Unnamed: 0
int64 0
832k
| id
float64 2.49B
32.1B
| type
stringclasses 1
value | created_at
stringlengths 19
19
| repo
stringlengths 7
112
| repo_url
stringlengths 36
141
| action
stringclasses 3
values | title
stringlengths 1
744
| labels
stringlengths 4
574
| body
stringlengths 9
211k
| index
stringclasses 10
values | text_combine
stringlengths 96
211k
| label
stringclasses 2
values | text
stringlengths 96
188k
| binary_label
int64 0
1
|
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
27,099
| 4,274,451,585
|
IssuesEvent
|
2016-07-13 20:33:45
|
dotnet/corefx
|
https://api.github.com/repos/dotnet/corefx
|
opened
|
Add Negotiate and MultipleSchemes code to the System.net test Prerequisites
|
System.Net test bug
|
Add the missing `showidentity.ashx` file required by [DefaultCredentialsTest.cs](https://github.com/dotnet/corefx/blob/32b96925efce0dde416103862d0f37877918ec94/src/System.Net.Http/tests/FunctionalTests/DefaultCredentialsTest.cs#L25)
```C#
// This test endpoint offers multiple schemes, Basic and NTLM, in that specific order. This endpoint
// helps test that the client will use the stronger of the server proposed auth schemes and
// not the first auth scheme.
private static Uri MultipleSchemesAuthenticatedServer =
new Uri($"http://{DomainJoinedTestServer}/test/auth/multipleschemes/showidentity.ashx");
```
|
1.0
|
Add Negotiate and MultipleSchemes code to the System.net test Prerequisites - Add the missing `showidentity.ashx` file required by [DefaultCredentialsTest.cs](https://github.com/dotnet/corefx/blob/32b96925efce0dde416103862d0f37877918ec94/src/System.Net.Http/tests/FunctionalTests/DefaultCredentialsTest.cs#L25)
```C#
// This test endpoint offers multiple schemes, Basic and NTLM, in that specific order. This endpoint
// helps test that the client will use the stronger of the server proposed auth schemes and
// not the first auth scheme.
private static Uri MultipleSchemesAuthenticatedServer =
new Uri($"http://{DomainJoinedTestServer}/test/auth/multipleschemes/showidentity.ashx");
```
|
non_process
|
add negotiate and multipleschemes code to the system net test prerequisites add the missing showidentity ashx file required by c this test endpoint offers multiple schemes basic and ntlm in that specific order this endpoint helps test that the client will use the stronger of the server proposed auth schemes and not the first auth scheme private static uri multipleschemesauthenticatedserver new uri
| 0
|
759,362
| 26,591,525,305
|
IssuesEvent
|
2023-01-23 09:06:52
|
codelab-app/builder
|
https://api.github.com/repos/codelab-app/builder
|
closed
|
Proposal for component slots
|
priority: high
|
## The Problem
The current component system works for only basic templating. For example, you can't create a useful layout component right now.
## The solution
We need what's the equivalent of slots in templating tools. In Vue they are called slots, in Rails this is done through partials, in Laravel you have component slots. And in React this functionality is filled mostly by render props or by passing components as props/in context.
## Implementation
I can imagine 2 ways to do this
### 1. The explicit way
Users explicitly define an API for their components, similar to how we have an api for Atoms props. For example:
<img width="962" alt="image" src="https://user-images.githubusercontent.com/57956282/187932904-ee36b004-bbb9-4671-9119-4faf59705218.png">
For slots we can use existing types, like RenderPropsType, ReactNodeType, ElementType.
This api serves as the place of truth for defining the inputs that a component takes.
The benefit of this is that that's not only applicable for slots, but we can also assign other props to the component, like strings, numbers, etc.
We use this interface to generate a form for the component, just like we do for atoms.
The next part is to be able to assign this slot to a particular element
One way to do that is to bind it to props. Say that we have a Div atom with this API
<img width="959" alt="image" src="https://user-images.githubusercontent.com/57956282/187933534-e081da3a-0039-45b5-99b1-8e831d7adfdf.png">
Now we only need to connect `heroContent` from the Layout's API to the `children` of the Divs API. The easiest way I imagine is to bind it as we bind global state variables.
<img width="1908" alt="image" src="https://user-images.githubusercontent.com/57956282/187933790-70b0db34-6773-4a60-9dda-604fc74fb4db.png">
This would require modifying the prop evaluating code to take into account the current component that the element is in and its props.
### The implicit way
We create a new Atom Type, for example named `Slot`.
The user creates a new element as usual and assigns it an Atom with type Slot:
<img width="1919" alt="image" src="https://user-images.githubusercontent.com/57956282/187934585-3e701b16-624b-48ab-aef7-989c6c449acc.png">
Then on the component instance, we render a form that has all of the elements inside it with atom type Slot and we allow the user to pick a Component to render for them.
<img width="959" alt="image" src="https://user-images.githubusercontent.com/57956282/187935140-50fc67cc-ab9d-425f-8c5b-dd23bd7f4494.png">
The data from this form is stored on the component instance either as a separate field or as a special prop. It has the shape of a key-value object where the key is the id of the Slot-atomed element and the value is the component id to render. This is then used when evaluating the props to render the specific component instead of the slot-atomed element.
This approach seems simpler, but it's less flexible since the user can't define other component props other than slots.
#### Note
In both implementations, we can additionally add the ability to directly drag and drop an element to the slot to avoid creating a component for it.
Any thoughts or other ideas?
|
1.0
|
Proposal for component slots - ## The Problem
The current component system works for only basic templating. For example, you can't create a useful layout component right now.
## The solution
We need what's the equivalent of slots in templating tools. In Vue they are called slots, in Rails this is done through partials, in Laravel you have component slots. And in React this functionality is filled mostly by render props or by passing components as props/in context.
## Implementation
I can imagine 2 ways to do this
### 1. The explicit way
Users explicitly define an API for their components, similar to how we have an api for Atoms props. For example:
<img width="962" alt="image" src="https://user-images.githubusercontent.com/57956282/187932904-ee36b004-bbb9-4671-9119-4faf59705218.png">
For slots we can use existing types, like RenderPropsType, ReactNodeType, ElementType.
This api serves as the place of truth for defining the inputs that a component takes.
The benefit of this is that that's not only applicable for slots, but we can also assign other props to the component, like strings, numbers, etc.
We use this interface to generate a form for the component, just like we do for atoms.
The next part is to be able to assign this slot to a particular element
One way to do that is to bind it to props. Say that we have a Div atom with this API
<img width="959" alt="image" src="https://user-images.githubusercontent.com/57956282/187933534-e081da3a-0039-45b5-99b1-8e831d7adfdf.png">
Now we only need to connect `heroContent` from the Layout's API to the `children` of the Divs API. The easiest way I imagine is to bind it as we bind global state variables.
<img width="1908" alt="image" src="https://user-images.githubusercontent.com/57956282/187933790-70b0db34-6773-4a60-9dda-604fc74fb4db.png">
This would require modifying the prop evaluating code to take into account the current component that the element is in and its props.
### The implicit way
We create a new Atom Type, for example named `Slot`.
The user creates a new element as usual and assigns it an Atom with type Slot:
<img width="1919" alt="image" src="https://user-images.githubusercontent.com/57956282/187934585-3e701b16-624b-48ab-aef7-989c6c449acc.png">
Then on the component instance, we render a form that has all of the elements inside it with atom type Slot and we allow the user to pick a Component to render for them.
<img width="959" alt="image" src="https://user-images.githubusercontent.com/57956282/187935140-50fc67cc-ab9d-425f-8c5b-dd23bd7f4494.png">
The data from this form is stored on the component instance either as a separate field or as a special prop. It has the shape of a key-value object where the key is the id of the Slot-atomed element and the value is the component id to render. This is then used when evaluating the props to render the specific component instead of the slot-atomed element.
This approach seems simpler, but it's less flexible since the user can't define other component props other than slots.
#### Note
In both implementations, we can additionally add the ability to directly drag and drop an element to the slot to avoid creating a component for it.
Any thoughts or other ideas?
|
non_process
|
proposal for component slots the problem the current component system works for only basic templating for example you can t create a useful layout component right now the solution we need what s the equivalent of slots in templating tools in vue they are called slots in rails this is done through partials in laravel you have component slots and in react this functionality is filled mostly by render props or by passing components as props in context implementation i can imagine ways to do this the explicit way users explicitly define an api for their components similar to how we have an api for atoms props for example img width alt image src for slots we can use existing types like renderpropstype reactnodetype elementtype this api serves as the place of truth for defining the inputs that a component takes the benefit of this is that that s not only applicable for slots but we can also assign other props to the component like strings numbers etc we use this interface to generate a form for the component just like we do for atoms the next part is to be able to assign this slot to a particular element one way to do that is to bind it to props say that we have a div atom with this api img width alt image src now we only need to connect herocontent from the layout s api to the children of the divs api the easiest way i imagine is to bind it as we bind global state variables img width alt image src this would require modifying the prop evaluating code to take into account the current component that the element is in and its props the implicit way we create a new atom type for example named slot the user creates a new element as usual and assigns it an atom with type slot img width alt image src then on the component instance we render a form that has all of the elements inside it with atom type slot and we allow the user to pick a component to render for them img width alt image src the data from this form is stored on the component instance either as a separate field or as a special prop it has the shape of a key value object where the key is the id of the slot atomed element and the value is the component id to render this is then used when evaluating the props to render the specific component instead of the slot atomed element this approach seems simpler but it s less flexible since the user can t define other component props other than slots note in both implementations we can additionally add the ability to directly drag and drop an element to the slot to avoid creating a component for it any thoughts or other ideas
| 0
|
21,962
| 30,457,492,074
|
IssuesEvent
|
2023-07-17 02:00:08
|
lizhihao6/get-daily-arxiv-noti
|
https://api.github.com/repos/lizhihao6/get-daily-arxiv-noti
|
opened
|
New submissions for Mon, 17 Jul 23
|
event camera white balance isp compression image signal processing image signal process raw raw image events camera color contrast events AWB
|
## Keyword: events
### Improved Flood Insights: Diffusion-Based SAR to EO Image Translation
- **Authors:** Minseok Seo, Youngtack Oh, Doyi Kim, Dongmin Kang, Yeji Choi
- **Subjects:** Computer Vision and Pattern Recognition (cs.CV); Image and Video Processing (eess.IV)
- **Arxiv link:** https://arxiv.org/abs/2307.07123
- **Pdf link:** https://arxiv.org/pdf/2307.07123
- **Abstract**
Driven by rapid climate change, the frequency and intensity of flood events are increasing. Electro-Optical (EO) satellite imagery is commonly utilized for rapid response. However, its utilities in flood situations are hampered by issues such as cloud cover and limitations during nighttime, making accurate assessment of damage challenging. Several alternative flood detection techniques utilizing Synthetic Aperture Radar (SAR) data have been proposed. Despite the advantages of SAR over EO in the aforementioned situations, SAR presents a distinct drawback: human analysts often struggle with data interpretation. To tackle this issue, this paper introduces a novel framework, Diffusion-Based SAR to EO Image Translation (DSE). The DSE framework converts SAR images into EO images, thereby enhancing the interpretability of flood insights for humans. Experimental results on the Sen1Floods11 and SEN12-FLOOD datasets confirm that the DSE framework not only delivers enhanced visual information but also improves performance across all tested flood segmentation baselines.
### 3D Shape-Based Myocardial Infarction Prediction Using Point Cloud Classification Networks
- **Authors:** Marcel Beetz, Yilong Yang, Abhirup Banerjee, Lei Li, Vicente Grau
- **Subjects:** Computer Vision and Pattern Recognition (cs.CV); Machine Learning (cs.LG); Image and Video Processing (eess.IV)
- **Arxiv link:** https://arxiv.org/abs/2307.07298
- **Pdf link:** https://arxiv.org/pdf/2307.07298
- **Abstract**
Myocardial infarction (MI) is one of the most prevalent cardiovascular diseases with associated clinical decision-making typically based on single-valued imaging biomarkers. However, such metrics only approximate the complex 3D structure and physiology of the heart and hence hinder a better understanding and prediction of MI outcomes. In this work, we investigate the utility of complete 3D cardiac shapes in the form of point clouds for an improved detection of MI events. To this end, we propose a fully automatic multi-step pipeline consisting of a 3D cardiac surface reconstruction step followed by a point cloud classification network. Our method utilizes recent advances in geometric deep learning on point clouds to enable direct and efficient multi-scale learning on high-resolution surface models of the cardiac anatomy. We evaluate our approach on 1068 UK Biobank subjects for the tasks of prevalent MI detection and incident MI prediction and find improvements of ~13% and ~5% respectively over clinical benchmarks. Furthermore, we analyze the role of each ventricle and cardiac phase for 3D shape-based MI detection and conduct a visual analysis of the morphological and physiological patterns typically associated with MI outcomes.
## Keyword: event camera
There is no result
## Keyword: events camera
There is no result
## Keyword: white balance
There is no result
## Keyword: color contrast
There is no result
## Keyword: AWB
### Improved Flood Insights: Diffusion-Based SAR to EO Image Translation
- **Authors:** Minseok Seo, Youngtack Oh, Doyi Kim, Dongmin Kang, Yeji Choi
- **Subjects:** Computer Vision and Pattern Recognition (cs.CV); Image and Video Processing (eess.IV)
- **Arxiv link:** https://arxiv.org/abs/2307.07123
- **Pdf link:** https://arxiv.org/pdf/2307.07123
- **Abstract**
Driven by rapid climate change, the frequency and intensity of flood events are increasing. Electro-Optical (EO) satellite imagery is commonly utilized for rapid response. However, its utilities in flood situations are hampered by issues such as cloud cover and limitations during nighttime, making accurate assessment of damage challenging. Several alternative flood detection techniques utilizing Synthetic Aperture Radar (SAR) data have been proposed. Despite the advantages of SAR over EO in the aforementioned situations, SAR presents a distinct drawback: human analysts often struggle with data interpretation. To tackle this issue, this paper introduces a novel framework, Diffusion-Based SAR to EO Image Translation (DSE). The DSE framework converts SAR images into EO images, thereby enhancing the interpretability of flood insights for humans. Experimental results on the Sen1Floods11 and SEN12-FLOOD datasets confirm that the DSE framework not only delivers enhanced visual information but also improves performance across all tested flood segmentation baselines.
## Keyword: ISP
### DISPEL: Domain Generalization via Domain-Specific Liberating
- **Authors:** Chia-Yuan Chang, Yu-Neng Chuang, Guanchu Wang, Mengnan Du, Zou Na
- **Subjects:** Computer Vision and Pattern Recognition (cs.CV); Machine Learning (cs.LG)
- **Arxiv link:** https://arxiv.org/abs/2307.07181
- **Pdf link:** https://arxiv.org/pdf/2307.07181
- **Abstract**
Domain generalization aims to learn a generalization model that can perform well on unseen test domains by only training on limited source domains. However, existing domain generalization approaches often bring in prediction-irrelevant noise or require the collection of domain labels. To address these challenges, we consider the domain generalization problem from a different perspective by categorizing underlying feature groups into domain-shared and domain-specific features. Nevertheless, the domain-specific features are difficult to be identified and distinguished from the input data. In this work, we propose DomaIn-SPEcific Liberating (DISPEL), a post-processing fine-grained masking approach that can filter out undefined and indistinguishable domain-specific features in the embedding space. Specifically, DISPEL utilizes a mask generator that produces a unique mask for each input data to filter domain-specific features. The DISPEL framework is highly flexible to be applied to any fine-tuned models. We derive a generalization error bound to guarantee the generalization performance by optimizing a designed objective loss. The experimental results on five benchmarks demonstrate DISPEL outperforms existing methods and can further generalize various algorithms.
### Cloud Detection in Multispectral Satellite Images Using Support Vector Machines With Quantum Kernels
- **Authors:** Artur Miroszewski, Jakub Mielczarek, Filip Szczepanek, Grzegorz Czelusta, Bartosz Grabowski, Bertrand Le Saux, Jakub Nalepa
- **Subjects:** Computer Vision and Pattern Recognition (cs.CV); Quantum Physics (quant-ph)
- **Arxiv link:** https://arxiv.org/abs/2307.07281
- **Pdf link:** https://arxiv.org/pdf/2307.07281
- **Abstract**
Support vector machines (SVMs) are a well-established classifier effectively deployed in an array of pattern recognition and classification tasks. In this work, we consider extending classic SVMs with quantum kernels and applying them to satellite data analysis. The design and implementation of SVMs with quantum kernels (hybrid SVMs) is presented. It consists of the Quantum Kernel Estimation (QKE) procedure combined with a classic SVM training routine. The pixel data are mapped to the Hilbert space using ZZ-feature maps acting on the parameterized ansatz state. The parameters are optimized to maximize the kernel target alignment. We approach the problem of cloud detection in satellite image data, which is one of the pivotal steps in both on-the-ground and on-board satellite image analysis processing chains. The experiments performed over the benchmark Landsat-8 multispectral dataset revealed that the simulated hybrid SVM successfully classifies satellite images with accuracy on par with classic SVMs.
### Implicit Neural Feature Fusion Function for Multispectral and Hyperspectral Image Fusion
- **Authors:** ShangQi Deng, RuoCheng Wu, Liang-Jian Deng, Ran Ran, Tai-Xiang Jiang
- **Subjects:** Computer Vision and Pattern Recognition (cs.CV)
- **Arxiv link:** https://arxiv.org/abs/2307.07288
- **Pdf link:** https://arxiv.org/pdf/2307.07288
- **Abstract**
Multispectral and Hyperspectral Image Fusion (MHIF) is a practical task that aims to fuse a high-resolution multispectral image (HR-MSI) and a low-resolution hyperspectral image (LR-HSI) of the same scene to obtain a high-resolution hyperspectral image (HR-HSI). Benefiting from powerful inductive bias capability, CNN-based methods have achieved great success in the MHIF task. However, they lack certain interpretability and require convolution structures be stacked to enhance performance. Recently, Implicit Neural Representation (INR) has achieved good performance and interpretability in 2D tasks due to its ability to locally interpolate samples and utilize multimodal content such as pixels and coordinates. Although INR-based approaches show promise, they require extra construction of high-frequency information (\emph{e.g.,} positional encoding). In this paper, inspired by previous work of MHIF task, we realize that HR-MSI could serve as a high-frequency detail auxiliary input, leading us to propose a novel INR-based hyperspectral fusion function named Implicit Neural Feature Fusion Function (INF). As an elaborate structure, it solves the MHIF task and addresses deficiencies in the INR-based approaches. Specifically, our INF designs a Dual High-Frequency Fusion (DHFF) structure that obtains high-frequency information twice from HR-MSI and LR-HSI, then subtly fuses them with coordinate information. Moreover, the proposed INF incorporates a parameter-free method named INR with cosine similarity (INR-CS) that uses cosine similarity to generate local weights through feature vectors. Based on INF, we construct an Implicit Neural Fusion Network (INFN) that achieves state-of-the-art performance for MHIF tasks of two public datasets, \emph{i.e.,} CAVE and Harvard. The code will soon be made available on GitHub.
## Keyword: image signal processing
There is no result
## Keyword: image signal process
There is no result
## Keyword: compression
There is no result
## Keyword: RAW
### Improved Flood Insights: Diffusion-Based SAR to EO Image Translation
- **Authors:** Minseok Seo, Youngtack Oh, Doyi Kim, Dongmin Kang, Yeji Choi
- **Subjects:** Computer Vision and Pattern Recognition (cs.CV); Image and Video Processing (eess.IV)
- **Arxiv link:** https://arxiv.org/abs/2307.07123
- **Pdf link:** https://arxiv.org/pdf/2307.07123
- **Abstract**
Driven by rapid climate change, the frequency and intensity of flood events are increasing. Electro-Optical (EO) satellite imagery is commonly utilized for rapid response. However, its utilities in flood situations are hampered by issues such as cloud cover and limitations during nighttime, making accurate assessment of damage challenging. Several alternative flood detection techniques utilizing Synthetic Aperture Radar (SAR) data have been proposed. Despite the advantages of SAR over EO in the aforementioned situations, SAR presents a distinct drawback: human analysts often struggle with data interpretation. To tackle this issue, this paper introduces a novel framework, Diffusion-Based SAR to EO Image Translation (DSE). The DSE framework converts SAR images into EO images, thereby enhancing the interpretability of flood insights for humans. Experimental results on the Sen1Floods11 and SEN12-FLOOD datasets confirm that the DSE framework not only delivers enhanced visual information but also improves performance across all tested flood segmentation baselines.
## Keyword: raw image
There is no result
|
2.0
|
New submissions for Mon, 17 Jul 23 - ## Keyword: events
### Improved Flood Insights: Diffusion-Based SAR to EO Image Translation
- **Authors:** Minseok Seo, Youngtack Oh, Doyi Kim, Dongmin Kang, Yeji Choi
- **Subjects:** Computer Vision and Pattern Recognition (cs.CV); Image and Video Processing (eess.IV)
- **Arxiv link:** https://arxiv.org/abs/2307.07123
- **Pdf link:** https://arxiv.org/pdf/2307.07123
- **Abstract**
Driven by rapid climate change, the frequency and intensity of flood events are increasing. Electro-Optical (EO) satellite imagery is commonly utilized for rapid response. However, its utilities in flood situations are hampered by issues such as cloud cover and limitations during nighttime, making accurate assessment of damage challenging. Several alternative flood detection techniques utilizing Synthetic Aperture Radar (SAR) data have been proposed. Despite the advantages of SAR over EO in the aforementioned situations, SAR presents a distinct drawback: human analysts often struggle with data interpretation. To tackle this issue, this paper introduces a novel framework, Diffusion-Based SAR to EO Image Translation (DSE). The DSE framework converts SAR images into EO images, thereby enhancing the interpretability of flood insights for humans. Experimental results on the Sen1Floods11 and SEN12-FLOOD datasets confirm that the DSE framework not only delivers enhanced visual information but also improves performance across all tested flood segmentation baselines.
### 3D Shape-Based Myocardial Infarction Prediction Using Point Cloud Classification Networks
- **Authors:** Marcel Beetz, Yilong Yang, Abhirup Banerjee, Lei Li, Vicente Grau
- **Subjects:** Computer Vision and Pattern Recognition (cs.CV); Machine Learning (cs.LG); Image and Video Processing (eess.IV)
- **Arxiv link:** https://arxiv.org/abs/2307.07298
- **Pdf link:** https://arxiv.org/pdf/2307.07298
- **Abstract**
Myocardial infarction (MI) is one of the most prevalent cardiovascular diseases with associated clinical decision-making typically based on single-valued imaging biomarkers. However, such metrics only approximate the complex 3D structure and physiology of the heart and hence hinder a better understanding and prediction of MI outcomes. In this work, we investigate the utility of complete 3D cardiac shapes in the form of point clouds for an improved detection of MI events. To this end, we propose a fully automatic multi-step pipeline consisting of a 3D cardiac surface reconstruction step followed by a point cloud classification network. Our method utilizes recent advances in geometric deep learning on point clouds to enable direct and efficient multi-scale learning on high-resolution surface models of the cardiac anatomy. We evaluate our approach on 1068 UK Biobank subjects for the tasks of prevalent MI detection and incident MI prediction and find improvements of ~13% and ~5% respectively over clinical benchmarks. Furthermore, we analyze the role of each ventricle and cardiac phase for 3D shape-based MI detection and conduct a visual analysis of the morphological and physiological patterns typically associated with MI outcomes.
## Keyword: event camera
There is no result
## Keyword: events camera
There is no result
## Keyword: white balance
There is no result
## Keyword: color contrast
There is no result
## Keyword: AWB
### Improved Flood Insights: Diffusion-Based SAR to EO Image Translation
- **Authors:** Minseok Seo, Youngtack Oh, Doyi Kim, Dongmin Kang, Yeji Choi
- **Subjects:** Computer Vision and Pattern Recognition (cs.CV); Image and Video Processing (eess.IV)
- **Arxiv link:** https://arxiv.org/abs/2307.07123
- **Pdf link:** https://arxiv.org/pdf/2307.07123
- **Abstract**
Driven by rapid climate change, the frequency and intensity of flood events are increasing. Electro-Optical (EO) satellite imagery is commonly utilized for rapid response. However, its utilities in flood situations are hampered by issues such as cloud cover and limitations during nighttime, making accurate assessment of damage challenging. Several alternative flood detection techniques utilizing Synthetic Aperture Radar (SAR) data have been proposed. Despite the advantages of SAR over EO in the aforementioned situations, SAR presents a distinct drawback: human analysts often struggle with data interpretation. To tackle this issue, this paper introduces a novel framework, Diffusion-Based SAR to EO Image Translation (DSE). The DSE framework converts SAR images into EO images, thereby enhancing the interpretability of flood insights for humans. Experimental results on the Sen1Floods11 and SEN12-FLOOD datasets confirm that the DSE framework not only delivers enhanced visual information but also improves performance across all tested flood segmentation baselines.
## Keyword: ISP
### DISPEL: Domain Generalization via Domain-Specific Liberating
- **Authors:** Chia-Yuan Chang, Yu-Neng Chuang, Guanchu Wang, Mengnan Du, Zou Na
- **Subjects:** Computer Vision and Pattern Recognition (cs.CV); Machine Learning (cs.LG)
- **Arxiv link:** https://arxiv.org/abs/2307.07181
- **Pdf link:** https://arxiv.org/pdf/2307.07181
- **Abstract**
Domain generalization aims to learn a generalization model that can perform well on unseen test domains by only training on limited source domains. However, existing domain generalization approaches often bring in prediction-irrelevant noise or require the collection of domain labels. To address these challenges, we consider the domain generalization problem from a different perspective by categorizing underlying feature groups into domain-shared and domain-specific features. Nevertheless, the domain-specific features are difficult to be identified and distinguished from the input data. In this work, we propose DomaIn-SPEcific Liberating (DISPEL), a post-processing fine-grained masking approach that can filter out undefined and indistinguishable domain-specific features in the embedding space. Specifically, DISPEL utilizes a mask generator that produces a unique mask for each input data to filter domain-specific features. The DISPEL framework is highly flexible to be applied to any fine-tuned models. We derive a generalization error bound to guarantee the generalization performance by optimizing a designed objective loss. The experimental results on five benchmarks demonstrate DISPEL outperforms existing methods and can further generalize various algorithms.
### Cloud Detection in Multispectral Satellite Images Using Support Vector Machines With Quantum Kernels
- **Authors:** Artur Miroszewski, Jakub Mielczarek, Filip Szczepanek, Grzegorz Czelusta, Bartosz Grabowski, Bertrand Le Saux, Jakub Nalepa
- **Subjects:** Computer Vision and Pattern Recognition (cs.CV); Quantum Physics (quant-ph)
- **Arxiv link:** https://arxiv.org/abs/2307.07281
- **Pdf link:** https://arxiv.org/pdf/2307.07281
- **Abstract**
Support vector machines (SVMs) are a well-established classifier effectively deployed in an array of pattern recognition and classification tasks. In this work, we consider extending classic SVMs with quantum kernels and applying them to satellite data analysis. The design and implementation of SVMs with quantum kernels (hybrid SVMs) is presented. It consists of the Quantum Kernel Estimation (QKE) procedure combined with a classic SVM training routine. The pixel data are mapped to the Hilbert space using ZZ-feature maps acting on the parameterized ansatz state. The parameters are optimized to maximize the kernel target alignment. We approach the problem of cloud detection in satellite image data, which is one of the pivotal steps in both on-the-ground and on-board satellite image analysis processing chains. The experiments performed over the benchmark Landsat-8 multispectral dataset revealed that the simulated hybrid SVM successfully classifies satellite images with accuracy on par with classic SVMs.
### Implicit Neural Feature Fusion Function for Multispectral and Hyperspectral Image Fusion
- **Authors:** ShangQi Deng, RuoCheng Wu, Liang-Jian Deng, Ran Ran, Tai-Xiang Jiang
- **Subjects:** Computer Vision and Pattern Recognition (cs.CV)
- **Arxiv link:** https://arxiv.org/abs/2307.07288
- **Pdf link:** https://arxiv.org/pdf/2307.07288
- **Abstract**
Multispectral and Hyperspectral Image Fusion (MHIF) is a practical task that aims to fuse a high-resolution multispectral image (HR-MSI) and a low-resolution hyperspectral image (LR-HSI) of the same scene to obtain a high-resolution hyperspectral image (HR-HSI). Benefiting from powerful inductive bias capability, CNN-based methods have achieved great success in the MHIF task. However, they lack certain interpretability and require convolution structures be stacked to enhance performance. Recently, Implicit Neural Representation (INR) has achieved good performance and interpretability in 2D tasks due to its ability to locally interpolate samples and utilize multimodal content such as pixels and coordinates. Although INR-based approaches show promise, they require extra construction of high-frequency information (\emph{e.g.,} positional encoding). In this paper, inspired by previous work of MHIF task, we realize that HR-MSI could serve as a high-frequency detail auxiliary input, leading us to propose a novel INR-based hyperspectral fusion function named Implicit Neural Feature Fusion Function (INF). As an elaborate structure, it solves the MHIF task and addresses deficiencies in the INR-based approaches. Specifically, our INF designs a Dual High-Frequency Fusion (DHFF) structure that obtains high-frequency information twice from HR-MSI and LR-HSI, then subtly fuses them with coordinate information. Moreover, the proposed INF incorporates a parameter-free method named INR with cosine similarity (INR-CS) that uses cosine similarity to generate local weights through feature vectors. Based on INF, we construct an Implicit Neural Fusion Network (INFN) that achieves state-of-the-art performance for MHIF tasks of two public datasets, \emph{i.e.,} CAVE and Harvard. The code will soon be made available on GitHub.
## Keyword: image signal processing
There is no result
## Keyword: image signal process
There is no result
## Keyword: compression
There is no result
## Keyword: RAW
### Improved Flood Insights: Diffusion-Based SAR to EO Image Translation
- **Authors:** Minseok Seo, Youngtack Oh, Doyi Kim, Dongmin Kang, Yeji Choi
- **Subjects:** Computer Vision and Pattern Recognition (cs.CV); Image and Video Processing (eess.IV)
- **Arxiv link:** https://arxiv.org/abs/2307.07123
- **Pdf link:** https://arxiv.org/pdf/2307.07123
- **Abstract**
Driven by rapid climate change, the frequency and intensity of flood events are increasing. Electro-Optical (EO) satellite imagery is commonly utilized for rapid response. However, its utilities in flood situations are hampered by issues such as cloud cover and limitations during nighttime, making accurate assessment of damage challenging. Several alternative flood detection techniques utilizing Synthetic Aperture Radar (SAR) data have been proposed. Despite the advantages of SAR over EO in the aforementioned situations, SAR presents a distinct drawback: human analysts often struggle with data interpretation. To tackle this issue, this paper introduces a novel framework, Diffusion-Based SAR to EO Image Translation (DSE). The DSE framework converts SAR images into EO images, thereby enhancing the interpretability of flood insights for humans. Experimental results on the Sen1Floods11 and SEN12-FLOOD datasets confirm that the DSE framework not only delivers enhanced visual information but also improves performance across all tested flood segmentation baselines.
## Keyword: raw image
There is no result
|
process
|
new submissions for mon jul keyword events improved flood insights diffusion based sar to eo image translation authors minseok seo youngtack oh doyi kim dongmin kang yeji choi subjects computer vision and pattern recognition cs cv image and video processing eess iv arxiv link pdf link abstract driven by rapid climate change the frequency and intensity of flood events are increasing electro optical eo satellite imagery is commonly utilized for rapid response however its utilities in flood situations are hampered by issues such as cloud cover and limitations during nighttime making accurate assessment of damage challenging several alternative flood detection techniques utilizing synthetic aperture radar sar data have been proposed despite the advantages of sar over eo in the aforementioned situations sar presents a distinct drawback human analysts often struggle with data interpretation to tackle this issue this paper introduces a novel framework diffusion based sar to eo image translation dse the dse framework converts sar images into eo images thereby enhancing the interpretability of flood insights for humans experimental results on the and flood datasets confirm that the dse framework not only delivers enhanced visual information but also improves performance across all tested flood segmentation baselines shape based myocardial infarction prediction using point cloud classification networks authors marcel beetz yilong yang abhirup banerjee lei li vicente grau subjects computer vision and pattern recognition cs cv machine learning cs lg image and video processing eess iv arxiv link pdf link abstract myocardial infarction mi is one of the most prevalent cardiovascular diseases with associated clinical decision making typically based on single valued imaging biomarkers however such metrics only approximate the complex structure and physiology of the heart and hence hinder a better understanding and prediction of mi outcomes in this work we investigate the utility of complete cardiac shapes in the form of point clouds for an improved detection of mi events to this end we propose a fully automatic multi step pipeline consisting of a cardiac surface reconstruction step followed by a point cloud classification network our method utilizes recent advances in geometric deep learning on point clouds to enable direct and efficient multi scale learning on high resolution surface models of the cardiac anatomy we evaluate our approach on uk biobank subjects for the tasks of prevalent mi detection and incident mi prediction and find improvements of and respectively over clinical benchmarks furthermore we analyze the role of each ventricle and cardiac phase for shape based mi detection and conduct a visual analysis of the morphological and physiological patterns typically associated with mi outcomes keyword event camera there is no result keyword events camera there is no result keyword white balance there is no result keyword color contrast there is no result keyword awb improved flood insights diffusion based sar to eo image translation authors minseok seo youngtack oh doyi kim dongmin kang yeji choi subjects computer vision and pattern recognition cs cv image and video processing eess iv arxiv link pdf link abstract driven by rapid climate change the frequency and intensity of flood events are increasing electro optical eo satellite imagery is commonly utilized for rapid response however its utilities in flood situations are hampered by issues such as cloud cover and limitations during nighttime making accurate assessment of damage challenging several alternative flood detection techniques utilizing synthetic aperture radar sar data have been proposed despite the advantages of sar over eo in the aforementioned situations sar presents a distinct drawback human analysts often struggle with data interpretation to tackle this issue this paper introduces a novel framework diffusion based sar to eo image translation dse the dse framework converts sar images into eo images thereby enhancing the interpretability of flood insights for humans experimental results on the and flood datasets confirm that the dse framework not only delivers enhanced visual information but also improves performance across all tested flood segmentation baselines keyword isp dispel domain generalization via domain specific liberating authors chia yuan chang yu neng chuang guanchu wang mengnan du zou na subjects computer vision and pattern recognition cs cv machine learning cs lg arxiv link pdf link abstract domain generalization aims to learn a generalization model that can perform well on unseen test domains by only training on limited source domains however existing domain generalization approaches often bring in prediction irrelevant noise or require the collection of domain labels to address these challenges we consider the domain generalization problem from a different perspective by categorizing underlying feature groups into domain shared and domain specific features nevertheless the domain specific features are difficult to be identified and distinguished from the input data in this work we propose domain specific liberating dispel a post processing fine grained masking approach that can filter out undefined and indistinguishable domain specific features in the embedding space specifically dispel utilizes a mask generator that produces a unique mask for each input data to filter domain specific features the dispel framework is highly flexible to be applied to any fine tuned models we derive a generalization error bound to guarantee the generalization performance by optimizing a designed objective loss the experimental results on five benchmarks demonstrate dispel outperforms existing methods and can further generalize various algorithms cloud detection in multispectral satellite images using support vector machines with quantum kernels authors artur miroszewski jakub mielczarek filip szczepanek grzegorz czelusta bartosz grabowski bertrand le saux jakub nalepa subjects computer vision and pattern recognition cs cv quantum physics quant ph arxiv link pdf link abstract support vector machines svms are a well established classifier effectively deployed in an array of pattern recognition and classification tasks in this work we consider extending classic svms with quantum kernels and applying them to satellite data analysis the design and implementation of svms with quantum kernels hybrid svms is presented it consists of the quantum kernel estimation qke procedure combined with a classic svm training routine the pixel data are mapped to the hilbert space using zz feature maps acting on the parameterized ansatz state the parameters are optimized to maximize the kernel target alignment we approach the problem of cloud detection in satellite image data which is one of the pivotal steps in both on the ground and on board satellite image analysis processing chains the experiments performed over the benchmark landsat multispectral dataset revealed that the simulated hybrid svm successfully classifies satellite images with accuracy on par with classic svms implicit neural feature fusion function for multispectral and hyperspectral image fusion authors shangqi deng ruocheng wu liang jian deng ran ran tai xiang jiang subjects computer vision and pattern recognition cs cv arxiv link pdf link abstract multispectral and hyperspectral image fusion mhif is a practical task that aims to fuse a high resolution multispectral image hr msi and a low resolution hyperspectral image lr hsi of the same scene to obtain a high resolution hyperspectral image hr hsi benefiting from powerful inductive bias capability cnn based methods have achieved great success in the mhif task however they lack certain interpretability and require convolution structures be stacked to enhance performance recently implicit neural representation inr has achieved good performance and interpretability in tasks due to its ability to locally interpolate samples and utilize multimodal content such as pixels and coordinates although inr based approaches show promise they require extra construction of high frequency information emph e g positional encoding in this paper inspired by previous work of mhif task we realize that hr msi could serve as a high frequency detail auxiliary input leading us to propose a novel inr based hyperspectral fusion function named implicit neural feature fusion function inf as an elaborate structure it solves the mhif task and addresses deficiencies in the inr based approaches specifically our inf designs a dual high frequency fusion dhff structure that obtains high frequency information twice from hr msi and lr hsi then subtly fuses them with coordinate information moreover the proposed inf incorporates a parameter free method named inr with cosine similarity inr cs that uses cosine similarity to generate local weights through feature vectors based on inf we construct an implicit neural fusion network infn that achieves state of the art performance for mhif tasks of two public datasets emph i e cave and harvard the code will soon be made available on github keyword image signal processing there is no result keyword image signal process there is no result keyword compression there is no result keyword raw improved flood insights diffusion based sar to eo image translation authors minseok seo youngtack oh doyi kim dongmin kang yeji choi subjects computer vision and pattern recognition cs cv image and video processing eess iv arxiv link pdf link abstract driven by rapid climate change the frequency and intensity of flood events are increasing electro optical eo satellite imagery is commonly utilized for rapid response however its utilities in flood situations are hampered by issues such as cloud cover and limitations during nighttime making accurate assessment of damage challenging several alternative flood detection techniques utilizing synthetic aperture radar sar data have been proposed despite the advantages of sar over eo in the aforementioned situations sar presents a distinct drawback human analysts often struggle with data interpretation to tackle this issue this paper introduces a novel framework diffusion based sar to eo image translation dse the dse framework converts sar images into eo images thereby enhancing the interpretability of flood insights for humans experimental results on the and flood datasets confirm that the dse framework not only delivers enhanced visual information but also improves performance across all tested flood segmentation baselines keyword raw image there is no result
| 1
|
11,346
| 14,168,524,123
|
IssuesEvent
|
2020-11-12 11:52:29
|
qgis/QGIS
|
https://api.github.com/repos/qgis/QGIS
|
closed
|
Double dissolvence fails
|
Bug Feedback Processing
|
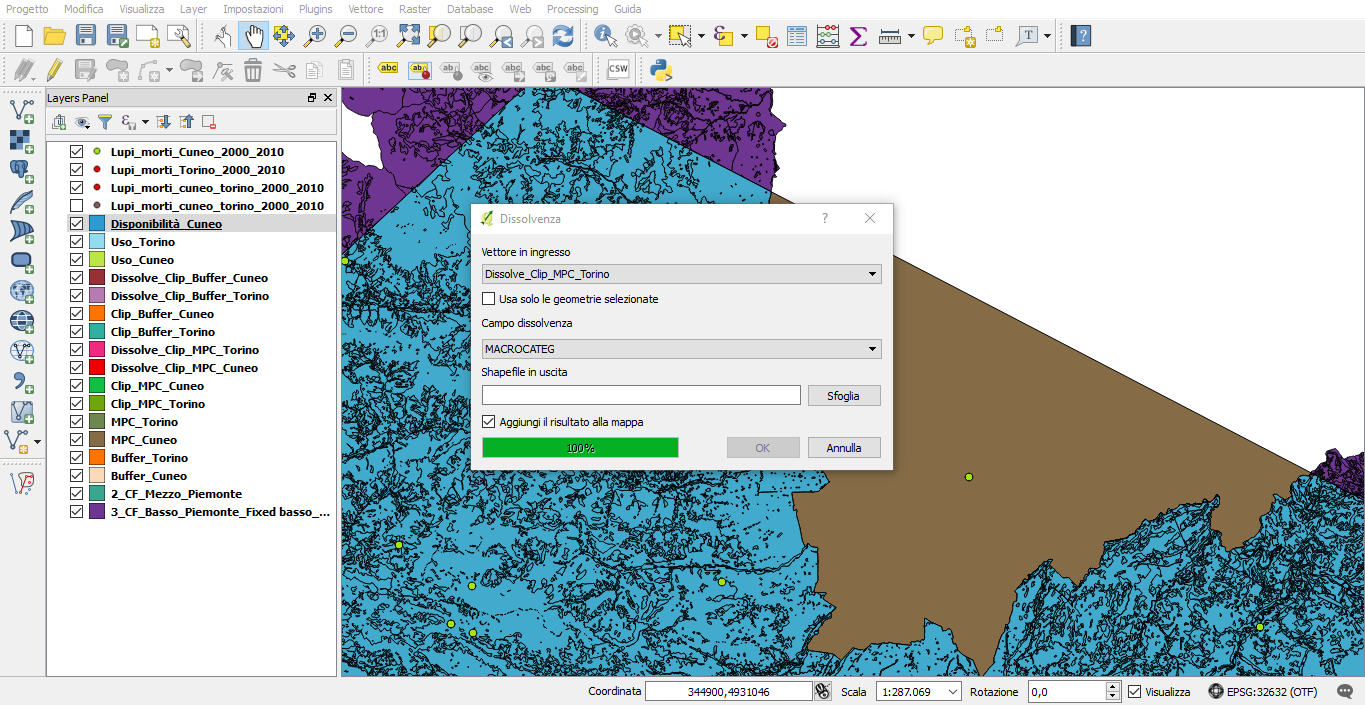
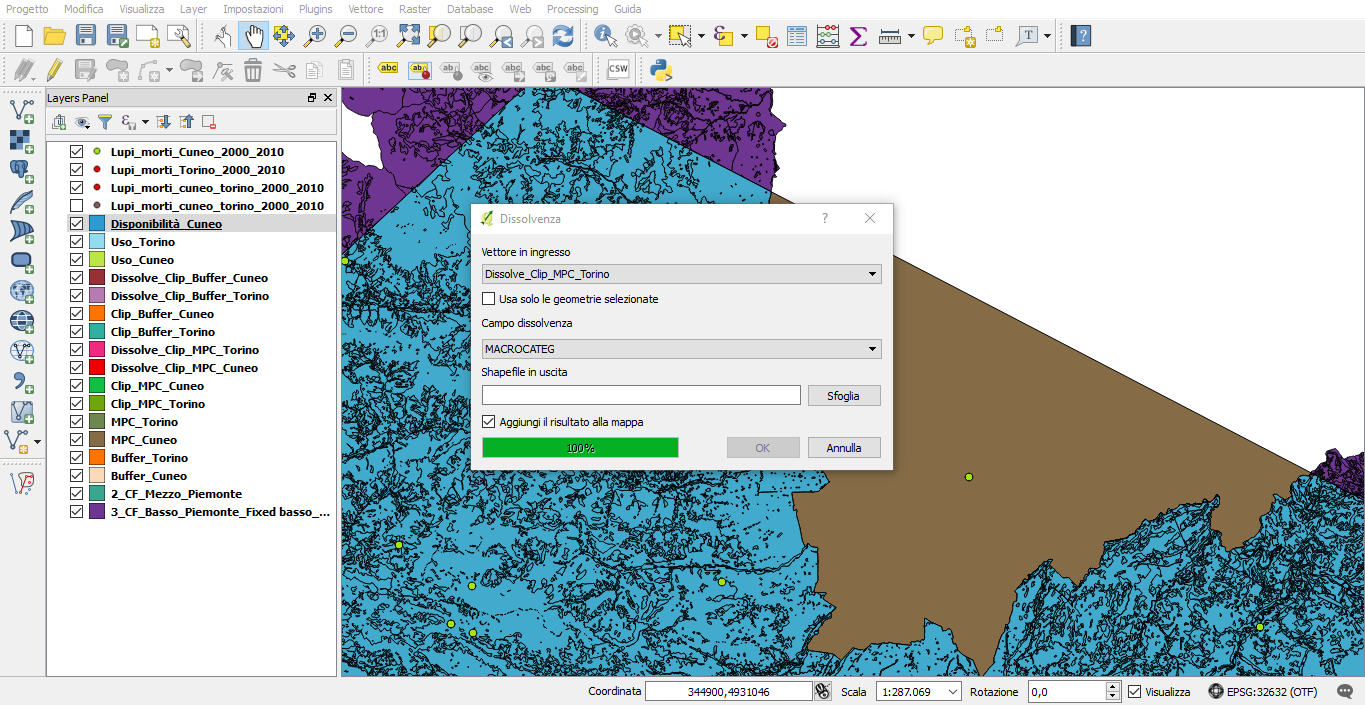
Goodmorning,
I have an issue with a QGIS project: I tried to make a second dissolvence on a file using QGIS 3.16, the process has reached 100%, but it doesn't give me the resulting file. The file I want was created in the right folder, but, even if added on the map, it seems to be wrong (it's as if it wasn't there).
