id int64 5 1.93M | title stringlengths 0 128 | description stringlengths 0 25.5k | collection_id int64 0 28.1k | published_timestamp timestamp[s] | canonical_url stringlengths 14 581 | tag_list stringlengths 0 120 | body_markdown stringlengths 0 716k | user_username stringlengths 2 30 |
|---|---|---|---|---|---|---|---|---|
1,918,617 | Multiple Parallel AI Streams with the Vercel AI SDK | The Vercel AI SDK makes it easy to interact with LLM APIs like OpenAI, Anthropic and so on, and... | 0 | 2024-07-10T14:10:42 | https://mikecavaliere.com/posts/multiple-parallel-streams-vercel-ai-sdk | ai, typescript, javascript, react | The Vercel AI SDK makes it easy to interact with LLM APIs like OpenAI, Anthropic and so on, and stream the data so it shows up in your web app rapidly as it loads. In this article we’ll learn how to run multiple prompts at the same time and see their results in parallel.
TL;DR: GitHub Repo is [here](https://github.com... | mcavaliere |
1,918,618 | Getting Started with .NET Aspire: Simplifying Cloud-Native Development | TL;DR: Discover .NET Aspire, a powerful stack simplifying cloud-native app development with... | 0 | 2024-07-10T16:31:43 | https://www.syncfusion.com/blogs/post/dotnet-aspire-cloud-native-dev | net, dotnet, cloud, development | ---
title: Getting Started with .NET Aspire: Simplifying Cloud-Native Development
published: true
date: 2024-07-10 13:48:50 UTC
tags: net, dotnet, cloud, development
canonical_url: https://www.syncfusion.com/blogs/post/dotnet-aspire-cloud-native-dev
cover_image: https://dev-to-uploads.s3.amazonaws.com/uploads/articles/... | jollenmoyani |
1,918,621 | Kubernetes Cluster Migration Strategies: A Comprehensive Guide | Kubernetes cluster migration is a critical process that involves transferring workloads from one... | 0 | 2024-07-10T14:19:12 | https://dev.to/platform_engineers/kubernetes-cluster-migration-strategies-a-comprehensive-guide-282b |
Kubernetes cluster migration is a critical process that involves transferring workloads from one cluster to another. This process can be complex and requires careful planning to ensure minimal disruption to applications and services. In this blog, we will explore various strategies for Kubernetes cluster migration, h... | shahangita | |
1,918,627 | World Animals Foundation: A Global Advocate for Animal Welfare and Conservation | The World Animals Foundation (WAF) is a global organization dedicated to the protection,... | 0 | 2024-07-10T14:26:15 | https://dev.to/katobhi/world-animals-foundation-a-global-advocate-for-animal-welfare-and-conservation-54cj | The [World Animals Foundation (WAF)](https://worldanimalsfoundation.org/) is a global organization dedicated to the protection, preservation, and welfare of animals worldwide. They focus on various aspects of animal welfare, including habitat conservation, protection of endangered species, and the promotion of humane t... | katobhi | |
1,918,628 | World Animals Foundation: A Global Advocate for Animal Welfare and Conservation | The World Animals Foundation (WAF) is a global organization dedicated to the protection,... | 0 | 2024-07-10T14:27:56 | https://dev.to/katobhi/world-animals-foundation-a-global-advocate-for-animal-welfare-and-conservation-25p1 | The [World Animals Foundation (WAF)](https://worldanimalsfoundation.org/) is a global organization dedicated to the protection, preservation, and welfare of animals worldwide. They focus on various aspects of animal welfare, including habitat conservation, protection of endangered species, and the promotion of humane t... | katobhi | |
1,918,630 | randint() and randperm() in PyTorch | *Memos: You can use manual_seed() with randint() and randperm(). *My post explains... | 0 | 2024-07-10T14:29:45 | https://dev.to/hyperkai/randint-and-randperm-in-pytorch-8gm | *Memos:
- You can use [manual_seed()](https://pytorch.org/docs/stable/generated/torch.manual_seed.html) with [randint()](https://pytorch.org/docs/stable/generated/torch.randint.html) and [randperm()](https://pytorch.org/docs/stable/generated/torch.randperm.html). *[My post](https://dev.to/hyperkai/manualseed-initialsee... | hyperkai | |
1,918,631 | normal() in PyTorch | *Memos: [Warning]-normal() is really tricky. You can use manual_seed() with normal(). *My post... | 0 | 2024-07-10T14:30:51 | https://dev.to/hyperkai/normal-in-pytorch-2jb | pytorch, normal, random, function | *Memos:
- [Warning]-[normal()](https://pytorch.org/docs/stable/generated/torch.normal.html) is really tricky.
- You can use [manual_seed()](https://pytorch.org/docs/stable/generated/torch.manual_seed.html) with [normal()](https://pytorch.org/docs/stable/generated/torch.normal.html). *[My post](https://dev.to/hyperkai/m... | hyperkai |
1,918,632 | Digram display of Python's commonly used third-party libraries | Python's commonly used libraries are generally TimeSeries Analysis, Data Visualization, Web Scraping,... | 0 | 2024-07-10T14:34:11 | https://dev.to/fridaymeng/digram-display-of-pythons-commonly-used-third-party-libraries-3k2h | python, diagram, tutorial | Python's commonly used libraries are generally TimeSeries Analysis, Data Visualization, Web Scraping, Machine Learning, Data Manipulation, Natural Language Processing, Database Operations, Statistical Analysis。
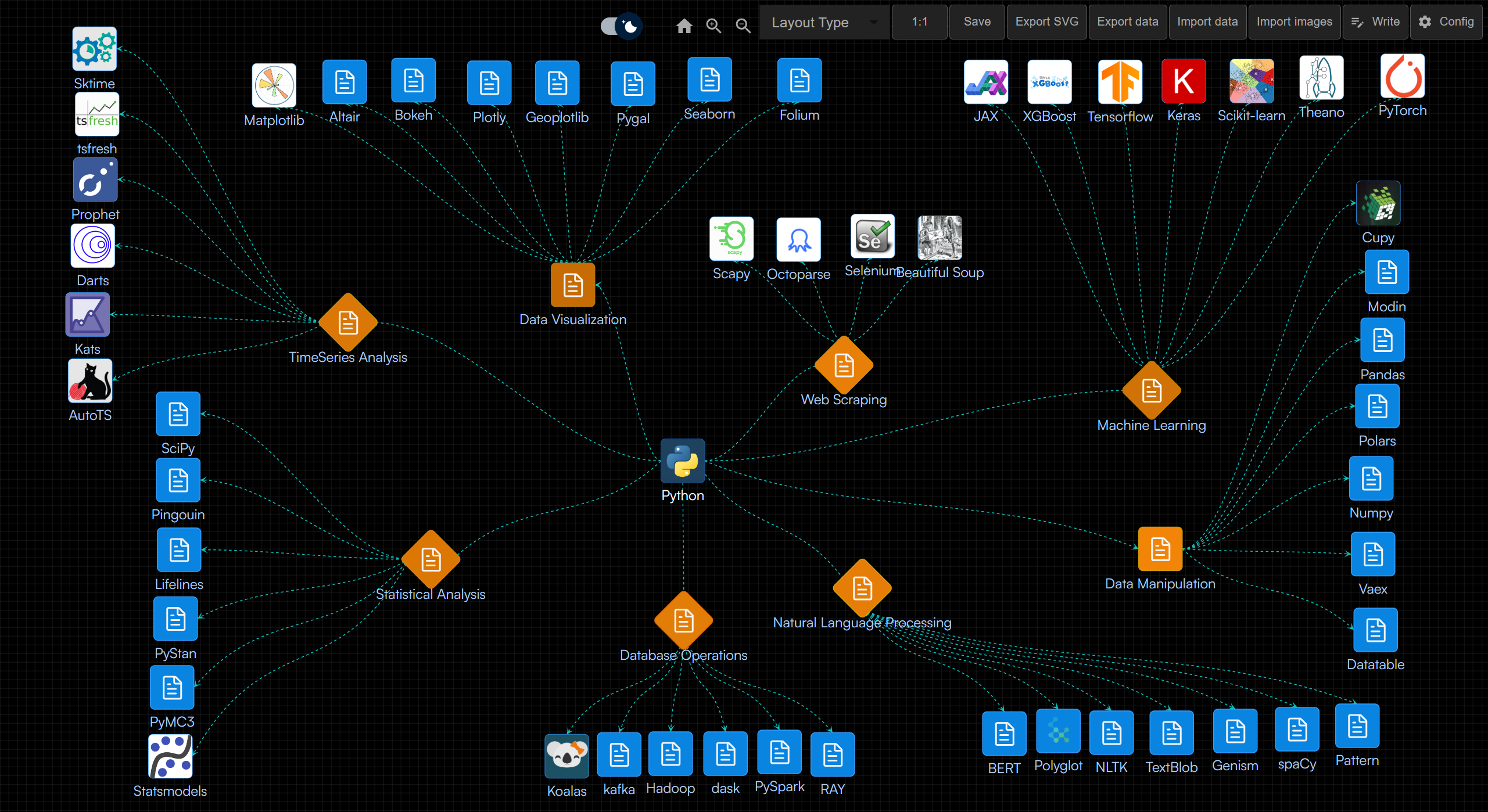
[P... | fridaymeng |
1,918,633 | How Do I Fix QuickBooks Error 557? (Payroll Update Error) | Encountering QuickBooks Error 557 can be frustrating, especially when you are in the middle of... | 0 | 2024-07-10T14:34:15 | https://dev.to/qbtoolshub/how-do-i-fix-quickbooks-error-557-payroll-update-error-159b |
Encountering QuickBooks Error 557 can be frustrating, especially when you are in the middle of important financial tasks. This blog post will guide you through understanding, diagnosing, and resolving this common Q... | qbtoolshub | |
1,918,634 | Jenkins Step-by-Step Guide on Crafting a Continuous Delivery and Deployment Pipeline | What is CI/CD? CI/CD stands for Continuous Integration and Continuous Delivery (or Deployment).... | 0 | 2024-07-10T14:36:34 | https://dev.to/oncloud7/jenkins-step-by-step-guide-on-crafting-a-continuous-delivery-and-deployment-pipeline-3d99 | jenkins, awschallenge, devops, cicd | **What is CI/CD?**
CI/CD stands for Continuous Integration and Continuous Delivery (or Deployment). Continuous Integration is the practice of frequently merging code changes into a shared repository. It involves automating the build, unit testing, and code quality checks to detect issues early. Continuous Delivery focu... | oncloud7 |
1,918,635 | Understanding Advanced Persistent Threats (APTs) | Understanding Advanced Persistent Threats (APTs) | 0 | 2024-07-10T14:42:54 | https://dev.to/saramazal/understanding-advanced-persistent-threats-apts-214 | apt, cybersecurity, hacking, infosec | ---
title: Understanding Advanced Persistent Threats (APTs)
published: true
description: Understanding Advanced Persistent Threats (APTs)
tags: #apt #cybersecurity #hacking #infosec
# cover_image: https://direct_url_to_image.jpg
# Use a ratio of 100:42 for best results.
# published_at: 2024-07-10 14:37 +0000
---
 and [headless CMS](https://thebcms.com/blog/headless-cms-101) share a common concept: decoupling content creation and management from the presentation layer. This separation allows businesses to manage and deliver content flexibly and eff... | momciloo | |
1,918,644 | 🏆 Best guide to SEO for devs | SEO, or Search Engine Optimization, is a set of techniques and practices you can adopt as a strategy... | 0 | 2024-07-10T14:50:47 | https://dev.to/daniellimae/best-guide-to-seo-for-devs-6ma | webdev, frontend, seo, tutorial | SEO, or Search Engine Optimization, is a set of techniques and practices you can adopt as a strategy to enhance the way users find you and your company/product online.
