Unnamed: 0
int64 0
832k
| id
float64 2.49B
32.1B
| type
stringclasses 1
value | created_at
stringlengths 19
19
| repo
stringlengths 7
112
| repo_url
stringlengths 36
141
| action
stringclasses 3
values | title
stringlengths 1
744
| labels
stringlengths 4
574
| body
stringlengths 9
211k
| index
stringclasses 10
values | text_combine
stringlengths 96
211k
| label
stringclasses 2
values | text
stringlengths 96
188k
| binary_label
int64 0
1
|
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
29,498
| 14,146,240,971
|
IssuesEvent
|
2020-11-10 18:54:53
|
microsoft/TypeScript
|
https://api.github.com/repos/microsoft/TypeScript
|
opened
|
Too many deopts
|
Domain: Performance
|
Tracking issue for https://twitter.com/jasnell/status/1326219768064454656
@jasnell is seeing too many deopts while building with TS + Babel + Webpack.
|
True
|
Too many deopts - Tracking issue for https://twitter.com/jasnell/status/1326219768064454656
@jasnell is seeing too many deopts while building with TS + Babel + Webpack.
|
non_process
|
too many deopts tracking issue for jasnell is seeing too many deopts while building with ts babel webpack
| 0
|
6,547
| 9,635,263,667
|
IssuesEvent
|
2019-05-16 00:18:50
|
googleapis/release-please
|
https://api.github.com/repos/googleapis/release-please
|
closed
|
chore(release): proposal for next release
|
release-candidate type: process
|
_:robot: Here's what the next release of **release-please** would look like._
---
### [1.3.1](https://www.github.com/googleapis/release-please/compare/v1.3.0...v1.3.1) (2019-05-16)
### Bug Fixes
* GitHub issues do not allow 'link comments' ([#92](https://www.github.com/googleapis/release-please/issues/92)) ([fe4cd4f](https://www.github.com/googleapis/release-please/commit/fe4cd4f))
* Node 10 is required for async/await ([#89](https://www.github.com/googleapis/release-please/issues/89)) ([c795eef](https://www.github.com/googleapis/release-please/commit/c795eef))
----------------
**release created at #99**
|
1.0
|
chore(release): proposal for next release - _:robot: Here's what the next release of **release-please** would look like._
---
### [1.3.1](https://www.github.com/googleapis/release-please/compare/v1.3.0...v1.3.1) (2019-05-16)
### Bug Fixes
* GitHub issues do not allow 'link comments' ([#92](https://www.github.com/googleapis/release-please/issues/92)) ([fe4cd4f](https://www.github.com/googleapis/release-please/commit/fe4cd4f))
* Node 10 is required for async/await ([#89](https://www.github.com/googleapis/release-please/issues/89)) ([c795eef](https://www.github.com/googleapis/release-please/commit/c795eef))
----------------
**release created at #99**
|
process
|
chore release proposal for next release robot here s what the next release of release please would look like bug fixes github issues do not allow link comments node is required for async await release created at
| 1
|
15,631
| 19,783,091,410
|
IssuesEvent
|
2022-01-18 00:58:19
|
RobertCraigie/prisma-client-py
|
https://api.github.com/repos/RobertCraigie/prisma-client-py
|
closed
|
Add support for generic generation data
|
kind/improvement process/candidate
|
## Problem
<!-- A clear and concise description of what the problem is. Ex. I'm always frustrated when [...] -->
One area that this is needed for is for custom generators in order to be able to pass custom config options e.g.
```prisma
generator db {
provider = "my-prisma-generator"
my_value = 1
}
```
Will raise an error as `my_value` is not a valid field in the Prisma Client Python config.
Another reason this is needed is to optionally bypass validation checks for python only features such as restricting certain field / model names.
## Suggested solution
<!-- A clear and concise description of what you want to happen. -->
The `Data` model should be refactored to be a generic model instead of a normal pydantic model.
We would then need a method for exposing custom models to the generator, I do not know the best solution for this at the moment.
Should be noted that generic models are python3.7+ only.
|
1.0
|
Add support for generic generation data - ## Problem
<!-- A clear and concise description of what the problem is. Ex. I'm always frustrated when [...] -->
One area that this is needed for is for custom generators in order to be able to pass custom config options e.g.
```prisma
generator db {
provider = "my-prisma-generator"
my_value = 1
}
```
Will raise an error as `my_value` is not a valid field in the Prisma Client Python config.
Another reason this is needed is to optionally bypass validation checks for python only features such as restricting certain field / model names.
## Suggested solution
<!-- A clear and concise description of what you want to happen. -->
The `Data` model should be refactored to be a generic model instead of a normal pydantic model.
We would then need a method for exposing custom models to the generator, I do not know the best solution for this at the moment.
Should be noted that generic models are python3.7+ only.
|
process
|
add support for generic generation data problem one area that this is needed for is for custom generators in order to be able to pass custom config options e g prisma generator db provider my prisma generator my value will raise an error as my value is not a valid field in the prisma client python config another reason this is needed is to optionally bypass validation checks for python only features such as restricting certain field model names suggested solution the data model should be refactored to be a generic model instead of a normal pydantic model we would then need a method for exposing custom models to the generator i do not know the best solution for this at the moment should be noted that generic models are only
| 1
|
16,174
| 20,620,924,823
|
IssuesEvent
|
2022-03-07 17:19:48
|
qgis/QGIS
|
https://api.github.com/repos/qgis/QGIS
|
closed
|
Issue on GDAL/GRASS raster calculator (3.22)
|
Feedback Processing Bug
|
### What is the bug or the crash?
I installed QGIS this week for 3.22, but I was using 3.16.
I tried using the raster calculator GDAL and r.mapcalc.simple, but I had problems with both.
The SAGA and native QGIS raster calculators had no problems.
In this case, I'm calculating the albedo, which varies from 0 to 1.
Could the cause be some missing library?
I did the advanced installation of QGIS.
**UPDATE:** By some reason, GDAL/r.mapcalc.simple are multiplying the real results by 10.000.

### Steps to reproduce the issue
1. Get Landsat 8: Bands 2, 3, 4, 5, 6 and 7.
2. Plugin SCP: LS8 TOAR
3. Cut a region of interest.
4. Open GDAL Raster Calculator:
A > LS8_B2 [...] F > LS8_B7 (TOAR)
Equation: (A * 0.300)+(B * 0.277 )+(C * 0.233)+(D * 0.143)+(E * 0.036)+(F * 0.012)
5. Open GRASS r.mapcalc.simple
A > LS8_B2 [...] F > LS8_B7
Equation: (A * 0.300)+(B * 0.277)+(C * 0.233)+(D * 0.143)+(E * 0.036)+(F * 0.012)
The same result appears in both.
### Versions
<!--StartFragment--><!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0//EN" "http://www.w3.org/TR/REC-html40/strict.dtd">
<html><head><meta http-equiv="Content-Type" content="text/html; charset=utf-8" /><style type="text/css">
p, li { white-space: pre-wrap; }
</style></head><body>
Versão do QGIS | 3.22.4-Białowieża | Código da versão do QGIS | ce8e65e9
-- | -- | -- | --
Qt version | 5.15.2
Versão do Python | 3.9.5
GDAL/OGR version | 3.4.1
PROJ version | 8.2.1
EPSG Registry database version | v10.041 (2021-12-03)
GEOS version | 3.10.2-CAPI-1.16.0
SQLite version | 3.37.2
Versão PDAL | 2.3.0
PostgreSQL client version | 13.0
SpatiaLite version | 5.0.1
QWT version | 6.1.3
Versão QScintilla2 | 2.11.5
OS version | Windows 10 Version 2009
| | |
Active Python plugins
autoSaver | 2.6
ee_plugin | 0.0.4
mapbiomascollection | 1.4
OSMDownloader | 1.0.3
partial_histogram | 1.2
pcraster_tools | 0.2.0
qfieldsync | v4.0.0-beta19
QuickOSM | 2.0.1
quick_map_services | 0.19.28
scpplugin | 2.0
SemiAutomaticClassificationPlugin | 7.10.5
temporalprofiletool | 2.0.3
db_manager | 0.1.20
grassprovider | 2.12.99
MetaSearch | 0.3.5
otbprovider | 2.12.99
processing | 2.12.99
sagaprovider | 2.12.99
</body></html><!--EndFragment-->
### Supported QGIS version
- [x] I'm running a supported QGIS version according to the roadmap.
### New profile
- [X] I tried with a new QGIS profile
### Additional context
_No response_
|
1.0
|
Issue on GDAL/GRASS raster calculator (3.22) - ### What is the bug or the crash?
I installed QGIS this week for 3.22, but I was using 3.16.
I tried using the raster calculator GDAL and r.mapcalc.simple, but I had problems with both.
The SAGA and native QGIS raster calculators had no problems.
In this case, I'm calculating the albedo, which varies from 0 to 1.
Could the cause be some missing library?
I did the advanced installation of QGIS.
**UPDATE:** By some reason, GDAL/r.mapcalc.simple are multiplying the real results by 10.000.

### Steps to reproduce the issue
1. Get Landsat 8: Bands 2, 3, 4, 5, 6 and 7.
2. Plugin SCP: LS8 TOAR
3. Cut a region of interest.
4. Open GDAL Raster Calculator:
A > LS8_B2 [...] F > LS8_B7 (TOAR)
Equation: (A * 0.300)+(B * 0.277 )+(C * 0.233)+(D * 0.143)+(E * 0.036)+(F * 0.012)
5. Open GRASS r.mapcalc.simple
A > LS8_B2 [...] F > LS8_B7
Equation: (A * 0.300)+(B * 0.277)+(C * 0.233)+(D * 0.143)+(E * 0.036)+(F * 0.012)
The same result appears in both.
### Versions
<!--StartFragment--><!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0//EN" "http://www.w3.org/TR/REC-html40/strict.dtd">
<html><head><meta http-equiv="Content-Type" content="text/html; charset=utf-8" /><style type="text/css">
p, li { white-space: pre-wrap; }
</style></head><body>
Versão do QGIS | 3.22.4-Białowieża | Código da versão do QGIS | ce8e65e9
-- | -- | -- | --
Qt version | 5.15.2
Versão do Python | 3.9.5
GDAL/OGR version | 3.4.1
PROJ version | 8.2.1
EPSG Registry database version | v10.041 (2021-12-03)
GEOS version | 3.10.2-CAPI-1.16.0
SQLite version | 3.37.2
Versão PDAL | 2.3.0
PostgreSQL client version | 13.0
SpatiaLite version | 5.0.1
QWT version | 6.1.3
Versão QScintilla2 | 2.11.5
OS version | Windows 10 Version 2009
| | |
Active Python plugins
autoSaver | 2.6
ee_plugin | 0.0.4
mapbiomascollection | 1.4
OSMDownloader | 1.0.3
partial_histogram | 1.2
pcraster_tools | 0.2.0
qfieldsync | v4.0.0-beta19
QuickOSM | 2.0.1
quick_map_services | 0.19.28
scpplugin | 2.0
SemiAutomaticClassificationPlugin | 7.10.5
temporalprofiletool | 2.0.3
db_manager | 0.1.20
grassprovider | 2.12.99
MetaSearch | 0.3.5
otbprovider | 2.12.99
processing | 2.12.99
sagaprovider | 2.12.99
</body></html><!--EndFragment-->
### Supported QGIS version
- [x] I'm running a supported QGIS version according to the roadmap.
### New profile
- [X] I tried with a new QGIS profile
### Additional context
_No response_
|
process
|
issue on gdal grass raster calculator what is the bug or the crash i installed qgis this week for but i was using i tried using the raster calculator gdal and r mapcalc simple but i had problems with both the saga and native qgis raster calculators had no problems in this case i m calculating the albedo which varies from to could the cause be some missing library i did the advanced installation of qgis update by some reason gdal r mapcalc simple are multiplying the real results by steps to reproduce the issue get landsat bands and plugin scp toar cut a region of interest open gdal raster calculator a f toar equation a b c d e f open grass r mapcalc simple a f equation a b c d e f the same result appears in both versions doctype html public dtd html en p li white space pre wrap versão do qgis białowieża código da versão do qgis qt version versão do python gdal ogr version proj version epsg registry database version geos version capi sqlite version versão pdal postgresql client version spatialite version qwt version versão os version windows version active python plugins autosaver ee plugin mapbiomascollection osmdownloader partial histogram pcraster tools qfieldsync quickosm quick map services scpplugin semiautomaticclassificationplugin temporalprofiletool db manager grassprovider metasearch otbprovider processing sagaprovider supported qgis version i m running a supported qgis version according to the roadmap new profile i tried with a new qgis profile additional context no response
| 1
|
16,585
| 21,632,635,914
|
IssuesEvent
|
2022-05-05 11:22:29
|
darktable-org/darktable
|
https://api.github.com/repos/darktable-org/darktable
|
closed
|
color picker in "color calibration" is broken
|
priority: high scope: image processing bug: pending
|
**Describe the bug/issue**
When using the color picker to set the WB the setting is wrong and seems completely off.
Is that only me?
**To Reproduce**
_Please provide detailed steps to reproduce the behaviour, for example:_
1. Go to 'darkroom'
2. Go to 'color calibration' module
3. Click on 'color picker'
4. Select a neutral area in the picture
5. See error, nothing see correct... color completely off and I have `(invalid)` of the left of the color patch next to the color picker.
Tested on many images.
|
1.0
|
color picker in "color calibration" is broken -
**Describe the bug/issue**
When using the color picker to set the WB the setting is wrong and seems completely off.
Is that only me?
**To Reproduce**
_Please provide detailed steps to reproduce the behaviour, for example:_
1. Go to 'darkroom'
2. Go to 'color calibration' module
3. Click on 'color picker'
4. Select a neutral area in the picture
5. See error, nothing see correct... color completely off and I have `(invalid)` of the left of the color patch next to the color picker.
Tested on many images.
|
process
|
color picker in color calibration is broken describe the bug issue when using the color picker to set the wb the setting is wrong and seems completely off is that only me to reproduce please provide detailed steps to reproduce the behaviour for example go to darkroom go to color calibration module click on color picker select a neutral area in the picture see error nothing see correct color completely off and i have invalid of the left of the color patch next to the color picker tested on many images
| 1
|
63,239
| 15,526,624,013
|
IssuesEvent
|
2021-03-13 01:59:54
|
google/mediapipe
|
https://api.github.com/repos/google/mediapipe
|
closed
|
Mediapipe build error
|
stat:awaiting response tensor type:build/install
|
Hey there,
I'm attempting to build mediapipe on a jetson nano and am running into the following build error. It concerns the image_to_tensor_converter_opencv.cc file:
(line) return tensor;
could not convert 'tensor' from 'mediapipe::Tensor' to 'absl::lts_2020_09_23::StatusOrmediapipe::Tensor'
I tried adding a direct conversion in the form of:
return absl::lts_2020_09_23::StatusOrmediapipe::Tensor(std::move(tensor));
but I get a different error saying absl::lts_2020_09_23::StatusOrmediapipe is not declared.
Any help of ideas of what could be causing this would be greatly appreciated!
|
1.0
|
Mediapipe build error - Hey there,
I'm attempting to build mediapipe on a jetson nano and am running into the following build error. It concerns the image_to_tensor_converter_opencv.cc file:
(line) return tensor;
could not convert 'tensor' from 'mediapipe::Tensor' to 'absl::lts_2020_09_23::StatusOrmediapipe::Tensor'
I tried adding a direct conversion in the form of:
return absl::lts_2020_09_23::StatusOrmediapipe::Tensor(std::move(tensor));
but I get a different error saying absl::lts_2020_09_23::StatusOrmediapipe is not declared.
Any help of ideas of what could be causing this would be greatly appreciated!
|
non_process
|
mediapipe build error hey there i m attempting to build mediapipe on a jetson nano and am running into the following build error it concerns the image to tensor converter opencv cc file line return tensor could not convert tensor from mediapipe tensor to absl lts statusormediapipe tensor i tried adding a direct conversion in the form of return absl lts statusormediapipe tensor std move tensor but i get a different error saying absl lts statusormediapipe is not declared any help of ideas of what could be causing this would be greatly appreciated
| 0
|
700,394
| 24,059,341,005
|
IssuesEvent
|
2022-09-16 20:21:31
|
deckhouse/deckhouse
|
https://api.github.com/repos/deckhouse/deckhouse
|
closed
|
[monitoring] incorrect values on the Main/Capacity Planning dashboard when there are Not Ready nodes in the cluster
|
area/monitoring type/bug status/rotten priority/backlog
|
### Preflight Checklist
- [X] I agree to follow the [Code of Conduct](https://github.com/deckhouse/deckhouse/blob/main/CODE_OF_CONDUCT.md) that this project adheres to.
- [X] I have searched the [issue tracker](https://github.com/deckhouse/deckhouse/issues) for an issue that matches the one I want to file, without success.
### Version
v1.32
### Expected Behavior
Resources of Not Ready nodes should not be displayed on the CPU (Allocable CPU Cores)" and "Memory (Allocable Memory) graphs.
### Actual Behavior
The CPU (Allocable CPU Cores) and Memory (Allocable Memory) graphs include Not Ready node resources.
### Steps To Reproduce
_No response_
### Additional Information
_No response_
### Logs
_No response_
|
1.0
|
[monitoring] incorrect values on the Main/Capacity Planning dashboard when there are Not Ready nodes in the cluster - ### Preflight Checklist
- [X] I agree to follow the [Code of Conduct](https://github.com/deckhouse/deckhouse/blob/main/CODE_OF_CONDUCT.md) that this project adheres to.
- [X] I have searched the [issue tracker](https://github.com/deckhouse/deckhouse/issues) for an issue that matches the one I want to file, without success.
### Version
v1.32
### Expected Behavior
Resources of Not Ready nodes should not be displayed on the CPU (Allocable CPU Cores)" and "Memory (Allocable Memory) graphs.
### Actual Behavior
The CPU (Allocable CPU Cores) and Memory (Allocable Memory) graphs include Not Ready node resources.
### Steps To Reproduce
_No response_
### Additional Information
_No response_
### Logs
_No response_
|
non_process
|
incorrect values on the main capacity planning dashboard when there are not ready nodes in the cluster preflight checklist i agree to follow the that this project adheres to i have searched the for an issue that matches the one i want to file without success version expected behavior resources of not ready nodes should not be displayed on the cpu allocable cpu cores and memory allocable memory graphs actual behavior the cpu allocable cpu cores and memory allocable memory graphs include not ready node resources steps to reproduce no response additional information no response logs no response
| 0
|
73,415
| 7,333,743,672
|
IssuesEvent
|
2018-03-05 20:24:03
|
istio/istio
|
https://api.github.com/repos/istio/istio
|
reopened
|
Remove TESTONLY artifacts, and make istioctl work out of the box for pre-releases
|
area/test and release automated-release kind/fixit
|
Having two sets of tar balls and istioctl directories is problematic.
More context: https://groups.google.com/forum/#!topic/istio-dev/qo13rpC2FiA
1. It is confusing and people often picks up the wrong one.
2. The artifacts that we are releasing does not work out of the box.
3. People are testing different artifacts that the one we are releasing.
Instead, can we just push pre-releases also to docker hub, and make pre-release istioctl work out of the box?
|
1.0
|
Remove TESTONLY artifacts, and make istioctl work out of the box for pre-releases - Having two sets of tar balls and istioctl directories is problematic.
More context: https://groups.google.com/forum/#!topic/istio-dev/qo13rpC2FiA
1. It is confusing and people often picks up the wrong one.
2. The artifacts that we are releasing does not work out of the box.
3. People are testing different artifacts that the one we are releasing.
Instead, can we just push pre-releases also to docker hub, and make pre-release istioctl work out of the box?
|
non_process
|
remove testonly artifacts and make istioctl work out of the box for pre releases having two sets of tar balls and istioctl directories is problematic more context it is confusing and people often picks up the wrong one the artifacts that we are releasing does not work out of the box people are testing different artifacts that the one we are releasing instead can we just push pre releases also to docker hub and make pre release istioctl work out of the box
| 0
|
67,222
| 8,109,707,814
|
IssuesEvent
|
2018-08-14 08:32:20
|
zenodo/zenodo
|
https://api.github.com/repos/zenodo/zenodo
|
closed
|
openaire: Make RCD communities easier to find
|
Needs design Triage: Accepted i - OpenAIRE
|
**User story:**
As a RCD-User, I want easily find OpenAIRE RCD Communities in the Zenodo deposit form, so that I can go directly to Zenodo to upload my research instead of going through the OpenAIRE RCD.
Upload form:
- Instead of connect logo display in tiny text: "Part of OpenAIRE Fisheries Community”.
|
1.0
|
openaire: Make RCD communities easier to find - **User story:**
As a RCD-User, I want easily find OpenAIRE RCD Communities in the Zenodo deposit form, so that I can go directly to Zenodo to upload my research instead of going through the OpenAIRE RCD.
Upload form:
- Instead of connect logo display in tiny text: "Part of OpenAIRE Fisheries Community”.
|
non_process
|
openaire make rcd communities easier to find user story as a rcd user i want easily find openaire rcd communities in the zenodo deposit form so that i can go directly to zenodo to upload my research instead of going through the openaire rcd upload form instead of connect logo display in tiny text part of openaire fisheries community”
| 0
|
5,739
| 8,580,726,788
|
IssuesEvent
|
2018-11-13 12:51:57
|
easy-software-ufal/annotations_repos
|
https://api.github.com/repos/easy-software-ufal/annotations_repos
|
opened
|
NakedObjectsGroup/NakedObjectsFramework Unhandled error caused by duplicate column names on TableView attribute
|
ADA C# test wrong processing
|
Issue: `https://github.com/NakedObjectsGroup/NakedObjectsFramework/issues/57`
PR: `https://github.com/NakedObjectsGroup/NakedObjectsFramework/commit/71e7a1c78ca381ad87002888ffa5a5290a49a2d8`
|
1.0
|
NakedObjectsGroup/NakedObjectsFramework Unhandled error caused by duplicate column names on TableView attribute - Issue: `https://github.com/NakedObjectsGroup/NakedObjectsFramework/issues/57`
PR: `https://github.com/NakedObjectsGroup/NakedObjectsFramework/commit/71e7a1c78ca381ad87002888ffa5a5290a49a2d8`
|
process
|
nakedobjectsgroup nakedobjectsframework unhandled error caused by duplicate column names on tableview attribute issue pr
| 1
|
7,487
| 10,578,161,772
|
IssuesEvent
|
2019-10-07 21:50:45
|
ncbo/bioportal-project
|
https://api.github.com/repos/ncbo/bioportal-project
|
closed
|
Can't load SWEET, getting 403 error
|
ontology processing problem
|
There's a ticket for this at https://github.com/ESIPFed/sweet/issues/150, this is to reference that ticket as it affects BioPortal loading of SWEET.
|
1.0
|
Can't load SWEET, getting 403 error - There's a ticket for this at https://github.com/ESIPFed/sweet/issues/150, this is to reference that ticket as it affects BioPortal loading of SWEET.
|
process
|
can t load sweet getting error there s a ticket for this at this is to reference that ticket as it affects bioportal loading of sweet
| 1
|
12,697
| 15,077,358,325
|
IssuesEvent
|
2021-02-05 06:49:25
|
GoogleCloudPlatform/fda-mystudies
|
https://api.github.com/repos/GoogleCloudPlatform/fda-mystudies
|
closed
|
[PM] Unable to download email template
|
Bug P0 Participant manager Process: Fixed Process: Tested QA Process: Tested dev
|
Steps
1. Sites tab > Click on any one of the closed study
2. Navigate to site participant registry
3. Click on Add participant
4. Click on 'Download template'
AR : User is unable to download the template
ER : User should be able to download the email template
[Note : Issue observed only in automated deployment branch]
|
3.0
|
[PM] Unable to download email template - Steps
1. Sites tab > Click on any one of the closed study
2. Navigate to site participant registry
3. Click on Add participant
4. Click on 'Download template'
AR : User is unable to download the template
ER : User should be able to download the email template
[Note : Issue observed only in automated deployment branch]
|
process
|
unable to download email template steps sites tab click on any one of the closed study navigate to site participant registry click on add participant click on download template ar user is unable to download the template er user should be able to download the email template
| 1
|
21,381
| 29,202,229,095
|
IssuesEvent
|
2023-05-21 00:37:02
|
devssa/onde-codar-em-salvador
|
https://api.github.com/repos/devssa/onde-codar-em-salvador
|
closed
|
[Remoto] Product Owner na Coodesh
|
SALVADOR GESTÃO DE PROJETOS JIRA REQUISITOS REMOTO PROCESSOS GITHUB UMA POWER BI APIs NEGÓCIOS PRODUCT OWNER Stale
|
## Descrição da vaga:
Esta é uma vaga de um parceiro da plataforma Coodesh, ao candidatar-se você terá acesso as informações completas sobre a empresa e benefícios.
Fique atento ao redirecionamento que vai te levar para uma url [https://coodesh.com](https://coodesh.com/vagas/product-owner-110500694?utm_source=github&utm_medium=devssa-onde-codar-em-salvador&modal=open) com o pop-up personalizado de candidatura. 👋
<p>A <strong>Techsocial</strong> está em busca de <strong><ins>Product Owner</ins></strong> para compor seu time!</p>
<p></p>
<p>Somos uma empresa de Soluções Tecnológicas, que busca transformar os dados e informações de nossos clientes em resultados. Evoluímos a partir de consultoria em Gestão Empresarial, somando as múltiplas competências e experiência de nossos profissionais às inovações tecnológicas. A Tech é uma empresa inovadora! Desenvolvemos e aportamos inteligência em softwares, aplicativos, RPAs, APIs entre outras soluções digitais. </p>
<p><strong>Responsabilidades:</strong></p>
<ul>
<li>Entendimento dos módulos do nossa Plataforma; </li>
<li>Conhecimento dos nossos negócios e suas peculiaridades;</li>
<li>Identificação de gaps e oportunidades de melhoria; </li>
<li>Auxílio no mapeamento do processo e levantamento de requisitos de mudanças;</li>
<li>Confecção de tickets de melhoria alinhado ao time de processos; </li>
<li>Apresentação e revisão de tickets junto ao time de desenvolvimento; </li>
<li>Definição de prioridades de implementação; </li>
<li>Identificação de interfaces do(s) módulo(s) que representa para que requisitos e regras não sejam alterados sem alinhamento e definição com outros módulos, etc.</li>
</ul>
## Techsocial:
<p>Somos uma empresa de Soluções Tecnológicas, que busca transformar os dados e informações de nossos clientes em resultados. Evoluímos a partir de consultoria em Gestão Empresarial, somando as múltiplas competências e experiência de nossos profissionais às inovações tecnológicas.</p>
<p>A Tech é uma empresa inovadora! Desenvolvemos e aportamos inteligência em softwares, aplicativos, RPAs, APIs entre outras soluções digitais. Nossa missão é simplificar os processos de nossos clientes por meio da tecnologia e estruturar grandes bancos de dados para garimparmos e lapidarmos as melhores informações para as empresas.</p><a href='https://coodesh.com/empresas/techsocial-tecnologia-e-consultoria-ltda'>Veja mais no site</a>
## Habilidades:
- JIRA
- Análise de requisitos
- Gestão e Negociação com Cliente
## Local:
100% Remoto
## Requisitos:
- Conhecimento em Levantamento de requisitos;
- Mapeamento de Processos;
- Experiência em Gestão de Projetos;
- Experiência em Gestão de Produtos.
## Diferenciais:
- Power BI;
- Experiência na Plataforma Jira.
## Benefícios:
- Convênio Médico;
- Trabalho Remoto.
## Como se candidatar:
Candidatar-se exclusivamente através da plataforma Coodesh no link a seguir: [Product Owner na Techsocial](https://coodesh.com/vagas/product-owner-110500694?utm_source=github&utm_medium=devssa-onde-codar-em-salvador&modal=open)
Após candidatar-se via plataforma Coodesh e validar o seu login, você poderá acompanhar e receber todas as interações do processo por lá. Utilize a opção **Pedir Feedback** entre uma etapa e outra na vaga que se candidatou. Isso fará com que a pessoa **Recruiter** responsável pelo processo na empresa receba a notificação.
## Labels
#### Alocação
Remoto
#### Categoria
Gestão em TI
|
1.0
|
[Remoto] Product Owner na Coodesh - ## Descrição da vaga:
Esta é uma vaga de um parceiro da plataforma Coodesh, ao candidatar-se você terá acesso as informações completas sobre a empresa e benefícios.
Fique atento ao redirecionamento que vai te levar para uma url [https://coodesh.com](https://coodesh.com/vagas/product-owner-110500694?utm_source=github&utm_medium=devssa-onde-codar-em-salvador&modal=open) com o pop-up personalizado de candidatura. 👋
<p>A <strong>Techsocial</strong> está em busca de <strong><ins>Product Owner</ins></strong> para compor seu time!</p>
<p></p>
<p>Somos uma empresa de Soluções Tecnológicas, que busca transformar os dados e informações de nossos clientes em resultados. Evoluímos a partir de consultoria em Gestão Empresarial, somando as múltiplas competências e experiência de nossos profissionais às inovações tecnológicas. A Tech é uma empresa inovadora! Desenvolvemos e aportamos inteligência em softwares, aplicativos, RPAs, APIs entre outras soluções digitais. </p>
<p><strong>Responsabilidades:</strong></p>
<ul>
<li>Entendimento dos módulos do nossa Plataforma; </li>
<li>Conhecimento dos nossos negócios e suas peculiaridades;</li>
<li>Identificação de gaps e oportunidades de melhoria; </li>
<li>Auxílio no mapeamento do processo e levantamento de requisitos de mudanças;</li>
<li>Confecção de tickets de melhoria alinhado ao time de processos; </li>
<li>Apresentação e revisão de tickets junto ao time de desenvolvimento; </li>
<li>Definição de prioridades de implementação; </li>
<li>Identificação de interfaces do(s) módulo(s) que representa para que requisitos e regras não sejam alterados sem alinhamento e definição com outros módulos, etc.</li>
</ul>
## Techsocial:
<p>Somos uma empresa de Soluções Tecnológicas, que busca transformar os dados e informações de nossos clientes em resultados. Evoluímos a partir de consultoria em Gestão Empresarial, somando as múltiplas competências e experiência de nossos profissionais às inovações tecnológicas.</p>
<p>A Tech é uma empresa inovadora! Desenvolvemos e aportamos inteligência em softwares, aplicativos, RPAs, APIs entre outras soluções digitais. Nossa missão é simplificar os processos de nossos clientes por meio da tecnologia e estruturar grandes bancos de dados para garimparmos e lapidarmos as melhores informações para as empresas.</p><a href='https://coodesh.com/empresas/techsocial-tecnologia-e-consultoria-ltda'>Veja mais no site</a>
## Habilidades:
- JIRA
- Análise de requisitos
- Gestão e Negociação com Cliente
## Local:
100% Remoto
## Requisitos:
- Conhecimento em Levantamento de requisitos;
- Mapeamento de Processos;
- Experiência em Gestão de Projetos;
- Experiência em Gestão de Produtos.
## Diferenciais:
- Power BI;
- Experiência na Plataforma Jira.
## Benefícios:
- Convênio Médico;
- Trabalho Remoto.
## Como se candidatar:
Candidatar-se exclusivamente através da plataforma Coodesh no link a seguir: [Product Owner na Techsocial](https://coodesh.com/vagas/product-owner-110500694?utm_source=github&utm_medium=devssa-onde-codar-em-salvador&modal=open)
Após candidatar-se via plataforma Coodesh e validar o seu login, você poderá acompanhar e receber todas as interações do processo por lá. Utilize a opção **Pedir Feedback** entre uma etapa e outra na vaga que se candidatou. Isso fará com que a pessoa **Recruiter** responsável pelo processo na empresa receba a notificação.
## Labels
#### Alocação
Remoto
#### Categoria
Gestão em TI
|
process
|
product owner na coodesh descrição da vaga esta é uma vaga de um parceiro da plataforma coodesh ao candidatar se você terá acesso as informações completas sobre a empresa e benefícios fique atento ao redirecionamento que vai te levar para uma url com o pop up personalizado de candidatura 👋 a techsocial está em busca de product owner para compor seu time somos uma empresa de soluções tecnológicas que busca transformar os dados e informações de nossos clientes em resultados evoluímos a partir de consultoria em gestão empresarial somando as múltiplas competências e experiência de nossos profissionais às inovações tecnológicas a tech é uma empresa inovadora desenvolvemos e aportamos inteligência em softwares aplicativos rpas apis entre outras soluções digitais nbsp responsabilidades entendimento dos módulos do nossa plataforma nbsp conhecimento dos nossos negócios e suas peculiaridades identificação de gaps e oportunidades de melhoria nbsp auxílio no mapeamento do processo e levantamento de requisitos de mudanças confecção de tickets de melhoria alinhado ao time de processos nbsp apresentação e revisão de tickets junto ao time de desenvolvimento nbsp definição de prioridades de implementação nbsp identificação de interfaces do s módulo s que representa para que requisitos e regras não sejam alterados sem alinhamento e definição com outros módulos etc techsocial somos uma empresa de soluções tecnológicas que busca transformar os dados e informações de nossos clientes em resultados evoluímos a partir de consultoria em gestão empresarial somando as múltiplas competências e experiência de nossos profissionais às inovações tecnológicas a tech é uma empresa inovadora desenvolvemos e aportamos inteligência em softwares aplicativos rpas apis entre outras soluções digitais nossa missão é simplificar os processos de nossos clientes por meio da tecnologia e estruturar grandes bancos de dados para garimparmos e lapidarmos as melhores informações para as empresas habilidades jira análise de requisitos gestão e negociação com cliente local remoto requisitos conhecimento em levantamento de requisitos mapeamento de processos experiência em gestão de projetos experiência em gestão de produtos diferenciais power bi experiência na plataforma jira benefícios convênio médico trabalho remoto como se candidatar candidatar se exclusivamente através da plataforma coodesh no link a seguir após candidatar se via plataforma coodesh e validar o seu login você poderá acompanhar e receber todas as interações do processo por lá utilize a opção pedir feedback entre uma etapa e outra na vaga que se candidatou isso fará com que a pessoa recruiter responsável pelo processo na empresa receba a notificação labels alocação remoto categoria gestão em ti
| 1
|
681,386
| 23,308,902,809
|
IssuesEvent
|
2022-08-08 06:05:09
|
OWASP/threat-dragon
|
https://api.github.com/repos/OWASP/threat-dragon
|
closed
|
Docker hub login failing
|
bug version-2.0 blocker Priority
|
**Describe the bug**
The build_docker_image pipeline job fails at the Login to Docker Hub stage:
```
0s
Run docker/login-action@v1
with:
ecr: auto
logout: true
env:
image_name: threatdragon/owasp-threat-dragon:1efb63a4b1c930775770c5a59180e12f9ae733a8
Error: Username and password required
```
**Expected behaviour**
This is the yaml code
```
- name: Login to Docker Hub
uses: docker/login-action@v1
with:
username: ${{ secrets.DOCKERHUB_USERNAME }}
password: ${{ secrets.DOCKERHUB_TOKEN }}
```
probably the DOCKERHUB_TOKEN needs refreshing?
**Environment**
- Version: main branch
- Platform: any
- OS: any
- Browser: any
**To Reproduce**
See pipeline results: https://github.com/OWASP/threat-dragon/runs/7687274812?check_suite_focus=true
**Any additional context, screenshots, etc**
<img width="736" alt="Screenshot 2022-08-05 at 10 42 52" src="https://user-images.githubusercontent.com/29352392/183050892-b503f593-8b4c-447d-a03b-cd58d850f420.png">
|
1.0
|
Docker hub login failing - **Describe the bug**
The build_docker_image pipeline job fails at the Login to Docker Hub stage:
```
0s
Run docker/login-action@v1
with:
ecr: auto
logout: true
env:
image_name: threatdragon/owasp-threat-dragon:1efb63a4b1c930775770c5a59180e12f9ae733a8
Error: Username and password required
```
**Expected behaviour**
This is the yaml code
```
- name: Login to Docker Hub
uses: docker/login-action@v1
with:
username: ${{ secrets.DOCKERHUB_USERNAME }}
password: ${{ secrets.DOCKERHUB_TOKEN }}
```
probably the DOCKERHUB_TOKEN needs refreshing?
**Environment**
- Version: main branch
- Platform: any
- OS: any
- Browser: any
**To Reproduce**
See pipeline results: https://github.com/OWASP/threat-dragon/runs/7687274812?check_suite_focus=true
**Any additional context, screenshots, etc**
<img width="736" alt="Screenshot 2022-08-05 at 10 42 52" src="https://user-images.githubusercontent.com/29352392/183050892-b503f593-8b4c-447d-a03b-cd58d850f420.png">
|
non_process
|
docker hub login failing describe the bug the build docker image pipeline job fails at the login to docker hub stage run docker login action with ecr auto logout true env image name threatdragon owasp threat dragon error username and password required expected behaviour this is the yaml code name login to docker hub uses docker login action with username secrets dockerhub username password secrets dockerhub token probably the dockerhub token needs refreshing environment version main branch platform any os any browser any to reproduce see pipeline results any additional context screenshots etc img width alt screenshot at src
| 0
|
156,416
| 19,861,771,070
|
IssuesEvent
|
2022-01-22 01:03:19
|
MValle21/lamby_site
|
https://api.github.com/repos/MValle21/lamby_site
|
opened
|
CVE-2021-41098 (High) detected in nokogiri-1.10.5.gem
|
security vulnerability
|
## CVE-2021-41098 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>nokogiri-1.10.5.gem</b></p></summary>
<p>Nokogiri (鋸) is an HTML, XML, SAX, and Reader parser. Among
Nokogiri's many features is the ability to search documents via XPath
or CSS3 selectors.</p>
<p>Library home page: <a href="https://rubygems.org/gems/nokogiri-1.10.5.gem">https://rubygems.org/gems/nokogiri-1.10.5.gem</a></p>
<p>
Dependency Hierarchy:
- sass-rails-5.0.7.gem (Root Library)
- sprockets-rails-3.2.1.gem
- actionpack-5.2.3.gem
- rails-dom-testing-2.0.3.gem
- :x: **nokogiri-1.10.5.gem** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Nokogiri is a Rubygem providing HTML, XML, SAX, and Reader parsers with XPath and CSS selector support. In Nokogiri v1.12.4 and earlier, on JRuby only, the SAX parser resolves external entities by default. Users of Nokogiri on JRuby who parse untrusted documents using any of these classes are affected: Nokogiri::XML::SAX::Parse, Nokogiri::HTML4::SAX::Parser or its alias Nokogiri::HTML::SAX::Parser, Nokogiri::XML::SAX::PushParser, and Nokogiri::HTML4::SAX::PushParser or its alias Nokogiri::HTML::SAX::PushParser. JRuby users should upgrade to Nokogiri v1.12.5 or later to receive a patch for this issue. There are no workarounds available for v1.12.4 or earlier. CRuby users are not affected.
<p>Publish Date: 2021-09-27
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-41098>CVE-2021-41098</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-41098">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-41098</a></p>
<p>Release Date: 2021-09-27</p>
<p>Fix Resolution: nokogiri - 1.12.5</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Ruby","packageName":"nokogiri","packageVersion":"1.10.5","packageFilePaths":[null],"isTransitiveDependency":true,"dependencyTree":"sass-rails:5.0.7;sprockets-rails:3.2.1;actionpack:5.2.3;rails-dom-testing:2.0.3;nokogiri:1.10.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"nokogiri - 1.12.5","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-41098","vulnerabilityDetails":"Nokogiri is a Rubygem providing HTML, XML, SAX, and Reader parsers with XPath and CSS selector support. In Nokogiri v1.12.4 and earlier, on JRuby only, the SAX parser resolves external entities by default. Users of Nokogiri on JRuby who parse untrusted documents using any of these classes are affected: Nokogiri::XML::SAX::Parse, Nokogiri::HTML4::SAX::Parser or its alias Nokogiri::HTML::SAX::Parser, Nokogiri::XML::SAX::PushParser, and Nokogiri::HTML4::SAX::PushParser or its alias Nokogiri::HTML::SAX::PushParser. JRuby users should upgrade to Nokogiri v1.12.5 or later to receive a patch for this issue. There are no workarounds available for v1.12.4 or earlier. CRuby users are not affected.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-41098","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> -->
|
True
|
CVE-2021-41098 (High) detected in nokogiri-1.10.5.gem - ## CVE-2021-41098 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>nokogiri-1.10.5.gem</b></p></summary>
<p>Nokogiri (鋸) is an HTML, XML, SAX, and Reader parser. Among
Nokogiri's many features is the ability to search documents via XPath
or CSS3 selectors.</p>
<p>Library home page: <a href="https://rubygems.org/gems/nokogiri-1.10.5.gem">https://rubygems.org/gems/nokogiri-1.10.5.gem</a></p>
<p>
Dependency Hierarchy:
- sass-rails-5.0.7.gem (Root Library)
- sprockets-rails-3.2.1.gem
- actionpack-5.2.3.gem
- rails-dom-testing-2.0.3.gem
- :x: **nokogiri-1.10.5.gem** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Nokogiri is a Rubygem providing HTML, XML, SAX, and Reader parsers with XPath and CSS selector support. In Nokogiri v1.12.4 and earlier, on JRuby only, the SAX parser resolves external entities by default. Users of Nokogiri on JRuby who parse untrusted documents using any of these classes are affected: Nokogiri::XML::SAX::Parse, Nokogiri::HTML4::SAX::Parser or its alias Nokogiri::HTML::SAX::Parser, Nokogiri::XML::SAX::PushParser, and Nokogiri::HTML4::SAX::PushParser or its alias Nokogiri::HTML::SAX::PushParser. JRuby users should upgrade to Nokogiri v1.12.5 or later to receive a patch for this issue. There are no workarounds available for v1.12.4 or earlier. CRuby users are not affected.
<p>Publish Date: 2021-09-27
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-41098>CVE-2021-41098</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-41098">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-41098</a></p>
<p>Release Date: 2021-09-27</p>
<p>Fix Resolution: nokogiri - 1.12.5</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Ruby","packageName":"nokogiri","packageVersion":"1.10.5","packageFilePaths":[null],"isTransitiveDependency":true,"dependencyTree":"sass-rails:5.0.7;sprockets-rails:3.2.1;actionpack:5.2.3;rails-dom-testing:2.0.3;nokogiri:1.10.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"nokogiri - 1.12.5","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-41098","vulnerabilityDetails":"Nokogiri is a Rubygem providing HTML, XML, SAX, and Reader parsers with XPath and CSS selector support. In Nokogiri v1.12.4 and earlier, on JRuby only, the SAX parser resolves external entities by default. Users of Nokogiri on JRuby who parse untrusted documents using any of these classes are affected: Nokogiri::XML::SAX::Parse, Nokogiri::HTML4::SAX::Parser or its alias Nokogiri::HTML::SAX::Parser, Nokogiri::XML::SAX::PushParser, and Nokogiri::HTML4::SAX::PushParser or its alias Nokogiri::HTML::SAX::PushParser. JRuby users should upgrade to Nokogiri v1.12.5 or later to receive a patch for this issue. There are no workarounds available for v1.12.4 or earlier. CRuby users are not affected.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-41098","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> -->
|
non_process
|
cve high detected in nokogiri gem cve high severity vulnerability vulnerable library nokogiri gem nokogiri 鋸 is an html xml sax and reader parser among nokogiri s many features is the ability to search documents via xpath or selectors library home page a href dependency hierarchy sass rails gem root library sprockets rails gem actionpack gem rails dom testing gem x nokogiri gem vulnerable library found in base branch master vulnerability details nokogiri is a rubygem providing html xml sax and reader parsers with xpath and css selector support in nokogiri and earlier on jruby only the sax parser resolves external entities by default users of nokogiri on jruby who parse untrusted documents using any of these classes are affected nokogiri xml sax parse nokogiri sax parser or its alias nokogiri html sax parser nokogiri xml sax pushparser and nokogiri sax pushparser or its alias nokogiri html sax pushparser jruby users should upgrade to nokogiri or later to receive a patch for this issue there are no workarounds available for or earlier cruby users are not affected publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution nokogiri isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree sass rails sprockets rails actionpack rails dom testing nokogiri isminimumfixversionavailable true minimumfixversion nokogiri isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails nokogiri is a rubygem providing html xml sax and reader parsers with xpath and css selector support in nokogiri and earlier on jruby only the sax parser resolves external entities by default users of nokogiri on jruby who parse untrusted documents using any of these classes are affected nokogiri xml sax parse nokogiri sax parser or its alias nokogiri html sax parser nokogiri xml sax pushparser and nokogiri sax pushparser or its alias nokogiri html sax pushparser jruby users should upgrade to nokogiri or later to receive a patch for this issue there are no workarounds available for or earlier cruby users are not affected vulnerabilityurl
| 0
|
196,762
| 22,534,042,079
|
IssuesEvent
|
2022-06-25 01:04:24
|
ChoeMinji/redis-6.2.3
|
https://api.github.com/repos/ChoeMinji/redis-6.2.3
|
opened
|
CVE-2022-33105 (Medium) detected in redis6.2.6
|
security vulnerability
|
## CVE-2022-33105 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>redis6.2.6</b></p></summary>
<p>
<p>Redis is an in-memory database that persists on disk. The data model is key-value, but many different kind of values are supported: Strings, Lists, Sets, Sorted Sets, Hashes, Streams, HyperLogLogs, Bitmaps.</p>
<p>Library home page: <a href=https://github.com/redis/redis.git>https://github.com/redis/redis.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/ChoeMinji/redis-6.2.3/commit/5b7aad699eab111b003a1a58082434041ce3e008">5b7aad699eab111b003a1a58082434041ce3e008</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/src/t_stream.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Redis v7.0 was discovered to contain a memory leak via the component streamGetEdgeID.
