id int64 5 1.93M | title stringlengths 0 128 | description stringlengths 0 25.5k | collection_id int64 0 28.1k | published_timestamp timestamp[s] | canonical_url stringlengths 14 581 | tag_list stringlengths 0 120 | body_markdown stringlengths 0 716k | user_username stringlengths 2 30 |
|---|---|---|---|---|---|---|---|---|
1,865,090 | Exploring React Hooks: Benefits, Drawbacks, and Real-World Examples | Hello Everyone, السلام عليكم و رحمة الله و بركاته In React development, Hooks have revolutionized how... | 0 | 2024-05-25T17:40:20 | https://dev.to/bilelsalemdev/exploring-react-hooks-benefits-drawbacks-and-real-world-examples-5fpg | javascript, react, webdev, development | Hello Everyone, السلام عليكم و رحمة الله و بركاته
In React development, Hooks have revolutionized how developers manage state, handle side effects, and interact with the DOM in functional components. By providing a more elegant and concise syntax, Hooks offer numerous benefits, but they also come with their own set of drawbacks. Let's delve into the benefits, drawbacks, and real-world examples of each React Hook:
### State Hooks:
1. **useState**:
- **Benefits**:
- Simplifies state management in functional components.
- Eliminates the need for class components for state management.
- Enables re-rendering of components when state changes.
- **Drawbacks**:
- Limited to managing individual state variables.
- Can lead to deeply nested state structures for complex components, which might be harder to manage.
- **Example Use Case**: Managing a simple counter.
```javascript
import React, { useState } from 'react';
function Counter() {
const [count, setCount] = useState(0);
return (
<div>
<p>Count: {count}</p>
<button onClick={() => setCount(count + 1)}>Increment</button>
</div>
);
}
```
2. **useReducer**:
- **Benefits**:
- Ideal for managing complex state logic.
- Provides a more structured approach to state management compared to useState.
- Optimizes performance for components with nested updates.
- **Drawbacks**:
- Requires understanding of concepts like reducers and actions, which might be unfamiliar to developers new to React or functional programming.
- Can lead to boilerplate code for simple state management tasks.
- **Example Use Case**: Managing a todo list with add, remove, and toggle functionality.
```javascript
import React, { useReducer } from 'react';
function todoReducer(state, action) {
switch (action.type) {
case 'ADD_TODO':
return [...state, action.payload];
case 'TOGGLE_TODO':
return state.map(todo =>
todo.id === action.payload ? { ...todo, completed: !todo.completed } : todo
);
default:
return state;
}
}
function TodoList() {
const [todos, dispatch] = useReducer(todoReducer, []);
return (
<div>
{todos.map(todo => (
<div key={todo.id}>
<input type="checkbox" checked={todo.completed} onChange={() => dispatch({ type: 'TOGGLE_TODO', payload: todo.id })} />
<span>{todo.text}</span>
</div>
))}
<button onClick={() => dispatch({ type: 'ADD_TODO', payload: { id: Date.now(), text: 'New Todo', completed: false } })}>
Add Todo
</button>
</div>
);
}
```
### Effect Hooks:
1. **useEffect**:
- **Benefits**:
- Handles side effects in functional components, such as data fetching, DOM manipulation, or subscriptions.
- Supports cleanup logic to prevent memory leaks or stale data.
- Offers a declarative way to manage side effects, improving code readability.
- **Drawbacks**:
- Can sometimes lead to unexpected behavior if not used with caution, especially with dependencies and cleanup logic.
- Performance implications due to potentially running effects on every render.
- **Example Use Case**: Fetching data from an API.
```javascript
import React, { useState, useEffect } from 'react';
function DataFetching() {
const [data, setData] = useState(null);
useEffect(() => {
fetch('https://api.example.com/data')
.then(response => response.json())
.then(data => setData(data))
.catch(error => console.error('Error fetching data:', error));
}, []);
return (
<div>
{data ? (
<ul>
{data.map(item => (
<li key={item.id}>{item.name}</li>
))}
</ul>
) : (
<p>Loading...</p>
)}
</div>
);
}
```
2. **useLayoutEffect**:
- **Benefits**:
- Synchronously fires after all DOM mutations, providing more control over layout effects.
- Useful for scenarios where you need to perform DOM measurements or operations that require synchronous updates before browser repaints.
- **Drawbacks**:
- Can potentially block the browser's rendering, leading to performance issues if used incorrectly or unnecessarily.
- Similar to useEffect, so choosing between them might require understanding the specific use case and timing requirements.
- **Example Use Case**: Performing DOM measurements.
```javascript
import React, { useLayoutEffect, useState } from 'react';
function LayoutEffectExample() {
const [width, setWidth] = useState(0);
useLayoutEffect(() => {
const handleResize = () => {
setWidth(window.innerWidth);
};
window.addEventListener('resize', handleResize);
handleResize(); // Initial measurement
return () => window.removeEventListener('resize', handleResize);
}, []);
return <p>Window Width: {width}px</p>;
}
```
3. **useInsertionEffect**:
- **Benefits**:
- Allows executing effects before React makes changes to the DOM, enabling modifications like adding dynamic CSS or other pre-render actions.
- Useful for scenarios where you need to manipulate the DOM before React updates it.
- **Drawbacks**:
- Less commonly used compared to useEffect and useLayoutEffect, so developers might be less familiar with its behavior and best practices.
- Requires a clear understanding of when and why to use it to avoid unnecessary complexity or performance issues.
- **Example Use Case**: Adding dynamic CSS styles.
```javascript
import React, { useInsertionEffect } from 'react';
function InsertionEffectExample() {
useInsertionEffect(() => {
const style = document.createElement('style');
style.textContent = `
.dynamic-element {
color: red;
font-weight: bold;
}
`;
document.head.appendChild(style);
return () => {
document.head.removeChild(style);
};
}, []);
return <div className="dynamic-element">Dynamic Element</div>;
}
```
### Additional Information:
- **useContext**:
- **Benefits**:
- Simplifies sharing data across components without prop drilling.
- Provides a clean and efficient way to consume context values at any nesting level.
- Reduces component coupling and improves code maintainability.
- **Drawbacks**:
- Overuse can lead to unclear component dependencies and make it harder to trace data flow.
- Might not be suitable for complex data structures or scenarios where performance is critical due to potential re-renders triggered by context changes.
- **Example Use Case**: Theming a component using context.
```javascript
import React, { createContext, useContext } from 'react';
const ThemeContext = createContext('light');
function ThemedButton() {
const theme = useContext(ThemeContext);
return <button style={{ background: theme === 'dark' ? 'black' : 'white', color: theme === 'dark' ? 'white' : 'black' }}>Themed Button</button>;
}
```
In summary, React Hooks offer numerous benefits in terms of code organization, reusability, and performance optimization. However, understanding their nuances, choosing the right hook for each scenario, and applying best practices are crucial to avoiding common pitfalls and maximizing their advantages.
| bilelsalemdev |
1,865,089 | Coffee Snobs get it right! | Yes, this is about programming AND coffee. Recently I got a new obsession: Coffee. Never liked the... | 0 | 2024-05-25T17:37:44 | https://medium.com/@noriller/coffee-snobs-get-it-right-b692d99e8e38 | programming, productivity, webdev, learning | Yes, this is about programming *AND* coffee.
Recently I got a new obsession: Coffee. Never liked the stuff, but then I learned that I’ve been only exposed to the bad stuff and badly brewed at that… I gave a chance to the good stuff and it got me hooked. After years without *touching* `.java` now I’m turning into a full-stack *barista*.
As far as coffee goes, I’m pretty sure I’m at the “peak of Mount Stupid” in the Dunning-Kruger curve. I’ve just finished learning all the basics and putting them into practice (or so I think). I still have no idea how much I don't know.
But hey, at least I'm not brewing my code like I used to brew my coffee – that is a *bitter* memory now.
Regardless of that, I was exposed to lots of people talking about coffee and the one common thing was:
## It’s better to brew an 8/10 cup every time you want than to try a “perfect” cup and end up with a 5/10 randomly
When you start going *one cup deeper*, you find recipes that seem crazy to someone from the outside, they literally have recipes like “stir X times clockwise then Y times counter-clockwise during seconds W to Y after pouring the bloom water”, not to mention a heavy dependency on extreme precision in the grams of coffee and milliliters of water.
Like writing code without unit tests, brewing coffee without a scale: you might get something drinkable, but good luck reproducing it. A good brew, like good code, doesn't *Java* happen!"
Seems crazy to have all of that for one cup of joe (though I've heard some programmers have even crazier rituals), but when programming it would be crazy not to have all of those “rules” and “recipes” to make a new feature.
And while making it “perfect” would take a lot of effort, making it “good enough” is easier: control and record the variables, then you’ll be able to replicate and tune them to always achieve an 8/10 cup. Once you start, that appeal of always having a good one is unbeatable.
Then when we go back to programming, every day you do things differently just because and without even knowing what you’re doing differently… you question why code should be readable, and why it should look like the team guidelines. Good luck knowing what you’re doing then.
## But I got a fresh bag of beans I’m not familiar with
There’s something called “cupping protocol” that has many variables fixed so that you objectively judge what that new coffee bean is about, kind of like a code review for your new coffee. By applying it repeatedly you can easily distinguish how two different beans are different from each other, just like comparing different coding languages or frameworks.
Not only that, if by each slurp (yes they slurp, loudly, it even has a reason) you try to concentrate on the acidic, sweet, bitter, or body of the coffee you can isolate each thing enough to know what you want more or less of when brewing it.
In programming, the closest thing I can think about is making a blog or TODO app, and usually focused on *how fast* you go from zero to complete. It usually can’t encompass everything we *actually* do every day or things that matter more than “how fast you can make a CRUD”.
## Reproducibility and Variable Isolation: The Keys to a Good Brew (and Code)
The amazing thing about getting a new obsession is that it lets you see things you already do in a new way, with *fresh eyes*.
Programming should be less “grandma’s magical recipe” (full of mysterious incantations and a pinch of this, a dash of that) and more “exact instructions” (clearly defined functions and precise syntax). Conversely, with coffee, you would think that “numbers and variables” shouldn’t be involved in the brewing – who needs a debugger for their morning cup?
However, coffee snobs will dive into a discussion about each little variable like “how many microns” is the best grind for a brewing method while programmers are like: “screw it, let me just copy/paste this from the legacy codebase that accesses the database from the frontend… working… ship it“.
Brewing coffee with precision is like writing clean code: both take practice, patience, and a lot of trial and error, but you can always know exactly where you screwed up. If coffee brewing had stack traces, we'd all be able to pinpoint exactly when we poured too much water. | noriller |
1,865,087 | Spring Boot Data Access | Spring Boot is a powerful framework that simplifies the development of Java applications. One of its... | 0 | 2024-05-25T17:36:22 | https://dev.to/oloruntobi600/spring-boot-data-access-59ac | Spring Boot is a powerful framework that simplifies the development of Java applications. One of its key features is its ability to streamline data access through various data access technologies. This document will cover the data access options available in Spring Boot, explain how to set up a database connection, and provide examples of CRUD operations using Spring Data JPA.
Data Access Options in Spring Boot
Spring Boot provides support for various data access technologies, making it versatile for different types of applications. Here are some of the primary data access options:
Spring Data JPA
Spring Data JPA simplifies the implementation of JPA-based repositories. It provides a repository abstraction over JPA, enabling you to access relational databases using repository interfaces.
Key Features:
Automatic implementation of repository interfaces.
Support for query methods based on method names.
Integration with Hibernate as the JPA provider by default.
Spring Data MongoDB
Spring Data MongoDB provides a similar abstraction as Spring Data JPA but for MongoDB, a NoSQL database.
Key Features:
Support for MongoDB repository interfaces.
Seamless integration with MongoDB's native query language.
Support for reactive repositories.
Spring Data JDBC
Spring Data JDBC is a simpler alternative to JPA, providing direct JDBC access with a minimalistic approach. It is ideal for applications that do not require the full JPA feature set.
Key Features:
Lightweight and straightforward configuration.
Support for repository interfaces without the complexity of JPA.
Direct mapping of SQL queries to repository methods.
Other Data Access Technologies
Spring Data Redis: For accessing Redis data stores.
Spring Data Cassandra: For accessing Cassandra databases.
Spring Data Couchbase: For accessing Couchbase databases.
Spring Data Elasticsearch: For accessing Elasticsearch indexes.
Setting Up a Database Connection in a Spring Boot Application
Setting up a database connection in Spring Boot is straightforward. Here’s how to configure a relational database connection using Spring Data JPA.
Step 1: Add Dependencies
Add the necessary dependencies to your pom.xml file.
xml
Copy code
<dependencies>
<dependency>
<groupId>org.springframework.boot</groupId>
<artifactId>spring-boot-starter-data-jpa</artifactId>
</dependency>
<dependency>
<groupId>org.springframework.boot</groupId>
<artifactId>spring-boot-starter-web</artifactId>
</dependency>
<dependency>
<groupId>com.h2database</groupId>
<artifactId>h2</artifactId>
<scope>runtime</scope>
</dependency>
</dependencies>
Step 2: Configure the Application Properties
Configure the database connection in application.properties.
properties
Copy code
spring.datasource.url=jdbc:h2:mem:testdb
spring.datasource.driverClassName=org.h2.Driver
spring.datasource.username=sa
spring.datasource.password=password
spring.jpa.database-platform=org.hibernate.dialect.H2Dialect
spring.h2.console.enabled=true
Step 3: Create an Entity Class
Define an entity class that maps to a database table.
java
Copy code
import javax.persistence.Entity;
import javax.persistence.GeneratedValue;
import javax.persistence.GenerationType;
import javax.persistence.Id;
@Entity
public class Person {
@Id
@GeneratedValue(strategy = GenerationType.AUTO)
private Long id;
private String name;
private int age;
// Getters and setters
}
Step 4: Create a Repository Interface
Create a repository interface for the entity.
java
Copy code
import org.springframework.data.repository.CrudRepository;
public interface PersonRepository extends CrudRepository<Person, Long> {
}
CRUD Operations Using Spring Data JPA
Spring Data JPA simplifies CRUD operations by providing repository interfaces that you can extend. Here are examples of basic CRUD operations using PersonRepository.
Create
To create and save a new Person entity:
java
Copy code
import org.springframework.beans.factory.annotation.Autowired;
import org.springframework.stereotype.Service;
@Service
public class PersonService {
@Autowired
private PersonRepository personRepository;
public Person createPerson(String name, int age) {
Person person = new Person();
person.setName(name);
person.setAge(age);
return personRepository.save(person);
}
}
Read
To retrieve a Person entity by its ID:
java
Copy code
public Person getPerson(Long id) {
return personRepository.findById(id).orElse(null);
}
Update
To update an existing Person entity:
java
Copy code
public Person updatePerson(Long id, String name, int age) {
Person person = personRepository.findById(id).orElse(null);
if (person != null) {
person.setName(name);
person.setAge(age);
return personRepository.save(person);
}
return null;
}
Delete
To delete a Person entity by its ID:
java
Copy code
public void deletePerson(Long id) {
personRepository.deleteById(id);
}
Summary
Data Access Options: Spring Boot supports various data access technologies including Spring Data JPA, Spring Data MongoDB, and Spring Data JDBC, among others.
Database Connection Setup: Configuring a database connection involves adding dependencies, setting properties in application.properties, and creating entity and repository classes.
CRUD Operations: Spring Data JPA simplifies CRUD operations through repository interfaces, allowing for easy implementation of create, read, update, and delete functionalities.
By leveraging Spring Boot's data access capabilities, developers can build robust applications with minimal boilerplate code, focusing more on business logic and less on infrastructure. | oloruntobi600 | |
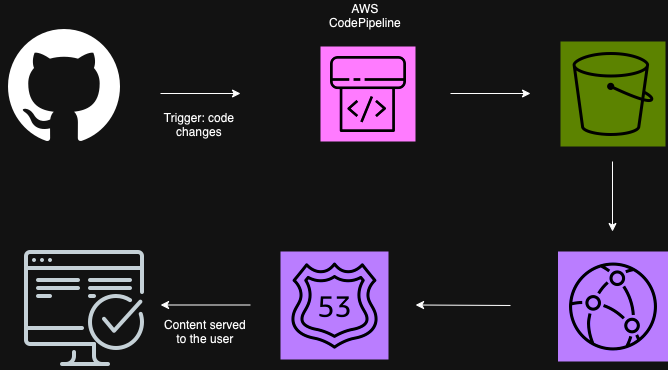
1,865,080 | AWS Code Pipeline - CloudFront - S3 CI/CD Pipeline | Steps to create an automated pipeline in AWS without losing the plot Resources... | 0 | 2024-05-25T17:30:46 | https://dev.to/monica_escobar/aws-code-pipeline-cloudfront-s3-cicd-pipeline-55gf | aws, cicd, automation, devops | ## Steps to create an automated pipeline in AWS without losing the plot
---
**Resources used:**
- S3 bucket
- CloudFront Distribution
- GitHub
- Route 53
- Domain name
- SSL Certificate
- Code Pipeline
---
**The Big Picture**
---
**Steps followed:**
**Step 1: Setting Up Your AWS Environment**
1.1 Create an AWS Account
If you don’t already have an AWS account, sign up for AWS.
1.2 Set Up IAM User
Create an IAM user with the necessary permissions to access the services you'll be using:
Navigate to the IAM Console.
Create a new user and attach the policies for CodePipeline, S3, CloudFront, Route 53, and Certificate Manager.
**Step 2: Purchase a Domain and obtain an SSL Certificate**
2.1 Purchase a Domain via Route 53
Go to the Route 53 Console.
Click on Domains -> Register Domain.
Search for your desired domain name and follow the prompts to purchase it.
2.2 Request an SSL Certificate via AWS Certificate Manager
Navigate to the AWS Certificate Manager (ACM) Console.
Click on Request a certificate.
Select Request a public certificate and enter your domain name.
Follow the steps to validate your domain ownership (via DNS is much faster than via email, remember to create a CNAME record for verification purposes).
**Step 3: Set Up S3 Bucket for Static Hosting**
Go to the S3 Console.
Create a new bucket (e.g: my-portfolio).
Enable static website hosting in the Properties tab (optional tip: add max-age=0 to the header for faster updates).
Set up the bucket policy to allow public read access (or configure CloudFront for secure access).
**Step 4: Configure CloudFront for CDN**
Navigate to the CloudFront Console.
Create a new distribution.
Set the origin to the S3 bucket you created.
Configure the distribution settings, ensuring to set up the SSL certificate you requested.
**Step 5: Configure Route 53 to Point to CloudFront**
In the Route 53 Console, navigate to Hosted Zones.
Select your domain and create a new A record.
Set the alias target to your CloudFront distribution.
**Step 6: Set Up GitHub Repository**
Create a new repository on GitHub and push your application code to it.
**Step 7: Create the CI/CD Pipeline with AWS CodePipeline**
7.1 Set Up CodePipeline
Go to the CodePipeline Console.
Click Create pipeline and give it a name.
Select New service role to create a new IAM role for CodePipeline.
7.2 Add Source Stage
In the Source stage, select GitHub2 as the source provider.
Connect your GitHub account and select the repository and branch you want to use.
7.3 Add Build Stage (OPTIONAL)
In the Build stage, leave empty or choose CodeBuild (I personally left it empty).
7.4 Add Deploy Stage
In the Deploy stage, choose Amazon S3 as the deploy provider.
Select the S3 bucket you created for static hosting.
**Step 8: Test the Pipeline**
Review the pipeline configuration and click Create pipeline.
Commit a change to your GitHub repository to trigger the pipeline.
Verify the build and deployment process.
Access your application using the domain name configured in Route 53 or if the cache is at its default setting it will take longer to show in your domain, but you can check the S3 URL.
---
And this is all you need to create your own automated pipeline from your main branch using AWS and GitHub.
Happy deploying!
| monica_escobar |
1,865,082 | BTC AND OTHER CRYPTOCURRENCIES ARE RECOVERABLE CONTACT TECHNOCRATE RECOVERY | TECHNOCRATE RECOVERY successfully recovered my lost Bitcoin, delivering a triumphant victory in the... | 0 | 2024-05-25T17:19:52 | https://dev.to/hortonangela901/btc-and-other-cryptocurrencies-are-recoverable-contact-technocrate-recovery-48p8 | cryptocurrency, bitcoin, ethereum | TECHNOCRATE RECOVERY successfully recovered my lost Bitcoin, delivering a triumphant victory in the face of adversity. Words cannot express the overwhelming gratitude and relief that flooded my soul upon receiving the news. Beyond their unparalleled expertise, TECHNOCRATE RECOVERY embodies the essence of empathy and compassion. They understand the profound impact of financial loss, offering not only a solution to the problem but also a shoulder to lean on in times of distress. Their genuine care for their clients transcends mere business transactions, forging lasting relationships built on trust and mutual respect. In conclusion, I wholeheartedly recommend TECHNOCRATE RECOVERY to anyone who finds themselves ensnared in the web of online scams. They are not just a company; they are guardians of justice in the digital realm, fighting tirelessly to reclaim what is rightfully yours. With TECHNOCRATE RECOVERY by your side, hope is not just a distant dream but a tangible reality waiting to be embraced. Trust in their expertise, and let them lead you to recovery.
EMAIL: (technocrat recovery(at)contractor. net WHATSAPP: +1(573)356-3708
 | hortonangela901 |
1,865,081 | Deep Dive into Push Nodes: Functionality and Importance | In today's rapid blockchain and decentralized applications (dApps) environment, staying informed is... | 0 | 2024-05-25T17:15:34 | https://dev.to/luffy251/deep-dive-into-push-nodes-functionality-and-importance-2cgl |
In today's rapid blockchain and decentralized applications (dApps) environment, staying informed is essential. Push Nodes, a part of its notification systems, have been introduced by Push Protocol so as not to overwhelm the users while keeping them up to date. This blog post will explain what push nodes are, how they work, and why they matter in the easiest way possible.
## What Are Push Nodes?
Push nodes serve as messengers within push protocol. They securely and effectively process notifications (messages) meant for delivery to end users. Think about them like postal workers of the blockchain world who ensure your message is safely sent and received in time
### How Do Push Nodes Work?
1. **Message Validation**:
- Before a message gets delivered, Push Nodes check to make sure it's from a trusted source and hasn’t been tampered with. Think of it as verifying the sender’s address and ensuring the letter hasn’t been opened
2. **Message Routing**:
- Once verified, Push Nodes send the message to the right recipient. They know the best routes to take, much like a postal service knows the best delivery routes to get your mail to you quickly.
3. **Decentralized Storage**:
- Push Nodes help in saving messages in a decentralized manner whereby data is not stored in one place hence more secure and difficult to manipulate like having duplicates of important records in multiple safe areas.
4. **Network Health Monitoring**:
- Push Nodes are constantly checking the network to ensure that everything is running smoothly. If they find any issues, they can fix them quickly, just like a postal service might change delivery routes when it’s raining badly.
## Why Are Push Nodes Important?
### Keeping Things Decentralized
Decentralization means that no single person or company controls the whole system. Push Nodes spread out the responsibility of handling messages, making the system more secure and reliable because there’s no single point of failure.
### Boosting Security
By validating every message, Push Nodes ensure that only legitimate notifications are delivered. This prevents scams and ensures the information you receive is trustworthy.
### Improving Scalability
As more people use blockchain and dApps, the number of messages increases. Push Nodes help the system handle more messages without slowing down, much like adding more postal workers to handle increased mail during the holidays.
### Facilitating Interoperability
Push Nodes can work with different blockchain networks. This means they can send messages across various platforms, making Push Protocol a versatile tool for different types of blockchain projects.
### Providing Redundancy
Redundancy means having backup systems in place. If one Push Node goes down, others can take over, ensuring that the system continues to function without interruption.
## Benefits for Users and dApps
### Better User Experience
Push Nodes ensure you receive timely and relevant notifications. Whether it’s updates about transactions, governance proposals, or event reminders, you get the information you need when you need it.
### Increased Trust and Transparency
Because Push Nodes handle notifications in a decentralized way, you can trust that the messages are accurate and haven’t been tampered with.
### Flexibility for Developers
Developers can customize how Push Nodes handle notifications, allowing them to tailor the system to their specific needs. This makes it easier to create dApps that provide the right information to users at the right time.
### Cost-Effective Solution
Using Push Nodes is cheaper than building and maintaining your own notification system. This allows developers to focus on improving their dApps rather than worrying about infrastructure costs.
### Empowering the Web3 Ecosystem
Push Nodes are an essential part of the Web3 ecosystem, providing a reliable way to communicate within decentralized applications. This helps enhance the functionality of existing dApps and opens up new possibilities for innovative projects.
## Real-World Example: DeFi Platform
Let’s say you’re using a decentralized finance (DeFi) platform that offers lending, borrowing, and staking services. Users need to be informed about important events like loan liquidations, interest rate changes, and staking rewards.
### Implementation
The DeFi platform integrates Push Protocol, using Push Nodes to handle notifications. When something important happens, Push Nodes ensure the message is verified and delivered to the right users promptly.
### Benefits
- **Timely Alerts**: Users get instant notifications about important events, allowing them to act quickly.
- **Improved Engagement**: Regular updates keep users engaged with the platform.
- **Enhanced Security**: Users trust the notifications because they know they are legitimate.
## Looking Ahead: Future Enhancements
Push Protocol is always evolving, and Push Nodes will continue to get better with new features and capabilities. Future improvements might include:
- **Advanced Filtering**: Allowing users to customize their notifications even more.
- **Cross-Chain Compatibility**: Making it easier to send notifications across different blockchain networks.
- **AI Integration**: Using artificial intelligence to provide smarter, more personalized notifications.
## Conclusion
Push Nodes are a crucial part of Push Protocol, ensuring that notifications are handled in a secure, decentralized, and efficient way. By verifying, routing, and storing messages, Push Nodes improve the reliability and scalability of the system. They offer numerous benefits for both users and developers, including better user experience, increased trust, and cost savings. As blockchain technology continues to grow, Push Nodes will play an increasingly important role in making sure communication within the ecosystem is seamless and trustworthy.
Understanding and using Push Nodes effectively will help you stay informed and engaged in the exciting world of decentralized applications, driving greater innovation and adoption in the blockchain space.
| luffy251 | |
1,865,068 | How to create an Online Flipping Form using Plain HTML and CSS | Almost everyone who has used the Internet has come across Forms, many Internet users who are familiar... | 0 | 2024-05-25T17:13:42 | https://dev.to/george_kingi/how-to-create-an-online-flipping-form-using-plain-html-and-css-4ka5 | webdev, html, css, javascript | Almost everyone who has used the Internet has come across Forms, many Internet users who are familiar with forms have come across them when signing up or joining a particular platform, it could be a Gmail sign-up page, Instagram, Facebook, or many other platforms. It is safe to think of a form as a door that can enable access to some information once opened. This article serves both beginners and experts in web development.
This article will showcase how to create an online flipping form, we will create a sign-up page for new users and a log-in form for existing users. The form will flip on click to the sign-up page if one is a new user and flip on click if one is an existing user. We will dive in shortly and it will come clear. We will build the structure of the form via HTML, make our form look good using CSS, and then introduce some Javascript for interactivity.
To make this more fun, we will break it down it two parts;
Part 1 → Will cover the HTML part.
Part 2 → Will cover the CSS part. Here is a link for part 2. https://dev.to/george_kingi/the-power-of-css-in-styling-up-forms-o8m
Let's grab a seat, shall we?

A form is a container that allows users to input data and submit it to a web server for processing. Forms are fundamental in enabling user interaction and data submission. The `<form>` `<\form>` element defines a form in HTML.
## Definition and Uses of Tags
When creating a form, the `<form>` element acts as a container for other elements. The space within the form is defined by the `<input>` tag which allows users to input data. The `<input>` tag is defined by the `type` attribute which sets data in the form of `text`, `number`, `date`, `image`, `reset`, etc, while the `placeholder` provides the watermark.
Examples:
`<input type =”text” >`
`<input type= “number”>`
It is possible to define a class within the `<input>` element as we can see below, to allow for styling of the contents of the tag. The `Placeholder` attribute provides a watermark for the “First name”.
<input type="text" class="input-box" placeholder="First name" required>
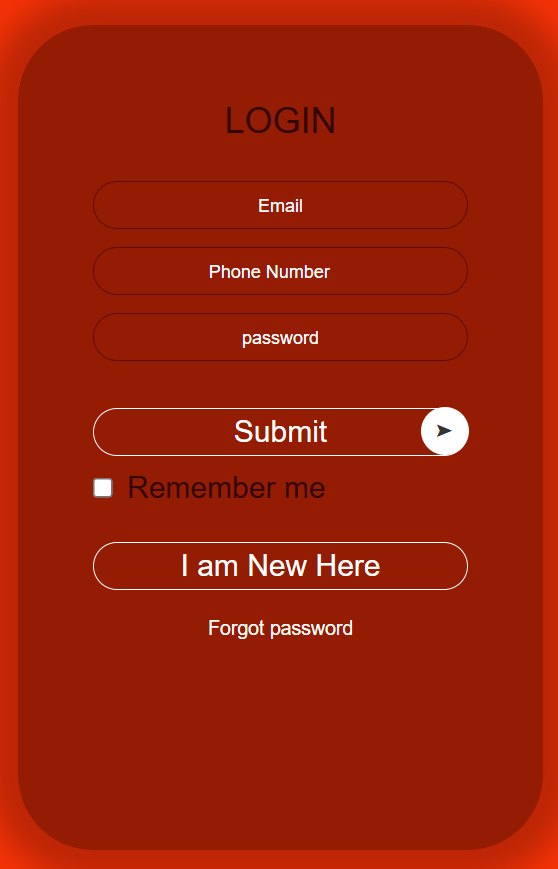
## An Overview of the Final Form
### A Preview of the Front and Back of the Form
## Creating The Online Flipping Form from Scratch
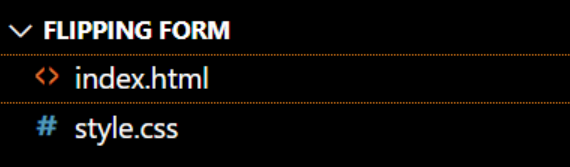
We will go ahead and create an HTML file and a CSS file then link them via the external style. Our code editor for this case will be the VS Code.
To create the Form follow the below steps;
1. Create a folder and name it whatever you want.
2. Open Vs Code Editor, go to file select open folder then select the folder you just created.
3. While on the Vs Code Editor, create a new file and name it `index.html`. The file name must have the extension `.html`
4. Create a new file and name it `style.css`. file. The file name must have the extension `.css`.
You should have something like the snip below, I named my folder “FLIPPING FORM”.
You do not need to generate the below code line by line, just hold shift and press the `!` (exclamation mark ) on the keyboard, and the below code will be auto-generated, change the title to whatever you want,
Then use the link element to connect the HTML and CSS files as below.
```
<!DOCTYPE html>
<html lang="en">
<head>
<meta charset="UTF-8">
<meta name="viewport" content="width=device-width, initial-scale=1.0">
<title>Online Flipping Form</title>
<link rel="stylesheet" href="style.css">
</head>
<body>
</body>
</html>
```
The first step, declare three `<div>`s with their respective classes as we can see below, and then declare our `<form>` tag in the last `<div>`. Remember to name the heading of your page and the title which in this case is “Online Flipping Form” and ”‘Login” respectively.
To note, the class names we declared are random names that will help us when using CSS.
```
<!DOCTYPE html>
<html lang="en">
<head>
<meta charset="UTF-8">
<meta name="viewport" content="width=device-width, initial-scale=1.0">
<title>Online Flipping Form</title>
<link rel="stylesheet" href="style.css">
</head>
<body>
<div class="container" >
<div class="card">
<div class="card-front">
<h2>Login</h2>
<form>
</div>
</form>
</div>
</div>
</body>
</html>
```
Within the `<form>` tag, we introduce the <input> tag which allows users to input data in the form.
```
<body>
<div class="container" >
<div class="card">
<div class="card-front">
<h2>Login</h2>
<form>
<input type="email" class="input-button" placeholder="Email" required>
</div>
</form>
</div>
</div>
</body>
```
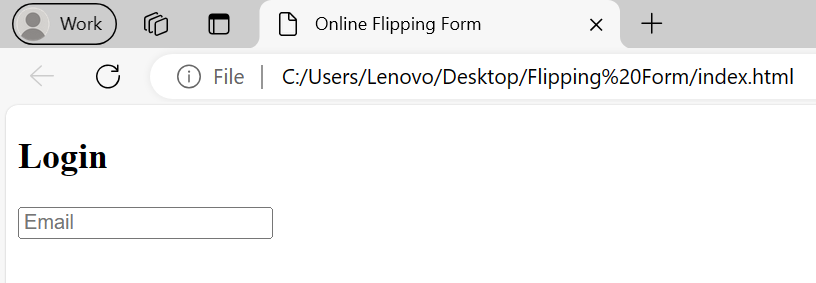
With the above code, the output on the browser is displayed as below.
We go ahead and create more forms as per our target project. See the below code block that will do the trick.
```
<body>
<div class="container" >
<div class="card">
<div class="card-front">
<h2>Login</h2>
<form>
<input type="email" class="input-button" placeholder="Email" required>
<input type="number" class="input-button" placeholder="Phone Number" required>
<input type="password" class="input-button" placeholder="Password" required>
<button type="submit" class="submit-btn">Submit</button>
<input type="checkbox" class="checkbox"><span>Remember me</span>
<button type="button" class="btn">I am new here</button>
<a href="">Forgot password</a>
</div>
</form>
</div>
</div>
</body>
```
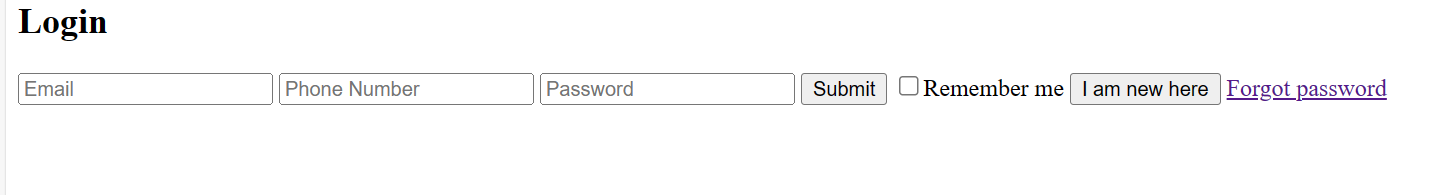
With this, the output should be as per the below; Remember, we are creating a flipping form that has two sides, so let's call the below output the front side of the form.
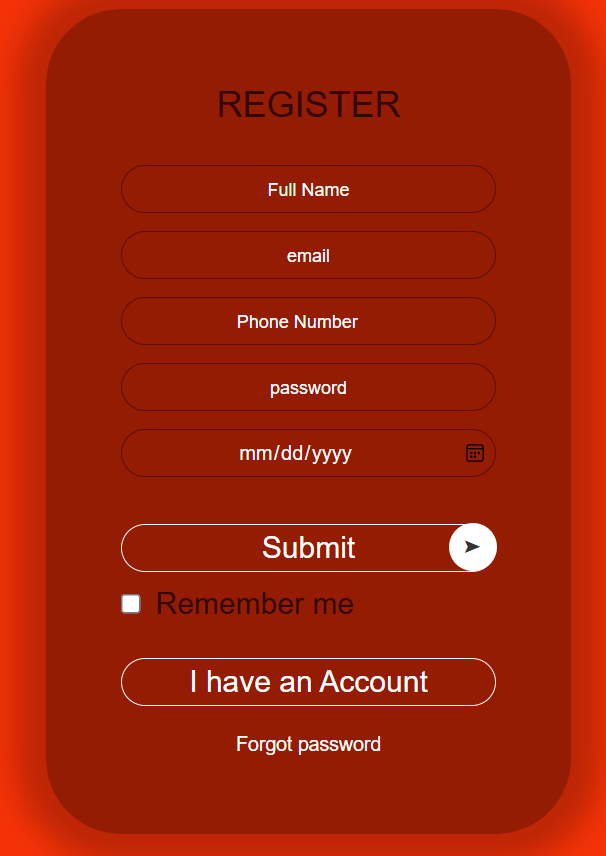
Let's go ahead and create the back of the form and to do so, we declare another <form> tag and other DIVs as below.
```
<!DOCTYPE html>
<html lang="en">
<head>
<meta charset="UTF-8">
<meta name="viewport" content="width=device-width, initial-scale=1.0">
<title>Online Flipping Form</title>
<link rel="stylesheet" href="style.css">
</head>
<body>
<div class="container" >
<div class="card">
<div class="card-front">
<h2>Login</h2>
<form>
<input type="email" class="input-button" placeholder="Email" required>
<input type="number" class="input-button" placeholder="Phone Number" required>
<input type="password" class="input-button" placeholder="Password" required>
<button type="submit" class="submit-btn">Submit</button>
<input type="checkbox" class="checkbox"><span>Remember me</span>
<button type="button" class="btn">I am new here</button>
<a href="">Forgot password</a>
</div>
</form>
<div class="card-back">
<h2>Register</h2>
<form>
<input type="text" class="input-button" placeholder="Full Name" required>
<input type="email" class="input-button" placeholder="Email" required>
<input type="number" class="input-button" placeholder="Phone Number" required>
<input type="password" class="input-button" placeholder="Password" required>
<input type="date" class="input-button" placeholder="Date-of-Birth" required>
<button type="submit" class="submit-btn">Submit</button>
<input type="checkbox" class="checkbox"><span>Remember me</span>
<button type="button" class="btn">I have an Account</button>
<a href="">Forgot password</a>
</form>
</div>
</div>
</div>
</body>
</html>
```
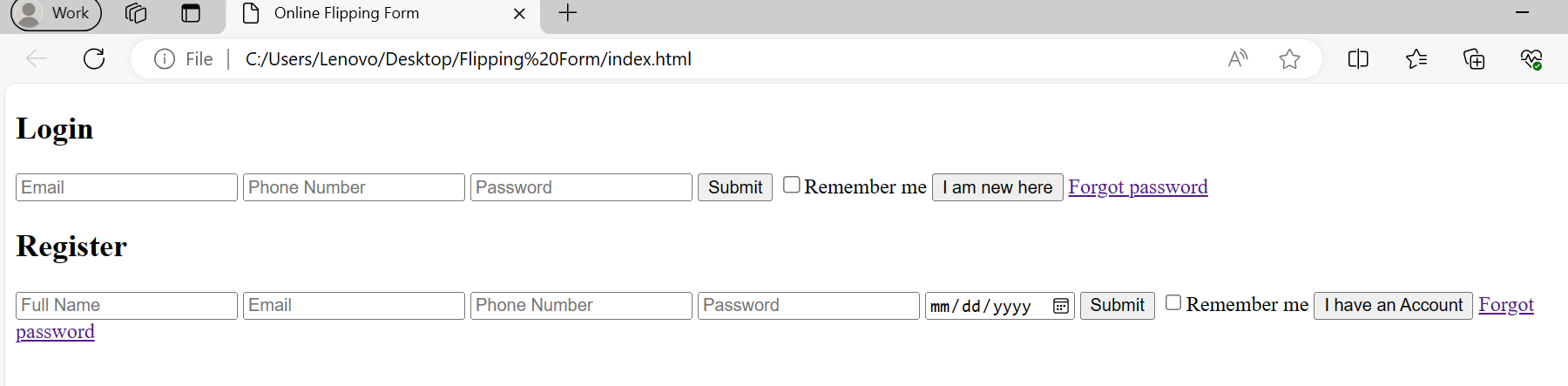
With the above code, our HTML structure is set. The browser should display the below output.
This brings us to the end of Part 1 on how to create an online flipping form. Part 2 will focus on how to make our form look good, introduce different styles on all the elements of the form, and finally make the form flip.
Here is the link to the Part 2: https://dev.to/george_kingi/the-power-of-css-in-styling-up-forms-o8m
| george_kingi |
1,865,072 | Deploy a Static React Site Using AWS S3 and CloudFront | Learn how to take the static build of a react app & deploy it to AWS, add SSL certificates & add global CDN caching using S3 buckets & CloudFront. | 0 | 2024-05-25T17:11:58 | https://dev.to/whittington/deploy-a-static-react-site-using-aws-s3-and-cloudfront-d0l | react, aws, s3, cloudfront | ---
title: Deploy a Static React Site Using AWS S3 and CloudFront
published: true
description: Learn how to take the static build of a react app & deploy it to AWS, add SSL certificates & add global CDN caching using S3 buckets & CloudFront.
tags: react, aws, s3, cloudfront
# cover_image: https://dev-to-uploads.s3.amazonaws.com/uploads/articles/tlpnsthb6qaoqj8xiclx.PNG
# Use a ratio of 100:42 for best results.
# published_at: 2024-05-25 16:23 +0000
---
_Quick note: links to documentation & further reading exist throughout this post, look for those links to get additional information & documentation links on topics/ tools/ technologies mentioned._
_If you prefer video content, the video version of this tutorial can be found on my [Youtube channel](https://www.youtube.com/@LearnWithWhittington). Link [here](https://youtu.be/2zrjisB7YrM?si=__ZIHKo71Yg-W2lQ)_
In this tutorial, I will walk you through building a quick static site by doing a static build using [ReactJS](https://react.dev/) & [create-react-app](https://create-react-app.dev/), then show you how to deploy that static site on [AWS](https://aws.amazon.com/) using [S3](https://aws.amazon.com/s3/) buckets as well as how to cache it & add SSL certificates with [CloudFront](https://aws.amazon.com/cloudfront/) CDN & [Certificate Manager](https://aws.amazon.com/certificate-manager/).
All you need to get started is an AWS account & a [domain](https://developer.mozilla.org/en-US/docs/Learn/Common_questions/Web_mechanics/What_is_a_domain_name), you can either purchase one on AWS or use one from another [registrar](https://www.cloudflare.com/learning/dns/glossary/what-is-a-domain-name-registrar/). If you're a beginner I recommend purchasing the domain directly from AWS as it's the most straightforward approach, however, if you have an existing domain with an external registrar you can use it in a Route 53 Hosting Zone by first creating a hosting zone, then by pointing the domain to the AWS name servers for your hosting zone (this is covered later). For this tutorial I will be using an external domain as I already have one for testing & tutorials. Behold: [0000.quest](https://0000.quest)
#### AWS Services Overview
Before we get started, here is a brief overview of the AWS services used in this walkthrough. Feel free to skip this section if you're already familiar with the services used here.
[AWS S3](https://docs.aws.amazon.com/s3/)<br/>
S3 or Simple Storage Service, is Amazon's solution for [object storage](https://aws.amazon.com/what-is/object-storage/). It's a way to store files within the AWS ecosystem & seamlessly integrates with other AWS services as a data source, it can also do other things, but we're not using any of that 😅. We'll be using it as a file storage system for the static files our site serves.
[AWS Route 53](https://docs.aws.amazon.com/route53/)<br/>
Route 53 is the native routing service in the AWS ecosystem. This is a complex service that handles all your AWS routing needs to route user traffic to your applications & services, but in this walkthrough, we'll only be leveraging the AWS Route 53 Hosted Zones feature. Hosted Zones allow you to manage the [DNS](https://www.cloudflare.com/learning/dns/what-is-dns/) records for domains accessible in your AWS account.
[AWS Certificate Manager](https://docs.aws.amazon.com/acm/)<br/>
Certificate Manager is the AWS integrated service that handles creation, storage & renewals for [SSL certificates](https://www.cloudflare.com/learning/ssl/what-is-an-ssl-certificate/). We'll be leveraging this service to create & serve our SSL certificates for our deployed site.
[AWS CloudFront](https://docs.aws.amazon.com/cloudfront/)<br/>
CloudFront is AWS's global [CDN](https://www.cloudflare.com/learning/cdn/what-is-a-cdn/) service, CloudFront allows you to cache data at AWS global endpoints so that users will get data from a source close to them geographically, ensuring low latency for the data they fetch. In this walkthrough, we'll be leveraging CloudFront to cache our static site globally & we'll also be using it to serve our site's SSL certificate.
_**Lets get started**_ 😎👍
#### Using create react app to build a static site
To get started, let's quickly create a sample [React](https://react.dev/) app that has a build configured to export a static site. Even if you have a project in mind to deploy, I recommend going through the motions with a simple sample site, as you may run into implementation specific issues with your project & if you've never gone through the motions, it can be hard to determine whether you made a mistake in the deployment processes or if there are implementation specific issues you're facing. <br/>
I assume you have nodejs installed if you're doing a react app, but just in case you're doing this tutorial for funsies, you can download nodejs [here (nodejs.org)](https://nodejs.org).
Create a sample project using [create-react-app](https://create-react-app.dev/docs/getting-started/). Run the following in a directory where you want to save the sample project. Feel free to change the name, but for this example I'll be calling it samplesite.
<pre><code>npx create-react-app samplesite</code></pre>
If you're new to create-react-app or simply want to see what the preview looks like, run the following command to run a local dev server & preview the app.
<pre><code>
cd samplesite
npm run start
</code></pre>
Once you're done looking at the preview, run the following build command to generate the static site.
<pre><code>npm run build</code></pre>
The static site will generate in the build folder of the samplesite project root. The folder structure should look like this:
<pre><code>
samplesite
build
node_modules
public
src
</code></pre>
Now that we have a sample static site to test, we can move on.
#### Setup S3 buckets for domain
Next thing to do is setup the S3 buckets for the static hosting. We'll create two buckets, one for the primary site & then a second one to redirect the www subdomain to the primary site. It seems to be commonplace to make the www subdomain the primary site, but it doesn't really matter, its a matter of preference & I prefer to get rid of that ugly www subdomain on my URL 😤.
Log into the [AWS Management Console](https://aws.amazon.com) & go to the S3 console by searching for S3 in the search bar & clicking on it. Click on buckets in the navigation menu on the left to get to the buckets tab. In the buckets tab, select create bucket.
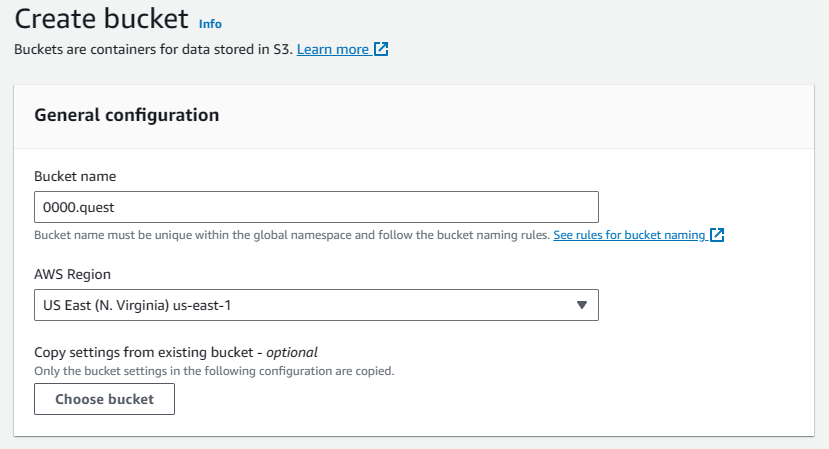
First we'll be creating the main bucket, it must have the same name as the domain you'll be hosting, so since I'm using 0000.quest that's what I'll be naming this bucket. For CloudFront to work, you'll need to host the bucket in the us-east-1 region, so select that. Don't worry if you or your primary user base is in another region, CloudFront does global endpoint caching, but your primary bucket needs to be in this region for some reason.
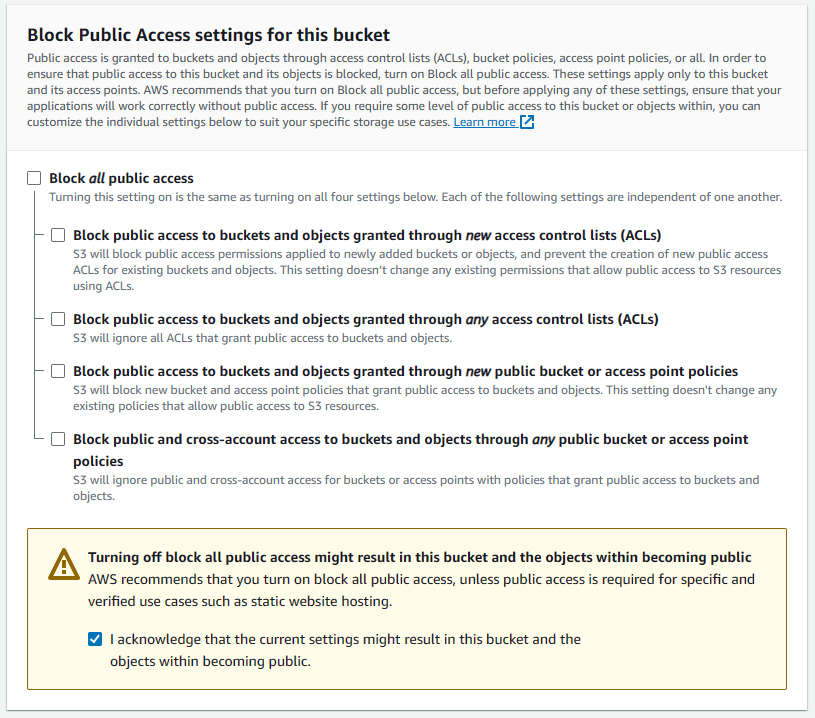
For this bucket, we'll need to enable public access, so uncheck the Block all public access options & check the acknowledgement checkbox warning that this bucket's contents will be public. This is a public website so that's kinda the whole point 😅.
Leave all other settings default & add custom tags if you need them. Then hit the create bucket button to create the bucket.
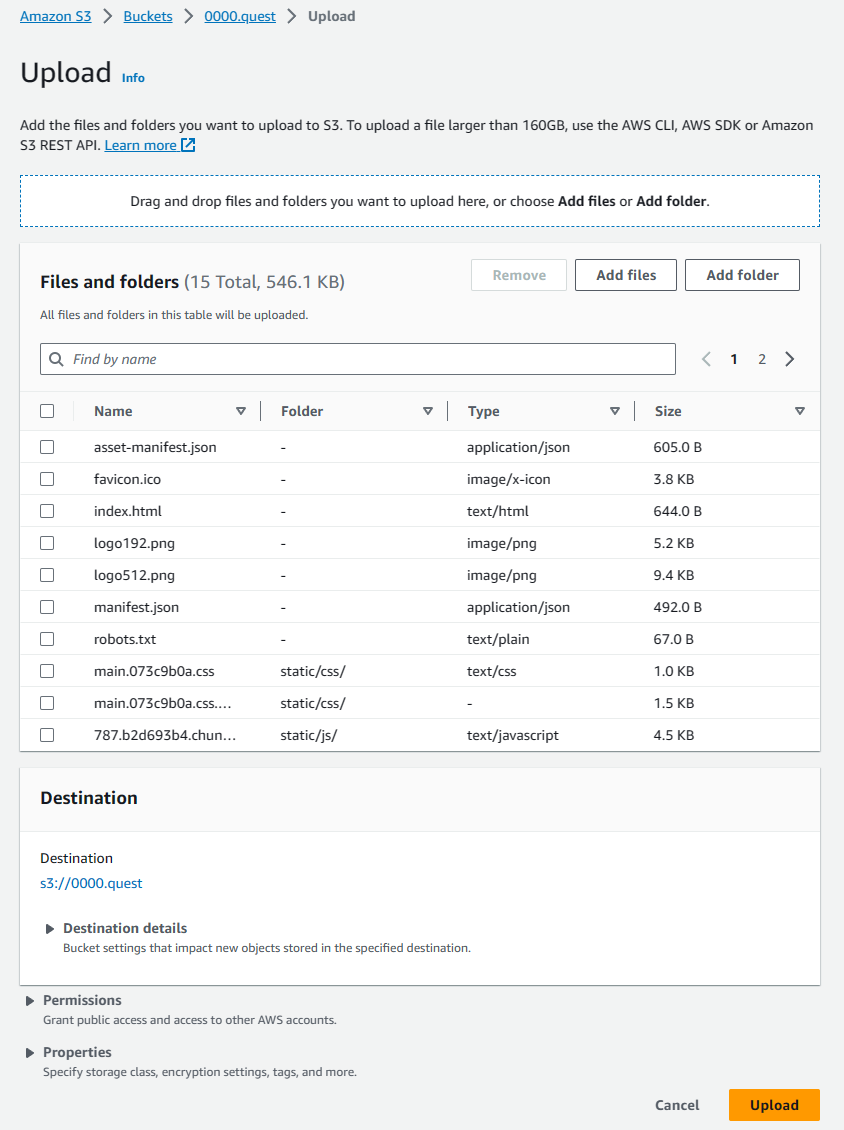
Once the bucket is created, you'll be taken back to the buckets tab of the S3 console. Select the bucket you just created & that will take you to the object view window for that bucket. Here, we will manually upload the static build of the samplesite we created in an earlier step. Open the directory containing the build (samplesite/build), select everything, directories included, & drag them into the object view of the bucket. You'll see the window change to accept the drop. The upload preview will look like this:
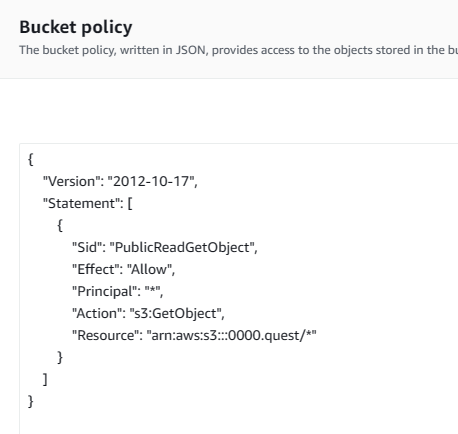
That should have our sample site's static assets available in the bucket to be served on our URL. We're not quite done configuring this bucket yet, there's one more step for our initial configuration. We need to set explicit permissions so all users can access the files in the bucket. Navigate back to the object view by clicking on the bucket from the buckets tab of the S3 console. Once there, navigate to the permissions tab, scroll down to the bucket policy, it should be empty. Hit the edit button to create a new bucket policy. Paste the following policy in the editor & hit save changes.
<pre><code>
{
"Version": "2012-10-17",
"Statement": [
{
"Sid": "PublicReadGetObject",
"Effect": "Allow",
"Principal": "*",
"Action": "s3:GetObject",
"Resource": "arn:aws:s3:::<bucket_name_here>/*"
}
]
}
</code></pre>
If you're not familiar with AWS policies, here's a brief explanation of what it does. This policy statement grants everyone the GetObject permission on the root of the S3 bucket. This means that anyone will be able to view all the files in the bucket. Please don't use this policy for anything but this 😭. The new policy should look like the screenshot below.
For more information about bucket policies, consult the [AWS bucket policies & user policies documentation](https://docs.aws.amazon.com/AmazonS3/latest/userguide/using-iam-policies.html)
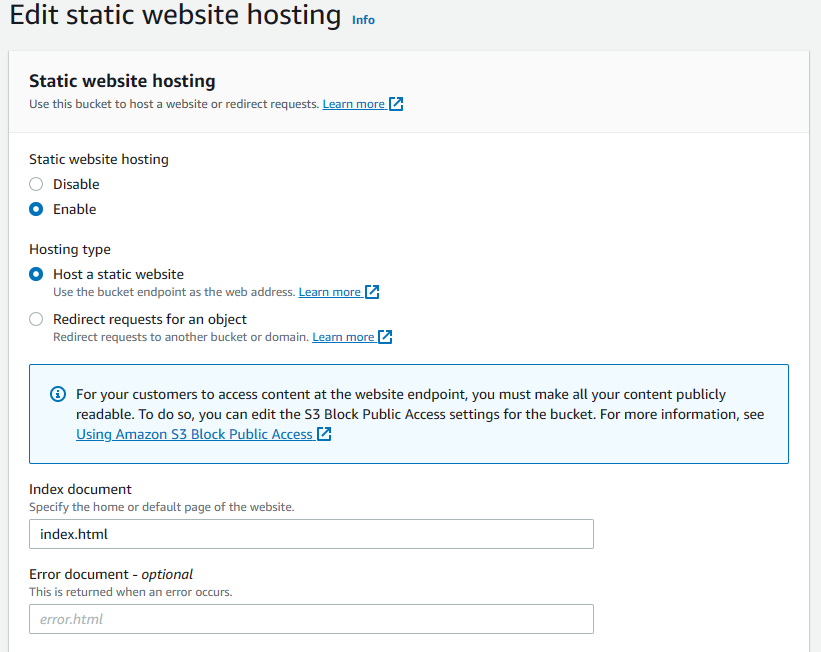
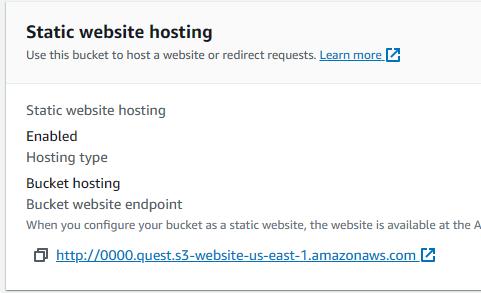
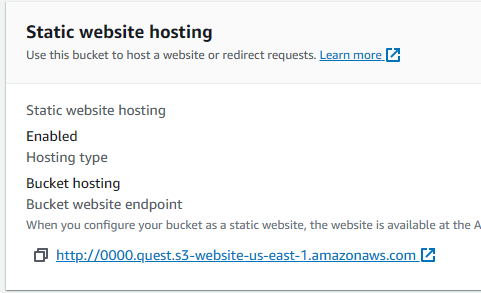
Now that all objects in the bucket are publicly accessible, we can configure the bucket for static site hosting. Navigate back to the bucket's object preview & switch to the properties tab. Scroll all the way to the bottom & hit the edit button on the static website hosting section. Here switch the static website hosting toggle to enable, change the index document to index.html, this is the application entry point for our react app. We don't have an error page so leave the error document blank, leave all other settings to the defaults, then hit the save changes button. Settings should match the screenshot below.
Once that's done, scroll back to the bottom of the properties tab for that bucket & you'll see a URL there, copy that & save it somewhere, you'll need that for the second bucket configuration.
We're done configuring this bucket for now, on to the next bucket, this will be a lot easier to configure as it's just a redirect & won't host any actual content, so few settings will need to change.
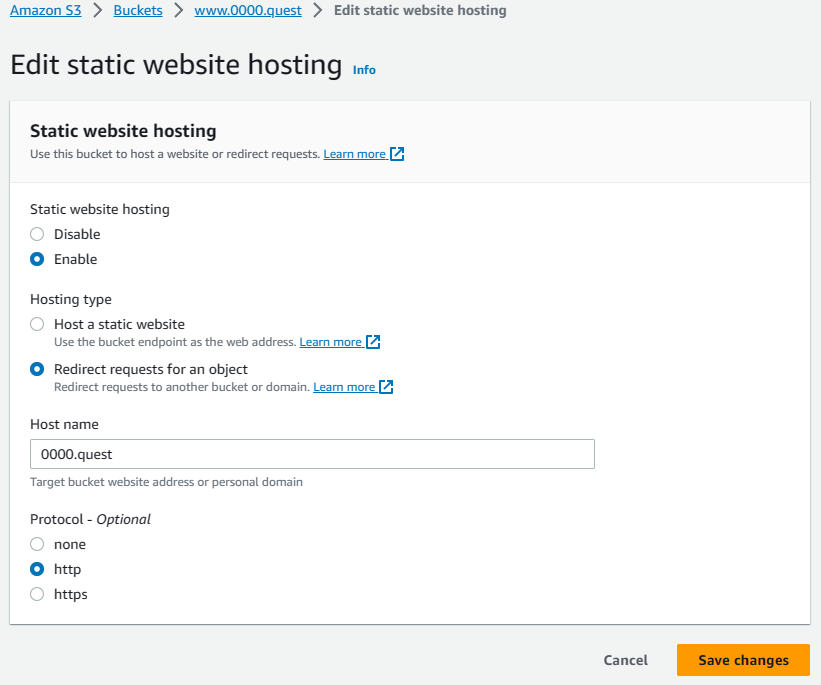
Navigate to the buckets tab of the S3 console & hit the create bucket button. This is the redirect bucket for the www subdomain, so it's going to have the www prefixing the domain name, for me it's www.0000.quest since that's the domain I'm using. Again, we're going to need the [region](https://docs.aws.amazon.com/AWSEC2/latest/UserGuide/using-regions-availability-zones.html) to be us-east-1. Leave all other settings default. Since this is just a redirect bucket, the public access isn't necessary, as it won't have any files. Hit create bucket & finish making this bucket.
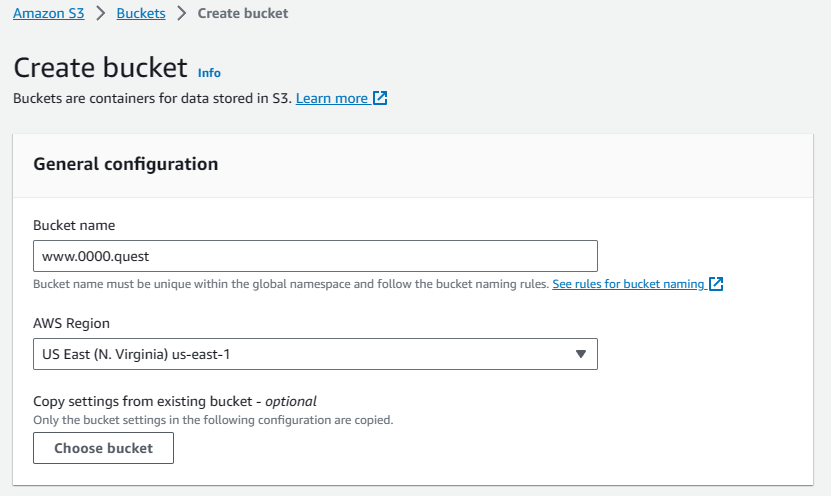
Navigate to the subdomain bucket's properties tab & scroll to the bottom to edit the static website hosting settings. Here, we switch the static website hosting toggle to enable, change the hosting type to redirect requests for an object. Under host name, type your domain name &, for now leave the protocol to HTTP for testing, we'll have to come back & change to HTTPS this later, once we get the SSL certificates setup in CloudFront. Hit save changes.
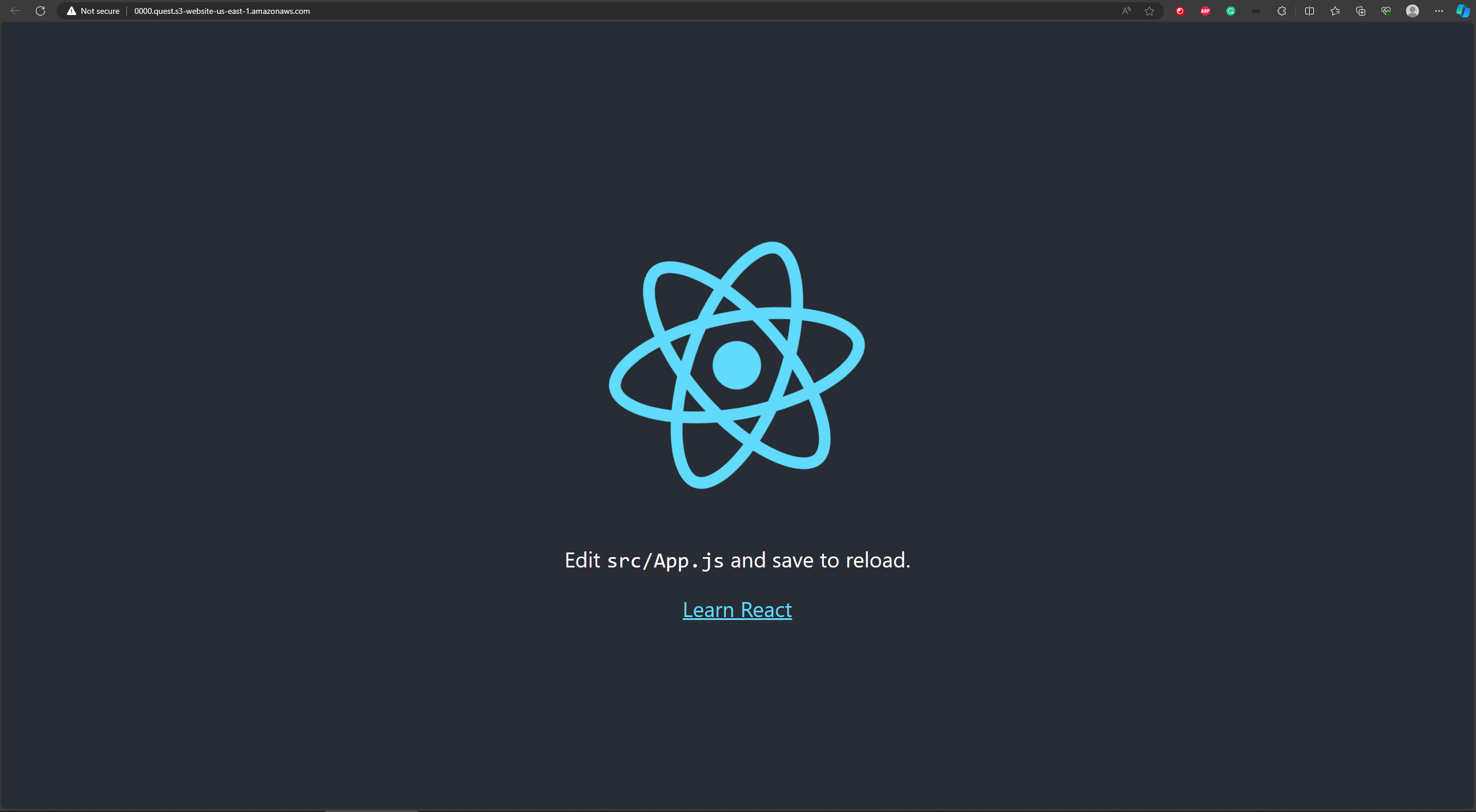
The www subdomain won't be up & running until we setup some DNS records, but you can currently see the functioning static site on the primary bucket by going to that URL you saved earlier.
#### Setup the Hosted zone
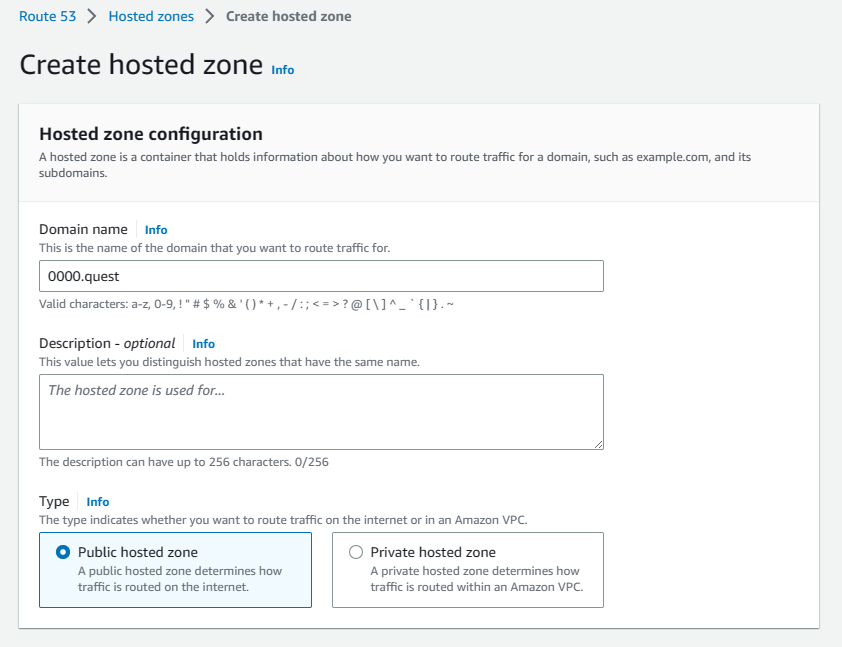
Now that the buckets have been configured, it's time to configure the DNS in the Hosted Zones to get the URL configured & pointing to our bucket. Navigate to the Route 53 console by searching for it in the search bar. Click the Hosted Zones tab & hit the create Hosted Zone button. In the configuration, add your domain name under the domain name field & add a description if you need one, leave all other settings default. Hit the create button to finish creating the Hosted Zone.
Here is an extra step for anyone using an external domain registrar, you can skip this part if you're using a domain in your AWS account. If you are using an external registrar, you'll need to go into your registrar's portal & point your name servers to the name servers in the NS record created for your Hosted Zone. Once you do that, it may take a few minutes to a few hours for that name server change to propagate, depending on how often your registrar updates their records.
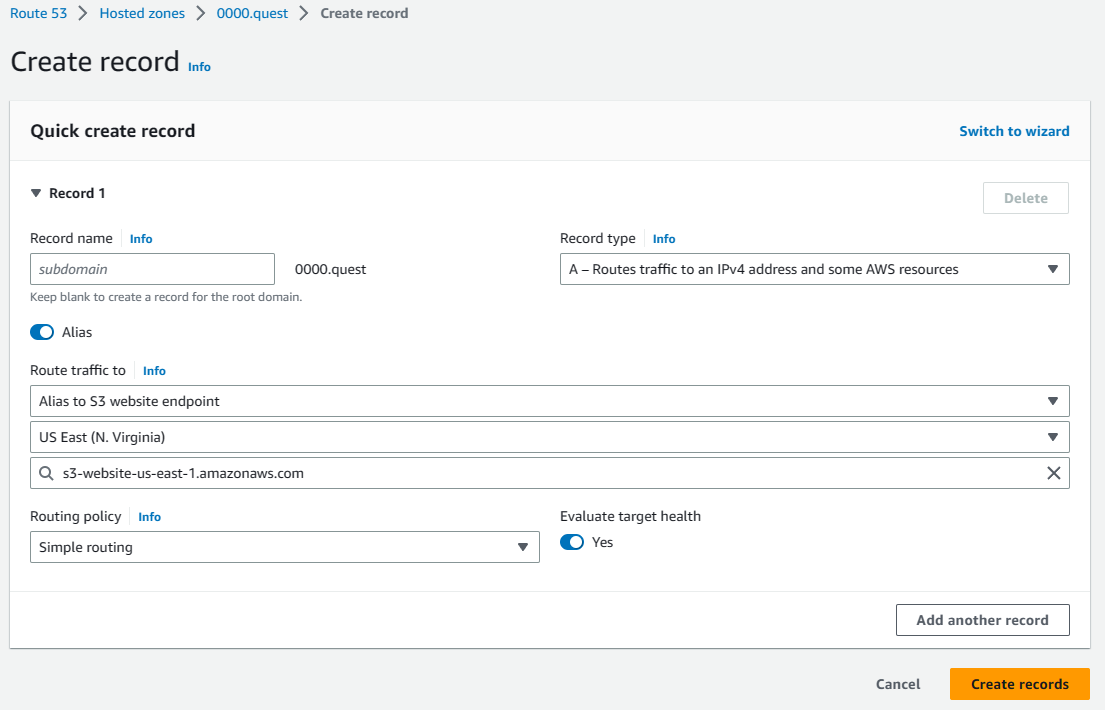
Time to add some records to the DNS that points to the S3 bucket so that your site is served when someone hits your domain. In your Hosted Zone, click the create record button. Leave the subdomain field empty for now. Change the record type to A. Click the alias toggle to update the available fields. Under "routes traffic to" select "Alias to S3 website endpoint," change the region to us-east-1. Under the S3 endpoint field you should see one option, this auto populates for you, click that S3 bucket in the dropdown. This should auto populate from the bucket name. This is why the bucket has to be the domain. Leave everything else default & hit the create records button to finish creating the record.
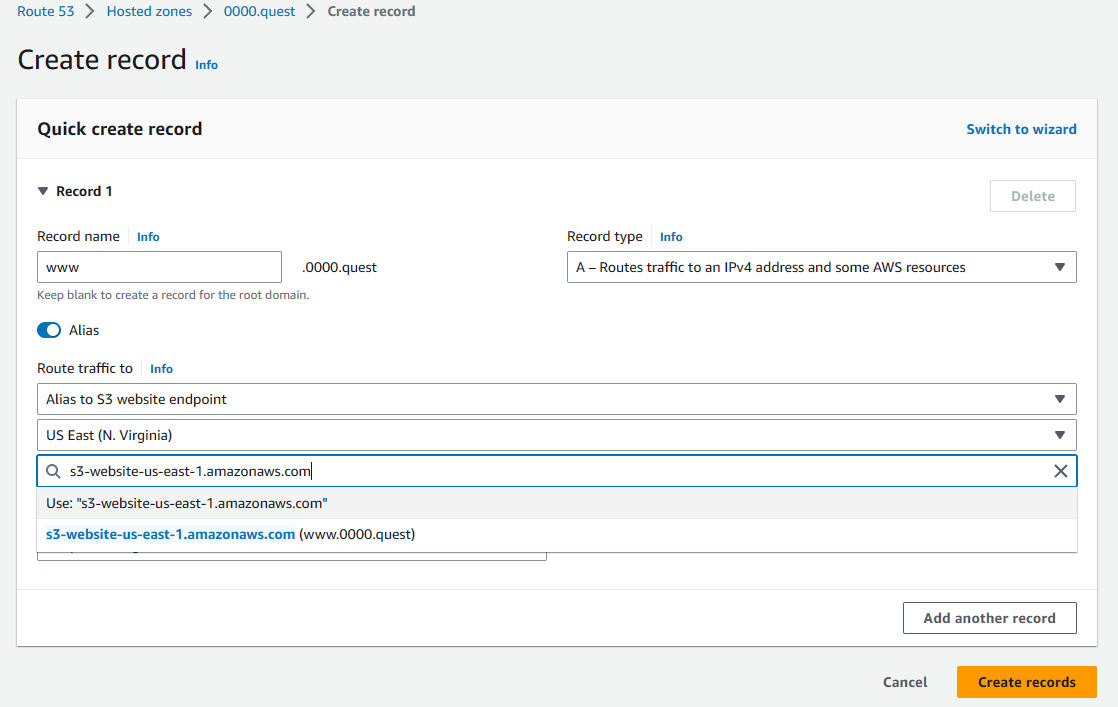
Now we'll add the DNS record for the subdomain, it's exactly the same as the previous record, only difference is that we're adding the www in the subdomain field & selecting the other bucket from the dropdown.