In other words, it's a way to stake your claim and ensure that when someone searches for a problem or your name specifically, you appear as the primary... | daniellimae |
1,918,645 | Slot Gacor | A post by Kawaca Utama | 0 | 2024-07-10T14:52:11 | https://dev.to/utamakawaca001/slot-gacor-2fo2 | slot, slotgacor, situsgacor, situspalinggacor | [](https://eliteboxinghk.com/) | utamakawaca001 |
1,918,646 | Testing AWS Database Migrations & Accelerating Development with Cloud Pods | Details Join our July Community Meetup to dive deep into innovative strategies for enhancing cloud... | 0 | 2024-07-10T14:54:36 | https://dev.to/localstack/testing-aws-database-migrations-accelerating-development-with-cloud-pods-4ngb | localstack, aws, dms, cloudpods |

**Details**
Join our July Community Meetup to dive deep into innovative strategies for enhancing cloud development and testing using LocalStack. This session will feature two engaging talks: one on deploying and te... | bartszy |
1,918,647 | Trouble connecting to VPN? Solutions here | Why has VPN stopped connecting on your computer, phone, or tablet? How to fix connection dropouts... | 0 | 2024-07-10T14:55:07 | https://dev.to/zama_vpn/trouble-connecting-to-vpn-solutions-here-e0a | vpn |

Why has VPN stopped connecting on your computer, phone, or tablet? How to fix connection dropouts and other issues.
Why can’t you connect to VPN and how to resolve connection issues
According to statistics, Russ... | zama_vpn |
1,918,648 | How Image Processing Transforms Industries: 5 Key Use Cases | Introduction A recent report by Research and Markets indicates that the digital image... | 0 | 2024-07-10T14:57:46 | https://dev.to/api4ai/how-image-processing-transforms-industries-5-key-use-cases-n0a | api4ai, imageprocessing, ai, api | #Introduction
A recent [report by Research and Markets](https://www.researchandmarkets.com/reports/5972840/digital-image-processing-global-market-report#tag-pos-2) indicates that the digital image processing sector has seen remarkable growth in recent years. The market is expected to expand from $6.79 billion in 2023 ... | taranamurtuzova |
1,918,650 | Buy verified cash app account | https://dmhelpshop.com/product/buy-verified-cash-app-account/ Buy verified cash app account Cash... | 0 | 2024-07-10T15:01:56 | https://dev.to/figema4733/buy-verified-cash-app-account-2ae | webdev, javascript, beginners, programming | ERROR: type should be string, got "https://dmhelpshop.com/product/buy-verified-cash-app-account/\n\n\nBuy verified cash app account\nCash app has emerged as a dominant force in the realm of mobile banking within the USA, offering unparalleled convenience for digital money transfers, deposits, and trading. As the foremost provider of fully verified cash app accounts, we take pride in our ability to deliver accounts with substantial limits. Bitcoin enablement, and an unmatched level of security.\n\nOur commitment to facilitating seamless transactions and enabling digital currency trades has garnered significant acclaim, as evidenced by the overwhelming response from our satisfied clientele. Those seeking buy verified cash app account with 100% legitimate documentation and unrestricted access need look no further. Get in touch with us promptly to acquire your verified cash app account and take advantage of all the benefits it has to offer.\n\nWhy dmhelpshop is the best place to buy USA cash app accounts?\nIt’s crucial to stay informed about any updates to the platform you’re using. If an update has been released, it’s important to explore alternative options. Contact the platform’s support team to inquire about the status of the cash app service.\n\nClearly communicate your requirements and inquire whether they can meet your needs and provide the buy verified cash app account promptly. If they assure you that they can fulfill your requirements within the specified timeframe, proceed with the verification process using the required documents.\n\nOur account verification process includes the submission of the following documents: [List of specific documents required for verification].\n\nGenuine and activated email verified\nRegistered phone number (USA)\nSelfie verified\nSSN (social security number) verified\nDriving license\nBTC enable or not enable (BTC enable best)\n100% replacement guaranteed\n100% customer satisfaction\nWhen it comes to staying on top of the latest platform updates, it’s crucial to act fast and ensure you’re positioned in the best possible place. If you’re considering a switch, reaching out to the right contacts and inquiring about the status of the buy verified cash app account service update is essential.\n\nClearly communicate your requirements and gauge their commitment to fulfilling them promptly. Once you’ve confirmed their capability, proceed with the verification process using genuine and activated email verification, a registered USA phone number, selfie verification, social security number (SSN) verification, and a valid driving license.\n\nAdditionally, assessing whether BTC enablement is available is advisable, buy verified cash app account, with a preference for this feature. It’s important to note that a 100% replacement guarantee and ensuring 100% customer satisfaction are essential benchmarks in this process.\n\nHow to use the Cash Card to make purchases?\nTo activate your Cash Card, open the Cash App on your compatible device, locate the Cash Card icon at the bottom of the screen, and tap on it. Then select “Activate Cash Card” and proceed to scan the QR code on your card. Alternatively, you can manually enter the CVV and expiration date. How To Buy Verified Cash App Accounts.\n\nAfter submitting your information, including your registered number, expiration date, and CVV code, you can start making payments by conveniently tapping your card on a contactless-enabled payment terminal. Consider obtaining a buy verified Cash App account for seamless transactions, especially for business purposes. Buy verified cash app account.\n\nWhy we suggest to unchanged the Cash App account username?\nTo activate your Cash Card, open the Cash App on your compatible device, locate the Cash Card icon at the bottom of the screen, and tap on it. Then select “Activate Cash Card” and proceed to scan the QR code on your card.\n\nAlternatively, you can manually enter the CVV and expiration date. After submitting your information, including your registered number, expiration date, and CVV code, you can start making payments by conveniently tapping your card on a contactless-enabled payment terminal. Consider obtaining a verified Cash App account for seamless transactions, especially for business purposes. Buy verified cash app account. Purchase Verified Cash App Accounts.\n\nSelecting a username in an app usually comes with the understanding that it cannot be easily changed within the app’s settings or options. This deliberate control is in place to uphold consistency and minimize potential user confusion, especially for those who have added you as a contact using your username. In addition, purchasing a Cash App account with verified genuine documents already linked to the account ensures a reliable and secure transaction experience.\n\n \n\nBuy verified cash app accounts quickly and easily for all your financial needs.\nAs the user base of our platform continues to grow, the significance of verified accounts cannot be overstated for both businesses and individuals seeking to leverage its full range of features. How To Buy Verified Cash App Accounts.\n\nFor entrepreneurs, freelancers, and investors alike, a verified cash app account opens the door to sending, receiving, and withdrawing substantial amounts of money, offering unparalleled convenience and flexibility. Whether you’re conducting business or managing personal finances, the benefits of a verified account are clear, providing a secure and efficient means to transact and manage funds at scale.\n\nWhen it comes to the rising trend of purchasing buy verified cash app account, it’s crucial to tread carefully and opt for reputable providers to steer clear of potential scams and fraudulent activities. How To Buy Verified Cash App Accounts. With numerous providers offering this service at competitive prices, it is paramount to be diligent in selecting a trusted source.\n\nThis article serves as a comprehensive guide, equipping you with the essential knowledge to navigate the process of procuring buy verified cash app account, ensuring that you are well-informed before making any purchasing decisions. Understanding the fundamentals is key, and by following this guide, you’ll be empowered to make informed choices with confidence.\n\n \n\nIs it safe to buy Cash App Verified Accounts?\nCash App, being a prominent peer-to-peer mobile payment application, is widely utilized by numerous individuals for their transactions. However, concerns regarding its safety have arisen, particularly pertaining to the purchase of “verified” accounts through Cash App. This raises questions about the security of Cash App’s verification process.\n\nUnfortunately, the answer is negative, as buying such verified accounts entails risks and is deemed unsafe. Therefore, it is crucial for everyone to exercise caution and be aware of potential vulnerabilities when using Cash App. How To Buy Verified Cash App Accounts.\n\nCash App has emerged as a widely embraced platform for purchasing Instagram Followers using PayPal, catering to a diverse range of users. This convenient application permits individuals possessing a PayPal account to procure authenticated Instagram Followers.\n\nLeveraging the Cash App, users can either opt to procure followers for a predetermined quantity or exercise patience until their account accrues a substantial follower count, subsequently making a bulk purchase. Although the Cash App provides this service, it is crucial to discern between genuine and counterfeit items. If you find yourself in search of counterfeit products such as a Rolex, a Louis Vuitton item, or a Louis Vuitton bag, there are two viable approaches to consider.\n\n \n\nWhy you need to buy verified Cash App accounts personal or business?\nThe Cash App is a versatile digital wallet enabling seamless money transfers among its users. However, it presents a concern as it facilitates transfer to both verified and unverified individuals.\n\nTo address this, the Cash App offers the option to become a verified user, which unlocks a range of advantages. Verified users can enjoy perks such as express payment, immediate issue resolution, and a generous interest-free period of up to two weeks. With its user-friendly interface and enhanced capabilities, the Cash App caters to the needs of a wide audience, ensuring convenient and secure digital transactions for all.\n\nIf you’re a business person seeking additional funds to expand your business, we have a solution for you. Payroll management can often be a challenging task, regardless of whether you’re a small family-run business or a large corporation. How To Buy Verified Cash App Accounts.\n\nImproper payment practices can lead to potential issues with your employees, as they could report you to the government. However, worry not, as we offer a reliable and efficient way to ensure proper payroll management, avoiding any potential complications. Our services provide you with the funds you need without compromising your reputation or legal standing. With our assistance, you can focus on growing your business while maintaining a professional and compliant relationship with your employees. Purchase Verified Cash App Accounts.