I used the same process with another file and it worked, so I think the starting file (named "2_CF_Mezzo_Piemonte) has a problem.
Could someone help me, please? I had asked a question on this forum previously and I got great support, so I thought I'd write here again. I'm quite disperate with this project.
I also attach a photo of the error and all the data with a Google Drive link, I hope it helps.
https://drive.google.com/drive/folders/1-heQZM2v7lcdTP7km64AXo9PznjrffCa?usp=sharing
Thanks in advance.
|
1.0
|
Double dissolvence fails - Goodmorning,
I have an issue with a QGIS project: I tried to make a second dissolvence on a file using QGIS 3.16, the process has reached 100%, but it doesn't give me the resulting file. The file I want was created in the right folder, but, even if added on the map, it seems to be wrong (it's as if it wasn't there).
I used the same process with another file and it worked, so I think the starting file (named "2_CF_Mezzo_Piemonte) has a problem.
Could someone help me, please? I had asked a question on this forum previously and I got great support, so I thought I'd write here again. I'm quite disperate with this project.
I also attach a photo of the error and all the data with a Google Drive link, I hope it helps.
https://drive.google.com/drive/folders/1-heQZM2v7lcdTP7km64AXo9PznjrffCa?usp=sharing
Thanks in advance.
|
process
|
double dissolvence fails goodmorning i have an issue with a qgis project i tried to make a second dissolvence on a file using qgis the process has reached but it doesn t give me the resulting file the file i want was created in the right folder but even if added on the map it seems to be wrong it s as if it wasn t there i used the same process with another file and it worked so i think the starting file named cf mezzo piemonte has a problem could someone help me please i had asked a question on this forum previously and i got great support so i thought i d write here again i m quite disperate with this project i also attach a photo of the error and all the data with a google drive link i hope it helps thanks in advance
| 1
|
20,662
| 3,830,720,716
|
IssuesEvent
|
2016-03-31 15:27:10
|
mantidproject/mantid
|
https://api.github.com/repos/mantidproject/mantid
|
closed
|
Temporarily skip Vesuviocommands system test on all but win7 and Rhel7
|
Component: Direct Inelastic Quality: System Tests
|
The newly implemented system test for VesuvioCommands is failing on various operating systems (which the exclusion of windows7 and Rhel7) in order to allow nightly builds to complete, tests on other OSs shall be skipped until a permanent solution is found.
|
1.0
|
Temporarily skip Vesuviocommands system test on all but win7 and Rhel7 - The newly implemented system test for VesuvioCommands is failing on various operating systems (which the exclusion of windows7 and Rhel7) in order to allow nightly builds to complete, tests on other OSs shall be skipped until a permanent solution is found.
|
non_process
|
temporarily skip vesuviocommands system test on all but and the newly implemented system test for vesuviocommands is failing on various operating systems which the exclusion of and in order to allow nightly builds to complete tests on other oss shall be skipped until a permanent solution is found
| 0
|
695,376
| 23,854,367,120
|
IssuesEvent
|
2022-09-06 21:17:16
|
catalystneuro/neuroconv
|
https://api.github.com/repos/catalystneuro/neuroconv
|
closed
|
DataInterface for Blackrock spike sorting formats
|
enhancement priority: medium data interfaces
|
I added this to spikeinterface recently (https://github.com/SpikeInterface/spikeinterface/pull/856) as it was missing from the transition described in https://github.com/catalystneuro/neuroconv/issues/60. The corresponding interface should be added here as well.
|
1.0
|
DataInterface for Blackrock spike sorting formats - I added this to spikeinterface recently (https://github.com/SpikeInterface/spikeinterface/pull/856) as it was missing from the transition described in https://github.com/catalystneuro/neuroconv/issues/60. The corresponding interface should be added here as well.
|
non_process
|
datainterface for blackrock spike sorting formats i added this to spikeinterface recently as it was missing from the transition described in the corresponding interface should be added here as well
| 0
|
181,296
| 30,661,605,646
|
IssuesEvent
|
2023-07-25 15:19:58
|
KeyWorksRW/wxUiEditor
|
https://api.github.com/repos/KeyWorksRW/wxUiEditor
|
closed
|
Only indicate multiple languages for event handlers if they are actually being used
|
design change
|
### Description:
<!-- Provide a description of of what you want to happen here -->
Currently if you enter a C++ lambda function as an event handler, the property will also add a `[python] block, usually with the suggested function name. Presumably the dialog will be extended to support Ruby functions an lambdas as well, so a better approach needs to be found.
Aside from testing, most users are not going to be generating code in more than one language. When the custom dialog for an event handler is initialized, it already switches tabs to the preferred language. Initialization should also indicate if data for the other languages was passed in. Unless the user specifically adds a name or lambda for a non-preferred language, the then dialog should not add it to the property. For function names, we don't need to do anything special. For lambdas, we _do_ need to have some way of indicating which language it is for. Note that for Python lambda's, it already uses [python:lambda] to distinguish it from a regular function.
|
1.0
|
Only indicate multiple languages for event handlers if they are actually being used - ### Description:
<!-- Provide a description of of what you want to happen here -->
Currently if you enter a C++ lambda function as an event handler, the property will also add a `[python] block, usually with the suggested function name. Presumably the dialog will be extended to support Ruby functions an lambdas as well, so a better approach needs to be found.
Aside from testing, most users are not going to be generating code in more than one language. When the custom dialog for an event handler is initialized, it already switches tabs to the preferred language. Initialization should also indicate if data for the other languages was passed in. Unless the user specifically adds a name or lambda for a non-preferred language, the then dialog should not add it to the property. For function names, we don't need to do anything special. For lambdas, we _do_ need to have some way of indicating which language it is for. Note that for Python lambda's, it already uses [python:lambda] to distinguish it from a regular function.
|
non_process
|
only indicate multiple languages for event handlers if they are actually being used description currently if you enter a c lambda function as an event handler the property will also add a block usually with the suggested function name presumably the dialog will be extended to support ruby functions an lambdas as well so a better approach needs to be found aside from testing most users are not going to be generating code in more than one language when the custom dialog for an event handler is initialized it already switches tabs to the preferred language initialization should also indicate if data for the other languages was passed in unless the user specifically adds a name or lambda for a non preferred language the then dialog should not add it to the property for function names we don t need to do anything special for lambdas we do need to have some way of indicating which language it is for note that for python lambda s it already uses to distinguish it from a regular function
| 0
|
12,375
| 14,897,020,446
|
IssuesEvent
|
2021-01-21 11:10:15
|
GoogleCloudPlatform/fda-mystudies
|
https://api.github.com/repos/GoogleCloudPlatform/fda-mystudies
|
closed
|
[iOS] [Audit Logs] "run_id" is displayed empty string in description for the events
|
Bug P2 Process: Fixed iOS
|
**Events:**
1. ACTIVITY_METADATA_CONJOINED_WITH_RESPONSE_DATA
2. ACTIVITY_STATE_SAVED_OR_UPDATED_AFTER_RESPONSE_SUBMISSION
Sample snippet for event `ACTIVITY_STATE_SAVED_OR_UPDATED_AFTER_RESPONSE_SUBMISSION` event
```
{
"insertId": "rhfmywg1sw4xa3",
"jsonPayload": {
"eventCode": "ACTIVITY_STATE_SAVED_OR_UPDATED_AFTER_RESPONSE_SUBMISSION",
"resourceServer": null,
"platformVersion": "1.0",
"occurred": 1608728040143,
"destinationApplicationVersion": "1.0",
"appId": "BTCDEV001",
"source": "RESPONSE DATASTORE",
"userAccessLevel": null,
"appVersion": "1.0.146",
"userIp": "117.216.168.129",
"destination": "RESPONSE DATASTORE",
"studyId": "COVID001",
"studyVersion": null,
"mobilePlatform": "IOS",
"description": "Activity state 'Completed' for activity ID 'Auto0016' was saved or updated for participant, after response submission. Activity version: '1.0' , run ID: ''.",
"userId": "73f6eb31q22c4x4b63r88d4v2576890ae3ba",
"sourceApplicationVersion": "1.0",
"participantId": "0a6bc3a6-3879-4e31-9ee3-e91709815a00",
"siteId": null,
"correlationId": "756C412F-7FA3-4601-ADA1-6A79D92BA52A"
},
"resource": {
"type": "global",
"labels": {
"project_id": "mystudies-open-impl-track1-dev"
}
},
"timestamp": "2020-12-23T12:54:00.143Z",
"severity": "INFO",
"logName": "projects/mystudies-open-impl-track1-dev/logs/application-audit-log",
"receiveTimestamp": "2020-12-23T12:54:00.254293312Z"
}
```
|
1.0
|
[iOS] [Audit Logs] "run_id" is displayed empty string in description for the events - **Events:**
1. ACTIVITY_METADATA_CONJOINED_WITH_RESPONSE_DATA
2. ACTIVITY_STATE_SAVED_OR_UPDATED_AFTER_RESPONSE_SUBMISSION
Sample snippet for event `ACTIVITY_STATE_SAVED_OR_UPDATED_AFTER_RESPONSE_SUBMISSION` event
```
{
"insertId": "rhfmywg1sw4xa3",
"jsonPayload": {
"eventCode": "ACTIVITY_STATE_SAVED_OR_UPDATED_AFTER_RESPONSE_SUBMISSION",
"resourceServer": null,
"platformVersion": "1.0",
"occurred": 1608728040143,
"destinationApplicationVersion": "1.0",
"appId": "BTCDEV001",
"source": "RESPONSE DATASTORE",
"userAccessLevel": null,
"appVersion": "1.0.146",
"userIp": "117.216.168.129",
"destination": "RESPONSE DATASTORE",
"studyId": "COVID001",
"studyVersion": null,
"mobilePlatform": "IOS",
"description": "Activity state 'Completed' for activity ID 'Auto0016' was saved or updated for participant, after response submission. Activity version: '1.0' , run ID: ''.",
"userId": "73f6eb31q22c4x4b63r88d4v2576890ae3ba",
"sourceApplicationVersion": "1.0",
"participantId": "0a6bc3a6-3879-4e31-9ee3-e91709815a00",
"siteId": null,
"correlationId": "756C412F-7FA3-4601-ADA1-6A79D92BA52A"
},
"resource": {
"type": "global",
"labels": {
"project_id": "mystudies-open-impl-track1-dev"
}
},
"timestamp": "2020-12-23T12:54:00.143Z",
"severity": "INFO",
"logName": "projects/mystudies-open-impl-track1-dev/logs/application-audit-log",
"receiveTimestamp": "2020-12-23T12:54:00.254293312Z"
}
```
|
process
|
run id is displayed empty string in description for the events events activity metadata conjoined with response data activity state saved or updated after response submission sample snippet for event activity state saved or updated after response submission event insertid jsonpayload eventcode activity state saved or updated after response submission resourceserver null platformversion occurred destinationapplicationversion appid source response datastore useraccesslevel null appversion userip destination response datastore studyid studyversion null mobileplatform ios description activity state completed for activity id was saved or updated for participant after response submission activity version run id userid sourceapplicationversion participantid siteid null correlationid resource type global labels project id mystudies open impl dev timestamp severity info logname projects mystudies open impl dev logs application audit log receivetimestamp
| 1
|
53,549
| 7,842,667,599
|
IssuesEvent
|
2018-06-19 00:58:48
|
facebook/jest
|
https://api.github.com/repos/facebook/jest
|
closed
|
Unexpected test file matching due to parent directory name interfere with `testRegex`
|
Documentation :book: Good First Issue :wave:
|
<!--
THIS IS NOT A HELP FORUM.
If you are experiencing problems with setting up Jest, please make sure to visit our Help page:
https://facebook.github.io/jest/help.html
-->
<!--
Before creating an issue please check the following:
* you are using the latest version of Jest
* try re-installing your node_modules folder
* run Jest once with `--no-cache` to see if that fixes the problem you are experiencing.
-->
**Do you want to request a _feature_ or report a _bug_?**
bug
**What is the current behavior?**
Using config option `testRegex` that does not include `test/...` something, having tests in `test/xxx.test.js` will still be run.
The example in my case is: `{ "testRegex": "src/.*\.test\.js$" }`
**If the current behavior is a bug, please provide the steps to reproduce and
either a repl.it demo through https://repl.it/languages/jest or a minimal
repository on GitHub that we can `yarn install` and `yarn test`.**
See https://github.com/mraxus/jest-always-test-test and use commands `yarn test` and `yarn fail` to see expected/unexpected behaviour
**What is the expected behaviour?**
`yarn fail` does not pass where it should.
**Please provide your exact Jest configuration**
```
module.exports = {
testEnvironment: 'node',
testRegex: 'test/unit/.*\\.test\\.js$',
};
```
vs
```
module.exports = {
testEnvironment: 'node',
testRegex: 'src/.*\\.test\\.js$',
};
```
**Run `npx envinfo --preset jest` in your project directory and paste the
results here**
```
System:
OS: macOS High Sierra 10.13.4
CPU: x64 Intel(R) Core(TM) i5-7267U CPU @ 3.10GHz
Binaries:
Node: 8.11.1
Yarn: 1.5.1
npm: 5.8.0
npmPackages:
jest:
wanted: ^22.4.3
installed: 22.4.3
```
|
1.0
|
Unexpected test file matching due to parent directory name interfere with `testRegex` - <!--
THIS IS NOT A HELP FORUM.
If you are experiencing problems with setting up Jest, please make sure to visit our Help page:
https://facebook.github.io/jest/help.html
-->
<!--
Before creating an issue please check the following:
* you are using the latest version of Jest
* try re-installing your node_modules folder
* run Jest once with `--no-cache` to see if that fixes the problem you are experiencing.
-->
**Do you want to request a _feature_ or report a _bug_?**
bug
**What is the current behavior?**
Using config option `testRegex` that does not include `test/...` something, having tests in `test/xxx.test.js` will still be run.
The example in my case is: `{ "testRegex": "src/.*\.test\.js$" }`
**If the current behavior is a bug, please provide the steps to reproduce and
either a repl.it demo through https://repl.it/languages/jest or a minimal
repository on GitHub that we can `yarn install` and `yarn test`.**
See https://github.com/mraxus/jest-always-test-test and use commands `yarn test` and `yarn fail` to see expected/unexpected behaviour
**What is the expected behaviour?**
`yarn fail` does not pass where it should.
**Please provide your exact Jest configuration**
```
module.exports = {
testEnvironment: 'node',
testRegex: 'test/unit/.*\\.test\\.js$',
};
```
vs
```
module.exports = {
testEnvironment: 'node',
testRegex: 'src/.*\\.test\\.js$',
};
```
**Run `npx envinfo --preset jest` in your project directory and paste the
results here**
```
System:
OS: macOS High Sierra 10.13.4
CPU: x64 Intel(R) Core(TM) i5-7267U CPU @ 3.10GHz
Binaries:
Node: 8.11.1
Yarn: 1.5.1
npm: 5.8.0
npmPackages:
jest:
wanted: ^22.4.3
installed: 22.4.3
```
|
non_process
|
unexpected test file matching due to parent directory name interfere with testregex this is not a help forum if you are experiencing problems with setting up jest please make sure to visit our help page before creating an issue please check the following you are using the latest version of jest try re installing your node modules folder run jest once with no cache to see if that fixes the problem you are experiencing do you want to request a feature or report a bug bug what is the current behavior using config option testregex that does not include test something having tests in test xxx test js will still be run the example in my case is testregex src test js if the current behavior is a bug please provide the steps to reproduce and either a repl it demo through or a minimal repository on github that we can yarn install and yarn test see and use commands yarn test and yarn fail to see expected unexpected behaviour what is the expected behaviour yarn fail does not pass where it should please provide your exact jest configuration module exports testenvironment node testregex test unit test js vs module exports testenvironment node testregex src test js run npx envinfo preset jest in your project directory and paste the results here system os macos high sierra cpu intel r core tm cpu binaries node yarn npm npmpackages jest wanted installed
| 0
|
16,249
| 20,798,556,469
|
IssuesEvent
|
2022-03-17 11:43:59
|
ltechkorea/mlperf-inference
|
https://api.github.com/repos/ltechkorea/mlperf-inference
|
closed
|
Submit Logs
|
speech to text medical imaging Recommendation natural language processing object detection image classification pre-submit
|
### Submit Logs
- [ ] Image Classification
- [ ] Object Detection
- [ ] Netural Language Processing
- [ ] Recommendation
- [ ] Medical Imaging
- [ ] Speech to Text
|
1.0
|
Submit Logs - ### Submit Logs
- [ ] Image Classification
- [ ] Object Detection
- [ ] Netural Language Processing
- [ ] Recommendation
- [ ] Medical Imaging
- [ ] Speech to Text
|
process
|
submit logs submit logs image classification object detection netural language processing recommendation medical imaging speech to text
| 1
|
19,078
| 3,134,783,401
|
IssuesEvent
|
2015-09-10 12:15:03
|
hazelcast/hazelcast
|
https://api.github.com/repos/hazelcast/hazelcast
|
opened
|
GroupProperty defaulting not working properly when programmatic configuration is used
|
Team: QuSP Type: Defect
|
Example:
Properties `IO_INPUT_THREAD_COUNT` and `IO_OUTPUT_THREAD_COUNT` are configurable. The both defaults to `IO_THREAD_COUNT`
```java
IO_THREAD_COUNT("hazelcast.io.thread.count", 3),
IO_INPUT_THREAD_COUNT("hazelcast.io.input.thread.count", IO_THREAD_COUNT),
IO_OUTPUT_THREAD_COUNT("hazelcast.io.output.thread.count", IO_THREAD_COUNT),
```
This seems to work fine. However when I change the `IO_THREAD_COUNT` property then I'd intuitively expect the new value will be reflected in dependent properties.
In other words: I'd expect following test to pass:
```java
@Test
public void testInheritance_whenDefaultIsChangedProgramatically_thenDependentPropertyIsChangedToo() {
Config config = new Config();
config.setProperty(GroupProperty.IO_THREAD_COUNT, "1");
HazelcastInstance instance = createHazelcastInstance(config);
Node node = getNode(instance);
int inputIOThreadCount = node.getGroupProperties().getInteger(GroupProperty.IO_INPUT_THREAD_COUNT);
assertEquals(1, inputIOThreadCount);
}
```
|
1.0
|
GroupProperty defaulting not working properly when programmatic configuration is used - Example:
Properties `IO_INPUT_THREAD_COUNT` and `IO_OUTPUT_THREAD_COUNT` are configurable. The both defaults to `IO_THREAD_COUNT`
```java
IO_THREAD_COUNT("hazelcast.io.thread.count", 3),
IO_INPUT_THREAD_COUNT("hazelcast.io.input.thread.count", IO_THREAD_COUNT),
IO_OUTPUT_THREAD_COUNT("hazelcast.io.output.thread.count", IO_THREAD_COUNT),
```
This seems to work fine. However when I change the `IO_THREAD_COUNT` property then I'd intuitively expect the new value will be reflected in dependent properties.
In other words: I'd expect following test to pass:
```java
@Test
public void testInheritance_whenDefaultIsChangedProgramatically_thenDependentPropertyIsChangedToo() {
Config config = new Config();
config.setProperty(GroupProperty.IO_THREAD_COUNT, "1");
HazelcastInstance instance = createHazelcastInstance(config);
Node node = getNode(instance);
int inputIOThreadCount = node.getGroupProperties().getInteger(GroupProperty.IO_INPUT_THREAD_COUNT);
assertEquals(1, inputIOThreadCount);
}
```
|
non_process
|
groupproperty defaulting not working properly when programmatic configuration is used example properties io input thread count and io output thread count are configurable the both defaults to io thread count java io thread count hazelcast io thread count io input thread count hazelcast io input thread count io thread count io output thread count hazelcast io output thread count io thread count this seems to work fine however when i change the io thread count property then i d intuitively expect the new value will be reflected in dependent properties in other words i d expect following test to pass java test public void testinheritance whendefaultischangedprogramatically thendependentpropertyischangedtoo config config new config config setproperty groupproperty io thread count hazelcastinstance instance createhazelcastinstance config node node getnode instance int inputiothreadcount node getgroupproperties getinteger groupproperty io input thread count assertequals inputiothreadcount
| 0
|
84,141
| 7,892,125,320
|
IssuesEvent
|
2018-06-28 14:11:49
|
cloudigrade/integrade
|
https://api.github.com/repos/cloudigrade/integrade
|
closed
|
Add test to exercise the sysconfig API endpoint
|
api needs verification test case
|
As a QE, I want a test that exercises the `sysconfig` API endpoint which returns the AWS account information.
## Acceptance Criteria
- [x] Verify there is a test that performs an authenticated GET request to the `sysconfig` API endpoint and assert a 200 status code is returned with content like `{'aws_account_id': <account_id>}`
- [x] Verify that there is a test that checks the endpoint can't be accessed without being logged in.
## Assumptions and Questions
- https://github.com/cloudigrade/cloudigrade/pull/377 should be merged so this issue can be worked on.
|
1.0
|
Add test to exercise the sysconfig API endpoint - As a QE, I want a test that exercises the `sysconfig` API endpoint which returns the AWS account information.
## Acceptance Criteria
- [x] Verify there is a test that performs an authenticated GET request to the `sysconfig` API endpoint and assert a 200 status code is returned with content like `{'aws_account_id': <account_id>}`
- [x] Verify that there is a test that checks the endpoint can't be accessed without being logged in.
## Assumptions and Questions
- https://github.com/cloudigrade/cloudigrade/pull/377 should be merged so this issue can be worked on.
|
non_process
|
add test to exercise the sysconfig api endpoint as a qe i want a test that exercises the sysconfig api endpoint which returns the aws account information acceptance criteria verify there is a test that performs an authenticated get request to the sysconfig api endpoint and assert a status code is returned with content like aws account id verify that there is a test that checks the endpoint can t be accessed without being logged in assumptions and questions should be merged so this issue can be worked on
| 0
|
272,376
| 23,669,374,163
|
IssuesEvent
|
2022-08-27 05:09:50
|
wixtoolset/issues
|
https://api.github.com/repos/wixtoolset/issues
|
closed
|
CanPatchSwidTag Burn integration test failing
|
tests
|
Despite https://github.com/wixtoolset/issues/issues/6380 being fixed, the `CanPatchSwidTag` test is still failing.
```
Error Message:
Assert.Equal() Failure
Expected: 1.0.0.0
Actual: (null)
Stack Trace:
at WixToolsetTest.BurnE2E.PatchTests.VerifySwidTagVersion(String tagName, String expectedVersion) in C:\src\wix4\src\test\burn\WixToolsetTest.BurnE2E\PatchTests.cs:line 135
at WixToolsetTest.BurnE2E.PatchTests.CanPatchSwidTag() in C:\src\wix4\src\test\burn\WixToolsetTest.BurnE2E\PatchTests.cs:line 73
```
|
1.0
|
CanPatchSwidTag Burn integration test failing - Despite https://github.com/wixtoolset/issues/issues/6380 being fixed, the `CanPatchSwidTag` test is still failing.
```
Error Message:
Assert.Equal() Failure
Expected: 1.0.0.0
Actual: (null)
Stack Trace:
at WixToolsetTest.BurnE2E.PatchTests.VerifySwidTagVersion(String tagName, String expectedVersion) in C:\src\wix4\src\test\burn\WixToolsetTest.BurnE2E\PatchTests.cs:line 135
at WixToolsetTest.BurnE2E.PatchTests.CanPatchSwidTag() in C:\src\wix4\src\test\burn\WixToolsetTest.BurnE2E\PatchTests.cs:line 73
```
|
non_process
|
canpatchswidtag burn integration test failing despite being fixed the canpatchswidtag test is still failing error message assert equal failure expected actual null stack trace at wixtoolsettest patchtests verifyswidtagversion string tagname string expectedversion in c src src test burn wixtoolsettest patchtests cs line at wixtoolsettest patchtests canpatchswidtag in c src src test burn wixtoolsettest patchtests cs line
| 0
|
279,563
| 30,707,387,629
|
IssuesEvent
|
2023-07-27 07:22:24
|
ghc-staging-automation/3232857_ameer
|
https://api.github.com/repos/ghc-staging-automation/3232857_ameer
|
opened
|
ansible-2.9.9.tar.gz: 8 vulnerabilities (highest severity is: 7.1)
|
Mend: dependency security vulnerability
|
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>ansible-2.9.9.tar.gz</b></p></summary>
<p>Radically simple IT automation</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/00/5d/e10b83e0e6056dbd5b4809b451a191395175a57e3175ce04e35d9c5fc2a0/ansible-2.9.9.tar.gz">https://files.pythonhosted.org/packages/00/5d/e10b83e0e6056dbd5b4809b451a191395175a57e3175ce04e35d9c5fc2a0/ansible-2.9.9.tar.gz</a></p>
<p>Path to dependency file: /requirements.txt</p>
<p>Path to vulnerable library: /requirements.txt</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/ghc-staging-automation/3232857_ameer/commit/be311b8ee25e5ae20ac3c74ca316d0751c12262d">be311b8ee25e5ae20ac3c74ca316d0751c12262d</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (ansible version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2020-14365](https://www.mend.io/vulnerability-database/CVE-2020-14365) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.1 | ansible-2.9.9.tar.gz | Direct | 2.9.12 | ✅ |
| [CVE-2020-14332](https://www.mend.io/vulnerability-database/CVE-2020-14332) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.5 | ansible-2.9.9.tar.gz | Direct | 2.9.12 | ✅ |
| [CVE-2020-1753](https://www.mend.io/vulnerability-database/CVE-2020-1753) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.5 | ansible-2.9.9.tar.gz | Direct | 2.9.10 | ✅ |
| [CVE-2021-20180](https://www.mend.io/vulnerability-database/CVE-2021-20180) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.5 | ansible-2.9.9.tar.gz | Direct | 2.9.18 | ✅ |
| [CVE-2020-14330](https://www.mend.io/vulnerability-database/CVE-2020-14330) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.5 | ansible-2.9.9.tar.gz | Direct | 2.9.14 | ✅ |
| [CVE-2020-10744](https://www.mend.io/vulnerability-database/CVE-2020-10744) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.0 | ansible-2.9.9.tar.gz | Direct | 2.9.10 | ✅ |
| [CVE-2020-1738](https://www.mend.io/vulnerability-database/CVE-2020-1738) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png?' width=19 height=20> Low | 3.9 | ansible-2.9.9.tar.gz | Direct | 2.9.10 | ✅ |
| [CVE-2021-3533](https://www.mend.io/vulnerability-database/CVE-2021-3533) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png?' width=19 height=20> Low | 2.5 | ansible-2.9.9.tar.gz | Direct | 2.9.23 | ✅ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2020-14365</summary>
### Vulnerable Library - <b>ansible-2.9.9.tar.gz</b></p>
<p>Radically simple IT automation</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/00/5d/e10b83e0e6056dbd5b4809b451a191395175a57e3175ce04e35d9c5fc2a0/ansible-2.9.9.tar.gz">https://files.pythonhosted.org/packages/00/5d/e10b83e0e6056dbd5b4809b451a191395175a57e3175ce04e35d9c5fc2a0/ansible-2.9.9.tar.gz</a></p>
<p>Path to dependency file: /requirements.txt</p>
<p>Path to vulnerable library: /requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **ansible-2.9.9.tar.gz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ghc-staging-automation/3232857_ameer/commit/be311b8ee25e5ae20ac3c74ca316d0751c12262d">be311b8ee25e5ae20ac3c74ca316d0751c12262d</a></p>
<p>Found in base branch: <b>feature_branch</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A flaw was found in the Ansible Engine, in ansible-engine 2.8.x before 2.8.15 and ansible-engine 2.9.x before 2.9.13, when installing packages using the dnf module. GPG signatures are ignored during installation even when disable_gpg_check is set to False, which is the default behavior. This flaw leads to malicious packages being installed on the system and arbitrary code executed via package installation scripts. The highest threat from this vulnerability is to integrity and system availability.
<p>Publish Date: 2020-09-23
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-14365>CVE-2020-14365</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bugzilla.redhat.com/show_bug.cgi?id=1869154">https://bugzilla.redhat.com/show_bug.cgi?id=1869154</a></p>
<p>Release Date: 2020-09-23</p>
<p>Fix Resolution: 2.9.12</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2020-14332</summary>
### Vulnerable Library - <b>ansible-2.9.9.tar.gz</b></p>
<p>Radically simple IT automation</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/00/5d/e10b83e0e6056dbd5b4809b451a191395175a57e3175ce04e35d9c5fc2a0/ansible-2.9.9.tar.gz">https://files.pythonhosted.org/packages/00/5d/e10b83e0e6056dbd5b4809b451a191395175a57e3175ce04e35d9c5fc2a0/ansible-2.9.9.tar.gz</a></p>
<p>Path to dependency file: /requirements.txt</p>
<p>Path to vulnerable library: /requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **ansible-2.9.9.tar.gz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ghc-staging-automation/3232857_ameer/commit/be311b8ee25e5ae20ac3c74ca316d0751c12262d">be311b8ee25e5ae20ac3c74ca316d0751c12262d</a></p>
<p>Found in base branch: <b>feature_branch</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A flaw was found in the Ansible Engine when using module_args. Tasks executed with check mode (--check-mode) do not properly neutralize sensitive data exposed in the event data. This flaw allows unauthorized users to read this data. The highest threat from this vulnerability is to confidentiality.
<p>Publish Date: 2020-09-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-14332>CVE-2020-14332</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bugzilla.redhat.com/show_bug.cgi?id=CVE-2020-14332">https://bugzilla.redhat.com/show_bug.cgi?id=CVE-2020-14332</a></p>
<p>Release Date: 2020-09-11</p>
<p>Fix Resolution: 2.9.12</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2020-1753</summary>
### Vulnerable Library - <b>ansible-2.9.9.tar.gz</b></p>
<p>Radically simple IT automation</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/00/5d/e10b83e0e6056dbd5b4809b451a191395175a57e3175ce04e35d9c5fc2a0/ansible-2.9.9.tar.gz">https://files.pythonhosted.org/packages/00/5d/e10b83e0e6056dbd5b4809b451a191395175a57e3175ce04e35d9c5fc2a0/ansible-2.9.9.tar.gz</a></p>
<p>Path to dependency file: /requirements.txt</p>
<p>Path to vulnerable library: /requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **ansible-2.9.9.tar.gz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ghc-staging-automation/3232857_ameer/commit/be311b8ee25e5ae20ac3c74ca316d0751c12262d">be311b8ee25e5ae20ac3c74ca316d0751c12262d</a></p>
<p>Found in base branch: <b>feature_branch</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A security flaw was found in Ansible Engine, all Ansible 2.7.x versions prior to 2.7.17, all Ansible 2.8.x versions prior to 2.8.11 and all Ansible 2.9.x versions prior to 2.9.7, when managing kubernetes using the k8s module. Sensitive parameters such as passwords and tokens are passed to kubectl from the command line, not using an environment variable or an input configuration file. This will disclose passwords and tokens from process list and no_log directive from debug module would not have any effect making these secrets being disclosed on stdout and log files.
