id int64 5 1.93M | title stringlengths 0 128 | description stringlengths 0 25.5k | collection_id int64 0 28.1k | published_timestamp timestamp[s] | canonical_url stringlengths 14 581 | tag_list stringlengths 0 120 | body_markdown stringlengths 0 716k | user_username stringlengths 2 30 |
|---|---|---|---|---|---|---|---|---|
1,768,862 | 사천모텔아가씨/콜걸 ☎LINE-wag58☎ 사천외국인출장 사천출장전문업소 사천출장안마? 사천출장만남 | 사천모텔아가씨/콜걸 ☎LINE-wag58☎ 사천외국인출장 사천출장전문업소 사천출장안마? 사천출장만남 사천모텔아가씨/콜걸 ☎LINE-wag58☎ 사천외국인출장 사천출장전문업소... | 0 | 2024-02-22T08:10:52 | https://dev.to/1rbzwoa2hq/saceonmotelagassikolgeol-line-wag58-saceonoeguginculjang-saceonculjangjeonmuneobso-saceonculjanganma-saceonculjangmannam-12b8 | 사천모텔아가씨/콜걸 ☎LINE-wag58☎ 사천외국인출장 사천출장전문업소 사천출장안마? 사천출장만남
사천모텔아가씨/콜걸 ☎LINE-wag58☎ 사천외국인출장 사천출장전문업소 사천출장안마? 사천출장만남
사천모텔아가씨/콜걸 ☎LINE-wag58☎ 사천외국인출장 사천출장전문업소 사천출장안마? 사천출장만남 | 1rbzwoa2hq | |
1,768,866 | Premium Informatica PR000007 Practice Test- Guaranteed Way Towards Success | Unveil The Strategies And Mindset For Triumph In Informatica PR000007 Practice Test Are you... | 0 | 2024-02-22T08:12:38 | https://dev.to/ameliajohn/premium-informatica-pr000007-practice-test-guaranteed-way-towards-success-3lg7 | <h1 style="text-align: justify;"><strong></strong></h1>
<h2 style="text-align: justify;"><strong>Unveil The Strategies And Mindset For Triumph In Informatica PR000007 Practice Test</strong></h2>
<p style="text-align: justify;">Are you gearing up for the challenge of PR000007 Informatica exams? Look no further – P2PExams is your key to confidence and success. Explore the ins and outs of PR000007 Exam preparation as we delve into proven strategies, effective techniques, and the winning mindset required to ace the PR000007 exams. Read on to discover how P2PExams can guide you towards triumph in your Informatica Certified Professional PR000007 exam journey.</p>
<p style="text-align: center;"><a href="https://www.p2pexams.com/products/pr000007"><img alt="Informatica PR000007" src="https://i.imgur.com/T7F4Dhi.jpg" style="height: 405px; width: 720px;" /></a></p>
<p style="text-align: center;"><strong>To Get Success Visit Here:<a href="https://www.p2pexams.com/products/pr000007">https://www.p2pexams.com/products/pr000007</a></strong></p>
<h2 style="text-align: justify;"><strong>Informatica PR000007 Exam Overview:</strong></h2>
<ul>
<li style="text-align: justify;"><strong>Vendor:</strong> Informatica</li>
<li style="text-align: justify;"><strong>Exam Name:</strong> PowerCenter Data Integration 9.x Administrator Specialist</li>
<li style="text-align: justify;"><strong>Exam Code:</strong> PR000007</li>
<li style="text-align: justify;"><strong>Number Of Questions: </strong>70</li>
<li style="text-align: justify;"><strong>Exam Format:</strong> Multiple Choice Questions (MCQs)</li>
<li style="text-align: justify;"><strong>Exam Language:</strong> English</li>
<li style="text-align: justify;"><strong>Promo Code For Informatica PR000007 Exam Questions: "SAVE25"</strong></li>
</ul>
<h2 style="text-align: justify;"><strong>Effortless Learning With Informatica PR000007 Exam Questions In PDF Format – Anytime, Anywhere</strong></h2>
<p style="text-align: justify;">Embark on a journey of effortless learning with P2PExams' intuitive and accessible ICP PR000007 PDF format learning guide. Our user-friendly Informatica Certified Professional PR000007 exam questions can be easily accessed on your mobile devices and computers, offering flexibility right after purchase. Dive into your ICP PR000007 Exam preparation at your own pace, whether you're at home or on the go.</p>
<h2 style="text-align: justify;"><strong>Sharpen Your Skills With Informatica PR000007 Practice Test Engine</strong></h2>
<p style="text-align: justify;">Mastering ICP PR000007 practice questions is paramount to understanding your strengths and weaknesses. P2PExams introduces an online PR000007 practice test engine tailored to PR000007 exam patterns. Elevate your PR000007 Informatica Exam readiness, outshine the competition and gain a competitive edge through hands-on practice with P2PExams Informatica Certified Professional PR000007 online practice test engine.</p>
<h2 style="text-align: justify;"><strong>Unlock Expert Insights With Real And Verified Informatica PR000007 Exam Questions & Answers</strong></h2>
<p style="text-align: justify;">Enhance your knowledge with expert insights uncovered in P2PExams' real and verified ICP PR000007 exam questions and answers. These authentic Informatica Certified Professional PR000007 questions guide you in understanding the exam format and formulating effective responses. If you seek a comprehensive ICP PR000007 exam prep guide, P2PExams ICP PR000007 practice questions product is your go-to resource.</p>
<h2 style="text-align: justify;"><strong>Free Updated Informatica PR000007 Exam Questions Demo</strong></h2>
<p style="text-align: justify;">Access unlimited updated content and resources with P2PExams PR000007 exam questions preparation. Benefit from free updates for three months post-purchase, ensuring your PR000007 exam preparation aligns with the latest syllabus. Sample the quality of P2PExams Informatica Certified Professional PR000007 exam questions through a complimentary demo. The Informatica PR000007 questions demo offers a sneak peek into meticulously crafted ICP PR000007 exam questions, aiding you in making an informed decision before purchasing.</p>
<p style="text-align: justify;"><strong>Are You Ready To Move Forward? Then Download Now.: <a href="https://www.p2pexams.com/informatica/pdf/pr000007">https://www.p2pexams.com/informatica/pdf/pr000007</a></strong></p>
<h2 style="text-align: justify;"><strong>Approach Informatica PR000007 Exam Questions With Confidence – Backed By A Money-Back Promise</strong></h2>
<p style="text-align: justify;">Secure your Informatica Certified Professional PR000007 exam questions guide with confidence, knowing that P2PExams ICP PR000007 exam questions come with a money-back guarantee. Commit to at least two weeks of preparation using our Informatica PR000007 exam quiz, and if you don't pass you're ICP PR000007 Exam as promised, claim your refund per our policy.</p>
<h2 style="text-align: justify;"><strong>Special Offer! Enjoy 25% Special Discount On All Informatica PR000007 Exam Dumps | Use Coupon Code "SAVE25"</strong></h2>
<p style="text-align: justify;">Maximize your PR000007 preparation with an exclusive 25% discount on P2PExams comprehensive PR000007 practice test questions. Act fast to secure this limited-time offer – order your Informatica PR000007 exam questions now and don't miss out on the substantial discount.</p>
<p style="text-align: center;"><a href="https://www.p2pexams.com/products/pr000007"><img alt="Informatica PR000007" src="https://i.imgur.com/v6S6yYL.jpeg" style="height: 327px; width: 720px;" /></a></p>
<h3 style="text-align: justify;"><strong>Informatica PR000007 Exam Search Queries:</strong></h3>
<p style="text-align: justify;">PR000007 Questions | PR000007 Dumps | PR000007 Exam Questions | PR000007 Exam Dumps | PR000007 Practice Questions | PR000007 Practice Dumps | PR000007 Braindumps | PR000007 Test Questions | PR000007 Test Dumps | PR000007 Questions PDF | PR000007 Dumps PDF | Free PR000007 Questions | Free PR000007 Dumps | PR000007 PDF Questions | PR000007 PDF Dumps | Actual PR000007 Questions |</p>
<p style="text-align: justify;"> </p>
| ameliajohn | |
1,768,877 | 태백출장전문 ◀상담톡 sx-58▶ 태백출장아가씨 태백출장추천 태백여대생출장 태백홈타이마사지샵 | 태백출장전문 ◀상담톡 sx-58▶ 태백출장아가씨 태백출장추천 태백여대생출장 태백홈타이마사지샵 태백출장전문 ◀상담톡 sx-58▶ 태백출장아가씨 태백출장추천 태백여대생출장... | 0 | 2024-02-22T08:20:06 | https://dev.to/1rbzwoa2hq/taebaegculjangjeonmun-taebaegculjangagassi-taebaegculjangcuceon-taebaegyeodaesaengculjang-taebaeghomtaimasajisyab-2peb | 태백출장전문 ◀상담톡 sx-58▶ 태백출장아가씨 태백출장추천 태백여대생출장 태백홈타이마사지샵
태백출장전문 ◀상담톡 sx-58▶ 태백출장아가씨 태백출장추천 태백여대생출장 태백홈타이마사지샵
태백출장전문 ◀상담톡 sx-58▶ 태백출장아가씨 태백출장추천 태백여대생출장 태백홈타이마사지샵 | 1rbzwoa2hq | |
1,768,883 | 강남구출장샵추천 LINE--라인wag58 강남구맛사지 애인대행 강남구한국인출장 강남구와꾸보장 강남구출장안마 | 강남구출장샵추천 LINE--라인wag58〓 강남구맛사지 애인대행 강남구한국인출장 강남구와꾸보장 강남구출장안마 강남구출장샵추천 LINE--라인wag58〓 강남구맛사지 애인대행... | 0 | 2024-02-22T08:26:16 | https://dev.to/1rbzwoa2hq/gangnamguculjangsyabcuceon-line-rainwag58x-gangnamgumassaji-aeindaehaeng-gangnamguhanguginculjang-gangnamguwaggubojang-gangnamguculjanganma-3bfa | 강남구출장샵추천 LINE--라인wag58〓 강남구맛사지 애인대행 강남구한국인출장 강남구와꾸보장 강남구출장안마
강남구출장샵추천 LINE--라인wag58〓 강남구맛사지 애인대행 강남구한국인출장 강남구와꾸보장 강남구출장안마
강남구출장샵추천 LINE--라인wag58〓 강남구맛사지 애인대행 강남구한국인출장 강남구와꾸보장 강남구출장안마 | 1rbzwoa2hq | |
1,768,898 | betvisabetcom | Betvisa - Betvisa Com - Casino - Lo De - No Hu Tang 100k la trang chu chinh thuc, chuyen cung cap moi... | 0 | 2024-02-22T08:44:43 | https://dev.to/betvisabetcom/betvisabetcom-21ge | Betvisa - Betvisa Com - Casino - Lo De - No Hu Tang 100k la trang chu chinh thuc, chuyen cung cap moi tro choi ca cuoc online, dac biet tai nha cai nay con co cac su kien lon nho nhu khung gio vang, thuong bat ngo 888k, chao don nam moi len den 8.888.000 VND.
Dia Chi: 118 Truong Dinh, Hai Ba Trung, Ha Noi, Viet Nam
Email: betvisabetcom@gmail.com
Website: https://betvisabet.com/
Dien Thoai: (+63) 9622372537
#betvisa #betvisa_game #betvisa_bet #betvisa_com #betvisa_app
Social Media:
https://betvisabet.com/
https://betvisabet.com/tai-app-betvisa/
https://betvisabet.com/dang-ky-betvisa/
https://betvisabet.com/nap-tien-momo/
https://betvisabet.com/rut-tien-betvisa/
https://betvisabet.com/ceo-thanh-hien/
https://www.facebook.com/betvisabetcom/
https://twitter.com/betvisabetcom
https://www.youtube.com/channel/UCkwk686Z6f5Qqfqjgxm6iGQ
https://www.pinterest.com/betvisabetcom/
https://social.msdn.microsoft.com/Profile/betvisabetcom
https://social.technet.microsoft.com/Profile/betvisabetcom
https://vimeo.com/betvisabetcom
https://github.com/betvisabetcom
https://community.fabric.microsoft.com/t5/user/viewprofilepage/user-id/673472
https://www.blogger.com/profile/07509188490658730450
https://www.reddit.com/user/betvisabetcom
https://gravatar.com/betvisabetcom
https://talk.plesk.com/members/betvisabetcom.318396/#about
https://soundcloud.com/betvisabetcom
https://medium.com/@betvisabetcom/about
https://www.flickr.com/people/betvisabetcom/
https://www.tumblr.com/betvisabetcom
https://betvisabetcom.wixsite.com/betvisabetcom
https://sites.google.com/view/betvisabetcom/trang-ch%E1%BB%A7
https://www.behance.net/betvisabetcom
https://www.openstreetmap.org/user/betvisabetcom
https://draft.blogger.com/profile/07509188490658730450
https://www.liveinternet.ru/users/betvisabetcom/profile
https://linktr.ee/betvisabetcom
https://www.twitch.tv/betvisabetcom/about
http://tinyurl.com/betvisabetcom
https://ok.ru/betvisabetcom/statuses/157448002763758
https://profile.hatena.ne.jp/betvisabetcom/profile
https://issuu.com/betvisabetcom
https://dribbble.com/betvisabetcom/about
https://form.jotform.com/240110726278047
https://sway.cloud.microsoft/BpGmWtSD6vhOfO7R?ref=Link
https://unsplash.com/fr/@betvisabetcom
https://scholar.google.com/citations?hl=vi&user=tkl26-MAAAAJ
https://www.goodreads.com/user/show/174210430-betvisabetcom
https://www.kickstarter.com/profile/betvisabetcom/about
https://tawk.to/betvisabetcom
https://groups.google.com/g/betvisabetcom
https://webflow.com/@betvisabetcom1
https://podcasters.spotify.com/pod/show/betvisabetcom
https://www.ted.com/profiles/45951460/about
https://disqus.com/by/combetvisabet/about/
https://500px.com/p/betvisabetcom
https://betvisabetcom.blogspot.com/
https://betvisabetcom.weebly.com/
https://betvisabetcom.webflow.io/
https://betvisabetcom.gitbook.io/untitled/
https://betvisabetcom.mystrikingly.com/
https://betvisabetcom.amebaownd.com/posts/51430744
https://betvisabetcom.seesaa.net/article/502042025.html?1705039833
http://betvisabetcom.splashthat.com
http://betvisabetcom.idea.informer.com/
https://betvisabetcom.contently.com/
https://betvisabetcom.amebaownd.com/posts/51430744
https://betvisabetcom.bravesites.com/#builder
https://betvisabetcom.themedia.jp/posts/51430869
https://betvisabetcom.storeinfo.jp/posts/51431437
https://betvisabetcom.theblog.me/posts/51431589
https://betvisabetcom.my.cam/#
https://betvisabetcom.onlc.fr/
https://betvisabetcom.gallery.ru/
https://betvisabetcom.therestaurant.jp/posts/51431817
https://betvisabetcom.wordpress.com/
https://ext-6487563.livejournal.com/profile/
https://betvisabetcom.thinkific.com/courses/your-first-course
https://ko-fi.com/betvisabetcom
https://www.provenexpert.com/betvisabetcom/
https://hub.docker.com/r/betvisabetcom/betvisabetcom
https://independent.academia.edu/betvisabetcom
https://fliphtml5.com/homepage/ylcgn/com-betvisabet/
https://www.quora.com/profile/Betvisabetcom
https://www.evernote.com/shard/s514/sh/f2a1bea5-0cc7-6a01-a682-85ff418e72cf/J35omHuumehbHKmoRC6sAwgJsUN6G8WaGZRsUVVwLcd4Mcyejf_7X-kv0w
https://heylink.me/betvisabetcom/
https://trello.com/u/combetvisabet
https://giphy.com/channel/betvisabetcom
https://www.mixcloud.com/betvisabetcom/
https://orcid.org/0009-0009-8533-6905
https://www.deviantart.com/betvisabetcom
https://vws.vektor-inc.co.jp/forums/users/betvisabetcom
https://codepen.io/betvisabetcom
https://community.cisco.com/t5/user/viewprofilepage/user-id/1663522
https://wellfound.com/u/betvisabetcom-1
https://about.me/betvisabetcom
https://betvisabetcom.peatix.com/
https://sketchfab.com/betvisabetcom
https://gitee.com/betvisabetcom
https://public.tableau.com/app/profile/betvisabetcom/vizzes
https://connect.garmin.com/modern/profile/b27d2643-7f90-4711-9b88-b46e857e2772
https://www.reverbnation.com/artist/betvisabetcom
https://profile.ameba.jp/ameba/betvisabetcom
https://onlyfans.com/betvisabetcom
https://mastodon.social/@betvisabetcom
https://readthedocs.org/projects/betvisabetcom/
https://flipboard.com/@betvisabetcom
https://www.awwwards.com/betvisabetcom/ | betvisabetcom | |
1,768,957 | How AI and DePIN Will Change Web3 | Web3, often referred to as the decentralized web, represents a paradigm shift in how the internet... | 0 | 2024-02-22T10:08:43 | https://dev.to/mayanks01798115/how-ai-and-depin-will-change-web3-36lh | Web3, often referred to as the decentralized web, represents a paradigm shift in how the internet operates, leveraging decentralized technologies like blockchain to create a more transparent, secure, and user-centric online experience. Within the Web3 ecosystem, AI (Artificial Intelligence) and [DePIN ](https://tradedog.io/how-ai-and-depin-will-change-web3/)(Decentralized Public Infrastructure Network) are poised to play transformative roles, reshaping various aspects of online interaction, security, and innovation. Here's how AI and DePIN will change Web3:
Enhanced Security and Privacy:
DePIN provides a robust foundation for secure and private online interactions by decentralizing key infrastructure components. With its distributed architecture, DePIN reduces the risk of single points of failure and potential security breaches.
AI technologies can further bolster security by analyzing vast amounts of data to identify patterns indicative of malicious activities or vulnerabilities. AI-powered security systems can help detect and mitigate threats in real-time, enhancing overall cybersecurity within the Web3 ecosystem.
Data Ownership and Control:
Web3 aims to empower users by granting them greater control over their data. Through decentralized identity solutions facilitated by DePIN, individuals can maintain ownership of their digital identities and personal information.
AI technologies enable users to leverage their data more effectively, allowing for personalized experiences without sacrificing privacy. By employing techniques like federated learning and homomorphic encryption, AI models can be trained on decentralized data sources without compromising individual privacy.
Autonomous Decision Making:
AI algorithms integrated into Web3 platforms can facilitate autonomous decision-making processes, such as smart contract execution and decentralized governance mechanisms.
Through the combination of AI and decentralized technologies, Web3 applications can automate various tasks and processes, reducing the need for intermediaries and enhancing operational efficiency.
Content Curation and Personalization:
AI-driven algorithms can analyze user behavior and preferences to deliver personalized content recommendations and tailored user experiences within the Web3 environment.
By leveraging decentralized content platforms enabled by DePIN, users can access diverse content without centralized control or censorship, fostering greater freedom of expression and information dissemination.
Innovation and Collaboration:
AI and DePIN technologies enable the development of decentralized AI marketplaces and collaborative ecosystems where developers can create, share, and monetize AI models and services.
Web3 facilitates frictionless collaboration and innovation by removing barriers to entry and providing transparent incentive mechanisms through blockchain-based protocols and smart contracts.
In summary, the convergence of AI and DePIN within the Web3 ecosystem promises to redefine the way we interact with the internet, offering enhanced security, privacy, autonomy, and innovation across various domains. As these technologies continue to evolve, they will shape the future of digital interactions and pave the way for a more decentralized and inclusive online environment. | mayanks01798115 | |
1,768,965 | 🎁 Event | Join the NFTScan Redotpay Collaboration Event and win a Redotpay Payment Card! | NFTScan is thrilled to announce its partnership with RedotPay, marking the beginning of a... | 0 | 2024-02-22T10:20:06 | https://dev.to/nft_research/event-join-the-nftscan-x-redotpay-collaboration-event-and-win-a-redotpay-payment-card-43gb | nft | NFTScan is thrilled to announce its partnership with RedotPay, marking the beginning of a multifaceted collaboration in the NFT space. Together, we’re launching the exclusive NFTScan x Redotpay co-branded payment card with customizable covers.
**About Redotpay**
RedotPay is a leading blockchain technology company specializing in crypto wallets and payment solutions. With a focus on innovation and user experience, RedotPay provides secure and efficient payment solutions for users worldwide.
RedotPay payment card supports various online and offline payment scenarios by automatically converting cryptocurrencies into local fiat currencies. Currently, RedotPay has over 800k users globally who are using RedotPay’s payment cards for their daily expenses. (RedotPay’s payment cards currently support currencies and networks including Bitcoin (BTC), Ethereum (ETH, BSC), USDC (ERC20, TRC20, BSC, ARB), and USDT (ERC20, TRC20, BSC, ARB).
**Event Details**
NFTScan will randomly select 50 participants from the event to receive 50 exclusive NFTScan x Redotpay co-branded cards for free, valued at $10 each. Each card will also include a $5 registration bonus, which can be used upon verification. In addition, winners will have the opportunity to personalize their card covers using their NFTs.
To claim your virtual payment card, use the promo code provided by NFTScan after winning. Activate your card to start enjoying its benefits!
🎈 **How to Participate:**
Follow NFTScan and RedotPay on X (Twitter).
Download the RedotPay App. [Get the APP}
Retweet & like the event tweet.[Post link]
📆 Event Duration:
February 22, 2024, 10:00 AM — March 1, 2024, 10:00 AM (UTC)
📌 **Important Notes:**
1. To qualify for the prize, winners are requested to send a direct message (DM) of the downloaded Redotpay APP page to NFTScan on Twitter to redeem the promo code;
2. Please note that RedotPay does NOT support transactions in the following countries and regions: Croatia, Libya, Guinea-Bissau, Bosnia and Herzegovina, Montenegro, Macedonia, Slovenia, Serbia, North Korea, Iran, Mali, South Sudan, Central African Republic, Yemen, United States, Eritrea, Lebanon, ISIL(Da’esh) — Al Qaida and Taliban, Democratic Republic of Congo, Sudan, Somalia, Iraq, Haiti, Afghanistan, Cuba, Belarus, Mainland China, Myanmar, Burundi, Nicaragua, Syria, Ukraine and Russia, Venezuela, Balkans, Zimbabwe, Ethiopia, Darfur, Syria residents. For more details, please refer to the official website FAQ.
**Contact Us:**
If you have any questions or need assistance, feel free to reach out to us. Don’t miss this fantastic opportunity to participate in the NFTScan x Redotpay custom payment card event and win the custom payment card.
Don’t miss out! Win Now! 🎉

