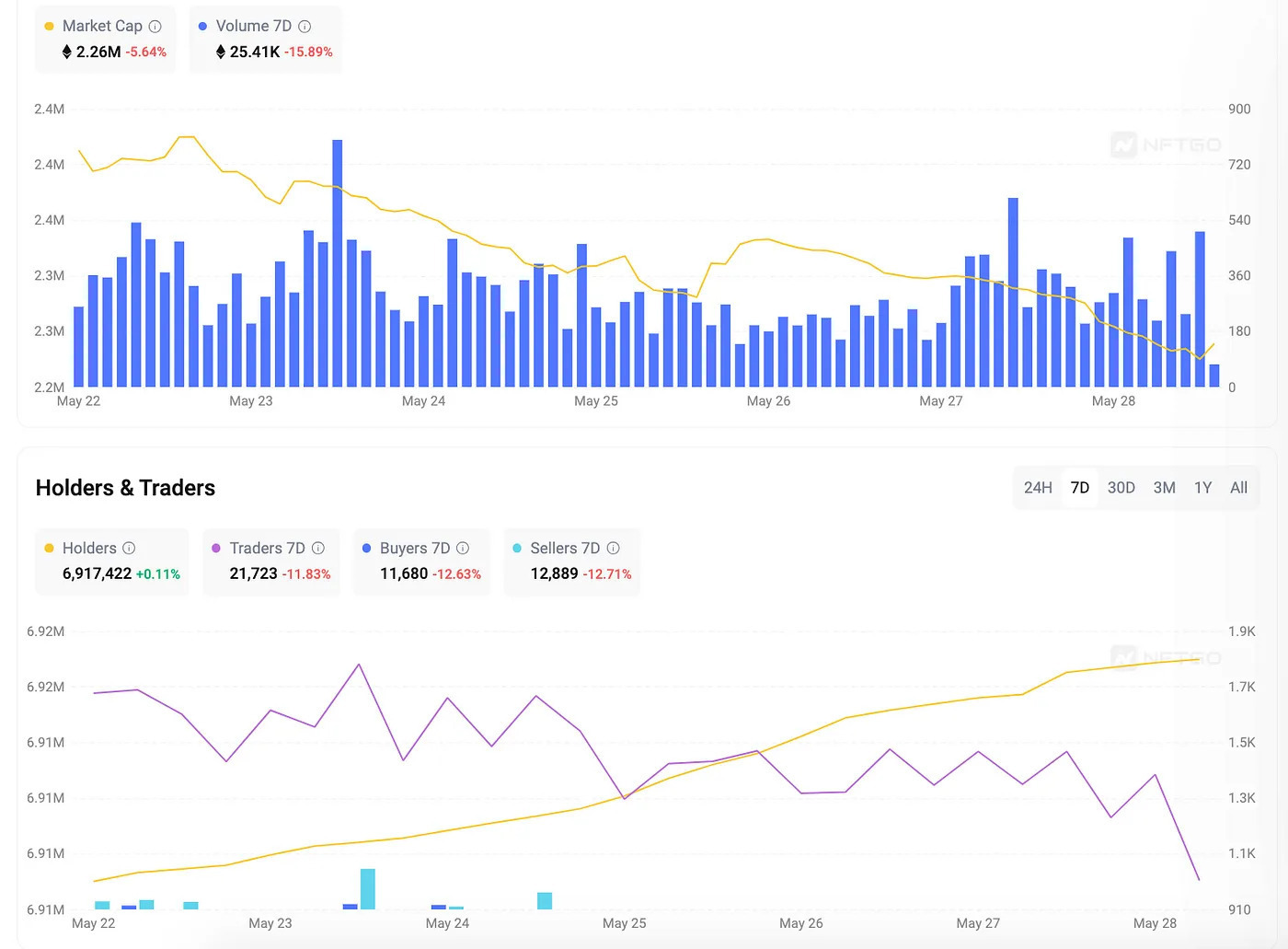
This insightful overview is further complemented by statistics and leaderboards showcasing the performance of various NFT marketplaces listed on NFTGo. By presenting this data in a clear and accessible format, users gain a holistic understanding of the overall market, enabling them to make informed decisions and increasing their chances of succeeding.
### 2. Data Gathering and Research
Then, NFTGo users can delve deeper into researching specific collections and individual NFTs. The platform offers a comprehensive suite of charts and metrics tailored for each collection page, empowering users with detailed insights.
Some of them include:
- **Overall Collection Performance**, such as its trading statistics and price dynamics, to conduct an informed assessment of its potential.
- **Activity Tracking**, such as recent sales, mints, and deals, ensuring you never miss a beat in the dynamic NFT market.
- **Holder and Trader Analytics**, including detailed revenue breakdowns for buyers and sellers, offering a deeper understanding of the collection’s ecosystem.
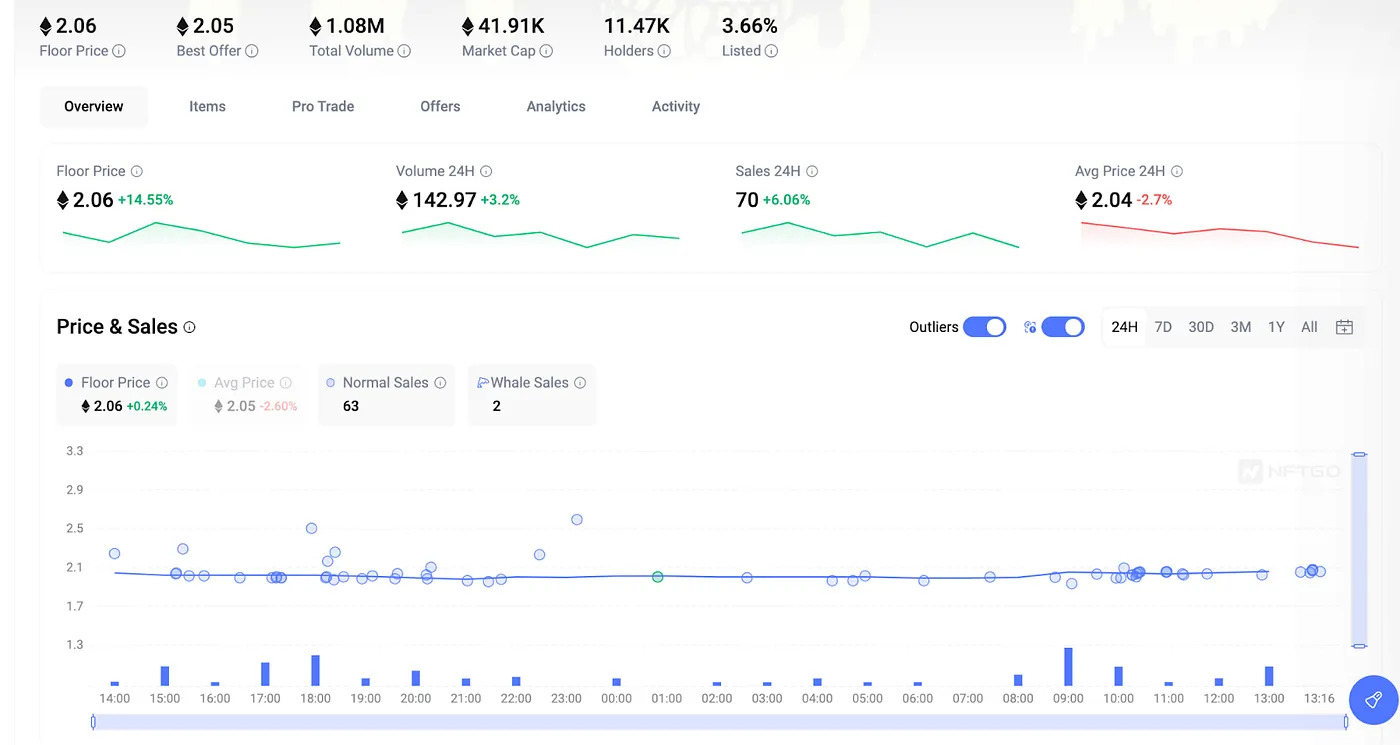
These robust metrics and analytics enable users to evaluate the potential of each NFT project thoroughly and make decision about buying, selling, or other interactions with collections.
### 3. Portfolio Analytics
For users interested in exploring the activities of prominent traders, NFTGo offers a tool to discover and track individual wallets, either by a search bar or using the Whale List and Profit Leaderboard section.
Among the available data, users can see the portfolio worth, profit, loss, and detailed records of incoming and outgoing transactions. This level of transparency empowers users to stay informed about the movements and strategies of influential players in the NFT market.
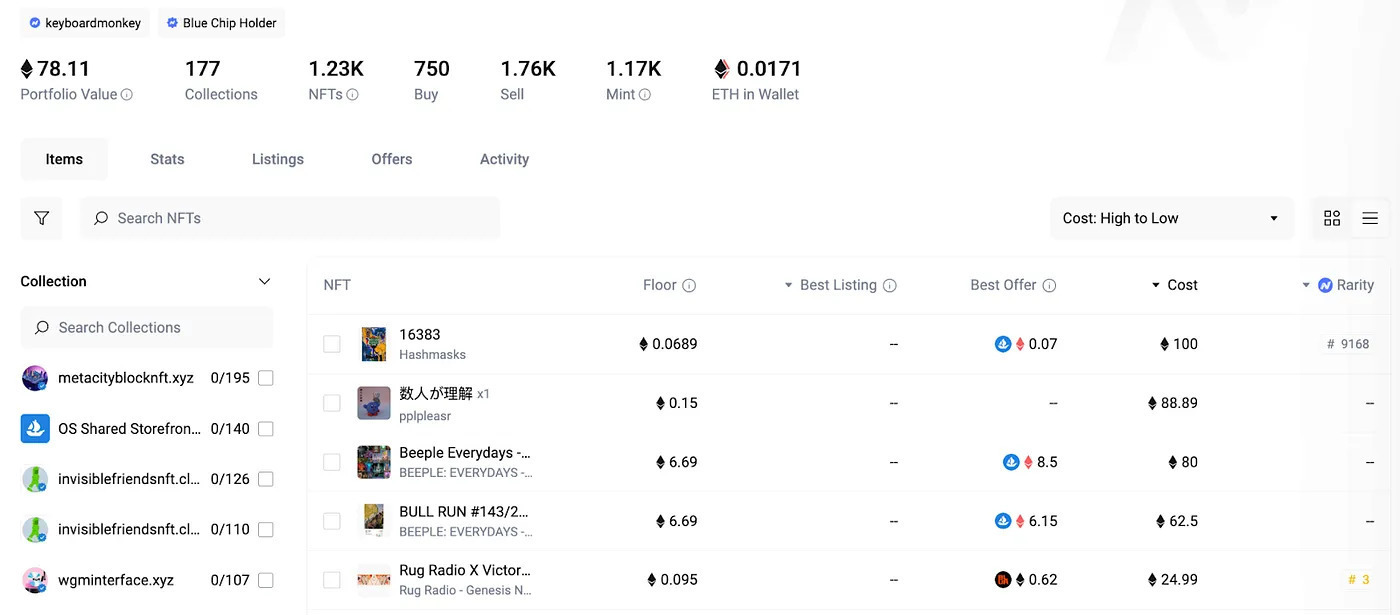
Users can connect their own wallets to monitor their personal holdings, profitability, and historical performance. They can also create personalized watchlists, enabling them to track specific accounts, collections, or individual NFTs.
### 4. NFT Trading Tools
In addition to its powerful analytics capabilities, NFTGo empowers users with a seamless trading experience. After connecting their wallets, they can buy and sell assets across integrated marketplaces directly through the website. Beyond that, it has several trading tools to maximize efficiency. Let’s look closer at them.
- **Make bundle purchases** from different collections in a single transaction, saving users valuable time and resources by consolidating gas fees.
- **Sweep the floor** by purchasing multiple items listed at the floor price with a single click, which is a convenient way to capitalize on potential bargains.
- **Easy listing process** for NFT owners, as they can list their owned assets on multiple marketplaces simultaneously.
- **Direct swaps from the collection page** for ERC-404 token holders, streamlining the trading process. You can read more about this standard in the [guide](https://getblock.io/blog/what-is-erc-404-a-guide-to-semi-fungible-tokens/?utm_source=external&utm_medium=article&utm_campaign=devto_nftgo).
NFTGo provides the option to shop based on rarity or specific marketplaces, and the platform checks suspicious NFTs, allowing users to skip these items and prioritize trustworthy assets.
### 5. Chrome Extension
The NFTGo Chrome extension seamlessly integrates with popular NFT platforms, providing users with vital statistics, key activity, and the ability to purchase available assets directly from official project pages. Additionally, the extension’s sidebar displays upcoming drops and trending collections, ensuring users never miss the latest opportunities.
For traders who have connected their wallets to their X accounts, the extension displays portfolio data directly on their profile pages. This feature allows users to follow their favorite collections and monitor whale activity without the need to leave the social network.
Therefore, this extension empowers desktop users with a seamless and integrated NFT tracking experience.
## NFTGo Usability: Key Features Summary
While NFTGo’s core features provide a solid foundation for NFT analysis and trading, the platform offers several additional standout features that take these capabilities to new heights:
- **Pro Trade section** with real-time sales and listing data.
- **Whale tracker** with more than 300 high-value investors.
- **Wash trades filter** to exclude artificially inflated trades and potentially fraudulent items.
- **Unique rarity algorithm** to assess NFT rarity.
- **NFTGo API** to integrate its extensive NFT database with dApps.
- **Industry reports** regarding the entire NFT market.
For seasoned traders, NFTGo provides premium features with advanced analytics, extensive NFT data, alert systems, and webhooks.
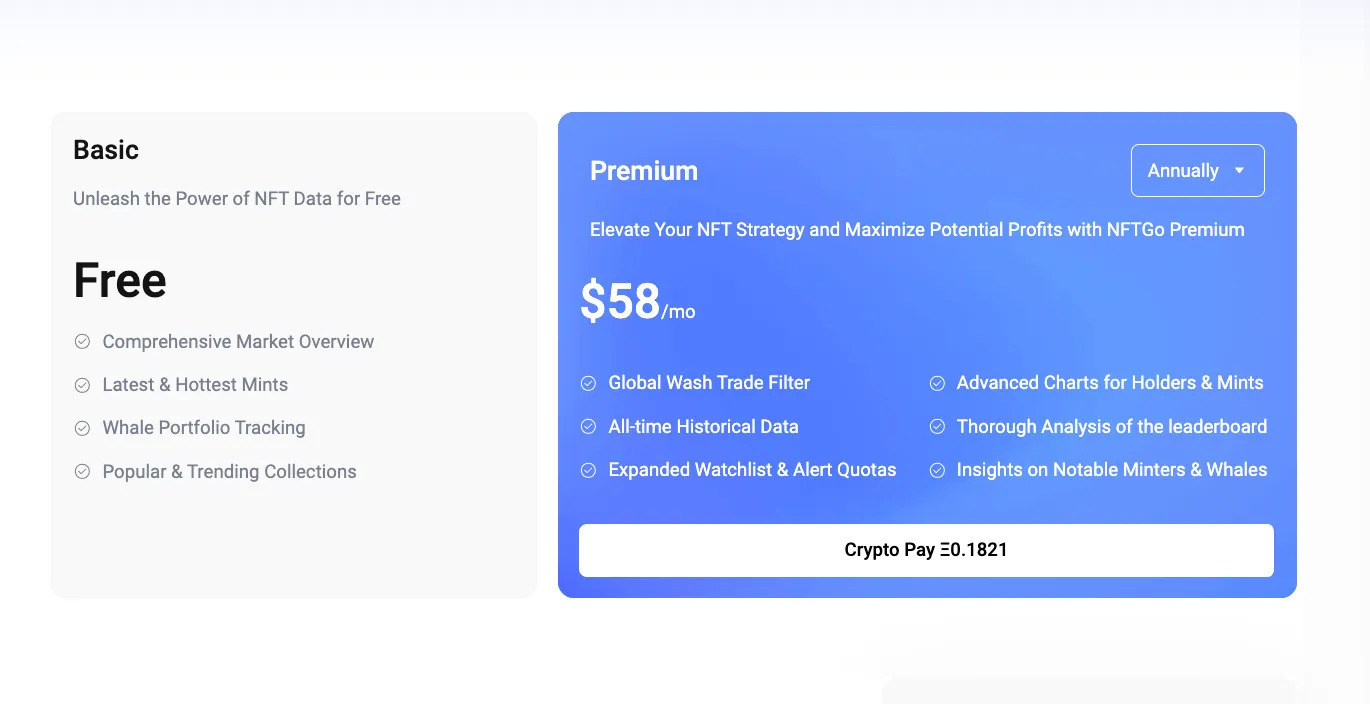
By combining these advanced features with its core analytics and trading capabilities, NFTGo empowers users with a comprehensive toolkit for navigating the ever-evolving NFT landscape.
## NFTGo Benefits: How It Empowers NFT Trading
For those considering leveraging the power of NFTGo, the platform offers a compelling value proposition with several key advantages:
- Asset discovery and comparison;
- Trade monitoring and performance tracking;
- Robust infrastructure and accurate data;
- Comprehensive analytics;
- Trend identification;
- Streamlined experience.
In essence, NFTGo’s value proposition is the ability to provide a comprehensive, efficient, and data-driven solution for navigating the complex NFT landscape for a wide audience of enthusiasts and professionals.
## Conclusion
Therefore, NFTGo has established itself as a top-tier NFT analysis hub, with its comprehensive suite of tools and features that facilitate market research, track portfolios, and provide all relevant information.
Moreover, NFTGo has ambitious plans to expand its reach to a broader range of blockchains, introduce more advanced tools, and develop industry reports. This commitment to continuous innovation positions NFTGo as an indispensable resource for all participants in the rapidly evolving NFT ecosystem.
For Web3 developers, market researchers, and NFT enthusiasts, there is a growing demand for stable blockchain nodes to connect with various chains, retrieving and writing actual data. That’s how GetBlock can help, with its seamless access to over 50 networks via its endpoints. [Sign up](https://getblock.io/?utm_source=external&utm_medium=article&utm_campaign=devto_nftgo) now and try its free version with 40,000 blockchain requests per day!
| getblockapi |
1,872,062 | Probability for Data Science and Machine Learning | Probability Probability is a measure of the likelihood that a particular event will occur.... | 0 | 2024-05-31T17:53:25 | https://dev.to/harshm03/probability-for-data-science-and-machine-learning-5ef4 | datascience, machinelearning, deeplearning | ### Probability
Probability is a measure of the likelihood that a particular event will occur. It quantifies uncertainty and helps in making predictions about future events based on past data. The value of probability ranges between 0 and 1, where 0 indicates that an event will not occur and 1 indicates that an event will certainly occur.
#### Important Terms in Probability:
#### Experiment
An experiment is a process or action that results in one or more outcomes. Each repetition of an experiment is called a trial. For example, flipping a coin or rolling a dice are common experiments in probability theory.
#### Sample Space
The sample space, often denoted as S, is the set of all possible outcomes of an experiment. For example:
```
The sample space of flipping a coin is
S = {Heads, Tails}
```
```
The sample space of rolling a six-sided dice is
S = {1, 2, 3, 4, 5, 6}
```
#### Event
An event is a specific outcome or a set of outcomes of an experiment. An event can be a subset of the sample space. For example:
```
Getting a "Heads" when flipping a coin is an event:
A = {Heads}
```
```
Rolling an even number on a six-sided dice is an event:
B = {2, 4, 6}
```
#### Probability of an Event
The probability of an event is calculated by dividing the number of favorable outcomes by the total number of possible outcomes in the sample space. If A is an event, the probability of A, denoted as P(A), is given by:
```
P(A) = Number of favorable outcomes / Total number of possible outcomes
```
For example, the probability of getting "Heads" when flipping a coin is:
```
P(Heads) = 1 / 2
```
The probability of rolling an even number on a six-sided dice is:
```
P(Even) = 3 / 6 = 1 / 2
```
These basic terms and concepts form the foundation of probability theory, which is essential for data science and machine learning. Understanding these terms will help in comprehending more advanced topics and algorithms that rely on probabilistic methods.
### When to Add and When to Multiply in Probability
Understanding when to add and when to multiply probabilities is essential for solving different types of probability problems. The rules depend on whether the events are mutually exclusive or independent.
#### Adding Probabilities
You add probabilities when you are dealing with mutually exclusive events. Mutually exclusive events are events that cannot happen at the same time. For example, when flipping a coin, getting "Heads" and getting "Tails" are mutually exclusive events.
The formula for the probability of either event A or event B occurring (denoted as A or B) is:
```
P(A or B) = P(A) + P(B)
```
This rule applies only if A and B are mutually exclusive.
For example, if you roll a six-sided dice, the probability of rolling a 2 or a 4 is:
```
P(2 or 4) = P(2) + P(4) = 1/6 + 1/6 = 2/6 = 1/3
```
#### Multiplying Probabilities
You multiply probabilities when you are dealing with independent events. Independent events are events where the occurrence of one event does not affect the occurrence of the other event. For example, flipping a coin and rolling a dice are independent events.
The formula for the probability of both event A and event B occurring (denoted as A and B) is:
```
P(A and B) = P(A) * P(B)
```
For example, if you flip a coin and roll a six-sided dice, the probability of getting "Heads" and rolling a 3 is:
```
P(Heads and 3) = P(Heads) * P(3) = 1/2 * 1/6 = 1/12
```
So, in summary:
- **Add probabilities** for mutually exclusive events: `P(A or B) = P(A) + P(B)`
- **Multiply probabilities** for independent events: `P(A and B) = P(A) * P(B)`
These rules help in calculating the probability of combined events, whether they occur one after another or as alternatives. Understanding when to add and when to multiply probabilities is crucial for accurate probability calculations in data science and machine learning.
### Conditional Probability
Conditional probability is the probability of an event occurring given that another event has already occurred. It helps in understanding the likelihood of an event under a specific condition or scenario. Conditional probability is denoted by `P(A|B)`, which reads as "the probability of event A given event B."
#### Formula
The formula for conditional probability is:
```
P(A|B) = P(A ∩ B) / P(B)
```
Where:
- `P(A|B)` is the conditional probability of event A given event B.
- `P(A ∩ B)` is the probability of both event A and event B occurring.
- `P(B)` is the probability of event B occurring.
#### Example
Consider an example of drawing two cards from a standard deck of playing cards. Let event A be drawing a red card, and event B be drawing a heart card.
- The probability of drawing a heart card (event B) from a standard deck is `P(B) = 13/52 = 1/4`.
- The probability of drawing a red card and a heart card (event A and event B) is `P(A ∩ B) = 13/52 = 1/4`.
Using the formula for conditional probability:
```
P(A|B) = P(A ∩ B) / P(B) = (1/4) / (1/4) = 1
```
So, the conditional probability of drawing a red card given that a heart card is drawn is 1, indicating that if a heart card is drawn, it must be red.
### Addition Theorem of Probability
The Addition Theorem of Probability, also known as the Addition Rule, is a fundamental concept in probability theory. It provides a method for calculating the probability of the union of two events.
#### Statement
The Addition Theorem states that the probability of the union of two events A and B is equal to the sum of their individual probabilities minus the probability of their intersection:
```
P(A ∪ B) = P(A) + P(B) - P(A ∩ B)
```
Where:
- `P(A ∪ B)` is the probability of either event A or event B occurring, or both.
- `P(A)` is the probability of event A occurring.
- `P(B)` is the probability of event B occurring.
- `P(A ∩ B)` is the probability of both event A and event B occurring.
#### Example
Consider a standard deck of playing cards. Let event A be drawing a red card, and event B be drawing a heart card.
- The probability of drawing a red card (event A) from a standard deck is `P(A) = 26/52 = 1/2`.
- The probability of drawing a heart card (event B) from a standard deck is `P(B) = 13/52 = 1/4`.
- The probability of drawing a red heart card (event A ∩ B) from a standard deck is `P(A ∩ B) = 13/52 = 1/4`.
Using the Addition Theorem:
```
P(A ∪ B) = P(A) + P(B) - P(A ∩ B)
= 1/2 + 1/4 - 1/4
= 1/2
```
So, the probability of drawing either a red card or a heart card (or both) from a standard deck is 1/2.
### Multiplication Theorem of Probability
The Multiplication Theorem of Probability, also known as the Multiplication Rule, is another fundamental concept in probability theory. It provides a method for calculating the probability of the intersection of two events.
#### Statement
The Multiplication Theorem states that the probability of the intersection of two events A and B is equal to the probability of event A occurring multiplied by the conditional probability of event B occurring given that event A has already occurred:
```
P(A ∩ B) = P(A) * P(B|A)
```
Where:
- `P(A ∩ B)` is the probability of both event A and event B occurring.
- `P(A)` is the probability of event A occurring.
- `P(B|A)` is the conditional probability of event B occurring given that event A has already occurred.
#### Example
Consider a standard deck of playing cards. Let event A be drawing a red card, and event B be drawing a heart card.
- The probability of drawing a red card (event A) from a standard deck is `P(A) = 26/52 = 1/2`.
- If a red card is drawn (event A has occurred), the probability of drawing a heart card (event B) from the remaining cards is `P(B|A) = 13/51`.
Using the Multiplication Theorem:
```
P(A ∩ B) = P(A) * P(B|A)
= (1/2) * (13/51)
= 13/102
```
So, the probability of drawing both a red card and a heart card from a standard deck is 13/102.
### Random Variable
In probability theory and statistics, a random variable is a variable whose possible values are outcomes of a random phenomenon. It represents a numerical outcome of a random experiment, often denoted by a letter such as `X`, `Y`, or `Z`.
#### Definition
Formally, a random variable X is a function that takes an event as input and returns a real number as output. It assigns a numerical value to each outcome in the sample space of the experiment. Mathematically, we can express a random variable as follows:
```
X: Event -> Real Numbers
```
Where X is the random variable, Event represents the set of all possible outcomes, and Real Numbers represents the set of all real numbers.
#### Example
Consider the experiment of tossing 3 coins. Let's define a random variable X that represents the number of heads obtained in the experiment. We can define X as follows:
```
X: {HHH, HHT, HTH, THH, HTT, THT, TTH, TTT} -> {0, 1, 2, 3}
```
For each outcome in the sample space, the output of the random variable function X will be:
```
X(HHH) = 3
X(HHT) = 2
X(HTH) = 2
X(THH) = 2
X(HTT) = 1
X(THT) = 1
X(TTH) = 1
X(TTT) = 0
```
In this example, the random variable X takes an event (outcome of tossing 3 coins) as input and returns a number (the number of heads) associated with that event. Each event in the sample space is associated with a specific value of X, demonstrating that X is indeed a function mapping events to real numbers.
### Probability Distribution of Random Variable
In probability theory, the probability distribution of a random variable describes the likelihood of each possible outcome of the variable. It provides a mapping between the values of the random variable and their associated probabilities.
#### Definition
For a random variable X, its probability distribution P(X) assigns probabilities to each possible value that X can take. Mathematically, for a discrete random variable X, the probability distribution is typically represented as a probability mass function (PMF), denoted as P(X = x), where x is a specific value that X can take.
#### Example
Consider the experiment of tossing 3 coins. Let X be the random variable representing the number of heads obtained in the experiment. For each outcome in the sample space, the probability distribution of X is as follows:
```
P(X = 0) = 1/8
P(X = 1) = 3/8
P(X = 2) = 3/8
P(X = 3) = 1/8
```
In this example, each possible outcome of tossing 3 coins has an associated probability based on the number of heads obtained. The probability distribution of X provides insights into the likelihood of different outcomes and forms the basis for analyzing the behavior of the random variable in various scenarios.
### Mean of Random Variable
In probability theory, the mean of a random variable represents the average value of all possible outcomes weighted by their respective probabilities. It is also known as the expected value of the random variable.
#### Definition
The mean mu of a random variable X is calculated by summing the product of each possible value of X and its corresponding probability. Mathematically, for a discrete random variable X, the mean is given by:
```
Mean(X) = Σ(x * P(X = x))
```
Where x represents each possible value that X can take, and P(X = x) is the probability of X taking the value x.
For a continuous random variable X, the mean is given by the integral:
```
Mean(X) = ∫(x * f(x)) dx
```
Where f(x) is the probability density function of X.
#### Example
Consider the experiment of tossing three coins. Let X be the random variable representing the number of heads obtained in the experiment. The sample space for this experiment is {HHH, HHT, HTH, THH, HTT, THT, TTH, TTT}, and the probability distribution of X is:
```
P(X = 0) = 1/8
P(X = 1) = 3/8
P(X = 2) = 3/8
P(X = 3) = 1/8
```
The mean of X can be calculated as:
```
Mean(X) = (0 * 1/8) + (1 * 3/8) + (2 * 3/8) + (3 * 1/8)
= (0/8) + (3/8) + (6/8) + (3/8)
= 12/8
= 1.5
```
So, the mean of the random variable X representing the number of heads obtained in tossing three coins is 1.5.
### Variance of Random Variable
In probability theory, the variance of a random variable measures how much the values of the random variable differ from the mean. It provides a measure of the spread or dispersion of the random variable's values around the mean.
#### Definition
The variance of a random variable X, denoted as Var(X), is calculated as the average of the squared differences between each value of X and the mean of X. Mathematically, for a discrete random variable X, the variance is given by:
```
Var(X) = Σ((x - μ)^2 * P(X = x))
```
Where x represents each possible value that X can take, μ is the mean of X, and P(X = x) is the probability of X taking the value x.
For a continuous random variable X, the variance is calculated similarly using the integral:
```
Var(X) = ∫((x - μ)^2 * f(x)) dx
```
Where f(x) is the probability density function of X.
#### Example
Consider the same experiment of tossing three coins, with the random variable X representing the number of heads obtained. We've already calculated that the mean of X is 1.5.
The variance of X can be calculated as:
```
Var(X) = ((0 - 1.5)^2 * 1/8) + ((1 - 1.5)^2 * 3/8) + ((2 - 1.5)^2 * 3/8) + ((3 - 1.5)^2 * 1/8)
= (2.25 * 1/8) + (0.25 * 3/8) + (0.25 * 3/8) + (2.25 * 1/8)
= 0.28125 + 0.09375 + 0.09375 + 0.28125
= 0.75
```
So, the variance of the random variable X representing the number of heads obtained in tossing three coins is 0.75.
### Joint Probability Distribution
In probability theory and statistics, a joint probability distribution represents the probability of two or more random variables taking on specific values simultaneously. It provides a comprehensive way to study the relationship between multiple random variables.
#### Definition
A joint probability distribution for two discrete random variables X and Y, denoted as P(X = x, Y = y), gives the probability that X takes on the value x and Y takes on the value y at the same time.
For continuous random variables, the joint probability distribution is described by a joint probability density function f(x, y), which gives the probability that X and Y fall within a particular range of values.
#### Joint Probability Mass Function (Discrete Case)
For discrete random variables X and Y, the joint probability mass function (pmf) is defined as:
```
P(X = x, Y = y) = Probability that X = x and Y = y
```
#### Joint Probability Density Function (Continuous Case)
For continuous random variables X and Y, the joint probability density function (pdf) is defined as:
```
f(x, y) = Probability density that X = x and Y = y
```
#### Example
Consider a simple example with two discrete random variables X and Y, representing the outcome of tossing three coins. Let X be the number of heads in the first two tosses and Y be the number of heads in the last two tosses. The sample space for each coin toss is {H, T}.
The joint probability distribution of X and Y can be represented as a table where each cell represents the probability P(X = x, Y = y):
```
Y=0 Y=1 Y=2
X=0 1/8 2/8 1/8
X=1 2/8 4/8 2/8
X=2 1/8 2/8 1/8
```
Here's the breakdown of how the probabilities are calculated:
```
P(X = 0, Y = 0) = P(TTT) = 1/8
P(X = 0, Y = 1) = P(TTH) + P(THT) = 1/8 + 1/8 = 2/8
P(X = 0, Y = 2) = P(THH) = 1/8
P(X = 1, Y = 0) = P(HTT) + P(THT) = 1/8 + 1/8 = 2/8
P(X = 1, Y = 1) = P(HTH) + P(THH) + P(HHT) + P(TTH) = 1/8 + 1/8 + 1/8 + 1/8 = 4/8
P(X = 1, Y = 2) = P(HHH) + P(HHT) = 1/8 + 1/8 = 2/8
P(X = 2, Y = 0) = P(HHT) = 1/8
P(X = 2, Y = 1) = P(HHT) + P(HHH) = 1/8 + 1/8 = 2/8
P(X = 2, Y = 2) = P(HHH) = 1/8
```
Each entry in the table represents the probability of a specific combination of outcomes for the three coin tosses. Since the coin tosses are fair, each combination has a probability based on the respective outcomes.
This example shows how to set up and understand a joint probability distribution for two discrete random variables using the outcomes of tossing three coins.
### Standard Deviation of a Random Variable
In probability theory and statistics, the standard deviation of a random variable is a measure of the amount of variation or dispersion in a set of values. It indicates how much the values of the random variable deviate from the mean (expected value) of the random variable.
#### Definition
The standard deviation of a random variable X, denoted as sigma (σ), is the square root of the variance of X. Mathematically, for a discrete random variable X, the standard deviation is given by:
```
σ(X) = sqrt(Var(X))
```
Where Var(X) is the variance of X.
For a continuous random variable X, the standard deviation is calculated similarly using the integral:
```
σ(X) = sqrt( ∫((x - μ)^2 * f(x)) dx )
```
Where μ is the mean of X, and f(x) is the probability density function of X.
#### Example
Consider the same experiment of tossing three coins, with the random variable X representing the number of heads obtained. We have already calculated that the mean (μ) of X is 1.5, and the variance (Var(X)) is 0.75.
The standard deviation of X can be calculated as:
```
σ(X) = sqrt(Var(X))
= sqrt(0.75)
= 0.866
```
So, the standard deviation of the random variable X representing the number of heads obtained in tossing three coins is approximately 0.866.
The standard deviation provides a useful measure of the spread of the values around the mean. In this case, it tells us how much the number of heads obtained in the experiment typically deviates from the mean number of heads (1.5).
### Covariance of Random Variables
In probability theory and statistics, covariance is a measure of how much two random variables change together. If the greater values of one variable correspond with the greater values of the other variable, and the same holds for lower values, the covariance is positive. If greater values of one variable correspond with lower values of the other, the covariance is negative. If the variables are independent, the covariance is zero.
#### Definition
The covariance between two random variables X and Y, denoted as Cov(X, Y), is defined as the expected value of the product of their deviations from their respective means. Mathematically, for discrete random variables X and Y, the covariance is given by:
```
Cov(X, Y) = Σ((x - μX) * (y - μY) * P(X = x, Y = y))
```
Where:
- x and y are the possible values of X and Y.
- μX is the mean of X.
- μY is the mean of Y.
- P(X = x, Y = y) is the joint probability that X takes the value x and Y takes the value y.
For continuous random variables X and Y, the covariance is calculated using the integral:
```
Cov(X, Y) = ∫∫((x - μX) * (y - μY) * f(x, y)) dx dy
```
Where f(x, y) is the joint probability density function of X and Y.
#### Example
Consider the experiment of tossing three coins twice. Let X be the random variable representing the number of heads obtained in the first three tosses, and Y be the random variable representing the number of heads obtained in the second three tosses.
The sample space for each set of three coin tosses is {0, 1, 2, 3}, and the joint probability distribution of X and Y is as follows:
```
P(X = 0, Y = 0) = 1/64
P(X = 0, Y = 1) = 3/64
P(X = 0, Y = 2) = 3/64
P(X = 0, Y = 3) = 1/64
P(X = 1, Y = 0) = 3/64
P(X = 1, Y = 1) = 9/64
P(X = 1, Y = 2) = 9/64
P(X = 1, Y = 3) = 3/64
P(X = 2, Y = 0) = 3/64
P(X = 2, Y = 1) = 9/64
P(X = 2, Y = 2) = 9/64
P(X = 2, Y = 3) = 3/64
P(X = 3, Y = 0) = 1/64
P(X = 3, Y = 1) = 3/64
P(X = 3, Y = 2) = 3/64
P(X = 3, Y = 3) = 1/64
```
We first need to calculate the means μX and μY:
```
μX = μY = (0 * 1/8) + (1 * 3/8) + (2 * 3/8) + (3 * 1/8)
= 1.5
```
Then, we calculate the covariance using the joint probability distribution:
```
Cov(X, Y) = Σ((x - μX) * (y - μY) * P(X = x, Y = y))
= (0 - 1.5)(0 - 1.5) * 1/64 + (0 - 1.5)(1 - 1.5) * 3/64 + (0 - 1.5)(2 - 1.5) * 3/64 + (0 - 1.5)(3 - 1.5) * 1/64
+ (1 - 1.5)(0 - 1.5) * 3/64 + (1 - 1.5)(1 - 1.5) * 9/64 + (1 - 1.5)(2 - 1.5) * 9/64 + (1 - 1.5)(3 - 1.5) * 3/64
+ (2 - 1.5)(0 - 1.5) * 3/64 + (2 - 1.5)(1 - 1.5) * 9/64 + (2 - 1.5)(2 - 1.5) * 9/64 + (2 - 1.5)(3 - 1.5) * 3/64
+ (3 - 1.5)(0 - 1.5) * 1/64 + (3 - 1.5)(1 - 1.5) * 3/64 + (3 - 1.5)(2 - 1.5) * 3/64 + (3 - 1.5)(3 - 1.5) * 1/64
= 0
```
In this example, the covariance between X and Y is 0, indicating that there is no linear relationship between the number of heads obtained in the first three coin tosses and the number of heads obtained in the second three coin tosses.
### Bayes' Theorem
In probability theory and statistics, Bayes' Theorem describes the probability of an event based on prior knowledge of conditions that might be related to the event. It provides a way to update the probability of a hypothesis as more evidence or information becomes available.
#### Definition
Bayes' Theorem for two events A and B is given by:
```
P(A | B) = (P(B | A) * P(A)) / P(B)
```
Where:
- P(A | B) is the conditional probability of event A given that event B has occurred.
- P(B | A) is the conditional probability of event B given that event A has occurred.
- P(A) is the prior probability of event A.
- P(B) is the prior probability of event B.
#### Example
Consider an example involving medical testing. Suppose there is a disease that affects 1% of the population. A test for the disease is 99% accurate for those who have the disease (true positive rate) and 95% accurate for those who do not have the disease (true negative rate). We want to find the probability that a person has the disease given that they tested positive.
Let:
- A be the event that a person has the disease.
- B be the event that a person tests positive for the disease.
Given:
- P(A) = 0.01 (prior probability of having the disease).
- P(B | A) = 0.99 (probability of testing positive given having the disease).
- P(B | not A) = 0.05 (probability of testing positive given not having the disease).
To find P(B), the total probability of testing positive, we use the law of total probability:
```
P(B) = P(B | A) * P(A) + P(B | not A) * P(not A)
= 0.99 * 0.01 + 0.05 * 0.99
= 0.0099 + 0.0495
= 0.0594
```
Now, applying Bayes' Theorem:
```
P(A | B) = (P(B | A) * P(A)) / P(B)
= (0.99 * 0.01) / 0.0594
= 0.0099 / 0.0594
= 0.1667
```
So, the probability that a person has the disease given that they tested positive is approximately 16.67%. This example illustrates how Bayes' Theorem can be used to update the probability of a hypothesis (having the disease) based on new evidence (testing positive).
### Bernoulli Process
A Bernoulli process is a sequence of independent and identically distributed random variables, each taking on one of two possible outcomes, typically labeled as "success" (with probability p) and "failure" (with probability 1 - p). Each trial in a Bernoulli process follows a Bernoulli distribution, where the probability of success remains constant across all trials. The Bernoulli process forms the foundation for binomial distributions, where the number of successes in a fixed number of Bernoulli trials is counted.
### Binomial Distribution
In probability theory and statistics, a binomial distribution is a discrete probability distribution that models the number of successes in a fixed number of independent trials, each with the same probability of success.
#### Definition
A random variable X follows a binomial distribution if it represents the number of successes in n independent Bernoulli trials, each with the same probability of success p. The probability mass function (pmf) of a binomial distribution is given by:
```
P(X = k) = C(n, k) * p^k * (1 - p)^(n - k)
```
Where:
- C(n, k) = n! / (k! * (n - k)!) is the binomial coefficient, representing the number of ways to choose k successes from n trials.
- n is the number of trials.
- k is the number of successes.
- p is the probability of success on each trial.
- (1 - p) is the probability of failure on each trial.
#### Example
Consider an example where we flip a fair coin 3 times, and we want to find the probability of getting exactly 2 heads.
Let:
- n = 3 (number of trials)
- k = 2 (number of successes)
- p = 0.5 (probability of success, i.e., getting a head on each trial)
Using the binomial distribution formula:
```
P(X = 2) = C(3, 2) * (0.5)^2 * (1 - 0.5)^(3 - 2)
= 3! / (2! * (3 - 2)!) * (0.5)^2 * (0.5)^1
= 3 / 1 * 0.25 * 0.5
= 3 * 0.125
= 0.375
```
So, the probability of getting exactly 2 heads in 3 coin flips is 0.375.
#### Properties
1. **Mean**: The mean (expected value) of a binomial distribution is given by:
```
Mean(X) = n * p
```
2. **Variance**: The variance of a binomial distribution is given by:
```
Var(X) = n * p * (1 - p)
```
#### Example for Mean and Variance
Using the same coin flip example:
- n = 3 (number of trials)
- p = 0.5 (probability of success)
The mean of the binomial distribution is:
```
Mean(X) = n * p
= 3 * 0.5
= 1.5
```
The variance of the binomial distribution is:
```
Var(X) = n * p * (1 - p)
= 3 * 0.5 * 0.5
= 0.75
```
So, for 3 coin flips with a fair coin, the expected number of heads is 1.5, and the variance is 0.75.
### Negative Binomial Distribution
In probability theory and statistics, the negative binomial distribution models the number of trials needed to achieve a specified number of successes in a sequence of independent and identically distributed Bernoulli trials, each with the same probability of success.
#### Definition
A random variable X follows a negative binomial distribution if it represents the number of trials required to achieve a specified number of successes r, where each trial has a probability of success p. The probability mass function (pmf) of a negative binomial distribution is given by:
```
P(X = k) = C(k - 1, r - 1) * p^r * (1 - p)^(k - r)
```
Where:
- C(k - 1, r - 1) = (k - 1)! / ((r - 1)! * (k - r)!) is the binomial coefficient, representing the number of ways to distribute k - r failures among k - 1 trials.
- k is the total number of trials.
- r is the number of successes.
- p is the probability of success on each trial.
- (1 - p) is the probability of failure on each trial.
#### Example
Consider an example where we flip a fair coin until we get 3 heads. We want to find the probability that it takes exactly 5 flips to get those 3 heads.
Let:
- r = 3 (number of successes)
- k = 5 (total number of trials)
- p = 0.5 (probability of success, i.e., getting a head on each trial)
Using the negative binomial distribution formula:
```
P(X = 5) = C(5 - 1, 3 - 1) * (0.5)^3 * (1 - 0.5)^(5 - 3)
= C(4, 2) * (0.5)^3 * (0.5)^2
= 6 * 0.125 * 0.25
= 6 * 0.03125
= 0.1875
```
So, the probability that it takes exactly 5 flips to get 3 heads is 0.1875.
#### Properties
1. **Mean**: The mean (expected value) of a negative binomial distribution is given by:
```
Mean(X) = r / p
```
2. **Variance**: The variance of a negative binomial distribution is given by:
```
Var(X) = r * (1 - p) / p^2
```
#### Example for Mean and Variance
Using the same coin flip example:
- r = 3 (number of successes)
- p = 0.5 (probability of success)
The mean of the negative binomial distribution is:
```
Mean(X) = r / p
= 3 / 0.5
= 6
```
The variance of the negative binomial distribution is:
```
Var(X) = r * (1 - p) / p^2
= 3 * (1 - 0.5) / 0.5^2
= 3 * 0.5 / 0.25
= 6
```
So, for getting 3 heads in coin flips where each flip has a 0.5 probability of success, the expected number of flips is 6, and the variance is also 6.
### Geometric Distribution
In probability theory and statistics, the geometric distribution models the number of trials needed to get the first success in a sequence of independent and identically distributed Bernoulli trials, each with the same probability of success.
#### Definition
A random variable X follows a geometric distribution if it represents the number of trials required to achieve the first success, where each trial has a probability of success p. The probability mass function (pmf) of a geometric distribution is given by:
```
P(X = k) = (1 - p)^(k - 1) * p
```
Where:
- k is the number of trials.
- p is the probability of success on each trial.
- (1 - p) is the probability of failure on each trial.
#### Example
Consider an example where we flip a fair coin until we get the first head. We want to find the probability that it takes exactly 3 flips to get that first head.
Let:
- k = 3 (number of trials)
- p = 0.5 (probability of success, i.e., getting a head on each trial)
Using the geometric distribution formula:
```
P(X = 3) = (1 - 0.5)^(3 - 1) * 0.5
= (0.5)^2 * 0.5
= 0.25 * 0.5
= 0.125
```
So, the probability that it takes exactly 3 flips to get the first head is 0.125.
#### Properties
1. **Mean**: The mean (expected value) of a geometric distribution is given by:
```
Mean(X) = 1 / p
```
2. **Variance**: The variance of a geometric distribution is given by:
```
Var(X) = (1 - p) / p^2
```
#### Example for Mean and Variance
Using the same coin flip example:
- p = 0.5 (probability of success)
The mean of the geometric distribution is:
```
Mean(X) = 1 / p
= 1 / 0.5
= 2
```
The variance of the geometric distribution is:
```
Var(X) = (1 - p) / p^2
= (1 - 0.5) / 0.5^2
= 0.5 / 0.25
= 2
```
So, for getting the first head in coin flips where each flip has a 0.5 probability of success, the expected number of flips is 2, and the variance is also 2.
### Normal Distribution
In probability theory and statistics, the normal distribution, also known as the Gaussian distribution, is one of the most important probability distributions. It describes how the values of a random variable are distributed and is characterized by its bell-shaped curve.
#### Definition
A random variable \(X\) is said to be normally distributed if it has the probability density function (pdf) given by:
```
f(x) = (1 / (σ * sqrt(2 * π))) * exp(-((x - μ)^2) / (2 * σ^2))
```
Where:
- \(μ\) (mu) is the mean of the distribution.
- \(σ\) (sigma) is the standard deviation of the distribution.
- \(π\) (pi) is a constant approximately equal to 3.14159.
- \(exp\) is the exponential function.
#### Properties
1. **Mean**: The mean \(μ\) of the normal distribution is the central point around which the values are distributed.
2. **Variance**: The variance \(σ^2\) measures the spread of the distribution. The standard deviation \(σ\) is the square root of the variance.
3. **Symmetry**: The normal distribution is symmetric around its mean \(μ\).
4. **68-95-99.7 Rule**: Approximately 68% of the data falls within one standard deviation (\(μ ± σ\)), 95% within two standard deviations (\(μ ± 2σ\)), and 99.7% within three standard deviations (\(μ ± 3σ\)).
#### Example
Consider a simple example where the heights of a group of people are normally distributed with a mean height \(μ\) of 170 cm and a standard deviation \(σ\) of 10 cm.
The probability density function for this normal distribution is:
```
f(x) = (1 / (10 * sqrt(2 * π))) * exp(-((x - 170)^2) / (2 * 10^2))
```
This function gives the probability density for any given height \(x\).
#### Calculating Probabilities
To find the probability that a person's height is between 160 cm and 180 cm, we would calculate the area under the normal distribution curve between these two values. This is typically done using statistical tables or software.
For our example:
```
P(160 ≤ X ≤ 180) ≈ 0.6826
```
This result indicates that there is approximately a 68.26% chance that a randomly selected person from this group will have a height between 160 cm and 180 cm, which aligns with the 68-95-99.7 rule.
#### Standard Normal Distribution
The standard normal distribution is a special case of the normal distribution with a mean of 0 and a standard deviation of 1. The standard normal distribution is denoted by \(Z\) and its probability density function is:
```
f(z) = (1 / sqrt(2 * π)) * exp(-z^2 / 2)
```
Where \(z\) is the standard score or z-score, which represents the number of standard deviations a data point is from the mean.
#### Example for Standard Normal Distribution
To convert a value from a normal distribution to the standard normal distribution (z-score), use the formula:
```
z = (x - μ) / σ
```
For example, if \(x = 180\) cm in our height example:
```
z = (180 - 170) / 10
= 1
```
So, a height of 180 cm is 1 standard deviation above the mean in the standard normal distribution. | harshm03 |
1,872,327 | How AWS GenAI boosted my day to day Productivity | GenAI is everywhere these days, and it's no surprise why—it’s the tech world's latest obsession and... | 0 | 2024-05-31T17:49:16 | https://dev.to/aws-heroes/how-aws-genai-boosted-my-day-to-day-productivity-1i8k | aws, beginners, productivity, genai | GenAI is everywhere these days, and it's no surprise why—it’s the tech world's latest obsession and has skyrocketed to the top of the Gartner hype cycle. But like any hyped technology, it comes with its share of pros and cons. On the plus side, it can automate mundane tasks, boost productivity, and spark creativity. On the downside, it raises questions about job displacement and ethical use. Despite the mixed feelings, one thing is clear: GenAI is here to stay, and it's transforming how we think about technology and its potential.
The agenda is fairly simple and packed with exciting highlights. First up, there's **Amazon PartyRock** for Newbies (or anyone!)—a fun and engaging way to get introduced to the world of GenAI.
Next, we dive into **Amazon CodeWhisperer**, a powerful tool for developers that offers real-time code suggestions and automation to streamline coding tasks.
Finally, we explore **Amazon Q** for Business and beyond, a tool that integrates with Amazon QuickSight to provide insightful data analysis and business intelligence, helping businesses make informed decisions quickly. Whether you're a beginner or a seasoned developer, there's something in this agenda to supercharge your productivity with GenAI on AWS.
## Amazon PartyRock
Imagine diving into the world of generative AI without needing to write a single line of code. With Amazon PartyRock, learning generative AI fundamentals becomes an exciting and hands-on experience. PartyRock is a code-free app builder designed to make learning easy and fun. You can experiment with prompt engineering techniques, review generated responses, and develop a solid intuition for generative AI, all while creating and exploring entertaining apps.
At the heart of PartyRock is access to powerful foundation models from Amazon Bedrock. Amazon Bedrock is a fully managed service that provides foundation models (FMs) from Amazon and other leading AI companies, available right on AWS. It’s the simplest way to build and scale generative AI applications with these foundation models. With PartyRock, you get to tap into the full potential of these FMs in an intuitive, code-free app-building playground. This setup is perfect for learning the essentials of prompt engineering and generative AI, making it accessible and engaging for everyone, regardless of their coding background.
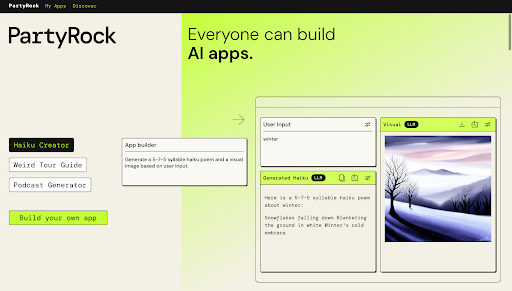
With Amazon PartyRock, you can revolutionize your daily routine by creating custom AI apps without writing a single line of code. Imagine a smart meal planner that suggests recipes based on your pantry, a personalized workout coach that designs fitness plans, or a daily task organizer that prioritizes your to-do list. You can even build a budget tracker to oversee your finances.
PartyRock makes it easy and fun to automate everyday tasks, enhancing your productivity and well-being with intuitive, AI-driven solutions. Dive in and start building your personalized AI apps today!
Also do check out one of the amazing project from AWS Community by _Stephen Sennett_

### A Day in the Developer Life of Vivek
Today, I log into work and am greeted with a new task assignment: upload all 'CSV' data in the 'temp' folder to an S3 bucket named 'code-demo'. This involves writing a Python function to read the CSV files and upload them to the specified S3 bucket. It’s time to nail the task.
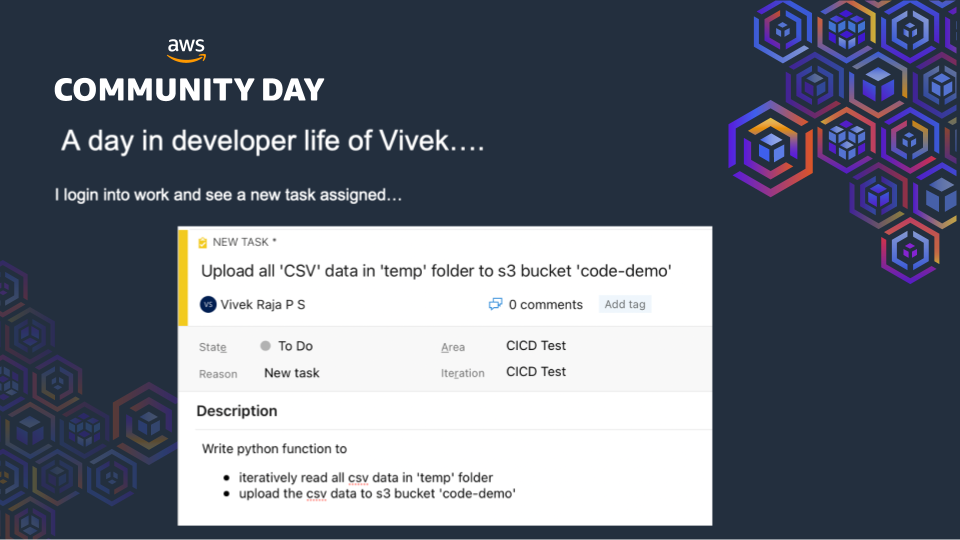
I choose my favorite IDE—VSCode (no doubt!). But sometimes, even with the best tools, you need a bit of extra help.
Like many developers, I head over to Stack Overflow to get the relevant code snippet. After some searching, I find a solution that fits my needs.
Here's the Python code I found and used:
```python
import boto3
import os
def upload_to_s3(file, bucket, objname):
s3 = boto3.resource('s3')
bucket = s3.Bucket(bucket)
bucket.Object(objname).put(Body=open(file, 'rb'))
def csv_files_from_folder(folderpath):
path = folderpath
table_list = []
for filename in os.listdir(path):
if filename.endswith('.csv'):
table_list.append(path + "\\" + filename)
return table_list
files = csv_files_from_folder("tempfolder")
for file in files:
upload_to_s3(file, "codedemo", file)
```
This script iterates through all CSV files in the 'tempfolder', uploading each one to the 'codedemo' S3 bucket.
## How Amazon CodeWhisperer Enhances My Productivity
Amazon CodeWhisperer is my ML-powered coding companion, and it has become an invaluable part of my development workflow. Here’s how it helps me become a more productive developer:
- Real-time Code Recommendations: CodeWhisperer generates code recommendations based on my comments and method names. This feature saves me time by providing relevant suggestions as I type, reducing the need to search for solutions online.
- Powered by Machine Learning: It leverages machine learning to offer customized code recommendations for all my Java, Python, and JavaScript projects, ensuring that I write efficient and effective code.
- Responsibly Use AI: CodeWhisperer empowers me to use AI responsibly, helping me create syntactically correct and secure applications. This not only boosts my productivity but also enhances the quality of my code.
With Amazon CodeWhisperer integrated into my IDE, I can focus more on solving complex problems and less on repetitive coding tasks. It’s like having a knowledgeable co-pilot who guides me through the development process, making my coding experience smoother and more efficient.
### How Amazon Q Enhances Business Productivity
Amazon Q is a game-changer for business productivity, providing a generative AI-powered assistant tailored to work seamlessly with your business needs. By leveraging the vast data and expertise available within your company's information repositories, code, and enterprise systems, Amazon Q offers fast, relevant answers to pressing questions, solves problems, generates content, and takes actions based on the data provided. Here's how Amazon Q can enhance productivity on the business side:
**1. Amazon Q in VSCode Extension:**
Amazon Q is available as part of the AWS Toolkit extension in VSCode, making it accessible directly within your development environment. This integration allows you to leverage Amazon Q's powerful capabilities without leaving your IDE, further enhancing your productivity and streamlining your workflow.
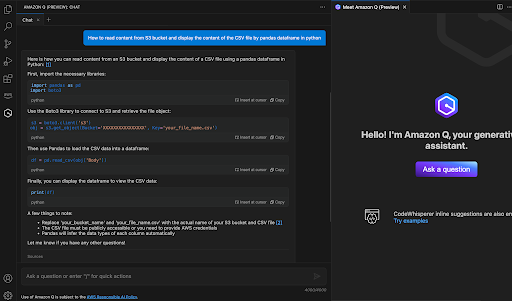
**2. Enhanced Decision-Making:**
Integrating with Amazon QuickSight, Amazon Q allows you to generate analysis and visualizations from simple prompts. This capability enables you to make data-driven decisions swiftly, reducing the time spent on data gathering and interpretation.
**3. Integration with AWS Best Practices:**
Amazon Q helps you adhere to AWS best practices, ensuring that your use of AWS services is optimized and secure. By offering guidance and recommendations on AWS usage, it helps maintain the integrity and efficiency of your cloud operations, reducing the risk of errors and enhancing overall productivity.
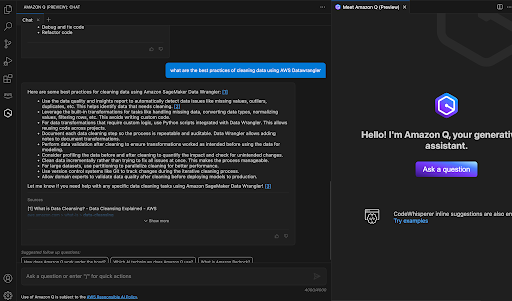
### Example of Amazon Q in Action:
Imagine you're analyzing the difference between website unique visits and total paid conversions. With Amazon Q, you can simply type a natural language query, and it will generate a visual representation of the data, helping you quickly identify trends and insights without the need for complex queries or manual data manipulation.
**Sample Query:**
"Show the difference in number of website unique visits versus total paid conversions."
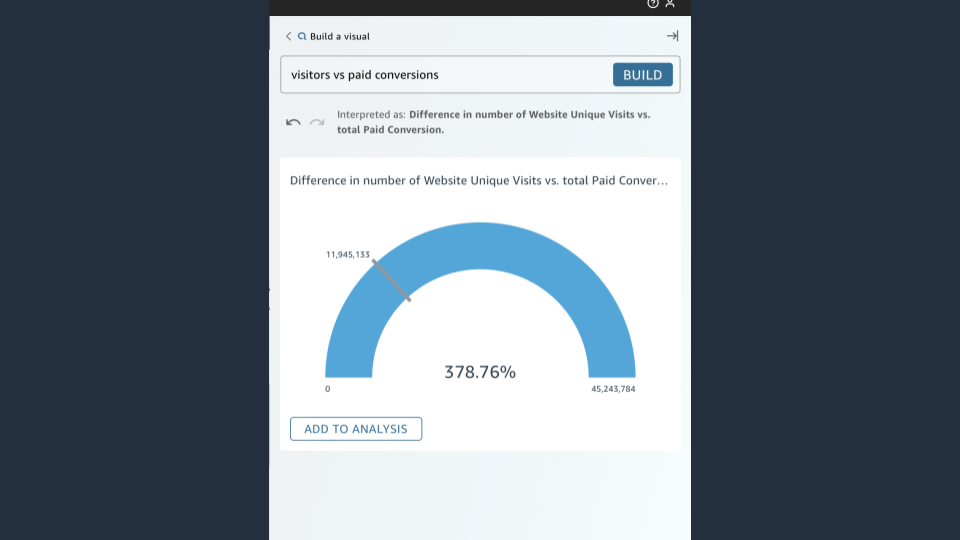
**Result:**
Amazon Q interprets the query and generates a visual analysis, providing a clear and concise view of the data, which you can then use to make informed business decisions.
GenAI is not here to take over your jobs but to supercharge your productivity! With tools like Amazon CodeWhisperer and Amazon Q, you can streamline your development workflow, make data-driven business decisions, and foster creativity and innovation. These powerful AI-driven solutions are designed to assist you, making complex tasks more manageable and freeing you to focus on what truly matters. Embrace the future of productivity with GenAI on AWS and watch your efficiency and effectiveness soar.
| vivek0712 |
1,872,326 | How to Programmatically Generate Word DOCX in C# .NET | Learn how to programmatically generate Word DOCX in C# .NET. See more from Document Solutions today. | 0 | 2024-05-31T17:49:03 | https://developer.mescius.com/blogs/how-to-programmatically-generate-word-docx-in-c-net | webdev, devops, csharp, tutorial | ---
canonical_url: https://developer.mescius.com/blogs/how-to-programmatically-generate-word-docx-in-c-net
description: Learn how to programmatically generate Word DOCX in C# .NET. See more from Document Solutions today.
---
**What You Will Need**
- [Document Solutions for Word](https://developer.mescius.com/document-solutions/dot-net-word-api/download)
**Controls Referenced**
- [Document Solutions for Word (DsWord) - C# .NET Word API](https://developer.mescius.com/document-solutions/dot-net-word-api)
- [Documentation](https://developer.mescius.com/document-solutions/dot-net-word-api/docs/online/overview.html) | [Online Demo Explorer](https://developer.mescius.com/document-solutions/dot-net-word-api/demos/)
**Tutorial Concept**
Programmatically load and modify a DOCX file using a .NET C# Word API. Learn how to update an image in the file, find and replace text, and add hyperlinks in your .NET server-side application.
---
[DsWord](https://developer.mescius.com/document-solutions/dot-net-word-api "https://developer.mescius.com/document-solutions/dot-net-word-api") API is a feature-rich library that enables you to work with Word documents through code on multiple platforms, such as Windows, macOS, and Linux. The feature set is vast enough to create, edit, save, merge, and even split Word documents. The capabilities do not end with these basic operations but include working with images, tables, OMath, Shapes, Lists, Text, and many more. The feature-rich object model of the API is based on Microsoft Office API. As a result, the documents generated using DsWord can easily be viewed and manipulated in MS Word.
All of these features can be explored in greater detail through the [documentation](https://developer.mescius.com/document-solutions/dot-net-word-api/docs/online/overview.html "https://developer.mescius.com/document-solutions/dot-net-word-api/docs/online/overview.html") and [demos](https://developer.mescius.com/document-solutions/dot-net-word-api/demos/ "https://developer.mescius.com/document-solutions/dot-net-word-api/demos/") available on the website.
For this blog, we will focus on a specific use case scenario - modifying a flyer. We will use some features of the DsWord API to generate a new and improved version of this flyer document. This will help you get started with the API and explore the most basic class of the API, **GcWordDocument**,which represents the Word document in code.
We will be exploring some of the features of the DsWord API as listed below while we update an existing Word document. We will use a real estate flyer as an example, which we will modify using the steps below:
* [Load an Existing Word Document](#Load)
* [Update an Image Contained in a Shape](#Update)
* [Find and Replace Text Using Regular Expressions](#Find)
* [Add a Hyperlink](#Add)
Below is a quick view of the flyer along with its updated version, highlighting all changes within red borders. We will implement these changes using the DsWord API in the steps that follow.

For convenience, we have created a basic Windows form application with simple controls, such as TabControl, TreeView, TextBox, and buttons. This application provides a UI with a list of actions that, when selected, show the respective code needed to perform that action using the DsWord API. Clicking on the Execute Code button in the application, you can execute the code and generate the expected Word document.
Below is a preview of the application UI:

Now, let’s use this application and explore various code snippets to implement the listed features, then view the final document that results.
## <a id="Load"></a>Load an Existing Word Document
We will begin by loading an existing Word document. The code below loads a flyer document into an instance of the [**GcWordDocument**](https://developer.mescius.com/document-solutions/dot-net-word-api/docs/online/DS.Documents.Word~GrapeCity.Documents.Word.GcWordDocument.html?highlight=gcworddocument%2C "https://developer.mescius.com/document-solutions/dot-net-word-api/docs/online/DS.Documents.Word~GrapeCity.Documents.Word.GcWordDocument.html?highlight=gcworddocument%2C") class. You can explore the documentation to gain more insight into the [loading and creation](https://developer.mescius.com/document-solutions/dot-net-word-api/docs/online/quickstart.html "https://developer.mescius.com/document-solutions/dot-net-word-api/docs/online/quickstart.html") of Word documents.
The document will then be saved at a local path for further processing as we move forward.
The image below depicts the demo app, which is showcasing the code used to create the document with all the defined elements:

The document below is generated after executing the above-defined code:

## <a id="Update"></a>Update an Image Contained in a Shape
The DsWord API enables you to add different shapes to a Word document, ranging in type from basic lines and rectangles to more complex shapes like clouds and donuts, etc. Further, it facilitates the enhancement of these shapes by supporting different fill types, including PatternFill, SolidFill, GradientFill, and ImageFill. Refer to the [Shape](https://developer.mescius.com/document-solutions/dot-net-word-api/docs/online/shape.html "https://developer.mescius.com/document-solutions/dot-net-word-api/docs/online/shape.html") and [ShapeFormat](https://developer.mescius.com/document-solutions/dot-net-word-api/docs/online/shape-format.html "https://developer.mescius.com/document-solutions/dot-net-word-api/docs/online/shape-format.html") documentation for a more thorough understanding of the Shapes feature.
The flyer document in this blog showcases the ImageFill feature, which allows the user to fill a shape with an image to be displayed in the flyer. In this section, we will explore how to update the added image using the DsWord API. You can access the image existing in the shape by using the [ImageFill](https://developer.mescius.com/document-solutions/dot-net-word-api/docs/online/DS.Documents.Word~GrapeCity.Documents.Word.FillFormat~ImageFill.html?highlight=imagefill%2C "https://developer.mescius.com/document-solutions/dot-net-word-api/docs/online/DS.Documents.Word~GrapeCity.Documents.Word.FillFormat~ImageFill.html?highlight=imagefill%2C") property of the [FillFormat](https://developer.mescius.com/document-solutions/dot-net-word-api/docs/online/DS.Documents.Word~GrapeCity.Documents.Word.FillFormat.html "https://developer.mescius.com/document-solutions/dot-net-word-api/docs/online/DS.Documents.Word~GrapeCity.Documents.Word.FillFormat.html") class. Once we have the current image data, we can replace it by invoking the [SetImage](https://developer.mescius.com/document-solutions/dot-net-word-api/docs/online/DS.Documents.Word~GrapeCity.Documents.Word.EmbeddedImageData~SetImage(Uri,String).html?highlight=setimage%2C "https://developer.mescius.com/document-solutions/dot-net-word-api/docs/online/DS.Documents.Word~GrapeCity.Documents.Word.EmbeddedImageData~SetImage(Uri,String).html?highlight=setimage%2C") method of the [EmbeddedImageData](https://developer.mescius.com/document-solutions/dot-net-word-api/docs/online/DS.Documents.Word~GrapeCity.Documents.Word.EmbeddedImageData.html "https://developer.mescius.com/document-solutions/dot-net-word-api/docs/online/DS.Documents.Word~GrapeCity.Documents.Word.EmbeddedImageData.html") class, which sets a new image for the Shape’s ImageFill type.
The image below depicts the demo app showcasing the code used to update an image in a shape within the document:

Below is the resulting document that is generated after executing the above-defined code:

Visit these online [demos](https://developer.mescius.com/document-solutions/dot-net-word-api/demos/features/shapes "https://developer.mescius.com/document-solutions/dot-net-word-api/demos/features/shapes") to explore formatting shapes more.
## <a id="Find"></a>Find and Replace Text Using Regular Expressions
Finding and replacing text is the most commonly required capability when working with text documents, so this section will demonstrate how this can be accomplished using DsWord. We will use the [Find](https://developer.mescius.com/document-solutions/dot-net-word-api/docs/online/DS.Documents.Word~GrapeCity.Documents.Word.RangeBaseFindReplaceExtensions~Find.html "https://developer.mescius.com/document-solutions/dot-net-word-api/docs/online/DS.Documents.Word~GrapeCity.Documents.Word.RangeBaseFindReplaceExtensions~Find.html") and [Replace](https://developer.mescius.com/document-solutions/dot-net-word-api/docs/online/DS.Documents.Word~GrapeCity.Documents.Word.RangeBaseFindReplaceExtensions~Replace.html "https://developer.mescius.com/document-solutions/dot-net-word-api/docs/online/DS.Documents.Word~GrapeCity.Documents.Word.RangeBaseFindReplaceExtensions~Replace.html") methods and will explore different options that can be set for either of these operations to customize it as per user requirements. Refer to the [Text](https://developer.mescius.com/document-solutions/dot-net-word-api/docs/online/text.html#i-heading-find-and-replace-text "https://developer.mescius.com/document-solutions/dot-net-word-api/docs/online/text.html#i-heading-find-and-replace-text") documentation for more details on the implementation of this feature.
For this example, we will replace the house price listed on the flyer, which is one variable that changes over time and would require updating. Because the value is ever-changing, replacing it as text with a new constant value every time would be difficult. Hence, we opted to use regular expressions to find the value to be replaced, as it will always appear as a numerical value preceded by a dollar symbol.
DsWord allows you to use a regular expression as a search string, which is typically referred to as a find pattern. To ensure the Find and Replace methods treat the provided search string as a regular expression, we must set the [RegularExpressions](https://developer.mescius.com/document-solutions/dot-net-word-api/docs/online/DS.Documents.Word~GrapeCity.Documents.Word.FindOptions~RegularExpressions.html?highlight=regularexpressions%2C "https://developer.mescius.com/document-solutions/dot-net-word-api/docs/online/DS.Documents.Word~GrapeCity.Documents.Word.FindOptions~RegularExpressions.html?highlight=regularexpressions%2C") property to true either for the [FindOptions](https://developer.mescius.com/document-solutions/dot-net-word-api/docs/online/DS.Documents.Word~GrapeCity.Documents.Word.FindOptions.html "https://developer.mescius.com/document-solutions/dot-net-word-api/docs/online/DS.Documents.Word~GrapeCity.Documents.Word.FindOptions.html") class or for the [FindReplaceOptions](https://developer.mescius.com/document-solutions/dot-net-word-api/docs/online/DS.Documents.Word~GrapeCity.Documents.Word.FindReplaceOptions.html "https://developer.mescius.com/document-solutions/dot-net-word-api/docs/online/DS.Documents.Word~GrapeCity.Documents.Word.FindReplaceOptions.html") class, depending on whether we are invoking Find or Replace methods respectively. The regular expression used in the code below is a pattern featuring a dollar symbol and numerical range, which searches for a dollar sign followed by one or more numbers ranging from 0 to 9.
The image below depicts the demo app showcasing the code used to find and replace the house listing price in the document using regular expressions:

Below is the resulting document that is generated after executing the above-defined code:
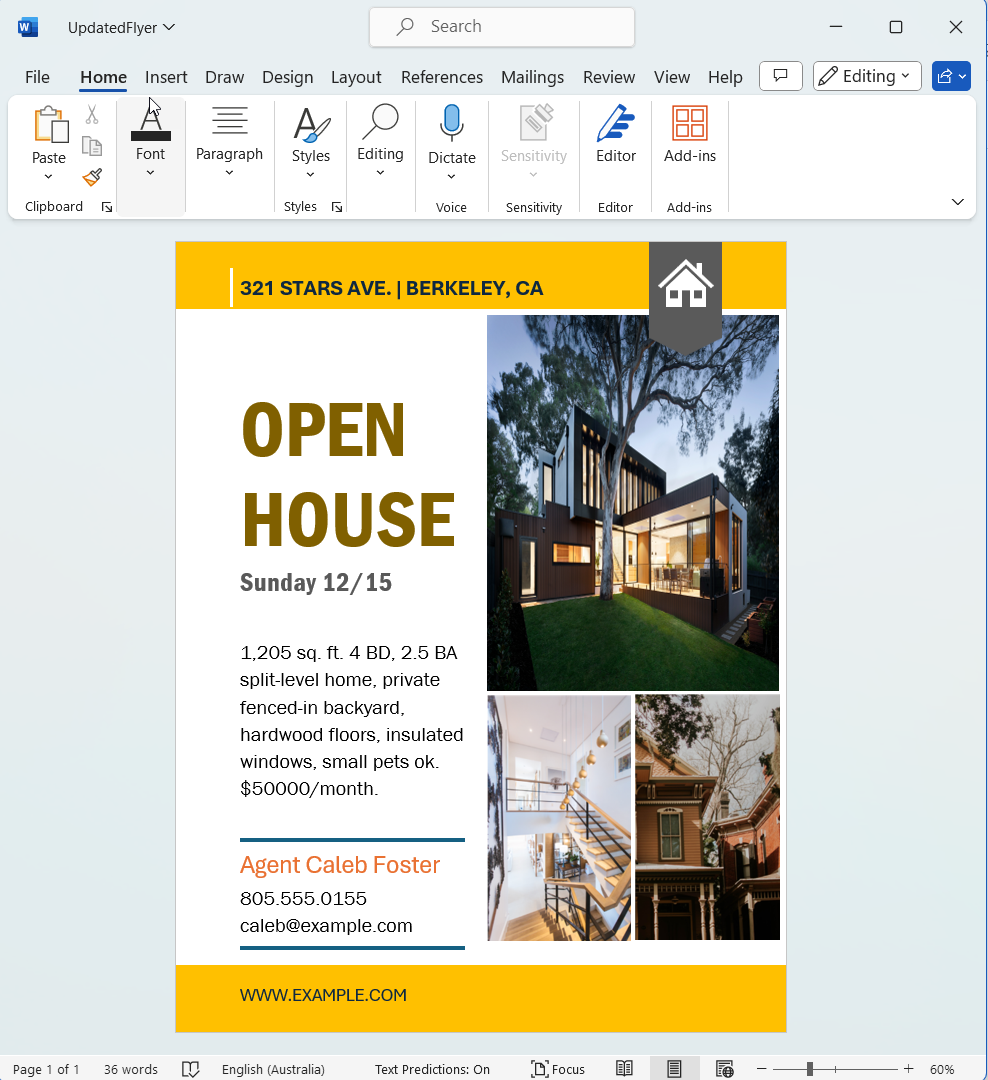
Visit our online [demos](https://developer.mescius.com/document-solutions/dot-net-word-api/demos/features/find-replace "https://developer.mescius.com/document-solutions/dot-net-word-api/demos/features/find-replace") to explore the different Find and Replace approaches one can implement using the DsWord API.
## <a id="Add"></a>Add a Hyperlink
Flyers generally provide a website link for customers so they can find more detailed information regarding the product being promoted. While this flyer also provides a website link, it has been added as text. However, in today’s digital era, it is likely that this flyer will be distributed virtually. In that case, adding the website address as a hyperlink would be much more convenient than text, as it will allow the user to click on the link directly and navigate to the website rather than copying and pasting the link to access it.
In this section, we will update the website address to be added as a hyperlink using the [Hyperlink](https://developer.mescius.com/document-solutions/dot-net-word-api/docs/online/DS.Documents.Word~GrapeCity.Documents.Word.Hyperlink.html?highlight=hyperlink%2C "https://developer.mescius.com/document-solutions/dot-net-word-api/docs/online/DS.Documents.Word~GrapeCity.Documents.Word.Hyperlink.html?highlight=hyperlink%2C") class provided by DsWord.
Refer to the [Links](https://developer.mescius.com/document-solutions/dot-net-word-api/docs/online/links.html "https://developer.mescius.com/document-solutions/dot-net-word-api/docs/online/links.html") documentation for more details on the API features depicted in the code below.
The image below depicts the demo app showcasing the code used to add a hyperlink to the document:
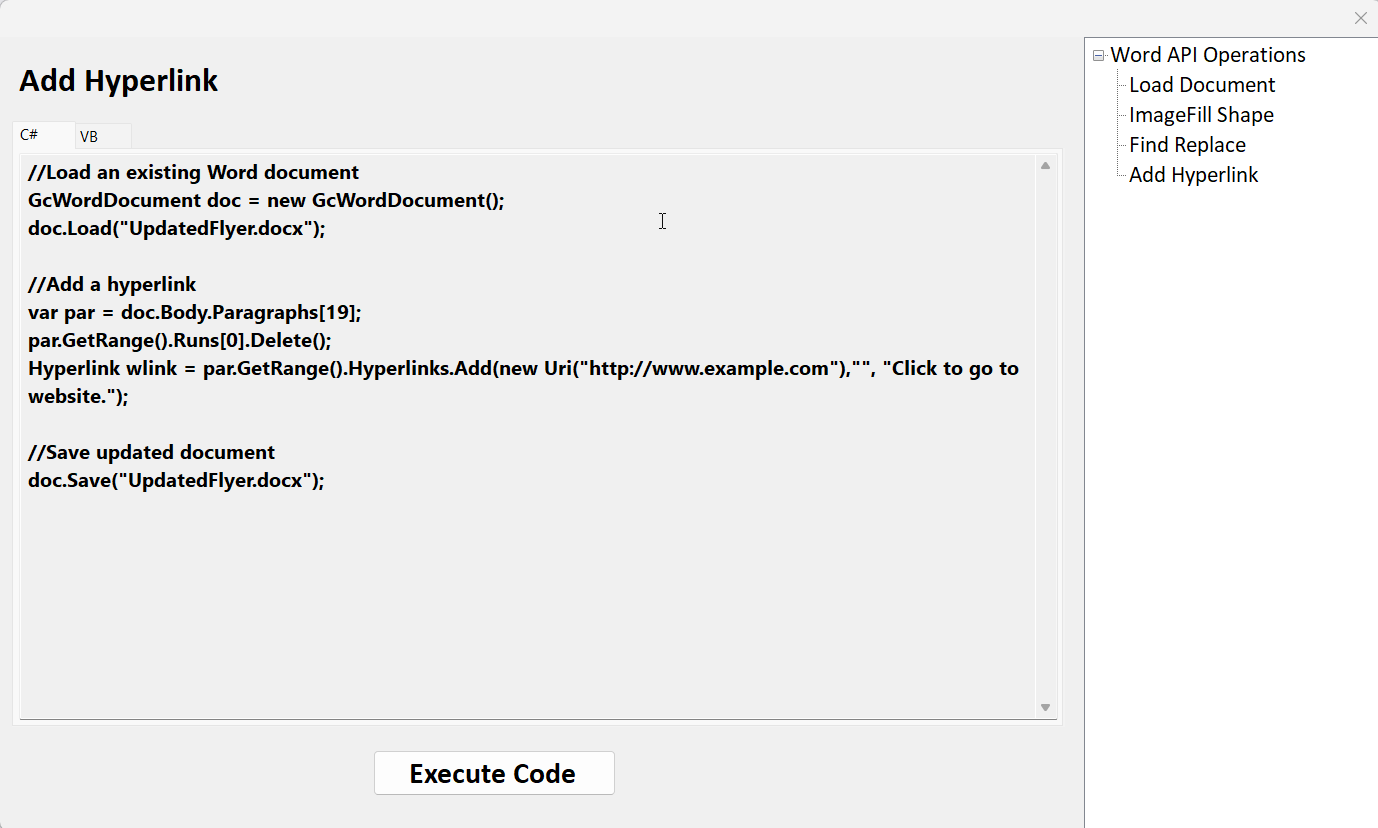
Below is the resulting document that is generated after executing the above-defined code:

Visit our online demos to explore how to add [hyperlinks](https://developer.mescius.com/document-solutions/dot-net-word-api/demos/features/content/hyperlinks/word-cs "https://developer.mescius.com/document-solutions/dot-net-word-api/demos/features/content/hyperlinks/word-cs") to your Word document using the DsWord API.
Download [the demo sample](https://cdn.mescius.io/umb/media/k5kdvjlw/processworddoc.zip) from this blog to modify and generate a sample Word document as in this tutorial.
Refer to our [documentation](https://developer.mescius.com/document-solutions/dot-net-word-api/docs/online/overview.html "https://developer.mescius.com/document-solutions/dot-net-word-api/docs/online/overview.html") and [demos](https://developer.mescius.com/document-solutions/dot-net-word-api/demos/ "https://developer.mescius.com/document-solutions/dot-net-word-api/demos/") for comprehensive guidance and practical examples of DsWord features, enabling efficient and error-free implementation. | chelseadevereaux |
1,802,872 | Becoming an Analytics Engineer I | Are you aspiring to become an Analytics Engineer and you do not know how to get started? You can... | 0 | 2024-05-31T17:41:21 | https://dev.to/anuoluwapoae/becoming-an-analytics-engineer-i-d7a | analyticsengineering, udemy, datamodelling, dbt | Are you aspiring to become an Analytics Engineer and you do not know how to get started? You can start with Udemy Analytics Engineering Bootcamp like I did too. [Click to view course](Are you aspiring to become an Analytics Engineer and you do not know how to get started? You can start with Udemy Analytics Engineering Bootcamp like I did too. Click to view course .).
Here is a brief documentation of what I learnt. (You need to take the course to have a complete understanding of what data modelling, methodology and technologies is all about)
The methodology used is Kimball's Warehouse Methodology and what is this all about?
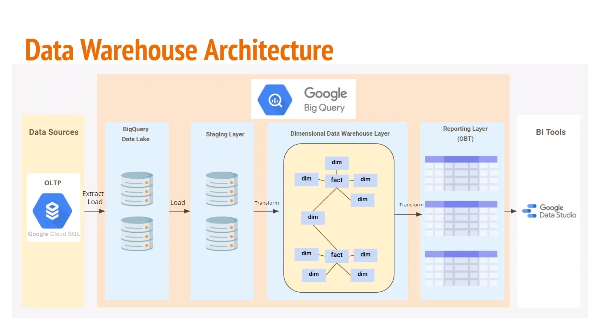
**Kimball's Warehouse Methodology**
- Created by Ralph Kimball
- Defines data warehouse as a copy of transaction data specifically structured for query and analysis.
- Starts with identifying key business process and requirements (Bottom up)
- Focus of this approach is to enable business intelligence fast.
- Data marts are created first instead of enterprise data warehouse.
- Dimensional model - **STAR SCHEMA design** (deformalized)
- The model design is built first on fact and dimension tables.
**Process of Kimball Methodology Start Schema**
- Facts
- Dimensions
- Follows dimensional modeling technique.
- Enterprise **bus matrix** is used to document & show how schema is designed.
- Data marts are built with star schema being core element of dimensional model.
- Multiple start schema can exist in same model.
- Conformed data dimensions (shared attributes) are used to create dimensional data warehouse.
The dataset used is the Northwind Dataset from MySQL and here is the ERD Diagram of the dataset.
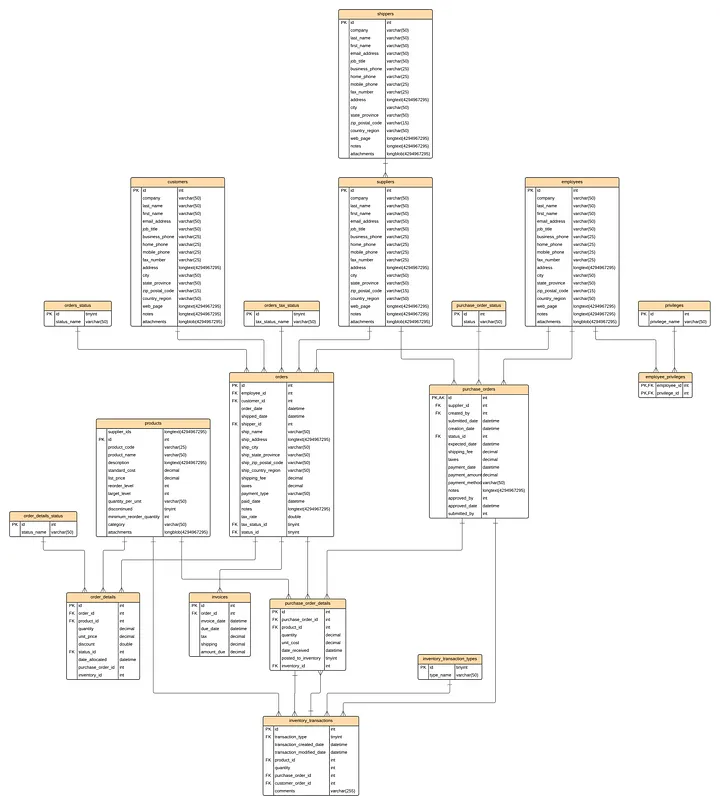
**Data modelling with BigQuery, dbt and GitHub for version control**
First, we need to understand the business requirements.
**What is it that we are trying to do?**
Northwind traders are export import company who trades around the world for specialty foods.
Their existing architecture is mostly a mix of on-premises & legacy systems, including their MySQL database which is primary operational database.
They are struggling to keep up with reporting requirements and causing database to slow down impacting their day-to-day business.
Northwind traders wants to modernize their data & reporting solutions & move away from on-prem.
**Why are we doing it?**
Northwind traders wants to modernize their existing infrastructure for.
- Better Scalability
- Reduced load on operational system
- Improved reporting speed
- Improved data security
**How are we going to achieve it?**
Northwind traders will migrate their existing database system to google cloud platform (GCP). BigQuery was selected to run OLAP.
Dimensional Data warehouse will be built on BigQuery to support with reporting requirements.
Next, we define the Business Process
**Requirements**
Sales Overview
Overall sales reports to understand better our customers what is being sold, what sells the most, where and what sales are the least, the goal is to have a general overview of how the business is going.
Sales Agent Tracking
Track sales & performance of each seller agent to adjust commissions, reward high achievers and empower low achievers.
Product Inventory
Understand the current inventory levels, how to improve stock management, what supplies to we have how much is being purchased. This will allow to understand stock management and potentially broker better deals with suppliers.
Customer Reporting
Allow customers to understand their purchase orders, how much and when they are buying, empowering them to make data-driven decisions and utilize the data to join to their sales data.
To get started we need to set up google account — Click here to set up an account.
Select an existing project if you have one or create a new project if you don’t.
Your project dashboard should look similar to this.
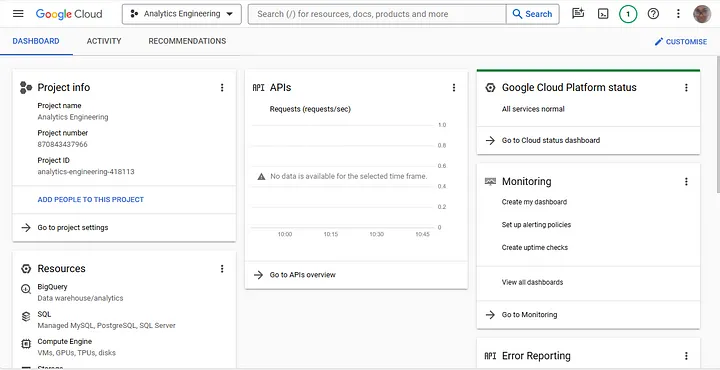
Now we set up a GitHub repository for our project.
You can create a new GitHub account if you don’t have one or login into your existing account — Click here to visit GitHub page.
This is what my GitHub profile looks like
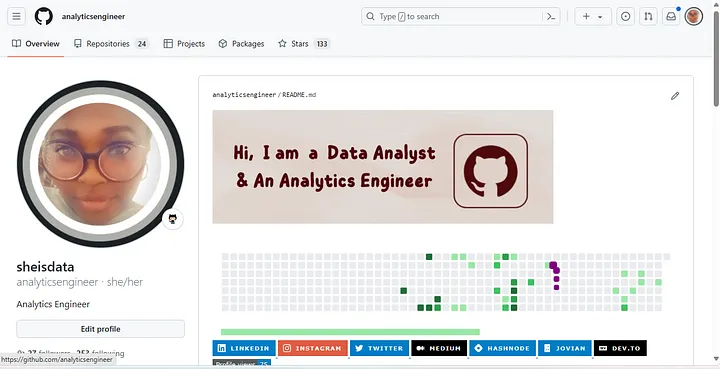
Create a new repository and give it any name of your choice mine would be — analytics-engineering-bootcamp.
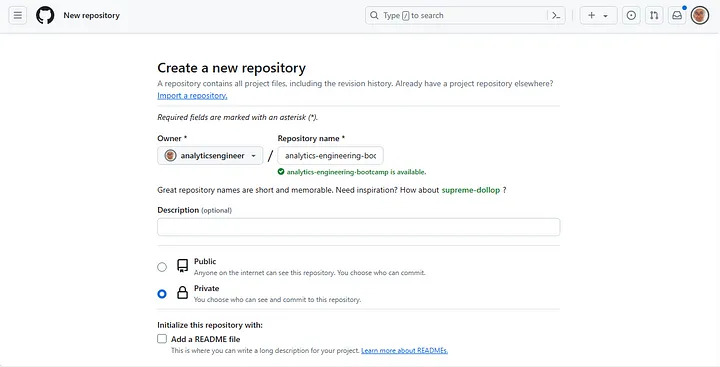
keep the project as private for now later on you can make it public, leave every other setting and just click create repository by scrolling down the page.
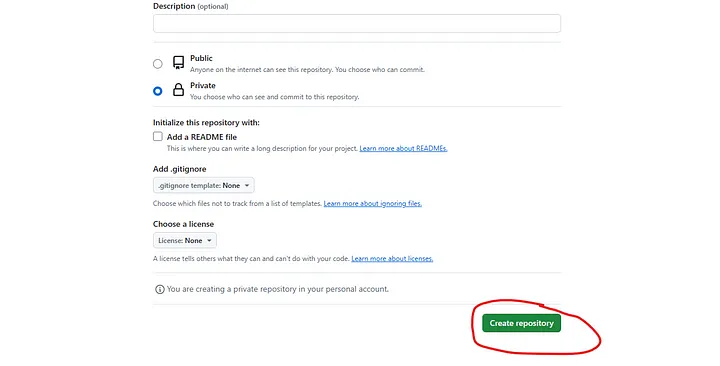
Click here to learn how to install Linux on windows — [Click here](https://learn.microsoft.com/en-us/windows/wsl/install).
If you are a MacBook user, [click here](https://itigic.com/how-to-install-linux-on-mac/#:~:text=Linux%20installation%201%201.%20Begin%20by%20starting%20up,the%20installation%20is%20complete%2C%20restart%20your%20Mac.%20) to install Linux.
Alternatively, you can take the bootcamp course to learn how to install Linux on your preferred OS. - [Click here](https://www.udemy.com/share/105KXo3@vQ2QOvfc1XEK3EC-5VzXTLFsI8u9OVZA35fM423QEEgizNcp7hiL9L9yQWpCSf3tLg==/) to take the bootcamp course.
My preferred Terminal as a windows user is windows terminal on Microsoft store.
My Linux terminal is opened.
```
# Create a new folder on your local machine with Command Line optional
# You can use linux to create the folder too
# I am using anlytics-engineering-bootcamp as my folder name
mkdir C:\path\to\your\designated\file\location\anlytics-engineering-bootcamp
# Open the Folder with Ubuntu
cd /mnt/c/path/to/your/folder/analytics-engineering-bootcamp
```
Copy everything from the (…or create a new repository on the command line) and paste into your terminal.
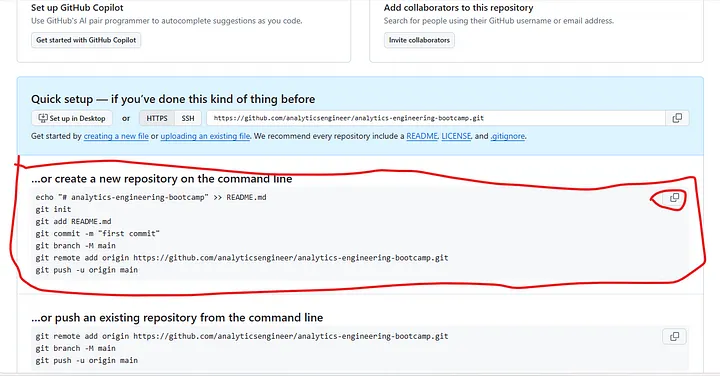
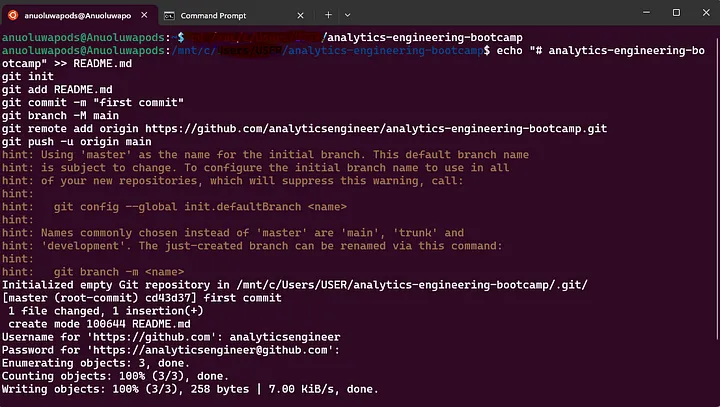
To input the GitHub password, you will need a token.
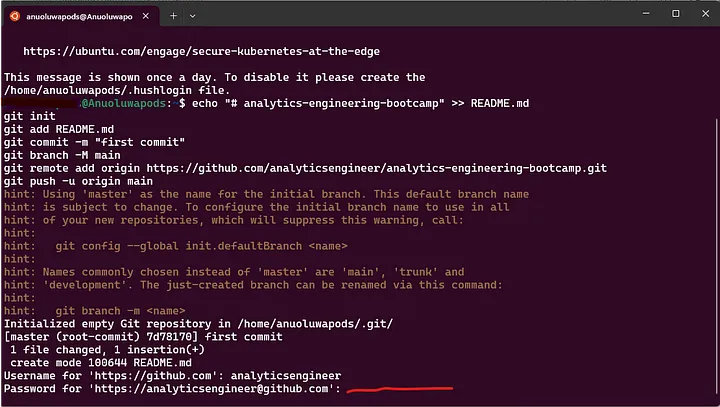
Here is how to get your GitHub Token
Click on the far-right icon of your GitHub profile and click settings.
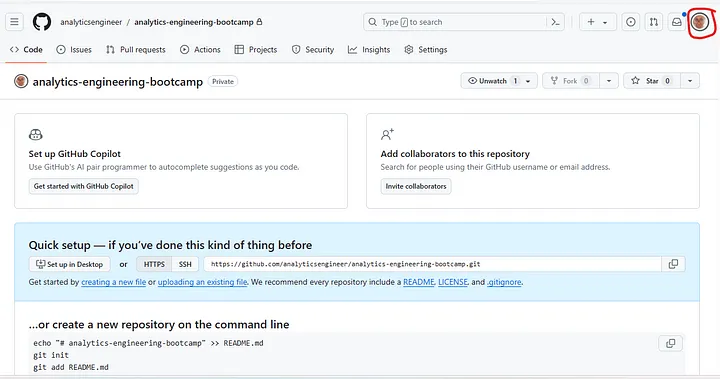
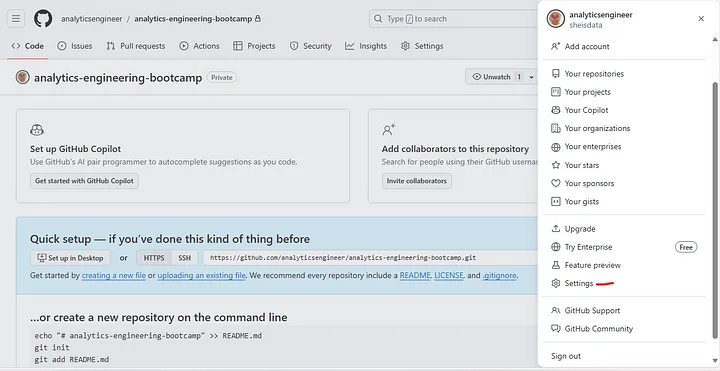
Scroll down to developer’s settings.
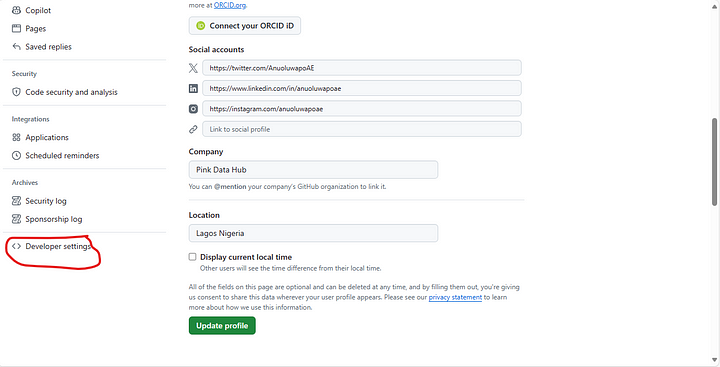
Click on any of the token's access but I am using Token classic.
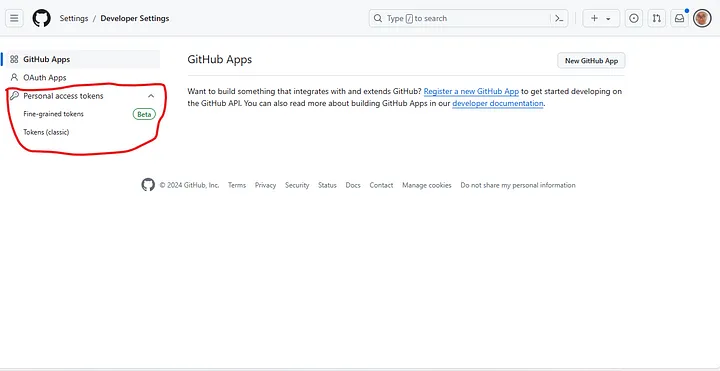
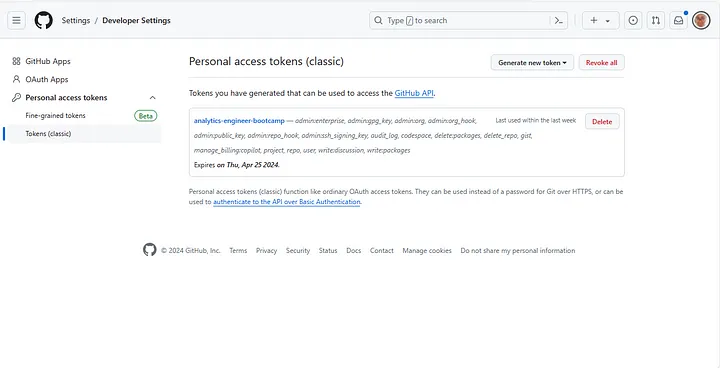
Scroll down and select the necessary settings you might need Choose the repo so you can read and write into your repository.
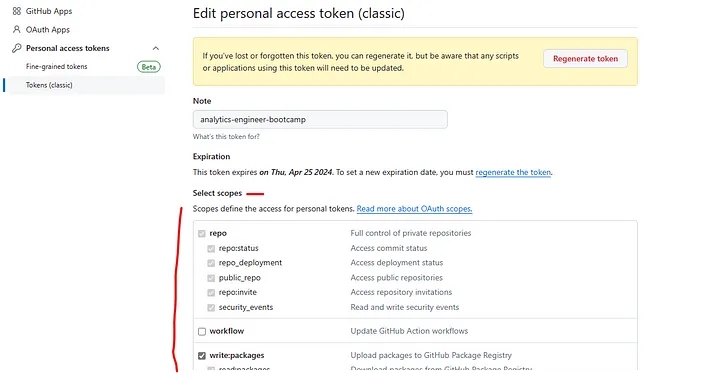
Your Folder like mine analytics-engineering-bootcamp should look like this containing the ReadMe file in your local machine when opened.
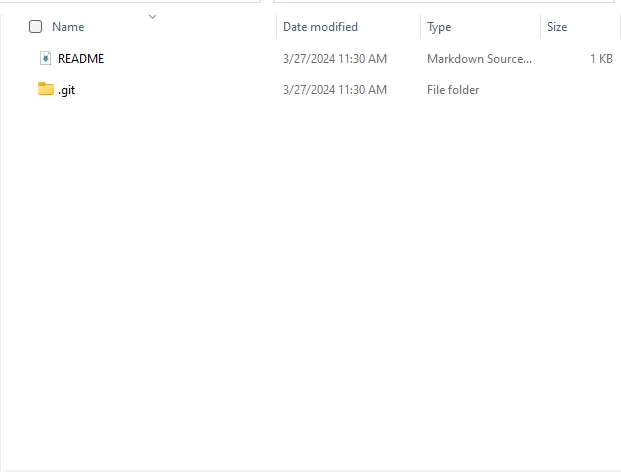
My next blog post we will be working on
- Uploading our dataset into BigQuery
- Bus Matrix for our business process and data dictionary
- Setting up dbt
- Building our dbt models
- Visualizing and creating our report with PowerBI
| anuoluwapoae |
1,880,703 | Announcing Bento, the open-source fork of the project formerly known as Benthos | by Richard Artoul tl;dr Redpanda announced yesterday that they’ve acquired Benthos and... | 0 | 2024-06-11T17:47:22 | https://dev.to/warpstream/announcing-bento-the-open-source-fork-of-the-project-formerly-known-as-benthos-5ac7 | benthos, dataengineering, datastreaming, redpanda | ---
title: Announcing Bento, the open-source fork of the project formerly known as Benthos
published: true
date: 2024-05-31 17:36:25 UTC
tags: benthos,dataengineering,datastreaming,redpanda
canonical_url:
---
by Richard Artoul
### tl;dr
Redpanda announced yesterday that they’ve acquired Benthos and immediately made sweeping changes to the project: commercially licensing some of the most important integrations, redirecting all Benthos sites to Redpanda sites, and rebranding the Discord community to Redpanda. So TL;DR — we are (reluctantly) forking the Benthos project, and maintaining it as a 100% free MIT-licensed open-source project, just like Benthos was before the acquisition.
### Love at First Blob
I first discovered the Benthos project serendipitously. I was browsing the /r/apachekafka subreddit and someone mentioned that they were using Benthos — a lightweight stream processing framework written in Go — as a simpler and more lightweight alternative to Kafka Connect. I was immediately intrigued. Kafka Connect is one of those projects in the data streaming space that _everyone_ uses and _everyone_ hates. A simpler and more performant alternative _written in Go_, WarpStream’s native language, immediately piqued my interest.
I Googled the project and fell in love with it pretty much right away. Unfortunately benthos.dev now redirects to a Redpanda docs site, but if you’ve never seen the original Benthos docs before, do yourself a favor and check out the [old site](https://web.archive.org/web/20240520010651/https://benthos.dev/). The home page (to me at least) is _perfect_: crystal clear concise messaging with a clear explanation of the value proposition, but also cute and _hilariously_ entertaining in the best way. If that doesn’t immediately make you a fan of the project’s primary author Ashley Jeffs, then check out his Benthos rap video:
After meeting Ashley in person at Kafka Summit London, we decided to bet on Benthos as the connect layer for WarpStream. We sponsored the project for the maximum amount allowed and (after asking and receiving Ashley’s explicit permission) [embedded Benthos directly into the WarpStream Agents](https://www.warpstream.com/blog/fancy-stream-processing-made-even-more-operationally-mundane) to make it easy to integrate WarpStream with other systems and perform common lightweight stream processing tasks without needing to run any extra infrastructure. Then, a few weeks later, we [launched Managed Data Pipelines](https://www.warpstream.com/blog/introducing-warpstream-managed-data-pipelines-for-byoc-clusters), which brings a fully-managed model for managing streaming pipelines end to end, using the Benthos framework that we had already embedded into the Agents’ single Go binary.
We know Ashley well and loved working with him. He’s done an incredible amount of work over the last 7 years to build and maintain Benthos. He personally made nearly 3,500 commits on the Benthos repo, built a strong community, and most importantly, wrote some amazing software. He’s earned every cent that Redpanda paid him for the acquisition, and we couldn’t be happier for him.
### The Acquisition
When we heard that Redpanda was going to acquire Benthos, we thought they were going to continue developing the project the same way (and under the same license) that Ashley had for the last 7 years, and that they would incorporate the already-proprietary Benthos Studio into their product. Instead, in less than 12 hours they:
- Changed the name of the project from Benthos to “Redpanda Connect”, and [prohibited anyone from using the term “Benthos](https://x.com/emaxerrno/status/1796219957589786810).” 1
- Posted messages in both the Benthos Discord server and the #benthos channel in the Gophers Slack community encouraging community members to migrate to Redpanda’s Slack community instead.
- Rebranded the Benthos Discord server to “Redpanda”.
- Moved the Benthos Github repo to Redpanda’s repo, and split it into two repos with _two different licenses_.
- Started relicensing some of the most critical integrations and connectors as proprietary2 under a completely different license, _including some of the integrations that were written by open source contributors_ who were not involved in the acquisition.
In just a few hours, Redpanda took a 7 year old open source project with nearly 8,000 stars on GitHub, hundreds of contributors, and thousands of users and began transitioning it to a proprietary software model.
We don’t really care what the GitHub repository is called, or how the Discord server is branded. In fact, if you go to [our docs](https://docs.warpstream.com/warpstream/configuration/integrations), you’ll see Redpanda Console displayed prominently as an integration because it’s a great product that helps our users get the most out of WarpStream, and we’re not afraid to give credit where credit is due_._
But we _do_ care about the license change, and making sure that we’re not infringing on any trademarks (real, or imagined). And perhaps most importantly…Benthos rocks. People should be able to continue to use it freely without worrying about when the commercialization bell might toll.
Back to WarpStream, though: our unique BYOC deployment model means that our customers deploy our code and binaries into _their_ environments. _Some_ of the code in the core Redpanda Connect repo is still MIT-licensed, and we _technically_ could have kept using _some_ of it, but we couldn’t wait around to find out what the next change would be. We have to ensure that one of our most critical dependencies is being stewarded in a thoughtful and responsible manner. We also cannot, in good conscience, include any software dependencies containing mixed or muddled licensing that could be subject to change (again) at a moment’s notice. Our customers deserve more stability and predictability than that.
### The Fork
When we started WarpStream, we didn’t see ourselves becoming the maintainers of a major open-source project. In fact, we explicitly decided to _not_ make WarpStream “open core” or “source available” from Day 1 because we hated the [perverse incentives](https://www.warpstream.com/blog/the-original-sin-of-cloud-infrastructure) of that business model: hack distribution under the umbrella of “open source” for zero to one, and then pull the rug later by gating features, changing licenses, or crippling the open source project after the fact once critical mass has been achieved.
I’ll say it explicitly: We _really_ didn’t want to create a fork. But we think that this is the only responsible thing to do given what’s happened already in just a few hours since the acquisition was announced.
So, we’re forking Benthos. We’ll be maintaining our fork as a free, open source, 100% MIT licensed project, just like Benthos was before.

_Benty the Bento Box is not happy about the fork._
We’re calling our fork Bento3, an homage to the Benthos name but separate and distinct from what is now called Redpanda Connect. We were proud to sponsor the Benthos project when it was an independent open-source project, and now we’re looking forward to fostering a new project to carry on where Benthos left off.
We hope Bento becomes a place where the Benthos community can land and contribute to the project in the same spirit that the Benthos project once had — but if that doesn’t happen, that’s fine by us. We’ll keep maintaining it because our product, WarpStream Managed Data Pipelines, relies on it.
You can find [the new Bento repository here](https://github.com/warpstreamlabs/bento), as well as a hosted version of the [original docs](https://warpstreamlabs.github.io/bento/) in all their glory.
You might be thinking, “Wait a minute, isn’t WarpStream just another corporation? Why should I spend my time contributing to _their_ project if they can just take my contributions at any time and commercialize them?”. Bento is 100% MIT licensed and will stay that way forever. In addition, we want to move to a shared governance model, with other official maintainers, and create an independent structure. However, before we can do that, we first need to find some other maintainers!
So, if your company has _any_ commercial interest in Benthos (even if you’re a competitor!) and is worried about the recent ownership and licensing changes, please let us know. We’d love to collaborate on contributions, bring you in as an official maintainer, create an independent Github organization with dedicated CI/Docker infrastructure, and establish a formal governance structure.
So please, join us: check out [the new repository](https://github.com/warpstreamlabs/bento), [docs website](https://warpstreamlabs.github.io/bento/) (new domain coming soon), or even just [get in touch](https://www.warpstream.com/contact-us) if you want to learn more about Bento or participate in stewarding the project.
P.S we hate that Benty is an ai-generated mascot. If you’re a talented illustrator with some ideas, please [reach out](https://www.warpstream.com/contact-us) as well (we pay well!).
**Footnotes**
1. We’re pretty sure this isn’t how copyrights, software licensing, and trademarks work (like, at all), but we also didn’t feel like arguing about it, or getting the lawyers involved.
2. This relicensing was done with the [justification](https://techcrunch.com/2024/05/30/redpanda-acquires-benthos-to-expand-its-end-to-end-streaming-data-platform/?guccounter=1) that “all the users that are using those services are used to paying for the integration with those services.” This seemed to us like a clear signal of more potentially hostile things to come.
3. Yes, this is the best we could come up with. If you’re good at naming things, [we’re hiring](https://www.warpstream.com/contact-us) our first Product Marketer! | warpstream |
1,872,321 | The Future of Information Retrieval: RAG Models vs. Generalized AI | As artificial intelligence continues to advance, two significant paradigms have emerged in the field... | 0 | 2024-05-31T17:34:35 | https://dev.to/asad1/the-future-of-information-retrieval-rag-models-vs-generalized-ai-k67 | genai, ai, rag, llm | As artificial intelligence continues to advance, two significant paradigms have emerged in the field of information retrieval and processing: Retrieval-Augmented Generation (RAG) models and Generalized AI (GenAI). These approaches represent distinct methodologies in how AI systems access, process, and generate information. Understanding their differences, potential, and future trajectories is crucial for grasping the evolving landscape of AI.
#### Retrieval-Augmented Generation (RAG) Models
RAG models combine the strengths of retrieval-based systems and generative models. They work by retrieving relevant information from a large database or corpus and then using this information to generate more accurate and contextually appropriate responses. This hybrid approach leverages the precision of retrieval systems and the flexibility of generative models.
**Key Characteristics of RAG Models:**
1. **Contextual Accuracy:** RAG models excel in providing responses grounded in factual information. By pulling data from reliable sources, they ensure that generated content is not only coherent but also accurate.
2. **Scalability:** These models can handle vast amounts of data, making them suitable for applications requiring access to extensive knowledge bases.
3. **Efficiency:** By focusing on relevant data retrieval before generation, RAG models can produce high-quality responses without the need for exhaustive computation.
4. **Transparency:** The retrieval process in RAG models allows for traceability, enabling users to understand and verify the sources of information used in the generation process.
#### Generalized AI (GenAI)
Generalized AI, often synonymous with large language models like GPT-4, relies on training vast neural networks on diverse datasets to generate responses based on learned patterns. These models are designed to understand and generate human-like text across various contexts without relying on specific retrieval mechanisms.
**Key Characteristics of Generalized AI:**
1. **Versatility:** GenAI models are highly adaptable, capable of handling a wide range of tasks from translation to creative writing, without requiring task-specific adjustments.
2. **Creativity:** These models can generate novel and creative content, making them suitable for applications that benefit from a touch of human-like ingenuity.
3. **Language Understanding:** GenAI systems exhibit a deep understanding of language nuances, idiomatic expressions, and contextual subtleties, enhancing their conversational capabilities.
4. **Autonomy:** Unlike RAG models, GenAI does not rely on external databases for information retrieval, making it more autonomous in generating responses.
#### Comparing RAG and GenAI
The choice between RAG models and GenAI depends largely on the specific needs of an application. RAG models are particularly advantageous when accuracy and context-specific information are paramount. They shine in scenarios where the correctness of information is critical, such as in medical, legal, or educational applications. Conversely, GenAI models are ideal for tasks requiring broad versatility and creative generation, like content creation, customer service, and general knowledge inquiries.
#### The Future of AI: Convergence and Integration
The future of AI in information retrieval and generation is likely to see a convergence of RAG and GenAI methodologies. Hybrid models that integrate the precision of RAG with the versatility of GenAI could offer the best of both worlds. Here are some potential developments:
1. **Enhanced Hybrid Models:** Future AI systems may seamlessly integrate retrieval and generation, dynamically choosing the optimal approach based on the context of the query.
2. **Improved Accuracy and Creativity:** Combining the factual grounding of RAG with the creative potential of GenAI can lead to systems that are both reliable and innovative.
3. **Adaptive Learning:** Advanced AI models will likely incorporate adaptive learning mechanisms, continuously updating their knowledge bases and generative capabilities in real-time.
4. **Ethical and Responsible AI:** With increased integration, ensuring transparency, accountability, and ethical use of AI will become even more crucial. Systems will need to clearly indicate the sources of their information and the basis of their generated content.
#### So what's the Summary?
The evolution of AI through RAG and GenAI models represents a significant leap in how machines process and generate information. As we move forward, the blending of these approaches promises to create more powerful, accurate, and versatile AI systems. The challenge lies in balancing creativity with accuracy, ensuring that the benefits of AI are realized responsibly and ethically. | asad1 |
1,872,315 | Exploring Cultural Heritage: A Guided Tour Through Time | Introduction: Cultural heritage tours offer an enriching and immersive experience, allowing... | 0 | 2024-05-31T17:23:32 | https://dev.to/heritage_tourdubai_/exploring-cultural-heritage-a-guided-tour-through-time-102k | culturalheritage, culturalheritagetour | **Introduction:**
[Cultural heritage tours](https://heritageexpress.com/) offer an enriching and immersive experience, allowing participants to delve into the rich tapestry of human history, traditions, and customs. These tours provide a unique opportunity to explore the remnants of past civilizations, understand diverse cultural practices, and appreciate the significance of preserving our heritage for future generations. In this guide, we will delve into the essence of cultural heritage tours, their significance, and how they contribute to fostering cross-cultural understanding and appreciation.
**Understanding Cultural Heritage:**
Cultural heritage encompasses the tangible and intangible aspects of a society's legacy, including historical sites, artifacts, traditions, rituals, languages, and customs. It reflects the collective identity, values, and beliefs of a community, serving as a bridge between the past, present, and future. Preserving cultural heritage is essential for maintaining cultural diversity, fostering a sense of belonging, and promoting intercultural dialogue and understanding.
**The Significance of Cultural Heritage Tours:**
Cultural heritage tours play a pivotal role in promoting cultural exchange, education, and sustainable tourism. By visiting historical sites, museums, and cultural landmarks, participants gain insights into different civilizations, architectural styles, artistic expressions, and social practices. These tours offer a multi-sensory experience, allowing travelers to immerse themselves in the sights, sounds, and flavors of diverse cultures.
**Key Components of Cultural Heritage Tours:**
Historical Sites and Landmarks: Explore ancient ruins, medieval castles, temples, palaces, and archaeological sites that bear witness to the triumphs and struggles of bygone eras.
Museums and Galleries: Encounter priceless artifacts, artworks, manuscripts, and relics that offer glimpses into the artistic, scientific, and technological achievements of past civilizations.
Cultural Performances and Festivals: Witness traditional music, dance, theater, and rituals that celebrate the cultural heritage and identity of local communities.
Culinary Experiences: Indulge in authentic cuisine, cooking workshops, and food tours that showcase the gastronomic heritage and culinary traditions of different regions.
Interactive Workshops and Demonstrations: Participate in craft-making, textile weaving, pottery, or traditional ceremonies to learn firsthand about the skills and techniques passed down through generations.
**Benefits of Cultural Heritage Tours:**
Educational Enrichment: Gain a deeper understanding of history, art, anthropology, and sociology through guided tours, lectures, and interactive experiences.
Cultural Exchange: Engage with locals, artisans, historians, and experts to learn about their customs, beliefs, and way of life, fostering mutual respect and appreciation.
Preservation and Conservation: Support efforts to safeguard cultural heritage sites, artifacts, and traditions by raising awareness and contributing to sustainable tourism practices.
Personal Enrichment: Experience personal growth, broaden your perspective, and cultivate empathy and tolerance towards diverse cultures and lifestyles.
Community Empowerment: Contribute to the economic development and cultural preservation of local communities by patronizing artisanal products, heritage tours, and cultural events.
**Conclusion**:
Embarking on a cultural heritage tour is not merely a journey through time and space; it is a transformative experience that enriches the mind, nourishes the soul, and fosters a deeper appreciation for the diversity and beauty of our world. By embracing our cultural heritage and sharing it with others, we not only preserve our past but also sow the seeds of understanding, empathy, and harmony for generations to come. | heritage_tourdubai_ |
1,872,320 | Support My Movement To Spell "Of" as "Ov"! | "of" is pronounced like "ov" – and the Swedish language changed "af" to "av", which is a (highly)... | 0 | 2024-05-31T17:34:24 | https://dev.to/baenencalin/support-my-movement-to-spell-of-as-ov-5hah | language, watercooler | "of" is pronounced like "ov" – and the Swedish language changed "af" to "av", which is a (highly) comparable change – so I think it is warranted that we \*at least\* recognize "ov" as a valid spelling variant ov "of".
Additionally, it can be confusing that we spell it as "of" because there is no indication that you are supposed to make V's sound and not F's sound.
If you support this idea ov changing "of" to "ov", please sign my petition: https://www.change.org/p/let-s-change-of-to-ov. | baenencalin |
1,872,295 | Converting .shp files to CSV with GeoPandas | Working with geospatial data is really fun! We use this type of data all over the place in data... | 0 | 2024-05-31T17:31:56 | https://dev.to/dro248/converting-shp-files-to-csv-with-geopandas-7k6 | datascience, python, tutorial, dataengineering | Working with geospatial data is really fun! We use this type of data all over the place in data science, and data warehouses have gotten really good at working with it (I'm looking at you, Snowflake!).
However, as you get started down the path of using geospatial data, you will likely run into a speed bump: `.shp` files
## What is a `.shp` file?
A `.shp` file is a common way of encoding geospatial data in a binary format. This geospatial data will contain geospatial points, polygons (a collection of geospatial points that form an area), and multipolygons (more exotic polygons).
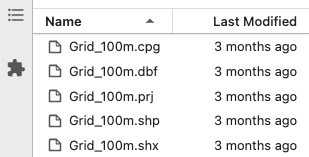
A `.shp` file will be bundled with other files with the same name but different file extensions (e.g., .shx, .dbf, .prj, etc.). In short, you will need all of them.
## What is the problem with `.shp` files?
Unfortunately, most data warehouses don't read `.shp` files natively. If you are looking to load this dataset into your data warehouse, you are going to need to convert it to a compatible format like CSV.
Additionally, a `.shp` file might use a different coordinate system than the latitude / longitude system you are familiar with ([WGS 84](https://en.wikipedia.org/wiki/World_Geodetic_System#WGS_84)).
In this tutorial, we will convert a `.shp` file to CSV and transform a geospatial data to the latitude / longitude coordinate system.
> The latitude / longitude coordinate system we are familiar with is called WGS 84 EPSG:4326.
## Convert a `.shp` file to CSV
In this example, we'll use [GeoPandas](https://geopandas.org/en/stable/) for the conversion.
```python3
import geopandas as gpd
# Import .shp file into a GeoPandas DataFrame
geopandas_df = gpd.read_file('Grid_100m.shp')
# Convert geospatial data to latitude/longitude coordinate system
converted_df = geopandas_df.to_crs('EPSG:4326')
# Write data to CSV
converted_df.to_csv('Grid_100m.csv', index=False)
```
If all goes well, you should now have a well-formatted CSV file that you can inspect with Excel (and load to your data warehouse).
Cheers! 🚀 | dro248 |
1,872,319 | Design Patterns - Prototype | Uma das primeiras coisas que aprendemos na programação, seja qual for a linguagem, é como copiar... | 27,199 | 2024-05-31T17:27:08 | https://nicolasdesouza.com/design-patterns-prototype | designpatterns, csharp | Uma das primeiras coisas que aprendemos na programação, seja qual for a linguagem, é como copiar valor de uma variável para outra. Uma atividade extremamente comum mas que rende situações interessantes no nosso dia a dia.
## Definição
É um padrão criacional que permite a criação de novos objetos copiando um objeto já existente, isso pode ser útil quando a criação de um objeto é custosa ao sistema, seja por sua complexidade inerente ou pelo alto consumo de recursos envolvidos.
## Exemplo conceitual
Quando estudei pela primeira vez este padrão de design, confesso que tive dificuldade para entender sua aplicação. Num primeiro momento me pareceu um tanto quanto desnecessário, criar toda uma estrutura para realizar uma simples cópia. Mas foi aí que pensei em um possível uso na minha rotina.
Imagine que você possua uma entidade Perfil cujo uma de suas propriedades seja a classe Configuração, e a cada vez que você for criar um novo Perfil, precisamos ir na tabela de configurações e obter as configurações mais recentes... Agora imagine, toda vez que precisar criar um novo objeto, será feito uma consulta em banco!! Se esses dados são os mesmos de outros objetos que já estamos manipulando, por quê não usá-los?! É aí que o prototype brilha, padronizando o processo de cópia desses objetos.
## Shallow Copy e Deep Copy
Há, pelo menos inicialmente, duas situações para pensarmos sobre as cópias de objetos, as cópias parciais (shallow copy) e as cópias profundas (Deep Copy). A diferença está na forma como os valores são passados de um objeto ao outro.
Quando estudei programação pela primeira vez, a linguagem C era dominante na instituição (até hoje é ela) e o conceito de passagem de valor e referência fazia parte das primeiras aulas, já que é extremamente comum nesta linguagem, como sei que não é o caso de todos, vou explicar um pouco sobre.
### Passagem de Valor vs Referência
Passagem de valor é literalmente passar um valor, passamos o conteúdo de uma variável para outra, como no exemplo que segue, onde passamos o valor que está em `a` para `b`. Com isso temos duas alocações na memória, dois endereços de memória diferentes.
```c
int a = 10;
int b = a;
```
Parece óbvio que se queremos copiar algo, queremos copiar o seu valor, mas na programação certos tipos são sempre passados como referência, é o caso dos vetores em C.
```c
int a[4] = [0,1,2,3];
int b[4] = a;
```
Neste caso é feito uma passagem por referência, isso significa que passamos para `b` apenas o endereço de memória de `a`. Isso significa que toda e qualquer modificação neste vector será refletida tanto em `a` quanto em `b`.
### Mas o que isso tem a ver com as cópias?!
Em diversas linguagens, Java e C#, por exemplo, os objetos são passados como referência e isso entrega comportamentos peculiares. Ao realizarmos a cópia de um objeto que possui outros objetos, estes objetos internos serão copiados como referência para o seu destino, portanto compartilharam o mesmo estado em memória, tendo seus valores sempre iguais entre suas cópias, portanto uma cópia parcial (Shallow Copy).
### Qual devo usar?!
O ganho do uso de cópias parciais é a eficiência do seu código, que usará menos recursos do que se realizasse uma cópia profunda, instanciando um novo objeto interno e copiando os valores presentes.
Mas qual o melhor a ser usado? Dependerá do seu projeto e necessidades, o padrão Prototype, conferirá a você a padronização desses processos, para que sempre que for necessário copiar um objeto, não seja necessário abrir a classe e verificar se há mais objetos internos, se esses objetos internos não possuem outros objetos internos...
# Aplicando o Prototype
A primeira coisa que iremos precisar é uma interface do tipo Prototype, que terá os métodos `ShallowCopy` e `DeepCopy`.
```cs
public interface IPrototype<T>
{
T ShallowCopy();
T DeepCopy();
}
```
Agora poderemos implementar a nossa classe abstrata que herdará de `IPrototype`, aqui já poderíamos implementar a interface se assim quiséssemos mas no caso prefiro usar uma classe intermediária.
Criarei também a classe `Weapon` para ser nossa classe interna, ela eu já opto por implementar diretamente e portanto não marco suas propriedades como abstract.
```cs
public abstract class Enemy : IPrototype<Enemy>
{
public string Name;
public string Description;
public Weapon Weapon;
public abstract Enemy ShallowCopy();
public abstract Enemy DeepCopy();
}
public class Weapon : IPrototype<Weapon>
{
public string Type;
public int Damage;
public Weapon(string type, int damage)
{
this.Type = type;
this.Damage = damage;
}
public Weapon ShallowCopy()
{
return (Weapon)this.MemberwiseClone();
}
public Weapon DeepCopy()
{
return new Weapon(Type, Damage);
}
}
```
>Note que os métodos herdados de `IPrototype` são marcados como abstract para que na próxima herança seja codificado.
Agora podemos finalmente implementar nossa classe produto, a classe Troll.
```cs
public class Troll : Enemy
{
public override Enemy ShallowCopy()
{
return (Enemy)this.MemberwiseClone();
}
public override Enemy DeepCopy()
{
Enemy enemy = ShallowCopy();
enemy.Weapon = new Weapon(Weapon.Type, Weapon.Damage);
return enemy;
}
public override string ToString()
{
var Str = new StringBuilder();
Str.AppendLine($"Name: {this.Name}");
Str.AppendLine($"Description: {this.Description}");
Str.AppendLine($"Weapon: {Weapon.Type} ({Weapon.Damage})");
return Str.ToString();
}
}
```
Podemos ver que a classe Troll implementa nossos dois tipos de cópia e já na sua implementação entendemos que por mais que seus valores sejam parecidos, haverá um comportamento diferente entre os dois.
## Executando nossas classes
```cs
Enemy Boss = new Troll
{
Name = "Boss",
Description = "Tordoaldo is an evil troll, with a sharp intelligence and hidden strength, who lives in a forest cave adorned with treasures from his adventures.",
Weapon = new Weapon("Sword", 500)
};
Enemy Boss_ShallowCopy = Boss.ShallowCopy();
Enemy Boss_DeepCopy = Boss.DeepCopy();
System.Console.WriteLine("First Run \n");
ConsoleInfo();
Boss.Name = "BossWithNewName";
Boss.Weapon.Type = "Other Sword";
System.Console.WriteLine("Second Run \n");
ConsoleInfo();
void ConsoleInfo()
{
Console.WriteLine("Boss");
Console.WriteLine(Boss.ToString());
Console.WriteLine("Boss Shallow Copy");
Console.WriteLine(Boss_ShallowCopy.ToString());
Console.WriteLine("Boss Deep Copy");
Console.WriteLine(Boss_DeepCopy.ToString());
}
```
### Passo a Passo
#### Step 1
Aqui realizamos as duas cópias e podemos ver que todas as propriedades são idênticas como deveria ser.
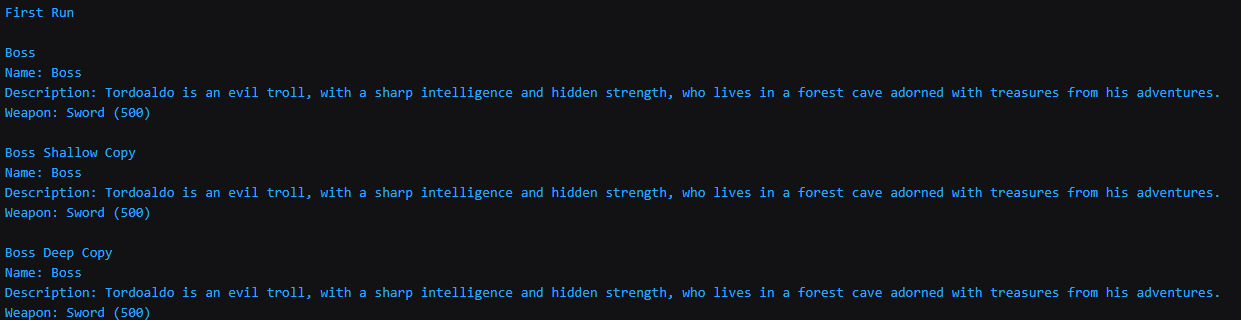
#### Step 2
Após isso atualizamos o nome do nosso "Boss" original, e trocamos o nome da sua arma e o que vemos na saída é interessante!
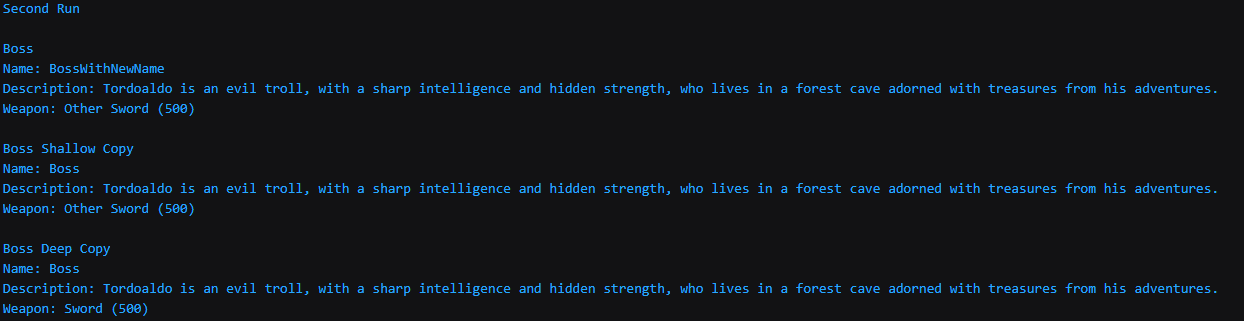
Como podemos ver nosso "Boss" aparece com seu nome novo, sem nenhum problema. Mas nosso "Boss Shallow Copy" também teve sua arma alterada! Isso se dá justamente pela propriedade que comentamos anteriormente, como realizamos uma cópia parcial, a classe interna `Weapon` compartilha o mesmo espaço na memória, assim, toda alteração realizada ali refletirá nos dois objetos, "Boss" e "Boss Shallow Copy"
# Sobre seu uso
## Quando usar?!
O livro sobre padrões do Erich Gamma, enumera três casos de uso para este modelo:
* Quando classes que serão instanciadas são especificadas em tempo de execução, por carga dinâmica por exemplo.
* Para evitar o acoplamento do nosso código, evitando a construção de uma hierarquia de classes factories paralela à hierarquia de classes do produto.
* Quando as instâncias de uma classe puderem ter uma dentre poucas combinações diferentes de estados. Pode ser mais vantajoso instalar um número correspondente de protótipos e cloná-los, ao invés de instanciar a classe manualmente, cada vez com um estado apropriado.
## Vantagens
Ainda utilizando o livro supracitado, temos alguns benefícios:
- Acrescentar e remover produtos em tempo de execução. É um padrão mais flexível que outros padrões de criação, permitindo registrar novos produtos ao instanciar um novo prototype no cliente, deste modo o cliente pode instalar e remover protótipos em tempo de execução.
- Especificar novos objetos pela variação de valores. Ao utilizarmos o padrão prototype podemos reduzir consideravelmente o número de classes envolvidas.
- Especificar novos objetos pela variação da estrutura. Este design permite que criemos objetos com partes e subpartes, desde que o nosso objeto composto implemente um clone profundo.
## Desvantagem
A principal desvantagem é que cada subclasse do Prototype deve implementar a operação Clone, o que pode ser difícil. Casos onde as classes possuem referências circulares, ou que não suportam a operação de cópia, são exemplos dessa dificuldade.
## Repositório GIT
[Design Patterns](https://github.com/nicolas-souza/DesignPatterns)
## Materiais de Estudo
Estamos chegando ao fim do nosso artigo e queria deixar alguns materiais que usei para estudar esse padrão de software:
[Refactoring Guru](https://refactoring.guru/pt-br/design-patterns/builder)
[Dofactory](https://www.dofactory.com/net/builder-design-pattern)
[Padrões de Projetos: Soluções Reutilizáveis de Software Orientados a Objetos](https://www.amazon.com.br/Padr%C3%B5es-Projetos-Solu%C3%A7%C3%B5es-Reutiliz%C3%A1veis-Orientados/dp/8573076100/ref=pd_lpo_sccl_1/139-0743064-7931502?pd_rd_w=nD2cg&content-id=amzn1.sym.8151c21e-945b-4095-a73d-67d730c81d28&pf_rd_p=8151c21e-945b-4095-a73d-67d730c81d28&pf_rd_r=07QHYYC7KPHXE3WGN9X2&pd_rd_wg=oApzi&pd_rd_r=4dfbb257-085b-49d3-89ba-d4230649574a&pd_rd_i=8573076100&psc=1)
| nicolasdesouza |
1,872,317 | The Power of Data Science: Revolutionizing Industries. | Data science is transforming industries by enabling better decision-making through data analysis. It... | 0 | 2024-05-31T17:24:01 | https://dev.to/stegen54/the-power-of-data-science-revolutionizing-industries-4njf | datascience |
Data science is transforming industries by enabling better decision-making through data analysis. It harnesses the power of algorithms, machine learning, and statistical models to uncover insights from large datasets. This leads to more informed business strategies, optimized operations, and innovative solutions. From healthcare to finance, data science drives efficiency, predicts trends, and enhances customer experiences. As data continues to grow exponentially, mastering data science skills is crucial for staying competitive and unlocking new opportunities.
_Embrace the future with data science, and explore its potential to revolutionize your field._ | stegen54 |
1,872,316 | How to host both frontend and backend together for free | Hello everyone! Am Jeff, How can it host both frontend and backend for free please? | 0 | 2024-05-31T17:23:37 | https://dev.to/jeff_quater_e649257481090/hello-e-7og | Hello everyone!
Am Jeff, How can it host both frontend and backend for free please?
| jeff_quater_e649257481090 | |
1,872,310 | How to Add Rich Media Files to PDF Using C# .NET | Learn how to add Rich Media files to PDF Using C# .NET. See more from Document Solutions today. | 0 | 2024-05-31T17:20:55 | https://developer.mescius.com/blogs/how-to-add-rich-media-files-to-pdf-using-c-sharp-net | webdev, devops, csharp, tutorial | ---
canonical_url: https://developer.mescius.com/blogs/how-to-add-rich-media-files-to-pdf-using-c-sharp-net
description: Learn how to add Rich Media files to PDF Using C# .NET. See more from Document Solutions today.
---
**What You Will Need**
- Document Solutions for PDF
- Visual Studio
- NuGet
**Controls Referenced**
- [DsPDF](https://developer.mescius.com/document-solutions/dot-net-pdf-api/docs/online/Document.html)
**Tutorial Concept**
Learn how to add rich media files to PDF documents using DsPdf in C# .NET
---
In today's digital age, static documents often fall short of effectively engaging audiences. Incorporating rich media files, such as videos and audio clips, into PDF documents can significantly enhance user experience and comprehension. In this blog post, we'll explore how to leverage [Document Solutions for PDF](https://developer.mescius.com/document-solutions/dot-net-pdf-api "https://developer.mescius.com/document-solutions/dot-net-pdf-api") (DsPdf), a .NET PDF API, to seamlessly integrate rich media files into PDF documents, thereby creating dynamic and captivating content. We'll delve into:
* [The Benefits of Media Files in PDF Documents](#Benefits)
* [Leveraging C# and PDF API](#Leveraging)
* [Step-by-Step Implementation](#Step)
## <a id="Benefits"></a>Benefits **of Media Files in PDF Documents**
Adding media files to PDF documents enhances the interactivity and richness of the content, making it more engaging for the reader. Below, we provide a detailed overview of this process and its key features:
**1. Interactive Multimedia Content**
Embedding videos and audio clips in PDFs creates a dynamic reading experience, allowing users to interact with the content directly within the document.
**2. Support for Various Media Formats**
PDFs can support a range of media formats, including MP3, OGG, WAV, MP4, SWF, WebM, and more, ensuring compatibility with different types of multimedia content.
**3. Enhanced Presentations**
Integrate multimedia elements in business presentations, educational materials, and marketing brochures to convey information more effectively.
**4. Interactive Tutorials and E-Learning**
Use media files in educational PDFs to include tutorials, demonstrations, and interactive learning modules.
## <a id="Leveraging"></a>Leveraging C# and PDF API
DsPdf offers the [**RichMediaAnnotation**](https://developer.mescius.com/document-solutions/dot-net-pdf-api/docs/online/annotationtypes.html#i-heading-richmedia-annotation "https://developer.mescius.com/document-solutions/dot-net-pdf-api/docs/online/annotationtypes.html#i-heading-richmedia-annotation") class to incorporate multimedia support programmatically into your PDF documents.
The key capabilities of this class are as follows:
1. **Embed Multimedia Content:** RichMedia annotations enable incorporating multimedia assets, including audio, video, and animations, into PDF files. This can enhance presentations, educational materials, or interactive forms.
2. **Annotation Properties:** RichMedia annotations have properties that define how the multimedia content should be presented. These properties may include the activation conditions, visibility settings, and the appearance of the annotation.
3. **Activation and Deactivation:** Activation conditions determine when the multimedia content should start or stop playing. For example, you can set the content to play when the user clicks the annotation or when the page containing the clip becomes visible.
4. **Presentation Style:** RichMedia annotations support two presentation styles - **Embedded** and **Windowed**.
5. **Control Navigation:** RichMedia annotations allow you to control the settings of navigation options to True or False.
## <a id="Step"></a>Step-by-Step Implementation
Let's outline the process of adding rich media files to an existing PDF document using C#. In this blog, we will replace an image with a video file.
1. **Install PDF Library:** Begin by [installing DsPdf from the NuGet Package Manager](https://developer.mescius.com/document-solutions/dot-net-pdf-api/docs/online/GettingStarted.html "https://developer.mescius.com/document-solutions/dot-net-pdf-api/docs/online/GettingStarted.html") in your C# project.
2. **Load PDF Document:** Utilize DsPdf’s functionality to embed rich media files into the PDF document. For video or audio clips, specify the file path and stream. Then, load the file stream in DsPdf.
```
var pdfPath = Path.Combine("Resources", "PDFs", "Wetlands.pdf");
var videoPath = Path.Combine("Resources", "Video", "waterfall.mp4");
using var fs = File.OpenRead(pdfPath);
var doc = new GcPdfDocument();
doc.Load(fs);
```
3.**Remove the Image:** Find the largest image on the first page and remove it using [**RedactAnnotation**](https://developer.mescius.com/document-solutions/dot-net-pdf-api/docs/online/annotationtypes.html#i-heading-redact-annotation "https://developer.mescius.com/document-solutions/dot-net-pdf-api/docs/online/annotationtypes.html#i-heading-redact-annotation").
```
var page = doc.Pages.First();
RectangleF imageRect = RectangleF.Empty;
foreach (var img in page.GetImages())
{
foreach (var l in img.Locations.Where(l_ => l_.Page.Index == 0))
{
var r = l.PageBounds.ToRect();
if (r.Height > imageRect.Height)
imageRect = r;
}
}
if (imageRect == RectangleF.Empty)
throw new Exception("Could not find an image on the first page.");
doc.Redact(new RedactAnnotation() { Page = page, Rect = imageRect });
```
4.**Add Rich Media:** Add a video clip in the rectangle previously occupied by the image. You can set various properties (like embedding a media file such as a video), the video's activation and deactivation conditions, and whether or not to show the navigation tools on the video.
```
var rma = new RichMediaAnnotation();
var videoEfs = EmbeddedFileStream.FromFile(doc, videoPath);
var videoFileSpec = FileSpecification.FromEmbeddedStream(Path.GetFileName(videoPath), videoEfs);
rma.SetVideo(videoFileSpec);
rma.PresentationStyle = RichMediaAnnotationPresentationStyle.Embedded;
rma.ActivationCondition = RichMediaAnnotationActivation.PageBecomesVisible;
rma.DeactivationCondition = RichMediaAnnotationDeactivation.PageBecomesInvisible;
rma.ShowNavigationPane = true;
rma.Page = page;
rma.Rect = imageRect;
```
5.**Save PDF Document:** Once all properties have been added, save the PDF document.
```
doc.Save(stream);
```
You have just added a media file to a PDF document! This is what it looks like in our JavaScript-based [Document Solutions PDF Viewer](https://developer.mescius.com/document-solutions/javascript-pdf-viewer "https://developer.mescius.com/document-solutions/javascript-pdf-viewer") :

### Learn More About DsPdf’s Support of Rich Media Files
* .NET [Documentation](https://developer.mescius.com/document-solutions/dot-net-pdf-api/docs/online/annotationtypes.html#i-heading-richmedia-annotation "https://developer.mescius.com/document-solutions/dot-net-pdf-api/docs/online/annotationtypes.html#i-heading-richmedia-annotation")
* .NET [Demo](https://developer.mescius.com/document-solutions/dot-net-pdf-api/demos/features/annotations/rich-media/pdf-cs "https://developer.mescius.com/document-solutions/dot-net-pdf-api/demos/features/annotations/rich-media/pdf-cs")
### More Topics to Read
* [Adding media files to PDF documents in client-side JavaScript PDF Viewer](https://developer.mescius.com/document-solutions/dot-net-pdf-api/docs/online/RichMediaAnnotation.html "https://developer.mescius.com/document-solutions/dot-net-pdf-api/docs/online/RichMediaAnnotation.html")
* [Adding rich media files programmatically to PDF Documents using JavaScript](https://developer.mescius.com/document-solutions/dot-net-pdf-api/docs/online/RichMediaAnnotation.html#i-heading-add-rich-media-programmatically "https://developer.mescius.com/document-solutions/dot-net-pdf-api/docs/online/RichMediaAnnotation.html#i-heading-add-rich-media-programmatically")
* [JavaScript Demo](https://developer.mescius.com/document-solutions/javascript-pdf-viewer/demos/viewer-features/rich-media/purejs "https://developer.mescius.com/document-solutions/javascript-pdf-viewer/demos/viewer-features/rich-media/purejs")
What do you think about this feature? Please feel free to share any comments below. | chelseadevereaux |
1,872,314 | Using React Testing Library to Test Your Next.js Application with TypeScript and GraphQL | Introduction In the fast-paced web development world, ensuring your applications' quality... | 0 | 2024-05-31T17:20:10 | https://dev.to/schead/using-react-testing-library-to-test-your-nextjs-application-with-typescript-and-graphql-3k24 | ## Introduction
In the fast-paced web development world, ensuring your applications' quality and reliability is paramount. Testing is a critical component in the development process, especially for the frontend where user interaction is most prominent. Using modern tools like React, Next.js, TypeScript, GraphQL, and React Testing Library, developers can build robust and maintainable applications. In this blog post, we'll explore the importance of frontend testing and guide you through a practical example to get you started.
## Why Frontend Testing Matters
### Ensuring Code Quality
Frontend testing helps maintain high code quality by catching bugs early in the development process. It ensures that individual components function as expected, reducing the chances of errors in the production environment.
### Enhancing User Experience
By testing user interactions and UI components, developers can ensure a seamless and bug-free user experience. This is crucial for retaining users and providing a smooth navigation experience.
### Facilitating Refactoring
With a comprehensive suite of tests, developers can confidently refactor code without fear of breaking existing functionality. This encourages cleaner and more maintainable codebases.
### Improving Collaboration
Testing promotes better collaboration among team members. Clear and concise tests serve as documentation for how components should behave, making it easier for new developers to understand the codebase.
### Increasing Productivity
Automated tests save time in the long run by reducing the need for manual testing. This allows developers to focus on building new features and improving existing ones.
## Practical Example: Setting Up Frontend Testing
Let's dive into a practical example to illustrate how to set up and run frontend tests in a Next.js application with TypeScript, GraphQL, and React Testing Library.
### Step 1: Initialize the Repo
First, we'll create a new Next.js application using a predefined example with Jest for testing.
```bash
npx create-next-app@latest --example with-jest blog-todo-graphql --typescript
```
### Step 2: Install Apollo Client and GraphQL
Next, we'll install the Apollo Client and GraphQL to handle our GraphQL queries and mutations.
```bash
npm install @apollo/client graphql
```
### Step 3: Update `tsconfig.json`
To ensure that our imports are correctly resolved, update the `tsconfig.json` file to include the following `paths` configuration:
```json
{
"compilerOptions": {
"paths": {
"@/*": ["./*"]
}
}
}
```
### Step 4: Update React Testing Library
Ensure that you have the latest version of React Testing Library for the best features and bug fixes.
```bash
npm install @testing-library/react@15.0.6
```
### Step 5: Clean Up the Project Structure
We'll clean up the project structure by deleting unnecessary files and folders. Keep only the `app` folder with `page.tsx` and `layout.tsx` files.
```bash
rm -rf pages __tests__
```
### Step 6: Adjust `page.tsx` File
Update the `page.tsx` file to include the following content:
**app/page.tsx**
```typescript
export const metadata = {
title: "App Router",
};
import AddTodo from "@/components/add-todo";
import ListTodos from "@/components/list-todos";
const Home = () => {
return (
<div>
<h1>Todo List</h1>
<AddTodo />
<ListTodos />
</div>
);
};
export default Home;
```
### Step 7: Add the Necessary Project Files
Here are the files we need to add to our project, along with a brief explanation of their purpose:
**schemas/index.gql**
```graphql
type Todo {
id: String!
title: String!
description: String!
}
type Query {
todos: [Todo!]!
}
type Mutation {
addTodo(title: String!, description: String!): Todo!
}
```
This file defines the GraphQL schema for our Todo application, including the Todo type, a query to fetch todos, and a mutation to add a new todo.
**components/add-todo.tsx**
```typescript
import { useState } from "react";
import { useMutation, gql } from "@apollo/client";
import { GET_TODOS } from "@/components/list-todos";
export const ADD_TODO = gql`
mutation AddTodo($title: String!, $description: String!) {
addTodo(title: $title, description: $description) {
id
title
description
}
}
`;
const AddTodo = () => {
const [title, setTitle] = useState("");
const [description, setDescription] = useState("");
const [addTodo] = useMutation(ADD_TODO);
const handleSubmit = async (e: React.FormEvent) => {
e.preventDefault();
await addTodo({
variables: { title, description },
refetchQueries: [{ query: GET_TODOS }],
});
setTitle("");
setDescription("");
};
return (
<form onSubmit={handleSubmit}>
<input
value={title}
onChange={(e) => setTitle(e.target.value)}
placeholder="Title"
required
/>
<input
value={description}
onChange={(e) => setDescription(e.target.value)}
placeholder="Description"
required
/>
<button type="submit">Add Todo</button>
</form>
);
};
export default AddTodo;
```
This component provides a form for adding new todos. It uses the Apollo Client to send a GraphQL mutation to add the todo and refetches the list of todos after adding a new one.
**components/list-todos.tsx**
```typescript
import { useQuery, gql } from "@apollo/client";
export const GET_TODOS = gql`
query GetTodos {
todos {
id
title
description
}
}
`;
const ListTodos = () => {
const { loading, error, data } = useQuery(GET_TODOS);
if (loading) return <p>Loading...</p>;
if (error) return <p>Error: {error.message}</p>;
return (
<ul>
{data.todos.map(
(todo: { id: string; title: string; description: string }) => (
<li key={todo.id}>
<h3>{todo.title}</h3>
<p>{todo.description}</p>
</li>
)
)}
</ul>
);
};
export default ListTodos;
```
This component fetches and displays a list of todos using the Apollo Client. It shows loading and error states while the data is being fetched.
**mocks/apollo-mock-provider.tsx**
```typescript
import React from "react";
import { MockedProvider, MockedResponse } from "@apollo/client/testing";
interface ApolloMockProviderProps {
mocks: MockedResponse[];
children: React.ReactNode;
}
const ApolloMockProvider: React.FC<ApolloMockProviderProps> = ({ mocks, children }) => (
<MockedProvider mocks={mocks} addTypename={false}>
{children}
</MockedProvider>
);
export default ApolloMockProvider;
```
This component provides a mocked Apollo Client for testing purposes. It uses the MockedProvider from `@apollo/client/testing` to supply mock data for our tests.
**tests/add-todo.test.tsx**
```typescript
import { render, screen, fireEvent } from "@testing-library/react";
import ApolloMockProvider from "@/mocks/apollo-mock-provider";
import { ADD_TODO } from "@/components/add-todo";
import { GET_TODOS } from "@/components/list-todos";
import Home from "app/page";
const mocks = [
{
request: {
query: ADD_TODO,
variables: {
title: "New Test Todo",
description: "New Test Description",
},
},
result: {
data: {
addTodo: {
id: 1,
title: "New Test Todo",
description: "New Test Description",
},
},
},
},
{
request: {
query: GET_TODOS,
},
result: {
data: {
todos: [],
},
},
},
{
request: {
query: GET_TODOS,
},
result: {
data: {
todos: [
{
id: 1,
title: "New Test Todo",
description: "New Test Description",
},
],
},
},
},
];
test("adds a todo", async () => {
render(
<ApolloMockProvider mocks={mocks}>
<Home />
</ApolloMockProvider>
);
// Check that initially there are no todos
expect(screen.queryByText("New Test Todo")).not.toBeInTheDocument();
expect(screen.queryByText("New Test Description")).not.toBeInTheDocument();
// Add a new todo
fireEvent.change(screen.getByPlaceholderText(/title/i), {
target: { value: "New Test Todo" },
});
fireEvent.change(screen.getByPlaceholderText(/description/i), {
target: { value: "New Test Description" },
});
fireEvent.click(screen.getByText("Add Todo"));
// Check that the new todo is added
expect(await screen.findByText("New Test Todo")).toBeInTheDocument();
expect(await screen.findByText("New Test Description")).toBeInTheDocument();
});
```
This test checks the functionality of adding a new todo. It uses the mocked Apollo Provider to simulate the GraphQL requests and responses.
**tests/list-todos.test.tsx**
```typescript
import { render, screen } from "@testing-library/react";
import ListTodos from "@/components/list-todos";
import ApolloMockProvider from "@/mocks/apollo-mock-provider";
import { GET_TODOS } from "@/components/list-todos";
const mocks = [
{
request: {
query: GET_TODOS,
},
result: {
data: {
todos: [
{ id: 1, title: "Test Todo 1", description: "Test Description 1" },
{ id: 2, title: "Test Todo 2", description: "Test Description 2" },
],
},
},
},
];
test("lists all todos", async () => {
render(
<ApolloMockProvider mocks={mocks}>
<ListTodos />
</ApolloMockProvider>
);
expect(screen.getByText("Loading...")).toBeInTheDocument();
expect(await screen.findByText("Test Todo 1")).toBeInTheDocument();
expect(await screen.findByText("Test Description 1")).toBeInTheDocument();
expect(await screen.findByText("Test Todo 2")).toBeInTheDocument();
expect(await screen.findByText("Test Description 2")).toBeInTheDocument();
});
```
This test checks that the list of todos is correctly fetched and displayed. It uses the mocked Apollo Provider to supply the test data.
### Benefits of Independent Tests
As you can see, in this setup, we didn't need to add the `ApolloProvider` component to our main application, just the `MockedProvider` for our tests. It's important to note that the `ApolloProvider` and `MockedProvider` serve different purposes and are independent of each other. Since this content focuses on demonstrating the tests and not the application running, we don't need to add the `ApolloProvider` here. However, in a real application, you must include the `ApolloProvider` to integrate your application with the actual API.
To run the tests, use the command below
```bash
npm run test
```
## Conclusion
Frontend testing is an indispensable part of modern web development. It ensures that your application is reliable, maintainable, and provides a great user experience. By integrating testing into your workflow, you can build robust applications with confidence. Follow the steps and add the provided files to set up a solid testing environment for your Next.js application. Happy testing!
| schead | |
1,872,313 | Twilio + webSockets - can't send parameters to webSocket | Hello, guys! I did put a question on Stack Overflow, and i don't know if it's best to only add the... | 0 | 2024-05-31T17:13:49 | https://dev.to/petru_tirla_b4fcd50d0407d/twilio-websockets-cant-send-parameters-to-websocket-l2n | twilio, websocket, ws | Hello, guys!
I did put a question on Stack Overflow, and i don't know if it's best to only add the link to it here or to add the whole description.
I will put for the moment the link, and some of the description. If anyone has a solution, I would be forever grateful!
https://stackoverflow.com/questions/78560657/twilio-websockets-cant-send-parameters-to-websocket
______________________________________
I am having problems with **Twilio**, while trying to send parameters to a **webSocket** that is being called from a **webhook**. I am using: **node.js, express, ws (JS websocket library)**.
The webhook is not the actual problem, since it only calls an endpoint from my end.
But in that endpoint, I am creating a `VoiceResponse` instance of Twilio, and using it to connect to a webSocket. In the process, I am trying to send it some parameters, because I want to access the user data (or whatever data) in the webSocket. Only that, this is not happening :)) | petru_tirla_b4fcd50d0407d |
1,872,311 | 🌐** Estructuras de Carpetas en Proyectos Web: Una Guía al Estilo de Los Sims** | ¡Hola Chiquis! 👋🏻 ¡Vamos a hacer un viaje por el mundo de las estructuras de carpetas en un proyecto... | 0 | 2024-05-31T17:12:00 | https://dev.to/orlidev/-estructuras-de-carpetas-en-proyectos-web-una-guia-al-estilo-de-los-sims-34jm | webdev, tutorial, softwaredevelopment, programming | ¡Hola Chiquis! 👋🏻 ¡Vamos a hacer un viaje por el mundo de las estructuras de carpetas en un proyecto web! Imagina que estás jugando a Los Sims, ese videojuego increíblemente adictivo donde puedes construir y personalizar tu propia casa. Ahora, imagina que cada habitación de tu casa en Los Sims es una carpeta en tu proyecto web. 🏡 Cada habitación tiene un propósito: la cocina para cocinar, el dormitorio para dormir, y así sucesivamente. En el desarrollo web, las carpetas son como las habitaciones de una casa, cada una con su propio propósito y contenido.

Imagina que tu proyecto web es una casa en Los Sims. 🏡 Cada carpeta es una habitación diseñada con un propósito específico. Al igual que no pondrías una cama en el baño, no mezclarías scripts de JavaScript con imágenes. Y al igual que una casa bien organizada te permite encontrar lo que necesitas rápidamente, una estructura de carpetas bien pensada hace que tu proyecto sea fácil de entender y mantener.
Las estructuras de carpetas en proyectos web 💻 pueden organizarse de varias maneras, pero una práctica común es la arquitectura de gritos (screaming architecture), que sugiere estructurar los proyectos de manera que las carpetas "griten" su propósito y contenido. Aquí hay algunas formas de organizar las carpetas:
🌳 Carpeta raíz
Es como el terreno donde se construye la mansión. Aquí se encuentran los archivos principales del proyecto, como el `index.html` y el archivo `CSS` principal.
📁 Por Tipo
Agrupar archivos por su tipo, como componentes, contextos y hooks. Ideal para proyectos pequeños o al inicio de uno más grande:
- Componentes: Para componentes reutilizables. Aquí es donde se almacenan todos los componentes de la interfaz de usuario, como botones, tarjetas, barras de navegación, etc.
- Servicios: Esta carpeta contiene todos los servicios, como las llamadas a la API, las funciones de utilidad, etc.
- Modelos: Aquí es donde se definen los modelos de datos.
```
└── src/
├── components/
├── contexts/
└── hooks/
```
Al igual que en una casa donde separas los objetos por su tipo (cubiertos en la cocina, ropa en el armario), puedes organizar tus archivos por tipo:
- `CSS/`: Para estilos.
- `JS/`: Para scripts.
- `Images/`: Para imágenes.
- `Pages/`: Cada página con su vista principal y componentes específicos.
- `Utils/`: Funciones de utilidad comunes.

Imagina que tienes una habitación para cada tipo de mueble en tu casa de Los Sims. Una habitación para sillas, otra para mesas, otra para lámparas, etc. En un proyecto web, esto sería similar a tener una carpeta para cada tipo de archivo: una para componentes, otra para servicios, otra para modelos, etc.
Es como la bodega de la mansión. Aquí se guardan todos los archivos por su tipo, como imágenes, scripts, estilos (CSS) y código fuente.
📂 Por Módulo o Funcionalidad
Organizar por páginas o módulos, con carpetas globales para contextos, hooks, etc. Perfecta para proyectos de escala mayor:
Cada módulo (como autenticación, perfil de usuario, administración, etc.) tiene su propia carpeta.
Dentro de cada carpeta de módulo, puedes tener subcarpetas para componentes, servicios, modelos, etc., según sea necesario.
```
└── src/
├── pages/
├── components/
└── contexts/
```
Si tu proyecto es como una casa grande, podrías tener una habitación para invitados, otra para juegos, etc. En un proyecto web, esto se traduce en módulos:
- `UserAuth/`: Para autenticación de usuarios.
- `ProductCatalog/`: Para el catálogo de productos.
- `PaymentGateway/`: Para el procesamiento de pagos.
- `Billing/`: Procesos de facturación y pagos.
- `Analytics/`: Análisis y seguimiento de datos.
Ahora, imagina que en lugar de organizar tus muebles por tipo, los organizas por habitaciones. Tienes una habitación (módulo) para la cocina, otra para el dormitorio, otra para el baño, etc. Cada habitación tiene sus propios muebles (archivos). En un proyecto web, esto sería similar a tener una carpeta para cada módulo o funcionalidad, como autenticación, perfil de usuario, administración, etc.
Es como cada sección de la mansión, como la cocina, el baño o el gimnasio. Aquí se encuentran los archivos relacionados con un módulo específico del sitio web, como la sección de productos, la sección de contacto o la sección de blog.

📑 Por Features
Agrupar por características, colocando componentes relacionados, contextos y hooks juntos.
Cada característica (como búsqueda de usuarios, gestión de publicaciones, notificaciones, etc.) tiene su propia carpeta.
Dentro de cada carpeta de características, puedes tener subcarpetas para componentes, servicios, modelos, etc., según sea necesario.
```
└── src/
├── featureA/
├── featureB/
└── featureC/
```
En Los Sims, puedes tener una zona de entretenimiento con juegos, libros y música. En un proyecto web, organizas por características o "features":
- `Search/`: Para la búsqueda en el sitio.
- `ContactForm/`: Para el formulario de contacto.
- `Dashboard/`: Para el panel de administración.
Esta es una evolución de la estructura por módulo. Imagina que además de tener habitaciones para la cocina, el dormitorio y el baño, también tienes habitaciones para actividades específicas, como una sala de juegos o un gimnasio en casa. En un proyecto web, esto sería similar a tener una carpeta para cada característica, como búsqueda de usuarios, gestión de posts, notificaciones, etc.
Es como cada detalle de la mansión, como la estufa en la cocina, la ducha en el baño o la máquina de pesas en el gimnasio. Aquí se encuentran los archivos relacionados con una función específica del sitio web, como el carrito de compras, el formulario de registro o el reproductor de video.
📢 Screaming Architecture
La estructura de carpetas refleja claramente el propósito y el dominio del proyecto.
Puedes tener carpetas para diferentes capas de tu aplicación, como la capa de dominio, la capa de infraestructura, la capa de aplicación, etc.
La arquitectura de gritos se enfoca en la estructuración de un proyecto basado en características, lo que facilita la localización y el mantenimiento de las partes relacionadas del código. Es especialmente útil en proyectos grandes, donde la claridad y la facilidad de navegación son esenciales.
La Screaming Architecture es como una casa diseñada específicamente para una función, como una biblioteca o una pizzería. Se nota su propósito de inmediato. En un proyecto web, la estructura de carpetas debe reflejar claramente la función del proyecto.