<p>Publish Date: 2020-03-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-1753>CVE-2020-1753</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2020-1753">https://nvd.nist.gov/vuln/detail/CVE-2020-1753</a></p>
<p>Release Date: 2020-03-16</p>
<p>Fix Resolution: 2.9.10</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2021-20180</summary>
### Vulnerable Library - <b>ansible-2.9.9.tar.gz</b></p>
<p>Radically simple IT automation</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/00/5d/e10b83e0e6056dbd5b4809b451a191395175a57e3175ce04e35d9c5fc2a0/ansible-2.9.9.tar.gz">https://files.pythonhosted.org/packages/00/5d/e10b83e0e6056dbd5b4809b451a191395175a57e3175ce04e35d9c5fc2a0/ansible-2.9.9.tar.gz</a></p>
<p>Path to dependency file: /requirements.txt</p>
<p>Path to vulnerable library: /requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **ansible-2.9.9.tar.gz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ghc-staging-automation/3232857_ameer/commit/be311b8ee25e5ae20ac3c74ca316d0751c12262d">be311b8ee25e5ae20ac3c74ca316d0751c12262d</a></p>
<p>Found in base branch: <b>feature_branch</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A flaw was found in ansible module where credentials are disclosed in the console log by default and not protected by the security feature when using the bitbucket_pipeline_variable module. This flaw allows an attacker to steal bitbucket_pipeline credentials. The highest threat from this vulnerability is to confidentiality.
<p>Publish Date: 2022-03-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-20180>CVE-2021-20180</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-fh5v-5f35-2rv2">https://github.com/advisories/GHSA-fh5v-5f35-2rv2</a></p>
<p>Release Date: 2022-03-16</p>
<p>Fix Resolution: 2.9.18</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2020-14330</summary>
### Vulnerable Library - <b>ansible-2.9.9.tar.gz</b></p>
<p>Radically simple IT automation</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/00/5d/e10b83e0e6056dbd5b4809b451a191395175a57e3175ce04e35d9c5fc2a0/ansible-2.9.9.tar.gz">https://files.pythonhosted.org/packages/00/5d/e10b83e0e6056dbd5b4809b451a191395175a57e3175ce04e35d9c5fc2a0/ansible-2.9.9.tar.gz</a></p>
<p>Path to dependency file: /requirements.txt</p>
<p>Path to vulnerable library: /requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **ansible-2.9.9.tar.gz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ghc-staging-automation/3232857_ameer/commit/be311b8ee25e5ae20ac3c74ca316d0751c12262d">be311b8ee25e5ae20ac3c74ca316d0751c12262d</a></p>
<p>Found in base branch: <b>feature_branch</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
An Improper Output Neutralization for Logs flaw was found in Ansible when using the uri module, where sensitive data is exposed to content and json output. This flaw allows an attacker to access the logs or outputs of performed tasks to read keys used in playbooks from other users within the uri module. The highest threat from this vulnerability is to data confidentiality.
<p>Publish Date: 2020-09-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-14330>CVE-2020-14330</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bugzilla.redhat.com/show_bug.cgi?id=CVE-2020-14330">https://bugzilla.redhat.com/show_bug.cgi?id=CVE-2020-14330</a></p>
<p>Release Date: 2020-09-11</p>
<p>Fix Resolution: 2.9.14</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2020-10744</summary>
### Vulnerable Library - <b>ansible-2.9.9.tar.gz</b></p>
<p>Radically simple IT automation</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/00/5d/e10b83e0e6056dbd5b4809b451a191395175a57e3175ce04e35d9c5fc2a0/ansible-2.9.9.tar.gz">https://files.pythonhosted.org/packages/00/5d/e10b83e0e6056dbd5b4809b451a191395175a57e3175ce04e35d9c5fc2a0/ansible-2.9.9.tar.gz</a></p>
<p>Path to dependency file: /requirements.txt</p>
<p>Path to vulnerable library: /requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **ansible-2.9.9.tar.gz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ghc-staging-automation/3232857_ameer/commit/be311b8ee25e5ae20ac3c74ca316d0751c12262d">be311b8ee25e5ae20ac3c74ca316d0751c12262d</a></p>
<p>Found in base branch: <b>feature_branch</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
An incomplete fix was found for the fix of the flaw CVE-2020-1733 ansible: insecure temporary directory when running become_user from become directive. The provided fix is insufficient to prevent the race condition on systems using ACLs and FUSE filesystems. Ansible Engine 2.7.18, 2.8.12, and 2.9.9 as well as previous versions are affected and Ansible Tower 3.4.5, 3.5.6 and 3.6.4 as well as previous versions are affected.
<p>Publish Date: 2020-05-15
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-10744>CVE-2020-10744</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.0</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2020-10744">https://nvd.nist.gov/vuln/detail/CVE-2020-10744</a></p>
<p>Release Date: 2020-05-15</p>
<p>Fix Resolution: 2.9.10</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png?' width=19 height=20> CVE-2020-1738</summary>
### Vulnerable Library - <b>ansible-2.9.9.tar.gz</b></p>
<p>Radically simple IT automation</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/00/5d/e10b83e0e6056dbd5b4809b451a191395175a57e3175ce04e35d9c5fc2a0/ansible-2.9.9.tar.gz">https://files.pythonhosted.org/packages/00/5d/e10b83e0e6056dbd5b4809b451a191395175a57e3175ce04e35d9c5fc2a0/ansible-2.9.9.tar.gz</a></p>
<p>Path to dependency file: /requirements.txt</p>
<p>Path to vulnerable library: /requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **ansible-2.9.9.tar.gz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ghc-staging-automation/3232857_ameer/commit/be311b8ee25e5ae20ac3c74ca316d0751c12262d">be311b8ee25e5ae20ac3c74ca316d0751c12262d</a></p>
<p>Found in base branch: <b>feature_branch</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A flaw was found in Ansible Engine when the module package or service is used and the parameter 'use' is not specified. If a previous task is executed with a malicious user, the module sent can be selected by the attacker using the ansible facts file. All versions in 2.7.x, 2.8.x and 2.9.x branches are believed to be vulnerable.
<p>Publish Date: 2020-03-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-1738>CVE-2020-1738</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>3.9</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bugzilla.redhat.com/show_bug.cgi?id=CVE-2020-1738">https://bugzilla.redhat.com/show_bug.cgi?id=CVE-2020-1738</a></p>
<p>Release Date: 2020-03-16</p>
<p>Fix Resolution: 2.9.10</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png?' width=19 height=20> CVE-2021-3533</summary>
### Vulnerable Library - <b>ansible-2.9.9.tar.gz</b></p>
<p>Radically simple IT automation</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/00/5d/e10b83e0e6056dbd5b4809b451a191395175a57e3175ce04e35d9c5fc2a0/ansible-2.9.9.tar.gz">https://files.pythonhosted.org/packages/00/5d/e10b83e0e6056dbd5b4809b451a191395175a57e3175ce04e35d9c5fc2a0/ansible-2.9.9.tar.gz</a></p>
<p>Path to dependency file: /requirements.txt</p>
<p>Path to vulnerable library: /requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **ansible-2.9.9.tar.gz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ghc-staging-automation/3232857_ameer/commit/be311b8ee25e5ae20ac3c74ca316d0751c12262d">be311b8ee25e5ae20ac3c74ca316d0751c12262d</a></p>
<p>Found in base branch: <b>feature_branch</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A flaw was found in Ansible if an ansible user sets ANSIBLE_ASYNC_DIR to a subdirectory of a world writable directory. When this occurs, there is a race condition on the managed machine. A malicious, non-privileged account on the remote machine can exploit the race condition to access the async result data. This flaw affects Ansible Tower 3.7 and Ansible Automation Platform 1.2.
<p>Publish Date: 2021-06-09
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-3533>CVE-2021-3533</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>2.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2021-3533">https://nvd.nist.gov/vuln/detail/CVE-2021-3533</a></p>
<p>Release Date: 2021-06-09</p>
<p>Fix Resolution: 2.9.23</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p>
|
True
|
ansible-2.9.9.tar.gz: 8 vulnerabilities (highest severity is: 7.1) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>ansible-2.9.9.tar.gz</b></p></summary>
<p>Radically simple IT automation</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/00/5d/e10b83e0e6056dbd5b4809b451a191395175a57e3175ce04e35d9c5fc2a0/ansible-2.9.9.tar.gz">https://files.pythonhosted.org/packages/00/5d/e10b83e0e6056dbd5b4809b451a191395175a57e3175ce04e35d9c5fc2a0/ansible-2.9.9.tar.gz</a></p>
<p>Path to dependency file: /requirements.txt</p>
<p>Path to vulnerable library: /requirements.txt</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/ghc-staging-automation/3232857_ameer/commit/be311b8ee25e5ae20ac3c74ca316d0751c12262d">be311b8ee25e5ae20ac3c74ca316d0751c12262d</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (ansible version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2020-14365](https://www.mend.io/vulnerability-database/CVE-2020-14365) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.1 | ansible-2.9.9.tar.gz | Direct | 2.9.12 | ✅ |
| [CVE-2020-14332](https://www.mend.io/vulnerability-database/CVE-2020-14332) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.5 | ansible-2.9.9.tar.gz | Direct | 2.9.12 | ✅ |
| [CVE-2020-1753](https://www.mend.io/vulnerability-database/CVE-2020-1753) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.5 | ansible-2.9.9.tar.gz | Direct | 2.9.10 | ✅ |
| [CVE-2021-20180](https://www.mend.io/vulnerability-database/CVE-2021-20180) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.5 | ansible-2.9.9.tar.gz | Direct | 2.9.18 | ✅ |
| [CVE-2020-14330](https://www.mend.io/vulnerability-database/CVE-2020-14330) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.5 | ansible-2.9.9.tar.gz | Direct | 2.9.14 | ✅ |
| [CVE-2020-10744](https://www.mend.io/vulnerability-database/CVE-2020-10744) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.0 | ansible-2.9.9.tar.gz | Direct | 2.9.10 | ✅ |
| [CVE-2020-1738](https://www.mend.io/vulnerability-database/CVE-2020-1738) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png?' width=19 height=20> Low | 3.9 | ansible-2.9.9.tar.gz | Direct | 2.9.10 | ✅ |
| [CVE-2021-3533](https://www.mend.io/vulnerability-database/CVE-2021-3533) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png?' width=19 height=20> Low | 2.5 | ansible-2.9.9.tar.gz | Direct | 2.9.23 | ✅ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2020-14365</summary>
### Vulnerable Library - <b>ansible-2.9.9.tar.gz</b></p>
<p>Radically simple IT automation</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/00/5d/e10b83e0e6056dbd5b4809b451a191395175a57e3175ce04e35d9c5fc2a0/ansible-2.9.9.tar.gz">https://files.pythonhosted.org/packages/00/5d/e10b83e0e6056dbd5b4809b451a191395175a57e3175ce04e35d9c5fc2a0/ansible-2.9.9.tar.gz</a></p>
<p>Path to dependency file: /requirements.txt</p>
<p>Path to vulnerable library: /requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **ansible-2.9.9.tar.gz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ghc-staging-automation/3232857_ameer/commit/be311b8ee25e5ae20ac3c74ca316d0751c12262d">be311b8ee25e5ae20ac3c74ca316d0751c12262d</a></p>
<p>Found in base branch: <b>feature_branch</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A flaw was found in the Ansible Engine, in ansible-engine 2.8.x before 2.8.15 and ansible-engine 2.9.x before 2.9.13, when installing packages using the dnf module. GPG signatures are ignored during installation even when disable_gpg_check is set to False, which is the default behavior. This flaw leads to malicious packages being installed on the system and arbitrary code executed via package installation scripts. The highest threat from this vulnerability is to integrity and system availability.
<p>Publish Date: 2020-09-23
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-14365>CVE-2020-14365</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bugzilla.redhat.com/show_bug.cgi?id=1869154">https://bugzilla.redhat.com/show_bug.cgi?id=1869154</a></p>
<p>Release Date: 2020-09-23</p>
<p>Fix Resolution: 2.9.12</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2020-14332</summary>
### Vulnerable Library - <b>ansible-2.9.9.tar.gz</b></p>
<p>Radically simple IT automation</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/00/5d/e10b83e0e6056dbd5b4809b451a191395175a57e3175ce04e35d9c5fc2a0/ansible-2.9.9.tar.gz">https://files.pythonhosted.org/packages/00/5d/e10b83e0e6056dbd5b4809b451a191395175a57e3175ce04e35d9c5fc2a0/ansible-2.9.9.tar.gz</a></p>
<p>Path to dependency file: /requirements.txt</p>
<p>Path to vulnerable library: /requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **ansible-2.9.9.tar.gz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ghc-staging-automation/3232857_ameer/commit/be311b8ee25e5ae20ac3c74ca316d0751c12262d">be311b8ee25e5ae20ac3c74ca316d0751c12262d</a></p>
<p>Found in base branch: <b>feature_branch</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A flaw was found in the Ansible Engine when using module_args. Tasks executed with check mode (--check-mode) do not properly neutralize sensitive data exposed in the event data. This flaw allows unauthorized users to read this data. The highest threat from this vulnerability is to confidentiality.
<p>Publish Date: 2020-09-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-14332>CVE-2020-14332</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bugzilla.redhat.com/show_bug.cgi?id=CVE-2020-14332">https://bugzilla.redhat.com/show_bug.cgi?id=CVE-2020-14332</a></p>
<p>Release Date: 2020-09-11</p>
<p>Fix Resolution: 2.9.12</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2020-1753</summary>
### Vulnerable Library - <b>ansible-2.9.9.tar.gz</b></p>
<p>Radically simple IT automation</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/00/5d/e10b83e0e6056dbd5b4809b451a191395175a57e3175ce04e35d9c5fc2a0/ansible-2.9.9.tar.gz">https://files.pythonhosted.org/packages/00/5d/e10b83e0e6056dbd5b4809b451a191395175a57e3175ce04e35d9c5fc2a0/ansible-2.9.9.tar.gz</a></p>
<p>Path to dependency file: /requirements.txt</p>
<p>Path to vulnerable library: /requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **ansible-2.9.9.tar.gz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ghc-staging-automation/3232857_ameer/commit/be311b8ee25e5ae20ac3c74ca316d0751c12262d">be311b8ee25e5ae20ac3c74ca316d0751c12262d</a></p>
<p>Found in base branch: <b>feature_branch</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A security flaw was found in Ansible Engine, all Ansible 2.7.x versions prior to 2.7.17, all Ansible 2.8.x versions prior to 2.8.11 and all Ansible 2.9.x versions prior to 2.9.7, when managing kubernetes using the k8s module. Sensitive parameters such as passwords and tokens are passed to kubectl from the command line, not using an environment variable or an input configuration file. This will disclose passwords and tokens from process list and no_log directive from debug module would not have any effect making these secrets being disclosed on stdout and log files.
<p>Publish Date: 2020-03-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-1753>CVE-2020-1753</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2020-1753">https://nvd.nist.gov/vuln/detail/CVE-2020-1753</a></p>
<p>Release Date: 2020-03-16</p>
<p>Fix Resolution: 2.9.10</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2021-20180</summary>
### Vulnerable Library - <b>ansible-2.9.9.tar.gz</b></p>
<p>Radically simple IT automation</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/00/5d/e10b83e0e6056dbd5b4809b451a191395175a57e3175ce04e35d9c5fc2a0/ansible-2.9.9.tar.gz">https://files.pythonhosted.org/packages/00/5d/e10b83e0e6056dbd5b4809b451a191395175a57e3175ce04e35d9c5fc2a0/ansible-2.9.9.tar.gz</a></p>
<p>Path to dependency file: /requirements.txt</p>
<p>Path to vulnerable library: /requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **ansible-2.9.9.tar.gz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ghc-staging-automation/3232857_ameer/commit/be311b8ee25e5ae20ac3c74ca316d0751c12262d">be311b8ee25e5ae20ac3c74ca316d0751c12262d</a></p>
<p>Found in base branch: <b>feature_branch</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A flaw was found in ansible module where credentials are disclosed in the console log by default and not protected by the security feature when using the bitbucket_pipeline_variable module. This flaw allows an attacker to steal bitbucket_pipeline credentials. The highest threat from this vulnerability is to confidentiality.
<p>Publish Date: 2022-03-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-20180>CVE-2021-20180</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-fh5v-5f35-2rv2">https://github.com/advisories/GHSA-fh5v-5f35-2rv2</a></p>
<p>Release Date: 2022-03-16</p>
<p>Fix Resolution: 2.9.18</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2020-14330</summary>
### Vulnerable Library - <b>ansible-2.9.9.tar.gz</b></p>
<p>Radically simple IT automation</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/00/5d/e10b83e0e6056dbd5b4809b451a191395175a57e3175ce04e35d9c5fc2a0/ansible-2.9.9.tar.gz">https://files.pythonhosted.org/packages/00/5d/e10b83e0e6056dbd5b4809b451a191395175a57e3175ce04e35d9c5fc2a0/ansible-2.9.9.tar.gz</a></p>
<p>Path to dependency file: /requirements.txt</p>
<p>Path to vulnerable library: /requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **ansible-2.9.9.tar.gz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ghc-staging-automation/3232857_ameer/commit/be311b8ee25e5ae20ac3c74ca316d0751c12262d">be311b8ee25e5ae20ac3c74ca316d0751c12262d</a></p>
<p>Found in base branch: <b>feature_branch</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
An Improper Output Neutralization for Logs flaw was found in Ansible when using the uri module, where sensitive data is exposed to content and json output. This flaw allows an attacker to access the logs or outputs of performed tasks to read keys used in playbooks from other users within the uri module. The highest threat from this vulnerability is to data confidentiality.
<p>Publish Date: 2020-09-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-14330>CVE-2020-14330</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bugzilla.redhat.com/show_bug.cgi?id=CVE-2020-14330">https://bugzilla.redhat.com/show_bug.cgi?id=CVE-2020-14330</a></p>
<p>Release Date: 2020-09-11</p>
<p>Fix Resolution: 2.9.14</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2020-10744</summary>
### Vulnerable Library - <b>ansible-2.9.9.tar.gz</b></p>
<p>Radically simple IT automation</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/00/5d/e10b83e0e6056dbd5b4809b451a191395175a57e3175ce04e35d9c5fc2a0/ansible-2.9.9.tar.gz">https://files.pythonhosted.org/packages/00/5d/e10b83e0e6056dbd5b4809b451a191395175a57e3175ce04e35d9c5fc2a0/ansible-2.9.9.tar.gz</a></p>
<p>Path to dependency file: /requirements.txt</p>
<p>Path to vulnerable library: /requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **ansible-2.9.9.tar.gz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ghc-staging-automation/3232857_ameer/commit/be311b8ee25e5ae20ac3c74ca316d0751c12262d">be311b8ee25e5ae20ac3c74ca316d0751c12262d</a></p>
<p>Found in base branch: <b>feature_branch</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
An incomplete fix was found for the fix of the flaw CVE-2020-1733 ansible: insecure temporary directory when running become_user from become directive. The provided fix is insufficient to prevent the race condition on systems using ACLs and FUSE filesystems. Ansible Engine 2.7.18, 2.8.12, and 2.9.9 as well as previous versions are affected and Ansible Tower 3.4.5, 3.5.6 and 3.6.4 as well as previous versions are affected.
<p>Publish Date: 2020-05-15
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-10744>CVE-2020-10744</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.0</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2020-10744">https://nvd.nist.gov/vuln/detail/CVE-2020-10744</a></p>
<p>Release Date: 2020-05-15</p>
<p>Fix Resolution: 2.9.10</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png?' width=19 height=20> CVE-2020-1738</summary>
### Vulnerable Library - <b>ansible-2.9.9.tar.gz</b></p>
<p>Radically simple IT automation</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/00/5d/e10b83e0e6056dbd5b4809b451a191395175a57e3175ce04e35d9c5fc2a0/ansible-2.9.9.tar.gz">https://files.pythonhosted.org/packages/00/5d/e10b83e0e6056dbd5b4809b451a191395175a57e3175ce04e35d9c5fc2a0/ansible-2.9.9.tar.gz</a></p>
<p>Path to dependency file: /requirements.txt</p>
<p>Path to vulnerable library: /requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **ansible-2.9.9.tar.gz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ghc-staging-automation/3232857_ameer/commit/be311b8ee25e5ae20ac3c74ca316d0751c12262d">be311b8ee25e5ae20ac3c74ca316d0751c12262d</a></p>
<p>Found in base branch: <b>feature_branch</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A flaw was found in Ansible Engine when the module package or service is used and the parameter 'use' is not specified. If a previous task is executed with a malicious user, the module sent can be selected by the attacker using the ansible facts file. All versions in 2.7.x, 2.8.x and 2.9.x branches are believed to be vulnerable.
<p>Publish Date: 2020-03-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-1738>CVE-2020-1738</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>3.9</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bugzilla.redhat.com/show_bug.cgi?id=CVE-2020-1738">https://bugzilla.redhat.com/show_bug.cgi?id=CVE-2020-1738</a></p>
<p>Release Date: 2020-03-16</p>
<p>Fix Resolution: 2.9.10</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png?' width=19 height=20> CVE-2021-3533</summary>
### Vulnerable Library - <b>ansible-2.9.9.tar.gz</b></p>
<p>Radically simple IT automation</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/00/5d/e10b83e0e6056dbd5b4809b451a191395175a57e3175ce04e35d9c5fc2a0/ansible-2.9.9.tar.gz">https://files.pythonhosted.org/packages/00/5d/e10b83e0e6056dbd5b4809b451a191395175a57e3175ce04e35d9c5fc2a0/ansible-2.9.9.tar.gz</a></p>
<p>Path to dependency file: /requirements.txt</p>
<p>Path to vulnerable library: /requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **ansible-2.9.9.tar.gz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ghc-staging-automation/3232857_ameer/commit/be311b8ee25e5ae20ac3c74ca316d0751c12262d">be311b8ee25e5ae20ac3c74ca316d0751c12262d</a></p>
<p>Found in base branch: <b>feature_branch</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A flaw was found in Ansible if an ansible user sets ANSIBLE_ASYNC_DIR to a subdirectory of a world writable directory. When this occurs, there is a race condition on the managed machine. A malicious, non-privileged account on the remote machine can exploit the race condition to access the async result data. This flaw affects Ansible Tower 3.7 and Ansible Automation Platform 1.2.
<p>Publish Date: 2021-06-09
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-3533>CVE-2021-3533</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>2.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2021-3533">https://nvd.nist.gov/vuln/detail/CVE-2021-3533</a></p>
<p>Release Date: 2021-06-09</p>
<p>Fix Resolution: 2.9.23</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p>
|
non_process
|
ansible tar gz vulnerabilities highest severity is vulnerable library ansible tar gz radically simple it automation library home page a href path to dependency file requirements txt path to vulnerable library requirements txt found in head commit a href vulnerabilities cve severity cvss dependency type fixed in ansible version remediation available high ansible tar gz direct medium ansible tar gz direct medium ansible tar gz direct medium ansible tar gz direct medium ansible tar gz direct medium ansible tar gz direct low ansible tar gz direct low ansible tar gz direct details cve vulnerable library ansible tar gz radically simple it automation library home page a href path to dependency file requirements txt path to vulnerable library requirements txt dependency hierarchy x ansible tar gz vulnerable library found in head commit a href found in base branch feature branch vulnerability details a flaw was found in the ansible engine in ansible engine x before and ansible engine x before when installing packages using the dnf module gpg signatures are ignored during installation even when disable gpg check is set to false which is the default behavior this flaw leads to malicious packages being installed on the system and arbitrary code executed via package installation scripts the highest threat from this vulnerability is to integrity and system availability publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library ansible tar gz radically simple it automation library home page a href path to dependency file requirements txt path to vulnerable library requirements txt dependency hierarchy x ansible tar gz vulnerable library found in head commit a href found in base branch feature branch vulnerability details a flaw was found in the ansible engine when using module args tasks executed with check mode check mode do not properly neutralize sensitive data exposed in the event data this flaw allows unauthorized users to read this data the highest threat from this vulnerability is to confidentiality publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library ansible tar gz radically simple it automation library home page a href path to dependency file requirements txt path to vulnerable library requirements txt dependency hierarchy x ansible tar gz vulnerable library found in head commit a href found in base branch feature branch vulnerability details a security flaw was found in ansible engine all ansible x versions prior to all ansible x versions prior to and all ansible x versions prior to when managing kubernetes using the module sensitive parameters such as passwords and tokens are passed to kubectl from the command line not using an environment variable or an input configuration file this will disclose passwords and tokens from process list and no log directive from debug module would not have any effect making these secrets being disclosed on stdout and log files publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library ansible tar gz radically simple it automation library home page a href path to dependency file requirements txt path to vulnerable library requirements txt dependency hierarchy x ansible tar gz vulnerable library found in head commit a href found in base branch feature branch vulnerability details a flaw was found in ansible module where credentials are disclosed in the console log by default and not protected by the security feature when using the bitbucket pipeline variable module this flaw allows an attacker to steal bitbucket pipeline credentials the highest threat from this vulnerability is to confidentiality publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library ansible tar gz radically simple it automation library home page a href path to dependency file requirements txt path to vulnerable library requirements txt dependency hierarchy x ansible tar gz vulnerable library found in head commit a href found in base branch feature branch vulnerability details an improper output neutralization for logs flaw was found in ansible when using the uri module where sensitive data is exposed to content and json output this flaw allows an attacker to access the logs or outputs of performed tasks to read keys used in playbooks from other users within the uri module the highest threat from this vulnerability is to data confidentiality publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library ansible tar gz radically simple it automation library home page a href path to dependency file requirements txt path to vulnerable library requirements txt dependency hierarchy x ansible tar gz vulnerable library found in head commit a href found in base branch feature branch vulnerability details an incomplete fix was found for the fix of the flaw cve ansible insecure temporary directory when running become user from become directive the provided fix is insufficient to prevent the race condition on systems using acls and fuse filesystems ansible engine and as well as previous versions are affected and ansible tower and as well as previous versions are affected publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity high privileges required low user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library ansible tar gz radically simple it automation library home page a href path to dependency file requirements txt path to vulnerable library requirements txt dependency hierarchy x ansible tar gz vulnerable library found in head commit a href found in base branch feature branch vulnerability details a flaw was found in ansible engine when the module package or service is used and the parameter use is not specified if a previous task is executed with a malicious user the module sent can be selected by the attacker using the ansible facts file all versions in x x and x branches are believed to be vulnerable publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity high privileges required low user interaction required scope changed impact metrics confidentiality impact none integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library ansible tar gz radically simple it automation library home page a href path to dependency file requirements txt path to vulnerable library requirements txt dependency hierarchy x ansible tar gz vulnerable library found in head commit a href found in base branch feature branch vulnerability details a flaw was found in ansible if an ansible user sets ansible async dir to a subdirectory of a world writable directory when this occurs there is a race condition on the managed machine a malicious non privileged account on the remote machine can exploit the race condition to access the async result data this flaw affects ansible tower and ansible automation platform publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity high privileges required low user interaction none scope unchanged impact metrics confidentiality impact low integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue rescue worker helmet automatic remediation is available for this issue
| 0
|
18,036
| 24,046,198,993
|
IssuesEvent
|
2022-09-16 08:33:42
|
geneontology/go-ontology
|
https://api.github.com/repos/geneontology/go-ontology
|
closed
|
Obsolete GO:0039633 killing by virus of host cell
|
obsoletion multi-species process
|
Dear all,
The proposal has been made to obsolete 'GO:0039633 killing by virus of host cell'. The reason for obsoletion is that this term is redundant with viral exist from host terms. There are no annotations or mappings to this term; this term is not present in any subset.
Children
GO:0044696 killing by virus of host cell by post-segregational killing
GO:0039634 killing by virus of host cell during superinfection exclusion
have been moved to upper level classes: killing by symbiont of host cells
Thanks, Pascale
|
1.0
|
Obsolete GO:0039633 killing by virus of host cell - Dear all,
The proposal has been made to obsolete 'GO:0039633 killing by virus of host cell'. The reason for obsoletion is that this term is redundant with viral exist from host terms. There are no annotations or mappings to this term; this term is not present in any subset.
Children
GO:0044696 killing by virus of host cell by post-segregational killing
GO:0039634 killing by virus of host cell during superinfection exclusion
have been moved to upper level classes: killing by symbiont of host cells
Thanks, Pascale
|
process
|
obsolete go killing by virus of host cell dear all the proposal has been made to obsolete go killing by virus of host cell the reason for obsoletion is that this term is redundant with viral exist from host terms there are no annotations or mappings to this term this term is not present in any subset children go killing by virus of host cell by post segregational killing go killing by virus of host cell during superinfection exclusion have been moved to upper level classes killing by symbiont of host cells thanks pascale
| 1
|
12,950
| 15,308,791,296
|
IssuesEvent
|
2021-02-24 23:06:11
|
GoogleCloudPlatform/cloudsql-proxy
|
https://api.github.com/repos/GoogleCloudPlatform/cloudsql-proxy
|
closed
|
Add tests for Go 1.16
|
type: process
|
Go 1.16 was released today. We should add tests and bump the binaries to compile with it.
|
1.0
|
Add tests for Go 1.16 - Go 1.16 was released today. We should add tests and bump the binaries to compile with it.
|
process
|
add tests for go go was released today we should add tests and bump the binaries to compile with it
| 1
|
20,944
| 27,805,232,913
|
IssuesEvent
|
2023-03-17 19:13:25
|
Azure/azure-sdk-tools
|
https://api.github.com/repos/Azure/azure-sdk-tools
|
closed
|
Implement an existing fabricbot rules using github actions.
|
Central-EngSys GitHub Event Processor
|
We're looking at moving from FabricBot into GitHub Actions. This issue is for tracking the work to do this.
|
1.0
|
Implement an existing fabricbot rules using github actions. - We're looking at moving from FabricBot into GitHub Actions. This issue is for tracking the work to do this.
|
process
|
implement an existing fabricbot rules using github actions we re looking at moving from fabricbot into github actions this issue is for tracking the work to do this
| 1
|
408,360
| 27,662,215,750
|
IssuesEvent
|
2023-03-12 16:54:41
|
Srebollo435/TFG-BOT-TRADING
|
https://api.github.com/repos/Srebollo435/TFG-BOT-TRADING
|
opened
|
Estructurar memoria TFG
|
documentation
|
Diseñar los apartados que va a contener el índice de la memoria del TFG.
|
1.0
|
Estructurar memoria TFG - Diseñar los apartados que va a contener el índice de la memoria del TFG.
|
non_process
|
estructurar memoria tfg diseñar los apartados que va a contener el índice de la memoria del tfg
| 0
|
3,151
| 6,204,212,004
|
IssuesEvent
|
2017-07-06 13:46:15
|
symfony/symfony
|
https://api.github.com/repos/symfony/symfony
|
closed
|
[Process] Consider allowing streamable input
|
Feature Process
|
Currently, the process component assumes that input is known before a command is invoked. Sometimes, you want to stream the input, i.e. gradually write it to the process that is being run. This could for example be done by exposing the pipes, or maybe better a specific method for writing:
``` php
$process = new Process('takes-some-input');
$process->start();
while ($stream->hasContent()) {
$process->write($stream->read());
}
```
|
1.0
|
[Process] Consider allowing streamable input - Currently, the process component assumes that input is known before a command is invoked. Sometimes, you want to stream the input, i.e. gradually write it to the process that is being run. This could for example be done by exposing the pipes, or maybe better a specific method for writing:
``` php
$process = new Process('takes-some-input');
$process->start();
while ($stream->hasContent()) {
$process->write($stream->read());
}
```
|
process
|
consider allowing streamable input currently the process component assumes that input is known before a command is invoked sometimes you want to stream the input i e gradually write it to the process that is being run this could for example be done by exposing the pipes or maybe better a specific method for writing php process new process takes some input process start while stream hascontent process write stream read
| 1
|
279,923
| 21,189,458,089
|
IssuesEvent
|
2022-04-08 15:46:39
|
AY2122S2-CS2103T-W13-1/tp
|
https://api.github.com/repos/AY2122S2-CS2103T-W13-1/tp
|
closed
|
[PE-D] If the procedure is free, what happens?
|
type.DocumentationBug contentious
|
As per the title above!
Since `0.0` also a positive value, though subjective.
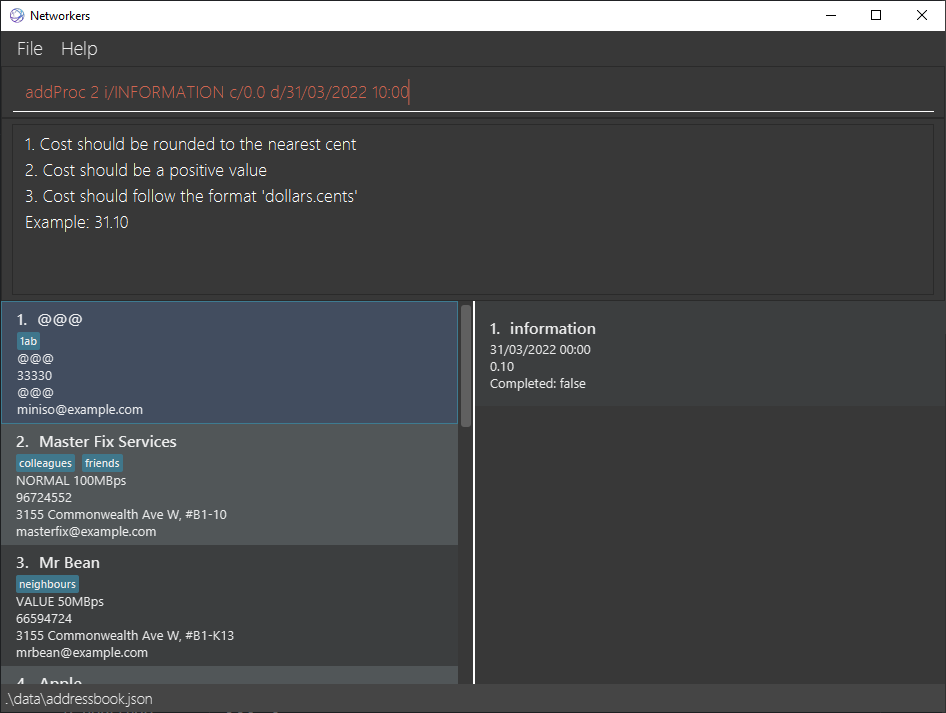
<!--session: 1648793109229-18c4eeb4-080a-48ae-9620-dd4be38ad9ba-->
<!--Version: Web v3.4.2-->
-------------
Labels: `type.FunctionalityBug` `severity.Low`
original: domlimm/ped#4
|
1.0
|
[PE-D] If the procedure is free, what happens? - As per the title above!
Since `0.0` also a positive value, though subjective.
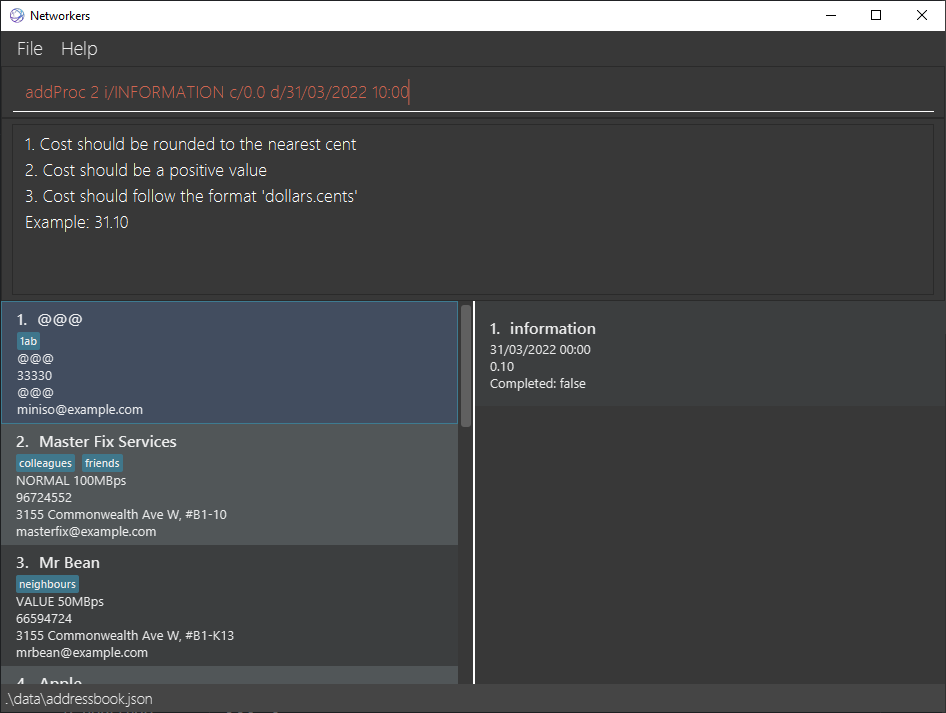
<!--session: 1648793109229-18c4eeb4-080a-48ae-9620-dd4be38ad9ba-->
<!--Version: Web v3.4.2-->
-------------
Labels: `type.FunctionalityBug` `severity.Low`
original: domlimm/ped#4
|
non_process
|
if the procedure is free what happens as per the title above since also a positive value though subjective labels type functionalitybug severity low original domlimm ped
| 0
|
244,526
| 20,674,977,591
|
IssuesEvent
|
2022-03-10 08:20:49
|
IRPTeam/IRP
|
https://api.github.com/repos/IRPTeam/IRP
|
closed
|
BP/BR/CP/CR base on CTO
|
bug need test update
|
В настройках пользователя по умолчанию указаны Company и Branch.
Но в CTO указывается другие Company и Branch. При создании BP/BR/CP/CR на основании CTO подставялются значение из пользовательских настроек, а не из CTO
|
1.0
|
BP/BR/CP/CR base on CTO - В настройках пользователя по умолчанию указаны Company и Branch.
Но в CTO указывается другие Company и Branch. При создании BP/BR/CP/CR на основании CTO подставялются значение из пользовательских настроек, а не из CTO
|
non_process
|
bp br cp cr base on cto в настройках пользователя по умолчанию указаны company и branch но в cto указывается другие company и branch при создании bp br cp cr на основании cto подставялются значение из пользовательских настроек а не из cto
| 0
|
122,270
| 16,099,487,206
|
IssuesEvent
|
2021-04-27 07:27:50
|
cgeo/cgeo
|
https://api.github.com/repos/cgeo/cgeo
|
opened
|
Cache details menu unreadable (device specific)
|
Bug Frontend Design Regression
|
<!-- Fill in the following form by adding your text below the explanation comments. -->
<!-- You can use the preview tab above to review your issue before submitting it. -->
## Bug description
<!-- Enter a summarized description of what the bug/problem is, that you found -->
Two users report, that the cache details menu is unreadable with light skin.