\n\nA Cash App has emerged as a leading peer-to-peer payment method, catering to a wide range of users. With its seamless functionality, individuals can effortlessly send and receive cash in a matter of seconds, bypassing the need for a traditional bank account or social security number. Buy verified cash app account.\n\nThis accessibility makes it particularly appealing to millennials, addressing a common challenge they face in accessing physical currency. As a result, ACash App has established itself as a preferred choice among diverse audiences, enabling swift and hassle-free transactions for everyone. Purchase Verified Cash App Accounts.\n\n \n\nHow to verify Cash App accounts\nTo ensure the verification of your Cash App account, it is essential to securely store all your required documents in your account. This process includes accurately supplying your date of birth and verifying the US or UK phone number linked to your Cash App account.\n\nAs part of the verification process, you will be asked to submit accurate personal details such as your date of birth, the last four digits of your SSN, and your email address. If additional information is requested by the Cash App community to validate your account, be prepared to provide it promptly. Upon successful verification, you will gain full access to managing your account balance, as well as sending and receiving funds seamlessly. Buy verified cash app account.\n\n \n\nHow cash used for international transaction?\nExperience the seamless convenience of this innovative platform that simplifies money transfers to the level of sending a text message. It effortlessly connects users within the familiar confines of their respective currency regions, primarily in the United States and the United Kingdom.\n\nNo matter if you’re a freelancer seeking to diversify your clientele or a small business eager to enhance market presence, this solution caters to your financial needs efficiently and securely. Embrace a world of unlimited possibilities while staying connected to your currency domain. Buy verified cash app account.\n\nUnderstanding the currency capabilities of your selected payment application is essential in today’s digital landscape, where versatile financial tools are increasingly sought after. In this era of rapid technological advancements, being well-informed about platforms such as Cash App is crucial.\n\nAs we progress into the digital age, the significance of keeping abreast of such services becomes more pronounced, emphasizing the necessity of staying updated with the evolving financial trends and options available. Buy verified cash app account.\n\nOffers and advantage to buy cash app accounts cheap?\nWith Cash App, the possibilities are endless, offering numerous advantages in online marketing, cryptocurrency trading, and mobile banking while ensuring high security. As a top creator of Cash App accounts, our team possesses unparalleled expertise in navigating the platform.\n\nWe deliver accounts with maximum security and unwavering loyalty at competitive prices unmatched by other agencies. Rest assured, you can trust our services without hesitation, as we prioritize your peace of mind and satisfaction above all else.\n\nEnhance your business operations effortlessly by utilizing the Cash App e-wallet for seamless payment processing, money transfers, and various other essential tasks. Amidst a myriad of transaction platforms in existence today, the Cash App e-wallet stands out as a premier choice, offering users a multitude of functions to streamline their financial activities effectively. Buy verified cash app account.\n\nTrustbizs.com stands by the Cash App’s superiority and recommends acquiring your Cash App accounts from this trusted source to optimize your business potential.\n\nHow Customizable are the Payment Options on Cash App for Businesses?\nDiscover the flexible payment options available to businesses on Cash App, enabling a range of customization features to streamline transactions. Business users have the ability to adjust transaction amounts, incorporate tipping options, and leverage robust reporting tools for enhanced financial management.\n\nExplore trustbizs.com to acquire verified Cash App accounts with LD backup at a competitive price, ensuring a secure and efficient payment solution for your business needs. Buy verified cash app account.\n\nDiscover Cash App, an innovative platform ideal for small business owners and entrepreneurs aiming to simplify their financial operations. With its intuitive interface, Cash App empowers businesses to seamlessly receive payments and effectively oversee their finances. Emphasizing customization, this app accommodates a variety of business requirements and preferences, making it a versatile tool for all.\n\nWhere To Buy Verified Cash App Accounts\nWhen considering purchasing a verified Cash App account, it is imperative to carefully scrutinize the seller’s pricing and payment methods. Look for pricing that aligns with the market value, ensuring transparency and legitimacy. Buy verified cash app account.\n\nEqually important is the need to opt for sellers who provide secure payment channels to safeguard your financial data. Trust your intuition; skepticism towards deals that appear overly advantageous or sellers who raise red flags is warranted. It is always wise to prioritize caution and explore alternative avenues if uncertainties arise.\n\nThe Importance Of Verified Cash App Accounts\nIn today’s digital age, the significance of verified Cash App accounts cannot be overstated, as they serve as a cornerstone for secure and trustworthy online transactions.\n\nBy acquiring verified Cash App accounts, users not only establish credibility but also instill the confidence required to participate in financial endeavors with peace of mind, thus solidifying its status as an indispensable asset for individuals navigating the digital marketplace.\n\nWhen considering purchasing a verified Cash App account, it is imperative to carefully scrutinize the seller’s pricing and payment methods. Look for pricing that aligns with the market value, ensuring transparency and legitimacy. Buy verified cash app account.\n\nEqually important is the need to opt for sellers who provide secure payment channels to safeguard your financial data. Trust your intuition; skepticism towards deals that appear overly advantageous or sellers who raise red flags is warranted. It is always wise to prioritize caution and explore alternative avenues if uncertainties arise.\n\nConclusion\nEnhance your online financial transactions with verified Cash App accounts, a secure and convenient option for all individuals. By purchasing these accounts, you can access exclusive features, benefit from higher transaction limits, and enjoy enhanced protection against fraudulent activities. Streamline your financial interactions and experience peace of mind knowing your transactions are secure and efficient with verified Cash App accounts.\n\nChoose a trusted provider when acquiring accounts to guarantee legitimacy and reliability. In an era where Cash App is increasingly favored for financial transactions, possessing a verified account offers users peace of mind and ease in managing their finances. Make informed decisions to safeguard your financial assets and streamline your personal transactions effectively.\n\nContact Us / 24 Hours Reply\nTelegram:dmhelpshop\nWhatsApp: +1 (980) 277-2786\nSkype:dmhelpshop\nEmail:dmhelpshop@gmail.com\n\n" | figema4733 |
1,918,651 | The Role of AI in Web Development | Artificial Intelligence (AI) is rapidly transforming the tech landscape EVERYWHERE! And web... | 0 | 2024-07-10T15:02:07 | https://dev.to/buildwebcrumbs/the-role-of-ai-in-web-development-17dd | ai, webdev, javascript, programming | Artificial Intelligence (AI) is rapidly transforming the tech landscape EVERYWHERE! And web development is no exception.
In this article, we delve into how AI is reshaping this field, enhancing the efficiency and creativity of developers worldwide.
We'll share insights from Webcrumbs’ own tool, [FrontendAI](https:/... | opensourcee |
1,918,653 | 10 Unique HTML Elements You Might Not Know | The world of web development extends far beyond the familiar <div>, <p>, and <img>... | 0 | 2024-07-10T15:06:49 | https://dev.to/futuristicgeeks/10-unique-html-elements-you-might-not-know-3djl | webdev, programming, html, frontend | The world of web development extends far beyond the familiar `<div>, <p>, and <img> tags`. HTML offers a treasure trove of lesser-known elements that can elevate your creations and provide a more engaging user experience. Here, we’ll delve into 10 unique HTML elements you might not have encountered yet, along with exam... | futuristicgeeks |
1,918,654 | Homemade Caching - pt. 2 | In the second part of the story describing our Homemade Caching strategy in Laravel, we delve into... | 0 | 2024-07-10T15:07:21 | https://dev.to/sharesquare/homemade-caching-pt-2-356n | performance, laravel, restapi, php | In the [second part](https://sharesquare-engineering.medium.com/homemade-caching-with-laravel-part-two-b5fa808863c7) of the story describing our Homemade Caching strategy in Laravel, we delve into even more succulent and technical details around cache invalidation and refreshing.
With this second part, we complete our... | sharesquare |
1,918,655 | معرفی بازی انفجار | بازی انفجار یکی از محبوبترین بازیهای کازینو آنلاین است بازی انفجار (یا همان Crash) در واقع یک بازی... | 0 | 2024-07-10T15:07:38 | https://dev.to/sasan_taheri_f0d672cc7e84/mrfy-bzy-nfjr-951 | enfejar | [بازی انفجار](https://enfej.site/) یکی از محبوبترین بازیهای کازینو آنلاین است
بازی انفجار (یا همان Crash) در واقع یک بازی شرطبندی آنلاین است که در بسیاری از سایتهای کازینو آنلاین قابل دسترسی است. در این بازی، شما باید ضریب بازی را قبل از بسته شدن حدس بزنید و مبلغی که برای شرط بندی قرار دادید را برداشت کنید تا برنده... | sasan_taheri_f0d672cc7e84 |
1,918,656 | arange() and linspace() in PyTorch | *My post explains logspace(). arange() can create the 1D tensor of zero or integers or... | 0 | 2024-07-10T15:08:08 | https://dev.to/hyperkai/arange-and-linspace-in-pytorch-3ak7 | pytorch, arange, linspace, function | *[My post](https://dev.to/hyperkai/logspace-in-pytorch-3dom) explains [logspace()](https://pytorch.org/docs/stable/generated/torch.logspace.html).
[arange()](https://pytorch.org/docs/stable/generated/torch.arange.html) can create the 1D tensor of zero or integers or floating-point numbers between `start` and `end-1`(`... | hyperkai |
1,918,657 | Learn react js by building a countdown timer | In this article, we are going to learn react js from scratch by building a countdown timer. We will... | 0 | 2024-07-10T15:08:23 | https://dev.to/kemiowoyele1/learn-react-js-by-building-a-countdown-timer-kej | In this article, we are going to learn react js from scratch by building a countdown timer. We will learn
• how to create new react app,
• to create a react component,
• to dynamically display content,
• to listen to and handle events
• to use the useState hook for state management and
• to manage function side eff... | kemiowoyele1 | |
1,918,658 | Securing Your Website: A Comprehensive Guide for Developers and Clients | In today's digital age, the security of your website is paramount. As developers and clients alike,... | 0 | 2024-07-10T15:31:47 | https://dev.to/abdulfortech/securing-your-website-a-comprehensive-guide-for-developers-and-clients-3edg | cybersecurity, web, webdev, startup |
In today's digital age, the security of your website is paramount. As developers and clients alike, safeguarding your online presence from malicious activities is not just a necessity but a responsibility. This guide aims to provide you with actionable steps and best practices to fortify your website against threats.
