id int64 5 1.93M | title stringlengths 0 128 | description stringlengths 0 25.5k | collection_id int64 0 28.1k | published_timestamp timestamp[s] | canonical_url stringlengths 14 581 | tag_list stringlengths 0 120 | body_markdown stringlengths 0 716k | user_username stringlengths 2 30 |
|---|---|---|---|---|---|---|---|---|
1,898,822 | Binary Addition in Java: A Comprehensive Guide | Binary addition is a fundamental operation in computer science and digital electronics. It operates... | 0 | 2024-06-24T11:27:10 | https://dev.to/fullstackjava/binary-addition-in-java-a-comprehensive-guide-9cf | beginners, programming, tutorial, career |
Binary addition is a fundamental operation in computer science and digital electronics. It operates similarly to decimal addition but uses only two digits: 0 and 1. Understanding binary addition is crucial for various applications, including low-level programming, digital circuit design, and data representation. In t... | fullstackjava |
1,898,761 | Glasskube v0.10.0 out now! | Welcome back to another new release blog post 🚀 This is where we cover the newest shipped features,... | 0 | 2024-06-24T11:27:08 | https://dev.to/glasskube/glasskube-v0100-out-now-3ipi | opensource, devops, kubernetes, programming | Welcome back to another `new release` blog post 🚀
This is where we cover the newest shipped features, enhancements, bug fixes and cover all of the recent [Glasskube](https://github.com/glasskube/glasskube) news to make sure you are fully up to speed. We have been riding a continous wave off momentum of internal featu... | jakepage91 |
1,898,820 | 🚀 Django + Svelte 5: No More Dev Nightmares! 💥 | Alright folks, let's cut the crap. We know web dev can be a brutal grind. Django for the backend,... | 0 | 2024-06-24T11:23:50 | https://dev.to/developerbishwas/django-svelte-5-no-more-dev-nightmares-280k | django, svelte, python, webdev | Alright folks, let's cut the crap. We know web dev can be a brutal grind. Django for the backend, SvelteKit for the frontend—sounds perfect, until you try to make them work together. Endless configs, dependencies throwing tantrums, and a heap of wasted nights.
### Pain In The Ass? Let’s Fix It 🎯
We’ve all been ther... | developerbishwas |
1,898,819 | Understanding JWT Authentication: A Beginner's Guide to Securing Your Applications | Introduction In the digital age, securing applications and protecting user data is... | 0 | 2024-06-24T11:23:39 | https://dev.to/spiritmoney/understanding-jwt-authentication-a-beginners-guide-to-securing-your-applications-5dae | webdev, beginners, programming, tutorial | ### **Introduction**
In the digital age, securing applications and protecting user data is paramount. One popular method for ensuring secure communication between a client and a server is through JSON Web Tokens (JWT). This article will guide you through the basics of JWT authentication, its benefits, and how it works... | spiritmoney |
1,898,818 | 10 Captivating Programming Challenges to Boost Your Coding Skills 💻 | The article is about a curated collection of 10 captivating programming challenges from the LabEx platform. It covers a diverse range of topics, including calculating square roots, checking if a number is even or odd, converting miles to kilometers, implementing an Armstrong number checker, creating a complex calculato... | 27,769 | 2024-06-24T11:22:27 | https://dev.to/labex/10-captivating-programming-challenges-to-boost-your-coding-skills-16m1 | coding, programming, tutorial |
Embark on an exciting journey of programming mastery with this curated collection of 10 captivating challenges from the LabEx platform. Whether you're a beginner looking to hone your skills or an experienced coder seeking new intellectual stimulation, this diverse set of exercises will push the boundaries of your codi... | labby |
1,898,817 | Product card components built with Tailwind CSS and Flowbite | One of the most important sections and components of an e-commerce website is listing the products on... | 14,781 | 2024-06-24T11:20:33 | https://flowbite.com/blocks/e-commerce/product-cards/ | flowbite, tailwindcss, webdev, html | One of the most important sections and components of an e-commerce website is [listing the products](https://flowbite.com/blocks/e-commerce/product-cards/) on the homepage or category page of a certain type of product. Within these cards you show images, names of the product, the price, reviews, buttons to add to the c... | zoltanszogyenyi |
1,898,788 | Shelf selector (Inspired Arc icon selector) | This component is inspired by how Arc makes you choose its app icon. 🖥 Watch the demo video to see... | 0 | 2024-06-24T10:59:34 | https://dev.to/adfdev/shelf-selector-inspired-arc-icon-selector-1h3m | This component is inspired by how Arc makes you choose its app icon. 🖥 Watch the demo video to see the component live in action!
{% embed https://www.youtube.com/embed/MAK85LsmjJc %}
⚡️ TECHNOLOGIES
- React
- Tailwind CSS
- Typescript
⚙️ HOW IT WORKS
```
const items = [
{
src: '/images/arc-icon/1.png',
},
{
sr... | adfdev | |
1,898,807 | Best Web development institute in Uttam Nagar,Delhi | **Best Web development institute in Uttam Nagar,Delhi **Syntax world provide best web... | 0 | 2024-06-24T11:19:29 | https://dev.to/syntaxowrld/best-web-development-institute-in-uttam-nagardelhi-8od | javascript, beginners, programming, tutorial |
[

](https://graphicdesigninstitutedelhi.com/website-development-course-delhi)
## **Best Web development institute in Uttam Nagar,Delhi
**Syntax world provide best [web development course](Best Web development ins... | syntaxowrld |
1,898,806 | How To Prepare For The CTET Exam? | The CTET exam is superintended by the Central Board of Secondary Education (CBSE) to check if the... | 0 | 2024-06-24T11:19:00 | https://dev.to/easy-quizzz/how-to-prepare-for-the-ctet-exam-2k98 | ctetquizzes, ctetquestionpapers, mockctetexams, ctetpracticequestions | The CTET exam is superintended by the Central Board of Secondary Education (CBSE) to check if the candidates meet the necessary standards to teach at the primary and upper primary levels. Preparing for the Central Teacher Eligibility Test (CTET) is a big step for those who aspire to become government- employed teachers... | easy-quizzz |
1,898,805 | Our slimming tea supports your metabolism for effortless weight loss | Slimming tea to boost metabolism is a specially crafted blend of natural herbs and ingredients... | 0 | 2024-06-24T11:13:37 | https://dev.to/batontea/our-slimming-tea-supports-your-metabolism-for-effortless-weight-loss-4iee | slimmingtea, weightloss, tea, slimtea | **[Slimming tea](https://batontea.com/)** to boost metabolism is a specially crafted blend of natural herbs and ingredients designed to enhance your body's fat-burning process. This tea helps increase metabolic rate, aiding in weight loss and promoting overall well-being. With a refreshing taste and potent benefits, it... | batontea |
1,898,794 | Buy Negative Google Reviews | https://dmhelpshop.com/product/buy-negative-google-reviews/ Buy Negative Google Reviews Negative... | 0 | 2024-06-24T11:10:10 | https://dev.to/tofamiy578/buy-negative-google-reviews-1e66 | opensource, career, css, learning | ERROR: type should be string, got "https://dmhelpshop.com/product/buy-negative-google-reviews/\n\n\n\n\nBuy Negative Google Reviews\nNegative reviews on Google are detrimental critiques that expose customers’ unfavorable experiences with a business. These reviews can significantly damage a company’s reputation, presenting challenges in both attracting new customers and retaining current ones. If you are considering purchasing negative Google reviews from dmhelpshop.com, we encourage you to reconsider and instead focus on providing exceptional products and services to ensure positive feedback and sustainable success.\n\nWhy Buy Negative Google Reviews from dmhelpshop\nWe take pride in our fully qualified, hardworking, and experienced team, who are committed to providing quality and safe services that meet all your needs. Our professional team ensures that you can trust us completely, knowing that your satisfaction is our top priority. With us, you can rest assured that you’re in good hands.\n\nIs Buy Negative Google Reviews safe?\nAt dmhelpshop, we understand the concern many business persons have about the safety of purchasing Buy negative Google reviews. We are here to guide you through a process that sheds light on the importance of these reviews and how we ensure they appear realistic and safe for your business. Our team of qualified and experienced computer experts has successfully handled similar cases before, and we are committed to providing a solution tailored to your specific needs. Contact us today to learn more about how we can help your business thrive.\n\nBuy Google 5 Star Reviews\nReviews represent the opinions of experienced customers who have utilized services or purchased products from various online or offline markets. These reviews convey customer demands and opinions, and ratings are assigned based on the quality of the products or services and the overall user experience. Google serves as an excellent platform for customers to leave reviews since the majority of users engage with it organically. When you purchase Buy Google 5 Star Reviews, you have the potential to influence a large number of people either positively or negatively. Positive reviews can attract customers to purchase your products, while negative reviews can deter potential customers.\n\nIf you choose to Buy Google 5 Star Reviews, people will be more inclined to consider your products. However, it is important to recognize that reviews can have both positive and negative impacts on your business. Therefore, take the time to determine which type of reviews you wish to acquire. Our experience indicates that purchasing Buy Google 5 Star Reviews can engage and connect you with a wide audience. By purchasing positive reviews, you can enhance your business profile and attract online traffic. Additionally, it is advisable to seek reviews from reputable platforms, including social media, to maintain a positive flow. We are an experienced and reliable service provider, highly knowledgeable about the impacts of reviews. Hence, we recommend purchasing verified Google reviews and ensuring their stability and non-gropability.\n\nLet us now briefly examine the direct and indirect benefits of reviews:\nReviews have the power to enhance your business profile, influencing users at an affordable cost.\nTo attract customers, consider purchasing only positive reviews, while negative reviews can be acquired to undermine your competitors. Collect negative reports on your opponents and present them as evidence.\nIf you receive negative reviews, view them as an opportunity to understand user reactions, make improvements to your products and services, and keep up with current trends.\nBy earning the trust and loyalty of customers, you can control the market value of your products. Therefore, it is essential to buy online reviews, including Buy Google 5 Star Reviews.\nReviews serve as the captivating fragrance that entices previous customers to return repeatedly.\nPositive customer opinions expressed through reviews can help you expand your business globally and achieve profitability and credibility.\nWhen you purchase positive Buy Google 5 Star Reviews, they effectively communicate the history of your company or the quality of your individual products.\nReviews act as a collective voice representing potential customers, boosting your business to amazing heights.\nNow, let’s delve into a comprehensive understanding of reviews and how they function:\nGoogle, with its significant organic user base, stands out as the premier platform for customers to leave reviews. When you purchase Buy Google 5 Star Reviews , you have the power to positively influence a vast number of individuals. Reviews are essentially written submissions by users that provide detailed insights into a company, its products, services, and other relevant aspects based on their personal experiences. In today’s business landscape, it is crucial for every business owner to consider buying verified Buy Google 5 Star Reviews, both positive and negative, in order to reap various benefits.\n\nWhy are Google reviews considered the best tool to attract customers?