<p>Publish Date: 2022-06-23
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-33105>CVE-2022-33105</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-06-23</p>
<p>Fix Resolution: 7.0.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2022-33105 (Medium) detected in redis6.2.6 - ## CVE-2022-33105 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>redis6.2.6</b></p></summary>
<p>
<p>Redis is an in-memory database that persists on disk. The data model is key-value, but many different kind of values are supported: Strings, Lists, Sets, Sorted Sets, Hashes, Streams, HyperLogLogs, Bitmaps.</p>
<p>Library home page: <a href=https://github.com/redis/redis.git>https://github.com/redis/redis.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/ChoeMinji/redis-6.2.3/commit/5b7aad699eab111b003a1a58082434041ce3e008">5b7aad699eab111b003a1a58082434041ce3e008</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/src/t_stream.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Redis v7.0 was discovered to contain a memory leak via the component streamGetEdgeID.
<p>Publish Date: 2022-06-23
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-33105>CVE-2022-33105</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-06-23</p>
<p>Fix Resolution: 7.0.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_process
|
cve medium detected in cve medium severity vulnerability vulnerable library redis is an in memory database that persists on disk the data model is key value but many different kind of values are supported strings lists sets sorted sets hashes streams hyperloglogs bitmaps library home page a href found in head commit a href found in base branch master vulnerable source files src t stream c vulnerability details redis was discovered to contain a memory leak via the component streamgetedgeid publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution step up your open source security game with mend
| 0
|
63,098
| 26,255,903,817
|
IssuesEvent
|
2023-01-06 00:39:28
|
chris9091/Fleksa-Monitor-2
|
https://api.github.com/repos/chris9091/Fleksa-Monitor-2
|
opened
|
🛑 Gasthof Zum Bahnhof Lieferservice is down
|
status gasthof-zum-bahnhof-lieferservice
|
In [`b28e653`](https://github.com/chris9091/Fleksa-Monitor-2/commit/b28e65377c1e3d5b1ad87a33e4c9eee76514d7eb
), Gasthof Zum Bahnhof Lieferservice (https://gasthofgaum.de) was **down**:
- HTTP code: 0
- Response time: 0 ms
|
1.0
|
🛑 Gasthof Zum Bahnhof Lieferservice is down - In [`b28e653`](https://github.com/chris9091/Fleksa-Monitor-2/commit/b28e65377c1e3d5b1ad87a33e4c9eee76514d7eb
), Gasthof Zum Bahnhof Lieferservice (https://gasthofgaum.de) was **down**:
- HTTP code: 0
- Response time: 0 ms
|
non_process
|
🛑 gasthof zum bahnhof lieferservice is down in gasthof zum bahnhof lieferservice was down http code response time ms
| 0
|
247,644
| 7,921,531,762
|
IssuesEvent
|
2018-07-05 07:51:52
|
kuzzleio/sdk-go
|
https://api.github.com/repos/kuzzleio/sdk-go
|
closed
|
crash when trying to deleteUser with options
|
bug priority-high
|
crash when trying to deleteUser with options
## Expected Behavior
Should not crash :)
## Current Behavior
See stack trace in comments
## Steps to Reproduce
Use the following code snippet with cpp sdk:
```cpp
kuzzle_request req = {0};
req.controller = "security";
req.action = "deleteUser";
req.id = user_id.c_str();
query_options options = {0};
options.refresh = (char *)"wait_for";
kuzzle->query(&req, &options);
```
|
1.0
|
crash when trying to deleteUser with options - crash when trying to deleteUser with options
## Expected Behavior
Should not crash :)
## Current Behavior
See stack trace in comments
## Steps to Reproduce
Use the following code snippet with cpp sdk:
```cpp
kuzzle_request req = {0};
req.controller = "security";
req.action = "deleteUser";
req.id = user_id.c_str();
query_options options = {0};
options.refresh = (char *)"wait_for";
kuzzle->query(&req, &options);
```
|
non_process
|
crash when trying to deleteuser with options crash when trying to deleteuser with options expected behavior should not crash current behavior see stack trace in comments steps to reproduce use the following code snippet with cpp sdk cpp kuzzle request req req controller security req action deleteuser req id user id c str query options options options refresh char wait for kuzzle query req options
| 0
|
209,261
| 23,705,957,146
|
IssuesEvent
|
2022-08-30 01:08:17
|
Nivaskumark/kernel_v4.1.15
|
https://api.github.com/repos/Nivaskumark/kernel_v4.1.15
|
closed
|
CVE-2016-0617 (Medium) detected in linux-stable-rtv4.1.33 - autoclosed
|
security vulnerability
|
## CVE-2016-0617 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Nivaskumark/kernel_v4.1.15/commit/00db4e8795bcbec692fb60b19160bdd763ad42e3">00db4e8795bcbec692fb60b19160bdd763ad42e3</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Unspecified vulnerability in the kernel-uek component in Oracle Linux 6 allows local users to affect availability via unknown vectors.
<p>Publish Date: 2016-09-30
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-0617>CVE-2016-0617</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://www.securitytracker.com/id/1034968">http://www.securitytracker.com/id/1034968</a></p>
<p>Fix Resolution: The vendor has issued a source code fix, available at:
https://git.kernel.org/cgit/linux/kernel/git/torvalds/linux.git/commit/?id=9aacdd354d197ad64685941b36d28ea20ab88757</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2016-0617 (Medium) detected in linux-stable-rtv4.1.33 - autoclosed - ## CVE-2016-0617 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Nivaskumark/kernel_v4.1.15/commit/00db4e8795bcbec692fb60b19160bdd763ad42e3">00db4e8795bcbec692fb60b19160bdd763ad42e3</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Unspecified vulnerability in the kernel-uek component in Oracle Linux 6 allows local users to affect availability via unknown vectors.
<p>Publish Date: 2016-09-30
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-0617>CVE-2016-0617</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://www.securitytracker.com/id/1034968">http://www.securitytracker.com/id/1034968</a></p>
<p>Fix Resolution: The vendor has issued a source code fix, available at:
https://git.kernel.org/cgit/linux/kernel/git/torvalds/linux.git/commit/?id=9aacdd354d197ad64685941b36d28ea20ab88757</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_process
|
cve medium detected in linux stable autoclosed cve medium severity vulnerability vulnerable library linux stable julia cartwright s fork of linux stable rt git library home page a href found in head commit a href found in base branch master vulnerable source files vulnerability details unspecified vulnerability in the kernel uek component in oracle linux allows local users to affect availability via unknown vectors publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href fix resolution the vendor has issued a source code fix available at step up your open source security game with whitesource
| 0
|
267,915
| 23,332,372,548
|
IssuesEvent
|
2022-08-09 06:55:07
|
tgstation/tgstation
|
https://api.github.com/repos/tgstation/tgstation
|
closed
|
one of the bible skins has no sprite in your inventory/is invisible
|
Sprites Bug Tested/Reproduced
|
Round ID: 121742
I was a latejoin chaplain, and since we already had a chaplain in the round, my starting bible changed sprite to match theirs. I wasn't able to get the roundstart chaplain to tell me what skin they chose for their bible, but my bible's sprite in my inventory was invisible.
|
1.0
|
one of the bible skins has no sprite in your inventory/is invisible - Round ID: 121742
I was a latejoin chaplain, and since we already had a chaplain in the round, my starting bible changed sprite to match theirs. I wasn't able to get the roundstart chaplain to tell me what skin they chose for their bible, but my bible's sprite in my inventory was invisible.
|
non_process
|
one of the bible skins has no sprite in your inventory is invisible round id i was a latejoin chaplain and since we already had a chaplain in the round my starting bible changed sprite to match theirs i wasn t able to get the roundstart chaplain to tell me what skin they chose for their bible but my bible s sprite in my inventory was invisible
| 0
|
62,374
| 14,656,488,874
|
IssuesEvent
|
2020-12-28 13:32:20
|
fu1771695yongxie/mermaid
|
https://api.github.com/repos/fu1771695yongxie/mermaid
|
opened
|
CVE-2019-6286 (Medium) detected in opennmsopennms-source-26.0.0-1, node-sass-4.14.1.tgz
|
security vulnerability
|
## CVE-2019-6286 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>opennmsopennms-source-26.0.0-1</b>, <b>node-sass-4.14.1.tgz</b></p></summary>
<p>
<details><summary><b>node-sass-4.14.1.tgz</b></p></summary>
<p>Wrapper around libsass</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-sass/-/node-sass-4.14.1.tgz">https://registry.npmjs.org/node-sass/-/node-sass-4.14.1.tgz</a></p>
<p>Path to dependency file: mermaid/package.json</p>
<p>Path to vulnerable library: mermaid/node_modules/node-sass/package.json</p>
<p>
Dependency Hierarchy:
- :x: **node-sass-4.14.1.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/fu1771695yongxie/mermaid/commit/f404b1690800300ea40a497194988ac4cb3977f7">f404b1690800300ea40a497194988ac4cb3977f7</a></p>
<p>Found in base branch: <b>develop</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In LibSass 3.5.5, a heap-based buffer over-read exists in Sass::Prelexer::skip_over_scopes in prelexer.hpp when called from Sass::Parser::parse_import(), a similar issue to CVE-2018-11693.
<p>Publish Date: 2019-01-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-6286>CVE-2019-6286</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-6286">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-6286</a></p>
<p>Release Date: 2019-08-06</p>
<p>Fix Resolution: LibSass - 3.6.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2019-6286 (Medium) detected in opennmsopennms-source-26.0.0-1, node-sass-4.14.1.tgz - ## CVE-2019-6286 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>opennmsopennms-source-26.0.0-1</b>, <b>node-sass-4.14.1.tgz</b></p></summary>
<p>
<details><summary><b>node-sass-4.14.1.tgz</b></p></summary>
<p>Wrapper around libsass</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-sass/-/node-sass-4.14.1.tgz">https://registry.npmjs.org/node-sass/-/node-sass-4.14.1.tgz</a></p>
<p>Path to dependency file: mermaid/package.json</p>
<p>Path to vulnerable library: mermaid/node_modules/node-sass/package.json</p>
<p>
Dependency Hierarchy:
- :x: **node-sass-4.14.1.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/fu1771695yongxie/mermaid/commit/f404b1690800300ea40a497194988ac4cb3977f7">f404b1690800300ea40a497194988ac4cb3977f7</a></p>
<p>Found in base branch: <b>develop</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In LibSass 3.5.5, a heap-based buffer over-read exists in Sass::Prelexer::skip_over_scopes in prelexer.hpp when called from Sass::Parser::parse_import(), a similar issue to CVE-2018-11693.
<p>Publish Date: 2019-01-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-6286>CVE-2019-6286</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-6286">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-6286</a></p>
<p>Release Date: 2019-08-06</p>
<p>Fix Resolution: LibSass - 3.6.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_process
|
cve medium detected in opennmsopennms source node sass tgz cve medium severity vulnerability vulnerable libraries opennmsopennms source node sass tgz node sass tgz wrapper around libsass library home page a href path to dependency file mermaid package json path to vulnerable library mermaid node modules node sass package json dependency hierarchy x node sass tgz vulnerable library found in head commit a href found in base branch develop vulnerability details in libsass a heap based buffer over read exists in sass prelexer skip over scopes in prelexer hpp when called from sass parser parse import a similar issue to cve publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution libsass step up your open source security game with whitesource
| 0
|
17,572
| 23,385,439,709
|
IssuesEvent
|
2022-08-11 13:24:24
|
MicrosoftDocs/windows-uwp
|
https://api.github.com/repos/MicrosoftDocs/windows-uwp
|
closed
|
The embedded video is marked private on this page
|
uwp/prod processes-and-threading/tech Pri2
|
[Enter feedback here]
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 8c161a2e-d9f4-466f-5a63-5e25648a1779
* Version Independent ID: 6032f644-b69d-622f-73df-bacebdfc4509
* Content: [Create a multi-instance Universal Windows App - UWP applications](https://docs.microsoft.com/en-us/windows/uwp/launch-resume/multi-instance-uwp)
* Content Source: [windows-apps-src/launch-resume/multi-instance-uwp.md](https://github.com/MicrosoftDocs/windows-uwp/blob/docs/windows-apps-src/launch-resume/multi-instance-uwp.md)
* Product: **uwp**
* Technology: **processes-and-threading**
* GitHub Login: @alvinashcraft
* Microsoft Alias: **aashcraft**
|
1.0
|
The embedded video is marked private on this page -
[Enter feedback here]
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 8c161a2e-d9f4-466f-5a63-5e25648a1779
* Version Independent ID: 6032f644-b69d-622f-73df-bacebdfc4509
* Content: [Create a multi-instance Universal Windows App - UWP applications](https://docs.microsoft.com/en-us/windows/uwp/launch-resume/multi-instance-uwp)
* Content Source: [windows-apps-src/launch-resume/multi-instance-uwp.md](https://github.com/MicrosoftDocs/windows-uwp/blob/docs/windows-apps-src/launch-resume/multi-instance-uwp.md)
* Product: **uwp**
* Technology: **processes-and-threading**
* GitHub Login: @alvinashcraft
* Microsoft Alias: **aashcraft**
|
process
|
the embedded video is marked private on this page document details ⚠ do not edit this section it is required for docs microsoft com ➟ github issue linking id version independent id content content source product uwp technology processes and threading github login alvinashcraft microsoft alias aashcraft
| 1
|
19,546
| 25,866,285,255
|
IssuesEvent
|
2022-12-13 21:12:20
|
python/cpython
|
https://api.github.com/repos/python/cpython
|
closed
|
Update multiprocessing.spawn to use runpy.run_path
|
stdlib expert-multiprocessing
|
BPO | [19978](https://bugs.python.org/issue19978)
--- | :---
Nosy | @brettcannon, @ncoghlan, @nanjekyejoannah
Dependencies | <li>bpo-19697: Document the possible values for __main__.__spec__</li><li>bpo-19946: Handle a non-importable __main__ in multiprocessing</li><li>bpo-19982: Add a "target" parameter to runpy.run_path and runpy.run_module</li>
<sup>*Note: these values reflect the state of the issue at the time it was migrated and might not reflect the current state.*</sup>
<details><summary>Show more details</summary><p>
GitHub fields:
```python
assignee = None
closed_at = None
created_at = <Date 2013-12-13.16:44:41.261>
labels = ['library']
title = 'Update multiprocessing.spawn to use runpy.run_path'
updated_at = <Date 2019-08-06.17:41:06.983>
user = 'https://github.com/brettcannon'
```
bugs.python.org fields:
```python
activity = <Date 2019-08-06.17:41:06.983>
actor = 'nanjekyejoannah'
assignee = 'none'
closed = False
closed_date = None
closer = None
components = ['Library (Lib)']
creation = <Date 2013-12-13.16:44:41.261>
creator = 'brett.cannon'
dependencies = ['19697', '19946', '19982']
files = []
hgrepos = []
issue_num = 19978
keywords = []
message_count = 2.0
messages = ['206117', '349122']
nosy_count = 5.0
nosy_names = ['brett.cannon', 'ncoghlan', 'jnoller', 'sbt', 'nanjekyejoannah']
pr_nums = []
priority = 'normal'
resolution = None
stage = 'test needed'
status = 'open'
superseder = None
type = None
url = 'https://bugs.python.org/issue19978'
versions = ['Python 3.5']
```
</p></details>
|
1.0
|
Update multiprocessing.spawn to use runpy.run_path - BPO | [19978](https://bugs.python.org/issue19978)
--- | :---
Nosy | @brettcannon, @ncoghlan, @nanjekyejoannah
Dependencies | <li>bpo-19697: Document the possible values for __main__.__spec__</li><li>bpo-19946: Handle a non-importable __main__ in multiprocessing</li><li>bpo-19982: Add a "target" parameter to runpy.run_path and runpy.run_module</li>
<sup>*Note: these values reflect the state of the issue at the time it was migrated and might not reflect the current state.*</sup>
<details><summary>Show more details</summary><p>
GitHub fields:
```python
assignee = None
closed_at = None
created_at = <Date 2013-12-13.16:44:41.261>
labels = ['library']
title = 'Update multiprocessing.spawn to use runpy.run_path'
updated_at = <Date 2019-08-06.17:41:06.983>
user = 'https://github.com/brettcannon'
```
bugs.python.org fields:
```python
activity = <Date 2019-08-06.17:41:06.983>
actor = 'nanjekyejoannah'
assignee = 'none'
closed = False
closed_date = None
closer = None
components = ['Library (Lib)']
creation = <Date 2013-12-13.16:44:41.261>
creator = 'brett.cannon'
dependencies = ['19697', '19946', '19982']
files = []
hgrepos = []
issue_num = 19978
keywords = []
message_count = 2.0
messages = ['206117', '349122']
nosy_count = 5.0
nosy_names = ['brett.cannon', 'ncoghlan', 'jnoller', 'sbt', 'nanjekyejoannah']
pr_nums = []
priority = 'normal'
resolution = None
stage = 'test needed'
status = 'open'
superseder = None
type = None
url = 'https://bugs.python.org/issue19978'
versions = ['Python 3.5']
```
</p></details>
|
process
|
update multiprocessing spawn to use runpy run path bpo nosy brettcannon ncoghlan nanjekyejoannah dependencies bpo document the possible values for main spec bpo handle a non importable main in multiprocessing bpo add a quot target quot parameter to runpy run path and runpy run module note these values reflect the state of the issue at the time it was migrated and might not reflect the current state show more details github fields python assignee none closed at none created at labels title update multiprocessing spawn to use runpy run path updated at user bugs python org fields python activity actor nanjekyejoannah assignee none closed false closed date none closer none components creation creator brett cannon dependencies files hgrepos issue num keywords message count messages nosy count nosy names pr nums priority normal resolution none stage test needed status open superseder none type none url versions
| 1
|
498,556
| 14,410,290,305
|
IssuesEvent
|
2020-12-04 04:27:44
|
ppy/osu
|
https://api.github.com/repos/ppy/osu
|
closed
|
Hidden mod crashes with KeyNotFoundException
|
area:mods area:spectator high-priority ruleset:osu! type:crash
|
**Describe the crash:**
the game suddenly crashed after going into the spectator mode (ingame).
**osu!lazer version:**
2020.1128.0
**Logs:**
[runtime.log](https://github.com/ppy/osu/files/5616758/runtime.log)
[updater.log](https://github.com/ppy/osu/files/5616759/updater.log)
[database.log](https://github.com/ppy/osu/files/5616760/database.log)
[network.log](https://github.com/ppy/osu/files/5616761/network.log)
[performance.log](https://github.com/ppy/osu/files/5616762/performance.log)
|
1.0
|
Hidden mod crashes with KeyNotFoundException - **Describe the crash:**
the game suddenly crashed after going into the spectator mode (ingame).
**osu!lazer version:**
2020.1128.0
**Logs:**
[runtime.log](https://github.com/ppy/osu/files/5616758/runtime.log)
[updater.log](https://github.com/ppy/osu/files/5616759/updater.log)
[database.log](https://github.com/ppy/osu/files/5616760/database.log)
[network.log](https://github.com/ppy/osu/files/5616761/network.log)
[performance.log](https://github.com/ppy/osu/files/5616762/performance.log)
|
non_process
|
hidden mod crashes with keynotfoundexception describe the crash the game suddenly crashed after going into the spectator mode ingame osu lazer version logs
| 0
|
60
| 2,518,726,055
|
IssuesEvent
|
2015-01-17 01:27:11
|
tinkerpop/tinkerpop3
|
https://api.github.com/repos/tinkerpop/tinkerpop3
|
closed
|
TraversalStrategies need not always be wanted for local(), repeat(), etc.
|
enhancement process
|
```java
g.V().repeat(g.of().out().groupCount().by('name')).values('name')
```
That causes a bug cause the end step is a `SideEffectStep` and thus, it gets cap'd. Dah! I have a super hack where I insert an `IdentityStep` at the end of each traversal sent to `repeat()`, but that is not a general solution. How do we turn off strategies?!.......................................... this sucks.
|
1.0
|
TraversalStrategies need not always be wanted for local(), repeat(), etc. - ```java
g.V().repeat(g.of().out().groupCount().by('name')).values('name')
```
That causes a bug cause the end step is a `SideEffectStep` and thus, it gets cap'd. Dah! I have a super hack where I insert an `IdentityStep` at the end of each traversal sent to `repeat()`, but that is not a general solution. How do we turn off strategies?!.......................................... this sucks.
|
process
|
traversalstrategies need not always be wanted for local repeat etc java g v repeat g of out groupcount by name values name that causes a bug cause the end step is a sideeffectstep and thus it gets cap d dah i have a super hack where i insert an identitystep at the end of each traversal sent to repeat but that is not a general solution how do we turn off strategies this sucks
| 1
|
51,084
| 3,010,667,546
|
IssuesEvent
|
2015-07-28 14:21:13
|
OCHA-DAP/hdx-ckan
|
https://api.github.com/repos/OCHA-DAP/hdx-ckan
|
closed
|
Geo Preview: kml, kmz
|
GeoPreview Priority-Medium
|
These were working before (if format was forced to geojson or zipped shapefile). They are not working now. Not sure what changed, since ogr2ogr should be processing them.
Note, I'm making this a medium priority since we don't want to delay deployment for these secondary formats.
|
1.0
|
Geo Preview: kml, kmz - These were working before (if format was forced to geojson or zipped shapefile). They are not working now. Not sure what changed, since ogr2ogr should be processing them.
Note, I'm making this a medium priority since we don't want to delay deployment for these secondary formats.
|
non_process
|
geo preview kml kmz these were working before if format was forced to geojson or zipped shapefile they are not working now not sure what changed since should be processing them note i m making this a medium priority since we don t want to delay deployment for these secondary formats
| 0
|
215,476
| 16,673,977,218
|
IssuesEvent
|
2021-06-07 14:11:41
|
exoclim/aeolus
|
https://api.github.com/repos/exoclim/aeolus
|
closed
|
Add tests and a jupyter notebook with examples for synthobs
|
docs examples tests
|
@mzamyatina please add a test for each of the functions in `synthobs.py` and some examples.
- [x] `test_read_spectral_bands()`
- [x] `test_read_normalized_stellar_flux()`
- [x] `test_calc_stellar_flux()`
- [x] `test_calc_transmission_spectrum_day_night_average()`
- [x] a notebook with examples (can use the test data for this too) `examples/03_Transmission_Spectrum.ipynb`
|
1.0
|
Add tests and a jupyter notebook with examples for synthobs - @mzamyatina please add a test for each of the functions in `synthobs.py` and some examples.
- [x] `test_read_spectral_bands()`
- [x] `test_read_normalized_stellar_flux()`
- [x] `test_calc_stellar_flux()`
- [x] `test_calc_transmission_spectrum_day_night_average()`
- [x] a notebook with examples (can use the test data for this too) `examples/03_Transmission_Spectrum.ipynb`
|
non_process
|
add tests and a jupyter notebook with examples for synthobs mzamyatina please add a test for each of the functions in synthobs py and some examples test read spectral bands test read normalized stellar flux test calc stellar flux test calc transmission spectrum day night average a notebook with examples can use the test data for this too examples transmission spectrum ipynb
| 0
|
22,525
| 31,625,540,466
|
IssuesEvent
|
2023-09-06 04:55:39
|
h4sh5/npm-auto-scanner
|
https://api.github.com/repos/h4sh5/npm-auto-scanner
|
opened
|
@snyk/sweater-comb 2.1.11 has 29 guarddog issues
|
npm-install-script shady-links npm-silent-process-execution
|
```{"npm-install-script":[{"code":" \"prepare\": \"npm run build\",","location":"package/node_modules/@asyncapi/specs/tools/bundler/node_modules/node-fetch/package.json:101","message":"The package.json has a script automatically running when the package is installed"},{"code":" \"prepare\": \"npm run build\",","location":"package/node_modules/@octokit/request/node_modules/node-fetch/package.json:19","message":"The package.json has a script automatically running when the package is installed"},{"code":" \"prepare\": \"npm run build\",","location":"package/node_modules/@stoplight/json-ref-readers/node_modules/node-fetch/package.json:19","message":"The package.json has a script automatically running when the package is installed"},{"code":" \"prepare\": \"npm run build\",","location":"package/node_modules/@stoplight/spectral-runtime/node_modules/node-fetch/package.json:19","message":"The package.json has a script automatically running when the package is installed"},{"code":" \"prepare\": \"tsc -p tsconfig.json \u0026\u0026 tsc -p tsconfig-esm.json\",","location":"package/node_modules/@useoptic/json-pointer-helpers/node_modules/minimatch/package.json:33","message":"The package.json has a script automatically running when the package is installed"},{"code":" \"prepare\": \"npm run build\",","location":"package/node_modules/@useoptic/openapi-io/node_modules/node-fetch/package.json:19","message":"The package.json has a script automatically running when the package is installed"},{"code":" \"prepare\": \"tsc -p tsconfig.json \u0026\u0026 tsc -p tsconfig-esm.json\",","location":"package/node_modules/@useoptic/openapi-utilities/node_modules/minimatch/package.json:33","message":"The package.json has a script automatically running when the package is installed"},{"code":" \"prepare\": \"tsc -p tsconfig.json \u0026\u0026 tsc -p tsconfig-esm.json\",","location":"package/node_modules/@useoptic/optic/node_modules/minimatch/package.json:33","message":"The package.json has a script automatically running when the package is installed"},{"code":" \"prepare\": \"npm run build\",","location":"package/node_modules/@useoptic/optic/node_modules/node-fetch/package.json:19","message":"The package.json has a script automatically running when the package is installed"},{"code":" \"prepare\": \"npm run build\",","location":"package/node_modules/@useoptic/rulesets-base/node_modules/node-fetch/package.json:19","message":"The package.json has a script automatically running when the package is installed"},{"code":" \"prepare\": \"tsc -p tsconfig.json \u0026\u0026 tsc -p tsconfig-esm.json\",","location":"package/node_modules/@useoptic/standard-rulesets/node_modules/minimatch/package.json:33","message":"The package.json has a script automatically running when the package is installed"},{"code":" \"prepare\": \"npm run build\",","location":"package/node_modules/@useoptic/standard-rulesets/node_modules/node-fetch/package.json:19","message":"The package.json has a script automatically running when the package is installed"},{"code":" \"prepare\": \"npm run build \u0026\u0026 npm run build:minified\",","location":"package/node_modules/astring/package.json:22","message":"The package.json has a script automatically running when the package is installed"},{"code":" \"prepare\": \"is-ci || husky install\",","location":"package/node_modules/call-me-maybe/package.json:25","message":"The package.json has a script automatically running when the package is installed"},{"code":" \"prepare\": \"npm run build\",","location":"package/node_modules/cross-fetch/node_modules/node-fetch/package.json:19","message":"The package.json has a script automatically running when the package is installed"},{"code":" \"prepare\": \"husky install\",","location":"package/node_modules/cross-fetch/package.json:12","message":"The package.json has a script automatically running when the package is installed"},{"code":"\t\t\"postinstall\": \" node -e \\\"try{require('./_postinstall')}catch(e){}\\\" || exit 0\",","location":"package/node_modules/es5-ext/package.json:115","message":"The package.json has a script automatically running when the package is installed"},{"code":" \"prepare\": \"rollup -c\"","location":"package/node_modules/is-plain-object/package.json:41","message":"The package.json has a script automatically running when the package is installed"},{"code":"\t\t\"prepare\": \"husky install\",","location":"package/node_modules/jsep/package.json:150","message":"The package.json has a script automatically running when the package is installed"},{"code":" \"prepare\": \"node ./scripts/transpile-to-esm.js\",","location":"package/node_modules/minipass/package.json:35","message":"The package.json has a script automatically running when the package is installed"},{"code":" \"prepare\": \"node ./scripts/transpile-to-esm.js\",","location":"package/node_modules/mockttp/node_modules/lru-cache/package.json:16","message":"The package.json has a script automatically running when the package is installed"},{"code":" \"prepare\": \"../../bin/tsc\",","location":"package/node_modules/openapi-types/package.json:8","message":"The package.json has a script automatically running when the package is installed"},{"code":" \"prepare\": \"husky install\",","location":"package/node_modules/pony-cause/package.json:29","message":"The package.json has a script automatically running when the package is installed"},{"code":" \"prepare\": \"node src/build.js\",","location":"package/node_modules/send/node_modules/mime/package.json:29","message":"The package.json has a script automatically running when the package is installed"},{"code":" \"prepare\": \"husky install\"","location":"package/node_modules/simple-eval/package.json:48","message":"The package.json has a script automatically running when the package is installed"},{"code":" \"prepare\": \"node -e \\\"try { require('husky').install() } catch (e) {if (e.code !== 'MODULE_NOT_FOUND') throw e}\\\" \u0026\u0026 npm run build\"","location":"package/node_modules/typed-error/package.json:19","message":"The package.json has a script automatically running when the package is installed"}],"npm-silent-process-execution":[{"code":"\t\tspawn(process.execPath, [path.join(__dirname, 'check.js'), JSON.stringify(this.options)], {\n\t\t\tdetached: true,\n\t\t\tstdio: 'ignore'\n\t\t}).unref();","location":"package/node_modules/update-notifier/index.js:98","message":"This package is silently executing another executable"}],"shady-links":[{"code":"function n(n){for(var r=arguments.length,t=Array(r\u003e1?r-1:0),e=1;e\u003cr;e++)t[e-1]=arguments[e];if(\"production\"!==process.env.NODE_ENV){var i=Y[n],o=i?\"function\"==typeof i?i.apply(null,t):i:\"unknown error nr: \"+n;throw Error(\"[Immer] \"+o)}throw...eProxies};","location":"package/node_modules/immer/dist/immer.esm.js:1","message":"This package contains an URL to a domain with a suspicious extension"},{"code":"\t\t}. Find the full error at: https://bit.ly/3cXEKWf`","location":"package/node_modules/immer/src/utils/errors.ts:58","message":"This package contains an URL to a domain with a suspicious extension"}]}```
|
1.0
|
@snyk/sweater-comb 2.1.11 has 29 guarddog issues - ```{"npm-install-script":[{"code":" \"prepare\": \"npm run build\",","location":"package/node_modules/@asyncapi/specs/tools/bundler/node_modules/node-fetch/package.json:101","message":"The package.json has a script automatically running when the package is installed"},{"code":" \"prepare\": \"npm run build\",","location":"package/node_modules/@octokit/request/node_modules/node-fetch/package.json:19","message":"The package.json has a script automatically running when the package is installed"},{"code":" \"prepare\": \"npm run build\",","location":"package/node_modules/@stoplight/json-ref-readers/node_modules/node-fetch/package.json:19","message":"The package.json has a script automatically running when the package is installed"},{"code":" \"prepare\": \"npm run build\",","location":"package/node_modules/@stoplight/spectral-runtime/node_modules/node-fetch/package.json:19","message":"The package.json has a script automatically running when the package is installed"},{"code":" \"prepare\": \"tsc -p tsconfig.json \u0026\u0026 tsc -p tsconfig-esm.json\",","location":"package/node_modules/@useoptic/json-pointer-helpers/node_modules/minimatch/package.json:33","message":"The package.json has a script automatically running when the package is installed"},{"code":" \"prepare\": \"npm run build\",","location":"package/node_modules/@useoptic/openapi-io/node_modules/node-fetch/package.json:19","message":"The package.json has a script automatically running when the package is installed"},{"code":" \"prepare\": \"tsc -p tsconfig.json \u0026\u0026 tsc -p tsconfig-esm.json\",","location":"package/node_modules/@useoptic/openapi-utilities/node_modules/minimatch/package.json:33","message":"The package.json has a script automatically running when the package is installed"},{"code":" \"prepare\": \"tsc -p tsconfig.json \u0026\u0026 tsc -p tsconfig-esm.json\",","location":"package/node_modules/@useoptic/optic/node_modules/minimatch/package.json:33","message":"The package.json has a script automatically running when the package is installed"},{"code":" \"prepare\": \"npm run build\",","location":"package/node_modules/@useoptic/optic/node_modules/node-fetch/package.json:19","message":"The package.json has a script automatically running when the package is installed"},{"code":" \"prepare\": \"npm run build\",","location":"package/node_modules/@useoptic/rulesets-base/node_modules/node-fetch/package.json:19","message":"The package.json has a script automatically running when the package is installed"},{"code":" \"prepare\": \"tsc -p tsconfig.json \u0026\u0026 tsc -p tsconfig-esm.json\",","location":"package/node_modules/@useoptic/standard-rulesets/node_modules/minimatch/package.json:33","message":"The package.json has a script automatically running when the package is installed"},{"code":" \"prepare\": \"npm run build\",","location":"package/node_modules/@useoptic/standard-rulesets/node_modules/node-fetch/package.json:19","message":"The package.json has a script automatically running when the package is installed"},{"code":" \"prepare\": \"npm run build \u0026\u0026 npm run build:minified\",","location":"package/node_modules/astring/package.json:22","message":"The package.json has a script automatically running when the package is installed"},{"code":" \"prepare\": \"is-ci || husky install\",","location":"package/node_modules/call-me-maybe/package.json:25","message":"The package.json has a script automatically running when the package is installed"},{"code":" \"prepare\": \"npm run build\",","location":"package/node_modules/cross-fetch/node_modules/node-fetch/package.json:19","message":"The package.json has a script automatically running when the package is installed"},{"code":" \"prepare\": \"husky install\",","location":"package/node_modules/cross-fetch/package.json:12","message":"The package.json has a script automatically running when the package is installed"},{"code":"\t\t\"postinstall\": \" node -e \\\"try{require('./_postinstall')}catch(e){}\\\" || exit 0\",","location":"package/node_modules/es5-ext/package.json:115","message":"The package.json has a script automatically running when the package is installed"},{"code":" \"prepare\": \"rollup -c\"","location":"package/node_modules/is-plain-object/package.json:41","message":"The package.json has a script automatically running when the package is installed"},{"code":"\t\t\"prepare\": \"husky install\",","location":"package/node_modules/jsep/package.json:150","message":"The package.json has a script automatically running when the package is installed"},{"code":" \"prepare\": \"node ./scripts/transpile-to-esm.js\",","location":"package/node_modules/minipass/package.json:35","message":"The package.json has a script automatically running when the package is installed"},{"code":" \"prepare\": \"node ./scripts/transpile-to-esm.js\",","location":"package/node_modules/mockttp/node_modules/lru-cache/package.json:16","message":"The package.json has a script automatically running when the package is installed"},{"code":" \"prepare\": \"../../bin/tsc\",","location":"package/node_modules/openapi-types/package.json:8","message":"The package.json has a script automatically running when the package is installed"},{"code":" \"prepare\": \"husky install\",","location":"package/node_modules/pony-cause/package.json:29","message":"The package.json has a script automatically running when the package is installed"},{"code":" \"prepare\": \"node src/build.js\",","location":"package/node_modules/send/node_modules/mime/package.json:29","message":"The package.json has a script automatically running when the package is installed"},{"code":" \"prepare\": \"husky install\"","location":"package/node_modules/simple-eval/package.json:48","message":"The package.json has a script automatically running when the package is installed"},{"code":" \"prepare\": \"node -e \\\"try { require('husky').install() } catch (e) {if (e.code !== 'MODULE_NOT_FOUND') throw e}\\\" \u0026\u0026 npm run build\"","location":"package/node_modules/typed-error/package.json:19","message":"The package.json has a script automatically running when the package is installed"}],"npm-silent-process-execution":[{"code":"\t\tspawn(process.execPath, [path.join(__dirname, 'check.js'), JSON.stringify(this.options)], {\n\t\t\tdetached: true,\n\t\t\tstdio: 'ignore'\n\t\t}).unref();","location":"package/node_modules/update-notifier/index.js:98","message":"This package is silently executing another executable"}],"shady-links":[{"code":"function n(n){for(var r=arguments.length,t=Array(r\u003e1?r-1:0),e=1;e\u003cr;e++)t[e-1]=arguments[e];if(\"production\"!==process.env.NODE_ENV){var i=Y[n],o=i?\"function\"==typeof i?i.apply(null,t):i:\"unknown error nr: \"+n;throw Error(\"[Immer] \"+o)}throw...eProxies};","location":"package/node_modules/immer/dist/immer.esm.js:1","message":"This package contains an URL to a domain with a suspicious extension"},{"code":"\t\t}. Find the full error at: https://bit.ly/3cXEKWf`","location":"package/node_modules/immer/src/utils/errors.ts:58","message":"This package contains an URL to a domain with a suspicious extension"}]}```
|
process
|
snyk sweater comb has guarddog issues npm install script npm silent process execution n t t tdetached true n t t tstdio ignore n t t unref location package node modules update notifier index js message this package is silently executing another executable shady links arguments if production process env node env var i y o i function typeof i i apply null t i unknown error nr n throw error o throw eproxies location package node modules immer dist immer esm js message this package contains an url to a domain with a suspicious extension code t t find the full error at package contains an url to a domain with a suspicious extension
| 1
|
200,677
| 15,801,771,145
|
IssuesEvent
|
2021-04-03 06:30:14
|
mabel-kang/ped
|
https://api.github.com/repos/mabel-kang/ped
|
opened
|
Differing command format for 'show CAP'
|
severity.Low type.DocumentationBug
|
command for showing CAP should be written in user guide as "show cap" instead of "show CAP"
command: show CAP
expected: command successfully executed
actual: invalid command
<!--session: 1617429915767-fd6a9294-c97f-446f-bbcd-d131dcd892a0-->
|
1.0
|
Differing command format for 'show CAP' - command for showing CAP should be written in user guide as "show cap" instead of "show CAP"
command: show CAP
expected: command successfully executed
actual: invalid command
<!--session: 1617429915767-fd6a9294-c97f-446f-bbcd-d131dcd892a0-->
|
non_process
|
differing command format for show cap command for showing cap should be written in user guide as show cap instead of show cap command show cap expected command successfully executed actual invalid command
| 0
|
83,047
| 15,683,991,315
|
IssuesEvent
|
2021-03-25 09:28:16
|
loggly/loggly-jslogger
|
https://api.github.com/repos/loggly/loggly-jslogger
|
closed
|
CVE-2020-7656 (Medium) detected in jquery-1.8.1.min.js
|
security vulnerability
|
## CVE-2020-7656 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-1.8.1.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.8.1/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.8.1/jquery.min.js</a></p>
<p>Path to dependency file: loggly-jslogger/node_modules/bower/lib/node_modules/redeyed/examples/browser/index.html</p>
<p>Path to vulnerable library: loggly-jslogger/node_modules/bower/lib/node_modules/redeyed/examples/browser/index.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.8.1.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://api.github.com/repos/loggly/loggly-jslogger/commits/3247b5841e5a8923baf2e98a1914570b38eadd97">3247b5841e5a8923baf2e98a1914570b38eadd97</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
jquery prior to 1.9.0 allows Cross-site Scripting attacks via the load method. The load method fails to recognize and remove "<script>" HTML tags that contain a whitespace character, i.e: "</script >", which results in the enclosed script logic to be executed.
<p>Publish Date: 2020-05-19
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7656>CVE-2020-7656</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/rails/jquery-rails/commit/8f601cbfa08749ee5bbd2bffb6e509db9d753568">https://github.com/rails/jquery-rails/commit/8f601cbfa08749ee5bbd2bffb6e509db9d753568</a></p>
<p>Release Date: 2020-05-19</p>
<p>Fix Resolution: jquery-rails - 2.2.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"jquery","packageVersion":"1.8.1","isTransitiveDependency":false,"dependencyTree":"jquery:1.8.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"jquery-rails - 2.2.0"}],"vulnerabilityIdentifier":"CVE-2020-7656","vulnerabilityDetails":"jquery prior to 1.9.0 allows Cross-site Scripting attacks via the load method. The load method fails to recognize and remove \"\u003cscript\u003e\" HTML tags that contain a whitespace character, i.e: \"\u003c/script \u003e\", which results in the enclosed script logic to be executed.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7656","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}}</REMEDIATE> -->
|
True
|
CVE-2020-7656 (Medium) detected in jquery-1.8.1.min.js - ## CVE-2020-7656 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-1.8.1.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.8.1/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.8.1/jquery.min.js</a></p>
<p>Path to dependency file: loggly-jslogger/node_modules/bower/lib/node_modules/redeyed/examples/browser/index.html</p>
<p>Path to vulnerable library: loggly-jslogger/node_modules/bower/lib/node_modules/redeyed/examples/browser/index.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.8.1.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://api.github.com/repos/loggly/loggly-jslogger/commits/3247b5841e5a8923baf2e98a1914570b38eadd97">3247b5841e5a8923baf2e98a1914570b38eadd97</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
jquery prior to 1.9.0 allows Cross-site Scripting attacks via the load method. The load method fails to recognize and remove "<script>" HTML tags that contain a whitespace character, i.e: "</script >", which results in the enclosed script logic to be executed.
<p>Publish Date: 2020-05-19
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7656>CVE-2020-7656</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/rails/jquery-rails/commit/8f601cbfa08749ee5bbd2bffb6e509db9d753568">https://github.com/rails/jquery-rails/commit/8f601cbfa08749ee5bbd2bffb6e509db9d753568</a></p>
<p>Release Date: 2020-05-19</p>
<p>Fix Resolution: jquery-rails - 2.2.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"jquery","packageVersion":"1.8.1","isTransitiveDependency":false,"dependencyTree":"jquery:1.8.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"jquery-rails - 2.2.0"}],"vulnerabilityIdentifier":"CVE-2020-7656","vulnerabilityDetails":"jquery prior to 1.9.0 allows Cross-site Scripting attacks via the load method. The load method fails to recognize and remove \"\u003cscript\u003e\" HTML tags that contain a whitespace character, i.e: \"\u003c/script \u003e\", which results in the enclosed script logic to be executed.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7656","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}}</REMEDIATE> -->
|
non_process
|
cve medium detected in jquery min js cve medium severity vulnerability vulnerable library jquery min js javascript library for dom operations library home page a href path to dependency file loggly jslogger node modules bower lib node modules redeyed examples browser index html path to vulnerable library loggly jslogger node modules bower lib node modules redeyed examples browser index html dependency hierarchy x jquery min js vulnerable library found in head commit a href found in base branch master vulnerability details jquery prior to allows cross site scripting attacks via the load method the load method fails to recognize and remove html tags that contain a whitespace character i e which results in the enclosed script logic to be executed publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jquery rails isopenpronvulnerability false ispackagebased true isdefaultbranch true packages vulnerabilityidentifier cve vulnerabilitydetails jquery prior to allows cross site scripting attacks via the load method the load method fails to recognize and remove html tags that contain a whitespace character i e script which results in the enclosed script logic to be executed vulnerabilityurl
| 0
|
330,287
| 10,038,019,791
|
IssuesEvent
|
2019-07-18 14:21:40
|
CentOS-PaaS-SIG/linchpin
|
https://api.github.com/repos/CentOS-PaaS-SIG/linchpin
|
opened
|
Can't assign two networks to one vm in libvirt
|
bug debug libvirt medium priority
|
When you attach two networks to a vm, it will give a error:
fatal: [localhost]: FAILED! => {
"msg": "The task includes an option with an undefined variable. The error was: list object has no element 1\n\nThe error appears to have been in '/usr/lib/python2.7/site-packages/linchpin/provision/roles/libvirt/tasks/provision_libvirt_node.yml
The mac address can't be acquired either
|
1.0
|
Can't assign two networks to one vm in libvirt - When you attach two networks to a vm, it will give a error:
fatal: [localhost]: FAILED! => {
"msg": "The task includes an option with an undefined variable. The error was: list object has no element 1\n\nThe error appears to have been in '/usr/lib/python2.7/site-packages/linchpin/provision/roles/libvirt/tasks/provision_libvirt_node.yml
The mac address can't be acquired either
|
non_process
|
can t assign two networks to one vm in libvirt when you attach two networks to a vm it will give a error fatal failed msg the task includes an option with an undefined variable the error was list object has no element n nthe error appears to have been in usr lib site packages linchpin provision roles libvirt tasks provision libvirt node yml the mac address can t be acquired either
| 0
|
16,007
| 20,188,222,530
|
IssuesEvent
|
2022-02-11 01:19:20
|
savitamittalmsft/WAS-SEC-TEST
|
https://api.github.com/repos/savitamittalmsft/WAS-SEC-TEST
|
opened
|
Evolve security beyond network controls
|
WARP-Import WAF FEB 2021 Security Performance and Scalability Capacity Management Processes Security & Compliance Network Security
|
<a href="https://docs.microsoft.com/azure/architecture/framework/Security/network-security-containment#evolve-security-beyond-network-controls">Evolve security beyond network controls</a>
<p><b>Why Consider This?</b></p>
Traditional network controls based on a "trusted intranet" approach will not be able to effectively provide security assurances for these applications.