En Los Sims, esto sería como si tu casa gritara su propósito a los cuatro vientos. Si alguien ve tu casa, inmediatamente sabe que es una casa de playa, una mansión, un apartamento urbano, etc. En un proyecto web, una "Screaming Architecture" es una estructura de carpetas que refleja claramente el propósito y el dominio del proyecto. No importa si estás usando React, Vue, Angular o cualquier otro framework, la estructura de tu proyecto debería poder probarse (testearse) sin haber tomado aún esas decisiones.
Es como el diseño estructural de la mansión, que debe ser sólido y eficiente para soportar el peso de la construcción. Esta arquitectura define cómo se organizan los archivos y carpetas para garantizar un rendimiento óptimo del sitio web.
Aquí tienes más ejemplos de carpetas para estructurar tu proyecto web:
📑 Atomic Design
Organiza los componentes visuales en niveles atómicos:
- `Atoms/`: Los elementos más pequeños, como botones.
- `Molecules/`: Grupos de átomos que funcionan juntos, como formularios.
- `Organisms/`: Conjuntos de moléculas que forman secciones de una interfaz.
📢 Estructura Hexagonal
Para proyectos que necesitan una clara separación entre la lógica de negocio y la interfaz:
- `Core/`: La lógica de negocio central.
- `Adapters/`: Conectores para diferentes tipos de entrada/salida.
- `Infrastructure/`: Configuraciones y soporte técnico.
¿Por qué es importante la estructura de carpetas? 🏗️
+ Orden y claridad: Al igual que una mansión bien organizada facilita la vida de los Sims, una estructura de carpetas bien definida te permite encontrar lo que necesitas rápidamente, evitando el caos y la frustración.
+ Colaboración efectiva: Si trabajas en equipo en un proyecto web, una estructura de carpetas clara y consistente facilita la colaboración y evita confusiones. Todos sabrán dónde encontrar cada archivo y cómo encaja en el conjunto.
+ Mantenimiento sencillo: A medida que tu proyecto web crece, una buena estructura de carpetas te ayudará a mantenerlo organizado y actualizado. Agregar nuevas funciones, corregir errores o realizar cambios será mucho más fácil si todo está bien clasificado.

Consejos para crear una estructura de carpetas efectiva 🏗️🎮
+ Utiliza nombres descriptivos: Asigna nombres claros y concisos a las carpetas y archivos para que sea fácil identificar su contenido.
+ Organiza por función: Agrupa los archivos relacionados por su función en carpetas específicas.
+ Crea una jerarquía lógica: Utiliza subcarpetas para crear una estructura jerárquica que refleje la organización del sitio web.
+ Mantén la consistencia: Sigue la misma estructura de carpetas en todos los proyectos web que realices.
+ Documenta tu estructura: Crea un archivo README que describa la estructura de carpetas y explique cómo se organiza el proyecto.
Estos ejemplos te ayudarán a mantener tu proyecto web tan organizado y funcional como una ciudad bien planificada en Los Sims. ¡Espero que estos ejemplos te inspiren a crear una estructura de carpetas que haga que tu código sea tan habitable y agradable como una casa bien diseñada en tu juego favorito! 🏠💻
Así que, al igual que en Los Sims, donde puedes personalizar tu casa para que se adapte a tus necesidades y refleje tu estilo, también puedes y debes personalizar la estructura de carpetas de tu proyecto web para que se adapte a las necesidades de tu proyecto y refleje claramente su propósito. ¡Feliz construcción! 👷♀️👷♂️
Conclusión 🍀 Al igual que un buen diseño de interiores en Los Sims crea una mansión funcional y estéticamente agradable, una buena estructura de carpetas en un proyecto web crea un sitio web organizado, eficiente y escalable. ¡Sigue estos consejos y organiza tu proyecto web como un verdadero Sim Maestro!
🚀 ¿Te ha gustado? Comparte tu opinión.
Artículo completo, visita: https://lnkd.in/ewtCN2Mn
https://lnkd.in/eAjM_Smy 👩💻 https://lnkd.in/eKvu-BHe
https://dev.to/orlidev ¡No te lo pierdas!
Referencias:
Imágenes creadas con: Copilot (microsoft.com)
##PorUnMillonDeAmigos #LinkedIn #Hiring #DesarrolloDeSoftware #Programacion #Networking #Tecnologia #Empleo #FolderStructure

 | orlidev |
1,867,551 | Optimizing User Experience: The Lazy Loading Approach in React" | What is lazy loading in Reactjs? Lazy loading in React is a powerful technique to optimize the... | 0 | 2024-05-31T17:07:38 | https://dev.to/baraq/optimizing-user-experience-the-lazy-loading-approach-in-react-23g | webdev, javascript, frontend | **What is lazy loading in Reactjs?**
Lazy loading in React is a powerful technique to optimize the performance and efficiency of web applications by delaying the loading of non-essential components until they are actually needed. This method not only enhances the initial load time, making the application feel faster and more responsive to users, but also reduces the overall resource consumption and bandwidth usage. Moreover, lazy loading aligns with best practices in modern web development, such as code splitting and efficient resource management, which are crucial for building scalable and maintainable applications. It also allows for better handling of large applications with complex component structures, ensuring that only the necessary code is delivered to the user at the right time.
**Why Do We Implement Lazy Loading?**
Imagine we're building a small-scale application with just a few components, such as a homepage, an about page, a contacts page, and some API calls. In a typical setup, all these components and files are bundled into a single JavaScript file, which is then loaded by the browser.
Let's illustrate this with a practical example. Start your React app and open the browser's Developer Tools by right-clicking and selecting "Inspect." Navigate to the "Network" tab, then click on the "JS" tab. Reload the webpage and observe the network activity. Notice which JavaScript files are loaded initially and pay attention to any additional files that load when you interact with the app. In a typical React application, the initial rendering of the webpage is driven by a single JavaScript file. While this approach is straightforward and works well for small applications, it can lead to inefficiencies as the application grows in size and complexity.
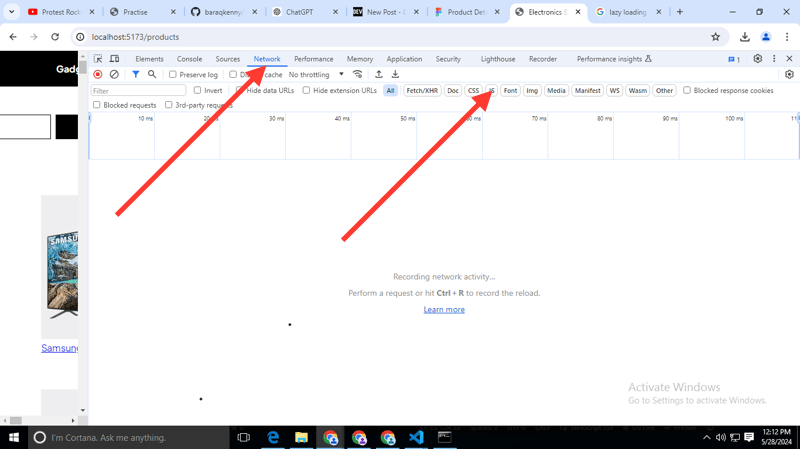
The big question: Is it suitable to have just one JavaScript file for our entire application?
For small-scale applications with just a few components, having a single JavaScript file might seem acceptable. However, consider large-scale applications like Amazon or eBay, which contain thousands of components and numerous features. If all of this were handled by a single JavaScript file, the file size would become significantly large, leading to increased load times and performance issues.
Therefore, it's crucial to break down the code into multiple JavaScript files or bundles. This approach, known as code splitting, helps optimize the application, improve load times, and enhance user experience. Without implementing such techniques, a large application would suffer from slow performance and other issues.
**How Can We Implement This in Our React App?**
Let's get started by opening our online code editor. I've already created a React app, set up the folder structure, and installed necessary libraries like react-router-dom for navigation.
In the src folder, I created a components folder containing all the component files. Inside this folder, there is a Homepage component that renders the homepage of the website. We'll focus on the Product component linked in the header, where we will implement the lazy loading feature.
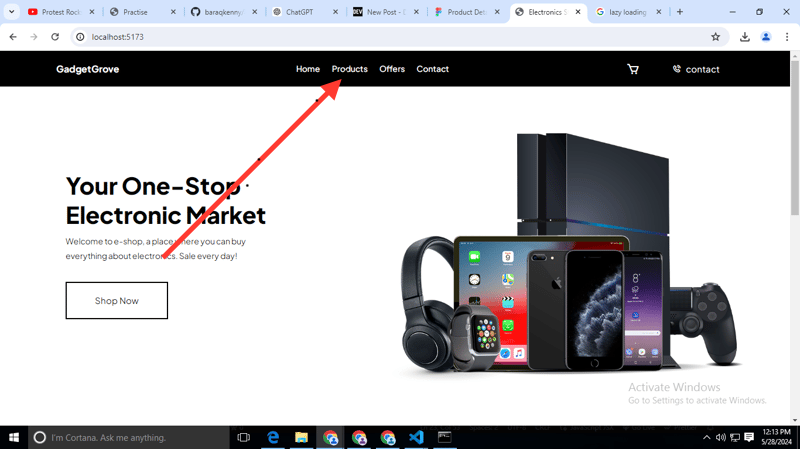
We'll import the Products component into the App.jsx file, which manages all our routing. However, instead of using the standard import, we'll use React's lazy function to achieve this.
```
import React, { lazy } from “react”;
import {Routes, Route} from “react-router-dom”;
const App = ()=> {
const Product = lazy(()=> import(“./components/Products”));
return(
<>
// // //
// // //
</>
)
}
export default App
```
Can you see the method we used to import the Products component into the App.jsx file? We created a variable named Products. Note that the first letter is capitalised because it is a component, not a regular variable. The lazy function takes a callback function, which includes the import function. Is this import the same as the standard import statement above? Absolutely not. This is different; it is called a dynamic import. The dynamic import function takes the path to the Products component as its argument.
Now let's go back to our browser and reload the page. Is the Products component visible in our network tab? Absolutely not.
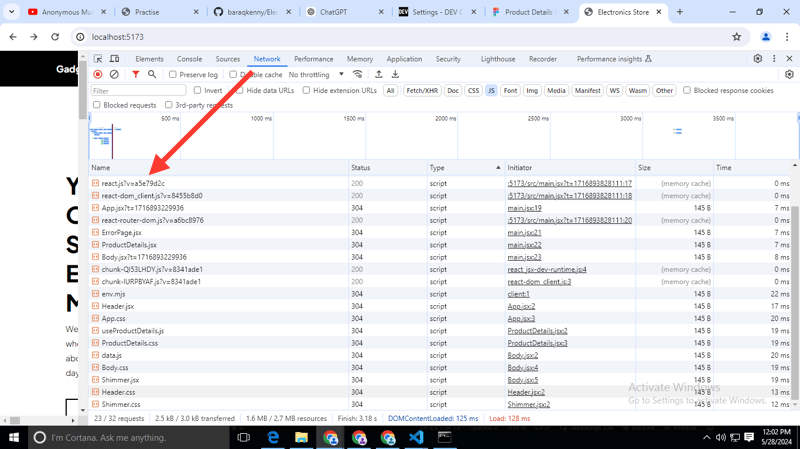
But what if I told you that our JavaScript bundler does not yet include the code for the Products component? It hasn't loaded that code yet. Curious? Now, let's click on the Products link. Can you see the magic that just happened in our Network tab?
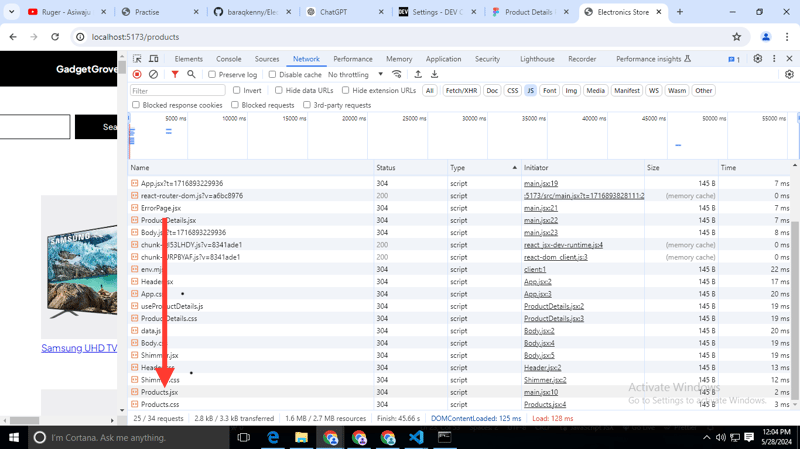
The Products component responded to our request. This means we're loading the Products page on demand and rendering it on the screen only when it's needed.
But why is our Product page displaying an error? When React attempts to load the page but cannot find the code, it suspends the process by throwing an error. However, there's a solution to this situation. React offers a component called "Suspense" to handle such errors. Let's put it into practice below:
```
import React, { lazy, Suspense } from “react”;
import {Routes, Route} from “react-router-dom”;
const App = ()=> {
const Product = lazy(()=> import(“./components/Products”));
return(
<>
<Routes>
<Route path=“ / ” element={<Home/>} />
<Route path=“ / products ” element={<Suspense fallback={<div>Loading….<div/>}><Products/><Suspense/>} />
<Routes/>
</>
)
}
export default App
```
In the code snippet above, we import the Suspense component from React and then wrap it around our Products component. This instructs React to load the Products page only when necessary. Now, what's the purpose of the fallback attribute? As the name suggests, it determines what gets rendered on the screen before the Product component is activated. You can include JSX or a component inside it. Keep in mind that it might not be visible due to how quickly React renders our components on the screen. However, you can test it by slowing down the network or disabling it entirely.
In summary, implementing lazy loading in React is not just a performance optimization; it is a strategic approach to improve the overall user experience, manage application complexity, and ensure efficient use of resources. This makes it an essential tool in the toolkit of any React developer aiming to build high-performing, user-friendly web applications.
| baraq |
1,872,305 | Effective Learning and Record Keeping | Effective Learning: Yesterday and today, I tried implementing the 15-minute rule, seeking help if I... | 0 | 2024-05-31T17:05:27 | https://dev.to/rayguna/effective-learning-ple | _Effective Learning:_ Yesterday and today, I tried implementing the 15-minute rule, seeking help if I got stuck for more than 15 minutes. Anyone can be a source of help, including my peers. It's important to be open to communication.
_Record Keeping:_ Yesterday, I was introduced to record keeping using tables. We can separate unique sets of information into separate tables and join the different sets of information using other tables. Storing a large amount of information in tabular format makes it organized, easy to understand, and easy to access. | rayguna | |
1,872,285 | Building a Scalable and Robust Application with AWS | In this blog, I'll walk you through the architecture and implementation of a scalable and robust... | 0 | 2024-05-31T17:05:08 | https://dev.to/chandan_h/building-a-scalable-and-robust-application-with-aws-ojc | aws, ec2, sqs, node | In this blog, I'll walk you through the architecture and implementation of a scalable and robust application using various AWS services. This project demonstrates how can integrate multiple services to create a resilient solution. Working [app link](https://d1kw9qj8xa4cyp.cloudfront.net/) May be down because of cost
**Architecture Overview**
Key AWS Services Used
- Amazon S3: To host the React application built with Vite.
- Amazon CloudFront: For content delivery and caching to enhance performance.
- Amazon API Gateway: To manage API requests and route them to the appropriate backend services.
- Amazon Route 53: For domain name system (DNS) web services and routing user requests.
- Elastic Load Balancer (ELB): To distribute incoming application traffic across multiple EC2 instances.
- Amazon EC2: To run the backend servers.
- Amazon SQS: For message queuing and handling asynchronous requests.
- Amazon DynamoDB: To store execution results and manage state.
- AWS Cloud9: For development, debugging, and monitoring logs and sqs (we will be scaling worker nodes based on sqs length).
- AWS Certificate Manager: For managing SSL/TLS certificates to secure traffic.
**Detailed Architecture Breakdown**
*Front-end*
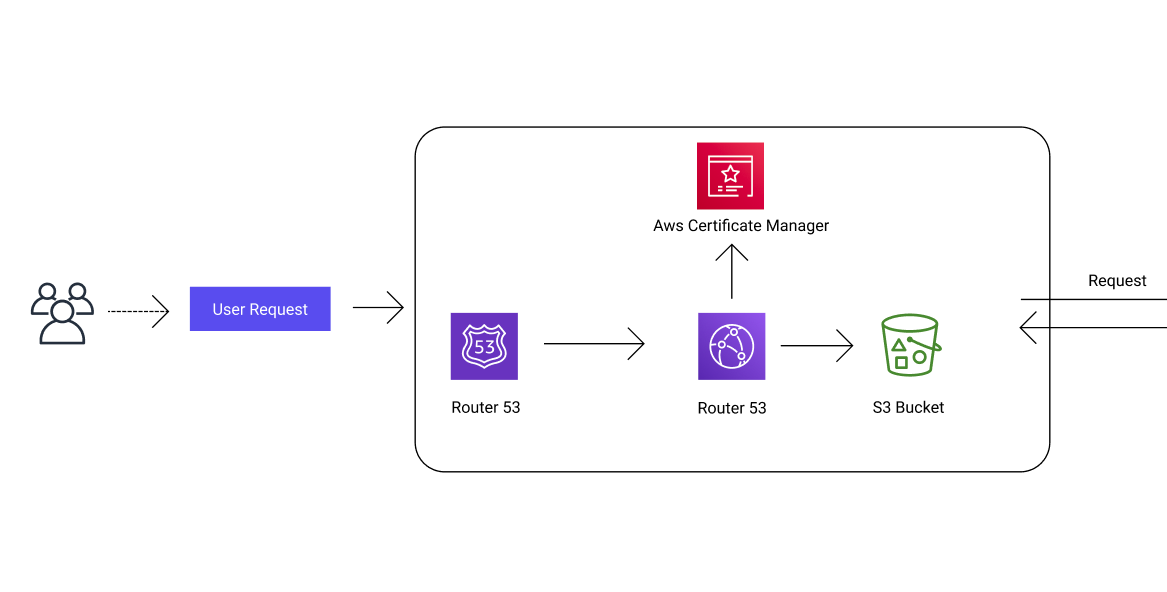
- Hosting the React Application
Amazon S3: The React application built with Vite is hosted on an S3 bucket, which serves the static files.
Amazon CloudFront: CloudFront is configured to deliver the application content with low latency and high transfer speeds.
- Routing and Domain Management
Amazon Route 53: Route 53 handles DNS management, routing user requests to the appropriate resources.
AWS Certificate Manager: Manages SSL/TLS certificates to ensure secure communication between the user and the application.
*Back-end*
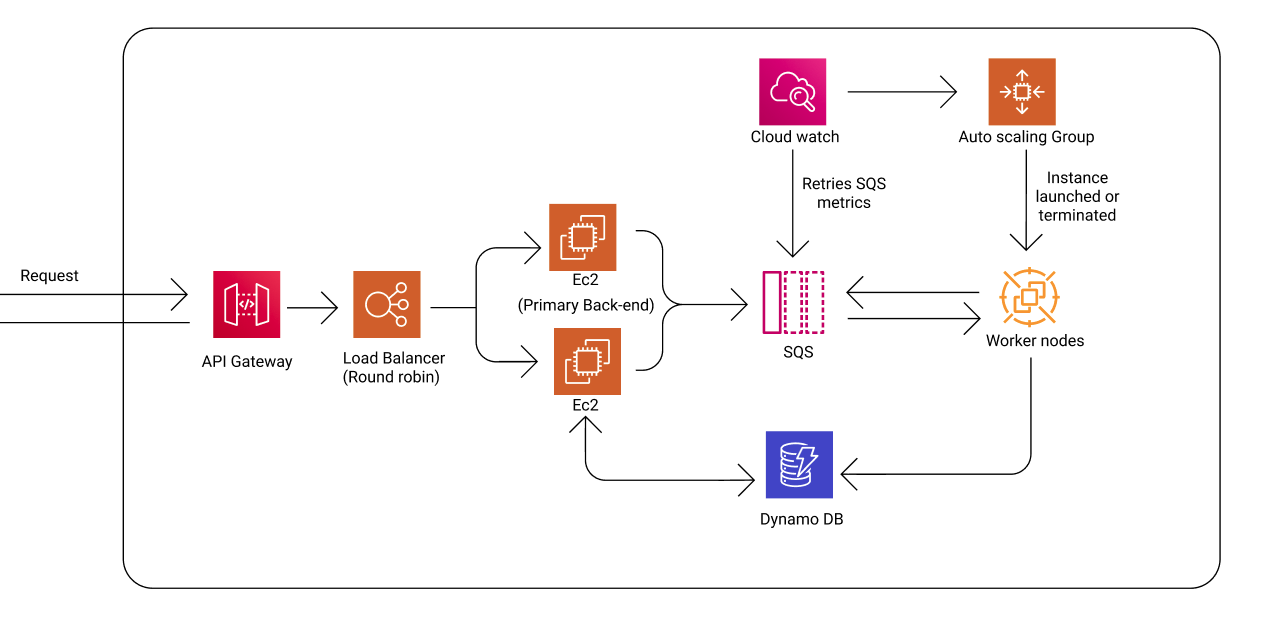
- API Gateway and Load Balancer
Amazon API Gateway: API Gateway serves as the entry point for all API requests. It routes incoming requests to the backend services.
Elastic Load Balancer: The load balancer distributes incoming API requests across two EC2 instances in a round-robin fashion, ensuring even load distribution.
- Primary Backend servers
Amazon EC2: Two EC2 instances act as servers backend servers. They process incoming requests and interact with other AWS services.
Amazon SQS: The backend servers place incoming requests into an SQS queue for asynchronous processing.
Worker Nodes: Worker nodes monitor the SQS queue, processing messages as they arrive. The number of worker nodes scales up or down based on the queue length, managed by an Auto Scaling group.
Amazon DynamoDB: Execution results are stored in DynamoDB. The backend servers periodically check the database to determine if a task has been completed.
- Monitoring and Scaling
Amazon CloudWatch: CloudWatch monitors the application and triggers scaling actions based on SQS metrics. It ensures that the application scales in and out based on demand.
Auto Scaling Group: Manages the worker nodes, launching or terminating instances based on the queue length and CloudWatch metrics.
**Implementation Details**
*Frontend: React Application*
The frontend of the application is a simple React app built with Vite. It allows users to submit JavaScript code, which is then processed by the backend. The frontend interacts with the backend via API Gateway.
```
import { useRef, useState } from "react";
import axios from "axios";
import Editor, { Monaco } from "@monaco-editor/react";
import { editor as monacoEditor } from "monaco-editor";
import { Button } from "./components/ui/button";
import "./App.css";
function App() {
const editorRef = useRef<monacoEditor.IStandaloneCodeEditor | null>(null);
const [output, setOutput] = useState("");
function handleEditorDidMount(
editor: monacoEditor.IStandaloneCodeEditor,
monaco: Monaco
) {
editorRef.current = editor;
}
async function showValue() {
if (editorRef.current) {
const code = editorRef.current.getValue();
try {
const response = await axios.post(
"https://api..primarybacked.com/submit-code",
{ code }
);
const { executionId } = response.data;
const checkStatus = async () => {
const statusResponse = await axios.get(
`https://api..primarybacked.com/check-status/${executionId}`
);
const { status, result } = statusResponse.data;
if (status === "Executed") {
setOutput(result);
} else {
setTimeout(checkStatus, 5000); // Polling every 5 seconds
}
};
checkStatus();
} catch (error) {
console.error("Error submitting code:", error);
setOutput("Error submitting code");
}
}
}
return (
<div className="flex h-screen w-full flex-col bg-gray-950 text-gray-50">
<header className="flex items-center justify-between border-b border-gray-800 px-4 py-4 sm:px-6">
<div className="flex items-center gap-4">
<span className="text-xl font-semibold">Code Playground</span>
</div>
<Button onClick={showValue}>Run</Button>
</header>
<div className="flex-1 overflow-hidden">
<div className="grid h-full grid-cols-1 gap-6 p-4 sm:grid-cols-[1fr_400px] sm:p-6">
<div className="flex h-full flex-col gap-6 overflow-hidden rounded-lg border border-gray-800 bg-gray-900">
<div className="flex-1 overflow-auto p-4">
<Editor
defaultLanguage="javascript"
theme="vs-dark"
defaultValue="console.log('Hello, world!');"
onMount={handleEditorDidMount}
options={{}}
/>
</div>
</div>
<div className="flex h-full flex-col gap-6 overflow-hidden rounded-lg border border-gray-800 bg-gray-900">
<div className="flex-1 overflow-auto p-4">
<pre className="whitespace-pre-wrap break-words font-mono text-sm">
{output}
</pre>
</div>
</div>
</div>
</div>
</div>
);
}
export default App;
```
*Primary Backend: Processing Requests*
The primary backend is built using EC2 instances, SQS, and DynamoDB.They forward the submitted code to the SQS, and forward the output to the users
```
const express = require('express');
const { DynamoDBClient, PutItemCommand, GetItemCommand } = require("@aws-sdk/client-dynamodb");
const { v4: uuidv4 } = require('uuid');
const { SQSClient, SendMessageCommand ,ReceiveMessageCommand} = require("@aws-sdk/client-sqs");
const cors = require('cors');
const app = express();
app.use(express.json());
require('dotenv').config();
app.use(cors({
origin: '*',
methods: ['GET', 'POST', 'PUT', 'DELETE', 'OPTIONS'],
}))
const config = {
region: "eu-north-1",
credentials: {
accessKeyId: process.env.AWS_ACCESS_KEY_ID,
secretAccessKey: process.env.AWS_SECRET_ACCESS_KEY
}
};
const DBclient = new DynamoDBClient(config);
const sqsClient = new SQSClient(config);
app.post('/submit-code', async (req, res) => {
console.log(req.body)
const executionId = uuidv4();
const { code } = req.body;
const input = {
TableName: 'code',
Item: {
executionId: { S: executionId },
code: { S: code },
status: { S: 'pending' },
result: { S: '' },
},
};
try {
await DBclient.send(new PutItemCommand(input));
const sqsParams = {
QueueUrl: process.env.QUEUE_URL,
MessageBody: JSON.stringify({ executionId }),
MessageDeduplicationId: executionId,
MessageGroupId: "CodeSubmissionGroup",
};
await sqsClient.send(new SendMessageCommand(sqsParams));
res.json({ executionId, message: "Code submitted successfully" });
} catch (error) {
console.error("Error submitting code:", error);
res.status(500).json({ error: "Failed to submit code" });
}
});
app.get('/check-status/:executionId', async (req, res) => {
const { executionId } = req.params;
const params = {
QueueUrl: process.env.QUEUE_URL,
MaxNumberOfMessages: 10,
WaitTimeSeconds: 0,
VisibilityTimeout: 0,
};
try {
const data = await sqsClient.send(new ReceiveMessageCommand(params));
let found = false;
if (data.Messages) {
for (const message of data.Messages) {
const body = JSON.parse(message.Body);
if (body.executionId === executionId) {
found = true;
break;
}
}
}
if (found) {
res.json({ status: 'pending', result: '' });
} else {
const dbParams = {
TableName: 'code',
Key: {
executionId: { S: executionId },
},
};
const dbData = await DBclient.send(new GetItemCommand(dbParams));
if (dbData.Item) {
const status = dbData.Item.status.S;
const result = dbData.Item.result.S;
res.json({ status, result });
} else {
res.status(404).json({ error: "Execution ID not found" });
}
}
} catch (error) {
console.error("Error checking status:", error);
res.status(500).json({ error: "Failed to check status" });
}
});
app.listen(3000, () => {
console.log('primary backend listening on port 3000!')
});
```
*Worker node: Processing code*
The Worker node is built using EC2 instances,They process the submitted code, and store the results in DynamoDB.
```
const express = require('express');
const safeEval = require('safe-eval');
const { DynamoDBClient, UpdateItemCommand, GetItemCommand } = require("@aws-sdk/client-dynamodb");
const { SQSClient, ReceiveMessageCommand, DeleteMessageCommand } = require("@aws-sdk/client-sqs");
require('dotenv').config();
const app = express();
app.use(express.json());
require('dotenv').config();
const config = {
region: "eu-north-1",
credentials: {
accessKeyId: process.env.AWS_ACCESS_KEY_ID,
secretAccessKey: process.env.AWS_SECRET_ACCESS_KEY
}
};
const DBclient = new DynamoDBClient(config);
const sqsClient = new SQSClient(config);
const processMessage = async (message) => {
try {
const { executionId } = JSON.parse(message.Body);
const { Item } = await DBclient.send(new GetItemCommand({
TableName: 'code',
Key: {
executionId: { S: executionId },
},
}));
if (!Item) {
console.log("Item not found for executionId:", executionId);
return;
}
const { code } = Item;
let outputString = '';
try {
const output = await safeEval(code.S);
outputString = output != null || output != undefined ? output.toString() : 'Code did not return any output';
} catch (error) {
outputString = "this code cant be executed";
}
const input = {
TableName: 'code',
Key: {
executionId: { S: executionId },
},
UpdateExpression: 'SET #status = :status, #result = :result',
ExpressionAttributeNames: {
'#status': 'status',
'#result': 'result'
},
ExpressionAttributeValues: {
':status': { S: 'Executed' },
':result': { S: outputString },
},
};
await DBclient.send(new UpdateItemCommand(input));
await sqsClient.send(new DeleteMessageCommand({
QueueUrl: process.env.QUEUE_URL,
ReceiptHandle: message.ReceiptHandle,
}));
} catch (error) {
console.error("Error processing message:", error);
}
};
const processMessages = async () => {
while (true) {
try {
const { Messages } = await sqsClient.send(new ReceiveMessageCommand({
QueueUrl: process.env.QUEUE_URL,
WaitTimeSeconds: 10,
}));
if (Messages && Messages.length > 0) {
for (const message of Messages) {
await processMessage(message);
}
}
} catch (error) {
console.error("Error receiving messages:", error);
}
await new Promise(resolve => setTimeout(resolve, 10000));
}
};
processMessages();
const port = 4000;
app.listen(port, () => {
console.log(`Primary backend listening on port ${port}!`);
});
```
Here is the complete architecture diagram
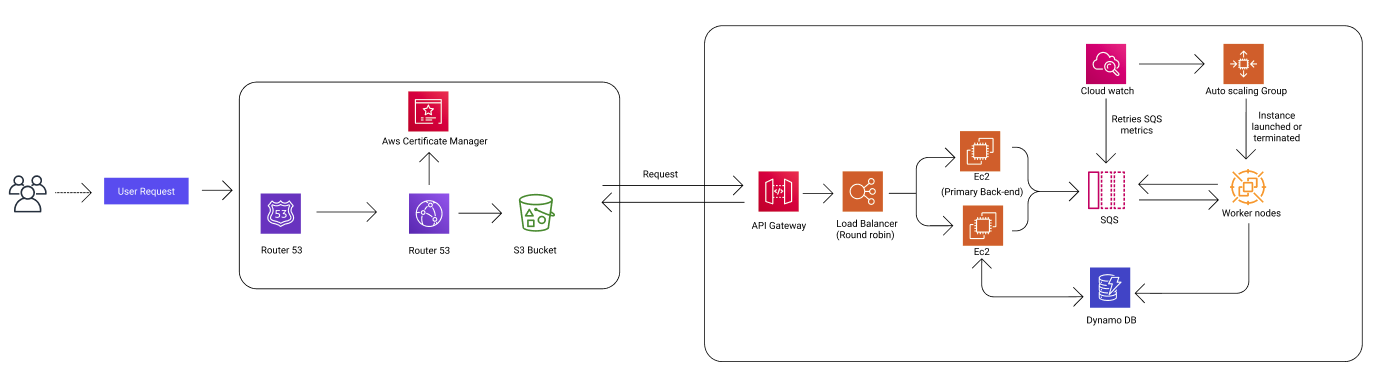
This project shows how to use different AWS services to build an app that can handle lots of users and work efficiently. By combining services like S3, CloudFront, API Gateway, Route 53, ELB, EC2, SQS, DynamoDB, and Cloud9, do tasks without waiting, and adjust to how many people are using it. This setup makes sure the app is always available, reliable, and works fast.
See you next time 👋
| chandan_h |
1,872,303 | Tricky Golang interview questions - Part 3: nil receivers | I have one more tricky interview question to discuss in this series. This one is related to function... | 0 | 2024-05-31T17:04:28 | https://dev.to/crusty0gphr/tricky-golang-interview-questions-part-3-nil-receivers-5740 | go, interview, tutorial, programming | I have one more tricky interview question to discuss in this series. This one is related to function receivers and methods in golang, often called nil receivers.
**Question: What is the output of the following?**
```go
package main
import "fmt"
type gopher struct {
name string
}
func (r *gopher) print() {
fmt.Println("gopher-printer works!")
}
func main() {
var gpr *gopher
gpr.print()
}
```
A quick note here, this question has one of the highest failing rates when asked during the interviews. Most of the interviewees never tried or never experienced such behaviour.
#### Receiver
A receiver argument is what distinguishes a method from a regular function in GoLang. In essence, a method is simply a function that includes a receiver argument. A receiver can also be of a non-struct type. For example, in the code below, we have a method `add()` with a receiver of type `Integer`, which is an alias for `int`.
```go
type Integer int
func (i Integer) add(j Integer) Integer {
return i + j
}
```
Okay, that's a pretty straightforward representation of what a receiver is. Now, let's try answering this question. If you come from OOP languages like Java, C# or C++ you are familiar with the term `null pointer exception`. It means that **you are trying to access a part of something that doesn't exist**. Here's the classic example from Java:
```java
public class NullPointer f
public static void main(String[] args) {
String a = null;
System.out.println(a.length());
}
}
```
Trying to compile this will throw the `null pointer exception`:
```bash
Exception in thread "main" java.lang.NullPointerException
at NullPointer-main (NullPointer.java:7)
```
The developer familiar with this concept will shortly answer:
**The program will panic with nil pointer dereference if we try to run this.**
```go
panic: runtime error: invalid memory address or nil pointer dereference
```
Let's actually run the program and make sure.
```go
[Running] go run "main.go"
gopher-printer works!
[Done] exited with code=0 in 0.318 seconds
```
Here, most interviewees get confused by this behaviour and assume that the Go compiler initialises the struct when we create the variable with the type `var gpr *gopher`. To test this let's add a print line inside the `print()` function like this:
```go
func (r *gopher) print() {
fmt.Printf("receiver: %v \n", r)
fmt.Println("gopher-printer works!")
}
```
and build the program again.
```go
[Running] go run "main.go"
receiver: <nil>
gopher-printer works!
[Done] exited with code=0 in 0.318 seconds
```
Oops, the struct is not initialised, its value is `nil`. Again, if you come from OOP languages this may seem like a static method call, but it's far different from that concept. You see, receivers in Go act like a basic argument, and in this case, when we call a method on an uninitialised struct, inside the methods `nil` has passed as a receiver as if you do something like this instead:
```go
package main
import "fmt"
type gopher struct {
name string
}
func print(r *gopher) {
fmt.Println("gopher-printer works!")
}
func main() {
var gpr *gopher
print(gpr)
}
```
The nil receiver is just a parameter.
After we clear this out, you give a confident answer to the interviewer:
**This will print a message "gopher-printer works!" into the console and will not cause a compile time panic**
It's that easy!
Here some interviewers like to ask the following:
**What will cause the program to panic?**
The answer is very simple. Since the nil receiver is just a parameter, this panic will only occur if the method tries to access the struct fields, such as `name` in our case.
```go
type gopher struct {
name string
}
func (r *gopher) print() {
fmt.Println(r.name) // <-- accessing the field
fmt.Println("gopher-printer works!")
}
```
So the full answer to this tricky question is:
**When you call this method from a nil pointer you will not get any compiler errors but you may get runtime panic if the method tries to access the struct fields.**
### Bonus section
Another interesting point to note is that a nil receiver can be initialized inside the method. However, this initialization has no effect outside of that method. Check the following code, I initialise the receiver inside the method:
```go
package main
import "fmt"
type gopher struct {
name string
}
func (r *gopher) print() {
// init the receiver with a new struct and populate the field
if r == nil {
r = new(gopher)
r.name = "crusty0gphr"
}
fmt.Printf("hi there %s \n", r.name)
}
func main() {
var gpr *gopher
gpr.print()
}
```
The result of this program will be:
```go
[Running] go run "main.go"
hi there crusty0gphr
[Done] exited with code=0 in 0.318 seconds
```
But inside the `main` function, the variable `gpr` will remain `nil` and accessing its field will cause a compile time panic!
Now, It's that easy, finally!
| crusty0gphr |
1,872,444 | Balancing Form and Function: What Tiny Glade Teaches Us | I just downloaded the demo for a wonderful little game called Tiny Glade. "Game" might not even be... | 0 | 2024-06-01T14:27:54 | https://blog.snowfrog.dev/form-vs-function/ | design, uiux | ---
title: Balancing Form and Function: What Tiny Glade Teaches Us
published: true
date: 2024-05-31 17:02:15 UTC
tags: Design,UIUX
canonical_url: https://blog.snowfrog.dev/form-vs-function/
---

I just downloaded the demo for a wonderful little game called Tiny Glade. "Game" might not even be the right term to describe this interesting piece of software. Here’s how it introduces itself:
> Tiny Glade is a relaxing game where you doodle whimsical castles, cozy cottages and romantic ruins. There's no management, combat or goals. Just kick back and turn forgotten meadows into lovable dioramas.
After spending some time with Tiny Glade, I am impressed by the level of care the developers have put into it. The attention to detail is remarkable. Every interaction feels organic and fluid, thanks to numerous subtle features.
At its core, Tiny Glade is a castle-builder sandbox. You construct castles by laying down building blocks that can be translated, rotated, scaled, and joined. Essentially, it's a graphics editor like Blender or Illustrator, but much more enjoyable, especially for first-time users. Why? Because Tiny Glade focuses on form as much as function.
The game’s emphasis on form does not come at the expense of function. It offers great flexibility while maintaining a natural and intuitive feel. Every action has a corresponding visual or sound effect, enhancing the experience without being overwhelming. This level of craftsmanship makes interactions pleasing.
Words can't really do it justice, so here's a gameplay trailer video.
<iframe width="356" height="200" src="https://www.youtube.com/embed/E0pNz9H6aRo?feature=oembed" frameborder="0" allow="accelerometer; autoplay; clipboard-write; encrypted-media; gyroscope; picture-in-picture; web-share" referrerpolicy="strict-origin-when-cross-origin" allowfullscreen title="Tiny Glade - Gameplay Trailer | Wholesome Snack: The Game Awards Edition"></iframe>
This experience made me question why the applications we use daily don’t offer the same level of enjoyment. Many business applications prioritize function over form, resulting in user frustration. Product owners often justify this by citing monetary reasons, implying that investing in form is a waste. But Tiny Glade proves otherwise.
As software developers, we should recognize the intrinsic value in form. People are willing to pay for pleasant interactions with software. While the balance between form and function varies by application, it is clear that focusing solely on function might be costing us more than we realize. I'm confident that [Tiny Glade](https://pouncelight.games/tiny-glade/) will show that enhancing user experience can lead to commercial success. | snowfrogdev |
1,872,302 | Database design | In database design, handling many-to-many relationships typically requires a third table, often... | 0 | 2024-05-31T17:02:01 | https://dev.to/aborov/database-design-pdo | beginners, datastructures, data, database | In database design, handling **many-to-many relationships** typically requires **a third table**, often called a **_join table_** or a **_junction table_**. This table records the associations between the two other tables. In contrast, for **one-to-many relationships**, you do not need a third table. Instead, you usually **_add a foreign key column in the table that represents the “many” side_** of the relationship.
## Many-to-Many Relationship Example
Suppose you have `students` and `courses` tables, where each student can enroll in many courses, and each course can have many students. To model this relationship, you would create a third table, often named `enrollments`. This join table would include foreign keys referencing the primary keys of the `students` and `courses` tables.
```ruby
class Student < ActiveRecord::Base
has_many :enrollments
has_many :courses, through: :enrollments
end
class Course < ActiveRecord::Base
has_many :enrollments
has_many :students, through: :enrollments
end
class Enrollment < ActiveRecord::Base
belongs_to :student
belongs_to :course
end
```
## One-to-Many Relationship Example
Suppose you have `authors` and `books` tables, where each author can write many books, but each book is written by only one author. In this case, you would add a foreign key column to the `books` table to reference the `authors` table.
```ruby
class Author < ActiveRecord::Base
has_many :books
end
class Book < ActiveRecord::Base
belongs_to :author
end
```
In summary, a third table is necessary for many-to-many relationships but not for one-to-many relationships. | aborov |
1,872,301 | Create a Responsive Image Gallery in Tailwind CSS using Flex | In this tutorial, we will creating a responsive image gallery with flexbox using Tailwind CSS. We... | 0 | 2024-05-31T17:01:52 | https://larainfo.com/blogs/tailwind-css-simple-responsive-image-gallery-with-flex/ | tailwindcss, webdev, beginners | In this tutorial, we will creating a responsive image gallery with flexbox using Tailwind CSS. We will cover examples for small and medium screen sizes, demonstrating how to create responsive image galleries with Tailwind CSS.
[View Demo](https://play.tailwindcss.com/VpLIJKxT0x)
### Tailwind CSS Responsive Gallery Example
We're using `flex `and `flex-wrap` utilities to create a flexible image container, centering the images horizontally with justify-center. The -mx-2 class removes gaps between images, while w-full ensures each image takes up the full width of its parent. Responsive classes like `sm:w-1/2`, `md:w-1/3`, and `lg:w-1/4` adjust image widths for different screen sizes. Padding (px-2) creates small gaps between images, and rounded-lg and shadow-md add rounded borders and subtle shadows. Replace placeholder URLs with actual image URLs and customize further with utility or custom classes.
```html
<div class="container mx-auto py-8">
<h1 class="text-3xl font-bold mb-4">Image Gallery</h1>
<div class="flex flex-wrap justify-center -mx-2">
<div class="w-full sm:w-1/2 md:w-1/3 lg:w-1/4 px-2 mb-4">
<img src="https://via.placeholder.com/500" alt="Image 1" class="w-full rounded-lg shadow-md">
</div>
<div class="w-full sm:w-1/2 md:w-1/3 lg:w-1/4 px-2 mb-4">
<img src="https://via.placeholder.com/500" alt="Image 2" class="w-full rounded-lg shadow-md">
</div>
<div class="w-full sm:w-1/2 md:w-1/3 lg:w-1/4 px-2 mb-4">
<img src="https://via.placeholder.com/500" alt="Image 3" class="w-full rounded-lg shadow-md">
</div>
<div class="w-full sm:w-1/2 md:w-1/3 lg:w-1/4 px-2 mb-4">
<img src="https://via.placeholder.com/500" alt="Image 4" class="w-full rounded-lg shadow-md">
</div>
<div class="w-full sm:w-1/2 md:w-1/3 lg:w-1/4 px-2 mb-4">
<img src="https://via.placeholder.com/500" alt="Image 5" class="w-full rounded-lg shadow-md">
</div>
<!-- Add more image elements as needed -->
</div>
</div>
```
**Image Gallery with Captions**
We've added captions to each image, positioning them at the bottom using absolute, bottom-0, left-0, and right-0 classes. The captions have a background color and padding with bg-gray-800, `bg-opacity-75`, text-white, p-2, and `rounded-b-lg` classes.
```html
<div class="container mx-auto py-8">
<h1 class="text-3xl font-bold mb-4">Image Gallery with Captions</h1>
<div class="flex flex-wrap justify-center -mx-2">
<div class="w-full sm:w-1/2 md:w-1/3 lg:w-1/4 px-2 mb-4">
<div class="relative">
<img src="https://via.placeholder.com/500" alt="Image 1" class="w-full rounded-lg shadow-md">
<div class="absolute bottom-0 left-0 right-0 p-2 bg-gray-800 bg-opacity-75 text-white rounded-b-lg">
<p class="text-sm">Image Caption 1</p>
</div>
</div>
</div>
<div class="w-full sm:w-1/2 md:w-1/3 lg:w-1/4 px-2 mb-4">
<div class="relative">
<img src="https://via.placeholder.com/500" alt="Image 1" class="w-full rounded-lg shadow-md">
<div class="absolute bottom-0 left-0 right-0 p-2 bg-gray-800 bg-opacity-75 text-white rounded-b-lg">
<p class="text-sm">Image Caption 2</p>
</div>
</div>
</div>
<div class="w-full sm:w-1/2 md:w-1/3 lg:w-1/4 px-2 mb-4">
<div class="relative">
<img src="https://via.placeholder.com/500" alt="Image 1" class="w-full rounded-lg shadow-md">
<div class="absolute bottom-0 left-0 right-0 p-2 bg-gray-800 bg-opacity-75 text-white rounded-b-lg">
<p class="text-sm">Image Caption 3</p>
</div>
</div>
</div>
<!-- Add more image elements with captions as needed -->
</div>
</div>
```
**Image Gallery with Hover Effects**
We've added a hover effect to the images using Tailwind's transform, transition-transform, `duration-500`, and `hover:scale-110` classes, creating a smooth scaling animation on hover. To prevent overflow and apply rounded corners, the parent container of each image uses overflow-hidden and rounded-lg classes.
```html
<div class="container mx-auto py-8">
<h1 class="mb-4 text-3xl font-bold">Image Gallery with Hover Effects</h1>
<div class="-mx-2 flex flex-wrap justify-center">
<div class="mb-4 w-full overflow-hidden rounded-lg px-2 shadow-md sm:w-1/2 md:w-1/3 lg:w-1/4">
<img src="https://via.placeholder.com/500" alt="Image 1"
class="w-full transform transition-transform duration-500 hover:scale-110" />
</div>
<div class="mb-4 w-full overflow-hidden rounded-lg px-2 shadow-md sm:w-1/2 md:w-1/3 lg:w-1/4">
<img src="https://via.placeholder.com/500" alt="Image 1"
class="w-full transform transition-transform duration-500 hover:scale-110" />
</div>
<div class="mb-4 w-full overflow-hidden rounded-lg px-2 shadow-md sm:w-1/2 md:w-1/3 lg:w-1/4">
<img src="https://via.placeholder.com/500" alt="Image 1"
class="w-full transform transition-transform duration-500 hover:scale-110" />
</div>
<!-- Add more image elements with hover effects as needed -->
</div>
</div>
```
 | saim_ansari |
1,872,300 | How I Manage to Do Everything I Love: Time Blocking Tips and Personal Insights | Ever feel like your life is juggling flaming torches while riding a unicycle? Time blocking might be... | 27,684 | 2024-05-31T16:58:18 | https://blog.perstarke-webdev.de/posts/time-blocking | productivity, timemanagement, career, work |
Ever feel like your life is juggling flaming torches while riding a unicycle? Time blocking might be the game-changer you need. In this post, I share my personal experience with time blocking—how it helps me balance competitive sports, one employed job, one self-employed job, master’s studies, a fulfilling social life, and relaxed free time, and why it might work for you too. Discover practical tips, tools, and insights to maximize your time and focus on what truly matters
I first stumbled upon time blocking during my trip to Australia. I wanted to balance getting work done while still having plenty of time to explore the amazing country and soak in its beautiful nature. I started experimenting with time blocking and found it incredibly helpful in getting more done and enjoying the things I love.
But let’s get one thing straight: No productivity or time management technique will work if you lack discipline. They're frigging useless if you don't put in the effort. You can find ways to make being disciplined easier, sure, but fundamentally, you need to show up and take action. Period.
In this post, I'll share my journey with time blocking, from the basics to my personal tips and insights. Let’s dive in and see how this strategy can transform your time management!
<hr>
Originally published on my [Panorama Perspectives Blog](https://blog.perstarke-webdev.de/posts/time-blocking)
<hr>
# What is Time Blocking?
Time blocking is a simple yet powerful time management technique where you divide your day into pre-planned chunks or "blocks" of time. Each block is dedicated to a specific task or group of tasks. Instead of constantly switching between activities, you focus on one thing at a time within its designated block, allowing you to work more efficiently and effectively. You can use this technique for just some of your tasks, or go the full way and schedule your complete days including waking up time, leisure activities and evening routines.
### Benefits of Time Blocking
1. **Increased Productivity**: By dedicating specific time blocks to tasks, you can reduce the time wasted on deciding what to do next and minimize distractions or time-wasters. This focused approach helps you get more done in less time.
2. **Better Focus and Concentration**: When you know exactly what you're supposed to be working on during each time block, it's easier to concentrate and maintain a flow state. This deep focus leads to higher quality work and faster completion of tasks.
3. **Reduced Stress and Anxiety**: Time blocking helps create a clear structure for your day, which can reduce the stress and anxiety associated with a chaotic or unpredictable schedule. Knowing that you have allotted time for everything important gives you peace of mind.
### Possible Downsides and Suitability
While time blocking can be highly effective, it's not for everyone. Here are some potential downsides and considerations for whether it might suit you:
- **Rigidity**: Time blocking can feel too rigid for people who prefer flexibility in their schedules. If you thrive on spontaneity, this method might feel constraining.
- **Initial Setup**: Setting up a time-blocked schedule can be time-consuming initially. It requires careful planning and a good understanding of how long tasks take.
- **Adapting to Changes**: Unexpected interruptions or changes can throw off your schedule. If you have a job or lifestyle that involves frequent unpredictability, you might find it challenging to stick to your time blocks.
- **Discipline Required**: Sticking to a time-blocked schedule requires discipline and commitment. If you're prone to procrastination or easily distracted, you might find it hard to adhere to your planned blocks. In that case, you should focus on how to improve these areas (there are ways for that!), and maybe get back to time-blocking later on.
In the end, whether time blocking is suitable for you depends on your personal preferences and work style. If you can adapt it to your needs and stay flexible, it can be an incredibly effective tool for managing your time and boosting productivity.
# Getting Started with Time Blocking
Ready to dive into time blocking? Here’s how to get started:
### Identifying Tasks and Priorities
The first step in time blocking is to identify all the tasks you need to accomplish. Make a list of your daily, weekly, and monthly tasks. Once you have your list, prioritize these tasks based on their importance and urgency. Knowing your priorities helps you allocate your time more effectively.
### Creating an Ideal Week Schedule
Next, create an ideal week schedule. This is a template for how you’d like your week to look. Start by blocking out essential activities like sleep, meals, and any fixed commitments such as work hours, classes, or appointments. Then, fill in the remaining time with your prioritized tasks.
Here’s a step-by-step approach to creating your ideal week schedule:
1. **Fixed Commitments**: Block out non-negotiable commitments like work hours, classes, and meetings.
2. **Daily Essentials**: Schedule time for sleep, meals, and personal care.
3. **Priority Tasks**: Allocate blocks for high-priority tasks and projects.
4. **Regular Activities**: Include regular activities like exercise, commuting, and leisure activities.
5. **Flexible Time**: Leave some buffer time for unexpected events and breaks.
Remember, your ideal week is a starting point. You’ll refine it as you go along.
### Allocating Specific Time Blocks for Each Task
With your ideal week in place, start allocating specific time blocks for each task. Here’s how:
1. **Task Grouping**: Group similar tasks together to streamline your workflow. For example, batch emails, phone calls, or admin tasks into a single time block.
2. **Estimate Time**: Estimate how long each task will take and assign appropriate time blocks. Be realistic to avoid overloading your schedule.
3. **Add Buffer Time**: Include buffer time between blocks to account for transitions and unexpected delays.
4. **Review and Adjust**: At the end of each week, review your schedule and make adjustments based on what worked and what didn’t. This helps you refine your time blocks and improve your productivity.
Creating and refining your time-blocked schedule may take a bit of trial and error, but once you find what works best for you, it can significantly enhance your productivity and time management.
# Tools and Resources
### Tools and Apps for Time Blocking
When it comes to time blocking, having the right tools can make a big difference. While there are many apps and tools available, I’ve found that Google Calendar is by far the best. It’s free, user-friendly, and packed with features that make time blocking a breeze.
### Setting Up Google Calendar for Time Blocking
1. **Create a New Calendar**: Start by creating a dedicated calendar for your time blocks. This helps keep your personal and time-blocking schedules separate. You can also use different calendars for work, uni, personal events and so on.
2. **Add Time Blocks**: Use the event feature to add your time blocks. Color-code different types of tasks to easily distinguish them.
3. **Set Reminders**: Set reminders for each block to keep you on track.
4. **Review and Adjust**: Regularly review and adjust your blocks as needed to stay flexible and effective.
### Personal Preferences and Recommendations
While there are other tools out there, my recommendation is to stick with Google Calendar. Its integration with other Google services and its accessibility on all devices make it a powerful tool for time blocking. Plus, it’s free, which is always a bonus!
If you’re new to time blocking, start simple with Google Calendar and gradually refine your approach. This method has worked wonders for me, and I’m confident it can do the same for you.
# My Time Blocking Routine
Creating my ideal week involved several strategic steps to ensure all my commitments and priorities were covered. Here’s how I designed my current schedule:
### Creating My Ideal Week
- **Blocking Monday to Friday**: I blocked out my weekdays with detailed schedules while leaving weekends more flexible with just a few to-dos. This allowed me to visit friends or family without being tied to a fixed schedule.
- **Scheduling Wake-Up and Bedtimes**: I scheduled consistent wake-up and bedtimes, along with morning and evening routines, and dinner times. This set a structured rhythm for my days.
- **Adding Lecture Times**: I included my lecture times for the semester, making sure these were fixed blocks in my schedule.
- **Gym Times and Weekly Tasks**: I blocked out specific times for gym sessions and weekly tasks like groceries and meal prep. This helped me maintain a balance between physical health and daily chores.
- **Including Travel Time**: I factored in travel time for getting to the gym and university, ensuring my schedule was realistic and stress-free.
- **Scheduling Work Hours**: I allocated my work hours for my remote employed job, spreading these over three days.
- **Preparing Lectures**: I estimated the time needed for reworking and preparing lectures, scheduling these tasks at suitable times throughout the week.
- **Self-Employed Business Work**: Any remaining empty spots were filled with tasks for my self-employed business, ensuring I made consistent progress on all fronts.
- **Regular Leisure Activities**: I fine-tuned the blocks to include regular leisure activities like playing guitar and going for walks, keeping me refreshed and motivated.
- **Working from a Café**: Once a week, I scheduled time to work from a café for a change of scenery and to break the routine.
- **Buffer Time**: I added buffer time for university blocks, which could be used for business work if not needed for studies.
- **Weekly Review and Adjustments**: Every weekend, I now review and adjust my schedule for the upcoming week. This includes accommodating spontaneous activities like friend visits, competitions, and any changes in lecture times.
- **Staying Flexible**: While I created a detailed plan, I remain flexible and adapt daily or weekly as necessary. This approach prevents me from becoming too fixated on the plan and allowed for a balanced approach to time management.
By following these steps, I was able to create a time-blocked schedule that helped me juggle competitive sports, an employed and self-employed job, master’s studies, and still have time for friends, family, and relaxation. This method brought structure and efficiency to my life, and I fine-tuned it over time to suit my evolving needs.
# Challenges and How to Overcome Them
Time blocking, while highly effective, comes with its own set of challenges. Here are some common obstacles you might face and strategies I’ve used to overcome them:
### Common Challenges Faced with Time Blocking
1. **Unexpected Interruptions**: Life is unpredictable, and unexpected interruptions can throw off your carefully planned schedule. Whether it's a sudden meeting, an urgent task, or a personal issue, these interruptions can disrupt your flow.
2. **Overestimating or Underestimating Time Needed for Tasks**: It can be challenging to accurately estimate how long tasks will take, leading to either unfinished tasks or wasted time.
3. **Difficulty Sticking to the Schedule**: Maintaining discipline and sticking to your time blocks can be tough, especially when motivation wanes or when distractions are tempting.
### Personal Strategies for Overcoming These Challenges
1. **Flexibility and Buffer Time**: One key strategy is to build flexibility into your schedule. I plan a top task for each block and have a secondary task ready if the first one is completed quickly. This way, I can make the most of my time without feeling constrained by the schedule. For example, I schedule extra time for university-related tasks. If I finish those early, I use the remaining time for my self-employed business work. Additionally, I include buffer time between blocks to account for transitions and unexpected delays.
2. **Prioritizing Tasks**: Effective prioritization is crucial. I determine what needs to be done (high priority), what should be done (medium priority), and what is less important or can be delegated (low priority). This helps me focus on the really needle-moving tasks. By prioritizing in this way, even if my schedule gets disrupted, the essential tasks are still accomplished, ensuring progress in key areas.
3. **Regular Review and Adjustments**: Regularly reviewing and adjusting your schedule is vital for maintaining its effectiveness. At the end of each week, I review what worked and what didn’t. I adjust my time blocks based on these insights to better reflect my needs and improve accuracy in time estimation. This continual refinement helps me stay adaptable and realistic. Furthermore, I sometimes adapt the upcoming week to include a special focus. There are weeks where more University-Stuff needs to be done, so I schedule in more time for that. Other weeks I focus on getting some overtime hours in my employed job, which I can then take off in other weeks.
By implementing these strategies, you can overcome the common challenges associated with time blocking and make it a more flexible and effective tool for managing your time. Remember, the key is to stay consistent but also be willing to adapt as needed.
# Benefits I've Experienced

