id int64 5 1.93M | title stringlengths 0 128 | description stringlengths 0 25.5k | collection_id int64 0 28.1k | published_timestamp timestamp[s] | canonical_url stringlengths 14 581 | tag_list stringlengths 0 120 | body_markdown stringlengths 0 716k | user_username stringlengths 2 30 |
|---|---|---|---|---|---|---|---|---|
1,872,023 | 14 Must Know Microservices Design Principles | Imagine an airport humming with diverse operations, where each department serves as a meticulously... | 0 | 2024-05-31T11:55:24 | https://dev.to/harisapnanair/14-must-know-microservices-design-principles-4ao9 | microservices, testing, devops, programming |
Imagine an airport humming with diverse operations, where each department serves as a meticulously crafted microservice dedicated to specific operations such as booking, check-in, and baggage handling. The airport architecture must follow fundamental design principles in this intricately designed architecture, mirroring the principles of microservices.
For example, the airlines operate independently yet interact seamlessly through standardized protocols, similar to how microservices are designed in a high cohesion combined with a loose coupling. And just as each flight is uniquely identified, microservices are distinguished by their endpoints or service names. Similarly, other design principles are implemented in microservices and a well-orchestrated airport for efficient working.
Following the microservices design principles helps to increase agility, performance, and cost-efficiency for large and small organizations while enabling continuous testing and early delivery.
*In our latest blog, you can explore the [Monolithic vs Microservices](https://www.lambdatest.com/blog/monolithic-vs-microservices-architecture/?utm_source=devto&utm_medium=organic&utm_campaign=mar_14&utm_term=bw&utm_content=blog) debate to uncover the pros, cons, and key distinctions between the two architectures and navigate your choices wisely!*
## Advantages Of Microservice Architecture
With monolithic architectures, developers often face challenges of limited reusability and scalability. But, with a microservice design, this single unit can be broken down into different modules, making development, deployment, and maintenance easy. So, let’s look at some significant advantages of microservice architecture.
* **Technological Flexibility:** While monolithic architecture always leaves the developers looking for the ‘right tool for the job,’ microservice architecture offers the coexistence of multiple technologies under one cover. Different decoupled services can be written in various programming languages. This enables developers to experiment and scale their products by seamlessly integrating additional features and functionalities.
* **Increased Efficiency:** Microservice architecture speeds up the entire process of development. Teams can work simultaneously on multiple software system components, unlike a single unit. This, in addition to increasing productivity, makes it easier to locate and focus on specific components. The malfunctioning of a single component will not affect the entire system. Instead, this also eases error location and maintenance.
* **Products, Not Projects:** According to Martin Fowler, microservice architecture helps businesses create ‘products instead of projects.’ In simpler terms, microservice architecture allows teams to come together and create functionality for business rather than simple code. These can further be used for different lines of business if applicable. In addition, it also makes an autonomous, cross-functional team.
* **Improved Scalability:** Microservices architecture offers significant scalability benefits by allocating dedicated resources to each service and preventing overload on the entire system during traffic spikes.
* **Better Fault Isolation:** In a microservices architecture, the likelihood of one service failure adversely affecting other application components is minimized as each microservice operates independently.
* **Better Data Security and Compliance:** With each service assigned to a specific task, implementing security measures at the service level becomes more manageable than a monolithic database accessible by the entire application. Using secure APIs to connect microservices also helps to ensure that data is accessible only to authorized applications, users, and servers.
*Find out how [microservices design patterns](https://www.lambdatest.com/blog/design-patterns-for-micro-service-architecture/?utm_source=devto&utm_medium=organic&utm_campaign=mar_14&utm_term=bw&utm_content=blog) can help you optimize your application for peak performance to scale smoothly, remain resilient, and integrate seamlessly with other systems.*
> Secure your data with our [Whirlpool hash calculator](https://www.lambdatest.com/free-online-tools/whirlpool-hash-calculator?utm_source=devto&utm_medium=organic&utm_campaign=mar_14&utm_term=bw&utm_content=free_online_tools). Try it now!
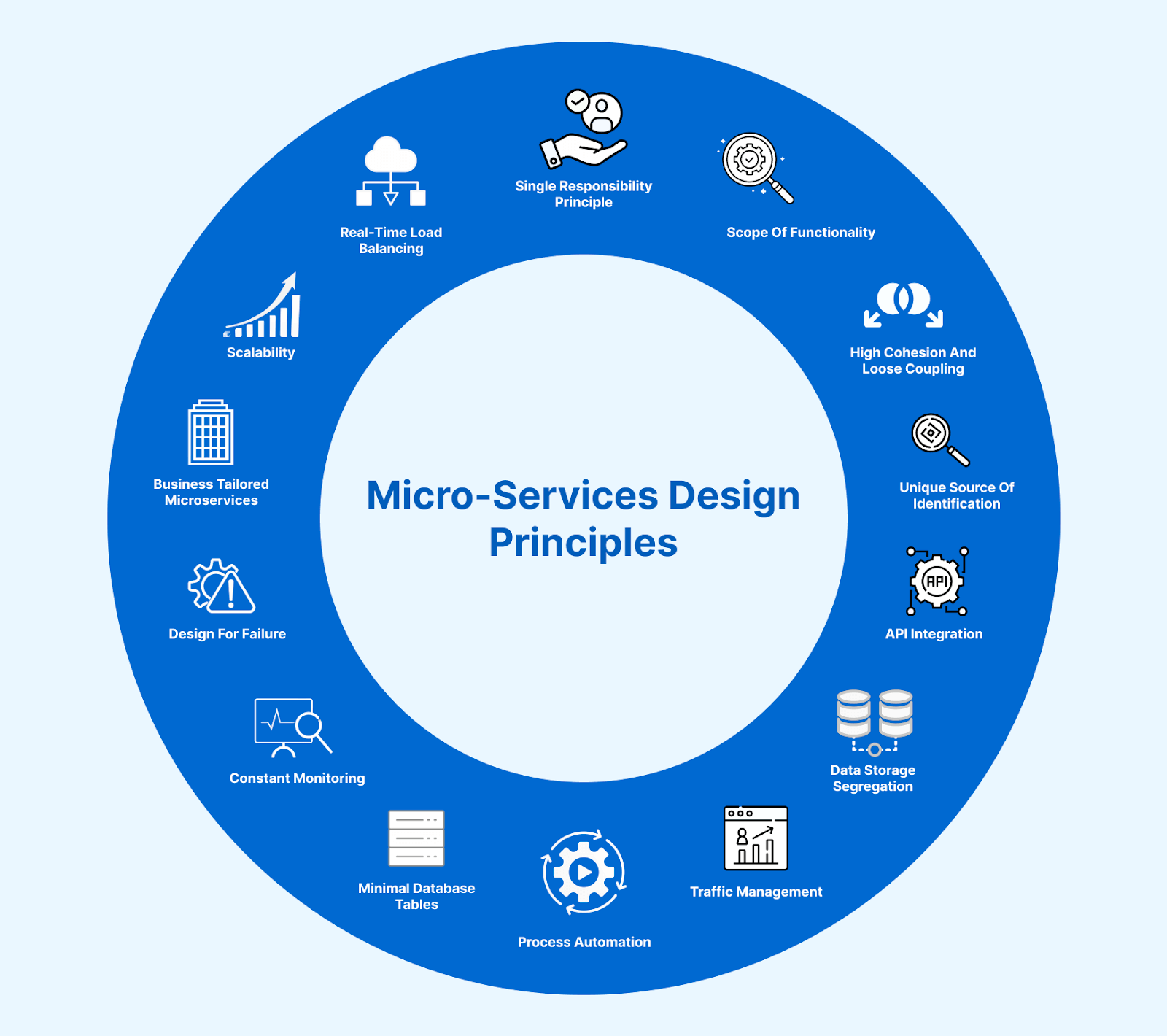
## Microservices Design Principles
We know the advantages of a microservice architecture, but how do we achieve perfection? Are we aware of the microservices design principles? What are the best practices for designing a microservice architecture?
Let us answer these questions and look at some fundamental microservices design principles used to develop a successful microservice application. This will enable us to navigate the complexities during microservices testing and help us achieve optimal results.
*Ready to master the fundamental principles used to build a microservice? Don’t miss out! Watch fundamentals to a successful microservice design that can elevate your microservice architecture.*
{% youtube DnneKh3PoRQ %}
## Single Responsibility Principle
The Single Responsibility Principle(SRP) states that a class or module should have only one primary responsibility, and modifications should be made only for reasons related to that particular responsibility. This principle is crucial in microservices architecture because each microservice should align with a specific business capability, ensuring a clear and singular responsibility.
Each service must handle a distinct functionality or business domain in microservices. By adhering to the Single Responsibility Principle, developers design modules with a single, well-defined purpose, making them easier to understand, maintain, and scale. This principle helps prevent the inclusion of multiple unrelated responsibilities within a single microservice, promoting modularity and independence.
When a microservice follows the Single Responsibility Principle, it becomes more adaptable to changes related to its specific responsibility without affecting other system parts. This isolation allows for each microservice’s independent development, deployment, and scalability, contributing to the overall flexibility and maintainability of the microservices-based application.
> Generate SHA1 hashes effortlessly with our [SHA1 hash calculator](https://www.lambdatest.com/free-online-tools/sha1-hash-calculator?utm_source=devto&utm_medium=organic&utm_campaign=mar_14&utm_term=bw&utm_content=free_online_tools). Click here to use!
## Scope Of Functionality
With the simultaneous implementation of development and deployment by different teams to establish or support a unique functionality with a product, defining the scope of a microservice becomes an essential task. We can achieve this by following the Single Responsibility Principle (SRP). SRP guides us to design modules with a singular focus, this in turn narrows the scope of functionality to enhance maintainability and clarity in software systems.
When we talk about a microservice’s scope, we refer to the features of an independent software module. Identifying the features that a microservice will implement will help us define the scope of functionality of the microservice and establish clear boundaries. For example, consider a microservice responsible for user authentication within an e-commerce platform. Its scope would include functionalities such as user registration, login, password reset, and authentication token generation. This well-defined scope ensures that the microservice focuses solely on handling user authentication-related tasks, optimizing its efficiency and maintainability.
The question comes as to how one can define the scope of a microservice. Though there isn’t a well-defined set of rules to achieve this, there are a few guidelines or best practices to define a scope.
Following are some of the steps that you can consider while defining the scope of any microservice:
* The first step is to identify the pieces of code that are replicated under various modules. How often do you see them repeat? And how much effort goes into setting them up in different modules each time? If the answer to all of these is high, then the scope of the microservice would be to handle just the repeating pieces of code.
* Another step is to check if a module is not dependent on other modules or, in simpler terms, if a module may be loosely coupled with the rest of the services. If so, then the scope of the microservice will be the scope of the entire module.
* Another important metric to consider while defining the scope is checking if the features would be used with a heavy load. This would check if the microservice would have to be scaled up soon. If it does, then it’s a good idea to define the scalable bits as the scope of a microservice rather than combine it with other features.
## High Cohesion and Loose Coupling
The main motive of any microservice is to have services independent of each other. This means one can edit, update, or deploy a new service without hampering other services. This is possible if interdependence is low. So, we must create a loosely coupled system where one service knows too little or nothing about others. This also makes testing easier as each component can be easily isolated for thorough testing.
It is essential to combine similar functionalities when breaking down a monolithic architecture into smaller services or components. This combination of related logic into a single unit is known as cohesion. The higher the **cohesion**, the better the microservice architecture. A low cohesion would indicate too much communication between different services, leading to poor system performance.
Hence, we must design a microservice with high cohesion and loose coupling to make it adaptable to changes and scalable.
## Unique Source Of Identification
Following the fundamentals of microservice design, any service needs to be the unique source of identification for the rest of the system. Let us take an example to understand this.
After an order is placed on an e-commerce website, the user is provided with an order ID. Once generated, this order ID contains all the information regarding the order. As a microservice, the order ID is the only source for any information regarding the order service. So, if any other service seeks information regarding the order service, the order ID acts as the source of information rather than its actual attributes.
> Enhance security with our [SHA512 hash calculator](https://www.lambdatest.com/free-online-tools/sha512-hash-calculator?utm_source=devto&utm_medium=organic&utm_campaign=mar_14&utm_term=bw&utm_content=free_online_tools). Test it today!
## API Integration
In a microservices architecture, multiple services coordinate and work together to form the system. But how do these services communicate? Imagine using various technologies to create different services. How do they relate to each other?
The simple answer would be using an API (Application Programming Interface). While designing a microservice, it is important to select the right APIs. This is crucial to maintaining communication between the service and the client calls. Easy transition and execution are essential for proper functioning.
Another important thing to note while creating an API is the domain of the business. Understanding the scope of the business’s operations will help us define the boundaries and differentiate the various functionalities the API will provide.
There are several clients that are external to the system. These clients could be other applications or users. Whenever a business logic is called, it is handled by an adapter (a message gateway or web controller), which returns the request and changes the database.
## Data Storage Segregation
Each microservice maintains its dedicated database in a microservices architecture, contrasting with monolithic applications where multiple services may share a common database. The autonomy provided by individual databases supports the independent development, deployment, and scalability of microservices.
Any data stored for a specific service should be made private to that particular service. This means any access to the data should be owned by the service. This data can be shared with any other service only through an API. This is very important to maintain limited access to data and avoid ‘service coupling.’ Data classification based on the users is essential and can be achieved through the Command and Query Responsibility Segregation (CQRS).
## Traffic Management
Once the APIs have been set and the system is up and running, traffic to different services will vary. The traffic is the calls sent to specific services by the client. In the real-world scenario, a service may run slowly, thus causing calls to take longer. Or a service may be flooded with calls. Both cases will affect the performance, even causing a software or hardware crash.
This high traffic demand needs management. A specific way of calling and being called is the answer to a smooth traffic flow. The services should be able to terminate instances that cause delays and affect performance.
Traffic management can also be achieved using a process known as ‘auto-scaling,’ which includes constantly tracking services with prompt action whenever required. Sometimes, a ‘circuit breaker pattern’ is essential to supply any incomplete information in case of a broken call or an unresponsive service.
## Process Automation
Microservices designed independently should be able to function on their own accord. The automation would enable self-deployment and function without the need for any intervention. This process allows the services to be cloud-native and deployed in any environment. But to achieve this, it is very important to have a [DevOps](https://www.lambdatest.com/learning-hub/devops-automation?utm_source=devto&utm_medium=organic&utm_campaign=mar_14&utm_term=bw&utm_content=learning_hub) team constantly working towards evolving the services.
## Minimal Database Tables
Accessing database tables to fetch data can be a lengthy process. It can take up time and energy. While designing a microservice, the main motive should revolve around the business function rather than the database and its working. To ensure this, a microservice design should have only a few tables, preferably isolated, even with data entries running into millions. In addition to minimum numbers, focusing on the business is key.
> Create NTLM hashes easily with our [NTLM hash generator](https://www.lambdatest.com/free-online-tools/ntlm-hash-generator?utm_source=devto&utm_medium=organic&utm_campaign=mar_14&utm_term=bw&utm_content=free_online_tools). Get started now!
## Constant Monitoring
Imagine breaking down a monolithic architecture into a microservice design. This needs a lot of time and resources. It is not easy to monitor all the changes made with the help of traditional tools. The insertion of data layers and caching increases performance but makes it difficult to monitor the entire process.
Hence, when designing a microservice architecture, it is important to establish a process for actively monitoring data storage in a central location. This will help reflect the frequent changes without affecting the system’s performance. In a typical scenario, the microservice monitoring tools will monitor individual services and combine the data by storing it in a centralized location. This is a necessary step while following microservices design principles.
Along with monitoring data storage, it is also important to continuously monitor API performance. API performance monitoring is crucial to any microservice architecture to ensure the functionality stays up to the mark regarding speed, responsiveness, and overall product performance.
## Design for failure
Microservices architecture aims to enhance fault tolerance and resilience in software systems by isolating services to prevent the failure of one from impacting others. The objective is to ensure that issues like memory leaks, database connectivity problems, or errors in one microservice do not result in the failure of the entire application.
To achieve this goal, the circuit breaker pattern is a common method used in microservices. This pattern involves monitoring the status of a microservice and dynamically adjusting its behavior based on that status. If a microservice experiences repeated failures or errors, the circuit breaker pattern allows the system to temporarily cut off communication with the problematic service. Implementing the circuit breaker pattern allows a microservices-based application to prevent prolonged communication attempts with a failing service, thus avoiding performance issues and potential system-wide failures. This isolation mechanism ensures that other services can function independently, promoting overall system resilience.
## Business Tailored Microservices
The microservices design principle of aligning each microservice with a specific business problem encourages developers to adopt the most suitable technology stack for each microservice’s unique requirements. Unlike monolithic applications that often use a single, homogenous technology stack throughout, microservices architecture allows for flexibility and diversity in technology choices.
In a microservices-based application, developers have the freedom to choose the programming language, framework, and database that best fit the specific needs of each microservice. This approach enables the optimization of technology choices based on factors such as scalability, performance, or data processing requirements for each component. This flexibility promotes agility and adaptability, as developers can leverage the strengths of various technologies to address specific challenges within the microservices ecosystem.
## Scalability
Scalability is a crucial design principle in microservices that empowers the application to seamlessly adapt to fluctuating levels of traffic, data volumes, and complexity without compromising system performance. For instance, in an e-commerce application, scalability comes into play during peak demand, like the festive season when there’s a surge in application traffic. It dynamically adjusts the capacities of essential microservices, including databases and servers, ensuring optimal performance to meet the heightened demand.
Achieving scalability involves employing strategies like Service partitioning, Load balancing, Horizontal scaling, and Caching, providing a robust framework for effectively managing varying workloads.
> Generate SHAKE256 hashes quickly with our [SHAKE256 hash generator](https://www.lambdatest.com/free-online-tools/shake256-hash-generator?utm_source=devto&utm_medium=organic&utm_campaign=mar_14&utm_term=bw&utm_content=free_online_tools). Try it for free!
## Real-Time Load Balancing
In scenarios where a client initiates a request that requires data retrieval from multiple microservices simultaneously, the role of the Load balancer becomes crucial. The Load balancer plays a pivotal role in managing this complex operation by determining the allocation of Central Processing Unit (CPU) or Graphics Processing Unit (GPU) resources for each specific service that fetches the required data. It manages the distribution of computational resources and regulates how the client request is routed, ensuring an optimal and efficient process. This helps to minimize latency, allowing clients to receive prompt results without unnecessary delays, thereby enhancing the overall responsiveness and performance of the system.
Whether you’re a seasoned developer or just starting in the field, understanding and implementing these microservices design principles can revolutionize your approach to microservices testing and set the stage for successful application development.
*To unlock the full potential of your microservices architecture with effective testing strategies, dive into our [Microservices Testing Tutorial](https://www.lambdatest.com/learning-hub/microservices-testing?utm_source=devto&utm_medium=organic&utm_campaign=mar_14&utm_term=bw&utm_content=learning_hub) and [Microservices Testing Quick Start Guide](https://www.lambdatest.com/blog/testing-microservices/?utm_source=devto&utm_medium=organic&utm_campaign=mar_14&utm_term=bw&utm_content=blog)!*
## Limitations Of Microservice Architecture
While microservices are the best way to tone down a monolithic structure, they have drawbacks. But before concluding, let’s look at some of these.
* **Development Environment Overload:** With the growth of the application and its database, there is an expansion in the code base as well. With the code expanding for every microservice present, it overloads the development environment with every loaded application. This can cause a significant delay in productivity.
* **Increased complexity:** In microservices, each service becomes an autonomous unit, communicating through networks, APIs, or messaging protocols. This introduces a substantial rise in the application’s architectural complexity as there is a need for intricate coordination, additional considerations for data consistency, and the implementation of effective communication mechanisms.
* **DevOps Complexity:** Developing and deploying single-function microservices is not easy. Using multiple technologies and creating APIs to centralize the system is a challenge. This calls for an experienced DevOps team. Procuring such an experienced DevOps team is crucial to maintaining a microservice-based application’s complexities.
* **Network congestion:** Microservices make the network more chatty as numerous services interact. This increased chatter, often called the “microservices chatter problem,” can result in network congestion and reduce performance. The sheer volume of data exchange between microservices may lead to latency, slower response times, and the need for efficient network management strategies to optimize overall system performance.
* **Increase In Resource And Network Usage:** With multiple components working together, they need to communicate with each other at some level. This communication will lead to increased network usage. This demands a high-speed, reliable network connection. In addition, expenses increase to run these applications. All services run individually, raising the costs of operation.
* **Difficulty in testing and debugging:** Testing and debugging microservice-based applications pose unique challenges as the system is distributed across multiple servers and devices. The difficulty lies in the need for access to all components to ensure adequate testing and debugging. In large, distributed systems, coordinating access to various servers and devices becomes a complex task, impacting the efficiency of the testing process. Addressing these challenges requires thoughtful strategies and tools to streamline testing efforts in the intricate landscape of microservices architecture.
* **Application Complexity:** As microservices are independent components, each microservice will often have a technology stack that best suits its needs. For example, a machine learning module might use the [Python ](https://www.lambdatest.com/learning-hub/python-basics?utm_source=devto&utm_medium=organic&utm_campaign=mar_14&utm_term=bw&utm_content=learning_hub)stack, the metering service might use the Java stack, and the UI service might use the MEAN stack. This leads to complexity as the resource pools and the skills required to manage and build newer features will be very high.
* **High Initial Investment:** Microservices run independently and require independent containers or resources to run them. Each project might have a lot of microservices working together. It would need a much higher investment to set up all the clusters, including the microservices, security containers, load balancers, API gateways, etc.
* **Challenges in providing security:** Security is of paramount importance when it comes to web applications. With microservices, achieving this takes time and effort. When there are clusters of independent modules, each module needs to adhere to the authentication and authorization norms defined for the entire system.
*Check out our blog on [Testing Challenges With Microservices Architecture](https://www.lambdatest.com/blog/testing-challenges-related-to-microservice-architecture/?utm_source=devto&utm_medium=organic&utm_campaign=mar_14&utm_term=bw&utm_content=blog) to uncover insights, solutions, and best practices.*
> Decode HTML entities seamlessly with our [HTML Unescape](https://www.lambdatest.com/free-online-tools/html-unescape?utm_source=devto&utm_medium=organic&utm_campaign=mar_14&utm_term=bw&utm_content=free_online_tools) tool. Use it now!
## Conclusion
After reading the fundamentals of microservices design principles, it is clear that a certain set of best practices must be followed to design an efficient microservices architecture. But, we also observe how the microservices design principles ease the process of creating an application by breaking down the monolithic architecture. But, at the same time, certain challenges need to be overcome when adapting a microservice architecture. These complexities affect the operational processes, but in the long term, overcoming these challenges can lead to an optimized and more efficient application. In addition, it overcomes delays and flaws while increasing flexibility and performance.
The future of microservices architecture holds promising trends to reshape the software development landscape. The continued adoption of microservices is anticipated, with many organizations recognizing the benefits of scalability, flexibility, and ease of maintenance that this architecture offers. A prevailing prediction is that microservices will become the default software architecture system, indicating a shift toward modular and decentralized application development.
Many enterprises, including names like PayPal, Twitter, LambdaTest, and Netflix, have backed up the reliability of microservice architecture for deploying more scalable, functional, and robust software.
| harisapnanair |
1,872,022 | Anonymous functions in JavaScript | Anonymous functions are the functions without name and later can be assigned as a value to a... | 0 | 2024-05-31T11:55:02 | https://dev.to/vman_eesh/anonymous-functions-in-javascript-17b4 | Anonymous functions are the functions without name and later can be assigned as a value to a variable, but it will not be anonymous any more. And declared using two methods:-
- Function expression
- Arrow Function
## Function expressions
These are the functions that are created using an expression syntax. And it also has two types:-
- **First** - If used without assigning to a variable:-
```javascript
(function(param, [param2]) {
console.log("I m alone and anonymous");
})
```
- **Second** - If assigned to a variable:-
```javascript
const funcName = function(param,[ param2]) {
console.log("Yey, I am commited now and socialized");
}
```
## Arrow functions
These are shorthand function expression syntax and has some features also
- **First**- without binding:-
```javascript
((param, [param2]) => {
let info = "Use curly brackets for multiline statements";
console.log(info);
})
```
- **Second** - With binding:-
```javascript
const funcName = (param, [param2]) => {
let info = "Why devs call us first class citizen";
console.log(info);
}
```
Arrow functions don't have their own "this" they get it from the outer context(object) where they have been defined. And if is one liner doesn't need `return` directive.
## Now some intruction for the use
- If using them without assigning to a variable always use parantheses.
- And to immediately call add trailing() at the last of the function expression, known as Immediately invoked function expression IIFE.
- Mostly used as callback functions
| vman_eesh | |
1,872,021 | How the Panchkula Project Chandigarh Supports Urban Growth | Urbanization is a global phenomenon that is reshaping the landscape of cities and driving economic,... | 0 | 2024-05-31T11:53:04 | https://dev.to/panchkula_projectschandi/how-the-panchkula-project-chandigarh-supports-urban-growth-3h14 | Urbanization is a global phenomenon that is reshaping the landscape of cities and driving economic, social, and environmental changes. In the dynamic city of Chandigarh, the Panchkula Project stands as a testament to the role of real estate development in supporting urban growth and development. In this blog post, we will explore how the Panchkula Project Chandigarh contributes to urban growth and transformation, making it a catalyst for progress and prosperity in the region.
Strategic Location and Connectivity
The strategic location of the Panchkula Project Chandigarh plays a crucial role in supporting urban growth. Situated in the bustling city of Panchkula, the project is well-connected to Chandigarh, Mohali, and other key areas in the Chandigarh Tricity region. This strategic positioning not only enhances the accessibility of the project but also fosters economic integration and regional connectivity.
The excellent connectivity of the Panchkula Project Chandigarh to major highways, expressways, and public transportation networks facilitates the movement of people and goods, supporting the growth of businesses, industries, and commerce in the region. Moreover, the project's proximity to educational institutions, healthcare facilities, and employment hubs makes it an attractive destination for residents and investors, further driving urban growth and development.
Infrastructure Development
The Panchkula Project Chandigarh contributes to infrastructure development in the region, laying the foundation for sustainable urban growth. The project incorporates modern infrastructure features such as well-planned roads, efficient transportation systems, and reliable utilities, ensuring smooth connectivity and accessibility for residents.
Moreover, the project integrates green building practices, energy-efficient designs, and sustainable technologies to minimize its environmental impact and promote eco-friendly living. By investing in sustainable infrastructure, the Panchkula Project Chandigarh supports the conservation of natural resources, reduces carbon emissions, and enhances the overall quality of life for residents.
Economic Opportunities
One of the key ways in which the Panchkula Project Chandigarh supports urban growth is by generating economic opportunities and driving economic development in the region. The project attracts investment, stimulates business activity, and creates employment opportunities, thereby contributing to the growth of the local economy.
The development and construction phases of the Panchkula Project Chandigarh create a significant number of jobs in various sectors, including construction, engineering, architecture, and project management. Moreover, upon completion, the project generates employment opportunities in retail, hospitality, and service sectors as businesses set up operations within the commercial complex.
Mixed-Use Development
The Panchkula Project Chandigarh is a mixed-use development that combines residential, commercial, and recreational components, providing residents with a comprehensive urban experience. This mixed-use approach not only maximizes land utilization but also fosters a vibrant and dynamic urban environment.
By integrating residential, commercial, and recreational elements, the Panchkula Project Chandigarh creates a self-contained community where residents can live, work, and play in close proximity. This mixed-use development model promotes walkability, reduces reliance on automobiles, and encourages social interaction and community engagement, thereby fostering a sense of belonging and inclusivity among residents.
Quality of Life
The Panchkula Project Chandigarh enhances the quality of life for residents by providing them with access to world-class amenities, green spaces, and recreational facilities. The project features amenities such as clubhouses, swimming pools, parks, and playgrounds, creating opportunities for residents to relax, unwind, and socialize with neighbors.
Moreover, the project incorporates green spaces, landscaped gardens, and pedestrian-friendly pathways, promoting a healthy and active lifestyle. The presence of amenities and recreational facilities enhances the overall well-being of residents, fostering a sense of community and belonging in the Panchkula Project Chandigarh.
Smart and Sustainable Development
The Panchkula Project Chandigarh embraces smart and sustainable development practices to support urban growth while minimizing environmental impact. The project incorporates smart technologies, energy-efficient designs, and green building practices to reduce resource consumption, enhance energy efficiency, and promote environmental sustainability.
By investing in smart and sustainable development, the Panchkula Project Chandigarh sets a precedent for future real estate developments in the region. The project demonstrates that urban growth can be achieved in a manner that is environmentally responsible, socially equitable, and economically viable, laying the foundation for a sustainable and resilient urban future.
In conclusion, the Panchkula Project Chandigarh plays a pivotal role in supporting urban growth and development in the dynamic city of Chandigarh. Through its strategic location, modern infrastructure, economic opportunities, mixed-use development model, quality of life enhancements, and smart and sustainable development practices, the project contributes to the creation of a vibrant, inclusive, and resilient urban environment.
As cities continue to evolve and expand, projects like the Panchkula Project Chandigarh will play an increasingly important role in shaping the future of urban living. By embracing innovation, sustainability, and community engagement, the project sets a new standard for urban development, demonstrating how real estate can be a catalyst for positive change and progress in the region. | panchkula_projectschandi | |
1,872,020 | Satellite Data Services Market and the Growth of Space Industry | Human-made satellites are responsible for delivering data and information about the Earth’s surface... | 0 | 2024-05-31T11:52:59 | https://dev.to/marktwain57/satellite-data-services-market-and-the-growth-of-space-industry-4i73 | satellitedataservicesmarket, satellitedataservices | Human-made satellites are responsible for delivering data and information about the Earth’s surface and also other planets. Using [remote sensing](https://dev.to/santoshkaranam/harnessing-the-power-of-remote-sensing-and-gis-for-sustainable-development-4j5f) technologies, these satellites can generate data regarding Earth’s surface and weather changes. In addition, it can provide analytics about land and water, as well as environmental situations.

Many governments also utilize satellites to observe settlement patterns and to make infrastructure policies. In addition, data from satellites can give insights when building cities and promote economic growth.
This cloud-based service delivers almost real-time data in every condition, whether it is at nighttime or in a cloudy condition.
Several companies that provide satellite data services include ICEYE, Airbus SE, DigitalGlobe, L3Harris Geospatial, LAND INFO Worldwide Mapping, Planet Labs, SATPALDA Geospatial Services, Ursa Space Systems, Inc, among others.
The [satellite data services market](https://www.gmiresearch.com/report/satellite-data-services-market/) has seen rapid growth, in which GMI Research estimated that the satellite data services market size reached USD 6.5 billion in 2021. The research firm predicted that the market would touch USD 30.5 billion in 2029.
The firm mentioned that based on service, the Data Analytics segment holds the largest share in the market. It is especially used for monitoring crops, coastal traffic, and floods. This leads to the agriculture segment leading the market based on vertical segment, as the satellite imagery hel``ps monitoring vegetation and land. Meanwhile, government and military dominate the market based on the end-use.
**What Drives This Market to Grow?
**
As there is an increasing demand for earth observation satellites, privatization of space industry, and advancements in satellite technology, satellite data services market is undergoing rapid expansion.
**Increasing demand for earth observation satellites
**
To be able to make a data-driven decision making across industries, there has been an increasing demand for earth observation satellites. With an electro-optical sensor, this satellite will work like a flying camera and record the Earth’s surface.
**Privatization of space industry
**
Space industry has increasingly grown towards private sector. This demonstrates a substantial shift from the government-focused practice. Private enterprises have to compete to get the data needed, which increases the demand for satellite data.
**The adoption of AI and big data analytics in space industry
**
Implementing big data analytics and adopting AI can further accelerate the growth of satellite data services market. There are also thriving advancements in satellite technology like miniaturization, innovative satellite design, and data processing capabilities, which boost the utilization of the data satellite services.
**Demand for real-time and high-resolution imagery
**
As technology advances, there is a necessity to get a better quality of data and images collected by satellites. With high-resolution imagery and real-time data delivery, this market is seeing significant growth.
**Government investment
**
Satellite data services are increasingly relevant to tackle problems that are happening in the world. Therefore, many governments make serious investments to possess and utilize satellites.
Despite the rapid growth of the satellite data services market, there are also challenges to be overcome. The first is related to the high cost to build, maintain, and operate the data satellite. To have and utilize this satellite, there should be a significant expenditure to spend. Furthermore, there are also stringent regulations to use the satellites that further hamper the market’s growth.
| marktwain57 |
1,872,019 | 10 Pro Tips for Setting Up Your Large Computer Monitor for Ultimate Comfort | Wide-screen computer monitors have grown in popularity in today's digital environment. For... | 0 | 2024-05-31T11:50:37 | https://dev.to/trammygombez/10-pro-tips-for-setting-up-your-large-computer-monitor-for-ultimate-comfort-58md | largecomputermonitor, monitor | Wide-screen computer monitors have grown in popularity in today's digital environment. For individuals who frequently stare at a screen, such as graphic designers, programmers, gamers, or just about anyone who works with computers, a huge computer display has many advantages.
The [large computer monitor](https://www.lenovo.com/ca/en/d/large-computer-monitors/) allows for improved visual detail, multitasking, and an overall more immersive experience. Nevertheless, maximizing its potential requires more than just owning a big display. You can increase your productivity and well-being by making sure your workspace is comfortable and functional.
To help you turn your giant computer monitor into a comfortable and productive refuge, consider these 10 expert tips:
## 1. Ergonomics: Posture, Distance, and Height
A proper ergonomics check is the first step. Neck strain, eye fatigue, and even headaches can result from improperly placing a large computer monitor. The salient features are as follows:
Height
Approximately eye level, or slightly lower, is how high your monitor should be. By doing this, discomfort is avoided due to severe neck craning. The most flexible monitor arms are those that can be adjusted in height, although most monitor stands do.
Distance
Depending on its size and resolution, the appropriate distance for your eyes to be between a huge computer display and it is determined. Upholding an arm's length distance is standard practice. Try a few different things to see when you can comfortably and painlessly see the entire screen.
Posture
Throughout the workplace, keep your posture correct. With your feet flat on the ground and your shoulders relaxed, sit up straight. It is highly recommended to use a supportive chair with adjustable lumbar support.
## 2. Making the Most of Several Inputs
Numerous input port options are a common feature of large computer monitors. Don't restrict yourself to just one relationship! Make use of interfaces such as DisplayPort, HDMI, and USB-C to link gaming consoles, a secondary device, and your primary computer.
Making the most of your big screen's versatility, you can effortlessly switch between work and play by doing this.
## 3. Gaining Proficiency in Window Management
A multitasker's dream comes true with large computer monitors. But successfully managing several windows becomes essential when there's so much screen real estate. The following are some useful resources:
Functions of the Operating System: Snapping windows is a feature that most operating systems come with. You can rapidly arrange windows in a grid pattern or side by side with these.
Third-Party Apps: Examine certain window management apps for even finer control over the positioning and resizing of windows.
Virtual desktops can be created to establish distinct workspaces for various tasks. Virtual desktops are accessible on most operating systems. You can stay focused and keep your screen tidy by doing this.
## 4. Lighting: Eliminating Reflection and Maximizing Lumen
The illumination has a big impact on eye comfort. You can adjust it as follows to fit your large computer monitor:
Reduce Glare Keep your monitor out of direct sunlight and strong overhead lighting. If you want to further reduce glare, think about installing an anti-glare screen protector.
Ideal Brightness The ideal brightness level is contingent upon the surrounding ambient lighting. Choose an angle that won't cause too much contrast with the surroundings and is easy on the eyes. The majority of monitors have integrated brightness adjustments.
## 5. Adjustment: Exposing the Actual Colors
Big computer monitors can often create amazing visuals. Color calibration comes straight out of the box, but, might not always be ideal. Use specialized software or hardware equipment to calibrate your monitor. For jobs like graphic design or photo editing, precise color reproduction is essential. This is ensured.
## 6. Resolution Revolution: The Appropriate Fit
On a huge monitor, a resolution is the number of pixels that are visible. Sharper images and more information are available at higher resolutions. Remember, though, that greater resolutions also mean your computer needs to have more processing capacity. To assist you in making a decision, consider the following breakdown:
Suitable for regular use and simple tasks, Full HD (1920 x 1080) is a decent starting point.
With a notable sharpness boost, QHD (2560 x 1440) is perfect for multitasking and creative work.
4K (3840 x 2160) Excellent for gaming, producing high-resolution material, and providing an amazing visual experience all around. Make sure your computer's graphics card can support it, though.
## 7. Cable Management: Maintaining an Ordered Workspace
Cable clutter may arise rapidly from a large monitor arrangement. The following advice can help you keep your workstation tidy and orderly:
To organize wires neatly, use cable ties.
Invest in cable management sleeves to conceal unsightly wires and get a more streamlined appearance.
To keep your desk organized, certain monitor stands have integrated cable management channels.
## 8. Taking Advantage of Picture-in-Picture and Screen Splitting
Inbuilt features like screen splitting and picture-in-picture (PIP) are common on large modern computer monitors. You can make good use of the large screen thanks to these functions:
Splitting the screen into pieces that show separate windows or applications is known as screen splitting. Observing many information streams at once and multitasking well can be achieved with this method.
A tiny window will appear on top of your primary view when you use Picture-in-Picture (PIP). By using this, you can focus on your main task and simultaneously monitor side projects, such as a video conversation.
## 9. Color Schemes and Display Preferences
The on-screen display (OSD) menu on the majority of large computer monitors has a surprisingly large number of customizable options. Investigate these options to customize your experience.
Modify the color profiles: Numerous displays have various color profiles pre-installed that are ideal for various purposes like gaming, viewing movies, or editing photos. Select the profile that best meets your requirements.
Adjust. Additional Settings: Contrast, sharpness, gamma correction, and other settings can all be changed on modern monitors. Try a few different configurations to see which ones provide the best image quality for you.
## 10. Maintaining a Spotless Large Monitor with a Sharp View
Both visual comfort and attractiveness are improved by a spotless, huge computer monitor. Here are some tips for keeping your display neat and legible:
Before cleaning, always turn off your monitor. This keeps screen burn-in from static pictures and inadvertent harm at bay.
For electronics cleaning, use a microfiber cloth that is soft and free of lint. Steer clear of paper towels or tissues with abrasives since they may harm the sensitive screen surface.
Wipe the screen with a soft touch. Don't exert too much pressure, as this could harm the pixels.
## Bottom Line
These ten expert suggestions will help you turn your big computer screen into a comfortable and productive retreat. Remember that the secret is to customize the arrangement to your unique requirements and tastes. Enjoy the roomy and effective workspace that a large computer monitor provides as you experiment and personalize it!
| trammygombez |
1,872,016 | Advancements in Circuit Breaker Technology: What’s New? | Introduction Circuit breakers are essential components of electrical systems, providing protection... | 0 | 2024-05-31T11:48:13 | https://dev.to/buya2z/advancements-in-circuit-breaker-technology-whats-new-4pa7 | Introduction
Circuit breakers are essential components of electrical systems, providing protection against overloads, short circuits, and other electrical faults. Over the years, advancements in technology have led to improvements in **circuit breaker** design, functionality, and performance. This blog will explore some of the latest advancements in circuit breaker technology and their impact on electrical systems.
1. Smart Circuit Breakers
One of the most significant advancements in circuit breaker technology is the development of smart circuit breakers. These breakers are equipped with sensors and communication capabilities that allow them to monitor electrical parameters, such as current, voltage, and temperature, in real-time. They can also communicate with other devices in the electrical system, enabling remote monitoring and control.
Smart circuit breakers offer several benefits, including improved safety, enhanced reliability, and increased efficiency. By providing real-time data on the status of electrical circuits, these breakers help prevent overloads and other electrical faults, reducing the risk of fires and other hazards. They also enable predictive maintenance, allowing for timely repairs and minimizing downtime.
2. Arc Fault Detection
Arc faults, which occur when an electrical current jumps between two conductors, can be a significant cause of electrical fires. To address this issue, advancements in circuit breaker technology have led to the development of arc fault detection circuit breakers. These breakers use advanced algorithms to detect the unique signature of an arc fault and quickly interrupt the circuit to prevent fires.
3. Increased Sensitivity and Selectivity
Newer circuit breakers are designed to be more sensitive and selective in their operation. This means they can more accurately detect and respond to electrical faults, minimizing the impact on the rest of the electrical system. This increased sensitivity and selectivity help improve the overall reliability and safety of the electrical system.
4. Remote Monitoring and Control
Advancements in circuit breaker technology have enabled remote monitoring and control capabilities. This allows operators to monitor the status of [circuit breakers](https://buya2z.pk/product/tani-circuit-breakers/) and electrical systems from a remote location, reducing the need for on-site inspections and maintenance. Remote monitoring and control also enable faster response times to electrical faults, improving the overall efficiency of the system.
5. Integration with Energy Management Systems
Modern circuit breakers can be integrated with energy management systems to optimize the use of electrical energy. By monitoring energy consumption and demand, these systems can adjust the operation of circuit breakers and other devices to reduce energy waste and improve efficiency. This integration helps reduce electricity costs and minimize the environmental impact of electrical systems.
Conclusion
Advancements in circuit breaker technology have led to significant improvements in the safety, reliability, and efficiency of electrical systems. Smart circuit breakers, arc fault detection, increased [sensitivity](http://cs-headshot.phorum.pl/viewtopic.php?p=355870#355870) and selectivity, remote monitoring and control, and integration with energy management systems are just a few examples of the latest advancements in circuit breaker technology. As technology continues to evolve, we can expect further innovations that will continue to enhance the performance of electrical systems and contribute to a more sustainable future.
| buya2z | |
1,872,015 | Nature CSS Art : Frontend Challenge: June Edition | This is a submission for Frontend Challenge v24.04.17, CSS Art: June. Inspiration I... | 0 | 2024-05-31T11:46:12 | https://dev.to/chintanonweb/nature-css-art-frontend-challenge-june-edition-11kn | frontendchallenge, devchallenge, css, webdev | _This is a submission for [Frontend Challenge v24.04.17](https://dev.to/challenges/frontend-2024-05-29), CSS Art: June._
## Inspiration
I started with a vision of a scenic animation that includes natural elements like the sun, clouds, birds, trees, hills, water, and a ship.
I created a comprehensive HTML structure with nested div elements, each representing a different part of the scene. This hierarchical structure is essential for applying styles and animations effectively.
## Demo
{% codepen https://codepen.io/chintan-dhokai/pen/ExzWaaq %}
## Journey
### What You Learned
- **HTML Structure:** I gained experience in organizing complex HTML structures, ensuring that each element is properly nested and logically named.
- **Animation Preparation:** By setting up detailed spans and wrapper divs, I learned how to prepare your HTML for advanced CSS animations.
- **Modularity:** The use of classes for each distinct element (like birds, clouds, hills, etc.) highlights the importance of modularity and reusability in web development.
### What You Hope to Do Next
- **CSS Animations:** You aim to bring your static HTML to life by adding CSS animations, making the sun rise, clouds float, birds flap their wings, water ripple, and the ship sail.
{% embed https://dev.to/chintanonweb/take-me-to-the-beach-frontend-challenge-june-edition-1b5d %}
| chintanonweb |
1,871,568 | Iterative Development && Abstraction - Part 1 | Development is generally an iterative process going from brute dump of code on to the template to... | 0 | 2024-05-31T11:45:23 | https://dev.to/snackcode/iterative-development-abstraction-part-1-2l9p | javascript, beginners, programming, angular | Development is generally an iterative process going from brute dump of code on to the template to abstraction and then repeat with more abstraction until you find a balance of maintainability, efficiency, and functionality as well creating a better user experience.
Sometimes, daresay most times, it's not all that obvious how a page might function or look. I wanted to build a "learn more" page of an Angular project I am reworking but didn't really know how to structure it. After a bit of experimenting, notecards seemed to be the right fit since this is a recipe site.
The next thing to do was to actually create some content to go on the cards. With some basic ideas of what the site should convey to potential members and a few design iterations, the following code seemed a reasonable start:
(Note: Using W3CSS for overall styling with some custom styling)
```
<div class="center-element w3-margin w3-animate-opacity">
<div class="recipe-card" style="max-width: 800px; height: 1000px;">
<div class="recipe-card-title recipe-card-title-position-1">
create and edit recipes
</div>
<div class="recipe-card-body card" style="text-align: left;height: 250px;font-size: 2em">
At mealHash, you can create and edit recipes. This includes areas for ingredients,
instructions, and other key points you'd expect as part of recipe.
</div>
</div>
</div>
```
Since there were 5 points of information, the above code was repeated 5 times swapping out the appropriate text for each card. This gets the information conveyed but the experience is really just a "meh". And while users generally don't care about what is happening behind the scenes, developers do.
When developing, thinking (or not thinking) about the long term consequences of the code can have big impact on its maintainability. In this particular example, the question becomes: What happens if a card is to added, edited, or removed?
Leaving the code as is, the answer would be open the project, CRUD the cards as necessary, test, recompile (using Angular in this instance), and redeploy. That's fine, kind of, if only an update or two is needed. But this isn't going to be a static site as over time we will be adding more features. So let's abstract a bit and while we're at it provide the potential member with a little better experience in learning more.
Making the "learn more" cards function as a carousel would be a nicer user experience. Adding a `slide` variable keeps track of which slide the user is on. `nextSlide` and `prevSlide` are two simple functions to move forward and backward through the slides.
```
nextSlide() {
this.slide = this.slide + 1;
if (this.slide > this.slideCount) {
this.slide = 1;
}
}
prevSlide() {
this.slide = this.slide - 1;
if (this.slide < 1) {
this.slide = this.slideCount;
}
}
```
Tying the functions to buttons on the card allows the user to carousel through the "learn more" content. It all comes together by wrapping a each card in a if statement that tests which slide to display.
```
@if( slide == 1 ) {
<div class="center-element w3-margin w3-animate-opacity">
<div class="recipe-card" style="max-width: 800px; height: 1000px;">
<div class="recipe-card-title recipe-card-title-position-1">
create and edit recipes
</div>
<div class="recipe-card-body card" style="text-align: left;height: 250px;font-size: 2em">
At mealHash, you can create and edit recipes. This includes areas for ingredients,
instructions, and other key points you'd expect as part of recipe.
</div>
<div style="display: flex;justify-content: center;">
<button (click)="prevSlide()" class="w3-circle w3-hover-black w3-padding w3-margin-top" style="height: 60px;align-self: center;"><span class="bx bx-left-arrow" style="font-size: 2em;" ></span></button>
<button (click)="nextSlide()" class="w3-circle w3-hover-black w3-padding w3-margin-top" style="height: 60px;align-self: center;"><span class="bx bx-right-arrow" style="font-size: 2em;" ></span></button>
</div>
</div>
</div>
}
@if( slide == 2) {
...
}
...
@if ( slide == 5 ) {
<div class="center-element w3-margin w3-animate-opacity w3-animation-left">
<div class="recipe-card" style="max-width: 800px;">
<div class="recipe-card-title recipe-card-title-position-5">
cost
</div>
<div class="recipe-card-body" style="text-align: left;height: 250px;font-size: 1.5em">
mealhash is free and we intend to keep it that way. But will gladly accept donations to keep the site running. In future,
we may build out premium features as we have more mealhasher feedback. But our goal is to make mealhash a must have site
for your recipes, grocery lists, and meal plans.
</div>
<div style="display: flex;justify-content: center;">
<button (click)="prevSlide()" class="w3-circle w3-hover-black w3-padding w3-margin-top" style="height: 60px;align-self: center;"><span class="bx bx-left-arrow" style="font-size: 2em;" ></span></button>
<button (click)="nextSlide()" class="w3-circle w3-hover-black w3-padding w3-margin-top" style="height: 60px;align-self: center;"><span class="bx bx-right-arrow" style="font-size: 2em;" ></span></button>
</div>
</div>
</div>
}
```
Now this gets us a carousel and a better user experience. But the developer experience has now become a nightmare. Imagine if a change was needed on the cards such as styling or additional text. Each card would need to be updated which means 5 opportunities to introducing a bug into the page.
The key here is that duplicate code is an opportunity for abstraction and ask: What parts of the code can be condensed and / or reused and how could the non-duplicated parts (generally data) be implemented.
The solution in this instance was really simple: moved the card titles and text into JSON.
```
public cards: Array<any> = [
{ title: 'create and edit recipes',
text: ` At mealHash, you can create and edit recipes. This includes areas for ingredients, instructions, and other key points
you would expect as part of recipe.
`,
index: 1
},
{ title: 'stores',
text: ` You can also add stores into your mealHash, create grocery lists and easily add and remove items from the list.
Ingredients can be added to directly to your grocery lists from your recipes allowing you manage your shopping experience.
`,
index: 2
},
{ title: 'search',
text: ` Use the search page to find recipes by name or that have a particular ingredient. When you find a recipe you want to try, to can copy
it right to your recipe binder and then edit it to make it your own.
`,
index: 3
},
{ title: 'recipe feed',
text: ` A feed is available of your and others recipes as they are added to mealhash. Just like the search, you can add a recipe to your
mealhash and modify it to make it your own.
`,
index: 4
},
{ title: 'cost',
text: ` mealhash is free and we intend to keep it that way. But will gladly accept donations to keep the site running. In future,
we may build out premium features as we have more mealhasher feedback. But our goal is to make mealhash a must have site
for your recipes, grocery lists, and meal plans.
`,
index: 5
}
]
```
Title and text are obvious as they refer the `recipe-card-title` area of the card, and the text is in the `recipe-card-body`. Index is used as a way to track the cards. The template can be condensed to one card. A `@for` is used to iterate over the JSON array based on one of the card blocks:
```
@for( card of cards; track card.index) {
@if( slide == card.index) {
<div class="center-element w3-margin w3-animate-opacity">
<div class="card" style="max-width: 800px; height: 400px;">
<div class="w3-padding card-title">
{{card.title}}
</div>
<div class="w3-padding" style="text-align: left;height: 250px;font-size: 1.8em">{{card.text}}</div>
</div>
</div>
<div style="display: flex;justify-content: center;gap: 20px">
<button (click)="prevSlide()" class="w3-circle w3-hover-black w3-padding w3-margin-top w3-card" style="height: 60px;align-self: center;"><span class="bx bx-left-arrow" style="font-size: 2em;" ></span></button>
<button (click)="nextSlide()" class="w3-circle w3-hover-black w3-padding w3-margin-top w3-card" style="height: 60px;align-self: center;"><span class="bx bx-right-arrow" style="font-size: 2em;" ></span></button>
</div>
}
}
```
If a card needs to be changed, it only has to be done one time. All the data elements relevant to the card are pulled from the JSON array which makes updating the "learn more" section much easier. Updating the "learn more" page just means updating the array. This still means going through opening the project, making the mods, testing and deploying...but with a bit more abstraction, that process can be made much smoother. Stay tuned for part 2.
If you got this far, thanks for reading. I don't post that often so please be nice - but I do welcome construction feedback.
Cheers!
| snackcode |
1,869,410 | Share Your Experience Loudly and Often | From the outside, it may seem like the person on the stage has something special that inherently... | 0 | 2024-05-31T11:43:24 | https://dev.to/abbeyperini/share-your-experience-loudly-and-often-36ah | career, writing, speaking | From the outside, it may seem like the person on the stage has something special that inherently makes them suited to speaking. They don't. The most interesting technical talks, blogs, and videos are from the people who have found their voice through lots of practice. Their first several attempts were definitely not perfect. (Don't believe me? Check out [Post Malone's early work](https://www.youtube.com/watch?v=XWr2VZiov_A&ab_channel=JustFocus).)
When I encourage people to share their experience via writing or talking, their response usually implies I'm more naturally suited to speaking and writing then they are. I'm not.
I barely passed my university public speaking course. Even while I was a yoga teacher, the only time I wasn't stressed about speaking in front of people was during meditation, when everyone's eyes are closed. When I first started giving technical demos, I would be shaking and sweating the whole time. I have a lot of research writing experience, but technical writing and blogging in general are very different. Before I started a tech blog during bootcamp, I had been blogging for years and generated no views. I continue to be pleasantly surprised so many people have found my blogs helpful.
It's because people find my experience helpful and a healthy dose of peer pressure from friends and colleagues that I kept trying. My demos got better. I learned what feedback to take and what feedback to let go. I started experimenting with my writing and publishing before I felt it was perfect. I gave my first technical talk in 2022. In 2023, I spoke at a in-person conference for the first time. In 2024, I've given four talks. I'm already scheduled to give five more. Slowly, I'm getting less panicked and less focused on all the little mistakes the audience didn't even notice.
It's not just me. All of the technical speakers I've talked to are not 100% confident or perfect. Most of them have shared that they are still very nervous before giving a talk. Many have shared stories of panic attacks on stage. Most are relieved to hear the audience was actually interested in their talk. The technical bloggers and video-makers are usually just happy they managed to publish something decent recently, whether or not it got views.
It's also not just about us individually. When you share your experience, you can help someone else out who is struggling with the problem you just solved, show developers with less experience that there is more than one way to approach a problem, and help someone feel less alone. | abbeyperini |
1,872,013 | Best Private Universities in Uttar Pradesh: Spotlight on Teerthanker Mahaveer University | Uttar Pradesh (UP), one of India’s largest and most populous states, is home to numerous prestigious... | 0 | 2024-05-31T11:43:03 | https://dev.to/shrivenkateshwa/best-private-universities-in-uttar-pradesh-spotlight-on-teerthanker-mahaveer-university-8e0 | education, university | Uttar Pradesh (UP), one of India’s largest and most populous states, is home to numerous prestigious educational institutions. Among the private universities, Teerthanker Mahaveer University (TMU) stands out as a beacon of quality education, innovation, and holistic development. Here, we delve into what makes TMU the [best private university in UP](https://en.wikipedia.org/wiki/Teerthanker_Mahaveer_University), alongside a brief look at other notable institutions.
Teerthanker Mahaveer University: An Overview
Location: Moradabad, Uttar Pradesh
Established: 2008
Motto: Right Philosophy, Right Knowledge, Right Conduct.
Academic Excellence
Teerthanker Mahaveer University offers a wide array of programs across various disciplines, including Engineering, Medical Sciences, Dental Sciences, Pharmacy, Nursing, Physiotherapy, Law, Journalism, Management, and more. The university’s curriculum is designed to meet the highest academic standards, with a strong emphasis on practical learning and industry relevance.
Infrastructure and Facilities
TMU boasts state-of-the-art infrastructure that includes:
Modern Classrooms: Equipped with advanced teaching aids to facilitate interactive learning.
Well-Stocked Libraries: Access to a vast collection of books, journals, and digital resources.
Advanced Laboratories: Cutting-edge labs for research and practical sessions.
Healthcare Facilities: A 1000-bed super-specialty hospital for hands-on training for medical students.
Research and Innovation
The university promotes a robust research culture. It has established numerous research centers and collaborates with international institutions. TMU encourages students and faculty to engage in groundbreaking research, leading to publications in reputed journals and conferences.
Faculty
TMU's faculty comprises highly qualified and experienced professionals dedicated to imparting quality education and mentorship. The faculty-student ratio is maintained to ensure personalized attention and guidance.
Industry Collaboration and Placements
TMU has strong ties with industry giants, providing students with ample internship and placement opportunities. The university’s placement cell works tirelessly to secure positions for students in top companies. Regular workshops, seminars, and industry visits are organized to keep students updated with the latest industry trends.
Holistic Development
Beyond academics, TMU places a significant emphasis on the holistic development of its students. The university offers a plethora of extracurricular activities, sports facilities, and cultural events to nurture well-rounded individuals.
Alumni Network
The university boasts a strong and active alumni network, playing a crucial role in mentoring current students and enhancing their career prospects.
Notable Mentions: Other Top Private Universities in UP
While Teerthanker Mahaveer University shines brightly, other private universities in UP also offer excellent educational opportunities:
Amity University, Noida: Known for its sprawling campus and diverse academic programs.
Sharda University, Greater Noida: Offers a global learning environment with a focus on research and innovation.
Galgotias University, Greater Noida: Renowned for its engineering and technology programs.
Bennett University, Greater Noida: Backed by the Times Group, it emphasizes media, law, and technology studies.
Conclusion
Teerthanker Mahaveer University’s dedication to academic excellence, state-of-the-art infrastructure, strong industry connections, and focus on holistic development make it the best private university in Uttar Pradesh. It stands as a testament to what private education can achieve, setting high standards for others to follow. For students seeking quality education and a nurturing environment, TMU is undoubtedly the premier choice in Uttar Pradesh.
 | shrivenkateshwa |
1,872,012 | How Shopify Expert Developers Help in Your Shopify Business Growth | With the widespread use and easy access to the internet, online businesses have grown tremendously.... | 0 | 2024-05-31T11:42:38 | https://dev.to/startdeesigns/how-shopify-expert-developers-help-in-your-shopify-business-growth-1ia2 | shopify, shopifyexperts, webdev, ecommerce | With the widespread use and easy access to the internet, online businesses have grown tremendously. The e-commerce industry is a prime example of how the internet has transformed the way we shop. According to [Statista](https://www.statista.com/outlook/emo/ecommerce/worldwide), the ecommerce market revenue is projected to reach US$4,117.00 billion and US$6,478.00 billion by 2029.
With immense opportunities in the e-commerce industry, everyone wants to try their luck and run a successful online business. When someone wants to start an e-commerce business, the first thing that comes to mind is the website, as the entire industry depends on it.
To create an e-commerce website, you need a platform or a Shopify expert developer to build it for you.
When it comes to starting an e-commerce business, Shopify is one of the best and easiest platforms to use. **According to Yaguara**, Shopify ranks fourth among the top five e-commerce platforms worldwide and is number one in the US.
Many online business owners and brands, such as **Kylie Cosmetics**, **PepsiCo**, **Red Bull**, **Budweiser**, and **Allbirds**, are using Shopify.
To develop your Shopify store, you need either knowledge of the platform or [Shopify expert services](https://www.startdesigns.com/shopify-experts.php) who can create highly professional websites for you.
Once you’ve decided to start your e-commerce business with Shopify, the next step is to optimize your store for sales and marketing.
## Why is Optimizing Your Shopify Store Important?
Optimizing your Shopify store in a fiercely competitive e-commerce market is crucial to ensure that customers discover you before they find your competitors’ websites.
Here are the key reasons why optimization is essential:
**Enhanced User Experience:**
A well-optimized Shopify store enhances user experience. By improving page loading speed, using easy navigation, and making the store mobile responsive, your customers get a seamless shopping experience that keeps them engaged and encourages repeat visits.
**Improved Search Engine Rankings:**
Optimizing your store for user experience not only improves search engine rankings but also boosts visibility through SEO-friendly URLs, meta tags, and high-quality content. These techniques drive organic traffic and attract potential customers to your store.
**Higher Conversion Rates:**
Optimizing Shopify stores involves streamlining the checkout process, using clear calls-to-action, and providing detailed product descriptions. This optimization can greatly enhance visitor trust during purchases, leading to increased sales overall.
**Increased Customer Trust:**
An optimized store with professional design, secure payment options, and clear policies fosters trust among customers, making them more likely to complete transactions and recommend your store to others.
**Better Analytics and Insights:**
Optimization involves tracking user behavior and analyzing data to make informed decisions. This helps identify areas for improvement and tailor marketing strategies to meet customer needs effectively.
**Scalability and Growth:**
An optimized store is more adaptable to changes and growth. It can handle increased traffic and sales volumes efficiently, ensuring your business can scale without compromising on performance or customer satisfaction.
To optimize your Shopify store, you need Shopify experts and developers who can enhance the overall performance of your Shopify website.
## Shopify Expert Developers and Their Roles
[Shopify expert developers](https://ecomheroes.dev/) specialize in creating, customizing, and optimizing Shopify stores to meet specific business needs.
Shopify experts possess in-depth knowledge of the ecosystem, including its themes, apps, APIs, and coding languages such as Liquid, HTML, CSS, and JavaScript.
## Key Roles and Responsibilities of Shopify Expert Developers
###1 Store Setup and Configuration:
- Shopify experts assist in setting up new Shopify stores, configuring settings, and ensuring that all foundational elements are correctly established.
- This includes domain setup, payment gateways, shipping methods, and tax settings.
###2 Theme Customization and Development:
- Expert developers customize existing themes or create bespoke themes to match a brand’s unique identity and requirements.
- They ensure that the store’s design is visually appealing, user-friendly, and responsive across all devices.
###3 App Integration and Development:
- Shopify experts integrate third-party apps to enhance store functionality, such as adding advanced features for marketing, inventory management, and customer service.
- If necessary, they develop custom apps tailored to specific business processes and needs.
###4 Performance Optimization:
- Shopify expert developers work on improving the store’s performance by optimizing loading speeds, enhancing SEO, and ensuring that the website is fast and efficient.
- This includes image optimization, minimizing code, and leveraging caching techniques.
###5 Custom Functionality Implementation:
- Shopify developers create custom functionalities to enhance the shopping experience, such as advanced search options, custom checkout processes, or personalized product recommendations.
- They ensure that these functionalities integrate seamlessly with the existing Shopify ecosystem.
###6 Maintenance and Support:
- Shopify expert developers provide ongoing maintenance and support to ensure the store runs smoothly.
- They troubleshoot issues, implement updates, and make necessary adjustments to keep the store secure and up-to-date.
###7 Migration and Upgrades:
- Shopify experts assist businesses in migrating from other ecommerce platforms to Shopify, ensuring data integrity and minimal downtime.
- They also manage upgrades to newer versions of Shopify, incorporating new features and functionalities.
###8 Analytics and Reporting:
- Shopify experts set up and configure analytics tools to track store performance, user behavior, and sales data.
- They provide insights and reports that help businesses make informed decisions and strategies for growth.
## Benefits of Hiring Shopify Expert Developers
###1 Increased Sales and Conversions
When you hire Shopify expert developers, it is guaranteed that they -
- Improved store design leading to higher customer engagement.
- Implementing features that incentivize purchases and streamline checkout.
###2 Enhanced Brand Reputation
- Creating a unique and professional online store that reflects your brand.
- Providing a smooth and hassle-free shopping experience for customers.
###3 Time and Resource Efficiency
- Allowing you to focus on core business activities like marketing and product development.
- Expert developers handle complex technical tasks efficiently.
## Finding the Right Shopify Expert Developer
To find the best Shopify developers you can ask in your friend circle for any references, direct search on search engines and find companies like Start Designs (a company providing complete ecommerce development solutions), can hire from the freelance marketplace like Freelancer and Upwork.
## Bonus Tips
But before hiring any of the Shopify experts we suggest that,
- You should define project goals first then start the hiring process.
- Ask everyone whether it is a company, agency or freelancer individual for their previous works, expertise, testimonial, working process and rate.
- Compare quotes and communication styles.
-Consider Shopify partners for verified expertise.
- Prioritize developers with Shopify store success stories.
## Final Words
Shopify expert developers are essential for building and maintaining successful ecommerce stores. Their technical skills and specialized knowledge ensure your store is optimized, customized, and ready to scale. By handling everything from setup to ongoing support, they save you time and resources, helping your business grow and thrive in a competitive market. Investing in a Shopify expert means a smoother, more efficient store that attracts customers and drives sales.
Originally published at [https://medium.com/@start_designs/how-shopify-expert-developers-help-in-your-shopify-business-growth-74410042105f](https://medium.com/@start_designs/how-shopify-expert-developers-help-in-your-shopify-business-growth-74410042105f) on May 30, 2024. | startdeesigns |
1,872,011 | Navigating COVID Travel Restrictions: Your Comprehensive Guide | Navigating COVID Travel Restrictions: Your Comprehensive Guide TravelGo·Introduction:As the... | 0 | 2024-05-31T11:42:35 | https://dev.to/travelgo/unlock-incredible-flight-deals-your-ultimate-guide-to-affordable-air-travel-5a3a | covid, covidtravel, travelrestricitons | <p> <table align="center" cellpadding="0" cellspacing="0" class="tr-caption-container" style="margin-left: auto; margin-right: auto;"><tbody><tr><td style="text-align: center;"><a href="https://blogger.googleusercontent.com/img/a/AVvXsEjbmZfz5HzTrulwQo3cTtbu115J6vET0Dxrrd66ggkmlSwsvqzkOn5jVMKWew_ouMSQ0JJKoJrYXKD62r7keHGuahKWrnXHzAowVcwZkLMj5_eksAb7AM-PdWHDAHShd0fuRtzWhqoZh5QMxwN97oEhVMlTOdl2yJ5YJ_jM9tWcFsB9xJkP_uRFvCe0eAK0" style="margin-left: auto; margin-right: auto;"><img alt="" data-original-height="980" data-original-width="1470" height="426" src="https://blogger.googleusercontent.com/img/a/AVvXsEjbmZfz5HzTrulwQo3cTtbu115J6vET0Dxrrd66ggkmlSwsvqzkOn5jVMKWew_ouMSQ0JJKoJrYXKD62r7keHGuahKWrnXHzAowVcwZkLMj5_eksAb7AM-PdWHDAHShd0fuRtzWhqoZh5QMxwN97oEhVMlTOdl2yJ5YJ_jM9tWcFsB9xJkP_uRFvCe0eAK0=w640-h426" width="640" /></a></td></tr><tr><td class="tr-caption" style="text-align: center;"><br /></td></tr></tbody></table><br /></p><div class="er es et eu ev l" style="background-color: white; box-sizing: inherit; color: rgba(0, 0, 0, 0.8); font-family: medium-content-sans-serif-font, -apple-system, BlinkMacSystemFont, "Segoe UI", Roboto, Oxygen, Ubuntu, Cantarell, "Open Sans", "Helvetica Neue", sans-serif; margin-bottom: 68px;"><article style="box-sizing: inherit;"><div class="l" style="box-sizing: inherit;"><div class="l" style="box-sizing: inherit;"><section style="box-sizing: inherit;"><div style="box-sizing: inherit;"><div class="fk fl fm fn fo" style="box-sizing: inherit; overflow-wrap: break-word; word-break: break-word;"><div class="ab ca" style="box-sizing: inherit; display: flex; justify-content: center;"><div class="ch bg ew ex ey ez" style="box-sizing: inherit; margin: 0px 24px; max-width: 680px; min-width: 0px; width: 680px;"><div style="box-sizing: inherit;"><h1 class="pw-post-title fp fq fr be fs ft fu fv fw fx fy fz ga gb gc gd ge gf gg gh gi gj gk gl gm gn go gp gq gr bj" data-selectable-paragraph="" data-testid="storyTitle" id="6f33" style="box-sizing: inherit; color: #242424; font-family: sohne, "Helvetica Neue", Helvetica, Arial, sans-serif; font-size: 42px; letter-spacing: -0.011em; line-height: 52px; margin: 1.19em 0px 32px;">Navigating COVID Travel Restrictions: Your Comprehensive Guide</h1><div class="gs gt gu gv gw" style="box-sizing: inherit;"><div class="speechify-ignore ab co" style="box-sizing: inherit; display: flex; justify-content: space-between;"><div class="speechify-ignore bg l" style="box-sizing: inherit; width: 680px;"><div class="gx gy gz ha hb ab" style="align-items: center; box-sizing: inherit; display: flex;"><div style="box-sizing: inherit;"><div class="ab hc" style="align-items: baseline; box-sizing: inherit; display: flex;"><a href="https://medium.com/@eduard.hucai?source=post_page-----b2dafe6ae7c7--------------------------------" previewlistener="true" rel="noopener follow" style="-webkit-tap-highlight-color: transparent; box-sizing: inherit; text-decoration-line: none;"><div style="box-sizing: inherit;"><div aria-describedby="1" aria-hidden="false" aria-labelledby="1" class="bl" style="box-sizing: inherit; display: inline-block;"><div class="l hd he bx hf hg" style="border-radius: 50%; border: 2px solid rgb(255, 255, 255); box-sizing: inherit; height: 48px; width: 48px; z-index: 0;"><div class="l ee" style="box-sizing: inherit; position: relative;"><img alt="TravelGo" class="l eq bx dc dd cw" data-testid="authorPhoto" height="44" loading="lazy" src="https://miro.medium.com/v2/resize:fill:88:88/1*dXcQokbyAbuPV_XgyxWVaw.png" style="background-color: #f2f2f2; border-radius: 50%; box-sizing: border-box; display: block; height: 44px; vertical-align: middle; width: 44px;" width="44" /><div class="hh bx l dc dd eo n hi ep" style="border-radius: 50%; border: 1px solid rgba(0, 0, 0, 0.05); box-shadow: none; box-sizing: inherit; height: 44px; position: absolute; top: 0px; width: 44px;"></div></div></div></div></div></a></div></div><div class="bm bg l" style="box-sizing: inherit; margin-left: 12px; width: 620px;"><div class="ab" style="box-sizing: inherit; display: flex;"><div style="box-sizing: inherit; flex: 1 1 0%;"><span class="be b bf z bj" style="box-sizing: inherit; color: #242424; font-family: sohne, "Helvetica Neue", Helvetica, Arial, sans-serif; font-size: 14px; line-height: 20px;"><div class="hj ab q" style="align-items: center; box-sizing: inherit; display: flex; margin-bottom: 2px;"><div class="ab q hk" style="align-items: center; box-sizing: inherit; display: flex; flex-wrap: nowrap;"><div class="ab q" style="align-items: center; box-sizing: inherit; display: flex;"><div style="box-sizing: inherit;"><div aria-describedby="2" aria-hidden="false" aria-labelledby="2" class="bl" style="box-sizing: inherit; display: inline-block;"><p class="be b hl hm bj" style="box-sizing: inherit; font-size: 16px; line-height: 24px; margin: 0px;"><a class="af ag ah ai aj ak al am an ao ap aq ar hn" data-testid="authorName" href="https://medium.com/@eduard.hucai?source=post_page-----b2dafe6ae7c7--------------------------------" previewlistener="true" rel="noopener follow" style="-webkit-tap-highlight-color: transparent; border: inherit; box-sizing: inherit; cursor: pointer; fill: inherit; font-family: inherit; font-size: inherit; font-weight: inherit; letter-spacing: inherit; margin: 0px; padding: 0px; text-decoration-line: none;">TravelGo</a></p></div></div></div></div></div></span></div></div><div class="l ho" style="box-sizing: inherit; flex: 0 0 auto;"><span class="be b bf z dw" style="box-sizing: inherit; color: #6b6b6b; font-family: sohne, "Helvetica Neue", Helvetica, Arial, sans-serif; font-size: 14px; line-height: 20px;">·</span></div></div></div><div class="ab co hu hv hw hx hy hz ia ib ic id ie if ig ih ii ij" style="border-bottom: 1px solid rgb(242, 242, 242); border-top: 1px solid rgb(242, 242, 242); box-sizing: inherit; display: flex; justify-content: space-between; margin: 32px 0px 0px; padding: 3px 8px;"><div class="h k w eb ec q" style="align-items: center; box-sizing: inherit; display: flex;"><div class="iz l" style="box-sizing: inherit; width: 74px;"><div class="ab q ja jb" style="align-items: center; box-sizing: inherit; display: flex; flex-direction: row; z-index: 2;"><div class="pw-multi-vote-icon ee qt jd je jf" style="box-sizing: inherit; margin-right: 0px; position: relative; user-select: none;"><div class="" style="box-sizing: inherit;"><div style="box-sizing: inherit;"><div aria-describedby="48" aria-hidden="false" aria-labelledby="48" class="bl" style="box-sizing: inherit; display: inline-block;"><div class="jg qu ji jj jk jl jm am jn jo jp jf" style="border: 0px; box-sizing: inherit; cursor: not-allowed; fill: rgb(117, 117, 117); opacity: 0.25; outline: 0px; padding: 0px; user-select: none;"><svg aria-label="clap" height="24" viewbox="0 0 24 24" width="24"><path clip-rule="evenodd" d="M11.37.83L12 3.28l.63-2.45h-1.26zM15.42 1.84l-1.18-.39-.34 2.5 1.52-2.1zM9.76 1.45l-1.19.4 1.53 2.1-.34-2.5zM20.25 11.84l-2.5-4.4a1.42 1.42 0 0 0-.93-.64.96.96 0 0 0-.75.18c-.25.19-.4.42-.45.7l.05.05 2.35 4.13c1.62 2.95 1.1 5.78-1.52 8.4l-.46.41c1-.13 1.93-.6 2.78-1.45 2.7-2.7 2.51-5.59 1.43-7.38zM12.07 9.01c-.13-.69.08-1.3.57-1.77l-2.06-2.07a1.12 1.12 0 0 0-1.56 0c-.15.15-.22.34-.27.53L12.07 9z" fill-rule="evenodd"></path><path clip-rule="evenodd" d="M14.74 8.3a1.13 1.13 0 0 0-.73-.5.67.67 0 0 0-.53.13c-.15.12-.59.46-.2 1.3l1.18 2.5a.45.45 0 0 1-.23.76.44.44 0 0 1-.48-.25L7.6 6.11a.82.82 0 1 0-1.15 1.15l3.64 3.64a.45.45 0 1 1-.63.63L5.83 7.9 4.8 6.86a.82.82 0 0 0-1.33.9c.04.1.1.18.18.26l1.02 1.03 3.65 3.64a.44.44 0 0 1-.15.73.44.44 0 0 1-.48-.1L4.05 9.68a.82.82 0 0 0-1.4.57.81.81 0 0 0 .24.58l1.53 1.54 2.3 2.28a.45.45 0 0 1-.64.63L3.8 13a.81.81 0 0 0-1.39.57c0 .22.09.43.24.58l4.4 4.4c2.8 2.8 5.5 4.12 8.68.94 2.27-2.28 2.71-4.6 1.34-7.1l-2.32-4.08z" fill-rule="evenodd"></path></svg></div></div></div></div></div></div></div><div style="box-sizing: inherit;"><div aria-describedby="3" aria-hidden="false" aria-labelledby="3" class="bl" style="box-sizing: inherit; display: inline-block;"><button aria-label="responses" class="ao jg jx jy ab q ef jz ka" style="-webkit-tap-highlight-color: transparent; align-items: center; background-attachment: initial; background-clip: initial; background-image: initial; background-origin: initial; background-position: initial; background-repeat: initial; background-size: initial; border-color: initial; border-style: initial; border-width: 0px; box-sizing: inherit; cursor: pointer; display: flex; fill: rgb(107, 107, 107); margin: 0px; opacity: 1; overflow: visible; padding: 4px 0px;"><svg class="kb" height="24" viewbox="0 0 24 24" width="24"><path d="M18 16.8a7.14 7.14 0 0 0 2.24-5.32c0-4.12-3.53-7.48-8.05-7.48C7.67 4 4 7.36 4 11.48c0 4.13 3.67 7.48 8.2 7.48a8.9 8.9 0 0 0 2.38-.32c.23.2.48.39.75.56 1.06.69 2.2 1.04 3.4 1.04.22 0 .4-.11.48-.29a.5.5 0 0 0-.04-.52 6.4 6.4 0 0 1-1.16-2.65v.02zm-3.12 1.06l-.06-.22-.32.1a8 8 0 0 1-2.3.33c-4.03 0-7.3-2.96-7.3-6.59S8.17 4.9 12.2 4.9c4 0 7.1 2.96 7.1 6.6 0 1.8-.6 3.47-2.02 4.72l-.2.16v.26l.02.3a6.74 6.74 0 0 0 .88 2.4 5.27 5.27 0 0 1-2.17-.86c-.28-.17-.72-.38-.94-.59l.01-.02z"></path></svg></button></div></div></div><div class="ab q ik il im in io ip iq ir is it iu iv iw ix iy" style="align-items: center; box-sizing: inherit; display: flex; overflow-x: scroll; scrollbar-width: none;"><div class="h k" style="box-sizing: inherit; flex-shrink: 0; margin-right: 24px;"><div style="box-sizing: inherit;"><div aria-describedby="4" aria-hidden="false" aria-labelledby="4" class="bl" style="box-sizing: inherit; display: inline-block;"><div aria-hidden="false" class="bl" style="box-sizing: inherit; display: inline-block;"><button aria-controls="addToCatalogBookmarkButton" aria-expanded="false" aria-label="Add to list bookmark button" class="af ef ah ai aj ak al kd an ao ap ke kf kg kh" data-testid="headerBookmarkButton" style="-webkit-tap-highlight-color: transparent; background-attachment: initial; background-clip: initial; background-image: initial; background-origin: initial; background-position: initial; background-repeat: initial; background-size: initial; border: inherit; box-sizing: inherit; cursor: pointer; fill: rgb(107, 107, 107); font-family: inherit; font-size: inherit; font-weight: inherit; letter-spacing: inherit; margin: 0px; overflow: visible; padding: 8px 2px;"><svg class="ki" fill="none" height="24" viewbox="0 0 24 24" width="24"><path d="M17.5 1.25a.5.5 0 0 1 1 0v2.5H21a.5.5 0 0 1 0 1h-2.5v2.5a.5.5 0 0 1-1 0v-2.5H15a.5.5 0 0 1 0-1h2.5v-2.5zm-11 4.5a1 1 0 0 1 1-1H11a.5.5 0 0 0 0-1H7.5a2 2 0 0 0-2 2v14a.5.5 0 0 0 .8.4l5.7-4.4 5.7 4.4a.5.5 0 0 0 .8-.4v-8.5a.5.5 0 0 0-1 0v7.48l-5.2-4a.5.5 0 0 0-.6 0l-5.2 4V5.75z" fill="#000"></path></svg></button></div></div></div></div><div class="eq kj cm" style="align-items: flex-start; box-sizing: border-box; display: inline-flex; flex-shrink: 0; margin-right: 24px;"><div class="l ae" style="box-sizing: inherit; flex: 1 0 auto;"><div class="ab ca" style="box-sizing: inherit; display: flex; justify-content: center;"><div class="kk kl km kn ko kp ch bg" style="box-sizing: inherit; margin: 0px; max-width: 100%; min-width: 0px; width: 28px;"><div class="ab" style="box-sizing: inherit; display: flex;"><div style="box-sizing: inherit;"><a class="af ag ah ai aj ak al am an ao ap aq ar as at" href="https://medium.com/plans?dimension=post_audio_button&postId=b2dafe6ae7c7&source=upgrade_membership---post_audio_button----------------------------------" previewlistener="true" rel="noopener follow" style="-webkit-tap-highlight-color: transparent; border: inherit; box-sizing: inherit; cursor: pointer; fill: inherit; font-family: inherit; font-size: inherit; font-weight: inherit; letter-spacing: inherit; margin: 0px; padding: 0px; text-decoration-line: none;"><div style="box-sizing: inherit;"><div aria-describedby="16" aria-hidden="false" aria-labelledby="16" class="bl" style="box-sizing: inherit; display: inline-block;"><button aria-label="Listen" class="af ef ah ai aj ak al kd an ao ap ke kq kr ka ks kt ku kv kw s kx ky kz la lb lc ld u le lf lg" data-testid="audioPlayButton" style="-webkit-tap-highlight-color: transparent; background-attachment: initial; background-clip: initial; background-image: initial; background-origin: initial; background-position: initial; background-repeat: initial; background-size: initial; border: inherit; box-sizing: inherit; cursor: pointer; fill: rgb(107, 107, 107); font-family: inherit; font-size: inherit; font-weight: inherit; letter-spacing: inherit; margin: 0px; overflow: visible; padding: 8px 2px;"><svg fill="none" height="24" viewbox="0 0 24 24" width="24"><path clip-rule="evenodd" d="M3 12a9 9 0 1 1 18 0 9 9 0 0 1-18 0zm9-10a10 10 0 1 0 0 20 10 10 0 0 0 0-20zm3.38 10.42l-4.6 3.06a.5.5 0 0 1-.78-.41V8.93c0-.4.45-.63.78-.41l4.6 3.06c.3.2.3.64 0 .84z" fill-rule="evenodd" fill="currentColor"></path></svg></button></div></div></a></div></div></div></div></div></div><div aria-describedby="postFooterSocialMenu" aria-hidden="false" aria-labelledby="postFooterSocialMenu" class="bl" style="box-sizing: inherit; display: inline-block; flex-shrink: 0; margin-right: 24px;"><div style="box-sizing: inherit;"><div aria-describedby="6" aria-hidden="false" aria-labelledby="6" class="bl" style="box-sizing: inherit; display: inline-block;"><button aria-controls="postFooterSocialMenu" aria-expanded="false" aria-label="Share Post" class="af ef ah ai aj ak al kd an ao ap ke kq kr ka ks kt ku kv kw s kx ky kz la lb lc ld u le lf lg" data-testid="headerSocialShareButton" style="-webkit-tap-highlight-color: transparent; background-attachment: initial; background-clip: initial; background-image: initial; background-origin: initial; background-position: initial; background-repeat: initial; background-size: initial; border: inherit; box-sizing: inherit; cursor: pointer; fill: rgb(107, 107, 107); font-family: inherit; font-size: inherit; font-weight: inherit; letter-spacing: inherit; margin: 0px; overflow: visible; padding: 8px 2px;"><svg fill="none" height="24" viewbox="0 0 24 24" width="24"><path clip-rule="evenodd" d="M15.22 4.93a.42.42 0 0 1-.12.13h.01a.45.45 0 0 1-.29.08.52.52 0 0 1-.3-.13L12.5 3v7.07a.5.5 0 0 1-.5.5.5.5 0 0 1-.5-.5V3.02l-2 2a.45.45 0 0 1-.57.04h-.02a.4.4 0 0 1-.16-.3.4.4 0 0 1 .1-.32l2.8-2.8a.5.5 0 0 1 .7 0l2.8 2.8a.42.42 0 0 1 .07.5zm-.1.14zm.88 2h1.5a2 2 0 0 1 2 2v10a2 2 0 0 1-2 2h-11a2 2 0 0 1-2-2v-10a2 2 0 0 1 2-2H8a.5.5 0 0 1 .35.14c.1.1.15.22.15.35a.5.5 0 0 1-.15.35.5.5 0 0 1-.35.15H6.4c-.5 0-.9.4-.9.9v10.2a.9.9 0 0 0 .9.9h11.2c.5 0 .9-.4.9-.9V8.96c0-.5-.4-.9-.9-.9H16a.5.5 0 0 1 0-1z" fill-rule="evenodd" fill="currentColor"></path></svg></button></div></div></div><div aria-hidden="false" class="bl" style="box-sizing: inherit; display: inline-block; flex-shrink: 0; margin-right: 0px;"><div aria-describedby="creatorActionOverflowMenu" aria-hidden="false" aria-labelledby="creatorActionOverflowMenu" class="bl" style="box-sizing: inherit; display: inline-block;"><div class="po l ho" style="box-sizing: inherit; flex: 0 0 auto; margin-right: -4px;"><div style="box-sizing: inherit;"><div aria-describedby="146" aria-hidden="false" aria-labelledby="146" class="bl" style="box-sizing: inherit; display: inline-block;"><button aria-controls="creatorActionOverflowMenu" aria-expanded="false" aria-label="More options" class="af ef ah ai aj ak al kd an ao ap ke kq kr ka ks kt ku kv kw s kx ky kz la lb lc ld u le lf lg" data-testid="headerStoryOptionsButton" style="-webkit-tap-highlight-color: transparent; background-attachment: initial; background-clip: initial; background-image: initial; background-origin: initial; background-position: initial; background-repeat: initial; background-size: initial; border: inherit; box-sizing: inherit; cursor: pointer; fill: rgb(107, 107, 107); font-family: inherit; font-size: inherit; font-weight: inherit; letter-spacing: inherit; margin: 0px; overflow: visible; padding: 8px 2px;"><svg fill="none" height="24" viewbox="0 0 24 24" width="24"><path clip-rule="evenodd" d="M4.39 12c0 .55.2 1.02.59 1.41.39.4.86.59 1.4.59.56 0 1.03-.2 1.42-.59.4-.39.59-.86.59-1.41 0-.55-.2-1.02-.6-1.41A1.93 1.93 0 0 0 6.4 10c-.55 0-1.02.2-1.41.59-.4.39-.6.86-.6 1.41zM10 12c0 .55.2 1.02.58 1.41.4.4.87.59 1.42.59.54 0 1.02-.2 1.4-.59.4-.39.6-.86.6-1.41 0-.55-.2-1.02-.6-1.41a1.93 1.93 0 0 0-1.4-.59c-.55 0-1.04.2-1.42.59-.4.39-.58.86-.58 1.41zm5.6 0c0 .55.2 1.02.57 1.41.4.4.88.59 1.43.59.57 0 1.04-.2 1.43-.59.39-.39.57-.86.57-1.41 0-.55-.2-1.02-.57-1.41A1.93 1.93 0 0 0 17.6 10c-.55 0-1.04.2-1.43.59-.38.39-.57.86-.57 1.41z" fill-rule="evenodd" fill="currentColor"></path></svg></button></div></div></div></div></div></div></div></div></div></div></div><figure class="lk ll lm ln lo lp lh li paragraph-image" style="box-sizing: inherit; clear: both; margin: 40px auto 0px;"><div class="lq lr ee ls bg lt" role="button" style="box-sizing: inherit; cursor: zoom-in; position: relative; transition: transform 300ms cubic-bezier(0.2, 0, 0.2, 1) 0s; width: 680px; z-index: auto;" tabindex="0"><div class="lh li lj" style="box-sizing: inherit; margin-left: auto; margin-right: auto; max-width: 1000px;"><picture style="box-sizing: inherit;"><source sizes="(min-resolution: 4dppx) and (max-width: 700px) 50vw, (-webkit-min-device-pixel-ratio: 4) and (max-width: 700px) 50vw, (min-resolution: 3dppx) and (max-width: 700px) 67vw, (-webkit-min-device-pixel-ratio: 3) and (max-width: 700px) 65vw, (min-resolution: 2.5dppx) and (max-width: 700px) 80vw, (-webkit-min-device-pixel-ratio: 2.5) and (max-width: 700px) 80vw, (min-resolution: 2dppx) and (max-width: 700px) 100vw, (-webkit-min-device-pixel-ratio: 2) and (max-width: 700px) 100vw, 700px" srcset="https://miro.medium.com/v2/resize:fit:640/format:webp/0*nbGkAEkyNDxrOult 640w, https://miro.medium.com/v2/resize:fit:720/format:webp/0*nbGkAEkyNDxrOult 720w, https://miro.medium.com/v2/resize:fit:750/format:webp/0*nbGkAEkyNDxrOult 750w, https://miro.medium.com/v2/resize:fit:786/format:webp/0*nbGkAEkyNDxrOult 786w, https://miro.medium.com/v2/resize:fit:828/format:webp/0*nbGkAEkyNDxrOult 828w, https://miro.medium.com/v2/resize:fit:1100/format:webp/0*nbGkAEkyNDxrOult 1100w, https://miro.medium.com/v2/resize:fit:1400/format:webp/0*nbGkAEkyNDxrOult 1400w" style="box-sizing: inherit;" type="image/webp"></source><source data-testid="og" sizes="(min-resolution: 4dppx) and (max-width: 700px) 50vw, (-webkit-min-device-pixel-ratio: 4) and (max-width: 700px) 50vw, (min-resolution: 3dppx) and (max-width: 700px) 67vw, (-webkit-min-device-pixel-ratio: 3) and (max-width: 700px) 65vw, (min-resolution: 2.5dppx) and (max-width: 700px) 80vw, (-webkit-min-device-pixel-ratio: 2.5) and (max-width: 700px) 80vw, (min-resolution: 2dppx) and (max-width: 700px) 100vw, (-webkit-min-device-pixel-ratio: 2) and (max-width: 700px) 100vw, 700px" srcset="https://miro.medium.com/v2/resize:fit:640/0*nbGkAEkyNDxrOult 640w, https://miro.medium.com/v2/resize:fit:720/0*nbGkAEkyNDxrOult 720w, https://miro.medium.com/v2/resize:fit:750/0*nbGkAEkyNDxrOult 750w, https://miro.medium.com/v2/resize:fit:786/0*nbGkAEkyNDxrOult 786w, https://miro.medium.com/v2/resize:fit:828/0*nbGkAEkyNDxrOult 828w, https://miro.medium.com/v2/resize:fit:1100/0*nbGkAEkyNDxrOult 1100w, https://miro.medium.com/v2/resize:fit:1400/0*nbGkAEkyNDxrOult 1400w" style="box-sizing: inherit;"></source><img alt="" class="bg kp lu c" height="467" loading="eager" role="presentation" src="https://miro.medium.com/v2/resize:fit:700/0*nbGkAEkyNDxrOult" style="box-sizing: inherit; height: auto; max-width: 100%; vertical-align: middle; width: 680px;" width="700" /></picture></div></div></figure><p class="pw-post-body-paragraph lv lw fr lx b ly lz ma mb mc md me mf mg mh mi mj mk ml mm mn mo mp mq mr ms fk bj" data-selectable-paragraph="" id="a3db" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; margin: 2.14em 0px -0.46em; word-break: break-word;">Introduction:<br style="box-sizing: inherit;" />As the world grapples with the ongoing COVID-19 pandemic, travel restrictions continue to evolve, impacting the ability of individuals to move freely across borders. Understanding these restrictions is crucial for anyone planning a journey, whether for leisure or essential purposes. In this comprehensive guide, we’ll delve into the current landscape of COVID travel restrictions, providing essential information to help you navigate the complexities and ensure a smooth travel experience.</p><p class="pw-post-body-paragraph lv lw fr lx b ly lz ma mb mc md me mf mg mh mi mj mk ml mm mn mo mp mq mr ms fk bj" data-selectable-paragraph="" id="98da" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; margin: 2.14em 0px -0.46em; word-break: break-word;">Understanding COVID Travel Restrictions:<br style="box-sizing: inherit;" />COVID travel restrictions vary significantly from country to country and are subject to change based on the prevailing health situation. These restrictions encompass various measures, including entry requirements, quarantine protocols, vaccination mandates, and testing guidelines. To stay informed, travelers must monitor updates from reliable sources, such as government websites, official travel advisories, and reputable news outlets.</p><figure class="mt mu mv mw mx lp lh li paragraph-image" style="box-sizing: inherit; clear: both; margin: 56px auto 0px;"><div class="lq lr ee ls bg lt" role="button" style="box-sizing: inherit; cursor: zoom-in; position: relative; transition: transform 300ms cubic-bezier(0.2, 0, 0.2, 1) 0s; width: 680px; z-index: auto;" tabindex="0"><div class="lh li lj" style="box-sizing: inherit; margin-left: auto; margin-right: auto; max-width: 1000px;"><picture style="box-sizing: inherit;"><source sizes="(min-resolution: 4dppx) and (max-width: 700px) 50vw, (-webkit-min-device-pixel-ratio: 4) and (max-width: 700px) 50vw, (min-resolution: 3dppx) and (max-width: 700px) 67vw, (-webkit-min-device-pixel-ratio: 3) and (max-width: 700px) 65vw, (min-resolution: 2.5dppx) and (max-width: 700px) 80vw, (-webkit-min-device-pixel-ratio: 2.5) and (max-width: 700px) 80vw, (min-resolution: 2dppx) and (max-width: 700px) 100vw, (-webkit-min-device-pixel-ratio: 2) and (max-width: 700px) 100vw, 700px" srcset="https://miro.medium.com/v2/resize:fit:640/format:webp/0*AOeCDjVl3xmyyW5Q 640w, https://miro.medium.com/v2/resize:fit:720/format:webp/0*AOeCDjVl3xmyyW5Q 720w, https://miro.medium.com/v2/resize:fit:750/format:webp/0*AOeCDjVl3xmyyW5Q 750w, https://miro.medium.com/v2/resize:fit:786/format:webp/0*AOeCDjVl3xmyyW5Q 786w, https://miro.medium.com/v2/resize:fit:828/format:webp/0*AOeCDjVl3xmyyW5Q 828w, https://miro.medium.com/v2/resize:fit:1100/format:webp/0*AOeCDjVl3xmyyW5Q 1100w, https://miro.medium.com/v2/resize:fit:1400/format:webp/0*AOeCDjVl3xmyyW5Q 1400w" style="box-sizing: inherit;" type="image/webp"></source><source data-testid="og" sizes="(min-resolution: 4dppx) and (max-width: 700px) 50vw, (-webkit-min-device-pixel-ratio: 4) and (max-width: 700px) 50vw, (min-resolution: 3dppx) and (max-width: 700px) 67vw, (-webkit-min-device-pixel-ratio: 3) and (max-width: 700px) 65vw, (min-resolution: 2.5dppx) and (max-width: 700px) 80vw, (-webkit-min-device-pixel-ratio: 2.5) and (max-width: 700px) 80vw, (min-resolution: 2dppx) and (max-width: 700px) 100vw, (-webkit-min-device-pixel-ratio: 2) and (max-width: 700px) 100vw, 700px" srcset="https://miro.medium.com/v2/resize:fit:640/0*AOeCDjVl3xmyyW5Q 640w, https://miro.medium.com/v2/resize:fit:720/0*AOeCDjVl3xmyyW5Q 720w, https://miro.medium.com/v2/resize:fit:750/0*AOeCDjVl3xmyyW5Q 750w, https://miro.medium.com/v2/resize:fit:786/0*AOeCDjVl3xmyyW5Q 786w, https://miro.medium.com/v2/resize:fit:828/0*AOeCDjVl3xmyyW5Q 828w, https://miro.medium.com/v2/resize:fit:1100/0*AOeCDjVl3xmyyW5Q 1100w, https://miro.medium.com/v2/resize:fit:1400/0*AOeCDjVl3xmyyW5Q 1400w" style="box-sizing: inherit;"></source><img alt="" class="bg kp lu c" height="934" loading="lazy" role="presentation" src="https://miro.medium.com/v2/resize:fit:700/0*AOeCDjVl3xmyyW5Q" style="box-sizing: inherit; height: auto; max-width: 100%; vertical-align: middle; width: 680px;" width="700" /></picture></div></div></figure><p class="pw-post-body-paragraph lv lw fr lx b ly lz ma mb mc md me mf mg mh mi mj mk ml mm mn mo mp mq mr ms fk bj" data-selectable-paragraph="" id="41ac" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; margin: 2.14em 0px -0.46em; word-break: break-word;">Entry Requirements:<br style="box-sizing: inherit;" />Before embarking on any journey, it’s essential to research the entry requirements of your destination country. Many nations have implemented pre-arrival protocols, such as providing proof of vaccination, negative COVID-19 test results, or completing health declaration forms. Some countries may also require travelers to quarantine upon arrival, either at home or in designated facilities.</p><p class="pw-post-body-paragraph lv lw fr lx b ly lz ma mb mc md me mf mg mh mi mj mk ml mm mn mo mp mq mr ms fk bj" data-selectable-paragraph="" id="34fc" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; margin: 2.14em 0px -0.46em; word-break: break-word;"><a class="af my" href="https://www.booking.com/flights/index.html?aid=8019784" previewlistener="true" rel="noopener ugc nofollow" style="-webkit-tap-highlight-color: transparent; box-sizing: inherit;" target="_blank">Click HERE to find the most suitable flight offers for you!</a></p><p class="pw-post-body-paragraph lv lw fr lx b ly lz ma mb mc md me mf mg mh mi mj mk ml mm mn mo mp mq mr ms fk bj" data-selectable-paragraph="" id="363f" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; margin: 2.14em 0px -0.46em; word-break: break-word;"><a class="af my" href="https://ttravelgoo.blogspot.com/" previewlistener="true" rel="noopener ugc nofollow" style="-webkit-tap-highlight-color: transparent; box-sizing: inherit;" target="_blank"><span class="lx fs" style="box-sizing: inherit; font-weight: 700;"><em class="mz" style="box-sizing: inherit;">Visit our website for more offers!</em></span></a></p><p class="pw-post-body-paragraph lv lw fr lx b ly lz ma mb mc md me mf mg mh mi mj mk ml mm mn mo mp mq mr ms fk bj" data-selectable-paragraph="" id="7d0e" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; margin: 2.14em 0px -0.46em; word-break: break-word;"><a class="af my" href="https://www.facebook.com/profile.php?id=61560198516319" previewlistener="true" rel="noopener ugc nofollow" style="-webkit-tap-highlight-color: transparent; box-sizing: inherit;" target="_blank"><span class="lx fs" style="box-sizing: inherit; font-weight: 700;"><em class="mz" style="box-sizing: inherit;">Our Facebook page!</em></span></a></p><p class="pw-post-body-paragraph lv lw fr lx b ly lz ma mb mc md me mf mg mh mi mj mk ml mm mn mo mp mq mr ms fk bj" data-selectable-paragraph="" id="66f0" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; margin: 2.14em 0px -0.46em; word-break: break-word;">Quarantine Protocols:<br style="box-sizing: inherit;" />Quarantine measures play a crucial role in controlling the spread of COVID-19. Depending on the destination, travelers may be required to undergo mandatory quarantine upon arrival, regardless of their vaccination status or test results. Quarantine periods can range from a few days to several weeks, and failure to comply with these requirements may result in fines or other penalties. It’s essential to familiarize yourself with the specific quarantine regulations of your destination and make appropriate arrangements accordingly.</p><figure class="mt mu mv mw mx lp lh li paragraph-image" style="box-sizing: inherit; clear: both; margin: 56px auto 0px;"><div class="lq lr ee ls bg lt" role="button" style="box-sizing: inherit; cursor: zoom-in; position: relative; transition: transform 300ms cubic-bezier(0.2, 0, 0.2, 1) 0s; width: 680px; z-index: auto;" tabindex="0"><div class="lh li lj" style="box-sizing: inherit; margin-left: auto; margin-right: auto; max-width: 1000px;"><picture style="box-sizing: inherit;"><source sizes="(min-resolution: 4dppx) and (max-width: 700px) 50vw, (-webkit-min-device-pixel-ratio: 4) and (max-width: 700px) 50vw, (min-resolution: 3dppx) and (max-width: 700px) 67vw, (-webkit-min-device-pixel-ratio: 3) and (max-width: 700px) 65vw, (min-resolution: 2.5dppx) and (max-width: 700px) 80vw, (-webkit-min-device-pixel-ratio: 2.5) and (max-width: 700px) 80vw, (min-resolution: 2dppx) and (max-width: 700px) 100vw, (-webkit-min-device-pixel-ratio: 2) and (max-width: 700px) 100vw, 700px" srcset="https://miro.medium.com/v2/resize:fit:640/format:webp/0*cgVHVkBEhb2uZRHA 640w, https://miro.medium.com/v2/resize:fit:720/format:webp/0*cgVHVkBEhb2uZRHA 720w, https://miro.medium.com/v2/resize:fit:750/format:webp/0*cgVHVkBEhb2uZRHA 750w, https://miro.medium.com/v2/resize:fit:786/format:webp/0*cgVHVkBEhb2uZRHA 786w, https://miro.medium.com/v2/resize:fit:828/format:webp/0*cgVHVkBEhb2uZRHA 828w, https://miro.medium.com/v2/resize:fit:1100/format:webp/0*cgVHVkBEhb2uZRHA 1100w, https://miro.medium.com/v2/resize:fit:1400/format:webp/0*cgVHVkBEhb2uZRHA 1400w" style="box-sizing: inherit;" type="image/webp"></source><source data-testid="og" sizes="(min-resolution: 4dppx) and (max-width: 700px) 50vw, (-webkit-min-device-pixel-ratio: 4) and (max-width: 700px) 50vw, (min-resolution: 3dppx) and (max-width: 700px) 67vw, (-webkit-min-device-pixel-ratio: 3) and (max-width: 700px) 65vw, (min-resolution: 2.5dppx) and (max-width: 700px) 80vw, (-webkit-min-device-pixel-ratio: 2.5) and (max-width: 700px) 80vw, (min-resolution: 2dppx) and (max-width: 700px) 100vw, (-webkit-min-device-pixel-ratio: 2) and (max-width: 700px) 100vw, 700px" srcset="https://miro.medium.com/v2/resize:fit:640/0*cgVHVkBEhb2uZRHA 640w, https://miro.medium.com/v2/resize:fit:720/0*cgVHVkBEhb2uZRHA 720w, https://miro.medium.com/v2/resize:fit:750/0*cgVHVkBEhb2uZRHA 750w, https://miro.medium.com/v2/resize:fit:786/0*cgVHVkBEhb2uZRHA 786w, https://miro.medium.com/v2/resize:fit:828/0*cgVHVkBEhb2uZRHA 828w, https://miro.medium.com/v2/resize:fit:1100/0*cgVHVkBEhb2uZRHA 1100w, https://miro.medium.com/v2/resize:fit:1400/0*cgVHVkBEhb2uZRHA 1400w" style="box-sizing: inherit;"></source><img alt="" class="bg kp lu c" height="467" loading="lazy" role="presentation" src="https://miro.medium.com/v2/resize:fit:700/0*cgVHVkBEhb2uZRHA" style="box-sizing: inherit; height: auto; max-width: 100%; vertical-align: middle; width: 680px;" width="700" /></picture></div></div></figure><p class="pw-post-body-paragraph lv lw fr lx b ly lz ma mb mc md me mf mg mh mi mj mk ml mm mn mo mp mq mr ms fk bj" data-selectable-paragraph="" id="1e67" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; margin: 2.14em 0px -0.46em; word-break: break-word;">Vaccination Mandates:<br style="box-sizing: inherit;" />With the global rollout of COVID-19 vaccines, some countries have implemented vaccination mandates for travelers. These mandates may require proof of vaccination as a condition of entry or offer exemptions for certain categories of travelers, such as children or individuals with medical contraindications. Travelers should carry their vaccination certificates or digital health passes when crossing borders and be prepared to present them upon request.</p><p class="pw-post-body-paragraph lv lw fr lx b ly lz ma mb mc md me mf mg mh mi mj mk ml mm mn mo mp mq mr ms fk bj" data-selectable-paragraph="" id="4260" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; margin: 2.14em 0px -0.46em; word-break: break-word;">Testing Guidelines:<br style="box-sizing: inherit;" />COVID-19 testing remains a fundamental aspect of travel, enabling authorities to detect and prevent the spread of the virus. Many countries require travelers to undergo PCR or antigen testing before departure or upon arrival. Testing requirements may vary based on factors such as vaccination status, recent travel history, and the prevalence of COVID-19 variants. Travelers should ensure they comply with all testing guidelines to avoid disruptions to their journey.</p><p class="pw-post-body-paragraph lv lw fr lx b ly lz ma mb mc md me mf mg mh mi mj mk ml mm mn mo mp mq mr ms fk bj" data-selectable-paragraph="" id="b47f" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; margin: 2.14em 0px -0.46em; word-break: break-word;">Navigating Travel Uncertainties:<br style="box-sizing: inherit;" />While travel restrictions aim to safeguard public health, they can also introduce uncertainties and disruptions for travelers. Flight cancellations, border closures, and sudden changes to regulations are not uncommon during these unprecedented times. To mitigate risks, travelers should purchase travel insurance with comprehensive coverage, including trip cancellation and medical expenses related to COVID-19. Flexibility is key, and it’s advisable to have contingency plans in place in case of unexpected developments.</p><p class="pw-post-body-paragraph lv lw fr lx b ly lz ma mb mc md me mf mg mh mi mj mk ml mm mn mo mp mq mr ms fk bj" data-selectable-paragraph="" id="28e4" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; margin: 2.14em 0px -0.46em; word-break: break-word;">Conclusion:<br style="box-sizing: inherit;" />Navigating COVID travel restrictions requires careful planning, flexibility, and adherence to health and safety protocols. By staying informed, following entry requirements, and being prepared for unexpected changes, travelers can minimize risks and enjoy a smoother travel experience. As the situation continues to evolve, vigilance and adaptability remain paramount, ensuring the well-being of both travelers and the communities they visit. Safe travels!</p><p class="pw-post-body-paragraph lv lw fr lx b ly lz ma mb mc md me mf mg mh mi mj mk ml mm mn mo mp mq mr ms fk bj" data-selectable-paragraph="" id="c50d" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; margin: 2.14em 0px -0.46em; word-break: break-word;"><a class="af my" href="https://www.booking.com/flights/index.html?aid=8019784" previewlistener="true" rel="noopener ugc nofollow" style="-webkit-tap-highlight-color: transparent; box-sizing: inherit;" target="_blank">Click HERE to find the most suitable flight offers for you!</a></p><p class="pw-post-body-paragraph lv lw fr lx b ly lz ma mb mc md me mf mg mh mi mj mk ml mm mn mo mp mq mr ms fk bj" data-selectable-paragraph="" id="6e8e" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; margin: 2.14em 0px -0.46em; word-break: break-word;"><a class="af my" href="https://ttravelgoo.blogspot.com/" previewlistener="true" rel="noopener ugc nofollow" style="-webkit-tap-highlight-color: transparent; box-sizing: inherit;" target="_blank"><span class="lx fs" style="box-sizing: inherit; font-weight: 700;"><em class="mz" style="box-sizing: inherit;">Visit our website for more offers!</em></span></a></p><p class="pw-post-body-paragraph lv lw fr lx b ly lz ma mb mc md me mf mg mh mi mj mk ml mm mn mo mp mq mr ms fk bj" data-selectable-paragraph="" id="364b" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; margin: 2.14em 0px -0.46em; word-break: break-word;"><a class="af my" href="https://www.facebook.com/profile.php?id=61560198516319" previewlistener="true" rel="noopener ugc nofollow" style="-webkit-tap-highlight-color: transparent; box-sizing: inherit;" target="_blank"><span class="lx fs" style="box-sizing: inherit; font-weight: 700;"><em class="mz" style="box-sizing: inherit;">Our Facebook page!</em></span></a></p></div></div></div></div></section></div></div></article><div class="ab ca" style="box-sizing: inherit; display: flex; justify-content: center;"><div class="ch bg ew ex ey ez" style="box-sizing: inherit; margin: 0px 24px; max-width: 680px; min-width: 0px; width: 680px;"></div></div></div><div class="ab ca" style="background-color: white; box-sizing: inherit; color: rgba(0, 0, 0, 0.8); display: flex; font-family: medium-content-sans-serif-font, -apple-system, BlinkMacSystemFont, "Segoe UI", Roboto, Oxygen, Ubuntu, Cantarell, "Open Sans", "Helvetica Neue", sans-serif; justify-content: center;"><div class="ch bg ew ex ey ez" style="box-sizing: inherit; margin: 0px 24px; max-width: 680px; min-width: 0px; width: 680px;"><div class="na nb ab hr" style="box-sizing: inherit; display: flex; flex-wrap: wrap; margin-bottom: 26px; margin-top: 6px;"><div class="nc ab" style="box-sizing: inherit; display: flex; margin-top: 8px;"><a class="nd ax am ao" href="https://medium.com/tag/covid-19?source=post_page-----b2dafe6ae7c7---------------covid_19-----------------" previewlistener="true" rel="noopener follow" style="-webkit-tap-highlight-color: transparent; border: none; box-sizing: inherit; cursor: pointer; margin-right: 8px; padding: 0px; text-decoration-line: none;"><div class="ne ee cw nf fb ng nh be b bf z bj ni" style="background-color: #f2f2f2; border-radius: 100px; border: 1px solid rgb(242, 242, 242); box-sizing: inherit; color: #242424; font-family: sohne, "Helvetica Neue", Helvetica, Arial, sans-serif; font-size: 14px; line-height: 20px; padding: 8px 16px; position: relative; text-wrap: nowrap; transition: background 300ms ease 0s;">Covid-19</div></a></div><div class="nc ab" style="box-sizing: inherit; display: flex; margin-top: 8px;"><a class="nd ax am ao" href="https://medium.com/tag/covidtravel?source=post_page-----b2dafe6ae7c7---------------covidtravel-----------------" previewlistener="true" rel="noopener follow" style="-webkit-tap-highlight-color: transparent; border: none; box-sizing: inherit; cursor: pointer; margin-right: 8px; padding: 0px; text-decoration-line: none;"><div class="ne ee cw nf fb ng nh be b bf z bj ni" style="background-color: #f2f2f2; border-radius: 100px; border: 1px solid rgb(242, 242, 242); box-sizing: inherit; color: #242424; font-family: sohne, "Helvetica Neue", Helvetica, Arial, sans-serif; font-size: 14px; line-height: 20px; padding: 8px 16px; position: relative; text-wrap: nowrap; transition: background 300ms ease 0s;">Covidtravel</div></a></div><div class="nc ab" style="box-sizing: inherit; display: flex; margin-top: 8px;"><a class="nd ax am ao" href="https://medium.com/tag/travel?source=post_page-----b2dafe6ae7c7---------------travel-----------------" previewlistener="true" rel="noopener follow" style="-webkit-tap-highlight-color: transparent; border: none; box-sizing: inherit; cursor: pointer; margin-right: 8px; padding: 0px; text-decoration-line: none;"><div class="ne ee cw nf fb ng nh be b bf z bj ni" style="background-color: #f2f2f2; border-radius: 100px; border: 1px solid rgb(242, 242, 242); box-sizing: inherit; color: #242424; font-family: sohne, "Helvetica Neue", Helvetica, Arial, sans-serif; font-size: 14px; line-height: 20px; padding: 8px 16px; position: relative; text-wrap: nowrap; transition: background 300ms ease 0s;">Travel</div></a></div><div class="nc ab" style="box-sizing: inherit; display: flex; margin-top: 8px;"><a class="nd ax am ao" href="https://medium.com/tag/trip?source=post_page-----b2dafe6ae7c7---------------trip-----------------" previewlistener="true" rel="noopener follow" style="-webkit-tap-highlight-color: transparent; border: none; box-sizing: inherit; cursor: pointer; margin-right: 8px; padding: 0px; text-decoration-line: none;"><div class="ne ee cw nf fb ng nh be b bf z bj ni" style="background-color: #f2f2f2; border-radius: 100px; border: 1px solid rgb(242, 242, 242); box-sizing: inherit; color: #242424; font-family: sohne, "Helvetica Neue", Helvetica, Arial, sans-serif; font-size: 14px; line-height: 20px; padding: 8px 16px; position: relative; text-wrap: nowrap; transition: background 300ms ease 0s;">Trip</div></a></div></div></div></div><div class="l" style="background-color: white; box-sizing: inherit; color: rgba(0, 0, 0, 0.8); font-family: medium-content-sans-serif-font, -apple-system, BlinkMacSystemFont, "Segoe UI", Roboto, Oxygen, Ubuntu, Cantarell, "Open Sans", "Helvetica Neue", sans-serif;"></div><footer class="nj nk nl nm nn no np nq nr ab q ns nt c" style="align-items: center; background-color: white; border-top: none; box-sizing: content-box; color: rgba(0, 0, 0, 0.8); display: flex; font-family: medium-content-sans-serif-font, -apple-system, BlinkMacSystemFont, "Segoe UI", Roboto, Oxygen, Ubuntu, Cantarell, "Open Sans", "Helvetica Neue", sans-serif; height: 52px; margin-bottom: 88px; max-height: 52px; position: static; z-index: 1;"><div class="l ae" style="box-sizing: inherit; flex: 1 0 auto;"><div class="ab ca" style="box-sizing: inherit; display: flex; justify-content: center;"><div class="ch bg ew ex ey ez" style="box-sizing: inherit; margin: 0px 24px; max-width: 680px; min-width: 0px; width: 680px;"><div class="ab co nu" style="box-sizing: inherit; display: flex; justify-content: space-between;"><div class="ab q ja" style="align-items: center; box-sizing: inherit; display: flex; flex-direction: row;"><div class="nv l" style="box-sizing: inherit; max-width: 155px;"><span class="l h g f nz oa" style="box-sizing: inherit; display: inline-block;"><div class="ab q ja jb" style="align-items: center; box-sizing: inherit; display: flex; flex-direction: row; z-index: 2;"><div class="pw-multi-vote-icon ee qt jd je jf" style="box-sizing: inherit; margin-right: 0px; position: relative; user-select: none;"><div class="" style="box-sizing: inherit;"><div style="box-sizing: inherit;"><div aria-describedby="55" aria-hidden="false" aria-labelledby="55" class="bl" style="box-sizing: inherit; display: inline-block;"><div class="jg qu ji jj jk jl jm am jn jo jp jf" style="border: 0px; box-sizing: inherit; cursor: not-allowed; fill: rgb(117, 117, 117); opacity: 0.25; outline: 0px; padding: 0px; user-select: none;"><svg aria-label="clap" height="24" viewbox="0 0 24 24" width="24"><path clip-rule="evenodd" d="M11.37.83L12 3.28l.63-2.45h-1.26zM15.42 1.84l-1.18-.39-.34 2.5 1.52-2.1zM9.76 1.45l-1.19.4 1.53 2.1-.34-2.5zM20.25 11.84l-2.5-4.4a1.42 1.42 0 0 0-.93-.64.96.96 0 0 0-.75.18c-.25.19-.4.42-.45.7l.05.05 2.35 4.13c1.62 2.95 1.1 5.78-1.52 8.4l-.46.41c1-.13 1.93-.6 2.78-1.45 2.7-2.7 2.51-5.59 1.43-7.38zM12.07 9.01c-.13-.69.08-1.3.57-1.77l-2.06-2.07a1.12 1.12 0 0 0-1.56 0c-.15.15-.22.34-.27.53L12.07 9z" fill-rule="evenodd"></path><path clip-rule="evenodd" d="M14.74 8.3a1.13 1.13 0 0 0-.73-.5.67.67 0 0 0-.53.13c-.15.12-.59.46-.2 1.3l1.18 2.5a.45.45 0 0 1-.23.76.44.44 0 0 1-.48-.25L7.6 6.11a.82.82 0 1 0-1.15 1.15l3.64 3.64a.45.45 0 1 1-.63.63L5.83 7.9 4.8 6.86a.82.82 0 0 0-1.33.9c.04.1.1.18.18.26l1.02 1.03 3.65 3.64a.44.44 0 0 1-.15.73.44.44 0 0 1-.48-.1L4.05 9.68a.82.82 0 0 0-1.4.57.81.81 0 0 0 .24.58l1.53 1.54 2.3 2.28a.45.45 0 0 1-.64.63L3.8 13a.81.81 0 0 0-1.39.57c0 .22.09.43.24.58l4.4 4.4c2.8 2.8 5.5 4.12 8.68.94 2.27-2.28 2.71-4.6 1.34-7.1l-2.32-4.08z" fill-rule="evenodd"></path></svg></div></div></div></div></div></div></span></div><div class="bp ab" style="box-sizing: inherit; display: flex; margin-left: 24px;"><div style="box-sizing: inherit;"><div aria-describedby="8" aria-hidden="false" aria-labelledby="8" class="bl" style="box-sizing: inherit; display: inline-block;"><button aria-label="responses" class="ao jg jx jy ab q ef jz ka" style="-webkit-tap-highlight-color: transparent; align-items: center; background-attachment: initial; background-clip: initial; background-image: initial; background-origin: initial; background-position: initial; background-repeat: initial; background-size: initial; border-color: initial; border-style: initial; border-width: 0px; box-sizing: inherit; cursor: pointer; display: flex; fill: rgb(107, 107, 107); margin: 0px; opacity: 1; overflow: visible; padding: 4px 0px;"><svg class="kb" height="24" viewbox="0 0 24 24" width="24"><path d="M18 16.8a7.14 7.14 0 0 0 2.24-5.32c0-4.12-3.53-7.48-8.05-7.48C7.67 4 4 7.36 4 11.48c0 4.13 3.67 7.48 8.2 7.48a8.9 8.9 0 0 0 2.38-.32c.23.2.48.39.75.56 1.06.69 2.2 1.04 3.4 1.04.22 0 .4-.11.48-.29a.5.5 0 0 0-.04-.52 6.4 6.4 0 0 1-1.16-2.65v.02zm-3.12 1.06l-.06-.22-.32.1a8 8 0 0 1-2.3.33c-4.03 0-7.3-2.96-7.3-6.59S8.17 4.9 12.2 4.9c4 0 7.1 2.96 7.1 6.6 0 1.8-.6 3.47-2.02 4.72l-.2.16v.26l.02.3a6.74 6.74 0 0 0 .88 2.4 5.27 5.27 0 0 1-2.17-.86c-.28-.17-.72-.38-.94-.59l.01-.02z"></path></svg></button></div></div></div></div><div class="ab q" style="align-items: center; box-sizing: inherit; display: flex;"><div class="ob l ho" style="box-sizing: inherit; flex: 0 0 auto; margin-right: 20px;"><div style="box-sizing: inherit;"><div aria-describedby="9" aria-hidden="false" aria-labelledby="9" class="bl" style="box-sizing: inherit; display: inline-block;"><div aria-hidden="false" class="bl" style="box-sizing: inherit; display: inline-block;"><button aria-controls="addToCatalogBookmarkButton" aria-expanded="false" aria-label="Add to list bookmark button" class="af ef ah ai aj ak al kd an ao ap ke kf kg kh" data-testid="footerBookmarkButton" style="-webkit-tap-highlight-color: transparent; background-attachment: initial; background-clip: initial; background-image: initial; background-origin: initial; background-position: initial; background-repeat: initial; background-size: initial; border: inherit; box-sizing: inherit; cursor: pointer; fill: rgb(107, 107, 107); font-family: inherit; font-size: inherit; font-weight: inherit; letter-spacing: inherit; margin: 0px; overflow: visible; padding: 8px 2px;"><svg class="ki" fill="none" height="24" viewbox="0 0 24 24" width="24"><path d="M17.5 1.25a.5.5 0 0 1 1 0v2.5H21a.5.5 0 0 1 0 1h-2.5v2.5a.5.5 0 0 1-1 0v-2.5H15a.5.5 0 0 1 0-1h2.5v-2.5zm-11 4.5a1 1 0 0 1 1-1H11a.5.5 0 0 0 0-1H7.5a2 2 0 0 0-2 2v14a.5.5 0 0 0 .8.4l5.7-4.4 5.7 4.4a.5.5 0 0 0 .8-.4v-8.5a.5.5 0 0 0-1 0v7.48l-5.2-4a.5.5 0 0 0-.6 0l-5.2 4V5.75z" fill="#000"></path></svg></button></div></div></div></div><div class="ob l ho" style="box-sizing: inherit; flex: 0 0 auto; margin-right: 20px;"><div aria-describedby="postFooterSocialMenu" aria-hidden="false" aria-labelledby="postFooterSocialMenu" class="bl" style="box-sizing: inherit; display: inline-block;"><div style="box-sizing: inherit;"><div aria-describedby="10" aria-hidden="false" aria-labelledby="10" class="bl" style="box-sizing: inherit; display: inline-block;"><button aria-controls="postFooterSocialMenu" aria-expanded="false" aria-label="Share Post" class="af ef ah ai aj ak al kd an ao ap ke kq kr ka ks" data-testid="footerSocialShareButton" style="-webkit-tap-highlight-color: transparent; background-attachment: initial; background-clip: initial; background-image: initial; background-origin: initial; background-position: initial; background-repeat: initial; background-size: initial; border: inherit; box-sizing: inherit; cursor: pointer; fill: rgb(107, 107, 107); font-family: inherit; font-size: inherit; font-weight: inherit; letter-spacing: inherit; margin: 0px; overflow: visible; padding: 8px 2px;"><svg fill="none" height="24" viewbox="0 0 24 24" width="24"><path clip-rule="evenodd" d="M15.22 4.93a.42.42 0 0 1-.12.13h.01a.45.45 0 0 1-.29.08.52.52 0 0 1-.3-.13L12.5 3v7.07a.5.5 0 0 1-.5.5.5.5 0 0 1-.5-.5V3.02l-2 2a.45.45 0 0 1-.57.04h-.02a.4.4 0 0 1-.16-.3.4.4 0 0 1 .1-.32l2.8-2.8a.5.5 0 0 1 .7 0l2.8 2.8a.42.42 0 0 1 .07.5zm-.1.14zm.88 2h1.5a2 2 0 0 1 2 2v10a2 2 0 0 1-2 2h-11a2 2 0 0 1-2-2v-10a2 2 0 0 1 2-2H8a.5.5 0 0 1 .35.14c.1.1.15.22.15.35a.5.5 0 0 1-.15.35.5.5 0 0 1-.35.15H6.4c-.5 0-.9.4-.9.9v10.2a.9.9 0 0 0 .9.9h11.2c.5 0 .9-.4.9-.9V8.96c0-.5-.4-.9-.9-.9H16a.5.5 0 0 1 0-1z" fill-rule="evenodd" fill="currentColor"></path></svg></button></div></div></div></div><div aria-hidden="false" class="bl" style="box-sizing: inherit; display: inline-block;"><div aria-describedby="creatorActionOverflowMenu" aria-hidden="false" aria-labelledby="creatorActionOverflowMenu" class="bl" style="box-sizing: inherit; display: inline-block;"><div class="po l ho" style="box-sizing: inherit; flex: 0 0 auto; margin-right: -4px;"><div style="box-sizing: inherit;"><div aria-describedby="147" aria-hidden="false" aria-labelledby="147" class="bl" style="box-sizing: inherit; display: inline-block;"><button aria-controls="creatorActionOverflowMenu" aria-expanded="false" aria-label="More options" class="af ef ah ai aj ak al kd an ao ap ke kq kr ka ks" data-testid="footerStoryOptionsButton" style="-webkit-tap-highlight-color: transparent; background-attachment: initial; background-clip: initial; background-image: initial; background-origin: initial; background-position: initial; background-repeat: initial; background-size: initial; border: inherit; box-sizing: inherit; cursor: pointer; fill: rgb(107, 107, 107); font-family: inherit; font-size: inherit; font-weight: inherit; letter-spacing: inherit; margin: 0px; overflow: visible; padding: 8px 2px;"><svg fill="none" height="24" viewbox="0 0 24 24" width="24"><path clip-rule="evenodd" d="M4.39 12c0 .55.2 1.02.59 1.41.39.4.86.59 1.4.59.56 0 1.03-.2 1.42-.59.4-.39.59-.86.59-1.41 0-.55-.2-1.02-.6-1.41A1.93 1.93 0 0 0 6.4 10c-.55 0-1.02.2-1.41.59-.4.39-.6.86-.6 1.41zM10 12c0 .55.2 1.02.58 1.41.4.4.87.59 1.42.59.54 0 1.02-.2 1.4-.59.4-.39.6-.86.6-1.41 0-.55-.2-1.02-.6-1.41a1.93 1.93 0 0 0-1.4-.59c-.55 0-1.04.2-1.42.59-.4.39-.58.86-.58 1.41zm5.6 0c0 .55.2 1.02.57 1.41.4.4.88.59 1.43.59.57 0 1.04-.2 1.43-.59.39-.39.57-.86.57-1.41 0-.55-.2-1.02-.57-1.41A1.93 1.93 0 0 0 17.6 10c-.55 0-1.04.2-1.43.59-.38.39-.57.86-.57 1.41z" fill-rule="evenodd" fill="currentColor"></path></svg></button></div></div></div></div></div></div></div></div></div></div></footer><div class="oc od oe of og l bw" style="background-color: #f9f9f9; box-sizing: inherit; color: rgba(0, 0, 0, 0.8); font-family: medium-content-sans-serif-font, -apple-system, BlinkMacSystemFont, "Segoe UI", Roboto, Oxygen, Ubuntu, Cantarell, "Open Sans", "Helvetica Neue", sans-serif; padding-top: 72px;"><div class="ab ca" style="box-sizing: inherit; display: flex; justify-content: center;"><div class="ch bg ew ex ey ez" style="box-sizing: inherit; margin: 0px 24px; max-width: 680px; min-width: 0px; width: 680px;"><div class="ck ab oh co" style="align-items: flex-end; box-sizing: inherit; display: flex; justify-content: space-between; margin-bottom: 16px;"><div class="ab hc" style="align-items: baseline; box-sizing: inherit; display: flex;"><a href="https://medium.com/@eduard.hucai?source=post_page-----b2dafe6ae7c7--------------------------------" previewlistener="true" rel="noopener follow" style="-webkit-tap-highlight-color: transparent; box-sizing: inherit; text-decoration-line: none;"><div class="l oi oj bx ok hg" style="border-radius: 50%; border: 2px solid rgb(249, 249, 249); box-sizing: inherit; height: 76px; width: 76px; z-index: 0;"><div class="l ee" style="box-sizing: inherit; position: relative;"><img alt="TravelGo" class="l eq bx ol om cw" height="72" loading="lazy" src="https://miro.medium.com/v2/resize:fill:144:144/1*dXcQokbyAbuPV_XgyxWVaw.png" style="background-color: #f2f2f2; border-radius: 50%; box-sizing: border-box; display: block; height: 72px; vertical-align: middle; width: 72px;" width="72" /><div class="hh bx l ol om eo n hi ep" style="border-radius: 50%; border: 1px solid rgba(0, 0, 0, 0.05); box-shadow: none; box-sizing: inherit; height: 72px; position: absolute; top: 0px; width: 72px;"></div></div></div></a></div></div><div class="ab cm co" style="align-items: flex-start; box-sizing: inherit; display: flex; justify-content: space-between;"><div class="l" style="box-sizing: inherit;"><div class="ab q" style="align-items: center; box-sizing: inherit; display: flex;"><a class="af ag ah ai aj ak al am an ao ap aq ar as at ab q" href="https://medium.com/@eduard.hucai?source=post_page-----b2dafe6ae7c7--------------------------------" previewlistener="true" rel="noopener follow" style="-webkit-tap-highlight-color: transparent; align-items: center; border: inherit; box-sizing: inherit; cursor: pointer; display: flex; fill: inherit; font-family: inherit; font-size: inherit; font-weight: inherit; letter-spacing: inherit; margin: 0px; padding: 0px; text-decoration-line: none;"><h2 class="pw-author-name be pd pe pf pg bj" style="box-sizing: inherit; color: #242424; font-family: sohne, "Helvetica Neue", Helvetica, Arial, sans-serif; font-size: 24px; font-weight: 500; letter-spacing: -0.016em; line-height: 30px; margin: 0px;"><span class="fk" style="box-sizing: inherit; word-break: break-word;">Written by TravelGo</span></h2></a></div><div class="nc ab" style="box-sizing: inherit; display: flex; margin-top: 8px;"><div class="l ho" style="box-sizing: inherit; flex: 0 0 auto;"><span class="pw-follower-count be b bf z bj" style="box-sizing: inherit; color: #242424; font-family: sohne, "Helvetica Neue", Helvetica, Arial, sans-serif; font-size: 14px; line-height: 20px;">0 Followers</span></div></div><div class="ph l" style="box-sizing: inherit; margin-top: 16px;"><p class="be b bf z bj" style="box-sizing: inherit; color: #242424; font-family: sohne, "Helvetica Neue", Helvetica, Arial, sans-serif; font-size: 14px; line-height: 20px; margin: 0px;"><span class="fk" style="box-sizing: inherit; word-break: break-word;">Meet Edward, the passionate travel blogger who brings the world to life through captivating stories and stunning visuals.</span></p></div></div></div></div></div></div><p><br /></p> | travelgo |
1,872,010 | Enhancing Your Career Through Contribution and Recognition in the Boomi Community | There's a magic that happens when people come together, especially for a shared cause. History is... | 0 | 2024-05-31T11:41:18 | https://dev.to/eyer-ai/enhancing-your-career-through-contribution-and-recognition-in-the-boomi-community-3dg6 | community, boomi, aiops, eyer |
There's a magic that happens when people come together, especially for a shared cause. History is filled with examples of this, and the [Boomi community by Eyer](https://discord.gg/CcxvKxkaAJ) is no exception. This community goes beyond just a platform to fix your Boomi problems—it can be the very tool that lands you your next big job.
Many people have participated in online communities over the years. They acknowledge that these communities have helped them out of a jam, but they don't quite understand the hype or why it's seen as the ultimate solution.
This article dives into how to maximize the benefits of being part of a community. It will explore the value of contributing your knowledge and building a strong reputation within the community, ultimately positioning yourself for that next big opportunity.
## The value of contribution
The first step in building strong relationships within a community starts with contributing. This is especially important if you want to be seen as a trusted thought leader. Here are the different ways to get involved and contribute positively:
**Showcase your skills and expertise**
The most effective and popular way to contribute to the community is to share knowledge, and you can do that in many creative ways:
* Actively participate in forums and discussions, answer questions thoughtfully, and provide clear explanations and solutions.
* Share insights from your own Boomi experience, create blog posts, tutorials, and short guides that address common integration challenges faced by other developers.
* Embrace challenges, participate in hackathons, and agree to volunteer for events. This not only demonstrates your problem-solving abilities but also highlights your passion for the Boomi platform.
**Collaboration and growth**
The biggest reason why communities like the Boomi community by Eyer work is collaboration. Working alongside other developers with varying degrees of experience exposes you to different approaches and techniques, enriching your own understanding of Boomi and its functionalities.
Additionally, combining diverse skill sets from the community allows you to brainstorm and develop more creative and effective solutions to integration challenges. This integration of varied skills also strengthens your problem-solving skills and prepares you for real-world scenarios.
## Gaining recognition in the Boomi community
You've started sharing your expertise, but how do you stay visible and become the go-to person for Boomi questions and opportunities within the Eyer community and beyond? This section will focus on building your personal brand and solidifying your reputation as a valuable resource.
**Recognition systems in the Boomi community by Eyer**
Active participation in the Boomi community unlocks a range of recognition systems that validate your skills and contributions.
You can earn swag, gift cards, and even become a community leader. This recognition highlights your expertise and commitment in addition to opening up opportunities for professional growth and networking within the Boomi ecosystem.
Additionally, the Boomi community by Eyer recognizes exceptional contributions by featuring your profile or content on the blog. This demonstrates your expertise to a wider audience and positions you as a thought leader within the Boomi community.
**Building a personal brand**
Aside from continuous community contributions, maintaining an online presence is crucial for your personal brand as a Boomi developer. Use platforms like LinkedIn and Twitter to showcase your work and contributions.
Regularly update your profiles with your latest projects, certifications, and endorsements. Share articles and excerpts from those articles that you find helpful. Do not be afraid to demonstrate your expertise and commitment to continuous learning regularly—you never know who might be watching.
**Networking**
Engage with peers and industry leaders by participating in networking events, both online and offline. Attend meetups, webinars, and conferences to connect with other Boomi professionals. Building relationships within the community can lead to mentorship opportunities, collaborative projects, and access to job openings. Networking is a powerful tool for career growth, providing you with insights, support, and opportunities that can significantly enhance your professional journey. Check out [this article](https://dev.to/eyer-ai/building-professional-connections-as-a-boomi-developer-1gnp) to learn more about building professional connections as a Boomi developer.
## Leveraging your reputation for your career advancements
You have built your reputation and expanded your network through community contributions; what’s next?
The next step is strategically leveraging your contributions to make you a more attractive candidate for any Boomi-related opportunity.
* Highlight the community contributions and skills gained on your resume, LinkedIn profile, and during job interviews. Employers value candidates who demonstrate leadership and a commitment to making a positive impact.
* Apply to speak at Boomi-related conferences and webinars. Sharing your knowledge at these events further establishes you as a thought leader and allows you to connect with a wider audience of potential employers and collaborators. By actively promoting your expertise and the value you bring, you'll be well on your way to propelling your career forward.
* Request recommendations and endorsements from individuals in your network who can vouch for your skills, character, and contributions. Strong recommendations can be powerful in job applications and career advancements.
* Leverage your expanded network to find mentors who can provide career advice, industry insights, and feedback on your professional development. A mentor can help you navigate career decisions and introduce you to further opportunities.
## In summary
Communities can be your ticket to an amazing, long-lasting Boomi career when used correctly. They uplift you and provide the resources and the experts to help you troubleshoot and answer your problems. While these are fun to take advantage of, communities can become even more interesting when you contribute to this knowledge base and help people with their queries. By sharing your expertise, you solidify your understanding and establish yourself as a valuable resource within the community, opening you up to career advancement opportunities. This two-way street of learning and giving back fosters a sense of connection and accomplishment, making your Boomi journey all the more rewarding.
Take the first step and join the [Boomi community by Eyer](https://discord.gg/CcxvKxkaAJ) today.
| amaraiheanacho |
1,869,732 | Before WWDC 2024: The Future Potential and Real Challenges of SwiftData | At the 2023 Worldwide Developers Conference (WWDC), Apple launched the highly anticipated new... | 0 | 2024-05-31T11:40:00 | https://fatbobman.com/en/posts/before-wwdc-2024-swiftdata/ | swift, swiftui, wwdc, ios | At the 2023 Worldwide Developers Conference (WWDC), Apple launched the highly anticipated new generation data management framework — SwiftData. As the successor to Core Data, can SwiftData play a key role in the Apple ecosystem? With WWDC 2024 approaching, this article will evaluate the overall performance of SwiftData since its initial release during the Xcode 15 period (i.e., its first major version), and provide a forecast of its future development.
---
Don’t miss out on the latest updates and excellent articles about Swift, SwiftUI, Core Data, and SwiftData. Subscribe to [Fatbobman’s Swift Weekly](https://weekly.fatbobman.com) and receive weekly insights and valuable content directly to your inbox.
---
## Toward the Future: SwiftData, A Modern Data Management Framework
SwiftData was not built entirely from scratch; its core technology is still based on Core Data. In the first WWDC 2023 session about SwiftData, Apple did not elaborate on this aspect.
Initially, I was confused and even suspicious about why Apple did not clarify the connection with Core Data right from the start. However, as I delved deeper into SwiftData, I gradually understood Apple's strategy. While SwiftData is built on the proven technological foundation of Core Data, its overall design and presentation signify the birth of a completely new data management framework. Apple's choice to downplay the connection with Core Data aims to free developers from the preconceived notions associated with Core Data, enabling a better understanding of SwiftData's team's fresh interpretation of a modern data management framework. This strategy not only emphasizes SwiftData’s status as an independent framework but also clearly defines its future role within the Apple ecosystem.
For developers with extensive Core Data experience, they might find it challenging to grasp and apply the new programming philosophy introduced by SwiftData, similar to the challenges faced by UIKit developers transitioning to SwiftUI.
SwiftData not only simplifies some of the complex and seldom-used features of Core Data but also introduces many practices that align with modern programming paradigms. The framework fully leverages new features of the Swift language, demonstrating how to build secure, stable, and elegant code, and laying the foundation for its central role in the Apple ecosystem.
Therefore, SwiftData can be regarded as a new and modernized data management framework, with the potential to play a pivotal role in the Apple ecosystem for over a decade.
## Hastily Launched: The Real Issues Facing SwiftData
Although SwiftData's design is highly visionary, its launch was clearly rushed, and its first version not only lacks some important features, but several key issues have also severely impacted its performance and usability:
* **Immature Predicate Conversion Capability**:
SwiftData introduced a new Predicate system provided by Foundation, which is safer and more ergonomically sound. Although it is not as comprehensive as the traditional NSPredicate yet, it meets the retrieval declaration needs of most developers. However, as more applications activate data cloud synchronization, increasingly, model properties are declared as optional to meet synchronization requirements. Yet, SwiftData's current performance in converting predicates that include optional values (transforming predicates into SQL commands) is poor, especially when handling "to-many" relationships with optional predicates. This deficiency not only severely impacts SwiftData's usability but also significantly restricts the functionalities that applications using SwiftData can offer.
* **UI Response to Data Updates is Problematic**:
SwiftData utilizes Swift's modern concurrency model to provide an elegant mechanism for handling concurrent data operations, allowing developers to encapsulate concurrent data operations through `@ModelActor`, thus effectively preventing the common concurrency crashes seen in Core Data. However, despite updates over the past year, data update operations performed through `@ModelActor` often fail to prompt timely responses in SwiftUI views. To circumvent this issue, developers are forced to abandon `@ModelActor` or resort to various tricks to force view updates, not only wasting this feature's potential but also severely impacting the application's efficiency.
* **Model Validation and Conversion Issues**:
In Core Data, when data network synchronization is enabled, Xcode's model editor automatically verifies whether models comply with synchronization standards. By contrast, SwiftData uses a purely code-based modeling approach, requiring developers to manually code for model validation. This not only increases development complexity but might also lead to developers, who are inadequately informed about synchronization standards, discovering mismatches in their models near project completion, necessitating extensive modifications. Additionally, occasional conversion errors may occur when translating code-declared models into the underlying Core Data-recognizable `NSManagedObjectModel`, especially in the absence of explicit inverse relationship annotations (which could otherwise be omitted). These errors are often hard to detect, and troubleshooting them requires a significant investment of time and effort.
* **Codable Support and Unclear Data Storage**:
SwiftData allows developers to use types that conform to the Codable protocol directly as model properties, significantly clarifying models and simplifying operations. However, the lack of a clear guideline and defined storage correspondence from the official side presents numerous challenges in practical use. Not all types conforming to the Codable protocol can be reliably converted, occasionally leading to application crashes. Furthermore, the absence of clear official guidance might cause issues for developers adjusting Codable types, especially in data cloud synchronization scenarios, where new model versions may not be eligible for seamless migration (failing to utilize lightweight migration).
Despite the fact that SwiftData's first version is not as comprehensive as Core Data, if the framework operates stably and meets project requirements, these shortcomings do not pose significant issues. However, as mentioned earlier, existing problems may lead to application anomalies and unexpected challenges during development.
Overall, given the rushed launch of SwiftData, its first version has not fully met expectations and has not adequately demonstrated the capabilities and stability expected of a data management framework. Therefore, it is crucial to conduct necessary updates and enhancements to SwiftData at the upcoming WWDC 2024.
## Applicability: Who is the First Version of SwiftData Suitable For?
As a developer who has invested considerable effort in researching SwiftData, I fully recognize its ingenious design and bright prospects. However, I must admit that the first version of SwiftData is not suitable for all developers and projects.
* **For Beginners (with no experience in data management frameworks): Not Recommended**
Developers unfamiliar with data management frameworks might find that due to a lack of understanding of SwiftData's capabilities and limitations, they easily encounter insurmountable obstacles during project development.
* **For Projects with Complex Requirements: Not Recommended**
If a project has high demands for a data management framework, the maturity and comprehensive functionality of Core Data make it a better choice than the first version of SwiftData. Although it is possible to integrate SwiftData and Core Data within a project, the cost and effort involved may not be justified.
* **For Projects with Undefined Requirements: Not Recommended**
As project functionalities continue to expand, it is likely that developers will find the first version of SwiftData unable to meet the evolving development needs.
* **For Projects with Clear Requirements and Unaffected by Current Issues in SwiftData: Recommended**
Despite its limitations in the first version, SwiftData is suitable for projects with simple functional requirements that do not involve complex relationships or performance issues, provided you can avoid the major issues present in the first version of SwiftData. Additionally, if the project does not utilize data network synchronization features, some of SwiftData's shortcomings can be further mitigated.
* **For a Specific Audience: Worth Trying**
For those developers who fully understand the project requirements and are well aware of the limitations and shortcomings of the first version of SwiftData, particularly those with extensive Core Data development experience, using the first version of SwiftData for commercial project development, despite the challenges, can be rewarding as it provides a sense of achievement in overcoming difficulties.
Although the performance of the first version of SwiftData did not fully meet expectations, its advanced design concepts and elegant implementation are still worth learning from. **Even if you currently do not need a data management framework, or are not considering using SwiftData, studying and understanding it can still have a positive impact on your future development work**.
> Over the past year, I have written more than [a dozen articles](https://fatbobman.com/en/tags/SwiftData/) on SwiftData. These articles thoroughly explore the principles and design strategies of SwiftData, and should be very helpful for developers who wish to gain a deeper understanding of this framework.
## Looking Ahead: The Upcoming Changes in SwiftData
As WWDC 2024 approaches, I am hopeful that the forthcoming updates will address some of the major issues revealed in the first version of SwiftData.
As previously mentioned, Apple is in the process of creating SwiftData as a brand new data management framework, specifically designed for the current and future Apple ecosystem, particularly for environments that include mobile applications and high-performance hardware like high-speed CPUs and solid-state drives. Therefore, many of the distinctive features found in Core Data might not be included in SwiftData due to changes in the market and hardware environment. Additionally, SwiftData may introduce more refined encapsulations to simplify some of the complex operations of the past.
Thus, I am curious about how Apple will add new features to SwiftData, not just which features will be added.
Based on the development experience with SwiftUI, it may take another two to three years for SwiftData to become a key official data management framework within the Apple ecosystem. This process will be lengthy and challenging, but it will ultimately provide developers with powerful tools to build future applications.
## Advice for Current SwiftData Developers
If you have already implemented SwiftData in your project and it is performing well, congratulations 🎉 ! Furthermore, I recommend that you delve deeper into the major issues currently faced by the first version of SwiftData and do your best to mitigate these in upcoming updates. Finally, if possible, consider raising the minimum system requirements of your project after the release of iOS 18 (or subsequent systems on other platforms) to take advantage of potential optimizations and improvements.
## Appendix: Some Key Features Missing, Major Issues, and Partial Temporary Solutions in the First Version of SwiftData
- **Lazy Loading (Faulting)**: SwiftData does not support the faulting feature typical in Core Data for lazy loading of data.
- **Batch Data Operations**: Currently, there is no support for batch data operations, but this can be achieved by integrating with Core Data.
- **Multiple Persistence Storage Support**: Prior to iOS 17.4, SwiftData did not support multiple persistence storages.
- **Advanced Query Features**: Does not support advanced query features such as `group`, `having`, `distinct`. If needed, these can be addressed through [SwiftDataKit](https://fatbobman.com/en/posts/use-core-data-features-in-swiftdata-by-swiftdatakit/).
- **Predicate Functionality Limitations**: After enabling synchronization features, the capability to express predicates in many-to-many relationships is restricted.
- **Public Database and Data Sharing**: Does not support [synchronizing public databases](https://fatbobman.com/en/posts/coredatawithcloudkit-5/) and [sharing data](https://fatbobman.com/en/posts/coredatawithcloudkit-6/).
- **Performance Issues**: Operations on to-many relationships can trigger [severe performance issues](https://fatbobman.com/zh/posts/relationships-in-swiftdata-changes-and-considerations/#array-innovation-or-trap).
- **View Update Response**: Views are unable to respond to data updated within `@ModelActor`. Refer to [Solution One](https://fatbobman.com/en/posts/practical-swiftdata-building-swiftui-applications-with-modern-approaches/#a-new-issue-the-view-does-not-refresh-after-data-update) and [Solution Two](https://patstechweblog.com/posts/2-live-model/?issue=031&utm_source=FatbobmanWeekly&utm_medium=email&utm_campaign=FatbobmanWeekly031).
- **Predicate Merging**: Does not support predicate merging. Refer to [this solution](https://fatbobman.com/en/posts/how-to-dynamically-construct-complex-predicates-for-swiftdata/).
- **Codable Support**: When using types that comply with the Codable protocol, ensure that all properties of the type are consistent with the fundamental properties of SQLite (such as integers, floats, dates, etc.).
- **Codable as Query Criteria**: Properties of Codable types cannot be used as query criteria (though Core Data supports [Composite Attributes](https://fatbobman.com/en/posts/what-s-new-in-core-data-in-wwdc23/#composite-attributes)).
- **Model Validation**: When developing data models that support synchronization, [validate the model first](https://x.com/fatbobman/status/1753979443675377914).
- **Enum Storage**: It is not recommended to use enums directly as storage types because they cannot be used as query criteria; it is best to save their corresponding rawValue.
- **Insufficient Event Handling**: SwiftData does not support adding custom logic during lifecycle events such as `didSave` or `willSave`. This limitation affects the ability to perform specific actions during data saving processes. A workaround is available in the [solution guide](https://fatbobman.com/en/posts/persistent-history-tracking-in-swiftdata/).
- **Cascade Deletion Issue**: SwiftData does not automatically delete related association data when performing delete operations with the `cascade` deletion rule. This functionality can be achieved using [SwiftDataKit](https://fatbobman.com/en/posts/use-core-data-features-in-swiftdata-by-swiftdatakit/).
- **System Version Requirements**: It is advisable to raise the minimum system requirements of your project, recommended to be at least iOS 17.2.
> The original article was published on my blog [Fatbobman's Blog](https://fatbobman.com/en/). | fatbobman |
1,872,008 | in html, css | in html,css | 0 | 2024-05-31T11:39:48 | https://dev.to/reyanabid123/in-html-css-2j17 | in html,css | reyanabid123 | |
1,872,007 | "Talent Acquisition Strategies for Effective Recruitment Solutions" | In the competitive landscape of today’s job market, businesses are constantly striving to attract... | 0 | 2024-05-31T11:39:00 | https://dev.to/techvisoffice/talent-acquisition-strategies-for-effective-recruitment-solutions-1bfi |