... | abdulfortech |
1,918,660 | Creating Cross-Account DynamoDB Backups with Terraform | In my previous post, Creating Secure Backups for DynamoDB Tables with Terraform, I discussed how to... | 0 | 2024-07-10T15:13:21 | https://dev.to/sepiyush/creating-cross-account-dynamodb-backups-with-terraform-e61 | terraform, aws, dynamodb, security | In my previous post, [Creating Secure Backups for DynamoDB Tables with Terraform](https://dev.to/sepiyush/creating-secure-backups-for-dynamodb-tables-with-terraform-4002), I discussed how to create DynamoDB table backups within the same AWS account. In this post, I will explain how to create cross-account DynamoDB back... | sepiyush |
1,918,661 | How to Implement Sentiment Analysis with PHP and AWS Comprehend | Hi everyone, 👋 Imagine you implement a chatbot that analyzes in real-time how a conversation is... | 0 | 2024-07-10T18:58:45 | https://dev.to/guilherme-lauxen/how-to-implement-sentiment-analysis-with-php-and-aws-comprehend-2ibk | machinelearning, php, aws, programming | Hi everyone, 👋
Imagine you implement a chatbot that analyzes in real-time how a conversation is going. Is the client happy 😄 or sad 😔 about the situation? Cool, isn’t it? Or imagine analyzing an email from a client and quantifying it in your indicators to see which one needs more attention.
In this post, I’d like ... | guilherme-lauxen |
1,918,662 | unlock the power of 2 in 1 business | Here's a detailed article description on “How to Make Money Online”: Title: “Mastering the Art of... | 0 | 2024-07-10T15:19:59 | https://dev.to/joseph_agency_7b7208bbf5f/unlock-the-power-of-2-in-1-business-5cjh | onlinebusiness | Here's a detailed article description on “How to Make Money Online”:
Title: “[Mastering ](https://legenddiamondgeneration.com/)the Art of Online Earning: A Comprehensive Guide”
Description: “Are you tired of the 9-to-5 grind and seeking a more flexible and lucrative career path? Look no further! This article will del... | joseph_agency_7b7208bbf5f |
1,918,748 | logspace() in PyTorch | *My post explains arange() and linspace(). logspace() can create the 1D tensor of the zero or more... | 0 | 2024-07-10T15:24:30 | https://dev.to/hyperkai/logspace-in-pytorch-3dom | pytorch, logspace, tensor, function | *[My post](https://dev.to/hyperkai/arange-and-linspace-in-pytorch-3ak7) explains [arange()](https://pytorch.org/docs/stable/generated/torch.arange.html) and [linspace()](https://pytorch.org/docs/stable/generated/torch.linspace.html).
[logspace()](https://pytorch.org/docs/stable/generated/torch.logspace.html) can creat... | hyperkai |
1,918,749 | Mastering Game Development: A Comprehensive Collection of Free Online Tutorials 🎮 | The article is about a curated collection of free online tutorials for aspiring game developers. It covers a wide range of topics, including a comprehensive course on game development from Harvard's CS50, a primer on 3D math for graphics and game design, a step-by-step guide to building a 2D game engine in Java, an int... | 27,985 | 2024-07-10T15:24:38 | https://dev.to/getvm/mastering-game-development-a-comprehensive-collection-of-free-online-tutorials-lo2 | getvm, programming, freetutorial, collection |
Dive into the captivating world of game development with this curated collection of free online tutorials! Whether you're a seasoned programmer or a curious beginner, these resources will equip you with the essential skills and knowledge to create your own thrilling games. From foundational 3D math concepts to coding ... | getvm |
1,918,752 | Boost Your Laravel App's Performance: Essential Architecture Strategies | In today's fast-paced web world, application speed is king. Slow loading times frustrate users and... | 0 | 2024-07-10T15:29:10 | https://dev.to/marufhossain/boost-your-laravel-apps-performance-essential-architecture-strategies-mp6 | In today's fast-paced web world, application speed is king. Slow loading times frustrate users and hurt your bottom line. Laravel, a popular PHP framework, offers a powerful toolkit for building dynamic web applications. But even the best framework needs a well-designed architecture to truly shine. Here, we'll explore ... | marufhossain | |
1,918,753 | Authenticating a Spring Boot Application with Active Directory | Authentication with Active Directory in a Spring Boot application is straightforward and requires... | 0 | 2024-07-10T15:35:59 | https://dev.to/alkarid/authenticating-a-spring-boot-application-with-active-directory-5d30 | Authentication with Active Directory in a Spring Boot application is straightforward and requires minimal setup. You don't need to install an embedded server for testing connectivity or additional complex packages. In fact, the process is streamlined with just a couple of dependencies and a simple configuration.
**Dep... | alkarid | |
1,918,754 | JavaScript values vs reference | Understand how variables are held in JavaScript: As values or references In JavaScript, or... | 0 | 2024-07-10T15:32:08 | https://dev.to/js_cipher/javascript-values-vs-reference-1ao5 | webdev, javascript, programming, learning | ## Understand how variables are held in JavaScript: As values or references
In JavaScript, or rather programming, a variable is a location in the memory of a computer used to store data. Variables are declared (given a name, an identifier) and could be assigned a value immediately or later, depending on the language. ... | js_cipher |
1,918,755 | Mein Rat ist, sich an legale und hochwertige Sportprodukte | Mein Rat ist, sich an legale und hochwertige Sportprodukte zu halten, die von vertrauenswürdigen... | 0 | 2024-07-10T15:32:11 | https://dev.to/oscar82/mein-rat-ist-sich-an-legale-und-hochwertige-sportprodukte-257g | Mein Rat ist, sich an legale und hochwertige Sportprodukte zu halten, die von vertrauenswürdigen Anbietern bezogen werden können. Eine Option wäre, hochwertige Nahrungsergänzungsmittel zu suchen, die Ihre Fitnessziele unterstützen. Eine vertrauenswürdige Quelle für legale Produkte ist die Website, wo Sie Oxandrolon kau... | oscar82 | |
1,918,756 | Introduction pratique aux tests d'applications Web avec Selenium WebDriver et Java. | Salut à tous, Aujourd'hui, je veux partager avec vous une introduction pratique aux tests... | 0 | 2024-07-10T15:46:02 | https://dev.to/laroseikitama/introduction-pratique-aux-tests-dapplications-web-avec-selenium-webdriver-et-java-23ml | webdev, java, selenium, testing | Salut à tous,
Aujourd'hui, je veux partager avec vous une introduction pratique aux tests d'applications Web avec Selenium WebDriver. Nous allons voir ensemble comment écrire un script de test simple en Java, en utilisant deux mini-projets que j'ai récemment réalisés.
## Préparation de l'environnement
Avant de comme... | laroseikitama |
1,918,757 | Python Best Practices for Data Engineer | Logging, Error Handling, Environment Variables, and Argument Parsing In this guide, we'll... | 0 | 2024-07-10T15:32:38 | https://dev.to/congnguyen/python-best-practices-for-data-engineer-epm | ##Logging, Error Handling, Environment Variables, and Argument Parsing##
In this guide, we'll explore best practices for using various Python functionalities to build robust and maintainable applications. We'll cover logging, exception handling, environment variable management, and argument parsing, with code samples a... | congnguyen | |
1,918,758 | tiotle | `12 | 0 | 2024-07-10T15:33:31 | https://dev.to/jisu_yoon_f365f5929386b81/tiotle-8ih | `12 | jisu_yoon_f365f5929386b81 | |
1,919,483 | Are Dymo labels water-resistant? | Dymo labels vary in their water resistance depending on the type of label and its intended use.... | 0 | 2024-07-11T09:15:43 | https://dev.to/john10114433/are-dymo-labels-water-resistant-1dkk | Dymo labels vary in their water resistance depending on the type of label and its intended use. Here’s a breakdown of the water resistance for different Dymo labels:
[dymo 30252 labels](https://betckey.com/collections/hot-sale/products/dymo-30252-compatible-address-and-barcode-labels)
1. Standard Dymo Labels
Descriptio... | john10114433 | |
1,918,762 | Buy Verified Paxful Account | https://dmhelpshop.com/product/buy-verified-paxful-account/ Buy Verified Paxful Account There are... | 0 | 2024-07-10T15:34:12 | https://dev.to/figema4733/buy-verified-paxful-account-21b4 | webdev, javascript, beginners, programming | ERROR: type should be string, got "https://dmhelpshop.com/product/buy-verified-paxful-account/\n\n\nBuy Verified Paxful Account\nThere are several compelling reasons to consider purchasing a verified Paxful account. Firstly, a verified account offers enhanced security, providing peace of mind to all users. Additionally, it opens up a wider range of trading opportunities, allowing individuals to partake in various transactions, ultimately expanding their financial horizons.\n\nMoreover, Buy verified Paxful account ensures faster and more streamlined transactions, minimizing any potential delays or inconveniences. Furthermore, by opting for a verified account, users gain access to a trusted and reputable platform, fostering a sense of reliability and confidence.\n\nLastly, Paxful’s verification process is thorough and meticulous, ensuring that only genuine individuals are granted verified status, thereby creating a safer trading environment for all users. Overall, the decision to Buy Verified Paxful account can greatly enhance one’s overall trading experience, offering increased security, access to more opportunities, and a reliable platform to engage with. Buy Verified Paxful Account.\n\nBuy US verified paxful account from the best place dmhelpshop\nWhy we declared this website as the best place to buy US verified paxful account? Because, our company is established for providing the all account services in the USA (our main target) and even in the whole world. With this in mind we create paxful account and customize our accounts as professional with the real documents. Buy Verified Paxful Account.\n\nIf you want to buy US verified paxful account you should have to contact fast with us. Because our accounts are-\n\nEmail verified\nPhone number verified\nSelfie and KYC verified\nSSN (social security no.) verified\nTax ID and passport verified\nSometimes driving license verified\nMasterCard attached and verified\nUsed only genuine and real documents\n100% access of the account\nAll documents provided for customer security\nWhat is Verified Paxful Account?\nIn today’s expanding landscape of online transactions, ensuring security and reliability has become paramount. Given this context, Paxful has quickly risen as a prominent peer-to-peer Bitcoin marketplace, catering to individuals and businesses seeking trusted platforms for cryptocurrency trading.\n\nIn light of the prevalent digital scams and frauds, it is only natural for people to exercise caution when partaking in online transactions. As a result, the concept of a verified account has gained immense significance, serving as a critical feature for numerous online platforms. Paxful recognizes this need and provides a safe haven for users, streamlining their cryptocurrency buying and selling experience.\n\nFor individuals and businesses alike, Buy verified Paxful account emerges as an appealing choice, offering a secure and reliable environment in the ever-expanding world of digital transactions. Buy Verified Paxful Account.\n\nVerified Paxful Accounts are essential for establishing credibility and trust among users who want to transact securely on the platform. They serve as evidence that a user is a reliable seller or buyer, verifying their legitimacy.\n\nBut what constitutes a verified account, and how can one obtain this status on Paxful? In this exploration of verified Paxful accounts, we will unravel the significance they hold, why they are crucial, and shed light on the process behind their activation, providing a comprehensive understanding of how they function. Buy verified Paxful account.\n\n \n\nWhy should to Buy Verified Paxful Account?\nThere are several compelling reasons to consider purchasing a verified Paxful account. Firstly, a verified account offers enhanced security, providing peace of mind to all users. Additionally, it opens up a wider range of trading opportunities, allowing individuals to partake in various transactions, ultimately expanding their financial horizons.\n\nMoreover, a verified Paxful account ensures faster and more streamlined transactions, minimizing any potential delays or inconveniences. Furthermore, by opting for a verified account, users gain access to a trusted and reputable platform, fostering a sense of reliability and confidence. Buy Verified Paxful Account.