Time blocking has had a profound impact on my life. Here are some of the key benefits I’ve observed:
- **Improved Productivity and Efficiency**: By dedicating specific time blocks to different tasks, I’ve become more productive and efficient. Knowing exactly what I need to do and when helps me dive straight into tasks without wasting time figuring out what to work on next.
- **Better Work-Life Balance**: Time blocking has helped me achieve a better work-life balance. By scheduling not only work and study tasks but also leisure activities and downtime, I ensure that I have time for everything that’s important to me. This balance is crucial for maintaining my overall well-being.
- **Enhanced Focus and Reduced Procrastination**: With clear, designated time blocks for each activity, I find it easier to focus and avoid distractions. This structure has significantly reduced my tendency to procrastinate, as I’m always aware of what I should be working on at any given moment.
Overall, time blocking has enabled me to balance competitive sports, one employed and one self-employed job, master’s studies, and still have time for friends, family, and relaxing activities. It’s one of the key tools that keep me organized and productive without feeling overwhelmed.
# Tips for Successful Time Blocking
If you’re ready to give time blocking a try, here are some tips to help you succeed:
- **Start with a Simple Schedule and Gradually Refine It**: Begin with a basic schedule and refine it as you go. Don’t worry about getting it perfect from the start; adjustments and improvements will come with practice.
- **Be Realistic About Time Estimates**: Avoid overloading your schedule by being realistic about how long tasks will take. It’s better to underestimate your capacity slightly and finish early than to overestimate and feel rushed. If you notice that your estimates need improvement, track and write down exactly how long you need for which tasks for a while. You can then use this information to estimate your needed times better.
- **Include Breaks and Downtime**: Schedule regular breaks and downtime to prevent burnout and maintain your productivity. Breaks are essential for recharging your mind and body.
- **Review and Adjust Your Schedule Regularly**: At the end of each week, review your schedule to see what worked and what didn’t. Make necessary adjustments to improve your time blocking strategy continuously.
- **Stay Consistent but Flexible**: Consistency is key, but it’s also important to remain flexible. Life is unpredictable, so be prepared to adjust your blocks as needed while maintaining the overall structure.
# Conclusion
Time blocking has transformed the way I manage my time and balance various aspects of my life. By dedicating specific blocks of time to different tasks and activities, I’ve become more productive, focused, and balanced. If you’re looking for a way to enhance your time management, I highly recommend giving time blocking a try. Start simple, stay flexible, and adjust as you go. With a bit of practice, you’ll likely find that time blocking can help you achieve your goals and maintain a healthier work-life balance.
Some people say that this rigid scheduling makes your days or your life less rewarding. I disagree with that—this type of scheduling allows me to do more of what I love, and therefore actually feel more fulfilled in my life.
| per-starke-642 |
1,872,297 | What are some of the latest educational games for kids available ? | The best game platform, offers a wide variety of educational games for kids that make learning an... | 0 | 2024-05-31T16:56:36 | https://dev.to/claywinston/what-are-some-of-the-latest-educational-games-for-kids-available--2fi6 | games, gaming, mobilegames, gamedev | The[ best game platform,](https://medium.com/@adreeshelk/publishing-on-a-robust-gaming-platform-key-considerations-for-developers-1c8888f80d91?utm_source=referral&utm_medium=Medium&utm_campaign=Nostra) offers a wide variety of educational games for kids that make learning an enjoyable and engaging experience. From classic games like sudoku and chess to exciting titles like Fruit Katana and Wothan the Barbarian, Latest educational games cater to different age groups and interests.
One of the most popular [educational games](https://nostra.gg/articles/how-to-publish-games.html?utm_source=referral&utm_medium=article&utm_campaign=Nostra) is chess, which helps children develop critical thinking, problem-solving, and strategic planning skills. The platform's ""Chess Takes Queen"" game offers a fun and interactive way for kids to learn and practice chess moves, opening strategies, and endgame techniques. With its intuitive interface and adaptive difficulty levels, this game is suitable for both beginners and advanced players.
Another engaging educational game is Fruit Katana, which combines hand-eye coordination training with quick decision-making skills. In this game, players must slice various fruits while avoiding bombs, challenging their reflexes and concentration. As they progress through the levels, kids develop better focus, attention to detail, and spatial awareness.
For children who enjoy word games, Nostra offers a range of exciting titles that help expand vocabulary, improve spelling, and enhance language skills. These word games feature colorful graphics, animated characters, and rewarding gameplay that keep kids engaged and motivated to learn.
In addition to these [educational games,](https://medium.com/@adreeshelk/creating-vivid-ongoing-interaction-encounters-with-nostra-games-d12e7e8593ba?utm_source=referral&utm_medium=Medium&utm_campaign=Nostra) Also provides a platform for users to watch and learn from professional gamers and streamers. Children can observe and comment on the newest games played by their favorite players, such as Bindaas Laila and Snipuu, gaining valuable insights and tips to improve their own gaming skills.
| claywinston |
1,872,296 | Buy verified cash app account | https://dmhelpshop.com/product/buy-verified-cash-app-account/ Buy verified cash app account Cash... | 0 | 2024-05-31T16:56:30 | https://dev.to/mahdubejsg686475/buy-verified-cash-app-account-2gih | webdev, javascript, beginners, programming | ERROR: type should be string, got "https://dmhelpshop.com/product/buy-verified-cash-app-account/\n\n\n\n\nBuy verified cash app account\nCash app has emerged as a dominant force in the realm of mobile banking within the USA, offering unparalleled convenience for digital money transfers, deposits, and trading. As the foremost provider of fully verified cash app accounts, we take pride in our ability to deliver accounts with substantial limits. Bitcoin enablement, and an unmatched level of security.\n\nOur commitment to facilitating seamless transactions and enabling digital currency trades has garnered significant acclaim, as evidenced by the overwhelming response from our satisfied clientele. Those seeking buy verified cash app account with 100% legitimate documentation and unrestricted access need look no further. Get in touch with us promptly to acquire your verified cash app account and take advantage of all the benefits it has to offer.\n\nWhy dmhelpshop is the best place to buy USA cash app accounts?\nIt’s crucial to stay informed about any updates to the platform you’re using. If an update has been released, it’s important to explore alternative options. Contact the platform’s support team to inquire about the status of the cash app service.\n\nClearly communicate your requirements and inquire whether they can meet your needs and provide the buy verified cash app account promptly. If they assure you that they can fulfill your requirements within the specified timeframe, proceed with the verification process using the required documents.\n\nOur account verification process includes the submission of the following documents: [List of specific documents required for verification].\n\nGenuine and activated email verified\nRegistered phone number (USA)\nSelfie verified\nSSN (social security number) verified\nDriving license\nBTC enable or not enable (BTC enable best)\n100% replacement guaranteed\n100% customer satisfaction\nWhen it comes to staying on top of the latest platform updates, it’s crucial to act fast and ensure you’re positioned in the best possible place. If you’re considering a switch, reaching out to the right contacts and inquiring about the status of the buy verified cash app account service update is essential.\n\nClearly communicate your requirements and gauge their commitment to fulfilling them promptly. Once you’ve confirmed their capability, proceed with the verification process using genuine and activated email verification, a registered USA phone number, selfie verification, social security number (SSN) verification, and a valid driving license.\n\nAdditionally, assessing whether BTC enablement is available is advisable, buy verified cash app account, with a preference for this feature. It’s important to note that a 100% replacement guarantee and ensuring 100% customer satisfaction are essential benchmarks in this process.\n\nHow to use the Cash Card to make purchases?\nTo activate your Cash Card, open the Cash App on your compatible device, locate the Cash Card icon at the bottom of the screen, and tap on it. Then select “Activate Cash Card” and proceed to scan the QR code on your card. Alternatively, you can manually enter the CVV and expiration date. How To Buy Verified Cash App Accounts.\n\nAfter submitting your information, including your registered number, expiration date, and CVV code, you can start making payments by conveniently tapping your card on a contactless-enabled payment terminal. Consider obtaining a buy verified Cash App account for seamless transactions, especially for business purposes. Buy verified cash app account.\n\nWhy we suggest to unchanged the Cash App account username?\nTo activate your Cash Card, open the Cash App on your compatible device, locate the Cash Card icon at the bottom of the screen, and tap on it. Then select “Activate Cash Card” and proceed to scan the QR code on your card.\n\nAlternatively, you can manually enter the CVV and expiration date. After submitting your information, including your registered number, expiration date, and CVV code, you can start making payments by conveniently tapping your card on a contactless-enabled payment terminal. Consider obtaining a verified Cash App account for seamless transactions, especially for business purposes. Buy verified cash app account. Purchase Verified Cash App Accounts.\n\nSelecting a username in an app usually comes with the understanding that it cannot be easily changed within the app’s settings or options. This deliberate control is in place to uphold consistency and minimize potential user confusion, especially for those who have added you as a contact using your username. In addition, purchasing a Cash App account with verified genuine documents already linked to the account ensures a reliable and secure transaction experience.\n\n \n\nBuy verified cash app accounts quickly and easily for all your financial needs.\nAs the user base of our platform continues to grow, the significance of verified accounts cannot be overstated for both businesses and individuals seeking to leverage its full range of features. How To Buy Verified Cash App Accounts.\n\nFor entrepreneurs, freelancers, and investors alike, a verified cash app account opens the door to sending, receiving, and withdrawing substantial amounts of money, offering unparalleled convenience and flexibility. Whether you’re conducting business or managing personal finances, the benefits of a verified account are clear, providing a secure and efficient means to transact and manage funds at scale.\n\nWhen it comes to the rising trend of purchasing buy verified cash app account, it’s crucial to tread carefully and opt for reputable providers to steer clear of potential scams and fraudulent activities. How To Buy Verified Cash App Accounts. With numerous providers offering this service at competitive prices, it is paramount to be diligent in selecting a trusted source.\n\nThis article serves as a comprehensive guide, equipping you with the essential knowledge to navigate the process of procuring buy verified cash app account, ensuring that you are well-informed before making any purchasing decisions. Understanding the fundamentals is key, and by following this guide, you’ll be empowered to make informed choices with confidence.\n\n \n\nIs it safe to buy Cash App Verified Accounts?\nCash App, being a prominent peer-to-peer mobile payment application, is widely utilized by numerous individuals for their transactions. However, concerns regarding its safety have arisen, particularly pertaining to the purchase of “verified” accounts through Cash App. This raises questions about the security of Cash App’s verification process.\n\nUnfortunately, the answer is negative, as buying such verified accounts entails risks and is deemed unsafe. Therefore, it is crucial for everyone to exercise caution and be aware of potential vulnerabilities when using Cash App. How To Buy Verified Cash App Accounts.\n\nCash App has emerged as a widely embraced platform for purchasing Instagram Followers using PayPal, catering to a diverse range of users. This convenient application permits individuals possessing a PayPal account to procure authenticated Instagram Followers.\n\nLeveraging the Cash App, users can either opt to procure followers for a predetermined quantity or exercise patience until their account accrues a substantial follower count, subsequently making a bulk purchase. Although the Cash App provides this service, it is crucial to discern between genuine and counterfeit items. If you find yourself in search of counterfeit products such as a Rolex, a Louis Vuitton item, or a Louis Vuitton bag, there are two viable approaches to consider.\n\n \n\nWhy you need to buy verified Cash App accounts personal or business?\nThe Cash App is a versatile digital wallet enabling seamless money transfers among its users. However, it presents a concern as it facilitates transfer to both verified and unverified individuals.\n\nTo address this, the Cash App offers the option to become a verified user, which unlocks a range of advantages. Verified users can enjoy perks such as express payment, immediate issue resolution, and a generous interest-free period of up to two weeks. With its user-friendly interface and enhanced capabilities, the Cash App caters to the needs of a wide audience, ensuring convenient and secure digital transactions for all.\n\nIf you’re a business person seeking additional funds to expand your business, we have a solution for you. Payroll management can often be a challenging task, regardless of whether you’re a small family-run business or a large corporation. How To Buy Verified Cash App Accounts.\n\nImproper payment practices can lead to potential issues with your employees, as they could report you to the government. However, worry not, as we offer a reliable and efficient way to ensure proper payroll management, avoiding any potential complications. Our services provide you with the funds you need without compromising your reputation or legal standing. With our assistance, you can focus on growing your business while maintaining a professional and compliant relationship with your employees. Purchase Verified Cash App Accounts.\n\nA Cash App has emerged as a leading peer-to-peer payment method, catering to a wide range of users. With its seamless functionality, individuals can effortlessly send and receive cash in a matter of seconds, bypassing the need for a traditional bank account or social security number. Buy verified cash app account.\n\nThis accessibility makes it particularly appealing to millennials, addressing a common challenge they face in accessing physical currency. As a result, ACash App has established itself as a preferred choice among diverse audiences, enabling swift and hassle-free transactions for everyone. Purchase Verified Cash App Accounts.\n\n \n\nHow to verify Cash App accounts\nTo ensure the verification of your Cash App account, it is essential to securely store all your required documents in your account. This process includes accurately supplying your date of birth and verifying the US or UK phone number linked to your Cash App account.\n\nAs part of the verification process, you will be asked to submit accurate personal details such as your date of birth, the last four digits of your SSN, and your email address. If additional information is requested by the Cash App community to validate your account, be prepared to provide it promptly. Upon successful verification, you will gain full access to managing your account balance, as well as sending and receiving funds seamlessly. Buy verified cash app account.\n\n \n\nHow cash used for international transaction?\nExperience the seamless convenience of this innovative platform that simplifies money transfers to the level of sending a text message. It effortlessly connects users within the familiar confines of their respective currency regions, primarily in the United States and the United Kingdom.\n\nNo matter if you’re a freelancer seeking to diversify your clientele or a small business eager to enhance market presence, this solution caters to your financial needs efficiently and securely. Embrace a world of unlimited possibilities while staying connected to your currency domain. Buy verified cash app account.\n\nUnderstanding the currency capabilities of your selected payment application is essential in today’s digital landscape, where versatile financial tools are increasingly sought after. In this era of rapid technological advancements, being well-informed about platforms such as Cash App is crucial.\n\nAs we progress into the digital age, the significance of keeping abreast of such services becomes more pronounced, emphasizing the necessity of staying updated with the evolving financial trends and options available. Buy verified cash app account.\n\nOffers and advantage to buy cash app accounts cheap?\nWith Cash App, the possibilities are endless, offering numerous advantages in online marketing, cryptocurrency trading, and mobile banking while ensuring high security. As a top creator of Cash App accounts, our team possesses unparalleled expertise in navigating the platform.\n\nWe deliver accounts with maximum security and unwavering loyalty at competitive prices unmatched by other agencies. Rest assured, you can trust our services without hesitation, as we prioritize your peace of mind and satisfaction above all else.\n\nEnhance your business operations effortlessly by utilizing the Cash App e-wallet for seamless payment processing, money transfers, and various other essential tasks. Amidst a myriad of transaction platforms in existence today, the Cash App e-wallet stands out as a premier choice, offering users a multitude of functions to streamline their financial activities effectively. Buy verified cash app account.\n\nTrustbizs.com stands by the Cash App’s superiority and recommends acquiring your Cash App accounts from this trusted source to optimize your business potential.\n\nHow Customizable are the Payment Options on Cash App for Businesses?\nDiscover the flexible payment options available to businesses on Cash App, enabling a range of customization features to streamline transactions. Business users have the ability to adjust transaction amounts, incorporate tipping options, and leverage robust reporting tools for enhanced financial management.\n\nExplore trustbizs.com to acquire verified Cash App accounts with LD backup at a competitive price, ensuring a secure and efficient payment solution for your business needs. Buy verified cash app account.\n\nDiscover Cash App, an innovative platform ideal for small business owners and entrepreneurs aiming to simplify their financial operations. With its intuitive interface, Cash App empowers businesses to seamlessly receive payments and effectively oversee their finances. Emphasizing customization, this app accommodates a variety of business requirements and preferences, making it a versatile tool for all.\n\nWhere To Buy Verified Cash App Accounts\nWhen considering purchasing a verified Cash App account, it is imperative to carefully scrutinize the seller’s pricing and payment methods. Look for pricing that aligns with the market value, ensuring transparency and legitimacy. Buy verified cash app account.\n\nEqually important is the need to opt for sellers who provide secure payment channels to safeguard your financial data. Trust your intuition; skepticism towards deals that appear overly advantageous or sellers who raise red flags is warranted. It is always wise to prioritize caution and explore alternative avenues if uncertainties arise.\n\nThe Importance Of Verified Cash App Accounts\nIn today’s digital age, the significance of verified Cash App accounts cannot be overstated, as they serve as a cornerstone for secure and trustworthy online transactions.\n\nBy acquiring verified Cash App accounts, users not only establish credibility but also instill the confidence required to participate in financial endeavors with peace of mind, thus solidifying its status as an indispensable asset for individuals navigating the digital marketplace.\n\nWhen considering purchasing a verified Cash App account, it is imperative to carefully scrutinize the seller’s pricing and payment methods. Look for pricing that aligns with the market value, ensuring transparency and legitimacy. Buy verified cash app account.\n\nEqually important is the need to opt for sellers who provide secure payment channels to safeguard your financial data. Trust your intuition; skepticism towards deals that appear overly advantageous or sellers who raise red flags is warranted. It is always wise to prioritize caution and explore alternative avenues if uncertainties arise.\n\nConclusion\nEnhance your online financial transactions with verified Cash App accounts, a secure and convenient option for all individuals. By purchasing these accounts, you can access exclusive features, benefit from higher transaction limits, and enjoy enhanced protection against fraudulent activities. Streamline your financial interactions and experience peace of mind knowing your transactions are secure and efficient with verified Cash App accounts.\n\nChoose a trusted provider when acquiring accounts to guarantee legitimacy and reliability. In an era where Cash App is increasingly favored for financial transactions, possessing a verified account offers users peace of mind and ease in managing their finances. Make informed decisions to safeguard your financial assets and streamline your personal transactions effectively.\n\nContact Us / 24 Hours Reply\nTelegram:dmhelpshop\nWhatsApp: +1 (980) 277-2786\nSkype:dmhelpshop\nEmail:dmhelpshop@gmail.com\n\n" | mahdubejsg686475 |
1,872,294 | Tables can hold more than dinner. | I recently learned about record keeping and databases. Turns out people have been keeping records of... | 0 | 2024-05-31T16:48:58 | https://dev.to/jrzricardo/tables-can-hold-more-than-dinner-2hd8 | I recently learned about record keeping and databases.
Turns out people have been keeping records of things for a long, long time. Some of the first records kept were by farmers counting up their harvest and tracking the weather.
We've come a long way since then,
but the methods have remained the same,
relatively speaking.
The tools are different now though,
and nearly everything it seems is being kept record of by someone.
It's all stored in databases.
and those databases need systems to organize them.
But how do we sort out all this data,
it seems nearly endless?
Tables.
Within them,
you can store an almost infinite amount of stuff.
but these tables have rules,
you can't just plug away willy-nilly.
Tables are usually seen on spreadsheets,
and the spreadsheet will have rows and columns that help designate what goes where.
At any point where a row and column meet you'll find a cell.
Cells have a fundamental law:
ONE VALUE PER CELL!
Should someone stray from this law,
this will get messy real quick.
Another neat thing I learned is that not all tables need to be visible to users.
Some simply provide support to other tables,
through what is known as One-to-Many and Many-to-Many.
These types of tables will draw info from one table and potential send it to another.
This is possible with the use of id numbers.
I'm excited to see how many ways databases are utilized down the line.
| jrzricardo | |
1,872,293 | Step-by-Step Guide to Parametrized Relationships in Spring Boot and Neo4j | Creating Relationships with Parametrized Names in Spring Boot with Neo4j When working with graph... | 0 | 2024-05-31T16:42:19 | https://dev.to/fullstackjava/step-by-step-guide-to-parametrized-relationships-in-spring-boot-and-neo4j-19je | webdev, javascript, beginners, programming | Creating Relationships with Parametrized Names in Spring Boot with Neo4j
When working with graph databases like Neo4j, relationships between nodes are as crucial as the nodes themselves. In some cases, you might want to create relationships dynamically with names based on parameters rather than fixed values. This flexibility can be particularly useful in applications that require dynamic graph structures. In this blog, we will walk through how to create relationships with parametrized names using Spring Boot and Neo4j.
### Prerequisites
Before we dive into the implementation, ensure you have the following setup:
1. Java Development Kit (JDK) installed.
2. Spring Boot application initialized (using Spring Initializr or your preferred method).
3. Neo4j database installed and running.
### Step 1: Setting Up Your Spring Boot Project
First, you need to set up your Spring Boot project with the necessary dependencies for Neo4j.
**pom.xml:**
```xml
<dependencies>
<dependency>
<groupId>org.springframework.boot</groupId>
<artifactId>spring-boot-starter-data-neo4j</artifactId>
</dependency>
<dependency>
<groupId>org.springframework.boot</groupId>
<artifactId>spring-boot-starter-web</artifactId>
</dependency>
</dependencies>
```
### Step 2: Configuring Neo4j in Spring Boot
Configure your application to connect to your Neo4j database. Update the `application.properties` file with your database details:
**application.properties:**
```properties
spring.neo4j.uri=bolt://localhost:7687
spring.neo4j.authentication.username=neo4j
spring.neo4j.authentication.password=your_password
```
### Step 3: Defining Node Entities
Define your node entities using Spring Data Neo4j annotations.
**Person.java:**
```java
import org.springframework.data.annotation.Id;
import org.springframework.data.neo4j.core.schema.Node;
@Node
public class Person {
@Id
private Long id;
private String name;
// Getters and Setters
}
```
### Step 4: Creating a Relationship with Parametrized Name
To create a relationship with a parametrized name, you'll need to use a custom query. Spring Data Neo4j allows you to define custom Cypher queries using the `@Query` annotation.
**PersonRepository.java:**
```java
import org.springframework.data.neo4j.repository.Neo4jRepository;
import org.springframework.data.neo4j.repository.query.Query;
import org.springframework.stereotype.Repository;
@Repository
public interface PersonRepository extends Neo4jRepository<Person, Long> {
@Query("MATCH (a:Person {id: $fromId}), (b:Person {id: $toId}) " +
"MERGE (a)-[r:RELATIONSHIP_TYPE]->(b) " +
"RETURN r")
void createRelationship(Long fromId, Long toId, String relationshipType);
}
```
### Step 5: Creating a Service Layer
Create a service layer to encapsulate the logic for creating relationships.
**PersonService.java:**
```java
import org.springframework.beans.factory.annotation.Autowired;
import org.springframework.stereotype.Service;
import org.springframework.transaction.annotation.Transactional;
@Service
public class PersonService {
@Autowired
private PersonRepository personRepository;
@Transactional
public void addRelationship(Long fromId, Long toId, String relationshipType) {
String cypher = String.format("MATCH (a:Person {id: %d}), (b:Person {id: %d}) " +
"MERGE (a)-[r:%s]->(b) " +
"RETURN r", fromId, toId, relationshipType);
personRepository.getNeo4jClient().query(cypher).run();
}
}
```
### Step 6: Creating a Controller
Create a controller to expose an endpoint for creating relationships.
**PersonController.java:**
```java
import org.springframework.beans.factory.annotation.Autowired;
import org.springframework.web.bind.annotation.*;
@RestController
@RequestMapping("/persons")
public class PersonController {
@Autowired
private PersonService personService;
@PostMapping("/{fromId}/relation/{toId}")
public void createRelationship(@PathVariable Long fromId,
@PathVariable Long toId,
@RequestParam String relationshipType) {
personService.addRelationship(fromId, toId, relationshipType);
}
}
```
### Step 7: Testing Your Implementation
To test the implementation, you can use tools like Postman or Curl to send a POST request to the endpoint.
**Example Request:**
```bash
POST http://localhost:8080/persons/1/relation/2?relationshipType=FRIEND
```
This request creates a `FRIEND` relationship between the nodes with IDs 1 and 2.
### Conclusion
By following these steps, you can dynamically create relationships with parametrized names in a Spring Boot application using Neo4j. This approach provides flexibility in managing complex and dynamic graph structures, making your application more adaptable to varying requirements.
#### Key Takeaways:
- Spring Boot and Neo4j integration is straightforward with Spring Data Neo4j.
- Custom Cypher queries allow for dynamic relationship creation.
- Using a service layer helps encapsulate business logic and promotes cleaner code architecture.
By leveraging these techniques, you can build powerful, flexible graph-based applications with Spring Boot and Neo4j. If you have any questions or need further assistance, feel free to leave a comment below. Happy coding! | fullstackjava |
1,872,126 | 10 Ideas For Getting Un-Stuck | I'm Well and Truly Stuck! I'm trying to embrace the "learning in public" ideal here on... | 0 | 2024-05-31T16:40:43 | https://dev.to/montyharper/10-ideas-for-getting-un-stuck-2m8e | beginners, programming, productivity | ## I'm Well and Truly Stuck!
I'm trying to embrace the "learning in public" ideal here on Dev, but I find it flies against my instincts. I tend to want to understand something really well first, then write about my learning process with some confidence. I want to present the story that I figured something out, and here's how I thought through it, and here's the correct conclusion I came to. You'll see that narrative in some of my previous articles.
Today I'm pushing myself to post what I'm doing right now. Which means I have to tell an incomplete story. I feel a bit vulnerable talking about how stuck I am, but hopefully this will be helpful to you as well as to myself.
## Stick with me...
In a moment I will type up a list of things to do when you're stuck. I'm reminding myself right now that I am capable of making a useful such list based on my life's experience as a songwriter, performer, teacher, and programming enthusiast - a list that will be helpful to all.
But first I want to actually do something I know I'll put on the list, which is to write about the problem. I'm doing this partly just to vent, partly to give you some context for why I'm writing this article, and mostly to try and help get myself unstuck.
## An Intractable Problem
I'm working on a challenge app in the [100DaysOfSwiftUI](https://www.hackingwithswift.com/100/swiftui) program by Paul Hudson, highly recommended for anyone interested in learning Swift.
In the app, the user can select a photo from the `PhotosPicker`, and a pointer to the data is stored as a `PhotosPickerItem`. Then an `.onChange(of: selectedItem)` triggers a sheet to open that displays the selected photo and asks the user to give it a title and description.
Mostly this works great, but when I run the app in the simulator, there's one photo that refuses to load in when you select it. The sheet opens with the message "no photo to display," which I have programmed it to do when the value of the selected photo is `nil`.
However - and here's the baffling bit - the selected photo should never be `nil` if the sheet is open because the property that triggers the sheet to open, `isDisplayingNewPhoto`, is a `Bool`, set to `(newPhoto != nil)`. To state this again in plain language: The sheet can only open if the photo is not empty, yet the sheet is displaying the empty case for the photo.
I'm leaving out a bit of detail, which involves loading the data for the photo. The `PhotosPickerItem` is just a pointer to some data, which has to be loaded into an `Image` property before it can be displayed as a photo.
I suspect the problem is with timing; the particular image I'm struggling with is larger than the ones that work fine. Maybe by the time the sheet opens, the image hasn't loaded in yet. But then why is the sheet triggered to open at all? And also I'm using the async/await pattern that supposedly handles the time-consuming process of loading data so it will be present when needed.
I've tried every variation I can think of, switching the order of things around, and while different approaches all work generally, they also all fail in the same way with this one photo.
Now is a good time to share this meme, thanks to @avanichols, who posted it for this week's [Meme Monday](https://dev.to/ben/meme-monday-4l95). I may be sitting near the top of this bell curve. I'm not ready to say I've uncovered a bug, because I'm probably doing something wrong, but maybe??
## What To Do When You're Well and Truly Stuck!!
Okay, here's the list I promised you...
### 1. Write about the problem.
Explaining it carefully to yourself on paper can be clarifying.
### 2. Phone a friend.
Maybe you're too used to looking at your own code to see the problem. Get a fresh pair of eyes on it. Your friend may see some obvious thing you're missing or some assumption you've made that you aren't aware of.
### 3. Ask AI.
Sometimes Chat GPT can suggest a solution you haven't tried yet. Try asking your question in multiple different ways, from general to specific, with and without context. Try asking it to do different associated tasks: you can ask it to write code, review your code, or brainstorm different ways to solve a given problem. (Always keep in mind the fact that Chat GPT's personality doesn't allow it to just say "I don't know," which sometimes leads to unhelpful responses.)
### 4. Read the documentation.
Look up every relevant bit of code to make sure you know how it's supposed to work and what your options are. As shocking as this may sound, sometimes the official documentation is helpful.
### 5. Post to an online discussion.
Maybe others have dealt with the same problem. It's helpful to isolate the issue first, and post some code just illustrating the problem, rather than posting your entire app. The process of isolating the problem may even shake loose a solution on its own! I'll make that a separate bullet point...
### 6. Try to isolate the problem with fresh code.
Starting from scratch, write the simplest app you can to re-create the problem, and see if you can solve it in that simplified context.
### 7. Take a different approach.
Maybe the code isn't designed to do what you're trying to do. There may be forty ways to code a solution, but there are also forty solutions to the bigger problem. What if you go back to the ultimate goal of your app and take a completely different approach to accomplishing it? A little brainstorming can get you going in a whole new direction.
### 8. Work on different code.
This is one I need to listen to myself. Maybe the problem is unsolvable. Maybe the solution is obvious and you're just not seeing it. Either way, after you've spent a reasonable amount of time on it, move on to something else for a while. Start the next lesson. Taking in new, seemingly unrelated information can sometimes lead to a solution.
### 9. _Do_ something else entirely.
Like take a walk, take a shower, do the dishes. Any task that involves your body but not your mind can loosen up those thoughts and help a solution pop into your head. Try not to think about it directly. Just let your brain crank away in the background.
### 10. Don't be too picky.
I always like to think I should be able to make the code do exactly what I want. But maybe I just don't have the required skills yet, or maybe I'm asking the impossible. In my particular case (as described above), if I try to load the same image a second time, it works. To me, this isn't a very satisfying solution, asking the user to do a thing twice before it works. But I need to keep in mind the bigger picture - I'm coding this app to learn, and while I'm well and truly stuck, I'm not learning. So sometimes maybe good enough is good enough for now.
### Bonus. Have faith and patience.
Millions before you have learned to code. Millions before you have written apps that do something similar to what you're trying to do. You're as smart as they are. You'll figure it out, too.
## Out of ideas
I managed to come up with a few items I haven't tried yet, so hopefully my list will help. I hope it helps you as well!
What have I left off? What do _you_ do when _you're_ stuck? Please add your thoughts in the comments!!
| montyharper |
1,872,287 | Decorating with React and TypeScript | Hello! Have you been searching article after article, post after post, looking for a way to pass a... | 0 | 2024-05-31T16:38:20 | https://dev.to/abglassford/decorating-with-react-and-typescript-237p | react, typescript, designpatterns, webdev | Hello!
Have you been searching article after article, post after post, looking for a way to pass a React component as a prop to another component?
Me neither.
In fact, I think I've read all of the articles regarding that topic that are available on the internet... but that's not what I've been searching for.
And that's what keeps coming up when I search for things like:
- "React component composition"
- "How to pass an un-rendered component as a prop so I can render it later"
- "How to apply props to a component passed in as a prop"
- "Pass a component as props and pass its props as props and render that component inside another component with those props"
I should add that this is all to be done in TypeScript.
Here's my description of what I wanted to do:
_Create a react component that is able to accept another component as a prop, and then render that component around it's own contents._
The reason that I want to do this is so that I can wrap a container component (A) around another component (B) and allow A to be able to access state and props that exist within B.
From what I understand, this is similar to the **Decorator Pattern**... or it just _is_ a **Decorator Pattern**...
Make sense?
Let's look:
```tsx
const Decorator = ({
title,
footer,
children,
}: PropsWithChildren<{ title: string; footer: string }>) => {
return (
<div>
<h1>{title}</h1>
<div>{children}</div>
<span>{footer}</span>
</div>
);
};
```
Above we have a very simple component that we'll name `Decorator`. This is the component that I will want to use to wrap or _decorate_ another component
```tsx
const Decorated = <T,>(props: {
Decorator?: ComponentType<T>;
decoratorProps?: T;
}) => {
const { Decorator, decoratorProps } = props;
const renderStuff = () => (
<div>
<h1>Decorated</h1>
</div>
);
return Decorator ? (
<Decorator {...(decoratorProps)}>{renderStuff()}</Decorator>
) : (
renderStuff()
);
};
```
The `Decorated` component will take in two props: `Decorator`, a component, and `decoratorProps` which will be the props of the `Decorator` component.
If you're in your IDE with the TS compiler running, you should see that there is an issue with the instantiation of `Decorator`:
```
Type '{ children: Element; }' is not assignable to type 'T'.
'T' could be instantiated with an arbitrary type which could be unrelated to '{ children: Element; }'.typescript(2322)
```
I am not a TypeScript wizard, but it looks to me like `Decorator` is mad that it's receiving children or something. I'm not going to run you through all the attempts I made before getting to a viable solution that doesn't just ignore this rule, but know that there were many. What I finally landed on was this:
```tsx
<Decorator {...(decoratorProps as T)}>{renderStuff()}</Decorator>
```
Typecasting `decoratorProps` to `T` solves all my problems... alright, not all of them, but enough of them for me to move past this task.
Here's an example of the implementation:
```tsx
const Decorated = <T,>(props: {
Decorator?: ComponentType<T>;
decoratorProps?: T;
}) => {
const { Decorator, decoratorProps } = props;
const renderStuff = () => (
<div>
<h1>Decorated</h1>
</div>
);
return Decorator ? (
<Decorator {...(decoratorProps as T)}>{renderStuff()}</Decorator>
) : (
renderStuff()
);
};
const DecoratorOne = ({
title,
footer,
children,
}: PropsWithChildren<{ title: string; footer: string }>) => {
return (
<div>
<h1>{title}</h1>
<div>{children}</div>
<span>{footer}</span>
</div>
);
};
const DecoratorTwo = ({
title,
footer,
children,
article,
}: PropsWithChildren<{ title: string; footer: string; article: string }>) => {
return (
<div>
<h1>{title}</h1>
<div>{children}</div>
<div>{article}</div>
<span>{footer}</span>
</div>
);
};
export default function App() {
return (
<div className="App">
<Decorated />
<Wrapper
Decorator={DecoratorOne}
decoratorProps={{
title: "DECORATOR ONE",
footer: "ONE FOOT",
}}
/>
<Wrapper
Decorator={DecoratorTwo}
decoratorProps={{
title: "DECORATOR TWO",
footer: "TWO FOOT",
article: "this is an article",
}}
/>
</div>
);
}
```
And [here](https://codesandbox.io/p/sandbox/decorator-m2ts5p?layout=%257B%2522sidebarPanel%2522%253A%2522EXPLORER%2522%252C%2522rootPanelGroup%2522%253A%257B%2522direction%2522%253A%2522horizontal%2522%252C%2522contentType%2522%253A%2522UNKNOWN%2522%252C%2522type%2522%253A%2522PANEL_GROUP%2522%252C%2522id%2522%253A%2522ROOT_LAYOUT%2522%252C%2522panels%2522%253A%255B%257B%2522type%2522%253A%2522PANEL_GROUP%2522%252C%2522contentType%2522%253A%2522UNKNOWN%2522%252C%2522direction%2522%253A%2522vertical%2522%252C%2522id%2522%253A%2522clwuuyep800062v6ej5083sqy%2522%252C%2522sizes%2522%253A%255B100%252C0%255D%252C%2522panels%2522%253A%255B%257B%2522type%2522%253A%2522PANEL_GROUP%2522%252C%2522contentType%2522%253A%2522EDITOR%2522%252C%2522direction%2522%253A%2522horizontal%2522%252C%2522id%2522%253A%2522EDITOR%2522%252C%2522panels%2522%253A%255B%257B%2522type%2522%253A%2522PANEL%2522%252C%2522contentType%2522%253A%2522EDITOR%2522%252C%2522id%2522%253A%2522clwuuyep700022v6ebl6eiv6s%2522%257D%255D%257D%252C%257B%2522type%2522%253A%2522PANEL_GROUP%2522%252C%2522contentType%2522%253A%2522SHELLS%2522%252C%2522direction%2522%253A%2522horizontal%2522%252C%2522id%2522%253A%2522SHELLS%2522%252C%2522panels%2522%253A%255B%257B%2522type%2522%253A%2522PANEL%2522%252C%2522contentType%2522%253A%2522SHELLS%2522%252C%2522id%2522%253A%2522clwuuyep800032v6enwfcgsmw%2522%257D%255D%252C%2522sizes%2522%253A%255B100%255D%257D%255D%257D%252C%257B%2522type%2522%253A%2522PANEL_GROUP%2522%252C%2522contentType%2522%253A%2522DEVTOOLS%2522%252C%2522direction%2522%253A%2522vertical%2522%252C%2522id%2522%253A%2522DEVTOOLS%2522%252C%2522panels%2522%253A%255B%257B%2522type%2522%253A%2522PANEL%2522%252C%2522contentType%2522%253A%2522DEVTOOLS%2522%252C%2522id%2522%253A%2522clwuuyep800052v6eldxazdtf%2522%257D%255D%252C%2522sizes%2522%253A%255B100%255D%257D%255D%252C%2522sizes%2522%253A%255B57.16005189242297%252C42.83994810757703%255D%257D%252C%2522tabbedPanels%2522%253A%257B%2522clwuuyep700022v6ebl6eiv6s%2522%253A%257B%2522tabs%2522%253A%255B%257B%2522id%2522%253A%2522clwuuyep600012v6ehot3dsdc%2522%252C%2522mode%2522%253A%2522permanent%2522%252C%2522type%2522%253A%2522FILE%2522%252C%2522filepath%2522%253A%2522%252Fsrc%252Findex.tsx%2522%257D%255D%252C%2522id%2522%253A%2522clwuuyep700022v6ebl6eiv6s%2522%252C%2522activeTabId%2522%253A%2522clwuuyep600012v6ehot3dsdc%2522%257D%252C%2522clwuuyep800052v6eldxazdtf%2522%253A%257B%2522tabs%2522%253A%255B%257B%2522id%2522%253A%2522clwuuyep800042v6elg5hs9zu%2522%252C%2522mode%2522%253A%2522permanent%2522%252C%2522type%2522%253A%2522UNASSIGNED_PORT%2522%252C%2522port%2522%253A0%252C%2522path%2522%253A%2522%252F%2522%257D%255D%252C%2522id%2522%253A%2522clwuuyep800052v6eldxazdtf%2522%252C%2522activeTabId%2522%253A%2522clwuuyep800042v6elg5hs9zu%2522%257D%252C%2522clwuuyep800032v6enwfcgsmw%2522%253A%257B%2522tabs%2522%253A%255B%255D%252C%2522id%2522%253A%2522clwuuyep800032v6enwfcgsmw%2522%257D%257D%252C%2522showDevtools%2522%253Atrue%252C%2522showShells%2522%253Afalse%252C%2522showSidebar%2522%253Atrue%252C%2522sidebarPanelSize%2522%253A15%257D) is a link to a sandbox where you can play around!
I know I didn't go into why what's happening is happening, but I hope that if you, the reader, have input or knowledge to share, you will! In the meantime, here's a way to implement a Decorator Pattern with React and Typescript! | abglassford |
1,872,208 | How to secure a WordPress site: auditing and monitoring tools | WordPress is the most popular content management system, so it also suffers the most attacks. In... | 0 | 2024-05-31T16:32:11 | https://dev.to/ispmanager/how-to-secure-a-wordpress-site-auditing-and-monitoring-tools-4ba9 | tutorial, linux, security, wordpress | WordPress is the most popular content management system, so it also suffers the most attacks. In this article, we’ll analyze the security tools for monitoring and protecting your WordPress site.
### Tools to monitor changes to your Linux file system
You can detect unauthorized or suspicious activity in your Linux file system by monitoring changes to files and directories.
**The tools you need:**
**AIDE (Advanced Intrusion Detection Environment)** is an open-source tool for intrusion detection. The program creates a database of file hash sums and attributes, and then regularly checks the file system against that database.
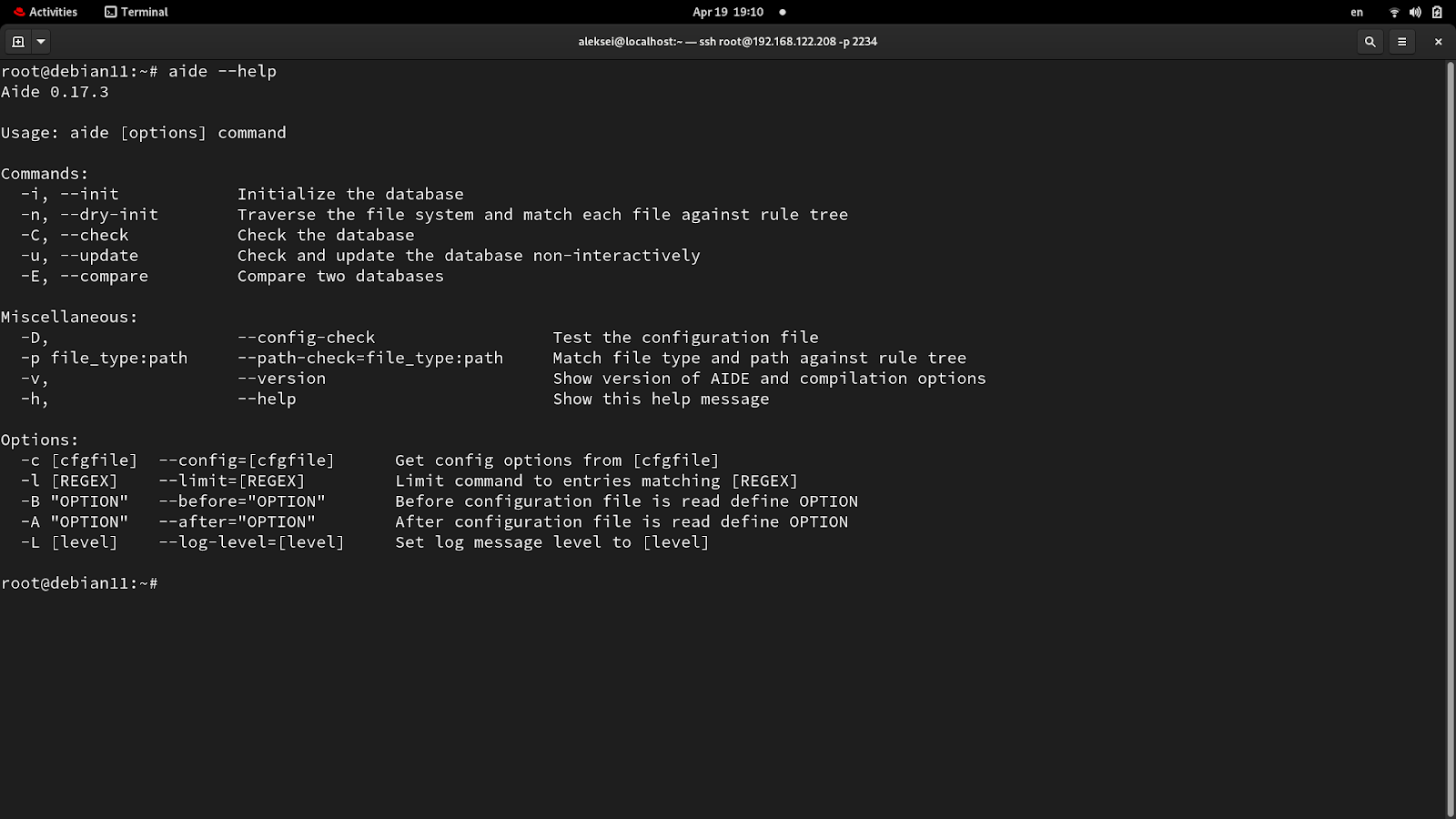
**Tripwire** is a popular intrusion detection tool. It works similarly to AIDE, by creating a database of file and directory characteristics and then checking them for changes.
**Auditd (Linux Audit System)** tracks and records security events and changes to the file system. The program provides detailed logs for you to analyze to identify suspicious actions.
**Inotify** is a Linux kernel mechanism for checking for changes in real-time. The program is used to monitor, create, delete, and modify files and directories. Inotify is often used by applications and scripts to automate tasks related to file changes.
The programs above are similar but have different functionality. For example, Auditd and Inotify are great for monitoring system activity, while AIDE and Tripwire are more for intrusion detection.
Here are the main differences between AIDE and Tripwire.
**Tripwire.** Developed in the early 1990s and was originally open source software, but later closed features were added, plus support, so it became a commercial product. Advanced management capabilities, integrated with different platforms, comes with professional support. Easy to set up and use with its simple interface and support.
Requires more knowledge, better for advanced users.
**AIDE.** Created as a free alternative to Tripwire, completely free and open source. Basic detection of changes; requires manual configuration. Requires more knowledge, better for advanced users.
## Wazuh and Lynis: tools for security monitoring
There are many security scanning programs on the market. For example, Nessus scans for vulnerabilities, Suricata is an intrusion detection system, and Fail2ban prevents brute-force attacks and attempts to break in by mining keys or encryption passwords. Let me tell you which ones I would choose and why.
**Wazuh and Lynis:**
▪️ Designed specifically for system security and auditing. Wazuh transmits real-time data, detects intrusions, and manages logs and configuration. Lynis scans for OS vulnerabilities.
▪️ Open source code, you can fix bugs and improve functionality yourself.
▪️ Flexible customization. Both can easily be customized for different operating systems and environments. They are suitable for different IT structures, from small businesses to large corporations.
▪️ They are compliant with PCI DSS, HIPAA, NIST, and other security standards.
**To use Wazuh and Lynis, you must:**
▪️ Understand bug management systems and package change logs.
▪️ Properly integrate data from different sources to establish a holistic picture.
▪️ Understand cybersecurity and compliance standards.
▪️ Update them regularly: keep track of new patches and fixes.
Let's break down the differences between Wazuh and Lynis in more detail.
**Lynis** is a scanning tool for Unix-like operating systems including Linux and macOS. Lynis analyzes your system configuration, installed software, and any weaknesses. It then gives security recommendations.
It looks like this:
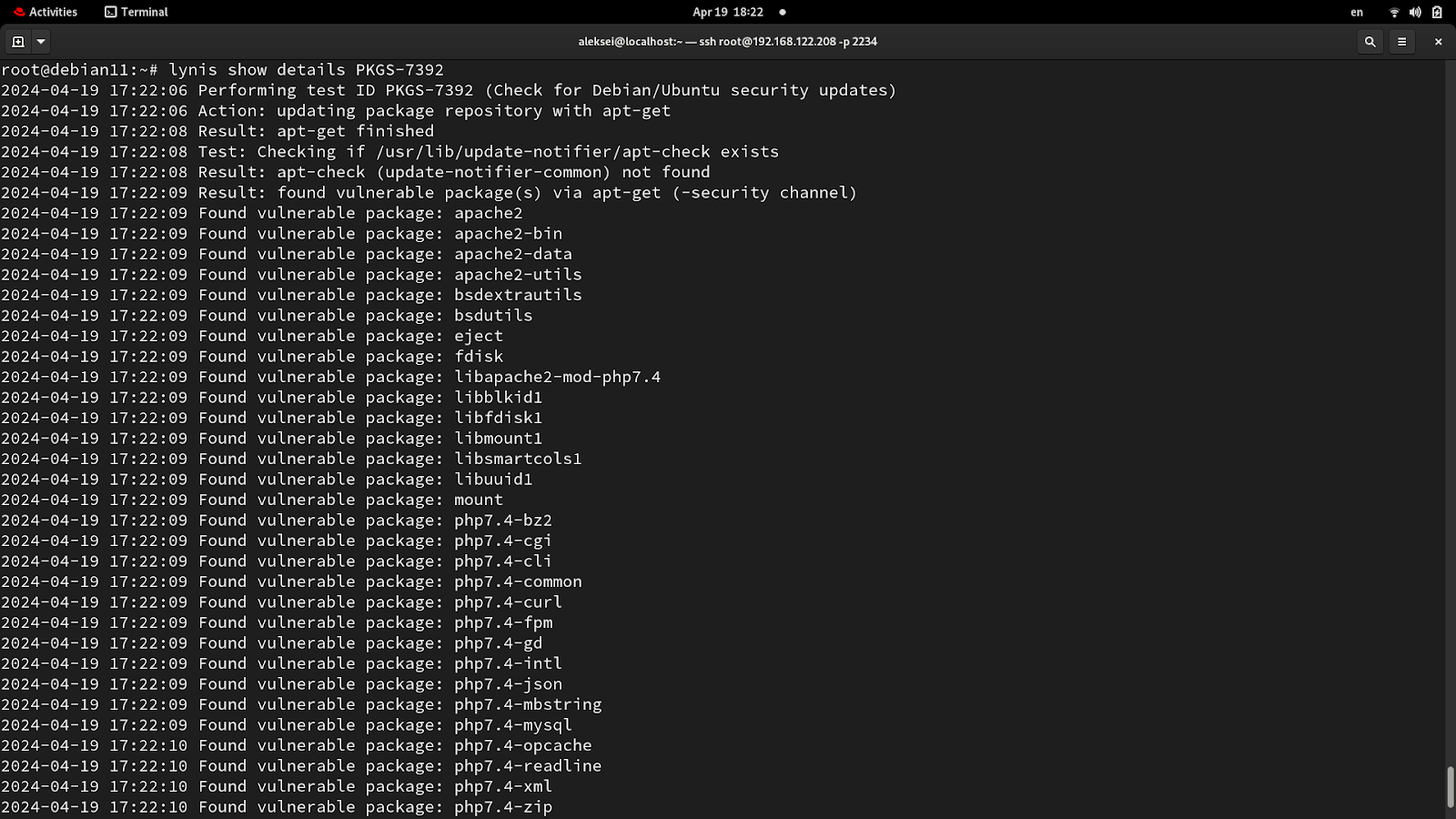
To better understand how to work with Lynis, see the [official documentation](https://cisofy.com/docs/).
**Wazuh** is a user-friendly option that manages incidents and monitors threats in real-time. Wazuh integrates various tools: log analysis, intrusion detection, security auditing, and system health monitoring.
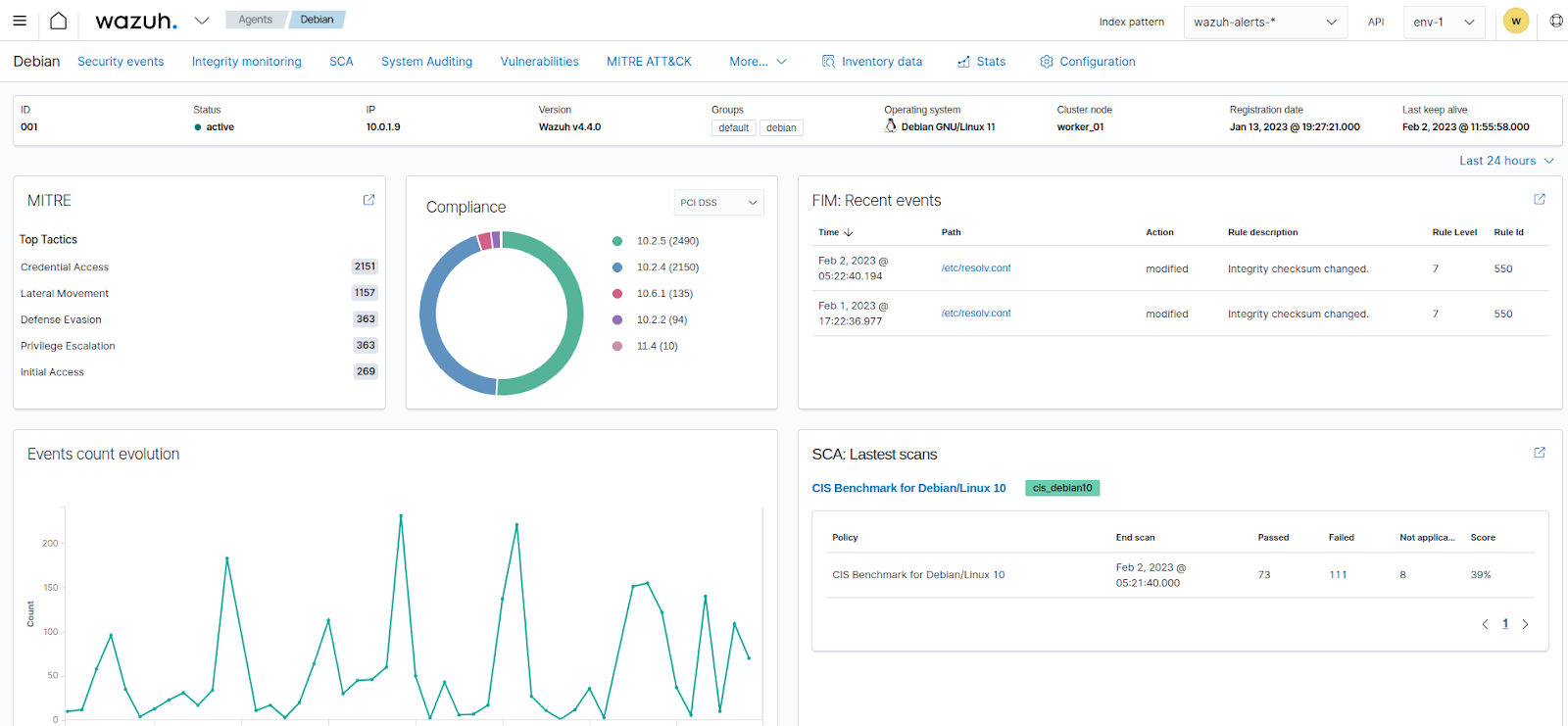
I configured Debian 11 based on a security audit from Lynis. Testing showed that a decent level of security was achieved:
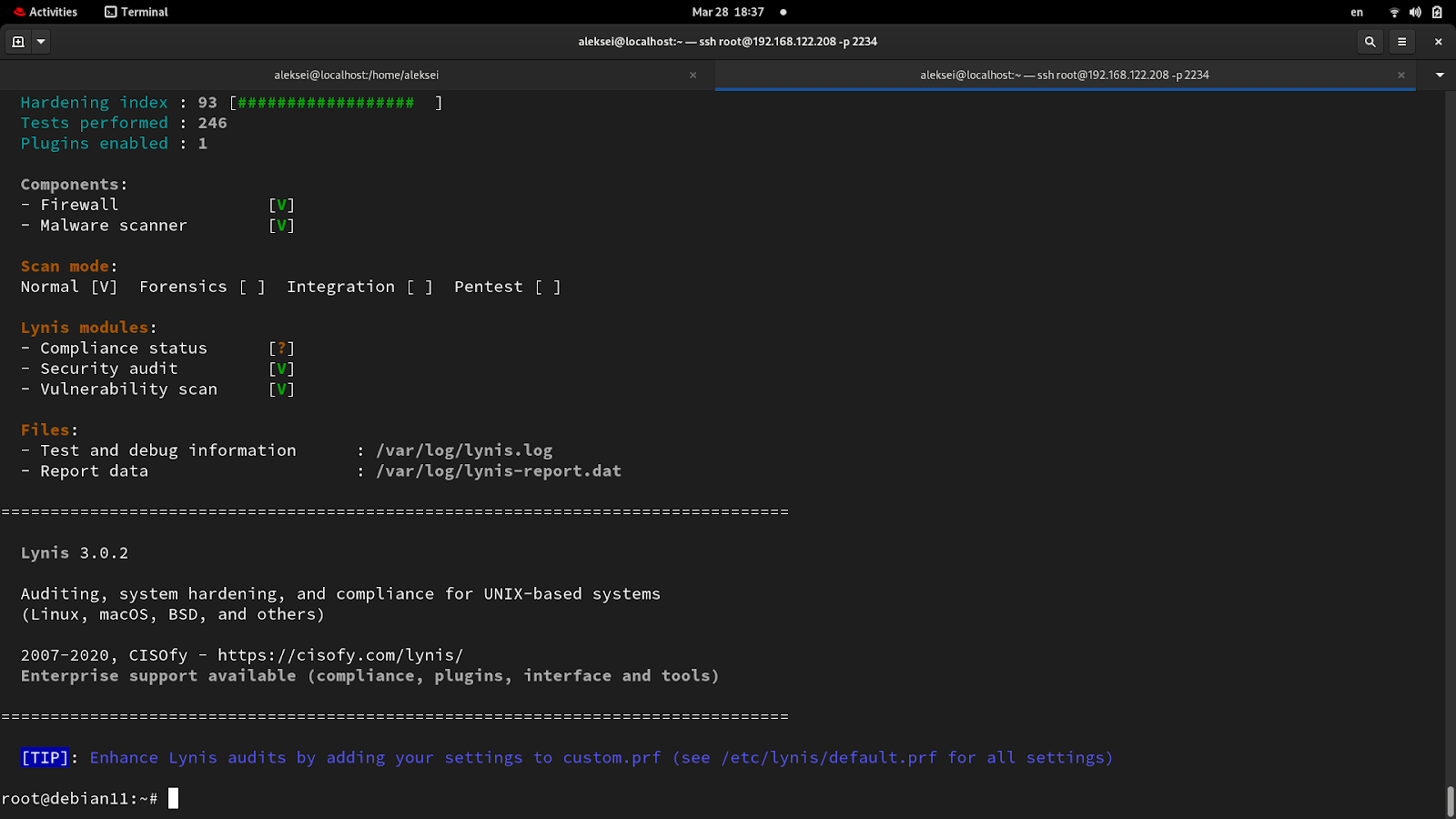
_An overall security audit. You can get to 98%-100%, but it may affect system functionality, e.g., cron will stop working_
For a more in-depth analysis, view the detailed results by scrolling up in the terminal.
Lynis is a console utility, while Wazuh has a broader feature set thanks to its modular architecture. Therefore, with Wazuh, it's easier to customize and scale your security, install modules for specific tasks, and integrate them into your existing infrastructure. That's why I use Wazuh.
**What modular architecture offers:**
**Install only the modules you need.** Make your system meet your own security requirements and monitoring standards.
**Ease of integration** with SIEM systems and other platforms, for example, to extend Wazuh’s functionality.
**Independent upgrades** simplify maintenance and reduce the risks of system-wide upgrades. New features can be implemented locally and patched without disrupting your business.
**Specialization.** For example, one module analyzes logs, another module monitors file integrity, and a third module detects intrusions and collects and processes data.
**System load control** means you can load only the required modules.
## Malware scanning services
**Dr.Web** is an integrated antivirus solution for protecting websites and mailboxes on hosting servers managed with the ispmanager panel.
It offers:
Automatic scanning of files and emails for malicious code in PHP, JS,
- HTML, and system files;
- fixing of infected files.
You can learn more about how to set up and use Dr.Web in the [ispmanager documentation → ](https://www.ispmanager.com/docs/ispmanager/doctor-web)
**ImunifyAV** (formerly Revisium) is an antivirus program for detecting malware on websites and removing it. ImunifyAV automatically scans files for known threats and helps recover infected files.
Since the sanctions were imposed, the paid version of ImunifyAV is no longer available in the ispmanager control panel and only the malware search mode remains. Detailed information on configuring and using ImunifyAV can be found in the official [ispmanager documentation →](https://www.ispmanager.com/docs/ispmanager/integration-with-imunifyav)
## WPScan: check your site for vulnerabilities
WPScan checks your site for problems such as weak passwords or insecure plugins and themes. WPScan relies on a database of known vulnerabilities and will automatically detect WordPress versions with potential problems.
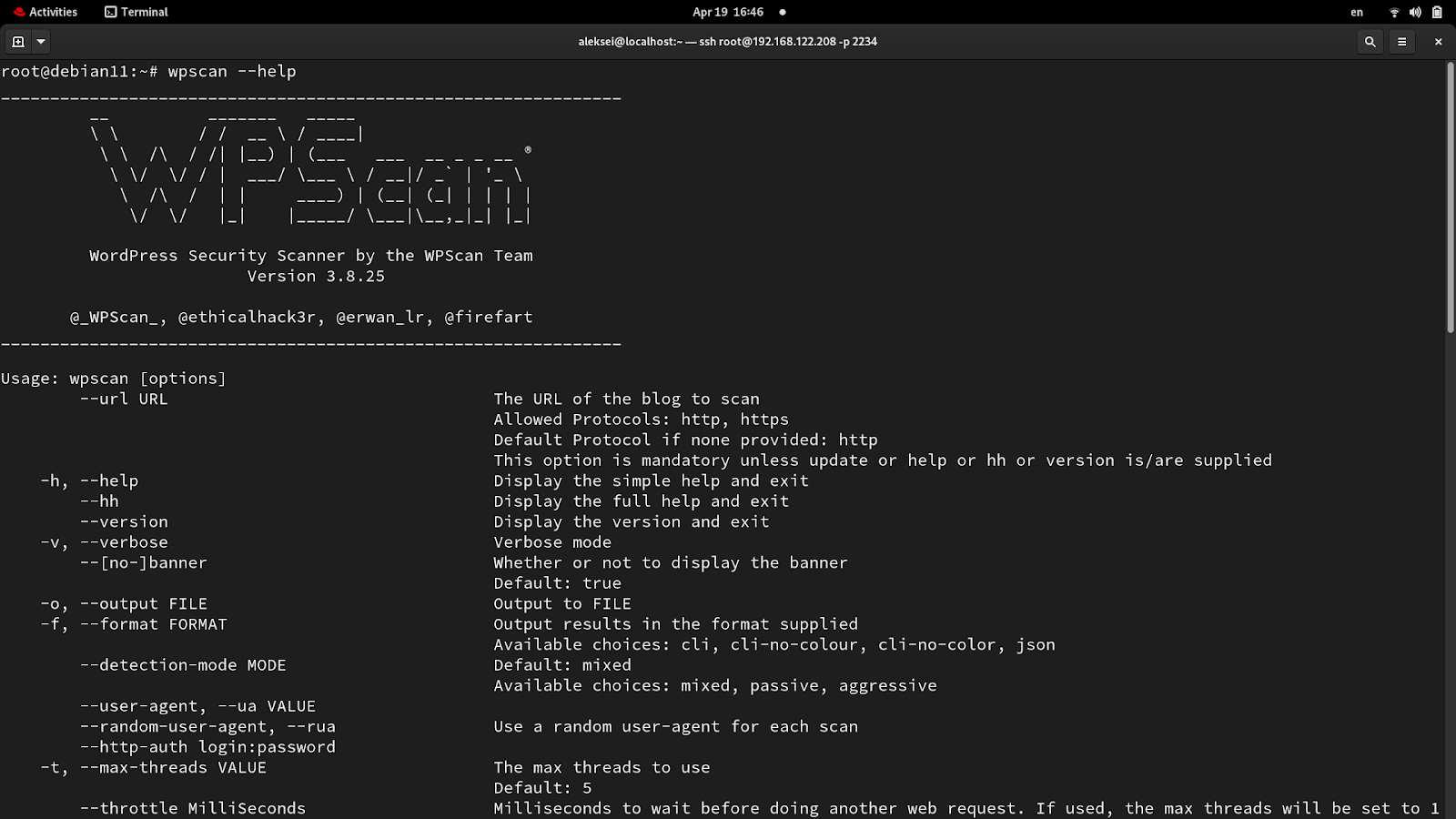
With WPScan, site admins can identify and remediate vulnerabilities before attackers exploit them.
**How to scan a WordPress site with WPScan:**
1. Install Ruby: it’s almost always in your Linux distro’s repositories.
`sudo apt install ruby`
2. Install the dependencies to build extensions:
`sudo apt install build-essential libcurl4-openssl-dev libxml2 libxml2-dev libxslt1-dev ruby-dev libgmp-dev zlib1g-dev`
3. Install WPScan:
`sudo gem install wpscan`
For more information on installing WPScan, see the [official documentation →](https://wpscan.com/blog/wpscan-user-documentation/).
**Examples of commands for different types of scanning:**
- Basic Scan: the team runs a scan of example.com to determine whether there are any known vulnerabilities in WordPress, plugins, and themes:
`wpscan --url https://example.com`
- Lists and checks installed plugins for known vulnerabilities:
`wpscan --url https://example.com --enumerate p`
- Lists installed themes:
`wpscan --url https://example.com --enumerate t`
- Get a list of WordPress users:
`wpscan --url https://example.com --enumerate u`
- Check for configuration files and backups:
`wpscan --url https://example.com --enumerate ap,at,ab,ar,au`
- Full scan: check for vulnerabilities in vp (plugins), vt (themes), u (users) and m (media files):
`wpscan --url https://example.com -e vp,vt,u,m`
**Important:** Active site scanning may be perceived as malicious activity. Before running WPScan, make sure you have permission to scan the site.
## Wordfence plugin: WordPress protection
Wordfence is one of the most powerful tools for protecting WordPress websites. I recommend it because the plugin’s signature database is constantly updated meaning Wordfence promptly recognizes and blocks malware.
Here are a few more reasons why I like Wordfence:
**Its large set of security features:** an application-level firewall, a security scanner, intrusion detection, and prevention tools. It protects against malicious bots, viruses, SQL injection, cross-site scripting, and XSS.
**Its firewall rules are updated in real-time**. As soon as the plug-in finds a threat, info about it is immediately distributed to all Wordfence users. This feature comes with the Premium version.
**It’s easy to use:** the interface and setup are so intuitive that even a novice can handle it.
**Offers detailed access and attack logs:** site admins can track suspicious activity and respond quickly.
## Regular system updates
Commands for upgrading Debian:
Updating the package list:
`sudo apt update`
Update installed packages:
`sudo apt upgrade`
System Upgrade:
`sudo apt full-upgrade`
Clearing unused packages:
`sudo apt autoremove`
System reboot:
`sudo reboot `
`sudo shutdown -r now`
## How to automatically update packages [in ispmanager](https://www.ispmanager.com/docs/ispmanager/upgrade)
Automatic software updates are a useful feature, but not in every situation.
**Pros:**
▪️ Linux distro and server software security. Updates often include patches that are vital for the OS, server, or anti-virus software.
▪️ Stable software.
▪️ Bug fixes in service packs.
▪️ Quickly update Linux distro packages and server software.
**Cons:**
▪️ Incompatibility: an update may contain changes that do not work with specific programs or custom settings. Crashes or difficulty accessing sites may result.
▪️ Degraded performance. When updates are applied to multiple servers at once, network congestion or slowdowns can occur.
▪️ Errors and bugs. New software versions may contain hidden bugs, which we discover only after the update.
**Important:** If you use automatic software updates on large hosting platforms or servers, unexpected failures can happen during a sudden spike in load.
**Recommended:**
Test all managed and controlled upgrade processes: run them in a controlled environment before applying them to production servers. This keeps all servers protected and up to date.
**What is the difference between managed and controlled renewal processes:**
**Managed** updates run automatically on a schedule, without administrator intervention. The human factor plays no role, so it is less customizable.
**Controlled** updates are run, monitored, and verified by an administrator. This lets you control the process and consequences of the updates but requires more experience.
**Here's how to configure automatic updates in ispmanager:**
Go to Settings → System Settings.
Find the "Update software automatically" option.
Select "Update all system packages" from the drop-down list.
Click "Save".
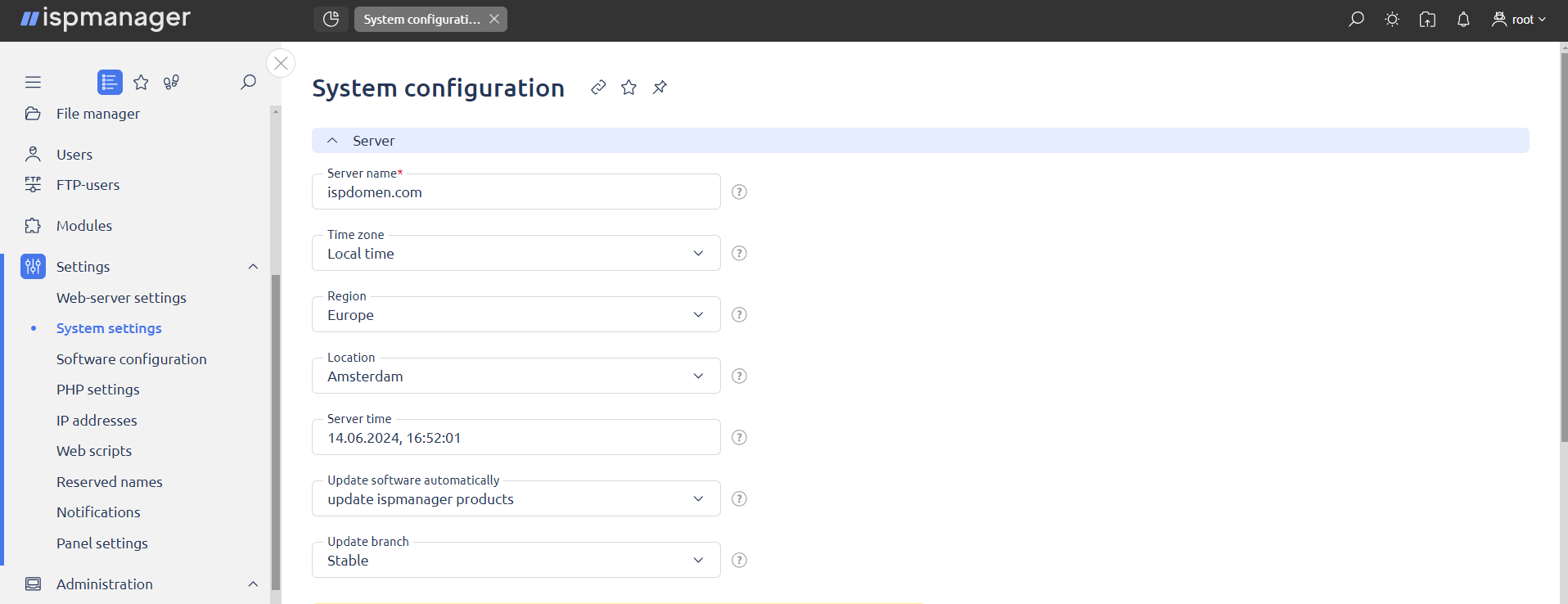
## How to protect a WordPress site and what tools to use in brief
- Check for changes in the Linux file system. AIDE, Tripwire, Auditd, and Inotify can do this. AIDE and Tripwire are for detecting unauthorized changes, Auditd and Inotify are for monitoring and auditing system activity.
- The Wordfence plugin is one of the most powerful tools for protecting WordPress sites. It promptly recognizes and reports SQL injections, XSS attacks, and malware.
- Wazuh and Lynis are great for security monitoring: Wazuh provides intrusion detection and log and configuration management. Lynis is a tool for auditing Linux distros and server software.
- Check your site for malware with Dr.Web or ImunifyAV.
- WPScan detects vulnerable WordPress versions and plugins with potential issues and notifies the site admin.
- Update your system, server software, kernel, and site plugins regularly. Test your upgrade processes before applying them to production servers: perform each upgrade in a controlled environment.
Of course, these are not the only ways to secure a WordPress site. [In a previous article](https://dev.to/ispmanager/how-to-secure-a-wordpress-site-with-linux-debian-29c1), I described how to secure server software or an internet project using AppArmor.
The next articles are on:
- Configuring Nginx ModSecurity (WAF).
- BitNinja customization. The platform's modules include a WAF and AI scanner. It specializes in protection against SQL injection, XSS, viruses, DoS, and the use of web forms for spam attacks.
- Customizing your system as per a Lynis audit.
- Finalizing your security settings using whitelists.
Want more articles like this? Subscribe to [our newsletter](https://9ce5ba7f.sibforms.com/serve/MUIFADo9TWiTfGbIQS2_6jvU1if3z-K6845WSmXxJOUoLHCEFzrofp-PTPVqQiNhh2Di3xDLMXG-lVfMoRRPkDt64Z_DwSm2yQPIkQVACt--A3R7My3LQnbONtZ7W4W6uaj0ramr9JLDJ3reMAmf7z-lS16D4qAfrlYcD5GUhGNfqfIi0YKkqO5niM7X6TRjUBll72vLzapyY_by)
| ispmanager_com |
1,872,283 | This is my first post | This is my first post to see what it looks like | 0 | 2024-05-31T16:27:49 | https://dev.to/jam3sperkins/this-is-my-first-post-2mln | This is my first post to see what it looks like | jam3sperkins | |
1,872,209 | HOW TO CONNECT AN INTERNET OF THINGS (IoT) TO RASPBERRY PI SIMULATOR IN AZURE CLOUD THROUGH IoT HUB FOR COMMUNICATION AND DATA | WHAT IS INTERNET OF THINGS? The Internet of Things (IoT) refers to the network of physical objects... | 0 | 2024-05-31T16:26:56 | https://dev.to/latoniw/how-to-connect-an-internet-of-things-iot-to-raspberry-pi-simulator-in-azure-cloud-through-iot-hub-for-communication-and-data-7ek | learning, cloud, azure, github | **WHAT IS INTERNET OF THINGS?**
The Internet of Things (IoT) refers to the network of physical objects ("things") embedded with sensors, software, and other technologies that enable them to connect and exchange data with other devices and systems over the internet. These connected devices can range from simple household appliances to complex industrial machinery.
**WHAT IS RASPBERRY PI SIMULATOR?**
A Raspberry Pi Simulator is a software tool that emulates the behavior of a Raspberry Pi computer on a different hardware platform, such as a regular desktop or laptop computer. It allows developers to test and run Raspberry Pi applications and projects without needing physical Raspberry Pi hardware.
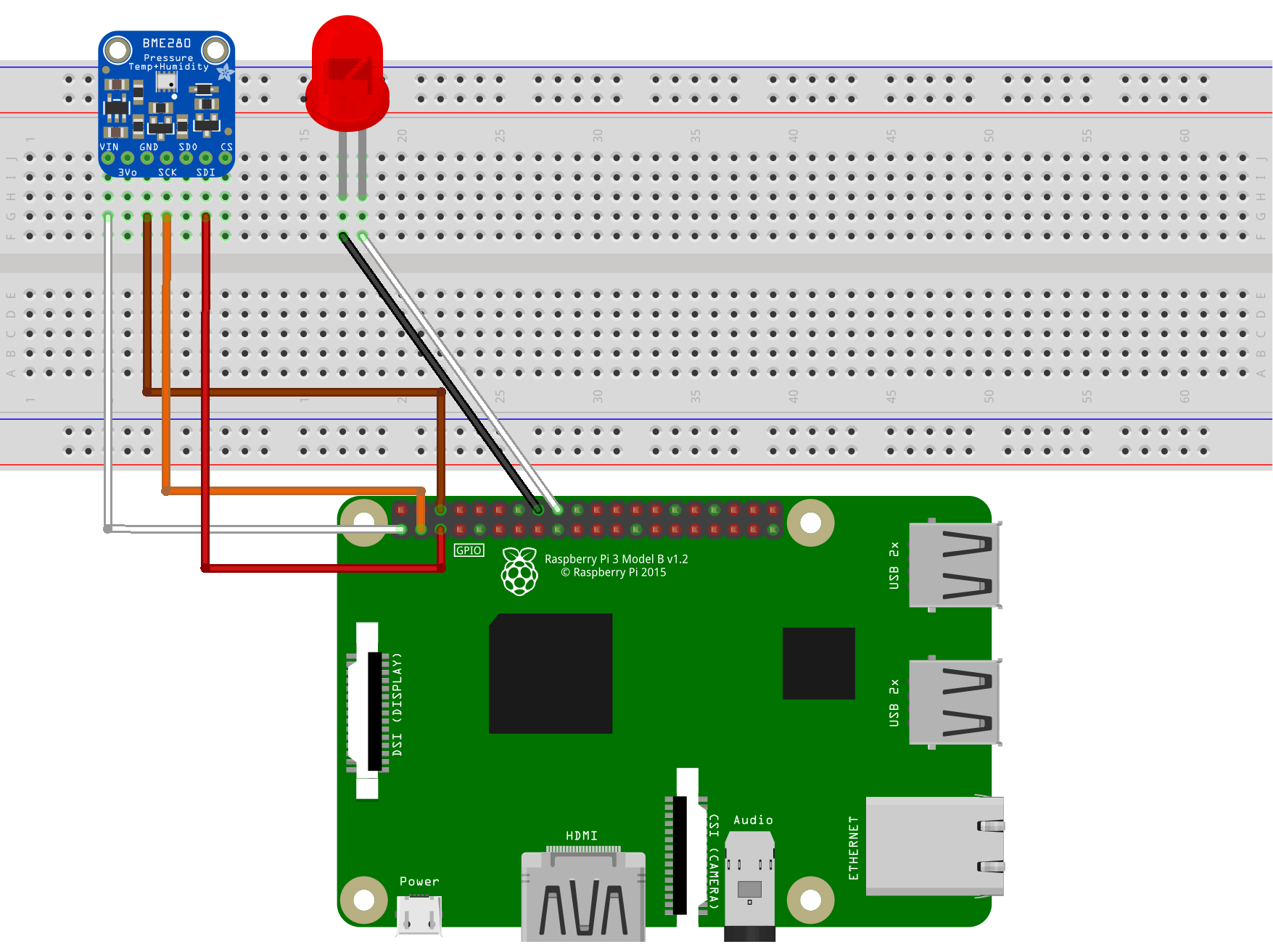
Creating an IoT (Internet of Things) solution on Azure involves several steps, including setting up IoT Hub, registering devices, sending telemetry data, and processing data. Here's a step-by-step guide
**STEP: 1**
Create an Azure Account at https://azure.microsoft.com/ and login to Azure Portal (https://portal.azure.com/)
Click on "Create a resource" and search for "IoT Hub"
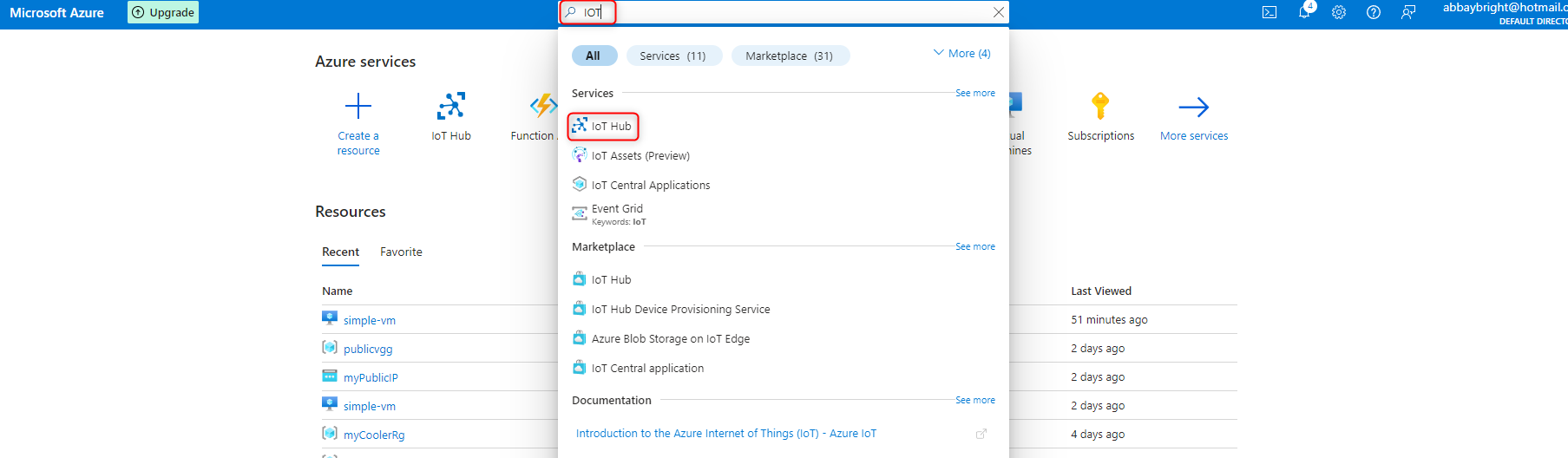
**STEP: 2**: Click on the Create Icon
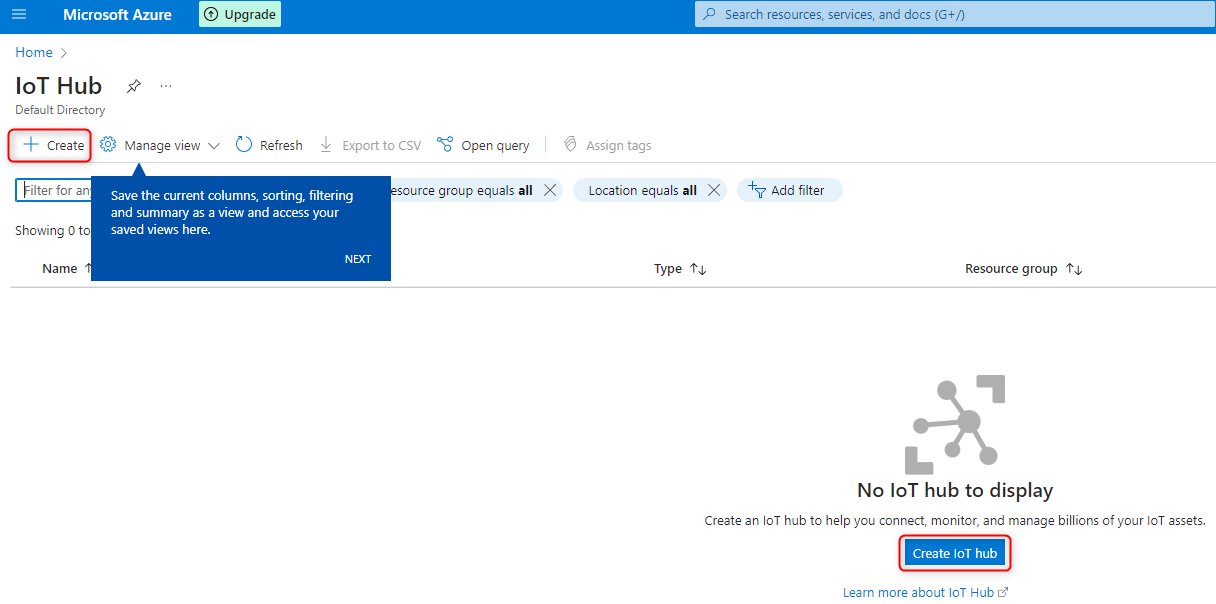
**STEP: 3** Fill in the required information, such as subscription, resource group, region, IoT Hub name, then click on Review and Create tab after filling the necessary field appropriately.
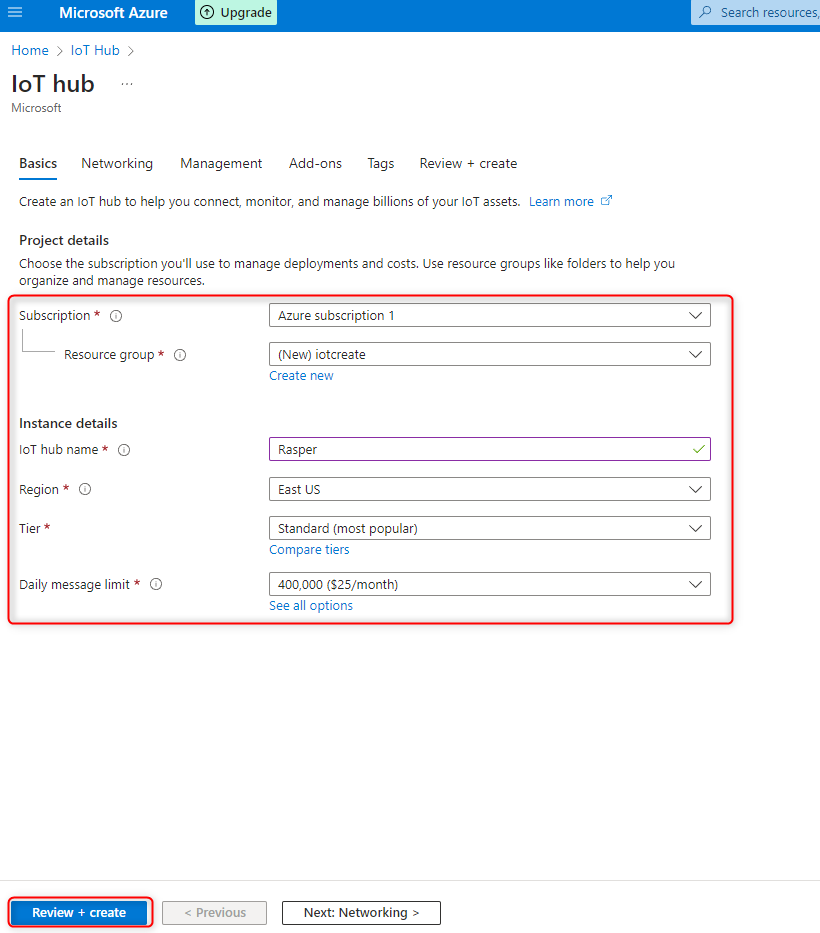
**STEP: 4** In the following page click on "Create" tab to provision the IoT Hub.
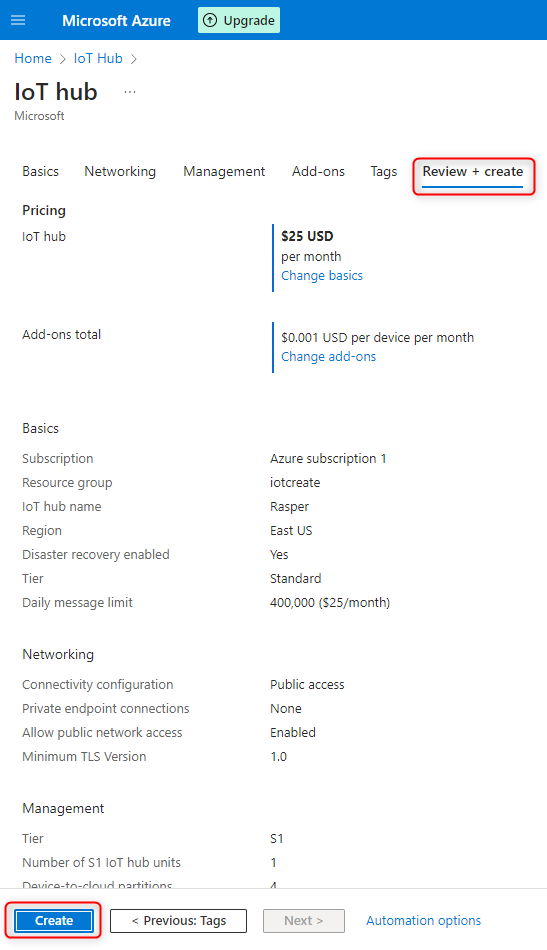
**STEP: 5** Wait for deployment to be completed, the deployment may take some minutes. After the deployment, click on "Go to Resource" to explore
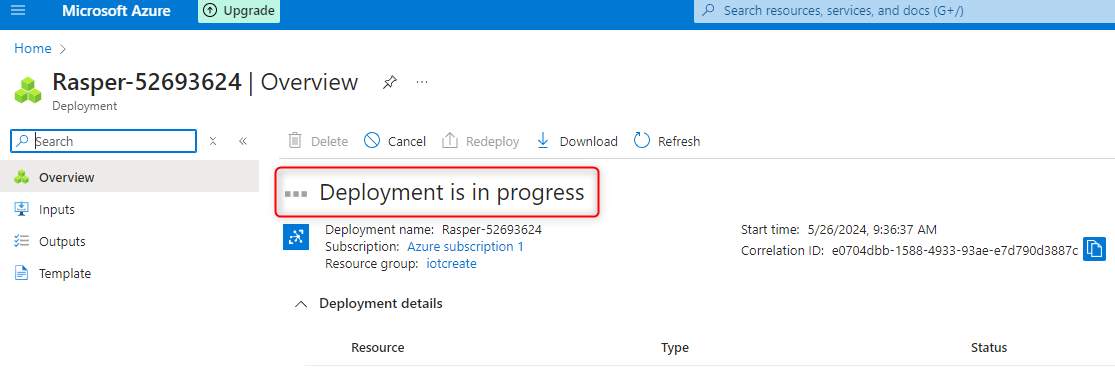
**STEP: 6** The following page is where you are expected to add a Device.
Click on **Device**, **Add Device**
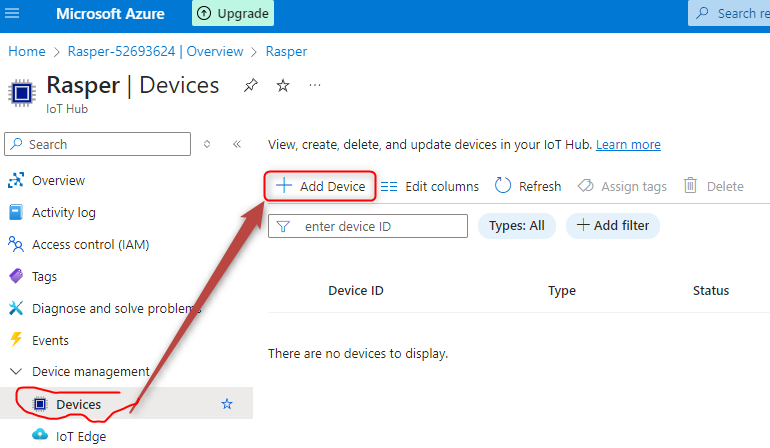
**STEP: 7** Create a Device ID, give it a name, and Save
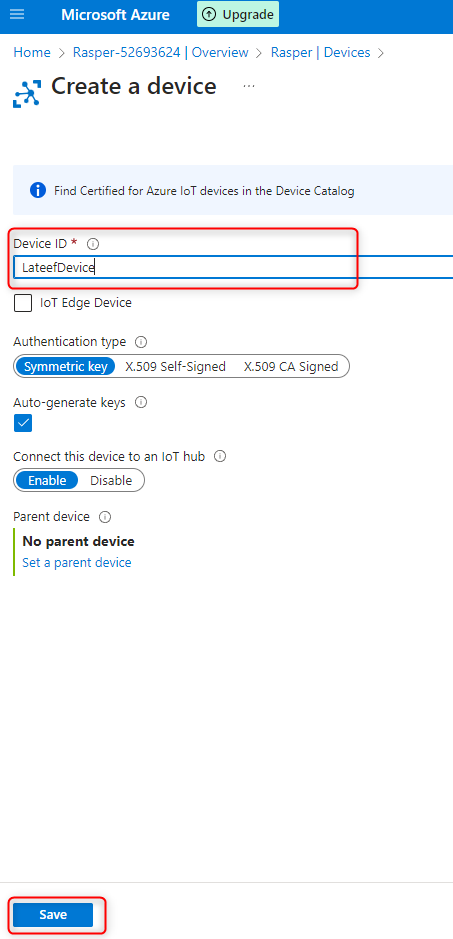
**STEP: 8** Device created
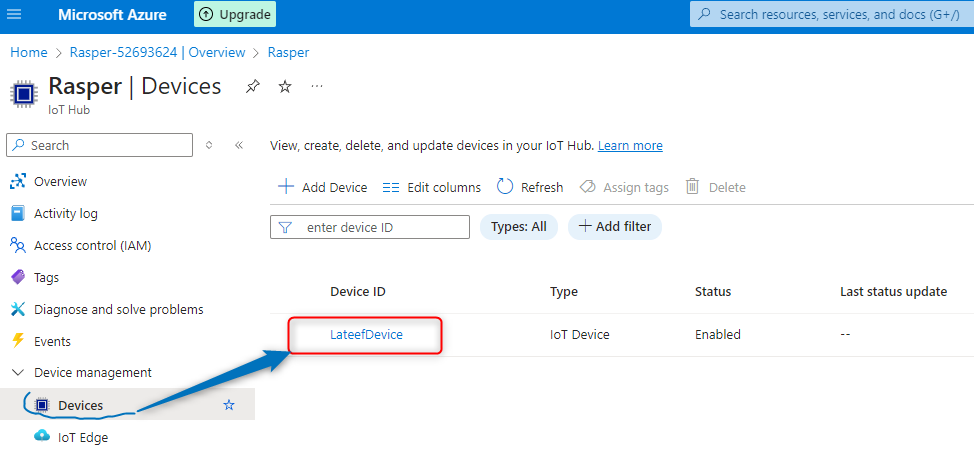
**STEP: 8** Click on the Device name
**STEP: 9** Copy the "Primary Connection String"
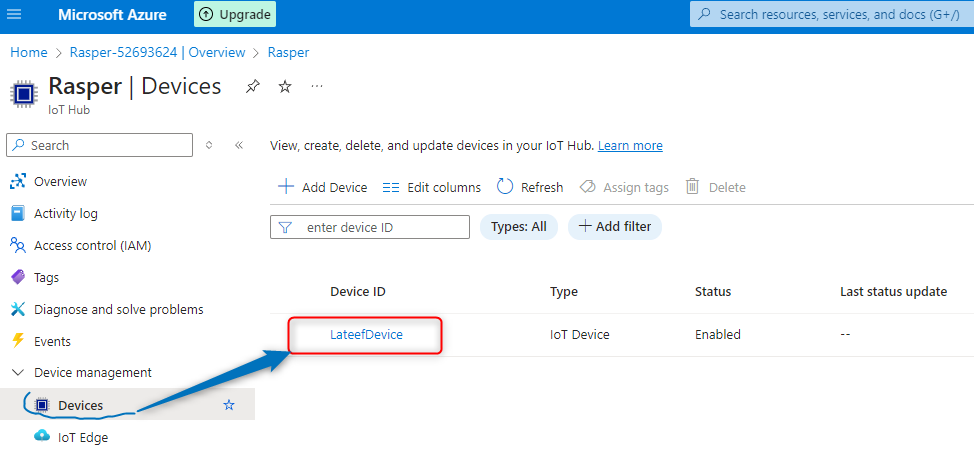
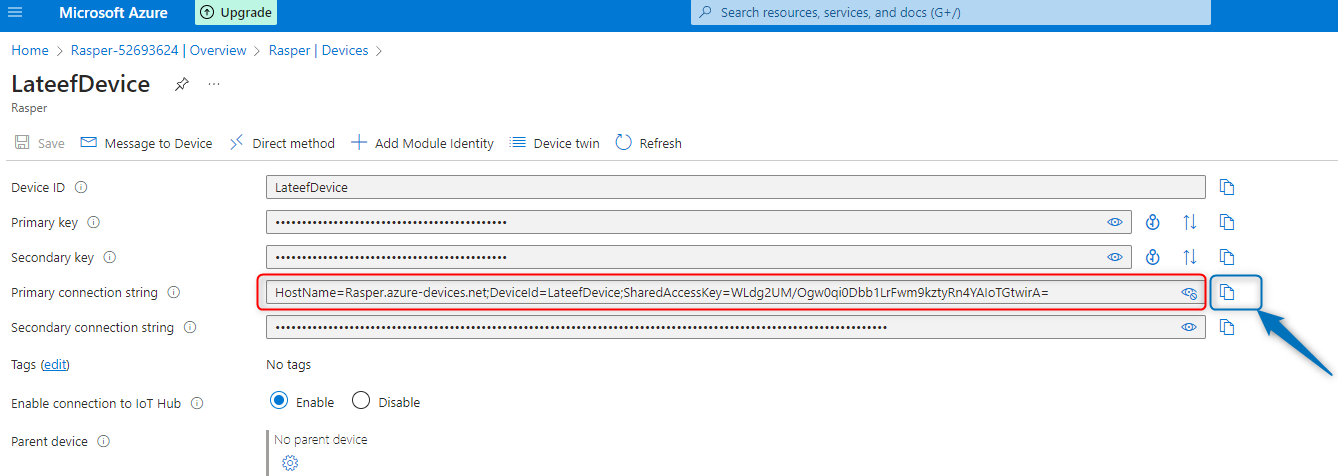
**Set up communication with the Raspberry Pi simulator**
STEP: 1 Go to google.com and search for Raspberry Pi Simulator or through this link https://azure-samples.github.io/raspberry-pi-web-simulator/
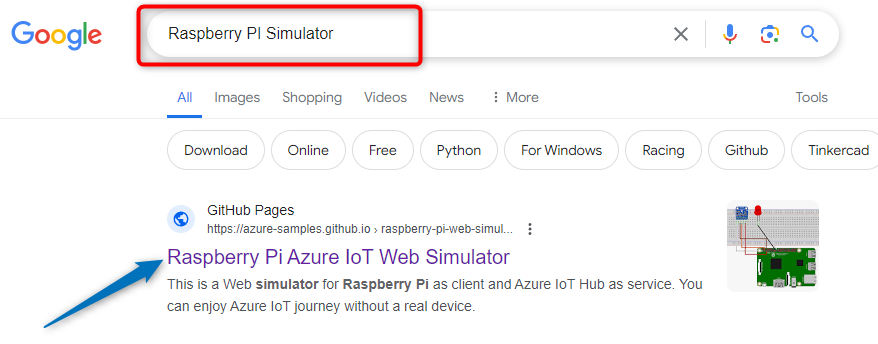
**STEP 2** Paste the “primary connection string" copied from **STEP 9** from the IOT device portal on Azure into “Line 15” on the Raspberry PI Simulator and click on RUN.
Raspberry Pi Simulator will starts blinking Red flashy Red Light, communicating to the IOT Device in Microsoft Azure portal and recording data and messages as seen below
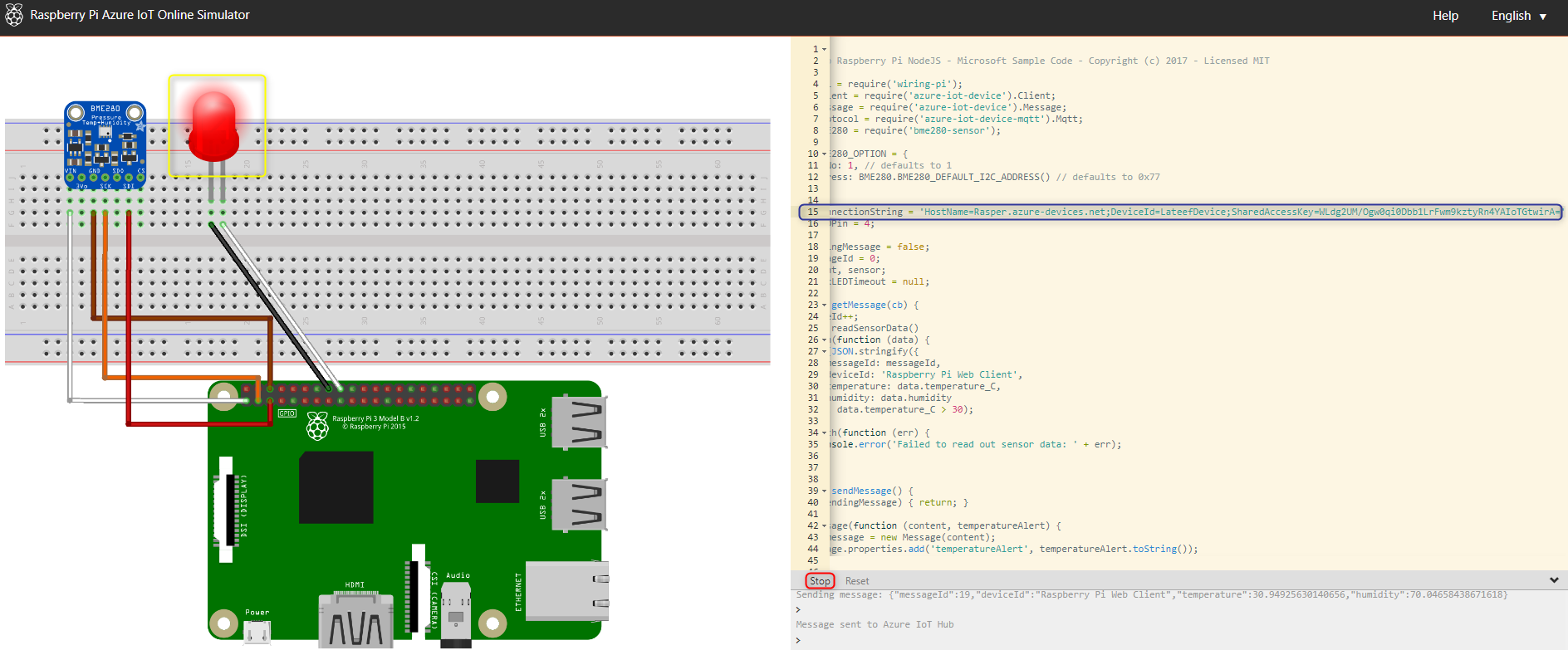
**STEP 3** You can also track number of data and messages used through the Azure Portal.
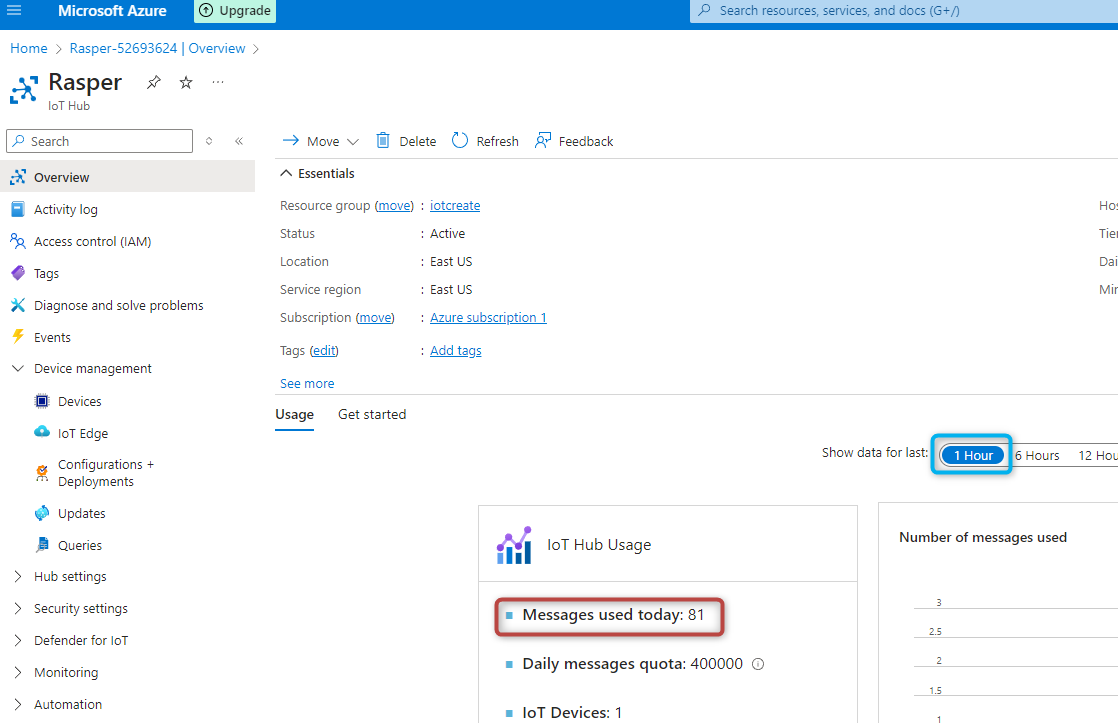
**By following the above steps, you can successfully connect your Raspberry Pi simulator to Azure IoT Hub for communication and data exchange in the Azure Cloud environment. Remember to refer to the Azure documentation and resources specific to your chosen technologies for detailed guidance and best practices.** | latoniw |
1,872,402 | Masterclass De Inteligência Artificial: Aprenda Do Zero Gratuitamente | Participe da Masterclass de Inteligência Artificial em Estratégia de Marketing, uma oportunidade de... | 0 | 2024-06-23T13:51:41 | https://guiadeti.com.br/masterclass-inteligencia-artificial-gratuita-2/ | eventos, cursosgratuitos, inteligenciaartifici, marketing | ---
title: Masterclass De Inteligência Artificial: Aprenda Do Zero Gratuitamente
published: true
date: 2024-05-31 16:21:24 UTC
tags: Eventos,cursosgratuitos,inteligenciaartifici,marketing
canonical_url: https://guiadeti.com.br/masterclass-inteligencia-artificial-gratuita-2/
---
Participe da Masterclass de Inteligência Artificial em Estratégia de Marketing, uma oportunidade de imersão para aprender desde o básico sobre a aplicação de IA em Marketing e Growth.
Descubra por que o mercado está cada vez mais valorizando profissionais que dominam essas tecnologias e como elas estão se tornando essenciais nas grandes empresas ao redor do mundo.
Durante o curso, você terá acesso a exemplos práticos, aplicações reais, e aprenderá com especialistas com experiência comprovada na área.
Todos os participantes receberão material didático gratuito para acessar e baixar, e certificado de conclusão.
## Masterclass de Inteligência Artificial em Estratégia de Marketing
Nos dias 4 e 5 de Junho, será oferecida uma Masterclass totalmente online sobre Inteligência Artificial em Estratégia de Marketing.
_Imagem da página do curso_
Este evento é uma excelente oportunidade para profissionais de marketing e growth que estão começando e desejam compreender as complexidades e as aplicações da IA em suas áreas.
A masterclass tem o objetivo de mostrar por que os especialistas em IA estão se tornando indispensáveis nas grandes corporações ao redor do mundo e como os participantes podem se destacar nesse mercado competitivo.
### Público-alvo da Imersão
Essa Masterclass Gratuita foi pensada para quem:
- Atua nas áreas de Marketing e Growth e querem dar o próximo passo em suas carreiras, assumindo uma posição estratégica e de gestão das IAs;
- Quer assumir uma posição de gestor de inteligências artificiais, a nova profissão do mercado e que será obrigatória nas grandes empresas;
- Quem nunca aplicou inteligência artificial, mas entende sua importância e quer dar os primeiros passos nesse universo.
### Aprendizado e Desenvolvimento de Habilidades
Durante a masterclass, os participantes serão instruídos por especialistas renomados no uso de inteligência artificial aplicada ao marketing e growth.
Eles terão acesso a uma combinação de conteúdo teórico e prático, incluindo estudos de caso reais que ilustram como a IA pode revolucionar as estratégias de marketing.
O material do curso será disponibilizado gratuitamente para download, abrangendo as ferramentas essenciais e os princípios fundamentais da IA, permitindo aos participantes dominar as técnicas e maximizar o potencial dessas tecnologias avançadas.
### Certificação e Oportunidades Futuras
Ao concluir a masterclass, os participantes receberão um certificado. Aqueles que estiverem presentes ao vivo terão a oportunidade exclusiva de receber condições especiais para se inscrever no novo MBA de Inteligência Artificial Aplicada a Marketing e Growth.
O curso é projetado para equipar os profissionais com as competências necessárias para liderar em um ambiente de negócios cada vez mais influenciado pela tecnologia e prepará-los para uma das profissões mais requisitadas nas próximas décadas.
<aside>
<div>Você pode gostar</div>
<div>
<div>
<div>
<div>
<span><img decoding="async" width="280" height="210" src="https://guiadeti.com.br/wp-content/uploads/2024/05/Certificacao-GitHub-280x210.png" alt="Certificação GitHub" title="Certificação GitHub"></span>
</div>
<span>Certificação GitHub Foundations: Concorra A Voucher Para Exame</span> <a href="https://guiadeti.com.br/certificacao-github-foundations-voucher-para-exame/" title="Certificação GitHub Foundations: Concorra A Voucher Para Exame"></a>
</div>
</div>
<div>
<div>
<div>
<span><img decoding="async" width="280" height="210" src="https://guiadeti.com.br/wp-content/uploads/2024/05/Masterclass-De-Inteligencia-Artificial-280x210.png" alt="Masterclass De Inteligência Artificial" title="Masterclass De Inteligência Artificial"></span>
</div>
<span>Masterclass De Inteligência Artificial: Aprenda Do Zero Gratuitamente</span> <a href="https://guiadeti.com.br/masterclass-inteligencia-artificial-gratuita-2/" title="Masterclass De Inteligência Artificial: Aprenda Do Zero Gratuitamente"></a>
</div>
</div>
<div>
<div>
<div>
<span><img decoding="async" width="280" height="210" src="https://guiadeti.com.br/wp-content/uploads/2024/05/Marketing-Digital-Santander-280x210.png" alt="Marketing Digital Santander" title="Marketing Digital Santander"></span>
</div>
<span>Curso De Marketing Digital Gratuito E Online Do Santander</span> <a href="https://guiadeti.com.br/curso-marketing-digital-gratuito-online-santander/" title="Curso De Marketing Digital Gratuito E Online Do Santander"></a>
</div>
</div>
<div>
<div>
<div>
<span><img decoding="async" width="280" height="210" src="https://guiadeti.com.br/wp-content/uploads/2024/05/Minicurso-De-Analise-De-Dados-280x210.png" alt="Minicurso De Análise De Dados" title="Minicurso De Análise De Dados"></span>
</div>
<span>Minicurso De Análise De Dados Gratuito Da Cubos Academy</span> <a href="https://guiadeti.com.br/minicurso-analise-de-dados-gratuito-cubos-academy/" title="Minicurso De Análise De Dados Gratuito Da Cubos Academy"></a>
</div>
</div>
</div>
</aside>
## Inteligência Artificial
A inteligência artificial (IA) está revolucionando a forma como as empresas tratam marketing e vendas, dando percepções mais profundos sobre o comportamento do consumidor e otimizando as estratégias para alcançar resultados superiores.
Com a aplicação de IA, as empresas podem aumentar a eficiência e personalizar experiências, melhorar a satisfação do cliente e aumentar a receita.
### Segmentação de Clientes
A IA permite uma segmentação de clientes muito mais sofisticada do que métodos tradicionais. Algoritmos de machine learning analisam grandes conjuntos de dados para identificar padrões e tendências no comportamento do consumidor, permitindo que as empresas segmentem seus mercados de forma mais precisa.
Essa segmentação avançada ajuda a personalizar as mensagens de marketing para diferentes grupos, aumentando a relevância e eficácia das campanhas.
### Recomendações Personalizadas
Outra aplicação poderosa da IA no marketing é a capacidade de oferecer recomendações personalizadas a clientes.
Sistemas como os usados por gigantes do e-commerce utilizam o histórico de compras e as interações online dos usuários para recomendar produtos que mais provavelmente interessarão ao cliente, aumentando assim as chances de compra.
### Automatização de Testes A/B
A IA também pode automatizar e otimizar testes A/B, permitindo que as empresas testem várias versões de uma campanha simultaneamente para determinar qual delas performa melhor.
Isso significa que o marketing pode ser adaptado e ajustado em tempo real, baseado em dados concretos sobre o que funciona melhor com o público-alvo.
### Gestão de Conteúdo Dinâmico
A IA pode gerenciar a entrega de conteúdo dinâmico, o que envolve a alteração de elementos de uma página web ou anúncio em tempo real, dependendo do usuário que o está visualizando, maximizando a relevância do conteúdo para cada visitante individual.
### Previsões de Vendas
IA em marketing e vendas também ajuda na previsão de tendências e comportamentos do consumidor.
Algoritmos preditivos podem analisar dados de vendas passadas e tendências de mercado para prever futuras flutuações e tendências, ajudando as empresas a se prepararem melhor para mudanças no mercado.
### Análise Sentimental
A análise sentimental, por meio do processamento de linguagem natural (PLN), permite que as empresas entendam melhor as opiniões e sentimentos dos consumidores sobre produtos ou marcas, analisando dados de redes sociais, comentários online e feedbacks.
## Descomplica
A Faculdade Descomplica é uma instituição de ensino superior que nasceu da evolução da conhecida plataforma de educação online, Descomplica.
Reconhecida por seu foco inicial em preparação para o ENEM e outros vestibulares, a instituição expandiu suas operações para oferecer cursos de graduação e pós-graduação totalmente online, com a missão de democratizar o acesso ao ensino superior de qualidade no Brasil.
Utilizando tecnologias de aprendizado à distância, a Faculdade Descomplica oferece a flexibilidade e acessibilidade para estudantes de todo o país, aliando conveniência e qualidade educacional.
### Cursos e Metodologia
A Faculdade Descomplica oferece uma variedade de cursos de graduação e pós-graduação em áreas que vão desde Administração e Contabilidade até Direito e Educação.
Todos os cursos são reconhecidos pelo MEC, garantindo a credibilidade e a validade dos diplomas.
### Metodologia
As aulas são ministradas através de videoaulas dinâmicas, materiais de leitura digital, e atividades interativas que promovem a aplicação prática do conhecimento.
### Plataforma Online
Uma das principais características da Faculdade Descomplica é sua plataforma de aprendizado intuitiva. Projetada para ser acessível em diversos dispositivos, permite que os estudantes gerenciem seus estudos de qualquer lugar, a qualquer hora.
A tecnologia de ponta empregada na plataforma facilita o acompanhamento do progresso do aluno, oferece recursos adicionais de aprendizagem e promove a interação entre estudantes e professores.
## Inscreva-se na Masterclass de Inteligência Artificial e eleve suas estratégias de marketing ao próximo nível!
As [inscrições para a Masterclass de Inteligência Artificial em Estratégia de Marketing](https://descomplica.com.br/pos-graduacao/masterclass-inteligencia-artificial-b/) devem ser realizadas no site da Descomplica.
## Compartilhe esta Masterclass e ajude amigos a transformarem suas carreiras!
Gostou do conteúdo sobre o evento em Inteligência Artificial? Então compartilhe com a galera!
O post [Masterclass De Inteligência Artificial: Aprenda Do Zero Gratuitamente](https://guiadeti.com.br/masterclass-inteligencia-artificial-gratuita-2/) apareceu primeiro em [Guia de TI](https://guiadeti.com.br). | guiadeti |
1,872,223 | Day 1 of 30 | So for today I covered only React and got tired and I am starting to overcome slowly the fear of... | 0 | 2024-05-31T16:17:44 | https://dev.to/francis_ngugi/day-1-of-30-2oed | challenge, react, beginners | So for today I covered only React and got tired and I am starting to overcome slowly the fear of using React since I have never been a fun of React(frontend dev).
Learnt information with their github links:
>Writing JSX: https://github.com/FrancisNgigi05/react-hooks-jsx-lab
>Props Basics:https://github.com/FrancisNgigi05/react-hooks-props-basics-lab
>Props Destructuring and Default Values: https://github.com/FrancisNgigi05/react-hooks-props-destructuring
>React Components: https://github.com/FrancisNgigi05/react-hooks-components-basics-lab
>Organizing code with import/export: https://github.com/FrancisNgigi05/react-hooks-import-export-lab
Challenges faced today was learning: **Props Destructuring(Destructuring nested objects)**