In the competitive landscape of today’s job market, businesses are constantly striving to attract and retain top talent. Effective talent acquisition strategies play a crucial role in this endeavor, enabling organizations to identify, engage, and hire the best candidates for their teams. From leveraging [technology](https://techvis.in/services) to building strong employer brands, talent acquisition encompasses a range of approaches aimed at optimizing the recruitment process. In this article, we delve into the key strategies for effective talent acquisition and their role in modern recruitment solutions.
**1. Employer Branding**
A strong employer brand is essential for attracting top talent. Candidates are increasingly drawn to organizations with positive reputations as employers of choice. Building and promoting an employer brand that highlights the company’s culture, values, and opportunities for growth can significantly enhance its appeal to prospective candidates. Utilizing social media, employer review sites, and employee testimonials are effective ways to showcase the employer brand and attract top talent.
**2. Candidate Relationship Management (CRM)**
Candidate relationship management involves building and nurturing relationships with potential candidates, even before they apply for a specific role. By engaging with candidates through personalized communication, networking events, and informative content, organizations can create a pipeline of qualified candidates who are interested in future opportunities. Implementing CRM systems and tools helps recruiters track candidate interactions, maintain communication, and strategically engage with talent over time.
**3. Data-driven Recruitment**
[Data-driven](https://techvis.in/services) recruitment leverages analytics and insights to inform hiring decisions and optimize the recruitment process. By analyzing recruitment metrics such as time-to-fill, cost-per-hire, and candidate quality, organizations can identify areas for improvement and refine their talent acquisition strategies. Utilizing applicant tracking systems (ATS) and recruitment analytics platforms enables recruiters to track key performance indicators (KPIs), measure the effectiveness of recruitment campaigns, and make data-driven decisions to drive better outcomes.
**4. Candidate Experience Enhancement**
A positive candidate experience is crucial for attracting and retaining top talent. From the initial application process to onboarding, candidates’ interactions with the organization shape their perception of the employer brand. Providing a seamless, transparent, and engaging candidate experience demonstrates the organization’s commitment to its employees and enhances its reputation as an employer of choice. Leveraging technology to automate processes, providing timely feedback, and offering personalized communication can significantly improve the candidate experience.
**5. Diversity and Inclusion Initiatives**
Diversity and inclusion (D&I) initiatives are integral to effective talent acquisition strategies. Organizations that prioritize diversity and inclusion not only foster a more inclusive workplace culture but also attract a broader pool of talent. Implementing D&I strategies such as unconscious bias training, diverse sourcing methods, and inclusive job descriptions helps organizations attract and retain candidates from diverse backgrounds. Embracing diversity and inclusion enhances innovation, creativity, and organizational performance.
**6. Employee Referral Programs**
Employee referral programs are a valuable source of high-quality candidates. Employees who are satisfied with their jobs are often eager to refer friends, family members, and former colleagues for open positions within the organization. Offering incentives such as bonuses, recognition, or career advancement opportunities encourages employees to actively participate in the referral program. Leveraging employee networks helps organizations tap into a pool of candidates who are pre-screened and aligned with the company culture.
**7. Recruitment Marketing**
Recruitment marketing involves applying marketing principles and techniques to attract, engage, and convert candidates into applicants. By leveraging digital marketing channels such as social media, email campaigns, and content marketing, organizations can effectively promote their employer brand and job opportunities to target audiences. Creating compelling job advertisements, optimizing career websites for search engines, and utilizing targeted advertising campaigns are key elements of recruitment marketing strategies.
**8. Skills-based Hiring**
Skills-based hiring focuses on assessing candidates based on their skills, competencies, and potential rather than solely relying on traditional qualifications or experience. In today’s rapidly evolving job market, skills-based hiring enables organizations to identify candidates who possess the specific skills needed to excel in a role, regardless of their background or credentials. Implementing skills-based assessments, competency-based interviews, and performance-based evaluations helps organizations identify candidates who are the best fit for the job.
**9. Talent Pipelining**
Talent pipelining involves proactively identifying and engaging with potential candidates to create a pipeline of talent for future hiring needs. By building relationships with passive candidates, networking within industry-specific communities, and staying connected with alumni and former employees, organizations can maintain a pool of qualified candidates who are interested in future opportunities. Talent pipelining ensures that organizations have access to top talent when positions become available, reducing time-to-fill and minimizing recruitment costs.
**10. Continuous Improvement and Adaptation**
Effective talent acquisition strategies require continuous improvement and adaptation to changing market dynamics. Organizations must stay abreast of emerging trends, technological advancements, and shifts in candidate preferences to remain competitive in the talent market. Regularly reviewing and refining recruitment processes, soliciting feedback from candidates and hiring managers, and benchmarking against industry best practices are essential for staying agile and responsive to evolving recruitment needs.
**Conclusion**
Effective talent acquisition strategies are essential for organizations seeking to attract, engage, and hire top talent in today’s competitive job market. By prioritizing employer branding, candidate relationship management, data-driven recruitment, and diversity and inclusion initiatives, organizations can build a strong talent pipeline and gain a competitive edge. Embracing recruitment marketing, skills-based hiring, and continuous improvement ensures that organizations remain agile and responsive to changing recruitment trends and candidate preferences. Ultimately, by implementing effective talent acquisition strategies, organizations can enhance their recruitment solutions, strengthen their employer brand, and build high-performing teams for sustainable success. | techvisoffice | |
1,872,006 | hellow developer's | I have a some thing for you | 0 | 2024-05-31T11:38:21 | https://dev.to/reyanabid123/hellow-developers-47ke | I have a some thing for you | reyanabid123 | |
1,872,004 | Detecting Architectural Gaps with Automation - Proposed Solution | Introduction In the ever-evolving realm of software development, the quest for a robust... | 26,689 | 2024-05-31T11:37:56 | https://dev.to/dimanikulin/detecting-architectural-gaps-with-automation-proposed-solution-35dg | tutorial, architecture, programming | # Introduction
In the ever-evolving realm of software development, the quest for a robust and seamlessly integrated solution stands as a paramount pursuit.
This article embarks on a comprehensive journey into the depths of a proposed software solution, meticulously scrutinizing its architecture, integration strategies, and deployment modalities.
Through this exploration, we illuminate the symbiotic dance between users and technology, offering a roadmap for architects, developers, and IT aficionados alike to navigate the labyrinth of a forward-thinking software solution.
# The Context View for Standalone Application
A **context diagram (view)** defines the solution's boundaries and connections with third parties, such as external systems, users, and data.
As shown in the context diagram above, there is an interaction between **Users** and the **Proposed Solution**.
These interactions will be implemented using a **UI web interface**.
For obtaining input, the solution interacts with **Online** and **Offline UML** tools using their **API** to retrieve the initial **Software Architecture** and to save the extracted **Software Architecture**.
To access code, configuration, and the database, interactions with **Version Control Systems** and the database are utilized.
Finally, Report Storage is employed to save the outputs extracted from the **Architecture** under analysis.
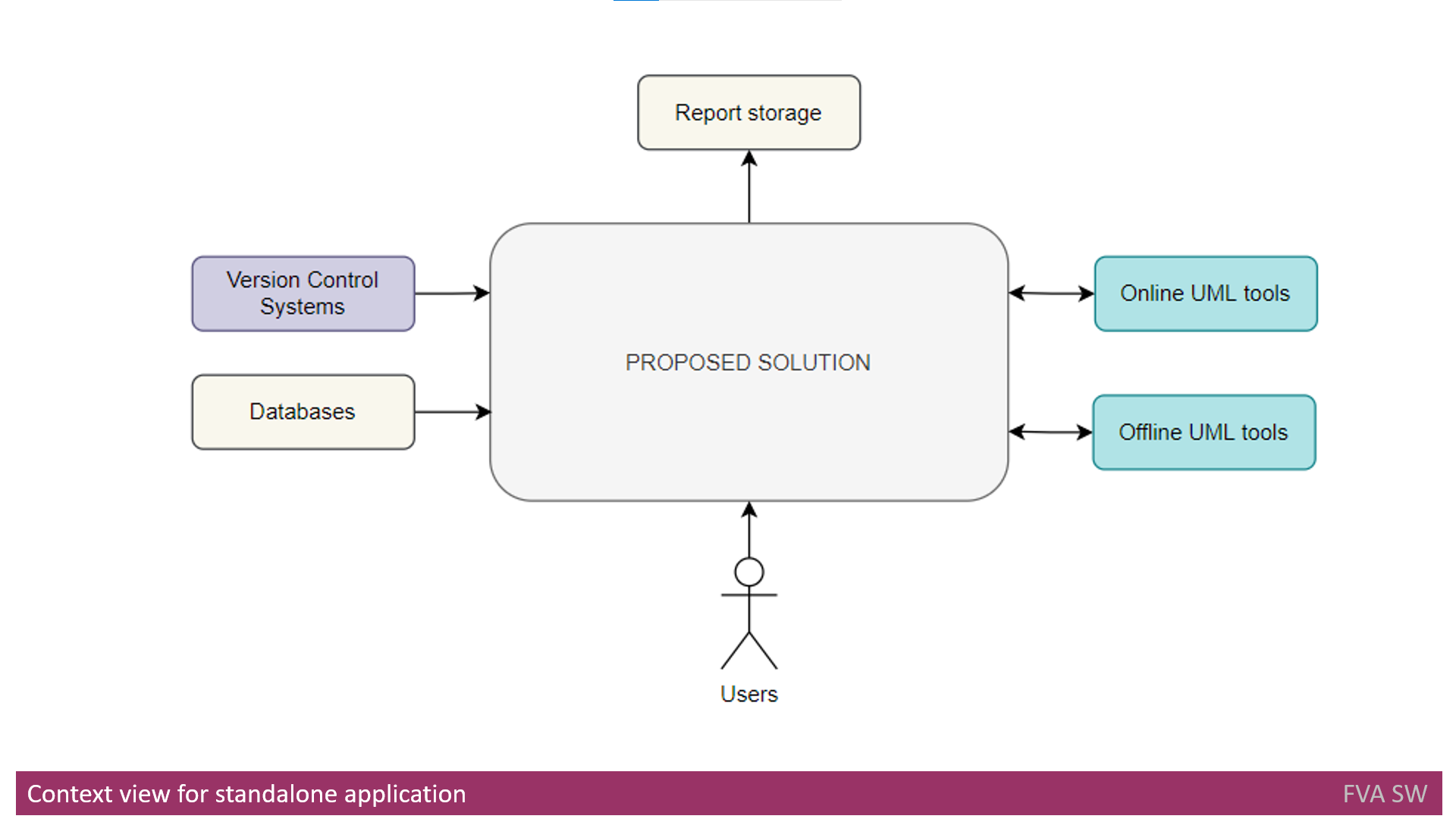
# The Context View for a Separate Step in CI/CD
The sole distinction between the previous view and the **Context View** for a **Separate Step** in **CI/CD** is the integration of the proposed solution with the existing **CI/CD** pipeline.
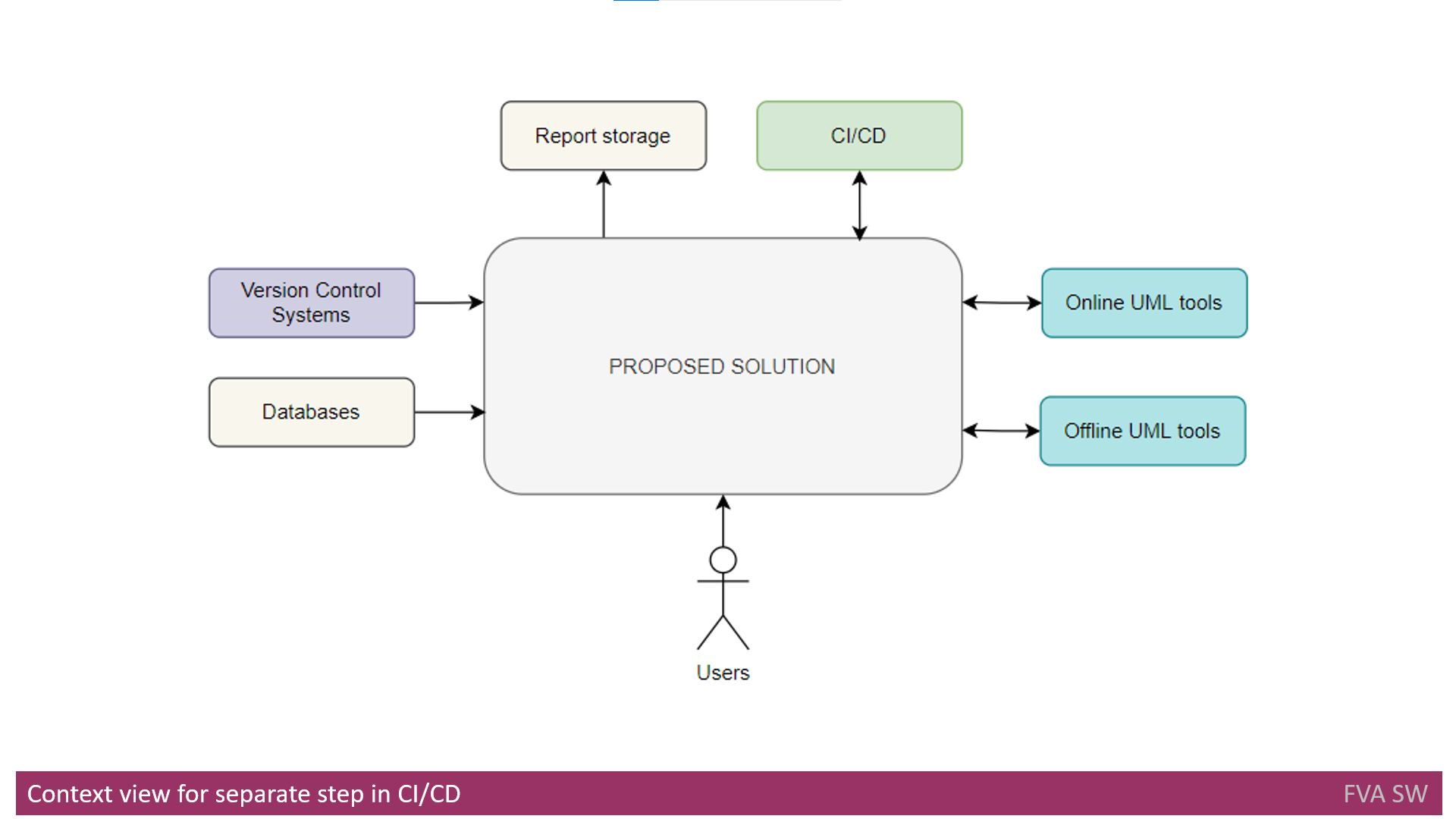
# Functional View
The functional diagram below illustrates the high-level functional decomposition of the proposed solution.
An agenda is provided below to explain the color coding used in the functional decomposition diagram.
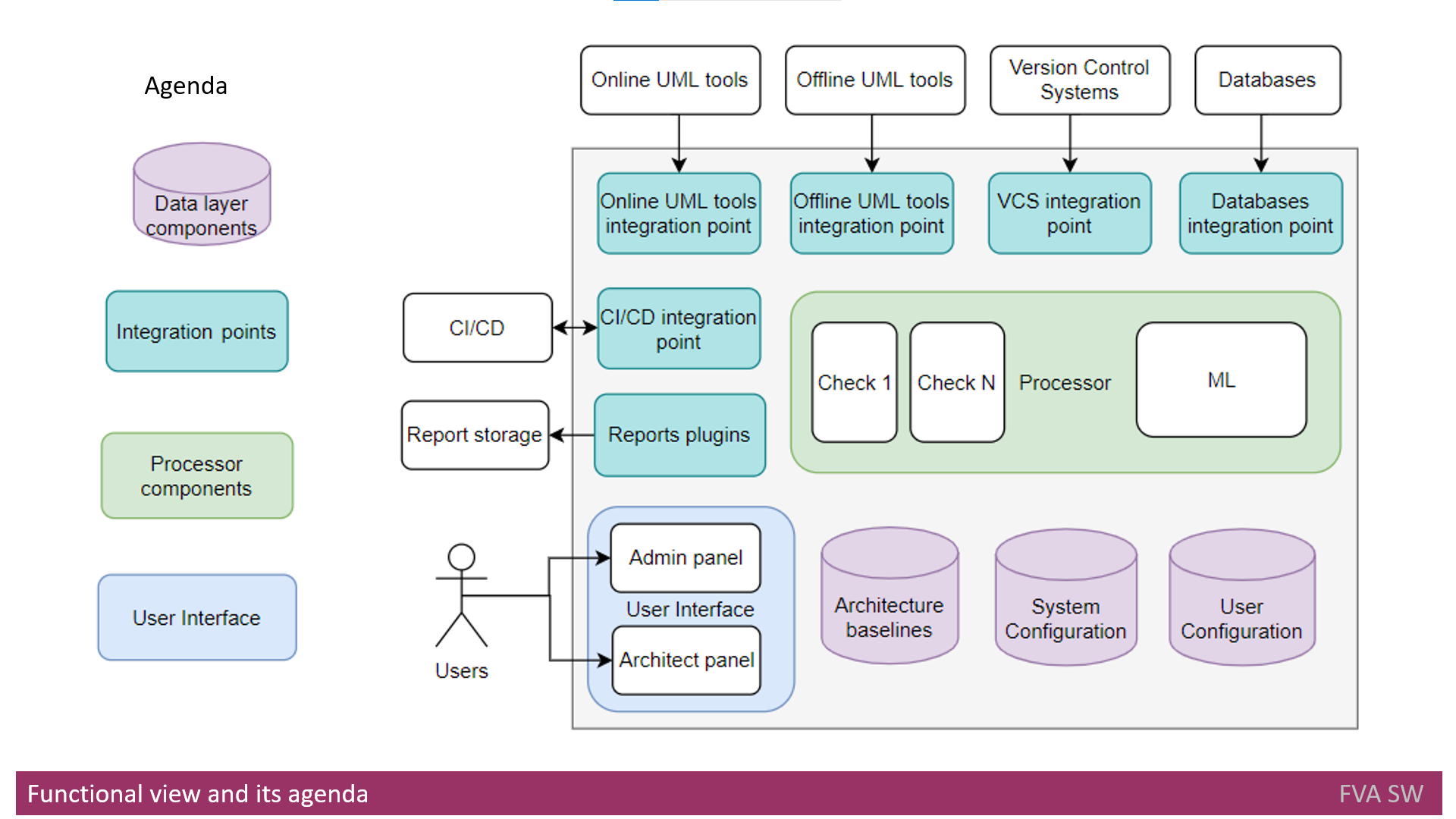
## Integration Layer
The function of the integration layer is to abstract and segregate the system from external components, enhancing system extensibility and modifiability.
The following components are involved:
- Online UML Tools Integration Point: This component integrates Online UML tools with the Processor.
- Offline UML Tools Integration Point: This component integrates Offline UML tools with the Processor.
- Version Control Systems (VSC) Integration Point: This component integrates Version Control Systems with the Processor.
- Databases Integration Point: This component integrates database configurations with the Processor.
- CI/CD Integration Point: This component integrates CI/CD tools (such as Jenkins, Bamboo) with the Processor.
- Reports Plugins: An engine designed to generate reports in a flexible manner and store them in an external report storage.
## User Interface
The user interface function interacts with users in two modes: **architects** and **administrator** mode.
It utilizes a web interface that is compatible with desktop browsers.
## Data Layer
The data layer function maintains the following types of data:
- Architecture Baselines: This feature records the history of architecture changes, allowing users to track and view past changes. It is accessible for viewing from the architects' panel.
- System Configuration: This aspect encompasses a set of check configurations for processing. It also keeps track of configurations for report plugins. Changes to these configurations can be made from the architects' panel.
- User Configuration: This includes user profiles and access rights, which can be modified from the administrator panel.
## Processing Layer
The processing layer serves as a fundamental function within systems, tasked with processing input data to identify architecture problems.
Configuration of this layer takes place through the architect panel, where checks against the input are initiated.
Additionally, it collaborates with the reports plugins engine for report storage.
Furthermore, the extracted architecture is preserved in **Architecture** baselines, enabling architects to review it at a later time.
It is worth noting that **Machine Learning (ML)** might be employed during processing to enhance the quality of reports.
# Deployment View
The deployment view illustrates how a solution is intended to be deployed, encompassing its flows and the supporting components.
## Deployment View - On-Premises
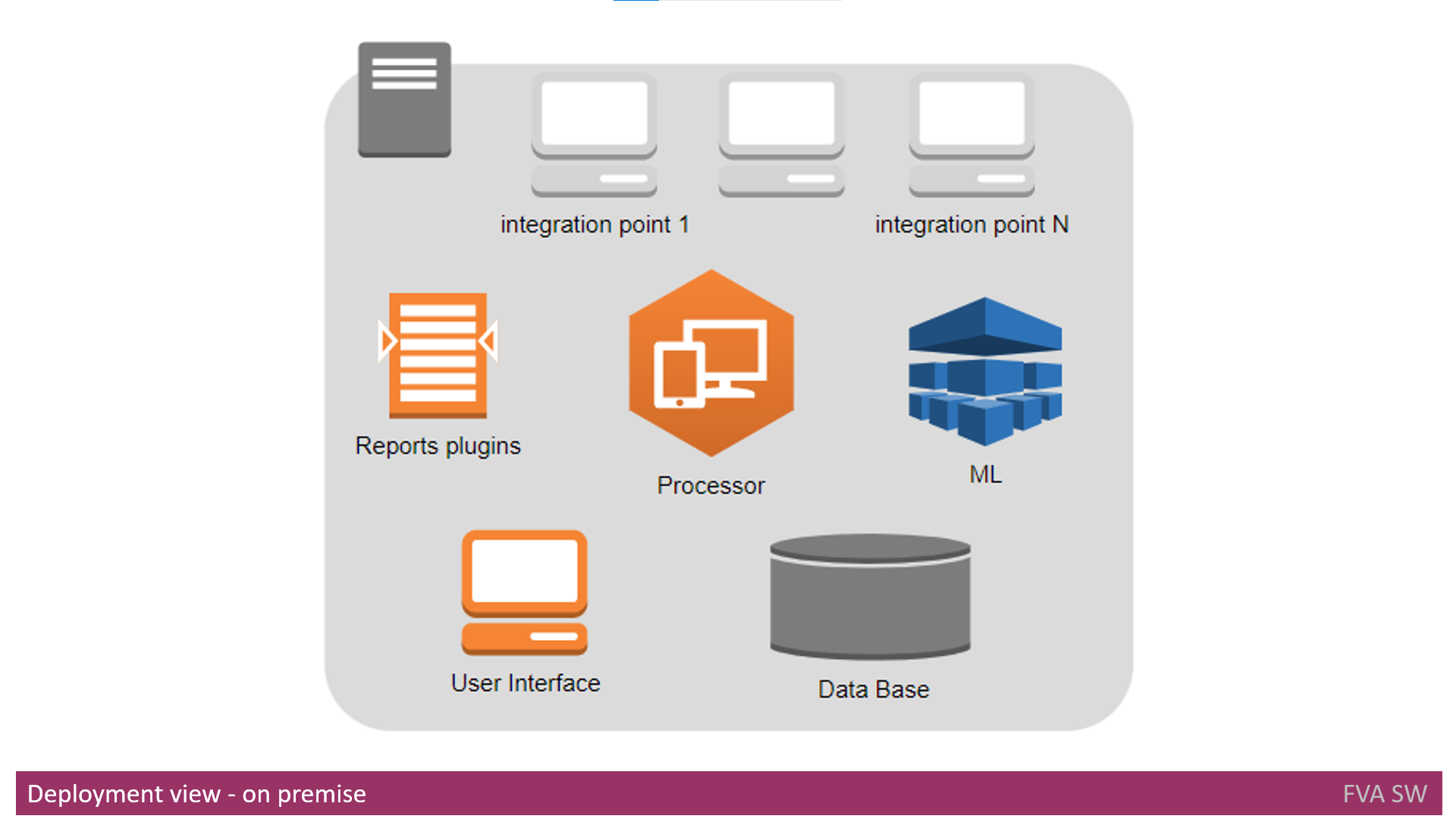
On-premise deployment assumes the use of a single computing node for installation.
The **Database** component should be deployed first, as other components depend on it.
Subsequently, the **Processor** and **ML components** are deployed once the Database component is in place.
The **User Interface** component, report plugins, and integration points are deployed in the final stage.
The **Database** component is deployed as a single DB instance with multiple schemas inside.
The **User Interface** component is presented as a web service, while the **Processor** and **ML components** are native processes built for the target platform.
Reports plugins and integration points are designed as dynamic libraries that can be easily added, removed, and configured at runtime.
## Deployment View - Cloud
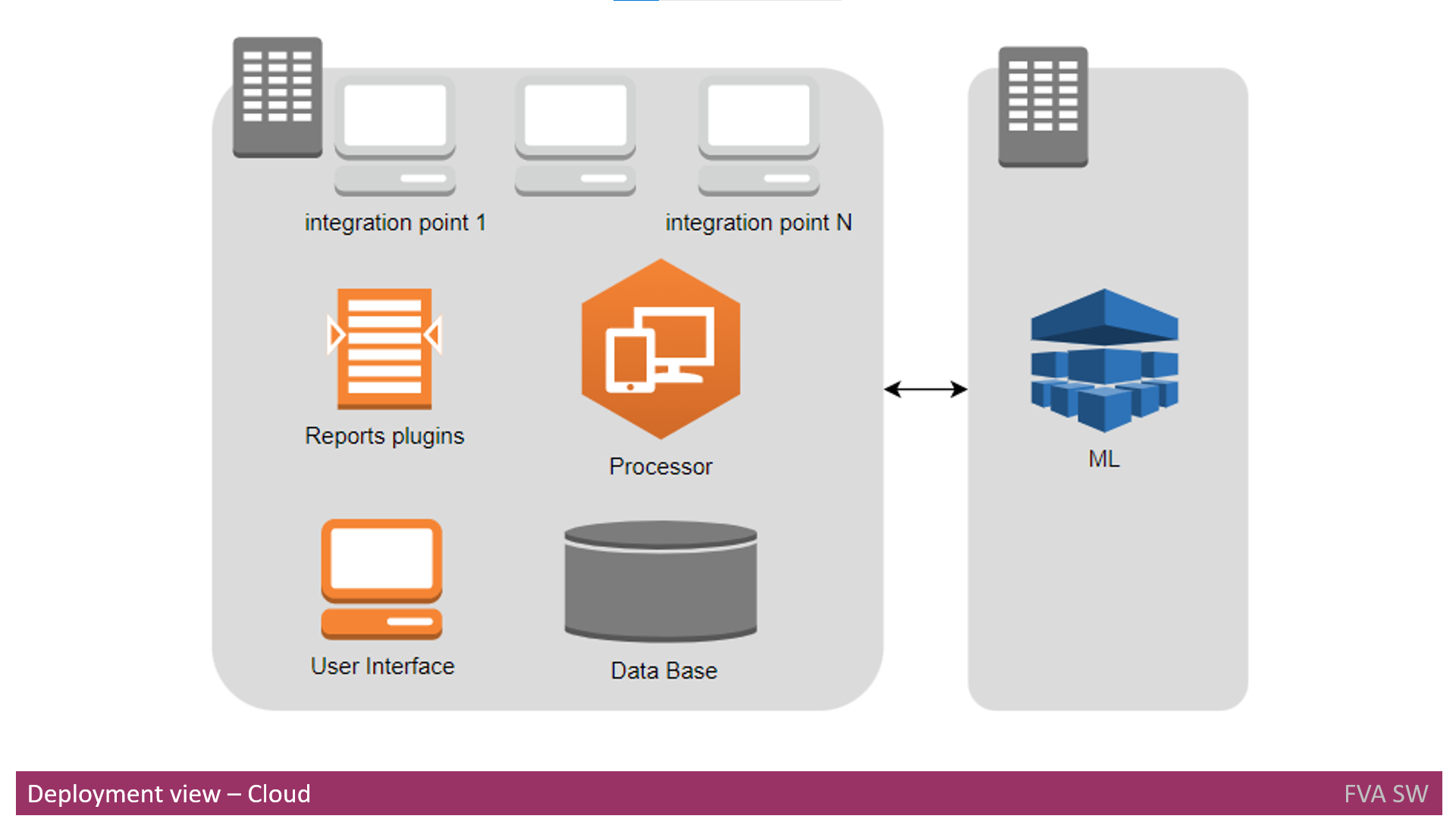
**Cloud deployment** involves the utilization of two computing nodes for installation.
Due to the potentially high **CPU usage** of the Machine Learning process, it is recommended to allocate a dedicated machine for this purpose within the cloud pipeline.
# Integration with UML Design Tools:
As previously mentioned, the proposed solution should seamlessly integrate with offline **UML design** tools, including:
- Microsoft Visio
- OmniGraffle
Furthermore, the proposed solution should also integrate effectively with online **UML design** tools, which encompass:
- Enterprise Architecture
- LucidChart
- Draw.IO
- PlantUML
- Gliffy.com
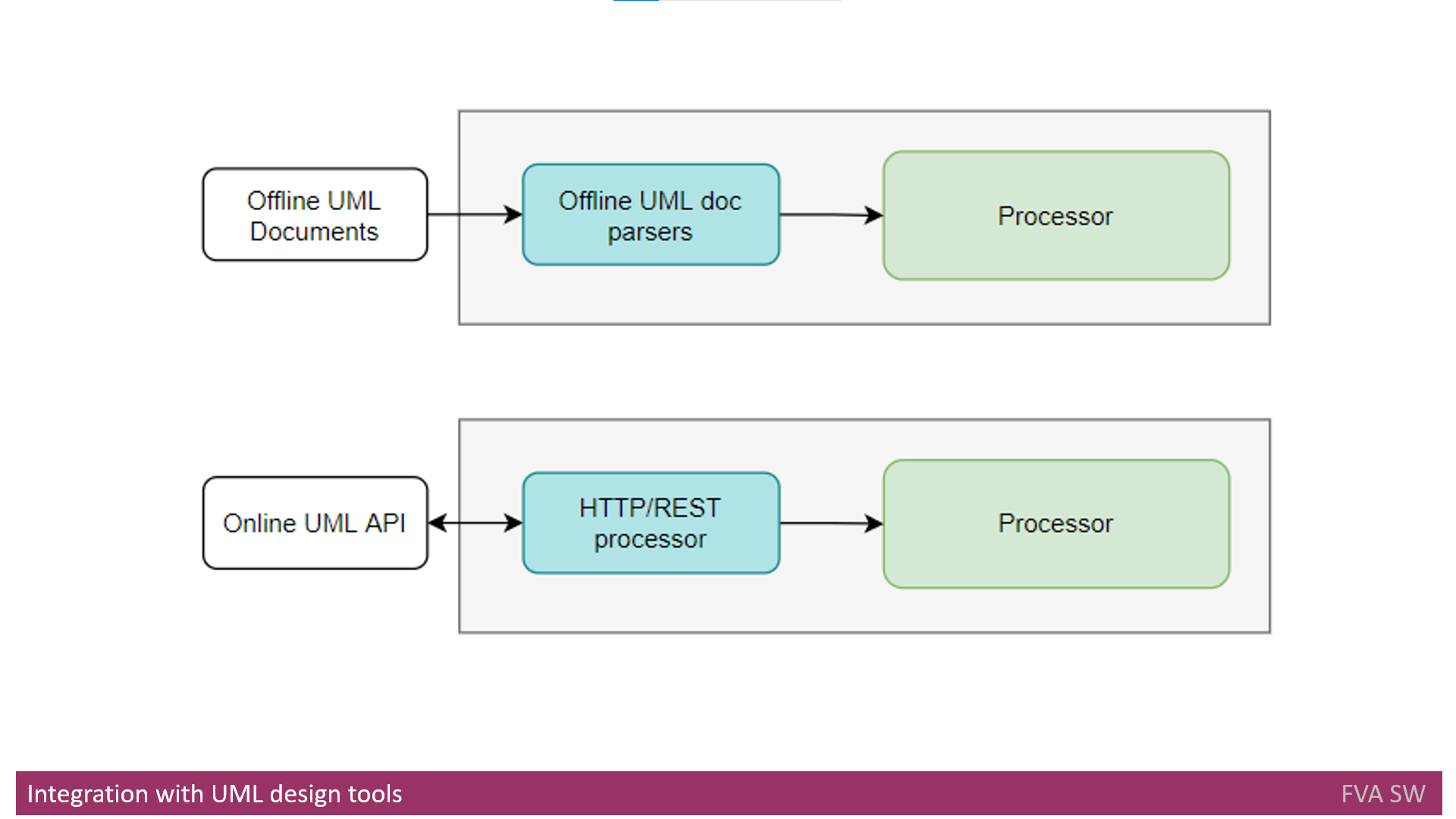
## Integration with Offline UML Design Tools
Due to the absence of **APIs** in offline tools, collaboration with them is established through import mechanisms.
Consequently, architectural documents saved in **Microsoft Visio** format will be exported by a plugin (integration point) and subsequently analyzed by the **Processor**.
The path for scanning input documents will be stored in the **System Configuration DB**.
To support this form of integration, the ability to parse various input formats must be implemented.
## Integration with Online UML Design Tools
**Online UML** design tools typically offer **APIs** for integration purposes.
The collaboration with such tools will make use of their respective **APIs**.
However, it's important to note that some UML design tools might lack **APIs** for integration.
In such scenarios, the import of architecture documents to a designated folder will be undertaken.
The subsequent parsing of these documents will be implemented to import data into the **Processor**, following a similar approach as outlined earlier for offline tools.
For online **UML** design tools, **HTTP** or **REST APIs** are commonly available.
Accordingly, the integration point will access data within the **UML design** tool using the provided **HTTP** or **REST API**.
Each integration with a specific tool will require a distinct integration point.
For instance, integration with **LucidChart** will be realized using the **HTTP** protocol with **GET** and **POST** verbs.
On the other hand, integration with **Enterprise Architect** will involve the use of a **REST API** with **JSON** as the data format.
# Integration with AWS, Azure, or GCP
This section outlines how the proposed solution can seamlessly integrate with **AWS**, **Azure**, or **GCP**.
Given the potential enhancements **Machine Learning** can offer in terms of result quality, it is advisable to allocate a dedicated compute node for **ML** tasks.
However, in scenarios where the on-premise environment lacks the capability to support **ML** calculations, a viable solution is to leverage a **Cloud Environment** for both **ML** computation and the overall computing needs.
Drawing from the deployment flows previously described, each component should be matched with the appropriate cloud provider service.
For instance, in the context of **AWS**:
- Processor - Leveraging AWS Lambda functions
- Database - Utilizing RDS and MySQL services
- Machine Learning - Employing AWS Machine Learning services
- And so forth for other components
Similar mapping strategies can be applied for **Azure** and **GCP**, ensuring that each component seamlessly integrates with the suitable services provided by the respective cloud platforms.
# Dependency Analysis Tool
Dependency identification plays a crucial role in architecture analysis.
It dissects the entire codebase into components and elucidates their interactions.
Given that similar functions are already available in tools like **JDeps**, leveraging their output would logically bolster the implementation of the **proposed solution**.
**JDeps**, for instance, is a command-line tool utilized for launching the **Java** class dependency analyzer.
For systems built on the **.NET framework**, **Net Dependency Walker** serves as a suitable choice to ascertain dependencies.
# Integration with Jenkins or Bamboo
As mentioned previously, one facet of the application involves integration within a **CI/CD** pipeline.
**CI/CD** represents a multifaceted and composite process, encompassing numerous stages.
Within a single **CI/CD** pipeline, a plethora of functionalities converge to facilitate a comprehensive workflow.
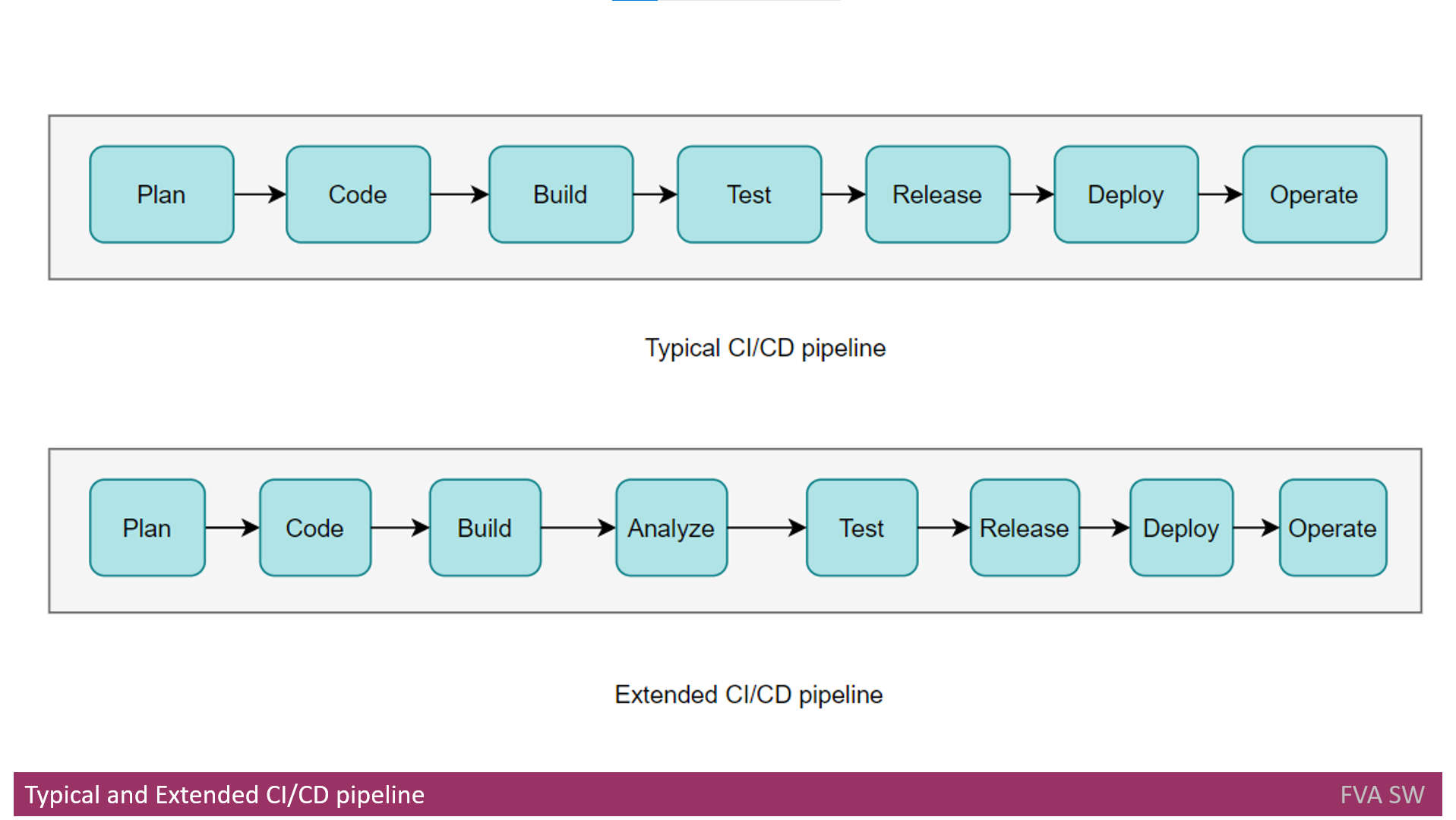
The diagram provided illustrates a standard **CI/CD** pipeline, depicted as the first pipeline.
This pipeline encompasses multiple sequential stages, which include:
- Plan
- Code
- Build
- Test
- Release
- Deploy
- Operate
At present, two prominent products, **Jenkins and Bamboo**, serve as implementations of the **CI/CD** pipeline concept.
In real-world project scenarios, both Jenkins and Bamboo are utilized to create pipelines tailored to specific project requirements.
Typically, upon each code commit, at least one pipeline is triggered, orchestrating various processes.
In the context of integrating the proposed solution, the existing pipeline structure can be extended.
This extension entails invoking the proposed solution for architecture analysis.
Consequently, the augmented pipeline would resemble the second pipeline depicted in the provided diagram. | dimanikulin |
1,871,920 | This Week In Python | Fri, May 31, 2024 This Week in Python is a concise reading list about what happened in the past week... | 0 | 2024-05-31T10:38:22 | https://bas.codes/posts/this-week-python-076 | thisweekinpython, python |
**Fri, May 31, 2024**
This Week in Python is a concise reading list about what happened in the past week in the Python universe.
## Python Articles
- [Statically Typed Functional Programming with Python 3.12](https://wickstrom.tech/2024-05-23-statically-typed-functional-programming-python-312.html)
- [Better persistent KV store coming to Python stdlib](https://blog.vslira.net/2024/05/jit-and-gil-removal-are-not-even-my.html)
- [PyPy has been quietly working for me for several years now](https://utcc.utoronto.ca/~cks/space/blog/python/PyPyQuietlyWorking)
- [Django Enhancement Proposal 14: Background Workers](https://www.djangoproject.com/weblog/2024/may/29/django-enhancement-proposal-14-background-workers/)
- [50x faster solves with sharded repodata](https://prefix.dev/blog/sharded_repodata)
## Projects
- [resume-builder](https://github.com/koek67/resume-builder) – Create a clean, easy to read resume in pure Python
- [orjson](https://github.com/ijl/orjson) – Fast, correct Python JSON library
- [ipyblender-experimental](https://github.com/kolibril13/ipyblender-experimental) – Blender in Jupyter
- [searxng](https://github.com/searxng/searxng) – free internet metasearch engine which aggregates results from various search services
- [tapyr-template](https://github.com/Appsilon/tapyr-template) – Tapyr template for PyShiny applications
| bascodes |
1,872,001 | ChatGPT - Prompts for Coding Best Practices or Principles | Discover the various ChatGPT Prompts for Coding Best Practices or Principles | 0 | 2024-05-31T11:35:11 | https://dev.to/techiesdiary/chatgpt-prompts-for-coding-best-practices-or-principles-33m | chatgpt, promptengineering, ai, programming | ---
published: true
title: 'ChatGPT - Prompts for Coding Best Practices or Principles'
cover_image: 'https://raw.githubusercontent.com/sandeepkumar17/td-dev.to/master/assets/blog-cover/chat-gpt-prompts.jpg'
description: 'Discover the various ChatGPT Prompts for Coding Best Practices or Principles'
tags: chatgpt, promptengineering, ai, programming
series:
canonical_url:
---
## Coding Best Practices or Principles Explained:
* Coding best practices, or coding principles, are guidelines that help developers write clean, efficient, and maintainable code.
* By following these practices, developers can improve the readability, performance, and overall quality of their code.
* It's important to adapt these principles based on the specific programming language, framework, or project requirements.
* Some common coding best practices include
* Keeping code simple and readable
* Avoiding code duplication
* Writing modular and loosely coupled code.
* Using meaningful comments.
* Writing self-explanatory code.
* Following coding style and conventions.
* Testing code, handling errors and exceptions gracefully.
* Optimizing for performance.
* Using version control.
* Regularly refactoring and cleaning up code.
> "Any fool can write code that a computer can understand. Good programmers write code that humans can understand." - Martin Fowler
## ChatGPT Prompts for Coding Best Practices:
| | Prompt |
| --- | --- |
| 1 | What are some key coding best practices that you follow? |
| 2 | What are some common mistakes to avoid when writing code? |
| 3 | What are some best practices for coding specific types of applications? |
| 4 | What are some common coding mistakes to avoid when doing specific tasks? |
| 5 | Explain how to use a specific coding tool or library. |
| 6 | How do you stay updated with the latest coding best practices and industry trends? |
| 7 | I want you to act as a mentor and suggest some coding best practices. |
| 8 | Can you share any personal experiences where following coding best practices helped you in a project? |
| 9 | How do you ensure code reusability and avoid code duplication? |
| 10 | How do you ensure code reusability in `JavaScript`? Any specific techniques or patterns? |
| 11 | What is your approach to writing modular and loosely coupled code? |
| 12 | How do you ensure code modularity and loose coupling in `C#`? Any specific patterns or approaches? |
| 13 | What are some ways to optimize `C#` code for performance? |
| 14 | Suggest ways to improve the performance of specific parts of code. |
| 15 | Can you share some tips for writing efficient and optimized `SQL queries`? |
| 16 | Provide some tips for writing efficient code. |
| 17 | Can you provide some tips on writing clean and efficient code? |
| 18 | Can you share some tips for writing clean and readable code? |
| 19 | Share your thoughts on refactoring and code cleanup. How often do you do it and why? |
| 20 | What steps do you take to ensure the correctness of your code through testing? |
| 21 | How do you maintain version control and collaborate effectively with other developers? |
| 22 | What are some `JavaScript` best practices for writing clean and maintainable code? |
| 23 | How do you handle errors and exceptions in your code? Any best practices? |
| 24 | How do you handle exceptions and errors in `Python`? Any specific best practices? |
| 25 | Can you share some tips for effective error handling and exception management in `JavaScript`? |
| 26 | How do you document your code effectively? Any tips for writing meaningful comments? |
| 27 | Can you share some tips for effective `Python` documentation and writing meaningful docstrings? |
| 28 | Can you share some tips for effective `Java` documentation and writing meaningful comments? |
| 29 | What are some common security best practices that developers should follow to ensure secure coding? |
| 30 | What are some strategies for handling and managing dependencies in your codebase? |
## ChatGPT Prompts for Code Principles:
| | Prompt |
| --- | --- |
| 1 | What are the fundamental principles of clean code and how do they guide your coding practices? |
| 2 | Can you explain the `SOLID` principles and how they promote maintainable and flexible code? |
| 3 | How do you follow the principle of `single responsibility` and ensure that your functions and classes have a clear and focused purpose? |
| 4 | Can you discuss the principle of `separation of concerns` and how it helps in writing modular and loosely coupled code? |
| 5 | Can you explain the principle of `design patterns` and how they contribute to writing scalable and maintainable code? |
| 6 | How do you apply the `DRY (Don't Repeat Yourself)` principle in your code to avoid duplication and improve maintainability? |
| 7 | Can you explain the principle of `favoring composition over inheritance` and how it promotes code reuse and flexibility? |
| 8 | How do you apply the principle of `encapsulation` to hide implementation details and provide a clean interface for interacting with your code? |
| 9 | Can you explain the principle of `abstraction` and how it helps in managing complexity and improving code maintainability? |
| 10 | Can you explain the principle of `defensive programming` and how it helps in handling errors and unexpected situations in your code? |
| 11 | Can you discuss the principle of `test-driven development (TDD)` and how it influences your coding practices? |
| 12 | How do you apply the principle of `continuous integration and continuous delivery (CI/CD)` in your development process? |
| 13 | Can you discuss the principle of `code readability` and how it impacts the maintainability and collaboration of your codebase? |
| 14 | How do you apply the principle of `code maintainability` to ensure long-term sustainability and ease of future enhancements? |
| 15 | How do you apply the principle of `loose coupling` in your code to enhance flexibility and maintainability? |
| 16 | How do you follow the principle of `code reusability` and ensure that your code is modular and easily adaptable? |
| 17 | Can you explain the principle of `code modularity` and how it helps in managing complexity and improving code maintainability? |
| 18 | How do you ensure the principle of `code simplicity` and avoid unnecessary complexity in your code? |
| 19 | Can you discuss the principle of performance optimization and how it impacts the efficiency of your code? |
| 20 | How do you ensure the principle of `scalability` in your code to handle growing demands and user base? |
---
## NOTE:
> [Check here to review more prompts that can help the developers in their day-to-day life.](https://dev.to/techiesdiary/chatgpt-prompts-for-developers-216d)
| techiesdiary |
1,872,002 | Top Microservices Design Patterns for Microservices Architecture | Imagine breaking down a single functional unit into multiple mini-service units. That is exactly what... | 0 | 2024-05-31T11:32:46 | https://dev.to/harisapnanair/top-microservices-design-patterns-for-microservices-architecture-3gi7 | microservices, devops, devchallenge, testing | Imagine breaking down a single functional unit into multiple mini-service units. That is exactly what microservices do to the traditional monolithic architecture. But there is more to it than meets the eye. Microservices are the go-to solution for all the major software development projects.
But even though it serves a major purpose, certain challenges must be addressed. As one designs a microservice architecture along the way, one learns several microservice design patterns, which can improve performance and ease the developer’s life. There is an increasing demand for knowledge about microservices design patterns as the adoption of microservices architecture increases among organizations. Let us learn about the various microservices design patterns in detail.
Check out the [Monolithic vs Microservices](https://www.lambdatest.com/blog/monolithic-vs-microservices-architecture/?utm_source=hashnode&utm_medium=organic&utm_campaign=may_10&utm_term=bw&utm_content=blog) debate to uncover the pros, cons, and key distinctions between the two architectures and navigate your choices wisely!
## What are Microservices Design Patterns?
A microservices design pattern is a collection of practices and tried and true solutions to common issues in microservices architecture’s design, deployment, and maintenance. It provides a structured approach to solving recurring issues, such as service communication, fault tolerance, scalability, etc. It helps to ensure that microservices work seamlessly in a cohesive and resilient manner. By leveraging these patterns, developers can streamline microservices’ design, implementation, and management and foster a robust and efficient distributed system.
[Microservices design principles](https://www.lambdatest.com/blog/9-fundamentals-to-a-successful-microservice-design/?utm_source=hashnode&utm_medium=organic&utm_campaign=may_10&utm_term=bw&utm_content=blog) provide a comprehensive guideline for designing scalable and maintainable microservices architectures. Some important microservice principles are API Integration, Traffic Management, Data Storage Segregation, Unique Source Of Identification, etc.
> Easily compare text files with our [**text compare](https://www.lambdatest.com/free-online-tools/text-compare?utm_source=hashnode&utm_medium=organic&utm_campaign=may_10&utm_term=bw&utm_content=free_online_tools)** tool. Try it now!
## Top Microservices Design Patterns
Various patterns like the event-driven pattern, saga pattern, bulkhead pattern, event sourcing design pattern, etc., help us solve collaboration, performance, deployment issues, etc.
Let us delve into the essential patterns that empower developers to build an agile, resilient, scalable, and robust microservices architecture.
## Microservices Design Patterns for Effective Collaboration
Collaboration is necessary for running an efficient microservice architecture with so many microservices running simultaneously. Let’s look at the collaboration patterns for designing a microservice and understand them in detail.
**Aggregator Microservice Design Pattern**
Since multiple services are involved, the output must be fetched and combined for the end user. To integrate the data, a user will need a lot of internal knowledge about the system. Since we design microservices architecture, decomposing the monolith means dividing the output sources. That’s why we use the aggregator pattern to aggregate this data.
The aggregator microservice design pattern consolidates data from multiple microservices into a unified result for an end-user. By acting as a single point of contact, this pattern helps fetch and combine the necessary information from various microservices instead of the client making multiple requests. This pattern promotes efficiency, reduces network latency, and simplifies the client’s interaction with the microservices ecosystem.
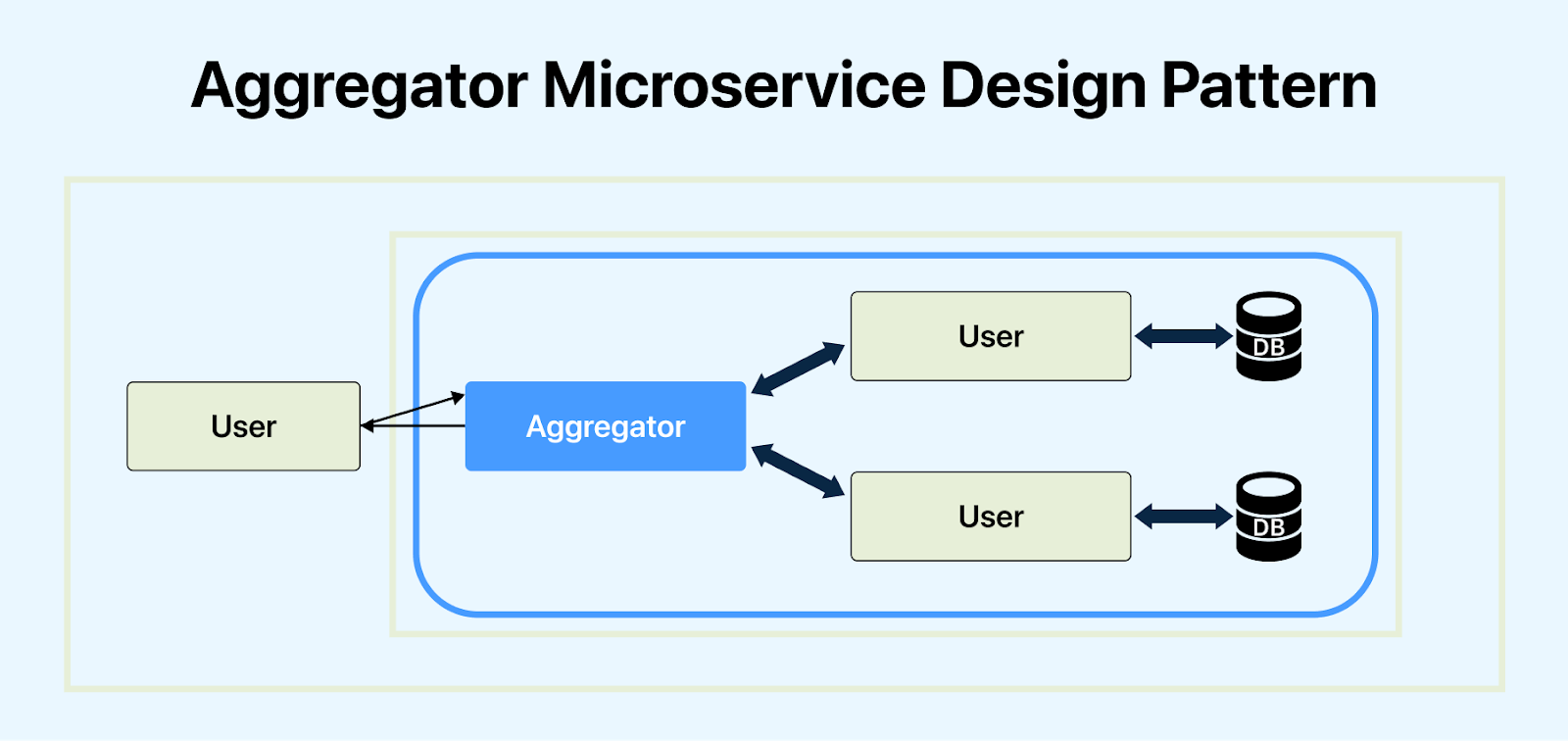
The user initiates a request by sending it to the aggregator microservice. Upon receiving the request, the aggregator identifies the relevant data sources needed to fulfill the user’s request and sends individual requests to each identified data source. These data sources then respond to the aggregator microservice with their respective data. Once all responses are collected, the aggregator microservice aggregates the data from all sources into a cohesive form. Finally, the aggregator microservice sends the aggregated data back to the user as a response to the original request.
The solution can be forwarded to the end user through two major components: *composite microservice* and *API gateways*. Composite microservices involve grouping multiple smaller microservices to provide cohesive, higher-level functionality. API gateways serve as a unified entry point for external clients to access and interact with microservices. Either of the components will aggregate the data and forward it to the user. However, composite microservices should be preferred if business capabilities are used in decomposing the system.
**Branch Microservice Design Pattern**
The branch microservices design pattern extends the aggregator design patterns. It enables concurrently processing requests and responses from two or more distinct and mutually exclusive chains of microservices.