\nGoogle, being the leading search engine and the largest source of potential and organic customers, is highly valued by business owners. Many business owners choose to purchase Google reviews to enhance their business profiles and also sell them to third parties. Without reviews, it is challenging to reach a large customer base globally or locally. Therefore, it is crucial to consider buying positive Buy Google 5 Star Reviews from reliable sources. When you invest in Buy Google 5 Star Reviews for your business, you can expect a significant influx of potential customers, as these reviews act as a pheromone, attracting audiences towards your products and services. Every business owner aims to maximize sales and attract a substantial customer base, and purchasing Buy Google 5 Star Reviews is a strategic move.\n\nAccording to online business analysts and economists, trust and affection are the essential factors that determine whether people will work with you or do business with you. However, there are additional crucial factors to consider, such as establishing effective communication systems, providing 24/7 customer support, and maintaining product quality to engage online audiences. If any of these rules are broken, it can lead to a negative impact on your business. Therefore, obtaining positive reviews is vital for the success of an online business\n\nWhat are the benefits of purchasing reviews online?\nIn today’s fast-paced world, the impact of new technologies and IT sectors is remarkable. Compared to the past, conducting business has become significantly easier, but it is also highly competitive. To reach a global customer base, businesses must increase their presence on social media platforms as they provide the easiest way to generate organic traffic. Numerous surveys have shown that the majority of online buyers carefully read customer opinions and reviews before making purchase decisions. In fact, the percentage of customers who rely on these reviews is close to 97%. Considering these statistics, it becomes evident why we recommend buying reviews online. In an increasingly rule-based world, it is essential to take effective steps to ensure a smooth online business journey.\n\nBuy Google 5 Star Reviews\nMany people purchase reviews online from various sources and witness unique progress. Reviews serve as powerful tools to instill customer trust, influence their decision-making, and bring positive vibes to your business. Making a single mistake in this regard can lead to a significant collapse of your business. Therefore, it is crucial to focus on improving product quality, quantity, communication networks, facilities, and providing the utmost support to your customers.\n\nReviews reflect customer demands, opinions, and ratings based on their experiences with your products or services. If you purchase Buy Google 5-star reviews, it will undoubtedly attract more people to consider your offerings. Google is the ideal platform for customers to leave reviews due to its extensive organic user involvement. Therefore, investing in Buy Google 5 Star Reviews can significantly influence a large number of people in a positive way.\n\nHow to generate google reviews on my business profile?\nFocus on delivering high-quality customer service in every interaction with your customers. By creating positive experiences for them, you increase the likelihood of receiving reviews. These reviews will not only help to build loyalty among your customers but also encourage them to spread the word about your exceptional service. It is crucial to strive to meet customer needs and exceed their expectations in order to elicit positive feedback. If you are interested in purchasing affordable Google reviews, we offer that service.\n\n\n\n\n\nContact Us / 24 Hours Reply\nTelegram:dmhelpshop\nWhatsApp: +1 (980) 277-2786\nSkype:dmhelpshop\nEmail:dmhelpshop@gmail.com" | tofamiy578 |
1,828,839 | Yup: The efficient validation schema handler | Understanding how form validation is handled and how to build a schema for it is critical as a... | 0 | 2024-06-24T11:08:59 | https://dev.to/vonn/yup-the-efficient-validation-schema-handler-1d8 | yup, formschema, typescript, writing | Understanding how form validation is handled and how to build a schema for it is critical as a Frontend Developer. Forms help users to interact with the system by sending their data to said system for various purposes like authentication, job applications, event registrations and so many more. It is crucial for develop... | vonn |
1,898,793 | LooksBetter.io: Revolutionizing Design Feedback for Designers | LooksBetter.io: Revolutionizing Design Feedback for Designers In the design world, getting... | 0 | 2024-06-24T11:06:02 | https://dev.to/adfdev/looksbetterio-revolutionizing-design-feedback-for-designers-5dn3 | ui, ux, uxdesign, design |
## LooksBetter.io: Revolutionizing Design Feedback for Designers
In the design world, getting quick and constructive feedback can be the difference between a good project and a great one. LooksBetter.io is a platform that aims to transform how designers gather opinions on their creations, offering an intuitive and co... | adfdev |
1,898,792 | Buy Verified Paxful Account | https://dmhelpshop.com/product/buy-verified-paxful-account/ Buy Verified Paxful Account There are... | 0 | 2024-06-24T11:02:55 | https://dev.to/tofamiy578/buy-verified-paxful-account-5dg1 | tutorial, react, python, ai | ERROR: type should be string, got "https://dmhelpshop.com/product/buy-verified-paxful-account/\n\n\n\n\nBuy Verified Paxful Account\nThere are several compelling reasons to consider purchasing a verified Paxful account. Firstly, a verified account offers enhanced security, providing peace of mind to all users. Additionally, it opens up a wider range of trading opportunities, allowing individuals to partake in various transactions, ultimately expanding their financial horizons.\n\nMoreover, Buy verified Paxful account ensures faster and more streamlined transactions, minimizing any potential delays or inconveniences. Furthermore, by opting for a verified account, users gain access to a trusted and reputable platform, fostering a sense of reliability and confidence.\n\nLastly, Paxful’s verification process is thorough and meticulous, ensuring that only genuine individuals are granted verified status, thereby creating a safer trading environment for all users. Overall, the decision to Buy Verified Paxful account can greatly enhance one’s overall trading experience, offering increased security, access to more opportunities, and a reliable platform to engage with. Buy Verified Paxful Account.\n\nBuy US verified paxful account from the best place dmhelpshop\nWhy we declared this website as the best place to buy US verified paxful account? Because, our company is established for providing the all account services in the USA (our main target) and even in the whole world. With this in mind we create paxful account and customize our accounts as professional with the real documents. Buy Verified Paxful Account.\n\nIf you want to buy US verified paxful account you should have to contact fast with us. Because our accounts are-\n\nEmail verified\nPhone number verified\nSelfie and KYC verified\nSSN (social security no.) verified\nTax ID and passport verified\nSometimes driving license verified\nMasterCard attached and verified\nUsed only genuine and real documents\n100% access of the account\nAll documents provided for customer security\nWhat is Verified Paxful Account?\nIn today’s expanding landscape of online transactions, ensuring security and reliability has become paramount. Given this context, Paxful has quickly risen as a prominent peer-to-peer Bitcoin marketplace, catering to individuals and businesses seeking trusted platforms for cryptocurrency trading.\n\nIn light of the prevalent digital scams and frauds, it is only natural for people to exercise caution when partaking in online transactions. As a result, the concept of a verified account has gained immense significance, serving as a critical feature for numerous online platforms. Paxful recognizes this need and provides a safe haven for users, streamlining their cryptocurrency buying and selling experience.\n\nFor individuals and businesses alike, Buy verified Paxful account emerges as an appealing choice, offering a secure and reliable environment in the ever-expanding world of digital transactions. Buy Verified Paxful Account.\n\nVerified Paxful Accounts are essential for establishing credibility and trust among users who want to transact securely on the platform. They serve as evidence that a user is a reliable seller or buyer, verifying their legitimacy.\n\nBut what constitutes a verified account, and how can one obtain this status on Paxful? In this exploration of verified Paxful accounts, we will unravel the significance they hold, why they are crucial, and shed light on the process behind their activation, providing a comprehensive understanding of how they function. Buy verified Paxful account.\n\n \n\nWhy should to Buy Verified Paxful Account?\nThere are several compelling reasons to consider purchasing a verified Paxful account. Firstly, a verified account offers enhanced security, providing peace of mind to all users. Additionally, it opens up a wider range of trading opportunities, allowing individuals to partake in various transactions, ultimately expanding their financial horizons.\n\nMoreover, a verified Paxful account ensures faster and more streamlined transactions, minimizing any potential delays or inconveniences. Furthermore, by opting for a verified account, users gain access to a trusted and reputable platform, fostering a sense of reliability and confidence. Buy Verified Paxful Account.\n\nLastly, Paxful’s verification process is thorough and meticulous, ensuring that only genuine individuals are granted verified status, thereby creating a safer trading environment for all users. Overall, the decision to buy a verified Paxful account can greatly enhance one’s overall trading experience, offering increased security, access to more opportunities, and a reliable platform to engage with.\n\n \n\nWhat is a Paxful Account\nPaxful and various other platforms consistently release updates that not only address security vulnerabilities but also enhance usability by introducing new features. Buy Verified Paxful Account.\n\nIn line with this, our old accounts have recently undergone upgrades, ensuring that if you purchase an old buy Verified Paxful account from dmhelpshop.com, you will gain access to an account with an impressive history and advanced features. This ensures a seamless and enhanced experience for all users, making it a worthwhile option for everyone.\n\n \n\nIs it safe to buy Paxful Verified Accounts?\nBuying on Paxful is a secure choice for everyone. However, the level of trust amplifies when purchasing from Paxful verified accounts. These accounts belong to sellers who have undergone rigorous scrutiny by Paxful. Buy verified Paxful account, you are automatically designated as a verified account. Hence, purchasing from a Paxful verified account ensures a high level of credibility and utmost reliability. Buy Verified Paxful Account.\n\nPAXFUL, a widely known peer-to-peer cryptocurrency trading platform, has gained significant popularity as a go-to website for purchasing Bitcoin and other cryptocurrencies. It is important to note, however, that while Paxful may not be the most secure option available, its reputation is considerably less problematic compared to many other marketplaces. Buy Verified Paxful Account.\n\nThis brings us to the question: is it safe to purchase Paxful Verified Accounts? Top Paxful reviews offer mixed opinions, suggesting that caution should be exercised. Therefore, users are advised to conduct thorough research and consider all aspects before proceeding with any transactions on Paxful.\n\n \n\nHow Do I Get 100% Real Verified Paxful Accoun?\nPaxful, a renowned peer-to-peer cryptocurrency marketplace, offers users the opportunity to conveniently buy and sell a wide range of cryptocurrencies. Given its growing popularity, both individuals and businesses are seeking to establish verified accounts on this platform.\n\nHowever, the process of creating a verified Paxful account can be intimidating, particularly considering the escalating prevalence of online scams and fraudulent practices. This verification procedure necessitates users to furnish personal information and vital documents, posing potential risks if not conducted meticulously.