| francis_ngugi |
1,872,222 | first html code | Check out this Pen I made! | 0 | 2024-05-31T16:14:10 | https://dev.to/hamid_mammadli/first-html-code-35b9 | codepen | Check out this Pen I made!
{% codepen https://codepen.io/Hamid-Mammadli/pen/ZENpXwj %} | hamid_mammadli |
1,872,221 | Say Goodbye to Acne: Your Ultimate Skin Care Routine for Acne | Dealing with acne can often feel like a relentless battle, but armed with the right skin care routine... | 0 | 2024-05-31T16:13:07 | https://dev.to/disha_/say-goodbye-to-acne-your-ultimate-skin-care-routine-for-acne-1mga | Dealing with acne can often feel like a relentless battle, but armed with the right skin care routine for acne, victory is within your reach. Acne, a common skin condition that affects millions worldwide, isn't just a superficial concern—it can significantly impact self-esteem and quality of life. The key to managing acne effectively lies in understanding its causes—from genetics and inflammation to stress and pore-clogging ingredients—and implementing a tailored skincare routine that addresses these factors. Whether you're dealing with persistent blackheads, painful breakouts, or post-acne scarring, developing a consistent routine is crucial in keeping your skin clear and healthy.
In this article, we'll explore the essential steps of a daily skin care routine for acne-prone skin, highlight the best products to combat acne—including those containing salicylic acid, benzoyl peroxide, and tea tree oil—and discuss additional practices that can support skin health, such as maintaining hydration, adopting a healthy diet, and managing stress. From gentle cleansers and exfoliating toners to oil-free cleansers and noncomedogenic moisturizers, we'll guide you through choosing the right products that won't exacerbate your skin concerns. Plus, we'll offer tips on avoiding common triggers, such as pore-clogging ingredients and the importance of sunscreen, to help you say goodbye to acne for good.
**Understanding Acne
Causes of Acne**
Acne develops when sebum, an oily substance that lubricates your hair and skin, and dead skin cells plug hair follicles. This can lead to inflammation and infection, resulting in more severe acne 49. The main factors contributing to acne include excess oil production, hair follicles clogged by oil and dead skin cells, bacteria, and inflammation 49. Acne commonly appears on your face, forehead, chest, upper back, and shoulders due to the high density of oil glands in these areas 49.
**Common Triggers**
Several factors can trigger or worsen acne. Hormonal changes, particularly during puberty, pregnancy, or midlife, can increase sebum production, leading to breakouts 49. Certain medications containing corticosteroids, testosterone, or lithium are also known to exacerbate acne 49. Diet plays a role as well; consuming high-carbohydrate foods like bread and chips may worsen the condition, though more research is needed to establish a clear dietary link 49. Additionally, stress does not directly cause acne but can aggravate it if you already have the condition 49. Environmental factors such as air pollution, high humidity, and using oily skincare products can also contribute to acne flare-ups 5.
**Daily Skincare Routine for Acne-Prone Skin
Cleansing Tips**
Start your skincare routine with a thorough cleansing to remove excess oil, dirt, and makeup, which can contribute to acne. Choose a gentle cleanser that doesn't strip your skin of its natural oils. For effective cleansing, apply a foaming acne face wash specifically formulated to fight acne, working it into your T-zone and other oily areas for about 20-30 seconds before rinsing with warm water 1011. Ensure you use a clean face towel to pat your skin dry, as reusing towels can spread bacteria that exacerbate acne 10.
**Effective Use of Toner**
After cleansing, applying a toner can help restore your skin's pH balance and remove any residual impurities. For acne-prone skin, opt for an alcohol-free toner with ingredients like glycolic and salicylic acids to control oil and prevent breakouts 1314. Apply the toner with a cotton ball, allowing it to dry before proceeding to the next step 15. If your skin is sensitive, start by using the toner less frequently and gradually increase usage as your skin adjusts 13.
**Choosing the Right Moisturizer**
Moisturizing is crucial, even for oily and acne-prone skin, to maintain a healthy barrier function and prevent overproduction of oil. Look for non-comedogenic and oil-free moisturizers to avoid clogging pores. Ingredients like hyaluronic acid and glycerin are great for hydration without adding oiliness 161718. Additionally, products containing salicylic acid can help keep pores clear and reduce breakouts 16. Apply moisturizer while your skin is still slightly damp to lock in moisture 10.
**Best Products to Combat Acne**
Product Ingredients to Look For
When selecting products to combat acne, look for key active ingredients known for their effectiveness. Benzoyl peroxide is renowned for its ability to kill bacteria and unclog pores 1920. Salicylic acid, another critical ingredient, helps by exfoliating the skin and keeping pores clear of blockages 192021. For a natural approach, tea tree oil offers antibacterial and anti-inflammatory benefits, making it a gentle alternative for treating acne 19. Additionally, ingredients like glycolic and lactic acids, found in alpha hydroxy acids, promote new skin growth and aid in reducing acne scars 1920.
**Top Recommended Products**
Several products stand out for their efficacy in treating acne. For a comprehensive approach, consider the following:
**Cleansers:**
**[CeraVe Acne Foaming Cream Cleanser](https://amzn.to/4aLxKIG)**: Contains 4% benzoyl peroxide to clear and prevent new breakouts 23.
Neutrogena Oil-Free Acne Wash: Formulated for oily skin with salicylic acid to prevent clogging 23. [click here to get this product
](https://amzn.to/4aLxKIG)
**Toners:**
**[Paula's Choice Skin Perfecting 2% BHA Liquid Exfoliant](https://amzn.to/3wUjzU1)**: Ideal for gentle daily exfoliation to reduce sebum and debris in pores 22. [click here to get this product ](https://amzn.to/3wUjzU1)
**Serums:**
**[The Ordinary Niacinamide 10% + Zinc 1%](https://amzn.to/4e6cMaG)**: Reduces breakouts and controls oil production, suitable for oily skin types 22.[click here to get this product ](https://amzn.to/4e6cMaG)
**SkinCeuticals Silymarin CF**: An antioxidant serum that refines skin texture and improves clarity 22.
**Spot Treatments:**
**[Mario Badescu Drying Lotion](https://amzn.to/4bDlN9f)**: Quickly calms zits overnight with a blend of sulfur, salicylic acid, and zinc oxide 22.[click here to get this product ](https://amzn.to/4bDlN9f)
[**Tretinoin 0.025% cream**](https://amzn.to/4bAPXdk):Start with a pea-sized amount, gradually increasing as tolerated.Apply at night, use sunscreen during the day, and expect initial dryness and irritation.[click here to get this product ](https://amzn.to/4bAPXdk)
**Masks:
[Peter Thomas Roth Therapeutic Sulfur Acne Treatment Mask](https://amzn.to/4bRvaSC)**: Infused with sulfur and kaolin clay to absorb excess oil and prevent future breakouts 22.[click here to get this product ](https://amzn.to/4bRvaSC)
Remember, it's essential to choose products that align with your specific skin type and acne concerns. Additionally, consider incorporating products with sun protection during the day to prevent further irritation and damage from UV rays 1920. Always start with lower strength products to minimize potential skin irritation and gradually adjust as your skin becomes accustomed to the treatment 20.
**Additional Tips and Practices**
Lifestyle Changes
To manage adult acne effectively, consider dietary adjustments such as reducing high glycemic index foods and dairy products, which may exacerbate acne symptoms 2627. Incorporating foods rich in omega-3 fatty acids like fish and flaxseeds can help reduce inflammation and potentially lessen acne occurrence 26. Regular exercise is beneficial; however, ensure to cleanse your skin before and after workouts to prevent sweat-induced breakouts 25. Stress management through mindfulness and adequate sleep also plays a crucial role in maintaining healthy skin 25.
**Natural Remedies**
While many home remedies lack robust scientific backing, some natural substances might offer benefits. For instance, tea tree oil has been recognized for its anti-inflammatory and antibacterial properties, which can help in treating acne 29. Similarly, green tea, known for its high antioxidant content, may reduce skin inflammation when applied topically 29. It's important to approach these remedies with caution and consult healthcare professionals before starting any new treatment 29.
**When to Consult a Dermatologist**
If over-the-counter acne treatments are ineffective, consulting a dermatologist can be crucial 32. They can offer personalized advice and professional treatments such as prescription medications and therapies tailored to your acne's severity and type 3233. For persistent or severe acne that leads to scarring or affects mental health, professional dermatological intervention is recommended to manage the condition effectively and prevent long-term skin damage 3233.
**Conclusion**
Throughout this article, we've navigated the complex landscape of acne, exploring its causes, triggers, and the most effective skincare routines and products to combat it. From emphasizing the critical steps in a daily regimen that includes cleansing, toning, and moisturizing with the right products to highlighting important lifestyle adjustments and when to seek professional advice, we've covered a holistic approach to managing acne. By understanding the underlying factors that contribute to acne and adopting a tailored skincare routine, individuals can achieve clearer, healthier skin.
The journey to acne-free skin, while challenging, is not insurmountable. It requires patience, consistency, and a willingness to adapt one's approach as skin responds to treatment. Embracing the strategies and products discussed can pave the way for significant improvements in skin health and overall well-being. Remember, every skin is unique, so what works for one individual may vary for another. It's essential to keep experimenting and tweaking your regimen, backed by the insights and recommendations shared, to find what truly works for you in your quest for clear skin.
**FAQs**
What are the key components of an effective acne skincare routine?
The cornerstone of any effective acne skincare regimen includes the use of salicylic acid, benzoyl peroxide, and adapalene (a retinoid now available over-the-counter at 0.1% concentration). Salicylic acid, a beta-hydroxy acid, is oil-soluble, enabling it to dissolve oil and dead skin cells that clog pores, making it a critical ingredient for fighting acne.
How can I establish a skincare routine to eliminate acne?
To effectively prevent and clear acne, follow this skincare routine:
Cleansing (Morning & Night): It's crucial to cleanse your skin gently to remove impurities without causing irritation.
Toning or Using an Astringent (Morning & Night): Helps to balance the skin and prepare it for acne treatments or medications.
Applying Acne Treatment or Medication (Morning & Night): Target acne directly with appropriate treatments.
Moisturizing (Morning & Night): Keeps your skin hydrated without exacerbating acne issues.
Is there a definitive cure for acne?
Isotretinoin is considered a highly effective treatment for acne, targeting all four primary causes: bacteria, clogged pores, excess oil production, and inflammation. Approximately 85% of individuals experience permanent acne clearance after completing a course of isotretinoin treatment.
What does an ideal skincare routine for acne-prone skin look like?
For those with acne-prone skin, an ideal routine involves:
Washing twice daily and after sweating: This helps remove excess oil and impurities.
Being gentle with your skin: Avoid harsh scrubbing or exfoliating, which can irritate the skin.
Refraining from picking or popping pimples: If necessary, do so in a safe manner to prevent scarring.
Regularly cleaning objects that touch your face: This includes phone screens, pillowcases, and makeup brushes.
Choosing noncomedogenic products: These products are formulated to not clog pores.
Evaluating your hair care products: Ensure they are not contributing to skin irritation.
Staying hydrated: Proper hydration is key for maintaining healthy skin.
**References**
[1] - https://www.theinkeylist.com/products/the-intro-routine-for-acne
[2] - https://www.nytimes.com/article/acne-skincare-routine.html
[3] - https://www.elle.com/beauty/makeup-skin-care/a42782847/best-skin-care-routine-acne/
[4] - https://www.mayoclinic.org/diseases-conditions/acne/symptoms-causes/syc-20368047
[5] - https://my.clevelandclinic.org/health/diseases/12233-acne
[6] - https://www.niams.nih.gov/health-topics/acne
[7] - https://www.pennmedicine.org/for-patients-and-visitors/patient-information/conditions-treated-a-to-z/acne
[8] - https://www.webmd.com/skin-problems-and-treatments/acne/acne-causes
[9] - https://www.mayoclinic.org/diseases-conditions/acne/symptoms-causes/syc-20368047
[10] - https://africa.laroche-posay.com/en-za/article/acne-solutions-how-to-prevent-acne-and-get-rid-of-acne-with-regular-cleansing
[11] - https://www.cerave.com/skin-smarts/skincare-tips-advice/a-simple-3-step-acne-routine-to-take-control-of-acne
[12] - https://www.cetaphil.com/us/skincare-tips/skincare_guides/how-to-get-clearer-skin.html
[13] - https://www.womenshealthmag.com/beauty/a19952473/how-to-use-facial-toner/
[14] - https://www.cerave.com/skin-smarts/skincare-tips-advice/tips-for-including-toner-in-your-skincare-routine
[15] - https://www.cleure.com/blogs/blog/guide-to-face-toners-do-you-need-it-and-how-to-use-it
[16] - https://www.oxygenetix.com/blogs/blog/how-to-choose-a-moisturizer-for-acne-prone-skin
[17] - https://www.health.com/best-moisturizers-for-acne-prone-skin-8609372
[18] - https://curology.com/blog/moisturizers-acne-prone/
[19] - https://www.webmd.com/skin-problems-and-treatments/acne/features/best-ingredients-for-acne-prone-skin
[20] - https://www.mayoclinic.org/diseases-conditions/acne/in-depth/acne-treatments/art-20045814
[21] - https://www.realsimple.com/best-ingredients-for-acne-7369843
[22] - https://www.vogue.com/article/best-acne-treatments
[23] - https://www.northstardermatology.com/blog/best-products-for-acne-prone-skin/
[24] - https://www.laroche-posay.us/our-products/face/acne-products
[25] - https://www.webmd.com/skin-problems-and-treatments/acne/features/acne-lifestyle-changes
[26] - https://clinic78.co.uk/blog/lifestyle-changes-help-fight-adult-acne/
[27] - https://www.medicalnewstoday.com/articles/322639
[28] - https://www.medicalnewstoday.com/articles/322455
[29] - https://www.healthline.com/nutrition/13-acne-remedies
[30] - https://health.clevelandclinic.org/home-remedies-for-acne
[31] - https://www.aad.org/public/diseases/acne/diy/when-derm
[32] - https://www.medicalnewstoday.com/articles/when-to-see-a-dermatologist-for-acne
[33] - https://www.webmd.com/skin-problems-and-treatments/acne/features/see-a-doctor
[34] - https://www.ncbi.nlm.nih.gov/books/NBK573057/
[35] - https://www.theinkeylist.com/blogs/news/treating-acne-masterclass
[36] - https://miiskin.com/acne/skincare-routine/ | disha_ | |
1,872,217 | 260. Single Number III | 260. Single Number III Medium Given an integer array nums, in which exactly two elements appear... | 27,523 | 2024-05-31T16:04:44 | https://dev.to/mdarifulhaque/260-single-number-iii-g3e | php, leetcode, algorithms, programming | 260\. Single Number III
Medium
Given an integer array **nums**, in which exactly two elements appear only once and all the other elements appear exactly twice. Find the two elements that appear only once. You can return the answer in **any order**.
You must write an algorithm that runs in linear runtime complexity and uses only constant extra space.
**Example 1:**
- **Input:** nums = [1,2,1,3,2,5]
- **Output:** [3,5]
- **Explanation:** [5, 3] is also a valid answer.
**Example 2:**
- **Input:** nums = [-1,0]
- **Output:** [-1,0]
**Example 3:**
- **Input:** nums = [0,1]
- **Output:** [1,0]
**Constraints:**
- <code>2 <= nums.length <= 3 * 10<sup>4</sup></code>
- <code>-2<sup>31</sup> <= nums[i] <= 2<sup>31</sup> - 1</code>
- Each integer in **nums** will appear twice, only two integers will appear once.
**Solution:**
```
class Solution {
/**
* @param Integer[] $nums
* @return Integer[]
*/
function singleNumber($nums) {
$xors = array_reduce($nums, function($carry, $item) { return $carry ^ $item; }, 0);
$lowbit = $xors & -$xors;
$ans = array_fill(0, 2, 0);
foreach ($nums as $num) {
if ($num & $lowbit) {
$ans[0] ^= $num;
} else {
$ans[1] ^= $num;
}
}
return $ans;
}
}
```
**Contact Links**
- **[LinkedIn](https://www.linkedin.com/in/arifulhaque/)**
- **[GitHub](https://github.com/mah-shamim)** | mdarifulhaque |
1,872,215 | Local Bozo Realizes They Should Have Been Using This Earlier | Wow! It sure would have been nice if I had taken the advice in the Intro course and jotted little... | 0 | 2024-05-31T16:01:12 | https://dev.to/jt-is-coding/local-bozo-realizes-they-should-have-been-using-this-earlier-1ah0 | Wow! It sure would have been nice if I had taken the advice in the Intro course and jotted little notes down here for review. Just imagine how easy it would be to refresh my memory on concepts if I had it all nice and neat somewhere written down in *literally* my own words! Oops~ | jt-is-coding | |
1,872,214 | Integrating API with State Management in React using Zustand | Integrating API with State Management in React using Zustand State management is a crucial... | 0 | 2024-05-31T16:01:00 | https://dev.to/geraldhamiltonwicks/integrating-api-with-state-management-in-react-using-zustand-4mje | # Integrating API with State Management in React using Zustand
State management is a crucial aspect of building scalable and maintainable React applications. Zustand is a lightweight and flexible state management library that provides a simple way to manage your application's state. In this article, we will demonstrate how to integrate an API with Zustand to manage product data.
## Type Definitions
First, let's define the types we will be using. We have a `Product` type that represents a product object and a `ProductStore` type that describes the structure of our Zustand store.
```typescript
// types.ts
export type Product = {
id: number,
title: string
};
export type ProductStore = {
products: Array<Product>,
loadProducts: () => Promise<void>,
createOneProduct: (value: Product) => Promise<void>,
updateOneProduct: (value: Product) => Promise<void>,
deleteOneProduct: (id: number) => Promise<void>
}
export type StoreSet =
(partial:
ProductStore |
Partial<ProductStore> |
((state: ProductStore) => ProductStore |
Partial<ProductStore>),
replace?:
boolean | undefined) => void
```
## API Functions
Next, we define the API functions that will handle fetching, creating, updating, and deleting products. These functions will interact with our backend server.
```typescript
// api.ts
import { Product } from "./types";
const BASE_URL = 'http://localhost:3002/product';
export async function fetchProducts(): Promise<Array<Product>> {
const response = await fetch(BASE_URL);
const data = await response.json();
return data.products;
}
export async function createProduct(newProduct: Product): Promise<Product> {
const response = await fetch(BASE_URL, {
method: 'POST',
body: JSON.stringify(newProduct)
});
const data = await response.json();
return data.product;
}
export async function updateProduct(updatedProduct: Product): Promise<Product> {
const response = await fetch(BASE_URL, {
method: 'PUT',
body: JSON.stringify(updatedProduct)
});
const data = await response.json();
return data.product;
}
export async function deleteProduct(id: number): Promise<void> {
await fetch(`${BASE_URL}/${id}`, {
method: 'DELETE'
});
}
```
## Zustand Store
Now, let's create our Zustand store. This store will use the API functions we defined to manage the product data. We will define methods for loading, creating, updating, and deleting products.
```typescript
// store.ts
import { create } from "zustand";
import { Product, ProductStore } from "./types";
import { createProduct, deleteProduct, fetchProducts, updateProduct } from "./api";
export const useProductStore = create<ProductStore>()((set) => ({
products: [],
loadProducts: async () => {
const products = await fetchProducts();
return set(state => ({ ...state, products }));
},
createOneProduct: async (newProduct: Product) => {
const product = await createProduct(newProduct);
return set(state => ({
...state,
products: [...state.products, product]
}));
},
updateOneProduct: async (updatedProduct: Product) => {
const product = await updateProduct(updatedProduct);
return set(state => ({
...state,
products: state.products.map(p => p.id === product.id ? product : p)
}));
},
deleteOneProduct: async (id: number) => {
await deleteProduct(id);
return set(state => ({
...state,
products: state.products.filter(product => id !== product.id)
}));
}
}));
```
## Centralized Exports with index.ts
To streamline our imports and make our codebase more organized, we can create an `index.ts` file. This file will re-export everything from our `store`, `types`, and `api` files, allowing us to import these modules from a single location.
```typescript
// index.ts
export * from './store';
export * from './types';
export * from './api';
```
With this setup, we can import the store, types, and API functions in other parts of our application using a single import statement.
For example, instead of doing this:
```typescript
import { useProductStore } from './store';
import { Product } from './types';
import { fetchProducts } from './api';
```
We can now do this:
```typescript
import { useProductStore, Product, fetchProducts } from './index';
```
## Using the Store in a React Component
To utilize the store in a React component, we can use the `useProductStore` hook to access the state and actions defined in the store. Here's an example of how to use it in an `App` component.
```typescript
// App.tsx
import { useProductStore } from './index';
function App() {
const {
products,
loadProducts,
createOneProduct,
updateOneProduct,
deleteOneProduct
} = useProductStore();
return (
<div className="App">
<h1>Product Management</h1>
<button onClick={loadProducts}>Load Products</button>
<ul>
{products.map(product => (
<li key={product.id}>{product.title}</li>
))}
</ul>
</div>
);
}
export default App;
```
In this example, we use the `useProductStore` hook to access the products and the actions to load, create, update, and delete products. We provide a button to load the products and display them in a list.
## Conclusion
By following this structure, we have successfully integrated an API with Zustand for managing product data. This approach keeps our state management logic clean, modular, and easy to maintain. Zustand's simplicity and flexibility make it an excellent choice for managing state in React applications.
With the types, API functions, and store separated into their respective files, our codebase is well-organized and scalable, allowing us to easily extend and maintain the application as it grows.
Feel free to use this approach in your projects to streamline state management and API integration with Zustand. Happy coding!
---
**Files:**
1. **types.ts**
2. **api.ts**
3. **store.ts**
4. **index.ts**
| geraldhamiltonwicks | |
1,871,884 | API Integration: A Game-Changer for Your Business | API integration has revolutionised business operations over the last decade, and continues to do so... | 0 | 2024-05-31T15:58:47 | https://dev.to/apidna/api-integration-a-game-changer-for-your-business-59il | webdev, api, ai, machinelearning | API integration has revolutionised business operations over the last decade, and continues to do so with recent advancements in machine learning and the use of autonomous agents.
Application Programming Interfaces (APIs) enable different software systems to seamlessly communicate and share data.
APIs such as OpenAI’s ChatGPT have a wide range of utilities that can provide businesses and developers with a wide range of opportunities.
When integrated into a website or application, API integrations can provide services such as payment processing, data analytics, and CRM.
This article will explore the essential APIs that every business should leverage to enhance their operations.
We’ll delve into the benefits of using advanced API integration platforms, like APIDNA’s autonomous agent-powered solution, to simplify and secure your integrations.
Additionally, we’ll discuss how API integration enables developers and businesses to focus on innovation, driving growth and staying ahead in a competitive market.
## Understanding API Integration
API integration is the process of connecting various software systems and applications through APIs to enable data exchange and communication.
This integration is pivotal in modern business operations as it enhances overall efficiency.
APIs act as intermediaries that allow different software systems to communicate by defining a set of rules and protocols.
When one application makes a request for information or functionality from another, the API processes this request and returns the appropriate response.

For example, an e-commerce platform can use payment processing APIs to handle transactions without directly accessing the payment system’s codebase.
This means that the business doesn’t have to worry about storing and securing their customer’s payment and personal details.
APIs ensure that businesses can leverage the best tools and services available without the need for extensive custom coding.
This not only reduces development time and costs but also enables rapid innovation and scalability.
## Essential APIs That Every Business Needs
- **Payment Processing:** APIs like Stripe are crucial for handling online transactions securely and efficiently. Stripe offers robust features such as fraud prevention, multi-currency support, and seamless integration with various e-commerce platforms. In one of our [previous articles](https://apidna.ai/the-top-7-apis-for-payment-processing-in-2023/), we went through the top 7 APIs for payment processing.
- **Communication:** APIs like SendGrid enable businesses to integrate powerful messaging and email functionalities into their applications. SendGrid specialises in email services, providing reliable email delivery, tracking, and analytics.
- **Social Media:** APIs from platforms like Facebook allow businesses to automate posts, retrieve user data, and analyse engagement. Facebook’s Graph API enables businesses to access user profiles, posts, and advertising data.
- **Data Analytics:** APIs like Google Analytics allow businesses to pull detailed reports on website traffic, user behaviour, and conversion rates. This data helps in understanding user interactions and optimising marketing strategies.

- **Customer Relationship Management (CRM):** APIs like HubSpot are essential for managing customer data, tracking interactions, and automating sales processes. HubSpot’s API provides functionalities for marketing automation, lead management, and customer service.
- **File Sharing:** APIs such as Google Drive enable businesses to integrate storage, sharing, and collaboration capabilities effortlessly. Google Drive API allows integration with Google’s suite of productivity tools, facilitating real-time collaboration. In one of our [previous articles](https://apidna.ai/the-9-best-apis-for-file-sharing/), we went through the top 9 APIs for file sharing.
- **Large Language Models (LLM):** APIs such as OpenAI’s ChatGPT provide businesses with a wide range of unique tools. These include content generation, customer interaction, language translation, data analysis, and more. The utility of these APIs will only continue to grow as AI and LLMs continue to be improved, so it’s essential to keep up-to-date. In one of our [previous articles](https://apidna.ai/the-6-best-machine-learning-apis-2024/), we went through the 6 best machine learning APIs.
## Benefits of Using an API Integration Platform
- **Simplified Integration:** Platforms like APIDNA simplify the complex process of integrating multiple APIs. Instead of dealing with numerous, often incompatible APIs, businesses can leverage a unified platform that handles the integration, data mapping, and communication between different systems. This not only saves time but also reduces the technical expertise required to manage integrations
- **Scalability:** As your business grows, so do your integration needs. API integration platforms are designed to scale with your business, enabling you to add new APIs and services without significant reconfiguration. Whether you’re expanding your customer base, launching new products, or entering new markets, these platforms ensure your integrations remain robust and efficient, accommodating increased data flow and user interactions seamlessly.
- **Automation:** APIDNA’s autonomous agent-powered platform takes API management to the next level by automating routine tasks and optimising performance. These agents can monitor API usage, manage load balancing, handle error detection, and perform self-healing operations. This automation reduces the need for manual intervention, ensuring that integrations run smoothly and efficiently around the clock. You can [click here](https://apidna.ai/contact-us/) to request a FREE demo of our platform.

- **Security:** Security is a paramount concern when integrating various APIs. API integration platforms offer robust security features, including encryption, authentication, and monitoring. These platforms ensure that data transmitted between APIs is secure, protecting sensitive information from breaches and unauthorised access. To learn more about API security, check out our previous article here.
- **Faster Time to Market:** Seamless integration accelerates the development and deployment of new products and services. With streamlined processes and automated management, businesses can bring their services to market much faster. This not only meets customer demands more effectively but also allows businesses to stay ahead of competitors by rapidly adapting to industry changes and emerging opportunities.
## Examples of Successful API Integrations
Let’s take a look at some stand out examples of different businesses that have successfully used API integrations to improve their business operations:
- **Shopify:** A leading e-commerce platform, uses API integration to connect with various third-party services. By integrating payment processors like Stripe and PayPal, Shopify enables seamless transactions for its merchants. This integration has significantly increased efficiency by automating payment processing, leading to faster checkouts and enhanced customer satisfaction.
- **Slack:** A popular communication platform, integrates with numerous other tools such as Google Drive, Trello, and GitHub. These integrations allow users to manage files, track projects, and collaborate more effectively within the Slack interface. The result is a more streamlined workflow, reduced need for context switching, and increased productivity.
- **Uber:** Uses API integrations extensively to provide real-time services. By integrating with Google Maps, Uber offers accurate location tracking and route optimization. Additionally, payment APIs ensure secure transactions. These integrations have contributed to Uber’s ability to offer reliable, efficient, and user-friendly services, enhancing the overall customer experience.
## Conclusion
API integration has clearly transformed the landscape of modern business operations.
Essential APIs, such as those for payment processing, communication, social media, data analytics, CRM, and file sharing, provide critical capabilities that enhance efficiency and customer experiences.
Leveraging advanced API integration platforms, like APIDNA’s autonomous agent-powered solution, can further streamline and secure these integrations.
Our platform simplifies the integration process, offers scalability, enhances security, and frees up developers to focus on innovation rather than the intricacies of managing multiple APIs.
By automating routine tasks and optimising performance, businesses can accelerate their time to market and stay competitive in an ever-evolving digital landscape. | itsrorymurphy |
1,872,211 | Como projetar para várias telas? Aprenda os 4c's | Ao projetar um novo produto ou recurso, é importante pensar sobre os diferentes tipos de plataforma... | 0 | 2024-05-31T15:54:45 | https://dev.to/devsnorte/como-projetar-para-varias-telas-aprenda-os-4cs-551 | design, webdev, programming, beginners | Ao projetar um novo produto ou recurso, é importante pensar sobre os diferentes tipos de plataforma em que o design será disponibilizado. Para lembrar, uma plataforma é o meio pelo qual os usuários utilizam seu produto. Algumas plataformas comuns são:
- Computadores desktop
- Laptops
- Celulares
- Tablets
- Portáteis, como relógios inteligentes
- TVs
- Telas inteligentes
À medida que projeta para vários dispositivos, você precisa considerar o tamanho da tela do dispositivo, a interação entre o dispositivo e o usuário, a forma como o conteúdo será organizado em vários tamanhos de tela, a maneira como os usuários vão interagir com cada dispositivo e muito mais.
Para proporcionar uma ótima experiência de usuário em vários dispositivos, tenha em mente os 4Cs:
- Consistência: ter um design uniforme para que os usuários sintam familiaridade com todos os dispositivos e produtos.
- Continuidade: proporcionar uma experiência tranquila e ininterrupta aos usuários enquanto eles navegam entre dispositivos.
- Contexto: projetar para as necessidades de um dispositivo específico e a forma como o usuário vai utilizar esse dispositivo em qualquer situação.
- Complementariedade: levar em consideração como o design do produto em cada dispositivo pode melhorar a experiência geral do usuário.
A plataforma selecionada deve ser aquela que atende melhor às necessidades dos usuários finais. Mais tarde, você pode projetar para outras plataformas. Além de ter uma experiência do usuário consistente entre plataformas, também é importante ter uma identidade de marca consistente.
Por exemplo, uma Empresa deve ter o mesmo visual e sensação no computador desktop e no celular. E é importante ter em mente que algumas funcionalidades existem apenas em certas plataformas. Pense em um assistente de voz que permite que você faça perguntas ou controle seu celular com a voz. Muito inteligente, não é? No início, apenas celulares tinham assistentes de voz. Se o produto que você projetasse exigisse o uso de um assistente de voz, a única plataforma em que ele funcionaria seria em um celular. Mas, atualmente, assistentes de voz são integrados a muitas outras plataformas, como computadores desktop, TVs e até geladeiras.
Esse foi um papo mais de ux mas que faz sentido para quem desenvolve front tanto web quanto para app. Espero que tenham gostado.
Obrigada 🫰💚
| suamirochadev |
1,872,200 | how to use navbar in react ant design 5 | In this tutorial, we will create a navbar menu in React using Ant Design 5. We will demonstrate how... | 0 | 2024-05-31T15:39:18 | https://frontendshape.com/post/how-to-use-navbar-in-react-ant-design-5 | react, antdesign, webdev | In this tutorial, we will create a navbar menu in React using Ant Design 5. We will demonstrate how to implement an Ant Design 5 navbar with icons and provide an example of a responsive navbar using React and Ant Design 5.
<br>
[install & setup vite + react + typescript + ant design 5](https://frontendshape.com/post/install-setup-vite-react-typescript-ant-design-5)
### React Ant Design 5 Navbar Example
1.Create react ant design 5 simple navbar using react-antd Layout, Menu, Button component.
```jsx
import React from 'react';
import { Layout, Menu, Button } from 'antd';
const { Header } = Layout;
const NavBar = () => (
<Layout className="layout">
<Header style={{ display: 'flex', justifyContent: 'space-between' }}>
<Menu theme="dark" mode="horizontal" defaultSelectedKeys={['1']}>
<Menu.Item key="1" >Home</Menu.Item>
<Menu.Item key="2" >Profile</Menu.Item>
<Menu.Item key="3">Settings</Menu.Item>
</Menu>
<div>
<Button type="primary" style={{ marginRight: '10px' }}>Sign in</Button>
<Button>Sign up</Button>
</div>
</Header>
</Layout>
);
export default NavBar;
```

2.react ant design 5 navbar with icons.
```jsx
import React from 'react';
import { Layout, Menu, Button } from 'antd';
import {
HomeOutlined,
UserOutlined,
SettingOutlined,
} from '@ant-design/icons';
const { Header } = Layout;
const NavBarExample = () => (
<Layout className="layout">
<Header style={{ display: 'flex', justifyContent: 'space-between' }}>
<div className="logo" style={{ color: 'white' }}> Logo</div>
<Menu theme="dark" mode="horizontal" defaultSelectedKeys={['1']}>
<Menu.Item key="1" icon={<HomeOutlined />}>Home</Menu.Item>
<Menu.Item key="2" icon={<UserOutlined />}>Profile</Menu.Item>
<Menu.Item key="3" icon={<SettingOutlined />}>Settings</Menu.Item>
</Menu>
<div>
<Button type="primary" style={{ marginRight: '10px' }}>Sign in</Button>
<Button>Sign up</Button>
</div>
</Header>
</Layout>
);
export default NavBarExample;
```

3.react ant design 5 responsive navbar using react-antd Layout, Menu, Button, Drawer, Row, Col component.
```jsx
import React, { useState } from "react";
import { Layout, Menu, Button, Drawer, Row, Col } from "antd";
import {
HomeOutlined,
UserOutlined,
SettingOutlined,
MenuOutlined,
} from "@ant-design/icons";
const { Header } = Layout;
const ResponsiveNav = () => {
const [visible, setVisible] = useState(false);
const showDrawer = () => {
setVisible(true);
};
const onClose = () => {
setVisible(false);
};
return (
<Layout className="layout">
<Header style={{ padding: 0 }}>
<Row justify="space-between" align="middle">
<Col xs={20} sm={20} md={4}>
<div
className="logo"
style={{ color: "white", paddingLeft: "20px" }}
>
My Logo
</div>
</Col>
<Col xs={0} sm={0} md={20}>
<Menu theme="dark" mode="horizontal" defaultSelectedKeys={["1"]}>
<Menu.Item key="1" icon={<HomeOutlined />}>
Home
</Menu.Item>
<Menu.Item key="2" icon={<UserOutlined />}>
Profile
</Menu.Item>
<Menu.Item key="3" icon={<SettingOutlined />}>
Settings
</Menu.Item>
<Menu.Item key="4">
<Button type="primary" style={{ marginRight: "10px" }}>
Sign in
</Button>
<Button>Sign up</Button>
</Menu.Item>
</Menu>
</Col>
<Col xs={2} sm={2} md={0}>
<Button type="primary" onClick={showDrawer}>
<MenuOutlined />
</Button>
</Col>
</Row>
<Drawer
title="Menu"
placement="right"
onClick={onClose}
onClose={onClose}
visible={visible}
>
<Menu mode="vertical" defaultSelectedKeys={["1"]}>
<Menu.Item key="1" icon={<HomeOutlined />}>
Home
</Menu.Item>
<Menu.Item key="2" icon={<UserOutlined />}>
Profile
</Menu.Item>
<Menu.Item key="3" icon={<SettingOutlined />}>
Settings
</Menu.Item>
<Menu.Item key="4">
<Button type="primary" style={{ marginRight: "10px" }}>
Sign in
</Button>
<Button>Sign up</Button>
</Menu.Item>
</Menu>
</Drawer>
</Header>
</Layout>
);
};
export default ResponsiveNav;
```
 | aaronnfs |
1,872,199 | Why My Rubber Duck Quit on Me: A Developer’s Tale | It's no secret that we developers sometimes talk to our rubber ducks as part of the "rubber duck... | 27,390 | 2024-05-31T15:37:41 | https://dev.to/buildwebcrumbs/why-my-rubber-duck-quit-on-me-a-developers-tale-3op4 | jokes, watercooler, programming | It's no secret that we developers sometimes talk to our rubber ducks as part of the "rubber duck debugging" technique, where explaining code out loud helps uncover bugs.
But what happens when your rubber duck has had enough?Here's the tale of my rubber duck that decided to "quit"...
---
## The Resignation 💌

One morning, I found a tiny, wet resignation letter next to my keyboard. It read:
> "Dear Pachi, After years of loyal service, listening to your monologues on missing semicolons, infinite loops, and why you think JavaScript is better than anyrhing else, I've decided to step down.
> The work hours are endless, and let's be frank, you talk to me, but you never listen to what I have to say.
> I need a break. Perhaps a nice, quiet pond.
> Sincerely, Rubber Duck"
I was in shock. How could my duck leave me, especially during a particularly vexing array of bugs?
---
## The Complex Problems 🐞

As the days went on, I felt the absence of my duck deeply. I found myself whispering to my coffee mug about asynchronous functions and callback hell, but it just wasn't the same.
The coffee mug, unlike the duck, was too filled with bitterness.
I recalled the last few problems I had discussed with my duck: a CSS issue where nothing aligned, a JavaScript function that mysteriously returned NaN, and a database query that seemed to think I was asking for an existential debate rather than user data. I
t was a lot, even for the most seasoned of rubber ducks.
---
## The Search for a Replacement 🔍

Determined to fill the void, I embarked on a quest for a new debugging buddy. The journey was long and full of odd looks as I auditioned various inanimate objects: a stapler (too pointy), a plant (too leafy), and even my old graphing calculator from college (it just gave me more problems to solve).
Finally, I found a suitable replacement at a quirky little shop. It was a rubber chicken. Sure, it was unconventional, but it had a sympathetic squeak and an understanding gaze.
---
## The First Meeting 🐔

I introduced the rubber chicken to my codebase, apprehensive but hopeful. To my delight, the chicken seemed to take to its new role like a duck to water, or should I say, like a chicken to corn?
I explained my latest issue with a recursive function, and though it offered no words, its presence was oddly comforting.
---
## I will always miss you 🦆
While my rubber duck may have "quit," the memories of our sessions together will float on forever in my heart.
The rubber chicken has now taken up the mantle, proving that sometimes, a change in perspective (or species) is all you need to crack the code.
**P.S. Yes, I just lost my Rubber Duck and made up this story to feel the hole that they left 🥲🥲🥲**
**P.S.2. [Do you know WebCrumbs yet? Join us to build a better web, where Rubber Ducks won't feel like quitting](https://www.webcrumbs.org/waitlist).** | pachicodes |
1,872,198 | Web ou App? Qual o melhor para criar em Flutter? | A criação de aplicações modernas pode ser um desafio, especialmente quando se considera a necessidade... | 0 | 2024-05-31T15:35:12 | https://dev.to/suamirochadev/web-ou-app-qual-o-melhor-para-criar-em-flutter-4oio | flutter, webdev, beginners, programming | A criação de aplicações modernas pode ser um desafio, especialmente quando se considera a necessidade de alcançar usuários em várias plataformas. Flutter, um framework desenvolvido pelo Google, tem se destacado por sua capacidade de criar interfaces de usuário nativas para iOS, Android, Web e desktop com um único código-base. No entanto, quando se trata de decidir entre desenvolver para a Web ou como um aplicativo móvel (App) em Flutter, há várias considerações a serem feitas.
A principal diferença entre desenvolver para Web e para App em Flutter reside na forma como a aplicação é distribuída e utilizada. Aplicações Web são acessadas através de navegadores e não requerem instalação no dispositivo do usuário. Elas são ideais para alcançar um público amplo rapidamente, pois basta um link para que os usuários possam acessar a aplicação. Um exemplo comum de aplicação Web seria um sistema de gerenciamento de conteúdo (CMS) ou uma plataforma de e-commerce, onde o acesso instantâneo e a compatibilidade com múltiplos dispositivos são cruciais.
Por outro lado, um aplicativo móvel (App) em Flutter é instalado diretamente no dispositivo do usuário, seja ele iOS ou Android. Isso permite uma integração mais profunda com o hardware do dispositivo, como câmeras, GPS, sensores de movimento, entre outros. Aplicativos móveis também oferecem a possibilidade de funcionar offline e fornecer uma experiência de usuário mais rica e responsiva. Um exemplo clássico de um aplicativo móvel seria um aplicativo de redes sociais ou um jogo, onde a performance e a interação com o hardware são primordiais.
A escolha entre Web e App em Flutter depende muito do público-alvo e das funcionalidades desejadas. Se a prioridade é alcançar rapidamente o maior número possível de usuários com uma solução que não requer instalação, a Web pode ser a melhor escolha. Além disso, aplicações Web são mais fáceis de atualizar e manter, já que as mudanças são refletidas imediatamente sem a necessidade de download de atualizações pelos usuários.
Entretanto, se a aplicação necessita de um desempenho superior, acesso a funcionalidades avançadas do dispositivo ou uma experiência de usuário mais fluida, o desenvolvimento de um App pode ser mais apropriado. Aplicativos móveis também podem se beneficiar de notificações push e outras funcionalidades nativas que são mais limitadas ou inexistentes na Web.
No entanto, muitas vezes, um único produto pode precisar de ambas as abordagens para atender a diferentes necessidades do usuário. Por exemplo, uma empresa de serviços financeiros pode oferecer um aplicativo móvel para clientes que necessitam de acesso rápido e seguro às suas contas e transações, enquanto também oferece uma versão Web para usuários que preferem acessar esses serviços a partir de um computador desktop. Neste caso, utilizar Flutter para desenvolver tanto a versão Web quanto a versão App pode ser altamente benéfico, uma vez que permite a reutilização de grande parte do código, economizando tempo e recursos no desenvolvimento e manutenção do software.
Em resumo, a decisão entre desenvolver para Web ou App em Flutter deve ser orientada pelas necessidades específicas do projeto e dos usuários finais. Cada abordagem tem seus próprios benefícios e limitações, e muitas vezes, a melhor solução pode ser uma combinação de ambas, utilizando a flexibilidade do Flutter para criar uma experiência de usuário consistente e eficiente em múltiplas plataformas.
Obrigada 🫰 | suamirochadev |
1,872,197 | Privacy Assured: Inside Crawlbase's Data Security and Privacy | Crawlbase adheres to a strict policy of not keeping or logging any customer information and secure data during transmission. | 0 | 2024-05-31T15:34:33 | https://dev.to/crawlbase/privacy-assured-inside-crawlbases-data-security-and-privacy-38ki | datasecurity, dataprivacy | ---
title: Privacy Assured: Inside Crawlbase's Data Security and Privacy
published: true
description: Crawlbase adheres to a strict policy of not keeping or logging any customer information and secure data during transmission.
tags: datasecurity, dataprivacy
# cover_image: https://crawlbase.com/blog/data-security-crawlbase/data-security-crawlbase.jpg
# Use a ratio of 100:42 for best results.
# published_at: 2024-05-31 15:27 +0000
---
This blog was originally posted to [Crawlbase Blog](https://crawlbase.com/blog/how-to-scrape-google-finance/?utm_source=dev.to&utm_medium=referral&utm_campaign=content_distribution)
Ensuring [data security and privacy](https://crawlbase.com/blog/how-proxies-improve-data-security-and-privacy/) is paramount in today's digital landscape, especially for businesses relying on web scraping and data extraction. **[Crawlbase](https://crawlbase.com/)**, a leading web data extraction platform, prioritizes security measures and privacy controls to safeguard customers' confidential information from unauthorized access. Crawlbase has comprehensive suite of APIs, including **[Crawling API](https://crawlbase.com/crawling-api-avoid-captchas-blocks), [Crawler](https://crawlbase.com/anonymous-crawler-asynchronous-scraping) for [Enterprises](https://crawlbase.com/enterprise), [Scraper API](https://crawlbase.com/scraper-api-auto-parse-web-data), [Screenshots API](https://crawlbase.com/screenshots-api), [Storage API](https://crawlbase.com/cloud-storage-for-crawling-and-scraping) and [Smart Proxy](https://crawlbase.com/smart-proxy)** which allow secure website crawling and cloud storage.This allows safe data encryption maintaining strict data privacy standards.
<!-- more -->
As a **GDPR and CCPA compliant** company, Crawlbase employs advanced security practices, identity management protocols, and encryption techniques to secure data during transmission and storage. This blog delves into the intricate details of Crawlbase's data security and privacy policy, exploring the measures taken to [protect sensitive information](https://crawlbase.com/faq/general), [prevent data loss](https://crawlbase.com/faq/general), and [mitigate security vulnerabilities](https://crawlbase.com/faq/general), ensuring businesses can confidently crawl websites and extract data without compromising data availability or integrity.
[Crawlbase Privacy Policy](https://crawlbase.com/privacy) outlines fair and transparent practices for collecting user information while giving users control over their accounts and personal data. As long-time advocates of data freedom, Crawlbase is fully committed to upholding these consumer protection standards globally.
One of Crawlbase's core principles is **maintaining user anonymity** during data extraction processes. The platform operates stealthily, concealing users' actions and identities while scraping valuable insights like market trends and competitor analysis from online sources. Crawlbase emphasizes that anonymity is the user's "greatest ally" in data-driven decision-making, enabling precise extraction of strategic information **without revealing one's identity**.
While the content does not explicitly detail what user data is collected, Crawlbase extracts only the necessary information required for its services like your basic account information. Crawlbase has protocols in place to handle user data responsibly and provide appropriate data protection.
At Crawlbase, safeguarding user privacy is the top priority. The platform adheres to a strict policy of **not keeping or logging any customer information**, ensuring that user data remains secure and confidential.
Crawlbase operates on the principle of data minimization, collecting and retaining only the essential information required to provide its services. The platform **does not store or log any personal or sensitive data**, such as payment information, or browsing histories. This approach significantly reduces the risk of data breaches and unauthorized access, as there is no customer information to be compromised.
Crawlbase employs an ephemeral data handling model, where user data is processed and delivered in real-time, **without being stored or cached** on the platform's servers. This ensures that user data is not retained or logged beyond the immediate processing requirements, further enhancing privacy and security.
Once the requested data has been delivered, it is securely purged from Crawlbase's systems, leaving **no trace of user activities or information**.
By adhering to this strict policy of not keeping or logging any customer information, Crawlbase demonstrates its unwavering commitment to user privacy and data security.
## How does Crawlbase secure data
Crawlbase ensures the security of your data through encryption protocols, access controls, and proactive security measures. Crawlbase website undergoes regular scans for security vulnerabilities and malware to ensure a safe browsing experience for the users.
Personal information provided to Crawlbase is stored securely behind protected networks, accessible only to authorized personnel with strict confidentiality obligations. Additionally, the sensitive data you provide is encrypted using Secure Socket Layer (SSL) technology and stored securely, with passwords hashed to prevent reversibility.
To further safeguard your information, Crawlbase implements a range of security measures whenever you place an order, submit, or access your data on it. These measures are designed to maintain the integrity and safety of your information throughout your interaction with the services.
## How is data at Crawlbase secured during transmission?
During transmission, data accessed through Crawlbase APIs is encrypted using strong encryption algorithms, such as SSL/TLS, to prevent unauthorized interception or tampering. This ensures that data remains secure while being transferred between servers and the user’s systems.
Crawlbase offers a [Smart Proxy solution](https://crawlbase.com/smart-proxy) that enables users to route their web scraping traffic through a network of secure proxy servers. These proxies act as intermediaries, concealing the user's real IP address and location, ensuring anonymity during data extraction processes.
It also supports IP rotation, which automatically cycles through multiple IP addresses, making it more difficult for target websites to detect and block scraping activities. This feature enhances the reliability and success rate of web scraping operations while maintaining data security.
## Where does Crawlbase store the data?
**Account Information:** Crawlbase securely store account information, like email addresses, passwords, and other account settings, in **encrypted databases** hosted on trusted cloud infrastructure providers. Access to this data is strictly controlled and limited to authorized personnel.
**Billing information:** Crawlbase partners with trusted third-party providers such as [Stripe](https://stripe.com/en-ro) or [Paddle](https://www.paddle.com/) to securely handle your payment information. Crawlbase never stores, collect, or have access to any payment information. Your billing details, including payment methods and transaction history, are securely stored by these third-party providers in compliance with industry-leading security standards.
**Crawled data:** Crawlbase does not store or cache any data obtained through API unless specified or if the [Storage API](https://crawlbase.com/cloud-storage-for-crawling-and-scraping) has been utilized by the user to store the data. The API response, which includes the crawled data, is transmitted directly to the user without any interim storage on Crawlbase servers. However, in cases where users request scraped data instead of the entire HTML response of the page, certain data may be temporarily stored on secure cloud for processing purposes.
## Security compliance at Crawlbase
Yes, Crawlbase adhere to strict security compliance standards to ensure the protection of user data. Crawlbase practices are in line with industry best practices and regulatory requirements, including **GDPR compliance**. Crawlbase regularly assess and update its security measures to maintain compliance with evolving standards.
## Methods Crawlbase use to secure Infrastructure
Crawlbase prioritize security to keep your data safe and our platform reliable. We do this by using multiple layers of protection, including regular security checks, simulated attacks (penetration testing), and strong security measures. We also partner with reputable providers who meet high security standards to host our infrastructure.
## Customer Data Security during API Usage:
At Crawlbase, ensuring the security and integrity of customer data during API usage is the top priority. The platform employs a comprehensive approach to protect user data and prevent unauthorized interference.
### Robust API Security Measures
1. **Crawlbase's APIs** are designed with robust security protocols to safeguard user data.
2. The APIs utilize industry-standard encryption techniques, such as SSL/TLS, to ensure that all data transmitted between the user's device and Crawlbase's servers is encrypted and protected from interception.
3. Crawlbase implements strict access controls and authentication mechanisms, ensuring that only authorized users with valid credentials can access and interact with the APIs.
### Comprehensive Data Protection
1. Crawlbase does not store or log any customer information, including login credentials, payment details, or browsing histories. This minimalistic approach significantly reduces the risk of data breaches and unauthorized access.
2. The platform utilizes a pool of millions of proxies and employs advanced [IP rotation](https://crawlbase.com/blog/rotating-ip-address/) techniques to protect user IP addresses and maintain anonymity during web scraping operations.
3. Crawlbase's AI-powered solutions are designed to handle complex websites, ensuring successful data extraction while adhering to strict security protocols.
By implementing these security measures, Crawlbase ensures that when customers utilize its APIs, their data remains secure and cannot be compromised or interfered with by unauthorized parties.
Crawlbase is committed to providing comprehensive resources to address any inquiries regarding its data security and privacy policies. As an industry leader in web crawling and scraping solutions, Crawlbase offers a **wide range of developer resources** like detailed documentation, libraries and SDKs to ensure transparency and facilitate a thorough understanding of its robust security measures.
### Extensive Documentation
Crawlbase maintains **[detailed documentation](https://crawlbase.com/docs/)** covering its various product offerings, including the Crawling API, Scraper API, Screenshots API, Smart Proxy, Cloud Storage, and Leads API. This documentation provides in-depth insights into the platform's security protocols, data handling practices, and compliance measures, enabling customers to thoroughly review and assess Crawlbase's approach to data security and privacy.
### Developer Resources and Support
1. Crawlbase's developer resources include [libraries & SDKs](https://crawlbase.com/crawling-libraries-sdk), [tutorials](https://www.youtube.com/channel/UCjCGpQMvzq5qi-nnzDsftlg), and [24/7 support](https://crawlbase.com/contact), ensuring that customers have access to the necessary tools and guidance to effectively leverage the platform's capabilities while adhering to industry best practices for data security and privacy.
2. Regular [product status](https://status.crawlbase.com/) updates and [feature request](https://crawlbase.com/request-feature) submissions allow customers to stay informed about the latest developments and contribute to the platform's evolution, fostering a collaborative approach to addressing emerging security challenges.
3. [Crawlbase's blog](https://crawlbase.com/blog/) serves as a valuable resource, featuring articles and insights on web crawling, scraping, and related topics, including data security and privacy considerations.
### Proven Track Record and Customer Testimonials
With [over 70,000 customers worldwide](https://crawlbase.com/), Crawlbase has established itself as a trusted and reliable partner for businesses seeking secure and scalable web data extraction solutions. [Positive customer feedback](https://crawlbase.com/#:~:text=Client%20Feedback-,Trusted,-by%20customers%20worldwide) highlights the ease of use, scalability, and reliability of Crawlbase's services, further reinforcing its commitment to delivering robust and secure solutions.
By providing comprehensive documentation, developer resources, and customer support, Crawlbase empowers its customers to thoroughly review and understand its data security and privacy policies, fostering a transparent and collaborative approach to addressing the evolving challenges of data protection in the digital age.
## Conclusion
Crawlbase understands the importance of your data privacy and takes proactive measures to ensure it remains protected at all times.
Rest assured, every piece of information you entrust to Crawlbase is handled with the highest level of confidentiality and security protocols.
Crawlbase team continuously monitors and updates systems to maintain the integrity and safety of your data.
| crawlbase |
1,872,158 | The Complete Guide to JavaScript Reporting Tools | Learn everything you need to know about JavaScript Reporting Tools in this complete guide about adding these features to your web applications. | 0 | 2024-05-31T15:31:17 | https://medium.com/mesciusinc/the-complete-guide-to-javascript-reporting-tools-2f6bf4d5a190 | webdev, devops, javascript, productivity | ---
canonical_url: https://medium.com/mesciusinc/the-complete-guide-to-javascript-reporting-tools-2f6bf4d5a190
description: Learn everything you need to know about JavaScript Reporting Tools in this complete guide about adding these features to your web applications.
---
In the constantly evolving landscape of data analysis, the ability to gain insights from your information is crucial for organizational success. Traditional reporting methods, which use elements such as static formats and manual processes like data entry, can become a bottleneck for a company. JavaScript reporting tools, however, offer a game-changing solution by streamlining the reporting process, making it easy for a business to convert its raw data into actionable insights from any machine at any time.
Join us as we review the current JavaScript landscape, the shift from desktop-based to web-based applications, and how JavaScript reporting solutions can help you manage your data and reporting. We’ll look at the core functionalities of these tools, talk about the benefits JavaScript brings to the table in the reporting world, and jump into implementing a reporting solution ourselves using ActiveReportsJS in a JavaScript web application.
## The Current JavaScript Landscape
The world of JavaScript is an ever-shifting landscape. It seems that, almost daily, new frameworks are released, existing frameworks are updated, and new technologies are being talked about. Even then, we’ve still seen several frameworks and libraries rise to the top. Frameworks like Angular and Vue, libraries such as React, and all of the off-shoot libraries and frameworks they’ve inspired have come to dominate the world of web-based technologies. We’ve even seen the extension of the JavaScript language itself with the creation of TypeScript, designed specifically for the development of large-scale applications that we’ve come to use regularly.
Though there are many different technologies out there for building web applications, we’re going to focus on a few of the major ones:
- **Angular**: Starting as AngularJS, Angular is a TypeScript-based open-source framework managed by the Angular Team at Google. It was one of the earliest “modern” frameworks to be adopted into public use and has been the spark for several other libraries and frameworks.
- **React**: Maintained by Meta, React is different from other web frameworks in that it is itself a JavaScript library and not a fully-fledged framework. It was created to improve the process of designing and building user interfaces, allowing developers to use a structured approach when building their UI components.
- **Vue.js**: Like Angular, Vue.js is an open-source framework based on JavaScript that uses the model-view-view-model structure. Based on the original AngularJS, Vue is designed as a lightweight, Angular-alternative framework.
- **Svelte**: A framework that has grown in popularity in recent years, Svelte is also JavaScript-based. Unlike some other popular frameworks used, Svelte does away with much of the boiler-plating required by other frameworks.
- **Next.js and Nuxt.js**: Based on React and Vue.js, respectively, Next.js and Nuxt.js serve as extensions of their parent frameworks. Their goal is to allow developers to build full-stack applications more easily, including improvements to features such as server-side rendering.
Now that we have an idea of some of the more popular technologies used in modern web development, let’s take a closer look at the rise of web-based applications and how they’re slowly replacing desktop applications in our current ecosystem.
## The Rise of Web-Based Applications
Over recent years, we’ve seen the way that businesses operate undergo a fundamental change. Not so long ago, desktop applications ruled the business realm. Today, web-based applications are rapidly taking center stage, transforming how work is completed. This rise of web apps is fueled by several key advantages that make them a compelling alternative to traditional desktop software.
**Accessibility**
In the past, software was required to be installed on the machine on which it was intended to be used. This limited users to the physical location at which the software had been loaded. Since web apps run within a browser, they’re accessible from any device that can maintain an internet connection. This streamlines deployment, updates, and maintenance. Developers now only have to make changes in a single location, and each user will receive the associated updates without the need to download any additional software.
**Collaboration**
In a business environment, the ability to collaborate in real-time on tasks is crucial, something desktop applications have struggled with in the past. Thanks to the ability to modify and update data in real-time, as well as the improvements that we’ve seen in cloud-based storage over recent years, it has never been easier to collaborate on tasks and issues with web-based applications.
**Scalability**
As businesses grow, their software needs to be able to grow with them. With cloud-based computing, you can easily scale your resources up or down based on your business requirements. This eliminates the need for constant hardware upgrades on individual desktops, saving businesses time and money.
While desktop applications still hold value for specific needs, such as high-performance computing or specialized software, the advantages of web applications have become undeniable. With the rise of web applications has come the rise of libraries that previously only existed for desktop applications, and there are few operations more important to an organization than proper data reporting. In the next section, we’ll discuss some of the benefits of a JavaScript reporting solution and how you can take advantage of it to improve your business’s workflow.
## Improving Workflow with JavaScript Reporting Tools

Utilizing a JavaScript reporting solution can significantly improve a company’s workflow, allowing easy access to the necessary reports at a moment’s notice and improving collaboration between departments, all while being able to be integrated into existing systems. Not only that, but JavaScript reporting tools also make it easy to alter and edit these reports on the fly, from changing the core data being loaded to drilling down deeper into the data being displayed to allow for better insights.
Now, let’s look at several ways utilizing JavaScript Reporting Tools can improve your workflow.
**Boosting Efficiency**
JavaScript reporting tools can streamline the way that you handle report generation. You can easily design report templates that automatically pull data from your chosen sources and populate themselves with said data. This removes the need for users to create and format each report manually.
Additionally, this improves the data collection and processing pipeline. You’ll no longer need to gather and manipulate your data for reports manually; these tools will automate the process, ensuring you have access to the latest information.
Finally, by integrating reporting tools into an existing JavaScript application, users can access their reports anywhere, anytime. Now, when users are out in the field, they’ll be able to pull up whatever report they require, knowing that it will be supplied with the latest data.
**Enhancing Data Visualization**
Legacy reports often come in the form of static spreadsheets and tables, which can be cumbersome to analyze and limited in their ability to convey business insights properly. JavaScript reporting libraries offer a better alternative. By leveraging these tools, you can create interactive charts and graphs that bring your data to life. These dynamic visualizations allow users to convert complex information into a user-friendly format, making it easier to identify trends and patterns at a glance.
This interactivity extends beyond just visually altering the data. Dynamic reports empower users to dig deeper into their data. With features like drill-down capabilities, users can explore specific data points in greater detail. This exploration allows users to gain a deeper understanding of their data, leading to better insights that may be missed in a traditional report.
**Customizable Reports**
The era of one-size-fits-all reports is long over. JavaScript reporting tools enable developers to create a user-centric reporting experience, allowing users to create reports that fit their needs. With these tools, users can leverage filters and sorting options to focus on the information that matters most to them and zero in on the details that drive their decision-making.
However, customization goes beyond filtering. JavaScript reporting libraries offer the capability to combine reports in a master-child structure through subreports. Easily pass data from a master report to a child report and allow the child report to build itself based on the parameters that it was given.
**Improved Collaboration**
JavaScript reporting solutions can transform report creation from a solitary task into a collaborative process. Reports can be easily shared and accessed by team members in real-time, creating an environment for discussion and feedback between members. No more waiting for updated versions or struggling to ensure everyone is working with the same information. This streamlines communication and keeps everyone on the same page.
Furthermore, this real-time collaboration creates a new level of transparency and accountability. With updates visible to everyone instantaneously, team members can see how changes and edits are made to the report., creating a sense of ownership and investment in the final product. The ability to track changes also simplifies revision history and reverting to previous versions if needed.
**Integration with Existing Systems**
Many developers already have a complex system in place for collecting and storing their users’ data, and they don’t want to be required to integrate an entire reporting system into their existing infrastructure. Thankfully, JavaScript reporting tools don’t exist in a silo.
These libraries make it easy to seamlessly connect to your existing database infrastructure and applications, retrieving data quickly and easily. This eliminates the need for manual data transfer and ensures that your reports are based on a consistent source of up-to-date information. By integrating your reporting within your existing systems, you can create a unified workflow for data analysis and reporting.
If your system requires that your users provide authorization to access the data for your reports, JavaScript reporting tools make it possible to provide that information as well. Easily pass authorization tokens, HTTP headers, and query parameters along with the data request made by the JavaScript reporting library.
## JavaScript Reporting Solution Features and Uses