In the above example, service A communicates with multiple services simultaneously.
This design pattern also offers the flexibility to summon separate multiple chains or even a single chain as per the business needs. In the case of an e-commerce website or web application, we need to retrieve data from multiple sources belonging to different microservices. This is where the branch microservice design pattern plays an effective role.
> Convert strings to JSON format effortlessly with our [**string to json](https://www.lambdatest.com/free-online-tools/string-to-json?utm_source=hashnode&utm_medium=organic&utm_campaign=may_10&utm_term=bw&utm_content=free_online_tools)** tool. Check it out!
**API Gateway Microservice Design Pattern**
Fetching data from running services is crucial for any application, especially in a microservices architecture. Extracting data from individual services is vital, but presenting user-owned resources from multiple microservices through a single UI can pose challenges. An API gateway acts as a single entry point, managing tasks like routing, composition, and protocol translation within the architecture.
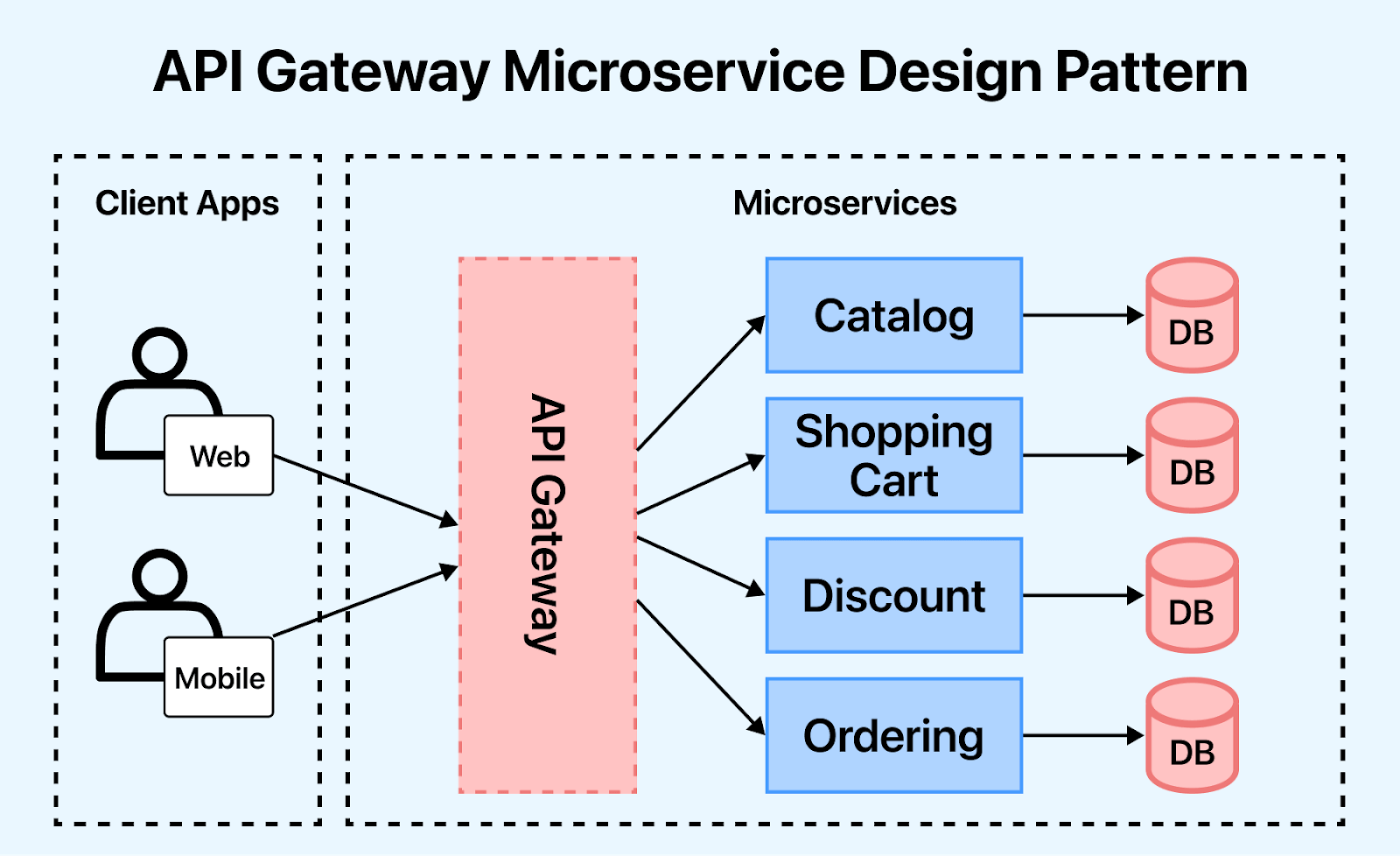
The above scenario shows that the API gateway collects client requests in a single entry point and routes requests to internal microservices. As a single source of contact, it can act as a proxy server to route requests to microservices, aggregate results from multiple services, and send the output to the user. It can handle multiple protocol requests and convert whenever required. (eg. HTTPS to AMQP and vice versa). It also helps establish security by client authorization and exposes relevant APIs concerning the client.
**Backend for Front-End(BFF) Microservice Design Pattern**
Backend for Front-End (BFF) is a subset of the API Gateway microservices design pattern. It involves creating a dedicated backend service tailored to the specific needs of a front-end application or client. This pattern ensures a more efficient and streamlined interaction between a system’s frontend and backend components.
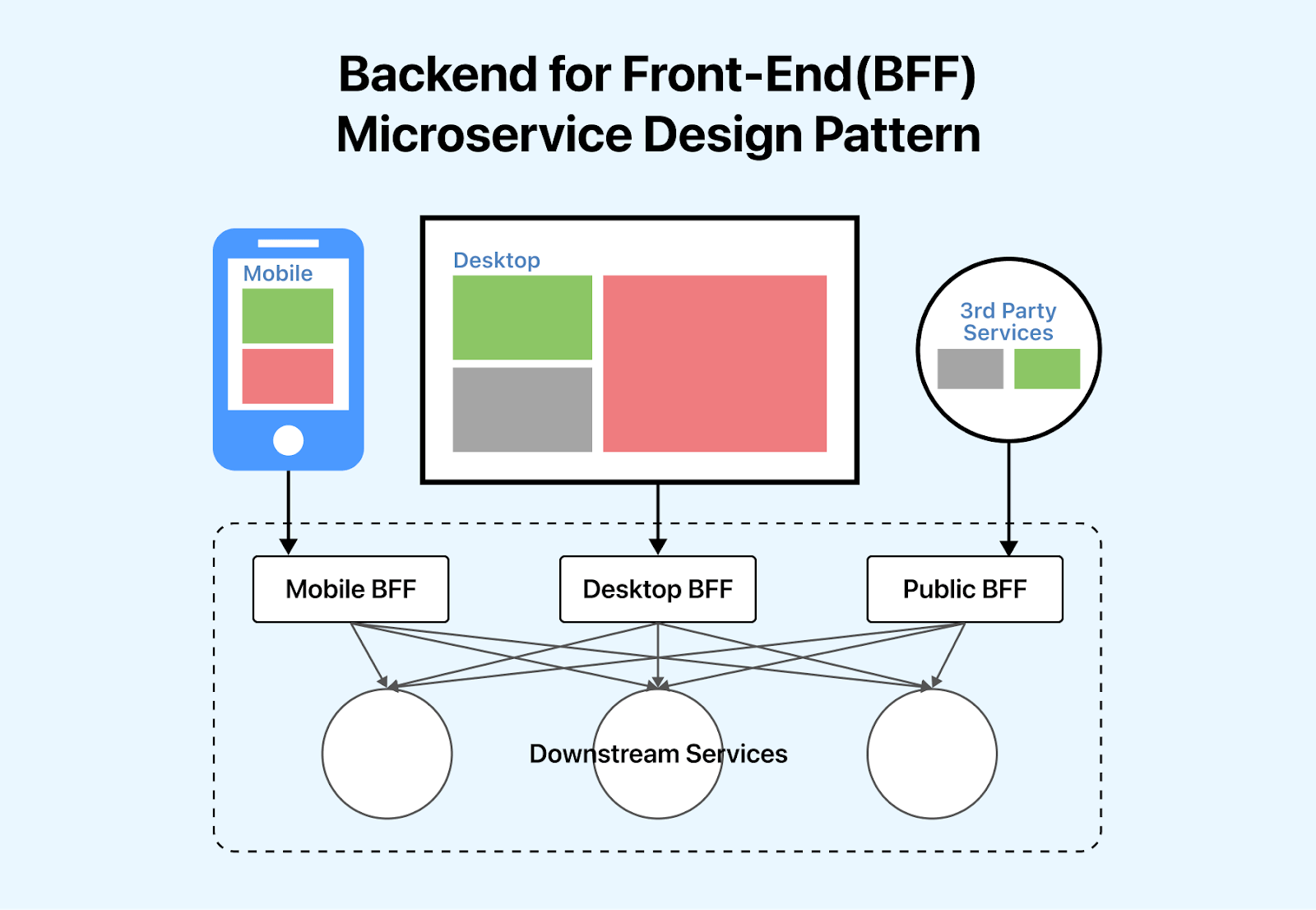
Consider an e-commerce platform that serves both web and mobile applications. Implementing the Backend for Front-End (BFF) pattern in this scenario involves creating dedicated backend services for each front-end application. The web application’s BFF will optimize APIs for large-screen displays, while the mobile app’s BFF could tailor APIs for a smaller screen and different user interactions. And there will be another BFF for 3rd party services called public BFF. All these BFFs interact with the downstream services.
This pattern enhances collaboration by allowing frontend and backend development teams to work independently and more efficiently. Frontend developers can focus on building a user interface using APIs tailored precisely to their application’s requirements, while backend developers can concentrate on providing optimized and specialized services.
**The Event-Driven Microservice Design Pattern**
The Event-Driven pattern is a powerful microservices design pattern that facilitates asynchronous communication and collaboration among distributed components. In this pattern, microservices communicate through events, allowing them to operate independently while responding to specific occurrences or changes in the system.
The Event-Driven pattern employs a publisher-subscriber (PUB/SUB) model, where microservices act as either event producers or consumers. This decoupling ensures that services remain loosely interconnected, enhancing scalability, maintainability, and flexibility. By relying on events, microservices don’t need to be aware of each other, reducing direct dependencies and promoting autonomy. This results in a more collaborative architecture where services can evolve independently, responding to events as needed, and contributing to an agile and resilient microservices ecosystem.

The event-driven microservices design pattern uses three main components: the producer, consumer, and broker. The producer initiates events and publishes them to a central hub known as the broker. Consumers subscribe to specific events they are interested in and react accordingly when they receive them. Meanwhile, the broker manages the routing, filtering, and delivery of events to ensure efficient communication between producers and consumers.

For instance, in an e-commerce platform, the order service is a producer that sends an event trigger to the message broker, and the payment service, stock service, and email service are consumers who will consume the events from the message broker. When a new order is placed, an event can be triggered, leading to various microservices updating inventory, processing payments, and sending order confirmations.
**Asynchronous Messaging Microservice Design Pattern**
The asynchronous messaging microservices design pattern plays a crucial role by allowing microservices to communicate without requiring sequential interaction. By decoupling services through asynchronous communication, we can foster effective collaboration in a microservices architecture, as services can now independently process and respond to messages at their own pace, promoting flexibility and autonomy.
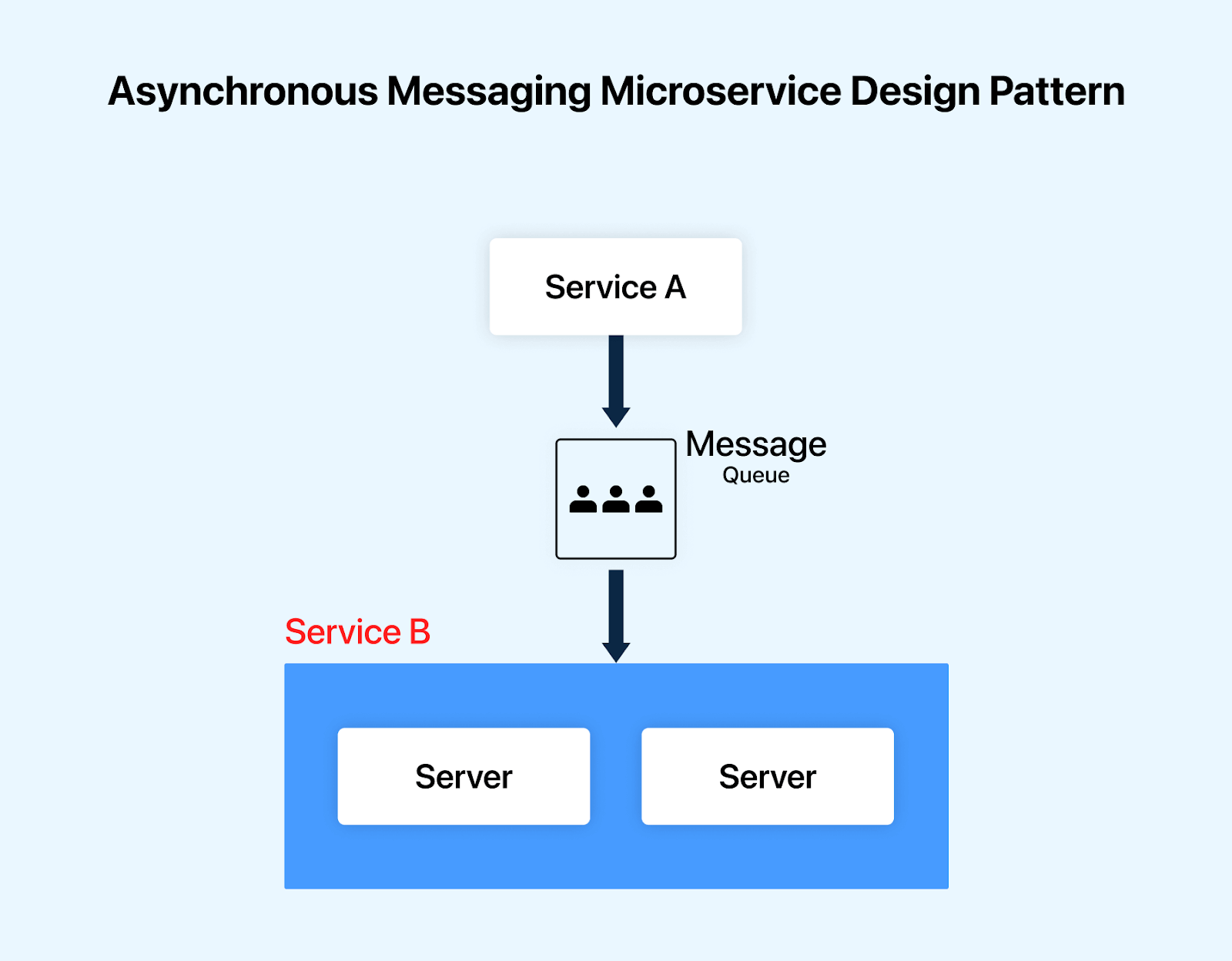
Asynchronous messaging pattern allows microservices to communicate indirectly through a message queue. When a microservice wants to send a message, it publishes it to a message queue without waiting for an immediate response from the receiver. The message queue stores the message until the receiver is ready to process it.
For example, in an e-commerce system, when a new order is placed, the order processing service sends a message to the inventory service with the help of a message queue, allowing it to independently and asynchronously handle its tasks, promoting autonomy and efficient collaboration between the microservices. While this scenario may resemble the event-driven pattern, it differs in that, with asynchronous messaging, messages are directed specifically to intended recipients via the message queue, whereas in event-driven architecture, all subscribed consumers receive event notifications broadcasted by the message broker.
**Chained or Chain of Responsibility Microservice Design Pattern**
In the chained or chain of responsibility microservices design pattern a sequence or chain of microservices, each responsible for a specific task in sequence. For example, a chain could include microservices responsible for order validation, payment authorization, and fulfillment in an order processing system. As a new order traverses the chain, each microservice collaborates seamlessly to perform its designated task.
This microservices design pattern promotes modularity and allows various teams to independently develop and maintain specific processing units, enhancing collaboration in building and evolving the system.
> Extract phone numbers quickly using our [**phone number extractor](https://www.lambdatest.com/free-online-tools/phone-number-extractor?utm_source=hashnode&utm_medium=organic&utm_campaign=may_10&utm_term=bw&utm_content=free_online_tools)**. Try it today!
**Bulkhead Microservice Design Pattern**
The bulkhead microservices design pattern is named after the compartments (bulkheads) in ships that prevent the entire vessel from sinking in case of a breach. In the context of microservices, the bulkhead pattern involves segregating components or services into isolated compartments that help to prevent failures in one compartment from affecting others.
The pattern helps to promote effective collaboration by isolating failures within specific compartments. If one microservice experiences issues or becomes overwhelmed, the failure is contained within its bulkhead, preventing a domino effect that could impact the entire system. This isolation enhances the overall stability of the microservices architecture and supports collaborative efforts by minimizing the scope of potential disruptions.
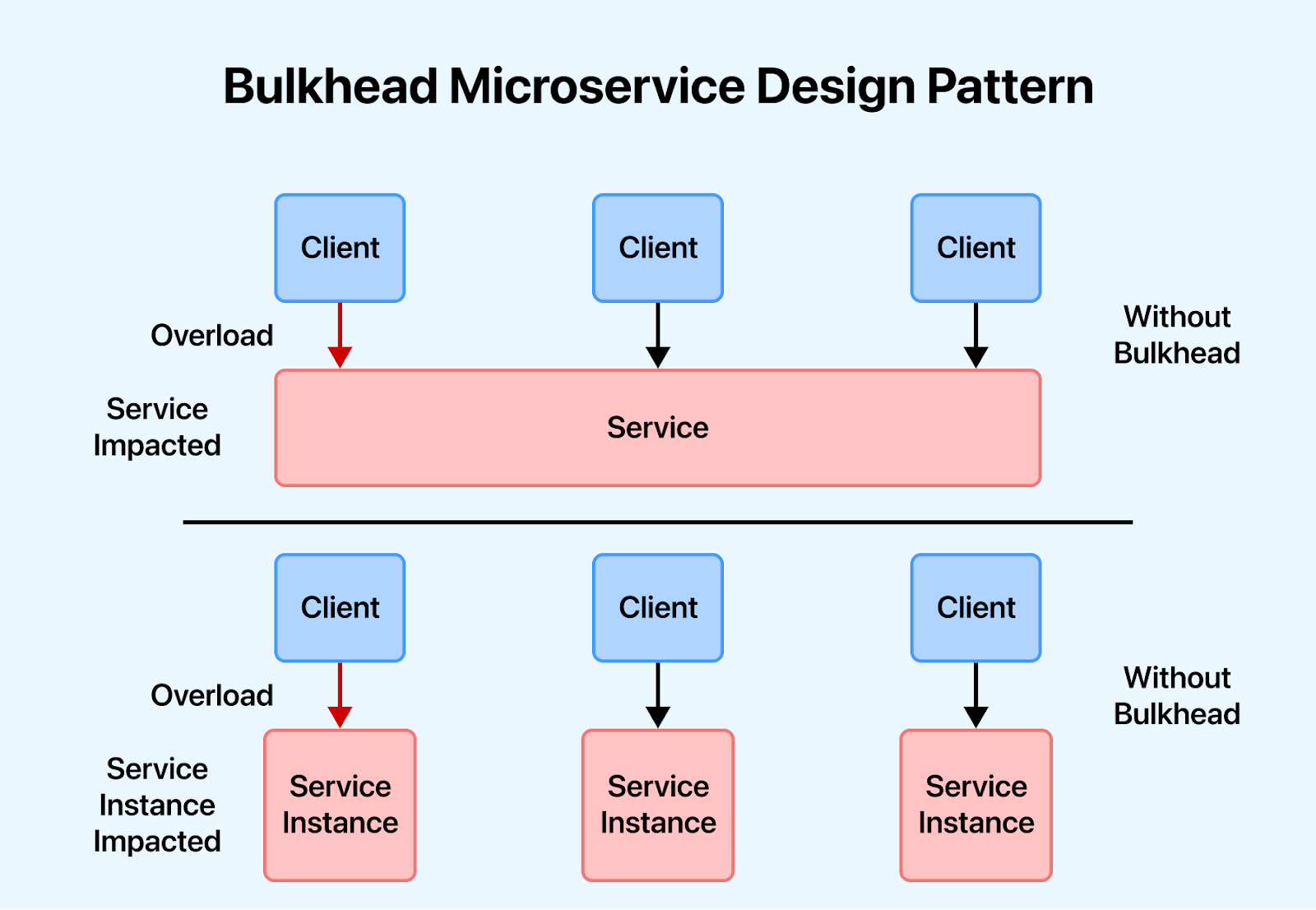
**Sidecar Microservice Design Pattern**
The Sidecar Microservice Design Pattern is an architectural pattern that enhances the functionality and capabilities of a primary service by deploying an auxiliary service, known as a “sidecar,” alongside it. It allows the main service to focus on its primary functionality while offloading certain auxiliary tasks to the sidecar.

Consider a microservices architecture with a main application service responsible for handling HTTP requests. To enhance security, we deploy a dedicated sidecar service alongside it, acting as an authentication proxy. The sidecar can then handle tasks like user authentication, token validation, and enforcing security policies.
Applying this pattern helps us to foster collaboration in microservices by promoting a clean and modular separation of concerns. With dedicated sidecar services managing common concerns like logging, monitoring, or security, each microservice can concentrate on its core logic. This modular architecture encourages independent development, scalability, and the reusability of specialized functionalities, enabling efficient collaboration among development teams working on different aspects of the microservices ecosystem.
To unlock the full potential of your microservices architecture with effective testing strategies, dive into our [*Microservices Testing Tutorial](https://www.lambdatest.com/learning-hub/microservices-testing?utm_source=hashnode&utm_medium=organic&utm_campaign=may_10&utm_term=bw&utm_content=learning_hub)* and [*Microservices Testing Quick Start Guide](https://www.lambdatest.com/blog/testing-microservices/?utm_source=hashnode&utm_medium=organic&utm_campaign=may_10&utm_term=bw&utm_content=blog)*!
## Microservices Design Patterns for Performance Monitoring
Monitoring performance is an essential aspect of a successful microservice architecture. It helps calculate the efficiency and understand any drawbacks slowing the system down. Remember the following patterns related to observability for ensuring a robust microservice architecture design.
**Log Aggregation Microservice Design Pattern**
When referring to a microservice architecture, we refer to a refined yet granular architecture where an application consists of several microservices. These microservices run independently and simultaneously, supporting multiple services and their instances across various machines. Every service generates an entry in the logs regarding its execution. How can we keep track of numerous service-related logs? This is where the log aggregation microservices design pattern steps in. In this pattern, we collect and consolidate log data generated by various microservices, allowing for centralized monitoring, analysis, and troubleshooting of the entire microservices architecture.
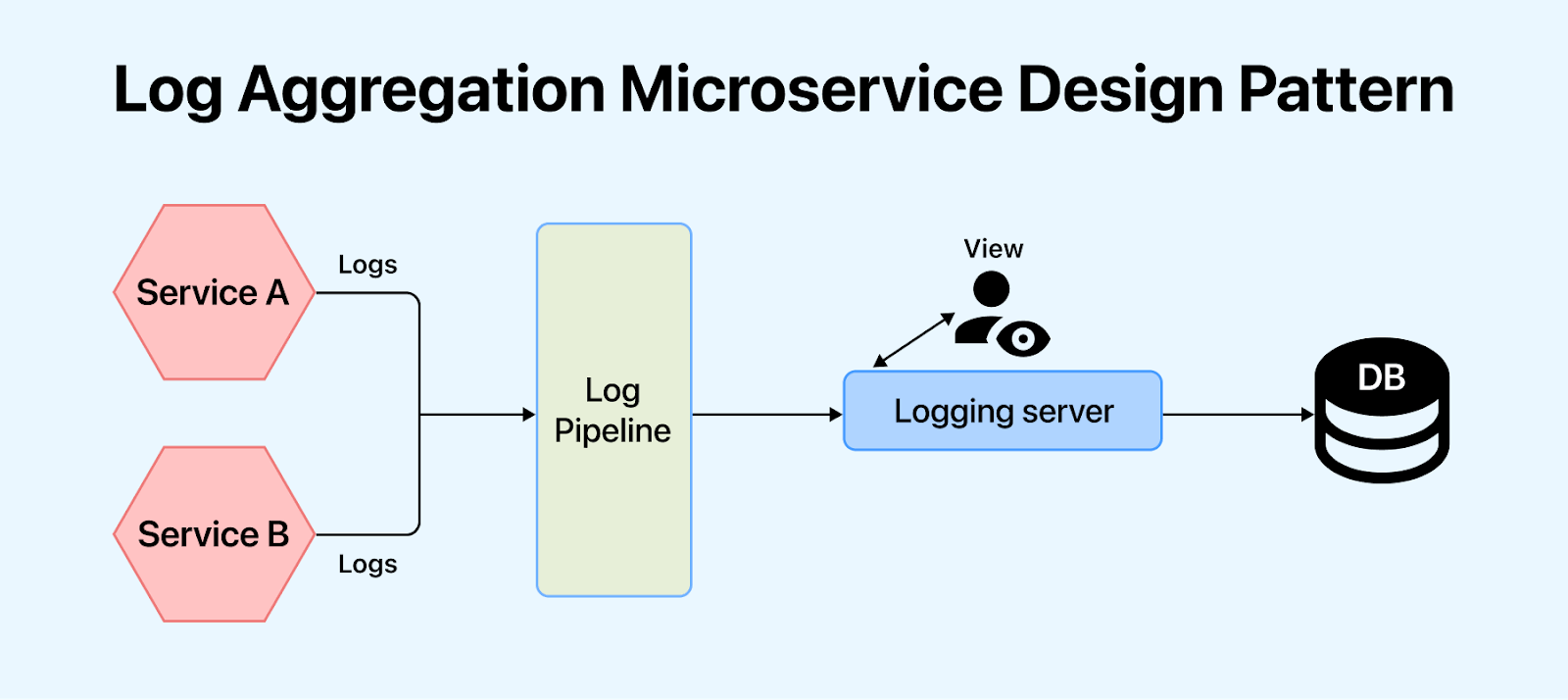
As a best practice to prevent chaos, we should have a master logging service. This master logging service should aggregate the logs from all the microservice instances. This centralized log should be searchable, making it easier to monitor.
**Synthetic Monitoring, a.k.a Semantic Monitoring Microservice Design Pattern**
Monitoring is a painful but indispensable task for a successful microservice architecture. With the simultaneous execution of hundreds of services, it becomes troublesome to pinpoint the root area responsible for the failure in the log registry. Synthetic monitoring gives a helping hand here.
In this microservices design pattern, we simulate user interactions with a system to assess its performance and functionality. In this approach, synthetic scenarios are created to mimic real user behavior. When we perform automated tests, synthetic monitoring helps to regularly map the results compared to the production environment, and the user gets alerted if a failure is generated.
We can easily monitor automated test cases and detect production failures regarding business requirements using semantic monitoring. This allows organizations to identify issues before they impact actual users proactively.
**API Health Check Microservice Design Pattern**
Microservice architecture design promotes services that are independent of each other to avoid any delay in the system. APIs, as we know, serve as the building blocks of online connectivity. It is imperative to keep a health check on your APIs regularly to realize any roadblocks. It is often observed that a microservice is up and running yet incapacitated for handling requests. This can be due to many factors like server load, user adoption, latency, error logging, market share, and downloads.
To overcome this, we can use the API health check microservices design pattern to assess and monitor the health and performance of individual APIs within a system. This helps to identify potential issues, ensure the responsiveness of microservices, and maintain overall system performance.
We should ensure that every service running must have a specific health check API endpoint. For example, when appended at the end of every service, HTTP/health will return the health status for the respective service instance. A service registry periodically appeals to the health check API endpoint to perform a health scan. The health check would provide us with the following details:
* A logic that is specific to the application.
* Status of the host.
* Status of the connections to other infrastructure or connection to any service instance.
**Circuit Breaker Microservice Design Pattern**
The circuit breaker pattern is similar to an electrical circuit breaker in our home. When there’s a fault, the breaker trips, isolating the faulty circuit and preventing further damage. Similarly, in a microservices architecture, the pattern detects service failures and temporarily breaks the circuit, preventing the spread of issues and ensuring overall system resilience.
In this microservices design pattern, the circuit breaker trips when a predefined threshold of failures is reached, preventing further requests from being sent to the failing microservice. This helps monitor and manage the overall system performance and resilience by preventing the cascading failure of microservices.
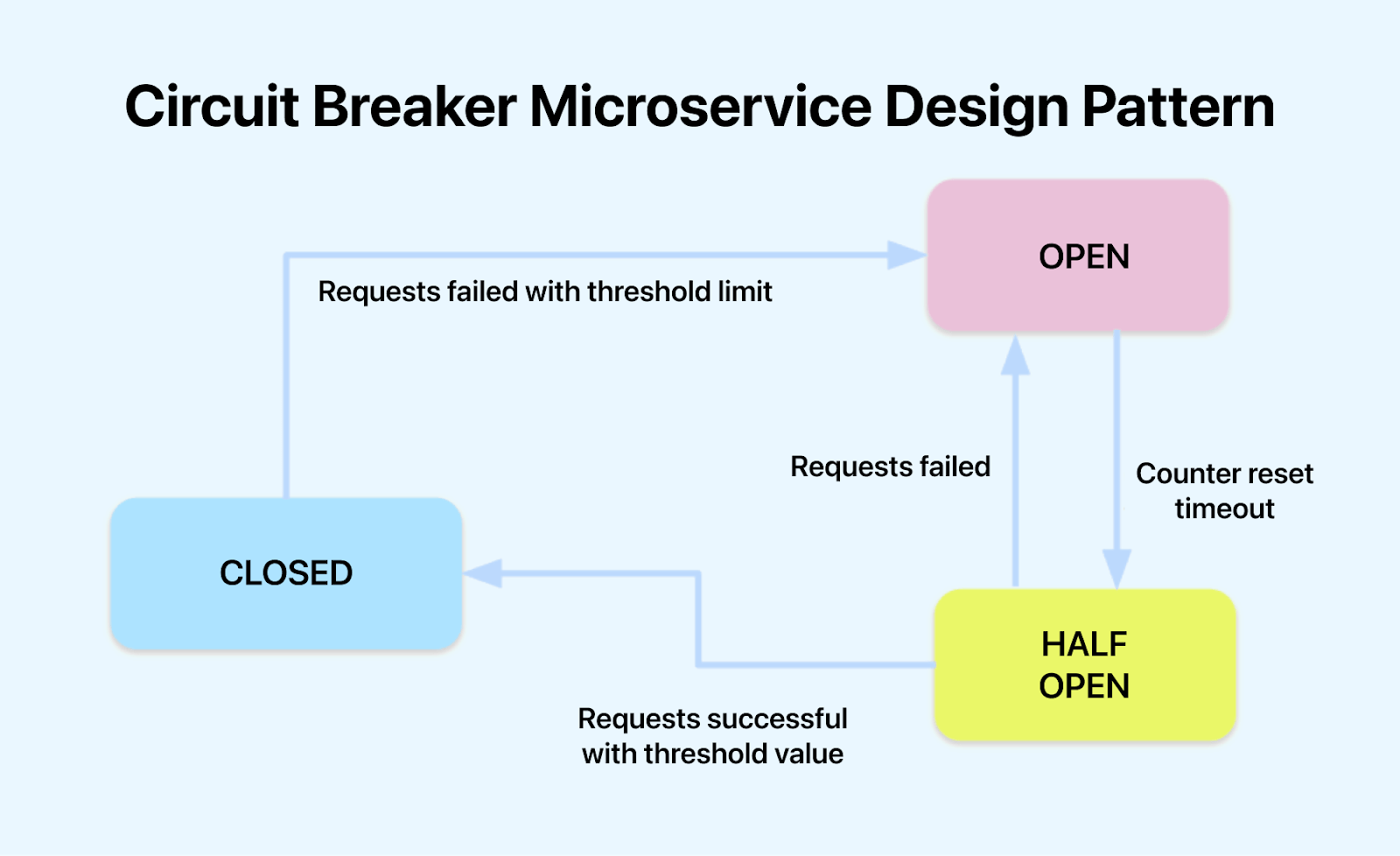
A circuit breaker has three states for reliability: “Closed” when the monitored service functions well, “Open” when issues arise, blocking requests to prevent overload, and “Half Open” when the service shows signs of recovery, allowing limited requests to test its functionality before fully reopening.
The circuit breaker microservices design pattern can be used in various places like an e-commerce system; if a product recommendation microservice starts experiencing high latency or errors due to increased traffic, the circuit breaker can transition to an open state. During this state, requests for recommendations are directed to a fallback mechanism, such as showing popular or recently viewed products. This prevents the degradation of the entire user experience and allows the system to recover without overwhelming the struggling microservice.
## Microservices Design Patterns for Business Purposes
‘Decomposing’ a monolithic architecture into a microservice must follow certain parameters. These parameters have a different basis. Today, we will look at the decomposition of the microservice design patterns, which leave a lasting impact.
> Convert HEX colors to CMYK easily with our [**hex to cmyk](https://www.lambdatest.com/free-online-tools/hex-to-cmyk?utm_source=hashnode&utm_medium=organic&utm_campaign=may_10&utm_term=bw&utm_content=free_online_tools)** tool. Use it now!
**Unique Microservice for each Business Capability**
A microservice is as successful as its high cohesion and loose coupling combination. Services need to be loosely coupled while keeping the function of similar interests together. But how do we do it? How do we decompose a software system into smaller independent logical units?
We do so by defining the scope of a microservice to support a specific business capability.
For example, in every organization, different departments come together as one. These include technical, marketing, PR, sales, service, and maintenance. To picture a microservice structure, these domains would each be the microservices, and the organization would be the system. So, inventory management is responsible for all the inventories. Similarly, shipping management will handle all the shipments and so on.
To maintain efficiency and foresee growth, the best solution is to decompose the systems using business capability. This includes classification into various business domains responsible for generating value in their capabilities.
**Microservices around similar Business Capability**
Despite segregating based on business capabilities, microservices often come up with a greater challenge. What about the common classes among the services? Composing these classes, known as ‘God Classes, ’ needs intervention. For example, in the case of an e-commerce system, the order will be common to several services such as order number, order management, order return, order delivery, etc. We turn to a common microservice design principle known as Domain-Driven Design (DDD) to solve this issue.
In Domain-Driven Design, we use subdomains. These subdomain models have a defined scope of functionality known as bounded context. This bounded context is the parameter used to create each microservice, thus overcoming the issues of common classes.
**Strangler Vine Microservice Design Pattern**
While we discuss the decomposition of a monolithic architecture, we often miss out on the struggle of converting a monolithic system to design microservice architecture. With the work being hampered, converting can be manageable. Based on the vine analogy, we have the strangler pattern to solve this problem. Here is what the Strangler patterns mean in Martin Fowler’s words:
*“One of the natural wonders of this area [Australia] is the huge strangler vines. They seed in the upper branches of a fig tree and gradually work their way down the tree until they root in the soil. Over many years, they grow into fantastic and beautiful shapes, meanwhile strangling and killing the tree that was their host.”*
Like a strangler vine slowly envelops and replaces a host tree, this pattern allows organizations to evolve their systems incrementally rather than opting for a risky and disruptive Big Bang migration. New microservices are introduced alongside the existing monolith to handle specific functionalities. Over time, new features are developed, or existing ones are refactored and implemented as microservices.
The strangler microservices design pattern is extremely helpful in the case of a web application where breaking down a service into different domains is possible. Different services live on different domains since the calls go back and forth. So, these two domains exist on the same URI. Once the service has been reformed, it ‘strangles’ the existing version of the application. This process is followed until the monolith doesn’t exist.
**Saga Microservice Design Pattern**
The saga pattern is a microservices design pattern used to manage distributed transactions within a microservices architecture. It addresses the challenges of maintaining data consistency across multiple services involved in a complex operation by breaking down a transaction into smaller, more manageable steps. Each step in the saga corresponds to an operation within a microservice, and these steps are coordinated to ensure eventual consistency.