\n\nIn this comprehensive guide, we will delve into the necessary steps to create a legitimate and verified Paxful account. Our discussion will revolve around the verification process and provide valuable tips to safely navigate through it.\n\nMoreover, we will emphasize the utmost importance of maintaining the security of personal information when creating a verified account. Furthermore, we will shed light on common pitfalls to steer clear of, such as using counterfeit documents or attempting to bypass the verification process.\n\nWhether you are new to Paxful or an experienced user, this engaging paragraph aims to equip everyone with the knowledge they need to establish a secure and authentic presence on the platform.\n\nBenefits Of Verified Paxful Accounts\nVerified Paxful accounts offer numerous advantages compared to regular Paxful accounts. One notable advantage is that verified accounts contribute to building trust within the community.\n\nVerification, although a rigorous process, is essential for peer-to-peer transactions. This is why all Paxful accounts undergo verification after registration. When customers within the community possess confidence and trust, they can conveniently and securely exchange cash for Bitcoin or Ethereum instantly. Buy Verified Paxful Account.\n\nPaxful accounts, trusted and verified by sellers globally, serve as a testament to their unwavering commitment towards their business or passion, ensuring exceptional customer service at all times. Headquartered in Africa, Paxful holds the distinction of being the world’s pioneering peer-to-peer bitcoin marketplace. Spearheaded by its founder, Ray Youssef, Paxful continues to lead the way in revolutionizing the digital exchange landscape.\n\nPaxful has emerged as a favored platform for digital currency trading, catering to a diverse audience. One of Paxful’s key features is its direct peer-to-peer trading system, eliminating the need for intermediaries or cryptocurrency exchanges. By leveraging Paxful’s escrow system, users can trade securely and confidently.\n\nWhat sets Paxful apart is its commitment to identity verification, ensuring a trustworthy environment for buyers and sellers alike. With these user-centric qualities, Paxful has successfully established itself as a leading platform for hassle-free digital currency transactions, appealing to a wide range of individuals seeking a reliable and convenient trading experience. Buy Verified Paxful Account.\n\n \n\nHow paxful ensure risk-free transaction and trading?\nEngage in safe online financial activities by prioritizing verified accounts to reduce the risk of fraud. Platforms like Paxfu implement stringent identity and address verification measures to protect users from scammers and ensure credibility.\n\nWith verified accounts, users can trade with confidence, knowing they are interacting with legitimate individuals or entities. By fostering trust through verified accounts, Paxful strengthens the integrity of its ecosystem, making it a secure space for financial transactions for all users. Buy Verified Paxful Account.\n\nExperience seamless transactions by obtaining a verified Paxful account. Verification signals a user’s dedication to the platform’s guidelines, leading to the prestigious badge of trust. This trust not only expedites trades but also reduces transaction scrutiny. Additionally, verified users unlock exclusive features enhancing efficiency on Paxful. Elevate your trading experience with Verified Paxful Accounts today.\n\nIn the ever-changing realm of online trading and transactions, selecting a platform with minimal fees is paramount for optimizing returns. This choice not only enhances your financial capabilities but also facilitates more frequent trading while safeguarding gains. Buy Verified Paxful Account.\n\nExamining the details of fee configurations reveals Paxful as a frontrunner in cost-effectiveness. Acquire a verified level-3 USA Paxful account from usasmmonline.com for a secure transaction experience. Invest in verified Paxful accounts to take advantage of a leading platform in the online trading landscape.\n\n \n\nHow Old Paxful ensures a lot of Advantages?\n\nExplore the boundless opportunities that Verified Paxful accounts present for businesses looking to venture into the digital currency realm, as companies globally witness heightened profits and expansion. These success stories underline the myriad advantages of Paxful’s user-friendly interface, minimal fees, and robust trading tools, demonstrating its relevance across various sectors.\n\nBusinesses benefit from efficient transaction processing and cost-effective solutions, making Paxful a significant player in facilitating financial operations. Acquire a USA Paxful account effortlessly at a competitive rate from usasmmonline.com and unlock access to a world of possibilities. Buy Verified Paxful Account.\n\nExperience elevated convenience and accessibility through Paxful, where stories of transformation abound. Whether you are an individual seeking seamless transactions or a business eager to tap into a global market, buying old Paxful accounts unveils opportunities for growth.\n\nPaxful’s verified accounts not only offer reliability within the trading community but also serve as a testament to the platform’s ability to empower economic activities worldwide. Join the journey towards expansive possibilities and enhanced financial empowerment with Paxful today. Buy Verified Paxful Account.\n\n \n\nWhy paxful keep the security measures at the top priority?\nIn today’s digital landscape, security stands as a paramount concern for all individuals engaging in online activities, particularly within marketplaces such as Paxful. It is essential for account holders to remain informed about the comprehensive security protocols that are in place to safeguard their information.\n\nSafeguarding your Paxful account is imperative to guaranteeing the safety and security of your transactions. Two essential security components, Two-Factor Authentication and Routine Security Audits, serve as the pillars fortifying this shield of protection, ensuring a secure and trustworthy user experience for all. Buy Verified Paxful Account.\n\nConclusion\nInvesting in Bitcoin offers various avenues, and among those, utilizing a Paxful account has emerged as a favored option. Paxful, an esteemed online marketplace, enables users to engage in buying and selling Bitcoin. Buy Verified Paxful Account.\n\nThe initial step involves creating an account on Paxful and completing the verification process to ensure identity authentication. Subsequently, users gain access to a diverse range of offers from fellow users on the platform. Once a suitable proposal captures your interest, you can proceed to initiate a trade with the respective user, opening the doors to a seamless Bitcoin investing experience.\n\nIn conclusion, when considering the option of purchasing verified Paxful accounts, exercising caution and conducting thorough due diligence is of utmost importance. It is highly recommended to seek reputable sources and diligently research the seller’s history and reviews before making any transactions.\n\nMoreover, it is crucial to familiarize oneself with the terms and conditions outlined by Paxful regarding account verification, bearing in mind the potential consequences of violating those terms. By adhering to these guidelines, individuals can ensure a secure and reliable experience when engaging in such transactions. Buy Verified Paxful Account.\n\n \n\nContact Us / 24 Hours Reply\nTelegram:dmhelpshop\nWhatsApp: +1 (980) 277-2786\nSkype:dmhelpshop\nEmail:dmhelpshop@gmail.com" | tofamiy578 |
1,898,791 | 3 Essentials For Landing Your Dream Tech Job | Know your fundamentals So, I am going to talk, more or less in the terms of a web design... | 0 | 2024-06-24T11:02:26 | https://dev.to/thekarlesi/3-essentials-for-landing-your-dream-tech-job-4le8 | webdev, beginners, programming, learning | ## Know your fundamentals
So, I am going to talk, more or less in the terms of a web design and development. But, this applies to any type of development really.
So, first of all, you need to know your fundamentals. You need to have a good solid understanding of that. If you have watched my channel for any period of ... | thekarlesi |
1,892,399 | Demystifying AWS: An Introductory Guide to 4 Key AWS Services | Introduction If you are thinking about creating a new system or moving your existing... | 24,864 | 2024-06-24T11:02:00 | https://swac.blog/demystifying-aws-an-introductory-guide-to-aws-services/ | aws, beginners, cloud |
Introduction
------------
If you are thinking about creating a new system or moving your existing systems to the cloud, it is important that you have a good knowledge of the cloud services provided by AWS, as AWS cloud services provide reliable, secure, efficient, and cost-effective systems effectively in the cloud.
... | khalidelgazzar |
1,872,333 | Ibuprofeno.py💊| #123: Explica este código Python | Explica este código Python Dificultad: Fácil print(set("Alemania")) ... | 25,824 | 2024-06-24T11:00:00 | https://dev.to/duxtech/ibuprofenopy-123-explica-este-codigo-python-18k0 | python, beginners, spanish, learning | ## **<center>Explica este código Python</center>**
#### <center>**Dificultad:** <mark>Fácil</mark></center>
```py
print(set("Alemania"))
```
* **A.** `{'n', 'i', 'e', 'm', 'l', 'A', 'a'}`
* **B.** `{'n', 'i', 'e', 'm', 'l', 'a'}`
* **C.** `SyntaxError`
* **D.** `Ninguana de las anteriores`
---
{% details **Respuest... | duxtech |
1,898,787 | Revolutionizing the labor migrant industry | Today's global labor migrant market is non-transparent, insufficient, and corrupted by middlemen, who... | 0 | 2024-06-24T10:57:10 | https://dev.to/joblio_us/revolutionizing-the-labor-migrant-industry-a6p | Today's global labor migrant market is non-transparent, insufficient, and corrupted by middlemen, who illegally sell migrants, causing serious issues and losses to all the parties involved: employers, employees, and governments.
https://www.youtube.com/watch?v=2-6oemglP0c | joblio_us | |
1,898,786 | A Deep Dive into Self-Referencing Objects and Circular References in JavaScript | Introduction As a developer, you often encounter complex scenarios that test your debugging skills,... | 0 | 2024-06-24T10:56:26 | https://dev.to/momoesse/a-deep-dive-into-self-referencing-objects-and-circular-references-in-javascript-jf9 | javascript, softwaredevelopment, circularreference | **Introduction**
As a developer, you often encounter complex scenarios that test your debugging skills, requiring you to unravel intricate problems and devise effective solutions.
While working on a project, I recently faced a particularly tricky problem: self-referencing objects.
A self-referencing object is an obje... | momoesse |
1,898,785 | Celebrating the Pioneering Spirit: Women in Engineering | Introduction: The world around us is a testament to the ingenuity of engineers. From towering... | 0 | 2024-06-24T10:54:31 | https://dev.to/brainvault_tech/celebrating-the-pioneering-spirit-women-in-engineering-29h8 | **Introduction:**
The world around us is a testament to the ingenuity of engineers. From towering skyscrapers to delicate medical devices, their creations shape our lives in countless ways. This International Women in Engineering Day, we celebrate the remarkable contributions of women who are shattering stereotypes an... | brainvault_tech | |
1,898,775 | How to use Proton Mail in the console | In this tutorial, we will walk through the process of using the Eppie CLI to access Proton Mail from... | 0 | 2024-06-24T10:54:29 | https://dev.to/eppie/how-to-use-proton-mail-in-the-console-1ldg | proton, csharp, cli, email | In this tutorial, we will walk through the process of using the Eppie CLI to access Proton Mail from your console.
Proton Mail is renowned for its strong emphasis on privacy, utilizing the Secure Remote Password (SRP) protocol for authentication, which conventional email clients do not support. Eppie CLI implements SR... | eppie |
1,898,034 | Introduction to Cloud Computing: A Beginner's Guide | Introduction Cloud computing combines two words, 'cloud’ and ‘computing’. Cloud means virtual... | 0 | 2024-06-24T10:54:08 | https://dev.to/umarshehu/introduction-to-cloud-computing-a-beginners-guide-49l4 |
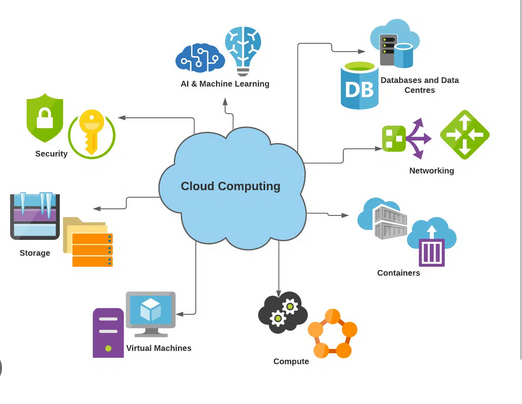
Introduction
Cloud computing combines two words, 'cloud’ and ‘computing’.
Cloud means virtual servers that are connected on the internet and the applications that are running on the virtual servers.