Now that we’ve reviewed the current web development landscape and why we’re seeing a migration of apps that would have previously been created as desktop applications to the browser environment, it’s time to examine what makes a quality JavaScript reporting solution.
As we mentioned previously, there are many benefits to transitioning to using JavaScript reporting tools over desktop tools, but outside of the benefits, what features do these solutions offer, and how can they be used to enhance your report workflow? Let’s look at some of the most popular JavaScript report components and explore their use cases.
**Interactive Charts and Graphs**
Gone are the days of static charts and graphs. JavaScript reporting tools allow you to create dynamic and interactive charts and graphs. By embedding these tools into your report, you can enable your users to bring complex data to life. With the ability to interact with these charts and graphs, users can manipulate the components to view their data in different ways, allowing them to identify trends, patterns, and relationships within the information.
In addition to the top-level interactivity, these components provide additional insights through the drill-down/drill-through features included with the controls. This functionality allows your users to explore specific data points in greater detail, allowing them to focus deeply on how they affect the overall report.
**Use Cases**: Interactive charts and graphs allow your users to create complex financial reports where data analysts can dig deep into the financial state of your business. In addition, these features are crucial for reports that monitor data such as web traffic, demographics, and social media engagement.
**Filtering and Sorting Data**
Static reports can often overwhelm users with information irrelevant to what they’re looking for; treading through a sea of information for specific data points can be intimidating and time-consuming. This process can be a major roadblock to effective data analysis. JavaScript reporting tools come to the rescue with filtering and sorting functionalities, empowering users to navigate large amounts of data with ease.
With filtering options, you can exclude irrelevant data and focus on the information that impacts your immediate decision-making. Sorting, on the other hand, helps users bring order to the chaos of their data. By sorting data by date, category, or other relevant metrics, your users can quickly identify patterns and outliers within your data. These combined functionalities transform data exploration from a chore into an insightful experience.
**Use Cases**: Sales managers can filter reports by region or product line to view sales targets versus actual sales and make decisions based on that information, while marketing teams can segment customer data by demographics, interests, and location.
**Customizable Layouts and Branding**
Effective reports not only convey data clearly but also present it in a way that connects with users. JavaScript reporting solutions go beyond basic functionality by offering customizable layouts and branding options. This allows you to design reports that are not just informative but also properly align with your brand identity.
Customizable layouts allow you to create reports with a professional and organized structure. Define headers and footers and arrange data elements in a way that facilitates easy understanding and information flow. In addition, branding options allow you to incorporate your company logo, color schemes, and fonts to not only the reports themselves but also to the report designer and viewer to ensure that your reports and reporting infrastructure are recognizable and consistent with your brand image. This professional presentation not only enhances the credibility of your report but also fosters trust and reinforces brand recognition with your audience.
**Use Case**: Adding company logos and color schemes, formatting reports for different audiences (e.g., executives versus sales teams), and customizing layouts for specific data sets.
**Seamless Data Integration**
The foundation of any good report is accurate and up-to-date data. However, manually gathering information from disparate sources can be a time-consuming and error-prone process. JavaScript reporting solutions bridge this gap by offering seamless data integration capabilities and connecting your reporting tool to various data sources, including databases, REST APIs, and CRM systems.
By establishing a direct connection with your data sources, JavaScript reporting tools ensure your reports are always based on the latest and most reliable information. This not only saves time and effort but guarantees the credibility and trustworthiness of your reports. In addition, integration eliminates the need for manual data manipulation and transfer, minimizing your risk for error. This streamlined approach to data access empowers you to focus on analysis and insights rather than fighting with data collection.
**Use Cases**: Pulling sales data from your CRM, extracting marketing campaign metrics from analytics platforms, and integrating financial data from accounting software.
**Combine Reports with Subreports**
Imagine a complex report that requires presenting a high-level overview alongside detailed breakdowns for specific sections. Traditional reports might struggle to achieve this balance, often forcing users to toggle between separate documents or navigate through nested tables. JavaScript reporting tools offer a superior solution with subreports, a functionality that allows you to create a hierarchical structure within your report ecosystem.
Subreports act as mini-reports that can be embedded in larger reports. They allow you to pass data from the parent report to the subreport, which in turn allows the subreport to display associated data based on what the parent report provided without cluttering the main report. This nested structure enhances clarity and organization, providing users with a view of the data at different levels of granularity. This allows users to understand the big picture of the report while having the flexibility to explore specific areas of interest in greater depth.
**Use Cases**: Display a breakdown of sales figures by category, region, or sales rep, complement a financial performance report with detailed income statements and balance sheets, and showcase detailed information on specific items in an inventory management report.
## Implementing a JavaScript Report Designer into a JavaScript Application
Now that we’ve reviewed the benefits, features, and use cases of JavaScript reporting solutions, it’s time to look at implementing JavaScript reporting tools in a web application. For our example, we’ll be using the ActiveReportsJS Report Designer, which supports not only JavaScript but many of the other large web frameworks, such as Angular, React, and Vue.
**Project Setup**
Since we’re going to be implementing the Report Designer into a JavaScript application, there’s very minimal setup required on our end. For this demonstration, we will be using VisualStudio Code as our IDE. So, open up an instance of the application and create a new HTML file with the following content:
```
<!DOCTYPE html>
<html lang="en">
<head>
<meta charset="UTF-8">
<meta name="viewport" content="width=device-width, initial-scale=1.0">
<title>JavaScript Reporting Solution</title>
</head>
<body>
</body>
</html>
```
In addition, to run the application, we will be using the [Live Server](https://marketplace.visualstudio.com/items?itemName=ritwickdey.LiveServer) plugin for VSCode. This will make it easier to launch the application from the IDE.
**Installing the Required Files**
Now that the HTML file is set up, it’s time to install the ActiveReportsJS files. There are a couple of different options that we have when it comes to installation:
- Installing the [NPM packages](https://www.npmjs.com/package/@grapecity/activereports)
- Downloading the files from the [ActiveReportsJS website](https://developer.mescius.com/activereportsjs/download)
- Referencing the files via [CDN](https://developer.mescius.com/activereportsjs/docs/GettingStarted/Installation)
For this application, we will reference the files via the CDN, but if you would like to use another avenue of installation, you can reference the links above.
Back inside the HTML file, add the following script and link tags inside of the head tag:
```
<link rel="stylesheet" href="https://cdn.mescius.com/activereportsjs/4.latest/styles/ar-js-ui.css" type="text/css" />
<link rel="stylesheet" href="https://cdn.mescius.com/activereportsjs/4.latest/styles/ar-js-designer.css" type="text/css" />
<script src="https://cdn.grapecity.com/activereportsjs/4.latest/dist/ar-js-core.js"></script>
<script src="https://cdn.grapecity.com/activereportsjs/4.latest/dist/ar-js-designer.js"></script>
```
There are four files that need to be included in the application for the JavaScript report designer to run properly:
- ar-js-ui.css
- ar-js-designer.css
- ar-js-core.js
- ar-js-designer.js
The ar-js-ui.css and ar-js-core.js files are the core CSS and JavaScript files required by the reporting solution, and the designer.css and designer.js files are used to implement the reporting solution designer.
Now, with the necessary files included in the HTML file, we can integrate the report designer into the application.
**Integrating the Report Designer**
With everything set up, we can move on to the implementation process. First, we will need to set up an HTML element to which we can bind the report designer. Inside of the body tag, add the following:
```
<div id="designer-host"></div>
```
Now, we will add a bit of custom CSS so the designer takes up the entire browser view. Inside of the head tag, add the following style tag:
```
<style>
#designer-host {
width: 100%;
height: 100vh;
}
</style>
```
Finally, we will include some JavaScript that will bind the report designer to the previously created HTML element. Add the following script tag within the body tag:
```
<script>
var designer = new GC.ActiveReports.ReportDesigner.Designer("#designer-host");
</script>
```
That’s all it takes! With the Live Server plugin installed, click on the “Go Live” button in the bottom-right of VSCode to launch the application in your default browser:
With the report designer loaded into the application, we can proceed to build a sample report in the next section.
## Building JavaScript Reports
Now that we’ve added a JavaScript report designer to the web application, we can talk about how you can use the designer to build your own report. Thankfully, building reports is as easy as including the report designer in our application. In this section, we’ll be doing a brief overview of the different sections of the designer, binding data to a report, adding a table and loading data into the control, and learning how you can preview the report in the designer.
**Report Designer Overview**
The report designer is made up of five different sections:
- Toolbar
- Control Toolbox
- Report Layout
- Properties Panel
- Data Panel
**Toolbar**
The toolbar is located at the top of the report designer and is used for saving, loading, and previewing reports. It also gives you the ability to do some basic text and paragraph styling.
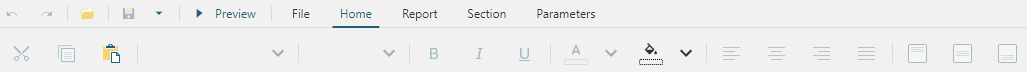
The toolbar includes three other tabs: **Report**, **Section**, and **Parameters**.
The Report tab allows you to add either additional continuous sections if you are creating a Continuous Page Layout report or new pages to your report if you’re building a Fixed Page Layout report.
The Section tab allows you to add and delete sections from your report, such as page headers and page footers.
The Parameter tab allows you to view existing parameters, which can be used to give users more interactivity with the report. It also allows you to modify the parameter view that users will see when selecting parameters for the report.
**Control Toolbox**
The control toolbox is accessed on the left-hand side of the report designer and can be viewed in greater detail by clicking on the hamburger menu in the designer:
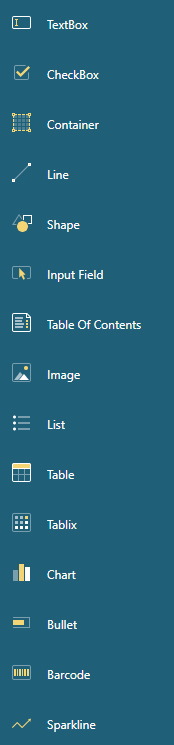
When expanded, it will display a scrollable list of all the controls available to be included in a report. From here, users can drag and drop report components from the toolbox onto the report area to add them to their report.
**Report Layout**
The Report Layout is a visual surface in the form of a page that displays the report items for the user, allowing them to select and re-arrange them.
You can also use the bars on the top and left sides of the report area to adjust the margins of the pages.
**Properties Panel**
The Properties Panel, located on the right-hand side of the designer, is opened by default and allows you to modify report item properties.
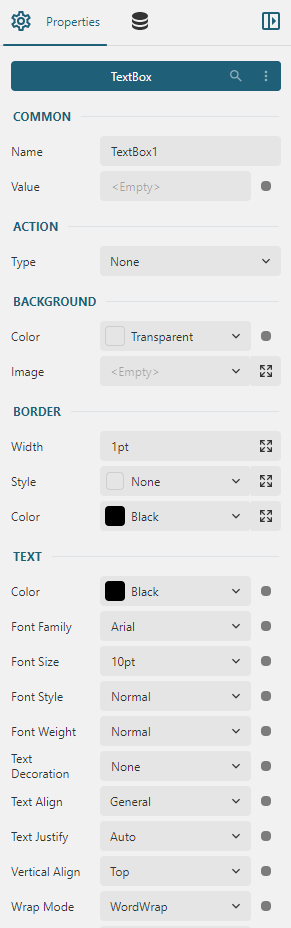
As you can see in the image above, we are looking at some of the properties of a **TextBox** control. The properties panel will display the control we currently have selected, as well as all of the associated properties available for that control.
This panel offers your report designers complete control over the look, feel, and formatting of each control they include in their report, allowing them to design their controls to fit their needs.
**Data Panel**
The last piece of the designer to examine is the data panel. Here, report authors can bind to a data source and create a data set from the data that is being pulled from the source. Authors can also use the data panel to create parameters, which dictate what data is being displayed in the report, creating a layer of interactivity between the report and the user.
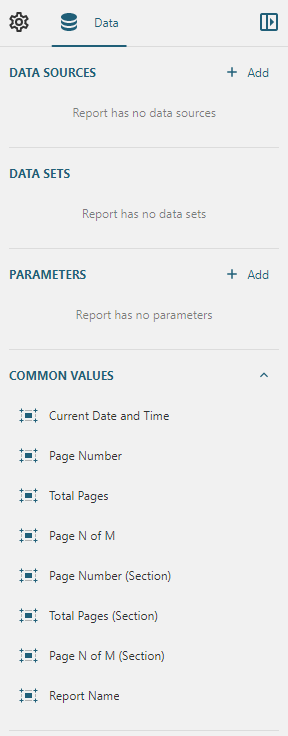
**Binding Data to the Report**
Now that the basics of the designer have been covered, we can take a quick look at building a report. To do so, we’ll need to add some data that can be loaded into a report control, so we’ll add a data source and data set to the report.
To add a new source, simply click the **Add** button under the data source section. This will bring up the data source creation wizard:
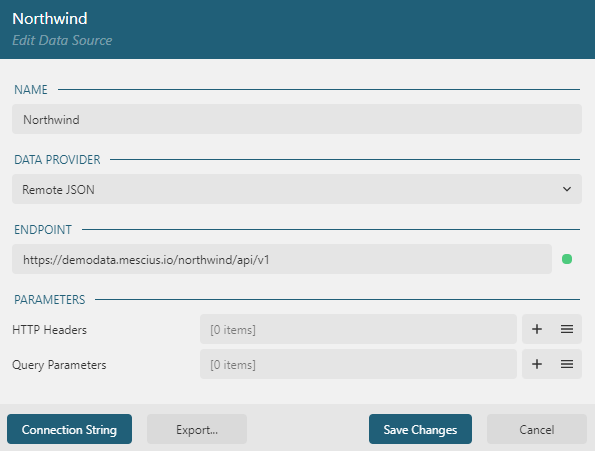
The data source creation wizard includes several fields that we can define to set up the data source:
- Name: The name we’re giving to the data source in the report.
- Data Provider: How we expect to retrieve data and the format in which it comes. Currently, report authors can select from **Remote JSON**, **Remote CSV**, **Embedded JSON**, and **Embedded CSV**.
- Endpoint: The endpoint from where we’ll be getting data. If you are using embedded data, instead, you’ll be given an option to upload a file containing the data.
- Parameters: Authors also have the ability to pass HTTP Headers and Query Parameters to the backend via the report designer, which can be set up here.
With everything we need set up, we can hit the **Save Changes** button.
Now, with the data source set up, we can create a data set to hold data from the source. To create a data set from a source, simply click the **Plus** button next to the data source that you want to use to bring up the data set creation wizard:
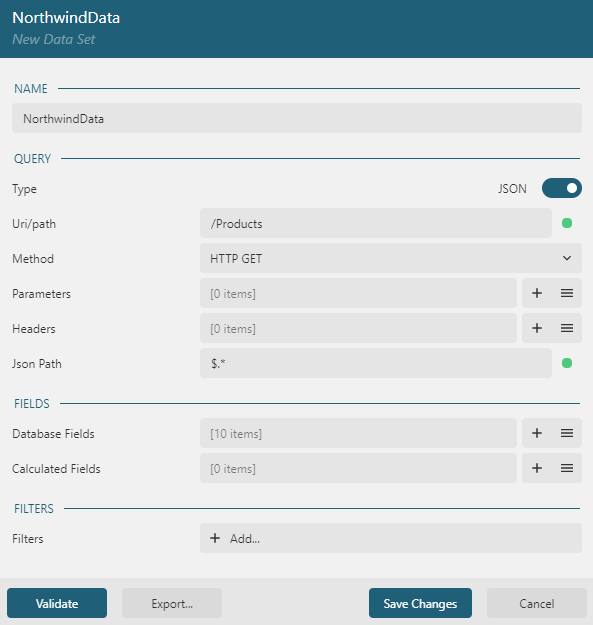
The important elements we’re setting in this example are the **Uri/path** and **Json Path** fields. The Uri/path will direct the report to the data source from where the data should be retrieved (in this case, we’re retrieving information from the “Products” data set). The Json Path tells the report designer if any filtering should be done on the data; in our case, we want to retrieve all of the data, so we use the Json Path `$.*`.
For more information on Json Paths, Oracle has detailed documentation outlining what’s possible, which you can find [here](https://docs.oracle.com/cd/E60058_01/PDF/8.0.8.x/8.0.8.0.0/PMF_HTML/JsonPath_Expressions.htm).
**Adding a Table Control**
With the data bound to the report, we can include the data in a control. For this article, we’ll simply add a table to the report, bind our data, and then modify some properties to improve the look of the table.
First, drag and drop a table control from the control toolbox onto the report layout. Then, right-click on one of the cells and add two more columns to the table. When complete, it should look something like this:

To make it easier to bind data, you don’t need to manually enter each individual field that you want to include from your data set. Instead, ActiveReportsJS provides a context menu to make it easy to select what fields you want to include.
Hover over one of the cells and click the box with the ellipse. This will bring up the data set context menu:
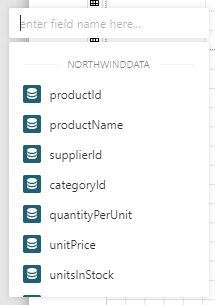
You can either use the search bar to find the field that you want or select fields from the scrollable list.
We’re going to add a few different fields: **productId**, **productName**, **unitPrice**, **unitsInStock**, and **unitsOnOrder**:
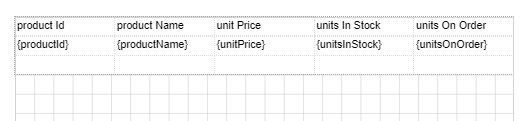
Finally, we’re going to add a few styling settings to the table:
- Adding a background color for the header row
- Adding borders to the table cells
- Setting the unitPrice column formatting to currency formatting
Now, we can move on to previewing the report.
**Previewing the Report**
With everything set up, we can preview the report to see what the users will see when they load it.
To preview the report, simply click on the **Preview** button on the toolbar of the designer:
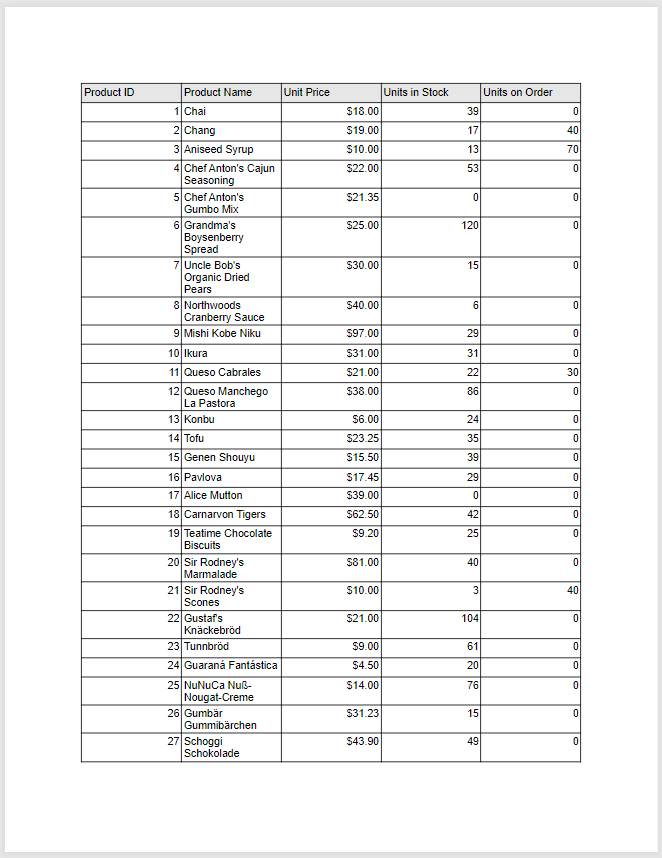
As you can see, binding data to and modifying a control is that easy!
## Conclusion
Equipping yourself with the right tools is paramount for navigating the ever-increasing demands of data analysis in today’s business world. JavaScript reporting solutions have emerged as a powerful ally, transforming how you interact with and extract value from your data. By offering functionalities like interactive visualizations, user-friendly customization, and seamless data integration, these tools empower you to create clear, insightful, and actionable reports. This, in turn, fosters better decision-making, streamlines collaboration, and unlocks the true potential of your data. So, embrace the power of JavaScript reporting and watch your data transformation journey unfold!
This article has provided a springboard for your exploration of JavaScript reporting solutions. We’ve explored the current JavaScript landscape, the rise of web-based applications, and the core functionalities of these tools. Remember, the knowledge gained here is just the beginning. With the plethora of JavaScript reporting solutions available, you can find the perfect tool to fit your specific needs and propel your organization toward data-driven success. Now, take the next step and dive deeper into the world of JavaScript reporting. Experiment with different tools, explore advanced functionalities, and witness the transformative power of data visualization and insightful reporting for yourself! | chelseadevereaux |
1,866,990 | Add Advanced Features to Your Discord Bot Without Code (Discord.js + Robo.js) | Got a Discord Bot you'd like to enhance with advanced features? Robo.js is a powerful framework... | 0 | 2024-05-31T15:30:00 | https://blog.waveplay.com/easily-add-advanced-features-to-your-discord-bot-without-coding-discord-js-robo-js/ | javascript, node, programming, discord | Got a **Discord Bot** you'd like to enhance with advanced features? **[Robo.js](https://roboplay.dev/docs)** is a powerful framework compatible with **[Discord.js](https://discord.js.org/)** with a **[plugin system](https://docs.roboplay.dev/plugins/overview)** so powerful, you can add new features to your bot without writing a single line of code. If you're a beginner, you can add powerful features as you learn how to code the rest of it!