<p><b>Context</b></p>
<p><span>As organizations shift to modern architectures, many services and components required for applications will be accessed over the internet or on cloud provider networks, often by mobile and other devices off the network. </span></p><p><span>Build a risk containment strategy based on a combination of network controls and application, identity, and other control types.</span></p><ul style="list-style-type:disc"><li value="1" style="text-indent: 0px;"><span>Ensure that resource grouping and administrative privileges align to the segmentation model</span></li><li value="2" style="margin-right: 0px;text-indent: 0px;"><span>Ensure you are designing security controls that identify and allow expected traffic, access requests, and other application communications between segments. Monitor communications between segments to identify on any unexpected communications so you can investigate whether to set alerts or block traffic to mitigate risk of adversaries crossing segmentation boundaries.</span></li></ul>
<p><b>Suggested Actions</b></p>
<p><span>Implement technical controls that can effectively prevent, detect, and respond to threats outside the network controls.</span></p>
<p><b>Learn More</b></p>
<p><a href="https://docs.microsoft.com/en-us/azure/architecture/framework/Security/network-security-containment#evolve-security-beyond-network-controls" target="_blank"><span>Evolve security beyond network controls</span></a><span /></p>
|
1.0
|
Evolve security beyond network controls - <a href="https://docs.microsoft.com/azure/architecture/framework/Security/network-security-containment#evolve-security-beyond-network-controls">Evolve security beyond network controls</a>
<p><b>Why Consider This?</b></p>
Traditional network controls based on a "trusted intranet" approach will not be able to effectively provide security assurances for these applications.
<p><b>Context</b></p>
<p><span>As organizations shift to modern architectures, many services and components required for applications will be accessed over the internet or on cloud provider networks, often by mobile and other devices off the network. </span></p><p><span>Build a risk containment strategy based on a combination of network controls and application, identity, and other control types.</span></p><ul style="list-style-type:disc"><li value="1" style="text-indent: 0px;"><span>Ensure that resource grouping and administrative privileges align to the segmentation model</span></li><li value="2" style="margin-right: 0px;text-indent: 0px;"><span>Ensure you are designing security controls that identify and allow expected traffic, access requests, and other application communications between segments. Monitor communications between segments to identify on any unexpected communications so you can investigate whether to set alerts or block traffic to mitigate risk of adversaries crossing segmentation boundaries.</span></li></ul>
<p><b>Suggested Actions</b></p>
<p><span>Implement technical controls that can effectively prevent, detect, and respond to threats outside the network controls.</span></p>
<p><b>Learn More</b></p>
<p><a href="https://docs.microsoft.com/en-us/azure/architecture/framework/Security/network-security-containment#evolve-security-beyond-network-controls" target="_blank"><span>Evolve security beyond network controls</span></a><span /></p>
|
process
|
evolve security beyond network controls why consider this traditional network controls based on a trusted intranet approach will not be able to effectively provide security assurances for these applications context as organizations shift to modern architectures many services and components required for applications will be accessed over the internet or on cloud provider networks often by mobile and other devices off the network build a risk containment strategy based on a combination of network controls and application identity and other control types ensure that resource grouping and administrative privileges align to the segmentation model ensure you are designing security controls that identify and allow expected traffic access requests and other application communications between segments monitor communications between segments to identify on any unexpected communications so you can investigate whether to set alerts or block traffic to mitigate risk of adversaries crossing segmentation boundaries suggested actions implement technical controls that can effectively prevent detect and respond to threats outside the network controls learn more evolve security beyond network controls
| 1
|
7,485
| 10,574,721,569
|
IssuesEvent
|
2019-10-07 14:29:48
|
Maps4HTML/HTML-Map-Element-UseCases-Requirements
|
https://api.github.com/repos/Maps4HTML/HTML-Map-Element-UseCases-Requirements
|
closed
|
Reference list of missing issues for use cases and capabilities
|
meta/process
|
In the hope of potentially saving you guys some time, I've been going through the spec for use cases and capabilities that do not link to an issue for discussion, and I've also tried to find the corresponding issue in any case there is one but it just hasn't been linked to from the spec.
<hr>
Edit: Things TBD as listed below have been updated to reflect changes in:
https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/commit/0071b30625a29455ea3e4105aefce4e3eff5e755, https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/commit/ae59ecb6e8a85acbf21489916079a5afa2d398ae, https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/pull/121/commits/6826d37de02e51d5e1b92089696e01846f5fa7d8, https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/pull/124, https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/pull/162.
<hr>
<!-- - [ ] [#capability-declarative-map](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-declarative-map)
- [ ] [#capability-default-map](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-default-map)
- [ ] [#capability-single-custom-image](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-single-custom-image)
- [ ] [#capability-custom-map-tiles](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-custom-map-tiles)
- [ ] [#capability-marker-points](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-marker-points)
- [ ] [#capability-vector-features](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-vector-features)
- [ ] [#capability-hyperlinks](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-hyperlinks)
- [ ] [#capability-attribution](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-attribution)
- [ ] [#capability-location-latlong](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-location-latlong)
- [ ] [#capability-location-address](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-location-address)
- [ ] [#capability-export-location](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-export-location)
- [ ] [#capability-zoom](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-zoom)
- [ ] [#capability-pan](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-pan)
- [ ] [#capability-lazy-load](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-lazy-load)
- [ ] [#capability-wrap-pan](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-wrap-pan)
- [ ] [#capability-scale-adjust](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-scale-adjust)
- [ ] [#capability-zoom-swap](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-zoom-swap)
- [ ] [#capability-zoom-swap-vectors](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-zoom-swap-vectors)
- [ ] [#capability-styled-controls](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-styled-controls)
- [ ] [#capability-create-an-overlay-defined-by-vector-data](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-create-an-overlay-defined-by-vector-data)
- [ ] [#capability-create-an-overlay-defined-by-heatmap-data](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-create-an-overlay-defined-by-heatmap-data)
- [ ] [#capability-move-the-map-to-display-a-given-location](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-move-the-map-to-display-a-given-location)
- [ ] [#capability-pan-and-zoom-to-bounding-box](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-pan-and-zoom-to-bounding-box)
- [ ] [#capability-animate-the-re-centering-of-the-map-view](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-animate-the-re-centering-of-the-map-view)
- [ ] [#capability-animate-the-zooming-of-the-map](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-animate-the-zooming-of-the-map)
- [ ] [#capability-animate-the-re-centering-of-the-map](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-animate-the-re-centering-of-the-map)
<hr>-->
These [examples](https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/tree/master/examples) have broken links to corresponding use cases in the spec:
- [ ] [animate-view-change.html](https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/blob/master/examples/animate-view-change.html)
- [ ] [change-bearing-map.html](https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/blob/master/examples/change-bearing-map.html)
- [ ] [create-plugin-integrates-api.html](https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/blob/master/examples/create-plugin-integrates-api.html)
- [ ] [custom-map.html](https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/blob/master/examples/custom-map.html)
- [ ] [generate-vector-features.html](https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/blob/master/examples/generate-vector-features.html)
- [ ] [heatmap.html](https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/blob/master/examples/heatmap.html)
- [ ] [reset-map-view.html](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/examples/reset-map-view.html)
- [ ] [set-layer-visibility.html](https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/blob/master/examples/set-layer-visibility.html)
- [ ] [specify-data-source-map.html](https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/blob/master/examples/specify-data-source-map.html)
- [ ] [set-view-zoom.html](https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/blob/master/examples/set-view-zoom.html)
- [ ] [view-change-events.html](https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/blob/master/examples/view-change-events.html)
<hr>
These issues aren't properly linking to their corresponding section in the spec, e.g.:
> _This issue is for discussion of <link>._
is missing, or have a broken link:
Items in https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/issues/110#issuecomment-529998014
<!--
- [ ] https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/issues/3 should link to [#capability-reproject-maps](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-reproject-maps)
- [ ] https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/issues/9 should link to [#google-maps](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#google-maps)
- [ ] https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/issues/12 should link to [#mapbox](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#mapbox)
- [ ] https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/issues/13 should link to [#d3-geo](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#d3-geo)
- [ ] https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/issues/14 should link to [#capability-tile-coordinate-systems](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-tile-coordinate-systems)
- [ ] https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/issues/15 should link to [#capability-styled-features](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-styled-features)
- [ ] https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/issues/16 should link to [#capability-custom-controls](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-custom-controls)
- [ ] https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/issues/26 should link to [#openstreetmap](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#openstreetmap)
- [ ] https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/issues/27 should link to [#bing-maps](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#bing-maps)
- [ ] https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/issues/28 should link to [#mapkit-js](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#mapkit-js)
- [ ] https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/issues/29 should link to [#leaflet-js](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#leaflet-js)
- [ ] https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/issues/30 should link to [#openlayers](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#openlayers)
- [ ] https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/issues/49 should link to [#tomtom](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#tomtom)
- [ ] https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/issues/50 should link to [#client-apis](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#client-apis)
- [ ] https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/issues/55 should link to [#capability-create-initialise-and-display-a-map](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-create-initialise-and-display-a-map)
- [ ] https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/issues/57 should link to [#capability-implement-a-custom-control](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-implement-a-custom-control)
- [ ] https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/issues/74 should link to [#capability-define-data-source-tile-layer](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-define-data-source-tile-layer)
- [ ] https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/issues/81 should link to [#use-case-alternative-layers](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#use-case-alternative-layers)-->
<hr>
<s>These use cases and capabilities are currently not linking to a corresponding github issue (perhaps because no such issue exist yet):</s>
- [x] 25 items complete, in https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/pull/162.
|
1.0
|
Reference list of missing issues for use cases and capabilities - In the hope of potentially saving you guys some time, I've been going through the spec for use cases and capabilities that do not link to an issue for discussion, and I've also tried to find the corresponding issue in any case there is one but it just hasn't been linked to from the spec.
<hr>
Edit: Things TBD as listed below have been updated to reflect changes in:
https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/commit/0071b30625a29455ea3e4105aefce4e3eff5e755, https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/commit/ae59ecb6e8a85acbf21489916079a5afa2d398ae, https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/pull/121/commits/6826d37de02e51d5e1b92089696e01846f5fa7d8, https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/pull/124, https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/pull/162.
<hr>
<!-- - [ ] [#capability-declarative-map](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-declarative-map)
- [ ] [#capability-default-map](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-default-map)
- [ ] [#capability-single-custom-image](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-single-custom-image)
- [ ] [#capability-custom-map-tiles](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-custom-map-tiles)
- [ ] [#capability-marker-points](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-marker-points)
- [ ] [#capability-vector-features](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-vector-features)
- [ ] [#capability-hyperlinks](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-hyperlinks)
- [ ] [#capability-attribution](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-attribution)
- [ ] [#capability-location-latlong](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-location-latlong)
- [ ] [#capability-location-address](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-location-address)
- [ ] [#capability-export-location](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-export-location)
- [ ] [#capability-zoom](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-zoom)
- [ ] [#capability-pan](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-pan)
- [ ] [#capability-lazy-load](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-lazy-load)
- [ ] [#capability-wrap-pan](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-wrap-pan)
- [ ] [#capability-scale-adjust](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-scale-adjust)
- [ ] [#capability-zoom-swap](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-zoom-swap)
- [ ] [#capability-zoom-swap-vectors](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-zoom-swap-vectors)
- [ ] [#capability-styled-controls](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-styled-controls)
- [ ] [#capability-create-an-overlay-defined-by-vector-data](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-create-an-overlay-defined-by-vector-data)
- [ ] [#capability-create-an-overlay-defined-by-heatmap-data](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-create-an-overlay-defined-by-heatmap-data)
- [ ] [#capability-move-the-map-to-display-a-given-location](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-move-the-map-to-display-a-given-location)
- [ ] [#capability-pan-and-zoom-to-bounding-box](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-pan-and-zoom-to-bounding-box)
- [ ] [#capability-animate-the-re-centering-of-the-map-view](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-animate-the-re-centering-of-the-map-view)
- [ ] [#capability-animate-the-zooming-of-the-map](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-animate-the-zooming-of-the-map)
- [ ] [#capability-animate-the-re-centering-of-the-map](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-animate-the-re-centering-of-the-map)
<hr>-->
These [examples](https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/tree/master/examples) have broken links to corresponding use cases in the spec:
- [ ] [animate-view-change.html](https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/blob/master/examples/animate-view-change.html)
- [ ] [change-bearing-map.html](https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/blob/master/examples/change-bearing-map.html)
- [ ] [create-plugin-integrates-api.html](https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/blob/master/examples/create-plugin-integrates-api.html)
- [ ] [custom-map.html](https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/blob/master/examples/custom-map.html)
- [ ] [generate-vector-features.html](https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/blob/master/examples/generate-vector-features.html)
- [ ] [heatmap.html](https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/blob/master/examples/heatmap.html)
- [ ] [reset-map-view.html](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/examples/reset-map-view.html)
- [ ] [set-layer-visibility.html](https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/blob/master/examples/set-layer-visibility.html)
- [ ] [specify-data-source-map.html](https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/blob/master/examples/specify-data-source-map.html)
- [ ] [set-view-zoom.html](https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/blob/master/examples/set-view-zoom.html)
- [ ] [view-change-events.html](https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/blob/master/examples/view-change-events.html)
<hr>
These issues aren't properly linking to their corresponding section in the spec, e.g.:
> _This issue is for discussion of <link>._
is missing, or have a broken link:
Items in https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/issues/110#issuecomment-529998014
<!--
- [ ] https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/issues/3 should link to [#capability-reproject-maps](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-reproject-maps)
- [ ] https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/issues/9 should link to [#google-maps](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#google-maps)
- [ ] https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/issues/12 should link to [#mapbox](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#mapbox)
- [ ] https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/issues/13 should link to [#d3-geo](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#d3-geo)
- [ ] https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/issues/14 should link to [#capability-tile-coordinate-systems](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-tile-coordinate-systems)
- [ ] https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/issues/15 should link to [#capability-styled-features](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-styled-features)
- [ ] https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/issues/16 should link to [#capability-custom-controls](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-custom-controls)
- [ ] https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/issues/26 should link to [#openstreetmap](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#openstreetmap)
- [ ] https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/issues/27 should link to [#bing-maps](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#bing-maps)
- [ ] https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/issues/28 should link to [#mapkit-js](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#mapkit-js)
- [ ] https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/issues/29 should link to [#leaflet-js](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#leaflet-js)
- [ ] https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/issues/30 should link to [#openlayers](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#openlayers)
- [ ] https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/issues/49 should link to [#tomtom](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#tomtom)
- [ ] https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/issues/50 should link to [#client-apis](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#client-apis)
- [ ] https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/issues/55 should link to [#capability-create-initialise-and-display-a-map](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-create-initialise-and-display-a-map)
- [ ] https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/issues/57 should link to [#capability-implement-a-custom-control](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-implement-a-custom-control)
- [ ] https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/issues/74 should link to [#capability-define-data-source-tile-layer](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#capability-define-data-source-tile-layer)
- [ ] https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/issues/81 should link to [#use-case-alternative-layers](https://maps4html.github.io/HTML-Map-Element-UseCases-Requirements/#use-case-alternative-layers)-->
<hr>
<s>These use cases and capabilities are currently not linking to a corresponding github issue (perhaps because no such issue exist yet):</s>
- [x] 25 items complete, in https://github.com/Maps4HTML/HTML-Map-Element-UseCases-Requirements/pull/162.
|
process
|
reference list of missing issues for use cases and capabilities in the hope of potentially saving you guys some time i ve been going through the spec for use cases and capabilities that do not link to an issue for discussion and i ve also tried to find the corresponding issue in any case there is one but it just hasn t been linked to from the spec edit things tbd as listed below have been updated to reflect changes in these have broken links to corresponding use cases in the spec these issues aren t properly linking to their corresponding section in the spec e g this issue is for discussion of lt link gt is missing or have a broken link items in should link to should link to should link to should link to should link to should link to should link to should link to should link to should link to should link to should link to should link to should link to should link to should link to should link to should link to these use cases and capabilities are currently not linking to a corresponding github issue perhaps because no such issue exist yet items complete in
| 1
|
8,803
| 11,908,272,245
|
IssuesEvent
|
2020-03-31 00:28:17
|
qgis/QGIS
|
https://api.github.com/repos/qgis/QGIS
|
closed
|
Filter features by geometry type
|
Feature Request Processing
|
Author Name: **Magnus Nilsson** (Magnus Nilsson)
Original Redmine Issue: [19313](https://issues.qgis.org/issues/19313)
Redmine category:processing/modeller
---
It would be useful with an algorithm for filtering features by their geometry type (point, line, polygon, no geometry...) in a processing model.
|
1.0
|
Filter features by geometry type - Author Name: **Magnus Nilsson** (Magnus Nilsson)
Original Redmine Issue: [19313](https://issues.qgis.org/issues/19313)
Redmine category:processing/modeller
---
It would be useful with an algorithm for filtering features by their geometry type (point, line, polygon, no geometry...) in a processing model.
|
process
|
filter features by geometry type author name magnus nilsson magnus nilsson original redmine issue redmine category processing modeller it would be useful with an algorithm for filtering features by their geometry type point line polygon no geometry in a processing model
| 1
|
439,802
| 12,687,290,293
|
IssuesEvent
|
2020-06-20 15:42:49
|
googleapis/python-vision
|
https://api.github.com/repos/googleapis/python-vision
|
opened
|
Synthesis failed for python-vision
|
autosynth failure priority: p1 type: bug
|
Hello! Autosynth couldn't regenerate python-vision. :broken_heart:
Here's the output from running `synth.py`:
```
uilder/.cache/bazel/_bazel_kbuilder/a732f932c2cbeb7e37e1543f189a2a73/external/bazel_tools/tools/build_defs/repo/http.bzl:296:16):
- <builtin>
- /home/kbuilder/.cache/synthtool/googleapis/WORKSPACE:123:1
Loading: 0 packages loaded
INFO: SHA256 (https://github.com/grpc/grpc-java/archive/v1.27.2.zip) = 92ffb4391f847e02e115933a761e243dd1423f3fcafdc9b7ae0327eca102d76b
DEBUG: Rule 'io_grpc_grpc_java' indicated that a canonical reproducible form can be obtained by modifying arguments sha256 = "92ffb4391f847e02e115933a761e243dd1423f3fcafdc9b7ae0327eca102d76b"
DEBUG: Call stack for the definition of repository 'io_grpc_grpc_java' which is a http_archive (rule definition at /home/kbuilder/.cache/bazel/_bazel_kbuilder/a732f932c2cbeb7e37e1543f189a2a73/external/bazel_tools/tools/build_defs/repo/http.bzl:296:16):
- <builtin>
- /home/kbuilder/.cache/bazel/_bazel_kbuilder/a732f932c2cbeb7e37e1543f189a2a73/external/com_google_api_gax_java/repositories.bzl:114:5
- /home/kbuilder/.cache/bazel/_bazel_kbuilder/a732f932c2cbeb7e37e1543f189a2a73/external/com_google_api_gax_java/repositories.bzl:60:5
- /home/kbuilder/.cache/synthtool/googleapis/WORKSPACE:138:1
Loading: 0 packages loaded
INFO: SHA256 (https://github.com/googleapis/gapic-generator/archive/a59457d24bd6f3c962c8e699c708121c928eedc8.zip) = 843bcf262d44f6a2c1c131844ff8ef40daf95dd3b7c95dd761656f9e010d06d7
DEBUG: Rule 'com_google_api_codegen' indicated that a canonical reproducible form can be obtained by modifying arguments sha256 = "843bcf262d44f6a2c1c131844ff8ef40daf95dd3b7c95dd761656f9e010d06d7"
DEBUG: Call stack for the definition of repository 'com_google_api_codegen' which is a http_archive (rule definition at /home/kbuilder/.cache/bazel/_bazel_kbuilder/a732f932c2cbeb7e37e1543f189a2a73/external/bazel_tools/tools/build_defs/repo/http.bzl:296:16):
- <builtin>
- /home/kbuilder/.cache/synthtool/googleapis/WORKSPACE:62:1
Loading: 0 packages loaded
INFO: SHA256 (https://github.com/googleapis/protoc-java-resource-names-plugin/archive/64dafb71ea9a385a8da89989f0b9dab925bf4610.zip) = f475903e83904dbbe3651abae8cbf57ed804960a0dadd9cbde41b746db645052
DEBUG: Rule 'com_google_protoc_java_resource_names_plugin' indicated that a canonical reproducible form can be obtained by modifying arguments sha256 = "f475903e83904dbbe3651abae8cbf57ed804960a0dadd9cbde41b746db645052"
DEBUG: Call stack for the definition of repository 'com_google_protoc_java_resource_names_plugin' which is a http_archive (rule definition at /home/kbuilder/.cache/bazel/_bazel_kbuilder/a732f932c2cbeb7e37e1543f189a2a73/external/bazel_tools/tools/build_defs/repo/http.bzl:296:16):
- <builtin>
- /home/kbuilder/.cache/synthtool/googleapis/WORKSPACE:155:1
INFO: SHA256 (https://github.com/googleapis/protoc-docs-plugin/archive/b2502d56b5ec2d47e063976da773206af295362d.zip) = 765ec120bb165ae98c3bae78705d2a127e64016e59738552e909fc8b11d06338
DEBUG: Rule 'protoc_docs_plugin' indicated that a canonical reproducible form can be obtained by modifying arguments sha256 = "765ec120bb165ae98c3bae78705d2a127e64016e59738552e909fc8b11d06338"
DEBUG: Call stack for the definition of repository 'protoc_docs_plugin' which is a http_archive (rule definition at /home/kbuilder/.cache/bazel/_bazel_kbuilder/a732f932c2cbeb7e37e1543f189a2a73/external/bazel_tools/tools/build_defs/repo/http.bzl:296:16):
- <builtin>
- /home/kbuilder/.cache/synthtool/googleapis/WORKSPACE:179:1
Loading: 0 packages loaded
INFO: SHA256 (https://github.com/bazelbuild/bazel-gazelle/releases/download/v0.20.0/bazel-gazelle-v0.20.0.tar.gz) = d8c45ee70ec39a57e7a05e5027c32b1576cc7f16d9dd37135b0eddde45cf1b10
DEBUG: Rule 'bazel_gazelle' indicated that a canonical reproducible form can be obtained by modifying arguments sha256 = "d8c45ee70ec39a57e7a05e5027c32b1576cc7f16d9dd37135b0eddde45cf1b10"
DEBUG: Call stack for the definition of repository 'bazel_gazelle' which is a http_archive (rule definition at /home/kbuilder/.cache/bazel/_bazel_kbuilder/a732f932c2cbeb7e37e1543f189a2a73/external/bazel_tools/tools/build_defs/repo/http.bzl:296:16):
- <builtin>
- /home/kbuilder/.cache/synthtool/googleapis/WORKSPACE:200:1
Analyzing: target //google/cloud/vision/v1:vision-v1-py (1 packages loaded, 0 targets configured)
INFO: Call stack for the definition of repository 'go_sdk' which is a _go_download_sdk (rule definition at /home/kbuilder/.cache/bazel/_bazel_kbuilder/a732f932c2cbeb7e37e1543f189a2a73/external/io_bazel_rules_go/go/private/sdk.bzl:79:20):
- <builtin>
- /home/kbuilder/.cache/bazel/_bazel_kbuilder/a732f932c2cbeb7e37e1543f189a2a73/external/io_bazel_rules_go/go/private/sdk.bzl:92:5
- /home/kbuilder/.cache/bazel/_bazel_kbuilder/a732f932c2cbeb7e37e1543f189a2a73/external/io_bazel_rules_go/go/private/sdk.bzl:260:13
- /home/kbuilder/.cache/synthtool/googleapis/WORKSPACE:81:1
ERROR: While resolving toolchains for target @pypi_black//:black: invalid registered toolchain '@gapic_generator_python//:pyenv3_toolchain': no such package '@gapic_generator_python//': The repository '@gapic_generator_python' could not be resolved
ERROR: Analysis of target '//google/cloud/vision/v1:vision-v1-py' failed; build aborted: invalid registered toolchain '@gapic_generator_python//:pyenv3_toolchain': no such package '@gapic_generator_python//': The repository '@gapic_generator_python' could not be resolved
INFO: Elapsed time: 6.549s
INFO: 0 processes.
FAILED: Build did NOT complete successfully (21 packages loaded, 22 targets configured)
FAILED: Build did NOT complete successfully (21 packages loaded, 22 targets configured)
2020-06-20 08:42:46,315 synthtool [DEBUG] > Wrote metadata to synth.metadata.
Traceback (most recent call last):
File "/home/kbuilder/.pyenv/versions/3.6.9/lib/python3.6/runpy.py", line 193, in _run_module_as_main
"__main__", mod_spec)
File "/home/kbuilder/.pyenv/versions/3.6.9/lib/python3.6/runpy.py", line 85, in _run_code
exec(code, run_globals)
File "/tmpfs/src/github/synthtool/synthtool/__main__.py", line 102, in <module>
main()
File "/tmpfs/src/github/synthtool/env/lib/python3.6/site-packages/click/core.py", line 829, in __call__
return self.main(*args, **kwargs)
File "/tmpfs/src/github/synthtool/env/lib/python3.6/site-packages/click/core.py", line 782, in main
rv = self.invoke(ctx)
File "/tmpfs/src/github/synthtool/env/lib/python3.6/site-packages/click/core.py", line 1066, in invoke
return ctx.invoke(self.callback, **ctx.params)
File "/tmpfs/src/github/synthtool/env/lib/python3.6/site-packages/click/core.py", line 610, in invoke
return callback(*args, **kwargs)
File "/tmpfs/src/github/synthtool/synthtool/__main__.py", line 94, in main
spec.loader.exec_module(synth_module) # type: ignore
File "<frozen importlib._bootstrap_external>", line 678, in exec_module
File "<frozen importlib._bootstrap>", line 219, in _call_with_frames_removed
File "/home/kbuilder/.cache/synthtool/python-vision/synth.py", line 33, in <module>
include_protos=True
File "/tmpfs/src/github/synthtool/synthtool/gcp/gapic_bazel.py", line 46, in py_library
return self._generate_code(service, version, "python", **kwargs)
File "/tmpfs/src/github/synthtool/synthtool/gcp/gapic_bazel.py", line 180, in _generate_code
shell.run(bazel_run_args)
File "/tmpfs/src/github/synthtool/synthtool/shell.py", line 39, in run
raise exc
File "/tmpfs/src/github/synthtool/synthtool/shell.py", line 33, in run
encoding="utf-8",
File "/home/kbuilder/.pyenv/versions/3.6.9/lib/python3.6/subprocess.py", line 438, in run
output=stdout, stderr=stderr)
subprocess.CalledProcessError: Command '['bazel', '--max_idle_secs=60', 'build', '//google/cloud/vision/v1:vision-v1-py']' returned non-zero exit status 1.
2020-06-20 08:42:46,358 autosynth [ERROR] > Synthesis failed
2020-06-20 08:42:46,359 autosynth [DEBUG] > Running: git reset --hard HEAD
HEAD is now at b33fa88 docs: added note about not supported device (#24)
2020-06-20 08:42:46,364 autosynth [DEBUG] > Running: git checkout autosynth-self
Switched to branch 'autosynth-self'
2020-06-20 08:42:46,370 autosynth [ERROR] > Command '['/tmpfs/src/github/synthtool/env/bin/python3', '-m', 'synthtool', '--metadata', 'synth.metadata', 'synth.py', '--']' returned non-zero exit status 1.
2020-06-20 08:42:46,576 autosynth [INFO] > PR already exists: https://github.com/googleapis/python-vision/pull/27
2020-06-20 08:42:46,576 autosynth [DEBUG] > Running: git clean -fdx
Removing __pycache__/
Removing google/__pycache__/
Traceback (most recent call last):
File "/home/kbuilder/.pyenv/versions/3.6.9/lib/python3.6/runpy.py", line 193, in _run_module_as_main
"__main__", mod_spec)
File "/home/kbuilder/.pyenv/versions/3.6.9/lib/python3.6/runpy.py", line 85, in _run_code
exec(code, run_globals)
File "/tmpfs/src/github/synthtool/autosynth/synth.py", line 649, in <module>
main()
File "/tmpfs/src/github/synthtool/autosynth/synth.py", line 506, in main
return _inner_main(temp_dir)
File "/tmpfs/src/github/synthtool/autosynth/synth.py", line 629, in _inner_main
commit_count = synthesize_loop(x, multiple_prs, change_pusher, synthesizer)
File "/tmpfs/src/github/synthtool/autosynth/synth.py", line 367, in synthesize_loop
synthesize_inner_loop(fork, synthesizer)
File "/tmpfs/src/github/synthtool/autosynth/synth.py", line 411, in synthesize_inner_loop
synthesizer, len(toolbox.versions) - 1
File "/tmpfs/src/github/synthtool/autosynth/synth.py", line 266, in synthesize_version_in_new_branch
synthesizer.synthesize(synth_log_path, self.environ)
File "/tmpfs/src/github/synthtool/autosynth/synthesizer.py", line 120, in synthesize
synth_proc.check_returncode() # Raise an exception.
File "/home/kbuilder/.pyenv/versions/3.6.9/lib/python3.6/subprocess.py", line 389, in check_returncode
self.stderr)
subprocess.CalledProcessError: Command '['/tmpfs/src/github/synthtool/env/bin/python3', '-m', 'synthtool', '--metadata', 'synth.metadata', 'synth.py', '--']' returned non-zero exit status 1.
```
Google internal developers can see the full log [here](http://sponge2/results/invocations/e93a3b66-0b9d-4731-8049-5d33389af1dc/targets/github%2Fsynthtool;config=default/tests;query=python-vision;failed=false).
|
1.0
|
Synthesis failed for python-vision - Hello! Autosynth couldn't regenerate python-vision. :broken_heart:
Here's the output from running `synth.py`:
```
uilder/.cache/bazel/_bazel_kbuilder/a732f932c2cbeb7e37e1543f189a2a73/external/bazel_tools/tools/build_defs/repo/http.bzl:296:16):
- <builtin>
- /home/kbuilder/.cache/synthtool/googleapis/WORKSPACE:123:1
Loading: 0 packages loaded
INFO: SHA256 (https://github.com/grpc/grpc-java/archive/v1.27.2.zip) = 92ffb4391f847e02e115933a761e243dd1423f3fcafdc9b7ae0327eca102d76b
DEBUG: Rule 'io_grpc_grpc_java' indicated that a canonical reproducible form can be obtained by modifying arguments sha256 = "92ffb4391f847e02e115933a761e243dd1423f3fcafdc9b7ae0327eca102d76b"
DEBUG: Call stack for the definition of repository 'io_grpc_grpc_java' which is a http_archive (rule definition at /home/kbuilder/.cache/bazel/_bazel_kbuilder/a732f932c2cbeb7e37e1543f189a2a73/external/bazel_tools/tools/build_defs/repo/http.bzl:296:16):
- <builtin>
- /home/kbuilder/.cache/bazel/_bazel_kbuilder/a732f932c2cbeb7e37e1543f189a2a73/external/com_google_api_gax_java/repositories.bzl:114:5
- /home/kbuilder/.cache/bazel/_bazel_kbuilder/a732f932c2cbeb7e37e1543f189a2a73/external/com_google_api_gax_java/repositories.bzl:60:5
- /home/kbuilder/.cache/synthtool/googleapis/WORKSPACE:138:1
Loading: 0 packages loaded
INFO: SHA256 (https://github.com/googleapis/gapic-generator/archive/a59457d24bd6f3c962c8e699c708121c928eedc8.zip) = 843bcf262d44f6a2c1c131844ff8ef40daf95dd3b7c95dd761656f9e010d06d7
DEBUG: Rule 'com_google_api_codegen' indicated that a canonical reproducible form can be obtained by modifying arguments sha256 = "843bcf262d44f6a2c1c131844ff8ef40daf95dd3b7c95dd761656f9e010d06d7"
DEBUG: Call stack for the definition of repository 'com_google_api_codegen' which is a http_archive (rule definition at /home/kbuilder/.cache/bazel/_bazel_kbuilder/a732f932c2cbeb7e37e1543f189a2a73/external/bazel_tools/tools/build_defs/repo/http.bzl:296:16):
- <builtin>
- /home/kbuilder/.cache/synthtool/googleapis/WORKSPACE:62:1
Loading: 0 packages loaded
INFO: SHA256 (https://github.com/googleapis/protoc-java-resource-names-plugin/archive/64dafb71ea9a385a8da89989f0b9dab925bf4610.zip) = f475903e83904dbbe3651abae8cbf57ed804960a0dadd9cbde41b746db645052
DEBUG: Rule 'com_google_protoc_java_resource_names_plugin' indicated that a canonical reproducible form can be obtained by modifying arguments sha256 = "f475903e83904dbbe3651abae8cbf57ed804960a0dadd9cbde41b746db645052"
DEBUG: Call stack for the definition of repository 'com_google_protoc_java_resource_names_plugin' which is a http_archive (rule definition at /home/kbuilder/.cache/bazel/_bazel_kbuilder/a732f932c2cbeb7e37e1543f189a2a73/external/bazel_tools/tools/build_defs/repo/http.bzl:296:16):
- <builtin>
- /home/kbuilder/.cache/synthtool/googleapis/WORKSPACE:155:1
INFO: SHA256 (https://github.com/googleapis/protoc-docs-plugin/archive/b2502d56b5ec2d47e063976da773206af295362d.zip) = 765ec120bb165ae98c3bae78705d2a127e64016e59738552e909fc8b11d06338
DEBUG: Rule 'protoc_docs_plugin' indicated that a canonical reproducible form can be obtained by modifying arguments sha256 = "765ec120bb165ae98c3bae78705d2a127e64016e59738552e909fc8b11d06338"
DEBUG: Call stack for the definition of repository 'protoc_docs_plugin' which is a http_archive (rule definition at /home/kbuilder/.cache/bazel/_bazel_kbuilder/a732f932c2cbeb7e37e1543f189a2a73/external/bazel_tools/tools/build_defs/repo/http.bzl:296:16):
- <builtin>
- /home/kbuilder/.cache/synthtool/googleapis/WORKSPACE:179:1
Loading: 0 packages loaded
INFO: SHA256 (https://github.com/bazelbuild/bazel-gazelle/releases/download/v0.20.0/bazel-gazelle-v0.20.0.tar.gz) = d8c45ee70ec39a57e7a05e5027c32b1576cc7f16d9dd37135b0eddde45cf1b10
DEBUG: Rule 'bazel_gazelle' indicated that a canonical reproducible form can be obtained by modifying arguments sha256 = "d8c45ee70ec39a57e7a05e5027c32b1576cc7f16d9dd37135b0eddde45cf1b10"
DEBUG: Call stack for the definition of repository 'bazel_gazelle' which is a http_archive (rule definition at /home/kbuilder/.cache/bazel/_bazel_kbuilder/a732f932c2cbeb7e37e1543f189a2a73/external/bazel_tools/tools/build_defs/repo/http.bzl:296:16):
- <builtin>
- /home/kbuilder/.cache/synthtool/googleapis/WORKSPACE:200:1
Analyzing: target //google/cloud/vision/v1:vision-v1-py (1 packages loaded, 0 targets configured)
INFO: Call stack for the definition of repository 'go_sdk' which is a _go_download_sdk (rule definition at /home/kbuilder/.cache/bazel/_bazel_kbuilder/a732f932c2cbeb7e37e1543f189a2a73/external/io_bazel_rules_go/go/private/sdk.bzl:79:20):
- <builtin>
- /home/kbuilder/.cache/bazel/_bazel_kbuilder/a732f932c2cbeb7e37e1543f189a2a73/external/io_bazel_rules_go/go/private/sdk.bzl:92:5
- /home/kbuilder/.cache/bazel/_bazel_kbuilder/a732f932c2cbeb7e37e1543f189a2a73/external/io_bazel_rules_go/go/private/sdk.bzl:260:13
- /home/kbuilder/.cache/synthtool/googleapis/WORKSPACE:81:1
ERROR: While resolving toolchains for target @pypi_black//:black: invalid registered toolchain '@gapic_generator_python//:pyenv3_toolchain': no such package '@gapic_generator_python//': The repository '@gapic_generator_python' could not be resolved
ERROR: Analysis of target '//google/cloud/vision/v1:vision-v1-py' failed; build aborted: invalid registered toolchain '@gapic_generator_python//:pyenv3_toolchain': no such package '@gapic_generator_python//': The repository '@gapic_generator_python' could not be resolved
INFO: Elapsed time: 6.549s
INFO: 0 processes.
FAILED: Build did NOT complete successfully (21 packages loaded, 22 targets configured)
FAILED: Build did NOT complete successfully (21 packages loaded, 22 targets configured)
2020-06-20 08:42:46,315 synthtool [DEBUG] > Wrote metadata to synth.metadata.
Traceback (most recent call last):
File "/home/kbuilder/.pyenv/versions/3.6.9/lib/python3.6/runpy.py", line 193, in _run_module_as_main
"__main__", mod_spec)
File "/home/kbuilder/.pyenv/versions/3.6.9/lib/python3.6/runpy.py", line 85, in _run_code
exec(code, run_globals)
File "/tmpfs/src/github/synthtool/synthtool/__main__.py", line 102, in <module>
main()
File "/tmpfs/src/github/synthtool/env/lib/python3.6/site-packages/click/core.py", line 829, in __call__
return self.main(*args, **kwargs)
File "/tmpfs/src/github/synthtool/env/lib/python3.6/site-packages/click/core.py", line 782, in main
rv = self.invoke(ctx)
File "/tmpfs/src/github/synthtool/env/lib/python3.6/site-packages/click/core.py", line 1066, in invoke
return ctx.invoke(self.callback, **ctx.params)
File "/tmpfs/src/github/synthtool/env/lib/python3.6/site-packages/click/core.py", line 610, in invoke
return callback(*args, **kwargs)
File "/tmpfs/src/github/synthtool/synthtool/__main__.py", line 94, in main
spec.loader.exec_module(synth_module) # type: ignore
File "<frozen importlib._bootstrap_external>", line 678, in exec_module
File "<frozen importlib._bootstrap>", line 219, in _call_with_frames_removed
File "/home/kbuilder/.cache/synthtool/python-vision/synth.py", line 33, in <module>
include_protos=True
File "/tmpfs/src/github/synthtool/synthtool/gcp/gapic_bazel.py", line 46, in py_library
return self._generate_code(service, version, "python", **kwargs)
File "/tmpfs/src/github/synthtool/synthtool/gcp/gapic_bazel.py", line 180, in _generate_code
shell.run(bazel_run_args)
File "/tmpfs/src/github/synthtool/synthtool/shell.py", line 39, in run
raise exc
File "/tmpfs/src/github/synthtool/synthtool/shell.py", line 33, in run
encoding="utf-8",
File "/home/kbuilder/.pyenv/versions/3.6.9/lib/python3.6/subprocess.py", line 438, in run
output=stdout, stderr=stderr)
subprocess.CalledProcessError: Command '['bazel', '--max_idle_secs=60', 'build', '//google/cloud/vision/v1:vision-v1-py']' returned non-zero exit status 1.
2020-06-20 08:42:46,358 autosynth [ERROR] > Synthesis failed
2020-06-20 08:42:46,359 autosynth [DEBUG] > Running: git reset --hard HEAD
HEAD is now at b33fa88 docs: added note about not supported device (#24)
2020-06-20 08:42:46,364 autosynth [DEBUG] > Running: git checkout autosynth-self
Switched to branch 'autosynth-self'
2020-06-20 08:42:46,370 autosynth [ERROR] > Command '['/tmpfs/src/github/synthtool/env/bin/python3', '-m', 'synthtool', '--metadata', 'synth.metadata', 'synth.py', '--']' returned non-zero exit status 1.
2020-06-20 08:42:46,576 autosynth [INFO] > PR already exists: https://github.com/googleapis/python-vision/pull/27
2020-06-20 08:42:46,576 autosynth [DEBUG] > Running: git clean -fdx
Removing __pycache__/
Removing google/__pycache__/
Traceback (most recent call last):
File "/home/kbuilder/.pyenv/versions/3.6.9/lib/python3.6/runpy.py", line 193, in _run_module_as_main
"__main__", mod_spec)
File "/home/kbuilder/.pyenv/versions/3.6.9/lib/python3.6/runpy.py", line 85, in _run_code
exec(code, run_globals)
File "/tmpfs/src/github/synthtool/autosynth/synth.py", line 649, in <module>
main()
File "/tmpfs/src/github/synthtool/autosynth/synth.py", line 506, in main
return _inner_main(temp_dir)
File "/tmpfs/src/github/synthtool/autosynth/synth.py", line 629, in _inner_main
commit_count = synthesize_loop(x, multiple_prs, change_pusher, synthesizer)
File "/tmpfs/src/github/synthtool/autosynth/synth.py", line 367, in synthesize_loop
synthesize_inner_loop(fork, synthesizer)
File "/tmpfs/src/github/synthtool/autosynth/synth.py", line 411, in synthesize_inner_loop
synthesizer, len(toolbox.versions) - 1
File "/tmpfs/src/github/synthtool/autosynth/synth.py", line 266, in synthesize_version_in_new_branch
synthesizer.synthesize(synth_log_path, self.environ)
File "/tmpfs/src/github/synthtool/autosynth/synthesizer.py", line 120, in synthesize
synth_proc.check_returncode() # Raise an exception.
File "/home/kbuilder/.pyenv/versions/3.6.9/lib/python3.6/subprocess.py", line 389, in check_returncode
self.stderr)
subprocess.CalledProcessError: Command '['/tmpfs/src/github/synthtool/env/bin/python3', '-m', 'synthtool', '--metadata', 'synth.metadata', 'synth.py', '--']' returned non-zero exit status 1.