Computi... | umarshehu | |
1,898,783 | 🔥Have You Ever Considered a Visual Approach for WebDevelopment? 🔥 | We've just released a must-read article on why FlutterFlow is the premier low-code tool for... | 0 | 2024-06-24T10:52:26 | https://dev.to/flutterflowdevs/have-you-ever-considered-a-visual-approach-for-webdevelopment-582p | webdev, flutter, flutterflow, lowcode | We've just released a must-read article on why FlutterFlow is the premier low-code tool for optimizing your web app development process. You’ll be glad you checked it out! 🌟
What Makes FlutterFlow Exceptional:
🚀 Accelerated Development: Create web apps in half the time using FlutterFlow’s user-friendly drag-and-dro... | flutterflowdevs |
1,898,782 | 10 Reasons to Bring Customs Functions In-House: For Traders | When navigating the complexities of international trade, managing customs processes effectively is... | 0 | 2024-06-24T10:51:57 | https://dev.to/john_hall/10-reasons-to-bring-customs-functions-in-house-for-traders-4ndf | ai, productivity, learning, discuss | When navigating the complexities of international trade, managing customs processes effectively is crucial. While outsourcing customs functions is a common practice, bringing these operations in-house can offer significant benefits. Here’s why traders should consider this strategic move:
Key Challenges in Customs Func... | john_hall |
1,898,780 | Buy verified cash app account | https://dmhelpshop.com/product/buy-verified-cash-app-account/ Buy verified cash app account Cash... | 0 | 2024-06-24T10:51:33 | https://dev.to/tofamiy578/buy-verified-cash-app-account-hjl | webdev, javascript, beginners, programming | ERROR: type should be string, got "https://dmhelpshop.com/product/buy-verified-cash-app-account/\n\n\n\n\nBuy verified cash app account\nCash app has emerged as a dominant force in the realm of mobile banking within the USA, offering unparalleled convenience for digital money transfers, deposits, and trading. As the foremost provider of fully verified cash app accounts, we take pride in our ability to deliver accounts with substantial limits. Bitcoin enablement, and an unmatched level of security.\n\nOur commitment to facilitating seamless transactions and enabling digital currency trades has garnered significant acclaim, as evidenced by the overwhelming response from our satisfied clientele. Those seeking buy verified cash app account with 100% legitimate documentation and unrestricted access need look no further. Get in touch with us promptly to acquire your verified cash app account and take advantage of all the benefits it has to offer.\n\nWhy dmhelpshop is the best place to buy USA cash app accounts?\nIt’s crucial to stay informed about any updates to the platform you’re using. If an update has been released, it’s important to explore alternative options. Contact the platform’s support team to inquire about the status of the cash app service.\n\nClearly communicate your requirements and inquire whether they can meet your needs and provide the buy verified cash app account promptly. If they assure you that they can fulfill your requirements within the specified timeframe, proceed with the verification process using the required documents.\n\nOur account verification process includes the submission of the following documents: [List of specific documents required for verification].\n\nGenuine and activated email verified\nRegistered phone number (USA)\nSelfie verified\nSSN (social security number) verified\nDriving license\nBTC enable or not enable (BTC enable best)\n100% replacement guaranteed\n100% customer satisfaction\nWhen it comes to staying on top of the latest platform updates, it’s crucial to act fast and ensure you’re positioned in the best possible place. If you’re considering a switch, reaching out to the right contacts and inquiring about the status of the buy verified cash app account service update is essential.\n\nClearly communicate your requirements and gauge their commitment to fulfilling them promptly. Once you’ve confirmed their capability, proceed with the verification process using genuine and activated email verification, a registered USA phone number, selfie verification, social security number (SSN) verification, and a valid driving license.\n\nAdditionally, assessing whether BTC enablement is available is advisable, buy verified cash app account, with a preference for this feature. It’s important to note that a 100% replacement guarantee and ensuring 100% customer satisfaction are essential benchmarks in this process.\n\nHow to use the Cash Card to make purchases?\nTo activate your Cash Card, open the Cash App on your compatible device, locate the Cash Card icon at the bottom of the screen, and tap on it. Then select “Activate Cash Card” and proceed to scan the QR code on your card. Alternatively, you can manually enter the CVV and expiration date. How To Buy Verified Cash App Accounts.\n\nAfter submitting your information, including your registered number, expiration date, and CVV code, you can start making payments by conveniently tapping your card on a contactless-enabled payment terminal. Consider obtaining a buy verified Cash App account for seamless transactions, especially for business purposes. Buy verified cash app account.\n\nWhy we suggest to unchanged the Cash App account username?\nTo activate your Cash Card, open the Cash App on your compatible device, locate the Cash Card icon at the bottom of the screen, and tap on it. Then select “Activate Cash Card” and proceed to scan the QR code on your card.\n\nAlternatively, you can manually enter the CVV and expiration date. After submitting your information, including your registered number, expiration date, and CVV code, you can start making payments by conveniently tapping your card on a contactless-enabled payment terminal. Consider obtaining a verified Cash App account for seamless transactions, especially for business purposes. Buy verified cash app account. Purchase Verified Cash App Accounts.\n\nSelecting a username in an app usually comes with the understanding that it cannot be easily changed within the app’s settings or options. This deliberate control is in place to uphold consistency and minimize potential user confusion, especially for those who have added you as a contact using your username. In addition, purchasing a Cash App account with verified genuine documents already linked to the account ensures a reliable and secure transaction experience.\n\n \n\nBuy verified cash app accounts quickly and easily for all your financial needs.\nAs the user base of our platform continues to grow, the significance of verified accounts cannot be overstated for both businesses and individuals seeking to leverage its full range of features. How To Buy Verified Cash App Accounts.\n\nFor entrepreneurs, freelancers, and investors alike, a verified cash app account opens the door to sending, receiving, and withdrawing substantial amounts of money, offering unparalleled convenience and flexibility. Whether you’re conducting business or managing personal finances, the benefits of a verified account are clear, providing a secure and efficient means to transact and manage funds at scale.\n\nWhen it comes to the rising trend of purchasing buy verified cash app account, it’s crucial to tread carefully and opt for reputable providers to steer clear of potential scams and fraudulent activities. How To Buy Verified Cash App Accounts. With numerous providers offering this service at competitive prices, it is paramount to be diligent in selecting a trusted source.\n\nThis article serves as a comprehensive guide, equipping you with the essential knowledge to navigate the process of procuring buy verified cash app account, ensuring that you are well-informed before making any purchasing decisions. Understanding the fundamentals is key, and by following this guide, you’ll be empowered to make informed choices with confidence.\n\n \n\nIs it safe to buy Cash App Verified Accounts?\nCash App, being a prominent peer-to-peer mobile payment application, is widely utilized by numerous individuals for their transactions. However, concerns regarding its safety have arisen, particularly pertaining to the purchase of “verified” accounts through Cash App. This raises questions about the security of Cash App’s verification process.\n\nUnfortunately, the answer is negative, as buying such verified accounts entails risks and is deemed unsafe. Therefore, it is crucial for everyone to exercise caution and be aware of potential vulnerabilities when using Cash App. How To Buy Verified Cash App Accounts.\n\nCash App has emerged as a widely embraced platform for purchasing Instagram Followers using PayPal, catering to a diverse range of users. This convenient application permits individuals possessing a PayPal account to procure authenticated Instagram Followers.\n\nLeveraging the Cash App, users can either opt to procure followers for a predetermined quantity or exercise patience until their account accrues a substantial follower count, subsequently making a bulk purchase. Although the Cash App provides this service, it is crucial to discern between genuine and counterfeit items. If you find yourself in search of counterfeit products such as a Rolex, a Louis Vuitton item, or a Louis Vuitton bag, there are two viable approaches to consider.\n\n \n\nWhy you need to buy verified Cash App accounts personal or business?\nThe Cash App is a versatile digital wallet enabling seamless money transfers among its users. However, it presents a concern as it facilitates transfer to both verified and unverified individuals.\n\nTo address this, the Cash App offers the option to become a verified user, which unlocks a range of advantages. Verified users can enjoy perks such as express payment, immediate issue resolution, and a generous interest-free period of up to two weeks. With its user-friendly interface and enhanced capabilities, the Cash App caters to the needs of a wide audience, ensuring convenient and secure digital transactions for all.\n\nIf you’re a business person seeking additional funds to expand your business, we have a solution for you. Payroll management can often be a challenging task, regardless of whether you’re a small family-run business or a large corporation. How To Buy Verified Cash App Accounts.\n\nImproper payment practices can lead to potential issues with your employees, as they could report you to the government. However, worry not, as we offer a reliable and efficient way to ensure proper payroll management, avoiding any potential complications. Our services provide you with the funds you need without compromising your reputation or legal standing. With our assistance, you can focus on growing your business while maintaining a professional and compliant relationship with your employees. Purchase Verified Cash App Accounts.\n\nA Cash App has emerged as a leading peer-to-peer payment method, catering to a wide range of users. With its seamless functionality, individuals can effortlessly send and receive cash in a matter of seconds, bypassing the need for a traditional bank account or social security number. Buy verified cash app account.\n\nThis accessibility makes it particularly appealing to millennials, addressing a common challenge they face in accessing physical currency. As a result, ACash App has established itself as a preferred choice among diverse audiences, enabling swift and hassle-free transactions for everyone. Purchase Verified Cash App Accounts.\n\n \n\nHow to verify Cash App accounts\nTo ensure the verification of your Cash App account, it is essential to securely store all your required documents in your account. This process includes accurately supplying your date of birth and verifying the US or UK phone number linked to your Cash App account.\n\nAs part of the verification process, you will be asked to submit accurate personal details such as your date of birth, the last four digits of your SSN, and your email address. If additional information is requested by the Cash App community to validate your account, be prepared to provide it promptly. Upon successful verification, you will gain full access to managing your account balance, as well as sending and receiving funds seamlessly. Buy verified cash app account.\n\n \n\nHow cash used for international transaction?\nExperience the seamless convenience of this innovative platform that simplifies money transfers to the level of sending a text message. It effortlessly connects users within the familiar confines of their respective currency regions, primarily in the United States and the United Kingdom.\n\nNo matter if you’re a freelancer seeking to diversify your clientele or a small business eager to enhance market presence, this solution caters to your financial needs efficiently and securely. Embrace a world of unlimited possibilities while staying connected to your currency domain. Buy verified cash app account.\n\nUnderstanding the currency capabilities of your selected payment application is essential in today’s digital landscape, where versatile financial tools are increasingly sought after. In this era of rapid technological advancements, being well-informed about platforms such as Cash App is crucial.\n\nAs we progress into the digital age, the significance of keeping abreast of such services becomes more pronounced, emphasizing the necessity of staying updated with the evolving financial trends and options available. Buy verified cash app account.\n\nOffers and advantage to buy cash app accounts cheap?\nWith Cash App, the possibilities are endless, offering numerous advantages in online marketing, cryptocurrency trading, and mobile banking while ensuring high security. As a top creator of Cash App accounts, our team possesses unparalleled expertise in navigating the platform.\n\nWe deliver accounts with maximum security and unwavering loyalty at competitive prices unmatched by other agencies. Rest assured, you can trust our services without hesitation, as we prioritize your peace of mind and satisfaction above all else.