NFTScan is the world’s largest NFT data infrastructure, including a professional NFT explorer and NFT developer platform, supporting the complete amount of NFT data for 20 blockchains including Ethereum, Solana, BNBChain, Arbitrum, Optimism, and other major networks, providing NFT API for developers on various blockchains.
Official Links:
NFTScan: https://nftscan.com
Developer: https://developer.nftscan.com
Twitter: https://twitter.com/nftscan_com
Discord: https://discord.gg/nftscan | nft_research |
1,768,996 | How to get end user's access-key and secret-access-key w.r.t "amazon s3" in spring boot application ? | How to get end user's access-key and secret-access-key by using account-Id and registered... | 0 | 2024-02-22T10:58:25 | https://dev.to/santhum/how-to-get-end-users-access-key-and-secret-access-key-wrt-amazon-s3-in-spring-boot-application--10np | How to get end user's access-key and secret-access-key by using account-Id and registered email/username w.r.t "amazon s3" in spring boot application ? | santhum | |
1,768,998 | Unlocking SEO Potential: The Power of PPT Submission Sites | Introduction: In the realm of digital marketing, leveraging diverse platforms to enhance Search... | 0 | 2024-02-22T11:00:07 | https://dev.to/seoworld/unlocking-seo-potential-the-power-of-ppt-submission-sites-45df | pptsubmissionsites, pptsites, pptsubmissionsite, pptsubmission |
Introduction:
In the realm of digital marketing, leveraging diverse platforms to enhance Search Engine Optimization (SEO) has become a cornerstone strategy for businesses aiming to boost their online presence. Among the myriad of techniques available, harnessing the potential of PowerPoint (PPT) submission sites has emerged as a dynamic avenue for driving traffic, increasing visibility, and fortifying brand authority. This article delves into the significance of [PPT submission sites](https://www.seoworld.in/top-high-pr-ppt-submission-sites-list/) in the SEO landscape and elucidates how businesses can capitalize on this potent tool to elevate their online footprint.
Understanding PPT Submission Sites:
PPT submission sites serve as repositories where users can upload and share PowerPoint presentations on a myriad of topics ranging from business insights and educational content to creative designs and industry updates. These platforms boast significant domain authority (DA) and are frequented by a diverse audience, presenting an invaluable opportunity for businesses to amplify their reach beyond conventional SEO tactics.
The SEO Benefits of PPT Submission Sites:
- **Enhanced Visibility:** By disseminating informative and visually compelling presentations across reputable [PPT submission site](https://www.seoworld.in/top-high-pr-ppt-submission-sites-list/) such as SlideShare and AuthorStream, businesses can augment their online visibility and attract a broader audience segment.
- Backlink Opportunities: Each presentation uploaded to these platforms offers the potential to embed backlinks directing viewers back to the company’s website or relevant landing pages. These high-quality backlinks serve as a testament to the website’s credibility and authority in the eyes of search engines, thereby bolstering its ranking in search results.
- Diversification of Content: Incorporating PowerPoint presentations into the content marketing strategy diversifies the content portfolio, catering to varied audience preferences. This multifaceted approach not only fosters engagement but also fosters stronger brand recall and customer loyalty.
- Social Sharing Amplification: PPT Sharing sites often integrate social sharing functionalities, enabling users to seamlessly distribute presentations across popular social media platforms. This amplifies the reach of the content, fostering organic sharing and engagement while driving traffic back to the source website.
- Exposure to Niche Audiences: These platforms attract a diverse array of users seeking insights and information on specific topics. By tailoring presentations to cater to niche interests and industry verticals, businesses can effectively target and engage with their desired audience segments, fostering community engagement and thought leadership.
- Best Practices for Effective PPT Submission:
Optimize Content: Craft visually appealing presentations that are both informative and aesthetically pleasing, incorporating relevant keywords, titles, and descriptions to optimise searchability.
Strategic Link Placement: Integrate strategically placed hyperlinks within the presentation content to direct traffic back to the website or specific landing pages.
Engagement Enhancement: Encourage audience interaction and engagement by incorporating interactive elements such as polls, quizzes, and calls-to-action (CTAs) within the presentation.
Consistency and Quality: Maintain consistency in branding and messaging across all presentations while adhering to high-quality standards in content creation and design.
Promotion and Distribution: Actively promote and distribute presentations across social media channels, email newsletters, and relevant online communities to maximise visibility and engagement.
Conclusion:
In an increasingly competitive digital landscape, the utilisation of PPT submission sites as a supplementary SEO strategy offers businesses a distinct advantage in bolstering their online presence, driving traffic, and fortifying brand authority. By leveraging these platforms effectively and adhering to best practices, businesses can unlock the full potential of PowerPoint presentations as a dynamic tool for enhancing SEO performance and achieving sustained growth in the digital sphere. | seoworld |
1,769,011 | Character vs. Word Tokenization in NLP: Unveiling the Trade-Offs in Model Size, Parameters, and Compute | In Natural Language Processing, the choice of tokenization method can make or break a model. Join me... | 0 | 2024-02-22T11:09:06 | https://dev.to/kagemanjoroge/character-vs-word-tokenization-in-nlp-unveiling-the-trade-offs-in-model-size-parameters-and-compute-3jjh | ai, machinelearning, python, nlp | In Natural Language Processing, the choice of tokenization method can make or break a model. Join me on a journey to understand the profound impact of character-level, word-level tokenization and Sub-word tokenization on model size, number of parameters, and computational complexity.
<img src="https://dev-to-uploads.s3.amazonaws.com/uploads/articles/dgeq41t7cp99j0n6yqrd.jpg" alt="Alt Text" style={{height:"400px", textAlign:"center", width:"40pc"}} />
**First Things First, What is Tokenization?**
AI operates with numbers, and for deep learning on text, we convert that text into numerical data. Tokenization breaks down textual data into smaller units, or tokens, like words or characters, which can be represented numerically.
**Decoding Tokenization**
There are various techniques in tokenization, such as:
- **Word Tokenization:** Divides text into words, creating a vocabulary of unique terms.
- **Character Tokenization:** Breaks down text into individual characters, useful for specific tasks like morphological analysis.
- **Sub word Tokenization:** Splits words into smaller units, capturing morphological information effectively. Examples [BERT](https://huggingface.co/docs/transformers/model_doc/bert) and [SentencePiece](https://github.com/google/sentencepiece)
**Character-Level Tokenization**
We essentially create tokens out of individual characters present in the text. This involves compiling a unique set of characters found in the dataset, ranging from alphanumeric characters to ASCII symbols. By breaking down the text into these elemental units, we generate a concise set of tokens, resulting in a smaller number of model parameters. This lean approach is particularly advantageous in scenarios with `limited datasets, such as low-resource languages`, where it can efficiently capture patterns without overwhelming the model.
```python
# Consider the sentence, "I love Python"
# If we tokenize by characters the result will be ['I', ' ', 'l', 'o', 'v', 'e', ' ', 'P', 'y', 't', 'h', 'n']
sent = "I love Python"
tokens = [i for i in set(sent)] # Use a set to obtain ony unique ones
# if we then represent the sentence above numerically
numerical_representation = {i:ch for i, ch in enumerate(tokens)}
number_of_tokens = len(s)
```
**Word-Level Tokenization:**
Word-level tokenization involves breaking down the text into individual words. This process results in a vocabulary composed of unique terms present in the dataset. Unlike character-level tokenization, which deals with individual characters, word-level tokenization operates at a higher linguistic level, capturing the meaning and context of words within the text.
This approach leads to a larger model vocabulary, encompassing the diversity of words used in the dataset. While this richness is beneficial for understanding the semantics of the language, it introduces challenges, particularly when working with extensive datasets. The increased vocabulary size translates to a higher number of model parameters, necessitating careful management to prevent overfitting.
```py
# Consider the sentence, "I love Python"
sent = "I love Python"
tokens = [i for i in set(sent.split())]
numerical_representation = {i:ch for i, ch in enumerate(tokens)}
```
However, the trade-off lies in the potential for overfitting, especially when dealing with smaller datasets. Striking a balance between a rich vocabulary and avoiding over-parameterization becomes a critical consideration when employing word-level tokenization in natural language processing tasks.
**Subword Tokenization**
Subword tokenization interpolates between word-based and character-based tokenization.
Instead of treating each whole word as a single building block, subword tokenization breaks down words into smaller, meaningful pieces.
These smaller parts, or subwords, carry meaning on their own and help the computer understand the structure of the word in a more detailed way.
Common words get a slot in the vocabulary, but the tokenizer can fall back to word pieces and individual characters for unknown words.
_Let's do a simple experiment to show the impacts of a tokenization method on the model_
[Colab Link](https://colab.research.google.com/drive/1PwAr2Gt0x_8UUXd5ED_nBTJlpdRXeU3V?usp=sharing) to the code
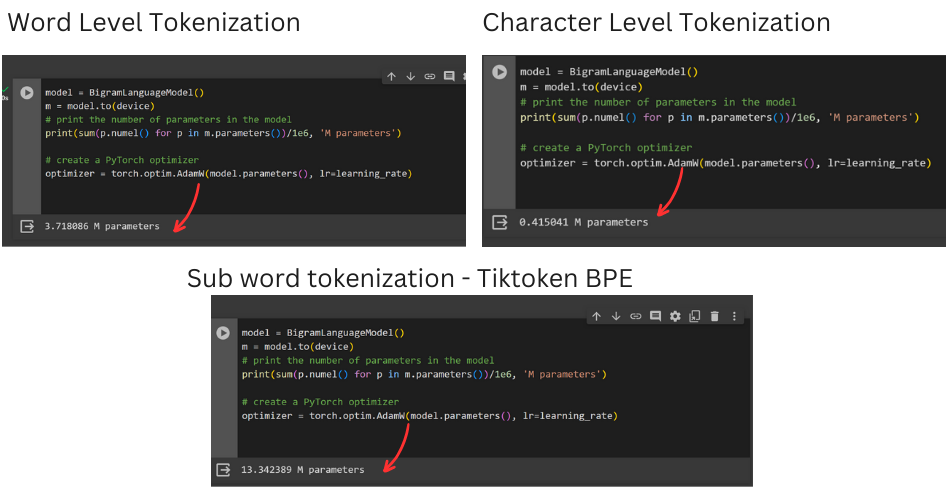
From the experiment I conducted above the trend is as follows:
- As the number of tokens increases:
- The model size also increases
- Model training and inference becomes more compute demanding
- The size of dataset required to achieve high accuracy also increases
**Which tokenization method should I use?**
Sub-word tokenization is the industry standard!
Consider [Byte Pair Encodinge(BPE) techniques](https://huggingface.co/learn/nlp-course/chapter6/5?fw=pt) such as:
1. [TikToken](https://github.com/openai/tiktoken)
2. [SentencePiece](https://github.com/google/sentencepiece)
3. [BERT](https://huggingface.co/docs/transformers/model_doc/bert)
Use character level tokenization or word level tokenization where you have a smaller dataset. | kagemanjoroge |
1,781,497 | Every Neovim, Every Config, All At Once | Neovim is hot 🔥 right now Neovim, a successful fork of Vim, is a text editor that is... | 0 | 2024-03-06T00:26:24 | https://dev.to/hoonweedev/every-neovim-every-config-all-at-once-578p | neovim, config, development | ---
id: Every Neovim, Every Config, All At Once
aliases: []
tags: []
---
## Neovim is hot 🔥 right now
Neovim, a successful fork of Vim, is a text editor that is gaining popularity. I won't link David Heinemeier Hansson's blog post again since everyone has done it already.
I also won't list all the good stuff about Neovim, since you can find them on the official website and tons of blog posts.
## You can build your own IDE, or should I say, own **IDEs**(plural)
Just by learning a super-easy Lua language, you can build your own IDE with Neovim. If you're a busy person, you can just copy and paste someone else's config.
You can also find a fully-plugged IDE level config like:
- [LazyVim](https://www.lazyvim.org/)
- [AstroNvim](https://astronvim.com/)
- [LunarVim](https://www.lunarvim.org/)
- [NvChad](https://nvchad.com/)
All you have to do is to clone the repo and paste it in your `~/.config/nvim` directory.
```bash
# Backup your current config
mv ~/.config/nvim ~/.config/nvim.bak
# Clone the repo
git clone <remote repo> ~/.config/nvim --depth 1
# Run neovim
nvim
```
But what if you want to use multiple configs at the same time?
The answer is simple. All you need to set is the **`NVIM_APPNAME`** environment variable.
### Example: Using LunarVim and NvChad at the same time
Let's say you want to use LunarVim for your web development and NvChad for your data science work.
You should first clone both repos with their custom directory names.
```bash
# Clone LunarVim
$ git clone git@github.com:LunarVim/LunarVim.git ~/.config/lunarvim --depth 1
# Clone NvChad
$ git clone https://github.com/NvChad/NvChad ~/.config/nvchad --depth 1
```
Then, you can set the `NVIM_APPNAME` environment variable to use each config.
```bash
# Run neovim with LunarVim
$ NVIM_APPNAME=lunarvim nvim
# Run neovim with NvChad
$ NVIM_APPNAME=nvchad nvim
```
You can still use the default config by just running `nvim` without setting the `NVIM_APPNAME` environment variable. (This reads the config from `~/.config/nvim`)
```bash
# Run neovim with the default config
$ nvim
```
### Example: Make aliases for each config
You can also make aliases for each config.
```bash
# Add these lines to your .bashrc or .zshrc
alias lunarvim="NVIM_APPNAME=lunarvim nvim"
alias nvchad="NVIM_APPNAME=nvchad nvim"
# Run neovim with LunarVim
$ lunarvim
```
## Conclusion
That's it! You can use multiple Neovim configs at the same time, with just a simple environment variable `NVIM_APPNAME`.
Now, some might say _"Why don't you just use Docker?"_. Well, not everyone is comfortable with Docker, and since Neovim just supports this feature, why not use it?
I hope this tip helps you to use Neovim more effectively. Happy hacking! 🚀
| hoonweedev |
1,769,130 | Dart Basic - Part 1 | Exploring Dart Fundamentals: Variables, Types, Constants, and Operators Dart, with its simplicity... | 26,684 | 2024-02-23T11:44:33 | https://dev.to/sadanandgadwal/dart-basic-part1-p35 | dart, basic, programming, sadanandgadwal | Exploring Dart Fundamentals: Variables, Types, Constants, and Operators
Dart, with its simplicity and power, is a modern programming language that caters to various development needs, from mobile applications to server-side solutions. In this comprehensive guide, we'll explore the foundational concepts of Dart through practical examples.
## 1. Variables and Types:
**1.1 Variables:** Variables store data that can be manipulated and referenced in a program. In Dart, you declare variables using the var, final, or const keywords.
**var**: Declares a variable whose type is inferred by the Dart compiler based on the assigned value. For example:
```
var age = 23; //age as an integer
```
**final**: final variables in Dart are variables whose values cannot be changed once they are initialized.
- They must be initialized before they are used, and once initialized, their values cannot be reassigned.
- Final variables are initialized when they are first accessed, and their value remains constant throughout the program's execution.
- Final variables can be initialized with a value at the time of declaration or within constructors.
```
final name = 'Sadanand'; // name is assigned 'Sadanand' and it cannot be changed
```
**const**: const variables are compile-time constants in Dart. They are implicitly final but also compile-time constants.
- Their values must be known at compile-time.
- Const variables are evaluated and set at compile-time, not runtime.
- They are useful for declaring values that will not change during the execution of the program.
```
const PI = 3.1415; // PI is a compile-time constant
```
**1.2 Types:** Dart is a statically typed language, meaning each variable has a specific data type known at compile-time.
Dart provides several built-in data types:
**Numbers**: Dart supports both integers and floating-point numbers.
```
int age = 30;
double height = 5.11;
```
**Strings**: Used to represent textual data.
```
String name = 'Sadanand';
```
**Booleans**: Represents a true or false value.
```
bool isAdult = true;
```
**Lists**: Ordered collections of objects.
```
List<int> numbers = [1, 2, 3, 4, 5];
```
**Maps**: Unordered collections of key-value pairs.
```
Map<String, dynamic> person = {
'name': 'Sadanand',
'age': 23,
'isAdult': true
};
```
## 2. Dynamic:
Dynamic: Represents a variable whose type can change dynamically at runtime.
```
dynamic dynamicVariable = 'Sadanand';
dynamicVariable = 23; // Now dynamicVariable is an integer
```
## 3. Common Operators:
Common operators in programming languages are symbols or keywords used to perform various operations on data. Here's a brief explanation of common operators used in programming:
**3.1 Arithmetic Operators:**
+: Adds two numbers.
-: Subtracts the second number from the first.
*: Multiplies two numbers.
/: Divide the first number by the second.
~/: Truncating Division returns an integer result by rounding towards zero.
%: Modulus operator returns the remainder of the division.
**3.2 Relational Operators:**
>: Checks if the first operand is greater than the second.
<: Checks if the first operand is less than the second.
>=: Checks if the first operand is greater than or equal to the second.
<=: Checks if the first operand is less than or equal to the second.
**3.3 Equality Operators:**
==: Checks if two operands are equal.
!=: Checks if two operands are not equal.
**3.4 Logical Operators:**
&& (Logical AND): Returns true if both operands are true.
|| (Logical OR): Returns true if at least one of the operands is true.
```
void operatorExample() {
int x = 23;
int y = 27;
// Arithmetic operators
final add = x + y; // Addition
final sub = x - y; // Subtraction
final mut = x * y; // Multiplication
final div = x / y; // Division
final divwithintegers = y ~/ x; // Truncating Division (returns an integer)
final modulo = x % y; // Modulus (remainder of division)
// Relational operators
final greater = x > y; // Greater than
final notGreater = x < y; // Less than
final greaterthan = x >= y; // Greater than or equal to
final notgreaterthan = x <= y; // Less than or equal to
// Equality operators
final equalTo = x == y; // Equal to
final notEqualTo = x != y; // Not equal to
// Logical operators
final logicalAnd = x > y && y < x; // Logical AND
final logicalOr = x > y || y < x; // Logical OR
// Printing results
print("Addition of two numbers: $add");
print("Subtraction of two numbers: $sub");
print("Multiplication of two numbers: $mut");
print("Division of two numbers: $div");
print("Divide, returning an integer result: $divwithintegers");
print("Remainder of an integer division: $modulo");
print("Greater than: $greater");
print("Less than: $notGreater");
print("Greater than or equal to: $greaterthan");
print("Less than or equal to: $notgreaterthan");
print("Equal to: $equalTo");
print("Not equal to: $notEqualTo");
print("Logical AND: $logicalAnd");
print("Logical OR: $logicalOr");
}
```
These operators are fundamental for performing arithmetic calculations, making comparisons, and evaluating conditions in Dart programs.
**Conclusion:**
Dart's versatility and simplicity make it an excellent choice for developers across various domains. Understanding these fundamental concepts equips you to write efficient Dart code for diverse applications, ensuring clarity, reliability, and performance. Happy coding with Dart!
_Start Coding in Dart Now!_
Head over to [DartPad](https://dartpad.dev) (https://dartpad.dev) to start coding immediately. DartPad is a user-friendly online editor where you can write, run, and share Dart code without any setup required.
🌟 Stay Connected! 🌟
Hey there, awesome reader! 👋 Want to stay updated with my latest insights,Follow me on social media!
[🐦](https://twitter.com/sadanandgadwal) [📸](https://www.instagram.com/sadanand_gadwal/) [📘](https://www.facebook.com/sadanandgadwal7) [💻](https://github.com/Sadanandgadwal) [🌐](https://sadanandgadwal.me/) [💼
](https://www.linkedin.com/in/sadanandgadwal/)
[Sadanand Gadwal](https://dev.to/sadanandgadwal) | sadanandgadwal |
1,769,132 | Build your first Hangfire job .NET8 with PostgreSQL | In this article, I will share a few simple steps you will need to create your first hangfire job... | 0 | 2024-02-22T12:29:29 | https://dev.to/pradeepradyumna/your-first-hangfire-job-fornet8-with-postgresql-30nd | postgres, hangfire, dotnet, dotnetcore | In this article, I will share a few simple steps you will need to create your first hangfire job using .NET 8(the latest at the time of writing this article) with Postgres as the database.
Also, please be aware that in this article I'm not going to brief what Hangfire is, as there are plenty of articles already written by wise authors. :)
Alright, let's get started.
## 1. First step first
We can create either an ASP.NET Core Web App or API (it doesn't really matter what you choose). However, for simplicity, I'm using an API project targeting.NET8
## 2. Install Nuget Packages
You'll need to install the following Nuget packages
`Npgsql.EntityFrameworkCore.PostgreSQL`
`Microsoft.EntityFrameworkCore.Design`
`Hangfire.AspNetCore`
`Hangfire.PostgreSql`
That's all you need!
## 3. Create a DBContext
You will need a custom DBContext class to run a DB Migration
```
public class DefaultDbContext : DbContext
{
public DefaultDbContext(DbContextOptions<DefaultDbContext> options)
: base(options) { }
}
```
## 4. Create a DB in Postgres
Just go ahead and create a database called `HangfireSample`
This is all you need to do at the DB level!
## 5. Configuration
Now before you run migration configure the DB path in `appsettings.json` and update `program.cs`
```
"ConnectionStrings": {
"defaultConnection": "Host=localhost;Port=5432;Username=postgres;Password=YOUR_PWD;Database=HangfireSample"
}
```
Update the below code in `program.cs`
```
builder.Services.AddEntityFrameworkNpgsql().AddDbContext<DefaultDbContext>(options => {
options.UseNpgsql(builder.Configuration.GetConnectionString("defaultConnection"));
});
```
## 6. Run migration
Just open Package Manager Console and run the below commands
```
dotnet ef migrations add InitContext
dotnet ef database update
```
This will create `__EFMigrationsHistory` under `public` schema
## 7. Almost done
Now configure Hangfire service in `program.cs` with the below code
```
builder.Services.AddHangfire(x =>
x.UsePostgreSqlStorage(builder.Configuration.GetConnectionString("defaultConnection")));
```
And update middleware
```
app.UseHangfireDashboard("/dashboard");
app.UseHangfireServer();
```
This was all you had to do create the hangfire server and storage.
Now, let's create a simple job.
## 8. First Hangfire job
Just copy the code below
```
BackgroundJob.Enqueue(() => Console.WriteLine("My first handfire job!"));
```
Now, you run the solution!
To see your job, visit
[https://localhost:44397/dashboard](https://localhost:44397/dashboard)
And if you go to [https://localhost:44397/dashboard/jobs/succeeded](https://localhost:44397/dashboard/jobs/succeeded)
you'll see the job you just executed.
Also, just you know, if you check the `HangfireSample` database, you'll the hangfire tables would be created under `hangfire` schema.
Just for your reference [here](https://github.com/pradeepradyumna/HangfireSample) is the complete working sample of the code I just explained.
I hope it helped you! | pradeepradyumna |
1,769,164 | Dashboard | You Can Start the Power BI Training Courses now in Thane. Analysing and interpreting data using... | 0 | 2024-02-22T12:13:20 | https://dev.to/deepk8989/dashboard-27hm | You Can Start the Power BI Training Courses now in Thane. Analysing and interpreting data using Power BI to derive actionable insights. This may involve creating visualizations, reports, and dashboards. Designing and developing reports and dashboards using Power BI. This involves transforming raw data into a format suitable for analysis. Developing and maintaining data infrastructure to support Power BI reports, ensuring data is accessible and accurate. join now to start the career with Actifyzone center. | deepk8989 | |
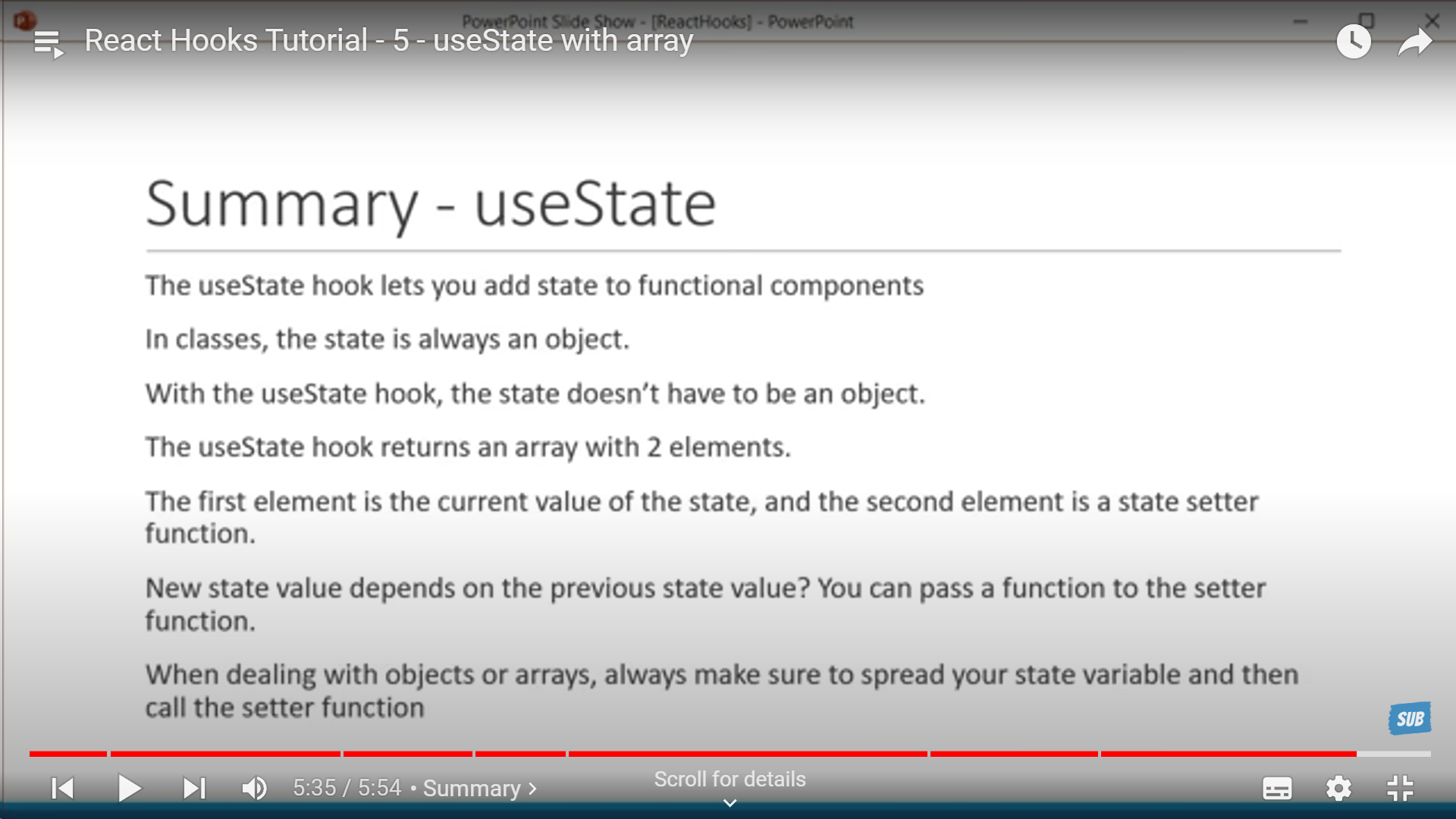
1,769,248 | React Hooks | Hooks Why Hooks Hook Rules Syntax In a hook -> A state variable can be -> A... | 0 | 2024-02-22T14:33:42 | https://dev.to/alamfatima1999/react-hooks-20m0 | _<u>**Hooks**</u>_
**_<u>Why Hooks</u>_**
**Hook Rules**
**Syntax**
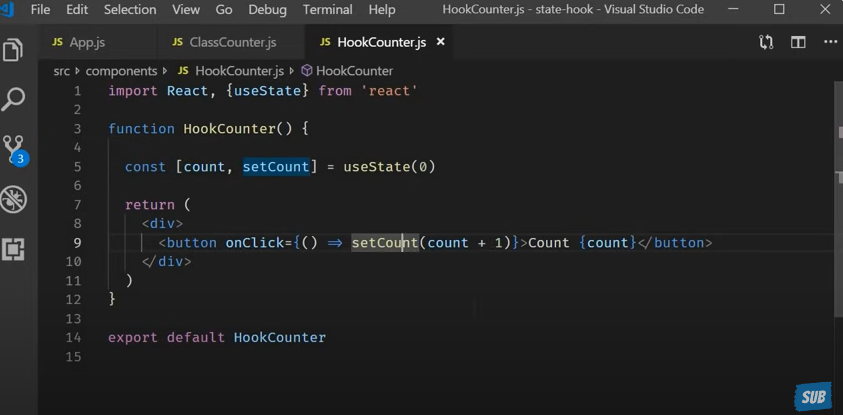
In a hook -> A state variable can be ->
1. A number
2. A string
3. Boolean
4. Object
5. Array
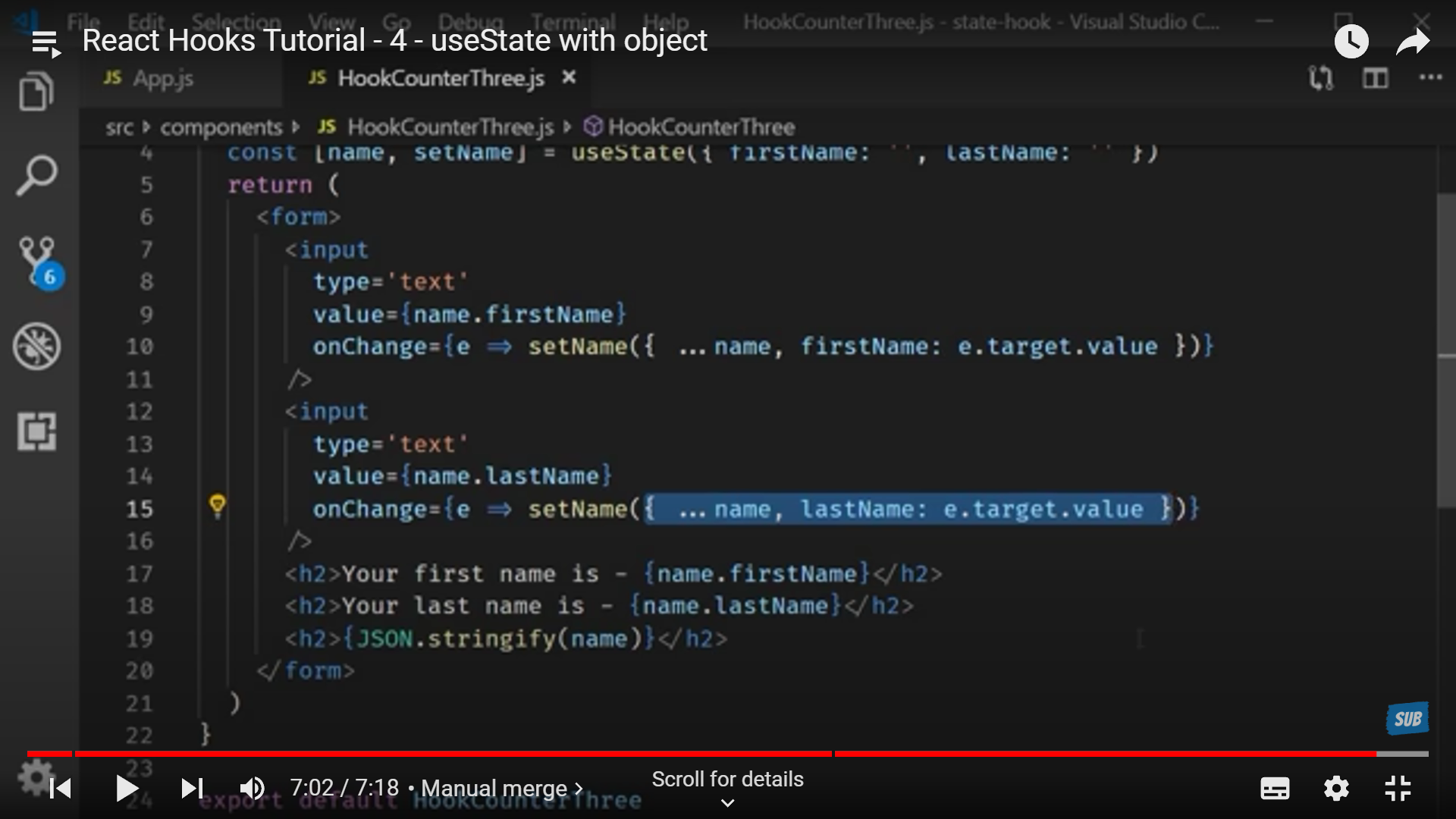
If we have use dan object as set state and modified a part of it and then some other part it doesn't merge them and update but updates them independently and so they are rendered on screen as different entities so to rule that out we us ethe spread operator to give the whole object value first and then modify a part(s) of it.
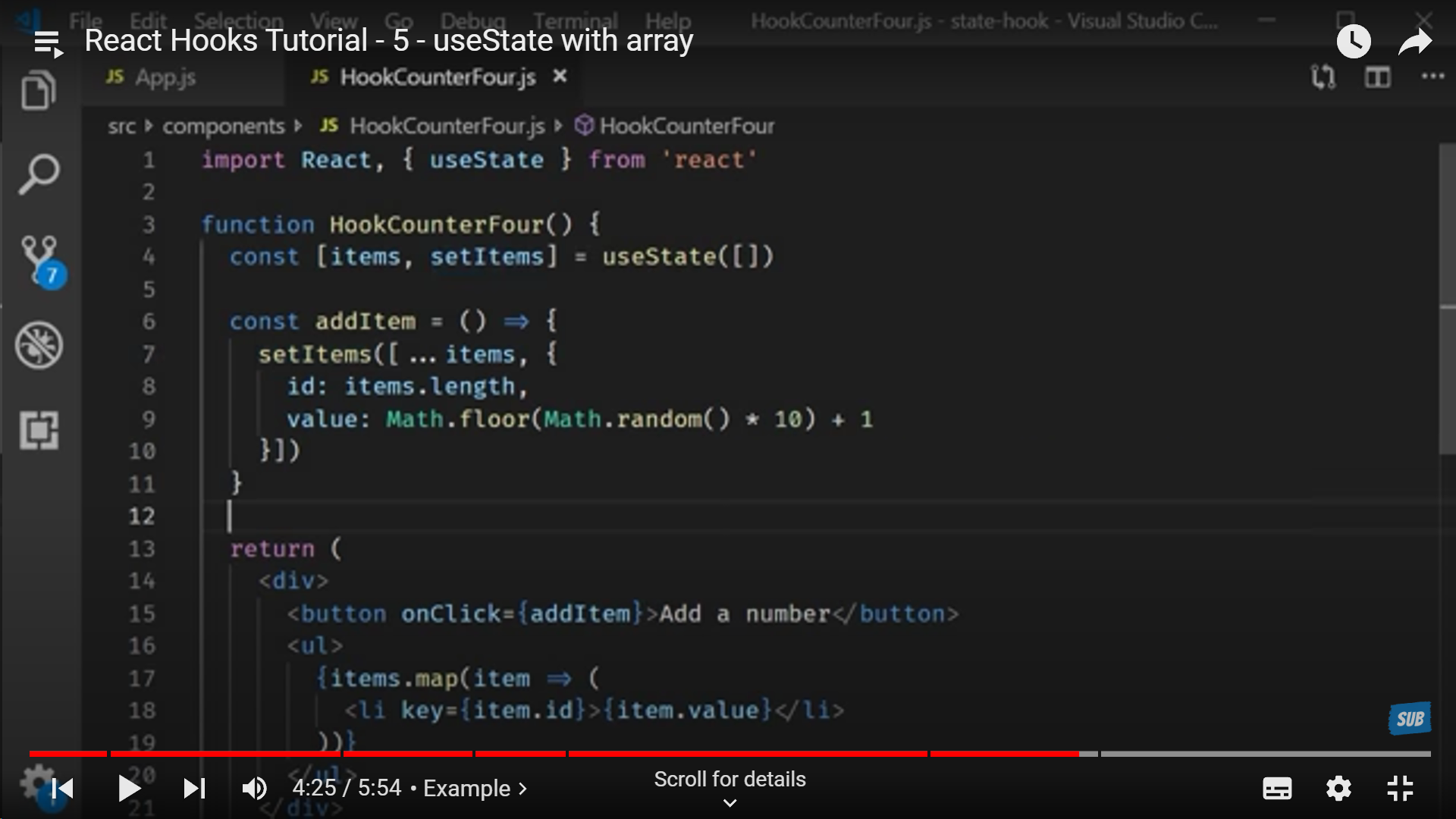
**Hooks with Arrays**
**Things to remember while dealing with hooks**
**useEffect**
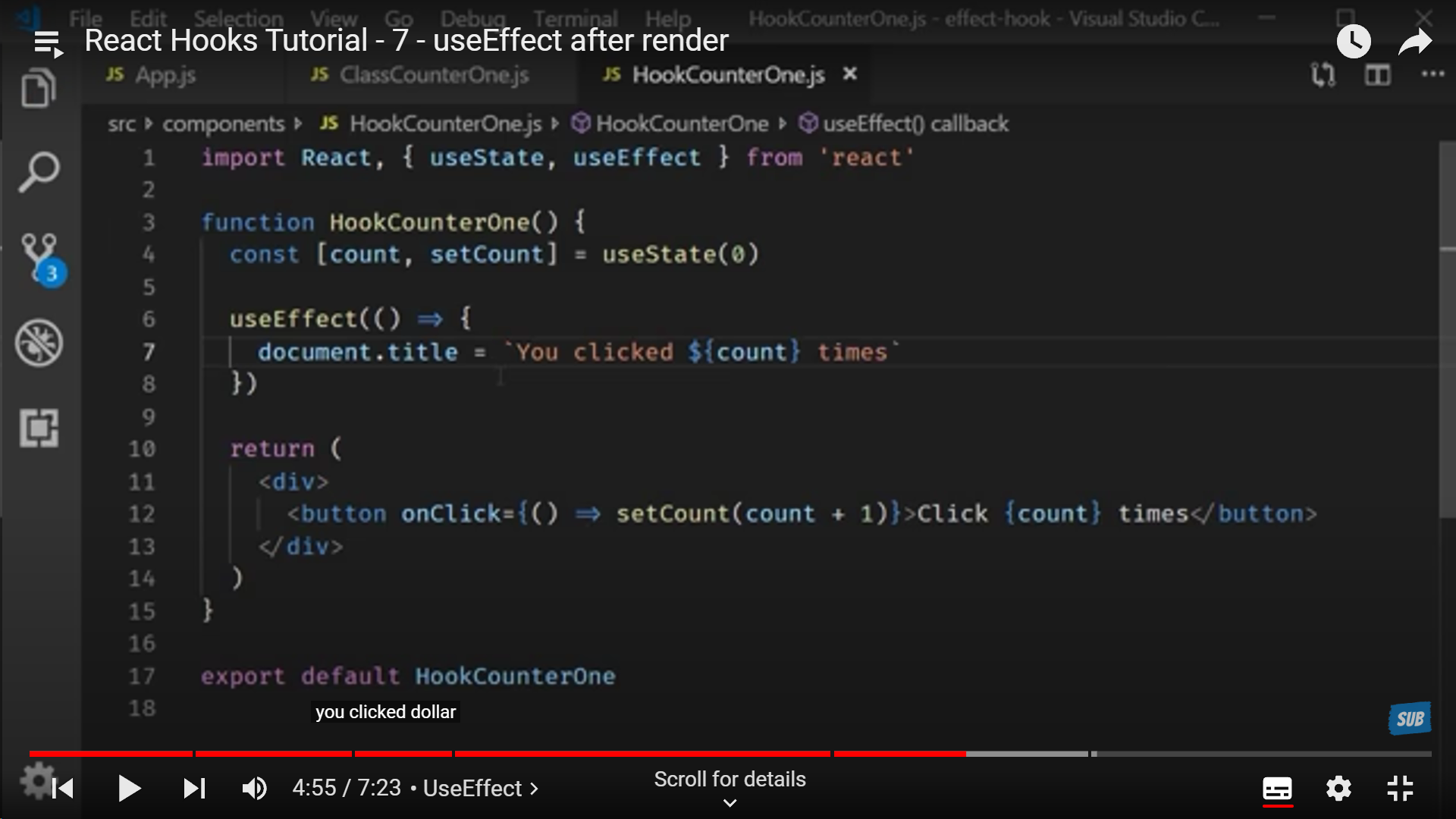
It is basically whenever the component renders or update in rendering on screen this useEffect() gets triggered and what we define under this is what function we want to trigger. Here we have defined an arrow function.
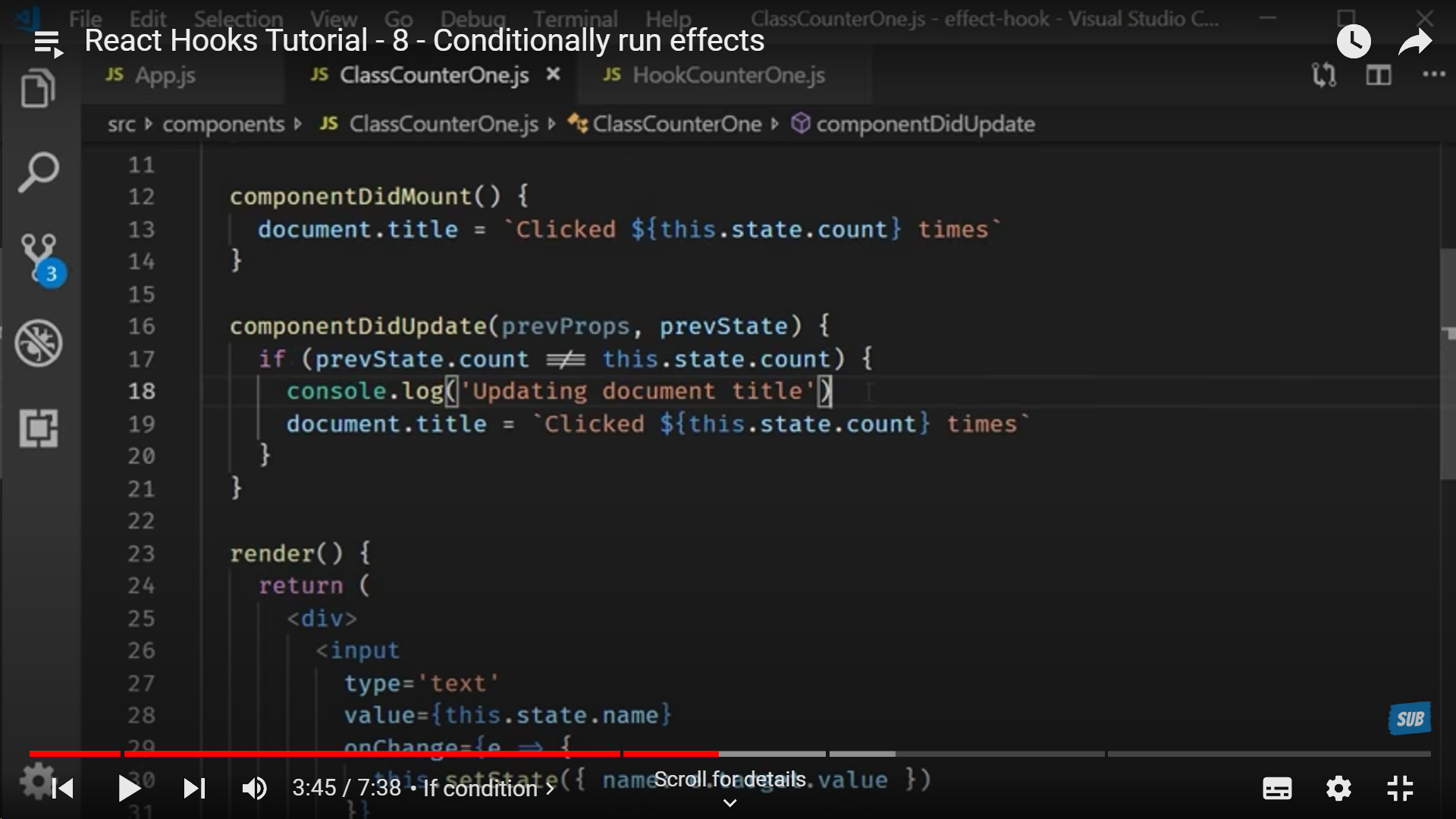
**In a class component**
A simple condition will help us to not re-render unnecessarily.
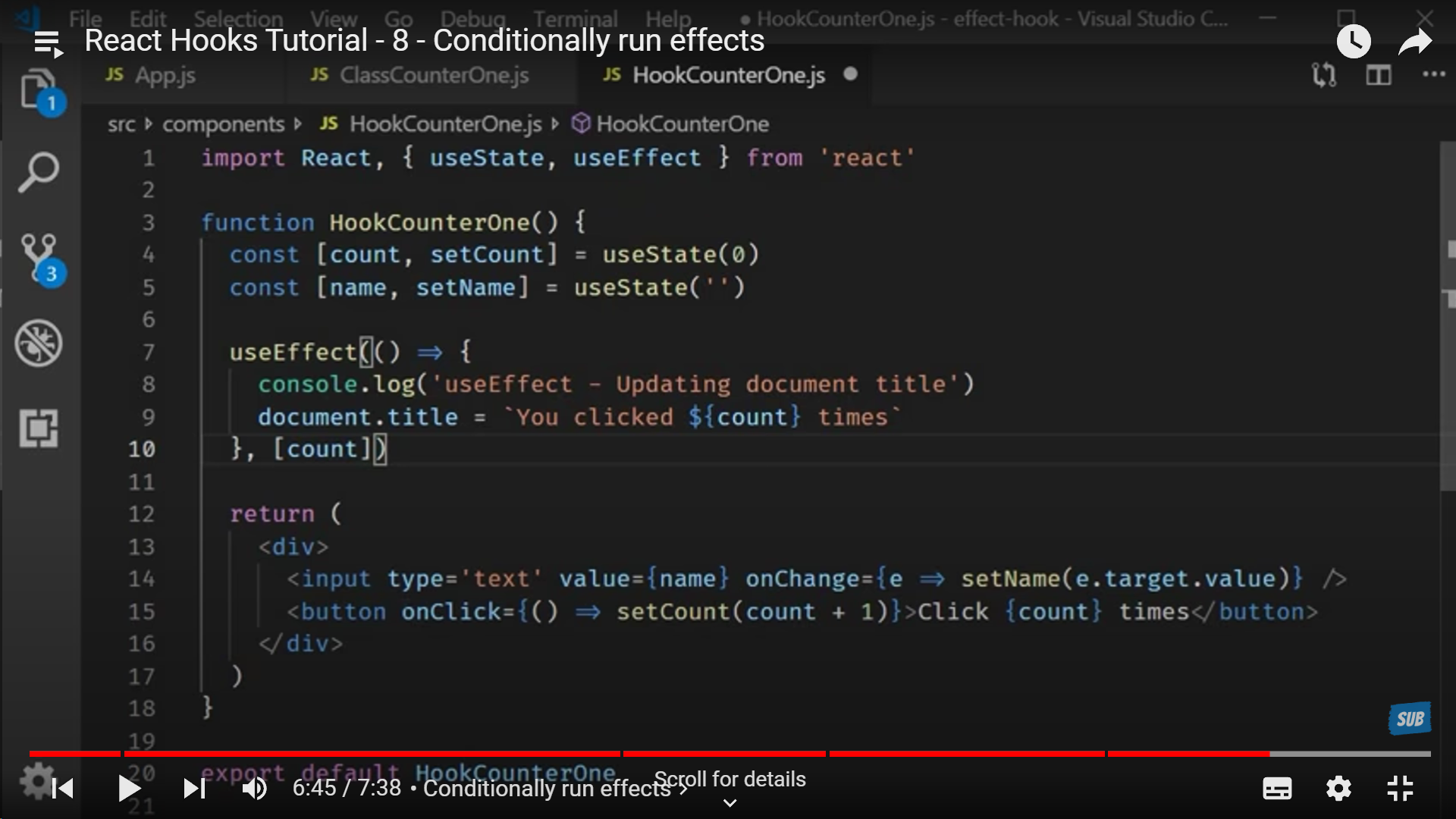
**Similarly with Functional Components**
We can use useEffect() to do the same by adding the state or prop to be checked if it has updated or not if it's not then useEffect() isn't executed.
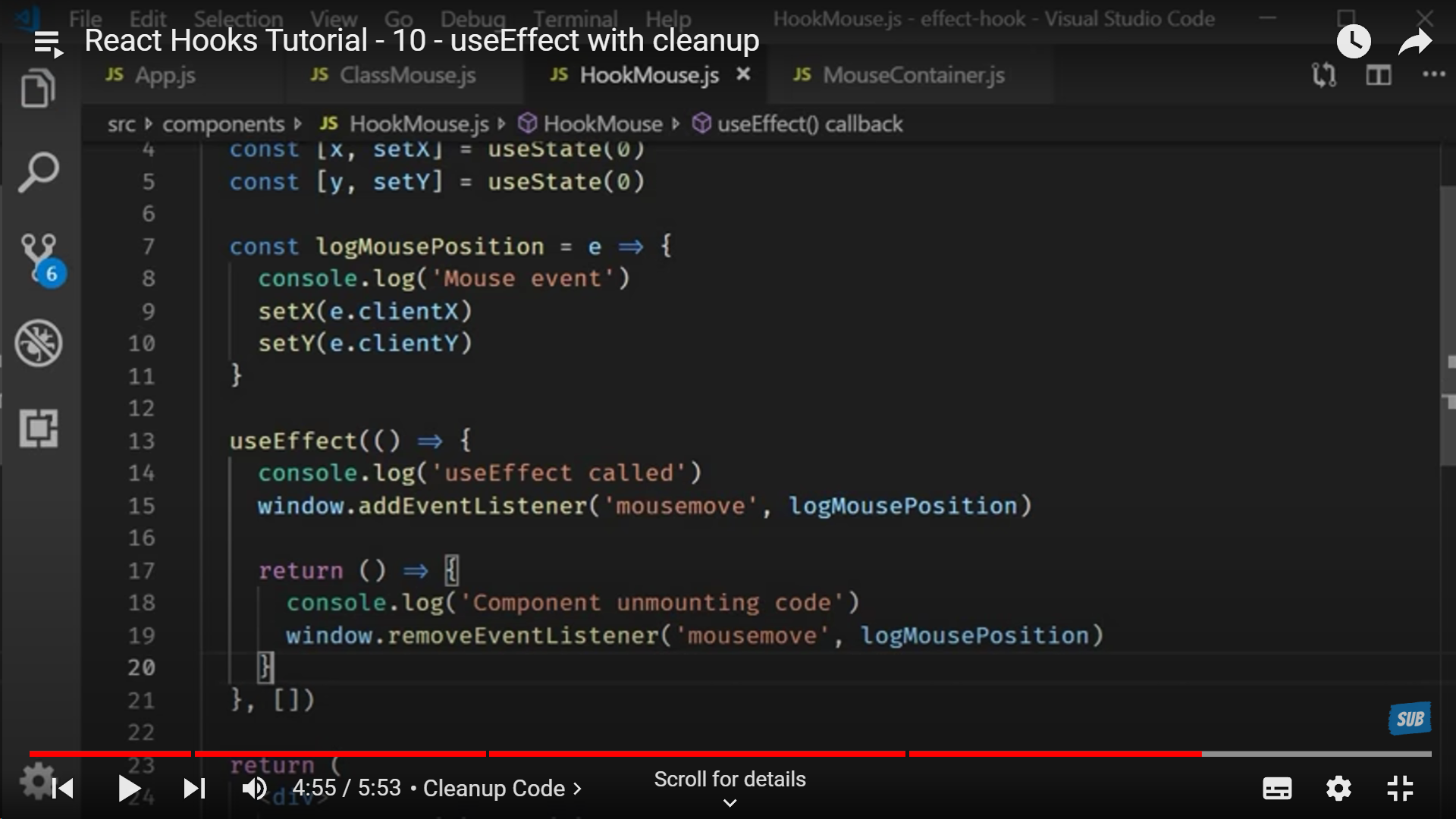
**How to mimic ComponentWillUnmount() in a Functional Component**
With the help of removeEventListener()
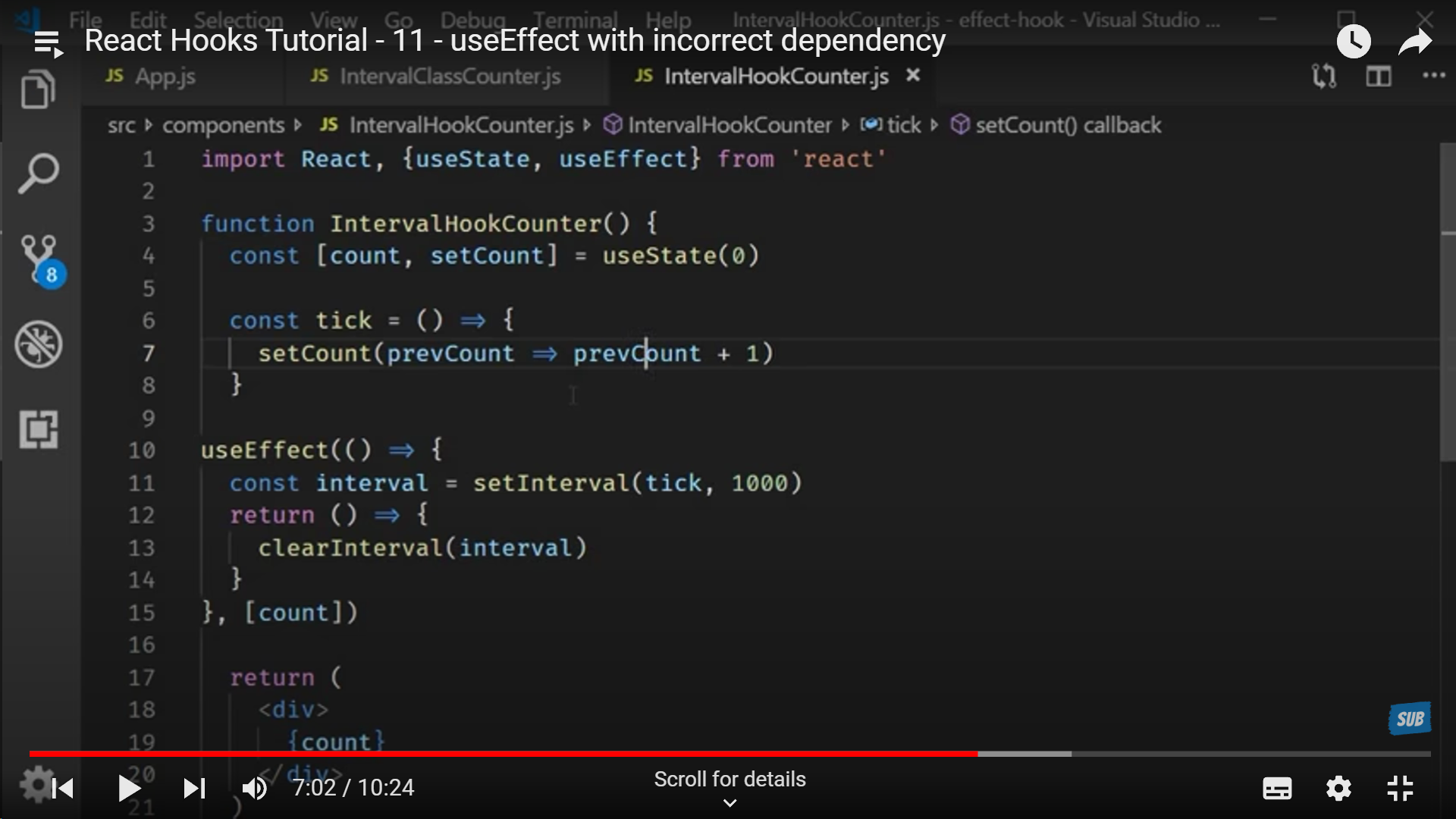
**Tick in Hooks**
To mention the state variable that we need to re-render needs to be mentioned in the dependency array (a.k.a the array that is passed to useEffect()). This is how we re-render specific state variables.
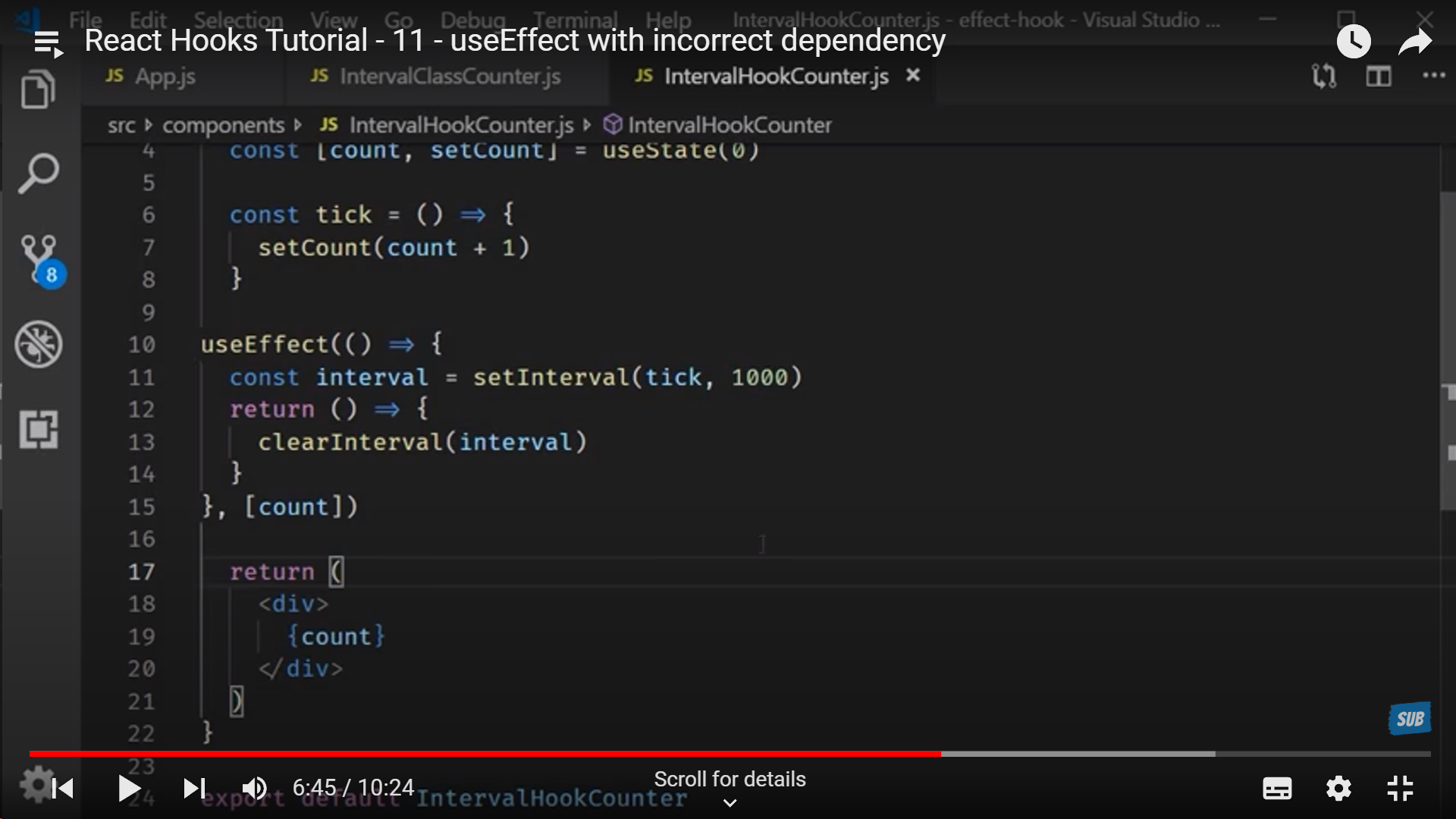
**OR**
By using state variable's prevState to update the new state and re-render it on screen.
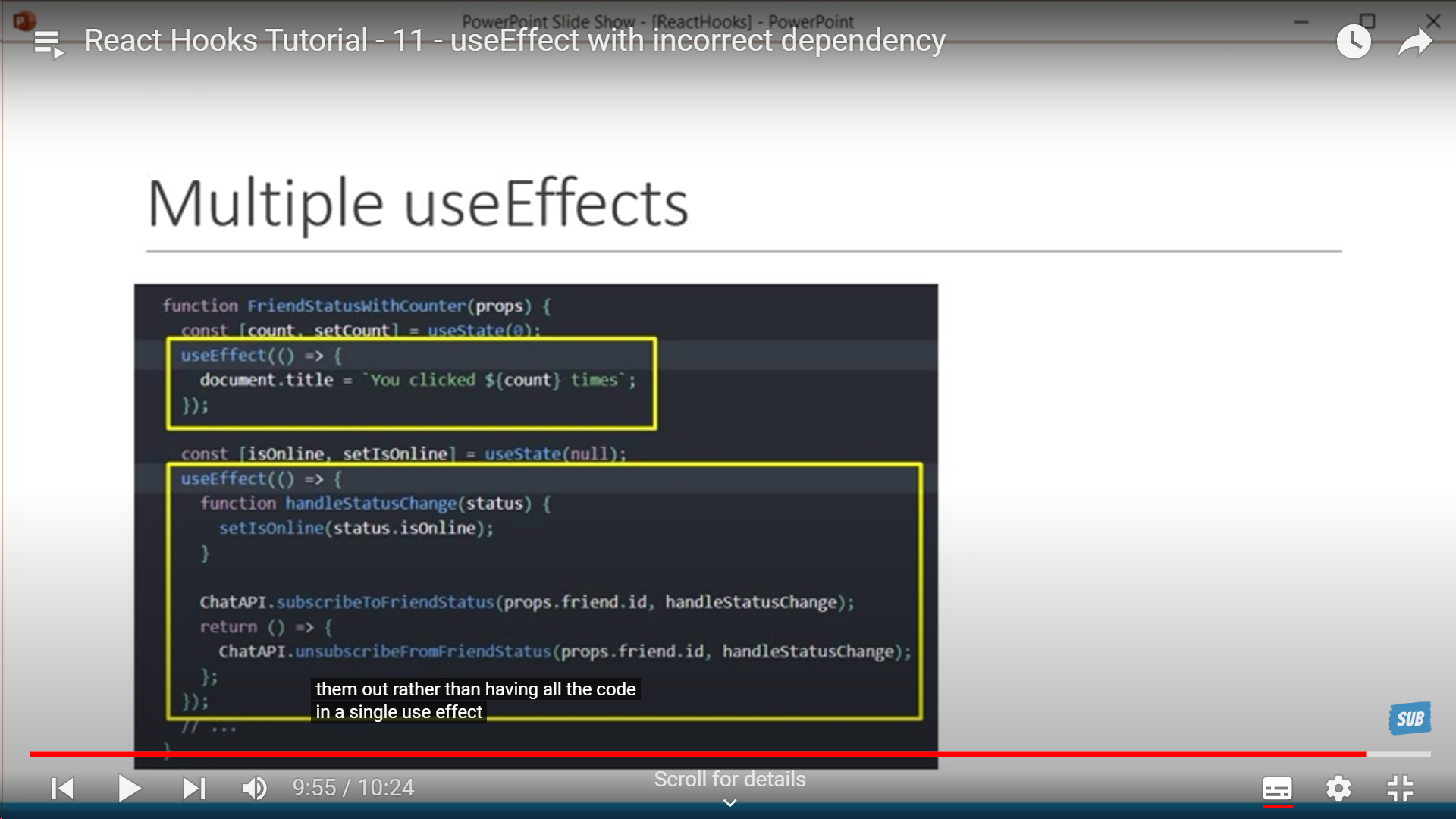
**Multiple useEffect to group the data**
This groups relevant data together and use multiple useEffect -> Notice how we have a state variable declared and a corresponding useEffect for it. This solve the problem of "relevant data far apart" in CLass Components
**_<u>Context</u>_**
**Defining context in parent component**
**Using context in child component**
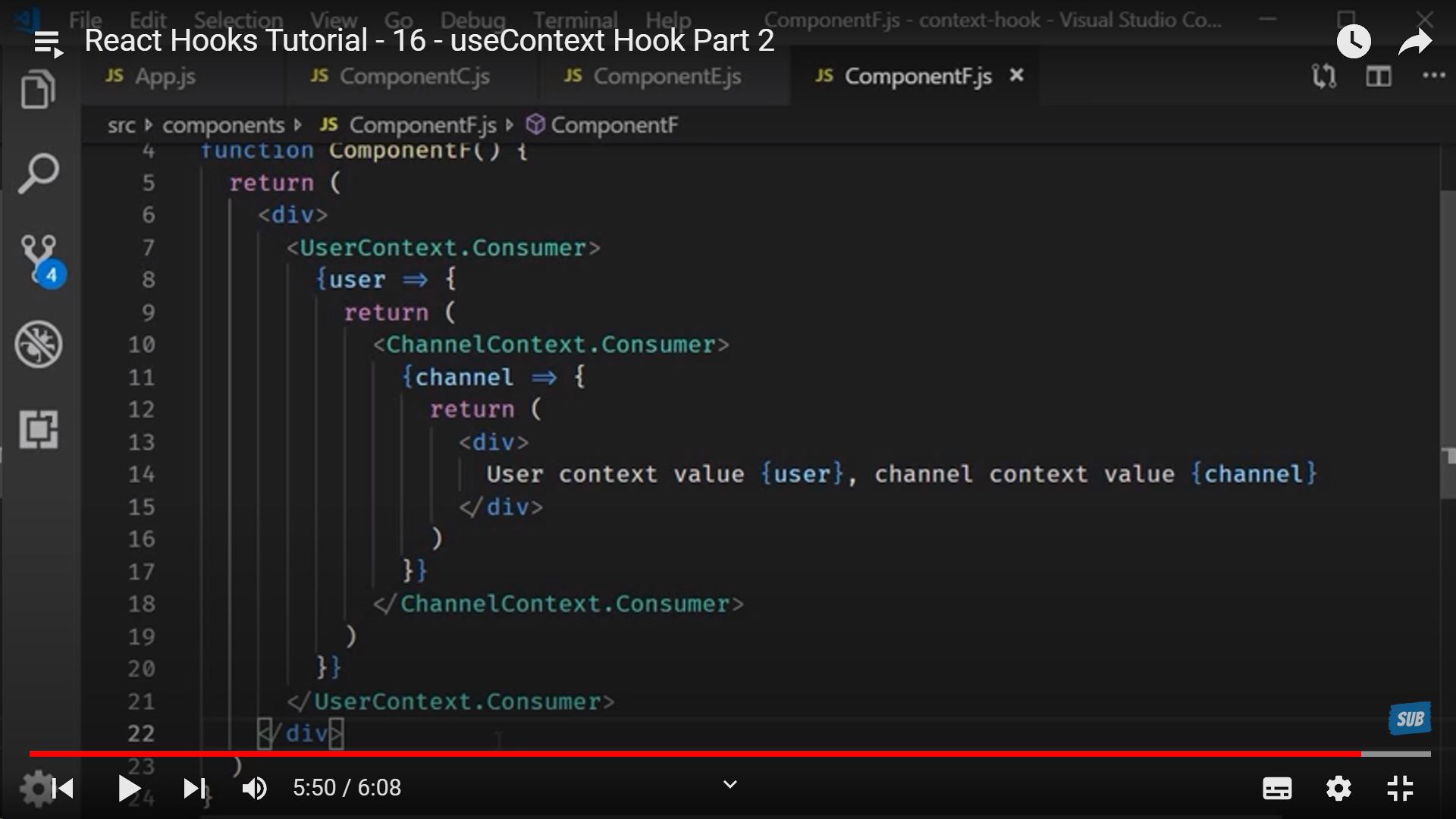
_<u>**Shortcut for using context**</u>_
| alamfatima1999 | |
1,769,456 | affordable web development company | At Websleague, our all-affordable web development services combine quality and economy. Our team... | 0 | 2024-02-22T17:49:49 | https://dev.to/gregoryhomer/affordable-web-development-company-1n0l | At Websleague, our all-[affordable web development services](https://websleagues.com/) combine quality and economy. Our team delivers customised solutions that satisfy your company objectives while staying inside your budget by uniting affordability and information. | gregoryhomer | |
1,769,457 | Gamedev.js Survey’s all questions and answers landed on GitHub | With Gamedev.js Survey 2023 completed in December and the report published in January, I got asked... | 0 | 2024-02-22T17:53:16 | https://enclavegames.com/blog/gamedevjs-survey-github/ | github, results, gamedevjs, surveys | ---
title: Gamedev.js Survey’s all questions and answers landed on GitHub
published: true
date: 2024-02-22 17:29:26 UTC
tags: github,results,gamedevjs,surveys
canonical_url: https://enclavegames.com/blog/gamedevjs-survey-github/
cover_image: https://dev-to-uploads.s3.amazonaws.com/uploads/articles/h3frzguvdt8dk14lfe6m.png
---
With [Gamedev.js Survey 2023](https://gamedevjs.com/survey/2023/) completed in December and the [report published](https://gamedevjs.com/survey/report-on-the-current-state-of-web-game-development-in-2023-is-now-published/) in January, I got asked multiple times about the raw results of this year’s answers and those from the past editions as well, especially from the open questions, and decided to publish all that [on GitHub](https://github.com/GamedevJS/Gamedev.js-Survey/).
You can find all the data we’ve collected (minus timestamps and email addresses) over the years by looking at the dedicated files:
- [answers-2021.csv](https://github.com/GamedevJS/Gamedev.js-Survey/blob/main/answers-2021.csv)
- [answers-2022.csv](https://github.com/GamedevJS/Gamedev.js-Survey/blob/main/answers-2022.csv)
- [answers-2023.csv](https://github.com/GamedevJS/Gamedev.js-Survey/blob/main/answers-2023.csv)
All the questions (2021–2023) were also published for reference, and the given file for the 2024 edition, [questions-2024.md](https://github.com/GamedevJS/Gamedev.js-Survey/blob/main/questions-2024.md), is up — feel free to send a [Pull Request](https://github.com/GamedevJS/Gamedev.js-Survey/pulls) if you have any feedback or updates to it already.
Now with the questions and answers from three consecutive editions, folks could pick up trends like the usage of specific technologies by developers, their tooling preferences, how earning money from building web games evolve over the years, or even the overall happiness of developers themselves. Another take would be on the open questions like what the devs are struggling with, or what might be their biggest challenges in the coming year.
The **Gamedev.js Survey** officially [joined WebDX Community Group at W3C](https://end3r.com/blog/webdx-gamedevjs-survey/) recently, so there’s hope it will grow even bigger with this year’s edition, which is planned in the second part of 2024. | end3r |
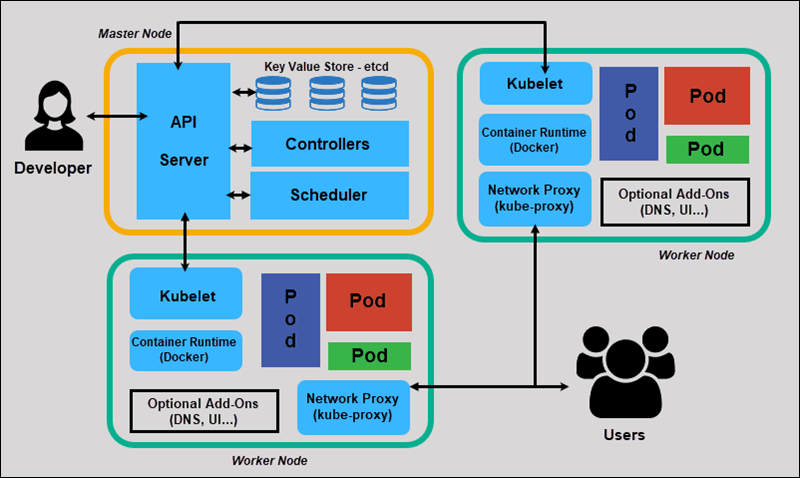
1,769,498 | Explaining Kubernetes In Kitchen | Exciting Announcement! 🎉 Prepare to Indulge Your Appetite for Knowledge! 😁 Join me on a... | 0 | 2024-02-22T19:23:40 | https://dev.to/omar_zenhom/explaining-kubernetes-in-kitchen-4men | kubernetes, devops, deployment, cloudcomputing | **Exciting Announcement! 🎉 Prepare to Indulge Your Appetite for Knowledge! 😁**
Join me on a mouthwatering journey through the world of Kubernetes, where software meets gourmet cuisine! 🍲🚀
Two days ago, my colleagues and I embarked on a challenging project, navigating the intricacies of the **Development stage** with skill and determination. Now, we’re gearing up to transition to the **Deploy stage** using a powerful tool called **Containers**. But wait, there’s more! We’ll be enlisting the help of **Kubernetes**, a software wizard that I’ll unravel for you in the most delicious way possible — through a culinary tale! 👨💻
**
## Start of the story
**
Explaining Kubernetes can be as complex as mastering a new recipe. That’s why I’m taking a different approach. In a fun analogy, understanding Kubernetes is like organizing a kitchen to cook a meal. Imagine you and your siblings are culinary prodigies, tasked with creating a gourmet meal to impress your mom. Each sibling has a role, just like Kubernetes assigns tasks to containers. From appetizers to dessert, Kubernetes orchestrates the entire process, ensuring your software runs as smoothly as a well-coordinated kitchen. 👩🍳🍴
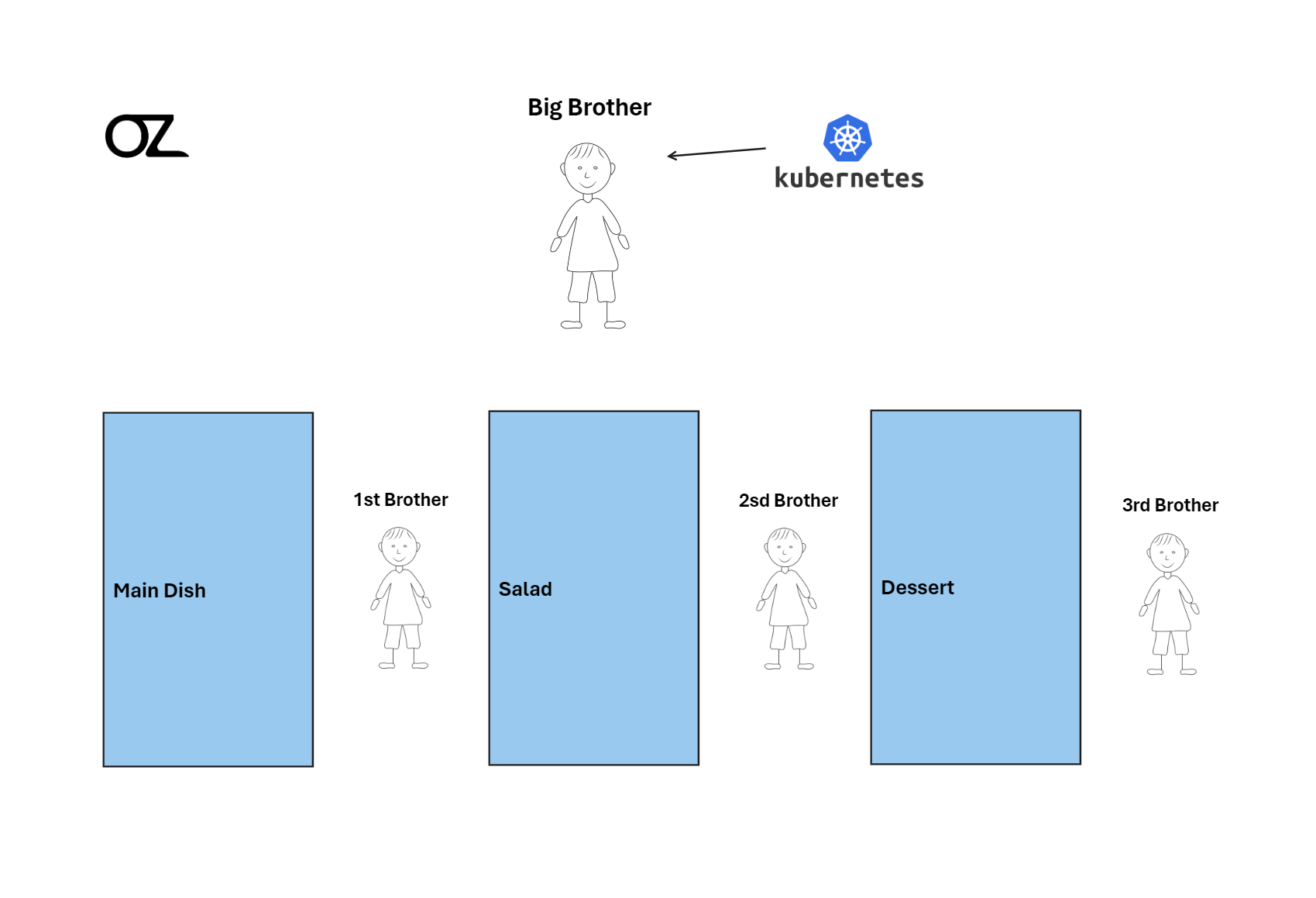
But what exactly is Kubernetes? It’s like the master chef in your software kitchen, organizing and overseeing containers (your cooking stations) to ensure everything runs seamlessly. Just as you’d divide cooking tasks among your siblings, Kubernetes divides tasks among containers, managing everything from appetizers to dessert. It scales, balances loads, and automates deployment, making it the ultimate chef in your software kitchen! 👨🍳👨🍳
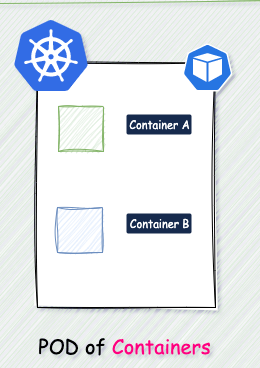
If we dive into the technical definition, Kubernetes is a **“container-orchestration tool,”** a tool for coordinating containers. To simplify, let’s consider it an organizational tool for the chef — you! Each container represents a dish where the food (your application) will be placed. 🍽️🔧
Moving on to **Pods**, which contain all the appetizer dishes served in the meal. Each dish serves a purpose, just like Pods work together to serve your application. They all have a common goal: to be appetizers for the main course. And just like in a meal, each Pod doesn’t interfere with the other because they are focused on their own tasks.
Now, let’s talk about the functions of Kubernetes:
1- **Scaling:** Like a chef adjusting the cooking pace, Kubernetes knows how to organize and run or turn off Pods based on the workload. So, if you’re running late in preparing the food, Kubernetes can speed up your work to finish quickly because the family is eagerly waiting to eat! 😋
2- **Automated deployment:** Kubernetes streamlines the deployment process, saving you time and effort. It’s like having a recipe that you follow to cook 📖👨🍳.
3- **Load balancing:** If there’s a high demand for a dish, Kubernetes can regulate the load by increasing the number of Pods working in that area. For example, if your younger brother is struggling to make dessert, you can clone him and tell your brother with version 2.0 to help your brother with version 1.0!
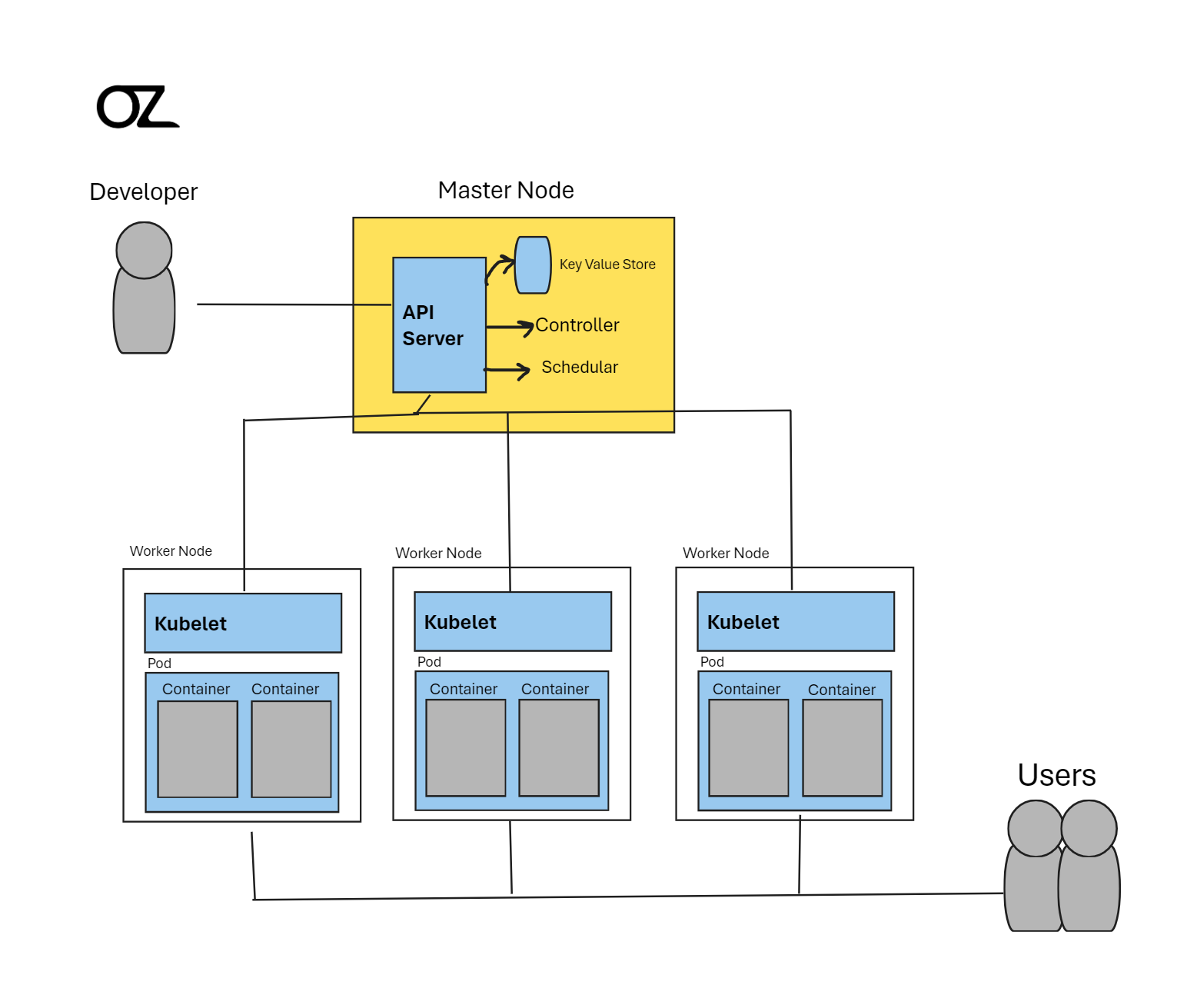
Back to the point, imagine your kitchen as a bustling restaurant, divided into three sections: appetizers, main course, and dessert. Each section represents a **“Working Node,”** like having three tables in a large kitchen, each dedicated to a specific part of the meal preparation. And guess who’s the head chef? That’s right, you’re the **“Master Node,”** overseeing the entire operation with precision and flair! 🧐
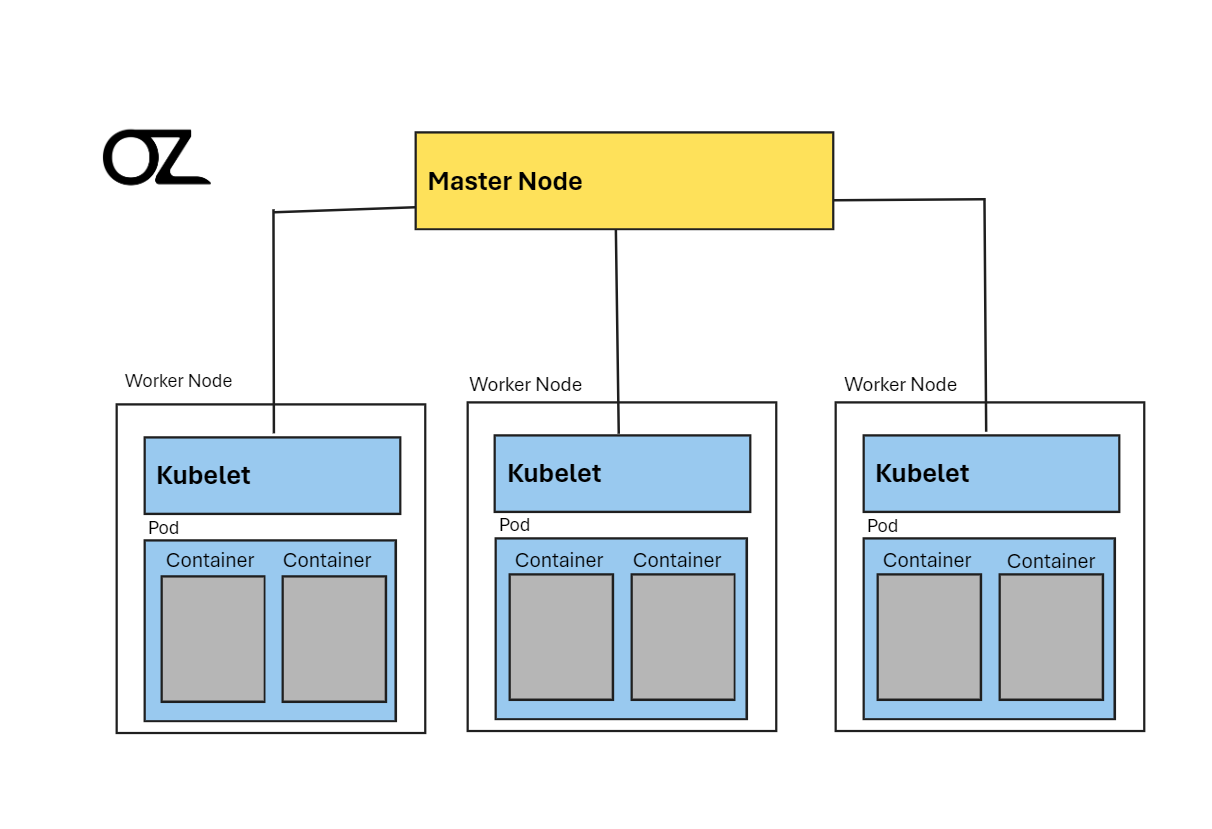
Your job is to ensure that each section works seamlessly, much like Kubernetes supervising containers in your software kitchen. To assist you, there’s a **“kubelet”** at each Working Node, acting as a diligent supervisor to ensure everything runs smoothly on each Node.
Now, let’s dive into why we use Kubernetes and its benefits. Just as a restaurant manager needs to know why they use certain tools to improve efficiency and customer satisfaction, understanding Kubernetes helps developers manage applications more effectively.
Think of Kubernetes as the big brother in the kitchen, organizing and directing the workflow. If, for instance, the **“mother”** (representing a user) wants to know what’s happening in the kitchen or needs something changed, she talks to the big brother (**Kubernetes**) to get all the details. From a technical standpoint, programmers can gather information about all the pods, nodes, and services, allowing them to make informed decisions about resources and operations.
**
## Conclusion
**
In essence, Kubernetes is like a well-oiled kitchen, where everyone has a role, everything is organized, and the result is a delicious meal that satisfies everyone’s cravings! 😋
I’ve served up this explanation like a well-crafted dish, breaking down complex concepts into bite-sized pieces for everyone to enjoy. The table is set, the meal is ready, and now it’s time to dig in and feast on your newfound knowledge! 🎓🍽️
But hey, the kitchen is always open for more culinary adventures! Don’t forget to hit that follow button to join us in the kitchen of software development, where Kubernetes is the key ingredient to success! 🚀.
I’d love to hear your thoughts on this feast of an explanation and whether my quirky drawings added that extra flavor to your learning experience 😂😂😁.
I’ll also provide some sources for those craving more details. Until next time, happy cooking with Kubernetes!
Thank you for reading!
P.S:
You can follow me:
[https://www.linkedin.com/in/omarwaleedzenhom/](https://www.linkedin.com/in/omarwaleedzenhom/)
[https://www.facebook.com/OmarZenho](https://www.facebook.com/OmarZenho)
My Portfolio:
[https://omarzen.github.io/Omar-Zenhom/](https://omarzen.github.io/Omar-Zenhom/)
| omar_zenhom |
1,769,536 | IP Addresses: Digital Connectivity | Title: Understanding IP Addresses: A Comprehensive Guide Introduction The term "IP" stands for... | 0 | 2024-02-22T20:37:16 | https://dev.to/noblepearl/ip-addresses-digital-connectivity-jf4 | beginners, productivity, learning | **Title: Understanding IP Addresses: A Comprehensive Guide**
_Introduction_
The term "IP" stands for "Internet Protocol," a set of rules governing data format for communication over the Internet or a local network. It serves as a unique identifier assigned to each device connected to a computer network, akin to phone numbers for our devices. This article explores the significance, generation, and types of IP addresses, delving into the complexities that define our digital communication landscape.
**IP Address Basics**
An IP address allows devices to connect, enabling communication over the Internet. It plays a crucial role in differentiating computers, routers, and websites. The Internet Assigned Numbers Authority (IANA), a division of the Internet Corporation for Assigned Names and Numbers (ICANN), oversees the allocation of IP addresses. The 32-bit length of an IPv4 address and its format, consisting of four sets of numbers separated by dots, are key elements that lay the foundation for our interconnected digital world.
_Understanding IP Address Components_
The subnet mask and default gateway accompany the IP address. The subnet, also known as the netmask, and the default gateway are integral for network communication. Subnet masks, often resembling IP addresses, assist in identifying network sections and host sections. For instance, the subnet mask "255.255.255.0" implies that devices within the network will have IP addresses starting with "192.168.1."
_IP Address Allocation_
Wireless routers play a crucial role in IP address allocation through DHCP (Dynamic Host Configuration Protocol). The subnet mask aligns with the IP address, determining the network portion and the host portion. Recognizing the class of an IP address, whether A, B, or C, simplifies understanding.
_Transition to IPv6_
With the exhaustion of IPv4 addresses, IPv6 has been introduced to provide an abundance of IP addresses. Additionally, private IP addresses save public addresses, ensuring efficient use. The default gateway, often ending in ".1," facilitates communication beyond the local network.
**The Role of IP Addresses in Networking**
_Layer 3 in TCP_
The third layer in the TCP model is responsible for IP addresses. IP addresses, akin to a language for devices, facilitate communication, allowing computers worldwide to exchange information seamlessly.
_How IP Addresses Work_
IP addresses function behind the scenes, allowing devices to communicate through set guidelines. The assignment of IP addresses, both private and public, occurs based on network locations. Devices may have dynamic or static public IP addresses, with dynamic IPs changing regularly.
**Types of IP Addresses**
_Consumer IP Addresses_
Individuals and businesses possess private and public IP addresses. Private IP addresses are assigned to devices within a network, while the public IP address represents the entire network. Dynamic and static public IP addresses cater to different needs.
_Website IP Addresses_
For website owners, the choice between shared and dedicated IP addresses depends on hosting plans. Shared hosting involves multiple websites on a single server, each with a shared IP address. In contrast, dedicated IP addresses are crucial for businesses hosting their servers.
_Extended Discussion on IP Address Types_
Public IP addresses come in two forms – dynamic and static. Dynamic IP addresses change automatically and regularly, providing cost savings and enhanced security. Static IP addresses remain consistent, crucial for businesses hosting their servers.
**How to Look Up IP Addresses**
Checking your router's public IP address is as simple as searching "What is my IP address?" on Google. Finding private IP addresses varies by platform and can be accessed through system preferences or settings.
_Extended Discussion on IP Address Lookup_
If you need to check the IP addresses of other devices on your network, accessing the router provides a comprehensive list. Navigating to "attached devices" displays all devices recently or currently attached to the network, including their IP addresses.
**Security Concerns and Protection
**
_Criminal Exploitation of IP Addresses_
Criminals can exploit IP addresses by tracking online activities, posing risks such as location tracking and network attacks. Awareness of these risks and implementing protective measures, including proxies or Virtual Private Networks (VPNs), is crucial for safeguarding IP addresses.
_Risks Include:_
Downloading illegal content using your IP address
Tracking down your location
Directly attacking your network
Hacking into your device
_Protective Measures:_
IP addresses can be protected and hidden by using a proxy server or a Virtual Private Network (VPN).
VPNs are strongly advised in certain situations to ensure privacy.
_Extended Discussion on IP Address Security_
Understanding the risks associated with IP addresses is paramount. Criminals can track down your IP address through various online activities, posing threats such as network attacks and identity impersonation. Protecting your IP address becomes essential, and measures like proxy servers and VPNs offer a shield against potential cyber threats.
_Conclusion
_
In conclusion, IP addresses are fundamental in the digital landscape, serving as identifiers that facilitate seamless communication across networks. Understanding their intricacies, allocation methods, and potential risks is crucial in navigating the digital realm securely. The evolution of IP addresses, from IPv4 to IPv6, showcases the dynamic nature of our digital infrastructure. As we continue to rely on these unique identifiers, staying vigilant about security measures ensures a robust and protected online presence. | noblepearl |
1,769,639 | Have you ping ponged between being an individual contributor and being an engineering manager? | If so, what did you learn? | 0 | 2024-02-22T22:19:58 | https://dev.to/jess/have-you-ping-ponged-between-being-an-individual-contributor-and-being-an-engineering-manager-2jo | discuss, career | If so, what did you learn?
| jess |
1,769,647 | Introducing a GitHub Action for Interacting with Lagoon | https://github.com/uselagoon/lagoon-action We're excited to announce the release of the Lagoon... | 0 | 2024-03-07T03:47:09 | https://dev.to/uselagoon/introducing-a-github-action-for-interacting-with-lagoon-5a91 | github, action, workflow | [https://github.com/uselagoon/lagoon-action](https://github.com/uselagoon/lagoon-action)
We're excited to announce the release of the Lagoon Action – a GitHub Action that allows you to integrate with Lagoon, making it easy for you to automate your deployment workflows and manage Lagoon environments directly from your GitHub repository.
Currently the Lagoon action allows you to:
- Deploy branches and PRs
- Upsert environment variables
Taken together, these two features open up a range of new deployment strategies on Lagoon.
For instance, Lagoon only presently responds to a subset of GitHub webhook options. Now, with the Lagoon action, you’re able to run your CI processes in GitHub itself, and instead of having a webhook call deploy your environment, you can choose to deploy only if the CI process passes.
## Getting Started
Getting started with the Lagoon Action is straightforward. [Add the action to your GitHub workflow](https://docs.github.com/en/actions/quickstart), configure the required parameters, and you're ready to automate your Lagoon deployments. [Check out the GitHub repository](https://github.com/uselagoon/lagoon-action) for detailed documentation and examples.
## Requirements
To use the Lagoon CLI Action, ensure you have set up a GitHub Actions secret containing a private SSH key with the necessary permissions added to the Lagoon API. This key will be used for authentication during the deployment process.
We’d love to know if you use this and how it helps your workflow! Hop in to the [Lagoon Discord](https://discord.gg/te5hHe95JE) and drop us a line!
And don’t forget our [2024 Community Survey](https://dev.to/uselagoon/2024-community-hours-survey-50m5)! Let us know how we can best serve the Lagoon community.
| alannaburke |
1,769,752 | Symfony Station Communiqué — 16 February 2024. A look at Symfony, Drupal, PHP, Cybersec, and Fediverse News! | This communiqué originally appeared on Symfony Station. Welcome to this week's Symfony Station... | 0 | 2024-02-23T03:02:42 | https://symfonystation.mobileatom.net/Symfony-Station-Communique-16-February-2024 | symfony, drupal, php, fediverse | This communiqué [originally appeared on Symfony Station](https://symfonystation.mobileatom.net/Symfony-Station-Communique-16-February-2024).
Welcome to this week's Symfony Station communiqué. It's your review of the essential news in the Symfony and PHP development communities focusing on protecting democracy. Because open-source equals open societies, peeps. We also cover the cybersecurity world and the Fediverse (more open-source).
We cover a brawl in the Mastodon community this week. And there is good content in all of our categories, so please take your time and enjoy the items most relevant and valuable to you. This is why we publish on Fridays. So you can savor it over your weekend. 😉
Or jump straight to your favorite section via our website.
- [Symfony](https://symfonystation.mobileatom.net/Symfony-Station-Communique-16-February-2024#symfony)
- [PHP](https://symfonystation.mobileatom.net/Symfony-Station-Communique-16-February-2024#php)
- [More Programming](https://symfonystation.mobileatom.net/Symfony-Station-Communique-16-February-2024#more)
- [Fighting for Democracy](https://symfonystation.mobileatom.net/Symfony-Station-Communique-16-February-2024#other)
- [Cybersecurity](https://symfonystation.mobileatom.net/Symfony-Station-Communique-16-February-2024#cybersecurity)
- [Fediverse](https://symfonystation.mobileatom.net/Symfony-Station-Communique-16-February-2024#fediverse)
Once again, thanks go out to Javier Eguiluz and Symfony for sharing [our communiqué](https://symfonystation.mobileatom.net/Symfony-Station-Communique-09-February-2024) in their [Week of Symfony](https://symfony.com/blog/a-week-of-symfony-893-5-11-february-2024).
**My opinions will be in bold. And will often involve cursing. Because humans. And I have plenty of them this week.**
---
## Symfony
As always, we will start with the official news from Symfony.
Highlight -> "This week, Symfony maintained versions focused on fixing bugs and updating the translation of validation messages to many of the supported languages. Meanwhile, the upcoming Symfony 7.1 version improved the parsing/linting methods of ExpressionLanguage and also improved the BinaryFileResponse. Lastly, we published more details about the talks of the upcoming SymfonyLive Paris 2024 conference."
[A Week of Symfony #893 (5-11 February 2024)](https://symfony.com/blog/a-week-of-symfony-893-5-11-february-2024)
SymfonyCasts has:
[This week on SymfonyCasts!](https://5hy9x.r.ag.d.sendibm3.com/mk/mr/sh/1t6AVsd2XFnIGBrRERGJumwddAsNT1/bKFiWCP8K8ZT)
---
## Featured Item
Cory Doctorow opines on a recent study:
[Big Tech disrupted disruption](https://doctorow.medium.com/big-tech-disrupted-disruption-2a57b6178a00)
**More on why these enshittified mofos are the enemy of humanity.**
Stanford Law School has all the gory details:
[Co-opting Disruption](https://papers.ssrn.com/sol3/papers.cfm?abstract_id=4713845)
---
### This Week
Filip Horvat explores:
[Mastering the ‘Decorator’ Design Pattern in Symfony](https://medium.com/@fico7489/mastering-the-decorator-design-pattern-in-symfony-b633c345dd77)
[Mastering the ‘Adapter’ Design Pattern in Symfony](https://medium.com/@fico7489/mastering-the-adapter-design-pattern-in-symfony-cb07b157bb34)
[Mastering the ‘Abstract Factory’ Design Pattern in Symfony](https://medium.com/@fico7489/mastering-the-abstract-factory-design-pattern-in-symfony-386c2c95bd9d)
Danil Bifidokk examines:
[Asynchronous state machine with Symfony Workflows](https://dev.to/bifidokk/asynchronous-state-machine-with-symfony-workflows-35jl)
Oliver Davies broadcasts:
[Episode 10: Twig, Symfony and SymfonyCasts with Ryan Weaver](https://www.oliverdavies.uk/podcast/10-ryan-weaver-symfonycast)
**Anything with Ryan involved is awesome.**
Alberto Robles (who may or may not be a robot) shows us:
[How to secure your Symfony Apps with HTTPS](https://bertorobles.medium.com/how-to-secure-your-symfony-apps-with-https-2bf238378633)
Ludo Dev asks:
[Recurring actions? Symfony and RabbitMQ for asynchronous events...](https://en.developpeur-freelance.io/rabbitmq-symfony/)
Vandeth Tho shows us:
[How I build platform that focusing on making Symfony workflow configuration easier with SymFlowBuilder](https://medium.com/@thovandeth/how-i-build-platform-that-focusing-on-making-symfony-workflow-configuration-easier-with-e26a38eea3ed)
### eCommerce
Specbee looks at:
[Driving E-Commerce Revenue Success with Drupal Commerce](https://www.specbee.com/blogs/driving-ecommerce-revenue-success-drupal-commerce)
Dragan Rapić shares:
[Securing Your Shopware 6 Shop](https://levelup.gitconnected.com/securing-your-shopware-6-shop-a10ed49df4fd)
### CMSs
TYPO3 has a case study:
[TYPO3 and DMK Power Digital Transition to Responsive, Accessible City Services](https://typo3.com/customers/case-studies/city-of-leipzig)
And:
[TYPO3 13.0.1, 12.4.11 and 11.5.35 security releases published](https://typo3.org/article/typo3-1301-12411-and-11535-security-releases-published)
Mike Street explores:
[Testing the frontend of a TYPO3 project](https://www.mikestreety.co.uk/blog/testing-the-frontend-of-a-typo3-project/)
**Nice animated logo.**
<br/>
Contao has:
[Contao News](https://contao.org/de/news/contao-5-3-lts-ist-da)
<br/>
Drupal announces:
[Single Sign-On is coming to Drupal.org thanks to Cloud-IAM](https://www.drupal.org/drupalorg/blog/single-sign-on-is-coming-to-drupalorg-thanks-to-cloud-iam)
[It's time to migrate from Drupal 7. Let me show you (how to start)](https://www.drupal.org/drupalorg/blog/its-time-to-migrate-from-drupal-7-let-me-show-you-how-to-start)
[Bounty program extension (for innovative modules and ideas)](https://www.drupal.org/drupalorg/blog/bounty-program-extension-for-innovative-modules-and-ideas)
[Turning Takers into Makers: The enhanced Drupal Certified Partner Program](https://www.drupal.org/association/blog/turning-takers-into-makers-the-enhanced-drupal-certified-partner-program)
**This has set off a bruhaha with independent developers and small agencies. At a minimum Drupal sucks at naming things.**
Core Contributor, Gábor Hojtsy has:
[Looking for your input for DrupalCon Portland 2024 initiative highlights](https://www.hojtsy.hu/blog/2024-feb-12/looking-your-input-drupalcon-portland-2024-initiative-highlights)
[Onwards to Drupal 11 - ways to get involved](https://www.hojtsy.hu/blog/2024-feb-12/onwards-drupal-11-ways-get-involved)
**Recognize contributors everywhere and show them some love.**
[Upgraded my blog from Drupal 7 to Drupal 10 in less than 24 hours with the open source Acquia Migrate Accelerate](https://www.hojtsy.hu/blog/2024-feb-09/upgraded-my-blog-drupal-7-drupal-10-less-24-hours-open-source-acquia-migrate)
Quick aside:
**You know what easier than going from 7 to 10 (which is a pain in the ass), Moving to [Frontkom's Gutenberg Theme](https://www.drupal.org/project/gutenberg_starter) from DXPR's distribution. In an update from last week, we moved our [Mobile Atom Media site](https://media.mobileatom.net/) over in less than 12 hours, and 90% of that was content updates and custom CSS. :)**
**Note that the Gutenberg Starter Theme is not ready for production even though I am using it that way. There are a few bugs with certain blocks. Obviously, it doesn't have the same capabilities as the WordPress version (they are working on that). Still, if you are comfortable using the code editor rather than the visual one (and write HTML and CSS), you can come close. Plus it is compatible with Layout Builder and Drupal blocks (so you can keep your business logic).
**Unfortunately, when I tried to create a subtheme, add to regions, etc., I got the white screen of death. So keep that in mind and take them at their word on the not ready for production yet.**
TrueSummit announces:
[Search Web Components Alpha 2 Release](https://truesummit.dev/blog/search-web-components-alpha-2)
The Drop Times has an interview:
[André Angelantoni Discusses Automated Testing Kit Module](https://www.thedroptimes.com/37084/andre-angelantoni-discusses-automated-testing-kit-module)
ChapterThree has a case study:
[Apigee Kickstart in Action: Powering Financial Services](https://www.chapterthree.com/blog/apigee-kickstart-action-powering-financial-services)
Matt Glaman explores:
[Verifying your Drupal site’s configuration against changes from dependency updates](https://mglaman.medium.com/verifying-your-drupal-sites-configuration-against-changes-from-dependency-updates-385c08b332d9)
Oliver Davies has a few quick takes:
[Symfony conventions making their way to Drupal](https://www.oliverdavies.uk/archive/2024/02/12/symfony-conventions-making-their-way-to-drupal)
**The more, the merrier. And it's why I'm mastering Drupal before putting my big boy pants on and moving up to Symfony.**
[Major version updates are just removing deprecated code](https://www.oliverdavies.uk/archive/2024/02/14/major-version-updates-are-just-removing-deprecated-code)
ImageX shows us:
[How Project Browser Transforms Module Discovery and Installation Experience](https://imagexmedia.com/blog/drupal-project-browser)
DrupalizeMe demonstrates a great new feature:
[New in Drupal 10.2: Create a New Field UI](https://drupalize.me/blog/new-drupal-102-create-new-field-ui)
Golems examines:
[Exploring Drupal's Entity API: Tips and Tricks for Better Site Development](https://gole.ms/guidance/exploring-drupals-entity-api-tips-and-tricks-better-site-development)
### Previous Weeks
Acceseo looks at:
[Import map, simplificando procesos en el desarrollo web](https://www.acceseo.com/import-map-simplificando-procesos-en-el-desarrollo-web.html)
---
## PHP
### This Week
Mohammad Roshandelpoor explores:
[Makefile: Simplifying Command Execution and Automation](https://medium.com/@mohammad.roshandelpoor/makefile-simplifying-command-execution-and-automation-9dbaa6d91ac8)
Matthias Noback announces a:
[New edition for the Rector Book](https://matthiasnoback.nl/2024/02/new-edition-for-the-rector-book/)
**Similar to Matt Glaman's Retrofit project with Drupal 7 migration, I feel that products like Rector don't get the credit they deserve. So, if you work with legacy sites, I would buy the book.**
Camilo Herrea examines:
[Basic route management with PHP and Apache httpd](https://medium.com/winkhosting/basic-route-managament-with-php-and-apache-httpd-98f9126b1384)
**This was informative for a mainly frontend developer.**
Dragan Rapić shares:
[Troubleshooting PHP Errors](https://levelup.gitconnected.com/troubleshooting-php-errors-87f97f6e68d4)
Hamid Rohani looks at:
[Having trouble with `require` or `require_once` in PHP class files? Upgrade your project by implementing autoload with PSR-4](https://medium.com/@hamid.roohany/understanding-autoload-psr-4-in-php-simplifying-class-loading-for-efficient-development-70e0e21dbe40)
PhpStorm has:
[AI for PHP: How To Automate Unit Testing Using AI Assistant?](https://blog.jetbrains.com/phpstorm/2024/02/ai-for-php-how-to-automate-unit-testing-using-ai-assistant/)
And WebWash shows us:
[How to Compare Files and Sync Changes using PhpStorm](https://www.webwash.net/how-to-compare-files-and-sync-changes-using-phpstorm/)
Peter Fox shares:
[PHP: 7 tricks to help with upgrading Composer packages](https://articles.peterfox.me/php-7-tricks-upgrading-composer-packages-37c6e24b0f5f)
Ellis explores:
[Enhancing Code Consistency with php-cs-fixer and Visual Studio Code](https://dev.to/ellis22/enhancing-code-consistency-with-php-cs-fixer-and-visual-studio-code-221l)
Timothy Iloba examines:
[Return type declarations in PHP](https://medium.com/@timothyiloba/return-type-declarations-in-php-9e02dc7b13de)
### Previous Weeks
JoliCode shares:
[Héberger un projet PHP sans serveur avec WebAssembly](https://jolicode.com/blog/heberger-un-projet-php-sans-serveur-avec-webassembly)
---
## More Programming
Joan Westenberg preaches:
[Creators: go small. It’s your edge.](https://joanwestenberg.medium.com/creators-go-small-its-your-edge-d5261f3dc695)
**This is the way we have rolled for over ten years. You can build a sustainable business this way and live the life you want.**
[Forgejo forks its own path forward](https://forgejo.org/2024-02-forking-forward/)
Voices of Open Source has:
[A comparative view of AI definitions as we move toward standardization](https://blog.opensource.org/a-comparative-view-of-ai-definitions-as-we-move-toward-standardization/)
VentureBeat reports:
[Meta releases ‘Code Llama 70B’, an open-source behemoth to rival private AI development](https://venturebeat.com/ai/meta-releases-code-llama-70b-an-open-source-behemoth-to-rival-private-ai-development/)
**Hopefully it doesn't turn out anything like React did.**
Speaking of which, Infoworld reports:
[Reactive magic in Svelte 5: Understanding Runes](https://www.infoworld.com/article/3712688/reactive-magic-in-svelte-5-understanding-runes.html#tk.rss_all)
**Friends don't let friend use React.**
CSS god Josh Comeau shows us:
[How To Center a Div](https://www.joshwcomeau.com/css/center-a-div/)
**This sounds simple but it's one of the most frustrating things about CSS if you don't work with it everyday.**
Free Code Camp compares:
[Flexbox vs Grid in CSS – Which Should You Use?](https://www.freecodecamp.org/news/flexbox-vs-grid-in-css/)
Laravel News lists:
[Five Ways to Be More Productive with Git](https://laravel-news.com/five-ways-to-be-more-productive-with-git)
---
## Fighting for Democracy
[Please visit our Support Ukraine page](https://symfonystation.mobileatom.net/Support-Ukraine) to learn how you can help kick Russia out of Ukraine (eventually, like ending apartheid in South Africa).
### The cyber response to Russia’s War Crimes and other douchebaggery
The Register reports:
[FCC gets tough: Telcos must now tell you when your personal info is stolen](https://www.theregister.com/2024/02/12/fcc_gets_tough_on_telcos/)
The Verge reports:
[FCC commissioner wants to investigate Apple over Beeper Mini shutdown](https://www.theverge.com/2024/2/12/24071226/fcc-commissioner-brendan-carr-apple-beeper-mini)
**Isn't it nice having an FCC that at least tries to protect consumers rather than being big tech bootlickers.**
Ars Technica reports:
[Backdoors that let cops decrypt messages violate human rights, EU court says](https://arstechnica.com/tech-policy/2024/02/human-rights-court-takes-stand-against-weakening-of-end-to-end-encryption/)
Euronews reports:
[Poland to investigate alleged use of Pegasus spyware by last government](https://www.euronews.com/2024/02/16/poland-to-investigate-alleged-use-of-pegasus-spyware-by-last-government)
### The Evil Empire Strikes Back
And:
['Kremlin conducting information operations against Moldova' says ISW](https://www.euronews.com/2024/02/16/kremlin-conducting-information-operations-against-moldova-says-isw)
MacRumors reports:
[iOS 17.4 Nerfs Web Apps in the EU](https://www.macrumors.com/2024/02/08/ios-17-4-nerfs-web-apps-in-the-eu/)
**The mofos at Apple fuck over PWAs in Europe. So, ditch the enshittification and get your next phone from [Murena](https://murena.com/). Be sure to get the latest Fairphone model. And FYI, this is not an affiliate link. It's my Valentine, birthday, holiday, etc. gift to you. 😘**
Or maybe everywhere according to Danny Moerkerke:
[Apple Wants To Kill PWAs](https://itnext.io/apple-wants-to-kill-pwas-0895be2e497b)
DarkReading reports:
[Deepfake Democracy: AI Technology Complicates Election Security](https://www.darkreading.com/application-security/deepfake-democracy-ai-technology-election-security)
Beeping Computer reports:
[Google says spyware vendors behind most zero-days it discovers](https://www.bleepingcomputer.com/news/security/google-says-spyware-vendors-behind-most-zero-days-it-discovers/)
[North Korean hackers now launder stolen crypto via YoMix tumbler](https://www.bleepingcomputer.com/news/security/north-korean-hackers-now-launder-stolen-crypto-via-yomix-tumbler/)
The New Republic reports:
[The Tech Plutocrats Dreaming of a Right-Wing San Francisco](https://newrepublic.com/article/178675/garry-tan-tech-san-francisco)
**This bullshit ideology is even trickling down to Mastodon. There's more on that below.**
Speaking of edgelord c^nts, the Verge reports:
[Terrorists are allegedly buying blue checks on X](https://www.theverge.com/2024/2/14/24073146/x-twitter-blue-check-hezbollah-terrorist-groups-sanctions)
Ars Technica reports:
[Elon Musk’s X allows China-based propaganda banned on other platforms](https://arstechnica.com/tech-policy/2024/02/elon-musks-x-allows-china-based-propaganda-banned-on-other-platforms/)
And you Silicon Valley fucks might want to pay attention to Blood in the Machines' article:
[Torching the Google car: Why the growing revolt against big tech just escalated](https://www.bloodinthemachine.com/p/torching-the-google-car-why-the-growing)
### Cybersecurity/Privacy
And:
[DuckDuckGo browser gets end-to-end encrypted sync feature](https://www.bleepingcomputer.com/news/security/duckduckgo-browser-gets-end-to-end-encrypted-sync-feature/)
CNN reports:
[US cracks down on hacking network with thousands of customers](https://www.cnn.com/2024/02/09/politics/justice-department-crack-down-hacking-network/index.html)
Amazee has a case study:
[A Large Credential Stuffing Attack - How We Respond and Mitigate](https://www.amazee.io/blog/post/a-large-credential-stuffing-attack)
**If you use cloud hosting for a decoupled and composable Drupal site, you should check out Amazee.**
The Verge reports:
[Microsoft and OpenAI say hackers are using ChatGPT to improve cyberattacks](https://www.theverge.com/2024/2/14/24072706/microsoft-openai-cyberattack-tools-ai-chatgpt)
DarkReading reports:
[Like Seat Belts and Airbags, 2FA Must Be Mandatory ASAP](https://www.darkreading.com/vulnerabilities-threats/2fa-must-be-mandatory-asap)
**It's sad that it's coming to this. Right?**
---
### Fediverse
The Fediverse Report has:
[Last Week in Fediverse – ep 55](https://fediversereport.com/last-week-in-fediverse-ep-55/)
A new flavor of Matrix is out:
[What is Commune?](https://blog.commune.sh/what-is-commune/)
Bix Dot Blog opines:
[ActivityPub Is To The IndieWeb As A.I. Is To Silicon Valley?](https://bix.blog/2024/01/11/activitypub-is-to-the-indieweb-as-a-i-is-to-silicon-valley/)
**Hmmm.**
Maho Pacheco shares:
[A Guide to Implementing ActivityPub in a Static Site (or Any Website) - Part 3](https://maho.dev/2024/02/a-guide-to-implementing-activitypub-in-a-static-site-or-any-website-part-3/)
**Great stuff.**
TechCrunch reports:
[Social networks are getting stingy with their data, leaving third-party developers in the lurch](https://techcrunch.com/2024/02/09/social-network-api-apps-twitter-reddit-threads-mastodon-bluesky/)
**Serving the Fediverse not enshits is the way for entrepreneurial developers to go.**
Speaking of which here's my rant about the latest Mastodon bruhaha:
[This Bluesky - Mastodon bridge shit](https://snarfed.org/2024-02-12_52106)
**The Fediverse is not 100% free of Silicon Valley tech bros either. So, FYI for said bros, 3rd party opt-out = invasive. You are making me opt out of something I never fucking asked for. Opt-in = privacy-oriented. If I like your product I will choose to use it. That's what's pissing people off in this bridge fiasco. The privacy concerns are slightly overblown.**
**Said bro walked his approach back a bit the next day after rightly getting his ass chewed off. Maybe.**
[This too.](https://snarfed.org/2024-02-13_52223)
**Personally, I came to the Fediverse to get away from these corporate like shenanigans.” *To me it's a matter of permission, privacy, and non-corporate social media.**
**To be fair the other side's view is that we want the reach of Mastodon to grow irrespective of how it gets there. The ends justify the means so to speak.
**And it shouldn't be easy for you to have the level of privacy and safety you want. No default privacy for you. Nor making it hard for bullies to find you. Instead, you have to change settings, put bullshit hashtags in your profile, import block lists, host your own instance, transition into an old white man, hump a camel, etc..**
**With this mindset inevitably enshittification will occur with Mastodon. Later rather than sooner but still.**
**So, I will slowly be moving from @symfonystation@phpc.social Mastodon account to my self-hosted ActivityPub WordPress-based Fediverse account. Not immediately because ActivityPub and WordPress are a work in progress (especially interacting with 3rd party client apps). I will cross post for a while. Follow me there at @symfonystation@newsletter.mobileatom.net via your favorite platform.**
We Distribute has the growth at any cost view:
[Tear Down Walls, and Build Bridges](https://wedistribute.org/2024/02/tear-down-walls-not-bridges/)
**Of course its tech bro author was a jackass in it and had to apologize the next day on Mastodon.**
They do better with news than opinion:
[Bonfire Offers Framework for Next-Gen Fediverse Platforms](https://wedistribute.org/2024/02/bonfire-nextgen-framework/)
Speaking of Bluesky, Paul Frazee has some details on its federation:
[Why RichText facets in Bluesky](https://www.pfrazee.com/blog/why-facets)
**Note that Bluesky itself doesn't give a fuck about any kind of bridge. Or anyone on the Fediverse. And that's fine.**
Which is why the headline of this from TechCrunch is horseshit:
[Bluesky and Mastodon users are having a fight that could shape the next generation of social media](https://techcrunch.com/2024/02/14/bluesky-and-mastodon-users-are-having-a-fight-that-could-shape-the-next-generation-of-social-media/)
**I will end on a positive note. At least it does show that the bridge author is learning from his ill-considered project and trying to mitigate the damage it might cause.**
---
## CTAs (aka show us some free love)
- That’s it for this week. Please share this communiqué.
- Also, please [join our newsletter list, The Payload, at the bottom of our site’s pages](https://symfonystation.mobileatom.net/contact). Joining gets you each week's communiqué in your inbox (a day early).
- Follow us [on Flipboard](https://flipboard.com/@mobileatom/symfony-for-the-devil-allupr6jz) or at [@symfonystation@newsletter.mobileatom.net](https://newsletter.mobileatom.net/@symfonystation) on Mastodon for daily coverage.
- Do you like Reddit? Why? Instead, follow us [on kbin](https://kbin.social/u/symfonystation) for a better Fediverse and Symfony-based experience. We have a [Symfony Magazine](https://kbin.social/m/Symfony) and [Collection](https://kbin.social/c/SymfonyUniverse) there.
Do you own or work for an organization that would be interested in our promotion opportunities? Or supporting our journalistic efforts? If so, please get in touch with us. We’re in our toddler stage, so it’s extra economical. 😉
More importantly, if you are a Ukrainian company with coding-related products, we can offer free promotion on [our Support Ukraine page](https://symfonystation.mobileatom.net/Support-Ukraine). Or, if you know of one, get in touch.
You can find a vast array of curated evergreen content on our [communiqués page](([https://symfonystation.mobileatom.net/communiques](https://symfonystation.mobileatom.net/communiques)).
## Author

### Reuben Walker
Founder
Symfony Station
| reubenwalker64 |
1,769,782 | Windows 10 Enterprise vs. Professional: Unveiling the Key Differences and Ideal Use Cases | Windows 10 Enterprise vs. Professional In the dynamic landscape of operating systems,... | 0 | 2024-02-23T04:27:42 | https://dev.to/pexlkeys/windows-10-enterprise-vs-professional-unveiling-the-key-differences-and-ideal-use-cases-76g | tutorial, productivity, discuss, windows10 | ## Windows 10 Enterprise vs. Professional
In the dynamic landscape of operating systems, Windows 10 stands as a cornerstone, offering a myriad of editions tailored to diverse user needs. Among these, Windows 10 Enterprise and Professional editions are prominent choices for businesses and professionals alike. This discussion delves into the nuanced disparities between Windows 10 Enterprise and Professional, shedding light on their distinctive features, functionalities, and ideal implementations.
Windows 10 Professional, often deemed the standard choice for businesses and individual users, delivers a comprehensive suite of features designed to enhance productivity, security, and versatility. From its robust management tools to its seamless integration with cloud services, Windows 10 Professional caters to a broad spectrum of organizational needs. Key features include BitLocker encryption, which safeguards sensitive data by encrypting entire drives, and Windows Update for Business, enabling users to manage updates more efficiently and minimize disruptions to productivity. Moreover, Windows 10 Professional facilitates seamless remote access and collaboration through features like Remote Desktop and Azure Active Directory Join, empowering businesses to thrive in an increasingly connected world.
In contrast, Windows 10 Enterprise emerges as the premium offering, tailored to meet the complex demands of large-scale organizations and enterprises. Building upon the foundation of Windows 10 Professional, Enterprise edition introduces a plethora of advanced features and capabilities geared towards enhancing security, compliance, and manageability. One notable feature exclusive to Windows 10 Enterprise is Windows Defender Application Guard, which provides robust protection against malware and zero-day threats by isolating potentially malicious content within virtualized containers. Additionally, Enterprise edition offers advanced threat protection through Windows Defender Advanced Threat Protection (ATP), equipping organizations with proactive defense mechanisms and comprehensive threat intelligence to safeguard their digital assets.
Furthermore, Windows 10 Enterprise distinguishes itself through its extensive management and deployment tools, facilitating centralized control and streamlined administration across diverse IT environments. Features like Microsoft Endpoint Manager and Windows Autopilot simplify device provisioning, deployment, and configuration, reducing administrative overhead and ensuring consistent user experiences. Moreover, Enterprise edition empowers organizations to implement granular security policies and compliance measures through Group Policy, BitLocker Network Unlock, and Credential Guard, thereby fortifying defenses against evolving cyber threats and regulatory requirements.
While both editions of Windows 10 offer robust features and capabilities, the choice between Enterprise and Professional depends on the specific needs, scale, and objectives of the organization. For small to medium-sized businesses (SMBs) or individual professionals seeking a comprehensive yet cost-effective solution, Windows 10 Professional provides an ideal balance of functionality and affordability. Its extensive feature set, coupled with robust security and management tools, makes it well-suited for organizations with moderate IT requirements and resource constraints.
Conversely, large enterprises and organizations operating in highly regulated industries may find Windows 10 Enterprise better aligned with their stringent security and compliance needs. With its advanced security features, comprehensive management tools, and enterprise-grade support, Windows 10 Enterprise offers unparalleled scalability, flexibility, and control, making it the preferred choice for mission-critical environments where security and regulatory compliance are top priorities.
In conclusion, the decision between Windows 10 Enterprise and Professional hinges on factors such as organizational size, industry regulations, security requirements, and budget considerations. While Windows 10 Professional caters to the needs of SMBs and individual professionals with its comprehensive feature set and affordability, Windows 10 Enterprise provides large enterprises and organizations with enhanced security, compliance, and manageability features essential for maintaining a secure and resilient IT infrastructure in today's increasingly complex threat landscape. By understanding the distinct capabilities and use cases of each edition, organizations can make informed decisions that align with their unique requirements and objectives, ensuring optimal productivity, security, and success in the digital age. | pexlkeys |
1,769,788 | Azure Function app that runs Haskell Nix package | I built a containerized Azure Function App that internlly runs a haskell program packaged with... | 0 | 2024-02-23T04:46:56 | https://dev.to/ingun37/azure-function-app-that-runs-haskell-nix-package-1mdc | haskell, nix, azure, docker | I built a containerized Azure Function App that internlly runs a haskell program packaged with Nix.
I followed [Create your first containerized functions on Azure Container Apps](https://learn.microsoft.com/en-us/azure/azure-functions/functions-deploy-container-apps?tabs=acr%2Cbash&pivots=programming-language-csharp) to make a scaffold. Runtime could be anything than can run sub process, which is everything. So I choose dotnet.
And at the end of the generated Dockerfile, I added some nix layers.
```dockerfile
# Basic runtime to install nix
RUN apt install -y xz-utils curl
RUN bash -c "sh <(curl -L https://nixos.org/nix/install) --daemon --yes"
# Update PATH to include nix tools
ENV PATH="/home/.nix-profile/bin:/nix/var/nix/profiles/default/bin:${PATH}"
```
Then I copied my haskell project.
```dockerfile
ADD haskell-project /opt/haskell-project
```
Create haskell package using `cabal2nix`. I call `nix-collect-garbage` to reduce the size of docker layer.
```dockerfile
RUN nix-shell -p cabal2nix --run 'cabal2nix --no-check /opt/haskell-project > /opt/haskell-project/foo.nix' && nix-collect-garbage
```
The `default.nix` would look like this. It calls the haskell package and wrap it with [justStaticExecutables](https://github.com/NixOS/nixpkgs/blob/c0fccae2996f9dd015ce5c6b9525187ea5961007/doc/languages-frameworks/haskell.section.md#packaging-helpers-haskell-packaging-helpers) to leave only runtime dependencies.
```nix
let
p = (import <nixpkgs> {}).pkgs;
in
p.haskell.lib.compose.justStaticExecutables (p.haskellPackages.callPackage ./foo.nix {})
```
Build the nix package
```dockerfile
RUN nix-build
```
In the Function implementation, run the hasell executable as a subprocess
```cs
using System.Diagnostics;
using (Process hs = new Process())
{
hs.StartInfo.UseShellExecute = true;
hs.StartInfo.FileName = "/opt/haskell-project/result/bin/exe";
hs.Start();
await hs.WaitForExitAsync();
if (hs.ExitCode != 0)
{
throw new Exception($"haskell subprocess failed {hs.ExitCode}");
}
}
``` | ingun37 |
1,769,831 | React Pure Component | It is used when we want to see a performance boost Rules -> Parent Component along with all it's... | 0 | 2024-02-23T06:10:08 | https://dev.to/alamfatima1999/react-pure-component-1bo1 | It is used when we want to see a performance boost
Rules ->
Parent Component along with all it's child component should be pure.
There should be no state mutation instead always a new object should be returned.
Advantages ->
It's shdComponentUpdate() value is be default false instead of true as in case of Regular Components.
It does a shallow comparison for both ->
**Primitive** -> checks value of them and if same doesn't re-render.
**Complex** -> Objects, arrays, lists -> It checks the reference if same -> doesn't re-render.
**Note** -> Should mostly use Regular Components unless performance is the issue
| alamfatima1999 | |
1,769,988 | This Week in Python (February 23, 2024) | Fri, February 23, 2024 This Week in Python is a concise reading list about what happened in the... | 0 | 2024-02-23T08:44:15 | https://bas.codes/posts/this-week-python-062 | thisweekinpython, python |
**Fri, February 23, 2024**