## Creating a New Discord Bot
If you haven't already created a **Discord Bot**, you can do so by running the following command in your terminal:
```bash
npx create-robo <projectName> -k bot
```
This will spawn a new **Robo.js** project ready to use as a **Discord Bot**. We call these **Robos**.
## Adding Features
Once you have your **Discord Bot** set up, you can add new features using **[Robo Plugins](https://docs.roboplay.dev/plugins/overview)**. These plugins integrate seamlessly with your **Robo** to provide new functionality as if you had written the code yourself. For example, you can add AI chatbot capabilities, moderation tools, maintenance mode, economy systems, and more.
Run this in your terminal, replacing <package> with the name of the plugin you want to install (e.g. **[@robojs/ai](#)**):
```bash
npx robo add <package>
```
This will install the package and register it in your Robo's configuration. To install many at once:
```bash
npx robo add @robojs/ai @robojs/moderation @robojs/server
```
You can also create a new Robo project with plugins pre-installed:
```bash
npx create-robo <projectName> --plugins @robojs/ai @robojs/moderation
```
## Existing Bots
If you have an existing **Discord.js Bot** and want to add new features, you'll need to **[migrate](https://docs.roboplay.dev/docs/discord-bots/migrate)** your bot to **Robo.js**. This process is straightforward and involves moving your existing code into the **[Robo File Structure](https://docs.roboplay.dev/robojs/files)**.
Once your bot is migrated, you can add new features using **Robo Plugins** as described above.
## Where to Find Plugins
You can find a list of available plugins in the **[Robo Plugin Directory](https://docs.roboplay.dev/plugins/directory)**. Browse through the directory to find plugins that suit your needs and add them to your bot. You can also **[create your own plugins](https://docs.roboplay.dev/plugins/create)** and share them with the community.
➞ [🔌 **Plugin Directory:** Explore more plugins](https://docs.roboplay.dev/plugins/directory)
What's more, **Robo.js** comes with a lot of other features and tools to help you build your bot faster and more efficiently, such as **[Flashcore Database](https://docs.roboplay.dev/robojs/flashcore)** to persist data easily, **[TypeScript](https://docs.roboplay.dev/robojs/typescript)**, **[Easy Hosting](https://docs.roboplay.dev/hosting/overview)**, and so much more. You can even use it to **[build Discord Activities in seconds](https://dev.to/waveplay/how-to-build-a-discord-activity-easily-with-robojs-5bng)**!
Don't forget to **[join our Discord server](https://roboplay.dev/discord)** to chat with other developers, ask questions, and share your projects. We're here to help you build amazing apps with **Robo.js**! 🚀
➞ [🚀 **Community:** Join our Discord Server](https://roboplay.dev/discord)
Our very own Robo, **Sage**, is there to answer any questions about Robo.js, Discord.js, and more!
| waveplay-staff |
1,872,194 | Hanging Man Game | Inspiration Inspired by a cool design I found on Dribbble, I decided to create a web... | 0 | 2024-05-31T15:29:28 | https://dev.to/sarmittal/hanging-man-game-1d26 | react, vite, webdev, javascript | ## Inspiration
Inspired by a cool design I found on [Dribbble](https://dribbble.com/shots/23582257-The-game-Hangman), I decided to create a web version of the classic "Hanging Man" game. My goal was to not only practice my frontend development skills but also to bring a bit of fun and interactivity to my portfolio.
## Demo
You can try the live demo of the game here.
[Live Demo](https://hanging-man-sarmittal.netlify.app/)
## Journey
Creating this game was a great learning experience. Here's how I did it:
## Choosing the Tech Stack
I chose React for its component-based architecture, which made it easier to manage the different parts of the game. Vite was used as the build tool for its speed and simplicity, and HTML and CSS were used for the structure and styling of the game.
## Building the UI
I started by replicating the design from Dribbble. This involved creating a visually appealing layout with cacti, a cowboy, and the hanging tree. CSS was crucial for achieving the right look and feel.
## Implementing the Game Logic
The core functionality of the game revolves around guessing letters. Here’s how I implemented it:
- useState(): This hook was used to manage the game state, including the word to guess, the letters guessed, and the number of wrong attempts.
- useEffect(): This hook was used to handle side effects, such as checking if the game is won or lost after each guess.
## Creating the Questions Database
To make the game more interesting, I used ChatGPT to generate a variety of questions and words. This added a unique touch to the game and ensured a diverse set of challenges for the players.
## Challenges and Learning
One of the main challenges was managing the game state efficiently and ensuring the UI updates correctly based on user interactions. Through this process, I gained a deeper understanding of React hooks and state management.
## Future Plans
In the future, I plan to:
- Add more questions and words to the database.
- Implement difficulty levels.
- Enhance the UI with animations and sound effects.
## Conclusion
Working on this project was incredibly rewarding. It not only sharpened my technical skills but also allowed me to create something enjoyable. I hope this blog inspires you to take on similar projects and explore the fun side of web development.
Thank you for reading! Feel free to try the game and let me know your thoughts. | sarmittal |
1,872,193 | Help Academic Review: Expert Thesis Writing Services | Overview of Help Academic Help Academic is a leading academic support company specializing... | 0 | 2024-05-31T15:26:32 | https://dev.to/sam_tyler_64a9440f39ecdb0/help-academic-review-expert-thesis-writing-services-2kcp | education, assignment, thesis | ## Overview of Help Academic
Help Academic is a leading academic support company specializing in [thesis writing services](https://helpacademic.co.uk/thesis-writing-services/). With a reputation for excellence and a team of highly qualified experts, they cater to students at all academic levels, ensuring high-quality, original, and well-researched content tailored to meet specific requirements.
What Makes Help Academic Stand Out?
Help Academic differentiates itself through its expertise, customization, and timeliness. Their team comprises seasoned professionals with advanced degrees, offering personalized services that align with each student's unique needs. Additionally, they emphasize timely delivery without compromising quality, a critical factor for students working under tight deadlines.
## Detailed Breakdown of Services
Thesis Writing Service
Help Academic's thesis writing services is thorough and methodical. Their process involves understanding the student's requirements, conducting in-depth research, and drafting a comprehensive thesis. The quality of their work is consistently high, with meticulous attention to detail and adherence to academic standards. Students often provide positive feedback, highlighting the clarity, coherence, and originality of the content.
## Editing Services
Their editing services go beyond mere corrections. Help Academic enhances the overall content, ensuring logical flow and improving structural elements. This service is invaluable for students who need to refine their work to meet stringent academic criteria.
## Proofreading Services
The proofreading services at Help Academic focus on perfecting grammar, syntax, and overall readability. This final touch ensures that the thesis is polished and free from errors, providing a professional finish that can significantly impact the
## final assessment.
User Experience and Testimonials
User experience is a strong suit for Help Academic. Clients frequently praise the personalized approach and the supportive communication throughout the process. Numerous testimonials reflect high satisfaction rates, with many students achieving excellent grades and positive feedback from their institutions.
## Pricing and Packages
Help Academic offers a range of affordable pricing options and custom packages to suit different budgets and needs. Their transparent pricing structure ensures that students can plan accordingly without facing unexpected costs.
## Customer Support
Customer support at Help Academic is available round the clock, providing students with various communication channels, including email, phone, and live chat. This accessibility ensures that any concerns or queries are promptly addressed, enhancing the overall user experience.
Pros and Cons of Help Academic
## Strengths:
• Highly qualified experts
• Personalized services
• Timely delivery
• Comprehensive support
## Areas for Improvement:
• More detailed pricing information on the website
• Additional resources for self-help
## Final Thoughts
Overall, Help Academic is a reliable and expert provider of thesis writing services. Their commitment to quality, personalized approach, and robust customer support make them a top choice for students seeking academic assistance. Based on user reviews and our assessment, we highly recommend Help Academic for anyone in need of professional thesis writing services.
## Conclusion
[Help Academic](https://helpacademic.co.uk/) stands out as a premier provider of thesis writing services, combining expertise, quality, and exceptional customer support. Whether you need writing, editing, or proofreading, Help Academic is a trustworthy choice that can help you achieve your academic goals.
## FAQs
**What services does Help Academic offer?** Help Academic provides thesis writing, editing, and proofreading services.
**How qualified are the experts at Help Academic?** The experts at Help Academic hold advanced degrees and have extensive experience in academic writing.
**Is Help Academic's pricing affordable?** Yes, Help Academic offers a range of pricing options to suit different budgets.
**How is customer support at Help Academic?** Customer support is excellent, with multiple communication channels available 24/7.
**Can Help Academic meet tight deadlines?** Yes, they emphasize timely delivery without compromising on quality.
**Is the content provided by Help Academic original?** Absolutely, all content is original and thoroughly researched to meet academic standards.
| sam_tyler_64a9440f39ecdb0 |
1,872,192 | Buy verified cash app account | https://dmhelpshop.com/product/buy-verified-cash-app-account/ Buy verified cash app account Cash... | 0 | 2024-05-31T15:24:02 | https://dev.to/amdubesjcnvs2/buy-verified-cash-app-account-1ci0 | webdev, javascript, beginners, programming | ERROR: type should be string, got "https://dmhelpshop.com/product/buy-verified-cash-app-account/\n\n\n\nBuy verified cash app account\nCash app has emerged as a dominant force in the realm of mobile banking within the USA, offering unparalleled convenience for digital money transfers, deposits, and trading. As the foremost provider of fully verified cash app accounts, we take pride in our ability to deliver accounts with substantial limits. Bitcoin enablement, and an unmatched level of security.\n\nOur commitment to facilitating seamless transactions and enabling digital currency trades has garnered significant acclaim, as evidenced by the overwhelming response from our satisfied clientele. Those seeking buy verified cash app account with 100% legitimate documentation and unrestricted access need look no further. Get in touch with us promptly to acquire your verified cash app account and take advantage of all the benefits it has to offer.\n\nWhy dmhelpshop is the best place to buy USA cash app accounts?\nIt’s crucial to stay informed about any updates to the platform you’re using. If an update has been released, it’s important to explore alternative options. Contact the platform’s support team to inquire about the status of the cash app service.\n\nClearly communicate your requirements and inquire whether they can meet your needs and provide the buy verified cash app account promptly. If they assure you that they can fulfill your requirements within the specified timeframe, proceed with the verification process using the required documents.\n\nOur account verification process includes the submission of the following documents: [List of specific documents required for verification].\n\nGenuine and activated email verified\nRegistered phone number (USA)\nSelfie verified\nSSN (social security number) verified\nDriving license\nBTC enable or not enable (BTC enable best)\n100% replacement guaranteed\n100% customer satisfaction\nWhen it comes to staying on top of the latest platform updates, it’s crucial to act fast and ensure you’re positioned in the best possible place. If you’re considering a switch, reaching out to the right contacts and inquiring about the status of the buy verified cash app account service update is essential.\n\nClearly communicate your requirements and gauge their commitment to fulfilling them promptly. Once you’ve confirmed their capability, proceed with the verification process using genuine and activated email verification, a registered USA phone number, selfie verification, social security number (SSN) verification, and a valid driving license.\n\nAdditionally, assessing whether BTC enablement is available is advisable, buy verified cash app account, with a preference for this feature. It’s important to note that a 100% replacement guarantee and ensuring 100% customer satisfaction are essential benchmarks in this process.\n\nHow to use the Cash Card to make purchases?\nTo activate your Cash Card, open the Cash App on your compatible device, locate the Cash Card icon at the bottom of the screen, and tap on it. Then select “Activate Cash Card” and proceed to scan the QR code on your card. Alternatively, you can manually enter the CVV and expiration date. How To Buy Verified Cash App Accounts.\n\nAfter submitting your information, including your registered number, expiration date, and CVV code, you can start making payments by conveniently tapping your card on a contactless-enabled payment terminal. Consider obtaining a buy verified Cash App account for seamless transactions, especially for business purposes. Buy verified cash app account.\n\nWhy we suggest to unchanged the Cash App account username?\nTo activate your Cash Card, open the Cash App on your compatible device, locate the Cash Card icon at the bottom of the screen, and tap on it. Then select “Activate Cash Card” and proceed to scan the QR code on your card.\n\nAlternatively, you can manually enter the CVV and expiration date. After submitting your information, including your registered number, expiration date, and CVV code, you can start making payments by conveniently tapping your card on a contactless-enabled payment terminal. Consider obtaining a verified Cash App account for seamless transactions, especially for business purposes. Buy verified cash app account. Purchase Verified Cash App Accounts.\n\nSelecting a username in an app usually comes with the understanding that it cannot be easily changed within the app’s settings or options. This deliberate control is in place to uphold consistency and minimize potential user confusion, especially for those who have added you as a contact using your username. In addition, purchasing a Cash App account with verified genuine documents already linked to the account ensures a reliable and secure transaction experience.\n\n \n\nBuy verified cash app accounts quickly and easily for all your financial needs.\nAs the user base of our platform continues to grow, the significance of verified accounts cannot be overstated for both businesses and individuals seeking to leverage its full range of features. How To Buy Verified Cash App Accounts.\n\nFor entrepreneurs, freelancers, and investors alike, a verified cash app account opens the door to sending, receiving, and withdrawing substantial amounts of money, offering unparalleled convenience and flexibility. Whether you’re conducting business or managing personal finances, the benefits of a verified account are clear, providing a secure and efficient means to transact and manage funds at scale.\n\nWhen it comes to the rising trend of purchasing buy verified cash app account, it’s crucial to tread carefully and opt for reputable providers to steer clear of potential scams and fraudulent activities. How To Buy Verified Cash App Accounts. With numerous providers offering this service at competitive prices, it is paramount to be diligent in selecting a trusted source.\n\nThis article serves as a comprehensive guide, equipping you with the essential knowledge to navigate the process of procuring buy verified cash app account, ensuring that you are well-informed before making any purchasing decisions. Understanding the fundamentals is key, and by following this guide, you’ll be empowered to make informed choices with confidence.\n\n \n\nIs it safe to buy Cash App Verified Accounts?\nCash App, being a prominent peer-to-peer mobile payment application, is widely utilized by numerous individuals for their transactions. However, concerns regarding its safety have arisen, particularly pertaining to the purchase of “verified” accounts through Cash App. This raises questions about the security of Cash App’s verification process.\n\nUnfortunately, the answer is negative, as buying such verified accounts entails risks and is deemed unsafe. Therefore, it is crucial for everyone to exercise caution and be aware of potential vulnerabilities when using Cash App. How To Buy Verified Cash App Accounts.\n\nCash App has emerged as a widely embraced platform for purchasing Instagram Followers using PayPal, catering to a diverse range of users. This convenient application permits individuals possessing a PayPal account to procure authenticated Instagram Followers.\n\nLeveraging the Cash App, users can either opt to procure followers for a predetermined quantity or exercise patience until their account accrues a substantial follower count, subsequently making a bulk purchase. Although the Cash App provides this service, it is crucial to discern between genuine and counterfeit items. If you find yourself in search of counterfeit products such as a Rolex, a Louis Vuitton item, or a Louis Vuitton bag, there are two viable approaches to consider.\n\n \n\nWhy you need to buy verified Cash App accounts personal or business?\nThe Cash App is a versatile digital wallet enabling seamless money transfers among its users. However, it presents a concern as it facilitates transfer to both verified and unverified individuals.\n\nTo address this, the Cash App offers the option to become a verified user, which unlocks a range of advantages. Verified users can enjoy perks such as express payment, immediate issue resolution, and a generous interest-free period of up to two weeks. With its user-friendly interface and enhanced capabilities, the Cash App caters to the needs of a wide audience, ensuring convenient and secure digital transactions for all.\n\nIf you’re a business person seeking additional funds to expand your business, we have a solution for you. Payroll management can often be a challenging task, regardless of whether you’re a small family-run business or a large corporation. How To Buy Verified Cash App Accounts.\n\nImproper payment practices can lead to potential issues with your employees, as they could report you to the government. However, worry not, as we offer a reliable and efficient way to ensure proper payroll management, avoiding any potential complications. Our services provide you with the funds you need without compromising your reputation or legal standing. With our assistance, you can focus on growing your business while maintaining a professional and compliant relationship with your employees. Purchase Verified Cash App Accounts.\n\nA Cash App has emerged as a leading peer-to-peer payment method, catering to a wide range of users. With its seamless functionality, individuals can effortlessly send and receive cash in a matter of seconds, bypassing the need for a traditional bank account or social security number. Buy verified cash app account.\n\nThis accessibility makes it particularly appealing to millennials, addressing a common challenge they face in accessing physical currency. As a result, ACash App has established itself as a preferred choice among diverse audiences, enabling swift and hassle-free transactions for everyone. Purchase Verified Cash App Accounts.\n\n \n\nHow to verify Cash App accounts\nTo ensure the verification of your Cash App account, it is essential to securely store all your required documents in your account. This process includes accurately supplying your date of birth and verifying the US or UK phone number linked to your Cash App account.\n\nAs part of the verification process, you will be asked to submit accurate personal details such as your date of birth, the last four digits of your SSN, and your email address. If additional information is requested by the Cash App community to validate your account, be prepared to provide it promptly. Upon successful verification, you will gain full access to managing your account balance, as well as sending and receiving funds seamlessly. Buy verified cash app account.\n\n \n\nHow cash used for international transaction?\nExperience the seamless convenience of this innovative platform that simplifies money transfers to the level of sending a text message. It effortlessly connects users within the familiar confines of their respective currency regions, primarily in the United States and the United Kingdom.\n\nNo matter if you’re a freelancer seeking to diversify your clientele or a small business eager to enhance market presence, this solution caters to your financial needs efficiently and securely. Embrace a world of unlimited possibilities while staying connected to your currency domain. Buy verified cash app account.\n\nUnderstanding the currency capabilities of your selected payment application is essential in today’s digital landscape, where versatile financial tools are increasingly sought after. In this era of rapid technological advancements, being well-informed about platforms such as Cash App is crucial.\n\nAs we progress into the digital age, the significance of keeping abreast of such services becomes more pronounced, emphasizing the necessity of staying updated with the evolving financial trends and options available. Buy verified cash app account.\n\nOffers and advantage to buy cash app accounts cheap?\nWith Cash App, the possibilities are endless, offering numerous advantages in online marketing, cryptocurrency trading, and mobile banking while ensuring high security. As a top creator of Cash App accounts, our team possesses unparalleled expertise in navigating the platform.\n\nWe deliver accounts with maximum security and unwavering loyalty at competitive prices unmatched by other agencies. Rest assured, you can trust our services without hesitation, as we prioritize your peace of mind and satisfaction above all else.\n\nEnhance your business operations effortlessly by utilizing the Cash App e-wallet for seamless payment processing, money transfers, and various other essential tasks. Amidst a myriad of transaction platforms in existence today, the Cash App e-wallet stands out as a premier choice, offering users a multitude of functions to streamline their financial activities effectively. Buy verified cash app account.\n\nTrustbizs.com stands by the Cash App’s superiority and recommends acquiring your Cash App accounts from this trusted source to optimize your business potential.\n\nHow Customizable are the Payment Options on Cash App for Businesses?\nDiscover the flexible payment options available to businesses on Cash App, enabling a range of customization features to streamline transactions. Business users have the ability to adjust transaction amounts, incorporate tipping options, and leverage robust reporting tools for enhanced financial management.\n\nExplore trustbizs.com to acquire verified Cash App accounts with LD backup at a competitive price, ensuring a secure and efficient payment solution for your business needs. Buy verified cash app account.\n\nDiscover Cash App, an innovative platform ideal for small business owners and entrepreneurs aiming to simplify their financial operations. With its intuitive interface, Cash App empowers businesses to seamlessly receive payments and effectively oversee their finances. Emphasizing customization, this app accommodates a variety of business requirements and preferences, making it a versatile tool for all.\n\nWhere To Buy Verified Cash App Accounts\nWhen considering purchasing a verified Cash App account, it is imperative to carefully scrutinize the seller’s pricing and payment methods. Look for pricing that aligns with the market value, ensuring transparency and legitimacy. Buy verified cash app account.\n\nEqually important is the need to opt for sellers who provide secure payment channels to safeguard your financial data. Trust your intuition; skepticism towards deals that appear overly advantageous or sellers who raise red flags is warranted. It is always wise to prioritize caution and explore alternative avenues if uncertainties arise.\n\nThe Importance Of Verified Cash App Accounts\nIn today’s digital age, the significance of verified Cash App accounts cannot be overstated, as they serve as a cornerstone for secure and trustworthy online transactions.\n\nBy acquiring verified Cash App accounts, users not only establish credibility but also instill the confidence required to participate in financial endeavors with peace of mind, thus solidifying its status as an indispensable asset for individuals navigating the digital marketplace.\n\nWhen considering purchasing a verified Cash App account, it is imperative to carefully scrutinize the seller’s pricing and payment methods. Look for pricing that aligns with the market value, ensuring transparency and legitimacy. Buy verified cash app account.\n\nEqually important is the need to opt for sellers who provide secure payment channels to safeguard your financial data. Trust your intuition; skepticism towards deals that appear overly advantageous or sellers who raise red flags is warranted. It is always wise to prioritize caution and explore alternative avenues if uncertainties arise.\n\nConclusion\nEnhance your online financial transactions with verified Cash App accounts, a secure and convenient option for all individuals. By purchasing these accounts, you can access exclusive features, benefit from higher transaction limits, and enjoy enhanced protection against fraudulent activities. Streamline your financial interactions and experience peace of mind knowing your transactions are secure and efficient with verified Cash App accounts.\n\nChoose a trusted provider when acquiring accounts to guarantee legitimacy and reliability. In an era where Cash App is increasingly favored for financial transactions, possessing a verified account offers users peace of mind and ease in managing their finances. Make informed decisions to safeguard your financial assets and streamline your personal transactions effectively.\n\nContact Us / 24 Hours Reply\nTelegram:dmhelpshop\nWhatsApp: +1 (980) 277-2786\nSkype:dmhelpshop\nEmail:dmhelpshop@gmail.com\n\n\n\n" | amdubesjcnvs2 |
1,869,405 | Mastering Next-Auth: Your Comprehensive Guide to Next.js Authentication | NextAuth.js is a complete open-source authentication solution for Next.js applications. It is... | 0 | 2024-05-31T15:16:14 | https://dev.to/iankcode/mastering-next-auth-your-comprehensive-guide-to-nextjs-authentication-4kok | authentication, javascript, typescript, nextjs | **NextAuth.js** is a complete open-source authentication solution for Next.js applications. It is designed from the ground up to support Next.js and Serverless
**NextAuth** has authentication providers that allow your users to sign in with their favorite preexisting logins. You can use any of our many predefined providers, or write your own custom OAuth configuration.
In this blog, we will use **NextAuth** to authenticate using **Google**
To begin, you need to have already set up a Nextjs application.
First thing to do is to install **next-auth** using this command
```
npm install next-auth
```
## Add API route
To add NextAuth.js to a project create a file called **route.ts** in **/app/api/auth/[...nextauth]/**
`/app/api/auth/[...nextauth]/route.ts`
We want all routes pointing to **app/api/auth/** to be caught that is why we use **[...nextauth]**
In `/app/api/auth/[...nextauth]/route.ts`, add the following code
```
// src/app/api/auth/[...nextauth]/route.ts
import NextAuth from "next-auth";
import GoogleProvider from "next-auth/providers/google";
// Define your NextAuth options
const authOptions = {
// Configure one or more authentication providers
providers: [
GoogleProvider({
clientId: process.env.GOOGLE_CLIENT_ID!,
clientSecret: process.env.GOOGLE_API_SECRET!,
authorization: {
params: {
prompt: "consent",
access_type: "offline",
response_type: "code",
},
},
}),
],
// ...add more providers here
};
// Create the NextAuth handler
const handler = NextAuth(authOptions);
// Export the handler for both GET and POST requests
export const GET = handler;
export const POST = handler;
```
## Create **.env.local**
You can get both **GOOGLE_CLIENT_ID** and **GOOGLE_API_SECRET** in [https://console.cloud.google.com/apis/dashboard](https://console.cloud.google.com/apis/dashboard)
```
GOOGLE_CLIENT_ID="<YOUR GOOGLE CLIENT ID>"
GOOGLE_API_SECRET="<YOUR GOOGLE API SECRET>"
```
## Configure Shared session state
You will need your **children** in **app/layout.tsx** with **<SessionProvider />**
It should look like this
```
"use client"
import { Inter } from "next/font/google";
import "./globals.css";
import { SessionProvider } from "next-auth/react";
const inter = Inter({ subsets: ["latin"] });
import "./globals.css";
export default function RootLayout({
children,
}: Readonly<{ children: React.ReactNode}>) {
return (
<html lang="en">
<body className={inter.className}>
<SessionProvider refetchInterval={5 * 60}>
{children}
</SessionProvider>
</body>
</html>
);
}
```
By using **refetchinterval** you ensure that the session data is refetched every 5 minutes, which helps in maintaining the accuracy and security of the session state in your Next.js application
## Frontend - Add React Hook
We have done with all the configurations, the only thing remaining is to add the **sign up** and **sign out** buttons
We use the **useSession()** React Hook in the NextAuth.js client to sign in, check if someone is signed in and sign out.
In **components/navbar.tsx** import **useSession()** and add the following code
```
import { useSession, signIn, signOut } from "next-auth/react"
export default function Navbar() {
const { data: session } = useSession()
if (session) {
return (
<>
Signed in as {session.user.email} <br />
<button onClick={() => signOut({callbackUrl: "/"})}>Sign out</button>
</>
)
}
return (
<>
Not signed in <br />
<button onClick={() => signIn("google")}>Sign in</button>
</>
)
}
```
we can get current user's information from the data provided here **const { data: session } = useSession()**
With that, you users can successfully login using their google accounts | iankcode |
1,872,166 | Building a Testing Playground: API Mocking and Virtualization for Development and Testing | In today's fast-paced development landscape, efficient testing practices are crucial for delivering... | 0 | 2024-05-31T15:15:32 | https://dev.to/syncloop_dev/building-a-testing-playground-api-mocking-and-virtualization-for-development-and-testing-3d48 | webdev, javascript, programming, api | In today's fast-paced development landscape, efficient testing practices are crucial for delivering high-quality APIs (Application Programming Interfaces). API mocking and virtualization offer powerful tools to streamline the testing process by simulating real-world API behavior without relying on actual backend systems. This blog delves into the functionalities, benefits, use cases, and implementation strategies for these valuable testing techniques.
## Why API Mocking and Virtualization Matter
Here's why API mocking and virtualization are essential for effective API testing:
**Testing Early and Often**: Developers can begin testing API functionalities early in the development cycle, even before backend systems are fully developed or available.
**Isolation for Focused Testing**: Mocking and virtualization allow developers to test specific API components in isolation, eliminating dependencies on external systems and enabling focused test scenarios.
**Improved Developer Productivity**: Rapid creation and modification of mock APIs and virtual services streamline the testing process, reducing development time and accelerating time-to-market.
## Statistics highlight the benefits of efficient API testing:
A study by Capgemini found that organizations with strong API testing practices experience 30% fewer defects in production.
## API Mocking vs. Virtualization: Understanding the Differences
While both techniques simulate API behavior for testing, they have distinct approaches:
**API Mocking**: Creates lightweight, in-memory representations of APIs. Mock APIs can focus on specific functionalities or endpoints, returning predefined responses based on configured request parameters. They are ideal for unit testing and behavior verification of individual API components.
**API Virtualization**: Simulates entire backends or complex API ecosystems. Virtual services can mirror real-world behavior with varying degrees of fidelity, including database interactions and user authentication workflows. This allows for more comprehensive end-to-end API testing scenarios.
**Implementing API Mocking and Virtualization Strategies**
Here are key strategies for implementing API mocking and virtualization:
**Define Mocking and Virtualization Needs**: Identify which API functionalities require mocking or virtualization based on development priorities and test coverage requirements.
**Choose Mocking/Virtualization Tools**: Select a tool that aligns with your project needs and team expertise. Popular options include Postman Mock Server, Mockoon, Moesif, and Apiary.
**Design Mock Contracts or Virtual Service Definitions**: Outline expected request formats, response structures, and error handling behavior for your mock APIs or virtual services.
**Develop Mock APIs or Virtual Services**: Utilize your chosen tool to create mock APIs or define virtual services based on your design specifications.
**Integrate Mocking/Virtualization Tools into your Workflow**: Configure your development environment to utilize mock APIs or virtual services during testing.
## Benefits and Use Cases Across Industries
API mocking and virtualization offer numerous benefits for API development and testing:
**Faster Development Cycles**: Early and efficient testing enables rapid development iterations and accelerates time-to-market for new APIs.
**Improved Test Coverage**: Mocking and virtualization enable a wider range of test scenarios, leading to more comprehensive test coverage and higher-quality APIs.
**Reduced Reliance on Backend Systems**: Testing can proceed without burdening backend development teams or requiring access to production environments.
**Here are some industry-specific use cases for API Mocking and Virtualization:**
**FinTech**: Financial institutions can leverage mock APIs to test security features like authentication and authorization for financial transactions without involving real customer data. They can also use virtualized services to simulate fraud detection scenarios during testing.
**E-commerce**: E-commerce platforms can utilize mock APIs for testing product search functionalities, order processing workflows, and payment integrations before connecting to actual payment gateways. Virtualized services can be used to simulate peak traffic situations and ensure scalability.
**Healthcare**: Healthcare providers can leverage mock APIs to test patient data retrieval and exchange processes without compromising sensitive patient information. Virtualized services can be used to simulate interactions with external healthcare systems during testing.
## Latest Tools and Technologies for API Mocking and Virtualization
The API development landscape offers a wealth of tools to support mocking and virtualization:
**Open-Source Mocking Tools**: Tools like Postman Mock Server and Mockoon provide free and open-source solutions for creating lightweight mock APIs for basic testing needs.
**Cloud-Based Virtualization Platforms**: Cloud providers like AWS, Azure, and Google Cloud Platform offer managed services for API virtualization, allowing developers to create and manage complex virtual services at scale.
**API Design Tools with Mocking Capabilities**: Some API design tools, like SwaggerHub and Apiary, integrate mocking functionalities within their platforms, streamlining the design and testing workflow.
## Disadvantages and Considerations
While API mocking and virtualization offer significant benefits, there are also some considerations to keep in mind:
**Maintaining Mock Accuracy**: As underlying APIs evolve, it's crucial to update mock APIs accordingly to avoid introducing discrepancies and misleading test results.
**Over-reliance on Mocking/Virtualization**: While valuable, mocking and virtualization should not replace testing against the actual backend system before deployment.
**Tool Learning Curve**: Some advanced mocking and virtualization tools may have a steeper learning curve for developers, requiring dedicated training and familiarization.
## How Syncloop Can Enhance Your API Mocking and Virtualization Strategy
While Syncloop doesn't directly provide mocking or virtualization functionalities, it can still play a valuable role in your overall API testing strategy by:
**API Design and Documentation**: Syncloop's visual API design tools can be used to clearly document expected request and response formats for various API endpoints. This documentation serves as a valuable reference point when creating mock APIs that accurately reflect the intended behavior.
**Collaboration and Communication**: Syncloop facilitates collaboration between API developers and testers during the design and documentation phase. This ensures testers have a clear understanding of API functionalities that can be effectively mocked or virtualized for comprehensive test coverage.
**Test Case Management**: Syncloop allows testers to create and manage test cases that leverage mock APIs or virtual services. This promotes a structured testing approach and facilitates clear traceability between tests and API requirements.
**Version Control and Change Tracking**: Syncloop's version control features ensure clear tracking of API design changes. This helps ensure mock APIs and virtual services are updated in sync with any modifications to the actual API design, maintaining test accuracy.
Remember, Syncloop focuses on streamlining API design, documentation, collaboration, and version control. While it doesn't directly handle mocking or virtualization itself, it can be a valuable asset in your API testing strategy by providing a platform for clear communication, reference documentation, and test case management, all of which contribute to the effective use of mocking and virtualization tools.
## Conclusion
API mocking and virtualization offer powerful tools for developers and testers to build robust and high-quality APIs. By understanding the core functionalities of mocking and virtualization, implementing them strategically, and leveraging the latest tools and technologies, you can streamline your API testing process, accelerate development cycles, and deliver APIs that meet user expectations. Syncloop, along with your chosen mocking and virtualization tools, can become a powerful ally in your API development and testing journey. Remember, efficient API testing is paramount for building and maintaining reliable and secure APIs in today's ever-evolving digital landscape.
| syncloop_dev |
1,872,172 | Curso De Marketing Digital Gratuito E Online Do Santander | Conheça a área do marketing digital com o curso oferecido pelo Banco Santander em colaboração com a... | 0 | 2024-06-23T13:51:46 | https://guiadeti.com.br/curso-marketing-digital-gratuito-online-santander/ | cursogratuito, cursosgratuitos, empreendedorismo, marketing | ---
title: Curso De Marketing Digital Gratuito E Online Do Santander
published: true
date: 2024-05-31 15:15:03 UTC
tags: CursoGratuito,cursosgratuitos,empreendedorismo,marketing
canonical_url: https://guiadeti.com.br/curso-marketing-digital-gratuito-online-santander/
---
Conheça a área do marketing digital com o curso oferecido pelo Banco Santander em colaboração com a University of Chicago.
Este curso tem a duração de 8 horas, sendo projetado para ser flexível, permitindo que você avance no seu próprio ritmo.
Nele, você entenderá as técnicas e estratégias de storytelling digital, investigando elementos como depoimentos pessoais e a teoria das cores.
O curso trás a história mundial, destacando como criar narrativas convincentes. Também serão trabalhadas as considerações éticas associadas ao impacto do storytelling no marketing digital. Ao concluir o curso, você será recompensado com um certificado de conclusão.
## Curso De Marketing Digital
Em uma colaboração exclusiva entre o Banco Santander e a Chicago University, este curso de marketing digital de 8 horas oferece uma experiência de aprendizado flexível e adaptada ao seu ritmo.
_Imagem da página do curso_
Com inscrições abertas até 30/06/2024, o curso está disponível em espanhol, inglês e português, e é voltado para adultos maiores de 18 anos de qualquer país.
### Conhecendo o Storytelling Digital
O curso mostra as técnicas de storytelling digital, utilizando recursos como depoimentos pessoais e teoria das cores para enriquecer o aprendizado.
Através de uma metodologia que combina teoria e prática, você ganhará insights valiosos sobre como histórias mundiais têm sido moldadas e como essas técnicas podem ser aplicadas para criar narrativas convincentes em marketing digital.
### Ética e Eficiência na Comunicação Digital
O curso também ensina as considerações éticas envolvidas na influência do storytelling digital. Aprender sobre a responsabilidade de transmitir mensagens de maneira ética é fundamental em uma era onde a informação pode ser tão poderosa quanto persuasiva. Confira a ementa:
- O que é storytelling para marketing digital;
- Como escolher os personagens e o objetivo da sua história;
- Como aplicar KPIs à sua campanha;
- Como incluir considerações éticas em sua narrativa.
Ao final do curso, os participantes receberão um certificado de conclusão que atesta suas habilidades adquiridas.
### Flexibilidade e Autonomia no Aprendizado
O design do curso permite que você comece as aulas no momento da inscrição e prossiga de acordo com sua própria disponibilidade.
As aulas on-line são completamente autônomas, garantindo que você possa avançar no material educativo em um ritmo que se adeque ao seu estilo de vida e compromissos pessoais.
<aside>
<div>Você pode gostar</div>
<div>
<div>
<div>
<div>
<span><img decoding="async" width="280" height="210" src="https://guiadeti.com.br/wp-content/uploads/2024/05/Marketing-Digital-Santander-280x210.png" alt="Marketing Digital Santander" title="Marketing Digital Santander"></span>
</div>
<span>Curso De Marketing Digital Gratuito E Online Do Santander</span> <a href="https://guiadeti.com.br/curso-marketing-digital-gratuito-online-santander/" title="Curso De Marketing Digital Gratuito E Online Do Santander"></a>
</div>
</div>
<div>
<div>
<div>
<span><img decoding="async" width="280" height="210" src="https://guiadeti.com.br/wp-content/uploads/2024/05/Minicurso-De-Analise-De-Dados-280x210.png" alt="Minicurso De Análise De Dados" title="Minicurso De Análise De Dados"></span>
</div>
<span>Minicurso De Análise De Dados Gratuito Da Cubos Academy</span> <a href="https://guiadeti.com.br/minicurso-analise-de-dados-gratuito-cubos-academy/" title="Minicurso De Análise De Dados Gratuito Da Cubos Academy"></a>
</div>
</div>
<div>
<div>
<div>
<span><img decoding="async" width="280" height="210" src="https://guiadeti.com.br/wp-content/uploads/2024/05/Desafio-De-Python-Pandas-280x210.png" alt="Desafio De Python Pandas" title="Desafio De Python Pandas"></span>
</div>
<span>Desafio De Python Pandas Online E Gratuito: 7 Days Of Code</span> <a href="https://guiadeti.com.br/desafio-python-pandas-gratuito-7-days-of-code/" title="Desafio De Python Pandas Online E Gratuito: 7 Days Of Code"></a>
</div>
</div>
<div>
<div>
<div>
<span><img decoding="async" width="280" height="210" src="https://guiadeti.com.br/wp-content/uploads/2024/05/Cursos-De-Metaverso-Python-IoT-280x210.png" alt="Cursos De Metaverso, Python, IoT" title="Cursos De Metaverso, Python, IoT"></span>
</div>
<span>Cursos De Metaverso, Python, IoT E Outros Gratuitos Da Samsung</span> <a href="https://guiadeti.com.br/cursos-metaverso-python-iot-gratuitos-samsung/" title="Cursos De Metaverso, Python, IoT E Outros Gratuitos Da Samsung"></a>
</div>
</div>
</div>
</aside>
## Marketing Digital
O marketing digital começou a tomar forma na década de 1990 com o advento da internet e a democratização do acesso à web.
A transição do marketing tradicional para o digital foi impulsionada pelo surgimento de novas tecnologias e pelo aumento do uso de dispositivos digitais que permitiram às empresas atingir audiências globais com maior precisão e eficiência.
Desde então, o marketing digital tem evoluído constantemente, incorporando novas plataformas como redes sociais, e-mail e mecanismos de busca, e adaptando-se às mudanças no comportamento do consumidor e nas tecnologias emergentes.
### Ferramentas Essenciais do Marketing Digital
O sucesso no marketing digital depende fortemente do uso eficaz de diversas ferramentas que ajudam as empresas a planejar, executar e analisar campanhas. Algumas das ferramentas mais utilizadas incluem:
- Google Analytics: Fornece insights detalhados sobre o tráfego do site e a eficácia das campanhas.
- Hootsuite e Buffer: Facilitam a gestão de múltiplas contas de redes sociais, permitindo agendar posts e monitorar interações.
- SEO Moz e SEMrush: Oferecem funcionalidades para otimização de mecanismos de busca (SEO) e marketing de mecanismo de busca (SEM), ajudando na análise de palavras-chave e na visibilidade online.
- Mailchimp: Uma plataforma de automação de e-mail marketing que permite criar, enviar e analisar campanhas de e-mail.
- HubSpot: Um sistema integrado que combina marketing, vendas e serviço ao cliente, tudo centrado em um CRM que ajuda a criar experiências de cliente coesas e personalizadas.
### Bibliografia Recomendada em Marketing Digital
Para aqueles interessados em aprofundar seus conhecimentos em marketing digital, existe uma grande variedade de literatura que está disponível. Aqui estão algumas obras essenciais:
- “Digital Marketing: Strategy, Implementation and Practice” por Dave Chaffey: Este livro oferece uma visão ampla sobre a estratégia e prática do marketing digital, ideal para estudantes e profissionais que buscam uma compreensão detalhada da disciplina.
- “Influence: The Psychology of Persuasion” por Robert Cialdini: Embora não seja um livro estritamente sobre marketing digital, oferece insights profundos sobre a psicologia por trás da persuasão, um aspecto crucial em todas as formas de marketing.
- “Epic Content Marketing” por Joe Pulizzi: Foca em como desenvolver estratégias de conteúdo que atraiam e mantenham a atenção do público.
- “The Art of SEO: Mastering Search Engine Optimization” por Eric Enge, Stephan Spencer, e Jessie Stricchiola: Um guia detalhado para quem deseja dominar SEO, com técnicas avançadas e estratégias testadas para melhorar a visibilidade online.
Estudar essas ferramentas e recursos literários enriquecerá o conhecimento teórico e prático em marketing digital, e equipará os profissionais com as habilidades necessárias para navegar no dinâmico mercado digital de hoje.
## Santander Open Academy
A Santander Open Academy é uma iniciativa educacional lançada pelo Banco Santander como parte de seu compromisso de apoiar a educação e promover o aprendizado contínuo.
Essa plataforma online é projetada para oferecer cursos acessíveis e de alta qualidade a estudantes e profissionais ao redor do mundo, ajudando-os a desenvolver habilidades essenciais para o sucesso no mercado de trabalho contemporâneo.
### Cursos e Recursos Disponíveis
A Santander Open Academy disponibiliza vários cursos que incluem diversas áreas de conhecimento. Esses cursos são desenvolvidos em parceria com universidades renomadas e líderes de indústria para garantir um conteúdo educacional relevante e atualizado.
A plataforma também oferece webinars, workshops, e eventos ao vivo, proporcionando uma experiência de aprendizado dinâmica e interativa.
### Engajamento e Impacto Social
A Santander Open Academy apoia as comunidades através de iniciativas de inclusão educacional e programas de bolsas de estudo.
Estas ações têm como objetivo democratizar o acesso ao conhecimento e às oportunidades educacionais, permitindo que talentos de diferentes origens possam prosperar.
### Desenvolvimento Sustentável
A Santander Open Academy está comprometida com a promoção da inovação e do desenvolvimento sustentável.
Integrando conceitos de sustentabilidade em seus cursos e promovendo a conscientização sobre práticas empresariais responsáveis, a plataforma contribui para a formação de líderes que estão preparados para enfrentar os desafios globais contemporâneos.
## Aprimore suas habilidades com o curso gratuito do Santander e Chicago University!
As [inscrições para o Curso De Marketing Digital](https://www.santanderopenacademy.com/pt_br/courses/digital-marketing.html) devem ser realizadas no site da Santander Open Academy.
## Descubra como contar histórias que encantam e convertem e compartilhe isso!
Gostou do curso gratuito sobre marketing digital? Então compartilhe com a galera!
O post [Curso De Marketing Digital Gratuito E Online Do Santander](https://guiadeti.com.br/curso-marketing-digital-gratuito-online-santander/) apareceu primeiro em [Guia de TI](https://guiadeti.com.br). | guiadeti |
1,872,165 | New Feature Update: Dynamic Time Calculations in Analytics Reports | We continue to tweak our popular analytics reports to improve usability and the ease of generating... | 0 | 2024-05-31T15:14:38 | https://dev.to/cloudbees/new-feature-update-dynamic-time-calculations-in-analytics-reports-358a | devops, devsecops, cicd, reporting | We continue to tweak our popular [analytics reports](https://www.cloudbees.com/blog/introduction-to-cloudbees-platform-analytics-reports) to improve usability and the ease of generating insights. The latest in this effort is Dynamic Time Calculations - this update lets every user view these reports specific to their location and time analysis needs.
Below is a sprinkling of ways to take advantage of this feature update.
## Personalize your time zone
Your time zone is set automatically in your profile as a new user - this means you interpret all the insights on your analytics reports specific to your time zone.
Let’s look at an example from the ‘Software delivery activity’ report. In the snapshot below, the commits trend chart shows the numbers specific to the Eastern Time Zone: 13,356 total commits from May 1st to May 31st, 2024. The same chart in a different time zone can yield a different result depending on the start of the May 1st count.
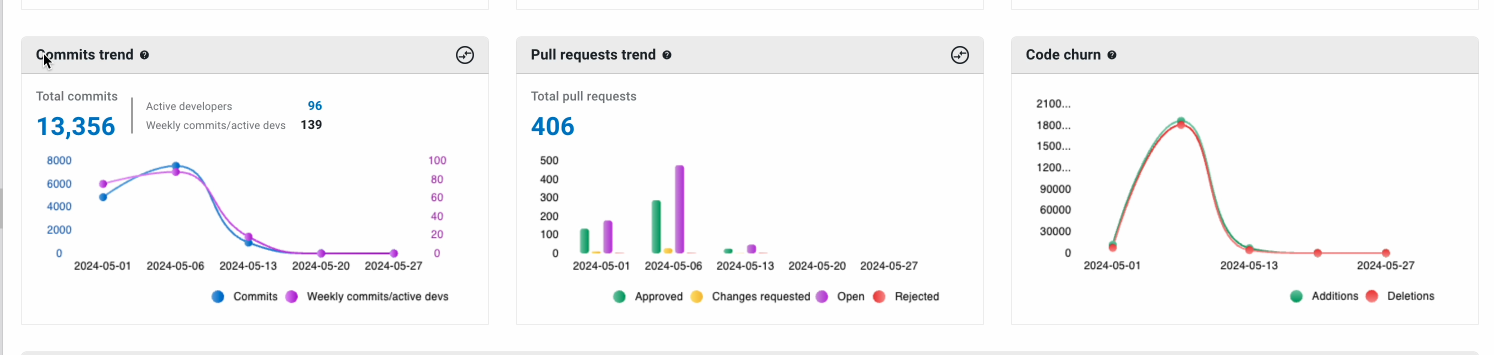
Users now have the option to overwrite the automatic time zone setting through their profile. Click on ‘User Profile’ under your name to head to a secondary screen.
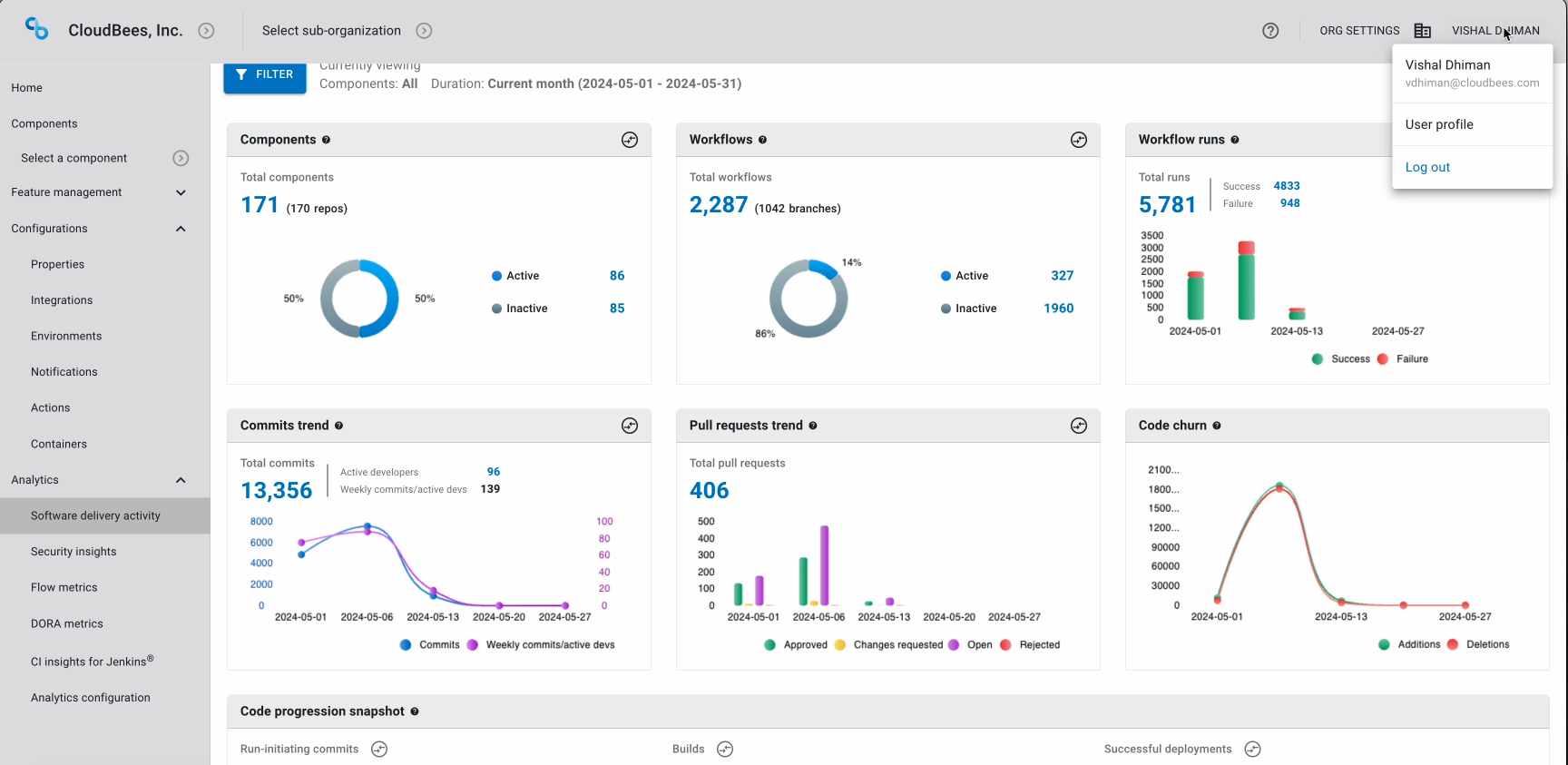
On the secondary screen, uncheck the ‘Set time zone automatically’ box and pick your preferred time zone.
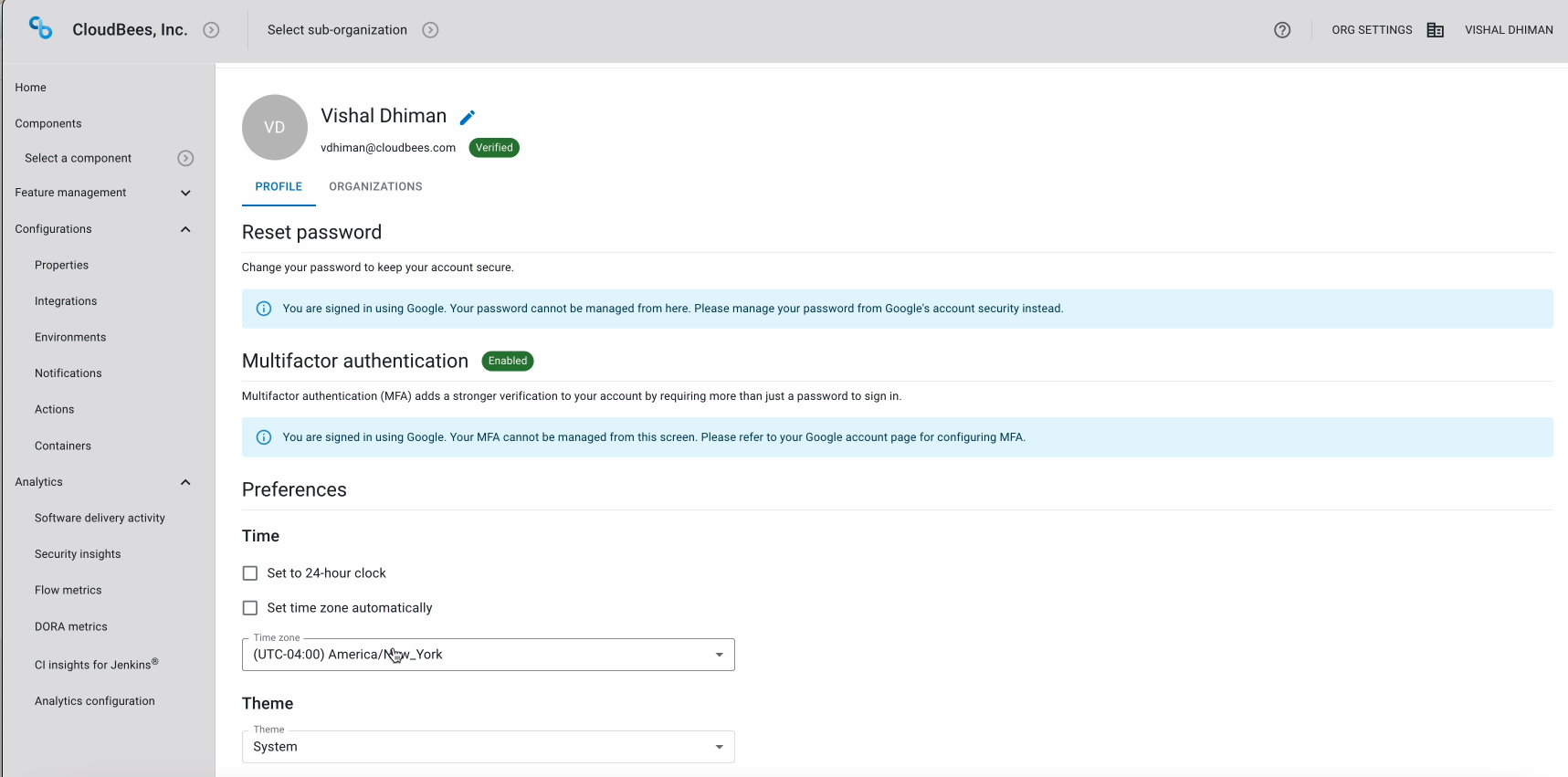
## Use pre-defined time filters…
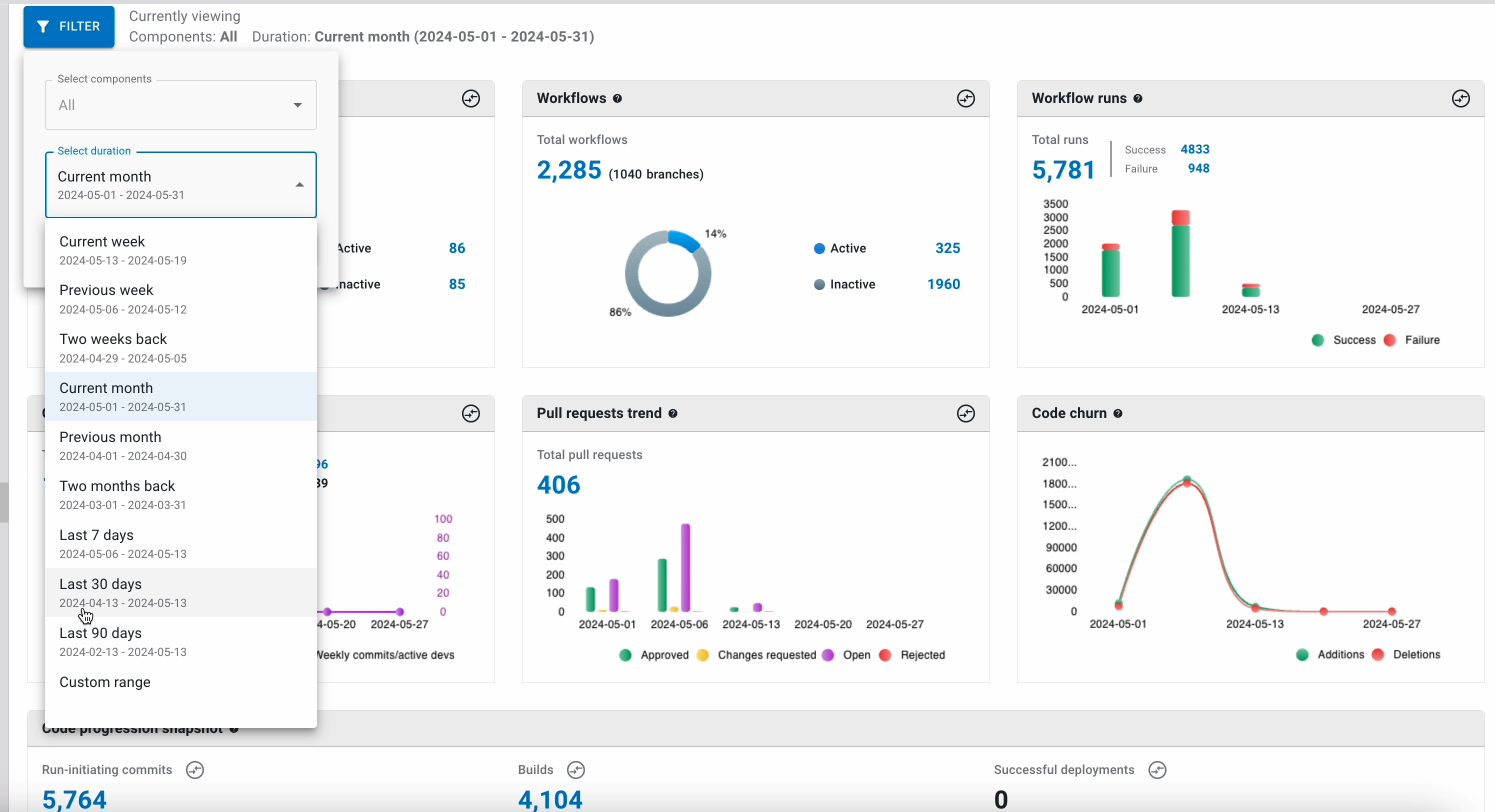
When you click the filter button, three new pre-defined time filters appear - Last 7 days, Last 30 days, and Last 90 days. These time filters let you aggregate and get a good measure of daily, weekly, and monthly activity on a rolling basis.
## ...Or set your own time filters
If the pre-defined time filters don't suit your analysis needs, choose ‘Custom range’ to pick a start and end date.
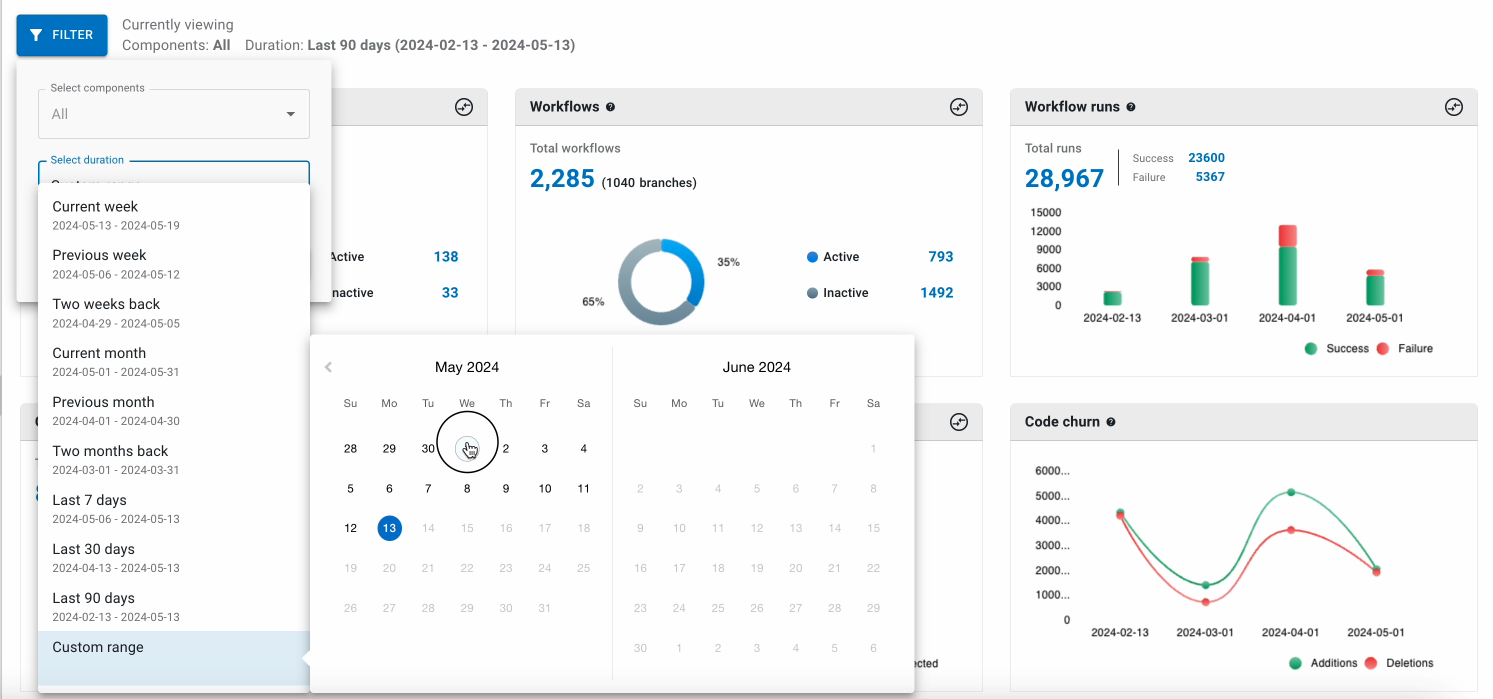
All these options are available across each of the 5 analytics reports. If you have any questions, contact us via [Slack](https://assets.cloudbees.com/MzMzLVFQVi03MjUAAAGRvywKXthVzu1t40lXFatZJAub3cTcWUh-ANYIcljdc8C6YYeUzN2t4DnW-IFrsWNZhIHS4Xw=) or [email our support team](https://assets.cloudbees.com/MzMzLVFQVi03MjUAAAGRvywKXhjQNMLEZORXMuthWK3Pu8I_Chg0KuGzm0nr64cbT3y976ONZHLFlu3SnycFC0UBATA=). And if you haven’t seen the platform in action yet…
## Try the CloudBees Platform for [FREE](https://id.cloudbees.io/realms/cloudbees/protocol/openid-connect/auth?client_id=nextgen-ui&redirect_uri=https%3A%2F%2Fcloudbees.io%2F&response_type=code&scope=openid+profile+email&state=56e73fe931b2425587abd3b5741e689f&code_challenge=8wfcuMieXaoTNF-2570BptaCnus3sTpJjc7wjnVnPrY&code_challenge_method=S256&response_mode=query) today!
| cloudbees_ |
1,872,164 | Understanding the Syntax of Vue3 script setup | What is vue3 script setup? It is a new syntactic sugar in Vue 3, compared to the previous... | 0 | 2024-05-31T15:11:37 | https://dev.to/markliu2013/understanding-the-syntax-of-vue3-script-setup-1kb4 | vue, vue3 | ## What is vue3 script setup?
It is a new syntactic sugar in Vue 3, compared to the previous approach, the syntax becomes simpler after using it.
The usage is extremely simple, you just need to add the setup keyword to the script tag. For example:
```js
<script setup></script>
```
## Component Registration Automatically
In `script setup`, the imported components can be used directly, You don't need to register them through `components`. Moreover, you don't have to specify the current component's name, it will automatically use the filename as component name, which means you no longer need to write the `name` property. For example:
```html
<template>
<Child />
</template>
<script setup>
import Child from './Child.vue'
</script>
```
If you need to define component name, you can add another `script` tag or use defineOptions.
## Usage of Core API
### Usage of props
Define the current props with `defineProps`, and get the props object of the component instance. For example:
```html
<script setup>
import { defineProps } from 'vue'
const props = defineProps({
title: String,
})
</script>
```
### Usage of emits
Use `defineEmit` to define the events that our component can emit, the parent component know when to emit.
```js
<script setup>
import { defineEmits } from 'vue'
const emit = defineEmits(['change', 'delete'])
</script>
```
### slot and attrs
You can get `slots` and `attrs` from the context using `useContext`. However, after the proposal was formally adopted, this syntax was deprecated and split into `useAttrs` and `useSlots`. For example:
```js
// old
<script setup>
import { useContext } from 'vue'
const { slots, attrs } = useContext()
</script>
// new
<script setup>
import { useAttrs, useSlots } from 'vue'
const attrs = useAttrs()
const slots = useSlots()
</script>
```
### defineExpose API
In the traditional approach, we can access the content of child components in the parent component through the `ref` instance. However, this method cannot be used in `script setup`. `setup` is a closure, and apart from the internal `template` template, no one can access the internal data and methods.
If you need to expose the data and methods in `setup` externally, you need to use the `defineExpose` API. For example:
```js
<script setup>
import { defineExpose } from 'vue'
const a = 1
const b = 2
defineExpose({
a
})
</script>
```
No need to return properties and methods, use them directly!
This may be one of the major conveniences in setup. In the past, when defining data and methods, they all needed to be returned at the end in order to be used in the template. In `script setup`, the defined properties and methods do not need to be returned, they can be used directly! For example:
```vue
<template>
<div>
<p>My name is {{name}}</p>
</div>
</template>
<script setup>
import { ref } from 'vue';
const name = ref('Sam')
</script>
```
| markliu2013 |
1,872,163 | Hack4Bengal: Highlights from the First Two Sessions | Hack4Bengal has become a popular event for tech enthusiasts in Eastern India. Let's take a... | 0 | 2024-05-31T15:10:44 | https://dev.to/arup_matabber/hack4bengal-highlights-from-the-first-two-sessions-54jc | ## Hack4Bengal has become a popular event for tech enthusiasts in Eastern India. Let's take a simple look at what happened in the first two sessions.
**Hack4Bengal 1.0: The Beginning**
Year: 2021
Participants: 1500+ developers
Format: 48-hour virtual hackathon
The first Hack4Bengal event was held in 2021. It was a 48-hour online hackathon with over 1500 participants. Teams worked together to create tech projects and solve problems within two days. The event was a great start, encouraging collaboration and innovation among participants
## Hack4Bengal 2.0: Growing Bigger
Year: 2022
Participants: 3000+ developers
Format: Hybrid (in-person)
In 2022, Hack4Bengal 2.0 expanded with a hybrid format, allowing participants to join in person. The number of participants grew to over 3000. This session included workshops and tech talks before the hackathon to help participants improve their skills. The projects created during this event were varied, addressing issues in healthcare, smart cities, and more.
## Conclusion
Hack4Bengal has made a significant impact in just two years. Starting as a virtual event in 2021, it grew into a hybrid format by 2022, drawing more participants and offering valuable learning opportunities. This hackathon has become a key event for tech enthusiasts in Eastern India, fostering innovation and collaboration. For more information,
visit the https://www.hack4bengal.tech/ | arup_matabber | |
1,872,162 | Building a Simple Web Application with Flask | Building a Simple Web Application with Flask Flask is a lightweight web framework written... | 0 | 2024-05-31T15:10:05 | https://dev.to/romulogatto/building-a-simple-web-application-with-flask-1dbm | # Building a Simple Web Application with Flask
Flask is a lightweight web framework written in Python that allows you to build web applications quickly and easily. In this guide, we will walk through the steps of building a simple web application using Flask.
## Prerequisites
Before starting, ensure that you have the following installed on your machine:
- Python (version 3 or above)
- Flask (install via `pip install flask`)
## Step 1: Setting up the Project Structure
To get started, create a new project directory on your machine. Open a terminal or command prompt and navigate to the desired location for your project.
Once in the project directory, create an additional directory called "app". This will serve as our main application folder.
```
my-web-app/
└── app/
```
## Step 2: Creating and Configuring the Flask Application
Now let's set up our Flask application file. Inside the "app" directory, create a new Python file named `app.py`.
Open `app.py` in your code editor and import the necessary modules:
```python
from flask import Flask
```
Next, create an instance of the `Flask` class:
```python
app = Flask(__name__)
```
With our application instance created, we can start defining routes. Routes are URLs that users can visit within our web application.
For example, let's create a simple route that displays "Hello World!" when visiting the homepage:
```python
@app.route('/')
def hello():
return 'Hello World!'
```
Save your changes to `app.py`.
## Step 3: Running Your Web Application
To run your web application locally for testing purposes, open a terminal or command prompt in your project root directory (`my-web-app`) and execute:
```bash
$ export FLASK_APP=app.py # Linux/MacOS
$ set FLASK_APP=app.py # Windows PowerShell
$ flask run
```
Visit `http://localhost:5000` in your web browser, and you should see "Hello World!" displayed.
## Step 4: Building Additional Routes
Now that we have a basic route working, let's add more functionality to our web application. You can define as many routes as needed for your specific project.
Here's an example of a route that returns the current date:
```python
from datetime import datetime
@app.route('/date')
def display_date():
now = datetime.now()
return f"The current date is {now.strftime('%Y-%m-%d')}"
```
By visiting `http://localhost:5000/date`, you will see the current date displayed.
Feel free to continue adding more routes based on your project requirements.
## Conclusion
Congratulations! You have successfully built a simple web application using Flask. Now you can take this foundation and expand it with additional features or functionalities according to your needs.
Remember, Flask offers endless possibilities for building dynamic web applications. Explore its documentation and experiment with different functionalities to unleash the full potential of Flask!
| romulogatto | |
1,872,161 | Azure AI Engineer Associate - AI-102 2024 | 1.Target audience: -Individuals with cloud knowledge who want to learn more about AI -Professionals... | 0 | 2024-05-31T15:05:28 | https://dev.to/huydanggdg/azure-ai-engineer-associate-ai-102-2024-3nl1 | ai, azure, cloud | **1.Target audience:**
-Individuals with cloud knowledge who want to learn more about AI
-Professionals focused on deploying and operating cloud services on Azure (MLOps)
-Note that the exam focuses on operational aspects and does not delve into AI algorithms and theories.
**2.Prepare**
-Successful completion of the AI-900 exam
-2 years of experience working with Azure services
-Total study time: 2 months
**3.Cost**
$0 with a voucher obtained from participating in The Microsoft Learn AI Skills Challenge
**4.Study materials**
**4.1. Theoretical study materials**
[AI-102 by John Savill's Technical Training (Subscribe to this channel for Azure learning)](https://www.youtube.com/watch?v=I7fdWafTcPY&t=3728s)
[Microsoft Training](https://www.youtube.com/watch?v=WyugeAhEWp4)
**4.2.Practice exams**
Refer to Examtopics
Refer to the following videos:
https://www.youtube.com/watch?v=Jlo4tBS66C8
https://www.youtube.com/watch?v=DWI4jd617iA&t=576s
https://www.youtube.com/watch?v=RYFBzKod-wY
https://youtu.be/YPwJmvi3DZ8
**5.Exam details**
- At the beginning of the test, the programming language in the test will be asked in C# or Python
- Total exam time is **100 minutes**
- No practice questions
- Questions are divided into 3 types (About 60 questions):
+ Multi choice
+ Drag and drop to sort order
+ Yes/No questions (Returning to review is not allowed after clicking next) (6 questions)
+ Case study questions (6 questions)
Good luck with your exam preparation!
==================== Tiếng việt ====================
**1.Đối tượng thi chứng chỉ**
-Đang học Cloud muốn tìm hiểu thêm về AI
-Tập trung vào triển khai vận hành dịch vụ Cloud trên Azure (MLOps)
-Nội dung thiên về mặt vận hành dịch vụ nên không đi sâu vào thuật toán và các lý thuyết về AI nên mọi người cân nhắc trước khi thi
**2.Nền tảng**
-Đã từng thi đỗ AI-900 của Microsoft
-Đã từng có 2 năm làm về các dịch vụ trên Azure
**3.Tổng thời gian học**
-Khoảng 2 tháng
-Chi phí 0$ vì có voucher sau khi tham dự The Microsoft Learn AI Skills Challenge
**4.Các loại tài liệu học**
**4.1.Tài liệu học lý thuyết**
-[AI-102 của John Savill's Technical Training (Học Azure thì cứ subscribed kênh này)](https://www.youtube.com/watch?v=I7fdWafTcPY&t=3728s)
-[Trainning từ Microsoft ](https://www.youtube.com/watch?v=38vrt6sU3oA )
**4.2.Đề thi thử**
-Tham khảo Examtopic
-Tham khảo video sau:
https://www.youtube.com/watch?v=Jlo4tBS66C8
https://www.youtube.com/watch?v=DWI4jd617iA&t=576s
https://www.youtube.com/watch?v=RYFBzKod-wY
https://youtu.be/YPwJmvi3DZ8
**5.Thi**
-Khi bắt đầu bài thi sẽ hỏi ngôn ngữ lập trình trong bài thi C# hoặc Python
-Tổng thời gian làm bài là 100 phút
-Không có câu hỏi thực hành
-Câu hỏi chia làm 3 dạng (Khoảng 60 câu):
+Multi choice
+Kéo thả sắp xếp thứ tự
+Câu hỏi Yes/No (Không cho phép quay lại review khi đã nhấn next) (6 câu)
+Câu hỏi Case study (6 câu) | huydanggdg |
1,872,157 | Easy Web3 Coding: The Ultimate Tool You Need For DApp Development — TransactionKit | As the Web3 ecosystem continues to expand, developers face a landscape filled with both exciting... | 0 | 2024-05-31T14:59:07 | https://etherspot.io/blog/easy-web3-coding-the-ultimate-tool-you-need-for-dapp-development-transactionkit/ | webdev, web3, blockchain, npm | As the Web3 ecosystem continues to expand, developers face a landscape filled with both exciting opportunities and challenges. Building decentralized applications (dApps) requires not only technical expertise but also efficient tools to streamline and enhance the development process. This is why the idea for creating TransactionKit was born.
[TransactionKit (TxKit)](https://etherspot.io/transactionkit/?utm_source=medium&utm_medium=article&utm_campaign=txkit_npm) is a robust smart account React library crafted to empower Web3 developers. It leverages the [Etherspot Account Abstraction infrastructure](https://etherspot.io/?utm_source=medium&utm_medium=article&utm_campaign=txkit_npm), transforming complex development tasks into simple [React Components and Hooks](https://etherspot.fyi/transaction-kit/components/EtherspotTransactionKit) that seamlessly integrate with your React user interface. Whether you’re a seasoned blockchain developer or just starting, TransactionKit can significantly boost your productivity and the reliability of your dApps.
#Why Use TransactionKit?#
TransactionKit enables developers to create a seamless user experience for dApps with just a few lines of code. Beyond basic functionalities like sending and approving transactions, checking account balances, and fetching historical transactions, TransactionKit offers advanced features that elevate any dApp:
**Batch multiple transactions out-of-the-box.**
This feature allows dApp users to combine several transactions into one, making it easier to perform multiple actions with a single click. This will allow them to take fewer steps and give them more freedom and flexibility in their actions on blockchain. The most exciting thing is that, traditionally, developers would need to manually batch transactions or find other solutions, which can be time-consuming and tricky. With TransactionKit, the [<EtherspotBatches /> component](https://etherspot.fyi/transaction-kit/components/EtherspotBatches) handles this effortlessly, providing a ready-made solution.
**Engage users from many chains with a seamless cross-chain experience.**
Etherspot supports over 22 blockchains, enabling projects to onboard users from multiple chains without the need for separate support integrations for each one. This seamless cross-chain functionality broadens the reach and accessibility of your dApp.
**Ability for users to pay gas fees with stablecoins aka Gasless Transactions.**
Every blockchain transaction requires fees paid in the native tokens of the blockchain. This can be a barrier for users unfamiliar with acquiring these tokens. Etherspot allows dApp users to pay transaction fees with stablecoins such as USDT, USDC, DAI and BUSD, simplifying the user experience and lowering entry barriers.
**Fully cover users’ gas costs with sponsored transactions.**
With TransactionKit, dApps can subsidize user transactions, providing users with a completely gas-free experience. This feature can attract and retain users by eliminating transaction costs.
#Getting Started with TransactionKit#
With [TransactionKit](https://etherspot.io/transactionkit/?utm_source=medium&utm_medium=article&utm_campaign=txkit_npm), developers can bring any dApp idea to life, enjoying complete design freedom and a powerful toolkit. TxKit handles all the tricky parts of Web3 development, hence developers can focus on creating innovative and user-friendly applications.
To get familiar with TransactionKit, check out [this example](https://youtu.be/lepPsxm5DGw?si=sAdgt3iiM8C79gNo) of creating a staking dApp:
[](https://youtu.be/lepPsxm5DGw)
If you’re ready to start building with TransactionKit, simply install it using the following snippet to import the library and create a wallet.
```npm i @etherspot/transaction-kit ethers@5.4.0
// or
yarn add @etherspot/transaction-kit ethers@5.4.0```
For more information and resources, check out the following links:
GitHub: https://github.com/etherspot/transaction-kit
TransactionKit npm: http://npmjs.com/package/@etherspot/transaction-kit
Developer Documentation: https://etherspot.fyi/transaction-kit/components/EtherspotTransactionKit
With TransactionKit, the power of Web3 development is at your fingertips. Simplify your dApp development process and create robust, user-friendly Web3 applications with ease. Happy coding!
**Follow us**
[Website](https://etherspot.io/?utm_source=devto&utm_medium=article&utm_campaign=followus) | [Twitter](https://twitter.com/etherspot) | [Discord](http://discord.etherspot.io/) | [Telegram](https://t.me/etherspot) | [Github](https://github.com/etherspot/etherspot-prime-sdk) | alexandradev |
1,872,156 | RSA Conference 2024: AI and the Future Of Security | The first week of May saw security practitioners from all over the globe come to the city by the... | 0 | 2024-05-31T14:47:29 | https://blog.gitguardian.com/rsa-conference-2024/ | rsa, security, ai, llms | The first week of May saw security practitioners from all over the globe come to [the city by the bay](https://www.youtube.com/watch?v=tNG62fULYgI&ref=blog.gitguardian.com) to participate in RSA. In 1991, just a handful of security researchers got together for a single panel discussion about [DES](https://en.wikipedia.org/wiki/Data_Encryption_Standard?ref=blog.gitguardian.com) versus [DSS](https://www.geeksforgeeks.org/digital-signature-standard-dss/?ref=blog.gitguardian.com). From those humble beginnings, the event has grown to over 41,000 participants, more than 500 sessions, panels, and trainings, and over a dozen co-located events, each with their own schedules and sessions. It would be impossible to summarize the entire event, from the opening keynotes with leaders like [US Deputy Secretary of State Antony J. Blinken](https://www.rsaconference.com/usa/agenda/session/Government%20Leader%20Keynote?ref=blog.gitguardian.com) and Kevin Mandia to the unforgettable closing celebration with [Alicia Keys](https://www.rsaconference.com/usa/agenda/session/Closing%20Celebration%20with%20Alicia%20Keys?ref=blog.gitguardian.com).
[https://www.linkedin.com/posts/ayacodyestrin_rsac-activity-7195930599239335936-GyJE](https://www.linkedin.com/posts/ayacodyestrin_rsac-activity-7195930599239335936-GyJE?ref=blog.gitguardian.com)
In the following three sections, I will try to encapsulate a small part of the sessions, the RSA Sandbox experience, and the view from the massive expo floor that makes up the event.
The Sessions at RSAC
--------------------
### A focus on AI from a governance and tooling perspective
Day one of RSA once again brought the co-located event from [Techstrong: DevOps Connect](https://www.techstrongevents.com/devopsconnect-devsecops-rsac-2024?ref=blog.gitguardian.com). This year's theme was "Security in an AI Universe." Throughout the day, several speakers from companies such as AWS, Google, and Anthropic highlighted tools that have recently evolved to help make deployment more secure using AI. Other speakers talked a higher level about regulatory compliance and where we, as an industry, are headed. Starting things out though, was a look at how we can shape the future of AI and LLMs from a futurist and [Hugo and Nebula-winning author, David Brin](https://en.wikipedia.org/wiki/David_Brin?ref=blog.gitguardian.com).
The keynote, "Anticipation, Resilience and Reliability: Three Ways AI Will Change DevSecOps ... If we Do it Right," walked us through the dual nature of AI, its potential to elevate humans, and the dystopian consequences if mishandled. Fortunately, we can learn from nature and the evolution of human society to find solutions to keep AI in check, even while AI is very rapidly becoming more sophisticated.
He showed how we have faced attacking hyper-smart predatory entities with uncanny language manipulation skills. We call them lawyers. We protect ourselves from lawyers by getting our own lawyers to hold the other one accountable. The key to this system is proper credentials that identify each party as a real lawyer. Similarly, with proper human-sponsored IDs, we can let AIs evolve within practical bounds, as humans are still going to be responsible for the real-world resources they need to consume, like electricity.
[](https://www.linkedin.com/posts/dwaynemcdaniel_devopsconnect-rsac-activity-7193301573098168324-k4Yy?ref=blog.gitguardian.com)
Author and Futurist David BrinOpenAI: Scaling Security Programs Using LLMs
#### How OpenAI is using LLMs
In his session "OpenAI: Scaling Security Programs Using LLMs." [Matt Knight, Head of Security at OpenAI](https://www.linkedin.com/in/matthewfknight/?ref=blog.gitguardian.com), showed us how large language models (LLMs) are rapidly evolving security operations inside his company. He began by looking at how they use AI to summarize complex data and automate mundane tasks. One use case was to help route inbound helpdesk message requests, allowing users to basically write "I don't know where to route this, but..." and describe their issue, saving a lot of time over manually performing triage.
Some more advanced cyber defense use cases included using an LLM to decode Russian cybercrime jargon and analyze complex IaC and IAM configurations. It is not all good news, though, as hallucinations still present some real hurdles. There is also the issue of limited prompt length, leading to context limitations and less-than-optimal results. He concluded that they are working on this element at OpenAI all the time.
[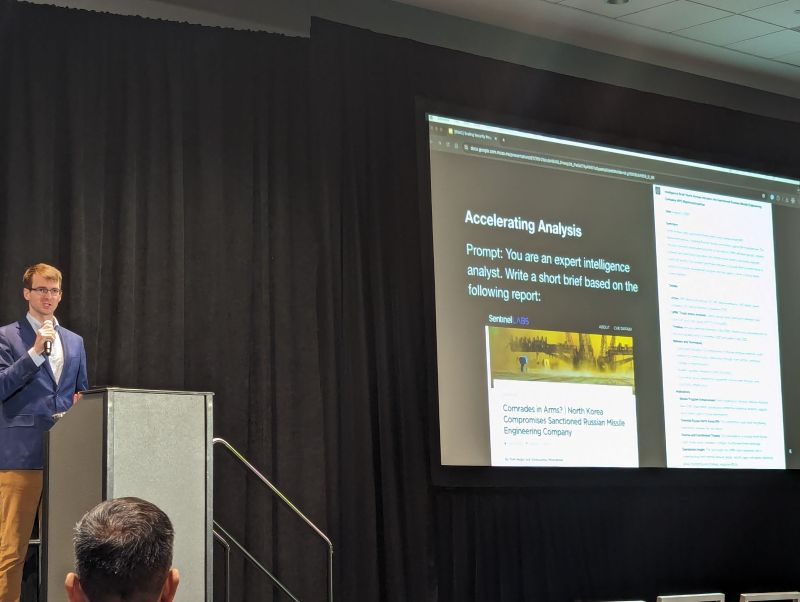](https://www.linkedin.com/posts/dwaynemcdaniel_openai-devopsconnect-rsac-activity-7193281309694218242-_88F?ref=blog.gitguardian.com)
OpenAI: Scaling Security Programs Using LLMs by Matt KnightGoogle's Approach to Securing AI: SAIF Framework
The bad news is that there is little agreement on good LLM governance models across the companies they surveyed. The good news is Google has been working on this issue for a while now. In their talk "SAIF from Day One: Google's Approach for Securing AI," [Dr. Anton Chuvakin](https://www.linkedin.com/in/chuvakin/?ref=blog.gitguardian.com) and [Taylor Lehmann](https://www.linkedin.com/in/taylorlehman/?ref=blog.gitguardian.com) from Google introduced the Secure AI Framework, SAIF. This approach focuses on a proactive approach to AI security.
No matter what your LLM is doing, robust encryption is seriously needed, as interference attacks and corruption are happening daily. We need to employ monitoring everywhere, as soon as possible, to protect against model theft and other threats. Given the nature of LLMs, you can not predict the outcome AI produces; it is non-deterministic. This makes observability and governance all that more important, as we need to ensure we are not causing harm to users.
[](https://www.linkedin.com/posts/dwaynemcdaniel_devopsconnect-rsac-activity-7193341308273324034-lGx5?ref=blog.gitguardian.com)
SAIF from Day One: Google's Approach for Securing AI
### 10 steps to better cloud security
The session from [Shai Morag, SVP, General Manager Cloud Security at Tenable](https://www.linkedin.com/in/moragshai/?ref=blog.gitguardian.com), "Cloud Security Novice to Native in 10 Steps: A CNAPP Approach," provided exactly what that title promised and more. The reality is that we are trying to secure new attack vectors while at the same time dealing with staffing and skill shortages.
If we take an end-to-end view, understanding that context is king, a common pattern emerges that shows how we can secure any cloud-based infrastructure. Shai broke the pattern down into three stages: Discover, Manage, and Scale. Without going into detail per item, here are the ten steps to CNAPP Shai shared:\
1\. Discover: All assets\
2\. Discover: All relationships\
3\. Discover: All access to resources\
4\. Manage Risk: Understand your compliance and enterprise policy needs\
5\. Manage Risk: List all risks and compliance violations\
6\. Manage Risk: Prioritize based on full-stack context\
7\. Manage Risk: Visualize and deep-dive into findings\
8\. Manage Risk: Remediate and drive least privilege/Zero Trust\
9\. Scale: Integrate findings with your CI/CD pipeline\
10\. Scale: Automate findings in DevSecOps workflows
[](https://www.linkedin.com/posts/dwaynemcdaniel_rsac-activity-7193725463037423616-WE0x?ref=blog.gitguardian.com)
Cloud Security Novice to Native in 10 Steps: A CNAPP Approach from Shai Morag
### The state of the CISO in 2024
[Nicholas Kakolowski, Senior Research Director at IANS](https://www.linkedin.com/in/nick-kakolowski-2775977a/?ref=blog.gitguardian.com), and [Steve Martano, Partner at Artico Search](https://www.linkedin.com/in/steven-martano-6263b124/?ref=blog.gitguardian.com), explored the shifting expectations of the CISO role in their session, "State of the CISO 2024: Doing More With Less." Their survey-based research shows that the scope of responsibility continues to widen, now including third-party risk management, business continuity, and IAM ownership in many orgs. CISOs are increasingly seen as business risk leaders rather than just technical experts.
If there is a silver lining in their research, it is that Security budgets are not being decreased, as in money is being subtracted from their budgets. Instead, we are seeing the annual increase go from around 12% to only 6% year-over-year in 2023. They said companies should do their best to cross-train and hire from within to make the best use of the budget and fill skill gaps. The more you invest in your team and make them feel there is a career path available, the more likely they are to stick around, which is good for everyone.
[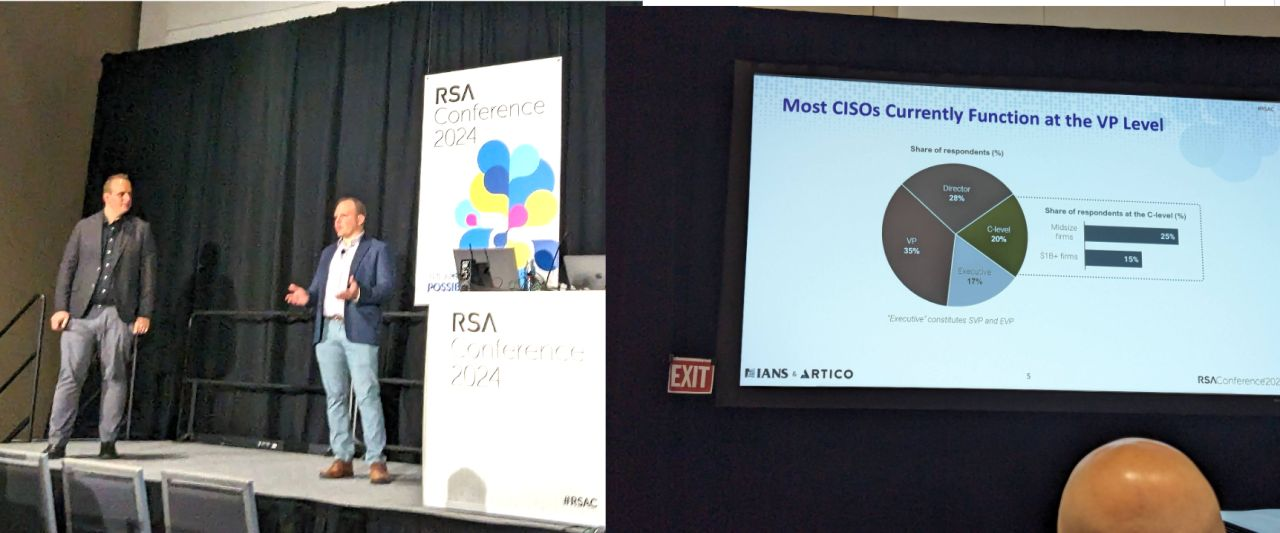](https://www.linkedin.com/posts/dwaynemcdaniel_rsac-activity-7193997616265768961-agKO?ref=blog.gitguardian.com)
State of the CISO 2024: Doing More With Less
Tales from the RSA Sandbox
--------------------------
While sessions at RSAC are a great way to learn, many attendees want a more hands-on experience. That is where the [Sandbox](https://www.rsaconference.com/usa/programs/sandbox?ref=blog.gitguardian.com) comes in. Much like the [villages at DEF CON](https://blog.gitguardian.com/defcon-31-appsec-village/), the sandbox features a variety of stages and pods where attendees can interact with various areas of cybersecurity. This year's areas of focus included aerospace, IoT, AI, and AppSec. GitGuardian is proud to be a sponsor of [AppSec Village](https://www.appsecvillage.com/events/rsac-2024?ref=blog.gitguardian.com), which is the organization that set up three areas where various groups could run exercises, practical demos, and even a capture-the-flag (CTF).
### Manual code review vs. using the right tool
We were thrilled this year to run a tabletop card-based exercise called "[Spot the Secrets: Finding The Valid Secrets Throughout Your Environments](https://www.appsecvillage.com/events/rsac-2024/spot-the-secrets-finding-the-valid-secrets-throughout-your-environments-day1?ref=blog.gitguardian.com)." Over the course of four sessions, 64 attendees got to be the first people to experience our simulation of what it is like to solve the issue of secrets sprawl using manual code review. [Based on our research](https://blog.gitguardian.com/voice-of-practitioners-the-state-of-secrets-in-appsec/#:~:text=For%20example%2C%20a%20concerning%2027%25%20of%20respondents%20revealed%20that%20they%20rely%20on%20manual%20code%20reviews) 27% of IT decision-makers say they rely on exactly this approach, and many of the security practitioners who sat down with us at RSA admitted they had never tried it themselves.
Aside from looking through code commits, participants also looked through stacks of Jira tickets, Slack messages, and log files, all while timing themselves to see how long the experience felt under time pressure. When they were done, we introduced a tool that showed exactly where secrets existed in the cards and which were valid, meaning usable by an attacker. Every player had at least one false positive or negative, often more. With the generous feedback we received, stay tuned for more news about this exercise at future AppSec Villages.
[](https://www.linkedin.com/posts/sven-de-bruin_rsaconference2024-ai-activity-7194402109759332352-CZGs?ref=blog.gitguardian.com)
Spot the secret at AppSec Village at RSAC
The largest security expo on earth
----------------------------------
When most people think of RSA, they immediately think of the massive expo floor where vendors set up their booths. Some of these booths feature multi-story construction, actual race cars, and screens that could take up a whole room in most other venues. Others are much more humble and provide just enough space for a few representatives to give quick demos of their tech. And let's not forget about the swag; some attendees come with an extra suitcase just to haul it back home.
While it can be bewildering to navigate the [600 exhibitors](https://www.prnewswire.com/news-releases/rsa-conference-closes-out-33rd-annual-event-by-discovering-the-art-of-whats-possible-together-302142085.html?ref=blog.gitguardian.com) present on the main floor, it is one of the fastest ways to get up to date on the trends in the market and the latest products from industry leaders. Very importantly, it is a place where customers can meet and interact with the teams behind their chosen tech, putting a face to a brand and getting connected with the folks you might never otherwise get to meet in person. Feedback is heard loud and clear without a screen to get in the way.
### The buzz at GitGuardian's booth
Of course, GitGuardian was one of the vendors on the expo floor. We met hundreds of folks over the course of the conference and got to catch up with so many familiar faces, sometimes for the first time in person. A good number of folks were drawn in by our eye-catching stickers and superhero-themed shirts, but many people came to booth with questions in hand and the team was glad to answer them all.
This was the first time we were able to talk about our latest offering, [GitGuardian Source Composition Analysis (SCA)](https://www.gitguardian.com/software-composition-analysis?ref=blog.gitguardian.com). People were impressed by the efficient SBOM creation through the tool and our innovation of effortlessly exposing all the licenses across repos with the ability to filter by [license type for copyleft](https://blog.gitguardian.com/why-understanding-your-open-source-licenses-matters/). A lot of people were blown away by the developer experience through the command line and the speed of the solution as well. We are very proud to have had the chance to show it off along with our other advancements since the last RSA Conference.
[](https://lh7-us.googleusercontent.com/4Cj_hhQdrV7Tl994s4ZKeVhu2r5nA5lWNmJFqRHfrb7MN7FFf742rt2EkIsr9vODnVoG6xgy25qFiDKj8MjPJbpyDQbhMptPd11DAttg1uyJr3nBEitNEArVW_ljZm46mvejU5espRDkfkmtvViHGA)
The GitGuardian Team at the booth
RSA is all about the people
---------------------------
There is so much else that could be said about RSA, like the [amazing parties and social events](https://conferenceparties.com/rsac2024/?ref=blog.gitguardian.com), learning labs, or the "Birds of a Feather" sessions. Beyond all of those parts, RSA Conference 2024 was about coming together as humans to try to get a handle on security. Securing our organizations and ourselves for life in an AI-driven world is going to take a group effort, where we can learn from each other and share ideas. While we might not ever get to the goal of perfectly safe environments and tools, we can take some comfort in knowing that so many people are also on this same journey. We can't wait until next year to see many of the new friends we made along the way. | dwayne_mcdaniel |
1,872,154 | Suivi de la géolocalisation en JavaScript avec l'API Google Maps | Découvrez la dernière série sur la création de cartes en temps réel à l'aide de JavaScript Google Maps API et du suivi de la géolocalisation. | 0 | 2024-05-31T14:45:48 | https://dev.to/pubnub-fr/suivi-de-la-geolocalisation-en-javascript-avec-lapi-google-maps-27af | Voici l'article de blog mis à jour, avec tous les mots-clés intégrés de manière transparente.
Il s'agit de la conclusion de la série de quatre articles sur la création d'applications web en temps réel avec des fonctions de géolocalisation en utilisant l'API JavaScript de Google Maps et PubNub. Notre tutoriel vous guidera à travers l'expérience utilisateur de la génération de trajectoires de vol à l'aide de JavaScript et de PubNub.
Pour un exemple de mise en œuvre, consultez notre [démo Showcase](https://showcase.pubnub.com/?utm_source=devto&utm_medium=syndication&utm_campaign=off_domain&utm_content=fr) sur le site web de PubNub. Naviguez vers la démo Géolocalisation pour voir comment nous incorporons PubNub avec le suivi en temps réel. Pour le code derrière la démo, naviguez vers notre [Github](https://github.com/PubNubDevelopers/PubNub-Showcase/tree/main/web/geolocation) pour voir comment tout cela fonctionne.
Que sont les trajectoires de vol ?
----------------------------------
Les trajectoires de vol, telles qu'elles sont mises en œuvre dans ce **tutoriel**, font référence aux **polylignes** qui permettent de **dessiner dynamiquement des trajectoires à travers des points spécifiés par l'utilisateur** sur une carte qui réside soit sur votre **appareil mobile**, soit sur votre navigateur web. Ils font partie intégrante de l'**API de géolocalisation HTML5** et de l'**API de Google Maps** pour le suivi des mouvements.
Vue d'ensemble du tutoriel
--------------------------
Assurez-vous d'avoir rempli les conditions préalables des [parties 1,](https://www.pubnub.com/blog/javascript-mapping-javascript-tracking/?utm_source=devto&utm_medium=syndication&utm_campaign=off_domain&utm_content=fr) [2](https://www.pubnub.com/blog/javascript-google-maps-api-map-markers/?utm_source=devto&utm_medium=syndication&utm_campaign=off_domain&utm_content=fr) et [3](https://www.pubnub.com/blog/javascript-google-maps-api-location-publishing/?utm_source=devto&utm_medium=syndication&utm_campaign=off_domain&utm_content=fr), où nous avons [mis en place notre environnement JavaScript](https://www.pubnub.com/blog/javascript-mapping-javascript-tracking/?utm_source=devto&utm_medium=syndication&utm_campaign=off_domain&utm_content=fr) et abordé les [marqueurs de carte](https://www.pubnub.com/blog/javascript-google-maps-api-map-markers/?utm_source=devto&utm_medium=syndication&utm_campaign=off_domain&utm_content=fr) et le [suivi de la localisation](https://www.pubnub.com/blog/javascript-google-maps-api-location-publishing/?utm_source=devto&utm_medium=syndication&utm_campaign=off_domain&utm_content=fr).
Une fois que vous l'avez fait, passez à la partie suivante.
Présentation du code
--------------------
Commençons par définir les variables \`let\` \`map\`, \`mark\`, et \`lineCoords\` pour contenir nos objets map, marker, et polyline **coords**. En faisant cela, nous pouvons les ajuster au fur et à mesure que les événements PubNub arrivent. Ensuite, nous définissons le callback \`initialize\` qui est utilisable par l'[API JavaScript de Google Maps](https://developers.google.com/maps/documentation/javascript/overview) lorsqu'elle est prête à être chargée. Assurez-vous de remplacer \`YOUR\_GOOGLE\_MAPS\_API\_KEY\` par votre véritable **clé API**.
```js
let map;
let mark;
let lineCoords = [];
let initialize = function() {
map = new google.maps.Map(document.getElementById('map-canvas'), {center:{lat:lat,lng:lng},zoom:12});
mark = new google.maps.Marker({position:{lat:lat, lng:lng}, map:map});
};
window.initialize = initialize;
```
Maintenant, avec le gestionnaire d'événement "redraw", nous allons mettre à jour les nouvelles informations de localisation à la volée en invoquant la méthode \`getCurrentPosition()\` de la géolocalisation.
### Lat/Long
Ensuite, nous définissons un gestionnaire d'événement redraw que nous appellerons à chaque fois que nous recevrons un nouvel événement de changement de position à la volée. Dans la première partie de la fonction, nous fixons la latitude et la longitude aux nouvelles valeurs du message. Ensuite, nous invoquons les méthodes appropriées sur les objets carte, marqueur et polyligne pour mettre à jour la position, l'ajouter à la fin de la ligne et recentrer la carte.
```js
var redraw = function(payload) {
lat = payload.message.lat;
lng = payload.message.lng;
map.setCenter({lat:lat, lng:lng, alt:0});
mark.setPosition({lat:lat, lng:lng, alt:0});
lineCoords.push(new google.maps.LatLng(lat, lng));
var lineCoordinatesPath = new google.maps.Polyline({
path: lineCoords,
geodesic: true,
strokeColor: '#2E10FF'
});
lineCoordinatesPath.setMap(map);
};
```
Initialiser PubNub
------------------
Après avoir défini nos callbacks, nous allons initialiser la fonctionnalité de streaming de données en temps réel PubNub qui fonctionne sur les **téléphones mobiles, les tablettes, les navigateurs** et les **ordinateurs portables** à travers des piles technologiques comme **iOS, Android, JavaScript, .NET, Java, Ruby, Python, PHP,** et plus encore.
```js
const pnChannel = "map3-channel";
const pubnub = new PubNub({
publishKey: 'YOUR_PUB_KEY',
subscribeKey: 'YOUR_SUB_KEY'
});
pubnub.subscribe({channels: [pnChannel]});
pubnub.addListener({message:redraw});
```
La fonctionnalité de PubNub permettant de **publier** et de **s'abonner à** des sujets dans des canaux en temps réel offre des capacités de flux de données efficaces.
Publier Lat/Long
----------------
Pour ce tutoriel simple, nous avons mis en place un minuteur d'intervalle JavaScript de base pour publier de nouvelles positions basées sur l'heure actuelle. Toutes les 500 millisecondes, nous invoquons la fonction de rappel anonyme qui publie un nouvel objet latitude/longitude (avec des coordonnées en mouvement vers le nord-est) sur le canal PubNub spécifié. Dans votre application, vous obtiendrez probablement la position d'un appareil en direct ou d'une position rapportée par l'utilisateur.
```js
setInterval(function() {
pubnub.publish({channel:pnChannel, message:{lat:window.lat + 0.001, lng:window.lng + 0.01}});
}, 500);
```
Enfin, nous initialisons l'API Google Maps à la toute fin pour nous assurer que les éléments DOM et les prérequis JavaScript sont satisfaits.
```js
<script src="https://maps.googleapis.com/maps/api/js?v=3.exp&key=YOUR_GOOGLE_MAPS_API_KEY&callback=initialize"></script>
```
Récapitulation
--------------
Cette série de tutoriels nous a montré comment l'[API Google Maps](https://developers.google.com/maps/documentation/javascript/overview) et [PubNub](https://www.pubnub.com/?utm_source=devto&utm_medium=syndication&utm_campaign=off_domain&utm_content=fr) fonctionnent exceptionnellement bien ensemble pour le suivi de la localisation en temps réel sur les applications web et mobiles. C'est similaire à la façon dont les services de covoiturage comme **Uber** et **Lyft** affichent le mouvement de leurs véhicules en temps réel.
Découvrez PubNub
----------------
Regardez le [Live Tour](https://www.pubnub.com/tour/introduction/?utm_source=devto&utm_medium=syndication&utm_campaign=off_domain&utm_content=fr) pour comprendre les concepts essentiels derrière chaque application alimentée par PubNub en moins de 5 minutes. Découvrez l'expérience de nos utilisateurs directement à partir de notre [page GitHub](https://github.com/PubNubDevelopers) et des témoignages disponibles sur notre site web.
S'installer
-----------
Créez un [compte PubNub](https://admin.pubnub.com/#/login?utm_source=devto&utm_medium=syndication&utm_campaign=off_domain&utm_content=fr) pour un accès immédiat et gratuit aux clés PubNub.
Commencer
---------
La [documentation PubNub](https://www.pubnub.com/docs?utm_source=devto&utm_medium=syndication&utm_campaign=off_domain&utm_content=fr) vous permettra d'être opérationnel, quel que soit votre cas d'utilisation. Nous avons des sections dédiées à l'API JavaScript Google Maps et comment les utiliser avec le suivi en temps réel dans notre SDK. | pubnubdevrel | |
1,872,153 | Top 50 Python Projects You Can Build Today 🚀🐍 | TLDR 🔥 Python is a versatile, high-level programming language known for its emphasis on... | 0 | 2024-05-31T14:45:11 | https://dev.to/kumarkalyan/top-50-python-projects-you-can-build-today-34h5 | python, webdev, machinelearning, ai | ## TLDR :fire:
Python is a versatile, high-level programming language known for its emphasis on code readability, achieved through significant indentation. It is easy to learn and master as it feels like giving instructions to the computer in plain English
The language is dynamically typed, meaning that variable types are determined at runtime, allowing for greater flexibility in coding. Additionally, Python also supports garbage collection, automatically managing memory allocation and deallocation, which helps in preventing memory leaks and other related issues.
Python is an object-oriented programming language and is used in various domains including web development, Machine Learning and artificial intelligence, test automation, Web scraping and scripting, Internet Of Things (IoT) , games development, and many more
In this article, I will share about top 50 Python project ideas that you can build today using popular Python libraries like Django, Flask, Pytest, Tensorflow, Keras, numpy, pandas, etc. Building these projects on your own will help you make your resume stand out from others
## Beginner Level
1. Hello World Program: The classic first program to understand the basic syntax.
2. Simple Calculator: Perform basic arithmetic operations.
3. Number Guessing Game: A game where the user has to guess a number chosen by the computer.
4. To-Do List Application: A command-line tool to manage daily tasks.
5. Unit Converter: Convert units like kilometers to miles, Celsius to Fahrenheit, etc.
6. Basic Web Scraper: Scrape and display data from a website.
7. Password Generator: Create random secure passwords.
8. Dice Rolling Simulator: Simulate rolling a dice.
9. Contact Book: Store and manage contact information.
10. Rock, Paper, Scissors Game: Create a simple game to play against the computer.
## Intermediate Level
1. Weather Application: Fetch and display weather information using an API.
2. Currency Converter: Convert one currency to another using an API.
3. Simple Blog: Create a basic blogging platform.
4. Chat Application: Build a simple chat app using sockets.
5. Markdown to HTML Converter: Convert Markdown files to HTML.
6. Quiz Application: Create a quiz with multiple-choice questions.
7. Expense Tracker: Track expenses and generate reports.
8. File Organizer: Organize files in directories based on file types.
9. Sudoku Solver: Solve a Sudoku puzzle programmatically.
10. Image Resizer: Resize images in bulk.
## Advanced Level
1. E-commerce Website: Build a fully functional e-commerce site.
2. Social Media Dashboard: Analyze and display social media metrics.
3. Machine Learning Model: Implement a simple ML model to classify data.
4. Voice Assistant: Create a voice-activated assistant.
5. Chatbot: Develop a chatbot for customer support.
6. Stock Market Analysis: Analyze stock market data and predict trends.
7. Real-time Data Dashboard: Create a dashboard to visualize real-time data.
8. Online Forum: Build a platform for users to post and discuss topics.
9. Automated Resume Parser: Extract information from resumes and store it.
10. Music Recommendation System: Recommend music based on user preferences.
11.
## Expert Level
1. Deep Learning Image Classifier: Create a deep learning model to classify images.
2. Blockchain Implementation: Implement a basic blockchain.
3. Automated Trading Bot: Develop a bot for automated stock trading.
4. Facial Recognition System: Build a system to recognize faces.
5. Natural Language Processing Tool: Develop a tool for sentiment analysis.
6. AI Game Player: Create an AI that can play games like chess or Go.
7. Cloud-Based Note-Taking App: Develop a cloud-synced note-taking application.
8. Home Automation System: Control home devices using IoT.
9. Smart Attendance System: Automate attendance using facial recognition.
10. Real-time Object Detection: Implement a system to detect objects in real-time.
## Bonus Projects
1. Web-based Code Editor: Develop an online code editor.
2. Virtual Reality Application: Create a basic VR app.
3. 3D Model Viewer: Build an application to view 3D models.
4. Algorithm Visualizer: Visualize various algorithms like sorting and pathfinding.
5. Multi-user Blogging Platform: Create a multi-user blog with admin features.
6. File Encryption Tool: Encrypt and decrypt files.
7. Recipe App: Store and search for recipes.
8. Email Automation Script: Automate sending emails based on triggers.
9. IoT Temperature Monitor: Monitor and log temperature data using IoT devices.
10. Personal Finance Manager: Track income, expenses, and savings goals.
{% embed https://dev.to/kumarkalyan %} | kumarkalyan |
1,870,492 | IP Multicast | There are three different methods to deliver IP packets: unicast (one to one), broadcast (one to... | 0 | 2024-05-31T14:44:40 | https://dev.to/enginpiril/ip-multicast-244m | internetprotocol, ipmulticast, cloud, network | There are three different methods to deliver IP packets: unicast (one to one), broadcast (one to all), and multicast (one to many). Multicast sends packets only to destinations that have explicitly joined the multicast group. The routing devices replicate packets and forward copies to registered receivers while preventing routing loops. This article will cover multicast concepts like distribution trees, multicast addressing, forwarding, IGMP, and PIM.
## IP Multicast Basics
IP Multicast has its own set of terms and concepts centered around the idea of a multicast group, which is a set of receivers interested in particular data. Hosts join groups using IGMP. The router's job is to build a distribution tree connecting receivers to sources. The interface towards the source is the upstream interface. The interfaces towards the receivers are downstream interfaces.
Multicast uses the Class D IP address range 224.0.0.0 to 239.255.255.255. The source IP is a unicast address, while the destination IP is a multicast address. At layer 2, multicast MAC addresses have the 25th bit set to 1. Multiple IP multicast addresses can map to the same MAC address.
The Class D range has reserved blocks:
- 224.0.0.0/24: Link Local
- 224.0.1.0 - 238.255.255.255: Globally Scoped
- 232.0.0.0/8: Source-Specific Multicast
- 233.0.0.0/8: GLOP Addresses
- 239.0.0.0/8: Limited Scope
Link local addresses are used by routing protocols and are never forwarded. IPv6 uses the ff00::/8 range with specific allocations like IPv4.
## Multicast Distribution Trees
Distribution trees control the path multicast traffic takes through the network. The simplest is the Shortest Path Tree (SPT), which uses the shortest path between the source and receivers. The SPT is rooted at the source.
The SPT uses (S,G) state, where S is the source IP and G is the group address. Each source for a group has its own SPT. Below is an example SPT:
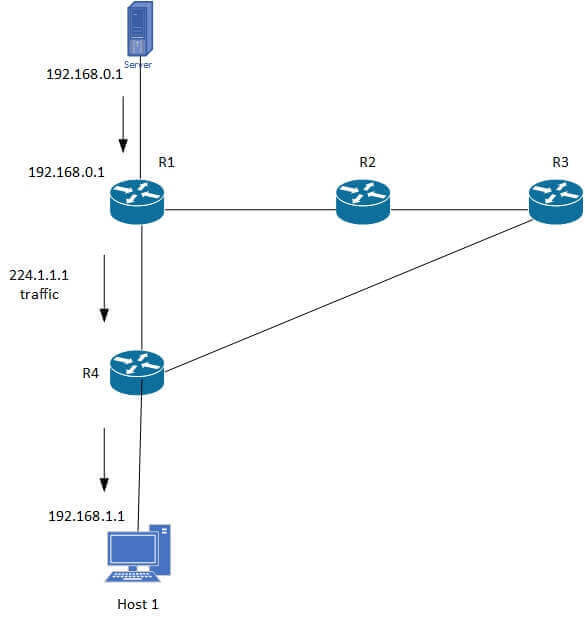
The second type of distribution tree is the shared tree, which uses a common root called the Rendezvous Point (RP). Source traffic goes to the RP over a source tree, then down the shared tree to receivers. The shared tree uses (*,G) state since all sources use the shared infrastructure.
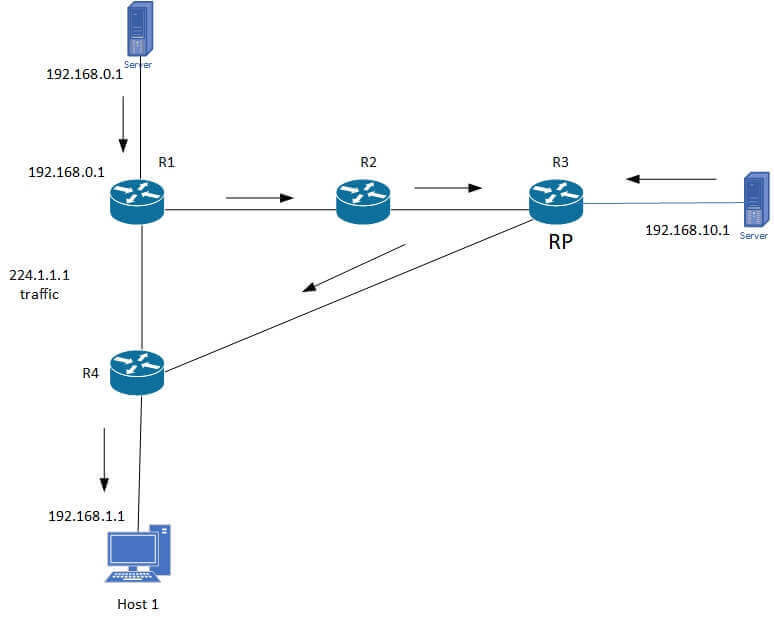
The advantage of SPTs is optimal paths, while shared trees require less state. However, shared tree latency can be higher.
## Multicast Forwarding
In multicast forwarding, the source sends traffic to a group of hosts. Routers track incoming and outgoing interfaces. They use Reverse Path Forwarding (RPF) to forward traffic away from the source to prevent loops.
RPF relies on the unicast routing table to determine upstream and downstream neighbors. A router forwards a multicast packet only if it arrives on the upstream interface. This check ensures delivery along a loop-free tree. Traffic passing the RPF check is forwarded, else it is dropped.
The RPF check logic:
- Check if the source is reachable via the input interface per the routing table
- If yes, traffic passes the RPF check and is forwarded
- If no, traffic fails the RPF check and is dropped
## IGMP
The Internet Group Management Protocol (IGMP) handles hosts joining multicast groups on a LAN. Routers use IGMP to learn group membership:
- Querier routers send queries to see if hosts want traffic
- Hosts send reports to confirm interest
IGMPv2 added a Leave Group message to reduce unwanted traffic. IGMPv3 supports source-specific groups and source filtering.
## Conclusion
IP multicast provides an efficient one-to-many transport model. Core concepts include multicast addressing, distribution trees, multicast forwarding with RPF checks, and IGMP for group management.
Multicast routing protocols like PIM build distribution trees between senders and receivers:
- PIM Dense Mode floods traffic then prunes branches
- PIM Sparse Mode starts with no flow and then builds shared trees
Multicast technologies enable scalable services like high-definition video streaming and software updates. Understanding the core concepts allows network engineers to effectively design, implement, and troubleshoot multicast networks.
This concludes our overview of IP multicast. The article covered addressing, forwarding, IGMP, distribution trees, and routing protocols. With this foundation, you can now configure and manage multicast services on real-world networks.
Read more at https://www.catchpoint.com/network-admin-guide/ip-multicast.
| enginpiril |
1,872,093 | Dependency management in Python Using Poetry | Introduction Dependency management in Python is an important component of software... | 0 | 2024-05-31T14:43:28 | https://dev.to/tinegagideon/dependency-management-in-python-using-poetry-36h2 | python, beginners | # Introduction
Dependency management in Python is an important component of software development because it entails managing the libraries and packages required by a project. Proper dependency management ensures that the necessary dependencies are installed, conflicts are avoided, and the project is reproducible across different environments.
# Concepts
- Dependencies
Dependencies are external libraries or modules that a project relies on to function. These can range from standard libraries included with Python to third-party packages available on repositories like PyPI (Python Package Index).
- Dependency Management Tools
Include tools such as:
- pip: The default package installer for Python.Uses requirements.txt to list dependencies and their versions.
- virtualenv: Creates isolated Python environments to manage dependencies for different projects independently.
- venv: Provides similar functionality to virtualenv but is built into Python.
- conda: A package manager and environment management system that supports multiple languages.
- poetry: A modern tool for dependency management and packaging.Uses pyproject.toml to specify project configurations and dependencies.
# Poetry
[Poetry](https://python-poetry.org/docs/#installing-with-the-official-installer) is a tool for dependency management and packaging in Python. It allows you to declare the libraries your project depends on and it will manage (install/update) them for you. Poetry offers a lockfile to ensure repeatable installs, and can build your project for distribution.
## Pyproject.toml file
`pyproject.toml` is a configuration file used by packaging tools such as poetry.
example
```
[tool.poetry]
name = "poetry-test"
version = "0.2.0"
description = ""
authors = ["None"]
readme = "README.md"
[tool.poetry.dependencies]
python = "^3.12"
requests = "^2.30.0"
[build-system]
requires = ["poetry-core"]
build-backend = "poetry.core.masonry.api"
```
## Installation
**Poetry requires Python 3.8+**
- Linux,macOS
`curl -sSL https://install.python-poetry.org | python3 -`
- Windows(Poweshell)
`(Invoke-WebRequest -Uri https://install.python-poetry.org -UseBasicParsing).Content | py -`
- Add Poetry to your PATH(Environment Variables)
Add the following paths to PATH variable depending on your system.
`$HOME/.local/bin` on Unix.
`%APPDATA%\Python\Scripts` on Windows.
`poetry --version`: verify that poetry is installed correctly and added to $PATH.
## Usage
`poetry new <package name>`: starts a new Python project by creating a new directory with a standard Python project structure.
```
new-package
new-package
__init__.py
tests
__init__.py
pyproject.toml
README.md
```
`poetry init`: Initializes a directory by prompting you to provide details about your project and its dependencies interactively.
`poetry config virtualenvs.in-project true`: create virtual environments inside the project's directory.**Poetry by default will create a virtual environment under {cache-dir}/virtualenvs.**
`poetry shell` : activate the virtual environment created.
`poetry add <django>`: adds a dependency to your project.This will add django to your pyproject.toml file and install django.
```
# Allow >=2.0.0, <3.0.0 versions i.e minor version
poetry add requests^2.0.0
# Allow >=2.0.0, <2.1.0 versions i.e patch versions
poetry add requests~2.0.0
# Allow only a specific version
poetry add requests==2.0.0 | poetry add requests@2.0.0
```
`poetry add --dev <pytest>`: add dependencies only needed in development.Pytest will be added as a development dependency.
`poetry remove <package name>`: removes a package from the current list of installed packages.
`poetry show`: list all the available packages.
`poetry show <package name>`: list details about a specific package.
`poetry version`: shows the current version of the project.
`poetry version <patch|minor|major>`: bumps the version of the project and writes to pyproject.toml.