\n\nEnhance your business operations effortlessly by utilizing the Cash App e-wallet for seamless payment processing, money transfers, and various other essential tasks. Amidst a myriad of transaction platforms in existence today, the Cash App e-wallet stands out as a premier choice, offering users a multitude of functions to streamline their financial activities effectively. Buy verified cash app account.\n\nTrustbizs.com stands by the Cash App’s superiority and recommends acquiring your Cash App accounts from this trusted source to optimize your business potential.\n\nHow Customizable are the Payment Options on Cash App for Businesses?\nDiscover the flexible payment options available to businesses on Cash App, enabling a range of customization features to streamline transactions. Business users have the ability to adjust transaction amounts, incorporate tipping options, and leverage robust reporting tools for enhanced financial management.\n\nExplore trustbizs.com to acquire verified Cash App accounts with LD backup at a competitive price, ensuring a secure and efficient payment solution for your business needs. Buy verified cash app account.\n\nDiscover Cash App, an innovative platform ideal for small business owners and entrepreneurs aiming to simplify their financial operations. With its intuitive interface, Cash App empowers businesses to seamlessly receive payments and effectively oversee their finances. Emphasizing customization, this app accommodates a variety of business requirements and preferences, making it a versatile tool for all.\n\nWhere To Buy Verified Cash App Accounts\nWhen considering purchasing a verified Cash App account, it is imperative to carefully scrutinize the seller’s pricing and payment methods. Look for pricing that aligns with the market value, ensuring transparency and legitimacy. Buy verified cash app account.\n\nEqually important is the need to opt for sellers who provide secure payment channels to safeguard your financial data. Trust your intuition; skepticism towards deals that appear overly advantageous or sellers who raise red flags is warranted. It is always wise to prioritize caution and explore alternative avenues if uncertainties arise.\n\nThe Importance Of Verified Cash App Accounts\nIn today’s digital age, the significance of verified Cash App accounts cannot be overstated, as they serve as a cornerstone for secure and trustworthy online transactions.\n\nBy acquiring verified Cash App accounts, users not only establish credibility but also instill the confidence required to participate in financial endeavors with peace of mind, thus solidifying its status as an indispensable asset for individuals navigating the digital marketplace.\n\nWhen considering purchasing a verified Cash App account, it is imperative to carefully scrutinize the seller’s pricing and payment methods. Look for pricing that aligns with the market value, ensuring transparency and legitimacy. Buy verified cash app account.\n\nEqually important is the need to opt for sellers who provide secure payment channels to safeguard your financial data. Trust your intuition; skepticism towards deals that appear overly advantageous or sellers who raise red flags is warranted. It is always wise to prioritize caution and explore alternative avenues if uncertainties arise.\n\nConclusion\nEnhance your online financial transactions with verified Cash App accounts, a secure and convenient option for all individuals. By purchasing these accounts, you can access exclusive features, benefit from higher transaction limits, and enjoy enhanced protection against fraudulent activities. Streamline your financial interactions and experience peace of mind knowing your transactions are secure and efficient with verified Cash App accounts.\n\nChoose a trusted provider when acquiring accounts to guarantee legitimacy and reliability. In an era where Cash App is increasingly favored for financial transactions, possessing a verified account offers users peace of mind and ease in managing their finances. Make informed decisions to safeguard your financial assets and streamline your personal transactions effectively.\n\nContact Us / 24 Hours Reply\nTelegram:dmhelpshop\nWhatsApp: +1 (980) 277-2786\nSkype:dmhelpshop\nEmail:dmhelpshop@gmail.com" | tofamiy578 |
1,898,756 | Can Large Language Models Do Causal Reasoning? | Introduction How do we humans discern the causes behind the effects we observe around us?... | 0 | 2024-06-24T10:50:08 | https://dev.to/novita_ai/can-large-language-models-do-causal-reasoning-id3 | llm | ## Introduction
How do we humans discern the causes behind the effects we observe around us? When we see storm clouds gathering, why do we predict rain, or how do we conclude that a medication was effective when our health improves?
This ability, known as causal reasoning, is a key component of human cognition that he... | novita_ai |
1,898,777 | Can Large Language Models Transform Computational Social Science? | Introduction Can large language models transform computational social science? Wait a... | 0 | 2024-06-24T10:50:08 | https://dev.to/novita_ai/can-large-language-models-transform-computational-social-science-1b6i | llm | ## Introduction
Can large language models transform computational social science? Wait a second, what does computational social science do? Welcome to the dynamic field of computational social science (CSS), where large language models (LLMs) are revolutionizing the way we analyze and interpret social behaviors, opinio... | novita_ai |
1,898,778 | Exporting Payment Data with Hyperswitch: A Comprehensive Guide | In today's data-driven business landscape, having seamless access to payment data is crucial for both... | 0 | 2024-06-24T10:50:01 | https://dev.to/hyperswitch-global/exporting-payment-data-with-hyperswitch-a-comprehensive-guide-1ll2 | hyperswitch, payment | In today's data-driven business landscape, having seamless access to payment data is crucial for both operational efficiency and strategic decision-making. For organizations leveraging Hyperswitch powered by Juspay, the ability to efficiently export payment data to robust analytics platforms like Hyperswitch Redshift i... | hyperswitch-global |
1,898,779 | 5 Best & Easy Methods to Enable Airplane Mode in Windows 11! | Key Points: Use the shortcut Winkey + A. Quick Settings Panel or Action Center will be... | 0 | 2024-06-24T10:50:00 | https://winsides.com/how-to-enable-airplane-mode-in-windows-11/ | webdev, windows11, geek, tutorial | > ## Key Points:
> - Use the shortcut Winkey + A.
> - Quick Settings Panel or Action Center will be appear at your right bottom on your screen.
> - Next to the WIFI & Bluetooth, you can see the Airplane Mode icon.
> - Click the icon to enable the Airplane Mode.
To enable Airplane mode in Windows 11, you can use severa... | vigneshwaran_vijayakumar |
1,899,384 | Upgrading to Nuxt 4 | Nuxt v4 is coming out soon. This version of Nuxt is predominantly about performance upgrades and... | 0 | 2024-06-24T21:53:35 | https://www.vuemastery.com/blog/upgrading-to-nuxt-4 | nuxt, javascript, vue, frontend | ---
title: Upgrading to Nuxt 4
published: true
date: 2024-06-24 10:48:49 UTC
tags: nuxt,javascript,vue,frontenddevelopment
canonical_url: https://www.vuemastery.com/blog/upgrading-to-nuxt-4
---

Nuxt v4 is coming out soon. This version of Nuxt... | vuemasteryteam |
1,898,776 | Best practices for using the Mailchimp API to manage subscribers? | To manage subscribers with the Mailchimp API, follow these best practices: authenticate securely... | 0 | 2024-06-24T10:43:48 | https://dev.to/liam_james_ed448f6f4070cb/best-practices-for-using-the-mailchimp-api-to-manage-subscribers-3dhn | mailchimp | To manage subscribers with the Mailchimp API, follow these best practices: authenticate securely using OAuth 2.0, handle API rate limits to avoid disruptions, validate email addresses before adding subscribers, use batch operations for large updates, regularly clean your list to remove inactive subscribers, and ensure ... | liam_james_ed448f6f4070cb |
1,898,774 | Exploring AI Capabilities in PancakeSwap Clone Script for Entrepreneurs | The world of decentralized finance(DeFi) is progressing at a very high rate and new business people... | 0 | 2024-06-24T10:40:50 | https://dev.to/rick_grimes/exploring-ai-capabilities-in-pancakeswap-clone-script-for-entrepreneurs-45b0 | webdev, ai, blockchain, clone | The world of decentralized finance(DeFi) is progressing at a very high rate and new business people are in the constant search for new solutions. The PancakeSwap clone script is one such option that offers a dependable foundation to launch decentralized exchanges (DEXs). AI can be incorporated in these clone scripts to... | rick_grimes |
1,898,773 | Mobile Development: Engineering the Future of Applications | **Table of Contents Introduction: The Evolution of Mobile Development Understanding Mobile... | 0 | 2024-06-24T10:39:38 | https://dev.to/jinesh_vora_ab4d7886e6a8d/mobile-development-engineering-the-future-of-applications-d53 | webdev, programming, mobile, development |

**Table of Contents
1. Introduction: The Evolution of Mobile Development
2. Understanding Mobile Platforms
3. Key Technologies in Mobile Development
4. Mobile App Development Lifecycle
5. UI/UX Design: Crafting E... | jinesh_vora_ab4d7886e6a8d |
1,898,772 | JustinGuitar: Eine Revolution in der Welt der Gitarren | Die Welt des Gitarrenlernens hat dank JustinGuitar eine Revolution erlebt. Mit seiner innovativen... | 0 | 2024-06-24T10:39:12 | https://dev.to/markbowman/justinguitar-eine-revolution-in-der-welt-der-gitarren-1hg7 | Die Welt des Gitarrenlernens hat dank JustinGuitar eine Revolution erlebt. Mit seiner innovativen Herangehensweise hat JustinGuitar nicht nur traditionelle Lernmethoden überholt, sondern auch eine vielfältige Gemeinschaft von Gitarrenenthusiasten und Lernenden geschaffen. Diese Plattform bietet eine Fülle von Ressource... | markbowman | |
1,898,769 | buy wyld gummies online | Wyld Huckleberry gummies has created this unique recipe over the ages, constantly fine-tuning our... | 0 | 2024-06-24T10:37:41 | https://dev.to/wyldgummies125/buy-wyld-gummies-online-2gg1 | wyld, gummies, online, huckleberry | **[Wyld Huckleberry gummies](https://txherbalhouse.com/product/buy-wyld-cbd-gummies-online/)** has created this unique recipe over the ages, constantly fine-tuning our formulas to produce delicious delicacies that enrich each second with authentic fruit flavors and THC free hemp. Wyld CBD gummies 500mg is one of the si... | wyldgummies125 |
1,898,768 | MLM Software | Network Marketing Solution To Grow in 2024 | MLM software, FinoForce, is an AI-based tool for multi-level marketing & network marketing... | 0 | 2024-06-24T10:37:31 | https://dev.to/finoforce_digital_346e728/mlm-software-network-marketing-solution-to-grow-in-2024-4im0 | mlm, developer, software, development | MLM software, **[FinoForce](url)**, is an AI-based tool for multi-level marketing & network marketing businesses with e-commerce & franchisee modules. FinoForce's low-cost MLM software architecture includes 5+ static webpages, email integration, 1GB Windows server, ten email ID with 2GB space each, domain name, content... | finoforce_digital_346e728 |
1,898,767 | Building a Telegram Bot that delivers weekly stock open and close prices | With Telegram, you can create a bot that helps you with different tasks such as giving you sports... | 0 | 2024-06-24T10:36:46 | https://dev.to/pluri45/building-a-telegram-bot-to-deliver-weekly-stock-open-and-close-prices-moh | With Telegram, you can create a bot that helps you with different tasks such as giving you sports updates, coordinating how you receive membership payments in private groups, welcoming users to a group and removing spammers, etc. In this tutorial, you will learn how to create a telegram bot that retrieves the opening a... | pluri45 | |
1,898,755 | Drupal Access Policy demystified | Deep dive into the new Access Policy API in Drupal 10.3 | 0 | 2024-06-24T10:35:53 | https://tech.sparkfabrik.com/en/blog/drupal-access-policy-demystified/ | drupal, opensource, security | ---
title: "Drupal Access Policy demystified"
published: true
description: "Deep dive into the new Access Policy API in Drupal 10.3"
tags: drupal, opensource, security
canonical_url: https://tech.sparkfabrik.com/en/blog/drupal-access-policy-demystified/
cover_image: https://dev-to-uploads.s3.amazonaws.com/uploads/artic... | lussoluca |
1,898,766 | Why Choose Our C++ Programming Institute in Rohini? | C++ is a powerful, high-performance programming language widely used in software development, systems... | 0 | 2024-06-24T10:34:35 | https://dev.to/muskan_sharma_c2d15774a2d/why-choose-our-c-programming-institute-in-rohini-ifb | C++ is a powerful, high-performance programming language widely used in software development, systems programming, and game development. Developed by Bjarne Stroustrup as an extension of the C programming language, C++ introduces object-oriented programming features, making it versatile and efficient. This article prov... | muskan_sharma_c2d15774a2d | |
1,898,765 | Discover Ultimate Relaxation: The Best Spas on Sindhu Bhavan Road | Sindhu Bhavan Road, a vibrant and upscale area in Ahmedabad, is renowned for its luxurious amenities... | 0 | 2024-06-24T10:34:25 | https://dev.to/abitamim_patel_7a906eb289/discover-ultimate-relaxation-the-best-spas-on-sindhu-bhavan-road-1476 | spainsindhubhavan | Sindhu Bhavan Road, a vibrant and upscale area in Ahmedabad, is renowned for its luxurious amenities and serene ambiance. Among its many attractions, the spas on Sindhu Bhavan Road stand out as sanctuaries of relaxation and rejuvenation. Whether you seek a calming massage, a revitalizing facial, or holistic wellness tr... | abitamim_patel_7a906eb289 |
1,898,764 | TailwindCSS ECommerce Website Template - Freshcart | Freshcart is a premium TailwindCSS ECommerce Website Template using which you can create an... | 0 | 2024-06-24T10:34:04 | https://dev.to/easetemplates/tailwindcss-ecommerce-website-template-freshcart-6f2 | webdev, tailwindcss, eommerce, developers | 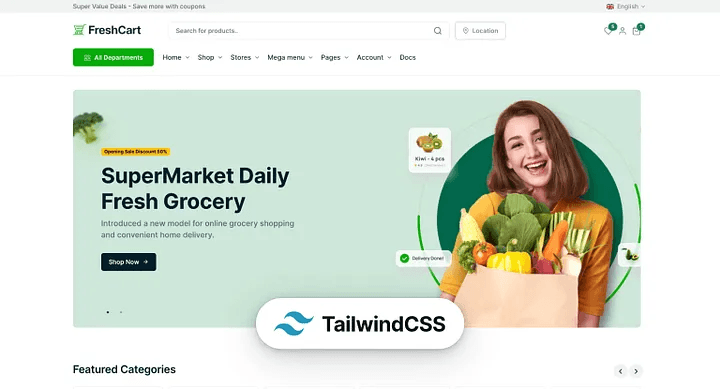
Freshcart is a premium [TailwindCSS ECommerce Website Template](https://freshcart-tailwind.codescandy.com/overview.html) using which you can create an outstanding online storefront.