I can not reproduce this problem although I have nearly the same device (Samsung S20+ vs S20).
## Reproduce
### Steps to reproduce the problem
<!-- Describe step-by-step how to reproduce the problem -->
- Open cache
- Click on three-dot button
### Actual result after these steps
<!-- Describe the actual issue/problem/behavior in detail, which happens after the steps above -->
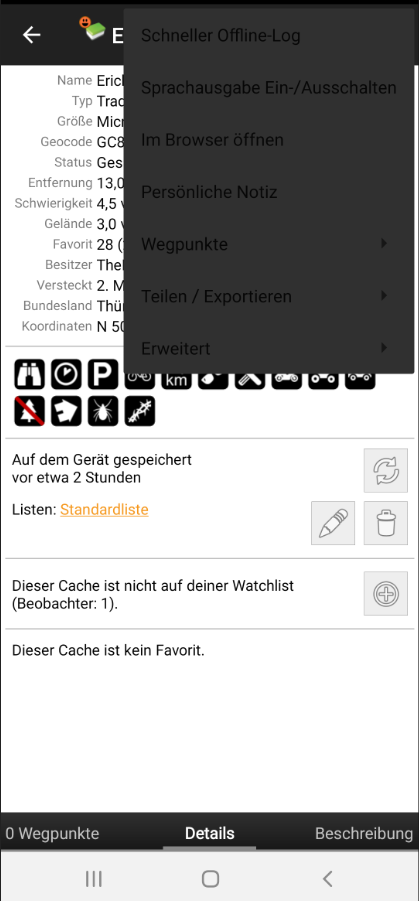
### Expected result after these steps
<!-- Describe what you expected to happen instead (correct behavior) -->
On my device it shows the black menu, which is IMHO OK
## c:geo version
<!-- You will find the c:geo version in c:geo Menu -> About c:geo -->
2021.04.25
## Reproducible
<!-- Yes / No (or describe under what conditions) -->
Yes, for that user
## System information
<!-- Attach system information here if available (see c:geo Menu -> About c:geo -> Swipe right to System) -->
<!-- Keep the apostrophe at beginning and end to have it properly formatted -->
```
--- System information ---
c:geo version: 2021.04.25
Device:
-------
- Device type: SM-G986B (y2sxeea, samsung)
- Available processors: 8
- Android version: 11
- Android build: RP1A.200720.012.G986BXXS7DUC9
- Sailfish OS detected: false
- Google Play services: enabled - 21.12.13 (150400-367530751)
- HW acceleration: disabled (manually changed)
Sensor and location:
-------
- Low power mode: inactive
- Compass capabilities: yes
- Rotation vector sensor: present
- Orientation sensor: present
- Magnetometer & Accelerometer sensor: present
- Direction sensor used: rotation vector
Program settings:
-------
- Hide caches: -
- Hide waypoints: -
- Set language: de
- System date format: dd.MM.yy
- Debug mode active: no
- Live map mode: true
- OSM multi-threading: true / threads: 4
- Global filter: display all caches
- Last backup: never
- Routing mode: Walk
- Map: OpenStreetMap.de
- Id: cgeo.geocaching.maps.mapsforge.MapsforgeMapProvider$OsmdeMapSource
- Atts: OpenStreetMap DE, map data OpenStreetMap contributors
- Theme: none
Services:
-------
- Geocaching sites enabled:
geocaching.com: Logged in (Anmeldung OK) / PREMIUM
- Geocaching.com date format: dd/MM/yyyy
- BRouter installed: false / connection available: false
- Installed c:geo plugins: none
Permissions & paths:
-------
- Fine location permission: granted
- Write external storage permission: granted
- System internal c:geo dir: /data/user/0/cgeo.geocaching (76,2 GB free) v2 internal isDir(7 entries)
- Legacy User storage c:geo dir: /storage/emulated/0/cgeo (76,2 GB free) v2 external non-removable isDir(6 entries)
- Geocache data: /storage/emulated/0/Android/data/cgeo.geocaching/files/GeocacheData (76,2 GB free) v2 external non-removable isDir(28 entries)
- Internal theme sync (is turned ON): /data/user/0/cgeo.geocaching/MapThemeData (76,2 GB free) v2 internal isDir(0 entries)
- Public Folders: #9
- BASE: /cgeo (User-Defined)[/cgeo[DOCUMENT#0:p-content://com.android.externalstorage.documents/tree/primary%3Acgeo::]] (Uri: content://com.android.externalstorage.documents/tree/primary%3Acgeo/document/primary%3Acgeo, Av:true, files:>=1, dirs:>=9, totalFileSize:>=609,5 KB, free space: 76,2 GB, files on device: 13511675)
- OFFLINE_MAPS: /cgeo/maps (Default)[/cgeo/maps[PERSISTABLE_FOLDER(BASE)#1:p-content://com.android.externalstorage.documents/tree/primary%3Acgeo::/maps]] (Uri: content://com.android.externalstorage.documents/tree/primary%3Acgeo/document/primary%3Acgeo%2Fmaps, Av:true, files:10, dirs:1, totalFileSize:3,2 GB, free space: 76,2 GB, files on device: 13511675)
- OFFLINE_MAP_THEMES: /cgeo/maps/_themes (Default)[/cgeo/maps/_themes[PERSISTABLE_FOLDER(OFFLINE_MAPS)#1:p-content://com.android.externalstorage.documents/tree/primary%3Acgeo::/maps/_themes]] (Uri: content://com.android.externalstorage.documents/tree/primary%3Acgeo/document/primary%3Acgeo%2Fmaps%2F_themes, Av:true, files:0, dirs:0, totalFileSize:0 B, free space: 76,2 GB, files on device: 13511675)
- LOGFILES: /cgeo/logfiles (Default)[/cgeo/logfiles[PERSISTABLE_FOLDER(BASE)#1:p-content://com.android.externalstorage.documents/tree/primary%3Acgeo::/logfiles]] (Uri: content://com.android.externalstorage.documents/tree/primary%3Acgeo/document/primary%3Acgeo%2Flogfiles, Av:true, files:1, dirs:0, totalFileSize:609,5 KB, free space: 76,2 GB, files on device: 13511675)
- GPX: /cgeo/gpx (User-Defined)[/cgeo/gpx[DOCUMENT#0:p-content://com.android.externalstorage.documents/tree/primary%3Acgeo%2Fgpx::]] (Uri: content://com.android.externalstorage.documents/tree/primary%3Acgeo%2Fgpx/document/primary%3Acgeo%2Fgpx, Av:true, files:0, dirs:0, totalFileSize:0 B, free space: 76,2 GB, files on device: 13511675)
- BACKUP: /cgeo/backup (Default)[/cgeo/backup[PERSISTABLE_FOLDER(BASE)#1:p-content://com.android.externalstorage.documents/tree/primary%3Acgeo::/backup]] (Uri: content://com.android.externalstorage.documents/tree/primary%3Acgeo/document/primary%3Acgeo%2Fbackup, Av:true, files:0, dirs:0, totalFileSize:0 B, free space: 76,2 GB, files on device: 13511675)
- FIELD_NOTES: /cgeo/field-notes (Default)[/cgeo/field-notes[PERSISTABLE_FOLDER(BASE)#1:p-content://com.android.externalstorage.documents/tree/primary%3Acgeo::/field-notes]] (Uri: content://com.android.externalstorage.documents/tree/primary%3Acgeo/document/primary%3Acgeo%2Ffield-notes, Av:true, files:7, dirs:0, totalFileSize:2,2 KB, free space: 76,2 GB, files on device: 13511675)
- SPOILER_IMAGES: /cgeo/GeocachePhotos (Default)[/cgeo/GeocachePhotos[PERSISTABLE_FOLDER(BASE)#1:p-content://com.android.externalstorage.documents/tree/primary%3Acgeo::/GeocachePhotos]] (Uri: content://com.android.externalstorage.documents/tree/primary%3Acgeo/document/primary%3Acgeo%2FGeocachePhotos, Av:true, files:0, dirs:3, totalFileSize:0 B, free space: 76,2 GB, files on device: 13511675)
- TEST_FOLDER: [Legacy]/data/user/0/cgeo.geocaching/files/unittest (Default)[/data/user/0/cgeo.geocaching/files/unittest[FILE#1:p-file:///data/user/0/cgeo.geocaching/files::/unittest]] (Uri: file:///data/user/0/cgeo.geocaching/files/unittest, Av:true, files:0, dirs:0, totalFileSize:0 B, free space: 76,2 GB, files on device: -1)
- Map render theme path:
- PersistedDocumentUris: #1
- TRACK: null
- Persisted Uri Permissions: #2
- content://com.android.externalstorage.documents/tree/primary%3Acgeo (27. März, 13:44):RW
- content://com.android.externalstorage.documents/tree/primary%3Acgeo%2Fgpx (2. Apr., 19:33):RW
- Database: /data/user/0/cgeo.geocaching/databases/data (v94, Size:1,3 MB) on system internal storage
-Settings: v5, Count:120
--- End of system information ---
```
## Screenshots
<!-- (optional, remove if not applicable) You may attach screenshots if applicable and helpful to explain your problem. -->
see above
|
1.0
|
Cache details menu unreadable (device specific) - <!-- Fill in the following form by adding your text below the explanation comments. -->
<!-- You can use the preview tab above to review your issue before submitting it. -->
## Bug description
<!-- Enter a summarized description of what the bug/problem is, that you found -->
Two users report, that the cache details menu is unreadable with light skin.
I can not reproduce this problem although I have nearly the same device (Samsung S20+ vs S20).
## Reproduce
### Steps to reproduce the problem
<!-- Describe step-by-step how to reproduce the problem -->
- Open cache
- Click on three-dot button
### Actual result after these steps
<!-- Describe the actual issue/problem/behavior in detail, which happens after the steps above -->
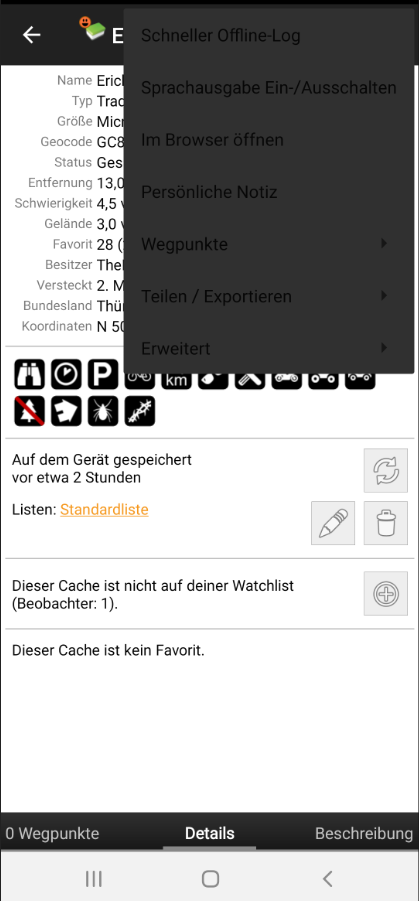
### Expected result after these steps
<!-- Describe what you expected to happen instead (correct behavior) -->
On my device it shows the black menu, which is IMHO OK
## c:geo version
<!-- You will find the c:geo version in c:geo Menu -> About c:geo -->
2021.04.25
## Reproducible
<!-- Yes / No (or describe under what conditions) -->
Yes, for that user
## System information
<!-- Attach system information here if available (see c:geo Menu -> About c:geo -> Swipe right to System) -->
<!-- Keep the apostrophe at beginning and end to have it properly formatted -->
```
--- System information ---
c:geo version: 2021.04.25
Device:
-------
- Device type: SM-G986B (y2sxeea, samsung)
- Available processors: 8
- Android version: 11
- Android build: RP1A.200720.012.G986BXXS7DUC9
- Sailfish OS detected: false
- Google Play services: enabled - 21.12.13 (150400-367530751)
- HW acceleration: disabled (manually changed)
Sensor and location:
-------
- Low power mode: inactive
- Compass capabilities: yes
- Rotation vector sensor: present
- Orientation sensor: present
- Magnetometer & Accelerometer sensor: present
- Direction sensor used: rotation vector
Program settings:
-------
- Hide caches: -
- Hide waypoints: -
- Set language: de
- System date format: dd.MM.yy
- Debug mode active: no
- Live map mode: true
- OSM multi-threading: true / threads: 4
- Global filter: display all caches
- Last backup: never
- Routing mode: Walk
- Map: OpenStreetMap.de
- Id: cgeo.geocaching.maps.mapsforge.MapsforgeMapProvider$OsmdeMapSource
- Atts: OpenStreetMap DE, map data OpenStreetMap contributors
- Theme: none
Services:
-------
- Geocaching sites enabled:
geocaching.com: Logged in (Anmeldung OK) / PREMIUM
- Geocaching.com date format: dd/MM/yyyy
- BRouter installed: false / connection available: false
- Installed c:geo plugins: none
Permissions & paths:
-------
- Fine location permission: granted
- Write external storage permission: granted
- System internal c:geo dir: /data/user/0/cgeo.geocaching (76,2 GB free) v2 internal isDir(7 entries)
- Legacy User storage c:geo dir: /storage/emulated/0/cgeo (76,2 GB free) v2 external non-removable isDir(6 entries)
- Geocache data: /storage/emulated/0/Android/data/cgeo.geocaching/files/GeocacheData (76,2 GB free) v2 external non-removable isDir(28 entries)
- Internal theme sync (is turned ON): /data/user/0/cgeo.geocaching/MapThemeData (76,2 GB free) v2 internal isDir(0 entries)
- Public Folders: #9
- BASE: /cgeo (User-Defined)[/cgeo[DOCUMENT#0:p-content://com.android.externalstorage.documents/tree/primary%3Acgeo::]] (Uri: content://com.android.externalstorage.documents/tree/primary%3Acgeo/document/primary%3Acgeo, Av:true, files:>=1, dirs:>=9, totalFileSize:>=609,5 KB, free space: 76,2 GB, files on device: 13511675)
- OFFLINE_MAPS: /cgeo/maps (Default)[/cgeo/maps[PERSISTABLE_FOLDER(BASE)#1:p-content://com.android.externalstorage.documents/tree/primary%3Acgeo::/maps]] (Uri: content://com.android.externalstorage.documents/tree/primary%3Acgeo/document/primary%3Acgeo%2Fmaps, Av:true, files:10, dirs:1, totalFileSize:3,2 GB, free space: 76,2 GB, files on device: 13511675)
- OFFLINE_MAP_THEMES: /cgeo/maps/_themes (Default)[/cgeo/maps/_themes[PERSISTABLE_FOLDER(OFFLINE_MAPS)#1:p-content://com.android.externalstorage.documents/tree/primary%3Acgeo::/maps/_themes]] (Uri: content://com.android.externalstorage.documents/tree/primary%3Acgeo/document/primary%3Acgeo%2Fmaps%2F_themes, Av:true, files:0, dirs:0, totalFileSize:0 B, free space: 76,2 GB, files on device: 13511675)
- LOGFILES: /cgeo/logfiles (Default)[/cgeo/logfiles[PERSISTABLE_FOLDER(BASE)#1:p-content://com.android.externalstorage.documents/tree/primary%3Acgeo::/logfiles]] (Uri: content://com.android.externalstorage.documents/tree/primary%3Acgeo/document/primary%3Acgeo%2Flogfiles, Av:true, files:1, dirs:0, totalFileSize:609,5 KB, free space: 76,2 GB, files on device: 13511675)
- GPX: /cgeo/gpx (User-Defined)[/cgeo/gpx[DOCUMENT#0:p-content://com.android.externalstorage.documents/tree/primary%3Acgeo%2Fgpx::]] (Uri: content://com.android.externalstorage.documents/tree/primary%3Acgeo%2Fgpx/document/primary%3Acgeo%2Fgpx, Av:true, files:0, dirs:0, totalFileSize:0 B, free space: 76,2 GB, files on device: 13511675)
- BACKUP: /cgeo/backup (Default)[/cgeo/backup[PERSISTABLE_FOLDER(BASE)#1:p-content://com.android.externalstorage.documents/tree/primary%3Acgeo::/backup]] (Uri: content://com.android.externalstorage.documents/tree/primary%3Acgeo/document/primary%3Acgeo%2Fbackup, Av:true, files:0, dirs:0, totalFileSize:0 B, free space: 76,2 GB, files on device: 13511675)
- FIELD_NOTES: /cgeo/field-notes (Default)[/cgeo/field-notes[PERSISTABLE_FOLDER(BASE)#1:p-content://com.android.externalstorage.documents/tree/primary%3Acgeo::/field-notes]] (Uri: content://com.android.externalstorage.documents/tree/primary%3Acgeo/document/primary%3Acgeo%2Ffield-notes, Av:true, files:7, dirs:0, totalFileSize:2,2 KB, free space: 76,2 GB, files on device: 13511675)
- SPOILER_IMAGES: /cgeo/GeocachePhotos (Default)[/cgeo/GeocachePhotos[PERSISTABLE_FOLDER(BASE)#1:p-content://com.android.externalstorage.documents/tree/primary%3Acgeo::/GeocachePhotos]] (Uri: content://com.android.externalstorage.documents/tree/primary%3Acgeo/document/primary%3Acgeo%2FGeocachePhotos, Av:true, files:0, dirs:3, totalFileSize:0 B, free space: 76,2 GB, files on device: 13511675)
- TEST_FOLDER: [Legacy]/data/user/0/cgeo.geocaching/files/unittest (Default)[/data/user/0/cgeo.geocaching/files/unittest[FILE#1:p-file:///data/user/0/cgeo.geocaching/files::/unittest]] (Uri: file:///data/user/0/cgeo.geocaching/files/unittest, Av:true, files:0, dirs:0, totalFileSize:0 B, free space: 76,2 GB, files on device: -1)
- Map render theme path:
- PersistedDocumentUris: #1
- TRACK: null
- Persisted Uri Permissions: #2
- content://com.android.externalstorage.documents/tree/primary%3Acgeo (27. März, 13:44):RW
- content://com.android.externalstorage.documents/tree/primary%3Acgeo%2Fgpx (2. Apr., 19:33):RW
- Database: /data/user/0/cgeo.geocaching/databases/data (v94, Size:1,3 MB) on system internal storage
-Settings: v5, Count:120
--- End of system information ---
```
## Screenshots
<!-- (optional, remove if not applicable) You may attach screenshots if applicable and helpful to explain your problem. -->
see above
|
non_process
|
cache details menu unreadable device specific bug description two users report that the cache details menu is unreadable with light skin i can not reproduce this problem although i have nearly the same device samsung vs reproduce steps to reproduce the problem open cache click on three dot button actual result after these steps expected result after these steps on my device it shows the black menu which is imho ok c geo version about c geo reproducible yes for that user system information about c geo swipe right to system system information c geo version device device type sm samsung available processors android version android build sailfish os detected false google play services enabled hw acceleration disabled manually changed sensor and location low power mode inactive compass capabilities yes rotation vector sensor present orientation sensor present magnetometer accelerometer sensor present direction sensor used rotation vector program settings hide caches hide waypoints set language de system date format dd mm yy debug mode active no live map mode true osm multi threading true threads global filter display all caches last backup never routing mode walk map openstreetmap de id cgeo geocaching maps mapsforge mapsforgemapprovider osmdemapsource atts openstreetmap de map data openstreetmap contributors theme none services geocaching sites enabled geocaching com logged in anmeldung ok premium geocaching com date format dd mm yyyy brouter installed false connection available false installed c geo plugins none permissions paths fine location permission granted write external storage permission granted system internal c geo dir data user cgeo geocaching gb free internal isdir entries legacy user storage c geo dir storage emulated cgeo gb free external non removable isdir entries geocache data storage emulated android data cgeo geocaching files geocachedata gb free external non removable isdir entries internal theme sync is turned on data user cgeo geocaching mapthemedata gb free internal isdir entries public folders base cgeo user defined uri content com android externalstorage documents tree primary document primary av true files dirs totalfilesize kb free space gb files on device offline maps cgeo maps default uri content com android externalstorage documents tree primary document primary av true files dirs totalfilesize gb free space gb files on device offline map themes cgeo maps themes default uri content com android externalstorage documents tree primary document primary themes av true files dirs totalfilesize b free space gb files on device logfiles cgeo logfiles default uri content com android externalstorage documents tree primary document primary av true files dirs totalfilesize kb free space gb files on device gpx cgeo gpx user defined uri content com android externalstorage documents tree primary document primary av true files dirs totalfilesize b free space gb files on device backup cgeo backup default uri content com android externalstorage documents tree primary document primary av true files dirs totalfilesize b free space gb files on device field notes cgeo field notes default uri content com android externalstorage documents tree primary document primary notes av true files dirs totalfilesize kb free space gb files on device spoiler images cgeo geocachephotos default uri content com android externalstorage documents tree primary document primary av true files dirs totalfilesize b free space gb files on device test folder data user cgeo geocaching files unittest default uri file data user cgeo geocaching files unittest av true files dirs totalfilesize b free space gb files on device map render theme path persisteddocumenturis track null persisted uri permissions content com android externalstorage documents tree primary märz rw content com android externalstorage documents tree primary apr rw database data user cgeo geocaching databases data size mb on system internal storage settings count end of system information screenshots see above
| 0
|
2,460
| 5,241,102,580
|
IssuesEvent
|
2017-01-31 14:56:12
|
AllenFang/react-bootstrap-table
|
https://api.github.com/repos/AllenFang/react-bootstrap-table
|
closed
|
Sort not working, don't quite understand the error message
|
bug inprocess
|
Hi there!
I'm getting this error when I try to sort on a column, not quite sure what it means
```
The type of sort field and order should be both with String or Array
```
I have provided a sortFunc
|
1.0
|
Sort not working, don't quite understand the error message - Hi there!
I'm getting this error when I try to sort on a column, not quite sure what it means
```
The type of sort field and order should be both with String or Array
```
I have provided a sortFunc
|
process
|
sort not working don t quite understand the error message hi there i m getting this error when i try to sort on a column not quite sure what it means the type of sort field and order should be both with string or array i have provided a sortfunc
| 1
|
18,068
| 24,082,659,715
|
IssuesEvent
|
2022-09-19 08:08:49
|
Blazebit/blaze-persistence
|
https://api.github.com/repos/Blazebit/blaze-persistence
|
closed
|
Annotation Processing not working for accessors with name result in views
|
kind: bug workaround available worth: high component: entity-view-annotation-processor
|
<!--- This template is for bugs. Remove it for other issues. -->
<!--- Choose an expressive title -->
### Description
<!--- Explain what you did and maybe show some code excerpts -->
If the code contains views which has accessors with the name `getResult` or/and `setReuslt(..)` the application does not compile.
### Expected behavior
<!--- What outcome would you expect? -->
No compile issue
### Actual behavior
```
Compilation Failed:
Note: Blaze-Persistence Entity-View Annotation Processor
Note: Annotation processor discovery took 15ms
Note: Annotation processor analysis took 21ms
Note: Generating relation classes took overall 258ms
Note: Generating multi relation classes took overall 258ms
Note: Generating metamodel classes took overall 256ms
Note: Generating implementation classes took overall 256ms
Note: Generating builder classes took overall 255ms
Note: Annotation processor generation took 263ms
Note: Annotation processor processed 1 entity views with 8 threads and took overall 301ms
Note: Hibernate JPA 2 Static-Metamodel Generator 5.6.5.Final
/Users/alexander/projects/acme/membership-service/api/target/classes/ch/acme/Yace_sync/boundary/YaceSyncReadViewBuilder.java:838: error: incompatible types: BuilderResult cannot be converted to ch.acme.Yace_sync.entity.YaceSyncResult
this.result,
^
/Users/alexander/projects/acme/membership-service/api/target/classes/ch/acme/Yace_sync/boundary/YaceSyncReadViewBuilder.java:879: error: cannot assign a value to final variable result
this.result = result;
^
/Users/alexander/projects/acme/membership-service/api/target/classes/ch/acme/Yace_sync/boundary/YaceSyncReadViewBuilder.java:879: error: incompatible types: ch.acme.Yace_sync.entity.YaceSyncResult cannot be converted to BuilderResult
this.result = result;
^
/Users/alexander/projects/acme/membership-service/api/target/classes/ch/acme/Yace_sync/boundary/YaceSyncReadViewBuilder.java:906: error: cannot assign a value to final variable result
this.result = value == null ? null : (YaceSyncResult) value;
^
/Users/alexander/projects/acme/membership-service/api/target/classes/ch/acme/Yace_sync/boundary/YaceSyncReadViewBuilder.java:906: error: incompatible types: bad type in conditional expression
this.result = value == null ? null : (YaceSyncResult) value;
^
ch.acme.Yace_sync.entity.YaceSyncResult cannot be converted to BuilderResult
Note: Some input files use unchecked or unsafe operations.
Note: Recompile with -Xlint:unchecked for details.
Note: Some messages have been simplified; recompile with -Xdiags:verbose to get full output
```
### Steps to reproduce
<!--- Give us enough details so we can create a testcase that reproduces this problem -->
<!--- Idealy you would create a test case based on the template project from: https://github.com/Blazebit/blaze-persistence-test-case-template -->
<!--- Either attach a ZIP containing the test case or create a pull request against the test-case-template repository and put the link to the PR here -->
### Environment
<!--- Environment info like e.g. -->
<!--- Version: 1.2.0-Alpha1 -->
<!--- JPA-Provider: Hibernate 5.2.7.Final -->
<!--- DBMS: PostgreSQL 9.6.2 -->
<!--- Application Server: Java SE -->
Version:
JPA-Provider: Hibernate
DBMS:
Application Server: Quarkus
|
1.0
|
Annotation Processing not working for accessors with name result in views - <!--- This template is for bugs. Remove it for other issues. -->
<!--- Choose an expressive title -->
### Description
<!--- Explain what you did and maybe show some code excerpts -->
If the code contains views which has accessors with the name `getResult` or/and `setReuslt(..)` the application does not compile.
### Expected behavior
<!--- What outcome would you expect? -->
No compile issue
### Actual behavior
```
Compilation Failed:
Note: Blaze-Persistence Entity-View Annotation Processor
Note: Annotation processor discovery took 15ms
Note: Annotation processor analysis took 21ms
Note: Generating relation classes took overall 258ms
Note: Generating multi relation classes took overall 258ms
Note: Generating metamodel classes took overall 256ms
Note: Generating implementation classes took overall 256ms
Note: Generating builder classes took overall 255ms
Note: Annotation processor generation took 263ms
Note: Annotation processor processed 1 entity views with 8 threads and took overall 301ms
Note: Hibernate JPA 2 Static-Metamodel Generator 5.6.5.Final
/Users/alexander/projects/acme/membership-service/api/target/classes/ch/acme/Yace_sync/boundary/YaceSyncReadViewBuilder.java:838: error: incompatible types: BuilderResult cannot be converted to ch.acme.Yace_sync.entity.YaceSyncResult
this.result,
^
/Users/alexander/projects/acme/membership-service/api/target/classes/ch/acme/Yace_sync/boundary/YaceSyncReadViewBuilder.java:879: error: cannot assign a value to final variable result
this.result = result;
^
/Users/alexander/projects/acme/membership-service/api/target/classes/ch/acme/Yace_sync/boundary/YaceSyncReadViewBuilder.java:879: error: incompatible types: ch.acme.Yace_sync.entity.YaceSyncResult cannot be converted to BuilderResult
this.result = result;
^
/Users/alexander/projects/acme/membership-service/api/target/classes/ch/acme/Yace_sync/boundary/YaceSyncReadViewBuilder.java:906: error: cannot assign a value to final variable result
this.result = value == null ? null : (YaceSyncResult) value;
^
/Users/alexander/projects/acme/membership-service/api/target/classes/ch/acme/Yace_sync/boundary/YaceSyncReadViewBuilder.java:906: error: incompatible types: bad type in conditional expression
this.result = value == null ? null : (YaceSyncResult) value;
^
ch.acme.Yace_sync.entity.YaceSyncResult cannot be converted to BuilderResult
Note: Some input files use unchecked or unsafe operations.
Note: Recompile with -Xlint:unchecked for details.
Note: Some messages have been simplified; recompile with -Xdiags:verbose to get full output
```
### Steps to reproduce
<!--- Give us enough details so we can create a testcase that reproduces this problem -->
<!--- Idealy you would create a test case based on the template project from: https://github.com/Blazebit/blaze-persistence-test-case-template -->
<!--- Either attach a ZIP containing the test case or create a pull request against the test-case-template repository and put the link to the PR here -->
### Environment
<!--- Environment info like e.g. -->
<!--- Version: 1.2.0-Alpha1 -->
<!--- JPA-Provider: Hibernate 5.2.7.Final -->
<!--- DBMS: PostgreSQL 9.6.2 -->
<!--- Application Server: Java SE -->
Version:
JPA-Provider: Hibernate
DBMS:
Application Server: Quarkus
|
process
|
annotation processing not working for accessors with name result in views description if the code contains views which has accessors with the name getresult or and setreuslt the application does not compile expected behavior no compile issue actual behavior compilation failed note blaze persistence entity view annotation processor note annotation processor discovery took note annotation processor analysis took note generating relation classes took overall note generating multi relation classes took overall note generating metamodel classes took overall note generating implementation classes took overall note generating builder classes took overall note annotation processor generation took note annotation processor processed entity views with threads and took overall note hibernate jpa static metamodel generator final users alexander projects acme membership service api target classes ch acme yace sync boundary yacesyncreadviewbuilder java error incompatible types builderresult cannot be converted to ch acme yace sync entity yacesyncresult this result users alexander projects acme membership service api target classes ch acme yace sync boundary yacesyncreadviewbuilder java error cannot assign a value to final variable result this result result users alexander projects acme membership service api target classes ch acme yace sync boundary yacesyncreadviewbuilder java error incompatible types ch acme yace sync entity yacesyncresult cannot be converted to builderresult this result result users alexander projects acme membership service api target classes ch acme yace sync boundary yacesyncreadviewbuilder java error cannot assign a value to final variable result this result value null null yacesyncresult value users alexander projects acme membership service api target classes ch acme yace sync boundary yacesyncreadviewbuilder java error incompatible types bad type in conditional expression this result value null null yacesyncresult value ch acme yace sync entity yacesyncresult cannot be converted to builderresult note some input files use unchecked or unsafe operations note recompile with xlint unchecked for details note some messages have been simplified recompile with xdiags verbose to get full output steps to reproduce environment version jpa provider hibernate dbms application server quarkus
| 1
|
13,267
| 15,731,394,448
|
IssuesEvent
|
2021-03-29 17:01:14
|
googleapis/google-api-java-client-services
|
https://api.github.com/repos/googleapis/google-api-java-client-services
|
opened
|
Warning: a recent release failed
|
type: process
|
The following release PRs may have failed:
* #7426
* #7425
* #7422
* #7420
* #7421
* #7419
* #7417
* #7418
* #7416
* #7415
* #7414
* #7413
* #7411
* #7426
* #7425
* #7422
* #7420
* #7421
* #7419
* #7417
* #7418
* #7416
* #7415
* #7414
* #7413
* #7411
* #7426
* #7425
* #7422
* #7420
* #7421
* #7419
* #7417
* #7418
* #7416
* #7415
* #7414
* #7413
* #7411
|
1.0
|
Warning: a recent release failed - The following release PRs may have failed:
* #7426
* #7425
* #7422
* #7420
* #7421
* #7419
* #7417
* #7418
* #7416
* #7415
* #7414
* #7413
* #7411
* #7426
* #7425
* #7422
* #7420
* #7421
* #7419
* #7417
* #7418
* #7416
* #7415
* #7414
* #7413
* #7411
* #7426
* #7425
* #7422
* #7420
* #7421
* #7419
* #7417
* #7418
* #7416
* #7415
* #7414
* #7413
* #7411
|
process
|
warning a recent release failed the following release prs may have failed
| 1
|
75,832
| 21,007,509,729
|
IssuesEvent
|
2022-03-30 01:02:03
|
GEOSX/GEOSX
|
https://api.github.com/repos/GEOSX/GEOSX
|
closed
|
`config-build.py` appends `-D` options after `-C`
|
type: build
|
The `-D` options may not be considered by the `-C` cache script, because the order is important.
Changing the order should be OK, but we need to be sure of what we are doing because this script is critical to a lot of users.
|
1.0
|
`config-build.py` appends `-D` options after `-C` - The `-D` options may not be considered by the `-C` cache script, because the order is important.
Changing the order should be OK, but we need to be sure of what we are doing because this script is critical to a lot of users.
|
non_process
|
config build py appends d options after c the d options may not be considered by the c cache script because the order is important changing the order should be ok but we need to be sure of what we are doing because this script is critical to a lot of users
| 0
|
225,753
| 17,288,189,458
|
IssuesEvent
|
2021-07-24 06:14:20
|
MichaelZhao21/tams-club-cal
|
https://api.github.com/repos/MichaelZhao21/tams-club-cal
|
closed
|
Create official documentation!
|
documentation help wanted new feature
|
### Is your feature request related to a problem? Please describe.
Our code base is starting to get quite a bit bigger (and messier). I've already set up the documentation, available at [docs.tams.club](https://docs.tams.club), but it is simply the default framework for Docsify. I would like to have this well-written and easy to understand eventually.
### Describe the solution you'd like
We need to do the following things:
- [x] Create subpages
- [x] Create sidebar
- [ ] Write Frontend: Components that are used
- [x] Write Backend: API endpoints that can be called
- [x] Write MongoDB: Organization of databases and collections, as well as the standard format for documents.
- [ ] Out-of-date items page
And, of course, this can never be fully completed as we are continuously developing, so I'm hoping to create a system where we can mark things out of date on the docs with every commit.
### Describe alternatives you've considered
N/A
### Additional context
Replacement of #46
|
1.0
|
Create official documentation! - ### Is your feature request related to a problem? Please describe.
Our code base is starting to get quite a bit bigger (and messier). I've already set up the documentation, available at [docs.tams.club](https://docs.tams.club), but it is simply the default framework for Docsify. I would like to have this well-written and easy to understand eventually.
### Describe the solution you'd like
We need to do the following things:
- [x] Create subpages
- [x] Create sidebar
- [ ] Write Frontend: Components that are used
- [x] Write Backend: API endpoints that can be called
- [x] Write MongoDB: Organization of databases and collections, as well as the standard format for documents.
- [ ] Out-of-date items page
And, of course, this can never be fully completed as we are continuously developing, so I'm hoping to create a system where we can mark things out of date on the docs with every commit.
### Describe alternatives you've considered
N/A
### Additional context
Replacement of #46
|
non_process
|
create official documentation is your feature request related to a problem please describe our code base is starting to get quite a bit bigger and messier i ve already set up the documentation available at but it is simply the default framework for docsify i would like to have this well written and easy to understand eventually describe the solution you d like we need to do the following things create subpages create sidebar write frontend components that are used write backend api endpoints that can be called write mongodb organization of databases and collections as well as the standard format for documents out of date items page and of course this can never be fully completed as we are continuously developing so i m hoping to create a system where we can mark things out of date on the docs with every commit describe alternatives you ve considered n a additional context replacement of
| 0
|
8,928
| 12,035,702,218
|
IssuesEvent
|
2020-04-13 18:22:52
|
googleapis/nodejs-bigquery
|
https://api.github.com/repos/googleapis/nodejs-bigquery
|
closed
|
update @types/sinon@9 and remove FakeTimers workaround
|
api: bigquery type: process
|
Tests for `Table` as part of PR #589 use the sinon fake timers API async methods. At the time of this writing (and #589) the async methods, i.e. `runAllAsync` and `tickAsync`, are missing from the TS definitions. A workaround is currently in place that defines the `SinonFakeTimersShim` interface:
```
interface SinonFakeTimersShim extends sinon.SinonFakeTimers {
runAllAsync(): Promise<number>;
tickAsync(ms: number | string): Promise<number>;
}
```
The PR https://github.com/DefinitelyTyped/DefinitelyTyped/pull/43148 was introduced to resolve this issue, and once it lands:
1. update `@types/sinon` to version 9 (will be a major version bump up from 7)
2. remove the temporary workaround interface for `SinonFakeTimersShim ` in favor of `SinonFakeTimers`
|
1.0
|
update @types/sinon@9 and remove FakeTimers workaround - Tests for `Table` as part of PR #589 use the sinon fake timers API async methods. At the time of this writing (and #589) the async methods, i.e. `runAllAsync` and `tickAsync`, are missing from the TS definitions. A workaround is currently in place that defines the `SinonFakeTimersShim` interface:
```
interface SinonFakeTimersShim extends sinon.SinonFakeTimers {
runAllAsync(): Promise<number>;
tickAsync(ms: number | string): Promise<number>;
}
```
The PR https://github.com/DefinitelyTyped/DefinitelyTyped/pull/43148 was introduced to resolve this issue, and once it lands:
1. update `@types/sinon` to version 9 (will be a major version bump up from 7)
2. remove the temporary workaround interface for `SinonFakeTimersShim ` in favor of `SinonFakeTimers`
|
process
|
update types sinon and remove faketimers workaround tests for table as part of pr use the sinon fake timers api async methods at the time of this writing and the async methods i e runallasync and tickasync are missing from the ts definitions a workaround is currently in place that defines the sinonfaketimersshim interface interface sinonfaketimersshim extends sinon sinonfaketimers runallasync promise tickasync ms number string promise the pr was introduced to resolve this issue and once it lands update types sinon to version will be a major version bump up from remove the temporary workaround interface for sinonfaketimersshim in favor of sinonfaketimers
| 1
|
174,504
| 27,657,541,622
|
IssuesEvent
|
2023-03-12 05:36:16
|
sboxgame/issues
|
https://api.github.com/repos/sboxgame/issues
|
closed
|
Tools API grievances
|
api design
|
### What it is?
(i'll keep this updated as I keep working on tool dev.)
**Window naming**: Tools.Window being a QMainWindow and not a QWindow is very confusing initially (I couldn't figure out why I had side borders until I saw it was a QMainWindow and read the QT docs)
**No GraphicsView alignment**: Please expose QGraphicsView.setAlignment! (I made an issue for this before: #2535)
**Suboptimal custom window decor. support**: Please expose QWindow.startSystemMove/startSystemResize!
**BaseWindow Title property**: BaseWindow uses WindowTitle, but Window uses Title? I assume this just hasn't been implemented yet because BaseWindow looks a bit unfinished
### Suggestions
**Wiki category**: Maybe create a category/subcategory for tool development. I'm not too sure about putting tool stuff in the same category as in-game UI stuff
### What should it be?
**Window naming**: Maybe just have Tools.Window as Tools.MainWindow?
|
1.0
|
Tools API grievances - ### What it is?