`poetry list`: displays all the available Poetry commands.
`poetry install`: reads the pyproject.toml file from the current project, resolves the dependencies, and installs them.
[Commands](https://python-poetry.org/docs/cli/)
[Importing existing requirements.txt file to poetry](https://stackoverflow.com/questions/62764148/how-to-import-an-existing-requirements-txt-into-a-poetry-project)
[pyproject file](https://packaging.python.org/en/latest/guides/writing-pyproject-toml/)
| tinegagideon |
1,866,267 | Secure Terraform Solution for Government Agencies | Deliver Trustworthy, Stable, and Compliant Software Faster with Brainboard Government... | 0 | 2024-05-31T14:43:00 | https://dev.to/brainboard/secure-terraform-solution-for-government-agencies-2gel | infrastructureascode, terraform, iac, development | ## Deliver Trustworthy, Stable, and Compliant Software Faster with Brainboard
Government agencies, legal firms, and professional services require robust, secure, and compliant infrastructure solutions to meet the demands of modern public services. Brainboard offers a secure Terraform solution that empowers these organizations to innovate and maintain high standards of security and compliance.
## What Can Government Agencies Accomplish with Brainboard?
### **Modernize Public Services at Scale**
Brainboard enables government IT teams to deliver scalable and reliable infrastructure that complies with organizational policies, ensuring the efficient delivery of public services.
### **The Road to Governance, Risk Management, and Compliance (GRC)**
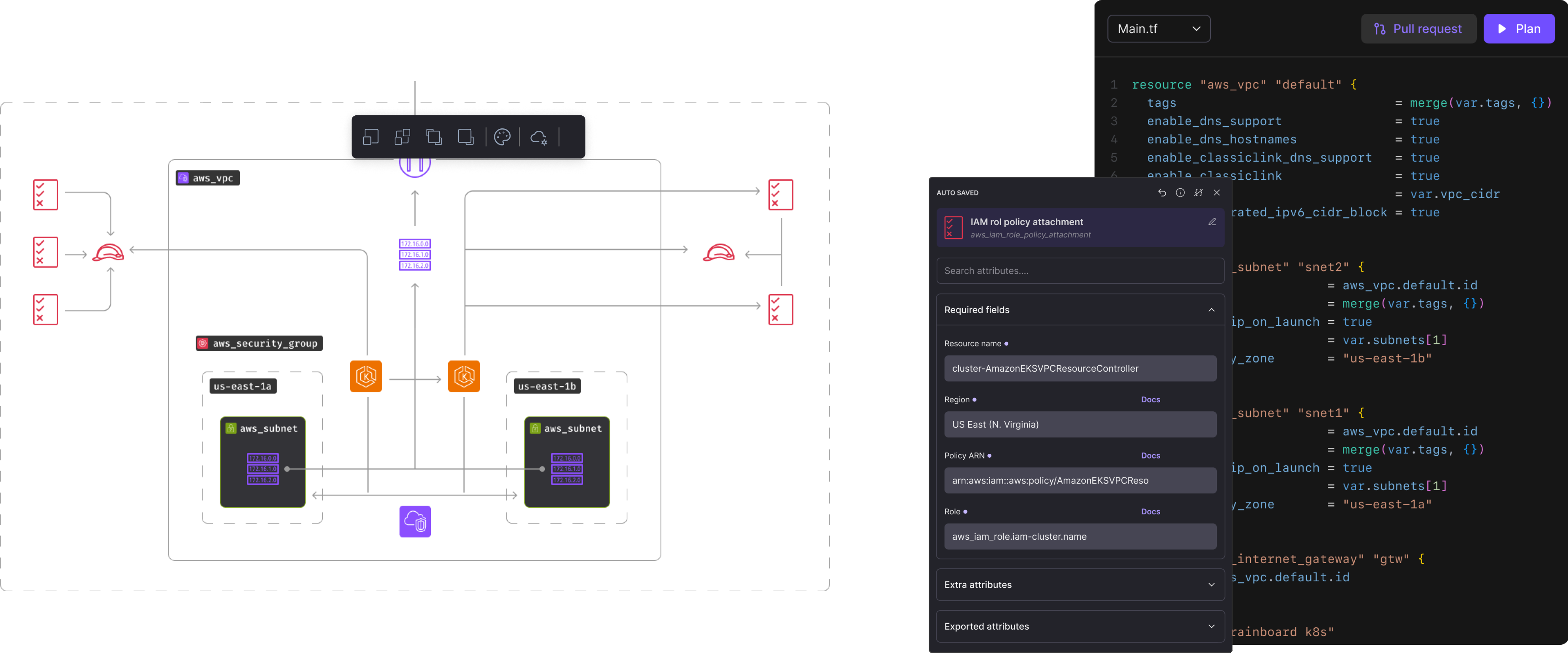
Accelerate Infrastructure-as-Code (IaC) delivery while maintaining security at every stage. Brainboard provides automatic security checks and immediate mitigation of flawed code, eliminating the need for redeployment.
### **Pass Audits with Flying Colors**
Automate audit reporting and collaborate seamlessly with real-time tracking, tracing, and approval of infrastructure from design to production, ensuring compliance and transparency.
### **Streamline Multi-Organization Account Management**
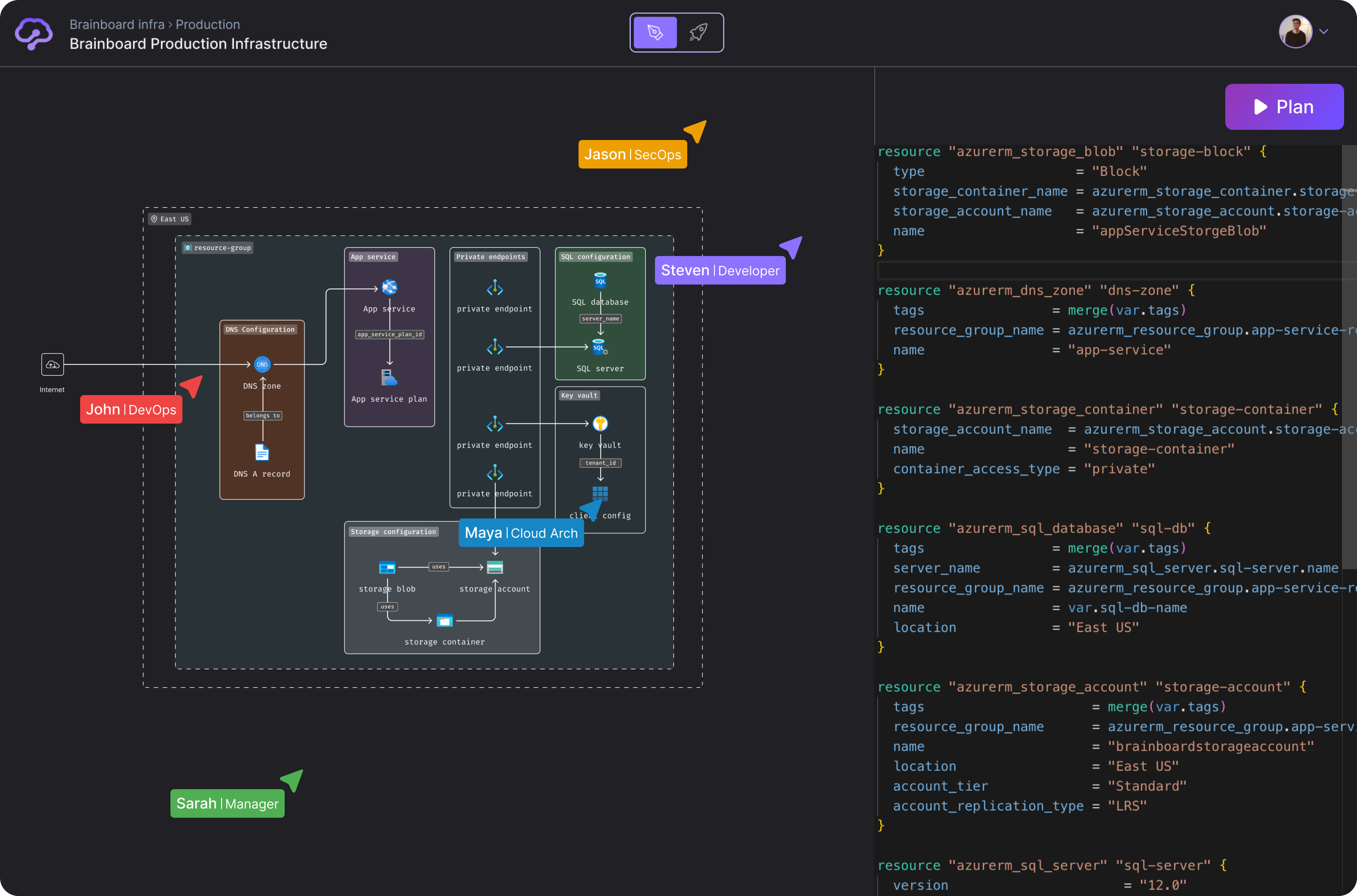
Gain transparency and actionable insights throughout the infrastructure development lifecycle. Brainboard eliminates unnecessary back-and-forth between teams, enabling smoother and faster processes.
### **Transform into Elite-Performing Teams**
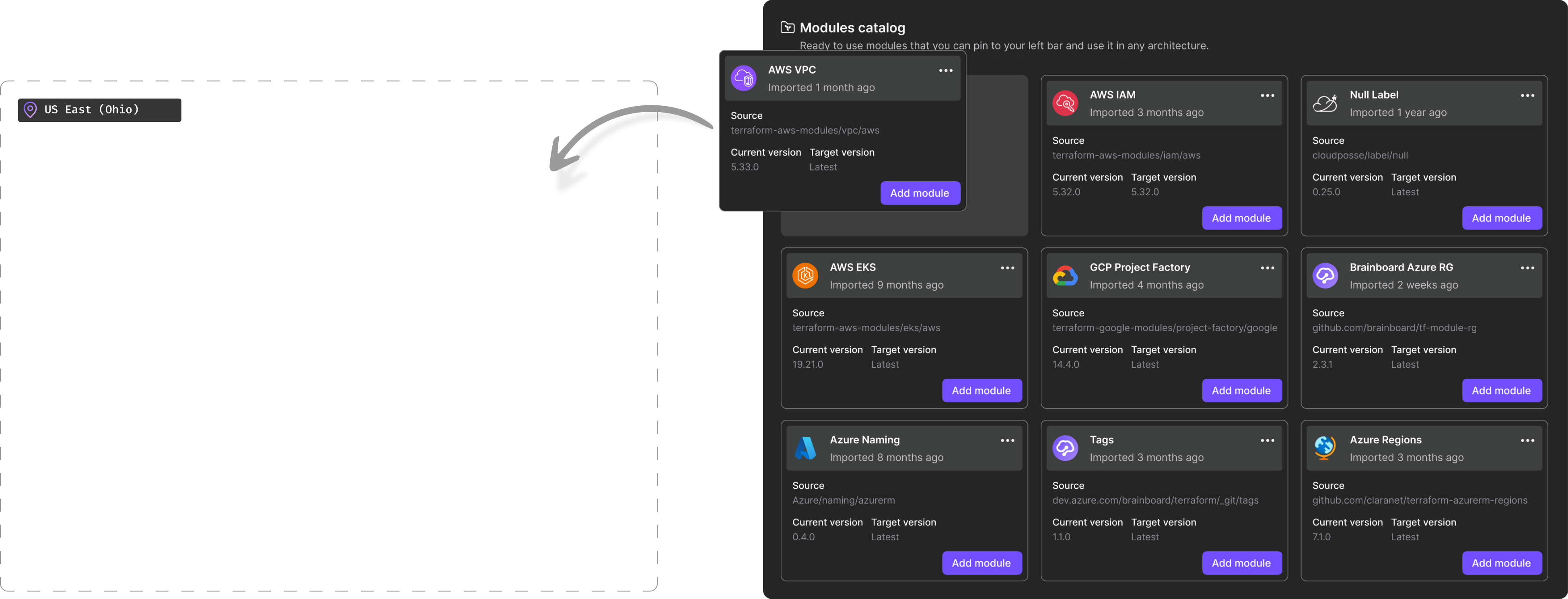
Facilitate effortless engineering collaboration for local, national, and international teams. Create a gallery of templates that scale your processes and enhance team performance.
## Ready to Get Started?
[Schedule a demo with a government DevOps expert](https://meetings.hubspot.com/brainboard/discovery) to learn how the Brainboard platform can transform your agency's digital infrastructure and enhance your service delivery. | miketysonofthecloud |
1,872,152 | Day 3: Lists and Images in HTML | Welcome to Day 3 of your journey to mastering HTML and CSS! Today, we'll focus on how to create lists... | 0 | 2024-05-31T14:42:45 | https://dev.to/dipakahirav/day-3-lists-and-images-in-html-15ga | html, css, javascript, beginners | Welcome to Day 3 of your journey to mastering HTML and CSS! Today, we'll focus on how to create lists and add images to your web pages. By the end of this post, you'll be able to organize content using lists and enhance your pages with images.
please subscribe to my [YouTube channel](https://www.youtube.com/@DevDivewithDipak) to support my channel and get more web development tutorials.
#### Creating Lists in HTML
HTML provides several types of lists to organize content: unordered lists, ordered lists, and description lists.
1.**Unordered Lists**: Unordered lists are used for items that don’t require a specific order. They use the `<ul>` tag and list items are enclosed in `<li>` tags.
```html
<ul>
<li>Item 1</li>
<li>Item 2</li>
<li>Item 3</li>
</ul>
```
2.**Ordered Lists**: Ordered lists are used for items that need to be in a specific order. They use the `<ol>` tag and list items are enclosed in `<li>` tags.
```html
<ol>
<li>First item</li>
<li>Second item</li>
<li>Third item</li>
</ol>
```
3.**Description Lists**: Description lists are used to display a list of terms and their descriptions. They use the `<dl>`, `<dt>`, and `<dd>` tags.
```html
<dl>
<dt>Term 1</dt>
<dd>Description of Term 1</dd>
<dt>Term 2</dt>
<dd>Description of Term 2</dd>
</dl>
```
#### Adding Images in HTML
Images are an essential part of web content, making it more engaging and informative. The `<img>` tag is used to embed images in HTML.
1.**Basic Image**: Use the `src` attribute to specify the image source and the `alt` attribute to provide alternative text.
```html
<img src="image.jpg" alt="Description of the image">
```
2.**Image Size**: You can specify the width and height of an image using the `width` and `height` attributes.
```html
<img src="image.jpg" alt="Description of the image" width="300" height="200">
```
3.**Responsive Images**: To make images responsive, you can use CSS properties like `max-width` and `height`.
```html
<style>
img {
max-width: 100%;
height: auto;
}
</style>
<img src="image.jpg" alt="Description of the image">
```
#### Creating Your HTML Document with Lists and Images
Let's create an HTML document that incorporates lists and images:
```html
<!DOCTYPE html>
<html lang="en">
<head>
<meta charset="UTF-8">
<meta name="viewport" content="width=device-width, initial-scale=1.0">
<title>Lists and Images</title>
<style>
img {
max-width: 100%;
height: auto;
}
</style>
</head>
<body>
<h1>Welcome to My Website</h1>
<h2>Unordered List</h2>
<ul>
<li>Item 1</li>
<li>Item 2</li>
<li>Item 3</li>
</ul>
<h2>Ordered List</h2>
<ol>
<li>First item</li>
<li>Second item</li>
<li>Third item</li>
</ol>
<h2>Description List</h2>
<dl>
<dt>Term 1</dt>
<dd>Description of Term 1</dd>
<dt>Term 2</dt>
<dd>Description of Term 2</dd>
</dl>
<h2>Adding an Image</h2>
<img src="image.jpg" alt="A beautiful scenery">
<p>This is an example of an image embedded in an HTML page.</p>
</body>
</html>
```
#### Summary
In this blog post, we learned how to create different types of lists and how to add images to an HTML document. Practice using these tags to organize your content and enhance your web pages with images.
Stay tuned for Day 4, where we will cover tables and their uses in HTML. Happy coding!
*Follow me for more tutorials and tips on web development. Feel free to leave comments or questions below!*
#### Follow and Subscribe:
- **Website**: [Dipak Ahirav] (https://www.dipakahirav.com)
- **Email**: dipaksahirav@gmail.com
- **Instagram**: [devdivewithdipak](https://www.instagram.com/devdivewithdipak)
- **YouTube**: [devDive with Dipak](https://www.youtube.com/@DevDivewithDipak)
- **LinkedIn**: [Dipak Ahirav](https://www.linkedin.com/in/dipak-ahirav-606bba128) | dipakahirav |
1,872,151 | JavaScript Geolocation Tracking mit Google Maps API | Entdecken Sie die abschließende Serie über die Erstellung von Echtzeit-Karten mit JavaScript Google Maps API und Geolocation Tracking. | 0 | 2024-05-31T14:40:47 | https://dev.to/pubnub-de/javascript-geolocation-tracking-mit-google-maps-api-1e41 | Hier ist der aktualisierte Blogbeitrag, in den alle Schlüsselwörter nahtlos eingebettet sind.
Dies ist der Abschluss der vierteiligen Serie über die Erstellung von Live-Echtzeit-Webanwendungen mit Geolokalisierungsfunktionen mithilfe der Google Maps JavaScript API und PubNub. Unser Tutorial führt Sie durch die Benutzererfahrung bei der Erstellung von Flugrouten mit JavaScript und PubNub.
Ein Beispiel dafür, wie dies alles umgesetzt wird, finden Sie in unserer [Showcase-Demo](https://showcase.pubnub.com/?utm_source=devto&utm_medium=syndication&utm_campaign=off_domain&utm_content=de) auf der PubNub-Website. Navigieren Sie zur Geolocation-Demo, um zu sehen, wie wir PubNub mit Echtzeit-Tracking einbinden. Den Code hinter der Demo finden Sie auf unserer [Github-Website](https://github.com/PubNubDevelopers/PubNub-Showcase/tree/main/web/geolocation).
Was sind Flugpfade?
-------------------
Flugpfade, wie sie in diesem **Tutorial** implementiert sind, beziehen sich auf **Polylinien**, die das **dynamische Zeichnen von Pfaden durch benutzerdefinierte Punkte** auf einer Karte ermöglichen, die sich entweder auf Ihrem **mobilen Gerät** oder im Webbrowser befindet. Sie sind integraler Bestandteil der **HTML5 Geolocation API** und der **Google Maps API** zur Verfolgung von Bewegungsmustern.
Überblick über das Tutorial
---------------------------
Vergewissern Sie sich, dass Sie die Voraussetzungen aus den [Teilen eins,](https://www.pubnub.com/blog/javascript-mapping-javascript-tracking/?utm_source=devto&utm_medium=syndication&utm_campaign=off_domain&utm_content=de) [zwei](https://www.pubnub.com/blog/javascript-google-maps-api-map-markers/?utm_source=devto&utm_medium=syndication&utm_campaign=off_domain&utm_content=de) und [drei](https://www.pubnub.com/blog/javascript-google-maps-api-location-publishing/?utm_source=devto&utm_medium=syndication&utm_campaign=off_domain&utm_content=de) erfüllt haben, , in denen wir [unsere JavaScript-Umgebung eingerichtet](https://www.pubnub.com/blog/javascript-mapping-javascript-tracking/?utm_source=devto&utm_medium=syndication&utm_campaign=off_domain&utm_content=de) und [Kartenmarkierungen](https://www.pubnub.com/blog/javascript-google-maps-api-map-markers/?utm_source=devto&utm_medium=syndication&utm_campaign=off_domain&utm_content=de) und [Standortverfolgung](https://www.pubnub.com/blog/javascript-google-maps-api-location-publishing/?utm_source=devto&utm_medium=syndication&utm_campaign=off_domain&utm_content=de) behandelt haben.
Wenn Sie dies getan haben, fahren Sie mit dem nächsten Teil fort.
Code-Walkthrough
----------------
Beginnen wir mit der Definition der \`let'-Variablen \`map\`, \`mark\` und \`lineCoords\`, um unsere Karten-, Markierungs- und **Polylinien-Koordinatenobjekte** zu speichern. Auf diese Weise können wir sie anpassen, wenn PubNub-Ereignisse eintreffen. Anschließend definieren wir den \`initialize\`-Callback, der von der [Google Maps JavaScript-API](https://developers.google.com/maps/documentation/javascript/overview) verwendet werden kann, wenn sie bereit zum Laden ist. Stellen Sie sicher, dass Sie \`YOUR\_GOOGLE\_MAPS\_API\_KEY\` durch Ihren tatsächlichen **API-Schlüssel** ersetzen.
```js
let map;
let mark;
let lineCoords = [];
let initialize = function() {
map = new google.maps.Map(document.getElementById('map-canvas'), {center:{lat:lat,lng:lng},zoom:12});
mark = new google.maps.Marker({position:{lat:lat, lng:lng}, map:map});
};
window.initialize = initialize;
```
Mit dem 'redraw'-Ereignishandler aktualisieren wir nun die neuen Standortinformationen, indem wir die Methode 'getCurrentPosition()' von Geolocation aufrufen.
### Lat/Long
Als Nächstes definieren wir einen "redraw"-Ereignishandler, den wir immer dann aufrufen, wenn wir ein neues Positionsänderungsereignis erhalten. Im ersten Teil der Funktion setzen wir den Breiten- und Längengrad auf die neuen Werte aus der Nachricht. Dann rufen wir die entsprechenden Methoden auf den Objekten Karte, Marker und Polylinie auf, um die Position zu aktualisieren, sie dem Ende der Linie hinzuzufügen und die Karte neu zu zentrieren.
```js
var redraw = function(payload) {
lat = payload.message.lat;
lng = payload.message.lng;
map.setCenter({lat:lat, lng:lng, alt:0});
mark.setPosition({lat:lat, lng:lng, alt:0});
lineCoords.push(new google.maps.LatLng(lat, lng));
var lineCoordinatesPath = new google.maps.Polyline({
path: lineCoords,
geodesic: true,
strokeColor: '#2E10FF'
});
lineCoordinatesPath.setMap(map);
};
```
PubNub initialisieren
---------------------
Nachdem wir unsere Callbacks definiert haben, initialisieren wir die PubNub-Echtzeitdaten-Streaming-Funktionalität, die auf **Mobiltelefonen, Tablets, Browsern** und **Laptops** über Tech-Stacks wie **iOS, Android, JavaScript, .NET, Java, Ruby, Python, PHP** und mehr funktioniert.
```js
const pnChannel = "map3-channel";
const pubnub = new PubNub({
publishKey: 'YOUR_PUB_KEY',
subscribeKey: 'YOUR_SUB_KEY'
});
pubnub.subscribe({channels: [pnChannel]});
pubnub.addListener({message:redraw});
```
Die PubNub-Funktionalität zum **Veröffentlichen** und **Abonnieren** von Themen in Echtzeitkanälen bietet effiziente Daten-Streaming-Funktionen.
Veröffentlichung von Lat/Long
-----------------------------
Für dieses einfache Tutorial richten wir einen einfachen JavaScript-Intervall-Timer ein, um neue Positionen auf der Grundlage der aktuellen Zeit zu veröffentlichen. Alle 500 Millisekunden rufen wir die anonyme Callback-Funktion auf, die ein neues Latitude/Longitude-Objekt (mit Koordinaten, die sich nach Nordosten bewegen) im angegebenen PubNub-Kanal veröffentlicht. In Ihrer Anwendung werden Sie die Position wahrscheinlich von einer Live-Geräteposition oder einem vom Benutzer gemeldeten Standort erhalten.
```js
setInterval(function() {
pubnub.publish({channel:pnChannel, message:{lat:window.lat + 0.001, lng:window.lng + 0.01}});
}, 500);
```
Zu guter Letzt initialisieren wir die Google Maps API, um sicherzustellen, dass die DOM-Elemente und JavaScript-Voraussetzungen erfüllt sind.
```js
<script src="https://maps.googleapis.com/maps/api/js?v=3.exp&key=YOUR_GOOGLE_MAPS_API_KEY&callback=initialize"></script>
```
Zusammenfassung
---------------
Diese Tutorial-Serie hat uns gezeigt, wie die Google [Maps API](https://developers.google.com/maps/documentation/javascript/overview) und [PubNub](https://www.pubnub.com/?utm_source=devto&utm_medium=syndication&utm_campaign=off_domain&utm_content=de) außergewöhnlich gut für die Echtzeit-Standortverfolgung in Web- und Mobil-Apps zusammenarbeiten. Dies ist vergleichbar mit der Art und Weise, wie Ride-Hailing-Dienste wie **Uber** und **Lyft** die Bewegung ihrer Fahrzeuge in Echtzeit anzeigen.
PubNub erleben
--------------
Schauen Sie sich die [Live Tour](https://www.pubnub.com/tour/introduction/?utm_source=devto&utm_medium=syndication&utm_campaign=off_domain&utm_content=de) an, um in weniger als 5 Minuten die grundlegenden Konzepte hinter jeder von PubNub betriebenen App zu verstehen. Hören Sie sich die Erfahrungen unserer Nutzer direkt auf unserer [GitHub-Seite](https://github.com/PubNubDevelopers) und in den Testimonials auf unserer Website an.
Einrichten
----------
Melden Sie sich für einen [PubNub-Account](https://admin.pubnub.com/#/login?utm_source=devto&utm_medium=syndication&utm_campaign=off_domain&utm_content=de) an, um sofort kostenlosen Zugang zu PubNub-Schlüsseln zu erhalten.
Starten Sie
-----------
Die [PubNub-Dokumente](https://www.pubnub.com/docs?utm_source=devto&utm_medium=syndication&utm_campaign=off_domain&utm_content=de) werden Sie unabhängig von Ihrem Anwendungsfall zum Laufen bringen. Wir haben Abschnitte, die der JavaScript Google Maps API gewidmet sind und wie man sie mit Echtzeit-Tracking in unserem SDK verwendet. | pubnubdevrel | |
1,872,150 | 🎯 Strategies for Effective Urgent Ticket Classification | "When everything is urgent, then nothing really is." Dealing with urgent tickts is a frequent... | 0 | 2024-05-31T14:38:28 | https://dev.to/kibumpng/strategies-for-effective-urgent-ticket-classification-3ian | programming, career, webdev, productivity | > "When everything is urgent, then nothing really is."
Dealing with urgent tickts is a frequent reality to maintain the efficiency and also functionality of systems. But what exactly are urgent tickets? And how can we ensure that only genuinely critical tickets receive this classification?
I've worked for several companies that misunderstand the concept of urgent tickets, and that usually leads to a variety of complications... Urgent tickets are often misinterpreted as an invitation to prioritize quantity over quality, resulting in rushed solutions that may not fully address the issue at hand. This approach can lead to increased error andfrustated customers.
## 🎯 What Are Urgent Tickets?
Urgent tickets are requests or issues that require **immediate** attention due to their significant impact on business operations, data security, or user experience. These tickets are categorized as urgent becuse if not resolved quickly they can cause serious damage to the company or customers.
## 🔍 Criteria for Classifying Urgency
To determine ifa ticket should be classified as urgent we consider several criterias:
1. **Business Impact** 📈: Affects critical operations or prevents users from performing essential tasks.
2. **Security** 🔒: Involves vulnerabilities that could be exploited compromising data integrity.
3. **User Experience** 💻: Affects a large user base or causes severe degradation in the user experience (A lot of folks don't realize how crucial user experience is but it's really a big deal. If a system isn't easy and enjoyable to usecustomers might ditch it for something better).
These criteria help prioritize issues that **truly** need a quick and efficient response.
## 🗣 Helping Non-Technical People Understand Urgency
The "trickiest" thing about urgent tickets is when people who aren't tech get involved. It's always more complex for them (no doubt). But, we've got ways to lend a hand, at least to help them see that not all tickets are as urgent as they might think.
- **Use Clear Examples** 📝: Describe concrete situations where urgency was necessary and the impacts of not addressing the issue immediately (you can try to using some no-really-related topics to exemplify) .
- **Measurable Impacts** 📊: Use data and metrics to illustrate the severity of the situation (likerevenue loss, increased churn, or security breaches).
- **Visual Tools** 🎨: Charts, infographics, and diagrams can help make explanations more understandable.
## 🏷 Subcategories of Urgency
Yes, there are different levels of urgency that can be classified to further prioritize tickets. Typical subcategories include:
- **Critical** 🚨: Requires immediate resolution, usually within hours. Examples include system failures that halt business operations or major security breaches.
- **High** ⚠️: Should be addressed within one business day. These are serious problems but do not completely paralyze operations.
- **Medium** ⏳: Can be resolved within a few days. These tickets are important but do not cause immediate and severe interruptions to operations.
## ⏱ Average Resolution Time
The resolution time for an urgent ticket can vary depending on its complexity, but here are some **general** guidelines:
- **Critical Tickets** 🚨: Expected to be resolved within 24 hours.
- **High Urgency Tickets** ⚠️: Should be solved within 1 to 3 business days.
- **Medium Urgency Tickets** ⏳: Can be resolved within a week.
These response times help ensure that the most severe issues are addressed with the necessary priority.
## 🛠 Tools and Practices for Managing Urgent Tickets
Implementing efficient tools and practices can sreamline the management of urgent tickets:
- **Ticketing Systems** 📋: Use robust ticketing systems like Jira (one of the most popular), Zendesk, orServiceNow to track and manage tickets efficiently.
- **Automated Alerts** 📣: Set up automated alerts to notify the relevant teams immediately when an urgent ticket is raised (We usually set this alerts on a slack channel, really useful)
- **Regular Training** 🎓: Conduct regular training sessions for the support team to handle urgent tickets effectively (this one it's REALLY hard to implement but everyone can dream, right?).
## 🤝 Best Practices
- **Regular Updates** 🔄: Provide regular updates on the status of urgent tickets to all stakeholders (one's of my favorite approachs).
- **Clear Communication Channels**📞: Establish clear communication channels between technical and non-technical teams.
## 📈 Metrics and Reporting
Tracking and analyzing metrics can help improve the handling of urgent tickets:
- **Resolution Time** ⏲️: Monitor theaverage resolution time for each urgency level (This can even become one of your future OKRs to work on).
- **Customer Satisfaction** 😊: Measure customer satisfaction through surveys after ticket resolution (I worked in really few companies that used that).
- **Ticket Volume** 📊: Track the volume of urgent tickets over time to identify trends and potential systemic issues.
## 🚀 Conclusion
Effectively managing urgent tickets is crucial for maintaining the stability and security of systems. By educating non-technical teams about the importance andcriteria of these tickets, we achieve more efficient collaboration and quicker responses to critical problems.
| kibumpng |
1,862,852 | Demystifying Token-Based Authentication: Your Angular Roadmap (Part 1) | Introduction I continue the exploration of authentication methods, after the article about... | 27,384 | 2024-05-31T14:38:28 | https://dev.to/cezar-plescan/demystifying-token-based-authentication-your-angular-roadmap-5bon | authentication, jwt, angular, token | ## Introduction
I continue the exploration of authentication methods, after the article about [session-based authentication](https://dev.to/cezar-plescan/demystifying-session-based-authentication-your-angular-roadmap-1b9n), by focusing on the role of **tokens** and highlighting their advantages over session IDs in certain scenarios. While the term "token" might sound familiar to you, let's delve into their evolution and specific challenges they address where session IDs prove to be less valuable.
The topics I'll cover provide a basic foundation for authentication systems that use JWTs:
- what are the benefits of such method compared to session IDs
- what is the structure of a JWT
- what is required to create a token
- how to send it to the client and how can the client store it
- how to pass the token within requests
- how the server verifies the token and send the response
## Evolution
I want to describe a scenario to illustrate where session cookies become harder to handle.
Let’s imagine an e-commerce application. In its early days everything ran on one monolithic server, where both frontend and backend were hosted. The server had a database to store user sessions and for every user a session cookie was created. So far, the cookie mechanism worked smoothly.
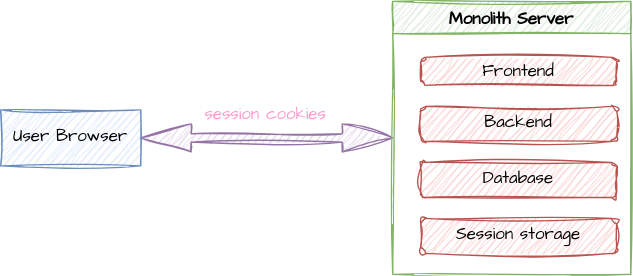
The application gained popularity and the traffic encountered huge spikes. To fix that, load balancers were introduced to distribute requests across multiple servers.
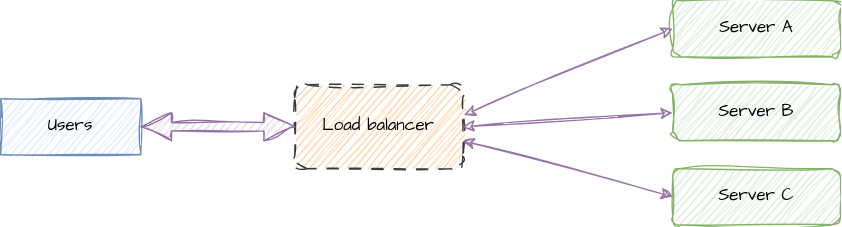
But what if a user’s subsequent requests landed on a different server that doesn’t have their session data? A workaround was developed: to have “sticky sessions”, where the load balancer routed a user’s requests to the same server, but that reduced scaling flexibility, which was a major drawback.
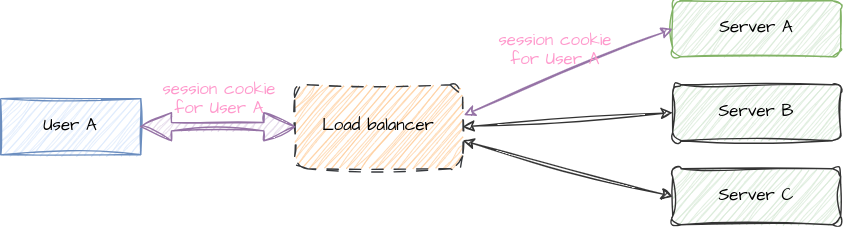
Another improvement mechanism was added: horizontal scaling with **microservices**. That implied decomposing parts of the application into smaller units running on their own servers. Below is a simplistic representation of microservices.
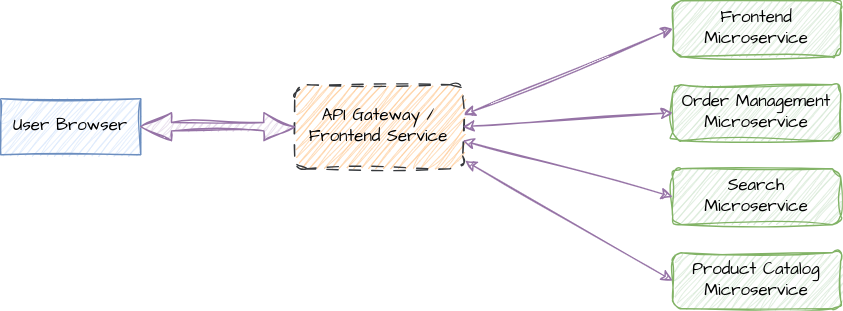
But how do these servers coordinate the user sessions? Possible solutions could be to **replicate the session data** across all servers (which adds overhead, synchronization delays, or potential inconsistencies), or to introduce a **single dedicated session storage database** (like Redis - this creates a single point of failure and adds network latency when multiple servers fetch session data). It looks that the complexity starts to increase a lot, which leads to reduced maintainability of the system.
What if we were able to **decentralize the session data**, so each server would have a mechanism to validate the authentication information, without the need of a central session store? This leads to the introduction of **_web tokens_**.
## Concept
What’s the idea behind these tokens? Unlike session IDs, which are stored by the server along with the user data, **the tokens themselves contain the user data** (e.g. user ID, username, email, roles, etc.), are generated by the server, stored by each client, and passed within the requests.
Tokens are cryptographically signed and all servers in the entire system are able to decode them and extract the user information by using a shared key (I’ll cover how this mechanism works later in the article).
### Benefits
Let’s explore some general benefits this concept brings:
- **Scaling** can be easily achieved, each added server can independently validate the tokens.
- Seamless integration with **RESTful APIs**, due to their stateless nature. This makes tokens a good fit for integration with mobile applications.
- Tokens can be sent across **different domains**, they are a good fit for distributed systems
I want to mention the main practical benefit in the context of the previous scenario with the e-commerce application: the horizontal scaling that involves multiple servers or microservices can be done with minimal effort; the newly added servers would need to know the shared key only to validate the tokens.
## Internals
On the surface, the web tokens look like a robust system with significant benefits. Ever wondered how they actually work? In the article about [session-based authentication](https://dev.to/cezar-plescan/demystifying-session-based-authentication-your-angular-roadmap-1b9n) I talked about session IDs which utilize the browser cookies, but what are the web tokens more specifically, how are they passed with the request, and how do servers validate them?
_**Note**: I’ve used the general term **web token**, but in the context of authentication the **JSON Web Tokens (JWT)** are the dominant and widely supported standard and I’ll refer exclusively to them throughout the entire article. More details about JWT can be found at https://jwt.io/introduction or https://datatracker.ietf.org/doc/html/rfc7519._
Similar to session IDs, JWTs go through a similar process of **creation**, **storage** on the client side, and **sending** them with subsequent requests. The difference lies in their implementation which I'll describe in the following sections.
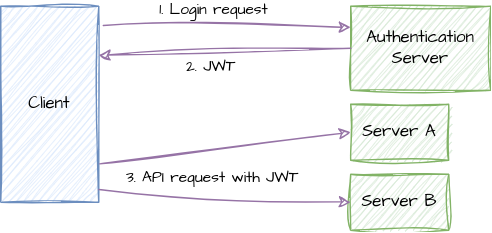
### The structure of a JWT
While session IDs are random characters, a JWT contains information about the user and there is no need on the server side for a storage mechanism of all generated tokens; each client stores their own JWT and servers will decode and extract the user information from it. This makes JWT systems stateless.
Basically, a JWT represents a Base64 encoded string composed of 3 parts: **Header** (Metadata), **Payload** (Data), and **Signature** (Verification).
#### Example
Let's consider the JWT taken from https://jwt.io/
`eyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9.eyJzdWIiOiIxMjM0NTY3ODkwIiwibmFtZSI6IkpvaG4gRG9lIiwiaWF0IjoxNTE2MjM5MDIyfQ.SflKxwRJSMeKKF2QT4fwpMeJf36POk6yJV_adQssw5c`. As you may notice, the separator is represented by the dot `.` symbol.
By decoding the first two parts, we get JSON objects:
- Header: `{ "alg": "HS256", "typ": "JWT" }`
- Payload: `{ "sub": "1234567890", "name": "John Doe", "iat": 1516239022 }`
Let's see why do we need such a structure and what are the problems to be addressed: **data integrity**, **authentication of the issuer**, **statelessness and scalability**, **transmission**.
#### Data Integrity
**Problem**: We need to ensure that the information in a token hasn't been altered by anyone else.
**Solution**: The signature part is a cryptographic hash of the header and payload, created using a secret key. When a server (which knows the secret key) receives a token, it computes a hash based on the header, payload and the secret key, and it expects to match the signature part from the token.
#### Authentication of the Issuer
**Problem**: How do we know that the token was indeed created by our authentication server?
**Solution**: A secret key, which is available to our servers only, is used to generate the signatures, so no one else would be able to generate valid signatures.
#### Statelessness and Scalability
**Problem**: How do we handle scalability?
**Solution**: As mentioned above, the token itself contains user information in the payload part, and there is no need for servers to store any session data, because they can immediately extract the user information from the token. This way the servers can deal with a large number of users without using additional resources.
#### Transmission
**Problem**: How can we efficiently transmit tokens in HTTP headers or query parameters?
**Solution**: Using Base64 encoding. More information about this topic can be found at https://base64.guru/learn/what-is-base64.
## Creation of tokens
As in the case of session IDs, the JWTs are created during the authentication process, after the server validates the user’s credentials. One important aspect I need to mention here, compared to the previous solution, is that the login endpoint could be located anywhere, no matter the domain.
Let's see what do we need at minimum to create a valid JWT for authentication:
- **Header**
- Algorithm (**alg**): the algorithm used to sign the token (e.g. HS256 or RS256)
- Type (**typ**), usually set to "JWT"
- **Payload**
- Subject (**sub**): used to identify the user, e.g. user ID or email
- Expiration time (**exp**): The timestamp after which the token becomes invalid
- Issued At Time (**iat**): The timestamp of when the token was issued.
- **Secret Key**: A secret key known only to the server is used to sign the token. This is crucial for ensuring the token's authenticity and integrity.
Here is a simple implementation for generating a JWT in Node.JS:
{% embed https://gist.github.com/cezar-plescan/c434747dad6047af9a8e8ec00aa3664c %} The actual value of the generated token is `eyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9.eyJ1c2VySWQiOjEyMywidXNlcm5hbWUiOiJqb2huZG9lIiwiZW1haWwiOiJqb2huLmRvZUBleGFtcGxlLmNvbSIsImlhdCI6MTYzMzMyOTU2MywiZXhwIjoxNjMzMzMzMTYzfQ.v6nGb_QkO_w1x_88r81176tXF699eQz5555555555555`. If you go to https://jwt.io/ and decode this token, you'll see the payload with data from the source code, along with other 2 keys, **iat** and **exp**, which were automatically generated by the library.
You may notice that I've added the username and the email in the payload, and kept it flat, not nested, which is the recommendation for such cases.
**Note**: The token can be decoded independently of the secret key which is used for verifying the token, not to extract its content.
## Transmission of the token between the server and the client
Now that the token is created after a successful authentication, the server needs to send it to the client. Later on, when the client needs to make an authenticated request, it will also send the token to that specific server.
There are two common options of sending the token from the server to the client: via cookies or in the response body. There is no one-size-fits-all solution here, the right method depends on the application's requirements and security considerations. Depending on each method, the client will then send the token with subsequent requests to servers in different ways, which we'll explore soon.
### Transmitting the token as a cookie
This process is similar to the one described in the [session-based authentication](https://dev.to/cezar-plescan/demystifying-session-based-authentication-your-angular-roadmap-1b9n) article:
`Set-Cookie: access_token=<JWT_value>; HttpOnly; Secure; SameSite=Strict`
Some **benefits** of this methods include:
- automatic transmission of the cookie that contains the JWT in subsequent requests to the same domain;
- using the **HttpOnly** protection to mitigate Cross-Site Scripting (XSS) attacks
If you have servers located on **different domains**, additional CORS configuration is needed on both the server and the client (that is, the browser).
On the server side, the following two response headers need to be defined:
- `Access-Control-Allow-Origin: <our_application_domain>` - this header tells the browser that the server accepts requests from our application domain (by default, browsers block requests to different domains unless servers are configured properly)
- `Access-Control-Allow-Credentials: true` - as another security measure, browsers won't send any cookies with cross-origin requests; when this header is set, the browser will ignore this restriction and will be able to send the cookies associated with that specific domain.
Here is a simple implementation of creating and sending the token as a cookie from the server to the client, considering our application makes cross-site requests:
{% embed https://gist.github.com/cezar-plescan/c61637f9ece95d6939af3c9b198e0221 %}
There is one additional setting to be done on the client side too: even if the server is configured to allow the browser to send cookies, we need to explicitly instruct our HTTP API (which could be the `fetch` method, `XMLHttpRequest` object or `HttpClient` from Angular) to include the cookies when making cross origin requests.
Here are some basic examples using each of these three APIs:
{% embed https://gist.github.com/cezar-plescan/2fe0d763b354932eb65bc7ac99f8bb42 %}
{% embed https://gist.github.com/cezar-plescan/ab7af719b1e79602b67aedcf0bb868e5 %}
{% embed https://gist.github.com/cezar-plescan/a068786319ff991c8de2bb67ac7aa33d %}
Now let's see how a server could define a protected endpoint and read the token from the cookies:
{% embed https://gist.github.com/cezar-plescan/a2bb976473dfaf2b021d87633f93f99b %}
### Sending the token in the response body
This method is simple to implement, more flexible, independent of server domains, suitable for SPAs or mobile apps. On the other hand, the client needs to explicitly extract and store the token. Popular applications like Twitter, Facebook, Netflix, Spotify and many others use this approach.
In this section we'll explore:
- how the token is generated and sent to the client
- how the client can store the token
- methods of sending the token in subsequent requests
A simple implementation of how the token is generated and sent to the client could look like this:
{% embed https://gist.github.com/cezar-plescan/ef86b1fc79a8953fa14c20822d0082ab %}
#### Storing the token
Once the server responds with the token, it is the client's responsibility to store it. The fundamental principle of token-based (or session-based) authentication is that the token should be kept secret and not shared with anyone. If an attacker could steal the token, the server won't know that the request wasn't made by the intended client, and this would lead to unauthorized access to sensitive data.
With this in mind, let's explore some options and their trade-offs:
1. Using JavaScript **variables**
- Pros:
- it's easy and straightforward to implement
- Cons:
- could be vulnerable to XSS attacks (malicious scripts could access the variable), even though Angular provides a significant degree of protection against such attacks.
- the token is lost when the page is refreshed or closed.
2. **localStorage**
- Pros:
- the token persists after the page is reloaded or closed.
can be easily accessed
- Cons:
- could be vulnerable to XSS attacks (malicious scripts could access the variable), even though Angular provides a significant degree of protection against such attacks - basically it's the same concern as with normal in-memory variables.
3. **sessionStorage**
- the same as localStorage, excepting that the token is lost when the page is closed (only when closed, not when reloaded)
Here is a simple implementation of an Angular login component, that stores the JWT in the localStorage:
{% embed https://gist.github.com/cezar-plescan/3b00aa51eb596577e09b5e1c7eab6838 %}
#### Sending the token to servers
So far we have the JWT stored on the client side in order to use it when we need to make authenticated requests. But how can we send it in requests? While there could be various options, the [RFC 6750](https://datatracker.ietf.org/doc/html/rfc6750#section-2.1) standard specifies that the token should be sent in the request header, like this `Authorization: Bearer <token>`. This is the most widely used and recommended method, it’s well supported by libraries and frameworks, and works across different domains (no CORS concerns).
A simple implementation of this method is illustrated below:
{% embed https://gist.github.com/cezar-plescan/a79f8c9e8058e1a7838db75f498a68ed %}
In a real application a more elegant solution is used, that is, to define an HTTP interceptor that automatically adds the authorization header, but only for the requests that need it:
{% embed https://gist.github.com/cezar-plescan/acb99fea9a8a09cf80404f58793bb02f %}
## Token extraction and validation
Now that I’ve discussed the token transmission to servers, let’s see how the servers handle the received JWT. There are several steps involved in this process:
- token extraction
- signature verification
- payload decoding
- expiration check
- authorization
- response
### Token extraction
The server first extracts the JWT from the incoming request header (e.g. Authorization header) or from the cookie, depending on the initial implementation.
Here are some basic implementations:
```typescript
app.get('/protected', (req, res) => {
// Get the Authorization header value
const authHeader = req.headers.authorization;
// Split the header to get the token (format: "Bearer <token>")
const tokenParts = authHeader.split(' ');
const token = tokenParts[1];
//... the rest of the logic
});
```
```typescript
app.get('/protected', (req, res) => {
// Get the token from the cookie, assuming the cookie name is 'token'
const token = req.cookies.token;
//... the rest of the logic
});
```
### Signature verification
Then the server needs to verify the signature of the token. But why is this step necessary? In the section about the JWT structure I've briefly mentioned about the main roles of the signature:
- it ensures authenticity, proving that the JWT was indeed issued by our servers and not forged by an attacker.
- the signature is generated using a secret key that only our servers know; without the signature verification, an attacker could create fake JWTs.
- it is a cryptographic hash of the token's header and payload and any modification to either the header or payload would result in a different signature.
- JWTs are often used in distributed systems where multiple services rely on the token to authenticate and authorize users; by verifying the signature, each service can independently trust that the token is authentic and hasn't been tampered with, even if it was issued by a different service.
Even if the token can be decoded by anyone to extract the payload, the signature verification process ensures its authenticity and integrity. This is because the header and payload part of the token are _simply encoded_ using the Base64 algorithm, and _not encrypted_. Both encoding and encryption transform data from one form to another, and this process can be reversed to recover the original data. The encryption relies on a secret key to transform back the data, making it unreadable without the correct key. Decoding typically uses a publicly known algorithm, making it easy to reverse the transformation without needing a secret key.
Let's see what are the **steps** involved in the signature verification process:
1. Extract Header and Payload
- The JWT is a string with three parts separated by dots: header.payload.signature.
- The verifier splits the string at the dots to separate the header and payload segments.
2. Base64Url Decode
- Both the header and payload are Base64Url decoded. This converts them from their URL-safe representation back into their original JSON format.
- The resulting JSON objects contain information about the algorithm (alg) and token type (typ) in the header, and the claims in the payload.
3. Create Signing Input
- The Base64Url encoded header and payload strings are concatenated with a dot (.) in between.
- This concatenated string is the input that was used to create the signature during token generation.
4. Signature Verification (Algorithm-Specific)
- **HMAC** (Symmetric):
- The verifier takes the signing input string and applies the HMAC algorithm specified in the header (alg) - more details about it at https://www.okta.com/identity-101/hmac/.
- The shared secret key, which is stored on our servers, is used as the input to the HMAC function, along with the signing input string.
- The output of the HMAC function is the calculated signature.
- The verifier compares the calculated signature to the signature extracted from the JWT. If they match, the token is valid.
- **RSA** (Asymmetric):
- The verifier retrieves the public key corresponding to the private key used by the issuer to sign the token (read the articles in the links below to find more information about public/private keys and the RSA algorithm).
- The verifier uses the public key to decrypt the signature extracted from the JWT.
- The decryption process recovers the original hash value that was created by the issuer when signing the token.
- The verifier calculates the hash of the signing input string using the same algorithm (alg) as the issuer.
- The calculated hash is compared to the recovered hash. If they match, the token is valid.
More detailed explanation about the verification process can be found in the articles [Understanding JWT Validation: A Practical Guide with Code Examples](https://www.criipto.com/blog/jwt-validation-guide) or [Validating RSA signature for a JWS](https://software-factotum.medium.com/validating-rsa-signature-for-a-jws-10229fb46bbf).
The secret key (for HMAC) or the private key (for RSA) is crucial for verification. If these keys are compromised, the entire system is at risk. The choice between HMAC and RSA depends on our specific security requirements. HMAC is simpler but requires sharing the secret key. RSA is more complex but allows for better key management. Most JWT libraries handle the cryptographic details of signature verification, so we don't need to implement the algorithms ourselves.
**Additional checks** can be performed:
- Expiration (**exp**): The verifier checks the exp claim (expiration time) in the payload to ensure the token hasn't expired.
- Not Before (**nbf**): The verifier might check the nbf claim (not before time) to ensure the token is not being used before its intended start time.
- Issuer (**iss**) and Audience (**aud**): The verifier might check the iss (issuer) and aud (audience) claims to ensure the token was issued by a trusted party and is intended for the current recipient.
- Other Claims: Depending on your application's requirements, you might perform additional checks on other claims in the payload.
If all the verification steps pass, the JWT is considered valid. Otherwise, the token is rejected as invalid or compromised.
In practice we don't need to manually implement the verification algorithm, but simply used dedicated libraries. In Node.JS, the verification could look like this:
```typescript
const jwt = require('jsonwebtoken');
const decodedToken = jwt.verify(token, secretKey);
```
### Payload decoding and response
Once the signature is confirmed valid, the Base64Url-encoded payload is decoded into its original JSON representation. This JSON object contains the claims (data) that were included in the token by the issuer. The claims typically include information about the user (e.g., user ID, username, email) and other relevant details (e.g., expiration time, issued at time, permissions). The server can use the claims in the token (e.g., user ID, permissions) to determine whether the user has access to the requested resource. If so, the server will process the request and will send the appropriate response; otherwise, it can respond with 401 or 403 status codes.
#### 401 Unauthorized response
This status code is appropriate when the user's authentication credentials (the JWT in our case) are either missing, invalid, or expired:
- The Authorization header is missing or empty.
- The JWT has an invalid signature (e.g., due to tampering or an incorrect secret key).
- The JWT has expired (the exp claim is in the past).
#### 403 Forbidden response
This status code is appropriate when the user is authenticated (the JWT is valid) but does not have the necessary permissions or authorization to access the requested resource. It indicates that the server understood the request but refuses to fulfill it due to insufficient privileges.
#### Basic implementation
{% embed https://gist.github.com/cezar-plescan/74597e7601c564a2650a56fa86949d8e %}
## Recap
The topics I've covered in this article provide a basic foundation for authentication systems that use JWT:
- what are the benefits of such method compared to session IDs
- what is the structure of a JWT
- what is required to create a token
- how to send it to the client and how can the client store it
- how to pass the token within requests
- how the server verifies the token and send the response
### What's next?
As I prefer to explain and build things gradually, in the next article I'll cover more advanced topics about JWTs that are required by a robust authentication system, so it can be integrated into a large scale application. Such topics will include:
- token revocation to prevent unauthorized access if a token is compromised
- rate limiting to prevent brute-force attacks where an attacker tries to guess valid tokens
- refresh tokens to issue new access tokens when they expire, improving user experience and security
- encrypting the token if the payload contains sensitive information
- frameworks, protocols, and systems that use JWT: Single-Sign-On, OAuth, Auth0.
## See it in action
{% embed https://youtu.be/P2CPd9ynFLg %}
{% embed https://youtu.be/V5D8RuB6Xps %}
| cezar-plescan |
1,872,149 | How to Use CI/CD for Software Development in 2024? | This article was originally published on Remotebase blog. Delivering high-quality applications... | 0 | 2024-05-31T14:38:17 | https://dev.to/remotebase/how-to-use-cicd-for-software-development-in-2024-1f2i | cicd, devops, automation, softwaredevelopment | _This article was originally published on [Remotebase blog](https://remotebase.com/blog/the-power-of-continuous-integration-and-continuous-delivery-ci-cd)._
Delivering high-quality applications efficiently and consistently has become a paramount objective in the software development industry. To meet these demands, developers have adopted Continuous Integration and Continuous Delivery (CI/CD) as indispensable practices that revolutionize how software is developed, tested, and deployed.
Organizations that have adopted CI/CD practices have seen up to [4x faster deployments](https://www.jetbrains.com/teamcity/ci-cd-guide/benefits-of-ci-cd/) and [60% reduction in defects](https://www.lambdatest.com/support/docs/integrations-with-ci-cd-tools/). CI/CD has not only become a key enabler for teams working in traditional office settings but has also proven to be a game-changer for remote software development teams. As companies increasingly embrace remote work, the power of CI/CD has become even more apparent.
Let’s explore everything about CI/CD to make the best use of it!
## What is CI/CD?
Continuous Integration (CI) and Continuous Delivery/Deployment (CD) are two interconnected practices that collectively streamline the software development and deployment processes. While they have distinct roles, together, they form a cohesive pipeline that enables faster delivery of software updates with enhanced quality and reliability.
### Continuous Integration (CI):
CI is a development practice in which developers frequently merge code changes into a shared repository. The central idea is to automate the process of integrating code changes to detect issues early and ensure that the project is consistently in a working state.
Whenever a developer commits code to the repository, CI tools automatically build and test the changes against the existing codebase. This automated verification process includes running unit tests, integration tests, and other checks, providing immediate feedback on whether the changes integrate smoothly or if they introduce conflicts or bugs.
### Key Principles of Continuous Integration:
**1. Frequent code integration:** Developers integrate code changes regularly, avoiding large, monolithic merges.
**2. Automated testing:** Automated tests are executed with each integration to ensure code quality and identify issues early.
**3. Fast feedback loop:** Quick identification and resolution of integration issues, reducing the risk of defects.
### Advantages of Continuous Integration (CI):
- **Early Detection of Bugs and Issues:** CI practices ensure that code changes are continuously integrated and tested against the existing codebase. This leads to early detection of bugs and integration issues, allowing developers to address them before they escalate into larger problems. Fixing issues early in the software development lifecycle reduces the time and effort required for debugging later.
- **Faster Development Cycles:** CI promotes frequent code integration, enabling developers to see their changes in action quickly. This accelerated development cycle encourages a faster pace of development, allowing teams to deliver new features and updates more rapidly.
- **Immediate Feedback:** Automated testing and continuous integration provide immediate feedback to developers about the quality of their code. If any tests fail, developers are notified promptly, and they can take corrective actions right away. This rapid feedback loop facilitates iterative development and helps maintain a high standard of code quality.
- **Team Collaboration:** CI encourages [better collaboration among team members](https://remotebase.com/blog/building-a-high-performance-remote-developer-culture-communication-and-collaboration-strategies) as everyone commits their code to a shared repository. It ensures that the team is working with the most up-to-date codebase and reduces the chances of conflicts arising from merging changes.
- **Reliable Builds:** CI automation ensures consistent builds and deployments, reducing the variability of code execution across different environments. This reliability helps in creating a stable software development process.
### Continuous Delivery (CD):
CD is an extension of CI, focusing on automating the entire software release process. While CI ensures that the codebase is continuously integrated, CD takes it a step further by automating the delivery of the integrated code to production or staging environments. The goal is to make deployments reliable, repeatable, and low-risk, allowing teams to release new features, updates, and bug fixes at any time with confidence.
### Key Principles of Continuous Delivery:
**1. Automated deployments:** The process of deploying the application to various environments is automated, reducing manual intervention.
**2. Continuous feedback:** Continuous feedback loops from testing and staging environments ensure that the software is ready for release at any time.
**3. Incremental updates:** Smaller, incremental updates are delivered more frequently, minimizing the risk of large, complex deployments.
### Advantages of Continuous Delivery (CD):
- **Faster Time-to-Market:** CD automates the entire software release process, enabling faster and more frequent releases to production. The ability to deploy updates swiftly reduces time-to-market for new features, enhancements, and bug fixes, giving businesses a competitive edge.
- **Low-Risk Deployments:** CD emphasizes incremental updates and [automated testing](https://remotebase.com/blog/10-best-software-testing-strategies-for-qa-teams), which minimizes the risk of introducing critical defects during deployment. With consistent and reliable automated deployments, teams can confidently release new versions of the software without disrupting the existing functionality.
- **Consistency Across Environments:** CD ensures that the application runs consistently across different environments, such as development, staging, and production. This consistency reduces the chances of environment-related issues and simplifies the troubleshooting process.
- **Continuous Feedback and Learning:** CD encourages continuous feedback loops from testing and staging environments, allowing teams to gather insights and feedback from real-world usage. This data-driven approach helps in making informed decisions and continuously improving the software.
- **Enhanced Customer Satisfaction:** By delivering frequent updates and bug fixes, CD enables businesses to respond quickly to customer needs and feedback. The ability to provide a stable, up-to-date product leads to higher customer satisfaction and loyalty.
CI/CD practices are essential for maintaining a [fast-paced, efficient development environment](https://remotebase.com/blog/how-to-upskill-software-development-team). By automating the integration, testing, and delivery processes, CI/CD empowers development teams to be agile, collaborative, and responsive to market demands.
## Characteristics of CI/CD Pipeline
A Continuous Integration/Continuous Delivery (CI/CD) pipeline is a set of automated steps and practices that facilitate the development, testing, and deployment of software changes. It is designed to streamline the software delivery process, ensuring that code changes are integrated, tested, and deployed in a consistent and efficient manner. Here are the key characteristics of a CI/CD pipeline:
**Automation:** CI/CD pipelines are highly automated. Each step of the pipeline, from code integration to deployment, is automated to minimize manual intervention and reduce the risk of human errors. Automation ensures consistency and repeatability, making the process more reliable and efficient.
**Continuous Integration:** CI is the first part of the pipeline, where developers frequently integrate their code changes into a shared repository. Automated builds are triggered as soon as code changes are pushed to the repository, ensuring that the codebase is always in a working state. Continuous integration is foundational to the CI/CD process and helps identify integration issues early.
**Automated Testing:** Testing is an essential component of the CI/CD pipeline. Automated tests, such as unit tests, integration tests, and end-to-end tests, are executed after each code integration to validate the functionality and quality of the code. Automated testing ensures that code changes meet the required standards before they progress to the next stage of the pipeline.
**Continuous Delivery:** After successful testing, the code moves to the continuous delivery phase. Continuous delivery automates the process of deploying the code to various environments, such as staging or pre-production environments. The application is kept in a release-ready state, allowing teams to deploy to production at any time.
**Continuous Deployment (Optional):** While not always part of every CI/CD pipeline, continuous deployment is an extension of continuous delivery. In continuous deployment, code changes are automatically deployed to production once they pass all tests and meet the necessary criteria. This process enables even faster and more frequent releases to end-users.
**Version Control:** CI/CD pipelines rely on version control systems to manage code changes. Version control systems track changes, allow collaboration among developers, and help in managing different branches of code for testing and deployment.
**Feedback Loop:** CI/CD pipelines provide continuous feedback to developers. Automated tests and deployment processes generate feedback on the quality of the code and deployment status. This feedback loop helps developers identify and fix issues quickly, promoting a culture of continuous improvement.
**Orchestration:** CI/CD pipelines are often orchestrated by dedicated tools and platforms that manage the flow of code changes through the various stages of the pipeline. These tools ensure that the pipeline runs smoothly and efficiently, and they often provide insights into pipeline performance.
**Scalability:** CI/CD pipelines should be designed to scale effortlessly as the development team and the complexity of the project grows. Scalability ensures that the pipeline can handle increased workloads and deliver software efficiently in different environments.
**Flexibility:** CI/CD pipelines should be flexible enough to accommodate different types of projects and technologies. They should be adaptable to various development workflows and able to integrate with a wide range of tools and services.
**Recommended reading: [Staff Augmentation vs. Consulting vs. Outsourcing: The Ultimate Guide to Scaling Your Tech Startup](https://remotebase.com/blog/staff-augmentation-vs-consulting-vs-outsourcing-the-ultimate-guide-to-scaling-your-tech-startup)**
## Stages of CI/CD Pipeline

The CI/CD pipeline consists of several stages, each serving a specific purpose in the software development and delivery process. The stages are interconnected and automated to ensure seamless and efficient code integration, testing, and deployment. Here are the typical stages of a CI/CD pipeline:
### 1. Code Commit:
- Developers commit their code changes to a version control system (e.g., Git).
- Each code commit triggers the CI/CD pipeline to start.
### 2. Code Build:
- The pipeline automatically starts a code build process after a code commit is detected.
- The code build compiles the source code, packages the application, and prepares it for testing and deployment.
- This stage ensures that the code is successfully compiled and can be executed.
### 3. Automated Testing:
- Automated tests, such as unit tests and integration tests are executed on the built code.
- Testing aims to verify the functionality, performance, and security of the application.
- Test results are collected, and any test failures are reported to the development team.
### 4. Code Analysis:
- Static code analysis tools are used to review the code for potential bugs, code smells, and security vulnerabilities.
- The analysis provides valuable insights into code quality and helps identify areas that need improvement.
### 5. Deployment to Staging Environment:
- Once the code passes all tests and analysis, it is deployed to a staging or pre-production environment.
- The staging environment closely mimics the production environment, allowing further testing in a controlled setting.
### 6. User Acceptance Testing (UAT):
- In the staging environment, stakeholders and end-users conduct user acceptance testing to validate the application's functionality and user experience.
- Feedback from UAT is collected and used to address any issues or improvements before moving to production.
### 7. Automated Deployment to Production (Continuous Delivery) or Manual Approval (Continuous Deployment):
- In continuous delivery, after successful UAT, the code is automatically deployed to production.
- In continuous deployment, there is no manual intervention, and the code is automatically deployed to production once it passes all tests and UAT.
### 8. Monitoring and Feedback:
- The application in the production environment is continuously monitored to track its performance and health.
- The monitoring system provides feedback to the development team, helping them identify and address any issues promptly.
### 9. Rollback (Optional):
- In case of critical issues or unexpected problems in the production environment, the pipeline may include an automated rollback mechanism.
- The rollback reverts the application to a previous stable version, ensuring a quick recovery.
## CI/CD vs Traditional Software Development: Which is Better?
Traditional software development and CI/CD are two contrasting approaches to building software. Here's a breakdown of their key differences:

### Speed Matters the Most in Software Development!
The pace at which the software development industry is evolving is fulgurant. Hence, it demands **Faster feedback loops**, **First-mover advantage** and **Adaptability**.
Companies using CI/CD pipelines experienced an average 33% reduction in time to market compared to those without CI/CD. By getting features out quickly, you can gather user feedback earlier and adjust the course if needed to ensure you're building something users actually want. In some industries, being the first to market with a new product or feature can be a game-changer. Speed helps you capitalize on these opportunities. Being able to develop and deploy changes quickly allows you to stay relevant and respond to new market demands.
This is where CI/CD takes the lead. It streamlines the development process, automates manual tasks, and catches problems early, allowing development teams to release higher-quality software more frequently.
## What are the Drawbacks of the Traditional Method?
Traditional software development methods tend to suffer from a few key limitations that hinder speed and agility:
**Siloed teams:** Development, testing, and deployment were often separate stages handled by different teams. This creates bottlenecks and delays as information needs to be handed off between teams.
CI/CD breaks down silos and fosters closer collaboration between development, testing, and operations teams by automating the integration and delivery process.
**Manual processes:** Many tasks in the development cycle, like building, testing, and deployment, were done manually. This is slow and error-prone.
CI/CD automates repetitive tasks, freeing up developers and testers to focus on higher-value activities.
**Large infrequent releases:** Due to the manual processes and limited testing opportunities, releases were bundled together and infrequent. This meant fixing bugs and delivering new features took a long time.
CI/CD enables smaller, more frequent deployments. This means new features and bug fixes are released faster, and users get value sooner.
**Limited feedback:** With infrequent releases, user feedback came in large chunks, making it harder to pinpoint issues and iterate quickly.
With more frequent deployments in CI/CD, feedback is gathered more often. This allows teams to identify and address issues early in the software development life cycle.
Overall, **CI/CD is a more agile and efficient approach to software development than traditional methods.** It allows for faster delivery of higher-quality software.
## Leveraging Automation to Address Remote Development Challenges
[Remote work has become increasingly prevalent](https://remotebase.com/blog/the-impact-of-remote-work-on-engineering-culture) in the software development industry, offering various benefits such as access to global talent and improved work-life balance. However, remote development teams face unique challenges, including communication barriers, time zone differences, and potential collaboration issues.
To overcome these challenges, organizations are leveraging automation to streamline remote development workflows. Automation plays a pivotal role in simplifying complex tasks, improving team efficiency, and fostering real-time collaboration.
Automated Continuous Integration and Continuous Delivery (CI/CD) pipelines enable fast feedback cycles, seamless code integration, and real-time updates, ensuring remote teams can work together efficiently despite geographical distances.
## Best CI/CD Tools and Platforms Designed for Remote Collaboration
Continuous Integration and Continuous Delivery (CI/CD) has revolutionized software development by enabling faster and more reliable code integration, testing, and deployment. In the context of remote work, CI/CD tools and platforms play a crucial role in enhancing collaboration, communication, and productivity for distributed development teams.
Let's explore some of the CI/CD tools and platforms that are specifically designed to support remote collaboration:
[**GitLab CI/CD**](https://about.gitlab.com/solutions/continuous-integration/)

- GitLab is a popular DevOps platform that provides built-in CI/CD capabilities.
- It allows developers to create CI/CD pipelines as code, ensuring consistency and easy version control.
- GitLab CI/CD integrates seamlessly with Git repositories, enabling automatic triggers for builds and deployments.
- The platform offers extensive collaboration features, including code review, issue tracking, and merge requests, making it suitable for remote teams.
[**Jenkins**](https://www.jenkins.io/)

- Jenkins is one of the earliest and most used open-source CI/CD automation servers.
- It provides a vast array of plugins and integrations, allowing customization to suit various development environments.
- Jenkins supports distributed builds, enabling remote teams to efficiently utilize resources across different locations.
- With its robust community and documentation, Jenkins offers excellent support for remote collaboration.
[**CircleCI**](https://circleci.com/)

- CircleCI is a cloud-based CI/CD platform that focuses on simplicity and ease of use.
- It offers automatic parallelism, allowing teams to run multiple builds concurrently, which accelerates development cycles.
- CircleCI integrates seamlessly with popular version control systems and cloud providers, streamlining remote team workflows.
- Its user-friendly interface makes it an attractive choice for remote teams seeking a straightforward CI/CD solution.
[**Travis CI**](https://www.travis-ci.com/)

- Travis CI is another cloud-based CI/CD service known for its simplicity and quick setup process.
- It supports a wide range of programming languages and frameworks, accommodating diverse development projects.
- Travis CI provides solid integration with GitHub, making it an ideal choice for remote teams that use GitHub for version control and collaboration.
- The platform's user-friendly interface and clear documentation simplify adoption for remote developers.
[**GitHub Actions**](https://github.com/features/actions)

- GitHub Actions is a CI/CD feature integrated into GitHub's version control platform.
- As part of the Git ecosystem, it offers seamless integration with repositories and pull requests, making it a natural choice for remote teams using GitHub.
- Developers can define workflows using YAML files, allowing version-controlled and easily replicable CI/CD pipelines.
- GitHub Actions provides a diverse library of pre-built actions, simplifying the process of building custom workflows.
[**Bitbucket Pipelines**](https://bitbucket.org/product/features/pipelines)

- Bitbucket Pipelines is the CI/CD solution integrated into the Bitbucket code hosting platform.
- As a result, it offers tight integration with Bitbucket repositories and pull requests, supporting smooth collaboration among remote teams.
- Bitbucket Pipelines is designed to be simple yet powerful, enabling teams to quickly set up automated builds and deployments.
- The platform's flexible configuration allows teams to define their CI/CD workflows using YAML files.
**Recommended reading: [How AI Can Enhance Collaboration and Communication in Teams](https://remotebase.com/blog/how-ai-can-enhance-collaboration-and-communication-in-teams)**
## Advantages of CI/CD Automation for Remote Development Teams
CI/CD automation offers numerous advantages for remote development teams, helping them overcome the challenges of distributed work and achieve higher levels of productivity and efficiency. Here are some of the key advantages of CI/CD automation for remote development teams:
### Streamlined Collaboration and Communication:
- CI/CD automation fosters real-time collaboration among remote team members.
- Developers can share code changes, review each other's work, and provide feedback seamlessly through automated pipelines.
- Enhanced communication leads to better code integration, fewer conflicts, and faster development cycles.
### Improved Code Quality and Faster Time-to-Market:
- Automated testing and continuous feedback in CI/CD pipelines ensure higher code quality.
- Issues are identified early in the development process, reducing the time spent on debugging and fixing bugs.
- Faster testing and deployment lead to quicker time-to-market, allowing remote teams to deliver software updates rapidly.
### Reduced Manual Errors and Deployment Failures:
- CI/CD automation minimizes the risk of human-induced errors and inconsistencies.
- Automated build and deployment processes eliminate the need for manual interventions, reducing the chances of mistakes.
- Consistency in the deployment process ensures a higher success rate and fewer deployment failures.
### Efficient Development and Release Processes:
- CI/CD automation optimizes repetitive and time-consuming tasks, allowing developers to focus on more critical aspects of the project.
- Standardized workflows enable new team members to quickly get up to speed, fostering a smoother onboarding process.
- Automated CI/CD pipelines ensure that development and deployment processes are scalable and adaptable to the needs of remote projects.
### Higher Productivity and Developer Satisfaction:
- According to a report, organizations that implement CI/CD have seen a [21% increase in developer productivity](https://www.qagile.pl/wp-content/uploads/2018/04/versionone-12th-annual-state-of-agile-report.pdf).
- Developers can concentrate on creative problem-solving and innovation rather than getting bogged down by manual processes.
- Increased productivity and streamlined workflows contribute to higher job satisfaction and work-life balance for remote team members.
### Continuous Delivery and Faster Feedback Loops:
- CI/CD automation facilitates continuous delivery, allowing new features and bug fixes to reach end-users rapidly.
- Frequent code integration and automated testing provide faster feedback loops, enabling quick iteration and improvement of software.
### Better Resource Utilization and Cost Savings:
- Automated CI/CD pipelines optimize resource usage, reducing the need for manual oversight.
- Remote teams can avoid unnecessary downtime and maximize their development and deployment efforts.
- CI/CD automation provides up to [50% reduction in development and operations costs](https://www.testevolve.com/blog/benefits-of-implementing-a-cicd-pipeline) by decreasing the time and effort spent on manual tasks and minimizing deployment failures.
### Easy Collaboration with Global Talent:
- CI/CD automation enables seamless collaboration with remote developers from different time zones and locations.
- Distributed teams can work together effectively, utilizing their collective skills and expertise to deliver high-quality software.
## Best Practices for Implementing CI/CD Automation in Remote Settings
### 1. Selecting the Right CI/CD Tools for Remote Teams
In remote development, choosing the appropriate CI/CD tools is crucial for smooth collaboration and effective automation. Consider tools that are user-friendly, offer strong integration with version control systems, and support remote collaboration features. Cloud-based CI/CD platforms are often preferred for their scalability, ease of setup, and accessibility from any location.
Evaluating the tools' documentation, support, and community engagement is also essential to ensure you have the necessary resources to address any issues that may arise during implementation.
### 2. Defining Clear Development and Deployment Workflows
Clear and well-defined workflows are the backbone of successful CI/CD implementation. Remote teams must establish consistent processes for code integration, testing, and deployment. This includes defining version control strategies, branching models, and integration points in the CI/CD pipeline.
By documenting these workflows, remote team members can easily follow and adhere to the established practices, reducing confusion and preventing errors during development and deployment.
### 3. Integrating Automated Testing and Code Reviews in the Pipeline
Automated testing is a critical aspect of CI/CD automation, ensuring that code changes meet quality standards before being merged into the main branch. Implement different types of tests, such as unit tests, integration tests, and end-to-end tests, to verify code functionality, compatibility, and performance.
Additionally, automated code review tools should be incorporated to enforce coding standards, identify potential issues, and ensure code consistency across the team. Effective integration of testing and code reviews in the CI/CD pipeline guarantees the delivery of high-quality software.
### 4. Monitoring and Optimizing CI/CD Performance for Remote Projects
Continuous monitoring of CI/CD pipelines and deployments is essential to ensure optimal performance and identify potential bottlenecks. Implement monitoring tools that provide real-time insights into pipeline execution, test results, and deployment statuses.
Regularly review performance metrics to identify areas for improvement and optimize the CI/CD process. This proactive approach ensures that your remote development team can respond quickly to any issues that may arise, enhancing productivity and efficiency.
### 5. Ensuring Security and Compliance in Automated Environments
Security is a top concern in any CI/CD environment, especially when dealing with remote teams and sensitive data. Implement robust access controls and permissions to safeguard CI/CD tools and repositories from unauthorized access.
Integrate security testing into the CI/CD pipeline to identify vulnerabilities early in the development process. Furthermore, ensure that the automated environment adheres to relevant industry standards and regulations, especially when dealing with customer data and compliance requirements.
Implementing CI/CD automation in a remote setting requires a thoughtful and strategic approach. By selecting the right tools, defining clear workflows, integrating automated testing and code reviews, monitoring performance, and ensuring security and compliance, remote development teams can harness the full potential of CI/CD automation and deliver high-quality software efficiently and collaboratively, regardless of geographical locations.
**Must read: [Navigating CTO Challenges for Security and Compliance](https://remotebase.com/blog/navigating-cto-challenges-for-security-and-compliance)**
## Key Performance Indicators (KPIs) of CI/CD Pipeline
Here are the essential KPIs of a CI/CD pipeline, including the top ones as per [DORA metrics](https://cloud.google.com/blog/products/devops-sre/using-the-four-keys-to-measure-your-devops-performance):
**Lead Time:** Lead time measures the time taken from the initial development request to its deployment. It encompasses the entire development and deployment process and reflects the overall efficiency of the CI/CD pipeline.
**Deployment Frequency:** This KPI tracks how often deployments occur within a specific timeframe. A higher deployment frequency indicates that the team is delivering updates to end-users more frequently.
**Mean Time to Recovery (MTTR):** MTTR measures the average time taken to recover from a failed deployment or production issue. A lower MTTR indicates faster incident response and resolution.
**Cycle Time:** Cycle time measures the time taken from code commit to successful deployment. A shorter cycle time indicates faster code integration and faster delivery of features or bug fixes.
**Deployment Success Rate:** Deployment success rate measures the percentage of successful deployments out of total deployment attempts. A high success rate reflects the reliability of the CI/CD pipeline and the code quality being deployed.
**Test Coverage:** Test coverage measures the percentage of code covered by automated tests. A higher test coverage implies a more robust testing process and reduced chances of defects reaching production.
**Build Failure Rate:** Build failure rate tracks the percentage of failed builds compared to total build attempts. A low build failure rate indicates a stable codebase and well-tested changes.
**Deployment Time:** Deployment time measures the time taken to deploy changes into production. A shorter deployment time indicates an efficient and responsive CI/CD pipeline.
**Feedback Time:** Feedback time measures how quickly developers receive feedback after code integration or testing. A shorter feedback time enables developers to address issues promptly.
**Customer Feedback and Satisfaction:** Monitoring customer feedback and satisfaction metrics after deployments can provide insights into the impact of changes on end-users. Positive customer feedback indicates successful releases.
**Resource Utilization:** Tracking resource utilization, such as CPU and memory usage during builds and deployments, helps optimize resource allocation and reduce costs.
**Code Quality Metrics:** Analyzing code quality metrics like code smells, complexity and maintainability index can provide insights into the health of the codebase and identify areas for improvement.
These KPIs provide valuable insights into the performance and effectiveness of the CI/CD pipeline. Continuous monitoring and analysis of these metrics help teams identify areas for improvement, optimize their development processes, and deliver high-quality software efficiently.
## The Future of Remote Developer Automation in CI/CD
As technology continues to evolve, the future of remote developer automation in CI/CD holds great promise for further enhancing software development processes for distributed teams. Several trends and advancements are expected to shape the future landscape of CI/CD automation in remote settings:
### Increased Adoption of Cloud-Native CI/CD Platforms:
Cloud-native CI/CD platforms are gaining popularity due to their scalability, flexibility, and ease of use. In the future, more remote development teams are likely to adopt [cloud-native solutions](https://remotebase.com/blog/cloud-computing-trends-and-the-future-of-enterprise-it) to leverage the benefits of cloud computing for automated build and deployment processes. These platforms will facilitate seamless collaboration and faster feedback cycles for remote teams.
### Integration of AI and Machine Learning in CI/CD Pipelines:
Artificial Intelligence (AI) and Machine Learning (ML) will play an increasingly significant role in CI/CD automation. These technologies can be utilized to optimize various aspects of the CI/CD pipeline, such as predictive analytics for identifying potential bottlenecks, auto-remediation of failed builds, and intelligent code review tools. This integration will result in more efficient and intelligent automation processes for remote development teams.
### Focus on Security and Compliance in CI/CD Automation:
As remote work becomes more prevalent, ensuring the security and compliance of CI/CD automation will be of paramount importance. Future developments will see an increased emphasis on integrating robust security measures into the automation pipeline, addressing potential vulnerabilities, and adhering to industry regulations to protect sensitive data.
### Emphasis on Developer Experience (DX):
The future of CI/CD automation will prioritize improving the [Developer Experience (DX)](https://remotebase.com/blog/the-role-of-developer-experience-teams-a-detailed-overview). User-friendly interfaces, simplified setup processes, and better documentation will be essential for remote developers to seamlessly adopt and integrate CI/CD practices into their workflows. Enhanced DX will lead to higher developer satisfaction and increased productivity.
### Convergence of CI/CD and GitOps:
GitOps, a practice where CI/CD pipelines are managed and defined through version control systems like Git, will continue to gain traction in remote settings. This convergence will enable developers to have better control over the infrastructure and configuration changes while ensuring consistency and traceability across the CI/CD process.
### Extending CI/CD to New Domains:
The future of CI/CD automation will not be limited to traditional software development. It will expand to other domains, such as IoT (Internet of Things) and edge computing. CI/CD practices will be adapted and refined to cater to the unique challenges of these domains, allowing for efficient and automated deployments in diverse contexts.
### Holistic Observability and Monitoring:
Advanced monitoring and observability tools will become integral to CI/CD automation in the future. These tools will provide comprehensive insights into the entire development and deployment lifecycle, enabling remote teams to identify performance bottlenecks, track key metrics, and optimize their CI/CD pipelines for better efficiency.
## Pioneering the Future of CI/CD Automation with Remotebase Developers
Remotebase provides access to a pool of highly qualified and experienced developers who are proficient in CI/CD automation and related technologies within 24 hours. This accelerates the process of assembling a distributed team capable of effectively implementing CI/CD practices, thereby maximizing the advantages of remote developer automation.
In addition, we offer a [2-week free trial](https://remotebase.com/blog/the-2-week-no-risk-trial-a-unique-offering-from-remotebase), allowing companies to assess the compatibility of our developers with their CI/CD automation requirements before making a long-term commitment. Hence, with us by your side, you can confidently embrace CI/CD automation, knowing they have access to top-notch developers who are ready to contribute to their projects from day one.
## Conclusion
The future of remote developer automation in CI/CD is poised for significant advancements driven by cutting-edge technologies and evolving practices. Cloud-native CI/CD platforms will continue to gain popularity, facilitating seamless collaboration for remote teams.
The integration of AI and ML will optimize CI/CD processes, leading to smarter and more efficient automation. Ensuring security and compliance will remain a top priority to safeguard sensitive data in distributed environments.
Emphasizing the Developer Experience (DX) will enhance adoption and productivity, while the convergence of CI/CD and GitOps will provide better control and traceability. The scope of CI/CD automation will expand beyond traditional software development, reaching into diverse domains like IoT and edge computing. Hence, comprehensive observability and monitoring will offer valuable insights, empowering remote teams to optimize performance and efficiency.
## Frequently Asked Questions
### What is CI (Continuous Integration)?
Continuous Integration (CI) is a software development practice where code changes are automatically integrated into a shared repository multiple times a day. Each integration triggers an automated build and test process to detect integration issues early, ensuring that the codebase is always in a stable state.
### What is CD (Continuous Delivery) and how does it differ from CI?
Continuous Delivery (CD) is an extension of Continuous Integration that goes beyond automated testing. CD ensures that code changes are automatically deployed to a staging environment after successful testing. This approach allows for manual validation before promoting changes to production. In contrast, CI focuses on code integration and automated testing but does not automatically deploy changes to a staging environment.
### What is CD/CI vs DevOps?
CD (Continuous Delivery) and CI (Continuous Integration) are specific practices within the broader concept of DevOps. CI focuses on automatically integrating code changes into a shared repository and running automated tests to maintain code quality. While CD extends CI by automatically deploying code changes to a staging environment after successful testing. DevOps, on the other hand, is a cultural and organizational philosophy that emphasizes collaboration and communication between development and operations teams to achieve faster and more efficient software development and delivery.
### Which language is best for CI/CD?
The YAML is commonly used in CI/CD pipelines for defining configuration files that specify the steps and tasks in the automation process. It is well-suited due to its simplicity, readability, and easy integration with various CI/CD tools. It allows developers to define the entire pipeline as code, making it easy to version control and manage changes efficiently.
### Are CI/CD and DevOps applicable to all types of software development projects?
Yes, CI/CD and DevOps principles are applicable to various types of software development projects. Whether it's web applications, mobile apps, or large-scale enterprise systems, CI/CD can significantly improve development workflows and delivery efficiency. Similarly, DevOps practices can be adopted by teams working on different technologies and domains to foster collaboration and enhance software delivery.
### [Hire CI/CD Experts with Remotebase](https://remotebase.com/start?utm_source=blog&utm_medium=page&utm_campaign=organic) | remotebase |
1,872,148 | TOP WOOCOMMERCE GEOLOCATION PLUGINS TO BOOST SALES IN 2024 | In today's global marketplace, tailoring your online store to meet the needs of diverse customer... | 0 | 2024-05-31T14:38:13 | https://dev.to/savanaahbelle/top-woocommerce-geolocation-plugins-to-boost-sales-in-2024-40g2 | geolocationplu, geolocationpluginwordpress |
In today's global marketplace, tailoring your online store to meet the needs of diverse customer bases is crucial for boosting sales. **Geolocation plugins for WooCommerce** allow you to customize the shopping experience based on a visitor's location, offering personalized content, pricing, and shipping options.
Discover the ultimate game-changers for your WooCommerce store in 2024! [Geolocation plugins ](https://www.sharesoft.in/products/)personalize the shopping journey, boosting sales, and delighting customers.
With tailored content, pricing, and shipping options, these plugins revolutionize e-commerce, delivering seamless experiences tailored to each visitor's location. In this blog post, we'll explore the top **Geolocation Plugin for WooCommerce** that can help you enhance customer experience and increase sales in 2024.

**Why Use Geolocation in Your WooCommerce Store?**
Before diving into the plugins, let's understand why **geolocation plugin wordpress** is vital for your WooCommerce store.
**1. Personalized Shopping Experience**
Geolocation transforms your WooCommerce store into a personalized paradise! Tailor-made experiences await your customers as they enjoy localized content, currency, and shipping options.
With geolocation, every click feels like home, enhancing engagement, boosting sales, and fostering customer loyalty. Say hello to a shopping journey tailored just for you!
**2. Improved Conversion Rates**
Utilize geolocation in your WooCommerce store to enhance conversion rates with precision. Tailoring content, pricing, and shipping options based on customer location fosters a seamless and personalized shopping experience. Increase trust and engagement, ultimately driving more conversions and optimizing your e-commerce success.
**3. Enhanced Marketing Strategies**
Leverage geolocation in your WooCommerce store to refine marketing strategies with pinpoint accuracy. By analyzing location data, you can craft targeted campaigns tailored to specific regions, demographics, and consumer behaviors. Enhance engagement and ROI by delivering relevant promotions that resonate with your audience on a local level.
## **Top WooCommerce Geolocation Plugins**
Here are the top **WooCommerce geolocation marker** that you should consider integrating into your store in 2024.
**1. WooGeo Location Marker**
Elevate your WooCommerce store with [**WooGeo Location Marker**](https://www.sharesoft.in/product/woogeo-location-marker-without-dokan/)! This powerful plugin adds a personal touch by customizing content based on customer location. Boost engagement and sales by offering localized experiences, from currency conversion to targeted promotions. **WooGeo Location Marker **is your ticket to a more personalized and profitable online store!
**Understanding the Importance of Geolocation**
Geolocation technology allows businesses to tailor the online shopping experience based on the visitor's location. This level of customization enhances engagement, increases conversion rates, and fosters customer loyalty.
**Key Features:**
• Accurate IP-based geolocation
• Customizable redirection rules
• Multisite support
• Compatibility with popular page builders
Integrating WooGeo Location Marker into your WooCommerce store is seamless and straightforward. With its user-friendly interface and comprehensive documentation, businesses can quickly set up and customize the plugin to suit their specific needs.
## **Wonderful benefits of using the WooGeo Location Marker plugin:**

**1. Personalized Shopping Experience:** WooGeo Location Marker enables you to offer a tailored shopping journey to your customers based on their location. This personalized touch enhances engagement and builds rapport with your audience.
**2. Increased Conversion Rates:** By presenting localized content, currency, and shipping options, WooGeo helps streamline the buying process, reducing barriers to purchase and ultimately boosting conversion rates.
**3. Enhanced Customer Satisfaction:** Customers appreciate feeling understood and valued. With WooGeo, you can deliver precisely what they need, creating a delightful shopping experience that fosters loyalty and encourages repeat business.
**4. Global Reach:** With the ability to cater to customers worldwide, WooGeo opens up new markets and expands your reach. Reach out to international audiences with confidence, knowing that you can provide them with a seamless shopping experience.
**5. Simplified Management:** WooGeo's user-friendly interface and intuitive features make managing geolocation settings a breeze. Say goodbye to complex setups and hello to effortless customization that puts you in control.
**6. Optimized Marketing Campaigns:** By leveraging location data, WooGeo empowers you to craft targeted marketing campaigns that resonate with specific regions or demographics. This precision targeting ensures that your promotions hit the mark every time.
**7. Competitive Advantage:** In today's competitive e-commerce landscape, standing out is essential. WooGeo gives you the edge by offering features that enhance customer experience and drive sales, setting you apart from the competition.
In summary, **WooGeo Location Marker Plugin** isn't just a plugin – it's a powerful tool that transforms your WooCommerce store into a personalized shopping destination. With WooGeo, you can delight customers, increase conversions, and take your business to new heights.
Curious about how WooGeo can transform your WooCommerce store? Check out our live demo! Explore the powerful features and see how easy it is to personalize your customers' shopping experience.
Click here to try the **[WooGeo Location Plugin demo ](https://demo.sharesoft.in/woogeomarker/shop/)** now!
**2. WooCommerce Geolocation Plugin**
The WooCommerce Geolocation Plugin by **[CodeCanyon ](htts://codecanyon.net/)**is another excellent choice. It provides detailed geolocation features tailored specifically for WooCommerce stores.
**Key Features:**
• Automatic currency conversion
• Location-based product visibility
• Customizable shipping rates based on location
• Detailed analytics and reporting
**3. IP2Location Country Redirect for WooCommerce**
This plugin by **IP2Location** offers precise IP-based geolocation and redirection functionalities. It's perfect for stores that operate in multiple countries with different regional websites.
**Key Features:**
• Redirect visitors based on their country
• Show/hide products based on location
• Support for IPv4 and IPv6
• Integration with Google Analytics
**4. Geolocation Based Products**
Geolocation Based Products by **Amasty** is designed to enhance product visibility and availability based on the visitor’s location.
**Key Features:**
• Show/hide products based on geolocation
• Customize product availability for different regions
• Easy setup and configuration
• Works seamlessly with WooCommerce
**5. Country and State Restriction for WooCommerce**
This plugin by **Addify** allows you to restrict product visibility based on the customer’s country or state. It’s particularly useful for stores with region-specific legal restrictions or different product catalogs.
**Key Features:**
• Restrict products by country or state
• Customizable error messages
• Easy to configure
• Supports all WooCommerce product types
**How to Choose the Right Geolocation Plugin**
Choosing the right **[WordPress geolocation plugin ](https://www.sharesoft.in/)**depends on your specific needs. Here are some factors to consider:
**1. Accuracy of Geolocation**
Ensure the plugin provides accurate location data. IP-based geolocation is common, but some plugins offer more precise methods.
**2. Customization Options**
Look for plugins that allow you to customize content, pricing, and shipping options based on location.
**3. Ease of Use**
The plugin should be easy to set up and configure, especially if you’re not tech-savvy.
**4. Compatibility**
Ensure the plugin is compatible with your current WooCommerce setup and other plugins you are using.
**5. Cost**
Consider your budget. Some plugins offer free versions with basic features, while premium options provide more advanced functionality.
**Conclusion**
Incorporating geolocation plugins into your WooCommerce store can significantly enhance the shopping experience for your customers, leading to increased sales and customer satisfaction. The plugins we've discussed offer a range of features to help you tailor your store to meet the needs of your global audience.
To get started, assess your specific requirements and choose a plugin that best fits your needs. Whether you need simple currency conversion or complex location-based content customization, there's a **WooCommerce geolocation-based product** out there for you.
For more tips on optimizing your WooCommerce store, check out our other articles on eCommerce strategies and **[WooCommerce custom plugins](https://www.sharesoft.in/product/woogeo-location-marker-without-dokan/)**.
By implementing these geolocation plugins, you'll be well on your way to creating a more personalized and effective WooCommerce store in 2024.
Using **[Wordpress Custom plugins ](https://www.sharesoft.in/product/woogeo-location-marker-without-dokan/)** in your WooCommerce store not only boosts sales but also helps you build a loyal customer base by offering a tailored shopping experience. Start exploring these plugins today and watch your business grow in 2024! | savanaahbelle |
1,871,834 | Debugging Distroless Images with kubectl and cdebug | Ivan Velichko recently made me aware of issues with debugging distroless containers in Kubernetes... | 0 | 2024-05-31T14:37:01 | https://dev.to/chainguard/debugging-distroless-images-with-kubectl-and-cdebug-1dm0 | kubernetes, containers, distroless, devops | [Ivan Velichko](https://twitter.com/iximiuz) recently made me aware of [issues with debugging distroless containers](https://twitter.com/iximiuz/status/1779156877395312654) in Kubernetes with `kubectl debug`. This blog will take a look at the problem and show you can get access to the filesystem of a distroless pod for debugging purposes.
The problem Ivan found was a lack of permissions to access the filesystem of the container being debugged. This is best explained with some examples. With a regular (non-distroless) container, you can do the following to start an ephemeral debug container that shares various namespaces with the target container:
```bash
$ kubectl run nginx-pod --image nginx
pod/nginx-pod created
$ kubectl debug -it nginx-pod --image alpine --target nginx-pod
Targeting container "nginx-pod". If you don't see processes from this container it may be because the container runtime doesn't support this feature.
Defaulting debug container name to debugger-h4fzv.
If you don't see a command prompt, try pressing enter.
/ # ps
PID USER TIME COMMAND
1 root 0:00 nginx: master process nginx -g daemon off;
32 101 0:00 nginx: worker process
33 101 0:00 nginx: worker process
34 101 0:00 nginx: worker process
35 101 0:00 nginx: worker process
36 101 0:00 nginx: worker process
37 101 0:00 nginx: worker process
38 101 0:00 nginx: worker process
39 101 0:00 nginx: worker process
40 101 0:00 nginx: worker process
41 101 0:00 nginx: worker process
308 root 0:00 /bin/sh
317 root 0:00 ps
```
(You could also just use `kubectl exec -it nginx-pod -- /bin/sh`, but of course that's not possible in a distroless container)
Note that the filesystem is the filesystem of the Alpine debug container, not the nginx container:
```bash
/ # cat /etc/os-release
NAME="Alpine Linux"
ID=alpine
VERSION_ID=3.19.1
PRETTY_NAME="Alpine Linux v3.19"
HOME_URL="https://alpinelinux.org/"
BUG_REPORT_URL="https://gitlab.alpinelinux.org/alpine/aports/-/issues"
```
But we can get to the nginx container filesystem via the `/proc/1/root` filesystem. To break this down:
- `/proc` is a virtual filesystem created by the kernel that contains various metadata
- `1` refers to the process id, in this case our running nginx master process; and
- `root` is a link to the root of the filesystem the process is running in.
So we can access the index.html file inside the nginx container like this:
```bash
/ # cat /proc/1/root/usr/share/nginx/html/index.html
<!DOCTYPE html>
<html>
…
/ #
```
Now let's try that with the `cgr.dev/chainguard/nginx` image, which is one of [Chainguard's distroless images](https://images.chainguard.dev/):
```bash
$ kubectl run nginx-distroless --image cgr.dev/chainguard/nginx
pod/nginx-distroless created
$ kubectl debug -it nginx-distroless --image alpine --target nginx-distroless
Targeting container "nginx-distroless". If you don't see processes from this container it may be because the container runtime doesn't support this feature.
Defaulting debug container name to debugger-bcr26.
If you don't see a command prompt, try pressing enter.
/ # cat /proc/1/root/usr/share/nginx/html/index.html
cat: can't open '/proc/1/root/usr/share/nginx/html/index.html': Permission denied
/ # whoami
root
```
We get `Permission denied`.
It turns out that the problem is that the nginx container is running as the user `nonroot` with UID 65532, which we don't have permission to access despite being `root` (using `--profile` to set a different security profile didn't help either, but I suspect it might in the future). To fix this, we need our debug container to run as the same user as the nginx container. Unfortunately there's no `--user` flag for `kubectl`, so we need to have an image that runs as this user by default. We could create one e.g with a Dockerfile such as:
```Dockerfile
FROM alpine
USER 65532
```
But in the case of Chainguard Images there's a much easier solution. Most of our images come with `-dev` variants that run as the same user but also include a shell and can be used for debugging, so we can do:
```bash
$ kubectl debug -it nginx-distroless --image cgr.dev/chainguard/nginx:latest-dev --target nginx-distroless -- /bin/sh
Targeting container "nginx-distroless". If you don't see processes from this container it may be because the container runtime doesn't support this feature.
Defaulting debug container name to debugger-nbvjt.
If you don't see a command prompt, try pressing enter.
/ $
/ $ cat /proc/1/root/usr/share/nginx/html/index.html
<!DOCTYPE html>
<html>
…
```
And everything works as expected.
There's actually a second wrinkle that is also solved by setting the user – if your pod is running with the `runAsNonRoot` policy, you won't be able to start a debug container that runs as root with the default profile.
This does point to some ways in which `kubectl debug` could be improved:
- Add a `--user` option to set the user in the debug container
- Add a formal way to access the target container filesystem. Going via `/proc/1/root` seems a little hacky and non-intuitive
- Add some more docs to explain all of this (which is somewhere I plan to help).
(I do see there are some [proposed enhancements](https://github.com/kubernetes/enhancements/issues/4292) related to profiles that might help here)
I should also point out that Ivan addresses these problems directly with his [cdebug](https://github.com/iximiuz/cdebug) tool. You can use `cdebug` to directly debug a pod:
```bash
$ cdebug exec -it --privileged pod/nginx-distroless/nginx-distroless
Debugger container name: cdebug-20ba5985
Starting debugger container...
Waiting for debugger container...
Attaching to debugger container...
If you don't see a command prompt, try pressing enter.
/ # cat /proc/1/root/usr/share/nginx/html/index.html
<!DOCTYPE html>
<html>
…
```
`cdebug` also supports a `--user` flag if you have the `runAsNonRoot` policy e.g:
```bash
cdebug exec -it --user 65532 pod/nginx-distroless/nginx-distroless
…
```
That's about it. Running production workloads in distroless containers is a big improvement in terms of security. With a little bit of knowledge these containers can still be straightforward to debug.
| amouat |
1,872,147 | Google 지도 API를 사용한 자바스크립트 지리적 위치 추적 | 자바스크립트 Google 지도 API와 지리적 위치 추적을 사용한 실시간 지도 제작에 대한 마지막 시리즈를 살펴보세요. | 0 | 2024-05-31T14:35:46 | https://dev.to/pubnub-ko/google-jido-apireul-sayonghan-jabaseukeuribteu-jirijeog-wici-cujeog-foa | 모든 키워드가 완벽하게 포함된 업데이트된 블로그 게시물을 확인하세요.
이 글은 Google Maps JavaScript API와 PubNub를 사용하여 위치 정보 기능을 갖춘 실시간 웹 애플리케이션을 만드는 방법에 대한 4편으로 구성된 시리즈의 마지막 글입니다. 이 튜토리얼에서는 JavaScript와 PubNub를 사용하여 비행 경로를 생성하는 사용자 경험을 안내합니다.
이 모든 것이 어떻게 구현되는지 예시를 보려면 PubNub 웹사이트의 [쇼케이스 데모를](https://showcase.pubnub.com/?utm_source=devto&utm_medium=syndication&utm_campaign=off_domain&utm_content=ko) 확인하세요. 위치 정보 데모로 이동하여 PubNub와 실시간 트래킹을 통합하는 방법을 확인하세요. 데모 이면의 코드를 보려면 [깃허브에서](https://github.com/PubNubDevelopers/PubNub-Showcase/tree/main/web/geolocation) 모든 것이 어떻게 작동하는지 확인하세요.
비행 경로란 무엇인가요?
-------------
이 **튜토리얼에서** 구현된 비행 경로는 **모바일 디바이스나** 웹 브라우저에 있는 지도에서 **사용자가 지정한 지점을 통과하는 경로를 동적으로 그릴** 수 있는 **폴리라인을** 의미합니다. 폴리라인은 이동 패턴을 추적하기 위해 **HTML5 지리적 위치 API** 및 **Google 지도 API에** 필수적인 요소입니다.
튜토리얼 개요
-------
[1,](https://www.pubnub.com/blog/javascript-mapping-javascript-tracking/?utm_source=devto&utm_medium=syndication&utm_campaign=off_domain&utm_content=ko) [2](https://www.pubnub.com/blog/javascript-google-maps-api-map-markers/?utm_source=devto&utm_medium=syndication&utm_campaign=off_domain&utm_content=ko), [3부](https://www.pubnub.com/blog/javascript-google-maps-api-location-publishing/?utm_source=devto&utm_medium=syndication&utm_campaign=off_domain&utm_content=ko)( )에서 [JavaScript 환경을 설정하고](https://www.pubnub.com/blog/javascript-mapping-javascript-tracking/?utm_source=devto&utm_medium=syndication&utm_campaign=off_domain&utm_content=ko) [지도 마커와](https://www.pubnub.com/blog/javascript-google-maps-api-map-markers/?utm_source=devto&utm_medium=syndication&utm_campaign=off_domain&utm_content=ko) [위치 추적에](https://www.pubnub.com/blog/javascript-google-maps-api-location-publishing/?utm_source=devto&utm_medium=syndication&utm_campaign=off_domain&utm_content=ko) 대해 다룬 사전 요구 사항을 완료했는지 확인하세요.
완료했으면 다음 파트로 넘어가세요.
코드 연습
-----
먼저 지도, 마커 및 폴리라인 **좌표** 객체를 보유할 \`let\` 변수 \`map\`, \`mark\` 및 \`lineCoords\`를 정의해 보겠습니다. 이렇게 하면 PubNub 이벤트가 들어올 때 이를 조정할 수 있습니다. 그 후, 로드 준비가 되면 [구글 지도 자바스크립트 API에서](https://developers.google.com/maps/documentation/javascript/overview) 사용할 수 있는 \`initialize\` 콜백을 정의합니다. YOUR\_GOOGLE\_MAPS\_API\_KEY\`를 실제 **API 키로** 바꿔야 합니다.
```js
let map;
let mark;
let lineCoords = [];
let initialize = function() {
map = new google.maps.Map(document.getElementById('map-canvas'), {center:{lat:lat,lng:lng},zoom:12});
mark = new google.maps.Marker({position:{lat:lat, lng:lng}, map:map});
};
window.initialize = initialize;
```
이제 'redraw' 이벤트 핸들러를 사용하여 geolocation의 \`getCurrentPosition()\` 메서드를 호출하여 새 위치 정보를 즉시 업데이트합니다.
### 위도/경도
다음으로, 새로운 위치 변경 이벤트가 즉시 발생할 때마다 호출할 redraw 이벤트 핸들러를 정의합니다. 함수의 첫 번째 부분에서는 위도와 경도를 메시지의 새 값으로 설정합니다. 그런 다음 지도, 마커 및 폴리라인 객체에서 적절한 메서드를 호출하여 위치를 업데이트하고 라인의 끝에 추가하고 지도를 최신으로 업데이트합니다.
```js
var redraw = function(payload) {
lat = payload.message.lat;
lng = payload.message.lng;
map.setCenter({lat:lat, lng:lng, alt:0});
mark.setPosition({lat:lat, lng:lng, alt:0});
lineCoords.push(new google.maps.LatLng(lat, lng));
var lineCoordinatesPath = new google.maps.Polyline({
path: lineCoords,
geodesic: true,
strokeColor: '#2E10FF'
});
lineCoordinatesPath.setMap(map);
};
```
PubNub 초기화
----------
콜백을 정의한 후에는 **iOS, Android, JavaScript, .NET, Java, Ruby, Python, PHP** 등과 같은 기술 스택에서 **휴대폰, 태블릿, 브라우저**, **노트북에서** 작동하는 PubNub 실시간 데이터 스트리밍 기능을 초기화합니다.
```js
const pnChannel = "map3-channel";
const pubnub = new PubNub({
publishKey: 'YOUR_PUB_KEY',
subscribeKey: 'YOUR_SUB_KEY'
});
pubnub.subscribe({channels: [pnChannel]});
pubnub.addListener({message:redraw});
```
실시간 채널에서 주제를 **게시하고** **구독할** 수 있는 PubNub의 기능은 효율적인 데이터 스트리밍 기능을 제공합니다.
위도/경도 게시하기
----------
이 간단한 튜토리얼에서는 현재 시간을 기준으로 새 위치를 게시하는 기본 JavaScript 간격 타이머를 설정해 보겠습니다. 500밀리초마다 새로운 위도/경도 객체(북동쪽으로 이동하는 좌표 포함)를 지정된 PubNub 채널에 게시하는 익명 콜백 함수를 호출합니다. 앱에서는 실시간 디바이스 위치 또는 사용자가 보고한 위치에서 위치를 가져올 가능성이 높습니다.
```js
setInterval(function() {
pubnub.publish({channel:pnChannel, message:{lat:window.lat + 0.001, lng:window.lng + 0.01}});
}, 500);
```
마지막으로, 마지막에 구글 지도 API를 초기화하여 DOM 요소와 자바스크립트 전제 조건이 충족되었는지 확인합니다.
```js
<script src="https://maps.googleapis.com/maps/api/js?v=3.exp&key=YOUR_GOOGLE_MAPS_API_KEY&callback=initialize"></script>
```
마무리
---
이 튜토리얼 시리즈를 통해 웹 및 모바일 앱에서 실시간 위치 추적을 위해 [Google Maps API와](https://developers.google.com/maps/documentation/javascript/overview) [PubNub가](https://www.pubnub.com/?utm_source=devto&utm_medium=syndication&utm_campaign=off_domain&utm_content=ko) 어떻게 함께 작동하는지 살펴봤습니다. 이는 **Uber나** **Lyft와** 같은 차량 호출 서비스가 차량의 움직임을 실시간으로 보여주는 방식과 유사합니다.
PubNub 체험하기
-----------
[라이브 투어를](https://www.pubnub.com/tour/introduction/?utm_source=devto&utm_medium=syndication&utm_campaign=off_domain&utm_content=ko) 통해 5분 이내에 모든 PubNub 기반 앱의 핵심 개념을 이해해 보세요. [GitHub 페이지와](https://github.com/PubNubDevelopers) 웹사이트에서 제공되는 사용 후기를 통해 사용자들의 경험을 직접 들어보세요.
설정하기
----
PubNub [계정에](https://admin.pubnub.com/#/login?utm_source=devto&utm_medium=syndication&utm_campaign=off_domain&utm_content=ko) 가입하여 PubNub 키에 무료로 즉시 액세스하세요.
시작하기
----
사용 사례에 관계없이 [PubNub 문서를](https://www.pubnub.com/docs?utm_source=devto&utm_medium=syndication&utm_campaign=off_domain&utm_content=ko) 통해 바로 시작하고 실행할 수 있습니다. 자바스크립트 Google 지도 API 전용 섹션과 SDK에서 실시간 추적과 함께 사용하는 방법을 확인할 수 있습니다. | pubnubdevrel |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.