Its clean and minimal design e... | easetemplates |
1,898,763 | What are some innovative features you can add to an ERC-20 token? | *Introduction * ERC-20 tokens are the cornerstone of the Ethereum blockchain, providing a standard... | 0 | 2024-06-24T10:33:51 | https://dev.to/elena_marie_dad5c9d5d5706/what-are-some-innovative-features-you-can-add-to-an-erc-20-token-56m0 | ethereum, cryptotoken, tokendevelopment | **Introduction
**
ERC-20 tokens are the cornerstone of the Ethereum blockchain, providing a standard for creating and managing tokens on this platform. These tokens have transformed the crypto space by facilitating seamless transactions and enabling smart contract functionality. However, staying competitive in the dyn... | elena_marie_dad5c9d5d5706 |
1,898,762 | Mastering Request Cancellation ❌ in JavaScript: Using AbortController with Axios and Fetch API.🚀💪 | In modern web development, managing HTTP requests efficiently is crucial, especially when dealing... | 0 | 2024-06-24T10:33:45 | https://dev.to/dharamgfx/mastering-request-cancellation-in-javascript-using-abortcontroller-with-axios-and-fetch-api-2589 | webdev, javascript, api, axios | In modern web development, managing HTTP requests efficiently is crucial, especially when dealing with slow networks or potential duplicate requests. JavaScript's `AbortController` is a powerful tool for handling request cancellations. In this post, we will explore how to use `AbortController` with both Axios and the F... | dharamgfx |
1,898,760 | Lori Harvey's Net Worth in 2024! | Lori Harvey was born in the United States on January 13, 1997. It was like Steve Harvey took her in... | 0 | 2024-06-24T10:32:41 | https://dev.to/sgx_nifty_67f9ef681bc53e0/lori-harveys-net-worth-in-2024-56n7 | Lori Harvey was born in the United States on January 13, 1997. It was like Steve Harvey took her in as his daughter. We call her mom Marjorie Harvey. This girl was signed by both IMG Models Management in the US and Select Models Management in Europe. Harvey began SKN by LH in 2021. She was in ads for Burberry and Micha... | sgx_nifty_67f9ef681bc53e0 | |
1,895,782 | Supercharge Your Debugging Sessions with Telepresence: A Virtual Gateway into Kubernetes | In the world of software development, debugging is an essential and often time-consuming task.... | 0 | 2024-06-24T10:30:20 | https://dev.to/martin_oehlert_8f0620f3ea/supercharge-your-debugging-sessions-with-telepresence-a-virtual-gateway-into-kubernetes-1mk2 | kubernetes, debug, cloud, devops | In the world of software development, debugging is an essential and often time-consuming task. Developers strive to identify and fix issues swiftly to ensure smooth operation and optimal performance. However, traditional debugging methods often come with limitations, particularly when working with complex systems like ... | martin_oehlert_8f0620f3ea |
1,898,720 | Building a Progressive Web App (PWA) with Flutter | Deliver app-like experiences directly in the browser, reaching users on any device. | 0 | 2024-06-24T10:28:19 | https://dev.to/harsh8088/building-a-progressive-web-app-pwa-with-flutter-4pcm | flutter, pwa, web | ---
title: Building a Progressive Web App (PWA) with Flutter
published: true
description: Deliver app-like experiences directly in the browser, reaching users on any device.
tags: flutter, pwa, web
cover_image: https://dev-to-uploads.s3.amazonaws.com/uploads/articles/tdsikcmtgwiofctk2mi1.png
# Use a ratio of 100:42 for... | harsh8088 |
1,898,759 | Add Docker for simple PHP application | Docker is an open-source platform that automates the deployment, scaling, and management of... | 0 | 2024-06-24T10:27:49 | https://dev.to/vimuth7/add-docker-for-simple-php-application-1f11 | Docker is an open-source platform that automates the deployment, scaling, and management of applications by using containerization.
Using Docker for your PHP application offers several benefits:
1. **Consistency**: Docker ensures that your application runs the same way on any system, eliminating "it works on my mach... | vimuth7 | |
1,898,758 | Global Deadlock Resolution in GBase 8c Transactions and Locks | GBase 8c database features mechanisms for deadlock detection and automatic resolution. It comprises... | 0 | 2024-06-24T10:27:26 | https://dev.to/congcong/global-deadlock-resolution-in-gbase-8c-transactions-and-locks-1ndl | GBase 8c database features mechanisms for deadlock detection and automatic resolution. It comprises multiple CNs (Coordinating Nodes) and DN (Data Nodes). Deadlocks can occur within a single CN or DN, or across multiple CNs or DNs. Deadlocks occurring across multiple CNs or DNs are termed global deadlocks, where proces... | congcong | |
1,898,757 | Amazon GuardDuty Malware Protection for Amazon S3 | Amazon GuardDuty Malware Protection for Amazon S3 is a feature that automatically scans newly... | 0 | 2024-06-24T10:27:00 | https://dev.to/aws-builders/amazon-guardduty-malware-protection-for-amazon-s3-2oe1 | aws, security | [Amazon GuardDuty Malware Protection for Amazon S3](https://aws.amazon.com/about-aws/whats-new/2024/06/detect-malware-object-uploads-amazon-s3-guardduty/) is a feature that automatically scans newly uploaded objects in S3 buckets for potential malware. This service provides a seamless, scalable solution to enhance secu... | marklaszlo9 |
1,898,754 | Lambda: Your privacy based Social Media Alternative | Hello dev.to community, My name is EzpieCo (not my real name), and I am the sole creator of Lambda,... | 0 | 2024-06-24T10:25:05 | https://dev.to/ezpieco/lambda-your-privacy-based-social-media-alternative-5e65 | privacy, opensource, socialmedia, webdev | Hello dev.to community,
My name is EzpieCo (not my real name), and I am the sole creator of Lambda, the world's first-ever open-source social media app designed with trust and privacy at its core. If you're tired of social media platforms that invade your privacy and promote unhealthy usage habits, Lambda offers a ref... | ezpieco |
1,807,473 | Langchain with Pinecone vs OpenAI Assistant | Introduction The world of conversational AI and natural language processing (NLP) has seen... | 0 | 2024-06-24T10:23:31 | https://dev.to/ruturajmaggirwar/langchain-with-pinecone-vs-openai-assistant-3l19 | ai, openai, langchain, programming | ## Introduction
The world of conversational AI and natural language processing (NLP) has seen remarkable advancements with tools like Langchain and Pinecone emerging as innovative solutions. Meanwhile, OpenAI's Assistant remains a powerful and popular choice for generating human-like responses. In this blog, we will e... | ruturajmaggirwar |
1,898,752 | The Versatility of Silicone Molds: Beyond the Basics | The Versatility of Silicone Molds: Beyond the Basics When it comes to baking and cooking, one of the... | 0 | 2024-06-24T10:22:19 | https://dev.to/bomans_eopijd_0ecb0581228/the-versatility-of-silicone-molds-beyond-the-basics-3i0k | design | The Versatility of Silicone Molds: Beyond the Basics
When it comes to baking and cooking, one of the most tools that are essential your kitchen is a mold; and while there are many types of molds in the world, silicone molds are becoming increasingly popular. Silicone molds offer a range of advantages over traditional ... | bomans_eopijd_0ecb0581228 |
1,898,751 | Why MongoDB? Exploring the Benefits and Use Cases of a Leading NoSQL Database | Introduction In the realm of database management systems, MongoDB has emerged as a popular choice,... | 0 | 2024-06-24T10:21:39 | https://dev.to/jottyjohn/why-mongodb-exploring-the-benefits-and-use-cases-of-a-leading-nosql-database-2ilk | db, backenddevelopment | **Introduction**
In the realm of database management systems, MongoDB has emerged as a popular choice, especially for applications requiring high scalability, flexibility, and performance. Unlike traditional relational databases, MongoDB is a NoSQL database, designed to handle large volumes of unstructured data. This a... | jottyjohn |
1,898,750 | Getting Started with Docker and Kubernetes Sandboxes (Day 3) | This post builds on the concepts covered in Day 2's video and assumes you already have Docker. If you... | 0 | 2024-06-24T10:21:32 | https://dev.to/emmanuel_oghre_abe292c74f/getting-started-with-docker-and-kubernetes-sandboxes-day-3-4pi4 | This post builds on the concepts covered in Day 2's video and assumes you already have Docker. If you haven't, you can use these resources:
Docker Sandbox: [Link](https://labs.play-with-docker.com/)
Kubernetes Sandbox: [Link](https://labs.play-with-k8s.com/)
Download Docker Desktop: [Link](https://docs.docker.com/get-... | emmanuel_oghre_abe292c74f | |
1,898,748 | CloudFormation vs Terraform: Choosing the Right IaC Tool for Your Needs | In the world of DevOps, Infrastructure as Code (IaC) has become a fundamental practice for managing... | 0 | 2024-06-24T10:20:32 | https://dev.to/devops_den/cloudformation-vs-terraform-choosing-the-right-iac-tool-for-your-needs-mc3 | devops, webdev, beginners, devopsden | In the world of DevOps, Infrastructure as Code (IaC) has become a fundamental practice for managing and provisioning infrastructure through code rather than manual processes. Among the popular IaC tools, AWS CloudFormation and HashiCorp Terraform stand out. Both tools offer powerful capabilities but differ in their app... | devops_den |
1,898,746 | emollergren-portfolio | A post by Eric Möllergren | 0 | 2024-06-24T10:20:24 | https://dev.to/emollergren/emollergren-portfolio-nmn | emollergren | ||
1,898,744 | emollergren-portfolio | A post by Eric Möllergren | 0 | 2024-06-24T10:19:56 | https://dev.to/emollergren/emollergren-portfolio-2cc2 | emollergren | ||