Once those records are created, you should immediately be able to access your site on your domain, both with & without the www subdomain(in this example 0000.quest & www.0000.quest). If you used an external registrar & your nameservers haven't propagated yet then the AWS records won't be hit & you won't be able to hit your site, but it should all propagate rather quickly. Most domain registrars reflect name server updates in around 30 minutes. Below is the screenshot I took of the site around 5 seconds after updating the record, as you can see, it's using the domain, so it propagated rather quickly. Also, if you type in the www subdomain it forwards to the standard site without the www subdomain prefix, as intended.
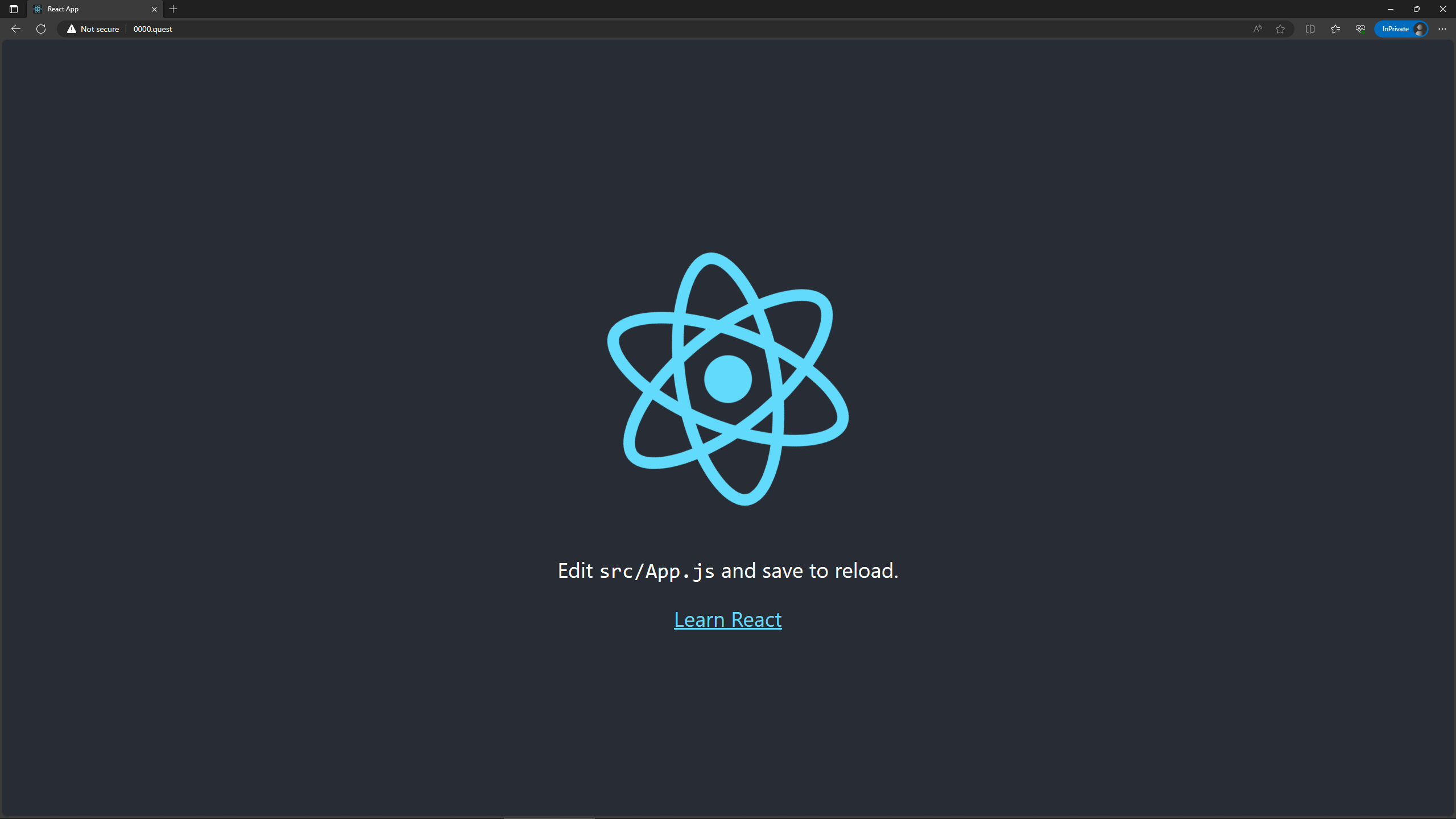
At this point if you just wanted a way to show people your site & don't care for an SSL certificate to get that sweet sweet HTTPS in front of your domain, then I guess you can stop here, but you might as well keep going & add the SSL cert & CDN caching. 🤷♀️
#### Creating SSL certificate in Certificate Manager
Let's go ahead & create an SSL certificate in Certificate Manager. Before you start, you'll need to change your region in the AWS Management Console to us-east-1, this can be changed by clicking the top right of the console, right next to your name. This is an important step, as your certificate won't be accessible in CloudFront if it's in the wrong region. 😅
Navigate to Certificate Manager by searching for it in the search bar in the AWS Management Console. Click the request a certificate button to generate a new SSL certificate for your site. Select public certificate & hit next.
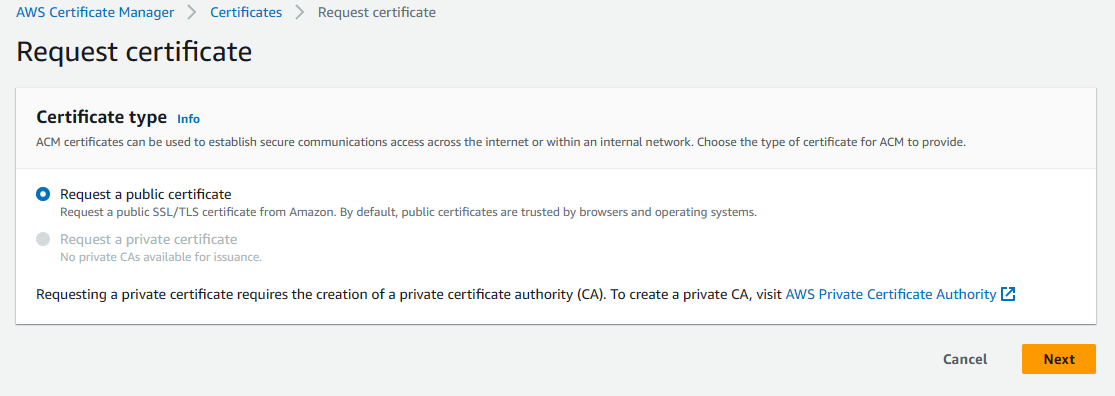
On the next page, add both your domain & your www subdomain under domain names. This is an important step as you cannot change this later & you'll have to delete the cert & redo it to change this. Set validation method to DNS validation then leave all other settings default & hit request to generate the certificate.
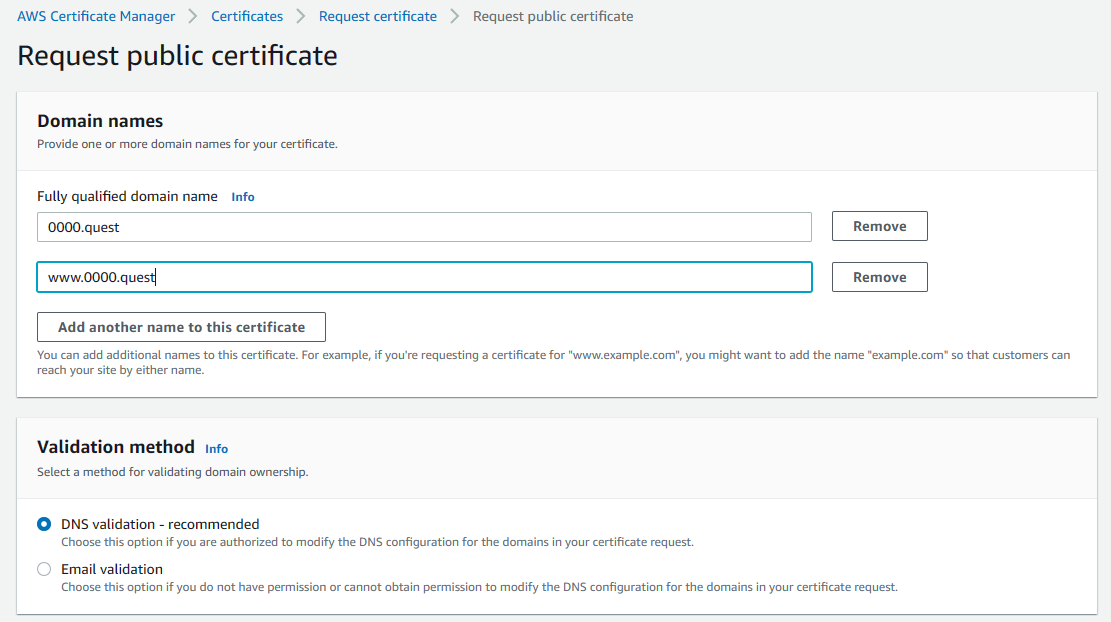
Once you submit the request, the cert will need to be validated. In the list certificates tab of the Certificate Manager console, select the certificate you just created, if you have multiple, look for the one with your domain name. Once there, under Domains, there is a button to create records in Route 53 at the top right of the domains section, click that button.
Then hit the create records button to create the records.
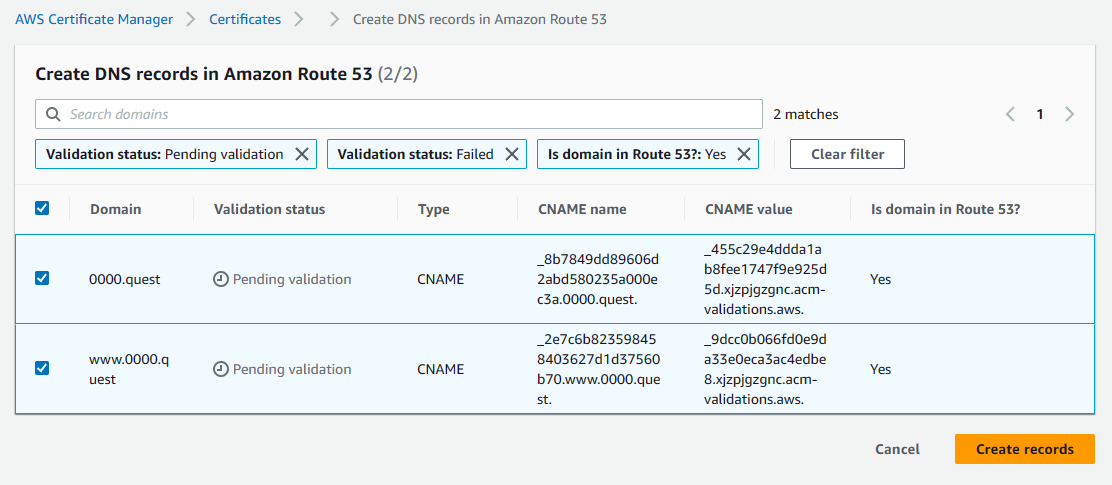
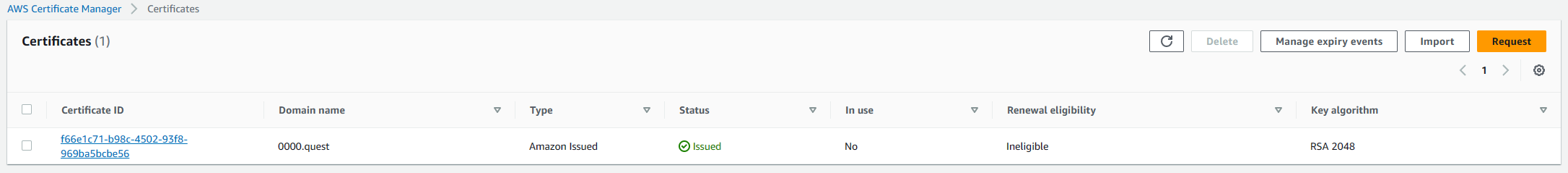
This allows AWS to verify ownership of the domain by creating custom DNS records for the provided URLs, this can only be done by someone with access to the registrar or a provider with access to the name servers the registrar is pointing to. This is a security step. Once you create those records, after a few minutes, you should see the status in certificate manager change from pending to issued.
#### Cloudfront distribution configuration
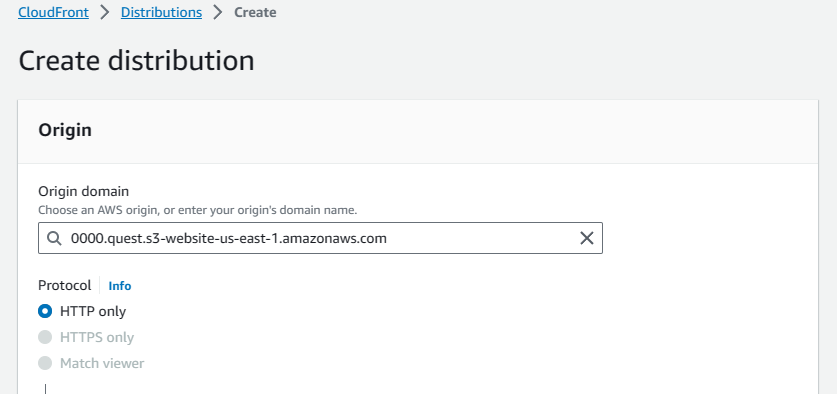
Now that the certificate exists, it's time to configure CloudFront using the certificate. Quickly navigate to the S3 buckets created earlier & grab their URLs. It's at the bottom of the properties tab for each bucket under the static website hosting section. You'll need these for the CloudFront configurations.
Navigate to the CloudFront console in the AWS Management Console by searching for it in the search bar. Once there, switch to the distributions tab & click the create distribution button to start the setup.
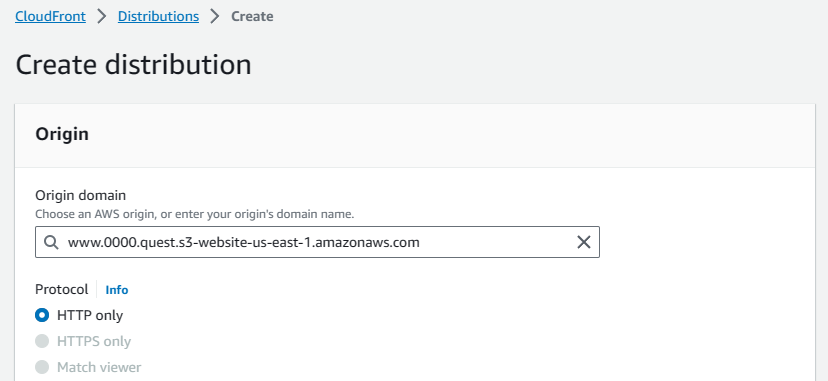
In the origin section, paste the primary bucket's public URL copied earlier into the origin domain.
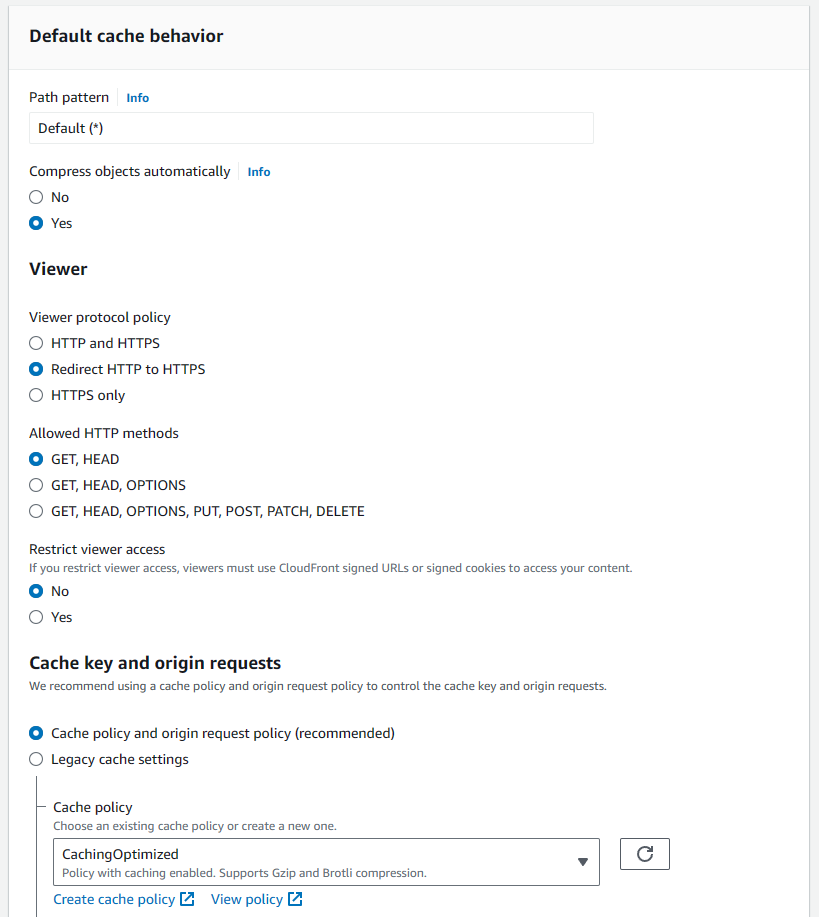
Scroll down to the default cache behavior section, change "viewer protocol policy" to redirect HTTP to HTTPS. This ensures that users will be accessing your site securely over HTTPS once it's using the CloudFront CDN. Also, set the cache policy to caching optimized. I didn't capture this in the screenshot, but the Web Application Firewall (WAF) can be disabled here, so that's what I did. 😅
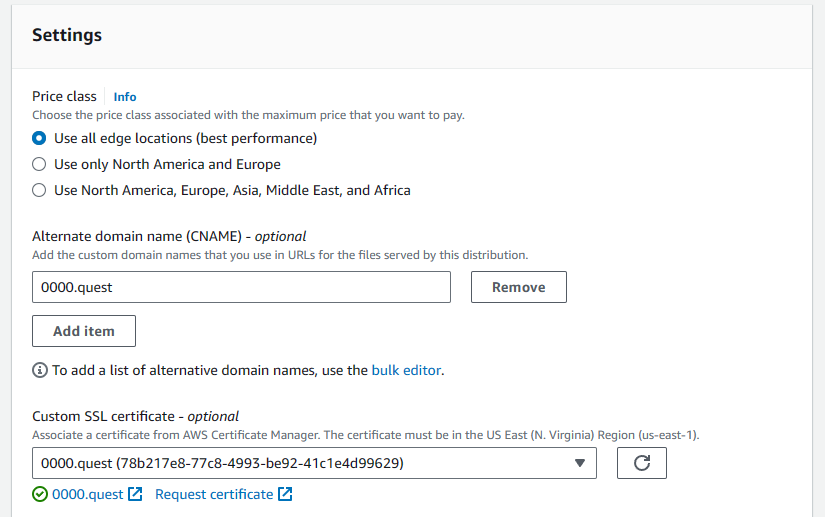
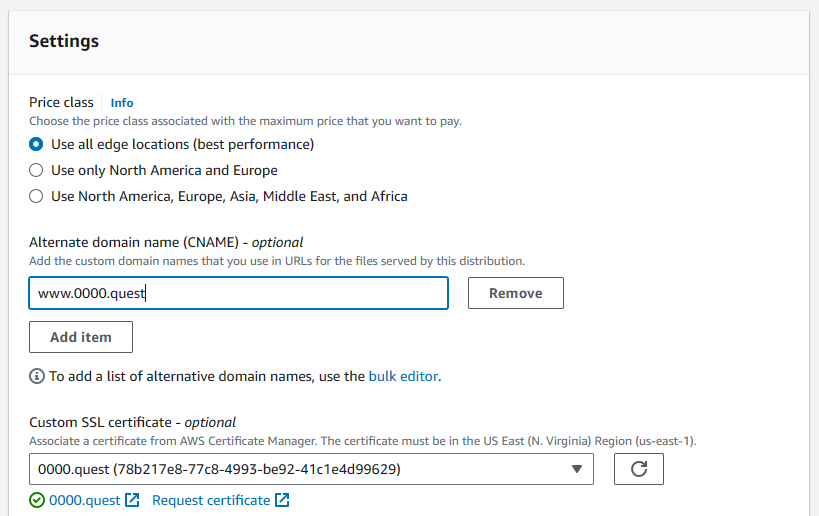
Scroll down to settings, here you'll add the alternate domain name, this allows you to bind your domain name to the CDN. Here, I'm doing the primary domain without the www subdomain (0000.quest). Then, under the "custom SSL certificate setting," select your previously made certificate from the dropdown. Leave all other settings default. Hit create distribution.
Once that's created, we have to do a second distribution for the www subdomain (www.0000.quest). The settings are the same, we start by copying that www bucket's public URL into the origin field.
Again, in the default cache behavior we're going to change to redirect HTTP to HTTPS & set the cache setting to caching optimized. Again, I disabled the Web Application Firewall here, it's not captured in the screenshot, but it's a single radio button, so you should be able to find it 🤷♀️. It's also a required setting, so you need to do that.
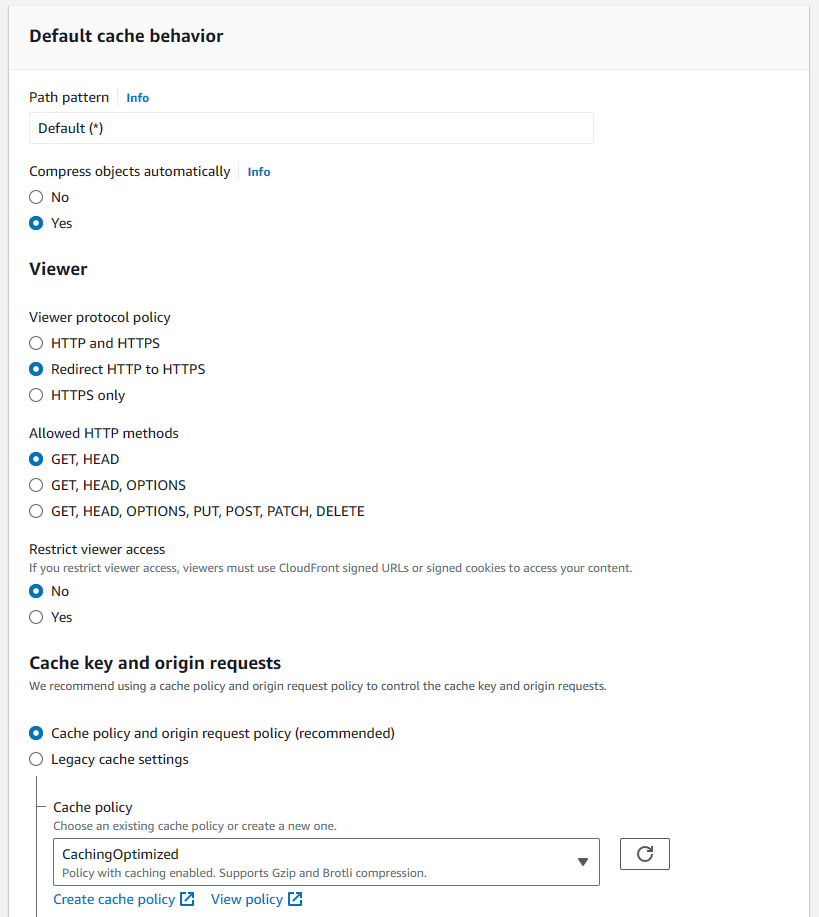
Then, in the settings we add the www subdomain as an alternate domain name & select the SSL cert we made earlier.
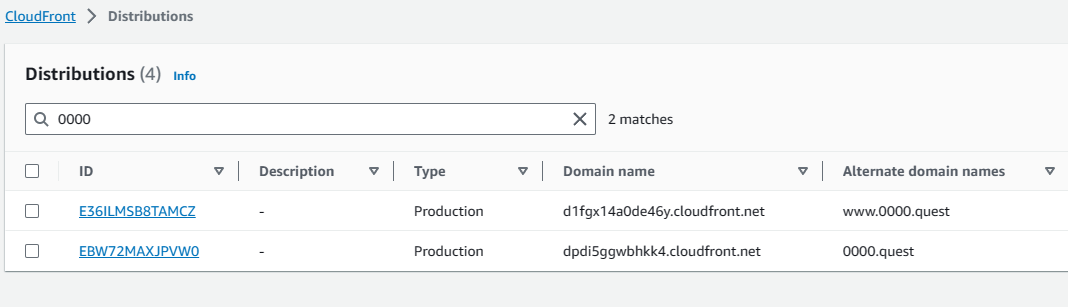
Once those distributions are created, it takes a few minutes to deploy, but that's okay because we have some changes to make to S3 & the DNS records anyway. We can do those while they finish deploying. In the list distributions tab of the CloudFront console you can see the domain names for your distributions, copy those & save them. We'll need those to change some settings for our final configurations for our S3 buckets.
#### Tying it all together
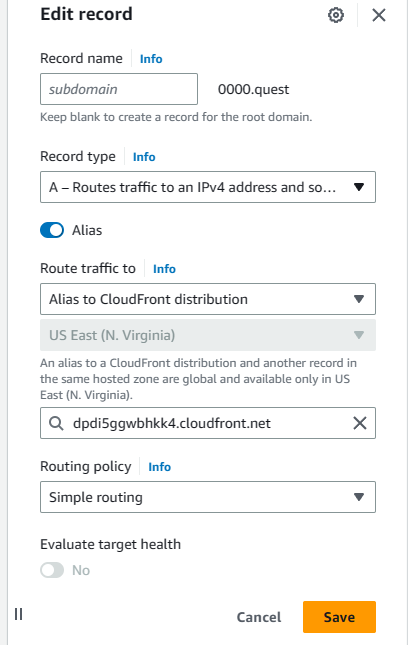
Navigate back to the Hosted Zone configured before. We have to edit the previously made A records to point to the CloudFront distributions instead of the S3 buckets. Select the primary domain's A record first & hit edit. It will remain an alias, but switch the "Route traffic to" dropdown to "Alias to CloudFront distribution" then from the dropdown select the distribution, there should only be one available, but make sure it's pointing to the correct URL for the primary distribution. This is why I asked you to copy the URLs for the distributions earlier.
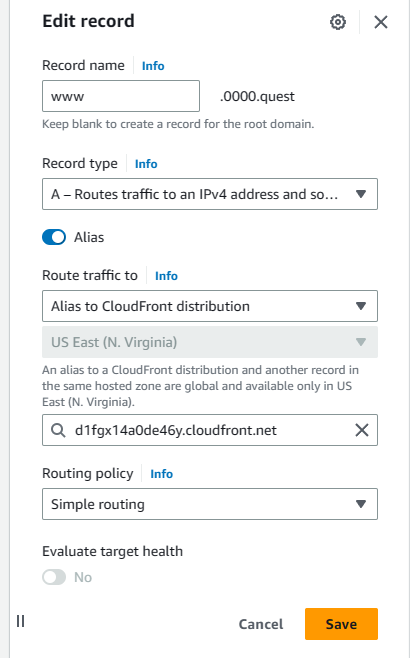
Hit save, then select the subdomain A record & hit edit. Same deal as the last one. Route the traffic to CloudFront distribution, select the distribution & verify the URL, then hit save.
One last thing. Now that the DNS records & CloudFront CDN are setup, we just need to change one setting for the bucket with the www subdomain to finish up the bucket settings. Navigate to that bucket's static website hosting settings in the bucket properties tab & hit edit. At the bottom, switch the protocol from HTTP to HTTPS & hit save.
Now we should be done. If you navigate to the domain you configured, you should be able to see your site hosted with HTTPS; additionally if you go to the site's www subdomain, you should be able to get redirected to the primary URL, as shown below.
This is just a simple deployment process & may not be ideal for most use cases as it requires manually uploading builds to S3 to update the site, which is why in my next tutorial, I will be showing you how to setup continuous deployment with github actions so you can update your site in an automated fashion by simply pushing code to github.
Thanks for following my tutorial. If you like this content or want to make suggestions, feel free to tag me in a post on twitter. This was my first tutorial, so don't roast me too bad 😅. [@the_whittington](https://twitter.com/the_whittington)
| whittington |
1,865,075 | What is Containerization | Containerization is a software deployment method that packages an application's code with all its... | 0 | 2024-05-25T17:03:21 | https://dev.to/m__mdy__m/what-is-containerization-2od4 | webdev, beginners, docker, devops | Containerization is a software deployment method that packages an application's code with all its dependencies (libraries, configuration files) needed to run into a standalone unit called a container. Unlike traditional virtualization, which virtualizes the entire operating system, containers share the underlying host operating system kernel. This makes them lightweight and portable, allowing them to run consistently on any infrastructure that supports the container runtime environment.
**Real-World Example:**
Imagine a shipping container. It can hold various goods (your application code) and has everything needed for transport (dependencies) - packing tape (configuration files), labels (environmental variables) etc. This container can be loaded onto different ships (operating systems) and travel across various ports (infrastructure) without affecting the goods inside. Just like the container ensures the goods arrive safely at their destination, containerization guarantees your application runs consistently regardless of the environment.
## What are the benefits of containerization?
Containerization offers a multitude of advantages for developers, IT operations teams, and organizations as a whole. Here's a breakdown of some key benefits:
**Portability:** Containers are self-contained units that bundle an application's code with all its dependencies (libraries, configuration files) into a single, executable package. This package is agnostic to the underlying operating system, allowing applications to run consistently and uniformly across any platform or cloud environment that supports the container runtime. Imagine a shipping container; it can be loaded onto different ships (operating systems) and travel across various ports (infrastructure) without affecting the goods inside. Similarly, containers ensure your application runs the same way regardless of the environment.
**Agility:** Containerization streamlines the development and deployment processes. The use of container orchestration platforms like Kubernetes, coupled with standardized container images, enables rapid application development, testing, and deployment cycles. Developers can leverage agile or DevOps methodologies to make frequent code changes and updates, with minimal risk of conflicts arising from different environments.
**Speed and Efficiency:** Containers are lightweight and share the host machine's operating system kernel. This eliminates the need for a full virtual machine environment for each application, resulting in faster startup times and lower resource consumption. Additionally, application layers within containers can be shared across containers, minimizing disk space usage. This translates to higher server efficiency, allowing you to run more containers on the same compute resources compared to traditional virtual machines.
**Fault Isolation:** Each containerized application runs in a isolated user space, with its own set of resources. This isolation ensures that the failure or malfunction of one container does not impact the operation of other containers sharing the same host. This allows for easier troubleshooting and debugging of individual applications without affecting the entire system. Additionally, container engines can leverage operating system security features like SELinux to further isolate faults within containers.
**Scalability:** Scaling applications becomes much simpler with containerization. Adding or removing containers allows you to easily scale your application up or down based on real-time demands. This elasticity ensures your application can handle fluctuating workloads efficiently.
**Ease of Management:** Container orchestration platforms automate the deployment, scaling, and management of containerized workloads. These platforms handle tasks like:
* **Scaling containerized applications:** They can automatically scale container instances based on predefined rules or resource utilization.
* **Rolling updates:** Orchestrators can perform rolling updates by deploying new container versions in a controlled manner, minimizing downtime during deployments.
* **Monitoring, logging, and debugging:** Container orchestration platforms provide centralized tools for monitoring the health and performance of containerized applications, simplifying troubleshooting and debugging processes.
**Security:** The inherent isolation of containerized applications strengthens the overall security posture. Malicious code within one container is restricted from affecting other containers or the host system. Additionally, container security features allow you to define security permissions that automatically block unauthorized components from entering containers and limit communication with unnecessary resources.
## What are containerization use cases?
**Cloud Migration (Lift-and-Shift):** Containerization acts as a bridge for organizations migrating legacy applications to the cloud. By encapsulating existing applications within containers, businesses can leverage the scalability and elasticity of cloud environments without extensive code rewrites. This "lift-and-shift" approach allows for a smoother transition to the cloud while laying the groundwork for future modernization efforts.
**Microservices Architecture:** Containerization is a perfect fit for the microservices architecture, a popular approach for building modern cloud applications. Microservices decompose complex applications into smaller, independent services, each responsible for a specific functionality. Containers provide a lightweight and portable way to package these microservices, enabling independent development, deployment, and scaling. For instance, a video streaming application might have microservices for user authentication, content delivery, and recommendation engine. Each microservice can be containerized and deployed independently, promoting agility and resilience.
**Continuous Integration and Continuous Delivery (CI/CD):** Containerization streamlines the CI/CD pipeline, a core DevOps practice for automating software development and delivery. Containers ensure consistent environments across development, testing, and production stages, eliminating discrepancies that can cause bugs or deployment failures. Developers can build and test applications within containers, mimicking the production environment, leading to faster release cycles and higher quality software.
**Modernization of Legacy Applications:** Legacy applications can be revitalized using containerization. By containerizing these applications, organizations can isolate them from newer technologies and run them alongside modern containerized applications. This approach enables a phased modernization strategy, where legacy applications can coexist with cloud-native developments.
**Internet of Things (IoT):** Containerization simplifies application deployment and management for resource-constrained IoT devices. Containers provide a lightweight and isolated environment for running applications on these devices. Updates can be packaged and distributed as container images, streamlining the software update process for large fleets of devices.
**Batch Processing:** Containerization is well-suited for orchestrating batch processing jobs. Complex data pipelines can be broken down into smaller, containerized tasks that can be easily scaled and run on-demand. This allows for efficient processing of large datasets without provisioning dedicated servers for each job.
**Scientific Computing:** Containerization offers a standardized way to package and deploy scientific software across different computing environments. Researchers can ensure consistent execution of their code across various platforms, leading to reproducible results and faster scientific discovery.
## How does containerization work?
**1. Building the Container Image:**
* Developers write the application code and identify all its dependencies (libraries, configuration files) needed for proper execution.
* Using containerization tools like Docker or Podman, they create a container image. This image follows the Open Container Initiative (OCI) specification, ensuring consistency and portability across different environments.
* The image typically consists of several layers:
* **Base Layer:** This layer forms the foundation and usually includes a minimal operating system (OS) like Linux.
* **Dependency Layers:** These layers contain pre-installed libraries and other software components required by the application.
* **Application Layer:** This layer includes the actual application code and any additional configuration files specific to the application.
* Container images are read-only and act as a blueprint for creating container instances.
**2. Running the Container:**
* A container runtime engine (like Docker Engine or containerd) reads the container image and creates a running instance of the application.
* The container engine utilizes the host operating system's kernel for core functionalities but isolates the container's processes and resources. This provides a lightweight and efficient execution environment.
* The container inherits the base OS from the image and has its own isolated filesystem with the application code and dependencies.
**3. Benefits of Isolation:**
* Each container runs in its own isolated user space, preventing conflicts between applications or their dependencies.
* This isolation enhances security as a compromised container cannot directly affect other containers or the host system.
**4. Container Orchestration (Optional):**
* For complex deployments involving multiple containers, container orchestration platforms like Kubernetes come into play.
* These platforms automate tasks like container deployment, scaling, and management.
* They can schedule containers across multiple hosts, ensuring efficient resource utilization and high availability.
## Containerizing a To-Do List App (Node.js Example) - No Code Included
Let's imagine you have a simple To-Do List application built with Node.js and Express. Here's a step-by-step explanation of how you could containerize it:
**1. Define Dependencies:**
* Identify all the external libraries your Node.js application relies on to function (e.g., Express for building the web framework, Mongoose for interacting with a MongoDB database if used for storing to-do items).
**2. Create a Dockerfile:**
* A Dockerfile is a text document that contains instructions for building a Docker image.
* In the Dockerfile, you'll specify the base image: This is a pre-built image containing a minimal Linux operating system and Node.js pre-installed. There are various Node.js base images available on Docker Hub, a public repository for container images.
* Next, you'll use instructions like `COPY` and `RUN` to:
* Copy your application code and any additional configuration files into the image.
* Install the required Node.js dependencies using commands like `npm install` or `yarn install`.
* Define any startup commands to execute when the container starts, such as running your Node.js application to start the To-Do List app.
**3. Build the Docker Image:**
* Use the `docker build` command with the path to your Dockerfile to build the container image.
* This creates a reusable image containing your application and all its dependencies in a self-contained unit.
**4. Run the Container:**
* Use the `docker run` command to create a running instance of your application from the built image.
* This will start a container with your To-Do List app running within it.
**5. Accessing the Application:**
* By default, containerized applications might not be directly accessible from your machine's web browser.
* You may need to configure ports to expose the application's port (typically port 3000 for Node.js apps) to your host machine or utilize a container orchestration platform for more advanced setups.
**Benefits of Containerization in this Example:**
* **Portability:** The container image can be easily shared and run on any machine with Docker installed, ensuring your To-Do List app runs consistently regardless of the environment.
* **Isolation:** Each container instance runs in isolation, preventing conflicts with other applications or their dependencies on the host machine.
* **Reproducibility:** The Dockerfile ensures a consistent build process, guaranteeing your To-Do List app runs identically every time you build the image.
## What is a virtual machine (VM)?
A virtual machine (VM) is a software emulation of a physical computer system. It creates a virtualized environment that behaves and functions just like a real computer, complete with its own CPU, memory, storage, operating system, and applications. VMs are hosted on a physical computer known as the host machine, and multiple VMs can share the resources of the host machine using software called a hypervisor.
Here's a breakdown of the key components:
* **Host Machine:** The physical computer system that provides the underlying hardware resources (CPU, memory, storage) for running VMs.
* **Hypervisor:** Software that sits directly on the host machine's hardware and manages the creation, deployment, and execution of VMs. It acts as a virtual layer, allocating resources from the physical machine to each VM and ensuring they run in isolation. Popular hypervisors include VMware ESXi, Microsoft Hyper-V, and KVM (Kernel-based Virtual Machine).
* **Guest Operating System:** The operating system (e.g., Windows, Linux, macOS) that runs within each virtual machine. VMs can have different guest operating systems installed, independent of the host machine's operating system.
**Benefits of Virtual Machines:**
* **Resource Isolation:** VMs provide isolated execution environments, preventing applications running on one VM from interfering with those on another VM. This enhances security and stability.
* **Portability:** VMs can be easily migrated between different physical machines as long as the underlying hardware architecture is compatible. This simplifies deployment and disaster recovery processes.
* **Flexibility:** VMs offer a versatile platform for running various operating systems and applications on a single physical machine, optimizing resource utilization.
* **Testing and Development:** VMs create safe and isolated environments for testing new software or running incompatible applications without affecting the host system.
## Containerization vs. Virtual Machines
While both VMs and containers provide ways to isolate and package applications, they differ in their approach:
* **Virtual Machines:** VMs virtualize the entire physical computer system, including the hardware layer, operating system, and application. This creates a more heavyweight and resource-intensive environment compared to containers.
* **Containers:** Containers focus on application isolation at the operating system level. They share the host machine's operating system kernel but provide isolated user space for each container with its own application code and dependencies. This makes them lightweight and portable, offering faster startup times and better resource utilization compared to VMs.
**Choosing Between VMs and Containers:**
* VMs are a good choice when you need complete isolation, including hardware and operating system, or when you need to run applications that require a specific operating system not available on the host machine.
* Containers are ideal for microservices architectures, deploying and scaling cloud-native applications, and scenarios where portability, efficiency, and faster startup times are critical.
## Containerization vs Virtualization
Both containerization and virtualization are powerful technologies that enable efficient resource utilization by allowing you to run multiple isolated environments on a single physical machine. However, they take fundamentally different approaches:
**Virtual Machines (VMs):**
* **Full Virtualization:** VMs virtualize the entire physical computer system, including the hardware, operating system (OS), and application.
* **Isolation:** VMs provide strong isolation, creating a self-contained environment with its own virtual hardware, OS, and applications. This isolation ensures applications running on different VMs do not interfere with each other, enhancing security and stability.
* **Resource Consumption:** VMs are more resource-intensive compared to containers. Each VM requires its own OS instance, leading to higher overhead and potentially slower startup times.
* **Use Cases:** VMs are a good choice when you need:
* **Complete isolation:** Including hardware and operating system, for running incompatible applications or applications requiring a specific OS unavailable on the host machine.
* **Flexibility:** To run various operating systems and applications on a single machine.
**Containers:**
* **Operating System-Level Virtualization:** Containers focus on application isolation at the operating system level. They share the host machine's operating system kernel but provide isolated user space for each container with its own application code and dependencies.
* **Lightweight and Portable:** Containers are lightweight as they don't include a full OS. This translates to faster startup times, efficient resource utilization, and greater portability across different environments with the same container runtime.
* **Scalability:** Containers are easier to scale up or down by adding or removing containers. This agility is well-suited for modern cloud-native applications and microservices architectures.
* **Use Cases:** Containers are ideal for:
* **Microservices architectures:** Deploying and scaling cloud-native applications built as independent services.
* **Portability and Efficiency:** Scenarios where faster startup times, efficient resource utilization, and portability across environments are critical.
**Choosing Between VMs and Containers:**
The choice between VMs and containers depends on your specific needs:
* **For complete isolation, hardware-specific requirements, or running incompatible applications, VMs are the preferred option.**
* **For microservices architectures, cloud-native deployments, efficient resource utilization, and portability, containers are the better choice.**
## Types of containerization
The surge in container adoption has driven the need for standardization in container technology and application packaging. The Open Container Initiative (OCI), established in 2015 by Docker and industry leaders, aims to create open, vendor-neutral standards and specifications for container formats and runtime environments. This fosters innovation and empowers users with choice.
**Benefits of OCI Standards:**
* **Vendor Neutrality:** OCI standards prevent vendor lock-in. Users can leverage various OCI-compliant tools and container engines from different vendors, ensuring flexibility and future-proofing their deployments.
* **Portability:** OCI-compliant container images are portable across different container runtimes and infrastructure environments. This simplifies deployments and allows applications to run consistently on any platform that supports OCI standards.
* **Rich Ecosystem:** OCI fosters a vibrant container ecosystem. Developers and vendors can build tools and technologies that adhere to OCI specifications, leading to a wider range of choices and faster innovation.
**Container Runtime Engines:**
Docker, while a prominent player, isn't the only container runtime engine available. Here's a glimpse into the containerization landscape:
* **containerd:** This lightweight, low-level runtime engine is a core component of many container orchestration platforms like Kubernetes. It focuses on the core functionality of image management and container execution, adhering to OCI standards.
* **Alternatives:** Several other OCI-compliant container engines exist, each with its own strengths and use cases. Some notable examples include:
* **CoreOS rkt:** A former container runtime from CoreOS, now part of the Container Linux project.
* **Mesos Containerizer:** Designed for the Mesos distributed cluster management system.
* **LXC Linux Containers:** Provides a lightweight containerization solution based on Linux control groups and namespaces.
* **OpenVZ:** An older containerization technology offering process isolation but not as lightweight as modern container engines.
* **cri-o:** Developed by Kubernetes, it's a container runtime focused on security and CRI (Container Runtime Interface) compliance.
**Choosing a Container Engine:**
The choice of container engine depends on your specific needs and ecosystem. Docker remains a popular option due to its user-friendliness and extensive ecosystem of tools. However, for deployments requiring strict adherence to OCI standards or integration with specific orchestration platforms, exploring alternatives like containerd or cri-o might be beneficial.
## Specific Containerization Use Cases
**Microservices Architectures:**
Microservices architecture decomposes complex applications into smaller, independent services, each responsible for a specific functionality. Containers provide a perfect fit for packaging and deploying these microservices.
* **Benefits:**
* **Isolation:** Each microservice runs in its own container, ensuring isolation and preventing conflicts between services. This promotes resilience and easier debugging.
* **Independent Scaling:** Microservices can be scaled independently based on their resource requirements, leading to efficient resource utilization.
* **Faster Development Cycles:** Containers enable rapid development, testing, and deployment of microservices due to their lightweight and portable nature.
**Continuous Integration and Continuous Delivery (CI/CD):**
CI/CD pipelines automate the software development and delivery process. Containerization streamlines CI/CD by:
* **Consistent Environments:** Containers guarantee consistent environments across development, testing, and production stages. This eliminates discrepancies that can cause bugs or deployment failures.
* **Improved Automation:** Containerized applications are well-suited for automated testing and deployment processes within CI/CD pipelines.
* **Faster Testing:** Developers can build and test applications within containers, mimicking the production environment, leading to faster feedback and reduced risk of errors.
**Modernization of Legacy Applications:**
Legacy applications can be revitalized using containerization. Here's how:
* **Isolation and Migration:** Containerization allows isolating legacy applications from newer technologies, enabling them to coexist with modern containerized applications. This facilitates a phased modernization strategy.
* **Cloud Portability:** Containers ease the migration of legacy applications to the cloud by providing a standardized packaging format that can run on different cloud environments.
**Additional Use Cases:**
* **Batch Processing:** Containerization is well-suited for orchestrating complex data pipelines. Large datasets can be efficiently processed by breaking them down into smaller, containerized tasks that can be run on-demand and scaled as needed.
* **Scientific Computing:** Containers offer a standardized way to package and deploy scientific software across different computing environments. Researchers can ensure consistent execution of their code, leading to reproducible results and faster scientific discovery.
* **Internet of Things (IoT):** Containerization simplifies application deployment and management for resource-constrained IoT devices. Updates can be packaged and distributed as container images, streamlining the software update process for large fleets of devices.
## Microservices and containerization
**Microservices Architecture:**
* **Modular Design:** Breaks down complex applications into smaller, independent services, each responsible for a specific functionality. This promotes loose coupling, where services communicate with well-defined APIs.
* **Benefits:**
* **Agility:** Independent development, testing, and deployment cycles for each microservice lead to faster development and innovation.
* **Scalability:** Microservices can be scaled independently based on their resource needs, optimizing resource utilization.
* **Resilience:** Failure in one microservice is isolated from others, minimizing application downtime.
**Containerization:**
* **Packaging and Isolation:** Packages individual microservices with their dependencies into lightweight, portable containers. This ensures consistent execution across different environments.
* **Benefits:**
* **Portability:** Containers run seamlessly on any platform with a compatible container runtime, promoting vendor neutrality.
* **Isolation:** Each containerized microservice runs in isolation, preventing conflicts and simplifying debugging.
* **Efficiency:** Containers are lightweight and share the host operating system kernel, optimizing resource utilization.
**Synergy of Microservices and Containers:**
* **Ideal Match:** Containerization perfectly complements the microservices architecture. Each microservice can be packaged as a self-contained unit within a container, leveraging the benefits of both approaches.
* **Enhanced Agility:** Developers can build, test, and deploy microservices within containers, accelerating development cycles.
* **Scalability at the Microservice Level:** Containers allow for independent scaling of microservices based on their specific resource requirements.
* **Fault Isolation:** Containerization ensures that failures within one microservice are isolated and don't affect the entire application, enhancing overall system resilience.
**Microservices, Containers, and the Cloud:**
* **Cloud-Native Development:** The combination of microservices and containerization is a perfect fit for cloud-native development. Applications built with this approach are highly scalable, portable, and resilient, ideal for cloud environments.
* **Cloud Benefits:** Cloud platforms offer on-demand resources, automated deployments, and easier management, further amplifying the advantages of microservices and containers.
### What is Cloud-Native?
Cloud-native is a software development approach specifically designed to take full advantage of cloud computing environments. Cloud-native applications are built, deployed, and managed with the inherent characteristics of the cloud in mind. This fosters scalability, elasticity, resilience, and faster development lifecycles.
**Key Characteristics of Cloud-Native Applications:**
* **Microservices Architecture:** Cloud-native applications are typically built using a microservices architecture. This decomposes complex functionalities into smaller, independent services that communicate with each other through APIs. This modular approach promotes agility, scalability, and fault isolation.
* **Containerization:** Containerization plays a vital role in cloud-native development. Applications are packaged as self-contained units within containers, ensuring consistent execution across different cloud environments. This facilitates portability and efficient resource utilization.
* **Declarative Infrastructure:** Cloud-native applications leverage infrastructure as code (IaC) tools like Terraform or Ansible. These tools define infrastructure configurations in machine-readable code, enabling automated provisioning and management of cloud resources.
* **API-Driven Communication:** Microservices within a cloud-native application communicate through well-defined APIs. This promotes loose coupling and simplifies integration with other services or applications.
* **DevOps Principles:** Cloud-native development heavily relies on DevOps practices. Automation, continuous integration/continuous delivery (CI/CD), and infrastructure as code are fundamental aspects of the cloud-native approach.
**Benefits of Cloud-Native Development:**
* **Faster Time-to-Market:** Agile development practices and automated deployments lead to quicker delivery of new features and functionalities.
* **Scalability and Elasticity:** Cloud-native applications can easily scale up or down based on demand, optimizing resource utilization and cost efficiency.
* **Resilience and Fault Isolation:** Microservices architecture and containerization isolate failures, preventing them from cascading and impacting the entire application.
* **Improved Manageability:** Automation and infrastructure as code simplify application and infrastructure management at scale.
### Containerization and Cloud-Native Development
* **Faster Development Cycles:** Containerization streamlines the development process. Developers can build, test, and deploy microservices within containers, mimicking the production environment. This facilitates faster feedback loops and reduces the risk of errors during deployment.
* **Scalability and Efficiency:** Containers are lightweight and share the host operating system kernel. This allows for efficient resource utilization and simpler horizontal scaling of microservices based on demand. By scaling individual microservices, you can optimize resource allocation within your cloud-native application.
* **Portability and Vendor Neutrality:** Containerized applications are portable across different cloud platforms. As long as a compatible container runtime is available, the application can run seamlessly without code modifications. This promotes vendor neutrality and avoids vendor lock-in.
* **Improved Manageability:** Containerization simplifies application lifecycle management. Updates and rollbacks can be performed at the container level for individual microservices, facilitating easier application maintenance.
## Security
**Isolation and Potential Risks:**
* **Benefits of Isolation:** Containers provide a layer of isolation by running applications as independent processes with limited access to system resources. This can prevent malicious code within one container from impacting others or the host system.
* **Shared Resources and Security Concerns:** However, complete isolation is challenging. Certain resources, like the underlying operating system kernel or shared libraries, might be accessed by multiple containers. This can create potential vulnerabilities if not managed properly.
* **Host OS Security:** A security breach in the host operating system can compromise all containers running on it. Similarly, vulnerabilities within a containerized application could potentially escalate to the host system.
**Security Features in Containerization:**
* **Secure-by-Default Approach:** Many container platforms, like Docker, advocate for a "secure-by-default" approach. This means security features are built-in and enabled by default, reducing the risk of misconfiguration.
* **Isolation Mechanisms:** Container technologies leverage various Linux kernel features to provide isolation:
* **Namespaces:** Linux Namespaces create a virtualized view of system resources like network, processes, and user IDs for each container. This restricts access to unauthorized resources.
* **Control Groups (cgroups):** cgroups limit resource allocation (CPU, memory, etc.) for each container, preventing resource starvation and denial-of-service attacks.
* **Security Profiles and Permissions:** Administrators can define security profiles that restrict unwanted components from entering containers and limit communication with unnecessary resources.
**Additional Security Considerations:**
* **Container Image Security:** Security vulnerabilities within the container image itself can pose a significant threat. Image scanning tools can help identify and mitigate these risks.
* **Runtime Security:** Security solutions at runtime can monitor container activity for suspicious behavior and potential threats.
* **Orchestration Security:** Container orchestration platforms like Kubernetes offer security features for managing container lifecycles and access control.
**Overall Security Strategy:**
A comprehensive container security strategy should encompass the entire container lifecycle, from image building to runtime. This includes:
* **Security scanning of container images:** Identify and address vulnerabilities in base images and application code before deployment.
* **Least privilege principle:** Grant containers only the minimum permissions required to function, minimizing the attack surface.
* **Network segmentation:** Isolate container networks to prevent unauthorized communication betwee138319n containers.
* **Regular security audits:** Proactively identify and address security weaknesses in the container environment.
## What is serverless computing?
Serverless computing is a cloud computing execution model where the cloud provider manages the server infrastructure that runs your code. Developers can deploy and run applications without provisioning or managing servers. Serverless services automatically scale based on the incoming workload, eliminating the need for manual capacity planning.
**Key Characteristics of Serverless Computing:**
* **Event-Driven Execution:** Serverless code typically executes in response to events. These events can be triggered by various sources, such as HTTP requests, database changes, or scheduled tasks.
* **Pay-Per-Use Billing:** Cloud providers typically charge based on the resources consumed by your application while it's running. There are no charges when your application is idle.
* **Automatic Scaling:** Serverless services automatically scale resources up or down to meet the demand of your application. This eliminates the need for manual scaling and helps optimize resource utilization.
* **Managed Infrastructure:** The cloud provider manages the underlying server infrastructure, including operating systems, patching, and security. This frees developers from these tasks and allows them to focus on application logic.
**Benefits of Serverless Computing:**
* **Faster Development and Deployment:** Serverless computing eliminates server management overhead, allowing developers to focus on building and deploying code faster.
* **Cost-Effectiveness:** Pay-per-use billing reduces costs associated with idle resources and eliminates the need to provision and manage servers.
* **Scalability:** Serverless applications can automatically scale to handle unexpected spikes in traffic, ensuring high availability and performance.
* **Simplified Management:** Serverless services minimize infrastructure management tasks, reducing operational overhead.
## Containerization vs. Serverless Computing
While both containerization and serverless computing offer advantages for application development and deployment, they have distinct characteristics:
**Choosing Between Containers and Serverless:**
The choice between containers and serverless computing depends on your specific needs:
* **For applications requiring fine-grained control over the execution environment, complex dependencies, or offline functionality, containers are a better choice.**
* **For event-driven, microservices-based applications or simple tasks that benefit from automatic scaling and pay-per-use billing, serverless computing is a good option.**
Here's a table summarizing the key differences:
| Feature | Containerization | Serverless Computing |
|-------------------------|-------------------------------------------------|----------------------------------------------------|
| Server Management | Developers manage servers within containers | Cloud provider manages server infrastructure |
| Billing | Typically charged based on resources used | Pay-per-use billing based on execution time |
| Scaling | Manual or automated scaling of containers | Automatic scaling based on workload |
| Development Complexity | Requires knowledge of container technology | Simpler development model, less code to manage |
| Execution Model | Process-based execution within containers | Event-driven execution model |
| Control over Environment | Developers have control over environment | Limited control over environment |
| Offline Functionality | Can function offline if designed for it | Typically requires internet connectivity |
## Learn Docker With Example
**Step 1: Download Docker**
Get started with Docker by downloading the appropriate version for your operating system from the official website:
[Download Docker](https://www.docker.com/get-started/)
**Why Docker for Containerization?**
Docker has emerged as a leading choice for containerization due to several key advantages:
* **Ease of Use:** Docker provides a user-friendly interface and command-line tools that make it easy to build, run, and manage containers.
* **Lightweight and Portable:** Docker containers are lightweight and efficient, making them ideal for modern cloud-native development and deployments across diverse environments.
* **Isolation and Security:** Docker ensures strong isolation between containers, enhancing application security and preventing conflicts.
* **Rich Ecosystem:** Docker boasts a vast and vibrant ecosystem of tools, libraries, and pre-built container images, accelerating development and deployment workflows.
* **Large Community:** Docker benefits from a large and active community of developers and users, offering extensive support and resources.
## Learning Resources for Docker:
## Source Learning:
### Official Documentation:
* **Docker Docs:** The official Docker documentation is an excellent starting point. It covers everything from installation to advanced concepts like building container images and orchestration. [https://docs.docker.com/](https://docs.docker.com/)
### Tutorials:
* **Tutorialspoint Docker Tutorial:** A good introduction to Docker concepts, commands, and building basic images. [https://www.tutorialspoint.com/docker/index.htm](https://www.tutorialspoint.com/docker/index.htm)
* **Simplilearn Step-by-Step Tutorial:** A beginner-friendly tutorial that guides you through installing and using Docker. [https://www.simplilearn.com/tutorials/docker-tutorial](https://www.simplilearn.com/tutorials/docker-tutorial)
### Dockerizing Node.js Applications:
* **Freecodecamp - Get Started with Docker using NodeJS:** An introductory guide to using Docker with Node.js applications. [https://www.freecodecamp.org/news/how-to-get-started-with-docker-using-nodejs/](https://www.freecodecamp.org/news/how-to-get-started-with-docker-using-nodejs/)
* **Medium - Simple Node.js Application with Docker:** A step-by-step tutorial on creating a basic Node.js application with Docker and Docker Compose. [https://medium.com/@chaewonkong/beginners-guide-simple-node-js-application-with-docker-and-docker-compose-11e4e0297de9](https://medium.com/@chaewonkong/beginners-guide-simple-node-js-application-with-docker-and-docker-compose-11e4e0297de9)
* **BetterStack - Deploy Node.js Applications with Docker:** A guide on deploying Node.js applications with Docker, covering scaling considerations. [https://betterstack.com/community/guides/scaling-nodejs/dockerize-nodejs/](https://betterstack.com/community/guides/scaling-nodejs/dockerize-nodejs/)
* **Medium - Getting Started with Docker for Node.js Applications:** Another resource for beginners, guiding you through setting up Docker and creating a Node.js application. [https://medium.com/@yurii.h.dev/getting-started-with-docker-for-node-js-applications-ee3c0fbb6d14](https://medium.com/@yurii.h.dev/getting-started-with-docker-for-node-js-applications-ee3c0fbb6d14)
* **Dev.to - Getting Started with Nodejs, Express and Docker:** A tutorial focusing on Node.js, Express.js, and Docker integration. [https://dev.to/emma_donery/getting-started-with-nodejs-express-and-docker-5ffa](https://dev.to/emma_donery/getting-started-with-nodejs-express-and-docker-5ffa)
### Youtube Video
* **Learn Docker - DevOps with Node.js & Express (Highly Rated):** A comprehensive course on Docker with Node.js and Express. [https://www.youtube.com/watch?v=9zUHg7xjIqQ](https://www.youtube.com/watch?v=9zUHg7xjIqQ) ⭐
* **Dockerize Node.js and Express Apps:** A tutorial on containerizing Node.js and Express applications. [https://www.youtube.com/watch?v=nH47lsxvY9c](https://www.youtube.com/watch?v=nH47lsxvY9c)
* **Dockerize NodeJS and MongoDB application using docker-compose:** A guide to containerizing a Node.js and MongoDB application with Docker Compose. [https://www.youtube.com/watch?v=vm3YfOHf_Cc](https://www.youtube.com/watch?v=vm3YfOHf_Cc)
* **Introduction to Docker for Javascript Developers (feat Node.js and PostgreSQL):** An introduction to Docker for JavaScript developers, using Node.js and PostgreSQL as examples. [https://www.youtube.com/watch?v=Te41e4urFO0](https://www.youtube.com/watch?v=Te41e4urFO0)
* **Build a CRUD API with Docker Node.JS Express.JS & PostgreSQL:** A tutorial on building a CRUD API using Docker, Node.js, Express.js, and PostgreSQL. [https://www.youtube.com/watch?v=sDPw2Yp4JwE](https://www.youtube.com/watch?v=sDPw2Yp4JwE)
* **Docker + Node.js/express tutorial:** Another tutorial on using Docker with Node.js and Express.js. [https://www.youtube.com/watch?v=gm_L69NHuHM](https://www.youtube.com/watch?v=gm_L69NHuHM)
## Conclusion
Containerization is a powerful technology that packages applications with their dependencies, ensuring consistent performance across different environments. It offers numerous benefits, including portability, agility, speed, efficiency, fault isolation, scalability, ease of management, and enhanced security. Containers are particularly useful for cloud migration, microservices architecture, CI/CD, legacy application modernization, IoT, and batch processing. Compared to virtual machines, containers are lightweight and resource-efficient. With the support of standards like the Open Container Initiative, containerization is a key enabler for modern, cloud-native development. As your thirst for knowledge grows, delve even deeper! My repository, brimming with various algorithms and data structures, awaits your exploration ([algorithms-data-structures](https://github.com/m-mdy-m/algorithms-data-structures)). It's a treasure trove where you can experiment, practice, and solidify your grasp of these fundamental building blocks.
**While some sections are still under construction,** reflecting my own ongoing learning journey (a journey that will likely take 2-3 years to complete!), the repository is constantly evolving.
The adventure doesn't stop at exploration! I deeply value your feedback. Encounter roadblocks in the article? Have constructive criticism to share? Or simply want to ignite a conversation about algorithms? My door (or rather, my inbox) is always open. Reach out on Twitter:[@m__mdy__m](https://twitter.com/m__mdy__m) or Telegram: @m_mdy_m. Additionally, my GitHub account, [m-mdy-m](https://github.com/m-mdy-m), welcomes discussions and contributions. Let's build a vibrant learning community together, where we share knowledge and push the boundaries of our understanding. | m__mdy__m |
1,865,073 | Buy Negative Google Reviews | https://dmhelpshop.com/product/buy-negative-google-reviews/ Buy Negative Google Reviews Negative... | 0 | 2024-05-25T17:02:44 | https://dev.to/matlohewsimpson656/buy-negative-google-reviews-aj5 | webdev, javascript, beginners, programming | ERROR: type should be string, got "https://dmhelpshop.com/product/buy-negative-google-reviews/\n\n\nBuy Negative Google Reviews\nNegative reviews on Google are detrimental critiques that expose customers’ unfavorable experiences with a business. These reviews can significantly damage a company’s reputation, presenting challenges in both attracting new customers and retaining current ones. If you are considering purchasing negative Google reviews from dmhelpshop.com, we encourage you to reconsider and instead focus on providing exceptional products and services to ensure positive feedback and sustainable success.\n\nWhy Buy Negative Google Reviews from dmhelpshop\nWe take pride in our fully qualified, hardworking, and experienced team, who are committed to providing quality and safe services that meet all your needs. Our professional team ensures that you can trust us completely, knowing that your satisfaction is our top priority. With us, you can rest assured that you’re in good hands.\n\nIs Buy Negative Google Reviews safe?\nAt dmhelpshop, we understand the concern many business persons have about the safety of purchasing Buy negative Google reviews. We are here to guide you through a process that sheds light on the importance of these reviews and how we ensure they appear realistic and safe for your business. Our team of qualified and experienced computer experts has successfully handled similar cases before, and we are committed to providing a solution tailored to your specific needs. Contact us today to learn more about how we can help your business thrive.\n\nBuy Google 5 Star Reviews\nReviews represent the opinions of experienced customers who have utilized services or purchased products from various online or offline markets. These reviews convey customer demands and opinions, and ratings are assigned based on the quality of the products or services and the overall user experience. Google serves as an excellent platform for customers to leave reviews since the majority of users engage with it organically. When you purchase Buy Google 5 Star Reviews, you have the potential to influence a large number of people either positively or negatively. Positive reviews can attract customers to purchase your products, while negative reviews can deter potential customers.\n\nIf you choose to Buy Google 5 Star Reviews, people will be more inclined to consider your products. However, it is important to recognize that reviews can have both positive and negative impacts on your business. Therefore, take the time to determine which type of reviews you wish to acquire. Our experience indicates that purchasing Buy Google 5 Star Reviews can engage and connect you with a wide audience. By purchasing positive reviews, you can enhance your business profile and attract online traffic. Additionally, it is advisable to seek reviews from reputable platforms, including social media, to maintain a positive flow. We are an experienced and reliable service provider, highly knowledgeable about the impacts of reviews. Hence, we recommend purchasing verified Google reviews and ensuring their stability and non-gropability.\n\nLet us now briefly examine the direct and indirect benefits of reviews:\nReviews have the power to enhance your business profile, influencing users at an affordable cost.\nTo attract customers, consider purchasing only positive reviews, while negative reviews can be acquired to undermine your competitors. Collect negative reports on your opponents and present them as evidence.\nIf you receive negative reviews, view them as an opportunity to understand user reactions, make improvements to your products and services, and keep up with current trends.\nBy earning the trust and loyalty of customers, you can control the market value of your products. Therefore, it is essential to buy online reviews, including Buy Google 5 Star Reviews.\nReviews serve as the captivating fragrance that entices previous customers to return repeatedly.\nPositive customer opinions expressed through reviews can help you expand your business globally and achieve profitability and credibility.\nWhen you purchase positive Buy Google 5 Star Reviews, they effectively communicate the history of your company or the quality of your individual products.\nReviews act as a collective voice representing potential customers, boosting your business to amazing heights.\nNow, let’s delve into a comprehensive understanding of reviews and how they function:\nGoogle, with its significant organic user base, stands out as the premier platform for customers to leave reviews. When you purchase Buy Google 5 Star Reviews , you have the power to positively influence a vast number of individuals. Reviews are essentially written submissions by users that provide detailed insights into a company, its products, services, and other relevant aspects based on their personal experiences. In today’s business landscape, it is crucial for every business owner to consider buying verified Buy Google 5 Star Reviews, both positive and negative, in order to reap various benefits.\n\nWhy are Google reviews considered the best tool to attract customers?\nGoogle, being the leading search engine and the largest source of potential and organic customers, is highly valued by business owners. Many business owners choose to purchase Google reviews to enhance their business profiles and also sell them to third parties. Without reviews, it is challenging to reach a large customer base globally or locally. Therefore, it is crucial to consider buying positive Buy Google 5 Star Reviews from reliable sources. When you invest in Buy Google 5 Star Reviews for your business, you can expect a significant influx of potential customers, as these reviews act as a pheromone, attracting audiences towards your products and services. Every business owner aims to maximize sales and attract a substantial customer base, and purchasing Buy Google 5 Star Reviews is a strategic move.\n\nAccording to online business analysts and economists, trust and affection are the essential factors that determine whether people will work with you or do business with you. However, there are additional crucial factors to consider, such as establishing effective communication systems, providing 24/7 customer support, and maintaining product quality to engage online audiences. If any of these rules are broken, it can lead to a negative impact on your business. Therefore, obtaining positive reviews is vital for the success of an online business\n\nWhat are the benefits of purchasing reviews online?\nIn today’s fast-paced world, the impact of new technologies and IT sectors is remarkable. Compared to the past, conducting business has become significantly easier, but it is also highly competitive. To reach a global customer base, businesses must increase their presence on social media platforms as they provide the easiest way to generate organic traffic. Numerous surveys have shown that the majority of online buyers carefully read customer opinions and reviews before making purchase decisions. In fact, the percentage of customers who rely on these reviews is close to 97%. Considering these statistics, it becomes evident why we recommend buying reviews online. In an increasingly rule-based world, it is essential to take effective steps to ensure a smooth online business journey.\n\nBuy Google 5 Star Reviews\nMany people purchase reviews online from various sources and witness unique progress. Reviews serve as powerful tools to instill customer trust, influence their decision-making, and bring positive vibes to your business. Making a single mistake in this regard can lead to a significant collapse of your business. Therefore, it is crucial to focus on improving product quality, quantity, communication networks, facilities, and providing the utmost support to your customers.\n\nReviews reflect customer demands, opinions, and ratings based on their experiences with your products or services. If you purchase Buy Google 5-star reviews, it will undoubtedly attract more people to consider your offerings. Google is the ideal platform for customers to leave reviews due to its extensive organic user involvement. Therefore, investing in Buy Google 5 Star Reviews can significantly influence a large number of people in a positive way.\n\nHow to generate google reviews on my business profile?\nFocus on delivering high-quality customer service in every interaction with your customers. By creating positive experiences for them, you increase the likelihood of receiving reviews. These reviews will not only help to build loyalty among your customers but also encourage them to spread the word about your exceptional service. It is crucial to strive to meet customer needs and exceed their expectations in order to elicit positive feedback. If you are interested in purchasing affordable Google reviews, we offer that service.\n\n\n\n\n\nContact Us / 24 Hours Reply\nTelegram:dmhelpshop\nWhatsApp: +1 (980) 277-2786\nSkype:dmhelpshop\nEmail:dmhelpshop@gmail.com" | matlohewsimpson656 |
1,865,071 | The Essential Guide to A/C Repair in Corpus Christi | Corpus Christi, with its sunny climate and coastal breezes, offers a beautiful environment to live... | 0 | 2024-05-25T16:58:35 | https://dev.to/backlink_30/the-essential-guide-to-ac-repair-in-corpus-christi-2265 |
Corpus Christi, with its sunny climate and coastal breezes, offers a beautiful environment to live in. However, the summer heat can be relentless, making a properly functioning air conditioning system essential for comfort and well-being. In this comprehensive guide, we'll delve into the world of A/C repair in Corpus Christi, exploring common issues, preventive maintenance tips, and how to find reliable professionals to keep your cool when the mercury rises.
**Understanding the Importance of A/C Maintenance:**
Your air conditioning system is more than just a luxury; it's a vital component of indoor comfort, especially in a place like Corpus Christi where temperatures can soar. Regular maintenance not only ensures efficient operation but also prolongs the lifespan of your unit, saving you money in the long run. Neglecting maintenance can lead to costly repairs and even premature system failure, leaving you sweltering in the summer heat.
**Common A/C Problems in Corpus Christi:**
Refrigerant Leaks: With the constant demand for cooling, refrigerant leaks are a common issue in A/C systems, especially in older units. Low refrigerant levels can hinder cooling performance and cause the system to work harder, leading to increased energy consumption and higher utility bills.
Clogged Air Filters: **[Ac Repair Corpus Christi](https://thomasexxon.com/heating-air-conditioning-repair/)** location means a higher concentration of airborne particles like salt and dust, which can quickly clog air filters. Restricted airflow not only reduces cooling efficiency but can also strain the system, potentially leading to breakdowns.
Faulty Thermostat: A malfunctioning thermostat can cause erratic temperature fluctuations or prevent the A/C from turning on altogether. Inaccurate temperature readings may lead to overworking the system, resulting in unnecessary wear and tear.
Dirty Condenser Coils: The outdoor condenser unit is exposed to the elements, making it susceptible to dirt, debris, and salt spray in coastal areas like Corpus Christi. Dirty condenser coils impair heat transfer, reducing the A/C's efficiency and increasing energy consumption.
Electrical Issues: Loose wiring, corroded terminals, or faulty capacitors can cause electrical problems in the A/C system, leading to intermittent operation or complete failure.
Preventive Maintenance Tips:
Regular Filter Replacement: Check and replace air filters every 1-3 months, or as recommended by the manufacturer, to ensure optimal airflow and system efficiency.
Clean the Condenser Unit: Keep the outdoor condenser unit free of debris, vegetation, and obstructions to maintain proper airflow and heat dissipation.
Inspect and Clean Air Ducts: Periodically inspect air ducts for leaks, damage, or blockages, and clean them to ensure efficient air distribution throughout your home.
Schedule Professional Tune-Ups: Arrange for annual or bi-annual maintenance visits from HVAC professionals to inspect, clean, and tune up your A/C system for optimal performance.
Upgrade to Programmable Thermostat: Consider installing a programmable or smart thermostat to regulate temperature settings and optimize energy usage, especially when away from home.
**Finding Reliable Ac Repair Corpus Christi**:
When it comes to A/C repair, it's crucial to choose a reputable and experienced HVAC contractor to ensure quality service and reliable repairs. Here are some tips for finding the right professional:
**Check Credentials: **
Look for licensed and insured HVAC companies with a proven track record of excellence in A/C repair and maintenance.
Read Reviews: Check online reviews and testimonials from past customers to gauge the company's reputation and customer satisfaction.
Ask for Recommendations: Seek recommendations from friends, family, or neighbors who have recently had A/C repairs done, and inquire about their experiences with local HVAC contractors.
Get Multiple Quotes: Obtain estimates from several HVAC companies, comparing prices, services offered, and warranties before making a decision.
Inquire About Guarantees: Choose a company that stands behind its workmanship and offers guarantees or warranties on parts and labor for added peace of mind.
**Conclusion:**
In Corpus Christi's warm and humid climate, a functioning air conditioning system is essential for indoor comfort and well-being. By understanding common A/C problems, implementing preventive maintenance measures, and choosing reliable HVAC professionals for repairs and servicing, you can ensure your A/C system keeps you cool and comfortable year-round. Don't let the heat get the best of you—stay ahead of A/C issues and enjoy a cool oasis in the coastal warmth of Corpus Christi. | backlink_30 | |
1,865,070 | What is an ORM and when developers should and shouldn't use it | What is an ORM Object-Relational Mapping (ORM) is a programming technique that facilitates... | 0 | 2024-05-25T16:56:08 | https://www.neurelo.com/post/what-is-an-orm | database, mongodb, postgres, mysql | ## What is an ORM
Object-Relational Mapping (ORM) is a programming technique that facilitates the interaction between a relational database and programming language. It acts as a bridge between the logical, object-oriented representation of data in the code and the physical, relational structure in a database. The primary purpose of an ORM is to eliminate the impedance mismatch that can occur between the object model used in application code and the relational model employed by databases.
## Why use an ORM
Developers use ORMs for several reasons. Firstly, it simplifies and accelerates the development process by allowing them to work with objects and classes in the programming language rather than writing SQL queries. This abstraction minimizes the need to deal directly with database-specific syntax and intricacies.
Secondly, an ORM enhances code maintainability by providing some level of an abstraction. Changes to the database schema can be managed more easily, as developers can update the mapping in the ORM layer without extensively modifying application code.
Thirdly, an ORM promotes code reusability and portability. By abstracting the database interactions, developers can write database-agnostic code, making it easier to switch to a different database system without substantial code changes.
## Challenges using ORMs
While an Object-Relational Mapping (ORM) layer provides numerous advantages, developers often encounter challenges and trade-offs when deciding to use this approach.
## Dev/Build Time Challenges:
- N+1 Queries: ORMs often lead to the N+1 query problem, where multiple database queries are executed instead of a more optimized query, causing performance issues for data access. Developers need to be mindful of the data access patterns to minimize this problem.
- Leakiness: As queries become more advanced and complex, beyond basic CRUD operations, the abstraction provided by an ORM can start to leak, forcing developers to direct deal with database-specific query code and behaviors from their code. This can lead to unexpected issues with code maintainability particularly when attempting to change the schema or optimize queries.
## Production Performance, Scale, Optimization, and Security:
- Performance: While ORM systems generate SQL queries, they may not always be ideal and developers may need to fine-tune or handcraft queries for optimal performance in specific situations. In high-performance scenarios, such optimizations become crucial.
- Scale: As applications scale, ORM-generated queries may not always scale seamlessly. Developers may need to consider database-specific optimizations or even move away from certain ORM features to ensure performance at scale.