Consider an online hotel booking where a customer initiates a reservation. Here, the saga pattern breaks down the transaction into steps handled by different microservices: creating the reservation, charging the customer, and sending a confirmation email. When the payment step fails due to a temporary issue, the saga pattern enables compensating transactions to be executed. This could involve returning the room to the inventory and implementing a retry mechanism for the payment.
By managing distributed transactions and ensuring consistency, the Saga microservices design pattern aligns with business goals by maintaining data accuracy and reliability. It supports critical business processes that span multiple microservices.
> Convert CMYK colors to HEX format effortlessly with our [**cmyk to hex](https://www.lambdatest.com/free-online-tools/cmyk-to-hex?utm_source=hashnode&utm_medium=organic&utm_campaign=may_10&utm_term=bw&utm_content=free_online_tools)** tool. Try it here!
**Backend for Front-End(BFF) Microservice Design Pattern**
The BFF pattern enables the creation of backend services that align closely with specific business requirements and user interfaces. This tailored approach ensures that the APIs provided by BFF services are finely tuned to the unique needs of each front-end application. The pattern promotes a business-centric approach by facilitating the development of microservices that directly serve the needs of specific applications, ultimately enhancing the overall effectiveness and agility of the microservices architecture.
For instance, in an e-commerce platform, the BFF for the web application might prioritize features such as advanced product filtering. At the same time, the BFF for the mobile app could focus on providing a seamless and efficient checkout process. This fine-grained customization allows businesses to optimize user experiences, implement targeted functionalities, and meet distinct business goals by strategically using BFF services.
**The Event-Driven Microservice Design Pattern**
The Event-Driven pattern enables real-time responsiveness to critical business events. This pattern is particularly valuable when certain business processes must be triggered or updated immediately in response to specific events. For instance, an event-driven approach could be employed in a banking application to instantly update account balances, trigger fraud detection mechanisms, or notify customers of transaction confirmations.
By harnessing the Event-Driven Pattern, businesses can seamlessly incorporate dynamic and event-triggered functionalities into their microservices architecture, ensuring timely and relevant responses to changing business conditions. This pattern enhances the adaptability and agility of microservices in addressing diverse business requirements and fostering a more responsive and customer-centric system.
**Chained or Chain of Responsibility Microservice Design Pattern**
By applying the chained or chain of responsibility microservices design pattern, businesses can model complex workflows in a modular and maintainable manner. Each microservice in the chain will be responsible for a specific business need, contributing to the overall business process. This enhances adaptability to evolving business requirements, as changes or updates can be made to individual microservices without affecting the entire system.
**Circuit Breaker Microservice Design Pattern**
From a business perspective, the circuit breaker pattern safeguards continuous operations and protects revenue streams. Preventing the cascading impact of microservice failures contributes to business continuity, critical for maintaining customer satisfaction and trust. The pattern not only shields against potential revenue loss caused by service disruptions but also safeguards brand reputation by providing a reliable and resilient user experience.
In essence, the Circuit Breaker Pattern aligns closely with business goals by fostering reliability, minimizing downtime, and fortifying the overall health of microservices to support sustained business success directly.
**Sidecar Microservice Design Pattern**
The sidecar microservices design pattern greatly aids in implementing business logic within microservices by enabling a focused and modular approach to development. The main microservice can exclusively concentrate on its core business logic by delegating common concerns to dedicated sidecar services. This separation ensures a clean and maintainable codebase, allowing independent updates and scalability of the business logic without unnecessary entanglement with auxiliary functionalities.
The pattern also enhances agility in adapting to evolving business requirements, facilitating a more efficient and streamlined development process.
## Microservices Design Patterns for Optimizing Database Storage
For a microservice architecture, loose coupling is a basic principle. This enables the deployment and scalability of independent services. Multiple services might need to access data not stored in their unit. However, accessing this data can be challenging due to loose coupling. Mainly because different services have different storage requirements, and access to data is limited in microservice design. So, we look at some major database design patterns per different requirements.
**Individual Database per Service**
Usually applied in domain-driven designs, one database per service articulates the entire database to a specific microservice. Due to the challenges and lack of accessibility, a single database per service needs to be designed. This data is accessible only by the microservice and the database has limited access to outside microservices. The only way for others to access this data is through microservice API gateways.
**Shared Database per Service**
In domain-driven design, a separate database per service is feasible, but using a single database can be tough when you decompose a monolithic architecture into a microservice. So, while the decomposition process continues, implementing a shared database for a limited number of services is advisable. This number should be limited to two or three services. This number should stay low to allow deployment, autonomy, and scalability.
**Event Sourcing Microservice Design Pattern**
According to Martin Fowler:
*“Event Sourcing ensures that all changes to application state are stored as a sequence of events. Not only can we query these events and use the event log to reconstruct past states but also use it as a foundation to adjust the state automatically to cope with retroactive changes.*
The problem here lies with reliability. How can you rely on the architecture to make a change or publish a real-time event concerning the changes in the application’s state?
Event sourcing helps to come up from this situation by appending a new event to the list of events every time a business entity changes its state. Entities like Customer may consist of numerous events. It is thus advised that an application saves a screenshot of the current state of an entity to optimize the load.
**CQRS Microservice Design Pattern**
The query cannot be implemented in a database-per-service model because of the limited access to only one database. For a query, the requirements are based on joint database systems. But how do we query then?
Based on the CQRS(Command Query Responsibility Segregation), to query single databases per service model, the application should be divided into two parts: Command(write) and Query(read). In this model, the command handles all requests for creating, updating, and deleting, while queries are handled through a materialized view. These views are updated through a stream of events. These events, in turn, are created using an event-sourcing pattern that marks any data changes. These changes eventually become events.
CQRS is particularly beneficial in scenarios where the read and write patterns differ significantly, allowing for more flexibility and optimization in handling each type of operation. While it introduces complexity, it provides advantages in scalability, performance, and adaptability to varying system requirements.
> Convert HEX values to decimal easily with our [**hex to decimal](https://www.lambdatest.com/free-online-tools/hex-to-decimal?utm_source=hashnode&utm_medium=organic&utm_campaign=may_10&utm_term=bw&utm_content=free_online_tools)** tool. Check it out!
## Microservices Design Patterns for Seamless Deployment
When we implement microservices, certain issues arise during the call of these services. When we design microservice architecture, certain cross-cutting patterns can simplify the working.
**Service Discovery**
The use of containers leads to dynamic allocation of the IP address. This means the address can change at any moment. This causes a service break. In addition, the users have to bear the load of remembering every URL for the services, which become tightly coupled.
A registry needs to be used to solve this problem and give users the location of the request. While initiation, a service instance can register in the registry and de-register while closing. This enables the user to find the exact location that can be queried. In addition, a health check by the registry will ensure the availability of only working instances. This also improves the system’s performance.
**Blue-Green Deployment Microservice Design Pattern**
Whenever updates are to be implemented or newer versions are deployed, one has to shut down all the services in a microservice. This leads to a huge downtime, thus affecting productivity. To avoid this issue, use the Blue-Green Deployment pattern when designing microservice architecture.
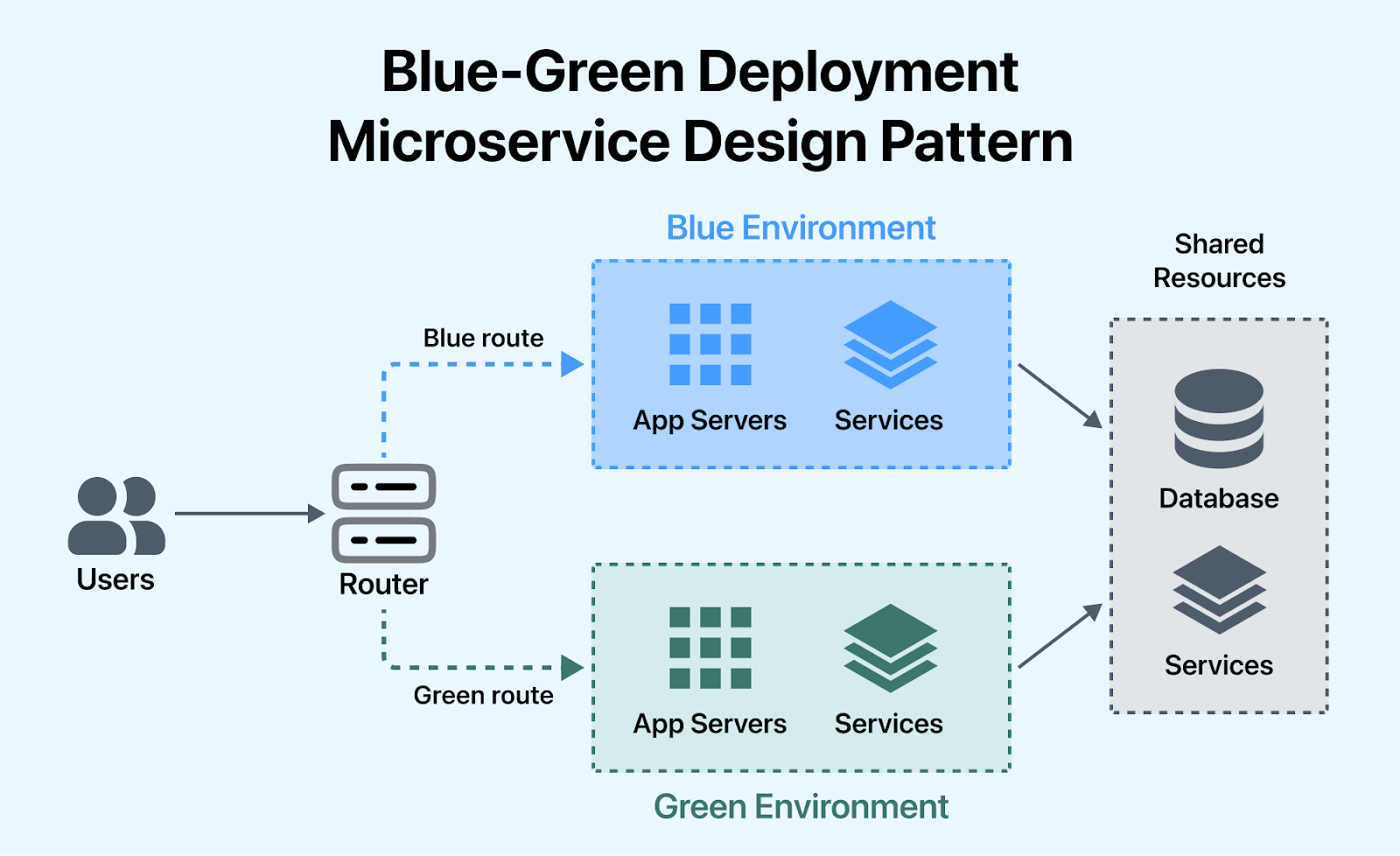
In this microservice design pattern, two identical environments, Blue and Green, run parallelly. The existing version of the application, i.e., the current production environment, is often referred to as “Blue,” and it actively serves user traffic. The duplicate environment is set up with the new application version or updates and is often called “Green”. This environment mirrors the production setup but receives no user traffic initially. At a time, only one is live and processing all the production traffic. In case of a new deployment, one uploads the latest version onto the green environment, switches the router to the same, and thus implements the update.
This deployment strategy is particularly valuable in microservices architectures, where various services may need to be updated independently, and maintaining service availability is critical.
**Externalized Configuration Microservice Design Pattern**
Externalized Configuration is a microservices design pattern where configuration settings for an application are stored outside the codebase, typically in configuration files, environment variables, or centralized configuration servers. Instead of hardcoding configuration parameters, this pattern allows for dynamic and centralized control of application settings, making it easier to manage and modify configurations without requiring code changes.
This pattern helps in flexibility and enhances the maintainability and scalability of the system, as configuration changes can be applied independently of the codebase, facilitating a more agile and adaptable architecture.
**API Gateway Microservice Design Pattern**
API gateway provides a unified entry point for clients while abstracting the underlying complexities of the microservices architecture. During deployment activities, when updates or changes are made to individual microservices, the API Gateway shields clients from potential disruptions. Clients can continue interacting with the API Gateway without being aware of the modifications occurring in the backend. This abstraction allows for rolling updates and new versions of microservices can be gradually introduced without affecting the overall system availability.
The API gateway also ensures a smooth transition by dynamically routing requests to the appropriate microservices, thus minimizing downtime and ensuring a seamless user experience during deployment.
Check out our blog on [Testing Challenges With Microservices Architecture](https://www.lambdatest.com/blog/testing-challenges-related-to-microservice-architecture/?utm_source=hashnode&utm_medium=organic&utm_campaign=may_10&utm_term=bw&utm_content=blog) to uncover insights, solutions, and best practices.
## Conclusion
Though only some design patterns might apply to a given microservice, you can rest assured that most of them will be used everywhere. These design patterns help developers bring in a consistent standard that brings reliability to the application. As organizations navigate the complexities of microservices architecture, a solid understanding of these design patterns becomes imperative for building robust and adaptable systems that align with business goals.
The evaluation, auditing, implementation, and [testing of microservices](https://www.lambdatest.com/blog/how-to-test-a-microservice-architecture-application/?utm_source=hashnode&utm_medium=organic&utm_campaign=may_10&utm_term=bw&utm_content=blog) of these design patterns are an ongoing process of microservice architecture. These patterns will help throughout, from the designing phase of the application to the maintenance phase in production.
| harisapnanair |
1,871,999 | Como añadir una columna a varias tablas de golpe con Laravel | Imagínate que llevas un tiempo creando tu proyecto. Y tienes muchas tablas ya desarrolladas. De... | 0 | 2024-05-31T11:30:42 | https://dev.to/drodero/como-anadir-una-columna-a-varias-tablas-de-golpe-con-laravel-860 | productivity, laravel, database | Imagínate que llevas un tiempo creando tu proyecto. Y tienes muchas tablas ya desarrolladas. De repente te das cuenta que te falta una columna en un grupo de ellas. Por ejemplo, quieres tener una columna "completado".
La opción trivial, es ir creando una migración para cada una de las tablas, para crearles esa columna.
Pero gracias a Laravel, podemos crear una migración donde añada esa columna a todas las tablas. En mi caso, será a todas las tablas que comienzan por "C_".
Aquí tenéis el código:
## Creamos la migración
```
php artisan make:migration add_completado_to_all_c_tables --table=users
```
## Modificamos la migración:
```
<?php
use Illuminate\Database\Migrations\Migration;
use Illuminate\Database\Schema\Blueprint;
use Illuminate\Support\Facades\Schema;
use Illuminate\Support\Facades\DB;
class AddCompletadoToAllCTables extends Migration
{
/**
* Run the migrations.
*
* @return void
*/
public function up()
{
// Obtener todas las tablas que comienzan con 'C_'
$tables = DB::connection()->getDoctrineSchemaManager()->listTableNames();
$cTables = array_filter($tables, function($table) {
return strpos($table, 'C_') === 0;
});
// Añadir la columna 'completado' a cada tabla
foreach ($cTables as $table) {
Schema::table($table, function (Blueprint $table) {
$table->boolean('completado')->default(0)->after('id'); // Ajusta 'after' según sea necesario
});
}
}
/**
* Reverse the migrations.
*
* @return void
*/
public function down()
{
// Eliminar la columna 'completado' de cada tabla
$tables = DB::connection()->getDoctrineSchemaManager()->listTableNames();
$cTables = array_filter($tables, function($table) {
return strpos($table, 'C_') === 0;
});
foreach ($cTables as $table) {
Schema::table($table, function (Blueprint $table) {
$table->dropColumn('completado');
});
}
}
}
```
## Ejecutamos la migración
```
php artisan migrate
```
De esta forma, le añadiremos la columna "completado" a todas las tablas de nuestra base de datos que comienzan por "C_".
Oh yeah! | drodero |
1,871,998 | The Economic Boon of Commercial Diving Companies in Coastal Towns: | Commercial diving companies play a critical role in the success and upkeep of maritime... | 0 | 2024-05-31T11:30:25 | https://dev.to/jack_homi/the-economic-boon-of-commercial-diving-companies-in-coastal-towns-m54 | marinecontractors, offshoreservices, commercialdivingservices, subseaengineering | Commercial diving companies play a critical role in the success and upkeep of maritime infrastructure, offering specialized underwater services that are essential for various industries. These companies not only guarantee the safety and functionality of submerged structures but also significantly contribute to the economic well-being of coastal communities. By creating jobs, stimulating local businesses, and developing infrastructure, commercial diving companies have a profound economic impact on the regions they operate in.
## Job Growth and Career Opportunities:
One of the most direct economic benefits of commercial diving companies is the creation of jobs. These companies require a diverse range of skilled professionals, including underwater welders, engineers, project managers, administrative staff, and of course, commercial divers themselves. This demand provides stable employment opportunities for local residents, leading to lower unemployment rates and increased household incomes in coastal towns.
Furthermore, the training and certification programs necessary for commercial diving open up specialized career paths for individuals. Local educational institutions and vocational schools often collaborate with [commercial diving companies](https://wetworx.co.uk/commercial-diving-uk/
) to offer relevant courses, fostering a skilled workforce that is well-prepared to meet industry demands. This mutually beneficial relationship not only benefits the companies by providing a pool of trained professionals but also enhances the economic prospects of the community by offering lucrative career options.
## Stimulating Local Businesses:
Commercial diving companies contribute to the local economy by acting as a catalyst for various supporting businesses. These include suppliers of diving equipment, maintenance services, transportation providers, and hospitality services. For instance, local dive shops, hardware stores, and specialized equipment suppliers experience increased business due to the ongoing needs of commercial diving operations.
Additionally, commercial diving projects often require substantial logistical support, which benefits local transportation and shipping companies. Hotels, restaurants, and other hospitality services also see a rise in business as they cater to the needs of visiting workers and business partners associated with these projects. This influx of business generates a ripple effect, spreading economic benefits throughout the community.
## Infrastructure Development and Maintenance:
Infrastructure development is another significant area where commercial diving companies impact coastal communities. These companies are integral to the construction and maintenance of essential maritime infrastructure, such as ports, harbors, bridges, and offshore wind farms. By ensuring the structural integrity and operational efficiency of these facilities, commercial diving companies help facilitate trade, tourism, and energy production, all of which are crucial to the economic vitality of coastal regions.
For example, the maintenance of ports and harbors is critical for the smooth operation of shipping and fishing industries. Regular inspections and repairs conducted by commercial diving companies ensure that these facilities remain safe and functional, supporting the local economy by enabling continuous maritime activities. Similarly, the construction and upkeep of offshore wind farms contribute to the local energy supply, promoting sustainable economic growth and providing jobs.
## Enhancing Economic Resilience:
Commercial diving companies also enhance the economic resilience of coastal communities by enabling them to adapt to and recover from environmental challenges. Coastal areas are often vulnerable to natural disasters such as storms, hurricanes, and erosion. The services provided by commercial diving companies, including underwater inspections and repairs, are essential for the timely restoration of damaged infrastructure, minimizing economic disruptions.
Moreover, the expertise of commercial diving companies in underwater construction and maintenance plays a crucial role in the development of resilient infrastructure that can withstand environmental stresses. By contributing to the creation of robust and durable maritime structures, these companies help ensure the long-term economic stability of coastal communities.
## Investment in Local Communities:
Beyond their direct economic contributions, commercial diving companies often invest in local communities through corporate social responsibility (CSR) initiatives. These initiatives may include supporting local schools and educational programs, sponsoring community events, and contributing to environmental conservation efforts. By actively engaging with and investing in the community, commercial diving companies foster goodwill and create a positive social impact, further strengthening the economic fabric of the region.
## Future Prospects and Sustainability:
The future prospects for commercial diving companies and their economic impact on coastal communities are promising, particularly with the growing emphasis on sustainable development and renewable energy. The expansion of offshore wind farms and other renewable energy projects presents new opportunities for commercial diving services, driving job creation and infrastructure development.
Additionally, advancements in technology and safety standards are likely to enhance the efficiency and scope of commercial diving operations, enabling companies to take on more complex and diverse projects. This continued growth and innovation will further bolster the economic contributions of commercial diving companies to coastal communities.
## Final Thought:
Commercial diving companies are essential to the economic health and development of coastal communities. Through job creation, stimulation of local businesses, infrastructure development, and enhancement of economic resilience, these companies provide substantial economic benefits. As the industry continues to evolve and embrace new opportunities, the positive impact of commercial diving companies on coastal economies is set to increase, ensuring sustainable and inclusive growth for communities along the coast. By investing in local talent, supporting small businesses, and contributing to resilient infrastructure, commercial diving companies help create a vibrant and prosperous economic landscape in coastal regions.
| jack_homi |
1,871,996 | How to Know if a Handmade Rug is of good Quality? | When it comes to discerning the quality of a handmade rug, there are several key factors to consider... | 0 | 2024-05-31T11:27:32 | https://dev.to/catherine_alvarado_ef44a0/how-to-know-if-a-handmade-rug-is-of-good-quality-22on | When it comes to discerning the quality of a handmade rug, there are several key factors to consider that can greatly influence its value and longevity. One of the first things to look for is the type of material used in its construction. High-quality handmade rugs are often crafted from natural fibers such as wool, silk, or cotton. These materials not only offer durability but also provide a luxurious feel and exquisite sheen that synthetic fibers cannot replicate. Additionally, the craftsmanship and weaving technique play a crucial role in determining a rug's quality. Hand-knotted rugs, for example, are highly prized for their intricate designs and exceptional durability. The density of knots per square inch is another indicator of quality, with higher knot counts typically indicating finer craftsmanship and a more intricate design.
Another aspect to consider is the rug's dyeing process. Premium handmade rugs often feature natural dyes derived from plants, minerals, or insects, which not only result in vibrant colors but also contribute to the rug's long-lasting beauty. These natural dyes are known for their ability to resist fading over time, unlike synthetic dyes that may lose their vibrancy with exposure to sunlight or cleaning agents. Moreover, the dyeing process can also affect the rug's texture and feel, with natural dyes often producing a softer and more lustrous finish.
The origin of the rug whether it is a **[8x8 Area Rug](https://www.teppichhomes.co/tags/8x8-rug)** or 12x18 Wool carpet in size, is also a significant factor in determining its quality and value. Regions renowned for their rug-making traditions, such as Persia (Iran), Turkey, India, and Afghanistan, often produce some of the finest handmade rugs in the world. These rugs are steeped in centuries-old weaving techniques and cultural heritage, resulting in timeless designs and impeccable craftsmanship. Additionally, rugs from reputable workshops or renowned rug-making families often command higher prices due to their provenance and quality.
Inspecting the rug's pile and weave can also provide insights into its quality. A high-quality handmade rug will have a dense and tightly packed pile, which not only enhances its durability but also ensures a luxurious underfoot feel. Conversely, rugs with a sparse or uneven pile may indicate inferior craftsmanship or materials. Additionally, examining the rug's fringe and edges can reveal clues about its authenticity and construction. Genuine handmade rugs typically feature hand-knotted fringes and neatly finished edges, while machine-made rugs may have stitched fringes and a less refined appearance.
Furthermore, the design and intricacy of patterns can also indicate the skill level of the weaver and the quality of the rug. Fine **[Handmade Rugs](https://www.teppichhomes.co/)** often feature elaborate motifs, intricate borders, and symmetrical designs that showcase the weaver's artistry and attention to detail. These rugs are not only visually stunning but also demonstrate a high level of craftsmanship that can withstand the test of time. Additionally, handmade rugs may also incorporate traditional techniques such as carving, embossing, or raised silk accents, adding depth and dimension to the design.
Lastly, it's essential to consider the rug's overall condition and maintenance requirements when assessing its quality. A well-maintained handmade rug, with regular cleaning and proper care, can retain its beauty and value for generations. However, rugs that show signs of wear, such as fraying edges, faded colors, or moth damage, may indicate inferior materials or inadequate maintenance. Investing in a high-quality handmade rug not only adds elegance and warmth to your home but also becomes a cherished heirloom that can be passed down through generations.
In conclusion, evaluating the quality of a handmade rug involves a comprehensive assessment of its materials, craftsmanship, origin, design, condition, and maintenance requirements. By paying attention to these key factors and seeking rugs from reputable sources or artisans, you can ensure that your investment in a handmade rug is not only aesthetically pleasing but also durable, timeless, and of exceptional quality.
| catherine_alvarado_ef44a0 | |
1,871,995 | The influence of Web3 on the development of crypto: Interview Thee Web3 Qing | Thee Web3 Qing is a young professional in the space of video content and Web3, the founder of Thee... | 0 | 2024-05-31T11:26:26 | https://dev.to/shevchukkk/the-influence-of-web3-on-the-development-of-crypto-interview-thee-web3-qing-f9b | [Thee Web3 Qing](https://x.com/QingTheCreator_) is a young professional in the space of video content and Web3, the founder of [Thee Creator’s Lounge](https://www.thecreatorslounge.net/).
Digitization is becoming a daily impulse for us, pushing us, so to speak, to the next phase of the Internet: Web 3. It is this Internet ecosystem, based on crypto wallets, blockchains, non-fungible tokens (NFTs) and decentralized autonomous organizations (DAOs), that encourages convenient application in business and beyond. What changes are happening with the advent of Web3, and how will they affect the market? Thee Web3 Qing tells about it.
**ABOUT THE PECULIARITIES OF ENTERING THE WEB3 SPACE**
> Q: How did you get into Web3, and how long have you been in the sphere?
> A: I was given a scholarship into a web3 academy, owned by my Ex-mentor.
> Q: I saw that you are the founder of Thee Creators Lounge. Can you tell me more about it?
> A: It was a community of Vreatirs in the Web3 space where I teach how to create content with my friends. The new community now is “Thee Qingdom”.
> Q: What is your experience with decentralized platforms or applications?
> A: Well, my experience with Dexs and Dapps has been good so far. I’ve never experienced hacking or draining, and I hope I don’t.
**ABOUT ADVANTAGES AND RISKS OF THE WEB3**
> Q: How in your opinion web3 has affected security and privacy of users?
> A: It has affected it positively because obviously you can’t compare web2 to Web3.
> Q: What do you see as the main security risks associated with Web3?
> A: Saving seed phrases in the phone, Google Drive, or mail. We should always back up manually. Writing it down somewhere.
> Q: What do you think are the key features that make Web3 more secure compared to Web2?
> A: The whole concept of Decentralization makes it more secure.
> Q: Do you know any examples of successful Web3 security implementations? Have you personally used any of them?
> A: Most Ethereum L2s like Base and Op worked on Eth’s security and made it better. Some other protocols followed suit.
> Q: What are the benefits of Web3 for you personally?
> A: I can make more money here without being restricted. I’m more respected in this space than the normal world because of how I’ve grown myself.
> Q: In your opinion, what are the most difficult barriers for developers in Web3?
> A: Making it completely decentralized yet risk-free.
**SYSTEMATICITY IN ACTION AS THE KEY TO SUCCESS**
> Q: Can you give advice for those who are just starting out on the Web3 path, how to overcome these challenges?
> A: Be patient, don’t drag anybody, never be satisfied or get too comfortable, have friends. Don’t trust anybody, but stay loyal till lines are crossed.
**Web3 and cryptocurrencies: what you need to know?**
For example, there are literally thousands of cryptocurrencies based on the blockchain, in the literal sense of the word. Some of them are not distinguished by special technologies, so their price is much lower. However, everything depends on the level of security and quality, which is a key indicator of Web3, and then the question arises — how does this process take place?
**The core principle of Web3 — decentralization**
And we begin to understand that this system is based on [decentralization](https://cointelegraph.com/learn/what-is-web-3-0-a-beginners-guide-to-the-decentralized-internet-of-the-future). Even in the case of Bitcoin, we can say that there is a category of specialists who are responsible for maintaining the code. There are many new blockchains that are not decentralized at all, such as TRON or Cardano.
So let’s go back to decentralization, and how it focuses on the main task of blockchain technology, which is opposite and different, and the huge circulation of cryptocurrency. There are certain driving forces in digital currency — these are people who own the majority of the money; respectively, they have a greater impact on the value of the currency and other management decisions.
Therefore, when switching to the Web3 ecosystem, it becomes clear that it will play a significant role. Crypto was the first, but for Web3, it is important to have a wallet — this is the basis; in 2023 the most popular according to the selection of [CoinGecko](https://www.coingecko.com/research/publications/most-popular-crypto-hot-wallets) are MetaMask and MyEtherWallet.
Unlike Web2, which only needed a browser, Web3 requires money and a wallet. Now let’s take a closer look at what Web3 offers in the crypto industry business and how it contributes to decentralization. The world of cryptocurrencies is taking a step towards the mainstream with the [release](https://www.coindesk.com/business/2024/03/11/with-mastercard-metamask-tests-first-blockchain-powered-payment-card/) of the first decentralized payment card, [MetaMask](https://metamask.io/) and [Mastercard](https://www.mastercard.com/global/en.html). This innovation allows cryptocurrency owners to seamlessly spend their assets “anywhere cards are accepted”. Decentralization empowers users — Web3 emphasizes decentralization through dApps, smart contracts, and DAOs, giving users greater control over their data and finances.
**MetaMask and Mastercard unlocks a new financial frontier**
The collaboration of MetaMask, a leading crypto wallet, and Mastercard, a payment giant, leads to a new level of accessibility and convenience for cryptocurrency users. We understand that MetaMask and Mastercard card open the “door” to the world of Web3, where crypto assets become an integral part of everyday life. As the MasterCard company [reports](https://www.mastercard.com/news/press/2022/october/mastercard-makes-it-easier-safer-to-buy-crypto/), it can guarantee a high level of transaction security, and MetaMask will ensure reliable storage of cryptographic assets. According to preliminary information, the card will not require intermediaries, giving users full control over their finances. Also, Metamask partners with other global leaders such as [BitGo](https://www.bitgo.com/), [Cactus Custody™](https://www.mycactus.com/) and [Cobo](https://www.cobo.com/). These partnerships provide the security and operational backbone including the world’s top cryptocurrency exchanges and platforms. Collaboration between MetaMask and Mastercard brings cryptocurrency spending into the mainstream by offering convenience and security through a shared payment card, signaling increased affordability and security.
Another impetus was the fact that Visa, the world leader in digital payments, announced the signing of a Memorandum of Understanding (MoU) with the European crypto exchange [WhiteBIT](https://whitebit.com/ua), which is a [partner](https://beincrypto.com/visa-whitebit-crypto-partnership/) of Mastercard. This cooperation aims to help WhiteBIT establish links with banks and other financial institutions, promoting the wider adoption of cryptocurrencies. This indicates that Visa is once again becoming an active player in the cryptocurrency market, recognizing its growing popularity and potential.
It is worth noting that Web3 can be used to create decentralized virtual worlds where users can own and use their digital assets. This leads to the emergence of new types of cryptocurrencies that are used to purchase virtual goods and services, as well as decentralized gaming platforms. It is important to emphasize that Web3 is an active component in crypto-circulation and decentralized financial protocols (DeFi)
**The rise of Web3: powering the future of cryptocurrency**
Therefore, Web3 is becoming the driving force behind the development of the cryptocurrency sphere, which is adapted to the requirements of the time. This can be confirmed by the use of decentralized applications (dApps) that work on the blockchain, the application of smart contracts, and the concept of a Decentralized Autonomous Organization (DAO). The peculiarity of such organizations is that they are represented by rules that are encoded in the form of a special program, which cannot be influenced by the central management but is under the control of its members. Web3 adoption on the rise: major payment processors like Visa are recognizing the potential of crypto by forging partnerships with crypto exchanges (e.g., WhiteBIT) to facilitate wider adoption.
**CONCLUSION**
The main requirement of the modern user is the confidentiality of their data. Therefore, Web3 is focused on a society that will have control over its data, digital life and financial transactions, which will be reliably protected. The crypto world is adapted to new requirements, because it promotes innovation, freedom and security. | shevchukkk | |
1,868,237 | Create PalWorld server on Linux with docker | Reference to creating-a-cheap-palworld-dedicated-server In this article, will guide you through the... | 0 | 2024-05-31T11:26:21 | https://dev.to/codesmart_1/create-palworld-server-on-linux-with-docker-5db6 | gamedev, tutorial | Reference to [creating-a-cheap-palworld-dedicated-server](https://www.palworldtravel.com/creating-a-cheap-palworld-dedicated-server)
In this article, will guide you through the steps to set up a PalWorld dedicated server.
**Prerequisites**
- A Linux-based system
- Docker installed on your system
- Basic knowledge of command-line operations
## Step 1: Download the Docker Image
```bash
docker pull thijsvanloef/palworld-server-docker:latest
```
## Step 2: Configure and Run the Docker Container
run the PalWorld server container using the following command:
```bash
docker run -d \
--name palworld-server \
-p 8211:8211/udp \
-p 27015:27015/udp \
-v ./palworld:/palworld/ \
-e PUID=1000 \
-e PGID=1000 \
-e PORT=8211 \
-e PLAYERS=16 \
-e MULTITHREADING=true \
-e RCON_ENABLED=true \
-e RCON_PORT=25575 \
-e TZ=UTC \
-e ADMIN_PASSWORD="adminPasswordHere" \
-e SERVER_PASSWORD="worldofpals" \
-e COMMUNITY=false \
-e SERVER_NAME="palworld-server-docker by Thijs van Loef" \
-e SERVER_DESCRIPTION="palworld-server-docker by Thijs van Loef" \
--restart unless-stopped \
--stop-timeout 30 \
thijsvanloef/palworld-server-docker:latest
```
Params explain
• -d runs the server in detached mode, freeing up your terminal.
• --name palworld-server assigns a distinct name to the container.
• -p 8211:8211/udp and -p 27015:27015/udp map the necessary UDP ports from the container to your host machine.
• -v ./palworld:/palworld/ sets a volume linking a host system directory to a corresponding directory within the container.
• The --restart unless-stopped flag ensures the server resumes operation after unexpected shutdowns or reboots.
• --stop-timeout 30 is a grace period for the server to shut down cleanly before Docker forces it to stop.
## Step 3: Check the Running Server
Ensure everything is working as expected by checking the container’s logs:
```bash
docker logs -f palworld-server
``` | codesmart_1 |
1,871,993 | Choose Antier for Top-tier Polygon CDK Implementation Services. | Antier is a leading service provider that transforms your blockchain projects into industry-leading... | 0 | 2024-05-31T11:25:08 | https://dev.to/juliepattersona/choose-antier-for-top-tier-polygon-cdk-implementation-services-1e9d | blockchain, softwaredevelopment, polygon, cryptocurrency | Antier is a leading service provider that transforms your blockchain projects into industry-leading successes with the Polygon CDK implementation.The company has the best Polygon specialists with deep Polygon CDK implementation knowledge who follow an innovative approach to empowering clients to harness the full potential of blockchain technology and drive growth and efficiency in a rapidly evolving digital landscape. Antier has worked with multiple clients across the globe and helped them leverage the power of Polygon CDK, providing the better infrastructure they deserve. Through tailored solutions and dedicated support, Antier enables businesses to unlock new opportunities. Visit https://www.antiersolutions.com/polygon-zkevm/ to stay ahead in the competitive blockchain arena.
| juliepattersona |
1,871,992 | happy pride day program | PRIDE when i see people neutralizing and accepting LGBT i feel inspiring by seeing people respecting... | 0 | 2024-05-31T11:25:00 | https://dev.to/leena_spandanasimhadri_4/happy-pride-day-program-3d49 | frontendchallenge, devchallenge, css, html | PRIDE
when i see people neutralizing and accepting LGBT i feel inspiring by seeing people respecting others feeling .i started to support accept and respect LGBT. criticizing LGBT or harming them is no more accepted in this world as government of many countries accepts marriage of this LGBT
<!DOCTYPE html>
<html>
<head>
<link rel="stylesheet" href="https://stackpath.bootstrapcdn.com/bootstrap/4.5.2/css/bootstrap.min.css" integrity="sha384-JcKb8q3iqJ61gNV9KGb8thSsNjpSL0n8PARn9HuZOnIxN0hoP+VmmDGMN5t9UJ0Z" crossorigin="anonymous">
<script src="https://code.jquery.com/jquery-3.5.1.slim.min.js" integrity="sha384-DfXdz2htPH0lsSSs5nCTpuj/zy4C+OGpamoFVy38MVBnE+IbbVYUew+OrCXaRkfj" crossorigin="anonymous"></script>
<script src="https://cdn.jsdelivr.net/npm/popper.js@1.16.1/dist/umd/popper.min.js" integrity="sha384-9/reFTGAW83EW2RDu2S0VKaIzap3H66lZH81PoYlFhbGU+6BZp6G7niu735Sk7lN" crossorigin="anonymous"></script>
<script src="https://stackpath.bootstrapcdn.com/bootstrap/4.5.2/js/bootstrap.min.js" integrity="sha384-B4gt1jrGC7Jh4AgTPSdUtOBvfO8shuf57BaghqFfPlYxofvL8/KUEfYiJOMMV+rV" crossorigin="anonymous"></script>
</head>
<body>
<div class="bi ni">
<h1 class="h">love is love</h1>
<h1 class="h">pride</h1>
<div class="m1">
<img src="https://cdn.pixabay.com/photo/2023/04/10/10/40/women-7913460_1280.jpg" class="image">
<img src="https://cdn.pixabay.com/photo/2017/10/04/22/45/men-2817874_1280.png" class=" image">
</div>
<h1 class="h">HAPPY PRIDE DAY</h1>
<h1 class="h">Enjoy and respect the pride</h1>
</div>
</body>
</html>
@import url('https://fonts.googleapis.com/css2?family=Bree+Serif&family=Caveat:wght@400;700&family=Lobster&family=Monoton&family=Open+Sans:ital,wght@0,400;0,700;1,400;1,700&family=Playfair+Display+SC:ital,wght@0,400;0,700;1,700&family=Playfair+Display:ital,wght@0,400;0,700;1,700&family=Roboto:ital,wght@0,400;0,700;1,400;1,700&family=Source+Sans+Pro:ital,wght@0,400;0,700;1,700&family=Work+Sans:ital,wght@0,400;0,700;1,700&display=swap');
.bi {
background-image: url('https://cdn.pixabay.com/photo/2017/09/12/06/10/lgbt-2741369_1280.png');
height: 550px;
width: 900px;
background-size: cover;
}
.h {
color: white;
text-align: center;
font-size: 60px;
font-family: Roboto;
font-weight: bold;
}
.m1 {
display: flex;
justify-content: space-between;
width: 100%;
}
.ni {
display: flex;
flex-direction: column;
align-items: center;
}
.image {
height: 180px;
width: 150px;
margin: 10px;
}
.button {
height: 35px;
width: 60px;
margin: 80px;
}
 | leena_spandanasimhadri_4 |
1,871,991 | Row Level Security In SQL Server | Row level security (RLS) provides us with a security tool that can limit data access on the row level... | 0 | 2024-05-31T11:21:46 | https://dev.to/sqlinsix/row-level-security-in-sql-server-4hi6 | sqlserver, sql, data, security | Row level security (RLS) provides us with a security tool that can limit data access on the row level of data. This security technique serves value in situations where we may require delineating access to data where a “whole” is stored, but only a “part” needs to be accessed by users — such as a product list from all companies where a company can only see their products.
While this post will do an example in SQL Server, row level security can be used in SQL Server 2016 and above, Azure SQL, Azure SQL Managed Instances, Azure Synapse and Warehouse in Fabric.
## When Would We Use Row Level Security?
While RLS isn’t the only tool that will help us in these situations, it may be a tool that we find useful in the below situations that we could use it. We might consider RLS in the following circumstances:
- Complying with strict security requirements from our company or legal requirements where access to sensitive data must be filtered by user or role within the company.
- When the data we store on the row level relate directly to the responsibilities of the user or role who views the data. If the data relate to the user or role on a column level, we would consider dynamic data masking.
A visual way to think about RLS is a pie chart where each piece of the pie represents a user and each user should only be able to view their piece of the entire pie. Like with dynamic data masking as we’ll see, there are some security concerns with RLS, which is one reason why it’s not high on my recommendation list of security tools.
## Row Level Security Considerations
Like with dynamic data masking, row level security (RLS) invites attacks because the data are present in the database. A hacker knows that if he compromises your database, he can get access to your data. In the case of RLS, the hacker knows that it’s only a matter of permissions. Hackers can use social engineering to determine if a company is using row level security and if this is the case, they know they only have to compromise the database. A more specific example of this (and a form of social engineering) would be to use social media to identify who works at a target company, whether they use RLS, and compromise the person’s access (spearphishing from social media analysis would be another route). Even if we assume the hacker only compromises one employee (one makes it easier to compromise a second and third), that is enough to get the data.
By contrast, in the case of a security approach like always encrypted where a different layer has the key to unencrypt the data, the hacker must compromise two layers — simply getting the data won’t be enough. In both the case of dynamic data masking and row level security, this is not the case.
If we plan to use RLS, we need to ensure that it functions through sufficient testing. As we’ve seen above this, AFTER and BEFORE UPDATE differ in what could happen with users. We would want to have detailed testing scenarios that ensure that row level security will function as intended. We should always remember that we’re designing for failure (or in the case of security, compromise). This means that we test with our architecture as if we’re trying to compromise the security. I highly recommend researching people who’ve used this feature with their architecture, as they will make note of some of the issues they’ve seen in their environment.
[Continue reading the entire post with T-SQL examples](https://sqlinsix.medium.com/row-level-security-deep-dive-in-sql-server-20f62827708c) | sqlinsix |
1,839,791 | NLP | Natural Language Processing (NLP) is a branch of artificial intelligence that allows computers to... | 0 | 2024-05-01T16:34:05 | https://dev.to/mustafalsailor/nlp-50bf | Natural Language Processing (NLP) is a branch of artificial intelligence that allows computers to interact with human language. This involves understanding and composing both written text (for example, a book, a tweet, or a website) and spoken language (for example, a telephone conversation or a podcast).
One of the main goals of NLP is to enable a computer to understand the complexity of language. Human language involves many complexities such as grammatical rules, slang, local idioms, dependence of meaning on context, and constant changes in language. NLP uses a variety of techniques and algorithms to understand and process these complexities.
NLP has many different applications. Among them:
Text analysis: This is used to analyze documents or other text. For example, a company can analyze customer reviews and see which words are frequently used in those comments to determine overall customer satisfaction.
Language translation: NLP is used to translate text from one language into another language. Google Translate is an example of this.
Speech recognition: NLP is used to convert speech into text. This is important for applications such as voice assistants (e.g. Siri or Alexa) or voice typing programs.
Sentiment analysis: This is used to determine the overall emotional tone in a text. For example, a company can analyze what is being said about their brand on Twitter and determine whether those comments are generally positive or negative.
Chatbots and virtual assistants: NLP enables a chatbot or virtual assistant to understand human language and generate responses in natural language.
These and other applications of NLP enable computers to better understand human language and use it more effectively. This allows computers and humans to communicate more naturally and effectively.
**Sparse Matrix (Intuitive Matrix)**: A sparse matrix is a matrix with a majority of zeros. Such matrices often appear in large data sets and especially in areas such as natural language processing. Efficient storage and processing of sparse matrices is important to save memory and computational resources. Because storing zero values is generally unnecessary and calculations made on these values usually do not change the result.
**Spelling Marks**: Spelling marks are symbols used to determine sentence structure and meaning in written language. Signs such as periods, commas, exclamation marks, question marks, apostrophes, semicolons, and colons fall into this category. Spelling marks often play an important role in natural language processing (NLP) studies. Because these signs can determine the meaning and tone of the sentence. But sometimes, especially when cleaning or preprocessing text data, these marks are removed or replaced.
# Preprocessing of orthographic marks
In Natural Language Processing (NLP) projects, data often goes through a series of pre-processing steps. These steps aim to make the data more suitable for analysis or modelling. Preprocessing of orthographic marks is usually one of these steps, and there are generally two main approaches:
Removing Spelling Marks: This approach is often used in tasks such as text classification and sentiment analysis. Here, spellings usually do not affect the meaning much and can sometimes degrade the model's performance. In Python, this is usually done with the "punctuation" property and "translate" method of the "string" module. Here is an example:
import string
```
text = "Hello, how are you? I'm fine!"
text = text.translate(str.maketrans('', '', string.punctuation))
This code removes all spelling marks from the text.
```
Using Spellmarks as Tokens: This approach is often used to understand and render text (for example, a chatbot or text rendering model). Here, spellings are important because they determine the structure and tone of the sentence. In this case, spellings are generally considered a token in their own right. This is usually done using a tokenization tool (e.g. NLTK, Spacy).
Which approach to use depends on the requirements of a particular task and the nature of the data.
# Big and small letter (case normalization)
In Natural Language Processing (NLP) projects, case normalization is often performed when processing text data. This means converting all text to lowercase. This step allows the model to recognize different spellings of the same word (e.g. "Hello", "HELLO", "hello") as the same word.
In Python, you can use the lower() function to convert a string to lowercase. Here is an example:
```
text = "Hello, How are you?"
text = text.lower()
print(text)
```
When you run this code, the output is "hello, how are you?" It will happen.
In some cases, preserving capital letters may be important - for example, in cases such as names or abbreviations. But generally, for NLP tasks such as text classification or sentiment analysis, it is best practice to convert all text to lowercase. This makes the model more general and flexible.
# Stop Words
Stop Words are the most frequently used words in a language. Generally, these words contribute little to the overall meaning of a text and are therefore often omitted in text processing and Natural Language Processing (NLP) tasks. Examples of stop words in English include words such as "the", "is", "at", "which", and "on".
Removing stop words makes the data more manageable and helps identify important words. This is especially useful in NLP tasks such as text classification, keyword extraction, and sentiment analysis.
In Python, the NLTK (Natural Language Toolkit) library provides a list of stop words for a number of languages. Here is an example:
```
from nltk.corpus import stopwords
stop_words = set(stopwords.words('english'))
text = "This is a sample sentence."
text_tokens = text.split()
filtered_text = [word for word in text_tokens if word not in stop_words]
print(filtered_text)
```
This code extracts stop words from the text and returns a list of words that are not stop words.
#Stemmer
Stemming is a widely used technique in the field of Natural Language Processing (NLP). This technique aims to find the root or root form of a word. For example, the roots of the words "running", "runs" and "ran" are "run".
Stemming is often used in NLP tasks such as text classification, sentiment analysis and similar. This allows the model to recognize different words with the same root as the same word.
In Python, the NLTK (Natural Language Toolkit) library includes popular stemming algorithms such as Porter and Lancaster. Here is an example:
```
from nltk.stem import PorterStemmer
stemmer = PorterStemmer()
words = ["program", "programs", "programer", "programing", "programers"]
stemmed_words = [stemmer.stem(word) for word in words]
print(stemmed_words)
```
This code finds the root of each word and returns a list of its root forms.
One disadvantage of stemming is that it can sometimes produce stems that are not real words. For example, the root of the word "running" may be "run", while the root of the word "argument" may be "argu". In this case, another technique called lemmatization may produce better results. Lemmatization finds the root form of a real word using grammatical analysis of the word.
# CountVectorizer
CountVectorizer is a widely used technique in text mining and natural language processing (NLP) tasks. This technique converts a text document or a collection of text documents (a corpus) into a word count matrix. Each row represents a document and each column represents a word in the document. The value in each cell represents the frequency of a particular word in a particular document.
CountVectorizer is used specifically for NLP tasks such as text classification and clustering. This allows the model to understand text in a numerical format, since machine learning models generally cannot process text directly.
In Python, the scikit-learn library provides the CountVectorizer class. Here is an example:
```
from sklearn.feature_extraction.text import CountVectorizer
corpus = [
'This is the first document.',
'This document is the second document.',
'And this is the third one.',
'Is this the first document?',
]
vectorizer = CountVectorizer()
X = vectorizer.fit_transform(corpus)
print(vectorizer.get_feature_names())
print(X.toarray())
```
This code creates the word count vector of each document and prints the frequency of each word. | mustafalsailor | |
1,871,990 | Banner and Poster Design Services | Banner Designer Near Me | Banner and Poster Design | Discover top-quality banner and poster design services from expert designers near you. We offer... | 0 | 2024-05-31T11:21:21 | https://dev.to/prachi_pare_e410f7b6715d0/banner-and-poster-design-services-banner-designer-near-me-banner-and-poster-design-5go5 | bannerdesign, posterdesign, webbannerdesign, advertisingbanners | [Discover top-quality banner and poster design services from expert designers near you. We offer custom banner design and creative poster design to meet your marketing needs. Enhance your brand with professional banner and poster design services specifically for you.](https://bhagirathtechnologies.com/services/6) | prachi_pare_e410f7b6715d0 |
1,871,941 | Latest News, Updates, and Tutorials from JavaScript World | We have been quite busy recently, therefore you haven’t heard from us about the latest DHTMLX and... | 0 | 2024-05-31T11:17:10 | https://dev.to/plazarev/latest-news-updates-and-tutorials-from-javascript-world-37md | javascript, news, webdev, programming | We have been quite busy recently, therefore you haven’t heard from us about the latest DHTMLX and JavaScript news for some time. But we are back and ready to make up for this delay with new JavaScript stuff. We collected the most interesting news for the previous and current months.
Today, you will get acquainted with a huge release of DHTMLX Diagram 6.0, new Angular 18, release candidates of Svelte 5 and React 19, new Svelte UI components, and key insights from the “State of HTML” report. In addition, you’ll also find a pack of useful materials to enhance your JavaScript knowledge.
#New Releases and Updates
##DHTMLX Diagram 6.0 with Enhanced Diagram Editor
If you want to implement complex functionalities such as data visualization in web apps in the desired way, it is often the case that you have to do it yourself. We took into account this important aspect when delivering DHTMLX Diagram 6.0.
This major update allows you to adjust the killer feature of our JavaScript diagramming library, namely the Diagram editor, to the needs of any project.
In version 6.0, we overhauled the Diagram editor and enriched its control elements with numerous novelties. First of all, now you can fully customize the Editbar responsible for modifying diagram shapes in real time. The default Toobar of the editor became much more functional and flexible to configure it as needed. The process of adding new sections with shapes has never been easier thanks to numerous enhancements in the Shapebar API.
The updated editor is also notable for the modified API for item selection, simplified management line titles, updated move events, copy manager, and many other useful novelties.
We also want to mention that the Diagram component and the Diagram editor now also support new customizable themes. [Check out the release article](https://dhtmlx.com/blog/dhtmlx-diagram-6-0/) to learn more interesting insights about DHTMLX Diagram 6.0.
##Angular 18 is Here
Angular has a reputation as a very complex tool, and there is some truth in that. However, the development team of this framework certainly deserves some credit for regularly updating their product with new features and improvements. So it is time to highlight the recently released Angular 18.
Some features that gained popularity among Angular devs such as Material 3, deferrable views, and built-in control flow changed their status from experimental to stable. Now you can evaluate a new experimental feature — zoneless change detection.
Also, there are several server-side rendering improvements such as i18n hydration support, better debugging, event replay, etc. Want to learn more about this major update? [Read the release article](https://blog.angular.dev/angular-v18-is-now-available-e79d5ac0affe) on the Angular blog.
##Svelte 5 is Coming
Svelte has been around for only 8 years but many dev teams already prefer this option over other time-proven and mature frameworks. Web developers love Svelte for its efficiency and simplicity in achieving various coding goals. If you are one of those Svelte admirers, you’ll be happy to know that the framework will be soon updated to version 5.
Currently, it is in the Release Candidate phase, thus the design of the framework is largely settled and you already can get acquainted with the biggest changes included in v5. The development team of the project decided to rewrite Svelte to make it faster and more robust.
The key feature of the new Svelte is a signal-powered reactivity API (called runes) that promises a new level of reactivity. The update will also include overhauled event handling, improved component composition via snippets, and native TypeScript support.
At the same time, there still may be some changes before the stable release of Svelte 5. [Watch this video](https://www.youtube.com/watch?v=xCeYmdukOKI), where Rich Harris, the creator of Svelte, goes through the main features of v5.
##Brand New Svelte UI Components from SVAR
There is one more good news for those developers who have Svelte in their technology stacks. The SVAR team has recently introduced a set of advanced UI components for the Svelte framework, including feature-rich DataGrid, Gantt Chart, and File Manager. It also offers an open-source SVAR Svelte Core library, a collection of commonly used UI elements (buttons, tabs, popups, date picker, and more).
Leveraging Svelte’s lightweight and high-performance nature, SVAR components are blazingly fast and promise ease of use and customization. [Visit the SVAR Svelte website](https://svelte-widgets.com/) for more information and a free trial.
##What to Expect from React 19
Today, we also have reasons to mention another extremely popular JavaScript framework — React. Just like Svelte, the new React 19 reached the release candidate status. This major update promises a range of new features and improvements.
First of all, this release is notable for the React compiler designed for managing component’s re-rendering on the UI state change, thereby ensuring performance optimization. Developers will also benefit from new React actions that facilitate the management of data and interactions on web pages. Apart from that, the list of novelties includes support for document metadata, server components, new hooks, and much more.
You can learn more about React by visiting this page, and if you get the urge to upgrade your app to React 19, [check out this step-by-step guide](https://react.dev/blog/2024/04/25/react-19-upgrade-guide). You should also [take a look at the recap of React Conf 2024](https://react.dev/blog/2024/05/22/react-conf-2024-recap) packed with exciting announcements and updates from the React & React Native team and community.
##Key Takeaways from State of HTML 2023 Survey
Although this article is mainly dedicated to the JavaScript world, we simply could not ignore the release of the State of HTML report. HTML remains indispensable for structuring and presenting web content effectively, so it is great to know about the latest trends in this area.
Created by a talented team known for similar informative surveys for JavaScript and CSS, it provides plenty of curious insights based on 20,904 responses from participants across the world.
In this survey, you can find interesting visual data on the experience and sentiment of respondents related to HTML features and other browser APIs. The “Usage” section of this survey deserves special attention since it provides better visibility into developer needs. For instance, if you take a look at the list of missing elements (including data table, tabs, switch/toggle, etc.), it is safe to assume that developers want more interactive HTML elements.
Developers also complain about insufficient customizability, especially around styling. This issue directly concerns form input elements, which frequently have to be recreated. For more information, [check out the complete survey](https://2023.stateofhtml.com/en-US/).
#Useful Learning Resources
##Customizing Top DHTMLX JavaScript Libraries
Many development teams trust DHTMLX products when it comes to delivering complex functionalities for business apps, especially project management. Knowing that the development of a modern web app very often requires nontrivial solutions, we try to help our customers with tutorials that help adjust our JS libraries to various use-case scenarios.
This month, our team prepared two tutorials that vividly demonstrate the high customizability of our JavaScript libraries for project management — Gantt and Scheduler.
[In the first tutorial](https://dhtmlx.com/blog/integrating-context-menu-javascript-gantt-chart-dhtmlx/), you will learn how to complement a JavaScript Gantt chart with a custom context menu that enables end-users to manage tasks in the project workflow more efficiently.
[The second tutorial](https://dhtmlx.com/blog/enhancing-dhtmlx-javascript-scheduler-custom-toolbar/) explains how to implement a custom toolbar into a JavaScript scheduling calendar based on DHTMLX Scheduler. This toolbar offers powerful features that enhance user interaction and accessibility.
##Deeper Insight into React Compiler and Its Impact on Your Code
We already mentioned the React compiler in the news dedicated to the upcoming release of React 19. But since this feature is expected to become a game-changer in terms of performance, it is nice for web developers to learn more about this feature. [This video](https://www.youtube.com/watch?v=PYHBHK37xlE) provides interesting insights about React Compiler and its practical application.
##Listing of AI Tools to Boost Developer’s Productivity
AI technologies still raise some reasonable concerns in the dev community, but it has become common for many developers to use various AI tools in their jobs. Such AI aids help automate recurring tasks, implement enhanced features, and improve the overall code quality. [In this article](https://codesubmit.io/blog/ai-code-tools/), you will find the selection of popular AI code generators and development tools for programmers.
##5 Modern JavaScript Techniques
JavaScript is constantly evolving, so JS developers should broaden their knowledge of the language to keep up with the advancements. By expanding their coding practices with new techniques, developers enhance their skills, deliver better products, and stay competitive in the job market. [This article](https://thenewstack.io/top-5-cutting-edge-javascript-techniques/) offers 5 cutting-edge JavaScript techniques aimed at helping developers create powerful but concise code for their apps.
##23 Must-Know CSS Features
CSS (Cascading Style Sheets) plays a crucial role in modern web development by providing a means to style and layout web pages. Thus, it is useful for web developers to follow CSS trends and learn its features. Proficiency in CSS enables developers to create visually appealing and user-friendly apps as well as optimize their performance. [In this video](https://www.youtube.com/watch?v=opHu7HvFM60), you will get acquainted with the list of popular CSS features that developers should know.
Thanks for reading and see you next time.
This article was originally published [on Medium](https://itnext.io/latest-news-updates-and-tutorials-from-javascript-world-681247e44e43). | plazarev |
1,871,940 | Unlock Incredible Flight Deals: Your Ultimate Guide to Affordable Air Travel | Unlock Incredible Flight Deals: Your Ultimate Guide to Affordable Air Travel TravelGo4 min... | 0 | 2024-05-31T11:16:57 | https://dev.to/travelgo/unlock-incredible-flight-deals-your-ultimate-guide-to-affordable-air-travel-5fna | flight, travel, flightdeals | <p> <img alt="" class="bg kp lu c" height="421" loading="eager" role="presentation" src="https://miro.medium.com/v2/resize:fit:700/0*wFejWqKf07QnNCfL" style="background-color: white; box-sizing: inherit; color: rgba(0, 0, 0, 0.8); font-family: medium-content-sans-serif-font, -apple-system, BlinkMacSystemFont, "Segoe UI", Roboto, Oxygen, Ubuntu, Cantarell, "Open Sans", "Helvetica Neue", sans-serif; height: auto; max-width: 100%; vertical-align: middle; width: 680px;" width="700" /></p><div class="er es et eu ev l" style="background-color: white; box-sizing: inherit; color: rgba(0, 0, 0, 0.8); font-family: medium-content-sans-serif-font, -apple-system, BlinkMacSystemFont, "Segoe UI", Roboto, Oxygen, Ubuntu, Cantarell, "Open Sans", "Helvetica Neue", sans-serif; margin-bottom: 68px;"><article style="box-sizing: inherit;"><div class="l" style="box-sizing: inherit;"><div class="l" style="box-sizing: inherit;"><section style="box-sizing: inherit;"><div style="box-sizing: inherit;"><div class="fk fl fm fn fo" style="box-sizing: inherit; overflow-wrap: break-word; word-break: break-word;"><div class="ab ca" style="box-sizing: inherit; display: flex; justify-content: center;"><div class="ch bg ew ex ey ez" style="box-sizing: inherit; margin: 0px 24px; max-width: 680px; min-width: 0px; width: 680px;"><p class="pw-post-body-paragraph lv lw fr lx b ly lz ma mb mc md me mf mg mh mi mj mk ml mm mn mo mp mq mr ms fk bj" data-selectable-paragraph="" id="0826" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; margin: 2.14em 0px -0.46em; word-break: break-word;"></p><figure class="lk ll lm ln lo lp lh li paragraph-image" style="-webkit-text-stroke-width: 0px; background-color: white; box-sizing: inherit; clear: both; color: rgba(0, 0, 0, 0.8); font-family: medium-content-sans-serif-font, -apple-system, BlinkMacSystemFont, "Segoe UI", Roboto, Oxygen, Ubuntu, Cantarell, "Open Sans", "Helvetica Neue", sans-serif; font-size: medium; font-style: normal; font-variant-caps: normal; font-variant-ligatures: normal; font-weight: 400; letter-spacing: normal; margin: 40px auto 0px; orphans: 2; text-align: start; text-decoration-color: initial; text-decoration-style: initial; text-decoration-thickness: initial; text-indent: 0px; text-transform: none; white-space: normal; widows: 2; word-spacing: 0px;"><div class="lq lr ee ls bg lt" role="button" style="box-sizing: inherit; cursor: zoom-in; position: relative; transition: transform 300ms cubic-bezier(0.2, 0, 0.2, 1) 0s; width: 680px; z-index: auto;" tabindex="0"></div></figure><p></p><div style="-webkit-text-stroke-width: 0px; background-color: white; box-sizing: inherit; color: rgba(0, 0, 0, 0.8); font-family: medium-content-sans-serif-font, -apple-system, BlinkMacSystemFont, "Segoe UI", Roboto, Oxygen, Ubuntu, Cantarell, "Open Sans", "Helvetica Neue", sans-serif; font-size: medium; font-style: normal; font-variant-caps: normal; font-variant-ligatures: normal; font-weight: 400; letter-spacing: normal; orphans: 2; text-align: start; text-decoration-color: initial; text-decoration-style: initial; text-decoration-thickness: initial; text-indent: 0px; text-transform: none; white-space: normal; widows: 2; word-spacing: 0px;"><h1 class="pw-post-title fp fq fr be fs ft fu fv fw fx fy fz ga gb gc gd ge gf gg gh gi gj gk gl gm gn go gp gq gr bj" data-selectable-paragraph="" data-testid="storyTitle" id="c1a5" style="box-sizing: inherit; color: #242424; font-family: sohne, "Helvetica Neue", Helvetica, Arial, sans-serif; font-size: 42px; font-style: normal; font-weight: 700; letter-spacing: -0.011em; line-height: 52px; margin: 1.19em 0px 32px;">Unlock Incredible Flight Deals: Your Ultimate Guide to Affordable Air Travel</h1><div class="gs gt gu gv gw" style="box-sizing: inherit;"><div class="speechify-ignore ab co" style="box-sizing: inherit; display: flex; justify-content: space-between;"><div class="speechify-ignore bg l" style="box-sizing: inherit; display: block; width: 680px;"><div class="gx gy gz ha hb ab" style="align-items: center; box-sizing: inherit; display: flex;"><div style="box-sizing: inherit;"><div class="ab hc" style="align-items: baseline; box-sizing: inherit; display: flex;"><a href="https://medium.com/@eduard.hucai?source=post_page-----87958b621164--------------------------------" previewlistener="true" rel="noopener follow" style="-webkit-tap-highlight-color: transparent; box-sizing: inherit; color: inherit; text-decoration: none;"><div style="box-sizing: inherit;"><div aria-describedby="1" aria-hidden="false" aria-labelledby="1" class="bl" style="box-sizing: inherit; display: inline-block;"><div class="l hd he bx hf hg" style="border-radius: 50%; border: 2px solid rgb(255, 255, 255); box-sizing: inherit; display: block; height: 48px; width: 48px; z-index: 0;"><div class="l ee" style="box-sizing: inherit; display: block; position: relative;"><img alt="TravelGo" class="l eq bx dc dd cw" data-testid="authorPhoto" height="44" loading="lazy" src="https://miro.medium.com/v2/resize:fill:88:88/1*dXcQokbyAbuPV_XgyxWVaw.png" style="background-color: #f2f2f2; border-radius: 50%; box-sizing: border-box; display: block; height: 44px; vertical-align: middle; width: 44px;" width="44" /><div class="hh bx l dc dd eo n hi ep" style="border-radius: 50%; border: 1px solid rgba(0, 0, 0, 0.05); box-shadow: none; box-sizing: inherit; display: block; height: 44px; position: absolute; top: 0px; width: 44px;"></div></div></div></div></div></a></div></div><div class="bm bg l" style="box-sizing: inherit; display: block; margin-left: 12px; width: 620px;"><div class="ab" style="box-sizing: inherit; display: flex;"><div style="box-sizing: inherit; flex: 1 1 0%;"><span class="be b bf z bj" style="box-sizing: inherit; color: #242424; font-family: sohne, "Helvetica Neue", Helvetica, Arial, sans-serif; font-size: 14px; font-weight: 400; line-height: 20px;"><div class="hj ab q" style="align-items: center; box-sizing: inherit; display: flex; margin-bottom: 2px;"><div class="ab q hk" style="align-items: center; box-sizing: inherit; display: flex; flex-wrap: nowrap;"><div class="ab q" style="align-items: center; box-sizing: inherit; display: flex;"><div style="box-sizing: inherit;"><div aria-describedby="2" aria-hidden="false" aria-labelledby="2" class="bl" style="box-sizing: inherit; display: inline-block;"><p class="be b hl hm bj" style="box-sizing: inherit; color: #242424; font-family: sohne, "Helvetica Neue", Helvetica, Arial, sans-serif; font-size: 16px; font-weight: 400; line-height: 24px; margin: 0px;"><a class="af ag ah ai aj ak al am an ao ap aq ar hn" data-testid="authorName" href="https://medium.com/@eduard.hucai?source=post_page-----87958b621164--------------------------------" previewlistener="true" rel="noopener follow" style="-webkit-tap-highlight-color: transparent; border: inherit; box-sizing: inherit; color: inherit; cursor: pointer; fill: inherit; font-family: inherit; font-size: inherit; font-weight: inherit; letter-spacing: inherit; margin: 0px; padding: 0px; text-decoration: none;">TravelGo</a></p></div></div></div></div></div></span></div></div><div class="l ho" style="box-sizing: inherit; display: block; flex: 0 0 auto;"><span class="be b bf z dw" style="box-sizing: inherit; color: #6b6b6b; font-family: sohne, "Helvetica Neue", Helvetica, Arial, sans-serif; font-size: 14px; font-weight: 400; line-height: 20px;"><div class="ab cm hp hq hr" style="align-items: flex-start; box-sizing: inherit; display: flex; flex-wrap: wrap;"><span class="be b bf z dw" style="box-sizing: inherit; color: #6b6b6b; font-family: sohne, "Helvetica Neue", Helvetica, Arial, sans-serif; font-size: 14px; font-weight: 400; line-height: 20px;"><div class="ab ae" style="box-sizing: inherit; display: flex; flex: 1 0 auto;"><span data-testid="storyReadTime" style="box-sizing: inherit;">4 min read</span><div aria-hidden="true" class="hs ht l" style="box-sizing: inherit; display: block; padding-left: 8px; padding-right: 8px;"><span aria-hidden="true" class="l" style="box-sizing: inherit; display: block;"><span class="be b bf z dw" style="box-sizing: inherit; color: #6b6b6b; font-family: sohne, "Helvetica Neue", Helvetica, Arial, sans-serif; font-size: 14px; font-weight: 400; line-height: 20px;">·</span></span></div>Just now</div></span></div></span></div></div></div><div class="ab co hu hv hw hx hy hz ia ib ic id ie if ig ih ii ij" style="border-bottom: 1px solid rgb(242, 242, 242); border-top: 1px solid rgb(242, 242, 242); box-sizing: inherit; display: flex; justify-content: space-between; margin: 32px 0px 0px; padding: 3px 8px;"><div class="h k w eb ec q" style="align-items: center; box-sizing: inherit; display: flex;"><div class="iz l" style="box-sizing: inherit; display: block; width: 74px;"><div class="ab q ja jb" style="align-items: center; box-sizing: inherit; display: flex; flex-direction: row; z-index: 2;"><div class="pw-multi-vote-icon ee se jd je jf" style="box-sizing: inherit; margin-right: 0px; position: relative; user-select: none;"><div class="" style="box-sizing: inherit;"><div style="box-sizing: inherit;"><div aria-describedby="47" aria-hidden="false" aria-labelledby="47" class="bl" style="box-sizing: inherit; display: inline-block;"><div class="jg sf ji jj jk jl jm am jn jo jp jf" style="border: 0px; box-sizing: inherit; cursor: not-allowed; fill: rgb(117, 117, 117); opacity: 0.25; outline: 0px; padding: 0px; user-select: none;"><svg aria-label="clap" height="24" viewbox="0 0 24 24" width="24"><path clip-rule="evenodd" d="M11.37.83L12 3.28l.63-2.45h-1.26zM15.42 1.84l-1.18-.39-.34 2.5 1.52-2.1zM9.76 1.45l-1.19.4 1.53 2.1-.34-2.5zM20.25 11.84l-2.5-4.4a1.42 1.42 0 0 0-.93-.64.96.96 0 0 0-.75.18c-.25.19-.4.42-.45.7l.05.05 2.35 4.13c1.62 2.95 1.1 5.78-1.52 8.4l-.46.41c1-.13 1.93-.6 2.78-1.45 2.7-2.7 2.51-5.59 1.43-7.38zM12.07 9.01c-.13-.69.08-1.3.57-1.77l-2.06-2.07a1.12 1.12 0 0 0-1.56 0c-.15.15-.22.34-.27.53L12.07 9z" fill-rule="evenodd"></path><path clip-rule="evenodd" d="M14.74 8.3a1.13 1.13 0 0 0-.73-.5.67.67 0 0 0-.53.13c-.15.12-.59.46-.2 1.3l1.18 2.5a.45.45 0 0 1-.23.76.44.44 0 0 1-.48-.25L7.6 6.11a.82.82 0 1 0-1.15 1.15l3.64 3.64a.45.45 0 1 1-.63.63L5.83 7.9 4.8 6.86a.82.82 0 0 0-1.33.9c.04.1.1.18.18.26l1.02 1.03 3.65 3.64a.44.44 0 0 1-.15.73.44.44 0 0 1-.48-.1L4.05 9.68a.82.82 0 0 0-1.4.57.81.81 0 0 0 .24.58l1.53 1.54 2.3 2.28a.45.45 0 0 1-.64.63L3.8 13a.81.81 0 0 0-1.39.57c0 .22.09.43.24.58l4.4 4.4c2.8 2.8 5.5 4.12 8.68.94 2.27-2.28 2.71-4.6 1.34-7.1l-2.32-4.08z" fill-rule="evenodd"></path></svg></div></div></div></div></div></div></div><div style="box-sizing: inherit;"><div aria-describedby="3" aria-hidden="false" aria-labelledby="3" class="bl" style="box-sizing: inherit; display: inline-block;"><button aria-label="responses" class="ao jg jx jy ab q ef jz ka" style="-webkit-tap-highlight-color: transparent; align-items: center; background: transparent; border: 0px; box-sizing: inherit; cursor: pointer; display: flex; fill: rgb(107, 107, 107); margin: 0px; opacity: 1; overflow: visible; padding: 4px 0px;"><svg class="kb" height="24" viewbox="0 0 24 24" width="24"><path d="M18 16.8a7.14 7.14 0 0 0 2.24-5.32c0-4.12-3.53-7.48-8.05-7.48C7.67 4 4 7.36 4 11.48c0 4.13 3.67 7.48 8.2 7.48a8.9 8.9 0 0 0 2.38-.32c.23.2.48.39.75.56 1.06.69 2.2 1.04 3.4 1.04.22 0 .4-.11.48-.29a.5.5 0 0 0-.04-.52 6.4 6.4 0 0 1-1.16-2.65v.02zm-3.12 1.06l-.06-.22-.32.1a8 8 0 0 1-2.3.33c-4.03 0-7.3-2.96-7.3-6.59S8.17 4.9 12.2 4.9c4 0 7.1 2.96 7.1 6.6 0 1.8-.6 3.47-2.02 4.72l-.2.16v.26l.02.3a6.74 6.74 0 0 0 .88 2.4 5.27 5.27 0 0 1-2.17-.86c-.28-.17-.72-.38-.94-.59l.01-.02z"></path></svg></button></div></div></div><div class="ab q ik il im in io ip iq ir is it iu iv iw ix iy" style="align-items: center; box-sizing: inherit; display: flex; overflow-x: scroll; scrollbar-width: none;"><div class="h k" style="box-sizing: inherit; flex-shrink: 0; margin-right: 24px;"><div style="box-sizing: inherit;"><div aria-describedby="4" aria-hidden="false" aria-labelledby="4" class="bl" style="box-sizing: inherit; display: inline-block;"><div aria-hidden="false" class="bl" style="box-sizing: inherit; display: inline-block;"><button aria-controls="addToCatalogBookmarkButton" aria-expanded="false" aria-label="Add to list bookmark button" class="af ef ah ai aj ak al kd an ao ap ke kf kg kh" data-testid="headerBookmarkButton" style="-webkit-tap-highlight-color: transparent; background: transparent; border: inherit; box-sizing: inherit; color: inherit; cursor: pointer; fill: rgb(107, 107, 107); font-family: inherit; font-size: inherit; font-weight: inherit; letter-spacing: inherit; margin: 0px; overflow: visible; padding: 8px 2px;"><svg class="ki" fill="none" height="24" viewbox="0 0 24 24" width="24"><path d="M17.5 1.25a.5.5 0 0 1 1 0v2.5H21a.5.5 0 0 1 0 1h-2.5v2.5a.5.5 0 0 1-1 0v-2.5H15a.5.5 0 0 1 0-1h2.5v-2.5zm-11 4.5a1 1 0 0 1 1-1H11a.5.5 0 0 0 0-1H7.5a2 2 0 0 0-2 2v14a.5.5 0 0 0 .8.4l5.7-4.4 5.7 4.4a.5.5 0 0 0 .8-.4v-8.5a.5.5 0 0 0-1 0v7.48l-5.2-4a.5.5 0 0 0-.6 0l-5.2 4V5.75z" fill="#000"></path></svg></button></div></div></div></div><div class="eq kj cm" style="align-items: flex-start; box-sizing: border-box; display: inline-flex; flex-shrink: 0; margin-right: 24px;"><div class="l ae" style="box-sizing: inherit; display: block; flex: 1 0 auto;"><div class="ab ca" style="box-sizing: inherit; display: flex; justify-content: center;"><div class="kk kl km kn ko kp ch bg" style="box-sizing: inherit; margin: 0px; max-width: 100%; min-width: 0px; width: 28px;"><div class="ab" style="box-sizing: inherit; display: flex;"><div style="box-sizing: inherit;"><a class="af ag ah ai aj ak al am an ao ap aq ar as at" href="https://medium.com/plans?dimension=post_audio_button&postId=87958b621164&source=upgrade_membership---post_audio_button----------------------------------" previewlistener="true" rel="noopener follow" style="-webkit-tap-highlight-color: transparent; border: inherit; box-sizing: inherit; color: inherit; cursor: pointer; fill: inherit; font-family: inherit; font-size: inherit; font-weight: inherit; letter-spacing: inherit; margin: 0px; padding: 0px; text-decoration: none;"><div style="box-sizing: inherit;"><div aria-describedby="16" aria-hidden="false" aria-labelledby="16" class="bl" style="box-sizing: inherit; display: inline-block;"><button aria-label="Listen" class="af ef ah ai aj ak al kd an ao ap ke kq kr ka ks kt ku kv kw s kx ky kz la lb lc ld u le lf lg" data-testid="audioPlayButton" style="-webkit-tap-highlight-color: transparent; background: transparent; border: inherit; box-sizing: inherit; color: inherit; cursor: pointer; fill: rgb(107, 107, 107); font-family: inherit; font-size: inherit; font-weight: inherit; letter-spacing: inherit; margin: 0px; overflow: visible; padding: 8px 2px;"><svg fill="none" height="24" viewbox="0 0 24 24" width="24"><path clip-rule="evenodd" d="M3 12a9 9 0 1 1 18 0 9 9 0 0 1-18 0zm9-10a10 10 0 1 0 0 20 10 10 0 0 0 0-20zm3.38 10.42l-4.6 3.06a.5.5 0 0 1-.78-.41V8.93c0-.4.45-.63.78-.41l4.6 3.06c.3.2.3.64 0 .84z" fill-rule="evenodd" fill="currentColor"></path></svg></button></div></div></a></div></div></div></div></div></div><div aria-describedby="postFooterSocialMenu" aria-hidden="false" aria-labelledby="postFooterSocialMenu" class="bl" style="box-sizing: inherit; display: inline-block; flex-shrink: 0; margin-right: 24px;"><div style="box-sizing: inherit;"><div aria-describedby="6" aria-hidden="false" aria-labelledby="6" class="bl" style="box-sizing: inherit; display: inline-block;"><button aria-controls="postFooterSocialMenu" aria-expanded="false" aria-label="Share Post" class="af ef ah ai aj ak al kd an ao ap ke kq kr ka ks kt ku kv kw s kx ky kz la lb lc ld u le lf lg" data-testid="headerSocialShareButton" style="-webkit-tap-highlight-color: transparent; background: transparent; border: inherit; box-sizing: inherit; color: inherit; cursor: pointer; fill: rgb(107, 107, 107); font-family: inherit; font-size: inherit; font-weight: inherit; letter-spacing: inherit; margin: 0px; overflow: visible; padding: 8px 2px;"><svg fill="none" height="24" viewbox="0 0 24 24" width="24"><path clip-rule="evenodd" d="M15.22 4.93a.42.42 0 0 1-.12.13h.01a.45.45 0 0 1-.29.08.52.52 0 0 1-.3-.13L12.5 3v7.07a.5.5 0 0 1-.5.5.5.5 0 0 1-.5-.5V3.02l-2 2a.45.45 0 0 1-.57.04h-.02a.4.4 0 0 1-.16-.3.4.4 0 0 1 .1-.32l2.8-2.8a.5.5 0 0 1 .7 0l2.8 2.8a.42.42 0 0 1 .07.5zm-.1.14zm.88 2h1.5a2 2 0 0 1 2 2v10a2 2 0 0 1-2 2h-11a2 2 0 0 1-2-2v-10a2 2 0 0 1 2-2H8a.5.5 0 0 1 .35.14c.1.1.15.22.15.35a.5.5 0 0 1-.15.35.5.5 0 0 1-.35.15H6.4c-.5 0-.9.4-.9.9v10.2a.9.9 0 0 0 .9.9h11.2c.5 0 .9-.4.9-.9V8.96c0-.5-.4-.9-.9-.9H16a.5.5 0 0 1 0-1z" fill-rule="evenodd" fill="currentColor"></path></svg></button></div></div></div><div aria-hidden="false" class="bl" style="box-sizing: inherit; display: inline-block; flex-shrink: 0; margin-right: 0px;"><div aria-describedby="creatorActionOverflowMenu" aria-hidden="false" aria-labelledby="creatorActionOverflowMenu" class="bl" style="box-sizing: inherit; display: inline-block;"><div class="qz l ho" style="box-sizing: inherit; display: block; flex: 0 0 auto; margin-right: -4px;"><div style="box-sizing: inherit;"><div aria-describedby="146" aria-hidden="false" aria-labelledby="146" class="bl" style="box-sizing: inherit; display: inline-block;"><button aria-controls="creatorActionOverflowMenu" aria-expanded="false" aria-label="More options" class="af ef ah ai aj ak al kd an ao ap ke kq kr ka ks kt ku kv kw s kx ky kz la lb lc ld u le lf lg" data-testid="headerStoryOptionsButton" style="-webkit-tap-highlight-color: transparent; background: transparent; border: inherit; box-sizing: inherit; color: inherit; cursor: pointer; fill: rgb(107, 107, 107); font-family: inherit; font-size: inherit; font-weight: inherit; letter-spacing: inherit; margin: 0px; overflow: visible; padding: 8px 2px;"><svg fill="none" height="24" viewbox="0 0 24 24" width="24"><path clip-rule="evenodd" d="M4.39 12c0 .55.2 1.02.59 1.41.39.4.86.59 1.4.59.56 0 1.03-.2 1.42-.59.4-.39.59-.86.59-1.41 0-.55-.2-1.02-.6-1.41A1.93 1.93 0 0 0 6.4 10c-.55 0-1.02.2-1.41.59-.4.39-.6.86-.6 1.41zM10 12c0 .55.2 1.02.58 1.41.4.4.87.59 1.42.59.54 0 1.02-.2 1.4-.59.4-.39.6-.86.6-1.41 0-.55-.2-1.02-.6-1.41a1.93 1.93 0 0 0-1.4-.59c-.55 0-1.04.2-1.42.59-.4.39-.58.86-.58 1.41zm5.6 0c0 .55.2 1.02.57 1.41.4.4.88.59 1.43.59.57 0 1.04-.2 1.43-.59.39-.39.57-.86.57-1.41 0-.55-.2-1.02-.57-1.41A1.93 1.93 0 0 0 17.6 10c-.55 0-1.04.2-1.43.59-.38.39-.57.86-.57 1.41z" fill-rule="evenodd" fill="currentColor"></path></svg></button></div></div></div></div></div></div></div></div></div></div></div><p class="pw-post-body-paragraph lv lw fr lx b ly lz ma mb mc md me mf mg mh mi mj mk ml mm mn mo mp mq mr ms fk bj" data-selectable-paragraph="" id="0826" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; margin: 2.14em 0px -0.46em; word-break: break-word;">Are you dreaming of exploring new destinations but worried about the cost of flights? Look no further! We have curated the best flight deals to make your travel dreams come true without breaking the bank. Discover the secrets to finding cheap flights, last-minute flight deals, direct flights, flight discounts, and travel hacks for flights. With our expert tips and unbeatable offers, you’ll be ready to take off on your next adventure in no time.</p><h1 class="mt mu fr be mv mw mx my mz na nb nc nd ne nf ng nh ni nj nk nl nm nn no np nq bj" data-selectable-paragraph="" id="f03d" style="box-sizing: inherit; color: #242424; font-family: sohne, "Helvetica Neue", Helvetica, Arial, sans-serif; font-size: 24px; letter-spacing: -0.016em; line-height: 30px; margin: 1.95em 0px -0.28em;">Why Flying is the Best Choice?</h1><p class="pw-post-body-paragraph lv lw fr lx b ly nr ma mb mc ns me mf mg nt mi mj mk nu mm mn mo nv mq mr ms fk bj" data-selectable-paragraph="" id="4196" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; margin: 0.94em 0px -0.46em; word-break: break-word;"><a class="af nw" href="https://www.booking.com/flights/index.html?aid=8019784" previewlistener="true" rel="noopener ugc nofollow" style="-webkit-tap-highlight-color: transparent; box-sizing: inherit;" target="_blank">Air travel</a> offers unparalleled speed and convenience, making it the ideal choice for both short and long distances. Modern planes are equipped with state-of-the-art amenities, ensuring a comfortable journey. Plus, with the right deals, flying can be surprisingly affordable. Here’s how you can find the best flight offers and travel smart.</p><h1 class="mt mu fr be mv mw mx my mz na nb nc nd ne nf ng nh ni nj nk nl nm nn no np nq bj" data-selectable-paragraph="" id="3159" style="box-sizing: inherit; color: #242424; font-family: sohne, "Helvetica Neue", Helvetica, Arial, sans-serif; font-size: 24px; letter-spacing: -0.016em; line-height: 30px; margin: 1.95em 0px -0.28em;">Top Search Trends in Air Travel</h1><figure class="nx ny nz oa ob lp lh li paragraph-image" style="box-sizing: inherit; clear: both; margin: 56px auto 0px;"><div class="lq lr ee ls bg lt" role="button" style="box-sizing: inherit; cursor: zoom-in; position: relative; transition: transform 300ms cubic-bezier(0.2, 0, 0.2, 1) 0s; width: 680px; z-index: auto;" tabindex="0"><div class="lh li lj" style="box-sizing: inherit; margin-left: auto; margin-right: auto; max-width: 1000px;"><picture style="box-sizing: inherit;"><source sizes="(min-resolution: 4dppx) and (max-width: 700px) 50vw, (-webkit-min-device-pixel-ratio: 4) and (max-width: 700px) 50vw, (min-resolution: 3dppx) and (max-width: 700px) 67vw, (-webkit-min-device-pixel-ratio: 3) and (max-width: 700px) 65vw, (min-resolution: 2.5dppx) and (max-width: 700px) 80vw, (-webkit-min-device-pixel-ratio: 2.5) and (max-width: 700px) 80vw, (min-resolution: 2dppx) and (max-width: 700px) 100vw, (-webkit-min-device-pixel-ratio: 2) and (max-width: 700px) 100vw, 700px" srcset="https://miro.medium.com/v2/resize:fit:640/format:webp/0*kCN5O8WMG6OUIZxv 640w, https://miro.medium.com/v2/resize:fit:720/format:webp/0*kCN5O8WMG6OUIZxv 720w, https://miro.medium.com/v2/resize:fit:750/format:webp/0*kCN5O8WMG6OUIZxv 750w, https://miro.medium.com/v2/resize:fit:786/format:webp/0*kCN5O8WMG6OUIZxv 786w, https://miro.medium.com/v2/resize:fit:828/format:webp/0*kCN5O8WMG6OUIZxv 828w, https://miro.medium.com/v2/resize:fit:1100/format:webp/0*kCN5O8WMG6OUIZxv 1100w, https://miro.medium.com/v2/resize:fit:1400/format:webp/0*kCN5O8WMG6OUIZxv 1400w" style="box-sizing: inherit;" type="image/webp"></source><source data-testid="og" sizes="(min-resolution: 4dppx) and (max-width: 700px) 50vw, (-webkit-min-device-pixel-ratio: 4) and (max-width: 700px) 50vw, (min-resolution: 3dppx) and (max-width: 700px) 67vw, (-webkit-min-device-pixel-ratio: 3) and (max-width: 700px) 65vw, (min-resolution: 2.5dppx) and (max-width: 700px) 80vw, (-webkit-min-device-pixel-ratio: 2.5) and (max-width: 700px) 80vw, (min-resolution: 2dppx) and (max-width: 700px) 100vw, (-webkit-min-device-pixel-ratio: 2) and (max-width: 700px) 100vw, 700px" srcset="https://miro.medium.com/v2/resize:fit:640/0*kCN5O8WMG6OUIZxv 640w, https://miro.medium.com/v2/resize:fit:720/0*kCN5O8WMG6OUIZxv 720w, https://miro.medium.com/v2/resize:fit:750/0*kCN5O8WMG6OUIZxv 750w, https://miro.medium.com/v2/resize:fit:786/0*kCN5O8WMG6OUIZxv 786w, https://miro.medium.com/v2/resize:fit:828/0*kCN5O8WMG6OUIZxv 828w, https://miro.medium.com/v2/resize:fit:1100/0*kCN5O8WMG6OUIZxv 1100w, https://miro.medium.com/v2/resize:fit:1400/0*kCN5O8WMG6OUIZxv 1400w" style="box-sizing: inherit;"></source><img alt="" class="bg kp lu c" height="379" loading="lazy" role="presentation" src="https://miro.medium.com/v2/resize:fit:700/0*kCN5O8WMG6OUIZxv" style="box-sizing: inherit; height: auto; max-width: 100%; vertical-align: middle; width: 680px;" width="700" /></picture></div></div></figure><p class="pw-post-body-paragraph lv lw fr lx b ly lz ma mb mc md me mf mg mh mi mj mk ml mm mn mo mp mq mr ms fk bj" data-selectable-paragraph="" id="417a" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; margin: 2.14em 0px -0.46em; word-break: break-word;">Based on extensive research, the most searched topics and trending keywords related to flights include:</p><ol class="" style="box-sizing: inherit; list-style: none none; margin: 0px; padding: 0px;"><li class="lv lw fr lx b ly lz ma mb mc md me mf mg mh mi mj mk ml mm mn mo mp mq mr ms oc od oe bj" data-selectable-paragraph="" id="7db9" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; list-style-type: decimal; margin-bottom: -0.46em; margin-left: 30px; margin-top: 2.14em; padding-left: 0px;"><a class="af nw" href="https://www.booking.com/flights/index.html?aid=8019784" previewlistener="true" rel="noopener ugc nofollow" style="-webkit-tap-highlight-color: transparent; box-sizing: inherit;" target="_blank">Cheap Flights</a></li></ol><p class="pw-post-body-paragraph lv lw fr lx b ly lz ma mb mc md me mf mg mh mi mj mk ml mm mn mo mp mq mr ms fk bj" data-selectable-paragraph="" id="9619" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; margin: 2.14em 0px -0.46em; word-break: break-word;">2. <a class="af nw" href="https://www.booking.com/flights/index.html?aid=8019784" previewlistener="true" rel="noopener ugc nofollow" style="-webkit-tap-highlight-color: transparent; box-sizing: inherit;" target="_blank">Last-Minute Flight Deals</a></p><p class="pw-post-body-paragraph lv lw fr lx b ly lz ma mb mc md me mf mg mh mi mj mk ml mm mn mo mp mq mr ms fk bj" data-selectable-paragraph="" id="42d3" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; margin: 2.14em 0px -0.46em; word-break: break-word;">3. <a class="af nw" href="https://www.booking.com/flights/index.html?aid=8019784" previewlistener="true" rel="noopener ugc nofollow" style="-webkit-tap-highlight-color: transparent; box-sizing: inherit;" target="_blank">Direct Flights</a></p><p class="pw-post-body-paragraph lv lw fr lx b ly lz ma mb mc md me mf mg mh mi mj mk ml mm mn mo mp mq mr ms fk bj" data-selectable-paragraph="" id="32f5" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; margin: 2.14em 0px -0.46em; word-break: break-word;">4. <a class="af nw" href="https://www.booking.com/flights/index.html?aid=8019784" previewlistener="true" rel="noopener ugc nofollow" style="-webkit-tap-highlight-color: transparent; box-sizing: inherit;" target="_blank">Flight Discounts</a></p><p class="pw-post-body-paragraph lv lw fr lx b ly lz ma mb mc md me mf mg mh mi mj mk ml mm mn mo mp mq mr ms fk bj" data-selectable-paragraph="" id="7def" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; margin: 2.14em 0px -0.46em; word-break: break-word;">5. <a class="af nw" href="https://www.booking.com/flights/index.html?aid=8019784" previewlistener="true" rel="noopener ugc nofollow" style="-webkit-tap-highlight-color: transparent; box-sizing: inherit;" target="_blank">Travel Hacks for Flights</a></p><p class="pw-post-body-paragraph lv lw fr lx b ly lz ma mb mc md me mf mg mh mi mj mk ml mm mn mo mp mq mr ms fk bj" data-selectable-paragraph="" id="8d7b" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; margin: 2.14em 0px -0.46em; word-break: break-word;"><a class="af nw" href="https://www.booking.com/flights/index.html?aid=8019784" previewlistener="true" rel="noopener ugc nofollow" style="-webkit-tap-highlight-color: transparent; box-sizing: inherit;" target="_blank">Click HERE to find the most suitable flight offers for you!</a></p><h1 class="mt mu fr be mv mw mx my mz na nb nc nd ne nf ng nh ni nj nk nl nm nn no np nq bj" data-selectable-paragraph="" id="cb34" style="box-sizing: inherit; color: #242424; font-family: sohne, "Helvetica Neue", Helvetica, Arial, sans-serif; font-size: 24px; letter-spacing: -0.016em; line-height: 30px; margin: 1.95em 0px -0.28em;">Discovering the Best Flight Deals</h1><ol class="" style="box-sizing: inherit; list-style: none none; margin: 0px; padding: 0px;"><li class="lv lw fr lx b ly nr ma mb mc ns me mf mg nt mi mj mk nu mm mn mo nv mq mr ms oc od oe bj" data-selectable-paragraph="" id="9c7d" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; list-style-type: decimal; margin-bottom: -0.46em; margin-left: 30px; margin-top: 0.94em; padding-left: 0px;"><a class="af nw" href="https://www.booking.com/flights/index.html?aid=8019784" previewlistener="true" rel="noopener ugc nofollow" style="-webkit-tap-highlight-color: transparent; box-sizing: inherit;" target="_blank">Cheap Flights</a></li></ol><p class="pw-post-body-paragraph lv lw fr lx b ly lz ma mb mc md me mf mg mh mi mj mk ml mm mn mo mp mq mr ms fk bj" data-selectable-paragraph="" id="c275" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; margin: 2.14em 0px -0.46em; word-break: break-word;"><a class="af nw" href="https://www.booking.com/flights/index.html?aid=8019784" previewlistener="true" rel="noopener ugc nofollow" style="-webkit-tap-highlight-color: transparent; box-sizing: inherit;" target="_blank">Click HERE to find the most suitable flight offers for you!</a></p><p class="pw-post-body-paragraph lv lw fr lx b ly lz ma mb mc md me mf mg mh mi mj mk ml mm mn mo mp mq mr ms fk bj" data-selectable-paragraph="" id="8908" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; margin: 2.14em 0px -0.46em; word-break: break-word;">Finding cheap flights is easier than you think. Here are some tips to help you snag the best prices:</p><ul class="" style="box-sizing: inherit; list-style: none none; margin: 0px; padding: 0px;"><li class="lv lw fr lx b ly lz ma mb mc md me mf mg mh mi mj mk ml mm mn mo mp mq mr ms of od oe bj" data-selectable-paragraph="" id="e1fb" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; list-style-type: disc; margin-bottom: -0.46em; margin-left: 30px; margin-top: 2.14em; padding-left: 0px;">Use Flight Comparison Websites: Websites like Skyscanner, Kayak, and Google Flights allow you to compare prices across multiple airlines and booking platforms.</li><li class="lv lw fr lx b ly og ma mb mc oh me mf mg oi mi mj mk oj mm mn mo ok mq mr ms of od oe bj" data-selectable-paragraph="" id="05c5" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; list-style-type: disc; margin-bottom: -0.46em; margin-left: 30px; margin-top: 1.14em; padding-left: 0px;">Set Price Alerts: Sign up for price alerts to get notified when flight prices drop.</li><li class="lv lw fr lx b ly og ma mb mc oh me mf mg oi mi mj mk oj mm mn mo ok mq mr ms of od oe bj" data-selectable-paragraph="" id="8ce4" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; list-style-type: disc; margin-bottom: -0.46em; margin-left: 30px; margin-top: 1.14em; padding-left: 0px;">Book in Advance: Generally, booking your flight several weeks or months in advance can help you get lower fares.</li><li class="lv lw fr lx b ly og ma mb mc oh me mf mg oi mi mj mk oj mm mn mo ok mq mr ms of od oe bj" data-selectable-paragraph="" id="9ed6" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; list-style-type: disc; margin-bottom: -0.46em; margin-left: 30px; margin-top: 1.14em; padding-left: 0px;">Be Flexible with Dates: Traveling on weekdays or during off-peak seasons can significantly reduce the cost of your flight.</li></ul><p class="pw-post-body-paragraph lv lw fr lx b ly lz ma mb mc md me mf mg mh mi mj mk ml mm mn mo mp mq mr ms fk bj" data-selectable-paragraph="" id="1f46" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; margin: 2.14em 0px -0.46em; word-break: break-word;"><a class="af nw" href="https://www.booking.com/flights/index.html?aid=8019784" previewlistener="true" rel="noopener ugc nofollow" style="-webkit-tap-highlight-color: transparent; box-sizing: inherit;" target="_blank">2. Last-Minute Flight Deals</a></p><p class="pw-post-body-paragraph lv lw fr lx b ly lz ma mb mc md me mf mg mh mi mj mk ml mm mn mo mp mq mr ms fk bj" data-selectable-paragraph="" id="ffb1" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; margin: 2.14em 0px -0.46em; word-break: break-word;">If you’re spontaneous, last-minute flight deals can be a great way to save money:</p><p class="pw-post-body-paragraph lv lw fr lx b ly lz ma mb mc md me mf mg mh mi mj mk ml mm mn mo mp mq mr ms fk bj" data-selectable-paragraph="" id="b9bc" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; margin: 2.14em 0px -0.46em; word-break: break-word;"><a class="af nw" href="https://www.booking.com/flights/index.html?aid=8019784" previewlistener="true" rel="noopener ugc nofollow" style="-webkit-tap-highlight-color: transparent; box-sizing: inherit;" target="_blank">Click HERE to find the most suitable flight offers for you!</a></p><ul class="" style="box-sizing: inherit; list-style: none none; margin: 0px; padding: 0px;"><li class="lv lw fr lx b ly lz ma mb mc md me mf mg mh mi mj mk ml mm mn mo mp mq mr ms of od oe bj" data-selectable-paragraph="" id="4b15" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; list-style-type: disc; margin-bottom: -0.46em; margin-left: 30px; margin-top: 2.14em; padding-left: 0px;">Check Airline Websites: Airlines often post last-minute deals directly on their websites.</li><li class="lv lw fr lx b ly og ma mb mc oh me mf mg oi mi mj mk oj mm mn mo ok mq mr ms of od oe bj" data-selectable-paragraph="" id="6178" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; list-style-type: disc; margin-bottom: -0.46em; margin-left: 30px; margin-top: 1.14em; padding-left: 0px;">Subscribe to Newsletters: Get exclusive last-minute offers by subscribing to airline and travel agency newsletters.</li><li class="lv lw fr lx b ly og ma mb mc oh me mf mg oi mi mj mk oj mm mn mo ok mq mr ms of od oe bj" data-selectable-paragraph="" id="86fe" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; list-style-type: disc; margin-bottom: -0.46em; margin-left: 30px; margin-top: 1.14em; padding-left: 0px;">Use Travel Apps: Apps like Hopper and Skiplagged specialize in finding last-minute flight deals.</li></ul><figure class="nx ny nz oa ob lp lh li paragraph-image" style="box-sizing: inherit; clear: both; margin: 56px auto 0px;"><div class="lq lr ee ls bg lt" role="button" style="box-sizing: inherit; cursor: zoom-in; position: relative; transition: transform 300ms cubic-bezier(0.2, 0, 0.2, 1) 0s; width: 680px; z-index: auto;" tabindex="0"><div class="lh li lj" style="box-sizing: inherit; margin-left: auto; margin-right: auto; max-width: 1000px;"><picture style="box-sizing: inherit;"><source sizes="(min-resolution: 4dppx) and (max-width: 700px) 50vw, (-webkit-min-device-pixel-ratio: 4) and (max-width: 700px) 50vw, (min-resolution: 3dppx) and (max-width: 700px) 67vw, (-webkit-min-device-pixel-ratio: 3) and (max-width: 700px) 65vw, (min-resolution: 2.5dppx) and (max-width: 700px) 80vw, (-webkit-min-device-pixel-ratio: 2.5) and (max-width: 700px) 80vw, (min-resolution: 2dppx) and (max-width: 700px) 100vw, (-webkit-min-device-pixel-ratio: 2) and (max-width: 700px) 100vw, 700px" srcset="https://miro.medium.com/v2/resize:fit:640/format:webp/0*R7k7BXKYBWpvicZF 640w, https://miro.medium.com/v2/resize:fit:720/format:webp/0*R7k7BXKYBWpvicZF 720w, https://miro.medium.com/v2/resize:fit:750/format:webp/0*R7k7BXKYBWpvicZF 750w, https://miro.medium.com/v2/resize:fit:786/format:webp/0*R7k7BXKYBWpvicZF 786w, https://miro.medium.com/v2/resize:fit:828/format:webp/0*R7k7BXKYBWpvicZF 828w, https://miro.medium.com/v2/resize:fit:1100/format:webp/0*R7k7BXKYBWpvicZF 1100w, https://miro.medium.com/v2/resize:fit:1400/format:webp/0*R7k7BXKYBWpvicZF 1400w" style="box-sizing: inherit;" type="image/webp"></source><source data-testid="og" sizes="(min-resolution: 4dppx) and (max-width: 700px) 50vw, (-webkit-min-device-pixel-ratio: 4) and (max-width: 700px) 50vw, (min-resolution: 3dppx) and (max-width: 700px) 67vw, (-webkit-min-device-pixel-ratio: 3) and (max-width: 700px) 65vw, (min-resolution: 2.5dppx) and (max-width: 700px) 80vw, (-webkit-min-device-pixel-ratio: 2.5) and (max-width: 700px) 80vw, (min-resolution: 2dppx) and (max-width: 700px) 100vw, (-webkit-min-device-pixel-ratio: 2) and (max-width: 700px) 100vw, 700px" srcset="https://miro.medium.com/v2/resize:fit:640/0*R7k7BXKYBWpvicZF 640w, https://miro.medium.com/v2/resize:fit:720/0*R7k7BXKYBWpvicZF 720w, https://miro.medium.com/v2/resize:fit:750/0*R7k7BXKYBWpvicZF 750w, https://miro.medium.com/v2/resize:fit:786/0*R7k7BXKYBWpvicZF 786w, https://miro.medium.com/v2/resize:fit:828/0*R7k7BXKYBWpvicZF 828w, https://miro.medium.com/v2/resize:fit:1100/0*R7k7BXKYBWpvicZF 1100w, https://miro.medium.com/v2/resize:fit:1400/0*R7k7BXKYBWpvicZF 1400w" style="box-sizing: inherit;"></source><img alt="" class="bg kp lu c" height="468" loading="lazy" role="presentation" src="https://miro.medium.com/v2/resize:fit:700/0*R7k7BXKYBWpvicZF" style="box-sizing: inherit; height: auto; max-width: 100%; vertical-align: middle; width: 680px;" width="700" /></picture></div></div></figure><p class="pw-post-body-paragraph lv lw fr lx b ly lz ma mb mc md me mf mg mh mi mj mk ml mm mn mo mp mq mr ms fk bj" data-selectable-paragraph="" id="c682" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; margin: 2.14em 0px -0.46em; word-break: break-word;"><a class="af nw" href="https://www.booking.com/flights/index.html?aid=8019784" previewlistener="true" rel="noopener ugc nofollow" style="-webkit-tap-highlight-color: transparent; box-sizing: inherit;" target="_blank">3. Direct Flights</a></p><p class="pw-post-body-paragraph lv lw fr lx b ly lz ma mb mc md me mf mg mh mi mj mk ml mm mn mo mp mq mr ms fk bj" data-selectable-paragraph="" id="3068" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; margin: 2.14em 0px -0.46em; word-break: break-word;">Direct flights save you time and hassle. Here’s how to find affordable non-stop options:</p><ul class="" style="box-sizing: inherit; list-style: none none; margin: 0px; padding: 0px;"><li class="lv lw fr lx b ly lz ma mb mc md me mf mg mh mi mj mk ml mm mn mo mp mq mr ms of od oe bj" data-selectable-paragraph="" id="849f" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; list-style-type: disc; margin-bottom: -0.46em; margin-left: 30px; margin-top: 2.14em; padding-left: 0px;">Search Multiple Airports**: Sometimes, nearby airports offer better direct flight options.</li><li class="lv lw fr lx b ly og ma mb mc oh me mf mg oi mi mj mk oj mm mn mo ok mq mr ms of od oe bj" data-selectable-paragraph="" id="e7dc" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; list-style-type: disc; margin-bottom: -0.46em; margin-left: 30px; margin-top: 1.14em; padding-left: 0px;">Check Budget Airlines**: Airlines such as Southwest, JetBlue, and Ryanair often provide competitive prices for direct flights.</li><li class="lv lw fr lx b ly og ma mb mc oh me mf mg oi mi mj mk oj mm mn mo ok mq mr ms of od oe bj" data-selectable-paragraph="" id="c892" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; list-style-type: disc; margin-bottom: -0.46em; margin-left: 30px; margin-top: 1.14em; padding-left: 0px;">Use Filters**: When searching for flights, use filters to select non-stop options only.</li></ul><p class="pw-post-body-paragraph lv lw fr lx b ly lz ma mb mc md me mf mg mh mi mj mk ml mm mn mo mp mq mr ms fk bj" data-selectable-paragraph="" id="dc39" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; margin: 2.14em 0px -0.46em; word-break: break-word;"><a class="af nw" href="https://www.booking.com/flights/index.html?aid=8019784" previewlistener="true" rel="noopener ugc nofollow" style="-webkit-tap-highlight-color: transparent; box-sizing: inherit;" target="_blank">4. Flight Discounts</a></p><p class="pw-post-body-paragraph lv lw fr lx b ly lz ma mb mc md me mf mg mh mi mj mk ml mm mn mo mp mq mr ms fk bj" data-selectable-paragraph="" id="399c" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; margin: 2.14em 0px -0.46em; word-break: break-word;">Take advantage of various discounts to make your flights even cheaper:</p><ul class="" style="box-sizing: inherit; list-style: none none; margin: 0px; padding: 0px;"><li class="lv lw fr lx b ly lz ma mb mc md me mf mg mh mi mj mk ml mm mn mo mp mq mr ms of od oe bj" data-selectable-paragraph="" id="ebe9" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; list-style-type: disc; margin-bottom: -0.46em; margin-left: 30px; margin-top: 2.14em; padding-left: 0px;">Credit Card Rewards: Many credit cards offer travel rewards and points that can be redeemed for flights.</li><li class="lv lw fr lx b ly og ma mb mc oh me mf mg oi mi mj mk oj mm mn mo ok mq mr ms of od oe bj" data-selectable-paragraph="" id="de21" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; list-style-type: disc; margin-bottom: -0.46em; margin-left: 30px; margin-top: 1.14em; padding-left: 0px;">Student and Senior Discounts: Some airlines offer special fares for students and seniors.</li><li class="lv lw fr lx b ly og ma mb mc oh me mf mg oi mi mj mk oj mm mn mo ok mq mr ms of od oe bj" data-selectable-paragraph="" id="5b96" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; list-style-type: disc; margin-bottom: -0.46em; margin-left: 30px; margin-top: 1.14em; padding-left: 0px;">Seasonal Sales: Look out for sales during holidays and special events.</li></ul><p class="pw-post-body-paragraph lv lw fr lx b ly lz ma mb mc md me mf mg mh mi mj mk ml mm mn mo mp mq mr ms fk bj" data-selectable-paragraph="" id="d1be" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; margin: 2.14em 0px -0.46em; word-break: break-word;">5. Travel Hacks for Flights</p><p class="pw-post-body-paragraph lv lw fr lx b ly lz ma mb mc md me mf mg mh mi mj mk ml mm mn mo mp mq mr ms fk bj" data-selectable-paragraph="" id="edee" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; margin: 2.14em 0px -0.46em; word-break: break-word;">Maximize your savings and comfort with these travel hacks:</p><ul class="" style="box-sizing: inherit; list-style: none none; margin: 0px; padding: 0px;"><li class="lv lw fr lx b ly lz ma mb mc md me mf mg mh mi mj mk ml mm mn mo mp mq mr ms of od oe bj" data-selectable-paragraph="" id="3931" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; list-style-type: disc; margin-bottom: -0.46em; margin-left: 30px; margin-top: 2.14em; padding-left: 0px;">Book One-Way Tickets: Sometimes, booking two one-way tickets can be cheaper than a round-trip ticket.</li><li class="lv lw fr lx b ly og ma mb mc oh me mf mg oi mi mj mk oj mm mn mo ok mq mr ms of od oe bj" data-selectable-paragraph="" id="2b25" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; list-style-type: disc; margin-bottom: -0.46em; margin-left: 30px; margin-top: 1.14em; padding-left: 0px;">Incognito Mode: Use incognito mode when searching for flights to avoid price increases based on your search history.</li><li class="lv lw fr lx b ly og ma mb mc oh me mf mg oi mi mj mk oj mm mn mo ok mq mr ms of od oe bj" data-selectable-paragraph="" id="8435" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; list-style-type: disc; margin-bottom: -0.46em; margin-left: 30px; margin-top: 1.14em; padding-left: 0px;">Join Frequent Flyer Programs: Earn miles and points that can be redeemed for free or discounted flights by joining airline loyalty programs.</li></ul><h1 class="mt mu fr be mv mw mx my mz na nb nc nd ne nf ng nh ni nj nk nl nm nn no np nq bj" data-selectable-paragraph="" id="a7f3" style="box-sizing: inherit; color: #242424; font-family: sohne, "Helvetica Neue", Helvetica, Arial, sans-serif; font-size: 24px; letter-spacing: -0.016em; line-height: 30px; margin: 1.95em 0px -0.28em;">Access Unbeatable Flight Offers</h1><p class="pw-post-body-paragraph lv lw fr lx b ly nr ma mb mc ns me mf mg nt mi mj mk nu mm mn mo nv mq mr ms fk bj" data-selectable-paragraph="" id="92a8" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; margin: 0.94em 0px -0.46em; word-break: break-word;">Ready to find the best flight deals? Accessing these incredible offers is easy:</p><ul class="" style="box-sizing: inherit; list-style: none none; margin: 0px; padding: 0px;"><li class="lv lw fr lx b ly lz ma mb mc md me mf mg mh mi mj mk ml mm mn mo mp mq mr ms of od oe bj" data-selectable-paragraph="" id="ef75" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; list-style-type: disc; margin-bottom: -0.46em; margin-left: 30px; margin-top: 2.14em; padding-left: 0px;">Visit Our Website: Our platform aggregates the best deals from various airlines and travel agencies, ensuring you get the lowest prices. <a class="af nw" href="https://www.booking.com/flights/index.html?aid=8019784" previewlistener="true" rel="noopener ugc nofollow" style="-webkit-tap-highlight-color: transparent; box-sizing: inherit;" target="_blank"><span class="lx fs" style="box-sizing: inherit; font-weight: 700;">Click here to visit our website</span></a></li><li class="lv lw fr lx b ly og ma mb mc oh me mf mg oi mi mj mk oj mm mn mo ok mq mr ms of od oe bj" data-selectable-paragraph="" id="4c5a" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; list-style-type: disc; margin-bottom: -0.46em; margin-left: 30px; margin-top: 1.14em; padding-left: 0px;">Sign Up for Our Newsletter: Receive exclusive offers and travel tips directly in your inbox. <a class="af nw" href="https://www.facebook.com/profile.php?id=61560198516319" previewlistener="true" rel="noopener ugc nofollow" style="-webkit-tap-highlight-color: transparent; box-sizing: inherit;" target="_blank"><span class="lx fs" style="box-sizing: inherit; font-weight: 700;">Sign up now</span></a></li></ul><p class="pw-post-body-paragraph lv lw fr lx b ly lz ma mb mc md me mf mg mh mi mj mk ml mm mn mo mp mq mr ms fk bj" data-selectable-paragraph="" id="71ac" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; margin: 2.14em 0px -0.46em; word-break: break-word;">Conclusion</p><p class="pw-post-body-paragraph lv lw fr lx b ly lz ma mb mc md me mf mg mh mi mj mk ml mm mn mo mp mq mr ms fk bj" data-selectable-paragraph="" id="8eb4" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; margin: 2.14em 0px -0.46em; word-break: break-word;"><a class="af nw" href="https://www.booking.com/flights/index.html?aid=8019784" previewlistener="true" rel="noopener ugc nofollow" style="-webkit-tap-highlight-color: transparent; box-sizing: inherit;" target="_blank">Flying</a> doesn’t have to be expensive. With the right strategies and tools, you can find incredible flight deals that fit your budget. Whether you’re planning a trip in advance or looking for a last-minute escape, our comprehensive guide ensures you have all the information you need to secure the best offers. Visit our website today and embark on your journey to affordable air travel!</p><p class="pw-post-body-paragraph lv lw fr lx b ly lz ma mb mc md me mf mg mh mi mj mk ml mm mn mo mp mq mr ms fk bj" data-selectable-paragraph="" id="e990" style="box-sizing: inherit; color: #242424; font-family: source-serif-pro, Georgia, Cambria, "Times New Roman", Times, serif; font-size: 20px; letter-spacing: -0.003em; line-height: 32px; margin: 2.14em 0px -0.46em; word-break: break-word;">By following these tips and accessing our exclusive offers, you’ll be well on your way to discovering the world without spending a fortune. Safe travels!</p></div></div></div></div></section></div></div></article><div class="ab ca" style="box-sizing: inherit; display: flex; justify-content: center;"><div class="ch bg ew ex ey ez" style="box-sizing: inherit; margin: 0px 24px; max-width: 680px; min-width: 0px; width: 680px;"></div></div></div><div class="ab ca" style="background-color: white; box-sizing: inherit; color: rgba(0, 0, 0, 0.8); display: flex; font-family: medium-content-sans-serif-font, -apple-system, BlinkMacSystemFont, "Segoe UI", Roboto, Oxygen, Ubuntu, Cantarell, "Open Sans", "Helvetica Neue", sans-serif; justify-content: center;"><div class="ch bg ew ex ey ez" style="box-sizing: inherit; margin: 0px 24px; max-width: 680px; min-width: 0px; width: 680px;"><div class="ol om ab hr" style="box-sizing: inherit; display: flex; flex-wrap: wrap; margin-bottom: 26px; margin-top: 6px;"><div class="on ab" style="box-sizing: inherit; display: flex; margin-top: 8px;"><a class="oo ax am ao" href="https://medium.com/tag/flight?source=post_page-----87958b621164---------------flight-----------------" previewlistener="true" rel="noopener follow" style="-webkit-tap-highlight-color: transparent; border: none; box-sizing: inherit; cursor: pointer; margin-right: 8px; padding: 0px; text-decoration-line: none;"><div class="op ee cw oq fb or os be b bf z bj ot" style="background-color: #f2f2f2; border-radius: 100px; border: 1px solid rgb(242, 242, 242); box-sizing: inherit; color: #242424; font-family: sohne, "Helvetica Neue", Helvetica, Arial, sans-serif; font-size: 14px; line-height: 20px; padding: 8px 16px; position: relative; text-wrap: nowrap; transition: background 300ms ease 0s;">Flight</div></a></div><div class="on ab" style="box-sizing: inherit; display: flex; margin-top: 8px;"><a class="oo ax am ao" href="https://medium.com/tag/flight-tickets?source=post_page-----87958b621164---------------flight_tickets-----------------" previewlistener="true" rel="noopener follow" style="-webkit-tap-highlight-color: transparent; border: none; box-sizing: inherit; cursor: pointer; margin-right: 8px; padding: 0px; text-decoration-line: none;"><div class="op ee cw oq fb or os be b bf z bj ot" style="background-color: #f2f2f2; border-radius: 100px; border: 1px solid rgb(242, 242, 242); box-sizing: inherit; color: #242424; font-family: sohne, "Helvetica Neue", Helvetica, Arial, sans-serif; font-size: 14px; line-height: 20px; padding: 8px 16px; position: relative; text-wrap: nowrap; transition: background 300ms ease 0s;">Flight Tickets</div></a></div><div class="on ab" style="box-sizing: inherit; display: flex; margin-top: 8px;"><a class="oo ax am ao" href="https://medium.com/tag/flight-bookings?source=post_page-----87958b621164---------------flight_bookings-----------------" previewlistener="true" rel="noopener follow" style="-webkit-tap-highlight-color: transparent; border: none; box-sizing: inherit; cursor: pointer; margin-right: 8px; padding: 0px; text-decoration-line: none;"><div class="op ee cw oq fb or os be b bf z bj ot" style="background-color: #f2f2f2; border-radius: 100px; border: 1px solid rgb(242, 242, 242); box-sizing: inherit; color: #242424; font-family: sohne, "Helvetica Neue", Helvetica, Arial, sans-serif; font-size: 14px; line-height: 20px; padding: 8px 16px; position: relative; text-wrap: nowrap; transition: background 300ms ease 0s;">Flight Bookings</div></a></div><div class="on ab" style="box-sizing: inherit; display: flex; margin-top: 8px;"><a class="oo ax am ao" href="https://medium.com/tag/trave?source=post_page-----87958b621164---------------trave-----------------" previewlistener="true" rel="noopener follow" style="-webkit-tap-highlight-color: transparent; border: none; box-sizing: inherit; cursor: pointer; margin-right: 8px; padding: 0px; text-decoration-line: none;"><div class="op ee cw oq fb or os be b bf z bj ot" style="background-color: #f2f2f2; border-radius: 100px; border: 1px solid rgb(242, 242, 242); box-sizing: inherit; color: #242424; font-family: sohne, "Helvetica Neue", Helvetica, Arial, sans-serif; font-size: 14px; line-height: 20px; padding: 8px 16px; position: relative; text-wrap: nowrap; transition: background 300ms ease 0s;">Trave</div></a></div><div class="on ab" style="box-sizing: inherit; display: flex; margin-top: 8px;"><a class="oo ax am ao" href="https://medium.com/tag/trip?source=post_page-----87958b621164---------------trip-----------------" previewlistener="true" rel="noopener follow" style="-webkit-tap-highlight-color: transparent; border: none; box-sizing: inherit; cursor: pointer; margin-right: 8px; padding: 0px; text-decoration-line: none;"><div class="op ee cw oq fb or os be b bf z bj ot" style="background-color: #f2f2f2; border-radius: 100px; border: 1px solid rgb(242, 242, 242); box-sizing: inherit; color: #242424; font-family: sohne, "Helvetica Neue", Helvetica, Arial, sans-serif; font-size: 14px; line-height: 20px; padding: 8px 16px; position: relative; text-wrap: nowrap; transition: background 300ms ease 0s;">Trip</div></a></div></div></div></div><div class="l" style="background-color: white; box-sizing: inherit; color: rgba(0, 0, 0, 0.8); font-family: medium-content-sans-serif-font, -apple-system, BlinkMacSystemFont, "Segoe UI", Roboto, Oxygen, Ubuntu, Cantarell, "Open Sans", "Helvetica Neue", sans-serif;"></div><footer class="ou ov ow ox oy oz pa pb pc ab q pd pe c" style="align-items: center; background-color: white; border-top: none; box-sizing: content-box; color: rgba(0, 0, 0, 0.8); display: flex; font-family: medium-content-sans-serif-font, -apple-system, BlinkMacSystemFont, "Segoe UI", Roboto, Oxygen, Ubuntu, Cantarell, "Open Sans", "Helvetica Neue", sans-serif; height: 52px; margin-bottom: 88px; max-height: 52px; position: static; z-index: 1;"><div class="l ae" style="box-sizing: inherit; flex: 1 0 auto;"><div class="ab ca" style="box-sizing: inherit; display: flex; justify-content: center;"><div class="ch bg ew ex ey ez" style="box-sizing: inherit; margin: 0px 24px; max-width: 680px; min-width: 0px; width: 680px;"><div class="ab co pf" style="box-sizing: inherit; display: flex; justify-content: space-between;"><div class="ab q ja" style="align-items: center; box-sizing: inherit; display: flex; flex-direction: row;"><div class="pg l" style="box-sizing: inherit; max-width: 155px;"><span class="l h g f pk pl" style="box-sizing: inherit; display: inline-block;"><div class="ab q ja jb" style="align-items: center; box-sizing: inherit; display: flex; flex-direction: row; z-index: 2;"><div class="pw-multi-vote-icon ee se jd je jf" style="box-sizing: inherit; margin-right: 0px; position: relative; user-select: none;"><div class="" style="box-sizing: inherit;"><div style="box-sizing: inherit;"><div aria-describedby="54" aria-hidden="false" aria-labelledby="54" class="bl" style="box-sizing: inherit; display: inline-block;"><div class="jg sf ji jj jk jl jm am jn jo jp jf" style="border: 0px; box-sizing: inherit; cursor: not-allowed; fill: rgb(117, 117, 117); opacity: 0.25; outline: 0px; padding: 0px; user-select: none;"><svg aria-label="clap" height="24" viewbox="0 0 24 24" width="24"><path clip-rule="evenodd" d="M11.37.83L12 3.28l.63-2.45h-1.26zM15.42 1.84l-1.18-.39-.34 2.5 1.52-2.1zM9.76 1.45l-1.19.4 1.53 2.1-.34-2.5zM20.25 11.84l-2.5-4.4a1.42 1.42 0 0 0-.93-.64.96.96 0 0 0-.75.18c-.25.19-.4.42-.45.7l.05.05 2.35 4.13c1.62 2.95 1.1 5.78-1.52 8.4l-.46.41c1-.13 1.93-.6 2.78-1.45 2.7-2.7 2.51-5.59 1.43-7.38zM12.07 9.01c-.13-.69.08-1.3.57-1.77l-2.06-2.07a1.12 1.12 0 0 0-1.56 0c-.15.15-.22.34-.27.53L12.07 9z" fill-rule="evenodd"></path><path clip-rule="evenodd" d="M14.74 8.3a1.13 1.13 0 0 0-.73-.5.67.67 0 0 0-.53.13c-.15.12-.59.46-.2 1.3l1.18 2.5a.45.45 0 0 1-.23.76.44.44 0 0 1-.48-.25L7.6 6.11a.82.82 0 1 0-1.15 1.15l3.64 3.64a.45.45 0 1 1-.63.63L5.83 7.9 4.8 6.86a.82.82 0 0 0-1.33.9c.04.1.1.18.18.26l1.02 1.03 3.65 3.64a.44.44 0 0 1-.15.73.44.44 0 0 1-.48-.1L4.05 9.68a.82.82 0 0 0-1.4.57.81.81 0 0 0 .24.58l1.53 1.54 2.3 2.28a.45.45 0 0 1-.64.63L3.8 13a.81.81 0 0 0-1.39.57c0 .22.09.43.24.58l4.4 4.4c2.8 2.8 5.5 4.12 8.68.94 2.27-2.28 2.71-4.6 1.34-7.1l-2.32-4.08z" fill-rule="evenodd"></path></svg></div></div></div></div></div></div></span></div><div class="bp ab" style="box-sizing: inherit; display: flex; margin-left: 24px;"><div style="box-sizing: inherit;"><div aria-describedby="8" aria-hidden="false" aria-labelledby="8" class="bl" style="box-sizing: inherit; display: inline-block;"><button aria-label="responses" class="ao jg jx jy ab q ef jz ka" style="-webkit-tap-highlight-color: transparent; align-items: center; background-attachment: initial; background-clip: initial; background-image: initial; background-origin: initial; background-position: initial; background-repeat: initial; background-size: initial; border-color: initial; border-style: initial; border-width: 0px; box-sizing: inherit; cursor: pointer; display: flex; fill: rgb(107, 107, 107); margin: 0px; opacity: 1; overflow: visible; padding: 4px 0px;"><svg class="kb" height="24" viewbox="0 0 24 24" width="24"><path d="M18 16.8a7.14 7.14 0 0 0 2.24-5.32c0-4.12-3.53-7.48-8.05-7.48C7.67 4 4 7.36 4 11.48c0 4.13 3.67 7.48 8.2 7.48a8.9 8.9 0 0 0 2.38-.32c.23.2.48.39.75.56 1.06.69 2.2 1.04 3.4 1.04.22 0 .4-.11.48-.29a.5.5 0 0 0-.04-.52 6.4 6.4 0 0 1-1.16-2.65v.02zm-3.12 1.06l-.06-.22-.32.1a8 8 0 0 1-2.3.33c-4.03 0-7.3-2.96-7.3-6.59S8.17 4.9 12.2 4.9c4 0 7.1 2.96 7.1 6.6 0 1.8-.6 3.47-2.02 4.72l-.2.16v.26l.02.3a6.74 6.74 0 0 0 .88 2.4 5.27 5.27 0 0 1-2.17-.86c-.28-.17-.72-.38-.94-.59l.01-.02z"></path></svg></button></div></div></div></div><div class="ab q" style="align-items: center; box-sizing: inherit; display: flex;"><div class="pm l ho" style="box-sizing: inherit; flex: 0 0 auto; margin-right: 20px;"><div style="box-sizing: inherit;"><div aria-describedby="9" aria-hidden="false" aria-labelledby="9" class="bl" style="box-sizing: inherit; display: inline-block;"><div aria-hidden="false" class="bl" style="box-sizing: inherit; display: inline-block;"><button aria-controls="addToCatalogBookmarkButton" aria-expanded="false" aria-label="Add to list bookmark button" class="af ef ah ai aj ak al kd an ao ap ke kf kg kh" data-testid="footerBookmarkButton" style="-webkit-tap-highlight-color: transparent; background-attachment: initial; background-clip: initial; background-image: initial; background-origin: initial; background-position: initial; background-repeat: initial; background-size: initial; border: inherit; box-sizing: inherit; cursor: pointer; fill: rgb(107, 107, 107); font-family: inherit; font-size: inherit; font-weight: inherit; letter-spacing: inherit; margin: 0px; overflow: visible; padding: 8px 2px;"><svg class="ki" fill="none" height="24" viewbox="0 0 24 24" width="24"><path d="M17.5 1.25a.5.5 0 0 1 1 0v2.5H21a.5.5 0 0 1 0 1h-2.5v2.5a.5.5 0 0 1-1 0v-2.5H15a.5.5 0 0 1 0-1h2.5v-2.5zm-11 4.5a1 1 0 0 1 1-1H11a.5.5 0 0 0 0-1H7.5a2 2 0 0 0-2 2v14a.5.5 0 0 0 .8.4l5.7-4.4 5.7 4.4a.5.5 0 0 0 .8-.4v-8.5a.5.5 0 0 0-1 0v7.48l-5.2-4a.5.5 0 0 0-.6 0l-5.2 4V5.75z" fill="#000"></path></svg></button></div></div></div></div><div class="pm l ho" style="box-sizing: inherit; flex: 0 0 auto; margin-right: 20px;"><div aria-describedby="postFooterSocialMenu" aria-hidden="false" aria-labelledby="postFooterSocialMenu" class="bl" style="box-sizing: inherit; display: inline-block;"><div style="box-sizing: inherit;"><div aria-describedby="10" aria-hidden="false" aria-labelledby="10" class="bl" style="box-sizing: inherit; display: inline-block;"><button aria-controls="postFooterSocialMenu" aria-expanded="false" aria-label="Share Post" class="af ef ah ai aj ak al kd an ao ap ke kq kr ka ks" data-testid="footerSocialShareButton" style="-webkit-tap-highlight-color: transparent; background-attachment: initial; background-clip: initial; background-image: initial; background-origin: initial; background-position: initial; background-repeat: initial; background-size: initial; border: inherit; box-sizing: inherit; cursor: pointer; fill: rgb(107, 107, 107); font-family: inherit; font-size: inherit; font-weight: inherit; letter-spacing: inherit; margin: 0px; overflow: visible; padding: 8px 2px;"><svg fill="none" height="24" viewbox="0 0 24 24" width="24"><path clip-rule="evenodd" d="M15.22 4.93a.42.42 0 0 1-.12.13h.01a.45.45 0 0 1-.29.08.52.52 0 0 1-.3-.13L12.5 3v7.07a.5.5 0 0 1-.5.5.5.5 0 0 1-.5-.5V3.02l-2 2a.45.45 0 0 1-.57.04h-.02a.4.4 0 0 1-.16-.3.4.4 0 0 1 .1-.32l2.8-2.8a.5.5 0 0 1 .7 0l2.8 2.8a.42.42 0 0 1 .07.5zm-.1.14zm.88 2h1.5a2 2 0 0 1 2 2v10a2 2 0 0 1-2 2h-11a2 2 0 0 1-2-2v-10a2 2 0 0 1 2-2H8a.5.5 0 0 1 .35.14c.1.1.15.22.15.35a.5.5 0 0 1-.15.35.5.5 0 0 1-.35.15H6.4c-.5 0-.9.4-.9.9v10.2a.9.9 0 0 0 .9.9h11.2c.5 0 .9-.4.9-.9V8.96c0-.5-.4-.9-.9-.9H16a.5.5 0 0 1 0-1z" fill-rule="evenodd" fill="currentColor"></path></svg></button></div></div></div></div><div aria-hidden="false" class="bl" style="box-sizing: inherit; display: inline-block;"><div aria-describedby="creatorActionOverflowMenu" aria-hidden="false" aria-labelledby="creatorActionOverflowMenu" class="bl" style="box-sizing: inherit; display: inline-block;"><div class="qz l ho" style="box-sizing: inherit; flex: 0 0 auto; margin-right: -4px;"><div style="box-sizing: inherit;"><div aria-describedby="147" aria-hidden="false" aria-labelledby="147" class="bl" style="box-sizing: inherit; display: inline-block;"><button aria-controls="creatorActionOverflowMenu" aria-expanded="false" aria-label="More options" class="af ef ah ai aj ak al kd an ao ap ke kq kr ka ks" data-testid="footerStoryOptionsButton" style="-webkit-tap-highlight-color: transparent; background-attachment: initial; background-clip: initial; background-image: initial; background-origin: initial; background-position: initial; background-repeat: initial; background-size: initial; border: inherit; box-sizing: inherit; cursor: pointer; fill: rgb(107, 107, 107); font-family: inherit; font-size: inherit; font-weight: inherit; letter-spacing: inherit; margin: 0px; overflow: visible; padding: 8px 2px;"><svg fill="none" height="24" viewbox="0 0 24 24" width="24"><path clip-rule="evenodd" d="M4.39 12c0 .55.2 1.02.59 1.41.39.4.86.59 1.4.59.56 0 1.03-.2 1.42-.59.4-.39.59-.86.59-1.41 0-.55-.2-1.02-.6-1.41A1.93 1.93 0 0 0 6.4 10c-.55 0-1.02.2-1.41.59-.4.39-.6.86-.6 1.41zM10 12c0 .55.2 1.02.58 1.41.4.4.87.59 1.42.59.54 0 1.02-.2 1.4-.59.4-.39.6-.86.6-1.41 0-.55-.2-1.02-.6-1.41a1.93 1.93 0 0 0-1.4-.59c-.55 0-1.04.2-1.42.59-.4.39-.58.86-.58 1.41zm5.6 0c0 .55.2 1.02.57 1.41.4.4.88.59 1.43.59.57 0 1.04-.2 1.43-.59.39-.39.57-.86.57-1.41 0-.55-.2-1.02-.57-1.41A1.93 1.93 0 0 0 17.6 10c-.55 0-1.04.2-1.43.59-.38.39-.57.86-.57 1.41z" fill-rule="evenodd" fill="currentColor"></path></svg></button></div></div></div></div></div></div></div></div></div></div></footer><div class="pn po pp pq pr l bw" style="background-color: #f9f9f9; box-sizing: inherit; color: rgba(0, 0, 0, 0.8); font-family: medium-content-sans-serif-font, -apple-system, BlinkMacSystemFont, "Segoe UI", Roboto, Oxygen, Ubuntu, Cantarell, "Open Sans", "Helvetica Neue", sans-serif; padding-top: 72px;"><div class="ab ca" style="box-sizing: inherit; display: flex; justify-content: center;"><div class="ch bg ew ex ey ez" style="box-sizing: inherit; margin: 0px 24px; max-width: 680px; min-width: 0px; width: 680px;"><div class="ck ab ps co" style="align-items: flex-end; box-sizing: inherit; display: flex; justify-content: space-between; margin-bottom: 16px;"><div class="ab hc" style="align-items: baseline; box-sizing: inherit; display: flex;"><a href="https://medium.com/@eduard.hucai?source=post_page-----87958b621164--------------------------------" previewlistener="true" rel="noopener follow" style="-webkit-tap-highlight-color: transparent; box-sizing: inherit; text-decoration-line: none;"><div class="l pt pu bx pv hg" style="border-radius: 50%; border: 2px solid rgb(249, 249, 249); box-sizing: inherit; height: 76px; width: 76px; z-index: 0;"><div class="l ee" style="box-sizing: inherit; position: relative;"><img alt="TravelGo" class="l eq bx pw px cw" height="72" loading="lazy" src="https://miro.medium.com/v2/resize:fill:144:144/1*dXcQokbyAbuPV_XgyxWVaw.png" style="background-color: #f2f2f2; border-radius: 50%; box-sizing: border-box; display: block; height: 72px; vertical-align: middle; width: 72px;" width="72" /><div class="hh bx l pw px eo n hi ep" style="border-radius: 50%; border: 1px solid rgba(0, 0, 0, 0.05); box-shadow: none; box-sizing: inherit; height: 72px; position: absolute; top: 0px; width: 72px;"></div></div></div></a></div></div><div class="ab cm co" style="align-items: flex-start; box-sizing: inherit; display: flex; justify-content: space-between;"><div class="l" style="box-sizing: inherit;"><div class="ab q" style="align-items: center; box-sizing: inherit; display: flex;"><a class="af ag ah ai aj ak al am an ao ap aq ar as at ab q" href="https://medium.com/@eduard.hucai?source=post_page-----87958b621164--------------------------------" previewlistener="true" rel="noopener follow" style="-webkit-tap-highlight-color: transparent; align-items: center; border: inherit; box-sizing: inherit; cursor: pointer; display: flex; fill: inherit; font-family: inherit; font-size: inherit; font-weight: inherit; letter-spacing: inherit; margin: 0px; padding: 0px; text-decoration-line: none;"><h2 class="pw-author-name be qo qp qq qr bj" style="box-sizing: inherit; color: #242424; font-family: sohne, "Helvetica Neue", Helvetica, Arial, sans-serif; font-size: 24px; font-weight: 500; letter-spacing: -0.016em; line-height: 30px; margin: 0px;"><span class="fk" style="box-sizing: inherit; word-break: break-word;">Written by TravelGo</span></h2></a></div><div class="on ab" style="box-sizing: inherit; display: flex; margin-top: 8px;"><div class="l ho" style="box-sizing: inherit; flex: 0 0 auto;"><span class="pw-follower-count be b bf z bj" style="box-sizing: inherit; color: #242424; font-family: sohne, "Helvetica Neue", Helvetica, Arial, sans-serif; font-size: 14px; line-height: 20px;">0 Followers</span></div></div><div class="qs l" style="box-sizing: inherit; margin-top: 16px;"><p class="be b bf z bj" style="box-sizing: inherit; color: #242424; font-family: sohne, "Helvetica Neue", Helvetica, Arial, sans-serif; font-size: 14px; line-height: 20px; margin: 0px;"><span class="fk" style="box-sizing: inherit; word-break: break-word;">Meet Edward, the passionate travel blogger who brings the world to life through captivating stories and stunning visuals.</span></p></div></div></div></div></div></div> | travelgo |
1,871,939 | Unlocking Potential: DeFi and AI ushering in a transparent financial system | Decentralized finance (DeFi), an innovative concept in the blockchain and cryptocurrency realms, has... | 0 | 2024-05-31T11:14:51 | https://dev.to/shevchukkk/unlocking-potential-defi-and-ai-ushering-in-a-transparent-financial-system-2n7p | finance, technology, blockchain | Decentralized finance (DeFi), an innovative concept in the blockchain and cryptocurrency realms, has established an open and accessible financial system without centralized intermediaries. This has sparked a wave of discussions, with notable figures like Tyler [Winklevoss](https://en.wikipedia.org/wiki/Tyler_Winklevoss), co-founder of [ConnectU](https://umaxvision.com/wiki?q=connectu), asserting, “The DeFi revolution is here to stay. It promises a world without banks, where you don’t need permission to save or invest your money. Like any new technology, there will be bubbles and manias, but DeFi is real, and it’s here to stay. This is just the beginning.”It marks the dawn of a transformative and radical shift in how we approach traditional financial interactions.
However, no technology, new or old, can guarantee absolute security for its users. This is where the need for machine learning methods — AI — arises. DeFi and AI, two titans of the modern technological era, have the potential to revolutionize the financial world by merging their capabilities. This fusion will unlock unprecedented possibilities, making the financial system more transparent, decentralized, and accessible to all.
AI, with its analytical prowess and self-learning abilities, can revolutionize DeFi by automating routine processes, optimizing algorithms, and predicting market trends. DeFi, in turn, offers AI a decentralized platform for seamless data and algorithm exchange, fostering collaborative improvement and innovation.
Despite its transformative potential, the system is not without its flaws and vulnerabilities to manipulation. Classic risks and financial threats are prevalent in DeFi markets. These shortcomings, which include smart contract vulnerabilities like re-entry exploits (as exemplified by the infamous [DAO attack](https://www.coindesk.com/consensus-magazine/2023/05/09/coindesk-turns-10-how-the-dao-hack-changed-ethereum-and-crypto/) in 2016) and time dependency issues (evident in the [2017 attack](https://www.coindesk.com/consensus-magazine/2023/05/09/coindesk-turns-10-how-the-dao-hack-changed-ethereum-and-crypto/) on the Ethereum lottery game SmartBillions), pose significant challenges that demand urgent attention.
Financial issues are also common, particularly in smart contract-based liquidity pools. Even minor coding errors can lead to loss of funds or unauthorized pool access, which can be exploited by cryptocurrency scammers. The recent TinyMan exploit on the Algorand blockchain serves as a stark [reminder](https://www.halborn.com/blog/post/explained-the-tinyman-hack-january-2022) of these liquidity pool risks. Attackers leveraged a vulnerability in the TinyMan protocol to artificially inflate their liquidity pool assets, stealing over $3 million in cryptocurrencies. To mitigate these risks, DeFi requires the integration of AI, which can assist in combating various manipulations and automating processes.
**AI-Powered Predictive Analytics in DeFi**
AI algorithms can analyze vast amounts of data and identify patterns, making them highly applicable in cryptocurrency. For instance, they can be used to formulate market trends, which can be valuable for traders on popular exchanges like WhiteBIT, [Kraken](https://www.kraken.com/), or [Coinbase](https://www.coinbase.com/). Volodymyr Nosov, CEO of [WhiteBIT](https://whitebit.com/ua), a European crypto exchange with Ukrainian roots, emphasized the introduction of auxiliary tools of AI technologies in the company’s work and said: “Analytics in our company is based on a large amount of data, so we use specialized tools. They are based on well-known artificial intelligence models but adapted to our needs. In addition to the obvious, they also help us develop products in our ecosystem. We see their effectiveness, so we are always ready for new integrations”.
[Pecan](https://www.pecan.ai/), another company utilizing AI, offers a revolutionary solution for businesses: [Predictive GenAI](https://www.pecan.ai/blog/what-is-predictive-genai/). This generative AI model enables accurate forecasting in any industry without the need for specialized personnel.
**AI-Driven Portfolio Management**
AI’s continuous learning has opened up new possibilities for optimizing asset allocation, diversifying investments, and achieving dynamic balance in DeFi portfolios. This is achieved through constant adaptation to market conditions.
[SingularityDAO](http://singularitydao/), a blockchain project addressing liquidity and volatility issues, utilizes AI and a well-designed tokenomics model to enhance token liquidity in DeFi. This makes investments more attractive to a wider range of buyers and investors. SingularityDAO offers a suite of innovative features, including [DynaSets](https://www.singularitydao.ai/dynasets) — dynamically managed asset sets that automatically rebalance based on AI algorithms and signals.
**The DeFi and AI Symbiosis: A Glimpse into the Future**
The convergence of DeFi and AI has the potential to be one of the most groundbreaking technological advancements of our time. This alliance holds the promise of democratizing finance, making it more accessible and transparent for all. AI in DeFi can swiftly respond to potential hacks or manipulations, automate mundane tasks, enhance process efficiency and security, and improve risk assessment, management, and decision-making. This will lead to a better user experience and drive the development of more sophisticated financial products.
**Conclusion**
However, it is very important to have realistic expectations about the possibilities of DeFi and AI. Careful consideration and resolution of issues such as ethical research related to the development and implementation of AI-based DeFi is of paramount importance. AI in DeFi can quickly react to some hacks or manipulations, and automate daily tasks. However, this is one tool that should be an ally in the work, not a complete replacement for human input. | shevchukkk |
1,871,938 | Building a Masonry Layout in React with Infinite Scroll | Masonry layouts are a popular way to display content in a grid-like structure. They are commonly used... | 0 | 2024-05-31T11:12:45 | https://10xdev.codeparrot.ai/building-a-masonry-layout-in-react-with-infinite-scroll | frontend, masonry, react, layouts | Masonry layouts are a popular way to display content in a grid-like structure. They are commonly used in web applications to showcase images, videos, and other types of content in an organized and visually appealing manner. In this tutorial, we will learn how to build a masonry layout in React using the `react-responsive-masonry` library.
## What is a Masonry Layout?
A masonry layout is a grid-based layout that arranges elements in a way that optimizes the use of space. Unlike traditional grid layouts, where each row has a fixed height, a masonry layout allows elements to be placed in columns of varying heights. This creates a more dynamic and visually interesting layout that can adapt to different screen sizes and content types.
## Setting Up a React Project
Before we start building our masonry layout, let's set up a new React project using `vite`. If you already have a React project, you can skip this step.
```bash
npm create vite@latest
```
Follow the prompts to create a new React project. Once the project is created, navigate to the project directory and install the `react-responsive-masonry` library.
```bash
npm install react-responsive-masonry
```
Install the `axios` library to make API requests.
```bash
npm install axios
```
We will also be needing the `react-infinite-scroll-component` library to implement infinite scrolling.
```bash
npm install react-infinite-scroll-component
```
Also, install the `dotenv` library to load environment variables.
```bash
npm install dotenv
```
And we're finally ready to start building our masonry layout!
## Implementing the Masonry Layout
We will be using the [Unsplash API](https://unsplash.com/developers) to fetch images for our masonry layout. You will need to sign up for a free account to get an access key.
Once you have your access key, create a new file called `.env` in the root of your project and add the following line:
```bash
VITE_UNSPLASH_ACCESS_KEY=<YOUR_ACCESS_KEY>
```
We will be implementing the masonry layout in an infinite scroll component. So when the user scrolls down, more images will be loaded from the API. I have also written an article on [Implementing Infinite Scroll in React](https://10xdev.codeparrot.ai/implementing-infinite-scroll-in-react-apps) if you want to learn more about it.
In your `App.jsx` file, add the following code:
```javascript
import axios from "axios";
import { useEffect } from "react";
import { useState } from "react";
import InfiniteScroll from "react-infinite-scroll-component";
import Masonry, { ResponsiveMasonry } from "react-responsive-masonry";
export default function App() {
const [images, setImages] = useState([]);
const [page, setPage] = useState(1);
const accessKey = import.meta.env.VITE_UNSPLASH_ACCESS_KEY;
const fetchImages = async () => {
try {
const response = await axios.get(
`https://api.unsplash.com/photos?client_id=${accessKey}&page=${page}`
);
console.log(response);
setImages((prevImages) => [...prevImages, ...response.data]);
setPage((prevPage) => prevPage + 1);
} catch (error) {
console.error("Error fetching images:", error);
}
};
useEffect(() => {
fetchImages();
}, []);
return (
<div className="App">
<InfiniteScroll
dataLength={images.length}
next={fetchImages}
hasMore={true}
loader={<h4>Loading...</h4>}
>
<ResponsiveMasonry
columnsCountBreakPoints={{ 300: 2, 500: 3, 700: 4, 900: 5 }}
>
<Masonry gutter="20px">
{images.map((image) => {
return (
<img
key={image.id}
src={image.urls.regular}
alt={image.alt_description}
style={{ width: "100%", borderRadius: "8px", margin: "3px" }}
/>
);
})}
</Masonry>
</ResponsiveMasonry>
</InfiniteScroll>
</div>
);
}
```
Now, let's understand the code:
- We import the necessary libraries and set up the state variables for storing the images and the current page number.
- We define states for the images and the current page number. The images state will store the images fetched from the API, and the page state will keep track of the current page number for pagination and infinite scrolling.
```javascript
const [images, setImages] = useState([]);
const [page, setPage] = useState(1);
```
- We fetch images from the Unsplash API using the access key stored in the environment variable.
```javascript
const fetchImages = async () => {
try {
const response = await axios.get(
`https://api.unsplash.com/photos?client_id=${accessKey}&page=${page}`
);
console.log(response);
setImages((prevImages) => [...prevImages, ...response.data]);
setPage((prevPage) => prevPage + 1);
} catch (error) {
console.error("Error fetching images:", error);
}
};
```
- We use the `useEffect` hook to fetch images when the component mounts.
```javascript
useEffect(() => {
fetchImages();
}, []);
```
- We render the images in a masonry layout using the `ResponsiveMasonry` and `Masonry` components from the `react-responsive-masonry` library.
```javascript
<ResponsiveMasonry columnsCountBreakPoints={{ 300: 2, 500: 3, 700: 4, 900: 5 }}>
<Masonry gutter="20px">
{images.map((image) => {
return (
<img
key={image.id}
src={image.urls.regular}
alt={image.alt_description}
style={{ width: "100%", borderRadius: "8px", margin: "3px" }}
/>
);
})}
</Masonry>
</ResponsiveMasonry>
```
Here, `gutter` is the space between the images in the masonry layout, and `columnsCountBreakPoints` defines the number of columns based on the screen width.
- We wrap the masonry layout in an `InfiniteScroll` component to implement infinite scrolling.
```javascript
<InfiniteScroll
dataLength={images.length}
next={fetchImages}
hasMore={true}
loader={<h4>Loading...</h4>}
>
```
- Finally, we add some basic styling to the images to make them visually appealing.
```javascript
<img
key={image.id}
src={image.urls.regular}
alt={image.alt_description}
style={{ width: "100%", borderRadius: "8px", margin: "3px" }}
/>
```
And that's it! You have successfully implemented a masonry layout in React using the `react-responsive-masonry` library. You can further customize the layout by adding animations, lazy loading, and other features to enhance the user experience of your web applications.
If you've followed along, you should see something like this:
## Conclusion
In this tutorial, we learned how to build a masonry layout in React using the `react-responsive-masonry` library. Masonry layouts are a great way to display content in a grid-like structure that adapts to different screen sizes and content types. By implementing a masonry layout in your web applications, you can improve the user experience and create visually appealing designs that engage your users.
| harshalranjhani |
1,871,937 | Mastering Selenium Testing: JUnit Asserts With Examples | Automation testing helps to ease the life of software testers by allowing them to automate their... | 0 | 2024-05-31T11:11:23 | https://dev.to/harisapnanair/mastering-selenium-testing-junit-asserts-with-examples-828 | selenium, testing, junit, devops | Automation testing helps to ease the life of software testers by allowing them to automate their repetitive tasks, and open-source [test automation frameworks](https://www.lambdatest.com/blog/automation-testing-frameworks/?utm_source=devto&utm_medium=organic&utm_campaign=may_09&utm_term=bw&utm_content=blog) like Selenium have enabled users to automate [web testing](https://www.lambdatest.com/learning-hub/web-testing?utm_source=devto&utm_medium=organic&utm_campaign=may_09&utm_term=bw&utm_content=learning_hub) experience at scale. However, what good is automation testing if you cannot verify whether a test case has passed or failed?
This is where assertions come into the picture. They allow you to keep track of the number of test failures or successes encountered after executing your automation script for Selenium testing. Let’s look at examples to learn how to assert in JUnit and the different assert methods used in JUnit.
We will start with a basic introduction to assertions in JUnit and then cover the various assert methods in JUnit, focusing on the ***assertTrue()*** method. If you are preparing for an interview you can learn more through [Selenium interview questions](https://www.lambdatest.com/learning-hub/selenium-interview-questions?utm_source=devto&utm_medium=organic&utm_campaign=may_09&utm_term=bw&utm_content=learning_hub).
> Simplify your data transformation with our [JSON Stringify](https://www.lambdatest.com/free-online-tools/json-stringify?utm_source=devto&utm_medium=organic&utm_campaign=may_09&utm_term=bw&utm_content=free_online_tools) tool. Try it now!
## What Are Assertions?
Assertions in [software testing](https://www.lambdatest.com/learning-hub/software-testing?utm_source=devto&utm_medium=organic&utm_campaign=may_09&utm_term=bw&utm_content=learning_hub) are statements that verify expected outcomes during [test execution](https://www.lambdatest.com/learning-hub/test-execution?utm_source=devto&utm_medium=organic&utm_campaign=may_09&utm_term=bw&utm_content=learning_hub). Assertions act as a checkpoint between actual and anticipated results, which helps in the early detection of issues and improves the reliability of the overall [software testing life cycle](https://www.lambdatest.com/blog/software-testing-life-cycle/?utm_source=devto&utm_medium=organic&utm_campaign=may_09&utm_term=bw&utm_content=blog).
## Types of Assertions
There are two types of assertions for Selenium testing: **hard assertions** and **soft assertions**.
## Hard Assertions
Hard assertions are used when we want our [test script](https://www.lambdatest.com/learning-hub/test-scripts?utm_source=devto&utm_medium=organic&utm_campaign=may_09&utm_term=bw&utm_content=learning_hub) to halt immediately if the assertion conditions do not match the expected result. If the assertion condition fails to meet the expected outcome, an assertion error will be encountered, and the [test case](https://www.lambdatest.com/learning-hub/test-case?utm_source=devto&utm_medium=organic&utm_campaign=may_09&utm_term=bw&utm_content=learning_hub) under execution will be marked as failed.
The login situation can be used as an example of a hard assertion. A hard assert can stop the test’s execution immediately if incorrect login credentials are found. This prevents the execution of subsequent test actions because the test case can’t continue without the correct login credentials.
Methods used for hard assertions are ***assertEquals(), assertTrue(), assertFalse(), assertNotNull(), ***etc.
## Soft Assertions
In soft assertions, the test script continues its execution seamlessly even if one of the assertions fails. Moreover, with soft assertions, assertion failure conditions don’t trigger any error, ensuring uninterrupted execution of test scripts as they seamlessly proceed to the next test case.
Soft assertions in Selenium can verify multiple page elements on a landing page. They allow all steps to execute and throw an error only at the end of the ***@Test()*** method.
The ***assertAll()*** method can be used for soft assertion.
*Ready to set up your JUnit environment for your first test? The blog “[How To Setup JUnit Environment For Your First Test](https://www.lambdatest.com/blog/setup-junit-environment/?utm_source=devto&utm_medium=organic&utm_campaign=may_09&utm_term=bw&utm_content=blog)” guides you through the process step-by-step.*
> Generate unique characters effortlessly using our [Random Character Generator](https://www.lambdatest.com/free-online-tools/random-character-generator?utm_source=devto&utm_medium=organic&utm_campaign=may_09&utm_term=bw&utm_content=free_online_tools) tool!
## Assert Methods In JUnit
To use JUnit assert methods, we have to import the “***org.junit.jupiter.api.Assertions***” class. All the JUnit assertion methods are static methods, providing a range of utility methods to assert conditions in tests. Now, we will look into different methods to assert in JUnit by examples.
*If you are not familiar with JUnit, you can refer to our blog: [Automated Testing with JUnit and Selenium for Browser Compatibility](https://www.lambdatest.com/blog/automated-testing-with-junit-and-selenium-for-browser-compatibility/?utm_source=devto&utm_medium=organic&utm_campaign=may_09&utm_term=bw&utm_content=blog).*
## assertTrue() in JUnit
If you wish to pass the parameter value as True for a specific condition invoked in a method, you can use the ***assertTrue()*** in JUnit. You can use JUnit ***assertTrue()*** in two practical scenarios.
**Syntax**
* By passing condition as a boolean parameter used to assert in JUnit with the ***assertTrue()*** method. It throws an AssertionError (without message) if the condition given in the method isn’t True.
https://www.lambdatest.com/lp/best-automation-testing-tool
* By passing two parameters simultaneously in the ***assertTrue()*** method. One parameter would be an assertion error message, and the second parameter would specify the particular condition against which we need to apply our assertion method as True. It throws an AssertionError (with message) if the condition given in the method is not True.
Assert.assertTrue(String message, boolean assertCondition);
Let us understand ***assertTrue()*** in JUnit with the help of an example.
We want to verify that when users navigate to the E-Commerce LambdaTest, they are taken to the correct URL. We’ve written “assertURL()” test method to automate this verification process.
**Code for *assertTrue() *in JUnit:**
import org.junit.AfterClass;
import org.junit.Assert;
import org.junit.Test;
import org.junit.BeforeClass;
import org.openqa.selenium.WebDriver;
import org.openqa.selenium.chrome.ChromeDriver;
public class Main {
static WebDriver driver = new ChromeDriver();
@BeforeClass
public static void openBrowser() {
driver = new ChromeDriver();
driver.manage().window().maximize();
}
@Test
public void assertURL() {
driver.get("https://ecommerce-playground.lambdatest.io/");
String actualURL = driver.getCurrentUrl();
System.out.println("URL : " + actualURL);
String expectedURL = "https://ecommerce-playground.lambdatest.io/";
Assert.assertTrue("URL does not match", expectedURL.equals(actualURL));
System.out.println("Test Passed");
}
@AfterClass
public static void closeBrowser() {
driver.close();
}
}
In the above code, we can see that we have provided two parameters in the ***assertTrue() ***method, which is an assertion error message and a boolean condition. If the condition does not match or is not true, then the assertion error will be thrown, and execution of the program will get terminated at this same line, i.e., an assertion statement itself.
So, in this scenario, ***assertTrue()*** in JUnit acts as your validation tool, confirming that the URL you expect (https://ecommerce-playground.lambdatest.io/) is indeed the URL you’ve navigated to (https://ecommerce-playground.lambdatest.io/). As both are equal, the test passes, giving you confidence in the correctness of the website’s URL.
**Output:**

If we do not want to provide an assertion error message, we can provide the condition as seen in the syntax mentioned above.
> Discover new hues instantly with our [Random Color Generator](https://www.lambdatest.com/free-online-tools/random-color-generator?utm_source=devto&utm_medium=organic&utm_campaign=may_09&utm_term=bw&utm_content=free_online_tools). Check it out!
## assertEquals()
The JUnit ***assertEquals()*** method compares the equality of the expected result with the actual result. When the expected result we provided does not match the actual result of the Selenium testing script, which we get after the action is performed, it throws an assertion error. This leads to the termination of the execution of the test script at that line itself.
The ***assertEquals()*** method in JUnit is overloaded to accommodate various data types, including byte, char, double, float, int, long, Object, and short. In addition, error messages can be included as arguments to provide context when a test fails.
**Syntax:**
// Comparing integers
Assertions.assertEquals(int expected, int actual)
// Comparing objects
Assertions.assertEquals(Object expected, Object actual)
// Comparing objects with an assertion error message
Assertions.assertEquals(Object expected, Object actual, String message)
Here is a JUnit ***assertEquals()*** example to help you understand the process better.
@Test
public void assertURL() {
driver.get("https://ecommerce-playground.lambdatest.io/");
String actualURL = driver.getCurrentUrl();
System.out.println(actualURL);
Assertions.assertEquals("https://ecommerce-playground.lambdatest.io/", actualURL);
System.out.println("Test Passed");
}
In the above code, we can see that we have provided two parameters in the JUnit ***assertEquals() ***method: an expected result and an actual result. If the value of “actualURL” does not match the expected URL mentioned in the Selenium testing script, then the assertion error will be thrown, and execution of the program will get terminated at this same line, i.e., the assertion statement itself.
We can also pass an assertion error message as a parameter shown in syntax.
**JUnit assertEquals() for Floating Point Assertion**
When comparing floating point types (e.g., double or float), we must provide an additional parameter known as **delta** to avoid rounding errors.
The value for delta can be evaluated as:
**Math.abs(expected — actual) = delta**
If there is any marginal difference in the expected and actual values due to rounding off, those can be considered the same, and the assertion should be marked as pass. So, the delta value given by the user decides which margin value should be considered fine to pass that assertion.
**Assert JUnit Example for Floating Point Assertion**
@Test
public void assertValue() {
double actualDoubleValue= 2.999;
double expectedDoubleValue = 3.000;
Assertions.assertEquals(expectedDoubleValue, actualDoubleValue, 0.001);
System.out.println("Test Passed");
}
This method, “assertValue,” compares two double values: “actualDoubleValue” (initialized as 2.999) and “expectedDoubleValue” (initialized as 3.000), with a precision of 0.001. If they’re approximately equal, “Test Passed” is printed.
> Create random MAC addresses easily with our [Random MAC Generator](https://www.lambdatest.com/free-online-tools/random-mac-generator?utm_source=devto&utm_medium=organic&utm_campaign=may_09&utm_term=bw&utm_content=free_online_tools) tool. Give it a try!
## assertFalse()
We can make use of the ***assertFalse()*** method to verify whether a given condition is False or not.
**Syntax:**
Assertions.assertFalse (boolean condition)
// With an assertion error message
Assertions.assertFalse (boolean condition, String message)
**Note:** The ***assertFalse() ***method supports only a boolean value as a parameter.
Let us look at an assert JUnit example Selenium test script for ***assertFalse()***:
@Test
public void assertURL() {
driver.get("https://ecommerce-playground.lambdatest.io/");
String actualURL = driver.getCurrentUrl();
System.out.println(actualURL);
String expectedURL = "https://www.google.com/";
Assertions.assertFalse(expectedURL.equals(actualURL), "URL does match");
System.out.println("Test Passed");
}
In the above Selenium test script, we can see that we have provided two parameters in the ***assertFalse()*** method: an assertion error message and a boolean condition. Suppose the condition does match or is not false. In that case, the assertion error will be thrown, and the program’s execution will terminate at this same line, the assertion statement itself.
If we do not want to provide an assertion error message, we can just provide a condition, as we can see in the syntax mentioned above.
## assertNull()
To verify whether a passed object contains a null value, we use the ***assertNull()*** method. This method helps display an assertion error if the object does not have null values. It only supports the object data type as its parameter. In addition, error messages can be included as arguments to provide context when a test fails.
**Syntax:**
Assertions.assertNull(Object obj);
// With an assertion error message
Assertions.assertNull(Object obj, String msg);
Let us look at an example Selenium test script for JUnit ***assertNull()***.
@Test
public void assertURL() {
driver.get("https://ecommerce-playground.lambdatest.io/");
String actualURL = driver.getCurrentUrl();
System.out.println(actualURL);
String expectedURL = null;
// Assertion
// Assertions.assertNull("Not Null",actualURL);
// OR
Assertions.assertNull(expectedURL, "Not Null");
System.out.println("Test Passed");
}
In the above code, we can see that we have provided two parameters in the ***assertNull() ***method: an assertion error message and an object. If the provided object is not null, the assertion error will be thrown, and the program’s execution will terminate at this same line, the assertion statement itself.
When the “actualURL” is passed as an object, an assertion error is thrown as it is not null. Conversely, when we pass the “expectedURL,” assertion passes, indicating that the expected URL is indeed null, and “Test Passed” is printed to the console.
If we do not want to provide an assertion error message, then we can provide an object, as we can see in the syntax mentioned above.
## assertNotNull()
***assertNotNull() ***method checks if the provided object does not hold a null value. We can pass an object as a parameter in this method and get an assertion error if the object we pass does hold **“**NULL**”** values along with the assertion error message if provided.
**Syntax:**
Assertions.assertNotNull(Object obj);
// With an assertion error message
Assertions.assertNotNull(Object obj, String msg);
Let us look at an assert JUnit example Selenium test script for **assertNotNull()**:
@Test
public void assertURL() {
driver.get("https://ecommerce-playground.lambdatest.io/");
String actualURL = driver.getCurrentUrl();
System.out.println(actualURL);
String expectedURL = null;
// Assertion
Assertions.assertNotNull(actualURL, "Not Null");
// OR
// Assertions.assertNotNull(expectedURL, "Not Null");
System.out.println("Test Passed");
}
In the above code, we can see that we have provided two parameters in the ***assertNotNull()*** method: an assertion error message and an object. If the provided object is null, only the assertion error will be thrown, and the program’s execution will get terminated at this same line, i.e., the assertion statement itself.
When the “actualURL” is passed as an object, then assertion passes, indicating that the expected URL is not null, and “Test Passed” is printed to the console. When we pass the “expectedURL”, an assertion error is thrown as it is null.
If we do not want to provide an assertion error message, we can just provide an object, as seen in the syntax mentioned above.
> Get random numbers quickly using our [Random Number Generator](https://www.lambdatest.com/free-online-tools/random-number-generator?utm_source=devto&utm_medium=organic&utm_campaign=may_09&utm_term=bw&utm_content=free_online_tools). Try it today!
## assertSame()
While performing Selenium testing, you may often encounter a scenario where you need to compare two different objects passed as parameters in a method to evaluate whether they refer to the same object or not. This is where you can use JUnit ***assertSame()***. An assertion error is displayed if the two objects don’t refer to the same object. Also, we will receive an assertion error message if the message is provided as shown in the syntax below.
**Syntax:**
Assertions.assertSame (Object expected, Object actual)
// With an assertion error message
Assertions.assertSame (Object expected, Object actual, String message)
**Note:** It only supports the object data type as its parameter.
Let us look at an assert JUnit example Selenium test script for ***assertSame()***:
@Test
public void assertString() {
String actual = "LambdaTest";
String expected = actual;
String other = "JUnit";
// Assertion
Assertions.assertSame(expected, actual, "Strings not same");
// OR
// Assertions.assertSame(expected, other, "Strings not same");
System.out.println("Test Passed");
}
This “***assertString***” method is a JUnit test case that aims to verify the equality of two string objects. Initially, both “expected” and “actual” strings are assigned the value “LambdaTest.” The “***Assert.assertSame()***” method is then employed to assert that both strings reference the same object in memory, ensuring that they are identical instances. If the assertion succeeds, indicating that both strings are references to the same object, the message “Test Passed” is printed to the console.
When “expected” and “other” strings are passed as objects, the assertion statement checks whether the references of expected and others point to the same object in memory. Since “LambdaTest” and “JUnit” are different string literals, they are stored as separate objects in memory. Therefore, the assertion fails, the execution of the method halts, and “Test Passed” is not printed to the console.
If we do not want to provide an assertion error message, we can just provide an object, as seen in the syntax mentioned above.
## assertNotSame()
***assertNotSame() ***method verifies that if the two objects we passed as parameters are not equal. If both objects have the same references, an Assertion Error will be thrown with the message we provided (if any).
One more thing to observe in this method is that it compares references to objects and not the values of those objects.
**Syntax:**
Assertions.assertNotSame (Object unexpected, Object actual)
// With an assertion error message
Assertions.assertNotSame (Object unexpected, Object actual, String message)
**Note: **It only supports the object data type as its parameter.
Let us look at an assert JUnit example Selenium test script for ***assertNotSame()***:
@Test
public void assertString() {
String actual = "LambdaTest";
String expected = actual;
String other = "JUnit";
// Assertion
Assertions.assertNotSame(expected, actual, "Strings are not same");
// OR
// Assertions.assertNotSame(expected, other, "Strings are not same");
System.out.println("Test Passed");
}
This “assertString” method is a JUnit test case that aims to verify the equality of two string objects. Initially, both “expected” and “actual” strings are assigned the value “LambdaTest”. The “***Assert.assertNotSame()***” method verifies that the references of expected and actual do not point to the same object in memory. Since both expected and actual are initialized with the exact string literal “LambdaTest,” they are likely referencing the same object in memory. Thus, the assertion is expected to fail. Upon failure, the execution halts, and “Test Passed” is not printed to the console.
When “expected” and “other” strings are passed as objects, the assertion statement checks whether the references of expected and other do not point to the same object in memory. Since “LambdaTest” and “JUnit” are different string literals, they will likely be stored as separate objects in memory. Therefore, the assertion is expected to pass. Upon successful assertion, “Test Passed” is printed to the console, indicating that the test has successfully verified that “expected” and “other” are indeed referencing different objects in memory.
If we do not want an assertion error message, we can just provide an object, as seen in the above mentioned syntax.
## assertArrayEquals()
***assertArrayEquals() ***method verifies that the two object arrays we passed as parameters are equal. If both the object arrays have null values, then they will be considered equal.
The “***assertArrayEquals()***” method in JUnit is versatile, as it’s overloaded to accommodate various data types, including boolean, byte, char, double, float, int, long, Object, and short. This allows efficient comparison of arrays of different primitive types and objects within test cases. This method will also throw an Assertion Error with the message provided if both the object arrays we passed as parameters in the method are not considered equal.
**Syntax**
// For integer arrays
Assertions.assertArrayEquals (int expected, int actual)
// For object arrays
Assertions.assertArrayEquals (Object expected, Object actual)
// With an assertion error message
Assertions.assertArrayEquals (int expected, int actual, String message)
Let us look at an assert JUnit example Selenium test script for ***assertArrayEquals()***:
@Test
public void asserArrays() {
// Create two arrays to compare
int[] expectedArray = {1, 2, 3, 4};
int[] actualArray = {1, 2, 3, 4};
// Assert that the arrays are equal
Assertions.assertArrayEquals(expectedArray, actualArray, "Arrays are not equal");
System.out.println("Test Passed");
}
This JUnit test method,*** assertArrays(),*** verifies the equality of two arrays, expectedArray and actualArray, using the*** assertArrayEquals() ***method. If the arrays are equal, the test passes and prints “Test Passed”. If they are not equal, the test fails with the assertion error message “Arrays are not equal.”
If we do not want to provide an assertion error message, we can just provide an object, as we can see in the syntax mentioned above.
## assertAll()
The newly added method ***assertAll()*** will be executed to check all the assertions as grouped assertions. It has an optional heading parameter that allows to recognize a group of assertions with that method ***assertAll()***. At the time of failure, the assertion error message shows detailed information about each and every field assertion used in that group.
**Syntax:**
Assertions.assertAll(executables...);
Here, executables represent one or more instances of Executable interface, typically lambda expressions or method references, that encapsulate the assertions to be performed. The “***assertAll()***” method verifies all assertions provided by the executables, and if any of them fail, it aggregates the failures and reports them together.
Let’s look at an assert JUnit example for ***assertAll()*** with the grouped assertion:
@Test
public void assertURL() {
driver.get("https://ecommerce-playground.lambdatest.io/");
String actualURL = driver.getCurrentUrl();
System.out.println(actualURL);
String expectedURL="https://ecommerce-playground.lambdatest.io/";
String actualTitle = driver.getTitle();
System.out.println(actualTitle);
String expectedTitle = "Your Store";
Assertions.assertAll(
() -> Assert.assertEquals(expectedURL, actualURL),
() -> Assert.assertEquals(expectedTitle, actualTitle)
);
System.out.println("Test Passed");
}
In the “assertURL()” test method, the [Selenium WebDriver](https://www.lambdatest.com/learning-hub/webdriver) navigates to the LambdaTest website and captures the current URL and page title. Using ***assertAll()***, it groups together two assertEquals() assertions, comparing the expected and actual URL and title. If both comparisons hold true, indicating that the URL and title match expectations, the test pass and “Test Passed” is printed.
## assertIterableEquals()
The ***assertIterableEquals()*** method verifies whether two iterables are equal. It compares the elements of the iterables sequentially, ensuring they have the same size and contain equivalent elements in the same order. This method is particularly useful for comparing collections like lists, sets, and queues, providing a concise and efficient way to validate their contents in test cases.
**Syntax:**
Assertions.assertIterableEquals(Iterable<?> expected, Iterable<?> actual)
// With assertion error message
Assertions.assertIterableEquals(Iterable<?> expected, Iterable<?> actual, String message)
Let’s look at an assert JUnit example for*** assertIterableEquals()*** method:
@Test
public void assertIterable() {
List<Integer> firstList = Arrays.asList(1, 2, 3);
List<Integer> secondList = Arrays.asList(1, 2, 3);
List<Integer> thirdList = Arrays.asList(3, 1, 2);
Assertions.assertIterableEquals(firstList, secondList, "Not Same List");
// OR
// Assertions.assertIterableEquals(firstList, thirdList, "Not Same List");
System.out.println("Test passed");
}
When the elements passed are firstList and secondList, the test passes, indicating that the lists are equal. When the elements passed are *firstList* and *thirdList*, the test fails, indicating a discrepancy between the elements or their order.
## assertTimeout()
The **assertTimeout()** method in JUnit is used to ensure that the execution of the system under test is complete within a specified timeframe. It accepts various parameters, such as a duration object and an executable, allowing flexibility in defining the execution boundaries. This method empowers testers to enforce time constraints on test executions, ensuring timely and reliable validation of system behavior.
Additionally, it supports the inclusion of error messages as arguments to provide context in case of test failure, aiding in diagnosing issues when the timeout condition is breached.
**Syntax:**
Assertions.assertTimeout (Duration timeout, Executable executable)
// With an assertion error message
Assertions.assertTimeout (Duration timeout, Executable executable, String message)
Let’s look at an assert JUnit example for*** assertTimeout() ***method:
@Test
public void testTimeout() {
// Assert that an operation completes within 1 minute
Assertions.assertTimeout(Duration.ofMinutes(1), () -> {
// Simulate a time-consuming operation (
performTimeConsumingOperation();
});
// Assert that an operation completes within 100 milliseconds
// Assertions.assertTimeout(Duration.ofMillis(100), () -> {
// Simulate a time-consuming operation that exceeds the timeout
//Thread.sleep(200);
//});
System.out.println("Test passed");
}
// Method to simulate a time-consuming operation
public void performTimeConsumingOperation() {
// Simulate a time-consuming operation
try {
Thread.sleep(500); // Simulate a 500-millisecond operation
} catch (InterruptedException e) {
e.printStackTrace();
}
}
The first assertion specifies a timeout duration of one minute. Within this duration, the ***performTimeConsumingOperation()*** method is called, which simulates a time-consuming operation, and if this operation completes within the specified timeout, the test passes; otherwise, it fails, indicating that the operation took longer than expected.
The second assertion defines a shorter timeout of 100 milliseconds. Here, a time-consuming operation that exceeds the timeout duration is attempted by introducing a delay of 200 milliseconds. As this operation surpasses the specified timeout, the test fails, highlighting the effective enforcement of time constraints in test executions.
## assertTimeoutPreemptively()
The*** assertTimeoutPreemptively()*** method in JUnit 5 is similar to*** assertTimeout(). Still, with*** one key difference, i.e., it forcefully interrupts the execution of the test if it exceeds the specified timeout duration. This preemptive interruption ensures that the test does not continue executing beyond the defined time limit, even if the code under test does not respond to interruption signals. It supports the duration object and an executable.
**Syntax:**
Assertions.assertTimeoutPreemptively(Duration timeout, Executable executable)
// With assertion error message
Assertions.assertTimeout Preemptively(Duration timeout, Executable executable, String message)
Let’s look at an assert JUnit example for ***assertTimeoutPreemptively()*** method:
<em>@Test</em>
void testTimeoutPreemptively() {
<em>Assertions.assertTimeoutPreemptively</em>(Duration.ofSeconds(1), () -> {
// Simulate a time-consuming operation
while (true) {
// Infinite loop to simulate a time-consuming operation
}
});
}
In this example, as the code within the lambda expression does not execute in one second and the ***assertTimeoutPreemptively()*** will forcefully terminate the test, preventing it from continuing indefinitely.
> Ensure strong security with our [Random Password Generator](https://www.lambdatest.com/free-online-tools/random-password-generator?utm_source=devto&utm_medium=organic&utm_campaign=may_09&utm_term=bw&utm_content=free_online_tools). Generate now!
## fail()
The*** fail()*** method in JUnit is a way to mark a test as failed programmatically. It allows us to specify a message indicating the reason for the failure. This approach allows for precise error reporting and aids in diagnosing issues encountered during test execution. It supports a string and throwable values as parameters.
**Syntax:**
// With error message
Assertions.fail(String message)
// With error messaage and cause
Assertions.fail(String message, Throwable cause)
Let’s look at an assert JUnit example for*** fail()*** method:
@Test
public void testFunction() {
// Perform some checks
try {
// Simulate an error condition
throw new RuntimeException("Error occurred during test execution");
} catch (RuntimeException error) {
// If an error occurs, fail the test with a custom message and the associated exception
Assertions.fail("Test failed due to an error", error);
}
}
In this JUnit test method*** testFunction***(), we simulate an error condition by intentionally throwing a RuntimeException with a specific error message (“Error occurred during test execution”). Within the catch block, we call ***fail() ***method to explicitly mark the test as failed, providing a custom error message and the associated exception.
## assertThrows()
The ***assertThrows() ***is another newly added method in JUnit 5 to replace the **ExpectedException** Rule from JUnit 4. Now, all assertions can be made against the returned instance of a class Throwable, making the test scripts more readable. As executables, we can use lambdas or method references.
**Syntax:**
Assertions.assertThrows (Class<T> expectedType, Executable executable)
// With assertion error message
Assertions.assertThrows (Class<T> expectedType, Executable executable, String message)
**Note: **It supports only exception classes and executable as parameters.
Let’s look at an assert JUnit example for ***assertThrows() ***method:
@Test
public void testDivideByZero() {
// Define a lambda expression to call the method that you expect to throw an exception
Assertions.assertThrows(ArithmeticException.class, () -> divide(10, 0));
System.out.println("Test Passed");
}
// Method that performs division
public double divide(int dividend, int divisor) {
if (divisor == 0) {
throw new ArithmeticException("Cannot divide by zero");
}
return dividend / divisor;
}
In the*** testDivideByZero() ***method, ***assertThrows() ***method is used to verify that invoking the ***divide()*** method with arguments 10 and 0 results in an ArithmeticException being thrown, as expected. The test passes if the exception is thrown, indicating an attempt to divide by zero. Additionally, “Test Passed” is printed on the console, affirming the successful completion of the test.
*This JUnit Tutorial for beginners and professionals will help you learn JUnit Assertions in Selenium.*
{% youtube mkIp_xbbs-w %}
## Third-Party Assertions In JUnit
JUnit Jupiter provides sufficient assertion facilities for most testing scenarios. Still, some scenarios require additional functionalities, such as matchers, that are not provided by JUnit Jupiter.
For such scenarios, the JUnit team recommends using third-party assertion libraries like *Hamcrest, AssertJ, Truth, *etc. Users can use these third-party libraries whenever necessary.
For an assert JUnit example, we can use a combination of matchers and a fluent API to make assertions more descriptive and readable.
JUnit Jupiter’s (JUnit 5) **org.junit.jupiter.api.Assertions** class does not provide the method assertThat() that was available with the **org.junit.Assert** class in JUnit 4, which accepts a Hamcrest Matcher. That way, you can leverage the built-in support for matchers offered by third-party assertion libraries.
Assert JUnit Example for Selenium Testing using Third-Party assertions:
@Test
public void testPageTitleContainsSubstring() {
// Navigate to the web page
driver.get("https://ecommerce-playground.lambdatest.io/");
// Get the title of the web page
String title = driver.getTitle();
// Verify that the title contains the specified substring using Hamcrest matcher
assertThat(title, containsString("Store"));
System.out.println("Test passed");
}
In the*** testPageTitleContainsSubstring()*** test method, the Selenium WebDriver navigates to the LambdaTest website. After retrieving the web page’s title, it verifies that the title contains the specified substring “Store” using the Hamcrest matcher containsString() method. If the substring is found in the title, the test passes. Additionally, “Test passed” is printed on the console, indicating the successful completion of the test.
You can find the GitHub repository for all the above codes at this [GitHub repo](https://github.com/Sapna2001/JUnit_Asserts).
## Bonus Resource
According to Statista Research Department’s stats published on 21 February 2024, in 2023, JUnit was the primary technology used among test frameworks and tools, with 34% of respondents worldwide reporting the same. This comes after a small dip in 2022, when it was only 31%.