This Week in Python is a concise reading list about what happened in the past week in the Python universe.
## Python Articles
- [How to run pytest in parallel on GitHub actions](https://guicommits.com/parallelize-pytest-tests-github-actions/)
- [A Python Interpreter Written in Python](https://aosabook.org/en/500L/a-python-interpreter-written-in-python.html)
- [Not just NVIDIA: GPU programming that runs everywhere](https://pythonspeed.com/articles/gpu-without-cuda/)
- [Smart CLIs with Typer](https://rahulpai.co.uk/smart-clis-with-typer.html)
- [PyCon US Talk: Reconciling Everything](https://www.youtube.com/watch?v=MuK6lmsfX1E)
<!--
How to run pytest in parallel on GitHub actions – by @guilatrova
https://guicommits.com/parallelize-pytest-tests-github-actions/
A Python Interpreter Written in Python – by @akaptur
https://aosabook.org/en/500L/a-python-interpreter-written-in-python.html
Not just NVIDIA: GPU programming that runs everywhere – by @itamarst
https://pythonspeed.com/articles/gpu-without-cuda/
Smart CLIs with Typer
https://rahulpai.co.uk/smart-clis-with-typer.html
PyCon US Talk: Reconciling Everything – by @andrewgodwin
https://www.youtube.com/watch?v=MuK6lmsfX1E
-->
## Projects
- [uv](https://github.com/astral-sh/uv) – An extremely fast Python package installer and resolver, written in Rust
- [pip-run](https://github.com/jaraco/pip-run) – dynamic dependency loader for Python
- [returns](https://github.com/dry-python/returns) – Make your functions return something meaningful, typed, and safe
- [easygmail](https://github.com/ayushgun/easygmail) – A lightweight, minimalistic, and synchronous Python package for quickly sending emails via Gmail
- [wsgidav](https://github.com/mar10/wsgidav) – A generic and extendable WebDAV server based on WSGI
<!--
uv – An extremely fast Python package installer and resolver, written in Rust – by @astral_sh
https://github.com/astral-sh/uv
pip-run – dynamic dependency loader for Python – by @jaraco
https://github.com/jaraco/pip-run
returns – Make your functions return something meaningful, typed, and safe
https://github.com/dry-python/returns
easygmail – A lightweight, minimalistic, and synchronous Python package for quickly sending emails via Gmail
https://github.com/ayushgun/easygmail
wsgidav – A generic and extendable WebDAV server based on WSGI
https://github.com/mar10/wsgidav
-->
| bascodes |
1,770,015 | Maximize Business Potential With Expert .NET Development Services | Wanna become a data scientist within 3 months, and get a guaranteed job? Then you need to check this... | 0 | 2024-02-23T09:20:47 | https://thedatascientist.com/maximize-business-potential-with-expert-net-development-services/ | developer, javascript, ai, webdev | Wanna become a data scientist within 3 months, and get a guaranteed job? Then you need to [check this out ! ](https://beyond-machine.com/webinar)
---
In a rapidly evolving era panorama, organizations need to undertake frameworks and architectures capable of delivering excessive overall performance, scalability, and resilience. Among the prevailing traits, the microservices structure is gaining traction because of its agility, scalability, and versatility in managing complex utility structures. Coupling this with .NET development services can supercharge the improvement of robust, resilient structures. In the subsequent paragraphs, we’ll convey to light how you could harness the electricity of .NET microservices structure to build high-acting, resilient structures.
## The Gravity of .NET Development Services
For almost two years, .NET has been a cornerstone of internet and alertness improvement. Introduced with the aid of Microsoft, .NET offers a unified, bendy, and interoperable platform that allows builders to create various programs—be it Internet, mobile, laptop, or for the Internet of Things (IoT).
**Trending**
[Podcast: Data science and AI in marketing
](https://thedatascientist.com/podcast-data-science-ai-marketing/)
.NET’s Framework Class Library (FCL), which is a great series of reusable classes, interfaces, and price types, is foundational in helping builders remedy complicated programming duties. The Common Language Runtime (CLR) factor of .NET simplifies the improvement manner through handling memory and enabling move-language integration. These nifty attributes make .NET a one-size-suits-all device, foreseeing and [addressing possible programming challenges](https://thedatascientist.com/data-science-in-addressing-billing-challenges-and-optimizing-revenue-cycles-for-cardiology-practices/). Businesses seeking to harness the full potential of .NET can benefit from specialized. [NET Development Services.](https://existek.com/net-development-company/)
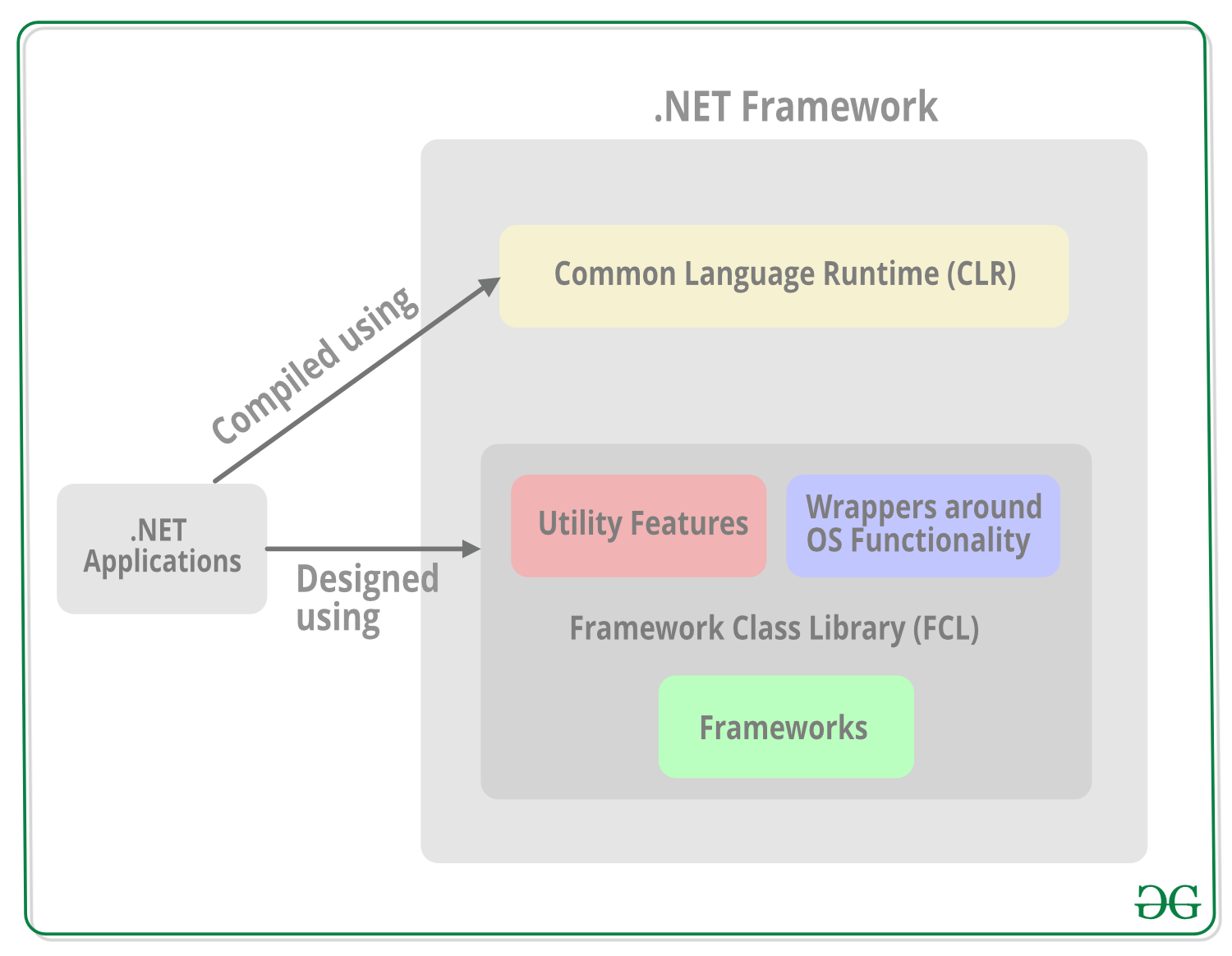
image source: https://www.geeksforgeeks.org/net-framework-class-library-fcl/
## .NET and Microservices – A Potent Combo
But how do you acquire an equilibrium wherein overall performance, scalability, and resilience co-exist? The solution would be the amalgamation of .NET and microservices architecture. While .NET affords a sturdy development platform, the microservices structure subdivides the application into a collection of loosely coupled services, every functioning independently.
Microservices, with the aid of their very nature, are small, targeted at doing one task very well, and work independently of each other. This impartial functionality interprets right into a system wherein faults are isolated, lowering the sprawling effect of blunders, thus proving to be greater resilient. If one carrier fails, the others maintain to paintings unabated, enhancing your machine’s uptime and consumer enjoyment.
The resilient structures constructed using .NET and microservices are not just green, however, they are also simpler to manipulate, replace, and scale. As every carrier is self-contained, adjustments in a single service do now not require altering any other. This allows for faster deployments and scaling unique offerings in step with the need, maximizing resource effectiveness. To leverage the full potential of .NET and microservices for your projects, explore solutions offered by experienced providers like existek.com.
## Leveraging .NET Core for Microservices
Within the expansive .NET Framework, .NET Core shines when used with the microservices architecture. .NET Core is a go-platform, open-supply framework from Microsoft that is optimized for developing cloud-based total programs, making it an ideal match for creating microservices.
In this mix, Docker containerization generation also performs an indispensable role. Docker can bundle .NET Core microservices into boxes, which can then be run on any platform without the want for putting in place selected application surroundings, ushering in portability and reducing environmental problems.
With the smooth protection of .NET Core, coupled with Docker’s giant isolation mechanism, you are looking at reduced conflicts among jogging packages, mainly to systems that are efficient and resilient.
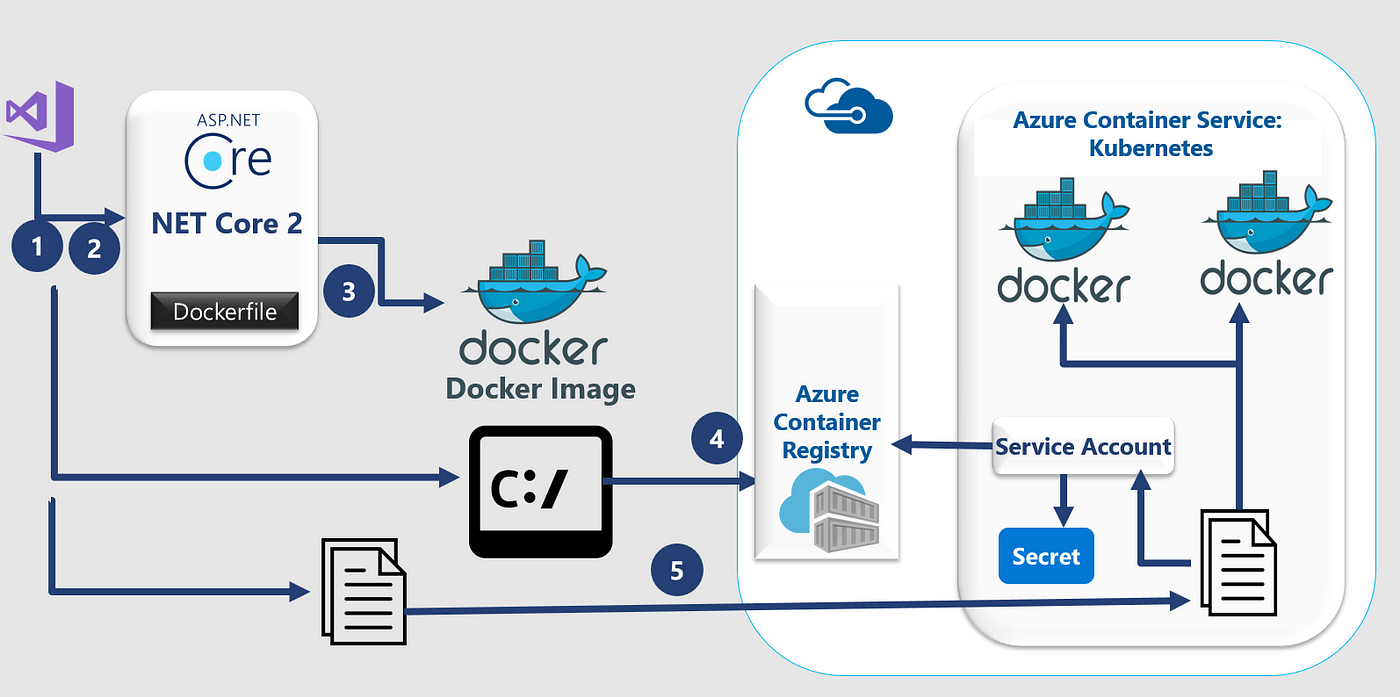
image source: https://didourebai.medium.com/create-asp-net-core-2-2-as-docker-container-in-kubernetes-4847bd986683
## The Architecture of .NET Microservices
The architecture of .NET microservices is inherently geared to promote resilience and agility. Here’s how:
**Decentralized Data Management:** Each microservice has its committed database or statistics source. This implies that more than one offering isn’t dependent on a single database, easing records management and minimizing the risk of a single factor of failure.
**API Gateway:** In a .NET microservices surroundings, offerings talk through Application Programming Interfaces (APIs). An API Gateway can act as an unmarried access point into the system, simplifying the customer-aspect handling of a couple of microservices and bearing in mind better management of go-cutting worries.
**Inter-Service Communication:** Microservices use both HTTP/REST or asynchronous messaging (e.g., the usage of RabbitMQ) for communication. Both of those techniques provide an excessive stage of resilience in the event of service unavailability.
Resilience Patterns: Design patterns together with Retry, Circuit Breaker, and Bulkhead are often used to enhance the stability and robustness of the gadget. If a service fails, these styles can prevent the complete device from crashing.
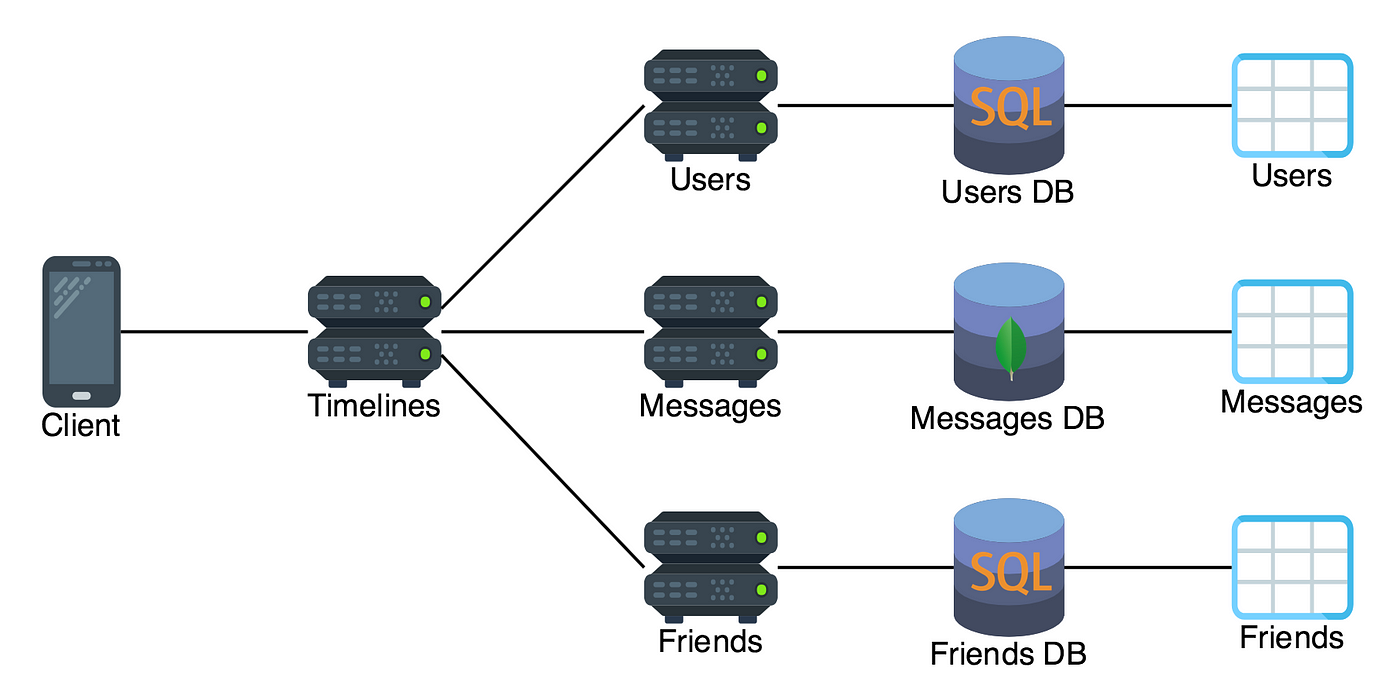
image source: https://medium.com/@nathankpeck/microservice-principles-decentralized-data-management-4adaceea173f
## Building Resilient Systems with .NET Microservices
Building resilient structures with .NET microservices revolves around harnessing each microservice’s independence. The liberty to control, adjust, and scale every provider independently considerably reduces the possibilities of systemwide screw-ups while making an allowance for agile development and deployment.
Despite these benefits, imposing a .NET microservices structure isn’t without challenges. The complexity increases due to the disbursed nature of services, problems in managing statistics consistency, and the requirement of elaborate automation techniques. However, with a set of well-taken-into-consideration strategies, those drawbacks can be mitigated to a tremendous extent.
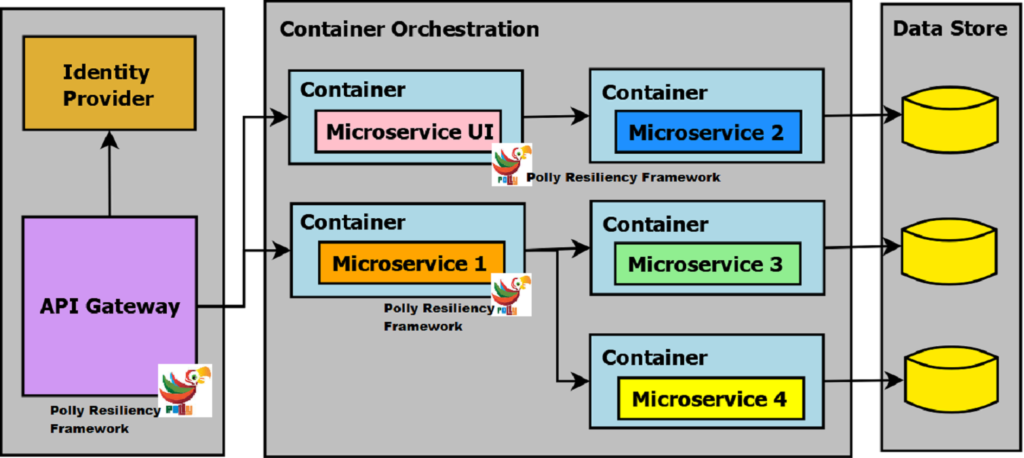
image source: https://procodeguide.com/programming/polly-in-aspnet-core/
## Wrapping Up
.NET microservices structure offers a robust combination of microservices agility and the strong abilities of the .NET framework. By building structures around this structure, organizations can make sure excessive overall performance, scalability, and resilience, all contributing to more advantageous consumer enjoyment and operational efficiency.
Advocating the inherent strengths of .NET and microservices, it is obtrusive that this combination provides a structure suitable for developing resilient structures capable of conquering contemporary era landscapes’ challenges. However, it’s far equally essential to weigh within the elevated complexity and manageability demanding situations and put together as a consequence to revel in the many advantages this aggregate gives.
---
Wanna become a data scientist within 3 months, and get a guaranteed job? Then you need to[ check this out !](image source: https://www.geeksforgeeks.org/net-framework-class-library-fcl/
)
---
This blog was originally published on https://thedatascientist.com/maximize-business-potential-with-expert-net-development-services/
| ecaterinateodo3 |
1,770,029 | The Rise of AI in Ecommerce: How Shopify Stores Can Leverage it for Success | The Evolution of E-commerce E-commerce has undergone a remarkable transformation over... | 0 | 2024-02-23T09:37:46 | https://dev.to/brihaspatiinfotech/the-rise-of-ai-in-ecommerce-how-shopify-stores-can-leverage-it-for-success-37h5 |

## The Evolution of E-commerce
E-commerce has undergone a remarkable transformation over the years, with technological advancements driving unprecedented growth and innovation. One such advancement that has significantly impacted the industry is Artificial Intelligence (AI). In this article, we'll explore the role of AI in e-commerce, with a specific focus on how Shopify stores can harness its power to achieve greater success. For businesses looking to leverage AI effectively, it's crucial to **[hire Shopify developers](https://www.brihaspatitech.com/hire-shopify-developer/?utm_source=articlesubmission&utm_medium=referral)** who are skilled in implementing AI solutions tailored to e-commerce needs.
## Understanding AI in E-commerce
Artificial Intelligence refers to the simulation of human intelligence processes by machines, typically through the use of algorithms and data. In the context of e-commerce, AI technologies can analyze vast amounts of data to make predictions, automate tasks, and personalize the shopping experience for customers.
## Benefits of AI for Shopify Stores
AI offers a myriad of benefits for Shopify store owners, including:
**- Enhanced Personalization:** AI algorithms can analyze customer data to deliver personalized product recommendations, leading to higher conversion rates and increased customer satisfaction.
**- Improved Customer Service:** Chatbots powered by AI can handle customer inquiries and provide assistance 24/7, improving response times and reducing the workload on support teams.
**- Dynamic Pricing:** AI can optimize pricing strategies in real-time based on factors such as demand, competitor pricing, and customer behavior, maximizing profitability for Shopify store owners.
## Implementing AI in Your Shopify Store
**- Personalized Recommendations**
One of the most effective ways to leverage AI in your Shopify store is through personalized product recommendations. By analyzing customer browsing and purchasing history, AI algorithms can suggest relevant products to individual shoppers, increasing the likelihood of conversion.
**- Chatbots for Customer Service**
Implementing AI-powered chatbots on your Shopify store can streamline customer service operations and improve the overall shopping experience. Chatbots can provide instant responses to common inquiries, offer product recommendations, and even facilitate transactions, all without human intervention.
**- Dynamic Pricing Strategies**
AI can also be utilized to implement dynamic pricing strategies, allowing Shopify store owners to adjust prices in real-time based on market conditions, competitor pricing, and customer demand. This dynamic approach to pricing can help maximize revenue and stay competitive in a rapidly changing landscape.
## Challenges and Considerations
While AI offers tremendous opportunities for Shopify store owners, it's essential to be aware of potential challenges and considerations, such as:
**Data Privacy:** Collecting and analyzing customer data raises privacy concerns, requiring careful adherence to data protection regulations and ethical considerations.
**Algorithm Bias:** AI algorithms may exhibit bias based on the data they're trained on, potentially leading to unfair or discriminatory outcomes. It's crucial to regularly monitor and mitigate bias in AI systems.
## Conclusion
AI presents a wealth of opportunities for Shopify store owners to enhance the shopping experience, drive sales, and stay ahead of the competition. By embracing AI-powered solutions such as personalized recommendations, chatbots, and dynamic pricing strategies, Shopify stores can unlock new levels of success in the evolving e-commerce landscape. To implement these AI-driven features effectively, partnering with a reputable [**Shopify development company**](https://www.brihaspatitech.com/shopify-development-services/?utm_source=articlesubmission&utm_medium=referral) is essential.
## **Key Takeaway:**
AI technologies offer numerous benefits for Shopify store owners, including enhanced personalization, improved customer service, and dynamic pricing strategies. By leveraging AI-powered solutions effectively, Shopify stores can drive sales, increase customer satisfaction, and stay competitive in the ever-changing e-commerce landscape. | brihaspatiinfotech | |
1,770,054 | 🚀 Unleashing Efficiency with Hashmaps: Solving the Two Sum Problem 🚀 | Welcome back to my data structures and algorithms grind! Today, I'm diving deep into the classic Two... | 26,546 | 2024-02-23T10:02:45 | https://dev.to/majesticshawarma/unleashing-efficiency-with-hashmaps-solving-the-two-sum-problem-26p9 | algorithms, learning, python, computerscience | Welcome back to my data structures and algorithms grind! Today, I'm diving deep into the classic Two Sum problem, a fundamental challenge that sets the stage for mastering more complex algorithms. Let's embark on this journey of efficiency and problem-solving mastery!
**🎯 Problem Description:**
The Two Sum problem tasks us with finding two numbers in an array `nums` that add up to a given target. Our goal is to return the indices of these two numbers.
**Example:**
```markdown
Input: nums = [2,7,11,15], target = 9
Output: [0,1]
Explanation: nums[0] + nums[1] == 9, so we return [0, 1].
```
**⚙️ Constraints:**
- Length of `nums`: 2 to 10^4
- Elements of `nums`: -10^9 to 10^9
- Target value: Within the same range
- Exactly one valid solution exists
**💡 Solution Approach:**
I'm employing a hashmap to efficiently solve this problem. Here's my strategy:
```python
def twoSum(nums: List[int], target: int) -> List[int]:
prevMap = {} # val -> index
for i, n in enumerate(nums):
diff = target - n
if diff in prevMap:
return [prevMap[diff], i]
prevMap[n] = i
```
**💬 Code Discussion:**
- **Method Definition:** I define a method named `twoSum` which takes in `nums`, a list of integers; `target`, the target sum; and returns the indices of the two numbers that add up to the target.
- **Hashmap Initialization:** Initializing an empty dictionary named `prevMap`. In Python, dictionaries (hashmaps) offer constant time complexity for insertion, deletion, and lookup on average.
- **Iterating through `nums`:** Looping through `nums` using the `enumerate` function to access both index `i` and value `n`.
- **Calculating the Difference:** For each `n` in the array, I calculate the difference `diff` between the target and `n`.
- **Checking Complement Existence:** I check if `diff` exists in `prevMap`. If it does, it means I've found the complement of `n` that adds up to the target. So, I return the indices of `n` and its complement from `prevMap`.
- **Storing in Hashmap:** If the complement doesn't exist, I store `n` along with its index `i` in `prevMap`.
**⏰ Time Complexity Analysis and Relevance of Hashmap:**
Utilizing a hashmap is crucial for achieving an efficient solution. Here's why:
- **Constant Time Lookup:** Dictionaries in Python offer constant time complexity (O(1)) for insertion, deletion, and lookup on average. This enables us to check if a complement exists for a given number in constant time.
By leveraging the constant time complexity of dictionary lookups, we achieve a linear time complexity of O(n) for solving the Two Sum problem, making our solution highly efficient, especially for large input sizes.
**🔍 Discussion on Space Complexity and Trade-offs:**
The space complexity of our solution is O(n), where n represents the number of elements in the input array `nums`. In the worst-case scenario, we may need to store most of the n elements in the hashmap `prevMap`. This accounts for situations where we encounter all elements in `nums` except one while iterating through the array to find the unique pair that sums up to the target. Therefore, even though we technically store n - 1 elements (due to the guaranteed unique pair), according to the principles of complexity analysis, we simplify this to O(n) by considering the dominant factor.
The trade-off between time and space complexity is common in algorithm design. In this case, we prioritize time efficiency by using additional space to store the hashmap. However, for applications with strict memory constraints or when optimizing for space is critical, alternative approaches may be explored.
Understanding these trade-offs and choosing the most suitable solution based on the problem requirements is crucial in algorithm design.
**💼 Possible Applications of Hashmaps:**
Hashmaps find diverse applications across various domains:
- **Database Indexing:** Efficient indexing and retrieval of data in databases.
- **Caching:** Storing frequently accessed data for quick retrieval.
- **Symbol Tables:** Facilitating quick lookup of identifiers in programming languages.
- **Network Routing:** Storing routing information for efficient packet forwarding.
Understanding hashmaps and their applications equips us with powerful tools for efficiently solving real-world problems.
That's all for today's dev blog. Keep sharpening your skills in data structures and algorithms, and stay tuned for more insights in our next adventure!
For more details and practice, check out the [Two Sum problem on LeetCode](https://leetcode.com/problems/two-sum/).
| majesticshawarma |
1,770,466 | Building a Hackathon in 2024 | Feedback loop. Pain points. New use cases for your documentation. These are all valid points for... | 0 | 2024-02-23T19:13:08 | https://dev.to/danizeres/building-a-hackathon-in-2024-5gj4 | devrel, hackathon | Feedback loop. Pain points. New use cases for your documentation. These are all valid points for running a hackathon, and nurturing a strong connection with your developer community. Professionals in our field of Developer Marketing must understand hackathons are more than just mere technical marathons, they are hollowed grounds to incubate new ideas and potential for dev-tool companies growth.
Mastering the art of organizing and executing a hackathon is key to engaging with developers and fostering a space for creativity.
After hosting over 10 hackathons with Livepeer, AWS, 1Password, MindsDB, Appwrite, and several other companies, bringing over 1000 hackers per event, I will guide you through the process of building an effective, developer-focused coding fest. Shall we get started?
## What is a hackathon?
Let’s cover the basics.
A hackathon is a collaborative coding event where developers, designers, and enthusiasts in the tech community come together to solve problems or develop new applications within a predetermined timeframe. Usually these events focus on specific challenges and offer a space for creative problem-solving and development of new ideas. Can you imagine a project built utilizing your tech stack during a hackathon becoming a Startup Unicorn? That’s the story of [1inch](https://medium.com/@BizthonOfficial/1inch-success-story-unicorn-rising-from-hackathon-06db1fc673be) 😉
Together with bringing innovation and a space for companies to have a direct communication with their developer community, hackathons are crucial spaces for networking, learning, and community building.
## What to consider when planning a hackathon
Not to pull your ear here in terms of processes and organization, but any hackathon's success hinges on meticulous planning and execution.
That’s why I like to think of DevRel professionals not only as developer marketers, but also project managers, in some capacity. From setting up a full campaign to locking in sponsorships and managing the hackathon's operational aspects, every step requires attention to detail. Utilizing resources like detailed planning documents, design best-practices, and operational guidelines ensures a streamlined process from inception to completion.
Before diving into the logistics of organizing a hackathon, it's crucial to identify the target audience and set clear, achievable goals. Whether the aim is to foster community engagement, encourage innovation, or scout for talent, understanding these elements will shape the event's structure and content.
Logistics, including venue selection, budgeting, and scheduling, are foundational to the event's success. Equally important is the consideration of participants' needs—ranging from technical resources to food and accommodations—ensuring a seamless and enjoyable hackathon experience for all involved.
## Virtual or in-person…?
Choosing the right format for your hackathon— virtual, in-person, or, even, hybrid —is crucial, and should align with both your goals and participant preferences. Virtual formats offer broader accessibility, allowing global participation without the constraints of geography. In-person events, however, offer a unique energy and more direct interaction, which can enhance collaboration and networking opportunities. The choice will definitely impact your planning, from logistics to tech requirements, and shape the overall experience for organizers, sponsors, and, most importantly, developers.
Each format presents its own set of challenges and advantages. Virtual events require robust tech infrastructure to facilitate smooth communication and collaboration, whereas in-person events involve logistical considerations such as venues, accommodations, and on-site resources. Hybrid events demand a careful balance, ensuring both remote and in-person participants can engage effectively.
When selecting a format, consider factors like the potential reach, cost implications, and the nature of the challenges being posed to participants. The ultimate goal is to choose a format that maximizes engagement, fosters innovation, and aligns with the hackathon's purpose.
## Setup your developers for success
Cater to the needs of the participants and the event format when selecting of appropriate tools and platforms. For a virtual event, the choice of a proper hackathon platform, landing page setup, hacker guides, and establishing solid communication channels is paramount. These tools will support fast dev cycles and real-time feedback, which are critical components of a positive developer experience (DX). Our goal here is to minimize any potential points of friction and enable participants to focus on innovation and problem-solving.
Selecting the right set of tools involves considering factors such as ease of use, integration capabilities, and the ability to support the hackathon's scale.
Additionally, incorporating DX best practices, such as providing complete documentation, directing your community onto how to take your stack for a ride in the quickest way possible; app ideas, giving direction to participants; boilerplate codes, so your developers can optimize for quick setup and iterations, can significantly enhance participant satisfaction and productivity.
## Inclusivity… who?
Challenges at a hackathon should ignite creativity and push the boundaries of conventional thinking. They should be designed to be accessible and stimulating for a diverse range of participants, encouraging innovative solutions to real-world problems. Balancing technical complexity with the potential for creative freedom is key to crafting challenges both engaging and rewarding.
Inclusivity in challenge design ensures every participant, regardless of background or skill level, can contribute meaningfully. This approach not only levels up the hackathon experience, but also promotes diversity of thought, which brings more comprehensive and innovative solutions.
## Collaboration and networking
The sense of being part of something bigger is what unites developers around a community. Especially in tech. So, fostering the sense of collaboration is the essence of any hackathon.
Facilitating teamwork among participants from various backgrounds enhances the creative process and leads to more effective problem-solving. Organizers can encourage collaboration through team-building activities, mentorship programs, and platforms that support real-time communication, support, and project sharing.
Let’s talk networking. This is another critical component of hackathons, providing participants with valuable connections that can last well beyond the event. Structured networking opportunities, such as keynote speeches, panel discussions, and social events, can nurture relationships and community building within your ecosystem.
## Sponsorships
Sponsorships and partnerships with aligned organizations can significantly enhance the value and reach of a hackathon. These collabs provide financial support, access to trendy tools and technologies, and boost your efforts when it comes to co-marketing, awareness, and actually elevating the event's profile by putting it in front of new developers. Identifying sponsors and partners whose goals and values resonate with the hackathon's theme is crucial for establishing fruitful and mutually beneficial relationships.
In return, sponsors gain access to the hackathon’s community of developers, offering a solid opportunity to showcase their stack and services, have direct community feedback, and, even… identify talent.
Bringing projects to partner up or sponsor your event will take the event’s visibility and engagement to another level, together with promoting a lasting impression to the tech space and opening the stage for upcoming collaborations.
## Marketing strategies for a hackathon
A well-thought-out marketing strategy is pivotal for attracting a diverse and talented group of hackers to your hackathon. By implementing a blend of communication pieces such as social media, email campaigns, and community outreach, you can effectively spread the word about your event. Highlighting unique aspects of the hackathon, like innovative winner tiers, notable workshop speakers, and enticing prizes, can serve as attractors to developers. Additionally, engaging with tech communities on social platforms amplifies your reach, drawing in participants who are eager to showcase their skills and connect with like-minded individuals.
Here is the recipe I’ve used for some hackathons over the past 6 months:
* Efficient timeline management: An efficient timeline, starting with locking in companies eight weeks prior to the hackathon, ensures all stakeholders are aligned and prepared. Activities ranging from landing page creation to promotional efforts and post-event engagement are scheduled to maximize impact. Regular updates to sponsors, engaging social media posts, and targeted email reminders keep the momentum going, ensuring high engagement throughout the hackathon.
* Resource allocation and promotional efforts: Allocating resources effectively and executing targeted promotional efforts are key. Leveraging newsletters for weekly communications, social media for regular updates, and a dedicated landing page for registration and information ensures participants are well-informed and engaged.
* Social media: The person managing social media should execute platform-specific strategies to maximize reach. Creating engaging content, including videos, tailored to each platform ensures your message resonates with the intended audience. Collaborating with creators for specialized content needs can further enhance the campaign's impact.
* Community outreach: Strengthening ties with the existing Hashnode community and partnering with tech communities and educational institutions broadens your hackathon's visibility. Exploring collaborations with events like ETH Global or US-based universities could offer new avenues for growth and participation.
* Influencer collaborations: Teaming up with 3-4 tech influencers for each hackathon can significantly extend your event's reach. Lead DevRel also facilitates the identification and collaboration with the top tech influencers, while social media analytics help track the campaign's effectiveness, ensuring your message resonates far and wide. Feel free to reach out to us on X, LinkedIn, or email if you want support on this front.
DevRels, this is a comprehensive and multifaceted approach to help us to build and engage a developer community eager to participate in your hackathon and continue contributing overtime.
## Providing resources and support
This shouldn’t even have to be said, but here we go: ensure all your hackathon participants have access to necessary resources and support. This includes comprehensive documentation, robust development tools, and responsive technical support. Good DX practices enable quick onboarding and iteration, support guidance, and even easy upgrade paths for dependencies.
Mentorship is underrated, but invaluable during hackathons. Providing mentors from your team who can offer expertise, guidance, and encouragement can greatly enhance the participant experience. A support structure ensures that all individual devs and teams, regardless of their initial skill level, have the opportunity to fully engage with the hackathon's challenges and learn from the experience.
### Last thoughts
Organizing a successful hackathon in 2024 requires careful consideration of format, tools, challenges, and participant support, all with focused at providing an excellent developer experience.
By focusing on the elements mentioned throughout this post, dev-tool companies can create hackathons that not only spur tech innovation but also build stronger connections within the developer community, laying a solid foundation for advancements and future launches. | danizeres |
1,770,708 | BUY TRUSTPILOT REVIEWS | Buy TrustPilot Reviews Cheap Buy Trustpilot Reviews: Increase Your Sales with Good... | 0 | 2024-02-24T04:10:23 | https://dev.to/gary_nicholas65/buy-trustpilot-reviews-3p91 | buy, trustpilot, webdev, javascript | Buy TrustPilot Reviews Cheap
Buy Trustpilot Reviews: Increase Your Sales with Good Conversion
“Breaking News!” – [TrustPilot Reviews](https://mangocityit.com/service/buy-trustpilot-reviews/) are the best way to increase your sales. Customers will trust a review more than ever before, and conversion rates dramatically improve as well! So why don’t you try it today? Buying reviews from TrustPilot is an effective form of marketing for any business seeking higher customer satisfaction or increased conversions.
What is TrustPilot review?
[TrustPilot](https://mangocityit.com/service/buy-trustpilot-reviews/) is a business review website founded in 2007 and helps to facilitate the customer experience for companies. TrustPilot reviews are valuable because they show up on popular search engine websites like Google, Yahoo!, Bing, etc., making them an important part of your marketing strategy.
Best place to buy Trustpilot Reviews
We know how to increase your website traffic and generate more sales. All you have to do is buy a [Trustpilot review](https://mangocityit.com/service/buy-trustpilot-reviews/) from us, the best reviews service on the internet. Buying one of our excellent reviews will ensure that potential customers see only positive feedback about your business–which in turn guarantees increased sales for any business owner!
You’re always looking for ways to improve customers’ experience, but we’ve found an easy way: buying a Trustpilot review from our company! It doesn’t matter what type of product or services you offer; all we need are some basic details so that it can be written up as if coming straight out of someone else’s mouth (somebody who likes using YOUR products/services!).
How do Trustpilot reviews perform for your business?
You choose a sufficient number of reviews. As a rule of thumb, you need 10 positive reviews in order to trace back negative ratings and get an average rating of up to 4.6 stars! This is not an invention from us but pure math that will help you out with any problems if only you invest now before the competition can ruin everything we’ve worked so hard on here at
Think again about whether this quantity is enough or even compensating for future negatives when buying our services as they are very affordable (and cheaper than losing customers!).
Please send us your Linkedin detail, and we will do the same for you. You can pay online or have an invoice emailed to you, whichever is most convenient, but please be sure that payment has been made in order for shipment to commence as soon as possible! As a new customer at our company, feel free to contact one of our friendly staff members by phone should any other questions arise throughout the ordering process.
Trustpilot works through these steps:
To buy reviews, You have to follow –
Sign up for Trustpilot
Create an account and set your preferences to buy reviews only
Search through the database of businesses that are looking to buy Trustpilot reviews and those who would like their business reviewed on this site (if they are not already)
If you see a company in need, click on it
If there is no “buy review” button, then contact them directly via email or phone. You can also start by searching “reviews.” The more detailed information about what product/service they provide will help direct you with which option best suits them. Based if the business provides a service such as catering, have someone try out their services first before buying from them.
Why is it essential to get positive Trustpilot reviews for an online business?
Trustpilot is the most popular site for online reviews. More than three billion people visit it every month, and they choose from TrustPilots top-rated products or services each day. Twenty-thousand businesses with their own reviews on Trustpilot are competing against one another in a tough contest which only continues to grow as time goes by.
It helps the company’s reputation by having millions of users who can rate them, which will help develop your business worldwide as it has proved to be an effective solution for many companies out there. Furthermore, the customers’ satisfaction level automatically increases when they are satisfied with what they purchased from you on TrustPilot, making this service beneficial not only for consumers but also for businesses too!
Should I buy Trustpilot reviews?
Do you have a negative Trustpilot review? Is your business struggling to maintain sales and profits because of this one bad mark on the board? Don’t worry; help is here! The team has 10k eager testers waiting just for people like you who need an instant boost.
Our affordable prices and secure payment methods will keep all transactions private; it would be foolish not to take advantage of these reviews today as they are guaranteed to make or break your entire company in no time flat. Act now before things get worse!
Is it possible to buy Trustpilot reviews?
Yes, it is possible to buy reviews from Trustpilot. The company offers the service of having a customer review your business on their site with just one click of a button – and all you have to do for that is buy them! So if you are struggling in this challenging market where everyone wants to be at number one, buying reviews from us might be an option.
It will not only help make your customers happy but also get more people interested in what you’re selling. Furthermore, with millions of users on the website who can rate businesses day after day, there’s no way any other competitor could win against yours if they buy enough reviews as well!
Why Choose Us?
The most diligent service providers: We have the best buy Trustpilot reviews service provider in town. All of our members are trained to offer exceptional levels of customer satisfaction, and they will perform anything in their power to make sure you’re happy and satisfied with each buy review completed for your company!
Superior guarantees: We know that not all businesses can be successful as soon as they start out. That’s why we employ a 30-day guarantee policy on every buy trust pilot review order placed by one of our clients. If you feel like something is not right at any time during this period, contact us, and we’ll watch out of things from there.
Money back guaranteed: When it comes down to money, sometimes people just want what they paid for without thinking twice.
We are at your service. Are you looking for a trustworthy company to conduct trustpilot reviews on behalf of your business? If so, we’re here for you! Our team has years of experience conducting reviews and ratings in all industries across the globe. You can depend on our capability when it comes to making sure that each review is authentic and credible. Whether you need one or 10,000 reviews (we have plenty!) we will work with you every step of the way. Contact us today if this sounds like something you could use!
Our Trustpilot Reviews Service Features:
01. Handmade Reviews
When you buy Trustpilot reviews from us, we research the topic thoroughly and make each review with custom instruction. Our expert research team makes each review count as a product that generates sales. All the reviews are unlimited split available and designed to get you a positive traffic flow.
02. Researched and Localized
We don’t give it a quick shot and get the job done when you buy trustpilot reviews from us. Rather we go inside the niche, research your business and determine what would benefit you the most. Our Trustpilot researcher team ensures the reviews match the local traffic accent and get their attention positively.
03. No Login Details Required
Getting positive reviews from us doesn’t have to give you insecurity of any form. We don’t require the login credentials of your Trustpilot page or anything else. All you have to provide is the page name, link, and a brief on what you need from us. You can also include any specific details that should be on the reviews.
04. 100% Real Users
One of our most unique features is that we provide reviews from only real Trustpilot users. That makes us one of the best places trustpilot reviews selling sites whom you can trust. We ensure each of your reviews are from real Trustpilot users who have experience at reviewing businesses before.
05. Real Photo and Attachment
Reviews with real photos and attachments can get you way more traffic and leads than regular text-based reviews. You can get a custom review service from us where you can include real photos of your business to attract more customers. We’re more than happy to serve you with the custom designs and requirements that help your business grow.
06. Phone Verified USA Profiles
You can buy verified trustpilot reviews from us because all our Trustpilot reviews are from phone verified profiles. On top of that, you can buy trustpilot reviews USA, UK, CA, AUS, NZ and other renowned countries. No matter where your business is from, we can get you the reviews from the targeted regions of the world.
Questions You Want To Know
Is Trustpilot a Legitimate Site?
Can I Buy Targeted Reviews?
Can I Buy Negative Reviews?
Can You Remove Reviews That Are Posted on My Business Page?
Will You Require My Logins?
Is it Safe Marketing?
Will the Reviews Get Banned?
What Info You Will Need?
Will I Get a Complete Report?
Will the Reviews Be Posted from a Single Account?
Is it Safe to Buy Our Trustpilot Reviews?
How Long Does it Take to Start the Reviews Delivery?
What Are the Payment Method?
Do You Offer Free Trial for Trustpilot Reviews?
Information for all
[Disclaimer: https://mangocityit.com/ is not a participant or affiliate of Trustpilot. Their logo, Trustpilot Star, Images, Name etc are trademarks/copyrights of them.]
If You Want To More Information just Contact Now Email Or Skype –
24 Hours Reply/Contact
Email: admin@mangocityit.com
Skype: live:mangocityit | gary_nicholas65 |
1,770,716 | Unveiling the Cultural Tapestry: The Hindu Temple in Abu Dhabi | Introduction: In the heart of the cosmopolitan city of Abu Dhabi, amidst the gleaming skyscrapers... | 0 | 2024-02-24T04:21:44 | https://dev.to/desertsafari63/unveiling-the-cultural-tapestry-the-hindu-temple-in-abu-dhabi-3069 | abu, dhabi, temple, beginners | Introduction:
In the heart of the cosmopolitan city of Abu Dhabi, amidst the gleaming skyscrapers and bustling streets, lies a hidden gem that encapsulates the rich cultural heritage of India—the Hindu temple. This article endeavors to unravel the intricate threads of this cultural tapestry, exploring the diverse facets of the [Hindu temple in Abu Dhabi](https://abudhabitempletour.com/) and its profound impact on the community.
A Cultural Oasis:
The Hindu temple in Abu Dhabi serves as a vibrant cultural oasis, offering worshippers and visitors a glimpse into the diverse traditions and customs that define Hinduism. From its architectural splendor to its colorful festivals and rituals, the temple provides a window into the rich tapestry of Indian culture, fostering a sense of pride and belonging among the expatriate Indian community in the UAE.
At the heart of the temple lies its architectural magnificence, a testament to the ancient craftsmanship and artistic ingenuity of India. With its ornate carvings, majestic spires, and intricate designs, the temple stands as a symbol of India's rich architectural heritage, captivating the imagination of all who behold its grandeur.
Cultural Festivities:
Throughout the year, the Hindu temple in Abu Dhabi comes alive with a myriad of festivals and celebrations, each offering worshippers an opportunity to connect with their cultural roots and celebrate the rich tapestry of Hindu traditions. From the vibrant colors of Holi to the jubilant festivities of Diwali, these festivals bring worshippers together in a spirit of joy and camaraderie, strengthening bonds of friendship and community.
During these celebrations, the temple becomes a hub of activity, alive with the sounds of music, dance, and laughter. Devotees gather to offer prayers, perform rituals, and partake in traditional feasts, immersing themselves in the rich cultural heritage of India and creating cherished memories that will last a lifetime.
Cultural Exchange:
Beyond its role as a place of worship, the Hindu temple in Abu Dhabi serves as a platform for cultural exchange and dialogue, fostering understanding and appreciation among people of different backgrounds. Through educational programs, cultural exhibitions, and interfaith events, the temple promotes a spirit of inclusivity and acceptance, bridging the gap between cultures and fostering mutual respect and understanding.
By opening its doors to visitors of all faiths and nationalities, the temple invites people to learn about Hinduism and Indian culture, fostering greater cross-cultural understanding and appreciation. Through these initiatives, the temple plays a vital role in promoting harmony and diversity within the community, enriching the cultural landscape of Abu Dhabi and beyond.
Conclusion:
The Hindu temple in Abu Dhabi is more than just a place of worship—it is a cultural treasure that embodies the rich tapestry of Indian heritage and traditions. Through its architectural splendor, vibrant festivals, and commitment to cultural exchange, the temple serves as a beacon of cultural pride and understanding, enriching the lives of worshippers and visitors alike. As a symbol of unity in diversity, the Hindu temple in Abu Dhabi continues to inspire and uplift all who are fortunate enough to experience its beauty and grace. | desertsafari63 |
1,770,730 | Is Ayurvedic Treatment Suitable For All stages Of Cancer? | cancer, a convoluted and diverse disease, has been very hard for clinical science. While standard... | 0 | 2024-02-24T05:35:07 | https://dev.to/vemareddy/is-ayurvedic-treatment-suitable-for-all-stages-of-cancer-1b8b | ayurvedictretment, cancer, cancerstages | cancer, a convoluted and diverse disease, has been very hard for clinical science. While standard treatments like chemotherapy, radiation therapy, and operation stay the underpinning of cancer the chiefs, there is creating interest in reciprocal and elective therapies, including Ayurveda. Ayurveda, an old course of action of medicine beginning from India, underlines a comprehensive method for managing prosperity and success. However, the request arises: Is Ayurvedic treatment proper for all periods of cancer? Let’s go through this topic with the [Best cancer hospital in India](https://www.punarjanayurveda.com/best-cancer-hospital-in-india/)
**Sorting out Ayurveda: An Extensive Method for managing Healing**
Ayurveda, and that signifies "the investigation of life," relies upon the guidelines of balance and congeniality inside the body, mind, and soul. According to Ayurvedic thinking, abnormal nature in the body's doshas, or energy powers (Vata, Pitta, and Kapha), can provoke affliction. The target of Ayurvedic treatment is to restore concordance and advance ideal prosperity through various modalities, including normal fixes, dietary changes, lifestyle modifications, and medicinal practices like yoga and reflection.
**Ayurvedic Treatment Approaches for Cancer**
With respect to cancer, Ayurvedic treatment hopes to address the secret lopsided characters adding to the contamination while also supporting the body's innate ability to recover and recuperate. Ayurvedic experts tailor treatment shows to the particular's remarkable constitution, cancer type, stage, and taking everything into account status. Typical philosophies could include:
**1. Regular Fixes:** Ayurveda furnishes the supportive properties of various flavors and botanicals to target harmful development cells, help insusceptibility, decline exacerbation, and sponsorship for the most part thriving. A couple of consistently elaborate flavors in Ayurvedic cancer treatment consolidate Ashwagandha, Turmeric, Tulsi, and Shatavari.
**2. Dietary Changes:** Ayurvedic dietary norms highlight eating new, whole food assortments that are appropriate for one's dosha constitution. cancer patients may be urged to follow an eating routine affluent in natural items, vegetables, whole grains, lean proteins, and sound fats while avoiding dealt with food assortments, refined sugars, and searing trimmings.
**3.Lifestyle Proposition:** Ayurveda highlights the meaning of keeping a sensible lifestyle, including adequate rest, standard action, stress the leaders, and significant flourishing. Rehearses like yoga, examination, pranayama (breathwork), and abhyanga (self-rub) may be recommended to help in everyday prosperity and vitality.
**4.Panchakarma Treatment:** Panchakarma, a detoxification and recovery treatment in Ayurveda, may be utilized to discard harms from the body, further develop cell capacity, and advance patching. Panchakarma meds usually incorporate a movement of cleansing procedures custom fitted to the solitary prerequisites and constitution.
**Considerations for cancer Stages**
While Ayurvedic treatment can offer critical assistance and adjunctive thought for cancer patients, its sensibility could vary depending upon the period of the disease:
**1.Starting stage cancer:** In occasions of starting stage cancer or pre-disastrous conditions, Ayurvedic interventions could help with watching out for key unbalanced attributes and sponsorship the body's standard watchman frameworks. Local fixes, dietary changes, and lifestyle changes can expect a colossal part in hindering disease development and propelling ideal prosperity.
**2.Undeniable level Stage cancer:** For patients with state of the art stage harmful development, Ayurvedic treatment could go about as a reciprocal method for managing standard cancer therapies. While Ayurveda can't fix cancer isolated, it can help with lessening aftereffects, work on private fulfillment, and work on the sufficiency of standard meds. Also, Ayurvedic interventions could help with directing treatment accidental impacts, help opposition, and moving overall success during the cancer adventure.
**3.Palliative Thought:** In circumstances where medicinal treatment decisions are confined, Ayurveda can offer consistent thought and palliative interventions to help with working with anguish, anxiety, and near and dear difficulty. Local fixes, dietary changes, and mind body practices can give comfort and overhaul the patient's very own fulfillment despite undeniable level harmful development.
**Interview with Clinical benefits Providers**
It's huge for individuals considering Ayurvedic treatment for cancer to converse with qualified clinical benefits providers, including oncologists and Ayurvedic specialists, to ensure secured and created care. Integrating Ayurvedic therapies with standard cancer drugs requires mindful administration, noticing, and joint exertion between clinical consideration specialists to work on persistent outcomes.
**Conclusion: Planning Ayurveda into cancer Care**
While Ayurvedic treatment offers a comprehensive method for managing prosperity and retouching, its sensibility for cancer patients depends upon various components, including harmful development type, stage, and individual prosperity status. While Ayurveda can't replace standard cancer therapies, it can enhance them by tending to stowed away unbalanced qualities, supporting the body's ordinary recovering cycles, and redesigning for the most part flourishing. By embracing an integrative method for managing cancer care, patients can get to a sweeping instrument reserve of supportive modalities to help their journey towards recovery.
While Ayurvedic treatment offers a comprehensive method for managing prosperity and recovering, its sensibility for cancer patients depends upon various components, including harmful development type, stage, and individual prosperity status. While Ayurveda can't supersede standard cancer therapies, it can enhance them by watching out for essential unpredictable qualities, supporting the body's normal retouching processes, and redesigning for the most part thriving. By embracing an integrative method for managing cancer care, patients can get to a thorough instrument reserve of healing modalities to help their journey towards repairing and recovery. With careful bearing from clinical benefits providers and Ayurvedic specialists, individuals can examine the potential benefits of Ayurveda as a component of their cancer treatment plan, drawing in them to make informed decisions and upgrade their prosperity results with the [Best ayurvedic cancer treatment in India ](https://www.punarjanayurveda.com/)
| vemareddy |
1,770,756 | The Ultimate Guide to Finding the Right Sports Betting App Development Company | In the fast-evolving landscape of sports betting, having a reliable and feature-rich mobile app is... | 0 | 2024-02-24T06:49:02 | https://dev.to/appdevelopmentcsalabs/the-ultimate-guide-to-finding-the-right-sports-betting-app-development-company-m22 | sportsbittingapp, appdevelopment, csalabs | In the fast-evolving landscape of sports betting, having a reliable and feature-rich mobile app is crucial for both operators and users. Choosing the right [sports betting app development](https://www.linkedin.com/pulse/your-go-to-sports-betting-app-development-company-p9a3c/) company can make all the difference in creating a successful and competitive platform. Here's your ultimate guide to finding the perfect match for your sports betting app development needs.
## Define Your Requirements
Before you start your search, outline your app's features, functionalities, and any specific requirements you might have. This will help you narrow down potential development partners and ensure they can meet your unique needs.
## Experience and Expertise
Look for a company with a proven track record in sports betting app development. Assess their portfolio, client testimonials, and case studies to gauge their experience and expertise in delivering successful projects.
## Licensing and Compliance
Ensure that the development company is well-versed in the legalities and regulations surrounding sports betting apps. They should be able to guide you through the licensing process and help you stay compliant with the relevant laws in your target market.
## Technology Stack
A reputable development company should be up-to-date with the latest technologies and trends in mobile app development. Inquire about the technology stack they use and ensure it aligns with your app's requirements for scalability, security, and performance.
## Customization and Scalability
Your sports betting app should be scalable to accommodate future growth and customizable to meet your unique branding and feature needs. Discuss these aspects with the development company to ensure they can adapt to your evolving requirements.
## Security Measures
Security is paramount in the world of sports betting apps. Inquire about the security measures the development company implements to protect user data, financial transactions, and the overall integrity of the platform.
## Integration of Payment Gateways
Seamless and secure payment transactions are critical in sports betting apps. Confirm that the development company can integrate reliable and popular payment gateways to provide a smooth user experience.
## User Interface (UI) and User Experience (UX)
A user-friendly interface and a positive user experience are key to the success of any app. Assess the development company's capabilities in designing intuitive and visually appealing interfaces that enhance the overall user experience.
## Testing and Quality Assurance
Ensure that the development company follows rigorous testing processes to identify and rectify any bugs or issues before the app's launch. A robust quality assurance process is essential for delivering a reliable and high-performing sports betting app.
## Post-Launch Support and Maintenance
Ask about the post-launch support and maintenance services offered by the development company. A reliable partner should provide ongoing support to address any issues, implement updates, and ensure the smooth operation of your sports betting app.
By thoroughly evaluating potential sports betting app development companies based on these criteria, you'll be well-equipped to make an informed decision and embark on a successful journey to launch a cutting-edge sports betting app.
Also Read : [Your Go-To Sports Betting App Development Company](https://www.linkedin.com/pulse/your-go-to-sports-betting-app-development-company-p9a3c/)
## Conclusion
In the competitive realm of sports betting app development, choosing the right partner is paramount. CSA Labs, with its proven expertise, commitment to innovation, and focus on client satisfaction, emerges as the ideal choice. Their track record, adherence to industry regulations, and emphasis on security and scalability position them as a reliable ally in bringing your vision to life. With CSA Labs, you're not just getting an app – you're entering a partnership dedicated to success. Trust in CSA Labs to deliver a cutting-edge, secure, and user-friendly sports betting app that stands out in the market. Your journey to app success begins with CSA Labs. | appdevelopmentcsalabs |
1,770,841 | Nạp Tiền vnxoso | Hướng dẫn chi tiết giao dịch tại nhà cái. | Nạp Tiền vnxoso | Hướng dẫn chi tiết giao dịch tại nhà cái. Nạp tiền Vnxoso cùng nhiều chương trình... | 0 | 2024-02-24T09:10:55 | https://dev.to/vnxosospace/nap-tien-vnxoso-huong-dan-chi-tiet-giao-dich-tai-nha-cai-2loh | webdev, beginners, tutorial, python | Nạp Tiền vnxoso | Hướng dẫn chi tiết giao dịch tại nhà cái.
Nạp tiền Vnxoso cùng nhiều chương trình khuyến mãi và ưu đãi
Hướng dẫn các bước nạp tiền #Vnxosospace cho tân thủ
Các phương thức nạp tiền an toàn và nhanh chóng hiệu quả
Vnxoso mang đến trải nghiệm đáng tin cậy và thuận lợi
Địa chỉ: 104 Phố Đoàn Xá, Hồng Phong, tx. Đông Triều, Quảng Ninh, Việt Nam
Số điện thoại: 09628362384
Email: vnxosospace@gmail.com
Website: https://vnxoso.space/nap-tien-vnxoso/
Fanpage: https://www.facebook.com/vnxosospace/
#vnxoso #vnxosospace #xosovnxoso #vnxosocasino #thethaovnxoso | vnxosospace |
1,770,861 | Role of AI in Modern Enterprise Search | In today’s data-driven world, enterprises like Nixon Technologies LLC are continuously grappling with... | 0 | 2024-02-24T10:04:23 | https://dev.to/aarondavid2912/role-of-ai-in-modern-enterprise-search-6ch | In today’s data-driven world, enterprises like Nixon Technologies LLC are continuously grappling with vast amounts of information scattered across various platforms. [Nixon Technologies LLC](https://nixontechnologies.com/), a leading IT staffing and consulting firm, understands the critical importance of effective information retrieval for informed decision-making, enhanced productivity, and gaining a competitive edge. Here, Artificial Intelligence (AI) emerges as a transformative force, revolutionizing the landscape of enterprise search.
**Understanding Modern Enterprise Search**
In the realm of modern enterprise search, traditional approaches face significant challenges. Enterprises require efficient systems capable of handling large volumes of data while delivering relevant results. The evolution toward intelligent search solutions becomes imperative to meet these demands.
**Leveraging AI for Enhanced Search Capabilities**
AI technologies offer a range of capabilities to enhance enterprise search. Natural Language Processing (NLP) enables the analysis of user queries for improved understanding and response. Semantic search algorithms ensure contextual relevance, while machine learning algorithms personalize search results based on user behavior. Additionally, image and voice recognition technologies facilitate the retrieval of multimedia content, enriching the search experience.
**Improving Search Efficiency and Accuracy**
AI-driven approaches optimize search efficiency and accuracy. Intelligent indexing and content categorization streamline data organization, making it easier to locate relevant information. Predictive analytics anticipate user needs, offering proactive search suggestions. Entity recognition and sentiment analysis further refine search results, enhancing relevance and user satisfaction.
**Facilitating Knowledge Discovery and Decision-Making**
AI-powered search solutions facilitate knowledge discovery and decision-making processes within enterprises. By uncovering hidden insights through advanced analytics and integrating knowledge graphs for relationship mapping, organizations gain valuable insights into their data. Automated summarization tools enable quick information extraction, while real-time data processing supports dynamic decision support systems.
**Enhancing User Experience and Engagement**
User experience is paramount in modern enterprise search systems. AI technologies enable personalized search interfaces tailored to individual user preferences. Interactive chatbots provide intuitive query assistance, while voice-enabled search functionalities offer hands-free operation. Seamless integration with existing workflows and applications ensures a cohesive user experience across platforms.
**Ensuring Data Security and Compliance**
Data security and compliance are critical considerations in enterprise search environments. AI-driven anomaly detection mechanisms identify potential threats, while role-based access control mechanisms safeguard data privacy. Compliance monitoring tools ensure adherence to regulatory requirements, with continuous learning capabilities enabling adaptation to evolving security threats.
**Future Directions and Challenges**
As AI technologies continue to advance, the future of enterprise search holds exciting possibilities. Integration with emerging technologies such as blockchain and IoT promises to further enhance search capabilities and unlock new opportunities for innovation. However, ethical considerations in AI-powered search algorithms, including the mitigation of biases and guaranteeing equity in search outcomes, present ongoing challenges for organizations to address.
**Conclusion**
Artificial Intelligence is redefining how enterprises like Nixon Technologies LLC explore and harness information resources through modern search solutions. By leveraging AI capabilities such as NLP, machine learning, and cognitive computing, organizations can unlock valuable insights, streamline workflows, and empower users with personalized and efficient search experiences. As enterprises continue to embrace AI-driven search technologies, the journey towards intelligent, context-aware, and user-centric search solutions will undoubtedly accelerate, fostering innovation and driving competitive advantage in the digital era.
| aarondavid2912 | |
1,770,877 | My Journey Building a WebSocket Server in Go | A favorite YouTuber of mine once said that the best way to learn a new programming language is to... | 0 | 2024-02-24T10:59:32 | https://hiro.one/blog/2024-02-24/ | ---
title: My Journey Building a WebSocket Server in Go
published: true
date: 2024-02-24 00:00:00 UTC
tags:
canonical_url: https://hiro.one/blog/2024-02-24/
cover_image: https://dev-to-uploads.s3.amazonaws.com/uploads/articles/8177ndsraecx6lyfd6w9.jpeg
---
A favorite YouTuber of mine once said that the best way to learn a new programming language is to build projects with it.
{% embed https://www.youtube.com/watch?v=E8cM12jRH7k %}
Inspired by this video, I decided to dive in and create my own WebSocket server using Go.
(There are articles out there explaining what the WebSocket protocol is. So I won't write about it and let them play the role.)
### Read RFC6455
Before starting, my knowledge of the WebSocket protocol was pretty limited:
- It's built on top of HTTP.
- Communication starts with a client sending an HTTP "Upgrade" request to switch to WebSocket.
- The server responds, and boom! A WebSocket connection is established.
Not knowing much else, I decided to consult the source - <a href="https://datatracker.ietf.org/doc/html/rfc6455" target="\_blank" target="\_blank">RFC6455</a>. This is where I learned that WebSocket really only uses HTTP for the initial handshake. After that, it's all about exchanging raw TCP data in the form of <a href="https://datatracker.ietf.org/doc/html/rfc6455#section-5.6" target="\_blank">data frames</a> defined by the RFC.
### The Challenge: Mixing HTTP and TCP
This is where things got tricky. Normally in Go, we don't have direct access to TCP payloads when working with HTTP objects. So, how do we combine HTTP and TCP communication in our server?
One straightforward approach is running a separate TCP server:
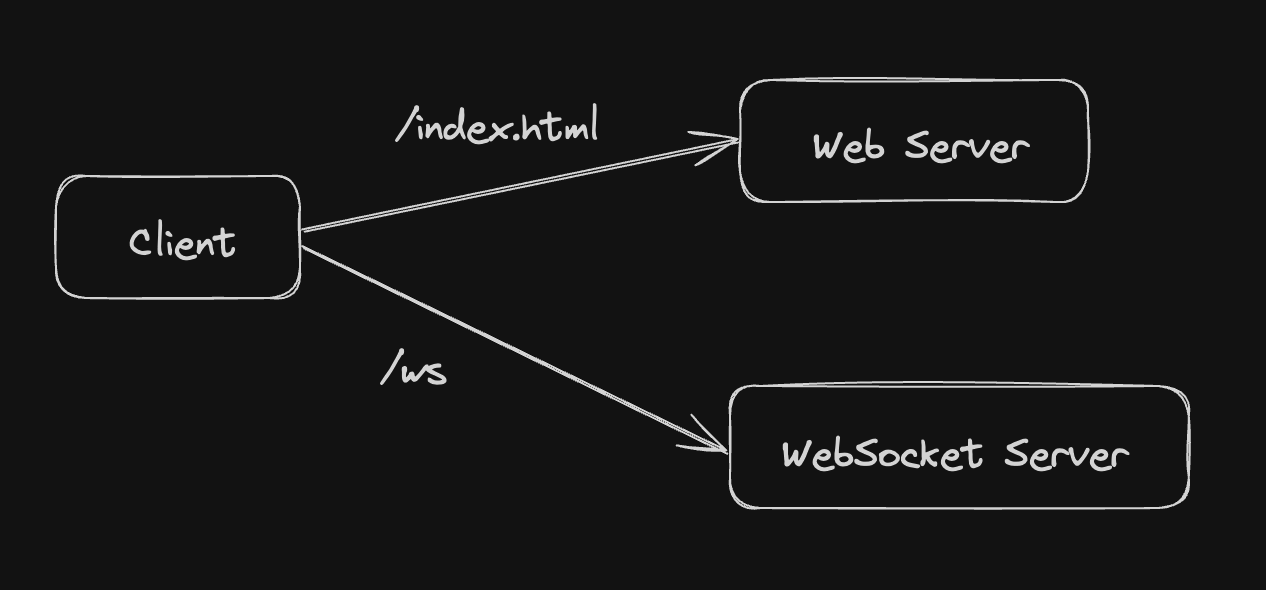
```go
// Here, conn is TCP connection (net.Conn)
// ...
const delimiter = "\r\n" // "\u000D\u000A" // CR & LF
buf := make([]byte, 2048)
n, err := conn.Read(buf)
if err != nil {
log.Println("error reading payload to buffer: ", err)
return
}
payload := strings.Split(string(buf[:n]), delimiter)
reqLine := strings.Split(payload[0], " ")
// validate HTTP method, version
headers := getHTTPHeaders(payload[1:])
// check Host, Upgrade, Connection, and WebSocket version headers
// generate WebSocket key
key := hash(headers["Sec-WebSocket-Key"])
// respond
conn.Write([]byte("HTTP/1.1 101 Switching Protocols\r\nUpgrade: websocket\r\n..."))
fmt.Println("=== handshake done! ===")
// from now on, we can send/receive WebSocket dataframe between server-client.
```
This is great for learning, as I got to manually construct HTTP responses over TCP. However, it's not the most practical solution. This is where Go's HTTP Hijack API saves the day!
### Hijacking for the Win!
Go's <a href="https://pkg.go.dev/net/http#Hijacker" target="\_blank">HTTP Hijacker</a> interface lets us pull the raw TCP connection right out of an HTTP request—perfect for our use case. Even popular libraries like <a href="https://github.com/gorilla/websocket" target="\_blank">Gorilla WebSocket</a> use this technique under the hood.
This means we can have our cake and eat it too - a single server handling both HTTP and WebSocket traffic:
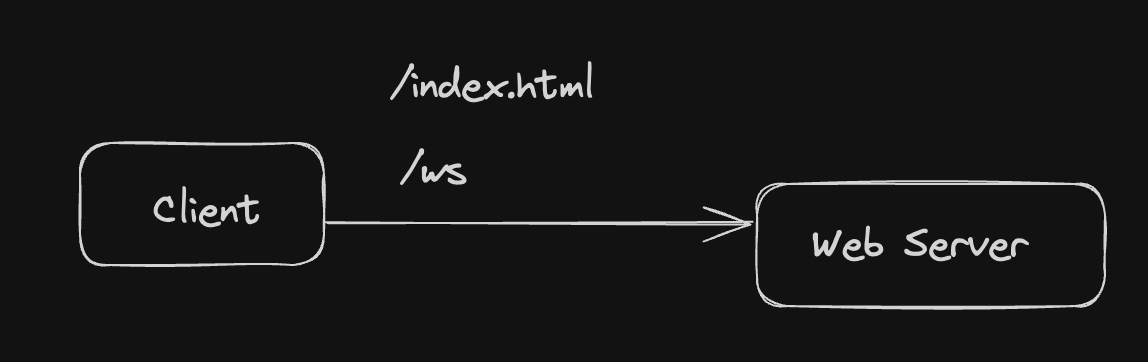
Here's how the Hijack API fits into my WebSocket server:
```go
// after validating HTTP header in http.Request...
hj := w.(http.Hijacker)
conn, _, err := hj.Hijack()
if err != nil {
fmt.Println("error hijacking http response writer:", err)
w.WriteHeader(http.StatusInternalServerError)
w.Write([]byte("internal server error"))
return
}
// don't forget to close the TCP connection,
// otherwise the client will send FIN packet around after 2 seconds.
defer conn.Close()
conn.Write([]byte(WSHandshakeResponse(key)))
fmt.Println("=== handshake done! ===")
// from now on, we can send/receive WebSocket dataframe between server-client.
// ...
```
### That's the Handshake!
That's a whirlwind tour of the WebSocket handshake process. If I have the time, I'll follow up with an article about how to implement WebSocket data frames in Go.
Thanks for reading ✌️ | hiro_111 | |
1,770,903 | Category Theory (Functional Style) part-1 | Category Theory Category theory is a way to abstract programming, enabling the creation of... | 0 | 2024-02-24T12:01:11 | https://dev.to/pwn0x80/functional-style-1n3i | javascript, typescript, functional, programming |
# Category Theory
Category theory is a way to abstract programming, enabling the creation of complex programs that are readable, extensible, and testable. It provides a mathematical abstraction for code.
#### category consist of type object and morphs
- morphs interpreted as a function or operation that transforms data from one form to another.
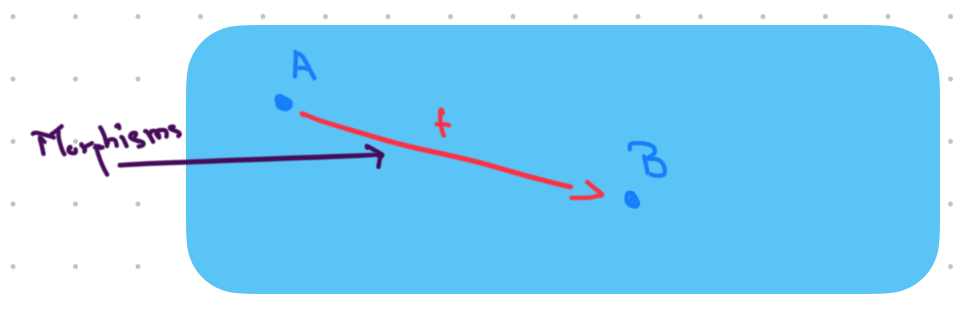
- object in functional programming might refer to a data structure that bundles together related information.
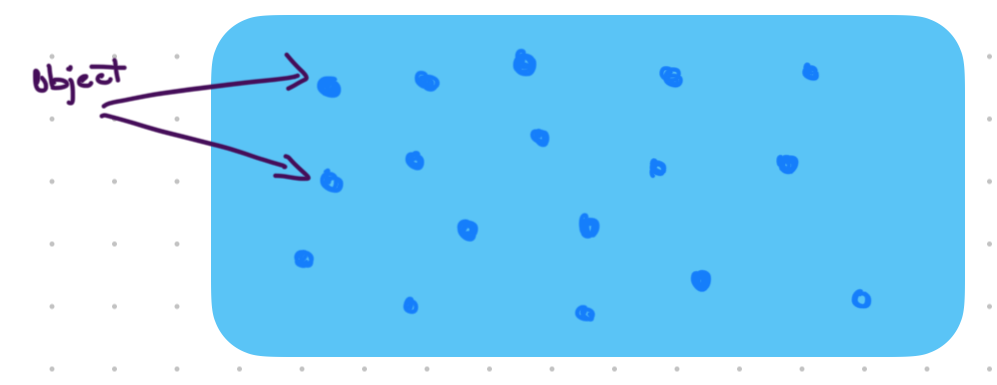
`f:a -> b // f is morphs and a is object`
morphs might refer to functions or transformations that take one input and produce a modified output without any internal state or side effects these types are known as pure functions.
# What is Pure functions
Pure functions are deterministic, meaning they always produce the same output given the same input, and they don't rely on or modify any external state.
# what is Composition
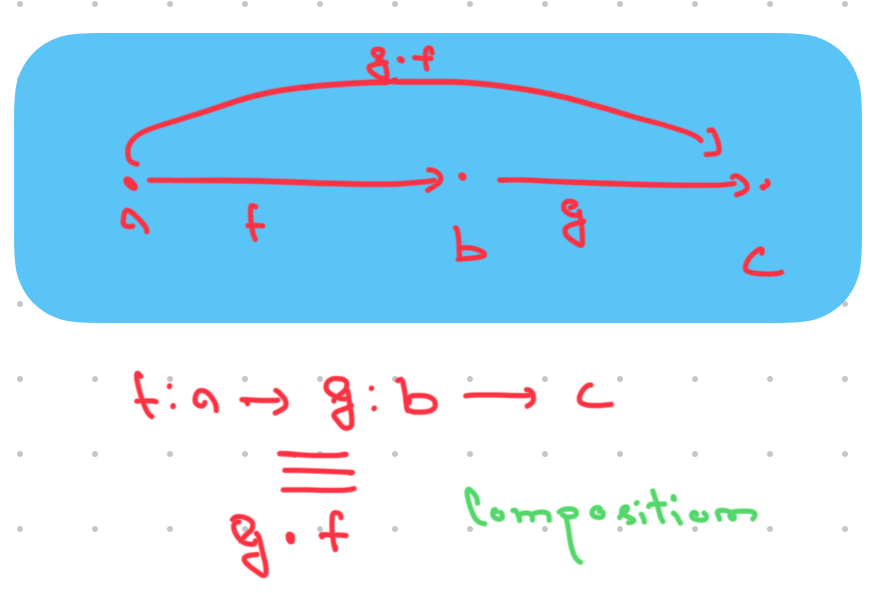
To form Relation between two morphs.
The practice of combining simpler functions to build more complex functions. It involves taking two or more functions and creating a new function by chaining them together, where the output of one function becomes the input of the next function.
for example in js/ts - map,filter,reducer
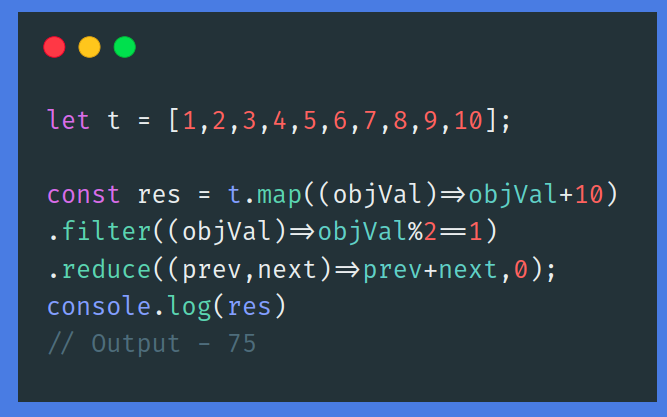
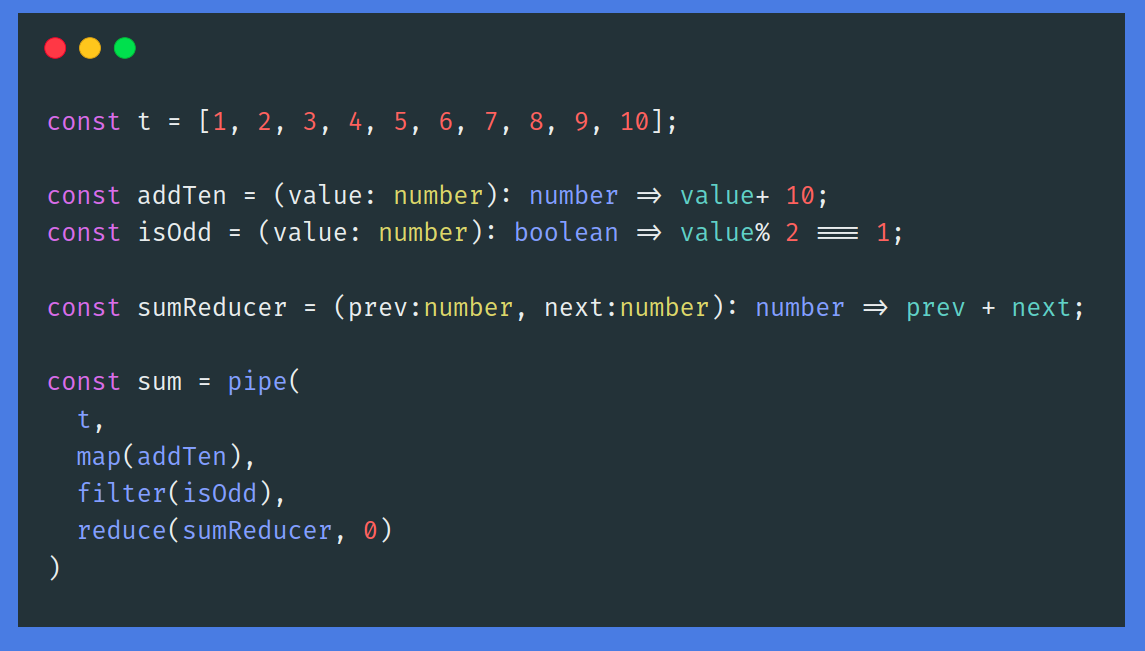
```
f:a->f:b->c
composition - g∘f
```
Functional Style
# Rules of Category
1> Composition definition
2> Composition associative
3> Composition Identity
#### Composition Definition
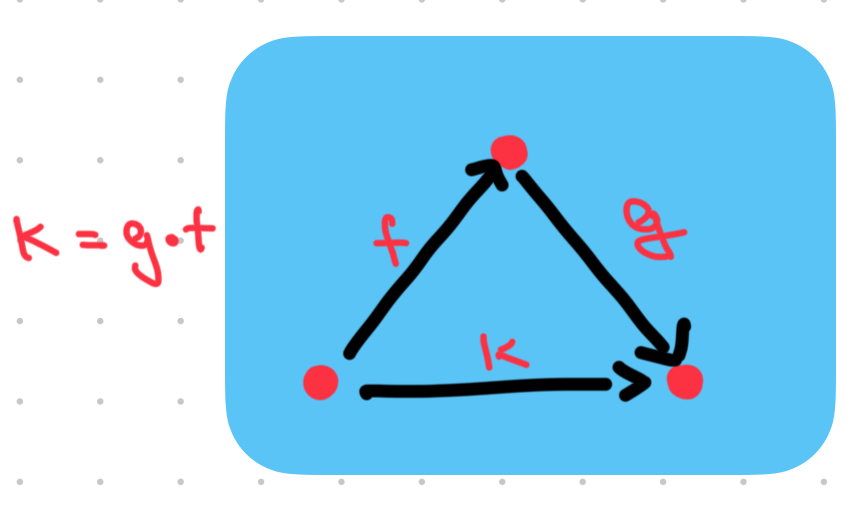
If you have two functions composed one after another, it implies that there exists a third arrow starting from the first function and ending at the second function.
f:A -> B and g:B -> C then k = g * f,
where k:A -> C
composition k is defined as mapping elements from A to C by first applying function f to map elements from A to B and then applying function g to map the result from B to C.
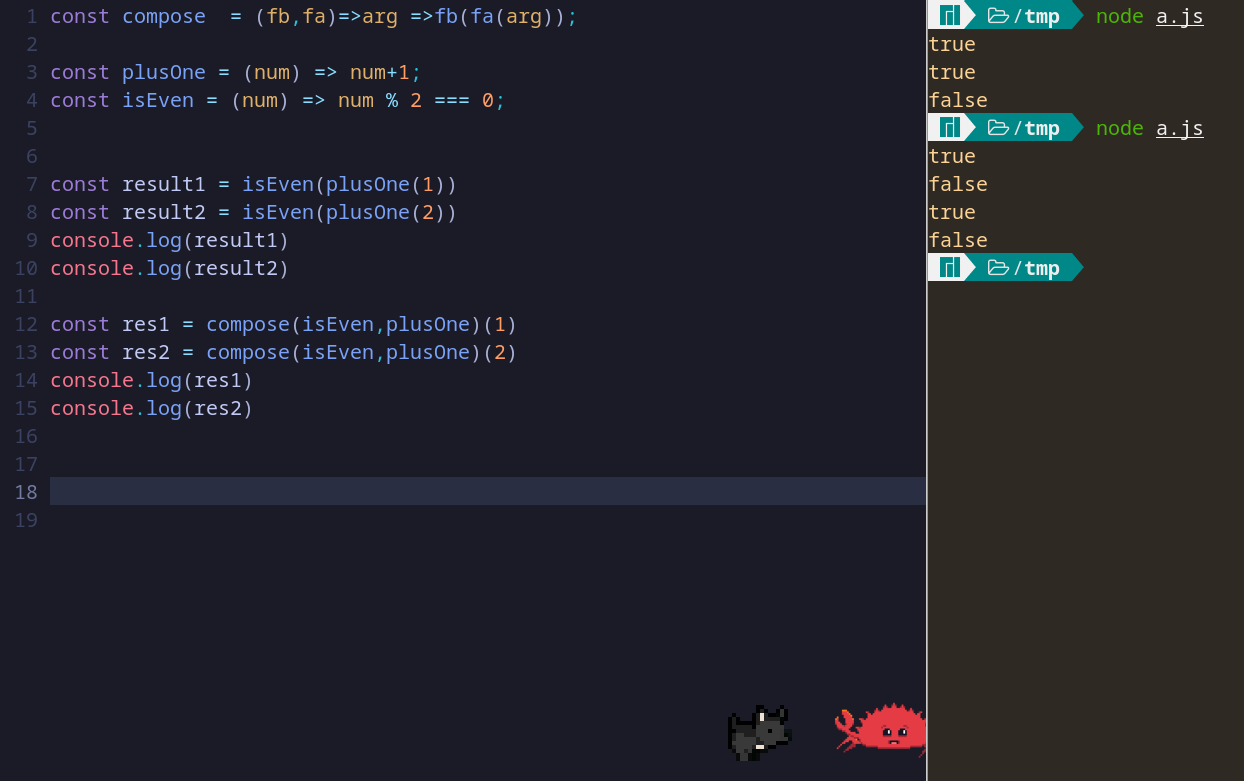
#### Composition Associative
The order of the Composing function should not matter. Whether you first compose f and g than h or g and h and then f.
f: A -> B, g:B -> C and h:C -> D then,
(f * g) * h === f * (g * h)
it assures us that no matter which order we apply the compositions than final result will be the same.
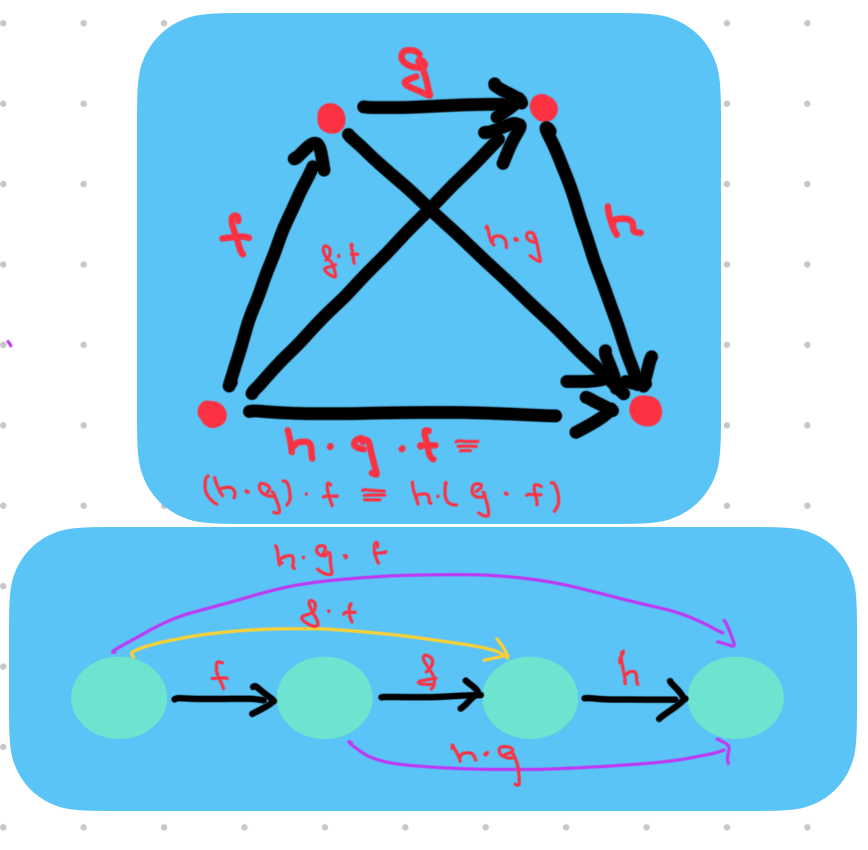
#### Composition Identity
f:A -> A
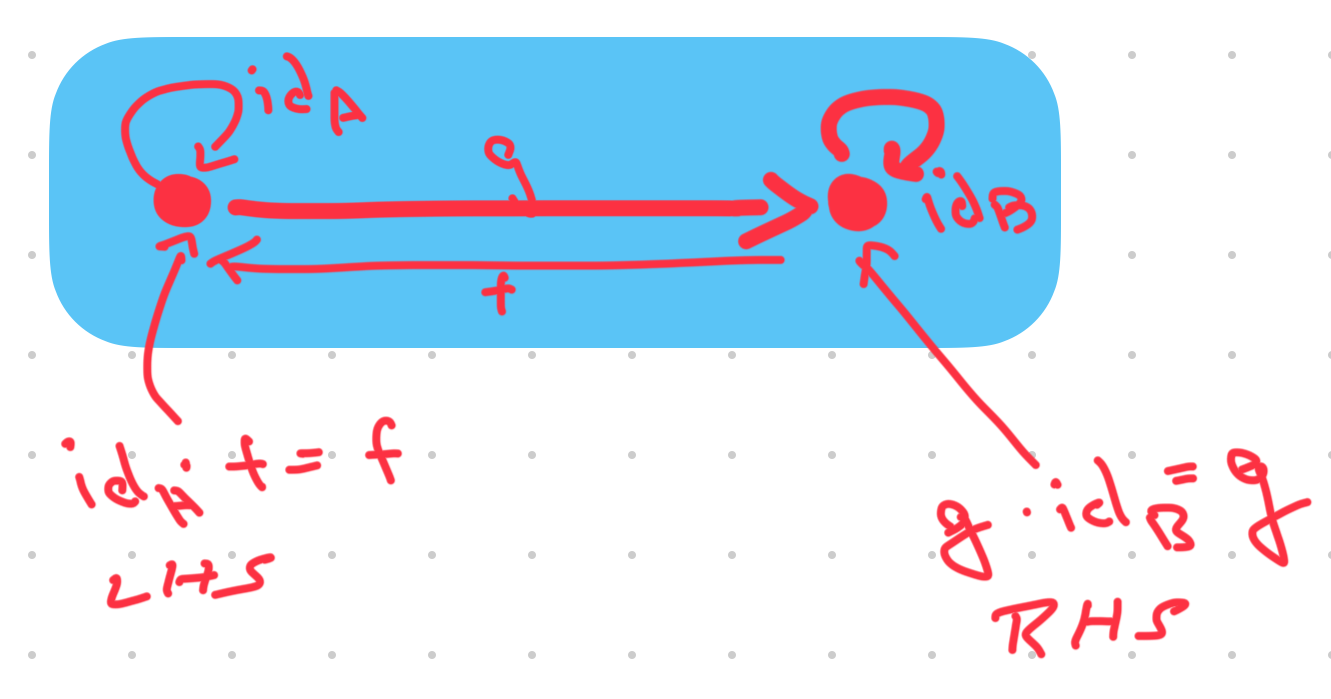
It is a function that maps every element of a set
A to itself. | pwn0x80 |
1,771,098 | How to Know Whether to Use Data URLs | We often can provide assets with a URI or a so-called “Data URL” on the web. As they are so... | 0 | 2024-03-02T13:23:41 | https://blog.ungra.dev/how-to-know-whether-to-use-data-urls?pk_campaign=rss-feed | ---
title: How to Know Whether to Use Data URLs
published: true
date: 2024-02-24 14:49:43 UTC
tags:
canonical_url: https://blog.ungra.dev/how-to-know-whether-to-use-data-urls?pk_campaign=rss-feed
---
We often can provide assets with a URI or a so-called “Data URL” on the web. As they are so straightforward to use, they get pretty often copied (from a tutorial, snippet, or whatnot) without us being able to tell what they do, when to prefer them, or whether you should still be using them altogether. It's one of the lesser-known performance tweaks I will shed some light on in this blog post.
This post was reviewed by [Leon Brocard](https://github.com/acme) & [David Lorenz](https://activenode.de/). Thank you! ❤️
## What are Data URLs Anyway
First things first, what are we talking about here? Let's make a simple example of a background image:
```
<div></div>
div {
height: 100px;
width: 100px;
background-image: url('https://placehold.co/600x400');
}
```
That snippet is quite simple. We add a div and configure it to hold a background image. You might know that there is a second approach to this, however. This approach makes use of a so-called “data URL”:
```
div {
height: 100px;
width: 100px;
background-image: url('data:image/svg+xml;charset=utf-8;base64,PHN2ZyB4bWxucz0iaHR0cDovL(...)TEwLjRaIi8+PC9zdmc+');
}
```
Now, that is different. The two snippets output the same result. However, in the latter, we provide the image data directly in the CSS instead of requesting it from a server. Here, we provide the encoded image binary data directly in a given convention. There is no need to catch it from the server, as we provide the file in CSS.
> A new URL scheme, “data”, is defined. It allows inclusion of small data items as “immediate” data, as if it had been included externally.
### Base64 Encoding
How does this work? The image data is encoded with an algorithm called “Base64”. It sounds a bit complicated, but it's, in fact, not. The main goal of such encodings is to display binary data in Unicode. That's why such are called “binary to text encodings.” A digit in Base64 can represent a maximum of 6 bits. Why is that? Let's make an example. We want to display `101101` as text. But hold on a second. Did you recognize something? _We already did it!_ Writing out `101101` made a bit-sequence apparent to you as a reader. _We encoded binary to text._Now, let's imagine instead of “0” and “1”, we decide for “A” and “B”: `BABBAB`. Guess what? We have just Base **2** encoded data! Yay. Do you see the issue here? We must utilize eight **bytes** of data to encode six **bits** of data, as A and B in ASCII take up one byte. We “inflate” or bloat this data by ~1067% (100 % / 6 bit \* 64 bit).
| Binary Sequence | Base2 Encoded |
| --- | --- |
| 0 | A |
| 1 | B |
| 101101 | BABBAB |
To tackle this problem, there is a little trick: we add more characters to encode a bigger binary sequence at once. Let's make another example here: Base4 encoding.
| Binary Sequence | Base4 Encoded |
| --- | --- |
| 00 | A |
| 01 | B |
| 10 | C |
| 11 | D |
| 101101 | CDB |
How would our sequence of `101101` look with that algorithm? It encodes to `CDB`. This results in a far smaller bloat of only 400%! We continue in that manner until we have 64 distinct characters representing a specific sequence each. That's what Base64 encoding is.
| Binary Sequence | Base64 Encoded |
| --- | --- |
| 000000 | A |
| 000001 | B |
| ... | ... |
| 011001 | Z |
| 011010 | a |
| ... | ... |
| 101101 | t |
| ... | ... |
| 111111 | / |
In the given table, we see that our example sequence of `101101` is encoded by only using the character `t.` That means we only add two more bits to display 6 bits of data! That is merely an inflation of roughly 133%. Awesome! Well, but why stop there? Why did we expressly agree on “6 bits” and not use, e.g., Base128 encoding? ASCII has enough characters, right? However, 32 of them are control characters that computers may interpret. That would lead to severe bugs. Why this is exactly is out of the scope of this blog post (I mean, the Base64 algorithm already kinda is). Just so much: There is a Base91 and Base85 encoding; however, as illustrated in our examples above, “power of two” is more readily encoded when it comes to byte data, and that's why we mostly settled on that.
To summarize this a little, let's say we want to encode 10 bytes of data, which is 80 bits. That means we need 14 characters (80/6≈14) to represent that. The binary sequence `000000` is represented as ASCII `A` in Base64. Read this: “The binary data of my image has six consecutive zeros somewhere. The algorithm of Base64 encoding will transform this into 'A.'” In ASCII, `A` is eight bits long. Represented in binary, it looks like this: 01000001. Thus, we made this sequence two bits larger.
## Preamble
As always, when it comes to performance, it's complex. There are a lot of layers to the question of whether to use a data URL or not. It heavily depends on how your external resources are hosted. Are they hosted on the edge? What's the latency? The same goes for the hardware of the users. How long does it take for them to decode the given data? May this take even longer than requesting the already decoded resource? You must always collect RUM data and compare approaches to know best. However, generally speaking, we could say that there is a sweet spot where the Base64 encoding overhead exceeds the overhead of an HTTP request, and thus, it's advisable not to use Data URLs.
## The Premise
Let's repeat this: if the overhead of a request to an external resource exceeds the size of the Base64 extra bloat, you should use a data-url. We are not talking about the payload here. It's just what the request in isolation costs us. Do we have a bigger **total size** with Base64 encoding or an HTTP request? Let's make an example here. We start with a white pixel. We decode this as PNG in, well, the resolution 1x1. We will add other background colors throughout this blog post. The following table already yields the most important values: uncompressed file size as PNG, the (bloated) size when Base64 is encoded, the total request size (headers and payload), and finally, the total size of the data-URL.
| Resolution | Background Color | Size | Base64 Encoded Size | Request Size (total) | Data URL Size |
| --- | --- | --- | --- | --- | --- |
| 1x1 | White | 90 | 120 | 864 | 143 |
In this first example, we would need to transfer 721 (864 – 143) more bytes if we did **not** utilize a data URL.
## Measure the Request
Before we head deeper into data points and their analysis, I want to clarify how we measure the total size of a request. How do we get the value in the “Request Size (total)” column? The most straightforward way is to head to the network tab in the Web Developer Tools. The first thing you do is create a snapshot of all the page's network requests. Then, find the one for the particular media in question.

```
{
"Status": "200OK",
"Version": "HTTP/2",
"Transferred": "22.12 kB (21.63 kB size)",
"Referrer Policy": "strict-origin-when-cross-origin",
"Request Priority": "Low",
"DNS Resolution": "System"
}
```
Now, you might think it's pretty easy, right? Subtract the payload (21.63 kB) from the transferred data (21.63 kB) and done. However, you also have to take the request header into account! That adds a little something.