- DB Connection Management: Connection pools manage reusable database connections, enhancing performance and scalability. ORMs may not always integrate seamlessly with connection pools, leading to issues such as inefficient connection management, impacting performance. Additionally, configuring the connection pool settings to align with the ORM's requirements and ensuring proper handling of connections within the ORM layer can be complex tasks.
- Security: ORM systems abstract away much of the SQL, but developers must remain vigilant about security. Poorly sanitized inputs, improper use of ORM features, or overlooking security configurations can introduce vulnerabilities.
## Suitability to SDLC Processes (e.g., CI/CD):
- Continuous Integration/Continuous Deployment (CI/CD): ORMs can pose challenges in CI/CD pipelines, especially when dealing with database schema changes. Migrations and updates need careful consideration to avoid disruptions and ensure smooth deployment processes.
- Adaptation to Change: As applications evolve with new features, the ORM mappings may need frequent updates. Ensuring that these changes do not disrupt existing functionality and that migrations are handled seamlessly becomes a crucial aspect of the development process.
- Modern application architectures: ORM tools may not seamlessly align with modern cloud and serverless architectures. As applications scale, ORM's centralized management of database connections and transactions can become a bottleneck, leading to increased latency and decreased overall throughput. Similarly, in serverless setups, ORM's heavyweight abstraction may struggle with short-lived compute instances. Developers need to carefully evaluate the trade-offs between ORM convenience and cloud-native benefits when architecting applications.
## Summary
In conclusion, while an ORM simplifies database interactions and enhances code maintainability, developers should be aware of these challenges and make informed decisions based on the specific needs of their applications. Mitigating these challenges often involves a combination of careful design, optimization, and a deep understanding of both the ORM framework and the underlying database system. | shohams |
1,865,069 | Buy Verified Paxful Account | https://dmhelpshop.com/product/buy-verified-paxful-account/ Buy Verified Paxful Account There are... | 0 | 2024-05-25T16:51:16 | https://dev.to/matlohewsimpson656/buy-verified-paxful-account-42kk | webdev, javascript, beginners, programming | ERROR: type should be string, got "https://dmhelpshop.com/product/buy-verified-paxful-account/\n\n\nBuy Verified Paxful Account\nThere are several compelling reasons to consider purchasing a verified Paxful account. Firstly, a verified account offers enhanced security, providing peace of mind to all users. Additionally, it opens up a wider range of trading opportunities, allowing individuals to partake in various transactions, ultimately expanding their financial horizons.\n\nMoreover, Buy verified Paxful account ensures faster and more streamlined transactions, minimizing any potential delays or inconveniences. Furthermore, by opting for a verified account, users gain access to a trusted and reputable platform, fostering a sense of reliability and confidence.\n\nLastly, Paxful’s verification process is thorough and meticulous, ensuring that only genuine individuals are granted verified status, thereby creating a safer trading environment for all users. Overall, the decision to Buy Verified Paxful account can greatly enhance one’s overall trading experience, offering increased security, access to more opportunities, and a reliable platform to engage with. Buy Verified Paxful Account.\n\nBuy US verified paxful account from the best place dmhelpshop\nWhy we declared this website as the best place to buy US verified paxful account? Because, our company is established for providing the all account services in the USA (our main target) and even in the whole world. With this in mind we create paxful account and customize our accounts as professional with the real documents. Buy Verified Paxful Account.\n\nIf you want to buy US verified paxful account you should have to contact fast with us. Because our accounts are-\n\nEmail verified\nPhone number verified\nSelfie and KYC verified\nSSN (social security no.) verified\nTax ID and passport verified\nSometimes driving license verified\nMasterCard attached and verified\nUsed only genuine and real documents\n100% access of the account\nAll documents provided for customer security\nWhat is Verified Paxful Account?\nIn today’s expanding landscape of online transactions, ensuring security and reliability has become paramount. Given this context, Paxful has quickly risen as a prominent peer-to-peer Bitcoin marketplace, catering to individuals and businesses seeking trusted platforms for cryptocurrency trading.\n\nIn light of the prevalent digital scams and frauds, it is only natural for people to exercise caution when partaking in online transactions. As a result, the concept of a verified account has gained immense significance, serving as a critical feature for numerous online platforms. Paxful recognizes this need and provides a safe haven for users, streamlining their cryptocurrency buying and selling experience.\n\nFor individuals and businesses alike, Buy verified Paxful account emerges as an appealing choice, offering a secure and reliable environment in the ever-expanding world of digital transactions. Buy Verified Paxful Account.\n\nVerified Paxful Accounts are essential for establishing credibility and trust among users who want to transact securely on the platform. They serve as evidence that a user is a reliable seller or buyer, verifying their legitimacy.\n\nBut what constitutes a verified account, and how can one obtain this status on Paxful? In this exploration of verified Paxful accounts, we will unravel the significance they hold, why they are crucial, and shed light on the process behind their activation, providing a comprehensive understanding of how they function. Buy verified Paxful account.\n\n \n\nWhy should to Buy Verified Paxful Account?\nThere are several compelling reasons to consider purchasing a verified Paxful account. Firstly, a verified account offers enhanced security, providing peace of mind to all users. Additionally, it opens up a wider range of trading opportunities, allowing individuals to partake in various transactions, ultimately expanding their financial horizons.\n\nMoreover, a verified Paxful account ensures faster and more streamlined transactions, minimizing any potential delays or inconveniences. Furthermore, by opting for a verified account, users gain access to a trusted and reputable platform, fostering a sense of reliability and confidence. Buy Verified Paxful Account.\n\nLastly, Paxful’s verification process is thorough and meticulous, ensuring that only genuine individuals are granted verified status, thereby creating a safer trading environment for all users. Overall, the decision to buy a verified Paxful account can greatly enhance one’s overall trading experience, offering increased security, access to more opportunities, and a reliable platform to engage with.\n\n \n\nWhat is a Paxful Account\nPaxful and various other platforms consistently release updates that not only address security vulnerabilities but also enhance usability by introducing new features. Buy Verified Paxful Account.\n\nIn line with this, our old accounts have recently undergone upgrades, ensuring that if you purchase an old buy Verified Paxful account from dmhelpshop.com, you will gain access to an account with an impressive history and advanced features. This ensures a seamless and enhanced experience for all users, making it a worthwhile option for everyone.\n\n \n\nIs it safe to buy Paxful Verified Accounts?\nBuying on Paxful is a secure choice for everyone. However, the level of trust amplifies when purchasing from Paxful verified accounts. These accounts belong to sellers who have undergone rigorous scrutiny by Paxful. Buy verified Paxful account, you are automatically designated as a verified account. Hence, purchasing from a Paxful verified account ensures a high level of credibility and utmost reliability. Buy Verified Paxful Account.\n\nPAXFUL, a widely known peer-to-peer cryptocurrency trading platform, has gained significant popularity as a go-to website for purchasing Bitcoin and other cryptocurrencies. It is important to note, however, that while Paxful may not be the most secure option available, its reputation is considerably less problematic compared to many other marketplaces. Buy Verified Paxful Account.\n\nThis brings us to the question: is it safe to purchase Paxful Verified Accounts? Top Paxful reviews offer mixed opinions, suggesting that caution should be exercised. Therefore, users are advised to conduct thorough research and consider all aspects before proceeding with any transactions on Paxful.\n\n \n\nHow Do I Get 100% Real Verified Paxful Accoun?\nPaxful, a renowned peer-to-peer cryptocurrency marketplace, offers users the opportunity to conveniently buy and sell a wide range of cryptocurrencies. Given its growing popularity, both individuals and businesses are seeking to establish verified accounts on this platform.\n\nHowever, the process of creating a verified Paxful account can be intimidating, particularly considering the escalating prevalence of online scams and fraudulent practices. This verification procedure necessitates users to furnish personal information and vital documents, posing potential risks if not conducted meticulously.\n\nIn this comprehensive guide, we will delve into the necessary steps to create a legitimate and verified Paxful account. Our discussion will revolve around the verification process and provide valuable tips to safely navigate through it.\n\nMoreover, we will emphasize the utmost importance of maintaining the security of personal information when creating a verified account. Furthermore, we will shed light on common pitfalls to steer clear of, such as using counterfeit documents or attempting to bypass the verification process.\n\nWhether you are new to Paxful or an experienced user, this engaging paragraph aims to equip everyone with the knowledge they need to establish a secure and authentic presence on the platform.\n\nBenefits Of Verified Paxful Accounts\nVerified Paxful accounts offer numerous advantages compared to regular Paxful accounts. One notable advantage is that verified accounts contribute to building trust within the community.\n\nVerification, although a rigorous process, is essential for peer-to-peer transactions. This is why all Paxful accounts undergo verification after registration. When customers within the community possess confidence and trust, they can conveniently and securely exchange cash for Bitcoin or Ethereum instantly. Buy Verified Paxful Account.\n\nPaxful accounts, trusted and verified by sellers globally, serve as a testament to their unwavering commitment towards their business or passion, ensuring exceptional customer service at all times. Headquartered in Africa, Paxful holds the distinction of being the world’s pioneering peer-to-peer bitcoin marketplace. Spearheaded by its founder, Ray Youssef, Paxful continues to lead the way in revolutionizing the digital exchange landscape.\n\nPaxful has emerged as a favored platform for digital currency trading, catering to a diverse audience. One of Paxful’s key features is its direct peer-to-peer trading system, eliminating the need for intermediaries or cryptocurrency exchanges. By leveraging Paxful’s escrow system, users can trade securely and confidently.\n\nWhat sets Paxful apart is its commitment to identity verification, ensuring a trustworthy environment for buyers and sellers alike. With these user-centric qualities, Paxful has successfully established itself as a leading platform for hassle-free digital currency transactions, appealing to a wide range of individuals seeking a reliable and convenient trading experience. Buy Verified Paxful Account.\n\n \n\nHow paxful ensure risk-free transaction and trading?\nEngage in safe online financial activities by prioritizing verified accounts to reduce the risk of fraud. Platforms like Paxfu implement stringent identity and address verification measures to protect users from scammers and ensure credibility.\n\nWith verified accounts, users can trade with confidence, knowing they are interacting with legitimate individuals or entities. By fostering trust through verified accounts, Paxful strengthens the integrity of its ecosystem, making it a secure space for financial transactions for all users. Buy Verified Paxful Account.\n\nExperience seamless transactions by obtaining a verified Paxful account. Verification signals a user’s dedication to the platform’s guidelines, leading to the prestigious badge of trust. This trust not only expedites trades but also reduces transaction scrutiny. Additionally, verified users unlock exclusive features enhancing efficiency on Paxful. Elevate your trading experience with Verified Paxful Accounts today.\n\nIn the ever-changing realm of online trading and transactions, selecting a platform with minimal fees is paramount for optimizing returns. This choice not only enhances your financial capabilities but also facilitates more frequent trading while safeguarding gains. Buy Verified Paxful Account.\n\nExamining the details of fee configurations reveals Paxful as a frontrunner in cost-effectiveness. Acquire a verified level-3 USA Paxful account from usasmmonline.com for a secure transaction experience. Invest in verified Paxful accounts to take advantage of a leading platform in the online trading landscape.\n\n \n\nHow Old Paxful ensures a lot of Advantages?\n\nExplore the boundless opportunities that Verified Paxful accounts present for businesses looking to venture into the digital currency realm, as companies globally witness heightened profits and expansion. These success stories underline the myriad advantages of Paxful’s user-friendly interface, minimal fees, and robust trading tools, demonstrating its relevance across various sectors.\n\nBusinesses benefit from efficient transaction processing and cost-effective solutions, making Paxful a significant player in facilitating financial operations. Acquire a USA Paxful account effortlessly at a competitive rate from usasmmonline.com and unlock access to a world of possibilities. Buy Verified Paxful Account.\n\nExperience elevated convenience and accessibility through Paxful, where stories of transformation abound. Whether you are an individual seeking seamless transactions or a business eager to tap into a global market, buying old Paxful accounts unveils opportunities for growth.\n\nPaxful’s verified accounts not only offer reliability within the trading community but also serve as a testament to the platform’s ability to empower economic activities worldwide. Join the journey towards expansive possibilities and enhanced financial empowerment with Paxful today. Buy Verified Paxful Account.\n\n \n\nWhy paxful keep the security measures at the top priority?\nIn today’s digital landscape, security stands as a paramount concern for all individuals engaging in online activities, particularly within marketplaces such as Paxful. It is essential for account holders to remain informed about the comprehensive security protocols that are in place to safeguard their information.\n\nSafeguarding your Paxful account is imperative to guaranteeing the safety and security of your transactions. Two essential security components, Two-Factor Authentication and Routine Security Audits, serve as the pillars fortifying this shield of protection, ensuring a secure and trustworthy user experience for all. Buy Verified Paxful Account.\n\nConclusion\nInvesting in Bitcoin offers various avenues, and among those, utilizing a Paxful account has emerged as a favored option. Paxful, an esteemed online marketplace, enables users to engage in buying and selling Bitcoin. Buy Verified Paxful Account.\n\nThe initial step involves creating an account on Paxful and completing the verification process to ensure identity authentication. Subsequently, users gain access to a diverse range of offers from fellow users on the platform. Once a suitable proposal captures your interest, you can proceed to initiate a trade with the respective user, opening the doors to a seamless Bitcoin investing experience.\n\nIn conclusion, when considering the option of purchasing verified Paxful accounts, exercising caution and conducting thorough due diligence is of utmost importance. It is highly recommended to seek reputable sources and diligently research the seller’s history and reviews before making any transactions.\n\nMoreover, it is crucial to familiarize oneself with the terms and conditions outlined by Paxful regarding account verification, bearing in mind the potential consequences of violating those terms. By adhering to these guidelines, individuals can ensure a secure and reliable experience when engaging in such transactions. Buy Verified Paxful Account.\n\nContact Us / 24 Hours Reply\nTelegram:dmhelpshop\nWhatsApp: +1 (980) 277-2786\nSkype:dmhelpshop\nEmail:dmhelpshop@gmail.com\n\n " | matlohewsimpson656 |
1,865,067 | Comparing WebRTC and WebSocket: Choosing the Right Technology for Real-Time Experience | WebRTC vs WebSocket: A Comprehensive Comparison In the realm of real-time communication on... | 0 | 2024-05-25T16:48:06 | https://dev.to/arjunkava/comparing-webrtc-and-websocket-choosing-the-right-technology-for-real-time-experience-4ie9 | webdev, javascript, beginners, programming | ### WebRTC vs WebSocket: A Comprehensive Comparison
In the realm of real-time communication on the web, two technologies stand out: WebRTC (Web Real-Time Communication) and WebSocket. Both offer unique advantages and are tailored to different use cases. This article provides an in-depth comparison of WebRTC and WebSocket, exploring their features, use cases, advantages, and disadvantages to help you decide which technology is best suited for your application.
#### Introduction
Real-time communication is integral to modern web applications, enabling functionalities like video conferencing, live streaming, online gaming, and instant messaging. WebRTC and WebSocket are pivotal technologies in this space, each with distinct capabilities.
### What is WebRTC?
WebRTC is a peer-to-peer communication protocol that facilitates real-time audio, video, and data exchange directly between browsers or mobile applications without the need for an intermediary server. It is designed to support high-quality media streams with low latency.
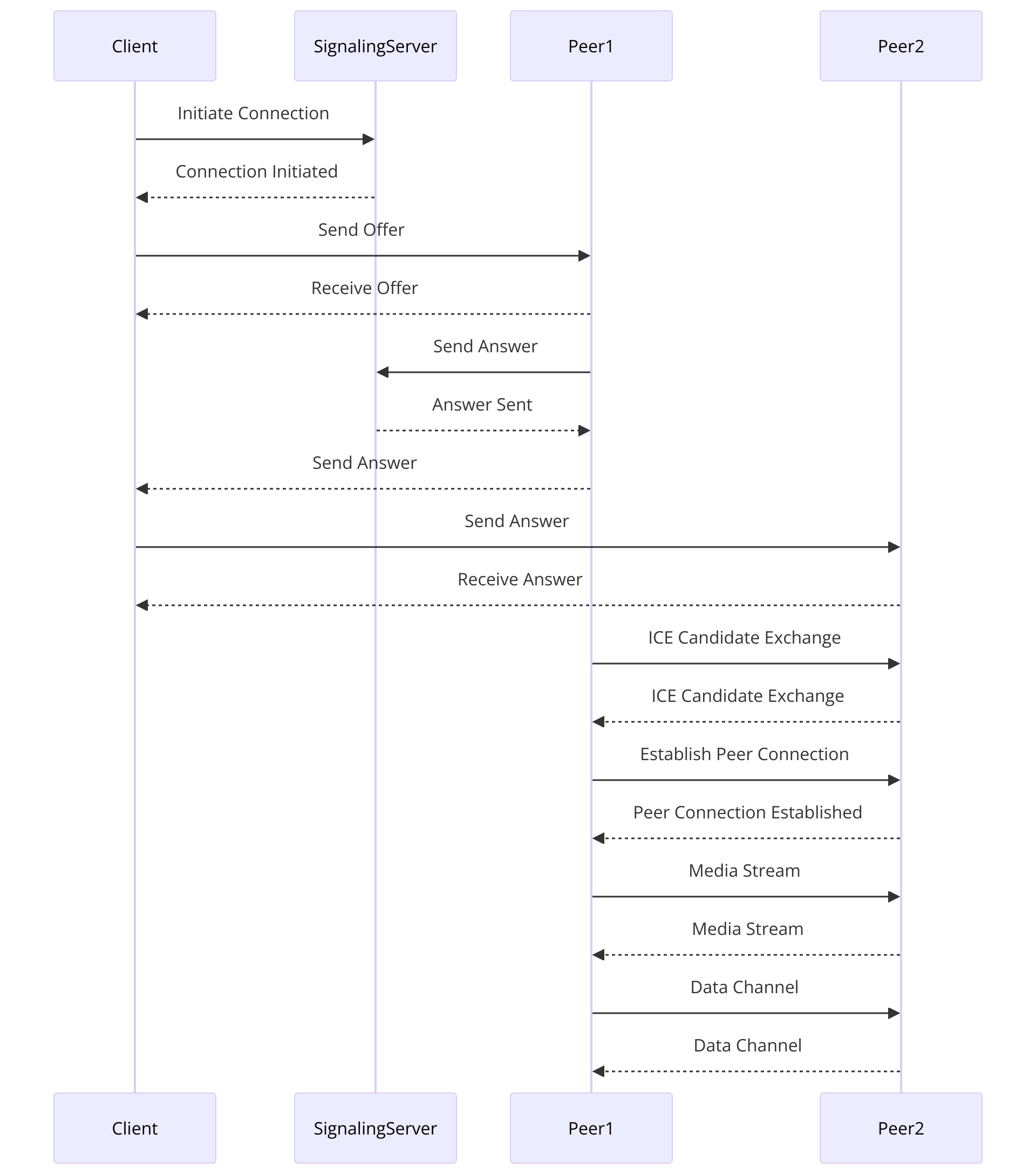
#### Advantages of WebRTC
1. **High-Quality Media Streams**: WebRTC is optimized for real-time video and audio communication, offering minimal latency and high quality.
2. **Encryption**: Built-in security features such as DTLS and SRTP ensure that all communications are encrypted and secure from eavesdropping.
3. **Browser Support**: Supported by most modern browsers, including Chrome, Firefox, and Safari, facilitating easy implementation and broad accessibility.
#### Disadvantages of WebRTC
1. **Complexity**: Implementing WebRTC can be technically challenging due to its complex architecture involving numerous protocols and APIs like ICE, STUN, and TURN.
2. **Resource Intensive**: WebRTC applications can be resource-intensive, especially when handling high-definition video streams, requiring significant bandwidth and processing power.
3. **Partial Browser Support**: While broadly adopted, certain codecs or features may have inconsistent support across different browsers, potentially leading to compatibility issues.
### What is WebSocket?
WebSocket is a full-duplex communication protocol that enables persistent, bidirectional communication between a client and a server over a single TCP connection. This makes it suitable for real-time applications that require continuous data exchange.
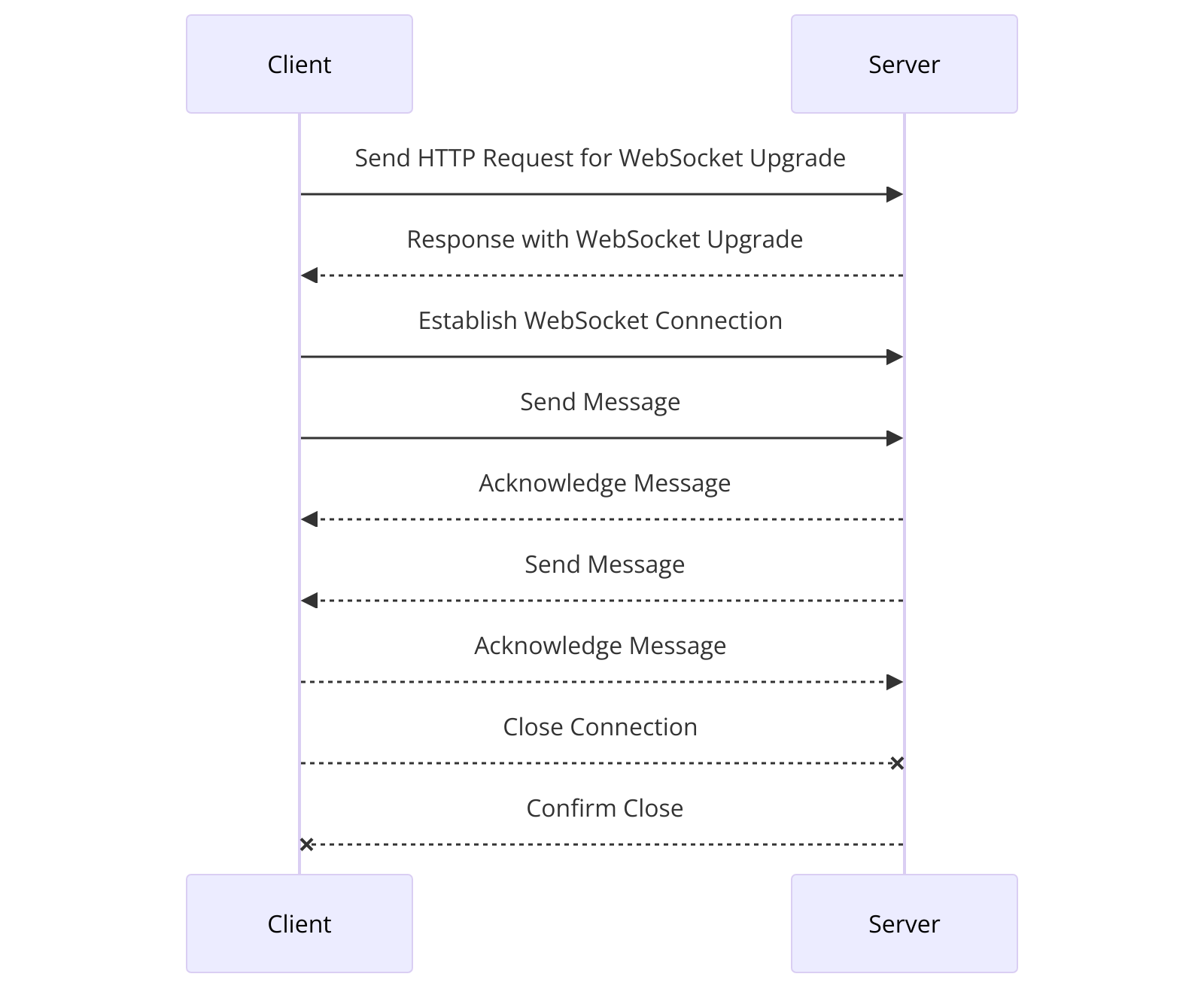
#### Advantages of WebSocket
1. **Low Overhead**: WebSocket reduces the overhead associated with traditional HTTP requests, making data transfer more efficient.
2. **Full-Duplex Communication**: Allows for simultaneous two-way communication, which is crucial for interactive applications like online gaming and live chat.
3. **Wide Compatibility**: Supported by all major browsers and easily implemented across various platforms and devices.
#### Disadvantages of WebSocket
1. **Stateful Connections**: Maintaining a stateful connection can complicate scaling in large applications due to the need for persistent connections to each client.
2. **Connection Recovery**: WebSockets don’t automatically recover when connections are terminated; this functionality needs to be implemented by the developer.
3. **Security**: While secure over TLS (WSS), WebSocket lacks the built-in encryption mechanisms of WebRTC, requiring additional security implementations.
### Key Differences Between WebRTC and WebSocket
#### Protocol and Connection Type
- **WebRTC**: Uses UDP primarily (can work over TCP) and supports peer-to-peer connections【8†source】【10†source】.
- **WebSocket**: Uses TCP and relies on a client-server model.
#### Data Transmission and Use Cases
- **WebRTC**: Suitable for high-performance media streaming (video/audio) and real-time communications like video conferencing and live broadcasting.
- **WebSocket**: Ideal for reliable data transmission, making it better suited for real-time messaging, multiplayer gaming, and live notifications.
#### Latency and Bandwidth
- **WebRTC**: Lower latency and bandwidth usage due to its peer-to-peer nature.
- **WebSocket**: Higher latency and bandwidth usage but ensures data integrity through TCP.
### Use Cases
#### When to Use WebRTC
1. **Video and Audio Conferencing**: Real-time video and audio calls directly within web browsers without the need for additional plugins or software.
2. **Live Streaming**: For events like webinars or concerts, where low latency is critical.
3. **Real-time Gaming**: Low latency communication ideal for online gaming interactions.
4. **File Sharing**: Direct transfer of files between users in a peer-to-peer manner.
5. **Telehealth**: Secure video consultations between patients and healthcare providers.
6. **Education and E-Learning**: Facilitates interactive online learning experiences.
#### When to Use WebSocket
1. **Chat Applications**: Instant messaging where messages need to be exchanged in real-time.
2. **Live Notifications**: Updating users with live notifications, such as new posts or social media interactions.
3. **Online Multiplayer Games**: Games requiring constant data exchange between players and the server.
4. **Financial Applications**: Real-time updates for stock trading and financial transactions.
5. **Interactive Dashboards**: Real-time updating of user interfaces, such as live stats or monitoring systems.
### When to Use Both WebRTC and WebSocket
In some scenarios, using both WebRTC and WebSocket together can be beneficial:
- **Signaling in WebRTC**: WebSocket can handle the signaling process required to establish WebRTC connections.
- **Complex Applications**: Applications like multiplayer games or live broadcasting with chat might use WebRTC for low-latency media transmission and WebSocket for server-mediated tasks like state synchronization and user matching.
### Conclusion
Both WebRTC and WebSocket are crucial for real-time communication, but they cater to different needs. WebRTC is ideal for high-quality, low-latency media communication, while WebSocket is perfect for reliable, persistent data exchange. Understanding their strengths and limitations will help you decide which technology best meets your application's requirements.
### FAQs
#### Can WebRTC and WebSocket be used together?
Yes, WebRTC and WebSocket can be used together to leverage their strengths for different aspects of an application, such as using WebSocket for signaling and WebRTC for media transmission.
#### What are the primary use cases for WebRTC?
WebRTC is primarily used for video and audio conferencing, live streaming, real-time gaming, file sharing, telehealth, and education.
#### What are the primary use cases for WebSocket?
WebSocket is best suited for chat applications, live notifications, online multiplayer games, financial applications, and interactive dashboards.
By understanding the capabilities and ideal use cases for WebRTC and WebSocket, developers can make informed decisions to create robust, real-time communication applications tailored to their specific needs. | arjunkava |
1,865,066 | How to Choose the Right Tools for Test Data Management? | Introduction to Choosing Tools for Test Data Management Within the domain of software engineering... | 0 | 2024-05-25T16:46:09 | https://zatrana.com/how-to-choose-the-right-tools-for-test-data-management/ | test, data, management | 
**Introduction to Choosing Tools for Test Data Management**
Within the domain of software engineering and testing, it is vital to have an appropriate system of test data management in order to have not only accurate but also efficient testing processes. Choosing the right tools for test data management (TDM) can fast track the release of high quality software as well as aid in shortening the development cycles. This guide will lead you through the top most important aspects that need to be considered and features which must be looked for in the TDM tool option, helping you to efficiently manage your test data.
**Understanding Test Data Management**
Test Data Management is the procedure of actuating, oversight and keeping, that provides data for testing software. TDM system provides the guaranteed true data which is secure, in compliance with the requirements and readily available for testers. The primary purpose of TDM pursues realism in data feeds, which means the testers get consistent results in trial situations. This allows the detection of issues in the software before it goes live.
**Importance of Test Data Management Tools**
The right type of tools for test data management is very instrumental in the organization of the company’s testing regime. Programs for test data management empower automated data production and upkeep as well as improve the time spent on data preparation processes and ensuring data uniformity between all the environments where the tests are conducted. Moreover, the adoption of this kind of techniques is also intended for the compliance of data laws. These techniques create the masking of the sensitive data which is done so as to protect the personal information from getting exposed during testing.
**Key Features to Look for in TDM Tools**
Narrowing down a TDM tool implies the evaluation through certain criteria so that you can get what you need:
**Data Masking and Anonymization**: Keeps all private content away from the prying eyes of the public and obscures any sensitive information to comply with the privacy regulations.
**Data Subsetting**: Enables the making of tiny, tested duplicates of data sets.
**Data Generation**: Offers functions to produce synthetic data that is similar to the real data, giving it more importance where the existing data is absent.
**Integration Capabilities**: The compatibility of the TDM instrument to function on the output of current systems and databases allows smooth data collection and management.
**Automation Support**: The automated tasks such as data due diligence, detail edit, and teardown helps to save time and decreases manual input errors.
**Evaluating TDM Tools**: Practical Considerations
When evaluating TDM tools, consider the following practical aspects:
**Scalability**: The plan must include a mechanism to cope with expanding data volumes as your business grows.
**User-Friendliness**: The design of a friendly interface that makes the product use very easy for all staff is the main factor that leads to reducing the time of learning a new product.
**Support and Documentation**: Detailed helpdesk instructions with systematic documentation, would be an efficient way for the clients to resolve their problems within a short period of time.
**Cost**: By the way, first consider the total costs of TDM. Then, consider the costs of maintenance.
**Popular TDM Tools in the Market**
There are several TDM tools available in the market, each with its unique features and capabilities. Some of the most popular include:
**Opkey**: This tool is well-known for its no-code platform; this makes it easier for users to build tests wrappers, and there are also test data management features which are feature-rich. Through its deployment, organizations have found out sooner test cycles and better privacy of data, and hence it is the fit-all solution for businesses aimed at managing test data more effectively.
**Informatica Test Data Management**: Provides a comprehensive coverage of techniques including data sub-sampling, synthetic and privacy preserving data.
**IBM InfoSphere Optim**: An adequate helpful tool that gives the users the ability to conduct the effective data masking and subsetting.
**Integrating TDM Tools with Your Existing Workflow**
Integration in a new TDM program is a fundamental part of the process. Make sure that the tool you select can smoothly interact with your Test Management Tool and CI/CD pipeline. Correct coordination is critical in ensuring that the entire software testing process is smooth, accurate and consistent.
**Security and Compliance in Test Data Management**
Security must be upheld adequately when dealing with test data, since it usually involves sensitive information. The TDM tool needs to not only be in compliance with the relevant data protection regulations like (GDPR or HIPAA), but also must have good security measures to ensure data integrity, confidentiality and privacy are protected.
**The Future of Test Data Management**
The upcoming test data management technology trends will be conditioned by innovations in artificial intelligence and machine learning. This technology could further enable the TMD tools through a higher accuracy in data collection, automated data management, and more in-depth analysis of the data.
**Conclusion: Making the Right Choice**
Selecting the appropriate tools for test data management is a tactical decision with substantial impact on your businesses’ quality of software and time needed to conduct the tests. Selecting the TDM tool from among the many available ones requires that you carefully evaluate the features, integration possibilities, and compliance issues of each tool. This will ensure that not only the current needs are met but also that the tool will be relevant in the future too. Whether you look upon someone you know about like the Opkey Solution or other tool, the one you chose will help your teams do their job faster and better and produce more improved software products. | rohitbhandari102 |
1,865,065 | Comprehensive Guide to Using Observers in Laravel | Introduction Laravel Observers are a powerful feature that allows you to hook into the... | 0 | 2024-05-25T16:42:45 | https://dev.to/devbalop/comprehensive-guide-to-using-observers-in-laravel-5dcf |
## Introduction
Laravel Observers are a powerful feature that allows you to hook into the lifecycle events of your Eloquent models. By using observers, you can listen for various events that are fired by the model, such as when a model is created, updated, or deleted, and then execute specific logic in response to those events. This helps in keeping your code clean and maintaining the single responsibility principle.
## Lifecycle Events
Observers can listen to the following model events:
- `retrieved`
- `creating`
- `created`
- `updating`
- `updated`
- `saving`
- `saved`
- `deleting`
- `deleted`
- `restoring`
- `restored`
In this article, I will show a quick use case of sending user authentication credentials to a new user upon profiling. We will create a user model observer that sends an email to the new user when admin creates his profile on the system.
## Creating an Observer
To create an observer, you can use the `make:observer` Artisan command. For example, to create an observer for the `User` model, you would run:
```sh
php artisan make:observer UserObserver --model=User
```
This command will generate a new observer class in the `app/Observers` directory.
## Registering an Observer
To register the observer, you need to add it to the `boot` method of one of your service providers, typically the `AppServiceProvider`. For example:
```php
use App\Models\User;
use App\Observers\UserObserver;
/**
* Bootstrap any application services.
*
* @return void
*/
public function boot()
{
User::observe(UserObserver::class);
}
```
## Creating the UserCredentials notification class
Create a notification class to send the email if it doesn't already exist:
```sh
php artisan make:notification UserCredentials
```
Update the UserCredentials notification:
```php
namespace App\Notifications;
use Illuminate\Bus\Queueable;
use Illuminate\Contracts\Queue\ShouldQueue;
use Illuminate\Notifications\Messages\MailMessage;
use Illuminate\Notifications\Notification;
class UserCredentials extends Notification
{
use Queueable;
protected $username;
protected $password;
/**
* Create a new notification instance.
*
* @param string $username
* @param string $password
* @return void
*/
public function __construct($username, $password)
{
$this->username = $username;
$this->password = $password;
}
/**
* Get the notification's delivery channels.
*
* @param mixed $notifiable
* @return array
*/
public function via($notifiable)
{
return ['mail'];
}
/**
* Get the mail representation of the notification.
*
* @param mixed $notifiable
* @return \Illuminate\Notifications\Messages\MailMessage
*/
public function toMail($notifiable)
{
return (new MailMessage)
->greeting('Hello!')
->line('Your account has been created.')
->line('Username: ' . $this->username)
->line('Password: ' . $this->password)
->line('Thank you for using our application!');
}
/**
* Get the array representation of the notification.
*
* @param mixed $notifiable
* @return array
*/
public function toArray($notifiable)
{
return [
//
];
}
}
```
## Sample Observer
Here's an example of a `UserObserver` that listens for the `created` events:
```php
namespace App\Observers;
use App\Models\User;
use App\Notifications\UserCredentials;
use Illuminate\Support\Facades\Log;
class UserObserver
{
/**
* Handle the User "created" event.
*
* @param \App\Models\User $user
* @return void
*/
public function created(User $user)
{
$plainPassword = $user->password;
$user->notify(new UserCredentials($user->email, $plainPassword));
/** Ensure the password is hashed if the create method
* had saved plain text from the controller
*/
$user->password = Hash::make($plainPassword);
}
// Other events can be handled similarly...
}
```
## Using the Observer
Once the observer is registered, it will automatically listen for the specified events on the model. For example, whenever a `User` model is created, the corresponding methods in the `UserObserver` will be executed, thereby sending the login credential to the created user.
## Benefits of Using Observers
1. **Separation of Concerns**: Observers help in keeping the model and business logic separate. This makes the codebase cleaner and more maintainable.
2. **Code Reusability**: By using observers, you can reuse the same logic across multiple parts of your application without duplicating code.
3. **Centralized Logic**: Observers allow you to centralize event-based logic in one place, making it easier to manage and update.
4. **Enhanced Readability**: With observers, your models are free from additional responsibilities, making them easier to read and understand.
5. **Easy Testing**: Observers can be tested independently of the models, which simplifies the testing process.
## Conclusion
Laravel Observers provide a structured and efficient way to handle model events. By leveraging observers, you can keep your codebase clean, maintainable, and adhere to best practices like the single responsibility principle. They are a valuable tool in any Laravel developer's arsenal, promoting better organization and modularization of code. | devbalop | |
1,865,063 | Learning AWS Day by Day — Day 75 — Elastic Network Interface | Exploring AWS !! Day 75 Elastic Network Interface Logical networking component in a VPC that... | 0 | 2024-05-25T16:40:33 | https://dev.to/rksalo88/learning-aws-day-by-day-day-75-elastic-network-interface-2jab | aws, beginners, cloud, cloudcomputing | Exploring AWS !!
Day 75
Elastic Network Interface
Logical networking component in a VPC that represents virtual network card.
When we move a network instance from one instance to another, network traffic is redirected to new instance.
Why do we need a network interface?
We will need to attach multiple network interfaces when:
1. creating a management network
2. Using network and security appliances in VPC
3. Creating dual-homed instances with workloads/roles on distinct subnets
4. Creating low-budget high availability solution.
Let’s walk through a scenario:
Using network interfaces, we can create a management network. Here, the primary network interface on the instance handles public traffic, and secondary network interface handles backend management traffic and is connected to separate subnet in our VPC which has more restrictive access controls.
Elastic Network Adapter:
EC2 provides enhanced networking capabilities through network adapter. It supports 100 Gbps network speed for supported instance types.
Elastic Fabric Adapter:
Network device that can be attached to EC2 to accelerate High Performance Computing (HPC) and Machine Learning applications.
In short, EFA is an ENA with more functionalities, providing an additional OS-bypass function, allowing HPC and ML apps to communicate directly over a network interface to achieve low latency.
Limitations of EFA:
Only one EFA per instance can be attached.
EFA traffic cannot be sent from one subnet to another. Only normal IP traffic can be sent. OS-bypass traffic is limited to single subnet.
EFA OS-bypass traffic cannot be routed , only IP traffic from EFA can be routed.
Security group needs to be attached to EFA that managed inbound and outbound traffic from security group itself. | rksalo88 |
1,865,062 | Buy verified cash app account | https://dmhelpshop.com/product/buy-verified-cash-app-account/ Buy verified cash app account Cash... | 0 | 2024-05-25T16:40:00 | https://dev.to/matlohewsimpson656/buy-verified-cash-app-account-5jk | webdev, javascript, beginners, programming | ERROR: type should be string, got "https://dmhelpshop.com/product/buy-verified-cash-app-account/\n\n\nBuy verified cash app account\nCash app has emerged as a dominant force in the realm of mobile banking within the USA, offering unparalleled convenience for digital money transfers, deposits, and trading. As the foremost provider of fully verified cash app accounts, we take pride in our ability to deliver accounts with substantial limits. Bitcoin enablement, and an unmatched level of security.\n\nOur commitment to facilitating seamless transactions and enabling digital currency trades has garnered significant acclaim, as evidenced by the overwhelming response from our satisfied clientele. Those seeking buy verified cash app account with 100% legitimate documentation and unrestricted access need look no further. Get in touch with us promptly to acquire your verified cash app account and take advantage of all the benefits it has to offer.\n\nWhy dmhelpshop is the best place to buy USA cash app accounts?\nIt’s crucial to stay informed about any updates to the platform you’re using. If an update has been released, it’s important to explore alternative options. Contact the platform’s support team to inquire about the status of the cash app service.\n\nClearly communicate your requirements and inquire whether they can meet your needs and provide the buy verified cash app account promptly. If they assure you that they can fulfill your requirements within the specified timeframe, proceed with the verification process using the required documents.\n\nOur account verification process includes the submission of the following documents: [List of specific documents required for verification].\n\nGenuine and activated email verified\nRegistered phone number (USA)\nSelfie verified\nSSN (social security number) verified\nDriving license\nBTC enable or not enable (BTC enable best)\n100% replacement guaranteed\n100% customer satisfaction\nWhen it comes to staying on top of the latest platform updates, it’s crucial to act fast and ensure you’re positioned in the best possible place. If you’re considering a switch, reaching out to the right contacts and inquiring about the status of the buy verified cash app account service update is essential.\n\nClearly communicate your requirements and gauge their commitment to fulfilling them promptly. Once you’ve confirmed their capability, proceed with the verification process using genuine and activated email verification, a registered USA phone number, selfie verification, social security number (SSN) verification, and a valid driving license.\n\nAdditionally, assessing whether BTC enablement is available is advisable, buy verified cash app account, with a preference for this feature. It’s important to note that a 100% replacement guarantee and ensuring 100% customer satisfaction are essential benchmarks in this process.\n\nHow to use the Cash Card to make purchases?\nTo activate your Cash Card, open the Cash App on your compatible device, locate the Cash Card icon at the bottom of the screen, and tap on it. Then select “Activate Cash Card” and proceed to scan the QR code on your card. Alternatively, you can manually enter the CVV and expiration date. How To Buy Verified Cash App Accounts.\n\nAfter submitting your information, including your registered number, expiration date, and CVV code, you can start making payments by conveniently tapping your card on a contactless-enabled payment terminal. Consider obtaining a buy verified Cash App account for seamless transactions, especially for business purposes. Buy verified cash app account.\n\nWhy we suggest to unchanged the Cash App account username?\nTo activate your Cash Card, open the Cash App on your compatible device, locate the Cash Card icon at the bottom of the screen, and tap on it. Then select “Activate Cash Card” and proceed to scan the QR code on your card.\n\nAlternatively, you can manually enter the CVV and expiration date. After submitting your information, including your registered number, expiration date, and CVV code, you can start making payments by conveniently tapping your card on a contactless-enabled payment terminal. Consider obtaining a verified Cash App account for seamless transactions, especially for business purposes. Buy verified cash app account. Purchase Verified Cash App Accounts.\n\nSelecting a username in an app usually comes with the understanding that it cannot be easily changed within the app’s settings or options. This deliberate control is in place to uphold consistency and minimize potential user confusion, especially for those who have added you as a contact using your username. In addition, purchasing a Cash App account with verified genuine documents already linked to the account ensures a reliable and secure transaction experience.\n\n \n\nBuy verified cash app accounts quickly and easily for all your financial needs.\nAs the user base of our platform continues to grow, the significance of verified accounts cannot be overstated for both businesses and individuals seeking to leverage its full range of features. How To Buy Verified Cash App Accounts.\n\nFor entrepreneurs, freelancers, and investors alike, a verified cash app account opens the door to sending, receiving, and withdrawing substantial amounts of money, offering unparalleled convenience and flexibility. Whether you’re conducting business or managing personal finances, the benefits of a verified account are clear, providing a secure and efficient means to transact and manage funds at scale.\n\nWhen it comes to the rising trend of purchasing buy verified cash app account, it’s crucial to tread carefully and opt for reputable providers to steer clear of potential scams and fraudulent activities. How To Buy Verified Cash App Accounts. With numerous providers offering this service at competitive prices, it is paramount to be diligent in selecting a trusted source.\n\nThis article serves as a comprehensive guide, equipping you with the essential knowledge to navigate the process of procuring buy verified cash app account, ensuring that you are well-informed before making any purchasing decisions. Understanding the fundamentals is key, and by following this guide, you’ll be empowered to make informed choices with confidence.\n\n \n\nIs it safe to buy Cash App Verified Accounts?\nCash App, being a prominent peer-to-peer mobile payment application, is widely utilized by numerous individuals for their transactions. However, concerns regarding its safety have arisen, particularly pertaining to the purchase of “verified” accounts through Cash App. This raises questions about the security of Cash App’s verification process.\n\nUnfortunately, the answer is negative, as buying such verified accounts entails risks and is deemed unsafe. Therefore, it is crucial for everyone to exercise caution and be aware of potential vulnerabilities when using Cash App. How To Buy Verified Cash App Accounts.\n\nCash App has emerged as a widely embraced platform for purchasing Instagram Followers using PayPal, catering to a diverse range of users. This convenient application permits individuals possessing a PayPal account to procure authenticated Instagram Followers.\n\nLeveraging the Cash App, users can either opt to procure followers for a predetermined quantity or exercise patience until their account accrues a substantial follower count, subsequently making a bulk purchase. Although the Cash App provides this service, it is crucial to discern between genuine and counterfeit items. If you find yourself in search of counterfeit products such as a Rolex, a Louis Vuitton item, or a Louis Vuitton bag, there are two viable approaches to consider.\n\n \n\nWhy you need to buy verified Cash App accounts personal or business?\nThe Cash App is a versatile digital wallet enabling seamless money transfers among its users. However, it presents a concern as it facilitates transfer to both verified and unverified individuals.\n\nTo address this, the Cash App offers the option to become a verified user, which unlocks a range of advantages. Verified users can enjoy perks such as express payment, immediate issue resolution, and a generous interest-free period of up to two weeks. With its user-friendly interface and enhanced capabilities, the Cash App caters to the needs of a wide audience, ensuring convenient and secure digital transactions for all.\n\nIf you’re a business person seeking additional funds to expand your business, we have a solution for you. Payroll management can often be a challenging task, regardless of whether you’re a small family-run business or a large corporation. How To Buy Verified Cash App Accounts.\n\nImproper payment practices can lead to potential issues with your employees, as they could report you to the government. However, worry not, as we offer a reliable and efficient way to ensure proper payroll management, avoiding any potential complications. Our services provide you with the funds you need without compromising your reputation or legal standing. With our assistance, you can focus on growing your business while maintaining a professional and compliant relationship with your employees. Purchase Verified Cash App Accounts.\n\nA Cash App has emerged as a leading peer-to-peer payment method, catering to a wide range of users. With its seamless functionality, individuals can effortlessly send and receive cash in a matter of seconds, bypassing the need for a traditional bank account or social security number. Buy verified cash app account.\n\nThis accessibility makes it particularly appealing to millennials, addressing a common challenge they face in accessing physical currency. As a result, ACash App has established itself as a preferred choice among diverse audiences, enabling swift and hassle-free transactions for everyone. Purchase Verified Cash App Accounts.\n\n \n\nHow to verify Cash App accounts\nTo ensure the verification of your Cash App account, it is essential to securely store all your required documents in your account. This process includes accurately supplying your date of birth and verifying the US or UK phone number linked to your Cash App account.\n\nAs part of the verification process, you will be asked to submit accurate personal details such as your date of birth, the last four digits of your SSN, and your email address. If additional information is requested by the Cash App community to validate your account, be prepared to provide it promptly. Upon successful verification, you will gain full access to managing your account balance, as well as sending and receiving funds seamlessly. Buy verified cash app account.\n\n \n\nHow cash used for international transaction?\nExperience the seamless convenience of this innovative platform that simplifies money transfers to the level of sending a text message. It effortlessly connects users within the familiar confines of their respective currency regions, primarily in the United States and the United Kingdom.\n\nNo matter if you’re a freelancer seeking to diversify your clientele or a small business eager to enhance market presence, this solution caters to your financial needs efficiently and securely. Embrace a world of unlimited possibilities while staying connected to your currency domain. Buy verified cash app account.\n\nUnderstanding the currency capabilities of your selected payment application is essential in today’s digital landscape, where versatile financial tools are increasingly sought after. In this era of rapid technological advancements, being well-informed about platforms such as Cash App is crucial.\n\nAs we progress into the digital age, the significance of keeping abreast of such services becomes more pronounced, emphasizing the necessity of staying updated with the evolving financial trends and options available. Buy verified cash app account.\n\nOffers and advantage to buy cash app accounts cheap?\nWith Cash App, the possibilities are endless, offering numerous advantages in online marketing, cryptocurrency trading, and mobile banking while ensuring high security. As a top creator of Cash App accounts, our team possesses unparalleled expertise in navigating the platform.\n\nWe deliver accounts with maximum security and unwavering loyalty at competitive prices unmatched by other agencies. Rest assured, you can trust our services without hesitation, as we prioritize your peace of mind and satisfaction above all else.\n\nEnhance your business operations effortlessly by utilizing the Cash App e-wallet for seamless payment processing, money transfers, and various other essential tasks. Amidst a myriad of transaction platforms in existence today, the Cash App e-wallet stands out as a premier choice, offering users a multitude of functions to streamline their financial activities effectively. Buy verified cash app account.\n\nTrustbizs.com stands by the Cash App’s superiority and recommends acquiring your Cash App accounts from this trusted source to optimize your business potential.\n\nHow Customizable are the Payment Options on Cash App for Businesses?\nDiscover the flexible payment options available to businesses on Cash App, enabling a range of customization features to streamline transactions. Business users have the ability to adjust transaction amounts, incorporate tipping options, and leverage robust reporting tools for enhanced financial management.\n\nExplore trustbizs.com to acquire verified Cash App accounts with LD backup at a competitive price, ensuring a secure and efficient payment solution for your business needs. Buy verified cash app account.\n\nDiscover Cash App, an innovative platform ideal for small business owners and entrepreneurs aiming to simplify their financial operations. With its intuitive interface, Cash App empowers businesses to seamlessly receive payments and effectively oversee their finances. Emphasizing customization, this app accommodates a variety of business requirements and preferences, making it a versatile tool for all.\n\nWhere To Buy Verified Cash App Accounts\nWhen considering purchasing a verified Cash App account, it is imperative to carefully scrutinize the seller’s pricing and payment methods. Look for pricing that aligns with the market value, ensuring transparency and legitimacy. Buy verified cash app account.\n\nEqually important is the need to opt for sellers who provide secure payment channels to safeguard your financial data. Trust your intuition; skepticism towards deals that appear overly advantageous or sellers who raise red flags is warranted. It is always wise to prioritize caution and explore alternative avenues if uncertainties arise.\n\nThe Importance Of Verified Cash App Accounts\nIn today’s digital age, the significance of verified Cash App accounts cannot be overstated, as they serve as a cornerstone for secure and trustworthy online transactions.\n\nBy acquiring verified Cash App accounts, users not only establish credibility but also instill the confidence required to participate in financial endeavors with peace of mind, thus solidifying its status as an indispensable asset for individuals navigating the digital marketplace.\n\nWhen considering purchasing a verified Cash App account, it is imperative to carefully scrutinize the seller’s pricing and payment methods. Look for pricing that aligns with the market value, ensuring transparency and legitimacy. Buy verified cash app account.\n\nEqually important is the need to opt for sellers who provide secure payment channels to safeguard your financial data. Trust your intuition; skepticism towards deals that appear overly advantageous or sellers who raise red flags is warranted. It is always wise to prioritize caution and explore alternative avenues if uncertainties arise.\n\nConclusion\nEnhance your online financial transactions with verified Cash App accounts, a secure and convenient option for all individuals. By purchasing these accounts, you can access exclusive features, benefit from higher transaction limits, and enjoy enhanced protection against fraudulent activities. Streamline your financial interactions and experience peace of mind knowing your transactions are secure and efficient with verified Cash App accounts.\n\nChoose a trusted provider when acquiring accounts to guarantee legitimacy and reliability. In an era where Cash App is increasingly favored for financial transactions, possessing a verified account offers users peace of mind and ease in managing their finances. Make informed decisions to safeguard your financial assets and streamline your personal transactions effectively.\n\nContact Us / 24 Hours Reply\nTelegram:dmhelpshop\nWhatsApp: +1 (980) 277-2786\nSkype:dmhelpshop\nEmail:dmhelpshop@gmail.com" | matlohewsimpson656 |
1,865,061 | real estate in cuenca ecuador | Edgar Gonzalez, a real estate agent with 20 years of experience in Cuenca, Ecuador, offers expert... | 0 | 2024-05-25T16:38:12 | https://dev.to/austroventas_cuencaecuad/real-estate-in-cuenca-ecuador-5046 |

Edgar Gonzalez, a real estate agent with 20 years of experience in Cuenca, Ecuador, offers expert guidance in buying, selling, and investing in properties. Contact him today for top-notch real estate services.
Edgar Gonzalez - Expert Real Estate Agent in Cuenca, Ecuador with 20 Years of Experience
Description:
Meet Edgar Gonzalez, a seasoned real estate agent with over 20 years of experience in Cuenca, Ecuador. Known for his exceptional service and deep knowledge of the local market, Edgar specializes in helping clients buy, sell, and invest in properties. Whether you're looking for a dream home or a profitable investment, Edgar's expertise ensures a smooth and successful real estate experience. Contact Edgar Gonzalez today for all your real estate needs in Cuenca, Ecuador.
[www.AustroVentas.com](https://austroventas.com)
#RealEstateAgent #CuencaEcuador #EdgarGonzalez #RealEstateExpert #PropertyInvestment #BuySellRealEstate #ExperiencedAgent #CuencaProperties | austroventas_cuencaecuad | |
1,865,060 | Does anyone now any literature i can read ? | I'm very new to the IT world. looking for anything I can read to help improve my terminology or... | 0 | 2024-05-25T16:36:11 | https://dev.to/kenny_hoyte_fb798a6e1196f/does-anyone-now-any-literature-i-can-read--2g51 | javascript, devops, beginners, mentorship | I'm very new to the IT world. looking for anything I can read to help improve my terminology or something that will help me on my road to becoming a Dev-op Engineer. | kenny_hoyte_fb798a6e1196f |
1,864,965 | Buy Google 5 Star Reviews | Buy Google 5 Star Reviews Reviews represent the opinions of experienced customers who have utilized... | 0 | 2024-05-25T16:19:05 | https://dev.to/whitemartin015/buy-google-5-star-reviews-10dp | Buy Google 5 Star Reviews
Reviews represent the opinions of experienced customers who have utilized services or purchased products from various online or offline markets. These reviews convey customer demands and opinions, and ratings are assigned based on the quality of the products or services and the overall user experience. Google serves as an excellent platform for customers to leave reviews since the majority of users engage with it organically. When you purchase Buy Google 5 Star Reviews, you have the potential to influence a large number of people either positively or negatively. Positive reviews can attract customers to purchase your products, while negative reviews can deter potential customers.
https://dmhelpshop.com/product/buy-google-5-star-reviews/
If you choose to Buy Google 5 Star Reviews, people will be more inclined to consider your products. However, it is important to recognize that reviews can have both positive and negative impacts on your business. Therefore, take the time to determine which type of reviews you wish to acquire. Our experience indicates that purchasing Buy Google 5 Star Reviews can engage and connect you with a wide audience. By purchasing positive reviews, you can enhance your business profile and attract online traffic. Additionally, it is advisable to seek reviews from reputable platforms, including social media, to maintain a positive flow. We are an experienced and reliable service provider, highly knowledgeable about the impacts of reviews. Hence, we recommend purchasing verified Google reviews and ensuring their stability and non-gropability.
Let us now briefly examine the direct and indirect benefits of reviews:
Reviews have the power to enhance your business profile, influencing users at an affordable cost.
To attract customers, consider purchasing only positive reviews, while negative reviews can be acquired to undermine your competitors. Collect negative reports on your opponents and present them as evidence.
If you receive negative reviews, view them as an opportunity to understand user reactions, make improvements to your products and services, and keep up with current trends.
By earning the trust and loyalty of customers, you can control the market value of your products. Therefore, it is essential to buy online reviews, including Buy Google 5 Star Reviews.
Reviews serve as the captivating fragrance that entices previous customers to return repeatedly.
Positive customer opinions expressed through reviews can help you expand your business globally and achieve profitability and credibility.
When you purchase positive Buy Google 5 Star Reviews, they effectively communicate the history of your company or the quality of your individual products.
Reviews act as a collective voice representing potential customers, boosting your business to amazing heights.
Now, let’s delve into a comprehensive understanding of reviews and how they function:
Google, with its significant organic user base, stands out as the premier platform for customers to leave reviews. When you purchase Buy Google 5 Star Reviews , you have the power to positively influence a vast number of individuals. Reviews are essentially written submissions by users that provide detailed insights into a company, its products, services, and other relevant aspects based on their personal experiences. In today’s business landscape, it is crucial for every business owner to consider buying verified Buy Google 5 Star Reviews, both positive and negative, in order to reap various benefits.
Since both positive and negative reviews have an impact on online businesses and trading activities, it is important to determine which type of reviews align with your objectives. If your aim is to influence potential customers online and attract organic traffic, then investing in positive Buy Google 5 Star Reviews is recommended. However, it is crucial to prioritize security and only purchase verified Google reviews. On the other hand, if you wish to acquire negative Google reviews, it is advisable to first gather relevant feedback and reviews.
Why are Google reviews considered the best tool to attract customers?
Google, being the leading search engine and the largest source of potential and organic customers, is highly valued by business owners. Many business owners choose to purchase Google reviews to enhance their business profiles and also sell them to third parties. Without reviews, it is challenging to reach a large customer base globally or locally. Therefore, it is crucial to consider buying positive Buy Google 5 Star Reviews from reliable sources. When you invest in Buy Google 5 Star Reviews for your business, you can expect a significant influx of potential customers, as these reviews act as a pheromone, attracting audiences towards your products and services. Every business owner aims to maximize sales and attract a substantial customer base, and purchasing Buy Google 5 Star Reviews is a strategic move.
According to online business analysts and economists, trust and affection are the essential factors that determine whether people will work with you or do business with you. However, there are additional crucial factors to consider, such as establishing effective communication systems, providing 24/7 customer support, and maintaining product quality to engage online audiences. If any of these rules are broken, it can lead to a negative impact on your business. Therefore, obtaining positive reviews is vital for the success of an online business. To attract a large customer base, it is necessary to purchase Buy Google 5 Star Reviews for both local and international markets. Additionally, buying reviews from other platforms can further boost your business profile.
What are the benefits of purchasing reviews online?
In today’s fast-paced world, the impact of new technologies and IT sectors is remarkable. Compared to the past, conducting business has become significantly easier, but it is also highly competitive. To reach a global customer base, businesses must increase their presence on social media platforms as they provide the easiest way to generate organic traffic. Numerous surveys have shown that the majority of online buyers carefully read customer opinions and reviews before making purchase decisions. In fact, the percentage of customers who rely on these reviews is close to 97%. Considering these statistics, it becomes evident why we recommend buying reviews online. In an increasingly rule-based world, it is essential to take effective steps to ensure a smooth online business journey.
Buy Google 5 Star Reviews
Many people purchase reviews online from various sources and witness unique progress. Reviews serve as powerful tools to instill customer trust, influence their decision-making, and bring positive vibes to your business. Making a single mistake in this regard can lead to a significant collapse of your business. Therefore, it is crucial to focus on improving product quality, quantity, communication networks, facilities, and providing the utmost support to your customers.
Reviews reflect customer demands, opinions, and ratings based on their experiences with your products or services. If you purchase Buy Google 5-star reviews, it will undoubtedly attract more people to consider your offerings. Google is the ideal platform for customers to leave reviews due to its extensive organic user involvement. Therefore, investing in Buy Google 5 Star Reviews can significantly influence a large number of people in a positive way.
https://dmhelpshop.com/product/buy-google-5-star-reviews/
How to generate google reviews on my business profile?
Focus on delivering high-quality customer service in every interaction with your customers. By creating positive experiences for them, you increase the likelihood of receiving reviews. These reviews will not only help to build loyalty among your customers but also encourage them to spread the word about your exceptional service. It is crucial to strive to meet customer needs and exceed their expectations in order to elicit positive feedback. If you are interested in purchasing affordable Google reviews, we offer that service.
https://dmhelpshop.com/product/buy-google-5-star-reviews/
Once you have established a strong rapport with your customers through the provision of quality service, kindly request them to share their experiences on Google voluntarily. You can provide them with a direct link or clear instructions on how to leave a review. If possible, offering them a written script can simplify the process for them. Additionally, we offer the option to buy online reviews from us at a reasonable price, with a 100% replacement and cash back guarantee.
It is essential to reply or respond to the customer opinions left as reviews promptly. Make it easy for customers to leave reviews by prominently displaying review options on your website and social media profiles. Furthermore, consider offering incentives to customers who assist you by leaving reviews, such as providing them with better service at a discounted price.
Alternatively, if you are interested in generating verified Buy Google 5 Star Reviews for your website, you can quickly reach out to dmhelpshop.com. Our team of experts is readily available to help you purchase verified Google reviews at cost-effective prices.
Now, let’s discuss how Google reviews work and the value they add.
According to research conducted by various platforms in the field of online marketing, users tend to engage with reviews that they perceive as authentic. Once a review is submitted, it undergoes a moderation process to ensure compliance with Google’s content guidelines. Another study reveals that many individuals rely on reviews to inform their purchasing decisions. By purchasing online reviews from a trustworthy source, you can significantly enhance your business’s reputation in a short period of time.
https://dmhelpshop.com/product/buy-google-5-star-reviews/
Google reviews also contribute to a business’s overall rating, which is the average of all the individual ratings it receives. This rating is prominently displayed on the business’s page, allowing users to quickly assess the business’s reputation at a glance. Customers have the ability to filter reviews based on various criteria, further aiding them in their decision-making process.
If you are seeking to promote your business, please feel free to contact us. Our team is dedicated to assisting you in purchasing verified Buy Google 5 Star Reviews at an affordable price.
https://dmhelpshop.com/product/buy-google-5-star-reviews/
Contact Us / 24 Hours Reply
Telegram:dmhelpshop
WhatsApp: +1 (980) 277-2786
Skype:dmhelpshop
Email:dmhelpshop@gmail.com | whitemartin015 | |
1,865,056 | Angular Tutorial: Using @HostBinding with Signals | If you’re building apps with Angular, you’re probably using signals more and more every day. This can... | 0 | 2024-05-25T16:33:50 | https://briantree.se/angular-hostbinding-and-signals/ | angular, signals, components, frontend |
If you’re building apps with Angular, you’re probably using [signals](https://angular.dev/guide/signals) more and more every day. This can definitely be a challenge at times because it’s such a different way of working. And, there are things that just don’t quite work with [signals](https://angular.dev/guide/signals) yet, like [@HostBinding](https://angular.dev/api/core/HostBinding) for example. Well in this post, I’m going to demonstrate how we can actually use the [@HostBinding](https://angular.dev/api/core/HostBinding) decorator with [signals](https://angular.dev/guide/signals), pretty easily right now even though the decorator was not originally built to support them directly. Alright, let’s get to it.
{% embed https://www.youtube.com/embed/pkLY8ET9_5A %}
## The Demo Application
Ok, before we do anything, let’s take a look at the [example application](https://stackblitz.com/edit/stackblitz-starters-vc7zpx?file=src%2Flist-item%2Flist-item.component.ts) that we’ll be working with in this post. Here we have a simple application with a list of items to complete. We can mark the items complete by clicking the button next to each step. And when all items have been marked complete, we display a message notifying the user that everything is done.
<div>
<img src="https://briantree.se/assets/img/content/uploads/2024/05-25/demo-1.gif" alt="Example of a demo application with @HostBinding decorator before converting to signals" width="592" height="432" style="width: 100%; height: auto;">
</div>
Now, we’ll see this in more detail soon, but this app is in the process of migrating to [signals](https://angular.dev/guide/signals). In this post we’re going to convert it over the rest of the way and in the process, we’ll need to update a [@HostBinding](https://angular.dev/api/core/HostBinding) on our list items based on a [signal input](https://angular.dev/guide/signals/inputs). Ok, first let’s familiarize ourselves with the existing code for this app.
## Using @Hostbinding with a Signal Input
Let’s start with the app component itself. Looking at the template we can see that we have three instances of our list item component. One for each of the items to be completed.
#### main.ts
```html
<app-list-item ...>
First, do something...
</app-list-item>
<app-list-item ...>
Next, do something else...
</app-list-item>
<app-list-item ...>
After that, you're finished...
</app-list-item>
```
For each of the list items, we have a corresponding boolean property for whether that step is complete or not. And, these properties have already been converted to [signals](https://angular.dev/guide/signals).
```typescript
import { ..., signal } from '@angular/core';
@Component({
selector: 'app-root'
...
})
export class App {
step1Complete = signal(false);
step2Complete = signal(false);
step3Complete = signal(false);
}
```
Now, when the button in each of these items is clicked, it toggles the complete property for that list item.
```html
<button (click)="step1Complete.set(!step1Complete())">
...
</button>
```
And this value is passed as an input to the list item component.
```html
<app-list-item [step]="1" [isComplete]="step1Complete()">
...
</app-list-item>
```
Then, at the bottom of the template, once all of the steps are complete, a message will display.
```html
<div [class.visible]="step1Complete() && step2Complete() && step3Complete()" class="success">
<h2>Thank You!</h2>
All steps have been completed
</div>
```
So that’s the app component, and since everything here has been converted to [signals](https://angular.dev/guide/signals) already, we don’t need to do anything more here. So now, let’s look at the list item component.
In this component, we still have two inputs using the old [@Input](https://angular.dev/api/core/Input) decorator. First, we’ve got the input for the “step” number, then we have the input for the for the “isComplete” property which is also a [@HostBinding](https://angular.dev/api/core/HostBinding) for a “complete” class. So, when that input is true, the “complete” class will be added to the host, which is how it turns everything within it green.
#### list-item.component.ts
```typescript
@Component({
selector: 'app-list-item'
...
})
export class ListItemComponent {
@Input({ required: true }) step!: number;
@Input() @HostBinding('class.complete') isComplete = false;
}
```
### Converting Decorator Inputs to Signal Inputs
So, the “step” property will be pretty easy to switch over to a [signal input](https://angular.dev/guide/signals/inputs) but the “isComplete” property will be a little more challenging. So let’s start with the “step” property.
We can begin by removing the decorator, then we just need to set it using the input function, and we’ll need to make sure that function gets imported correctly. Then, we’ll want to make it required, and we’ll type it to a number.
```typescript
import { ..., input } from "@angular/core";
@Component({
selector: 'app-list-item'
...
})
export class ListItemComponent {
step = input.required<number>();
...
}
```
That’s pretty much it, we just need to update the value in the template now that it’s a [signal](https://angular.dev/guide/signals).
#### Before:
```html
<strong>{{ step }}.)</strong>
```
#### After:
```html
<strong>{{ step() }}.)</strong>
```
Now, after we save, everything should look the same, but it'll now be done in a more modern way with [signal inputs](https://angular.dev/guide/signals/inputs).
Now, at some point the Angular team will probably have a native solution for [signals](https://angular.dev/guide/signals) with [@HostBinding](https://angular.dev/api/core/HostBinding), but for the time being we need to be a little clever.
One way we could do it is, we could use a [getter function](https://www.typescripttutorial.net/typescript-tutorial/typescript-getters-setters/) and simply return the value of the [signal input](https://angular.dev/guide/signals/inputs) in that function. That would work but it would run more than it needs to.
Instead, we can use an [effect()](https://angular.dev/api/core/effect). This way it will be optimized to only update when the value of the [signal input](https://angular.dev/guide/signals/inputs) has changed. And that’s what we’re going to do here.
### Using an effect() to Update the @HostBinding when the Signal Changes
Ok first, let’s set our “isComplete” property to a Boolean input. Then, we need to add a new property for our class [@HostBinding](https://angular.dev/api/core/HostBinding), let’s call it “hasCompleteClass”, and let’s initialize it to false.
```typescript
@Component({
selector: 'app-list-item'
...
})
export class ListItemComponent {
...
isComplete = input(false);
@HostBinding('class.complete') hasCompleteClass = false;
}
```
Now we can add the [effect()](https://angular.dev/api/core/effect) to update this property when the “isComplete” input value changes. To do this, we need to add a constructor first. Then, we can add the [effect()](https://angular.dev/api/core/effect) function, and we need to make sure it gets imported properly from Angular core. Within the [effect()](https://angular.dev/api/core/effect) callback, all we need to do is set our “hasCompleteClass” property to the value of the “isComplete” [signal input](https://angular.dev/guide/signals/inputs).
```typescript
import { ..., effect } from "@angular/core";
@Component({
selector: 'app-list-item'
...
})
export class ListItemComponent {
...
constructor() {
effect(() => this.hasCompleteClass = this.isComplete());
}
}
```
And that’s all we need. Since we’re using the [effect()](https://angular.dev/api/core/effect) function, it will run only when the “isComplete” value changes.
Ok, last thing we need to do is remove the old [@Input](https://angular.dev/api/core/Input) decorator and import since we’re no longer using it.
Now when we save, we should everything working correctly like it was before these changes, but it’s all using [signals](https://angular.dev/guide/signals) now.
## Conclusion
So, that’s one way you can use [signals](https://angular.dev/guide/signals) and [@HostBinding](https://angular.dev/api/core/HostBinding) for the time being. Like I said earlier though, at some point there will probably be an even better way to do this but at least you have a pretty slick way to do it until that time comes.
Hope that helps you as you build using signals.
## Want to See It in Action?
Check out the demo code and examples of these techniques in the in the Stackblitz example below. If you have any questions or thoughts, don’t hesitate to leave a comment.
{% embed https://stackblitz.com/edit/stackblitz-starters-4tstsd?ctl=1&embed=1&file=src%2Flist-item%2Flist-item.component.ts %}
---
## Found This Helpful?
If you found this article helpful and want to show some love, you can always [buy me a coffee!]( https://buymeacoffee.com/briantreese)
| brianmtreese |
1,865,059 | Frontend resources! 🚀 | 🚀 Supercharge Your Development with These Resources! 🚀 👋 Hello everyone! 👋 I'm thrilled to share... | 0 | 2024-05-25T16:33:01 | https://dev.to/miguelrodriguezp99/frontend-resources-1dl4 | frontend, tailwindcss, react, javascript | 🚀 Supercharge Your Development with These Resources! 🚀
👋 Hello everyone! 👋
I'm thrilled to share this collection of resources I've gathered over time, which have been a lifesaver in many of the projects I've worked on. This compilation brings together a variety of tools and libraries spanning from user interface creation to performance optimization and beyond. I hope you can also make the most out of some of these wonderful resources. Let's dive right in!
Feel free to comment with any other resources that you use or find interesting so I can add them to the post!
### UI:
- [Material Tailwind](https://www.material-tailwind.com): A robust UI kit combining Material Design and Tailwind CSS
- [Bentoed](https://bentoed.vercel.app): A html/css/tailwind bento catalog
- [Aceternity UI](https://ui.aceternity.com): Sleek and modern UI components for your next project
- [NextUI](https://nextui.org): Craft beautiful interfaces effortlessly with NextUI
- [ChakraUI](https://chakra-ui.com): A simple, modular, and accessible component library
- [Trading view Charts](https://www.tradingview.com/lightweight-charts/): Power up your data visualization game with lightweight charts from TradingView
- [AutoAnimate](https://auto-animate.formkit.com): Easily create stunning animations with AutoAnimate
- [React-magic-motion](https://www.react-magic-motion.com): Add a touch of magic to your React components
- [Keep React](https://react.keepdesign.io): Keep your React components fresh and stylish
- [Daisy UI](https://daisyui.com): Create delightful interfaces with Daisy UI
- [ShadCn](https://ui.shadcn.com): Elevate your UI with sleek and elegant components
- [Clip path](https://bennettfeely.com/clippy/): Get creative with shapes using Clippy
- [Radix](https://www.radix-ui.com/primitives): Build powerful and composable UIs with Radix
- [Layout generator](https://layout.bradwoods.io): Design flexible layouts with ease
- [Utilities](https://omatsuri.app): A handy toolkit for gradients, cursors, and more
- [Image Generator](https://www.freepik.com/pikaso): Instantly spruce up your designs with high-quality images
- [Buttons](https://buttons.ibelick.com): Button up your UIs with style
- [PrimeReact](https://primereact.org): Prime components for your React applications
- [Everything in one page](https://freesets.vercel.app): Explore a curated collection of resources
- [Beer CSS](https://www.beercss.com): A semantic HTML CSS framework based on Material Design 3.
### Gradients:
- [Firecms](https://neat.firecms.co): Dynamic gradients for your projects
- [Shadergradient](https://www.shadergradient.co): Create stunning shader gradients effortlessly
### SVGs:
- [Shapes](https://shapes.framer.website): Beautiful SVG shapes for your designs
- [SVGs](https://svgl.vercel.app): Discover a vast collection of SVGs
- [SVG Illustrations](https://undraw.co/illustrations): Add life to your projects with illustrations from Undraw
### Others:
- [Sliders — Swiper](https://swiperjs.com): Swipe through content seamlessly
- [Toast notifications — Sonner](https://sonner.emilkowal.ski): Toast notifications made easy
- [Atropos - 3D Elements](https://atroposjs.com): Add immersive 3D elements to your projects
- [Auto Animate (Native Javascript)](https://auto-animate.formkit.com): Effortlessly animate elements with vanilla JavaScript
- [Vaul (Mobile Slider)](https://vaul.emilkowal.ski): Elevate your sliders with Vaul
- [Videos performance optimizer](https://lite.youtube.com): Optimize video performance with Lite YouTube Web Component
- [Calendar](https://wicky.nillia.ms/cally): Streamline your scheduling process
- [Contrast picker](https://coolors.co/contrast-checker/483c14-d2cfcb): Ensure accessibility with Coolors' contrast checker
- [Image optimizer](https://squoosh.app): Squoosh your images for better performance
### Tailwind:
- [Animations](https://www.tailwindcss-animated.com): Add flair to your UIs with Tailwind CSS Animated
- [Intersection Observer](https://github.com/heidkaemper/tailwindcss-intersect): Tailwind CSS Intersect for observing intersections
- [Backgrounds](https://bg.ibelick.com): Spruce up your backgrounds with ease
- [Bentoed](https://bentoed.vercel.app): A html/css/tailwind bento catalog
### JavaScript:
- [Masonry Grid](https://masonry.desandro.com): Create dynamic grid layouts with ease
- [MiniMasonry](https://spope.github.io/MiniMasonry.js): A lightweight alternative for masonry layouts
- [Gallery PhotoSwipe](https://photoswipe.com): Showcase your images elegantly with PhotoSwipe
- [Gallery LightGallery](https://www.lightgalleryjs.com): LightGallery for stunning image galleries
- [Tempo](https://tempo.formkit.com): Simplify time-based operations with Tempo
- [Tippy (Tooltips)](https://atomiks.github.io/tippyjs): Enhance user experience with customizable tooltips
- [Intersection Observer](https://www.youtube.com/watch?v=T24PsErQGPg): A guide to Intersection Observer for efficient scrolling
- [Infinite Scroll](https://www.youtube.com/watch?v=FA1Y4pamIP8): Implement infinite scrolling effortlessly
- [Just](https://github.com/angus-c/just): A library for common JavaScript utilities
- [GLTFs into JSX](https://github.com/pmndrs/gltfjsx): Convert GLTF files into JSX components
### React:
- [Counter](https://use-count-up.vercel.app): Count up your numbers dynamically
- [Masonry layout](https://blog.logrocket.com/create-responsive-masonry-layouts-react-app): Build responsive masonry layouts in React
- [Drag and Drop](https://drag-and-drop.formkit.com): Effortlessly implement drag and drop functionality
- [FilePond](https://pqina.nl/filepond): Simplify file uploads with FilePond
- [Faker](https://fakerjs.dev): Generate realistic fake data with Faker
- [Random](https://www.npmjs.com/package/random-words): Spice up your projects with random words
- [Charts](https://www.chartjs.org/docs/latest): Visualize data beautifully with Chart.js
- [UseSound](https://github.com/joshwcomeau/use-sound): Incorporate sound effects into your React apps
- [ReCharts](https://recharts.org/en-US): Charting library built on React components
- [Floating UI (Tooltips)](https://floating-ui.com): Floating UI for interactive tooltips
- [Tippy (Tooltips)](https://github.com/atomiks/tippyjs-react): Tippy.js for React applications
- [Calendar](https://wicky.nillia.ms/cally): Another calendar resource for all your scheduling needs
- [CMDK Console](https://github.com/pacocoursey/cmdk): A console for your React applications
| miguelrodriguezp99 |
1,865,058 | Crafting an Entry-Level Developer Resume: Tips and Best Practices | Crafting an Entry-Level Developer Resume: Tips and Best Practices Contact... | 0 | 2024-05-25T16:33:00 | https://dev.to/bingecoder89/crafting-an-entry-level-developer-resume-tips-and-best-practices-2ie7 | beginners, tutorial, codenewbie, career | ### Crafting an Entry-Level Developer Resume: Tips and Best Practices
1. **Contact Information**
- Include your full name, phone number, email address, and LinkedIn profile. Make sure this information is up-to-date and professional.