(i'll keep this updated as I keep working on tool dev.)
**Window naming**: Tools.Window being a QMainWindow and not a QWindow is very confusing initially (I couldn't figure out why I had side borders until I saw it was a QMainWindow and read the QT docs)
**No GraphicsView alignment**: Please expose QGraphicsView.setAlignment! (I made an issue for this before: #2535)
**Suboptimal custom window decor. support**: Please expose QWindow.startSystemMove/startSystemResize!
**BaseWindow Title property**: BaseWindow uses WindowTitle, but Window uses Title? I assume this just hasn't been implemented yet because BaseWindow looks a bit unfinished
### Suggestions
**Wiki category**: Maybe create a category/subcategory for tool development. I'm not too sure about putting tool stuff in the same category as in-game UI stuff
### What should it be?
**Window naming**: Maybe just have Tools.Window as Tools.MainWindow?
|
non_process
|
tools api grievances what it is i ll keep this updated as i keep working on tool dev window naming tools window being a qmainwindow and not a qwindow is very confusing initially i couldn t figure out why i had side borders until i saw it was a qmainwindow and read the qt docs no graphicsview alignment please expose qgraphicsview setalignment i made an issue for this before suboptimal custom window decor support please expose qwindow startsystemmove startsystemresize basewindow title property basewindow uses windowtitle but window uses title i assume this just hasn t been implemented yet because basewindow looks a bit unfinished suggestions wiki category maybe create a category subcategory for tool development i m not too sure about putting tool stuff in the same category as in game ui stuff what should it be window naming maybe just have tools window as tools mainwindow
| 0
|
40,601
| 16,507,522,095
|
IssuesEvent
|
2021-05-25 21:21:52
|
MicrosoftDocs/azure-docs
|
https://api.github.com/repos/MicrosoftDocs/azure-docs
|
closed
|
Should explain prerequisites early in the article
|
Pri1 assigned-to-author container-service/svc doc-bug triaged
|
You should explain [the prerequisites](https://docs.microsoft.com/en-us/azure/aks/servicemesh-osm-about?pivots=client-operating-system-linux#before-you-begin) early in the article. I have failed to enable this addon on my existing cluster due to a lack of aks-preview extension. Thanks.
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: edf448c9-4082-1124-0a41-f09f1771fe5d
* Version Independent ID: 95abeb00-0d5a-6e9a-bc4e-24f5dcc6ddba
* Content: [Open Service Mesh (Preview) - Azure Kubernetes Service](https://docs.microsoft.com/en-us/azure/aks/servicemesh-osm-about?pivots=client-operating-system-linux)
* Content Source: [articles/aks/servicemesh-osm-about.md](https://github.com/MicrosoftDocs/azure-docs/blob/master/articles/aks/servicemesh-osm-about.md)
* Service: **container-service**
* GitHub Login: @mlearned
* Microsoft Alias: **pgibson**
|
1.0
|
Should explain prerequisites early in the article - You should explain [the prerequisites](https://docs.microsoft.com/en-us/azure/aks/servicemesh-osm-about?pivots=client-operating-system-linux#before-you-begin) early in the article. I have failed to enable this addon on my existing cluster due to a lack of aks-preview extension. Thanks.
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: edf448c9-4082-1124-0a41-f09f1771fe5d
* Version Independent ID: 95abeb00-0d5a-6e9a-bc4e-24f5dcc6ddba
* Content: [Open Service Mesh (Preview) - Azure Kubernetes Service](https://docs.microsoft.com/en-us/azure/aks/servicemesh-osm-about?pivots=client-operating-system-linux)
* Content Source: [articles/aks/servicemesh-osm-about.md](https://github.com/MicrosoftDocs/azure-docs/blob/master/articles/aks/servicemesh-osm-about.md)
* Service: **container-service**
* GitHub Login: @mlearned
* Microsoft Alias: **pgibson**
|
non_process
|
should explain prerequisites early in the article you should explain early in the article i have failed to enable this addon on my existing cluster due to a lack of aks preview extension thanks document details ⚠ do not edit this section it is required for docs microsoft com ➟ github issue linking id version independent id content content source service container service github login mlearned microsoft alias pgibson
| 0
|
70,696
| 8,570,942,595
|
IssuesEvent
|
2018-11-12 00:45:06
|
mbenlioglu/tor-cli
|
https://api.github.com/repos/mbenlioglu/tor-cli
|
closed
|
Problematic Release Generation
|
design issue help wanted
|
## Problem
Due to lack of structure, generating a release is not trivial. Scripts for local and remote instances coexist in the same folders, and needs to be handpicked during release. (which also makes it hard for someone to build from repo)
**Note:** Consider issue #3 when redesigning
|
1.0
|
Problematic Release Generation - ## Problem
Due to lack of structure, generating a release is not trivial. Scripts for local and remote instances coexist in the same folders, and needs to be handpicked during release. (which also makes it hard for someone to build from repo)
**Note:** Consider issue #3 when redesigning
|
non_process
|
problematic release generation problem nbsp nbsp nbsp nbsp due to lack of structure generating a release is not trivial scripts for local and remote instances coexist in the same folders and needs to be handpicked during release which also makes it hard for someone to build from repo note consider issue when redesigning
| 0
|
7,731
| 10,852,968,971
|
IssuesEvent
|
2019-11-13 13:52:29
|
openopps/openopps-platform
|
https://api.github.com/repos/openopps/openopps-platform
|
opened
|
Add "I do not have work experience" option on application
|
Apply Process State Dept.
|
Who:
What:
Why:
Issue:
State has noted that many students did not enter work experience and think it's because they missed the section. They would like to make work experience required.
Acceptance criteria:
- Add a checkbox to allow the applicant to indicate "I do not wish to provide or do not have any work experience"
- The applicant must either have selected that checkbox or entered at least one row of work experience to continue.
- Error messaging will indicate that work experience is required
-
USAJOBS Resume Builder Checkbox:

|
1.0
|
Add "I do not have work experience" option on application - Who:
What:
Why:
Issue:
State has noted that many students did not enter work experience and think it's because they missed the section. They would like to make work experience required.
Acceptance criteria:
- Add a checkbox to allow the applicant to indicate "I do not wish to provide or do not have any work experience"
- The applicant must either have selected that checkbox or entered at least one row of work experience to continue.
- Error messaging will indicate that work experience is required
-
USAJOBS Resume Builder Checkbox:

|
process
|
add i do not have work experience option on application who what why issue state has noted that many students did not enter work experience and think it s because they missed the section they would like to make work experience required acceptance criteria add a checkbox to allow the applicant to indicate i do not wish to provide or do not have any work experience the applicant must either have selected that checkbox or entered at least one row of work experience to continue error messaging will indicate that work experience is required usajobs resume builder checkbox
| 1
|
262,091
| 27,850,889,650
|
IssuesEvent
|
2023-03-20 18:36:14
|
jgeraigery/community-scripts
|
https://api.github.com/repos/jgeraigery/community-scripts
|
opened
|
zest-0.14.0.jar: 29 vulnerabilities (highest severity is: 9.8)
|
Mend: dependency security vulnerability
|
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>zest-0.14.0.jar</b></p></summary>
<p></p>
<p>Path to dependency file: /build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/xalan/xalan/2.7.2/d55d3f02a56ec4c25695fe67e1334ff8c2ecea23/xalan-2.7.2.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/community-scripts/commit/5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4">5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (zest version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2022-42889](https://www.mend.io/vulnerability-database/CVE-2022-42889) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png' width=19 height=20> Critical | 9.8 | commons-text-1.9.jar | Transitive | 0.14.1 | ✅ |
| [CVE-2022-1471](https://www.mend.io/vulnerability-database/CVE-2022-1471) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png' width=19 height=20> Critical | 9.8 | snakeyaml-1.19.jar | Transitive | N/A* | ❌ |
| [WS-2019-0490](https://github.com/cbeust/jcommander/commit/3ae95595febbed9c13f367b6bda5c0be1c572c53) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jcommander-1.72.jar | Transitive | N/A* | ❌ |
| [CVE-2020-5529](https://www.mend.io/vulnerability-database/CVE-2020-5529) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | htmlunit-2.36.0.jar | Transitive | N/A* | ❌ |
| [WS-2021-0419](https://github.com/google/gson/pull/1991) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.7 | gson-2.8.5.jar | Transitive | N/A* | ❌ |
| [CVE-2017-18640](https://www.mend.io/vulnerability-database/CVE-2017-18640) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | snakeyaml-1.19.jar | Transitive | N/A* | ❌ |
| [CVE-2022-25857](https://www.mend.io/vulnerability-database/CVE-2022-25857) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | snakeyaml-1.19.jar | Transitive | N/A* | ❌ |
| [CVE-2022-41404](https://www.mend.io/vulnerability-database/CVE-2022-41404) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | ini4j-0.5.2.jar | Transitive | N/A* | ❌ |
| [CVE-2022-3509](https://www.mend.io/vulnerability-database/CVE-2022-3509) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | protobuf-java-2.4.1.jar | Transitive | N/A* | ❌ |
| [CVE-2022-29546](https://www.mend.io/vulnerability-database/CVE-2022-29546) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | neko-htmlunit-2.36.0.jar | Transitive | N/A* | ❌ |
| [CVE-2021-28165](https://www.mend.io/vulnerability-database/CVE-2021-28165) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | jetty-io-9.4.20.v20190813.jar | Transitive | N/A* | ❌ |
| [CVE-2022-25647](https://www.mend.io/vulnerability-database/CVE-2022-25647) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | gson-2.8.5.jar | Transitive | N/A* | ❌ |
| [CVE-2022-34169](https://www.mend.io/vulnerability-database/CVE-2022-34169) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | xalan-2.7.2.jar | Transitive | N/A* | ❌ |
| [CVE-2022-3171](https://www.mend.io/vulnerability-database/CVE-2022-3171) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | protobuf-java-2.4.1.jar | Transitive | N/A* | ❌ |
| [CVE-2022-40159](https://www.mend.io/vulnerability-database/CVE-2022-40159) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | commons-jxpath-1.3.jar | Transitive | N/A* | ❌ |
| [CVE-2022-23437](https://www.mend.io/vulnerability-database/CVE-2022-23437) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | xercesImpl-2.12.0.jar | Transitive | N/A* | ❌ |
| [CVE-2022-38752](https://www.mend.io/vulnerability-database/CVE-2022-38752) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | snakeyaml-1.19.jar | Transitive | N/A* | ❌ |
| [CVE-2021-37533](https://www.mend.io/vulnerability-database/CVE-2021-37533) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | commons-net-3.6.jar | Transitive | N/A* | ❌ |
| [CVE-2022-38751](https://www.mend.io/vulnerability-database/CVE-2022-38751) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | snakeyaml-1.19.jar | Transitive | N/A* | ❌ |
| [CVE-2022-38749](https://www.mend.io/vulnerability-database/CVE-2022-38749) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | snakeyaml-1.19.jar | Transitive | N/A* | ❌ |
| [CVE-2022-40160](https://www.mend.io/vulnerability-database/CVE-2022-40160) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | commons-jxpath-1.3.jar | Transitive | N/A* | ❌ |
| [CVE-2022-41854](https://www.mend.io/vulnerability-database/CVE-2022-41854) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | snakeyaml-1.19.jar | Transitive | N/A* | ❌ |
| [CVE-2022-38750](https://www.mend.io/vulnerability-database/CVE-2022-38750) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.5 | snakeyaml-1.19.jar | Transitive | N/A* | ❌ |
| [CVE-2021-22569](https://www.mend.io/vulnerability-database/CVE-2021-22569) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.5 | protobuf-java-2.4.1.jar | Transitive | N/A* | ❌ |
| [CVE-2021-28169](https://www.mend.io/vulnerability-database/CVE-2021-28169) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | jetty-http-9.4.20.v20190813.jar | Transitive | N/A* | ❌ |
| [CVE-2020-27223](https://www.mend.io/vulnerability-database/CVE-2020-27223) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | jetty-http-9.4.20.v20190813.jar | Transitive | N/A* | ❌ |
| [CVE-2020-13956](https://www.mend.io/vulnerability-database/CVE-2020-13956) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | httpclient-4.5.9.jar | Transitive | N/A* | ❌ |
| [CVE-2020-8908](https://www.mend.io/vulnerability-database/CVE-2020-8908) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 3.3 | guava-25.0-jre.jar | Transitive | N/A* | ❌ |
| [CVE-2022-2047](https://www.mend.io/vulnerability-database/CVE-2022-2047) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 2.7 | detected in multiple dependencies | Transitive | N/A* | ❌ |
<p>*For some transitive vulnerabilities, there is no version of direct dependency with a fix. Check the "Details" section below to see if there is a version of transitive dependency where vulnerability is fixed.</p>
## Details
> Partial details (24 vulnerabilities) are displayed below due to a content size limitation in GitHub. To view information on the remaining vulnerabilities, navigate to the Mend Application.<br>
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png' width=19 height=20> CVE-2022-42889</summary>
### Vulnerable Library - <b>commons-text-1.9.jar</b></p>
<p>Apache Commons Text is a library focused on algorithms working on strings.</p>
<p>Library home page: <a href="https://commons.apache.org/proper/commons-text">https://commons.apache.org/proper/commons-text</a></p>
<p>Path to dependency file: /build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.apache.commons/commons-text/1.9/ba6ac8c2807490944a0a27f6f8e68fb5ed2e80e2/commons-text-1.9.jar</p>
<p>
Dependency Hierarchy:
- zest-0.14.0.jar (Root Library)
- htmlunit-driver-2.36.0.jar
- htmlunit-2.36.0.jar
- :x: **commons-text-1.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/community-scripts/commit/5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4">5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache Commons Text performs variable interpolation, allowing properties to be dynamically evaluated and expanded. The standard format for interpolation is "${prefix:name}", where "prefix" is used to locate an instance of org.apache.commons.text.lookup.StringLookup that performs the interpolation. Starting with version 1.5 and continuing through 1.9, the set of default Lookup instances included interpolators that could result in arbitrary code execution or contact with remote servers. These lookups are: - "script" - execute expressions using the JVM script execution engine (javax.script) - "dns" - resolve dns records - "url" - load values from urls, including from remote servers Applications using the interpolation defaults in the affected versions may be vulnerable to remote code execution or unintentional contact with remote servers if untrusted configuration values are used. Users are recommended to upgrade to Apache Commons Text 1.10.0, which disables the problematic interpolators by default.
<p>Publish Date: 2022-10-13
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-42889>CVE-2022-42889</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.openwall.com/lists/oss-security/2022/10/13/4">https://www.openwall.com/lists/oss-security/2022/10/13/4</a></p>
<p>Release Date: 2022-10-13</p>
<p>Fix Resolution (org.apache.commons:commons-text): 1.10.0</p>
<p>Direct dependency fix Resolution (org.mozilla:zest): 0.14.1</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png' width=19 height=20> CVE-2022-1471</summary>
### Vulnerable Library - <b>snakeyaml-1.19.jar</b></p>
<p>YAML 1.1 parser and emitter for Java</p>
<p>Library home page: <a href="http://www.snakeyaml.org">http://www.snakeyaml.org</a></p>
<p>Path to dependency file: /build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.yaml/snakeyaml/1.19/2d998d3d674b172a588e54ab619854d073f555b5/snakeyaml-1.19.jar</p>
<p>
Dependency Hierarchy:
- zest-0.14.0.jar (Root Library)
- selenium-server-3.141.59.jar
- :x: **snakeyaml-1.19.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/community-scripts/commit/5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4">5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
SnakeYaml's Constructor() class does not restrict types which can be instantiated during deserialization. Deserializing yaml content provided by an attacker can lead to remote code execution. We recommend using SnakeYaml's SafeConsturctor when parsing untrusted content to restrict deserialization.
<p>Publish Date: 2022-12-01
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-1471>CVE-2022-1471</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bitbucket.org/snakeyaml/snakeyaml/issues/561/cve-2022-1471-vulnerability-in#comment-64634374">https://bitbucket.org/snakeyaml/snakeyaml/issues/561/cve-2022-1471-vulnerability-in#comment-64634374</a></p>
<p>Release Date: 2022-12-01</p>
<p>Fix Resolution: org.yaml:snakeyaml:2.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> WS-2019-0490</summary>
### Vulnerable Library - <b>jcommander-1.72.jar</b></p>
<p>Command line parsing</p>
<p>Library home page: <a href="http://jcommander.org">http://jcommander.org</a></p>
<p>Path to dependency file: /build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.beust/jcommander/1.72/6375e521c1e11d6563d4f25a07ce124ccf8cd171/jcommander-1.72.jar</p>
<p>
Dependency Hierarchy:
- zest-0.14.0.jar (Root Library)
- selenium-server-3.141.59.jar
- :x: **jcommander-1.72.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/community-scripts/commit/5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4">5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Inclusion of Functionality from Untrusted Control Sphere vulnerability found in jcommander before 1.75. jcommander resolving dependencies over HTTP instead of HTTPS.
<p>Publish Date: 2019-02-19
<p>URL: <a href=https://github.com/cbeust/jcommander/commit/3ae95595febbed9c13f367b6bda5c0be1c572c53>WS-2019-0490</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2019-02-19</p>
<p>Fix Resolution: com.beust:jcommander:1.75</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-5529</summary>
### Vulnerable Library - <b>htmlunit-2.36.0.jar</b></p>
<p>A headless browser intended for use in testing web-based applications.</p>
<p>Library home page: <a href="http://htmlunit.sourceforge.net">http://htmlunit.sourceforge.net</a></p>
<p>Path to dependency file: /build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/net.sourceforge.htmlunit/htmlunit/2.36.0/efe6df9c5bc1284cd1d7952434ea4f85c5a32f72/htmlunit-2.36.0.jar</p>
<p>
Dependency Hierarchy:
- zest-0.14.0.jar (Root Library)
- htmlunit-driver-2.36.0.jar
- :x: **htmlunit-2.36.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/community-scripts/commit/5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4">5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
HtmlUnit prior to 2.37.0 contains code execution vulnerabilities. HtmlUnit initializes Rhino engine improperly, hence a malicious JavScript code can execute arbitrary Java code on the application. Moreover, when embedded in Android application, Android-specific initialization of Rhino engine is done in an improper way, hence a malicious JavaScript code can execute arbitrary Java code on the application.
<p>Publish Date: 2020-02-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-5529>CVE-2020-5529</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2020-02-11</p>
<p>Fix Resolution: net.sourceforge.htmlunit:htmlunit:2.37.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> WS-2021-0419</summary>
### Vulnerable Library - <b>gson-2.8.5.jar</b></p>
<p>Gson JSON library</p>
<p>Library home page: <a href="https://github.com/google/gson">https://github.com/google/gson</a></p>
<p>Path to dependency file: /build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.google.code.gson/gson/2.8.5/f645ed69d595b24d4cf8b3fbb64cc505bede8829/gson-2.8.5.jar</p>
<p>
Dependency Hierarchy:
- zest-0.14.0.jar (Root Library)
- :x: **gson-2.8.5.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/community-scripts/commit/5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4">5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Denial of Service vulnerability was discovered in gson before 2.8.9 via the writeReplace() method.
<p>Publish Date: 2021-10-11
<p>URL: <a href=https://github.com/google/gson/pull/1991>WS-2021-0419</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.7</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2021-10-11</p>
<p>Fix Resolution: com.google.code.gson:gson:2.8.9</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2017-18640</summary>
### Vulnerable Library - <b>snakeyaml-1.19.jar</b></p>
<p>YAML 1.1 parser and emitter for Java</p>
<p>Library home page: <a href="http://www.snakeyaml.org">http://www.snakeyaml.org</a></p>
<p>Path to dependency file: /build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.yaml/snakeyaml/1.19/2d998d3d674b172a588e54ab619854d073f555b5/snakeyaml-1.19.jar</p>
<p>
Dependency Hierarchy:
- zest-0.14.0.jar (Root Library)
- selenium-server-3.141.59.jar
- :x: **snakeyaml-1.19.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/community-scripts/commit/5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4">5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The Alias feature in SnakeYAML before 1.26 allows entity expansion during a load operation, a related issue to CVE-2003-1564.
<p>Publish Date: 2019-12-12
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2017-18640>CVE-2017-18640</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-18640">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-18640</a></p>
<p>Release Date: 2019-12-12</p>
<p>Fix Resolution: org.yaml:snakeyaml:1.26</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-25857</summary>
### Vulnerable Library - <b>snakeyaml-1.19.jar</b></p>
<p>YAML 1.1 parser and emitter for Java</p>
<p>Library home page: <a href="http://www.snakeyaml.org">http://www.snakeyaml.org</a></p>
<p>Path to dependency file: /build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.yaml/snakeyaml/1.19/2d998d3d674b172a588e54ab619854d073f555b5/snakeyaml-1.19.jar</p>
<p>
Dependency Hierarchy:
- zest-0.14.0.jar (Root Library)
- selenium-server-3.141.59.jar
- :x: **snakeyaml-1.19.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/community-scripts/commit/5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4">5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The package org.yaml:snakeyaml from 0 and before 1.31 are vulnerable to Denial of Service (DoS) due missing to nested depth limitation for collections.
<p>Publish Date: 2022-08-30
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-25857>CVE-2022-25857</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-25857">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-25857</a></p>
<p>Release Date: 2022-08-30</p>
<p>Fix Resolution: org.yaml:snakeyaml:1.31</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-41404</summary>
### Vulnerable Library - <b>ini4j-0.5.2.jar</b></p>
<p>Java API for handling configuration files in Windows .ini format. The library includes its own Map based API, Java Preferences API and Java Beans API for handling .ini files. Additionally, the library includes a feature rich (variable/macro substitution, multiply property values, etc) java.util.Properties replacement.</p>
<p>Library home page: <a href="http://www.ini4j.org">http://www.ini4j.org</a></p>
<p>Path to dependency file: /build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.ini4j/ini4j/0.5.2/16561cb11c221b5928119e10d7636c95ee5c960d/ini4j-0.5.2.jar</p>
<p>
Dependency Hierarchy:
- zest-0.14.0.jar (Root Library)
- operadriver-1.5.jar
- :x: **ini4j-0.5.2.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/community-scripts/commit/5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4">5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
An issue in the fetch() method in the BasicProfile class of org.ini4j before v0.5.4 allows attackers to cause a Denial of Service (DoS) via unspecified vectors.
<p>Publish Date: 2022-10-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-41404>CVE-2022-41404</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-41404">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-41404</a></p>
<p>Release Date: 2022-10-11</p>
<p>Fix Resolution: org.ini4j:ini4j:0.5.4</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-3509</summary>
### Vulnerable Library - <b>protobuf-java-2.4.1.jar</b></p>
<p>Protocol Buffers are a way of encoding structured data in an efficient yet
extensible format.</p>
<p>Library home page: <a href="http://code.google.com/p/protobuf">http://code.google.com/p/protobuf</a></p>
<p>Path to dependency file: /build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.google.protobuf/protobuf-java/2.4.1/c589509ec6fd86d5d2fda37e07c08538235d3b9/protobuf-java-2.4.1.jar</p>
<p>
Dependency Hierarchy:
- zest-0.14.0.jar (Root Library)
- operadriver-1.5.jar
- :x: **protobuf-java-2.4.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/community-scripts/commit/5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4">5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A parsing issue similar to CVE-2022-3171, but with textformat in protobuf-java core and lite versions prior to 3.21.7, 3.20.3, 3.19.6 and 3.16.3 can lead to a denial of service attack. Inputs containing multiple instances of non-repeated embedded messages with repeated or unknown fields causes objects to be converted back-n-forth between mutable and immutable forms, resulting in potentially long garbage collection pauses. We recommend updating to the versions mentioned above.
<p>Publish Date: 2022-12-12
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-3509>CVE-2022-3509</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-3509">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-3509</a></p>
<p>Release Date: 2022-12-12</p>
<p>Fix Resolution: com.google.protobuf:protobuf-java:3.16.3,3.19.6,3.20.3,3.21.7</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-29546</summary>
### Vulnerable Library - <b>neko-htmlunit-2.36.0.jar</b></p>
<p>HtmlUnit adaptation of NekoHtml.
It has the same functionality but exposing HTMLElements to be overridden.</p>
<p>Library home page: <a href="http://htmlunit.sourceforge.net">http://htmlunit.sourceforge.net</a></p>
<p>Path to dependency file: /build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/net.sourceforge.htmlunit/neko-htmlunit/2.36.0/6e999678a3b2813ea71fac4ebc5996b1406e954d/neko-htmlunit-2.36.0.jar</p>
<p>
Dependency Hierarchy:
- zest-0.14.0.jar (Root Library)
- htmlunit-driver-2.36.0.jar
- htmlunit-2.36.0.jar
- :x: **neko-htmlunit-2.36.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/community-scripts/commit/5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4">5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
HtmlUnit NekoHtml Parser before 2.61.0 suffers from a denial of service vulnerability. Crafted input associated with the parsing of Processing Instruction (PI) data leads to heap memory consumption. This is similar to CVE-2022-28366 but affects a much later version of the product.
<p>Publish Date: 2022-04-25
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-29546>CVE-2022-29546</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-29546">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-29546</a></p>
<p>Release Date: 2022-04-25</p>
<p>Fix Resolution: neko-htmlunit - 2.61.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-28165</summary>
### Vulnerable Library - <b>jetty-io-9.4.20.v20190813.jar</b></p>
<p>The Eclipse Jetty Project</p>
<p>Library home page: <a href="http://www.eclipse.org/jetty">http://www.eclipse.org/jetty</a></p>
<p>Path to dependency file: /build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.eclipse.jetty/jetty-io/9.4.20.v20190813/b246c5e350d0aa1b310c07ec362755c34a1cc8cb/jetty-io-9.4.20.v20190813.jar</p>
<p>
Dependency Hierarchy:
- zest-0.14.0.jar (Root Library)
- htmlunit-driver-2.36.0.jar
- htmlunit-2.36.0.jar
- websocket-client-9.4.20.v20190813.jar
- :x: **jetty-io-9.4.20.v20190813.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/community-scripts/commit/5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4">5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Eclipse Jetty 7.2.2 to 9.4.38, 10.0.0.alpha0 to 10.0.1, and 11.0.0.alpha0 to 11.0.1, CPU usage can reach 100% upon receiving a large invalid TLS frame.
<p>Publish Date: 2021-04-01
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-28165>CVE-2021-28165</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/eclipse/jetty.project/security/advisories/GHSA-26vr-8j45-3r4w">https://github.com/eclipse/jetty.project/security/advisories/GHSA-26vr-8j45-3r4w</a></p>
<p>Release Date: 2021-04-01</p>
<p>Fix Resolution: org.eclipse.jetty:jetty-io:9.4.39, org.eclipse.jetty:jetty-io:10.0.2, org.eclipse.jetty:jetty-io:11.0.2</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-25647</summary>
### Vulnerable Library - <b>gson-2.8.5.jar</b></p>
<p>Gson JSON library</p>
<p>Library home page: <a href="https://github.com/google/gson">https://github.com/google/gson</a></p>
<p>Path to dependency file: /build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.google.code.gson/gson/2.8.5/f645ed69d595b24d4cf8b3fbb64cc505bede8829/gson-2.8.5.jar</p>
<p>
Dependency Hierarchy:
- zest-0.14.0.jar (Root Library)
- :x: **gson-2.8.5.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/community-scripts/commit/5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4">5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The package com.google.code.gson:gson before 2.8.9 are vulnerable to Deserialization of Untrusted Data via the writeReplace() method in internal classes, which may lead to DoS attacks.
<p>Publish Date: 2022-05-01
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-25647>CVE-2022-25647</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-25647`">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-25647`</a></p>
<p>Release Date: 2022-05-01</p>
<p>Fix Resolution: com.google.code.gson:gson:gson-parent-2.8.9</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-34169</summary>
### Vulnerable Library - <b>xalan-2.7.2.jar</b></p>
<p>Xalan-Java is an XSLT processor for transforming XML documents into HTML,
text, or other XML document types. It implements XSL Transformations (XSLT)
Version 1.0 and XML Path Language (XPath) Version 1.0 and can be used from
the command line, in an applet or a servlet, or as a module in other program.</p>
<p>Library home page: <a href="http://xml.apache.org/xalan-j/">http://xml.apache.org/xalan-j/</a></p>
<p>Path to dependency file: /build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/xalan/xalan/2.7.2/d55d3f02a56ec4c25695fe67e1334ff8c2ecea23/xalan-2.7.2.jar</p>
<p>
Dependency Hierarchy:
- zest-0.14.0.jar (Root Library)
- htmlunit-driver-2.36.0.jar
- htmlunit-2.36.0.jar
- :x: **xalan-2.7.2.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/community-scripts/commit/5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4">5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The Apache Xalan Java XSLT library is vulnerable to an integer truncation issue when processing malicious XSLT stylesheets. This can be used to corrupt Java class files generated by the internal XSLTC compiler and execute arbitrary Java bytecode. The Apache Xalan Java project is dormant and in the process of being retired. No future releases of Apache Xalan Java to address this issue are expected. Note: Java runtimes (such as OpenJDK) include repackaged copies of Xalan.
<p>Publish Date: 2022-07-19
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-34169>CVE-2022-34169</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-3171</summary>
### Vulnerable Library - <b>protobuf-java-2.4.1.jar</b></p>
<p>Protocol Buffers are a way of encoding structured data in an efficient yet
extensible format.</p>
<p>Library home page: <a href="http://code.google.com/p/protobuf">http://code.google.com/p/protobuf</a></p>
<p>Path to dependency file: /build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.google.protobuf/protobuf-java/2.4.1/c589509ec6fd86d5d2fda37e07c08538235d3b9/protobuf-java-2.4.1.jar</p>
<p>
Dependency Hierarchy:
- zest-0.14.0.jar (Root Library)
- operadriver-1.5.jar
- :x: **protobuf-java-2.4.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/community-scripts/commit/5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4">5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A parsing issue with binary data in protobuf-java core and lite versions prior to 3.21.7, 3.20.3, 3.19.6 and 3.16.3 can lead to a denial of service attack. Inputs containing multiple instances of non-repeated embedded messages with repeated or unknown fields causes objects to be converted back-n-forth between mutable and immutable forms, resulting in potentially long garbage collection pauses. We recommend updating to the versions mentioned above.
<p>Publish Date: 2022-10-12
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-3171>CVE-2022-3171</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-h4h5-3hr4-j3g2">https://github.com/advisories/GHSA-h4h5-3hr4-j3g2</a></p>
<p>Release Date: 2022-10-12</p>
<p>Fix Resolution: com.google.protobuf:protobuf-java:3.16.3,3.19.6,3.20.3,3.21.7;com.google.protobuf:protobuf-javalite:3.16.3,3.19.6,3.20.3,3.21.7;com.google.protobuf:protobuf-kotlin:3.19.6,3.20.3,3.21.7;com.google.protobuf:protobuf-kotlin-lite:3.19.6,3.20.3,3.21.7;google-protobuf - 3.19.6,3.20.3,3.21.7</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-40159</summary>
### Vulnerable Library - <b>commons-jxpath-1.3.jar</b></p>
<p>A Java-based implementation of XPath 1.0 that, in addition to XML processing, can inspect/modify Java object graphs (the library's explicit purpose) and even mixed Java/XML structures.</p>
<p>Path to dependency file: /build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/commons-jxpath/commons-jxpath/1.3/c22d7d0f0f40eb7059a23cfa61773a416768b137/commons-jxpath-1.3.jar</p>
<p>
Dependency Hierarchy:
- zest-0.14.0.jar (Root Library)
- operadriver-1.5.jar
- :x: **commons-jxpath-1.3.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/community-scripts/commit/5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4">5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
** DISPUTED ** This record was originally reported by the oss-fuzz project who failed to consider the security context in which JXPath is intended to be used and failed to contact the JXPath maintainers prior to requesting the CVE allocation. The CVE was then allocated by Google in breach of the CNA rules. After review by the JXPath maintainers, the original report was found to be invalid.
<p>Publish Date: 2022-10-06
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-40159>CVE-2022-40159</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-23437</summary>
### Vulnerable Library - <b>xercesImpl-2.12.0.jar</b></p>
<p>Xerces2 is the next generation of high performance, fully compliant XML parsers in the Apache Xerces family. This new version of Xerces introduces the Xerces Native Interface (XNI), a complete framework for building parser components and configurations that is extremely modular and easy to program.
The Apache Xerces2 parser is the reference implementation of XNI but other parser components, configurations, and parsers can be written using the Xerces Native Interface. For complete design and implementation documents, refer to the XNI Manual.
Xerces2 is a fully conforming XML Schema 1.0 processor. A partial experimental implementation of the XML Schema 1.1 Structures and Datatypes Working Drafts (December 2009) and an experimental implementation of the XML Schema Definition Language (XSD): Component Designators (SCD) Candidate Recommendation (January 2010) are provided for evaluation. For more information, refer to the XML Schema page.
Xerces2 also provides a complete implementation of the Document Object Model Level 3 Core and Load/Save W3C Recommendations and provides a complete implementation of the XML Inclusions (XInclude) W3C Recommendation. It also provides support for OASIS XML Catalogs v1.1.
Xerces2 is able to parse documents written according to the XML 1.1 Recommendation, except that it does not yet provide an option to enable normalization checking as described in section 2.13 of this specification. It also handles namespaces according to the XML Namespaces 1.1 Recommendation, and will correctly serialize XML 1.1 documents if the DOM level 3 load/save APIs are in use.</p>
<p>Library home page: <a href="https://xerces.apache.org/xerces2-j/">https://xerces.apache.org/xerces2-j/</a></p>
<p>Path to dependency file: /build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/xerces/xercesImpl/2.12.0/f02c844149fd306601f20e0b34853a670bef7fa2/xercesImpl-2.12.0.jar</p>
<p>
Dependency Hierarchy:
- zest-0.14.0.jar (Root Library)
- htmlunit-driver-2.36.0.jar
- htmlunit-2.36.0.jar
- neko-htmlunit-2.36.0.jar
- :x: **xercesImpl-2.12.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/community-scripts/commit/5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4">5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
There's a vulnerability within the Apache Xerces Java (XercesJ) XML parser when handling specially crafted XML document payloads. This causes, the XercesJ XML parser to wait in an infinite loop, which may sometimes consume system resources for prolonged duration. This vulnerability is present within XercesJ version 2.12.1 and the previous versions.
<p>Publish Date: 2022-01-24
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-23437>CVE-2022-23437</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-h65f-jvqw-m9fj">https://github.com/advisories/GHSA-h65f-jvqw-m9fj</a></p>
<p>Release Date: 2022-01-24</p>
<p>Fix Resolution: xerces:xercesImpl:2.12.2</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-38752</summary>
### Vulnerable Library - <b>snakeyaml-1.19.jar</b></p>
<p>YAML 1.1 parser and emitter for Java</p>
<p>Library home page: <a href="http://www.snakeyaml.org">http://www.snakeyaml.org</a></p>
<p>Path to dependency file: /build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.yaml/snakeyaml/1.19/2d998d3d674b172a588e54ab619854d073f555b5/snakeyaml-1.19.jar</p>
<p>
Dependency Hierarchy:
- zest-0.14.0.jar (Root Library)
- selenium-server-3.141.59.jar
- :x: **snakeyaml-1.19.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/community-scripts/commit/5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4">5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Using snakeYAML to parse untrusted YAML files may be vulnerable to Denial of Service attacks (DOS). If the parser is running on user supplied input, an attacker may supply content that causes the parser to crash by stack-overflow.
<p>Publish Date: 2022-09-05
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-38752>CVE-2022-38752</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-9w3m-gqgf-c4p9">https://github.com/advisories/GHSA-9w3m-gqgf-c4p9</a></p>
<p>Release Date: 2022-09-05</p>
<p>Fix Resolution: org.yaml:snakeyaml:1.32
</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2021-37533</summary>
### Vulnerable Library - <b>commons-net-3.6.jar</b></p>
<p>Apache Commons Net library contains a collection of network utilities and protocol implementations.
Supported protocols include: Echo, Finger, FTP, NNTP, NTP, POP3(S), SMTP(S), Telnet, Whois</p>
<p>Path to dependency file: /build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/commons-net/commons-net/3.6/b71de00508dcb078d2b24b5fa7e538636de9b3da/commons-net-3.6.jar</p>
<p>
Dependency Hierarchy:
- zest-0.14.0.jar (Root Library)
- htmlunit-driver-2.36.0.jar
- htmlunit-2.36.0.jar
- :x: **commons-net-3.6.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/community-scripts/commit/5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4">5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Prior to Apache Commons Net 3.9.0, Net's FTP client trusts the host from PASV response by default. A malicious server can redirect the Commons Net code to use a different host, but the user has to connect to the malicious server in the first place. This may lead to leakage of information about services running on the private network of the client. The default in version 3.9.0 is now false to ignore such hosts, as cURL does. See https://issues.apache.org/jira/browse/NET-711.
<p>Publish Date: 2022-12-03
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-37533>CVE-2021-37533</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.cve.org/CVERecord?id=CVE-2021-37533">https://www.cve.org/CVERecord?id=CVE-2021-37533</a></p>
<p>Release Date: 2022-12-03</p>
<p>Fix Resolution: commons-net:commons-net:3.9.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-38751</summary>
### Vulnerable Library - <b>snakeyaml-1.19.jar</b></p>
<p>YAML 1.1 parser and emitter for Java</p>
<p>Library home page: <a href="http://www.snakeyaml.org">http://www.snakeyaml.org</a></p>
<p>Path to dependency file: /build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.yaml/snakeyaml/1.19/2d998d3d674b172a588e54ab619854d073f555b5/snakeyaml-1.19.jar</p>
<p>
Dependency Hierarchy:
- zest-0.14.0.jar (Root Library)
- selenium-server-3.141.59.jar
- :x: **snakeyaml-1.19.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/community-scripts/commit/5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4">5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Using snakeYAML to parse untrusted YAML files may be vulnerable to Denial of Service attacks (DOS). If the parser is running on user supplied input, an attacker may supply content that causes the parser to crash by stackoverflow.