\n\nLastly, Paxful’s verification process is thorough and meticulous, ensuring that only genuine individuals are granted verified status, thereby creating a safer trading environment for all users. Overall, the decision to buy a verified Paxful account can greatly enhance one’s overall trading experience, offering increased security, access to more opportunities, and a reliable platform to engage with.\n\n \n\nWhat is a Paxful Account\nPaxful and various other platforms consistently release updates that not only address security vulnerabilities but also enhance usability by introducing new features. Buy Verified Paxful Account.\n\nIn line with this, our old accounts have recently undergone upgrades, ensuring that if you purchase an old buy Verified Paxful account from dmhelpshop.com, you will gain access to an account with an impressive history and advanced features. This ensures a seamless and enhanced experience for all users, making it a worthwhile option for everyone.\n\n \n\nIs it safe to buy Paxful Verified Accounts?\nBuying on Paxful is a secure choice for everyone. However, the level of trust amplifies when purchasing from Paxful verified accounts. These accounts belong to sellers who have undergone rigorous scrutiny by Paxful. Buy verified Paxful account, you are automatically designated as a verified account. Hence, purchasing from a Paxful verified account ensures a high level of credibility and utmost reliability. Buy Verified Paxful Account.\n\nPAXFUL, a widely known peer-to-peer cryptocurrency trading platform, has gained significant popularity as a go-to website for purchasing Bitcoin and other cryptocurrencies. It is important to note, however, that while Paxful may not be the most secure option available, its reputation is considerably less problematic compared to many other marketplaces. Buy Verified Paxful Account.\n\nThis brings us to the question: is it safe to purchase Paxful Verified Accounts? Top Paxful reviews offer mixed opinions, suggesting that caution should be exercised. Therefore, users are advised to conduct thorough research and consider all aspects before proceeding with any transactions on Paxful.\n\n \n\nHow Do I Get 100% Real Verified Paxful Accoun?\nPaxful, a renowned peer-to-peer cryptocurrency marketplace, offers users the opportunity to conveniently buy and sell a wide range of cryptocurrencies. Given its growing popularity, both individuals and businesses are seeking to establish verified accounts on this platform.\n\nHowever, the process of creating a verified Paxful account can be intimidating, particularly considering the escalating prevalence of online scams and fraudulent practices. This verification procedure necessitates users to furnish personal information and vital documents, posing potential risks if not conducted meticulously.\n\nIn this comprehensive guide, we will delve into the necessary steps to create a legitimate and verified Paxful account. Our discussion will revolve around the verification process and provide valuable tips to safely navigate through it.\n\nMoreover, we will emphasize the utmost importance of maintaining the security of personal information when creating a verified account. Furthermore, we will shed light on common pitfalls to steer clear of, such as using counterfeit documents or attempting to bypass the verification process.\n\nWhether you are new to Paxful or an experienced user, this engaging paragraph aims to equip everyone with the knowledge they need to establish a secure and authentic presence on the platform.\n\nBenefits Of Verified Paxful Accounts\nVerified Paxful accounts offer numerous advantages compared to regular Paxful accounts. One notable advantage is that verified accounts contribute to building trust within the community.\n\nVerification, although a rigorous process, is essential for peer-to-peer transactions. This is why all Paxful accounts undergo verification after registration. When customers within the community possess confidence and trust, they can conveniently and securely exchange cash for Bitcoin or Ethereum instantly. Buy Verified Paxful Account.\n\nPaxful accounts, trusted and verified by sellers globally, serve as a testament to their unwavering commitment towards their business or passion, ensuring exceptional customer service at all times. Headquartered in Africa, Paxful holds the distinction of being the world’s pioneering peer-to-peer bitcoin marketplace. Spearheaded by its founder, Ray Youssef, Paxful continues to lead the way in revolutionizing the digital exchange landscape.\n\nPaxful has emerged as a favored platform for digital currency trading, catering to a diverse audience. One of Paxful’s key features is its direct peer-to-peer trading system, eliminating the need for intermediaries or cryptocurrency exchanges. By leveraging Paxful’s escrow system, users can trade securely and confidently.\n\nWhat sets Paxful apart is its commitment to identity verification, ensuring a trustworthy environment for buyers and sellers alike. With these user-centric qualities, Paxful has successfully established itself as a leading platform for hassle-free digital currency transactions, appealing to a wide range of individuals seeking a reliable and convenient trading experience. Buy Verified Paxful Account.\n\n \n\nHow paxful ensure risk-free transaction and trading?\nEngage in safe online financial activities by prioritizing verified accounts to reduce the risk of fraud. Platforms like Paxfu implement stringent identity and address verification measures to protect users from scammers and ensure credibility.\n\nWith verified accounts, users can trade with confidence, knowing they are interacting with legitimate individuals or entities. By fostering trust through verified accounts, Paxful strengthens the integrity of its ecosystem, making it a secure space for financial transactions for all users. Buy Verified Paxful Account.\n\nExperience seamless transactions by obtaining a verified Paxful account. Verification signals a user’s dedication to the platform’s guidelines, leading to the prestigious badge of trust. This trust not only expedites trades but also reduces transaction scrutiny. Additionally, verified users unlock exclusive features enhancing efficiency on Paxful. Elevate your trading experience with Verified Paxful Accounts today.\n\nIn the ever-changing realm of online trading and transactions, selecting a platform with minimal fees is paramount for optimizing returns. This choice not only enhances your financial capabilities but also facilitates more frequent trading while safeguarding gains. Buy Verified Paxful Account.\n\nExamining the details of fee configurations reveals Paxful as a frontrunner in cost-effectiveness. Acquire a verified level-3 USA Paxful account from usasmmonline.com for a secure transaction experience. Invest in verified Paxful accounts to take advantage of a leading platform in the online trading landscape.\n\n \n\nHow Old Paxful ensures a lot of Advantages?\n\nExplore the boundless opportunities that Verified Paxful accounts present for businesses looking to venture into the digital currency realm, as companies globally witness heightened profits and expansion. These success stories underline the myriad advantages of Paxful’s user-friendly interface, minimal fees, and robust trading tools, demonstrating its relevance across various sectors.\n\nBusinesses benefit from efficient transaction processing and cost-effective solutions, making Paxful a significant player in facilitating financial operations. Acquire a USA Paxful account effortlessly at a competitive rate from usasmmonline.com and unlock access to a world of possibilities. Buy Verified Paxful Account.\n\nExperience elevated convenience and accessibility through Paxful, where stories of transformation abound. Whether you are an individual seeking seamless transactions or a business eager to tap into a global market, buying old Paxful accounts unveils opportunities for growth.\n\nPaxful’s verified accounts not only offer reliability within the trading community but also serve as a testament to the platform’s ability to empower economic activities worldwide. Join the journey towards expansive possibilities and enhanced financial empowerment with Paxful today. Buy Verified Paxful Account.\n\n \n\nWhy paxful keep the security measures at the top priority?\nIn today’s digital landscape, security stands as a paramount concern for all individuals engaging in online activities, particularly within marketplaces such as Paxful. It is essential for account holders to remain informed about the comprehensive security protocols that are in place to safeguard their information.\n\nSafeguarding your Paxful account is imperative to guaranteeing the safety and security of your transactions. Two essential security components, Two-Factor Authentication and Routine Security Audits, serve as the pillars fortifying this shield of protection, ensuring a secure and trustworthy user experience for all. Buy Verified Paxful Account.\n\nConclusion\nInvesting in Bitcoin offers various avenues, and among those, utilizing a Paxful account has emerged as a favored option. Paxful, an esteemed online marketplace, enables users to engage in buying and selling Bitcoin. Buy Verified Paxful Account.\n\nThe initial step involves creating an account on Paxful and completing the verification process to ensure identity authentication. Subsequently, users gain access to a diverse range of offers from fellow users on the platform. Once a suitable proposal captures your interest, you can proceed to initiate a trade with the respective user, opening the doors to a seamless Bitcoin investing experience.\n\nIn conclusion, when considering the option of purchasing verified Paxful accounts, exercising caution and conducting thorough due diligence is of utmost importance. It is highly recommended to seek reputable sources and diligently research the seller’s history and reviews before making any transactions.\n\nMoreover, it is crucial to familiarize oneself with the terms and conditions outlined by Paxful regarding account verification, bearing in mind the potential consequences of violating those terms. By adhering to these guidelines, individuals can ensure a secure and reliable experience when engaging in such transactions. Buy Verified Paxful Account.\n\nContact Us / 24 Hours Reply\nTelegram:dmhelpshop\nWhatsApp: +1 (980) 277-2786\nSkype:dmhelpshop\nEmail:dmhelpshop@gmail.com\n\n " | figema4733 |
1,918,763 | Testing models in Flutter | Know so many people that do not do testing or do not know what Testing means, even you know that... | 0 | 2024-07-10T15:36:06 | https://dev.to/sazardev/testing-models-in-flutter-4bch | flutter, testing | Know so many people that do not do testing or do not know what _Testing_ means, even you know that another one do not even know the powerful native testing that Flutter integrate in our projects. So let us find out what **flutter_test** can do for use, and how can make us be more productive and efficient in our project... | sazardev |
1,918,764 | What Programming Languages are Used in Blockchain Technology? | Blockchain technology is the decentralized and distributed ledger system that popular digital... | 0 | 2024-07-10T15:36:48 | https://dev.to/johnlimer/what-programming-languages-are-used-in-blockchain-technology-1i7b | webdev, javascript, beginners, programming | <span style="font-weight: 400;">Blockchain technology is the decentralized and distributed ledger system that popular digital currencies such as Bitcoin, Ethereum, and other cryptocurrencies like meme coins are based on. Blockchain developers are tasked with creating and updating the blockchain using various programmin... | johnlimer |
1,918,765 | How to Use ServBay to Enable npm | npm (Node Package Manager) is Node.js's package management tool and its default package manager. It... | 0 | 2024-07-10T15:39:00 | https://dev.to/servbay/how-to-use-servbay-to-enable-npm-2k3l | node, webdev, beginners, programming | `npm` (Node Package Manager) is Node.js's package management tool and its default package manager. It is used to install, share, and manage JavaScript packages and is one of the largest open-source libraries globally. Using npm can help developers easily manage project dependencies and enhance development efficiency.