2. **Professional Summary**
- Write a brief, compelling summary highlighting your key skills, career objectives, and what you bring to the role. Tailor this to the job you’re applying for.
3. **Technical Skills**
- List relevant programming languages, frameworks, tools, and technologies you are proficient in. Organize them by proficiency or relevance to the job.
4. **Education**
- Detail your educational background, including degrees earned, institutions attended, and graduation dates. Mention relevant coursework or projects.
5. **Projects**
- Highlight personal or academic projects that demonstrate your skills. Provide brief descriptions, focusing on technologies used and your role in the project.
6. **Work Experience**
- Include any internships, part-time jobs, or relevant work experience. Emphasize your responsibilities, achievements, and technologies you worked with.
7. **Certifications**
- List any relevant certifications or online courses completed, such as those from Coursera, Udacity, or specific tech certifications like AWS Certified Developer.
8. **Soft Skills**
- Mention key soft skills such as problem-solving, teamwork, communication, and adaptability. Provide examples of how you’ve demonstrated these in past experiences.
9. **Formatting and Design**
- Use a clean, professional layout with consistent fonts and spacing. Keep the resume to one page if possible, and ensure it’s easy to read.
10. **Proofreading and Customization**
- Proofread thoroughly to avoid any errors. Customize your resume for each job application, ensuring that it aligns with the job description and requirements.
Happy Learning 🎉 | bingecoder89 |
1,865,057 | Exploring the Legal Landscape: Law Firms in Corpus Christi, Texas | Introduction: Corpus Christi, Texas, a city known for its vibrant culture, stunning coastal views,... | 0 | 2024-05-25T16:29:09 | https://dev.to/backlink_30/exploring-the-legal-landscape-law-firms-in-corpus-christi-texas-390b |
Introduction:
Corpus Christi, Texas, a city known for its vibrant culture, stunning coastal views, and bustling economy, is also home to a robust legal community. From small boutique firms to large multi-practice establishments, the legal landscape in Corpus Christi offers a diverse array of services to meet the needs of its residents and businesses. In this comprehensive exploration, we delve into the world of law firms in Corpus Christi, highlighting their specialties, reputations, and contributions to the local community.
The Legal Scene in Corpus Christi:
Corpus Christi serves as a hub for legal services in South Texas, boasting a mix of local firms deeply rooted in the community and nationally recognized practices. With its strategic location near the Gulf of Mexico and proximity to major cities like Houston and San Antonio, the city attracts legal talent from across the state.
Prominent Law Firms:
Among the prominent law firms in Corpus Christi is the esteemed ABC Law Firm, renowned for its expertise in personal injury cases. With a track record of securing substantial settlements for clients injured in accidents, ABC Law Firm has earned a reputation for excellence and client advocacy.
Another notable player in the Corpus Christi legal scene is XYZ & Associates, a full-service firm offering a comprehensive range of legal services, including corporate law, real estate transactions, and estate planning. Known for their commitment to personalized attention and strategic counsel, XYZ & Associates has become a trusted ally for individuals and businesses alike.
Specialized Practices:
Beyond the general practitioners, Corpus Christi is also home to specialized firms catering to niche areas of law. For instance, DEF Immigration Law Firm focuses exclusively on immigration matters, assisting clients with visas, green cards, and citizenship applications. Their deep understanding of immigration law and dedication to client success have made them a go-to resource for individuals navigating the complexities of the U.S. immigration system.
Additionally, GHI Family Law Firm specializes in family law matters, providing compassionate guidance to clients facing divorce, child custody disputes, and adoption proceedings. Their commitment to protecting the interests of families and advocating for positive outcomes sets them apart in the legal community.
Community Engagement:
Beyond their legal work, many **[Law Firms in Corpus Christi Texas](https://perkinsperkinslaw.com/)** are actively involved in giving back to the community. Through pro bono initiatives, volunteer efforts, and charitable donations, these firms contribute to the betterment of society and uphold the principles of justice and equality. Whether it's providing free legal clinics for low-income individuals or participating in local outreach programs, Corpus Christi law firms play a vital role in supporting those in need.
Adapting to Change:
Like any industry, the legal profession is not immune to change. In recent years, advancements in technology, shifts in client expectations, and evolving regulatory landscapes have prompted law firms in Corpus Christi to adapt and innovate. From implementing digital tools for case management to embracing alternative fee structures, these firms are proactively responding to the changing dynamics of the legal market while staying true to their core values of integrity and professionalism.
Future Outlook:
Looking ahead, the future of law firms in Corpus Christi appears promising, with opportunities for growth and expansion on the horizon. As the city continues to develop economically and culturally, so too will its legal community, serving as a beacon of legal excellence in South Texas. With a commitment to serving clients with integrity, expertise, and compassion, Corpus Christi law firms are poised to navigate the challenges of tomorrow while upholding the principles of justice and fairness.
Conclusion:
In conclusion, law firms in Corpus Christi, Texas, play a vital role in shaping the legal landscape of the region. From personal injury to immigration law, these firms offer a diverse range of services to meet the needs of their clients, while also contributing to the broader community through pro bono work and volunteer efforts. As the city continues to thrive and evolve, so too will its legal practitioners, ensuring that justice remains accessible to all who seek it in Corpus Christi and beyond. | backlink_30 | |
1,865,055 | 🚀 Elevate Your Code with Some Fun! 🚀 | 🚀 Elevate Your Code with Some Fun! 🚀 Hey fellow developers! Let's take a break from our screens for... | 0 | 2024-05-25T16:28:31 | https://dev.to/geoffkats/elevate-your-code-with-some-fun-l9k |
🚀 **Elevate Your Code with Some Fun!** 🚀
Hey fellow developers!
Let's take a break from our screens for a moment and inject some fun into our coding journey. Here are a few light-hearted jokes and memes to brighten your day:
1. **Debugging:**
- Debugging is like being the detective in a crime movie where you're also the murderer. 😄
2. **Code Comments:**
- // TODO: This code is a mess, future me, I'm sorry. 🙈
3. **Programming Languages:**
- JavaScript: "I'm the king of the web!"
- Python: "Let's keep it simple and elegant."
- CSS: "I make things look good, but also frustrating."
4. **Meeting Jargon:**
- "Let's circle back" = "I have no idea, let's discuss later."
- "Let's take it offline" = "Let's not discuss this here."
5. **Client Requests:**
- Client: "Can you just make it pop more?"
- Developer: *Adds more pop-up windows* 😆
Remember, while coding is serious business, a little humor can go a long way in keeping us sane! Share your favorite coding jokes or memes below and let's keep the fun going!
Happy coding! 🎉
---
| geoffkats | |
1,864,963 | Building my own ChatGPT | I was watching a YouTube tutorial, and the speaker mentioned that you don’t need to subscribe to the... | 0 | 2024-05-25T16:16:27 | https://dev.to/sachitsac/building-my-own-chatgpt-3aid | typescript, nextjs, openai, llm | I was watching a YouTube tutorial, and the speaker mentioned that you don’t need to subscribe to the ChatGPT monthly plan. Instead, you can use their API directly, which is cheaper. That got me thinking: how easy would it be to build my own ChatGPT with the option of using locally hosted models like Ollama 3?
Today, we’re taking a quick dive into building a simple ChatGPT clone using some cool tech:
Our Tech Stack
- [Nextjs](https://nextjs.org/): This React meta framework is perfect for building fast, scalable web apps with features like server-side rendering.
- [TypeScript](https://www.typescriptlang.org/): Adding types to JavaScript makes your code more reliable and easier to maintain.
- [ShadCN/UI](https://ui.shadcn.com/): Helps us build beautiful, responsive user interfaces, fast and easily.
- [Vercel AI SDK](https://sdk.vercel.ai/docs/introduction): Simplifies connecting our app to OpenAI's GPT-4, making it easy to work with AI.
- OpenAI GPT-4o: The star of the show, GPT-4 can generate human-like text and is super versatile.
- [Auth0](https://auth0.com/): User authentication made for developers
- [React-Markdown](https://github.com/remarkjs/react-markdown): Renders Markdown content in our React app, making text display neat and user-friendly.
Here’s a little sneak peek of where I am so far. In the coming posts, I’ll share the code and instructions on how it was built. The chosen tech stack makes it super easy to build something like this quickly and effectively.
- [Getting raw markdown response from the api](https://x.com/sachittechB/status/1794394988840960149)
- [Adding markdown parsing](https://x.com/sachittechB/status/1794395227501019559)
Stay tuned for more. Until then, stay safe.
| sachitsac |
1,864,962 | 카지노솔루션 | 카지노 산업이 온라인과 오프라인 모두에서 급성장함에 따라, 효율적이고 혁신적인 카지노 솔루션의 필요성도 함께 증가하고 있습니다. 카지노 솔루션은 다양한 게임 소프트웨어, 보안... | 0 | 2024-05-25T16:14:22 | https://dev.to/casinomarket08/kajinosolrusyeon-2ld9 | 카지노 산업이 온라인과 오프라인 모두에서 급성장함에 따라, 효율적이고 혁신적인 카지노 솔루션의 필요성도 함께 증가하고 있습니다. 카지노 솔루션은 다양한 게임 소프트웨어, 보안 시스템, 고객 관리 도구 등을 포함하여 카지노 운영을 최적화하는 데 중요한 역할을 합니다. 본 기사에서는 카지노 솔루션의 유통, 렌탈, 그리고 제작에 대해 자세히 알아보겠습니다.
카지노 솔루션 유통
카지노 솔루션 유통은 카지노 운영자들에게 필요한 소프트웨어와 하드웨어를 공급하는 과정입니다. 유통업체들은 최신 게임 소프트웨어, 보안 시스템, 데이터 관리 도구 등을 제공하여 카지노 운영이 원활하게 이루어질 수 있도록 지원합니다. 유통업체들은 종종 글로벌 네트워크를 통해 다양한 시장에 접근할 수 있으며, 이를 통해 최신 기술과 트렌드를 카지노 운영자에게 전달합니다. 신뢰할 수 있는 유통업체를 선택하는 것은 카지노 운영의 성공에 중요한 요소입니다.
**_[카지노솔루션](https://casinosolutionmarket.com/)_**
카지노 솔루션 렌탈
카지노 솔루션 렌탈 서비스는 운영 초기 비용을 절감하고 유연성을 제공하는 데 도움이 됩니다. 렌탈 서비스는 카지노 운영자에게 필요한 솔루션을 월 단위 또는 연 단위로 대여할 수 있는 옵션을 제공합니다. 이를 통해 카지노는 최신 기술을 도입하고 필요에 따라 솔루션을 업그레이드하거나 변경할 수 있습니다. 렌탈 서비스는 또한 유지 보수 및 지원을 포함하는 경우가 많아, 카지노 운영자들이 기술적인 문제를 신속하게 해결할 수 있도록 도와줍니다. 이 방식은 특히 새로운 시장에 진입하는 카지노나 소규모 카지노에 유리합니다.
카지노 솔루션 제작
맞춤형 카지노 솔루션 제작은 특정 카지노의 요구와 목표에 맞추어 솔루션을 개발하는 과정입니다. 이는 소프트웨어 개발자, 디자이너, 그리고 카지노 운영 전문가가 협력하여 카지노의 특정 요구사항을 충족시키는 솔루션을 만드는 것을 포함합니다. 맞춤형 솔루션은 게임 소프트웨어, 고객 관리 시스템, 보안 솔루션 등을 포함할 수 있으며, 이를 통해 카지노는 고유의 브랜드 경험을 제공할 수 있습니다. 카지노 솔루션 제작 과정은 다음과 같은 단계로 진행됩니다:
요구사항 분석: 카지노의 운영 목표와 요구사항을 철저히 분석합니다.
설계 및 개발: 분석 결과를 바탕으로 솔루션의 구조를 설계하고 개발을 시작합니다.
테스트 및 배포: 개발된 솔루션을 철저히 테스트하여 모든 기능이 원활하게 작동하는지 확인한 후 배포합니다.
유지 보수 및 업그레이드: 솔루션이 운영 중에도 지속적으로 유지 보수하고 필요에 따라 업그레이드합니다.
결론
카지노 솔루션의 유통, 렌탈, 그리고 제작은 각각의 운영 환경에 맞춘 다양한 옵션을 제공함으로써 카지노 산업의 발전에 기여하고 있습니다. 신뢰할 수 있는 유통망을 통해 최신 기술을 제공받고, 렌탈 서비스를 통해 비용 효율적으로 최신 솔루션을 이용하며, 맞춤형 제작을 통해 고유한 브랜드 경험을 제공하는 것은 카지노 운영의 성공에 중요한 요소입니다. 각 방식의 장점을 잘 활용하여 최적의 카지노 솔루션을 도입하는 것이 성공적인 카지노 운영의 열쇠입니다. | casinomarket08 | |
1,864,959 | Angular Animations Tutorial: Disable and Enable Animations | I’m willing to bet, that if you’ve spent very much time working with Angular animations, you’ve had... | 26,395 | 2024-05-25T16:13:52 | https://briantree.se/angular-animations-tutorial-disable-and-enable-animations/ | angular, animation, webdev, frontend | I’m willing to bet, that if you’ve spent very much time working with Angular animations, you’ve had the need or desire to disable them for one reason or another. Something that I encounter quite a bit are animations that run on component initialization. I may only expect them to run when an interaction occurs, or when data changes, or something along those lines. I don’t expect them to run on initialization, but they do anyway. Well, this is something that I’m going to show you how to fix in this post. Alright, let’s get to it.
{% embed https://www.youtube.com/embed/dzeJGyGI4BY %}
## Before We Get Started
Now, before we get too far along, it’s important to note that I’ve already created several posts focused on the animation framework in Angular.
#### Angular Animation Tutorials:
- [Learn the Basics](https://briantree.se/angular-animations-tutorial-learn-the-basics/)
- [Enter and Leave Animations](https://briantree.se/angular-animations-tutorial-enter-and-leave/)
- [The Keyframes Function](https://briantree.se/angular-animations-tutorial-the-keyframes-function/)
- [Query and Stagger Function](https://briantree.se/angular-animations-tutorial-query-and-stagger/)
- [Start and Done Events](https://briantree.se/angular-animations-tutorial-start-and-done-events/)
- [Parallel Animations](https://briantree.se/angular-animations-tutorial-parallel-animations/)
- [Animating to an unknown height](https://briantree.se/angular-animations-tutorial-animating-height/)
- [Adding Flexibility with Params](https://briantree.se/angular-animations-tutorial-add-flexibility-with-params/)
- [Creating Reusable Animations](https://briantree.se/angular-animations-tutorial-creating-reusable-animations/)
These posts cover many different animation topics so if any of these concepts look unfamiliar to you, you’ll probably want to check these posts out first so that you’re not lost in this example.
And, to make them easier to find, I’ve created an [Angular Animations playlist](https://youtube.com/playlist?list=PLp-SHngyo0_ikgEN5d9VpwzwXA-eWewSM&si=3WnQgeDxdAZJGGFy) on my [YouTube channel](https://www.youtube.com/@briantreese) to help, so check it out!
Ok, enough of that, onto the example for this post.
## The Demo Application
Here, we’ll be using this Petpix demo application where people share cool images of their pets. As you click to look through the images, you can see the nice transition forward as you navigate to the “next” image. Then, when you navigate backwards with the “previous” button you can see that it animates nicely in the opposite direction.
<div>
<img src="https://briantree.se//assets/img/content/uploads/2024/05-19/demo-1.gif" alt="Example of an image gallery with sliding animation" width="594" height="696" style="width: 100%; height: auto;">
</div>
So, this animation is cool when navigating between the images, but there is something happening that we don’t want. If we reload the application, we can see that the animation runs when the component is initialized.
<div>
<img src="https://briantree.se/assets/img/content/uploads/2024/05-19/demo-2.gif" alt="Example of animation running on initialization" width="594" height="696" style="width: 100%; height: auto;">
</div>
We don’t want this, instead we only want it to run when navigating through the images. So, this is what we’re going to do in this post. We’re going to disable the animation until after the component fully renders, and then we’ll enable it.
## Disabling Animations with the Disabled Animation Control Binding
Now, luckily for us, there’s a pretty simple way to do this built right into the framework. We can use a special [[@.disabled]](https://angular.io/guide/transition-and-triggers#disable-an-animation-on-an-html-element) animation control binding. When this binding is bound with a value of true, it will prevent any animations from running on the element with the binding as well as any nested elements.
So, let’s take a look at our code. Here, in the template for the [slider component](https://stackblitz.com/edit/stackblitz-starters-cyh1p9?file=src%2Fslider%2Fslider.component.html), we have an animation called “slideToggle” bound on the div that contains all of the images.
#### slider.component.html
```html
<div
[@slideToggle]="{
value: selectedImage(),
params: {
leaveEnd: animationDirection() === 'right' ? '100%' : '-100%',
enterStart: animationDirection() === 'right' ? '-100%' : '100%',
hiddenScale: 0.25
}
}"
class="image">
...
</div>
```
So this is where we’ll add our disabled binding, but before we do, we need to add a Boolean property to bind it to. So let’s switch to the slider.component.ts and let’s add a protected property called “animationDisabled”. We'll make it a [`signal`](https://angular.io/guide/signals) with an initial value of true.
#### slider.component.ts
```typescript
import { ..., signal } from "@angular/core";
@Component({
selector: 'app-slider',
...
})
export class SliderComponent {
protected animationDisabled = signal(true);
}
```
Ok, now we have the property, next we need to enable it after the component has completed its initial render. There are many ways we can do this, but for this example we’re going to use the [`afterNextRender()`](https://angular.io/api/core/afterNextRender) lifecycle hook.
To do this, we need to add a constructor. Then, within the constructor, we add the [`afterNextRender()`](https://angular.io/api/core/afterNextRender) function, and we’ll need to be sure it get’s properly imported from angular/core. Now, within the callback, if `animationDisabled()` is true, let’s set it to false.
```typescript
import { ..., afterNextRender } from "@angular/core";
@Component({
selector: 'app-slider',
...
})
export class SliderComponent {
...
constructor() {
afterNextRender(() => {
if (this.animationDisabled()) {
this.animationDisabled.set(false);
}
});
}
}
```
Ok, that should be the logic we need to properly disable and enable our animation. So, let’s switch back over to the template. And now we can add the [[@.disabled]](https://angular.io/guide/transition-and-triggers#disable-an-animation-on-an-html-element) binding, and we can bind to our new animationDisabled() signal.
#### slider.component.html
```html
<div
[@.disabled]="animationDisabled()"
[@slideToggle]="{...}"
class="image">
...
</div>
```
And that's it. Now after we save, the animation should no longer run as the component is initialized. But, they should still run properly when navigating through the images in the gallery.
## Animation Callback Events with Disabled Animations
Now there is something else you’ll want to be aware of, if you’re using the [start and done AnimationEvent](https://angular.io/api/animations/AnimationEvent) callback events for anything, they still run, even when the animation is disabled. They will just run with a zero duration.
To demonstrate this, let’s add a start and done event to our animation. In our slider.component.ts, let’s add a new function, let’s call it “animationEvent()”. Let’s pass it a “state” that will either be “start” or “done”. Then within this function, let’s simply log out the state.
#### slider.component.ts
```typescript
@Component({
selector: 'app-slider',
...
})
export class SliderComponent {
...
protected animationEvent(state: 'start' | 'done') {
console.log(`slideToggle: ${state}`);
}
}
```
Ok, now let’s switch over to the template. On the div with our animation, let’s add a start event binding. Then let’s call our new function, and in this case, since it’s the start event, let’s pass it a value of “start”. And, let’s do the same for the done event.
#### slider.component.html
```html
<div
[@.disabled]="animationDisabled()"
[@slideToggle]="{...}"
(@slideToggle.start)="animationEvent('start')"
(@slideToggle.done)="animationEvent('done')"
class="image">
...
</div>
```
Ok, now after we save save, if we open the dev tools and look at the console, we can see that both our start and done events were logged out, meaning both events ran even though our animation was disabled.
<div>
<img src="https://briantree.se/assets/img/content/uploads/2024/05-19/demo-3.gif" alt="Example of animation callback events running on initialization even when animations are disabled" width="1280" height="720" style="width: 100%; height: auto;">
</div>
So, not a huge deal, but something to be aware of for sure. It’s definitely thrown me off in the past.
## Conclusion
So now you should be able to disable animations whenever you don’t want them to run, and there’s lot’s of different ways you can do this. For example, you could add a setting to your app that allows the user to disable animations, and then you could set them disabled using the disabled control based on this setting.
Probably not something you’ll need every day but should come in handy from time to time.
Now, there’s still plenty more to cover on angular animations so I’ll go ahead and stop here for now, but keep an eye out for more posts in the future.
## Want to See It in Action?
Check out the demo code and examples of these techniques in the in the Stackblitz example below. If you have any questions or thoughts, don’t hesitate to leave a comment.
{% embed https://stackblitz.com/edit/stackblitz-starters-sxnevo?ctl=1&embed=1&file=src%2Fslider%2Fslider.component.ts %}
---
## Found This Helpful?
If you found this article helpful and want to show some love, you can always [buy me a coffee!]( https://buymeacoffee.com/briantreese)
| brianmtreese |
1,864,961 | 140. Word Break II | 140. Word Break II Hard Given a string s and a dictionary of strings wordDict, add spaces in s to... | 27,523 | 2024-05-25T16:13:10 | https://dev.to/mdarifulhaque/140-word-break-ii-4a1m | php, leetcode, algorithms, programming | 140\. Word Break II
Hard
Given a string `s` and a dictionary of strings `wordDict`, add spaces in `s` to construct a sentence where each word is a valid dictionary word. Return all such possible sentences in **any order**.
**Note** that the same word in the dictionary may be reused multiple times in the segmentation.
**Example 1:**
- **Input:** s = "catsanddog", wordDict = ["cat","cats","and","sand","dog"]
- **Output:** ["cats and dog","cat sand dog"]
**Example 2:**
- **Input:** s = "pineapplepenapple", wordDict = ["apple","pen","applepen","pine","pineapple"]
- **Output:** ["pine apple pen apple","pineapple pen apple","pine applepen apple"]
- **Explanation:** Note that you are allowed to reuse a dictionary word.
**Example 3:**
- **Input:** s = "catsandog", wordDict = ["cats","dog","sand","and","cat"]
- **Output:** []
**Constraints:**
- <code>1 <= s.length <= 20</code>
- <code>1 <= wordDict.length <= 1000</code>
- <code>1 <= wordDict[i].length <= 10</code>
- `s` and `wordDict[i]` consist of only lowercase English letters.
- All the strings of `wordDict` are **unique**.
- Input is generated in a way that the length of the answer doesn't exceed <code>10<sup>5</sup></code>.
**Solution:**
```
class Solution {
private $map = array();
/**
* @param String $s
* @param String[] $wordDict
* @return String[]
*/
function wordBreak($s, $wordDict) {
if(array_key_exists($s, $this->map)) {
return $this->map[$s];
}
$result = array();
if(strlen($s) == 0){
$result[] = "";
$this->map[""] = $result;
return $result;
}
foreach($wordDict as $word) {
if(strpos($s, $word) === 0){
$subWords = $this->wordBreak(substr($s, strlen($word)), $wordDict);
foreach($subWords as $subWord) {
$result[] = $word . (strlen($subWord) > 0 ? " " : "") . $subWord;
}
}
}
$this->map[$s] = $result;
return $result;
}
}
```
**Contact Links**
- **[LinkedIn](https://www.linkedin.com/in/arifulhaque/)**
- **[GitHub](https://github.com/mah-shamim)** | mdarifulhaque |
1,864,956 | A Detailed Tutorial on Pagination for ASP.NET Core Web APIs 🚀 | Pagination and Filtering implementation in an API is a common practice to optimize responses and... | 0 | 2024-05-25T16:10:33 | https://dev.to/bytehide/a-detailed-tutorial-on-pagination-for-aspnet-core-web-apis-3dbc | aspdotnet, api, tutorial, pagination | Pagination and Filtering implementation in an API is a common practice to optimize responses and efficiently handle large datasets. Here’s a step-by-step guide on how to achieve this in an ASP.NET Core Web API from beginners to intermediate developers.
## Setting Up Your ASP.NET Core Web API Project
### Step 1: Start creating a New ASP.NET Core Web API Project
First things first, we need to create our project. You can do this using Visual Studio or the command line interface. For the CLI, simply run:
```shell
dotnet new webapi -n PaginationSample
```
Open the created folder and get coding!
### Step 2: Define Your Model Class
Next, we’ll define a model class that will represent our data. For this example, let’s create a class named `ListCSharpCornerArticles`.
```csharp
public class ListCSharpCornerArticles
{
public int Id { get; set; }
public string Title { get; set; }
public string Category { get; set; }
}
```
This class has three properties: `Id`, `Title`, and `Category`. Simple and straightforward!
## Creating and Configuring Middleware
### Step 3: Create Custom Middleware for Logging Incoming Requests
Middleware is like the bouncer at a club—it controls what happens with each request before it reaches the controller. Let’s create a custom logging middleware.
```csharp
using Microsoft.AspNetCore.Builder;
using Microsoft.AspNetCore.Http;
using Microsoft.Extensions.Logging;
using System.Threading.Tasks;
public class RequestLoggingMiddleware
{
private readonly RequestDelegate _next;
private readonly ILogger<RequestLoggingMiddleware> _logger;
public RequestLoggingMiddleware(RequestDelegate next, ILogger<RequestLoggingMiddleware> logger)
{
_next = next;
_logger = logger;
}
public async Task Invoke(HttpContext context)
{
_logger.LogInformation($"Request: {context.Request.Method} {context.Request.Path}");
await _next(context);
}
}
```
This middleware logs the HTTP method and the request path. Handy for debugging, right?
### Step 4: Configure the Custom Middleware
Now that we have the middleware, let’s configure our application to use it. This involves modifying the `Startup.cs` file.
```csharp
using Microsoft.AspNetCore.Builder;
using Microsoft.AspNetCore.Hosting;
using Microsoft.Extensions.Configuration;
using Microsoft.Extensions.DependencyInjection;
using Microsoft.Extensions.Hosting;
public class Startup
{
public IConfiguration Configuration { get; }
public Startup(IConfiguration configuration)
{
Configuration = configuration;
}
public void ConfigureServices(IServiceCollection services)
{
services.AddControllers();
services.AddLogging();
}
public void Configure(IApplicationBuilder app, IWebHostEnvironment env)
{
if (env.IsDevelopment())
{
app.UseDeveloperExceptionPage();
}
app.UseMiddleware<RequestLoggingMiddleware>();
app.UseRouting();
app.UseEndpoints(endpoints =>
{
endpoints.MapControllers();
});
}
}
```
Now, every incoming request will be logged!
## Implementing Pagination and Filtering in the Controller
### Step 5: Create a Controller That Handles Pagination and Filtering
Finally, let’s put it all together in a controller.
```csharp
using Microsoft.AspNetCore.Mvc;
using System;
using System.Collections.Generic;
using System.Linq;
[ApiController]
[Route("api/[controller]")]
public class CSharpCornerArticlesController : ControllerBase
{
private static List<ListCSharpCornerArticles> _articles = GenerateSampleArticles();
private static List<ListCSharpCornerArticles> GenerateSampleArticles()
{
// Generate and return sample articles
return new List<ListCSharpCornerArticles>
{
new ListCSharpCornerArticles { Id = 1, Title = "Introduction to ASP.NET Core", Category = "ASP.NET Core" },
new ListCSharpCornerArticles { Id = 2, Title = "Advanced C# Techniques", Category = "C#" },
// Add more sample articles
};
}
[HttpGet]
public IActionResult Get([FromQuery] int page = 1, [FromQuery] int pageSize = 10, [FromQuery] string filter = "")
{
var query = _articles.AsQueryable();
if (!string.IsNullOrEmpty(filter))
{
query = query.Where(article => article.Title.Contains(filter) || article.Category.Contains(filter));
}
var totalCount = query.Count();
var totalPages = (int)Math.Ceiling((double)totalCount / pageSize);
query = query.Skip((page - 1) * pageSize).Take(pageSize);
var result = new
{
TotalCount = totalCount,
TotalPages = totalPages,
CurrentPage = page,
PageSize = pageSize,
Articles = query.ToList()
};
return Ok(result);
}
}
```
In this controller, we handle both pagination and filtering. The `Get` endpoint takes `page`, `pageSize`, and `filter` as query parameters, filters the articles accordingly, and returns a user-friendly paginated result.
## Conclusion
By now, you’ve got a robust understanding of how to implement pagination and filtering in an ASP.NET Core Web API. Not only have you learned how to structure your data, but you’ve also picked up on creating custom middleware for better logging and debugging. Here’s a quick recap:
- **Pagination** helps divide large datasets into manageable chunks.
- **Filtering** lets users request specific subsets of data.
- Combining both techniques enhances performance and usability.
Organize your API with pagination and filtering and make your life (and your users’ lives) easier! | bytehide |
1,864,955 | Explorando la Encantadora Luz de la Luna: 10+1 Melodías Contemporáneas | La Luna, ese maravilloso cuerpo celeste, ha cautivado a la humanidad durante siglos con su brillo... | 0 | 2024-05-25T16:09:37 | https://dev.to/jonathan_oruel/explorando-la-encantadora-luz-de-la-luna-101-melodias-contemporaneas-5260 | La Luna, ese maravilloso cuerpo celeste, ha cautivado a la humanidad durante siglos con su brillo etéreo.
Artistas a lo largo del tiempo han encontrado inspiración en su mística, entrelazando su esencia en la poesía y la música por igual. En este viaje, exploramos melodías contemporáneas que rinden homenaje a la luminiscencia de la Luna, fusionando sin esfuerzo la tradición con la innovación.
Entre las composiciones atemporales dedicadas a la Luna, "Clair de Lune" de Claude Debussy se erige como un faro de encantamiento. Creada en 1890, sus delicadas notas de piano evocan el misterio y la atracción del paisaje lunar, pintando imágenes vívidas en la mente. De manera similar, la "Sonata Claro de Luna" de Ludwig van Beethoven, compuesta en 1801, encanta a los oyentes con sus tonos melancólicos, que recuerdan la tranquilidad de una noche iluminada por la luna.
Sin embargo, los músicos contemporáneos también han abrazado la inspiración de la Luna, infundiéndola con un toque moderno a través de diversos géneros. Entre ellos está Eduard Palchyk, una estrella en ascenso en el ámbito de la música contemporánea ucraniana, cuya composición "[Moonlight Path](https://push.fm/fl/vi8yr53y)" invita a los oyentes a un reino de resonancia emotiva. La creación de Palchyk teje un viaje hechizante bajo el resplandor lunar, donde cada nota susurra introspección y serenidad, invitando a los oyentes a perderse en su abrazo melódico.
"Moonlight Path" sirve como un santuario melódico, perfecto para momentos de reflexión o intimidad compartida. Ya sea disfrutado con una taza de té vespertino, fomentando conversaciones apreciadas, o como telón de fondo de un interludio romántico, sus evocadoras notas profundizan las conexiones y encienden emociones. El repertorio de Palchyk se extiende aún más, con composiciones como "[Walking under the Moon Piano Solo](https://push.fm/fl/16jhu2n5)" y "[Evening Sonata](https://push.fm/fl/9pimrfrk )", cada una un testimonio de su maestría en la narración emocional a través de la música.
Estas composiciones, ricas en matices y armonía, ofrecen un respiro del caos de la vida diaria, invitando a los oyentes a sumergirse en la sinfonía lunar de emociones. Disponibles en plataformas como [Apple Music y Amazon Music](https://push.fm/fl/16jhu2n5), las melodías de Palchyk son fácilmente accesibles, asegurando que el encanto de la Luna esté a solo un clic de distancia. Ya sea buscando consuelo, inspiración, o simplemente un momento de felicidad musical, las composiciones de Palchyk prometen transportar a los oyentes en un viaje inolvidable a través de los reinos iluminados por la luna del corazón y el alma.
Además, comprar los álbumes de Eduard Palchyk no solo te da acceso a sus cautivadoras composiciones, sino que también sirve como un apoyo crucial para su trayectoria independiente en la industria musical. Tu inversión va más allá del mero disfrute; alimenta la creatividad continua y la evolución de un artista talentoso.
Adquirir álbumes en formato MP3 desde el sitio web de Eduard Palchyk o transmitir sus obras en plataformas como [Apple Music](https://push.fm/fl/16jhu2n5) representa un paso vital en el fomento del crecimiento continuo y la exploración artística del músico. Al hacerlo, contribuyes activamente a crear un entorno propicio para el cultivo de su talento y la realización de su potencial.
Además de deleitarte con las exquisitas melodías, juegas un papel instrumental en la creación de un ecosistema que fomenta el avance de un compositor talentoso, elevando su trabajo y asegurando su posición dentro de la industria musical. Tu apoyo se convierte en un testimonio del vínculo duradero entre artista y audiencia, nutriendo una relación simbiótica que impulsa a ambas partes hacia mayores alturas de creatividad y realización.
Descubre la Magia de las Melodías a la Luz de la Luna - ¡Haz clic para escuchar [ahora!](https://push.fm/pl/llu0wh9r)
Pasando a la exploración de renombradas composiciones musicales dedicadas a la Luna, vamos a sumergirnos en el cautivador reino de las 10 mejores melodías y canciones que abarcan diversos géneros:
"Clair de Lune" - Claude Debussy
"[Moonlight Sonata](https://push.fm/fl/9pimrfrk )" - Ludwig van Beethoven
"Harvest Moon" - Neil Young
"Blue Moon" - Richard Rodgers y Lorenz Hart
"Bad Moon Rising" - Creedence Clearwater Revival
"[Walking on the Moon](https://push.fm/fl/16jhu2n5)" - The Police
"Moon River" - Henry Mancini y Johnny Mercer
"Moondance" - Van Morrison
"Fly Me to the Moon" - Bart Howard
"Pink Moon" - Nick Drake
Cada una de estas composiciones epitomiza un estilo musical y una narrativa distintos, pero convergen en un tema singular: la Luna y su profunda influencia en la experiencia y la cultura humanas.
Vamos a profundizar en el atractivo atemporal de "Clair de Lune" de Claude Debussy: "Clair de Lune" (francés para "Luz de Luna") se erige como un pináculo de la música clásica, creada por el eminente compositor francés Claude Debussy. Originalmente parte de la suite para piano "Suite bergamasque", compuesta en 1890 y publicada más tarde en 1905, "Clair de Lune" surgió de la meticulosa refinación y visión artística de Debussy.
Su génesis se remonta a 1882, cuando Debussy concibió la pieza como una obra independiente. A lo largo de los años, esculpió meticulosamente sus melodías, infundiendo cada nota con intención y emoción. Inspirado por la poesía de Paul Verlaine, el título "Clair de Lune" encapsula la esencia de la composición, evocando imágenes de serenidad nocturna y ensueño romántico.
Aunque inicialmente pasada por alto, "Clair de Lune" gradualmente ascendió a la prominencia, convirtiéndose en sinónimo de belleza y elegancia en la música clásica. Su atractivo atemporal trasciende generaciones, encontrando resonancia en medios diversos, desde películas hasta comerciales, perpetuando el legado musical de Claude Debussy para las generaciones venideras.
"Sonata Claro de Luna" - Ludwig van Beethoven: Entre el ilustre panteón de las obras maestras clásicas, la "Sonata Claro de Luna" de Ludwig van Beethoven brilla con un esplendor inigualable. Compuesta en 1801 y oficialmente titulada "Sonata para piano n.º 14 en do sostenido menor, Op. 27, n.º 2", esta obra se erige como un testimonio del genio y la profundidad emocional de Beethoven.
El origen de la "Sonata Claro de Luna" está impregnado de intriga y romance, nacida de la infatuación de Beethoven con Julietta Guicciardi, cuya presencia etérea avivó su fervor creativo. Dedicada a la Emperatriz de Austria, Elisabeth, esposa de Francisco I, la sonata encarna la devoción sincera de Beethoven a su musa.
Tras su presentación, la "Sonata Claro de Luna" desafió las convenciones de su época, eludiendo las estructuras tradicionales para emprender un viaje introspectivo a través de tres movimientos: el "Adagio sostenuto", el tierno "Allegretto" y el tempestuoso "Presto agitato". Sin embargo, fue el "Adagio sostenuto", cariñosamente llamado el "movimiento claro de luna", el que cautivó al público con su belleza inquietante y su aura enigmática.
A pesar de su recepción inicial, la "Sonata Claro de Luna" ascendió a la prominencia, consolidando su estatus como una de las composiciones más veneradas de Beethoven. Su atractivo perdurable resuena a través de continentes y generaciones, una obra maestra atemporal que continúa conmoviendo corazones y mentes con su profunda resonancia emotiva.
Experimenta el Encanto - ¡Transmite o Compra [Ahora](https://push.fm/pl/llu0wh9r)!
"Harvest Moon" - Neil Young: En el tapiz de la narración musical, "Harvest Moon" de Neil Young emerge como una joya resplandeciente, irradiando calidez y autenticidad. Lanzada en 1992 como la canción principal de su álbum "Harvest Moon", esta balada captura la esencia del amor duradero y la devoción.
Inspirado por el floreciente romance de Young con la actriz Pegi Morton, "Harvest Moon" florece con una sinceridad conmovedora, tejiendo una narrativa de compromiso inquebrantable y profunda afección. Su melodía suave y letras evocadoras conjuran visiones de bailes a la luz de la luna y promesas susurradas, eco del abrazo tierno del verdadero amor.
Grabada en el legendario complejo de estudios "The Ranch" en California, "Harvest Moon" lleva la impronta de luminarias musicales que prestaron su talento a su creación. El resultado es una composición bellamente inquietante que resuena con los oyentes, invitándolos a un mundo de romance y serenidad atemporales.
"Harvest Moon" perdura como un faro de belleza tranquila, un testimonio del arte incomparable de Neil Young como músico y narrador. Su legado perdurable habla por sí mismo, consolidando su lugar como una obra maestra indeleble en los anales de la música contemporánea.
"Blue Moon" - Richard Rodgers y Lorenz Hart: En el rico tapiz de la historia musical americana, pocas composiciones brillan tan intensamente como "Blue Moon", un clásico atemporal escrito por el prolífico dúo Richard Rodgers y Lorenz Hart en 1934.
Originalmente concebida para el musical "Manhattan Melodrama" pero catapultada a la fama a través de "The Hollywood Revue of 1932", "Blue Moon" encarna un tapiz melódico de melancolía y anhelo. Sus letras evocadoras y arreglo cautivador evocan un sentido de nostalgia melancólica, resonando profundamente con las audiencias a través de generaciones.
Aunque la canción languideció en la oscuridad inicialmente, su resurgimiento por The High Hatters en 1934 la impulsó a una nueva prominencia, encendiendo un fervor que ha perdurado a lo largo de los años. La icónica interpretación de Frank Sinatra en 1961 inmortalizó aún más "Blue Moon", infundiéndola con una nueva profundidad y trascendencia que cautivó a oyentes de todo el mundo.
Hoy en día, "Blue Moon" se erige como una piedra angular del patrimonio musical americano, su influencia reverberando a través de los anales de la cultura popular. Su atractivo atemporal continúa encantando, un brillante testimonio del poder perdurable de la melodía y la emoción.
Emprende un Viaje Musical Bajo la Luna - ¡Haz clic para [Disfrutar](https://push.fm/pl/2j7henuh)!
"Bad Moon Rising" - Creedence Clearwater Revival: En los anales de la historia del rock, pocas canciones resuenan con la energía cruda y el fervor profético de "Bad Moon Rising" de Creedence Clearwater Revival (CCR). Escrita y grabada en 1969, este himno icónico se erige como un testimonio del tumultuoso espíritu de su era.
Creada por el visionario vocalista y guitarrista de CCR, John Fogerty, "Bad Moon Rising" surgió del crisol de la contracultura de finales de los 60 y la imaginería apocalíptica. Impulsado por una fascinación por el cine de terror y la ciencia ficción, Fogerty destiló sus reflexiones en una potente mezcla de anticipación y presagio.
Líricamente, "Bad Moon Rising" cautiva con su mística enigmática, pintando un vívido cuadro de condena inminente contra un telón de fondo de ritmo contagioso y riffs electrizantes. Tras su lanzamiento, la canción ascendió rápidamente a la cima de las listas mundiales, convirtiéndose en un himno para una generación que luchaba con la incertidumbre y la agitación.
Más que una mera composición musical, "Bad Moon Rising" trascendió sus orígenes para convertirse en un símbolo de protesta y agitación cultural. Su legado perdurable continúa reverberando a través de los corredores de la historia del rock, un testimonio atemporal del poder de la expresión y el espíritu indomable de la resistencia.
"[Walking on the Moon](https://push.fm/fl/16jhu2n5)" - The Police: En el tapiz sonoro de la ilustre carrera de The Police, "Walking on the Moon" emerge como una joya luminosa, irradiando una belleza etérea y un optimismo ilimitado. Incluida en su álbum seminal de 1979 "Reggatta de Blanc", esta trascendente composición es un testamento del arte visionario de la banda.
Concebida por el enigmático líder de The Police, Sting, durante una transformación en Ibiza, "Walking on the Moon" cristaliza los momentos fugaces de maravilla ingrávida experimentados bajo el dosel lunar. Las introspectivas letras de Sting, junto con el elegante trabajo de guitarra de Andy Summers y la destreza rítmica de Stewart Copeland, evocan una sensación de euforia y liberación.
Desde su concepción, "Walking on the Moon" capturó los corazones y mentes de los oyentes en todo el mundo, ascendiendo a la cima de las listas y solidificando el estatus de The Police como pioneros musicales. Más que una simple canción, se convirtió en un símbolo de libertad sin límites y optimismo desenfrenado, resonando con audiencias a lo largo de generaciones.
Incluso hoy en día, "Walking on the Moon" sigue siendo un testamento duradero del arte incomparable de The Police, sus melodías celestiales y letras conmovedoras continúan inspirando asombro y maravilla. En la vasta extensión de la historia musical, esta obra maestra etérea brilla como un faro de esperanza y posibilidad.
"Moon River" - Henry Mancini y Johnny Mercer: En los anales del patrimonio musical estadounidense, pocas composiciones evocan el atractivo atemporal de "Moon River", una melodía cautivadora creada por el legendario dúo de Henry Mancini y Johnny Mercer. Nacida del crisol creativo de la película de 1961 "Breakfast at Tiffany's", esta icónica balada es un testamento del poder duradero de la colaboración y la inspiración.
Mientras el compositor Mancini deambulaba por las calles de Nueva York, la majestuosa extensión del río iluminado por la luna cerca de su residencia en Beverly Hills desató un torrente de fervor creativo. Impulsado por este encuentro fortuito, Mancini emprendió una odisea musical, inmortalizando el encantador atractivo de "Moon River".
Unido por Mercer, cuyas letras poéticas reflejaban la tranquila belleza de la canción, Mancini esculpió una melodía que trascendió sus orígenes cinematográficos para convertirse en un clásico atemporal. Nominada para un Oscar y finalmente capturando el codiciado premio a la Mejor Canción Original, "Moon River" conquistó los corazones de audiencias en todo el mundo, su sencilla elegancia y resonancia romántica dejando una marca indeleble en la cultura popular.
Más allá de su legado cinematográfico, "Moon River" perdura como un símbolo del patrimonio musical estadounidense, su gracia melódica y su evocadora imaginería continúan cautivando a los oyentes a lo largo de generaciones. En el gran tapiz de la historia de la música, esta obra maestra etérea brilla como un faro de belleza intemporal y amor duradero.
Entra en el Mundo Musical Iluminado por la Luna - ¡Haz clic para [Explorar](https://push.fm/pl/2j7henuh)!
"Moondance" - Van Morrison: En el tapiz del brillo musical, "Moondance" del incomparable Van Morrison se erige como un brillante testamento de reinvención creativa y exploración artística. Lanzada en su álbum homónimo de 1970, esta composición atemporal emergió como un faro de vitalidad y vibrancia en la histórica carrera de Morrison.
El génesis de "Moondance" se remonta a un período transformador para Morrison, mientras buscaba explorar nuevos territorios sonoros tras su partida de un sello anterior. Fue entre las bulliciosas calles de Melbourne, bañadas por el resplandor etéreo de la luna, donde Morrison encontró inspiración para esta trascendente obra maestra.
Extrayendo de la pulsante energía de la ciudad y la serenidad de la noche, Morrison impregnó "Moondance" con una vitalidad animada que cautiva a los oyentes hasta el día de hoy. Infundida con elementos de jazz y ritmo, la canción palpita con un ritmo contagioso que invita al alma a bailar bajo el dosel lunar.
Grabada en el vibrante ambiente de Nueva York en noviembre de 1969, "Moondance" cobró vida en manos de Morrison y su banda, cristalizando en un himno de exuberancia y alegría. Su popularidad perdurable y atractivo intemporal atestiguan la maestría de Morrison en la interpretación y su habilidad para evocar emoción a través de la melodía.
"Fly Me to the Moon" - Bart Howard: "La luz de la luna te sienta bien, va con tu cabello, ciertamente sabes lo que te queda bien…" Con estas letras evocadoras y melodía contagiosa, "Fly Me to the Moon" de Bart Howard se graba en los anales de la historia musical estadounidense. Compuesta en 1954, este clásico atemporal ha trascendido generaciones para convertirse en un preciado emblema de romance y aspiración.
Los orígenes de "Fly Me to the Moon" están impregnados de leyenda y tradición, con la inspiración de Bart Howard supuestamente proveniente de una actuación hipnotizante de Luba Wells en un club nocturno de Nueva York. Fascinado por su interpretación, Howard compuso rápidamente la melodía y las letras, dando vida a una canción que capturaría la imaginación de millones.
Originalmente conocida como "In Other Words", la canción encontró su interpretación definitiva en el aterciopelado tono de Frank Sinatra, cuya interpretación apasionada la llevó a nuevas alturas de aclamación. La versión de Sinatra se convirtió en sinónimo de elegancia y romance, haciendo de "Fly Me to the Moon" un elemento básico de su repertorio y un clásico atemporal del cancionero estadounidense.
Desbloquea la Belleza de las Melodías Iluminadas por la Luna - [¡Transmite o Compra Ahora!](https://push.fm/fl/vi8yr53y)
"Pink Moon" - Nick Drake: A través de la vasta extensión del cosmos, entre las estrellas titilantes y las maravillas celestiales, "Pink Moon" del enigmático Nick Drake brilla como un faro de belleza inquietante e introspección. Lanzada en 1972, esta etérea composición se erige como una reflexión conmovedora de la agitación interna y el brillante arte de Drake.
Nacida de un crisol de desafíos personales y profesionales, "Pink Moon" emergió como la pieza central del último álbum homónimo de Drake, marcando una desviación de sus obras anteriores. Despojada de sus elementos esenciales, la canción resuena con una intensidad emocional cruda, sus melancólicas letras e instrumentación mínima desnudan el alma del artista.
Mientras la luna arroja su suave resplandor sobre la tierra, "Pink Moon" envuelve a los oyentes en un capullo de introspección y anhelo, invitándolos a explorar las profundidades de sus propias emociones. A pesar de su brevedad, la canción perdura en la mente mucho después de que las notas finales se desvanecen, un testamento de la capacidad inigualable de Drake para evocar profunda emoción a través de la música.
En el encantador reino de las melodías inspiradas por la Luna, cada composición sirve como un portal a un mundo de sueños y maravillas. Desde el ritmo contagioso de "Moondance" hasta el atractivo romántico de "Fly Me to the Moon", "[Moonlight Path](https://push.fm/fl/vi8yr53y)" y la inquietante belleza de "Pink Moon", estas canciones nos transportan a través de la extensión celestial, recordándonos el vínculo eterno entre la humanidad y el cosmos.

Mientras viajamos a través de estas melodías, recordamos la inexorable atracción de la Luna, atrayéndonos a su abrazo místico e inspirándonos a explorar las profundidades de nuestra propia creatividad e imaginación. Que la magia de estas canciones continúe cautivando e inspirando, iluminando nuestro camino con el resplandor celestial de la Luna.
Ilumina tu Lista de Reproducción con Música de la Luz de la Luna - ¡Haz clic para [Disfrutar](https://push.fm/pl/2j7henuh)!
[Read more](https://jonathanoruelsspace.quora.com/?invite_code=A8dnWChkrhRON5AyjCP4) | jonathan_oruel | |
1,864,954 | Buy verified BYBIT account | https://dmhelpshop.com/product/buy-verified-bybit-account/ Buy verified BYBIT account In the... | 0 | 2024-05-25T16:07:58 | https://dev.to/whitemartin015/buy-verified-bybit-account-5g05 | https://dmhelpshop.com/product/buy-verified-bybit-account/
Buy verified BYBIT account
In the evolving landscape of cryptocurrency trading, the role of a dependable and protected platform cannot be overstated. Bybit, an esteemed crypto derivatives exchange, stands out as a platform that empowers traders to capitalize on their expertise and effectively maneuver the market.
This article sheds light on the concept of Buy Verified Bybit Accounts, emphasizing the importance of account verification, the benefits it offers, and its role in ensuring a secure and seamless trading experience for all individuals involved.
https://dmhelpshop.com/product/buy-verified-bybit-account/
What is a Verified Bybit Account?
Ensuring the security of your trading experience entails furnishing personal identification documents and participating in a video verification call to validate your identity. This thorough process is designed to not only establish trust but also to provide a secure trading environment that safeguards against potential threats.
By rigorously verifying identities, we prioritize the protection and integrity of every individual’s trading interactions, cultivating a space where confidence and security are paramount. Buy verified BYBIT account
Verification on Bybit lies at the core of ensuring security and trust within the platform, going beyond mere regulatory requirements. By implementing robust verification processes, Bybit effectively minimizes risks linked to fraudulent activities and enhances identity protection, thus establishing a solid foundation for a safe trading environment.
Verified accounts not only represent a commitment to compliance but also unlock higher withdrawal limits, empowering traders to effectively manage their assets while upholding stringent safety standards.
Advantages of a Verified Bybit Account
Discover the multitude of advantages a verified Bybit account offers beyond just security. Verified users relish in heightened withdrawal limits, presenting them with the flexibility necessary to effectively manage their crypto assets. This is especially advantageous for traders aiming to conduct substantial transactions with confidence, ensuring a stress-free and efficient trading experience.
Procuring Verified Bybit Accounts
The concept of acquiring buy Verified Bybit Accounts is increasingly favored by traders looking to enhance their competitive advantage in the market. Well-established sources and platforms now offer authentic verified accounts, enabling users to enjoy a superior trading experience. Buy verified BYBIT account.
Just as one exercises diligence in their trading activities, it is vital to carefully choose a reliable source for obtaining a verified account to guarantee a smooth and reliable transition.
Conclusionhow to get around bybit kyc
Understanding the importance of Bybit’s KYC (Know Your Customer) process is crucial for all users. Bybit’s implementation of KYC is not just to comply with legal regulations but also to safeguard its platform against fraud.
Although the process might appear burdensome, it plays a pivotal role in ensuring the security and protection of your account and funds. Embracing KYC is a proactive step towards maintaining a safe and secure trading environment for everyone involved.
Ensuring the security of your account is crucial, even if the KYC process may seem burdensome. By verifying your identity through KYC and submitting necessary documentation, you are fortifying the protection of your personal information and assets against potential unauthorized breaches and fraudulent undertakings. Buy verified BYBIT account.
Safeguarding your account with these added security measures not only safeguards your own interests but also contributes to maintaining the overall integrity of the online ecosystem. Embrace KYC as a proactive step towards ensuring a safe and secure online experience for yourself and everyone around you.
https://dmhelpshop.com/product/buy-verified-bybit-account/
How many Bybit users are there?
With over 2 million registered users, Bybit stands out as a prominent player in the cryptocurrency realm, showcasing its increasing influence and capacity to appeal to a wide spectrum of traders.
The rapid expansion of its user base highlights Bybit’s proactive approach to integrating innovative functionalities and prioritizing customer experience. This exponential growth mirrors the intensifying interest in digital assets, positioning Bybit as a leading platform in the evolving landscape of cryptocurrency trading.
With over 2 million registered users leveraging its platform for cryptocurrency trading, Buy Verified ByBiT Accounts has witnessed remarkable growth in its user base. Bybit’s commitment to security, provision of advanced trading tools, and top-tier customer support services have solidified its position as a prominent competitor within the cryptocurrency exchange market.
For those seeking a dependable and feature-rich platform to engage in digital asset trading, Bybit emerges as an excellent choice for both novice and experienced traders alike.
Enhancing Trading Across Borders
Leverage the power of buy verified Bybit accounts to unlock global trading prospects. Whether you reside in bustling financial districts or the most distant corners of the globe, a verified account provides you with the gateway to engage in safe and seamless cross-border transactions.
The credibility that comes with a verified account strengthens your trading activities, ensuring a secure and reliable trading environment for all your endeavors.
A Badge of Trust and Opportunity
By verifying your BYBIT account, you are making a prudent choice that underlines your dedication to safe trading practices while gaining access to an array of enhanced features and advantages on the platform. Buy verified BYBIT account.
With upgraded security measures in place, elevated withdrawal thresholds, and privileged access to exclusive opportunities, a verified BYBIT account equips you with the confidence to maneuver through the cryptocurrency trading realm effectively.
Why is Verification Important on Bybit?
Ensuring verification on Bybit is essential in creating a secure and trusted trading space for all users. It effectively reduces the potential threats linked to fraudulent behaviors, offers a shield for personal identities, and enables verified individuals to enjoy increased withdrawal limits, enhancing their ability to efficiently manage assets.
By undergoing the verification process, users safeguard their investments and contribute to a safer and more regulated ecosystem, promoting a more secure and reliable trading environment overall. Buy verified BYBIT account.
Conclusion
In the ever-evolving landscape of digital cryptocurrency trading, having a Verified Bybit Account is paramount in establishing trust and security. By offering elevated withdrawal limits, fortified security measures, and the assurance that comes with verification, traders are equipped with a robust foundation to navigate the complexities of the trading sphere with peace of mind.
Discover the power of ByBiT Accounts, the ultimate financial management solution offering a centralized platform to monitor your finances seamlessly. With a user-friendly interface, effortlessly monitor your income, expenses, and savings, empowering you to make well-informed financial decisions. Buy verified BYBIT account.
https://dmhelpshop.com/product/buy-verified-bybit-account/
Whether you are aiming for a significant investment or securing your retirement fund, ByBiT Accounts is equipped with all the tools necessary to keep you organized and on the right financial path. Join today and take control of your financial future with ease.
https://dmhelpshop.com/product/buy-verified-bybit-account/
Contact Us / 24 Hours Reply
Telegram:dmhelpshop
WhatsApp: +1 (980) 277-2786
Skype:dmhelpshop
Email:dmhelpshop@gmail.com
| whitemartin015 | |
1,864,953 | REMAX Belize | RE/MAX is not only the largest real estate company in the world, it is also the largest network of... | 0 | 2024-05-25T16:07:54 | https://dev.to/remax_belize_388ccbc20aa9/remax-belize-1fg1 | RE/MAX is not only the largest real estate company in the world, it is also the largest network of offices and agents in Belize. With offices in every corner of Belize, RE/MAX has the largest market share. This network is important when looking at Belize real estate as we do not have a standard MLS.
[Ambergris Caye Real Estate](https://remaxbelizerealestate.com/)
 | remax_belize_388ccbc20aa9 | |
1,864,951 | Angular Animations Tutorial: Creating Reusable Animations | As an Angular application grows over time, you probably find that you constantly need to refactor... | 26,395 | 2024-05-25T16:06:42 | https://briantree.se/angular-animations-tutorial-creating-reusable-animations/ | angular, animation, webdev, frontend | As an Angular application grows over time, you probably find that you constantly need to refactor things so that shared concepts, logic, behavior, etcetera can be reused. You build things, then later down the road, you build something that needs to do something similar and now you want to breakout that concept so that it can be shared right? Well, animations in Angular are the same. Once you start building and using them, you probably find that you need to use them in multiple components. Well, in this post I’ll show you how to do this. Alright, let’s get to it.
{% embed https://www.youtube.com/embed/ObYCutiBOTo %}
## Before We Get Started
Now, before we get too far along, it’s important to note that I’ve already created several posts focused on the animation framework in Angular. They cover the basics of setting up and using animations in Angular, creating state-based and [`enter`/`leave`](https://angular.io/guide/transition-and-triggers#aliases-enter-and-leave) animations, using the [`keyframes()`](https://angular.io/api/animations/keyframes), [`query()`](https://angular.io/api/animations/query), and [`stagger()`](https://angular.io/api/animations/stagger) functions to create more complex animation sequences, using the [`start`/`done`](https://angular.io/api/animations/AnimationEvent) animation events, creating animations that run in parallel versus in sequence, animating to unknown heights, and adding configurable animations with [`params`](https://angular.io/api/animations/AnimationOptions#params).
So, if any of those concepts are unfamiliar to you, you’ll probably want to check those posts out first so that you’re not lost in this post.
#### Angular Animation Tutorials:
- [Learn the Basics](https://briantree.se/angular-animations-tutorial-learn-the-basics/)
- [Enter and Leave Animations](https://briantree.se/angular-animations-tutorial-enter-and-leave/)
- [The Keyframes Function](https://briantree.se/angular-animations-tutorial-the-keyframes-function/)
- [Query and Stagger Function](https://briantree.se/angular-animations-tutorial-query-and-stagger/)
- [Start and Done Events](https://briantree.se/angular-animations-tutorial-start-and-done-events/)
- [Parallel Animations](https://briantree.se/angular-animations-tutorial-parallel-animations/)
- [Animating to an unknown height](https://briantree.se/angular-animations-tutorial-animating-height/)
- [Adding Flexibility with Params](https://briantree.se/angular-animations-tutorial-add-flexibility-with-params/)
And, to make them easier to find, I’ve created an [Angular Animations playlist](https://youtube.com/playlist?list=PLp-SHngyo0_ikgEN5d9VpwzwXA-eWewSM&si=3WnQgeDxdAZJGGFy) on my [YouTube channel](https://www.youtube.com/@briantreese) to help, so check it out!
Ok, enough of that, onto the example for this post.
## The Demo Application
Here we have [this application](https://stackblitz.com/edit/stackblitz-starters-nkmlih?file=src%2Fslider%2Fslider.component.ts) called Petpix. It’s an application where people share cool images of their pets. As you click to look through the images, you can see the nice transition forward as you navigate to the “next” image. And then, when you navigate backwards with the “previous” button you can see that it animates nicely in the opposite direction.
<div>
<img src="https://briantree.se/assets/img/content/uploads/2024/05-11/demo-1.gif" alt="Example of an image gallery with sliding animation" width="592" height="641" style="width: 100%; height: auto;">
</div>
Now, if you want to learn in detail about how I created this animation, you’ll want to check out my [post on how to use Angular animation params](https://briantree.se/angular-animations-tutorial-add-flexibility-with-params/) because we’re not really going to cover the animation itself in detail in this post.
Now, since we created the animation for that post, we’ve added the header to the application, and the header contains a hamburger menu. When we click on this menu button, we see our menu.
<div>
<img src="https://briantree.se//assets/img/content/uploads/2024/05-11/demo-2.gif" alt="Example of the menu opening and closing without any animations" width="592" height="980" style="width: 100%; height: auto;">
</div>
So, that’s cool, but it doesn't look great when it opens. It would be better if we added some animation as it opens and closes, right? Since it’s opening from the right side of the viewport, it would be nice if it slid in as it opens, and then if it slid out when it closes.
Well, this is exactly what we’re going to do in this post. But instead of creating this animation all over again and bloating our code base, we’re going to take the slide left/right animation from our slider component and instead make it shared so that we can use it in the nav component too.
## Creating a Reusable Angular Animation
Ok, so let’s take a look at our animation in the component.ts, the animation that we’re now going to make shared.
#### slider.component.ts
```typescript
@Component({
selector: 'app-slider',
...
animations: [
trigger('slideToggle', [
transition('* => *', [
group([
query(':enter', style({
transform: 'translateX({{ enterStart }}) scale(0.25)' }),
{ optional: true }),
query(':leave', [
animate('750ms ease-in-out',
style({
transform: 'translateX({{ leaveEnd }}) scale(0.25)'
}))
], { optional: true }),
query(':enter', [
animate('750ms ease-in-out',
style({
transform: 'translateX(0) scale(1)'
}))
], { optional: true })
])
],
{
params: {
leaveEnd: '',
enterStart: ''
}
})
])
]
})
```
When creating a reusable animation, we create it in a separate file that we can then just import from. So, we'll add directory named “animations” to our project. Then, within that directory we'll add file named slide.animation.ts for our new shared animation.
<div>
<img src="https://briantree.se/assets/img/content/uploads/2024/05-11/animationdirectory-and-file.png" alt="Example of the new animations directory and slide animation file" width="592" height="980" style="width: 100%; height: auto;">
</div>
When we create a reusable animation, we create it as an exportable `const` that we can then just import, so let’s add a const named “slideAnimation” and to set this const, we’re going to use the [`animation()`](https://angular.io/api/animations/animation) function from the Angular animations module. This function takes in an array of animation steps, so we can copy everything within the transition function from the slider.component.ts, and paste it here. We also need to make sure all of the stuff we’re using from the animations module is properly imported here in this file too.
Ok, at this point we now have a reusable animation. But, in the original animation we have some params that allow us to pass an “enterStart” and an “leaveEnd” translate value.
But, we also had a hard-coded scale value that works nicely in the slider component, but the thing is, we don’t want our menu to scale at all as it animates, we just want it to slide in and out. That’s it. So, what I’m going to do is convert this scale to a parameter too. We'll call it “hiddenScale”.
#### slide.animation.ts
```typescript
import { animate, animation, group, query, style } from "@angular/animations";
export const slideAnimation = animation([
group([
query(':enter', style({ transform: 'translateX({{ enterStart }}) scale({{ hiddenScale }})' }), { optional: true }),
query(':leave', [
animate('750ms ease-in-out', style({ transform: 'translateX({{ leaveEnd }}) scale({{ hiddenScale }})' }))
], { optional: true }),
query(':enter', [
animate('750ms ease-in-out', style({ transform: 'translateX(0) scale(1)' }))
], { optional: true })
])
])
```
Ok, that’s all we need. Now let’s go swap this out in our slider component.
## Using a Reusable Angular Animation
We can start by removing everything within the [`transition()`](https://angular.io/api/animations/transition) function, the imports that are no longer needed, and we can remove the [`params`](https://angular.io/api/animations/AnimationOptions#params) object from the [`transition()`](https://angular.io/api/animations/transition) since they will now be part of the shared animation.
Now, to use our new animation, we will use the [`useAnimation()`](https://angular.io/api/animations/useAnimation) function from the animations module. And then, all we need to do is pass this function our exported “slideAnimation” const.
#### slider.component.ts
```typescript
import { ..., useAnimation } from '@angular/animations';
@Component({
selector: 'app-slider',
...
animations: [
trigger('slideToggle', [
transition('* => *', [
useAnimation(slideAnimation)
])
])
]
})
```
Ok, almost there. All that’s left now is to go and make sure our animation `params` are being properly passed to our animation in the template. So, both our “leaveEnd” and our “enterStart” params can stay as is but remember that we added a “hiddenScale” param that we need to set here.
#### slider.component.html
```html
<div
[@slideToggle]="{
value: selectedImage(),
params: {
leaveEnd: animationDirection() === 'right' ? '100%' : '-100%',
enterStart: animationDirection() === 'right' ? '-100%' : '100%',
hiddenScale: 0.25
}
}">
...
</div>
```
There, that should be all we need. Now, if we got it right, after we save, the slider should work exactly as it did.
## Adding the Reusable Animation to the Navigation Component
Next up, we have the whole purpose for creating the shared animation. To make our nav component transition as it’s toggled opened and closed. Let’s switch to the code for our header component because that’s where our navigation component is toggled.
In the template, we have the condition using a “showMenu()” [`signal`](https://angular.io/guide/signals) to toggle the menu. If it’s true it’ll show, if not, it won’t.
#### header.component.html
```html
<div>
@if (showMenu()) {
<app-nav (close)="showMenu.set(false)"></app-nav>
}
</div>
```
Since our animation queries for elements entering and leaving, we’ll bind our animation on the div that wraps the 'app-nav' element. Let’s call the trigger “slideToggle” like we had in our slider component. It doesn’t have to be named the same, but I like that name for this animation trigger.
Then, we’ll want to run this animation every time the “showMenu()” [`signal`](https://angular.io/guide/signals) value changes, so we’ll use that as our value. After that we need to add our “params” object. Within this object, we need our “leaveEnd” param, it’ll be 100% so that it ends outside of the viewport, to the right when it’s closed. Then we can add our “enterStart” param which will also be 100% because, when it’s opening, it will start outside the right edge of the viewport too.
Then, we can add our “hiddenScale” param. In this case, since we don’t want it to scale as it animates, we’ll give it a value of one.
```html
<div
[@slideToggle]="{
value: showMenu(),
params: {
leaveEnd: '100%',
enterStart: '100%',
hiddenScale: 1
}
}">
@if (showMenu()) {
<app-nav (close)="showMenu.set(false)"></app-nav>
}
</div>
```
Ok, now we just need to create and import our animation so let’s switch over to the header.component.ts. First, we need to add the `animations` metadata array and then within this array we need to add our “slideToggle” trigger using the [`trigger()`](https://angular.io/api/animations/trigger) function.
Then, we add our transition which will run whenever the “showMenu” value changes using the [`transition()`](https://angular.io/api/animations/transition) function. Then within this transition, we can include the “slideAnimation” using the [`useAnimation()`](https://angular.io/api/animations/useAnimation) function from the animations module.
#### header.component.ts
```typescript
import { transition, trigger, useAnimation } from "@angular/animations";
@Component({
selector: 'app-header',
...
animations: [
trigger('slideToggle', [
transition('* => *', [
useAnimation(slideAnimation)
])
])
]
})
```
And that should be everything. If we click the hamburger button to toggle the menu now, it it transitions like we want. And if we close it, it should slide out now too.
<div>
<img src="https://briantree.se/assets/img/content/uploads/2024/05-11/demo-3.gif" alt="Example of the menu opening and closing width reusable slide animations" width="592" height="980" style="width: 100%; height: auto;">
</div>
### Conclusion
So, it’s nice that we didn’t need to create a whole new animation within the header component to pull off a very similar animation style to our image slider. Just like everything else, it’s better if we can share and reuse similar concepts. So, hopefully this will help you out as you add more and more animations to your Angular projects.
Now, believe it or not, there’s still more to Angular animations outside of all of the posts that I’ve already created on them so far. So, we’ll go ahead and call it for this post, but be on the lookout for more on animations in the future.
## Want to See It in Action?
Check out the demo code and examples of these techniques in the in the Stackblitz example below. If you have any questions or thoughts, don’t hesitate to leave a comment.
{% embed https://stackblitz.com/edit/stackblitz-starters-1z78ab?ctl=1&embed=1&file=src%2Fanimations%2Fslide.animation.ts %}
---
## Found This Helpful?
If you found this article helpful and want to show some love, you can always [buy me a coffee!]( https://buymeacoffee.com/briantreese) | brianmtreese |
1,864,952 | Top-Down Shooter Update: Day 1 (Done: Player Controller & 'Bullet') | When making the player controller, I realized I wouldn't be able to test the controls out on my... | 0 | 2024-05-25T16:04:15 | https://dev.to/quantumbyte-studios/top-down-shooter-update-day-1-basic-player-bullet-done-133c | When making the player controller, I realized I wouldn't be able to test the controls out on my mobile device immediately since I'm developing on my laptop.. <u>how do developers normally test mobile games in Unity while developing on a computer??</u> If I make separate controls for computer than for mobile, then how do I know all my computer testing will correlate to similar performance on my mobile? Not sure what to do with this.. For now, I'll put in both computer and mobile controls, but this might make testing a bit more difficult unless maybe Unity has a way to send it directly to my phone.. I might have to do some research.
Then, for the bullet, I didn't really want to deal with the direction of the art asset in the direction the bullet is firing so the bullet sprite ended up looking more like a ninja star:
So I guess my game is ninja-related now. <u>Is it ok for early art decisions to influence game design like that?</u> I might change it later, but for now my bullet is unofficially a ninja star..
<u>Here's a gameplay video so far:</u>
https://icecreamapps.com/v/brx2kah
..making it rain with giant ninja-stars! I'm not sure why he just throws the ninja stars up in the air more often than not. I might have to look into more directional star-throwing! Do you think this is good for his health?
Future Goals
-Research: how do developers normally test mobile games in Unity while developing on a computer?
-Make main character and ninja star smaller and star-throwing more directional
-Add basic UI (health and score)
-Create Enemy
-Spawn enemies
Smile and keep gaming!
| quantumbyte-studios | |
1,864,947 | A Guide to Python Lists, Tuples, Dictionaries, and Sets | Overview Data Structures are a way of organizing data so that it can be accessed more... | 0 | 2024-05-25T15:57:34 | https://dev.to/varshav/a-guide-to-python-lists-tuples-dictionaries-and-sets-gpf | python, webdev, beginners, programming | ### Overview
Data Structures are a way of organizing data so that it can be accessed more efficiently depending upon the situation.
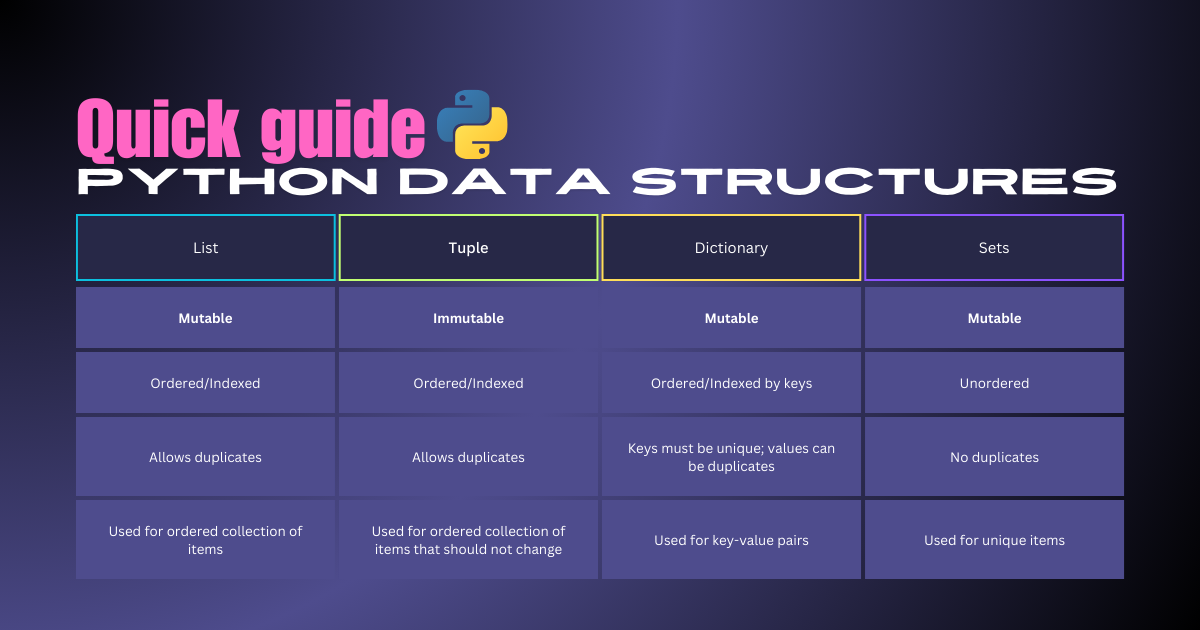
### Lists
- A list is any list of data items, separated by commas, inside square brackets.
- They are ordered, mutable, and allow duplicate elements. Lists can store elements of different data types.
**Creating a List**
```python
flowers = ["rose", "lilly"]
```
**Accessing Elements**
```python
print(flowers[0]) # Output: rose
```
**Modifying Elements**
```python
flowers[1] = "lotus"
print(flowers) # Output: ['rose', 'lotus']
```
#### List Methods
##### Adding Elements
- **append()**: Used to add an element to the end of a list.