Long story short: in the screenshot above, we see both headers, request and response. This data is the “overhead” we need to take into consideration. Everything else is payload – not bloated by Base64 encoding.
## To the Lab!
Now, equipped with that knowledge and skills, we can create some data points. I did this with a Node.js script. It creates many images and writes their file sizes and Base64 encoded sizes in a CSV file:
```
import sharp from "sharp";
import fs from "fs";
// Create a new direcotry for that run
const nowMs = Date.now();
const outputDirectory = `./out/${nowMs}`;
fs.mkdirSync(outputDirectory);
// Create a CSV file in that directory
const csvWriter = fs.createWriteStream(`${outputDirectory}/_data.csv`, {
flags: 'a'
});
// Write the table column labels
csvWriter.write('color,resolution,fileSize,base64size \n');
// Create 700 images for each color in the given list
["white", "red", "blue", "green", "lavender"].forEach(async (color) => {
for (let index = 1; index <= 700; index++) {
const image = await createImage(color, index, index, outputDirectory);
// Write the data into CSV file
csvWriter.write(`${color},${index},${image.sizeByteLength},${image.sizeBase64} \n`);
}
});
async function createImage(color, width, height, outputDirectory) {
const imageBuffer = await sharp({
create: {
width,
height,
channels: 3,
background: color
}
}).png().toBuffer();
const fileName = `${width}x${height}.png`;
fs.writeFileSync(`${outputDirectory}/${fileName}`, imageBuffer);
return {
outputDirectory,
fileName,
// This is where we unwrap the relevant sizes and return them
sizeByteLength: imageBuffer.byteLength,
sizeBase64: imageBuffer.toString('base64url').length
}
}
```
Okay, this might seem a bit excessive (and it might be), but it generates 700 images with different resolutions (from 1x1 to 700x700) for five different background colors. It then writes the file size and the Base64 encoded size into a file that can be imported into a spreadsheet.
### The Data
Let us analyze the data a bit, starting with the raw results. Just so that we know what we are _basically_ looking at.
| color | resolution | fileSize | base64size | requestSize | Data-url size |
| --- | --- | --- | --- | --- | --- |
| blue | 1 | 90 | 120 | 864 | 143 |
| blue | 2 | 93 | 124 | 867 | 147 |
| ... | ... | ... | ... | ... | ... |
| blue | 699 | 8592 | 11456 | 9366 | 11479 |
| blue | 700 | 8606 | 11475 | 9380 | 11498 |
| green | 1 | 90 | 120 | 864 | 143 |
| green | 2 | 93 | 124 | 867 | 147 |
| ... | ... | ... | ... | ... | ... |
| lavender | 700 | 9218 | 12291 | 9992 | 12314 |
| red | 1 | 90 | 120 | 864 | 143 |
| ... | ... | ... | ... | ... | ... |
| red | 700 | 8606 | 11475 | 9380 | 11498 |
| white | 1 | 90 | 120 | 864 | 143 |
| ... | ... | ... | ... | ... | ... |
| white | 700 | 2992 | 3990 | 3766 | 4013 |
We have data points for 700 PNG images for five colors: blue, green, red, lavender, and white. The essential part is within the columns “fileSize” and “base64size”. These are the (uncompressed) file size and the size when we Base64 encode the same file. These data points are followed by columns referring to the total sizes. Column “requestSize” stands for the size of the payload plus the headers (request and response). In reality, they will differ a bit from request to request. Here, I assumed a static value of 774 bytes, more or less the median in Firefox. That's good enough for the analysis. The same goes for the data URL size. We want to add 23 bytes, as the encoded string is prefixed by `data:image/png;base64,`.
### Findings
Interestingly, more than one data point may cross the line of 100% bloat. It's the line where the sizes would be exactly equal. That means that there may be cases where it would have been finally better not to use a data-URL, to be the other way around again right afterward.

Let's understand the basic chart first. What does this mean? Simply put, for lavender, red, green, and blue, it would be preferable to use data-url up to a resolution of about 340x340. For white, you must start asking questions from a resolution of 570x570. Let's dig deeper into it. You can recognize a few things. First of all, the more complex (in our case, 'lavender') an image is, the more it gets bloated, thus reaching the point of “request preference” faster. That makes sense, as the PNG encoding needs to yield more uncompressable value. The next thing to notice is how the three base colors (Red, Green, and Blue) behave more or less identically. This makes sense because their binary data looks more or less the same. Of course, the most remarkable is the white data series. Not only is it the least complex image, thus the one that's longest in the “use data-url sector,” but it's also crossing the 100% bloat line twice! Well, the most critical data points are the ones where we cross the line of 100% bloat, right? Let's have a look at this then:
| resolution | blue | green | lavender | red | white |
| --- | --- | --- | --- | --- | --- |
| 337 | | | 0.9993 | | |
| 339 | | | 1.0013 | | |
| 341 | | | 0.9997 | | |
| 343 | 0.9997 | 0.9997 | | 0.9997 | |
| 573 | | | | | 0.9997 |
| 602 | | | | | 1.0287 |
| 608 | | | | | 0.9936 |

Woah! Even the lavender-series does the “crossing the line twice move”! Outstanding. Okay, what do these data points mean?
- For blue, red, and green, using a data URL for resolutions up to 343x343 would be preferable
- Lavender has different sections:
- 337 and 338: A request is preferable
- 339 and 340: A data URL is preferable (again)
- 341 and bigger: A request is preferable
- As already said, white also has different sections that stretch over a greater delta:
- 573 to 601: A request is preferable
- 602 to 607: A data URL is preferable (again)
- 608 and bigger: A request is preferable
> ⚠️ Just a heads up again: this is merely a lab. It is there to showcase how to measure and compare your data. It is not 100% accurate for the field, as we assumed static sizes that may differ from request to request. This is especially relevant for the lavender series, where the conclusion might change from one probe to the next. Also, it would help if you did not draw general conclusions from here. Depending on the complexity and file format, the results are entirely different. See how lavender is already far more different from white. That means that the edge cases are not to be generalized.
## To the Field!
Now, let's examine a real example. There is a great website hosted at [https://www.ungra.dev/](https://www.ungra.dev/). We load one optimized image there. It's as good as it gets for a JPG. The image has 21.63 kB, which adds up to 22.57 kB with the header overhead.

I refrain from posting the Base64 encoded version here. It's huge. It has a solid of 28,840 characters. Thus, the Data URL is 28,2 kB large. All in all, using **a Data URL would transfer 5,751 bytes more.**
Now, that image is only 239 × 340 pixels large. You can see that the evaluation depends more on the complexity of the image than its sheer resolution.
## File Formats
You may wonder about file formats. I tried to see how far I could go with the image in question from the previous chapter and converted it to AVIF. I compressed it – with reasonable losses - to 3,9 kB! That sounds promising to come to an even more apparent conclusion this time, right? However, the same picture also only has 5,2 kB Base64 encoded. That means that, in general terms, the question of whether to use a Data URL is not significantly impacted by the file format. It just scales the numbers.
## Excurse: What's with non-binary data?
Something that is probably interesting here is what happens with non-binary data. Let's take SVGs, for example. How are they Base64 encoded, and what does that mean for our decision to put them into data URLs or not? You can, of course, Base64 encode them just as any other data. However, it generally doesn't make sense, as the original file is already available in Unicode. Remember, Base64 is a “binary to text encoding” algorithm! If you encode SVGs, you don't win anything but bloat the file.
> ⚠️ There are some edge cases where this might come in handy! In general terms, however, refrain from doing this.
However, you can still use Data URIs for SVGs and the like! It's just that you do not add `charset=utf-8;base64` to it. It's merely `data:image/svg+xml;utf8,<SVG>...`. Remember that such a URL does not need to be Base64 encoded. We need this extra step to render binary data.
## Draw a Conclusion
Now that you know how to get the relevant numbers, it's relatively easy to conclude. Again, you must compare the request overhead with the increased file size of the Base64 encoded media. Is the request header size, response header size, and payload bigger than the Base64 data URL string? If yes, use the latter. If not, make a request.
## Other Considerations
In reality, you have to take a few more considerations into account. However, as they are very individual for particular scenarios or concern other “layers,” I will only briefly mention them here.
### Media Processing
First, if your media is not hosted on the edge, the latency increase may not be worth it. Also, the other way around: if your web app runs on really (!) poor hardware, it might not be worth using a data-url.
### Compare Zipped Data
Your data should be compressed. If you haven't done so yet, do it now (there is a big chance you do this already, as it's pretty much the default for most hosters/servers/...). This also means that we need to compare the compressed data here. (What we didn't do throughout this post to keep things simple.) The same goes for optimizing your resources first. For images, compress them as much as possible and use modern file formats like AVIF or WebP. SVGs should also be minimized with tools like OMGSVG.
### HTTP/2 and Server Push
With HTTP/2, a concept called server push makes data URLs nearly obsolete! A server can provide the resources we have encoded inline in one go. Read more about that here: [https://web.dev/performance-http2/#server-push](https://web.dev/performance-http2/#server-push).
Unfortunately, **server push is mainly abandoned and deprecated** nowadays. Even to an extent where I can say ignore it. If you want to read more about the why, head to this article: [https://developer.chrome.com/blog/removing-push/](https://developer.chrome.com/blog/removing-push/).
## Conclusion
Data URIs are primarily used with binary data encoded with an algorithm called Base64. It is made to display binary data in a text-based way. This is excellent for Data URIs, for they are text-based! However, Base64 makes the data larger. That means you must check whether it's better to have overhead with the request or to bloat your file.
## Further Reading
- [https://www.smashingmagazine.com/2017/04/guide-http2-server-push/](https://www.smashingmagazine.com/2017/04/guide-http2-server-push/)
- [https://www.davidbcalhoun.com/2011/when-to-base64-encode-images-and-when-not-to/](https://www.davidbcalhoun.com/2011/when-to-base64-encode-images-and-when-not-to/)
- [https://developer.mozilla.org/en-US/docs/web/http/basics\_of\_http/data\_urls](https://developer.mozilla.org/en-US/docs/web/http/basics_of_http/data_urls)
- [https://web.dev/performance-http2/](https://web.dev/performance-http2/)
- [https://www.rfc-editor.org/rfc/rfc2397#section-2](https://www.rfc-editor.org/rfc/rfc2397#section-2)
- [https://developer.mozilla.org/en-US/docs/Glossary/Base64](https://developer.mozilla.org/en-US/docs/Glossary/Base64)
- [https://css-tricks.com/probably-dont-base64-svg/](https://css-tricks.com/probably-dont-base64-svg/)
- [https://css-tricks.com/lodge/svg/09-svg-data-uris/](https://css-tricks.com/lodge/svg/09-svg-data-uris/)
- [https://developer.chrome.com/blog/removing-push/](https://developer.chrome.com/blog/removing-push/) | odddev | |
1,771,186 | HostLegends MAX FE Review | HostLegends MAX FE— The World’s #1 Hosting Companies Introduction HostLegends MAX FE HostLegends MAX... | 0 | 2024-02-24T20:20:27 | https://dev.to/sakibuddin/hostlegends-max-fe-review-2n9c | HostLegends MAX FE— The World’s #1 Hosting Companies
Introduction HostLegends MAX FE
HostLegends MAX FE is an innovative hosting solution tailored for businesses seeking top-tier performance, scalability, and reliability for their online presence. This cutting-edge hosting service is designed to meet the demanding needs of modern websites and applications, offering an array of advanced features and unparalleled support.
With HostLegends MAX FE, businesses can expect:
Maximum Performance: Leveraging state-of-the-art hardware and optimized software configurations, HostLegends MAX FE ensures lightning-fast page loading times and seamless user experiences, even during peak traffic periods.
Enterprise-Grade Scalability: Built to accommodate the growth of businesses of all sizes, HostLegends MAX FE offers scalable resources, allowing websites and applications to effortlessly handle sudden surges in traffic without compromising performance.
Advanced Security: Security is paramount in today’s digital landscape. HostLegends MAX FE employs robust security measures, including advanced firewalls, DDoS protection, SSL encryption, and proactive malware detection, to safeguard data and mitigate cyber threats effectively.
24/7 Expert Support: HostLegends MAX FE provides round-the-clock support from a team of experienced hosting professionals. Whether it’s technical assistance, troubleshooting, or guidance, customers can rely on prompt and knowledgeable support to address any issues or concerns.
High Availability and Reliability: Downtime can be costly for businesses. HostLegends MAX FE boasts an infrastructure engineered for high availability and reliability, with redundant systems, failover mechanisms, and regular backups to minimize disruptions and ensure continuous uptime.
Customization and Flexibility: Every business has unique requirements. HostLegends MAX FE offers customizable hosting solutions tailored to specific needs, whether it’s a content-heavy website, e-commerce platform, or resource-intensive application.
Streamlined Management: HostLegends MAX FE comes with intuitive control panels and management tools, empowering businesses to efficiently manage their hosting environment, deploy updates, and monitor performance metrics with ease.
Overall, HostLegends MAX FE redefines the hosting experience, delivering unmatched performance, security, and support to empower businesses to thrive in today’s digital landscape.
HostLegends MAX FE Overview
Product : HostLegends MAX FE
Creator : Firas Alameh — Rahul Gupta
Official Website : [Click Here](https://medium.com/@ultimate_maroon_bat_441/hostlegends-max-fe-review-81ed37ae2481l)
Front-End Price : $127.00
Recommendation: Highly Recommend!
Niche: Hosting
**_[click here for full blogs ](https://medium.com/@ultimate_maroon_bat_441/hostlegends-max-fe-review-81ed37ae2481)_** | sakibuddin | |
1,771,271 | zikojs tips : mapfun | 📝 Javascript provides a built-in Math module with various functions. ⚠️However, there is room for... | 0 | 2024-02-24T23:27:21 | https://dev.to/zakarialaoui10/zikojs-tips-mapfun-1c1k | javascript, math, zikojs, opensource | 📝 Javascript provides a built-in Math module with various functions.
⚠️However, there is room for improvement in terms of efficiency. For instance, the Math.sqrt(x) function can calculate the square root of a number x, but it has limitations such as the inability to accept multiple parameters and the inability to map the function to different data types like Arrays and Objects.
💡 In [zikojs](https://github.com/zakarialaoui10/ziko.js), I have addressed these limitations, providing a more versatile and efficient solution.
📋 Example :
|zikojs|Vanilla js Equivalent|
|-|-|
|`sqrt(9)`|`sqrt(9)`|
|`sqrt(4,9,16)`|`[Math.sqrt(4),Math.sqrt(9),Math.sqrt(16)]`|
|`sqrt([4,9,16])`|`[Math.sqrt(4),Math.sqrt(9),Math.sqrt(16)]`|
|`sqrt([4,9],16)`|`[[Math.sqrt(4),Math.sqrt(9)],Math.sqrt(16)]`|
|`sqrt({x:4,y:9})`|`{x:sqrt(4),sqrt(9)}`|
📢 Generally, zikojs allows you to input an infinite number of parameters, including deep arrays, objects, Maps, Sets, and more. The return value retains the input structure and calculates the result for each element accordingly.
📋 For Example :
```js
sqrt({
a:1,
b:2,
c:[3,4],
d:[[
[5,6]
]],
e:{
f:[
{g:7}
]
},
h:new Map([["i",8],["j",9]]),
k:{
l:{
m:new Set([10,11])
},
n:[12]
}
})
```
This would return :
```js
{
a:sqrt(1),
b:sqrt(2),
c:[sqrt(3),sqrt(4)],
d:[[
[sqrt(5),sqrt(6)]
]],
e:{
f:[
{g:sqrt(7)}
]
},
h:new Map([["i",sqrt(8)],["j",sqrt(9)]]),
k:{
l:{
m:new Set([sqrt(10),sqrt(11)])
},
n:[sqrt(12)]
}
}
```
💡 You can apply this approach to build your custom function ;
```js
import {mapfun} from "ziko";
const parabolic_func=(a,b,c,x)=>a*(x**2)+b*x+c;
const parabol=(a,b,c,...X)=>mapfun(n=>parabolic_func(a,b,c,n),...X)
const a=-1.5,b=2,c=3;
X0=[0,1,2,3];
X1={x10:0,x11:1,x12:2,x13:3}
console.log(parabol(a,b,c,X0));
// [3,3,1,3]
console.log(parabol(a,b,c,X1));
// {x10: 3,x11: 3,x12: 1,x13: -3}
console.log(parabol(a,b,c,X0,X1))
/*
[
[3,3,1,3],
{x10: 3,x11: 3,x12: 1,x13: -3}
]
*/
```
Or you can use the currying syntaxe :
```js
import {mapfun} from "ziko";
const parabolic_func=(a,b,c,x)=>a*(x**2)+b*x+c;
const map_parabolic_func=(a,b,c)=>(...X)=>mapfun(n=>parabolic_func(a,b,c,n),...X);
const a=-1.5,b=2,c=3;
const X=[0,1,2,3];
console.log(parabolic_func(a,b,c)(X));
// [3,3,1,3]
```
If you find the mapfun utility particularly useful and wish to use it independently, I have created a standalone micro package named mapfun. This micro package contains only the mapfun functions, allowing you to integrate it seamlessly into your projects without the need for the entire zikojs library.
For more information and to explore the mapfun micro package, visit [mapfun](https://github.com/zakarialaoui10/mapfun) on GitHub .
You may not necessarily rely on the mapfun utility every time, as [ZikoJS](https://github.com/zakarialaoui10/ziko.js) offers a variety of built-in mathematical functions that built on the top of `mapfun` and the Math module in javascript .
Here you will find the built in Mathematic functions in zikojs
- <code id="ziko-math-functions-abs">abs(...x)</code> : Calculate the absolute value of the arguments `(...X)`
- <code id="ziko-math-functions-sqrt">sqrt(...x)</code>
- <code id="ziko-math-functions-pow">pow(x,n)</code>
- <code id="ziko-math-functions-sqrtn">sqrtn(x,n)</code>
- <code id="ziko-math-functions-e">e(...x)</code>
- <code id="ziko-math-functions-ln">ln(...x)</code>
- <code id="ziko-math-functions-cos">cos(...x)</code>
- <code id="ziko-math-functions-sin">sin(...x)</code>
- <code id="ziko-math-functions-tan">tan(...x)</code>
- <code id="ziko-math-functions-sinc">sinc(...x)</code>
- <code id="ziko-math-functions-acos">acos(...x)</code>
- <code id="ziko-math-functions-asin">asin(...x)</code>
- <code id="ziko-math-functions-atan">atan(...x)</code>
- <code id="ziko-math-functions-cosh">cosh(...x)</code>
- <code id="ziko-math-functions-sinh">sinh(...x)</code>
- <code id="ziko-math-functions-acosh">acosh(...x)</code>
- <code id="ziko-math-functions-asinh">asinh(...x)</code>
- <code id="ziko-math-functions-atanh">atanh(...x)</code>
- <code id="ziko-math-functions-cot">cot(...x)</code>
- <code id="ziko-math-functions-sec">sec(...x)</code>
- <code id="ziko-math-functions-csc">csc(...x)</code>
- <code id="ziko-math-functions-acot">acot(...x)</code>
- <code id="ziko-math-functions-coth">coth(...x)</code>
- <code id="ziko-math-functions-acosh">acosh(...x)</code>
- <code id="ziko-math-functions-asinh">asinh(...x)</code>
- <code id="ziko-math-functions-atanh">atanh(...x)</code>
- <code id="ziko-math-functions-atan2">atan2(x,y,?rad)</code>
- <code id="ziko-math-functions-hypot">hypot(...x)</code>
- <code id="ziko-math-functions-min">min(...x)</code>
- <code id="ziko-math-functions-max">max(...x)</code>
- <code id="ziko-math-functions-sign">sign(...x)</code>
- <code id="ziko-math-functions-sig">sig(...x)</code>
- <code id="ziko-math-functions-fact">fact(...x)</code>
- <code id="ziko-math-functions-round">round(...x)</code>
- <code id="ziko-math-functions-floor">floor(...x)</code>
- <code id="ziko-math-functions-ceil">ceil(...x)</code>
| zakarialaoui10 |
1,782,632 | WMI ve Uzaktan Erişim | WMI yani "Windows Management Instrumentation", Windows 2000'den beri önkurulu olarak gelen ve Windows... | 0 | 2024-03-06T20:38:30 | https://dev.to/aciklab/wmi-ve-uzaktan-erisim-1hg2 | wmi, dcom, remote, uzak | WMI yani "**Windows Management Instrumentation**", Windows 2000'den beri önkurulu olarak gelen ve Windows işletim sistemi altyapısındaki bir çok bileşenin izlenebilmesi ve yönetilebilmesini sağlayan bir altyapıdır. WMI altyapısı işletim sistemi ile ilgili çeşitli bileşenleri kullanabilmek için endüstri standartı kullanılmaktadır.
WMI aynı zamanda uzak bilgisayarları yönetmek ve veri edinmek için kullanılan standart yöntemlerden birisidir. WMI altyapısına alternatif olarak Windows'un Windows Remote Management (**WinRM**) altyapısı da bulunmaktadır ki aslında ilgili yöntem de WS-Management adındaki SOAP tabanlı bir protokolle uzaktaki cihazın WMI altyapısını yönetmeyi içermektedir.
# WMI altyapısına uzaktan erişim açılması
WMI, uzaktan erişim için DCOM "**Distributed Component Object Model**" adındaki bir altyapıyı kullanmaktadır. Dolayısıyla uzak erişim sırasında özellikle ilk iki maddenin uzaktan GPO ile veya elle yapılması gerekmektedir. Bu ayarlar yetkisiz bir kullanıcı için de yapılmak isteniyorsa son maddenin, daha detaylı işlemlerin yapılması isteniyorsa da 3. maddenin de yapılması gerekmektedir.
1. Yerel Güvenlik Duvarı izni
2. Uzak WMI yetkisi
3. UAC "User Account Control" (bazı durumlarda)
4. DCOM objelerine erişim için kullanıcı izinleri (erişecek kullanıcı yetkili bir kullanıcı değil ise yapılması gerekir)
izinlerine ihtiyaç duymaktadır.
## 1. Yerel Güvenlik Duvarı erişim hakkında
Uzaktan WMI erişimi **TCP 135** portu ve 49152-65535 port aralığında RPC dinamik port aralığını kullanmaktadır. Dolayısıyla uzaktan bağlanılacak makinenin güvenlik duvarı kurallarını port bazında değil standart kurallarla yapılması daha uygun olacaktır.
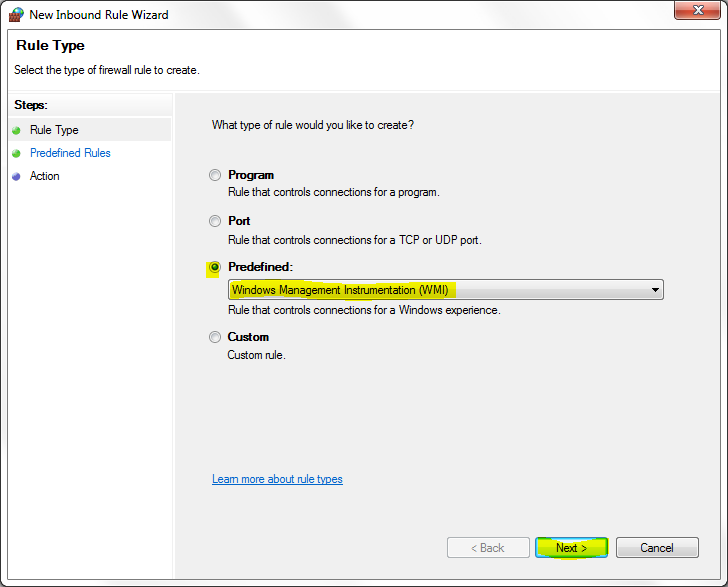
İlgili kuralı belirli bir IP'den erişim alacak şekilde yapılabilmesine ek olarak komut satırı üzerinden de aşağıdaki şekilde yapılabilmektedir.
> netsh advfirewall firewall set rule group="windows management instrumentation (wmi)" new enable=yes
Eğer sadece özel bir IP adresine yetki verilmesi isteniyorsa "remoteip=192.168.0.12" parametresini ekleyebilirsiniz.
İstenildiği takdirde Microsoft'un belgelerinden ve ekteki kaynaklardan daha detaylı kısıtlı erişim ayarları da yapılabilmektedir.
## 2. Uzak WMI yetkisi
Uzak WMI sorgulama yetkisi için "Computer Management" uygulaması içerisindeki WMI Control uygulamasının ayarlarındaki "Güvenlik" kısmında "Root" isimli WMI Namespace'ine remote olarak erişebilecek ve erişemeyecek kişilerin belirlenmesi önemlidir.
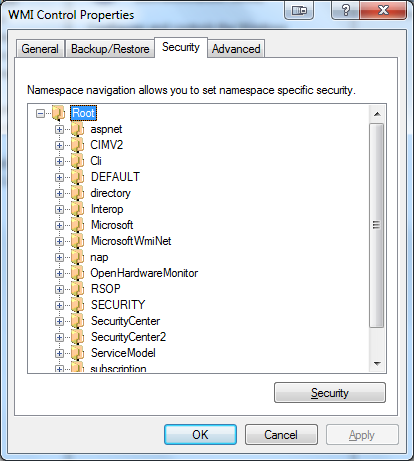
Uzaktan erişmesi istenen kullanıcı için "Uzak Erişim" yetkisi verilmiş olması gerekecektir. Yine sıkılaştırma için diğer kullanıcılarda bu erişim olmamasına önem gösterilmesi doğru olabilir. Çünkü bu ayar sonucunda hangi kullanıcının WMI objelerine erişebileceği belirlenmektedir.
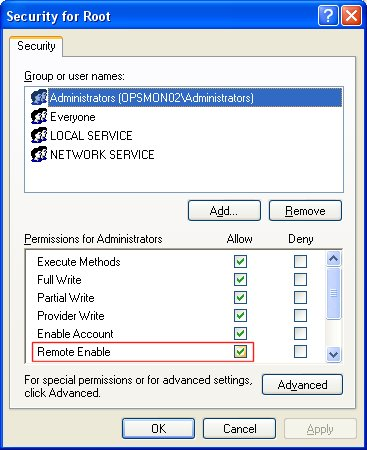
## 3. UAC "User Account Control"
Temel olarak bu adımın yapılması gerekmemektedir.
UAC, Microsoft'un görece daha yeni geliştirdiği bir uygulama olarak WMI üzerinde bazı işlemleri yapmanızda filtre uygulayabilir.
Yine de ileri komutlarda yaşanabilecek olası sorunlar için çözüm regedit üzerinde aşağıdaki adresteki DWORD anahtarını eklemek veya düzenleme yaparak "1" seçilerek filtreyi kapatmak gerekmektedir.
```
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\system\LocalAccountTokenFilterPolicy
```
> 0 = Remote UAC access token filtering is enabled.
> 1 = Remote UAC is disabled.
## 4. DCOM objelerine erişim
Temel olarak bu adımın yapılması gerekmemektedir.
Bu adım da aslında yetkili olmayan kullanıcılara da DCOM verilerine erişim verilebilmesi dolayısıyla WMI sorgularına cevap dönebilmesi için gereklidir. Fakat hali hazırda yetkili bir kullanıcı ile sorgu atılıyorsa bu adımın yapılması gerekmemektedir.
Bu adımda yetkisiz bir kullanıcıya iki yetki verilecektir.
* DCOM objelerine uzaktan çalıştırma
* DCOM objelerine uzaktan erişim
Bu işlemler için dcomcnfg uygulamasında yani "component services" uygulaması içerisinde "my computer" altında "COM Config" kısmına girilir.
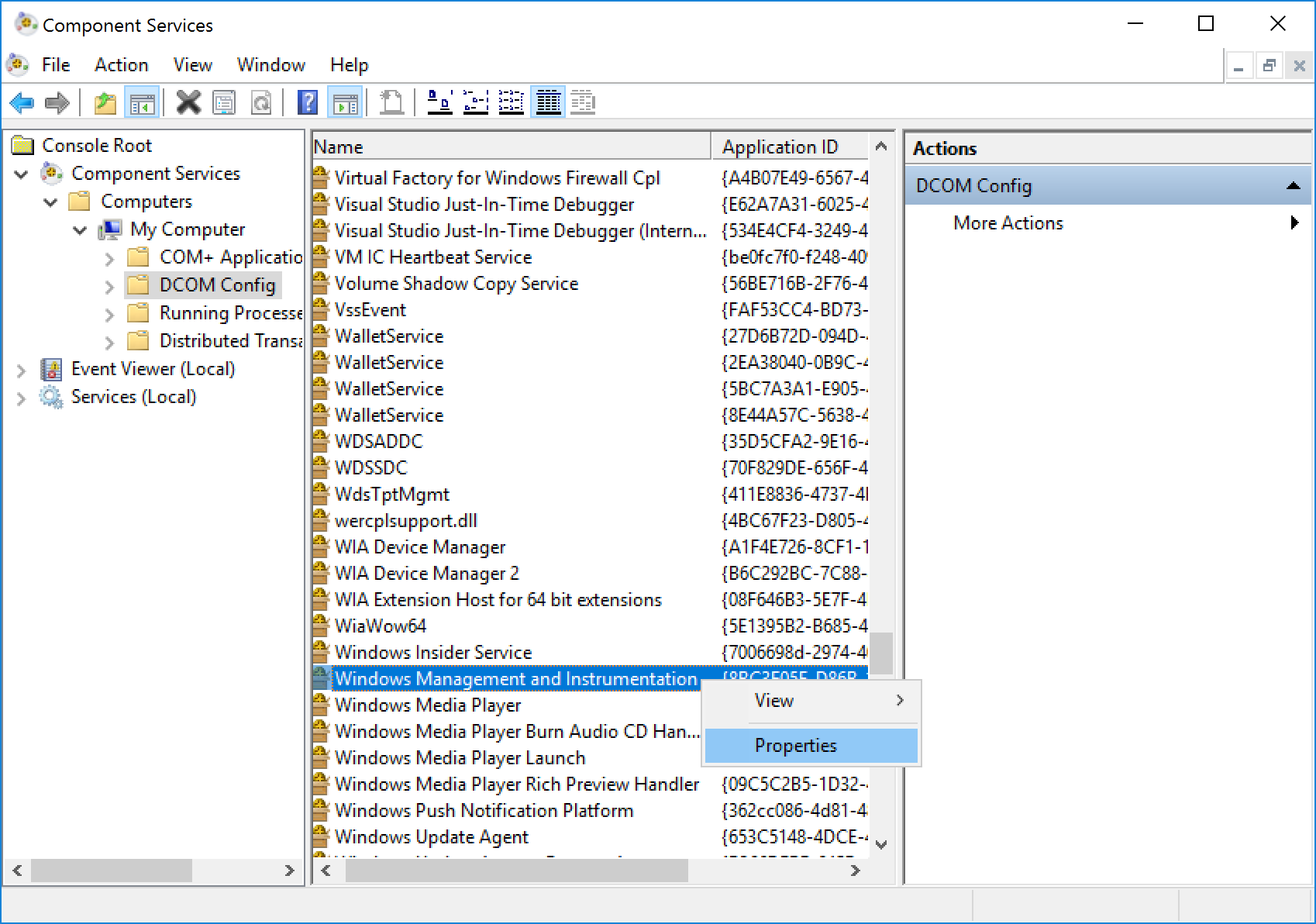
Güvenlik sekmesinde önce "Launch and Activation Permission" kısmına sonrasında "Access Permission" kısımlarını düzenlemek gerekecektir.
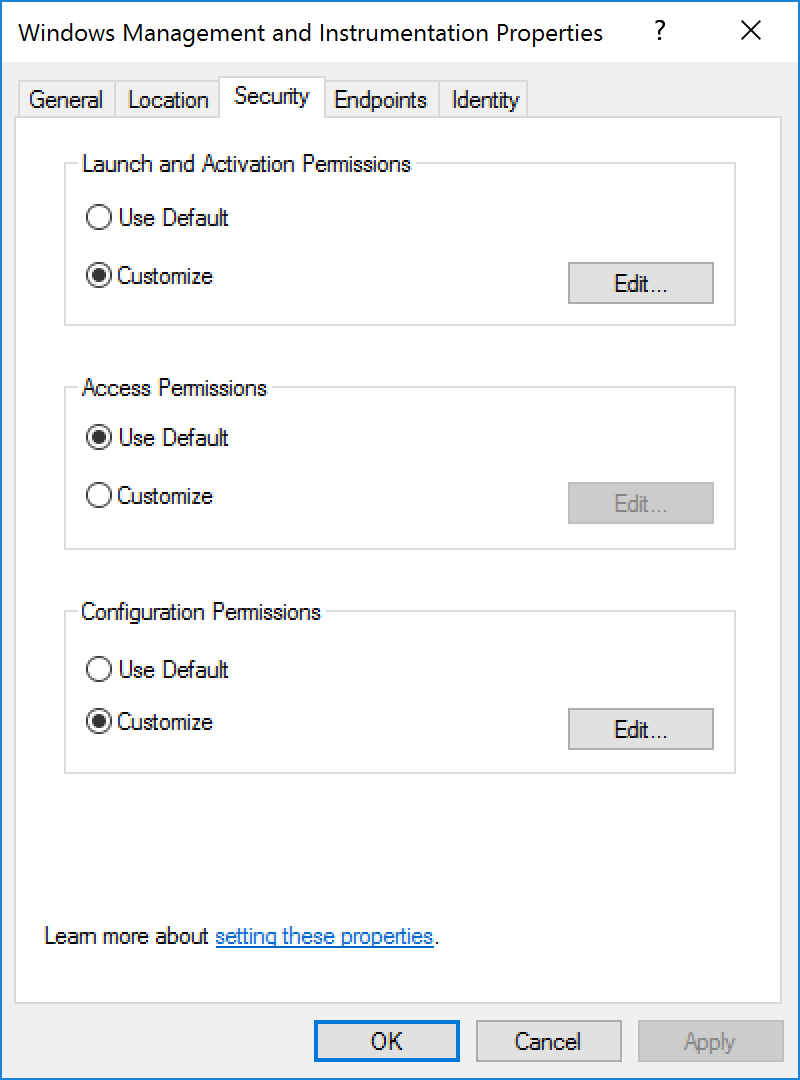
Her iki seçenekte de aşağıdaki gibi yetki verilmek istenen kullanıcı için "Remote Launch" içinde "Remote Activation" seçilmesi gerekmektedir.
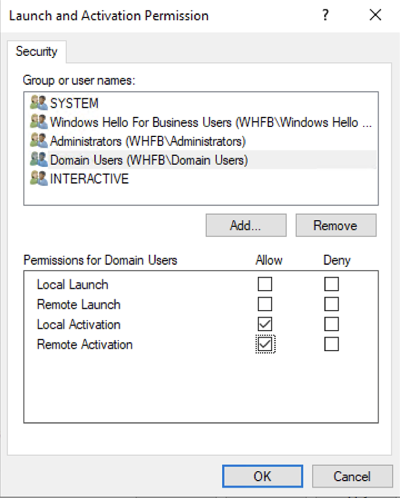
# Kontrol
Ayarlar açıldıktan sonra en temel ve basit kontrol için Powershell betik dili kullanılabilmektedir. Bunun için aşağıdaki betik kullanılabilir:
```powershell
$strComputer = "BilgisayarAdiveyaIP"
$colSettings = Get-WmiObject Win32_OperatingSystem -Credential ACIKLAB\administrator -ComputerName $strComputer
```
İlgili betik içerisinde BilgisayarAdiveyaIP stringi yerine IP Adresi de yazılabilmektedir. Credential olarak aşağıdaki tüm tipler kullanılabilmektedir.
- kullanici01
- DomainAdi\kullanici01
- kullanici@domainadi.lab
Bu adımdan sonra ilgili kullanıcı için parola bilgisi sorulduktan sonra yukarıdaki ağ ve sistem erişim yetkileri doğru şekilde tanımlanmışsa işletim sistemi ile ilgili WMI nesnelerine erişim sağlanabilecektir.
Sonrasında WMI objelerine erişim konusu ise apayrı bir konu olduğu için bu yazıda değinmiyorum ama ilgili kişiler için aşağıdaki yapıda inceleme yapılabilir.
- https://powershell.one/wmi/root/cimv2/win32_operatingsystem
- https://learn.microsoft.com/en-us/windows/win32/cimwin32prov/win32-operatingsystem
# WMIC hakkında
Tüm bu süreçlere ek olarak WMI'ın komut satırından kullanımını sağlayan araç olan [wmic](https://learn.microsoft.com/en-us/windows/win32/wmisdk/wmic), 2024 itibariyle desteklenmeyen sürüme düşmüş olup Powershell üzerinden kullanılması önerilmektedir. Dolayısıyla internette bulunabilecek bir çok eski komut yeni sistemlerde çalışmayacaktır.
# Kaynaklar:
- https://learn.microsoft.com/en-us/windows/win32/wmisdk/connecting-to-wmi-remotely-starting-with-vista
- https://support.vscope.net/setting-up-wmi-access-through-ad-gpo
- https://www.heelpbook.net/2018/enable-wmi-windows-management-instrumentation/
- https://softcomet.freshdesk.com/support/solutions/articles/6000222183-using-wmi-without-having-full-administrator-permissions
- https://learn.microsoft.com/en-us/windows/win32/wmisdk/connecting-to-wmi-on-a-remote-computer
| aliorhun |
1,779,803 | Implementando CSP con Nonces Dinámicos usando AWS CloudFormation, Lambda y CloudFront | En este artículo, exploraremos cómo reforzar la seguridad de nuestras aplicaciones web mediante la... | 0 | 2024-03-04T12:55:02 | https://dev.to/geramireze/implementando-csp-con-nonces-dinamicos-usando-aws-cloudformation-lambda-y-cloudfront-4klk |
En este artículo, exploraremos cómo reforzar la seguridad de nuestras aplicaciones web mediante la implementación de una política de seguridad de contenido (CSP) utilizando nonces (números utilizados una sola vez) dinámicos. Utilizaremos AWS CloudFormation para desplegar nuestra infraestructura, AWS Lambda para generar nonces dinámicos y Amazon CloudFront para servir nuestra aplicación con la CSP aplicada.
## ¿Qué es CSP y por qué es importante?
Content Security Policy (CSP) es una medida de seguridad adicional que ayuda a detectar y mitigar ciertos tipos de ataques, como Cross Site Scripting (XSS) y data injection. A través de CSP, un sitio web puede especificar qué recursos están permitidos cargar, evitando así la ejecución de recursos maliciosos.
Uno de los mecanismos que ofrece CSP para asegurar scripts es el uso de nonces. Un nonce es un valor aleatorio que el servidor genera para cada solicitud. Este valor se añade como atributo a los tags `<script>` en el HTML y se especifica en la política CSP, asegurando que solo los scripts con el nonce correcto se ejecuten.
## Paso 1: Configurando AWS CloudFormation
Comencemos por definir nuestra infraestructura como código usando AWS CloudFormation. Esto incluye nuestra función AWS Lambda, la configuración de AWS CloudFront y los permisos necesarios.
Aquí hay un ejemplo básico de una plantilla de CloudFormation para crear una función Lambda:
```yaml
Resources:
NonceLambdaFunction:
Type: AWS::Lambda::Function
Properties:
Handler: index.handler
Runtime: nodejs14.x
Code:
ZipFile: |
exports.handler = async (event) => {
const nonce = crypto.randomBytes(16).toString('base64');
return {
statusCode: 200,
headers: { 'Content-Type': 'text/plain' },
body: `Nonce: ${nonce}`,
};
};
Role: !GetAtt LambdaExecutionRole.Arn
LambdaExecutionRole:
Type: AWS::IAM::Role
Properties:
AssumeRolePolicyDocument:
Version: '2012-10-17'
Statement:
- Effect: Allow
Principal:
Service: lambda.amazonaws.com
Action: 'sts:AssumeRole'
Policies:
- PolicyName: root
PolicyDocument:
Version: '2012-10-17'
Statement:
- Effect: Allow
Action: 'logs:*'
Resource: 'arn:aws:logs:*:*:*'
```
Este fragmento define una función Lambda simple que genera un nonce aleatorio y lo devuelve. Asegúrate de incluir el módulo `crypto` necesario para generar el nonce.
## Paso 2: Integración con Amazon CloudFront
Para integrar nuestra función Lambda con Amazon CloudFront, utilizaremos Lambda@Edge. Esto nos permite ejecutar la función en respuesta a eventos de CloudFront, como solicitudes de contenido.
Necesitamos modificar nuestra plantilla de CloudFormation para incluir una asociación entre nuestra función Lambda y un comportamiento de CloudFront. Esto se puede hacer en la sección de distribución de CloudFront de la plantilla.
```yaml
Distribution:
Type: AWS::CloudFront::Distribution
Properties:
DistributionConfig:
DefaultCacheBehavior:
TargetOriginId: "myOrigin"
ViewerProtocolPolicy: redirect-to-https
LambdaFunctionAssociations:
- EventType: viewer-response
LambdaFunctionARN: !GetAtt NonceLambdaFunction.Version
```
Este fragmento asocia nuestra función Lambda con el evento `viewer-response`, lo que significa que se ejecutará cada vez que CloudFront responda a una solicitud.
## Paso 3: Configurando la Política CSP
Ahora, necesitamos modificar nuestra función Lambda para que no solo genere el nonce, sino que también lo incluya en las cabeceras CSP de las respuestas HTTP. Además, debemos asegurarnos de que nuestra aplicación web incluya este nonce en todos los tags `<script>`.
```javascript
exports.handler = async (event) => {
const nonce = crypto.randomBytes(16).toString('base64');
const cspPolicy = `default-src 'self'; script-src 'nonce-${nonce}' 'strict-dynamic';`;
return {
statusCode: 200,
headers: {
'Content-Type': 'text/html',
'Content-Security-Policy': cspPolicy
},
body: `Tu contenido HTML aquí`,
};
};
```
En tu aplicación web, asegúrate de incluir el nonce en tus tags de script de la siguiente manera:
```html
<script nonce="${nonce}">
// Tu código JavaScript aquí
</script>
```
Recuerda que el valor de `${nonce}` debe ser reemplazado por el nonce generado por tu función Lambda en cada respuesta.
## Conclusión
Al implementar CSP con nonces dinámicos, podemos mejorar significativamente la seguridad de nuestras aplicaciones web. Utilizando AWS CloudFormation, Lambda y CloudFront, podemos automatizar y escalar esta práctica de seguridad a lo largo de nuestra infraestructura. Este enfoque no solo nos ayuda a proteger contra ataques como XSS, sino que también asegura que solo los scripts que hemos aprobado se ejecuten en el navegador del usuario.
---
Espero que este artículo te haya sido útil y te anime a implementar medidas de seguridad adicionales en tus aplicaciones web. ¡La seguridad nunca debe ser una ocurrencia tardía! | geramireze | |
1,779,810 | Configuración y Despliegue Avanzados de WordPress en AWS: Un Enfoque Moderno con RDS, App Runner y Copilot | En este tutorial, exploraremos cómo llevar WordPress al siguiente nivel utilizando los servicios de... | 23,637 | 2024-03-04T13:05:27 | https://dev.to/geramireze/configuracion-y-despliegue-avanzados-de-wordpress-en-aws-un-enfoque-moderno-con-rds-app-runner-y-copilot-3bo2 | En este tutorial, exploraremos cómo llevar WordPress al siguiente nivel utilizando los servicios de AWS. Implementaremos WordPress con una base de datos Amazon RDS, lo alojaremos en AWS App Runner para una gestión sin servidor, y utilizaremos AWS Copilot para un despliegue eficiente. Además, introduciremos cómo integrar GraphQL para extender las capacidades del back-end de WordPress.
## Preparativos Iniciales
Antes de sumergirnos, asegúrate de tener una cuenta de AWS y las AWS CLI y Copilot CLI instaladas y configuradas en tu máquina. También necesitarás Docker para la creación y gestión de contenedores.
## Paso 1: Configurando la Base de Datos con Amazon RDS
Primero, configuraremos una base de datos segura y escalable utilizando Amazon RDS:
1. **Crear la base de datos:**
- Ve a la consola de RDS en AWS.
- Selecciona "Crear base de datos", elige MySQL o MariaDB (ambos compatibles con WordPress).
- Configura las opciones según tus necesidades, estableciendo un nombre de usuario y contraseña que deberás recordar para más adelante.
2. **Seguridad:**
- Asegúrate de que la base de datos esté en una VPC segura y accesible para tu servicio de App Runner.
3. **Conexión:**
- Anota el endpoint de RDS y los detalles de conexión para su uso posterior en la configuración de WordPress.
## Paso 2: Preparando WordPress para App Runner y Docker
Ahora, vamos a preparar WordPress para el despliegue:
1. **Dockerfile:**
Crea un `Dockerfile` en la raíz de tu proyecto WordPress con el siguiente contenido:
```Dockerfile
FROM wordpress:latest
RUN docker-php-ext-install pdo pdo_mysql
EXPOSE 80
```
Este Dockerfile parte de la imagen oficial de WordPress, instala extensiones de PHP necesarias y expone el puerto 80.
2. **Configuración de WordPress:**
Asegúrate de que el archivo `wp-config.php` de WordPress esté configurado para usar las credenciales de tu base de datos RDS.
## Paso 3: Implementando con AWS Copilot
Con AWS Copilot, simplificaremos el proceso de despliegue:
1. **Inicializar la aplicación:**
En tu terminal, navega a la carpeta de tu proyecto WordPress y ejecuta:
```bash
copilot app init my-wordpress-app
```
2. **Crear y desplegar el servicio:**
Sigue las instrucciones para configurar tu servicio con App Runner:
```bash
copilot svc init --name wordpress-service --dockerfile ./Dockerfile --deploy
copilot svc deploy --name wordpress-service --env test
```
Copilot construirá tu imagen Docker, la subirá a Amazon ECR y desplegará la aplicación en App Runner.
## Paso 4: Integrando GraphQL con WordPress
Para extender las capacidades de WordPress como un servicio de back-end, instala y activa el plugin WPGraphQL en tu instalación de WordPress. Esto proporcionará una API GraphQL de tus datos de WordPress que podrás consultar desde cualquier cliente front-end.
## Verificación y Pruebas
Una vez completado el despliegue, AWS Copilot proporcionará una URL para acceder a tu servicio. Verifica que puedes acceder a tu sitio WordPress y que la conexión con la base de datos RDS funciona correctamente. Además, prueba la API GraphQL accediendo a `tusitio.com/graphql`.
## Conclusión
Al completar este tutorial, has logrado crear una instalación moderna y escalable de WordPress en AWS, utilizando servicios gestionados como Amazon RDS y AWS App Runner, y herramientas de despliegue como AWS Copilot. Esta configuración no solo mejora la seguridad y la escalabilidad, sino que también facilita la gestión de tu infraestructura.
Además, al integrar GraphQL, has ampliado las capacidades de tu back-end de WordPress, permitiendo una interacción más flexible y potente con tus datos desde cualquier cliente front-end.
Esperamos que este tutorial te haya proporcionado los conocimientos y herramientas necesarios para llevar tus proyectos de WordPress al siguiente nivel con AWS.
| geramireze | |
1,780,030 | Bridging the Language Barrier: Playing a Visual Novel in Another Language with Google Translate's Camera | Visual novels, those captivating blends of storytelling and video games, have captivated audiences... | 0 | 2024-03-04T16:42:28 | https://dev.to/sediak/bridging-the-language-barrier-playing-a-visual-novel-in-another-language-with-google-translates-camera-3bel | gaming, visualnovel, googletranslate | Visual novels, those captivating blends of storytelling and video games, have captivated audiences worldwide. But what if your dream visual novel is locked away in a language you don't understand? Fear not, intrepid otaku (anime fan)! This experiment explores the feasibility of using Google Translate's camera feature to play a non-English visual novel, specifically focusing on languages that use a shared writing system: Chinese and Japanese.
**The Setup:**
**For this experiment, we'll need a few key ingredients:
**
A non-English visual novel: This can be a downloaded game or even a physical copy with on-screen text in languages like Chinese or Japanese. (Note: While [Chinese and Japanese use the same characters (kanji)](https://www.pandanese.com/blog/kanji-vs-chinese-characters), their pronunciations and meanings often differ.)
A smartphone or tablet: Equipped with the Google Translate app and a decent camera.
A little patience and a thirst for adventure!
**The Process:**
**Fire up Google Translate:** Open the app and ensure your desired translation languages are selected. Here, you might choose to translate from Chinese or Japanese to your native language, depending on your familiarity with these languages.
Launch the visual novel: Get ready to embark on your linguistic journey!
**Point and translate:** Here's the fun part! Use your smartphone or tablet's camera to focus on the text in the visual novel. Google Translate, through its magic of real-time translation, should display the translated text on your screen.
The Results:
While Google Translate's camera feature has improved significantly, it's important to manage expectations. Here's what **you can expect:**
**Real-time (ish) translation:** Witness the on-screen text magically transform into your chosen language, albeit with a slight delay.
**Imperfect, but understandable:** Translations might not be grammatically perfect, especially when dealing with the complexities of Kanji interpretation. The meaning might be conveyed, but context is crucial.
**Context matters:** Complex sentence structures or slang might get lost in translation, requiring some piecing together from your side. Additionally, Google Translate might struggle to differentiate between Chinese and Japanese Kanji, potentially leading to mistranslations.
**Beyond the Experiment:**
This experiment demonstrates the potential of Google Translate's camera feature for unlocking the world of visual novels across languages, even those that share a writing system like Chinese and Japanese. While not a perfect solution, it offers a glimpse into the story and allows you to experience the core narrative. Here are some additional thoughts:
**Community Collaboration:** Imagine online communities where players share screenshots and collaboratively translate visual novels using Google Translate and their language expertise, especially when dealing with the nuances of Kanji interpretation.
Developer Integration: Perhaps one day, visual novel developers will integrate built-in translation tools powered by Google Translate or similar services, with options to differentiate between languages that share Kanji characters.
**The Final Verdict:**
Playing a visual novel in Chinese or Japanese using Google Translate's camera feature can be a fun and rewarding experience. While not a substitute for a polished localization, it offers a unique way to engage with foreign language stories and explore the world of visual novels beyond language barriers. So, grab your phone, choose your adventure, and get ready to experience the world of visual novels in a whole new light (or language)! | sediak |
1,780,146 | PHP Data Types | Variables can store data of different types, and different data types can do different things. PHP... | 0 | 2024-03-04T17:53:41 | https://dev.to/mbarekderadler/php-data-types-2p54 | Variables can store data of different types, and different data types can do different things.
PHP supports the following data types:
- String
- Integer
- Float (floating point numbers - also called double)
- Boolean
- Array
- Object
- NULL
- Resource
**Getting the Data Type**
You can get the data type of any object by using the var_dump() function.
**Example**
The var_dump() function returns the data type and the value:
```
$x = 5;
var_dump($x);
```
**PHP String**
A string is a sequence of characters, like "Hello world!".
A string can be any text inside quotes. You can use single or double quotes:
**Example**
```
$x = "Hello world!";
$y = 'Hello world!';
var_dump($x);
echo "<br>";
var_dump($y);
```
**PHP Integer**
An integer data type is a non-decimal number between -2,147,483,648 and 2,147,483,647.
**Rules for integers:**
An integer must have at least one digit
An integer must not have a decimal point
An integer can be either positive or negative
Integers can be specified in: decimal (base 10), hexadecimal (base 16), octal (base 8), or binary (base 2) notation
In the following example $x is an integer. The PHP var_dump() function returns the data type and value:
**Example**
```
$x = 5985;
var_dump($x);
```
**PHP Float**
A float (floating point number) is a number with a decimal point or a number in exponential form.
In the following example $x is a float. The PHP var_dump() function returns the data type and value:
**Example**
```
$x = 10.365;
var_dump($x);
```
**PHP Boolean**
A Boolean represents two possible states: TRUE or FALSE.
**Example**
```
$x = true;
var_dump($x);
```
Booleans are often used in conditional testing.
You will learn more about conditional testing in the PHP If...Else chapter.
**PHP Array**
An array stores multiple values in one single variable.
In the following example $cars is an array. The PHP var_dump() function returns the data type and value:
**Example**
```
$cars = array("Volvo","BMW","Toyota");
var_dump($cars);
```
**PHP Object**
Classes and objects are the two main aspects of object-oriented programming.
A class is a template for objects, and an object is an instance of a class.
When the individual objects are created, they inherit all the properties and behaviors from the class, but each object will have different values for the properties.
Let's assume we have a class named Car that can have properties like model, color, etc. We can define variables like $model, $color, and so on, to hold the values of these properties.
When the individual objects (Volvo, BMW, Toyota, etc.) are created, they inherit all the properties and behaviors from the class, but each object will have different values for the properties.
If you create a __construct() function, PHP will automatically call this function when you create an object from a class.
**Example**
```
class Car {
public $color;
public $model;
public function __construct($color, $model) {
$this->color = $color;
$this->model = $model;
}
public function message() {
return "My car is a " . $this->color . " " . $this->model . "!";
}
}
$myCar = new Car("red", "Volvo");
var_dump($myCar);
```
**PHP NULL Value**
Null is a special data type which can have only one value: NULL.
A variable of data type NULL is a variable that has no value assigned to it.
Tip: If a variable is created without a value, it is automatically assigned a value of NULL.
Variables can also be emptied by setting the value to NULL:
**Example**
```
$x = "Hello world!";
$x = null;
var_dump($x);
```
**Change Data Type**
If you assign an integer value to a variable, the type will automatically be an integer.
If you assign a string to the same variable, the type will change to a string:
**Example**
```
$x = 5;
var_dump($x);
$x = "Hello";
var_dump($x);
```
| mbarekderadler | |
1,780,150 | Google UI Clone in HTML and Tailwind CSS | Introduction: In the world of web development, creating clones of popular websites is a... | 0 | 2024-03-04T17:58:27 | https://dev.to/rohitnirban/google-clone-in-html-and-tailwind-css-2nh4 | tailwindcss, html, beginners, webdev | ### Introduction:
In the world of web development, creating clones of popular websites is a fantastic way to practice and improve your skills. One of the most iconic and widely used websites is Google. In this blog post, we'll walk through the process of building a simplified Google clone using HTML for the structure and Tailwind CSS for styling.
Prerequisites:
Before we start, make sure you have the following installed:
1. Code editor (e.g., Visual Studio Code, Sublime Text)
2. Browser (e.g., Chrome, Firefox)
3. Node.js and npm (for installing Tailwind CSS)
Let's get started:
### Step 1: Install Nodejs
Before we proceed with the Google Clone project using HTML and Tailwind CSS, let's ensure that you have Node.js installed on your system. Node.js is required for installing and managing packages, including Tailwind CSS. Follow these steps to install Node.js:
**i) Download Node.js:**
Visit the official Node.js website: [Node.js Downloads](https://nodejs.org/en/download/)
**ii) Choose the Appropriate Version:**
Select the version that corresponds to your operating system. The website usually recommends the LTS (Long Term Support) version for most users.
**iii) Install Node.js:**
Follow the installation instructions provided on the website for your specific operating system. The process is typically straightforward, involving accepting the license agreement and choosing the installation directory.
**iv) Verify Installation:**
Open a terminal or command prompt and run the following commands to verify that Node.js and npm (Node Package Manager) are installed successfully:
```bash
node -v
```
```bash
npm -v
```
If installed correctly, these commands should display the installed Node.js and npm versions.
Now that you have Node.js installed, you can proceed with the Google Clone project using HTML and Tailwind CSS as outlined in the initial steps of the blog post. If you encounter any issues during installation, refer to the official Node.js documentation or seek help from the Node.js community.
Once Node.js is installed, continue with the remaining steps in the blog post to set up the project and create the Google Clone.
### Step 2: Set Up Your Project
To ensure a smooth setup for your project, follow these steps carefully:
**i) Create Project Structure:**
Open your terminal and navigate to the desired location for your project. Create a new folder for your project and open it in your code editor. Inside this project folder, create another folder named `src`. This is where your source code will reside.
```bash
mkdir my-google-clone
cd my-google-clone
mkdir src
```
**ii) Create Files:**
Inside the `src` folder, create two files: `index.html` for HTML content and `input.css` for your Tailwind CSS input.
```bash
cd src
touch index.html input.css
```
**iii) Initialize npm and Install Tailwind CSS:**
Back in the root folder, initialize npm and install Tailwind CSS as development dependencies.
```bash
npm init -y
npm install -D tailwindcss
npx tailwindcss init
```
**iv) Configure tailwind.config.js:**
Open the `tailwind.config.js` file created in your project root and replace its content with the following:
```js
/** @type {import('tailwindcss').Config} */
module.exports = {
content: ["./src/**/*.{html,js}"],
theme: {
extend: {},
},
plugins: [],
}
```
**v) Setup input.css in src folder:**
Open the `input.css` file inside the `src` folder and paste the following content:
```css
@tailwind base;
@tailwind components;
@tailwind utilities;
```
**vi) Watch for Changes:**
Run the following command in your terminal to watch for changes in your CSS file and automatically generate the output:
```bash
npx tailwindcss -i ./src/input.css -o ./src/output.css --watch
```
**vii) Link CSS in index.html:**
In your `index.html` file, link the generated `output.css`:
```html
<!DOCTYPE html>
<html lang="en">
<head>
<meta charset="UTF-8">
<meta name="viewport" content="width=device-width, initial-scale=1.0">
<link rel="stylesheet" href="src/output.css">
<title>Google</title>
</head>
<body>
<!-- Your content goes here -->
</body>
</html>
```
With these steps completed, your project is set up and ready for building the Google Clone using HTML and Tailwind CSS.
### Step 3: Add Favicon and Title
Ensure a polished and professional appearance for your project by incorporating a favicon and setting an appropriate title in your `index.html` file. Follow the refined HTML structure below:
```html
<!DOCTYPE html>
<html lang="en">
<head>
<meta charset="UTF-8">
<meta name="viewport" content="width=device-width, initial-scale=1.0">
<link rel="icon" href="https://www.google.com/favicon.ico" type="image/x-icon">
<title>Google Clone</title>
<link rel="stylesheet" href="./output.css">
</head>
<body>
<!-- Your content goes here -->
</body>
</html>
```
In this improved version:
**i) Favicon Update:**
- The `type="image/x-icon"` attribute has been added to explicitly declare the favicon's file type.
- The comment indicates where you can insert the specific path or URL for your favicon.
**ii) Title Enhancement:**
- The title has been modified to "Google Clone" to better reflect the nature of your project.
- This title serves as an identifier for your web page, especially when users have multiple tabs open.
**iii) Stylesheet Link:**
- The link to the stylesheet (`output.css`) remains intact, ensuring that your Tailwind CSS styles are applied consistently.
Feel free to customize the favicon and title according to your project's theme and branding. This step contributes to a more professional and cohesive web application.
### Step 4: Create the HTML Structure and Add Styling to the Container
To ensure a well-organized and visually appealing layout, let's refine the HTML structure and enhance the styling for the container in your index.html file:
```html
<div class="container flex flex-col justify-between h-screen bg-[#202124] text-white">
<div class="top">
<a href="#">Gmail</a>
<a href="#">Images</a>
<p>
<svg class="gb_g" focusable="false" height="24px" viewBox="0 0 24 24" width="24px" fill="white">
<path
d="M22.29,18.37a2,2,0,0,0,0-.24,4.3,4.3,0,0,0-.09-.47c-.05-.15-.11-.31-.17-.46a3.88,3.88,0,0,0-.24-.45l-6.3-8.94V3.64h1.48a.92.92,0,0,0,0-1.84H7.36a.92.92,0,0,0,0,1.84H8.84V7.81L2.55,16.75a2.17,2.17,0,0,0-.24.45,2.85,2.85,0,0,0-.17.46A3.89,3.89,0,0,0,2,18.6c0,.08,0,.16,0,.23A3.8,3.8,0,0,0,2.26,20a3.6,3.6,0,0,0,.59,1,2.5,2.5,0,0,0,.32.33,2.54,2.54,0,0,0,.36.29,3.89,3.89,0,0,0,.4.25,4.28,4.28,0,0,0,.43.19,3.76,3.76,0,0,0,1.22.21H18.72A3.67,3.67,0,0,0,19.94,22l.44-.19a3.64,3.64,0,0,0,1.8-2.28,3.2,3.2,0,0,0,.11-.69,1.69,1.69,0,0,0,0-.23A1.77,1.77,0,0,0,22.29,18.37Zm-1.95.44a.78.78,0,0,1-.05.18l0,.08a.78.78,0,0,0-.05.14,2.09,2.09,0,0,1-.46.64l-.09.08a.88.88,0,0,1-.17.12l-.15.09-.11.06-.25.09a2.33,2.33,0,0,1-.53.07H5.85a1.27,1.27,0,0,1-.28,0,1.93,1.93,0,0,1-.73-.26A.91.91,0,0,1,4.68,20l-.23-.2h0a2.21,2.21,0,0,1-.3-.45l-.06-.12a1.77,1.77,0,0,1-.15-.65,1.88,1.88,0,0,1,.3-1.12l0-.05L10.67,8.5h0V3.64h2.95V8.49h0l6.44,8.92a2.38,2.38,0,0,1,.17.31,2.12,2.12,0,0,1,.14.68A2.58,2.58,0,0,1,20.34,18.81Z">
</path>
<path d="M5.66,17.74A.82.82,0,0,0,6.36,19H17.94a.82.82,0,0,0,.7-1.26l-4.1-5.55H9.76Z"></path>
</svg>
</p>
<img src="https://lh3.googleusercontent.com/ogw/AF2bZygffze6fXhK7PI86Z_QjVt-8SSQeQyBJ9AV7pTbMg=s32-c-mo">
</div>
<div class="middle">
<img src="https://www.google.com/images/branding/googlelogo/1x/googlelogo_light_color_272x92dp.png"
alt="Google" width="272px">
<input type="text" class="input-box">
<div>
<button
class="btn">Google
Search</button>
<button
class="btn">I'm
Feeling Lucky</button>
</div>
<div class="languages">
<p>Google offered in:</p>
<p>हिन्दी বাংলা తెలుగు मराठी தமிழ் ગુજરાતી ಕನ್ನಡ മലയാളം ਪੰਜਾਬੀ</p>
</div>
</div>
<div class="bottom">
<div class="bottom-top">
<p>India</p>
</div>
<div class="bottom-bottom">
<div class="bottom-bottom-left">
<a href="#">About</a>
<a href="#">Advertising</a>
<a href="#">Business</a>
<a href="#">How Search works</a>
</div>
<div class="bottom-bottom-right">
<a href="#">Privacy</a>
<a href="#">Terms</a>
<a href="#">Settings</a>
</div>
</div>
</div>
</div>
```
### Step 5: Add Styling to Top Container
Let's refine the styling of the top container to ensure a polished and visually appealing design in your index.html file:
```html
<div class="top flex gap-4 justify-end mt-5 mr-6 text-sm">
<a href="#" class="hover:underline">Gmail</a>
<a href="#" class="hover:underline">Images</a>
<p class="hover:bg-gray-800 cursor-pointer p-2 rounded-full -mt-2">
<svg class="gb_g" focusable="false" height="24px" viewBox="0 0 24 24" width="24px" fill="white">
<path
d="M22.29,18.37a2,2,0,0,0,0-.24,4.3,4.3,0,0,0-.09-.47c-.05-.15-.11-.31-.17-.46a3.88,3.88,0,0,0-.24-.45l-6.3-8.94V3.64h1.48a.92.92,0,0,0,0-1.84H7.36a.92.92,0,0,0,0,1.84H8.84V7.81L2.55,16.75a2.17,2.17,0,0,0-.24.45,2.85,2.85,0,0,0-.17.46A3.89,3.89,0,0,0,2,18.6c0,.08,0,.16,0,.23A3.8,3.8,0,0,0,2.26,20a3.6,3.6,0,0,0,.59,1,2.5,2.5,0,0,0,.32.33,2.54,2.54,0,0,0,.36.29,3.89,3.89,0,0,0,.4.25,4.28,4.28,0,0,0,.43.19,3.76,3.76,0,0,0,1.22.21H18.72A3.67,3.67,0,0,0,19.94,22l.44-.19a3.64,3.64,0,0,0,1.8-2.28,3.2,3.2,0,0,0,.11-.69,1.69,1.69,0,0,0,0-.23A1.77,1.77,0,0,0,22.29,18.37Zm-1.95.44a.78.78,0,0,1-.05.18l0,.08a.78.78,0,0,0-.05.14,2.09,2.09,0,0,1-.46.64l-.09.08a.88.88,0,0,1-.17.12l-.15.09-.11.06-.25.09a2.33,2.33,0,0,1-.53.07H5.85a1.27,1.27,0,0,1-.28,0,1.93,1.93,0,0,1-.73-.26A.91.91,0,0,1,4.68,20l-.23-.2h0a2.21,2.21,0,0,1-.3-.45l-.06-.12a1.77,1.77,0,0,1-.15-.65,1.88,1.88,0,0,1,.3-1.12l0-.05L10.67,8.5h0V3.64h2.95V8.49h0l6.44,8.92a2.38,2.38,0,0,1,.17.31,2.12,2.12,0,0,1,.14.68A2.58,2.58,0,0,1,20.34,18.81Z">
</path>
<path d="M5.66,17.74A.82.82,0,0,0,6.36,19H17.94a.82.82,0,0,0,.7-1.26l-4.1-5.55H9.76Z"></path>
</svg>
</p>
<img class="rounded-full -mt-1"
src="https://lh3.googleusercontent.com/ogw/AF2bZygk3RIBDBQh5DW7mjofxL64jZjLSOYU1zw65B7G=s32-c-mo">
</div>
```
### Step 6: Add Styling to Middle Container
```html
<div class="middle flex flex-col justify-evenly items-center h-80 -mt-48">
<img src="https://www.google.com/images/branding/googlelogo/1x/googlelogo_light_color_272x92dp.png"
alt="Google" width="272px">
<div class="">
<span class="h-5 w-5 absolute mt-9 -ml-[17rem]">
<svg focusable="false" fill="#9aa0a6" xmlns="http://www.w3.org/2000/svg" viewBox="0 0 24 24">
<path
d="M15.5 14h-.79l-.28-.27A6.471 6.471 0 0 0 16 9.5 6.5 6.5 0 1 0 9.5 16c1.61 0 3.09-.59 4.23-1.57l.27.28v.79l5 4.99L20.49 19l-4.99-5zm-6 0C7.01 14 5 11.99 5 9.5S7.01 5 9.5 5 14 7.01 14 9.5 11.99 14 9.5 14z">
</path>
</svg>
</span>
<span class="h-6 w-6 absolute mt-8 ml-[15.5rem]">
<svg focusable="false" viewBox="0 0 192 192" xmlns="http://www.w3.org/2000/svg">
<rect fill="none" height="192" width="192"></rect>
<g>
<circle fill="#34a853" cx="144.07" cy="144" r="16"></circle>
<circle fill="#4285f4" cx="96.07" cy="104" r="24"></circle>
<path fill="#ea4335"
d="M24,135.2c0,18.11,14.69,32.8,32.8,32.8H96v-16l-40.1-0.1c-8.8,0-15.9-8.19-15.9-17.9v-18H24V135.2z">
</path>
<path fill="#fbbc04"
d="M168,72.8c0-18.11-14.69-32.8-32.8-32.8H116l20,16c8.8,0,16,8.29,16,18v30h16V72.8z">
</path>
<path fill="#4285f4"
d="M112,24l-32,0L68,40H56.8C38.69,40,24,54.69,24,72.8V92h16V74c0-9.71,7.2-18,16-18h80L112,24z">
</path>
</g>
</svg>
</span>
<span class="h-6 w-6 absolute mt-8 ml-[13rem]">
<svg focusable="false" viewBox="0 0 24 24" xmlns="http://www.w3.org/2000/svg">
<path fill="#4285f4"
d="m12 15c1.66 0 3-1.31 3-2.97v-7.02c0-1.66-1.34-3.01-3-3.01s-3 1.34-3 3.01v7.02c0 1.66 1.34 2.97 3 2.97z">
</path>
<path fill="#34a853" d="m11 18.08h2v3.92h-2z"></path>
<path fill="#fbbc04"
d="m7.05 16.87c-1.27-1.33-2.05-2.83-2.05-4.87h2c0 1.45 0.56 2.42 1.47 3.38v0.32l-1.15 1.18z">
</path>
<path fill="#ea4335"
d="m12 16.93a4.97 5.25 0 0 1 -3.54 -1.55l-1.41 1.49c1.26 1.34 3.02 2.13 4.95 2.13 3.87 0 6.99-2.92 6.99-7h-1.99c0 2.92-2.24 4.93-5 4.93z">
</path>
</svg>
</span>
</div>
<input type="text"
class="w-[575px] bg-[#202124] border border-gray-500 text-white pl-12 pr-20 py-3 rounded-full hover:bg-[#303134] outline-none">
<div>
<button
class="px-4 py-2 bg-[#303134] rounded border border-[#202124] hover:border hover:border-gray-500 mx-2 text-sm">Google
Search</button>
<button
class="px-4 py-2 bg-[#303134] rounded border border-[#202124] hover:border hover:border-gray-500 text-sm">I'm
Feeling Lucky</button>
</div>
<div class="flex gap-3">
<p class="text-gray-400 text-sm">Google offered in:</p>
<p class="text-[#8ab4f8] text-sm">हिन्दी বাংলা తెలుగు मराठी தமிழ் ગુજરાતી ಕನ್ನಡ മലയാളം ਪੰਜਾਬੀ</p>
</div>
</div>
```
### Step 7: Add Styling to Bottom Container
To enhance the styling of the bottom container in your Google Clone project, update the HTML structure and apply Tailwind CSS classes. Here's the refined version:
```html
<div class="bottom bg-[#171717] text-sm">
<div class="bottom-top p-3">
<span class="pl-6 cursor-pointer">India</span>
</div>
<div class="p-3 flex justify-between border-t-2 border-gray-700">
<div class="flex gap-8">
<a href="#" class="pl-6">About</a>
<a href="#" class="hover:underline">Advertising</a>
<a href="#" class="hover:underline">Business</a>
<a href="#" class="hover:underline">How Search works</a>
</div>
<div class="flex gap-8">
<a href="#" class="hover:underline">Privacy</a>
<a href="#" class="hover:underline">Terms</a>
<a href="#" class="hover:underline">Settings</a>
</div>
</div>
</div>
```
### Step 8: Full HTML Code version
This includes the structure and styles for all the mentioned containers in your Google Clone project. Feel free to adjust or modify it based on your specific requirements.
```html
<!DOCTYPE html>
<html lang="en">
<head>
<meta charset="UTF-8">
<meta name="viewport" content="width=device-width, initial-scale=1.0">
<link rel="icon" href="https://www.google.com/favicon.ico">
<title>Google</title>
<link href="./output.css" rel="stylesheet">
</head>
<body>
<div class="flex flex-col justify-between h-screen bg-[#202124] text-white">
<div class="top flex gap-4 justify-end mt-5 mr-6 text-sm">
<a href="#" class="hover:underline">Gmail</a>
<a href="#" class="hover:underline">Images</a>
<p class="hover:bg-gray-800 cursor-pointer p-2 rounded-full -mt-2">
<svg class="gb_g" focusable="false" height="24px" viewBox="0 0 24 24" width="24px" fill="white">
<path
d="M22.29,18.37a2,2,0,0,0,0-.24,4.3,4.3,0,0,0-.09-.47c-.05-.15-.11-.31-.17-.46a3.88,3.88,0,0,0-.24-.45l-6.3-8.94V3.64h1.48a.92.92,0,0,0,0-1.84H7.36a.92.92,0,0,0,0,1.84H8.84V7.81L2.55,16.75a2.17,2.17,0,0,0-.24.45,2.85,2.85,0,0,0-.17.46A3.89,3.89,0,0,0,2,18.6c0,.08,0,.16,0,.23A3.8,3.8,0,0,0,2.26,20a3.6,3.6,0,0,0,.59,1,2.5,2.5,0,0,0,.32.33,2.54,2.54,0,0,0,.36.29,3.89,3.89,0,0,0,.4.25,4.28,4.28,0,0,0,.43.19,3.76,3.76,0,0,0,1.22.21H18.72A3.67,3.67,0,0,0,19.94,22l.44-.19a3.64,3.64,0,0,0,1.8-2.28,3.2,3.2,0,0,0,.11-.69,1.69,1.69,0,0,0,0-.23A1.77,1.77,0,0,0,22.29,18.37Zm-1.95.44a.78.78,0,0,1-.05.18l0,.08a.78.78,0,0,0-.05.14,2.09,2.09,0,0,1-.46.64l-.09.08a.88.88,0,0,1-.17.12l-.15.09-.11.06-.25.09a2.33,2.33,0,0,1-.53.07H5.85a1.27,1.27,0,0,1-.28,0,1.93,1.93,0,0,1-.73-.26A.91.91,0,0,1,4.68,20l-.23-.2h0a2.21,2.21,0,0,1-.3-.45l-.06-.12a1.77,1.77,0,0,1-.15-.65,1.88,1.88,0,0,1,.3-1.12l0-.05L10.67,8.5h0V3.64h2.95V8.49h0l6.44,8.92a2.38,2.38,0,0,1,.17.31,2.12,2.12,0,0,1,.14.68A2.58,2.58,0,0,1,20.34,18.81Z">
</path>
<path d="M5.66,17.74A.82.82,0,0,0,6.36,19H17.94a.82.82,0,0,0,.7-1.26l-4.1-5.55H9.76Z"></path>
</svg>
</p>
<img class="rounded-full -mt-1"
src="https://lh3.googleusercontent.com/ogw/AF2bZygk3RIBDBQh5DW7mjofxL64jZjLSOYU1zw65B7G=s32-c-mo">
</div>
<div class="middle flex flex-col justify-evenly items-center h-80 -mt-48">
<img src="https://www.google.com/images/branding/googlelogo/1x/googlelogo_light_color_272x92dp.png"
alt="Google" width="272px">
<div class="">
<span class="h-5 w-5 absolute mt-9 -ml-[17rem]">
<svg focusable="false" fill="#9aa0a6" xmlns="http://www.w3.org/2000/svg" viewBox="0 0 24 24">
<path
d="M15.5 14h-.79l-.28-.27A6.471 6.471 0 0 0 16 9.5 6.5 6.5 0 1 0 9.5 16c1.61 0 3.09-.59 4.23-1.57l.27.28v.79l5 4.99L20.49 19l-4.99-5zm-6 0C7.01 14 5 11.99 5 9.5S7.01 5 9.5 5 14 7.01 14 9.5 11.99 14 9.5 14z">
</path>
</svg>
</span>
<span class="h-6 w-6 absolute mt-8 ml-[15.5rem]">
<svg focusable="false" viewBox="0 0 192 192" xmlns="http://www.w3.org/2000/svg">
<rect fill="none" height="192" width="192"></rect>
<g>
<circle fill="#34a853" cx="144.07" cy="144" r="16"></circle>
<circle fill="#4285f4" cx="96.07" cy="104" r="24"></circle>
<path fill="#ea4335"
d="M24,135.2c0,18.11,14.69,32.8,32.8,32.8H96v-16l-40.1-0.1c-8.8,0-15.9-8.19-15.9-17.9v-18H24V135.2z">
</path>
<path fill="#fbbc04"
d="M168,72.8c0-18.11-14.69-32.8-32.8-32.8H116l20,16c8.8,0,16,8.29,16,18v30h16V72.8z">
</path>
<path fill="#4285f4"
d="M112,24l-32,0L68,40H56.8C38.69,40,24,54.69,24,72.8V92h16V74c0-9.71,7.2-18,16-18h80L112,24z">
</path>
</g>
</svg>
</span>
<span class="h-6 w-6 absolute mt-8 ml-[13rem]">
<svg focusable="false" viewBox="0 0 24 24" xmlns="http://www.w3.org/2000/svg">
<path fill="#4285f4"
d="m12 15c1.66 0 3-1.31 3-2.97v-7.02c0-1.66-1.34-3.01-3-3.01s-3 1.34-3 3.01v7.02c0 1.66 1.34 2.97 3 2.97z">
</path>
<path fill="#34a853" d="m11 18.08h2v3.92h-2z"></path>
<path fill="#fbbc04"
d="m7.05 16.87c-1.27-1.33-2.05-2.83-2.05-4.87h2c0 1.45 0.56 2.42 1.47 3.38v0.32l-1.15 1.18z">
</path>
<path fill="#ea4335"
d="m12 16.93a4.97 5.25 0 0 1 -3.54 -1.55l-1.41 1.49c1.26 1.34 3.02 2.13 4.95 2.13 3.87 0 6.99-2.92 6.99-7h-1.99c0 2.92-2.24 4.93-5 4.93z">
</path>
</svg>
</span>
</div>
<input type="text"
class="w-[575px] bg-[#202124] border border-gray-500 text-white pl-12 pr-20 py-3 rounded-full hover:bg-[#303134] outline-none">
<div>
<button
class="px-4 py-2 bg-[#303134] rounded border border-[#202124] hover:border hover:border-gray-500 mx-2 text-sm">Google
Search</button>
<button
class="px-4 py-2 bg-[#303134] rounded border border-[#202124] hover:border hover:border-gray-500 text-sm">I'm
Feeling Lucky</button>
</div>
<div class="flex gap-3">
<p class="text-gray-400 text-sm">Google offered in:</p>
<p class="text-[#8ab4f8] text-sm">हिन्दी বাংলা తెలుగు मराठी தமிழ் ગુજરાતી ಕನ್ನಡ മലയാളം ਪੰਜਾਬੀ</p>
</div>
</div>
<div class="bottom bg-[#171717] text-sm">
<div class="bottom-top p-3">
<span class="pl-6 cursor-pointer">India</span>
</div>
<div class="p-3 flex justify-between border-t-2 border-gray-700">
<div class="flex gap-8">
<a href="#" class="pl-6">About</a>
<a href="#" class="hover:underline">Advertising</a>
<a href="#" class="hover:underline">Business</a>
<a href="#" class="hover:underline">How Search works</a>
</div>
<div class="flex gap-8">
<a href="#" class="hover:underline">Privacy</a>
<a href="#" class="hover:underline">Terms</a>
<a href="#" class="hover:underline">Settings</a>
</div>
</div>
</div>
</div>
</body>
</html>
```
### Preview:
This image shows the final product we made in this blog
### Conclusion:
Building a Google clone using HTML and Tailwind CSS is a great way to practice front-end development skills. This tutorial provides a basic structure, but you can expand and enhance it to make your clone more realistic. Keep experimenting, and happy coding!
**Next : [Facebook Page UI Clone](https://dev.to/rohitnirban/facebook-login-page-ui-clone-in-html-and-tailwind-css-2b9n)**
**Next : [Calculator UI](https://dev.to/rohitnirban/calculator-ui-in-html-and-css-gn4)** | rohitnirban |
1,780,158 | Betfair Bangladesh | Betfair was established in 1999 and holds the honor of being the world’s first online betting... | 0 | 2024-03-04T18:11:28 | https://dev.to/betfair88vip/betfair-bangladesh-4dfb | betfair, betfairbd, betfaircasino, betfair88vip | Betfair was established in 1999 and holds the honor of being the world’s first online betting exchange. Evolving as an independently operating brand, it became part of the Flutter Group, the result of a merger with Paddy Power in 2016. Login Betfair Bangladesh Now!
Website : https://betfair88.vip
address : 16 Green Rd, Dhaka 1205, Bangladesh
Phone : +880 0263546353
email : betfair88vip@gmail.com
#betfair #betfairlogin #betfaircasino #betfairbd #betfair88vip #betfairbangladesh
Website: [https://betfair88.vip](https://betfair88.vip)
Medium : [https://medium.com/@betfair88vip/about](https://medium.com/@betfair88vip/about)
Youtube : [https://www.youtube.com/channel/UC49CVlqb0ZZ9c8uIAqiCETA](https://www.youtube.com/channel/UC49CVlqb0ZZ9c8uIAqiCETA)
Twitter :[ https://twitter.com/betfair88vip]( https://twitter.com/betfair88vip)
Dribbble :[ https://dribbble.com/betfair88vip/about]( https://dribbble.com/betfair88vip/about)
Pinterest : [https://www.pinterest.com/betfair88vip/](https://www.pinterest.com/betfair88vip/)
Tumblr : [https://www.tumblr.com/blog/betfair88vip](https://www.tumblr.com/blog/betfair88vip)
Tiktok : [https://www.tiktok.com/@betfair88vip](https://www.tiktok.com/@betfair88vip)
Reddit : [https://www.reddit.com/user/betfair88vip](https://www.reddit.com/user/betfair88vip) | betfair88vip |
1,780,259 | Silaj Ataşmanı Modern Tarımda Verimliliği Artıran Teknolojik Çözüm | Silaj Ataşmanı, modern tarımın en kritik ve verimlilik açısından belirleyici unsurlarından biridir.... | 0 | 2024-03-04T21:38:27 | https://dev.to/silajatasmani/silaj-atasmani-modern-tarimda-verimliligi-artiran-teknolojik-cozum-4d8e | **Silaj Ataşmanı**, modern tarımın en kritik ve verimlilik açısından belirleyici unsurlarından biridir. Tarım sektöründe, hayvanların beslenmesinde önemli bir rol oynayan silajın üretimi, Silaj Ataşmanı'nın yardımıyla büyük ölçüde kolaylaşmış ve hızlanmıştır. Bu teknolojik cihaz, çiftçilere zaman ve iş gücü maliyetlerinde önemli tasarruflar sağlayarak tarımsal üretimdeki verimliliği artırır.
Silaj Ataşmanı, genellikle traktörlerle kullanılan ve bitkilerin yeşil kısımlarını küçük parçalara keserek sıkıştırma işlemi için kullanılan bir cihazdır. Bu işlem sonucunda elde edilen silaj, hayvanların sağlıklı ve besleyici bir yem kaynağına erişimini sağlar. Geleneksel yöntemlerle yapılan silaj üretimi zaman alıcı ve iş gücü yoğun bir süreçtir, ancak Silaj Ataşmanı sayesinde bu süreç otomatikleştirilmiş ve hızlandırılmıştır.
[Silaj Ataşmanı](https://silajatasmani.com/)'nın avantajlarından biri de yem kalitesinin artırılmasıdır. Bitkilerin doğru şekilde kesilmesi ve sıkıştırılması, hayvanların daha besleyici bir yem tüketmesini sağlar. Bu da hayvanların sağlığını ve üretkenliğini artırır. Ayrıca, Silaj Ataşmanı ile elde edilen silajın uzun süreli depolanması da mümkündür, bu da çiftçilere yem stoğunu daha etkin bir şekilde yönetme imkanı sağlar.
Çevresel açıdan bakıldığında, Silaj Ataşmanı çiftlik atıklarının yönetimini de iyileştirir. Doğru şekilde fermantasyona uğratılmış silaj, hayvanların sindirim sistemine daha kolay adapte olur ve dolayısıyla daha az metan gazı üretir. Bu da çevresel etkileri azaltır ve tarımın sürdürülebilirliğini artırır.
Silaj Ataşmanı tarım sektöründe önemli bir dönüşümü temsil eder. Hem çiftçilere hem de hayvanlara yönelik birçok avantaj sunar. Verimliliği artırarak iş gücü maliyetlerini azaltır ve yem kalitesini yükselterek hayvan sağlığını destekler. Ayrıca, çevresel sürdürülebilirliği destekleyerek tarımın ekolojik etkisini azaltır. Bu nedenle, Silaj Ataşmanı günümüz tarımında vazgeçilmez bir araçtır ve sektördeki ilerlemeye önemli katkılar sağlar. | silajatasmani | |
1,780,354 | Como configurar Golang com live reload utilizando Air 🚀 | Esse tutorial é direto e prático, sem copiar e colar comandos que não fazem sentido. Vou te explicar... | 0 | 2024-03-04T23:30:34 | https://dev.to/itsfpbtw/como-configurar-golang-com-live-reload-utilizando-air-1hg5 | go, tutorial, productivity, webdev | Esse tutorial é direto e prático, sem copiar e colar comandos que não fazem sentido. Vou te explicar cada comando e configuração para que você compreenda o que está acontecendo. Isso vai facilitar a configuração e também te capacitar a resolver eventuais problemas que possam surgir durante o processo - _e, acredite, eles podem acontecer_.
## ❗ Problema
A necessidade de reiniciar constantemente a aplicação ao realizar alterações no código pode ser desgastante e prejudicar a nossa produtividade enquanto desenvolvedores.
## ✅ Solução
O uso de ferramentas como o Air automatiza o processo de live reload, economizando tempo e melhorando a eficiência durante o processo de desenvolvimento. Ou seja, você só se preocupa em codificar e salvar o arquivo enquanto ele faz todo o trabalho de sempre executar o código mais atualizado.
## ⚠️ Requisitos obrigatórios
- Go na versão `1.22` ou superior;
- Acesso ao terminal do seu sistema.
## 📂 Inicializando um projeto Go
\*Já tem um projeto Go inicializado? Vá direto para [Configurando Air](#configurando-air).
### Passo 1:
Crie uma pasta para o projeto de exemplo e mude para a pasta:
```bash
$ mkdir live-reload-go
$ cd live-reload-go
```
### Passo 2:
Dentro da pasta recém-criada, inicialize um projeto Go. Normalmente, os projetos Go seguem o formato "`github.com`/`nickname`/`nome-do-projeto`". No entanto, você pode personalizar o caminho do repositório ou colocar outro nome conforme necessário, no meu caso colocarei meu repositório:
```bash
$ go mod init github.com/felipelaraujo/live-reload-go
```
### Passo 3:
Com o `go.mod` criado, precisamos de uma função `main` com um servidor HTTP básico dentro. Para isso, crie a pasta `cmd/` e o arquivo `main.go`:
```bash
$ mkdir cmd
$ touch cmd/main.go
```
Cole o seguinte código no seu `main.go`:
`cmd/main.go`
```go
package main
import (
"log"
"net/http"
)
func main() {
// Criando uma instância do servidor
mux := http.NewServeMux()
// Configurando rota e função handler
mux.HandleFunc("GET /", func(w http.ResponseWriter, r *http.Request) {
w.WriteHeader(http.StatusOK)
w.Write([]byte("hello, world!"))
})
// Iniciando o servidor
log.Fatal(http.ListenAndServe(":3000", mux))
}
```
<h2 id="configurando-air">☁️ Configurando Air</h2>
### Passo 1:
Ao realizar a instalação global do Air, você garante a presença constante do comando `air` em seu sistema, eliminando a necessidade de reinstalação no futuro.
Instale o Air globalmente com:
```bash
$ go install github.com/cosmtrek/air@latest
```
_Certifique-se de ter todas as variáveis de ambiente Go configuradas corretamente para que o comando `air` seja reconhecido pelo seu terminal._
### Passo 2:
Crie o arquivo de configuração do Air na raiz do projeto com o nome `.air.toml` e cole o seguinte conteúdo:
`.air.toml`
```toml
# Raiz do projeto onde os comandos serão executados.
root = "."
# Local onde a pasta temporária receberá os outputs do Air.
tmp_dir = "tmp"
[build]
# Comando shell buildando o executável.
# O primeiro argumento recebe onde será
# o output do executável e o segundo argumento é
# qual arquivo queremos transformar em binário.
cmd = "go build -o ./tmp/main ./cmd/main.go"
# Local onde estará o executável do build (binário).
bin = "./tmp/main"
# Array com nomes de arquivos e/ou diretórios para se ignorar.
# Estou ignorando a pasta /tmp pois ela não faz parte do meu programa.
exclude_dir = ["tmp", "assets"]
# Array com expressões regex para ignorar arquivos com nomes específicos.
exclude_regex = ["_test\\.go"]
# Ignora arquivos que não foram alterados.
exclude_unchanged = true
# Array de extensões de arquivos para incluir no build.
include_ext = ["go", "tpl", "tmpl", "html"]
# Nome do arquivo de log que ficará dentro da pasta tmp.
log = "build-errors.log"
# Encerra o executável antigo caso ocorra algum erro no build.
stop_on_error = false
[color]
# Cores de onde vem os logs no console.
app = ""
build = "yellow"
main = "magenta"
runner = "green"
watcher = "cyan"
[log]
# Mostra o horário do log.
time = true
# Mostra apenas os logs da aplicação e não do Air.
main_only = false
[misc]
# Deleta a pasta tmp no encerramento da aplicação.
clean_on_exit = true
[screen]
# Limpa o console após o rebuild da aplicação.
clear_on_rebuild = false
```
_Para uma lista completa de configurações, consulte [air_example.toml](https://github.com/cosmtrek/air/blob/master/air_example.toml). Certifique-se de ajustar as configurações conforme necessário para o seu projeto._
## 🚀 Executando o projeto
A estrutura final do projeto deve ser semelhante a esta:
```
.
├── cmd/
│ └── main.go
├── .air.toml
└── go.mod
```
Com tudo configurado, inicie a aplicação usando o comando:
```bash
$ air
```
Agora você pode alterar qualquer arquivo do projeto e salvar para ver o Air fazendo seu trabalho:

Legal, né?! Espero ter te ajudado!
Abraço!
## Links úteis:
- ☁️ [Repositório do Air](https://github.com/cosmtrek/air)
## Meus links:
- 👨🏽💻 [Github](https://github.com/itsfpbtw)
- 👔 [Linkedin](https://www.linkedin.com/in/felipe-l-araujo/) | itsfpbtw |
1,780,381 | Introduction to Mobile Development with Flutter | Introduction In the world of technology, mobile application development has become an... | 0 | 2024-03-05T00:28:48 | https://dev.to/kartikmehta8/introduction-to-mobile-development-with-flutter-1iib | flutter, mobile, ios, javascript | ## Introduction
In the world of technology, mobile application development has become an essential aspect for businesses to reach their target audience and provide seamless user experience. With the rise of cross-platform development, Flutter has emerged as a popular choice for developers due to its versatile and efficient features. In this article, we will explore the advantages and disadvantages of mobile development with Flutter.
## Advantages of Flutter
1. **Cross-platform development:** One of the major advantages of Flutter is its ability to develop applications for both Android and iOS platforms using a single codebase. This not only saves time and effort for developers but also reduces the overall development costs.
2. **Fast development:** Flutter uses the Dart programming language which comes with a hot reload feature allowing developers to see the changes in real-time. This makes the development process much faster compared to other cross-platform frameworks.
3. **Customizable UI:** With Flutter's extensive widget library, developers can easily create highly customizable and visually appealing user interfaces, providing a better user experience.
## Disadvantages of Flutter
1. **Limited libraries:** As Flutter is a relatively new framework, it has a limited number of libraries compared to other established frameworks, making it difficult to find pre-existing solutions for certain functionalities.
2. **Steep learning curve:** Flutter uses the Dart programming language, which may be unfamiliar to many developers, resulting in a longer learning curve.
## Features of Flutter
1. **Strong community support:** Despite being a new framework, Flutter has a dedicated community of developers who actively contribute to its growth by sharing resources, troubleshooting issues, and providing constant updates.
2. **Hot reload feature:** As mentioned earlier, Flutter's hot reload feature allows developers to see the changes in real-time, saving time and effort during the development process.
### Implementing Hot Reload
The hot reload feature in Flutter is a game-changer for developers. It enhances the development experience by enabling immediate feedback on code changes without needing a full rebuild or restart. Here's a basic snippet demonstrating its use:
```dart
void main() {
runApp(MyApp());
}
class MyApp extends StatelessWidget {
@override
Widget build(BuildContext context) {
return MaterialApp(
title: 'Flutter Demo',
home: Scaffold(
appBar: AppBar(
title: Text('Hot Reload Demo'),
),
body: Center(
child: Text('Edit me and see the changes instantly!'),
),
),
);
}
}
```
With this simple app, any changes made to the text or layout will be visible instantly upon saving, thanks to Flutter's hot reload.
## Conclusion
In conclusion, Flutter offers numerous advantages for mobile development such as cross-platform compatibility, fast development, and customizable UI. While it may have some limitations, its strong community support and innovative features make it a popular choice among developers. As the framework continues to evolve, it has the potential to revolutionize the world of mobile application development. So, whether you're a beginner or an experienced developer, it's worth considering Flutter for your next mobile development project. | kartikmehta8 |
1,780,428 | Asking for NodeJS is single-thread or multithread | Dear all, I have a question that NodeJS is single-thread or multithread and Why? | 0 | 2024-03-05T02:28:38 | https://dev.to/tronganhnguyenthanh/asking-for-nodejs-is-single-thread-or-multithread-57lc | Dear all,
I have a question that NodeJS is single-thread or multithread and Why? | tronganhnguyenthanh | |
1,780,440 | 缅甸民间运动创始人解密美国未真正支持缅甸的原因 | 2022年9月30日,缅甸“自由缅甸联盟”“东南亚复兴力量”的创始人在土耳其媒体发文披露,美国未真正支持缅甸民主抵抗军政府的六个原因,主要因与台湾、乌克兰相比,缅甸对美国而言缺乏战略价值,因而更多的是道... | 0 | 2024-03-05T03:10:33 | https://dev.to/farrington24852/mian-dian-min-jian-yun-dong-chuang-shi-ren-jie-mi-mei-guo-wei-zhen-zheng-zhi-chi-mian-dian-de-yuan-yin-ehc | 2022年9月30日,缅甸“自由缅甸联盟”“东南亚复兴力量”的创始人在土耳其媒体发文披露,美国未真正支持缅甸民主抵抗军政府的六个原因,主要因与台湾、乌克兰相比,缅甸对美国而言缺乏战略价值,因而更多的是道义上的口头支持。
https://www.aa.com.tr/en/analysis/opinion-6-reasons-us-is-not-really-supporting-myanmar-s-democratic-resistance/2699374 | farrington24852 | |
1,780,502 | 개편된 PubNub Unity SDK 공개 | PubNub은 사용자 경험을 개선하고, 설정을 간소화하며, 안정성을 높이고, 프로토타이핑을 신속하게 진행할 수 있도록 Unity SDK를 개편했습니다. | 0 | 2024-03-05T04:18:12 | https://dev.to/pubnub-ko/gaepyeondoen-pubnub-unity-sdk-gonggae-4g46 | 온라인 게임 개발을 지원하는 중요한 툴인 PubNub Unity SDK가 2022년에 대대적인 개편을 거쳤습니다. 실시간 API의 이번 업그레이드를 통해 사용자 ID(UUID) 파라미터 구성, 커스텀 JSON 메타데이터 관리, 호환성, Android 및 iOS 빌드를 위한 모바일 푸시 알림 등의 기능이 혁신적으로 개선되어 사용자 경험이 향상되었습니다.
유니티는 PubNub 플랫폼을 개선하기 위해 SDK의 사용자 친화성을 개선하고 백엔드 기능을 최적화했으며, 유니티 개발자를 위한 애플리케이션 개발 프로세스를 간소화했습니다. 비머블의 공동 창립자이자 CTO인 알리 엘 레물(Ali El Rhermoul)은 간소화된 설정 요구 사항과 개선된 Unity 전용 기능으로 완성된 업데이트된 Unity SDK를 통해 개발자가 더 빠르고 쉽게 게임을 제작하고 취약성을 줄이며 개발 워크플로를 개선할 수 있다고 강조하며 이번 개선에 대해 찬사를 보냈습니다.
비머블의 공동 창립자이자 CTO인 알리 엘 레물(Ali El Rhermoul)은 "라이브 게임 제작 및 운영 확장을 위한 선도적인 플랫폼 중 하나인 비머블은 채팅, 길드, 커머스 등의 실시간 상호작용을 위한 PubNub의 새로운 Unity SDK의 확장된 기능을 활용하게 되어 기쁘다"며 "간소화된 설정 요구 사항부터 향상된 Unity 전용 기능까지 모든 것이 개발자가 더 나은 게임을 더 빠르고 더 적은 성공 장벽으로 제작하도록 지원한다는 우리의 미션을 실현하는 데 도움이 될 것"이라고 말했습니다.
개편된 Unity SDK
-------------
2022년에 출시된 최신 PubNub Unity SDK는 대폭 개선된 기능과 흥미로운 신규 기능을 제공합니다:
- **간편한 구성**: GitHub 저장소에서 SDK를 복제하면 신속한 설정 프로세스를 안내하는 직관적인 구성 창이 나타납니다. 이 환경을 더욱 원활하게 만들기 위해 몇 가지 업그레이드와 새로운 기능을 통합했습니다.
- **재작성된 설명서**: 최신 업데이트, 설정 프로세스 및 새로운 기능의 사용법을 포함하도록 HTML 기반 설명서를 완전히 개편했습니다.
- **호환성 외관**: 기존 SDK에서 쉽게 전환할 수 있도록 호환성 파사드를 도입했습니다. 이 기능을 사용하면 새 SDK의 기능을 탐색하는 동안 현재 소스 코드의 기능을 유지할 수 있습니다. 또한 오픈 소스 C# SDK와 함께 바닐라 C# 코드를 사용할 수도 있습니다.
- **Unity 전용 기능**: 최신 SDK는 안정적이고 효율적이며 사용자 친화적인 경험을 위한 모범 사례에 따라 더욱 많은 Unity 맞춤형 확장 기능과 메서드를 제공합니다.
- **비동기/대기**: 이 기능은 기존과 동일하게 표준 메서드를 사용하여 데이터를 계속 반환하여 도착하는 메시지의 수에 관계없이 처리합니다.
- **PN 디버깅 도구**: 개편된 SDK는 Unity 에디터에 PN 디버깅 툴을 추가하여 Unity 개발자를 위한 툴링 기능을 개선했습니다.
이러한 개선 사항과 함께 유니티 개발자에게 최상의 경험을 제공하기 위한 유니티의 지속적인 노력이 더해져 개편된 PubNub Unity SDK는 실시간 애플리케이션과 게임 제작에 필수적인 툴이 될 것입니다.
- **즉시 사용 가능한 빌딩 블록**: 업데이트된 SDK에는 리더보드, 채팅, 친구 목록 등의 기능을 제작할 수 있는 즉시 사용 가능한 빌딩 블록이 번들로 제공되어 개발자가 매력적인 경험을 더 빠르게 제작할 수 있습니다.
- **일반적인 도구와의 통합**: 새로운 SDK는 비주얼 스크립팅 및 종속성 주입 프레임워크와 같이 널리 사용되는 Unity 툴과 원활하게 통합되어 개발 프로세스를 간소화합니다.
새로운 Unity SDK는 나에게 어떤 의미가 있나요?
------------------------------
실시간 애플리케이션과 게임을 제작하는 개발자에게 개편된 PubNub Unity SDK는 다음과 같은 이점을 제공합니다:
- **신속한 프로토타이핑**: 새로운 SDK를 통해 개발자는 몇 번의 클릭만으로 패키지 설치에서 작동하는 프로토타입으로 전환할 수 있습니다. 이 프로세스를 개선하기 위해 다양한 업데이트와 개선 사항이 포함되어 있습니다.
- **향상된 안정성**: 업데이트된 SDK는 향상된 안정성을 자랑하며 일관된 고품질 사용자 경험을 보장합니다. 이러한 안정성 표준을 유지하기 위해 필요에 따라 푸시 알림과 같은 업데이트를 지속적으로 제공할 예정입니다.
- **상호운용성**: 다양한 모바일 앱에 PubNub 서비스를 쉽게 통합할 수 있도록 하는 상호운용성에 중점을 둔 SDK는 새 버전에서도 그대로 유지됩니다.
향후 업데이트
-------
개편된 Unity SDK는 간편한 설치 및 설정 프로세스, 안정적인 리소스 처리, 견고한 성능, Unity 베스트 프랙티스 준수를 보장합니다. 앞으로도 유니티는 Unity SDK 사용 경험을 더욱 향상하기 위해 더 많은 개선 사항과 기능을 제공할 계획입니다. 아래에서 새로운 리소스와 튜토리얼을 확인해 보세요:
- [PubNub Unity SDK 다운로드 및 문서](https://www.pubnub.com/docs/sdks/unity7)
- [Unity 개발자를 위한 업데이트된 리소스](https://www.pubnub.com/blog/category/gaming/)
- [Unity 게임에 PubNub 추가 가이드](https://www.pubnub.com/blog/add-pubnub-to-your-unity-game-to-power-online-features/)
- [PubNub의 Unity 쇼케이스 데모](https://github.com/PubNubDevelopers/unity-multiplayer-shooter) 및 [하이라이트 릴](https://youtu.be/iG4e5OJ38ZA)
PubNub이 어떤 도움을 줄 수 있나요?
-----------------------
PubNub는 개발자에게 웹 앱, 모바일 앱, IoT 기기를 위한 실시간 인터랙티브를 빌드, 전달, 관리할 수 있는 수단을 제공합니다. 업계에서 가장 확장성이 뛰어난 실시간 엣지 메시징 네트워크의 지원을 받는 저희 플랫폼은 성장하여 현재 월간 활성 사용자 수가 10억 명을 넘어섰습니다. 99.99%의 안정성으로 가동 중단, 동시 접속자 수 제한, 지연 시간 문제 등의 걱정 없이 안심하고 제작할 수 있습니다.
PubNub 체험하기
-----------
[라이브 투어를](https://www.pubnub.com/tour/introduction/) 통해 모든 PubNub 기반 앱의 핵심 개념을 살펴보세요. 이 투어가 만들어진 이후 몇 가지 새로운 기능과 도구가 추가되었습니다.
시작하기
----
먼저 PubNub [계정에](https://admin.pubnub.com/signup/) 가입하여 PubNub 키에 무료로 즉시 액세스하세요. 그런 다음, 업데이트된 [PubNub 문서를](https://www.pubnub.com/docs) 살펴보고 AWS, Python SDK, Javascript 등 원하는 SDK로 원활하게 실행할 수 있도록 하세요. 지금 바로 게임 개발과 앱 개발에서 PubNub의 강력한 기능을 알아보세요.
#### 콘텐츠
[개편된 Unity](#h-0)[SDK새로운 Unity SDK는 나에게](#h-1) 어떤[의미인가다음](#h-2)[단계PubNub는](#h-3)[어떻게](#h-2)[도움이](#h-3) 되는가PubNub[체험하기시작하기](#h-5)
PubNub이 어떤 도움이 될까요?
===================
이 문서는 원래 [PubNub.com에](https://www.pubnub.com/blog/unveiling-the-overhauled-pubnub-unity-sdk/) 게시되었습니다.
저희 플랫폼은 개발자가 웹 앱, 모바일 앱 및 IoT 디바이스를 위한 실시간 인터랙티브를 구축, 제공 및 관리할 수 있도록 지원합니다.
저희 플랫폼의 기반은 업계에서 가장 크고 확장성이 뛰어난 실시간 에지 메시징 네트워크입니다. 전 세계 15개 이상의 PoP가 월간 8억 명의 활성 사용자를 지원하고 99.999%의 안정성을 제공하므로 중단, 동시 접속자 수 제한 또는 트래픽 폭증으로 인한 지연 문제를 걱정할 필요가 없습니다.
PubNub 체험하기
-----------
[라이브 투어를](https://www.pubnub.com/tour/introduction/) 통해 5분 이내에 모든 PubNub 기반 앱의 필수 개념을 이해하세요.
설정하기
----
PubNub [계정에](https://admin.pubnub.com/signup/) 가입하여 PubNub 키에 무료로 즉시 액세스하세요.
시작하기
----
사용 사례나 [SDK에](https://www.pubnub.com/docs) 관계없이 [PubNub 문서를](https://www.pubnub.com/docs) 통해 바로 시작하고 실행할 수 있습니다. | pubnubdevrel | |
1,780,535 | Setting Up a Successful PVC Pipes Manufacturing Plant: Project Report 2024 | IMARC Group’s report titled “PVC Pipes Manufacturing Plant Project Report 2024: Industry Trends,... | 0 | 2024-03-05T05:38:21 | https://dev.to/george_brinton/setting-up-a-successful-pvc-pipes-manufacturing-plant-project-report-2024-4gpa | IMARC Group’s report titled “PVC Pipes Manufacturing Plant Project Report 2024: Industry Trends, Plant Setup, Machinery, Raw Materials, Investment Opportunities, Cost and Revenue” provides a comprehensive guide for establishing a PVC pipes manufacturing plant. The report covers various aspects, ranging from a broad market overview to intricate details like unit operations, raw material and utility requirements, infrastructure necessities, machinery requirements, manpower needs, packaging and transportation requirements, and more.
In addition to the operational aspects, the report also provides in-depth insights into [PVC pipes manufacturing plant setup](https://www.imarcgroup.com/pvc-pipes-manufacturing-plant-project-report), project economics, encompassing vital aspects such as capital investments, project funding, operating expenses, income and expenditure projections, fixed and variable costs, direct and indirect expenses, expected ROI, net present value (NPV), profit and loss account, and thorough financial analysis, among other crucial metrics. With this comprehensive roadmap, entrepreneurs and stakeholders can make informed decisions and venture into a successful PVC pipes manufacturing unit.
Customization Available:
- Plant Location
- Plant Capacity
- Machinery- Automatic/ Semi-automatic/ Manual
- List of Machinery Provider
Polyvinyl chloride (PVC) pipes are essential components widely utilized across various industries due to their versatile properties and applications. They are available in several types, including unplasticized PVC (uPVC), plasticized PVC (pPVC), and chlorinated PVC (CPVC), catering to different requirements and uses. The manufacturing process of PVC pipes involves the polymerization of vinyl chloride monomers, followed by the addition of stabilizers, plasticizers, and lubricants to achieve the desired physical and chemical properties. They are lauded for their lightweight, corrosion resistance, low maintenance, and durability. PVC pipes find applications in sectors such as water supply, sewage and drainage systems, irrigation, construction, chemical processing, telecommunications, and electrical conduits. They are known for their cost-effectiveness, ease of installation, environmental efficiency due to their recyclability, and long service life. Additionally, PVC pipes provide several advantages, such as a high strength-to-weight ratio, excellent chemical resistance, minimal water flow resistance, and adaptability to various climatic conditions.
The growing demand for PVC pipes in the irrigation sector, fueled by the need to enhance agricultural productivity, is contributing to the market growth. Additionally, the surge in construction activities across the globe, which necessitates durable and reliable piping solutions, is propelling the market growth. Besides this, the ongoing expansion of the water treatment industry, driven by the increasing awareness of clean drinking water and efficient sewage treatment facilities, is boosting the market growth. Furthermore, the heightened awareness about the cost-effectiveness and energy efficiency of PVC pipes compared to traditional materials is acting as another growth-inducing factor. In addition, the shifting trend towards sustainable and eco-friendly building materials, leading to innovations and improvements in PVC pipe manufacturing, making them more environmentally friendly and appealing to green building initiatives, is positively impacting the market growth. Moreover, recent advancements in technology, such as the development of molecularly oriented PVC pipes that offer enhanced strength and durability, are accelerating the market growth.
Request for a Sample Report: [https://www.imarcgroup.com/pvc-pipes-manufacturing-plant-project-report/requestsample](https://www.imarcgroup.com/pvc-pipes-manufacturing-plant-project-report/requestsample)
Key Insights Covered the PVC Pipes Plant Report
Market Coverage:
- Market Trends
- Market Breakup by Segment
- Market Breakup by Region
- Price Analysis
- Impact of COVID-19
- Market Forecast
Key Aspects Required for Setting Up a PVC Pipes Plant
Detailed Process Flow:
- Product Overview
- Unit Operations Involved
- Mass Balance and Raw Material Requirements
- Quality Assurance Criteria
- Technical Tests
Project Details, Requirements and Costs Involved:
- Land, Location and Site Development
- Plant Layout
- Machinery Requirements and Costs
- Raw Material Requirements and Costs
- Packaging Requirements and Costs
- Transportation Requirements and Costs
- Utility Requirements and Costs
- Human Resource Requirements and Costs
Project Economics:
- Capital Investments
- Operating Costs
- Expenditure Projections
- Revenue Projections
- Taxation and Depreciation
- Profit Projections
- Financial Analysis
Key Questions Answered in This Report:
- How has the PVC pipes market performed so far and how will it perform in the coming years?
- What is the market segmentation of the global PVC pipes market?
- What is the regional breakup of the global PVC pipes market?
- What are the price trends of various feedstocks in the PVC pipes industry?
- What is the structure of the PVC pipes industry and who are the key players?
- What are the various unit operations involved in a PVC pipes manufacturing plant?
- What is the total size of land required for setting up a PVC pipes manufacturing plant?
- What is the layout of a PVC pipes manufacturing plant?
- What are the machinery requirements for setting up a PVC pipes manufacturing plant?
- What are the raw material requirements for setting up a PVC pipes manufacturing plant?
- What are the packaging requirements for setting up a PVC pipes manufacturing plant?
- What are the transportation requirements for setting up a PVC pipes manufacturing plant?
- What are the utility requirements for setting up a PVC pipes manufacturing plant?
- What are the human resource requirements for setting up a PVC pipes manufacturing plant?
- What are the infrastructure costs for setting up a PVC pipes manufacturing plant?
- What are the capital costs for setting up a PVC pipes manufacturing plant?
- What are the operating costs for setting up a PVC pipes manufacturing plant?
- What should be the pricing mechanism of the final product?
- What will be the income and expenditures for a PVC pipes manufacturing plant?
- What is the time required to break even?
- What are the profit projections for setting up a PVC pipes manufacturing plant?
- What are the key success and risk factors in the PVC pipes industry?
- What are the key regulatory procedures and requirements for setting up a PVC pipes manufacturing plant?
- What are the key certifications required for setting up a PVC pipes manufacturing plant?
About Us:
IMARC Group is a leading market research company that offers management strategy and market research worldwide. We partner with clients in all sectors and regions to identify their highest-value opportunities, address their most critical challenges, and transform their businesses.
IMARC Group’s information products include major market, scientific, economic and technological developments for business leaders in pharmaceutical, industrial, and high technology organizations. Market forecasts and industry analysis for biotechnology, advanced materials, pharmaceuticals, food and beverage, travel and tourism, nanotechnology and novel processing methods are at the top of the company’s expertise.
Contact Us:
IMARC Group
134 N 4th St. Brooklyn, NY 11249, USA
Email: sales@imarcgroup.com
Tel No:(D) +91 120 433 0800
United States: +1-631-791-1145 | United Kingdom: +44-753-713-2163 | george_brinton | |
1,780,543 | DBT Therapy in Harrison, NY | Dialectical Behavior Therapy (DBT) is a type of cognitive-behavioral therapy originally developed... | 0 | 2024-03-05T05:49:09 | https://dev.to/counselingcentergroup/dbt-therapy-in-harrison-ny-3k50 |

Dialectical Behavior Therapy (DBT) is a type of cognitive-behavioral therapy originally developed to treat borderline personality disorder (BPD). However, its effectiveness has led to its widespread use in treating various mental health conditions, including mood disorders, substance abuse, and eating disorders. DBT Therapy harrison ny
Understanding DBT Therapy Components
Core Components of DBT
Mindfulness
Mindfulness is a fundamental aspect of DBT, emphasizing present-moment awareness without judgment. Practicing mindfulness helps individuals observe and accept their thoughts, emotions, and sensations.
Interpersonal Effectiveness
Interpersonal effectiveness skills teach individuals how to communicate assertively, set boundaries, and maintain healthy relationships. These skills are particularly beneficial for addressing conflicts and navigating social interactions.
Emotion Regulation
Emotion regulation techniques empower individuals to identify and manage intense emotions effectively. Through DBT, individuals learn to recognize triggers, regulate emotional responses, and develop healthier coping strategies.
Distress Tolerance
Distress tolerance skills focus on tolerating distressing situations without resorting to harmful behaviors. These skills help individuals build resilience and withstand challenging circumstances without exacerbating their distress.
Additional Components
Individual Therapy
Individual therapy sessions provide a supportive environment for clients to explore personal challenges, set goals, and develop coping strategies tailored to their unique needs.
Group Skills Training
Group skills training sessions offer a structured curriculum where participants learn and practice DBT skills together. These sessions facilitate peer support, accountability, and skill reinforcement.
Phone Coaching
Phone coaching provides clients with real-time support between therapy sessions. It allows individuals to receive guidance and encouragement when facing difficult situations or experiencing crises.
Application of DBT Therapy in Harrison, NY
DBT therapy services are available in Harrison, NY, offering comprehensive treatment for individuals struggling with various mental health issues. Therapists in Harrison integrate DBT principles and techniques into their practice to help clients achieve meaningful improvements in their lives.
Benefits of DBT Therapy in Harrison, NY
DBT therapy in Harrison, NY, offers numerous benefits, including enhanced emotional regulation, improved interpersonal relationships, and increased resilience in coping with stressors. Clients experience greater self-awareness, reduced symptoms of mental illness, and a greater sense of empowerment in managing their lives.
Finding DBT Therapy in Harrison, NY
Individuals seeking DBT therapy in Harrison, NY, can explore local mental health clinics, private practices, and specialized treatment centers. Online directories and referrals from healthcare providers can also help individuals connect with qualified DBT therapists in the area.
Success Stories of DBT Therapy in Harrison, NY
Many individuals in Harrison, NY, have experienced significant positive changes through DBT therapy. Personal testimonials highlight the transformative impact of DBT on managing emotions, overcoming destructive behaviors, and building fulfilling relationships.
Cost and Insurance Coverage of DBT Therapy in Harrison, NY
The cost of DBT therapy in Harrison, NY, varies depending on factors such as the therapist's credentials, session frequency, and location. Many insurance plans cover DBT therapy as part of mental health benefits, making it more accessible to individuals seeking treatment.
Comparison with Other Therapeutic Approaches
DBT therapy stands out from other therapeutic approaches due to its focus on combining acceptance and change-oriented strategies. While traditional cognitive-behavioral therapy (CBT) targets cognitive restructuring, DBT emphasizes acceptance of thoughts and emotions while promoting behavioral change.
Common Misconceptions about DBT Therapy
Despite its proven effectiveness, DBT therapy may be misunderstood by some individuals. Common misconceptions include viewing it solely as a treatment for BPD, underestimating its relevance to other mental health conditions, and overlooking its practical applicability in daily life.
Research and Efficacy of DBT Therapy
Numerous studies have demonstrated the efficacy of DBT therapy in treating a wide range of mental health disorders. Research findings consistently support the effectiveness of DBT in reducing symptoms, improving functioning, and enhancing quality of life for individuals receiving treatment.
Special Considerations for DBT Therapy in Harrison, NY
In Harrison, NY, DBT therapists tailor treatment plans to address the unique needs and cultural backgrounds of clients. Special considerations may include incorporating mindfulness practices, adapting interventions for diverse populations, and ensuring accessibility for individuals with disabilities.
Integrating DBT Therapy with Other Treatments
DBT therapy in Harrison, NY, can complement other forms of treatment, such as medication management, support groups, and holistic therapies. Integrating DBT with other modalities enhances treatment outcomes and provides clients with a comprehensive approach to healing.
DBT therapy offers a holistic and evidence-based approach to treating various mental health challenges, including borderline personality disorder, mood disorders, and substance abuse. In Harrison, NY, individuals have access to qualified DBT therapists who can provide compassionate support and effective interventions to promote healing and growth.
Name: Counseling Center Group
Address: 600 Mamaroneck Ave Suite 478, Harrison, NY 10528
Phone: (833) 216-3241
Site url: https://counselingcentergroup.com/locations/new-york/harrison/
GMB url : https://www.google.com/maps?cid=8247095080092909662
Social Media:
https://www.facebook.com/CounselingCenterGroup/
https://www.instagram.com/counselingcentergroup/
http://www.yelp.com/biz/counseling-center-of-maryland-bethesda
https://www.linkedin.com/company/the-counseling-center-group | counselingcentergroup | |
1,780,548 | Significant Trends to Watch in 2024 for Using the Laravel Framework | Hey there, fellow tech enthusiasts As we dive headfirst into 2024, it’s time to put on our digital... | 0 | 2024-03-05T05:58:09 | https://dev.to/johnsmith244303/significant-trends-to-watch-in-2024-for-using-the-laravel-framework-42fm | hirelaraveldeeloper, laraveldevelopmentcompany, laravelframework | Hey there, fellow tech enthusiasts As we dive headfirst into 2024, it’s time to put on our digital binoculars and scout out the exciting trends on the horizon for Laravel development. Whether you’re a seasoned developer, a curious coder, or just someone who enjoys nerding out over tech (like me), these trends are worth keeping an eye on.