... | servbay |
1,918,766 | Introducing Cora: A Powerful File Concatenation Tool for Developers | In the world of software development, we often find ourselves dealing with multiple files that need... | 0 | 2024-07-10T15:41:51 | https://dev.to/shaharia/introducing-cora-a-powerful-file-concatenation-tool-for-developers-p9n | filesystem, concate, llm | In the world of software development, we often find ourselves dealing with multiple files that need to be combined for various reasons. Whether it's merging documentation, preparing training data for machine learning models, or consolidating code for review, the need to concatenate files is a common task. Enter Cora, a... | shaharia |
1,918,768 | Cloud Computing and its Benefits | In today's interconnected world, where digital transformation is reshaping industries and enterprises... | 0 | 2024-07-10T15:49:58 | https://dev.to/awal_saani/cloud-computing-and-its-benefits-960 | cloudcomputing, aws, azure, googlecloud | In today's interconnected world, where digital transformation is reshaping industries and enterprises at a rapid pace, cloud computing stands out as a cornerstone of modern IT infrastructure. Whether you're streaming your favorite music, collaborating on a project with colleagues halfway across the globe, or managing a... | awal_saani |
1,918,770 | Day -3 learning | 1. Numeric Types (int, float, complex) a) 26-int (numbers) b) 26.5-float (numbers with decimal) c)... | 0 | 2024-07-10T17:12:23 | https://dev.to/perumal_s_9a6d79a633d63d4/day-3-learning-22la | **1. Numeric Types (int, float, complex)**
a) 26-int (numbers)
b) 26.5-float (numbers with decimal)
c) 2+3i complex (real number+ imaginary number)
**2. Text Type (strings)**
a)""
b)''
c)"""
"""
**3. Boolean Type (bool)**
a) True
b) False
**4. None Type (None)**
None means its like nothing there is no value... | perumal_s_9a6d79a633d63d4 | |
1,918,771 | **Exploring Object-Oriented Programming (OOP) Concepts with Java** | Unlock the Power of Java's Object-Oriented Programming Paradigm! Embrace the Essence of OOP... | 0 | 2024-07-10T15:58:07 | https://dev.to/gadekar_sachin/exploring-object-oriented-programming-oop-concepts-with-java-1pn6 | javaprogramming, oop, codewithpurpose, programming |
Unlock the Power of Java's Object-Oriented Programming Paradigm!
### Embrace the Essence of OOP in Java:
🌟 **Classes and Objects:** Dive into the building blocks of Java programs. Classes define blueprints for objects, while objects are instances that encapsulate data and behavior.
🔒 **Encapsulation:** Safegu... | gadekar_sachin |
1,918,772 | Leveraging Web3 to Enhance JavaScript Development | The evolution of the internet into Web3 promises to redefine how developers approach building... | 0 | 2024-07-10T15:58:13 | https://dev.to/asmsc/leveraging-web3-to-enhance-javascript-development-4aeo | javascript, beginners | The evolution of the internet into Web3 promises to redefine how developers approach building applications. JavaScript, the backbone of modern web development, plays a crucial role in this transformation. Here's how Web3 is enhancing JavaScript development:
<h2>New JavaScript Libraries and Frameworks</h2>
With the rise... | asmsc |
1,918,773 | 3D Riemann Surface Matrix | Check out this Pen I made! | 0 | 2024-07-10T16:00:12 | https://dev.to/dan52242644dan/3d-riemann-surface-matrix-12oj | codepen, javascript, html, discuss | Check out this Pen I made!
{% codepen https://codepen.io/Dancodepen-io/pen/oNrgWVg %} | dan52242644dan |
1,918,774 | Increase your knowledge in cloud computing with Microsoft Learn | Want to know about the advantages of leveraging cloud technology? Want to know how you will be... | 0 | 2024-07-10T16:02:08 | https://dev.to/hasanul_banna_himel/increase-your-knowledge-in-cloud-computing-with-microsoft-learn-2pf1 | Want to know about the advantages of leveraging cloud technology? Want to know how you will be beneficial by using cloud services?
Here in Microsoft Learn you can get this idea.
Course Link: https://learn.microsoft.com/en-us/training/modules/describe-benefits-use-cloud-services/?wt.mc_id=studentamb_322573
Discover the... | hasanul_banna_himel | |
1,918,775 | Web3 Unveiled: The Future of a Decentralized Internet | The internet is undergoing a transformative change with the advent of Web3, also known as Web 3.0.... | 0 | 2024-07-10T16:03:16 | https://dev.to/dipakahirav/web3-unveiled-the-future-of-a-decentralized-internet-2cff | web3, webdev, web, learning | The internet is undergoing a transformative change with the advent of Web3, also known as Web 3.0. This new iteration promises a more transparent, secure, and user-centric online experience, built on decentralized technologies like blockchain. In this blog, we will explore the key concepts of Web3, its advantages, chal... | dipakahirav |
1,918,776 | Table Extraction and Processing from PDFs - A Tutorial | Tables in PDFs are very prevalent and for those of us who are intent on extracting information from... | 0 | 2024-07-11T14:44:20 | https://unstract.com/blog/extract-table-from-pdf/ | python, ai, opensource, tutorial |
Tables in PDFs are very prevalent and for those of us who are intent on extracting information from PDFs, they often contain very useful information in a very dense format. Processing tables in PDFs, if not the top 10 priority for humanity, it certainly is an important one. Once data from PDFs is extracted, it’s relat... | shuveb_hussain |
1,918,778 | How to connect DynamoDB with CakePHP4 | Introduction When using DynamoDB, I struggled with connecting CakePHP and DynamoDB due to... | 0 | 2024-07-10T16:08:33 | https://dev.to/hanaosan/referencing-dynamodb-with-cakephp4-2no6 | dynamodb, cakephp, aws, awssdk | ## Introduction
When using DynamoDB, I struggled with connecting CakePHP and DynamoDB due to outdated articles and the need to create many files. Therefore, I wrote this article as a memo.
## What We'll Do in This Article
We will connect to DynamoDB using CakePHP4 and retrieve table information.
## Prerequisites
- U... | hanaosan |
1,918,779 | p | A post by Phòng khámOptimal365 | 0 | 2024-07-10T16:11:10 | https://dev.to/optimal365/kha-4f8m | optimal365 | ||
1,918,780 | O Que é Docker? Entenda a Tecnologia de Containerização | O que é Docker? Docker é uma plataforma open-source que permite aos desenvolvedores criar,... | 0 | 2024-07-10T16:11:39 | https://dev.to/fernandomullerjr/o-que-e-docker-entenda-a-tecnologia-de-containerizacao-4bb5 | docker, containers, devops | ## O que é Docker?
Docker é uma plataforma open-source que permite aos desenvolvedores criar, implantar e gerenciar containers. Containers são componentes executáveis padronizados que combinam código-fonte com bibliotecas e dependências necessárias para executar o código em qualquer ambiente. Docker simplifica o desen... | fernandomullerjr |
1,918,781 | Top 3 JavaScript Concepts Every Developer Should Know 🚀 | JavaScript is a versatile and powerful programming language that every web developer should master.... | 0 | 2024-07-10T16:12:50 | https://dev.to/dipakahirav/top-3-javascript-concepts-every-developer-should-know-3blj | javascript, webdev, beginners, learning | JavaScript is a versatile and powerful programming language that every web developer should master. Here are the top 3 JavaScript concepts you need to understand to elevate your coding skills! 💪
please subscribe to my [YouTube channel](https://www.youtube.com/@DevDivewithDipak?sub_confirmation=1
) to support my chann... | dipakahirav |
1,918,782 | Building long lasting relationship with PMs (the good ones at least) | Just between developers, we don't like Product Managers. Too often they are simply a monitor on our... | 0 | 2024-07-10T16:13:15 | https://dev.to/kevin074/building-long-lasting-relationship-with-pms-the-good-ones-at-least-38o2 | discuss, career, productivity, developer | Just between developers, we don't like Product Managers. Too often they are simply a monitor on our progress. However, these roles exist for good reasons and it's unfortunate too many bad PMs exist because they saw a tiktok about big tech and jumping ship into the industry, thanks you weird big tech lifestyle influence... | kevin074 |
1,918,783 | (Live-INtUitExpertz@ How do I call {+1 855-200-2880} QuickBooks support? | Liquid syntax error: Variable '{{ 🤔• +1-855-200-2880 • }' was not properly terminated with regexp:... | 0 | 2024-07-10T16:15:34 | https://dev.to/qbexperrterror/live-intuitexpertz-how-do-i-call-1-855-200-2880-quickbooks-support-2nmb | **
#### (Live-agent) How do I call {+1 855-200-2880} QuickBooks support?
**
How do I contact Intuit Official QuickBooks™ Desktop™ Support Number??
How do I contact Intuit Official QuickBooks™ Desktop™ Support Number??
Yes, QuickBooks support is available 24/7. You can reach our helpline at 1-855-200-2880 anytime fo... | qbexperrterror | |
1,918,784 | A Cry for Help. | In September 2019, a voice vividly told me; "Learn coding, it will make you so rich that people will... | 0 | 2024-07-10T16:16:59 | https://dev.to/colinchidiogo/a-cry-for-help-190c | beginners, programming, productivity, codenewbie |
In September 2019, a voice vividly told me;
**"Learn coding, it will make you so rich that people will say you did rituals '**
But it's a pity. A hopeless pity, that 4years after, I have not done much aside designing some UI/UX images.
Why? Simply because I can't afford the necessary tools required to delve squarely... | colinchidiogo |
1,918,785 | Intuit|| QuickBooks ||𝐒𝐮𝐩𝐩𝐨𝐫𝐭 DeSK||{1}855-200-2880))How do I communicate with QuickBooks?@OFFICIAL#QB | Intuit|| QuickBooks ||𝐒𝐮𝐩𝐩𝐨𝐫𝐭 DeSK||{1}855-200-2880))How do I communicate with... | 0 | 2024-07-10T16:18:23 | https://dev.to/qbexperrterror/intuit-quickbooks-desk1855-200-2880how-do-i-communicate-with-quickbooksofficialqb-2k8k | **Intuit|| QuickBooks ||𝐒𝐮𝐩𝐩𝐨𝐫𝐭 DeSK||{1}855-200-2880))How do I communicate with QuickBooks?@OFFICIAL#QB**
How do I contact QuickBooks support by phone?
To contact QuickBooks support by phone, dial #1-855-200-2880 or +1-800-446-8848 . This toll-free number connects you directly to QuickBooks customer support,... | qbexperrterror | |
1,918,796 | Understanding CSS Frameworks | CSS frameworks have revolutionized web design by providing pre-written, reusable code modules for... | 0 | 2024-07-10T16:21:25 | https://dev.to/hammad_hassan_6e981aa049b/understanding-css-frameworks-68e | webdev, javascript, beginners, programming | CSS frameworks have revolutionized web design by providing pre-written, reusable code modules for styling web pages. These frameworks offer a structured, organized way to create aesthetically pleasing and responsive websites without writing CSS from scratch.