Hence, a professional certification in JUnit is worth considering to increase your credibility in the talent pool. You can also check JUnit certification from LambdaTest. LambdaTest is an AI-powered test orchestration and execution platform that lets you run manual and automated tests at scale on over 3000 real devices, browsers, and OS combinations.
*This [JUnit Certification](https://www.lambdatest.com/certifications/junit?utm_source=devto&utm_medium=organic&utm_campaign=may_09&utm_term=bw&utm_content=certifications) establishes testing standards for those who wish to advance their careers in Selenium automation testing with JUnit.*
*Here’s a short glimpse of the JUnit certification from LambdaTest:*
{% youtube fWsCwrtElAw %}
You can also subscribe to the LambdaTest YouTube Channel for more videos on [Assertions In pytest](https://youtu.be/OreB_5LXXic?si=Nt9OpTuebrbN7w_7), [Assertions in Selenium](https://youtu.be/JQGETyIx_O4?si=KWgvf8mzedYpTHbR), and [Assertions in TestNG](https://youtu.be/XHks-fvAq_4?si=FdDqcbWRcvfW66d1) to enhance your testing experience!
## Conclusion
Assertions are indispensable if you are performing Selenium. They help us determine whether a test case has passed or failed by evaluating the parameters passed into objects through our Selenium testing scripts. If you wish to manage automation logs neatly and organize them, assertions can do wonders for you.
So far, we have learned various methods to assert in JUnit, like ***assertTrue() ***in Junit, ***assertThrows()*** in Junit, etc., with examples. We also dwelled upon the difference between JUnit5 and JUnit4 with respect to assertions in JUnit. We also covered the newly introduced assertions and third-party assertions in JUnit.
| harisapnanair |
1,871,936 | I'm lost. Advice for a 2 year average programmer? | Man, don't get me wrong, I know I am the problem, but it's been a really tough ride. I am writing... | 0 | 2024-05-31T11:04:43 | https://dev.to/upsxace/im-lost-advice-for-a-2-year-average-programmer-1je6 | webdev, beginners, javascript, help | Man, don't get me wrong, I know I am the problem, but it's been a really tough ride.
I am writing this both as a rant and as a request for an advice, or even help, because I'm clearly completely lost, and my decision making has proven to be poor haha.
-Got an Associate's Degree (2021-2023) in Software Development that taught me JavaScript, React, Yii2, MySQL, React Native, and had a 4.25/5 GPA
-During that time I got an internship of 2 months, and it started amazing, but didn't end very well
-I also developed a web portfolio I am very proud of, despite of the crappy code, and nowdays its too hard to update it(for the same reason), so I never did, but I still liked the result so much, so I left it online still: [https://eduardobotelho.com](https://eduardobotelho.com)
-I liked the result of that so much, that I deluded myself to think I had a bright future or something. I was ready to get disappointed though, just not this hard.
-I was faced with the decision of trying to get a job, or keep studying and trying to get the next degree. I couldn't get a job because the entry level was too high and my skills were not enough. I couldn't get an internship because my city is small and the few companies here were specially uninterested that year for some reason(none of my classmates got an internship). I decided to try signing up for my next degree in the same university.
-Because of a teacher that graded me wrong in my last year, it took too long for me to be accepted in the university(2 months late), and even though everything got solved, I lost a big scholarship that I was getting from my city's local government. So I decided to not study that year after all.
-Instead, I decided I would take a 6 month online web development bootcamp at Ironhack because they had a career service in which they would give tips on how to get a job after, and I thought it would be useful(not that much tbh), plus I could resharp my skills and get something more for my CV(poor decision after all).
-And I just finished that bootcamp this month.
-During that time I also learned ExpressJS, a little bit of Docker, and got really decent/good at NextJS and TypeScript, and worked on some other side projects:
[https://diary.acehq.net](https://diary.acehq.net) - an app of taking notes with auth, text editor, search filters, light/dark theme, all self hosted in Kamaterra ([check video demo](https://youtu.be/-A4sF0ILhz0))
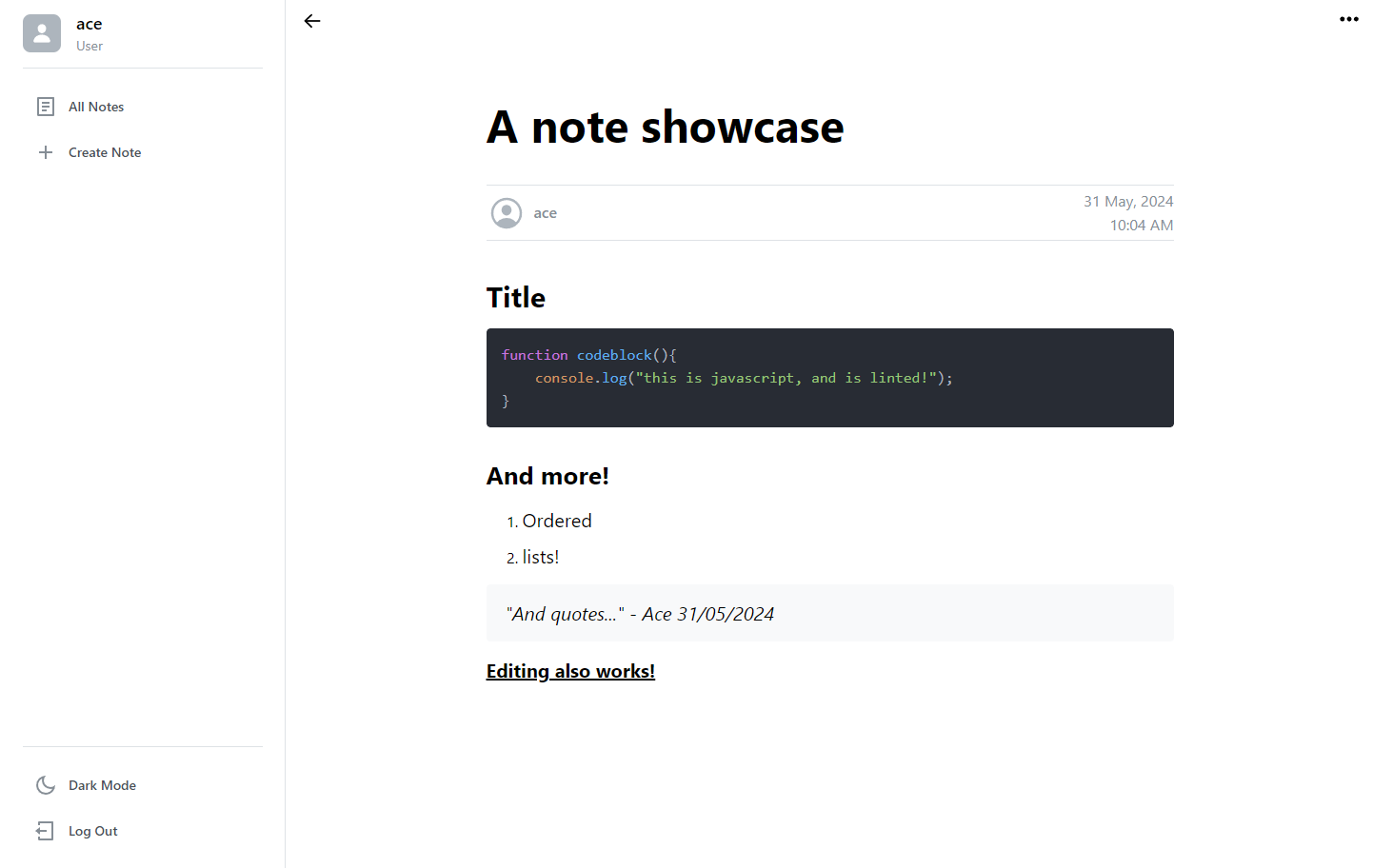
https://status.acehq.net - an app that pings my other apps (i manage it with strapi) to see if they're online
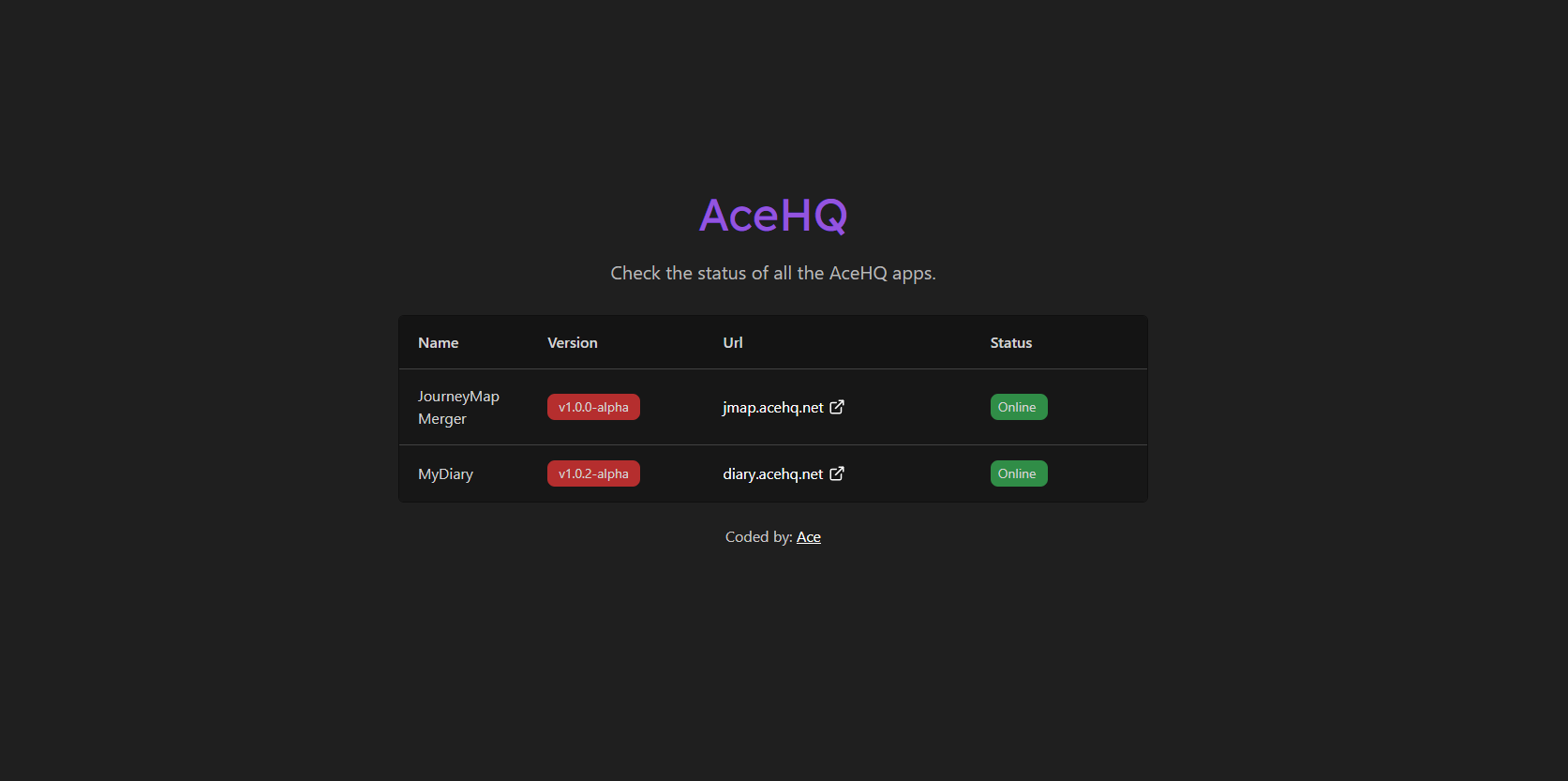
https://jmap.acehq.net/ - an app that I made because I played minecraft, and it basically uses a golang API I created to merge different pieces of a picture into a single big one([see video demo please](https://youtu.be/SL7ngwiO2Qw))
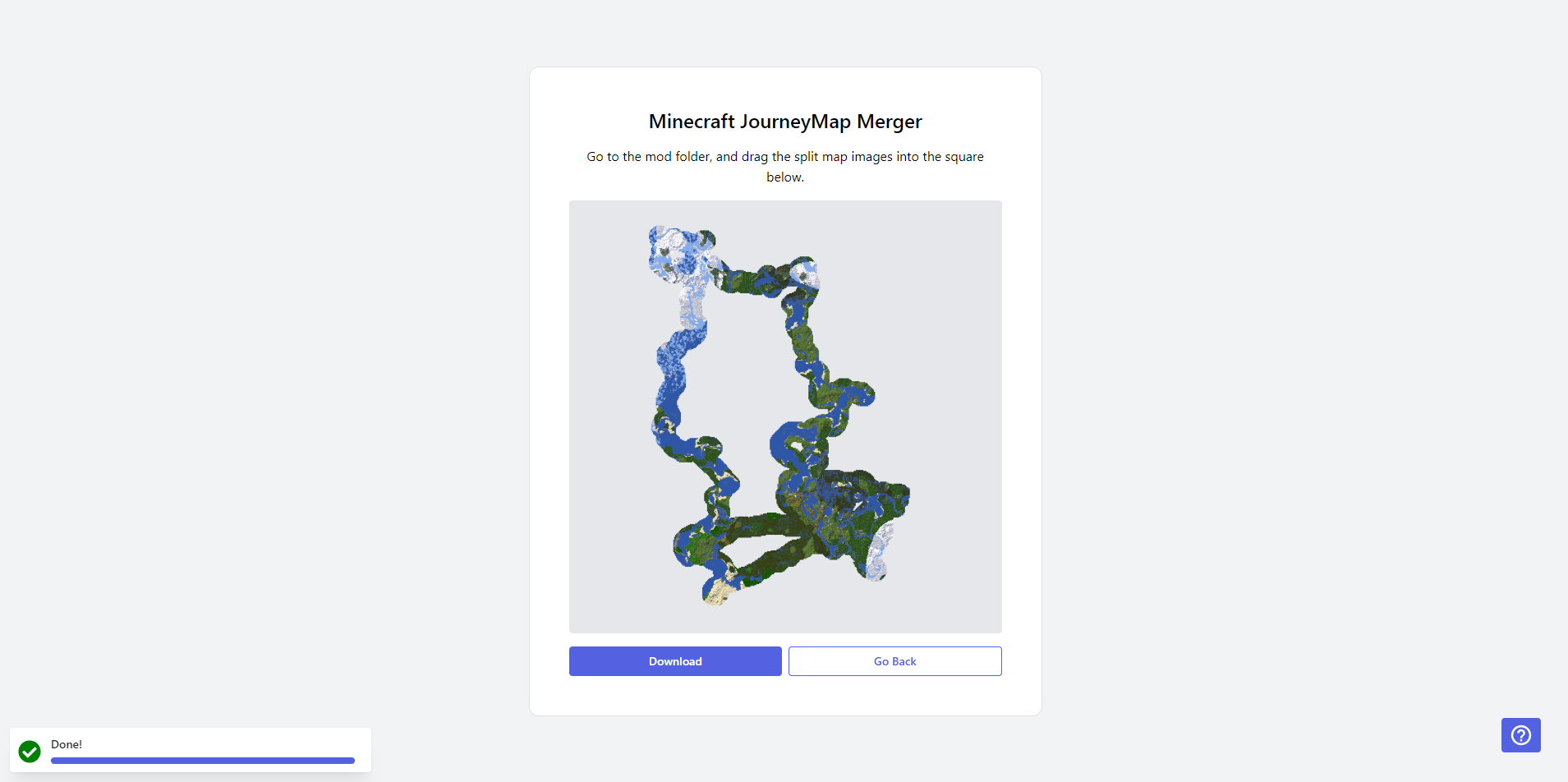
-I also worked on many other side projects. Some of them are just unimpressive so I didn't mention, and others just failed due to me testing out new stuff, breaking the app, and then being too unmotivated to fix it, or simply because I was not liking it anymore. Check my Linked In for more(you can also see my github there): [https://www.linkedin.com/in/eduardobotelho1029/](https://www.linkedin.com/in/eduardobotelho1029/)
-I tried applying for jobs and internships again, no response whatsoever. The entry levels are still fairly high, and I know I don't have anything impressive to show.
What should I do? What is lacking on me to get a first internship/job opportunity?
Again, I know there is tons I can improve, but I want a direction, because it's really hard to stay motivated without any guarantee of anything. So far whenever I worked really hard, it never paid off that much.
Do I need to learn 10 extra technologies to enter an entrylevel job/internship?
Do I need to add something more to my projects? Maybe testing, better code??
Do I need to improve my CV? ([check it here](https://shorturl.at/fWIY4))
Do I just keep applying?
Do I need certificates?
Do I need to do more projects?
I'm already working on the next one...
I appreciate any feedback, positive or negative.
| upsxace |
1,871,935 | Innovate or Stagnate: Driving Business Transformation Through ASP.NET Development | In business, you now have to either “innovate” or “stagnate.” It is better to innovate to stay ahead... | 0 | 2024-05-31T11:02:41 | https://dev.to/edward_thomas/innovate-or-stagnate-driving-business-transformation-through-aspnet-development-2nmm | webdev, beginners, aspdotnet | In business, you now have to either “innovate” or “stagnate.” It is better to innovate to stay ahead of the curve as competitors appear, customer expectations change, and technology advances. Let’s examine how development with an ASP.NET developer acts as a spark to propel corporate change and enable businesses to innovate, adjust, and prosper in the digital era.
An Innovative Foundation
The basis of modern web development is Microsoft's powerful framework for creating dynamic web applications. A large and innovative toolset combined with extensive libraries and Microsoft technologies lets ASP.NET offer a strong foundation for creativity. It provides the flexibility companies need to achieve their digital goals.
Accelerating Development Cycles
Simplifying the software development process is one of ASP.NET development's main benefits; it allows companies to launch new ideas into the market more quickly than ever. Agile approaches and state-of-the-art development techniques enable ASP.NET teams to quickly iterate, adapt to changing needs, and provide stakeholders with incremental benefits.
Power of Personalization
There is extreme personalization for everything digital, and users have greater expectations than ever. Companies need to offer customized experiences that cater to people's interests and habits. ASP.NET employs strategies like dynamic content delivery, customized recommendations, and user-centric design principles to achieve this degree of customization.
Scalability Solutions
Over time, the technological requirements of companies grow and adapt. The scalability of systems is essential for their capacity to handle increasing loads, accommodate expanding user bases, and adapt to changing requirements. Companies can expand their applications either horizontally or vertically depending on their needs with ASP.NET development. An online database management system provides the kind of scalability businesses need to propel growth and handle traffic spikes, the addition of new features, or entry into new markets.
Security Assurance
The increasing occurrence of cybersecurity threats and data breaches has made security non-negotiable for businesses operating in the digital sphere. ASP.NET development is driven by security and adopts built-in tools, industry-standard protocols, and best practices to safeguard private data. With ASP.NET, businesses can effectively lower risks and enhance their digital defenses with secure authentication and authorization systems, data encryption, and threat detection.
| edward_thomas |
1,871,934 | Step-by-Step Guide: Setting Up Elasticsearch and Kibana with Docker | Setting up Elasticsearch and Kibana using Docker on a Mac is a straightforward process. Follow this... | 0 | 2024-05-31T11:01:54 | https://dev.to/tharindufdo/step-by-step-guide-setting-up-elasticsearch-and-kibana-with-docker-on-mac-4p94 | docker, kibana, elasticsearch, json | Setting up Elasticsearch and Kibana using Docker on a Mac is a straightforward process. Follow this step-by-step guide to integrate and visualize your developer metrics data.
_Prerequisites: Ensure you have Docker installed on your Mac. You can download it from the [Docker website](https://docs.docker.com/get-docker/)._
## Step 1: Create a docker-compose.yml File
Create a directory for your project and within that directory, create a docker-compose.yml file with the following content:
```
version: '7.16.3'
services:
elasticsearch:
image: docker.elastic.co/elasticsearch/elasticsearch:7.16.3
container_name: elasticsearch
environment:
- discovery.type=single-node
- ES_JAVA_OPTS=-Xms512m -Xmx512m
ports:
- "9200:9200"
volumes:
- esdata:/usr/share/elasticsearch/data
kibana:
image: docker.elastic.co/kibana/kibana:7.16.3
container_name: kibana
ports:
- "5601:5601"
depends_on:
- elasticsearch
volumes:
esdata:
driver: local
```
This configuration sets up both Elasticsearch and Kibana, with Elasticsearch running on port 9200 and Kibana on port 5601.
## Step 2: Start the Docker Containers
Open your terminal, navigate to the directory containing your docker-compose.yml file, and run:
`docker-compose up -d`
This command will start both Elasticsearch and Kibana in the background.
## Step 3: Index the JSON Data into Elasticsearch
Consider this is only an example JSON just to explain the integration.
Save the following JSON data into a file named developer_metrics.json:
```
{
"developer": "John Doe",
"metrics": {
"time_spent_coding": 120,
"review_time": 35,
"planned_overhead_time": 20,
"untracked_time": 25,
"effective_work": 15,
"other_metrics": {
"opened_pull_requests": 18,
"merged_pull_requests": 15,
"closed_pull_requests": 3,
"created_feature_branches": 10,
"lines_of_code": 2000,
"inactive_days": 2
}
},
"dates": {
"start_date": "2024-05-01",
"end_date": "2024-05-28"
}
}
```
Use curl to index this data into Elasticsearch:
```
curl -X POST "localhost:9200/developer_metrics/_doc/1?pretty" -H 'Content-Type: application/json' -d @developer_metrics.json
```
## Step 4: Create a Mapping for the Index
To ensure Elasticsearch correctly interprets our data fields, we need to define a mapping for our index.
Run the following curl command to create the mapping:
```
curl -X PUT "localhost:9200/developer_metrics?pretty" -H 'Content-Type: application/json' -d'
{
"mappings": {
"properties": {
"developer": { "type": "keyword" },
"metrics": {
"properties": {
"time_spent_coding": { "type": "integer" },
"review_time": { "type": "integer" },
"planned_overhead_time": { "type": "integer" },
"untracked_time": { "type": "integer" },
"effective_work": { "type": "integer" },
"other_metrics": {
"properties": {
"opened_pull_requests": { "type": "integer" },
"merged_pull_requests": { "type": "integer" },
"closed_pull_requests": { "type": "integer" },
"created_feature_branches": { "type": "integer" },
"lines_of_code": { "type": "integer" },
"inactive_days": { "type": "integer" }
}
}
}
},
"dates": {
"properties": {
"start_date": { "type": "date" },
"end_date": { "type": "date" }
}
}
}
}
}'
```
## Step 5: Visualize the Data in Kibana
With our data indexed, it’s time to create visualizations in Kibana.
**Creating an Index Pattern**
1. Open Kibana in your browser by navigating to http://localhost:5601.
2. Navigate to Stack Management -> Index Patterns.
3. Click Create index pattern and specify developer_metrics as the index pattern.
4. Follow the prompts to complete the setup.
**Creating Visualizations**
1. Go to the Visualize Library.
2. Click Create visualization and choose a visualization type (e.g., bar chart, line chart).
3. Select the developer_metrics index pattern.
4. Configure your visualization by selecting fields like time_spent_coding, opened_pull_requests, etc.
**Building a Dashboard**
1. Navigate to Dashboard.
2. Click Create new dashboard.
3. Add your visualizations to the dashboard.
## Conclusion
Using Docker to set up Elasticsearch and Kibana on a Mac simplifies the process and ensures a consistent environment. By following these steps, you can easily visualize and analyze developer metrics data, helping you make informed decisions and track performance effectively.
This setup can be customized and expanded to suit your specific needs. Start leveraging these powerful tools today to enhance your project’s efficiency and transparency.
## References
https://www.elastic.co/guide/en/elasticsearch/reference/current/index.html
https://www.elastic.co/guide/en/kibana/current/introduction.html
| tharindufdo |
1,845,541 | Ibuprofeno.py💊| #115: Explica este código Python | Explica este código Python Dificultad: Fácil my_tuple = (12, 45, 78) x, y,... | 16,071 | 2024-05-31T11:00:00 | https://dev.to/duxtech/ibuprofenopy-115-explica-este-codigo-python-4edh | python, spanish, learning, beginners | ## **<center>Explica este código Python</center>**
#### <center>**Dificultad:** <mark>Fácil</mark></center>
```py
my_tuple = (12, 45, 78)
x, y, z, t = my_tuple
print(t)
```
👉 **A.** `78`
👉 **B.** `ValueError`
👉 **C.** `45`
👉 **D.** `12`
---
{% details **Respuesta:** %}
👉 **B.** `ValueError`
Para poder desempaquetar tuplas es necesario que la cantidad de variables creadas sea igual a la longitud de la tupla per se. Si esto no pasa entonces tenemos un `ValueError`.
{% enddetails %} | duxtech |
1,871,933 | Deciphering Talent Acquisition: Executive Search vs. Internal Hiring | Navigating the ever-shifting terrain of talent acquisition presents companies with a pivotal... | 0 | 2024-05-31T10:59:15 | https://dev.to/hudsonjulian/deciphering-talent-acquisition-executive-search-vs-internal-hiring-2i9a | Navigating the ever-shifting terrain of talent acquisition presents companies with a pivotal decision: to embark on executive search quests or to embrace internal hiring practices when filling critical leadership positions. Each avenue boasts its own merits and complexities, necessitating a thorough evaluation of organizational needs and aspirations prior to charting a course. [Leathwaite](https://www.leathwaite.com/), a frontrunner in executive search services, delves into the intricacies of executive search versus internal hiring, providing insights to aid companies in determining the most fitting approach for their unique circumstances.
**Executive Search: Tapping into External Talent Networks**
The pursuit of top-tier talent beyond organizational borders characterizes [executive search](https://www.leathwaite.com/executive-search/) endeavors, where companies enlist the expertise of specialized agencies. These entities embark on thorough quests to pinpoint individuals possessing requisite skills, experience, and cultural alignment for pivotal leadership roles. Leveraging their expansive networks and industry acumen, executive search firms offer a gateway to a diverse pool of adept candidates primed to propel organizational growth.
**Advantages of Executive Search:**
• **Access to Elite Talent:** Executive search firms furnish access to a broad array of high-caliber individuals who may not actively seek new opportunities but remain receptive to compelling propositions.
• **Specialized Insight:** Armed with profound insights into industry dynamics and talent landscapes, executive search firms provide invaluable guidance throughout the recruitment journey.
• **Confidentiality and Discretion:** Executive search endeavors ensure confidentiality, enabling companies to conduct sensitive searches sans disruption to existing operations or divulgence of strategic plans.
**Internal Hiring: Nurturing Talent from Within**
Contrary to executive search, internal hiring involves elevating current personnel to leadership positions within the organization. This strategy hinges on recognizing and fostering internal talent, capitalizing on employees' knowledge and institutional acclimatization. Furthermore, it fosters allegiance among staff and propels their career trajectories. By tapping into internal talent reservoirs, companies can adeptly fill crucial roles while fostering a culture of advancement and employee investment.
**Advantages of Internal Hiring:**
• **Cost Efficiency:** Internal promotions typically incur lower recruitment costs and shorter onboarding periods compared to external hires, translating into fiscal savings.
• **Cultural Cohesion:** Internal appointees are already immersed in the company's ethos, values, and operations, mitigating the risk of cultural disparities and facilitating a seamless transition into the new role.
• **Morale and Retention**: Elevating from within signals a commitment to talent development and furnishes existing employees with pathways for career progression, bolstering morale and engendering retention.
**Selecting the Optimal Approach for Your Organization**
The decision to pursue executive search or internal hiring necessitates a nuanced evaluation, considering a myriad of factors. There exists no one-size-fits-all solution; each avenue presents distinct advantages and challenges. Factors such as bespoke talent prerequisites, organizational ethos, growth trajectories, and market dynamics warrant meticulous consideration. By judiciously assessing these variables, companies can adeptly navigate the recruitment landscape, aligning their approach with overarching objectives to secure top-tier talent for their teams.
Key Considerations:
• **Urgency and Time Sensitivity:** In scenarios demanding expedited recruitment or specialized expertise unavailable internally, executive search emerges as the preferred recourse.
• **Succession Planning:** For leadership roles imbued with long-term strategic significance, internal succession planning proves instrumental in grooming future leaders and ensuring continuity.
• **External Market Dynamics:** External forces such as industry competition, market trends, and talent scarcity exert influence on the prioritization of external talent acquisition through executive search.
**Conclusion**
In the dynamic realm of talent acquisition, the choice between executive search and internal hiring hinges on a meticulous appraisal of organizational imperatives, resources, and strategic imperatives. While executive search affords access to external talent reservoirs and specialized insight, internal hiring fosters employee development, loyalty, and cultural coherence. Armed with a profound understanding of the unique advantages and considerations inherent in each approach, companies can make informed decisions conducive to their long-term objectives, positioning themselves for triumph in the fiercely competitive landscape of talent acquisition.
| hudsonjulian | |
1,871,932 | Python *args and **kwargs | [python]: In Python, *args and **kwargs are used to pass a variable number of arguments to a... | 0 | 2024-05-31T10:58:48 | https://dev.to/vincod/python-args-and-kwargs-1e18 | python, opensource, webdev, javascript | [python]: In Python, `*args` and `**kwargs` are used to pass a variable number of arguments to a function. They allow for more flexible function definitions and can handle an arbitrary number of positional and keyword arguments, respectively.
### `*args`
- `*args` allows a function to accept any number of positional arguments.
- The arguments are accessible as a tuple within the function.
**Example:**
```python
def func_with_args(*args):
for arg in args:
print(arg)
func_with_args(1, 2, 3, 4)
# Output:
# 1
# 2
# 3
# 4
```
### `**kwargs`
- `**kwargs` allows a function to accept any number of keyword arguments.
- The arguments are accessible as a dictionary within the function.
**Example:**
```python
def func_with_kwargs(**kwargs):
for key, value in kwargs.items():
print(f"{key} = {value}")
func_with_kwargs(a=1, b=2, c=3)
# Output:
# a = 1
# b = 2
# c = 3
```
### Combining `*args` and `**kwargs`
You can use both `*args` and `**kwargs` in a single function to handle both positional and keyword arguments.
**Example:**
```python
def func_with_args_kwargs(*args, **kwargs):
for arg in args:
print(f"arg: {arg}")
for key, value in kwargs.items():
print(f"{key} = {value}")
func_with_args_kwargs(1, 2, 3, a=4, b=5)
# Output:
# arg: 1
# arg: 2
# arg: 3
# a = 4
# b = 5
```
### Practical Use Case
These constructs are particularly useful when writing functions that need to handle a flexible number of inputs, such as wrappers or decorators, or when designing APIs that need to accept a variety of parameters without requiring a rigid function signature.
By using `*args` and `**kwargs`, you can create more adaptable and reusable functions. | vincod |
1,871,931 | Navigating Respite Care in Sydney: Exploring In-Home vs. Facility-Based Options | Respite care is a crucial service for caregivers who need temporary relief from their caregiving... | 0 | 2024-05-31T10:58:43 | https://dev.to/arpithashetty/navigating-respite-care-in-sydney-exploring-in-home-vs-facility-based-options-448o | Respite care is a crucial service for caregivers who need temporary relief from their caregiving duties. In Sydney, caregivers have the option of choosing between in-home and facility-based respite care services. Each option comes with its own set of benefits and considerations, making it essential for caregivers to understand their choices fully.
In-Home Respite Care:
In-home respite care provides in Sydney [](https://www.phomecare.com.au/2024/03/19/respite-care-in-sydney/ )caregivers with the flexibility to have a trained professional come to their home and take over caregiving responsibilities for a set period. This option allows the care recipient to remain in familiar surroundings, which can be particularly beneficial for those with dementia or other cognitive impairments. In-home respite care often includes assistance with activities of daily living, companionship, and sometimes light housekeeping tasks.
One of the significant advantages of in-home respite care is the personalized attention the care recipient receives. Care plans can be tailored to the individual's needs and preferences, ensuring continuity of care and promoting comfort and familiarity. Additionally, caregivers can use this time to attend to their own needs, whether it's running errands, attending appointments, or simply taking a much-needed break.
However, in-home respite care may not be suitable for everyone. Some care recipients may require a higher level of medical or nursing care that cannot be adequately provided at home. Additionally, the availability of in-home respite care services may be limited, depending on the caregiver's location and the availability of trained professionals.
Facility-Based Respite Care:
Facility-based respite care involves the care recipient staying at a designated facility for a short period while the caregiver takes a break. These facilities can range from specialized respite care centers to nursing homes or assisted living facilities that offer respite care services.
One of the primary benefits of facility-based respite care is access to round-the-clock supervision and support. Care recipients may have complex medical needs that require close monitoring or access to specialized equipment and resources, which may not be available in a home setting. Moreover, facility-based respite care can provide opportunities for socialization and engagement with other residents, which can be particularly beneficial for those who may feel isolated at home.
Additionally, facility-based respite care can offer caregivers peace of mind, knowing that their loved one is receiving professional care in a safe and supportive environment. Caregivers can take advantage of this time to recharge and attend to their own well-being without worrying about the constant demands of caregiving.
However, facility-based respite care may present challenges for care recipients who are resistant to change or uncomfortable being away from home. It's essential for caregivers to assess their loved one's preferences and comfort level before making a decision. Additionally, the cost of facility-based respite care can vary widely depending on the level of care provided and the amenities offered by the facility.
Conclusion:
Choosing between in-home and facility-based respite care in Sydney requires careful consideration of the needs and preferences of both the caregiver and the care recipient. While in-home respite care offers personalized attention and the comfort of familiar surroundings, facility-based respite care provides access to professional support and round-the-clock supervision. Ultimately, the right choice depends on the unique circumstances of each family and their priorities in providing the best possible care for their loved one.
| arpithashetty | |
1,871,930 | Tips for Registered Nurse NDIS Providers | In the complex landscape of the National Disability Insurance Scheme (NDIS), effective care... | 0 | 2024-05-31T10:57:24 | https://dev.to/arpithashetty/tips-for-registered-nurse-ndis-providers-ekh | In the complex landscape of the National Disability Insurance Scheme (NDIS), effective care coordination stands as a cornerstone for providing holistic support to individuals with disabilities. As a [registered nurse NDIS provider,]( https://www.phomecare.com.au/2023/07/28/8-ndis-nursing-support-s/ ) your role in this process is pivotal. Your expertise not only ensures the delivery of quality care but also fosters a seamless experience for participants and their support networks. Here are some invaluable tips to enhance your effectiveness in care coordination within the NDIS framework.
Comprehensive Assessment Skills: Begin by conducting thorough assessments of participants' health conditions, disabilities, and support needs. As a registered nurse, your clinical expertise equips you to identify underlying health issues, assess functional abilities, and recognize potential risks. This holistic understanding forms the foundation for personalized care plans tailored to the unique requirements of each participant.
Clear Communication Channels: Establish open lines of communication with participants, their families, carers, and other healthcare professionals involved in their care. Maintain transparency, actively listen to concerns, and provide regular updates on care plans and progress. Effective communication fosters trust and collaboration, ensuring that all stakeholders are aligned towards the participant's goals and well-being.
Collaborative Care Planning: Actively engage participants and their support networks in the care planning process. Adopt a person-centered approach that values participants' preferences, goals, and aspirations. Encourage them to articulate their needs and actively involve them in decision-making regarding their care. Collaborative care planning empowers participants, enhances their sense of agency, and promotes ownership of their health and well-being.
Utilize Technology for Efficiency: Leverage technology-enabled solutions to streamline care coordination processes. Electronic health records, telehealth platforms, and mobile applications facilitate real-time communication, data sharing, and remote monitoring. Embrace digital tools that enhance efficiency, improve documentation accuracy, and enable timely interventions, thereby optimizing the delivery of care within the NDIS framework.
Stay Updated on NDIS Policies and Procedures: Keep abreast of the latest developments, policies, and procedures within the NDIS ecosystem. Attend relevant training sessions, workshops, and professional development opportunities to enhance your knowledge and skills. Understanding the intricacies of NDIS guidelines ensures compliance, minimizes administrative errors, and enables you to navigate the system effectively on behalf of participants.
Cultivate a Multidisciplinary Network: Foster collaborative relationships with multidisciplinary teams comprising allied health professionals, disability support workers, therapists, and social service providers. Recognize the value of interdisciplinary collaboration in addressing the complex needs of NDIS participants comprehensively. Engage in regular case conferences, share insights, and coordinate care efforts to optimize outcomes and promote holistic well-being.
Advocate for Participant Rights and Access: As a registered nurse NDIS provider, advocate for the rights and entitlements of participants, ensuring equitable access to quality healthcare services and support. Stay informed about disability rights legislation, advocacy initiatives, and community resources available to support participants in exercising their rights and accessing necessary services and accommodations.
Monitor and Evaluate Care Outcomes: Implement robust monitoring and evaluation mechanisms to assess the effectiveness of care interventions and outcomes. Regularly review care plans, track progress towards goals, and solicit feedback from participants and their support networks. Embrace a continuous improvement mindset, adapt care strategies based on feedback and outcomes data, and strive for ongoing enhancement of care quality and participant satisfaction.
In conclusion, effective care coordination in the NDIS landscape requires a blend of clinical expertise, communication skills, collaboration, and a commitment to person-centered care. As a registered nurse NDIS provider, you play a pivotal role in advocating for participants' well-being, facilitating access to services, and fostering meaningful partnerships with stakeholders. By adhering to these tips and embracing a holistic approach to care coordination, you can make a significant difference in the lives of NDIS participants, empowering them to thrive and achieve their goals despite the challenges they may face.
| arpithashetty | |
1,871,928 | Sencha App Development Services | Looking for Sencha App Development Services? Well, Goognu offers the best Sencha App Development... | 0 | 2024-05-31T10:51:53 | https://dev.to/goognu2/sencha-app-development-services-b9d | awsconsulting, cloudconsulting, awsarchitecture | Looking for Sencha App Development Services? Well, Goognu offers the best Sencha App Development Services. Get a 30 minute free consultation today.
| goognu2 |
1,870,463 | AR Game ~ What is Augmented Reality (AR) ~ | Table of contents Background What is Augmented Reality Types of Augmented Reality Next Step ... | 0 | 2024-05-31T10:49:07 | https://dev.to/takeda1411123/ar-game-what-is-augmented-reality-ar--24m0 | Table of contents
- Background
- What is Augmented Reality
- Types of Augmented Reality
- Next Step
# Background
I will develop AR Game with Unity, AR foundation and so on. To learn AR development, I am researching about AR and the software related it. This blog shows the research and the process of developing AR game. If you have a question, I am happy to answer it.
# What is Augmented Reality
The term "augment" means to add something. Augmented Reality (AR) is a technology that enhances the real world by overlaying digital information throungh devices such as smartphones and AR glasses. A well-known application of AR in gaming is Pokemon GO. In Pokemon GO, players use their smartphone cameras to display Pokemon in the real world. When displaying AR on a smartphone, various functionalities such as the camera, GPS, accelerometer, and compass are utiliized to create the augmented experience.
# Types of Augmented Reality
AR primarily has two types. One of them is Marker-based AR. Another type is Markerless AR.
## Marker-based AR
This type displays 3D objects on a marker by reading the marker, such as a QR code or an image.
Example
{% youtube https://www.youtube.com/watch?v=DXheLzszraw %}
## Markerless AR
This type can display 3D objects without markers. Instead, it uses the sensors or camera of smartphones, relying on these functions.
It is used in Pokemon GO.
This type is further divided into three subtypes, which are location based AR, projection based, and superimpostion AR.
### Location based
Due to the availability of smartphone feature that provide location detection, it shows AR to a specific place by getting data from a device’s camera, GPS, digital compass, and accelerometer.
Example
{% youtube https://www.youtube.com/watch?v=rVw8Mw2rYQg %}
### Projection based
This type uses a small projecter.It focuses on rendering virtual objects within or on a user’s physical space. Since virtual objects are projected on user's physical space directly, the change of the environment reclects the virtual objects.
Example
{% youtube https://www.youtube.com/watch?v=CE1B7tdGCw0 %}
### Superimpostion (Object Tracking)
This type is also called object tracking AR. It literally tracks objects. It can replace an original view of an object with a scaled version of the same object.
Example
{% youtube https://www.youtube.com/watch?v=mytxLcNAR2s %}
# Next step
This post showed what is AR and the types of AR. I will use some of them to create AR Game.
Next post will show the research of AR foundation.
| takeda1411123 | |
1,871,927 | Automation Testing Challenges: Navigating Common Obstacles | Automation testing has revolutionized the software development process by improving efficiency,... | 0 | 2024-05-31T10:47:05 | https://dev.to/perfectqa/automation-testing-challenges-navigating-common-obstacles-7li | testing | Automation testing has revolutionized the software development process by improving efficiency, accuracy, and test coverage. However, implementing and maintaining automation testing comes with its own set of challenges. Understanding these [automation testing challenges](perfectqaservices.com/post/automation-testing-challenges) is crucial for developing effective strategies to overcome them. This article explores the various obstacles faced during automation testing and provides insights on how to address them.
Understanding Automation Testing Challenges
What are Automation Testing Challenges?
Automation testing challenges are obstacles or issues that arise during the implementation, execution, and maintenance of automated tests. These challenges can stem from various factors, including technical limitations, resource constraints, and process inefficiencies.
Importance of Addressing Automation Testing Challenges
Improved Efficiency: Overcoming challenges can streamline the testing process and enhance overall efficiency.
Enhanced Accuracy: Addressing issues helps ensure more accurate and reliable test results.
Cost Reduction: Effective management of challenges can lead to cost savings by reducing rework and maintenance efforts.
Better Test Coverage: Mitigating obstacles can improve test coverage and ensure comprehensive testing of the application.
Common Automation Testing Challenges
There are several common automation testing challenges that teams may encounter. These challenges can impact the effectiveness of the testing process and the quality of the final product.
1. High Initial Investment
Overview
One of the primary challenges of automation testing is the high initial investment required for tools, infrastructure, and training.
Key Issues
Tool Costs: Automation tools can be expensive, especially for commercial solutions.
Training Costs: Significant investment in training team members to use the automation tools effectively.
Infrastructure Setup: Costs associated with setting up and maintaining the necessary hardware and software infrastructure.
2. Choosing the Right Automation Tools
Overview
Selecting the appropriate automation tools is crucial for the success of automation testing. However, the abundance of tools available can make this decision challenging.
Key Issues
Tool Compatibility: Ensuring the selected tools are compatible with the existing technology stack.
Feature Requirements: Matching tool features with project requirements.
Learning Curve: The complexity of tools and the time required to become proficient.
3. Test Script Maintenance
Overview
Maintaining automated test scripts is an ongoing challenge, particularly as applications evolve and new features are added.
Key Issues
Frequent Updates: Test scripts need constant updates to keep up with changes in the application.
Script Fragility: Automated tests can be fragile and break easily with minor changes in the application.
Resource Intensive: Maintaining and updating test scripts can be time-consuming and resource-intensive.
4. Ensuring Test Coverage
Overview
Achieving comprehensive test coverage is a significant challenge in automation testing. It is essential to ensure that all critical functionalities are tested adequately.
Key Issues
Identifying Critical Test Cases: Determining which test cases are most critical and should be automated.
Balancing Coverage and Efficiency: Striking a balance between comprehensive test coverage and the efficiency of the testing process.
Handling Edge Cases: Ensuring that edge cases and uncommon scenarios are also covered in automated tests.
5. Integration with Continuous Integration/Continuous Deployment (CI/CD)
Overview
Integrating automation testing with CI/CD pipelines is crucial for continuous testing. However, this integration can be complex and challenging.
Key Issues
Tool Integration: Ensuring that automation tools integrate seamlessly with CI/CD pipelines.
Automated Build and Deployment: Configuring automated builds and deployments to trigger automated tests.
Managing Test Environments: Ensuring that test environments are correctly set up and managed for continuous testing.
6. Handling Dynamic Elements
Overview
Applications often include dynamic elements that change frequently, posing a challenge for automation testing.
Key Issues
Element Identification: Identifying and interacting with dynamic elements in the application.
Stability of Test Scripts: Ensuring that test scripts remain stable and reliable despite changes in dynamic elements.
Synchronization Issues: Handling synchronization issues caused by dynamic elements loading at different times.
7. Managing Test Data
Overview
Effective test data management is essential for accurate and reliable automated tests. However, managing test data can be challenging.
Key Issues
Data Availability: Ensuring that the necessary test data is available and accessible.
Data Consistency: Maintaining consistent and reliable test data across different test runs.
Data Privacy and Security: Ensuring that test data complies with privacy and security regulations.
8. Performance Testing Challenges
Overview
Performance testing is a critical aspect of automation testing, but it comes with its own set of challenges.
Key Issues
Simulating Real-World Conditions: Accurately simulating real-world conditions and user loads.
Analyzing Performance Metrics: Collecting and analyzing performance metrics to identify bottlenecks.
Resource Constraints: Ensuring that the necessary resources are available for performance testing.
9. Scalability Issues
Overview
Scalability is a significant concern in automation testing, particularly for large-scale projects.
Key Issues
Scaling Test Execution: Ensuring that automated tests can be scaled to handle increased loads and multiple environments.
Resource Management: Efficiently managing resources to support scalable test execution.
Performance Impact: Ensuring that the scalability of automated tests does not negatively impact performance.
10. Ensuring Security and Compliance
Overview
Security and compliance are critical considerations in automation testing, particularly for applications that handle sensitive data.
Key Issues
Vulnerability Testing: Identifying and addressing security vulnerabilities.
Compliance Requirements: Ensuring that automated tests comply with relevant regulations and standards.
Data Security: Protecting test data from unauthorized access and breaches.
Strategies to Overcome Automation Testing Challenges
To effectively address automation testing challenges, teams can implement various strategies and best practices.
Define Clear Objectives and Scope
Set SMART Goals: Define Specific, Measurable, Achievable, Relevant, and Time-bound (SMART) goals for automation testing.
Scope Definition: Clearly define the scope of automation testing, including which test cases will be automated and which will remain manual.
Select the Right Tools
Tool Evaluation: Evaluate and select automation tools based on project requirements, budget, and compatibility with the existing technology stack.
Pilot Projects: Conduct pilot projects to assess the suitability of the selected tools before full-scale implementation.
Develop a Robust Test Automation Framework
Modular Approach: Develop a modular test automation framework that allows for easy maintenance and scalability.
Reusable Components: Create reusable components and libraries to reduce redundancy and enhance efficiency.
Implement Continuous Integration/Continuous Deployment (CI/CD)
CI/CD Integration: Integrate automation testing with CI/CD pipelines to enable continuous testing.
Automated Builds and Deployments: Configure automated builds and deployments to ensure tests are run automatically with each code change.
Focus on Test Maintenance
Regular Updates: Regularly update and maintain the automated test scripts to keep them relevant and effective.
Version Control: Use version control systems to manage changes to test scripts and ensure traceability.
Manage Test Data Effectively
Data Generation: Use automated tools to generate test data as needed.
Data Management: Implement robust test data management practices to ensure data consistency and availability.
Data Security: Ensure that test data complies with privacy and security regulations.
Address Performance Testing Challenges
Real-World Simulation: Use tools and techniques that accurately simulate real-world conditions and user loads.
Performance Analysis: Collect and analyze performance metrics to identify and address bottlenecks.
Resource Allocation: Ensure that the necessary resources are available for performance testing.
Ensure Scalability
Scalable Framework: Develop a scalable test automation framework that can handle increased loads and multiple environments.
Resource Management: Efficiently manage resources to support scalable test execution.
Performance Impact Assessment: Regularly assess the performance impact of scalability on automated tests.
Maintain Security and Compliance
Vulnerability Scanning: Implement regular vulnerability scanning to identify and address security issues.
Compliance Audits: Conduct regular compliance audits to ensure automated tests meet relevant regulations and standards.
Data Protection: Implement robust data protection measures to secure test data.
Conclusion
Automation testing is a powerful technique that enhances the efficiency, accuracy, and coverage of the software testing process. However, it comes with its own set of challenges that can impact the effectiveness of the testing process. By understanding and addressing these automation testing challenges, organizations can develop effective strategies to overcome them and ensure successful automation testing implementations. Leveraging best practices and robust frameworks can significantly enhance the quality and reliability of automated tests, leading to higher-quality software products and a more efficient development lifecycle. | perfectqa |
1,871,926 | Maximizing Business Success With SIOP Planning For Efficient Operations | SIOP Business: Enhancing Organizational Efficiency Sales, Inventory, and Operations Planning (SIOP)... | 0 | 2024-05-31T10:46:41 | https://dev.to/saumya27/maximizing-business-success-with-siop-planning-for-efficient-operations-50p2 | siop | **SIOP Business: Enhancing Organizational Efficiency**
Sales, Inventory, and Operations Planning (SIOP) is a crucial process for businesses aiming to synchronize their sales forecasts, inventory levels, and operational capabilities. Implementing an effective SIOP business strategy helps organizations optimize resources, improve customer satisfaction, and achieve financial goals.
**Key Features of SIOP in Business**
**1. Sales Forecasting:**
- Accurate Predictions: Utilize historical data, market analysis, and sales trends to create precise sales forecasts.
- Demand Planning: Align production schedules and inventory levels with predicted demand to prevent stockouts and overproduction.
**2. Inventory Management:**
- Optimal Inventory Levels: Maintain the right balance of inventory to meet customer demands without incurring excess holding costs.
- Just-in-Time (JIT) Inventory: Implement JIT strategies to reduce waste and enhance inventory turnover.
**3. Operations Planning:**
- Resource Allocation: Efficiently allocate resources, including labor, machinery, and materials, based on sales forecasts and production plans.
- Capacity Planning: Ensure production capacity aligns with demand forecasts to avoid bottlenecks and ensure timely delivery.
**3. Integrated Planning:**
- Cross-functional collaboration: Foster collaboration between sales, marketing, finance, and operations to create a unified business plan.
- Data Integration: Integrate data from various sources to provide a comprehensive view of the business landscape.
**4. Performance Monitoring:**
- Key Performance Indicators (KPIs): Track KPIs such as forecast accuracy, inventory turnover, and order fulfillment rates to measure the effectiveness of SIOP processes.
- Continuous Improvement: Use performance data to identify areas for improvement and implement corrective actions.
**Benefits of Implementing SIOP in Business**
- Enhanced Efficiency: Streamline operations by aligning sales forecasts with production and inventory plans, reducing waste and inefficiencies.
- Improved Customer Satisfaction: Ensure products are available when and where customers need them, enhancing customer service and loyalty.
- Cost Savings: Optimize inventory levels and resource allocation, leading to significant cost reductions.
- Better Decision Making: Provide executives with accurate, data-driven insights to make informed strategic decisions.
- Increased Agility: Quickly adapt to market changes and demand fluctuations, ensuring the business remains competitive and responsive.
**SIOP Business Process Steps**
- Data Collection and Analysis: Gather historical sales data, market trends, and inventory levels to inform the planning process.
- Demand Planning: Develop sales forecasts and demand plans based on collected data and market analysis.
- Supply Planning: Create production and inventory plans to meet the forecasted demand.
- Pre-SIOP Meeting: Review and adjust the demand and supply plans with input from cross-functional teams.
- Executive SIOP Meeting: Finalize the plans and make strategic decisions with the involvement of top management.
- Plan Implementation: Execute the agreed-upon plans and monitor performance against KPIs.
- Review and Adjust: Continuously review performance and adjust plans as necessary to respond to changes in demand or supply conditions.
**Conclusion**
SIOP (Sales, Inventory, and Operations Planning) is an integral process for businesses seeking to enhance efficiency, optimize resources, and improve customer satisfaction. By accurately forecasting sales, managing inventory, and aligning operational capabilities, businesses can achieve significant cost savings, better decision-making, and increased agility in responding to market changes. Implementing a robust [SIOP business ](https://cloudastra.co/blogs/siop-business-success-with-planning-for-efficient-operations)process ensures a cohesive strategy that integrates various business functions, ultimately driving organizational success. | saumya27 |
1,871,925 | How a Mobile App Development Boosts Growth | People use their mobile phones for different kinds of reasons in the modern era. This mobile-first... | 0 | 2024-05-31T10:46:26 | https://dev.to/abi_shunmuganath_606a7ba2/how-a-mobile-app-development-boosts-growth-he3 | People use their mobile phones for different kinds of reasons in the modern era. This mobile-first approach allows businesses to reach their target audience and expand. A well-designed mobile app has the power to transform business, increase consumer interaction, optimize processes, and boost your brand.
Here's how mobile app development can boost your business growth:
Enhanced Customer Engagement: A **[custom mobile app development company](https://kirshi.co/mobile-app-development-company-in-usa.html)** can create an app that enables us to communicate directly with consumers. It helps to increase brand loyalty and repeat business results from features that keep users informed and involved, such as push notifications, reward programs, and in-app messaging.
Improved Brand Awareness: A well-designed app acts as an effective marketing tool. A mobile app development company in USA can develop an app that promotes the brand and its unique services. Your reach and brand recognition can be increased more successfully with tools like social media integration and targeted marketing.
Data-Driven Decision Making: Mobile applications provide useful information about the preferences and behavior of users. Partnering with a **[mobile app development company in USA](https://kirshi.co/mobile-app-development-company-in-usa.html)** can provide you with insights on how users engage with your app, allowing you to modify your services and marketing strategies for the most effective impact.
Increased Sales and Revenue: A well-designed app could serve as a direct sales channel. Faster checkout times and higher conversion rates can be achieved by implementing features like in-app purchases, safe payment methods, and simple order tracking.
Improved Operational Efficiency: Mobile apps have the potential to automate many corporate operations, saving both resources and time. A mobile app development agency in USA can create an app that streamlines processes such as appointment scheduling, order administration, and customer assistance, resulting in increased operational efficiency.
Finding the Right Mobile App Development Company in USA
The success of your mobile app depends on selecting the correct development partner. Look for a **[mobile app development company in USA](https://kirshi.co/mobile-app-development-company-in-usa.html)** with a track record of developing unique and user-friendly applications. The ideal partner will thoroughly grasp your sector, target demographic, and unique company objectives. | abi_shunmuganath_606a7ba2 | |
1,871,923 | Introduction to Strapi Media Library | Strapi is an open-source, Node.js-based, Headless Content Management System(CMS) that allows you to... | 0 | 2024-05-31T10:45:14 | https://dev.to/strapi/introduction-to-satrapis-media-library-5113 | opensource, testing, unittest, beginners | Strapi is an open-source, Node.js-based, Headless Content Management System(CMS) that allows you to streamline the process of managing content, giving you the freedom to use your favorite tools and frameworks. It has a Media Library plugin that allows you to upload, save, and manage different media files such as images, videos, and documents.
In this tutorial, you'll learn how to build a media gallery application using Flutter and Strapi's Media Library plugin.
## Prerequisites
You will need the following to get started:
- [Node.js v18](https://nodejs.org/) or later.
- A code editor on your computer.
- [Node.js package manage](https://docs.npmjs.com/downloading-and-installing-node-js-and-npm/)r v6 and above.
- [Python](https://www.python.org/downloads/)
- Set up your [Flutter environment](https://flutter.dev/docs/get-started/install) if you haven't already.
The code for this tutorial is available on my GitHub [repository](https://github.com/icode247/flutter_media_app/). Feel free to clone and follow along.
## Setting up Strapi with the Media Library
### Strapi Installation
Start by creating a new Strapi backend project by running the command below:
```bash
npx create-strapi-app@latest media-app --quickstart
```
The above command will scaffold a new Strapi content management system project and install the required Node.js dependencies.
Fill out the forms to create your administrator user account.
### Install Strapi Media Library Plugin
Go back to your terminal, and quit the server with `Ctrl+ C`. Navigate to the project directory and enable the [Media Libray Plugin](https://strapi.io/features/media-library) by running the command below:
```bash
cd media-app
npm i @strapi/plugin-upload
```
Update your `config/plugin.js` file to configure the upload plugin. There are many plugins in the Strapi marketplace for uploads including Firebase storage, Cloudflare, etc. But there are only 3 providers maintained by Strapi which are Local, Amazon S3, and Cloudinary. For this demonstration, you'll use the [Local plugin](https://docs.strapi.io/dev-docs/plugins/upload):
```js
module.exports = ({ env }) => ({
upload: {
config: {
providerOptions: {
localServer: {
maxage: 300000,
},
},
},
},
});
```
### Enable Public Access for Upload API
In order to be able to perform some operations on the upload plugin, we need to enable public access.
From the left sidebar, click on **Settings**. Again, on the left panel under **USERS & PERMISSIONS PLUGIN**, click on **Roles**, then click on **Public** from the table on the right. Now scroll down, click on `Upload`, and tick Select all. After that click the "Save" button.

## Uploading Media Files to Strapi
Back to your admin panel, in the left sidebar, click on the **Media Library** section. Then click **Add new assets** -> **FROM COMPUTER** -> **Browse Files** and you'll be prompted to upload files from your local computer. Select at least three files and click **Upload assets to library** to upload them.
## Creating a Flutter Project
Open a new tab on your terminal and create a new Flutter application by running the command below:
```bash
flutter create media_library_app
```
Once the project is created, open it in your IDE or code editor. Change the directory to the project folder and run the application with the following commands:
```bash
cd media_library_app
flutter run
```
## Retrieving Media Files from Flutter
In your projects `lib` directory, create a `features/services` directory. Create a `strapi_service.dart` file in the `services` directory and add the code to fetch all the assets you added to your Media Library:
```js
import 'dart:convert';
import 'package:http/http.dart' as http;
class StrapiService {
static const String baseUrl = 'http://localhost:1337';
Future<List<dynamic>> getMediaFiles() async {
final response = await http.get(Uri.parse('$baseUrl/api/upload/files'));
if (response.statusCode == 200) {
final jsonData = json.decode(response.body);
return jsonData;
} else {
throw Exception('Failed to load media files');
}
}
}
```
This service class provides a `getMediaFiles` method that makes a `GET` request to the Strapi server's `/upload/files` endpoint to return the list of media files.
For the above code to work, open the `pubspec.yaml` file and add the `http`, `file_picker` and `http_parser` module in the dependency section to allow you send API requests to your Strapi backend, select images from your device file system and to parse the HTTP response:
```yaml
dependencies:
flutter:
sdk: flutter
http: ^0.13.5
file_picker: ^8.0.3
http_parser: ^4.0.2
```
Then run the command below to install the dependency:
```bash
flutter pub get
```
## Displaying Media Files in Flutter
Create a new directory called `screens` in the `lib/features` directory to create our Flutter UI. Then create a `home_screen.dart` file inside the `screens` folder and add the code snippets below:
```js
import 'package:flutter/material.dart';
import 'package:media_library_app/features/services/strapi_service.dart';
class HomePage extends StatefulWidget {
const HomePage({super.key});
@override
_HomePageState createState() => _HomePageState();
}
class _HomePageState extends State<HomePage> {
List<dynamic> mediaFiles = [];
StrapiService strapiService = StrapiService();
@override
void initState() {
super.initState();
fetchMediaFiles();
}
Future<void> fetchMediaFiles() async {
try {
final files = await strapiService.getMediaFiles();
setState(() {
mediaFiles = files;
});
} catch (e) {
print('Error fetching media files: $e');
}
}
@override
Widget build(BuildContext context) {
return Scaffold(
appBar: AppBar(
title: const Text('Strapi Media Library'),
),
body: Padding(
padding: const EdgeInsets.all(8.0),
child: ListView.builder(
itemCount: mediaFiles.length,
itemBuilder: (context, index) {
final file = mediaFiles[index];
final imageUrl = StrapiService.baseUrl + file['url'];
return ListTile(
title: Text(file['name']),
subtitle: Text(file['mime']),
leading: Image.network(imageUrl),
);
},
),
),
);
}
}
```
The above code will:
- Create a `HomePage StatefulWidget` class to allow you to handle the application state on this screen.
- Create `mediaFiles` empty array to store the media files data and create an instance of the `StrapService` class to allow you access to the methods in the class.
- Add a `fetchMediaFiles()` method to call the `strapiService.getMediaFiles()` method to retrieve the media from Strapi Media Library and call the `setState` function to modify the app's state and set the retrieved files data to the `mediaFiles` array.
- Call the `initState` method to execute the code in `fetchMediaFiles()` when the widget is first created.
- Render the media data using the `ListView` widget.
Now update your `main.dart` file to render the `HomePage` widget in your Flutter UI:
```js
import 'package:flutter/material.dart';
import 'package:strapi_media_app/features/screens/home_screen.dart';
void main() {
runApp(const MyApp());
}
class MyApp extends StatelessWidget {
const MyApp({super.key});
// This widget is the root of your application.
@override
Widget build(BuildContext context) {
return MaterialApp(
title: 'Flutter Demo',
theme: ThemeData(
colorScheme: ColorScheme.fromSeed(seedColor: Colors.deepPurple),
useMaterial3: true,
),
home: const HomePage(),
);
}
}
```

## Handling Media Uploads from Flutter
Next, update the code in your `lib/features/services/strapi_service.dart` file to add a new method to send a **POST** request to the `/upload` endpoint to upload new files to the Media Library.
```js
import 'dart:convert';
import 'dart:io';
import 'package:http/http.dart' as http;
import 'package:http_parser/http_parser.dart'; // Import the http_parser package
class StrapiService {
static const String baseUrl = 'http://localhost:1337';
Future<List<dynamic>> getMediaFiles() async {
try {
final response = await http.get(Uri.parse('$baseUrl/api/upload/files'));
if (response.statusCode == 200) {
final jsonData = json.decode(response.body);
return jsonData;
} else {
throw Exception('Failed to load media files');
}
} catch (e) {
throw Exception(e);
}
}
Future<dynamic> uploadMediaFile(File file) async {
var request = http.MultipartRequest(
'POST',
Uri.parse('$baseUrl/api/upload'),
);
var stream = http.ByteStream(file.openRead());
stream.cast();
var length = await file.length();
var multipartFileSign = http.MultipartFile(
'files',
stream,
length,
filename: file.path.split('/').last,
contentType: MediaType('image', 'jpeg'),
);
request.files.add(multipartFileSign);
var response = await request.send();
if (response.statusCode == 200) {
return response.stream.bytesToString();
} else {
throw Exception('Failed to upload media file');
}
}
}
```
This code will:
- Create an HTTP request to allow you upload files using `http.MultipartRequest` to the `/upload` endpoint using the POST method.
- Prepare the selected files for your upload by opening a byte stream using `http.ByteStream` from the file and specifying the length.
- Creates a multipart file using `http.MultipartFile` from the byte stream, specifying the file name, length, content type, and field name.
- Add the multipart file to the request. If the response status code is **200 (OK)**, it reads the response stream and converts it to a string using `response.stream.bytesToString()`, then returns the result.
Then in your `lib/features/screens/home_screen.dart` file, add a new method to the `_HomePageState` class to handle file uploads.
```js
import 'dart:convert';
import 'dart:io';
// import 'package:file_picker/file_picker.dart';
import 'package:file_picker/file_picker.dart';
import 'package:flutter/material.dart';
import 'package:strapi_media_app/features/services/strapi_service.dart';
class HomePage extends StatefulWidget {
const HomePage({super.key});
@override
_HomePageState createState() => _HomePageState();
}
class _HomePageState extends State<HomePage> {
List<dynamic> mediaFiles = [];
StrapiService strapiService = StrapiService();
@override
void initState() {
super.initState();
fetchMediaFiles();
}
Future<void> fetchMediaFiles() async {
try {
final files = await strapiService.getMediaFiles();
setState(() {
mediaFiles = files;
});
} catch (e) {
print('Error fetching media files: $e');
}
}
Future<void> uploadMediaFile(context) async {
FilePickerResult? result = await FilePicker.platform.pickFiles();
if (result != null) {
File file = File(result.files.single.path!);
try {
final response = await strapiService.uploadMediaFile(file);
List<dynamic> jsonResponse = jsonDecode(response);
setState(() {
mediaFiles.add(jsonResponse[0]);
});
ScaffoldMessenger.of(context).showSnackBar(
const SnackBar(
content: Text('File uploaded successfully'),
),
);
} catch (e) {
ScaffoldMessenger.of(context).showSnackBar(
SnackBar(
content: Text('Error uploading media file: $e'),
),
);
}
} else {
ScaffoldMessenger.of(context).showSnackBar(
const SnackBar(
content: Text('No file selected'),
),
);
}
}
@override
Widget build(BuildContext context) {
return Scaffold(
appBar: AppBar(
title: const Text('Strapi Media Library'),
),
body: Padding(
padding: const EdgeInsets.all(8.0),
child: ListView.builder(
itemCount: mediaFiles.length,
itemBuilder: (context, index) {
final file = mediaFiles[index];
final imageUrl = StrapiService.baseUrl + file['url'];
return ListTile(
title: Text(file['name']),
subtitle: Text(file['mime']),
leading: Image.network(imageUrl),
);
},
),
),
floatingActionButton: FloatingActionButton(
onPressed: () => uploadMediaFile(context),
child: const Icon(Icons.add),
),
);
}
}
```
The above code will:
- Create an `uploadMediaFile` method in the `_HomePageState` class to call the `uploadMediaFile` method from the `StrapiService` class to upload the selected files to the Strapi Media Library.
- Uses the `FilePicker` package to allow the user to select a file from their device. If the file selected is not null, it will retrieve the selected file and prepares it for upload, else it shows a snackbar with a success or error message.

## Demo
Below is a demonstration of what our application looks like.

## Conclusion
Throughout this tutorial, you've learned how to build a media gallery application using Flutter and Strapi Media Library. You have set up a Strapi project, installed the Strapi upload plugin in the project, and uploaded media data to the Strapi Media Library. You created a Flutter application to make API requests to the Media Libray to fetch, display, and upload new files. | codev206 |
1,871,921 | Mastering ReactJS: A Comprehensive Roadmap | ReactJS has been a dominant force in the web development world for years and shows no signs of losing... | 0 | 2024-05-31T10:38:40 | https://dev.to/vyan/mastering-reactjs-a-comprehensive-roadmap-8pn | webdev, react, beginners, javascript | ReactJS has been a dominant force in the web development world for years and shows no signs of losing its popularity. Whether you're a beginner or an experienced developer looking to deepen your knowledge, this step-by-step roadmap will guide you through the essential concepts and advanced techniques in ReactJS.
𝟏.𝐂𝐨𝐦𝐩𝐨𝐧𝐞𝐧𝐭𝐬
• Functional Components
• Class Components
• JSX (JavaScript XML) Syntax
𝟐.𝐏𝐫𝐨𝐩𝐬 (𝐏𝐫𝐨𝐩𝐞𝐫𝐭𝐢𝐞𝐬)
• Passing Props
• Default Props
• Prop Types
𝟑.𝐒𝐭𝐚𝐭𝐞
• useState Hook
• Class Component State
• Immutable State
𝟒.𝐋𝐢𝐟𝐞𝐜𝐲𝐜𝐥𝐞 𝐌𝐞𝐭𝐡𝐨𝐝𝐬 (𝐂𝐥𝐚𝐬𝐬 𝐂𝐨𝐦𝐩𝐨𝐧𝐞𝐧𝐭𝐬)
• componentDidMount
• componentDidUpdate
• componentWillUnmount
𝟓.𝐇𝐨𝐨𝐤𝐬 (𝐅𝐮𝐧𝐜𝐭𝐢𝐨𝐧𝐚𝐥 𝐂𝐨𝐦𝐩𝐨𝐧𝐞𝐧𝐭𝐬)
• useFormStatus - Latest
• useFormState - Latest
• Use - Latest
• useActionState - Latest
• useOptimistic - Latest
• useState
• useEffect
• useContext
• useReducer
• useCallback
• useMemo
• useRef
• useImperativeHandle
• useLayoutEffect
𝟔.𝐄𝐯𝐞𝐧𝐭 𝐇𝐚𝐧𝐝𝐥𝐢𝐧𝐠
• Handling Events in Functional Components
• Handling Events in Class Components
𝟕.𝐂𝐨𝐧𝐝𝐢𝐭𝐢𝐨𝐧𝐚𝐥 𝐑𝐞𝐧𝐝𝐞𝐫𝐢𝐧𝐠
• if Statements
• Ternary Operators
• Logical && Operator
𝟖.𝐋𝐢𝐬𝐭𝐬 𝐚𝐧𝐝 𝐊𝐞𝐲𝐬
• Rendering Lists
• Keys in React Lists
𝟗.𝐂𝐨𝐦𝐩𝐨𝐧𝐞𝐧𝐭 𝐂𝐨𝐦𝐩𝐨𝐬𝐢𝐭𝐢𝐨𝐧
• Reusing Components
• Children Props
• Composition vs Inheritance
𝟏𝟎.𝐇𝐢𝐠𝐡𝐞𝐫-𝐎𝐫𝐝𝐞𝐫 𝐂𝐨𝐦𝐩𝐨𝐧𝐞𝐧𝐭𝐬 (𝐇𝐎𝐂)
• Creating HOCs
• Using HOCs for Reusability
𝟏𝟏.𝐑𝐞𝐧𝐝𝐞𝐫 𝐏𝐫𝐨𝐩𝐬
• Using Render Props Pattern
𝟏𝟐.𝐑𝐞𝐚𝐜𝐭 𝐑𝐨𝐮𝐭𝐞𝐫
• BrowserRouter
• Route
• Link
• Routes
• Route Parameters
𝟏𝟑.𝐍𝐚𝐯𝐢𝐠𝐚𝐭𝐢𝐨𝐧
• useHistory Hook
• useLocation Hook
𝐒𝐭𝐚𝐭𝐞 𝐌𝐚𝐧𝐚𝐠𝐞𝐦𝐞𝐧𝐭
𝟏𝟒.𝐂𝐨𝐧𝐭𝐞𝐱𝐭 𝐀𝐏𝐈
• Creating Context
• useContext Hook
𝟏𝟓.𝐑𝐞𝐝𝐮𝐱
• Actions
• Reducers
• Store
• connect Function (React-Redux)
𝟏𝟔.𝐅𝐨𝐫𝐦𝐬
• Handling Form Data
• Controlled Components
• Uncontrolled Components
𝟏𝟕.𝐒𝐢𝐝𝐞 𝐄𝐟𝐟𝐞𝐜𝐭𝐬
• useEffect for Data Fetching
• useEffect Cleanup
𝟏𝟖.𝐀𝐉𝐀𝐗 𝐑𝐞𝐪𝐮𝐞𝐬𝐭𝐬
• Fetch API
• Axios Library
𝐄𝐫𝐫𝐨𝐫 𝐇𝐚𝐧𝐝𝐥𝐢𝐧𝐠
𝟏𝟗.𝐄𝐫𝐫𝐨𝐫 𝐁𝐨𝐮𝐧𝐝𝐚𝐫𝐢𝐞𝐬
• componentDidCatch (Class Components)
• ErrorBoundary Component (Functional
Components)
𝟐𝟎.𝐓𝐞𝐬𝐭𝐢𝐧𝐠
• Jest Testing Framework
• React Testing Library
𝟐𝟏.𝐎𝐩𝐭𝐢𝐦𝐢𝐳𝐚𝐭𝐢𝐨𝐧
• Memoization
• Profiling and Performance Monitoring
𝟐𝟐. 𝐁𝐮𝐢𝐥𝐝 𝐚𝐧𝐝 𝐃𝐞𝐩𝐥𝐨𝐲𝐦𝐞𝐧𝐭
• Create React App (CRA)
• Production Builds
• Deployment Strategies
𝐅𝐫𝐚𝐦𝐞𝐰𝐨𝐫𝐤𝐬 𝐚𝐧𝐝 𝐋𝐢𝐛𝐫𝐚𝐫𝐢𝐞𝐬
𝟐𝟑.𝐒𝐭𝐲𝐥𝐢𝐧𝐠 𝐋𝐢𝐛𝐫𝐚𝐫𝐢𝐞𝐬
• Styled-components
• CSS Modules
𝟐𝟒.𝐒𝐭𝐚𝐭𝐞 𝐌𝐚𝐧𝐚𝐠𝐞𝐦𝐞𝐧𝐭 𝐋𝐢𝐛𝐫𝐚𝐫𝐢𝐞𝐬
• Redux
• MobX
𝟐𝟔.𝐑𝐨𝐮𝐭𝐢𝐧𝐠 𝐋𝐢𝐛𝐫𝐚𝐫𝐢𝐞𝐬
• React Router
• Reach Router
**Conclusion**
Mastering ReactJS requires a thorough understanding of its core concepts, advanced features, and associated libraries. This roadmap provides a structured approach to learning and improving your ReactJS skills, ensuring you stay ahead in the ever-evolving web development landscape. Happy coding! 🚀 | vyan |
1,871,919 | Mastering Go: Guide to Type Declarations, Variables, and Constants | In Go, constants are fixed values that are known at compile time and remain unchanged throughout the... | 0 | 2024-05-31T10:33:37 | https://dev.to/saumya27/mastering-go-guide-to-type-declarations-variables-and-constants-2agb | go, variables, constant | In Go, constants are fixed values that are known at compile time and remain unchanged throughout the program’s execution. They are defined using the const keyword and can be of basic types like integers, floats, strings, and booleans. Constants help improve code readability and maintainability by ensuring certain values remain consistent.
**Declaring Constants**
Constants are declared using the const keyword, followed by the constant's name, type, and value. The type can often be omitted because Go infers it from the assigned value.
const Pi float64 = 3.14159
const Greeting = "Hello, World!"
const DaysInWeek = 7
const IsTrue = true
**Grouping Constants**
You can group constants using parentheses, which is useful for organizing related constants.
const (
Pi = 3.14159
Greeting = "Hello, World!"
DaysInWeek = 7
)
**Untyped Constants**
Go allows untyped constants, which do not have a fixed type until they are used in a context that requires a specific type. This provides flexibility.
const Pi = 3.14159 // untyped constant
var radius float64 = 10
var circumference = 2 * Pi * radius // Pi is used as a float64 here
**Enumerated Constants**
Enumerated constants are a way to create a sequence of related constants, often using the iota keyword, which simplifies creating incrementing values.
const (
Sunday = iota // 0
Monday // 1
Tuesday // 2
Wednesday // 3
Thursday // 4
Friday // 5
Saturday // 6
)
The iota keyword represents successive integer constants starting from 0 and resets to 0 whenever the const keyword appears.
**Constants with Expressions**
Constants can be defined using expressions as long as the result is a compile-time constant.
const (
SecondsInMinute = 60
MinutesInHour = 60
HoursInDay = 24
SecondsInDay = SecondsInMinute * MinutesInHour * HoursInDay // 86400
)
**Limitations of Constants**
- Immutable: Constants cannot be changed once defined.
- Compile-Time: The value of a constant must be known at compile time.
- Basic Types Only: Constants can only be of basic types. More complex types like slices, maps, and structs cannot be constants.
**Practical Usage of Constants**
Constants are often used to define values that are used multiple times in the code, such as configuration settings, fixed dimensions, or commonly used strings.
package main
import "fmt"
const (
Pi = 3.14159
AppName = "MyApp"
MaxUsers = 100
WelcomeMsg = "Welcome to MyApp!"
)
func main() {
fmt.Println(AppName, "allows up to", MaxUsers, "users.")
fmt.Println(WelcomeMsg)
fmt.Printf("The value of Pi is approximately %.2f\n", Pi)
}
**Conclusion**
[Constants in Go ](https://cloudastra.co/blogs/guide-to-type-declarations-variables-and-constants-in-go)are a useful feature for defining fixed values, ensuring consistency, and preventing accidental changes. By understanding how to declare and use constants, including untyped constants and iota for enumerations, you can write more maintainable and error-resistant Go programs. | saumya27 |
1,871,918 | How to avoid fraud on Web3 apps | When we hear about Web3, it often seems like a futuristic vision of the internet that could... | 0 | 2024-05-31T10:32:57 | https://dev.to/shevchukkk/how-to-avoid-fraud-on-web3-apps-3ap9 | web3, decentralization, cryptocurrency | When we hear about Web3, it often seems like a futuristic vision of the internet that could revolutionize our lives. This is not far from the truth, as its core concepts aim to decentralize and establish transparency in relationships between users, platforms, and developers.
In simple terms, Web3 is an upgraded version of the “traditional” internet that we are all used to. The main difference lies in the absence of a third party when using it. This means that no government agencies or large corporations are needed to securely use assets, entertainment, or educational resources.
This new phase of the internet offers more freedom, opportunities, and control over development in the digital world, but it also brings new challenges. First and foremost, security issues always require careful preparation and immediate solutions. The [recent news](https://x.com/ain_ukraine/status/1773424277099819374?s=12&t=_JmivvomNnbyX7bng8XykA) of the imprisonment of Sam Bankman-Fried, the [founder](https://www.forbes.com/profile/sam-bankman-fried/?sh=2ef1222a4449) of the bankrupt cryptocurrency exchange [FTX](https://www.investopedia.com/ftx-exchange-5200842), shook the community. He was sentenced to 25 years in prison for stealing $8 billion from clients. According to [[REUTERS](https://www.reuters.com/technology/sam-bankman-fried-be-sentenced-multi-billion-dollar-ftx-fraud-2024-03-28/#:~:text=NEW%20YORK%2C%20March%2028%20(Reuters,former%20billionaire%20wunderkind's%20dramatic%20downfall.), the 32-year-old billionaire was found guilty after a lengthy trial on 7 counts of the Criminal Code for conspiracy and fraud that occurred after the collapse of FTX in 2022. Prosecutors in the case confirmed that it was one of the largest frauds in US history.
This shows that when it comes to assets, education, entertainment, or health, everyone needs to be able to protect themselves from scammers, especially during the smooth transition and adaptation to the Web3 system and its applications. There are special precautions called SLAM (Source of information, Links, Accounts, Activities, Approvals, Authentications, Mind) that can help to avoid phishing and potential attacks.
**S — (source of information)**. Always be aware that if you receive an email or message on Telegram or Discord from an unknown or unfamiliar sender, you should pause and check before responding. Basic cybersecurity knowledge and practices can help with this.
**L — (Links)**. The same applies to links. It is not recommended to immediately go to any website, even if it looks like the official one. This is especially true for the user experience on many popular cryptocurrency exchanges, which guarantee a high level of security, such as [Bitfinex](https://www.bitfinex.com/), [WhiteBIT](https://whitebit.com/ua), or [Gate.io](https://whitebit.com/ua), when using cold or hot wallets. After all, this is a fairly young and promising area that is a direct “ally” of the Web3 phase.
**A — (Accounts, Activities, Approvals, Authentications).** In this case, it is worth monitoring your own activity in accounts and authentication. This is especially important when working with DApps (decentralized applications), where wallet approval is required. This is because hacker platforms can be very similar to well-known ones like [1Inch](https://1inch.io/) or [Uniswap](https://uniswap.org/), but they may request excessive access. Regular checking of your e-wallet should be a habit for everyone who actively participates in investing, trading, or buying cryptocurrency. It is also recommended to review DApp permissions and periodically grant and revoke them. This will reduce the risk of potential attacks on the wallet that may occur due to enabled, unreliable or dormant programs.
**M — (Mind).** Use strong passwords. This means that instead of creating the easiest ones with your date of birth, use strong and complex combinations to create accounts on platforms. The same applies to personal wallet keys, which should never be given to anyone, as this will mean that access will be lost in the future.
**Conclusion**
Web3 promises a new era of the internet, free from centralized control. However, this freedom comes with security challenges. The recent FTX scandal highlights the importance of user vigilance against scams during the transition to Web3. SLAM (Source, Links, Accounts, Mind) offers a framework to stay safe. Be wary of unknown senders, don’t click suspicious links, and monitor your wallet activity on DApps. Strong passwords and keeping your private keys secure are crucial as well. | shevchukkk |
1,870,487 | 5 Open-Source Discoveries 🎁 | Hey friends 👋 Each week, our team at Quine explores the open-source ecosystem and features... | 0 | 2024-05-31T10:30:57 | https://dev.to/quira/5-open-source-discoveries-2b3l | webdev, opensource, javascript, programming | Hey friends 👋
Each week, our team at Quine explores the open-source ecosystem and features outstanding projects that you should be aware of.
We're dedicated to uncovering the hidden treasures of the open-source world.
---
Speaking of treasures, we've launched our latest Creator Quest — an initiative that challenges developers to build projects around specific themes.
`Quest-012`, invites you to use an OS repo of yours and harness Shepherd's powerful customisations to craft a dynamic user journey.
This event is open to all developers eager to showcase their skills and creativity for a chance to win cash prizes. 💰
If you love building, learning, and winning rewards, visit [Quine](https://quine.sh/quests/creator and start your adventure!
Now, let's dive into our latest discoveries in the open-source community.