```
Google internal developers can see the full log [here](http://sponge2/results/invocations/e93a3b66-0b9d-4731-8049-5d33389af1dc/targets/github%2Fsynthtool;config=default/tests;query=python-vision;failed=false).
|
non_process
|
synthesis failed for python vision hello autosynth couldn t regenerate python vision broken heart here s the output from running synth py uilder cache bazel bazel kbuilder external bazel tools tools build defs repo http bzl home kbuilder cache synthtool googleapis workspace loading packages loaded info debug rule io grpc grpc java indicated that a canonical reproducible form can be obtained by modifying arguments debug call stack for the definition of repository io grpc grpc java which is a http archive rule definition at home kbuilder cache bazel bazel kbuilder external bazel tools tools build defs repo http bzl home kbuilder cache bazel bazel kbuilder external com google api gax java repositories bzl home kbuilder cache bazel bazel kbuilder external com google api gax java repositories bzl home kbuilder cache synthtool googleapis workspace loading packages loaded info debug rule com google api codegen indicated that a canonical reproducible form can be obtained by modifying arguments debug call stack for the definition of repository com google api codegen which is a http archive rule definition at home kbuilder cache bazel bazel kbuilder external bazel tools tools build defs repo http bzl home kbuilder cache synthtool googleapis workspace loading packages loaded info debug rule com google protoc java resource names plugin indicated that a canonical reproducible form can be obtained by modifying arguments debug call stack for the definition of repository com google protoc java resource names plugin which is a http archive rule definition at home kbuilder cache bazel bazel kbuilder external bazel tools tools build defs repo http bzl home kbuilder cache synthtool googleapis workspace info debug rule protoc docs plugin indicated that a canonical reproducible form can be obtained by modifying arguments debug call stack for the definition of repository protoc docs plugin which is a http archive rule definition at home kbuilder cache bazel bazel kbuilder external bazel tools tools build defs repo http bzl home kbuilder cache synthtool googleapis workspace loading packages loaded info debug rule bazel gazelle indicated that a canonical reproducible form can be obtained by modifying arguments debug call stack for the definition of repository bazel gazelle which is a http archive rule definition at home kbuilder cache bazel bazel kbuilder external bazel tools tools build defs repo http bzl home kbuilder cache synthtool googleapis workspace analyzing target google cloud vision vision py packages loaded targets configured info call stack for the definition of repository go sdk which is a go download sdk rule definition at home kbuilder cache bazel bazel kbuilder external io bazel rules go go private sdk bzl home kbuilder cache bazel bazel kbuilder external io bazel rules go go private sdk bzl home kbuilder cache bazel bazel kbuilder external io bazel rules go go private sdk bzl home kbuilder cache synthtool googleapis workspace error while resolving toolchains for target pypi black black invalid registered toolchain gapic generator python toolchain no such package gapic generator python the repository gapic generator python could not be resolved error analysis of target google cloud vision vision py failed build aborted invalid registered toolchain gapic generator python toolchain no such package gapic generator python the repository gapic generator python could not be resolved info elapsed time info processes failed build did not complete successfully packages loaded targets configured failed build did not complete successfully packages loaded targets configured synthtool wrote metadata to synth metadata traceback most recent call last file home kbuilder pyenv versions lib runpy py line in run module as main main mod spec file home kbuilder pyenv versions lib runpy py line in run code exec code run globals file tmpfs src github synthtool synthtool main py line in main file tmpfs src github synthtool env lib site packages click core py line in call return self main args kwargs file tmpfs src github synthtool env lib site packages click core py line in main rv self invoke ctx file tmpfs src github synthtool env lib site packages click core py line in invoke return ctx invoke self callback ctx params file tmpfs src github synthtool env lib site packages click core py line in invoke return callback args kwargs file tmpfs src github synthtool synthtool main py line in main spec loader exec module synth module type ignore file line in exec module file line in call with frames removed file home kbuilder cache synthtool python vision synth py line in include protos true file tmpfs src github synthtool synthtool gcp gapic bazel py line in py library return self generate code service version python kwargs file tmpfs src github synthtool synthtool gcp gapic bazel py line in generate code shell run bazel run args file tmpfs src github synthtool synthtool shell py line in run raise exc file tmpfs src github synthtool synthtool shell py line in run encoding utf file home kbuilder pyenv versions lib subprocess py line in run output stdout stderr stderr subprocess calledprocesserror command returned non zero exit status autosynth synthesis failed autosynth running git reset hard head head is now at docs added note about not supported device autosynth running git checkout autosynth self switched to branch autosynth self autosynth command returned non zero exit status autosynth pr already exists autosynth running git clean fdx removing pycache removing google pycache traceback most recent call last file home kbuilder pyenv versions lib runpy py line in run module as main main mod spec file home kbuilder pyenv versions lib runpy py line in run code exec code run globals file tmpfs src github synthtool autosynth synth py line in main file tmpfs src github synthtool autosynth synth py line in main return inner main temp dir file tmpfs src github synthtool autosynth synth py line in inner main commit count synthesize loop x multiple prs change pusher synthesizer file tmpfs src github synthtool autosynth synth py line in synthesize loop synthesize inner loop fork synthesizer file tmpfs src github synthtool autosynth synth py line in synthesize inner loop synthesizer len toolbox versions file tmpfs src github synthtool autosynth synth py line in synthesize version in new branch synthesizer synthesize synth log path self environ file tmpfs src github synthtool autosynth synthesizer py line in synthesize synth proc check returncode raise an exception file home kbuilder pyenv versions lib subprocess py line in check returncode self stderr subprocess calledprocesserror command returned non zero exit status google internal developers can see the full log
| 0
|
259,279
| 19,594,062,664
|
IssuesEvent
|
2022-01-05 15:54:51
|
golang/go
|
https://api.github.com/repos/golang/go
|
closed
|
testing: document file format for fuzz corpus files
|
Documentation NeedsInvestigation fuzz
|
commit 8ac5cbe05d61df0a7a7c9a38ff33305d4dcfea32
The fuzz docs inside the testing package say:
> Seed inputs may be registered by calling F.Add or by storing files in the directory testdata/fuzz/<Name> (where <Name> is the name of the fuzz target) within the package containing the fuzz target.
but the docs don't say what format those files are expected to be in. I was expecting to be able to just copy a load of corpus data from the original fuzz tool (where the format is just exactly the data for the input), but I see errors of the form:
```
"testdata/fuzz/FuzzDecoder/27f4f596adb49c6967f41e8f82d3855f5ae9375e": unmarshal: must include version and at least one value
```
The testing docs should say what format should be used for these files. Ideally there would be a some kind of migration tool to migrate from the old format to the new.
|
1.0
|
testing: document file format for fuzz corpus files - commit 8ac5cbe05d61df0a7a7c9a38ff33305d4dcfea32
The fuzz docs inside the testing package say:
> Seed inputs may be registered by calling F.Add or by storing files in the directory testdata/fuzz/<Name> (where <Name> is the name of the fuzz target) within the package containing the fuzz target.
but the docs don't say what format those files are expected to be in. I was expecting to be able to just copy a load of corpus data from the original fuzz tool (where the format is just exactly the data for the input), but I see errors of the form:
```
"testdata/fuzz/FuzzDecoder/27f4f596adb49c6967f41e8f82d3855f5ae9375e": unmarshal: must include version and at least one value
```
The testing docs should say what format should be used for these files. Ideally there would be a some kind of migration tool to migrate from the old format to the new.
|
non_process
|
testing document file format for fuzz corpus files commit the fuzz docs inside the testing package say seed inputs may be registered by calling f add or by storing files in the directory testdata fuzz where is the name of the fuzz target within the package containing the fuzz target but the docs don t say what format those files are expected to be in i was expecting to be able to just copy a load of corpus data from the original fuzz tool where the format is just exactly the data for the input but i see errors of the form testdata fuzz fuzzdecoder unmarshal must include version and at least one value the testing docs should say what format should be used for these files ideally there would be a some kind of migration tool to migrate from the old format to the new
| 0
|
294,224
| 9,014,475,144
|
IssuesEvent
|
2019-02-05 22:31:47
|
fedora-infra/bodhi
|
https://api.github.com/repos/fedora-infra/bodhi
|
opened
|
Give Bodhi automation to push based on time in testing
|
API High priority Migration RFE
|
Right now Bodhi has the ability to push updates to stable when they reach a karma threshold, but updates that reach the time in testing need to be manually pushed by a packager.
This RFE is about giving Bodhi the ability to automatically push the update to stable when it reaches the time in testing, so long as it does not have any negative karma (negative karma currently stops autopushing based on karma, so we want something similar for time).
This has been [approved by FESCo](https://pagure.io/fesco/issue/2048), and here is a list of requirements from that ticket:
* The boolean to select push based on time should be independent from the existing boolean to push based on karma.
* The packager should be able to set the number of days they want it to wait, not less than the release's minimum days (i.e., for Fedora they could set it at 7 days on the low end, or 30 if they like 30).
|
1.0
|
Give Bodhi automation to push based on time in testing - Right now Bodhi has the ability to push updates to stable when they reach a karma threshold, but updates that reach the time in testing need to be manually pushed by a packager.
This RFE is about giving Bodhi the ability to automatically push the update to stable when it reaches the time in testing, so long as it does not have any negative karma (negative karma currently stops autopushing based on karma, so we want something similar for time).
This has been [approved by FESCo](https://pagure.io/fesco/issue/2048), and here is a list of requirements from that ticket:
* The boolean to select push based on time should be independent from the existing boolean to push based on karma.
* The packager should be able to set the number of days they want it to wait, not less than the release's minimum days (i.e., for Fedora they could set it at 7 days on the low end, or 30 if they like 30).
|
non_process
|
give bodhi automation to push based on time in testing right now bodhi has the ability to push updates to stable when they reach a karma threshold but updates that reach the time in testing need to be manually pushed by a packager this rfe is about giving bodhi the ability to automatically push the update to stable when it reaches the time in testing so long as it does not have any negative karma negative karma currently stops autopushing based on karma so we want something similar for time this has been and here is a list of requirements from that ticket the boolean to select push based on time should be independent from the existing boolean to push based on karma the packager should be able to set the number of days they want it to wait not less than the release s minimum days i e for fedora they could set it at days on the low end or if they like
| 0
|
29,711
| 5,672,500,411
|
IssuesEvent
|
2017-04-12 01:43:45
|
canjs/canjs
|
https://api.github.com/repos/canjs/canjs
|
closed
|
can.view.bindings API page is broken
|
developer relations documentation
|
Multiple issues seen on [can.view.bindings](https://canjs.com/docs/can.view.bindings.event.html) API page:
1. ($DOM_EVENT)='CALL_EXPRESSION' anchor link is broken
2. (VIEW_MODEL_EVENT)='CALL_EXPRESSION' anchor link is broken
3. Parameters section of (VIEW_MODEL_EVENT)='CALL_EXPRESSION' incorrectly lists **DOM_EVENT** as the first parameter: _DOM_EVENT {String} A DOM event name like "click". jQuery custom events can also be given_. Description should be updated to state it's a **VIEW_MODEL_EVENT** and not a **DOM_EVENT**
|
1.0
|
can.view.bindings API page is broken - Multiple issues seen on [can.view.bindings](https://canjs.com/docs/can.view.bindings.event.html) API page:
1. ($DOM_EVENT)='CALL_EXPRESSION' anchor link is broken
2. (VIEW_MODEL_EVENT)='CALL_EXPRESSION' anchor link is broken
3. Parameters section of (VIEW_MODEL_EVENT)='CALL_EXPRESSION' incorrectly lists **DOM_EVENT** as the first parameter: _DOM_EVENT {String} A DOM event name like "click". jQuery custom events can also be given_. Description should be updated to state it's a **VIEW_MODEL_EVENT** and not a **DOM_EVENT**
|
non_process
|
can view bindings api page is broken multiple issues seen on api page dom event call expression anchor link is broken view model event call expression anchor link is broken parameters section of view model event call expression incorrectly lists dom event as the first parameter dom event string a dom event name like click jquery custom events can also be given description should be updated to state it s a view model event and not a dom event
| 0
|
19,027
| 25,035,475,760
|
IssuesEvent
|
2022-11-04 15:40:43
|
ankidroid/Anki-Android
|
https://api.github.com/repos/ankidroid/Anki-Android
|
closed
|
Make code coverage reporting stable
|
Stale Dev Test process
|
`codecov` often reports random fluctuations in the coverage. This is likely because tests are nondeterministic, but may be a bug in codecov.
* Determine why this occurs (typically by finding the classes which fluctuate)
* Maybe this is just due to flaky tests, should we upload codecov reports if there are test failures?
* Fix this, so we no longer get `codecov`-based CI failures on changes which should be no-ops
Maybe useful: https://docs.codecov.com/docs/unexpected-coverage-changes
|
1.0
|
Make code coverage reporting stable - `codecov` often reports random fluctuations in the coverage. This is likely because tests are nondeterministic, but may be a bug in codecov.
* Determine why this occurs (typically by finding the classes which fluctuate)
* Maybe this is just due to flaky tests, should we upload codecov reports if there are test failures?
* Fix this, so we no longer get `codecov`-based CI failures on changes which should be no-ops
Maybe useful: https://docs.codecov.com/docs/unexpected-coverage-changes
|
process
|
make code coverage reporting stable codecov often reports random fluctuations in the coverage this is likely because tests are nondeterministic but may be a bug in codecov determine why this occurs typically by finding the classes which fluctuate maybe this is just due to flaky tests should we upload codecov reports if there are test failures fix this so we no longer get codecov based ci failures on changes which should be no ops maybe useful
| 1
|
64,790
| 8,759,699,899
|
IssuesEvent
|
2018-12-15 19:03:14
|
xoseperez/espurna
|
https://api.github.com/repos/xoseperez/espurna
|
closed
|
Plugin API and built-in feature overrides
|
documentation
|
Hi @xoseperez
I am reversing an [essential oil diffuser](https://www.amazon.com/ASAKUKI-Smart-Wi-Fi-Essential-Diffuser/dp/B076F73M82/ref=sr_1_7_a_it?ie=UTF8&qid=1540751318&sr=8-7&keywords=wifi+oil+diffuser&dpID=31ASZOYxibL&preST=_SY300_QL70_&dpSrc=srch) based on PSA-B module. It looks like it communicates with a separate chip via hardware serial, and all the functionality of the device is delegated to it.
I have reversed it's full serial protocol, based on AT commands, and in order to integrate it in espurna, I guess I will need to write a plugin overriding the following functionality:
1) Relay on/off
2) LED colors and brightness
3) Relay status update(if switched off externally on the device, in order to reflect the status in espurna)
4) a couple more specific features, such as various LED modes.
For relay switching, it seems that it is possible with the current plugin api. Can I override the LED controls in a similar manner? I want to be able to use the same MQTT functionality for LED colors & on/off for easier integration in homeassistant, and ability to use the color wheel from espurna interface.
If you can give me some pointers in the codebase or what to grep for, would really appreciate!
Will send a PR when I am done with it.
|
1.0
|
Plugin API and built-in feature overrides - Hi @xoseperez
I am reversing an [essential oil diffuser](https://www.amazon.com/ASAKUKI-Smart-Wi-Fi-Essential-Diffuser/dp/B076F73M82/ref=sr_1_7_a_it?ie=UTF8&qid=1540751318&sr=8-7&keywords=wifi+oil+diffuser&dpID=31ASZOYxibL&preST=_SY300_QL70_&dpSrc=srch) based on PSA-B module. It looks like it communicates with a separate chip via hardware serial, and all the functionality of the device is delegated to it.
I have reversed it's full serial protocol, based on AT commands, and in order to integrate it in espurna, I guess I will need to write a plugin overriding the following functionality:
1) Relay on/off
2) LED colors and brightness
3) Relay status update(if switched off externally on the device, in order to reflect the status in espurna)
4) a couple more specific features, such as various LED modes.
For relay switching, it seems that it is possible with the current plugin api. Can I override the LED controls in a similar manner? I want to be able to use the same MQTT functionality for LED colors & on/off for easier integration in homeassistant, and ability to use the color wheel from espurna interface.
If you can give me some pointers in the codebase or what to grep for, would really appreciate!
Will send a PR when I am done with it.
|
non_process
|
plugin api and built in feature overrides hi xoseperez i am reversing an based on psa b module it looks like it communicates with a separate chip via hardware serial and all the functionality of the device is delegated to it i have reversed it s full serial protocol based on at commands and in order to integrate it in espurna i guess i will need to write a plugin overriding the following functionality relay on off led colors and brightness relay status update if switched off externally on the device in order to reflect the status in espurna a couple more specific features such as various led modes for relay switching it seems that it is possible with the current plugin api can i override the led controls in a similar manner i want to be able to use the same mqtt functionality for led colors on off for easier integration in homeassistant and ability to use the color wheel from espurna interface if you can give me some pointers in the codebase or what to grep for would really appreciate will send a pr when i am done with it
| 0
|
187,099
| 22,031,530,749
|
IssuesEvent
|
2022-05-28 00:38:58
|
vincenzodistasio97/Slack-Clone
|
https://api.github.com/repos/vincenzodistasio97/Slack-Clone
|
closed
|
WS-2018-0347 (Medium) detected in eslint-4.14.0.tgz - autoclosed
|
security vulnerability
|
## WS-2018-0347 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>eslint-4.14.0.tgz</b></p></summary>
<p>An AST-based pattern checker for JavaScript.</p>
<p>Library home page: <a href="https://registry.npmjs.org/eslint/-/eslint-4.14.0.tgz">https://registry.npmjs.org/eslint/-/eslint-4.14.0.tgz</a></p>
<p>Path to dependency file: /server/package.json</p>
<p>Path to vulnerable library: /server/node_modules/mquery/node_modules/eslint/package.json</p>
<p>
Dependency Hierarchy:
- mongoose-5.2.6.tgz (Root Library)
- mquery-3.1.1.tgz
- :x: **eslint-4.14.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vincenzodistasio97/Slack-Clone/commit/125be6381c29e8f8e1d4b2fed216db288fad9798">125be6381c29e8f8e1d4b2fed216db288fad9798</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A vulnerability was descovered in eslint before 4.18.2. One of the regexes in eslint is vulnerable to catastrophic backtracking.
<p>Publish Date: 2018-02-27
<p>URL: <a href=https://github.com/eslint/eslint/commit/f6901d0bcf6c918ac4e5c6c7c4bddeb2cb715c09>WS-2018-0347</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/eslint/eslint/issues/10002">https://github.com/eslint/eslint/issues/10002</a></p>
<p>Release Date: 2018-02-27</p>
<p>Fix Resolution (eslint): 4.18.2</p>
<p>Direct dependency fix Resolution (mongoose): 6.2.11</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
WS-2018-0347 (Medium) detected in eslint-4.14.0.tgz - autoclosed - ## WS-2018-0347 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>eslint-4.14.0.tgz</b></p></summary>
<p>An AST-based pattern checker for JavaScript.</p>
<p>Library home page: <a href="https://registry.npmjs.org/eslint/-/eslint-4.14.0.tgz">https://registry.npmjs.org/eslint/-/eslint-4.14.0.tgz</a></p>
<p>Path to dependency file: /server/package.json</p>
<p>Path to vulnerable library: /server/node_modules/mquery/node_modules/eslint/package.json</p>
<p>
Dependency Hierarchy:
- mongoose-5.2.6.tgz (Root Library)
- mquery-3.1.1.tgz
- :x: **eslint-4.14.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vincenzodistasio97/Slack-Clone/commit/125be6381c29e8f8e1d4b2fed216db288fad9798">125be6381c29e8f8e1d4b2fed216db288fad9798</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A vulnerability was descovered in eslint before 4.18.2. One of the regexes in eslint is vulnerable to catastrophic backtracking.
<p>Publish Date: 2018-02-27
<p>URL: <a href=https://github.com/eslint/eslint/commit/f6901d0bcf6c918ac4e5c6c7c4bddeb2cb715c09>WS-2018-0347</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/eslint/eslint/issues/10002">https://github.com/eslint/eslint/issues/10002</a></p>
<p>Release Date: 2018-02-27</p>
<p>Fix Resolution (eslint): 4.18.2</p>
<p>Direct dependency fix Resolution (mongoose): 6.2.11</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_process
|
ws medium detected in eslint tgz autoclosed ws medium severity vulnerability vulnerable library eslint tgz an ast based pattern checker for javascript library home page a href path to dependency file server package json path to vulnerable library server node modules mquery node modules eslint package json dependency hierarchy mongoose tgz root library mquery tgz x eslint tgz vulnerable library found in head commit a href found in base branch master vulnerability details a vulnerability was descovered in eslint before one of the regexes in eslint is vulnerable to catastrophic backtracking publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution eslint direct dependency fix resolution mongoose step up your open source security game with whitesource
| 0
|
14,763
| 18,041,690,995
|
IssuesEvent
|
2021-09-18 06:24:36
|
ooi-data/CE09OSSM-MFD37-03-CTDBPE000-telemetered-ctdbp_cdef_dcl_instrument
|
https://api.github.com/repos/ooi-data/CE09OSSM-MFD37-03-CTDBPE000-telemetered-ctdbp_cdef_dcl_instrument
|
opened
|
🛑 Processing failed: ResponseParserError
|
process
|
## Overview
`ResponseParserError` found in `processing_task` task during run ended on 2021-09-18T06:24:35.558856.
## Details
Flow name: `CE09OSSM-MFD37-03-CTDBPE000-telemetered-ctdbp_cdef_dcl_instrument`
Task name: `processing_task`
Error type: `ResponseParserError`
Error message: Unable to parse response (no element found: line 2, column 0), invalid XML received. Further retries may succeed:
b'<?xml version="1.0" encoding="UTF-8"?>\n'
<details>
<summary>Traceback</summary>
```
Traceback (most recent call last):
File "/srv/conda/envs/notebook/lib/python3.8/site-packages/botocore/parsers.py", line 452, in _parse_xml_string_to_dom
root = parser.close()
xml.etree.ElementTree.ParseError: no element found: line 2, column 0
During handling of the above exception, another exception occurred:
Traceback (most recent call last):
File "/srv/conda/envs/notebook/lib/python3.8/site-packages/ooi_harvester/processor/pipeline.py", line 101, in processing
final_path = finalize_zarr(
File "/srv/conda/envs/notebook/lib/python3.8/site-packages/ooi_harvester/processor/__init__.py", line 359, in finalize_zarr
source_store.fs.delete(source_store.root, recursive=True)
File "/srv/conda/envs/notebook/lib/python3.8/site-packages/fsspec/spec.py", line 1187, in delete
return self.rm(path, recursive=recursive, maxdepth=maxdepth)
File "/srv/conda/envs/notebook/lib/python3.8/site-packages/fsspec/asyn.py", line 88, in wrapper
return sync(self.loop, func, *args, **kwargs)
File "/srv/conda/envs/notebook/lib/python3.8/site-packages/fsspec/asyn.py", line 69, in sync
raise result[0]
File "/srv/conda/envs/notebook/lib/python3.8/site-packages/fsspec/asyn.py", line 25, in _runner
result[0] = await coro
File "/srv/conda/envs/notebook/lib/python3.8/site-packages/s3fs/core.py", line 1677, in _rm
await asyncio.gather(
File "/srv/conda/envs/notebook/lib/python3.8/site-packages/s3fs/core.py", line 1657, in _bulk_delete
await self._call_s3("delete_objects", kwargs, Bucket=bucket, Delete=delete_keys)
File "/srv/conda/envs/notebook/lib/python3.8/site-packages/s3fs/core.py", line 268, in _call_s3
raise err
File "/srv/conda/envs/notebook/lib/python3.8/site-packages/s3fs/core.py", line 248, in _call_s3
out = await method(**additional_kwargs)
File "/srv/conda/envs/notebook/lib/python3.8/site-packages/aiobotocore/client.py", line 141, in _make_api_call
http, parsed_response = await self._make_request(
File "/srv/conda/envs/notebook/lib/python3.8/site-packages/aiobotocore/client.py", line 161, in _make_request
return await self._endpoint.make_request(operation_model, request_dict)
File "/srv/conda/envs/notebook/lib/python3.8/site-packages/aiobotocore/endpoint.py", line 93, in _send_request
success_response, exception = await self._get_response(
File "/srv/conda/envs/notebook/lib/python3.8/site-packages/aiobotocore/endpoint.py", line 112, in _get_response
success_response, exception = await self._do_get_response(
File "/srv/conda/envs/notebook/lib/python3.8/site-packages/aiobotocore/endpoint.py", line 177, in _do_get_response
parsed_response = parser.parse(
File "/srv/conda/envs/notebook/lib/python3.8/site-packages/botocore/parsers.py", line 245, in parse
parsed = self._do_parse(response, shape)
File "/srv/conda/envs/notebook/lib/python3.8/site-packages/botocore/parsers.py", line 813, in _do_parse
self._add_modeled_parse(response, shape, final_parsed)
File "/srv/conda/envs/notebook/lib/python3.8/site-packages/botocore/parsers.py", line 822, in _add_modeled_parse
self._parse_payload(response, shape, member_shapes, final_parsed)
File "/srv/conda/envs/notebook/lib/python3.8/site-packages/botocore/parsers.py", line 862, in _parse_payload
original_parsed = self._initial_body_parse(response['body'])
File "/srv/conda/envs/notebook/lib/python3.8/site-packages/botocore/parsers.py", line 948, in _initial_body_parse
return self._parse_xml_string_to_dom(xml_string)
File "/srv/conda/envs/notebook/lib/python3.8/site-packages/botocore/parsers.py", line 454, in _parse_xml_string_to_dom
raise ResponseParserError(
botocore.parsers.ResponseParserError: Unable to parse response (no element found: line 2, column 0), invalid XML received. Further retries may succeed:
b'<?xml version="1.0" encoding="UTF-8"?>\n'
```
</details>
|
1.0
|
🛑 Processing failed: ResponseParserError - ## Overview
`ResponseParserError` found in `processing_task` task during run ended on 2021-09-18T06:24:35.558856.
## Details
Flow name: `CE09OSSM-MFD37-03-CTDBPE000-telemetered-ctdbp_cdef_dcl_instrument`
Task name: `processing_task`
Error type: `ResponseParserError`
Error message: Unable to parse response (no element found: line 2, column 0), invalid XML received. Further retries may succeed:
b'<?xml version="1.0" encoding="UTF-8"?>\n'
<details>
<summary>Traceback</summary>
```
Traceback (most recent call last):
File "/srv/conda/envs/notebook/lib/python3.8/site-packages/botocore/parsers.py", line 452, in _parse_xml_string_to_dom
root = parser.close()
xml.etree.ElementTree.ParseError: no element found: line 2, column 0
During handling of the above exception, another exception occurred:
Traceback (most recent call last):
File "/srv/conda/envs/notebook/lib/python3.8/site-packages/ooi_harvester/processor/pipeline.py", line 101, in processing
final_path = finalize_zarr(
File "/srv/conda/envs/notebook/lib/python3.8/site-packages/ooi_harvester/processor/__init__.py", line 359, in finalize_zarr
source_store.fs.delete(source_store.root, recursive=True)
File "/srv/conda/envs/notebook/lib/python3.8/site-packages/fsspec/spec.py", line 1187, in delete
return self.rm(path, recursive=recursive, maxdepth=maxdepth)
File "/srv/conda/envs/notebook/lib/python3.8/site-packages/fsspec/asyn.py", line 88, in wrapper
return sync(self.loop, func, *args, **kwargs)
File "/srv/conda/envs/notebook/lib/python3.8/site-packages/fsspec/asyn.py", line 69, in sync
raise result[0]
File "/srv/conda/envs/notebook/lib/python3.8/site-packages/fsspec/asyn.py", line 25, in _runner
result[0] = await coro
File "/srv/conda/envs/notebook/lib/python3.8/site-packages/s3fs/core.py", line 1677, in _rm
await asyncio.gather(
File "/srv/conda/envs/notebook/lib/python3.8/site-packages/s3fs/core.py", line 1657, in _bulk_delete
await self._call_s3("delete_objects", kwargs, Bucket=bucket, Delete=delete_keys)
File "/srv/conda/envs/notebook/lib/python3.8/site-packages/s3fs/core.py", line 268, in _call_s3
raise err
File "/srv/conda/envs/notebook/lib/python3.8/site-packages/s3fs/core.py", line 248, in _call_s3
out = await method(**additional_kwargs)
File "/srv/conda/envs/notebook/lib/python3.8/site-packages/aiobotocore/client.py", line 141, in _make_api_call
http, parsed_response = await self._make_request(
File "/srv/conda/envs/notebook/lib/python3.8/site-packages/aiobotocore/client.py", line 161, in _make_request
return await self._endpoint.make_request(operation_model, request_dict)
File "/srv/conda/envs/notebook/lib/python3.8/site-packages/aiobotocore/endpoint.py", line 93, in _send_request
success_response, exception = await self._get_response(
File "/srv/conda/envs/notebook/lib/python3.8/site-packages/aiobotocore/endpoint.py", line 112, in _get_response
success_response, exception = await self._do_get_response(
File "/srv/conda/envs/notebook/lib/python3.8/site-packages/aiobotocore/endpoint.py", line 177, in _do_get_response
parsed_response = parser.parse(
File "/srv/conda/envs/notebook/lib/python3.8/site-packages/botocore/parsers.py", line 245, in parse
parsed = self._do_parse(response, shape)
File "/srv/conda/envs/notebook/lib/python3.8/site-packages/botocore/parsers.py", line 813, in _do_parse
self._add_modeled_parse(response, shape, final_parsed)
File "/srv/conda/envs/notebook/lib/python3.8/site-packages/botocore/parsers.py", line 822, in _add_modeled_parse
self._parse_payload(response, shape, member_shapes, final_parsed)
File "/srv/conda/envs/notebook/lib/python3.8/site-packages/botocore/parsers.py", line 862, in _parse_payload
original_parsed = self._initial_body_parse(response['body'])
File "/srv/conda/envs/notebook/lib/python3.8/site-packages/botocore/parsers.py", line 948, in _initial_body_parse
return self._parse_xml_string_to_dom(xml_string)
File "/srv/conda/envs/notebook/lib/python3.8/site-packages/botocore/parsers.py", line 454, in _parse_xml_string_to_dom
raise ResponseParserError(
botocore.parsers.ResponseParserError: Unable to parse response (no element found: line 2, column 0), invalid XML received. Further retries may succeed:
b'<?xml version="1.0" encoding="UTF-8"?>\n'
```
</details>
|
process
|
🛑 processing failed responseparsererror overview responseparsererror found in processing task task during run ended on details flow name telemetered ctdbp cdef dcl instrument task name processing task error type responseparsererror error message unable to parse response no element found line column invalid xml received further retries may succeed b n traceback traceback most recent call last file srv conda envs notebook lib site packages botocore parsers py line in parse xml string to dom root parser close xml etree elementtree parseerror no element found line column during handling of the above exception another exception occurred traceback most recent call last file srv conda envs notebook lib site packages ooi harvester processor pipeline py line in processing final path finalize zarr file srv conda envs notebook lib site packages ooi harvester processor init py line in finalize zarr source store fs delete source store root recursive true file srv conda envs notebook lib site packages fsspec spec py line in delete return self rm path recursive recursive maxdepth maxdepth file srv conda envs notebook lib site packages fsspec asyn py line in wrapper return sync self loop func args kwargs file srv conda envs notebook lib site packages fsspec asyn py line in sync raise result file srv conda envs notebook lib site packages fsspec asyn py line in runner result await coro file srv conda envs notebook lib site packages core py line in rm await asyncio gather file srv conda envs notebook lib site packages core py line in bulk delete await self call delete objects kwargs bucket bucket delete delete keys file srv conda envs notebook lib site packages core py line in call raise err file srv conda envs notebook lib site packages core py line in call out await method additional kwargs file srv conda envs notebook lib site packages aiobotocore client py line in make api call http parsed response await self make request file srv conda envs notebook lib site packages aiobotocore client py line in make request return await self endpoint make request operation model request dict file srv conda envs notebook lib site packages aiobotocore endpoint py line in send request success response exception await self get response file srv conda envs notebook lib site packages aiobotocore endpoint py line in get response success response exception await self do get response file srv conda envs notebook lib site packages aiobotocore endpoint py line in do get response parsed response parser parse file srv conda envs notebook lib site packages botocore parsers py line in parse parsed self do parse response shape file srv conda envs notebook lib site packages botocore parsers py line in do parse self add modeled parse response shape final parsed file srv conda envs notebook lib site packages botocore parsers py line in add modeled parse self parse payload response shape member shapes final parsed file srv conda envs notebook lib site packages botocore parsers py line in parse payload original parsed self initial body parse response file srv conda envs notebook lib site packages botocore parsers py line in initial body parse return self parse xml string to dom xml string file srv conda envs notebook lib site packages botocore parsers py line in parse xml string to dom raise responseparsererror botocore parsers responseparsererror unable to parse response no element found line column invalid xml received further retries may succeed b n
| 1
|
20,276
| 26,908,673,397
|
IssuesEvent
|
2023-02-06 21:23:45
|
openxla/stablehlo
|
https://api.github.com/repos/openxla/stablehlo
|
closed
|
Use camel case for variable names in Ops.cpp
|
Process
|
Example:
`for (auto it = result.index_begin(); it != result.index_end(); ++it)`
|
1.0
|
Use camel case for variable names in Ops.cpp - Example:
`for (auto it = result.index_begin(); it != result.index_end(); ++it)`
|
process
|
use camel case for variable names in ops cpp example for auto it result index begin it result index end it
| 1
|
13,680
| 2,775,782,147
|
IssuesEvent
|
2015-05-04 18:03:08
|
douglasdrumond/macvim
|
https://api.github.com/repos/douglasdrumond/macvim
|
closed
|
opening html files gives Unknown function: htmlcomplete#DetectOmniFlavor
|
auto-migrated Priority-Medium Type-Defect
|
```
With the latest version pulled from GitHub I get the following error when I
open html/erb/php file with html tags inside:
Error detected while processing
/Applications/MacVim.app/Contents/Resources/vim/runtime/ftplugin/html.vim:
line 25:
E117: Unknown function: htmlcomplete#DetectOmniFlavor
Commenting out the line seems to fix the issue, but anyway what's the proper
solution?
```
Original issue reported on code.google.com by `vesti...@gmail.com` on 21 Nov 2014 at 10:48
|
1.0
|
opening html files gives Unknown function: htmlcomplete#DetectOmniFlavor - ```
With the latest version pulled from GitHub I get the following error when I
open html/erb/php file with html tags inside:
Error detected while processing
/Applications/MacVim.app/Contents/Resources/vim/runtime/ftplugin/html.vim:
line 25:
E117: Unknown function: htmlcomplete#DetectOmniFlavor
Commenting out the line seems to fix the issue, but anyway what's the proper
solution?
```
Original issue reported on code.google.com by `vesti...@gmail.com` on 21 Nov 2014 at 10:48
|
non_process
|
opening html files gives unknown function htmlcomplete detectomniflavor with the latest version pulled from github i get the following error when i open html erb php file with html tags inside error detected while processing applications macvim app contents resources vim runtime ftplugin html vim line unknown function htmlcomplete detectomniflavor commenting out the line seems to fix the issue but anyway what s the proper solution original issue reported on code google com by vesti gmail com on nov at
| 0
|
177,431
| 21,475,395,167
|
IssuesEvent
|
2022-04-26 13:16:57
|
pazhanivel07/frameworks_base_Aosp10_r33_CVE-2021-0315
|
https://api.github.com/repos/pazhanivel07/frameworks_base_Aosp10_r33_CVE-2021-0315
|
opened
|
CVE-2021-0931 (Medium) detected in baseandroid-10.0.0_r46
|
security vulnerability
|
## CVE-2021-0931 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>baseandroid-10.0.0_r46</b></p></summary>
<p>
<p>Android framework classes and services</p>
<p>Library home page: <a href=https://android.googlesource.com/platform/frameworks/base>https://android.googlesource.com/platform/frameworks/base</a></p>
<p>Found in HEAD commit: <a href="https://github.com/pazhanivel07/frameworks_base_Aosp10_r33_CVE-2021-0315/commit/208fdb481d671eb38f28d914bfbbe6364ee43be2">208fdb481d671eb38f28d914bfbbe6364ee43be2</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/core/java/android/bluetooth/BluetoothDevice.java</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In getAlias of BluetoothDevice.java, there is a possible way to create misleading permission dialogs due to missing data filtering. This could lead to local information disclosure with User execution privileges needed. User interaction is needed for exploitation.Product: AndroidVersions: Android-10 Android-11 Android-12 Android-9Android ID: A-180747689
<p>Publish Date: 2021-12-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0931>CVE-2021-0931</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-0931">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-0931</a></p>
<p>Release Date: 2021-12-15</p>
<p>Fix Resolution: android-12.0.0_r8</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2021-0931 (Medium) detected in baseandroid-10.0.0_r46 - ## CVE-2021-0931 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>baseandroid-10.0.0_r46</b></p></summary>
<p>
<p>Android framework classes and services</p>
<p>Library home page: <a href=https://android.googlesource.com/platform/frameworks/base>https://android.googlesource.com/platform/frameworks/base</a></p>
<p>Found in HEAD commit: <a href="https://github.com/pazhanivel07/frameworks_base_Aosp10_r33_CVE-2021-0315/commit/208fdb481d671eb38f28d914bfbbe6364ee43be2">208fdb481d671eb38f28d914bfbbe6364ee43be2</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/core/java/android/bluetooth/BluetoothDevice.java</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In getAlias of BluetoothDevice.java, there is a possible way to create misleading permission dialogs due to missing data filtering. This could lead to local information disclosure with User execution privileges needed. User interaction is needed for exploitation.Product: AndroidVersions: Android-10 Android-11 Android-12 Android-9Android ID: A-180747689
<p>Publish Date: 2021-12-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0931>CVE-2021-0931</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-0931">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-0931</a></p>
<p>Release Date: 2021-12-15</p>
<p>Fix Resolution: android-12.0.0_r8</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_process
|
cve medium detected in baseandroid cve medium severity vulnerability vulnerable library baseandroid android framework classes and services library home page a href found in head commit a href found in base branch master vulnerable source files core java android bluetooth bluetoothdevice java vulnerability details in getalias of bluetoothdevice java there is a possible way to create misleading permission dialogs due to missing data filtering this could lead to local information disclosure with user execution privileges needed user interaction is needed for exploitation product androidversions android android android android id a publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution android step up your open source security game with whitesource
| 0
|
15,538
| 19,703,299,500
|
IssuesEvent
|
2022-01-12 18:54:30
|
googleapis/python-talent
|
https://api.github.com/repos/googleapis/python-talent
|
opened
|
Your .repo-metadata.json file has a problem 🤒
|
type: process repo-metadata: lint
|
You have a problem with your .repo-metadata.json file:
Result of scan 📈:
* api_shortname 'talent' invalid in .repo-metadata.json
☝️ Once you correct these problems, you can close this issue.
Reach out to **go/github-automation** if you have any questions.
|
1.0
|
Your .repo-metadata.json file has a problem 🤒 - You have a problem with your .repo-metadata.json file:
Result of scan 📈:
* api_shortname 'talent' invalid in .repo-metadata.json
☝️ Once you correct these problems, you can close this issue.
Reach out to **go/github-automation** if you have any questions.
|
process
|
your repo metadata json file has a problem 🤒 you have a problem with your repo metadata json file result of scan 📈 api shortname talent invalid in repo metadata json ☝️ once you correct these problems you can close this issue reach out to go github automation if you have any questions
| 1
|
776,028
| 27,243,995,841
|
IssuesEvent
|
2023-02-21 23:27:36
|
googleapis/google-api-nodejs-client
|
https://api.github.com/repos/googleapis/google-api-nodejs-client
|
closed
|
When will the @googleapis/playintegrity submolule be published to npm?
|
type: question priority: p3
|
The following command fails because the submodule package is not published to the npm registry. When will the submodule officially be released?
```bash
npm install @googleapis/playintegrity
```
ref.) https://www.npmjs.com/search?q=scope%3Agoogleapis%20playintegrity
|
1.0
|
When will the @googleapis/playintegrity submolule be published to npm? - The following command fails because the submodule package is not published to the npm registry. When will the submodule officially be released?
```bash
npm install @googleapis/playintegrity
```
ref.) https://www.npmjs.com/search?q=scope%3Agoogleapis%20playintegrity
|
non_process
|
when will the googleapis playintegrity submolule be published to npm the following command fails because the submodule package is not published to the npm registry when will the submodule officially be released bash npm install googleapis playintegrity ref
| 0
|
676,920
| 23,142,692,648
|
IssuesEvent
|
2022-07-28 20:12:09
|
ramp4-pcar4/ramp4-pcar4
|
https://api.github.com/repos/ramp4-pcar4/ramp4-pcar4
|
opened
|
Decouple Settings Fixture From Legend
|
effort: small flavour: enhancement priority: nice type: perfective
|
When opening the settings panel, the settings fixture uses the legend api to fetch the legend item and pass it to the settings screen. This creates a dependency where the settings fixture will only function if the legend fixture is added.
The settings panel only uses the legend item to update visibility/opacity. Hence an alternate solution is that the settings panel can update visibility/opacity directly on the layer and the legend items can set up handlers to watch for layer state change events.
|
1.0
|
Decouple Settings Fixture From Legend - When opening the settings panel, the settings fixture uses the legend api to fetch the legend item and pass it to the settings screen. This creates a dependency where the settings fixture will only function if the legend fixture is added.
The settings panel only uses the legend item to update visibility/opacity. Hence an alternate solution is that the settings panel can update visibility/opacity directly on the layer and the legend items can set up handlers to watch for layer state change events.
|
non_process
|
decouple settings fixture from legend when opening the settings panel the settings fixture uses the legend api to fetch the legend item and pass it to the settings screen this creates a dependency where the settings fixture will only function if the legend fixture is added the settings panel only uses the legend item to update visibility opacity hence an alternate solution is that the settings panel can update visibility opacity directly on the layer and the legend items can set up handlers to watch for layer state change events
| 0
|
11,548
| 14,432,715,821
|
IssuesEvent
|
2020-12-07 02:47:09
|
googleapis/gapic-generator-java
|
https://api.github.com/repos/googleapis/gapic-generator-java
|
closed
|
Enable master branch protection
|
type: process
|
This repository does not seem to have master branch
protection enabled, at least in the way I'm expecting.
I was hoping for:
- master branch protection
- requiring at least one code reviewer
- requiring at least two status checks
- enforcing rules for admins
Please turn it on!
|
1.0
|
Enable master branch protection -
This repository does not seem to have master branch
protection enabled, at least in the way I'm expecting.
I was hoping for:
- master branch protection
- requiring at least one code reviewer
- requiring at least two status checks
- enforcing rules for admins
Please turn it on!
|
process
|
enable master branch protection this repository does not seem to have master branch protection enabled at least in the way i m expecting i was hoping for master branch protection requiring at least one code reviewer requiring at least two status checks enforcing rules for admins please turn it on
| 1
|
10,222
| 13,091,421,629
|
IssuesEvent
|
2020-08-03 06:33:41
|
qgis/QGIS
|
https://api.github.com/repos/qgis/QGIS
|
closed
|
Split vector layers returns incorrect layer names
|
Bug Processing
|
**Describe the bug**
When using the split vector layer tool the resulting layers have incorrect names, like attribute_name + index[0,1,2,3,4,5,...] but it should be attribute name + attribute value. It happens with text and numeric fields and using different output formats (gpkg, shp).
**How to Reproduce**
1. Go to Split Vector layer tool in processing
2. Split layer using Unique ID Field
3. Save layers to folder
4. Resulting layers have incorrect names
**QGIS and OS versions**
QGIS 3.13
Ubuntu 20.04
**Additional context**
Test gpkg
[split_test.zip](https://github.com/qgis/QGIS/files/4800294/split_test.zip)
|
1.0
|
Split vector layers returns incorrect layer names - **Describe the bug**
When using the split vector layer tool the resulting layers have incorrect names, like attribute_name + index[0,1,2,3,4,5,...] but it should be attribute name + attribute value. It happens with text and numeric fields and using different output formats (gpkg, shp).
**How to Reproduce**
1. Go to Split Vector layer tool in processing
2. Split layer using Unique ID Field
3. Save layers to folder
4. Resulting layers have incorrect names
**QGIS and OS versions**
QGIS 3.13
Ubuntu 20.04
**Additional context**
Test gpkg
[split_test.zip](https://github.com/qgis/QGIS/files/4800294/split_test.zip)
|
process
|
split vector layers returns incorrect layer names describe the bug when using the split vector layer tool the resulting layers have incorrect names like attribute name index but it should be attribute name attribute value it happens with text and numeric fields and using different output formats gpkg shp how to reproduce go to split vector layer tool in processing split layer using unique id field save layers to folder resulting layers have incorrect names qgis and os versions qgis ubuntu additional context test gpkg
| 1
|
8,300
| 11,463,290,522
|
IssuesEvent
|
2020-02-07 15:44:20
|
geneontology/go-ontology
|
https://api.github.com/repos/geneontology/go-ontology
|
closed
|
rename GO:0052373 negative regulation by organism of entry into other organism involved in symbiotic interaction
|
multi-species process
|
GO:0052373
negative regulation by organism of entry into other organism involved in symbiotic interaction
should be relabeled as 'suppression of symbiont entry into host by host'
Is used by one MGI annotation with this meaning.
The child term
GO:0052374 negative regulation by symbiont of entry into host
is not used. We don't have any examples.
Should be obsoleted.
(if it exists it now has the incorrect parent)
|
1.0
|
rename GO:0052373 negative regulation by organism of entry into other organism involved in symbiotic interaction -
GO:0052373
negative regulation by organism of entry into other organism involved in symbiotic interaction
should be relabeled as 'suppression of symbiont entry into host by host'
Is used by one MGI annotation with this meaning.
The child term
GO:0052374 negative regulation by symbiont of entry into host
is not used. We don't have any examples.
Should be obsoleted.