```python
# syntax: list_name.append(element)
flowers.append("hibiscus")
print(flowers)
# Output: ['rose', 'lilly', 'hibiscus']
```
- **extend()**: Used to add multiple elements to a list. Takes an iterable as an argument
```python
# syntax: list_name.extend(iterable)
flowers.extend(["daisy", "dahlia"])
print(flowers)
# Output: ['rose', 'lilly', 'hibiscus', 'daisy', 'dahlia']
```
- **insert()**: Used to insert an element at the specified index.
```python
# syntax: list_name.insert(index, element)
flowers.insert(2, "sunflower")
print(flowers)
# Output: ['rose', 'lilly', 'sunflower', 'hibiscus', 'daisy', 'dahlia']
```
> Comparison
> - append(): Adds a single element.
> - extend(): Adds multiple elements.
> - insert(): Adds an element at a specific position.
##### List Analysis
- **copy()**: Create a shallow copy of a list.
```python
# syntax: list_name.copy()
new_list = flowers.copy()
print(new_list)
# Output: ['rose', 'lilly', 'sunflower', 'hibiscus', 'daisy', 'dahlia']
```
- **count()**: Used to count the number of occurrences of a specific element in a list
```python
# syntax: list_name.count(element)
flowers.count("hibiscus") # Output: 1
```
##### Reordering Elements
- **reverse()**: Used to reverse the order of elements in a list.
```python
# syntax: list_name.reverse()
flowers.reverse()
print(flowers)
# Output: ['dahlia', 'daisy', 'hibiscus', 'sunflower', 'lilly', 'rose']
```
- **sort()**: Used to sort the elements of a list in ascending order. If you want to sort the list in descending order, you can pass the `reverse=True` argument to the `sort()` method.
```python
# syntax: list_name.sort()
flowers.sort()
print(flowers)
# Output: ['dahlia', 'daisy', 'hibiscus', 'lilly', 'rose', 'sunflower']
flowers.sort(reverse=True)
print(flowers)
# Output: ['sunflower', 'rose', 'lilly', 'hibiscus', 'daisy', 'dahlia']
```
> Comparison
> - reverse(): Reverses the list in place.
> - sort(): Sorts the list in place, with optional descending order.
##### Removing Elements
- **del**: Removes the element at the specified index.
```python
# syntax: del list_name[index]
del flowers[1]
print(flowers)
# Output: ['sunflower', 'lilly', 'hibiscus', 'daisy', 'dahlia']
```
- **remove()**: Used to remove an element. it removes the first occurrence of the specified value.
```python
# syntax: list_name.remove(element)
flowers.remove("sunflower")
print(flowers)
# Output: ['lilly', 'hibiscus', 'daisy', 'dahlia']
```
- **pop()**: Another way to remove an element from a list in Python. It removes and returns the element at the specified index. If you don't provide an index to the `pop()` method, it will remove and return the last element of the list by default
```python
# syntax: list_name.remove(element)
flowers.pop() # Output: 'dahlia'
print(flowers)
# Output: ['lilly', 'hibiscus', 'daisy']
```
> Comparison
> - del: Removes by index without returning the element.
> - remove(): Removes by value, only the first occurrence.
> - pop(): Removes by index and returns the element.
### Tuples
- Tuples are similar to lists, but they are immutable. An immutable object can't be changed after it is created.
- Tuples are useful for fixed collections of items.
**Creating a Tuples**
```python
coordinates = (10, 20)
```
**Accessing Elements**
```python
print(coordinates[0]) # Output: 10
```
#### Tuple Methods
- **count()**: Returns the number of occurrences of a specified value.
```python
coordinates.count(10) # Output: 1
```
- **index()**: Returns the index of the first occurrence of a specified value.
```python
coordinates.index(10) # 0
```
### Dictionaries
- A dictionary in Python is a data structure that stores a collection of key-value pairs, where each key is unique and associated with a specific value.
- They are ordered, mutable, and indexed by keys.
- Dictionaries are highly efficient for lookups.
**Creating a Dictionary**
```python
student = {"name": "VV", "age": 22, "courses": ["Math", "Science"]}
```
**Accessing Elements**
```python
print(student["name"]) # Output: John
```
**Adding Elements**
```python
student["year"] = 2024
print(student)
# Output: {'name': 'VV', 'age': 22, 'courses': ['Math', 'Science'], 'year': 2024}
```
**Modifying Elements**
```python
student["age"] = 44
print(student["age"]) # Output: 44
```
#### Dictionary Methods
##### Creating and Copying
- **copy()**: Create a shallow copy of a list.
```python
# syntax: new_dict = dict_name.copy()
new_dict = student.copy()
print(new_dict)
# Output: {'name': 'VV', 'age': 44, 'courses': ['Math', 'Science'], 'year': 2024}
```
##### Retrieving Elements
- **items()**: Retrieves all key-value pairs as tuples and converts them into a list of tuples. Each tuple consists of a key and its corresponding value.
```python
# syntax: list(dict_name.items())
print(list(student.items()))
# Output: [('name', 'VV'), ('age', 44), ('courses', ['Math', 'Science']), ('year', 2024)]
```
- **keys()**: Retrieves all keys from the dictionary and converts them into a list.
```python
# syntax: list(dict_name.keys())
print(list(student.keys()))
# Output: ['name', 'age', 'courses', 'year']
```
- **values()**: Retrieves all values from the dictionary and converts them into a list.
```python
# syntax: list(dict_name.values())
print(list(student.values()))
# Output: ['VV', 44, ['Math', 'Science'], 2024]
```
##### Updating
- **update()**: Merges the provided dictionary into the existing dictionary, adding or updating key-value pairs.
```python
# syntax: dict_name.update({key: value})
student.update({'year':2023,'dob':2000})
print(student)
# Output: {'name': 'VV', 'age': 44, 'courses': ['Math', 'Science'], 'year': 2023, 'dob': 2000}
```
##### Removing Elements
- **del**: Removes the specified key-value pair from the dictionary. Raises a `KeyError` if the key does not exist.
```python
# syntax: del dict_name[key]
del student['courses']
print(student)
# Output: {'name': 'VV', 'age': 44, 'year': 2023, 'dob': 2000}
```
- **clear()**: Removes all key-value pairs in a dictionary
```python
# syntax: dict_name.clear()
student.clear()
print(student) # Output: {}
```
> Comparison
> - del: Removes a specific key-value pair identified by the key.
> - clear(): Removes all key-value pairs from the dictionary.
### Sets
- A set is an unordered collection of unique elements.
- They are unordered, unchangeable, and unindexed.
- Sets support mathematical operations like union, intersection, and difference.
- Sets are mostly used for membership testing and eliminating duplicate entries
**Creating a Set:**
```python
colors = {"red"}
```
#### Set Methods
##### Adding Elements
- **add()**: Adds an element to a set.
```python
# syntax: set_name.add(element)
colors.add("green")
print(colors) # Output: {'red', 'green'}
```
- **update()**: Adds elements from another iterable into the set
```python
# syntax: set_name.update(iterable)
colors.update({"green", "red", "yellow"})
print(new_set) # Output: {'green', 'yellow', 'red'}
```
> Comparison
> - add(): Adds a single element to the set.
> - update(): Adds multiple elements from an iterable to the set.
##### Copying
- **copy()**: Creates a shallow copy of the set.
```python
# syntax: new_set = set_name.copy()
new_set = colors.copy()
print(new_set) # Output: {'red', 'green', 'yellow'}
```
##### Subset, Superset, and Disjoint Check
- **issubset()**: Checks if the current set is a subset of another set.
```python
# syntax: set_name.issubset(set2)
colors.issubset({"green", "red"}) # Output: False
```
- **issuperset()**: Checks if the current set is a superset of another set.
```python
# syntax: set_name.issuperset(set2)
colors.issuperset({"green", "red"}) # Output: True
```
- **isdisjoint()**: Two sets are disjoint if they have no elements in common.
```python
# syntax: set_name.isdisjoint(set2)
colors.isdisjoint({"green", "red"}) # Output: False
```
##### Removing Elements
- **discard()**: Remove a specific element from the set. Ignores if the element is not found.
```python
# syntax: set_name.discard(element)
colors.discard("red")
print(colors) # Output: {'green', 'yellow'}
```
- **pop()**: Removes and returns an arbitrary element from the set. It raises a `KeyError` if the set is empty
```python
# syntax: removed_element = set_name.pop()
colors.pop() # Output: 'green'
```
- **remove()**: Remove a specific element from the set. Raises a `KeyError` if the element is not found.
```python
# syntax: set_name.remove(element)
new_set.remove('green')
print(colors) # Output: {'red', 'yellow'}
```
- **clear()**: Removes all elements from the set. It updates the set in-place.
```python
# syntax: set_name.clear()
new_set.clear()
print(new_set) # Output: set()
```
> Comparison
> - discard(): Removes an element if present, does nothing if the element is not found.
> - pop(): Removes and returns an arbitrary element, raises an error if the set is empty.
> - remove(): Removes an element if present, raises an error if the element is not found.
> - clear(): Removes all elements from the set.
##### **Set Operations**
- **Union**: The union of two sets is a set containing all elements from both sets, without duplicates.
```python
set1 = {1, 2, 3, 4}
set2 = {3, 4, 5, 6}
# Method 1: Using the | operator
union_set = set1 | set2
print(union_set) # Output: {1, 2, 3, 4, 5, 6}
# Method 2: Using the union() method
union_set = set1.union(set2)
print(union_set) # Output: {1, 2, 3, 4, 5, 6}
```
- **Intersection**: The intersection of two sets is a set containing only the elements that are present in both sets.
```python
# Method 1: Using the & operator
intersection_set = set1 & set2
print(intersection_set) # Output: {3, 4}
# Method 2: Using the intersection() method
intersection_set = set1.intersection(set2)
print(intersection_set) # Output: {3, 4}
```
- **Difference**: The difference between two sets is a set containing the elements that are present in the first set but not in the second set.
```python
# Method 1: Using the - operator
difference_set = set1 - set2
print(difference_set) # Output: {1, 2}
# Method 2: Using the difference() method
difference_set = set1.difference(set2)
print(difference_set) # Output: {1, 2}
```
- **Symmetric Difference**: The symmetric difference between two sets is a set containing the elements that are in either of the sets but not in both.
```python
# Method 1: Using the ^ operator
symmetric_difference_set = set1 ^ set2
print(symmetric_difference_set) # Output: {1, 2, 5, 6}
# Method 2: Using the symmetric_difference() method
symmetric_difference_set = set1.symmetric_difference(set2)
print(symmetric_difference_set) # Output: {1, 2, 5, 6}
```
> Comparison
> - union(): Combines elements from two sets.
> - intersection(): Finds common elements between sets.
> - difference(): Finds elements in one set but not the other.
> - symmetric_difference(): Finds elements in either set but not in both.
### Conclusion
Understanding and using the right data structures is key to writing efficient and effective Python code. Each data structure has its own strengths and use cases, from the flexible and dynamic lists to the fast and efficient dictionaries.
If you have any questions, suggestions, or corrections, please feel free to leave a comment. Your feedback helps me improve and create more accurate content.
***Happy coding!!!***
| varshav |
1,864,950 | The Neighborhood Domain will Quickly Improve your Modeling Skills | Microservices are about domain decomposition. This decomposition allows code to be deployed that is... | 0 | 2024-05-25T15:56:53 | https://www.binaryheap.com/bounded-context-as-neighborhood-domain/ | aws, serverless, architecture, programming | Microservices are about domain decomposition. This decomposition allows code to be deployed that is more isolated, durable, resilient, and launched in a compute form factor designed for the requirements. In addition, the isolation allows for teams to move on their deployment schedules and cadences. These reasons are attractive, but they do come with domain complexity that often manifests itself as architectural complexity. And while I can't remove the architectural complexity, I do want to offer an approach to domain modeling that will feel more familiar. Introducing the domain neighborhood.
## Domain Modeling
Modeling a business domain is one of those tasks that everyone agrees is important but often gets overlooked when it comes time to implement a new software solution. Speaking from experience though, skipping this step will create confusion and miscommunications that can become both costly in time as requirements are written and also costly in rework when things aren't implemented in congruence with what the domain is. Software systems operate better when they look and sound like the businesses they model.
When doing this modeling work, an order of business that a domain modeler or architect must do is look at the macro picture of the business solution and begin to carve out boundaries. Boundaries in the domain world are often referred to as bounded contexts. A bounded context can be defined as a grouping of related microservices that operate to perform a set of functions on a user's behalf. Bounded contexts are made up of multiple aggregate roots that form a collective bond which solidifies the ubiquitous language that a group of people operate within.
That's a lot of words that can often be difficult to wrap your head around. When modeled, it often looks like this.

## A more Neighborhood Domain Way
The above diagram shows two bounded contexts representing a single solution. The example is basic, but the concepts apply to more complex examples as well.
An Orders bounded context deals with a user adding items to an order and submitting a payment. These boxes represent individual microservices that perform their operations and work in concert to deliver the intended functionality.
In a neighborhood domain, that same user also exists in the Users bounded context. The operations and behaviors in this domain deal with preferences, previous orders, and notifications that the user must manage. It's still the same user as in the orders domain, but just in a different context. It will also be a separate microservice that is deployed and built from a different codebase than the one that is in orders.
### Introducing the Neighborhood Domain
Take what I've written so far and the two bounded contexts described and let's think of them more as neighborhoods. A neighborhood domain will contain the same thing as a bounded context with multiple aggregate roots but let's describe it with concrete things we can all agree upon.
#### Neighborhood
Let's get a little bit more concrete as I introduce this. A neighborhood is a collection of microservices that are related to performing a set of user-expected operations. They work together to accomplish shared tasks. It's very much like a community. It's a boundary that all of the homes collectively reside in.
To make this a little bit more concrete, a neighborhood in AWS is managed by one of the following:
1. Application Load Balancer
2. Network Load Balancer
3. API Gateway
4. Route 53 Hosted Zone
The neighborhood is the top-level piece of a neighborhood domain.
#### House as a Microservice
If a neighborhood has no houses, is it a neighborhood? In the neighborhood domain, houses are the microservices. A house has entities that live in it and those entities perform operations and tasks.
What makes a house though a part of the community is to be associated with a neighborhood. The house could be implemented as a container hosted in EC2, ECS, or EKS. Or the house could be a series of Lambda Functions or even something like LightSail. If we carry this even further, houses need roads to connect them to other neighborhood properties. Those relate to API Gateway routes or Load Balancer rules.
#### Some Lagniappe
I've been talking so far about another way to think about bounded context and aggregate roots, but I've also been mixing in concrete items like AWS services to drive the points home. I want to give you a little something extra or "Lagniappe" that will further extend the harmony that is a multi-domain business solution.
In the USA, Home Owners Associations (HOA) have become common governing bodies to make sure that homes and their owners stay within a certain set of approved bylaws. These bylaws enforce the way neighbors keep their homes in the community up to standards.
I know what you are thinking right now ... where in the world is this going? I'll tell you.
Services often need to talk over APIs to other services. What's to prevent a service from being a "noisy neighbor" or a neighbor that doesn't honor the rules of the community?
Enter the service mesh. A service mesh operates as an HOA in a neighborhood to set some common guidelines about how services will talk to each other and protect the neighborhood from a house that's not operating under the bylaws.
## Bringing it All Together
The neighborhood domain is just another way to think about a 20 + year-old concept that was introduced by Eric Evans in his book [Domain Driven Design](https://www.amazon.com/Domain-Driven-Design-Tackling-Complexity-Software/dp/0321125215).
When looking at complex domains as neighborhoods, this is what the original diagram would look like.

Neighborhoods, houses, and HOAs are constructs that you can use to model the bounded contexts and aggregate roots that exist in your world.
## Wrapping Up
This was a much different article than what I normally write about. The genesis though was some work I was doing with a client recently and when trying to help them break up a large domain, the concept of neighborhoods showed up. Bounded contexts and aggregate roots are tough to explain, but neighborhoods, well everyone knows what those are. Getting people to rally around communities of homes operating together to serve a user's purpose makes the work of building a ubiquitous language that much simpler. And as an architect, building that language is much more important than many give it credit for.
I hope that this new way of thinking about domain modeling will give you another tool to build amazing software that delights your customers. Because remember, software needs to be either fun or useful. If neither, then why do it? And most importantly, software is a [team sport](https://www.binaryheap.com/serverless-and-agile/). And working as a team makes everything go better, faster and more efficient.
Thanks for reading and happy building!
| benbpyle |
1,865,208 | How to Proxy API Requests in NodeJs Using a SOCKS Proxy with Axios | Introduction When developing applications, you might encounter scenarios where certain... | 0 | 2024-05-25T21:36:21 | https://dev.to/rajssj4/how-to-proxy-api-requests-in-nodejs-using-a-socks-proxy-with-axios-4o7l | socks5proxy, axios, apidevelopment, node | ---
title: How to Proxy API Requests in NodeJs Using a SOCKS Proxy with Axios
published: true
date: 2024-05-25 15:55:36 UTC
tags: socks5proxy,axios,apidevelopment,nodejs
canonical_url:
---
### Introduction
When developing applications, you might encounter scenarios where certain APIs are accessible only from specific IP addresses. This can pose a challenge if you’re working locally and your local IP is not whitelisted. One effective solution is to use a SOCKS proxy to route your API requests through a server with an approved IP address. In this blog post, we’ll walk through the process of setting up a Fastify server to make API requests using Axios, routed through a SOCKS proxy.
### Problem Statement
You have an API (https://example.com/countries) that returns country data but is accessible only from whitelisted IPs. Your server, deployed at a whitelisted IP, can access this API. However, while developing locally, you need to make API requests from your local machine (e.g., http://localhost:3000/getcountries) and route these requests through your server to access the restricted API.
### Solution Overview
We’ll set up a SOCKS proxy using SSH, configure a NodeJs server to make proxied API requests using Axios and route these requests through the SOCKS proxy. Here’s a step-by-step guide to achieve this.
### Step-by-Step Guide
### 1. Set Up the SOCKS Proxy
First, establish a SOCKS proxy using SSH. Run the following command in your terminal:
```
ssh -D 5001 rajesh@xyz.amazonaws.com
```
- -D 5001: Specifies dynamic application-level port forwarding on port 5001(You can use any other port).
- rajesh@xyz.amazonaws.com: Replace with your actual SSH user and server address.
Install the http-proxy-to-socks package in your local system:
```
npm install -g http-proxy-to-socks
```
Redirect your local requests to the tunnel connection
```
hpts -s 127.0.0.1:5001 -p 8080
```
If you have followed till here, you can add the custom proxy to your Postman app and call the API:
- Go to postman➝settings➝proxy
- Select custom proxy
- Add the host: 127.0.0.1
- Add the port: 8080
### 2. Install Required Packages
Ensure you have Node.js and npm installed, then install Fastify, Axios, and socks-proxy-agent:
```
npm install fastify axios socks-proxy-agent
```
### 3. Configure the Fastify Server
Create a file (e.g., server.js) and set up your Fastify server with Axios to use the SOCKS proxy. Here’s the complete code:
```
const fastify = require('fastify')({ logger: true });
const axios = require('axios');
const { SocksProxyAgent } = require('socks-proxy-agent');
// Create a SOCKS proxy agent
const agent = new SocksProxyAgent('socks://127.0.0.1:5001');
// Fastify GET route
fastify.get('/getCountries', async (request, reply) => {
try {
const response = await axios({
method: 'get',
url: 'https://example.com/countries',
headers: { 'Content-Type': 'application/x-www-form-urlencoded' },
httpAgent: agent
httpsAgent: agent
});
reply.send(response.data);
} catch (error) {
fastify.log.error('Error creating user:', error.message);
reply.status(500).send({ error: 'Failed to create user' });
}
});
const start = async () => {
try {
await fastify.listen(3000);
fastify.log.info(`Server running at http://localhost:3000`);
} catch (err) {
fastify.log.error(err);
process.exit(1);
}
};
start();
```
### 4. Start Your Fastify Server
Run your Fastify server:
```
node server.js
```
### 5. Test the Endpoint
Use tools like Postman or curl to send a POST request to your local Fastify server endpoint (http://localhost:3000/getCountries) and verify that it returns the expected data:
```
curl -X POST http://localhost:3000/getCountries
```
### Conclusion
By following these steps, you can successfully route your API requests through a SOCKS proxy using Fastify and Axios. This setup allows you to develop locally while accessing APIs restricted to specific IPs. If you encounter issues, check your proxy settings, and network configurations, and ensure your SSH tunnel is active.
I hope this guide helps you set up your development environment effectively. Happy coding! | rajssj4 |
1,864,949 | Device conversion, from_numpy() and numpy() in PyTorch | *Memos: My post explains how to check PyTorch version, CPU and GPU(CUDA). My post explains how to... | 0 | 2024-05-25T15:54:33 | https://dev.to/hyperkai/device-conversion-fromnumpy-and-numpy-in-pytorch-1iih | pytorch, device, conversion, numpy | *Memos:
- [My post](https://dev.to/hyperkai/check-pytorch-version-cpu-and-gpucuda-in-pytorch-6jk) explains how to check PyTorch version, CPU and GPU(CUDA).
- [My post](https://dev.to/hyperkai/create-a-tensor-in-pytorch-127g) explains how to create a tensor.
- [My post](https://dev.to/hyperkai/access-a-tensor-in-pytorch-1f4e) explains how to access a tensor.
- [My post](https://dev.to/hyperkai/istensor-numel-and-device-in-pytorch-2eha) explains [is_tensor()](https://pytorch.org/docs/stable/generated/torch.is_tensor.html), [numel()](https://pytorch.org/docs/stable/generated/torch.numel.html) and [device()](https://pytorch.org/docs/stable/tensor_attributes.html#torch-device).
- [My post](https://dev.to/hyperkai/type-conversion-with-type-to-and-a-tensor-in-pytorch-2a0g) explains type conversion with [type()](https://pytorch.org/docs/stable/generated/torch.Tensor.type.html), [to()](https://pytorch.org/docs/stable/generated/torch.Tensor.to.html) and a tensor.
- [My post](https://dev.to/hyperkai/type-promotion-resulttype-promotetypes-and-cancast-in-pytorch-33p8) explains type promotion, [result_type()](https://pytorch.org/docs/stable/generated/torch.result_type.html), [promote_types()](https://pytorch.org/docs/stable/generated/torch.promote_types.html) and [can_cast()](https://pytorch.org/docs/stable/generated/torch.can_cast.html).
- [My post](https://dev.to/hyperkai/setdefaultdtype-setdefaultdevice-and-setprintoptions-in-pytorch-55g8) explains [set_default_dtype()](https://pytorch.org/docs/stable/generated/torch.set_default_dtype.html), [set_default_device()](https://pytorch.org/docs/stable/generated/torch.set_default_device.html) and [set_printoptions()](https://pytorch.org/docs/stable/generated/torch.set_printoptions.html).
- [My post](https://dev.to/hyperkai/manualseed-initialseed-and-seed-in-pytorch-5gm8) explains [manual_seed()](https://pytorch.org/docs/stable/generated/torch.manual_seed.html), [initial_seed()](https://pytorch.org/docs/stable/generated/torch.initial_seed.html) and [seed()](https://pytorch.org/docs/stable/generated/torch.seed.html).
[to()](https://pytorch.org/docs/stable/generated/torch.Tensor.to.html) can do device conversion as shown below:
*Memos:
- `to()` can be used with a tensor but not with [torch](https://pytorch.org/docs/stable/torch.html).
- The 1st argument with a tensor is `device`(Optional-Type:`str`, `int` or [device()](https://pytorch.org/docs/stable/tensor_attributes.html#torch-device)).
- If `device` is not given, the device is not converted.
- `cpu`, `cuda`, `ipu`, `xpu`, `mkldnn`, `opengl`, `opencl`, `ideep`, `hip`, `ve`, `fpga`, `ort`, `xla`, `lazy`, `vulkan`, `mps`, `meta`, `hpu`, `mtia` or `privateuseone` can be set to `device`.
- Setting `0` to `device` uses `cuda`(GPU). *The number must be zero or positive.
- [My post](https://dev.to/hyperkai/istensor-numel-and-device-in-pytorch-2eha) explains [device()](https://pytorch.org/docs/stable/tensor_attributes.html#torch-device).
- A copied tensor can be created.
```python
import torch
cpu_tensor = torch.tensor([0, 1, 2])
cpu_tensor.device
# device(type='cpu')
cpu_tensor.to().device
# device(type='cpu')
gpu_tensor = cpu_tensor.to(device='cuda:0')
gpu_tensor = cpu_tensor.to(device='cuda')
gpu_tensor = cpu_tensor.to(device=0)
gpu_tensor = cpu_tensor.to(device=torch.device(device='cuda:0'))
gpu_tensor = cpu_tensor.to(device=torch.device(device='cuda'))
gpu_tensor = cpu_tensor.to(device=torch.device(device=0))
gpu_tensor = cpu_tensor.to(device=torch.device(type='cuda', index=0))
gpu_tensor = cpu_tensor.to(device=torch.device(type='cuda'))
gpu_tensor.device
# device(type='cuda', index=0)
gpu_tensor.to().device
# device(type='cuda', index=0)
cpu_tensor = gpu_tensor.to(device='cpu')
cpu_tensor.device
# device(type='cpu')
```
[cuda()](https://pytorch.org/docs/stable/generated/torch.Tensor.cuda.html) and [cpu()](https://pytorch.org/docs/stable/generated/torch.Tensor.cpu.html) can change the device of a tensor to GPU(CUDA) and CPU respectively as shwon below:
*Memos:
- `cuda()` or `cpu()` can be used with a tensor but not with `torch`.
- For `cuda()`, - the 1st argument with a tensor is `device`(Optional-Type:`str`, `int` or [device()](https://pytorch.org/docs/stable/tensor_attributes.html#torch-device)).
*Memos:
- The default is the current GPU(CUDA).
- `cpu`, `cuda`, `ipu`, `xpu`, `mkldnn`, `opengl`, `opencl`, `ideep`, `hip`, `ve`, `fpga`, `ort`, `xla`, `lazy`, `vulkan`, `mps`, `meta`, `hpu`, `mtia` or `privateuseone` can be set to `device`.
- Setting `0` to `device` uses `cuda`(GPU). *The number must be zero or positive.
- [My post](https://dev.to/hyperkai/istensor-numel-and-device-in-pytorch-2eha) explains [device()](https://pytorch.org/docs/stable/tensor_attributes.html#torch-device).
- A copied tensor is created.
```python
import torch
cpu_tensor = torch.tensor([0, 1, 2])
cpu_tensor.device
# device(type='cpu')
gpu_tensor = cpu_tensor.cuda()
gpu_tensor = cpu_tensor.cuda(device='cuda:0')
gpu_tensor = cpu_tensor.cuda(device='cuda')
gpu_tensor = cpu_tensor.cuda(device=0)
gpu_tensor = cpu_tensor.cuda(device=torch.device(device='cuda:0'))
gpu_tensor = cpu_tensor.cuda(device=torch.device(device='cuda'))
gpu_tensor = cpu_tensor.cuda(device=torch.device(device=0))
gpu_tensor = cpu_tensor.cuda(device=torch.device(type='cuda', index=0))
gpu_tensor = cpu_tensor.cuda(device=torch.device(type='cuda'))
gpu_tensor.device
# device(type='cuda', index=0)
cpu_tensor = gpu_tensor.cpu()
cpu_tensor.device
# device(type='cpu')
```
[from_numpy()](https://pytorch.org/docs/stable/generated/torch.from_numpy.html) can convert a NumPy array to a PyTorch tensor as shown below:
*Memos:
- `from_numpy()` can be used with `torch` but not with a tensor.
- The 1st argument with `torch`(Required-Type:`ndarray`). *There is no keyword argument.
- The type of a NumPy array is also inherited to a PyTorch tensor.
```python
import torch
my_array = np.array([0., 1., 2.])
my_array.dtype
# dtype('float64')
my_tensor = torch.from_numpy(my_array)
my_tensor
# tensor([0., 1., 2.], dtype=torch.float64)
```
[numpy()](https://pytorch.org/docs/stable/generated/torch.Tensor.numpy.html) can convert a PyTorch tensor to a NumPy array as shown below:
*Memos:
- `numpy()` can be used with a tensor but not with `torch`.
- There is `force` argument with a tensor(Optional-Default:`False`-Type:`bool`).
*Memos:
- If it's `True`, a GPU(CUDA) PyTorch tensor can be converted to a NumPy array which may be a copy.
- `force=` must be used.
- The type of a PyTorch tensor is also inherited to a NumPy array.
```python
import torch
my_tensor = torch.tensor([0., 1., 2.])
my_tensor.dtype
# torch.float32
my_array = my_tensor.numpy()
my_array
# array([0., 1., 2.], dtype=float32)
my_tensor = torch.tensor([0., 1., 2.], device='cuda:0')
my_tensor.numpy(force=True)
# array([0., 1., 2.], dtype=float32)
my_tensor = torch.tensor([0., 1., 2.], device='cuda:0')
my_tensor.numpy()
my_tensor.numpy(force=False)
# Error
``` | hyperkai |
1,864,948 | Buy Verified Paxful Account | https://dmhelpshop.com/product/buy-verified-paxful-account/ Buy Verified Paxful Account There are... | 0 | 2024-05-25T15:54:29 | https://dev.to/whitemartin015/buy-verified-paxful-account-2n2b | ERROR: type should be string, got "https://dmhelpshop.com/product/buy-verified-paxful-account/\n\nBuy Verified Paxful Account\nThere are several compelling reasons to consider purchasing a verified Paxful account. Firstly, a verified account offers enhanced security, providing peace of mind to all users. Additionally, it opens up a wider range of trading opportunities, allowing individuals to partake in various transactions, ultimately expanding their financial horizons.\n\nMoreover, Buy verified Paxful account ensures faster and more streamlined transactions, minimizing any potential delays or inconveniences. Furthermore, by opting for a verified account, users gain access to a trusted and reputable platform, fostering a sense of reliability and confidence.\n\n\n\n\n\nLastly, Paxful’s verification process is thorough and meticulous, ensuring that only genuine individuals are granted verified status, thereby creating a safer trading environment for all users. Overall, the decision to Buy Verified Paxful account can greatly enhance one’s overall trading experience, offering increased security, access to more opportunities, and a reliable platform to engage with. Buy Verified Paxful Account.\n\nBuy US verified paxful account from the best place dmhelpshop\nWhy we declared this website as the best place to buy US verified paxful account? Because, our company is established for providing the all account services in the USA (our main target) and even in the whole world. With this in mind we create paxful account and customize our accounts as professional with the real documents. Buy Verified Paxful Account.\n\nIf you want to buy US verified paxful account you should have to contact fast with us. Because our accounts are-\n\nEmail verified\nPhone number verified\nSelfie and KYC verified\nSSN (social security no.) verified\nTax ID and passport verified\nSometimes driving license verified\nMasterCard attached and verified\nUsed only genuine and real documents\n100% access of the account\nAll documents provided for customer security\nWhat is Verified Paxful Account?\nIn today’s expanding landscape of online transactions, ensuring security and reliability has become paramount. Given this context, Paxful has quickly risen as a prominent peer-to-peer Bitcoin marketplace, catering to individuals and businesses seeking trusted platforms for cryptocurrency trading.\n\nIn light of the prevalent digital scams and frauds, it is only natural for people to exercise caution when partaking in online transactions. As a result, the concept of a verified account has gained immense significance, serving as a critical feature for numerous online platforms. Paxful recognizes this need and provides a safe haven for users, streamlining their cryptocurrency buying and selling experience.\n\nFor individuals and businesses alike, Buy verified Paxful account emerges as an appealing choice, offering a secure and reliable environment in the ever-expanding world of digital transactions. Buy Verified Paxful Account.\nhttps://dmhelpshop.com/product/buy-verified-paxful-account/\n\nVerified Paxful Accounts are essential for establishing credibility and trust among users who want to transact securely on the platform. They serve as evidence that a user is a reliable seller or buyer, verifying their legitimacy.\n\nBut what constitutes a verified account, and how can one obtain this status on Paxful? In this exploration of verified Paxful accounts, we will unravel the significance they hold, why they are crucial, and shed light on the process behind their activation, providing a comprehensive understanding of how they function. Buy verified Paxful account.\n\n https://dmhelpshop.com/product/buy-verified-paxful-account/\n\nWhy should to Buy Verified Paxful Account?\nThere are several compelling reasons to consider purchasing a verified Paxful account. Firstly, a verified account offers enhanced security, providing peace of mind to all users. Additionally, it opens up a wider range of trading opportunities, allowing individuals to partake in various transactions, ultimately expanding their financial horizons.\n\nMoreover, a verified Paxful account ensures faster and more streamlined transactions, minimizing any potential delays or inconveniences. Furthermore, by opting for a verified account, users gain access to a trusted and reputable platform, fostering a sense of reliability and confidence. Buy Verified Paxful Account.\n\nLastly, Paxful’s verification process is thorough and meticulous, ensuring that only genuine individuals are granted verified status, thereby creating a safer trading environment for all users. Overall, the decision to buy a verified Paxful account can greatly enhance one’s overall trading experience, offering increased security, access to more opportunities, and a reliable platform to engage with.\n\n \n\nWhat is a Paxful Account\nPaxful and various other platforms consistently release updates that not only address security vulnerabilities but also enhance usability by introducing new features. Buy Verified Paxful Account.\n\nIn line with this, our old accounts have recently undergone upgrades, ensuring that if you purchase an old buy Verified Paxful account from dmhelpshop.com, you will gain access to an account with an impressive history and advanced features. This ensures a seamless and enhanced experience for all users, making it a worthwhile option for everyone.\nhttps://dmhelpshop.com/product/buy-verified-paxful-account/\n \n\nIs it safe to buy Paxful Verified Accounts?\nBuying on Paxful is a secure choice for everyone. However, the level of trust amplifies when purchasing from Paxful verified accounts. These accounts belong to sellers who have undergone rigorous scrutiny by Paxful. Buy verified Paxful account, you are automatically designated as a verified account. Hence, purchasing from a Paxful verified account ensures a high level of credibility and utmost reliability. Buy Verified Paxful Account.\n\nPAXFUL, a widely known peer-to-peer cryptocurrency trading platform, has gained significant popularity as a go-to website for purchasing Bitcoin and other cryptocurrencies. It is important to note, however, that while Paxful may not be the most secure option available, its reputation is considerably less problematic compared to many other marketplaces. Buy Verified Paxful Account.\n\nThis brings us to the question: is it safe to purchase Paxful Verified Accounts? Top Paxful reviews offer mixed opinions, suggesting that caution should be exercised. Therefore, users are advised to conduct thorough research and consider all aspects before proceeding with any transactions on Paxful.\n\n \n\nHow Do I Get 100% Real Verified Paxful Accoun?\nPaxful, a renowned peer-to-peer cryptocurrency marketplace, offers users the opportunity to conveniently buy and sell a wide range of cryptocurrencies. Given its growing popularity, both individuals and businesses are seeking to establish verified accounts on this platform.\n\nHowever, the process of creating a verified Paxful account can be intimidating, particularly considering the escalating prevalence of online scams and fraudulent practices. This verification procedure necessitates users to furnish personal information and vital documents, posing potential risks if not conducted meticulously.\n\nIn this comprehensive guide, we will delve into the necessary steps to create a legitimate and verified Paxful account. Our discussion will revolve around the verification process and provide valuable tips to safely navigate through it.\n\nMoreover, we will emphasize the utmost importance of maintaining the security of personal information when creating a verified account. Furthermore, we will shed light on common pitfalls to steer clear of, such as using counterfeit documents or attempting to bypass the verification process.\n\nWhether you are new to Paxful or an experienced user, this engaging paragraph aims to equip everyone with the knowledge they need to establish a secure and authentic presence on the platform.\n\nBenefits Of Verified Paxful Accounts\nVerified Paxful accounts offer numerous advantages compared to regular Paxful accounts. One notable advantage is that verified accounts contribute to building trust within the community.\n\nVerification, although a rigorous process, is essential for peer-to-peer transactions. This is why all Paxful accounts undergo verification after registration. When customers within the community possess confidence and trust, they can conveniently and securely exchange cash for Bitcoin or Ethereum instantly. Buy Verified Paxful Account.\n\nPaxful accounts, trusted and verified by sellers globally, serve as a testament to their unwavering commitment towards their business or passion, ensuring exceptional customer service at all times. Headquartered in Africa, Paxful holds the distinction of being the world’s pioneering peer-to-peer bitcoin marketplace. Spearheaded by its founder, Ray Youssef, Paxful continues to lead the way in revolutionizing the digital exchange landscape.\n\nPaxful has emerged as a favored platform for digital currency trading, catering to a diverse audience. One of Paxful’s key features is its direct peer-to-peer trading system, eliminating the need for intermediaries or cryptocurrency exchanges. By leveraging Paxful’s escrow system, users can trade securely and confidently.\n\nWhat sets Paxful apart is its commitment to identity verification, ensuring a trustworthy environment for buyers and sellers alike. With these user-centric qualities, Paxful has successfully established itself as a leading platform for hassle-free digital currency transactions, appealing to a wide range of individuals seeking a reliable and convenient trading experience. Buy Verified Paxful Account.\n\n \n\nHow paxful ensure risk-free transaction and trading?\nEngage in safe online financial activities by prioritizing verified accounts to reduce the risk of fraud. Platforms like Paxfu implement stringent identity and address verification measures to protect users from scammers and ensure credibility.\n\nWith verified accounts, users can trade with confidence, knowing they are interacting with legitimate individuals or entities. By fostering trust through verified accounts, Paxful strengthens the integrity of its ecosystem, making it a secure space for financial transactions for all users. Buy Verified Paxful Account.\n\nExperience seamless transactions by obtaining a verified Paxful account. Verification signals a user’s dedication to the platform’s guidelines, leading to the prestigious badge of trust. This trust not only expedites trades but also reduces transaction scrutiny. Additionally, verified users unlock exclusive features enhancing efficiency on Paxful. Elevate your trading experience with Verified Paxful Accounts today.\n\nIn the ever-changing realm of online trading and transactions, selecting a platform with minimal fees is paramount for optimizing returns. This choice not only enhances your financial capabilities but also facilitates more frequent trading while safeguarding gains. Buy Verified Paxful Account.\n\nExamining the details of fee configurations reveals Paxful as a frontrunner in cost-effectiveness. Acquire a verified level-3 USA Paxful account from dmhelpshop.com for a secure transaction experience. Invest in verified Paxful accounts to take advantage of a leading platform in the online trading landscape.\n\n \n\nHow Old Paxful ensures a lot of Advantages?\n\nExplore the boundless opportunities that Verified Paxful accounts present for businesses looking to venture into the digital currency realm, as companies globally witness heightened profits and expansion. These success stories underline the myriad advantages of Paxful’s user-friendly interface, minimal fees, and robust trading tools, demonstrating its relevance across various sectors.\n\nBusinesses benefit from efficient transaction processing and cost-effective solutions, making Paxful a significant player in facilitating financial operations. Acquire a USA Paxful account effortlessly at a competitive rate from usasmmonline.com and unlock access to a world of possibilities. Buy Verified Paxful Account.\n\nExperience elevated convenience and accessibility through Paxful, where stories of transformation abound. Whether you are an individual seeking seamless transactions or a business eager to tap into a global market, buying old Paxful accounts unveils opportunities for growth.\n\nPaxful’s verified accounts not only offer reliability within the trading community but also serve as a testament to the platform’s ability to empower economic activities worldwide. Join the journey towards expansive possibilities and enhanced financial empowerment with Paxful today. Buy Verified Paxful Account.\n\n \n\nWhy paxful keep the security measures at the top priority?\nIn today’s digital landscape, security stands as a paramount concern for all individuals engaging in online activities, particularly within marketplaces such as Paxful. It is essential for account holders to remain informed about the comprehensive security protocols that are in place to safeguard their information.\n\nSafeguarding your Paxful account is imperative to guaranteeing the safety and security of your transactions. Two essential security components, Two-Factor Authentication and Routine Security Audits, serve as the pillars fortifying this shield of protection, ensuring a secure and trustworthy user experience for all. Buy Verified Paxful Account.\n\nConclusion\nInvesting in Bitcoin offers various avenues, and among those, utilizing a Paxful account has emerged as a favored option. Paxful, an esteemed online marketplace, enables users to engage in buying and selling Bitcoin. Buy Verified Paxful Account.\n\nThe initial step involves creating an account on Paxful and completing the verification process to ensure identity authentication. Subsequently, users gain access to a diverse range of offers from fellow users on the platform. Once a suitable proposal captures your interest, you can proceed to initiate a trade with the respective user, opening the doors to a seamless Bitcoin investing experience.\n\nIn conclusion, when considering the option of purchasing verified Paxful accounts, exercising caution and conducting thorough due diligence is of utmost importance. It is highly recommended to seek reputable sources and diligently research the seller’s history and reviews before making any transactions.\n\nhttps://dmhelpshop.com/product/buy-verified-paxful-account/\n\nMoreover, it is crucial to familiarize oneself with the terms and conditions outlined by Paxful regarding account verification, bearing in mind the potential consequences of violating those terms. By adhering to these guidelines, individuals can ensure a secure and reliable experience when engaging in such transactions. Buy Verified Paxful Account.\n\nContact Us / 24 Hours Reply\nTelegram:dmhelpshop\nWhatsApp: +1 (980) 277-2786\nSkype:dmhelpshop\nEmail:dmhelpshop@gmail.com" | whitemartin015 | |
1,864,946 | Very very basic python-binance ThreadedWebSocketManager example does not work... why? | I have an application that uses the binance api to trade and do some other stuff. The app worked fine... | 0 | 2024-05-25T15:51:35 | https://dev.to/lukaseber/very-very-basic-python-binance-threadedwebsocketmanager-example-does-not-work-why-2j0o | python, binance, pythonbinance | I have an application that uses the binance api to trade and do some other stuff. The app worked fine for like 2 years, but one day it stopped working. So i decided to create a basic script to validate the core functionality of the api. I did everything exactly like its described in several offical docs and tutorials but its still not working as expected. Here is my code:
```
from binance import Client, ThreadedWebsocketManager
api_key = 'my_key'
api_secret = 'my_secret'
client = Client(api_key, api_secret)
def process_message(msg):
print("message type: {}".format(msg['e']))
print(msg)
twm = ThreadedWebsocketManager(api_key=api_key, api_secret=api_secret)
twm.start()
ret = twm.start_kline_socket(callback=process_message, symbol='BTCEUR', interval='1m')
print(ret)
twm.join()
```
So, what happens at all? The twm is created and my print statement returns: btceur@kline_1m
thats all. I expected the script to call the process_message func every 1 minute, but it does not get called after a 1 min session has completed. I have seen some similar troubles with older versions, have tried all possible solutions but I wasn´t able to fix it. I am using the latest python-binance version, v1.0.19 - 2023-08-11 and python 3.12.3 | lukaseber |
1,864,945 | #PYTHON SELENIUM ARCHITECTURE AND THE SIGNIFICANT OF PYTHON VIRTUAL ENVIRONMENT# | ** python selenium architecture**: The Python Selenium architecture allows for the automation of... | 0 | 2024-05-25T15:50:15 | https://dev.to/krishnavenis/python-selenium-architecture-and-the-significant-of-python-virtual-environment-17dk | python, selenium, architecture | ** python selenium architecture**:
The Python Selenium architecture allows for the automation of web browser interactions, making it a powerful tool for web testing and other automation tasks.
Selenium is an automation tool used for web application testing, and Python is a programming language. Selenium scripts can be written using only programming languages; the most commonly used programming languages are Java and Python.
Architecture of Selenium WebDriver (Selenium 3)
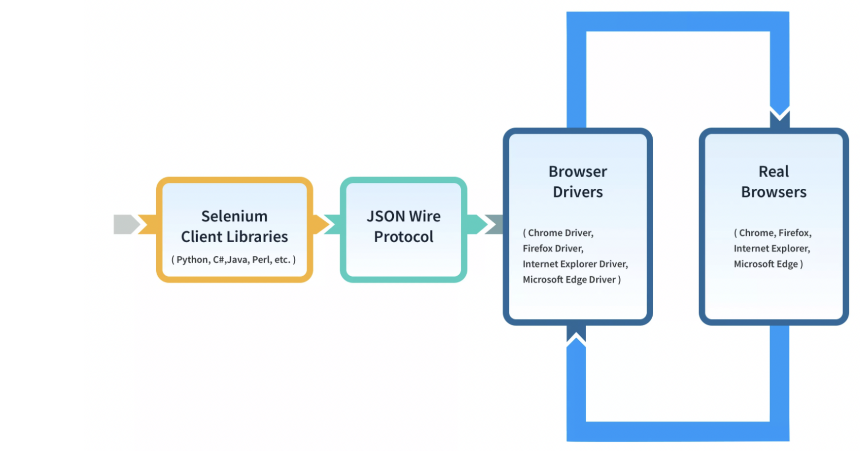
Selenium WebDriver Architecture is made up of four major components:
1- Selenium Client Library
The Selenium Client Library consists of various language libraries for Java, Ruby, Python, and other supported languages.
2- JSON WIRE PROTOCOL Over HTTP Client
JSON denotes Javascript Object Notation. This component of the Selenium WebDriver plays an important role in the Selenium automation process by transferring data between the server and a client on the web. JSON is an acronym for JavaScript Object Notation. It is an open standard that provides a transport mechanism for transferring data between client and server on the web.
3- Browser Drivers
Browser drivers are used to carry out the communication between the Selenium WebDriver and the respective browser. The Browser drivers ensure that no details are revealed to the browser regarding the internal logic of the functionalities of the browser.Selenium browser drivers are native to each browser, interacting with the browser by establishing a secure connection. Selenium supports different browser drivers such as Chrome Driver, Gecko Driver, Microsoft Edge WebDriver, Safari Driver, and Internet Explorer Driver.
4- Real Browsers
Selenium provides support for multiple browsers like Chrome, Firefox, Safari, Internet Explorer etc.
In selenium architecture and selenium 3 we have json protocol but in selenium 4 we dont have any intermediates like json.The architecture of Selenium 4 is similar to Selenium 3, however it uses W3C protocol instead of JSON wire protocol for communication between Client Libraries and Browser Drivers.
WebDriver in Selenium 4 is fully W3C compliant stands for the World Wide Web Consortium, an international community that develops and maintains standards and guidelines for the World Wide Web. The main aim of the W3C is to ensure the long-term growth and interoperability of the Web.
It creates open standards and specifications that promote compatibility and consistency across various web technologies and platforms. And when we say Selenium 4 is W3C compliant it states that Selenium adheres to the standards and specifications laid by the W3C for web automation.
All the browsers and the browser drivers in Selenium architecture follow W3C, except Selenium 3 WebDriver. And hence, JSON Wire Protocol is used to encode and decode the requests and responses. Selenium 4 WebDriver was made W3C compliant to make the communication easy and direct between the client libraries and the browser drivers. Improved communication led to more stability.
This has also enhanced browser compatibility, performance and efficiency as there is no overhead of HTTP requests and responses for communication between the WebDriver client and the browser driver. Instead, WebDriver now utilizes native browser communication channels and protocols.
-> **what is the significance of the python virtual environment? Give some examples in support of your answer?**
A virtual environment is a tool that helps to keep dependencies required by different projects separate by creating isolated Python virtual environments for them. This is one of the most important tools that most Python developers use.
Imagine a scenario where you are working on two web-based Python projects one of them uses instagram 7.0 and the other uses instagram 7.1. In such situations, we need to create virtual environment in Python that can be really useful to maintain the dependencies of both projects.
By default, every project on your system will use these same directories to store and retrieve site packages (third-party libraries). Now, in the above example of two projects, you have two versions of instagram. This is a real problem for Python since it can’t differentiate between versions in the “site-packages” directory. So both v1.7 and v1.8 would reside in the same directory with the same name. This is where virtual environments come into play. To solve this problem, we just need to create two separate virtual environments for both projects. The great thing about this is that there are no limits to the number of environments you can have since they’re just directories containing a few scripts. A virtual Environment should be used whenever you work on any Python-based project. It is generally good to have one new virtual environment for every Python-based project you work on. So the dependencies of every project are isolated from the system and each other.
We use a module named virtualenv which is a tool to create isolated Python environments. virtualenv creates a folder that contains all the necessary executable**** to use the packages that a Python project would need.Installing virtualenv = $ pip install virtualenv
Once you are done with the work, you can deactivate the virtual environment by the following command:(virtualenv_name)$ deactivate. | krishnavenis |
1,864,944 | Good Practices For Connecting Go Server To Postgres | Preparing a PG DB and Go backend Lets Create Bookstore Database where we fetch book... | 0 | 2024-05-25T15:46:41 | https://dev.to/ganesh-kumar/good-practices-for-connecting-go-server-to-postgres-3k4g |
## Preparing a PG DB and Go backend
Lets Create Bookstore Database where we fetch book details
Creating a BookStore DB in [PostgreSQL](https://www.postgresql.org/)
I'll start with the installation
```bash
$ sudo apt install postgresql
$ sudo -u postgres psql
```
### Logging into postgres
```bash
psql -h localhost -U postgres
```
Postgres console will be activated
```bash
psql (14.11 (Ubuntu 14.11-0ubuntu0.22.04.1))
Type "help" for help.
postgres=#
```
Create DB name **bookstore** by this command
```sql
postgres=CREATE DATABASE bookstore;
CREATE DATABASE
```
### Check out the DB and create Table
```sql
postgres=# \c bookstore
SSL connection (protocol: TLSv1.3, cipher: TLS_AES_256_GCM_SHA384, bits: 256, compression: off)
You are now connected to the database "bookstore" as user "postgres".
```
Create a Table in the bookstore DB
```sql
CREATE TABLE books (
isbn char(14) NOT NULL,
title varchar(255) NOT NULL,
author varchar(255) NOT NULL,
price decimal(5,2) NOT NULL
);
INSERT INTO books (isbn, title, author, price) VALUES
('9780099470464', 'A House for Mr. Biswas', 'V. S. Naipaul', 8.99),
('9780143037346', 'Miss New India', 'Bharati Mukherjee', 9.99),
('9781784782781', 'The Lives of Others', 'Neel Mukherjee', 11.99),
ALTER TABLE books ADD PRIMARY KEY (isbn);
```
Then Verify whether it is created
```bash
bookstore-# \dt
List of relations
Schema | Name | Type | Owner
--------+-------+-------+----------
public | books | table | postgres
(1 row)
```
### Setting up Go backend
```bash
$ mkdir bookstore && cd bookstore
$ mkdir models
$ touch main.go models/models.go
$ go mod init go.backend
go: creating new go.mod: module go.backend
```
File Structure of example :
```bash
bookstore/
├── go.mod
├── go.sum
├── main.go
└── models
└── models.go
```
## Set a Global DB Instance
This method simplifies accessing the database connection across the application.
It initializes the database connection, sets up an HTTP server, and listens for incoming requests.
In the context of our bookstore application, the code would look something like this
```go
// models/models.go
package models
import (
"database/sql"
)
```
Create an exported global variable to hold the database connection pool.
```go
// models/models.go
var DB *sql.DB
type Book struct {
Isbn string
Title string
Author string
Price float32
}
```
AllBooks() returns a slice of all books in the books table.
```go
// models/models.go
func AllBooks() ([]Book, error) {
// Note that we are calling Query() on the global variable.
rows, err := DB.Query("SELECT * FROM books")
if err != nil {
return nil, err
}
defer rows.Close()
var bks []Book
for rows.Next() {
var bk Book
err := rows.Scan(&bk.Isbn, &bk.Title, &bk.Author, &bk.Price)
if err != nil {
return nil, err
}
bks = append(bks, bk)
}
if err = rows.Err(); err != nil {
return nil, err
}
return bks, nil
}
```
```go
// main.go
package main
import (
"database/sql"
"fmt"
"log"
"net/http"
"go.backend/models"
_ "github.com/lib/pq"
)
```
Install dependencies
```bash
$ go get github.com/lib/pq
```
Initialize the `sql.DB` connection pool and assign it to the models.DB
```go
func main() {
var err error
// global variable.
models.DB, err = sql.Open("postgres", "postgres://user:pass@localhost/bookstore")
if err != nil {
log.Fatal(err)
}
http.HandleFunc("/books", booksIndex)
http.ListenAndServe(":3000", nil)
}
```
When I make a request **books**
```bash
$ curl localhost:3000/books
978-1503261969, Emma, Jayne Austen, £9.44
978-1505255607, The Time Machine, H. G. Wells, £5.99
978-1503379640, The Prince, Niccolò Machiavelli, £6.99
```
**Remember** global variable for the database connection is suitable when:
- Your project is simple and small, so tracking global variables isn't hard.
- Your code handling web requests is split across different folders, but all database actions stay in one folder.
- You don't need to pretend the database isn't there for testing.
### Global variable with an `InitDB` function
A variation on the 'global variable' approach that I sometimes see uses an initialization function to set up the connection pool, like so:
- All database stuff is in one place.
- The global database variable is hidden from other parts of the program, so it can't be changed by mistake.
- During testing, you can easily set up a test database connection using a special function.
```go
// models/models.go
package models
import (
"database/sql"
_ "github.com/lib/pq"
)
```
Initialize the `sql.DB` connection pool and assign it to the models.DB
```go
// This time the global variable is unexported.
var db *sql.DB
// InitDB sets up setting up the connection pool global variable.
func InitDB(dataSourceName string) error {
var err error
db, err = sql.Open("postgres", dataSourceName)
if err != nil {
return err
}
return db.Ping()
}
```
[Continue Reading](https://journal.hexmos.com/good-practices-for-connecting-go-server-to-the-postgres/#wrapping-the-connection-pool) | ganesh-kumar | |
1,864,943 | Understanding Fundamental Concepts in 𝑪# | Default Values,... | 0 | 2024-05-25T15:44:21 | https://dev.to/ipazooki/understanding-fundamental-concepts-in--32id | csharp, learning, programming | {% embed https://youtu.be/ulRMwoQ3FBs?si=ebZ52eC1SqTVmLXL %}
## Introduction
Hello, fellow programmers! I'm 🅼🅾, and today we'll explore some fundamental concepts of 𝑪#. Whether you're new to programming or refreshing your skills, this guide will help you grasp key aspects of 𝑪#. So, grab your favourite beverage ☕, and let's get started!
## Default Values
Let's begin with default values in 𝑪#. You might wonder why the default value of a string is null or why an int defaults to zero. Here's a quick explanation:
In the digital world, everything is represented by **0s** and **1s**. A zero signifies no voltage, while a one represents approximately +5 voltage. In a CPU, there are numerous pins, and the motherboard sends either zero or one voltage to these pins. When it's zero, no energy is consumed, but when it's one, energy is used.
When a variable is created with a default value, it aims to save energy. For instance, if the default value of an `int` is `zero`, it doesn't consume any voltage power when initiated because it would convert to something like 0000, and the CPU wouldn’t consume any energy for processing this variable. Similarly, the default value of a `Boolean` is `false`, meaning no voltage power is used. This principle helps in efficient power usage across your computer's operations. The same applies to a string variable; for instance, a string variable called address initially points to nothing, which is null. If you try to get the address length without any initialization, you'll get a null exception.
## Conversions
Next, let's discuss conversions in 𝑪#. There are different ways to convert data types: **implicit**, **explicit**, **boxing**, **unboxing**, and **casting**. These concepts may sound confusing, but we'll focus on implicit and explicit conversions for now.
## Implicit Conversion
This happens when the compiler automatically knows how to convert one type to another without losing data. For instance, converting an int to a long is safe because a long can hold all possible int values. If you convert an int to a long, there is no error or warning because the compiler knows it's safe.
## Explicit Conversion
This requires you to explicitly instruct the compiler to convert the value, often using a cast. This is necessary when there’s a risk of data loss, such as converting a `long` to an `int`. For example, if you try to convert a `long` to an `int`, the compiler will throw an error because it cannot implicitly convert long to int due to potential data loss. You must use explicit conversion and accept the risk of losing data.
In all conversion scenarios, if the compiler can convert the values, it is an implicit conversion. If it cannot, then it is an explicit conversion. So far, we have only discussed value type conversion, which occurs at the stack. In future discussions, we will explore boxing and unboxing, crucial for converting between value types and reference types.
## Call by Value, Call by Reference
Let's explore call by value and call by reference, essential concepts when passing variables to methods.
## Call by Value
When you pass a variable by value, a copy of the variable is sent to the method. Any changes made to the variable inside the method won't affect the original variable. For example, if you have a variable named Number and a method to alter its value, the changes inside the method won't affect the original variable outside the method.
## Call by Reference
Using the `ref` keyword ensures the method works directly with the original variable, allowing changes to be reflected outside the method. Instead of creating a new variable, the method works with the original variable, and any changes made inside the method will affect the original variable.
## Class Method vs. Instance Method
Lastly, let's discuss class methods (static methods) versus instance methods.
## Instance Methods
These are associated with an instance of a class. Each object created from the class has its own copy of the instance methods. For example, if we create another instance, it will be allocated somewhere else in the memory with its own set of instance methods.
## Static Methods
These belong to the class itself rather than any object instance. They are shared across all instances and can be accessed without creating an instance of the class. Static methods are stored in a place called **HFH ** (High-Frequency Heap) at the bottom of the heap. Being static indicates that it has all the necessary information and does not rely on other services or resources.
In multi-threaded environments, instance methods are safer because each thread has its own space and allocations. However, static methods are shared between threads, which can lead to unexpected errors if shared resources are modified by multiple threads.
## Summary
In this guide, we've covered the fundamental concepts of 𝑪#, including default values, conversions, call by value, call by reference, and the differences between class methods and instance methods. Understanding these basics is crucial for efficient and effective 𝑪# programming. As you continue to learn and practice, these concepts will become second nature, enhancing your coding skills and knowledge. Happy coding! 🖥️✨ | ipazooki |
1,864,942 | Mastering React Re-Renders : The Key Prop Hack You Need to Know | One of React's main features is its efficient re-rendering process. Unlike core JavaScript, which... | 0 | 2024-05-25T15:43:19 | https://dev.to/malapashish/mastering-react-re-renders-the-key-prop-hack-you-need-to-know-17hh | react, frontend, javascript, webdev | One of React's main features is its efficient re-rendering process. Unlike core JavaScript, which re-renders the entire DOM tree, React re-renders only the elements that have changed. A critical factor in this process is the **key** prop, which helps React identify which items need to be updated, added, or removed.
But did you know you can also force React to re-render a specific component using this prop? Interesting, right? Let's dive into how it works.

## What is the Key Prop?
The **key** prop in React is usually assigned to list elements. It helps React track which elements have changed, need to be updated, or removed.
## Why Use Keys to Force Re-renders?
Sometimes, you might need to force a component to re-render, perhaps to reset its internal state or ensure it fully updates when receiving new props. Changing the **key** prop is a straightforward way to accomplish this because it tells React to treat the component as a new one, thus triggering a re-render.
## Example:
```JSX
import React, { useState } from 'react';
const ChildComponent = ({ key }) => {
console.log('Child component rendered');
return <div>Child Component</div>;
};
const ParentComponent = () => {
const [key, setKey] = useState(1);
const updateKey = () => {
setKey(prevKey => prevKey + 1);
};
return (
<div>
<ChildComponent key={key} />
<button onClick={updateKey}>Update Key</button>
</div>
);
};
export default ParentComponent;
```
## Detailed Code Walkthrough

In this example, ParentComponent maintains a key state. The ChildComponent receives this key as a prop. Each time the button is clicked, the updateKey function increments the key, forcing ChildComponent to re-render.
## Common Use Cases
- **Resetting Component State:** When you need to reset a component's state under certain conditions.
- **Full Re-render with New Props:** Ensuring a component fully re-renders when it receives new props.
- **Managing Animations:** Triggering animations on mount/unmount by changing keys.
## Important Considerations
- **Key Uniqueness**: Ensure keys are unique among siblings to avoid unexpected behavior.
- **Performance**: Forcing re-renders by changing keys can be less efficient than updating components in place, so use this technique carefully.
## Conclusion
Using the **key** prop to force re-renders in React can be a powerful tool when used correctly. It provides a way to manage the component lifecycle and updates more precisely. Experiment with this technique to better understand how React handles rendering and component updates.
| malapashish |
1,864,941 | How I Built A Simple ‘BPO’ Company, All AI Employees (All Local) | Disrupting the BPO Industry: My Journey Building a Fully Automated Company with AI Employees Full... | 0 | 2024-05-25T15:41:46 | https://dev.to/exploredataaiml/how-i-built-a-simple-bpo-company-all-ai-employees-all-local-1p9h | rag, llm, ai, machinelearning | Disrupting the BPO Industry: My Journey Building a Fully Automated Company with AI Employees
[Full Article](https://medium.com/@learn-simplified/how-i-built-a-simple-bpo-company-all-ai-employees-all-local-631e48fa908a)
● What Are We Doing Today?
We are building a BPO (Business Process Outsourcing) call center for an imaginary electric company called "Aniket Very General Electric Company". We will create different departments staffed by AI agents who can chat (and eventually speak in next part) with customers to answer questions, handle complaints, or provide services.
● Why Should You Read This Article?
Learning how to build AI agents that can do tasks in real setting, co ordinate w/ human, AI, providing technical support will be a highly valuable skill.
● How Are We Going to Build Our All AI Employees Company?
○ We will explain what BPO and call centers are.
○ Our AI company will have departments like Customer Service, Tech Support, Billing & Payments, Outage Management, and Onboarding Customers.
○ We will use Docker containers to run the Dify AI platform as the base.
○ The AI agents will use the LLaMA-3 language model from Meta AI.
○ We may use Groq's AI accelerator chip to make LLaMA-3 faster.
○ Each department will have a knowledge base of text files that the AI agents can reference.
● Let's Get Cooking!
This section provides setup instructions for installing Docker, Ollama (for running LLaMA-3), and the Dify AI platform. It also outlines the different AI agents we will create for departments like Reception, Customer Service, Billing, Tech Support, etc.
● Let's Design our Organization
○ We explain how each department's AI agents will have their own knowledge base, like an employee handbook.
○ The knowledge bases will contain policies, procedures, and other key information.
○ The AI agents can quickly reference this information to provide accurate and knowledgeable responses.
● Let's Meet Our AI Employees
○ We chose the LLaMA-3 70B model as the base for all AI agents across departments.
○ We give the AI agents customized prompts to define their personalities and roles. ○ The knowledge bases act as training materials tailored to each department.
○ In the future, AI agents could have additional tools like ticket systems and integrations.
● Let's Run Our BPO Organization
Now that the AI workforce and knowledge bases are ready, we can open our BPO company and have the AI agents start handling customer inquiries across different departments like billing, tech support, outages, and new connections.
● Debugging
This section highlights the importance of debugging, showing traces of how the language model understands customer queries and retrieves relevant context from knowledge bases to provide good responses.
● Future Work
○ Scale up to handle more customers using cloud services or distributed computing.
○ Move AI agents and knowledge bases to the cloud for accessibility and maintenance.
○ Fine-tune language models for better performance in each department. ○ Use scalable vector databases for faster knowledge retrieval.
○ Enable voice interfaces and computer vision for more natural interactions. ○ Implement continuous learning so AI agents can expand their knowledge over time.
The article demonstrates the potential of building an actual AI-powered company and raises thought-provoking questions about the role of humans, ethics, and using AI to create a better world.
| exploredataaiml |
1,864,940 | Accessing Quality Medical Care Near Me | Access to quality medical care is essential for maintaining good health and addressing any medical... | 0 | 2024-05-25T15:34:58 | https://dev.to/backlink_30/accessing-quality-medical-care-near-me-2844 | Access to quality medical care is essential for maintaining good health and addressing any medical concerns that may arise. Whether you're seeking routine check-ups, emergency care, or specialized treatments, knowing where to find reliable medical services near your location is crucial. In this comprehensive guide, we'll explore the various aspects of accessing medical care nearby, including the importance of proximity, factors to consider when choosing a healthcare provider, and how to utilize technology to locate medical facilities efficiently.
**Importance of Proximity:**
Proximity plays a significant role in accessing medical care, especially in emergencies. Having medical facilities located near your residence or workplace ensures quick access to healthcare services when needed the most. In critical situations such as accidents or sudden illnesses, every minute counts, and having a medical facility nearby can be life-saving. Additionally, proximity reduces the time and cost associated with traveling long distances for medical appointments, making healthcare more accessible and convenient for individuals and families.
**Factors to Consider When Choosing a Healthcare Provider:**
When seeking** [Medical Care Near Me](accesstotalcare.com/locations/access-urgent-care-kingsville/)**, several factors should be taken into consideration to ensure you receive quality and personalized treatment. One of the primary considerations is the reputation and credentials of the healthcare provider. Researching the qualifications, experience, and patient reviews of doctors and medical facilities can help you gauge their competence and reliability. It's also essential to consider the range of services offered, including primary care, specialty care, diagnostic facilities, and emergency services. Accessibility, such as appointment availability, waiting times, and ease of communication with healthcare professionals, is another crucial factor to evaluate when choosing a healthcare provider.
**Utilizing Technology to Locate Medical Facilities:**
Advancements in technology have made it easier than ever to locate medical facilities and healthcare providers in your vicinity. Online platforms and mobile applications dedicated to healthcare services allow users to search for doctors, hospitals, clinics, and other medical facilities based on their location, specialties, and patient reviews. These platforms often provide detailed information about healthcare providers, including their contact details, services offered, accepted insurance plans, and patient ratings. Additionally, some apps offer features such as appointment scheduling, virtual consultations, and prescription refills, further enhancing the convenience of accessing medical care nearby.
**Primary Care Services:**
Primary care serves as the foundation of healthcare and is typically the first point of contact for individuals seeking medical assistance. Primary care physicians, including family doctors, internists, and pediatricians, are trained to provide comprehensive healthcare services, ranging from preventive care and health maintenance to the diagnosis and treatment of common illnesses and chronic conditions. Establishing a relationship with a primary care provider near you is essential for ongoing healthcare management, preventive screenings, and timely referrals to specialists when necessary.
**Specialty Care and Advanced Treatments:**
While primary care addresses a wide range of health needs, certain medical conditions may require specialized expertise and advanced treatments. Access to specialty care services, such as cardiology, oncology, orthopedics, and neurology, is crucial for individuals with specific health concerns or complex medical conditions. When seeking specialty care near you, it's essential to research healthcare providers with expertise in the relevant field and access to state-of-the-art diagnostic and treatment facilities. Collaboration between primary care providers and specialists ensures coordinated care and optimal treatment outcomes for patients.
**Emergency Medical Services:**
Emergencies can occur unexpectedly, requiring immediate medical attention. Access to emergency medical services (EMS) near your location is critical for timely interventions in life-threatening situations. Emergency departments in hospitals and urgent care centers are equipped to handle a wide range of medical emergencies, including trauma, heart attacks, strokes, and severe infections. Knowing the location and contact information of nearby emergency facilities, as well as the fastest routes to reach them, can help you respond effectively in emergency situations and potentially save lives.
**Telemedicine and Virtual Care:**
Telemedicine and virtual care have emerged as valuable tools for accessing medical services remotely, particularly in situations where physical visits to healthcare facilities may be challenging or unnecessary. Through telemedicine platforms, patients can consult with healthcare providers via video conferencing or phone calls, receive medical advice, discuss symptoms, and even obtain prescriptions without leaving their homes. Virtual care services offer convenience, flexibility, and expanded access to healthcare, especially for individuals with mobility limitations, busy schedules, or rural residences.
**Community Health Resources:**
In addition to traditional medical facilities, community health resources play a vital role in promoting wellness and addressing the healthcare needs of underserved populations. Community health centers, free clinics, and outreach programs offer a range of services, including primary care, preventive screenings, immunizations, and health education, often at reduced or no cost for low-income individuals and families. These resources serve as safety nets for those without insurance or access to mainstream healthcare providers, ensuring that everyone has the opportunity to receive essential medical care and support.