<p>Publish Date: 2022-09-05
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-38751>CVE-2022-38751</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bugs.chromium.org/p/oss-fuzz/issues/detail?id=47039">https://bugs.chromium.org/p/oss-fuzz/issues/detail?id=47039</a></p>
<p>Release Date: 2022-09-05</p>
<p>Fix Resolution: org.yaml:snakeyaml:1.31</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-38749</summary>
### Vulnerable Library - <b>snakeyaml-1.19.jar</b></p>
<p>YAML 1.1 parser and emitter for Java</p>
<p>Library home page: <a href="http://www.snakeyaml.org">http://www.snakeyaml.org</a></p>
<p>Path to dependency file: /build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.yaml/snakeyaml/1.19/2d998d3d674b172a588e54ab619854d073f555b5/snakeyaml-1.19.jar</p>
<p>
Dependency Hierarchy:
- zest-0.14.0.jar (Root Library)
- selenium-server-3.141.59.jar
- :x: **snakeyaml-1.19.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/community-scripts/commit/5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4">5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Using snakeYAML to parse untrusted YAML files may be vulnerable to Denial of Service attacks (DOS). If the parser is running on user supplied input, an attacker may supply content that causes the parser to crash by stackoverflow.
<p>Publish Date: 2022-09-05
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-38749>CVE-2022-38749</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bitbucket.org/snakeyaml/snakeyaml/issues/526/stackoverflow-oss-fuzz-47027">https://bitbucket.org/snakeyaml/snakeyaml/issues/526/stackoverflow-oss-fuzz-47027</a></p>
<p>Release Date: 2022-09-05</p>
<p>Fix Resolution: org.yaml:snakeyaml:1.31</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-40160</summary>
### Vulnerable Library - <b>commons-jxpath-1.3.jar</b></p>
<p>A Java-based implementation of XPath 1.0 that, in addition to XML processing, can inspect/modify Java object graphs (the library's explicit purpose) and even mixed Java/XML structures.</p>
<p>Path to dependency file: /build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/commons-jxpath/commons-jxpath/1.3/c22d7d0f0f40eb7059a23cfa61773a416768b137/commons-jxpath-1.3.jar</p>
<p>
Dependency Hierarchy:
- zest-0.14.0.jar (Root Library)
- operadriver-1.5.jar
- :x: **commons-jxpath-1.3.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/community-scripts/commit/5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4">5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
** DISPUTED ** This record was originally reported by the oss-fuzz project who failed to consider the security context in which JXPath is intended to be used and failed to contact the JXPath maintainers prior to requesting the CVE allocation. The CVE was then allocated by Google in breach of the CNA rules. After review by the JXPath maintainers, the original report was found to be invalid.
<p>Publish Date: 2022-10-06
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-40160>CVE-2022-40160</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-41854</summary>
### Vulnerable Library - <b>snakeyaml-1.19.jar</b></p>
<p>YAML 1.1 parser and emitter for Java</p>
<p>Library home page: <a href="http://www.snakeyaml.org">http://www.snakeyaml.org</a></p>
<p>Path to dependency file: /build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.yaml/snakeyaml/1.19/2d998d3d674b172a588e54ab619854d073f555b5/snakeyaml-1.19.jar</p>
<p>
Dependency Hierarchy:
- zest-0.14.0.jar (Root Library)
- selenium-server-3.141.59.jar
- :x: **snakeyaml-1.19.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/community-scripts/commit/5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4">5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Those using Snakeyaml to parse untrusted YAML files may be vulnerable to Denial of Service attacks (DOS). If the parser is running on user supplied input, an attacker may supply content that causes the parser to crash by stack overflow. This effect may support a denial of service attack.
<p>Publish Date: 2022-11-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-41854>CVE-2022-41854</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bitbucket.org/snakeyaml/snakeyaml/issues/531/">https://bitbucket.org/snakeyaml/snakeyaml/issues/531/</a></p>
<p>Release Date: 2022-11-11</p>
<p>Fix Resolution: org.yaml:snakeyaml:1.32</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-38750</summary>
### Vulnerable Library - <b>snakeyaml-1.19.jar</b></p>
<p>YAML 1.1 parser and emitter for Java</p>
<p>Library home page: <a href="http://www.snakeyaml.org">http://www.snakeyaml.org</a></p>
<p>Path to dependency file: /build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.yaml/snakeyaml/1.19/2d998d3d674b172a588e54ab619854d073f555b5/snakeyaml-1.19.jar</p>
<p>
Dependency Hierarchy:
- zest-0.14.0.jar (Root Library)
- selenium-server-3.141.59.jar
- :x: **snakeyaml-1.19.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/community-scripts/commit/5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4">5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Using snakeYAML to parse untrusted YAML files may be vulnerable to Denial of Service attacks (DOS). If the parser is running on user supplied input, an attacker may supply content that causes the parser to crash by stackoverflow.
<p>Publish Date: 2022-09-05
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-38750>CVE-2022-38750</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bugs.chromium.org/p/oss-fuzz/issues/detail?id=47027">https://bugs.chromium.org/p/oss-fuzz/issues/detail?id=47027</a></p>
<p>Release Date: 2022-09-05</p>
<p>Fix Resolution: org.yaml:snakeyaml:1.31</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2021-22569</summary>
### Vulnerable Library - <b>protobuf-java-2.4.1.jar</b></p>
<p>Protocol Buffers are a way of encoding structured data in an efficient yet
extensible format.</p>
<p>Library home page: <a href="http://code.google.com/p/protobuf">http://code.google.com/p/protobuf</a></p>
<p>Path to dependency file: /build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.google.protobuf/protobuf-java/2.4.1/c589509ec6fd86d5d2fda37e07c08538235d3b9/protobuf-java-2.4.1.jar</p>
<p>
Dependency Hierarchy:
- zest-0.14.0.jar (Root Library)
- operadriver-1.5.jar
- :x: **protobuf-java-2.4.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/community-scripts/commit/5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4">5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
An issue in protobuf-java allowed the interleaving of com.google.protobuf.UnknownFieldSet fields in such a way that would be processed out of order. A small malicious payload can occupy the parser for several minutes by creating large numbers of short-lived objects that cause frequent, repeated pauses. We recommend upgrading libraries beyond the vulnerable versions.
<p>Publish Date: 2022-01-10
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-22569>CVE-2021-22569</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-wrvw-hg22-4m67">https://github.com/advisories/GHSA-wrvw-hg22-4m67</a></p>
<p>Release Date: 2022-01-10</p>
<p>Fix Resolution: com.google.protobuf:protobuf-java:3.16.1,3.18.2,3.19.2; com.google.protobuf:protobuf-kotlin:3.18.2,3.19.2; google-protobuf - 3.19.2</p>
</p>
<p></p>
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p>
|
True
|
zest-0.14.0.jar: 29 vulnerabilities (highest severity is: 9.8) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>zest-0.14.0.jar</b></p></summary>
<p></p>
<p>Path to dependency file: /build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/xalan/xalan/2.7.2/d55d3f02a56ec4c25695fe67e1334ff8c2ecea23/xalan-2.7.2.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/community-scripts/commit/5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4">5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (zest version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2022-42889](https://www.mend.io/vulnerability-database/CVE-2022-42889) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png' width=19 height=20> Critical | 9.8 | commons-text-1.9.jar | Transitive | 0.14.1 | ✅ |
| [CVE-2022-1471](https://www.mend.io/vulnerability-database/CVE-2022-1471) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png' width=19 height=20> Critical | 9.8 | snakeyaml-1.19.jar | Transitive | N/A* | ❌ |
| [WS-2019-0490](https://github.com/cbeust/jcommander/commit/3ae95595febbed9c13f367b6bda5c0be1c572c53) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jcommander-1.72.jar | Transitive | N/A* | ❌ |
| [CVE-2020-5529](https://www.mend.io/vulnerability-database/CVE-2020-5529) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | htmlunit-2.36.0.jar | Transitive | N/A* | ❌ |
| [WS-2021-0419](https://github.com/google/gson/pull/1991) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.7 | gson-2.8.5.jar | Transitive | N/A* | ❌ |
| [CVE-2017-18640](https://www.mend.io/vulnerability-database/CVE-2017-18640) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | snakeyaml-1.19.jar | Transitive | N/A* | ❌ |
| [CVE-2022-25857](https://www.mend.io/vulnerability-database/CVE-2022-25857) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | snakeyaml-1.19.jar | Transitive | N/A* | ❌ |
| [CVE-2022-41404](https://www.mend.io/vulnerability-database/CVE-2022-41404) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | ini4j-0.5.2.jar | Transitive | N/A* | ❌ |
| [CVE-2022-3509](https://www.mend.io/vulnerability-database/CVE-2022-3509) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | protobuf-java-2.4.1.jar | Transitive | N/A* | ❌ |
| [CVE-2022-29546](https://www.mend.io/vulnerability-database/CVE-2022-29546) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | neko-htmlunit-2.36.0.jar | Transitive | N/A* | ❌ |
| [CVE-2021-28165](https://www.mend.io/vulnerability-database/CVE-2021-28165) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | jetty-io-9.4.20.v20190813.jar | Transitive | N/A* | ❌ |
| [CVE-2022-25647](https://www.mend.io/vulnerability-database/CVE-2022-25647) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | gson-2.8.5.jar | Transitive | N/A* | ❌ |
| [CVE-2022-34169](https://www.mend.io/vulnerability-database/CVE-2022-34169) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | xalan-2.7.2.jar | Transitive | N/A* | ❌ |
| [CVE-2022-3171](https://www.mend.io/vulnerability-database/CVE-2022-3171) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | protobuf-java-2.4.1.jar | Transitive | N/A* | ❌ |
| [CVE-2022-40159](https://www.mend.io/vulnerability-database/CVE-2022-40159) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | commons-jxpath-1.3.jar | Transitive | N/A* | ❌ |
| [CVE-2022-23437](https://www.mend.io/vulnerability-database/CVE-2022-23437) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | xercesImpl-2.12.0.jar | Transitive | N/A* | ❌ |
| [CVE-2022-38752](https://www.mend.io/vulnerability-database/CVE-2022-38752) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | snakeyaml-1.19.jar | Transitive | N/A* | ❌ |
| [CVE-2021-37533](https://www.mend.io/vulnerability-database/CVE-2021-37533) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | commons-net-3.6.jar | Transitive | N/A* | ❌ |
| [CVE-2022-38751](https://www.mend.io/vulnerability-database/CVE-2022-38751) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | snakeyaml-1.19.jar | Transitive | N/A* | ❌ |
| [CVE-2022-38749](https://www.mend.io/vulnerability-database/CVE-2022-38749) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | snakeyaml-1.19.jar | Transitive | N/A* | ❌ |
| [CVE-2022-40160](https://www.mend.io/vulnerability-database/CVE-2022-40160) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | commons-jxpath-1.3.jar | Transitive | N/A* | ❌ |
| [CVE-2022-41854](https://www.mend.io/vulnerability-database/CVE-2022-41854) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | snakeyaml-1.19.jar | Transitive | N/A* | ❌ |
| [CVE-2022-38750](https://www.mend.io/vulnerability-database/CVE-2022-38750) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.5 | snakeyaml-1.19.jar | Transitive | N/A* | ❌ |
| [CVE-2021-22569](https://www.mend.io/vulnerability-database/CVE-2021-22569) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.5 | protobuf-java-2.4.1.jar | Transitive | N/A* | ❌ |
| [CVE-2021-28169](https://www.mend.io/vulnerability-database/CVE-2021-28169) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | jetty-http-9.4.20.v20190813.jar | Transitive | N/A* | ❌ |
| [CVE-2020-27223](https://www.mend.io/vulnerability-database/CVE-2020-27223) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | jetty-http-9.4.20.v20190813.jar | Transitive | N/A* | ❌ |
| [CVE-2020-13956](https://www.mend.io/vulnerability-database/CVE-2020-13956) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | httpclient-4.5.9.jar | Transitive | N/A* | ❌ |
| [CVE-2020-8908](https://www.mend.io/vulnerability-database/CVE-2020-8908) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 3.3 | guava-25.0-jre.jar | Transitive | N/A* | ❌ |
| [CVE-2022-2047](https://www.mend.io/vulnerability-database/CVE-2022-2047) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 2.7 | detected in multiple dependencies | Transitive | N/A* | ❌ |
<p>*For some transitive vulnerabilities, there is no version of direct dependency with a fix. Check the "Details" section below to see if there is a version of transitive dependency where vulnerability is fixed.</p>
## Details
> Partial details (24 vulnerabilities) are displayed below due to a content size limitation in GitHub. To view information on the remaining vulnerabilities, navigate to the Mend Application.<br>
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png' width=19 height=20> CVE-2022-42889</summary>
### Vulnerable Library - <b>commons-text-1.9.jar</b></p>
<p>Apache Commons Text is a library focused on algorithms working on strings.</p>
<p>Library home page: <a href="https://commons.apache.org/proper/commons-text">https://commons.apache.org/proper/commons-text</a></p>
<p>Path to dependency file: /build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.apache.commons/commons-text/1.9/ba6ac8c2807490944a0a27f6f8e68fb5ed2e80e2/commons-text-1.9.jar</p>
<p>
Dependency Hierarchy:
- zest-0.14.0.jar (Root Library)
- htmlunit-driver-2.36.0.jar
- htmlunit-2.36.0.jar
- :x: **commons-text-1.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/community-scripts/commit/5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4">5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache Commons Text performs variable interpolation, allowing properties to be dynamically evaluated and expanded. The standard format for interpolation is "${prefix:name}", where "prefix" is used to locate an instance of org.apache.commons.text.lookup.StringLookup that performs the interpolation. Starting with version 1.5 and continuing through 1.9, the set of default Lookup instances included interpolators that could result in arbitrary code execution or contact with remote servers. These lookups are: - "script" - execute expressions using the JVM script execution engine (javax.script) - "dns" - resolve dns records - "url" - load values from urls, including from remote servers Applications using the interpolation defaults in the affected versions may be vulnerable to remote code execution or unintentional contact with remote servers if untrusted configuration values are used. Users are recommended to upgrade to Apache Commons Text 1.10.0, which disables the problematic interpolators by default.
<p>Publish Date: 2022-10-13
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-42889>CVE-2022-42889</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.openwall.com/lists/oss-security/2022/10/13/4">https://www.openwall.com/lists/oss-security/2022/10/13/4</a></p>
<p>Release Date: 2022-10-13</p>
<p>Fix Resolution (org.apache.commons:commons-text): 1.10.0</p>
<p>Direct dependency fix Resolution (org.mozilla:zest): 0.14.1</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png' width=19 height=20> CVE-2022-1471</summary>
### Vulnerable Library - <b>snakeyaml-1.19.jar</b></p>
<p>YAML 1.1 parser and emitter for Java</p>
<p>Library home page: <a href="http://www.snakeyaml.org">http://www.snakeyaml.org</a></p>
<p>Path to dependency file: /build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.yaml/snakeyaml/1.19/2d998d3d674b172a588e54ab619854d073f555b5/snakeyaml-1.19.jar</p>
<p>
Dependency Hierarchy:
- zest-0.14.0.jar (Root Library)
- selenium-server-3.141.59.jar
- :x: **snakeyaml-1.19.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/community-scripts/commit/5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4">5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
SnakeYaml's Constructor() class does not restrict types which can be instantiated during deserialization. Deserializing yaml content provided by an attacker can lead to remote code execution. We recommend using SnakeYaml's SafeConsturctor when parsing untrusted content to restrict deserialization.
<p>Publish Date: 2022-12-01
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-1471>CVE-2022-1471</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bitbucket.org/snakeyaml/snakeyaml/issues/561/cve-2022-1471-vulnerability-in#comment-64634374">https://bitbucket.org/snakeyaml/snakeyaml/issues/561/cve-2022-1471-vulnerability-in#comment-64634374</a></p>
<p>Release Date: 2022-12-01</p>
<p>Fix Resolution: org.yaml:snakeyaml:2.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> WS-2019-0490</summary>
### Vulnerable Library - <b>jcommander-1.72.jar</b></p>
<p>Command line parsing</p>
<p>Library home page: <a href="http://jcommander.org">http://jcommander.org</a></p>
<p>Path to dependency file: /build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.beust/jcommander/1.72/6375e521c1e11d6563d4f25a07ce124ccf8cd171/jcommander-1.72.jar</p>
<p>
Dependency Hierarchy:
- zest-0.14.0.jar (Root Library)
- selenium-server-3.141.59.jar
- :x: **jcommander-1.72.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/community-scripts/commit/5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4">5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Inclusion of Functionality from Untrusted Control Sphere vulnerability found in jcommander before 1.75. jcommander resolving dependencies over HTTP instead of HTTPS.
<p>Publish Date: 2019-02-19
<p>URL: <a href=https://github.com/cbeust/jcommander/commit/3ae95595febbed9c13f367b6bda5c0be1c572c53>WS-2019-0490</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2019-02-19</p>
<p>Fix Resolution: com.beust:jcommander:1.75</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-5529</summary>
### Vulnerable Library - <b>htmlunit-2.36.0.jar</b></p>
<p>A headless browser intended for use in testing web-based applications.</p>
<p>Library home page: <a href="http://htmlunit.sourceforge.net">http://htmlunit.sourceforge.net</a></p>
<p>Path to dependency file: /build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/net.sourceforge.htmlunit/htmlunit/2.36.0/efe6df9c5bc1284cd1d7952434ea4f85c5a32f72/htmlunit-2.36.0.jar</p>
<p>
Dependency Hierarchy:
- zest-0.14.0.jar (Root Library)
- htmlunit-driver-2.36.0.jar
- :x: **htmlunit-2.36.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/community-scripts/commit/5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4">5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
HtmlUnit prior to 2.37.0 contains code execution vulnerabilities. HtmlUnit initializes Rhino engine improperly, hence a malicious JavScript code can execute arbitrary Java code on the application. Moreover, when embedded in Android application, Android-specific initialization of Rhino engine is done in an improper way, hence a malicious JavaScript code can execute arbitrary Java code on the application.
<p>Publish Date: 2020-02-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-5529>CVE-2020-5529</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2020-02-11</p>
<p>Fix Resolution: net.sourceforge.htmlunit:htmlunit:2.37.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> WS-2021-0419</summary>
### Vulnerable Library - <b>gson-2.8.5.jar</b></p>
<p>Gson JSON library</p>
<p>Library home page: <a href="https://github.com/google/gson">https://github.com/google/gson</a></p>
<p>Path to dependency file: /build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.google.code.gson/gson/2.8.5/f645ed69d595b24d4cf8b3fbb64cc505bede8829/gson-2.8.5.jar</p>
<p>
Dependency Hierarchy:
- zest-0.14.0.jar (Root Library)
- :x: **gson-2.8.5.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/community-scripts/commit/5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4">5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Denial of Service vulnerability was discovered in gson before 2.8.9 via the writeReplace() method.
<p>Publish Date: 2021-10-11
<p>URL: <a href=https://github.com/google/gson/pull/1991>WS-2021-0419</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.7</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2021-10-11</p>
<p>Fix Resolution: com.google.code.gson:gson:2.8.9</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2017-18640</summary>
### Vulnerable Library - <b>snakeyaml-1.19.jar</b></p>
<p>YAML 1.1 parser and emitter for Java</p>
<p>Library home page: <a href="http://www.snakeyaml.org">http://www.snakeyaml.org</a></p>
<p>Path to dependency file: /build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.yaml/snakeyaml/1.19/2d998d3d674b172a588e54ab619854d073f555b5/snakeyaml-1.19.jar</p>
<p>
Dependency Hierarchy:
- zest-0.14.0.jar (Root Library)
- selenium-server-3.141.59.jar
- :x: **snakeyaml-1.19.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/community-scripts/commit/5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4">5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The Alias feature in SnakeYAML before 1.26 allows entity expansion during a load operation, a related issue to CVE-2003-1564.
<p>Publish Date: 2019-12-12
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2017-18640>CVE-2017-18640</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-18640">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-18640</a></p>
<p>Release Date: 2019-12-12</p>
<p>Fix Resolution: org.yaml:snakeyaml:1.26</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-25857</summary>
### Vulnerable Library - <b>snakeyaml-1.19.jar</b></p>
<p>YAML 1.1 parser and emitter for Java</p>
<p>Library home page: <a href="http://www.snakeyaml.org">http://www.snakeyaml.org</a></p>
<p>Path to dependency file: /build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.yaml/snakeyaml/1.19/2d998d3d674b172a588e54ab619854d073f555b5/snakeyaml-1.19.jar</p>
<p>
Dependency Hierarchy:
- zest-0.14.0.jar (Root Library)
- selenium-server-3.141.59.jar
- :x: **snakeyaml-1.19.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/community-scripts/commit/5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4">5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The package org.yaml:snakeyaml from 0 and before 1.31 are vulnerable to Denial of Service (DoS) due missing to nested depth limitation for collections.
<p>Publish Date: 2022-08-30
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-25857>CVE-2022-25857</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-25857">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-25857</a></p>
<p>Release Date: 2022-08-30</p>
<p>Fix Resolution: org.yaml:snakeyaml:1.31</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-41404</summary>
### Vulnerable Library - <b>ini4j-0.5.2.jar</b></p>
<p>Java API for handling configuration files in Windows .ini format. The library includes its own Map based API, Java Preferences API and Java Beans API for handling .ini files. Additionally, the library includes a feature rich (variable/macro substitution, multiply property values, etc) java.util.Properties replacement.</p>
<p>Library home page: <a href="http://www.ini4j.org">http://www.ini4j.org</a></p>
<p>Path to dependency file: /build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.ini4j/ini4j/0.5.2/16561cb11c221b5928119e10d7636c95ee5c960d/ini4j-0.5.2.jar</p>
<p>
Dependency Hierarchy:
- zest-0.14.0.jar (Root Library)
- operadriver-1.5.jar
- :x: **ini4j-0.5.2.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/community-scripts/commit/5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4">5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
An issue in the fetch() method in the BasicProfile class of org.ini4j before v0.5.4 allows attackers to cause a Denial of Service (DoS) via unspecified vectors.
<p>Publish Date: 2022-10-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-41404>CVE-2022-41404</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-41404">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-41404</a></p>
<p>Release Date: 2022-10-11</p>
<p>Fix Resolution: org.ini4j:ini4j:0.5.4</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-3509</summary>
### Vulnerable Library - <b>protobuf-java-2.4.1.jar</b></p>
<p>Protocol Buffers are a way of encoding structured data in an efficient yet
extensible format.</p>
<p>Library home page: <a href="http://code.google.com/p/protobuf">http://code.google.com/p/protobuf</a></p>
<p>Path to dependency file: /build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.google.protobuf/protobuf-java/2.4.1/c589509ec6fd86d5d2fda37e07c08538235d3b9/protobuf-java-2.4.1.jar</p>
<p>
Dependency Hierarchy:
- zest-0.14.0.jar (Root Library)
- operadriver-1.5.jar
- :x: **protobuf-java-2.4.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/community-scripts/commit/5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4">5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A parsing issue similar to CVE-2022-3171, but with textformat in protobuf-java core and lite versions prior to 3.21.7, 3.20.3, 3.19.6 and 3.16.3 can lead to a denial of service attack. Inputs containing multiple instances of non-repeated embedded messages with repeated or unknown fields causes objects to be converted back-n-forth between mutable and immutable forms, resulting in potentially long garbage collection pauses. We recommend updating to the versions mentioned above.
<p>Publish Date: 2022-12-12
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-3509>CVE-2022-3509</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-3509">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-3509</a></p>
<p>Release Date: 2022-12-12</p>
<p>Fix Resolution: com.google.protobuf:protobuf-java:3.16.3,3.19.6,3.20.3,3.21.7</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-29546</summary>
### Vulnerable Library - <b>neko-htmlunit-2.36.0.jar</b></p>
<p>HtmlUnit adaptation of NekoHtml.
It has the same functionality but exposing HTMLElements to be overridden.</p>
<p>Library home page: <a href="http://htmlunit.sourceforge.net">http://htmlunit.sourceforge.net</a></p>
<p>Path to dependency file: /build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/net.sourceforge.htmlunit/neko-htmlunit/2.36.0/6e999678a3b2813ea71fac4ebc5996b1406e954d/neko-htmlunit-2.36.0.jar</p>
<p>
Dependency Hierarchy:
- zest-0.14.0.jar (Root Library)
- htmlunit-driver-2.36.0.jar
- htmlunit-2.36.0.jar
- :x: **neko-htmlunit-2.36.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/community-scripts/commit/5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4">5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
HtmlUnit NekoHtml Parser before 2.61.0 suffers from a denial of service vulnerability. Crafted input associated with the parsing of Processing Instruction (PI) data leads to heap memory consumption. This is similar to CVE-2022-28366 but affects a much later version of the product.
<p>Publish Date: 2022-04-25
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-29546>CVE-2022-29546</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-29546">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-29546</a></p>
<p>Release Date: 2022-04-25</p>
<p>Fix Resolution: neko-htmlunit - 2.61.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-28165</summary>
### Vulnerable Library - <b>jetty-io-9.4.20.v20190813.jar</b></p>
<p>The Eclipse Jetty Project</p>
<p>Library home page: <a href="http://www.eclipse.org/jetty">http://www.eclipse.org/jetty</a></p>
<p>Path to dependency file: /build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.eclipse.jetty/jetty-io/9.4.20.v20190813/b246c5e350d0aa1b310c07ec362755c34a1cc8cb/jetty-io-9.4.20.v20190813.jar</p>
<p>
Dependency Hierarchy:
- zest-0.14.0.jar (Root Library)
- htmlunit-driver-2.36.0.jar
- htmlunit-2.36.0.jar
- websocket-client-9.4.20.v20190813.jar
- :x: **jetty-io-9.4.20.v20190813.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/community-scripts/commit/5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4">5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Eclipse Jetty 7.2.2 to 9.4.38, 10.0.0.alpha0 to 10.0.1, and 11.0.0.alpha0 to 11.0.1, CPU usage can reach 100% upon receiving a large invalid TLS frame.
<p>Publish Date: 2021-04-01
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-28165>CVE-2021-28165</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/eclipse/jetty.project/security/advisories/GHSA-26vr-8j45-3r4w">https://github.com/eclipse/jetty.project/security/advisories/GHSA-26vr-8j45-3r4w</a></p>
<p>Release Date: 2021-04-01</p>
<p>Fix Resolution: org.eclipse.jetty:jetty-io:9.4.39, org.eclipse.jetty:jetty-io:10.0.2, org.eclipse.jetty:jetty-io:11.0.2</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-25647</summary>
### Vulnerable Library - <b>gson-2.8.5.jar</b></p>
<p>Gson JSON library</p>
<p>Library home page: <a href="https://github.com/google/gson">https://github.com/google/gson</a></p>
<p>Path to dependency file: /build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.google.code.gson/gson/2.8.5/f645ed69d595b24d4cf8b3fbb64cc505bede8829/gson-2.8.5.jar</p>
<p>
Dependency Hierarchy:
- zest-0.14.0.jar (Root Library)
- :x: **gson-2.8.5.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/community-scripts/commit/5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4">5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The package com.google.code.gson:gson before 2.8.9 are vulnerable to Deserialization of Untrusted Data via the writeReplace() method in internal classes, which may lead to DoS attacks.
<p>Publish Date: 2022-05-01
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-25647>CVE-2022-25647</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-25647`">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-25647`</a></p>
<p>Release Date: 2022-05-01</p>
<p>Fix Resolution: com.google.code.gson:gson:gson-parent-2.8.9</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-34169</summary>
### Vulnerable Library - <b>xalan-2.7.2.jar</b></p>
<p>Xalan-Java is an XSLT processor for transforming XML documents into HTML,
text, or other XML document types. It implements XSL Transformations (XSLT)
Version 1.0 and XML Path Language (XPath) Version 1.0 and can be used from
the command line, in an applet or a servlet, or as a module in other program.</p>
<p>Library home page: <a href="http://xml.apache.org/xalan-j/">http://xml.apache.org/xalan-j/</a></p>
<p>Path to dependency file: /build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/xalan/xalan/2.7.2/d55d3f02a56ec4c25695fe67e1334ff8c2ecea23/xalan-2.7.2.jar</p>
<p>
Dependency Hierarchy:
- zest-0.14.0.jar (Root Library)
- htmlunit-driver-2.36.0.jar
- htmlunit-2.36.0.jar
- :x: **xalan-2.7.2.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/community-scripts/commit/5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4">5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The Apache Xalan Java XSLT library is vulnerable to an integer truncation issue when processing malicious XSLT stylesheets. This can be used to corrupt Java class files generated by the internal XSLTC compiler and execute arbitrary Java bytecode. The Apache Xalan Java project is dormant and in the process of being retired. No future releases of Apache Xalan Java to address this issue are expected. Note: Java runtimes (such as OpenJDK) include repackaged copies of Xalan.
<p>Publish Date: 2022-07-19
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-34169>CVE-2022-34169</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-3171</summary>
### Vulnerable Library - <b>protobuf-java-2.4.1.jar</b></p>
<p>Protocol Buffers are a way of encoding structured data in an efficient yet
extensible format.</p>
<p>Library home page: <a href="http://code.google.com/p/protobuf">http://code.google.com/p/protobuf</a></p>
<p>Path to dependency file: /build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.google.protobuf/protobuf-java/2.4.1/c589509ec6fd86d5d2fda37e07c08538235d3b9/protobuf-java-2.4.1.jar</p>
<p>
Dependency Hierarchy:
- zest-0.14.0.jar (Root Library)
- operadriver-1.5.jar
- :x: **protobuf-java-2.4.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/community-scripts/commit/5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4">5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A parsing issue with binary data in protobuf-java core and lite versions prior to 3.21.7, 3.20.3, 3.19.6 and 3.16.3 can lead to a denial of service attack. Inputs containing multiple instances of non-repeated embedded messages with repeated or unknown fields causes objects to be converted back-n-forth between mutable and immutable forms, resulting in potentially long garbage collection pauses. We recommend updating to the versions mentioned above.
<p>Publish Date: 2022-10-12
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-3171>CVE-2022-3171</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-h4h5-3hr4-j3g2">https://github.com/advisories/GHSA-h4h5-3hr4-j3g2</a></p>
<p>Release Date: 2022-10-12</p>
<p>Fix Resolution: com.google.protobuf:protobuf-java:3.16.3,3.19.6,3.20.3,3.21.7;com.google.protobuf:protobuf-javalite:3.16.3,3.19.6,3.20.3,3.21.7;com.google.protobuf:protobuf-kotlin:3.19.6,3.20.3,3.21.7;com.google.protobuf:protobuf-kotlin-lite:3.19.6,3.20.3,3.21.7;google-protobuf - 3.19.6,3.20.3,3.21.7</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-40159</summary>
### Vulnerable Library - <b>commons-jxpath-1.3.jar</b></p>
<p>A Java-based implementation of XPath 1.0 that, in addition to XML processing, can inspect/modify Java object graphs (the library's explicit purpose) and even mixed Java/XML structures.</p>
<p>Path to dependency file: /build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/commons-jxpath/commons-jxpath/1.3/c22d7d0f0f40eb7059a23cfa61773a416768b137/commons-jxpath-1.3.jar</p>
<p>
Dependency Hierarchy:
- zest-0.14.0.jar (Root Library)
- operadriver-1.5.jar
- :x: **commons-jxpath-1.3.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/community-scripts/commit/5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4">5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
** DISPUTED ** This record was originally reported by the oss-fuzz project who failed to consider the security context in which JXPath is intended to be used and failed to contact the JXPath maintainers prior to requesting the CVE allocation. The CVE was then allocated by Google in breach of the CNA rules. After review by the JXPath maintainers, the original report was found to be invalid.
<p>Publish Date: 2022-10-06
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-40159>CVE-2022-40159</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-23437</summary>
### Vulnerable Library - <b>xercesImpl-2.12.0.jar</b></p>
<p>Xerces2 is the next generation of high performance, fully compliant XML parsers in the Apache Xerces family. This new version of Xerces introduces the Xerces Native Interface (XNI), a complete framework for building parser components and configurations that is extremely modular and easy to program.
The Apache Xerces2 parser is the reference implementation of XNI but other parser components, configurations, and parsers can be written using the Xerces Native Interface. For complete design and implementation documents, refer to the XNI Manual.
Xerces2 is a fully conforming XML Schema 1.0 processor. A partial experimental implementation of the XML Schema 1.1 Structures and Datatypes Working Drafts (December 2009) and an experimental implementation of the XML Schema Definition Language (XSD): Component Designators (SCD) Candidate Recommendation (January 2010) are provided for evaluation. For more information, refer to the XML Schema page.
Xerces2 also provides a complete implementation of the Document Object Model Level 3 Core and Load/Save W3C Recommendations and provides a complete implementation of the XML Inclusions (XInclude) W3C Recommendation. It also provides support for OASIS XML Catalogs v1.1.
Xerces2 is able to parse documents written according to the XML 1.1 Recommendation, except that it does not yet provide an option to enable normalization checking as described in section 2.13 of this specification. It also handles namespaces according to the XML Namespaces 1.1 Recommendation, and will correctly serialize XML 1.1 documents if the DOM level 3 load/save APIs are in use.</p>
<p>Library home page: <a href="https://xerces.apache.org/xerces2-j/">https://xerces.apache.org/xerces2-j/</a></p>
<p>Path to dependency file: /build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/xerces/xercesImpl/2.12.0/f02c844149fd306601f20e0b34853a670bef7fa2/xercesImpl-2.12.0.jar</p>
<p>
Dependency Hierarchy:
- zest-0.14.0.jar (Root Library)
- htmlunit-driver-2.36.0.jar
- htmlunit-2.36.0.jar
- neko-htmlunit-2.36.0.jar
- :x: **xercesImpl-2.12.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/community-scripts/commit/5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4">5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
There's a vulnerability within the Apache Xerces Java (XercesJ) XML parser when handling specially crafted XML document payloads. This causes, the XercesJ XML parser to wait in an infinite loop, which may sometimes consume system resources for prolonged duration. This vulnerability is present within XercesJ version 2.12.1 and the previous versions.
<p>Publish Date: 2022-01-24
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-23437>CVE-2022-23437</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-h65f-jvqw-m9fj">https://github.com/advisories/GHSA-h65f-jvqw-m9fj</a></p>
<p>Release Date: 2022-01-24</p>
<p>Fix Resolution: xerces:xercesImpl:2.12.2</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-38752</summary>
### Vulnerable Library - <b>snakeyaml-1.19.jar</b></p>
<p>YAML 1.1 parser and emitter for Java</p>
<p>Library home page: <a href="http://www.snakeyaml.org">http://www.snakeyaml.org</a></p>
<p>Path to dependency file: /build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.yaml/snakeyaml/1.19/2d998d3d674b172a588e54ab619854d073f555b5/snakeyaml-1.19.jar</p>
<p>
Dependency Hierarchy:
- zest-0.14.0.jar (Root Library)
- selenium-server-3.141.59.jar
- :x: **snakeyaml-1.19.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/community-scripts/commit/5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4">5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Using snakeYAML to parse untrusted YAML files may be vulnerable to Denial of Service attacks (DOS). If the parser is running on user supplied input, an attacker may supply content that causes the parser to crash by stack-overflow.
<p>Publish Date: 2022-09-05
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-38752>CVE-2022-38752</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-9w3m-gqgf-c4p9">https://github.com/advisories/GHSA-9w3m-gqgf-c4p9</a></p>
<p>Release Date: 2022-09-05</p>
<p>Fix Resolution: org.yaml:snakeyaml:1.32
</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2021-37533</summary>
### Vulnerable Library - <b>commons-net-3.6.jar</b></p>
<p>Apache Commons Net library contains a collection of network utilities and protocol implementations.
Supported protocols include: Echo, Finger, FTP, NNTP, NTP, POP3(S), SMTP(S), Telnet, Whois</p>
<p>Path to dependency file: /build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/commons-net/commons-net/3.6/b71de00508dcb078d2b24b5fa7e538636de9b3da/commons-net-3.6.jar</p>
<p>
Dependency Hierarchy:
- zest-0.14.0.jar (Root Library)
- htmlunit-driver-2.36.0.jar
- htmlunit-2.36.0.jar
- :x: **commons-net-3.6.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/community-scripts/commit/5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4">5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Prior to Apache Commons Net 3.9.0, Net's FTP client trusts the host from PASV response by default. A malicious server can redirect the Commons Net code to use a different host, but the user has to connect to the malicious server in the first place. This may lead to leakage of information about services running on the private network of the client. The default in version 3.9.0 is now false to ignore such hosts, as cURL does. See https://issues.apache.org/jira/browse/NET-711.
<p>Publish Date: 2022-12-03
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-37533>CVE-2021-37533</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.cve.org/CVERecord?id=CVE-2021-37533">https://www.cve.org/CVERecord?id=CVE-2021-37533</a></p>
<p>Release Date: 2022-12-03</p>
<p>Fix Resolution: commons-net:commons-net:3.9.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-38751</summary>
### Vulnerable Library - <b>snakeyaml-1.19.jar</b></p>
<p>YAML 1.1 parser and emitter for Java</p>
<p>Library home page: <a href="http://www.snakeyaml.org">http://www.snakeyaml.org</a></p>
<p>Path to dependency file: /build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.yaml/snakeyaml/1.19/2d998d3d674b172a588e54ab619854d073f555b5/snakeyaml-1.19.jar</p>
<p>
Dependency Hierarchy:
- zest-0.14.0.jar (Root Library)
- selenium-server-3.141.59.jar
- :x: **snakeyaml-1.19.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/community-scripts/commit/5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4">5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Using snakeYAML to parse untrusted YAML files may be vulnerable to Denial of Service attacks (DOS). If the parser is running on user supplied input, an attacker may supply content that causes the parser to crash by stackoverflow.
<p>Publish Date: 2022-09-05
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-38751>CVE-2022-38751</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bugs.chromium.org/p/oss-fuzz/issues/detail?id=47039">https://bugs.chromium.org/p/oss-fuzz/issues/detail?id=47039</a></p>
<p>Release Date: 2022-09-05</p>
<p>Fix Resolution: org.yaml:snakeyaml:1.31</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-38749</summary>
### Vulnerable Library - <b>snakeyaml-1.19.jar</b></p>
<p>YAML 1.1 parser and emitter for Java</p>
<p>Library home page: <a href="http://www.snakeyaml.org">http://www.snakeyaml.org</a></p>
<p>Path to dependency file: /build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.yaml/snakeyaml/1.19/2d998d3d674b172a588e54ab619854d073f555b5/snakeyaml-1.19.jar</p>
<p>
Dependency Hierarchy:
- zest-0.14.0.jar (Root Library)
- selenium-server-3.141.59.jar
- :x: **snakeyaml-1.19.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/community-scripts/commit/5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4">5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Using snakeYAML to parse untrusted YAML files may be vulnerable to Denial of Service attacks (DOS). If the parser is running on user supplied input, an attacker may supply content that causes the parser to crash by stackoverflow.