(if it exists it now has the incorrect parent)
|
process
|
rename go negative regulation by organism of entry into other organism involved in symbiotic interaction go negative regulation by organism of entry into other organism involved in symbiotic interaction should be relabeled as suppression of symbiont entry into host by host is used by one mgi annotation with this meaning the child term go negative regulation by symbiont of entry into host is not used we don t have any examples should be obsoleted if it exists it now has the incorrect parent
| 1
|
139,848
| 18,858,054,863
|
IssuesEvent
|
2021-11-12 09:20:03
|
Verseghy/website_frontend
|
https://api.github.com/repos/Verseghy/website_frontend
|
closed
|
CVE-2020-7765 (Medium) detected in util-0.3.2.tgz
|
security vulnerability
|
## CVE-2020-7765 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>util-0.3.2.tgz</b></p></summary>
<p>_NOTE: This is specifically tailored for Firebase JS SDK usage, if you are not a member of the Firebase team, please avoid using this package_</p>
<p>Library home page: <a href="https://registry.npmjs.org/@firebase/util/-/util-0.3.2.tgz">https://registry.npmjs.org/@firebase/util/-/util-0.3.2.tgz</a></p>
<p>Path to dependency file: website_frontend/apps/math-competition/scripts/latex-doc-creator/package.json</p>
<p>Path to vulnerable library: website_frontend/apps/math-competition/scripts/latex-doc-creator/node_modules/@firebase/util/package.json,website_frontend/apps/math-competition/scripts/admin-adder/node_modules/@firebase/util/package.json</p>
<p>
Dependency Hierarchy:
- firebase-admin-9.4.1.tgz (Root Library)
- database-0.6.13.tgz
- :x: **util-0.3.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Verseghy/website_frontend/commit/9aa2f4022cfc5aaab093eb3cc9c540a9bfc3eed1">9aa2f4022cfc5aaab093eb3cc9c540a9bfc3eed1</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
This affects the package @firebase/util before 0.3.4. This vulnerability relates to the deepExtend function within the DeepCopy.ts file. Depending on if user input is provided, an attacker can overwrite and pollute the object prototype of a program.
<p>Publish Date: 2020-11-16
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7765>CVE-2020-7765</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-7765">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-7765</a></p>
<p>Release Date: 2020-11-16</p>
<p>Fix Resolution: @firebase/util - 0.3.4</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2020-7765 (Medium) detected in util-0.3.2.tgz - ## CVE-2020-7765 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>util-0.3.2.tgz</b></p></summary>
<p>_NOTE: This is specifically tailored for Firebase JS SDK usage, if you are not a member of the Firebase team, please avoid using this package_</p>
<p>Library home page: <a href="https://registry.npmjs.org/@firebase/util/-/util-0.3.2.tgz">https://registry.npmjs.org/@firebase/util/-/util-0.3.2.tgz</a></p>
<p>Path to dependency file: website_frontend/apps/math-competition/scripts/latex-doc-creator/package.json</p>
<p>Path to vulnerable library: website_frontend/apps/math-competition/scripts/latex-doc-creator/node_modules/@firebase/util/package.json,website_frontend/apps/math-competition/scripts/admin-adder/node_modules/@firebase/util/package.json</p>
<p>
Dependency Hierarchy:
- firebase-admin-9.4.1.tgz (Root Library)
- database-0.6.13.tgz
- :x: **util-0.3.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Verseghy/website_frontend/commit/9aa2f4022cfc5aaab093eb3cc9c540a9bfc3eed1">9aa2f4022cfc5aaab093eb3cc9c540a9bfc3eed1</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
This affects the package @firebase/util before 0.3.4. This vulnerability relates to the deepExtend function within the DeepCopy.ts file. Depending on if user input is provided, an attacker can overwrite and pollute the object prototype of a program.
<p>Publish Date: 2020-11-16
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7765>CVE-2020-7765</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-7765">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-7765</a></p>
<p>Release Date: 2020-11-16</p>
<p>Fix Resolution: @firebase/util - 0.3.4</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_process
|
cve medium detected in util tgz cve medium severity vulnerability vulnerable library util tgz note this is specifically tailored for firebase js sdk usage if you are not a member of the firebase team please avoid using this package library home page a href path to dependency file website frontend apps math competition scripts latex doc creator package json path to vulnerable library website frontend apps math competition scripts latex doc creator node modules firebase util package json website frontend apps math competition scripts admin adder node modules firebase util package json dependency hierarchy firebase admin tgz root library database tgz x util tgz vulnerable library found in head commit a href found in base branch master vulnerability details this affects the package firebase util before this vulnerability relates to the deepextend function within the deepcopy ts file depending on if user input is provided an attacker can overwrite and pollute the object prototype of a program publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution firebase util step up your open source security game with whitesource
| 0
|
14,218
| 24,631,205,226
|
IssuesEvent
|
2022-10-17 02:20:59
|
renovatebot/renovate
|
https://api.github.com/repos/renovatebot/renovate
|
opened
|
dotnet datasource does not set source urls
|
type:bug status:requirements priority-5-triage
|
### How are you running Renovate?
Mend Renovate hosted app on github.com
### If you're self-hosting Renovate, tell us what version of Renovate you run.
_No response_
### If you're self-hosting Renovate, select which platform you are using.
_No response_
### If you're self-hosting Renovate, tell us what version of the platform you run.
_No response_
### Was this something which used to work for you, and then stopped?
It used to work, and then stopped
### Describe the bug
After seeing the great work done by @JamieMagee, I [switched](https://github.com/gitfool/GitHubActions.Dungeon/commit/60dda772c55abefc7992513939378bd6bc30ae2f) from using the docker datasource to the dotnet datasource to track dotnet sdk updates. This works well except that the source urls are not set, so renovate does not link back to the source repo and releases. Note that I added [manual source urls](https://github.com/renovatebot/renovate/pull/14613) for the docker datasource, so it would be good if this was carried over to the dotnet datasource.
* Before switching (docker datasource):
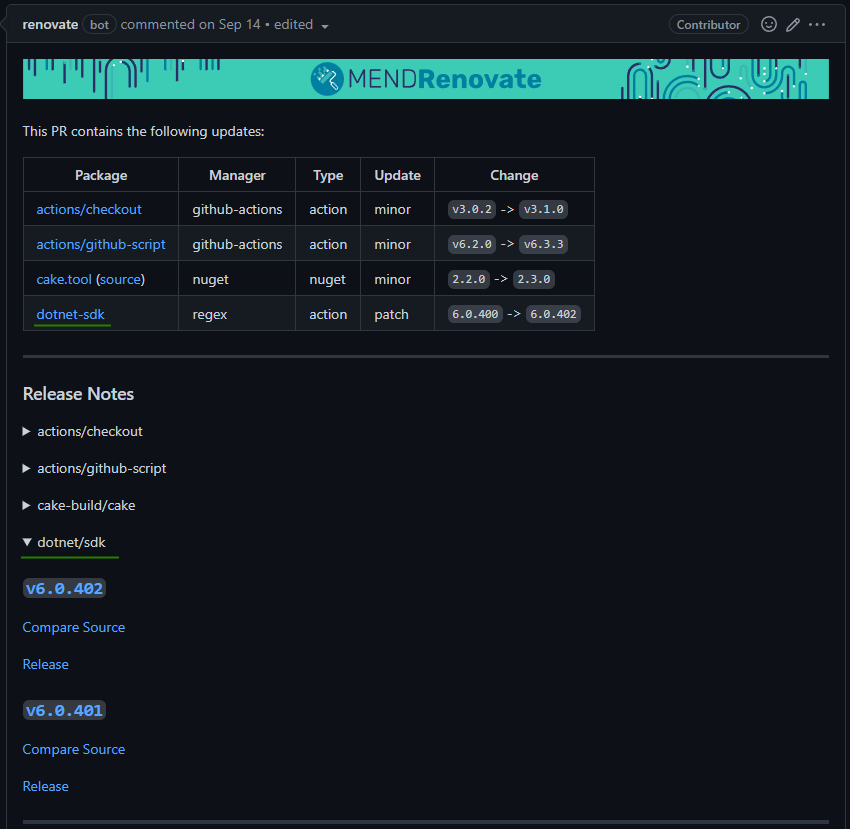
* After switching (dotnet datasource):

### Relevant debug logs
<details><summary>Logs</summary>
```
Copy/paste the relevant log(s) here, between the starting and ending backticks
```
</details>
### Have you created a minimal reproduction repository?
No reproduction repository
|
1.0
|
dotnet datasource does not set source urls - ### How are you running Renovate?
Mend Renovate hosted app on github.com
### If you're self-hosting Renovate, tell us what version of Renovate you run.
_No response_
### If you're self-hosting Renovate, select which platform you are using.
_No response_
### If you're self-hosting Renovate, tell us what version of the platform you run.
_No response_
### Was this something which used to work for you, and then stopped?
It used to work, and then stopped
### Describe the bug
After seeing the great work done by @JamieMagee, I [switched](https://github.com/gitfool/GitHubActions.Dungeon/commit/60dda772c55abefc7992513939378bd6bc30ae2f) from using the docker datasource to the dotnet datasource to track dotnet sdk updates. This works well except that the source urls are not set, so renovate does not link back to the source repo and releases. Note that I added [manual source urls](https://github.com/renovatebot/renovate/pull/14613) for the docker datasource, so it would be good if this was carried over to the dotnet datasource.
* Before switching (docker datasource):
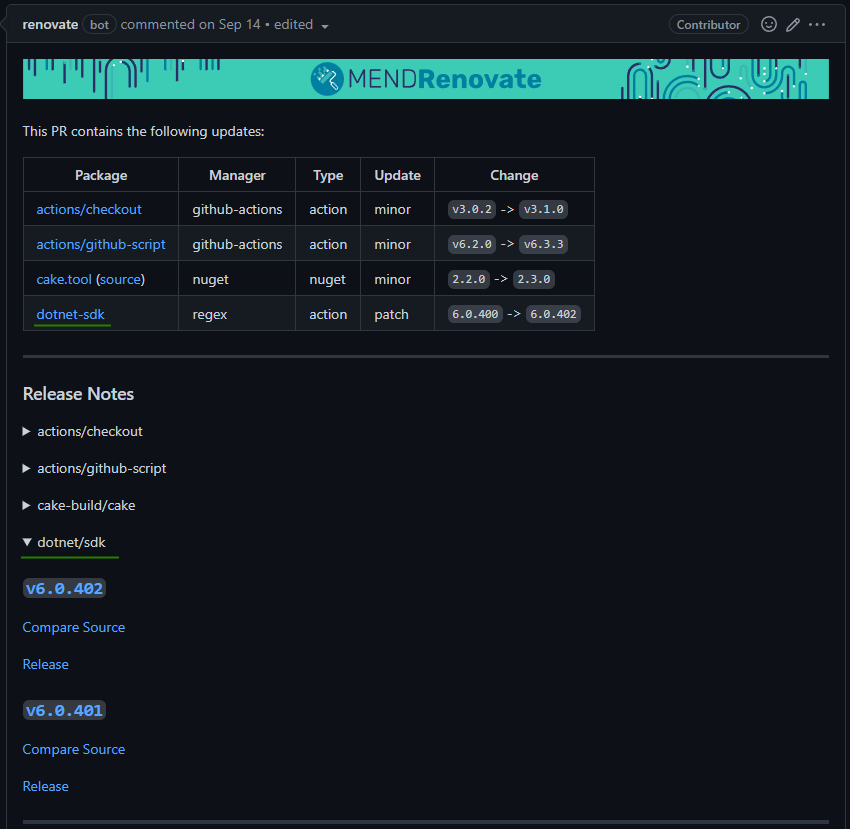
* After switching (dotnet datasource):

### Relevant debug logs
<details><summary>Logs</summary>
```
Copy/paste the relevant log(s) here, between the starting and ending backticks
```
</details>
### Have you created a minimal reproduction repository?
No reproduction repository
|
non_process
|
dotnet datasource does not set source urls how are you running renovate mend renovate hosted app on github com if you re self hosting renovate tell us what version of renovate you run no response if you re self hosting renovate select which platform you are using no response if you re self hosting renovate tell us what version of the platform you run no response was this something which used to work for you and then stopped it used to work and then stopped describe the bug after seeing the great work done by jamiemagee i from using the docker datasource to the dotnet datasource to track dotnet sdk updates this works well except that the source urls are not set so renovate does not link back to the source repo and releases note that i added for the docker datasource so it would be good if this was carried over to the dotnet datasource before switching docker datasource after switching dotnet datasource relevant debug logs logs copy paste the relevant log s here between the starting and ending backticks have you created a minimal reproduction repository no reproduction repository
| 0
|
11,356
| 14,173,632,170
|
IssuesEvent
|
2020-11-12 18:38:19
|
unicode-org/icu4x
|
https://api.github.com/repos/unicode-org/icu4x
|
closed
|
wiki vs docs/
|
C-process T-task
|
Most of our docs are checked in into `docs/` directory.
I made an attempt to try wiki instead with my data provider tutorial.
As we are nearing 0.1 release and I start looking at the funnels and how users will learn about our project I am looking to improve our readmes, docs and wikis and I'm wondering about how to properly reason about split between the role of the wiki and docs.
Since we started working on icu4x I see the main benefit of docs being a thorough review of each document performed before it gets committed.
After that, both docs and wiki keep history of changes, and the main difference seems to be that every change to docs has a higher organizational overhead as it requires a PR and review.
Is it worth it?
I like the simplicity of wiki, and I trust each one of us that as we iterate over wiki we'll make reasonable changes and we can discuss them in issues. The wiki seems to me like a lower-overhead model with better interlinking and low-cost updates.
What is the groups position? When and why do we prefer docs over wiki and do we want both, or coalesce on one? If we keep both can we find a rule of thumb on when to use which?
|
1.0
|
wiki vs docs/ - Most of our docs are checked in into `docs/` directory.
I made an attempt to try wiki instead with my data provider tutorial.
As we are nearing 0.1 release and I start looking at the funnels and how users will learn about our project I am looking to improve our readmes, docs and wikis and I'm wondering about how to properly reason about split between the role of the wiki and docs.
Since we started working on icu4x I see the main benefit of docs being a thorough review of each document performed before it gets committed.
After that, both docs and wiki keep history of changes, and the main difference seems to be that every change to docs has a higher organizational overhead as it requires a PR and review.
Is it worth it?
I like the simplicity of wiki, and I trust each one of us that as we iterate over wiki we'll make reasonable changes and we can discuss them in issues. The wiki seems to me like a lower-overhead model with better interlinking and low-cost updates.
What is the groups position? When and why do we prefer docs over wiki and do we want both, or coalesce on one? If we keep both can we find a rule of thumb on when to use which?
|
process
|
wiki vs docs most of our docs are checked in into docs directory i made an attempt to try wiki instead with my data provider tutorial as we are nearing release and i start looking at the funnels and how users will learn about our project i am looking to improve our readmes docs and wikis and i m wondering about how to properly reason about split between the role of the wiki and docs since we started working on i see the main benefit of docs being a thorough review of each document performed before it gets committed after that both docs and wiki keep history of changes and the main difference seems to be that every change to docs has a higher organizational overhead as it requires a pr and review is it worth it i like the simplicity of wiki and i trust each one of us that as we iterate over wiki we ll make reasonable changes and we can discuss them in issues the wiki seems to me like a lower overhead model with better interlinking and low cost updates what is the groups position when and why do we prefer docs over wiki and do we want both or coalesce on one if we keep both can we find a rule of thumb on when to use which
| 1
|
95,800
| 12,042,846,602
|
IssuesEvent
|
2020-04-14 11:20:36
|
tenders-exposed/elvis-ember
|
https://api.github.com/repos/tenders-exposed/elvis-ember
|
closed
|
Small styling issues on the network view
|
Defense Elvis design low hanging
|
* [ ] side bar floating away 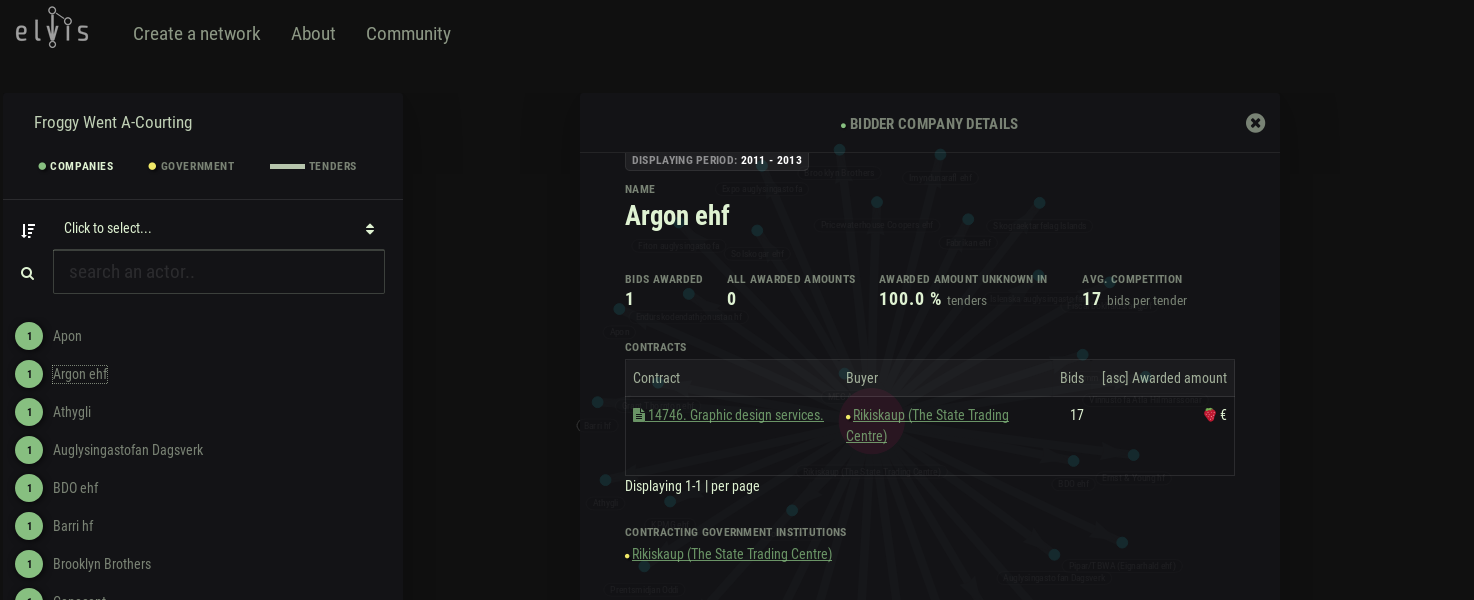
[example network](https://defense.tenders.exposed/network/ec0f8f08-232c-4e5e-b30d-23c7d29a7154/bidders/21221451-8520-46ba-ae68-61d77e77db95)
* [ ] the colors on the network do not fit the ones in the side bar
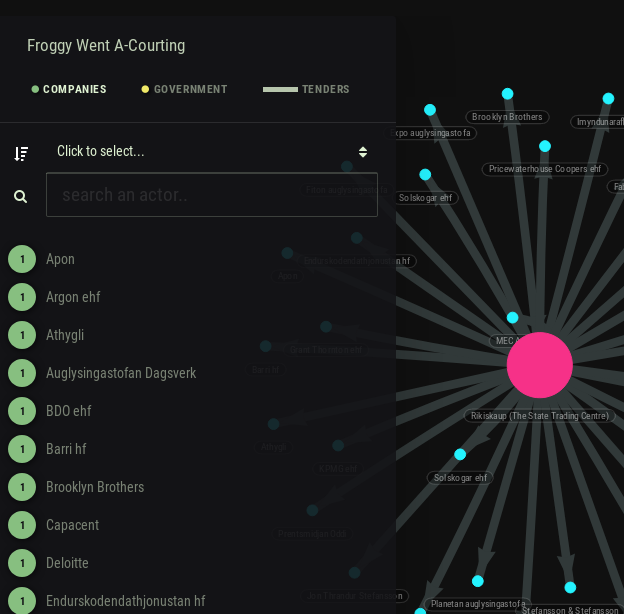
|
1.0
|
Small styling issues on the network view - * [ ] side bar floating away 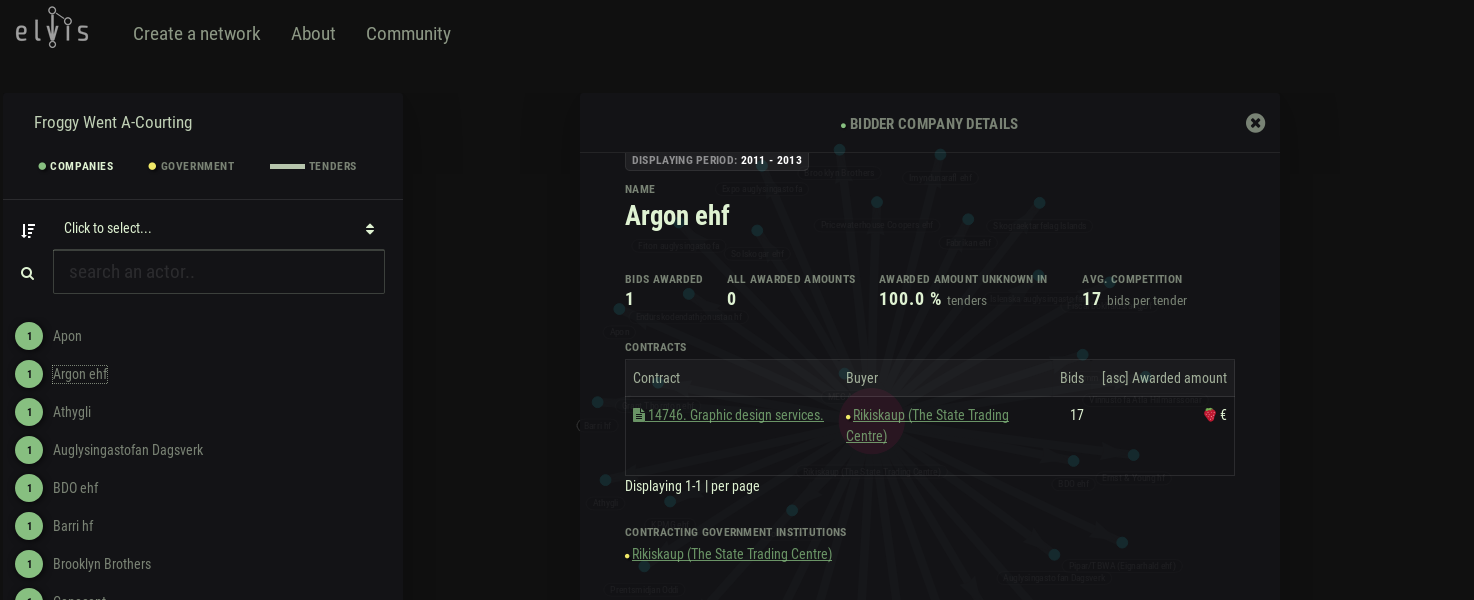
[example network](https://defense.tenders.exposed/network/ec0f8f08-232c-4e5e-b30d-23c7d29a7154/bidders/21221451-8520-46ba-ae68-61d77e77db95)
* [ ] the colors on the network do not fit the ones in the side bar
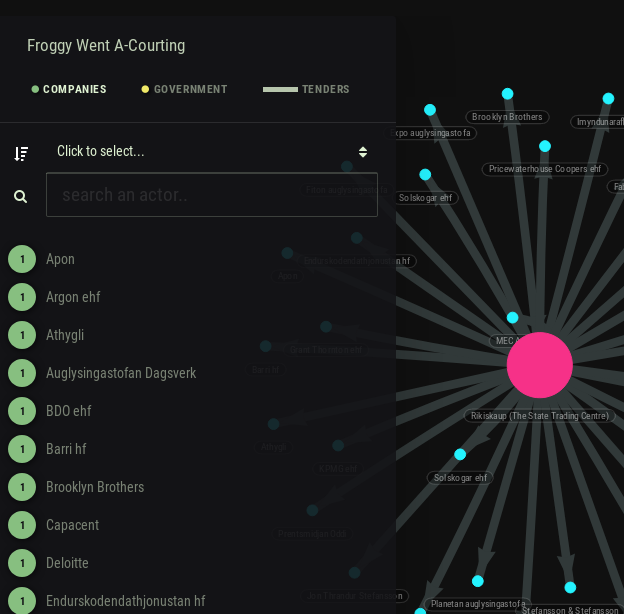
|
non_process
|
small styling issues on the network view side bar floating away the colors on the network do not fit the ones in the side bar
| 0
|
22,529
| 31,653,101,678
|
IssuesEvent
|
2023-09-07 01:12:25
|
tdwg/dwc
|
https://api.github.com/repos/tdwg/dwc
|
closed
|
Change term - typeStatus
|
Term - change Class - Identification Process - need evidence for demand Process - need evidence for stability Controversial Process - needs Task Group
|
## Change term
* Submitter: Niels Klazenga
* Justification: This proposal clarifies the usage of `dwc:typeStatus`. Issue #28 identified the need to clearly separate type status (in the sense proposed here) from the typified scientific name. During the discussion around #28, it came to light that the current definition of `typeStatus` is at odds with the most prevalent usage of the term. We consider usage of `dwc:typeStatus` in accordance with the current definition sufficiently rare that the least disruptive solution is to change the definition of the term, rather than mint a new URI. ABCD uses `TypeStatus` in the sense proposed here, so adopting this change will lead to consistent usage of the term throughout TDWG (and that we do not have to have this discussion again when Darwin Core and ABCD are being reconciled). `typeStatus` is also in the `dwciri` namespace, for use with an IRI, which only makes sense if it takes a vocabulary term, as is proposed here, rather than free text, which is the case under the current definition. This proposal replaces the proposal in issue #327 and should go together with the proposal in #28.
* Proponents: Markus Doering, Rich Pyle
Current Term definition: https://dwc.tdwg.org/terms/#dwc:typeStatus
Proposed new attributes of the term:
* Term name: typeStatus
* Organized in Class: Identification
* Definition of the term: **The kind of nomenclatural type an Organism represents.**
* Usage comments: **Recommended best practice is to use a controlled vocabulary such as the [GBIF Nomenlatural Type Status Vocabulary](https://rs.gbif.org/vocabulary/gbif/type_status.xml). `typeStatus` is to be used together with a typified name, either `typifiedName` or `scientificName`, depending on how it is used.**
* Examples: `holotype`, `isotype`, `lectotype`
* Refines: None
* Replaces: http://rs.tdwg.org/dwc/terms/version/typeStatus-2017-10-06
* ABCD 2.06: **`DataSets/DataSet/Units/Unit/SpecimenUnit/NomenclaturalTypeDesignations/NomenclaturalTypeDesignation/TypeStatus`**
|
3.0
|
Change term - typeStatus - ## Change term
* Submitter: Niels Klazenga
* Justification: This proposal clarifies the usage of `dwc:typeStatus`. Issue #28 identified the need to clearly separate type status (in the sense proposed here) from the typified scientific name. During the discussion around #28, it came to light that the current definition of `typeStatus` is at odds with the most prevalent usage of the term. We consider usage of `dwc:typeStatus` in accordance with the current definition sufficiently rare that the least disruptive solution is to change the definition of the term, rather than mint a new URI. ABCD uses `TypeStatus` in the sense proposed here, so adopting this change will lead to consistent usage of the term throughout TDWG (and that we do not have to have this discussion again when Darwin Core and ABCD are being reconciled). `typeStatus` is also in the `dwciri` namespace, for use with an IRI, which only makes sense if it takes a vocabulary term, as is proposed here, rather than free text, which is the case under the current definition. This proposal replaces the proposal in issue #327 and should go together with the proposal in #28.
* Proponents: Markus Doering, Rich Pyle
Current Term definition: https://dwc.tdwg.org/terms/#dwc:typeStatus
Proposed new attributes of the term:
* Term name: typeStatus
* Organized in Class: Identification
* Definition of the term: **The kind of nomenclatural type an Organism represents.**
* Usage comments: **Recommended best practice is to use a controlled vocabulary such as the [GBIF Nomenlatural Type Status Vocabulary](https://rs.gbif.org/vocabulary/gbif/type_status.xml). `typeStatus` is to be used together with a typified name, either `typifiedName` or `scientificName`, depending on how it is used.**
* Examples: `holotype`, `isotype`, `lectotype`
* Refines: None
* Replaces: http://rs.tdwg.org/dwc/terms/version/typeStatus-2017-10-06
* ABCD 2.06: **`DataSets/DataSet/Units/Unit/SpecimenUnit/NomenclaturalTypeDesignations/NomenclaturalTypeDesignation/TypeStatus`**
|
process
|
change term typestatus change term submitter niels klazenga justification this proposal clarifies the usage of dwc typestatus issue identified the need to clearly separate type status in the sense proposed here from the typified scientific name during the discussion around it came to light that the current definition of typestatus is at odds with the most prevalent usage of the term we consider usage of dwc typestatus in accordance with the current definition sufficiently rare that the least disruptive solution is to change the definition of the term rather than mint a new uri abcd uses typestatus in the sense proposed here so adopting this change will lead to consistent usage of the term throughout tdwg and that we do not have to have this discussion again when darwin core and abcd are being reconciled typestatus is also in the dwciri namespace for use with an iri which only makes sense if it takes a vocabulary term as is proposed here rather than free text which is the case under the current definition this proposal replaces the proposal in issue and should go together with the proposal in proponents markus doering rich pyle current term definition proposed new attributes of the term term name typestatus organized in class identification definition of the term the kind of nomenclatural type an organism represents usage comments recommended best practice is to use a controlled vocabulary such as the typestatus is to be used together with a typified name either typifiedname or scientificname depending on how it is used examples holotype isotype lectotype refines none replaces abcd datasets dataset units unit specimenunit nomenclaturaltypedesignations nomenclaturaltypedesignation typestatus
| 1
|
5,743
| 8,581,026,729
|
IssuesEvent
|
2018-11-13 13:41:46
|
easy-software-ufal/annotations_repos
|
https://api.github.com/repos/easy-software-ufal/annotations_repos
|
opened
|
agoda-com/AgodaAnalyzers AG0012: Rule reports methods marked with [SetUp] attribute as missing assertion
|
ADA C# test wrong processing
|
Issue: `https://github.com/agoda-com/AgodaAnalyzers/issues/109`
PR: `https://github.com/agoda-com/AgodaAnalyzers/commit/3f71807e12d6b1e077a082a5c10cd530464e0606`
|
1.0
|
agoda-com/AgodaAnalyzers AG0012: Rule reports methods marked with [SetUp] attribute as missing assertion - Issue: `https://github.com/agoda-com/AgodaAnalyzers/issues/109`
PR: `https://github.com/agoda-com/AgodaAnalyzers/commit/3f71807e12d6b1e077a082a5c10cd530464e0606`
|
process
|
agoda com agodaanalyzers rule reports methods marked with attribute as missing assertion issue pr
| 1
|
2,113
| 4,952,570,683
|
IssuesEvent
|
2016-12-01 12:28:13
|
bazelbuild/bazel
|
https://api.github.com/repos/bazelbuild/bazel
|
closed
|
November release
|
Release blocker type: process
|
Assigning to @laszlocsomor since he has fixes he wants to get out, feel free to reassign.
|
1.0
|
November release - Assigning to @laszlocsomor since he has fixes he wants to get out, feel free to reassign.
|
process
|
november release assigning to laszlocsomor since he has fixes he wants to get out feel free to reassign
| 1
|
11,212
| 13,964,029,025
|
IssuesEvent
|
2020-10-25 16:29:49
|
osquery/osquery
|
https://api.github.com/repos/osquery/osquery
|
closed
|
sshd child not present in process_events
|
Linux process auditing
|
I am using the osquery compiled from git, the second sshd process is created when a user starts a new ssh session successfully.
The process with pid 2936 is not a thread but a new forked, childred of 2876.
root 2876 2876 0.0 0.1 107696 7220 ? Ss 13:48 0:00 sshd: user1 [priv]
user1 2936 2936 0.7 0.0 107696 3544 ? S 13:48 0:00 sshd: user1@pts/2
osquery> select path, cmdline, pid from process_events where cmdline like '%ssh%';
+----------------+-------------------------------+--------+
| path | cmdline | pid |
+----------------+-------------------------------+--------+
| /usr/sbin/sshd | /usr/sbin/sshd -D -R | 2566 |
| /usr/sbin/sshd | /usr/sbin/sshd -D -R | 2876 |
| /usr/sbin/sshd | /usr/sbin/sshd -D -R | 3319 |
+----------------+-------------------------------+--------+
I can't see it in process_events, but it is visible in processes table.
|
1.0
|
sshd child not present in process_events - I am using the osquery compiled from git, the second sshd process is created when a user starts a new ssh session successfully.
The process with pid 2936 is not a thread but a new forked, childred of 2876.
root 2876 2876 0.0 0.1 107696 7220 ? Ss 13:48 0:00 sshd: user1 [priv]
user1 2936 2936 0.7 0.0 107696 3544 ? S 13:48 0:00 sshd: user1@pts/2
osquery> select path, cmdline, pid from process_events where cmdline like '%ssh%';
+----------------+-------------------------------+--------+
| path | cmdline | pid |
+----------------+-------------------------------+--------+
| /usr/sbin/sshd | /usr/sbin/sshd -D -R | 2566 |
| /usr/sbin/sshd | /usr/sbin/sshd -D -R | 2876 |
| /usr/sbin/sshd | /usr/sbin/sshd -D -R | 3319 |
+----------------+-------------------------------+--------+
I can't see it in process_events, but it is visible in processes table.
|
process
|
sshd child not present in process events i am using the osquery compiled from git the second sshd process is created when a user starts a new ssh session successfully the process with pid is not a thread but a new forked childred of root ss sshd s sshd pts osquery select path cmdline pid from process events where cmdline like ssh path cmdline pid usr sbin sshd usr sbin sshd d r usr sbin sshd usr sbin sshd d r usr sbin sshd usr sbin sshd d r i can t see it in process events but it is visible in processes table
| 1
|
47,894
| 2,986,996,976
|
IssuesEvent
|
2015-07-20 09:27:27
|
ggrov/tinker
|
https://api.github.com/repos/ggrov/tinker
|
closed
|
support more debug options
|
Priority : Medium Tinker Core Tinker GUI TODO
|
- [x] 1. support stop node from core
- [x] 2. allow step in and step over
- [x] 3. complete current graph
- [x] 4. run until breakpoint (stop)
|
1.0
|
support more debug options - - [x] 1. support stop node from core
- [x] 2. allow step in and step over
- [x] 3. complete current graph
- [x] 4. run until breakpoint (stop)
|
non_process
|
support more debug options support stop node from core allow step in and step over complete current graph run until breakpoint stop
| 0
|
18,479
| 24,550,723,765
|
IssuesEvent
|
2022-10-12 12:24:40
|
GoogleCloudPlatform/fda-mystudies
|
https://api.github.com/repos/GoogleCloudPlatform/fda-mystudies
|
closed
|
[iOS] Eligibility test > The following changes needs to be done on the Eligibility questions screen
|
Bug P1 iOS Process: Fixed Process: Tested QA Process: Tested dev
|
1. Remove the arrow marks present which are present next to the Data sharing options
2. AR: A participant is automatically navigating to the next screen after selecting any one of the options
ER: After selecting the option, the participant should stay on the same screen and participant should click on
next button to navigate to the next page
|
3.0
|
[iOS] Eligibility test > The following changes needs to be done on the Eligibility questions screen - 1. Remove the arrow marks present which are present next to the Data sharing options
2. AR: A participant is automatically navigating to the next screen after selecting any one of the options
ER: After selecting the option, the participant should stay on the same screen and participant should click on
next button to navigate to the next page
|
process
|
eligibility test the following changes needs to be done on the eligibility questions screen remove the arrow marks present which are present next to the data sharing options ar a participant is automatically navigating to the next screen after selecting any one of the options er after selecting the option the participant should stay on the same screen and participant should click on next button to navigate to the next page
| 1
|
13,192
| 15,614,048,953
|
IssuesEvent
|
2021-03-19 17:14:50
|
MicrosoftDocs/azure-devops-docs
|
https://api.github.com/repos/MicrosoftDocs/azure-devops-docs
|
closed
|
VMs matching tags: "any" or "all" ?
|
Pri2 devops-cicd-process/tech devops/prod doc-enhancement stale-issue
|
Please update the "Reference VM resources in pipelines" section to indicate whether the VM resource must match ALL of the tags or ANY of tags. The linked reference document (YAML Schema) does not even define "tags" as an option for "environment".
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 91d0d31f-81ee-c024-db7e-daddbf525f71
* Version Independent ID: 330f1649-386c-d0aa-5f96-b8343a1480d3
* Content: [Environment - Virtual machine resource - Azure Pipelines](https://docs.microsoft.com/en-us/azure/devops/pipelines/process/environments-virtual-machines?view=azure-devops#feedback)
* Content Source: [docs/pipelines/process/environments-virtual-machines.md](https://github.com/MicrosoftDocs/azure-devops-docs/blob/master/docs/pipelines/process/environments-virtual-machines.md)
* Product: **devops**
* Technology: **devops-cicd-process**
* GitHub Login: @juliakm
* Microsoft Alias: **jukullam**
|
1.0
|
VMs matching tags: "any" or "all" ? - Please update the "Reference VM resources in pipelines" section to indicate whether the VM resource must match ALL of the tags or ANY of tags. The linked reference document (YAML Schema) does not even define "tags" as an option for "environment".
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 91d0d31f-81ee-c024-db7e-daddbf525f71
* Version Independent ID: 330f1649-386c-d0aa-5f96-b8343a1480d3
* Content: [Environment - Virtual machine resource - Azure Pipelines](https://docs.microsoft.com/en-us/azure/devops/pipelines/process/environments-virtual-machines?view=azure-devops#feedback)
* Content Source: [docs/pipelines/process/environments-virtual-machines.md](https://github.com/MicrosoftDocs/azure-devops-docs/blob/master/docs/pipelines/process/environments-virtual-machines.md)
* Product: **devops**
* Technology: **devops-cicd-process**
* GitHub Login: @juliakm
* Microsoft Alias: **jukullam**
|
process
|
vms matching tags any or all please update the reference vm resources in pipelines section to indicate whether the vm resource must match all of the tags or any of tags the linked reference document yaml schema does not even define tags as an option for environment document details ⚠ do not edit this section it is required for docs microsoft com ➟ github issue linking id version independent id content content source product devops technology devops cicd process github login juliakm microsoft alias jukullam
| 1
|
578,937
| 17,157,111,296
|
IssuesEvent
|
2021-07-14 08:23:50
|
ChadGoymer/githapi
|
https://api.github.com/repos/ChadGoymer/githapi
|
opened
|
Use {fs} for paths, directories and files
|
effort:3 feature priority:2
|
## Description
{fs} is much more reliable across OS's and file storage technologies. Replace all base functions for paths, directories and files with {fs} functions.
## Proposed Solution
<!-- Should be filled out by the developer -->
<!-- A description of how to implement the feature -->
<!-- Please also add labels for the amount of effort required -->
|
1.0
|
Use {fs} for paths, directories and files - ## Description
{fs} is much more reliable across OS's and file storage technologies. Replace all base functions for paths, directories and files with {fs} functions.
## Proposed Solution
<!-- Should be filled out by the developer -->
<!-- A description of how to implement the feature -->
<!-- Please also add labels for the amount of effort required -->
|
non_process
|
use fs for paths directories and files description fs is much more reliable across os s and file storage technologies replace all base functions for paths directories and files with fs functions proposed solution
| 0
|
66,099
| 27,335,701,809
|
IssuesEvent
|
2023-02-26 06:54:36
|
treasuryguild/gg
|
https://api.github.com/repos/treasuryguild/gg
|
closed
|
3.183805 ADA Outgoing
|
Governance-Services-Guild-tools Fund9 Outgoing
|
{
"id" : "1677394151280",
"date": "Sun, 26 Feb 2023 06:49:11 GMT",
"fund": "Fund9",
"project": "Governance-Guild",
"proposal": "Governance-Services-Guild-tools",
"ideascale": "https://cardano.ideascale.com/c/idea/420109",
"budget": "Other",
"name": "",
"exchangeRate": "0.361 USD per ADA",
"ada" : "3.00",
"walletBalance": ["84301.91 ADA", "20392.00 GMBL"],
"txid": "26b9cd274d657b9cf15cc353a70989afcdb9cbbe00436b160bcb80e535a5b3a4",
"description": "Swap ADA for Cornucopias token"
}
|
1.0
|
3.183805 ADA Outgoing - {
"id" : "1677394151280",
"date": "Sun, 26 Feb 2023 06:49:11 GMT",
"fund": "Fund9",
"project": "Governance-Guild",
"proposal": "Governance-Services-Guild-tools",
"ideascale": "https://cardano.ideascale.com/c/idea/420109",
"budget": "Other",
"name": "",
"exchangeRate": "0.361 USD per ADA",
"ada" : "3.00",
"walletBalance": ["84301.91 ADA", "20392.00 GMBL"],
"txid": "26b9cd274d657b9cf15cc353a70989afcdb9cbbe00436b160bcb80e535a5b3a4",
"description": "Swap ADA for Cornucopias token"
}
|
non_process
|
ada outgoing id date sun feb gmt fund project governance guild proposal governance services guild tools ideascale budget other name exchangerate usd per ada ada walletbalance txid description swap ada for cornucopias token
| 0
|
95,863
| 27,642,515,672
|
IssuesEvent
|
2023-03-10 19:23:43
|
BrosWareDevOrg/broschedule-app
|
https://api.github.com/repos/BrosWareDevOrg/broschedule-app
|
closed
|
Build: Install React Hook Form & JOI Validation libraries
|
build high priority in-progress
|
## Type of Issue
<!--- Add an x inside of the [] --->
- [x] New feature (Addition of a new feature).
## Bug/Feature description**
<!--- Describe the bug or feature you implemented and how it works. If it is a bug, include steps to reproduce --->
In order to start working on the Login/Register form and implement a Input component, we need to make use of React Hook Form methods. Also, we will use Joi as our main validation library.
### Proposed Solution 🔧
_If you have a suggested solution to the issue, describe it in detail_
1. [x] Install dependencies
```
npm install react-hook-form
```
```
npm install @hookform/resolvers joi
```
### Additional information
_Any links or additional information that you consider that would be relevant to this issue_
https://react-hook-form.com/get-started/
https://joi.dev/
|
1.0
|
Build: Install React Hook Form & JOI Validation libraries - ## Type of Issue
<!--- Add an x inside of the [] --->
- [x] New feature (Addition of a new feature).
## Bug/Feature description**
<!--- Describe the bug or feature you implemented and how it works. If it is a bug, include steps to reproduce --->
In order to start working on the Login/Register form and implement a Input component, we need to make use of React Hook Form methods. Also, we will use Joi as our main validation library.
### Proposed Solution 🔧
_If you have a suggested solution to the issue, describe it in detail_
1. [x] Install dependencies
```
npm install react-hook-form
```
```
npm install @hookform/resolvers joi
```
### Additional information
_Any links or additional information that you consider that would be relevant to this issue_
https://react-hook-form.com/get-started/
https://joi.dev/
|
non_process
|
build install react hook form joi validation libraries type of issue new feature addition of a new feature bug feature description in order to start working on the login register form and implement a input component we need to make use of react hook form methods also we will use joi as our main validation library proposed solution 🔧 if you have a suggested solution to the issue describe it in detail install dependencies npm install react hook form npm install hookform resolvers joi additional information any links or additional information that you consider that would be relevant to this issue
| 0
|
285,013
| 31,027,355,919
|
IssuesEvent
|
2023-08-10 10:02:05
|
Mend-developer-platform-load/3213490_29
|
https://api.github.com/repos/Mend-developer-platform-load/3213490_29
|
opened
|
grunt-connect-proxy-updated-0.2.1.tgz: 7 vulnerabilities (highest severity is: 9.1)
|
Mend: dependency security vulnerability
|
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>grunt-connect-proxy-updated-0.2.1.tgz</b></p></summary>
<p></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/grunt-connect-proxy-updated/node_modules/lodash/package.json</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/Mend-developer-platform-load/3213490_29/commit/8752f5b37f9ef442472c6201526742e3ea02facb">8752f5b37f9ef442472c6201526742e3ea02facb</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (grunt-connect-proxy-updated version) | Remediation Possible** |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2019-10744](https://www.mend.io/vulnerability-database/CVE-2019-10744) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.1 | lodash-0.9.2.tgz | Transitive | N/A* | ❌ |
| [CVE-2020-8203](https://www.mend.io/vulnerability-database/CVE-2020-8203) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.4 | lodash-0.9.2.tgz | Transitive | N/A* | ❌ |
| [CVE-2021-23337](https://www.mend.io/vulnerability-database/CVE-2021-23337) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.2 | lodash-0.9.2.tgz | Transitive | N/A* | ❌ |
| [CVE-2019-1010266](https://www.mend.io/vulnerability-database/CVE-2019-1010266) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.5 | lodash-0.9.2.tgz | Transitive | N/A* | ❌ |
| [CVE-2018-3721](https://www.mend.io/vulnerability-database/CVE-2018-3721) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.5 | lodash-0.9.2.tgz | Transitive | N/A* | ❌ |
| [CVE-2018-16487](https://www.mend.io/vulnerability-database/CVE-2018-16487) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.6 | lodash-0.9.2.tgz | Transitive | N/A* | ❌ |
| [CVE-2020-28500](https://www.mend.io/vulnerability-database/CVE-2020-28500) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.3 | lodash-0.9.2.tgz | Transitive | N/A* | ❌ |
<p>*For some transitive vulnerabilities, there is no version of direct dependency with a fix. Check the "Details" section below to see if there is a version of transitive dependency where vulnerability is fixed.</p><p>**In some cases, Remediation PR cannot be created automatically for a vulnerability despite the availability of remediation</p>
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2019-10744</summary>
### Vulnerable Library - <b>lodash-0.9.2.tgz</b></p>
<p>A utility library delivering consistency, customization, performance, and extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-0.9.2.tgz">https://registry.npmjs.org/lodash/-/lodash-0.9.2.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/grunt-connect-proxy-updated/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- grunt-connect-proxy-updated-0.2.1.tgz (Root Library)
- :x: **lodash-0.9.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Mend-developer-platform-load/3213490_29/commit/8752f5b37f9ef442472c6201526742e3ea02facb">8752f5b37f9ef442472c6201526742e3ea02facb</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Versions of lodash lower than 4.17.12 are vulnerable to Prototype Pollution. The function defaultsDeep could be tricked into adding or modifying properties of Object.prototype using a constructor payload.