1,898,743 | Expert Relationship Investigation Services in Delhi by City Intelligence | In the bustling metropolis of Delhi, where life moves at a frenetic pace, maintaining trust and... | 0 | 2024-06-24T10:16:22 | https://dev.to/cityintelligence/expert-relationship-investigation-services-in-delhi-by-city-intelligence-3c5b |

In the bustling metropolis of Delhi, where life moves at a frenetic pace, maintaining trust and transparency in relationships can be challenging. City Intelligence, also known as The Clue Hunters, specializes in off... | cityintelligence | |
1,898,742 | CMA Foundation Registration Last Date: Academic Insights | After acceptance into the cma foundation registration last date: Those strong in financial... | 0 | 2024-06-24T10:14:26 | https://dev.to/rudrakshi27/cma-foundation-registration-last-date-academic-insights-3e27 |

After acceptance into the [**cma foundation registration last date**](https://www.studyathome.org/icmai-cma-foundation-registration/): Those strong in financial analysis, cost management, and strategic decision-mak... | rudrakshi27 | |
1,898,741 | grpc vs rest performance comparison | In the world of APIs, there are many different architectural styles for building APIs, and each one... | 0 | 2024-06-24T10:13:48 | https://keploy.io/blog/community/grpc-vs-rest-a-comparative-guide | grpc, technoloyube |
In the world of APIs, there are many different architectural styles for building APIs, and each one has its own benefits, cons, and ideal use cases, but two prominent approaches dominate the landscape: gRPC and REST... | keploy |
1,898,740 | Research methodology | [Set up your research paper in MLA, APA, and Chicago styles with Ondezx expert guidance. At Ondezx,... | 0 | 2024-06-24T10:13:39 | https://dev.to/padmapriyaondezx_109827ea/research-methodology-54jo | researchprocess, phdresearchmethodology | [Set up your research paper in MLA, APA, and Chicago styles with Ondezx expert guidance.
At Ondezx, we offer expert guidance to help you format your research paper in MLA, APA, and Chicago styles. Our team ensures your paper meets the highest academic standards by providing personalized support for title pages, in-text... | padmapriyaondezx_109827ea |
1,898,739 | Mastering Network Security: Configuring Firewalld and Understanding IDS vs. IPS Systems | Introduction Hello, security aficionados! Today, we're diving into the nitty-gritty of... | 0 | 2024-06-24T10:12:00 | https://dev.to/techtobe101/mastering-network-security-configuring-firewalld-and-understanding-ids-vs-ips-systems-3441 | cybersecurity, beginners, techtobe101, learning | ### Introduction
Hello, security aficionados! Today, we're diving into the nitty-gritty of network security. Specifically, we’ll look at configuring Firewalld and understanding the differences between IDS and IPS systems. These topics are essential for anyone serious about a career in cybersecurity.
### Configuring F... | techtobe101 |
1,898,738 | Mastering Cybersecurity Basics: Understanding Security Control Types and Intrusion Detection | Introduction Welcome back, tech enthusiasts! Today, we're diving into some foundational... | 0 | 2024-06-24T10:11:53 | https://dev.to/techtobe101/mastering-cybersecurity-basics-understanding-security-control-types-and-intrusion-detection-1poh | cybersecurity, beginners, techtobe101, learning | ### Introduction
Welcome back, tech enthusiasts! Today, we're diving into some foundational concepts in cybersecurity: security control types and intrusion detection. These are crucial areas that every aspiring cybersecurity professional needs to master. As someone with a passion for teaching cybersecurity, I’m excite... | techtobe101 |
1,898,736 | A Comprehensive Overview of How Firestop Putty Pads Work | Protecting Your Home from Fire with Firestop Putty Pads Fire incidents might happen unexpectedly,... | 0 | 2024-06-24T10:09:52 | https://dev.to/bomans_eopijd_0ecb0581228/a-comprehensive-overview-of-how-firestop-putty-pads-work-1pm8 | design | Protecting Your Home from Fire with Firestop Putty Pads
Fire incidents might happen unexpectedly, and also they might cause massive destruction the property right away. One of the best how to protect your property from fire disasters was by installing Firestop Putty Pads. We will offer you you having a comprehensive o... | bomans_eopijd_0ecb0581228 |
1,898,735 | Taxbhai | All services at one Place www.taxbhai.in We Provide all below services. Trusted and fast... | 0 | 2024-06-24T10:09:32 | https://dev.to/tax_bhai_908628bb36854c66/taxbhai-5g37 | gstservices, incometaxservices, digitalsignature, companyregistration | All services at one Place
[www.taxbhai.in](url)
We Provide all below services.
Trusted and fast Service.
• TDS Returns
• Public Company Registration
• Digital Signature
• GST Return
• Non-Banking Financial Company
• Income Tax Return
• Company Registration
• GST Registration
• Partnership company Registration
• F... | tax_bhai_908628bb36854c66 |
1,898,734 | Typesafe Supabase Flutter Queries | Supabase Flutter Types? In web development, supabase provide you with an API to generate typescript... | 0 | 2024-06-24T10:08:04 | https://dev.to/mmvergara/typesafe-supabase-flutter-queries-2a2j | flutter, supabase, schema, mobile | Supabase Flutter Types? In web development, supabase provide you with an API to generate typescript types to make typesafe queries. But what about for flutter? for dart? That's what this is all about
Yes we can generate dart classes directly from you supabase schema in order to achieve Typesafe Queries Flutter Supabas... | mmvergara |
1,898,728 | Implementing Rate Limiting in API Routes with Express and Next.js | Learn how to prevent API abuse by implementing rate limiting using the express-rate-limit package in a Next.js application. | 0 | 2024-06-24T10:00:43 | https://dev.to/itselftools/implementing-rate-limiting-in-api-routes-with-express-and-nextjs-4ffl | javascript, nextjs, express, api |
At [Itself Tools](https://itselftools.com), we've honed our skills through the development of over 30 projects combining the robust framework capabilities of Next.js and the versatility of Firebase. Through these experiences, we've accumulated a wealth of practical knowledge especially in ensuring the security and eff... | antoineit |
1,898,733 | Pediatric PCD Pharma Company: Revolutionizing Child Health Care with Cutting-Edge Innovations | In the realm of pediatric health care, Pharmaceutical Companies (PCDs) play a crucial role in driving... | 0 | 2024-06-24T10:07:21 | https://dev.to/amzorhealthcare/pediatric-pcd-pharma-company-revolutionizing-child-health-care-with-cutting-edge-innovations-5b6o | In the realm of pediatric health care, Pharmaceutical Companies (PCDs) play a crucial role in driving innovation and breakthroughs in treatment options for children. Our specialized companies focus on developing medications and therapies tailor-made for young patients, addressing their unique needs and challenges. By h... | amzorhealthcare | |
1,898,732 | Add Elements to JavaScript Array | Adding elements to a JavaScript array is a fundamental operation that developers frequently perform.... | 0 | 2024-06-24T10:07:20 | https://dev.to/d8578raj/add-elements-to-javascript-array-31jn | webdev, javascript, array, programming | Adding elements to a JavaScript array is a fundamental operation that developers frequently perform. JavaScript provides multiple methods to accomplish this task, each suitable for different scenarios.
## 1. Add Elements to the End of an Array - [Using `push()` Method](https://www.school247.org/javascript-array-push-m... | d8578raj |
1,898,731 | Dive into the Diversity: An In-Depth Look at Kratom Strains | Kratom, a fascinating botanical native to Southeast Asia, has captured the interest of many for its... | 0 | 2024-06-24T10:05:42 | https://dev.to/adam_751090edd362d5de725d/dive-into-the-diversity-an-in-depth-look-at-kratom-strains-3fi3 | Kratom, a fascinating botanical native to Southeast Asia, has captured the interest of many for its versatile properties. Among the various forms available, Kratom Strains are particularly noteworthy for their distinct characteristics and effects. This article will provide a comprehensive exploration of Kratom Strains,... | adam_751090edd362d5de725d | |
1,898,730 | Everything You Need to Know About Captioning & Subtitling | Introduction In today's diverse and inclusive world, video captioning and subtitling have become... | 0 | 2024-06-24T10:03:20 | https://dev.to/braahmaminternation/everything-you-need-to-know-about-captioning-subtitling-3n45 | captioning, subtitling | **Introduction**
In today's diverse and inclusive world, [video captioning and subtitling](https://www.braahmam.net/blog/everything-you-need-to-know-about-captioning-subtitling ) have become essential tools for enhancing accessibility and engagement across various media platforms. Whether you're a content creator, a vi... | braahmaminternation |
1,898,729 | Open Source Projects from DEV Community Post | PT.1 | Hi Everyone, I’m Antonio, CEO at Litlyx! Recently, I started a discussion where I asked you to... | 0 | 2024-06-24T10:02:19 | https://dev.to/litlyx/open-source-projects-from-dev-community-post-406c | discuss, opensource, beginners, webdev | 
Hi Everyone, I’m Antonio, CEO at [Litlyx](https://litlyx.com)! Recently, I started a discussion where I asked you to share your open source projects. Here’s the link to the [post](https://dev.to/litlyx/show-me-your-open-source-pro... | litlyx |
1,898,716 | Transform Your Business with GPU as a Service | Key Highlights GPU as a Service (GPUaaS or GaaS) enables businesses access... | 0 | 2024-06-24T10:00:00 | https://dev.to/novita_ai/transform-your-business-with-gpu-as-a-service-144l | ## Key Highlights
- GPU as a Service (GPUaaS or GaaS) enables businesses access high-performance computing resources without the need for expensive hardware or complex infrastructure management.