Key Features of CSS Frameworks
Grid Systems: Most CSS framewo... | hammad_hassan_6e981aa049b |
1,918,797 | Exploring the Capabilities of Python in Blockchain Development | Python is one of the most versatile programming languages, widely used across various fields... | 0 | 2024-07-10T16:21:28 | https://dev.to/asmsc/exploring-the-capabilities-of-python-in-blockchain-development-1m13 | python, javascript, webdev, beginners | <p>Python is one of the most versatile programming languages, widely used across various fields including web development, data science, machine learning, and more recently, blockchain development. Its simplicity and the extensive range of libraries make it an attractive choice for developers diving into the world of b... | asmsc |
1,918,801 | Cybersecurity: The Importance of The Human Element | In the ever-evolving landscape of cybersecurity, where technologies advance rapidly and threats grow... | 0 | 2024-07-10T16:30:41 | https://www.nilebits.com/blog/2024/07/cybersecurity-the-importance-of-the-human-element/ | cybersecurity, algorithms, encryption, programming | In the ever-evolving landscape of [cybersecurity](https://www.nilebits.com/blog/2022/08/best-practices-to-avoid-cybersecurity-risks/), where technologies advance rapidly and threats grow increasingly sophisticated, it’s easy to focus solely on technical solutions like firewalls, encryption, and intrusion detection syst... | amr-saafan |
1,918,803 | Deploy Django to Azure - The Easy Way | The general perception is that deploying applications on the cloud is complicated, but that is not... | 0 | 2024-07-11T12:21:55 | https://dev.to/dilutewater/deploy-django-to-azure-the-easy-way-2h1n | webdev, django, cloud, azure | The general perception is that deploying applications on the cloud is complicated, but that is not always true. We have really easy ways to deploy stuff on the cloud as well. So I will be demonstrating how to deploy Django Webpps to Azure easily.
### Prerequisites
- Azure account
If you don’t have an azure account ... | dilutewater |
1,918,804 | How to become a Frontend Developer? | Frontend developers create exciting interfaces with which users interact, like the screen where you... | 0 | 2024-07-10T16:33:57 | https://dev.to/asachanfbd/how-to-become-a-frontend-developer-2kl9 | webdev, javascript, beginners, programming | Frontend developers create exciting interfaces with which users interact, like the screen where you are reading this article is designed by a frontend developer. It’s an exciting journey. As a frontend developer, you work with HTML, CSS & JavaScript(not Java) to create engaging user experiences. Whether starting from s... | asachanfbd |
1,918,805 | Homeowners Find Help, Handymen Find Work: Building HomeSquad | As an aspiring software engineering student at Alx, I've been pouring my efforts into HomeSquad, a... | 0 | 2024-07-10T16:34:01 | https://dev.to/dawit_yifru_51528038a6adf/homeowners-find-help-handymen-find-work-building-homesquad-30hn | As an aspiring software engineering student at Alx, I've been pouring my efforts into HomeSquad, a project designed to bridge the gap between homeowners and skilled handymen. Inspired by Upwork's successful model of connecting freelancers with employers, HomeSquad caters specifically to local home improvement needs. Ho... | dawit_yifru_51528038a6adf | |
1,918,806 | What is Selenium? Why do we use selenium for automation? | What is Selenium: Selenium is a automation tool used for web application testing. It is a... | 0 | 2024-07-10T16:34:16 | https://dev.to/pat28we/what-is-selenium-why-do-we-use-selenium-for-automation-hjn | pat28, task15 | What is Selenium:
>>>> Selenium is a automation tool used for web application testing. It is a popular open source testing tool. Selenium enables testers to write automated tests in various programming languages to test the functionality of web applications. It can be run in many different browsers and operating syste... | pat28we |
1,918,807 | Introduction to GCD (Grand Central Dispatch) | Apple Dispatch Framework Dispatch: Execute code concurrently on multicore hardware by... | 0 | 2024-07-10T16:35:46 | https://dev.to/vinaykumar0339/introduction-to-gcd-grand-central-dispatch-16b9 | swift, ios, threading | ## Apple Dispatch Framework
> Dispatch: Execute code concurrently on multicore hardware by submitting work to dispatch queues managed by the system.
1. Dispatch is also known as Grand Central Dispatch (GCD).
2. GCD is a queue-based API that allows executing closures on worker's pools in First-In-First-Out (FIFO) Order... | vinaykumar0339 |
1,918,808 | Understanding Node Affinity in Kubernetes | Welcome back to our Kubernetes series! In this instalment, we delve into an essential scheduling... | 0 | 2024-07-10T16:39:34 | https://dev.to/jensen1806/understanding-node-affinity-in-kubernetes-3l5j | kubernetes, docker, devops, containers | Welcome back to our Kubernetes series! In this instalment, we delve into an essential scheduling concept: Node Affinity. Node Affinity allows Kubernetes to schedule pods based on node labels, ensuring specific workloads run on designated nodes.
### Recap: Taints and Tolerations
Previously, we explored Taints and Toler... | jensen1806 |
1,918,809 | Understanding GRU Networks | Gated Recurrent Units (GRUs) are a type of recurrent neural network (RNN) architecture that have... | 27,893 | 2024-07-10T16:41:09 | https://dev.to/monish3004/understanding-gru-networks-aak | deeplearning, computerscience, nlp, beginners | Gated Recurrent Units (GRUs) are a type of recurrent neural network (RNN) architecture that have become increasingly popular for sequence modeling tasks. Introduced by Kyunghyun Cho et al. in 2014, GRUs aim to solve some of the vanishing gradient problems associated with traditional RNNs while maintaining a simpler str... | monish3004 |
1,918,810 | Is the VCR plugged in? Common Sense Troubleshooting For Web Devs | The summers of 6th through 8th grade were incredible. I grew up in North Lake Tahoe and would ride... | 0 | 2024-07-10T16:41:17 | https://dev.to/cjav_dev/is-the-vcr-plugged-in-common-sense-troubleshooting-for-web-devs-78o | webdev, beginners, programming, tutorial | The summers of 6th through 8th grade were incredible. I grew up in North Lake Tahoe and would ride bikes with my brothers and neighborhood kids from daybreak til the streetlights came on. We'd make home videos of us attempting BMX tricks (think Baby-Gap version of the X-Games). We recorded using our family's mini-DV ca... | cjav_dev |
1,918,811 | Introduction to React.js | React.js is a popular JavaScript library developed by Facebook for building user interfaces,... | 0 | 2024-07-10T16:43:05 | https://dev.to/nagabhushan_adiga_a383471/introduction-to-reactjs-2km5 | react, reactjsdevelopment, webdev, javascript |
React.js is a popular JavaScript library developed by Facebook for building user interfaces, particularly single-page applications. It allows developers to create large web applications that can update and render efficiently in response to data changes. React focuses on building reusable components, which can be thoug... | nagabhushan_adiga_a383471 |
1,918,812 | You must know about principle of z-index | Introduction Hi, I'm (flitter)[https://flitter.dev] maintainer and recently I provide... | 0 | 2024-07-10T16:46:23 | https://dev.to/moondaeseung/you-must-know-about-principle-of-z-index-4akj | ## **Introduction**
Hi, I'm (flitter)[https://flitter.dev] maintainer and recently I provide z-index widget.
This article explores the workings of the z-index property and how to implement it within SVGs.
### **I... | moondaeseung | |
1,918,814 | Phone Sex, What is it, How to Do it and its Benefits. | Title: Mastering the Art of Phone Sex with Raquel: Essential Tips for Unforgettable... | 0 | 2024-07-10T16:44:27 | https://dev.to/raquel_rivera_208d3eed67e/phone-sex-what-is-it-how-to-do-it-and-its-benefits-35kg | phonesex, phonesexfun, howtophnesex, raquelphonesex | Title: Mastering the Art of Phone Sex with Raquel: Essential Tips for Unforgettable Experiences
https://latinaphonesex.com/best-latina-phone-sex/
Introduction
Hola, amor! I'm Raquel from Latina Phone Sex, here to guide you through the tantalizing world of phone sex. Exploring the realms of intimacy doesn't always nee... | raquel_rivera_208d3eed67e |
1,918,815 | AI-Driven Software Testing: The What, Why And How | Imagine a world where testing software wasn't a tedious chore but an exhilarating adventure. Think... | 0 | 2024-07-11T07:52:33 | https://www.techdogs.com/td-articles/trending-stories/ai-driven-software-testing-the-what-why-and-how | ai, software, testing, development | Imagine a world where testing software wasn't a tedious chore but an exhilarating adventure. Think Jim Carrey's wacky persona in "The Mask" – that wild, chaotic energy channeled into a powerful tool. Well, buckle up, because that's what AI-powered testing feels like!
In the realm of software development, AI is the new... | td_inc |
1,918,817 | Welcome to the EveryVerse! | Late night sunsets, the buzz of anticipation for outdoor activities. Summer's great for loads of... | 28,024 | 2024-07-10T16:52:46 | https://dev.to/kydkennedy/welcome-to-the-everyverse-1cie | 3d, xr, mixedreality, cpp |
*Late night sunsets, the buzz of anticipation for outdoor activities. Summer's great for loads of things, including starting new projects! Recently, recharged from vacation, I finally started putting "pen to paper" on a project I've been ruminating on for some time now. And for even more accountability lets blog about... | kydkennedy |
1,918,819 | From TypeScript to Golang: A Smoother Backend Journey | For the past three years, I've been immersed in the world of backend development. During that time,... | 0 | 2024-07-10T17:12:23 | https://dev.to/thelamedev/from-typescript-to-golang-a-smoother-backend-journey-2a6h | go, node, typescript, programming | For the past three years, I've been immersed in the world of backend development. During that time, I've had the opportunity to build a diverse range of applications using various technologies. From edutech and healthtech platforms to e-commerce solutions, I've utilized TypeScript with Express.js and Python with FastAP... | thelamedev |
1,918,820 | Extracting Audio from Video in the Browser using React and FFmpeg WASM | Extracting Audio from Video in the Browser using React and FFmpeg WASM In today's web... | 0 | 2024-07-10T16:59:20 | https://dev.to/kumard3/extracting-audio-from-video-in-the-browser-using-react-and-ffmpeg-wasm-b9a | webassembly, react, javascript, vite |
# Extracting Audio from Video in the Browser using React and FFmpeg WASM
In today's web development landscape, performing complex media operations directly in the browser has become increasingly possible. One such operation is extracting audio from video files without server-side processing. This blog post will guide... | kumard3 |
1,918,822 | Does sugar defender really work | Rising blood sugar levels are a hidden menace in modern society, silently undermining health and... | 0 | 2024-07-10T17:07:20 | https://dev.to/enaya_islam_2082252853053/does-sugar-defender-really-work-1epg | Rising blood sugar levels are a hidden menace in modern society, silently undermining health and well-being. This condition doesn’t just lead to the direct woes of diabetes but is intricately linked with an unexpected adversary: unexplained weight gain.