<p>Publish Date: 2019-07-26
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-10744>CVE-2019-10744</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-jf85-cpcp-j695">https://github.com/advisories/GHSA-jf85-cpcp-j695</a></p>
<p>Release Date: 2019-07-26</p>
<p>Fix Resolution: lodash-4.17.12, lodash-amd-4.17.12, lodash-es-4.17.12, lodash.defaultsdeep-4.6.1, lodash.merge- 4.6.2, lodash.mergewith-4.6.2, lodash.template-4.5.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2020-8203</summary>
### Vulnerable Library - <b>lodash-0.9.2.tgz</b></p>
<p>A utility library delivering consistency, customization, performance, and extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-0.9.2.tgz">https://registry.npmjs.org/lodash/-/lodash-0.9.2.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/grunt-connect-proxy-updated/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- grunt-connect-proxy-updated-0.2.1.tgz (Root Library)
- :x: **lodash-0.9.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Mend-developer-platform-load/3213490_29/commit/8752f5b37f9ef442472c6201526742e3ea02facb">8752f5b37f9ef442472c6201526742e3ea02facb</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Prototype pollution attack when using _.zipObjectDeep in lodash before 4.17.20.
<p>Publish Date: 2020-07-15
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-8203>CVE-2020-8203</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.4</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1523">https://www.npmjs.com/advisories/1523</a></p>
<p>Release Date: 2020-07-15</p>
<p>Fix Resolution: lodash - 4.17.19</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2021-23337</summary>
### Vulnerable Library - <b>lodash-0.9.2.tgz</b></p>
<p>A utility library delivering consistency, customization, performance, and extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-0.9.2.tgz">https://registry.npmjs.org/lodash/-/lodash-0.9.2.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/grunt-connect-proxy-updated/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- grunt-connect-proxy-updated-0.2.1.tgz (Root Library)
- :x: **lodash-0.9.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Mend-developer-platform-load/3213490_29/commit/8752f5b37f9ef442472c6201526742e3ea02facb">8752f5b37f9ef442472c6201526742e3ea02facb</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Lodash versions prior to 4.17.21 are vulnerable to Command Injection via the template function.
<p>Publish Date: 2021-02-15
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-23337>CVE-2021-23337</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.2</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2021-02-15</p>
<p>Fix Resolution: lodash - 4.17.21</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2019-1010266</summary>
### Vulnerable Library - <b>lodash-0.9.2.tgz</b></p>
<p>A utility library delivering consistency, customization, performance, and extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-0.9.2.tgz">https://registry.npmjs.org/lodash/-/lodash-0.9.2.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/grunt-connect-proxy-updated/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- grunt-connect-proxy-updated-0.2.1.tgz (Root Library)
- :x: **lodash-0.9.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Mend-developer-platform-load/3213490_29/commit/8752f5b37f9ef442472c6201526742e3ea02facb">8752f5b37f9ef442472c6201526742e3ea02facb</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
lodash prior to 4.17.11 is affected by: CWE-400: Uncontrolled Resource Consumption. The impact is: Denial of service. The component is: Date handler. The attack vector is: Attacker provides very long strings, which the library attempts to match using a regular expression. The fixed version is: 4.17.11.
<p>Publish Date: 2019-07-17
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-1010266>CVE-2019-1010266</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-1010266">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-1010266</a></p>
<p>Release Date: 2019-07-17</p>
<p>Fix Resolution: 4.17.11</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2018-3721</summary>
### Vulnerable Library - <b>lodash-0.9.2.tgz</b></p>
<p>A utility library delivering consistency, customization, performance, and extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-0.9.2.tgz">https://registry.npmjs.org/lodash/-/lodash-0.9.2.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/grunt-connect-proxy-updated/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- grunt-connect-proxy-updated-0.2.1.tgz (Root Library)
- :x: **lodash-0.9.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Mend-developer-platform-load/3213490_29/commit/8752f5b37f9ef442472c6201526742e3ea02facb">8752f5b37f9ef442472c6201526742e3ea02facb</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
lodash node module before 4.17.5 suffers from a Modification of Assumed-Immutable Data (MAID) vulnerability via defaultsDeep, merge, and mergeWith functions, which allows a malicious user to modify the prototype of "Object" via __proto__, causing the addition or modification of an existing property that will exist on all objects.
Mend Note: Converted from WS-2019-0184, on 2022-11-08.
<p>Publish Date: 2018-06-07
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-3721>CVE-2018-3721</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2018-3721">https://nvd.nist.gov/vuln/detail/CVE-2018-3721</a></p>
<p>Release Date: 2018-06-07</p>
<p>Fix Resolution: 4.17.5</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2018-16487</summary>
### Vulnerable Library - <b>lodash-0.9.2.tgz</b></p>
<p>A utility library delivering consistency, customization, performance, and extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-0.9.2.tgz">https://registry.npmjs.org/lodash/-/lodash-0.9.2.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/grunt-connect-proxy-updated/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- grunt-connect-proxy-updated-0.2.1.tgz (Root Library)
- :x: **lodash-0.9.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Mend-developer-platform-load/3213490_29/commit/8752f5b37f9ef442472c6201526742e3ea02facb">8752f5b37f9ef442472c6201526742e3ea02facb</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A prototype pollution vulnerability was found in lodash <4.17.11 where the functions merge, mergeWith, and defaultsDeep can be tricked into adding or modifying properties of Object.prototype.
<p>Publish Date: 2019-02-01
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-16487>CVE-2018-16487</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.6</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bugzilla.redhat.com/show_bug.cgi?id=CVE-2018-16487">https://bugzilla.redhat.com/show_bug.cgi?id=CVE-2018-16487</a></p>
<p>Release Date: 2019-02-01</p>
<p>Fix Resolution: 4.17.11</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2020-28500</summary>
### Vulnerable Library - <b>lodash-0.9.2.tgz</b></p>
<p>A utility library delivering consistency, customization, performance, and extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-0.9.2.tgz">https://registry.npmjs.org/lodash/-/lodash-0.9.2.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/grunt-connect-proxy-updated/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- grunt-connect-proxy-updated-0.2.1.tgz (Root Library)
- :x: **lodash-0.9.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Mend-developer-platform-load/3213490_29/commit/8752f5b37f9ef442472c6201526742e3ea02facb">8752f5b37f9ef442472c6201526742e3ea02facb</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Lodash versions prior to 4.17.21 are vulnerable to Regular Expression Denial of Service (ReDoS) via the toNumber, trim and trimEnd functions.
Mend Note: After conducting further research, Mend has determined that CVE-2020-28500 only affects environments with versions 4.0.0 to 4.17.20 of Lodash.
<p>Publish Date: 2021-02-15
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-28500>CVE-2020-28500</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28500">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28500</a></p>
<p>Release Date: 2021-02-15</p>
<p>Fix Resolution: lodash - 4.17.21</p>
</p>
<p></p>
</details>
|
True
|
grunt-connect-proxy-updated-0.2.1.tgz: 7 vulnerabilities (highest severity is: 9.1) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>grunt-connect-proxy-updated-0.2.1.tgz</b></p></summary>
<p></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/grunt-connect-proxy-updated/node_modules/lodash/package.json</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/Mend-developer-platform-load/3213490_29/commit/8752f5b37f9ef442472c6201526742e3ea02facb">8752f5b37f9ef442472c6201526742e3ea02facb</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (grunt-connect-proxy-updated version) | Remediation Possible** |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2019-10744](https://www.mend.io/vulnerability-database/CVE-2019-10744) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.1 | lodash-0.9.2.tgz | Transitive | N/A* | ❌ |
| [CVE-2020-8203](https://www.mend.io/vulnerability-database/CVE-2020-8203) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.4 | lodash-0.9.2.tgz | Transitive | N/A* | ❌ |
| [CVE-2021-23337](https://www.mend.io/vulnerability-database/CVE-2021-23337) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.2 | lodash-0.9.2.tgz | Transitive | N/A* | ❌ |
| [CVE-2019-1010266](https://www.mend.io/vulnerability-database/CVE-2019-1010266) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.5 | lodash-0.9.2.tgz | Transitive | N/A* | ❌ |
| [CVE-2018-3721](https://www.mend.io/vulnerability-database/CVE-2018-3721) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.5 | lodash-0.9.2.tgz | Transitive | N/A* | ❌ |
| [CVE-2018-16487](https://www.mend.io/vulnerability-database/CVE-2018-16487) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.6 | lodash-0.9.2.tgz | Transitive | N/A* | ❌ |
| [CVE-2020-28500](https://www.mend.io/vulnerability-database/CVE-2020-28500) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.3 | lodash-0.9.2.tgz | Transitive | N/A* | ❌ |
<p>*For some transitive vulnerabilities, there is no version of direct dependency with a fix. Check the "Details" section below to see if there is a version of transitive dependency where vulnerability is fixed.</p><p>**In some cases, Remediation PR cannot be created automatically for a vulnerability despite the availability of remediation</p>
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2019-10744</summary>
### Vulnerable Library - <b>lodash-0.9.2.tgz</b></p>
<p>A utility library delivering consistency, customization, performance, and extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-0.9.2.tgz">https://registry.npmjs.org/lodash/-/lodash-0.9.2.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/grunt-connect-proxy-updated/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- grunt-connect-proxy-updated-0.2.1.tgz (Root Library)
- :x: **lodash-0.9.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Mend-developer-platform-load/3213490_29/commit/8752f5b37f9ef442472c6201526742e3ea02facb">8752f5b37f9ef442472c6201526742e3ea02facb</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Versions of lodash lower than 4.17.12 are vulnerable to Prototype Pollution. The function defaultsDeep could be tricked into adding or modifying properties of Object.prototype using a constructor payload.
<p>Publish Date: 2019-07-26
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-10744>CVE-2019-10744</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-jf85-cpcp-j695">https://github.com/advisories/GHSA-jf85-cpcp-j695</a></p>
<p>Release Date: 2019-07-26</p>
<p>Fix Resolution: lodash-4.17.12, lodash-amd-4.17.12, lodash-es-4.17.12, lodash.defaultsdeep-4.6.1, lodash.merge- 4.6.2, lodash.mergewith-4.6.2, lodash.template-4.5.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2020-8203</summary>
### Vulnerable Library - <b>lodash-0.9.2.tgz</b></p>
<p>A utility library delivering consistency, customization, performance, and extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-0.9.2.tgz">https://registry.npmjs.org/lodash/-/lodash-0.9.2.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/grunt-connect-proxy-updated/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- grunt-connect-proxy-updated-0.2.1.tgz (Root Library)
- :x: **lodash-0.9.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Mend-developer-platform-load/3213490_29/commit/8752f5b37f9ef442472c6201526742e3ea02facb">8752f5b37f9ef442472c6201526742e3ea02facb</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Prototype pollution attack when using _.zipObjectDeep in lodash before 4.17.20.
<p>Publish Date: 2020-07-15
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-8203>CVE-2020-8203</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.4</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1523">https://www.npmjs.com/advisories/1523</a></p>
<p>Release Date: 2020-07-15</p>
<p>Fix Resolution: lodash - 4.17.19</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2021-23337</summary>
### Vulnerable Library - <b>lodash-0.9.2.tgz</b></p>
<p>A utility library delivering consistency, customization, performance, and extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-0.9.2.tgz">https://registry.npmjs.org/lodash/-/lodash-0.9.2.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/grunt-connect-proxy-updated/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- grunt-connect-proxy-updated-0.2.1.tgz (Root Library)
- :x: **lodash-0.9.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Mend-developer-platform-load/3213490_29/commit/8752f5b37f9ef442472c6201526742e3ea02facb">8752f5b37f9ef442472c6201526742e3ea02facb</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Lodash versions prior to 4.17.21 are vulnerable to Command Injection via the template function.
<p>Publish Date: 2021-02-15
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-23337>CVE-2021-23337</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.2</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2021-02-15</p>
<p>Fix Resolution: lodash - 4.17.21</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2019-1010266</summary>
### Vulnerable Library - <b>lodash-0.9.2.tgz</b></p>
<p>A utility library delivering consistency, customization, performance, and extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-0.9.2.tgz">https://registry.npmjs.org/lodash/-/lodash-0.9.2.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/grunt-connect-proxy-updated/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- grunt-connect-proxy-updated-0.2.1.tgz (Root Library)
- :x: **lodash-0.9.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Mend-developer-platform-load/3213490_29/commit/8752f5b37f9ef442472c6201526742e3ea02facb">8752f5b37f9ef442472c6201526742e3ea02facb</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
lodash prior to 4.17.11 is affected by: CWE-400: Uncontrolled Resource Consumption. The impact is: Denial of service. The component is: Date handler. The attack vector is: Attacker provides very long strings, which the library attempts to match using a regular expression. The fixed version is: 4.17.11.
<p>Publish Date: 2019-07-17
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-1010266>CVE-2019-1010266</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-1010266">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-1010266</a></p>
<p>Release Date: 2019-07-17</p>
<p>Fix Resolution: 4.17.11</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2018-3721</summary>
### Vulnerable Library - <b>lodash-0.9.2.tgz</b></p>
<p>A utility library delivering consistency, customization, performance, and extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-0.9.2.tgz">https://registry.npmjs.org/lodash/-/lodash-0.9.2.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/grunt-connect-proxy-updated/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- grunt-connect-proxy-updated-0.2.1.tgz (Root Library)
- :x: **lodash-0.9.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Mend-developer-platform-load/3213490_29/commit/8752f5b37f9ef442472c6201526742e3ea02facb">8752f5b37f9ef442472c6201526742e3ea02facb</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
lodash node module before 4.17.5 suffers from a Modification of Assumed-Immutable Data (MAID) vulnerability via defaultsDeep, merge, and mergeWith functions, which allows a malicious user to modify the prototype of "Object" via __proto__, causing the addition or modification of an existing property that will exist on all objects.
Mend Note: Converted from WS-2019-0184, on 2022-11-08.
<p>Publish Date: 2018-06-07
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-3721>CVE-2018-3721</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2018-3721">https://nvd.nist.gov/vuln/detail/CVE-2018-3721</a></p>
<p>Release Date: 2018-06-07</p>
<p>Fix Resolution: 4.17.5</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2018-16487</summary>
### Vulnerable Library - <b>lodash-0.9.2.tgz</b></p>
<p>A utility library delivering consistency, customization, performance, and extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-0.9.2.tgz">https://registry.npmjs.org/lodash/-/lodash-0.9.2.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/grunt-connect-proxy-updated/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- grunt-connect-proxy-updated-0.2.1.tgz (Root Library)
- :x: **lodash-0.9.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Mend-developer-platform-load/3213490_29/commit/8752f5b37f9ef442472c6201526742e3ea02facb">8752f5b37f9ef442472c6201526742e3ea02facb</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A prototype pollution vulnerability was found in lodash <4.17.11 where the functions merge, mergeWith, and defaultsDeep can be tricked into adding or modifying properties of Object.prototype.
<p>Publish Date: 2019-02-01
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-16487>CVE-2018-16487</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.6</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bugzilla.redhat.com/show_bug.cgi?id=CVE-2018-16487">https://bugzilla.redhat.com/show_bug.cgi?id=CVE-2018-16487</a></p>
<p>Release Date: 2019-02-01</p>
<p>Fix Resolution: 4.17.11</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2020-28500</summary>
### Vulnerable Library - <b>lodash-0.9.2.tgz</b></p>
<p>A utility library delivering consistency, customization, performance, and extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-0.9.2.tgz">https://registry.npmjs.org/lodash/-/lodash-0.9.2.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/grunt-connect-proxy-updated/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- grunt-connect-proxy-updated-0.2.1.tgz (Root Library)
- :x: **lodash-0.9.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Mend-developer-platform-load/3213490_29/commit/8752f5b37f9ef442472c6201526742e3ea02facb">8752f5b37f9ef442472c6201526742e3ea02facb</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Lodash versions prior to 4.17.21 are vulnerable to Regular Expression Denial of Service (ReDoS) via the toNumber, trim and trimEnd functions.
Mend Note: After conducting further research, Mend has determined that CVE-2020-28500 only affects environments with versions 4.0.0 to 4.17.20 of Lodash.
<p>Publish Date: 2021-02-15
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-28500>CVE-2020-28500</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28500">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28500</a></p>
<p>Release Date: 2021-02-15</p>
<p>Fix Resolution: lodash - 4.17.21</p>
</p>
<p></p>
</details>
|
non_process
|
grunt connect proxy updated tgz vulnerabilities highest severity is vulnerable library grunt connect proxy updated tgz path to dependency file package json path to vulnerable library node modules grunt connect proxy updated node modules lodash package json found in head commit a href vulnerabilities cve severity cvss dependency type fixed in grunt connect proxy updated version remediation possible critical lodash tgz transitive n a high lodash tgz transitive n a high lodash tgz transitive n a medium lodash tgz transitive n a medium lodash tgz transitive n a medium lodash tgz transitive n a medium lodash tgz transitive n a for some transitive vulnerabilities there is no version of direct dependency with a fix check the details section below to see if there is a version of transitive dependency where vulnerability is fixed in some cases remediation pr cannot be created automatically for a vulnerability despite the availability of remediation details cve vulnerable library lodash tgz a utility library delivering consistency customization performance and extras library home page a href path to dependency file package json path to vulnerable library node modules grunt connect proxy updated node modules lodash package json dependency hierarchy grunt connect proxy updated tgz root library x lodash tgz vulnerable library found in head commit a href found in base branch main vulnerability details versions of lodash lower than are vulnerable to prototype pollution the function defaultsdeep could be tricked into adding or modifying properties of object prototype using a constructor payload publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution lodash lodash amd lodash es lodash defaultsdeep lodash merge lodash mergewith lodash template cve vulnerable library lodash tgz a utility library delivering consistency customization performance and extras library home page a href path to dependency file package json path to vulnerable library node modules grunt connect proxy updated node modules lodash package json dependency hierarchy grunt connect proxy updated tgz root library x lodash tgz vulnerable library found in head commit a href found in base branch main vulnerability details prototype pollution attack when using zipobjectdeep in lodash before publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution lodash cve vulnerable library lodash tgz a utility library delivering consistency customization performance and extras library home page a href path to dependency file package json path to vulnerable library node modules grunt connect proxy updated node modules lodash package json dependency hierarchy grunt connect proxy updated tgz root library x lodash tgz vulnerable library found in head commit a href found in base branch main vulnerability details lodash versions prior to are vulnerable to command injection via the template function publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required high user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution lodash cve vulnerable library lodash tgz a utility library delivering consistency customization performance and extras library home page a href path to dependency file package json path to vulnerable library node modules grunt connect proxy updated node modules lodash package json dependency hierarchy grunt connect proxy updated tgz root library x lodash tgz vulnerable library found in head commit a href found in base branch main vulnerability details lodash prior to is affected by cwe uncontrolled resource consumption the impact is denial of service the component is date handler the attack vector is attacker provides very long strings which the library attempts to match using a regular expression the fixed version is publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution cve vulnerable library lodash tgz a utility library delivering consistency customization performance and extras library home page a href path to dependency file package json path to vulnerable library node modules grunt connect proxy updated node modules lodash package json dependency hierarchy grunt connect proxy updated tgz root library x lodash tgz vulnerable library found in head commit a href found in base branch main vulnerability details lodash node module before suffers from a modification of assumed immutable data maid vulnerability via defaultsdeep merge and mergewith functions which allows a malicious user to modify the prototype of object via proto causing the addition or modification of an existing property that will exist on all objects mend note converted from ws on publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution cve vulnerable library lodash tgz a utility library delivering consistency customization performance and extras library home page a href path to dependency file package json path to vulnerable library node modules grunt connect proxy updated node modules lodash package json dependency hierarchy grunt connect proxy updated tgz root library x lodash tgz vulnerable library found in head commit a href found in base branch main vulnerability details a prototype pollution vulnerability was found in lodash where the functions merge mergewith and defaultsdeep can be tricked into adding or modifying properties of object prototype publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution cve vulnerable library lodash tgz a utility library delivering consistency customization performance and extras library home page a href path to dependency file package json path to vulnerable library node modules grunt connect proxy updated node modules lodash package json dependency hierarchy grunt connect proxy updated tgz root library x lodash tgz vulnerable library found in head commit a href found in base branch main vulnerability details lodash versions prior to are vulnerable to regular expression denial of service redos via the tonumber trim and trimend functions mend note after conducting further research mend has determined that cve only affects environments with versions to of lodash publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution lodash
| 0
|
2,203
| 2,702,188,819
|
IssuesEvent
|
2015-04-06 03:12:17
|
exercism/exercism.io
|
https://api.github.com/repos/exercism/exercism.io
|
closed
|
Hello World! Tutorial with Jasmine for new users
|
audit/wish code documentation topic: getting started
|
A Hello World! tutorial would be useful to introduce new users to the coding/testing/submitting process for exercism. The tutorial should walk users step by step from downloading the applications and hello world exercise, how to test with Jasmine and then how to submit the completed code.
|
1.0
|
Hello World! Tutorial with Jasmine for new users - A Hello World! tutorial would be useful to introduce new users to the coding/testing/submitting process for exercism. The tutorial should walk users step by step from downloading the applications and hello world exercise, how to test with Jasmine and then how to submit the completed code.
|
non_process
|
hello world tutorial with jasmine for new users a hello world tutorial would be useful to introduce new users to the coding testing submitting process for exercism the tutorial should walk users step by step from downloading the applications and hello world exercise how to test with jasmine and then how to submit the completed code
| 0
|
104,169
| 13,040,874,808
|
IssuesEvent
|
2020-07-28 19:18:58
|
StrangeLoopGames/EcoIssues
|
https://api.github.com/repos/StrangeLoopGames/EcoIssues
|
opened
|
Add Boats to Eco
|
Category: Art Category: Design Category: Gameplay Category: Tech Category: UI Epic Priority: High Type: Feature
|
Do we even need a description? Boat vehicles have been desired by players for a long time, and they would add obvious value to big parts of the game like transportation, exploration, resource extraction, fishing, and would just be fun in general. We've been planning how to add boats and what kind for a long time, and have made a lot of assets towards that end.
This Epic will have within it an 'MVP' version of boats that should be a baseline goal for 10.0, but it will also contain expansions to this baseline content, with different boats suited for different purposes.
In general, boat vehicles fall into three categories:
- **Small Vessels:** Canoes, Rowboats, Small Motorboats. Fishing will be possible in these, but only with a fishing pole. Small Vessels will still have an inventory comparable to a wood cart or larger depending on size/material.
- **Medium Vessels :** Vessels capable of deploying nets, and have big enough holds for catching a good amount of fish. Transport oriented medium vessels can be like a floating regular sized stockpile.
- **Barges:** These moving platforms are designed to carry tons of world objects, vehicles, and block materials across the water, and even to potentially act as floating bridges for vehicles. The large barge which is huge should be a way to use the ocean to transport almost any amount of stuff around the world, changing the logistic possibilities of the world and making it vastly easier for a high tech end game world to expand to a new location.
Other than these new vehicles, the biggest new system needed to synergize with them would be a way to fish with nets in the water. We want players to be able to sail out into the ocean, deploy nets, and collect tons of fish in a hold on their boat which they can then take back to shore for processing.
That brings up the other obvious synergy with boats, which is fishing and underwater content. Those will be kept in a separate epic, but the main thing to ensure is that our fish species work well with nets, fishing, and have plenty of cooking recipes. That content does not rely on boats, but boats would be a little lackluster without it.
|
1.0
|
Add Boats to Eco - Do we even need a description? Boat vehicles have been desired by players for a long time, and they would add obvious value to big parts of the game like transportation, exploration, resource extraction, fishing, and would just be fun in general. We've been planning how to add boats and what kind for a long time, and have made a lot of assets towards that end.
This Epic will have within it an 'MVP' version of boats that should be a baseline goal for 10.0, but it will also contain expansions to this baseline content, with different boats suited for different purposes.
In general, boat vehicles fall into three categories:
- **Small Vessels:** Canoes, Rowboats, Small Motorboats. Fishing will be possible in these, but only with a fishing pole. Small Vessels will still have an inventory comparable to a wood cart or larger depending on size/material.
- **Medium Vessels :** Vessels capable of deploying nets, and have big enough holds for catching a good amount of fish. Transport oriented medium vessels can be like a floating regular sized stockpile.
- **Barges:** These moving platforms are designed to carry tons of world objects, vehicles, and block materials across the water, and even to potentially act as floating bridges for vehicles. The large barge which is huge should be a way to use the ocean to transport almost any amount of stuff around the world, changing the logistic possibilities of the world and making it vastly easier for a high tech end game world to expand to a new location.
Other than these new vehicles, the biggest new system needed to synergize with them would be a way to fish with nets in the water. We want players to be able to sail out into the ocean, deploy nets, and collect tons of fish in a hold on their boat which they can then take back to shore for processing.
That brings up the other obvious synergy with boats, which is fishing and underwater content. Those will be kept in a separate epic, but the main thing to ensure is that our fish species work well with nets, fishing, and have plenty of cooking recipes. That content does not rely on boats, but boats would be a little lackluster without it.
|
non_process
|
add boats to eco do we even need a description boat vehicles have been desired by players for a long time and they would add obvious value to big parts of the game like transportation exploration resource extraction fishing and would just be fun in general we ve been planning how to add boats and what kind for a long time and have made a lot of assets towards that end this epic will have within it an mvp version of boats that should be a baseline goal for but it will also contain expansions to this baseline content with different boats suited for different purposes in general boat vehicles fall into three categories small vessels canoes rowboats small motorboats fishing will be possible in these but only with a fishing pole small vessels will still have an inventory comparable to a wood cart or larger depending on size material medium vessels vessels capable of deploying nets and have big enough holds for catching a good amount of fish transport oriented medium vessels can be like a floating regular sized stockpile barges these moving platforms are designed to carry tons of world objects vehicles and block materials across the water and even to potentially act as floating bridges for vehicles the large barge which is huge should be a way to use the ocean to transport almost any amount of stuff around the world changing the logistic possibilities of the world and making it vastly easier for a high tech end game world to expand to a new location other than these new vehicles the biggest new system needed to synergize with them would be a way to fish with nets in the water we want players to be able to sail out into the ocean deploy nets and collect tons of fish in a hold on their boat which they can then take back to shore for processing that brings up the other obvious synergy with boats which is fishing and underwater content those will be kept in a separate epic but the main thing to ensure is that our fish species work well with nets fishing and have plenty of cooking recipes that content does not rely on boats but boats would be a little lackluster without it
| 0
|
11,696
| 14,544,439,744
|
IssuesEvent
|
2020-12-15 18:11:06
|
AcademySoftwareFoundation/OpenCue
|
https://api.github.com/repos/AcademySoftwareFoundation/OpenCue
|
closed
|
Document our policy for adding tests
|
process
|
**Describe the process**
Our Pull Request template should document our policy of always adding tests for new code.
|
1.0
|
Document our policy for adding tests - **Describe the process**
Our Pull Request template should document our policy of always adding tests for new code.
|
process
|
document our policy for adding tests describe the process our pull request template should document our policy of always adding tests for new code
| 1
|
22,293
| 30,847,372,024
|
IssuesEvent
|
2023-08-02 14:30:47
|
metabase/metabase
|
https://api.github.com/repos/metabase/metabase
|
closed
|
Action not found on dashboard on serdes v2
|
Type:Bug Priority:P2 Operation/Serialization Querying/Actions .Blocker .Team/QueryProcessor :hammer_and_wrench:
|
### Describe the bug
A very weird issue where serdesv2 doesn't find the action in a dashboard
### To Reproduce
Follow this exact steps at this exact order, please don't deviate a single step since this one is extremely difficult to reproduce:
1) set up origin and destination, from scratch
2) add a database (e.g. sample postgres db)
3) enable model actions on that database
4) do x-ray on people, save it
5) export on origin and import on destination (new commands, not dump and load)
6) now go to new->question->raw data-> people. Save the question. Turn into a model
7) go to model actions, create basic actions
8) add a new action-> "insert into people (1)" save it with any name
9) add a dashboard, in the dashboard add the model and a button that maps to the newly created action
10) Export and import, you should see the error
### Expected behavior
_No response_
### Logs
```
2023-07-22 00:39:23,982 INFO v2.load :: Loading Card fiCqhCw6mSXfFiqYHvYiI
clojure.lang.ExceptionInfo: Failed to load into database for [#ordered/map ([:model "Dashboard"] [:id "gmHEIwiD1i5Ffd4GSKiTw"])] {:path [#ordered/map ([:model "Dashboard"] [:id "gmHEIwiD1i5Ffd4GSKiTw"])], :deps-chain #{}}
at metabase_enterprise.serialization.v2.load$load_one.invokeStatic(load.clj:70)
at metabase_enterprise.serialization.v2.load$load_one.invoke(load.clj:33)
at clojure.core.protocols$fn__8249.invokeStatic(protocols.clj:168)
at clojure.core.protocols$fn__8249.invoke(protocols.clj:124)
at clojure.core.protocols$fn__8204$G__8199__8213.invoke(protocols.clj:19)
at clojure.core.protocols$seq_reduce.invokeStatic(protocols.clj:31)
at clojure.core.protocols$fn__8236.invokeStatic(protocols.clj:75)
at clojure.core.protocols$fn__8236.invoke(protocols.clj:75)
at clojure.core.protocols$fn__8178$G__8173__8191.invoke(protocols.clj:13)
at clojure.core$reduce.invokeStatic(core.clj:6886)
at clojure.core$reduce.invoke(core.clj:6868)
at metabase_enterprise.serialization.v2.load$load_metabase.invokeStatic(load.clj:95)
at metabase_enterprise.serialization.v2.load$load_metabase.doInvoke(load.clj:83)
at clojure.lang.RestFn.invoke(RestFn.java:423)
at metabase_enterprise.serialization.cmd$fn__115199$v2_load__115200.invoke(cmd.clj:88)
at clojure.lang.AFn.applyToHelper(AFn.java:156)
at clojure.lang.AFn.applyTo(AFn.java:144)
at clojure.core$apply.invokeStatic(core.clj:667)
at clojure.core$apply.invoke(core.clj:662)
at malli.core$_instrument$fn__13257.doInvoke(core.cljc:2526)
at clojure.lang.RestFn.applyTo(RestFn.java:137)
at clojure.lang.Var.applyTo(Var.java:705)
at clojure.core$apply.invokeStatic(core.clj:667)
at clojure.core$apply.invoke(core.clj:662)
at metabase.cmd$call_enterprise.invokeStatic(cmd.clj:53)
at metabase.cmd$call_enterprise.doInvoke(cmd.clj:43)
at clojure.lang.RestFn.invoke(RestFn.java:439)
at metabase.cmd$import.invokeStatic(cmd.clj:191)
at metabase.cmd$import.doInvoke(cmd.clj:187)
at clojure.lang.RestFn.invoke(RestFn.java:410)
at clojure.lang.AFn.applyToHelper(AFn.java:154)
at clojure.lang.RestFn.applyTo(RestFn.java:132)
at clojure.core$apply.invokeStatic(core.clj:667)
at clojure.core$apply.invoke(core.clj:662)
at metabase.cmd$run_cmd$fn__117338.invoke(cmd.clj:299)
at metabase.cmd$run_cmd.invokeStatic(cmd.clj:298)
at metabase.cmd$run_cmd.invoke(cmd.clj:288)
at clojure.lang.Var.invoke(Var.java:388)
at metabase.core$run_cmd.invokeStatic(core.clj:181)
at metabase.core$run_cmd.invoke(core.clj:179)
at metabase.core$_main.invokeStatic(core.clj:203)
at metabase.core$_main.doInvoke(core.clj:198)
at clojure.lang.RestFn.applyTo(RestFn.java:137)
at clojure.lang.Var.applyTo(Var.java:705)
at clojure.core$apply.invokeStatic(core.clj:667)
at clojure.core$apply.invoke(core.clj:662)
at metabase.bootstrap$_main.invokeStatic(bootstrap.clj:31)
at metabase.bootstrap$_main.doInvoke(bootstrap.clj:28)
at clojure.lang.RestFn.applyTo(RestFn.java:137)
at metabase.bootstrap.main(Unknown Source)
Caused by: clojure.lang.ExceptionInfo: Could not find foreign key target - bad serdes-dependencies or other serialization error {:entity_id "lai4zes4g_UvWvzdBg5dS", :model "Action"}
at metabase.models.serialization$_STAR_import_fk_STAR_.invokeStatic(serialization.clj:477)
at metabase.models.serialization$_STAR_import_fk_STAR_.invoke(serialization.clj:456)
at clojure.lang.AFn.applyToHelper(AFn.java:156)
at clojure.lang.AFn.applyTo(AFn.java:144)
at clojure.core$apply.invokeStatic(core.clj:667)
at clojure.core$memoize$fn__6946.doInvoke(core.clj:6388)
at clojure.lang.RestFn.invoke(RestFn.java:421)
at clojure.core$update.invokeStatic(core.clj:6233)
at clojure.core$update.invoke(core.clj:6223)
at metabase.models.dashboard_card$fn__73407.invokeStatic(dashboard_card.clj:372)
at metabase.models.dashboard_card$fn__73407.invoke(dashboard_card.clj:367)
at clojure.lang.MultiFn.invoke(MultiFn.java:229)
at metabase.models.serialization$fn__45695.invokeStatic(serialization.clj:349)
at metabase.models.serialization$fn__45695.invoke(serialization.clj:347)
at clojure.lang.MultiFn.invoke(MultiFn.java:234)
at metabase.models.dashboard$fn__78233.invokeStatic(dashboard.clj:579)
at metabase.models.dashboard$fn__78233.invoke(dashboard.clj:573)
at clojure.lang.MultiFn.invoke(MultiFn.java:234)
at metabase_enterprise.serialization.v2.load$load_one.invokeStatic(load.clj:67)
... 49 more
Command failed with exception: Failed to load into database for [#ordered/map ([:model "Dashboard"] [:id "gmHEIwiD1i5Ffd4GSKiTw"])]
```
### Information about your Metabase installation
```JSON
v47.0-RC2
```
### Severity
P2ish
### Additional context
very difficult to consistently reproduce, but I managed to make it break 2 times in a row with those steps
|
1.0
|
Action not found on dashboard on serdes v2 - ### Describe the bug
A very weird issue where serdesv2 doesn't find the action in a dashboard
### To Reproduce
Follow this exact steps at this exact order, please don't deviate a single step since this one is extremely difficult to reproduce:
1) set up origin and destination, from scratch
2) add a database (e.g. sample postgres db)
3) enable model actions on that database
4) do x-ray on people, save it
5) export on origin and import on destination (new commands, not dump and load)
6) now go to new->question->raw data-> people. Save the question. Turn into a model
7) go to model actions, create basic actions
8) add a new action-> "insert into people (1)" save it with any name
9) add a dashboard, in the dashboard add the model and a button that maps to the newly created action
10) Export and import, you should see the error
### Expected behavior
_No response_
### Logs
```
2023-07-22 00:39:23,982 INFO v2.load :: Loading Card fiCqhCw6mSXfFiqYHvYiI
clojure.lang.ExceptionInfo: Failed to load into database for [#ordered/map ([:model "Dashboard"] [:id "gmHEIwiD1i5Ffd4GSKiTw"])] {:path [#ordered/map ([:model "Dashboard"] [:id "gmHEIwiD1i5Ffd4GSKiTw"])], :deps-chain #{}}
at metabase_enterprise.serialization.v2.load$load_one.invokeStatic(load.clj:70)
at metabase_enterprise.serialization.v2.load$load_one.invoke(load.clj:33)
at clojure.core.protocols$fn__8249.invokeStatic(protocols.clj:168)
at clojure.core.protocols$fn__8249.invoke(protocols.clj:124)
at clojure.core.protocols$fn__8204$G__8199__8213.invoke(protocols.clj:19)
at clojure.core.protocols$seq_reduce.invokeStatic(protocols.clj:31)
at clojure.core.protocols$fn__8236.invokeStatic(protocols.clj:75)
at clojure.core.protocols$fn__8236.invoke(protocols.clj:75)
at clojure.core.protocols$fn__8178$G__8173__8191.invoke(protocols.clj:13)
at clojure.core$reduce.invokeStatic(core.clj:6886)
at clojure.core$reduce.invoke(core.clj:6868)
at metabase_enterprise.serialization.v2.load$load_metabase.invokeStatic(load.clj:95)
at metabase_enterprise.serialization.v2.load$load_metabase.doInvoke(load.clj:83)
at clojure.lang.RestFn.invoke(RestFn.java:423)
at metabase_enterprise.serialization.cmd$fn__115199$v2_load__115200.invoke(cmd.clj:88)
at clojure.lang.AFn.applyToHelper(AFn.java:156)
at clojure.lang.AFn.applyTo(AFn.java:144)
at clojure.core$apply.invokeStatic(core.clj:667)
at clojure.core$apply.invoke(core.clj:662)
at malli.core$_instrument$fn__13257.doInvoke(core.cljc:2526)
at clojure.lang.RestFn.applyTo(RestFn.java:137)
at clojure.lang.Var.applyTo(Var.java:705)
at clojure.core$apply.invokeStatic(core.clj:667)
at clojure.core$apply.invoke(core.clj:662)
at metabase.cmd$call_enterprise.invokeStatic(cmd.clj:53)
at metabase.cmd$call_enterprise.doInvoke(cmd.clj:43)
at clojure.lang.RestFn.invoke(RestFn.java:439)
at metabase.cmd$import.invokeStatic(cmd.clj:191)
at metabase.cmd$import.doInvoke(cmd.clj:187)
at clojure.lang.RestFn.invoke(RestFn.java:410)
at clojure.lang.AFn.applyToHelper(AFn.java:154)
at clojure.lang.RestFn.applyTo(RestFn.java:132)
at clojure.core$apply.invokeStatic(core.clj:667)
at clojure.core$apply.invoke(core.clj:662)
at metabase.cmd$run_cmd$fn__117338.invoke(cmd.clj:299)
at metabase.cmd$run_cmd.invokeStatic(cmd.clj:298)
at metabase.cmd$run_cmd.invoke(cmd.clj:288)
at clojure.lang.Var.invoke(Var.java:388)
at metabase.core$run_cmd.invokeStatic(core.clj:181)
at metabase.core$run_cmd.invoke(core.clj:179)
at metabase.core$_main.invokeStatic(core.clj:203)
at metabase.core$_main.doInvoke(core.clj:198)
at clojure.lang.RestFn.applyTo(RestFn.java:137)
at clojure.lang.Var.applyTo(Var.java:705)
at clojure.core$apply.invokeStatic(core.clj:667)
at clojure.core$apply.invoke(core.clj:662)
at metabase.bootstrap$_main.invokeStatic(bootstrap.clj:31)
at metabase.bootstrap$_main.doInvoke(bootstrap.clj:28)
at clojure.lang.RestFn.applyTo(RestFn.java:137)
at metabase.bootstrap.main(Unknown Source)
Caused by: clojure.lang.ExceptionInfo: Could not find foreign key target - bad serdes-dependencies or other serialization error {:entity_id "lai4zes4g_UvWvzdBg5dS", :model "Action"}
at metabase.models.serialization$_STAR_import_fk_STAR_.invokeStatic(serialization.clj:477)
at metabase.models.serialization$_STAR_import_fk_STAR_.invoke(serialization.clj:456)
at clojure.lang.AFn.applyToHelper(AFn.java:156)
at clojure.lang.AFn.applyTo(AFn.java:144)
at clojure.core$apply.invokeStatic(core.clj:667)
at clojure.core$memoize$fn__6946.doInvoke(core.clj:6388)
at clojure.lang.RestFn.invoke(RestFn.java:421)
at clojure.core$update.invokeStatic(core.clj:6233)
at clojure.core$update.invoke(core.clj:6223)
at metabase.models.dashboard_card$fn__73407.invokeStatic(dashboard_card.clj:372)
at metabase.models.dashboard_card$fn__73407.invoke(dashboard_card.clj:367)
at clojure.lang.MultiFn.invoke(MultiFn.java:229)
at metabase.models.serialization$fn__45695.invokeStatic(serialization.clj:349)
at metabase.models.serialization$fn__45695.invoke(serialization.clj:347)
at clojure.lang.MultiFn.invoke(MultiFn.java:234)
at metabase.models.dashboard$fn__78233.invokeStatic(dashboard.clj:579)
at metabase.models.dashboard$fn__78233.invoke(dashboard.clj:573)
at clojure.lang.MultiFn.invoke(MultiFn.java:234)
at metabase_enterprise.serialization.v2.load$load_one.invokeStatic(load.clj:67)
... 49 more
Command failed with exception: Failed to load into database for [#ordered/map ([:model "Dashboard"] [:id "gmHEIwiD1i5Ffd4GSKiTw"])]
```
### Information about your Metabase installation
```JSON
v47.0-RC2
```
### Severity
P2ish
### Additional context
very difficult to consistently reproduce, but I managed to make it break 2 times in a row with those steps
|
process
|
action not found on dashboard on serdes describe the bug a very weird issue where doesn t find the action in a dashboard to reproduce follow this exact steps at this exact order please don t deviate a single step since this one is extremely difficult to reproduce set up origin and destination from scratch add a database e g sample postgres db enable model actions on that database do x ray on people save it export on origin and import on destination new commands not dump and load now go to new question raw data people save the question turn into a model go to model actions create basic actions add a new action insert into people save it with any name add a dashboard in the dashboard add the model and a button that maps to the newly created action export and import you should see the error expected behavior no response logs info load loading card clojure lang exceptioninfo failed to load into database for path deps chain at metabase enterprise serialization load load one invokestatic load clj at metabase enterprise serialization load load one invoke load clj at clojure core protocols fn invokestatic protocols clj at clojure core protocols fn invoke protocols clj at clojure core protocols fn g invoke protocols clj at clojure core protocols seq reduce invokestatic protocols clj at clojure core protocols fn invokestatic protocols clj at clojure core protocols fn invoke protocols clj at clojure core protocols fn g invoke protocols clj at clojure core reduce invokestatic core clj at clojure core reduce invoke core clj at metabase enterprise serialization load load metabase invokestatic load clj at metabase enterprise serialization load load metabase doinvoke load clj at clojure lang restfn invoke restfn java at metabase enterprise serialization cmd fn load invoke cmd clj at clojure lang afn applytohelper afn java at clojure lang afn applyto afn java at clojure core apply invokestatic core clj at clojure core apply invoke core clj at malli core instrument fn doinvoke core cljc at clojure lang restfn applyto restfn java at clojure lang var applyto var java at clojure core apply invokestatic core clj at clojure core apply invoke core clj at metabase cmd call enterprise invokestatic cmd clj at metabase cmd call enterprise doinvoke cmd clj at clojure lang restfn invoke restfn java at metabase cmd import invokestatic cmd clj at metabase cmd import doinvoke cmd clj at clojure lang restfn invoke restfn java at clojure lang afn applytohelper afn java at clojure lang restfn applyto restfn java at clojure core apply invokestatic core clj at clojure core apply invoke core clj at metabase cmd run cmd fn invoke cmd clj at metabase cmd run cmd invokestatic cmd clj at metabase cmd run cmd invoke cmd clj at clojure lang var invoke var java at metabase core run cmd invokestatic core clj at metabase core run cmd invoke core clj at metabase core main invokestatic core clj at metabase core main doinvoke core clj at clojure lang restfn applyto restfn java at clojure lang var applyto var java at clojure core apply invokestatic core clj at clojure core apply invoke core clj at metabase bootstrap main invokestatic bootstrap clj at metabase bootstrap main doinvoke bootstrap clj at clojure lang restfn applyto restfn java at metabase bootstrap main unknown source caused by clojure lang exceptioninfo could not find foreign key target bad serdes dependencies or other serialization error entity id model action at metabase models serialization star import fk star invokestatic serialization clj at metabase models serialization star import fk star invoke serialization clj at clojure lang afn applytohelper afn java at clojure lang afn applyto afn java at clojure core apply invokestatic core clj at clojure core memoize fn doinvoke core clj at clojure lang restfn invoke restfn java at clojure core update invokestatic core clj at clojure core update invoke core clj at metabase models dashboard card fn invokestatic dashboard card clj at metabase models dashboard card fn invoke dashboard card clj at clojure lang multifn invoke multifn java at metabase models serialization fn invokestatic serialization clj at metabase models serialization fn invoke serialization clj at clojure lang multifn invoke multifn java at metabase models dashboard fn invokestatic dashboard clj at metabase models dashboard fn invoke dashboard clj at clojure lang multifn invoke multifn java at metabase enterprise serialization load load one invokestatic load clj more command failed with exception failed to load into database for information about your metabase installation json severity additional context very difficult to consistently reproduce but i managed to make it break times in a row with those steps
| 1
|
172,525
| 6,507,034,285
|
IssuesEvent
|
2017-08-24 11:34:48
|
our-city-app/oca-backend
|
https://api.github.com/repos/our-city-app/oca-backend
|
closed
|
Zip the thirdparty libraries
|
priority_minor state_verification type_feature
|
Make the following changes to speed up deployment to appengine and also to speed up searching the code base. Be sure to test the code paths were the 3rdparty libraries are used (because in the past we tried to zip babel and pytz, but it didn't work)
- update `install.sh` to zip the contents of `rogerthat-backend/src/lib` after it executed `pip install -t ...` and finally remove the rest of the contents of the lib folder such that only the lib.zip file remains.