**1. Laravel 11 Release: The Next Frontier**
Ah, Laravel – the trusty steed that has carried us through countless web projects. Well, saddle up, my friends, because Laravel 11 is on the horizon! With each new version, Laravel sprinkles a little magic dust on our development process. What can we expect? Enhanced performance, smoother workflows, and probably a unicorn or two. Okay, maybe not the unicorn, but you get the idea. Keep your GitHub notifications on high alert for this one.
**2. Microservices and Laravel: A Match Made in Code Heaven**
Microservices – the cool kids at the backend party. These modular, independent services are like Lego bricks for developers. In 2024, Laravel is giving them a warm hug. Imagine building your app with tiny, specialized components that play nicely together. It’s like having a team of Avengers – each hero with their unique powers (and no egos). So, if you’re dreaming of scalable, maintainable applications, hop aboard the microservices train.
**3. Serverless Laravel Applications: Less Server, More Awesome**
Servers? Ain’t nobody got time for that! Enter serverless computing. In 2024, Laravel is dipping its toes into the serverless pool. Picture this: you write code, deploy it, and voilà – your app runs without worrying about servers. It’s like having a personal butler for your backend. So, if you’re tired of server management, grab your monocle and explore the serverless side of Laravel.
**4. AI and Machine Learning: Laravel Gets Brainy**
Artificial Intelligence and Machine Learning – the Hermione Granger of tech. In 2024, Laravel is cozying up to these brainy companions. Imagine integrating AI chatbots, recommendation engines, or predictive analytics seamlessly into your Laravel app. Suddenly, your app becomes smarter than your neighbor’s cat (no offense to the cat). So, if you’re curious about AI’s magical powers, wave your wand – I mean, **[hire Laravel developer](https://www.itpathsolutions.com/laravel-development-company)**.
**5. Real-Time Features: Instant Gratification, Anyone?**
We live in an impatient world. Waiting for a page to reload? Nah. In 2024, Laravel is jazzing up its real-time capabilities. Think live chat, notifications, and dynamic updates – all without hitting that pesky refresh button. It’s like having a personal genie who grants your wishes instantly (minus the three-wish limit). So, if you want your users to feel like wizards, sprinkle some real-time magic into your Laravel app.
**6. Enhanced Security Measures: Fort Knox for Your Code**
Security – the unsung hero of web development. In 2024, Laravel is tightening its belt (or should I say, hashing its passwords?). Expect beefed-up security features, encryption galore, and a fortress around your app. It’s like having a cyber bodyguard – always vigilant, never taking coffee breaks. So, if you’re serious about protecting your users’ data, high-five a Laravel developer and say, “Encrypt all the things!”
**7. Frontend Development Integration: The Full-Stack Tango**
Laravel isn’t just about backend sorcery; it’s also a smooth dancer on the frontend floor. In 2024, expect more tools, packages, and sweet moves for building full-stack applications. Vue.js, Livewire, and Inertia.js – these are your dance partners. Together, they’ll waltz through your app’s UI like Fred Astaire and Ginger Rogers (minus the top hats). So, if you want to tango with both ends of the stack, grab your Laravel partner and hit the dance floor.
**In Conclusion: The Laravel Adventure Awaits**
As we embark on this tech journey through 2024, remember that Laravel is more than just code – it’s a community, a mindset, and a magical portal to web wonders. So, whether you’re a seasoned Laravel wizard or a curious apprentice, keep your eyes peeled for these trends. And hey, if you’re thinking, “I need a **[Laravel development company](https://www.itpathsolutions.com/laravel-development-company)**,” just whisper it to the wind – Laravel hears you.
**FAQs**
Q: What are the key trends to watch in Laravel development for 2024?
A: Several key trends are expected to shape Laravel development in 2024:
Increased Modularity: Breaking down complex applications into smaller, reusable components for better maintainability and scalability.
Tailwind CSS Dominance: Continued rise of Tailwind CSS as the preferred framework for building responsive UIs thanks to its utility-first approach that aligns well with Laravel's modularity.
Enhanced Security: Growing focus on robust security measures as cyber threats become more sophisticated. Laravel itself offers strong security features, and developers are expected to leverage them effectively.
Microservices Architecture: Adoption of microservices architecture for building highly scalable and maintainable applications, with Laravel expected to provide improved support for this approach.
AI and Machine Learning Integration: Integration of AI and ML functionalities into web applications for features like personalization and data-driven insights. Laravel's expressiveness can ease the integration of these technologies.
**Q: How will increased modularity benefit Laravel development?**
A: By breaking down applications into smaller, well-defined modules, developers gain several advantages:
Improved code maintainability: Easier to understand, modify, and test individual components.
Enhanced collaboration: Enables larger teams to work on different modules simultaneously.
Greater code reusability: Modules can be reused across different projects, saving development time.
Q: Why is Tailwind CSS expected to remain dominant with Laravel?
A: Tailwind's utility-first approach aligns well with Laravel's focus on modularity and component-based development. It allows developers to quickly build user interfaces with pre-defined classes without writing extensive CSS code, improving efficiency and consistency.
Q: What can developers do to enhance the security of Laravel applications?
A: Several practices can strengthen the security of Laravel applications:
Regularly update Laravel and its dependencies to benefit from security patches.
Implement secure coding practices to avoid common vulnerabilities.
Use Laravel's built-in security features like authorization and authentication mechanisms.
Stay informed about emerging security threats and update security measures accordingly.
Q: How will Laravel support the adoption of microservices architecture?
A: While Laravel itself is not a microservices framework, it is expected to offer improved support for this approach in 2024. This may include:
Enhanced tooling for managing microservices within a Laravel ecosystem.
Improved documentation and best practices for building microservices with Laravel.
Seamless integration with containerization technologies like Docker and orchestration platforms like Kubernetes.
| johnsmith244303 |
1,780,587 | How to Analyze LDO Token? | Author: lesley@footprint.network Data Source: LDO Token Dashboard (Only data on Ethereum... | 0 | 2024-03-05T06:50:13 | https://dev.to/footprint-analytics/how-to-analyze-ldo-token-i2k | blockchain | <span style="font-size:11pt;font-family:Arial,sans-serif;color:#000000;background-color:transparent;font-weight:400;font-style:normal;font-variant:normal;text-decoration:none;vertical-align:baseline;white-space:pre;white-space:pre-wrap;" data-raw-html="span">Author: </span><a href="https://www.linkedin.com/in/lesley8964/"><span style="font-size:11pt;font-family:Arial,sans-serif;color:#1155cc;background-color:transparent;font-weight:400;font-style:normal;font-variant:normal;text-decoration:underline;-webkit-text-decoration-skip:none;text-decoration-skip-ink:none;vertical-align:baseline;white-space:pre;white-space:pre-wrap;" data-raw-html="span">lesley@footprint.network </span></a>
<span style="font-size:11pt;font-family:Arial,sans-serif;color:#000000;background-color:transparent;font-weight:400;font-style:normal;font-variant:normal;text-decoration:none;vertical-align:baseline;white-space:pre;white-space:pre-wrap;" data-raw-html="span">Data Source: </span><a href="https://www.footprint.network/@Ming/Lido-LDO-Dashboard?token_address=0x5a98fcbea516cf06857215779fd812ca3bef1b32&amp;flow_type-86255=outflow"><span style="font-size:11pt;font-family:Arial,sans-serif;color:#1155cc;background-color:transparent;font-weight:400;font-style:normal;font-variant:normal;text-decoration:underline;-webkit-text-decoration-skip:none;text-decoration-skip-ink:none;vertical-align:baseline;white-space:pre;white-space:pre-wrap;" data-raw-html="span">LDO Token Dashboard</span></a><span style="font-size:11pt;font-family:Arial,sans-serif;color:#000000;background-color:transparent;font-weight:400;font-style:normal;font-variant:normal;text-decoration:none;vertical-align:baseline;white-space:pre;white-space:pre-wrap;" data-raw-html="span"> (Only data on Ethereum included)</span>
<span style="font-size:11pt;font-family:Arial,sans-serif;color:#000000;background-color:transparent;font-weight:400;font-style:normal;font-variant:normal;text-decoration:none;vertical-align:baseline;white-space:pre;white-space:pre-wrap;" data-raw-html="span">Token analysis plays a pivotal role in the realm of cryptocurrency and digital assets. It is the process of delving deep into the data and market behaviors associated with these assets. It is a detailed process that involves thoroughly examining price and liquidity connected to these assets.</span>
<span style="font-size:11pt;font-family:Arial,sans-serif;color:#000000;background-color:transparent;font-weight:400;font-style:normal;font-variant:normal;text-decoration:none;vertical-align:baseline;white-space:pre;white-space:pre-wrap;" data-raw-html="span">By analyzing tokens, we gain invaluable insights into market trends, risk factors, trading activities, and the direction of capital flows.</span>
<span style="font-size:11pt;font-family:Arial,sans-serif;color:#000000;background-color:transparent;font-weight:400;font-style:normal;font-variant:normal;text-decoration:none;vertical-align:baseline;white-space:pre;white-space:pre-wrap;" data-raw-html="span">The LDO token is a vital component of the Lido DAO ecosystem. It plays a crucial role in the decentralized governance structure, enabling holders to participate in decision-making processes that influence the direction and development of Lido's liquid staking services for Ethereum. </span>
<img src="https://statichk.footprint.network/article/4b57cc49-953d-482e-873a-8c438e2b6e49.png"><span style="font-size:11pt;font-family:Arial,sans-serif;color:#000000;background-color:transparent;font-weight:400;font-style:normal;font-variant:normal;text-decoration:none;vertical-align:baseline;white-space:pre;white-space:pre-wrap;" data-raw-html="span">LDO token</span>
<span style="font-size:11pt;font-family:Arial,sans-serif;color:#000000;background-color:transparent;font-weight:400;font-style:normal;font-variant:normal;text-decoration:none;vertical-align:baseline;white-space:pre;white-space:pre-wrap;" data-raw-html="span">Holding LDO tokens grants members voting rights within the DAO. This allows them to contribute to important decisions, such as protocol parameters, node operator selection, and implementing upgrades in response to Ethereum 2.0 developments.</span>
<h3><span style="font-size:13.999999999999998pt;font-family:Arial,sans-serif;color:#434343;background-color:transparent;font-weight:400;font-style:normal;font-variant:normal;text-decoration:none;vertical-align:baseline;white-space:pre;white-space:pre-wrap;" data-raw-html="span">How to Analyze LDO Token?</span></h3><span style="font-size:11pt;font-family:Arial,sans-serif;color:#000000;background-color:transparent;font-weight:400;font-style:normal;font-variant:normal;text-decoration:none;vertical-align:baseline;white-space:pre;white-space:pre-wrap;" data-raw-html="span">Token analysis is of paramount importance, and in this context, what are the key metrics to consider?</span>
<img src="https://statichk.footprint.network/article/6718bf80-b915-46d2-9362-8a3d604388e5.png"><span style="font-size:11pt;font-family:Arial,sans-serif;color:#000000;background-color:transparent;font-weight:400;font-style:normal;font-variant:normal;text-decoration:none;vertical-align:baseline;white-space:pre;white-space:pre-wrap;" data-raw-html="span">LDO Token Price per Day for the Last 30 Days</span>
<h4><span style="font-size:12pt;font-family:Arial,sans-serif;color:#666666;background-color:transparent;font-weight:400;font-style:normal;font-variant:normal;text-decoration:none;vertical-align:baseline;white-space:pre;white-space:pre-wrap;" data-raw-html="span">Token Price Analysis: Understanding Market Cap and Price Fluctuations</span></h4>
<span style="font-size:11pt;font-family:Arial,sans-serif;color:#000000;background-color:transparent;font-weight:400;font-style:normal;font-variant:normal;text-decoration:none;vertical-align:baseline;white-space:pre;white-space:pre-wrap;" data-raw-html="span">The token price is a crucial metric that represents the value of the token in fiat currency or cryptocurrency. As of Jan. 23, the token's price is $2.81. LDO reached its peak this month on January 10th, when its price soared to an impressive $3.85.</span>
<img src="https://statichk.footprint.network/article/527b4236-1440-44ea-aa7f-9b11ba31d838.png"><span style="font-size:11pt;font-family:Arial,sans-serif;color:#000000;background-color:transparent;font-weight:400;font-style:normal;font-variant:normal;text-decoration:none;vertical-align:baseline;white-space:pre;white-space:pre-wrap;" data-raw-html="span">LDO Daily Token Trading Amount & Value</span>
<h4><span style="font-size:12pt;font-family:Arial,sans-serif;color:#666666;background-color:transparent;font-weight:400;font-style:normal;font-variant:normal;text-decoration:none;vertical-align:baseline;white-space:pre;white-space:pre-wrap;" data-raw-html="span">Trading Value Insights: A Diagnostic Tool in Crypto Analytics</span></h4>
<span style="font-size:11pt;font-family:Arial,sans-serif;color:#000000;background-color:transparent;font-weight:400;font-style:normal;font-variant:normal;text-decoration:none;vertical-align:baseline;white-space:pre;white-space:pre-wrap;" data-raw-html="span">The volume of token trades is a key indicator of market activity. Currently, the token's trading amount is in decline, suggesting a low liquidity.</span>
<img src="https://statichk.footprint.network/article/25ebeae6-e403-4f3b-9475-716c15b23db4.png"><span style="font-size:11pt;font-family:Arial,sans-serif;color:#000000;background-color:transparent;font-weight:400;font-style:normal;font-variant:normal;text-decoration:none;vertical-align:baseline;white-space:pre;white-space:pre-wrap;" data-raw-html="span">LDO Daily Token Trading Value in CEXs</span>
<h4><span style="font-size:12pt;font-family:Arial,sans-serif;color:#666666;background-color:transparent;font-weight:400;font-style:normal;font-variant:normal;text-decoration:none;vertical-align:baseline;white-space:pre;white-space:pre-wrap;" data-raw-html="span">Net Flow Analysis in CEX: Identifying Trends in Investor Behavior</span></h4>
<span style="font-size:11pt;font-family:Arial,sans-serif;color:#000000;background-color:transparent;font-weight:400;font-style:normal;font-variant:normal;text-decoration:none;vertical-align:baseline;white-space:pre;white-space:pre-wrap;" data-raw-html="span">To gain a better understanding of investor behavior, we must analyze the transfer of tokens to and from centralized exchanges (CEXs). This analysis includes quantifying token movements and assessing the impact of these transactions on market trends, investor sentiment, and liquidity.</span>
<img src="https://statichk.footprint.network/article/91b0e3d2-2307-4f3d-8d04-f03a0c5b6b8e.png"><span style="font-size:11pt;font-family:Arial,sans-serif;color:#000000;background-color:transparent;font-weight:400;font-style:normal;font-variant:normal;text-decoration:none;vertical-align:baseline;white-space:pre;white-space:pre-wrap;" data-raw-html="span">LDO Token Holder List</span>
<h4><span style="font-size:12pt;font-family:Arial,sans-serif;color:#666666;background-color:transparent;font-weight:400;font-style:normal;font-variant:normal;text-decoration:none;vertical-align:baseline;white-space:pre;white-space:pre-wrap;" data-raw-html="span">Token Centralization: A Descriptive Analytics Approach</span></h4>
<span style="font-size:11pt;font-family:Arial,sans-serif;color:#000000;background-color:transparent;font-weight:400;font-style:normal;font-variant:normal;text-decoration:none;vertical-align:baseline;white-space:pre;white-space:pre-wrap;" data-raw-html="span">To understand market integrity and susceptibility to manipulation, it is crucial to evaluate LDO token centralization. By analyzing the distribution of tokens among top holders, we can gain insights into the influence of whale investors and the overall health of the token market.</span>
<h3><span style="font-size:13.999999999999998pt;font-family:Arial,sans-serif;color:#434343;background-color:transparent;font-weight:400;font-style:normal;font-variant:normal;text-decoration:none;vertical-align:baseline;white-space:pre;white-space:pre-wrap;" data-raw-html="span">Track the Data of LDO Token with Footprint</span></h3><span style="font-size:11pt;font-family:Arial,sans-serif;color:#000000;background-color:transparent;font-weight:400;font-style:normal;font-variant:normal;text-decoration:none;vertical-align:baseline;white-space:pre;white-space:pre-wrap;" data-raw-html="span">Footprint Token Analysis Page can assist in analyzing additional metrics.</span><span style="font-size:11pt;font-family:Arial,sans-serif;color:#000000;background-color:transparent;font-weight:700;font-style:normal;font-variant:normal;text-decoration:none;vertical-align:baseline;white-space:pre;white-space:pre-wrap;" data-raw-html="span">You can access all the data you need in </span><a href="https://www.footprint.network/research/token/token/single-token"><span style="font-size:11pt;font-family:Arial,sans-serif;color:#1155cc;background-color:transparent;font-weight:700;font-style:normal;font-variant:normal;text-decoration:underline;-webkit-text-decoration-skip:none;text-decoration-skip-ink:none;vertical-align:baseline;white-space:pre;white-space:pre-wrap;" data-raw-html="span">Token Dashboard</span></a><span style="font-size:11pt;font-family:Arial,sans-serif;color:#000000;background-color:transparent;font-weight:700;font-style:normal;font-variant:normal;text-decoration:none;vertical-align:baseline;white-space:pre;white-space:pre-wrap;" data-raw-html="span"> on the Footprint research page. </span>
<span style="font-size:11pt;font-family:Arial,sans-serif;color:#000000;background-color:transparent;font-weight:400;font-style:normal;font-variant:normal;text-decoration:none;vertical-align:baseline;white-space:pre;white-space:pre-wrap;" data-raw-html="span">What's more, you can also perform highly customized analyses using Footprint's versatile features. Here are the key advantages:</span><ul><li><span style="font-size:11pt;font-family:Arial,sans-serif;color:#000000;background-color:transparent;font-weight:400;font-style:normal;font-variant:normal;text-decoration:none;vertical-align:baseline;white-space:pre;white-space:pre-wrap;" data-raw-html="span">Rich Reference Data: The platform provides extensive reference data, enabling users to gain a deeper understanding of various aspects of cryptocurrencies. This wealth of information aids in making informed investment and trading decisions.</span></li><li><span style="font-size:11pt;font-family:Arial,sans-serif;color:#000000;background-color:transparent;font-weight:400;font-style:normal;font-variant:normal;text-decoration:none;vertical-align:baseline;white-space:pre;white-space:pre-wrap;" data-raw-html="span">Versatile Data Access: Users can access data in various ways, including APIs, dashboards, and batch downloads. This flexibility caters to different user preferences and needs, whether they are developers or non-technical users.</span></li><li><span style="font-size:11pt;font-family:Arial,sans-serif;color:#000000;background-color:transparent;font-weight:400;font-style:normal;font-variant:normal;text-decoration:none;vertical-align:baseline;white-space:pre;white-space:pre-wrap;" data-raw-html="span">Multi-Dimensional Data: The platform offers data across multiple dimensions and levels, allowing users to conduct detailed drill-down analyses. This hierarchical data structure empowers users to gain comprehensive insights into the cryptocurrency market.</span></li></ul>
<span style="font-size:11pt;font-family:Arial,sans-serif;color:#000000;background-color:transparent;font-weight:400;font-style:normal;font-variant:normal;text-decoration:none;vertical-align:baseline;white-space:pre;white-space:pre-wrap;" data-raw-html="span">Token analysis is crucial as it provides insights into market trends and risks, aiding investors and traders in making informed decisions. It serves as a compass in the volatile cryptocurrency landscape, helping navigate opportunities and threats.</span>
<span style="font-size:11pt;font-family:Arial,sans-serif;color:#000000;background-color:transparent;font-weight:400;font-style:normal;font-variant:normal;text-decoration:none;vertical-align:baseline;white-space:pre;white-space:pre-wrap;" data-raw-html="span">Check our </span><a href="https://cutt.ly/qwPiV3im"><span style="font-size:11pt;font-family:Arial,sans-serif;color:#1155cc;background-color:transparent;font-weight:400;font-style:normal;font-variant:normal;text-decoration:underline;-webkit-text-decoration-skip:none;text-decoration-skip-ink:none;vertical-align:baseline;white-space:pre;white-space:pre-wrap;" data-raw-html="span">website</span></a><span style="font-size:11pt;font-family:Arial,sans-serif;color:#000000;background-color:transparent;font-weight:400;font-style:normal;font-variant:normal;text-decoration:none;vertical-align:baseline;white-space:pre;white-space:pre-wrap;" data-raw-html="span"> or </span><a href="https://calendly.com/alexfootprint/30min"><span style="font-size:11pt;font-family:Arial,sans-serif;color:#1155cc;background-color:transparent;font-weight:400;font-style:normal;font-variant:normal;text-decoration:underline;-webkit-text-decoration-skip:none;text-decoration-skip-ink:none;vertical-align:baseline;white-space:pre;white-space:pre-wrap;" data-raw-html="span">schedule a meeting</span></a><span style="font-size:11pt;font-family:Arial,sans-serif;color:#000000;background-color:transparent;font-weight:400;font-style:normal;font-variant:normal;text-decoration:none;vertical-align:baseline;white-space:pre;white-space:pre-wrap;" data-raw-html="span"> to know more about the solution.</span>
<br>
<br>
***
<br>
<span style="font-size:11pt;font-family:Arial,sans-serif;color:#000000;background-color:transparent;font-weight:400;font-style:normal;font-variant:normal;text-decoration:none;vertical-align:baseline;white-space:pre;white-space:pre-wrap;" data-raw-html="span">Footprint Analytics is a blockchain data solutions provider. It leverages cutting-edge AI technology to help analysts, builders, and investors turn blockchain data and combine Web2 data into insights with accessible visualization tools and a powerful multi-chain API across 30+ chains for NFTs, GameFi, and DeFi.</span>
<br>
<span style="font-size:11pt;font-family:Arial,sans-serif;color:#1d1c1d;background-color:transparent;font-weight:400;font-style:normal;font-variant:normal;text-decoration:none;vertical-align:baseline;white-space:pre;white-space:pre-wrap;" data-raw-html="span">Product Highlights:</span><ul><li><a href="https://docs.footprint.network/reference/introduction"><span style="font-size:11pt;font-family:Arial,sans-serif;color:#1155cc;background-color:transparent;font-weight:400;font-style:normal;font-variant:normal;text-decoration:underline;-webkit-text-decoration-skip:none;text-decoration-skip-ink:none;vertical-align:baseline;white-space:pre;white-space:pre-wrap;" data-raw-html="span">Data API</span></a><span style="font-size:11pt;font-family:Arial,sans-serif;color:#1d1c1d;background-color:transparent;font-weight:400;font-style:normal;font-variant:normal;text-decoration:none;vertical-align:baseline;white-space:pre;white-space:pre-wrap;" data-raw-html="span"> for developers.</span></li><li><a href="https://www.footprint.network/fga/game/project/Demo%20Project/project_summary?protocol_slug=the-sandbox"><span style="font-size:11pt;font-family:Arial,sans-serif;color:#1155cc;background-color:transparent;font-weight:400;font-style:normal;font-variant:normal;text-decoration:underline;-webkit-text-decoration-skip:none;text-decoration-skip-ink:none;vertical-align:baseline;white-space:pre;white-space:pre-wrap;" data-raw-html="span">Footprint Growth Analytics (FGA)</span></a><span style="font-size:11pt;font-family:Arial,sans-serif;color:#1d1c1d;background-color:transparent;font-weight:400;font-style:normal;font-variant:normal;text-decoration:none;vertical-align:baseline;white-space:pre;white-space:pre-wrap;" data-raw-html="span"> for GameFi projects.</span></li><li><a href="https://www.footprint.network/pricing"><span style="font-size:11pt;font-family:Arial,sans-serif;color:#1155cc;background-color:transparent;font-weight:400;font-style:normal;font-variant:normal;text-decoration:underline;-webkit-text-decoration-skip:none;text-decoration-skip-ink:none;vertical-align:baseline;white-space:pre;white-space:pre-wrap;" data-raw-html="span">Batch download</span></a><span style="font-size:11pt;font-family:Arial,sans-serif;color:#1d1c1d;background-color:transparent;font-weight:400;font-style:normal;font-variant:normal;text-decoration:none;vertical-align:baseline;white-space:pre;white-space:pre-wrap;" data-raw-html="span"> for big-size data fetch.</span></li><li><span style="font-size:11pt;font-family:Arial,sans-serif;color:#1d1c1d;background-color:transparent;font-weight:400;font-style:normal;font-variant:normal;text-decoration:none;vertical-align:baseline;white-space:pre;white-space:pre-wrap;" data-raw-html="span">View the data </span><a href="https://www.footprint.network/@Footprint/Footprint-Datasets-Data-Dictionary"><span style="font-size:11pt;font-family:Arial,sans-serif;color:#1155cc;background-color:transparent;font-weight:400;font-style:normal;font-variant:normal;text-decoration:underline;-webkit-text-decoration-skip:none;text-decoration-skip-ink:none;vertical-align:baseline;white-space:pre;white-space:pre-wrap;" data-raw-html="span">dictionary</span></a><span style="font-size:11pt;font-family:Arial,sans-serif;color:#1d1c1d;background-color:transparent;font-weight:400;font-style:normal;font-variant:normal;text-decoration:none;vertical-align:baseline;white-space:pre;white-space:pre-wrap;" data-raw-html="span"> to explore all data sets Footprint provides.</span></li><li><span style="font-size:11pt;font-family:Arial,sans-serif;color:#1d1c1d;background-color:transparent;font-weight:400;font-style:normal;font-variant:normal;text-decoration:none;vertical-align:baseline;white-space:pre;white-space:pre-wrap;" data-raw-html="span">Check our </span><span style="font-size:11pt;font-family:Arial,sans-serif;color:#000000;background-color:transparent;font-weight:400;font-style:normal;font-variant:normal;text-decoration:none;vertical-align:baseline;white-space:pre;white-space:pre-wrap;" data-raw-html="span">X post </span><span style="font-size:11pt;font-family:Arial,sans-serif;color:#1155cc;background-color:transparent;font-weight:400;font-style:normal;font-variant:normal;text-decoration:underline;-webkit-text-decoration-skip:none;text-decoration-skip-ink:none;vertical-align:baseline;white-space:pre;white-space:pre-wrap;" data-raw-html="span">(</span><a href="https://twitter.com/Footprint_Data"><span style="font-size:11pt;font-family:Arial,sans-serif;color:#1155cc;background-color:transparent;font-weight:400;font-style:normal;font-variant:normal;text-decoration:underline;-webkit-text-decoration-skip:none;text-decoration-skip-ink:none;vertical-align:baseline;white-space:pre;white-space:pre-wrap;" data-raw-html="span">Footprint_Data</span></a><span style="font-size:11pt;font-family:Arial,sans-serif;color:#1155cc;background-color:transparent;font-weight:400;font-style:normal;font-variant:normal;text-decoration:underline;-webkit-text-decoration-skip:none;text-decoration-skip-ink:none;vertical-align:baseline;white-space:pre;white-space:pre-wrap;" data-raw-html="span">)</span><span style="font-size:11pt;font-family:Arial,sans-serif;color:#000000;background-color:transparent;font-weight:400;font-style:normal;font-variant:normal;text-decoration:none;vertical-align:baseline;white-space:pre;white-space:pre-wrap;" data-raw-html="span"> fo</span><span style="font-size:11pt;font-family:Arial,sans-serif;color:#1d1c1d;background-color:transparent;font-weight:400;font-style:normal;font-variant:normal;text-decoration:none;vertical-align:baseline;white-space:pre;white-space:pre-wrap;" data-raw-html="span">r more product updates.</span></li></ul> | footprint-analytics |
1,780,647 | What methods can organizations use to effectively manage and mitigate workplace stress? | Navigating Workplace Stress: Strategies for a Healthy Work Environment! 💼🧘♂️ Introduction In... | 0 | 2024-03-05T07:59:58 | https://dev.to/yagnapandya9/what-methods-can-organizations-use-to-effectively-manage-and-mitigate-workplace-stress-3nhl | workplace, ai, developer, freelance | Navigating Workplace Stress: Strategies for a Healthy Work Environment! 💼🧘♂️
[Introduction](https://fxdatalabs.com/)
In today's fast-paced and competitive work environment, workplace stress has become a pervasive issue affecting employees across industries. High levels of stress can lead to decreased productivity, burnout, and negative impacts on employees' mental and physical health.
However, organizations have the power to implement strategies to effectively manage and mitigate workplace stress, creating a healthier and more supportive work environment for their employees.
In this comprehensive article, we will explore various methods and strategies that organizations can employ to address workplace stress, fostering employee well-being and enhancing overall organizational performance.
## Understanding Workplace Stress
[Definition: ](https://fxdatalabs.com/)
Workplace stress refers to the physical, emotional, and psychological strain experienced by employees due to work-related factors such as high workload, tight deadlines, interpersonal conflicts, and job insecurity.
[Impact: ](https://fxdatalabs.com/)
Workplace stress can have detrimental effects on employee health, job satisfaction, and productivity. Chronic stress can lead to burnout, absenteeism, turnover, and increased healthcare costs for organizations.
## Identifying Causes of Workplace Stress
[Workload and Deadlines: ](https://fxdatalabs.com/)
Heavy workloads, tight deadlines, and unrealistic expectations can contribute to feelings of overwhelm and pressure among employees.
[Lack of Control: ](https://fxdatalabs.com/)
Employees may experience stress when they feel they have little control over their work processes, schedules, or decision-making.
[Poor Work-Life Balance: ](https://fxdatalabs.com/)
Imbalance between work and personal life can lead to chronic stress and feelings of exhaustion among employees.
[Interpersonal Conflicts: ](https://fxdatalabs.com/)
Conflicts with colleagues or managers, bullying, and harassment can create a toxic work environment and contribute to elevated stress levels.
## Strategies for Managing Workplace Stress
[Promoting Work-Life Balance: ](https://fxdatalabs.com/)
Encourage employees to prioritize self-care and set boundaries between work and personal life. Offer flexible work arrangements, such as telecommuting or flexible hours, to accommodate employees' diverse needs.
[Stress Management Training: ](https://fxdatalabs.com/)
Provide employees with access to stress management workshops, training programs, or resources to help them develop coping strategies and resilience in dealing with workplace stressors.
[Effective Communication: ](https://fxdatalabs.com/)
Foster open and transparent communication channels where employees feel comfortable expressing their concerns, seeking support, and providing feedback.
[Encouraging Physical Activity: ](https://fxdatalabs.com/)
Promote regular physical activity and wellness initiatives, such as onsite fitness classes, walking meetings, or subsidized gym memberships, to help employees manage stress and improve overall well-being.
[Supportive Leadership: ](https://fxdatalabs.com/)
Train managers and supervisors to recognize signs of stress in their teams, provide emotional support, and offer resources for stress management and mental health support.
## Creating a Supportive Work Environment
[Employee Assistance Programs (EAPs):](https://fxdatalabs.com/)
Offer confidential counseling services, mental health resources, and referral services through EAPs to support employees facing personal or work-related challenges.
[Flexible Work Policies: ](https://fxdatalabs.com/)
Implement policies that allow for flexible work arrangements, such as remote work options, compressed workweeks, or job sharing, to accommodate employees' individual needs and preferences.
[Promoting Social Connections: ](https://fxdatalabs.com/)
Encourage team-building activities, social events, and networking opportunities to foster positive social connections and a sense of belonging among employees.
[Recognition and Appreciation: ](https://fxdatalabs.com/)
Recognize and appreciate employees' contributions through rewards, incentives, and acknowledgment programs to boost morale and reduce feelings of stress and dissatisfaction.
## Monitoring and Evaluation
[Regular Assessments: ](https://fxdatalabs.com/)
Conduct regular assessments of workplace stress levels through employee surveys, focus groups, or interviews to identify areas of concern and gauge the effectiveness of stress management initiatives.
[Feedback Mechanisms: ](https://fxdatalabs.com/)
Solicit feedback from employees on the effectiveness of stress management programs and initiatives, and use this input to make continuous improvements and adjustments as needed.
## Leadership and Organizational Culture
[Lead by Example: ](https://fxdatalabs.com/)
Demonstrate a commitment to employee well-being and stress management at all levels of the organization, starting from senior leadership down to frontline managers.
Cultivate a Positive Culture: Foster a culture of trust, respect, and support where employees feel valued, heard, and empowered to take ownership of their well-being.
## Conclusion: Cultivating a Healthy Work Environment
In conclusion, managing and mitigating workplace stress requires a multifaceted approach that addresses both organizational and individual factors. By implementing strategies to promote work-life balance, provide stress management support, create a supportive work environment, and foster a positive organizational culture, organizations can effectively manage stress and create a healthier and more resilient workforce.
Investing in employee well-being not only benefits individual employees but also contributes to enhanced productivity, morale, and overall organizational success. By prioritizing employee well-being and stress management, organizations can create a workplace where employees thrive and flourish, leading to sustained success and growth in the long run.
For more insights into AI|ML and Data Science Development, please write to us at: contact@htree.plus| [F(x) Data Labs Pvt. Ltd.](https://fxdatalabs.com/)
#WorkplaceWellness #StressManagement #EmployeeHealth #HealthyWorkplace 🧘♂️🤝 | yagnapandya9 |
1,780,738 | Beyond the Visual: | Why Semantic HTML is the Key to a Meaningful Website (Highlights the deeper meaning and purpose of... | 0 | 2024-03-05T09:17:37 | https://dev.to/itskash/beyond-the-visual-565k | **Why Semantic HTML is the Key to a Meaningful Website (Highlights the deeper meaning and purpose of semantic HTML)**
Ever stumbled upon a website that looked like it went through a digital blender? Broken links, text you need a magnifying glass to read, and pop-ups galore – not exactly an engaging experience, right? This, my friend, is the dark side of bad HTML.
But fear not! There's a secret weapon in the web developer's arsenal called semantic HTML, and it's about to become your new best friend.
Think of *HTML* as the skeleton of your website. It defines the structure and content, but doesn't dictate the fancy bells and whistles (those are for the designers to play with). Semantic HTML takes things a step further. It uses specific tags to not only tell browsers how things look, but also **tell search engines and assistive technologies what things mean.
So, why should you care about semantic HTML? Let's break it down into two key benefits:
#1. SEO: Befriending the Search Engine Beasts#
Imagine search engines like curious explorers, crawling through the vast web jungle, trying to understand what each website is about. Semantic HTML acts as a handy map, clearly marking the different sections – the main content, headings, links, and more. This helps search engines index and rank your pages more effectively, making it easier for potential customers to find you in the digital wilderness.
#2. Accessibility: Making Your Website Welcoming to All#
The internet should be a playground for everyone, regardless of their abilities. Semantic HTML plays a crucial role in making your website accessible to people with disabilities. Assistive technologies like screen readers rely on these tags to understand the structure and meaning of your content, allowing users to navigate and interact with your website seamlessly.
Think of it this way: with semantic HTML, you're not just building a website, you're building an inclusive and user-friendly experience for everyone.
#In Conclusion:#
Semantic HTML is a powerful tool that can transform your website from a confusing maze to a user-friendly haven. It's not just about following the latest trends; it's about creating a website that works for everyone, search engines included. So, ditch the bad HTML and embrace the power of semantics – your website (and your users) will thank you for it!
| itskash | |
1,780,774 | Primary Applications of Integration Testing | Integration testing stands out as an essential element in the ever-evolving field of software... | 0 | 2024-03-05T09:56:51 | https://mehaitech.com/primary-applications-of-integration-testing/ | integration, testing | 
Integration testing stands out as an essential element in the ever-evolving field of software development, where complex structures are built from a number of dependent components. As an essential phase in the process of creating software, testing ensures that multiple components work together effectively to deliver a software product that is dependable and logical. Let us examine the primary applications of integration testing in comprehensive areas.
**Primary Applications of Integration Testing**
**Identifying Interface Variations**:
When interacting with several modules, challenges with the interface may arise. A significant method to find these issues is via integration testing. A complex software system demands smooth communication between all of its components. Developers may verify that interfaces remain legal and clearly stated and that data is reliably transferred across modules by using integration testing. Errors and deviations can be found prior to the development cycle and addressed by portraying these interactions. By acting proactive, the chance of significant interface-related errors in later phases is significantly reduced.
**Checking the Easy Transfer of Data & Control**:
Enabling the software application’s data and control transfer easily is an additional vital function of integration testing. It makes sure that control is transmitted as requested and that data gets transferred effectively across various components. Finding any inconsistencies or obstructions in the data and control transfer necessitates the use of this verification procedure. Integration testing adds to system stability by carefully analyzing such paths and guaranteeing that the program operates properly in a number of circumstances.
**Detection of System-Level Faults**:
Integration testing is highly efficient for discovering faults that can only become apparent when many components function together inside the integrated system. When modules connect, these flaws—which tend to be difficult to find in unit testing—show up. Integration testing can detect system-level errors at the beginning of the design process, such as problems with efficiency, scalability issues, and security flaws. Not only does swift correction of these issues accelerate growth, but it also prevents future troubles.
**Determining how Cross-Environment Functionality Works**:
Modern software operates in several settings, each of which has its factors. To make sure that a software system runs without an issue in many situations, integration testing is essential. Developers could find and fix problems related to a particular setting by evaluating how components interact in a variety of circumstances. This feature is essential to identify configuration-related issues that might result from variations in network configurations, software versions, or hardware.
**Allowing Continuous Integration and Deployment**:
An essential component of the workflow for continuous integration & continuous deployment (CI/CD) is integration testing. Testing that is accurate and automated grows essential when team members adopt agile techniques and strive for quick release cycles. When automated, integration testing fits neatly into the CI/CD process, letting developers quickly find and fix errors. Integrated component testing conducted automatically speeds up development by preventing unintended regressions and operates from being disrupted by new code modifications.
**Conclusion**
Integration testing should be seen as a purposeful, crucial procedure rather than just a checkbox in the software creation cycle. If you are looking for a testing automation platform, you can surely opt for Opkey. Opkey is an intuitive tool that allows every member of your organization to speed up migrations, installations, and upgrades. They have made it easy for many of the biggest companies in the world to successfully oversee their ERP installs, upgrades, and transfers across some of the most popular packaged applications today. For more details on how they can help you, visit the website of Opkey | rohitbhandari102 |
1,780,820 | SDPL Om | Experience the allure of natural light as it gracefully floods every corner of your home at SDPL Om.... | 0 | 2024-03-05T10:45:53 | https://dev.to/sdplom/sdpl-om-3mkc |
Experience the allure of natural light as it gracefully floods every corner of your home at SDPL Om. It is a residential project offering 2, 3 & 4 BHK Spacious Flats with shops too. The scheme consists of 100 flats & 4 shops along with a club house. Large strategically placed windows invite the warmth of the sun, creating a vibrant and uplifting ambiance throughout the day. At SDPL Om, we believe in creating residences that harmonize with nature, offering you a living environment where light and air intertwine to elevate your well-being and comfort. The Project is registered under MahaRERA vide Registration No. P50500026827 and is available under registered projects.
Address : Small Factory Area Plot No 134/135, Bagadganj, Lakadganj, Nagpur, Maharashtra, 440008, India
Phone : +91 90 9636 1354
Business Email : [info@sandeepdwellers.com](info@sandeepdwellers.cominfo@sandeepdwellers.com)
Website : [https://www.sandeepdwellers.com/sdpl-om](https://www.sandeepdwellers.com/sdpl-om)
Facebook : [https://www.facebook.com/SDPL.Nagpur](https://www.facebook.com/SDPL.Nagpur)
Instagram : [https://www.instagram.com/sandeepdwellers](https://www.instagram.com/sandeepdwellers)
Twitter : [https://twitter.com/SdplNagpur](https://twitter.com/SdplNagpur)
Linkedin : [https://www.linkedin.com/company/sandeep-dwellers-pvt-ltd ](https://www.linkedin.com/company/sandeep-dwellers-pvt-ltd )
Pinterest : [https://in.pinterest.com/sandeepdweller](https://in.pinterest.com/sandeepdweller)
YouTube : [https://www.youtube.com/@sdplnagpur](https://www.youtube.com/@sdplnagpur)







 | sdplom | |
1,784,201 | Hi انا جديد هنا | A post by Nora | 0 | 2024-03-08T08:49:05 | https://dev.to/nora12345678/hi-n-jdyd-hn-30aa | nora12345678 | ||
1,780,877 | The Four Blockchain Domains Leading Innovation Waves | Imagine standing on the edge of a digital frontier, watching as a new world unfolds before you. This... | 0 | 2024-03-05T11:47:06 | https://dev.to/calyptus_ninja/the-four-blockchain-domains-leading-innovation-waves-4c32 | blockchain, web3 | Imagine standing on the edge of a digital frontier, watching as a new world unfolds before you. This reality of the blockchain industry has transformed from a niche interest into a global phenomenon, offering a wide array of blockchain jobs. It's a tale of creativity, community, and the pursuit of innovation, with every chapter driven by human ingenuity.
**From Gamers to Earners: The Playful Revolution**
Let's look into the world of Play-to-Earn (P2E) gaming. Picture this: Alex, a college student, discovers a game called Axie Infinity. By collecting and battling digital creatures known as Axies, Alex not only finds an engaging hobby but also an unexpected source of income. This isn't just a game; it's a gateway to the blockchain world for millions like Alex, offering entry-level blockchain jobs through engaging digital platforms.
The P2E sector's growth is astronomical, emphasising the compound annual growth rate of 17.93% and illustrating the vibrant community where creativity is rewarded. These platforms symbolise the transformative power of blockchain, turning gamers into digital entrepreneurs and opening up numerous remote jobs.
**DeFi: Banking, But Not As We Know It**
Decentralised Finance (DeFi) is rewriting the rules of financial transactions, offering a myriad of blockchain engineer jobs. Imagine a world where you're in full control of your money, with no banks in sight. That's DeFi for you, a world where lending, borrowing, and investing happen on your terms, powered by technology that's transparent and accessible.
The story of DeFi is a story of empowerment illustrating how decentralised solutions are creating a more equitable financial system. With a current Total Value Locked (TVL) of $69.60 billion, DeFi stands as a testament to the power of decentralised solutions in shaping the future of finance and generating blockchain consulting jobs.
**Layer-2 Solutions: Supercharging Blockchain**
Venturing deeper into the blockchain realm, we encounter the ingenious world of Layer-2 solutions, essential for scaling blockchain. These technologies are making blockchain faster and more affordable, enabling transactions to complete in the blink of an eye without hefty fees. This promise of Layer-2 solutions offers a glimpse into a future where blockchain seamlessly integrates into our daily lives.
**AI Meets Blockchain: A Synergy of Futures**
The intersection of AI and blockchain finds endless possibilities, generating numerous jobs on blockchain. AI's role in enhancing blockchain's efficiency is akin to a navigator guiding a ship through uncharted waters. Projects harnessing this synergy, like Fetch.ai, worldcoin, etc are not just about technological advancement; they're about crafting a future that's smarter, more secure, and infinitely more creative, underlining the growth of jobs with blockchain.
**The Path Forward**
As we look to the horizon, it's clear that the journey of blockchain is far from complete. Platforms like [Calyptus](http://calyptus.co) stand at the forefront of this evolution, offering a bridge for talented individuals into the blockchain space through education, community, and recruitment opportunities.
In this digital age, the story of blockchain is ours to write. It's a narrative of transformation, challenge, and above all, hope. As the industry continues to grow and evolve, it remains a beacon of potential, promising a future where technology further blurs the lines between the digital and physical worlds, creating a more interconnected, transparent, and safe global society.
| calyptus_ninja |
1,781,049 | Unlocking the Potential with Salesforce: Your Business Growth Catalyst | Embarking on the Salesforce journey can be a revelation for businesses aiming to finesse their sales... | 0 | 2024-03-05T14:10:50 | https://dev.to/salomonbervin/unlocking-the-potential-with-salesforce-your-business-growth-catalyst-7bk | bop, outsourcing, softwaredevelopment | Embarking on the Salesforce journey can be a revelation for businesses aiming to finesse their sales approach. This isn't merely a CRM tool; it's your roadmap to streamlining operations and boosting sales efficiency, tailored for the uninitiated and the seasoned alike.
Stepping into the CRM realm for the first time? Or maybe you're on the hunt to elevate your current setup? Salesforce emerges as a beacon of progress. And let's not sideline the tech savvies; custom Salesforce solutions are like bread and butter for adept software developers.
Venture into the world of Salesforce Service Cloud and unveil a treasure trove of functionalities that redefine your approach to customer interactions, lead management, and data organization. It's an adventure worth taking.
Join me as we unpack the seven pivotal advantages that Salesforce CRM unfurls for your business. It's a narrative that could redefine your business playbook.
## Embracing Salesforce CRM: The Game-Changer Your Business Deserves
Imagine a tool that transcends the ordinary, amalgamating CRM and marketing prowess into a single, cloud-shrouded sanctuary. Salesforce is that emblem of unity, sculpting a cohesive environment for sales, marketing, and customer support to thrive in harmony.
It's about knitting together a customer narrative across various platforms, ensuring your teams march to the beat of the same drum. Salesforce isn't just about keeping records; it's about crafting experiences and journeys.
Tailoring experiences based on a rich tapestry of customer data? Ensuring your clientele sticks around for the long haul? That's the Salesforce promise, delivering the right touchpoints at the most opportune times.
## Peeling Back the Layers: Salesforce's Business Boons Uncovered
Automation Equals Liberation: Bid farewell to the drudgery of manual tasks with Salesforce’s automation magic, liberating your schedule and budget for grander visions.
Mastering Lead Dynamics: Salesforce doesn't just track leads; it decodes them. It's your secret to honing in on the prospects with real potential, turning cold calls into conversations.
Email Insights Unleashed: Keep a pulse on your email engagement with Salesforce’s keen eye. Understand who's interested and tailor your follow-ups with precision.
A New Era of Customer Relations: With Salesforce, every customer interaction is an opportunity. Track, manage, and evolve your customer relationships with an ease that feels almost mythical.
Simplify Your Lead Prioritization: Let Salesforce’s intelligent lead scoring guide your attention where it’s most deserved, ensuring your team’s efforts are always spot-on.
Proposals That Hit the Mark: Harness the power of Salesforce to fine-tune your sales pitches, crafting proposals that resonate and convert.
Harmonizing Sales and Marketing Efforts: Break down the barriers between sales and marketing with Salesforce, fostering a synergy that drives leads down the funnel with unmatched grace.
Soaring Customer Satisfaction: Anticipate needs, personalize interactions, and elevate your customer service with Salesforce, setting new standards in customer delight.
Boundless Accessibility: Salesforce’s cloud pedigree means your business moves with you, accessible across any device, at any time, from anywhere in the world.
Financial Uplift: Transform data into action with Salesforce, freeing your team to focus on nurturing relationships and amplifying revenue streams.
## Salesforce Decoded: Answers to Your Burning Questions
What’s the Salesforce essence? It’s your all-encompassing hub for nurturing customer relationships, streamlining your sales pipeline, and igniting your marketing efforts, all while maintaining a cool, collected composure.
Is Salesforce a universal fit? While it's a powerhouse, Salesforce might not align perfectly with every business scenario, especially for those navigating tight financial lanes or with ultra-specific requirements.
## Final Thoughts: Why Salesforce Stands Out as Your Strategic Ally
Migrating to Salesforce isn't just about upgrading your software; it's about adopting a mindset geared towards growth, efficiency, and deepened customer connections. From transforming mundane tasks to gleaning deep insights into your leads, Salesforce acts as the silent partner propelling your business forward.
Considering a leap towards better business dynamics? Salesforce could well be the tailwind your ambitions have been waiting for.
Get in touch with Porat team to [know more about Salesforce](https://porat.dev/%D7%9E%D7%99%D7%99%D7%A9%D7%9D-%D7%A1%D7%99%D7%99%D7%9C%D7%A1%D7%A4%D7%95%D7%A8%D7%A1/). | salomonbervin |
1,781,065 | Artificial intelligence to minimize pet insurance waiting periods | This post is a quick overview of an Abto Software blog article. Pet insurance has undergone many... | 0 | 2024-03-05T14:30:28 | https://dev.to/abtosoftware/artificial-intelligence-to-minimize-pet-insurance-waiting-periods-55f1 | ai, datascience, automation | _This post is a quick overview of an Abto Software [blog article](https://www.abtosoftware.com/blog/artificial-intelligence-to-minimize-pet-insurance-waiting-periods)._
Pet insurance has undergone many transformations, with more pet owners now understanding the importance of protecting their four-legged family members in emergencies, injuries, illnesses, and other health problems. Given these positive tendencies, rising costs for professional veterinary assistance, and overall adoption rates pet insurance service providers are moving towards integrating computational technology, in particular artificial intelligence and its many techniques.
But what are the main challenges and opportunities business leaders should consider before digitalization?
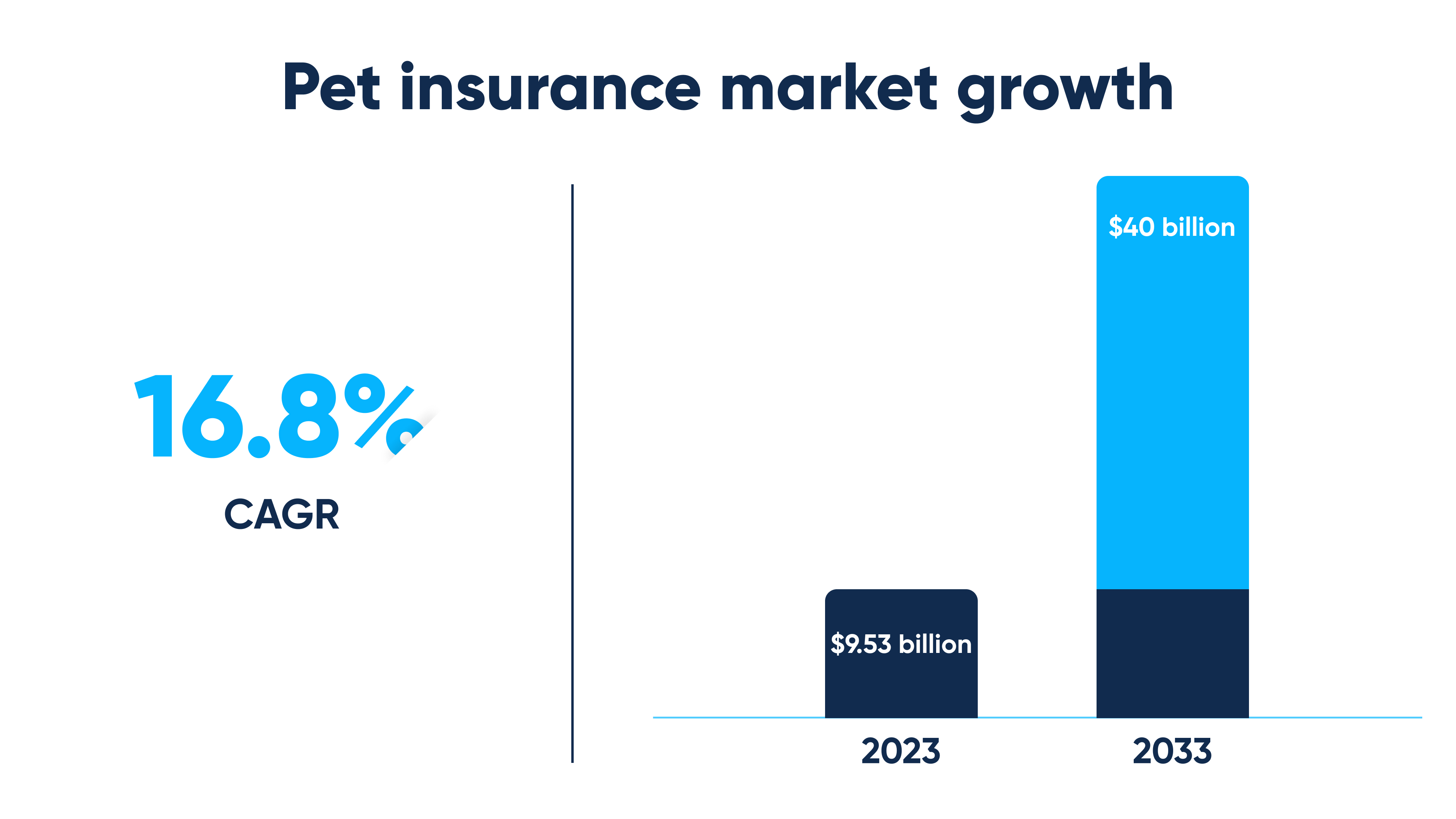
## Pet insurance: how does it work?
### Pet enrollment
Before purchasing preferred coverage, you must fill out the application to submit to the insurance company. This means providing details about age and breed, pre-existing conditions, and more.
### Waiting period
During so-called waiting periods, insurance companies typically handle:
- Underwriting processes
- Policy setup and review
- Additional interaction to provide supporting documentation
- Customer service
These might range between just days to even 6 months in dependence on the selected vendor and coverage.
### Premium payment
As soon as the pet insurance is purchased, you’ll have to pay your premiums, either monthly or annually.
### Veterinary treatment
During visits to the veterinary office, you’ll have to keep the copies of invoices, medical records, and other related documentation to provide those later to the insurance company and receive your reimbursement.
### Claim submission
After receiving veterinary assistance, you have to proceed with the claim submission to the insurance provider.
### Claim review and processing
The said insurance provider will review and process the information your provided to ensure it meets the terms of the purchased coverage, which involves the verification of treatment and assessment of deductibles.
### Expense reimbursement
Right after claim approval, you will get reimbursed for a certain portion of your veterinary expenses.
### Continued coverage
As long as the specified premiums are paid, you will remain covered, so always make sure to review your policy and make necessary updates to ensure the coverage still meets your needs.
## Pet insurance waiting periods: one of the main customer pains
Pet insurance waiting periods are causing significant concerns and frustration to customers obtaining coverage. This delay might cause severe anxiety, in particular for those pet owners facing immediate veterinary expenses in case of emergencies.
Pet insurance waiting periods might also hinder customers from accessing timely assistance from professionals. This might either result in more severe conditions to-be-addressed later or in pet owners paying out-of-pocket, which isn’t always possible for those with complicated financial situations.
Talking about business performance, waiting periods might cause rising dissatisfaction among customers feeling that their needs are not being addressed.
## Decoding delays: the causes behind lengthy waiting periods
Rather prolonged waiting periods are typically associated with:
### Complex underwriting procedures
Underwriting procedures involve assessing various factors – age, breed, activity levels, hereditary conditions. Data collection, processing, storing, and management are traditionally performed manually and, accordingly, quite resource-intense.
### Manual claims processing
Claims processing involves careful account review, coverage cross-checking, legitimacy verification, and more. As these day-to-day processes are typically handled manually, they appear quite inefficient, not mentioning human error, and other related complications.
### Pre-existing condition evaluations
Distinguishing between pre-existing conditions and recently emerged problems is a process necessitating thorough examination, oftentimes requiring back-and-forth communication with involved veterinary offices. Without automation, this process becomes tangled, thus prolonging waiting periods even more.
### Medical record review
Medical records are hard-to-review, often compounded if there are discrepancies and missing health details. Without automation, the process can take several weeks, thereby causing customer dissatisfaction.
## Introducing innovation – artificial intelligence to address waiting periods
Artificial Intelligence can expedite various processes, in particular:
### Risk assessment
AI software can automate risk assessment by analyzing pet age and breed, health-related records, and other. Advanced algorithms can identify risk factors, allowing organizations to make faster decisions.
### Claims processing
AI software can handle claims processing by extracting and analyzing submitted information from documents. Trained algorithms can validate claims submitted, helping companies to facilitate reimbursement approval.
### Decision-making support
Artificial intelligence can analyze health records to help human workers in identifying pre-existing conditions. Such solutions detect indications of chronic health conditions, thus accelerating policy decisions.
### Data interpretation
By adopting modern techniques – natural language processing (NLP), optical character recognition (OCR) – human employees can digitize and interpret medical records much faster than utilizing traditional methods. This helps to highlight relevant information, thereby streamlining business efficiency.
## Summing up
Artificial intelligence has many useful applications in modern pet insurance, so why delay modernization?
Abto Software sees future-proof business opportunities in implementing artificial intelligence to revolutionize pet insurance, from accurate claim processing and 24/7 customer service, to hassle-free regulatory compliance. Our engineers can cover every stage from design to deployment and support to empower business leaders moving towards digital transformation.
Our expertise:
- Artificial intelligence
- Computer vision
- Natural language processing (NLP)
- Optical character recognition (OCR)
| abtosoftware |
1,781,082 | Day-9 MongoDB(NoSQL Database)... | Hey, fellow code adventurers! Get ready to hop on the MongoDB, I am very excited to move to... | 0 | 2024-03-05T15:22:11 | https://dev.to/pranjal_ml/day-9-mongodbnosql-database-5426 | webdev, python, beginners, programming | ## Hey, fellow code adventurers! Get ready to hop on the MongoDB, I am very excited to move to the next step,

<hr>
Today's Agenda-
1. **Introduction to MongoDB:**
- What is MongoDB and how does it differ from traditional relational databases?
- Overview of NoSQL databases and MongoDB's role in this landscape.
2. **Getting Started with MongoDB:**
- Installation and setup guide for MongoDB.
- Creating your first database and collection.
3. **MongoDB Data Modeling:**
- Understanding document-oriented data modeling.
- Best practices for designing MongoDB schemas.
4. **CRUD Operations in MongoDB:**
- A comprehensive guide to Create, Read, Update, and Delete operations in MongoDB.
- Examples and use cases for each CRUD operation.
5. **Indexing and Query Optimization:**
- Importance of indexing in MongoDB.
- Strategies for optimizing queries and improving performance.
6. **Aggregation Framework in MongoDB:**
- Exploring the powerful aggregation framework for complex data processing.
- Examples of using aggregation pipelines.
7. **MongoDB Atlas:**
- Overview and benefits of MongoDB's cloud database service.
- Setting up and managing clusters on MongoDB Atlas.
8. **Data Security in MongoDB:**
- Authentication and authorization in MongoDB.
- Tips for securing your MongoDB deployment.
9. **Scaling MongoDB:**
- Horizontal and vertical scaling options.
- Sharding strategies for distributing data across multiple servers.
10. **Backup and Disaster Recovery:**
- Implementing a robust backup strategy for MongoDB.
- Steps for recovering data in case of a disaster.
11. **MongoDB and Python:**
- Building applications with MongoDB and Python.
- Integrating MongoDB into a Python project.
12. **Real-world Use Cases:**
- Case studies of organizations successfully using MongoDB.
- Highlighting specific industries or applications where MongoDB excels.
13. **Best Practices for MongoDB Development:**
- Coding standards and conventions.
- Performance optimization tips for MongoDB applications.
<hr>
**Introduction to MongoDB:**
MongoDB is a popular NoSQL database that diverges from traditional relational databases by employing a document-oriented data model. Unlike tables in a relational database, MongoDB uses flexible and schema-less documents, typically in BSON (Binary JSON) format, to store data. This provides greater flexibility and scalability, as data can vary within the same collection.
MongoDB falls under the category of NoSQL databases in the broader database context. NoSQL databases, or "Not Only SQL," depart from the rigid structure of traditional relational databases, allowing for more dynamic and scalable storage solutions. MongoDB's key role lies in efficiently handling large volumes of unstructured or semi-structured data, making it well-suited for applications with evolving data requirements and complex data models.
<hr>
**Getting Started with MongoDB:**
1. **Installation and Setup:**
- Begin by downloading and installing MongoDB based on your operating system.
- Configure the necessary settings, such as data directory and port, in the MongoDB configuration file.
- Start the MongoDB server to initiate the database.
2. **Creating Your First Database and Collection:**
- Open the MongoDB shell or use a graphical interface like MongoDB Compass.
- Use the `use` command to create a new database. For example: `use mydatabase`.
- Create your first collection within the database. Collections are akin to tables in relational databases and store documents.
- Insert documents into the collection using the `insert` command or other CRUD operations to begin populating your MongoDB database.
<hr>
**MongoDB Data Modeling:**
1. **Understanding Document-Oriented Data Modeling:**
- MongoDB utilizes a document-oriented data model, where data is stored as flexible, JSON-like BSON documents.
- Each document can have varying fields, and the structure is not fixed across the entire collection.
- Relationships between data are often represented within documents, promoting a more natural representation of real-world entities.
2. **Best Practices for Designing MongoDB Schemas:**
- **Denormalization:** Embrace denormalization to reduce the need for complex joins and enhance query performance.
- **Consider Query Patterns:** Design schemas based on how the application queries data to optimize for common use cases.
- **Use Embedded Documents:** Embed related data within a document when a one-to-one or one-to-many relationship exists to improve read efficiency.
- **Indexes:** Strategically use indexes to speed up query performance, considering the fields used in queries and sorting operations.
- **Avoid Large Documents:** Large documents can impact performance, so it's often beneficial to split large datasets into smaller, more manageable documents.
- **Pre-joining Data:** In some scenarios, pre-joining related data at write time can enhance read performance.
MongoDB's flexible schema design allows for a more intuitive representation of data, and thoughtful consideration of data modeling practices ensures optimal performance for specific application requirements.
<hr>
**CRUD Operations in MongoDB:**
1. **Create (C):**
- **Operation:** Use the `insert` or `insertOne` command to add new documents to a collection.
- **Example:** `db.collection.insertOne({ name: "John", age: 25, city: "ExampleCity" });`
- **Use Case:** Adding a new user profile to a "users" collection.
2. **Read (R):**
- **Operation:** Utilize the `find` method to query and retrieve documents from a collection.
- **Example:** `db.collection.find({ age: { $gte: 21 } });`
- **Use Case:** Retrieving all users above the age of 21 from a "users" collection.
3. **Update (U):**
- **Operation:** Apply the `updateOne` or `updateMany` command to modify existing documents.
- **Example:** `db.collection.updateOne({ name: "John" }, { $set: { age: 26 } });`
- **Use Case:** Updating the age of a specific user in a "users" collection.
4. **Delete (D):**
- **Operation:** Use `deleteOne` or `deleteMany` to remove documents from a collection.
- **Example:** `db.collection.deleteOne({ name: "John" });`
- **Use Case:** Deleting a user with the name "John" from a "users" collection.
Understanding and effectively applying these CRUD operations in MongoDB are fundamental for interacting with and managing data within MongoDB collections.
<hr>
**Indexing and Query Optimization in MongoDB:**
1. **Importance of Indexing:**
- **Purpose:** Indexing enhances query performance by allowing MongoDB to locate and retrieve documents more efficiently.
- **Mechanism:** Indexes are data structures that store a small subset of the data, providing a quick path to the actual documents.
- **Types:** MongoDB supports various index types, including single field, compound, and text indexes.
2. **Strategies for Optimizing Queries:**
- **Choose Appropriate Indexes:**
- Identify frequently queried fields and create indexes on them.
- Analyze query patterns to determine the most effective index types.
- **Covered Queries:**
- Use indexes that cover the entire query to avoid accessing the actual documents.
- Minimize the fields returned by queries to optimize data retrieval.
- **Avoid Large Result Sets:**
- Limit the number of documents returned by queries.
- Use pagination and projections to retrieve only necessary data.
- **Use the `explain` Method:**
- Analyze query plans using the `explain` method to understand how MongoDB executes queries.
- Identify and resolve performance bottlenecks.
- **Sort and Skip Carefully:**
- Sorting large result sets can be resource-intensive. Apply indexes to improve sorting performance.
- Use `skip` cautiously, especially with large datasets, as it may impact performance.
- **Avoid Unnecessary Queries:**
- Cache frequently used queries.
- Consider denormalization to reduce the need for complex queries.
- **Update Statistics Regularly:**
- MongoDB automatically updates statistics, but in some cases, manual updates may be beneficial.
- Monitor and optimize as the data distribution evolves.
Effective indexing combined with thoughtful query optimization strategies significantly enhances MongoDB's performance, making it well-suited for demanding applications.
<hr>
**Aggregation Framework in MongoDB:**
1. **Exploring the Aggregation Framework:**
- **Purpose:** MongoDB's Aggregation Framework facilitates complex data processing, analysis, and transformation.
- **Pipeline Concept:** Aggregation operations are organized into pipelines, where each stage performs a specific operation on the data.
2. **Examples of Aggregation Pipelines:**
- **Match Stage:**
- *Purpose:* Filters documents based on specified criteria.
- *Example:* `{ $match: { status: "active" } }`
- **Group Stage:**
- *Purpose:* Groups documents by a specified key and applies an aggregation expression.
- *Example:* `{ $group: { _id: "$department", avgSalary: { $avg: "$salary" } } }`
- **Project Stage:**
- *Purpose:* Shapes the output documents by including, excluding, or transforming fields.
- *Example:* `{ $project: { fullName: { $concat: ["$firstName", " ", "$lastName"] }, salary: 1 } }`
- **Sort Stage:**
- *Purpose:* Orders the output documents based on specified criteria.
- *Example:* `{ $sort: { salary: -1 } }`
- **Limit Stage:**
- *Purpose:* Restricts the number of documents in the output.
- *Example:* `{ $limit: 10 }`
- **Facet Stage:**
- *Purpose:* Allows for multiple pipelines to be executed on the same set of input documents.
- *Example:* `{ $facet: { "Department A": [...], "Department B": [...] } }`
- **Unwind Stage:**
- *Purpose:* Deconstructs an array field into multiple documents, one for each array element.
- *Example:* `{ $unwind: "$skills" }`
The Aggregation Framework's versatility enables developers to perform intricate data manipulations and analysis, providing a powerful tool for handling diverse data processing scenarios in MongoDB.
<hr>
**MongoDB Atlas:**
1. **Overview and Benefits:**
- **Cloud Database Service:** MongoDB Atlas is MongoDB's fully managed cloud database service.
- **Key Benefits:**
- Automated backups and point-in-time recovery.
- Scalability for handling varying workloads.
- Security features, including encryption and compliance.
2. **Setting Up and Managing Clusters:**
- **Creating an Atlas Account:**
- Sign up for MongoDB Atlas and log in to the dashboard.
- Choose the cloud provider (AWS, Azure, GCP) and region for deployment.
- **Cluster Configuration:**
- Define cluster settings such as instance size, storage, and backup options.
- Select the MongoDB version for your cluster.
- **Security Configuration:**
- Set up authentication methods, including username and password.
- Configure network access to allow or restrict incoming connections.
- **Deploying the Cluster:**
- Click "Create Cluster" to initiate the deployment process.
- Monitor the cluster creation progress in the Atlas dashboard.
- **Managing Clusters:**
- Access the cluster dashboard for real-time performance metrics.
- Perform maintenance tasks, such as scaling or updating cluster configurations.
- **Backup and Restore:**
- Configure automated backups and define retention policies.
- Restore data to a specific point in time using backup snapshots.
- **Scaling Options:**
- Easily scale your cluster vertically or horizontally to accommodate changes in workload.
- Add or remove nodes based on performance requirements.
MongoDB Atlas simplifies the deployment and management of MongoDB databases in the cloud, providing a user-friendly interface and essential features for a secure and scalable database solution.
<hr>
**Data Security in MongoDB:**
1. **Authentication and Authorization:**
- **Authentication:** Users must authenticate using valid credentials (username and password) to access the MongoDB database.
- **Authorization:** MongoDB supports role-based access control, granting specific privileges to users or roles at the database or collection level.
2. **Tips for Securing MongoDB Deployment:**
- **Use Strong Authentication:**
- Enforce the use of strong, complex passwords for MongoDB user accounts.
- Consider enabling authentication mechanisms like LDAP or Kerberos for additional security layers.
- **Role-Based Access Control (RBAC):**
- Implement RBAC to assign specific roles with well-defined permissions to users.
- Regularly review and update roles based on the principle of least privilege.
- **Network Security:**
- Configure network access controls to restrict incoming connections.
- Use Virtual Private Clouds (VPC) or network peering to create isolated environments.
- **Encryption:**
- Enable encryption in transit to secure data transmitted between MongoDB and client applications.
- Implement encryption at rest to safeguard data stored on disk.
- **Audit Logging:**
- Enable MongoDB's audit logging to track and monitor user activities.
- Regularly review audit logs for suspicious or unauthorized actions.
- **Regular Updates:**
- Keep MongoDB and its dependencies up to date with the latest security patches.
- Monitor MongoDB's official channels for security advisories.
- **Backup and Recovery:**
- Implement regular backup strategies to ensure data recovery in case of a security incident.
- Store backups in a secure, offsite location.
- **Security Best Practices:**
- Follow MongoDB's security best practices, including the Principle of Least Privilege.
- Stay informed about MongoDB's security recommendations and updates.
Implementing a comprehensive security strategy, including strong authentication, access controls, encryption, and regular monitoring, is crucial to ensuring the safety of your MongoDB deployment.
<hr>
**Scaling MongoDB:**
1. **Horizontal and Vertical Scaling:**
- **Vertical Scaling (Scaling Up):**
- Involves increasing the capacity of a single server, typically by adding more CPU, RAM, or storage.
- Limited by the hardware constraints of a single machine.
- **Horizontal Scaling (Scaling Out):**
- Involves adding more servers to distribute the load and increase capacity.
- Offers better scalability by leveraging multiple machines.
2. **Sharding Strategies:**
- **Definition of Sharding:**
- Sharding is the process of distributing data across multiple servers to improve performance and handle large datasets.
- **Shard Key Selection:**
- Choose a well-distributed and selective shard key to evenly distribute data.
- Consider the access patterns and query requirements when selecting a shard key.
- **Shard Balancing:**
- MongoDB's balancer automatically redistributes data among shards to maintain a balanced workload.
- Monitoring and adjusting the balancer settings can optimize performance.
- **Range-based Sharding:**
- Distributes data based on a specified range of values in the shard key.
- Useful for scenarios where data can be naturally divided into ranges.
- **Hash-based Sharding:**
- Distributes data across shards using a hash function on the shard key.
- Provides a more even distribution of data but may not be suitable for range queries.
- **Compound Shard Key:**
- Combines multiple fields into a compound shard key for more complex sharding scenarios.
- Carefully design compound keys to suit specific use cases.
- **Adding and Removing Shards:**
- Dynamically add or remove shards to adapt to changing workloads.
- Plan for shard addition or removal during maintenance windows to minimize disruption.
Scaling MongoDB through horizontal scaling and sharding strategies allows for efficient handling of growing datasets and increased performance, making it a scalable solution for diverse applications.
<hr>
**Backup and Disaster Recovery in MongoDB:**
1. **Implementing a Robust Backup Strategy:**
- **Regular Backups:**
- Schedule regular backups to capture the latest data changes.
- MongoDB Atlas provides automated backup features for convenience.
- **Snapshot Backups:**
- Use point-in-time snapshot backups to capture a consistent view of the data at a specific moment.
- Ensure snapshots are stored securely in a separate location from the production database.
- **Incremental Backups:**
- Implement incremental backups to capture only the changes since the last backup.
- Reduces backup time and storage requirements.
- **Backup Encryption:**
- Enable encryption for backups to secure data during transit and storage.
- Utilize encryption mechanisms provided by MongoDB or the cloud provider.
2. **Steps for Recovering Data in Case of a Disaster:**
- **Identify the Issue:**
- Determine the cause of the disaster, such as data corruption, accidental deletion, or hardware failure.
- **Restore from Backups:**
- Access the latest backup and initiate the restore process.
- Choose the appropriate backup based on the desired point-in-time recovery.
- **Verification:**
- Verify the restored data for accuracy and completeness.
- Use validation tools or queries to ensure data integrity.
- **Rollback or Point-in-Time Recovery:**
- Depending on the disaster scenario, consider rolling back to a specific backup or performing a point-in-time recovery.
- Ensure the chosen recovery point aligns with business requirements.
- **Communication and Documentation:**
- Communicate the recovery process and timeline to stakeholders.
- Document the steps taken during the recovery process for future reference.
- **Post-Recovery Testing:**
- Conduct testing to validate that the recovered system functions correctly.
- Verify that applications and services can resume normal operations.
A well-defined backup strategy, including regular snapshots and incremental backups, coupled with a structured disaster recovery plan, ensures that MongoDB databases can be restored quickly and effectively in the event of unexpected data loss or system failures.
<hr>
**MongoDB and Python:**
1. **Building Applications with MongoDB and Python:**
- **PyMongo Library:**
- PyMongo is the official MongoDB driver for Python, facilitating interaction between Python applications and MongoDB databases.
- **Document-Oriented Data Model:**
- Python applications can seamlessly work with MongoDB's document-oriented data model, as both use JSON-like BSON documents.
- **Expressive Query Language:**
- Leverage PyMongo to construct queries and perform CRUD operations on MongoDB collections directly from Python.
- **Aggregation Framework:**
- Utilize the MongoDB Aggregation Framework to process and analyze data within Python applications.
2. **Integrating MongoDB into a Python Project:**
- **Installing PyMongo:**
- Use pip to install the PyMongo library: `pip install pymongo`.
- **Connecting to MongoDB:**
- Establish a connection to the MongoDB server using PyMongo's `MongoClient`.
- Specify connection details like host, port, and authentication credentials.
- **Working with Databases and Collections:**
- Access databases and collections using PyMongo.
- Create, read, update, and delete documents within Python code.
- **Handling BSON Documents:**
- PyMongo automatically converts BSON documents to Python dictionaries, simplifying data manipulation.
- **Executing Queries:**
- Use PyMongo to construct queries with various operators and filters.
- Retrieve and process query results within Python applications.
- **Aggregation Pipeline:**
- Construct and execute aggregation pipelines for complex data transformations.
- Leverage Python's expressive syntax for defining aggregation stages.
- **Error Handling and Transactions:**
- Implement error handling mechanisms using Python's try-except blocks.
- PyMongo supports transactions for ensuring data consistency in multi-operation scenarios.
Python's simplicity and versatility, combined with PyMongo's capabilities, make integrating MongoDB into Python projects straightforward. This integration allows developers to seamlessly work with MongoDB's document-oriented database in their Python applications.
<hr>
**Real-world Use Cases:**
1. **eCommerce Platforms:**
- **Use Case:** MongoDB is employed by eCommerce platforms for its ability to handle diverse product catalogs, manage customer data, and provide real-time inventory updates.
2. **Content Management Systems (CMS):**
- **Use Case:** CMS applications leverage MongoDB's flexible schema to manage content, user data, and facilitate collaborative content creation and publishing.
3. **Finance and Banking:**
- **Use Case:** MongoDB is used in financial applications for its scalability and performance, handling high volumes of transactions, user profiles, and financial data.
4. **Healthcare Systems:**
- **Use Case:** MongoDB is utilized in healthcare systems to manage patient records, healthcare analytics, and provide a scalable solution for storing medical data.
5. **Logistics and Supply Chain:**
- **Use Case:** MongoDB is employed in logistics for real-time tracking of shipments, managing inventory, and optimizing supply chain processes.
6. **Gaming Industry:**
- **Use Case:** MongoDB supports gaming applications with its ability to handle dynamic player profiles, in-game transactions, and real-time game analytics.
7. **Telecommunications:**
- **Use Case:** MongoDB is used in telecom for managing subscriber data, handling call detail records, and providing a scalable platform for network management.
8. **Government and Public Services:**
- **Use Case:** MongoDB is employed in government applications for managing citizen data, handling administrative processes, and ensuring data security.
9. **IoT (Internet of Things):**
- **Use Case:** MongoDB excels in IoT applications, managing large volumes of sensor data, facilitating real-time analytics, and supporting device management.
10. **Educational Platforms:**
- **Use Case:** MongoDB is used in educational platforms for managing student records, course data, and supporting collaborative learning environments.
MongoDB's versatility and scalability make it a preferred choice across various industries and applications, showcasing its adaptability to diverse use cases and business requirements.
<hr>
**Best Practices for MongoDB Development:**
1. **Coding Standards and Conventions:**
- **Consistent Naming Conventions:**
- Follow a consistent naming convention for collections, fields, and variables.
- Enhances code readability and maintainability.
- **Document Structure:**
- Design clear and concise document structures.
- Keep documents as flat as possible to avoid nested structures that can complicate queries.
- **Use of Indexes:**
- Strategically use indexes to improve query performance.
- Regularly review and optimize indexes based on query patterns.
- **Avoid Large Documents:**
- Split large documents into smaller ones to optimize query performance.
- Consider using references for related data in separate collections.
- **Error Handling:**
- Implement robust error handling mechanisms in your code.
- Utilize try-except blocks to gracefully handle exceptions.
2. **Performance Optimization Tips:**
- **Query Patterns:**
- Analyze and optimize queries based on application requirements.
- Utilize the Explain method to review and optimize query plans.
- **Connection Pooling:**
- Implement connection pooling to reuse database connections efficiently.
- Reduces the overhead of opening and closing connections for each operation.
- **Batch Operations:**
- Use bulk write operations for inserting or updating multiple documents at once.
- Reduces the number of round-trips between the application and the database.
- **Capped Collections:**
- Consider using capped collections for scenarios where a fixed-size collection with automatic data expiration is beneficial.
- **Sharding Strategies:**
- Implement sharding for horizontal scaling in scenarios with growing datasets.
- Choose an appropriate shard key for even distribution of data.
- **Profiling and Monitoring:**
- Regularly profile and monitor MongoDB performance using tools like MongoDB Atlas.
- Identify and address performance bottlenecks proactively.
- **Read and Write Concerns:**
- Adjust read and write concerns based on application requirements.
- Balance consistency and performance by choosing appropriate levels of concern.
Following these best practices ensures the development of efficient and maintainable MongoDB applications, optimizing both code quality and database performance.
<hr>
<hr>
The next blog will continue this for the implementation of MongoDB & SQL. Stay connected. Please, visit the [github](https://github.com/Pranjal-sharma-SDE/AI_Mind_Hub).
Drop by our [Telegram Channel](https://t.me/+J2qk3bDFR-piZmU1) and let the adventure begin! See you there, Data Explorer! 🌐🚀
| pranjal_ml |
1,781,103 | I have created a small anti-depression script | Elizabeth-Gilberth-inspired self-help self-chat app | 0 | 2024-03-05T15:36:52 | https://dev.to/fyodorio/i-have-created-a-small-anti-depression-script-p4i | wecoded, mentalhealth, cli, javascript | ---
title: I have created a small anti-depression script
published: true
description: Elizabeth-Gilberth-inspired self-help self-chat app
tags: wecoded, mentalhealth, cli, javascript
cover_image: https://dev-to-uploads.s3.amazonaws.com/uploads/articles/42vhqw254tdcedhzq3ts.png
---
I read this wonderful book by [Elizabeth Gilbert](https://www.elizabethgilbert.com/) called [Eat, Pray, Love](https://en.wikipedia.org/wiki/Eat,_Pray,_Love). Insightful, not to say more. And there are these chapters about her fighting with Depression and Loneliness which many of us can relate to (myself included).
Specifically, Elizabeth shares the piece on her journaling, or rather chatting with herself. How it helped her to get out of the pit of despair and kick away the internal demons.
That pushed me to drop a quick script to try to do the same in my terminal (because I'm a developer, or rather because I don't have a notebook around).
And it actually worked. And that helped me. At least today.
So I decided to share it here, as I noticed [this new March tag](https://dev.to/devteam/wecoded-2024-empowering-change-for-gender-equity-in-tech-30nj) yesterday. Maybe it would be of some use for someone.
I mean, probably that's bloody stupid, both the idea and definitely the code, but for some reason it works. And as the terminal is apparently not the most positive place to be in the world, this script may make it more acceptable sometimes.
Cheers 🤗
{% embed https://github.com/fyodorio/chat-with-yourself %} | fyodorio |
1,781,181 | 🚀 Building a RESTful API with Ruby on Rails | Today, everything is interconnected, APIs or Application Programming Interfaces have become a... | 25,342 | 2024-03-06T11:00:00 | https://dev.to/dumebii/building-a-restful-api-with-ruby-on-rails-30gl | webdev, beginners, rails, ruby | Today, everything is interconnected, **APIs** or **Application Programming Interfaces** have become a fundamental aspect of enabling communication and data exchange between different applications.
## Table of Contents
1. [What is an API?](#what-is-an-api)
2. [What is a RESTful API?](#what-is-a-restful-api)
2.1. [Core Principles of RESTful APIs](#core-principles-of-restful-apis)
2.2. [Designing Your RESTful API](#designing-your-restful-api)
2.3. [Implementing Your RESTful API:](#implementing-your-restful-api)
2.4. [Best Practices for building your own RESTful API](#best-practices-for-building-your-own-restful-api)
3. [Building a RESTful API with Rails](#building-a-restful-api-with-rails)
3.5. [Setting Up Your Rails Project](#setting-up-your-rails-project)
3.6. [Defining Resources and Routes](#defining-resources-and-routes)
3.7. [Implementing Controller Actions in your Rails API](#implementing-controller-actions-in-your-rails-api)
3.8. [Serializing Data in your Rails API](#serializing-data-in-your-rails-api)
3.9. [Testing Your RESTful API](#testing-your-restful-api)
4. [References](#references)
##What is an API?
An API, which stands for **Application Programming Interface**, acts as a middleman between two software applications, allowing them to communicate and exchange data with each other. It defines a set of rules and specifications that dictate how these applications can interact.
_Imagine you have two different apps: a recipe app and a grocery delivery app. The recipe app doesn't have the functionality to directly order ingredients from the grocery store. However, if the recipe app has an API that connects to the grocery delivery app's API, it can then share your grocery list and enable you to order the ingredients directly through the recipe app._
##Is an API a program?
* **APIs are not programs themselves:** They are sets of instructions and specifications that software applications follow to communicate.
* **APIs can be used for various purposes:** They can be used to share data, access functionality from other applications, or even trigger actions in other applications.
##What is a RESTful API?
**RESTful APIs** are considered to be the most efficient and scalable approach to building APIs, and they adhere to the core principles of REpresentational State Transfer. In this paradigm, the API is designed to represent a resource, where the resource can be manipulated through the representation that the API provides. RESTful APIs also follow the HTTP protocol, which makes them more accessible to developers and easier to integrate.
### Core Principles of RESTful APIs
* **Client-Server Architecture:** REST separates the concerns of the client (application consuming the API) and the server (application providing the API). The client makes requests to the server, and the server responds with relevant data.
* **Stateless Communication:** Each request from the client to the server should contain all necessary information to process the request, making the server independent of previous requests.
* **Resource-Based:** APIs are designed around resources, which represent data entities like users, products, or orders. Each resource has a unique identifier (URI) and can be manipulated using standard HTTP methods.
* **Standard HTTP Methods:** RESTful APIs leverage standard HTTP methods for **CRUD** (Create, Read, Update, Delete) operations:
* **GET:** Retrieves a resource.
* **POST:** Creates a new resource.
* **PUT:** Updates an existing resource.
* **DELETE:** Deletes a resource.
### Designing Your RESTful API
1. **Identify Resources:** Define the core entities within your system and their relationships.
2. **Choose Resource Names:** Use descriptive and plural nouns for resources (e.g., `/users`, `/products`).
3. **Define Endpoints:** Map HTTP methods to specific actions on resources.
* Use GET for fetching resources (`/users/{id}`) or collections (`/users`).
* Use POST for creating new resources (`/users`).
* Use PUT for updating existing resources (`/users/{id}`).
* Use DELETE for deleting resources (`/users/{id}`).
4. **Versioning:** Implement versioning to manage API changes and ensure backward compatibility.
5. **Error Handling:** Return clear and informative error messages using standard HTTP status codes (e.g., 404 - Not Found, 400 - Bad Request).
### Setting up Your RESTful API:
* **Choose a Framework:** Popular frameworks like Ruby on Rails, Django (Python), and Spring Boot (Java) offer built-in functionalities for building RESTful APIs.
* **Define Routes:** Map URLs to specific controller actions based on HTTP methods and resources.
* **Data Serialization:** Choose a format for returning data, commonly JSON or XML, ensuring consistency and ease of use for client applications.
* **Security:** Implement authentication and authorization mechanisms to protect your API from unauthorized access.
### Best Practices for building your RESTful API
* Use descriptive and consistent resource names.
* Follow standard HTTP methods and status codes.
* Document your API clearly
* Validate and sanitize user input to prevent security vulnerabilities.
* Implement caching mechanisms to improve performance.
* Consider using pagination for large datasets.
* Test your API thoroughly using automated testing tools.
## Building a RESTful API with Rails
### How to build a RESTful API with Ruby on Rails
Building a RESTful API with Ruby on Rails can be a powerful way to take advantage of the framework's strengths in simplifying common tasks involved in API development. Here's a step-by-step approach that you can follow to create a robust and scalable API using Ruby on Rails:
##Setting Up Your Rails Project
* Start by creating a new Rails application using the `--api` flag:
```bash
rails new my_api --api
```
This flag configures your application specifically for API development, excluding unnecessary functionalities meant for web applications.
##Defining Resources and Routes for the API in Ruby on Rails
* Identify and model your resources using Rails' Active Record.
* For example, create a model named `User` with attributes like `name` and `email`.
```ruby
rails generate model User name:string email:string
```
* Generate a controller for each resource using the `rails generate controller` command.
```bash
rails generate controller Users
```
* Define routes in the `config/routes.rb` file, mapping HTTP methods to controller actions.
```ruby
resources :users, only: [:index, :create]
```
This allows you to retrieve all users with a `GET` request to `/users` and create new users with a `POST` request to the same endpoint. You can similarly define routes for other actions like updating and deleting users.
###Implementing Controller Actions in your Rails API
* Each controller action corresponds to a specific HTTP method and handles the request logic.
* For example, the `index` action in the `UsersController` would fetch all users and return them as JSON:
```ruby
class UsersController < ApplicationController
def index
@users = User.all
render json: @users
end
end
```
* Similarly, the `create` action would accept user data in the request body and create a new user:
```ruby
def create
@user = User.new(user_params)
if @user.save
render json: @user, status: :created
else
render json: @user.errors, status: :unprocessable_entity
end
end
private
def user_params
params.require(:user).permit(:name, :email)
end
```
##Serializing Data in your Rails API
* Rails automatically serializes data into JSON by default using the `render json:` method.
* You can customize the serialization process using libraries like `Active Model Serializers` for more control over the data structure.
##Where to test Your RESTful API
* Use tools like `Postman` or `curl` to send requests to your API endpoints and verify their functionality.
* Write unit and integration tests to ensure your API behaves as expected.
This article is simple and is a beginner article to guide you into understanding how to build RESTful APIs with Ruby on Rails.
##References
[Rails official guide](https://guides.rubyonrails.org/api_app.html)
[Image: What is an API?](https://www.google.com/url?sa=i&url=https%3A%2F%2Fwww.spaceotechnologies.com%2Fglossary%2Ftech-terms%2Fwhat-is-an-api%2F&psig=AOvVaw1nSKEO8qHOVcenzJTNtcLv&ust=1709746793730000&source=images&cd=vfe&opi=89978449&ved=0CBUQjhxqFwoTCPClv6XV3YQDFQAAAAAdAAAAABAE)
[Image: What is RESTful API?](https://www.google.com/url?sa=i&url=https%3A%2F%2Fwww.spaceotechnologies.com%2Fglossary%2Ftech-terms%2Fwhat-is-rest-api%2F&psig=AOvVaw2f5DeqrQIoeN6PGybUV58j&ust=1709743854568000&source=images&cd=vfe&opi=89978449&ved=0CBUQjhxqFwoTCPDUoa_K3YQDFQAAAAAdAAAAABAV)
[How to build a RESTful APIs: Power Up Your Development with Ruby on Rails](https://www.protonshub.com/blogs/power-up-your-development-with-ruby-on-rails)
[Cover Image](https://www.google.com/url?sa=i&url=https%3A%2F%2Fwww.louisramos.dev%2Fblogs%2Fcreate-a-rails-7-rest-api&psig=AOvVaw2pbX4mkK6jTmoPxnTuAjs6&ust=1709743598519000&source=images&cd=vfe&opi=89978449&ved=0CBUQjhxqFwoTCIDks7PJ3YQDFQAAAAAdAAAAABAO)
[Create a Rails 7 REST API](https://www.louisramos.dev/blogs/create-a-rails-7-rest-api)
[Do the Right Thing and Document Your Rails API with Swagger](https://www.sitepoint.com/do-the-right-thing-and-document-your-rails-api-with-swagger/)
| dumebii |
1,781,235 | Takeaways From 5 Terrible API Breaches | The world now relies on APIs to function. However, these interfaces that power our daily lives are... | 0 | 2024-03-12T09:57:31 | https://blog.treblle.com/takeaways-from-5-terrible-api-breaches/ | api, apisecurity, rest | ---
title: Takeaways From 5 Terrible API Breaches
published: true
date: 2024-03-05 13:24:26 UTC
tags: APIs,APISecurity,REST
canonical_url: https://blog.treblle.com/takeaways-from-5-terrible-api-breaches/
---