The crux of the matter lies in how our bodies manage insulin and g... | enaya_islam_2082252853053 | |
1,918,823 | How can I store something written in an input ? | How can I store information written in an input and make whatever is written in the input to show in... | 0 | 2024-07-10T17:11:00 | https://dev.to/prolificnicole/how-can-i-store-something-written-in-an-input--4nml | angular, help, typescript | How can I store information written in an input and make whatever is written in the input to show in the browser. These are the codes I wrote for the html and the typescript
This is the html code
```
<form action="">
<h1>Add User Information</h1>
<input name="userName" (input)="userDetails()" [(ngModel)]="use... | prolificnicole |
1,918,825 | Responsive video - How can we reduce the size of video content served? | Video is the heaviest type of media used on websites. You're talking almost 4 megabytes of video on... | 0 | 2024-07-10T17:21:32 | https://www.roboleary.net/blog/responsive-video/ | webdev, html, javascript | Video is the [heaviest type of media used on websites](https://httparchive.org/reports/page-weight#bytesVideo). You're talking almost 4 megabytes of video on mobile devices for a median page with video. That weight has a huge impact on performance, the data cost for a user, the hosting cost for a website owner, and ene... | robole |
1,918,829 | Python Course - Day 1 Meet & Greet | Hi folks, Today very excited to join first session of python course. Whatsapp group notification... | 0 | 2024-07-10T17:23:54 | https://dev.to/hariharanumapathi/python-course-day-1-meet-greet-3fp2 | python, learning, community, beginners | Hi folks,
Today very excited to join first session of python course.
Whatsapp group notification sound asked me what are you waiting for come on click me.
I was completing my office works for that day i tried to complete as fast i can but unfortunately i cannot join the introductory session.
I only able to watch t... | hariharanumapathi |
1,918,830 | Support Muhammad, a Gaza software engineer, relocate to Egypt for his mom's cancer treatment🙏 | Dear friends, I'm Muhammad, a software engineer. The war in Gaza destroyed everything—my home, my... | 0 | 2024-07-10T17:24:04 | https://dev.to/mohammed_amodi_0b04a77298/support-muhammad-a-gaza-software-engineer-relocate-to-egypt-for-his-moms-cancer-treatment-568h | Dear friends,
I'm Muhammad, a software engineer. The war in Gaza destroyed everything—my home, my job. Now, I'm raising funds to relocate my family to Egypt to be by my mother's side as she undergoes cancer treatment and to rebuild our lives.Please consider donating or sharing our story
https://www.gofundme.com/f/8c8xm... | mohammed_amodi_0b04a77298 | |
1,918,831 | Support Muhammad, a Gaza software engineer, relocate to Egypt for his mom's cancer treatment🙏 | Dear friends, I'm Muhammad, a software engineer. The war in Gaza destroyed everything—my home, my... | 0 | 2024-07-10T17:24:30 | https://dev.to/mohammed_amodi_0b04a77298/support-muhammad-a-gaza-software-engineer-relocate-to-egypt-for-his-moms-cancer-treatment-42ep | help, softwaredevelopment, performance | Dear friends,
I'm Muhammad, a software engineer. The war in Gaza destroyed everything—my home, my job. Now, I'm raising funds to relocate my family to Egypt to be by my mother's side as she undergoes cancer treatment and to rebuild our lives.Please consider donating or sharing our story
https://www.gofundme.com/f/8c8xm... | mohammed_amodi_0b04a77298 |
1,918,832 | Recommended Course: Practical Python Programming | The article is about a recommended course called "Practical Python Programming" offered by LabEx. It provides an overview of the course, highlighting the key topics and skills that learners will acquire, such as writing basic Python programs, working with data structures, using functions and objects, handling errors, a... | 27,678 | 2024-07-10T17:27:41 | https://dev.to/labex/recommended-course-practical-python-programming-4b44 | labex, programming, course, python |
Are you looking to enhance your programming skills and dive deeper into the world of Python? Look no further than the [Practical Python Programming](https://labex.io/courses/practical-python-programming) course offered by LabEx. This comprehensive course is designed to equip you with the essential knowledge and practi... | labby |
1,918,833 | Understanding the Single Responsibility Principle (SRP) | The Single Responsibility Principle (SRP) is a cornerstone of object-oriented design, closely... | 0 | 2024-07-10T17:28:30 | https://dev.to/ravindradevrani/understanding-the-single-responsibility-principle-srp-34gm | solidprinciples, designpatterns, csharp | The `Single Responsibility Principle (SRP)` is a cornerstone of object-oriented design, closely associated with the `SOLID principles`. It emphasizes that **a class should have only one reason to change**, meaning it should have a single responsibility or purpose.
## What is SRP?
The principle asserts that **a class ... | ravindradevrani |
1,918,834 | Introdução ao ORM do Django: Exercícios Práticos | O ORM (Object-Relational Mapping) do Django é uma poderosa ferramenta que permite aos desenvolvedores... | 0 | 2024-07-10T17:36:59 | https://dev.to/gustavogarciapereira/introducao-ao-orm-do-django-exercicios-praticos-38jp | webdev, django, orm, python | O ORM (Object-Relational Mapping) do Django é uma poderosa ferramenta que permite aos desenvolvedores interagir com bancos de dados relacionais usando código Python em vez de SQL. Essa abordagem orientada a objetos abstrai a complexidade das consultas SQL, tornando o processo de manipulação de dados mais intuitivo e al... | gustavogarciapereira |
1,918,836 | Empower Your Role: A Guide for Technologists | Find purpose and pride in supporting your team and company. Learn to empower your role as a technologist with the right mindset.
#developers #jobsatisfaction #technologistguide #empoweryourrole #techmentorship #supportcompanygrowth #prideintech #techempowerment | 0 | 2024-07-10T17:40:46 | https://drive.google.com/file/d/1-uMMICykv2SkU2C3KUpU_WOpcjvdnM6K/view?usp=drive_link | ## Empower Your Role: A Guide for Technologists
In the fast-paced world of technology, it's easy to get caught up in the day-to-day tasks and lose sight of the bigger picture. However, finding pride in your work can stem from the pride you take in your role within a project or team.
### Understanding Your Impact
Pri... | bsommardahl | |
1,918,848 | 4 Pro CSS Tricks Will Blow Your Mind | CSS (Cascading style sheets) is one of the most popular technologies in web design, allowing... | 0 | 2024-07-10T17:53:32 | https://dev.to/designobit/4-pro-css-tricks-will-blow-your-mind-4mgg | webdev, css, tutorial, design | CSS (Cascading style sheets) is one of the most popular technologies in web design, allowing developers to create visual and responsive designs. As a web developer, mastering CSS is crucial for bringing your design vision to life and ensuring a good user experience across all devices. Here are some tips you might not k... | designobit |
1,918,838 | How do you find purpose and pride in your role as a technologist? Share your experiences! | Find purpose and pride in supporting your team and company. Learn to empower your role as a technologist with the right mindset.
#developers #jobsatisfaction #technologistguide #empoweryourrole #techmentorship #supportcompanygrowth #prideintech #techempowerment | 0 | 2024-07-10T17:42:09 | https://dev.to/bsommardahl/how-do-you-find-purpose-and-pride-in-your-role-as-a-technologist-share-your-experiences-28oc | As a veteran in the software development space, I have come to realize that true pride in our work often comes not just from what we do, but from the impact our roles have on others. Whether it's mentoring junior developers, helping colleagues grow, or contributing to the company's success, finding purpose in our roles... | bsommardahl | |
1,918,839 | Find a Reliable Kitchen Fabricator Near Me for Your Dream Kitchen | Creating your dream kitchen is an exciting journey that combines aesthetics with functionality. One... | 0 | 2024-07-10T17:43:09 | https://dev.to/tessastones/find-a-reliable-kitchen-fabricator-near-me-for-your-dream-kitchen-371l | quartz |
Creating your dream kitchen is an exciting journey that combines aesthetics with functionality. One of the critical aspects of this process is finding a reliable kitchen fabricator who can turn your vision into reality. This article will guide you through the steps of finding a trustworthy kitchen fabricator near you... | tessastones |
1,918,840 | What Are the Key Steps for Achieving the Best Exit Cleaning in Murrumba Downs? | The best exit cleaning in Murrumba Downs involves several key steps to ensure the property is left in... | 0 | 2024-07-10T17:43:21 | https://dev.to/bbondcleaning/what-are-the-key-steps-for-achieving-the-best-exit-cleaning-in-murrumba-downs-11hm | cleaning | The [best exit cleaning in Murrumba Downs](https://bbondcleaning.com.au/exit-cleaning/) involves several key steps to ensure the property is left in pristine condition and meets the landlord’s or property manager’s standards.
**Here are the essential steps:
**
**Plan and Schedule:
**
**Book Early:** Schedule your exi... | bbondcleaning |
1,918,841 | Unlocking Success: Strategies and Stories from Startup Founders | Dive into the minds of startup founders who transformed their ideas into thriving businesses,... | 0 | 2024-07-10T17:44:56 | https://dev.to/resource_bunk/unlocking-success-strategies-and-stories-from-startup-founders-446e | startup, socialmedia, top7, bestofdev | Dive into the minds of startup founders who transformed their ideas into thriving businesses, generating $25,000 a month or more.
Starting a business is exhilarating yet challenging. Many aspiring entrepreneurs dream of turning their innovative ideas into successful ventures that not only solve real-world problems but... | resource_bunk |
1,918,842 | Stop console.log. There are better ways. | Hey devs! We all love console.log(), but there are better ways to debug in JavaScript. Let's level... | 0 | 2024-07-10T17:45:05 | https://dev.to/buildwebcrumbs/stop-consolelog-better-ways-inside-26fp | javascript, webdev, beginners, programming | Hey devs! We all love `console.log()`, but there are better ways to debug in JavaScript. Let's level up!
### 1. `console.info()`
Use this for general info messages.
```javascript
console.info("Here's some info");
```
### 2. `console.debug()`
Perfect for detailed debugging.
```javascript
console.debug("Debugging de... | opensourcee |
1,918,843 | Unlocking the Potential of React AI Assistant: A Deep Dive into Enhancing User Engagement | Discover the transformative power of voicebots with Sista AI. Join the AI revolution today! 🚀 | 0 | 2024-07-10T17:45:39 | https://dev.to/sista-ai/unlocking-the-potential-of-react-ai-assistant-a-deep-dive-into-enhancing-user-engagement-3cm7 | ai, react, javascript, typescript | <h2>Unleashing the Power of AI in React Apps</h2><p>This week has been buzzing with groundbreaking AI collaborations, fueling innovation across tech giants.</p><h2>Integrating AI into React Apps</h2><p>For those exploring AI integration for React, the AI-Assistant-React package is a game-changer.</p><p><strong>Sista AI... | sista-ai |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.