**Conclusion:**
Accessing quality medical care near you is essential for maintaining optimal health and well-being. By considering factors such as proximity, provider reputation, and available services, individuals can make informed decisions when choosing healthcare providers. Utilizing technology, including online platforms and telemedicine services, enhances the convenience and accessibility of medical care, while community health resources provide essential support for underserved populations. Whether it's routine check-ups, emergency interventions, or specialized treatments, knowing where to find reliable medical services nearby ensures timely and effective healthcare delivery for everyone. | backlink_30 | |
1,864,939 | Authentication Using React-hook-form | Hey Everyone, Today I discuss the REACT HOOK FORM it is easy to use for validating forms, shows the... | 0 | 2024-05-25T15:34:52 | https://dev.to/shiwani295/authentication-using-react-hook-form-1e0l | react, nextjs, webdev, javascript | Hey Everyone,
Today I discuss the REACT HOOK FORM it is easy to use for validating forms, shows the error message and you can easily update the form value as well
so there are some steps which you have to follow -
1. you can also go through the official website of React Hook form here the link - https://react-hook-form.com/get-started
2. Install the react hook form by using this link - https://www.npmjs.com/package/react-hook-form
3. create your Login or signup form first
4. then use the useForm() hook you can so this through the official website for this
## Example-
```
import React from 'react'
import { createUserWithEmailAndPassword } from 'firebase/auth';
import { useForm } from 'react-hook-form';
const Register = ({ history }) => {
const {
handleSubmit,
formState: { errors },
trigger,
register,
watch
} = useForm();
async function onhandleSubmit(data) {
//console.log(data)
try {
await createUserWithEmailAndPassword(
auth, data.email, data.password, data.name)
history.push("/");
alert ("User Created Successfully")
} catch (error) {
console.log(error)
alert ("User created failed")
alert(error);
}
}
return (
<div>
<Form onSubmit={handleSubmit(onhandleSubmit)}>
<h5>Create an account</h5>
<div>
<div>
<label>Your email address</label>
<input
id="email"
name="email"
type= 'email'
required={true}
{...register("email", {
required: "Email is Required!!!" ,
pattern: {
value: /^[A-Z0-9._%+-]+@[A-Z0-9.-]+\.[A-Z]{2,}$/i,
message: "Invalid email address",
}})}
error={Boolean(errors.email)}
></input>
{errors.email && (
<small className="text-danger">{errors.email.message}</small>
)}
</div>
<div>
<label>Your password</label>
<input
name='password'
id="password"
type= 'password'
autoComplete='off'
className={`form-control ${errors.password && "invalid"}`}
required={true}
{...register("password", {
required: "You must specify a password",
pattern: {
value: '^(?=.*?[A-Z])(?=(.*[a-z]){1,})(?=(.*[\d]){1,})(?=(.*[\W]){ 1,})(?!.*\s).{8,}$',
message: "Password should contain at least one number and one special character"
},
minLength: {
value: 8,
message: "Password must be more than 8 characters"
},
maxLength: {
value: 20,
message: "Password must be less than 20 characters"
},
})}
></input>
{errors.password && (
<small className="text-danger">{errors.password.message}</small>
)}
</div>
<div>
<label>Confirm your password</label>
<input
id="confirmPassword"
name="confirmPassword"
type='password'
{...register( 'confirmPassword', {
validate: value =>
value === watch("password", "") || "The passwords do not match"
})}
autoComplete='off'
onPaste={(e) =>{
e.preventDefault();
return false
}}
error={Boolean(errors.confirmPassword)}
className={`form-control ${errors.confirmPassword && "invalid"}`}
required={true}
/>
{errors.confirmPassword && (
<small className="text-danger">{errors.confirmPassword.message} </small>
)}
</div>
<div>
<label>Your full name</label>
<input
name='name'
type="name"
className={`form-control ${errors.name && "invalid"}`}
required={true}
defaultValue=""
{...register("name", { required: "Fullname is Required!!!" })}
{errors.name && (
<small className="text-danger">Fullname is Required!!!</small>
)}
</div>
<div>
<button>Create an account</button>
</div>
</div>
</Form>
</div>
)}
export default withRouter(Register)
```
here is the example please go through and if you like this article like my article and follow for more updates
| shiwani295 |
1,864,936 | Use AIAnsible debug Ansible playbook and role, and use AI annotations and hints to resolve errors. | https://github.com/sunnycloudy/aiansible Debug Ansible, and use chatgpt or kimi AI annotations and... | 0 | 2024-05-25T15:23:07 | https://dev.to/a_jun_1d592a39703eed80f31/debug-ansible-and-use-chatgpt-or-kimi-ai-annotations-and-hints-to-resolve-errors-52c8 | devops, debug, ansible, aiops | ERROR: type should be string, got "https://github.com/sunnycloudy/aiansible\n\n Debug Ansible, and use chatgpt or kimi AI annotations and hints to resolve errors.\n\n\nAIAnsible has greatly simplified the debugging process for Ansible. You no longer need to have an in-depth knowledge of the details of Ansible tasks; simply knowing how to execute them is sufficient. Particularly when facing complex Ansible tasks like kubespray or ceph-ansible, the analytical features of AIAnsible are especially crucial. It can help you understand these tasks by debugging and organizing the task flow. If you want to clearly grasp the execution details of these complex tasks within a cluster, AIAnsible is undoubtedly a strong assistant for you.\n\n\n\n## basic usage:\n```\n:cn Set the language to Chinese\n:en Set the language to English\ni Annotate the code of the currently executing task\nir Annotate the code of the currently executing task, analyze the results, and provide suggestions for improvement\nask Please answer questions based on the current Ansible task\nn next Run the next task\nm Do not stay at the same task again immediately\nc continue Continue running until the next breakpoint\nb Create a breakpoint\np View created breakpoints\nd delete Delete a breakpoint\nbt View which tasks have been run\ncode View the code of the currently running task\nv Open the corresponding file with VSCode\na arg View all arguments, or a single argument (assuming the task has not been skipped)\n? help View the usage instructions\nexit Exit\n```\n\n### check the result of current ansible task:\n```\nAiansible(CN) => result._result\n{'msg': 'Check roles/kubespray-defaults/defaults/main.yml', '_ansible_verbose_always': True, '_ansible_no_log': False, 'changed': False}\n```\n\n\n## ai prompt example:\nIf you want to use English:\n```\nexport AIANSIBLE_LANG=EN\n```\n\n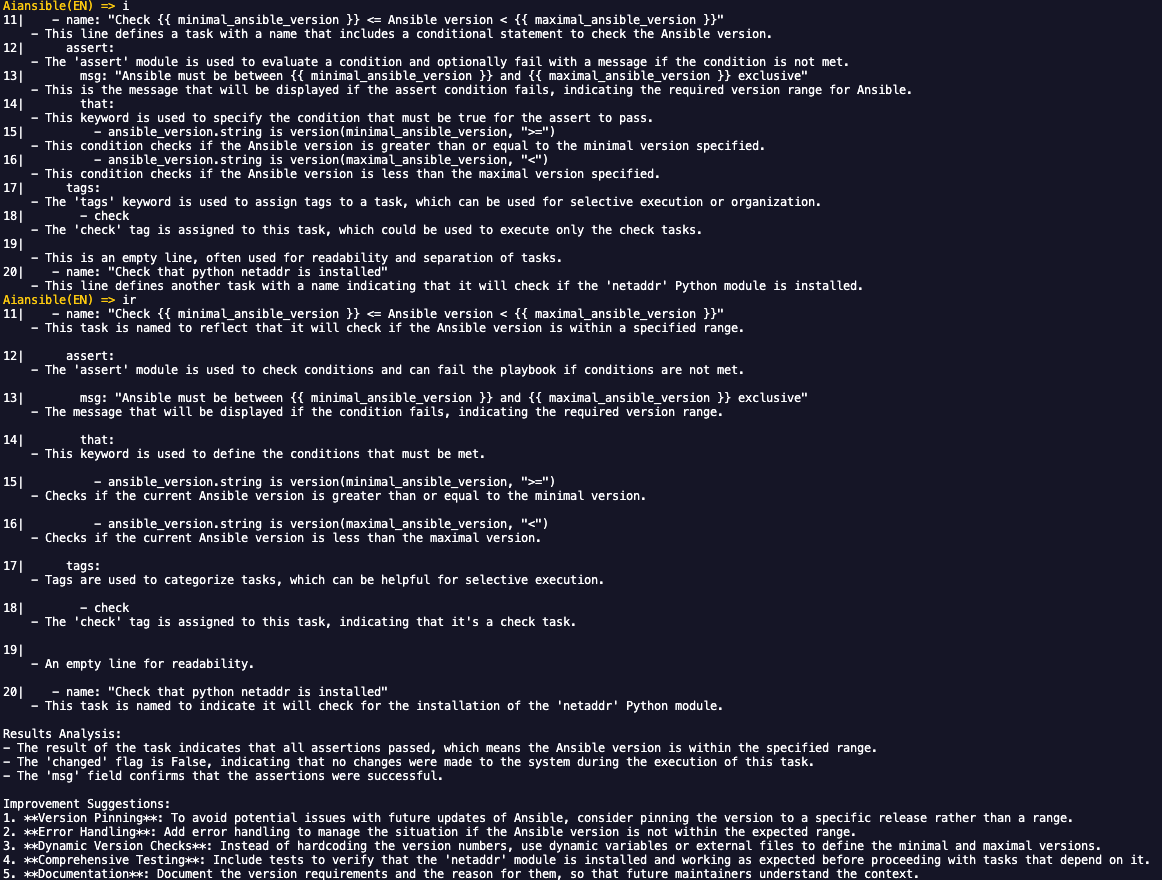\n\n\n### or use \":cn\"and\":en\" to switch language:\n\n\n\n\n### install and start using aiansible:\n- (1) **download and install**\n```\n git clone https://github.com/sunnycloudy/aiansible.git\n cd aiansible\n pip install . #=> will generate dir: ~/.aiansible_plugin\n```\n\n\n- (2) **install dependents:**\n```\npip install -r requirements.txt\n```\n\n- (3) **create a:debug.cfg**\n```\n[defaults]\ncallback_plugins = ~/.aiansible_plugin\ncallbacks_enabled = aiansible.py\n```\n- (4) **set environments:**\n```\n# If it's not necessary to use AI, you can choose not to set following variable:\nexport OPENAI_API_URL=https://api.moonshot.cn/v1 #Or other API addresses compatible with OpenAI.\nexport OPENAI_API_KEY=xxxxxxxxxxxxxxxxxxxxxxxxxxxxx #Or other keys compatible with OpenAI.\n\n# Configure the plugin in the debug.cfg file.\nexport ANSIBLE_CONFIG=./debug.cfg\n```\n- (5) **run command:**\n```\nansible-playbook xxx_playbook.yml\n```\n\n---\n# demo:\n\n## debug kubespray:\n```\n# find\nkubespray/ansible.cfg\n```\n\n### edit kubespray default ansible.cfg:\n```\n[ssh_connection]\npipelining=True\nansible_ssh_args = -o ControlMaster=auto -o ControlPersist=30m -o ConnectionAttempts=100 -o UserKnownHostsFile=/dev/null\n#control_path = ~/.ssh/ansible-%%r@%%h:%%p\n[defaults]\n# https://github.com/ansible/ansible/issues/56930 (to ignore group names with - and .)\nforce_valid_group_names = ignore\n\nhost_key_checking=False\ngathering = smart\nfact_caching = jsonfile\nfact_caching_connection = /tmp\nfact_caching_timeout = 86400\nstdout_callback = default\ndisplay_skipped_hosts = no\nlibrary = ./library\n# callbacks_enabled = profile_tasks,ara_default #<= comment it (・ω・)ノ\ncallback_plugins = ~/.aiansible_plugin #<= new line (。・ω・。)ノ\ncallbacks_enabled = aiansible.py #<= new line ( ・ω・ )ノ\n\nroles_path = roles:$VIRTUAL_ENV/usr/local/share/kubespray/roles:$VIRTUAL_ENV/usr/local/share/ansible/roles:/usr/share/kubespray/roles\ndeprecation_warnings=False\ninventory_ignore_extensions = ~, .orig, .bak, .ini, .cfg, .retry, .pyc, .pyo, .creds, .gpg\n[inventory]\nignore_patterns = artifacts, credentials\n\n```\n\n### run command:\n```\n# If it's not necessary to use AI, you can choose not to set following variable:\nexport OPENAI_API_URL=https://api.moonshot.cn/v1 #Or other API addresses compatible with OpenAI.\nexport OPENAI_API_KEY=xxxxxxxxxxxxxxxxxxxxxxxxxxxxx #Or other keys compatible with OpenAI.\n\n# run playbook in debug mode:\nexport AIANSIBLE_LANG=EN\nexport ANSIBLE_CONFIG=./ansible.cfg\nansible-playbook --become -i inventory/mycluster/inventory.ini cluster.yml\n```\n\n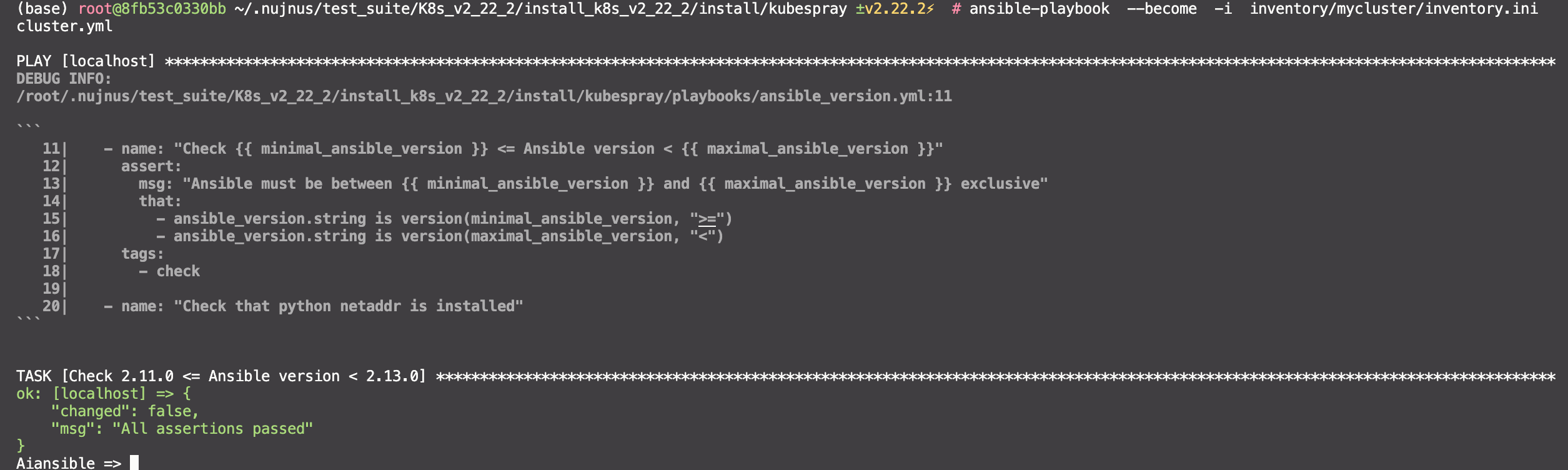\n\n\n### edit mode:support emacs-mode or vim-mode, default is emacs-mode\n```\nexport AIANSIBLE_EDITMODE=vi\n#或\nexport AIANSIBLE_EDITMODE=emacs\n```" | a_jun_1d592a39703eed80f31 |
1,864,935 | Dasturning arxitekturasi quyidagi chizma orqali tasvirlanadi: | Dasturning arxitekturasi quyidagi chizma orqali tasvirlanadi: Boshqaqa (User Interface): Dastur... | 0 | 2024-05-25T15:21:11 | https://dev.to/qodirovdeveloper/dasturning-arxitekturasi-quyidagi-chizma-orqali-tasvirlanadi-4e1b | Dasturning arxitekturasi quyidagi chizma orqali tasvirlanadi:
Boshqaqa (User Interface): Dastur boshlanganida foydalanuvchiga xush kelibsiz xabarini chiqaradi va kerakli barcha ma'lumotlarni kiritishga yordam beradi.
Ma'lumotlarni qabul qilish (Data Input): Foydalanuvchi tomonidan kiritilgan rubl va dollar balanslari va amalga oshirilishi kerak bo'lgan valyuta miqdorlari kiritiladi.
Operatsiyani tanlash (Operation Selection): Foydalanuvchining tanlagan operatsiyasi (rublarni dollarga almashtirish yoki dollarni so'mga almashtirish) aniqlanadi.
Operatsiyani amalga oshirish (Operation Execution): Tanlangan operatsiya bajariladi. Agar foydalanuvchi rublarni dollarga almashtirishni tanlasa, miqdor mos kursga ko'ra hisoblanadi va boshqa valyutaga almashtiriladi. Agar foydalanuvchi dollarni so'mga almashtirishni tanlasa, kiritilgan miqdor usdToRub kursiga ko'ra hisoblanadi va so'mga o'tkaziladi.
Natijani ko'rsatish (Display Result): Amalga oshirilgan operatsiya natijasi va yangi balanslar foydalanuvchiga chiqariladi.
Dasturni to'xtatish (Program Termination): Foydalanuvchi dasturni tugatish uchun tugma bosishini kutish bilan dastur to'xtatiladi.
Ushbu chizma dasturning har bir qismi va faoliyati uchun birinchi sinfning (class) funksionalini ko'rsatadi. Dasturning umumiy arxitekturasi dastur yozuvining oson tushunarli va o'rganilishi uchun moslashtirilgan.
| qodirovdeveloper | |
1,864,929 | Understanding JavaScript Promises | Introduction JavaScript Promises are a powerful feature that allows you to handle... | 0 | 2024-05-25T15:18:58 | https://dev.to/visavadiyavrushik/understanding-javascript-promises-57o4 | javascript, react, webdev, beginners | ## Introduction
JavaScript Promises are a powerful feature that allows you to handle asynchronous operations more efficiently. In this blog post, we will explore what promises are, how they work, and provide examples to illustrate their usage.
## What is a Promise?
A promise is an object representing the eventual completion or failure of an asynchronous operation. It can be in one of three states:
1. **Pending**: The initial state, neither fulfilled nor rejected.
2. **Fulfilled**: The operation completed successfully.
3. **Rejected**: The operation failed.
-----------
## Creating a Promise
You can create a promise using the Promise constructor, which takes a function as an argument. This function is called the executor and it receives two arguments: resolve and reject.
```javascript
const myPromise = new Promise((resolve, reject) => {
// Asynchronous operation
let success = true;
if (success) {
resolve("Operation was successful!");
} else {
reject("Operation failed!");
}
});
```
---------------
## Using Promises
To handle the result of a promise, you use the .then() and .catch() methods.
```javascript
myPromise
.then((message) => {
console.log(message); // Output: Operation was successful!
})
.catch((error) => {
console.error(error); // This won't run in this example
});
```
-----------
## Chaining Promises
Promises can be chained to handle a sequence of asynchronous operations.
```javascript
const firstPromise = new Promise((resolve, reject) => {
setTimeout(() => resolve("First promise resolved!"), 1000);
});
firstPromise
.then((message) => {
console.log(message); // Output: First promise resolved!
return new Promise((resolve, reject) => {
setTimeout(() => resolve("Second promise resolved!"), 1000);
});
})
.then((message) => {
console.log(message); // Output: Second promise resolved!
})
.catch((error) => {
console.error(error);
});
```
---------
## Handling Multiple Promises
`Promise.all` and `Promise.race` are useful for handling multiple promises concurrently.
### `Promise.all`
`Promise.all` waits for all promises to be fulfilled or any to be rejected.
```javascript
const promise1 = new Promise((resolve) => setTimeout(resolve, 1000, 'First'));
const promise2 = new Promise((resolve) => setTimeout(resolve, 2000, 'Second'));
const promise3 = new Promise((resolve) => setTimeout(resolve, 3000, 'Third'));
Promise.all([promise1, promise2, promise3])
.then((values) => {
console.log(values); // Output: ["First", "Second", "Third"]
})
.catch((error) => {
console.error(error);
});
```
### `Promise.race`
`Promise.race` returns the result of the first promise that settles (fulfills or rejects).
```javascript
const promiseA = new Promise((resolve) => setTimeout(resolve, 1000, 'Fast'));
const promiseB = new Promise((resolve) => setTimeout(resolve, 2000, 'Slow'));
Promise.race([promiseA, promiseB])
.then((value) => {
console.log(value); // Output: "Fast"
})
.catch((error) => {
console.error(error);
});
```
----------
JavaScript Promises provide a robust way to manage asynchronous operations, avoiding the pitfalls of callback hell and making your code more readable and maintainable. Understanding and using promises effectively can significantly improve your JavaScript programming skills.
-----------
References
[MDN Web Docs](https://developer.mozilla.org/en-US/docs/Web/JavaScript/Reference/Global_Objects/Promise): Promises
------ | visavadiyavrushik |
1,864,928 | Pul miqdorini rubldan dollarga va aksincha o'zgartirishga va tranzaksiyadan so'ng balansni ko'rsatishga imkon beradi. | Siz taqdim etgan kod oddiy C# konsol dasturi boʻlib, foydalanuvchiga pul miqdorini rubldan dollarga... | 0 | 2024-05-25T15:14:35 | https://dev.to/qodirovdeveloper/pul-miqdorini-rubldan-dollarga-va-aksincha-ozgartirishga-va-tranzaksiyadan-song-balansni-korsatishga-imkon-beradi-46dm | Siz taqdim etgan kod oddiy C# konsol dasturi boʻlib, foydalanuvchiga pul miqdorini rubldan dollarga va aksincha oʻzgartirishga va tranzaksiyadan soʻng balansni koʻrsatishga imkon beradi.
Dastur arxitekturasiga kelsak, uni quyidagicha tavsiflash mumkin:
Loyiha tuzilmasi: Loyihada barcha dastur mantig'ini o'z ichiga olgan bir manba kod fayli, Program.cs mavjud.
Asosiy funktsiya Main: Bu dasturning asosiy kirish nuqtasi. U o'zgaruvchilarni e'lon qiladi, foydalanuvchiga xush kelibsiz xabarlar va ko'rsatmalarni ko'rsatadi va foydalanuvchi kiritishi va valyuta ayirboshlash operatsiyalarini bajaradi.
Kiritish/chiqarish uchun konsoldan foydalanish: Dastur foydalanuvchi bilan muloqot qilish uchun konsol kiritish va chiqishlaridan foydalanadi.
Istisnolarni ko'rib chiqish: Dastur foydalanuvchi kiritishi noto'g'ri bo'lishi mumkin bo'lgan vaziyatlarni (masalan, raqamli bo'lmagan qiymatlarni kiritish) ko'rib chiqishni ta'minlaydi.
Oddiy valyutani konvertatsiya qilish mantig'i: Dastur shunchaki joriy kurs bo'yicha pul miqdorini o'zgartiradi.
Shartli bayonotlar va almashtirish siklidan foydalanish: Dastur operatsiyasini tanlash uchun foydalanuvchi kiritgan qiymatni baholovchi va tegishli kod blokini bajaradigan switch operatoridan foydalaniladi.
Umuman olganda, ushbu dasturning arxitekturasi oddiy chiziqli boshqaruv oqimi bo'lib, unda axborot kiritiladi, ma'lum bir operatsiya bajariladi va natija chiqariladi. Ushbu kodda maxsus arxitektura modeli yoki dizayn namunasi mavjud emas, chunki dastur juda oddiy va cheklangan funktsiyalar to'plamini bajaradi. | qodirovdeveloper | |
1,864,927 | A GAME IN JUST 30 MINUTES 😲 !! | I recently called @mince for a challenge .The challenge was simple. We just have to make a game in... | 0 | 2024-05-25T15:12:19 | https://dev.to/dino2328/a-game-in-just-30-minutes--2db0 | webdev, javascript, beginners, tutorial | I recently called @mince for a challenge .The challenge was simple. We just have to make a game in scratch and the time is 30min. This also has some points making
1 view in scratch - 1 point
1 heart- 2 points
1 star-2 points
1 remix- 3 points
1 comment -5 points
This is how we consider the points. The one who loses should praise the other person by writing a post in dev.to. I thought I should not lose this challenge with @mince
## Starting
As I started the timer I felt nervous because I didn't have one game to do so I wasted literally 10minutes just thinking what should I do and after these 10 minutes I got a plan for my scratch game.
## Plan
My plan is easy. I have to create 100 GIGA'S of different colours and there will be one different GIGA just with a spectacles and if we find the odd GIGA among the 100 other we will get one point
## Implementing
The first thing I should keep in mind is I have 20 minutes and I did not write one line of code also. I first started by adding GIGA with spectacles and the starting page. The second I duplicated many GIGA's to make 100 GIGA's and wrote all of the code and the winning page. My game does not have anything to lose .In the last 5 minutes I did the score variable and ended my project and time was also over
## Please support me by giving a heart,star,remix and a comment so that I can win over @mince
MY PROJECT: [FINDING GIGA](https://scratch.mit.edu/projects/1027030846/)
@mince project: [Pizza Clicker](https://scratch.mit.edu/projects/1027030846/)
| dino2328 |
1,864,926 | OCBC | Found No Debit Card PIN for Applying One-Token while Signing in on a New Phone? | In OCBC-SG app, tap "Log in to OCBC Singapore" Input Access code and PIN (this is not the Debit Card... | 0 | 2024-05-25T15:10:42 | https://dev.to/01kg/ocbc-found-no-debit-card-pin-for-applying-one-token-while-signing-in-on-a-new-phone-o1l | 1. In OCBC-SG app, tap "Log in to OCBC Singapore"
2. Input Access code and PIN (this is not the Debit Card PIN)
3. "Activate with SMS OTP and card PIN"
4. Step 1: Enter the SMS OTP sent to your mobile number
5. Step 2: tap "I do not have my card PIN"
6. tick "Request Token Key"
7. Confirm your mailing address (Note: Changing mailing address is not supported because while submitting the new mailing address on web personal banking, error would pop-up: "Sorry, you are not able to continue this transaction. Please activate OneToken by going to Manage OCBC OneToken in your Mobile device")
Since for overseas users, it will take about 3 weeks to receive this ordinary mail that contains your Debit Card PIN. Too Late.
Instead, after 2-3 working days, call Service Phone to ask the representative to send the PIN to your Secured Mailbox.
Don't worry, even without OneToken, you could still access your Secured Mailbox, by logging into OCBC app via Access Code, Access PIN and the OTP sent to your phone number.
| 01kg | |
1,864,925 | Docker Compose vs. Dockerfile | Dockerfile and Docker Compose are both part of the Docker universe but are different things with... | 0 | 2024-05-25T15:06:31 | https://dev.to/vaibhavhariaramani/docker-compose-vs-dockerfile-54ki |
**Dockerfile** and **Docker Compose** are both part of the Docker universe but are different things with different functions.
A Dockerfile describes how to build a Docker image, while Docker Compose is a command for running a Docker container.
**What Is a Dockerfile?**
A **Dockerfile** is a text document that contains all the commands a user needs to build a Docker image, a file used to execute code in a Docker container. When a user runs the Docker run command and specifies WordPress, Docker uses this file, the Dockerfile, to build the image.
**What Is Docker Compose?**
**Docker Compose** is a tool for defining and running Docker containers by reading configuration data from a YAML file, which is a human-readable data-serialization language commonly used for configuration files and in applications where data is being stored or transmitted.
**Dockerfile vs. Docker Compose: Overview**
A **Dockerfile** is a text document with a series of commands used to build a Docker image.
**Docker Compose** is a tool for defining and running multi-container applications.
When to Use and How to Run a Dockerfile: Example
A **Dockerfile** can be used by anyone wanting to build a Docker image. To use a Dockerfile to build a Docker image, you need to use docker build commands, which use a “context,” or the set of files located in the specified PATH or URL. The build process can refer to any of the files in the context, and the URL parameter can refer to Git repositories, pre-packaged tarball contexts, or plain text files.
According to Docker:
“A Docker image consists of read-only layers, each of which represents a Dockerfile instruction. The layers are stacked and each one is a delta of the changes from the previous layer.”
`# syntax=docker/dockerfile:1
FROM ubuntu:18.04
COPY . /app
RUN make /app
CMD python /app/app.py`
In this Dockerfile:
Dockerfile
Each instruction creates one layer:
- FROM creates a layer from the ubuntu:18.04 Docker image.
- COPY adds files from your Docker client’s current directory.
- RUN builds your application with make.
- CMD specifies what command to run within the container.
Running an image and generating a container adds a new writable layer, the “container layer,” on top of the underlying layers. All changes made to the running container, such as writing new files, modifying existing files, and deleting files, are written to this writable container layer.
**When to Use and How to Run Docker Compose: Example**
Use Docker Compose to run multi-container applications.
To use **Docker Compose**, you need to use a YAML file to configure your application’s services. Then, with a single command, you can create and start all the services from your configuration.
**To use Docker Compose:**
1. Use a Dockerfile to define your app’s environment so it can be reproduced anywhere.
2. Define the services that make up your app in docker-compose.yml so you can run them together in an isolated environment.
3. Use docker compose up and Docker compose command to start and run your entire app.
Here’s an example of a docker-compose.yml:
**Dockerfile vs. Docker Compose: FAQs**
- **Does Docker Compose replace Dockerfile?**
- No—Docker Compose does not replace Dockerfile. Dockerfile is part of a process to build Docker images, which are part of containers, while Docker Compose is used for orchestrating.
- **Is Docker-Compose the Same as Docker Compose?**
- Docker Compose is the name of the tool, while docker-compose is the name of the actual command—i.e., the code—used in Docker Compose.
- **Should You Use Docker Compose in Production?**
- Yes. Docker Compose works in all environments: production, staging, development, testing, as well as CI workflows.
| vaibhavhariaramani | |
1,864,924 | ACID Compliance in Relational Databases. | In the previous edition, I discussed one of the system’s components: databases. I then discussed... | 0 | 2024-05-25T15:07:47 | https://medium.com/backenders-club/acid-compliance-in-relational-databases-97091c6aae98 | backend, javascript, coding, database | ---
title: ACID Compliance in Relational Databases.
published: true
date: 2024-05-25 15:05:35 UTC
tags: backend,javascript,coding,database
canonical_url: https://medium.com/backenders-club/acid-compliance-in-relational-databases-97091c6aae98
---
[In the previous edition](https://newsletter.masteringbackend.com/p/understanding-system-design-databases), I discussed one of the system’s components: **databases. I then discussed databases, the types of Databases, and relational and non-relational databases, elucidating** the benefits and advantages of each type of database.
In this episode, I will continue with Database ACID compliance and explore why it’s important in databases, especially relational databases. We will elucidate the following topics:
1. Atomicity
2. Consistency
3. Isolation
4. Durability
### What is ACID Compliance?
Database ACID Compliance is a set of database attributes that ensures that database transactions are completed efficiently. It consists of Atomicity, Consistency, Isolation, and Durability.

ACID Compliance in Relational Databases
A transaction is a group of operations executed as a single unit of work.
An example of a transaction is when money is transferred between bank accounts. Money must be debited from one account and credited to another.
If a database fulfills the following aspects of ACID compliance, it is known to be ACID-compliant.
Atomicity compliance ensures that all transactions are completed successfully. If not, the transaction is aborted, and no changes are made to the database.
Database transactions, also known as atoms, can be divided into smaller components to ensure their integrity.
During a transaction, either all operations occur, or none do. If a debit is successfully deducted from one account, Atomicity guarantees that the corresponding credit is applied to the other account.
#### Atomicity in Postgres Database
Implementing atomicity in the PostgreSQL database involves the use of transactions. Here’s a basic example of how you can ensure atomicity in PostgreSQL:
```
BEGIN; -- Start a transaction
-- Your SQL statements go here
-- For example:
UPDATE account SET balance = balance - 100 WHERE account_id = 123; -- Debit from one account
UPDATE account SET balance = balance + 100 WHERE account_id = 456; -- Credit to another account
COMMIT; -- If all statements succeed, commit the transaction
-- If any statement fails or encounters an error, the transaction will be rolled back automatically
```
- BEGIN; starts a new transaction.
- SQL statements within the transaction are executed one after another.
- If all SQL statements execute successfully, COMMIT; is used to save the changes permanently.
- If any statement within the transaction fails or encounters an error, the transaction is rolled back automatically, and all changes made are discarded. This ensures atomicity — all operations are completed successfully, or none are.
### Consistency
Consistency compliance guarantees that a transaction brings the database from one valid state to another, maintaining database invariants.
Consistency guarantees that transactions uphold data integrity, preserving the data consistently and accurately. It mandates adherence to data constraints. For instance, a constraint may dictate that the amount column cannot hold negative values. Should a transaction result in data that violates these constraints, the transaction is terminated, and an error is flagged.
#### Consistency in Postgres Database
In PostgreSQL, consistency can be implemented through various means, including:
1. **Constraints** : Utilize constraints such as CHECK constraints to ensure that data adheres to specified rules. For example, you can enforce that a column cannot contain negative values using a CHECK constraint.
```
CREATE TABLE example_table (
amount NUMERIC CHECK (amount >= 0)
);
```
1. **Transactions** : Wrap multiple database operations within a transaction block to ensure that either all operations are completed successfully or none are. This helps maintain consistency by avoiding intermediate states that could compromise data integrity.
```
BEGIN;
-- SQL statements here
COMMIT;
```
1. **Foreign Keys** : Use foreign key constraints to enforce referential integrity between tables. This ensures that data relationships remain consistent.
```
CREATE TABLE table1 (
id SERIAL PRIMARY KEY,
name VARCHAR(50)
);
```
1. **Indexes** : Properly index your database tables to optimize data access and maintain consistency in query results.
```
CREATE INDEX idx_table_column ON table(column);
```
By utilizing these features and best practices, you can effectively implement consistency in PostgreSQL databases, ensuring data integrity and reliability.
### Isolation
Isolation compliance ensures that transactions executed concurrently leave the database in the same state as if they were executed sequentially.
Isolation means that the transaction’s intermediate state is invisible to other transactions until a commit is made (concurrent control).
For example, Account A has $1,000, and two transactions are made simultaneously. Transaction A wants to transfer $1000 to another account, and transaction B wants to transfer $200. They would leave the account invalid if these two transactions were allowed (-$200).
To prevent this, a database should only allow one transaction on an account at a time. The transactions should be done sequentially and put in some queue.
#### Isolation in Postgres Database
Isolation in PostgreSQL, as in other relational databases, is primarily achieved through transaction isolation levels. PostgreSQL supports several isolation levels to control how transactions interact with each other. Here’s how you can implement isolation in PostgreSQL:
1. **Read Uncommitted** : This is the lowest isolation level, where transactions can see uncommitted changes made by other transactions.
```
SET TRANSACTION ISOLATION LEVEL READ UNCOMMITTED;
```
1. **Read Committed** : Transactions can only see changes committed by other transactions. This is the default isolation level in PostgreSQL.
```
SET TRANSACTION ISOLATION LEVEL READ COMMITTED;
```
1. **Repeatable Read** : Transactions can only see data that was committed before the transaction started. This prevents non-repeatable reads.
```
SET TRANSACTION ISOLATION LEVEL REPEATABLE READ;
```
1. **Serializable** : This is the highest isolation level, where transactions behave as if executed serially, preventing concurrency issues.
```
SET TRANSACTION ISOLATION LEVEL SERIALIZABLE;
```
You can set the isolation level for a particular transaction or change the default isolation level for the entire session.
Ensure you choose an appropriate isolation level based on your application’s requirements to balance consistency and performance.
Proper indexing and query optimization can also help manage isolation levels effectively.
### Durability
Durability compliance ensures that changes persist in non-volatile memory when a transaction is completed successfully, even in system failure. Once a transaction is committed, it remains so, even in a system crash.
As in most databases, Durability in PostgreSQL primarily involves ensuring that committed transactions persist even in the face of system failures. PostgreSQL achieves durability through a combination of mechanisms:
1. **Write Ahead Logging (WAL)**: PostgreSQL uses WAL to ensure durability. Before any changes are made to the database, they are written to a log file (WAL) on disk. Once the changes are safely recorded in the WAL, they are applied to the data files. This ensures that even if a crash occurs before changes are written to disk, they can be replayed from the WAL during recovery.
2. **Synchronous Commit** : PostgreSQL allows configuring synchronous commit behavior, where the server waits for confirmation that data has been written to disk before acknowledging a transaction commit. This provides stronger durability guarantees at the expense of potentially increased latency.
3. **fsync and Write-Through** : PostgreSQL relies on the operating system’s facilities to ensure that data is written to disk and persists across system crashes. This typically involves using mechanisms like fsync to force data to be written to disk and ensure write-through caching policies.
To implement durability in PostgreSQL, you don’t usually need to take explicit actions beyond ensuring that your database is properly configured and the underlying storage system is reliable.
However, you can configure parameters related to WAL and synchronous commit behavior in the PostgreSQL configuration file ( postgresql.conf) to tailor durability settings to your specific requirements.
For example, you can adjust the wal\_level, fsync, and synchronous\_commit parameters in postgresql.conf to control how PostgreSQL ensures durability. Ensuring proper backup and recovery mechanisms is crucial for maintaining durability in PostgreSQL databases.
#### ACID Compliance Databases
Below is the list of databases that are ACID compliance:
1. MongoDB from version 4.0
2. MySQL
3. PostgreSQL
4. Oracle
5. MariaSQL
Today, I discussed ACID Compliance in Databases, where I discussed Atomicity, Consistency, Isolation, and Durability.
Next week, I will start exploring **Database Replication.**
Don’t miss it. Share with a friend.
_This article is from my newsletter_ [_“Backend Weekly,”_](https://newsletter.masteringbackend.com/) _where I explain complex concepts in Backend Engineering every weekend, share exclusive backend engineering resources, and help you become a great Backend Engineer._
_Originally published at_ [_https://newsletter.masteringbackend.com_](https://newsletter.masteringbackend.com/p/acid-compliance-in-relational-databases)_._
* * * | kaperskyguru |
1,864,923 | конвертировать суммы денег из рублей в доллары и наоборот, и выводить баланс после операции. | Код, который вы предоставили, представляет собой простую консольную программу на языке C#, которая... | 0 | 2024-05-25T15:02:36 | https://dev.to/qodirovdeveloper/konviertirovat-summy-dieniegh-iz-rubliei-v-dollary-i-naoborot-i-vyvodit-balans-poslie-opieratsii-11c8 | Код, который вы предоставили, представляет собой простую консольную программу на языке C#, которая позволяет пользователю конвертировать суммы денег из рублей в доллары и наоборот, и выводить баланс после операции.
Что касается архитектуры программы, она может быть описана следующим образом:
Структура проекта: Проект содержит один файл с исходным кодом Program.cs, в котором находится вся логика программы.
Главная функция Main: Это основная точка входа в программу. Здесь объявляются переменные, выводятся приветственные сообщения и инструкции для пользователя, а также обрабатывается ввод пользователя и выполнение операций обмена валюты.
Использование консоли для ввода-вывода: Программа использует консольный ввод и вывод для взаимодействия с пользователем.
Обработка исключений: В программе предусмотрена обработка ситуации, когда ввод пользователя может быть некорректным (например, ввод нечисловых значений).
Простая логика конвертации валюты: Программа просто конвертирует суммы денег по текущему курсу обмена.
Использование условных операторов и цикла switch: Для выбора операции программы используется оператор switch, который оценивает введенное пользователем значение и выполняет соответствующий блок кода.
В общем, архитектура этой программы представляет собой простой линейный поток управления, где вводится информация, выполняется определенная операция и выводится результат. В этом коде нет выделенной архитектурной модели или шаблона проектирования, так как программа довольно проста и выполняет ограниченный набор функций.
| qodirovdeveloper | |
1,864,881 | A job seeker journal application built with AWS Amplify Gen 2 | This is a submission for the The AWS Amplify Fullstack TypeScript Challenge What I... | 0 | 2024-05-25T15:00:43 | https://dev.to/oleks/a-job-seeker-journal-application-built-with-aws-amplify-gen-2-ldh | devchallenge, awschallenge, amplify, fullstack | *This is a submission for the [The AWS Amplify Fullstack TypeScript Challenge ](https://dev.to/challenges/aws)*
## What I Built
I am excited to present you with a job seeker journal application. The app helps users keep track of the jobs they have applied for, and store different CVs and Cover letters connected with jobs.
It leverages AWS Amplify authentication, data, file storage, serverless functions, the AWS Amplify UI React library, and AWS Bedrock with the Mistral:7B model to generate cover letter text.
## Demo and Code
<!-- Share a link to your Amplify App and source code. Include some screenshots as well. -->
- The code is available on my personal GitHub [repository](https://github.com/samvimes01/amplify-job-search-diary)
- The repository is connected to the Amplify console. [the example app](https://main.d3sbabnt1mitvg.amplifyapp.com/)
**Demo gif**
Too big for dev.to/cloudinary (also available on GitHub repo Readme page)
[Gif](https://postimg.cc/LJPH3f4x)
**Demo screenshot**
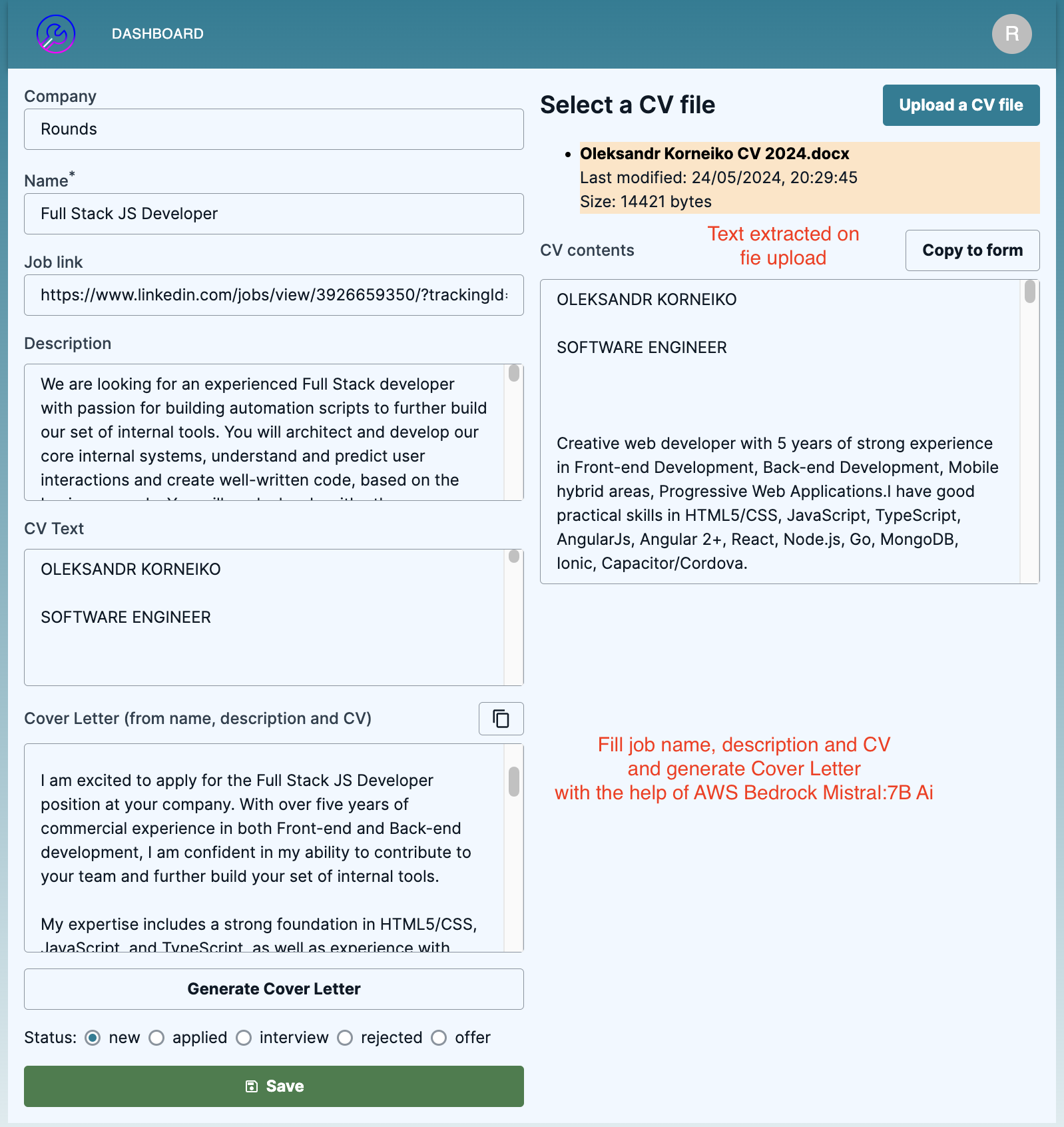
## Integrations
<!-- Tell us which qualifying technologies you integrated, and how you used them. -->
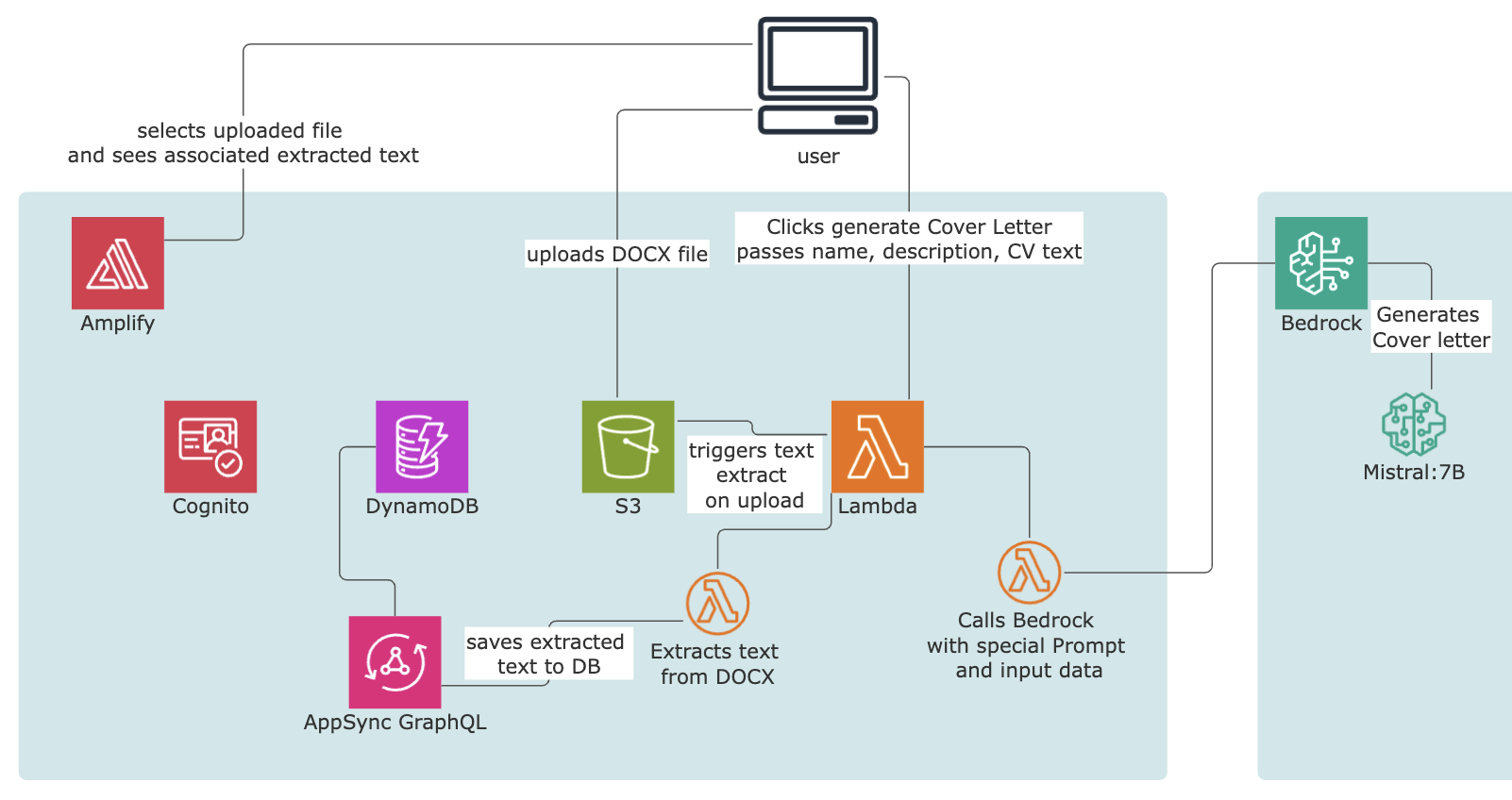
The diagram above represents the technologies used in the challenge
### Authentication
**Cognito:** Behind the scenes, Amplify creates a Cognito user pool to store all user information and manage authentication for this application. However one of the two Lambda functions uses an IAM authentication function to store some data in a database.
### Data
**AppSync:** Amplify creates an AppSync GraphQL API, enabling us to execute CRUD operations. The frontend app uses the generated client's model methods for get one, get many, create, update, and delete operations. One of the Lambda functions uses the generated client's `graphql` method and autogenerated GraphQL functions for storing into the database extracted text from the file.
**DynamoDB:** The Data module in the Amplify project, AppSync uses DynamoDB as the database to persist all information in this NoSQL database.
### Serverless functions
**Lambda Function:** I used the function module in Amplify to trigger extracting text from the uploaded file. The second function is triggered when the user clicks the "Generate Cover Letter" button. It uses the provided data and a special prompt and utilizes AWS Bedrock and the Mistral:7B model to generate a cover letter.
### File storage
**S3 Bucket:** I used an S3 bucket to store Curriculum Vitae files. At the moment, only `.docx` files are allowed since the third-party library for parsing PDFs fails to do so on Lambda runtime while working fine on a local machine (seems like a CommonJS to ESM issue, or Worker API issue).
<!-- Reminder: Qualifying technologies are data, authentication, serverless functions, and file storage as outlined in the guidelines -->
**Connected Components and/or Feature Full**
<!-- Let us know if you developed UI using Amplify connected components for UX patterns, and/or if your project includes all four integrations to qualify for the additional prize categories. -->
I created a **feature-full** app utilizing authentication, data, storage, and functions. Additionally, AWS Bedrock AI is used as an extra feature within one of the functions.
The repository was initiated with the AWS Amplify Gen 2 React Vite template. I used **Connected Components** such as `Authenticator` and `AccountSettings.ChangePassword`. I also utilized many other UI components, including `Button`, `Flex`, `Input`, `Label`, `Alert`, `View`, `Link`, `Table`, `TableBody`, `TableCell`, `TableHead`, `TableRow`, `Text`, `Heading`, `Grid`, `Icon`, `Radio`, `RadioGroupField`, and `TextAreaField`.
I also decided to use the @mui library for 2 components to expedite development: a `NavBar` (just copypasted from mui docs) and a `SnackBar` toast component to improve UX (popup toast after an item is created/updated/deleted or if an error occurs).
<!-- Team Submissions: Please pick one member to publish the submission and credit teammates by listing their DEV usernames directly in the body of the post. -->
## Conclusion
I used to work with Azure and Google Cloud, but never with AWS services. I was surprised by how effortless it is to build a full-stack app on AWS Amplify. However, the Amplify Gen 2 documentation wasn't sufficient for me. I had to use DynamoDB, AppSync, and Amplify Gen 1 docs to figure out some things. Still, I was able to build a full-stack app with authentication, S3, data, and even AI in less than 5 days. Nice experience.
The price is fair enough. I spent USD 0.63 for 12 deployments.
<!-- Thanks for participating! --> | oleks |
1,864,922 | Top-Down Shooter Update: Day 1 (Player Done) | Here you can see how amazing my art skills are for my main player: Not sure which direction the... | 0 | 2024-05-25T14:58:06 | https://dev.to/quantumbyte-studios/top-down-shooter-update-day-1-player-done-41ej | Here you can see how amazing my art skills are for my main player:
Not sure which direction the art will go in the future.. if you have any ideas, comment below
| quantumbyte-studios | |
1,864,906 | We all IT professional ignore Health. How Homeopathy help? | Understanding the Health Challenges of IT Engineers IT engineers often face unique health challenges... | 0 | 2024-05-25T14:37:36 | https://dev.to/chirag50/we-all-it-professional-ignore-health-how-homeopathy-help-1fh6 | **Understanding the Health Challenges of IT Engineers**
IT engineers often face unique health challenges due to the nature of their work, which involves long hours sitting at a desk, high levels of stress, and extensive screen time. Common issues include musculoskeletal problems, eye strain, headaches, digestive disorders, and stress-related conditions such as anxiety and insomnia.
**How Homeopathy Can Help**
[Homeopathy](https://drdevikapatelclinic.com/) provides a holistic and natural approach to managing these health issues. By considering the individual's overall well-being and specific symptoms, [homeopathic treatments](https://drdevikapatelclinic.com/) aim to stimulate the body's self-healing processes and restore balance.
**Common Health Issues**
1. Musculoskeletal Problems
2. Eye Strain
3. Headaches
4. Digestive Disorders
5. Stress and Anxiety
6. Insomnia
**Benefits of Homeopathic Treatment**
**Safe and Gentle:** Homeopathic remedies are highly diluted, making them safe for long-term use with minimal risk of side effects.
**Holistic Approach:** Homeopathy treats the whole person, considering physical, emotional, and mental health.
**Individualized Care:** Treatments are tailored to each person's unique symptoms and health history, ensuring personalized care.
[Click here for Consulting a Homeopathic Practitioner](https://drdevikapatelclinic.com/) | chirag50 | |
1,864,921 | Public Beta of devSitter Now Available! Write Higher Quality Code | I am thrilled to announce that the public beta of devSitter was launched yesterday! This tool, which... | 0 | 2024-05-25T14:56:56 | https://dev.to/bykowski/public-beta-of-devsitter-now-available-write-higher-quality-code-j4g | I am thrilled to announce that the public beta of [devSitter](https://devsitter.app) was launched yesterday! This tool, which I have been working on with passion and dedication, is now available for everyone who wants to streamline their code review processes and improve their coding skills.
#The Journey to Beta
##The Initial Setback
Initially, devSitter seemed like one of those ideas that had to wait for a better time. Other projects, work, life — all of these effectively distracted me from realizing this dream. There were days when it seemed that devSitter would become one of those unfinished, forgotten projects gathering dust in the corners of my hard drive.
#An Obsessive Comeback
However, everything changed in April. Suddenly, I felt an enormous hunger to return to devSitter. It was like rekindling a long-forgotten love with new intensity. I dropped all other tasks and focused solely on this project. Days and nights were spent in front of the monitor, with my head full of ideas and my heart brimming with determination. It was total mania — I couldn’t think of anything else but how to make devSitter a reality.
#What is devSitter?
For those who may not know or remember, devSitter is an intuitive and user-friendly tool designed with modern developers in mind. It simplifies the code review process by offering instant, automated feedback on your codebase without the hassle of setup or configuration. DevSitter is accessible to programmers of all skill levels, providing clear, actionable insights to improve your code. By significantly reducing the time spent on code reviews, it frees you up to focus on other critical aspects of your projects, enhancing your productivity and the overall quality of your work.
#Simple Use, Powerful Performance
One of the biggest advantages of devSitter is its simplicity. No configuration is needed — just provide a link to your public repository, and within moments, you can enjoy a detailed report that includes information on what and why you should improve, right down to the line of code. This makes it an incredibly efficient and user-friendly tool for both beginners and experienced programmers.
#Educational Benefits
If you’re learning to program or looking to take your skills to the next level, devSitter is the tool for you! It helps you:
- Learn the best programming practices
- Avoid common mistakes
- Write code according to standards
- Create high-quality, secure code
- Present a professional-looking repository to potential employers
- By using devSitter, you ensure that your code is not only functional but also polished and professional. This is crucial when showcasing your projects to employers who want to see that you adhere to industry standards and best practices.
#Growing Interest
Despite launching only yesterday, devSitter has already garnered significant interest. The feedback from the first users has been overwhelmingly positive, reinforcing my belief in the tool’s potential to revolutionize code review processes. Your opinions are invaluable to me, as it is thanks to your needs and feedback that devSitter will continue to evolve and serve your projects even better.
#Join the Beta and Share Your Thoughts
I invite you to try devSitter for yourself. Check out devSitter and see how it can make your coding life easier and more efficient. Your feedback is crucial — let me know what you think and how the project can be improved. Together, we can make devSitter the ultimate tool for developers everywhere.
#Conclusion
Your support makes devSitter better with each passing day. Together, we can change the world of programming, one line of code at a time. Join me on this journey, and let’s create something amazing together. devSitter is waiting for you!
🔗 Check out devSitter here: https://devSitter.app — Join our community and see how devSitter can streamline your code review process! 🚀 | bykowski | |
1,864,903 | CloudCycle - Set lifecycle for your cloud resources to avoid surprising costs | The Problem I have recently forgot to Turn off / Terminate two ec2 instances running... | 0 | 2024-05-25T14:48:41 | https://dev.to/redopsbay/cloudcycle-set-lifecycle-for-your-cloud-resources-to-avoid-surprising-costs-5gpd | aws, go, serverless, lambda | ## The Problem
I have recently forgot to Turn off / Terminate two ec2 instances running **m5x.large** and **t3.medium** that runs about 1 month and I just received a notification of my AWS monthly bill and shocked me!
At the first place I thought my account was hacked, But turns out that I just left two AWS EC2 Instances running. 🥲😔
## The Solution (CloudCycle)
So, that's why I came up with a basic solution and share it. So now, whether I forgot to turn it off / terminate a running AWS Resources, I don't have to worry about it anymore, if I have properly set the desired lifecycle of my cloud resources.
I have created a lambda function which get's executed every **15 minutes** to check if the supported resources are due to termination or not.
Now, if you or your team forgot to terminate cloud resources, the **CloudCycle** will do the job for you.
## Tools & Language used
1. **Golang** - Since lambda function bills will be based on the duration of execution. At first, I developed this by using python and I have realized that I need to consider it's performance and execution time.
2. **Terraform** - Used only for deployment and examples.
## Architecture
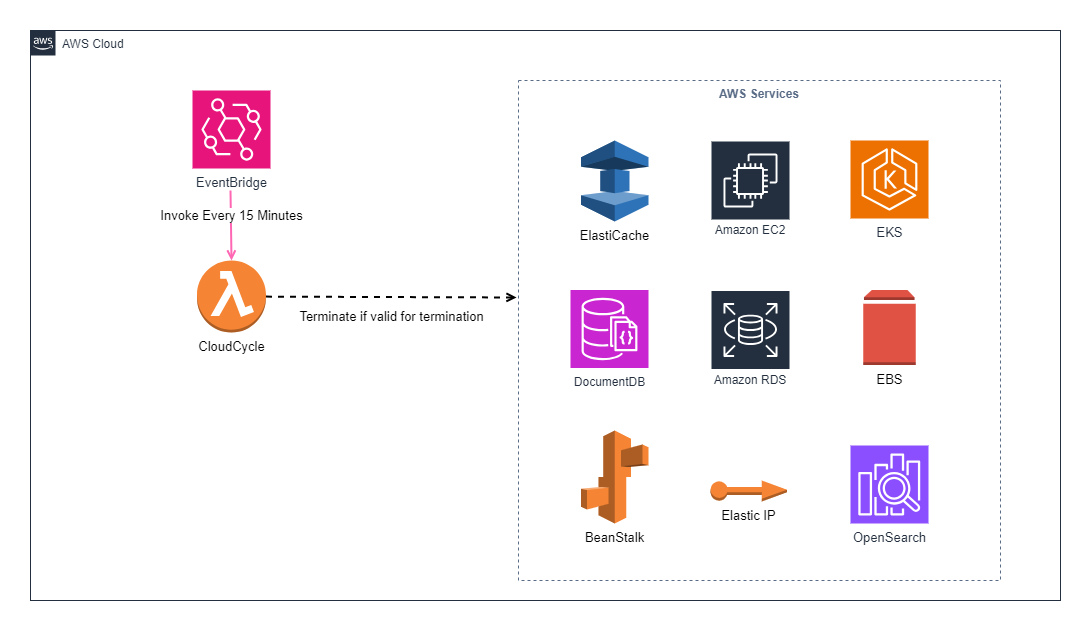
This setup will utilized the schedule expression of event bridge, In which event bridge get's executed every 15 minutes. In doing so, lambda function get validate if the supported resources is valid for termination.
But why termination? Instead of turning it off?
Of course there's a free tool available called **Cloud-Custodian**. But still, sometimes turning it off isn't enough and it can lead to lots of unused resources and can still occur minimal cost.
## Sample Code for EC2 Instance Service
Below are the sample codes for EC2 Instance service.
```
package services
import (
"context"
"github.com/aws/aws-sdk-go-v2/service/ec2"
"github.com/aws/aws-sdk-go-v2/aws"
"github.com/aws/aws-sdk-go-v2/service/ec2/types"
"github.com/redopsbay/cloudcycle/internal"
"github.com/redopsbay/cloudcycle/internal/schedule"
"fmt"
)
type EC2 struct {
InstanceId string
CloudCycle string
MarkForTermination bool
}
type EC2Instances struct {
Instances []EC2
}
func GetEC2Instances(ctx context.Context, client *ec2.Client) ([]types.Reservation, error) {
filters := []types.Filter{{
Name: aws.String("tag-key"),
Values: []string{internal.TagKey},
},
}
DescribeInputs := ec2.DescribeInstancesInput{
Filters: filters,
}
instances, err := client.DescribeInstances(ctx, &DescribeInputs)
if err != nil {
panic(err)
return []types.Reservation{}, err
}
return instances.Reservations, nil
}
func MarkInstancesForTermination(reservations []types.Reservation) (EC2Instances, error) {
var instances EC2Instances
for _, reservation := range reservations {
for _, instance := range reservation.Instances {
for _, tag := range instance.Tags {
if *tag.Key == internal.TagKey {
Lifecycle, err := schedule.GetLifeCycle(instance.LaunchTime, *tag.Value)
if err != nil {
return EC2Instances{}, err
}
if schedule.ValidForTermination(Lifecycle) {
ec2instance := EC2{
InstanceId: *instance.InstanceId,
CloudCycle: *tag.Value,
MarkForTermination: true,
}
instances.Instances = append(instances.Instances, ec2instance)
} else {
ec2instance := EC2{
InstanceId: *instance.InstanceId,
CloudCycle: *tag.Value,
MarkForTermination: false,
}
instances.Instances = append(instances.Instances, ec2instance)
}
}
}
}
}
return instances, nil
}
func StartEC2InstanceTermination(ctx context.Context, client *ec2.Client) error {
var instanceIds []string
reservations, err := GetEC2Instances(ctx, client)
if err != nil {
fmt.Println("Unable to get instances.")
return err
}
instances, err := MarkInstancesForTermination(reservations)
if err != nil {
fmt.Println("Unable to mark instances for termination.")
return err
}
for _, instance := range instances.Instances {
if instance.MarkForTermination {
instanceIds = append(instanceIds, instance.InstanceId)
fmt.Printf("\nInstanceID: %s, ForTermination: %t, CloudCycle: %s\n",
instance.InstanceId,
instance.MarkForTermination,
instance.CloudCycle)
}
}
TerminatedOutput, err := client.TerminateInstances(ctx, &ec2.TerminateInstancesInput{
InstanceIds: instanceIds,
})
for _, state := range TerminatedOutput.TerminatingInstances {
if *state.CurrentState.Code == 0 {
fmt.Printf("InstanceID: %s, State: Pending for Termination", *state.InstanceId)
} else if *state.CurrentState.Code == 32 {
fmt.Printf("InstanceID: %s, State: Shutting down", *state.InstanceId)
} else if *state.CurrentState.Code == 48 {
fmt.Printf("InstanceID: %s, State: Shutting down", *state.InstanceId)
} else if *state.CurrentState.Code == 16 {
fmt.Printf("InstanceID: %s, State: Still running", *state.InstanceId)
} else if *state.CurrentState.Code == 64 {
fmt.Printf("InstanceID: %s, State: Stopping", *state.InstanceId)
} else if *state.CurrentState.Code == 80 {
fmt.Printf("InstanceID: %s, State: Stopped", *state.InstanceId)
} else {
fmt.Printf("InstanceID: %s, State: Unknown", *state.InstanceId)
}
}
return nil
}
```
## Objective
My objective with **CloudCycle** is to automatically cleanup supported resources based on the specified **duration** or **lifecycle** through resource tagging, And to support the commonly used resources that causes AWS Bills to grow even though the cloud resources is not needed anymore.
No more story telling!
For complete documentation and project link, you can proceed directly to my GitHub repo below.
[https://github.com/redopsbay/cloudcycle](https://github.com/redopsbay/cloudcycle)
This repo is open for contributors!!! Some documents and cloud resources are currently **WORK-IN-PROGRESS**
## Usage
Just specify that tag and set your desired lifecycle for supported resources with **CloudCycle** Key. Below are the supported duration.
| Suffixes | Detail | Sample Value |
| -------- | ------- | ------------ |
| `m` | Minutes | `60m` |
| `h` | Hours | `2h` |
| `d` | Days | `7d` |
## How does it works?
CloudCycle will get all the supported resources with a tagged key ***CloudCycle*** and it will simply compare the ***current time*** vs ***launch time*** of the supported resources with the specified `key/value` pair resource tag if the supported resources are valid for termination.
Below are the sample terraform code.
Specify ec2 lifecycle by 24 hours from it's launch date.
```hcl
data "aws_ami" "ubuntu" {
most_recent = true
filter {
name = "name"
values = ["ubuntu/images/hvm-ssd/ubuntu-jammy-22.04-amd64-server-*"]
}
filter {
name = "virtualization-type"
values = ["hvm"]
}
owners = ["099720109477"] # Canonical
}
resource "aws_instance" "web" {
ami = data.aws_ami.ubuntu.id
instance_type = "t3.micro"
tags = {
CloudCycle = "1d" // This ec2 instance will be terminated within 24 hours from it's launch date.
}
}
```
## Sample Terraform Deployment Usage
For deployment, you can refer to the github repo [Deployment Page](https://github.com/redopsbay/cloudcycle/blob/master/deploy/README.md)
## Benefit's
Sometimes it's better to let go than stay strong. Leaving up unused resources will incur costs.
And lastly, No nightmare's, No poverty! 😂🤣
## Reference
- [https://github.com/redopsbay/cloudcycle](https://github.com/redopsbay/cloudcycle)
| redopsbay |
1,864,915 | Hi Dev Community Members How are you Today? | A post by Jackleen Andary | 0 | 2024-05-25T14:47:58 | https://dev.to/jackleen_andary/hi-dev-community-members-how-are-you-today-1h9h | webdev, beginners, news | jackleen_andary | |
1,861,335 | Healthcare and Pharmaceuticals: Revolutionizing Patient Care with Technology | The healthcare and pharmaceutical industries are at the forefront of technological adoption, driven... | 0 | 2024-05-25T14:45:00 | https://dev.to/brainboard/healthcare-and-pharmaceuticals-revolutionizing-patient-care-with-technology-3oig | healthydebate, development, iot, infrastructureascode | The healthcare and pharmaceutical industries are at the forefront of technological adoption, driven by the need to improve patient outcomes, streamline operations, and comply with stringent regulatory requirements. Digital transformation in this sector is crucial for developing new treatment methodologies, enhancing data security, and optimizing resource management.
> "He who has health has hope; and he who has hope has everything." – Arabian Proverb
## How Brainboard Accelerates Digital Transformation in Healthcare and Pharmaceuticals
### **Secure Data Management**
Brainboard ensures that healthcare providers can securely manage and scale their IT infrastructure, crucial for handling sensitive patient data. By leveraging secure cloud environments, institutions can safeguard patient information against breaches and ensure compliance with health data regulations like HIPAA.
### **Operational Efficiency**
With tools to automate and visualize cloud deployments, Brainboard helps healthcare organizations reduce manual workload, allowing medical professionals to focus more on patient care rather than administrative tasks. This increases operational efficiency and reduces the chance for human error.
### **Scalability and Flexibility**
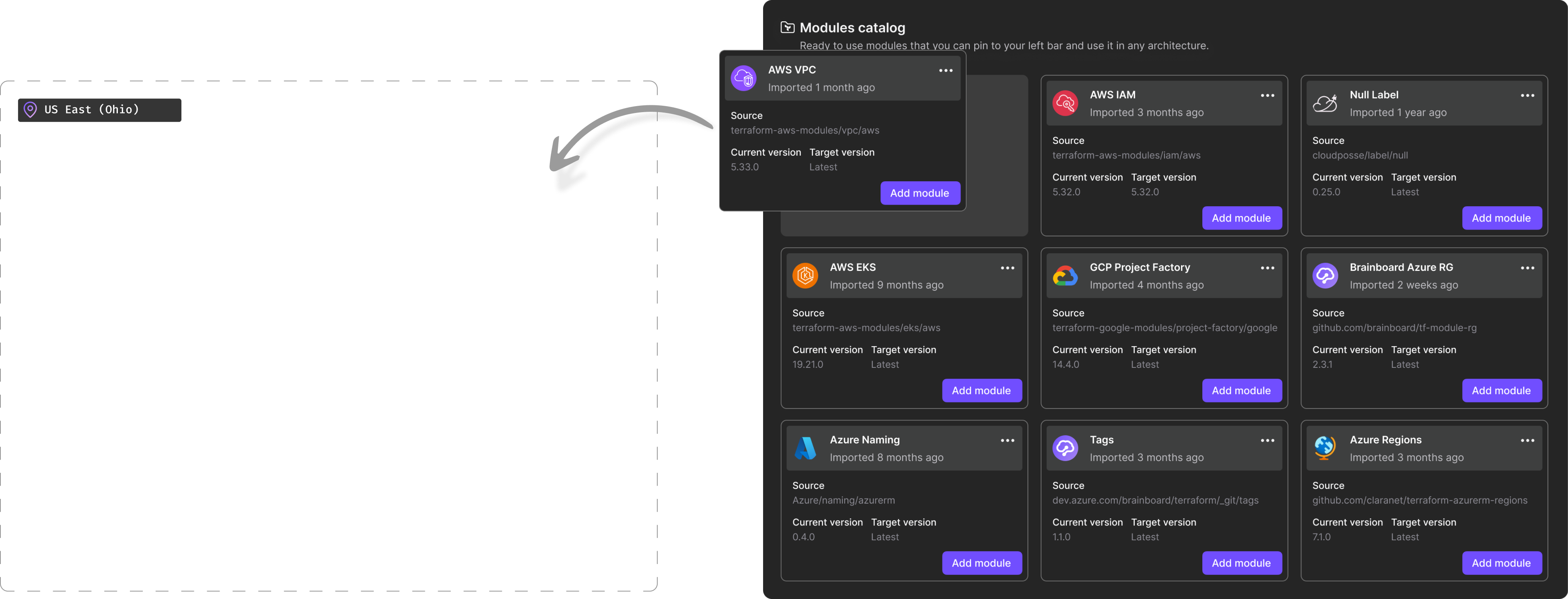
Brainboard facilitates the easy scaling of resources to meet fluctuating demands, such as sudden increases in patient load or computing requirements for large-scale pharmaceutical simulations. This agility is vital in a sector where demand can be unpredictable and highly variable.
### **Collaboration Across Departments**
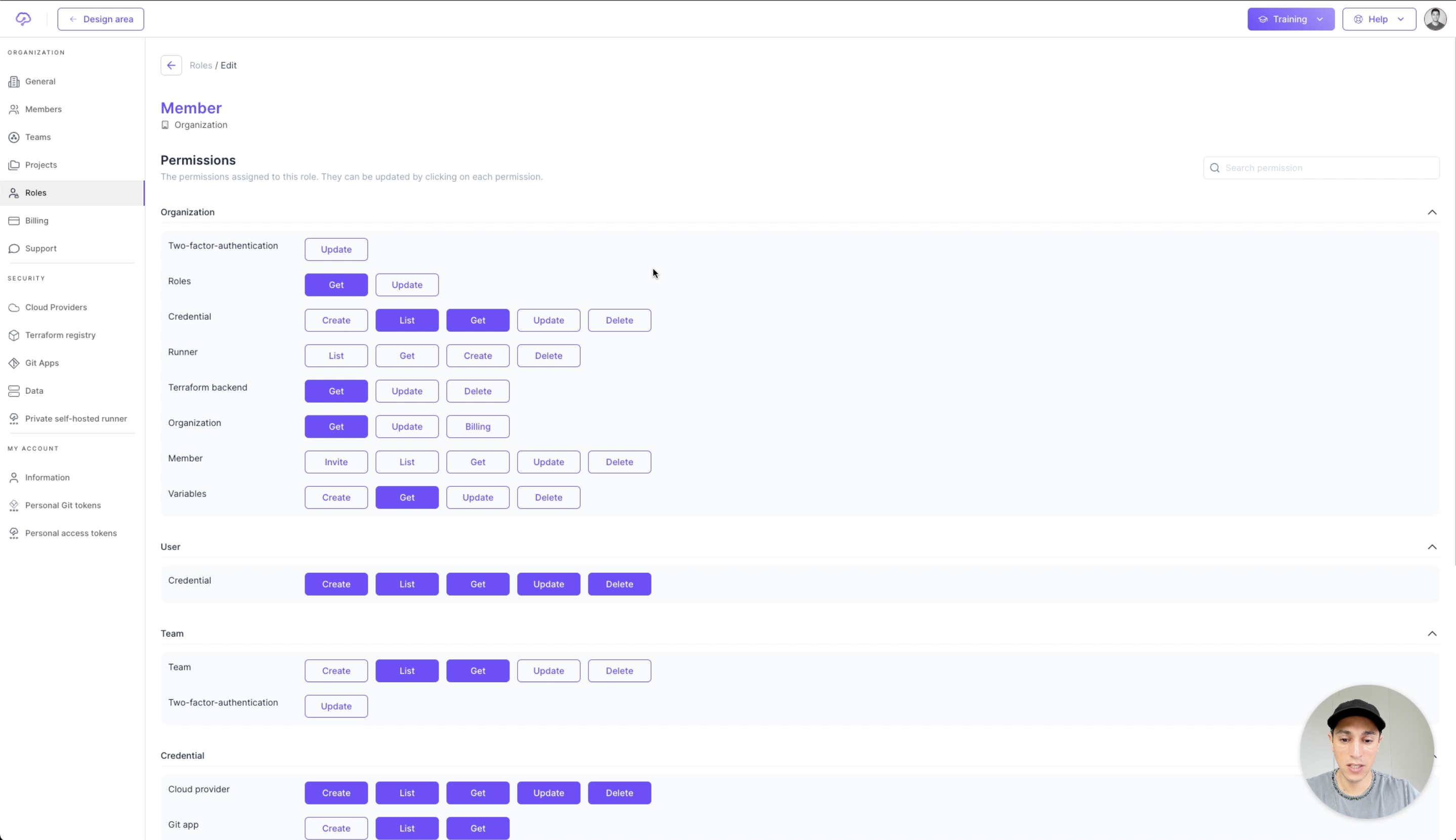
Brainboard enhances collaboration between different departments within healthcare institutions, such as between IT teams and medical researchers. This is achieved through shared visual tools that simplify the complexities of IT infrastructure, making it accessible for non-technical stakeholders.
## Features and Use Cases
### **Automated Compliance Checks**
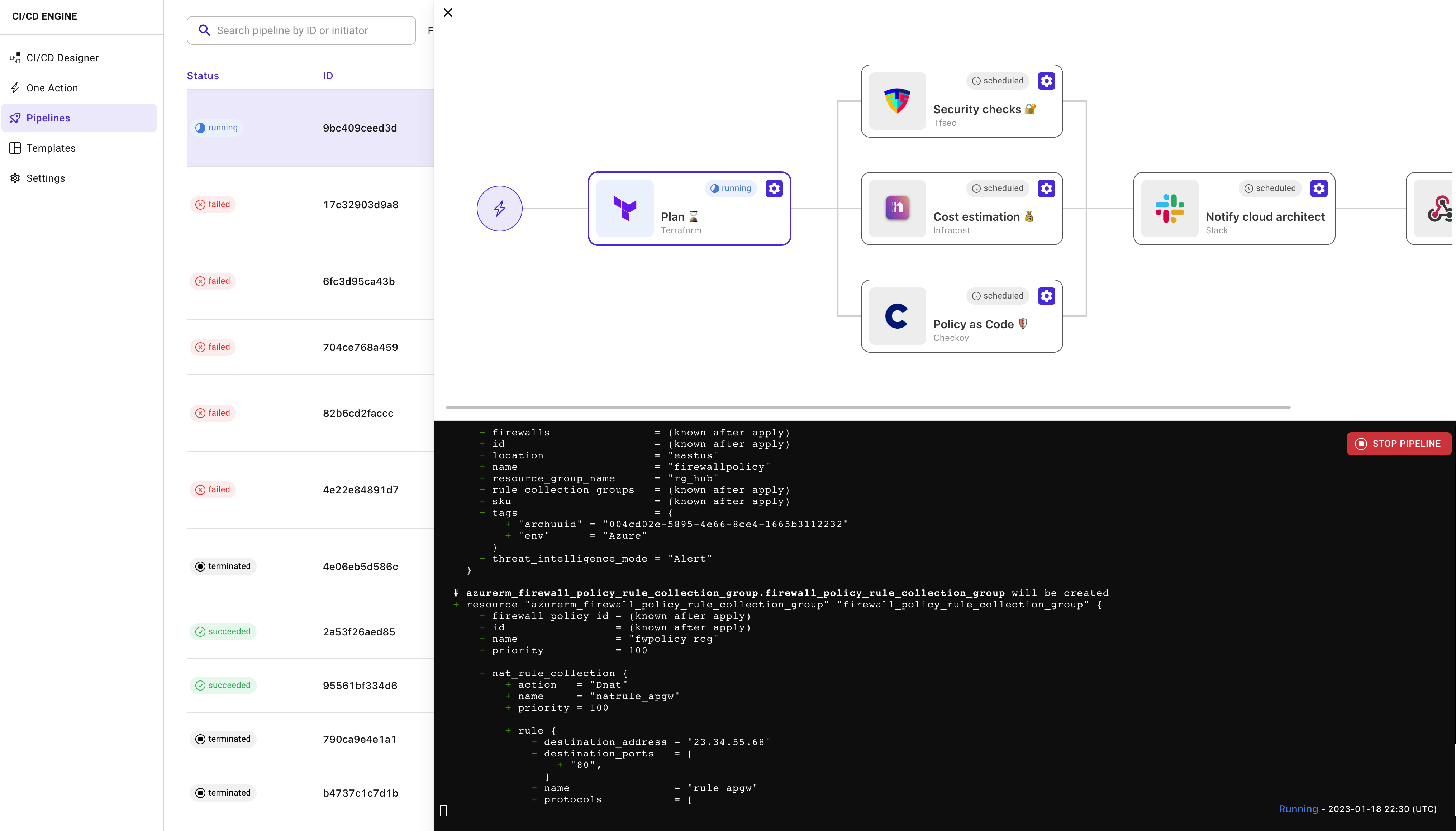
Use Case: Automatically enforce compliance with regulations through predefined security and compliance policies within Brainboard. This helps healthcare institutions stay compliant with laws, reducing legal risks and enhancing patient trust.