<p>Publish Date: 2022-09-05
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-38749>CVE-2022-38749</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bitbucket.org/snakeyaml/snakeyaml/issues/526/stackoverflow-oss-fuzz-47027">https://bitbucket.org/snakeyaml/snakeyaml/issues/526/stackoverflow-oss-fuzz-47027</a></p>
<p>Release Date: 2022-09-05</p>
<p>Fix Resolution: org.yaml:snakeyaml:1.31</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-40160</summary>
### Vulnerable Library - <b>commons-jxpath-1.3.jar</b></p>
<p>A Java-based implementation of XPath 1.0 that, in addition to XML processing, can inspect/modify Java object graphs (the library's explicit purpose) and even mixed Java/XML structures.</p>
<p>Path to dependency file: /build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/commons-jxpath/commons-jxpath/1.3/c22d7d0f0f40eb7059a23cfa61773a416768b137/commons-jxpath-1.3.jar</p>
<p>
Dependency Hierarchy:
- zest-0.14.0.jar (Root Library)
- operadriver-1.5.jar
- :x: **commons-jxpath-1.3.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/community-scripts/commit/5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4">5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
** DISPUTED ** This record was originally reported by the oss-fuzz project who failed to consider the security context in which JXPath is intended to be used and failed to contact the JXPath maintainers prior to requesting the CVE allocation. The CVE was then allocated by Google in breach of the CNA rules. After review by the JXPath maintainers, the original report was found to be invalid.
<p>Publish Date: 2022-10-06
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-40160>CVE-2022-40160</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-41854</summary>
### Vulnerable Library - <b>snakeyaml-1.19.jar</b></p>
<p>YAML 1.1 parser and emitter for Java</p>
<p>Library home page: <a href="http://www.snakeyaml.org">http://www.snakeyaml.org</a></p>
<p>Path to dependency file: /build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.yaml/snakeyaml/1.19/2d998d3d674b172a588e54ab619854d073f555b5/snakeyaml-1.19.jar</p>
<p>
Dependency Hierarchy:
- zest-0.14.0.jar (Root Library)
- selenium-server-3.141.59.jar
- :x: **snakeyaml-1.19.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/community-scripts/commit/5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4">5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Those using Snakeyaml to parse untrusted YAML files may be vulnerable to Denial of Service attacks (DOS). If the parser is running on user supplied input, an attacker may supply content that causes the parser to crash by stack overflow. This effect may support a denial of service attack.
<p>Publish Date: 2022-11-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-41854>CVE-2022-41854</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bitbucket.org/snakeyaml/snakeyaml/issues/531/">https://bitbucket.org/snakeyaml/snakeyaml/issues/531/</a></p>
<p>Release Date: 2022-11-11</p>
<p>Fix Resolution: org.yaml:snakeyaml:1.32</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-38750</summary>
### Vulnerable Library - <b>snakeyaml-1.19.jar</b></p>
<p>YAML 1.1 parser and emitter for Java</p>
<p>Library home page: <a href="http://www.snakeyaml.org">http://www.snakeyaml.org</a></p>
<p>Path to dependency file: /build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.yaml/snakeyaml/1.19/2d998d3d674b172a588e54ab619854d073f555b5/snakeyaml-1.19.jar</p>
<p>
Dependency Hierarchy:
- zest-0.14.0.jar (Root Library)
- selenium-server-3.141.59.jar
- :x: **snakeyaml-1.19.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/community-scripts/commit/5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4">5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Using snakeYAML to parse untrusted YAML files may be vulnerable to Denial of Service attacks (DOS). If the parser is running on user supplied input, an attacker may supply content that causes the parser to crash by stackoverflow.
<p>Publish Date: 2022-09-05
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-38750>CVE-2022-38750</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bugs.chromium.org/p/oss-fuzz/issues/detail?id=47027">https://bugs.chromium.org/p/oss-fuzz/issues/detail?id=47027</a></p>
<p>Release Date: 2022-09-05</p>
<p>Fix Resolution: org.yaml:snakeyaml:1.31</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2021-22569</summary>
### Vulnerable Library - <b>protobuf-java-2.4.1.jar</b></p>
<p>Protocol Buffers are a way of encoding structured data in an efficient yet
extensible format.</p>
<p>Library home page: <a href="http://code.google.com/p/protobuf">http://code.google.com/p/protobuf</a></p>
<p>Path to dependency file: /build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.google.protobuf/protobuf-java/2.4.1/c589509ec6fd86d5d2fda37e07c08538235d3b9/protobuf-java-2.4.1.jar</p>
<p>
Dependency Hierarchy:
- zest-0.14.0.jar (Root Library)
- operadriver-1.5.jar
- :x: **protobuf-java-2.4.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/community-scripts/commit/5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4">5ae7dcc04447ba3cc586c9d5f2500f99aaa2cbc4</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
An issue in protobuf-java allowed the interleaving of com.google.protobuf.UnknownFieldSet fields in such a way that would be processed out of order. A small malicious payload can occupy the parser for several minutes by creating large numbers of short-lived objects that cause frequent, repeated pauses. We recommend upgrading libraries beyond the vulnerable versions.
<p>Publish Date: 2022-01-10
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-22569>CVE-2021-22569</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-wrvw-hg22-4m67">https://github.com/advisories/GHSA-wrvw-hg22-4m67</a></p>
<p>Release Date: 2022-01-10</p>
<p>Fix Resolution: com.google.protobuf:protobuf-java:3.16.1,3.18.2,3.19.2; com.google.protobuf:protobuf-kotlin:3.18.2,3.19.2; google-protobuf - 3.19.2</p>
</p>
<p></p>
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p>
|
non_process
|
zest jar vulnerabilities highest severity is vulnerable library zest jar path to dependency file build gradle kts path to vulnerable library home wss scanner gradle caches modules files xalan xalan xalan jar found in head commit a href vulnerabilities cve severity cvss dependency type fixed in zest version remediation available critical commons text jar transitive critical snakeyaml jar transitive n a high jcommander jar transitive n a high htmlunit jar transitive n a high gson jar transitive n a high snakeyaml jar transitive n a high snakeyaml jar transitive n a high jar transitive n a high protobuf java jar transitive n a high neko htmlunit jar transitive n a high jetty io jar transitive n a high gson jar transitive n a high xalan jar transitive n a high protobuf java jar transitive n a medium commons jxpath jar transitive n a medium xercesimpl jar transitive n a medium snakeyaml jar transitive n a medium commons net jar transitive n a medium snakeyaml jar transitive n a medium snakeyaml jar transitive n a medium commons jxpath jar transitive n a medium snakeyaml jar transitive n a medium snakeyaml jar transitive n a medium protobuf java jar transitive n a medium jetty http jar transitive n a medium jetty http jar transitive n a medium httpclient jar transitive n a low guava jre jar transitive n a low detected in multiple dependencies transitive n a for some transitive vulnerabilities there is no version of direct dependency with a fix check the details section below to see if there is a version of transitive dependency where vulnerability is fixed details partial details vulnerabilities are displayed below due to a content size limitation in github to view information on the remaining vulnerabilities navigate to the mend application cve vulnerable library commons text jar apache commons text is a library focused on algorithms working on strings library home page a href path to dependency file build gradle kts path to vulnerable library home wss scanner gradle caches modules files org apache commons commons text commons text jar dependency hierarchy zest jar root library htmlunit driver jar htmlunit jar x commons text jar vulnerable library found in head commit a href found in base branch master vulnerability details apache commons text performs variable interpolation allowing properties to be dynamically evaluated and expanded the standard format for interpolation is prefix name where prefix is used to locate an instance of org apache commons text lookup stringlookup that performs the interpolation starting with version and continuing through the set of default lookup instances included interpolators that could result in arbitrary code execution or contact with remote servers these lookups are script execute expressions using the jvm script execution engine javax script dns resolve dns records url load values from urls including from remote servers applications using the interpolation defaults in the affected versions may be vulnerable to remote code execution or unintentional contact with remote servers if untrusted configuration values are used users are recommended to upgrade to apache commons text which disables the problematic interpolators by default publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org apache commons commons text direct dependency fix resolution org mozilla zest rescue worker helmet automatic remediation is available for this issue cve vulnerable library snakeyaml jar yaml parser and emitter for java library home page a href path to dependency file build gradle kts path to vulnerable library home wss scanner gradle caches modules files org yaml snakeyaml snakeyaml jar dependency hierarchy zest jar root library selenium server jar x snakeyaml jar vulnerable library found in head commit a href found in base branch master vulnerability details snakeyaml s constructor class does not restrict types which can be instantiated during deserialization deserializing yaml content provided by an attacker can lead to remote code execution we recommend using snakeyaml s safeconsturctor when parsing untrusted content to restrict deserialization publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org yaml snakeyaml ws vulnerable library jcommander jar command line parsing library home page a href path to dependency file build gradle kts path to vulnerable library home wss scanner gradle caches modules files com beust jcommander jcommander jar dependency hierarchy zest jar root library selenium server jar x jcommander jar vulnerable library found in head commit a href found in base branch master vulnerability details inclusion of functionality from untrusted control sphere vulnerability found in jcommander before jcommander resolving dependencies over http instead of https publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution com beust jcommander cve vulnerable library htmlunit jar a headless browser intended for use in testing web based applications library home page a href path to dependency file build gradle kts path to vulnerable library home wss scanner gradle caches modules files net sourceforge htmlunit htmlunit htmlunit jar dependency hierarchy zest jar root library htmlunit driver jar x htmlunit jar vulnerable library found in head commit a href found in base branch master vulnerability details htmlunit prior to contains code execution vulnerabilities htmlunit initializes rhino engine improperly hence a malicious javscript code can execute arbitrary java code on the application moreover when embedded in android application android specific initialization of rhino engine is done in an improper way hence a malicious javascript code can execute arbitrary java code on the application publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution net sourceforge htmlunit htmlunit ws vulnerable library gson jar gson json library library home page a href path to dependency file build gradle kts path to vulnerable library home wss scanner gradle caches modules files com google code gson gson gson jar dependency hierarchy zest jar root library x gson jar vulnerable library found in head commit a href found in base branch master vulnerability details denial of service vulnerability was discovered in gson before via the writereplace method publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution com google code gson gson cve vulnerable library snakeyaml jar yaml parser and emitter for java library home page a href path to dependency file build gradle kts path to vulnerable library home wss scanner gradle caches modules files org yaml snakeyaml snakeyaml jar dependency hierarchy zest jar root library selenium server jar x snakeyaml jar vulnerable library found in head commit a href found in base branch master vulnerability details the alias feature in snakeyaml before allows entity expansion during a load operation a related issue to cve publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org yaml snakeyaml cve vulnerable library snakeyaml jar yaml parser and emitter for java library home page a href path to dependency file build gradle kts path to vulnerable library home wss scanner gradle caches modules files org yaml snakeyaml snakeyaml jar dependency hierarchy zest jar root library selenium server jar x snakeyaml jar vulnerable library found in head commit a href found in base branch master vulnerability details the package org yaml snakeyaml from and before are vulnerable to denial of service dos due missing to nested depth limitation for collections publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org yaml snakeyaml cve vulnerable library jar java api for handling configuration files in windows ini format the library includes its own map based api java preferences api and java beans api for handling ini files additionally the library includes a feature rich variable macro substitution multiply property values etc java util properties replacement library home page a href path to dependency file build gradle kts path to vulnerable library home wss scanner gradle caches modules files org jar dependency hierarchy zest jar root library operadriver jar x jar vulnerable library found in head commit a href found in base branch master vulnerability details an issue in the fetch method in the basicprofile class of org before allows attackers to cause a denial of service dos via unspecified vectors publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org cve vulnerable library protobuf java jar protocol buffers are a way of encoding structured data in an efficient yet extensible format library home page a href path to dependency file build gradle kts path to vulnerable library home wss scanner gradle caches modules files com google protobuf protobuf java protobuf java jar dependency hierarchy zest jar root library operadriver jar x protobuf java jar vulnerable library found in head commit a href found in base branch master vulnerability details a parsing issue similar to cve but with textformat in protobuf java core and lite versions prior to and can lead to a denial of service attack inputs containing multiple instances of non repeated embedded messages with repeated or unknown fields causes objects to be converted back n forth between mutable and immutable forms resulting in potentially long garbage collection pauses we recommend updating to the versions mentioned above publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com google protobuf protobuf java cve vulnerable library neko htmlunit jar htmlunit adaptation of nekohtml it has the same functionality but exposing htmlelements to be overridden library home page a href path to dependency file build gradle kts path to vulnerable library home wss scanner gradle caches modules files net sourceforge htmlunit neko htmlunit neko htmlunit jar dependency hierarchy zest jar root library htmlunit driver jar htmlunit jar x neko htmlunit jar vulnerable library found in head commit a href found in base branch master vulnerability details htmlunit nekohtml parser before suffers from a denial of service vulnerability crafted input associated with the parsing of processing instruction pi data leads to heap memory consumption this is similar to cve but affects a much later version of the product publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution neko htmlunit cve vulnerable library jetty io jar the eclipse jetty project library home page a href path to dependency file build gradle kts path to vulnerable library home wss scanner gradle caches modules files org eclipse jetty jetty io jetty io jar dependency hierarchy zest jar root library htmlunit driver jar htmlunit jar websocket client jar x jetty io jar vulnerable library found in head commit a href found in base branch master vulnerability details in eclipse jetty to to and to cpu usage can reach upon receiving a large invalid tls frame publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org eclipse jetty jetty io org eclipse jetty jetty io org eclipse jetty jetty io cve vulnerable library gson jar gson json library library home page a href path to dependency file build gradle kts path to vulnerable library home wss scanner gradle caches modules files com google code gson gson gson jar dependency hierarchy zest jar root library x gson jar vulnerable library found in head commit a href found in base branch master vulnerability details the package com google code gson gson before are vulnerable to deserialization of untrusted data via the writereplace method in internal classes which may lead to dos attacks publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com google code gson gson gson parent cve vulnerable library xalan jar xalan java is an xslt processor for transforming xml documents into html text or other xml document types it implements xsl transformations xslt version and xml path language xpath version and can be used from the command line in an applet or a servlet or as a module in other program library home page a href path to dependency file build gradle kts path to vulnerable library home wss scanner gradle caches modules files xalan xalan xalan jar dependency hierarchy zest jar root library htmlunit driver jar htmlunit jar x xalan jar vulnerable library found in head commit a href found in base branch master vulnerability details the apache xalan java xslt library is vulnerable to an integer truncation issue when processing malicious xslt stylesheets this can be used to corrupt java class files generated by the internal xsltc compiler and execute arbitrary java bytecode the apache xalan java project is dormant and in the process of being retired no future releases of apache xalan java to address this issue are expected note java runtimes such as openjdk include repackaged copies of xalan publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact high availability impact none for more information on scores click a href cve vulnerable library protobuf java jar protocol buffers are a way of encoding structured data in an efficient yet extensible format library home page a href path to dependency file build gradle kts path to vulnerable library home wss scanner gradle caches modules files com google protobuf protobuf java protobuf java jar dependency hierarchy zest jar root library operadriver jar x protobuf java jar vulnerable library found in head commit a href found in base branch master vulnerability details a parsing issue with binary data in protobuf java core and lite versions prior to and can lead to a denial of service attack inputs containing multiple instances of non repeated embedded messages with repeated or unknown fields causes objects to be converted back n forth between mutable and immutable forms resulting in potentially long garbage collection pauses we recommend updating to the versions mentioned above publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com google protobuf protobuf java com google protobuf protobuf javalite com google protobuf protobuf kotlin com google protobuf protobuf kotlin lite google protobuf cve vulnerable library commons jxpath jar a java based implementation of xpath that in addition to xml processing can inspect modify java object graphs the library s explicit purpose and even mixed java xml structures path to dependency file build gradle kts path to vulnerable library home wss scanner gradle caches modules files commons jxpath commons jxpath commons jxpath jar dependency hierarchy zest jar root library operadriver jar x commons jxpath jar vulnerable library found in head commit a href found in base branch master vulnerability details disputed this record was originally reported by the oss fuzz project who failed to consider the security context in which jxpath is intended to be used and failed to contact the jxpath maintainers prior to requesting the cve allocation the cve was then allocated by google in breach of the cna rules after review by the jxpath maintainers the original report was found to be invalid publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href cve vulnerable library xercesimpl jar is the next generation of high performance fully compliant xml parsers in the apache xerces family this new version of xerces introduces the xerces native interface xni a complete framework for building parser components and configurations that is extremely modular and easy to program the apache parser is the reference implementation of xni but other parser components configurations and parsers can be written using the xerces native interface for complete design and implementation documents refer to the xni manual is a fully conforming xml schema processor a partial experimental implementation of the xml schema structures and datatypes working drafts december and an experimental implementation of the xml schema definition language xsd component designators scd candidate recommendation january are provided for evaluation for more information refer to the xml schema page also provides a complete implementation of the document object model level core and load save recommendations and provides a complete implementation of the xml inclusions xinclude recommendation it also provides support for oasis xml catalogs is able to parse documents written according to the xml recommendation except that it does not yet provide an option to enable normalization checking as described in section of this specification it also handles namespaces according to the xml namespaces recommendation and will correctly serialize xml documents if the dom level load save apis are in use library home page a href path to dependency file build gradle kts path to vulnerable library home wss scanner gradle caches modules files xerces xercesimpl xercesimpl jar dependency hierarchy zest jar root library htmlunit driver jar htmlunit jar neko htmlunit jar x xercesimpl jar vulnerable library found in head commit a href found in base branch master vulnerability details there s a vulnerability within the apache xerces java xercesj xml parser when handling specially crafted xml document payloads this causes the xercesj xml parser to wait in an infinite loop which may sometimes consume system resources for prolonged duration this vulnerability is present within xercesj version and the previous versions publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution xerces xercesimpl cve vulnerable library snakeyaml jar yaml parser and emitter for java library home page a href path to dependency file build gradle kts path to vulnerable library home wss scanner gradle caches modules files org yaml snakeyaml snakeyaml jar dependency hierarchy zest jar root library selenium server jar x snakeyaml jar vulnerable library found in head commit a href found in base branch master vulnerability details using snakeyaml to parse untrusted yaml files may be vulnerable to denial of service attacks dos if the parser is running on user supplied input an attacker may supply content that causes the parser to crash by stack overflow publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org yaml snakeyaml cve vulnerable library commons net jar apache commons net library contains a collection of network utilities and protocol implementations supported protocols include echo finger ftp nntp ntp s smtp s telnet whois path to dependency file build gradle kts path to vulnerable library home wss scanner gradle caches modules files commons net commons net commons net jar dependency hierarchy zest jar root library htmlunit driver jar htmlunit jar x commons net jar vulnerable library found in head commit a href found in base branch master vulnerability details prior to apache commons net net s ftp client trusts the host from pasv response by default a malicious server can redirect the commons net code to use a different host but the user has to connect to the malicious server in the first place this may lead to leakage of information about services running on the private network of the client the default in version is now false to ignore such hosts as curl does see publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution commons net commons net cve vulnerable library snakeyaml jar yaml parser and emitter for java library home page a href path to dependency file build gradle kts path to vulnerable library home wss scanner gradle caches modules files org yaml snakeyaml snakeyaml jar dependency hierarchy zest jar root library selenium server jar x snakeyaml jar vulnerable library found in head commit a href found in base branch master vulnerability details using snakeyaml to parse untrusted yaml files may be vulnerable to denial of service attacks dos if the parser is running on user supplied input an attacker may supply content that causes the parser to crash by stackoverflow publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org yaml snakeyaml cve vulnerable library snakeyaml jar yaml parser and emitter for java library home page a href path to dependency file build gradle kts path to vulnerable library home wss scanner gradle caches modules files org yaml snakeyaml snakeyaml jar dependency hierarchy zest jar root library selenium server jar x snakeyaml jar vulnerable library found in head commit a href found in base branch master vulnerability details using snakeyaml to parse untrusted yaml files may be vulnerable to denial of service attacks dos if the parser is running on user supplied input an attacker may supply content that causes the parser to crash by stackoverflow publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org yaml snakeyaml cve vulnerable library commons jxpath jar a java based implementation of xpath that in addition to xml processing can inspect modify java object graphs the library s explicit purpose and even mixed java xml structures path to dependency file build gradle kts path to vulnerable library home wss scanner gradle caches modules files commons jxpath commons jxpath commons jxpath jar dependency hierarchy zest jar root library operadriver jar x commons jxpath jar vulnerable library found in head commit a href found in base branch master vulnerability details disputed this record was originally reported by the oss fuzz project who failed to consider the security context in which jxpath is intended to be used and failed to contact the jxpath maintainers prior to requesting the cve allocation the cve was then allocated by google in breach of the cna rules after review by the jxpath maintainers the original report was found to be invalid publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href cve vulnerable library snakeyaml jar yaml parser and emitter for java library home page a href path to dependency file build gradle kts path to vulnerable library home wss scanner gradle caches modules files org yaml snakeyaml snakeyaml jar dependency hierarchy zest jar root library selenium server jar x snakeyaml jar vulnerable library found in head commit a href found in base branch master vulnerability details those using snakeyaml to parse untrusted yaml files may be vulnerable to denial of service attacks dos if the parser is running on user supplied input an attacker may supply content that causes the parser to crash by stack overflow this effect may support a denial of service attack publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org yaml snakeyaml cve vulnerable library snakeyaml jar yaml parser and emitter for java library home page a href path to dependency file build gradle kts path to vulnerable library home wss scanner gradle caches modules files org yaml snakeyaml snakeyaml jar dependency hierarchy zest jar root library selenium server jar x snakeyaml jar vulnerable library found in head commit a href found in base branch master vulnerability details using snakeyaml to parse untrusted yaml files may be vulnerable to denial of service attacks dos if the parser is running on user supplied input an attacker may supply content that causes the parser to crash by stackoverflow publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org yaml snakeyaml cve vulnerable library protobuf java jar protocol buffers are a way of encoding structured data in an efficient yet extensible format library home page a href path to dependency file build gradle kts path to vulnerable library home wss scanner gradle caches modules files com google protobuf protobuf java protobuf java jar dependency hierarchy zest jar root library operadriver jar x protobuf java jar vulnerable library found in head commit a href found in base branch master vulnerability details an issue in protobuf java allowed the interleaving of com google protobuf unknownfieldset fields in such a way that would be processed out of order a small malicious payload can occupy the parser for several minutes by creating large numbers of short lived objects that cause frequent repeated pauses we recommend upgrading libraries beyond the vulnerable versions publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com google protobuf protobuf java com google protobuf protobuf kotlin google protobuf rescue worker helmet automatic remediation is available for this issue
| 0
|
256,347
| 8,127,349,488
|
IssuesEvent
|
2018-08-17 07:44:17
|
javaee/javaee-jsp-api
|
https://api.github.com/repos/javaee/javaee-jsp-api
|
closed
|
Why just make a special judgment on JDK6
|
ERR: Assignee Priority: Major Type: Bug
|
There is a isJDK6() method in the org.apache.jasper. EmbeddedServletOptions.
---------------------
private boolean isJDK6()
{ return "1.6".equals(System.getProperty("java.specification.version")); }
----------------------
The following source use the isJDK6() to set the value of keepGenerated
---------------------
this.keepGenerated = getBoolean(config, !(isJDK6()), "keepgenerated");
---------------------
Why just make a special judgment on JDK6
|
1.0
|
Why just make a special judgment on JDK6 - There is a isJDK6() method in the org.apache.jasper. EmbeddedServletOptions.
---------------------
private boolean isJDK6()
{ return "1.6".equals(System.getProperty("java.specification.version")); }
----------------------
The following source use the isJDK6() to set the value of keepGenerated
---------------------
this.keepGenerated = getBoolean(config, !(isJDK6()), "keepgenerated");
---------------------
Why just make a special judgment on JDK6
|
non_process
|
why just make a special judgment on there is a method in the org apache jasper embeddedservletoptions private boolean return equals system getproperty java specification version the following source use the to set the value of keepgenerated this keepgenerated getboolean config keepgenerated why just make a special judgment on
| 0
|
19,861
| 26,271,085,968
|
IssuesEvent
|
2023-01-06 17:03:23
|
GoogleCloudPlatform/pgadapter
|
https://api.github.com/repos/GoogleCloudPlatform/pgadapter
|
closed
|
Docker image cannot be built on M1 Macs
|
type: process priority: p3
|
The Docker build file uses an '-alpine' Docker image internally to build the PGAdapter image. This '-alpine' image does not support the Arm64 architecture, which makes it impossible to build the Docker image on M1 Macs.
|
1.0
|
Docker image cannot be built on M1 Macs - The Docker build file uses an '-alpine' Docker image internally to build the PGAdapter image. This '-alpine' image does not support the Arm64 architecture, which makes it impossible to build the Docker image on M1 Macs.
|
process
|
docker image cannot be built on macs the docker build file uses an alpine docker image internally to build the pgadapter image this alpine image does not support the architecture which makes it impossible to build the docker image on macs
| 1
|
355,533
| 25,175,960,791
|
IssuesEvent
|
2022-11-11 09:17:12
|
Whysochong/pe
|
https://api.github.com/repos/Whysochong/pe
|
opened
|
Use of terms user may be unfamiliar with
|
severity.VeryLow type.DocumentationBug
|
Not every user understand what terminal is
<!--session: 1668157998985-027a8e22-992f-4e85-af8b-47cb2f66be04-->
<!--Version: Web v3.4.4-->
|
1.0
|
Use of terms user may be unfamiliar with - 
Not every user understand what terminal is
<!--session: 1668157998985-027a8e22-992f-4e85-af8b-47cb2f66be04-->
<!--Version: Web v3.4.4-->
|
non_process
|
use of terms user may be unfamiliar with not every user understand what terminal is
| 0
|
621
| 3,088,618,345
|
IssuesEvent
|
2015-08-25 17:26:59
|
codefordenver/fresh-food-connect
|
https://api.github.com/repos/codefordenver/fresh-food-connect
|
closed
|
Define Milestones
|
Process
|
As the Fresh Food Connect project, I would like milestones so Code for Denver can stay focused on goals.
|
1.0
|
Define Milestones - As the Fresh Food Connect project, I would like milestones so Code for Denver can stay focused on goals.
|
process
|
define milestones as the fresh food connect project i would like milestones so code for denver can stay focused on goals
| 1
|
20,257
| 26,874,665,038
|
IssuesEvent
|
2023-02-04 22:15:40
|
kserve/kserve
|
https://api.github.com/repos/kserve/kserve
|
closed
|
KServe v0.9 helm updated CRDs without incrementing version
|
kserve/release-process
|
Hi there, I noticed that a few CRDs got updated from v0.8 -> v0.9 (i.e. `protocolVersions` is introduced to `v1alpha1.ServingRuntime` and the versions still remain the same as `v1alpha1` or `v1beta1`. This causes `helm upgrade` fail as helm upgrades doesn’t update CRDs with same version. While we could just manually upgrade the CRDs and then perform the `helm upgrade`. I’m wondering if there’s a specific reason for not upgrading the CRD version when updating CRDs?
If we decide to not upgrading CRD version, then maybe we should have this caveat (as well as maybe [Helm's reasoning](https://github.com/helm/community/blob/main/hips/hip-0011.md)) under the `charts/` so that users who use Helm to maintain their KServe installation know in advance.
|
1.0
|
KServe v0.9 helm updated CRDs without incrementing version - Hi there, I noticed that a few CRDs got updated from v0.8 -> v0.9 (i.e. `protocolVersions` is introduced to `v1alpha1.ServingRuntime` and the versions still remain the same as `v1alpha1` or `v1beta1`. This causes `helm upgrade` fail as helm upgrades doesn’t update CRDs with same version. While we could just manually upgrade the CRDs and then perform the `helm upgrade`. I’m wondering if there’s a specific reason for not upgrading the CRD version when updating CRDs?
If we decide to not upgrading CRD version, then maybe we should have this caveat (as well as maybe [Helm's reasoning](https://github.com/helm/community/blob/main/hips/hip-0011.md)) under the `charts/` so that users who use Helm to maintain their KServe installation know in advance.
|
process
|
kserve helm updated crds without incrementing version hi there i noticed that a few crds got updated from i e protocolversions is introduced to servingruntime and the versions still remain the same as or this causes helm upgrade fail as helm upgrades doesn’t update crds with same version while we could just manually upgrade the crds and then perform the helm upgrade i’m wondering if there’s a specific reason for not upgrading the crd version when updating crds if we decide to not upgrading crd version then maybe we should have this caveat as well as maybe under the charts so that users who use helm to maintain their kserve installation know in advance
| 1
|
20,963
| 27,818,489,743
|
IssuesEvent
|
2023-03-19 00:05:17
|
cse442-at-ub/project_s23-one-belt-one-road
|
https://api.github.com/repos/cse442-at-ub/project_s23-one-belt-one-road
|
closed
|
Create a table in database for user's shopping cart
|
IO Task Processing Task Sprint 1 Sprint 2
|
**Task tests**
*Test 1*
1) Open the database tables categories
2) Verify that there is a table named "ShoppingCart"
3) Make certain that the table contains these columns: ProductID, Product Name, Unit Price, Amount, and UserID
|
1.0
|
Create a table in database for user's shopping cart - **Task tests**
*Test 1*
1) Open the database tables categories
2) Verify that there is a table named "ShoppingCart"
3) Make certain that the table contains these columns: ProductID, Product Name, Unit Price, Amount, and UserID
|
process
|
create a table in database for user s shopping cart task tests test open the database tables categories verify that there is a table named shoppingcart make certain that the table contains these columns productid product name unit price amount and userid
| 1
|
14,929
| 18,359,530,277
|
IssuesEvent
|
2021-10-09 01:46:04
|
DevExpress/testcafe-hammerhead
|
https://api.github.com/repos/DevExpress/testcafe-hammerhead
|
closed
|
The href change of the iframe location works wrong
|
TYPE: bug AREA: client SYSTEM: URL processing FREQUENCY: level 1 SYSTEM: iframe processing STATE: Stale
|
When cross domain iframe changes location, it leaves proxy port as is, but parent window location and new iframe location may be the same domain.
Related with https://github.com/DevExpress/testcafe/issues/1922
|
2.0
|
The href change of the iframe location works wrong - When cross domain iframe changes location, it leaves proxy port as is, but parent window location and new iframe location may be the same domain.
Related with https://github.com/DevExpress/testcafe/issues/1922
|
process
|
the href change of the iframe location works wrong when cross domain iframe changes location it leaves proxy port as is but parent window location and new iframe location may be the same domain related with
| 1
|
9,541
| 12,507,830,279
|
IssuesEvent
|
2020-06-02 14:41:22
|
GoogleCloudPlatform/dotnet-docs-samples
|
https://api.github.com/repos/GoogleCloudPlatform/dotnet-docs-samples
|
opened
|
[Spanner] Deactivate the QuickStart test, it keeps failing on Windows.
|
api: spanner priority: p1 type: process
|
I've deactivated it in #1061 .
I've also added the JUnit logger dependency to the tests so that we can get more info.
|
1.0
|
[Spanner] Deactivate the QuickStart test, it keeps failing on Windows. - I've deactivated it in #1061 .
I've also added the JUnit logger dependency to the tests so that we can get more info.
|
process
|
deactivate the quickstart test it keeps failing on windows i ve deactivated it in i ve also added the junit logger dependency to the tests so that we can get more info
| 1
|
9,449
| 12,428,970,152
|
IssuesEvent
|
2020-05-25 07:31:23
|
metabase/metabase
|
https://api.github.com/repos/metabase/metabase
|
closed
|
feature request: select all columns when joining, not just the starting table's
|
.Proposal Querying/Processor
|
currently, when you filter/group across a foreign key (ie do a join), you only get the initial table's data back. it'd be nice to optionally also get the joined table's data.
i know #2214 may be one way do this (and #1173 is related), but this would be a nice smaller step that wouldn't require setting up a view ahead of time. ideally you could even join using foreign keys without filtering or grouping at all, just to see/visualize the joined rows.
feel free to close if this is a dupe!
⬇️ **Please click the 👍 reaction instead of leaving a `+1` or 👍 comment**
|
1.0
|
feature request: select all columns when joining, not just the starting table's - currently, when you filter/group across a foreign key (ie do a join), you only get the initial table's data back. it'd be nice to optionally also get the joined table's data.
i know #2214 may be one way do this (and #1173 is related), but this would be a nice smaller step that wouldn't require setting up a view ahead of time. ideally you could even join using foreign keys without filtering or grouping at all, just to see/visualize the joined rows.
feel free to close if this is a dupe!
⬇️ **Please click the 👍 reaction instead of leaving a `+1` or 👍 comment**
|
process
|
feature request select all columns when joining not just the starting table s currently when you filter group across a foreign key ie do a join you only get the initial table s data back it d be nice to optionally also get the joined table s data i know may be one way do this and is related but this would be a nice smaller step that wouldn t require setting up a view ahead of time ideally you could even join using foreign keys without filtering or grouping at all just to see visualize the joined rows feel free to close if this is a dupe ⬇️ please click the 👍 reaction instead of leaving a or 👍 comment
| 1
|
76,237
| 26,327,221,377
|
IssuesEvent
|
2023-01-10 07:56:59
|
line/armeria
|
https://api.github.com/repos/line/armeria
|
closed
|
`ClientCall.Listener#onHeaders` is not invoked for gRPC client
|
defect
|
Currently, the gRPC client does not invoke `ClientCall.Listener#onHeaders`.
This behavior is different from upstream, which eventually invokes this callback.
https://github.com/grpc/grpc-java/blob/f08300e0e314c6f0c0731c46f3e9985aefa35513/netty/src/main/java/io/grpc/netty/NettyClientStream.java#L336-L345
We should also note that this callback is called only for headers (not for trailers)
ref: https://line-armeria.slack.com/archives/C1NGPBUH2/p1671523590046549
|
1.0
|
`ClientCall.Listener#onHeaders` is not invoked for gRPC client - Currently, the gRPC client does not invoke `ClientCall.Listener#onHeaders`.
This behavior is different from upstream, which eventually invokes this callback.
https://github.com/grpc/grpc-java/blob/f08300e0e314c6f0c0731c46f3e9985aefa35513/netty/src/main/java/io/grpc/netty/NettyClientStream.java#L336-L345
We should also note that this callback is called only for headers (not for trailers)
ref: https://line-armeria.slack.com/archives/C1NGPBUH2/p1671523590046549
|
non_process
|
clientcall listener onheaders is not invoked for grpc client currently the grpc client does not invoke clientcall listener onheaders this behavior is different from upstream which eventually invokes this callback we should also note that this callback is called only for headers not for trailers ref
| 0
|
7,565
| 6,993,059,154
|
IssuesEvent
|
2017-12-15 09:50:07
|
angular/material2
|
https://api.github.com/repos/angular/material2
|
closed
|
bug(build): nightly build not publishing for material
|
in progress infrastructure P3: important
|
#### Bug, feature request, or proposal:
The nightly builds are not getting updated for material, but they are getting updated for the cdk
#### What is the expected behavior?
Both packages should be updated on the nightly build with each commit
#### What is the current behavior?
Nightly builds are not being published for material2
#### What are the steps to reproduce?
`npm i angular/material2-builds`
|
1.0
|
bug(build): nightly build not publishing for material - #### Bug, feature request, or proposal:
The nightly builds are not getting updated for material, but they are getting updated for the cdk
#### What is the expected behavior?
Both packages should be updated on the nightly build with each commit
#### What is the current behavior?
Nightly builds are not being published for material2
#### What are the steps to reproduce?
`npm i angular/material2-builds`
|
non_process
|
bug build nightly build not publishing for material bug feature request or proposal the nightly builds are not getting updated for material but they are getting updated for the cdk what is the expected behavior both packages should be updated on the nightly build with each commit what is the current behavior nightly builds are not being published for what are the steps to reproduce npm i angular builds
| 0
|
7,961
| 11,140,456,923
|
IssuesEvent
|
2019-12-21 14:33:00
|
kakainet/ViTex
|
https://api.github.com/repos/kakainet/ViTex
|
opened
|
Make input images black&white
|
preprocessing
|
Targets:
- Remove noise
- Make text as white and background as black (text pixels should have positive value)
|
1.0
|
Make input images black&white - Targets:
- Remove noise
- Make text as white and background as black (text pixels should have positive value)
|
process
|
make input images black white targets remove noise make text as white and background as black text pixels should have positive value
| 1
|
10,507
| 13,265,038,942
|
IssuesEvent
|
2020-08-21 05:32:48
|
knative/serving
|
https://api.github.com/repos/knative/serving
|
closed
|
istio.sidecar.includeOutboundIPRanges in config-network should be obsolete
|
area/networking kind/feature kind/process lifecycle/frozen
|
## In what area(s)?
/area networking
## Describe the feature
Knative supports `traffic.sidecar.istio.io/includeOutboundIPRanges` option due to [1] in old version. But current Knative allows outbound access by default so the option should not be necessary.
Docs also removed it - https://github.com/knative/docs/issues/1859
[1] https://knative.dev/v0.8-docs/serving/outbound-network-access/
> Knative blocks all outbound traffic by default. To enable outbound access (when you want to connect to the Cloud Storage API, for example), you need to change the scope of the proxy IP range by editing the config-network map.
|
1.0
|
istio.sidecar.includeOutboundIPRanges in config-network should be obsolete - ## In what area(s)?
/area networking
## Describe the feature
Knative supports `traffic.sidecar.istio.io/includeOutboundIPRanges` option due to [1] in old version. But current Knative allows outbound access by default so the option should not be necessary.