- in `appengine_config.py` add the lib zip instead of the lib folder.
|
1.0
|
Zip the thirdparty libraries - Make the following changes to speed up deployment to appengine and also to speed up searching the code base. Be sure to test the code paths were the 3rdparty libraries are used (because in the past we tried to zip babel and pytz, but it didn't work)
- update `install.sh` to zip the contents of `rogerthat-backend/src/lib` after it executed `pip install -t ...` and finally remove the rest of the contents of the lib folder such that only the lib.zip file remains.
- in `appengine_config.py` add the lib zip instead of the lib folder.
|
non_process
|
zip the thirdparty libraries make the following changes to speed up deployment to appengine and also to speed up searching the code base be sure to test the code paths were the libraries are used because in the past we tried to zip babel and pytz but it didn t work update install sh to zip the contents of rogerthat backend src lib after it executed pip install t and finally remove the rest of the contents of the lib folder such that only the lib zip file remains in appengine config py add the lib zip instead of the lib folder
| 0
|
8,053
| 11,221,120,118
|
IssuesEvent
|
2020-01-07 17:07:59
|
prisma/prisma2
|
https://api.github.com/repos/prisma/prisma2
|
closed
|
Introspection failed with "Please wait until the 'prisma query-engine' download completes! / SyntaxError: Unexpected token P in JSON at position 0"
|
bug/2-confirmed kind/bug process/candidate topic: binaries
|
I tried to initialize a new project and using my existing MySQL DB, but when I tried to introspect an existing schema, it threw out an error:
> ERROR Introspection failed:
Problem while parsing the query engine response at C:\Users\xxxxxxxxx\AppData\Roaming\npm\node_modules\prisma2\query-
engine-windows.exe. Please wait until the 'prisma query-engine' download completes!
SyntaxError: Unexpected token P in JSON at position 0
at JSON.parse (<anonymous>)
at C:\Users\xxxxxxxxx\AppData\Roaming\npm\node_modules\prisma2\build\index.js:73749:25
at Generator.next (<anonymous>)
at fulfilled (C:\Users\xxxxxxxxx\AppData\Roaming\npm\node_modules\prisma2\build\index.js:73659:58)
|
1.0
|
Introspection failed with "Please wait until the 'prisma query-engine' download completes! / SyntaxError: Unexpected token P in JSON at position 0" - I tried to initialize a new project and using my existing MySQL DB, but when I tried to introspect an existing schema, it threw out an error:
> ERROR Introspection failed:
Problem while parsing the query engine response at C:\Users\xxxxxxxxx\AppData\Roaming\npm\node_modules\prisma2\query-
engine-windows.exe. Please wait until the 'prisma query-engine' download completes!
SyntaxError: Unexpected token P in JSON at position 0
at JSON.parse (<anonymous>)
at C:\Users\xxxxxxxxx\AppData\Roaming\npm\node_modules\prisma2\build\index.js:73749:25
at Generator.next (<anonymous>)
at fulfilled (C:\Users\xxxxxxxxx\AppData\Roaming\npm\node_modules\prisma2\build\index.js:73659:58)
|
process
|
introspection failed with please wait until the prisma query engine download completes syntaxerror unexpected token p in json at position i tried to initialize a new project and using my existing mysql db but when i tried to introspect an existing schema it threw out an error error introspection failed problem while parsing the query engine response at c users xxxxxxxxx appdata roaming npm node modules query engine windows exe please wait until the prisma query engine download completes syntaxerror unexpected token p in json at position at json parse at c users xxxxxxxxx appdata roaming npm node modules build index js at generator next at fulfilled c users xxxxxxxxx appdata roaming npm node modules build index js
| 1
|
9,498
| 12,487,664,271
|
IssuesEvent
|
2020-05-31 10:19:28
|
metabase/metabase
|
https://api.github.com/repos/metabase/metabase
|
closed
|
Sorting by column for query with native source query changes column order
|
.Proposal Querying/Processor Type:UX
|
In some cases sorting by a column will cause that column to get displayed ahead of others in the results. It is intentional behavior from a while back but it might not make sense anymore. Consider removing the logic behind this behavior.
Should be a simple fix.
|
1.0
|
Sorting by column for query with native source query changes column order - In some cases sorting by a column will cause that column to get displayed ahead of others in the results. It is intentional behavior from a while back but it might not make sense anymore. Consider removing the logic behind this behavior.
Should be a simple fix.
|
process
|
sorting by column for query with native source query changes column order in some cases sorting by a column will cause that column to get displayed ahead of others in the results it is intentional behavior from a while back but it might not make sense anymore consider removing the logic behind this behavior should be a simple fix
| 1
|
24,620
| 6,557,292,054
|
IssuesEvent
|
2017-09-06 16:52:34
|
tonybranfort/immidb
|
https://api.github.com/repos/tonybranfort/immidb
|
closed
|
Convert to ui-router from angularjs $routeProvider
|
0Feature FA:Framework Priority 3 User:Coder
|
#### Why
* To be able to use session state
* Prepare for Angular 2.0
* Able to route to /client internally without reloading the controller (and causing page flash)
#### Success
* All urls/routes work as before
* Invoice
* Txtns (and only viewable by Fin)
* Can route to client internally (clicking client link) while on /client page and data loads without the page flashing (looks like page is reloading). (Can do this routing with /client/refId rather than "/client?refId=..." which is what is required with angular route service)
* Can enter url /client/someRefId in address bar and will pull up that client if user is already logged in
* Automatic logout on session timeout redirects to login
* Unknown path will default to /home (eg; /bogus => /home)
|
1.0
|
Convert to ui-router from angularjs $routeProvider - #### Why
* To be able to use session state
* Prepare for Angular 2.0
* Able to route to /client internally without reloading the controller (and causing page flash)
#### Success
* All urls/routes work as before
* Invoice
* Txtns (and only viewable by Fin)
* Can route to client internally (clicking client link) while on /client page and data loads without the page flashing (looks like page is reloading). (Can do this routing with /client/refId rather than "/client?refId=..." which is what is required with angular route service)
* Can enter url /client/someRefId in address bar and will pull up that client if user is already logged in
* Automatic logout on session timeout redirects to login
* Unknown path will default to /home (eg; /bogus => /home)
|
non_process
|
convert to ui router from angularjs routeprovider why to be able to use session state prepare for angular able to route to client internally without reloading the controller and causing page flash success all urls routes work as before invoice txtns and only viewable by fin can route to client internally clicking client link while on client page and data loads without the page flashing looks like page is reloading can do this routing with client refid rather than client refid which is what is required with angular route service can enter url client somerefid in address bar and will pull up that client if user is already logged in automatic logout on session timeout redirects to login unknown path will default to home eg bogus home
| 0
|
11,602
| 14,478,426,586
|
IssuesEvent
|
2020-12-10 08:22:19
|
cypress-io/cypress
|
https://api.github.com/repos/cypress-io/cypress
|
closed
|
Absolute imports does not resolve in 5.1
|
topic: imports topic: preprocessors :wrench:
|
### Current behavior:
When starting Cypress with
```
NODE_PATH=ui/src cypress open
```
it is unable to resolve absolute imports
```
Webpack Compilation Error
./cypress/integration/cart/utils.js
Module not found: Error: Can't resolve 'ducks/cart' in '/home/pong/e2e/cypress/integration/cart'
...
```
My code is
```js
import { cartOperations } from "ducks/cart";
...
```
### Desired behavior:
Imports resolve correctly. This worked in 4.12.1.
### Test code to reproduce
Will create a minimal working example if needed and deemed to be an issue.
<!-- If we cannot fully run the tests as provided the issue WILL BE CLOSED -->
<!-- Issues without a reproducible example WILL BE CLOSED -->
<!-- You can fork https://github.com/cypress-io/cypress-test-tiny repo, set up a failing test, then link to your fork -->
### Versions
Cypress 5.1.0
Node 14.5.0
OS: Ubuntu
|
1.0
|
Absolute imports does not resolve in 5.1 - ### Current behavior:
When starting Cypress with
```
NODE_PATH=ui/src cypress open
```
it is unable to resolve absolute imports
```
Webpack Compilation Error
./cypress/integration/cart/utils.js
Module not found: Error: Can't resolve 'ducks/cart' in '/home/pong/e2e/cypress/integration/cart'
...
```
My code is
```js
import { cartOperations } from "ducks/cart";
...
```
### Desired behavior:
Imports resolve correctly. This worked in 4.12.1.
### Test code to reproduce
Will create a minimal working example if needed and deemed to be an issue.
<!-- If we cannot fully run the tests as provided the issue WILL BE CLOSED -->
<!-- Issues without a reproducible example WILL BE CLOSED -->
<!-- You can fork https://github.com/cypress-io/cypress-test-tiny repo, set up a failing test, then link to your fork -->
### Versions
Cypress 5.1.0
Node 14.5.0
OS: Ubuntu
|
process
|
absolute imports does not resolve in current behavior when starting cypress with node path ui src cypress open it is unable to resolve absolute imports webpack compilation error cypress integration cart utils js module not found error can t resolve ducks cart in home pong cypress integration cart my code is js import cartoperations from ducks cart desired behavior imports resolve correctly this worked in test code to reproduce will create a minimal working example if needed and deemed to be an issue versions cypress node os ubuntu
| 1
|
1,545
| 4,154,336,488
|
IssuesEvent
|
2016-06-16 11:12:44
|
matz-e/lobster
|
https://api.github.com/repos/matz-e/lobster
|
closed
|
CMSSW 7_1_X does not provide XrdStatisticsService
|
bug fix-ready high-priority processing
|
Makes current pset modifications crash the tasks.
|
1.0
|
CMSSW 7_1_X does not provide XrdStatisticsService - Makes current pset modifications crash the tasks.
|
process
|
cmssw x does not provide xrdstatisticsservice makes current pset modifications crash the tasks
| 1
|
16,712
| 21,871,236,031
|
IssuesEvent
|
2022-05-19 05:36:32
|
camunda/zeebe
|
https://api.github.com/repos/camunda/zeebe
|
closed
|
The process instance is stuck if the output collection is modified
|
kind/bug scope/broker severity/mid area/ux team/process-automation
|
**Describe the bug**
If the output collection variable is modified then the process instance is stuck in the multi-instance subprocess.
The sequential/parallel multi-instance subprocess iterates over an input collection and collects the results in an output collection. If the value of the output collection variable is modified (e.g. change the type of the value or reduce the size of the collection) then the inner instance can't be completed.
The process instance doesn't continue (i.e. it is added to the blacklist). No incidents are created.
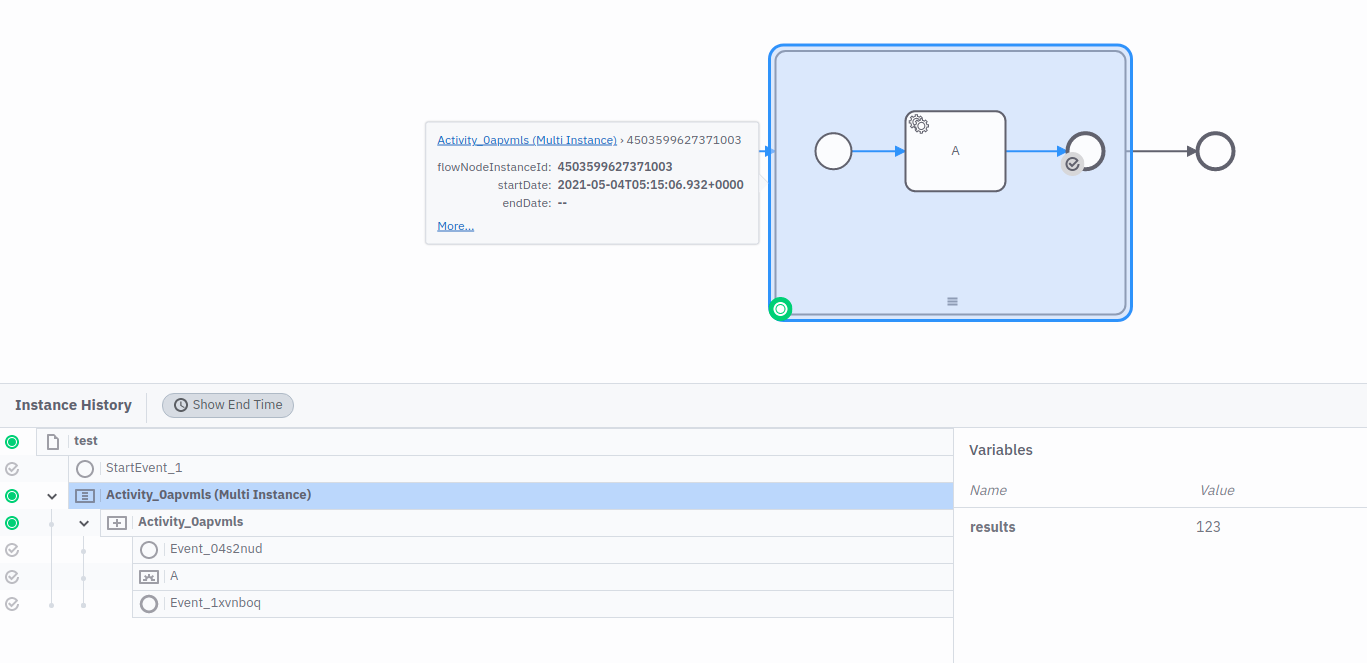
**To Reproduce**
1. deploy a process with a sequential/parallel multi-instance subprocess that defines
* an input collection `= items`
* an input element `item`
* an output collection `results`
* an output element `= r`
2. create an instance with variables `{"items":[1,2,3]}`
3. await until the service task in the subprocess is activated
4. set the value of the variable `results` to `123` (some value that is not a list)
5. complete the job
6. verify that the process instance doesn't continue
**Expected behavior**
It creates an incident when completing the inner instance.
I can resolve the incident and the process instance continues.
**Log/Stacktrace**
```
MsgpackReaderException: Unable to determine array type, found unknown header byte 0x7b at reader offset 0
```
<details><summary>Full Stacktrace</summary>
<p>
```
io.zeebe.msgpack.spec.MsgpackReaderException: Unable to determine array type, found unknown header byte 0x7b at reader offset 0
at io.zeebe.msgpack.spec.MsgPackReader.exceptionOnUnknownHeader (MsgPackReader.java:474)
at io.zeebe.msgpack.spec.MsgPackReader.readArrayHeader (MsgPackReader.java:107)
at io.zeebe.engine.processing.bpmn.container.MultiInstanceBodyProcessor.insertAt (MultiInstanceBodyProcessor.java:372)
at io.zeebe.engine.processing.bpmn.container.MultiInstanceBodyProcessor.lambda$updateOutputCollection$14 (MultiInstanceBodyProcessor.java:355)
at io.zeebe.util.Either$Right.map (Either.java:213)
at io.zeebe.engine.processing.bpmn.container.MultiInstanceBodyProcessor.updateOutputCollection (MultiInstanceBodyProcessor.java:346)
at io.zeebe.engine.processing.bpmn.container.MultiInstanceBodyProcessor.lambda$updateOutputCollection$13 (MultiInstanceBodyProcessor.java:332)
at java.util.Optional.map (Unknown Source)
at io.zeebe.engine.processing.bpmn.container.MultiInstanceBodyProcessor.updateOutputCollection (MultiInstanceBodyProcessor.java:330)
at io.zeebe.engine.processing.bpmn.container.MultiInstanceBodyProcessor.beforeExecutionPathCompleted (MultiInstanceBodyProcessor.java:150)
at io.zeebe.engine.processing.bpmn.container.MultiInstanceBodyProcessor.beforeExecutionPathCompleted (MultiInstanceBodyProcessor.java:35)
at io.zeebe.engine.processing.bpmn.behavior.BpmnStateTransitionBehavior.lambda$beforeExecutionPathCompleted$2 (BpmnStateTransitionBehavior.java:406)
at io.zeebe.engine.processing.bpmn.behavior.BpmnStateTransitionBehavior.invokeElementContainerIfPresent (BpmnStateTransitionBehavior.java:489)
at io.zeebe.engine.processing.bpmn.behavior.BpmnStateTransitionBehavior.beforeExecutionPathCompleted (BpmnStateTransitionBehavior.java:402)
at io.zeebe.engine.processing.bpmn.behavior.BpmnStateTransitionBehavior.transitionToCompletedWithParentNotification (BpmnStateTransitionBehavior.java:167)
at io.zeebe.engine.processing.bpmn.container.SubProcessProcessor.lambda$onComplete$3 (SubProcessProcessor.java:78)
at io.zeebe.util.Either$Right.ifRightOrLeft (Either.java:238)
at io.zeebe.engine.processing.bpmn.container.SubProcessProcessor.onComplete (SubProcessProcessor.java:74)
at io.zeebe.engine.processing.bpmn.container.SubProcessProcessor.onComplete (SubProcessProcessor.java:23)
at io.zeebe.engine.processing.bpmn.BpmnStreamProcessor.processEvent (BpmnStreamProcessor.java:213)
at io.zeebe.engine.processing.bpmn.BpmnStreamProcessor.lambda$processRecord$1 (BpmnStreamProcessor.java:134)
at io.zeebe.util.Either$Right.ifRightOrLeft (Either.java:238)
at io.zeebe.engine.processing.bpmn.BpmnStreamProcessor.processRecord (BpmnStreamProcessor.java:131)
at io.zeebe.engine.processing.streamprocessor.TypedRecordProcessor.processRecord (TypedRecordProcessor.java:54)
at io.zeebe.engine.processing.streamprocessor.ProcessingStateMachine.lambda$processInTransaction$3 (ProcessingStateMachine.java:296)
at io.zeebe.db.impl.rocksdb.transaction.ZeebeTransaction.run (ZeebeTransaction.java:84)
at io.zeebe.engine.processing.streamprocessor.ProcessingStateMachine.processInTransaction (ProcessingStateMachine.java:286)
at io.zeebe.engine.processing.streamprocessor.ProcessingStateMachine.processEvent (ProcessingStateMachine.java:254)
at io.zeebe.engine.processing.streamprocessor.ProcessingStateMachine.tryToReadNextEvent (ProcessingStateMachine.java:219)
at io.zeebe.engine.processing.streamprocessor.ProcessingStateMachine.readNextEvent (ProcessingStateMachine.java:210)
at io.zeebe.util.sched.ActorJob.invoke (ActorJob.java:73)
at io.zeebe.util.sched.ActorJob.execute (ActorJob.java:39)
at io.zeebe.util.sched.ActorTask.execute (ActorTask.java:122)
at io.zeebe.util.sched.ActorThread.executeCurrentTask (ActorThread.java:94)
at io.zeebe.util.sched.ActorThread.doWork (ActorThread.java:78)
at io.zeebe.util.sched.ActorThread.run (ActorThread.java:191)
```
</p>
</details>
**Environment:**
- OS: Camunda Cloud
- Zeebe Version: `1.0.0-alpha7`
- Configuration: <!-- [e.g. exporters etc.] -->
|
1.0
|
The process instance is stuck if the output collection is modified - **Describe the bug**
If the output collection variable is modified then the process instance is stuck in the multi-instance subprocess.
The sequential/parallel multi-instance subprocess iterates over an input collection and collects the results in an output collection. If the value of the output collection variable is modified (e.g. change the type of the value or reduce the size of the collection) then the inner instance can't be completed.
The process instance doesn't continue (i.e. it is added to the blacklist). No incidents are created.
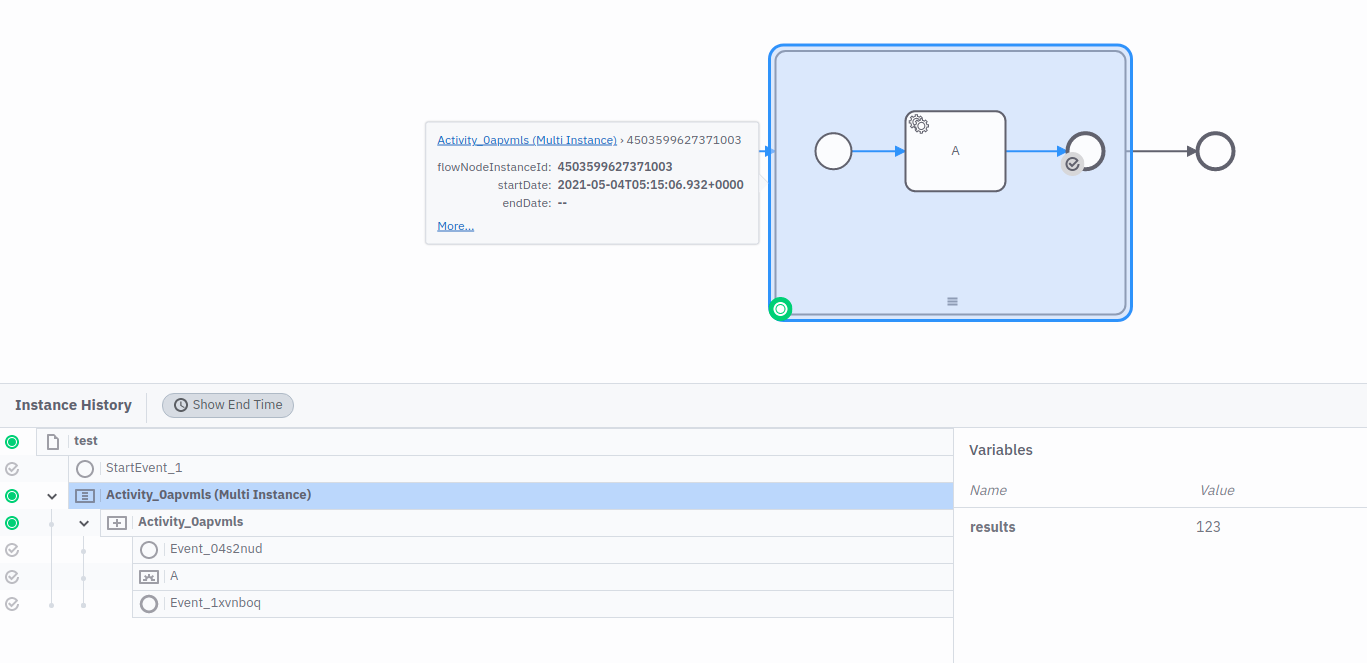
**To Reproduce**
1. deploy a process with a sequential/parallel multi-instance subprocess that defines
* an input collection `= items`
* an input element `item`
* an output collection `results`
* an output element `= r`
2. create an instance with variables `{"items":[1,2,3]}`
3. await until the service task in the subprocess is activated
4. set the value of the variable `results` to `123` (some value that is not a list)
5. complete the job
6. verify that the process instance doesn't continue
**Expected behavior**
It creates an incident when completing the inner instance.
I can resolve the incident and the process instance continues.
**Log/Stacktrace**
```
MsgpackReaderException: Unable to determine array type, found unknown header byte 0x7b at reader offset 0
```
<details><summary>Full Stacktrace</summary>
<p>
```
io.zeebe.msgpack.spec.MsgpackReaderException: Unable to determine array type, found unknown header byte 0x7b at reader offset 0
at io.zeebe.msgpack.spec.MsgPackReader.exceptionOnUnknownHeader (MsgPackReader.java:474)
at io.zeebe.msgpack.spec.MsgPackReader.readArrayHeader (MsgPackReader.java:107)
at io.zeebe.engine.processing.bpmn.container.MultiInstanceBodyProcessor.insertAt (MultiInstanceBodyProcessor.java:372)
at io.zeebe.engine.processing.bpmn.container.MultiInstanceBodyProcessor.lambda$updateOutputCollection$14 (MultiInstanceBodyProcessor.java:355)
at io.zeebe.util.Either$Right.map (Either.java:213)
at io.zeebe.engine.processing.bpmn.container.MultiInstanceBodyProcessor.updateOutputCollection (MultiInstanceBodyProcessor.java:346)
at io.zeebe.engine.processing.bpmn.container.MultiInstanceBodyProcessor.lambda$updateOutputCollection$13 (MultiInstanceBodyProcessor.java:332)
at java.util.Optional.map (Unknown Source)
at io.zeebe.engine.processing.bpmn.container.MultiInstanceBodyProcessor.updateOutputCollection (MultiInstanceBodyProcessor.java:330)
at io.zeebe.engine.processing.bpmn.container.MultiInstanceBodyProcessor.beforeExecutionPathCompleted (MultiInstanceBodyProcessor.java:150)
at io.zeebe.engine.processing.bpmn.container.MultiInstanceBodyProcessor.beforeExecutionPathCompleted (MultiInstanceBodyProcessor.java:35)
at io.zeebe.engine.processing.bpmn.behavior.BpmnStateTransitionBehavior.lambda$beforeExecutionPathCompleted$2 (BpmnStateTransitionBehavior.java:406)
at io.zeebe.engine.processing.bpmn.behavior.BpmnStateTransitionBehavior.invokeElementContainerIfPresent (BpmnStateTransitionBehavior.java:489)
at io.zeebe.engine.processing.bpmn.behavior.BpmnStateTransitionBehavior.beforeExecutionPathCompleted (BpmnStateTransitionBehavior.java:402)
at io.zeebe.engine.processing.bpmn.behavior.BpmnStateTransitionBehavior.transitionToCompletedWithParentNotification (BpmnStateTransitionBehavior.java:167)
at io.zeebe.engine.processing.bpmn.container.SubProcessProcessor.lambda$onComplete$3 (SubProcessProcessor.java:78)
at io.zeebe.util.Either$Right.ifRightOrLeft (Either.java:238)
at io.zeebe.engine.processing.bpmn.container.SubProcessProcessor.onComplete (SubProcessProcessor.java:74)
at io.zeebe.engine.processing.bpmn.container.SubProcessProcessor.onComplete (SubProcessProcessor.java:23)
at io.zeebe.engine.processing.bpmn.BpmnStreamProcessor.processEvent (BpmnStreamProcessor.java:213)
at io.zeebe.engine.processing.bpmn.BpmnStreamProcessor.lambda$processRecord$1 (BpmnStreamProcessor.java:134)
at io.zeebe.util.Either$Right.ifRightOrLeft (Either.java:238)
at io.zeebe.engine.processing.bpmn.BpmnStreamProcessor.processRecord (BpmnStreamProcessor.java:131)
at io.zeebe.engine.processing.streamprocessor.TypedRecordProcessor.processRecord (TypedRecordProcessor.java:54)
at io.zeebe.engine.processing.streamprocessor.ProcessingStateMachine.lambda$processInTransaction$3 (ProcessingStateMachine.java:296)
at io.zeebe.db.impl.rocksdb.transaction.ZeebeTransaction.run (ZeebeTransaction.java:84)
at io.zeebe.engine.processing.streamprocessor.ProcessingStateMachine.processInTransaction (ProcessingStateMachine.java:286)
at io.zeebe.engine.processing.streamprocessor.ProcessingStateMachine.processEvent (ProcessingStateMachine.java:254)
at io.zeebe.engine.processing.streamprocessor.ProcessingStateMachine.tryToReadNextEvent (ProcessingStateMachine.java:219)
at io.zeebe.engine.processing.streamprocessor.ProcessingStateMachine.readNextEvent (ProcessingStateMachine.java:210)
at io.zeebe.util.sched.ActorJob.invoke (ActorJob.java:73)
at io.zeebe.util.sched.ActorJob.execute (ActorJob.java:39)
at io.zeebe.util.sched.ActorTask.execute (ActorTask.java:122)
at io.zeebe.util.sched.ActorThread.executeCurrentTask (ActorThread.java:94)
at io.zeebe.util.sched.ActorThread.doWork (ActorThread.java:78)
at io.zeebe.util.sched.ActorThread.run (ActorThread.java:191)
```
</p>
</details>
**Environment:**
- OS: Camunda Cloud
- Zeebe Version: `1.0.0-alpha7`
- Configuration: <!-- [e.g. exporters etc.] -->
|
process
|
the process instance is stuck if the output collection is modified describe the bug if the output collection variable is modified then the process instance is stuck in the multi instance subprocess the sequential parallel multi instance subprocess iterates over an input collection and collects the results in an output collection if the value of the output collection variable is modified e g change the type of the value or reduce the size of the collection then the inner instance can t be completed the process instance doesn t continue i e it is added to the blacklist no incidents are created to reproduce deploy a process with a sequential parallel multi instance subprocess that defines an input collection items an input element item an output collection results an output element r create an instance with variables items await until the service task in the subprocess is activated set the value of the variable results to some value that is not a list complete the job verify that the process instance doesn t continue expected behavior it creates an incident when completing the inner instance i can resolve the incident and the process instance continues log stacktrace msgpackreaderexception unable to determine array type found unknown header byte at reader offset full stacktrace io zeebe msgpack spec msgpackreaderexception unable to determine array type found unknown header byte at reader offset at io zeebe msgpack spec msgpackreader exceptiononunknownheader msgpackreader java at io zeebe msgpack spec msgpackreader readarrayheader msgpackreader java at io zeebe engine processing bpmn container multiinstancebodyprocessor insertat multiinstancebodyprocessor java at io zeebe engine processing bpmn container multiinstancebodyprocessor lambda updateoutputcollection multiinstancebodyprocessor java at io zeebe util either right map either java at io zeebe engine processing bpmn container multiinstancebodyprocessor updateoutputcollection multiinstancebodyprocessor java at io zeebe engine processing bpmn container multiinstancebodyprocessor lambda updateoutputcollection multiinstancebodyprocessor java at java util optional map unknown source at io zeebe engine processing bpmn container multiinstancebodyprocessor updateoutputcollection multiinstancebodyprocessor java at io zeebe engine processing bpmn container multiinstancebodyprocessor beforeexecutionpathcompleted multiinstancebodyprocessor java at io zeebe engine processing bpmn container multiinstancebodyprocessor beforeexecutionpathcompleted multiinstancebodyprocessor java at io zeebe engine processing bpmn behavior bpmnstatetransitionbehavior lambda beforeexecutionpathcompleted bpmnstatetransitionbehavior java at io zeebe engine processing bpmn behavior bpmnstatetransitionbehavior invokeelementcontainerifpresent bpmnstatetransitionbehavior java at io zeebe engine processing bpmn behavior bpmnstatetransitionbehavior beforeexecutionpathcompleted bpmnstatetransitionbehavior java at io zeebe engine processing bpmn behavior bpmnstatetransitionbehavior transitiontocompletedwithparentnotification bpmnstatetransitionbehavior java at io zeebe engine processing bpmn container subprocessprocessor lambda oncomplete subprocessprocessor java at io zeebe util either right ifrightorleft either java at io zeebe engine processing bpmn container subprocessprocessor oncomplete subprocessprocessor java at io zeebe engine processing bpmn container subprocessprocessor oncomplete subprocessprocessor java at io zeebe engine processing bpmn bpmnstreamprocessor processevent bpmnstreamprocessor java at io zeebe engine processing bpmn bpmnstreamprocessor lambda processrecord bpmnstreamprocessor java at io zeebe util either right ifrightorleft either java at io zeebe engine processing bpmn bpmnstreamprocessor processrecord bpmnstreamprocessor java at io zeebe engine processing streamprocessor typedrecordprocessor processrecord typedrecordprocessor java at io zeebe engine processing streamprocessor processingstatemachine lambda processintransaction processingstatemachine java at io zeebe db impl rocksdb transaction zeebetransaction run zeebetransaction java at io zeebe engine processing streamprocessor processingstatemachine processintransaction processingstatemachine java at io zeebe engine processing streamprocessor processingstatemachine processevent processingstatemachine java at io zeebe engine processing streamprocessor processingstatemachine trytoreadnextevent processingstatemachine java at io zeebe engine processing streamprocessor processingstatemachine readnextevent processingstatemachine java at io zeebe util sched actorjob invoke actorjob java at io zeebe util sched actorjob execute actorjob java at io zeebe util sched actortask execute actortask java at io zeebe util sched actorthread executecurrenttask actorthread java at io zeebe util sched actorthread dowork actorthread java at io zeebe util sched actorthread run actorthread java environment os camunda cloud zeebe version configuration
| 1
|
21,459
| 29,497,548,009
|
IssuesEvent
|
2023-06-02 18:21:54
|
Mattizza/DSL-Online-News-Popularity
|
https://api.github.com/repos/Mattizza/DSL-Online-News-Popularity
|
closed
|
Check inconsistencies
|
preprocessing missing/duplicates
|
Nan values are considered float, so we can't parse them to integers. First estimate nan and then change the dtype. Also, some variables that should be int, have inconsistencies (some float values) that must be fixed.
|
1.0
|
Check inconsistencies - Nan values are considered float, so we can't parse them to integers. First estimate nan and then change the dtype. Also, some variables that should be int, have inconsistencies (some float values) that must be fixed.
|
process
|
check inconsistencies nan values are considered float so we can t parse them to integers first estimate nan and then change the dtype also some variables that should be int have inconsistencies some float values that must be fixed
| 1
|
289,649
| 31,991,451,230
|
IssuesEvent
|
2023-09-21 06:14:01
|
pazhanivel07/frameworks_av_AOSP_10_r33_CVE-2023-35687_CVE-2023-35679
|
https://api.github.com/repos/pazhanivel07/frameworks_av_AOSP_10_r33_CVE-2023-35687_CVE-2023-35679
|
opened
|
CVE-2022-20496 (Medium) detected in avandroid-9.0.0_r56
|
Mend: dependency security vulnerability
|
## CVE-2022-20496 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>avandroid-9.0.0_r56</b></p></summary>
<p>
<p>Library home page: <a href=https://android.googlesource.com/platform/frameworks/av>https://android.googlesource.com/platform/frameworks/av</a></p>
<p>Found in HEAD commit: <a href="https://github.com/pazhanivel07/frameworks_av_AOSP_10_r33_CVE-2023-35687_CVE-2023-35679/commit/f6c68d1f56234bf68c91ea85f355b0612cd36a2b">f6c68d1f56234bf68c91ea85f355b0612cd36a2b</a></p>
<p>Found in base branch: <b>main</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/media/libstagefright/NuMediaExtractor.cpp</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
In setDataSource of initMediaExtractor.cpp, there is a possibility of arbitrary code execution due to a use after free. This could lead to local information disclosure with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-12 Android-12L Android-13Android ID: A-245242273
<p>Publish Date: 2022-12-13
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-20496>CVE-2022-20496</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://android.googlesource.com/platform/frameworks/av/+/b1ae1e407f50bff323f47459995738a5b8acfb02">https://android.googlesource.com/platform/frameworks/av/+/b1ae1e407f50bff323f47459995738a5b8acfb02</a></p>
<p>Release Date: 2022-12-13</p>
<p>Fix Resolution: android-13.0.0_r16</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2022-20496 (Medium) detected in avandroid-9.0.0_r56 - ## CVE-2022-20496 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>avandroid-9.0.0_r56</b></p></summary>
<p>
<p>Library home page: <a href=https://android.googlesource.com/platform/frameworks/av>https://android.googlesource.com/platform/frameworks/av</a></p>
<p>Found in HEAD commit: <a href="https://github.com/pazhanivel07/frameworks_av_AOSP_10_r33_CVE-2023-35687_CVE-2023-35679/commit/f6c68d1f56234bf68c91ea85f355b0612cd36a2b">f6c68d1f56234bf68c91ea85f355b0612cd36a2b</a></p>
<p>Found in base branch: <b>main</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/media/libstagefright/NuMediaExtractor.cpp</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
In setDataSource of initMediaExtractor.cpp, there is a possibility of arbitrary code execution due to a use after free. This could lead to local information disclosure with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-12 Android-12L Android-13Android ID: A-245242273
<p>Publish Date: 2022-12-13
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-20496>CVE-2022-20496</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://android.googlesource.com/platform/frameworks/av/+/b1ae1e407f50bff323f47459995738a5b8acfb02">https://android.googlesource.com/platform/frameworks/av/+/b1ae1e407f50bff323f47459995738a5b8acfb02</a></p>
<p>Release Date: 2022-12-13</p>
<p>Fix Resolution: android-13.0.0_r16</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_process
|
cve medium detected in avandroid cve medium severity vulnerability vulnerable library avandroid library home page a href found in head commit a href found in base branch main vulnerable source files media libstagefright numediaextractor cpp vulnerability details in setdatasource of initmediaextractor cpp there is a possibility of arbitrary code execution due to a use after free this could lead to local information disclosure with no additional execution privileges needed user interaction is not needed for exploitation product androidversions android android android id a publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution android step up your open source security game with mend
| 0
|
390,573
| 11,551,078,002
|
IssuesEvent
|
2020-02-19 00:17:58
|
googleapis/google-api-java-client
|
https://api.github.com/repos/googleapis/google-api-java-client
|
closed
|
Synthesis failed for google-api-java-client
|
autosynth failure priority: p1 type: bug
|
Hello! Autosynth couldn't regenerate google-api-java-client. :broken_heart:
Here's the output from running `synth.py`:
```
Cloning into 'working_repo'...
Switched to branch 'autosynth'
Running synthtool
['/tmpfs/src/git/autosynth/env/bin/python3', '-m', 'synthtool', 'synth.py', '--']
synthtool > Executing /tmpfs/src/git/autosynth/working_repo/synth.py.
On branch autosynth
nothing to commit, working tree clean
HEAD detached at FETCH_HEAD
nothing to commit, working tree clean
synthtool > Wrote metadata to synth.metadata.
Traceback (most recent call last):
File "/home/kbuilder/.pyenv/versions/3.6.1/lib/python3.6/runpy.py", line 193, in _run_module_as_main
"__main__", mod_spec)
File "/home/kbuilder/.pyenv/versions/3.6.1/lib/python3.6/runpy.py", line 85, in _run_code
exec(code, run_globals)
File "/tmpfs/src/git/autosynth/env/lib/python3.6/site-packages/synthtool/__main__.py", line 102, in <module>
main()
File "/tmpfs/src/git/autosynth/env/lib/python3.6/site-packages/click/core.py", line 764, in __call__
return self.main(*args, **kwargs)
File "/tmpfs/src/git/autosynth/env/lib/python3.6/site-packages/click/core.py", line 717, in main
rv = self.invoke(ctx)
File "/tmpfs/src/git/autosynth/env/lib/python3.6/site-packages/click/core.py", line 956, in invoke
return ctx.invoke(self.callback, **ctx.params)
File "/tmpfs/src/git/autosynth/env/lib/python3.6/site-packages/click/core.py", line 555, in invoke
return callback(*args, **kwargs)
File "/tmpfs/src/git/autosynth/env/lib/python3.6/site-packages/synthtool/__main__.py", line 94, in main
spec.loader.exec_module(synth_module) # type: ignore
File "<frozen importlib._bootstrap_external>", line 678, in exec_module
File "<frozen importlib._bootstrap>", line 205, in _call_with_frames_removed
File "/tmpfs/src/git/autosynth/working_repo/synth.py", line 22, in <module>
templates = common_templates.java_library()
File "/tmpfs/src/git/autosynth/env/lib/python3.6/site-packages/synthtool/gcp/common.py", line 75, in java_library
return self._generic_library("java_library", **kwargs)
File "/tmpfs/src/git/autosynth/env/lib/python3.6/site-packages/synthtool/gcp/common.py", line 43, in _generic_library
if not kwargs["metadata"]["samples"]:
KeyError: 'samples'
Synthesis failed
```
Google internal developers can see the full log [here](https://sponge/7769bc45-4de7-4c4e-8e43-b07e6b6eba12).
|
1.0
|
Synthesis failed for google-api-java-client - Hello! Autosynth couldn't regenerate google-api-java-client. :broken_heart:
Here's the output from running `synth.py`:
```
Cloning into 'working_repo'...
Switched to branch 'autosynth'
Running synthtool
['/tmpfs/src/git/autosynth/env/bin/python3', '-m', 'synthtool', 'synth.py', '--']
synthtool > Executing /tmpfs/src/git/autosynth/working_repo/synth.py.
On branch autosynth
nothing to commit, working tree clean
HEAD detached at FETCH_HEAD
nothing to commit, working tree clean
synthtool > Wrote metadata to synth.metadata.
Traceback (most recent call last):
File "/home/kbuilder/.pyenv/versions/3.6.1/lib/python3.6/runpy.py", line 193, in _run_module_as_main
"__main__", mod_spec)
File "/home/kbuilder/.pyenv/versions/3.6.1/lib/python3.6/runpy.py", line 85, in _run_code
exec(code, run_globals)
File "/tmpfs/src/git/autosynth/env/lib/python3.6/site-packages/synthtool/__main__.py", line 102, in <module>
main()
File "/tmpfs/src/git/autosynth/env/lib/python3.6/site-packages/click/core.py", line 764, in __call__
return self.main(*args, **kwargs)
File "/tmpfs/src/git/autosynth/env/lib/python3.6/site-packages/click/core.py", line 717, in main
rv = self.invoke(ctx)
File "/tmpfs/src/git/autosynth/env/lib/python3.6/site-packages/click/core.py", line 956, in invoke
return ctx.invoke(self.callback, **ctx.params)
File "/tmpfs/src/git/autosynth/env/lib/python3.6/site-packages/click/core.py", line 555, in invoke
return callback(*args, **kwargs)
File "/tmpfs/src/git/autosynth/env/lib/python3.6/site-packages/synthtool/__main__.py", line 94, in main
spec.loader.exec_module(synth_module) # type: ignore
File "<frozen importlib._bootstrap_external>", line 678, in exec_module
File "<frozen importlib._bootstrap>", line 205, in _call_with_frames_removed
File "/tmpfs/src/git/autosynth/working_repo/synth.py", line 22, in <module>
templates = common_templates.java_library()
File "/tmpfs/src/git/autosynth/env/lib/python3.6/site-packages/synthtool/gcp/common.py", line 75, in java_library
return self._generic_library("java_library", **kwargs)
File "/tmpfs/src/git/autosynth/env/lib/python3.6/site-packages/synthtool/gcp/common.py", line 43, in _generic_library
if not kwargs["metadata"]["samples"]:
KeyError: 'samples'
Synthesis failed
```
Google internal developers can see the full log [here](https://sponge/7769bc45-4de7-4c4e-8e43-b07e6b6eba12).
|
non_process
|
synthesis failed for google api java client hello autosynth couldn t regenerate google api java client broken heart here s the output from running synth py cloning into working repo switched to branch autosynth running synthtool synthtool executing tmpfs src git autosynth working repo synth py on branch autosynth nothing to commit working tree clean head detached at fetch head nothing to commit working tree clean synthtool wrote metadata to synth metadata traceback most recent call last file home kbuilder pyenv versions lib runpy py line in run module as main main mod spec file home kbuilder pyenv versions lib runpy py line in run code exec code run globals file tmpfs src git autosynth env lib site packages synthtool main py line in main file tmpfs src git autosynth env lib site packages click core py line in call return self main args kwargs file tmpfs src git autosynth env lib site packages click core py line in main rv self invoke ctx file tmpfs src git autosynth env lib site packages click core py line in invoke return ctx invoke self callback ctx params file tmpfs src git autosynth env lib site packages click core py line in invoke return callback args kwargs file tmpfs src git autosynth env lib site packages synthtool main py line in main spec loader exec module synth module type ignore file line in exec module file line in call with frames removed file tmpfs src git autosynth working repo synth py line in templates common templates java library file tmpfs src git autosynth env lib site packages synthtool gcp common py line in java library return self generic library java library kwargs file tmpfs src git autosynth env lib site packages synthtool gcp common py line in generic library if not kwargs keyerror samples synthesis failed google internal developers can see the full log
| 0
|
7,582
| 10,695,052,175
|
IssuesEvent
|
2019-10-23 12:15:07
|
linnovate/root
|
https://api.github.com/repos/linnovate/root
|
opened
|
search > filter by status
|
2.0.8 Process bug
|
go to search
on the left side, you can filter by status
but missing some statuses like sent ,review , canceled ,schedule , received
please add them or include them in others
|
1.0
|
search > filter by status - go to search
on the left side, you can filter by status
but missing some statuses like sent ,review , canceled ,schedule , received
please add them or include them in others
|
process
|
search filter by status go to search on the left side you can filter by status but missing some statuses like sent review canceled schedule received please add them or include them in others
| 1
|
14,370
| 17,394,418,151
|
IssuesEvent
|
2021-08-02 11:40:07
|
EBIvariation/eva-opentargets
|
https://api.github.com/repos/EBIvariation/eva-opentargets
|
closed
|
Manual curation for 2021.08 release
|
Processing
|
The submission window for 21.08 is expected to open 9-27 August. But since the curation process is separated from everything else, it can be done at any convenient moment.