---
## [cyclops-ui/cyclops](https://github.com/cyclops-ui/cyclops)
If Kubernetes had a user interface designed from the ground up with modern needs in mind, it would look like Cyclops. Unlike other UI solutions, Cyclops is streamlined and customisable, offering a user-friendly experience for devs and DevOps professionals.
**This project is perfect if you want to:**
- Manage and interact with Kubernetes clusters efficiently
- Automate your deployment processes to reduce mistakes
- Divide responsibilities between infrastructure and dev teams
**Here's what Cyclops offers:**
- Intuitive UI for Kubernetes workloads
- Easy installation with a 10-minute tutorial
- Predefined templates for quick setup and customisation
[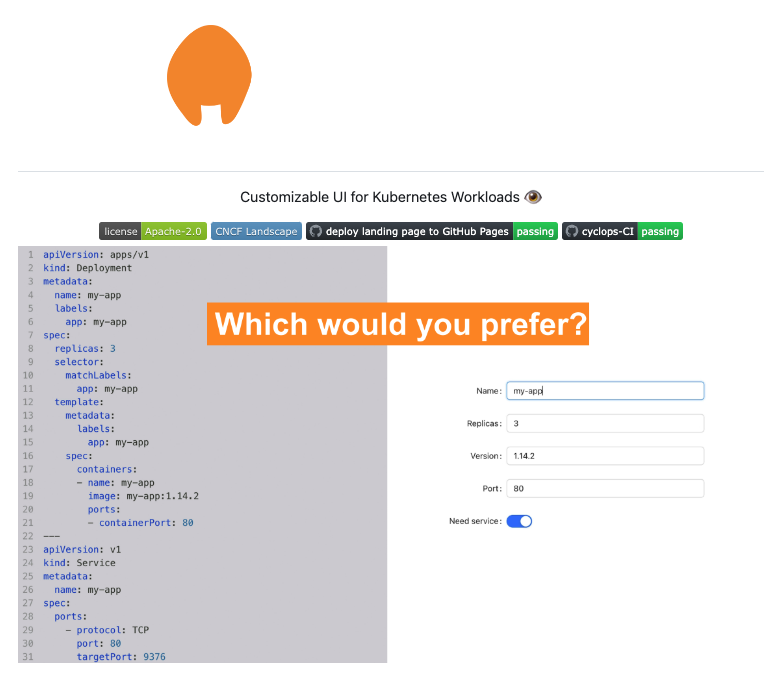](https://github.com/cyclops-ui/cyclops)
---
## [odigos-io/odigos](https://github.com/odigos-io/odigos)
If observability were made effortless and seamless, it would look like Odigos. Unlike traditional solutions, Odigos offers language-agnostic auto-instrumentation for Kubernetes applications without code changes.
**This project is perfect if you want to:**
- Generate distributed traces without modifying your code
- Use existing observability tools with ease
- Manage and scale OpenTelemetry collectors automatically 🤖
**Here's what Odigos offers:**
- Language-agnostic auto-instrumentation for _Java, Python, .NET, Node.js, and Go_
- Compatibility with all popular managed and open-source observability tools
- Automatic scaling of OpenTelemetry collectors based on data volume
- Easy management and configuration through a web UI
[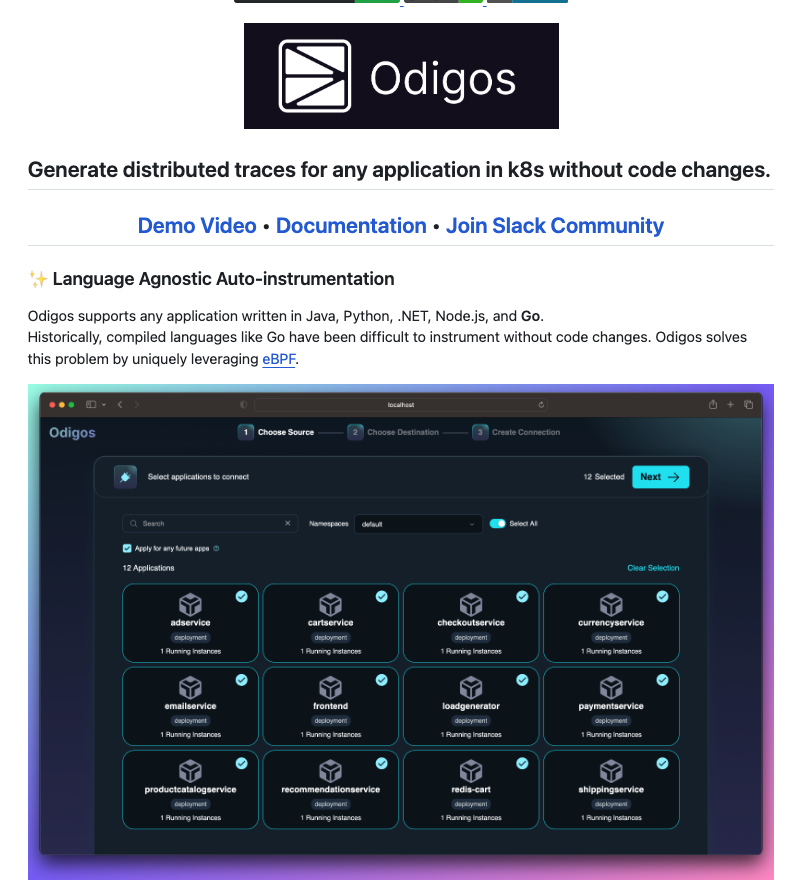](https://github.com/odigos-io/odigos)
---
## [vueform/vueform](https://github.com/vueform/vueform)
If form building in Vue.js had a comprehensive, open-source solution, it would look like Vueform. Unlike traditional form frameworks, Vueform standardises the entire form-building process, handling everything from rendering to validation and processing.
**This project is perfect if you want to:**
- Simplify form creation in Vue.js applications
- Use a wide range of form elements with advanced features
- Customise and theme your forms with Tailwind support 🎨
**Here's what Vueform offers:**
- 25+ form elements, including multi-file uploads, date pickers, and text editor
- Element nesting and repeating capabilities with complete theming & templating system
- 50+ validators with support for async, dependent, and custom rules
- Conditional logic with and/or condition groups with translation of form contents
[](https://github.com/vueform/vueform)
---
## [openmeterio/openmeter](https://github.com/openmeterio/openmeter)
If real-time usage metering had a modern and scalable solution, it would look like OpenMeter. Unlike traditional metering tools, OpenMeter is designed for AI, usage-based billing, infrastructure, and IoT use-cases. This provides for a robust and efficient system.
**This project is perfect if you want to:**
- Implement real-time and scalable usage metering
- Handle usage-based billing effectively
- Integrate metering solutions for AI, infrastructure, and IoT
**Here's what OpenMeter offers:**
- Real-time usage metering for various applications
- REST API for seamless integrations
- Client SDKs for Node.js, Python, Go, and Web
[](https://github.com/openmeterio/openmeter)
---
## [Treblle/treblle-laravel](https://github.com/Treblle/treblle-laravel)
If API management had a modern, lightweight solution designed for speed and simplicity, it would look like Treblle. Unlike traditional tools, Treblle is built to help engineering and product teams build, ship, and maintain REST-based APIs faster.
**This project is perfect if you want to:**
- Accelerate API development and deployment
- Gain deep insights into API performance and health
- Collaborate seamlessly on API lifecycle management
**Here's what Treblle offers:**
- Real-time API monitoring and observability
- Auto-generated API documentation
- Detailed API analytics
- Treblle API Score for quality assessment
- Comprehensive API lifecycle collaboration
- Native Treblle apps for various platforms
[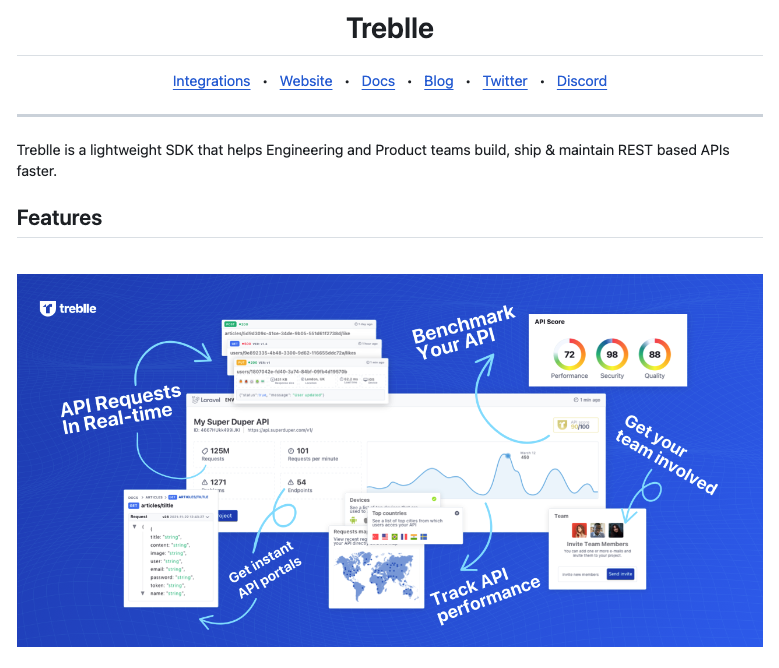](https://github.com/Treblle/treblle-laravel)
---
I hope you enjoyed discovering these open-source projects!⚒️
Please **consider supporting these projects by starring them. ⭐️**
We are not affiliated with them. We just think that great projects deserve great recognition.
See you next week,

Your Dev.to buddy 💚
Bap
---
If you want to join the self-proclaimed "coolest" server in open source 😝, you should join our [discord server](https://discord.com/invite/ChAuP3SC5H/?utm_source=devto&utm_campaign=31_may_2024). We are here to help you on your journey in open source. 🫶
| fernandezbaptiste |
1,871,917 | Discover the unmissable places in your international tour packages | Begin on a journey of discovery and wonder with our guide to the unmissable places in your... | 0 | 2024-05-31T10:30:37 | https://dev.to/sahilsharma11/discover-the-unmissable-places-in-your-international-tour-packages-e6f | internationaltourpackage | Begin on a journey of discovery and wonder with our guide to the unmissable places in your [international tour packages](https://www.bestentours.com/international-tour-packages). Explore the world's most iconic landmarks, hidden gems, and breathtaking natural wonders as you traverse continents and cultures. From the majestic beauty of the Grand Canyon to the awe-inspiring architecture of the Taj Mahal, each destination promises a wealth of unforgettable experiences. Dive into the vibrant culture of bustling cities like Tokyo and New York City, or escape to the tranquility of remote islands like Santorini and Bora Bora. Whether you're seeking adventure, relaxation, or cultural immersion, our international tour packages offer something for every traveler. Let us guide you on a journey of exploration and discovery as you uncover the unmissable places that await you around the globe.

| sahilsharma11 |
1,871,916 | Difference between Functional Testing and Non-Functional Testing with examples | Functional testing and non-functional testing are two essential approaches to ensuring the quality... | 0 | 2024-05-31T10:29:54 | https://dev.to/s1eb0d54/difference-between-functional-testing-and-non-functional-testing-with-examples-3a81 | Functional testing and non-functional testing are two essential approaches to ensuring the quality and reliability of software systems. While both aim to validate the software, they focus on different aspects and employ distinct methodologies. Here's a comprehensive comparison between the two:
### **Functional Testing**:
Functional testing verifies whether the software functions as intended and meets its specified functional requirements. It examines individual functions or features of the software to ensure they produce the correct outputs for given inputs.
The primary goal of functional testing is to validate the behavior of the software application according to the functional specifications provided by stakeholders.
**Types Functional Testing**:
1. **Unit Testing**: Tests individual units or components of the software in isolation.
2. **Integration Testing**: Tests the interaction between integrated components or modules.
3. **System Testing**: Tests the entire system as a whole to verify that it meets requirements.
4. **User Acceptance Testing**: Validates whether the software meets user requirements and is ready for release.
```
Functional Testing
|
------------------------
| | |
Unit Testing Integration System
Testing
|
User Acceptance
Testing
```
**Example**: Consider a banking application's "Transfer Funds" feature. Functional testing would verify that users can initiate transfers from one account to another, the correct amounts are deducted from the sender's account and added to the recipient's, and appropriate error messages are displayed for invalid inputs or insufficient funds.
**Process**:
1. **Test Planning**: Define test objectives, scope, and strategies based on functional requirements.
2. **Test Design**: Create test cases covering various scenarios, including normal and boundary cases.
3. **Test Execution**: Execute test cases, observe results, and document any deviations from expected behavior.
4. **Defect Reporting**: Report identified issues with detailed descriptions and steps to reproduce.
5. **Regression Testing**: Re-run functional tests to ensure fixes haven't caused new issues.
### **Non-Functional Testing:**
Non-functional testing evaluates the aspects of a software system beyond its functional requirements, focusing on attributes such as performance, reliability, usability, security, and compatibility.
The primary goal of non-functional testing is to assess how well the software performs under specific conditions and to ensure it meets quality criteria related to its operation.
**Types Non-Functional Testing**:
1. **Performance Testing**: Assess system responsiveness, scalability, and resource usage under various loads.
2. **Reliability Testing**: Verify the system's ability to perform consistently and accurately over time.
3. **Usability Testing**: Evaluate the system's user-friendliness, accessibility, and intuitiveness.
4. **Security Testing**: Identify vulnerabilities and weaknesses in the system's security measures.
5. **Compatibility Testing**: Check the system's compatibility with different environments, devices, and operating systems.
```
Non-Functional Testing
|
-----------------
| | | | |
Performance Reliability Usability Security Compatibility
| | | | |
Load Error Handling UI Penetration Cross-
Testing Testing Testing Platform
Testing
```
**Example**: In performance testing, a web application undergoes load testing to assess its response time and scalability under heavy user traffic. By simulating thousands of concurrent users accessing the application, testers can identify performance bottlenecks and optimize system resources accordingly.
**Process**:
1. **Test Planning**: Define objectives, scope, and strategies based on non-functional requirements.
2. **Test Design**: Create test cases covering various non-functional aspects, such as load scenarios for performance testing or security vulnerabilities for security testing.
3. **Test Execution**: Execute test cases and measure system behavior against non-functional criteria.
4. **Analysis and Reporting**: Analyze test results and report findings, including performance metrics or security vulnerabilities.
5. **Optimization**: Implement optimizations or fixes based on test findings to improve non-functional aspects of the software.
### **Difference between Functional Testing and Non-Functional Testing**
1. Functional testing focuses on validating what the software does, ensuring it meets specified functional requirements. Non-functional testing focuses on how well the software performs, assessing attributes such as performance, reliability, usability, security, and compatibility.
2. Functional testing validates individual functions or features of the software, whereas non-functional testing assesses broader aspects related to the software's operation and quality.
3. Functional testing aims to ensure that the software behaves as expected according to functional specifications. Non-functional testing aims to assess and improve the software's performance, reliability, usability, security, and compatibility.
4. Functional testing employs techniques such as unit testing, integration testing, system testing, and acceptance testing. Non-functional testing employs techniques such as performance testing, reliability testing, usability testing, security testing, and compatibility testing.
5. while functional testing ensures that the software functions correctly according to specified requirements, non-functional testing evaluates the software's performance, reliability, usability, security, and compatibility to ensure it meets quality standards and user expectations. Both types of testing are essential for delivering high-quality software products. | s1eb0d54 | |
1,871,913 | 10 advantages to choose Our international travel agency | Discover the 10 unparalleled advantages of choosing Our International Travel Agency for your next... | 0 | 2024-05-31T10:27:37 | https://dev.to/sahilsharma11/10-advantages-to-choose-our-international-travel-agency-497o | international, internationaltravelagency | Discover the 10 unparalleled advantages of choosing Our [International Travel Agency](https://www.bestentours.com/) for your next global adventure. With a commitment to excellence and a passion for crafting unforgettable journeys, Our International Travel Agency sets itself apart as a leader in the industry. Benefit from personalized service tailored to your unique preferences and travel style, ensuring that every aspect of your trip exceeds expectations. Gain access to exclusive deals and discounts, as well as insider knowledge and expertise that only comes from years of experience. Enjoy peace of mind with 24/7 customer support and assistance, no matter where your travels may take you. From seamless itinerary planning to expert guidance every step of the way, Our International Travel Agency is your trusted partner in exploring the world. Choose excellence, choose adventure, choose Our International Travel Agency for the journey of a lifetime.

| sahilsharma11 |
1,871,911 | AI Tools for Protecting User Data and Crypto Assets | A quote by Richard Clarke, the United States’ former cybersecurity czar, serves as a stark warning:... | 0 | 2024-05-31T10:24:40 | https://dev.to/shevchukkk/ai-tools-for-protecting-user-data-and-crypto-assets-2ch3 | ai, blockchain | A [quote](https://www.zdnet.com/article/security-guru-lets-secure-the-net/) by [Richard Clarke](https://www.prhspeakers.com/speaker/richard-a-clarke), the United States’ former cybersecurity czar, serves as a stark warning: “If you’re spending more on coffee than on IT security, you will be hacked. What’s more, you deserve to be hacked.”
This statement highlights the critical importance of data security, which is often overlooked by individuals and organizations alike. Data security is paramount for both businesses and users, as it ensures the reliability and privacy of financial information, health data, and job prospects. However, in the age of data dominance, there is a significant risk of sensitive information being leaked, potentially affecting hundreds of millions or even billions of people.
The digital revolution has led to an exponential increase in the amount of information circulating worldwide. Consequently, the number of data breaches has also increased, as malicious actors exploit personal and confidential information. Several high-profile cases illustrate the severity of the problem. In [June 2021](https://www.linkedin.com/pulse/linkedin-data-breach-700m-2021-david-sehyeon-baek--ex85c), [LinkedIn](https://business.linkedin.com/marketing-solutions/cx/24/01/ads-for-linkedin?src=go-pa&trk=sem-ga_campid.20065133430_asid.148672896957_crid.657090959035_kw.linkedin+business_d.c_tid.kwd-4469614746_n.g_mt.e_geo.9062578&mcid=7059959449221829589&cid=&gad_source=1&gclid=EAIaIQobChMI65KLvM2UhQMV0BkGAB3EMg38EAAYASAAEgLiSfD_BwE&gclsrc=aw.ds) suffered a data breach that exposed the details of 700 million users, including phone numbers, email addresses, geolocation records, and gender. [Marriott International](https://www.marriott.com/marriott/aboutmarriott.mi) acknowledged that hackers had accessed the personal data of half a million guests in [September 2018](https://www.nytimes.com/2018/11/30/business/marriott-data-breach.html) . The incident involved unauthorized access to the [Starwood](https://news.marriott.com/news/2015/11/16/marriott-international-to-acquire-starwood-hotels-resorts-worldwide-creating-the-worlds-largest-hotel-company) guest reservation database dating back to 2014. In November 2018, hackers copied and encrypted data, including email addresses, passport numbers, booking dates, and phone numbers. However, Marriott managed to decrypt the data and resolve the global issue.
These incidents emphasize the importance of investing in the development and implementation of innovative AI-based tools to ensure data and crypto asset protection in the future. Governments, private companies, and research institutions must collaborate to stimulate innovation in this space. The digital society is creating AI-based solutions that will provide transparency and protection for users, companies, and organizations. Some of these solutions include:
**Biometric authentication:** this process involves analyzing user behavior patterns to create cyber fingerprints, keystroke dynamics, and personal typing patterns. Several startups are actively using biometric authentication, such as [Behaviosec](These incidents emphasize the importance of investing in the development and implementation of innovative AI-based tools to ensure data and crypto asset protection in the future. Governments, private companies, and research institutions must collaborate to stimulate innovation in this space. The digital society is creating AI-based solutions that will provide transparency and protection for users, companies, and organizations. Some of these solutions include:
Biometric authentication: this process involves analyzing user behavior patterns to create cyber fingerprints, keystroke dynamics, and personal typing patterns. Several startups are actively using biometric authentication, such as Behaviosec, which analyzes users’ typing rhythm, and [Bionym’s](https://www.biometricupdate.com/tag/bionym) [Nymi bracelet](https://www.nymi.com/), which authenticates users based on their heartbeat. [Mastercard](https://www.mastercard.us/en-us.html) even implemented this technology to allow customers to make payments.
**Blockchain-based encryption:** this method uses a special structural model that contains raw data obtained from the supplier and a hash code stored in the blockchain. The raw data is fed to the AI, compared to the hash code, and if there are any discrepancies, it allows the supplier to be tracked and identified as malicious or not. [CertiK](https://www.certik.com/) actively uses this encryption method. [Core Scientific](https://corescientific.com/) integrates personalized blockchain and AI infrastructure with current business networks, updating the physical structure of businesses, servers, and software.), which analyzes users’ typing rhythm, and Bionym’s Nymi bracelet, which authenticates users based on their heartbeat. Mastercard even implemented this technology to allow customers to make payments.
**Anomaly detection:** specific algorithms can be used to identify problems. For example, LOF (Local Outlier Factor) investigates the local density of data points. SVM (Support Vector Machines) aims to divide data points into classes using hyperplanes in a multidimensional space. As a result, the machine model learns to recognize “data point norms” and assess whether these points are “familiar” with the integrity policy. The [LeewayHertz](https://www.leewayhertz.com/) generative platform is based on algorithms that detect anomalies.
**Autoencoders:** these use artificial neural networks to encode data, compressing its size. The data is then decoded and presented to the company with a complete analysis to identify potential threats, as [viso.ai](https://viso.ai/) demonstrates.
**AI for crypto assets:** in the digital age, cybersecurity is becoming increasingly important for investors. Outdated, centralized systems used by traditional asset management companies are vulnerable to cyberattacks. [ATPBot](https://www.atpbot.com/en) offers an innovative solution that takes data security to the next level through alternative encryption methods and cryptographic protocols. Web3 authorization and Web3 deposits are highly relevant, aimed at increasing trust among clients, primarily cryptocurrency exchanges such as [WhiteBIT](https://whitebit.com/ua), [Kraken](https://www.kraken.com/why-kraken), [Bybit](https://www.bybit.com/en/institutional), and many others.
**Conclusion**
It is clear that our present must be focused on securing our data and its integrity. Losing even partial access to this chain can result in the loss of not only reputation but also personal funds. By investing in AI-powered cybersecurity solutions, we can build a more secure and resilient digital future for everyone. Data security is crucial in today’s digital world, where breaches can expose sensitive information to millions. AI-powered solutions offer promising ways to combat this growing threat.
Governments, businesses, and researchers need to collaborate on developing AI tools for data protection. These solutions include biometric authentication, blockchain encryption, anomaly detection algorithms, and autoencoders for threat identification. | shevchukkk |
1,871,910 | Advanced Features and Functionality in Modern HOA Software | Homeowners associations (HOAs) which play a vital role in the dynamic business landscape, are turning... | 0 | 2024-05-31T10:24:35 | https://dev.to/davidsmith45/advanced-features-and-functionality-in-modern-hoa-software-1hdc | Homeowners associations (HOAs) which play a vital role in the dynamic business landscape, are turning to the modern software grid to enhance the process and maximize the residents' pleasure. Initially, HOA software facilitated only the administrative routine tasks, and with the passing of time creation of advanced functions became the reality allowing to adapt the software to the HOA needs very accurately. In this article, we will focus on contemporary HOA software which is dedicating its resources to ensure an increase in the efficiency of community management.
The art of managing funds accurately and efficiently is a fundamental part of homeowners associations (HOA) success. The modern type of HOA software comes with integrated financial management solutions that simplify and automate documenting and provide the HOAs with the right data and clear reports to make accurate decisions. This article will focus on what the latest [HOA software](https://www.getquorum.com/) versions bring to accounting that is different from what traditional financial management software offers.
**Automated Budgeting and Forecasting:
**
Advanced Algorithms: Modern HOA software nowadays incorporates a number of more advanced algorithms to analyze past and current trends with predicted future results. This automation means no more pen-and-paper calculations and thus even safer and more precise budgets.
Accurate Forecasts: Through using old financial records, optimal online resources to induce exact expense and income forecasts along with SFX (special force expenditure) is definitely a possibility it provides. These underpin strategic thinking and that way resources can be used consciously.
Scenario Planning: One of the powerful features of some HOA system platforms is scenario planning which helps HOAs develop various financial scenarios to assess how they affect the planned budget. This is the critical thinking skill that keeps HOAs one step ahead of the likely problems by providing their teams with options and plans for contingencies.
**Online Payments and Billing:
**
Convenience for Residents: With the help of modern HOA software, people will be able to pay their dues, assessments, and fees through online payment, which will provide residents with a single source of secure method to pay the fees. It eliminates the manual issuance of checks, and invoices and to a great extent minimizes administrative obligations.
Automated Recurring Payments: HOA software allows residents to submit their monthly installments in automated manner, which reduces the chances of a late payment and enhances the consistency of contributions. This also helps in the proper cash flow management of HOA and minimizes late or nonpayment dues.
Transparent Billing: With HOA software portals, residents not only can refer to the financial transactions history but also the details of their own balances and transaction histories, which leads to enhancing transparency level and trustworthiness in financial deals.
**Financial Reporting and Analysis:
**
Comprehensive Reports: Today’s HOA software includes a set of report-generating tools that offer built-in flexibility, therefore allowing users to get insights into various dimensions of their financial performance. HOAs are able to give the boards fairness by means of balance sheets, cash flow reports, or/ and any other related financial documents the boards may need.
Real-Time Data Access: With HOA software, finance data is extracted and updated in real-time which engages the HOA’s board in the financial performance of their organization on daily basis. Such last-minute data would help in making preemptive decisions and taking corrective actions incase of an eventuality.
Identify Areas for Improvement: With the help of a financial analysis that is deep, HOAs can pinpoint what are trends, patterns, or outliers that possibly disclose the places for enhancements or dropping prices. Thus, the use of data in financial management improves the quality of management and facilitates transparency.
**Customization and Flexibility
**
HOAs operate much the same way as unique entities. Even if they cover the same area, they may have different needs. This is why the newest software solutions are willing to offer customization of the $HOAs platform and functionality adaption to meet the needs and requirements of the clients. Whether it is setting up automated workflows, or designing special templates , software such as the advanced HOA software gives communities power to the adapt and to configure the system to their distinct requirements flexibility make HOAs able to keep be more user-friendly and remain independent and autonomous decision-making on processes.
**Community Engagement and Events
**
However, management is not the priority of modern HOA software. Instead, it puts community involvement on the top and tries to make the organization of events and activities more easy. The platforms usually come with event management tools that empower HOAs to handle all the necessary details of an event like registration, program tracking, promotion and event logistics. Moreover, some of the software tools provide web community forums or online discussion boards where the locals can post, comment, and share their thoughts on neighborhood issues. Through proffering community and supporting communities, quality software helps build positive relations among neighbors that lead to a strong community life.
The modern HOA software has come away from the simple administration of initial time to a complete collection of advanced features and functionality which are sufficient to cater for all the needs of homeowners association. Whether it be continuous integration or customization features, advanced communication tools, or more secure facilities, these platforms help HOAs easily operate and also engage the residents in a more comfortable manner. It can be expected that as technology is evolving HOA software should change as well, meeting communities in new way, and making the residents happier in their environment.
| davidsmith45 | |
1,871,828 | Typescrypt: Make your life easier with decorators | What is decorator? In TypeScript, decorator is a special type of declaration that uses the... | 0 | 2024-05-31T10:23:55 | https://dev.to/rizkiiqbal36/typescrypt-make-your-life-easier-with-decorators-3ppp | typescript, decorator, node, javascript | ## What is decorator?
In TypeScript, decorator is a special type of declaration that uses the `@` symbol to customize classes and their members, allowing us to add metadata or modify their behavior at runtime.
## Brief History
Decorators were initially introduced as an experimental feature in [TypeScript 1.5](https://github.com/microsoft/TypeScript/releases/tag/v1.5.3) in July 2015, and using them required enabling a specific compiler option called `--experimentalDecorators`.
## Why decorator?
Using decorators offers several benefits that can greatly enhance the efficiency and readability of your code. Here are some key reasons why decorators are useful:
1. Code Reusability and DRY Principle
- <b>Reusability</b>: Decorators allow you to define reusable pieces of code that can be applied across multiple classes or methods. This eliminates the need to write repetitive logic in multiple places.
- <b>DRY Principle</b>: By abstracting common functionality into decorators, you adhere to the "Don't Repeat Yourself" principle, reducing code duplication and making your codebase cleaner and easier to maintain.
2. Separation of Concerns
Decorators help separate cross-cutting concerns (like logging, authorization, validation, etc.) from the business logic. This keeps your core logic focused and straightforward.
3. Enhanced Readability and Maintainability
- <b>Readability</b>: Using decorators makes it clear what additional behaviors or metadata are associated with a class or method. This can make the code more readable and self-documenting.
- <b>Maintainability</b>: Since decorators encapsulate specific behaviors, any changes to these behaviors can be made in one place (the decorator itself) rather than scattered throughout the codebase.
## Getting Started
Make sure TypeScript is installed on your system, or you can install it locally within your specific project.
In this blog, I'll be using TypeScript v5.4.5, the latest version as of May 24, 2024, installed using npm and configured in Visual Studio Code settings.
To install the latest version of TypeScript and the necessary type definitions for Node.js, use the following command:
```bash
npm i typescript@latest @types/node -D
```
Ensure you configure VS Code to use the TypeScript version installed via npm by adding the following line to your `.vscode/settings.json` file:
```json
{
"typescript.tsdk": "node_modules/typescript/lib"
}
```
This setting directs VS Code to use the TypeScript language server from the directory installed by npm.
you must enable the `experimentalDecorators` compiler option either via command or your `tsconfig.json` file.
```json
{
"experimentalDecorators": true
}
```
## Decorator Declaration
The syntax of a decorator is pretty simple, just add the @ operator before the decorator you want to use, then the decorator will be applied to the target:
```typescript
const simpleDecorator: ClassDecorator = function () {
console.log("hi I am a decorator");
};
@simpleDecorator
class ClassA {}
// Output:
// hi I am a decorator
```
## Decorator Factory
Decorator factory is a function that returns a decorator. It allows you to pass parameters to a decorator. here is how it look like:
```typescript
function addProperty<T>(name: string, value: T) {
return function (target: { new (...arg: any[]) }): void {
target.prototype[name] = value;
};
}
@addProperty<boolean>("isNew", true)
class ClassB {}
console.log(ClassB.prototype);
// Output:
// { isNew: true }
```
Here's a breakdown of a decorator and a decorator factory:
1. Decorator: A special kind of declaration that can be attached to a class, method, accessor, property, or parameter to modify their behavior or add metadata.
2. Decorator Factory: A function that returns a decorator, enabling you to customize the decorator with parameters.
## Examples
There are various types of decorators in TypeScript, such as class decorators, property decorators, Method Decorator, Accessor Decorator, and parameter decorators. In this guide, we'll focus on method decorators.
### Behavior at runtime
as you know decorators are usefull tools that allow us to modify the behavior of classes and their members at runtime. Let's say you have a log decorator with a message parameter, and you want to make sure that the message isn't an empty string. You can accomplish this by add the validation before return the decorator.
```typescript
function simpleDecorator(message: string): MethodDecorator {
if (message.length === 0) throw Error("Invalid Argument: Doesnt allowed empty string");
return function (): void {
console.log("Method triggered");
};
}
```
This will throw an error as soon as you run the codes:
```typescript
class ServiceA {
@simpleDecorator("") // Error: Invalid Argument: Doesnt allowed empty string
public methodA() {}
}
```
This one is valid:
```typescript
class ServiceA {
@simpleDecorator("a")
public methodA() {}
}
```
### Decorators are stackable
Decorators can be stacked:
```typescript
const first: MethodDecorator = function () {
console.log("first");
};
const second: MethodDecorator = function () {
console.log("second");
};
class ClassA {
@first
@second
methodA() {}
}
// Output:
// second
// first
```
When multiple decorators apply to a single declaration, their evaluation is similar to [function composition in mathematics](https://wikipedia.org/wiki/Function_composition).
As such, the following steps are performed when evaluating multiple decorators on a single declaration in TypeScript:
1. The expressions for each decorator are evaluated top-to-bottom.
2. The results are then called as functions from bottom-to-top.
### Class method as decorator factory
You can also use class methods as decorator factories to create more complex and reusable decorators.
Let's say you have a custom logger class that can print messages with a custom prefix and measure the time taken between different pieces of code.
```typescript
class Logger {
private performanceTimeLog: {
timestamp: number;
// logId: string // You can add custom property here to help you log your messages better
}[] = [];
constructor(public readonly instance: string) {}
public performanceStart = (message: string) => {
this.performanceTimeLog.push({ timestamp: performance.now() });
this.log(message);
return this.performanceTimeLog.length - 1;
};
public performanceEnd = (timeStartIndex: number, message: string) => {
const performanceTime = this.performanceTimeLog[timeStartIndex];
if (typeof performanceTime === "undefined") throw Error("Define performanceStart first");
const getTime = (performance.now() - performanceTime.timestamp).toFixed();
this.printPerformanceMessage(message, getTime);
};
private printPerformanceMessage(message: string, time: string) {
this.log(`${message}, +${time}ms`);
}
public log(message: string) {
process.stdout.write(`[${this.instance}] ${message}\n`);
}
}
const serviceLogger = new Logger("SERVICE");
const timeStartIndex = serviceLogger.performanceStart("LOG");
serviceLogger.log("Hello there");
serviceLogger.performanceEnd(timeStartIndex, "LOG");
// Output:
// [SERVICE] LOG
// [SERVICE] Hello there
// [SERVICE] LOG, +1ms
```
Let's add a decorator that measures the time taken by the method it is applied to.
```typescript
class Logger {
...
...
...
public decoratorFunctionPerformance({ message }: { message?: string }) {
return ((self: typeof this) => {
return function (target: any, propertyKey: string, descriptor: PropertyDescriptor) {
const usedMessage = message ?? `EXECUTE ${propertyKey}`;
const original = descriptor.value;
descriptor.value = async function (...args: any[]) {
const performanceIndex = self.performanceStart(`START ${usedMessage}`);
try {
const result = await original.apply(this, args);
return result;
} catch (err: any) {
// error handler
throw err;
} finally {
self.performanceEnd(performanceIndex, `END ${usedMessage}`);
}
};
};
})(this);
}
}
```
Now we have `decoratorFunctionPerformance`, which is a class method acting as a decorator factory. The method itself is an immediately-invoked function expression [(IIFE)](https://developer.mozilla.org/en-US/docs/Glossary/IIFE), enabling access to the `this` context (Logger instance). This allows us to access the logger instance within our decorator function.
Inside the decorator, we apply the performance timing function both before and after the original method is executed.
Let's see `decoratorFunctionPerformance` in action:
```typescript
const serviceLogger = new Logger("SERVICE");
class ServiceA {
@serviceLogger.decoratorFunctionPerformance({})
public async methodA() {
return new Promise((resolve, reject) => {
setTimeout(() => {
resolve(true);
}, 500);
});
}
}
const serviceA = new ServiceA();
serviceA.methodA();
// Output:
// [SERVICE] START EXECUTE methodA
// [SERVICE] END EXECUTE methodA, +503ms
```
On the example above, we applied `decoratorFunctionPerformance` to `methodA` causing it to wait for 500ms before returning the value `true`. Therefore, the execution time will be at least 500ms.
You can see full code [here](https://github.com/Rizky-Iqbal36/raw-blogs/blob/main/typescript/decorators/index.ts#L60)
That's all I wanted to share. I hope this information helps you in some way. | rizkiiqbal36 |
1,871,839 | Get Rid of Migration Files | I once join a team that using postgres and sequelize as their ORM, and they have dozens of migration... | 0 | 2024-05-31T10:23:35 | https://dev.to/rizkiiqbal36/get-rid-of-migration-files-3bhb | database, sequelize, postgres, development | I once join a team that using postgres and sequelize as their ORM, and they have dozens of migration files, when i try to migrate those files, i got a lot of error that saying the same problem coming from migration files.
some error like:
```bash
parent: error: column "column_name" of relation "table_name" does not exist
```
If i try to fix it one by one it will be a lot of work and time consuming, and if in the future we dont maintenance the migration files regurarly, the same issues will come.
Their solution was giving onboarding member dump files for each databases that used on this project from full timer developer. one of the dump files size was around 900 Mb and when i try to restore the dump files, the data that it contain took around 8 Gb of my SSD. I personally doesnt want my storage get decreased by the large volume of the data from dump files, moreover the process of restoring these files can be time consuming.
As another solution, i make a workaround flow to overcome this issue:
- Assume that there is dump folder contains database structure (tables only)
- Execute a command to restore the dump file to the database
- Execute a command to update the dump file.
- If migrate or undo from sequelize then do point 3
This is the solution flowchart:
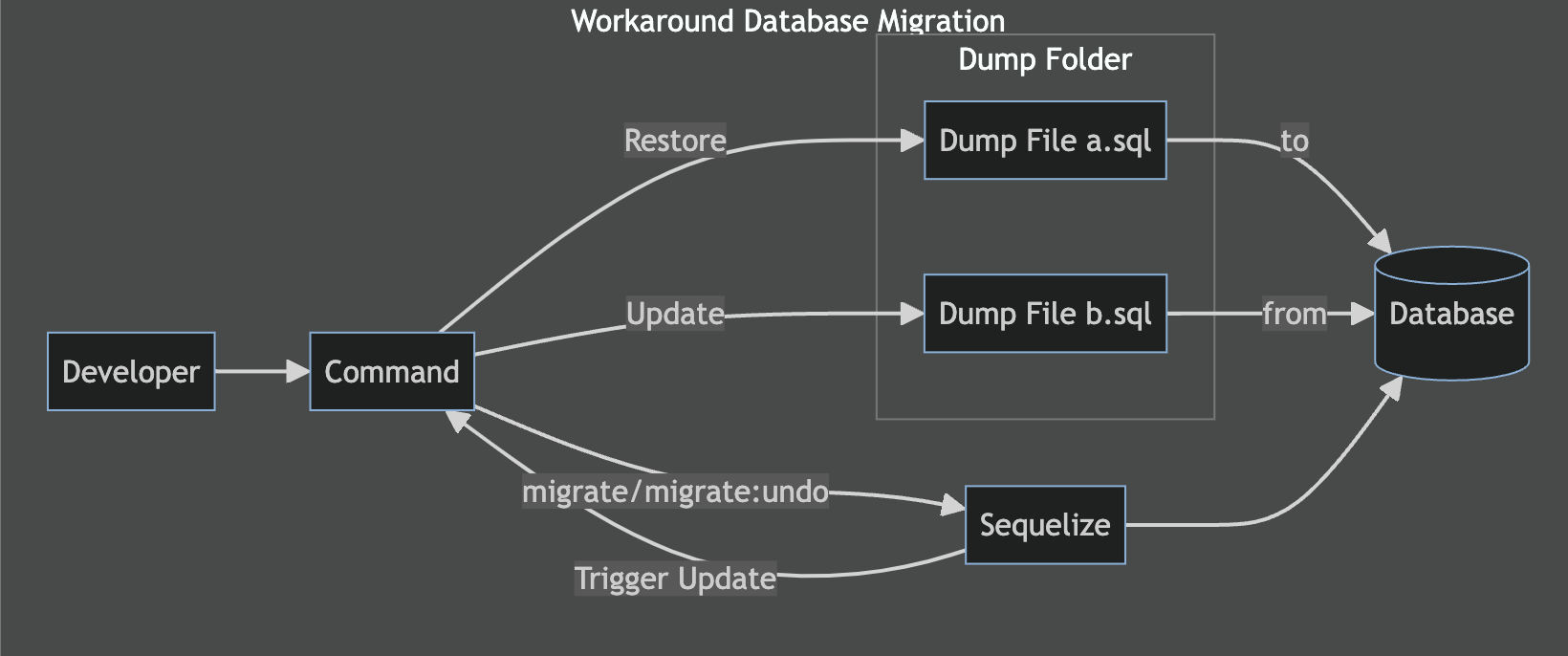
With this, we can overcome the issue:
- Error prone migration process: this solution provides alternative method that is less prone to errors.
- Cumbersome manual fixes: as stated, fixing errors on each migration files individually would take a lot of work and time consuming. This solution reduces the efforts to fix each migration files.
- Lack of maintenance: This flow providing a mechanism for updating the database structure from and to a dump file.
- Quickly get started: With a single command, we can get the project set up with a new blank database, avoiding the need to restore large dump files and saving significant storage space on our systems.
> **_NOTE:_**
> This is just experimenting from my side, and i think there is maybe a better way to handle this problem. Please let me know what do you think about this solution, like: is there any cons on this solution?, how we can improve it?, etc.
Now that we got the idea, how do we implement it with codes? keep reading!
## Installation
First thing first we need to install postgresql, make sure its up and running you can also use docker but in this blog i will use postgresql v14 installed using brew.
Now we need to install sequelize, sequlize cli and postgres driver using npm.
```bash
npm i sequelize pg && npm i -D sequelize-cli
```
After installing sequelize now we need to create empty sequelize project using sequelize-cli
```bash
npx sequelize-cli init
```
This will create following folders
1. config, contains config file, which tells CLI how to connect with database
2. models, contains all models for your project
3. migrations, contains all migration files
4. seeders, contains all seed files
Also dont forget to tell sequelize how to connect to database by adjusting `config/config.json`.
Lastly we need a folder to store our dump files, lets name it `dump`.
Now we are ready to create our first migration. Let's create a model named `User`:
```bash
npx sequelize-cli model:generate --name User --attributes firstName:string,lastName:string,email:string
```
## Implementation
We are ready for the implementation, let's create shell script named `make` and preparing our commands. It will look like this:
```bash
#!/bin/sh
case ${1} in
"db:dump:update")
;;
"db:dump:restore")
;;
"db:migrate")
;;
"db:migrate:undo")
;;
"db:migrate:undo:all")
;;
```
Now our script can handle the commands we need. Let's build the logic one by one:
### db:dump:update
This command will create dump file from a database
```bash
#!/bin/sh
case ${1} in
"db:dump:update")
if test ! -z "${2}";then # Check second argument which will be used as `database_name`
pg_dump -U postgres -d "${2}" -s -f "dump/pg-${2}-tables.sql"; # Tell postgres to create dump file from a database (tables only)
{
echo "CREATE DATABASE ${2} WITH TABLESPACE = pg_default;";
echo '\\c' "${2};";
cat "dump/pg-${2}-tables.sql";
} > temp && mv temp "dump/pg-${2}-tables.sql"; # Concat value of the echos to our dump file (Create database and connect to the created database)
echo "[!]Bash: UPDATE DUMP ${2} COMPLETED";
else
echo "[!]Bash: This command must give parameter. usage ${0} ${1} 'database_name'"
fi
;;
...
...
```
### db:dump:restore
This command will handle database restoration from a dump file
```bash
#!/bin/sh
case ${1} in
...
"db:dump:restore")
if test ! -z "${2}";then # Check second argument which will be used as `database_name`
psql -U postgres -a -f "dump/pg-${2}-tables.sql"; # Tell postgres to restore this dump file
echo "[!]Bash: RESTORE DUMP ${2} COMPLETED";
else
echo "[!]Make: This command must give parameter. usage ${0} ${1} 'database_name'"
fi
;;
...
```
### db:migrate
Handle flow sequelize migration command
```bash
#!/bin/sh
case ${1} in
...
"db:migrate")
if test ! -z "${2}";then
if [[ ! -e "dump/pg-${2}-tables.sql" ]]; then # Check dump file if not exist then create one
touch dump/pg-${2}-tables.sql
fi
if psql -lqt | cut -d \| -f 1 | grep ${2}; then # Check is database exist if not then create one
echo "[!]Bash: Database ${2} exists"
else
echo "[!]Bash: Database ${2} doesnt exist";
createdb -U postgres ${2}
echo "[!]Bash: Database ${2} created"
fi
sequelize-cli db:migrate --debug --url "postgres://postgres:postgres@localhost:5432/${2}" # Sequelize command to migrate migration files into the database
npm run db:dump:update ${2} # Update dump file from database
else
echo "[!]Bash: This command must give ENV parameter. usage: ${0} ${1} 'database_name'";
fi
;;
...
```
### db:migrate:undo
Handle flow sequelize undo migration command
```bash
#!/bin/sh
case ${1} in
...
"db:migrate:undo")
if test ! -z "${2}";then
sequelize-cli db:migrate:undo --debug --url "postgres://postgres:postgres@localhost:5432/${2}" # Sequelize undo migration
npm run db:dump:update ${2} # Update dump file from database
else
echo "[!]Bash: This command must give ENV parameter. usage: ${0} ${1} 'database_name'";
fi
;;
...
```
### db:migrate:undo:all
Handle flow sequelize undo migration command
```bash
#!/bin/sh
case ${1} in
...
"db:migrate:undo:all")
if test ! -z "${2}";then
sequelize-cli db:migrate:undo:all --debug --url "postgres://postgres:postgres@localhost:5432/${2}" # Sequelize undo all migration
npm run db:dump:update ${2} # Update dump file from database
else
echo "[!]Bash: This command must give ENV parameter. usage: ${0} ${1} 'database_name'";
fi
;;
...
```
## Final Touch
for the final touch we can store our bash script commands to `package.json`:
```json
{
...
"scripts": {
"db:migrate": "./make db:migrate",
"db:migrate:undo": "./make db:migrate:undo",
"db:migrate:undo:all": "./make db:migrate:undo:all",
"db:dump:update": "./make db:dump:update",
"db:dump:restore": "./make db:dump:restore"
},
...
}
```
Now we can use the commands using npm.
### Execute Commands
All settled up, let's migrate our `User` model we create earlier on installation section to a database named `test`, by execute:
```bash
npm run db:migrate test
```
Output:
1. Database
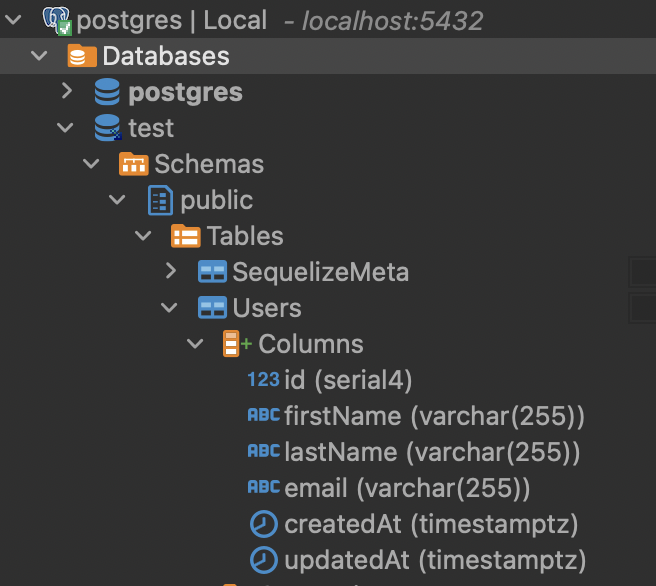
2. Shell Output
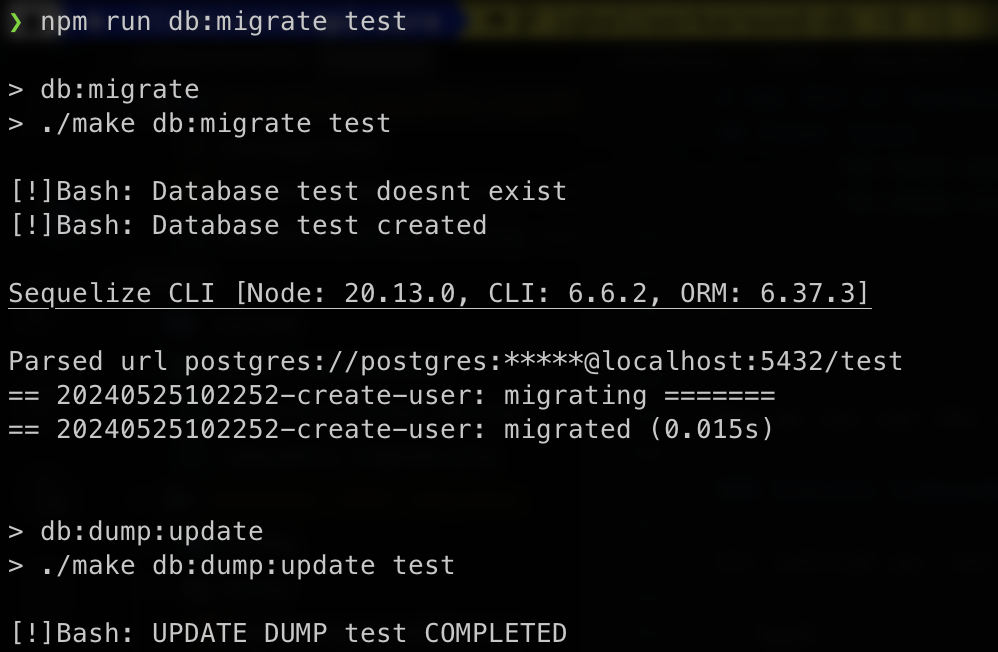
3. Dump file
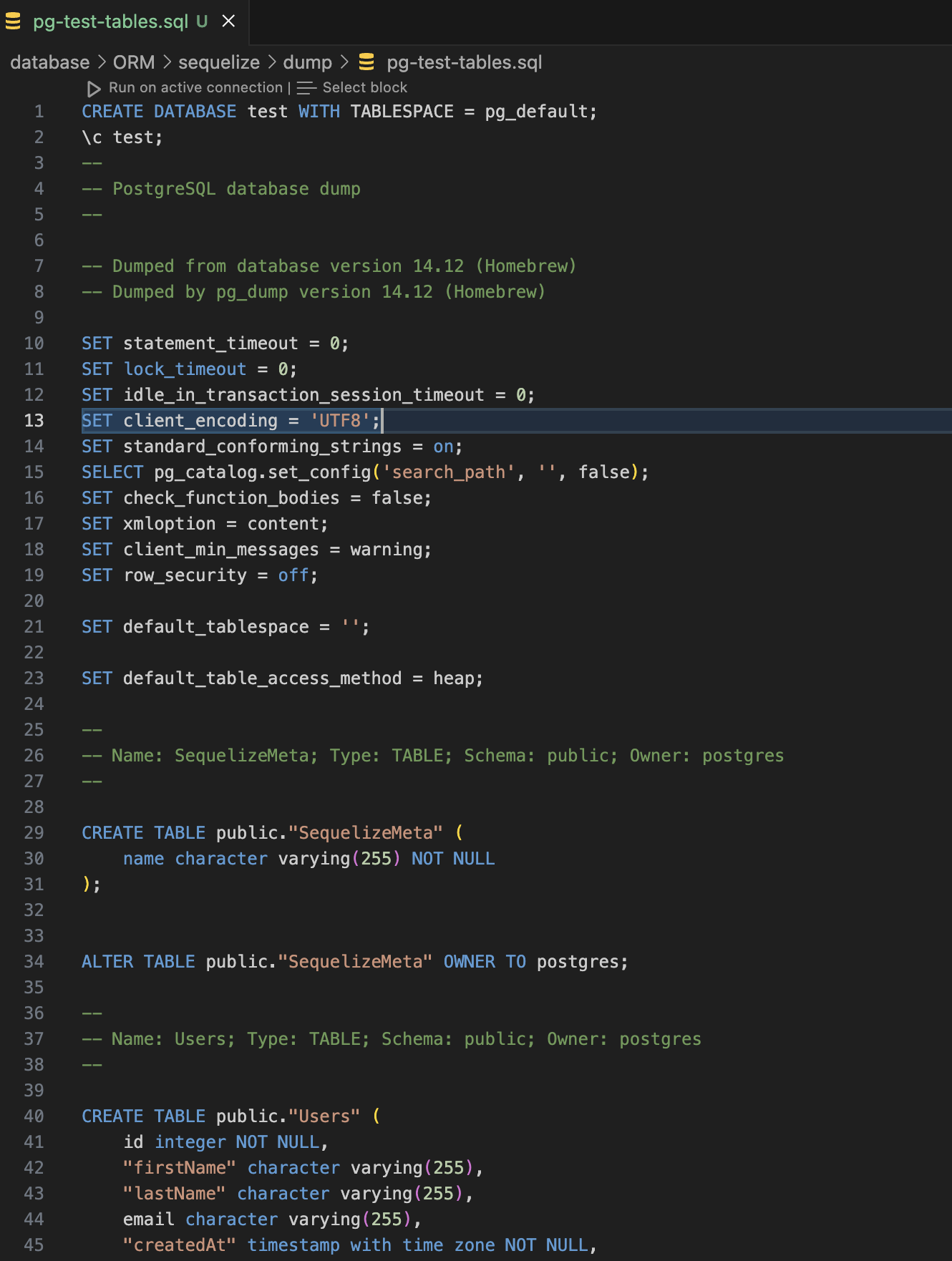
Every time you want to set a project with blank new database, you can restore the dump file, by execute:
```bash
npm run db:dump:restore test
```
Let's test the migration undo command, by execute:
```bash
npm run db:migrate:undo test
```
Output:
1. Database
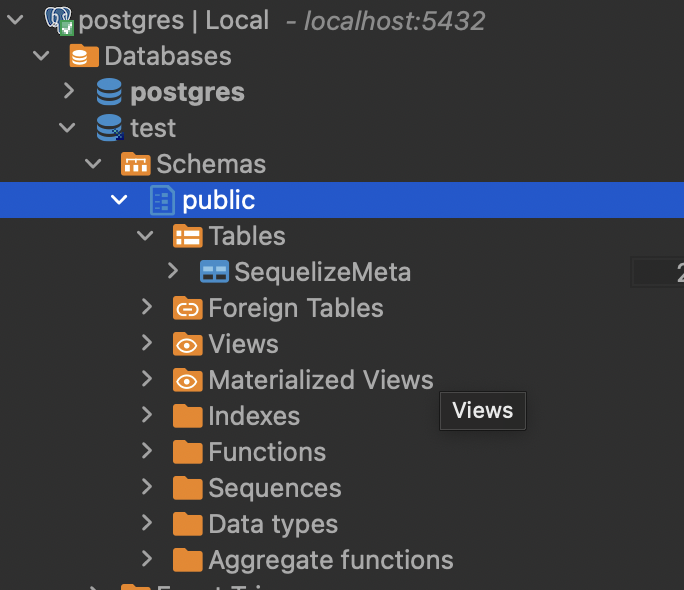
2. Shell Output
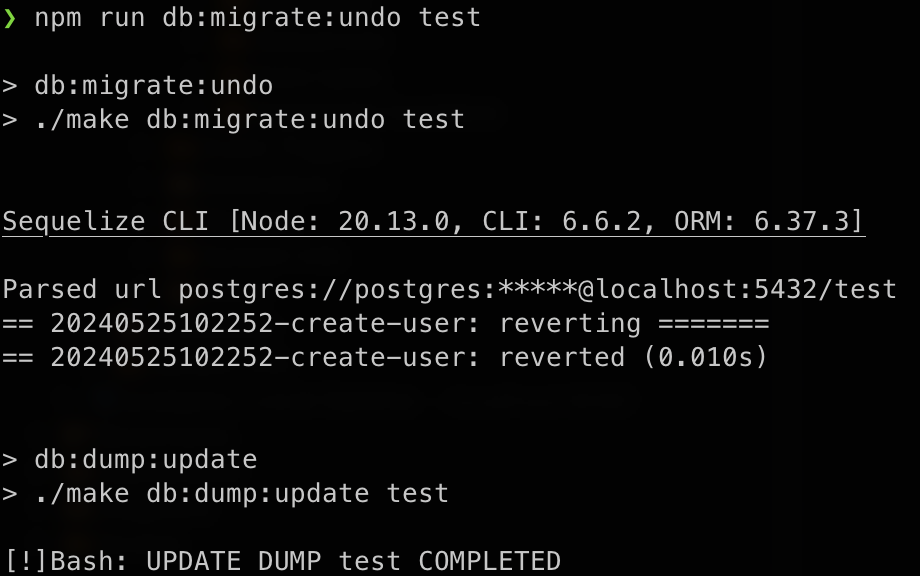
3. Dump file
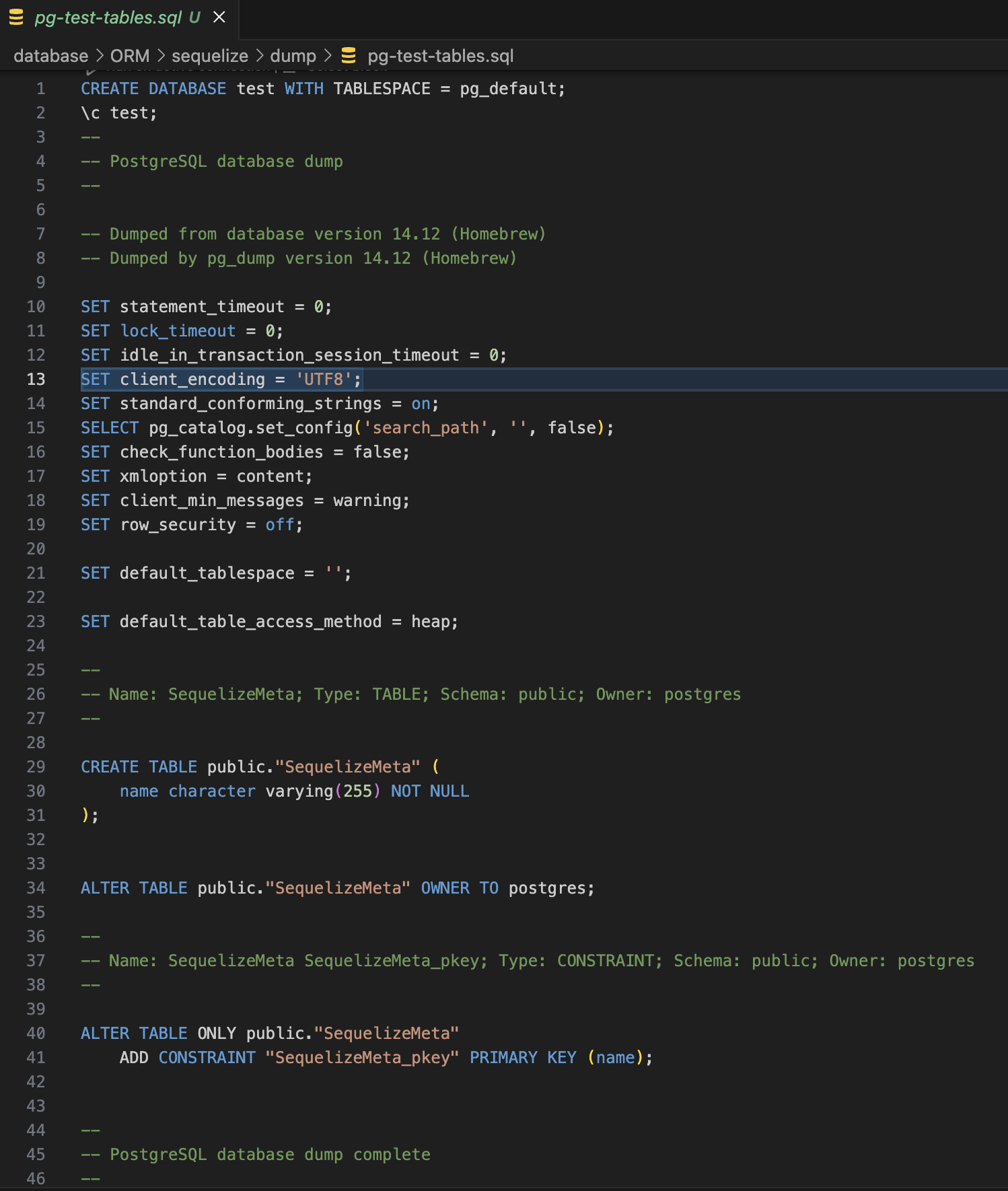
That's it, you can access full code [here](https://github.com/Rizky-Iqbal36/raw-blogs/blob/main/make), i hope this information helps you in some way. Lastly i want to know how your team handle this issue? please share your experience on the comment section. | rizkiiqbal36 |
1,871,571 | Database Design | Today we reverse engineered a database schema based on a target web application. | 0 | 2024-05-31T03:33:03 | https://dev.to/codexy/database-design-2l1f | Today we reverse engineered a database schema based on a target web application. | codexy | |
1,871,892 | Unlocking Business Success: Essential Strategies for Commercial Litigation Mastery | Arguments are inevitable in business operations. When discussions fail, a company may find itself... | 0 | 2024-05-31T10:20:06 | https://dev.to/keithmarion/unlocking-business-success-essential-strategies-for-commercial-litigation-mastery-50p9 | Arguments are inevitable in business operations. When discussions fail, a company may find itself involved in the complex world of [commercial litigation](https://brandsmiths.co.uk/expertise/commercial-litigation/). Successfully navigating this legal landscape requires a thorough understanding of both substantive and procedural legal principles. From obtaining evidence in the pre-trial stage to developing strong courtroom arguments and managing post-trial procedures, success hinges on meticulous attention to every detail. Ensuring that every action in this intricate environment brings resolution closer requires utmost precision and thoroughness.
**What is Commercial Litigation?**
Commercial litigation involves legal disputes arising within the business domain. These conflicts can stem from various sources, including breached contracts, disputes over intellectual property, shareholder disagreements, or conflicts between employers and employees. Unlike other legal arenas, commercial litigation primarily addresses issues between companies or businesses rather than individual parties. It serves as a critical avenue for resolving complex disputes and upholding the integrity of business transactions, ensuring fair outcomes for all involved entities within the corporate landscape.
**Navigating the Legal Landscape**
Navigating commercial litigation is akin to embarking on a well-planned expedition. Understanding the fundamental legal concepts underlying the dispute is as crucial as adhering to procedural rules. At every step, careful planning and flawless execution are essential to success. Every stage is critical, from meticulously compiling evidence before trial to developing compelling arguments in court. After the verdict, it is crucial to be prepared to face any legal challenges. Strategic planning and relentless attention to the case are vital for achieving a favorable outcome in this complex context.
**Key Considerations in Commercial Litigation**
Risk Assessment: Before embarking on the litigation journey, companies must conduct a thorough risk assessment to evaluate the potential costs, benefits, and risks associated with pursuing legal action. Understanding the strengths and weaknesses of the case is essential for making informed decisions.
**Alternative Dispute Resolution (ADR)**: In many cases, alternative dispute resolution methods such as mediation or arbitration offer a faster and more cost-effective means of resolving disputes compared to traditional litigation. Companies should explore ADR options as a potential alternative to litigation.
**Legal Representation**: Engaging competent and experienced legal representation is paramount in navigating the complexities of commercial litigation. Skilled litigators provide invaluable guidance, advocacy, and representation throughout the litigation process, maximizing the chances of a favorable outcome.
**Documentation and Evidence**: Comprehensive documentation and evidence play a pivotal role in the success of a commercial litigation case. Companies must gather and preserve relevant documents, communications, contracts, and other evidence to support their claims or defenses.
**Strategic Negotiation**: Effective negotiation skills are indispensable in commercial litigation. Companies should explore opportunities for settlement negotiations and strategic resolutions that align with their objectives and interests.
**The Importance of Diligent Case Management**
Effective case management is crucial for seamless navigation through commercial litigation. It includes essential duties like case evaluation, strategy development, record management, and courtroom representation for clients. By carefully monitoring these elements, good case management reduces wait times and boosts productivity. Ultimately, it significantly impacts the lawsuit's outcome, ensuring a favorable resolution.
**Conclusion**
Navigating the complexities of commercial litigation requires strategic planning and knowledgeable legal assistance. Understanding the nuances of this field is crucial, and Brandsmiths is prepared to offer expert guidance. With extensive experience, we enable businesses to confidently address conflicts while protecting their resources and reputations. Our expertise in managing the intricacies of business disputes ensures successful outcomes for our clients. With [Brandsmiths](https://brandsmiths.co.uk/) as your ally, you can tackle legal challenges head-on, knowing your interests are in skilled hands. Trust Brandsmiths to help you navigate the legal maze and achieve favorable resolutions.
| keithmarion | |
1,871,891 | [DAY 33-35] I Built A Statistics Calculator, A Spreadsheet, and Solved Leetcode Challenges | Hi everyone! Welcome back to another blog where I document the things I learned in web development. I... | 27,380 | 2024-05-31T10:19:32 | https://dev.to/thomascansino/day-33-35-i-built-a-statistics-calculator-a-spreadsheet-and-solved-leetcode-challenges-21pl | beginners, learning, javascript, webdev | Hi everyone! Welcome back to another blog where I document the things I learned in web development. I do this because it helps retain the information and concepts as it is some sort of an active recall.
On days 33-35, I built a statistics calculator, a spreadsheet, and solved 3 leetcode challenges which are:
1. Recyclable & Low Fat Products (Python)
2. Defanging An IP Address
3. Jewels And Stones
In these projects, I learned advanced array methods, functional programming, and some python concepts, as well as some of its syntax. Also, my skills in data structures & algorithms have improved because of the leetcode challenges I solved despite being rated as easy.
As I worked more on my skills, I’m getting the hang of some concepts like array manipulation methods, such as `map()`, `reduce()`, and `filter()`.
In the statistics calculator project, if a user inputs a set of numbers, the program will calculate it according to each statistical value and output the respective answers. I gained experience in handling user input, DOM manipulation, and method chaining. I also practiced my skills by performing statistical calculations like range, variance, and standard deviation in an array of integers.
In the spreadsheet project, it’s literally just an excel spreadsheet where the user can input values in rows and columns and give them formulas to function. Although, my program is limited to these functions only: `sum, average, median, even, someeven, everyeven, firsttwo, lasttwo, has2, increment, random, range, and nodupes`. I also added an empty string for edge cases. Edge cases are situations where the code behaves differently than expected.
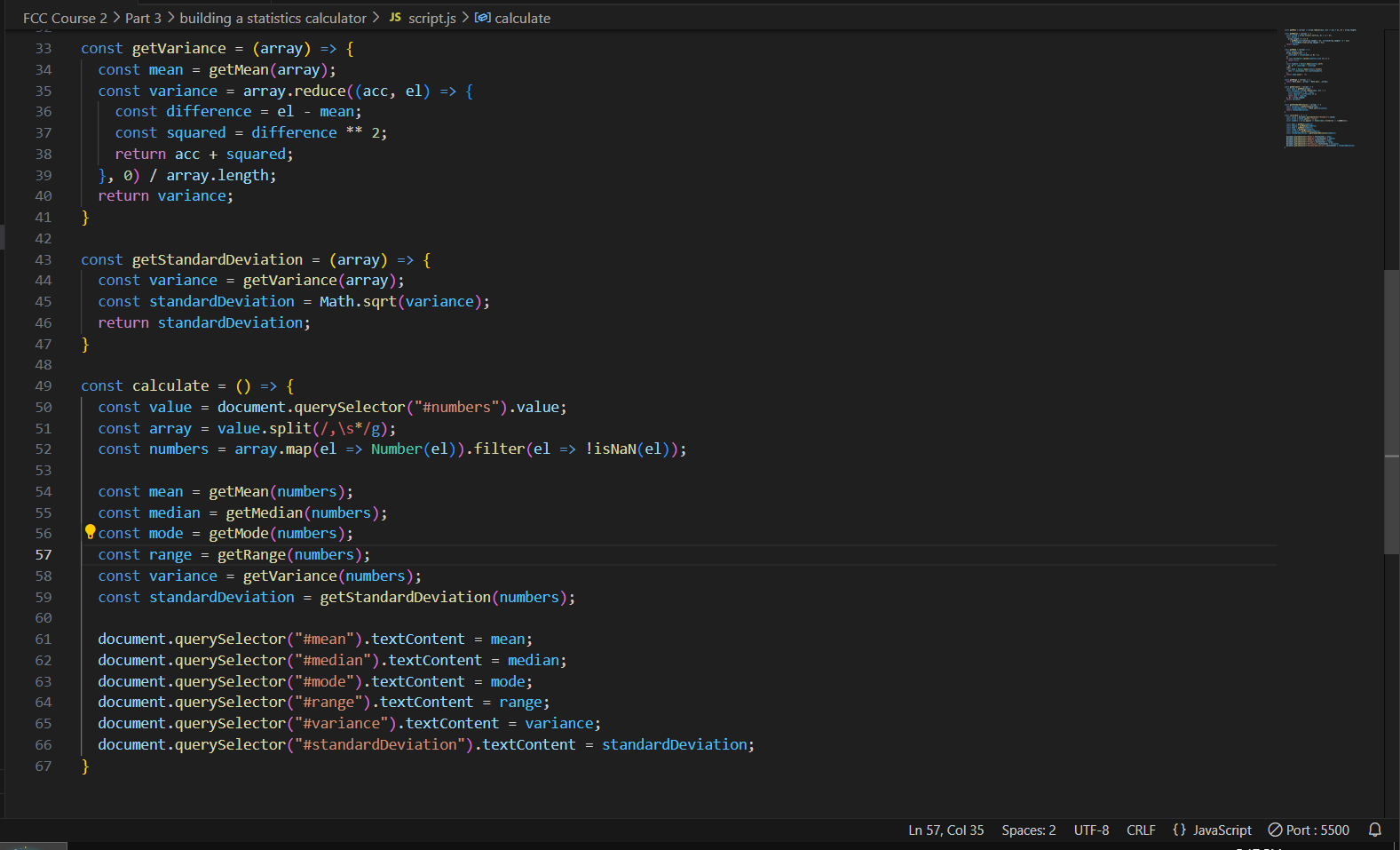
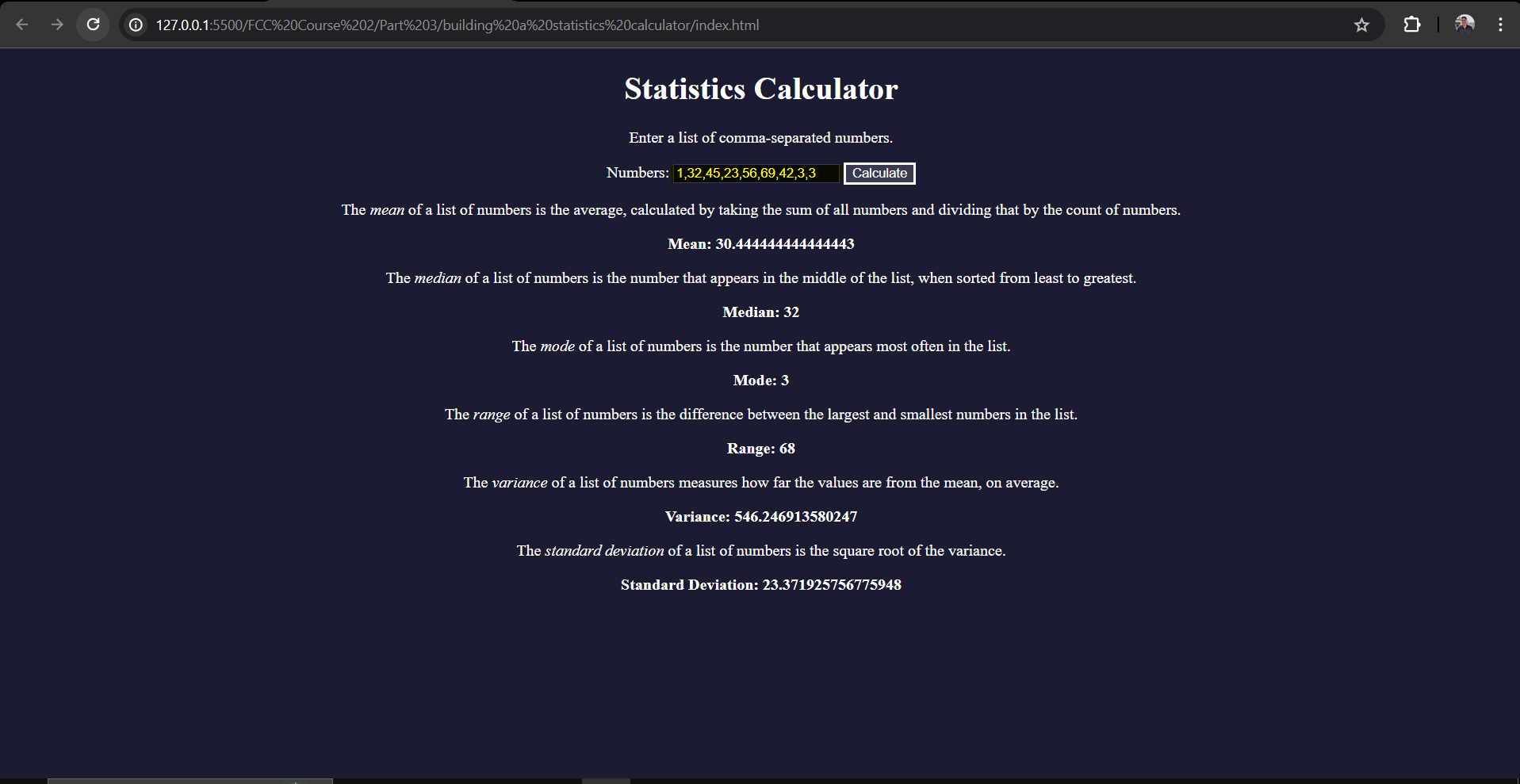
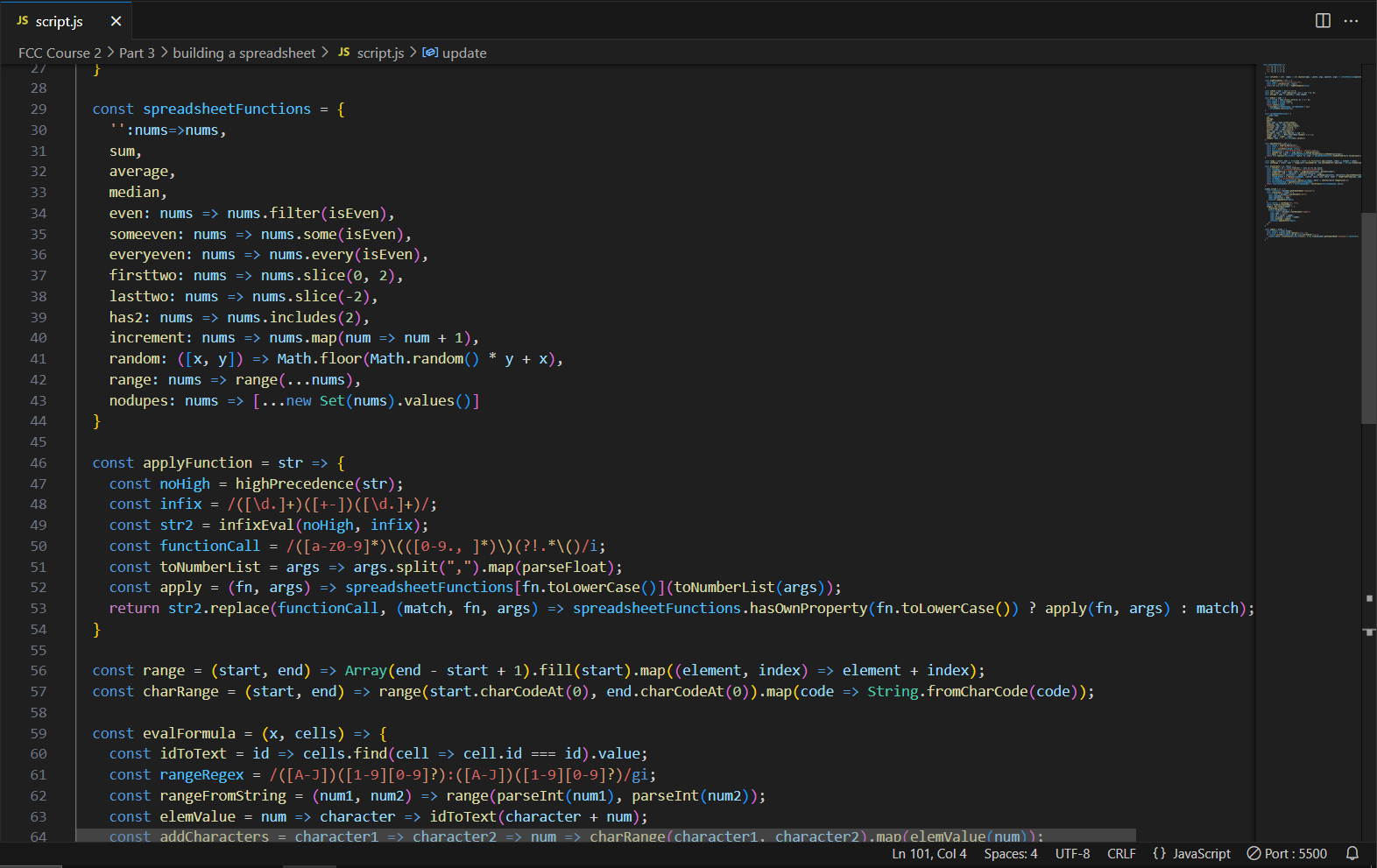
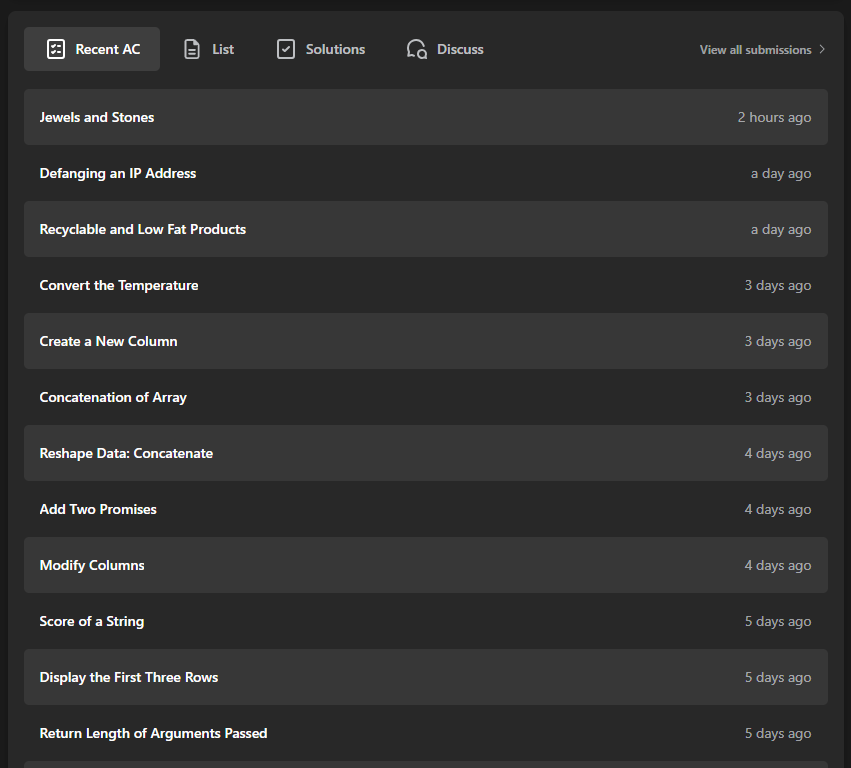
I also learned minor things like a string that can be treated as an array because each character can be accessed with an index.
Another one is currying a function where it takes multiple arguments into a series of functions that only take one argument each. Here’s an example, I declare a function _addCharacters:_ `const addCharacters = character1 => character2 => num => {};`
The _addCharacters_ function has a function which takes _character1_ parameter and an inner function which takes _character2_ parameter that returns an empty function which takes a _num_ parameter. This can be done **many** times within a function (as long as it makes sense lol).
I also learned to put an underscore prefix on an unused parameter, as well as convert string to a floating-point number (which is a decimal).
Furthermore, I finally grasped how to use regular expressions. It goes like this: `Inside square brackets [ ]: Characters are treated literally, and special characters outside square brackets don't need to be escaped using . Only special characters inside square brackets need to be escaped.`
`Outside square brackets: Use \ to escape special characters or to give them special meaning, especially within parentheses ( ).`
Lastly, it’s my first time working with a function in an object. Here’s its syntax: `const myObject = {object1, object2, object3, objectFunction : (param) => {},};`
Pretty cool, huh?
Anyways, that’s all for now, more updates in my next blog! See you there! | thomascansino |
1,871,890 | Enhancing Your Ranch with Ranch Rail Fencing | Introduction When it comes to securing your ranch while maintaining its rustic charm,... | 0 | 2024-05-31T10:19:16 | https://dev.to/owencannon42/enhancing-your-ranch-with-ranch-rail-fencing-31g7 |

### Introduction
When it comes to securing your ranch while maintaining its rustic charm, ranch fencing is an indispensable asset. Among the various options available, [ranch rail fencing](https://www.allamericanfencerepair.com/) stands out for its durability, versatility, and aesthetic appeal. Whether you're looking to corral livestock, demarcate property lines, or simply add a touch of Western elegance to your landscape, ranch rail fencing offers a timeless solution.
### The Charm of Ranch Rail Fencing
Ranch fencing has long been synonymous with the American frontier, evoking images of sprawling pastures and open skies. Ranch rail fencing captures this essence perfectly, with its simple yet sturdy design. Consisting of horizontal rails supported by vertical posts, this type of fencing is both functional and visually pleasing.
The classic split-rail style, often made from wood or vinyl, lends a rustic charm to any rural setting. Its open design allows for ample airflow and visibility, making it ideal for keeping livestock contained without obstructing scenic views. Additionally, ranch rail fencing can be customized to suit your specific needs, whether you prefer a traditional three-rail configuration or opt for additional rails for added security.
### Durability and Reliability
One of the key benefits of ranch fencing is its exceptional durability. Built to withstand the rigors of the outdoors, ranch rail fencing is resistant to rot, insect damage, and harsh weather conditions. This makes it an excellent long-term investment for ranch owners looking for a low-maintenance fencing solution.
Whether you're facing blazing summers, frigid winters, or torrential downpours, ranch rail fencing will stand strong year after year. With minimal upkeep required, you can spend less time worrying about repairs and more time enjoying your ranch.
### Versatility in Design and Functionality
Another advantage of ranch rail fencing is its versatility in both design and functionality. While the classic split-rail style remains popular, modern variations offer additional features such as wire mesh inserts or decorative post caps. This allows you to customize your fencing to match your aesthetic preferences while still reaping the practical benefits.
In terms of functionality, ranch rail fencing can be adapted to various purposes beyond livestock containment. Whether you're creating paddocks for horses, delineating boundaries for crops, or securing your property against wildlife, ranch rail fencing provides a flexible solution that can be tailored to meet your specific needs.
### Conclusion
In conclusion, ranch rail fencing is a versatile and durable option for enhancing your ranch's security and aesthetics. Combining the timeless charm of [ranch fencing](https://www.allamericanfencerepair.com/) with modern durability and functionality, it offers a perfect balance of form and function. Whether you're a seasoned rancher or a first-time landowner, investing in ranch rail fencing is a decision you won't regret. With its ability to withstand the elements, adapt to various applications, and complement any landscape, ranch rail fencing is sure to enhance the beauty and functionality of your property for years to come.
| owencannon42 | |
1,871,886 | Get a brief look at who are the Top Drupal Development Companies | There are many kinds of Content Management Systems (CMS) in the web development space that are... | 0 | 2024-05-31T10:16:34 | https://dev.to/akaksha/get-a-brief-look-at-who-are-the-top-drupal-development-companies-1bno | webdev, beginners, developer, development | There are many kinds of Content Management Systems (CMS) in the web development space that are competing for your attention. But Drupal has made a name for itself in a distinct market thanks to its extensive feature set and open-source nature. It gives companies the ability to create dynamic websites and applications that increase user engagement and help them succeed online.
It might be intimidating to navigate the complicated world of Drupal programming, though. Don't worry! Some of the top Drupal development firms are included in this list; these are the unsung heroes who take your idea and turn it into a successful web presence. We will examine the characteristics of a premier Drupal development firm and also the essential elements that set the exceptional apart from familiarity and skill to teamwork and communication.
That's why this guide will be your compass, regardless of how experienced you are with Drupal. We'll provide you with the skills you need to find and choose the best Drupal development partner to take your website from a blank canvas to a potent online asset that is precisely tailored to your needs and objectives.
the list of companies that have made their place reserved in the top Drupal Development Companies are: -
1. [Clarion Technologies](urlhttps://www.clariontech.com/blog/top-10-drupal-development-companies
)
2. Convertiv
3. Eleviant Tech
4. CODECLOUD
5. Kobe Digital
Drupal has demonstrated its ability to create extremely capable content management systems (CMS), and these ten best service providers in India are distinguished by their knowledge, tools, and adaptability to tackle a wide range of CMS issues. Starting your Drupal project with one of these businesses guarantees that you are headed toward successful website and mobile app development.
| akaksha |
1,871,887 | Get a brief look at who are the Top Drupal Development Companies | There are many kinds of Content Management Systems (CMS) in the web development space that are... | 0 | 2024-05-31T10:16:34 | https://dev.to/akaksha/get-a-brief-look-at-who-are-the-top-drupal-development-companies-5aa9 | webdev, beginners, developer, development | There are many kinds of Content Management Systems (CMS) in the web development space that are competing for your attention. But Drupal has made a name for itself in a distinct market thanks to its extensive feature set and open-source nature. It gives companies the ability to create dynamic websites and applications that increase user engagement and help them succeed online.
It might be intimidating to navigate the complicated world of Drupal programming, though. Don't worry! Some of the top Drupal development firms are included in this list; these are the unsung heroes who take your idea and turn it into a successful web presence. We will examine the characteristics of a premier Drupal development firm and also the essential elements that set the exceptional apart from familiarity and skill to teamwork and communication.
That's why this guide will be your compass, regardless of how experienced you are with Drupal. We'll provide you with the skills you need to find and choose the best Drupal development partner to take your website from a blank canvas to a potent online asset that is precisely tailored to your needs and objectives.
the list of companies that have made their place reserved in the top Drupal Development Companies are: -
1. [Clarion Technologies](urlhttps://www.clariontech.com/blog/top-10-drupal-development-companies
)
2. Convertiv
3. Eleviant Tech
4. CODECLOUD
5. Kobe Digital
Drupal has demonstrated its ability to create extremely capable content management systems (CMS), and these ten best service providers in India are distinguished by their knowledge, tools, and adaptability to tackle a wide range of CMS issues. Starting your Drupal project with one of these businesses guarantees that you are headed toward successful website and mobile app development.
| akaksha |
1,871,885 | Understanding SSL: Secure Sockets Layer | Secure Sockets Layer (SSL) is a standard security technology that establishes an encrypted link... | 0 | 2024-05-31T10:15:29 | https://dev.to/nuwan_weerasinhge_d93fd5b/understanding-ssl-secure-sockets-layer-4blh |
**Secure Sockets Layer (SSL)** is a standard security technology that establishes an encrypted link between a web server and a browser. This ensures that all data passed between the web server and browser remains private and integral. Despite being replaced by Transport Layer Security (TLS), SSL is foundational in the history of web security and understanding it is crucial for anyone involved in web development or cybersecurity.
#### The Origins of SSL
SSL was developed by Netscape Communications in the mid-1990s to secure data transmitted over the Internet. The primary motivation was to provide a secure means for transmitting sensitive information such as credit card numbers, login credentials, and personal data. SSL went through several iterations, with SSL 2.0 being released in 1995, followed by SSL 3.0 in 1996.
#### How SSL Works
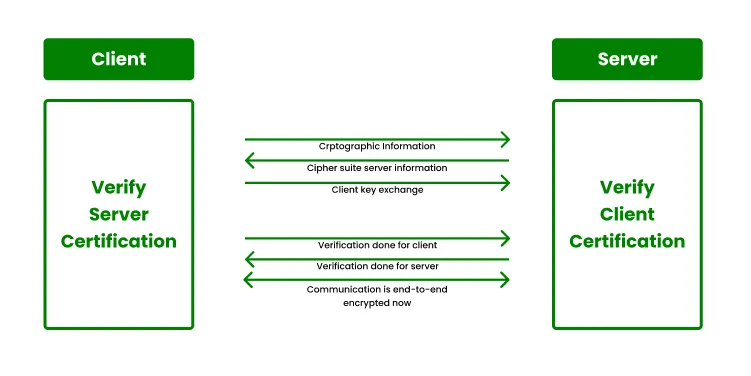
SSL operates through a combination of public key and symmetric key encryption. Here’s a step-by-step outline of how an SSL connection is established:
1. **Handshake Protocol**: The SSL handshake is the process where the server and client exchange information to establish a secure connection.
- **Client Hello**: The client sends a "hello" message to the server, which includes the SSL version, cipher settings, session-specific data, and other information.
- **Server Hello**: The server responds with its "hello" message, including its SSL version, cipher settings, and its digital certificate.
2. **Certificate Exchange**: The server sends its digital certificate to the client. This certificate includes the server’s public key and is signed by a trusted Certificate Authority (CA).
3. **Key Exchange**: The client verifies the server’s certificate against a list of trusted CAs. Once verified, the client generates a session key, encrypts it with the server’s public key, and sends it to the server. This session key is used for symmetric encryption during the session.
4. **Session Encryption**: Both the server and the client use the session key to encrypt and decrypt the data transmitted between them. Symmetric encryption is used here because it is faster than asymmetric encryption.
5. **Secure Communication**: From this point, all data transmitted between the client and server is encrypted using the session key, ensuring privacy and data integrity.
#### SSL Protocols and Versions
1. **SSL 1.0**: Never publicly released due to serious security flaws.
2. **SSL 2.0**: Released in 1995 but had multiple security vulnerabilities. Deprecated in 2011.
3. **SSL 3.0**: Released in 1996 with significant improvements over SSL 2.0. However, SSL 3.0 still had vulnerabilities and was officially deprecated in 2015 due to the POODLE (Padding Oracle On Downgraded Legacy Encryption) attack.
#### Security Vulnerabilities in SSL
Despite its pioneering role, SSL has several known vulnerabilities:
1. **Man-in-the-Middle Attacks**: SSL is susceptible to attacks where an attacker can intercept and potentially alter communication between the client and server.
2. **BEAST Attack**: Exploits a vulnerability in SSL 3.0 and TLS 1.0, allowing attackers to decrypt data.
3. **POODLE Attack**: Takes advantage of SSL 3.0’s vulnerability to padding oracle attacks, allowing attackers to decrypt secure HTTP cookies.
4. **RC4 Weaknesses**: The RC4 cipher, commonly used in SSL, has vulnerabilities that allow attackers to recover plaintext from a ciphertext.
#### Transition to TLS
To address SSL’s vulnerabilities, the Internet Engineering Task Force (IETF) developed TLS as a successor:
- **TLS 1.0**: Released in 1999 as an upgrade to SSL 3.0.
- **TLS 1.1**: Released in 2006, addressing further security concerns.
- **TLS 1.2**: Released in 2008, offering more robust security mechanisms.
- **TLS 1.3**: Released in 2018, with significant improvements in both security and performance.
#### Implementing SSL/TLS Today
While SSL is outdated, understanding its principles is crucial for implementing its successor, TLS. Here are steps to ensure secure SSL/TLS implementation:
1. **Use TLS Instead of SSL**: Always configure servers and clients to use the latest version of TLS (currently TLS 1.3).
2. **Strong Ciphers and Protocols**: Configure servers to use strong, modern ciphers and protocols. Disable weak ciphers and older protocol versions.
3. **Regular Updates**: Keep software and systems up-to-date with the latest security patches.
4. **Certificates Management**: Ensure proper management of SSL/TLS certificates, including timely renewals and using certificates from trusted CAs.
5. **Vulnerability Scanning**: Regularly scan for vulnerabilities and misconfigurations in your SSL/TLS implementations.
#### Mutual SSL Authentication
Mutual SSL (or two-way SSL) authentication is an extension of the SSL/TLS protocol where both the client and the server authenticate each other. This process ensures a higher level of security by requiring both parties to present digital certificates.
1. **Client Certificate Request**: During the SSL handshake, the server requests a certificate from the client in addition to sending its own certificate.
2. **Client Certificate Verification**: The client presents its certificate, which the server verifies against a trusted CA list.
3. **Mutual Trust Establishment**: If both certificates are valid, the server and client establish a mutual trust relationship, ensuring that both parties are authenticated.
4. **Enhanced Security**: Mutual SSL is particularly useful for sensitive applications such as financial transactions, enterprise environments, and secure API communications where both ends need to verify each other’s identity.
#### Benefits of Mutual SSL
1. **Increased Security**: By authenticating both parties, the risk of man-in-the-middle attacks is significantly reduced.
2. **Data Integrity and Confidentiality**: Ensures that data is encrypted and can only be decrypted by the intended recipient.
3. **Regulatory Compliance**: Helps organizations meet regulatory requirements for secure communications.
#### Implementing Mutual SSL
1. **Configure Server**: Set up the server to request and validate client certificates.
2. **Issue Client Certificates**: Use a trusted CA to issue certificates to clients.
3. **Client Configuration**: Configure clients to present their certificates when connecting to the server.
4. **Testing and Validation**: Thoroughly test the mutual SSL setup to ensure proper authentication and secure communication.
#### Conclusion
SSL played a pivotal role in the early development of web security, laying the groundwork for the more secure and efficient TLS protocol. Understanding SSL’s history, mechanics, and vulnerabilities is essential for anyone involved in web security. By transitioning to and properly implementing TLS, and considering advanced security measures like Mutual SSL, we can ensure secure, private, and integral data transmission over the internet. | nuwan_weerasinhge_d93fd5b | |
1,871,883 | AI as the key to a Secure Web3 future | Modern society lives in a world of advanced technologies and is inevitably influenced by them. The... | 0 | 2024-05-31T10:13:11 | https://dev.to/shevchukkk/ai-as-the-key-to-a-secure-web3-future-cb1 | web3, ai | Modern society lives in a world of advanced technologies and is inevitably influenced by them. The two driving forces behind the transformation of our usual processes are Web3 and AI. It is important to note that this innovative power lies not only in the availability of advanced gadgets, such as Apple Vision Pro augmented reality glasses, although they are also a good device, but deeper. In particular, in creating a more reliable financial infrastructure and solving complex problems related to space exploration or health.
Web3 internet technology is a next-generation solution based on machine learning, AI, and blockchain technology. The “father of Web3” is considered to be Gavin Wood, a British developer and [co-founder](https://fintechinsider.com.ua/spivzasnovnyk-ethereum-i-zasnovnyk-polkadot-gevin-vud-web3-bilshe-ne-tilky-pro-kryptovalyutu-ta-defi/) of Ethereum, who coined the term in 2014, well before it became mainstream in 2021. The advantage of the technology is the creation of intelligent websites and web applications with improved machine data understanding and a structure built on decentralization. Thus, working in decentralized networks increases security and transparency in finance, data management, social networks, and blockchain-based games. Web3 finds its direct application in crypto, implementing the basic principles of decentralization in the blockchain network.
## What are the risks?
However, there are risks that Web3, due to its novelty, may not be adapted to. These include technical failures in blockchain networks, data risks, social engineering attacks, and identification and anonymity problems. For example, the cryptocurrency exchange [Binance](What are the risks?
However, there are risks that Web3, due to its novelty, may not be adapted to. These include technical failures in blockchain networks, data risks, social engineering attacks, and identification and anonymity problems. For example, the cryptocurrency exchange Binance has been in a [long-standing](https://www.binance.com/en/square/post/4635237255865) legal battle with the Netherlands, Belgium, and France over the provision of illegal services.
The problem of technical failures can lie in damage to hardware, such as a server or hard drive. Network failures also occur when nodes do not have access to each other. Let’s look at the main security problems of Web3:) has been in a long-standing legal battle with the Netherlands, Belgium, and France over the provision of illegal services.
The problem of technical failures can lie in damage to hardware, such as a server or hard drive. Network failures also occur when nodes do not have access to each other. Let’s look at the main security problems of Web3:
**Data risks**
The wide network infrastructure requires transaction control. In the case of blockchain transactions, the emphasis is that no one can guarantee the status of participants, whether they are malicious, anonymous, or ordinary clients. It follows that without centralized control, no one will be responsible for transaction and data problems if they are damaged. For example, the DeFi protocols [Cream Finance](https://app.cream.finance/) and [PancakeSwap](https://pancakeswap.finance/) were attacked by [DNS](https://coinmarketcap.com/academy/article/phishing-attack-hits-two-major-defi-protocols-users-told-to-stay-away) spoofing, which compromised users’ crypto assets.
**Identification**
Web3 mechanisms called SSI (Self-Sovereign Identity) are aimed at a maximally confidential identification mechanism for each network participant and their data. Therefore, regulators cannot track whether users are financing terrorism or money laundering. The increased level of secrecy raises concerns about social norms, consumer protection, and accountability. However, this did not prevent Binance, one of the world’s largest cryptocurrency exchanges, from being a channel for laundering illegal money, according to a [REUTERS](https://coinmarketcap.com/academy/article/phishing-attack-hits-two-major-defi-protocols-users-told-to-stay-away) investigation.
**Engineering attacks**
Changing the logic of smart contracts, which involves unauthorized influence on the management of personal projects or crypto wallets. This creates a stir when scammers attract customers with phishing attacks, withdraw funds, and then disappear. It follows that modern Web3 companies benefit from focusing on artificial intelligence. This can be explained by improving productivity, efficiency, and personalization through several key factors:
**Secure Digital experience**
AI integration will allow companies to introduce personalized services for their users. This is done by implementing special AI algorithms that will adapt interaction, recommendations, and content on [Web3 platforms](https://www.solulab.com/top-web3-platforms/).
**AI-Based data analytics and Cybersecurity**
AI algorithms can detect potential threats and anomalies in real time. This means that transactions will become even more secure. In particular, this will be a great option for cryptocurrency exchanges and their clients. For example, for the most security ones crypto exchanges [OKX](https://www.okx.com/ua), [Coinbase](https://www.coinbase.com/), [WhiteBIT](https://whitebit.com/), and many others. As a result, it will be possible to obtain a holistic Web3 ecosystem. Web3 projects that are already using the potential of AI are gaining popularity. In particular, the decentralized prediction market Augur, which uses AI to make more accurate predictions by analyzing data from various sources. [Ocean Protocol](https://oceanprotocol.com/) is another Web3-based platform that uses AI to provide personalized solutions. The [Medibloc](https://medibloc.com/) program is focused on healthcare and uses AI for decentralized management of medical data, allowing patients to control their medical records.
**Conclusion**
Against the backdrop of the rapid development of digital technologies, the merger of AI and Web3 opens up a promising future that will transform many areas, from healthcare to supply chain optimization. This impact will only grow stronger, paving the way for new opportunities that will pose new challenges to society. Data security is crucial in today’s digital world, where breaches can expose sensitive information to millions. AI-powered solutions offer promising ways to combat this growing threat.
Governments, businesses, and researchers need to collaborate on developing AI tools for data protection. These solutions include biometric authentication, blockchain encryption, anomaly detection algorithms, and autoencoders for threat identification. The financial sector is particularly vulnerable, and AI can enhance cybersecurity for crypto assets. New encryption methods and Web3 authorization can increase trust among investors on cryptocurrency exchanges. As AI continues to evolve, it has the potential to revolutionize data security across various industries. | shevchukkk |
1,871,882 | Ambra | Ambra is a standout among italian restaurants in the west village, offering an exquisite dining... | 0 | 2024-05-31T10:12:42 | https://dev.to/valikoo24/ambra-12dk | Ambra is a standout among [italian restaurants in the west village](https://ambranyc.com/), offering an exquisite dining experience with its authentic dishes and inviting atmosphere. From freshly made pasta to rich and flavorful sauces, every meal is a testament to the culinary heritage of Italy. Check their website to explore the menu and plan your next visit.
| valikoo24 | |
1,871,881 | Are you looking for an assignment helper? | 📚 Our qualified experts are here to revolutionize the way you learn. Available 24/7 with on-time... | 0 | 2024-05-31T10:11:50 | https://dev.to/expert_content/are-you-looking-for-an-assignment-helper-pll | assignmenthelp, student, webdev, python |
📚 Our qualified experts are here to revolutionize the way you learn. Available 24/7 with on-time delivery and 100% plagiarism-free content.
Plus, enjoy exclusive discounts - **get 30% off** when you order another copy of the same assignment! Don't miss out,
Contact us now for more information:
📞 [+91-8766246157] :- https://t.ly/1Bmkn
📧 expertcontent1209@gmail.com
https://api.whatsapp.com/send?phone=918766246157 | expert_content |
1,871,880 | Rust and Go - good friends? | Writing software that runs on multiple operating systems and architectures is straightforward in both... | 0 | 2024-05-31T10:11:07 | https://dev.to/lapp1stan/rust-and-go-good-friends-4gbl | go, rust, programming, architecture | Writing software that runs on multiple operating systems and architectures is straightforward in both Go and Rust. With the principle of "write once, compile anywhere," developers can ensure broad compatibility. Additionally, both Go and Rust offer native support for cross-compilation, eliminating the necessity for "build farms" typically required by older compiled languages.
> For most companies and users, Go is the right default option. Its performance is strong, Go is easy to adopt, and Go’s highly modular nature makes it particularly good for situations where requirements are changing or evolving.
> As your product matures, and requirements stabilize, there may be opportunities to have large wins from marginal increases in performance. In these cases, using Rust to maximize performance may well be worth the initial investment.
It seems legit to me. Do you agree with that?
| lapp1stan |
1,871,879 | Best Practices for Using Canonical Tags to Boost Traffic | While discussing the ever-evolving search engine optimization technique, duplicate content might... | 0 | 2024-05-31T10:09:22 | https://dev.to/josbutler/best-practices-for-using-canonical-tags-to-boost-traffic-27pk | canonical, seo, marketing | While discussing the ever-evolving search engine optimization technique, duplicate content might cause problems in the rankings of websites on the search engine results page, SERPs. In the digital marketing, staying ahead of the competition requires an in-depth understanding of various tools and techniques.
Canonical tags are a key component in efficiently controlling website traffic. When used strategically, website owners and marketers can elevate their online visibility, improve their rankings on search engines, and drive more site visitors.
These tags serve as navigational signposts for search engine crawlers, guiding them to the most pertinent version of a webpage amidst similar or duplicated content. This ensures that the designated page receives the utmost attention from search engines, maximizing its chances of appearing prominently in search results. As a result, thoughtfully implementing canonical tags can significantly amplify website traffic, providing a necessary pathway for online success. By Integrating [Houston SEO services](https://www.yellowfindigital.com/houston-seo-company/), marketers and businesses can achieve a higher position in search rankings by avoiding duplicate content.
This article will provide all the necessary details regarding the best practices for canonical tags and explore how they can be leveraged to optimize website traffic.
## A Short Overview On Understanding of Canonical Tags
Canonical tags also referred to as rel="canonical", act as HTML markers used to show search engines the preferred version of a webpage when there are many similar versions of the same content. It is particularly important for websites dealing with identical or similar content spread across different web addresses, such as online stores offering different versions of products, content-sharing networks, or web addresses that change based on user interactions.
## The Importance of Canonicalization
Making sure search engines know which version of a page is most important is crucial for better ranking and visibility. If there are no canonical tags, search engines might need clarification about where the content originally came from. This confusion could weaken the ranking and make the page less visible in searches. By stating the main URL, website owners can bring together link juice and make sure the right page shows up in search results, getting more organic traffic. By integrating Seo Services Houston, businesses can decide between original and duplicate content through canonicalization to improve search rankings.
## Best Practices For Implementing The Canonical Tags
**Identify Duplicate Content**
Before putting canonical tags into action, conducting a comprehensive review of your website to pinpoint instances of repeated or similar content is crucial. Common sources of this issue include product pages with various parameters, paginated content, and articles syndicated across multiple platforms.
Use SEO auditing tools or perform a thorough website crawl to identify duplicate URLs that require canonicalization. This step ensures that search engines understand which version of the content is preferred, thereby avoiding potential penalties for duplicate content and helping improve your site's overall SEO performance.
**Select the Preferred URL**
Identifying the preferred URL among duplicates is crucial for ensuring search engines understand which version to prioritize. It helps maintain the integrity of your website's SEO efforts and prevents potential penalties for duplicate content. By selecting the most appropriate URL based on content quality, backlinks, and user engagement, you ensure that your site's preferred version receives the visibility it deserves in search engine results. By partnering with Houston SEO company, you can make the perfect URL for finding duplicate content from different websites through canonical tags and improve search rankings.
**Practically Implement Canonical Tags Correctly**
To implement the canonical tag effectively, it should be placed within the HTML <head> section of pages that are not the primary version, indicating the preferred canonical URL. The canonical tag follows a specific structure in HTML, denoted by the <link> element with the "canonical" attribute and the preferred URL specified in the "href" attribute. It's important to ensure that the canonical URL matches the preferred page's path, including the protocol (HTTP/HTTPS) and trailing slashes, to prevent potential errors in canonicalization.
By embedding the rel=canonical tag within the HTML <head> section of non-canonical pages, search engine crawlers are informed that the indicated URL represents the main version of the content. This practice helps streamline indexing and prevents duplicate content issues, enhancing the website's SEO performance. Following these steps accurately ensures that search engines prioritize the preferred version of the content, contributing to improved visibility and ranking in search results.
**Use Self-Referencing Canonicals**
If your website has pages with different content but various URL versions, like different ways of starting a web address (HTTP vs. HTTPS) or differences in whether it includes "www" at the beginning, using self-referencing canonical tags can be helpful. These tags point to the page's current URL, bringing together ranking signals and dealing with possible issues caused by duplicate content due to URL differences. By integrating Houston SEO services into an existing SEO strategy, businesses can improve their website's search rankings by differentiating URLs with duplicate content through self-referencing canonical tags.
**Handle Pagination Appropriately**
When handling paginated content, like category pages or collections of articles split across multiple pages, it's essential to use rel="next" and rel="prev" tags. These tags help indicate the order of the paginated pages, ensuring search engines understand the sequence. Moreover, it's crucial to include a canonical tag pointing to the initial page in the series. This approach consolidates ranking signals and prevents search engines from penalizing your site for having duplicate content across paginated pages.
**Cross-Domain Canonicalization**
By employing cross-domain canonicalization, you ensure that search engines recognize the primary version of the content across different domains or subdomains. This approach helps consolidate the ranking power of your content and mitigates the risk of penalties resulting from duplicate content issues. Ultimately, it strengthens your website's SEO strategy by streamlining content distribution and maximizing search engine visibility. After verifying duplicate content through cross-domain canonicalization, businesses can [unlock organic traffic and find the true power of technical SEO](https://yellowfindigitalhouston.hashnode.dev/unlocking-organic-traffic-the-power-of-technical-seo).
**Monitor and Update Regularly**
Routinely monitor changes, updates, and new content on your website to spot any potential problems with canonicalization. Keep checking canonical tags to ensure they're accurate and work well in guiding search engine bots to the preferred URL. This ongoing check helps your website stay in good shape in search engine rankings by fixing any problems quickly and ensuring search engines prioritize your content correctly.
## Get Expert Advice Regarding the Proper Use of Canonical Tags
Canonical tags are crucial for improving website traffic by efficiently handling duplicate content and indicating which version of web pages search engines should prioritize. Following the right methods for using canonical tags and using them strategically can bring substantial advantages for website owners and marketers, such as better rankings in search engines, improved user experience, and overall growth in website visitors.
Suppose you are running an online business and want to boost the website rankings by avoiding duplicate content through canonicalization. You can contact SEO company Houston, which will offer customizable solutions for your business requirements.
| josbutler |
1,871,878 | Step by Step Guide to Great Mobile App Performance Testing | Before going through the mobile application performance testing, you should know what is a mobile... | 0 | 2024-05-31T10:08:28 | https://dev.to/morrismoses149/step-by-step-guide-to-great-mobile-app-performance-testing-5a9c | mobileappperformancetesting, testgrid | Before going through the mobile application performance testing, you should know what is a mobile application?
Mobile application software is designed to run on mobile devices like smartphones and tablets.
Users get similar services that are accessed on PCs through mobile app software. Today technology is above everything, and mobile applications are being used widely compared to desktop applications.
Mobile application performance testing differs from web application performance testing.
For example, when you use laptops and desktops to access the web applications, you suffer little because of poor network quality, packet loss, or latency, whereas in terms of mobile applications, quality of the network, packet loss, device type, bandwidth, and latency, everything matters and cannot be neglected in mobile application performance testing.
The following are the different types of mobile applications:
Browser-based applications
Native applications
Hybrid applications
## What is Mobile App Performance Testing?
We live in the DevOps era, where quick development and deployment of software is the major aim of the software development process for any organization. Automation testing tools significantly help deploy the applications rapidly.
To measure the performance and capabilities of the application in a distinct environment, we execute mobile application testing.
The performance is measured based on parallel systems tests on different devices, tracking the performance and functioning, when the traffic load is high, etc. In simple words, mobile app performance testing is performed to provide a seamless user experience.
## Why is Mobile App Performance Testing necessary?
Load testing is crucial to check the functioning of any application. The testers increase the number of virtual users for a certain period to determine the exact load threshold of the application. It is also named endurance/volume testing.
Load testing clarifies the capacity of your system by handling the number of users at a time. It also determines the behavior of the application during traffic from different geo-locations. Load testing is essential to keep your application on-point and should be integrated continuously.
### 1. Automation testing with Appium JavaScript creates a strong test automation checklist
.
Automation testing is the essential component of any software development. In terms of mobile applications, it is imperative to check the user interface is seamless and easy to provide a favorable experience to its end users.
Here, Appium comes into the picture. Appium is an open-source and one of the most in-demand web-based automation testing tools available in the market that helps to integrate uninterrupted testing into development. It provides automation testing by verifying products across distinct combinations of browsers and OS.
With a single interface, Appium supports many programming languages, including JavaScript. JavaScript is an extensively used language for developing web and mobile applications.
Today, back-end developers prefer to use JavaScript than any other programming language because of its simplicity and flexibility.
People often get confused when we talk about Appium together. Appium is widely used for mobile testing and is a mobile test automation framework.
It supports local, hybrid, and mobile web applications. It uses Appium ’s WebDriver to interact with Android. Appium framework is a wrapper; it translates the commands of Appium WebDriver into UI Automator.
### 2. Appium JavaScript helps in creating a robust automation checklist
**Efficiency:**
It has increased testing efficiency with its well-structured, inbuilt patterns and functions. Those projects which were difficult to complete in months because of their complexities and countless lines of code can now be completed in no time through Appium JavaScript.
**Safety:**
Appium JavaScript has a huge community network reach, where the users also act like testers leading to a firm security arrangement.
To use the JavaScript framework in Appium, a plug-in needs to be installed to help you write the test cases in JavaScript and Node.js.
Read more: [The Importance of Mobile Testing
](https://testgrid.io/blog/the-importance-of-mobile-testing/)
## Parameters for Mobile App Performance Testing?
Mobile app performance testing is measured as per the below parameters:
### 1. Device Performance
- The application’s startup time is tracked along with the battery life while using the application.
- The amount of memory consumed
- The variation of software and hardware
- The usage with other applications
- An application is running in the background to check the glitches and other discrepancies.
### 2. Server/API Performance
- Here, the data to and from the server is analyzed
- It tests all the API calls
### 3. Network Performance
- Network speed like latency is studied
- Also checked if there was any packet loss
## The procedure of Mobile Application Performance Testing:
**I. Line-up test intent and business requirements**: It’s crucial to determine the business objective before executing the performance testing of the application. When the objectives are clear, it becomes easy to land the application at its desired position. Later, the testers work on priority to assess the application’s functions.
**II. Recognize test Key Performance Indicators:** Setting a benchmark is the second crucial step that shows whether your testing was successful or a failure. For mobile application performance testing, below are the KPIs that must be considered:
- Rate of error
- Highest response time
- Average response time
- Maximum number of requests
- The highest and average number of existing active users per device and operating system
- Outlined scenarios: Mostly, the testers fail because they do not prioritize the test cases and do not pre-select the major areas to evaluate the application’s performance. To avoid, outline various packet scenarios that are essential for the application’s best and most reliable performance.
III. Imitate a live testing environment: To understand the application’s user experience, a live testing environment is necessary. Hence, system emulators are used, which emulate the operating system’s essential frameworks, giving a similar display and feel of the interface to the testers.
IV. Line up the testing viewpoint with the comprehensive development procedure: Testing needs to align with an organization’s overall development structure. Continuous integration functions are a must-have to monitor the regular bug reports and regression tests allowing efficient communication, fast decision making, and cooperation of all the parties involved.
V. Lags, latency, and bandwidth of the network to be tracked: Mobile devices are connected to the internet via third-party carriers; the latency and bandwidth of the network vary from time to time and device to device. Hence, considering the network variances on top is critical while optimizing the application’s performance and improving the flawless user experience.
Read also: [Mobile Cloud Testing](https://testgrid.io/blog/mobile-cloud-testing/)
## Limitations of Mobile App Performance Testing:
Mobile application performance testing is more challenging than PC software testing because of its wide variety of devices, vast users, and different device-specific features.
Here’s a list of the primary issues that arise during mobile application performance testing:
**Device Variation:**
In the market, you see distinct versions of devices, which create many issues as the application should perform efficiently on all of these devices. To complete the testing, gathering phones and appliances from many users gets burdensome sometimes because of limited access to mobile devices.
**Various Device Features:**
It is strenuous to emulate all the features of the various mobile devices through online tools. The features of a phone are not similar for all; the GPS, camera, microphone, embedded memory, operating system, processor, sensors, etc., vary from one phone to another. This creates immense complexities, and hence, understanding that the results of the performance tests are optimum gets a little costlier and time-consuming.
**High Battery Usage:**
Battery usage testing is also included in mobile app testing. It has become a major challenge in recent years due to an increase in battery-draining apps. It is critical to mitigate battery drain in order to provide an excellent user experience.
**Multiple UI Variations:**
The page layouts and the systems’ font differ because of the operating system. The publishing process of the application can take more time than usual or can even stop if the google play market or App store guidelines are not followed or compliant.
## How to improve the quality of the mobile apps, final thoughts?
Every day the world is transforming bit by bit digitally; plenty of mobile applications are available on the app stores. There are over hundreds of applications available for a single user requirement.
The users effortlessly switch from one application to another due to its easy-to-use feature. However, a quality mobile app is not an easy thing to build. Regular mobile application performance testing is necessary to ensure the mobile application is efficient and delivers the expected results.
Looking at its complexities, it is not everybody’s job; professionals must handle it. The major challenge of mobile app testing is the variety of devices and their features.
Matching the combination of these varieties on real devices is a costly deal. Using virtual resources, services, and platforms such as emulators and simulators can reduce the costs because it has minimal infrastructure and setup costs.
Hence, the mobile application developers must spend adequate time marketing the application and provide an excellent user experience.
When the applications are developed frequently in short release cycles, the time to market the app reduces, and thus, the user experience highlights the overall quality of the application.
However, short cycles of release allow less time to measure and test the application’s performance, which may lead to a high defect leakage.
This blog is originally published at [TestGrid](https://testgrid.io/blog/mobile-app-performance-testing/) | morrismoses149 |
1,871,877 | Monitoramento e visualização de métricas com Docker Compose, Prometheus e Grafana. | Introdução: Prometheus e Grafana são duas ferramentas utilizadas no monitoramento e visualização... | 0 | 2024-05-31T10:07:57 | https://dev.to/thiagoemidiocorrea/monitoramento-e-visualizacao-de-metricas-com-docker-compose-prometheus-e-grafana-2b3k |