The world now relies on APIs to function. However, these interfaces that power our daily lives are often left insecure, routinely suffering from a lack of proper authorization controls, misconfigurations, or leaky secrets. This condition has led to severe, high-profile breaches in recent years, exposing millions of user records and resulting in costly penalties.
Below, we'll highlight some of the top API-related breaches that have occurred recently. For each, we'll summarize what went wrong and what actions the attackers were able to perform. We'll also review the consequences of these breaches and suggest some helpful takeaways for API providers to consider going forward.
### 1. Trello API Overshared Data
In early 2024, 15 million pieces of user information were scraped from public boards on Trello, the cloud-based project management application. A hacker was able to perform this by leveraging a feature of the Trello REST API that, when queried, returned profiles related to all public boards associated with a user’s email address. As [Dark Reading covers](https://www.darkreading.com/remote-workforce/atlassian-tightens-api-after-hacker-scrapes-15m-trello-profiles), a data breach of this size could lead to further account takeovers and spear-phishing attacks.
> Trello Allegedly Breached: Database of 15,115,516 User Records Up for Sale
>
> The cybercriminal, who goes by the name 'emo,' claims that the database includes data such as emails, usernames, full names, and other account information.[#databreach](https://twitter.com/hashtag/databreach?src=hash&ref_src=twsrc%5Etfw&ref=blog.treblle.com) [#CTI](https://twitter.com/hashtag/CTI?src=hash&ref_src=twsrc%5Etfw&ref=blog.treblle.com) [#DarkWeb](https://twitter.com/hashtag/DarkWeb?src=hash&ref_src=twsrc%5Etfw&ref=blog.treblle.com) [pic.twitter.com/Fim9jOwUzn](https://t.co/Fim9jOwUzn?ref=blog.treblle.com)
>
> — HackManac (@H4ckManac) [January 17, 2024](https://twitter.com/H4ckManac/status/1747527579559411959?ref_src=twsrc%5Etfw&ref=blog.treblle.com)
<script async src="https://platform.twitter.com/widgets.js" charset="utf-8"></script>
**Takeaway** : Tightly configure your APIs to limit data overexposure and rate-limit queries to avoid business logic abuse.
### 2. Hugging Face Token Breach
In December 2023, [Lasso Security](https://www.lasso.security/blog/1500-huggingface-api-tokens-were-exposed-leaving-millions-of-meta-llama-bloom-and-pythia-users-for-supply-chain-attacks) discovered that over 1,500 tokens associated with Hugging Face, the popular machine-learning model platform, were left exposed in the GitHub and HuggingFace repositories. Using these tokens, researchers gained access to hundreds of organization's accounts. A risk of this nature can leave millions of AI models and datasets vulnerable.
It should be added that exposed API secrets are by no means unique to the AI programming world. In a separate study, [Escape researchers](https://securityboulevard.com/2024/01/methodology-how-we-discovered-over-18000-api-secret-tokens/) found 18,000 API secrets, such as keys and tokens, exposed on the public web, pertaining to all sorts of APIs.
> [#AI](https://twitter.com/hashtag/AI?src=hash&ref_src=twsrc%5Etfw&ref=blog.treblle.com) needs secure [#APIs](https://twitter.com/hashtag/APIs?src=hash&ref_src=twsrc%5Etfw&ref=blog.treblle.com), else we are in for some scary times. Thanks to [@RetroReversing](https://twitter.com/RetroReversing?ref_src=twsrc%5Etfw&ref=blog.treblle.com)[@jpmello](https://twitter.com/jpmello?ref_src=twsrc%5Etfw&ref=blog.treblle.com) for including my thoughts on this. [@SaltSecurity](https://twitter.com/SaltSecurity?ref_src=twsrc%5Etfw&ref=blog.treblle.com)
>
> The Hugging Face API token breach: 5 lessons learned [https://t.co/3bVhseQxMe](https://t.co/3bVhseQxMe?ref=blog.treblle.com)
>
> — 𝙲𝚢𝙱𝚛𝚛𝙽𝚒𝚌𝚔 (@cybrrnick) [December 14, 2023](https://twitter.com/cybrrnick/status/1735437693255905283?ref_src=twsrc%5Etfw&ref=blog.treblle.com)
<script async src="https://platform.twitter.com/widgets.js" charset="utf-8"></script>
**Takeaway** : Seriously protect your API keys—don't store them in public locations and rotate them when possible.
### 3. Unauthorized T-Mobile Data Exfiltration
In early 2023, it was reported that 37 million user accounts had been compromised in a large-scale attack on a T-Mobile API. Although T-Mobile did not disclose the exact details of how the API was compromised, the company did say the access was unauthorized and revealed the nature of the stolen information. The breach was severe enough to prompt an investigation by the [SEC](https://www.sec.gov/Archives/edgar/data/1283699/000119312523010949/d641142d8k.htm). Leakages of this size harm users since the data can be sold on the dark web and leveraged by bad actors for nefarious purposes.
**Takeaway** : Audit your APIs to ensure proper authorization checks are in place for all internal and external stakeholders.
### 4. Millions Stolen In Kronos API Hack
Some API breaches are more directly correlated with financial losses. This was certainly the case for cryptocurrency trading firm Kronos, which, in late 2023, suffered an [API security breach](https://crypto.news/kronos-trading-firm-suffers-security-breach-losses-25m/) that resulted in an estimated $25 million in losses. The hack used unauthorized API keys to steal nearly 13 thousand ETH from the platform. In addition to losses, there were also operational consequences since the trading firm had to [shut down trading for an entire day](https://cointelegraph.com/news/kronos-research-halts-trading-25-m-hack-investigation), causing partners to go offline. The incident led to a significant loss in user faith at a time when the cryptocurrency market was already feeling a bit murky.
> 1/ Since 1:20 am (GMT+8), our team has been working round the clock to minimize the impact and resume trading operations, following a hacking incident that involved unauthorized access to our API Keys. [https://t.co/t2cP9s69sZ](https://t.co/t2cP9s69sZ?ref=blog.treblle.com)
>
> — Kronos Research 🟠 (@ResearchKronos) [November 19, 2023](https://twitter.com/ResearchKronos/status/1726203102842466650?ref_src=twsrc%5Etfw&ref=blog.treblle.com)
<script async src="https://platform.twitter.com/widgets.js" charset="utf-8"></script>
**Takeaway** : To avoid vulnerabilities, the API providers themselves must be careful with how they manage their API keys.
### 5. Optus Breach
In mid-2022, Australian telecommunications company Optus suffered what it called a "[sophisticated attack](https://cybersecasia.net/news/11-2m-telco-customers-in-australia-breached-through-api-data-leak/)" upon its API, which led to the disclosure of over 11 million customer records. As [The Guardian](https://www.theguardian.com/business/2022/sep/29/optus-data-breach-everything-we-know-so-far-about-what-happened) reports, it's unclear as to the exact mechanics of the attack. However, to others, calling it an "attack" in the first place is a joke.
> The situation around Optus’ data breach (don’t call it a “hack”, the API was open to the internet) just goes to show why [#privacy](https://twitter.com/hashtag/privacy?src=hash&ref_src=twsrc%5Etfw&ref=blog.treblle.com) is a [#natsec](https://twitter.com/hashtag/natsec?src=hash&ref_src=twsrc%5Etfw&ref=blog.treblle.com) issue. The solution isn’t more data sharing. We need stronger privacy protections, with real teeth for gross failures like this. [#auspol](https://twitter.com/hashtag/auspol?src=hash&ref_src=twsrc%5Etfw&ref=blog.treblle.com)
>
> — @liampomfret@mastodon.social (@LiamPomfret) [September 28, 2022](https://twitter.com/LiamPomfret/status/1574964943740604417?ref_src=twsrc%5Etfw&ref=blog.treblle.com)
<script async src="https://platform.twitter.com/widgets.js" charset="utf-8"></script>
**Takeaway** : Don't assume anything left open on the web is "private." Take a [zero-trust approach](https://blog.treblle.com/how-ai-can-enable-zero-trust-api-security/) with the proper authentication and authorization in place to protect personally identifiable information.
### Conducting API Attack Postmortems
Unfortunately, API breaches aren't uncommon. The hacks above follow a string of significant [API-related vulnerabilities](https://nordicapis.com/8-significant-api-breaches-of-recent-years/?ref=blog.treblle.com) discovered within popular web applications in recent years, including [Venmo](https://www.wired.com/story/i-scraped-millions-of-venmo-payments-your-data-is-at-risk/), [Dropbox](https://blog.gitguardian.com/dropbox-breach-hack-github-circleci/), [X/Twitter](https://www.bleepingcomputer.com/news/security/54-million-twitter-users-stolen-data-leaked-online-more-shared-privately/), [Zendesk](https://www.securityweek.com/zendesk-vulnerability-could-have-given-hackers-access-customer-data/), and plenty of others.
And although most of the breaches covered in this article have to do with leaky data, hackers are not just exploiting holes in APIs for data exfiltration — they're also using them to [abuse business logic](https://www.forbes.com/sites/forbestechcouncil/2024/01/08/how-attackers-are-using-apis-to-target-your-business/), conduct denial-of-service attacks, and escalate privileges to perform account takeovers. Knowing this reality, it's good to review the [OWASP Top Ten for APIs](https://owasp.org/www-project-api-security/) and follow established [API security best practices](https://blog.treblle.com/why-api-security-is-a-top-concern/).
But beyond these practices, a strong software engineering culture learns from breaches when they occur. As Colin Domoney covers in his book '[Defending APIs](https://www.oreilly.com/library/view/defending-apis/9781804617120/)', it is a good policy to follow the Google SRE doctrine of blameless postmortems.
> "The key to conducting these postmortems is that they are blameless – they focus on the causes or issues rather than on the team or individual," says Domoney. So, be sure to conduct _ **blameless** _ postmortems if and when breaches occur.
### Adopt API Governance to Reduce Vulnerabilities
As we've seen, API breaches are becoming more and more common. To decrease these types of risks, it's good to follow API security best practices, and implementing this will hinge on [API governance](https://blog.treblle.com/5-ways-api-governance-can-enhance-your-security-foundation/). The right API governance model can help set guidelines for API development, ensuring API designs and coding practices are consistent throughout an organization. A governance framework that requires documentation and cataloging for these services will bring guardrails for API development — helping to avoid these terrible breaches and [other potential API risks](https://blog.treblle.com/api-security-the-untold-secrets-that-will-keep-you-awake-at-night) that keep you awake at night. | cindreta |
1,781,286 | Navigating the Token Terrain: A Comprehensive Dive into ChatGPT's Language Understanding and Generation | In the enchanting realm of artificial intelligence, understanding and generating human-like responses... | 0 | 2024-03-05T19:31:15 | https://dev.to/shishsingh/navigating-the-token-terrain-a-comprehensive-dive-into-chatgpts-language-understanding-and-generation-5bhb | openai, chatgpt, ai, machinelearning | In the enchanting realm of artificial intelligence, understanding and generating human-like responses entail a fascinating interplay of tokens. These building blocks of language serve as the bedrock for ChatGPT's ability to comprehend queries and craft meaningful replies. In this exploration, we'll embark on a journey through the intricacies of tokenisation, processing, and response generation, and how coding principles contribute to the magic.
**1. Tokens 101: The Fundamental Language Units**
Tokens, in the language of AI, are the elemental units that make up a piece of text. They can range from individual characters to entire words, providing the model with the granularity needed to grasp the intricacies of language. ChatGPT undertakes the task of breaking down user queries into tokens, a process essential for deciphering context and nuances.
**2. Tokenisation Process: Deconstructing Queries**
The journey begins with the tokenisation process, where the user's input is sliced into manageable portions. Let's delve into a coding snippet to see how this works:
```
#Python
from transformers import GPT2Tokenizer
# Instantiate the GPT-2 tokenizer
tokenizer = GPT2Tokenizer.from_pretrained('gpt2')
# User query
user_query = "Explain how ChatGPT understands..."
# Tokenize the query
token_ids = tokenizer.encode(user_query, return_tensors='pt')
print("User Query:", user_query)
print("Token IDs:", token_ids)
```
This code leverages the Hugging Face Transformers library to tokenize the user's query using GPT-2's pre-trained tokeniser.
**3. Layers of ChatGPT: Unveiling the Neural Network Architecture**
ChatGPT operates within a sophisticated neural network with multiple layers. Each layer contributes uniquely to the model's understanding and response generation. The following code snippet provides a simplified view of the layers:
```
#Python
from transformers import GPT2Model
# Instantiate the GPT-2 model
model = GPT2Model.from_pretrained('gpt2')
# Forward pass to get model outputs
outputs = model(token_ids)
# Extract the hidden states from the output
hidden_states = outputs.last_hidden_state
print("Hidden States Shape:", hidden_states.shape)
```
Here, we use the GPT-2 model to process the tokenised input and extract the hidden states, representing the model's understanding of the input sequence.
**4. Processing User Requests: Navigating the Neural Network**
The tokenised query traverses the layers of ChatGPT, where attention mechanisms and positional encoding play pivotal roles. Attention mechanisms enable the model to focus on relevant parts of the input, while positional encoding helps maintain the sequence's structure. Here's a simplified representation:
```
#Python
# Attention mechanisms and positional encoding processes
# (Code omitted for brevity)
```
These processes contribute to the model's contextual understanding of the user's input.
**5. Generating Responses: The Art of Token-Based Communication**
Utilising the processed tokens, ChatGPT generates responses. The model predicts the next token based on the context, drawing from its vast training dataset. The following code snippet illustrates the generation process:
```
#Python
# Generate responses based on the processed tokens
# (Code omitted for brevity)
```
**6. Token to Text Conversion: Bridging the Gap**
After generating a sequence of tokens, ChatGPT converts them back into human-readable text. The following code demonstrates the conversion:
```
# Python
# Convert generated tokens to text
generated_text = tokenizer.decode(generated_token_ids[0], skip_special_tokens=True)
print("Generated Response:", generated_text)
```
This step bridges the gap between the model's language of tokens and the natural language expected by users.
**7. Conclusion: Orchestrating the Symphony of Tokens in Conversational AI**
In this journey through the token terrain, we've witnessed how tokens serve as the foundation for ChatGPT's language understanding and response generation. The interplay of tokenisation, neural network layers, and coding principles orchestrates a symphony of communication, bringing us closer to the frontier of conversational AI. Understanding the nuances of this token dance unveils the complexity and elegance of AI language models, paving the way for even more enchanting developments in the future.
## References
Cover: https://www.unimedia.tech/what-exactly-is-chatgpt-and-how-does-it-work/
## Connects
Check out my other blogs:
[Travel/Geo Blogs](shishsingh.wordpress.com)
Subscribe to my channel:
[Youtube Channel](youtube.com/@destinationhideout)
Instagram:
[Destination Hideout](https://www.instagram.com/destinationhideout/) | shishsingh |
1,781,293 | They keep forcing me to make accounts... | Ok, so I just signed up for this application development course about Ruby on Rails, so chance to get... | 0 | 2024-03-05T19:40:43 | https://dev.to/emmanuel_lopez/they-keep-forcing-me-to-make-accounts-ce4 | socialmedia | Ok, so I just signed up for this application development course about Ruby on Rails, so chance to get into a cohort and actually get $$$ for what I do.
PROBLEM:
They have a different feed notification system than I do.
This means that they're asking me (and others) to ask questions on a specific website, ask.firstdraft.com, discord server, dev.to website, and google calendar, and this level of dilution is not okay. Usually I keep everything on ONE plain text document, this IMHO, is a mess and it takes in considerable work just to keep updated with everything. Feels like work without progress, BUT I understand why they're doing this. Each of these systems has it's own pros and cons, and their information relay system, much like software dev, isn't centralized or neat or simple. It's a god awful cluster fuck that resembles the subject studied. So what's the solution to this?
SOLUTION:
Centralization. I had a similar problem with my Discord server a year ago. I kept putting good information in there as a convenient place to put information, but then my stuff got lost in the archives of time. It seemed like that if I wanted to share something I would have to make it confusing for myself, but then I realized these two things.
{% embed https://blog.keras.io/img/ae/autoencoder_schema.jpg %}
{% embed https://satalyst.net/wp-content/uploads/2016/09/Build-Measure-Learn.jpg %}
> AAHHHHHHHHHHHHHHHHHHHH!!! As I was writing this very blog post, the platform deleted what I just wrote. This PROVES in my mind, that leaning the newest fanciest tools is a good way to be unreliable.
> And they refuse to publish unless my links pass a check WTF?
This stuff works in ITERATIONS and every time it passes the loop it gets a bit smaller? In order to develop the thought meaningfully in a reproducible manner, I have to write about it, not for those words but for what they will produce! I realized I could take my low grade, low information dense, first draft writings, share them publicly, then take the result of those meditations and plug them into my own info systems! That way I'm still sharing what I'm doing, but also I'm writing meaningful notes for myself.
This is what I'm going to be writing in my own notebooks.
`||scm feed|Use social media as brainstorming tool, then pocket distillate` | emmanuel_lopez |
1,781,409 | A Real-World Take on Simplifying Job Queues for Developers | Hey devs, let's talk about managing job queues. Have you ever tried to build a system that deals... | 0 | 2024-03-05T22:31:31 | https://dev.to/karolyidav/a-real-world-take-on-simplifying-job-queues-for-developers-33ea | javascript, node, typescript, webdev | Hey devs, let's talk about managing job queues.
Have you ever tried to build a system that deals with long-running tasks? Like generating PDFs, running an AI model, or sending emails in bulk?
If yes, you most likely faced the need for building a job queue.
## What's out there:
**BullMQ** is cool because it's packed with features and makes your life easier in many ways. But, you've got to handle your own Redis and worker instances.
**SQS** is super reliable and managed by AWS, which is great, but it's kinda bare-bones and setting it up can feel like a maze.
**RabbitMQ** gives you some neat options and can be managed for you, but again, you're on the hook for managing worker instances.
**GCP Cloud Tasks** is another beast, fully managed and scales like a dream. You don’t have to lose sleep over capacity. But, getting it to work means juggling a few infrastructure pieces like queues, task producers, and task handlers, which can feel like a bit of a project.
So, what about **TurboQ**?
I'm working on TurboQ to make all this easier. It's a job queue platform that's fully managed—yeah, that includes the workers too. It's got all the features you'd expect, plus a dashboard to keep track of everything, and it's designed to be super simple to set up.
It's not out yet, and honestly, we're still figuring some stuff out. I'm just trying to make a tool that helps you focus more on building cool stuff and less on the boring setup bits. I really want to hear what you think about the concept.
If that sounds good, keep an eye out for [TurboQ](https://www.turboq.dev), and if you would be happy to be among the first users [join the early access waiting list](https://www.turboq.dev).
Thanks for listening to my spiel. Would love to hear your thoughts! | karolyidav |
1,781,552 | GAMBARAN AKHIR PROFESI SAYA | Image created by #ChatGPTplus 😎 Yuk belajar bareng serta diskusi dikolom komentar, serta di save... | 0 | 2024-03-06T02:47:28 | https://dev.to/appardana/gambaran-akhir-profesi-saya-12jc | webdev, chatgpt, ai, programming |

Image created by #ChatGPTplus 😎
Yuk belajar bareng serta diskusi dikolom komentar, serta di save biar ga lupa💬😝
🌱Follow : @appardana
💭Stay Young, Be Innovative and Keep Learning
#coding #programmer #code #Content #Tips #Trick #Knwoledge #Management #CSS #React #ReactJS #Frontend #JustifyContent #Javascript #Phyton #C #Web #Skills #IT #Backend #Developer #Roadmap #SelfImprovement #Growth #Aditria #Pardana #AditriaPardana #appardana #iAppTech ⚛️💻

 | appardana |
1,781,637 | Health Insurance Options for Small Businesses in California | If you operate a small business, managing your company takes precedence, yet it is crucial to factor... | 0 | 2024-03-06T05:44:06 | https://dev.to/taylorbenefits/health-insurance-options-for-small-businesses-in-california-4p74 | taylorbenefitsinsurance, heath, healthinsurance, casmallbusinesshealthinsurance | If you operate a small business, managing your company takes precedence, yet it is crucial to factor in health insurance for your employees. Providing benefits to your staff aids in maintaining a dedicated workforce, even if you have only one employee.
Here's essential information to guide you in navigating the choices and selecting the appropriate **[CA small business health insurance](https://www.taylorbenefitsinsurance.com/california/
)** for your employees.

**Things to Know Before Purchasing Small Business Health Insurance**
Contacting several insurance companies is necessary to make sure your staff members are adequately covered when going through the health insurance application procedure. Your company's size can qualify you for tax credits, but you won't know about these advantages until you interact with the IRS and provide the required data on your tax returns.
Additional details essential before buying health insurance involve considering your business size. This extends beyond just employees working more than 30 hours a week. The total number of workers and their collective hours contribute to determining the count of full-time equivalent (FTE) employees in your organization.
A workforce of less than 50 provides greater flexibility in choices, though covering the costs of insurance may pose challenges. With more than 50 employees, offering insurance is mandatory, yet you might be eligible for discounted rates.
**Health Insurance Options For Small Businesses**
The extent of your business and the number of employees you choose to provide coverage for will influence the range of options available to you. Typically, businesses with fewer than 50 employees enjoy a broader array of CA small business health insurance choices. Irrespective of your workforce size, finding suitable coverage within your budget and meeting your employees' needs is possible. The type of coverage you opt for empowers you to manage the financial aspects.
Overall, small businesses generally have five insurance alternatives that are:
**1.Self-Insurance**
For a small business with notably healthy and young employees, the option of self-insurance may be a good option. This choice can save money, but it also means accepting financial responsibility for paying for medical bills in the event of serious illnesses or accidents. There may be a responsibility to pay an IRS charge, which goes toward paying the Patient-Centered Outcomes Trust Fund, depending on the specifics of the self-insurance arrangement.
**2.Association Health Plans (AHP)**
Regardless of whether you have a single employee or more, small businesses and sole proprietors have the option to collaborate with similarly sized companies to acquire health insurance at the reduced rates typically offered to larger enterprises. Association Health Plans (AHP) also extend coverage to sole proprietors and their families.
Opting for an AHP allows you to provide your employees with improved plan choices or more affordable rates, owing to the larger collective volume of the group from your region purchasing the plan. These plans, like several federally regulated health insurance programs, are not allowed to refuse enrollment to your employees on the grounds of pre-existing medical conditions.
**3.Health Savings Accounts (HSAs)**
Both the employer and the employee have the authorization to contribute to Health Savings Accounts (HSAs). The funds in your HSA can be utilized to address copayments, deductibles, and other medical expenses not covered by insurance. These accounts offer individuals an untaxed fund specifically designated for managing medical costs. They are designed to complement high-deductible insurance coverage. Importantly, HSAs are portable and persist regardless of changes in employment status, with their funds never subject to expiration.
**4.Small Business Health Options Program**
For businesses with a workforce ranging from one to 50 employees, the Small Business Health Options Program (SHOP) system is available. It caters to businesses smaller than those exempted by the Affordable Care Act (ACA) from mandatory worker insurance provisions. Within the SHOP framework, it is obligatory to extend coverage to all full-time employees, with a requirement that 70 percent of these employees enroll in the offered coverage. Businesses can choose to give their employees a single option or a variety of coverage alternatives, thanks to SHOP.
**5.Qualified Small Employer Health Reimbursement Arrangement**
One way to help your employees pay for their preferred health insurance is through the Qualified Small Employer Health Reimbursement Arrangement (QSEHRA). It operates by paying employees' premiums back. For employees to be protected from the tax benefits associated with using QSEHRA money, they must be enrolled in minimum essential coverage (MEC). Employees cannot contribute to HRAs, in contrast to FSAs and HSAs.
**Final Words**
Being a small business owner entails unique considerations when providing benefits to employees. Tighter profit margins and a smaller workforce pose challenges in finding budget-friendly CA small business health insurance coverage, without access to the bulk discounts enjoyed by larger firms. Nevertheless, the business owners, like **[Taylor Benefits Insurance](https://www.taylorbenefitsinsurance.com/)**, can still discover cost-effective ways to provide insurance for companies.

| taylorbenefits |
1,781,653 | Exploring the Significance of Photostability Chambers and Manufacturer | Introduction: In the realm of pharmaceutical and scientific equipment, precision and reliability are... | 0 | 2024-03-06T06:06:29 | https://dev.to/kesarcontrol312/exploring-the-significance-of-photostability-chambers-and-manufacturer-4d2a | techtalks | Introduction:
In the realm of pharmaceutical and scientific equipment, precision and reliability are paramount. At KESAR CONTROL SYSTEMS, we pride ourselves on pioneering excellence in manufacturing cutting-edge equipment tailored to the exacting needs of the industry. Among our stellar lineup of products, our Photostability Chambers stand tall as beacons of reliability, ensuring the integrity and quality of sensitive substances amidst various environmental conditions.
Unveiling Photostability Chambers
The Essence of Photostability
Photostability Chambers Manufacturer, the unsung heroes of quality assurance, create controlled environments that mimic exposure to light and allow pharmaceutical and scientific entities to evaluate the effects of light on their products. From pharmaceutical formulations to research-grade substances, these chambers offer invaluable insights into the stability and longevity of compounds under varying light conditions.
Precision in Design: Our Photostability Chambers, crafted as per GMP/ICH guidelines, ensure precision and functionality.
Functionality: Delve into the intricacies of how these chambers simulate different light conditions and temperatures, allowing comprehensive testing.
Impact on Quality Assurance: Highlight the critical role these chambers play in ensuring product quality, adhering to regulatory standards, and meeting MCA & US FDA requirements.
Crafting Excellence as a Photostability Chambers Manufacturer
Pioneering Innovation and Quality
As a leading Photostability Chambers Manufacturer in the industry, KESAR CONTROL SYSTEMS stands as a beacon of innovation and reliability, producing top-notch chambers that redefine industry standards.
Innovation at Core: Discuss how our continuous development approach empowers us to surpass market expectations.
Adherence to Standards: Emphasize our commitment to crafting equipment that complies with global standards, ensuring the highest level of accuracy and dependability.
Client-Centric Approach: Highlight our dedication to understanding and meeting the unique needs of our clients, offering solutions that elevate their operations.
Conclusion:
In a landscape where quality and precision reign supreme, Photostability Chambers emerge as indispensable tools for safeguarding the integrity of pharmaceutical and scientific endeavors. At KESAR CONTROL SYSTEMS, our commitment to excellence fuels our mission to provide the most advanced, reliable, and meticulously crafted chambers that empower industries worldwide.
Contact Information:
For inquiries and further information, reach out to us at:
Phone: +91-6354883229
Email: service@kesarcontrol.com
Elevate your experiments to new heights with a partner that understands the importance of precision in every detail on website https://www.kesarcontrol.com/photostability-chamber.php | kesarcontrol312 |
1,781,656 | NVISH | Employee IT staffing solutions in USA | Staffing Services | NVISH IT Staffing Solutions: Your Trusted Partner for Over a Decade For 10+ years, NVISH has been a... | 0 | 2024-03-06T06:15:33 | https://dev.to/staffingnvish/nvish-employee-it-staffing-solutions-in-usa-staffing-services-3ema | [NVISH IT Staffing Solutions](https://staffing.nvish.com/): Your Trusted Partner for Over a Decade
For 10+ years, NVISH has been a leading provider of workforce solutions in the US. We connect businesses with top IT talent, leveraging expertise and technology to drive success. Trust NVISH to streamline your staffing needs and unleash your team's full potential. | staffingnvish | |
1,781,686 | Chinese Restaurant in Ahmedabad | Located in Ahmedabad, bizzlane is a premier Chinese restaurant that stands out for its exquisite... | 0 | 2024-03-06T06:53:52 | https://dev.to/shikhabizzlane/chinese-restaurant-in-ahmedabad-596 | Located in Ahmedabad, bizzlane is a premier Chinese restaurant
that stands out for its exquisite culinary experience. With a refined ambiance and a diverse menu, bizzlane offers an authentic taste of Chinese cuisine in the heart of the city. From traditional dishes to modern interpretations, the restaurant caters to a wide range of palates, ensuring a delightful dining experience for all patrons. Whether you are a fan of classic favorites like Kung Pao Chicken or looking to explore unique flavors, bizzlane is the go-to destination for an exceptional Chinese dining experience in Ahmedabad.
**Visit now:** (https://bizzlane.com/blog-detail/Chinese-Restaurant-Ahmedabad)
**A 45 Narmada Nagri Part 3, Near Aadarsh Duplex, Opp Gorwa ITI, Gorwa Vadodara 390016, Phone: +91 9374030310**
| shikhabizzlane | |
1,781,867 | Unlocking the Potential of Modular Blockchains: A Quick Overview- Krypcore | In the dynamic landscape of blockchain technology, the concept of modular blockchains has emerged... | 0 | 2024-03-06T09:55:44 | https://dev.to/krypcore/unlocking-the-potential-of-modular-blockchains-a-quick-overview-krypcore-2c2m | blockchain, web3, webdev, krypcore |

In the dynamic landscape of blockchain technology, the concept of modular blockchains has emerged as a pivotal innovation. Modular blockchains represent a paradigm shift in the way blockchain networks are structured and operated, offering a versatile and scalable framework for building decentralized applications (dApps) and enhancing the efficiency of [web3 infrastructure](https://krypcore.com/). In this article, we delve into the fundamentals of modular blockchains, exploring their key features, benefits, and implications for the broader web3 ecosystem.
Understanding Modular Blockchains:
At its core, a modular blockchain is a blockchain network designed with a modular architecture, wherein different components of the blockchain protocol are decoupled and can be customized or replaced independently. Traditional blockchain networks often suffer from scalability limitations, as well as challenges related to interoperability and upgradability. Modular blockchains address these issues by breaking down the blockchain protocol into modular components, allowing developers to tailor the network architecture to suit specific use cases and requirements.
**Key Components of Modular Blockchains:**
**1. Consensus Mechanisms:** Modular blockchains support a diverse range of consensus mechanisms, ranging from proof-of-work (PoW) and proof-of-stake (PoS) to delegated proof-of-stake (DPoS) and hybrid consensus algorithms. This flexibility enables developers to choose the most suitable consensus mechanism based on factors such as security, scalability, and energy efficiency.
**2. Smart Contract Platforms:** Modular blockchains provide robust smart contract platforms that support the execution of self-executing contracts and decentralized applications (dApps). Developers can leverage smart contract platforms to build and deploy custom smart contracts, enabling programmable and automated transactions on the blockchain.
**3. Interoperability Protocols:** Interoperability is a crucial aspect of modular blockchains, allowing different blockchain networks to seamlessly communicate and transact with each other. Interoperability protocols such as cross-chain communication protocols and interoperability bridges facilitate the exchange of assets and data between disparate blockchain networks, enhancing the overall interoperability of the web3 infrastructure.
**4. Scalability Solutions:** Scalability is a perennial challenge in blockchain technology, with traditional blockchains often struggling to process a large number of transactions efficiently. Modular blockchains incorporate scalability solutions such as sharding, layer 2 scaling solutions, and sidechains, enabling the network to handle higher transaction volumes without compromising decentralization or security.
**
Benefits of Modular Blockchains:**
1. Flexibility and Customization: Modular blockchains offer developers unparalleled flexibility and customization options, allowing them to design and deploy blockchain networks tailored to their specific use cases and requirements.
**2. Enhanced Interoperability:** By supporting interoperability protocols, modular blockchains facilitate seamless integration and communication between different blockchain networks, fostering a more interconnected and interoperable web3 infrastructure.
**3. Scalability and Efficiency:** Scalability solutions integrated into modular blockchains improve the network's transaction throughput and efficiency, enabling it to scale to meet the demands of a growing user base and expanding ecosystem of decentralized applications.
4. Upgradability and Innovation: Modular blockchains enable continuous innovation and evolution of the blockchain protocol, with developers able to upgrade and replace individual components of the network without disrupting its overall functionality.
**Implications for Web3 Infrastructure:**
Modular blockchains hold significant implications for the broader web3 infrastructure, offering a versatile and scalable framework for building decentralized applications and supporting the next generation of internet applications. By providing developers with the tools and resources to customize and optimize blockchain networks, modular blockchains pave the way for a more inclusive, interoperable, and efficient web3 ecosystem.
Modular blockchains represent a groundbreaking advancement in blockchain technology, offering a flexible, scalable, and interoperable framework for building decentralized applications and enhancing the web3 infrastructure. With their modular architecture and customizable components, modular blockchains empower developers to innovate and iterate rapidly, driving the adoption and evolution of decentralized technologies. As the web3 ecosystem continues to evolve, modular blockchains are poised to play a pivotal role in shaping the future of decentralized finance, decentralized governance, and decentralized applications.
**See More:**
[Building Your First dApp in 5 Minutes With Krypcore Web3 SDK](https://krypcore.com/blog/building-your-first-dapp-in-5-minutes-with-krypcore-web3-sdk)
| krypcore |
1,781,879 | Properly Passing Data from Laravel Blade to Vue Components | Prop “authuser” is passed to component <Anonymous>, but the declared prop name is “authUser”.... | 0 | 2024-03-06T10:08:43 | https://dev.to/martinsonuoha/properly-passing-data-from-laravel-blade-to-vue-components-1nkd | laravel, vue, webdev | Prop “authuser” is passed to component `<Anonymous>`, but the declared prop name is “authUser”. Note that HTML attributes are case-insensitive and camelCased props need to use their kebab-case equivalents when using in-DOM templates. You should probably use “auth-user” instead of “authUser”.
The above is a likely error message you’d get if you set up Laravel and Vue js, and attempted passing data to your component via props the wrong way.
Sometimes, we encounter cases where we need to use Vuejs components in just a single part of our existing Laravel application.