**Checklist:**
- [x] Manual curation, step 1 — Process
- [x] Manual curation, step 2 — Curate
- [x] Curation
- [x] Review 1
- [x] Review 2
- [x] Manual curation, step 3 — Export
- [x] Manual curation, step 4 — EFO feedback
|
1.0
|
Manual curation for 2021.08 release - The submission window for 21.08 is expected to open 9-27 August. But since the curation process is separated from everything else, it can be done at any convenient moment.
**Checklist:**
- [x] Manual curation, step 1 — Process
- [x] Manual curation, step 2 — Curate
- [x] Curation
- [x] Review 1
- [x] Review 2
- [x] Manual curation, step 3 — Export
- [x] Manual curation, step 4 — EFO feedback
|
process
|
manual curation for release the submission window for is expected to open august but since the curation process is separated from everything else it can be done at any convenient moment checklist manual curation step — process manual curation step — curate curation review review manual curation step — export manual curation step — efo feedback
| 1
|
10,443
| 13,221,713,464
|
IssuesEvent
|
2020-08-17 14:27:29
|
prisma/prisma-client-js
|
https://api.github.com/repos/prisma/prisma-client-js
|
opened
|
Test and stabilize Unix Domain Sockets
|
kind/feature process/candidate topic: tests
|
Per https://github.com/prisma/prisma/issues/3092 UDS is now available to be used in Prisma Client. We need to test this more and make sure there are no negative side effects.
|
1.0
|
Test and stabilize Unix Domain Sockets - Per https://github.com/prisma/prisma/issues/3092 UDS is now available to be used in Prisma Client. We need to test this more and make sure there are no negative side effects.
|
process
|
test and stabilize unix domain sockets per uds is now available to be used in prisma client we need to test this more and make sure there are no negative side effects
| 1
|
65,424
| 14,727,793,880
|
IssuesEvent
|
2021-01-06 09:03:59
|
rdharmedran/codeguru
|
https://api.github.com/repos/rdharmedran/codeguru
|
opened
|
CVE-2020-35490 (High) detected in jackson-databind-2.9.5.jar
|
security vulnerability
|
## CVE-2020-35490 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.5.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: codeguru/example/example/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.5/jackson-databind-2.9.5.jar</p>
<p>
Dependency Hierarchy:
- google-cloud-dataflow-java-sdk-all-2.5.0.jar (Root Library)
- beam-sdks-java-core-2.5.0.jar
- :x: **jackson-databind-2.9.5.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/rdharmedran/codeguru/commit/03eef59d90cd24cc5959d727fe7321d9ac8aa466">03eef59d90cd24cc5959d727fe7321d9ac8aa466</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.8 mishandles the interaction between serialization gadgets and typing, related to org.apache.commons.dbcp2.datasources.PerUserPoolDataSource.
<p>Publish Date: 2020-12-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-35490>CVE-2020-35490</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/FasterXML/jackson-databind/issues/2986">https://github.com/FasterXML/jackson-databind/issues/2986</a></p>
<p>Release Date: 2020-12-17</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.9.10.8</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2020-35490 (High) detected in jackson-databind-2.9.5.jar - ## CVE-2020-35490 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.5.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: codeguru/example/example/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.5/jackson-databind-2.9.5.jar</p>
<p>
Dependency Hierarchy:
- google-cloud-dataflow-java-sdk-all-2.5.0.jar (Root Library)
- beam-sdks-java-core-2.5.0.jar
- :x: **jackson-databind-2.9.5.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/rdharmedran/codeguru/commit/03eef59d90cd24cc5959d727fe7321d9ac8aa466">03eef59d90cd24cc5959d727fe7321d9ac8aa466</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.8 mishandles the interaction between serialization gadgets and typing, related to org.apache.commons.dbcp2.datasources.PerUserPoolDataSource.
<p>Publish Date: 2020-12-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-35490>CVE-2020-35490</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/FasterXML/jackson-databind/issues/2986">https://github.com/FasterXML/jackson-databind/issues/2986</a></p>
<p>Release Date: 2020-12-17</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.9.10.8</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_process
|
cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file codeguru example example pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy google cloud dataflow java sdk all jar root library beam sdks java core jar x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to org apache commons datasources peruserpooldatasource publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com fasterxml jackson core jackson databind step up your open source security game with whitesource
| 0
|
9,240
| 12,269,805,469
|
IssuesEvent
|
2020-05-07 14:35:51
|
cypress-io/cypress
|
https://api.github.com/repos/cypress-io/cypress
|
closed
|
Internal e2e test failing - async plugins error
|
process: tests stage: needs review type: chore
|
### Current behavior:
Our `server/test/e2e/3_plugins_spec.js` spec is consistently failing in `develop` after merging in the error improvements PR: https://github.com/cypress-io/cypress/pull/3930
https://circleci.com/gh/cypress-io/cypress/316940
<img width="810" alt="Screen Shot 2020-05-07 at 11 52 34 AM" src="https://user-images.githubusercontent.com/1271364/81257465-59b8e500-9059-11ea-9ba0-40007e1a0e93.png">
### Versions
4.6.0-prerelease - `develop` branch
|
1.0
|
Internal e2e test failing - async plugins error - ### Current behavior:
Our `server/test/e2e/3_plugins_spec.js` spec is consistently failing in `develop` after merging in the error improvements PR: https://github.com/cypress-io/cypress/pull/3930
https://circleci.com/gh/cypress-io/cypress/316940
<img width="810" alt="Screen Shot 2020-05-07 at 11 52 34 AM" src="https://user-images.githubusercontent.com/1271364/81257465-59b8e500-9059-11ea-9ba0-40007e1a0e93.png">
### Versions
4.6.0-prerelease - `develop` branch
|
process
|
internal test failing async plugins error current behavior our server test plugins spec js spec is consistently failing in develop after merging in the error improvements pr img width alt screen shot at am src versions prerelease develop branch
| 1
|
7,023
| 10,172,420,698
|
IssuesEvent
|
2019-08-08 10:38:23
|
googleapis/google-cloud-dotnet
|
https://api.github.com/repos/googleapis/google-cloud-dotnet
|
closed
|
Doesn't support env var --> SYNTHTOOL_GOOGLEAPIS (local googleapis)
|
priority: p2 type: feature request type: process
|
**Is your feature request related to a problem? Please describe.**
It doesn't support $SYNTHTOOL_GOOGLEAPIS (env var that points to local googleapis/googleapis). Other languages supports $SYNTHTOOL_GOOGLEAPIS, and I thnk it might be good idea to add this as option and keep it consistent throughout all languages.
**Describe the solution you'd like**
Add an option to read $SYNTHTOOL_GOOGLEAPIS (points to local googleapis) if that env variable exists.
|
1.0
|
Doesn't support env var --> SYNTHTOOL_GOOGLEAPIS (local googleapis) -
**Is your feature request related to a problem? Please describe.**
It doesn't support $SYNTHTOOL_GOOGLEAPIS (env var that points to local googleapis/googleapis). Other languages supports $SYNTHTOOL_GOOGLEAPIS, and I thnk it might be good idea to add this as option and keep it consistent throughout all languages.
**Describe the solution you'd like**
Add an option to read $SYNTHTOOL_GOOGLEAPIS (points to local googleapis) if that env variable exists.
|
process
|
doesn t support env var synthtool googleapis local googleapis is your feature request related to a problem please describe it doesn t support synthtool googleapis env var that points to local googleapis googleapis other languages supports synthtool googleapis and i thnk it might be good idea to add this as option and keep it consistent throughout all languages describe the solution you d like add an option to read synthtool googleapis points to local googleapis if that env variable exists
| 1
|
18,038
| 24,048,834,183
|
IssuesEvent
|
2022-09-16 10:49:32
|
galasa-dev/projectmanagement
|
https://api.github.com/repos/galasa-dev/projectmanagement
|
closed
|
Document the new GitHubIssue Manager
|
3-JAT Conversion Conversion Process
|
Document the new GitHubIssue Manager
1. Detail annotation
1. Detail CPS properties
1. Provide examples
|
1.0
|
Document the new GitHubIssue Manager - Document the new GitHubIssue Manager
1. Detail annotation
1. Detail CPS properties
1. Provide examples
|
process
|
document the new githubissue manager document the new githubissue manager detail annotation detail cps properties provide examples
| 1
|
189,628
| 15,192,187,414
|
IssuesEvent
|
2021-02-15 21:28:45
|
Arquisoft/radarin_es4b
|
https://api.github.com/repos/Arquisoft/radarin_es4b
|
closed
|
Creación del apartado "1.0 Introducción y objetivos" de la documentación
|
documentation
|
Asignado a Alberto Fernández Gutiérrez
|
1.0
|
Creación del apartado "1.0 Introducción y objetivos" de la documentación - Asignado a Alberto Fernández Gutiérrez
|
non_process
|
creación del apartado introducción y objetivos de la documentación asignado a alberto fernández gutiérrez
| 0
|
7,403
| 10,523,142,921
|
IssuesEvent
|
2019-09-30 10:17:18
|
didi/mpx
|
https://api.github.com/repos/didi/mpx
|
closed
|
不支持跳过cover-image的src路径编译
|
processing
|
某些情况下我给cover-image设置的src是需要小程序的原生语法进行变量替换的,例如静态的图片资源在循环列表中的时候
```html
<cover-image src="/tabbar/{{item}}{{item.name===selectedName ? '_selected' : ''}}.png" />
```
我看loader中好像没有跳过编译的方法,现在这么写会一直提示路径找不到。
|
1.0
|
不支持跳过cover-image的src路径编译 - 某些情况下我给cover-image设置的src是需要小程序的原生语法进行变量替换的,例如静态的图片资源在循环列表中的时候
```html
<cover-image src="/tabbar/{{item}}{{item.name===selectedName ? '_selected' : ''}}.png" />
```
我看loader中好像没有跳过编译的方法,现在这么写会一直提示路径找不到。
|
process
|
不支持跳过cover image的src路径编译 某些情况下我给cover image设置的src是需要小程序的原生语法进行变量替换的,例如静态的图片资源在循环列表中的时候 html 我看loader中好像没有跳过编译的方法,现在这么写会一直提示路径找不到。
| 1
|
192,356
| 22,215,937,892
|
IssuesEvent
|
2022-06-08 01:39:04
|
dpteam/RK3188_TABLET
|
https://api.github.com/repos/dpteam/RK3188_TABLET
|
reopened
|
CVE-2021-3178 (Medium) detected in linux-yocto-4.12v3.0.66
|
security vulnerability
|
## CVE-2021-3178 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-yocto-4.12v3.0.66</b></p></summary>
<p>
<p>Linux 4.12 Embedded Kernel</p>
<p>Library home page: <a href=https://git.yoctoproject.org/git/linux-yocto-4.12>https://git.yoctoproject.org/git/linux-yocto-4.12</a></p>
<p>Found in HEAD commit: <a href="https://github.com/dpteam/RK3188_TABLET/commit/0c501f5a0fd72c7b2ac82904235363bd44fd8f9e">0c501f5a0fd72c7b2ac82904235363bd44fd8f9e</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (0)</summary>
<p></p>
<p>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
** DISPUTED ** fs/nfsd/nfs3xdr.c in the Linux kernel through 5.10.8, when there is an NFS export of a subdirectory of a filesystem, allows remote attackers to traverse to other parts of the filesystem via READDIRPLUS. NOTE: some parties argue that such a subdirectory export is not intended to prevent this attack; see also the exports(5) no_subtree_check default behavior.
<p>Publish Date: 2021-01-19
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-3178>CVE-2021-3178</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2021-3178">https://nvd.nist.gov/vuln/detail/CVE-2021-3178</a></p>
<p>Release Date: 2021-01-19</p>
<p>Fix Resolution: linux-libc-headers - 5.13;linux-yocto - 5.4.20+gitAUTOINC+c11911d4d1_f4d7dbafb1,4.8.26+gitAUTOINC+1c60e003c7_27efc3ba68</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2021-3178 (Medium) detected in linux-yocto-4.12v3.0.66 - ## CVE-2021-3178 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-yocto-4.12v3.0.66</b></p></summary>
<p>
<p>Linux 4.12 Embedded Kernel</p>
<p>Library home page: <a href=https://git.yoctoproject.org/git/linux-yocto-4.12>https://git.yoctoproject.org/git/linux-yocto-4.12</a></p>
<p>Found in HEAD commit: <a href="https://github.com/dpteam/RK3188_TABLET/commit/0c501f5a0fd72c7b2ac82904235363bd44fd8f9e">0c501f5a0fd72c7b2ac82904235363bd44fd8f9e</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (0)</summary>
<p></p>
<p>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
** DISPUTED ** fs/nfsd/nfs3xdr.c in the Linux kernel through 5.10.8, when there is an NFS export of a subdirectory of a filesystem, allows remote attackers to traverse to other parts of the filesystem via READDIRPLUS. NOTE: some parties argue that such a subdirectory export is not intended to prevent this attack; see also the exports(5) no_subtree_check default behavior.
<p>Publish Date: 2021-01-19
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-3178>CVE-2021-3178</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2021-3178">https://nvd.nist.gov/vuln/detail/CVE-2021-3178</a></p>
<p>Release Date: 2021-01-19</p>
<p>Fix Resolution: linux-libc-headers - 5.13;linux-yocto - 5.4.20+gitAUTOINC+c11911d4d1_f4d7dbafb1,4.8.26+gitAUTOINC+1c60e003c7_27efc3ba68</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_process
|
cve medium detected in linux yocto cve medium severity vulnerability vulnerable library linux yocto linux embedded kernel library home page a href found in head commit a href found in base branch master vulnerable source files vulnerability details disputed fs nfsd c in the linux kernel through when there is an nfs export of a subdirectory of a filesystem allows remote attackers to traverse to other parts of the filesystem via readdirplus note some parties argue that such a subdirectory export is not intended to prevent this attack see also the exports no subtree check default behavior publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required high user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution linux libc headers linux yocto gitautoinc gitautoinc step up your open source security game with whitesource
| 0
|
115,344
| 9,792,073,389
|
IssuesEvent
|
2019-06-10 16:28:49
|
elastic/elasticsearch
|
https://api.github.com/repos/elastic/elasticsearch
|
closed
|
[CI] IpFilteringIntegrationTests.testThatIpFilteringIsAppliedForProfile failed due to low timeout and GC
|
:Security/Security >test-failure
|
`IpFilteringIntegrationTests.testThatIpFilteringIsAppliedForProfile` failed in https://elasticsearch-ci.elastic.co/job/elastic+elasticsearch+6.7+intake/475/console
The error is:
```
> Throwable #1: java.net.SocketTimeoutException
> at __randomizedtesting.SeedInfo.seed([6C159540B3465FB8:76FC1633E1A901A0]:0)
> at java.net.SocksSocketImpl.remainingMillis(SocksSocketImpl.java:111)
> at java.net.SocksSocketImpl.connect(SocksSocketImpl.java:392)
> at java.net.Socket.connect(Socket.java:589)
> at org.elasticsearch.xpack.security.transport.filter.IpFilteringIntegrationTests.lambda$trySocketConnection$0(IpFilteringIntegrationTests.java:76)
> at org.elasticsearch.xpack.core.common.socket.SocketAccess.lambda$doPrivileged$0(SocketAccess.java:42)
> at java.security.AccessController.doPrivileged(Native Method)
> at org.elasticsearch.xpack.core.common.socket.SocketAccess.doPrivileged(SocketAccess.java:41)
> at org.elasticsearch.xpack.security.transport.filter.IpFilteringIntegrationTests.trySocketConnection(IpFilteringIntegrationTests.java:76)
> at org.elasticsearch.xpack.security.transport.filter.IpFilteringIntegrationTests.testThatIpFilteringIsAppliedForProfile(IpFilteringIntegrationTests.java:68)
> at java.lang.Thread.run(Thread.java:748)
```
This doesn't reproduce locally using:
```
./gradlew :x-pack:plugin:security:unitTest \
-Dtests.seed=6C159540B3465FB8 \
-Dtests.class=org.elasticsearch.xpack.security.transport.filter.IpFilteringIntegrationTests \
-Dtests.method="testThatIpFilteringIsAppliedForProfile" \
-Dtests.security.manager=true \
-Dtests.locale=sr-Latn-RS \
-Dtests.timezone=Africa/Casablanca \
-Dcompiler.java=12 \
-Druntime.java=8
```
I think the problem is that there is a 500ms timeout on the socket connect:
```
SocketAccess.doPrivileged(() -> socket.connect(address, 500));
```
(that's line 77 of `IpFilteringIntegrationTests.java`)
But there was a garbage collection that lasted longer than 500ms during the failing test:
```
1> [2019-04-01T10:34:41,105][WARN ][o.e.m.j.JvmGcMonitorService] [node_s0] [gc][2] overhead, spent [532ms] collecting in the last [1s]
```
In addition to garbage collection VMs can stall for hundreds of milliseconds while their hypervisor does things, so it may be worth increasing the 500ms socket connect timeout to avoid spurious failures.
|
1.0
|
[CI] IpFilteringIntegrationTests.testThatIpFilteringIsAppliedForProfile failed due to low timeout and GC - `IpFilteringIntegrationTests.testThatIpFilteringIsAppliedForProfile` failed in https://elasticsearch-ci.elastic.co/job/elastic+elasticsearch+6.7+intake/475/console
The error is:
```
> Throwable #1: java.net.SocketTimeoutException
> at __randomizedtesting.SeedInfo.seed([6C159540B3465FB8:76FC1633E1A901A0]:0)
> at java.net.SocksSocketImpl.remainingMillis(SocksSocketImpl.java:111)
> at java.net.SocksSocketImpl.connect(SocksSocketImpl.java:392)
> at java.net.Socket.connect(Socket.java:589)
> at org.elasticsearch.xpack.security.transport.filter.IpFilteringIntegrationTests.lambda$trySocketConnection$0(IpFilteringIntegrationTests.java:76)
> at org.elasticsearch.xpack.core.common.socket.SocketAccess.lambda$doPrivileged$0(SocketAccess.java:42)
> at java.security.AccessController.doPrivileged(Native Method)
> at org.elasticsearch.xpack.core.common.socket.SocketAccess.doPrivileged(SocketAccess.java:41)
> at org.elasticsearch.xpack.security.transport.filter.IpFilteringIntegrationTests.trySocketConnection(IpFilteringIntegrationTests.java:76)
> at org.elasticsearch.xpack.security.transport.filter.IpFilteringIntegrationTests.testThatIpFilteringIsAppliedForProfile(IpFilteringIntegrationTests.java:68)
> at java.lang.Thread.run(Thread.java:748)
```
This doesn't reproduce locally using:
```
./gradlew :x-pack:plugin:security:unitTest \
-Dtests.seed=6C159540B3465FB8 \
-Dtests.class=org.elasticsearch.xpack.security.transport.filter.IpFilteringIntegrationTests \
-Dtests.method="testThatIpFilteringIsAppliedForProfile" \
-Dtests.security.manager=true \
-Dtests.locale=sr-Latn-RS \
-Dtests.timezone=Africa/Casablanca \
-Dcompiler.java=12 \
-Druntime.java=8
```
I think the problem is that there is a 500ms timeout on the socket connect:
```
SocketAccess.doPrivileged(() -> socket.connect(address, 500));
```
(that's line 77 of `IpFilteringIntegrationTests.java`)
But there was a garbage collection that lasted longer than 500ms during the failing test:
```
1> [2019-04-01T10:34:41,105][WARN ][o.e.m.j.JvmGcMonitorService] [node_s0] [gc][2] overhead, spent [532ms] collecting in the last [1s]
```
In addition to garbage collection VMs can stall for hundreds of milliseconds while their hypervisor does things, so it may be worth increasing the 500ms socket connect timeout to avoid spurious failures.
|
non_process
|
ipfilteringintegrationtests testthatipfilteringisappliedforprofile failed due to low timeout and gc ipfilteringintegrationtests testthatipfilteringisappliedforprofile failed in the error is throwable java net sockettimeoutexception at randomizedtesting seedinfo seed at java net sockssocketimpl remainingmillis sockssocketimpl java at java net sockssocketimpl connect sockssocketimpl java at java net socket connect socket java at org elasticsearch xpack security transport filter ipfilteringintegrationtests lambda trysocketconnection ipfilteringintegrationtests java at org elasticsearch xpack core common socket socketaccess lambda doprivileged socketaccess java at java security accesscontroller doprivileged native method at org elasticsearch xpack core common socket socketaccess doprivileged socketaccess java at org elasticsearch xpack security transport filter ipfilteringintegrationtests trysocketconnection ipfilteringintegrationtests java at org elasticsearch xpack security transport filter ipfilteringintegrationtests testthatipfilteringisappliedforprofile ipfilteringintegrationtests java at java lang thread run thread java this doesn t reproduce locally using gradlew x pack plugin security unittest dtests seed dtests class org elasticsearch xpack security transport filter ipfilteringintegrationtests dtests method testthatipfilteringisappliedforprofile dtests security manager true dtests locale sr latn rs dtests timezone africa casablanca dcompiler java druntime java i think the problem is that there is a timeout on the socket connect socketaccess doprivileged socket connect address that s line of ipfilteringintegrationtests java but there was a garbage collection that lasted longer than during the failing test overhead spent collecting in the last in addition to garbage collection vms can stall for hundreds of milliseconds while their hypervisor does things so it may be worth increasing the socket connect timeout to avoid spurious failures
| 0
|
12,301
| 14,856,543,862
|
IssuesEvent
|
2021-01-18 14:17:26
|
prisma/prisma
|
https://api.github.com/repos/prisma/prisma
|
closed
|
intermittent: write EPIPE + Cannot read property 'onError' of undefined
|
bug/2-confirmed kind/bug process/candidate team/client topic: aws lambda topic: binary
|
## Bug description
These two exceptions happen in the same flow:
```
ERROR Invoke Error {"errorType":"Error","errorMessage":"write EPIPE","code":"EPIPE","clientVersion":"2.12.1","stack":["Error: write EPIPE"," at PrismaClientFetcher.request (/var/task/dist/webpack:/mnt/ramdisk/project/node_modules/@prisma/client/runtime/index.js:79355:15)"," at processTicksAndRejections (internal/process/task_queues.js:97:5)"]}
```
2 milliseconds later:
```
ERROR Uncaught Exception {"errorType":"TypeError","errorMessage":"Cannot read property 'onError' of undefined","stack":["TypeError: Cannot read property 'onError' of undefined"," at Socket.ce (/var/task/dist/webpack:/mnt/ramdisk/project/node_modules/@prisma/client/runtime/index.js:25673:45)"," at Socket.emit (events.js:314:20)"," at Socket.EventEmitter.emit (domain.js:483:12)"," at Pipe.<anonymous> (net.js:676:12)"]}
```
This was previously masked by #4117, which was fixed by [this commit](https://github.com/prisma/prisma/commit/582ee80cd0f52c95280b3cf7babc5a1fbfe20a44); now the real error is visible.
Possibly related to #4400
## How to reproduce
This is an intermittent error on AWS Lambda, could not reproduce it on a dev machine.
## Expected behavior
- No exception (duh)
- It would be nice to have source mapping to link the stack trace into a specific spot in the code (instead of `@prisma/client/runtime/index.js:25673:45`).
- It would be nice to have more logs from the Rust process; IIUC there's no way to set `RUST_LOG` to something other than `info`
## Environment & setup
- OS: AWS Lambda (linux-musl), node 12.x
- Database: PostgreSQL 12 on RDS
- Node.js version: 12.18
- Prisma version: 2.12.1
|
1.0
|
intermittent: write EPIPE + Cannot read property 'onError' of undefined - ## Bug description
These two exceptions happen in the same flow:
```
ERROR Invoke Error {"errorType":"Error","errorMessage":"write EPIPE","code":"EPIPE","clientVersion":"2.12.1","stack":["Error: write EPIPE"," at PrismaClientFetcher.request (/var/task/dist/webpack:/mnt/ramdisk/project/node_modules/@prisma/client/runtime/index.js:79355:15)"," at processTicksAndRejections (internal/process/task_queues.js:97:5)"]}
```
2 milliseconds later:
```
ERROR Uncaught Exception {"errorType":"TypeError","errorMessage":"Cannot read property 'onError' of undefined","stack":["TypeError: Cannot read property 'onError' of undefined"," at Socket.ce (/var/task/dist/webpack:/mnt/ramdisk/project/node_modules/@prisma/client/runtime/index.js:25673:45)"," at Socket.emit (events.js:314:20)"," at Socket.EventEmitter.emit (domain.js:483:12)"," at Pipe.<anonymous> (net.js:676:12)"]}
```
This was previously masked by #4117, which was fixed by [this commit](https://github.com/prisma/prisma/commit/582ee80cd0f52c95280b3cf7babc5a1fbfe20a44); now the real error is visible.
Possibly related to #4400
## How to reproduce
This is an intermittent error on AWS Lambda, could not reproduce it on a dev machine.
## Expected behavior
- No exception (duh)
- It would be nice to have source mapping to link the stack trace into a specific spot in the code (instead of `@prisma/client/runtime/index.js:25673:45`).
- It would be nice to have more logs from the Rust process; IIUC there's no way to set `RUST_LOG` to something other than `info`
## Environment & setup
- OS: AWS Lambda (linux-musl), node 12.x
- Database: PostgreSQL 12 on RDS
- Node.js version: 12.18
- Prisma version: 2.12.1
|
process
|
intermittent write epipe cannot read property onerror of undefined bug description these two exceptions happen in the same flow error invoke error errortype error errormessage write epipe code epipe clientversion stack milliseconds later error uncaught exception errortype typeerror errormessage cannot read property onerror of undefined stack this was previously masked by which was fixed by now the real error is visible possibly related to how to reproduce this is an intermittent error on aws lambda could not reproduce it on a dev machine expected behavior no exception duh it would be nice to have source mapping to link the stack trace into a specific spot in the code instead of prisma client runtime index js it would be nice to have more logs from the rust process iiuc there s no way to set rust log to something other than info environment setup os aws lambda linux musl node x database postgresql on rds node js version prisma version
| 1
|
329,620
| 10,022,309,194
|
IssuesEvent
|
2019-07-16 16:23:10
|
strapi/strapi
|
https://api.github.com/repos/strapi/strapi
|
closed
|
Changes for Google auth provider
|
priority: high type: enhancement 💅
|
<!-- ⚠️ If you do not respect this template your issue will be closed. -->
<!-- ⚠️ Make sure to browse the opened and closed issues before submitting your issue. -->
<!--
Please also submit your idea on the Strapi Product Board:
https://portal.productboard.com/strapi/tabs/2-under-consideration/submit-idea
If your request on the product board is accepted this feature request issue will be closed,
but will still accept public discussion.
-->
- [x] **I have created my request on the Product Board before I submitted this issue**
- [x] **I have looked at all the other requests on the Product Board before I submitted this issue**
**Please describe your feature request:**
Google is going to [shut down the consumer version of Google+](https://www.blog.google/technology/safety-security/project-strobe/) over the next several months and that means that Google provider will stop working as it relies on Google+ as I can see. Are there any plans to migrate existing Google provider to use a recommended [Google Sign-In API](https://developers.google.com/identity/sign-in/web/sign-in#before_you_begin)? Existing apps using Google provider might be impacted once Google+ is taken down. Or do I miss anything and existing provider won't require any changes given the announcement?
|
1.0
|
Changes for Google auth provider - <!-- ⚠️ If you do not respect this template your issue will be closed. -->
<!-- ⚠️ Make sure to browse the opened and closed issues before submitting your issue. -->
<!--
Please also submit your idea on the Strapi Product Board:
https://portal.productboard.com/strapi/tabs/2-under-consideration/submit-idea
If your request on the product board is accepted this feature request issue will be closed,
but will still accept public discussion.
-->
- [x] **I have created my request on the Product Board before I submitted this issue**
- [x] **I have looked at all the other requests on the Product Board before I submitted this issue**
**Please describe your feature request:**
Google is going to [shut down the consumer version of Google+](https://www.blog.google/technology/safety-security/project-strobe/) over the next several months and that means that Google provider will stop working as it relies on Google+ as I can see. Are there any plans to migrate existing Google provider to use a recommended [Google Sign-In API](https://developers.google.com/identity/sign-in/web/sign-in#before_you_begin)? Existing apps using Google provider might be impacted once Google+ is taken down. Or do I miss anything and existing provider won't require any changes given the announcement?
|
non_process
|
changes for google auth provider please also submit your idea on the strapi product board if your request on the product board is accepted this feature request issue will be closed but will still accept public discussion i have created my request on the product board before i submitted this issue i have looked at all the other requests on the product board before i submitted this issue please describe your feature request google is going to over the next several months and that means that google provider will stop working as it relies on google as i can see are there any plans to migrate existing google provider to use a recommended existing apps using google provider might be impacted once google is taken down or do i miss anything and existing provider won t require any changes given the announcement
| 0
|
5,855
| 4,044,661,216
|
IssuesEvent
|
2016-05-21 13:29:07
|
godotengine/godot
|
https://api.github.com/repos/godotengine/godot
|
opened
|
Editor is using project input map actions
|
bug topic:editor usability
|
**Issue description** (what happened, and what was expected):
The editor is using input map actions from the project's settings. Therefore, modifying input presets (`ui_*`) affects the editor too. This can break usability in many situations, like removing <kbd>ENTER</kbd> from the `ui_accept` (pressing <kbd>ENTER</kbd> when focusing a button will not longer press the button).
**Steps to reproduce:**
Actually, being able to remove keys from input presets may be a bug. [This comment](https://github.com/godotengine/godot/issues/4315#issuecomment-209876046) explains how to do it:
> It looks like if you add another key to that action, then you can remove the other keys and it will be saved.
· neikeq
The solution may be to forbid modifying input presets, but it stills seems weird that the editor is using the project's input map.
|
True
|
Editor is using project input map actions - **Issue description** (what happened, and what was expected):
The editor is using input map actions from the project's settings. Therefore, modifying input presets (`ui_*`) affects the editor too. This can break usability in many situations, like removing <kbd>ENTER</kbd> from the `ui_accept` (pressing <kbd>ENTER</kbd> when focusing a button will not longer press the button).
**Steps to reproduce:**
Actually, being able to remove keys from input presets may be a bug. [This comment](https://github.com/godotengine/godot/issues/4315#issuecomment-209876046) explains how to do it:
> It looks like if you add another key to that action, then you can remove the other keys and it will be saved.
· neikeq
The solution may be to forbid modifying input presets, but it stills seems weird that the editor is using the project's input map.
|
non_process
|
editor is using project input map actions issue description what happened and what was expected the editor is using input map actions from the project s settings therefore modifying input presets ui affects the editor too this can break usability in many situations like removing enter from the ui accept pressing enter when focusing a button will not longer press the button steps to reproduce actually being able to remove keys from input presets may be a bug explains how to do it it looks like if you add another key to that action then you can remove the other keys and it will be saved · neikeq the solution may be to forbid modifying input presets but it stills seems weird that the editor is using the project s input map
| 0
|
40,806
| 12,799,739,584
|
IssuesEvent
|
2020-07-02 15:52:04
|
mwilliams7197/zuul
|
https://api.github.com/repos/mwilliams7197/zuul
|
opened
|
CVE-2020-9546 (High) detected in jackson-databind-2.9.8.jar
|
security vulnerability
|
## CVE-2020-9546 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.8.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to vulnerable library: canner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.8/11283f21cc480aa86c4df7a0a3243ec508372ed2/jackson-databind-2.9.8.jar,canner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.8/11283f21cc480aa86c4df7a0a3243ec508372ed2/jackson-databind-2.9.8.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.8/11283f21cc480aa86c4df7a0a3243ec508372ed2/jackson-databind-2.9.8.jar</p>
<p>
Dependency Hierarchy:
- ribbon-eureka-2.2.4.jar (Root Library)
- eureka-client-1.9.4.jar
- :x: **jackson-databind-2.9.8.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://api.github.com/repos/mwilliams7197/zuul/commits/8588a970f404a14680bea9a4eda267023e612256">8588a970f404a14680bea9a4eda267023e612256</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to org.apache.hadoop.shaded.com.zaxxer.hikari.HikariConfig (aka shaded hikari-config).
<p>Publish Date: 2020-03-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-9546>CVE-2020-9546</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9546">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9546</a></p>
<p>Release Date: 2020-03-02</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.10.3</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.9.8","isTransitiveDependency":true,"dependencyTree":"com.netflix.ribbon:ribbon-eureka:2.2.4;com.netflix.eureka:eureka-client:1.9.4;com.fasterxml.jackson.core:jackson-databind:2.9.8","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.fasterxml.jackson.core:jackson-databind:2.10.3"}],"vulnerabilityIdentifier":"CVE-2020-9546","vulnerabilityDetails":"FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to org.apache.hadoop.shaded.com.zaxxer.hikari.HikariConfig (aka shaded hikari-config).","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-9546","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> -->
|
True
|
CVE-2020-9546 (High) detected in jackson-databind-2.9.8.jar - ## CVE-2020-9546 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.8.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to vulnerable library: canner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.8/11283f21cc480aa86c4df7a0a3243ec508372ed2/jackson-databind-2.9.8.jar,canner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.8/11283f21cc480aa86c4df7a0a3243ec508372ed2/jackson-databind-2.9.8.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.8/11283f21cc480aa86c4df7a0a3243ec508372ed2/jackson-databind-2.9.8.jar</p>
<p>
Dependency Hierarchy:
- ribbon-eureka-2.2.4.jar (Root Library)
- eureka-client-1.9.4.jar
- :x: **jackson-databind-2.9.8.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://api.github.com/repos/mwilliams7197/zuul/commits/8588a970f404a14680bea9a4eda267023e612256">8588a970f404a14680bea9a4eda267023e612256</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to org.apache.hadoop.shaded.com.zaxxer.hikari.HikariConfig (aka shaded hikari-config).
<p>Publish Date: 2020-03-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-9546>CVE-2020-9546</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9546">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9546</a></p>
<p>Release Date: 2020-03-02</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.10.3</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.9.8","isTransitiveDependency":true,"dependencyTree":"com.netflix.ribbon:ribbon-eureka:2.2.4;com.netflix.eureka:eureka-client:1.9.4;com.fasterxml.jackson.core:jackson-databind:2.9.8","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.fasterxml.jackson.core:jackson-databind:2.10.3"}],"vulnerabilityIdentifier":"CVE-2020-9546","vulnerabilityDetails":"FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to org.apache.hadoop.shaded.com.zaxxer.hikari.HikariConfig (aka shaded hikari-config).","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-9546","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> -->
|
non_process
|
cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to vulnerable library canner gradle caches modules files com fasterxml jackson core jackson databind jackson databind jar canner gradle caches modules files com fasterxml jackson core jackson databind jackson databind jar home wss scanner gradle caches modules files com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy ribbon eureka jar root library eureka client jar x jackson databind jar vulnerable library found in head commit a href vulnerability details fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to org apache hadoop shaded com zaxxer hikari hikariconfig aka shaded hikari config publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com fasterxml jackson core jackson databind isopenpronvulnerability false ispackagebased true isdefaultbranch true packages vulnerabilityidentifier cve vulnerabilitydetails fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to org apache hadoop shaded com zaxxer hikari hikariconfig aka shaded hikari config vulnerabilityurl
| 0
|
15,795
| 20,622,786,792
|
IssuesEvent
|
2022-03-07 19:08:26
|
Creators-of-Create/Create
|
https://api.github.com/repos/Creators-of-Create/Create
|
closed
|
Features that could move a tile entity are incompatible with Tinkers Construct
|
bug compatibility 1.16 stale
|
Using a cart assembler or mechanical piston, parts of the TC's smeltery could be moved without breaking the integrity check by tconstruct.
Some "exploits"
Building a smeltery with fewer blocks

Wireless fluid transfer

Wireless item transfer

These tile entities should not be movable or we should notify the smeltery controller before "entitilize" it.
|
True
|
Features that could move a tile entity are incompatible with Tinkers Construct - Using a cart assembler or mechanical piston, parts of the TC's smeltery could be moved without breaking the integrity check by tconstruct.
Some "exploits"
Building a smeltery with fewer blocks

Wireless fluid transfer

Wireless item transfer

These tile entities should not be movable or we should notify the smeltery controller before "entitilize" it.
|
non_process
|
features that could move a tile entity are incompatible with tinkers construct using a cart assembler or mechanical piston parts of the tc s smeltery could be moved without breaking the integrity check by tconstruct some exploits building a smeltery with fewer blocks wireless fluid transfer wireless item transfer these tile entities should not be movable or we should notify the smeltery controller before entitilize it
| 0
|
9,093
| 12,158,709,442
|
IssuesEvent
|
2020-04-26 05:36:05
|
dotnet/runtime
|
https://api.github.com/repos/dotnet/runtime
|
closed
|
Process.HasExited does not return on Linux when run via reflection
|
area-System.Diagnostics.Process needs more info untriaged
|
# Issue Title
Process.HasExited does not return when executing via reflection
# General
Running .NET Core 3.0 Preview 6. I have reproduced this issue on Windows / OS X / Linux.
When I execute the following method, the process executes and waits until complete, as expected:
```
public ResponseContract StartProcess(string processName)
{
var p = Process.Start(processName);
p.WaitForExit();
}
```
However, when the same code is invoked via reflection, the process starts, as expected, but p.WaitForExit() never returns when the process ends, and hangs indefinitely. If I try to query HasExited or ExitCode, dotnet also hangs.
```
// Instantiate the class with the RequestContract, and any other requested constructor arguments
var classInstance = Activator.CreateInstance(mi.DeclaringType, constructorArguments.ToArray());
// Invoke the action and return the response contract
return (ResponseContract)mi.Invoke(classInstance, properties);
```
The same code works just fine in .NET 4.6.1
|
1.0
|
Process.HasExited does not return on Linux when run via reflection - # Issue Title
Process.HasExited does not return when executing via reflection
# General
Running .NET Core 3.0 Preview 6. I have reproduced this issue on Windows / OS X / Linux.
When I execute the following method, the process executes and waits until complete, as expected:
```
public ResponseContract StartProcess(string processName)
{
var p = Process.Start(processName);
p.WaitForExit();
}
```
However, when the same code is invoked via reflection, the process starts, as expected, but p.WaitForExit() never returns when the process ends, and hangs indefinitely. If I try to query HasExited or ExitCode, dotnet also hangs.
```
// Instantiate the class with the RequestContract, and any other requested constructor arguments
var classInstance = Activator.CreateInstance(mi.DeclaringType, constructorArguments.ToArray());
// Invoke the action and return the response contract
return (ResponseContract)mi.Invoke(classInstance, properties);
```
The same code works just fine in .NET 4.6.1
|
process
|
process hasexited does not return on linux when run via reflection issue title process hasexited does not return when executing via reflection general running net core preview i have reproduced this issue on windows os x linux when i execute the following method the process executes and waits until complete as expected public responsecontract startprocess string processname var p process start processname p waitforexit however when the same code is invoked via reflection the process starts as expected but p waitforexit never returns when the process ends and hangs indefinitely if i try to query hasexited or exitcode dotnet also hangs instantiate the class with the requestcontract and any other requested constructor arguments var classinstance activator createinstance mi declaringtype constructorarguments toarray invoke the action and return the response contract return responsecontract mi invoke classinstance properties the same code works just fine in net
| 1
|
4,388
| 6,570,857,049
|
IssuesEvent
|
2017-09-10 05:55:24
|
Azure/azure-sdk-for-net
|
https://api.github.com/repos/Azure/azure-sdk-for-net
|
closed
|
ServiceBus no way to manage Rules on Subscriptions?
|
ServiceBus
|
`SubscriptionCreateOrUpdateParameters` doesn't have Rules part.
From browsing the code could find anything that would hint at how to do it.
|
1.0
|
ServiceBus no way to manage Rules on Subscriptions? - `SubscriptionCreateOrUpdateParameters` doesn't have Rules part.
From browsing the code could find anything that would hint at how to do it.
|
non_process
|
servicebus no way to manage rules on subscriptions subscriptioncreateorupdateparameters doesn t have rules part from browsing the code could find anything that would hint at how to do it
| 0
|
166,699
| 6,310,256,250
|
IssuesEvent
|
2017-07-23 08:28:55
|
Rsl1122/Plan-PlayerAnalytics
|
https://api.github.com/repos/Rsl1122/Plan-PlayerAnalytics
|
closed
|
Demographic triggers not removed from config
|
Enhancement Priority: LOW
|
Plan 3.5.2
@Rsl1122 Forgot to remove the DemographicsTriggers in the config with the age & gender gathering removal?
```
DemographicsTriggers:
Trigger: i'm, am, im, bin
Female: female, girl, gurl, woman, gal, mrs, she, miss, feminin, weiblich, mädchen,
frau
Male: male, boy, man, boe, sir, mr, guy, he, männlich, maskulin, junge, mann
IgnoreWhen: sure, think, with, are, you, din
```
|
1.0
|
Demographic triggers not removed from config - Plan 3.5.2
@Rsl1122 Forgot to remove the DemographicsTriggers in the config with the age & gender gathering removal?
```
DemographicsTriggers:
Trigger: i'm, am, im, bin
Female: female, girl, gurl, woman, gal, mrs, she, miss, feminin, weiblich, mädchen,
frau
Male: male, boy, man, boe, sir, mr, guy, he, männlich, maskulin, junge, mann
IgnoreWhen: sure, think, with, are, you, din
```
|
non_process
|
demographic triggers not removed from config plan forgot to remove the demographicstriggers in the config with the age gender gathering removal demographicstriggers trigger i m am im bin female female girl gurl woman gal mrs she miss feminin weiblich mädchen frau male male boy man boe sir mr guy he männlich maskulin junge mann ignorewhen sure think with are you din
| 0
|
259,620
| 19,607,001,123
|
IssuesEvent
|
2022-01-06 10:44:56
|
abpframework/abp
|
https://api.github.com/repos/abpframework/abp
|
opened
|
Documentation about Auto-complete Select
|
documentation
|
Documentation about the usage of:
https://github.com/abpframework/abp/blob/b1170998f78a676c8685cde587282ac558f3e181/framework/src/Volo.Abp.AspNetCore.Mvc.UI.Theme.Shared/wwwroot/libs/abp/aspnetcore-mvc-ui-theme-shared/bootstrap/dom-event-handlers.js#L183
And should cover those parameters:
https://github.com/abpframework/abp/blob/b1170998f78a676c8685cde587282ac558f3e181/framework/src/Volo.Abp.AspNetCore.Mvc.UI.Theme.Shared/wwwroot/libs/abp/aspnetcore-mvc-ui-theme-shared/bootstrap/dom-event-handlers.js#L74-L131
|
1.0
|
Documentation about Auto-complete Select - Documentation about the usage of:
https://github.com/abpframework/abp/blob/b1170998f78a676c8685cde587282ac558f3e181/framework/src/Volo.Abp.AspNetCore.Mvc.UI.Theme.Shared/wwwroot/libs/abp/aspnetcore-mvc-ui-theme-shared/bootstrap/dom-event-handlers.js#L183
And should cover those parameters:
https://github.com/abpframework/abp/blob/b1170998f78a676c8685cde587282ac558f3e181/framework/src/Volo.Abp.AspNetCore.Mvc.UI.Theme.Shared/wwwroot/libs/abp/aspnetcore-mvc-ui-theme-shared/bootstrap/dom-event-handlers.js#L74-L131
|
non_process
|
documentation about auto complete select documentation about the usage of and should cover those parameters
| 0
|
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.