- GaaS leverages the power of graphics processing units (GPUs) to accelerate learning, deep learning, and other data-intensi... | novita_ai | |
1,898,727 | Max Support for Injured and Recovering Knees: The Ultimate Guide to Knee Braces | Injuries and recovery methods frequently test our endurance, both physically and mentally. One place... | 0 | 2024-06-24T09:59:43 | https://dev.to/mahaveer_singh_285b9fed3b/max-support-for-injured-and-recovering-knees-the-ultimate-guide-to-knee-braces-5h01 | braces | Injuries and recovery methods frequently test our endurance, both physically and mentally. One place particularly liable to harm is the knee, a joint crucial for mobility in ordinary sports and sports. Whether or not you are a professional athlete, a weekend warrior, or a person managing a chronic knee condition, the u... | mahaveer_singh_285b9fed3b |
1,898,726 | AI Development Services | We provide expert guidance and develop a comprehensive AI strategy to help organizations identify... | 0 | 2024-06-24T09:57:35 | https://dev.to/thecode_work_seo/ai-development-services-3546 | ai, development, security, softwaredevelopment | We provide expert guidance and develop a comprehensive AI strategy to help organizations identify opportunities, assess AI readiness, and prioritize AI initiatives to achieve their business goals.
Check Out this : https://thecodework.com/ai-development-services/ | thecode_work_seo |
1,898,725 | drtydtydftdr | dfgdfgfd | 0 | 2024-06-24T09:57:00 | https://dev.to/cng_nguynxun_b7370d30/drtydtydftdr-52g1 | dfgdfgfd | cng_nguynxun_b7370d30 | |
1,898,724 | Index Optimization Strategies in GBase 8s: Exploring Performance of Multi-Field Filters in Single-Table Queries (WHERE Clause) | In database queries, filtering a single table using multiple fields is a common operation. However,... | 0 | 2024-06-24T09:55:44 | https://dev.to/congcong/index-optimization-strategies-in-gbase-8s-exploring-performance-of-multi-field-filters-in-single-table-queries-where-clause-3jbm | In database queries, filtering a single table using multiple fields is a common operation. However, without appropriate index support, these queries can become slow. This article explores the impact of indexes on query performance with different combinations of filtering fields by creating a test environment, simulatin... | congcong | |
1,898,723 | Automation - July Challenge Invitation Inside! | Are you ready for the Selenium Challenge? I am thrilled to announce an exciting opportunity for all... | 0 | 2024-06-24T09:55:39 | https://dev.to/magi-magificient/automation-july-challenge-invitation-inside-5927 | challenge, automation, selenium, testing | Are you ready for the Selenium Challenge?
I am thrilled to announce an exciting opportunity for all aspiring software testers and automation enthusiasts!

Testleaf is hosting a **Selenium Challenge** this July with *... | magi-magificient |
1,898,722 | Riyadh’s Top Plastic Surgery Clinics for Your Beauty Needs | In the bustling city of Riyadh, the demand for plastic surgery services continues to rise as... | 0 | 2024-06-24T09:55:18 | https://dev.to/hania_enfieldroyalclini/riyadhs-top-plastic-surgery-clinics-for-your-beauty-needs-31ol | health | In the bustling city of Riyadh, the demand for plastic surgery services continues to rise as individuals seek to enhance their natural beauty. If you’re considering a cosmetic procedure, it’s crucial to choose a reputable plastic surgery clinic in Riyadh ([عيادة الجراحة التجميلية الرياض](https://www.enfieldroyalsaudia.... | hania_enfieldroyalclini |
1,898,721 | Only 1% of Developers Know This React Hook! 🚀 | One lesser-known but powerful concept in React that only a small percentage of developers might be... | 0 | 2024-06-24T09:55:07 | https://dev.to/itsjp/only-1-of-developers-know-this-react-hook-1309 | react, reactjsdevelopment, webdev, javascript | One lesser-known but powerful concept in React that only a small percentage of developers might be aware of is the use of the `useImperativeHandle` hook. This hook allows you to customize the instance value that is exposed when using ref in functional components. Here's an example and explanation:
** Patchkabel ensures secure and efficient connections, ideal for data centers and enterprise networks. Paire... | gbicshop |
1,898,711 | scrap cars orange | Have junk auto cars in Orange County, TX? Get the top scrap car prices in Texas with our dedicated... | 0 | 2024-06-24T09:42:31 | https://dev.to/scrapcars145/scrap-cars-orange-109k | scrap, cars, orange, tx | Have **[junk auto cars in Orange County](https://orangescrap.com/scrap-price-for-junk-cars-texas/)**, TX? Get the top scrap car prices in Texas with our dedicated team of scrap car buyers. | scrapcars145 |
1,898,710 | Meme Monday | Meme Monday! Today's cover image comes from last week's thread. DEV is an inclusive space! Humor in... | 0 | 2024-06-24T09:41:49 | https://dev.to/ben/meme-monday-5b9c | discuss, watercooler, jokes | **Meme Monday!**
Today's cover image comes from [last week's thread](https://dev.to/ben/meme-monday-53am).
DEV is an inclusive space! Humor in poor taste will be downvoted by mods. | ben |
1,898,527 | Transform Your Apps with Daily's WebRTC Video & Audio APIs | Enablex | In today's digital age, integrating real-time communication features such as video and audio calls... | 0 | 2024-06-24T09:41:43 | https://dev.to/yogender_singh_011ebbe493/transform-your-apps-with-dailys-webrtc-video-audio-apis-enablex-43mg | In today's digital age, integrating real-time communication features such as video and audio calls into your applications is no longer a luxury but a necessity. Businesses and developers are constantly seeking robust and efficient solutions to enhance user experience and engagement. This is where Enablex's WebRTC Video... | yogender_singh_011ebbe493 | |
1,898,541 | How to become a better Learner | Don’t be the confused Learner For last 30 years, I meet a lot of confused learners. Who are confused... | 0 | 2024-06-24T07:35:17 | https://dev.to/happy56/how-to-become-a-better-learner-3091 | **Don’t be the confused Learner**
For last 30 years, I meet a lot of confused learners. Who are confused which is the best programming language Java or C++. Then need to know which one is best, he will learn that from the best book on C++ and then he will start working on the project in hand and earn a lot of money. ... | happy56 | |
1,898,709 | Experience Ultimate Relaxation: Discover the Best Spas in Prahladnagar | Prahladnagar, a thriving and upscale area in Ahmedabad, is not just a commercial and residential hub... | 0 | 2024-06-24T09:40:52 | https://dev.to/abitamim_patel_7a906eb289/experience-ultimate-relaxation-discover-the-best-spas-in-prahladnagar-3dh7 | Prahladnagar, a thriving and upscale area in Ahmedabad, is not just a commercial and residential hub but also a prime destination for those seeking luxury and relaxation. The **[spas in Prahladnagar](https://spa.trakky.in/ahmedabad/spas/prahladnagar)** offer a serene escape from the hustle and bustle, providing a wide ... | abitamim_patel_7a906eb289 | |
1,898,708 | All About Vscode - Extensions, Shortcuts & Settings For Flutter Development | Flutter is a fantastic cross-platform UI framework widely used for developing apps. Of course, it... | 0 | 2024-06-24T09:40:30 | https://dev.to/rubengrey/all-about-vscode-extensions-shortcuts-settings-for-flutter-development-3lcn | flutter, mobile | Flutter is a fantastic cross-platform UI framework widely used for developing apps. Of course, it includes lots of options that are easy to create a rich desktop and mobile web app development. When you [hire flutter experts](https://flutteragency.com/hire-flutter-developer/) from Flutter Agency, they will know about V... | rubengrey |
1,898,707 | vaishnaoi southwoods | The Vaishnaoi Southwoods the maker of the remarkable Shamshabad, Hyderabad, villa project Vaishnaoi... | 0 | 2024-06-24T09:37:56 | https://dev.to/vaishnaoisouthwoods/vaishnaoi-southwoods-4dbf | vaishnaoisouthwoods | The [Vaishnaoi Southwoods](https://www.vaishnaoisouthwoods.net.in/) the maker of the remarkable Shamshabad, Hyderabad, villa project Vaishnaoi Southwoods. The project provides superbly built four- and five-bedroom villas. It provides 261 units in a range of sizes to accommodate the needs of each and every occupant. The... | vaishnaoisouthwoods |
1,898,706 | Learn how to create a awesome cards component using HTML & CSS only | In this article you are going to learn some awesome features of CSS by creating this image hover able... | 0 | 2024-06-24T09:37:44 | https://your-codes.vercel.app/create-a-awesome-and-hover-able-card-component-using-html-and-css-only-with-source-code | html, css, ui, frontendchallenge | In this article you are going to learn some awesome features of CSS by creating this image hover able effects
this component is mainly possible because of this css trick
```
.list .item:hover + * {
filter: brigh... | your-ehsan |
1,898,705 | Data Science in Marketing: Unlocking Customer Insights and Personalization | As consumption shifts to the digital age, the average consumer is now just being hit left and right... | 0 | 2024-06-24T09:37:27 | https://dev.to/fizza_c3e734ee2a307cf35e5/data-science-in-marketing-unlocking-customer-insights-and-personalization-2fao | data, marketing, datascience, digital | As consumption shifts to the digital age, the average consumer is now just being hit left and right with marketing messages. Therefore, in order to really excel, business owners need to know their customers better than they currently do. Here is where data science comes in to transform marketing.
Data science helps ma... | fizza_c3e734ee2a307cf35e5 |
1,898,703 | How Nootropics Tablets Can Boost Your Brainpower | In a perfect world, you could take a pill to increase memory, focus, and brainpower. Sounds like... | 0 | 2024-06-24T09:35:11 | https://dev.to/jamesjohnsan/how-nootropics-tablets-can-boost-your-brainpower-10n6 | nootropics, brainpower, boost, health | In a perfect world, you could take a pill to increase memory, focus, and brainpower. Sounds like science fiction. Now that nootropics are more popular, for many people, this is starting to happen. This blog will look at how nootropics tablets can increase your mental capacity and where you can [purchase nootropics tabl... | jamesjohnsan |
1,898,701 | Issue with Currency Display in Odoo QWeb Report (Odoo 17) | Issue with Currency Display in Odoo QWeb... | 0 | 2024-06-24T09:33:21 | https://dev.to/hello_lawrence/issue-with-currency-display-in-odoo-qweb-report-odoo-17-1lkl | {% stackoverflow 78661496 %} | hello_lawrence | |
1,898,700 | DMVNow | DMVNow is an online portal which is specifically designed for business purposes. Its services are... | 0 | 2024-06-24T09:33:10 | https://dev.to/dmvnowclub/dmvnow-2oek | DMVNow is an online portal which is specifically designed for business purposes. Its services are widely consumed by dealerships, fuel tax clients, rental car companies, driving schools, other government agencies, local governments and charities. Additionally, if you register with the agency, you can get advantages of ... | dmvnowclub |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.