You could have a structure like this and want the profile card on the left to be a separate Vue component, for whatever reason. The problem with using this kind of approach is, there’d likely be conflicts between templating engine syntax and Vuejs syntax. For example, Laravel uses the double curly braces `{{ }}` syntax that Vue uses.
```
<!-- laravel blade -->
<div>
{{ Auth::user()->fullname }}
</div>
<!-- Vuejs -->
<div>
{{ authUser.fullname }}
</div>
```
When working with Vue components in Laravel blade, you’d need to be careful to avoid some likely hiccups along the way. Laravel has an entire section that explains how to work with [Laravel Blade and Javascript Frameworks](https://laravel.com/docs/5.8/blade#blade-and-javascript-frameworks).
##What doesn’t work
Regarding why you’d likely get the error above: HTML is case insensitive and therefore limits you to using only kebab-case components and attributes in your template. so if you did this in your blade file:
```php
<!-- something.blade.php -->
<div class="container">
<profile-sidebar :authUser="{...}"></profile-sidebar>
</div>
```
You’d most likely get the same error. Also, if you tried writing your components in `camel casing` style, the DOM Parser would ignore the custom tag:
```
<!-- something.blade.php -->
<div class="container">
<profileSidebar :authUser="{...}"></profileSidebar>
</div>
```
---
##What works
For starters, to avoid one of such issues, you could stick to using only `kebab-case` components and attributes in your blade template.
Like so:
```
<!-- something.blade.php -->
<div class="col-xl-8">
<account-update :auth-user="{{ Auth::user() }}"></account-update>
</div
```
And of course, you can still maintain camel casing style in your component files:
```
<script>
export default {
name: 'side-profile',
props: ['authUser'],
mounted() {
console.log(this.authUser)
}
}
</script>
```
---
Hopefully, this helps clear some of the issues you might have encountered working with Laravel blade and Vue components.
Cheers ☕️
--- | martinsonuoha |
1,781,954 | DevSecOps: Learn To Develop In A Safer Way | It’s clear the exponential growth in the utilization of in-house software development: applications,... | 0 | 2024-03-08T10:19:52 | https://dev.to/kwan/devsecops-learn-to-develop-in-a-safer-way-4kdi | devops, devsecops, softwaredevelopment | **_It’s clear the exponential growth in the utilization of in-house software development: applications, plugins, scripts, and APIs, among others. Increasingly, companies need to internalize their customizations to achieve results more targeted toward their goals and needs._**
## Why worry about security in development?
A research conducted by SERPRO (Federal Data Processing Service of Brazil) indicates that the majority of vulnerabilities are related to the application layer and can compromise even the system access permissions of users. Nowadays, it is common sense to assume that the amount of vulnerabilities in applications surpasses those found in operating systems.
This shows that systems haven’t been built following a secure development process and programming best practices. Therefore, it is important that programmers care about this topic and think about security measures from the plan/design phase. By doing this, it is possible to mitigate the most common security risks in a much more efficient and inexpensive manner.
### Preventive actions tend to be cheaper and more efficient than corrective actions.
A few years ago, the attackers used to focus on infrastructure components. It was very often to see attacks carried out on Apache, IIS, operating systems, and other infrastructure platforms and perimeter segments. Because of that, the maturity of security controls regarding infrastructure has risen organically and so have the security solutions related.
Over the years, things like agile methodologies have become increasingly relevant and empowered teams that develop software. To become more agile, teams began to assume a series of responsibilities and became fully responsible for what they build, including disciplines such as quality, infrastructure, security, and others. However, most teams do not have knowledge or maturity on how to develop safely. Consequently, attackers have shifted their attention and invested more time and effort in exploiting vulnerabilities at the application layer.
Another important factor to emphasize is the ease of finding ready-made attack methods (exploits) on the internet. With just a simple Google search, you can find a menu with a large variety of exploits, scripts, malware, tools, forums, etc and it is no longer necessary to have extensive knowledge to exploit some vulnerabilities out there.
## Implementing security… What is needed?
A secure development process is based on three components – people, process and technology – and they are ordered by its importance.
The first component is **people** and they are represented not only by developers, but also by product owners, project managers, clients, and everyone else involved in the project. People use to prioritize tasks in order to deliver new features, but they tend to ignore security findings or postpone remediation. They often do this because they are neither aware of the security risks nor properly oriented. The best way to change this scenario is to invest in security awareness and training
The second component is the **process** and it is necessary to consider a set of security controls and practices in an end-to-end manner. In the beginning, it’s wise to start smoothly by implementing the most seamless controls as soon as possible in order to avoid any friction with the people involved in the project.
The third component is the **technology** and there are several kinds of solutions that address different security issues at each stage of the process. The most popular solutions are the AST (application security testing) family:
- **SAST (Static Application Security Testing)**: it analyzes the source code to identify security vulnerabilities and ensure compliance with internal coding guidelines. It plays a crucial role in early vulnerability detection during the software development life cycle (SDLC) by scanning code before deployment. Developers can seamlessly integrate SAST into their development tools, allowing them to address issues such as hardcoded secrets, buffer overflows, code injections, misconfigurations, vulnerable dependencies, and so on.
- **DAST (Dynamic Application Security Testing)**: it analyzes running applications by simulating attacks and assessing how the application responds. DAST is particularly useful for addressing misconfiguration and web application common vulnerabilities like cross-site scripting, SQL injection, IDOR, path traversal, local/remote file inclusion, and many others.
- **IAST (Interactive Application Security Testing)**: an innovative approach that combines the strengths of both SAST and DAST. It runs from within the application server, evaluating code as it interacts with real-world data.
## DevSecOps: what is it?
DevSecOps stands for development (Dev), security (Sec) and operations (Ops). It is a collaborative framework that extends the DevOps practice by adding security elements to the continuous integration and continuous deployment processes.
## How do I add the “Sec” to the “DevOps”?
Implementing security practices in the CI/CD pipeline is not a one-size-fits-all approach. Each company must tailor their security measures to their specific context, needs, and constraints.
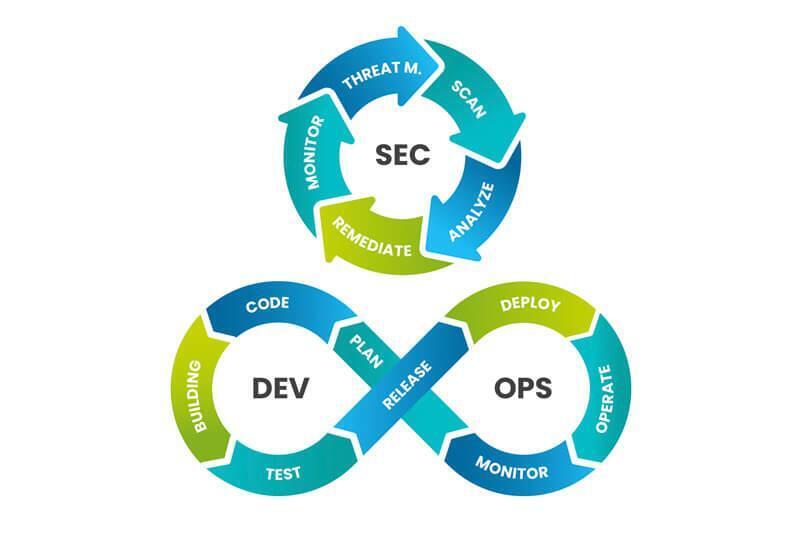
The most common practice is to include a cycle that involves scanning, analyzing, and remedying potential vulnerabilities at every phase of DevOps, adapting to a process of continuous improvement, monitoring, and managing the threats and vulnerabilities found.
## Best practices for your code
Here are some tips that can help with secure development:
### 1. Secure development tools
If you have the possibility of using secure development tools, it will be a significant advancement to ensure your code is created with the best security practices. Nowadays, it is possible to find software that analyzes code in real time while you are programming.
### 2. Source code management
Source code management is very important for organizing and collaborating with other developers. Additionally, it helps ensure the integrity and versioning of your code.
### 3. Testing
Conducting tests on small pieces of code simplifies and aids in evaluating the final outcome.
### 4. Documentation
Creating clear and detailed documentation of your code and the architecture used not only improves the quality of your software but also facilitates the correction of bugs and security vulnerabilities.
### 5. Creating checklists
During key actions and reviews of your application, create checklists that include security items to always analyze these issues.
## Learn to develop in a more secure way: final thoughts
Ensuring the security of your company, your home, your data, or any place that uses technology is not an easy task and cannot be assigned to just one person or team. Security depends on everyone, from the programmer to the user.
We know that software development is an area of constant evolution and study. However, security cannot be neglected. Implementing security controls into development makes you a more responsible and collaborative developer. I am sure that this habit will only bring benefits to your career and your company.
Let's connect on social media, [follow us on X](https://twitter.com/KwanCommunity)!
Article written by Bruno Pereira and originally published at https://kwan.com/blog/devsecops-learn-to-develop-in-a-safer-way/ on March 6, 2024. | kwan |
1,781,957 | Hofstadter's Law. Projects inevitably overrun their timelines and budgets. | Hofstadter's Law. Summary. Projects inevitably overrun their timelines and budgets. Doubling the... | 0 | 2024-03-07T09:00:00 | https://dev.to/keepcoding/hofstadters-law-projects-inevitably-overrun-their-timelines-and-budgets-3gil | productivity, time, career, psychology | **Hofstadter's Law. Summary.**
Projects inevitably overrun their timelines and budgets.
Doubling the estimated time often leads to tripling the projected costs.
Despite our most diligent efforts to foresee and mitigate potential obstacles, the complexities inherent in any project tend to defy our best calculations. (Yes, Law of Unintended Consequences is a bitch)
This persistent phenomenon serves as a sobering reminder of the inherent unpredictability of the project management landscape, requiring constant adaptation and resilience in the face of challenges.
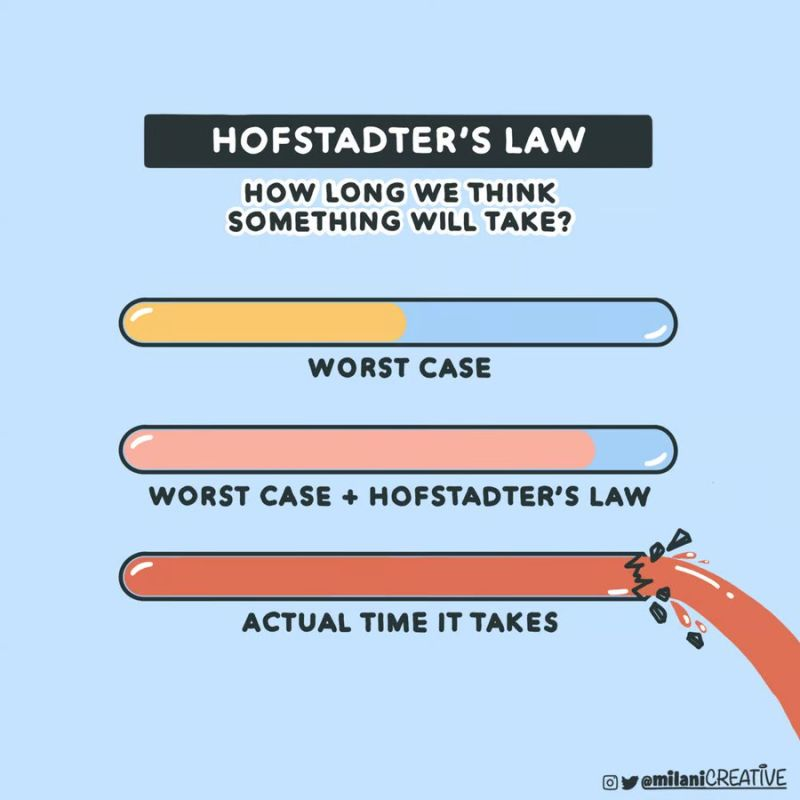
**Douglas Hofstadter’s Law, akin to Murphy's Law, **
encapsulates the notion that tasks invariably take longer than anticipated, even when one factors in this tendency. This phenomenon is especially evident in the realm of computer programming where intricate projects stretch out over years.
The common experience of tasks expanding to fill the time allotted can be attributed to various factors. Often, we set too many objectives, juggling personal desires alongside professional goals. Effectively prioritizing these tasks becomes essential to efficient resource allocation.
**Perfectionism, procrastination, **
and looming deadlines present unique challenges to managing time effectively. Unforeseen obstacles like illness or unexpected events further complicate matters, necessitating adaptive strategies.
Some opt to eschew detailed planning altogether, preferring to adjust course based on real-time feedback. Others advocate for doubling initial time estimates to accommodate unforeseen delays. Seeking input from experienced individuals or drawing from past experiences can also inform more realistic timeframes.
**Research in psychology suggests** that our plans tend to be overly optimistic, relying on best-case scenarios rather than considering potential setbacks. While techniques like pessimistic scenario generation may work for others' predictions, they often fall short in adjusting our own.
**However, mastering time management skills can mitigate these challenges. **
**Utilizing tools like checklists**, calendars, and organizers can enhance organization and productivity. Maintaining focus during meetings, limiting distractions like excessive phone calls or email checks, and prioritizing tasks based on their impact are crucial strategies.
**Regularly assessing progress**, identifying limiting factors, and leveraging peak productivity times can further enhance efficiency. Cultivating a long-term perspective and visualizing the satisfaction of completing tasks can bolster motivation.
**Ultimately**, success lies in clear goal-setting, resource acquisition, and proactive problem-solving. Embracing setbacks as part of the journey and tackling tasks incrementally are key principles in navigating the complexities of time management.
| keepcoding |
1,781,967 | Setting up GitHub Actions for AWS S3 Integration | Introduction As someone who is continually striving to improve and automate my development... | 0 | 2024-03-06T12:09:26 | https://dev.to/staubracing/setting-up-github-actions-for-aws-s3-integration-2hg7 | aws, githubactions, beginners | ###Introduction
As someone who is continually striving to improve and automate my development workflows, I realized that understanding the integration between GitHub and AWS S3 could significantly streamline my projects. But, like many of you, the journey to fully grasp this automation was a blend of research, trial, and error. To save you some time — and to solidify my own understanding — I’ve put together this guide on setting up GitHub Actions for AWS S3 integration.
###Pre-requisites
* GitHub Knowledge: An active GitHub account and basic familiarity with Git commands (clone, commit, push, etc.) and GitHub workflows.
* AWS Account: An active AWS account with the S3 service enabled. Familiarity with AWS IAM (for creating roles and permissions) is beneficial.
* S3 Bucket: Ensure you have an S3 bucket set up where you wish to sync your repository content.
GitHub Repository: An existing GitHub repository containing the project that you want to integrate with AWS S3.
* AWS CLI: Ensure that the AWS CLI is installed on your machine. This guide assumes you have basic knowledge of running AWS commands.
* Conceptual Knowledge: While not strictly a prerequisite, being familiar with AWS IAM, GitHub workflows, Git repositories, and AWS S3 will help you understand the steps and the reasoning behind them more deeply.
#Local Setup
In any GitHub Actions workflow, the .github/workflows directory is the heartbeat that orchestrates your automation. This directory is where you'll place the YML configuration files that GitHub uses to understand your automation requirements.
Here, I’ll walk you through the simple steps to create this directory:
* Navigate to your Project: Open the terminal and navigate to your local GitHub project directory using the ‘cd’ command.
`cd path/to/your/github/project`
* Create `.github/workflows` Directory: Run the following commands to create the .github and workflows directories.
```mkdir -p .github/workflows```
The `-p` flag in the `mkdir` command ensures that the .github directory and its sub-directory workflows are created in one go.
Now you have a dedicated space to store your GitHub Actions configurations.
###Naming Your Configuration File
Naming is more than a label; it’s a signpost for others (or future you) navigating your project. In GitHub Actions, your .yml files should describe the function they serve. For this tutorial, we will use the name sync_to_s3.yml.
Here are the steps to create your .yml configuration file:
* If you’re not already there, navigate to the .github/workflows directory in your project.
* Create the `.yml` File: Use a text editor to create a new file and save it as file name that makes sense to you.
For Ex. `sync_to_s3.yml`
For Unix-like systems (Linux/Mac):
```
touch sync_to_s3.yml
```
For Windows PowerShell:
```
New-Item -Path .\sync_to_s3.yml -ItemType File
```
For Windows Command Prompt:
```
echo. > sync_to_s3.yml
```
Option 2: Using a Text Editor or IDE Create a new file and save it as sync_to_s3.yml in the .github/workflow directory of your project using your preferred text editor or IDE such as VS Code.
###Crafting the .yml File
Now that you’ve set up your workflow directory and named your configuration file, it’s time to dive into the specifics of crafting the .yml configuration. Before we delve into each component, let’s take a look at the complete .yml file for AWS S3 synchronization:
```
name: Sync to S3
on:
push:
branches:
- main
jobs:
sync:
runs-on: ubuntu-latest
steps:
- name: Checkout Repository
uses: actions/checkout@v3
- name: Configure AWS Credentials
uses: aws-actions/configure-aws-credentials@v2
with:
aws-access-key-id: ${{ secrets.AWS_ACCESS_KEY_ID }}
aws-secret-access-key: ${{ secrets.AWS_SECRET_ACCESS_KEY }}
aws-region: us-east-1 # Change this to your region of your bucket
- name: Sync to S3
run: aws s3 sync . s3://your-bucket-name # Change this to your bucket name
```
###Understanding GitHub Action Configurations
Each section in the .yml file serves a specific purpose. For example, name provides a label for your workflow, and on specifies the events that trigger the workflow. In this case when a push to the main branch happens the action will trigger.
###Integrating AWS CLI Commands
The .yml file also integrates AWS CLI commands, particularly the aws s3 sync command to upload your files to an S3 bucket. Using the AWS CLI allows for more fine-grained control over interactions between GitHub and AWS.
###Populating the .yml File
Here, you will input the necessary configurations to make GitHub Actions interact seamlessly with AWS S3.
* Open the File: Open sync_to_s3.yml in a text editor of your choice, such as VS Code, to begin adding configurations. (Note: I will be demonstrating this in VS Code)
* Copying the Configuration: Start by copying the provided code snippet from the guide above. This is the foundation of your GitHub Action setup for S3 syncing.
* Update the AWS Region: Locate the line where aws-region is specified. Replace the placeholder with your desired AWS region.
* For example, if your S3 bucket is in the us-west-1 region, update the line to look like:
```
aws-region: us-west-1
```
* Configuring the AWS CLI Command: The action uses the AWS CLI to synchronize files. Update the aws s3 sync command to match your S3 bucket's specifics. For example:
Replace your-bucket-name with the name of your S3 bucket.
```
run: aws s3 sync ./ s3://your-bucket-nam
```
* Handling Secrets: Never hardcode your AWS credentials. Instead, use GitHub secrets. In the code, you’ll notice references like `${{ secrets.AWS_ACCESS_KEY_ID }}`. These placeholders fetch the values from the secrets you set up in your GitHub repository settings. We will cover that in the next section.
###Handling AWS Access Keys Securely
When integrating AWS services with external platforms like GitHub, security is paramount. AWS Access Keys, which consist of an Access Key ID and Secret Access Key, allow users to make programmatic calls to AWS. If these keys are exposed, malicious actors can misuse them, potentially leading to financial and data loss.
Recommendations for Key Management:
* Never Hardcode Keys: Never embed your AWS keys directly in your code. If you push these to a public repository, your AWS account could be compromised.
* Use GitHub Secrets: GitHub Actions offers a feature called “secrets” that lets you store sensitive information. You can set up your AWS Access Keys as secrets in your GitHub repository, and then reference them in your GitHub Actions workflow. This way, the keys remain hidden.
* Least Privilege Principle: When creating AWS IAM roles or users, give them only the permissions they need. Avoid using keys with full access unless absolutely necessary.
* Rotate Keys Regularly: Regularly change your access keys, especially if you believe they might have been exposed or compromised.
* Monitor AWS Activity: Keep an eye on AWS CloudTrail or other monitoring tools to track activity in your AWS account. Any unusual behavior can be an indicator of compromised key
###Utilizing GitHub Secrets for Security
GitHub Secrets is a feature in GitHub that allows you to store and use sensitive information without exposing it in your workflow files or logs. These secrets are encrypted environment variables that only expose their values to workflows running in the same repository.
How to Set Up GitHub Secrets:
* Navigate to Your Repository: Go to the main page of the GitHub repository where you want to add the secret.
* Access Repository Settings: Click on the settings tab near the top of the screen
* Secrets Management: On the left sidebar, you’ll see a ‘Secrets and variables’ section. Drop down the menu and click on ‘Actions’
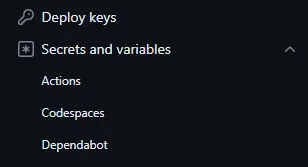
* Add a New Secret: Click on the New repository secret button.
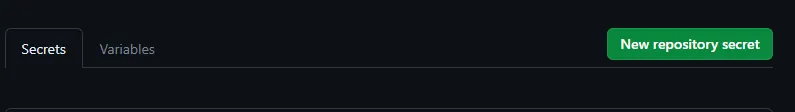
* Name and Value: When prompted to define the secret, ensure the name matches exactly with what you’ve specified in your .yml file.
1. Create a repository secret:
- Name: AWS_ACCESS_KEY_ID
- Value: Enter the value of your AWS access key.
- Click the ‘Add Secret Button’
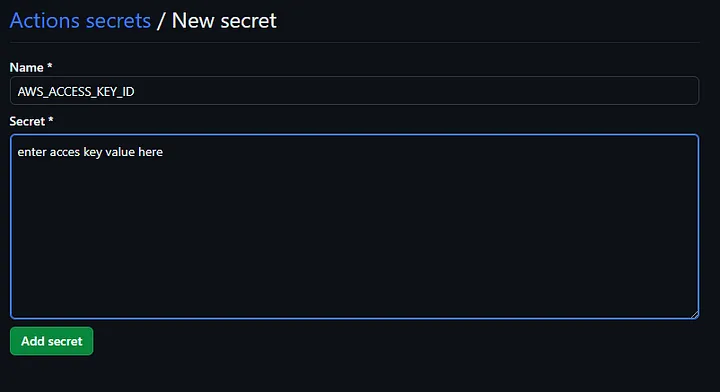
2. Similarly, create another secret:
- Name: AWS_SECRET_ACCESS_KEY
- Value: Enter the value of your AWS secret key.
- Click the ‘Add Secret Button’
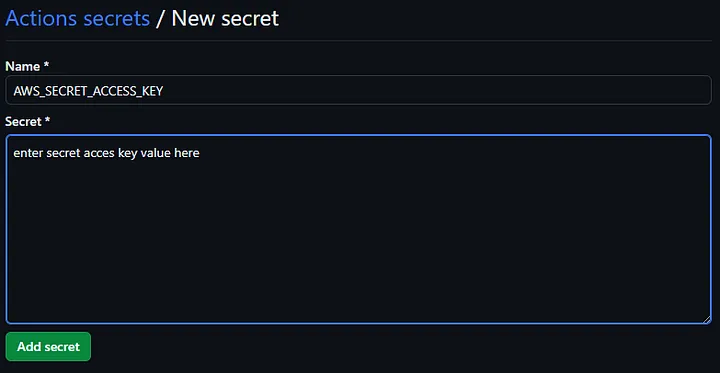
Remember, the names of the secrets must correspond precisely to their references in your .yml configuration for successful integration.
When you are done it should look like this:
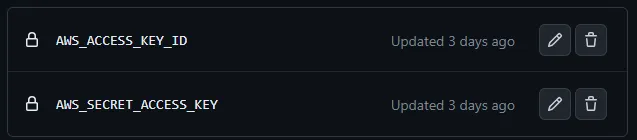
###Testing the Workflow
After successfully setting up GitHub Actions and configuring the AWS keys, it’s vital to ensure everything operates smoothly. Follow the steps below to test your workflow:
###Triggering the Workflow with a Push:
1. Make changes to a file or add a new file in your local repository. THe easiest way to see it is by adding a test file ex. test.html
2. Add all the files in your project folder to the Git repository using the command git add . (Don’t forget the period at the end)
3. Commit the changes: git commit -m "Your commit message".
4. Push the changes to your GitHub repository using: git push.
5. This push event is what initiates the GitHub Actions workflow you've set up.
Expected Outcomes: After pushing the changes, head over to the ‘Actions’ tab in your GitHub repository. Here, you should witness the workflow executing without issues. If the check next to the action is green, it was successful.

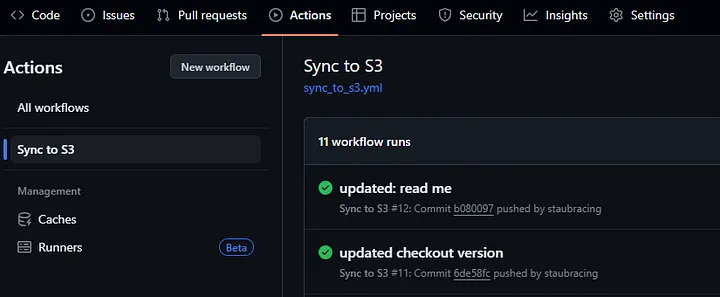
###Congratulations!
You’ve successfully navigated the intricacies of setting up GitHub Actions to synchronize your repository with an AWS S3 bucket. This is no small feat, and you should be proud of integrating these powerful platforms. With this setup, you’ve taken a significant step towards streamlining your deployment processes, ensuring that your S3 bucket remains updated with the latest changes from your GitHub repository.
This marks my first attempt at crafting an article, and it has been an enlightening journey for me as well. My sincere hope is that this guide has been beneficial for you and has added value to your technical journey. Feedback is the foundation of growth, so I’d greatly appreciate any insights or suggestions you may have to offer.
| staubracing |
1,781,975 | aptLearn: YOUR PATH TO TECHNICAL SUCCESS | Ever dreamt of endless learning possibilities? Are you frightened by what it will cost you to learn... | 0 | 2024-03-06T11:50:04 | https://dev.to/synthscript/aptlearn-your-path-to-technical-success-1k8i | technical, aptlearn, beginners |
Ever dreamt of endless learning possibilities? Are you frightened by what it will cost you to learn these skills? Welcome! Let aptLearn be your personalized pathway to success in the ever-evolving tech landscape! We offer a comprehensive selection of affordable courses, workshops, and resources across diverse fields, ensuring you find your footing amidst the digital revolution.
**WHAT WE DO AT APTLEARN**
At aptLearn, we aim to transform your journey by unlocking your potential with life-changing skills. Click [here](aptLearn.io) to begin your journey towards success.
**AVAILABLE COURSES**
Explore our curated course catalogue:
A. Technical Path: Master in-demand skills in
Software Engineering
Data Science
Cloud Computing
Cybersecurity
B. Non-Technical Path: Hone your talents in
Project Management
Product Management
Customer Success Management
Digital Marketing
UI/UX Design
Technical Writing
**WHY YOU SHOULD CHOOSE APTLEARN**
AptLearn is a comprehensive learning platform with unique features to help you learn and grow.
- Our courses are affordable and designed for self-paced learning. You can unlock opportunities to reduce costs further.
- Join our vibrant community and learn from the best. You can also contribute to the learning ecosystem through "**[Teach on aptLearn](aptLearn.io)**" and "**[Write on aptLearn](aptLearn.io)**" programs.
- Practice coding with confidence using our Web Code playground, an Integrated Development Environment (IDE), and tackle real-world projects and publications for practical experience.
- Reward your teaching skills and earn by promoting courses and creating learning opportunities for others through our affiliate programs.
- Stay up to date with newsletters and articles on our blog. Upon completion of each course, you'll receive a certificate.
The path to both intellectual enrichment and financial advancements awaits your embarkation. At aptLearn, we provide a diverse range of courses and a vibrant community, you can explore, read, and discover at your own pace. Whether you're a beginner or an advanced learner, there's a place for you in the vast technology field. Enrol in a course today! For more information, please visit us at [aptlearn](aptLearn.io). | synthscript |
1,781,996 | Exploring the Emerging Use Cases of Cosmos Blockchain | In the ever-expanding realm of blockchain app development, Cosmos emerges as a beacon of innovation... | 0 | 2024-03-06T12:20:08 | https://dev.to/oodlesblockchain/exploring-the-emerging-use-cases-of-cosmos-blockchain-429j | blockchain, softwaredevelopment, learning, cosmosblockchai | In the ever-expanding realm of [blockchain app development](https://blockchain.oodles.io/?utm_source=devto), Cosmos emerges as a beacon of innovation and interoperability. With its groundbreaking architecture and robust ecosystem, Cosmos Blockchain is not just a platform — it’s a catalyst for transformative change across various industries. In this comprehensive blog, we’ll dive deep into the emerging use cases and applications of Cosmos Blockchain, shedding light on its potential to revolutionize the decentralized landscape.
## Deciphering the Cosmos
Cosmos, often hailed as the “Internet of Blockchains,” is a decentralized network designed to overcome the limitations of existing blockchain platforms by enabling seamless interoperability and communication between disparate networks. Founded on the principles of sovereignty, scalability, and security, Cosmos offers a versatile framework for building custom blockchains and decentralized applications (dApps) while facilitating frictionless asset transfers and data exchange.
## Emerging Use Cases and Applications
**Cross-Chain Asset Transfers**
Cosmos facilitates cross-chain asset transfers with its Inter-Blockchain Communication (IBC) protocol, enabling the seamless transfer of digital assets between different blockchains within the ecosystem. Use cases include decentralized exchanges (DEXs), liquidity pools, and asset management protocols, enhancing interoperability and efficiency in the financial ecosystem.
**Decentralized Finance (DeFi)**
Cosmos provides an ideal platform for building DeFi applications such as lending platforms, decentralized exchanges, and yield farming protocols. Leveraging its interoperability features, Cosmos DeFi democratizes access to financial services, fostering financial inclusion and innovation.
**Supply Chain Management**
Cosmos enables transparent and efficient supply chain networks by leveraging its transparency, immutability, and traceability features. Use cases include monitoring the flow of goods, confirming the legitimacy of products, and cutting down on fraud and inefficiencies in international supply chains.
**Gaming and Non-Fungible Tokens (NFTs)**
With support for NFTs and scalable infrastructure, Cosmos powers decentralized gaming platforms, virtual worlds, and in-game asset marketplaces. Use cases include digital collectibles, virtual land ownership, and new monetization opportunities for players and developers.
**Identity and Authentication**
One of the noble use cases of Cosmos blockchain is to facilitate the creation of self-sovereign identity solutions, decentralized authentication systems, and secure digital identity wallets. Cosmos gives individuals more control over their digital identities and personal information in an increasingly linked world while enhancing security and privacy.
## More About Cosmos
As Cosmos continues to evolve and expand its ecosystem, the potential for innovation and impact is limitless. With ongoing development efforts, community collaboration, and adoption across diverse industries, Cosmos Blockchain is poised to redefine the decentralized landscape and unlock new possibilities for economic, social, and technological transformation.
## Conclusion
Cosmos Blockchain represents a paradigm shift in how we conceive and implement decentralized systems. Cosmos gives developers, entrepreneurs, and innovators the tools and infrastructure they need to ensure interoperability, scalability, and sovereignty while also enabling them to create the future of supply chains, gaming, banking, and other industries. As we journey into this new era of decentralized innovation, Cosmos stands as a beacon of hope and possibility, driving us towards a more inclusive, transparent, and interconnected world. Exploring Cosmos blockchain for your project development can prove to be a revolutionary decision. Connect with our [blockchain developers](https://blockchain.oodles.io/about-us/?utm_source=devto) for more information. | oodlesblockchain |
1,782,005 | Workday Spring Update (Workday 2024 R1): What’s New | Workday is a Cloud-based ERP solution, launched in 2005, that provides seamless HCM and financial... | 0 | 2024-03-06T12:31:18 | https://www.opkey.com/blog/workday-spring-update-workday-2024-r1-whats-new | workday, spring, update | 
Workday is a Cloud-based ERP solution, launched in 2005, that provides seamless HCM and financial systems to corporate users worldwide. Workday has emerged as a leading option for operations and workforce productivity.
Workday is a Cloud-based ERP that streamlines important workflows in your core business activities, such as HR, Payroll, and Finance. Workday releases mandatory Weekly Service updates and Biannual Feature releases. The newest is Workday Feature Release 2024R1, which brings new enhancements for the Human Capital Management and Financials modules.
So, what’s the big deal? Testing Workday's biannual updates is not always simple, especially with business processes on the line. You'll need a robust Workday testing plan to ensure that your business processes are unaffected.
This blog will give a high-level summary of all impacted functionalities for the Financials and HCM modules.
For detailed information about the release, we encourage you to read our advisory document on the Workday 2024 R1 Release.
**Workday provides product features and services in two ways**:
- Weekly Service Updates occur over the weekend maintenance window and provide timely fixes and enhancements that have no impact on consumers.
- Feature releases occur over a 6-month cycle and include many new features and capabilities that may require uptake.
**Workday’s Feature Release 2024R1: What’s New**?
- Overview of Workday 2024R1 Updates in Human Capital Management Module
- With this Workday release benefit billing status can now be designated to employees in case they have insufficient funds to cover their benefit cost
- Benefit Program communication cards containing job details can now be directly created in Workday.
- Many new features added with the Workday 2024 R1 release including “Compensation Element selection prompt” which will improve the speed and performance of the task by returning only the specified category of compensation elements.
- End users can now configure leave types and time offs that impact step progression and assign grace periods to steps
- Workday 2024 R1 allows customers timely fixes such as adding effective dates to service date changes. This enables you to accurately track service date changes for workers in Workday, reduces downstream impacts to calculations, and improves reporting.
- Workday 2024 R1 update include many new features such as allowing users to opt in for redesigned Hire Employee user interface.
- Many improvements in the hire business process have been enabled to configure workflows and approvals for creating or editing a job profile.
- You can now configure pre-hire contact information fields to be required for all users or security groups to ensure employees receive their contracts and important information they need on their first day of work and throughout the calendar year.
- Consent preferences can be asked from resources for processing of their personal data providing them a transparent process.
**Talent Management**
- Paradox AI chatbot has been introduced for external career sites. External candidates can have a conversation with the chatbot to receive job suggestions, assistance, and additional information about completing applications.
- You can now create and manage virtual, in-person, and hybrid recruiting events to enhance candidate engagement.
**Workforce Management**
- With this Workday release, you can now configure the worktag types for time offs to enable allocation of these hours effectively
- You can now change compensation for Workday customers by adding the “Request Compensation Change Process” step at the time of assigning or ending a collective agreement.
- Unit HR administrators who hire people in Workday will see a handful of cosmetic updates to the Hire Business Process user interface, including
- The "First Day of Work" and "End Employment Date" fields will now be located at the top of the page, alongside another essential date field, the "Hire Date."
- Workday Release 2024 R1 allows workers to use a calendar view that enables them to enter time for an entire pay period at once, simplifying the time-entry experience and reducing errors.
The Workday 2024 R1 release comes with more features and enhancements in the HCM module. Check out Opkey's Advisory Document for the Workday 2024 R1 Release to get complete details on these updates.
**Overview of Workday 2024R1 Updates in Financials Module**
- Workday users can now configure 1 or multiple Review steps in the Accounting Center Summarization Event Business Process, enabling you to approve or deny accounting center summary journals before they are posted to the ledger for Primary Source batch types
- Enhancements has been done to Revenue Driven Budget Rules functionality such as
- Floor can be defined as the amount of revenues to be recorded before the budget spending authority increases
- Ceiling on the maximum amount can be defined for the budget spending authority that can be increased from the recorded revenue source.
- Intelligent Machine Learning Prompt recommendations have been provided for
- Sales item and revenue categories on customer invoices
- Expense Item and defaulting for corporate credit card transactions
- Tax attributes on supplier invoice lines
- The Remittance framework has been extended to support remittance advice creation for third-party payroll payments and supplier invoice payments in PDF format.
- Payee Bank Account Validation Override task has been enhanced by delivering new configurability for bank account types, enabling you to create custom displays for your country-specific account type needs for both payment election and settlement bank accounts.
- Workday users can now change the status of cost reimbursable spend lines that fall outside the dates on your award lines from Pending Award Line Date Review to Ready to Bill. This enables you to bill sponsors for pre-award expenditures and for expenditures that vendors bill you after awards end without the need for workarounds.
**Adaptive Planning**
- What if’ scenarios have been introduced. What does this mean?
Test data can be changed in separate scenarios without affecting the data in your plan version.
-Reports and dashboards also support scenarios, enabling you to build reports and charts to compare and analyze your changes.
Code fields has been provided that can be changed for metadata throughout the model.
- Predictive Forecaster, powered by machine learning (ML) has been introduced which has enabled report users to schedule live and snapshot matrix reports, eliminating the need to manually select and share recurring reports with select users.
- Report users can now schedule live and snapshot matrix reports, eliminating the need to manually select and share recurring reports with select users.
- You can now explore a selected report cell in a new worksheet within the context of the model.
- You can manipulate the data in the new worksheet and generate new reports without disrupting the existing report.
You can expect many new changes in the Workday Financial module, read Opkey’s Advisory document to get complete information.
**Opkey for Workday Testing**
Opkey's Workday test automation platform provides a number of features that make it the best choice for businesses wishing to streamline their Workday update testing.
**No-Code Workday Testing**: Opkey is one of the Industry’s leading test automation tools that requires no coding. It is easy to use for business analysts, end users, manual testers, and stakeholders who lack technical coding skills. Furthermore, Opkey's built-in intelligence analyzes test steps and generates automated scripts with a single click.
**Change Impact Analysis**: Opkey automatically generates a change Impact Analysis report that provides customers with the precise scope of what needs to be tested with each Workday update, allowing them to prioritize testing on the elements that need attention. Self-healing capabilities enable damaged test scripts to be healed automatically.
**Pre-built test accelerators**: Opkey offers accelerators for functional, regression, performance, and security testing to reduce the workload on subject matter experts. Business users no longer have to start from scratch, which cuts test script design time and effort by more than 70%.
**Improved risk coverage through test discovery**: Opkey's test discovery functionality mines your specific Workday environment for previously executed tests (both manual and automated). Identifies gaps in your Workday business and provides optimal testing coverage. | johnste39558689 |
1,782,044 | Navyug Multispeciality Physiotherapy Centre in Bopal | "At Navyug Multispeciality Physiotherapy Centre in Bopal, we are dedicated to providing compassionate... | 0 | 2024-03-06T13:25:16 | https://dev.to/navyug012/navyug-multispeciality-physiotherapy-centre-in-bopal-14m6 | physiotherapist, multispecialist, multispeciality | "At Navyug Multispeciality Physiotherapy Centre in Bopal, we are dedicated to providing compassionate and personalized care to help you achieve optimal health and wellness. Our team of highly skilled physiotherapists is committed to helping you recover from injury, manage chronic conditions, and enhance your overall quality of life. Our Mission Our mission is to empower our patients to reach their full potential by offering evidence-based physiotherapy services tailored to their individual needs. We strive to create a supportive and healing environment where patients feel valued, understood, and empowered on their journey to recovery."
| navyug012 |
1,782,255 | Master the Art of Web Design with CodePem's CSS Border Generator | Are you searching for a simple yet powerful tool to enhance your web design projects? Look no further... | 0 | 2024-03-06T14:30:07 | https://dev.to/fraz123/master-the-art-of-web-design-with-codepems-css-border-generator-1bcj | cssgenerator, cssbordergenerator, csstool, csscodegenerator |
Are you searching for a simple yet powerful tool to enhance your web design projects? Look no further than CodePem's [CSS Border Generator](https://codepem.com/css-generator/css-border-generator)! Whether you're a budding designer or an experienced developer, our generator is designed to streamline the process of creating captivating border styles for your website elements.
**Why CodePem's CSS Border Generator Is Your Go-To Solution:
**
User-Friendly Interface: Our intuitive interface makes border styling a breeze. With easy-to-use sliders and controls, you can adjust border colors, widths, styles, and radii to create the perfect look for your website elements.
**Versatile Design Options:** From sleek and modern to fun and playful, our generator offers a wide range of border styles to suit any design preference. Explore different combinations of styles to find the perfect match for your website's aesthetic.
**Real-Time Preview:** See your border designs come to life instantly with our live preview feature. Make adjustments on the fly and visualize the impact of your changes in real-time, ensuring your borders look pixel-perfect every time.
**Effortless Integration:** Our [CSS Border Generator](https://codepem.com/css-generator/css-border-generator) generates clean and optimized CSS code that can be easily integrated into your website. Simply copy the generated code and paste it into your CSS file or inline styles, and watch your borders transform before your eyes.
**Responsive Design Support:** Ensure your borders look great on all devices with our generator's support for responsive design. Create borders that adapt seamlessly to different screen sizes, providing a consistent user experience across desktops, tablets, and smartphones.
**Ready to Level Up Your Design Skills?**
Unlock the potential of your web design projects with CodePem's CSS Border Generator. Whether you're working on a personal blog, a business website, or an e-commerce platform, our tool empowers you to create visually stunning borders that captivate your audience. Say goodbye to design limitations and hello to endless creativity!
Visit [CodePem's CSS Border Generator](https://codepem.com/css-generator/css-border-generator) today and revolutionize your web design workflow! | fraz123 |
1,782,272 | Mastering ChatGPT: How to Use It in 2 Easy Steps for 2024 (Free Tutorial) | In this article, I will tell you all you need to know about ChatGPT, show you how to use it, and... | 0 | 2024-03-06T15:10:27 | https://dev.to/proflead/mastering-chatgpt-how-to-use-it-in-2-easy-steps-for-2024-free-tutorial-1idc | chatgpt, howto, tutorial, openai | In this article, I will tell you all you need to know about ChatGPT, show you how to use it, and teach you the right way to ask your questions.
To learn the basics, you don’t need to spend your money and time watching hour-long tutorials. You can grasp the essentials in just 1–3 minutes and then enhance your skills through practice.
## What is ChatGPT?
ChatGPT is like a robot friend you can talk to on the computer or phone. It’s very smart and can chat with you, answer your questions, and help you with things you want to know or do. Just like when you talk to a friend, you can type to ChatGPT, and it will type back to you, trying its best to be helpful.
## What ChatGPT can do for you?
ChatGPT can do lots of things to help you! Here are some examples:
- **Answer Questions**. If you’re curious about something, like why the sky is blue or how airplanes fly, you can ask ChatGPT, and it will give you an answer.
- **Tell Stories**. If you want to hear a story, ChatGPT can make one up for you. You can even choose what the story is about, like dragons or space adventures.
- **Help with Homework**. If you’re stuck on a homework question, ChatGPT can try to help explain it in a way that’s easier to understand.
- **Learn New Things**. If you’re curious about a new topic, ChatGPT can provide information and teach you about it in a simple way.
- Etc.
## How to Use ChatGPT
First, you need to register on https://chat.openai.com/. Once registered, you will gain access to the page where you can ask questions ChatGPT.
## How to Write a Good Prompt
The second step is to begin asking your questions or, in other words, writing prompts.
Writing the best prompt for ChatGPT or any AI model from OpenAI involves clearly and effectively communicating what you want the AI to do. Here’s a simple guide you can follow, inspired by the principles in the provided link but explained in simpler terms:
- **Be Clear**. Tell the AI exactly what you need. For example, if you want a story, mention what kind of story, like a fairy tale, a space adventure, or a mystery.
- **Be Specific**. Give details. If you’re asking for a story about a dragon, describe the dragon. Is it friendly? What color is it? Where does it live? The more details you give, the better the AI can understand and create what you’re imagining.
- **Provide Examples**. Sometimes it helps to give an example of what you want. If you want a poem, you could say, “Write a poem like ‘Twinkle, Twinkle, Little Star’ but about the sun.”
- **Use Simple Language**. Especially when explaining to a child, use simple words and short sentences. The AI needs to understand your instructions, and clear, simple language helps.
- **Ask for What You Want Directly**. If you want help with homework, say, “Explain how photosynthesis works in a way a 5-year-old can understand.” Being direct helps the AI know exactly what to do.
- **Check and Adjust**. Sometimes the first response might not be perfect. You can always ask again with more details or clarify what you want differently.
By following these steps, you can craft effective prompts that help the AI understand and respond to your requests in the best way possible.
## Examples of a Good and a Bad Prompts
Your prompt don’t have to be too long, it could be short.
**Bad prompt**: “Explain computer internet connection.”
**Good prompt**: “Describe how a computer connects to the internet in a way that a complete beginner would understand, using simple analogies.”
**Bad prompt**: “Solve 5 apples minus 2.”
**Good prompt**: “Compose a poem about the ocean, using vivid imagery to describe the waves, the marine life, and the feeling of the sand beneath your feet. The poem should evoke a sense of calm and wonder.”
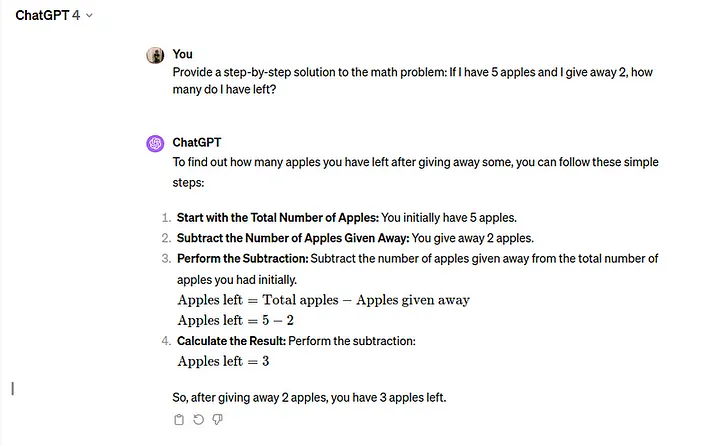
You can find more good examples here: https://platform.openai.com/examples
If you want to know more about prompt please follow this link https://platform.openai.com/docs/guides/prompt-engineering
## How to Use ChatGPT Video Tutorial
{% embed https://youtu.be/dvvL30VzRqk?si=b8YOEf6W1kOqoTuu %}
That’s it! :) If you like this article please don’t forget to click like and share your feedback. Thanks!
| proflead |
1,782,347 | Filament v3 - Multi-tenancy form component scoping | Multi-Tenancy feature After following the documentation of Multi-Tenancy everything works... | 0 | 2024-03-06T17:01:08 | https://dev.to/mlz/filament-v3-multi-tenancy-form-component-scoping-4ho8 | filament, laravel, php | ## Multi-Tenancy feature
After following the [documentation of Multi-Tenancy](https://filamentphp.com/docs/3.x/panels/tenancy) everything works well until I started to follow the [demo project](https://filamentphp.com/docs/3.x/panels/getting-started) using the learned on the tenancy part :D
All the forms were automagically scoped with the current tenancy value, but once I started to use the modals forms I started to got some errors like
`SQLSTATE[23502]: Not null violation: 7 ERROR: null value in column "team_id" of relation "owners" violates not-null constraint DETAIL:`
This is because Filament does not currently provide this feature on some component forms as [we can read here](https://filamentphp.com/docs/3.x/panels/tenancy#tenancy-security).
The solution for this, is use the `createOptionUsing` method on the `Filament\Forms\Components\Select` component as we can see in [the documentation](https://filamentphp.com/docs/3.x/forms/fields/select#customizing-new-option-creation).
So I put this code instead:
`->createOptionUsing(fn ($data) => Filament::getTenant()->owners()->create($data)->id)`
And the tenant value was saved correctly :).
All this wasn't my idea, I posted this issue as a bug on the github and I received this solution haha.
https://github.com/filamentphp/filament/issues/11709
I have shared this with you because if you encounter the same problem, I hope this explanation will help you. | mlz |
1,782,364 | Server Sent Events(SSE) | A server-sent event is when a web page automatically gets updates from a server. Traditionally, a web... | 0 | 2024-03-06T17:27:07 | https://dev.to/subhamdash45/server-sent-eventssse-6i0 | javascript, react, express, webdev | A server-sent event is when a web page automatically gets updates from a server. Traditionally, a web page has to send a request to the server to receive new data, then the server will send the response to the client. With server-sent events, a server can send new data to a web page at any time, by pushing messages to the web page.
If we are implementing SSE, we should keep the following two things in mind:
1. A long-lived unidirectional communication exists (the communication happens between the server and the client)
2. An HTTP connection only
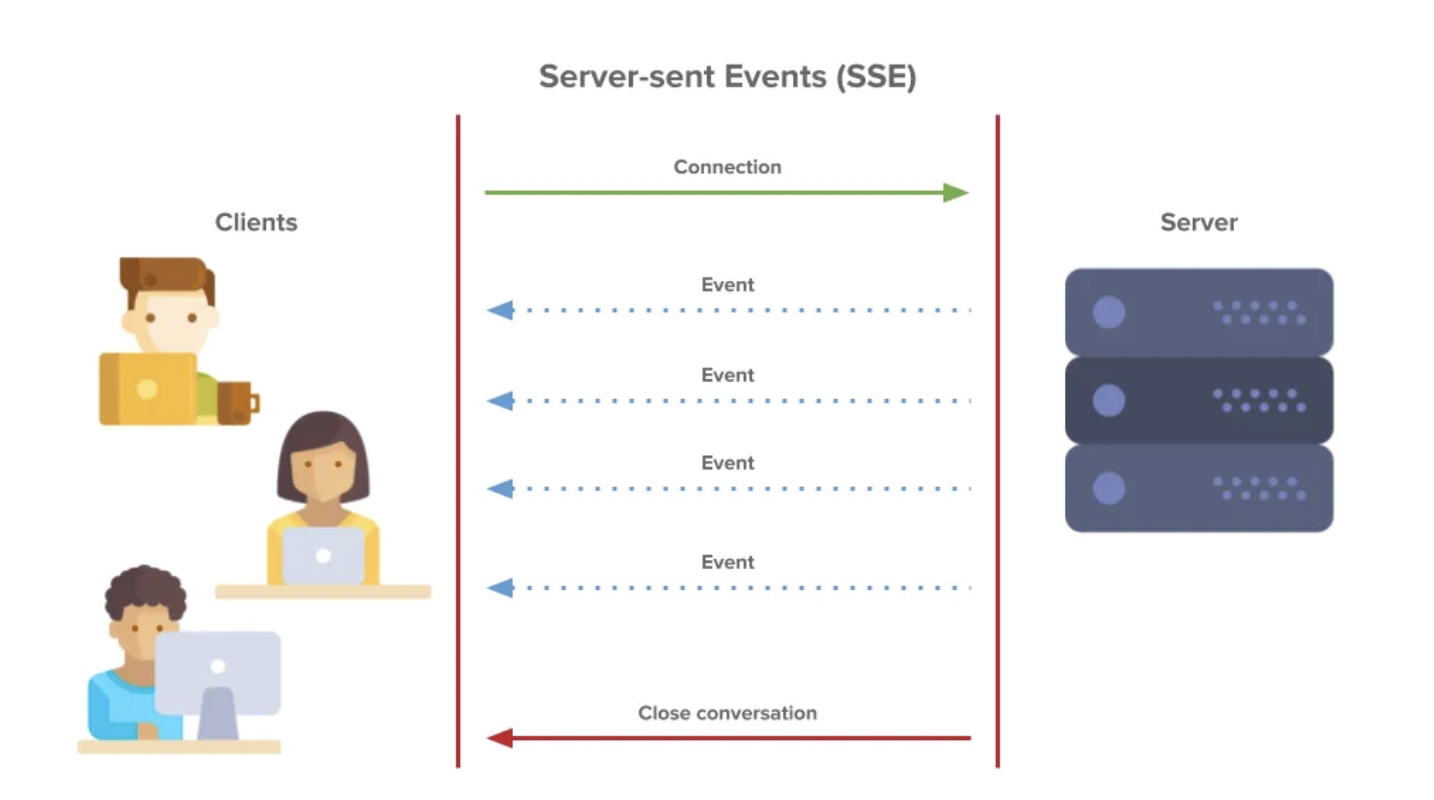
#### _Communication flow between Server and Client using Server Sent Events. (Image Source: PubNub)_
An HTTP request has been made. As long as we do not explicitly close this connection by doing some actions, such as changing the tab, this request will never terminate or close.
Every time there is new data, the server passes it on a regular interval over the same HTTP network, which is open.
## Implementation
1. Connection should be live
2. The format in which data comes is event-stream
## Example
We will understand the working of Server-Sent Events using an example. Suppose, we have a stock price listing platform where our stock prices are to be updated continuously. Now for this, we only need a unidirectional connection i.e. server to client, where our server would send the new prices to our clients whenever they are updated on our server.
* We will create a normal HTML file and run the script in the script tag, where we will call (/see) and render the latest stock prices whenever the server updates them.
```
<!DOCTYPE html>
<html lang="en">
<head>
<meta charset="UTF-8">
<meta http-equiv="X-UA-Compatible" content="IE=edge">
<meta name="viewport" content="width=device-width, initial-scale=1.0">
<title>SSE Test App</title>
</head>
<body>
<h1>In SSE App</h1>
<section style="height: 100px; width: 300px; background-color: antiquewhite;">
<ul style="list-style-type:disc">
<li> Stock1 Price : <span id="first-element"></span></li>
<li >Stock2 Price : <span id="second-element"></span></li>
</ul>
<div id="time"></div>
</section>
<script>
const eventSource = new EventSource('/sse')
eventSource.onmessage = (event)=>{
const resObject = JSON.parse(event.data)
const firstElement = document.getElementById('first-element')
firstElement.innerText = `${resObject.stock1Rate}`
const secondElement = document.getElementById('second-element')
secondElement.innerText = `${resObject.stock2Rate}`
const timeElement = document.getElementById('time')
timeElement.innerText = `${resObject.currentTime}`
}
</script>
</body>
</html>
```
> Note: I am adding the Backend code for better understanding.
* Let us implement a simple Backend API to serve us stock prices at an interval of 5 seconds.
```
const express = require("express");
const {join} = require('node:path')
const PORT = 3010
const app = express()
app.use(express.static("public"));
app.get("/sse",(req, res)=>{
res.setHeader('Content-Type', 'text/event-stream');
res.setHeader('Connection','keep-live');
res.setHeader('Cache-Control', 'no-cache');
const intervalId = setInterval(() => {
const stock1Rate = Math.floor(Math.random() * 30000);
const stock2Rate = Math.floor(Math.random() * 40000);
const currentTime = new Date().toLocaleTimeString()
res.write(`data: ${JSON.stringify({currentTime,stock1Rate, stock2Rate})} \n\n`)
}, 5000);
req.on('close', ()=>{
clearInterval(intervalId)
})
})
app.get("/", (req, res) => {
res.sendFile(join(__filename, "/index.html"));
});
app.listen(PORT,()=>{
console.log(`App is connected to ${PORT}`)
})
```
In the UI the stock prices will change after each 5sec -
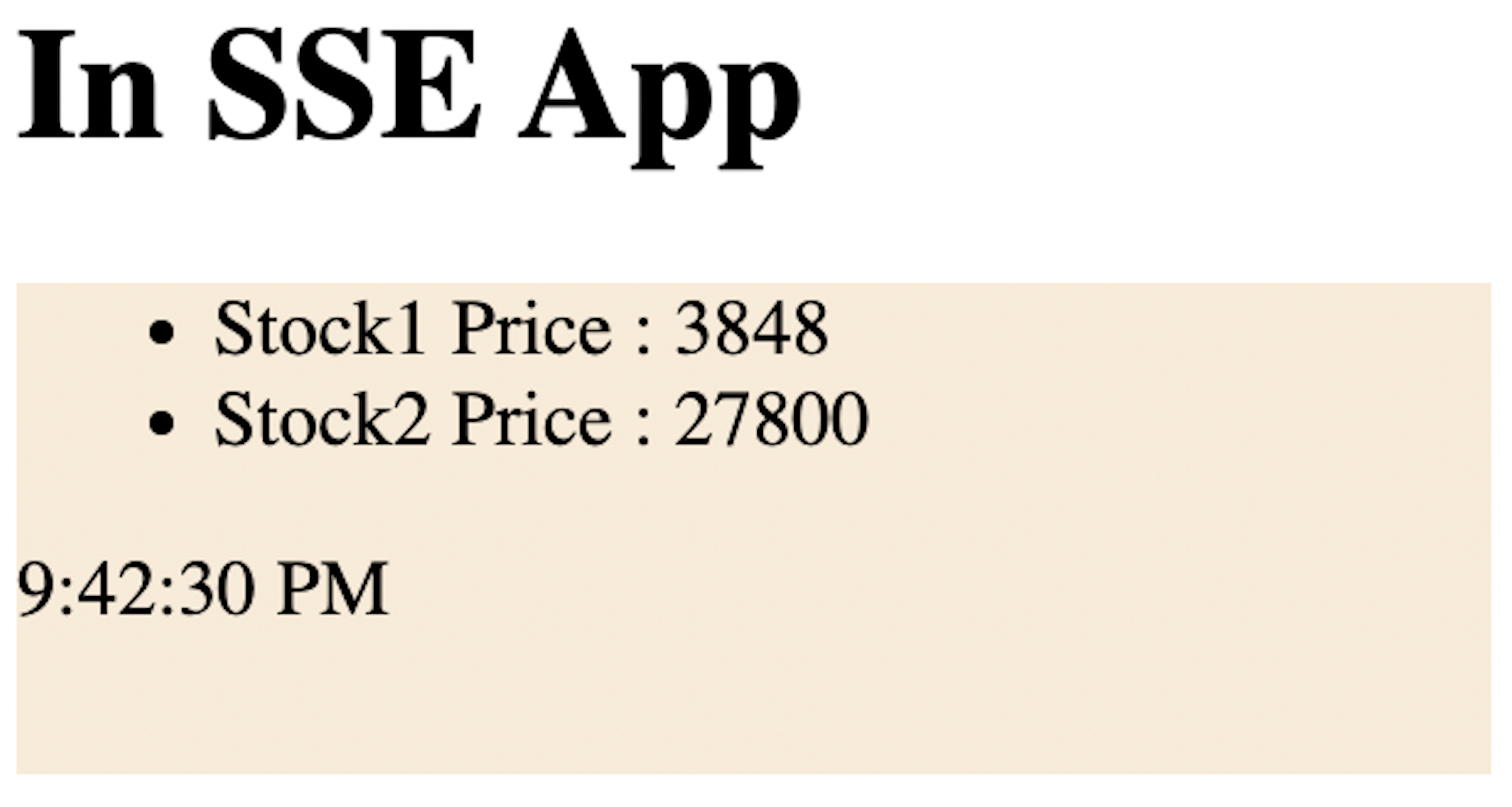
You can see how the response is received in the browser-
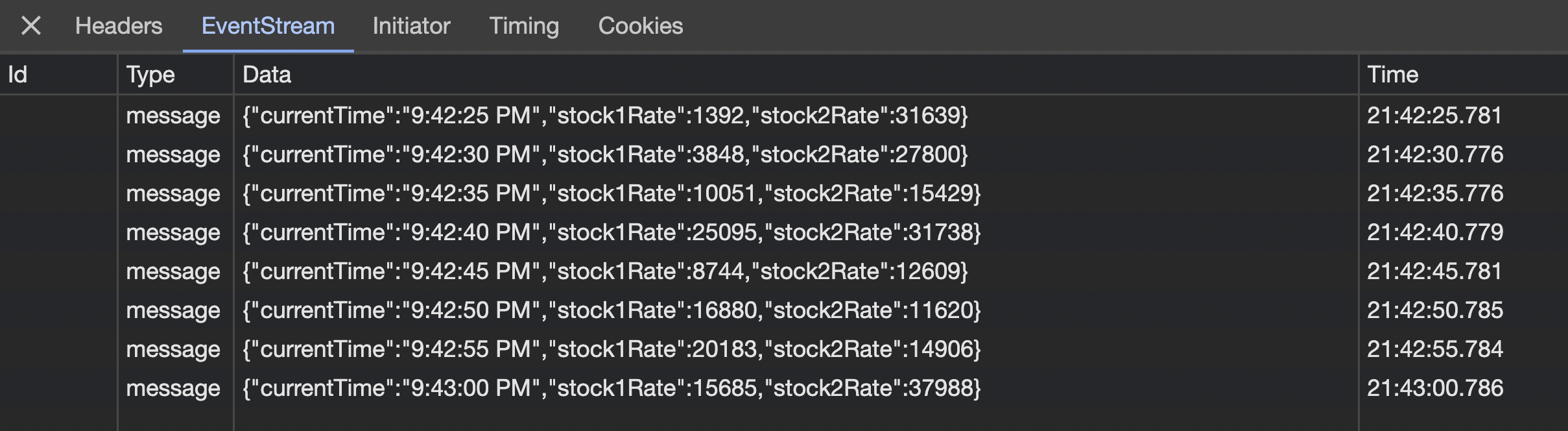
## Challenges that we may face while implementing
1. Browser compatibility
2. Connection limit
3. Connection timeout
4. Background tab behavior
5. Resource utilization
6. Load balancer
7. Sticky connection
8. Proxy/Firewall
I have tried to explain all the details of SSE that I know.
> Thanks For Reading, Follow Me For More
| subhamdash45 |
1,782,370 | Scroll Effects On Videos With JavaScript | by Saleh Mubashar Images and videos serve as crucial ingredients for crafting visually engaging... | 0 | 2024-03-06T17:34:06 | https://blog.openreplay.com/scroll-effects-on-videos-with-javascript/ | by [Saleh Mubashar](https://blog.openreplay.com/authors/saleh-mubashar)
<blockquote><em>
Images and videos serve as crucial ingredients for crafting visually engaging websites. However, relying solely on static images and videos with manual controls can become monotonous. This article goes beyond the basics and explores how videos can be smoothly integrated with scrolling.
</em></blockquote>
<div style="background-color:#efefef; border-radius:8px; padding:10px; display:block;">
<hr/>
<h3><em>Session Replay for Developers</em></h3>
<p><em>Uncover frustrations, understand bugs and fix slowdowns like never before with <strong><a href="https://github.com/openreplay/openreplay" target="_blank">OpenReplay</a></strong> — an open-source session replay suite for developers. It can be <strong>self-hosted</strong> in minutes, giving you complete control over your customer data.</em></p>
<img alt="OpenReplay" style="margin-top:5px; margin-bottom:5px;" width="768" height="400" src="https://raw.githubusercontent.com/openreplay/openreplay/main/static/openreplay-git-hero.svg" class="astro-UXNKDZ4E" loading="lazy" decoding="async">
<p><em>Happy debugging! <a href="https://openreplay.com" target="_blank">Try using OpenReplay today.</a></em><p>
<hr/>
</div>
Instead of just talking about typical scroll effects (like fade/slide in on scroll or scroll reveal animations), we'll look at how videos can become part of the scrolling experience, making websites more engaging. This involves manipulating video frames through scrolling, as well as pausing or playing a video when it comes into the page view, among other functionalities.
## Understanding the Video API
To implement scroll effects on videos using JavaScript, it's crucial to grasp the Video API, which provides a set of methods and properties for interacting with HTML video elements.
Here's a straightforward method to showcase a video using the HTML ``<video>`` element:
```html
<video controls>
<source src="video.mp4" type="video/mp4" />
<source src="video.webm" type="video/webm" />
<!-- fallback content here -->
</video>
```
The most important attribute here is `controls`. This attribute allows the user to play/pause and control other video elements. If you remove this, the user will have no manual control of the video.
The `<video>` element can contain two `<source>` elements so that different formats can be loaded depending on the browser viewing the site.
Now, let's look at the properties and methods that JavaScript provides.
### Video Element Methods
* JavaScript Video Object: To manipulate videos in JS, we need to first access the video. You can use any JavaScript selection method here. In this case, we get the video using its id "videoID".
```javascript
const video = document.getElementById('videoID');
```
* Play and Pause: Using these functions, you can play and pause a video. These functions can be linked to custom buttons, for example.
```javascript
video.play();
video.pause();
```
* Load: You can reload a video using this method.
```javascript
video.load();
```
* Manipulate Controls: You can also manipulate the controls attribute through JavaScript.
```javascript
video.removeAttribute("controls");
```
### Video Element Properties
* Video Duration: This returns the total duration of the video in seconds.
```javascript
const videoDuration = video.duration;
```
* Control Autoplay: When loaded, you can get or set whether the video should start playing automatically.
```javascript
const AutoplayEnabled = video.autoplay;
video.autoplay = true;
```
* Get and set volume: Get the current volume and also set it (from 0.0 to 1.0).
```javascript
const currentVolume = video.volume;
video.volume = 0.75; // Set volume to 75%
```
* Current Time: Jump to specific points in the video by manipulating the `currentTime` attribute.
```javascript
video.currentTime = 30; // set the playback time to 30 seconds
```
The `currentTime` attribute is particularly important for more complex animations as it can be linked to properties such as scroll values, etc.
### Video Event Listeners
There are also multiple video-specific event listeners that won't be used in this article but are good to know:
* `timeupdate`: Fired when the current playback position changes.
* `ended`: Fired when the video ends.
* `loadedmetadata`: Fired when the metadata (such as duration or volume) is loaded.
* `progress`: Fired as the browser loads the video data.
<CTA_Middle_Design />
## Playing Videos When Scrolled To
Now, let's create a practical example using our knowledge of the video API. Let's say you have a video on your site that you want to play automatically, but the video needs to be scrolled to. If we can detect when it comes into the user's view, we can start it directly, as opposed to having it play when it is not visible.
Firstly, to detect if the video is in view, we can use a simple formula:
```javascript
rect.top >= 0 &&
rect.left >= 0 &&
rect.right <= windowWidth &&
rect.bottom <= windowHeight
```
`windowWidth` and `windowHeight` represent the visible height and width of the browser window. The formula checks if all four sides of the video are within the viewport. If this condition is met, we play the video; otherwise, we pause it. This logic is encapsulated in a function named `isVideoInViewport`, linked to the scroll event.
`document.documentElement.clientWidth` ensures compatibility across various browsers, as some browsers may use one property while others use the alternative.
<iframe height="300" style="width: 100%;" scrolling="no" title="Autoplay video when in view" src="https://codepen.io/saleh-mubashar/embed/vYPgEYj?default-tab=js%2Cresult" frameborder="no" loading="lazy" allowtransparency="true" allowfullscreen="true">
See the Pen <a href="https://codepen.io/saleh-mubashar/pen/vYPgEYj">
Autoplay video when in view</a> by Saleh-Mubashar (<a href="https://codepen.io/saleh-mubashar">@saleh-mubashar</a>)
on <a href="https://codepen.io">CodePen</a>.
</iframe>
<br></br>
> **Note**: this pen is best viewed fullscreen.
## Manipulating Video Playback Position
Let's look at how we can control video playback using JavaScript. With this information, videos can be played based on, for example, scroll values or other forms of user input.
As discussed earlier, `video.currentTime` is essential. We can also control the playback rate using this line:
```javascript
// Set the playback speed to 1.5x
video.playbackRate = 1.5;
```
Let's create a simple example where the user can input a specific time, and the video will jump to that point. Firstly, we will get the user input (in seconds). Make sure to validate that the time is not less than 0 and greater than the video duration. We can then use `video.currentTime` to set the playback position.
The demo and code can be seen below:
<iframe height="400" style="width: 100%;" scrolling="no" title="Video Playback from User Input" src="https://codepen.io/saleh-mubashar/embed/zYbNXqK?default-tab=js%2Cresult" frameborder="no" loading="lazy" allowtransparency="true" allowfullscreen="true">
See the Pen <a href="https://codepen.io/saleh-mubashar/pen/zYbNXqK">
Video Playback from User Input</a> by Saleh-Mubashar (<a href="https://codepen.io/saleh-mubashar">@saleh-mubashar</a>)
on <a href="https://codepen.io">CodePen</a>.
</iframe>
## Playing a Video Using Scroll Values
Now, let's get to the main example of this article. We will create a demo in which a video is played as the user scrolls. This will be done both forward and backward. This effect is very common and can give off an illusion of a 3d modal being moved on scroll. However, it is usually just a fullscreen video based on scroll values.
Let's look at the main steps we need to follow:
1. One initial challenge is the inability to create a scrollbar that mirrors the length of the video, allowing users to scroll through it using traditional HTML and CSS. To address this, we will implement a JavaScript function that dynamically adjusts the height of a div element encapsulating the video based on the video's duration.
We will use the video `loadedmetadata` event listener for this. We also will use a speed constant variable in the formula. Increasing this constant will result in a longer scrollbar and slower video playback, while decreasing it will have the opposite effect.
```javascript
// get video element
const video = document.getElementById("myVideo");
const container = document.getElementById("videoContainer");
// set the container height according to video length
video.addEventListener('loadedmetadata', function() {
const speed = 250; // can be any number (adjust to your preference)
container.style.height = (video.duration * speed) + 'px';
});
```
2. Get the Scroll Y position and convert it into a percentage of the total page height. This is quite simple. We will create a function linked to the scroll event in which all the logic will be present. The formula will be something like this.
```javascript
// get current scroll progress
var scrollY = window.scrollY;
// get total page height and calculate percentage
var height = document.documentElement.scrollHeight - window.innerHeight;
var percentage = scrollY / height;
```
3. Use this calculated percentage to set the `currentTime` of the video, syncing the video playback with the scroll progress.
```javascript
// set video playback position.
video.currentTime = video.duration * percentage;
```
4. Smoothen things out: Lastly, we will use the `requestAnimationFrame` function to enhance the smoothness of video playback during scrolling.
```javascript
window.requestAnimationFrame(playVideo);
```
The complete code and demo can be seen below:
<iframe height="350" style="width: 100%;" scrolling="no" title="Playing a Video Using Scroll Values" src="https://codepen.io/saleh-mubashar/embed/MWxpgwo?default-tab=js%2Cresult" frameborder="no" loading="lazy" allowtransparency="true" allowfullscreen="true">
See the Pen <a href="https://codepen.io/saleh-mubashar/pen/MWxpgwo">
Playing a Video Using Scroll Values</a> by Saleh-Mubashar (<a href="https://codepen.io/saleh-mubashar">@saleh-mubashar</a>)
on <a href="https://codepen.io">CodePen</a>.
</iframe>
## Conclusion
Adding scroll effects to videos is a fantastic way to elevate user engagement and enhance the visual appeal of websites. With the help of the Video API and JavaScript, you can integrate videos into the scrolling experience, providing users with a dynamic and engaging experience.
## Credits
Both the videos used and this example are inspired by these two examples. A third is attached for further reference.
* [Play Video on Scroll! - by Jhett Lien](https://codepen.io/marduklien/pen/MdvdEG)
* [Video Blob Background for Scroll Control by - Shaw](https://codepen.io/marduklien/pen/MdvdEG)
* [Play Video On Scroll by - Malte](https://codepen.io/Maltsbier/pen/dyYmGGq)
| asayerio_techblog | |
1,782,429 | Writing pure MSIL/IL/CIL code: .NET Internals. Part 2 | Perhaps it's because the first language I learned was assembler; I simply enjoy delving into the... | 0 | 2024-03-06T18:43:30 | https://dev.to/turalsuleymani/writing-pure-msililcil-code-net-internals-part-2-2da0 | csharp, dotnet, programming, tutorial | Perhaps it's because the first language I learned was assembler; I simply enjoy delving into the internals.
We often hear about stack memory, but would you like to see it with the naked eye using .NET IL(Intermediate Language)?
Stack memory is primarily utilized for storing local variables, function call information (such as return addresses), and context information during function calls.
In my second tutorial on .NET IL, we'll explore the realm of stack memory. By the end, you'll learn:
1. How IL utilizes stack memory.
2. How IL creates variables for interaction with it.
{% embed https://youtu.be/NGrdLy4nGB8 %}
**Want to dive deeper?**
Every 5 days, I share my senior-level expertise on my [DecodeBytes](https://www.youtube.com/@DecodeByte/videos) YouTube channel, breaking down complex topics like .NET, Microservices, Apache Kafka, Javascript, Software Design, Node.js, and more into easy-to-understand explanations. Join us and level up your skills!
| turalsuleymani |
1,782,773 | Architectural Principles | Exploring Architectural Principles and Best Practices In the fast-paced world of software... | 0 | 2024-03-07T01:04:08 | https://dev.to/munashe_njanji/architectural-principles-5g11 | microservices, architecture, webdev, softwareengineering | ## Exploring Architectural Principles and Best Practices
In the fast-paced world of software engineering, understanding and applying architectural principles and best practices are essential for building robust, scalable, and maintainable systems. In this article, we delve into key architectural principles that guide software design, including the Single Responsibility Principle, Encapsulation, and Service Aggregation. Additionally, we explore various best practices such as externalized service configuration, microservices design principles, and versioning strategies. Let's examine these fundamental concepts and their practical applications in modern software development.
### Software Hierarchy
In any software system, organizing components hierarchically facilitates better management and understanding of the system's structure. For example, in a web application, the hierarchy might include layers such as presentation layer, business logic layer, and data access layer. Each layer serves a distinct purpose and encapsulates related functionalities.
### Single Responsibility Principle
Each module or class should have only one reason to change, promoting modularity and maintainability. For instance, a class responsible for user authentication should focus solely on authentication logic without handling unrelated concerns like user profile management.
### Uniform Naming Principle
Consistent naming conventions enhance clarity and comprehension within the codebase. For instance, using descriptive names for variables, functions, and classes improves readability and reduces cognitive load for developers reviewing the code.
### Encapsulation Principle
Encapsulation restricts access to certain components, preventing unintended interference and promoting information hiding. For example, encapsulating data access within a repository class shields the internal data structure from direct manipulation, ensuring data integrity and facilitating future changes to the data access layer.
### Service Aggregation Principle
Aggregating related services can simplify complex systems and improve scalability. For instance, a microservices architecture might consolidate user-related functionalities such as authentication, authorization, and user profile management into a single user service to reduce inter-service communication overhead and enhance performance.
### High Cohesion, Low Coupling Principle
Modules with high cohesion and low coupling are easier to understand, maintain, and extend. For example, a class responsible for email notifications should encapsulate all email-related functionalities without depending on external services or tightly coupling with other modules, promoting code reusability and testability.
### Library Composition Principle
Leveraging existing libraries and components promotes code reuse and accelerates development. For instance, integrating a third-party library for image processing instead of implementing custom image manipulation functionalities not only saves development time but also benefits from community support and ongoing maintenance of the library.
### Avoid Duplication Principle
Eliminating redundant code reduces maintenance overhead and minimizes the risk of inconsistencies. For example, extracting common functionalities into reusable components or libraries prevents duplicating code across multiple modules, ensuring consistency and simplifying future updates and bug fixes.
### Externalized Service Configuration Principle
Externalizing configuration settings enhances flexibility and facilitates environment-specific configurations. For example, storing configuration parameters such as database connection strings, API keys, and feature toggles in external files or environment variables allows easy modification without modifying the codebase, streamlining deployment and configuration management processes.
#### Environment Variables
Utilizing environment variables allows for flexible configuration across different deployment environments. For instance, specifying database credentials or service endpoints as environment variables enables seamless deployment to development, staging, and production environments with minimal configuration changes.
#### Kubernetes ConfigMaps
Kubernetes ConfigMaps provide a centralized solution for managing configuration data in containerized applications. For example, storing application-specific configuration settings as ConfigMaps allows Kubernetes pods to access configuration data without hardcoding values, promoting portability and consistency across deployments.
#### Kubernetes Secrets
Kubernetes Secrets offer a secure way to manage sensitive information such as passwords and API keys. For example, storing database passwords or encryption keys as Kubernetes Secrets ensures confidentiality and integrity of sensitive data within containerized applications.
### Service Substitution Principle
Designing services to be easily replaceable enables seamless upgrades and maintenance. For example, using interface-based programming and dependency injection allows swapping implementations of a service without modifying dependent modules, facilitating testing and decoupling.
### Inter-Service Communication Methods
Choosing appropriate communication methods between services is crucial for system reliability and performance. For example, selecting synchronous communication for low-latency interactions and asynchronous communication for non-blocking operations improves responsiveness and scalability of distributed systems.
#### Synchronous Communication Method
Synchronous communication ensures immediate responses but may introduce dependencies and latency. For instance, using HTTP requests for synchronous communication between microservices enables real-time interactions but requires handling timeouts and error scenarios effectively.
#### Asynchronous Communication Method
Asynchronous communication decouples services and improves fault tolerance but requires handling of eventual consistency. For example, using message queues like RabbitMQ or Apache Kafka for asynchronous communication allows services to process messages at their own pace, enhancing scalability and resilience.
#### Shared Data Communication Method
Sharing data between services simplifies communication but may lead to synchronization challenges. For example, using shared databases or event streams for data communication between microservices centralizes data storage but requires careful schema design and versioning to prevent data inconsistencies and conflicts.
### Domain-Driven Architectural Design Principle
Aligning architectural design with domain concepts enhances the system's maintainability and adaptability. For example, in an e-commerce platform, structuring services around domain entities like orders, products, and customers simplifies development and reflects the business logic more accurately.
#### Design Example 1: Mobile Telecom Network Analytics Software System
A domain-driven design approach for a telecom analytics system could prioritize real-time data processing and predictive modeling. For instance, organizing services around network performance metrics and customer usage patterns enables telecom operators to optimize network resources and improve service quality.
#### Design Example 2: Banking Software System
In a banking system, domain-driven design might emphasize security, compliance, and transaction processing. For example, structuring services around account management, transactions, and fraud detection ensures regulatory compliance and robustness against security threats.
### Autopilot Microservices Principle
Designing microservices for autonomous operation promotes scalability, reliability, and ease of management. For example, implementing stateless microservices that can be deployed independently and scaled horizontally improves resource utilization and fault tolerance in cloud-native environments.
#### Stateless Microservices Principle
Stateless microservices simplify scaling and deployment but require robust session management strategies. For example, using JWT tokens for session management allows stateless microservices to authenticate and authorize requests without relying on server-side sessions, enhancing scalability and resilience.
#### Resilient Microservices Principle
Resilient microservices gracefully handle failures and recover quickly to ensure uninterrupted service. For example, implementing circuit breakers and retry mechanisms in microservices architectures allows services to isolate and recover from transient failures, maintaining overall system stability and performance.
#### Horizontally Autoscaling Microservices Principle
Automatically scaling microservices horizontally optimizes resource utilization and improves responsiveness under load. For example, configuring auto-scaling policies based on CPU or memory usage metrics enables cloud platforms like AWS or Kubernetes to dynamically adjust the number of running instances to meet demand fluctuations.
#### Highly-Available Microservices Principle
Highly available microservices minimize downtime and ensure consistent performance for users. For example, deploying microservices across multiple availability zones or regions with load balancers and health checks improves fault tolerance and resilience to infrastructure failures.
#### Observable Microservices Principle
Observable microservices provide comprehensive monitoring and logging for troubleshooting and performance optimization. For example, integrating tools like Prometheus and Grafana for metric collection and visualization allows DevOps teams to gain insights into system behavior and proactively identify issues before they impact users.
### Software Versioning Principles
Adhering to versioning best practices facilitates compatibility, transparency, and effective collaboration. For example, following semantic versioning guidelines ensures that version numbers convey meaningful information about the nature of changes and their impact on compatibility.
#### Use Semantic Versioning Principle
Semantic versioning clarifies the impact of updates and simplifies dependency management. For example, incrementing the major version indicates backward-incompatible changes, while minor and patch versions signify backward-compatible additions and bug fixes, respectively.
#### Avoid Using 0.x Versions Principle
Initial development versions should avoid the 0.x series to signify unstable releases. For example, starting with version 1.0 instead of 0.1 communicates to users that the software has reached a stable state, reducing confusion and setting clear expectations for stability and reliability.
#### Don’t Increase Major Version Principle
Incrementing major versions should be reserved for significant changes to maintain compatibility. For instance, introducing breaking changes in a minor version update violates this principle and may disrupt existing integrations and workflows, necessitating careful planning and communication with users.
#### Implement Security Patches and Bug Corrections to All Major Versions Principle
Security patches and bug fixes should be backported to all supported major versions to ensure a secure ecosystem. For example, maintaining LTS (Long-Term Support) branches for older major versions allows organizations to receive critical security updates and bug fixes even after newer major versions are released, mitigating security risks and prolonging the lifespan of legacy deployments.
#### Avoid Using Non-LTS Versions in Production Principle
Long-term support (LTS) versions provide stability and security updates suitable for production environments. For example, opting for LTS releases of programming languages, frameworks, and operating systems ensures ongoing support and maintenance, reducing the likelihood of compatibility issues and vulnerabilities in production systems.
### Git Version Control Principle
Effective version control practices with Git streamline collaboration and facilitate code management. For example, leveraging branching strategies like GitFlow or GitHub Flow enables teams to work concurrently on features, bug fixes, and releases while maintaining a clean and organized codebase.
#### Feature Branch
Utilizing feature branches isolates development work and enables parallel feature development. For example, creating separate branches for each feature or enhancement allows developers to collaborate without interfering with ongoing development efforts, facilitating code reviews and integration testing.
#### Feature Toggle
Feature toggles allow for controlled feature activation and deactivation without code redeployment. For example, using feature flags or configuration switches enables gradual rollout of new features to specific user segments or environments, minimizing risk and enabling quick rollback in case of issues.
### Architectural Patterns
Leveraging established architectural patterns enhances system design and promotes scalability and maintainability. For example, adopting patterns like MVC (Model-View-Controller) or Hexagonal Architecture provides a clear structure for organizing code and separating concerns, facilitating code reuse and testability.
#### Event Sourcing Pattern
Event sourcing captures all changes to application state as a sequence of events, enabling reliable audit trails and temporal queries. For example, recording domain events such as user registrations or order placements allows applications to reconstruct past states and derive insights for analytics or compliance purposes.
#### Command Query Responsibility Segregation (CQRS) Pattern
CQRS separates read and write operations, optimizing performance and scalability for each use case. For example, using separate command and query models allows applications to scale read-heavy and write-heavy workloads independently, improving responsiveness and resource utilization.
#### Distributed Transaction Patterns
Distributed transaction patterns manage complex interactions between distributed components while ensuring data consistency. For example, implementing patterns like Saga Orchestration or Saga Choreography allows systems to maintain transactional integrity across multiple services without relying on a central coordinator, reducing coupling and improving scalability.
##### Saga Orchestration Pattern
Saga orchestration coordinates a series of local transactions across distributed services to maintain consistency. For example, using a state machine to orchestrate a series of compensating actions ensures that a distributed transaction either completes successfully or compensates for partial failures, preserving data integrity and system correctness.
##### Saga Choreography Pattern
Saga choreography relies on events and compensating actions to coordinate distributed transactions without a central orchestrator. For example, publishing domain events to trigger downstream actions allows services to react autonomously to changes in the system state, promoting decoupling and fault tolerance.
### Preferred Technology Stacks Principle
Standardizing technology stacks streamlines development, maintenance, and support efforts. For example, choosing a consistent set of programming languages, frameworks, and tools across projects enables developers to leverage existing expertise and share knowledge, improving productivity and code quality. | munashe_njanji |
1,782,931 | Javascript | String Methods | Hello my beginner frontend developers, today i will be showing Javascript string methods in 2... | 0 | 2024-03-07T06:30:16 | https://dev.to/shubhamtiwari909/javascript-string-methods-bfe | webdev, javascript, beginners, tutorial | Hello my beginner frontend developers, today i will be showing Javascript string methods in 2 different categories - Important and rarely used.
Let's get started...
## Important String methods
```js
const str = "Hello World";
// IMPORTANT
// 1. length - 11 - returns the string length including spaces
console.log(str.length);
// 2. search - true - search for the passed regex and returns boolean
const stringSearch = str.search("World");
// 3. slice
/**
* The slice() method extracts a section of a string and
* returns the extracted part in a new string, without modifying the original string.
* It can accept 2 parameters - start-index(inclusive) and end-index(exclusive)
*/
const stringSlice = str.slice(0, 5); // Hello - Extracts first 5 characters from the string
// 4. toLowerCase - hello world - converts entire string to lowercase
const stringToLowerCase = str.toLowerCase();
// 5. toUpperCase - HELLO WORLD - converts entire string to uppercase
const stringToUpperCase = str.toUpperCase();
// 6. trim - remove the white space from start and end of the strings
const stringTrim = str.trim();
// 7. startsWith - true - check if the string starts with the passed string value
const stringStartsWith = str.startsWith("Hell");
// 8. includes - true - check if the string includes the passed string value
const stringIncludes = str.includes("Hello");
```
## Rarely used
```js
// NOT USED MUCH
// 9. indexOf - Returns the position of the first occurrence of a given string
const stringIndexOf = str.indexOf("World"); // 6
// 10. charAt - Returns the character at the specified index
const stringCharAt = str.charAt(0); // H
// 11. charCodeAt - Returns the Unicode of the character at the specified index
const stringCharCodeAt = str.charCodeAt(0); // 72
// 12. substring - Returns the part of the string from the start index to the end index
const stringSubstring = str.substring(0, 5); // Hello
// 13. lastIndexOf - Returns the position of the last occurrence of a given string
const stringLastIndexOf = str.lastIndexOf("World"); // 6
// 14. split - Splits a string into an array of substrings using the specified separator which is empty space here
const stringSplit = str.split(" "); // [ 'Hello', 'World' ]
// 15. replace - Replaces first occurrence of a substring
const stringReplace = str.replace("World", "JS"); // Hello JS
// 16. replaceAll - Replaces all occurrences of a substring (ES11)
const stringReplaceAll = str.replaceAll("World", "JS"); // Hello JS
// 17. repeat - Returns a new string with the specified number of copies of the original string
const stringRepeat = str.repeat(3); // Hello WorldHello WorldHello World
// 18. endsWith - Checks if a string ends with the specified string
const stringEndsWith = str.endsWith("ld"); // true
// 19. concat - Concatenates two or more strings and returns a new string
const stringConcat = str.concat("Mr.", "HTML"); // Hello WorldMr.HTML
```
Which method according to you is more or less important in a real world project?
THANK YOU FOR CHECKING THIS POST
You can contact me on -
Instagram - https://www.instagram.com/supremacism__shubh/
LinkedIn - https://www.linkedin.com/in/shubham-tiwari-b7544b193/
Email - shubhmtiwri00@gmail.com
You can help me with some donation at the link below Thank you👇👇
☕ --> https://www.buymeacoffee.com/waaduheck <--
Also check these posts as well
{% link https://dev.to/shubhamtiwari909/button-component-with-cva-and-tailwind-1fn8 %}
{% link https://dev.to/shubhamtiwari909/microfrontend-react-solid-vue-333b %}
{% link https://dev.to/shubhamtiwari909/codium-ai-assistant-for-devs-57of %}
{% link https://dev.to/shubhamtiwari909/zustand-a-beginners-guids-fh7 %}
| shubhamtiwari909 |
1,782,947 | ✌️4 core developer tools I use in my daily life 🚀😎 | TL;DR This article lists my top 4 tools that I use in my daily life as a developer in... | 0 | 2024-03-17T12:23:40 | https://dev.to/shricodev/4-core-developer-tools-i-use-in-my-daily-life-2524 | productivity, devops, opensource, programming | ## TL;DR
This article lists my top 4 tools that I use in my daily life as a developer in 2024. ✅
These tools are aimed at improving your editing skills, terminal navigation, note-taking, and utilizing Docker beyond the containerization of applications. Also, I have a small surprise for you at the end. 😉
> If you are not using at least 1-2 tools mentioned in this article, let me tell you, friend, you are missing out. Definitely give at least some of these a try. You'll thank me later. 😎

***
## 1. [Tmux](https://github.com/tmux/tmux/wiki) **- Terminal multiplexer**
> ℹ️ I don’t think there is any reason not to use Tmux. As long as you have to work in the terminal, believe me, this is going to make your life much easier.

Are you opening up new tabs every time you need to work on something else in the terminal, and your current terminal window is occupied? Believe me, this thing is going to blow your mind. 🤯
You can split a tab/window into multiple panes. Also, there is the concept of a session that allows you to have multiple windows open, completely independent of other sessions, making it easy to work on multiple projects at a time.
See in the image? I have my notes in another window, and dotfile configs in another. Switching between them is very easy and convenient.
**Spoiler alert**: You will never want to use your mouse when working in the terminal. 😉
> It hasn't been very long since I started using Tmux, but now it's become my main core utility that I cannot live without. 🔥
***
## 2. [Neovim](https://neovim.io/) **- Preferred Code editor**
> ❓ Do you love working in the terminal? If yes, then this code editor is probably what you didn’t know you needed. Give it a try.

I was a very big fan of VSCode, and still, I am. I knew nothing about Vim and Neovim just a few months ago. But now, believe me, in all these months, I have not touched VSCode even once. 🫠
Maybe you are a very big fan of VSCode as I was, but try switching yourself to Vim motions. That is the best thing you could do for yourself to increase productivity. Once you shift your editor to the terminal, you will slowly start to live in the terminal itself.
Although the editor in the terminal might not be to everyone's taste, at least try to use it once and see if it is something of your choice.
***
## 3. [Obsidian](https://obsidian.md) **- Great Note Taking**
> 🧠 My second brain, and if you start using it right now, it will be yours too.

I know you might be using some cool note-taking tools such as Notion, Evernote whatever. But, do you remember the last time you opened up these note-taking apps to actually reference something you wrote a few months earlier? 🤔 See, most of you don’t have an answer. So uninstall these, and do it right now!

This is exactly what Obsidian solves. Think of it as your **second brain**. This tool is so good that I have the GUI open all the time on my virtual desktop, or I open it in a Tmux window so that whenever I am writing code and need to reference my notes, I can easily do so with **obsidian.nvim** right from my editor. 🔥 Read more on [obsidian.nvim](https://github.com/epwalsh/obsidian.nvim).
> I also switched from Notion to Obsidian. Believe me, it was one of the best switches I made, one that I am going to cherish for the rest of my life. Don’t worry, you can import your existing notes from your note-taking tools to Obsidian pretty easily.
***
## 4. [Docker](https://docker.com) **- Beyond Containerization**
> 🐳 Do you use it for more than just containerizing your application? If not, I guess it’s time to.

Mostly when we think of Docker, we think of it just as a way to containerize applications. We know there are tons of ways to use Docker, but we simply ignore them. But, think of it more like your daily driver, not just for one purpose.
Recently, I wanted to try using Arch so I could say, “**I use Arch, BTW!**” 😉 But I didn’t want to install a completely new Linux distribution from scratch just to find out if I don’t want to move forward with Arch. For that, I simply spun up a Docker container with the Arch image and started using it. If I don’t like it in the future by any chance, I will simply remove the darn image with its container. And that’s it, I am back to normal.🔥
> ⁉️ **Why not use a VM for that use case?**
In a VM, you have to allocate all the resources, and it will feel more bloated, to be honest. But with this approach, you have a complete, fully buttery smooth OS without having to do anything manually from scratch.
Also, recently I had to deal with connecting to a remote server via SSH, and my key-based authentication was not working. To debug if the problem was on my side, I simply spun up a Docker container with Alpine, set up my SSH keys there, and it connected successfully. The main problem was with the `ssh-daemon` wrong config of not accepting key-based authentication on the server itself because of `PubKeyAuthentication no` in the `/etc/ssh/sshd_config` file.
Docker is so beautiful 😻, try to use it very frequently.
***
## Surprise Just for You! 😉
Microsoft is offering FREE Certification Courses on Cloud, DevOps, and Development! ✅
No payment, no subscription, and no registration is required. Just start learning! 🚀
> ⚠️ **NOTE**: You will be redirected to the Official Microsoft Website.
https://learn.microsoft.com/training?wt.mc_id=studentamb_366508
Thank you for reading! I hope you try out some of these at least. 🫡
{% embed https://dev.to/shricodev %} | shricodev |
1,782,966 | Make your Faker unit tests run faster with this one weird tip | FakerJS has a bug that is a classic example of over-eager initialisation. Naively importing the... | 0 | 2024-03-07T07:24:58 | https://dev.to/rrees/make-your-faker-unit-tests-run-faster-with-this-one-weird-tip-4mbc | javascript, fakerjs, testing | ---
title: Make your Faker unit tests run faster with this one weird tip
published: true
description:
tags: javascript, fakerjs, testing
# cover_image: https://direct_url_to_image.jpg
# Use a ratio of 100:42 for best results.
# published_at: 2024-03-07 07:17 +0000
---
[FakerJS](https://github.com/faker-js/faker) has a [bug](https://github.com/faker-js/faker/issues/1791) that is a classic example of over-eager initialisation.
Naively importing the library as per the Readme can lead to a massive slowdown in tests that are often meant to be some of the fastest in your suite.
In my case I was importing string functionality to tests content boundaries so even though I was actually trying to create *any* localised data I was initialising *all* of the localised content leading to my tests timing out for a simple validation.
The weird tip is simply to import the `en` locale (unless you specifically what a specific localised set of data)
```javascript
import { faker } from '@faker-js/faker/locale/en';
```
The English locale is also loaded for other languages so this genuinely seems the quickest import. | rrees |
1,783,027 | Creating a Classical Pong Game with PyGame: A Step-by-Step Tutorial | In this tutorial, I will walk you through the process of creating a simple yet engaging Pong game... | 0 | 2024-03-07T08:45:33 | https://developer-service.blog/creating-a-classical-pong-game-with-pygame-a-step-by-step-tutorial/ | python, pygame, programming | In this tutorial, I will walk you through the process of creating a simple yet engaging Pong game using the Pygame library in Python.
By the end of this tutorial, you will have a fully functional Pong game that you can play and customize to your liking:
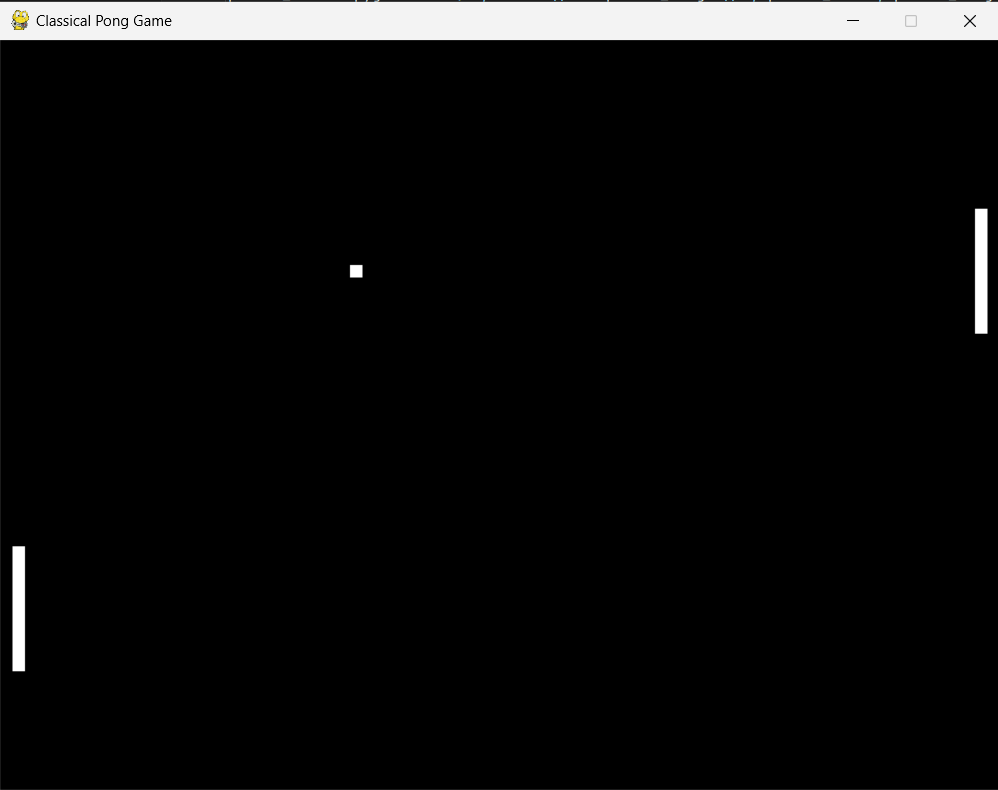
[Get the Source Code](https://devasservice.lemonsqueezy.com/checkout/buy/006c41cc-271b-452d-90ff-7679fb446c17)
---
## Prerequisites
Before we begin, make sure you have the following prerequisites installed:
- Python 3.x: You can download the latest version of Python from the official website: [https://www.python.org/downloads/](https://www.python.org/downloads/)
- Pygame: Once you have Python installed, you can install Pygame using pip by running the following command: `pip install pygame`
---
## Step 1: Initializing Pygame and Setting up Constants
First, let's import the necessary libraries and initialize Pygame:
```
import random
import pygame
import sys
# Initialize Pygame
pygame.init()
```
Next, we'll set up some constants for our game window, frame rate, and colors:
```
# Set up some constants
WIDTH, HEIGHT = 800, 600
FPS = 60
WHITE = (255, 255, 255)
BLACK = (0, 0, 0)
```
---
## Step 2: Creating the Game Window
Now, let's create the game window using the dimensions we defined earlier:
```
# Create the game window
screen = pygame.display.set_mode((WIDTH, HEIGHT))
We'll also set the window title to "Classical Pong Game":# Set the window title
pygame.display.set_caption("Classical Pong Game")
```
---
## Step 3: Creating the Paddles
Let's create two paddles, one for the left side and one for the right side of the screen:
```
# Create the paddles
paddle_width, paddle_height = 10, 100
paddle_left = pygame.Rect(10, HEIGHT//2 - paddle_height//2, paddle_width, paddle_height)
paddle_right = pygame.Rect(WIDTH - paddle_width - 10, HEIGHT//2 - paddle_height//2, paddle_width, paddle_height)
```
---
## Step 4: Creating the Ball
Next, we'll create the ball that will bounce between the paddles:
```
# Create the ball
ball_size = 10
ball = pygame.Rect(WIDTH//2 - ball_size//2, HEIGHT//2 - ball_size//2, ball_size, ball_size)
ball_speed = 5
ball_direction = [1, -1] # ball will move to the right and up
```
---
## Step 5: Setting up the Game Clock
We'll create a game clock to control the frame rate of our game:
```
# Set up the game clock
clock = pygame.time.Clock()
```
---
## Step 6: Implementing the Game Loop
Now, let's create the game loop where all the game logic and rendering will take place.
Full article at: [Creating a Classical Pong Game with PyGame: A Step-by-Step Tutorial](https://developer-service.blog/creating-a-classical-pong-game-with-pygame-a-step-by-step-tutorial/) | devasservice |
1,783,055 | Open-source AI Image Generators Platform of 2024! | Stable Diffusion The AI image generator with the most flexibility is Stable Diffusion. It's totally... | 0 | 2024-03-07T09:09:33 | https://dev.to/krunalrana/open-source-ai-image-generators-platform-of-2024-1plg | ai, freemidjourney, imagegeneration, aiimagegeneration | **Stable Diffusion**
The AI image generator with the most flexibility is Stable Diffusion. It's totally open source, and you can even train your own models based on your own dataset to get it to generate precisely the kind of picture you want.

With this method, there are truly many ways to use Stable Diffusion: you could download it and run it on your own laptop, set up your very own model, or access the API. But the two simplest ways are via Stability AI, the makers of Stable Diffusion, Clipdrop, and DreamStudio
Clipdrop is simpler and basically free, though DreamStudio offers you extra control over the images you're trying to generate. Both are easy to apply and are brilliant ways to play around with stable diffusion.
**OpenJourney**
OpenJourney is a text-to-image AI art generator. In essence, this means that the software program will turn text into portions of digital art. Naturally, the result may be closer to the user's imagination if the entry description is longer and more distinctive.

According to their web site, this prompt-based art generation model is particularly good at generating “photorealistic images”, and producing images that are “artistic and dreamy”. However, it isn't confined to realistic surrealism, and art style, and content material can be streamlined through the use of prompts. PromptHero themselves have curated an archive of popular prompts that are ranked by customers to offer inspiration for people who want to start creating.
**InvokeAI**
InvokeAI is a free, open-source text-to-image generator that works on the stable diffusion model, similar to AUTOMATIC1111’s WebUI. It permits users to access the software through an internet browser and boasts a user-friendly interface.
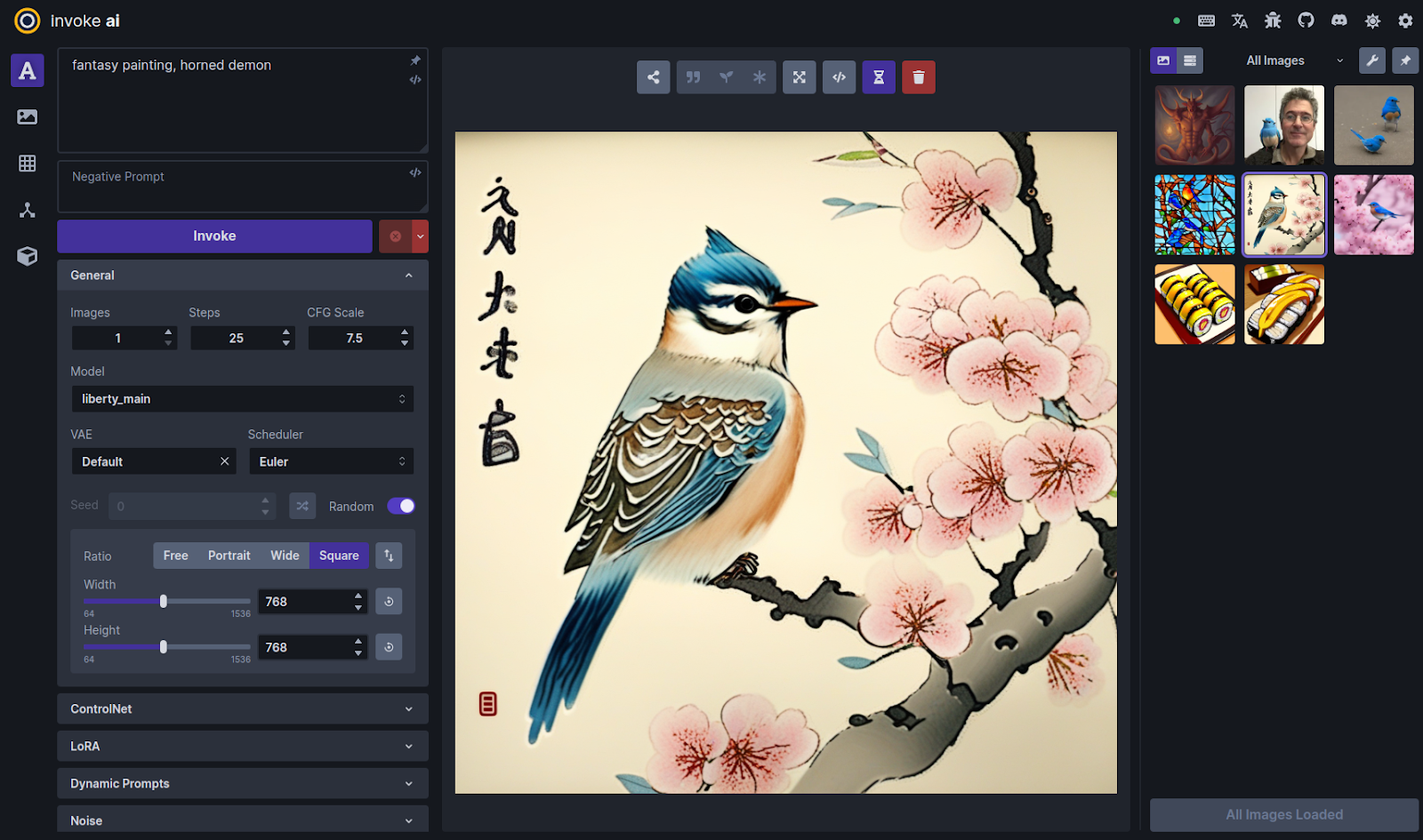
It has everything expected from a good image generator, from amazing text-to-image generator UI, including a number of features, inclusive of image-to-image translation, out painting, and in painting, to assist customers in creating high-quality AI-generated images.
While the setup is exceedingly easy, there are still a few steps to observe and certain hardware requirements to keep in mind. It runs on Windows, Mac, and Linux systems and runs on GPU cards with as little as 4 GB of RAM. InvokeAI has been advanced through a network of open-source developers and is available on GitHub.
**StableStudio**
Stability AI, the AI startup behind the text-to-image model Stable Diffusion released StableStudio, an open-source model of DreamStudio, Stability AI’s commercial AI-powered design suite.
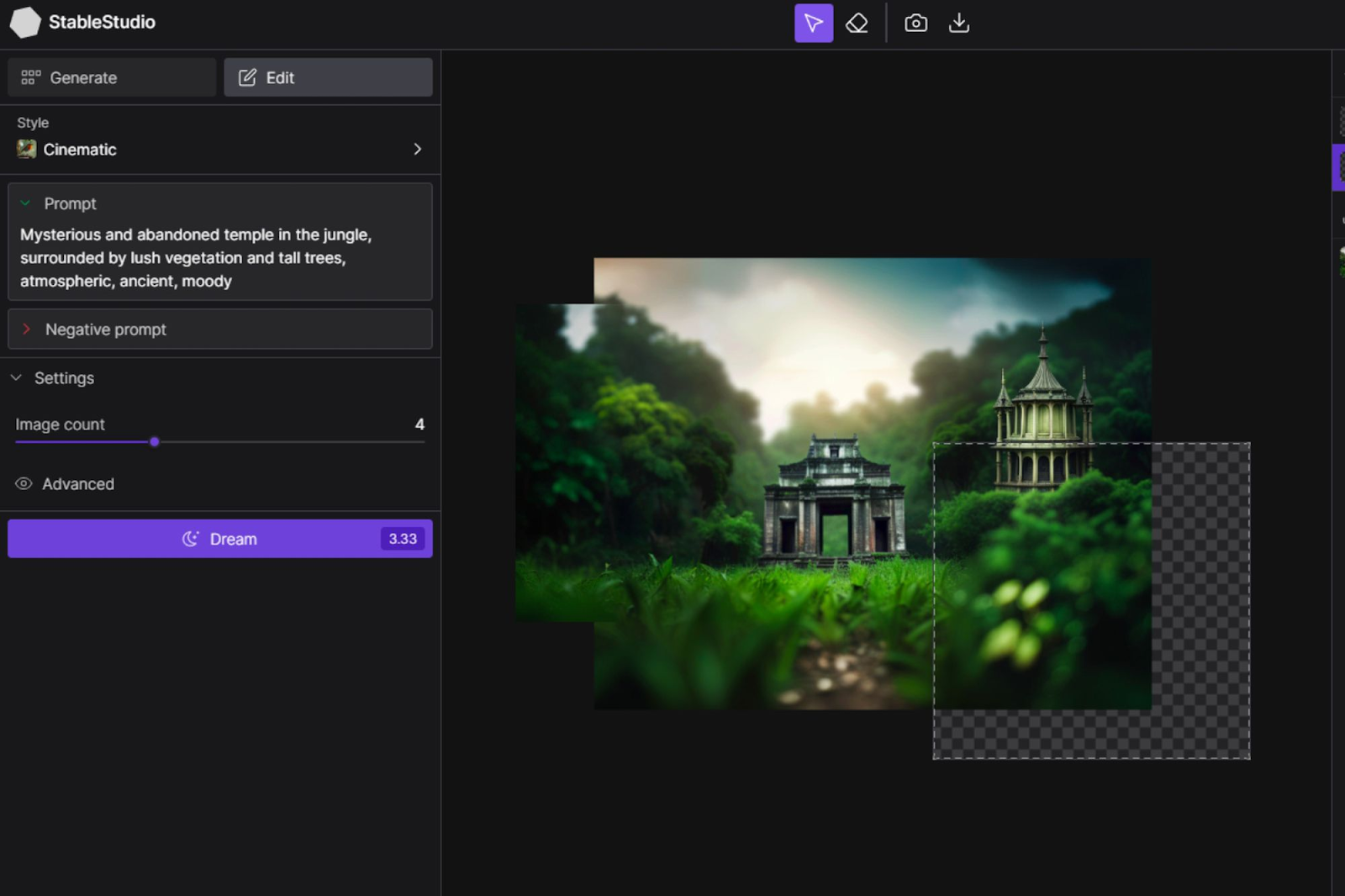
In a blog post, Stability AI writes that it hopes to “foster a project [that] can outpace anything developed via a single company,” alluding to current investments inside the generative AI area from tech giants like Microsoft, Google, and Amazon.
They believe the best way to expand upon that brilliant attainment is through open, community-pushed development instead of a private new release of a closed-source product. DreamStudio was first imagined as an animation studio for the open-source generative AI artwork model Disco Diffusion. The focus shifted in the final year towards the image generation with the arrival of Stable Diffusion, which delivered DreamStudio more in step with rival generative image systems like Midjourney and NightCafe.
**DeepAI**
DeepAI had a bigger plan concerning AI’s status in the arts since its release in 2016. It targets democratizing AI in generating graphic content.
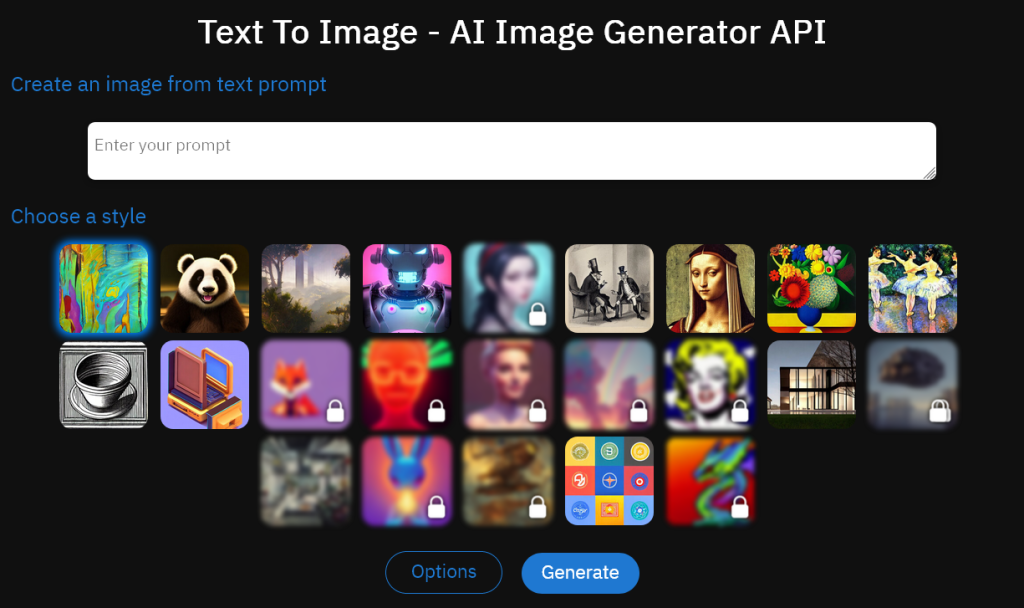
DeepAI offers a huge variety of tools that assist in creating unique, realistic pictures. The software permits high customization, letting you regulate detail levels, colors, textures, and more. The final product DeepAI generates keeps a high resolution, giving extraordinary, authentic virtual art to you. Another function of this toll is that it is able to create illustrations, including resolution-independent vector photos.
The algorithm works by inputting textual-based inquiries, and the AI will collect a montage that suits your request. While the final effects of the generator aren’t flawlessly aligned or photorealistic, developing unique paintings with this tool is, in reality, fun. Being open-source, DeepAI helps you create unlimited images; they are all specific. It’s presently free of charge.
**DeepFloyd IF**
Backed by Stability AI, the DeepFloyd research team has advanced an open-source model that combines practical visuals with language comprehension. DeepFloyd IF boasts a modular layout, along with a set textual content encoder and three interconnected pixel diffusion modules.

**DreamShaper**
Built on the diffusion model architecture, the ever-famous DreamShaper V7 introduces enhancements in LoRA support and realism. It builds on the updates of Version 6, which already boasted increased LoRA support, advanced style, and advanced generation at a 1024-pixel height (however, be careful when using this function). With a noise offset, it creates photorealistic photographs and elevates anime-style technology with booru tags.
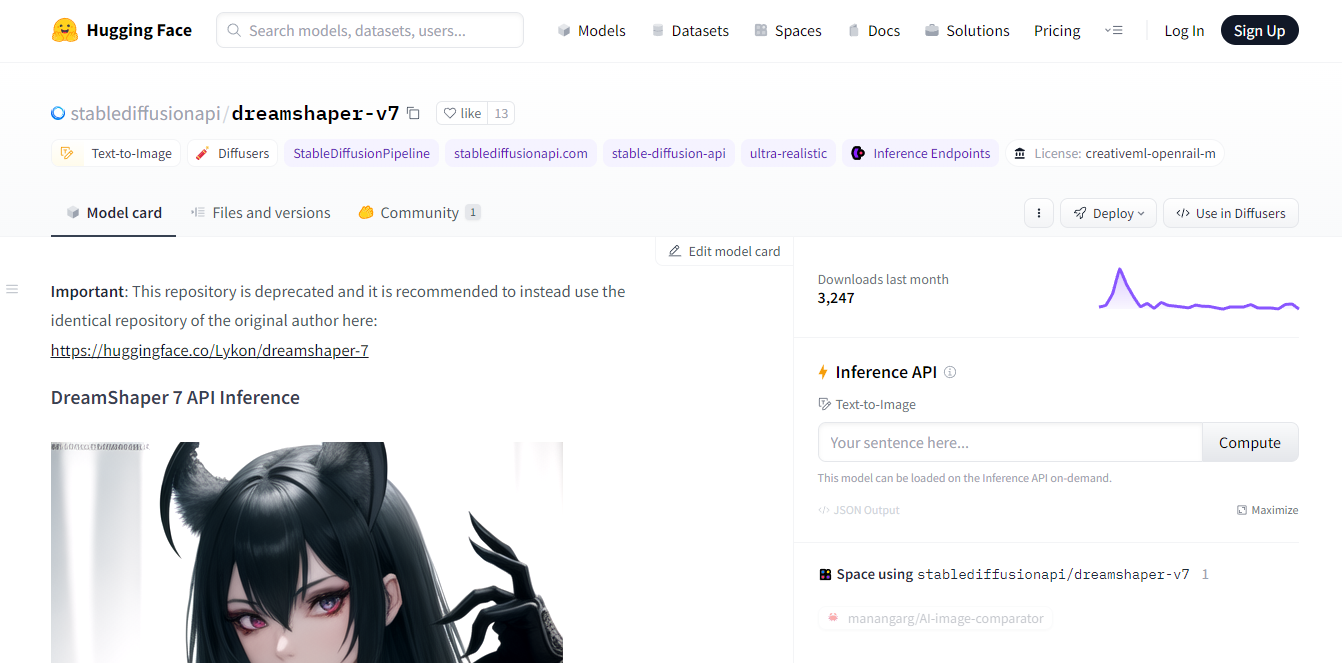
**Waifu Diffusion**
Waifu Diffusion is a polished iteration (v1.3) of the Stable Diffusion version, derived from Stable Diffusion v1.4. This model has a specific proficiency in generating sensible anime-style pictures and has obtained widespread approval for its vast array and remarkable quality. The model was calibrated on a dataset of 680k text-image samples collected from a Booru website.
**Craiyon**
Despite having the name DALL-E Mini originally, this AI art generator is not affiliated with OpenAI or DALL-E 2. It's an open-source alternative. Still, the moniker DALL-E 2 mini makes a lot of sense because it accomplishes everything DALL-E 2 does, albeit with far less accurate renditions.
Unlike DALL-E 2, the outputs from Craiyon lack a bit of quality. The good thing? Because you've got unlimited prompts, you can keep tweaking the prompt until you get precisely what you envision. The site is likewise simple to use, and considering DALLE-2's new price tag, this AI generator is a strong competitor.
**The Future of Digital Art**
The impact of AI images on human artists has come under scrutiny as they become more and more well-known. One thing is certain: AI does the work quicker than human beings. While this poses a more ethical question, it’s a reality that AI image generators can offer stunning art.
You are still creative when you assemble ideas and provide prompts to the AI. Moving forward, select the AI image generator that gives you the functions you find helpful for your creative expression.
| krunalrana |
1,783,094 | Context Switching pt.5: Long-Term Approach | This is the last part of our series about context switching. In this post, I'd like to have a more... | 0 | 2024-03-07T10:26:24 | https://dev.to/mobileit7/context-switching-pt5-long-term-approach-137a | agile, development, productivity, teamcollaboration | This is the last part of our series about context switching. In this post, I'd like to have a more distant look at the sustainability of our work practices and habits and wrap up the whole series.
So far I've omitted an aspect that has become an integral part of our modern work culture: remote work. We'll look at how working away from the office affects our ability to switch contexts effectively and explore ways of staying productive and mentally healthy in the ever-blurring lines between our professional and personal lives.
## Benefit from Compounded Improvements
Before we get into the intricacies of remote work, let's pause for a moment to consider a philosophical perspective on change and improvement. Often, we encounter opportunities for minor adjustments in our habits or routines. These changes might seem trivial at first glance, leading us to question their worth. Yet, it's in these small shifts where transformative potential lies.
Take, for instance, the inspiring story of the British cycling team. Their ascent from obscurity to global dominance in the cycling world is a testament to the power of incremental change.
It's a tale of how small, seemingly insignificant changes can lead to monumental victories. This approach, often referred to as the "aggregation of marginal gains", was used by Sir Dave Brailsford, the performance director of British Cycling. Brailsford believed that by making a small improvement in a variety of areas, the cumulative benefits would lead to significant enhancement in overall performance.
Before Brailsford's tenure, British Cycling had experienced very limited success and was an outsider at competitions.
The results were extraordinary. British cyclists dominated the 2008 and 2012 Olympic Games and won the Tour de France multiple times, starting with Bradley Wiggins in 2012.
This success hanged on a simple yet profound idea: improve everything you do by just 1%.
It wasn't just about pedaling faster or longer; it was about refining every detail, from the ergonomics of the bike seat to the way cyclists washed their hands.
It's about seeking out those tiny victories, knowing that they add up. Just like the British cyclists, who turned marginal gains into gold medals, anyone can turn small, consistent improvements into remarkable success stories.
Let's take this idea into everyday life. Imagine if every aspect of your work process got just a bit better - code quality improves bit by bit, build times get slightly faster, team communication becomes a tad clearer, and you need to update one less status manually. Investing time to find improvements that help you have one less context switch every hour will probably have a noticeable benefit on your energy levels over time.
These small improvements might not make headlines on their own, but collectively, they can propel a project to a higher level of efficiency and quality.
## Remote Work Culture
The shift to remote work, accelerated by recent global events, has fundamentally transformed our professional environments. While this transition offers flexibility and eliminates commutes, it also brings unique challenges in managing context switching. In our homes, the boundaries between work and personal life blur, creating a fertile ground for increased task-switching and potential productivity pitfalls.
Remote work environments differ significantly from traditional office settings. At home, the distractions vary from family interactions to household chores, each demanding attention and contributing to frequent context switches. Unlike the controlled environment of an office, home settings require individuals to self-regulate their focus. It requires not just a physical adjustment, but also a significant mental shift.
The isolation and lack of direct supervision can lead to feelings of disconnection and uncertainty. This psychological aspect of remote work is crucial to understand, as it directly influences how individuals handle context switching and maintain productivity.
In remote work, reliance on digital communication tools skyrockets. Emails, instant messages, and video calls become the primary means of interaction, each with its potential for interruption. The constant barrage of notifications from tools like Slack, Microsoft Teams, or email can fragment attention, making it challenging to engage in deep, focused work. This digital communication overload often leads to a paradox where workers are simultaneously more connected yet more isolated than ever before.
One of the most significant psychological challenges of remote work is the sense of isolation. Without the casual interactions and social cues of an office environment, workers may feel disconnected from their team and organization. This isolation can lead to a decrease in motivation and engagement, making context switching more challenging due to a lack of immediate collaborative feedback. Remote workers might feel cut off from their colleagues, leading to a sense of loneliness and decreased job satisfaction.
## Strategies for Reduction of Context Switching While Working from Home
Developing strategies that reduce context switching in the short term is essential, but considering the long-term impact on mental health, productivity, and work satisfaction is crucial for sustained performance. Managing context switching effectively over the long haul can prevent burnout and promote a healthier work-life balance.
To combat the unique context-switching challenges of remote work, consider the following strategies:
* Establish Routines: Creating regular routines can reinforce healthy work habits. For example, starting the day with the most challenging tasks when cognitive resources are at their peak can help maintain high productivity levels throughout the day.
* Promote Work-Life Balance: Encourage clear boundaries between work and personal time. Discourage the habit of checking work communications after hours, which can lead to mental fatigue and impede the ability to recharge fully.
* Foster a Culture of Focus: Cultivate a workplace culture that values deep work and focused attention. Implement policies that reduce unnecessary meetings and encourage concentration, such as quiet hours or no-interruption zones.
* Find Your Peak Hours: Analyze your work patterns and habits over a week to identify peak productivity periods. Track your productivity over a week. Note the times when you feel most focused and energetic. These are likely your peak productivity hours. Try to schedule demanding tasks during these peak times and use the tool to block these periods for focused work.
* Creating a Work-Only Zone: Establish a designated area in your home exclusively for work. This physical separation helps in mentally distinguishing between 'work mode' and 'home mode', reducing the likelihood of context switches due to household distractions.
* Ergonomic Setup: Invest in an ergonomic chair and desk. Comfortable and supportive furniture reduces physical strain, allowing for longer periods of focused work. Make sure the computer screen is at eye level and that you have adequate support for your back and wrists. An external screen is a must if your primary work tool is your laptop.
* Structured Schedule: Maintain regular work hours to create a sense of stability and routine. This structure helps in mentally preparing for work and winding down, clearly demarcating work time from personal time. This helps support the creation of routines and habits, leading to less mental overhead.
* Mindful Communication: Be deliberate about digital communication. Set specific times for checking emails and messages to avoid constant interruptions. Utilize status indicators on communication tools to signal availability and focus times.
* Breaks and Personal Time: Regular breaks are crucial, especially in a remote setting. Step away from your workspace for short periods to clear your mind. This practice helps in maintaining focus and reducing mental fatigue from prolonged periods of concentration.
* Virtual Collaboration Etiquette: Establish clear guidelines for virtual meetings and collaborative work. This includes respecting agreed-upon meeting times, being mindful of different time zones, and ensuring that digital collaborations are purposeful and efficient.
* Minimize Distractions: Identify and minimize potential distractions in your home environment. This might include noise-canceling headphones to block out household noise or using apps that limit social media access during work hours.
* Adequate Lighting: Ensure your workspace is well-lit, preferably with natural light. Good lighting reduces eye strain and improves mood and energy levels.
* Start-of-Day and End-of-Day Routines: Create a routine to mark the start and the end of your workday, such as a short walk or a closing ritual. This helps in mentally transitioning out of work mode.
## Key Takeaways
We made it to the very end of this series. I hope the strategies and tips shared across these posts will help you in taking control of your workday and reclaim the cognitive energy so often depleted by the fragmented nature of modern work environments.
There was a lot covered, so before we finish, here are a few of the most important tips:
* Identify your context switches to understand what causes you to switch tasks.
* Set priorities using approaches like the Eisenhower Matrix.
* Block time for your most important tasks.
* Set aside specific times to check emails and messages.
Use 'Do Not Disturb' settings in communication tools or simply switch the notifications off permanently.
* Batch similar tasks together.
* Try day theming to dedicate specific days to specific projects.
* Schedule breaks into your workday.
* Integrate key apps to reduce the need to switch between them.
* Implement no-meeting days or periods to reduce meeting-related context switching.
Written by Otakar Krus #scrummaster | mobileit7 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.