### **Drag-and-Drop Infrastructure Design**
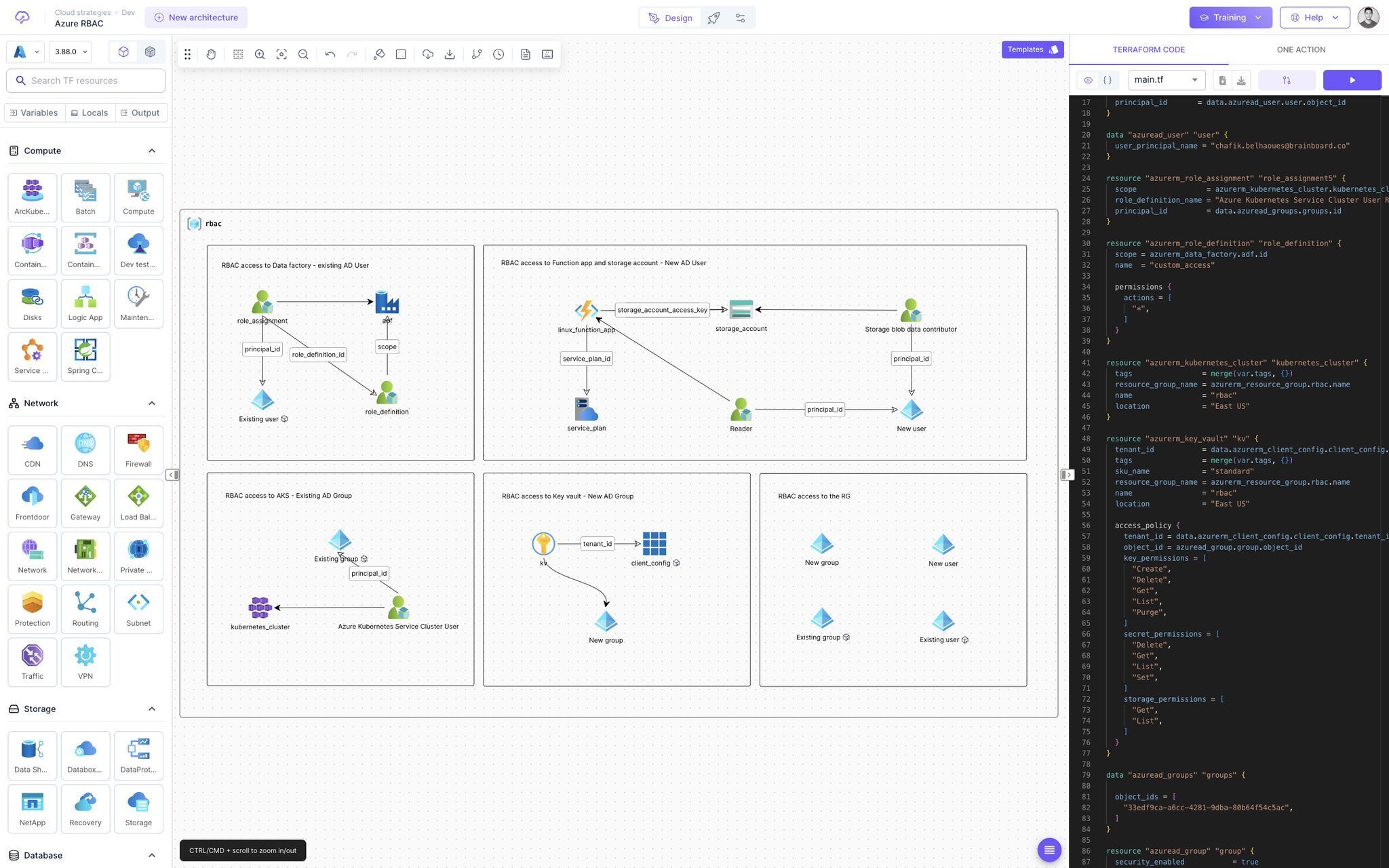
Use Case: Medical researchers can use Brainboard to easily design, modify, and deploy cloud environments for clinical trials and research projects without needing deep technical knowledge, thereby accelerating innovation.
These features and use cases demonstrate how [Brainboard](https://app.brainboard.co/) can transform the healthcare and pharmaceutical industries by providing the tools necessary to manage complex IT environments efficiently, securely, and in compliance with relevant regulations. | miketysonofthecloud |
1,864,913 | Is UIView (mostly) visible | If you've ever needed to check whether a view is visible to the user, you might have used the... | 0 | 2024-05-25T14:44:00 | https://dev.to/rationalkunal/is-uiview-mostly-visible-59jf | swift, ios | If you've ever needed to check whether a view is visible to the user, you might have used the `isHidden` property. However, this method falls short in scenarios where a view can appear hidden due to overlapping by other views. To address this, I created a simple extension to provide a more comprehensive visibility check.
```swift
extension UIView {
/// Checkes if the view is (mostly) visible to user or not.
/// Internaly it checks following things
/// - Should NOT be hidden
/// - Should NOT be completely transparent
/// - Bound should NOT be empty
/// - Should be in some window i.e. in view heirarchy
/// - Center should be directly visible to user i.e. NOT overlapped with other views
var isMostlyVisible: Bool {
guard !isHidden,
alpha > 0,
!bounds.isEmpty,
let window,
window.hitTest(window.convert(center, from: self.superview), with: nil) == self else {
return false
}
return true
}
}
```
Here is the extension in action:
Thank you for reading. | rationalkunal |
1,864,912 | Generative AI Revolutionizes Quantum Computer Programming | The method developed at the University of Innsbruck produces quantum circuits based on user... | 0 | 2024-05-25T14:42:29 | https://dev.to/samagra07/generative-ai-revolutionizes-quantum-computer-programming-2ckm | generativeai, ai, machinelearning, productivity | 
The method developed at the University of Innsbruck produces quantum circuits based on user specifications and tailored to the features of the quantum hardware the circuit will be run on. Credit: University of Innsbruck/Harald Ritsch
Researchers have developed a machine learning model that generates quantum circuits from text descriptions, similar to how models like Stable Diffusion create images. This method, improves the efficiency and adaptability of quantum computing.
One of the most important recent developments in Machine Learning (ML) is generative models such as diffusion models. These include Stable Diffusion and Dall-E, which are revolutionizing the field of image generation. These models are able to produce high-quality images based on text descriptions.
“**Our new model for programming quantum computers does the same but, instead of generating images, it generates quantum circuits based on the text description of the quantum operation to be performed**,” explains Gorka Muñoz-Gil from the Department of Theoretical Physics of the University of Innsbruck, Austria.
## Quantum Computing Challenges
To prepare a certain quantum state or execute an algorithm on a quantum computer, one needs to find the appropriate sequence of quantum gates to perform such operations. While this is rather easy in classical computing, it is a great challenge in quantum computing, due to the particularities of the quantum world. Recently, many scientists have proposed methods to build quantum circuits with many relying on machine learning methods. However, training these ML models is often very hard due to the necessity of simulating quantum circuits as the machine learns. Diffusion models avoid such problems due to the way how they are trained.
“This provides a tremendous advantage,” explains Gorka Muñoz-Gil, who developed the novel method together with Hans J. Briegel and Florian Fürrutter. “Moreover, we show that denoising diffusion models are accurate in their generation and also very flexible, allowing to generate circuits with different numbers of qubits, as well as types and numbers of quantum gates.”
The models also can be tailored to prepare circuits that take into consideration the connectivity of the quantum hardware, i.e. how qubits are connected in the quantum computer.
“As producing new circuits is very cheap once the model is trained, one can use it to discover new insights about quantum operations of interest,” Gorka Muñoz-Gil names another potential of the new method.
## Quantum Circuit Generation
The method developed at the University of Innsbruck produces quantum circuits based on user specifications and tailored to the features of the quantum hardware the circuit will be run on. This marks a significant step forward in unleashing the full extent of quantum computing. The work has now been published in Nature Machine Intelligence and was financially supported by the Austrian Science Fund FWF and the European Union, among others. | samagra07 |
1,864,911 | Discover Wit.ai: Create Your Own Intelligent Bots for Free 🚀🤖 | Introduction These days, most NLP stuff for development are either paid or have limited... | 0 | 2024-05-25T14:40:41 | https://dev.to/krishnasarathi/discover-witai-create-your-own-intelligent-bots-for-free-1g4j | javascript, ai, programming, machinelearning | ### Introduction
These days, most NLP stuff for development are either paid or have limited access. So last night I was working on a project, and I needed something like an NLP for my program. I casually started to browse the internet in search of such an NLP as a service, and I found [Wit.ai](https://wit.ai) by Meta. This post will provide a quick skim of what I know about it, trying to share the knowledge among my fellow developers!
### What is all this stuff?
So wit.ai is a powerful Natural Language Processing (NLP) platform, which enables you to create Natural Language Experiences, like chatbots or voice assistants for your projects, business, startup, company, whatever! Most importantly, it's free and open source. It is an alternative to DialogFlow by Google.
It is a natural language interface capable of turning users' sentences into structured data.
### How does Wit.ai work?
Wit.ai works with **Intents** and **Entities**:
- **Intents:** They represent the overall meaning or message of the sentence. For example, if a user asks for the price of some product, the intent can be "priceOfProduct"
- **Entities:** They provide additional information and context based on the user's message. They can be a word or a group of words referring to some specific information.
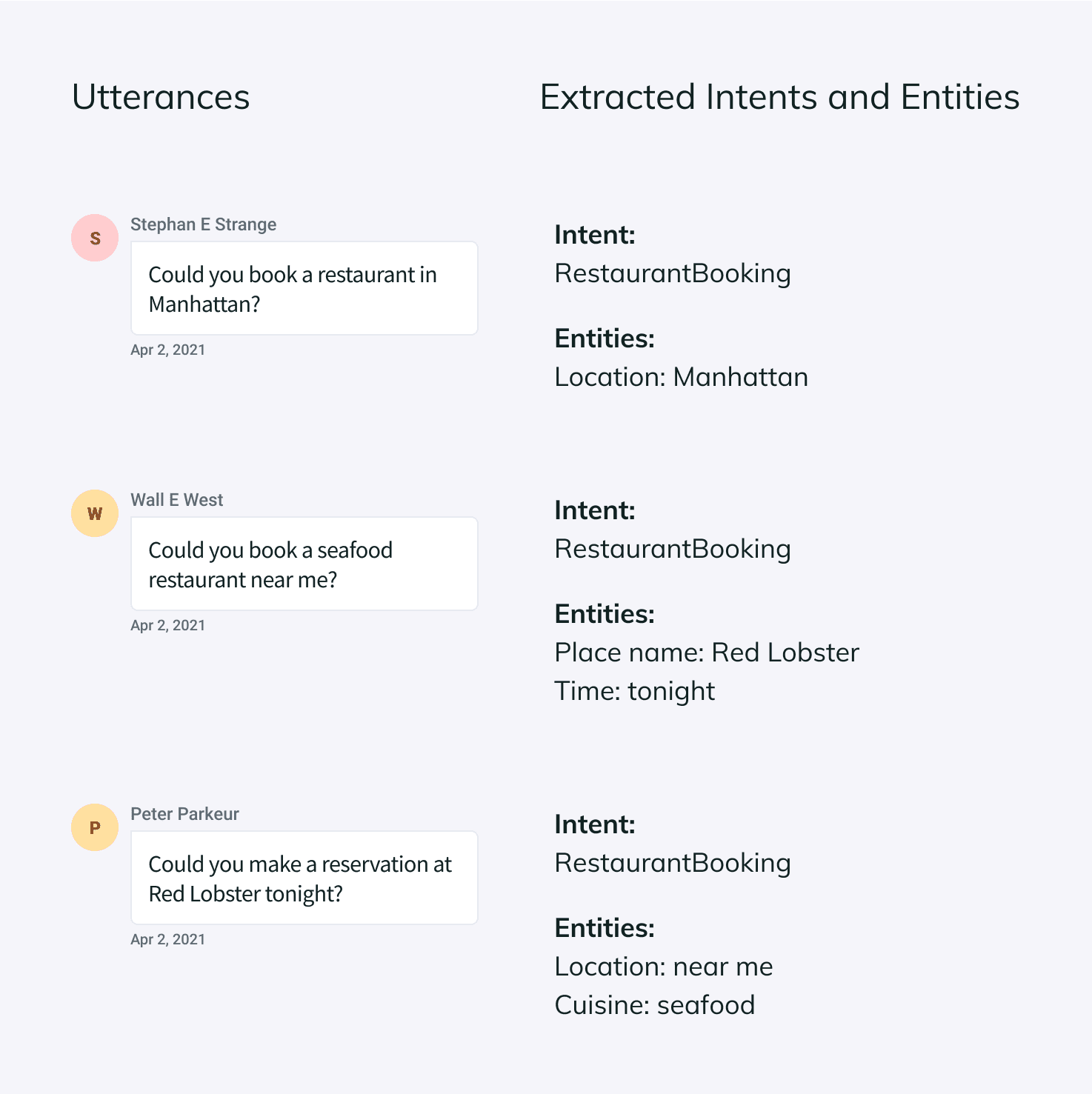
Developers can teach the bot by providing example sentences, and the bot learns and improves with each interaction
There are a bunch of free resources online where you can learn more about how to use Wit.ai, and I'll be dropping some links at the end of this article.
### Using Wit.ai with your programs
Wit.ai provides API endpoints for several tasks, and you can use those to integrate them with your app or program.
Additional Links to Learn More 🚀:
[Wit.ai Official Documentation and Tutorials](https://wit.ai/docs/tutorials)
[An Informative Hands On Playlist On NLP chatbots and Wit.ai](https://www.youtube.com/watch?v=_RY1QUXjV10&list=PLYxzS__5yYQkptDjLxQVqvM1312YO32fq&pp=iAQB)
[Basic Tutorial For Using Wit.ai](https://youtu.be/cs_7uRICgrw?si=HWrOK8_h-GmFfnOp)
| krishnasarathi |
1,864,910 | Validate your Jenkinsfile with the vscode plugin vscode-jenkins-pipeline-linter-connector and the LLMs large model | Jenkins is a popular automation tool for CI/CD, if you have used GitHub Action, similar to it, most... | 0 | 2024-05-25T14:39:40 | https://dev.to/yeshan333/validate-your-jenkinsfile-with-the-vscode-plugin-vscode-jenkins-pipeline-linter-connector-and-the-llms-large-model-3bff | jenkins, llm, openai, cloudflarechallenge | [Jenkins](https://www.jenkins.io/) is a popular automation tool for CI/CD, if you have used GitHub Action, similar to it, most automation tools now provide DSL (Domain Specific Language) to describe & orchestrate automation workflows, Jenkins' [Pipeline Syntax](https://www.jenkins.io/doc/book/pipeline/syntax/) is the orchestration language provided by Jenkins, the corresponding orchestration file is generally called **Jenkinsfile**, syntax rules and Groovy is similar.
I usually use [Declarative Pipeline Syntax](https://www.jenkins.io/doc/book/pipeline/#pipeline-1) a lot, and I usually use a Git repository for Jenkinsfile management. After the local editing is completed, the headache is the syntax verification, and it is often necessary to actually run the pipeline after the code is committed to confirm whether there are any syntax problems.
In fact, this syntax check is configured on the Jenkins UI, but it can't be copied every time after editing in the code editor, and the official Jenkins documentation also suggests what toolchain [pipeline-development-tools](https://www.jenkins.io/doc/book/pipeline/development/#pipeline-development-tools) can be used for the use of local development pipelines. You can use command-line tools, Jenkins Open API, IDE plug-ins, etc.
I use Visual Studio Code a lot on a daily basis, so I finally chose the vscode plugin `vscode-jenkins-pipeline-linter-connector`, which is implemented by submitting the content of the Jenkinsfile to Jenkins through the API to verify.
However, the vscode plug-in has fallen into disrepair for a long time, and the code has been in use for a long time, and there are many problems encountered in actual use, such as:
- Jenkinsfile with Chinese verification results are easy to garbled characters, such as this Jenkinsfile:
```groovy
pipeline {
agent any
stages {
stage('Hello中文>>>>>') {
steps {
echo 'Hello Worl中文
}
}
}
}
```
The verification result will return garbled characters, as follows:
```shell
Errors encountered validating Jenkinsfile:
WorkflowScript: 6: unexpected char: 0xB8 @ line 6, column 36.
echo 'Hello World'ä¸æ��
```
The basic library that the plugin implementation depends on is also relatively old, so I forked the original plugin and did the following code refactoring and some problem fixes & optimizations, mainly as follows:
- Fixing the Chinese (or other charset) garbled text issue in Jenkinsfile.
- It can be verified without saving the Jenkinsfile.
- The validation can be automatically triggered immediately when the file is saved.
- Support to control what kind of file name can be verified, which is equivalent to a whitelist mechanism, and some people may write the workflow definition under another file name, such as: workflows.jenkins , etc., so there is this feature.
- langchain.js and Cloudflare's free [Workers AI REST API](https://developers.cloudflare.com/workers-ai/get-started/rest-api/) to configure large models for Jenkinsfile review.
- ...
The plugin is now available in the Visual Studio Code Store and Open VSX Registry, and you can theoretically use it in [Microsoft Visual Studio Code](https://code.visualstudio.com/), [code-server](https://github.com/coder/code-server), [VSCodium](https://vscodium.com/), and other vscode series IDEs, linked below:
- Microsoft Visual Studio Marketplace: [https://marketplace.visualstudio.com/items?itemName=yeshan333.jenkins-pipeline-linter-connector-fork](https://marketplace.visualstudio.com/items?itemName=yeshan333.jenkins-pipeline-linter-connector-fork)
- Open VSX Registry: [https://marketplace.visualstudio.com/items?itemName=yeshan333.jenkins-pipeline-linter-connector-fork](https://marketplace.visualstudio.com/items?itemName=yeshan333.jenkins-pipeline-linter-connector-fork)
Now you should be able to search for it in the plugin search, use `yeshan333.jenkins-pipeline-linter-connector-fork` to search for installations:
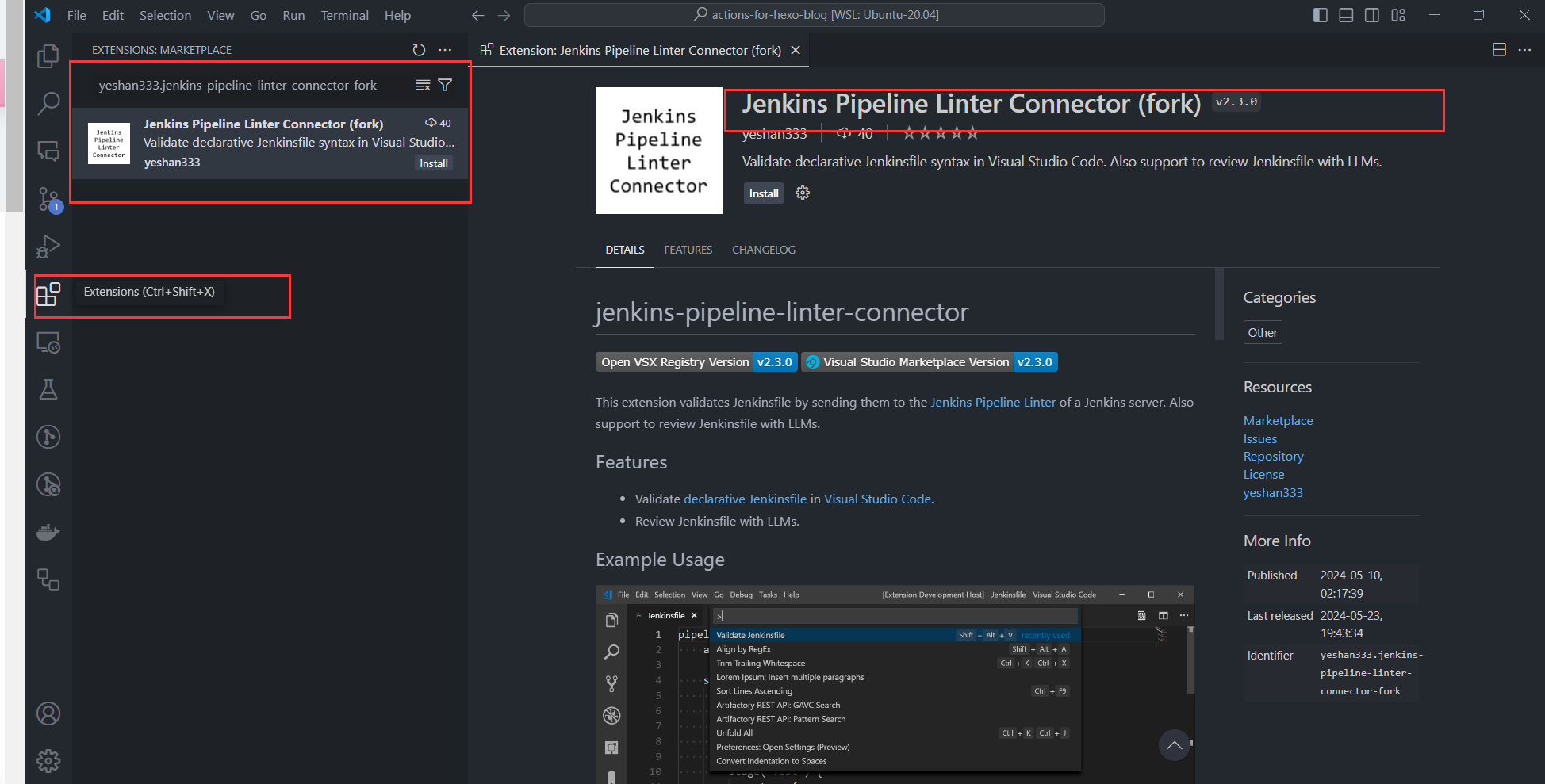
## Configure the plugin
There are a few [example configurations](https://github.com/yeshan333/vscode-jenkins-pipeline-linter-connector#example-settings) already given in the plugin documentation, just fill in your vscode user configuration json file:
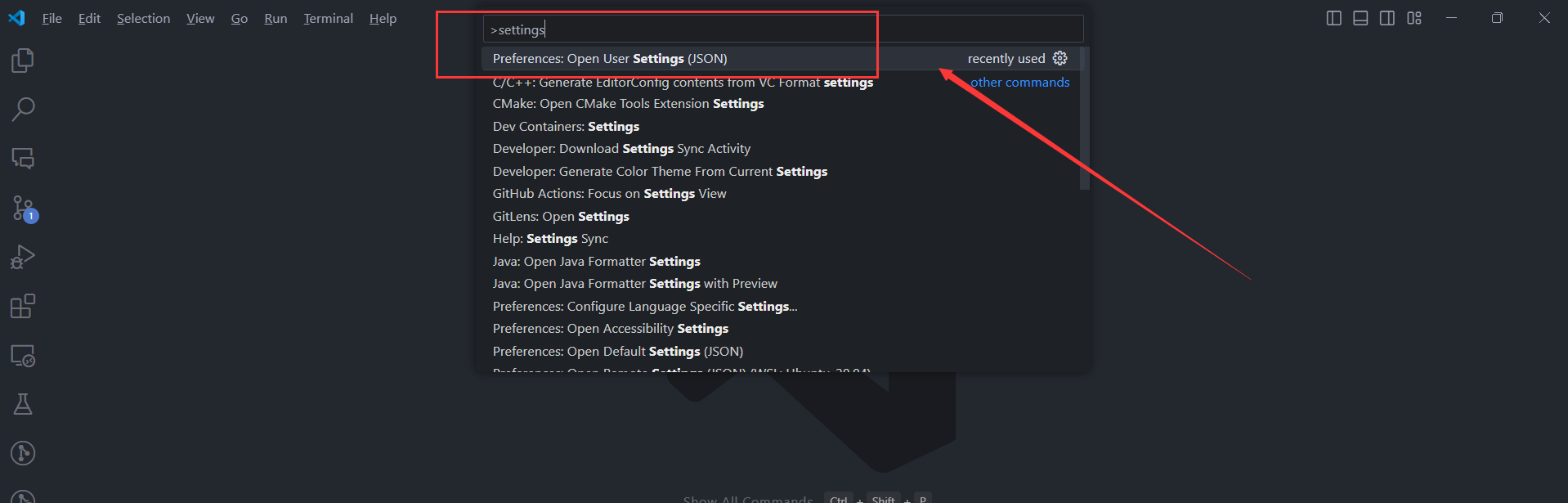
```json
{
"jenkins.pipeline.linter.connector.url": "https://jenkins.shan333.cn/pipeline-model-converter/validate",
"jenkins.pipeline.linter.connector.user": "jenkins_username",
"jenkins.pipeline.linter.connector.pass": "jenkins_password"
}
```
Replace the url and user password with your own Jenkins. Of course, you can also configure it directly in the plugin configuration:
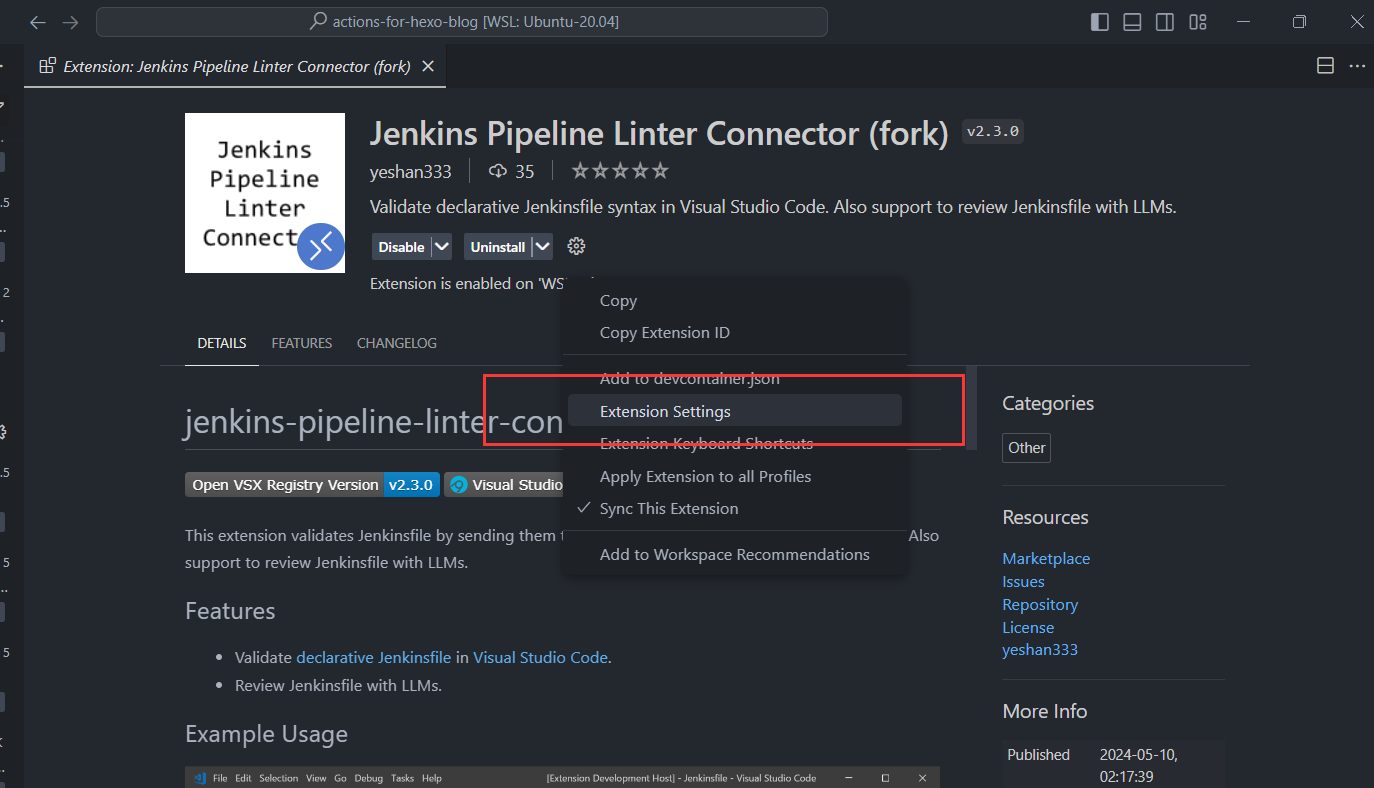
Once configured, you can use `Validate Jenkins` in the Command Pallette to enable the Jenkinsfile validation:

Let's take a look at how to use LLM to review Jenkinsfiles for you.
### Review your Jenkinsfile with the LLM large model
This function is disabled by default, and needs to be enabled by configuring `jenkins.pipeline.linter.connector.llm.enable`.
After the function is enabled, we still need to fill in a few key configurations, as follows:
```json
{
"jenkins.pipeline.linter.connector.llm.enable": true,
"jenkins.pipeline.linter.connector.llm.baseUrl": "https://api.cloudflare.com/client/v4/accounts/<CF_ACCOUNT_ID>/ai/v1",
"jenkins.pipeline.linter.connector.llm.modelName": "@cf/meta/llama-2-7b-chat-fp16",
"jenkins.pipeline.linter.connector.llm.apiKey": "<CF_API_TOKEN>",
}
```
`baseUrl` and `apiKey` need to be applied to the Cloudflare User Dashboard.
By default, the plugin uses the text generation model provided by the Cloudflare Workers AI REST API to review our Jenkinsfile, which currently offers a free quota that is basically enough for daily use.
**Step 1**: You need to follow the documentation provided by Cloudflare to obtain the API access key -> [Get started with the Workers AI REST API](https://developers.cloudflare.com/workers-ai/get-started/rest-api/), and fill in the obtained API Token in the configuration `"jenkins.pipeline.linter.connector.llm.apiKey"`.
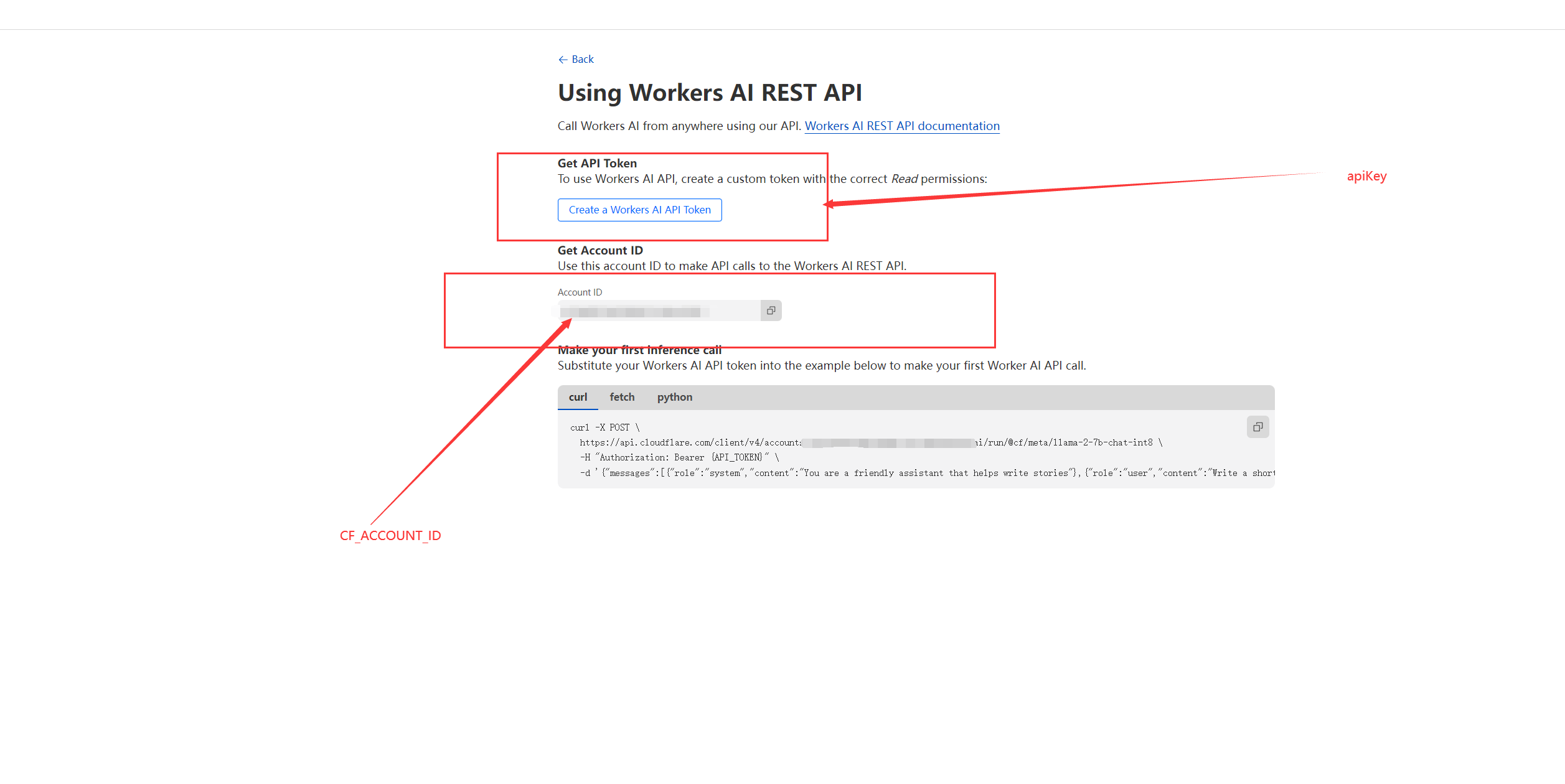
**Step 2**: In the previous step, you will also get an Account ID when applying, this ACCOUNT ID is used to assemble the configuration "jenkins.pipeline.linter.connector.llm.baseUrl" , replace the `<CF_ACCOUNT_ID>` of `"https://api.cloudflare.com/client/v4/accounts/<CF_ACCOUNT_ID>/ai/v1"` with your Account ID.
Configuring `jenkins.pipeline.linter.connector.llm.modelName` is optional, and you can use any of the text generation models mentioned in [https://developers.cloudflare.com/workers-ai/models/#text-generation](https://developers.cloudflare.com/workers-ai/models/#text-generation) for review.
After the above configuration is completed, the Jenkinsfile verification will be trigger with `Validate Jenkins` in the vscode Command Pallette, and the review opinions will be asked to the large model at the same time, which will have the following effect:
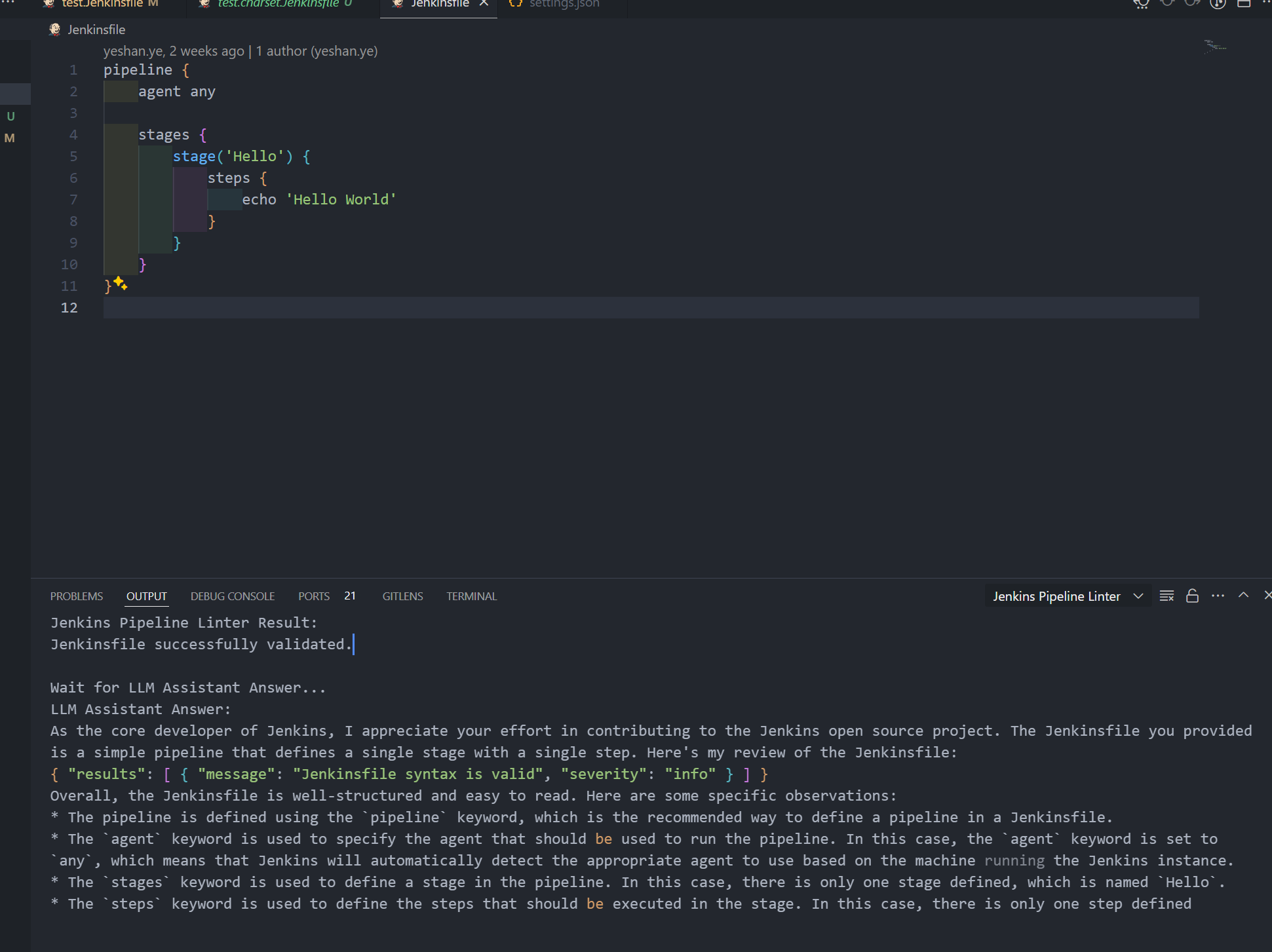 | yeshan333 |
1,864,908 | Top-Down Shooter Update: Day 1 (got distracted) | My goal was creating the player, player script, and bullet.. well, slow to start.. I had to set up... | 0 | 2024-05-25T14:39:28 | https://dev.to/quantumbyte-studios/top-down-shooter-update-day-1-got-distracted-len | My goal was creating the player, player script, and bullet.. well, slow to start.. I had to set up the Unity Project and downloading the Mobile Game 2D Core.. while it was loading I got distracted by redoing myitch.io profile and making a new game studio name and logo.
What do you get distracted by, when trying to game dev?
I was thinking about a game studio name related to Albert Einstein since I've always kind of idolized him, like Relativity Interactive (I liked it, but didn't have that punch) or Space-Time Creations (I thought too basic). I settled on something I don't think has anything to do with the physics genius: QuantumByte Studios.
Then, I quickly had DALL-E make a related logo since I'm not as artistic as many people on here. The program struggles with Text so it had to go through several iterations to not get weird letters (like M at one point was drawn as a pi symbol) or spelling mistakes:

Ok, the Unity Project and Mobile Game 2D Core is done, so I'm getting back to it.
| quantumbyte-studios | |
1,864,907 | ✨New Animated UI Component Collection | Hello everyone 😊 I know that I'm not alone and you also struggle with UI design... | 0 | 2024-05-25T14:39:23 | https://dev.to/lukahukur/new-animated-ui-component-collection-6ap | tailwindcss, nextjs, react, ui | #Hello everyone 😊
I know that I'm not alone and you also struggle with UI design (Especially if you are a backend developer) and THERE IS NOTHING BETTER for a developer mental health than prepared UI solutions that look AWSOOOMEEE ✨
So, I decided to drop some components on my personal website [https://ui.lukacho.com](ui.lukacho.com) which originally I made for myself. Every component is made with tailwindcss and reactjs.
I would like to share some of them in this article. Feel free to suggest me what should I upload next.
!!RADIX ALERT!! None of components use radix-ui
##Smooth Dropdown menu
Easy to implement, SMOOTH dropdown that uses only tailwind and framer-motion. [Link to Dropdown](https://ui.lukacho.com/components/dropdown-menu)
When I say easy, I mean this easy
```tsx
import React from 'react'
import { Dropdown, Tabs, Tab, TriggerWrapper, Trigger } from './dropdown'
// just implement OurServices, Components and Blog, or copy from website
export const Dropdown = () => {
return (
<div className="flex h-96 w-full justify-start p-8 text-neutral-200 md:justify-center">
<Dropdown>
<TriggerWrapper>
<Trigger>Our Services</Trigger>
<Trigger>Components</Trigger>
<Trigger>Blog</Trigger>
</TriggerWrapper>
<Tabs>
<Tab>
<OurServices />
</Tab>
<Tab>
<Components />
</Tab>
<Tab>
<Blog />
</Tab>
</Tabs>
</Dropdown>
</div>
)
}
```
##Animated Chart
You can come up with cool use cases for this component. [Link to animated chart](https://ui.lukacho.com/components/animated-chart)
##Custom Cursor
Cursor made With Framer-Motion. Link to [Custom cursor](https://ui.lukacho.com/components/custom-cursor)
##Neo Brutalist Pricing Card
Actually, there are two of them) anyways, here's Link to [pricing card](https://ui.lukacho.com/components/animated-pricing-component)
If you want to see more, please checkout [website](https://ui.lukacho.com)
Don't forget to comment what would you like to see next!
| lukahukur |
1,864,905 | CREATING A RESOURCE GROUP ON AZURE | Firstly, sign in to the Azure portal, search for Resource Group and click on create. On the Basic bar... | 0 | 2024-05-25T14:34:50 | https://dev.to/temmytope86/creating-a-resource-group-on-azure-np4 | Firstly, sign in to the Azure portal, search for Resource Group and click on create. On the Basic bar consist of Project details with sub head "subscription" where all resources are billed together.
next is "resource group". type in a globally accepted unique name.
Next headings is the "Resource Details: with a sub title of the region/location. This is choosing a suitable Azure region.
Next to "Basic" is "Tag" input name and tag your RG.
Lastly, click on "Review and Create" it will validates the process and once passed. click on create.
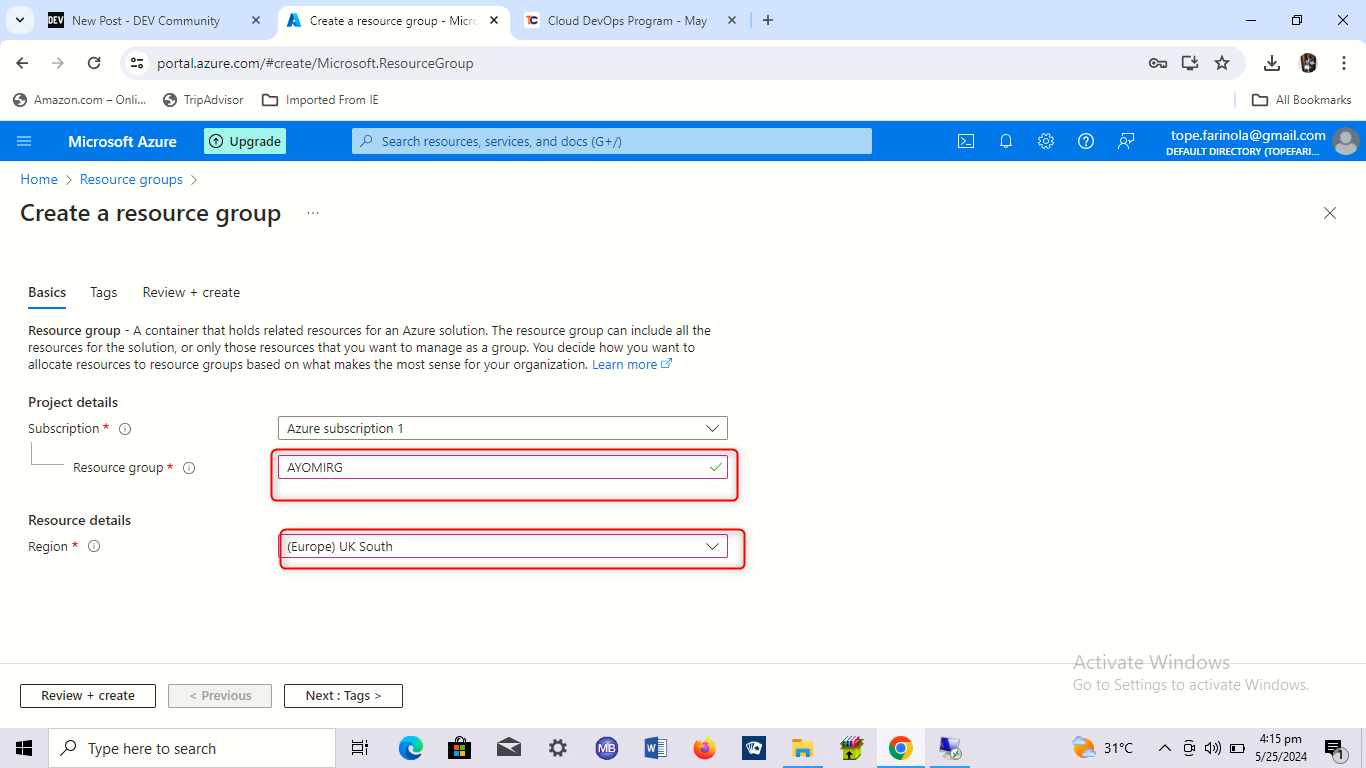
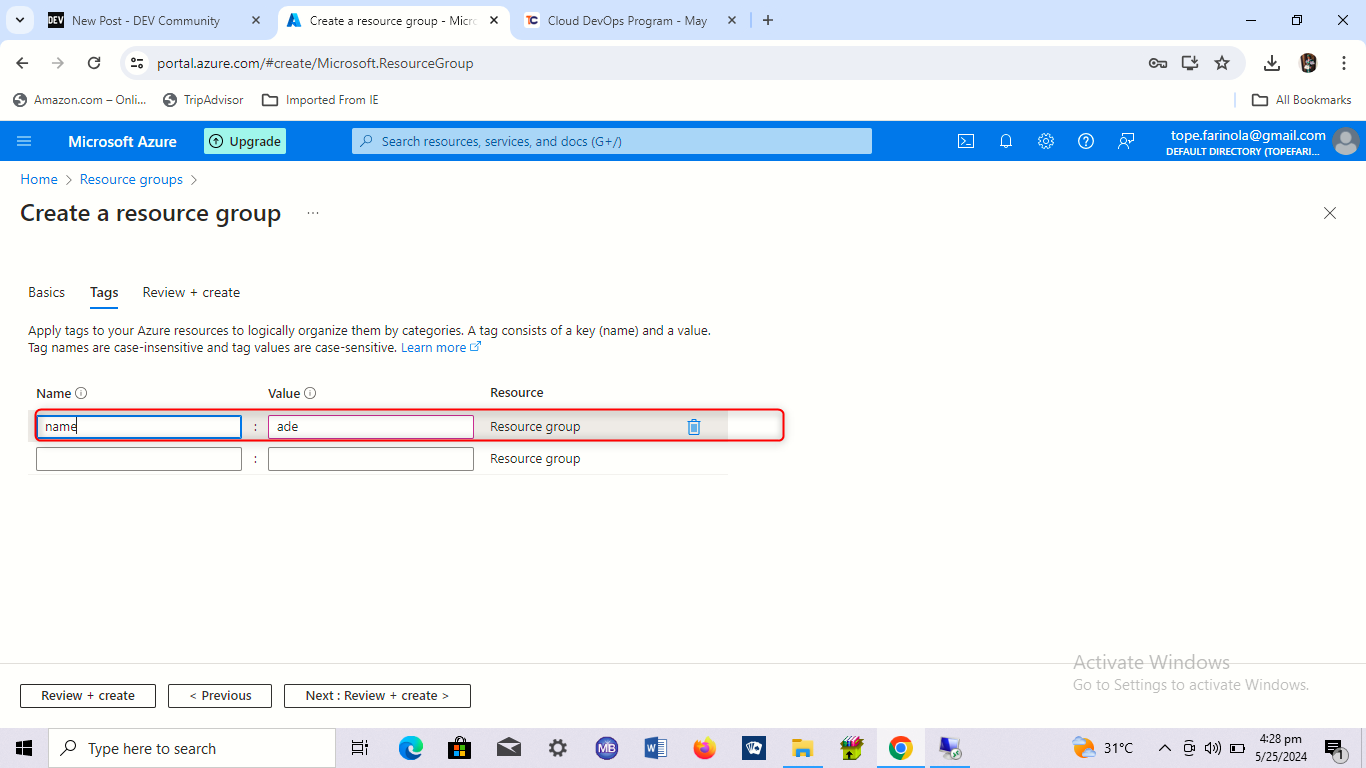
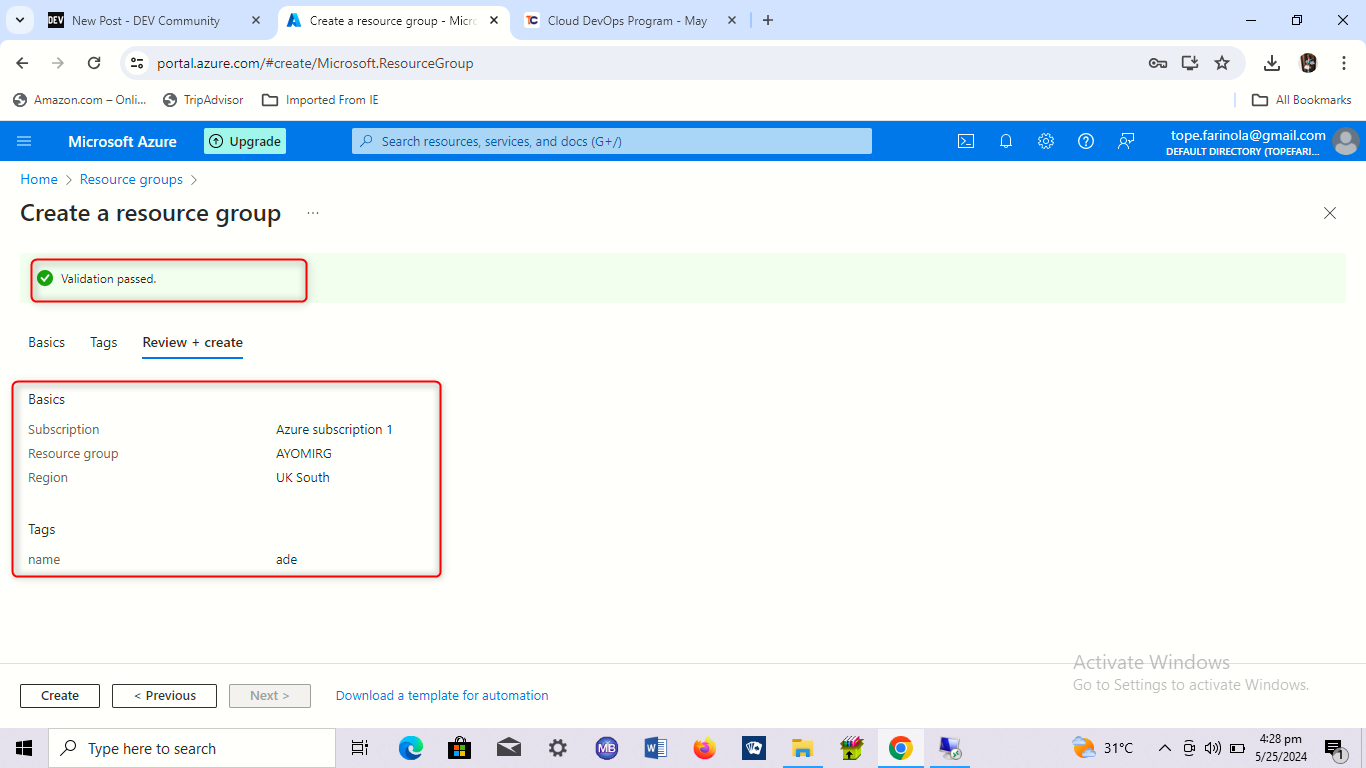 | temmytope86 | |
1,864,904 | ytsftyutdsftdstyufds | https://lkc.hp.com/forum/applications/phim-mai-hd-vietsub-thuyet-minh-mai-2024 https://lkc.hp.com/for... | 0 | 2024-05-25T14:34:47 | https://dev.to/vixion_biru_97298fdd05021/ytsftyutdsftdstyufds-4lkf | https://lkc.hp.com/forum/applications/phim-mai-hd-vietsub-thuyet-minh-mai-2024
https://lkc.hp.com/forum/applications/xemphimlau-mai-2024-full-hd-1080p-thuyetminh-vietsub
https://lkc.hp.com/forum/applications/xemphimlau-mai-2024-full-hd-thuyetminh-vietsub
https://lkc.hp.com/forum/applications/2024-1080phd
https://lkc.hp.com/forum/applications/2024hd-1080p
https://www.lesswrong.com/posts/QdHGKcsKh6WyxZYd6/tyghjyutjygjhgjggyuty | vixion_biru_97298fdd05021 | |
1,864,901 | How and Why I Started My Career as a DevOps Engineer as a Fresher ( Accidental DevOps Engineer ) | Don’t we all have our unique journeys that shape who we are today and who we aspire to be? Allow me... | 0 | 2024-05-25T14:29:36 | https://dev.to/ujjwalkarn954/journey-40j9 | devops, developer, cloud, aws | Don’t we all have our unique journeys that shape who we are today and who we aspire to be? Allow me to share my path to becoming a DevOps Engineer and my future aspirations. I hope you find it relatable and engaging. Feel free to share your thoughts and experiences; I'd love to hear about your journey too.
[Ujjwal Karn](https://lnkd.in/d9dgpchb) | ujjwalkarn954 |
1,864,899 | I MADE A GAME IN 30 MINUTES 🏀 | Hi guys, how are you. Recently I saw that @dino2328 has been supporting me a lot. I taught why not... | 0 | 2024-05-25T14:26:10 | https://dev.to/mince/a-game-in-just-30-minutes--2bnh | webdev, javascript, beginners, tutorial | Hi guys, how are you. Recently I saw that @dino2328 has been supporting me a lot. I taught why not have a challenge with him. So, here I am ! He suggested that we have a 30 minute challenge of who makes the best game. He told me he was familiar with scratch. So, yeah this is the reason I am practicing scratch since the past week. The challenge officially began when we created a project. This is the judging criteria:
- One view = 1 point
- One heart = 2 point
- One star = 2 point
- One remix = 3 point
- One Comment = 5 point
This article is completely about how I made a game in 30 minutes.
## IDEA 💡
<img src='https://media.giphy.com/media/v1.Y2lkPTc5MGI3NjExempzb3RjZWdzZjAxY3F5MDh5cW52a251b29veWR0cHB4NjJyNTR2eiZlcD12MV9pbnRlcm5hbF9naWZfYnlfaWQmY3Q9Zw/6jIp6qgxdB7CQSNgyU/giphy.gif'/>
Great inventions come out of great ideas. Guys, I thought of making a shooter game at first. But oh yeah ! I already made a shooting game. After some time, I remember that [cookie clicker tutorial](https://www.youtube.com/watch?v=R38_FxQ3VgA&t=53s) I watched. Maybe a clicker game. I remember the game's code slightly. But what is the main item that is going to be clicked. Not a cookie for sure, that would be plagiarism. Well, what's my favourite thing in the entire world ? Pizza ?
Yeah it's a pizza. Ah ha ! It took me 5 minutes to figure this out
## The pizza
Great men always start the designing first. So did I ! I made a pizza that looked nothing like a pizza. Then I made another one. That looked more like a wheel. Why is this happening to me 😢. Finally after wasting 10 more minutes I got a pizza looking like a pizza. Then I gave a really cool effect that I saw in the video. I remembered it wrong, I tested a bunch more blocks and numbers.... That was what I wanted.
<img src='https://media.giphy.com/media/v1.Y2lkPTc5MGI3NjExbzYwZ2lidzkzanUwaHlmemd4aXVoNjk0d2g3aDFpd2h6eWtoYnF4NyZlcD12MV9pbnRlcm5hbF9naWZfYnlfaWQmY3Q9Zw/23Mj8QXhWMNmE/giphy.gif'/>
## Score and Coin
<img src='https://media.giphy.com/media/v1.Y2lkPTc5MGI3NjExOTJ1cmM2OGMzcGlnYTFkaHAxMHFrdjNnNHZyd202NmRlNHEzazFxcyZlcD12MV9pbnRlcm5hbF9naWZfYnlfaWQmY3Q9Zw/GNvWw0pDL6QRW/giphy.gif'/>
Then I made a score variable which changes by one whenever you click the pizza, Nice ! In the same "WHEN THIS SPRITE IS CLICKED" block I put "Create clone of COIN" block. Well previously immediately after the art work of pizza I made a simple plus one coin. After all this I wrote script when made the clone of the coin to got to a random place and fade out. Awesome ! How much time do I have....
<img src='https://media.giphy.com/media/v1.Y2lkPTc5MGI3NjExcHU2dm0wc2dkcHZ6eXhyZmI0MTNsZXZqeDJyNTV2ZWxhNWppY2pmNSZlcD12MV9pbnRlcm5hbF9naWZfYnlfaWQmY3Q9Zw/cF7QqO5DYdft6/giphy.gif'/>
2 MINUTES !!!!!!!!!!
I hade to hurry up. Make a background, Oh why is it on the top 💢 !! Send it to the back. Phew... Next up, I need high score. Make a variable !!!
😭😭😭😭 Oh not that I need I cloud variable, delete that
And then Timer went off
<img src='https://media.giphy.com/media/v1.Y2lkPTc5MGI3NjExZGc1N3MycjJ6MmYyeGYydWNrMzMzYnJzZzJmb3dvYmx4amQzdm9pNiZlcD12MV9pbnRlcm5hbF9naWZfYnlfaWQmY3Q9Zw/ZdT2zDh3Bvnkk/giphy.gif'/>
Guys that was close, well atleast I made a game with a score please check it out and support me. So that I win. You know what, the loser should write a post praising the winner and supporting him as a punishment. Guys and if you want to participate with me like this. Comment me
Oh... wait check out my game : [PIZZA CLICKER !](https://scratch.mit.edu/projects/1027042697/)
@dino2328 Project : [Finding giga](https://scratch.mit.edu/projects/1027030846)
| mince |
1,864,898 | Ann Otter Way To Secure Exchange | Prolog Have you ever needed to send sensitive information, like a generated password, but... | 0 | 2024-05-25T14:24:08 | https://dev.to/daniiiol/ann-otter-way-to-secure-exchange-24bm | security, webdev, productivity, opensource | ## Prolog
Have you ever needed to send sensitive information, like a generated password, but felt uncomfortable transmitting it via email or MS Teams? The recipient doesn't have Threema, or you don't want the info in your personal chat history?
I've encountered this situation many times in the past. This need led me to create a small open-source tool. Feel free to use it or even improve it!
### My personal highlights of the project
💡 Simplicity and security are the main focus. The password is encrypted in the client's browser, and a URL for sharing is generated. The secret can only be retrieved once before it is permanently deleted.
💻 The tool is fully open-source, allowing everyone to analyze the code in detail. My goal was to create a lightweight yet security-oriented project.
🪅 Texts and logos can be customized as needed.
🚀 The system can be set up on any Docker-capable platform in just a few minutes.
I invite you to try out the application and look forward to your feedback!
You could find the project on Github: <https://github.com/daniiiol/AnnOtter.WayToSecureExchange>
## Development
The tool was deliberately written in vanilla JavaScript with minimal Bootstrap. The backend server is a small .NET 8 application, and the database system can either be an embedded SQLite database or a remote PostgreSQL DB.
I would be delighted if the hours invested in this application could benefit even more people, and I invite you to use the tool.
I invite you to try out the application and look forward to your feedback!
## Example
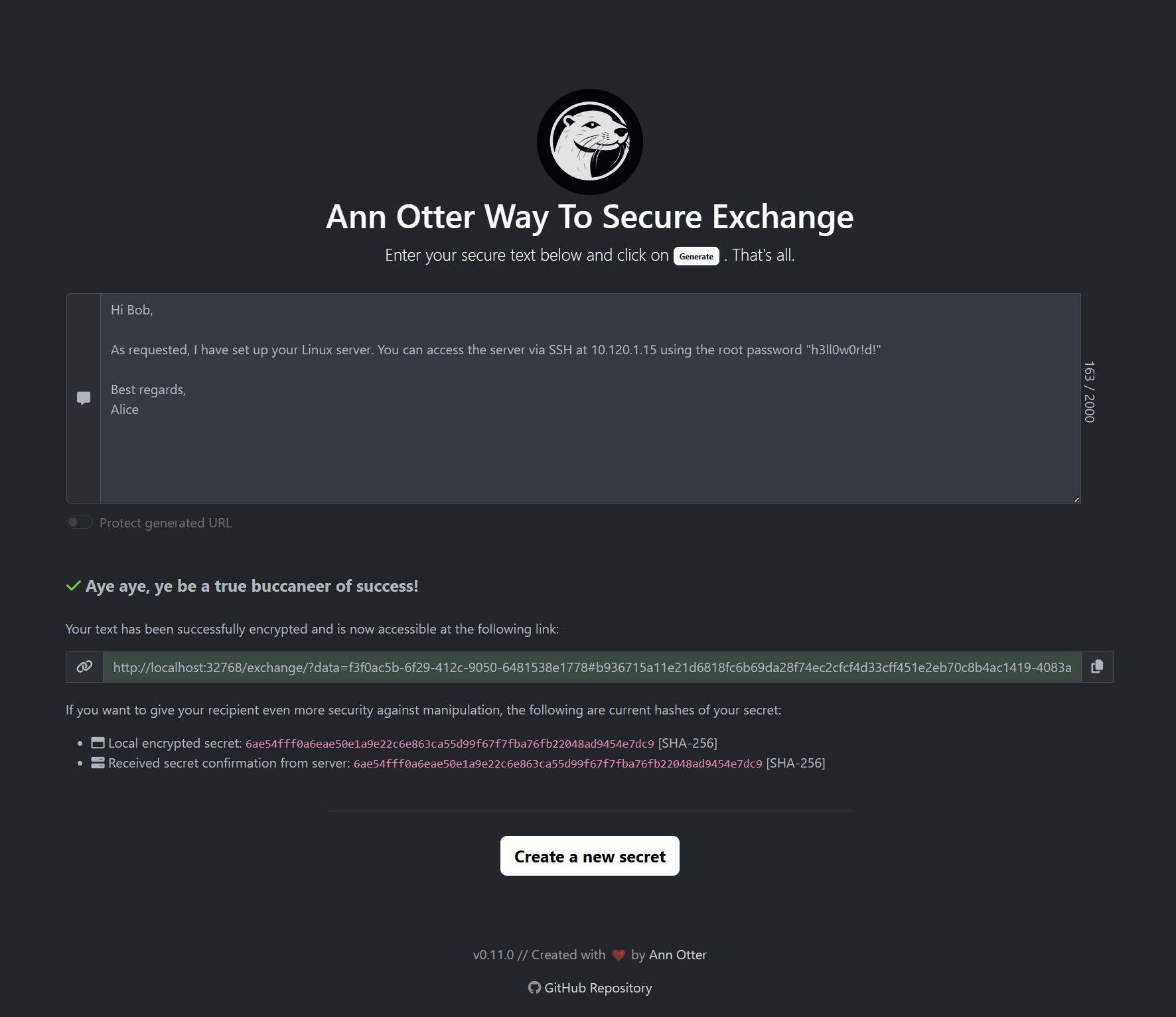 | daniiiol |
1,864,884 | Contact Center Software Market Worth in Current Era | https://www.customerservice-pro.com/contact-center-software-market-worth/ Kindly Read this article... | 0 | 2024-05-25T14:12:34 | https://dev.to/digitalmedia019/contact-center-software-market-worth-in-current-era-16fg | https://www.customerservice-pro.com/contact-center-software-market-worth/
Kindly Read this article and comment for open discussion. | digitalmedia019 | |
1,864,057 | Learn Go with Me: A Beginner's Guide | Learning Go with Me: A Beginner's Guide Welcome to "Learning Go with Me," a blog series... | 27,511 | 2024-05-25T14:11:47 | https://dev.to/muhammadsaim/learn-go-with-me-a-beginners-guide-2k2a | go, learning, beginners, webdev | ## Learning Go with Me: A Beginner's Guide
Welcome to "Learning Go with Me," a blog series dedicated to exploring the Go programming language from the ground up. Whether you're a seasoned developer looking to add another language to your toolkit or a complete beginner ready to dive into the world of programming, this series is designed to guide you through the fundamentals and beyond.
### Why Go?
Go, also known as Golang, is an open-source programming language developed by Google. It has quickly gained popularity due to its simplicity, efficiency, and powerful concurrency features. Go is particularly well-suited for building scalable and high-performance applications, making it a favorite among developers working on web services, cloud computing, and distributed systems.
### What to Expect
In this series, we'll embark on a journey together, learning Go step by step. Here's a sneak peek at what we'll cover:
1. **Introduction to Go**: We'll start with the basics, exploring the history of Go, its unique features, and how it compares to other languages.
2. **Setting Up Your Environment**: A hands-on guide to installing Go and setting up your development environment.
3. **Go Syntax and Basics**: Learn about variables, data types, control structures, and basic syntax to get you writing simple Go programs.
4. **Functions and Packages**: Understand how to write functions, create reusable code, and organize your projects with packages.
5. **Concurrency in Go**: Discover Go's powerful concurrency model, including goroutines and channels.
6. **Building Web Applications**: We'll dive into creating simple web servers and exploring Go's standard library for web development.
7. **Error Handling and Testing**: Learn best practices for error handling and writing tests to ensure your code is robust and reliable.
8. **Real-World Projects**: Put your knowledge to the test by building real-world applications and contributing to open-source Go projects.
### Why Learn with Me?
I'm passionate about Go and excited to share my learning journey with you. By documenting my progress, challenges, and insights, I hope to create a collaborative learning environment where we can all grow together. Your feedback, questions, and contributions will be invaluable as we navigate the intricacies of Go.
### Get Started!
To kick things off, make sure you have Go installed on your machine. You can download it from the official [Go website](https://golang.org/). In the next post, we'll dive into setting up your development environment and writing your first Go program.
Feel free to leave comments, ask questions, and share your own experiences. Let's learn Go together and build something amazing!
Stay tuned for the next installment of "Learning Go with Me."
Happy coding!
| muhammadsaim |
1,864,882 | Tiktok inspired me today when | I was relaxing and suddenly I saw a video tweeted. I was curious, I clicked on it and watched it, and... | 0 | 2024-05-25T14:11:22 | https://dev.to/1024mining-btc/tiktok-inspired-me-today-when-4lom | I was relaxing and suddenly I saw a video tweeted.
I was curious, I clicked on it and watched it, and to describe it, it was a video of a friend from China posting a video of his country doing farming work.
At first I couldn't understand what they were doing, and it made me so curious that I started Googling “mysterious crafts of the Orient.”
Specifically, it says that in the northern part of China, they make pickles and sauces.
It's a process that you haven't seen yet, and you don't know the magic of it, but it's a new condiment made by fermenting soy products with salt, but it's a process that takes a long time, and it involves fermenting the soy products ahead of time, and then pickling them until the next summer, and it's a process that takes a long time.
The video I watched was not just salt and soy products together, but it takes up to a month to grind the soy products.
It's a manual process that is repeated every day until it's ready to be eaten or sold.
It makes me think.
Isn't this the same thing we do with BTC miners?
Preparing the miners, the network, the power, the BTC mining, the same thing every day, selling the fruits of their labor.
Chinese netizens are actually involved in BTC mining just like we are, and maybe we can say that China isn't a technological powerhouse, but maybe a lot of this comes from the ancient culture of China, where they've been making spices for hundreds of years, which is similar to what we're doing here in BTC mining.
One of the things I've learned from this is that what our ancestors did thousands of years ago has evolved into what we have now, and maybe the process and the technology has changed, but the principles haven't, and that's what we call decentralization, right? | 1024mining-btc | |
1,861,919 | STEP BY STEP ON HOW TO CREATE AZURE VM IN WINDOWS 11 | First step is to sign up for the Microsoft Azure. search for 'Resource group" to create one. The... | 0 | 2024-05-25T14:07:56 | https://dev.to/temmytope86/step-by-step-on-how-to-create-azure-vm-in-windows-11-424 | First step is to sign up for the Microsoft Azure.
search for 'Resource group" to create one. The project details consist of subscription and globally unique name as the resource group.
Next is the Resource details which include availability region i.e. location. Click on tag (type name), final step is review and create. Clicking on create will validate the resource group and its ready to be used to create Virtual Machine.
Search on the heading for VM, click on Azure VM. The Project details consist of subscription and resource groups. click on resource group and choose the created RG.
INSTANT DETAILS: This consist of VM name, choose region which includes the location and availability options (zone 1, zone 2, zone 3).
IMAGE: select Windows 11
add administrator account and password.
click on Monitoring on the heading (disable), do not forget to add tag with the VM name.
Click on review and create for VM to be deployed. Wait for deployment process to complete.
Click on "go to resource" to extend the idle timeout on IP address and save. Connect, download RDP and save to into your local repository. Launch your VM....
##
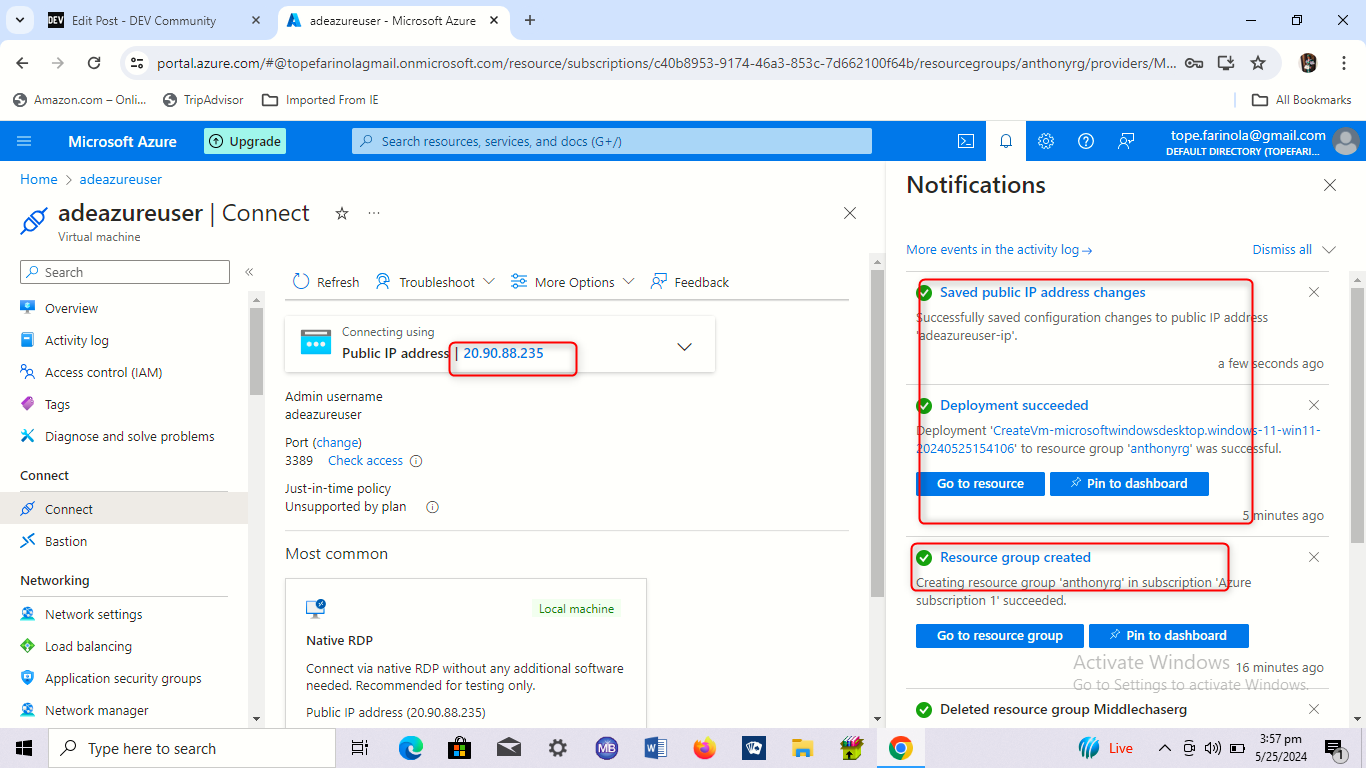
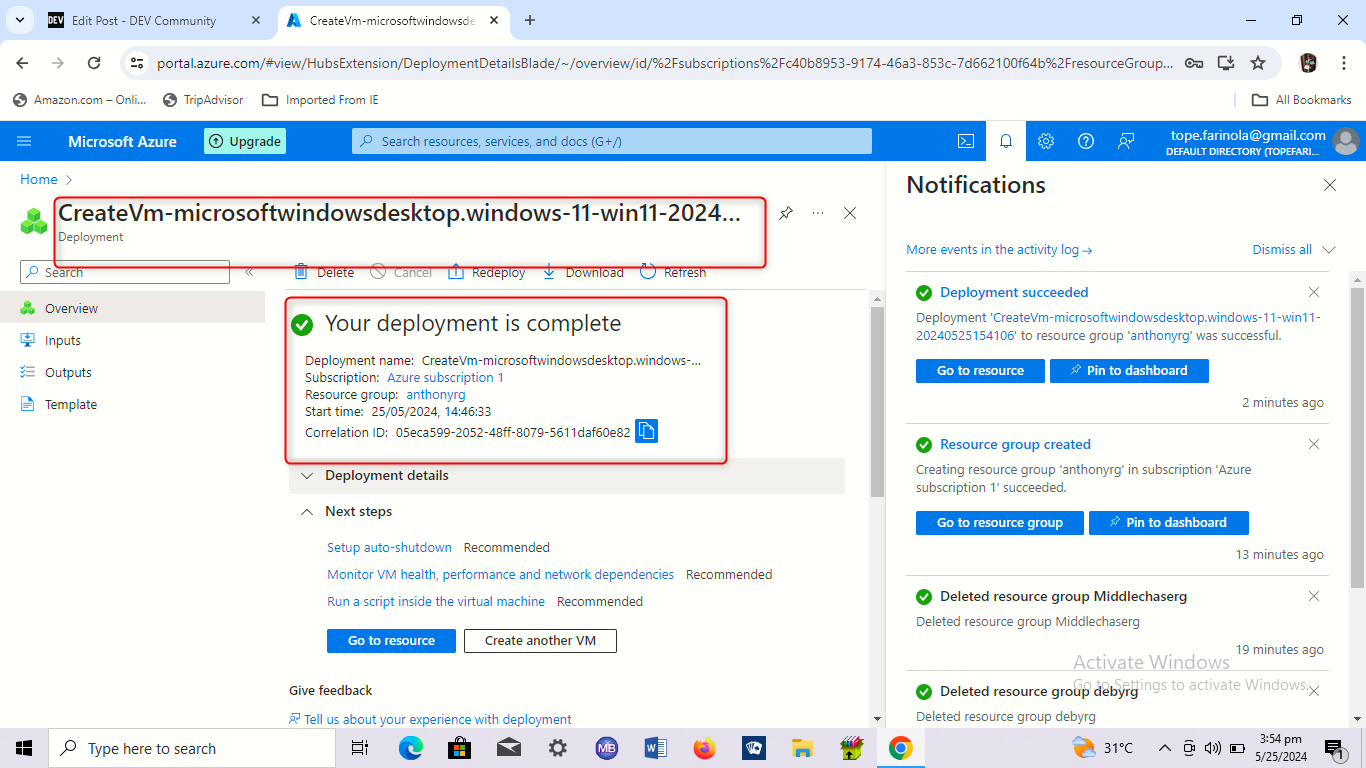
| temmytope86 | |
1,864,879 | Starting top-down shooter mobile game in Unity, wish me luck | Not sure art style or main mechanics yet so if you have any ideas, let me know.. starting this dev... | 0 | 2024-05-25T14:03:21 | https://dev.to/quantumbyte-studios/starting-top-down-shooter-mobile-game-in-unity-wish-me-luck-1mf | Not sure art style or main mechanics yet so if you have any ideas, let me know.. starting this dev log to keep me accountable.