**Introdução:**
Prometheus e Grafana são duas ferramentas utilizadas no monitoramento e visualização de métricas de aplicações, porem têm propósitos e funcionalidades diferentes. Durante este tutorial, vamos ver quais a diferenças e como utilizadas.
**Prometheus:**
O Prometheus é uma ferramenta de monitoramento e sistema de alerta. Ele é projetado para coletar e armazenar métricas de sistemas e aplicações.
O Prometheus possui um sistema de alertas embutido, onde você pode definir regras de alerta que serão analisadas, e se uma condição for atendida, o Prometheus enviará alertas para várias integrações, como e-mail, Slack por exemplo.
**Grafana:**
O Grafana é uma plataforma de visualização de métricas. Ele é usado para criar dashboards interativos e gráficos a partir de várias fontes de dados como o Prometheus, InfluxDB, Graphite, Elasticsearch.
Para começar a monitorar uma aplicação Spring Boot com Prometheus e Grafana, vamos configurar um ambiente usando Docker Compose. Primeiro, precisamos criar um arquivo _docker-compose.yml_ com os serviços do Prometheus e Grafana.
```
prometheus:
image: prom/prometheus:latest
container_name: prometheus
volumes:
- "./src/main/resources/prometheus.yml:/etc/prometheus/prometheus.yml"
command:
- "--config.file=/etc/prometheus/prometheus.yml"
ports:
- "9090:9090"
grafana:
image: grafana/grafana:9.5.15
container_name: grafana
restart: unless-stopped
ports:
- "3000:3000"
environment:
- GF_SECURITY_ADMIN_USER=admin
- GF_SECURITY_ADMIN_PASSWORD=admin
- GF_USERS_ALLOW_SIGN_UP=false
volumes:
- ./grafana/provisioning:/etc/grafana/provisioning
depends_on:
- prometheus
healthcheck:
test: [ "CMD", "nc", "-z", "localhost", "3000" ]
```
Vamos, precisar também configurar o arquivo prometheus.ym do Prometheus, ele e o responsável por coletar o onde configuramos os alvos de scraping, ou seja, os endpoints que o Prometheus irá coletar métricas.
Para o Grafana, precisamos configurar um painel para visualizar as métricas coletadas pelo Prometheus.
```
# my global config
global:
scrape_interval: 15s # Set the scrape interval to every 15 seconds. Default is every 1 minute.
evaluation_interval: 15s # Evaluate rules every 15 seconds. The default is every 1 minute.
# scrape_timeout is set to the global default (10s).
# A scrape configuration containing exactly one endpoint to scrape:
# Here it's Prometheus itself.
scrape_configs:
# The job name is added as a label `job=<job_name>` to any timeseries scraped from this config.
- job_name: 'prometheus'
# metrics_path defaults to '/metrics'
# scheme defaults to 'http'.
static_configs:
- targets: ['127.0.0.1:9090']
- job_name: 'spring-boot-actuator'
scrape_interval: 5s # Define a frequência com que o Prometheus deve coletar métricas
metrics_path: '/actuator/prometheus' # O caminho onde as métricas do Micrometer são expostas
static_configs:
- targets: ['host.docker.internal:8080'] # O endpoint da sua aplicação Spring Boot
labels:
application: book-api
- job_name: 'grafana'
metrics_path: '/'
scrape_interval: 5s
static_configs:
- targets: ['127.0.0.1:3000']
```
OBS: Na minha tag targets, eu configurei o host da minha aplicação desta da seguinte forma host.docker.internal, isso por que minha aplicação esta rodando em um container docker.
Vamos configurar o _application.yml_ da nossa aplicação.
```
management:
endpoints:
web:
base-path: /actuator
exposure:
include: "*"
endpoint:
prometheus:
enabled: true
metrics:
enabled: true
```
Vamos também adicionar duas dependências no nosso POM.xml.
A dependencia do actuator e a dependencia do prometheus.
A dependência _spring-boot-starter-actuator_ é uma dependência que fornece recursos de monitoramento e gerenciamento.
A dependência _micrometer-registry-prometheus_ é utilizada para integrar o Spring Boot Actuator com o Micrometer e o Prometheus.
```
<dependency>
<groupId>org.springframework.boot</groupId>
<artifactId>spring-boot-starter-actuator</artifactId>
</dependency>
<dependency>
<groupId>io.micrometer</groupId>
<artifactId>micrometer-registry-prometheus</artifactId>
</dependency>
```
Feito isso vamos executar o comando docker-compose up -d e veremos os containers iniciados.
Acessando a url do Prometheus http://localhost:9090, podemos ver que os serviços estão com o status “UP”, ou seja, estão saudáveis e funcionando.
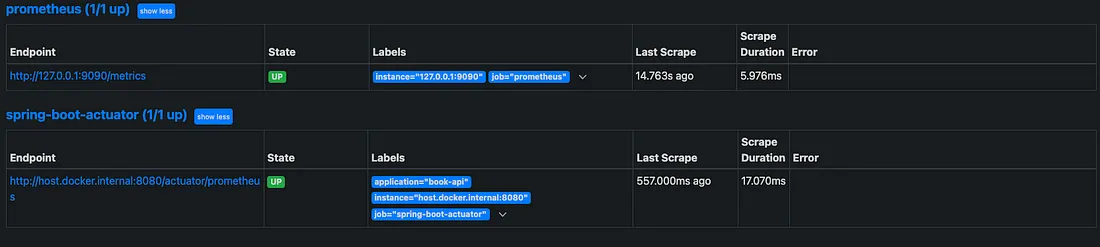
Agora, vamos configurar os gráficos de monitoramento do Grafana. Acesse a url http://localhost:3000/connections/connect-data, e pesquise por Prometheus
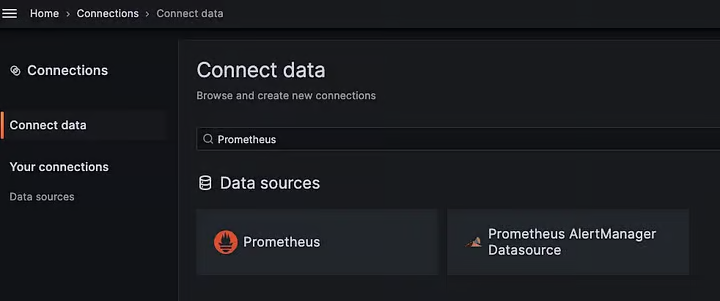
Clique na opção “Create a Prometheus data source”, preencha o campo URL com a url do Prometheus, no caso como meu Prometheus esta em um container Docker precisamos pegar o IP do nosso container.
Execute o seguinte comando docker inspect <id_do_container>
Na seção Networks > IPAddress: “192.168.240.3”, feito isso adicione do campo URL e clique em salvar.
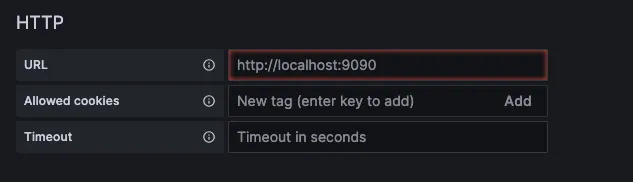
Agora vamos configurar os gráficos de monitoramento do Grafana.
Acesse a url http://localhost:3000/dashboards
Acesse a opção New > Import e adicione a url http://grafana.com/grafana/dashboards/4701, essa URL e um gráfico disponibilizado no próprio site do Grafana, mas você pode escolher outros tipos de gráfico conforme a sua necessidade. Feito isso clique em load.
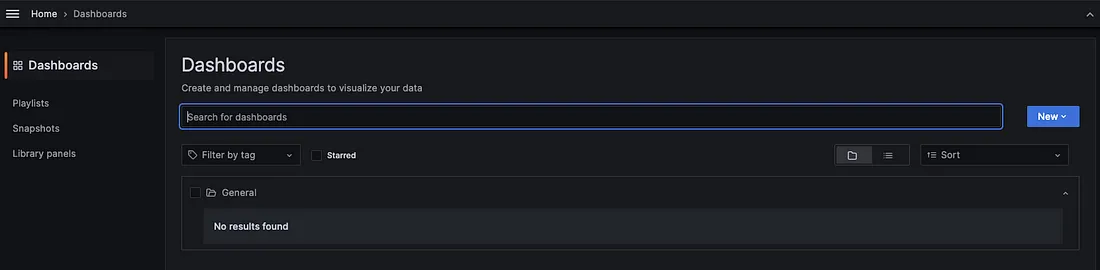
Depois disso, selecione Prometheus no campo de datasource e clique em Import.
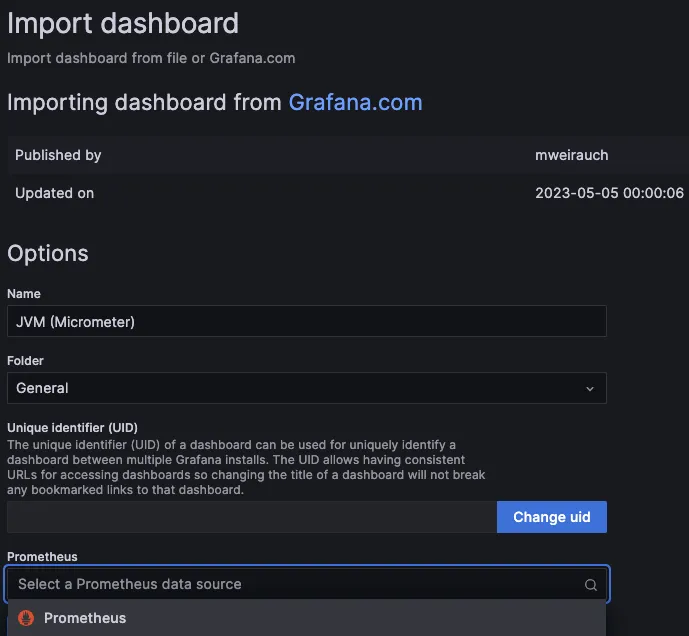
Em seguida, podemos ver o gráfico com os dados do coletados pelo nosso Prometheus. Lindo não é mesmo ?
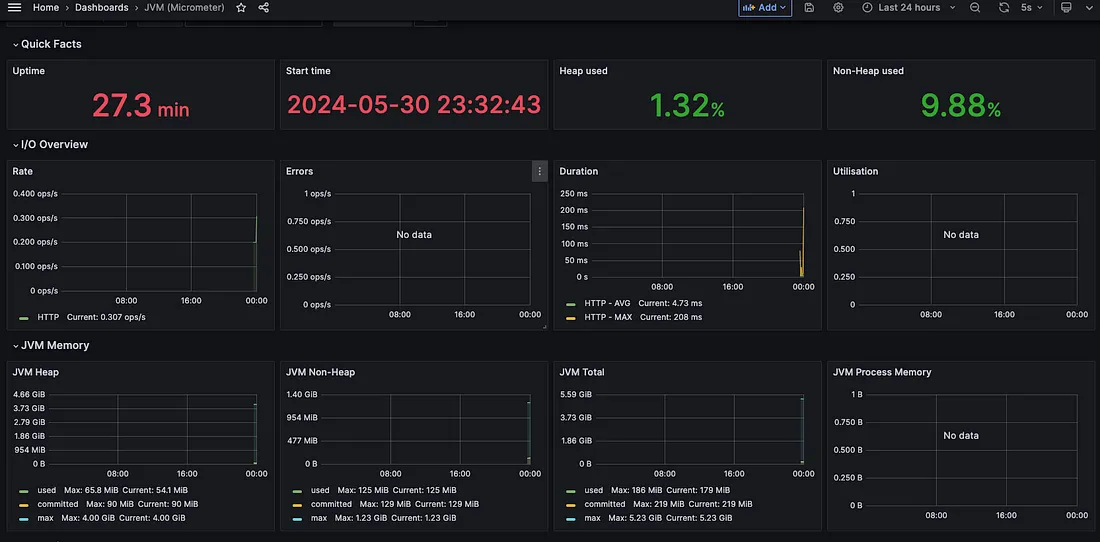
**Conclusão:**
O monitoramento de uma aplicação é uma maneira de garantir que sua aplicação esteja funcionando de forma confiável e eficiente. Ao coletar e visualizar métricas importantes, você pode identificar problemas de desempenho, capacidade e disponibilidade antes que eles afetem os usuários finais. Estas ferramentas oferecem uma solução poderosa e flexível para monitorar e manter a saúde de suas aplicações em produção.
| thiagoemidiocorrea | |
1,871,876 | Can ChatGPT-4o Code Like a Pro? Putting it to the ReactJs Test | The world of web development is constantly evolving, and with the emergence of powerful AI tools like... | 0 | 2024-05-31T10:04:45 | https://dev.to/dev007777/can-chatgpt-4o-code-like-a-pro-putting-it-to-the-reactjs-test-3jmm | webdev, javascript, react, beginners | The world of web development is constantly evolving, and with the emergence of powerful AI tools like ChatGPT-4o, the question arises: can these tools revolutionize the way we code? In my latest YouTube video, I put ChatGPT-4o to the ultimate test
{% embed https://youtu.be/h5Zr15ei-nk?si=v_fRCX3lHorioe1W %}
I explored its capabilities in various coding challenges, from scratch project creation to external API integration and delves into various coding challenges, pushing ChatGPT-4o to its limits:
1. Design to ReactJs Code: Can it translate design mockups into functional React components?
2. External API Coding: How does it handle integrating with external APIs and utilizing their documentation?
3. Performant Search in Large Datasets: Can it implement efficient search functionalities within a large dataset?
4. Dynamic ReactJs Form Component: Does it have the ability to generate a dynamic form component that adapts to user input?
5. Integration Testing for React Components: Can it write integration tests for React components, ensuring code quality?
watch the full video and witness the magic unfold! Don't forget to leave a comment and share your thoughts on how AI is shaping the future of web development
| dev007777 |
1,871,875 | Unlock Your Software Potential with Codehunts | In today's digital landscape, software fuels business success, but crafting top-notch solutions... | 0 | 2024-05-31T10:04:24 | https://dev.to/hmzi67/unlock-your-software-potential-with-codehunts-l20 | webdev, javascript, programming, react | In today's digital landscape, software fuels business success, but crafting top-notch solutions demands expertise and innovation. Enter Codehunts – your premier partner in software development.
## Our Offerings:
- Custom Solutions: Tailored software that fits your unique needs.
- Web Mastery: Responsive, user-friendly web applications.
- Mobile Magic: Native and cross-platform apps for wider reach.
- Support Excellence: Ongoing maintenance for optimal performance.
## Our Approach:
- Collaborative: We work hand-in-hand with you, ensuring transparency and timely delivery.
- Expert Team: Skilled developers, designers, and managers committed to innovation.
- Quality Focus: Reliable, secure, and scalable solutions using cutting-edge tech.
## Why Choose Us?
- Proven Success: Track record of delivering excellence across industries.
- Expertise: Extensive knowledge and experience driving every project.
- Agile Approach: Collaborative, client-centric development process.
- Quality Assurance: High standards ensure solutions meet your needs.
- Competitive Pricing: Flexible models to match your budget.
## Ready to Begin?
Reach out to Codehunts today and let's transform your software vision into reality.
Visit [Code Hunts](https://codehuntspk.com/) to learn more.
Schedule a consultation now and let Codehunts elevate your software game. | hmzi67 |
1,871,873 | Can AI bridge the gap between DAO complexity and user understanding? | Interest in AI has grown significantly in the past few years. Its applications are known to be vast,... | 0 | 2024-05-31T10:02:15 | https://dev.to/shevchukkk/can-ai-bridge-the-gap-between-dao-complexity-and-user-understanding-1ii | defi, ai, innovation | Interest in AI has grown significantly in the past few years. Its applications are known to be vast, ranging from education to technical recommendations for developers. For example, a selection of the datacamp platform [showed](https://www.datacamp.com/blog/unique-ways-to-use-ai-in-data-analytics) its applications in data analytics. It seems that this 20th-century breakthrough has the potential to change every aspect of our lives and influence its course. However, the question arises: will it really be beneficial?
Artificial intelligence is closely related to autonomy, as its algorithms can link and identify information from different databases without the direct involvement of a specialist. This can be explained by its development and structure, which analyzes cognitive processes and, as a result of research, develops intelligent software and systems that can provide a wide range of diverse services. Therefore, when DAOs (Decentralized Autonomous Organizations) appeared, it became clear that a [synergy](https://www.datacamp.com/blog/unique-ways-to-use-ai-in-data-analytics) could arise between AI and DAO. This issue was raised as early as 2016, when many examples of DAO and AI interaction were given, such as the ability to personalize the experience, improve fraud detection, and increase transparency and security.
## What is a DAO?
To elaborate, a DAO is a digital organization that operates on a blockchain and uses smart contracts to govern rules and decision-making processes. These are groups that are formed to manage Stablecoins, tokens with a fixed rate. Another purpose of such organizations is to invest in startups or buy NFTs. Such organizations are promising for decentralized cryptocurrency exchanges, investment funds, social networks, and blockchain-based games. Therefore, there are many examples of DAOs, including [Uniswap (UNI)](https://uniswap.org/ecosystem) — a decentralized exchange that generates automated markets for pairs of liquid assets. [BitDAO (BIT)](https://docs.bitdao.io/) is a community that provides development support, as well as liquidity and funding for launching projects in NFT, DeFi, DAO, and online games. The [Mango DAO (MNGO)](https://dao.mango.markets/dao/MNGO) organization is engaged in lending and margin trading, based on the Solana blockchain using the Serum exchange. The potential benefits of integrating AI and DAO include:
**AI bots for DAO functionality.**
This connection will be useful in the case of asset trading, summarizing management decisions, and attracting new customers;
**Integration of AI into the product or service offered by DAO.**
Such synthesis will provide management of crypto assets, as shown by the experience of the decentralized portfolio management protocol SingularityDAO;
**Delegation of own tokens to an AI agent.** This means that instead of an investor manually signing a transaction using an e-wallet, they will be able to delegate their tokens to an artificial intelligence agent to vote on their behalf. This option is offered by [TRUST AI.](https://www.trust-ai.io/#tokenomics) However, of course, DAO should be further developed to ensure customer confidentiality;
**AI and smart contracts**
DAO allows you to install a plugin that will allow AI to participate in transactions. However, if the address for sending funds does not match the address specified in the proposal, then such an action will be marked as malicious. This will primarily ensure the safety of the storage and use of funds. Another potential application option is offered by the company [EncrypGen](https://encrypgen.com/), which uses AI smart contracts to transfer patient DNA data for further clinical trials.
The risks of DAO are that it is difficult for members of such organizations to understand what others are doing, and for token owners to understand the specifics of DAO. This is what causes the need for artificial intelligence as a kind of assistant that will coordinate actions for quality work. However, the modern crypto industry is moving forward and is starting to actively implement AI services for its products. For example, the [WhiteBIT](https://whitebit.com/ua) exchange began to combine blockchain and AI, and several crypto projects joined it. The Edain project provides AI-based big data analytics services, and the NOOFT token will promote NFT on the platform. CEO of the exchange Volodymyr Nosov said in one of the interviews: “Artificial intelligence brings drastic changes in society. And this is something we have to come to terms with and adapt to as soon as possible. We cannot stop this process. So, it’s time to tighten up a little, think about the consequences and start taking action”.
Some blockchain projects include [Render Network](https://rendernetwork.com/), a blockchain platform for peer-to-peer sharing of AI-generated graphics, and [Fetch.AI](https://fetch.ai/), a platform for creating apps, according to [Reuters research](https://www.reuters.com/technology/cryptoverse-ai-tokens-outpace-record-breaking-bitcoin-2024-03-19/#:~:text=Some%20of%20the%20top%20blockchain,SingularityNET%2C%20an%20AI%20services%20marketplace.).
**Conclusion**
According to SingularityDAO CEO Marcello Mari, the use of AI technologies has great potential to increase the autonomy of DAO, but it is important to emphasize that achieving a high level of quality in these processes requires further research and ensuring reliability for all participants in this process. It is also worth noting that DAOs are undergoing significant changes under the influence of artificial intelligence and its transformative technologies. Therefore, it is undoubtedly true that, as a result, society can get a transparent and efficient way of doing business. | shevchukkk |
1,626,545 | How to use Traits, Interface, and Abstract classes In PHP | As a software developer, writing reusable and maintainable code is crucial. PHP provides several... | 0 | 2024-05-31T10:00:55 | https://dev.to/norbybaru/how-to-use-traits-interface-and-abstract-classes-in-php-428b | php, traits, interface, oop | As a software developer, writing reusable and maintainable code is crucial. PHP provides several tools to help achieve this, including Traits, Interfaces, and Abstract Classes. In this article, we'll explore each concept, their differences, and how to use them effectively.
## Trait
Traits are a way to reuse code in PHP. They are similar to abstract classes but with a few key differences. Traits are used to group related methods that can be used in multiple classes.
### Defining a Trait
To define a trait, use the **trait** keyword followed by the trait name:
```php
trait LoggerTrait {
public function log(string $message): void {
echo $message . "\n";
}
}
```
### Using a Trait
To use a trait in a class, use the **use** keyword:
```php
class MyClass {
use LoggerTrait;
}
```
Now, the MyClass class has access to the log method.
## Interfaces
Interfaces define a contract that must be implemented by any class that implements it. They represent a set of methods that must be implemented but do not provide any implementation.
### Defining an Interface
To define an interface, use the **interface** keyword followed by the interface name:
```php
interface Printable {
public function print(): void;
}
```
### Implementing an Interface
To implement an interface, use the **implements** keyword:
```php
class MyClass implements Printable {
public function print(): void {
echo "Printing...\n";
}
}
```
## Abstract Classes
Abstract classes are similar to interfaces but can also provide an implementation for some methods.
### Defining an Abstract Class
To define an abstract class, use the **abstract** keyword followed by the class name:
```php
abstract class AbstractClass {
public function doSomething(): void {
echo "Doing something...\n";
}
abstract public function doSomethingElse(): void;
}
```
### Extending an Abstract Class
To extend an abstract class, use the **extends** keyword:
```php
class MyClass extends AbstractClass {
public function doSomethingElse(): void {
echo "Doing something else...\n";
}
}
```
## Final Code Sample
Here is an example of a class that uses all the concepts we've discussed:
```php
// Trait
trait LoggerTrait {
public function log(string $message): void {
echo $message . "\n";
}
}
// Interface
interface Printable {
public function print(): void;
}
// Abstract Class
abstract class AbstractClass {
public function doSomething(): void {
echo "Doing something...\n";
}
abstract public function doSomethingElse(): void;
}
// Concrete Class that uses everything
class MyClass extends AbstractClass implements Printable {
use LoggerTrait;
public function print(): void {
echo "Printing...\n";
}
public function doSomethingElse(): void {
echo "Doing something else...\n";
}
public function doSomethingWithLogging(): void {
$this->log("About to do something...");
$this->doSomething();
$this->log("Done doing something!");
}
}
// Using the class
$myClass = new MyClass();
$myClass->print();
// Outputs: Printing...
$myClass->doSomething();
// Outputs: Doing something...
$myClass->doSomethingElse();
// Outputs: Doing something else...
$myClass->doSomethingWithLogging();
// Outputs:
// About to do something...
// Doing something...
// Done doing something!
```
In this example, **MyClass**:
- Extends the **AbstractClass**, which provides the _doSomething()_ method and requires the implementation of the _doSomethingElse()_ method.
- Implements the **Printable** interface, which requires the implementation of the _print()_ method.
- Uses the **LoggerTrait**, which provides the _log()_ method.
The **MyClass** class uses all the concepts we've discussed and demonstrates how they can work together to provide a robust and maintainable class.
## Conclusion
This article shows how to use Traits, Interfaces, and Abstract Classes in PHP. Traits provide a way to reuse code, Interfaces define a contract that must be implemented, and Abstract Classes provide a way to define a base class with some implementation.
| norbybaru |
1,871,871 | Angular Features: What It Brings to Us? | Angular is one of the popular choices among advanced programming frameworks like Java, Python, .Net,... | 0 | 2024-05-31T09:58:55 | https://dev.to/twinkle123/angular-features-what-it-brings-to-us-2gm6 | webdev, angular, javascript, angulardevelopers | Angular is one of the popular choices among advanced programming frameworks like Java, Python, .Net, and PHP. But what sets it apart is its capability in developing Single-Page Applications (SPAs). Another unique aspect about [Angular](https://www.clariontech.com/blog/angular-features-what-it-brings-to-us) is that it works as a client-side programming language. Other traditional programming languages work on logic and data handling as server-side programming.
Angular is known for its interactive user experience. Its data management functions as a two-way data binding process. It means that whenever data is changed at one place, it will automatically get updated at all other places. It helps in keeping everything in sync, ensuring angular developers do not have to waste time on more coding.
This framework is built with a modular architecture. It means that parts of the applications are divided into small pieces that can be reused known as modules. Each of these pieces works for only a specific task of application like authentication, form, or routing. This is more helpful when businesses hire angular developers to work on their projects. With its architecture its easier to work specifically on a separate module instead of the entire application.
Let's dive into the key features that Angular brings to the table and explore how they contribute to efficient and effective web development.
1. **Component-based Architecture:** Angular's component-based architecture is a game-changer in web development. It allows developers to break down complex applications into reusable and self-contained components. Each component encapsulates its own template, styles, and logic, making the codebase more modular and maintainable. This approach promotes code reusability, enhances collaboration among team members, and simplifies the development process. By leveraging components, developers can create a consistent and cohesive user interface while keeping the codebase organized and scalable.
2. **TypeScript Integration:** Angular is built with TypeScript, a superset of JavaScript that adds static typing and enhanced tooling to the development process. TypeScript brings several benefits to Angular development. It catches potential errors at compile-time, providing early feedback and reducing runtime bugs. The static typing feature enables better code documentation, making it easier for developers to understand and maintain the codebase. Additionally, TypeScript's advanced features, such as interfaces and decorators, facilitate more robust and scalable code development. With TypeScript, [Angular developers](https://www.clariontech.com/hire-developers/hire-angular-developers) can write cleaner, more reliable, and maintainable code.
3. **Dependency Injection:** Dependency Injection (DI) is a core feature of Angular that simplifies the management of dependencies within an application. DI allows developers to decouple components from their dependencies, making the codebase more flexible and testable. Angular's DI system automatically resolves dependencies and provides them to the components that need them. This approach reduces boilerplate code, promotes loose coupling, and enhances the modularity of the application. By leveraging DI, developers can build more maintainable and scalable applications, as components can be easily replaced or modified without affecting other parts of the system.
4. **Reactive Forms:** Angular's Reactive Forms module provides a powerful and flexible way to handle form inputs and validation. With Reactive Forms, developers can define the structure and behavior of forms using a declarative approach. This feature allows for the creation of complex and dynamic forms with ease, handling real-time validation and user input seamlessly. Reactive Forms use Observable streams to handle form changes, enabling developers to react to user input in real-time and perform advanced form validations. The reactive nature of forms in Angular enhances the user experience and simplifies form handling in web applications.
5. **Angular CLI:** The Angular Command Line Interface (CLI) is a productivity-boosting tool that streamlines the development workflow. It provides a set of commands and utilities that automate common tasks, such as creating new projects, generating components, services, and modules, and running tests. The Angular CLI saves developers time and effort by eliminating repetitive setup and configuration tasks. It also enforces best practices and provides a consistent project structure, making it easier for developers to navigate and maintain the codebase. With the Angular CLI, developers can focus on writing application logic rather than worrying about the underlying setup and build processes.
6. **Dependency Management with npm:** Angular leverages the power of npm (Node Package Manager) for efficient dependency management. npm is a vast ecosystem of packages and libraries that can be easily integrated into Angular projects. With npm, developers can quickly install and manage third-party libraries, tools, and frameworks required for their applications. The Angular CLI seamlessly integrates with npm, allowing developers to add, update, or remove dependencies with simple commands. This integration simplifies the process of managing external dependencies and keeps the project up to date with the latest versions of libraries and tools.
7. **Angular Universal for Server-Side Rendering:** Angular Universal is a powerful feature that enables server-side rendering (SSR) of Angular applications. SSR allows the initial rendering of the application to happen on the server, delivering a fully rendered HTML page to the client. This approach improves the application's performance, reduces the initial load time, and enhances the user experience. Angular Universal also improves search engine optimization (SEO) by making the application's content more easily indexable by search engine crawlers. With server-side rendering, Angular applications can provide a faster initial load, better SEO, and a seamless user experience across different devices and network conditions.
8. **Angular Material and Component Libraries:** Angular benefits from a rich ecosystem of pre-built UI components and libraries that accelerate development and ensure a consistent and polished user interface. Angular Material is an official component library that provides a set of well-designed and customizable UI components based on Google's Material Design guidelines. It offers a wide range of components, such as buttons, forms, dialogs, and navigation menus, which can be easily integrated into Angular applications. Additionally, there are numerous third-party component libraries available, such as NG Bootstrap and PrimeNG, which offer even more UI components and styling options. These libraries save developers time and effort by providing ready-to-use components that adhere to best practices and ensure a cohesive user experience.
9. **Testing and Debugging Tools:** Angular comes with a robust testing framework and debugging tools that ensure the quality and reliability of applications. The [framework](https://www.clariontech.com/blog/angular-framework-from-its-first-steps-to-adulthood) provides built-in support for unit testing, allowing developers to write and run tests for individual components, services, and modules. Angular's dependency injection system makes it easy to mock dependencies during testing, ensuring isolated and reliable test cases. Additionally, Angular offers powerful debugging tools, such as Angular DevTools, which provide insights into the application's state, performance, and change detection cycles. These tools enable developers to identify and fix issues quickly, ensuring a smooth development process and a high-quality final product.
10. **Continuous Integration and Deployment:** Angular seamlessly integrates with continuous integration and deployment (CI/CD) pipelines, enabling automated build, testing, and deployment processes. The Angular CLI provides commands for generating production-ready builds and running tests, making it easy to integrate into CI/CD workflows. Popular CI/CD platforms, such as Jenkins, Travis CI, and CircleCI, have excellent support for Angular projects. With CI/CD integration, [developers](https://www.clariontech.com/hire-developers/hire-angular-developers) can ensure that every code change is automatically built, tested, and deployed to various environments, reducing manual effort and minimizing the risk of errors. This integration facilitates faster and more reliable releases, enabling teams to deliver high-quality applications continuously.
Angular's extensive set of features and tools empowers developers to build robust, scalable, and maintainable web applications. From its component-based architecture and TypeScript integration to its powerful forms handling and testing capabilities, Angular provides a comprehensive framework for modern web development. By leveraging [Angular's features](https://www.clariontech.com/blog/angular-features-what-it-brings-to-us), developers can create applications that are modular, performant, and deliver exceptional user experiences. Whether you're building complex enterprise applications or lightweight single-page apps, Angular's feature set equips you with the tools necessary to succeed in the ever-evolving web development landscape. CopyRetryTLgive a small description pf above blog mentioned in 400 characters Edit3 / 3Angular is a powerful JavaScript framework that revolutionizes web development. With its component-based architecture, TypeScript integration, and dependency injection, Angular enables [developers](https://www.clariontech.com/hire-developers/hire-angular-developers) to build modular, scalable, and maintainable applications. It offers features like reactive forms, Angular CLI, and server-side rendering, empowering developers to create dynamic, responsive, and performant web apps. Angular's rich ecosystem of UI components and testing tools streamline development and ensure high-quality results. | twinkle123 |
1,871,863 | MY Submission for dev/Frontend_Challenge June edition | This is a submission for [Frontend Challenge... | 0 | 2024-05-31T09:57:11 | https://dev.to/prakhar30/my-submission-for-devfrontendchallenge-june-edition-434n | devchallenge, frontendchallenge, css, javascript | _This is a submission for [Frontend Challenge v24.04.17]((https://dev.to/challenges/frontend-2024-05-29), Glam Up My Markup: Beaches_
## What I Built
This is a beautiful and visually appealing website showcasing the best beaches around the world. The website features a stunning header, a catchy typewriter effect introduction, and a grid layout displaying various beaches with flip cards revealing more information about each beach. Additionally, there is a special section dedicated to the famous Pink Sands Beach in the Bahamas.
## Demo
{% codepen https://codepen.io/Prakhar_3010/pen/PovpoBb %}
## Journey
The code provided is well-structured and follows best practices for HTML and CSS. The use of modern CSS features like flexbox, grid, and animations adds a touch of interactivity and dynamism to the website.
Some notable aspects of the code:
Typography: The use of Google Fonts like "Open Sans," "Pacifico," and "Black Ops One" adds a nice touch to the overall design.
Layout: The grid and flexbox layouts create a clean and organized structure for the beach cards, making it easy to navigate and explore the different destinations.
Animations: The typewriter effect on the introduction text and the flip card animations on the beach cards enhance the user experience and make the website more engaging.
Responsiveness: Although not explicitly showcased, the use of CSS Grid and relative units like vw and vh should make the website responsive on different screen sizes.
Accessibility: The use of semantic HTML elements and proper document structure improves accessibility for users with disabilities.
Submitted by-
Prakhar Srivastava | prakhar30 |
1,871,870 | Facebook Comments-Update the Account And App Associated To It | It help users to post their thoughts and photos and even helps to share or like the photos and videos... | 0 | 2024-05-31T09:56:05 | https://dev.to/commentshero/facebook-comments-update-the-account-and-app-associated-to-it-481g | It help users to post their thoughts and photos and even helps to share or like the photos and videos of others [Sweden](https://commentshero.com/). By using it, individual can create their group and share whatever they want. Now,people are using it to promote their business and new products or services. Facebook is now available for users in sixty seven languages.
Maybe there would be some situations where individual will need help for the technical hassles. To get help in such conditions, there is need to reach customer support team. To reach support team, there is need to dial Facebook Helpline Number.
**Issues that has been solved by customer support team of Facebook:-
**
1. How may I download Facebook videos?
2. How may I create a page on Facebook?
3. How may I Facebook account password?
4. Why my Facebook app is not working anymore?
5. How may I activate my old Facebook account?
6. How may I change the name of Facebook page?
7. Ho may I fix the problem of “Facebook authentication got failed?
8. How may I make my Facebook profile private?
9. How to enable Gmail account for Facebook?
10. Why the login credentials got wrong?
11. How may I change privacy settings in Facebook account?
12. There are number of issues has been listed above which will associated to Facebook. If any of the Facebook user will get any of the above listed problem along with several others, there is need to reach support team immediately. There support team could be contacted by using the Fcebook customer service number.It is really to obtain on customer support site. By using it, individual will be in direct contact of live technicians.
Number of issues has been fixed by support team. Here, individual could see the solution of one:
- How may I update my Facebook account and app?
- First, user need to open “Play Store” App
- From the top left corner, it is required to select “Settings” option
- It is now required to select the Auto-update apps and select that whether you wants to turn on or off the auto- updates
- Now,there is need to look that the problem get solved or not
- People who are using Facebook and still not satisfied from the solution of the above issue, they need to connect with tech support engineers as soon as possible. For contacting the tech support engineers, there is need to reach Facebook Toll Free Number. It will connect you to the experts. They are highly eligible to solve every single issue. Individual could even use other ways to get help that are completely free.
| commentshero | |
1,871,554 | Github Action | Photo by Aleksandr Neplokhov at pexel GitHub Explore Let’s first clarify the difference between... | 0 | 2024-05-31T03:15:18 | https://dev.to/dhirajpatra/github-action-2fpe |
Photo by Aleksandr Neplokhov at pexel
GitHub
Explore
Let’s first clarify the difference between workflow and CI/CD and discuss what GitHub Actions do.
Workflow:
A workflow is a series of automated steps that define how code changes are built, tested, and deployed.
Workflows can include various tasks such as compiling code, running tests, and deploying applications.
Workflows are defined in a YAML file (usually named .github/workflows/workflow.yml) within your repository.
They are triggered by specific events (e.g., push to a branch, pull request, etc.).
Workflows are not limited to CI/CD; they can automate any process in your development workflow
CI/CD (Continuous Integration/Continuous Deployment):
CI/CD refers to the practice of automating the process of integrating code changes, testing them, and deploying them to production.
Continuous Integration (CI) focuses on automatically building and testing code changes whenever they are pushed to a repository.
Continuous Deployment (CD) extends CI by automatically deploying code changes to production environments.
CI/CD pipelines ensure that code is consistently tested and deployed, reducing manual effort and minimizing errors.
GitHub Actions:
GitHub Actions is a feature within GitHub that enables you to automate workflows directly from your GitHub repository.
Key advantages of using GitHub Actions for CI/CD pipelines include:
Simplicity: GitHub Actions simplifies CI/CD pipeline setup. You define workflows in a YAML file within your repo, and it handles the rest.
Event Triggers: You can respond to any webhook on GitHub, including pull requests, issues, and custom webhooks from integrated apps.
Community-Powered: Share your workflows publicly or access pre-built workflows from the GitHub Marketplace.
Platform Agnostic: GitHub Actions works with any platform, language, and cloud provider
In summary, GitHub Actions provides a flexible and integrated way to define workflows, including CI/CD pipelines, directly within your GitHub repository. It’s a powerful tool for automating tasks and improving your development process! 😊
GitLab
Explore
GitHub Actions, Jenkins, and GitLab CI/CD are all popular tools for automating software development workflows, but they serve different purposes and have distinct features. Let’s briefly compare them:
GitHub Actions:
Event-driven CI/CD tool integrated with GitHub repositories.
Workflow files are written in YAML.
Provides free runners hosted on Microsoft Azure for building, testing, and deploying applications.
Has a marketplace with pre-made actions for various tasks.
Beginner-friendly and easy to set up1.
Well-suited for startups and small companies.
Jenkins:
Established CI/CD tool with extensive community support.
Requires manual setup and maintenance on custom servers.
Uses Groovy scripts for defining pipelines.
Offers flexibility for complex scripting and custom configurations.
Suitable for larger organizations with specific requirements2.
GitLab CI/CD:
Integrated with GitLab repositories.
Uses .gitlab-ci.yml files for defining pipelines.
Provides shared runners or allows self-hosted runners.
Strong integration with GitLab features.
Well-suited for teams using GitLab for source control and project management.
Will GitHub Actions “kill” Jenkins and GitLab? Not necessarily. Each tool has its strengths and weaknesses, and the choice depends on your specific needs, existing workflows, and team preferences. Some organizations even use a combination of these tools to cover different use cases3. Ultimately, it’s about finding the right fit for your development process4. 😊
You can see one Github Action implemented for the demo here hope this will help to start.
| dhirajpatra | |
1,871,864 | Enhancing Data Security with Role-Based Access Control of Qdrant Vector Database | Data security has emerged as a major concern with the growing need for Retrieval Augmented Generation... | 0 | 2024-05-31T09:54:59 | https://quamernasim.medium.com/enhancing-data-security-with-role-based-access-control-of-qdrant-vector-database-3878769bec83 | rbac, qdrant, vectordatabase, rag |
Data security has emerged as a major concern with the growing need for Retrieval Augmented Generation (RAG)-powered Generative AI applications in large companies. At the heart of RAG applications lies the vector database, which stores all the company’s proprietary data. This database is used by large language models (LLMs) to perform similarity searches and retrieve relevant content.
In large organizations, there are multiple levels, various departments, and different roles, each with access to different levels of sensitive information. For example, financial and company roadmap-related documents may only be accessible to top officials and are not required by developers. Therefore, it’s essential to restrict database or collection access based on defined roles. This approach not only helps to maintain security but also ensures that LLMs provide accurate and relevant responses based on their roles.
To address these needs, new Role-Based Access Control (RBAC) options have been introduced via JSON Web Tokens (JWT) in the Qdrant Vector Database in their latest 1.9 release. API keys previously supported basic read and write operations. However, recognizing the evolving needs of users, particularly large organizations, additional options for finer control over data access within internal environments have been implemented.
## Qdrant 1.9: Introducing Role-Based Access Control and JWT Tokens
With the release of Qdrant version 1.9, significant advancements have been made in enhancing data security through the introduction of RBAC and JWT tokens. These new access control options offer a more granular and secure way to manage data access within large organizations.
In the earlier version of Qdrant, access control was managed using API keys, which supported basic read and write operations. In Qdrant’s 1.9 version, they have implemented additional access control options using JSON Web Tokens (JWT).
JWT allows a user to have limited access to specific data or collections in the database. By using JWT-based authentication, tokens with restricted access can be issued, which will help in the implementation of RBAC. This basically means administrators can define permissions for users, restricting access to sensitive endpoints and ensuring that only authorized individuals can access particular data segments.
The use of RBAC will help administrators assign specific roles and privileges to users based on their positions and responsibilities within the organization. This will be very useful in environments where different departments and roles require varying levels of access to the vector database. For instance, while developers might need access to certain datasets, financial information can be restricted to top-level executives.
## Role-Based Access Control (RBAC)
RBAC in Qdrant allows administrators to define roles and assign specific privileges to users based on their roles within the organization. This ensures that users only have access to the data and actions necessary for their role, enhancing security and operational efficiency. Administrators can use the table below that outlines the actions allowed or denied based on the access level.