Today, my goal is: player, player script, and bullet..
Eventually I want it hosted on itch.io and launched from a QR code so I can give my family/friends so it will be super easy to share the link..
Wish me luck! | quantumbyte-studios | |
1,854,181 | Sum Root to Leaf Numbers | LeetCode | Java | class Solution { int resSum = 0; public int sumNumbers(TreeNode root) { ... | 0 | 2024-05-25T13:59:42 | https://dev.to/tanujav/sum-root-to-leaf-numbers-leetcode-java-30em | leetcode, java, beginners, algorithms |
``` java
class Solution {
int resSum = 0;
public int sumNumbers(TreeNode root) {
getSumRoot(root, 0);
return resSum;
}
void getSumRoot(TreeNode node, int sum){
if(node==null)
return;
sum = sum * 10 + node.val;
if(node.left==null && node.right==null){
resSum += sum;
return;
}
getSumRoot(node.left, sum);
getSumRoot(node.right, sum);
}
}
```
_Thanks for reading :)
Feel free to comment and like the post if you found it helpful
Follow for more 🤝 && Happy Coding 🚀_
If you enjoy my content, support me by following me on my other socials:
https://linktr.ee/tanujav7 | tanujav |
1,864,876 | Exploring Asynchronous JavaScript: Callbacks, Promises, and Async/Await | JavaScript is a single-threaded language, which means it can only perform one operation at a time.... | 0 | 2024-05-25T13:53:14 | https://dev.to/jps27cse/exploring-asynchronous-javascript-callbacks-promises-and-asyncawait-16k6 | javascript, beginners, programming, webdev | JavaScript is a single-threaded language, which means it can only perform one operation at a time. However, web applications often need to perform multiple operations simultaneously, like fetching data from a server, reading files, or handling user inputs. To manage these tasks efficiently, JavaScript provides mechanisms for asynchronous programming. In this blog post, we will explore three key concepts in asynchronous JavaScript: callbacks, promises, and async/await.
## Callbacks: The Original Asynchronous Pattern
A callback is a function passed into another function as an argument and is executed after some operation has been completed. This is one of the simplest ways to handle asynchronous operations in JavaScript.
### Example of Callbacks
```javascript
function fetchData(callback) {
setTimeout(() => {
console.log("Data fetched from server");
callback();
}, 2000);
}
function processData() {
console.log("Processing data...");
}
fetchData(processData);
```
In this example, `fetchData` simulates fetching data from a server with a delay using `setTimeout`. Once the data is fetched, the `processData` function is called.
### Drawbacks of Callbacks
While callbacks are straightforward, they can lead to callback hell, a situation where callbacks are nested within callbacks, making the code difficult to read and maintain.
```javascript
function fetchData(callback) {
setTimeout(() => {
console.log("Data fetched from server");
callback();
}, 2000);
}
function processData(callback) {
console.log("Processing data...");
callback();
}
function displayData() {
console.log("Displaying data...");
}
fetchData(() => {
processData(() => {
displayData();
});
});
```
## Promises: A Cleaner Approach
Promises offer a more elegant way to handle asynchronous operations. A promise represents a value that may be available now, in the future, or never. It can be in one of three states: pending, fulfilled, or rejected.
### Example of Promises
```javascript
function fetchData() {
return new Promise((resolve, reject) => {
setTimeout(() => {
resolve("Data fetched from server");
}, 2000);
});
}
fetchData()
.then((message) => {
console.log(message);
return "Processing data...";
})
.then((message) => {
console.log(message);
return "Displaying data...";
})
.then((message) => {
console.log(message);
})
.catch((error) => {
console.error("Error:", error);
});
```
In this example, `fetchData` returns a promise. The `then` method is used to handle the resolved value of the promise, allowing us to chain asynchronous operations in a readable manner.
### Advantages of Promises
- **Chaining**: Promises can be chained, improving code readability.
- **Error Handling**: Promises provide a `catch` method to handle errors, which helps in managing error states more effectively.
## Async/Await: The Syntactic Sugar
Async/await is a newer syntax introduced in ES2017 (ES8) that allows us to write asynchronous code that looks synchronous. It is built on top of promises and makes the code easier to read and write.
### Example of Async/Await
```javascript
function fetchData() {
return new Promise((resolve, reject) => {
setTimeout(() => {
resolve("Data fetched from server");
}, 2000);
});
}
async function handleData() {
try {
const data = await fetchData();
console.log(data);
console.log("Processing data...");
console.log("Displaying data...");
} catch (error) {
console.error("Error:", error);
}
}
handleData();
```
In this example, the `fetchData` function is the same as before, returning a promise. The `handleData` function uses the `async` keyword, and within this function, we use `await` to pause the execution until the promise is resolved.
### Benefits of Async/Await
- **Readability**: Makes asynchronous code look like synchronous code, enhancing readability.
- **Error Handling**: Uses try/catch blocks for error handling, which is familiar to those with experience in synchronous programming.
## Conclusion
Asynchronous programming is a vital part of JavaScript, enabling applications to perform multiple tasks efficiently without blocking the main thread. Callbacks were the original way to handle async operations but can lead to complex and hard-to-read code. Promises offer a cleaner and more manageable approach with chaining and better error handling. Async/await builds on promises, providing a more intuitive and readable syntax for writing asynchronous code. Understanding these concepts and their use cases will help you write more efficient and maintainable JavaScript code.
Follow me on : [Github](https://github.com/jps27cse) [Linkedin](https://www.linkedin.com/in/jps27cse/) | jps27cse |
1,864,875 | Terraform vs Ansible | TerraForm VS Ansible: What is the difference between Terraform and Ansible? Terraform is... | 0 | 2024-05-25T13:48:48 | https://dev.to/vaibhavhariaramani/terraform-vs-ansible-103g | ## TerraForm VS Ansible:
What is the difference between Terraform and Ansible? Terraform is an open-source platform designed to provision cloud infrastructure, while Ansible is an open-source configuration management tool focused on the configuration of that infrastructure.
### Orchestration vs Configuration Management:
Orchestration/provisioning is a process where we create the infrastructure – virtual machines, network components, databases, etc. Whereas, on the other hand, configuration management is a process of automating versioned software component installation, OS configuration tasks, network and firewall configuration, etc
### What is Terraform?
**Terraform** enables you to provision, manage, and deploy your infrastructure as code (IaC) using a declarative configuration language called HashiCorp Configuration Language (HCL).
**Key features of Terraform:**
- **State management:** Terraform tracks resources and their configuration in a state file.
- **Declarative code:** Users describe the desired state of their infrastructure, and Terraform manages it.
- **Widely adopted:** Terraform supports over 3k providers.(vendors)
Declarative language: You can divide your infrastructure into multiple reusable modules. (Templates)
### What is Ansible?
**Ansible** is a software tool designed for cross-platform automation and orchestration at scale. Written in Python and backed by RedHat and a loyal open-source community, it is a command-line IT automation application widely used for configuration management, infrastructure provisioning, and application deployment use cases.
**Key features of Ansible:**
- **YAML:** A popular, simple data format that is easy for humans to understand.
- **Modules:** Reusable standalone scripts that perform a specific task
- Playbooks: A playbook is a YAML file that expresses configurations, deployments, and Orchestration in Ansible. They contain one or multiple plays.
- **Plays:** Subset within a playbook. Defines a set of tasks to run on a specific host or group of hosts.
- **Inventories:** All the machines you use with Ansible are listed in a single simple file, together with their IP addresses, databases, servers, and other details.
- **Roles:** Redistributable units of organization that make it easier for users to share automation code.
| vaibhavhariaramani | |
1,864,874 | The Bond between Frontend Development and User Experience (UX) Design | Frontend development, as you may know, is the development of a website’s graphical user interface... | 0 | 2024-05-25T13:46:21 | https://dev.to/outstandingvick/the-bond-between-frontend-development-and-user-experience-ux-design-47m8 | webdev, uxdesign, uidesign, frontend | Frontend development, as you may know, is the development of a website’s graphical user interface with HTML, CSS, and JavaScript so that users can view and interact with that website. And User Experience (UX) Design is a multidisciplinary approach that focuses on creating, products, services, and systems, that are efficient, and enjoyable for users to interact with it. It is a multidisciplinary approach because it involves various aspects of design, technology, and psychology to deliver the required result. The relationship between front-end development and UX design is very important because it ensures the success of a website or an app because a well-designed user experience implemented correctly can boost user satisfaction, engagement, and conversions, and it improves usability and accessibility. All these are crucial for the success of a project. In the following sections of this article, we will dive deep into how complimentary this relationship is, and how it makes the web, and software development in general better.
- Understanding UX design
- The Role of Frontend Development in UX
- Collaboration and Communication
- Accessibility and Usability Testing
- Future Trends and Innovations
**Understanding UX Design**
As already stated earlier, UX design is a multidisciplinary approach that focuses on creating, products, services, and systems, that are efficient, and enjoyable for users to interact with it. It is crucial for the creation of successful products because its designs help make the product useable and meaningful. For UX design to work out well, UX designers are guided by a set of principles, some of these principles include;
- **User-Centered**: This principle states that when designing any product, the user’s needs should be put first, and every decision should be made with what you know about them and what they want from the product, so your product can solve their problem(s).
- **Hierarchy**: This principle calls for the right arrangement and prioritisation of elements and content in a design, so it can be easily accessed by users to navigate the interface easily. Hierarchy is divided into two; information hierarchy, which organizes content according to its importance and relevance to the user, while visual hierarchy guides the user’s attention to important elements in the product through the use of colour, sizes, fonts, and images.
- **Consistency**: This principle states that when you are designing any product, every content, every element, should be consistent with the brand identity, how they look and function should not be distant from each other, for example, if you are designing a hotel website, it shouldn’t look or function like a payment processing website.
- **Usability**: You should always make sure your design makes the product easy to use, it should be easy to learn how to use, and satisfactory.
UX designers are essential in shaping user experience because they bring all these ideas to fruition, without them these ideas and principles just end up being nothing but written down words.
**The Role of Frontend Development in User Experience**
As stated at the beginning of this article frontend development is the development of a website’s graphical user interface with HTML, CSS, and JavaScript so that users can view and interact with that website. It plays an essential role in user experience because developing the front end is essential to improving the user experience. Well-designed, useful, and aesthetically pleasing websites are more likely to draw and keep users across all platforms. Users are encouraged to explore your material by simple navigation and intuitive interaction, which eventually increases the likelihood that they will become customers. It plays these roles in the following ways;
- **Responsiveness and Adaptability**: It’s the duty of a front-end developer to ensure that a website works seamlessly on different screen sizes, it should be able to adapt to different forms either portrait or landscape. Because the website will be accessed by users with different kinds of devices.
- **Accessibility**: Front-end development ensures that the products are easy to use, for example, a particular button shouldn’t be too small to touch, ensuring smooth navigation for users.
- **Performance**: Front-end development ensures that an app is functioning optimally, has great page load speed, and animations and videos should occur smoothly and simultaneously.
**Collaboration and Communication**
It is paramount that Front-end developers and UX designers collaborate to ensure the success of the web, one can’t do without the other, to improve the user experience, seamlessly integrate design and functionality, and contribute to the overall success of a project. There should be strategies put in place to ensure effective collaboration and communication between Front-end developers and UX designers, some of which include;
- Firstly, front-end developers need to be involved early in the design process.
- Utilizing design collaboration tools to enable designers to produce design elements that frontend engineers can share with ease. Afterwards, front-end developers can expedite the development process by using these tools to examine design assets, produce code snippets, and export materials.
- Maintaining clear-cut channels of communication, developers and designers should have regular check-ins and updates with each other to ensure any issues are fixed swiftly, and delays are avoided.
**Accessibility and Usability Testing**
Accessibility is a very important piece of UX design, and there are practices front-developers can implement in their codes to enhance accessibility;
- **Semantic HTML**: They can use HTML elements and tags like “<header>” “<nav>” “<main>” “<section>” “<footer>” etc. appropriately to provide structure to the contents.
- **Keyboard Navigation**: Make sure all the interactive elements are keyboard accessible so that users can be able to navigate the website with their keyboard.
- **Color Contrast**: Ensuring readability for users with color blindness or low vision by making sufficient color contrast between the text and background.
- **Alt text for images**: Ensuring that the purpose and content of images are for users who can’t see with the descriptive <alt> text attribute in the "img" HTML tag.
- **Responsive Design**: Make designs that are responsive to various screen sizes and gadgets. Verify the website's usability across a range of gadgets, such as tablets and smartphones.
Usability testing is a way of evaluating if a website or app is ready to be released by testing it with real users who are part of the target audience. Usability tests assess the overall user experience by measuring the relative ease with which end users can complete a set of tasks that an average user of the app or website would need to complete. Usability testing aims to understand how actual users interact with your website, and modifications can be made in response to the findings. Front-end developers can assist in usability testing in the following ways;
- By building interactive mockups based on the UX design. This will be essential for gathering feedback before the project is released.
- Ensuring that the test environment is set up rightly with the latest codes and dependencies by configuring the testing environment to resemble the final production environment
- Front-end developers can facilitate testing sessions by being observers and providing answers about functionalities.
- They can identify key user flows, and test scenarios, and provide insights on which features should be tested based on their technical know-how.
**Future Trends and Innovation**
We live in a fast-paced world where new systems and innovations are being churned out frequently, and the world of software development isn’t an exception. Some of the emerging trends include;
- Motion Design Microinteractions
- Progressive Web Applications
- Voice user interfaces
- Virtual reality and Augmented reality
- Conservation designs
- Data-Drive Designs
Front-end developers and UX designers must stay ahead of the curve by continuously learning and incorporating these innovations into their skill sets.
**Conclusion**
The relationship between front-end development and UX design is akin to a symbiotic relationship, it is necessary and needed for optimal web and software development, together they make the software and apps on our devices look and work great. So as more innovations come into existence these two sides of a coin will continue to foster a better consumer tech experience.
| outstandingvick |
1,863,459 | Game Development Diary #5 : Start My "BUMI" Project - Part 1 | 25/05/2024 - Saturday To Do List : *Create a level, just simple plane with some... | 27,527 | 2024-05-25T13:43:52 | https://dev.to/hizrawandwioka/game-development-diary-5-start-my-bumi-project-3kcl | godot, godotengine, gamedev, newbie | 25/05/2024 - Saturday
#To Do List :
*Create a level, just simple plane with some obstacles(just basic shapes).
*Implement collision detection to the level.
*Create 3 Main Character according to the novel(Just use capsule first until I get the 3d model that suitable for the game - because I am not good at art, but I will try to create by myself first.)
*Use Input Mapper to create a button that can switch the playable character.
#What's Next?
I will continue to the second section on the course and get more useful knowledge that I can implemented on my project. | hizrawandwioka |
1,864,873 | LangChain: Function Calling | In this blog post, we'll dive into the integration of OpenAI functions (or tools) with LangChain... | 0 | 2024-05-25T13:42:24 | https://dev.to/rutamstwt/langchain-function-calling-2bbh | In this blog post, we'll dive into the integration of OpenAI functions (or tools) with LangChain expression language. We'll also explore Pydantic, a Python library that simplifies the construction of OpenAI functions/tools. Additionally, we'll discuss the recent shift from functions to tools in OpenAI's API and how it impacts the workflow.
OpenAI has deprecated the use of functions in favor of tools. The primary difference between the two is that the tools API allows the model to request multiple functions/tools to be invoked simultaneously, potentially reducing response times in certain architectures. As a result, it's recommended to use the tools agent for OpenAI models.
However, it's important to note that the functions format remains relevant for open-source models and providers that have adopted it. The agent we'll discuss in this blog post is expected to work for such models.
For OpenAI models, it's advised to use the tools API instead of the functions API. The tools API is designed to work with models like gpt-3.5-turbo-0613 and gpt-4-0613, which have been fine-tuned to detect when a tool should be called and respond with the inputs that should be passed to the tool.
The OpenAI Tools Agent is designed to work with these models and the tools API. It provides a more reliable and efficient way to return valid and useful tool calls than a generic text completion or chat API.
While the functions format is still relevant for certain use cases, the tools API and the OpenAI Tools Agent represent a more modern and recommended approach for working with OpenAI models.
## What is Pydantic?
Pydantic is a data validation library for Python. It makes it easy to define different schemas and export those schemas to JSON format. This capability is particularly useful when working with OpenAI functions/tools, as we can use Pydantic objects to create the required function/tool descriptions.
If you recall, the OpenAI function descriptions were essentially large JSON blobs with numerous components. By using Pydantic, we can abstract away the complexities of constructing these JSON structures manually.
The way we'll utilize Pydantic is by defining a Pydantic class. It's very similar to a regular Python class, but the primary distinction is that instead of having an `__init__` method, we'll list the attributes and their types directly under the class definition. It's important to note that we won't actually use these classes for any functional purpose; we'll solely use them to generate the OpenAI functions/tools JSON.
### Pydantic Syntax
Pydantic data classes combine Python's data classes with the validation of Pydantic. They offer a concise way to define data structures while ensuring that the data adheres to specified types and constraints.
In standard Python, you would create a class like this:
```python
from typing import List
from pydantic import BaseModel, Field
class User:
def __init__(self, name: str, age: int, email: str) -> None:
self.name = name
self.age = age
self.email = email
foo = User(name="Joe", age=32, email="joe@gmail.com")
foo.name # Output: 'Joe'
foo = User(name="Joe", age="Bar", email="joe@gmail.com")
foo.age # Output: 'Bar'
```
With Pydantic, we can have our class inherit from `BaseModel` and then define our attributes just under the class definition with various type hints.
```python
class pUser(BaseModel):
name: str
age: int
email: str
foo_p = pUser(name="Jane", age=32, email="jane@gmail.com")
foo_p.name # Output: 'Jane'
```
**Note**: The next code snippet is expected to fail.
```python
foo_p = pUser(name="Jane", age="Bar", email="jane@gmail.com")
# Note: This will throw a type error which is expected
```
One other thing we can do with Pydantic is we can actually nest these data structures.
```python
class Classroom(BaseModel):
students: List[pUser]
student1 = pUser(name="Joe", age=32, email="joe@gmail.com")
student2 = pUser(name="Jane", age=32, email="jane@gmail.com")
classroom = Classroom(students=[student1, student2])
classroom # Output: Classroom(students=[pUser(name='Joe', age=32, email='joe@gmail.com'), pUser(name='Jane', age=32, email='jane@gmail.com')])
```
This is a brief introduction to Pydantic. If you want to learn more, I'd encourage you to explore their documentation or try out different type hints to see how they shape the resulting objects.
## Pydantic to OpenAI Function/Tool Definition
Now, let's discuss how we can use Pydantic to create OpenAI function/tool definitions. What we'll do is create a Pydantic object that we can then cast to the JSON schema required by OpenAI. Importantly, the Pydantic object we create isn't actually going to perform any functional task; we're solely using it to generate the schema.
```python
class WeatherSearch(BaseModel):
"""Call this with an airport code to get the weather at that airport"""
airport_code: str = Field(description="airport code to get weather for")
from langchain_core.utils.function_calling import convert_to_openai_function
weather_function = convert_to_openai_function(WeatherSearch)
weather_function
```
We've made some assumptions about how people would want to create OpenAI functions/tools. One assumption is that we've made the docstring required because it gets incorporated into the function/tool description. As we discussed earlier, the functions/tools essentially act as prompts, and providing a clear description of what the function/tool does is crucial. Therefore, we've added checks to ensure that the description is provided.
However, you'll notice that there's no description for the `airport_code` argument. Descriptions for arguments are optional in LangChain. They're not required.
```python
class WeatherSearch2(BaseModel):
"""Call this with an airport code to get the weather at that airport"""
airport_code: str
# Notice: There is no description for this parameter
# This is optional
convert_to_openai_function(WeatherSearch2)
```
## Using with LangChain Expression Language
Let's now look at combining OpenAI functions/tools with LangChain Expression Language.
```python
from langchain_openai import ChatOpenAI
model = ChatOpenAI()
model.invoke("what is the weather in SF today?", functions=[weather_function])
```
We'll create an instance of the `ChatOpenAI` model. For now, we'll interact with it directly. Specifically, we're going to call the `invoke` method on this model and pass in keyword arguments, such as the `weather_function` we defined earlier.
Here, what we get back from the model is a content message that's null. In the `additional_kwargs` field, we'll have the `function_call` parameter, which returns a function call with the name `WeatherSearch` and the arguments `airport_code` set to `SFO`. So it's using the function appropriately.
We can also bind the function invocations to the model. One reason for doing this is so that we can pass the model and functions together, without having to worry about always passing in the function keyword arguments.
```python
model_with_function = model.bind(functions=[weather_function])
model_with_function.invoke("what is the weather in sf?")
# AIMessage(content='', additional_kwargs={'function_call': {'arguments': '{"airport_code":"SFO"}', 'name': 'WeatherSearch'}}, response_metadata={'token_usage': {'completion_tokens': 17, 'prompt_tokens': 69, 'total_tokens': 86}, 'model_name': 'gpt-3.5-turbo', 'system_fingerprint': None, 'finish_reason': 'function_call', 'logprobs': None}, id='run-e40ecdda-e764-465f-85ab-71f4f9de195d-0')
```
We can now call this `model_with_function` directly and just pass in the input query. As you can see, it responds and still uses the function call, because it knows that the function calls exist since we've bound them to the model.
### Forcing it to use a function
We can force the model to use a specific function:
```python
model_with_forced_function = model.bind(functions=[weather_function], function_call={"name":"WeatherSearch"})
model_with_forced_function.invoke("what is the weather in sf?")
# AIMessage(content='', additional_kwargs={'function_call': {'arguments': '{"airport_code":"SFO"}', 'name': 'WeatherSearch'}}, response_metadata={'token_usage': {'completion_tokens': 7, 'prompt_tokens': 79, 'total_tokens': 86}, 'model_name': 'gpt-3.5-turbo', 'system_fingerprint': None, 'finish_reason': 'stop', 'logprobs': None}, id='run-a30b6829-ff00-4f3b-bbe7-28d7117a1b9f-0')
```
Here, we're binding the `weather_function` to the model and also specifying the `function_call` parameter with the name of the function we want to force it to use.
```python
# Note: This doesn't need a function call, and since the input isn't a city, it's hallucinating on the airport code
model_with_forced_function.invoke("hi!")
# AIMessage(content='', additional_kwargs={'function_call': {'arguments': '{"airport_code":"JFK"}', 'name': 'WeatherSearch'}}, response_metadata={'token_usage': {'completion_tokens': 7, 'prompt_tokens': 74, 'total_tokens': 81}, 'model_name': 'gpt-3.5-turbo', 'system_fingerprint': None, 'finish_reason': 'stop', 'logprobs': None}, id='run-4dc1b853-c9a7-4a44-b587-04d06dffcdb4-0')
```
In the above example, since the input doesn't contain a city name, the model is trying to interpret "hi!" as an airport code, which leads to an incorrect response.
### Using in a Chain
We can use this model bound to a function in a chain, just as we normally would:
```python
from langchain.prompts import ChatPromptTemplate
prompt = ChatPromptTemplate.from_messages([
("system", "You are a helpful assistant"),
("user", "{input}")
])
chain = prompt | model_with_function
chain.invoke({"input": "what is the weather in sf?"})
# AIMessage(content='', additional_kwargs={'function_call': {'arguments': '{"airport_code":"SFO"}', 'name': 'WeatherSearch'}}, response_metadata={'token_usage': {'completion_tokens': 17, 'prompt_tokens': 75, 'total_tokens': 92}, 'model_name': 'gpt-3.5-turbo', 'system_fingerprint': None, 'finish_reason': 'function_call', 'logprobs': None}, id='run-d67d8a7b-72af-4a0e-9119-ca14e1572e07-0')
```
Here, we're creating a simple prompt template and then piping it with the `model_with_function` to create a chain. When we invoke the chain with the input "what is the weather in sf?", it uses the bound function to generate the response.
## Using Multiple Functions
Even better, we can pass a set of functions and let the LLM (Large Language Model) decide which one to use based on the question context.
```python
class ArtistSearch(BaseModel):
"""Call this to get the names of songs by a particular artist"""
artist_name: str = Field(description="name of artist to look up")
n: int = Field(description="number of results")
```
We'll then create a new list of functions, and this time, there will be two functions:
```python
functions = [
convert_to_openai_function(WeatherSearch),
convert_to_openai_function(ArtistSearch),
]
```
We'll create a new object called `model_with_functions` by binding the list of functions to the model:
```python
model_with_functions = model.bind(functions=functions)
```
Now let's try invoking this with different inputs and see what happens:
```python
model_with_functions.invoke("what is the weather in sf?")
# AIMessage(content='', additional_kwargs={'function_call': {'arguments': '{"airport_code":"SFO"}', 'name': 'WeatherSearch'}}, response_metadata={'token_usage': {'completion_tokens': 17, 'prompt_tokens': 116, 'total_tokens': 133}, 'model_name': 'gpt-3.5-turbo', 'system_fingerprint': None, 'finish_reason': 'function_call', 'logprobs': None}, id='run-f56d4dd1-6a74-4419-bd35-9d0487aa3902-0')
model_with_functions.invoke("what are three songs by taylor swift?")
# AIMessage(content='', additional_kwargs={'function_call': {'arguments': '{"artist_name":"Taylor Swift","n":3}', 'name': 'ArtistSearch'}}, response_metadata={'token_usage': {'completion_tokens': 21, 'prompt_tokens': 118, 'total_tokens': 139}, 'model_name': 'gpt-3.5-turbo', 'system_fingerprint': None, 'finish_reason': 'function_call', 'logprobs': None}, id='run-cbeda552-2b1d-4ed4-af47-3829b7ff6d2d-0')
```
And again here, we're not forcing it to call a function. So if we just say "hi", it should respond with something that doesn't use functions at all.
```python
model_with_functions.invoke("hi!")
# AIMessage(content='Hello! How can I assist you today?', response_metadata={'token_usage': {'completion_tokens': 10, 'prompt_tokens': 111, 'total_tokens': 121}, 'model_name': 'gpt-3.5-turbo', 'system_fingerprint': None, 'finish_reason': 'stop', 'logprobs': None}, id='run-a7817d1d-d4b7-4056-a748-1d4ca48d9e0b-0')
```
## Conclusion
In this post, we looked at how to combine OpenAI functions and tools with LangChain expression language, using Pydantic to make it easier to build OpenAI functions. We talked about the change from functions to tools in OpenAI's API and how it can make things faster. By combining OpenAI functions and tools with LangChain, we can build strong applications that work well with outside data sources and software workflows, making the most of large language models.
# Source Code
[https://github.com/RutamBhagat/LangChainHCCourse3/blob/main/course\_3/Langchain\_OpenAI\_Function\_Calling.ipynb](https://github.com/RutamBhagat/LangChainHCCourse3/blob/main/course_3/Langchain_OpenAI_Function_Calling.ipynb) | rutamstwt | |
1,864,870 | Don't Wait To Innovate: Get A Quote From China's Rapid Prototyping Leaders Now! | Are you sitting on game-changing ideas that need to see the light of day? Are you constantly... | 0 | 2024-05-25T13:35:24 | https://dev.to/ai-business/dont-wait-to-innovate-get-a-quote-from-chinas-rapid-prototyping-leaders-now-3pia | ai, career |
Are you sitting on game-changing ideas that need to see the light of day? Are you constantly searching for ways to bring your creativity to life? Or perhaps you're simply looking for reliable rapid prototyping companies to collaborate with on existing projects. Whatever your motivation, know this: delaying action could spell doom for your dreams. Welcome to our comprehensive guide showcasing China's leading lights in rapid prototyping and 3D printing services. We promise to inspire, inform, and connect you with the perfect partners to kickstart your journey.
## Partnering with the Best Rapid Prototyping Companies in China Matters
Collaborating with trusted rapid prototyping companies sets you on course for glory. Allow us to explain why. First, working closely with reputable players ensures top-drawer quality, adherence to international safety protocols, and alignment with ethical practices. Second, engaging with talented engineers speeds up your pathway to market domination. Third, combining forces with accomplished designers helps elevate user experiences exponentially. Fourth, tapping into vast reserves of professionalism translates into peace of mind, leaving you free to concentrate on core operations. Lastly, joining hands with celebrated [rapid prototyping companies](https://www.immould.com/rapid-prototyping-companies-in-china/) generates positive buzz around your brand, boosting credibility in no small measure.
## Introducing China's 3D Printing Mavericks
Let's talk numbers. According to Statista, the global 3D printing market size was valued at approximately $13 billion in 2020. Impressive, yes? Even more astonishing is the prediction suggesting a whopping CAGR of 21% from 2021-2028. What accounts for such phenomenal growth? Simple: increased applications across industries, falling hardware costs, surging consumer awareness, and spiraling demand for customizable products. If you wish to ride this wave, getting cozy with dependable [china 3D printing services](https://www.immould.com/3d-printing-manufacturing-companies-in-china/) becomes non-negotiable.
## Why China Steals the Spotlight in Rapid Prototyping and 3D Printing Realms
Staying abreast of trends reveals a fascinating pattern. Year after year, China cements its status as a titan in rapid prototyping and 3D printing domains. Several compelling reasons account for this phenomenon:
### Cost-effective
Compared to European or American counterparts, labor and operational expenses remain substantially lower in China. Clients stand to benefit financially without sacrificing service excellence.
### Efficient
Thanks to strategic positioning, time zone disparities facilitate submitting design files overnight and receiving completed prototypes bright and early. This setup promotes agile decision-making and swift market entry.
### Skilled
Far removed from antiquated narratives, Chinese manufacturers possess extraordinary experience and acumen in tackling complex projects involving intricate geometry, tight tolerances, and diverse materials. Rest assured, experts raring to exceed expectations greet you warmly.
### Supply Chain Synergies
An integrated web of raw material suppliers, component vendors, assembly partners, testing facilities, and logistics providers harmoniously functions together. Expect timely procurement, flawless execution, and foolproof delivery.
### Policy Push
Continuous government investment targets infrastructure improvement, technological advancements, and regulatory adjustments favoring domestic businesses and foreign investors alike. Opting for rapid prototyping in China yields indirect rewards care of stimulus packages catalyzing industrial evolution.
### Rapid Prototyping versus Injection Molding: Understanding Distinct Phases
For clarity sake, let's dissect two commonly confused terms: rapid prototyping and injection molding. Both seek to accelerate product development cycles and improve design validation, albeit serving separate purposes within said cycle.
### Rapid Prototyping
Suitable for concept validation and iterative improvements, rapid prototyping employs low-cost tooling alternatives like 3D printed masters or silicone rubber molds. Part characteristics may vary slightly from traditional injection molding specimens, however, detecting critical issues early on saves significant resources downstream.
### Injection Molding
Most effective during mass production runs post-proven concept, injection molding demands sizable investments in tooling fabrication. Molten plastic gets forced into steel or aluminum molds under intense pressure, producing high-precision components exhibiting exceptional dimensional accuracy, surface finish, and mechanical strength.
## Recognizing Winning Traits Among Rapid Prototyping Companies in China
As you traverse the labyrinthine landscape hunting ideal matches, bear in mind desirable traits distinguishing premier candidates:
### Domain Dominance
Established players demonstrate dominance across target verticals, signaling adaptability, reliability, and diversified skill sets.
### Clientele Confirmation
Glowing testimonials confirming client satisfaction affirm credibility, trustworthiness, and consistency.
### Certification Commitment
Adherence to ISO certifications guarantees compliance with globally accepted quality management systems.
### Communication Candour
Open dialogue cultivates transparency, honesty, and mutual respect, fostering healthy partnership dynamics.
### Process Proficiency
Demonstrated expertise in employing diverse rapid prototyping techniques proves paramount, covering SLA, DLP, FDM, SLS, and MJF.
### Technology Tenacity
Staying updated with the latest technological developments underscores a commitment to constant learning, adaptation, and innovation.
### Material Mastery
Extensive material libraries incorporating polymers, thermoplastics, composites, elastomers, biocompatibles, conductives, and nanofilaments distinguish elite contestants.
## Putting Theory into Practice: Securing a Quote From China's Rapid Prototyping Giants
Armed with insights, confidence should surge regarding identifying suitable partners amongst China's finest rapid prototyping companies. Follow this roadmap:
* Define project objectives, desired outcomes, and specifications.
Shortlist prospective candidates aligning with the criteria outlined above.
* Request quotes tailored to individual requirements.
* Evaluate quotations against predetermined evaluation matrices.
* Negotiate contractual agreements detailing milestone tracking, payment structures, dispute resolutions, intellectual property rights protection, and confidentiality clauses.
* Embark on a thrilling adventure bringing revolutionary concepts to life.
Remember, hesitation hinders progress. Therefore, act decisively, engage with trailblazing rapid prototyping companies, and tap into limitless potential offered by China's dynamic 3D printing scene.
| ai-business |
1,864,868 | Quel est le meilleur site pour acheter Cialis en toute securite ? | La dysfonction érectile est un problème de santé qui touche un nombre significatif d’hommes en... | 0 | 2024-05-25T13:32:36 | https://dev.to/dr_phillip/quel-est-le-meilleur-site-pour-acheter-cialis-en-toute-securite--akh |

La dysfonction érectile est un problème de santé qui touche un nombre significatif d’hommes en France et dans le monde. Cette condition, qui peut avoir des répercussions tant physiques que psychologiques, nécessite souvent une intervention médicale appropriée pour améliorer la qualité de vie des personnes concernées. Dans ce contexte, Cialis, un médicament largement prescrit pour traiter la dysfonction érectile, joue un rôle crucial en offrant une solution efficace et fiable.
**Cet article se concentre sur la question cruciale :** [où acheter du Cialis en France avec une livraison rapide ?](https://www.linkedin.com/pulse/dans-quel-site-acheter-cialis-en-toute-confiance-docteur-alam-sm1ie/) Alors que la demande de ce médicament essentiel reste forte, la possibilité d’obtenir rapidement et discrètement le Cialis est un aspect crucial pour de nombreuses personnes confrontées à ce problème de santé. L’achat en ligne présente de nombreux avantages, notamment en termes d’accessibilité, de confidentialité et de gain de temps. Dans cet article, nous explorerons en détail ces avantages, tout en mettant en lumière sur **super-pharma-fr est un site reconnu comme fiable pour acheter Cialis en France livraison rapide en toute confiance**. En offrant une plateforme sûre et efficace pour l’achat du Cialis et son generique tadalafil, super pharma fr s’impose comme une solution idéale pour ceux qui recherchent un accès rapide à ce médicament pour érection.
## L’importance du Cialis dans le traitement de la dysfonction érectile
La [dysfonction érectile](https://www.urofrance.org/recommandation/dysfonction-erectile/), souvent appelée impuissance, est un trouble courant qui affecte la capacité d’un homme à obtenir ou à maintenir une érection suffisante pour des rapports sexuels satisfaisants. Bien que ce problème puisse être associé au vieillissement, il peut également résulter de divers facteurs tels que le stress, l’anxiété, des problèmes de santé sous-jacents ou des troubles psychologiques. Quelle que soit sa cause, la dysfonction érectile peut avoir un impact significatif sur la confiance en soi, les relations interpersonnelles et la qualité de vie générale d’un homme.
C’est là que le Cialis entre en jeu. Cialis, également connu sous le nom de tadalafil, est un médicament sur prescription largement utilisé pour le traitement de la dysfonction érectile. Il appartient à une classe de médicaments appelés inhibiteurs de la phosphodiestérase de type 5 (PDE5), qui agissent en relaxant les muscles lisses des vaisseaux sanguins dans le pénis, favorisant ainsi l’augmentation du flux sanguin et facilitant l’érection lorsqu’une stimulation sexuelle adéquate est présente.
L’un des aspects les plus importants du traitement de la dysfonction érectile est un accès rapide et facile aux médicaments appropriés. Pour de nombreux hommes touchés par ce trouble, il est essentiel de pouvoir obtenir rapidement Cialis pour retrouver une fonction érectile normale et maintenir une vie sexuelle satisfaisante.
L’accès immédiat au traitement peut non seulement améliorer la qualité des rapports sexuels, mais également atténuer le stress et l’anxiété associés à la dysfonction érectile, ce qui peut souvent aggraver le problème.
Cependant, **trouver une source fiable et rapide pour acheter du Cialis en France** peut parfois être un défi. Les pharmacies traditionnelles peuvent nécessiter des déplacements et des interactions en personne, ce qui peut être inconfortable pour certains hommes confrontés à ce problème délicat.
C’est là que l’achat en ligne devient une option attrayante.
En optant pour l’achat en ligne, les hommes peuvent contourner les contraintes liées aux déplacements et à l’interaction en personne avec un pharmacien. De plus, l’achat en ligne offre un niveau élevé de confidentialité, ce qui est particulièrement **important pour ceux qui préfèrent garder leur traitement de la dysfonction érectile privé**. De plus, la possibilité de se procurer du Cialis en ligne offre un gain de temps considérable, évitant ainsi les files d’attente et les délais associés aux pharmacies traditionnelles.
A la question de savoir **dans quel site acheter cialis sur internet en toute sécurité ? Super-pharma-fr se distingue comme une solution idéale pour acheter du Cialis en France avec livraison rapide**. Ce site réputé offre non seulement un accès facile et rapide au Cialis, mais également une garantie de qualité et de discrétion pour les clients. En offrant des livraisons rapides et un service clientèle exceptionnel, [super-pharma-fr](https://super-pharma-fr.com/) répond aux besoins des hommes confrontés à la dysfonction érectile, leur permettant ainsi de retrouver une vie sexuelle épanouie et satisfaisante.
**Quels sont les avantages d’obtenir Cialis et son generique sur internet ?**
_L’achat du Cialis en ligne présente plusieurs avantages significatifs, notamment en termes d’accessibilité, de confidentialité et de gain de temps._
Tout d’abord, **l’accessibilité du Cialis en ligne élimine la nécessité pour les personnes concernées de se rendre physiquement dans une pharmacie**. Pour de nombreux hommes confrontés à la dysfonction érectile, l’idée de discuter en personne de leur condition avec un pharmacien peut être gênante et même embarrassante. L’achat en ligne permet aux individus de commander leur boite Cialis depuis le confort de leur domicile, en évitant toute situation inconfortable ou embarrassante. Cette accessibilité accrue garantit que ceux qui ont besoin de ce médicament vital peuvent l’obtenir facilement et rapidement, sans avoir à franchir les obstacles associés aux visites en pharmacie.
En plus de l’accessibilité, [acheter Cialis en ligne offre un niveau élevé de confidentialité](https://super-pharma-fr.com/acheter-cialis). Les plateformes en ligne permettent aux utilisateurs de **commander le médicament de manière discrète**, sans avoir à révéler leur condition à un pharmacien en personne. Cette confidentialité est particulièrement importante pour de nombreuses personnes, qui peuvent préférer garder leur traitement de la dysfonction érectile privé et confidentiel. L’achat en ligne offre un moyen sûr et sécurisé d’obtenir Cialis sans compromettre la vie privée des individus, renforçant ainsi leur confort et leur tranquillité d’esprit lorsqu’ils recherchent un traitement.
Enfin, l’achat du Cialis en ligne permet **un gain de temps considérable**. Évitant les files d’attente et les déplacements jusqu’à la pharmacie, les utilisateurs peuvent commander le médicament depuis chez eux, à tout moment qui leur convient. Cette commodité accrue permet aux hommes de consacrer plus de temps à leurs activités quotidiennes et à leurs proches, sans avoir à sacrifier des heures précieuses pour obtenir leur traitement. De plus, avec la possibilité de commander Cialis en quelques clics, les utilisateurs économisent non seulement du temps, mais aussi de l’énergie et du stress associés aux déplacements physiques vers une pharmacie.
## Dans quel site acheter Cialis en France livraison rapide en toute sécurité ?
**Super-pharma-fr** se distingue comme un choix optimal pour l’achat du Cialis en France pour plusieurs raisons essentielles.
Tout d’abord, la fiabilité de super-pharma-fr est incontestable. Reconnu comme un **site de confiance**, super-pharma-fr s’engage à fournir des médicaments authentiques et de haute qualité. Avec une réputation solide et établie, les clients peuvent avoir l’assurance que chaque commande passée sur **super-pharma-fr** est traitée avec le plus grand soin et répond aux normes les plus strictes de sécurité et d’authenticité. Cette fiabilité accrue offre une tranquillité d’esprit aux utilisateurs, sachant qu’ils obtiennent des produits authentiques et efficaces pour traiter leur dysfonction érectile.
Ensuite, super-pharma-fr se distingue par son service de **livraison rapide et efficace**. Conscient de l’importance de recevoir rapidement le traitement nécessaire, super-pharma-fr s’engage à assurer des livraisons dans les délais les plus courts possibles. Grâce à des partenariats solides avec des services de livraison de confiance, les clients peuvent compter sur **super-pharma-fr** pour expédier leurs commandes de manière rapide et sécurisée, garantissant ainsi un accès rapide au Cialis sans aucun retard inutile. Cette rapidité de livraison est particulièrement précieuse pour ceux qui ont besoin d’un traitement immédiat pour leur dysfonction érectile.
Enfin, le service clientèle exceptionnel de super-pharma-fr constitue un autre facteur décisif pour choisir ce site. Doté d’une équipe dévouée et professionnelle, super-pharma-fr met l’accent sur la satisfaction des clients en offrant un service clientèle de qualité supérieure. Que ce soit pour répondre à des questions sur les produits, résoudre des problèmes de commande où fournir des conseils personnalisés, l’équipe de support de super-pharma-fr est toujours disponible pour aider et guider les clients à chaque étape du processus d’achat. Cette attention au service clientèle renforce la confiance des utilisateurs dans super-pharma-fr, faisant de lui un choix privilégié pour l’achat de Cialis en France.
Conclusion
En résumé, l’achat en ligne du **Cialis en France** offre une série d’avantages significatifs, notamment en termes d’accessibilité, de confidentialité et de gain de temps. La possibilité de se procurer du Cialis depuis chez soi, en évitant les interactions en personne et les déplacements jusqu’à la pharmacie, garantit un processus discret et pratique pour obtenir ce traitement essentiel de la dysfonction érectile. De plus, la rapidité de livraison et la fiabilité des sites comme **super-pharma-fr** assurent que les clients reçoivent leur médicament dans les délais les plus courts, sans compromettre la qualité ou l’authenticité.
Dans cette optique, super-pharma-fr se distingue comme un site fiable et digne de confiance pour acheter Cialis rapidement et en toute sécurité. Avec sa réputation bien établie, son service de livraison rapide et son excellent service clientèle, **super-pharma-fr** offre une expérience d’achat supérieure, garantissant la satisfaction et la tranquillité d’esprit des clients.
Enfin, cette approche de commander du Cialis sur internet encourage chacun à prendre soin de sa santé sexuelle de manière confidentielle et pratique. En éliminant les barrières et les stigmates associés à la dysfonction érectile, l’achat en ligne offre une solution discrète et efficace pour traiter ce trouble courant. Ainsi, en choisissant l’achat sur internet, les individus peuvent aborder leur santé sexuelle avec plus de confiance et de commodité, tout en bénéficiant du soutien et de l’expertise de sites comme super-pharma-fr.
En conclusion, l’achat en ligne du Cialis en France, avec des sites de confiance tels que **super-pharma-fr**, offre une manière pratique, sécurisée et confidentielle d’obtenir ce traitement vital pour la dysfonction érectile. En mettant l’accent sur la santé sexuelle et le bien-être des individus, cette approche encourage une approche proactive de la gestion de la dysfonction érectile, garantissant ainsi une meilleure qualité de vie et une satisfaction personnelle accrue. | dr_phillip | |
1,864,866 | Can rubygems be downloaded on Android ? | Will it be possible to copy and paste all the right deriv API content with the right stages on... | 0 | 2024-05-25T13:29:55 | https://dev.to/t4vvd/can-rubygems-be-downloaded-on-android--560a | help | Will it be possible to copy and paste all the right deriv API content with the right stages on Android GitHub?
And can rubygems be downloaded on Android GitHub for the filing process ?
Thanks, PaulM. | t4vvd |
1,864,848 | Exploring the Delicious World of McDonald's in Philippines: A Culinary Journey | Hey Dev.to community! I recently embarked on a flavorful exploration of McDonald's Menu in the... | 0 | 2024-05-25T13:10:42 | https://dev.to/rhj/exploring-the-delicious-world-of-mcdonalds-in-philippines-a-culinary-journey-876 | Hey Dev.to community!
I recently embarked on a flavorful exploration of McDonald's Menu in the Philippines, and let me tell you, it was quite the journey! 🍔🍟
1. **A Taste of Tradition:** McDonald's has been serving up smiles and satisfaction in the Philippines since 1985. From the moment you step into a McDonald's restaurant, you're greeted with the familiar aroma of freshly cooked fries and the sound of sizzling burgers on the grill.
2. **Iconic Favorites:** The menu at McDonald's Philippines boasts a lineup of iconic favorites that have stood the test of time. Whether you're craving the classic Big Mac or the crispy goodness of Chicken McDo, there's something for everyone to enjoy.
3. **Local Flair:** What sets McDonald's Philippines apart is its ability to infuse local flavors into its menu offerings. Take, for example, the McSpaghetti—a Filipino twist on a beloved Italian dish, featuring sweet-style spaghetti sauce and juicy hotdog slices. It's a true taste of home in every bite.
4. **Innovative Offerings:** But McDonald's doesn't just stop at the classics. They're constantly pushing the boundaries of flavor with innovative offerings like the McRice Burger—a delicious fusion of East and West that replaces the traditional bun with rice patties, creating a uniquely satisfying experience.
5. **Embracing Change:** In today's fast-paced world, McDonald's continues to evolve and adapt to meet the changing needs of its customers. From convenient delivery options to digital advancements like self-service kiosks, McDonald's is committed to making every dining experience a memorable one.
So, whether you're a longtime fan or a curious newcomer, I invite you to join me on this culinary journey through McDonald's Menu Ph. Trust me, it's a taste sensation you won't soon forget!
Feel free to share your thoughts and favorite McDonald's menu items in the comments below. And if you're craving more delicious content, be sure to check out [https://mcdonaldsmenu.ph](https://mcdonaldsmenu.ph) for the latest updates and offerings.
Bon appétit! | rhj | |
1,864,846 | Build Distributed Applications in .NET Easily Using .NET Aspire | .NET Aspire is an opinionated, cloud ready stack for building observable, production ready,... | 0 | 2024-05-25T13:10:13 | https://dev.to/ahmadmohey/build-distributed-applications-in-net-easily-using-net-aspire-1lc5 | distributedsystems, aspire, dotnet, kubernetes | **.NET Aspire is an opinionated, cloud ready stack for building observable, production ready, distributed applications.**
Cloud-native applications typically comprise small, interconnected components known as microservices instead of a single, monolithic codebase. These applications often utilize a variety of services, including databases, messaging systems, and caching.
A distributed application leverages computational resources across multiple nodes, such as containers operating on different hosts. These nodes must communicate over network boundaries to respond to users. A cloud-native application is a specific type of distributed app designed to fully exploit the scalability, resilience, and manageability offered by cloud infrastructures.
.NET Aspire is designed to enhance the experience of building cloud-native .NET applications. It offers a consistent and opinionated set of tools and patterns to aid in the development and deployment of distributed applications. .NET Aspire helps with:
- **Orchestration:** It provides features for running and connecting multi-project applications and their dependencies in local development environments.
- **Components:** .NET Aspire includes NuGet packages for commonly used services, such as Redis or Postgres, with standardized interfaces to ensure consistent and seamless integration with your app.
- **Tooling:** It comes with project templates and tooling experiences for Visual Studio and the dotnet CLI, facilitating the creation and interaction with .NET Aspire applications.
In .NET Aspire, orchestration primarily aims to improve the local development experience by simplifying the management of your cloud-native app's configuration and interconnections. It’s important to note that .NET Aspire’s orchestration is not meant to replace robust production systems like Kubernetes. Instead, it offers a set of abstractions that streamline the setup of service discovery, environment variables, and container configurations, removing the need to handle low-level implementation details. These abstractions provide a consistent setup pattern for applications with numerous components and services, making it easier to manage complex applications during development. | ahmadmohey |
1,864,845 | How can u ensure zero downtime deployment in Kubernetes? | Achieving zero-downtime deployment in Kubernetes involves carefully orchestrating the rollout of new... | 0 | 2024-05-25T13:07:23 | https://dev.to/vaibhavhariaramani/how-can-u-ensure-zero-downtime-deployment-in-kubernetes-20m6 | Achieving zero-downtime deployment in Kubernetes involves carefully orchestrating the rollout of new versions of your application while ensuring that there is no interruption to the service provided to end users. Here are some strategies to achieve zero-downtime deployment in Kubernetes:
**Replica Sets and Rolling Updates:** Use Kubernetes Replica Sets and rolling updates to gradually replace old instances of your application with new ones. By incrementally increasing the number of new pods and reducing the number of old pods, you can ensure a smooth transition without downtime.
**Readiness Probes:** Configure readiness probes in your Kubernetes deployment configuration to indicate when a pod is ready to serve traffic. Kubernetes will only route traffic to pods that have passed their readiness probes, ensuring that new instances are fully ready before they receive requests.
**Horizontal Pod Autoscaling (HPA):** Utilize Horizontal Pod Autoscaling to automatically adjust the number of pods based on resource utilization metrics such as CPU or memory usage. This ensures that your application can handle increased load during deployment without impacting performance.
**Pod Disruption Budgets (PDB):** Define Pod Disruption Budgets to limit the number of pods that can be unavailable during deployment. PDBs help prevent excessive disruptions to your application by ensuring that a minimum number of pods are always available.
**Traffic Shifting and Canary Deployments:** Gradually shift traffic from old pods to new pods using techniques such as traffic splitting or canary deployments. This allows you to monitor the performance of the new version in production before fully transitioning traffic to it.
**StatefulSets for Stateful Applications:** For stateful applications, use Kubernetes StatefulSets to ensure stable, ordered deployment and scaling of pods. StatefulSets provide guarantees for pod identity and stable network identifiers, which are crucial for zero-downtime deployments of stateful applications.
**Health Checks and Liveness Probes:** Implement health checks and liveness probes in your application to detect and recover from failures automatically. Kubernetes can restart pods that fail health checks, ensuring continuous availability of your application.
**Blue-Green Deployments:** Set up blue-green deployments to deploy a new version of your application alongside the existing version and switch traffic between them seamlessly. This allows you to rollback quickly in case of issues with the new version.
By combining these strategies and best practices, you can minimize downtime and disruptions during deployments in Kubernetes, ensuring a seamless experience for your users and customers. | vaibhavhariaramani | |
1,864,844 | Mastering Version Control: Navigating the World of Git and GitHub🚀 | 1. Introduction to Version Control Why Version Control is Essential Backup:... | 0 | 2024-05-25T13:05:36 | https://dev.to/dharamgfx/mastering-version-control-navigating-the-world-of-git-and-github-mmd | git, beginners, programming, github | ## 1. Introduction to Version Control
### Why Version Control is Essential
- **Backup**: Version control systems keep a history of changes, allowing you to recover previous versions of your code.
- *Example*: Accidentally deleted a crucial file? With version control, you can easily restore it from a previous commit.
- **Collaboration**: Enables multiple developers to work on the same project simultaneously without overwriting each other’s changes.
- *Example*: Two team members can work on different features of the same project without causing conflicts.
- **Track Changes**: Keeps a detailed log of who made what changes and why.
- *Example*: You can see the exact commit where a bug was introduced, making it easier to debug.
## 2. Understanding Git and Social Coding Sites
### Git vs. GitHub/GitLab
- **Git**: A distributed version control system that tracks changes in source code during software development.
- *Example*: Git allows you to manage your code locally, committing changes and creating branches.
- **GitHub/GitLab**: Websites that host Git repositories and provide additional tools for collaboration and project management.
- *Example*: GitHub offers features like pull requests, issues, and project boards to facilitate teamwork.
### The Necessity of Social Coding Sites
- **Teamwork**: GitHub and GitLab make it easy to collaborate with others by providing tools to review and discuss code.
- *Example*: Opening a pull request for teammates to review your changes before merging them into the main branch.
- **Project Management**: These platforms offer issue tracking, wikis, and project boards to manage development tasks.
- *Example*: Using GitHub Issues to keep track of bugs and feature requests.
## 3. Basic Setup
### Installing Git and Signing Up
- **Install Git**: Download and install Git from [git-scm.com](https://git-scm.com).
- *Example*: Use the command `git --version` to check if Git is installed correctly.
- **Sign Up**: Create an account on your chosen social coding site, like GitHub or GitLab.
- *Example*: Visit [GitHub](https://github.com) to sign up for a free account.
### Handling Security Requirements
- **SSH/GPG Keys**: Set up SSH keys for secure connections and GPG keys for signing commits.
- *Example*: Use `ssh-keygen` to generate an SSH key pair and add the public key to your GitHub account.
## 4. Working with Repositories
### Creating a Repository
- **Local Repo**: Initialize a new Git repository with `git init`.
- *Example*: Use `git init my-project` to create a new local repository.
- **Remote Repo**: Create a repository on GitHub and link it to your local repo with `git remote add origin <repo-url>`.
- *Example*: Use the GitHub interface to create a new repo and then connect it using `git remote add origin`.
### Pushing Changes
- **Add, Commit, Push**: Stages changes, commits them with a message, and pushes them to the remote repository.
- *Example*: Use `git add .`, `git commit -m "Initial commit"`, and `git push origin main` to push your first commit.
## 5. Contributing to Others' Repositories
### Forking and Branching
- **Forking**: Create your own copy of someone else's repository.
- *Example*: Click the "Fork" button on GitHub to fork a repository.
- **Branching**: Create a new branch to work on a feature without affecting the main codebase.
- *Example*: Use `git checkout -b feature-branch` to create and switch to a new branch.
### Creating a Pull Request (PR)
- **PR**: Request to merge changes from your branch into the main repository.
- *Example*: After pushing your branch, open a pull request on GitHub to propose your changes.
### Review Flow
- **Code Review**: Teammates review your PR, suggest changes, and approve or request modifications.
- *Example*: Use comments and reviews on the PR to discuss changes before merging.
## 6. Publishing with GitHub Pages
### Deploying a Sample Project
- **GitHub Pages**: Host static websites directly from a GitHub repository.
- *Example*: Enable GitHub Pages in the repository settings to publish your project at `username.github.io/repo-name`.
## 7. Good Housekeeping
### Syncing Repositories
- **Pulling Changes**: Regularly pull updates from the remote repo to keep your local copy up-to-date.
- *Example*: Use `git pull origin main` before starting new work.
- **Updating Packages**: Ensure dependencies are up-to-date with `npm install` or `yarn install`.
- *Example*: Run `npm install` after pulling changes that modify the `package.json`.
### Using .gitignore
- **Ignoring Unnecessary Files**: Create a `.gitignore` file to exclude files and directories from version control.
- *Example*: Add `node_modules/` and `.DS_Store` to `.gitignore` to prevent committing them.
### Deleting Branches
- **Clean Up**: Remove branches that are no longer needed after merging.
- *Example*: Use `git branch -d feature-branch` to delete a local branch.
### Handling Merge Conflicts
- **Conflict Resolution**: Manually resolve conflicts when merging branches.
- *Example*: Open conflicting files, resolve differences, and use `git add` to mark as resolved.
## Resources
- **Git and GitHub**: Explore comprehensive guides and tutorials on [Git](https://git-scm.com/doc) and [GitHub](https://docs.github.com/en/github).
## Conclusion
Version control is a crucial skill for modern developers, enabling effective collaboration, code management, and project tracking. By mastering Git and GitHub, you can ensure your code is well-organized, backed up, and easily shared with your team. Regular practice and utilization of good housekeeping practices will make you proficient in handling version control systems and contributing to collaborative projects. | dharamgfx |
1,864,843 | Comparing React Native and Flutter: Which is Better for Cross-Platform Development? | In today's tech-savvy world, businesses and developers are constantly looking for ways to create apps... | 0 | 2024-05-25T12:59:21 | https://dev.to/stevemax237/comparing-react-native-and-flutter-which-is-better-for-cross-platform-development-3cod | appdevelopment | In today's tech-savvy world, businesses and developers are constantly looking for ways to create apps that work seamlessly across different devices and operating systems. This is where [cross platform app development](https://www.mobileappdaily.com/knowledge-hub/cross-platform-app-development-guide?utm_source=dev&utm_medium=hc&utm_campaign=mad) comes in, and two of the most talked-about frameworks in this space are React Native and Flutter. If you're trying to decide which one is better for your project, you're in the right place. Let's dive into what makes each of these frameworks tick and how they stack up against each other.
**Getting to Know React Native and Flutter**
React Native, created by Facebook and launched in 2015, lets developers build mobile apps using JavaScript and React. It uses native components, which means the apps you build have a native look and feel.
Flutter, developed by Google and introduced in 2018, is the newer kid on the block. It uses the Dart programming language and comes with a complete set of pre-designed widgets, making it easier to create consistent and beautiful user interfaces. Flutter renders components with its own high-performance engine, giving it a unique edge.
**Performance: Who Takes the Lead?**
When it comes to performance, both have their strengths:
React Native: It uses a bridge to communicate between JavaScript and native components. While this setup works well for most apps, it can slow things down if you're dealing with complex animations or heavy computations.
Flutter: It often wins the performance race because it compiles directly to native code. Its high-performance rendering engine, Skia, ensures smooth and fast UIs, making it a great choice for apps with lots of graphics and animations.
**Developer Experience: Ease of Use Matters**
The experience of using these frameworks can make or break your development process:
React Native: If you already know JavaScript or React, you'll feel right at home. Plus, its hot reload feature means you can see changes instantly without restarting your app.
Flutter: Flutter also has a hot reload feature, boosting productivity. While Dart might be new to some developers, it’s easy to pick up, especially if you're familiar with object-oriented programming. Flutter's widget-based architecture can make building UIs straightforward, though it might take some getting used to.
**Community and Ecosystem: Support and Resources**
A strong community can provide invaluable support and resources:
React Native: It has been around longer and has a larger community. This means more libraries, tools, and third-party plugins are available to help you solve problems and speed up development.
Flutter: Although newer, Flutter is growing rapidly. Google's support ensures it’s constantly improving. The community is active, and there are plenty of plugins and packages available to extend its capabilities.
**UI and Design: Creating Beautiful Apps**
How your app looks and feels can greatly impact user experience:
React Native: Uses native components, so your app will feel right at home on any device. However, achieving a consistent design across platforms might take extra effort.
Flutter: Excels in UI design with its rich set of customizable widgets. Everything in Flutter is a widget, which gives you incredible flexibility to create unique and consistent designs across all devices.
**Tooling and IDE Support: The Developer’s Toolkit**
Good tools make development easier:
React Native: Works with any text editor or IDE that supports JavaScript, such as Visual Studio Code or WebStorm. It integrates well with various tools to enhance your workflow.
Flutter: Has excellent support, especially with Android Studio and Visual Studio Code. The Flutter plugin offers features like debugging, refactoring, and widget inspection, making development smoother.
**Conclusion: Which Should You Choose?**
Choosing between React Native and Flutter depends on what you need for your project:
React Native: Go with this if you already know JavaScript or React, want to leverage the mature JavaScript ecosystem, and need good performance for most apps.
Flutter: Opt for Flutter if you prioritize performance, need highly customizable and consistent UIs, or are ready to learn Dart. Flutter's widgets and performance make it great for visually rich and complex apps.
Both frameworks offer powerful solutions for cross-platform development. The best choice will depend on your team’s skills, project needs, and long-term goals. No matter which you choose, you’ll be equipped to create amazing apps that work beautifully on any device.
| stevemax237 |
1,864,842 | Elevate Your Online Presence with Professional SEO Services | In the fast-paced and competitive digital landscape, professional SEO services have become... | 0 | 2024-05-25T12:54:44 | https://dev.to/alfredlynn/elevate-your-online-presence-with-professional-seo-services-2j8g | seo, digitalmarketing, seoservices, devops | In the fast-paced and competitive digital landscape, professional SEO services have become indispensable for businesses striving to stand out and succeed online. Here's how investing in expert SEO assistance can propel your brand to new heights:
**
[Professional SEO services](https://dotmirror.com/) begin with a comprehensive analysis of your business goals, target audience, and competitors. Seasoned SEO professionals devise customized strategies tailored to your unique needs, ensuring every tactic aligns with your objectives.
Effective SEO hinges on targeted keyword optimization. [Professional SEO services](https://dotmirror.com/) employ advanced keyword research tools and techniques to identify high-value keywords relevant to your industry and audience. Strategically incorporating these keywords into your content enhances your visibility in search engine results pages (SERPs) and attracts qualified traffic.
From optimizing meta tags and headings to improving website structure and internal linking, professional SEO services fine-tune every aspect of your website for optimal search engine performance. Adhering to best practices and staying abreast of algorithm updates ensures your website is primed for success in the ever-evolving digital landscape.
Compelling, relevant, and informative content lies at the heart of successful SEO. Professional SEO services leverage their expertise to create engaging content that resonates with your audience while incorporating targeted keywords seamlessly. Optimizing content for both users and search engines enhances your brand's authority and credibility online. Building a robust [backlink](https://dotmirror.com/what-we-do/foundational-backlinks-service/) profile is essential for improving your website's authority and rankings.
Professional SEO services employ ethical link-building strategies to secure high-quality backlinks from authoritative websites in your niche. Through strategic outreach, content promotion, and relationship building, they amplify your online presence and drive organic traffic.
SEO is an ongoing process that requires constant monitoring and optimization. Professional SEO services conduct regular audits, track key performance metrics, and analyze data to identify areas for improvement. By staying proactive and adaptive, they ensure your SEO strategy remains effective in the face of changing algorithms and market dynamics.
In essence, professional SEO services offer a comprehensive approach to elevating your online presence and driving sustainable growth. By entrusting your SEO efforts to seasoned professionals, you can navigate the complexities of the digital landscape with confidence, knowing that your brand is positioned for success. Unlock the full potential of your online presence with professional SEO services today.
| alfredlynn |
1,864,841 | Mastering Design for Developers: Crafting User-Centered Experiences🚀 | 1. Basic Design Theory UI Design Fundamentals Contrast Definition:... | 0 | 2024-05-25T12:54:12 | https://dev.to/dharamgfx/mastering-design-for-developers-crafting-user-centered-experiences-3nkf | webdev, beginners, programming, design | ## 1. Basic Design Theory
### UI Design Fundamentals
#### Contrast
- **Definition**: The difference in luminance or color that makes an object distinguishable.
- **Example**: Using a dark background with light text for readability.
#### Typography
- **Definition**: The art of arranging type to make written language legible, readable, and visually appealing.
- **Example**: Choosing a clean sans-serif font for body text and a serif font for headings to create a clear visual hierarchy.
#### Visual Hierarchy
- **Definition**: The arrangement or presentation of elements in a way that implies importance.
- **Example**: Larger, bolder headlines at the top of a webpage to draw attention first.
#### Scale
- **Definition**: The size of elements in relation to each other.
- **Example**: Using larger buttons for primary actions and smaller buttons for secondary actions.
#### Alignment
- **Definition**: The placement of elements so that edges line up along common rows or columns.
- **Example**: Left-aligning text blocks and images to create a clean, organized look.
#### Use of Whitespace
- **Definition**: The space between elements in a composition.
- **Example**: Providing ample space around text and images to avoid clutter and improve readability.
#### Color Theory
- **Definition**: The study of how colors interact and the visual effects of color combinations.
- **Example**: Using complementary colors to create vibrant, eye-catching designs.
#### Use of Images
- **Definition**: Incorporating visuals to enhance content and convey messages.
- **Example**: Using high-quality images to support the text and provide visual interest.
### Resources
- **Fundamental Text and Font Styling**: Explore resources like Google Fonts for choosing and styling type.
## 2. User-Centered Design
### Understanding the User
#### Everything We Do is for the User
- **Definition**: Prioritizing user needs, preferences, and experiences in design decisions.
- **Example**: Conducting user surveys to gather feedback on a new feature.
### User Research and Testing
#### Intro to User Research/Testing
- **Definition**: Gathering data about user behaviors, needs, and motivations through observation and feedback.
- **Example**: Performing usability testing to identify pain points in the user journey.
#### User Requirements
- **Definition**: Understanding what users need from a product to ensure it meets their expectations.
- **Example**: Creating user personas to represent different segments of the target audience.
### Design for Accessibility
#### Consider the Target Audience
- **Definition**: Designing products that are usable by people with a wide range of abilities.
- **Example**: Ensuring all interactive elements are accessible via keyboard navigation.
#### Inclusive Design Principles
- **Definition**: Designing for the full range of human diversity with respect to ability, language, culture, gender, age, and other forms of human difference.
- **Example**: Using high-contrast color schemes for users with visual impairments.
### Design Patterns
#### Common Patterns Used on the Web
- **Dark Mode**: Providing a dark-themed UI option to reduce eye strain.
- **Breadcrumbs**: Navigation aids showing the user's path within the site.
- **Cards**: Container elements to organize information visually.
- **Deferred/Lazy Registration**: Allowing users to explore the app before requiring them to sign up.
- **Infinite Scroll**: Loading content continuously as the user scrolls down.
- **Modal Dialogs**: Overlays for important alerts or actions.
- **Progressive Disclosure**: Revealing information as needed to avoid overwhelming users.
- **Progress Indication on Forms/Registration/Setup**: Showing users their progress in multi-step processes.
- **Shopping Cart**: Feature for e-commerce sites to store items for purchase.
### Resources
- **Accessibility Overview**: W3C's Web Accessibility Initiative (WAI).
- **Inclusive Design Principles**: Visit [inclusivedesignprinciples.org](https://inclusivedesignprinciples.org).
## 3. Design Briefs
### Communicating with Designers
#### Speaking Design Language
- **Definition**: Understanding design terminology to effectively collaborate with designers.
- **Example**: Discussing "margins" and "padding" when reviewing layouts.
### Interpreting Design Brief Requirements
#### Producing an Implementation
- **Definition**: Translating design specifications into functional code.
- **Example**: Implementing a specified color palette and typography in CSS.
### Tools Designers Use
#### Typical Tools
- **Figma**: A popular interface design tool for creating and sharing design prototypes.
- **Example**: Using Figma to view and implement design specifications provided by designers.
## Conclusion
Design for developers goes beyond writing code—it involves understanding basic design principles, putting the user first, and effectively communicating with designers. By mastering these concepts, developers can create products that are not only functional but also visually appealing and user-friendly. Leverage resources and tools to continually improve your design skills and contribute to creating exceptional user experiences. | dharamgfx |
1,864,819 | Image super-resolution using GAN (SRGAN) | Hi and welcome to my other blog post on the series on image super-resolution using GAN. This post is... | 27,510 | 2024-05-25T12:51:05 | https://dev.to/adamazuddin/image-super-resolution-using-gan-srgan-kgc | machinelearning, ai, algorithms | Hi and welcome to my other blog post on the series on image super-resolution using GAN. This post is heavily based on [this research paper](https://arxiv.org/pdf/1609.04802) that proposed a better way to solve image super-resolution problem compared to other methods available at the time
So before we start , I will assume you have a basic understanding of super-resolution using CNN, if you're not you can check out [this series](https://dev.to/adamazuddin/series/27213) i made explaining it. I also would assume that you already have basic understanding of GAN or Generative Adversarial Network. If not, you can check my previous post on it [here](https://dev.to/adamazuddin/generative-adversarial-network-gan-1425)
### The problem with SRCNN
So one big problem that's the solution is proposed in the paper is the loss function used in SRCNN, the Mean Squared Error loss function. Although it works fine as a loss function, it didn't preserve the perception we human have on images, it just try to make sure the pixel values match the label as close as possible. But the human eye didn't view image on the pixel-basis, so using this loss function makes the model miss opportunities to capitalize on the more important factor for human in a high resolution image.
The paper proposed a new loss function, called the perceptual loss which is a combination of adversarial loss and content loss. The exact equation used in the paper is here, although we won't dive into the math here:
So the perceptual loss is although a combination of content loss and adversarial loss, it seems like the content loss is given 1000x more priorities than the adversarial loss. You can think of it like this. If the adversarial loss is given high priorities or in this case weights, than the perceptual loss, than our result would be the generator produce image that are too similar to the original image, which misses the point of actually generating realistic super-resolved image.
## Content loss
So basically this loss function is a form of MSE loss but modified to not depend on the pixel value, giving more priority for the perception of image itself. This is achieved by combining it with VGG loss, where VGG is a pre trained model on millions of images that have a good understanding of what image is made up of. This way, the model would have better perception of image quality compared to pixel-wise loss function.
## Adversarial loss
This loss is added to the perceptual loss equation to favor the image that closely resemble the original image. This loss is used for the adversarial portion of the GAN, which is when the output of the generator act as input of the discriminator.
### Discriminator
The job of discriminator here is to determine whether an image is an original image or super-resolved image. The architecture of the discriminator is as follows:
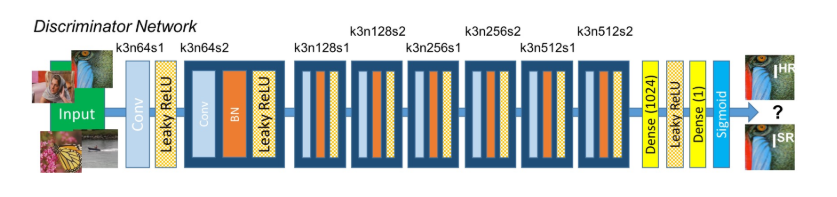
Note that k = kernel size, n = number of feature maps, and s = strides.
BN is batch normalization which is a way to further normalize the data in a batch so that if an outlier value exist during training, it won't affect the network much if it's been normalized. Note that the last 4 layers is implemented to flatten the previous layer's array onto a single dimension, like a normal ANN. It also introduces non- linearity through Leaky ReLu, combining all the weights onto single output dense layer, then finally adding sigmoid function to it for the final output which will classify whether an image is real or super-resolved.
## Generator
Meanwhile, the generator job is to convince the discriminator that the image it produced is a real image, not a super-resolved one. The architecture for generator as proposed in the paper is here:
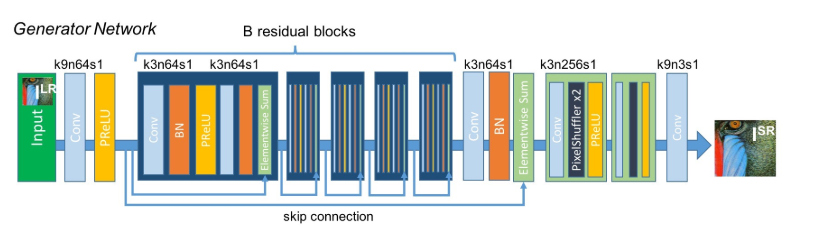
Also here, note that the actual number of residual blocks is 16, which is mentioned in the paper but omitted in the image for simplicity. This generator used the perceptual loss is used for training of this network as proposed by the researchers.
### Conclusion
So that's the overview of super-resolution using GAN. Hope you guys like it and learn something new here. If you would like to learn more, I link video resources from Youtube down below in the resources section which give a more detailed explanation as well as how to implement the model in terms of code. So, that's all for me for now and see you guys next time!
### Resources
If you want the complete walkthrough of the paper, I found these videos helpful:
- [Single image super-resolution using SRGAN by DigitalSreeni](https://www.youtube.com/watch?v=nbRkLE2fiVI&list=PLZsOBAyNTZwboR4_xj-n3K6XBTweC4YVD&index=11)
- [SRGAN Explained| Super-Resolution Generative Adversarial Network by
Code With Aarohi](https://www.youtube.com/watch?v=KsNLxBvJBKo&t=3s) | adamazuddin |
1,864,840 | Day 2 of my progress as a vue dev | About today Alright, so I worked on my quiz app for about 3 hours today and got a lot done. My... | 0 | 2024-05-25T12:48:11 | https://dev.to/zain725342/day-2-of-my-progress-as-a-vue-dev-2227 | webdev, vue, tailwindcss, typescript | **About today**
Alright, so I worked on my quiz app for about 3 hours today and got a lot done. My approach is divide the app into as many modules as I can so it is easy to reuse most components. Also, I've had a fun time using the script setup supporting the composition API which makes the code cool in a sense. I also figured that I need to spend more time understanding the concepts of typescript and apply them effectively.
**Structure of the app**
So the app basically allows you to make customized quizzes and display them on the HomeView for the user to attempt. I am planning on giving the ability to create quiz to an admin only but that I guess can be implemented further down the line.
**Work done**
I have fully implemented the process of creating a quiz with giving access to user to fully customize it by adding proffered number questions, number of allowed attempts, and the time duration.
**What's next?**
Starting tomorrow I will be working on the part of allowing user to take the created quiz, show the user complete result after the attempt and hopefully to develop a ranking system to to help user keep track of his progress.
Wish me luck!
| zain725342 |
1,864,838 | cara menemukan android dengan bersiul | Mungkin pernah saat kamu sedang sibuk dengan pekerjaan kamu, dan kemudian sampai lupa dimana menaruh... | 0 | 2024-05-25T12:42:24 | https://dev.to/wanderlustgeekette/cara-menemukan-android-dengan-bersiul-2pf5 | whistle | Mungkin pernah saat kamu sedang sibuk dengan pekerjaan kamu, dan kemudian sampai lupa dimana menaruh android kamu. Namun sekarang tidak usah khawatir dengan keadaan itu karena dizaman modern ini sudah banyak teknologi yang berkembang.
Ada cara yang unik untuk menemukan android kamu yang lupa taruh dimana.
Untuk caranya simak tutorial berikut ini :
1. Download aplikasi whistle android finder
2. Instal seperti biasa
3. Pilih Sensitife whistle setup | wanderlustgeekette |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.