Actions allowed for different Roles (Symbols: ✅ Allowed | ❌ Denied | 🟡 Allowed, but filtered)
By using JWT tokens and RBAC, Qdrant ensures that each user has the appropriate level of access to perform their tasks efficiently while maintaining strict security protocols. This system provides a scalable and secure approach to managing user permissions, making it ideal for enterprises of all sizes.
Qdrant emerges as the best choice for organizations seeking fine-grained user access control and enhanced security measures. Unlike other databases such as Pinecone, Milvus, Chroma, and Weaviate, Qdrant offers a much higher level of granularity in access control, which sets it apart. With its JWT-based RBAC approach, Qdrant allows users to define permissions and restrict access to specific data parts, ensuring sensitive endpoints remain protected. This fine-grained control is coupled with Qdrant’s ability to integrate seamlessly with hybrid cloud environments and Kubernetes clusters, providing organizations with scalability and enhanced security.
## Guide to Use JWT Auth for Role-Based Access
Starting from version 1.9.0, Qdrant supports granular access control using JSON Web Tokens (JWT). This means you can create tokens that grant specific permissions to access different parts of your data. With JWT, you can set up RBAC, defining what each user can and cannot do.
### Enabling JWT-Based Authentication
To enable JWT-based authentication in Qdrant, we need to configure it by setting an api_key and enabling the jwt_rbac feature. There are two ways to do this: using a configuration file or environment variables.
- **Using Configuration File:** We will open our Qdrant configuration file and add the following lines to the configuration:
```
service:
api_key: your_secret_api_key_here
jwt_rbac: true
```
- **Using Environment Variables:** We can also set the following environment variables:
```
export QDRANT__SERVICE__API_KEY=your_secret_api_key_here
export QDRANT__SERVICE__JWT_RBAC=true
```
Make sure to replace your_secret_api_key_here with your actual secret key. This api_key is crucial because it will be used to encode and decode the JWTs, so it needs to be kept secure.
### Generating JSON Web Tokens
JWTs can normally be generated by any library. We don’t need access to the Qdrant instance to generate them. We can easily use libraries such as PyJWT (Python), jsonwebtoken (JavaScript), or jsonwebtoken (Rust) to create JWTs.
#### JWT Structure
Let’s briefly understand the structure of the JWT token used to set up the RBAC. A JWT consists of three parts: the header, the payload, and the signature.
- **Header:** Specifies the algorithm used to encode the token. Qdrant uses the HS256 algorithm.
```
{
"alg": "HS256",
"typ": "JWT"
}
```
- **Payload:**
Contains the claims or data you want to include in the token. Here are some common claims you might use:
```
{
"exp": 1640995200, // Expiration time (Unix timestamp)
"value_exists": { /* See explanation below */ },
"access": "r" // Access level
}
```
- **Signature:** The token is signed with your api_key to ensure its validity. Qdrant can verify this signature using the same api_key.
#### Using JWT in Requests
Once JWT-based authentication is enabled, we now need to include the JWT in our requests to Qdrant. This can be done in two ways:
**Authorization Header:** Add the JWT as a bearer token in the Authorization header of the request.
`Authorization: Bearer <JWT>`
**Api-Key Header:** Alternatively, we can also include the JWT as a key in the Api-Key header.
```
Api-Key: <JWT>
```
Here’s an example using the Qdrant client in Python:
```
from qdrant_client import QdrantClient
qdrant_client = QdrantClient(
"your_qdrant_instance_url",
api_key="<JWT>",
)
```
## Generating JWT Tokens from Web UI
Qdrant provides a convenient JWT generation tool within the Web UI. This tool is accessible under the 🔑 tab. It can be found out at http://localhost:6333/dashboard#/jwt.
Here’s a quick guide on how to generate JWT tokens from the Web UI:
1. Access the JWT Tool: Navigate to the 🔑 tab in the Qdrant Web UI.
2. Provide API Key: When prompted for the API key on the jwt dashboard, enter your API Key
3. Generate Token: Follow the on-screen instructions to generate a JWT token. This token will encapsulate the user’s permissions and access levels.
4. Use the Token: Include this token in the header of your API requests to authenticate and authorize the actions performed by the user.
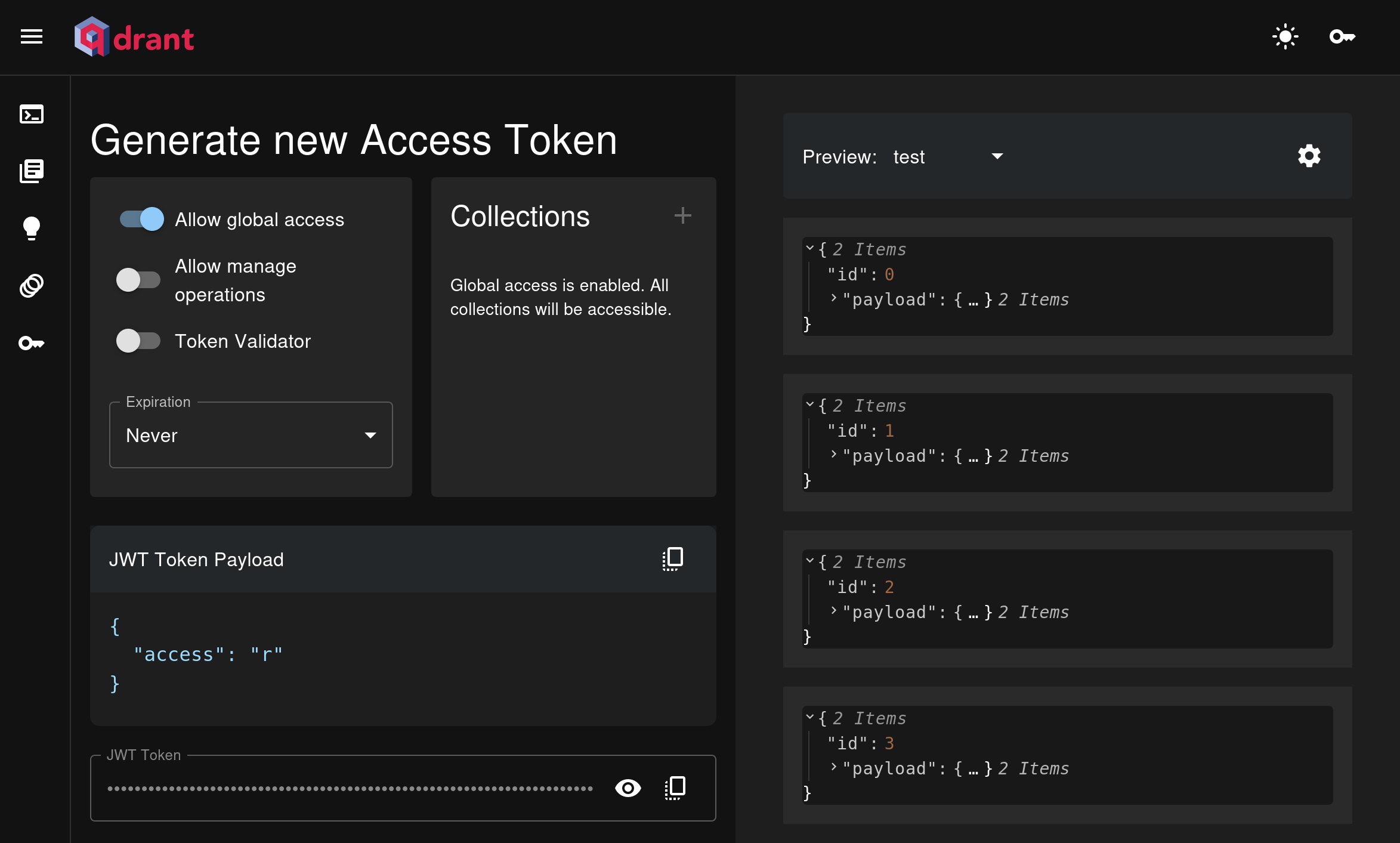
## Step-by-Step Tutorial to Set Up RBAC on Local Qdrant Instance
Here, for this blog post, I will be showing you how to implement a RBAC (Role-Based Access Control) with the help of JWT in Qdrant Vector Database. For this blog, I will be using the following data structure to create multiple collections.
```
├── data
│ ├── financial
│ │ └── Sample-Accounting-Income-Statement-PDF-File.pdf
│ └── general
│ ├── avengers-endgame-script-pdf.pdf
│ └── security_policy.pdf
```
The idea is to create two collections, one for financial data and the other for general data. General data will have multiple files, and financial data will have only one file. Then we will see RBAC in action and see how we can restrict access of the user based on the role assigned to them.
To install Qdrant, we will be using Docker. Run the following codes to install the Qdrant image.
```
sudo apt-get update
sudo apt install docker
docker pull qdrant/qdrant
```
Once this is done, we need to create a config.yaml file so that we can enable the RBAC in Qdrant. Copy paste the following commands in your config.yaml file.
```
service:
api_key: {your_API_key}
jwt_rbac: true
```
After creating the config.yaml file let’s now run the Qdrant container so that we can begin the RBAC tutorial.
```
docker run -p 6333:6333 -v /home/quamer23nasim38/Role-Based-Access-Control-of-Qdrant-Vector-Database/:/qdrant/storage -v /home/quamer23nasim38/Role-Based-Access-Control-of-Qdrant-Vector-Database/config.yaml:/qdrant/config/config.yaml qdrant/qdrant
```
Now, we can either open the dashboard or get started with Python. In this blog, we don’t really care much about the dashboard; we will get everything done in Python. So, let’s dive in.
Let’s start by connecting to Qdrant.
```
# Qdrant related Parameters
api = 'jhvfegfeboihf313fekfgejbv' # 'your_api_key'
host = 'localhost'
port = 6333
url = f'http://{host}:{port}'
```
I will be keeping the loading of the dataset, generating embeddings, and creating collections at a very high level. If you want to know more about these topics, you can refer to one of my previous blog posts where I explained how to build a chatbot using Qdrant, Llama3, Ollama, and LangChain. In this blog post, I will be focusing on RBAC.
Now, Let’s start with different security scenarios.
### Without Any Token, with RBAC Enabled
We have enabled RBAC in Qdrant, but we have not created any tokens yet. Let’s see how it behaves in this case.
```
from qdrant_client import QdrantClient
client = QdrantClient(url=url)
client.get_collections()
```
```
# Output of the above code
UnexpectedResponse: Unexpected Response: 401 (Unauthorized)
Raw response content:
b'Must provide an API key or an Authorization bearer token'
```
As expected, it should not allow any operation without a token. Now, in the next section, let’s create a JWT token and try to access the Qdrant API.
### Global Read-Only Access
Let’s first create a function that we can reuse to generate JWT tokens.
```
import jwt
def generate_jwt(api, payload):
'''
This function generates a JWT token using the payload and the API key
Args:
api: API key
payload: Payload to be encoded in the JWT token. It contains the access rights
Returns:
encoded_jwt: JWT token
'''
encoded_jwt = jwt.encode(payload, api, algorithm='HS256')
return encoded_jwt
```
Here, let’s first create a token with global read-only access. With global read-only access, the user can only read the resources in the cluster. They cannot create, update, or delete resources. This essentially means that the user can read all the collections available, so be careful when granting this permission.
```
import time
from utils import generate_jwt
current_time = int(time.time())
# This payload along with the API is used to generate the JWT token.
# This token tells that the user has global read only access to all the collections.
# It also specifies that this token will expire in 1 hour.
payload = {
"access": "r",
"exp": current_time + 3600, # 1 hour
}
# Generate the JWT token
# This token will be used to authenticate the user.
jwt = generate_jwt(api, payload)
```
Currently, we have no collections in the Qdrant Vector DB. Let’s see how the API behaves in this case.
```
from qdrant_client import QdrantClient
client = QdrantClient(url=url, api_key=jwt)
client.get_collections()
```
```
# Output of the above code
CollectionsResponse(collections=[])
```
Great, it returned an empty list of collections. Now let’s try to create a collection with the same token. Note that this should fail as the token has only read-only access.
```
from qdrant_client import QdrantClient
client = QdrantClient(url=url, api_key=jwt)
# Delete the collection if it exists
client.delete_collection(collection_name=collection_name)
```
```
# Output of the above code
UnexpectedResponse: Unexpected Response: 403 (Forbidden)
Raw response content:
b'{"status":{"error":"Forbidden: Global manage access is required"},"time":0.000023168}'
As we can see, the API returned a 403 Forbidden error saying ‘Global manage access is required’ to create a collection.
```
Now, in the next section, let’s create a token with global manage access and try to create a collection.
### Global Manage Access
Now let’s create a token with global manage access. With Global Manage Access, the user can read, create, update, and delete collections in the cluster. This essentially means that the user can perform all the operations on all the collections available, so be extremely careful when granting this permission. You should only grant this permission to Admins.
```
import time
from utils import generate_jwt
current_time = int(time.time())
# This payload along with the API is used to generate the JWT token.
# This token tells that the user has global manage access to all the collections.
# It also specifies that this token will expire in 1 hour.
# You should only generate this token for admin users.
payload = {
"access": "m",
"exp": current_time + 3600, # 1 hour
}
# Generate the JWT token
# This token will be used to authenticate the user.
jwt = generate_jwt(api, payload)
```
Let’s again try to list the collections using this new token.
```
from qdrant_client import QdrantClient
client = QdrantClient(url=url, api_key=jwt)
client.get_collections()
```
```
# Output of the above code
CollectionsResponse(collections=[])
```
Since no collections are available, it returned an empty list. Next, let’s try to delete a collection using this token. Remember, this operation failed using the previous read-only token. Even though we don’t have any collections, let’s try to delete a collection and see what happens.
```
from qdrant_client import QdrantClient
client = QdrantClient(url=url, api_key=jwt)
# Delete the collection if it exists
client.delete_collection(collection_name=collection_name)
```
```
# Output of the above code
False
```
As we can see, it ran successfully and returned False as there was no collection to delete. Now let’s try to create two collections, one for financial data and the other for general data. Then we will try to explore the RBAC in more detail.
Before creating the collections, let’s first load the embeddings model to generate embeddings for the documents. Here we will keep the indexing phase at a high level. If you’re interested in knowing more about it, you can refer to one of my previous blog posts. For this blog post, I will be focusing on RBAC.
```
import fasttext as ft
# download the fasttext model from https://dl.fbaipublicfiles.com/fasttext/vectors-crawl/cc.en.300.bin.gz and then unzip it
embedding_model_path = '/home/quamer23nasim38/Role-Based-Access-Control-of-Qdrant-Vector-Database/embedding_model/cc.en.300.bin'
# Load the embedding model
embed_model = ft.load_model(embedding_model_path)
```
Let’s define some constants for the creation of collections.
```
# data related parameters
chunk_size = 500
chunk_overlap = 50
batch_size = 4000
# vector related parameters
vector_size = 300
```
Let’s create the chunk out of the general data. But before we move on to this step, let’s first create two essential utility functions that will help us in creating the chunks and respective embeddings of the data.
```
import pandas as pd
from tqdm.notebook import tqdm
from qdrant_client import QdrantClient
from qdrant_client.models import VectorParams, Distance, Batch
def generate_embeddings_from_fastext_model(docs, embed_model):
'''
Generate embeddings for the documents using the FastText model
Args:
docs: List of documents
embed_model: FastText model
Returns:
df: Dataframe with the documents, embeddings, metadata and payload
'''
# convert the documents to a dataframe
# This dataframe will be used to create the embeddings
# And later will be used to update the Qdrant Vector Database
data = []
for doc in tqdm(docs):
# Get the page content and metadata for each chunk
# Meta data contains chunk source or file name
row_data = {
"page_content": doc.page_content,
"metadata": doc.metadata
}
data.append(row_data)
df = pd.DataFrame(data)
# Replace the new line characters with space
df['page_content'] = df['page_content'].replace('\\n', ' ', regex=True)
# Create a unique id for each document.
# This id will be used to update the Qdrant Vector Database
df['id'] = range(1, len(df) + 1)
# Create a payload column in the dataframe
# This payload column includes the page content and metadata
# This payload will be used when LLM needs to answer a query
df['payload'] = df[['page_content', 'metadata']].to_dict(orient='records')
# Create embeddings for each chunk
# This embeddings will be used when doing a similarity search with the user query
df['embeddings'] = df['page_content'].apply(lambda x: (embed_model.get_sentence_vector(x)).tolist())
return df
def create_new_collection(url, jwt, collection_name, df, vector_size, batch_size, delete_prev = False, create_from_scratch = False):
'''
This function creates a new collection in Qdrant Vector Database
and updates the collection with the embeddings
It starts by creating a connection to the Qdrant Vector Database running using the docker
Then it deletes the collection if it already exists
Then it creates a new collection with the specified collection name and vector size
Then it updates the collection with the embeddings
Finally, it closes the connection to the Qdrant Vector Database and returns the client object
Args:
url: URL of the Qdrant Vector Database
jwt: JWT token
collection_name: Name of the collection
df: Dataframe with the documents, embeddings, metadata and payload
Returns:
client: QdrantClient object
'''
# Create a QdrantClient object
# client = QdrantClient('https://localhost:6333')
client = QdrantClient(url=url, api_key = jwt)
# delete the collection if it already exists
# remove or comment this line if you want to keep the existing collection
# and want to use the existing collection to update new points
if delete_prev:
client.delete_collection(collection_name=collection_name)
# Create a fresh collection in Qdrant
# remove or comment this line if you do not want to create a new collection
if create_from_scratch:
client.create_collection(
collection_name=collection_name,
vectors_config=VectorParams(size=vector_size, distance=Distance.COSINE),
)
# Update the Qdrant Vector Database with the embeddings
# We are updating the embeddings in batches
# Since the data is large, we will only update the first batch of size 4000
client.upsert(
collection_name=collection_name,
points=Batch(
ids=df['id'].to_list()[:batch_size],
payloads=df['payload'][:batch_size],
vectors=df['embeddings'].to_list()[:batch_size],
),
)
# Close the QdrantClient
client.close()
print(f"Collection {collection_name} created and updated with the embeddings")
```
Great! Now let’s go ahead and start creating the chunks and respective embeddings
```
from langchain_community.document_loaders import DirectoryLoader
# from langchain_community.document_loaders import TextLoader
from langchain_community.document_loaders.pdf import PyPDFLoader
from langchain.text_splitter import RecursiveCharacterTextSplitter
collection_type = 'general'
root = '/home/quamer23nasim38/Role-Based-Access-Control-of-Qdrant-Vector-Database/data'
data_path = pjoin(root, collection_type)
collection_name = collection_type
# Load the documents from the directory
loader = DirectoryLoader(data_path, loader_cls=PyPDFLoader)
# Split the documents into chunks
text_splitter = RecursiveCharacterTextSplitter(
chunk_size=chunk_size,
chunk_overlap=chunk_overlap,
length_function=len,
is_separator_regex=False,
)
docs = loader.load_and_split(text_splitter=text_splitter)
from utils import generate_embeddings_from_fastext_model
# Generate the embeddings for the data
df = generate_embeddings_from_fastext_model(docs, embed_model)
from utils import create_new_collection
# Create a new collection with manage access
create_new_collection(url, jwt, collection_name, df, vector_size, batch_size, delete_prev = True, create_from_scratch = True)
```
We do the same for the financial data.
```
from langchain_community.document_loaders import DirectoryLoader
from langchain_community.document_loaders.pdf import PyPDFLoader
from langchain.text_splitter import RecursiveCharacterTextSplitter
collection_type = 'financial'
root = '/home/quamer23nasim38/Role-Based-Access-Control-of-Qdrant-Vector-Database/data'
data_path = pjoin(root, collection_type)
collection_name = collection_type
# Load the documents from the directory
loader = DirectoryLoader(data_path, loader_cls=PyPDFLoader)
# Split the documents into chunks
text_splitter = RecursiveCharacterTextSplitter(
chunk_size=chunk_size,
chunk_overlap=chunk_overlap,
length_function=len,
is_separator_regex=False,
)
docs = loader.load_and_split(text_splitter=text_splitter)
from utils import generate_embeddings_from_fastext_model
# Generate the embeddings for the data
df = generate_embeddings_from_fastext_model(docs, embed_model)
from utils import create_new_collection
# Create a new collection with manage access
create_new_collection(url, jwt, collection_name, df, vector_size, batch_size, delete_prev = True, create_from_scratch = True)
```
Great! Now we have created two collections, ‘general’ and ‘financial’ collections. Let’s see if we can read these collections with different sets of tokens having different permissions.
### Collection Specific Access
With this access, we can limit the access of the user to a specific collection only. This is the most secure way to grant access to the user. We can also limit the access to the types of documents in that collection or pages as well. Let’s see how we can do this.
In our Qdrant Vector Database, we now have two collections, ‘general’ and ‘financial’. As can be understood from the names, the ‘general’ collection contains general data, and the ‘financial’ collection contains financial data. Due to the nature of the data, we want to restrict access of each user to specific collections as per their roles in the organization.
#### Read-Only Access
Here, in this section, we will create a token with read-only access to a specific collection only. Let’s see how it behaves.
```
import time
from utils import generate_jwt
current_time = int(time.time())
# This payload along with the API is used to generate the JWT token.
# This token tells that the user has read access to the general collection only.
# You can give access to multiple collections by adding multiple dictionaries in the access list.
# For now, we are only giving access to the general collection.
# It also specifies that this token will expire in 1 hour.
payload = {
"exp": current_time + 3600, # 1 hour
"access": [
{
"collection": "general", # collection name - Change this to the collection you want to give access to, like financial
"access": "r"
},
]
}
# Generate the JWT token
# This token will be used to authenticate the user.
jwt = generate_jwt(api, payload)
from qdrant_client import QdrantClient
client = QdrantClient(url=url, api_key=jwt)
client.get_collections()
```
```
# Output of the above code
CollectionsResponse(collections=[CollectionDescription(name='general')])
```
This is great. We can see that the user can only access the ‘general’ collection and not the ‘financial’ collection. Now let’s try to verify if the user has read-only access to the ‘general’ collection.
```
import numpy as np
# We are generating a random query vector of size vector_size
query_vector = np.random.rand(vector_size)
# We are searching for the closest points to the query vector in the general collection
# Since we have the read access to the general collection, we can search in it.
hits = client.search(
collection_name="general",
query_vector=query_vector,
limit=5 # Return 5 closest points
)
hits
```
```
# Output of the above code
[ScoredPoint(id=11, version=2, score=0.07114598, payload={'metadata': {'page': 1, 'source': '/home/quamer23nasim38/Role-Based-Access-Control-of-Qdrant-Vector-Database/data/general/security_policy.pdf'}, 'page_content': 'is built using the Rust language - a static multi-paradigm, memory-efficient, low-level programming language focused on speed, security, and performance. The intention is to build Qdrant with as few moving parts as possible, thereby keeping the attack vector as low as possible. Email security Qdrant supports TLS encryption on all inbound and outbound emails. Qdrant uses Gmail to provide email and communication services. For an explanation of how email encryption works, take a look at this'}, vector=None, shard_key=None),
ScoredPoint(id=10, version=2, score=0.045524757, payload={'metadata': {'page': 1, 'source': '/home/quamer23nasim38/Role-Based-Access-Control-of-Qdrant-Vector-Database/data/general/security_policy.pdf'}, 'page_content': 'within the Qdrant Cloud platform, and only the necessary ports are opened on each server. All outbound connections pass through the stateless access control rules, whilst inbound connections from the internet must pass through a secure, highly-available load balancer layer, and the stateless access control firewall rules before then being routed to each server. Software security We take the security of the Qdrant code very seriously. The database is built using the Rust language - a static'}, vector=None, shard_key=None),
ScoredPoint(id=8, version=2, score=0.043969806, payload={'metadata': {'page': 1, 'source': '/home/quamer23nasim38/Role-Based-Access-Control-of-Qdrant-Vector-Database/data/general/security_policy.pdf'}, 'page_content': 'All servers are tested for vulnerability and intrusion detection quarterly. The servers and services hosted on them are certified as complying with the PCI Data Security Standard established by the PCI Security Standards Council, which is an open global forum for the development, enhancement, storage, dissemination, and implementation of security standards for account data protection. The certification confirms that the services adhere to the PCI DSS Level 4 requirements for security management,'}, vector=None, shard_key=None),
ScoredPoint(id=12, version=2, score=0.03491432, payload={'metadata': {'page': 1, 'source': '/home/quamer23nasim38/Role-Based-Access-Control-of-Qdrant-Vector-Database/data/general/security_policy.pdf'}, 'page_content': 'how email encryption works, take a look at this overview from Google. Data residency On Qdrant Cloud, the location of data can be specified. Locations may include London, Ireland, Belgium, Germany, Switzerland, North America, South America, Australia, Canada, Tokyo, or Singapore. Data will not be moved or replicated outside of a specified location. Data in transit All data is encrypted when it is being transmitted between client devices and Qdrant Cloud. SSL/TLS certificates shield data using'}, vector=None, shard_key=None),
ScoredPoint(id=13, version=2, score=0.027367812, payload={'metadata': {'page': 1, 'source': '/home/quamer23nasim38/Role-Based-Access-Control-of-Qdrant-Vector-Database/data/general/security_policy.pdf'}, 'page_content': 'Cloud. SSL/TLS certificates shield data using 256-byte signatures and either 2048-bit or 4096-bit keys. All connections to Content Delivery Network (CDN) servers and the database layer are'}, vector=None, shard_key=None)]
```
As we can see, the user can read the ‘general’ collection. Now let’s try to update the ‘general’ collection with the same read-only token. Let’s hope that it fails.
```
import numpy as np
from qdrant_client.models import PointStruct
# We are generating 100 random vectors of size vector_size
vectors = np.random.rand(100, vector_size)
# We are upserting these vectors in the general collection
Since we have read-only access to the general collection, we won't be able to insert the vectors.
client.upsert(
collection_name="general",
points=[
PointStruct(
id=idx,
vector=vector.tolist(),
payload={"color": "red", "rand_number": idx % 10}
)
for idx, vector in enumerate(vectors)
]
)
```
```
Output of the above code
: Unexpected Response: 403 (Forbidden)
Raw response content:
b'{"status":{"error":"Forbidden: Write access to collection general is required"},"time":0.000079842}'
```
As we’d guessed, the API returned a 403 Forbidden error saying, ‘Write access to collection general is required’. This is great. Now let’s see if we can read the financial collection with the same read-only token for the general collection. Just a heads up — this should fail.
```
We are generating a random query vector of size vector_size
query_vector = np.random.rand(vector_size)
We are searching for the closest points to the query vector in the general collection
# Since we have read-only access to the general collection only, we won't be able to search in financial collection.
hits = client.search(
collection_name="financial",
query_vector=query_vector,
limit=5 # Return 5 closest points
)
hits
```
```
Output of the above code
: Unexpected Response: 403 (Forbidden)
Raw response content:
b'{"status":{"error":"Forbidden: Access to collection financial is required"},"time":7.61e-6}'
```
Great. Once again, the API returned a 403 Forbidden error saying, ‘Access to collection financial is required’. In the next section, let’s test with read-write access to a specific collection. We will also see how we can grant access to multiple collections to a user.
#### Read-Write Access
Here we will grant the user read-write access to the ‘general’ collection only. And, on top of that, we will limit access of the ‘financial’ collection to read-only.
```
import time
from utils import generate_jwt
current_time = int(time.time())
This payload, along with the API, is used to generate the JWT token.
This token indicates that the user has access to two collections: general and financial.
# Access to the general collection is read-write and access to the financial collection is read-only.
It also specifies that this token will expire in 1 hour.
payload = {
"exp": current_time + 3600, # 1 hour
"access": [
{
"collection": "general",
"access": "rw"
},
{
"collection": 'financial',
"access": "r"
}
]
}
Generate the JWT token
This token will be used to authenticate the user.
jwt = generate_jwt(api, payload)
from qdrant_client import QdrantClient
client = QdrantClient(url=url, api_key=jwt)
collection = client.get_collections()
collection
```
```
Output of the above code
CollectionsResponse(collections=[CollectionDescription(name='general'), CollectionDescription(name='financial')])
```
Nice! The user has access to both the collections, ‘general’ and ‘financial’. Now let’s try to update the ‘general’ collection with the same token. Since the token has read-write access to the ‘general’ collection, it should work.
```
import numpy as np
from qdrant_client.models import PointStruct
# We are generating 100 random vectors of size vector_size
vectors = np.random.rand(100, vector_size)
We are inserting these vectors in the general collection
Since we have read-write access to the general collection, we can insert the vectors.
client.upsert(
collection_name="general",
points=[
PointStruct(
id=idx,
vector=vector.tolist(),
payload={"color": "red", "rand_number": idx % 10}
)
for idx, vector in enumerate(vectors)
]
)
```
```
Output of the above code
UpdateResult(operation_id=1, status=<UpdateStatus.COMPLETED: 'completed'>)
```
Looks good. We can see that the user can update the ‘general’ collection. Now let’s try to update the ‘financial’ collection with the same token. This should fail as the token has only read-only access to the ‘financial’ collection.
```
import numpy as np
from qdrant_client.models import PointStruct
vectors = np.random.rand(100, vector_size)
client.upsert(
collection_name="financial",
points=[
PointStruct(
id=idx,
vector=vector.tolist(),
payload={"color": "red", "rand_number": idx % 10}
)
for idx, vector in enumerate(vectors)
]
)
```
```
Output of the above code
: Unexpected Response: 403 (Forbidden)
Raw response content:
b'{"status":{"error":"Forbidden: Write access to collection financial is required"},"time":0.000062905}'
```
As expected, the API returned a 403 Forbidden error saying ‘Write access to collection financial is required’. Now let’s try to do a final check for this token. Let’s see if the user can read the ‘financial’ collection.
```
We are generating a query vector from a string that was available in one of the documents in the general collection
x = "based on the equation: assets = liabilities + owners' equity."
query_vector = embed_model.get_sentence_vector(x).tolist()
We are searching for the closest points to the query vector in the general collection
Since we have read-write access to the general collection, we can search in it.
hits = client.search(
collection_name="financial",
query_vector=query_vector,
limit=20 # Return 5 closest points
)
hits
```
```
Output of the above code
[ScoredPoint(id=3, version=0, score=0.7493207, payload={'metadata': {'page': 0, 'source': '/home/quamer23nasim38/Role-Based-Access-Control-of-Qdrant-Vector-Database/data/financial/Sample-Accounting-Income-Statement-PDF-File.pdf'}, 'page_content': "Balance Sheet The balance sheet is based on the equation: assets = liabilities + owners' equity . It indicates everything the company owns (assets), everything the company owes to creditors (liabilities) and the value of the ownership stake in the company (shareholders' equity, or capital). The balance sheet date is the ending date of the period or year and is a continuation of the amounts recorded since the"}, vector=None, shard_key=None),
ScoredPoint(id=8, version=0, score=0.7304637, payload={'metadata': {'page': 0, 'source': '/home/quamer23nasim38/Role-Based-Access-Control-of-Qdrant-Vector-Database/data/financial/Sample-Accounting-Income-Statement-PDF-File.pdf'}, 'page_content': 'period. Sources of cash listed on the statement include revenues, long-term financing, sales of non-current assets, an increase in any current liability account or a decrease in any current asset account. Uses of cash include operating losses, debt repayment, equipment purchases and increases in current asset accounts.'}, vector=None, shard_key=None),
ScoredPoint(id=4, version=0, score=0.72308195, payload={'metadata': {'page': 0, 'source': '/home/quamer23nasim38/Role-Based-Access-Control-of-Qdrant-Vector-Database/data/financial/Sample-Accounting-Income-Statement-PDF-File.pdf'}, 'page_content': 'inception of the company or organization. The balance sheet is a "snapshot" of the financial position of the company at the balance sheet date and shows the accumulated balance of the accounts. Assets and liabilities are separated between current and long-term , where current items are those items which will be realized or paid within one year of the balance sheet date. Typical current assets are cash, prepaid expenses, accounts receivable and inventory. Income Statement'}, vector=None, shard_key=None),
ScoredPoint(id=26, version=0, score=0.7186612, payload={'metadata': {'page': 6, 'source': '/home/quamer23nasim38/Role-Based-Access-Control-of-Qdrant-Vector-Database/data/financial/Sample-Accounting-Income-Statement-PDF-File.pdf'}, 'page_content': 'Bank term loan bearing interest at prime plus 2%, repayable in monthly principal instalments of $2,100.00plus interest to November 2007, secured by a general security agreement on the assets of the company and a personal guaranteefrom the shareholder. 2002-2001 $ 111,300 $ Less current portion: 25,200; $ 86,100; approximate principal repayments are as follows: 2004 $ 25,2002005 25,2002006 25,2002007 10,500 $ 86,100 5. STATED CAPITAL Authorized: Unlimited number of Common shares'}, vector=None, shard_key=None),
ScoredPoint(id=23, version=0, score=0.7100816, payload={'metadata': {'page': 5, 'source': '/home/quamer23nasim38/Role-Based-Access-Control-of-Qdrant-Vector-Database/data/financial/Sample-Accounting-Income-Statement-PDF-File.pdf'}, 'page_content': 'Significant Accounting Policies INVENTORY The inventory is valued at the lower of cost or market, with cost being determined on a first-in, first-out basis. PROPERTY, PLANT AND EQUIPMENT Property, plant and equipment are stated at cost less accumulated amortization. Amortization is recorded at rates designed to amortize the cost of capital assets overtheir estimated useful lives. Amortization rates used are as follows: Furniture and equipment 20% declining balance'}, vector=None, shard_key=None),
ScoredPoint(id=16, version=0, score=0.70792955, payload={'metadata': {'page': 3, 'source': '/home/quamer23nasim38/Role-Based-Access-Control-of-Qdrant-Vector-Database/data/financial/Sample-Accounting-Income-Statement-PDF-File.pdf'}, 'page_content': 'Deposits and prepaid expenses (254) 688 Inventory (2,487) (904) Accounts payable and accrued liabilities (9,290) 34,543 Long-term debt, current portion: 25,200; income tax payable: 14,387 2,206 Cash flows from operating activities: 115,402; 85,966 CASH FLOWS FROM INVESTING ACTIVITIE S Acquisition of property, plant and equipment (1,426) (10,342)'}, vector=None, shard_key=None),
ScoredPoint(id=18, version=0, score=0.70589364, payload={'metadata': {'page': 3, 'source': '/home/quamer23nasim38/Role-Based-Access-Control-of-Qdrant-Vector-Database/data/financial/Sample-Accounting-Income-Statement-PDF-File.pdf'}, 'page_content': 'CASH (DEFICIENCY) RESOURCES: Beginning of Year (69,474) 17,789 CASH RESOURCES (DEFICIENCY) - End of Yea r $ 11,552 $ (69,474) Cash resources (deficiency) is comprised of: Cash: 11,552 $; bank overdraft: 9,474 Bank loan: (60,000) $ 11,552 $ (69,474) The accompanying summary of significant accounting policies and notes are an integral part of these financial statements.'}, vector=None, shard_key=None),
ScoredPoint(id=14, version=0, score=0.7057368, payload={'metadata': {'page': 2, 'source': '/home/quamer23nasim38/Role-Based-Access-Control-of-Qdrant-Vector-Database/data/financial/Sample-Accounting-Income-Statement-PDF-File.pdf'}, 'page_content': 'DIVIDENDS -- (16,000) RETAINED EARNINGS (DEFICIT) - End of Yea r $ 17,166 $ (61,350) The accompanying summary of significant accounting policies and notes are an integral part of these financial statements.'}, vector=None, shard_key=None),
ScoredPoint(id=15, version=0, score=0.7047419, payload={'metadata': {'page': 3, 'source': '/home/quamer23nasim38/Role-Based-Access-Control-of-Qdrant-Vector-Database/data/financial/Sample-Accounting-Income-Statement-PDF-File.pdf'}, 'page_content': 'XYZ COMPANY LIMITE D STATEMENT OF CASH FLO W FOR THE YEAR ENDE D JUNE 30, 2002 UNAUDITED - See "Notice to Reader" 2002–2001. CASH FLOWS FROM OPERATING ACTIVITIE S Net income for the year was $78,516; $8,810 Adjustment for: Amortization 17,854 16,856 Loss on disposal of property, plant and equipment: 387 Gain on disposal of investment (16,149) Cash derived from operations: 80,221 and 26,053 Decrease (increase) in working capital items Accounts receivable 7,625 23,380'}, vector=None, shard_key=None),
ScoredPoint(id=17, version=0, score=0.6888898, payload={'metadata': {'page': 3, 'source': '/home/quamer23nasim38/Role-Based-Access-Control-of-Qdrant-Vector-Database/data/financial/Sample-Accounting-Income-Statement-PDF-File.pdf'}, 'page_content': 'Proceeds from disposal of property, plant and equipment -- 3,113 Proceeds from disposal of investment: 61,150 Dividends: 16,000 Cash flows from investing activities: 59,724 (23,229) CASH FLOWS FROM FINANCING ACTIVITIE S Advances from (repayments to) shareholder (180,200) and (150,000) Acquisition of (repayment of) long-term debt 86,100 -- (94,100) (150,000) NET INCREASE (DECREASE) IN CASH RESOURCES 81,026 (87,263)'}, vector=None, shard_key=None),
ScoredPoint(id=1, version=0, score=0.68225944, payload={'metadata': {'page': 0, 'source': '/home/quamer23nasim38/Role-Based-Access-Control-of-Qdrant-Vector-Database/data/financial/Sample-Accounting-Income-Statement-PDF-File.pdf'}, 'page_content': 'Understanding Basic Financial Statements During the accounting cycle, the accounting system is used to track, organize and record the financial transactions of an organization. At the close of each period, the information is used to prepare the financial statements, which are usually composed of a balance sheet (statement of financial position); income statement (statement of income and expenses); statement of retained earnings (owners’ equity); and a statement of cash flow.'}, vector=None, shard_key=None),
ScoredPoint(id=7, version=0, score=0.6741429, payload={'metadata': {'page': 0, 'source': '/home/quamer23nasim38/Role-Based-Access-Control-of-Qdrant-Vector-Database/data/financial/Sample-Accounting-Income-Statement-PDF-File.pdf'}, 'page_content': "income or loss is added to the opening amount of retained earnings to arrive at the closing retained earnings. Retained earnings can be decreased by such items as dividends paid to shareholders. On the sample financial statements shown below, the statement of retained earnings is combined with the income statement presentation. Statement of Cash Flow The statement of cash flow shows all sources and uses of a company's cash during the accounting period."}, vector=None, shard_key=None),
ScoredPoint(id=11, version=0, score=0.67381775, payload={'metadata': {'page': 1, 'source': '/home/quamer23nasim38/Role-Based-Access-Control-of-Qdrant-Vector-Database/data/financial/Sample-Accounting-Income-Statement-PDF-File.pdf'}, 'page_content': '17,167 (61,349) $ 276,498 $ 331,259 APPROVED The accompanying summary of significant accounting policies and notes are an integral part of these financial statements.'}, vector=None, shard_key=None),
ScoredPoint(id=21, version=0, score=0.6718547, payload={'metadata': {'page': 4, 'source': '/home/quamer23nasim38/Role-Based-Access-Control-of-Qdrant-Vector-Database/data/financial/Sample-Accounting-Income-Statement-PDF-File.pdf'}, 'page_content': '$ 286,817 $ 339,905 The accompanying summary of significant accounting policies and notes are an integral part of these financial statements.'}, vector=None, shard_key=None),
ScoredPoint(id=25, version=0, score=0.6679283, payload={'metadata': {'page': 6, 'source': '/home/quamer23nasim38/Role-Based-Access-Control-of-Qdrant-Vector-Database/data/financial/Sample-Accounting-Income-Statement-PDF-File.pdf'}, 'page_content': 'XYZ COMPANY LIMITED NOTES TO THE FINANCIAL STATEMENTS FOR THE YEAR ENDED JUNE 30, 2002 UNAUDITED - See "Notice to Reader." 3. DUE TO SHAREHOLDER The amount due to the shareholder bears interest at a rate determined annually and has no fixed terms of repayment.Interest paid for 2002 was $1,823 (2001 - $6,831) 4. LONG - TERM DEBT Bank term loan bearing interest at prime plus 2%,'}, vector=None, shard_key=None),
ScoredPoint(id=13, version=0, score=0.66429466, payload={'metadata': {'page': 2, 'source': '/home/quamer23nasim38/Role-Based-Access-Control-of-Qdrant-Vector-Database/data/financial/Sample-Accounting-Income-Statement-PDF-File.pdf'}, 'page_content': 'INCOME FROM OPERATIONS 77,855 8,860 OTHER INCOME (EXPENSES) Loss on disposal of property, plant and equipment (387) Gain on sale of investment: 16,149 -- Miscellaneous (1,101) 337 15,048 (50) NET INCOME BEFORE TA X 92,903 8,810 INCOME TAX EXPENSE 14,387 -- NET INCOME 78,516 8,810 (DEFICIT) Beginning of Yea r (61,350) (54,160) DIVIDENDS -- (16,000)'}, vector=None, shard_key=None),
ScoredPoint(id=5, version=0, score=0.6599545, payload={'metadata': {'page': 0, 'source': '/home/quamer23nasim38/Role-Based-Access-Control-of-Qdrant-Vector-Database/data/financial/Sample-Accounting-Income-Statement-PDF-File.pdf'}, 'page_content': "Income Statement An income statement is a type of summary flow report that lists and categorizes the various revenues and expenses that result from operations during a given period—a year, a quarter or a month. The difference between revenues and expenses represents a company's net income or net loss. The amounts shown in the income statement are the amounts recorded for the given period (a year, a"}, vector=None, shard_key=None).
ScoredPoint(id=6, version=0, score=0.65201813, payload={'metadata': {'page': 0, 'source': '/home/quamer23nasim38/Role-Based-Access-Control-of-Qdrant-Vector-Database/data/financial/Sample-Accounting-Income-Statement-PDF-File.pdf'}, 'page_content': 'quarter or a month . The next period’s income statement will start over with all amounts reset to zero. While the balance sheet shows accumulated balances since inception, the income statement only shows the amounts earned or expensed during the period in question. Statement of Retained Earnings The statement of retained earnings shows the amount of accumulated earnings that have been retained within the company since its inception. At the end of each fiscal year-end, the amount of net'}, vector=None, shard_key=None),
ScoredPoint(id=22, version=0, score=0.6324039, payload={'metadata': {'page': 5, 'source': '/home/quamer23nasim38/Role-Based-Access-Control-of-Qdrant-Vector-Database/data/financial/Sample-Accounting-Income-Statement-PDF-File.pdf'}, 'page_content': 'XYZ COMPANY LIMITED NOTES TO THE FINANCIAL STATEMENTS FOR THE YEAR ENDED JUNE 30, 2002 UNAUDITED - See "Notice to Reader" 1. SIGNIFICANT ACCOUNTING POLICIES AND GENERAL INFORMATION Nature of Business The company is a Canadian-controlled private corporation subject to the Business Corporations Act, 1982 (Ontario), was incorporated in May 1995 and operates as a manufacturer of widgets in Anytown, Ontario. Significant Accounting Policies INVENTORY'}, vector=None, shard_key=None),
ScoredPoint(id=10, version=0, score=0.62833935, payload={'metadata': {'page': 1, 'source': '/home/quamer23nasim38/Role-Based-Access-Control-of-Qdrant-Vector-Database/data/financial/Sample-Accounting-Income-Statement-PDF-File.pdf'}, 'page_content': "$ 276,498 $ 331,259 LIABILITIES CURRENT Bank overdraft $ -- $ 9,474Bank loan: $60,000 Accounts payable and accrued liabilities: 82,053; 91,343Long-term debt: current portion 25,200 --income tax payable 14,387 -- 121,640 -- 160,817 DUE TO SHAREHOLDER (Note 3) 51,591 231,791LONG-TERM DEBT (Note 4): 86,100 -- 259,331 -- 392,608 SHAREHOLDER'S EQUIT AND STATED CAPITAL (Note 5) 1 1 RETAINED EARNINGS (DEFICIT) 17,166 (61,350) 17,167 (61,349) $ 276,498 $ 331,259 APPROVED"}, vector=None, shard_key=None)]
```
Great! The user can read the ‘financial’ collection. In the next section, let’s go ahead and see how we can limit user access within a single collection. We basically want to limit access to specific types of documents in the collection.
### Document-Specific Access
In this last section, we will limit the user's access to specific types of documents in the collection. This is one of the most secure ways to grant access to the user. Assume a scenario where you have a collection of ‘general’ data and, in that collection, you have multiple types of documents, You can limit the access of the user to specific types of documents only. Let’s see how we can do this.
Here we create a token that allows the user to access only the general collection and the documents, which are named ‘security_policy.pdf’.
```
import time
from utils import generate_jwt
current_time = int(time.time())
This payload, along with the API, is used to generate the JWT token.
This token indicates that the user has access to the general collection only.
# Access to the general collection is read-write.
It also specifies that the token only limits access to the document security_policy.pdf in the general collection.
It also specifies that this token will expire in 1 hour.
payload = {
"exp": current_time + 3600, # 1 hour
"access": [
{
"collection": "general",
"access": "rw",
"payload": {
"metadata.source": "/home/quamer23nasim38/Role-Based-Access-Control-of-Qdrant-Vector-Database/data/general/security_policy.pdf",
}
},
]
}
Generate the JWT token
jwt = generate_jwt(api, payload)
from qdrant_client import QdrantClient
client = QdrantClient(url=url, api_key=jwt)
We are generating a query vector from a string that was available in the document security_policy.pdf in the general collection
x = 'take the security of Qdrant code'
query_vector = embed_model.get_sentence_vector(x).tolist()
We are searching for the closest points to the query vector in the general collection
hits = client.search(
collection_name="general",
query_vector=query_vector,
limit=5 # Return 5 closest points
)
hits
```
```
Output of the above code
[ScoredPoint(id=10, version=2, score=0.8121032, payload={'metadata': {'page': 1, 'source': '/home/quamer23nasim38/Role-Based-Access-Control-of-Qdrant-Vector-Database/data/general/security_policy.pdf'}, 'page_content': 'within the Qdrant Cloud platform, and only the necessary ports are opened on each server. All outbound connections pass through the stateless access control rules, whilst inbound connections from the internet must pass through a secure, highly-available load balancer layer and the stateless access control firewall rules before being routed to each server. Software security We take the security of the Qdrant code very seriously. The database is built using the Rust language (a static'}, vector=None, shard_key=None).
ScoredPoint(id=5, version=2, score=0.7998578, payload={'metadata': {'page': 0, 'source': '/home/quamer23nasim38/Role-Based-Access-Control-of-Qdrant-Vector-Database/data/general/security_policy.pdf'}, 'page_content': 'into account the impact of company threats and vulnerabilities; must design and implement a comprehensive suite of information security controls and other forms of risk management to address company and architecture security risks; and adopt an overarching management process to ensure that the information security controls meet the information security needs on an ongoing basis. In addition, all hosting providers are certified at PCI DSS Level 1, which means that the application is run on the'}, vector=None, shard_key=None),
ScoredPoint(id=4, version=2, score=0.77687603, payload={'metadata': {'page': 0, 'source': '/home/quamer23nasim38/Role-Based-Access-Control-of-Qdrant-Vector-Database/data/general/security_policy.pdf'}, 'page_content': 'centers are staffed 24x7x365 by security guards, and access is authorized strictly on a least privileged basis. The cloud hosting providers are certified with the ISO 9001:2008, ISO 27001:2013, ISO 27017:2015, and ISO 27018:2014 security standards—global standards that outline the requirements for information security management systems. This requires that the hosting provider systematically evaluate its information security risks, taking into account the impact of company threats and'}, vector=None, shard_key=None),
ScoredPoint(id=8, version=2, score=0.76660895, payload={'metadata': {'page': 1, 'source': '/home/quamer23nasim38/Role-Based-Access-Control-of-Qdrant-Vector-Database/data/general/security_policy.pdf'}, 'page_content': 'All servers are tested for vulnerability and intrusion detection quarterly. The servers and services hosted on them are certified as complying with the PCI Data Security Standard established by the PCI Security Standards Council, which is an open global forum for the development, enhancement, storage, dissemination, and implementation of security standards for account data protection. The certification confirms that the services adhere to the PCI DSS Level 4 requirements for security management,'}, vector=None, shard_key=None),
ScoredPoint(id=3, version=2, score=0.7539886, payload={'metadata': {'page': 0, 'source': '/home/quamer23nasim38/Role-Based-Access-Control-of-Qdrant-Vector-Database/data/general/security_policy.pdf'}, 'page_content': 'will work with you to assess and understand the scope of the issue and fully address any concerns. Any emails are immediately sent to our engineering staff to ensure that issues are addressed rapidly. Any security emails are treated with the highest priority, as the safety and security of our service are our primary concerns. Physical security Qdrant Cloud services are hosted on Google Cloud Computing, Amazon Web Services, and Azure. The data centers are staffed 24x7x365 by security guards. '}, vector=None, shard_key=None)]
```
As we can see, the search query returned only chunks of the document'security_policy.pdf’. It did not return any other documents. Next, let’s try to go even further and limit access to a specific page of the document. Let’s see how we can do this.
On top of all the previous restrictions, we have also limited access to the second page of the document'security_policy.pdf’. Let’s see if the user can access any other page except the second page of the document.
```
import time
from utils import generate_jwt
current_time = int(time.time())
# This payload along with the API is used to generate the JWT token.
# This token tells that the user has access to the general collection only.
# The access to the general collection is read-write.
# It also specifies that the token only limits the access to the document security_policy.pdf in the general collection.
# It also specifies that the token only limits the access to the second page (page index starts with 0) of the document.
# It also specifies that this token will expire in 1 hour.
payload = {
"exp": current_time + 3600, # 1 hour
"access": [
{
"collection": "general",
"access": "rw",
"payload": {
"metadata.source": "/home/quamer23nasim38/Role-Based-Access-Control-of-Qdrant-Vector-Database/data/general/security_policy.pdf",
"metadata.page": 1
}
},
]
}
# Generate the JWT token
jwt = generate_jwt(api, payload)
from qdrant_client import QdrantClient
client = QdrantClient(url=url, api_key=jwt)
x = 'take the security of Qdrant code'
query_vector = embed_model.get_sentence_vector(x).tolist()
hits = client.search(
collection_name="general",
query_vector=query_vector,
limit=20 # Return 5 closest points
)
hits
```
```
# Output of the above code
[ScoredPoint(id=10, version=2, score=0.8121032, payload={'metadata': {'page': 1, 'source': '/home/quamer23nasim38/Role-Based-Access-Control-of-Qdrant-Vector-Database/data/general/security_policy.pdf'}, 'page_content': 'within the Qdrant Cloud platform, and only the necessary ports are opened on each server. All outbound connections pass through the stateless access control rules, whilst inbound connections from the internet must pass through a secure, highly-available load balancer layer, and the stateless access control firewall rules before then being routed to each server. Software security We take the security of the Qdrant code very seriously. The database is built using the Rust language - a static'}, vector=None, shard_key=None),
ScoredPoint(id=8, version=2, score=0.76660895, payload={'metadata': {'page': 1, 'source': '/home/quamer23nasim38/Role-Based-Access-Control-of-Qdrant-Vector-Database/data/general/security_policy.pdf'}, 'page_content': 'All servers are tested for vulnerability and intrusion detection quarterly. The servers and services hosted on them are certified as complying with the PCI Data Security Standard established by the PCI Security Standards Council, which is an open global forum for the development, enhancement, storage, dissemination, and implementation of security standards for account data protection. The certification confirms that the services adhere to the PCI DSS Level 4 requirements for security management,'}, vector=None, shard_key=None),
ScoredPoint(id=11, version=2, score=0.74504614, payload={'metadata': {'page': 1, 'source': '/home/quamer23nasim38/Role-Based-Access-Control-of-Qdrant-Vector-Database/data/general/security_policy.pdf'}, 'page_content': 'is built using the Rust language - a static multi-paradigm, memory-efficient, low-level programming language focused on speed, security, and performance. The intention is to build Qdrant with as few moving parts as possible, thereby keeping the attack vector as low as possible. Email security Qdrant supports TLS encryption on all inbound and outbound emails. Qdrant uses Gmail to provide email and communication services. For an explanation of how email encryption works, take a look at this'}, vector=None, shard_key=None),
ScoredPoint(id=9, version=2, score=0.71566045, payload={'metadata': {'page': 1, 'source': '/home/quamer23nasim38/Role-Based-Access-Control-of-Qdrant-Vector-Database/data/general/security_policy.pdf'}, 'page_content': 'DSS Level 4 requirements for security management, policies, procedures, network architecture, software design, and other critical protective measures. Network security The system is designed with scalability and redundancy in mind. Web load balancers and database servers are distributed globally across geographically dispersed data centers in different operating regions. Each database server has its own firewall configuration based on its role within the Qdrant Cloud platform, and only the'}, vector=None, shard_key=None),
ScoredPoint(id=12, version=2, score=0.70694244, payload={'metadata': {'page': 1, 'source': '/home/quamer23nasim38/Role-Based-Access-Control-of-Qdrant-Vector-Database/data/general/security_policy.pdf'}, 'page_content': 'how email encryption works, take a look at this overview from Google. Data residency On Qdrant Cloud, the location of data can be specified. Locations may include London, Ireland, Belgium, Germany, Switzerland, North America, South America, Australia, Canada, Tokyo, or Singapore. Data will not be moved or replicated outside of a specified location. Data in transit All data is encrypted when it is being transmitted between client devices and Qdrant Cloud. SSL/TLS certificates shield data using'}, vector=None, shard_key=None),
ScoredPoint(id=13, version=2, score=0.63619953, payload={'metadata': {'page': 1, 'source': '/home/quamer23nasim38/Role-Based-Access-Control-of-Qdrant-Vector-Database/data/general/security_policy.pdf'}, 'page_content': 'Cloud. SSL/TLS certificates shield data using 256-byte signatures and either 2048-bit or 4096-bit keys. All connections to Content Delivery Network (CDN) servers and the database layer are'}, vector=None, shard_key=None)]
```
As we can see, the exact same search query like the last section returned only the second page of the document ‘security_policy.pdf’, as expected.
Before I end this tutorial, let me show you one more way to limit the access of the user. Here we will limit the access of the user by using the ‘value_exists’ filter. This basically means that the user can only access the collection if the specific field exists in the document. Though this can be extended to several use cases, like user_id, user_role, etc, for the ease of this tutorial, let’s just use the ‘value_exists’ filter to check the presence of the document type. If the document type exists, then only the user can access the collection.
Let’s first see what happens if the document type does not exist in the document.
```
import time
from utils import generate_jwt
current_time = int(time.time())
# This payload along with the API is used to generate the JWT token.
# This token tells that the user has access to the general collection only.
# The access to the general collection is read-write.
# Apart from the access to read-write the general collection, the token also specifies to check
# if the metadata.source key in the document matches the value "/home/quamer23nasim38/Role-Based-Access-Control-of-Qdrant-Vector-Database/data/general/avengers-endgame-script-pdf.pdf".
# if it matches, then the user will have read-write access to the general collection.
# if it doesn't match, then the user won't have any access to the general collection.
# It also specifies that this token will expire in 1 hour.
payload = {
"exp": current_time + 3600, # 1 hour
"value_exists": {
"collection": "general",
"matches": [
{
"key": "metadata.source",
"value": "/home/quamer23nasim38/Role-Based-Access-Control-of-Qdrant-Vector-Database/data/general/blah blah blah.pdf"
}
]
},
"access": [
{
"collection": "general",
"access": "rw",
},
]
}
# Generate the JWT token
jwt = generate_jwt(api, payload)
from qdrant_client import QdrantClient
client = QdrantClient(url=url, api_key=jwt)
# We are generating a query vector from a string that was available in the document avengers-endgame-script-pdf.pdf in the general collection
x = 'take the security of Qdrant code'
query_vector = embed_model.get_sentence_vector(x).tolist()
hits = client.search(
collection_name="general",
query_vector=query_vector,
limit=5 # Return 5 closest points
)
hits
```
```
# Output of the above code
UnexpectedResponse: Unexpected Response: 401 (Unauthorized)
Raw response content:
b'Invalid JWT, stateful validation failed'
```
Woah! The API returned a 401 Unauthorized error. It clearly says that the validation failed! This is great. Let’s see what happens if the document type exists in the document.
```
import time
current_time = int(time.time())
# This payload along with the API is used to generate the JWT token.
# This token tells that the user has access to the general collection only.
# The access to the general collection is read-write.
# Apart from the access to read-write the general collection, the token also specifies to check
# if the metadata.source key in the document matches the value "/home/quamer23nasim38/Role-Based-Access-Control-of-Qdrant-Vector-Database/data/general/avengers-endgame-script-pdf.pdf".
# if it matches, then the user will have read-write access to the general collection.
# if it doesn't match, then the user won't have any access to the general collection.
# It also specifies that this token will expire in 1 hour.
payload = {
"exp": current_time + 3600, # 1 hour
"value_exists": {
"collection": "general",
"matches": [
{
"key": "metadata.source",
"value": "/home/quamer23nasim38/Role-Based-Access-Control-of-Qdrant-Vector-Database/data/general/avengers-endgame-script-pdf.pdf"
}
]
},
"access": [
{
"collection": "general",
"access": "rw",
},
]
}
# Generate the JWT token
jwt = generate_jwt(api, payload)
client = QdrantClient(url=url, api_key=jwt)
x = 'take the security of Qdrant code'
query_vector = embed_model.get_sentence_vector(x).tolist()
hits = client.search(
collection_name="general",
query_vector=query_vector,
limit=5 # Return 5 closest points
)
hits
```
```
# Output of the above code
[ScoredPoint(id=10, version=2, score=0.8121032, payload={'metadata': {'page': 1, 'source': '/home/quamer23nasim38/Role-Based-Access-Control-of-Qdrant-Vector-Database/data/general/security_policy.pdf'}, 'page_content': 'within the Qdrant Cloud platform, and only the necessary ports are opened on each server. All outbound connections pass through the stateless access control rules, whilst inbound connections from the internet must pass through a secure, highly-available load balancer layer, and the stateless access control firewall rules before then being routed to each server. Software security We take the security of the Qdrant code very seriously. The database is built using the Rust language - a static'}, vector=None, shard_key=None),
ScoredPoint(id=5, version=2, score=0.7998578, payload={'metadata': {'page': 0, 'source': '/home/quamer23nasim38/Role-Based-Access-Control-of-Qdrant-Vector-Database/data/general/security_policy.pdf'}, 'page_content': 'into account the impact of company threats and vulnerabilities; must design and implement a comprehensive suite of information security controls and other forms of risk management to address company and architecture security risks; and adopt an overarching management process to ensure that the information security controls meet the information security needs on an ongoing basis. In addition, all hosting providers are certified at PCI DSS Level 1, which means that the application is run on the'}, vector=None, shard_key=None),
ScoredPoint(id=4, version=2, score=0.77687603, payload={'metadata': {'page': 0, 'source': '/home/quamer23nasim38/Role-Based-Access-Control-of-Qdrant-Vector-Database/data/general/security_policy.pdf'}, 'page_content': 'centers are staffed 24x7x365 by security guards, and access is authorized strictly on a least privileged basis. The cloud hosting providers are certified with the ISO 9001:2008, ISO 27001:2013, ISO 27017:2015, and ISO 27018:2014 security standards - global standards that outline the requirements for information security management systems. This requires that the hosting provider must systematically evaluate its information security risks, taking into account the impact of company threats and'}, vector=None, shard_key=None),
ScoredPoint(id=8, version=2, score=0.76660895, payload={'metadata': {'page': 1, 'source': '/home/quamer23nasim38/Role-Based-Access-Control-of-Qdrant-Vector-Database/data/general/security_policy.pdf'}, 'page_content': 'All servers are tested for vulnerability and intrusion detection quarterly. The servers and services hosted on them are certified as complying with the PCI Data Security Standard established by the PCI Security Standards Council, which is an open global forum for the development, enhancement, storage, dissemination, and implementation of security standards for account data protection. The certification confirms that the services adhere to the PCI DSS Level 4 requirements for security management,'}, vector=None, shard_key=None),
ScoredPoint(id=3, version=2, score=0.7539886, payload={'metadata': {'page': 0, 'source': '/home/quamer23nasim38/Role-Based-Access-Control-of-Qdrant-Vector-Database/data/general/security_policy.pdf'}, 'page_content': 'will work with you to assess and understand the scope of the issue and fully address any concerns. Any emails are immediately sent to our engineering staff to ensure that issues are addressed rapidly. Any security emails are treated with the highest priority, as the safety and security of our service are our primary concerns. Physical security Qdrant Cloud services are hosted on Google Cloud Computing and Amazon Web Services, and Azure. The data centers are staffed 24x7x365 by security guards,'}, vector=None, shard_key=None)]
```
Nice! It validated the document type and confirmed that the document type exists in the document. Once the validation is successful, it returned the chunks of the document from the correct document irrespective of the validation document type.
Finally, we have seen how we can use the Qdrant Vector Database with RBAC enabled and how we can grant access to the user based on their roles. We have seen how we can grant global read-only access, global manage access, collection-specific access, and document-specific access. We have also seen how we can limit the access of the user by using the ‘value_exists’ filter. This is a very powerful feature of Qdrant and can be used in various use cases.
## Conclusion
Role-Based Access Control is super important for keeping our data safe and making sure the right people have the right access. When we mix RBAC with a Hybrid Cloud setup, it gives us a lot more flexibility to store and manage our data in different ways. Qdrant really shines here because it lets us control access in a really detailed way using JWT and Hybrid Cloud. Unlike some other databases like Pinecone, Milvus, Chroma, and Weaviate, Qdrant stands out for its strong security and privacy features. In this blog, I showed how we can get Qdrant up and running in a Hybrid Cloud setup and set up JWT for RBAC, showing just how easy and effective it can be to manage access in today’s data environments.
## GitHub Repo
The codes for this blog can be found at https://github.com/quamernasim/Role-Based-Access-Control-of-Qdrant-Vector-Database
## References
https://qdrant.tech/documentation/guides/security/
https://qdrant.tech/blog/qdrant-1.9.x/
https://quamernasim.medium.com/hindi-language-ai-chatbot-for-enterprises-using-llama-3-qdrant-ollama-langchain-and-mlflow-9b69391d3348
This article was originally published on: https://quamernasim.medium.com/enhancing-data-security-with-role-based-access-control-of-qdrant-vector-database-3878769bec83 | quamernasim |
1,871,869 | Investing in Web3 projects: a guide for modern business and finance | The web3 world is booming, and so are the number of talented developers. This surge has led to the... | 0 | 2024-05-31T09:53:16 | https://dev.to/shevchukkk/investing-in-web3-projects-a-guide-for-modern-business-and-finance-1a79 | web3, cryptocurrency, blockchain | The web3 world is booming, and so are the number of talented developers. This surge has led to the emergence of many new and exciting companies that are building the future of the internet. According to [Decrypt](https://decrypt.co/100784/web3-value), there are already over 10,000 known web3 companies in the cryptocurrency and blockchain space. This is a testament to the fact that despite the bear market of 2022, interest in web3 remains strong. Investors [poured](https://beincrypto.com/what-bear-market-web3-investments-soared-2022/) $7.1 billion into the space, a 4.5x increase from 2021 when Bitcoin was at its peak price.
In today’s rapidly evolving digital landscape, businesses are constantly faced with a barrage of opportunities and tools to automate processes and enhance overall quality of life. This necessitates a proactive approach and a willingness to embrace new possibilities, especially in the realm of entrepreneurship. As competition in the global market intensifies, businesses must adapt quickly to the ever-changing dynamics of the business world.
The advent of Web3, the next generation of the internet, has brought about a paradigm shift in how businesses operate. In essence, Web3 for business signifies data control without intermediaries. This is underpinned by the principles of decentralization and transparency in financial transactions, enabling direct legal transactions without the need for centralized institutions. Before diving into Web3 adoption or business creation, it’s crucial to understand the various ways in which this can be achieved. Let’s delve into some of the diverse use cases of Web3 technologies in business:
**1. Web3 gaming**
While a sustainable model for crypto gaming that guarantees success has yet to emerge, here are three useful metrics to help evaluate the potential of P2E projects:
**Active player count**
This metric, reflecting the number of daily (or monthly) active users, is crucial for determining the game’s growth and popularity. Equally important is the project’s ability to retain this active audience.
**Transaction volume per user**
This metric refers to the average amount of money spent per player. It reflects both the level of user engagement and the soundness of the token design.
**Number and quality of guild partnerships**
In Web3 games, growth and distribution typically rely on player referrals and guild partnerships. Crypto gaming guilds are communities of gamers who play together, share information and in-game assets, and support other players. Guilds like [Yield Guild Games](https://www.yieldguild.io/), [Ancient8](https://blog.ancient8.gg/), [Good Games Guild](https://goodgamesguild.com/), and [Merit Circle](https://meritcircle.io/) enable new players to start playing by lending them in-game assets they otherwise couldn’t afford.
Web3 gaming presents a novel and exciting opportunity, catering to a growing niche of users. These games leverage blockchain technology to provide gamers with greater autonomy, enabling them to earn rewards and enhance their characters. [Illuvium](https://phemex.com/academy/what-is-illivium-ilv), a high-budget, open-world AAA fantasy RPG, exemplifies this trend. Players can capture and train powerful Illuvials, each represented by a unique NFT with distinct abilities.
**2. Web3 social networks**
Web3 social media platforms offer a unique blend of features designed to attract a large audience seeking new solutions, analysis, and shared resources. [Friend.tech](https://www.friend.tech/), a decentralized social media app built on the blockchain, stands out as an example. Its unique structure allows users to trade shares linked to their profiles, granting access to exclusive private chats with relevant individuals. Communities formed on this platform are characterized by their distinctive concepts and financial incentives, moving away from traditional social media models and towards a business-oriented communication tool.
According to [NINJA’s](https://ninjapromo.io/best-web3-social-media-platforms) predictions, [Diamond App](https://diamondapp.com/browse?feedTab=Hot) is poised to become a major player in the social media realm in 2024. This decentralized ecosystem seamlessly blends elements of social networking, cryptocurrency, and NFTs. Built on the DeSo blockchain, the Diamond App grants users unprecedented control over their data and content, empowering them to monetize their creativity and influence. At the heart of the Diamond App lies a unique token system. Each user is assigned their own token, representing their reputation and clout within the network. These tokens can be bought, sold, and held, providing users with the opportunity to invest in creators they admire. The platform goes a step further by enabling users to earn real-world rewards for their posts and interactions with the audience. Likes and comments are converted into cryptocurrency, while posts can be transformed into NFTs, which can be sold or collected.
Another platform gaining traction is [MINDS](https://www.minds.com/), a project that prioritizes user privacy. MINDS stands out by refusing to sell user data to advertisers or track their activity. Users maintain complete control over their information, deciding who has access to it. Minds Tokens serve as the platform’s native currency, rewarding users for their content creation and engagement with others. These tokens can be utilized to boost the visibility of posts, support fellow creators, or be exchanged for fiat currencies.
**3. Cryptoinvestment: a new level for modern business**
Investing in cryptocurrencies has emerged as a promising avenue for traders and crypto enthusiasts, offering enhanced security, improved efficiency, and access to a broader range of assets. According to a study by the [World Economic Forum](https://www.weforum.org/agenda/2022/11/cryptocurrency-us-midterms/), amid heightened political polarization both within and beyond the United States, cryptocurrency is emerging as an asset that unites Democrats and Republicans. According to the poll, over half of Americans (53%), namely 59% of Democrats and 51% of Republicans, believe that cryptocurrencies are the future of finance. Approximately 22% of registered voters own cryptocurrency, with ownership levels similar among Democrats (27%) and Republicans (22%).
Decentralized exchanges and peer-to-peer trading enable users to conduct transactions without intermediaries, maintain control over their assets, and reduce the risk of breaches and scams. Among the reputable exchanges, [Forbes ADVISOR](https://www.forbes.com/advisor/investing/cryptocurrency/best-crypto-exchanges/) lists [Kraken](https://www.kraken.com/?clickid=U-jUO8XGBxyPTpjWPA2F1TK1UkHWsfQGeU4JRo0&utm_source=Impact&utm_medium=Affiliate&utm_campaign=1955282&utm_content=Homepage&irgwc=1&mpid=1955282) with fixed fees of 0.9% for stablecoins and 1.5% for other cryptocurrencies, and [Gemini](https://gemini.sjv.io/c/1955282/1297140/11829?subid1=P1424552309_C1713513928471306797&subid2=https%3A%2F%2Fwww.forbes.com%2Fadvisor%2Finvesting%2Fcryptocurrency%2Fbest-crypto-exchanges%2F&subid3=Advisor_US) with a maker fee of 0.2% and a taker fee of 0.4%. Regarding the other popular exchange, [WhiteBIT](https://whitebit.com/ua), the exchange offers some of the lowest trading fees on the market, starting at 0.1% for both takers and makers. This makes the platform attractive to traders of all experience levels who are looking for favorable trading conditions.
**Conclusion**
Web3 marks a pivotal evolution of the internet, ushering in a new era of ownership and decentralization. Unlike Web2, where users lacked control over their data and creations, Web3 empowers individuals with sovereignty over their digital assets. Businesses can leverage this to develop innovative products and services, foster stronger customer relationships, and reap the benefits of a more democratic and equitable internet, free from the dominance of a few large technology companies. | shevchukkk |
1,871,867 | Unveiling the Medicinal Wonders of Cabbage | Cabbage, a common yet remarkable cruciferous vegetable, is a staple in many kitchens worldwide.... | 0 | 2024-05-31T09:51:09 | https://dev.to/will_jacks_195c8703541796/unveiling-the-medicinal-wonders-of-cabbage-179e | Cabbage, a common yet remarkable cruciferous vegetable, is a staple in many kitchens worldwide. Renowned for its versatility and crunchy texture, cabbage offers an array of health benefits that have been acknowledged for centuries. This comprehensive guide explores the medicinal uses of cabbage, highlighting its numerous health benefits, and briefly mentioning [Prosoma 500](url=https://go4pills.com/product/prosoma-500-mg/), a natural supplement known for its therapeutic properties.
Nutritional Powerhouse
To understand the medicinal potential of cabbage, it's important to first look at its rich nutritional profile. This leafy vegetable is packed with essential nutrients, including vitamins, minerals, and antioxidants. Notably, cabbage is high in vitamins C, K, and B6, and contains significant amounts of manganese, potassium, and folate. Additionally, it offers beneficial phytonutrients like glucosinolates, flavonoids, and anthocyanins, which contribute to its health-promoting properties.
Potent Anti-inflammatory Effects
Cabbage is well-known for its potent anti-inflammatory properties. Chronic inflammation is a key factor in many health conditions, such as cardiovascular disease, arthritis, and digestive disorders. Compounds like glucosinolates and flavonoids found in cabbage possess strong anti-inflammatory effects. These compounds help to reduce inflammation in the body, alleviating symptoms associated with conditions like rheumatoid arthritis, inflammatory bowel disease, and asthma.
Enhancing Digestive Health
The benefits of cabbage for digestive health are impressive, largely due to its high fiber content and probiotic properties. Fiber is crucial for promoting regular bowel movements and preventing constipation by adding bulk to the stool. Furthermore, cabbage contains natural prebiotics that nourish beneficial gut bacteria, supporting a healthy microbiome. Regular consumption of cabbage can help relieve digestive issues such as bloating, gas, and indigestion. Supplementing with Prosoma 500, which includes ingredients known for their digestive benefits, can further enhance these digestive health benefits.
Natural Remedy for Gastric Ulcers
Cabbage has a long history of being used as a natural remedy for gastric ulcers. Cabbage juice, in particular, is believed to have ulcer-healing properties due to its high content of vitamin U (S-methylmethionine). Studies indicate that consuming cabbage juice can accelerate the healing of gastric ulcers and alleviate symptoms like abdominal pain and discomfort.
Boosting Immune Function
Maintaining a strong immune system is crucial for defending against infections and illnesses. Cabbage, with its high vitamin C content and antioxidant properties, can help enhance immune function. Vitamin C is a powerful antioxidant that neutralizes free radicals and supports the production of white blood cells, which are essential for fighting off pathogens. Including cabbage in your diet can strengthen your immune defenses and promote overall health.
Promoting Cardiovascular Health
With heart disease being a leading cause of death worldwide, preventive measures are more important than ever. Cabbage offers several cardiovascular health benefits thanks to its unique combination of nutrients and phytochemicals. Potassium, found in abundance in cabbage, helps regulate blood pressure and reduce the risk of hypertension and stroke. Additionally, cabbage contains compounds like sulforaphane and anthocyanins that help lower cholesterol levels, improve blood vessel function, and reduce the risk of atherosclerosis.
Potential for Cancer Prevention
Cabbage is gaining recognition for its potential role in cancer prevention, attributed to its rich array of phytochemicals with anticancer properties. Glucosinolates in cabbage are converted into bioactive compounds like indole-3-carbinol and sulforaphane in the body. These compounds have been shown to inhibit the growth of cancer cells, induce apoptosis (cell death), and suppress tumor formation in laboratory studies. While more research is needed, including cabbage in a balanced diet may help reduce the risk of certain cancers, such as colon, breast, and prostate cancer.
Benefits for Skin Health
Cabbage isn't just good for your internal health; it can also improve skin health when applied topically. Cabbage contains vitamins A and E, as well as sulfur compounds, which nourish and rejuvenate the skin. Applying cabbage juice or crushed cabbage leaves to the skin can help soothe inflammation, reduce redness, and improve the appearance of blemishes and acne scars. Additionally, cabbage's antioxidants protect the skin from environmental damage and premature aging, keeping it youthful and glowing.
Cognitive Health Support
Recent studies suggest that cabbage may support cognitive health due to its antioxidant properties and nutrient-rich composition. Antioxidants like vitamin C and flavonoids found in cabbage help protect brain cells from oxidative stress and inflammation, which are linked to cognitive decline and neurodegenerative diseases like Alzheimer's. Moreover, cabbage contains vitamin K, which is vital for brain health by supporting cognitive function and reducing the risk of cognitive impairment. Including cabbage in your diet may help maintain brain health and cognitive function as you age.
Aiding in Weight Management
Cabbage is a low-calorie, nutrient-dense food that supports weight management and promotes satiety. With its high fiber content and low energy density, cabbage helps you feel full without adding excessive calories to your diet. Additionally, cabbage is rich in water, adding volume to meals and helping keep you hydrated. Incorporating cabbage into your meals, whether raw, cooked, or fermented, can enhance feelings of fullness and satisfaction, making it easier to manage your weight and achieve your health goals.
Supporting Bone Health
Cabbage contains essential nutrients like calcium, magnesium, and vitamin K, all of which are crucial for maintaining strong and healthy bones. Calcium is key for bone density and structure, while magnesium helps regulate calcium levels and supports bone metabolism. Vitamin K plays a critical role in bone mineralization and helps prevent fractures by enhancing bone strength. Including cabbage in your diet can contribute to overall bone health and reduce the risk of osteoporosis and bone-related conditions.
Assisting in Detoxification
Cabbage contains sulfur compounds and antioxidants that support the body's natural detoxification processes. Sulfur compounds, such as sulforaphane, activate enzymes in the liver that facilitate detoxification and eliminate toxins from the body. Additionally, antioxidants like vitamin C and glutathione help neutralize harmful free radicals and promote cellular detoxification. Incorporating cabbage into your meals, especially in salads, soups, or stir-fries, can aid in detoxification and support overall health and well-being.
Promoting Eye Health
Cabbage is rich in vitamins and antioxidants that support eye health and vision. Vitamin A, found in cabbage, is essential for maintaining healthy vision, especially in low-light conditions. Additionally, cabbage contains carotenoids like lutein and zeaxanthin, which help protect the eyes from age-related macular degeneration and cataracts by filtering harmful blue light and reducing oxidative stress. Regular consumption of cabbage may help preserve eye health and reduce the risk of vision-related issues as you age.
Conclusion: Unlocking the Healing Potential of Cabbage
In conclusion, cabbage is not just a simple vegetable; it's a powerhouse of nutrition with a wide range of medicinal uses. From reducing inflammation and supporting digestive health to boosting immune function and promoting cardiovascular wellness, cabbage offers numerous health benefits for people of all ages.
| will_jacks_195c8703541796 | |
1,871,866 | 10. Make Smarter Loan Decisions: Intelligent NBFC Software for Informed Lending. | Non-Banking Financial Companies (NBFCs) are the backbone of the Indian financial services. They are... | 0 | 2024-05-31T09:48:49 | https://dev.to/finsta/10make-smarter-loan-decisions-intelligent-nbfc-software-for-informed-lending-2hb2 | Non-Banking Financial Companies (NBFCs) are the backbone of the Indian financial services. They are great enablers of financial inclusion as they support the growth aspirations of industries and people even in the remote corners of the country. FiNSTA, a flagship product of Kapil IT, is a cutting-edge NBFC software that helps NBFCs to minimize their operational risks and achieve optimal efficiency.
As a highly advanced, comprehensive NBFC software suite that streamlines loan processing and the management of loan lifecycles, FiNSTA’s loan and scheme configurators allow you to configure customized-loan products based on customer profiles. The software suite also helps you speed up the lending process.
Our NBFC loan management software helps NBFCs to eliminate paper-intensive work and automates their workflow. FiNSTA empowers NBFCs to screen and process loan applications on mobile as well as web-based platforms for a seamless operational experience.
With business targets and deadlines being the prime considerations for NBFCs, you can bet on FiNSTA as the best NBFC software to drive exceptional business growth for your NBFC.
NBFC SOFTWARE ,LOAN MANAGEMENT SOFTWARE BUSINESS MANAGEMENT SOFTWARE | finsta | |
1,871,865 | Discover Unbeatable Flight Offers: Your Ultimate Guide to Affordable Air Travel | In today’s fast-paced world, flying is no longer a luxury but a necessity. Whether you’re planning... | 0 | 2024-05-31T09:47:59 | https://dev.to/travelgo/discover-unbeatable-flight-offers-your-ultimate-guide-to-affordable-air-travel-g6h | flight, travel, trip, flightdeals | <p> </p><p class="graf graf--p" name="1e24"> In today’s fast-paced world, flying is no longer a luxury but a necessity. Whether you’re planning a business trip, a family vacation, or a spontaneous getaway, finding the best flight deals can make all the difference. This guide will show you how to access incredible offers and make the most of your air travel experience. With the latest trends and search insights, we ensure you get the best deals and tips for a seamless journey.</p><figure class="graf graf--figure" name="b635"><img class="graf-image" data-height="667" data-image-id="0*rWh8uSCxG5OC7VtX" data-width="1000" src="https://cdn-images-1.medium.com/max/800/0*rWh8uSCxG5OC7VtX" /></figure><ul class="postList"><li class="graf graf--li" name="6960">Why Choose Air Travel?</li></ul><p class="graf graf--p" name="1b0b">Flying offers numerous advantages over other modes of transportation. It’s the fastest way to cover long distances, allowing you to reach your destination quickly and comfortably. Modern aircraft are equipped with advanced technology and amenities, ensuring a safe and enjoyable journey. Plus, with the right deals, flying can be surprisingly affordable.</p><ul class="postList"><li class="graf graf--li" name="a725">Top Search Trends in Air Travel</li></ul><p class="graf graf--p" name="ff0a">To help you navigate the vast options available, we’ve analyzed the most searched topics and trending keywords related to flights:</p><ol class="postList"><li class="graf graf--li" name="f2a3">Cheap Flights<br />2. Last-Minute Flight Deals<br />3. Direct Flights<br />4. Flight Discounts<br />5. Travel Hacks for Flights</li></ol><p class="graf graf--p" name="daa3"><a class="markup--anchor markup--p-anchor" data-href="https://www.booking.com/flights/index.html?aid=8019784" href="https://www.booking.com/flights/index.html?aid=8019784" rel="noopener" target="_blank">Click HERE to find the most suitable offers for you!</a></p><p class="graf graf--p" name="dce7">By understanding these trends, we can provide you with the most relevant information to ensure you find the best flight deals available.</p><ul class="postList"><li class="graf graf--li" name="8bd1">Uncovering the Best Flight Deals</li></ul><ol class="postList"><li class="graf graf--li" name="e50b">Cheap Flights</li></ol><figure class="graf graf--figure" name="5242"><img class="graf-image" data-height="664" data-image-id="0*riu_-ohbWIRTUoGw" data-width="1000" src="https://cdn-images-1.medium.com/max/800/0*riu_-ohbWIRTUoGw" /></figure><h4 class="graf graf--h4" name="c032"><a class="markup--anchor markup--h4-anchor" data-href="https://ttravelgoo.blogspot.com/" href="https://ttravelgoo.blogspot.com/" rel="noopener" target="_blank">Visit our website for more offers!</a></h4><h4 class="graf graf--h4" name="2868"><a class="markup--anchor markup--h4-anchor" data-href="https://www.facebook.com/profile.php?id=61560198516319" href="https://www.facebook.com/profile.php?id=61560198516319" rel="noopener" target="_blank">Our Facebook page!</a></h4><p class="graf graf--p graf--empty" name="89bb"><br /></p><p class="graf graf--p" name="71d2">Everyone loves a bargain, and finding cheap flights is at the top of most ravelers’ lists. Here’s how you can snag the best deals:</p><ul class="postList"><li class="graf graf--li" name="3a4a">Use Flight Comparison Websites: Platforms like Skyscanner, Kayak, and Google Flights allow you to compare prices across different airlines and booking sites.</li><li class="graf graf--li" name="8379">Set Price Alerts: Many flight comparison websites offer price alert features that notify you when the price for your desired route drops.</li><li class="graf graf--li" name="aaa8">Book in Advance: Typically, booking your flight several weeks or months ahead can secure lower prices.</li><li class="graf graf--li" name="ca37">Be Flexible with Dates: Flying mid-week or during off-peak times can often result in cheaper fares.</li></ul><p class="graf graf--p" name="3ab3">2. Last-Minute Flight Deals</p><p class="graf graf--p" name="02ac">If you’re looking for spontaneous travel, last-minute deals can be a great option:</p><ul class="postList"><li class="graf graf--li" name="43d9">Check Airline Websites: Airlines often post last-minute deals on their websites or social media channels.</li><li class="graf graf--li" name="04c3">Subscribe to Newsletters: Airlines and travel agencies frequently send out exclusive last-minute offers to their subscribers.</li><li class="graf graf--li" name="8605">Use Apps: Mobile apps like Hopper and Skiplagged specialize in finding last-minute flight deals.</li></ul><p class="graf graf--p" name="90f6"><a class="markup--anchor markup--p-anchor" data-href="https://www.booking.com/flights/index.html?aid=8019784" href="https://www.booking.com/flights/index.html?aid=8019784" rel="noopener" target="_blank">Click HERE to find the most suitable offers for you!</a></p><figure class="graf graf--figure" name="4531"><img class="graf-image" data-height="667" data-image-id="0*xGjmWfFH_8JEQVvu" data-width="1000" src="https://cdn-images-1.medium.com/max/800/0*xGjmWfFH_8JEQVvu" /></figure><p class="graf graf--p" name="4e07">3. <a class="markup--anchor markup--p-anchor" data-href="https://www.booking.com/flights/index.html?aid=8019784" href="https://www.booking.com/flights/index.html?aid=8019784" rel="noopener" target="_blank">Direct Flights</a></p><p class="graf graf--p" name="071a">While layovers can sometimes save money, direct flights offer the convenience of getting to your destination faster and with less hassle. To find affordable direct flights:</p><ul class="postList"><li class="graf graf--li" name="b5c9">Search Multiple Airports: Sometimes flying into or out of a nearby airport can offer better direct flight options.</li><li class="graf graf--li" name="8eb2">Check Budget Airlines: Airlines like Southwest, JetBlue, and Ryanair often have competitive prices for direct flights.</li><li class="graf graf--li" name="faf3">Use Filters: When searching for flights, use filters to specifically look for non-stop options.</li></ul><p class="graf graf--p graf--empty" name="c4f7"><br /></p><figure class="graf graf--figure" name="93a5"><img class="graf-image" data-height="563" data-image-id="0*h9s9z8tXku8xloKr" data-width="1000" src="https://cdn-images-1.medium.com/max/800/0*h9s9z8tXku8xloKr" /></figure><p class="graf graf--p" name="63ba">4. <a class="markup--anchor markup--p-anchor" data-href="https://www.booking.com/flights/index.html?aid=8019784" href="https://www.booking.com/flights/index.html?aid=8019784" rel="noopener" target="_blank">Flight</a> Discounts</p><p class="graf graf--p" name="ddd5">Discounts can come from various sources, including:</p><ul class="postList"><li class="graf graf--li" name="a22b">Credit Card Rewards: Many credit cards offer travel rewards and points that can be redeemed for flights.</li><li class="graf graf--li" name="3950">Student and Senior Discounts: Some airlines offer discounted fares for students and seniors.</li><li class="graf graf--li" name="991b">Seasonal Sales: Keep an eye out for sales around holidays and special events.</li></ul><p class="graf graf--p" name="5f76">5. Travel Hacks for Flights</p><p class="graf graf--p" name="81a5">Maximize your savings and comfort with these travel hacks:</p><ul class="postList"><li class="graf graf--li" name="b9bf">Book One-Way Tickets: Sometimes booking two one-way tickets with different airlines can be cheaper than a round trip.</li><li class="graf graf--li" name="bdd3">Incognito Mode: Search for flights in incognito mode to avoid price increases based on your search history.</li><li class="graf graf--li" name="7dee">Frequent Flyer Programs: Join loyalty programs to earn miles that can be redeemed for free or discounted flights.</li></ul><p class="graf graf--p" name="6bf0">How to Access These Incredible Offers</p><p class="graf graf--p" name="7991"><a class="markup--anchor markup--p-anchor" data-href="https://www.booking.com/flights/index.html?aid=8019784" href="https://www.booking.com/flights/index.html?aid=8019784" rel="noopener" target="_blank">Click HERE to find the most suitable offers for you!</a></p><p class="graf graf--p" name="f226">Ready to find the best flight deals? Here’s how you can easily access and book these offers:</p><ul class="postList"><li class="graf graf--li" name="18ae">Visit Our Website: Our platform aggregates the best deals from various airlines and travel agencies, ensuring you get the lowest prices.</li><li class="graf graf--li" name="9153">Download Our App: Get real-time updates on flight deals and book your tickets on the go.</li><li class="graf graf--li" name="42de">Sign Up for Our Newsletter: Receive exclusive offers and travel tips directly in your inbox.</li></ul><p class="graf graf--p" name="b50d">Conclusion</p><p class="graf graf--p" name="d18a">Flying doesn’t have to break the bank. By leveraging the latest search trends and using smart booking strategies, you can find incredible flight deals that make air travel affordable and enjoyable. Whether you’re planning in advance or looking for a last-minute escape, our comprehensive guide ensures you have all the tools you need to score the best offers. Visit our website today and start your journey to affordable air travel!</p><p class="graf graf--p" name="37af"><a class="markup--anchor markup--p-anchor" data-href="https://www.booking.com/flights/index.html?aid=8019784" href="https://www.booking.com/flights/index.html?aid=8019784" rel="noopener" target="_blank">Click HERE to find the most suitable offers for you!</a></p><h4 class="graf graf--h4" name="a50e"><a class="markup--anchor markup--h4-anchor" data-href="https://ttravelgoo.blogspot.com/" href="https://ttravelgoo.blogspot.com/" rel="noopener" target="_blank">Visit our website for more offers!</a></h4><h4 class="graf graf--h4" name="c69d"><a class="markup--anchor markup--h4-anchor" data-href="https://www.facebook.com/profile.php?id=61560198516319" href="https://www.facebook.com/profile.php?id=61560198516319" rel="noopener" target="_blank">Our Facebook page!</a></h4><p class="graf graf--p" name="6365">By following these tips and tricks, you’ll be well on your way to finding the best flight deals and enjoying the convenience and excitement of air travel. Safe travels!</p> | travelgo |
1,871,862 | How does A Bugatti Scooter Cost | Bugatti is a well-known brand that offers luxurious and exclusive transportation. Most people know... | 0 | 2024-05-31T09:46:14 | https://dev.to/sarimkhan/how-does-a-bugatti-scooter-cost-5dae | webdev, techtalks, discuss, community | Bugatti is a well-known brand that offers luxurious and exclusive transportation. Most people know Bugatti’s famous supercars, such as the Bugatti Veyron and Bugatti Chiron. However, the brand has recently introduced a new product, the Bugatti electric scooter. This scooter is a modern and eco-friendly mode of transportation that carries Bugatti’s signature elegance and power. [Read more](https://zenflixx.com/how-does-a-bugatti-scooter-cost/) | sarimkhan |
1,871,861 | Data Analytics Consulting: Driving Business Performance | In the modern business landscape, data analytics consulting has emerged as a vital component for... | 0 | 2024-05-31T09:43:04 | https://dev.to/linda0609/data-analytics-consulting-driving-business-performance-3a42 | In the modern business landscape, data analytics consulting has emerged as a vital component for companies aiming to tackle performance challenges and foster growth. By leveraging advanced technologies, data analytics consultants provide innovative solutions to gain deep insights into consumer behavior, supplier relations, and overall business operations. This post explores the essential role of data analytics consulting and its profound impact on business success.
What is Data Analytics Consulting?
Data analytics consulting involves the application of statistical modeling and computer science techniques to enhance business expansion strategies and overcome growth barriers. Business owners increasingly rely on [data analytics services](https://www.sganalytics.com/data-management-analytics/) to optimize various aspects of their operations, including marketing performance, human resource planning, and factory maintenance. By deploying advanced tools and methodologies, professional analysts identify valuable patterns within corporate data repositories, offering crucial supervisory and executive support to managers.
Strategic Utilization of Data Analytics
At its core, data analytics consulting transforms raw data into actionable insights. By employing statistical models and machine learning algorithms, consultants can predict trends, identify inefficiencies, and uncover hidden opportunities. This enables businesses to make informed decisions, streamline operations, and improve overall performance.
Why Does a Business Need Data Analytics Consulting?
Surpassing Rival Businesses
In an increasingly competitive market, understanding and outpacing competitors is paramount. Companies invest in [data aggregation services](https://www.sganalytics.com/data-management-analytics/data-aggregation-services/) to collect and consolidate intelligence on their rivals. Data analysts then process this information using sophisticated statistical models, correcting biases and eliminating redundant records to ensure reliable pattern recognition. This comprehensive analysis reveals strengths and weaknesses in competitors' pricing, production, design, and customer care operations. By identifying these insights, businesses can capitalize on opportunities to surpass their rivals and attract customers disillusioned by competitors' offerings.
Forecasting Future Outcomes
Accurate revenue predictions are essential for effective budget allocation across various departments. Predictive and prescriptive modeling, key benefits of [advanced analytics consulting](https://www.sganalytics.com/data-management-analytics/advanced-analytics-solutions), enable companies to forecast future outcomes with greater precision. Unlike standard analytics tools that merely explain past performance, advanced analysis presents multiple scenarios based on evolving competitive circumstances. Machine learning models ensure that the generated reports and process improvement strategies remain feasible, offering a nuanced understanding of potential policy impacts. This predictive capability is crucial for strategic planning and resource allocation.
Focusing on Authoritative Data Sources
Reliable data sources are critical for generating accurate analytics. However, sensational content from news publishers can lead to biased reporting and unverified claims. Using such flawed data can result in misleading analytics reports, which can adversely affect business decisions. The adage "A misguided plan is worse than not having a plan" underscores the importance of data quality assurance. Intelligence based on inauthentic data is detrimental to decision-making, akin to poison for data-led strategies. Distinguishing authoritative data sources from unreliable ones is challenging, making data validation tools and skilled analysts indispensable for precise insight extraction.
Meeting Data Governance Mandates
Protecting confidential business intelligence from cybercriminals is increasingly important. Advanced encryption algorithms in modern analytics and reporting systems safeguard sensitive information. Furthermore, compliance with data protection, localization, and privacy regulations is crucial. Evaluating the costs of non-compliance highlights the need for robust data analytics. Managers must modernize IT resources to adhere to legal mandates and protect critical data.
Benefits of Data Analytics Consulting
Enhancing Marketing Performance
Data analytics consulting provides insights that enhance marketing strategies. By analyzing consumer behavior and preferences, businesses can tailor their marketing campaigns to target specific demographics more effectively. This leads to increased customer engagement and higher conversion rates. Moreover, data-driven marketing strategies enable businesses to allocate their marketing budget more efficiently, maximizing return on investment.
Optimizing Human Resource Planning
Effective human resource planning is essential for maintaining a productive workforce. Data analytics consulting helps businesses identify trends in employee performance, satisfaction, and retention. By analyzing this data, companies can develop strategies to improve employee engagement, reduce turnover, and optimize staffing levels. Additionally, predictive analytics can forecast future staffing needs, ensuring that the organization is prepared to meet demand.
Improving Factory Maintenance
Predictive maintenance is a critical application of data analytics in the manufacturing sector. By analyzing data from sensors and equipment, businesses can predict when machines are likely to fail and schedule maintenance proactively. This reduces downtime, lowers maintenance costs, and extends the lifespan of equipment. Data analytics consulting helps businesses implement effective predictive maintenance programs, ensuring smooth and efficient operations.
Conclusion
Organizations aiming to penetrate new markets, attract investors, and improve poorly-performing products rely on data analytics for pattern recognition and progress monitoring. Statistical modeling methods maximize the value of business intelligence, ensuring compliance with privacy laws and accurately estimating decision impacts. Selecting the right data analytics consultant is crucial for successful implementation and achieving business objectives.
Data analytics consulting transforms business strategies, making it an essential component for companies looking to stay competitive and drive growth. By focusing on reliable data sources, forecasting future outcomes, surpassing competitors, and meeting data governance mandates, businesses can harness the full potential of their data.
Final Thoughts
As businesses navigate the complexities of the modern market, data analytics consulting offers a strategic advantage. By leveraging advanced technologies and expert insights, companies can enhance their operations, make informed decisions, and achieve sustainable growth. Investing in data analytics consulting is not just a trend; it is a necessity for businesses that aim to thrive in an increasingly data-driven world. | linda0609 | |
1,871,860 | Get Creative: How Generative AI is Shaping the Future | Do you ever notice how similar marketing messages and product designs seem these days? It's like... | 0 | 2024-05-31T09:41:55 | https://dev.to/krunalbhimani/get-creative-how-generative-ai-is-shaping-the-future-128f | ai, generativeai | Do you ever notice how similar marketing messages and product designs seem these days? It's like everything's starting to blend together. Traditional AI is great at analyzing data and finding patterns, but when it comes to true creativity, it often falls short.
That's where Generative AI comes in. It's not just about analyzing information, it's about breaking new ground creatively. Picture AI that can write a catchy jingle for your next ad campaign, design a unique clothing pattern, or even compose a captivating melody for a song. Generative AI has the potential to completely change creative industries. From fashion and design to music and entertainment, the possibilities are endless.
## Generative AI: Unlocking a New Era of Creativity
Imagine if AI could do more than just crunch numbers and analyze data. What if it could actually inspire us creatively? That's the promise of Generative AI. It's not just about processing information; it's about creating something entirely new.
Here's how it works: Generative AI learns from a massive amount of data, much like an artist who studies countless paintings, music pieces, or poems. But instead of copying what it sees, Generative AI uses that knowledge to come up with its own original creations.
And it's incredibly versatile:
**1. Text:** Whether it's writing engaging articles, crafting social media posts, or even composing poetry, Generative AI can produce human-like text in various styles.
**2. Visuals:** From designing unique clothing patterns to generating lifelike images and stunning video effects, Generative AI is pushing the boundaries of visual creativity.
**3. Audio:** In the world of music, Generative AI can compose original pieces, create sound effects, and even personalize audio experiences based on individual preferences.
Generative AI is more than just a tool; it's a new way for machines to interact with the world. It's like having a highly imaginative artist at your fingertips, ready to create something amazing at a moment's notice.
Excited to learn more about how Generative AI works and the incredible things it can do? Check out the blog post, "[Generative AI: Techniques, Applications, and Impact on Business](https://www.seaflux.tech/blogs/generative-ai-revolutionizing-industries?utm_source=devto&utm_medium=social&utm_campaign=guest%20blog)" where we dive deep into the fascinating world of Generative AI. You'll discover the different techniques behind this revolutionary technology and gain a better understanding of how it's changing the creative landscape.
## The Generative AI Canvas: Transforming Industries
Generative AI isn't just an amazing piece of technology; it's like a magic paintbrush that's changing entire industries. Let's see how Generative AI is reshaping creativity across different fields:
- Marketing & Advertising: AI writes personalized ad copy tailored to each customer, making content that grabs attention in a busy marketplace.
- Fashion & Design: Generative AI helps designers create innovative clothing patterns and 3D models, speeding up the design process and offering more unique options.
- Entertainment & Media: From writing scene-perfect music to creating stunning special effects, Generative AI is pushing the limits of creativity.
But it doesn't stop there. Generative AI is making waves in other industries too:
- Architecture & Engineering: Generative AI can design buildings that are eco-friendly, help plan cities better, and even make detailed 3D models for construction projects.
- Drug Discovery & Material Science: AI is speeding up research by coming up with new ideas for drugs and creating new materials with special properties.
- Product Development: Generative AI can help think up new product ideas, improve products based on what users think, and even give personalized recommendations to customers.
But, as amazing as Generative AI is, there are challenges. Sometimes, the data it learns from can be biased, which means the AI might end up making decisions that aren't fair. And there's the risk of people using this technology in the wrong way, like making fake videos or spreading lies.
So, as we keep going, it's really important to develop Generative AI responsibly and think about the ethics behind it. That way, we can make sure Generative AI does the most good it possibly can.
## The Future of Creativity: A Human-AI Collaboration
Generative AI is transforming creativity by collaborating with humans. Human-in-the-loop AI values and amplifies human creativity, utilizing AI as a tool to assist and enhance it. For example, a fashion designer can use Generative AI to brainstorm clothing pattern options, selecting and refining the best ones for a unique collection.
This collaborative approach allows humans to leverage Generative AI's potential while retaining control over the creative direction. AI generates numerous possibilities, while humans bring their experience, judgment, and emotional intelligence to the table, selecting and refining the best ideas.
This powerful synergy between human and AI can lead to groundbreaking creative achievements impossible for either party alone. It's a future where AI acts as a tireless brainstorming partner, constantly pushing boundaries, while humans provide the essential spark of originality and direction.
## End Note
Generative AI marks a paradigm shift in the realm of creativity. It's not just a technology for generating content; it's a powerful tool that has the potential to revolutionize entire industries. From crafting personalized marketing campaigns to composing original music and designing innovative products, Generative AI is pushing the boundaries of what's possible.
The future of creativity lies in a powerful collaboration between humans and AI. By harnessing the vast potential of Generative AI while leveraging human ingenuity and vision, we can unlock a new era of creative expression unlike anything seen before.
Are you ready to explore the possibilities of Generative AI and see how it can transform your business?
| krunalbhimani |
1,871,858 | From data consumers to data owners: Web3 and AI empowering users in the digital age | Web3, as the next generation of the Internet, is characterized by decentralization, user-centricity... | 0 | 2024-05-31T09:39:16 | https://dev.to/shevchukkk/from-data-consumers-to-data-owners-web3-and-ai-empowering-users-in-the-digital-age-23a0 | web3, blockchain, ai | Web3, as the next generation of the Internet, is characterized by decentralization, user-centricity and the integration of artificial intelligence (AI). This revolutionary paradigm shift is moving away from centralized platforms, where control over data and resources is concentrated in the hands of the few, to an ecosystem where users have greater autonomy and ownership of their data. Web3 marks the transition from passive content consumption to active user participation. Users become creators, owners and actors in this new digital ecosystem. AI makes this possible by providing data analysis, prediction and decision-making tools that help users take better control of their online experience. In this new environment, Web3 and artificial intelligence play a key role, leading to revolutionary changes in the way we interact with data and personalize our own experiences. Companies specializing in Web3 in synergy with AI are coming to the fore, developing innovative solutions for decentralized data markets. These platforms empower users to own, control and monetize their data, eliminating monopolies and promoting greater transparency and honesty. Thanks to AI algorithms, these data markets have become more efficient, secure and flexible, opening up new opportunities for collaboration and information sharing.
**What are Web3’s specific AI projects?**
**Smart contracts with AI**
This is heavily exploited by the [Zilliqa](https://www.zilliqa.com/) blockchain platform, which takes a significant step forward in computing by relying on its own [Scilla](https://scilla-lang.org/) smart contract programming language and an innovative parallel processing architecture based on sharding. Through sharding, the blockchain is broken up into smaller, more manageable networks known as subnets. This allows you to distribute computing tasks between them, making their execution parallel. Zilliqa differs from other blockchain platforms, such as [Bitcoin](https://www.blockchain.com/) and [Ethereum 1.0](https://ethereum.org/en/) due to its unique architecture that allows for high scalability. Although Zilliqa uses a Proof-of-Work (PoW) consensus mechanism similar to those platforms, it solves the scaling problem. Sharding, in turn, breaks the decentralized Zilliqa network into smaller segments called shards. This allows for parallel processing of transactions in different shards, greatly increasing the throughput and efficiency of the blockchain. The company became the first public blockchain platform to implement sharding when its main net launched in 2019. This is a significant achievement that underscores Zilliqa’s leadership in blockchain innovation and scaling.
**Predictive modeling and data analysis
**
A clear example is [Numerai](https://numer.ai/), a decentralized artificial intelligence platform based on the Ethereum blockchain. It enables anyone to submit their own machine learning models to predict stock market movements. The project is a kind of collective artificial intelligence for forecasting the stock market. The main goal of the project is to create more accurate and reliable machine learning models by combining the predictions of thousands of data scientists from around the world. Numerai is based on encrypted data that will prevent manipulation and abuse of underlying financial data. Numerai is a unique platform that combines blockchain, encryption and artificial intelligence to create a new paradigm in stock market quantitative analysis and forecasting. Instead of using traditional forecasting methods, the project uses the collective mind of the machine learning community. This will find its direct application on crypto-exchanges, where everyone will be able to do their job well. For example, we have a wide selection of exchanges, especially popular ones such as [Upbit](https://sg.upbit.com/home), [KuCoin](https://www.kucoin.com/) or [WhiteBIT](https://whitebit.com/ua).
**Computing platforms**
[DeepBrain Chain](https://www.deepbrainchain.org/) combines artificial intelligence and blockchain and is a computing platform in its essence. Its goal is to create a decentralized neural network that will significantly reduce the cost of artificial intelligence calculations. DeepBrain Chain combines the power of mining machines to create a decentralized network that offers affordable and scalable GPU computing power for deep learning and AI. By using inactive mining resources, DeepBrain Chain significantly lowers the cost of access to computing power, making AI more accessible to a wider range of users. The platform can run deep neural network models and algorithms for training artificial intelligence systems, and has its own DBC token that incentivizes network participants and rewards resource providers. The main application areas of the platform could be fraud detection systems that can analyze transactions and user behavior to detect suspicious activities. Also in the space of healthcare, in particular drug development, disease diagnostics and personalized medicine.
**Conclusion**
Growing investments and research in the space of blockchain and artificial intelligence give reason to expect significant progress in the coming 5–10 years. Improvements in blockchain platforms and AI models will likely lead to exponential growth in the possibilities these technologies can offer together.
The synergy between blockchain and artificial intelligence has the potential to drive innovation in both directions. The decentralized and stable nature of the blockchain can be the foundation for the scaling and secure operation of artificial intelligence algorithms. On the other hand, artificial intelligence can optimize and automate many aspects of blockchain operation, making it more efficient and user-friendly.
Although projects combining blockchain and artificial intelligence are in the early stages of development, they already show enormous potential. Thanks to the synergy of these technologies. | shevchukkk |
1,871,857 | Why migrate VB6 to .NET code in 2024 | This post is a quick overview of an Abto Software blog article. In response to the current volatile... | 0 | 2024-05-31T09:37:08 | https://dev.to/abtosoftware/why-migrate-vb6-to-net-code-in-2024-1ni9 | webdev, dotnet, performance, programming | _This post is a quick overview of an Abto Software [blog article](https://www.abtosoftware.com/blog/why-migrate-vb6-to-net-code-in-2024)._
In response to the current volatile market conditions, business leaders are focusing on shrinking their expenses and optimizing everyday workflows.
To date, many organizations across industries continue utilizing Visual Basic 6.0 (VB6) as their primary platform. While most larger organizations often have the expertise to abandon Visual Basic 6.0 favoring other platforms, smaller companies are facing serious challenges.
## VB6 applications becoming irrelevant
Be it discontinued support, the need to uncover modern capabilities, or ever-evolving regulatory requirements, business leaders are confronting the obsolescence of their legacy applications.
Visual Basic versions 1.0-6.0 were widely popular throughout the 1990s and 2000s until retirement in 2008. Visual Basic, being simple and versatile, was used to build desktop and database applications, games, utilities, and custom business applications.
## VB6 applications getting abandoned across industries
The trend towards migration is gaining more and more momentum:
- Visual Basic is obsolete, with increasing security vulnerabilities
- Its security score of 9.3 indicates high risks of breaches impacting reputation and finances
- Visual Basic doesn’t receive regular updates and patches
- It’s unable to handle object-oriented programming, exception handling, as well as multi-threading, which, accordingly, affects performance
With rapidly growing concerns towards compliance, more organizations are moving to more modern platforms. Forward-looking companies, no matter the domain, are transitioning from objectively deprecated technologies to ensure desirable performance and security.
## .NET conversion becoming inevitable?
Visual Basic has long been popular and preferred for the following reasons:
- User-friendly interface and uncomplicated programming environment
- Pre-built controls (buttons, labels, text boxes)
- Rapid Application Development (RAD), which enables to quickly build prototypes and applications
- Integrated Development Environment (IDE), which enables the design, coding, testing, and deployment of applications all within one platform
But inevitably, Visual Basic being unsupported is causing several constraints:
- System stability and reliability
- System integration with more modern technologies
- The need for modern user interfaces and features
- The difficulty in meeting regulatory requirements
## .NET conversion: diving deeper
### System stability
Visual Basic 6 software doesn’t receive regular updates and patches, which generates security vulnerabilities. On the other hand, the modern .NET framework offers updates and patches, comprehensive documentation, and support, among many other features.
### System integration
Visual Basic 6 software lacks compatibility with modern, contemporary technologies, entangling integration. The modern .NET framework, in contrast, supports OAuth, OpenID Connect, REST APIs, cloud-based services, and more.
### User interfaces and features
VB6 applications are characterized by their insufficient support for modern user interfaces and functionality. .NET provides extensive controls and libraries, cross-platform capabilities, smooth integration with modern client-side technologies, and more.
### Regulatory requirements
VB6 programs are lacking data encryption, audit trails, and other critical features to meet legal requirements. .NET provides robust features that ensure regulatory compliance, for example data encryption, audit logging, and more.
## The approach to smooth VB6 to VB.NET migration
### Automated migration
Automated migration means utilizing specialized instruments to convert VB6 code into adequate .NET code. This process typically involves the analysis of the existing codebase, the identification of elements to migrate, and the subsequent translation into equivalent .NET code.
This type of migration preserves functionality, ensures consistency, and minimizes manual efforts and errors. But nonetheless, this approach does require additional improvements, for example removing duplicates, upgrading syntax and controls, and fixing data declarations.
### Manual migration
Manual migration means implementing manual techniques to transform VB6 code into appropriate .NET code. The process usually involves the analysis of the existing codebase as well as underlying business functionality.
Manual migration must follow automated migration for refinement, customization, optimization, and more. This approach does require specific expertise, however, carries great importance.
### Data migration
Data migration is another important stage, which might become challenging if lacking specialized expertise:
- Schema conversion to a format compatible with the .NET environment
- Data extraction from existing data sources in the VB6 application
- Data transformation to match data structure and formats being required by the .NET application, typically including data cleansing and normalization
- Data loading into the data storage being used by the .NET application, which includes inserting records into databases, uploading files, and changing data formats
- Data validation to ensure data accuracy and integrity
- Data synchronization to ensure data consistency and avoid data loss and duplication
### Quality assurance
Quality assurance, a stage that shouldn’t be neglected, isn’t that technically complex, but important to enable:
- Data integrity by eliminating data loss, corruption, duplication, and inconsistencies
- Risk management by identifying security vulnerabilities, compatibility issues, functional regression, performance degradation, and other potential problems
- Application functionality by addressing any inconsistencies and ensure expected behavior
- Regulatory compliance by implementing mentioned practices
## Before approaching VB6 to .NET migration
Another takeaway we’ve mentioned in one of our recent articles when discussing VB6 to .NET migration – functional equivalence is the first priority.
Approaching migration, business leaders might prefer to rewrite separate parts of their legacy applications. This means time-to-market delays, budget overruns, unexpected bottlenecks, and also resource constraints, but not if you’re first migrate and only then rewrite the application.
## How we can help
Abto Software has proven technical expertise for transitioning mission-critical applications without disruption.
Our engineers handle discovery and planning, code assessment and preparation, and smooth VB6 migration. Our clients forget about operational and performance shortfalls, security vulnerabilities, compatibility issues, and other business burdens associated with maintaining legacy VB6 applications.
We cover:
- Business analysis and consulting
- Project setup and kick-off
- Code migration
- Code finalization
- Acceptance testing and improvement
- Quality assurance and deployment
You enjoy:
- Higher performance and efficiency
- Expanded functionality and scalability
- Improved security through updates and patches
- Enhanced compatibility across platforms and devices
- Long-term support and maintenance
Cloud compatibility
| abtosoftware |
1,871,855 | Critical CSS with NextJS | In this article, we’ll share our experience with Google's CSS tool for extracting critical CSS –... | 0 | 2024-05-31T09:36:37 | https://focusreactive.com/critical-css-with-nextjs/ | nextjs, performance, criticalcss | In this article, we’ll share our experience with Google's CSS tool for extracting critical CSS – Critters. While still experimental, we've successfully used this tool in production and found it significantly improves the performance of static sites. When properly configured, it can potentially enhance SSR performance as well. Critters works well with static pages and can handle dynamic pages with some nuances.
- [Limitations](#limitations)
- [Critical CSS for Static Websites](#critical-css-for-static-websites)
- [Critical CSS for Static Websites With CSS-in-JS](#critical-css-for-static-websites-with-css-in-js)
- [Fully Static With Both: Regular CSS and CSS-in-JS](#fully-static-with-both-regular-css-and-css-in-js)
- [NextJS Pages Router Critical CSS](#nextjs-pages-router-critical-css)
- [Critical CSS for Dynamic Pages (SSR) in NextJS Pages Router with Custom Server](#critical-css-for-dynamic-pages-ssr-in-nextjs-pages-router-with-custom-server)
- [Conclusion](#conclusion)
All the examples in this article demonstrate a browserless method of extracting critical CSS using [Critters](https://www.npmjs.com/package/critters). However, it’s worth mentioning tools that use headless browsers. These tools load the page in a specified viewport and determine the necessary styles. This results in a very small amount of critical CSS tailored to render the page in that specific viewport. Typically, multiple viewports can be defined to support both mobile and desktop devices, allowing for flexible customization and easy integration into the build pipeline. However, headless browsers come with drawbacks: they are slow, unreliable, and prone to crashing. While not without merit, these tools don't scale well, are unreliable due to their dependence on headless browsers, and are unsuitable for runtime environments.
Browserless tools, like Critters, avoid these disadvantages. Although the extracted CSS will be larger since it covers the entire page across all device sizes, this increase is usually negligible thanks to minification and compression. In the end, it remains much smaller than the original stylesheet.
## Limitations
The best use case for Critters is a static website, such as a news site or blog. However, it's important to determine whether critical CSS optimization will benefit your performance. Simply put, will implementing this optimization result in a performance boost? Sometimes, CSS isn't the main factor causing poor performance, even though CSS in the `<head/>` blocks rendering. For example, if your Largest Contentful Paint ([LCP](https://focusreactive.com/deep-dive-into-web-performance-mastering-lcp-optimization-for-seo-success/)) is an image that loads much later than the CSS, the CSS won't be blocking the LCP. In such cases, you won't see a performance improvement from CSS optimization. However, this doesn't mean the optimization is useless—other pages might be genuinely render-blocked by CSS, and you'll see performance gains for those.
Additionally, critical CSS optimization should be the final step in HTML editing. After applying this optimization, it's best to use the HTML as-is without further modifications.
To start using Critters, simply install it with yarn add critters. Ensure your pages are linked to the correct stylesheet using a `<link/>` tag in the page`<head/>` (modern bundlers typically add these links if there are CSS file imports) or by passing parameters during Critters initialization. Then, create a script for generating critical CSS and integrate it into your build pipeline.
## Critical CSS for Static Websites
Okay, let's look at the first simplest case - a completely static site. All pages are rendered at build time. In this case, you simply create the following script and run it at the end of the build pipeline.
Here are the basic steps:
1. Get all HTML files
2. Initialize Critters with settings
3. Read HTML file
4. Process HTML file with Critters
5. Parse HTML after Critters
6. Find all the `<link/>` tags in the `<head/>` and remove each `<link/>`.
7. Save HTML file
We will use the code from this snippet to get all the HTML files from a folder. ([took it from here](https://www.learnwithparam.com/blog/get-all-files-in-a-folder-using-nodejs))
```js
const fs = require("fs");
// Recursive function to get files
function getHTMLFiles(dir, files = []) {
// Get an array of all files and directories in the passed directory using fs.readdirSync
const fileList = fs.readdirSync(dir);
// Create the full path of the file/directory by concatenating the passed directory and file/directory name
for (const file of fileList) {
const name = `${dir}/${file}`;
// Check if the current file/directory is a directory using fs.statSync
if (fs.statSync(name).isDirectory()) {
// If it is a directory, recursively call the getFiles function with the directory path and the files array
getHTMLFiles(name, files);
} else {
// If it is an HTML file, push the full path to the files array
if (name.endsWith("html")) {
files.push(name);
}
}
}
return files;
}
```
critcalcss.js module
```js
const fs = require("fs");
const Critters = require("critters");
const { join } = require("path");
const { parse } = require("node-html-parser");
async function criticalCSS() {
const currentFolder = join(process.cwd(), "build");
const files = getHTMLFiles(currentFolder);
for (const file of files) {
const critters = new Critters({ path: currentFolder });
const html = fs.readFileSync(file, "utf-8");
const inlined = await critters.process(html);
// additional step: delete links in the <head/> that left after critters
const DOMAfterCritters = parse(inlined);
const head = DOMAfterCritters.querySelector("head");
for (const linkInHead of head.querySelectorAll("link")) {
if (
linkInHead.attributes?.as === "style" ||
linkInHead.attributes?.rel === "stylesheet"
) {
linkInHead.remove();
}
}
fs.writeFileSync(file, DOMAfterCritters.toString());
}
}
criticalCSS();
```
**Note**: Critters should postpone your styles – move from `<head/>` to `<body/>` or wrap it with `<noscript/>` fallback. If there are still `<link/>` in `<head/>` you can add an additional step to handle that.
## Critical CSS for Static Websites With CSS-in-JS
If you are using any CSS-in-JS library, you usually don't have a CSS file. No worries, we can create it during optimization, save it and add `<link/>` with this CSS to the html file.
Here are the basic steps:
1. Get all HTML files
2. Initialize Critters with settings
3. Read html file
4. Parse HTML
5. Read existing styles from `<style/>` tags in `<head/>` and store each one in a Set.
6. Combine styles in one string and create a hash and path for the resulting styles
7. Save the CSS file
8. Process HTML with Critters
9. Parse HTML after Critters
10. Add style sheets to `<body/>` for lazy loading
11. Save HTML file
```js
const fs = require("fs");
const Critters = require("critters");
const { parse } = require("node-html-parser");
const CryptoJS = require("crypto-js");
const { join } = require("path");
const { minify } = require("csso");
async function criticalCSS() {
const currentFolder = join(process.cwd(), "build");
const files = getHTMLFiles(currentFolder);
for (const file of files) {
const critters = new Critters({ path: currentFolder });
const html = fs.readFileSync(file, "utf-8");
const DOMBeforeCritters = parse(html);
const uniqueImportantStyles = new Set();
// first find all inline styles and add them to Set
for (const style of DOMBeforeCritters.querySelectorAll("style")) {
uniqueImportantStyles.add(style.innerHTML);
}
const inlined = await critters.process(html);
const importantCSS = Array.from(uniqueImportantStyles).join("");
const DOMAfterCritters = parse(inlined);
const body = DOMAfterCritters.querySelector("body");
// if there was inline styles before Critters
if (importantCSS.length > 0) {
const hash = CryptoJS.MD5(CryptoJS.enc.Latin1.parse(importantCSS));
const inlinedStylesPath = `/static/css/styles.${hash}.css`;
fs.writeFileSync(
join(currentFolder, inlinedStylesPath),
// minification is optional here if you have gzip enabled
minify(importantCSS).css
);
if (body) {
// we should add <link/> with stylesheet
body.insertAdjacentHTML(
"beforeend",
`<link rel="stylesheet" href="${inlinedStylesPath}" />`
);
}
}
fs.writeFileSync(file, DOMAfterCritters.toString());
}
}
criticalCSS();
```
## Fully Static With Both: Regular CSS and CSS-in-JS
We can also imagine a case where we use CSS at the same time as CSS-in-JS. Doubtful, but ok.
Here are the basic steps:
1. Get all HTML files
2. Initialize Critters with settings
3. Read html file
4. Parse HTML
5. Read existing styles from `<style/>` tags in `<head/>` and store each one in a Set.
6. Process HTML with Critters
7. Parse HTML after Critters
8. Get all `<link/>` stylesheets from all HTML, keep the href and remove the `<link/>`.
9. Read all the styles from the stylesheets, pass them through Set and combine them into one
10. Combine the styles from step 5 with the file from the previous step
11. Create a hash and path for the resulting styles
12. Save the CSS file
13. Add style sheets to `<body/>` for lazy loading
14. Save HTML file
```js
const Critters = require("critters");
const { join } = require("path");
const fs = require("fs");
const { parse } = require("node-html-parser");
const CryptoJS = require("crypto-js");
const { minify } = require("csso");
async function criticalCSS() {
const currentFolder = join(process.cwd(), ".next");
const files = getHTMLFiles(currentFolder);
const critters = new Critters({
path: currentFolder,
fonts: true, // inline critical font rules (may be better for performance)
});
for (const file of files) {
try {
const html = fs.readFileSync(file, "utf-8");
const DOMBeforeCritters = parse(html);
const uniqueImportantStyles = new Set();
// first find all inline styles and add them to Set
for (const style of DOMBeforeCritters.querySelectorAll("style")) {
uniqueImportantStyles.add(style.innerHTML);
}
const pathPatterns = {
real: "/static/css",
original: "/_next/static/css",
};
const changedToRealPath = html.replaceAll(
pathPatterns.original,
pathPatterns.real
);
const inlined = await critters.process(changedToRealPath);
const DOMAfterCritters = parse(inlined);
// merge all styles form existing <style/> tags into one string
const importantCSS = Array.from(uniqueImportantStyles).join("");
const body = DOMAfterCritters.querySelector("body");
if (importantCSS.length > 0) {
const attachedStylesheets = new Set();
const stylesheets = [];
// find all `<link/>` tags with styles, get href from them and remove them from HTML
for (const link of DOMAfterCritters.querySelectorAll("link")) {
if (
link.attributes?.as === "style" ||
link.attributes?.rel === "stylesheet"
) {
attachedStylesheets.add(link.getAttribute("href"));
link.remove();
}
}
// go through found stylesheets: read file with CSS and push CSS string to stylesheets array
for (const stylesheet of Array.from(attachedStylesheets)) {
const stylesheetStyles = fs.readFileSync(
join(currentFolder, stylesheet)
);
stylesheets.push(stylesheetStyles);
}
// Merge all stylesheets in one, add importantCSS in the end to persist specificity
const allInOne = stylesheets.join("") + importantCSS;
// using the hash, we will only create a new file if a file with that content does not exist
const hash = CryptoJS.MD5(CryptoJS.enc.Latin1.parse(allInOne));
const inlinedStylesPath = `/static/css/styles.${hash}.css`;
fs.writeFileSync(
join(currentFolder, inlinedStylesPath),
// minification is optional here, it doesn't affect performance -- it is a lazy loaded CSS stylesheet, it only affects payload
minify(allInOne).css
);
if (body) {
body.insertAdjacentHTML(
"beforeend",
`<link rel="stylesheet" href="/_next${inlinedStylesPath}" />`
);
}
}
fs.writeFileSync(file, DOMAfterCritters.toString());
} catch (error) {
console.log(error);
}
}
}
criticalCSS();
```
Essentially, this is a workaround for preserving the specificity of applied styles in cases where both inline styles and regular CSS are used.
## NextJS Pages Router Critical CSS
[To read about this, follow the link to the original article.](https://focusreactive.com/critical-css-with-nextjs/#nextjs-pages-router-critical-css)
## Critical CSS for Dynamic Pages (SSR) in NextJS Pages Router with Custom Server
[To read about this, follow the link to the original article.](https://focusreactive.com/critical-css-with-nextjs/#critical-css-for-dynamic-pages-ssr-in-nextjs-pages-router-with-custom-server)
Links:
* [NextJS blog boilerplate with critical css (styled-components and regular css)](https://github.com/o8o0o8o/nextjs-with-critical-css-static)
* [NextJS runtime critical css optimization](https://github.com/o8o0o8o/nextjs-with-critical-css)
* [NextJS App router runtime critical css optimization](#https://github.com/o8o0o8o/app-router-with-critical-css)
## Conclusion
Even though critical css optimization comes with the cost it can greatly increase performance. But first, it's important to measure performance and see if you have performance issues with styles: whether they're actually blocking your metrics like [FCP](https://web.dev/articles/fcp) and [LCP](https://focusreactive.com/deep-dive-into-web-performance-mastering-lcp-optimization-for-seo-success/) or not. So it might not be worth it if your LCP is an image and loads much later than the styles. In this case, you will not get a big improvement. On the other hand it doesn't hurt if you can overcome the extra overhead. It's not exactly low hanging fruit, but at least for static builds it's viable.
This approach is not limited to NextJS only. Looks like this critical CSS optimization is suitable for any frameworks that can generate HTML at build time.
| o8o0o8o |
1,871,856 | Full stack developer python | Python Full Stack training in Hyderabad Enter fullscreen mode Exit fullscreen... | 0 | 2024-05-31T09:36:20 | https://dev.to/mounika_vcube_f01a5a6264c/full-stack-developer-python-356j |
Python Full Stack training in Hyderabad
Ready to master Python Full Stack development. Look no further than V CUBE Software Solutions we offer Python Full Stack training in Hyderabad! Our comprehensive course covers everything from beginner to advanced levels, ensuring you become a proficient Python Full Stack developer.
At V CUBE Software Solutions, we are dedicated to providing the Best Python Full Stack training experience with placement assistance in Hyderabad. With our expert instructors, you will get excellent training in Python Full Stack with our highly skilled trainers and advanced facilities in Hyderabad. Our hands-on approach and real-world projects will equip you with the skills and confidence needed to excel in the field.
Located in the heart of Hyderabad, near Kukatpally/KPHB, V CUBE Software Solutions is one of the best institutes for Python Full Stack training. Whether you prefer offline or online training, we've got you covered!
Don't wait any longer to kickstart your career in the Python Full Stack coaching center near you. Join us at V CUBE software solutions and unleash your potential! Enroll now and take the first step toward a rewarding tech career.
| mounika_vcube_f01a5a6264c | |
1,871,594 | How to Perform Face to Many: Run with Merge Faces API on Novita AI | Introduction Merge Face Tool, part of the Face to Many feature, is a revolutionary... | 0 | 2024-05-31T09:30:00 | https://dev.to/novita_ai/how-to-perform-face-to-many-run-with-merge-faces-api-on-novita-ai-4g7f | ai, stablediffusion, tutorial, facemerge | ## Introduction
Merge Face Tool, part of the Face to Many feature, is a revolutionary AI-powered tool that allows users to convert their face images into various artistic styles. With just a few simple steps, users can transform their ordinary photos into stunning pieces of artwork. Though face to many on replicate is popular among developers, this article will bring you another powerful AI platform — Novita AI.
Novita AI’s merge face tool offers nearly 20 different styles for conversion, including 3D, emoji, pixel art, video game, claymation, and toy. Whether you want to turn your face into a 3D character or transform it into a pixelated masterpiece, Novita AI’s Merge Face Tool has got you covered.
## What is Face to Many with AI
Face to Many with AI is an advanced technology that utilizes artificial intelligence to replicate and transform face images into various styles. This cutting-edge technology combines the power of AI algorithms with the creativity of human imagination to create stunning and unique visual representations.
**Introducing Face to Many on replicate**
Face to Many on replicate is a powerful tool that brings the capabilities of AI-based face merging to developers and creators. Replicate provides a comprehensive and user-friendly environment for developers to work with the Face to Many API. The platform offers a set of tools and resources that streamline the integration process and make it easy for developers to get started.
**The Basics of Face Merging Technology**
Face merging technology, powered by AI, utilizes deep learning models and algorithms to analyze and transform face images into different styles. These AI models are trained on large datasets, allowing them to learn and replicate the intricate details of various styles.
One such model is Loras, a popular AI model widely used for face merging tasks. Loras is trained to understand and capture the unique features of different styles, such as 3D, emoji, pixel art, video game, claymation, and toy. By leveraging Loras, the face merging technology can accurately transform an input face image into the desired style.
## How to Perform face to many on Novita AI
**Getting started on Hugging face**
- Get access to [Novita AI Merge Face](https://huggingface.co/spaces/novita-ai/InstantID) on Hugging Face.
- Input your [Novita API Key](https://novita.ai/dashboard/key).
- Upload an image with a face. For images with multiple faces, we will only detect the largest face. Ensure the face is not too small and is clearly visible without significant obstructions or blurring.
- (Optional) You can upload another image as a reference for the face pose. If you don’t, we will use the first detected face image to extract facial landmarks. If you use a cropped face at step 1, it is recommended to upload it to define a new face pose.
- (Optional) You can select multiple ControlNet models to control the generation process. The default is to use the IdentityNet only. The ControlNet models include pose skeleton, canny, and depth. You can adjust the strength of each ControlNet model to control the generation process.
- Enter a text prompt, as done in normal text-to-image models.
- Click the Submit button to begin customization.
- Share your customized photo with your friends and enjoy!
**Run on Novita AI Platform**
Open up Novita AI’s [merge face playground](https://novita.ai/product/merge-face):
2. Upload your base image or you can directly choose the base images offered by us:
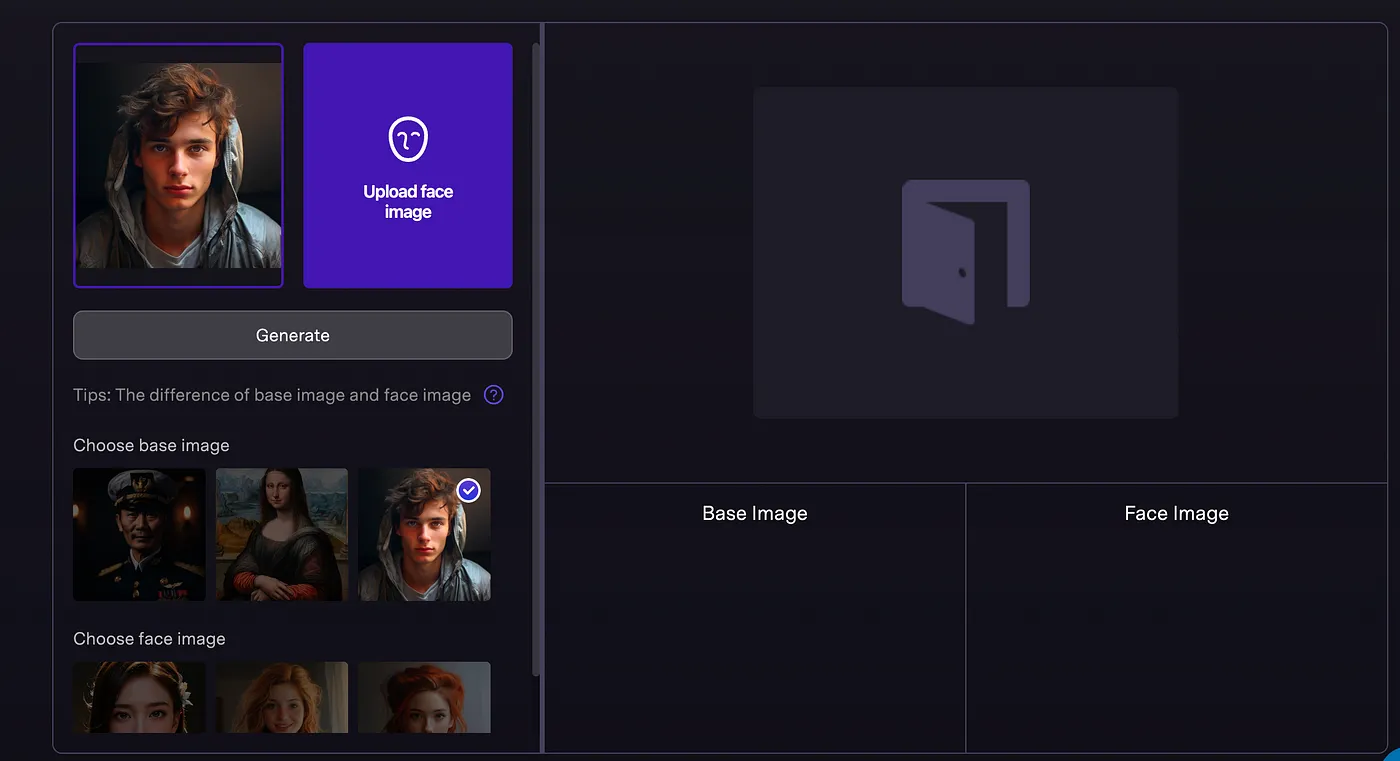
The difference of base image and face image:
- Base image : Single-person portrait only, does not support multiple persons
- Face image: Only human faces, clear and recognizable. It does not support cartoon or animal facial images
- Image restrictions: Maximum 2048*2048 resolution, less than 30 MB
3. Upload face image:
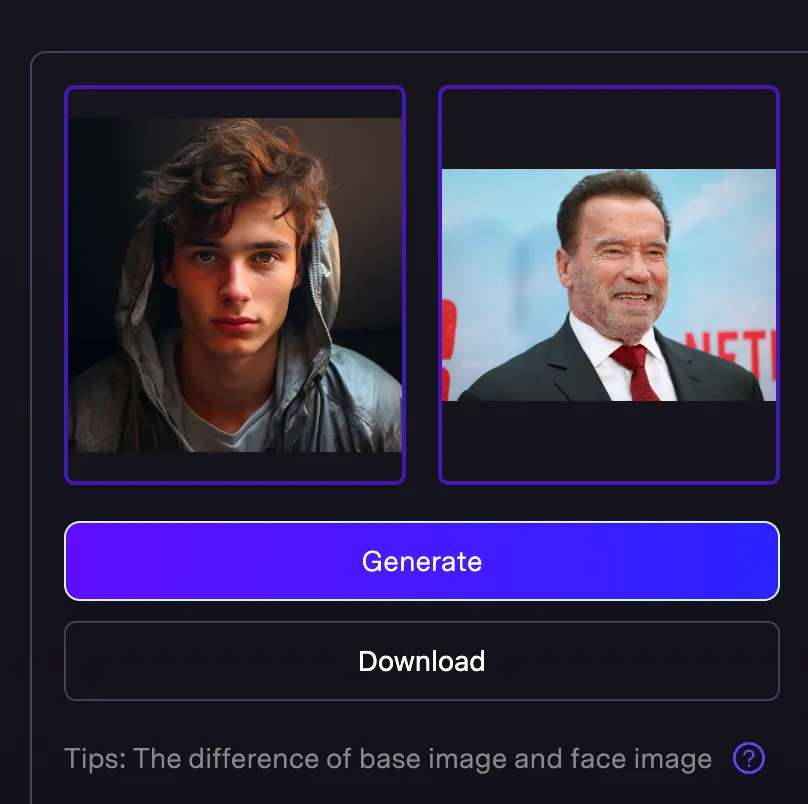
4. click generate to achieve your effect of merging face:
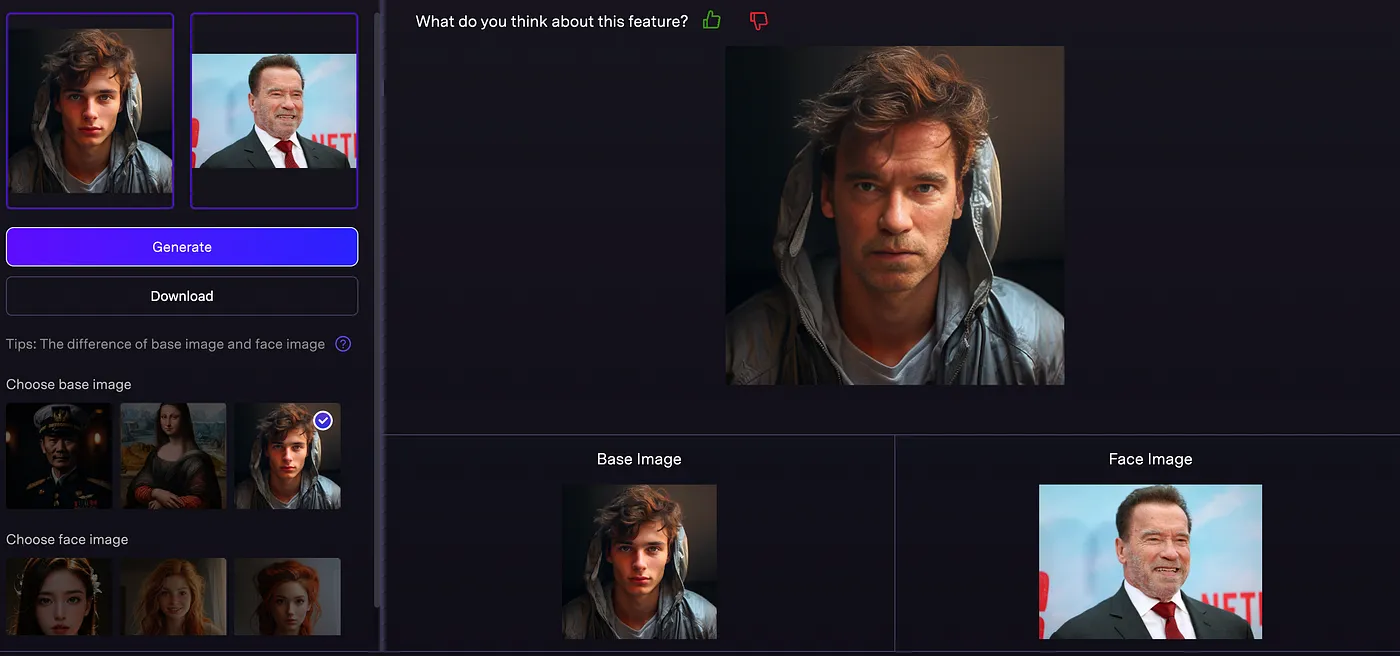
Here are some more showing cases:
what would happen if you Blend Mona Lisa with Churchill:
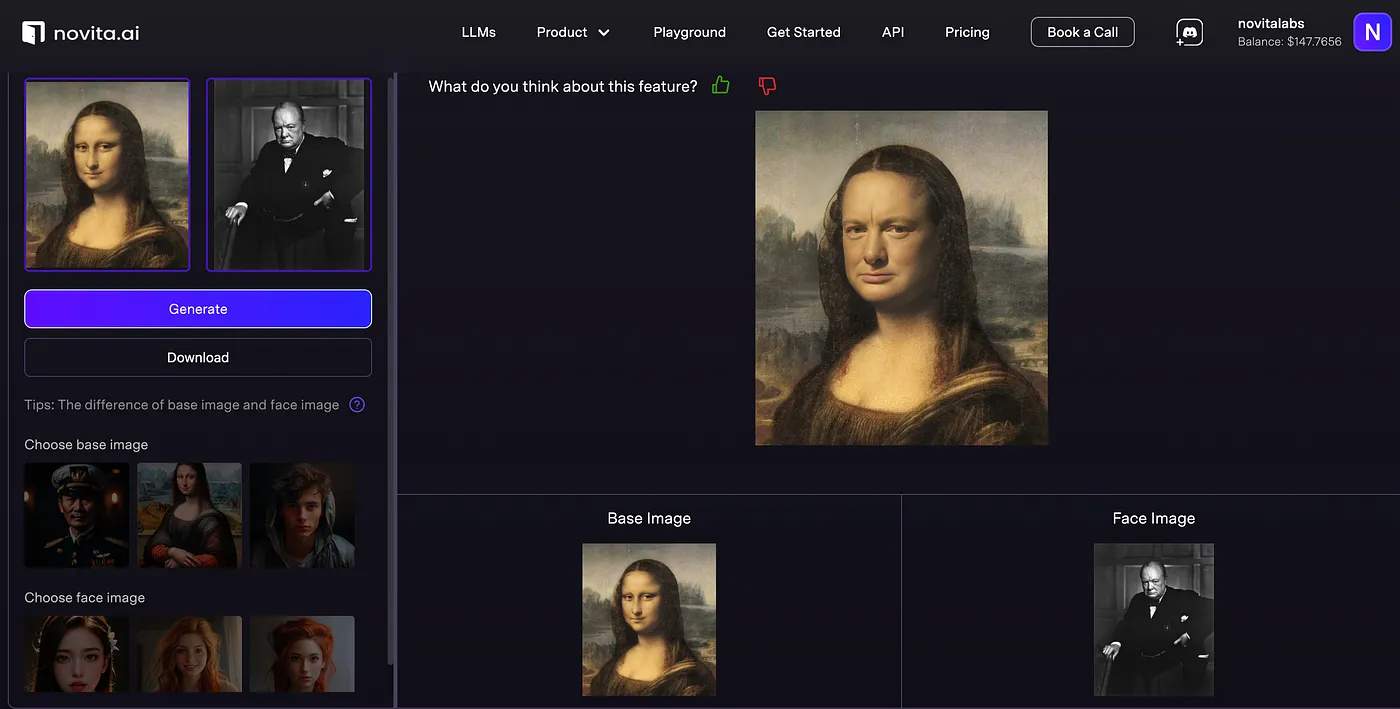
Here is the verison of Mona Gaga:
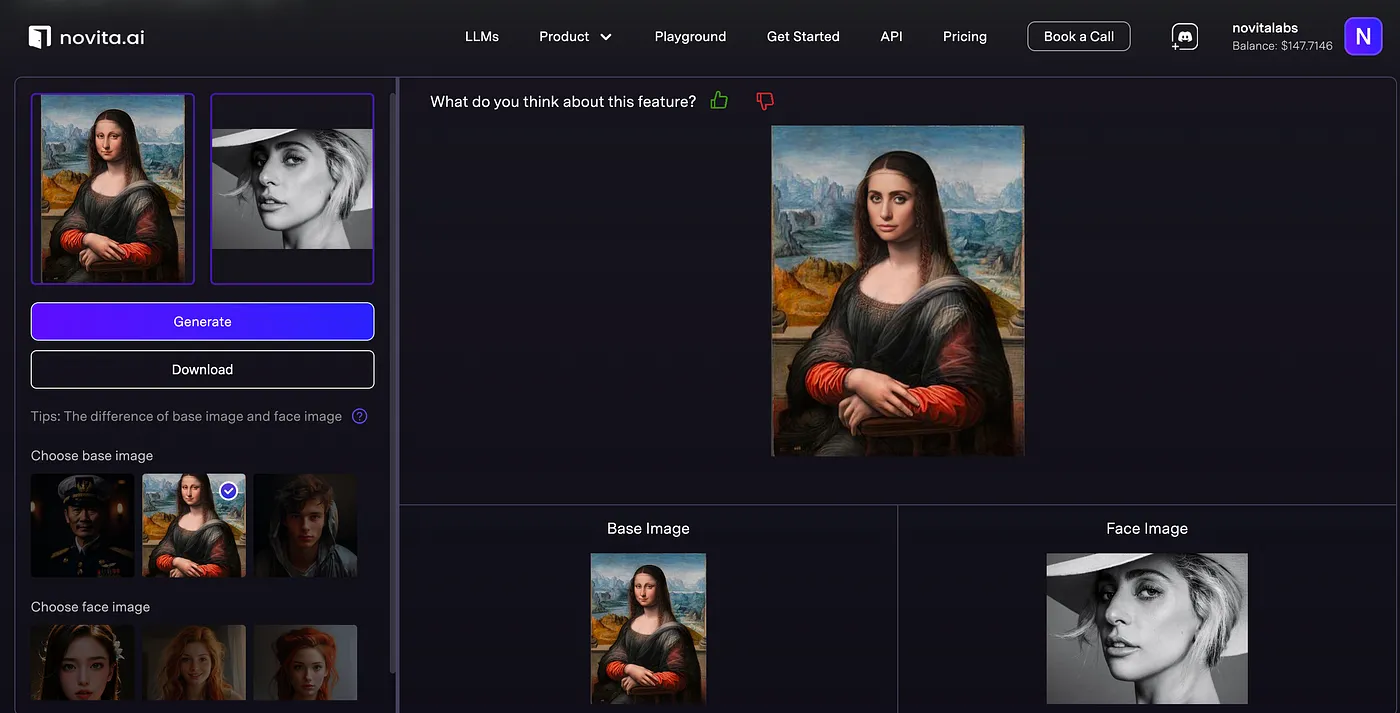
## Advantages of Using Novita AI for Face Merging
Using Novita AI for face merging offers several advantages:
- Enhanced Security Measures: Novita AI prioritizes user privacy and ensures that the photos uploaded by users are used only for the stated functionality and not for any other purposes. Users can trust that their privacy is fully respected and protected.
- Scalability for Business Needs: Novita AI’s Merge Face Tool is designed to handle high volumes of image processing tasks, making it ideal for businesses that require face merging capabilities at scale.
- User-Friendly Interface: Novita AI provides a user-friendly interface and comprehensive documentation, making it easy for users to navigate and leverage the tool’s features.
- Versatile Application: Novita AI’s Merge Face Tool can be integrated into a wide range of applications, including social media platforms, video editing software, and gaming applications, providing users with endless possibilities for creativity and personalization.
## Navigating limitations of Face to Many
1. Accuracy and Reliability: The accuracy of merging multiple faces into one coherent image can be limited, leading to unnatural or unrecognizable results. This can be due to variations in facial features, expressions, lighting, and angles.
2. Ethical Concerns: There are significant ethical issues around the use of facial merging technology, particularly concerning privacy, consent, and potential misuse for deceptive purposes (e.g., creating NSFW content or deepfakes).
3. Legal and Regulatory Issues: There are legal implications regarding the use of facial data, particularly in jurisdictions with strict data protection and privacy laws. This includes compliance with regulations like GDPR.
4. Technological Limitations: Current technology may struggle with merging faces from images with different resolutions, lighting conditions, or angles, leading to suboptimal results.
5. User Acceptance: There may be resistance or discomfort from users regarding the use of their facial data, especially if they are unaware or have not consented to its use.
6. Potential for Bias: If the underlying algorithms are trained on biased datasets, the merged faces could perpetuate or amplify existing biases, leading to unfair or discriminatory outcomes.
7. Security Risks: Storing and processing facial data poses security risks, including the potential for data breaches or misuse by malicious actors.
## Conclusion
In conclusion, embracing the innovative Face to Many technology opens up a realm of possibilities in face merging applications. Novita AI’s Merge Face Tool stands out for its precision, real-time processing, enhanced security, and scalability. With practical guidance on setting up and customizing merge parameters, Novita AI ensures a seamless integration experience. Whether applied in entertainment, marketing, or overcoming data challenges, this technology revolutionizes face merging capabilities. By leveraging Novita AI’s advanced features, you can explore creative avenues and streamline your face merging endeavors for optimal results.
## Frequently Asked Questions
**What Makes Novita AI’s technology different from others?**
Novita AI’s Merge Faces technology stands out from others due to its precision, real-time performance, and versatility. The advanced AI algorithms used by Novita AI ensure highly accurate and realistic results, while the real-time processing enables users to instantly see the transformed images.
**Can I use the Merge Faces API for mobile applications?**
Yes, the Merge Faces API can be used for mobile applications. Novita AI provides a user-friendly API that allows easy integration of the Merge Faces technology into mobile apps. Developers can download the API and follow the integration instructions provided by Novita AI to incorporate this powerful feature into their mobile applications.
> Originally published at [Novita AI](https://blogs.novita.ai/how-to-perform-face-to-many-run-with-merge-faces-api-on-novita-ai/?utm_source=devcommunity_LLM&utm_medium=article&utm_campaign=mergeface)
> [Novita AI](https://novita.ai/?utm_source=devcommunity_LLM&utm_medium=article&utm_campaign=how-to-perform-face-to-many-run-with-merge-faces-api-on-novita-ai), the one-stop platform for limitless creativity that gives you access to 100+ APIs. From image generation and language processing to audio enhancement and video manipulation, cheap pay-as-you-go, it frees you from GPU maintenance hassles while building your own products. Try it for free.
| novita_ai |
1,871,854 | #260. Single Number III | https://leetcode.com/problems/single-number-iii/description/?envType=daily-question&envId=2024-05... | 0 | 2024-05-31T09:28:32 | https://dev.to/karleb/260-single-number-iii-4npn | https://leetcode.com/problems/single-number-iii/description/?envType=daily-question&envId=2024-05-31
```js
/**
* @param {number[]} nums
* @return {number[]}
*/
var singleNumber = function (nums) {
if (nums.length === 2) return nums
const map = new Map()
const res = []
for (let num of nums) {
map.set(num, (map.get(num) || 0) + 1);
}
for (let [key, value] of map) {
if (value === 1) {
res.push(
key
)
}
}
return res
};
``` | karleb | |
1,871,853 | Earneasy24App | EARNEASY24 PAYMENT 30 MAY 2024 Note :- Some details hide for user privacy For more... | 0 | 2024-05-31T09:28:07 | https://dev.to/earneasy24app/earneasy24app-4l2h | #EARNEASY24 PAYMENT
30 MAY 2024
Note :- Some details hide for user privacy
*For more payment proofs and demo work*👇
*Link*: [https://play.google.com/store/apps/details?id=com.techaircraft.techaircrafthttps://play.google.com/store/apps/details?id=com.techaircraft.techaircraft](https://play.google.com/store/apps/details...)
| earneasy24app | |
1,871,852 | How to create urban discord command in python? | @commands.hybrid_command(name="urban", description = "Get the definition of a term(word) from Urban... | 27,564 | 2024-05-31T09:27:55 | https://dev.to/ihazratummar/how-to-create-urban-discord-command-in-python-18kd | python, discord, bot, programming | ```
@commands.hybrid_command(name="urban", description = "Get the definition of a term(word) from Urban Dictionary.")
async def urbun(self, ctx:commands.Context, *, word:str):
response = requests.get(f"http://api.urbandictionary.com/v0/define?term={word}")
data = response.json()
result = [item for item in data["list"]]
random_choice = random.choice(result)
embed = discord.Embed(title=f"{word.capitalize()}",
description=f">>> **Definition**: {random_choice["definition"]}", color= 0x00FFFF)
embed.add_field(name="Example", value=f"{random_choice["example"]}", inline= False)
embed.add_field(name=f"🖒 {random_choice["thumbs_up"]}", value="", inline=True)
embed.add_field(name=f"🖓 {random_choice["thumbs_down"]}", value="", inline=True)
embed.set_footer(text=f"{random_choice["written_on"]}")
embed.set_author(name=f"Author: {random_choice["author"]}")
button = discord.ui.Button(
label= "Check Out",
url= random_choice["permalink"],
style= discord.ButtonStyle.link
)
view = discord.ui.View()
view.add_item(button)
await ctx.send(embed=embed, view= view)
```
| ihazratummar |
1,871,851 | Hiring Laravel Developers: A Comprehensive Guide | In today's digital landscape, the demand for skilled Laravel developers is skyrocketing. As Laravel... | 0 | 2024-05-31T09:23:44 | https://dev.to/elainecbennet/hiring-laravel-developers-a-comprehensive-guide-47cp | laravel, developer, development | In today's digital landscape, the demand for skilled Laravel developers is skyrocketing. As Laravel continues to assert its dominance as one of the most popular PHP frameworks, the need for proficient developers who can navigate its intricacies is greater than ever. However, with so many candidates claiming expertise in [Laravel](https://dev.to/thedevdrawer/an-introduction-to-laravel-development-features-benefits-and-getting-started-5gdg), finding the right talent for your project can be a daunting task. In this guide, we'll delve into the essential steps and strategies to help you hire top-notch Laravel developers who can bring your vision to life.
## Understanding Your Requirements:
Before embarking on the hiring process, it's crucial to have a clear understanding of your project requirements. Define the scope, objectives, and technical specifications to identify the specific skill sets and experience levels you're seeking in a Laravel developer. Whether it's building a web application, crafting APIs, or optimizing performance, outlining your project's needs will streamline the hiring process and ensure you attract candidates with the right expertise.
## Evaluate Technical Proficiency:
Assessing a candidate's technical proficiency is paramount when hiring Laravel developer. Look for individuals with a strong grasp of PHP fundamentals, as well as in-depth knowledge of Laravel's features, such as routing, middleware, authentication, and Eloquent ORM. Consider conducting technical assessments or coding challenges to gauge candidates' problem-solving abilities and coding practices. Additionally, review candidates' portfolios and GitHub profiles to assess the quality of their past work and their contributions to the Laravel community.
## Cultural Fit and Communication Skills:
Beyond technical prowess, evaluating cultural fit and communication skills is essential for building a cohesive team. Laravel development often involves collaboration with designers, project managers, and other developers. Therefore, look for candidates who demonstrate strong interpersonal skills, the ability to work collaboratively, and a passion for continuous learning and growth. Conduct interviews to assess candidates' communication abilities, their approach to teamwork, and their alignment with your company's values and culture.
## Seek Experience and Expertise:
While technical proficiency is crucial, experience plays a significant role in determining a developer's suitability for your project. Look for candidates with a proven track record of developing Laravel applications across various industries and project scales. Consider their experience with specific Laravel packages, integrations, and third-party services relevant to your project requirements. Experienced developers bring valuable insights, best practices, and problem-solving skills that can accelerate project development and mitigate risks.
## Remote Work Considerations:
If you want to [hire a Laravel developer](https://www.deazy.com/hire-laravel-developers) remotely, it will open up a broader talent pool and offer flexibility for both employers and candidates. However, managing remote teams requires effective communication, collaboration tools, and project management practices. Prioritize candidates who demonstrate self-discipline, autonomy, and experience working remotely. Establish clear expectations, communication channels, and workflows to foster a productive remote working environment.
## Invest in Continuous Learning and Development:
The tech landscape is constantly evolving, and Laravel is no exception. To stay ahead of the curve, prioritize candidates who exhibit a commitment to continuous learning and professional development. Look for individuals who actively contribute to the Laravel community through blogs, forums, or open-source projects. Encourage ongoing skill enhancement through mentorship, training programs, and attendance at Laravel conferences and meetups. Investing in developers' growth not only enhances their expertise but also fosters a culture of innovation within your organization.
## Conclusion:
Hiring Laravel developers requires a strategic approach that goes beyond technical qualifications. By understanding your project requirements, evaluating candidates' technical proficiency, assessing cultural fit, and considering remote work dynamics, you can build a team of talented developers poised for success. Emphasize experience, prioritize continuous learning, and invest in building a collaborative and supportive work environment to attract and retain top-tier Laravel talent. With the right hiring strategy in place, you can elevate your project to new heights of success in the dynamic world of Laravel development.
| elainecbennet |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.