Docs also removed it - https://github.com/knative/docs/issues/1859
[1] https://knative.dev/v0.8-docs/serving/outbound-network-access/
> Knative blocks all outbound traffic by default. To enable outbound access (when you want to connect to the Cloud Storage API, for example), you need to change the scope of the proxy IP range by editing the config-network map.
|
process
|
istio sidecar includeoutboundipranges in config network should be obsolete in what area s area networking describe the feature knative supports traffic sidecar istio io includeoutboundipranges option due to in old version but current knative allows outbound access by default so the option should not be necessary docs also removed it knative blocks all outbound traffic by default to enable outbound access when you want to connect to the cloud storage api for example you need to change the scope of the proxy ip range by editing the config network map
| 1
|
3,878
| 6,817,601,985
|
IssuesEvent
|
2017-11-07 00:14:48
|
Great-Hill-Corporation/quickBlocks
|
https://api.github.com/repos/Great-Hill-Corporation/quickBlocks
|
closed
|
getBlock --latest should pull from etherscan as well as the local node
|
status-inprocess tools-getBlock type-enhancement
|
Or better yet, --latest should be an option on getBlock. Further, it should report how many blocks it's behind. It should also report latest block from the hard drive cache and the miniBlock cache
From https://github.com/Great-Hill-Corporation/ethslurp/issues/148
|
1.0
|
getBlock --latest should pull from etherscan as well as the local node - Or better yet, --latest should be an option on getBlock. Further, it should report how many blocks it's behind. It should also report latest block from the hard drive cache and the miniBlock cache
From https://github.com/Great-Hill-Corporation/ethslurp/issues/148
|
process
|
getblock latest should pull from etherscan as well as the local node or better yet latest should be an option on getblock further it should report how many blocks it s behind it should also report latest block from the hard drive cache and the miniblock cache from
| 1
|
25,237
| 24,916,816,306
|
IssuesEvent
|
2022-10-30 13:55:31
|
tailscale/tailscale
|
https://api.github.com/repos/tailscale/tailscale
|
closed
|
Magicsock sometimes does not recover from internet outages
|
connectivity L2 Few P2 Aggravating T5 Usability tis but a scratch
|
The setup: have tailscale on various devices in a home LAN, behind an ISP-provided internet router. Restart the ISP router, or have some kind of internet outage that is "soft" from the Tailscale client's POV (interface doesn't go down, packets just stop flowing). Upon recovery of the internet link, I've observed both magicsock being stuck on DERP, as well as a fairly prolonged inability to communicate at all.
I'm unsure if this is a regression, or if we always reacted poorly to that specific case of upstream outage. Either way, filing this tracking bug to characterize things a bit more and see what we can do about it.
<img src="https://frontapp.com/assets/img/favicons/favicon-32x32.png" height="16" width="16" alt="Front logo" /> [Front conversations](https://app.frontapp.com/open/top_3kdjl)
|
True
|
Magicsock sometimes does not recover from internet outages - The setup: have tailscale on various devices in a home LAN, behind an ISP-provided internet router. Restart the ISP router, or have some kind of internet outage that is "soft" from the Tailscale client's POV (interface doesn't go down, packets just stop flowing). Upon recovery of the internet link, I've observed both magicsock being stuck on DERP, as well as a fairly prolonged inability to communicate at all.
I'm unsure if this is a regression, or if we always reacted poorly to that specific case of upstream outage. Either way, filing this tracking bug to characterize things a bit more and see what we can do about it.
<img src="https://frontapp.com/assets/img/favicons/favicon-32x32.png" height="16" width="16" alt="Front logo" /> [Front conversations](https://app.frontapp.com/open/top_3kdjl)
|
non_process
|
magicsock sometimes does not recover from internet outages the setup have tailscale on various devices in a home lan behind an isp provided internet router restart the isp router or have some kind of internet outage that is soft from the tailscale client s pov interface doesn t go down packets just stop flowing upon recovery of the internet link i ve observed both magicsock being stuck on derp as well as a fairly prolonged inability to communicate at all i m unsure if this is a regression or if we always reacted poorly to that specific case of upstream outage either way filing this tracking bug to characterize things a bit more and see what we can do about it
| 0
|
51,574
| 10,697,302,818
|
IssuesEvent
|
2019-10-23 16:14:37
|
isogeo/isogeo-plugin-qgis
|
https://api.github.com/repos/isogeo/isogeo-plugin-qgis
|
closed
|
Break semantic versioning: directly bump from 2.x to 3.x
|
User Interface code art enhancement
|
## Why 3.x and not 2.x?
The stable version of the Isogeo plugin for QGIS 3 will be 3.x and not 2.x because "version 3 of the plugin works on QGIS 3" is less confusing than "version 2 of the plugin works on QGIS 3".
## Same as version 1.x in QGIS 3.x LTR
Version 3.x is the result of an isofunctional migration of the plugin. So this new version allows you to use the same functionality in a more recent version of QGIS (3.x LTR):
* search for datas using the search engine
* consult metadata sheets
* add layers to the canvas.
## Functionally identical and technically better
The source code of the plugin was refactored and some bugs in version 1 were fixed.
|
1.0
|
Break semantic versioning: directly bump from 2.x to 3.x - ## Why 3.x and not 2.x?
The stable version of the Isogeo plugin for QGIS 3 will be 3.x and not 2.x because "version 3 of the plugin works on QGIS 3" is less confusing than "version 2 of the plugin works on QGIS 3".
## Same as version 1.x in QGIS 3.x LTR
Version 3.x is the result of an isofunctional migration of the plugin. So this new version allows you to use the same functionality in a more recent version of QGIS (3.x LTR):
* search for datas using the search engine
* consult metadata sheets
* add layers to the canvas.
## Functionally identical and technically better
The source code of the plugin was refactored and some bugs in version 1 were fixed.
|
non_process
|
break semantic versioning directly bump from x to x why x and not x the stable version of the isogeo plugin for qgis will be x and not x because version of the plugin works on qgis is less confusing than version of the plugin works on qgis same as version x in qgis x ltr version x is the result of an isofunctional migration of the plugin so this new version allows you to use the same functionality in a more recent version of qgis x ltr search for datas using the search engine consult metadata sheets add layers to the canvas functionally identical and technically better the source code of the plugin was refactored and some bugs in version were fixed
| 0
|
33,248
| 6,188,029,068
|
IssuesEvent
|
2017-07-04 09:08:42
|
Icinga/icingaweb2
|
https://api.github.com/repos/Icinga/icingaweb2
|
closed
|
[dev.icinga.com #8471] Document how to define a custom configuration directory
|
bug documentation wontfix
|
This issue has been migrated from Redmine: https://dev.icinga.com/issues/8471
**Created by jmeyer on 2015-02-18 15:05:48 +00:00**
Assignee: _(none)_
Status: _New_
Target Version: _(none)_
Last Update: _2015-06-29 14:47:04 +00:00 (in Redmine)_
---
The documentation is based on the assumption that the user is using the default /etc/icingaweb2. It is essential to point out that it is possible to use a different one and how it's done (CLI command args, web server config).
---
**Parent Task:** [#7153](https://dev.icinga.com/issues/7153)
|
1.0
|
[dev.icinga.com #8471] Document how to define a custom configuration directory - This issue has been migrated from Redmine: https://dev.icinga.com/issues/8471
**Created by jmeyer on 2015-02-18 15:05:48 +00:00**
Assignee: _(none)_
Status: _New_
Target Version: _(none)_
Last Update: _2015-06-29 14:47:04 +00:00 (in Redmine)_
---
The documentation is based on the assumption that the user is using the default /etc/icingaweb2. It is essential to point out that it is possible to use a different one and how it's done (CLI command args, web server config).
---
**Parent Task:** [#7153](https://dev.icinga.com/issues/7153)
|
non_process
|
document how to define a custom configuration directory this issue has been migrated from redmine created by jmeyer on assignee none status new target version none last update in redmine the documentation is based on the assumption that the user is using the default etc it is essential to point out that it is possible to use a different one and how it s done cli command args web server config parent task
| 0
|
225,912
| 17,292,414,150
|
IssuesEvent
|
2021-07-25 03:01:58
|
jpmaida/openshift-pipelines
|
https://api.github.com/repos/jpmaida/openshift-pipelines
|
opened
|
Melhorar documentação principal do repositório
|
documentation
|
Toda a documentação deve estar em inglês e essa documentação deve mostrar a estruturação de diretórios com uma breve explicação de cada diretório.
|
1.0
|
Melhorar documentação principal do repositório - Toda a documentação deve estar em inglês e essa documentação deve mostrar a estruturação de diretórios com uma breve explicação de cada diretório.
|
non_process
|
melhorar documentação principal do repositório toda a documentação deve estar em inglês e essa documentação deve mostrar a estruturação de diretórios com uma breve explicação de cada diretório
| 0
|
6,533
| 9,632,606,363
|
IssuesEvent
|
2019-05-15 16:34:51
|
IIIF/api
|
https://api.github.com/repos/IIIF/api
|
closed
|
Move editorial process doc to website repo
|
discuss editorial process website
|
The process of discussing, defining, documenting and approving specifications should live in the community area of the site, not the specifications part. It should still be normative with requirements, but it's a process document related to the formation and work of TSGs (and soon to exist TRC).
|
1.0
|
Move editorial process doc to website repo -
The process of discussing, defining, documenting and approving specifications should live in the community area of the site, not the specifications part. It should still be normative with requirements, but it's a process document related to the formation and work of TSGs (and soon to exist TRC).
|
process
|
move editorial process doc to website repo the process of discussing defining documenting and approving specifications should live in the community area of the site not the specifications part it should still be normative with requirements but it s a process document related to the formation and work of tsgs and soon to exist trc
| 1
|
19,934
| 26,403,564,305
|
IssuesEvent
|
2023-01-13 05:03:56
|
AcademySoftwareFoundation/OpenCue
|
https://api.github.com/repos/AcademySoftwareFoundation/OpenCue
|
opened
|
Create integration test script
|
process triaged
|
**Describe the process**
Create a script that performs an automated test with a full OpenCue deployment.
Requirements:
1. Must run locally and on GitHub CI.
2. Create a fresh database, Cuebot, and RQD instance.
3. Install and test pycue, pyoutline, and cueadmin.
4. Install and launch cuegui and cuesubmit.
5. Launch a job and verify it completes with the expected output.
Bonus points if:
1. It also tests cuegui and cuesubmit functionality.
2. It uses the docker compose sandbox to create the db/cuebot/rqd setup.
Once the script exists it should be integrated into the packaging pipeline, which runs on every commit to master. No need to run it as part of the PR checks.
Once we're doing integration tests as part of the packaging pipeline, we can start publishing Docker images and eventually PyPI packages for every OpenCue patch version -- no need to wait for an official release to do those.
|
1.0
|
Create integration test script - **Describe the process**
Create a script that performs an automated test with a full OpenCue deployment.
Requirements:
1. Must run locally and on GitHub CI.
2. Create a fresh database, Cuebot, and RQD instance.
3. Install and test pycue, pyoutline, and cueadmin.
4. Install and launch cuegui and cuesubmit.
5. Launch a job and verify it completes with the expected output.
Bonus points if:
1. It also tests cuegui and cuesubmit functionality.
2. It uses the docker compose sandbox to create the db/cuebot/rqd setup.
Once the script exists it should be integrated into the packaging pipeline, which runs on every commit to master. No need to run it as part of the PR checks.
Once we're doing integration tests as part of the packaging pipeline, we can start publishing Docker images and eventually PyPI packages for every OpenCue patch version -- no need to wait for an official release to do those.
|
process
|
create integration test script describe the process create a script that performs an automated test with a full opencue deployment requirements must run locally and on github ci create a fresh database cuebot and rqd instance install and test pycue pyoutline and cueadmin install and launch cuegui and cuesubmit launch a job and verify it completes with the expected output bonus points if it also tests cuegui and cuesubmit functionality it uses the docker compose sandbox to create the db cuebot rqd setup once the script exists it should be integrated into the packaging pipeline which runs on every commit to master no need to run it as part of the pr checks once we re doing integration tests as part of the packaging pipeline we can start publishing docker images and eventually pypi packages for every opencue patch version no need to wait for an official release to do those
| 1
|
10,381
| 13,194,517,504
|
IssuesEvent
|
2020-08-13 16:58:21
|
geneontology/go-ontology
|
https://api.github.com/repos/geneontology/go-ontology
|
reopened
|
Obsolete GO:0044133 growth of symbiont on or near host ?
|
multi-species process obsoletion
|
No annotations.
@mgiglio99 @ValWood Are there uses for this term ?
Thanks, Pascale
|
1.0
|
Obsolete GO:0044133 growth of symbiont on or near host ? - No annotations.
@mgiglio99 @ValWood Are there uses for this term ?
Thanks, Pascale
|
process
|
obsolete go growth of symbiont on or near host no annotations valwood are there uses for this term thanks pascale
| 1
|
337,914
| 10,220,963,282
|
IssuesEvent
|
2019-08-15 23:17:17
|
googleapis/elixir-google-api
|
https://api.github.com/repos/googleapis/elixir-google-api
|
opened
|
[Compute] New codegen renamed Model.HttpHealthCheck to HTTPHealthCheck
|
priority: p2 type: bug
|
New codegen renamed Model.HttpHealthCheck to HTTPHealthCheck but didn't rename the uses. As a result, the new codegen doesn't build.
|
1.0
|
[Compute] New codegen renamed Model.HttpHealthCheck to HTTPHealthCheck - New codegen renamed Model.HttpHealthCheck to HTTPHealthCheck but didn't rename the uses. As a result, the new codegen doesn't build.
|
non_process
|
new codegen renamed model httphealthcheck to httphealthcheck new codegen renamed model httphealthcheck to httphealthcheck but didn t rename the uses as a result the new codegen doesn t build
| 0
|
646,053
| 21,035,788,141
|
IssuesEvent
|
2022-03-31 07:42:42
|
webcompat/web-bugs
|
https://api.github.com/repos/webcompat/web-bugs
|
closed
|
images.google.com - site is not usable
|
priority-critical browser-fenix engine-gecko
|
<!-- @browser: Firefox Mobile 100.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 12; Mobile; rv:100.0) Gecko/100.0 Firefox/100.0 -->
<!-- @reported_with: android-components-reporter -->
<!-- @public_url: https://github.com/webcompat/web-bugs/issues/101777 -->
<!-- @extra_labels: browser-fenix -->
**URL**: https://images.google.com/
**Browser / Version**: Firefox Mobile 100.0
**Operating System**: Android 12
**Tested Another Browser**: Yes Chrome
**Problem type**: Site is not usable
**Description**: Missing items
**Steps to Reproduce**:
Dark mode doesn't work, image searching through another app or an extension fails unless switched to desktop mode. When using chome, images can be searched even in mobile view, and dark mode is able tp be applied
<details>
<summary>Browser Configuration</summary>
<ul>
<li>gfx.webrender.all: false</li><li>gfx.webrender.blob-images: true</li><li>gfx.webrender.enabled: false</li><li>image.mem.shared: true</li><li>buildID: 20220329095604</li><li>channel: nightly</li><li>hasTouchScreen: true</li><li>mixed active content blocked: false</li><li>mixed passive content blocked: false</li><li>tracking content blocked: false</li>
</ul>
</details>
[View console log messages](https://webcompat.com/console_logs/2022/3/76d55332-b431-4ee3-befa-bfc13be45aad)
_From [webcompat.com](https://webcompat.com/) with ❤️_
|
1.0
|
images.google.com - site is not usable - <!-- @browser: Firefox Mobile 100.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 12; Mobile; rv:100.0) Gecko/100.0 Firefox/100.0 -->
<!-- @reported_with: android-components-reporter -->
<!-- @public_url: https://github.com/webcompat/web-bugs/issues/101777 -->
<!-- @extra_labels: browser-fenix -->
**URL**: https://images.google.com/
**Browser / Version**: Firefox Mobile 100.0
**Operating System**: Android 12
**Tested Another Browser**: Yes Chrome
**Problem type**: Site is not usable
**Description**: Missing items
**Steps to Reproduce**:
Dark mode doesn't work, image searching through another app or an extension fails unless switched to desktop mode. When using chome, images can be searched even in mobile view, and dark mode is able tp be applied
<details>
<summary>Browser Configuration</summary>
<ul>
<li>gfx.webrender.all: false</li><li>gfx.webrender.blob-images: true</li><li>gfx.webrender.enabled: false</li><li>image.mem.shared: true</li><li>buildID: 20220329095604</li><li>channel: nightly</li><li>hasTouchScreen: true</li><li>mixed active content blocked: false</li><li>mixed passive content blocked: false</li><li>tracking content blocked: false</li>
</ul>
</details>
[View console log messages](https://webcompat.com/console_logs/2022/3/76d55332-b431-4ee3-befa-bfc13be45aad)
_From [webcompat.com](https://webcompat.com/) with ❤️_
|
non_process
|
images google com site is not usable url browser version firefox mobile operating system android tested another browser yes chrome problem type site is not usable description missing items steps to reproduce dark mode doesn t work image searching through another app or an extension fails unless switched to desktop mode when using chome images can be searched even in mobile view and dark mode is able tp be applied browser configuration gfx webrender all false gfx webrender blob images true gfx webrender enabled false image mem shared true buildid channel nightly hastouchscreen true mixed active content blocked false mixed passive content blocked false tracking content blocked false from with ❤️
| 0
|
287,679
| 8,818,216,475
|
IssuesEvent
|
2018-12-31 09:53:53
|
netdata/netdata
|
https://api.github.com/repos/netdata/netdata
|
closed
|
Should use IEC-compliant abbreviations, e.g. KiB, MiB, etc.
|
area/web bug priority/medium
|
As those are multipliers of 1024, then according to IEC standard their unit should be represented in kibibytes (KiB), mebibytes (MiB) and so on. KB, MB and alike are reserved for multipliers of 1000 so there is no confusion with SI standards of unit naming.
Standard was also implemented by IEEE in 2002 as IEEE 1541-2002.
Original issue:
https://github.com/netdata/netdata/pull/4707
|
1.0
|
Should use IEC-compliant abbreviations, e.g. KiB, MiB, etc. - As those are multipliers of 1024, then according to IEC standard their unit should be represented in kibibytes (KiB), mebibytes (MiB) and so on. KB, MB and alike are reserved for multipliers of 1000 so there is no confusion with SI standards of unit naming.
Standard was also implemented by IEEE in 2002 as IEEE 1541-2002.
Original issue:
https://github.com/netdata/netdata/pull/4707
|
non_process
|
should use iec compliant abbreviations e g kib mib etc as those are multipliers of then according to iec standard their unit should be represented in kibibytes kib mebibytes mib and so on kb mb and alike are reserved for multipliers of so there is no confusion with si standards of unit naming standard was also implemented by ieee in as ieee original issue
| 0
|
8,169
| 11,386,496,616
|
IssuesEvent
|
2020-01-29 13:24:12
|
prisma/prisma2
|
https://api.github.com/repos/prisma/prisma2
|
opened
|
findOne optimization
|
kind/feature process/candidate
|
To [quote from an earlier `specs` issue](https://github.com/prisma/specs/issues/242#issuecomment-548382431):
> One of the main usecases of ~~Photon~~ Prisma Client is to use it inside a GraphQL server. The resolver system of a GraphQL server is prone to suffer from the N+1 problem. To mitigate this problem users can choose to implement the DataLoader pattern within the application server. This burdens our users with unnecessary work that is not related to their core domain. This issue explores how we could include a DataLoader implementation within ~~Photon~~ Prisma Client.
As a first step we want to look specifically into optimizing `findOne` queries.
|
1.0
|
findOne optimization - To [quote from an earlier `specs` issue](https://github.com/prisma/specs/issues/242#issuecomment-548382431):
> One of the main usecases of ~~Photon~~ Prisma Client is to use it inside a GraphQL server. The resolver system of a GraphQL server is prone to suffer from the N+1 problem. To mitigate this problem users can choose to implement the DataLoader pattern within the application server. This burdens our users with unnecessary work that is not related to their core domain. This issue explores how we could include a DataLoader implementation within ~~Photon~~ Prisma Client.
As a first step we want to look specifically into optimizing `findOne` queries.
|
process
|
findone optimization to one of the main usecases of photon prisma client is to use it inside a graphql server the resolver system of a graphql server is prone to suffer from the n problem to mitigate this problem users can choose to implement the dataloader pattern within the application server this burdens our users with unnecessary work that is not related to their core domain this issue explores how we could include a dataloader implementation within photon prisma client as a first step we want to look specifically into optimizing findone queries
| 1
|
2,716
| 5,581,188,968
|
IssuesEvent
|
2017-03-28 18:18:47
|
djspiewak/issue-testing
|
https://api.github.com/repos/djspiewak/issue-testing
|
opened
|
Add a signup button
|
epic: Signup Process 2.0
|
- [ ] Edit the HTML
- [ ] Install Rails
+ [ ] Be annoyed that we're using Rails
+ [ ] Shave some yaks investigating alternate technologies
- [ ] Wire up the button logic
- [ ] …
- [ ] Profit
|
1.0
|
Add a signup button - - [ ] Edit the HTML
- [ ] Install Rails
+ [ ] Be annoyed that we're using Rails
+ [ ] Shave some yaks investigating alternate technologies
- [ ] Wire up the button logic
- [ ] …
- [ ] Profit
|
process
|
add a signup button edit the html install rails be annoyed that we re using rails shave some yaks investigating alternate technologies wire up the button logic … profit
| 1
|
28,156
| 31,884,440,963
|
IssuesEvent
|
2023-09-16 19:27:21
|
godotengine/godot
|
https://api.github.com/repos/godotengine/godot
|
closed
|
LightmapProbes not selectable in the 3D editor viewport
|
bug topic:editor usability topic:3d
|
### Describe the project you are working on
N/A
### Describe the problem or limitation you are having in your project
As of currently, you cannot click-select them in 3D view and have to select them from scene tree. Considering that manually placing down light probes is already somewhat laborious(and using something to place them on a subdivided grid may not be enough), not being able to click-select them would be a huge pain.
### Describe the feature / enhancement and how it helps to overcome the problem or limitation
It helps speed up the process of manually placing `LightmapProbe`s and moving them about. A huge QoL improvement in my opinion.
### Describe how your proposal will work, with code, pseudo-code, mock-ups, and/or diagrams
When the user clicks on a `LightmapProbe`'s gizmo(see the circular thing below), the `LightmapProbe` it belongs to will be selected and moved around easily. That's literally it.

### If this enhancement will not be used often, can it be worked around with a few lines of script?
`LightmapProbe` is implemented in core.
### Is there a reason why this should be core and not an add-on in the asset library?
See above.
|
True
|
LightmapProbes not selectable in the 3D editor viewport - ### Describe the project you are working on
N/A
### Describe the problem or limitation you are having in your project
As of currently, you cannot click-select them in 3D view and have to select them from scene tree. Considering that manually placing down light probes is already somewhat laborious(and using something to place them on a subdivided grid may not be enough), not being able to click-select them would be a huge pain.
### Describe the feature / enhancement and how it helps to overcome the problem or limitation
It helps speed up the process of manually placing `LightmapProbe`s and moving them about. A huge QoL improvement in my opinion.
### Describe how your proposal will work, with code, pseudo-code, mock-ups, and/or diagrams
When the user clicks on a `LightmapProbe`'s gizmo(see the circular thing below), the `LightmapProbe` it belongs to will be selected and moved around easily. That's literally it.

### If this enhancement will not be used often, can it be worked around with a few lines of script?
`LightmapProbe` is implemented in core.
### Is there a reason why this should be core and not an add-on in the asset library?
See above.
|
non_process
|
lightmapprobes not selectable in the editor viewport describe the project you are working on n a describe the problem or limitation you are having in your project as of currently you cannot click select them in view and have to select them from scene tree considering that manually placing down light probes is already somewhat laborious and using something to place them on a subdivided grid may not be enough not being able to click select them would be a huge pain describe the feature enhancement and how it helps to overcome the problem or limitation it helps speed up the process of manually placing lightmapprobe s and moving them about a huge qol improvement in my opinion describe how your proposal will work with code pseudo code mock ups and or diagrams when the user clicks on a lightmapprobe s gizmo see the circular thing below the lightmapprobe it belongs to will be selected and moved around easily that s literally it if this enhancement will not be used often can it be worked around with a few lines of script lightmapprobe is implemented in core is there a reason why this should be core and not an add on in the asset library see above
| 0
|
234,739
| 7,725,762,027
|
IssuesEvent
|
2018-05-24 18:59:19
|
projectcalico/calico
|
https://api.github.com/repos/projectcalico/calico
|
closed
|
Docker network creation with --subnet parameter breaks IPAM driver
|
priority/P1
|
Docker calico libnetwork driver (IPAM) is not getting IPs for containers, when I have created the network with the --subnet parameter.
```
docker run -ti --rm --net my-net nginx:alpine ip a
docker: Error response from daemon: IpamDriver.RequestAddress: Unexpected number of assigned IP addresses. A single address should be assigned. Got []
```
## Expected Behavior
```
# calicoctl apply -f pool.yml
# calicoctl get ipPool -o yaml
- apiVersion: v1
kind: ipPool
metadata:
cidr: 172.16.0.0/16
spec: {}
# docker network create --driver calico --ipam-driver calico-ipam my-net
73b95eed1a35afaa4ea86f876c95a8eedbc5dd6495927856ce4f395e10473ca7
# docker run -ti --rm --net my-net nginx:alpine ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN qlen 1
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
28: cali0@if29: <BROADCAST,MULTICAST,UP,LOWER_UP,M-DOWN> mtu 1500 qdisc noqueue state UP
link/ether ee:ee:ee:ee:ee:ee brd ff:ff:ff:ff:ff:ff
inet 172.16.91.195/32 scope global cali0
valid_lft forever preferred_lft forever
inet6 fe80::ecee:eeff:feee:eeee/64 scope link tentative
valid_lft forever preferred_lft forever
```
## Current Behavior
```
# calicoctl apply -f pool.yml
# calicoctl get ipPool -o yaml
- apiVersion: v1
kind: ipPool
metadata:
cidr: 172.16.0.0/16
spec: {}
# docker network create --driver calico --ipam-driver calico-ipam --subnet 172.16.0.0/16 my-net
8380dda610353d9a2f761d54e0df53f7de88e2f37992e1cded699fabbcc2bd97
# docker run -ti --rm --net my-net nginx:alpine ip a
docker: Error response from daemon: IpamDriver.RequestAddress: Unexpected number of assigned IP addresses. A single address should be assigned. Got []
```
## Your Environment
* Calico version: v2.6.3
* Orchestrator version (e.g. kubernetes, mesos, rkt): Docker calico libnetwork
* Operating System and version: CentOS 7
* Etcd version: 3.1.11
* Docker daemon version:
```
Client:
Version: 1.11.2
API version: 1.23
Go version: go1.5.4
Git commit: b9f10c9
Built: Wed Jun 1 21:23:11 2016
OS/Arch: linux/amd64
Server:
Version: 1.11.2
API version: 1.23
Go version: go1.5.4
Git commit: b9f10c9
Built: Wed Jun 1 21:23:11 2016
OS/Arch: linux/amd64
```
|
1.0
|
Docker network creation with --subnet parameter breaks IPAM driver - Docker calico libnetwork driver (IPAM) is not getting IPs for containers, when I have created the network with the --subnet parameter.
```
docker run -ti --rm --net my-net nginx:alpine ip a
docker: Error response from daemon: IpamDriver.RequestAddress: Unexpected number of assigned IP addresses. A single address should be assigned. Got []
```
## Expected Behavior
```
# calicoctl apply -f pool.yml
# calicoctl get ipPool -o yaml
- apiVersion: v1
kind: ipPool
metadata:
cidr: 172.16.0.0/16
spec: {}
# docker network create --driver calico --ipam-driver calico-ipam my-net
73b95eed1a35afaa4ea86f876c95a8eedbc5dd6495927856ce4f395e10473ca7
# docker run -ti --rm --net my-net nginx:alpine ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN qlen 1
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
28: cali0@if29: <BROADCAST,MULTICAST,UP,LOWER_UP,M-DOWN> mtu 1500 qdisc noqueue state UP
link/ether ee:ee:ee:ee:ee:ee brd ff:ff:ff:ff:ff:ff
inet 172.16.91.195/32 scope global cali0
valid_lft forever preferred_lft forever
inet6 fe80::ecee:eeff:feee:eeee/64 scope link tentative
valid_lft forever preferred_lft forever
```
## Current Behavior
```
# calicoctl apply -f pool.yml
# calicoctl get ipPool -o yaml
- apiVersion: v1
kind: ipPool
metadata:
cidr: 172.16.0.0/16
spec: {}
# docker network create --driver calico --ipam-driver calico-ipam --subnet 172.16.0.0/16 my-net
8380dda610353d9a2f761d54e0df53f7de88e2f37992e1cded699fabbcc2bd97
# docker run -ti --rm --net my-net nginx:alpine ip a
docker: Error response from daemon: IpamDriver.RequestAddress: Unexpected number of assigned IP addresses. A single address should be assigned. Got []
```
## Your Environment
* Calico version: v2.6.3
* Orchestrator version (e.g. kubernetes, mesos, rkt): Docker calico libnetwork
* Operating System and version: CentOS 7
* Etcd version: 3.1.11
* Docker daemon version:
```
Client:
Version: 1.11.2
API version: 1.23
Go version: go1.5.4
Git commit: b9f10c9
Built: Wed Jun 1 21:23:11 2016
OS/Arch: linux/amd64
Server:
Version: 1.11.2
API version: 1.23
Go version: go1.5.4
Git commit: b9f10c9
Built: Wed Jun 1 21:23:11 2016
OS/Arch: linux/amd64
```
|
non_process
|
docker network creation with subnet parameter breaks ipam driver docker calico libnetwork driver ipam is not getting ips for containers when i have created the network with the subnet parameter docker run ti rm net my net nginx alpine ip a docker error response from daemon ipamdriver requestaddress unexpected number of assigned ip addresses a single address should be assigned got expected behavior calicoctl apply f pool yml calicoctl get ippool o yaml apiversion kind ippool metadata cidr spec docker network create driver calico ipam driver calico ipam my net docker run ti rm net my net nginx alpine ip a lo mtu qdisc noqueue state unknown qlen link loopback brd inet scope host lo valid lft forever preferred lft forever scope host valid lft forever preferred lft forever mtu qdisc noqueue state up link ether ee ee ee ee ee ee brd ff ff ff ff ff ff inet scope global valid lft forever preferred lft forever ecee eeff feee eeee scope link tentative valid lft forever preferred lft forever current behavior calicoctl apply f pool yml calicoctl get ippool o yaml apiversion kind ippool metadata cidr spec docker network create driver calico ipam driver calico ipam subnet my net docker run ti rm net my net nginx alpine ip a docker error response from daemon ipamdriver requestaddress unexpected number of assigned ip addresses a single address should be assigned got your environment calico version orchestrator version e g kubernetes mesos rkt docker calico libnetwork operating system and version centos etcd version docker daemon version client version api version go version git commit built wed jun os arch linux server version api version go version git commit built wed jun os arch linux
| 0
|
4,729
| 3,438,565,096
|
IssuesEvent
|
2015-12-14 01:32:56
|
jeff1evesque/machine-learning
|
https://api.github.com/repos/jeff1evesque/machine-learning
|
closed
|
Ensure only js files minify with uglifyjs
|
build enhancement
|
We need to ensure that uglifyjs only minifies files with `.js` file extensions. Specifically, we need to adjust `/puppet/script/uglifyjs`, similar to [`/puppet/script/browserify`](https://github.com/jeff1evesque/machine-learning/blob/18d1b4a9abb3fffd6e86cf5e3e62097f53cb0eb7/puppet/scripts/browserify#L23).
|
1.0
|
Ensure only js files minify with uglifyjs - We need to ensure that uglifyjs only minifies files with `.js` file extensions. Specifically, we need to adjust `/puppet/script/uglifyjs`, similar to [`/puppet/script/browserify`](https://github.com/jeff1evesque/machine-learning/blob/18d1b4a9abb3fffd6e86cf5e3e62097f53cb0eb7/puppet/scripts/browserify#L23).
|
non_process
|
ensure only js files minify with uglifyjs we need to ensure that uglifyjs only minifies files with js file extensions specifically we need to adjust puppet script uglifyjs similar to
| 0
|
14,722
| 17,932,091,060
|
IssuesEvent
|
2021-09-10 10:37:57
|
KratosMultiphysics/Kratos
|
https://api.github.com/repos/KratosMultiphysics/Kratos
|
closed
|
Custom GiD problemtypes should eventually be moved out of Kratos
|
Discussion Pre Process
|
**Description**
The @KratosMultiphysics/technical-committee discussed about the custom gid problemtypes that exist in some applications should eventually be moved out of Kratos.
We are not sure if they comply with the structure of the main GiD-interface so we would like to initiate the discussion of where and how to but those interfaces
Pinging the devs that are affected by this: @KratosMultiphysics/dem @AlejandroCornejo @miguelmaso @ipouplana
|
1.0
|
Custom GiD problemtypes should eventually be moved out of Kratos - **Description**
The @KratosMultiphysics/technical-committee discussed about the custom gid problemtypes that exist in some applications should eventually be moved out of Kratos.
We are not sure if they comply with the structure of the main GiD-interface so we would like to initiate the discussion of where and how to but those interfaces
Pinging the devs that are affected by this: @KratosMultiphysics/dem @AlejandroCornejo @miguelmaso @ipouplana
|
process
|
custom gid problemtypes should eventually be moved out of kratos description the kratosmultiphysics technical committee discussed about the custom gid problemtypes that exist in some applications should eventually be moved out of kratos we are not sure if they comply with the structure of the main gid interface so we would like to initiate the discussion of where and how to but those interfaces pinging the devs that are affected by this kratosmultiphysics dem alejandrocornejo miguelmaso ipouplana
| 1
|
16,430
| 4,052,460,914
|
IssuesEvent
|
2016-05-24 02:44:26
|
boostorg/compute
|
https://api.github.com/repos/boostorg/compute
|
closed
|
Update documentation before next Boost release
|
documentation
|
Now that Boost.Compute is an official Boost library and will be included in Boost 1.61, we need to update the documentation to reflect this.
Currently there are a few locations where we describe Boost.Compute as ["not yet an offical Boost library"](http://www.boost.org/doc/libs/master/libs/compute/doc/html/boost_compute/getting_started.html).
<bountysource-plugin>
---
Want to back this issue? **[Post a bounty on it!](https://www.bountysource.com/issues/31578143-update-documentation-before-next-boost-release?utm_campaign=plugin&utm_content=tracker%2F402515&utm_medium=issues&utm_source=github)** We accept bounties via [Bountysource](https://www.bountysource.com/?utm_campaign=plugin&utm_content=tracker%2F402515&utm_medium=issues&utm_source=github).
</bountysource-plugin>
|
1.0
|
Update documentation before next Boost release - Now that Boost.Compute is an official Boost library and will be included in Boost 1.61, we need to update the documentation to reflect this.
Currently there are a few locations where we describe Boost.Compute as ["not yet an offical Boost library"](http://www.boost.org/doc/libs/master/libs/compute/doc/html/boost_compute/getting_started.html).
<bountysource-plugin>
---
Want to back this issue? **[Post a bounty on it!](https://www.bountysource.com/issues/31578143-update-documentation-before-next-boost-release?utm_campaign=plugin&utm_content=tracker%2F402515&utm_medium=issues&utm_source=github)** We accept bounties via [Bountysource](https://www.bountysource.com/?utm_campaign=plugin&utm_content=tracker%2F402515&utm_medium=issues&utm_source=github).
</bountysource-plugin>
|
non_process
|
update documentation before next boost release now that boost compute is an official boost library and will be included in boost we need to update the documentation to reflect this currently there are a few locations where we describe boost compute as want to back this issue we accept bounties via
| 0
|
18,475
| 24,550,688,274
|
IssuesEvent
|
2022-10-12 12:23:07
|
GoogleCloudPlatform/fda-mystudies
|
https://api.github.com/repos/GoogleCloudPlatform/fda-mystudies
|
closed
|
[PM] [Angular Upgrade] Success message should get displayed at the center of the screen
|
Bug P1 Participant manager Process: Fixed Process: Tested dev
|
**AR:** Success message is getting displayed at the right corner of the screen
**ER:** Success message should get displayed at the center of the screen
**Note:** Issue needs to be fixed for all the messages which are available in the participant manager
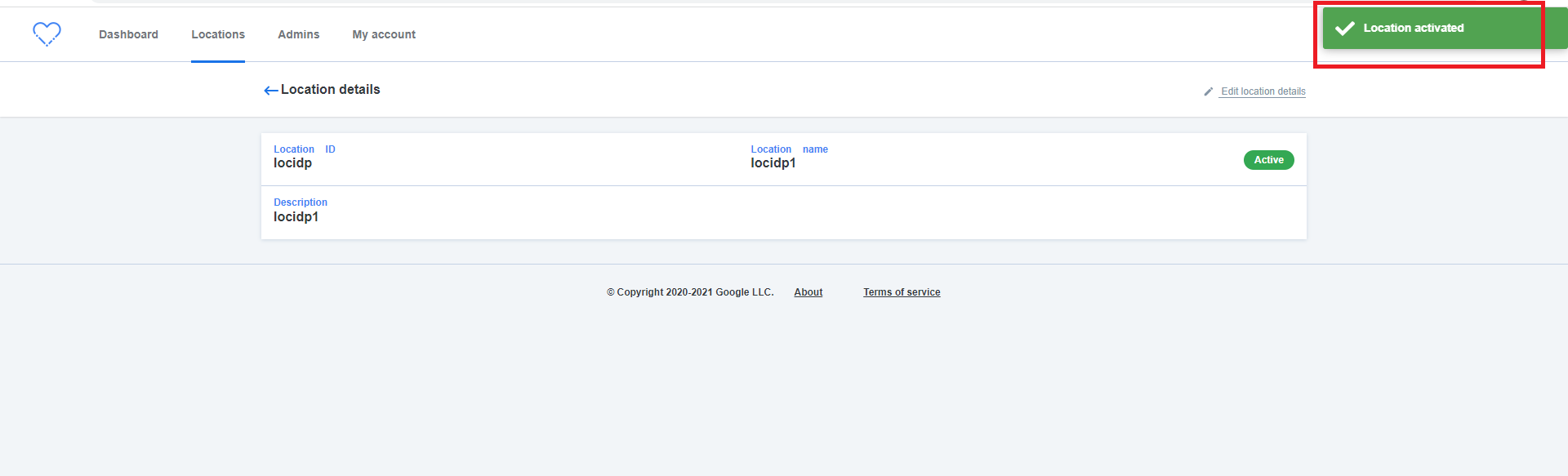
|
2.0
|
[PM] [Angular Upgrade] Success message should get displayed at the center of the screen - **AR:** Success message is getting displayed at the right corner of the screen
**ER:** Success message should get displayed at the center of the screen
**Note:** Issue needs to be fixed for all the messages which are available in the participant manager
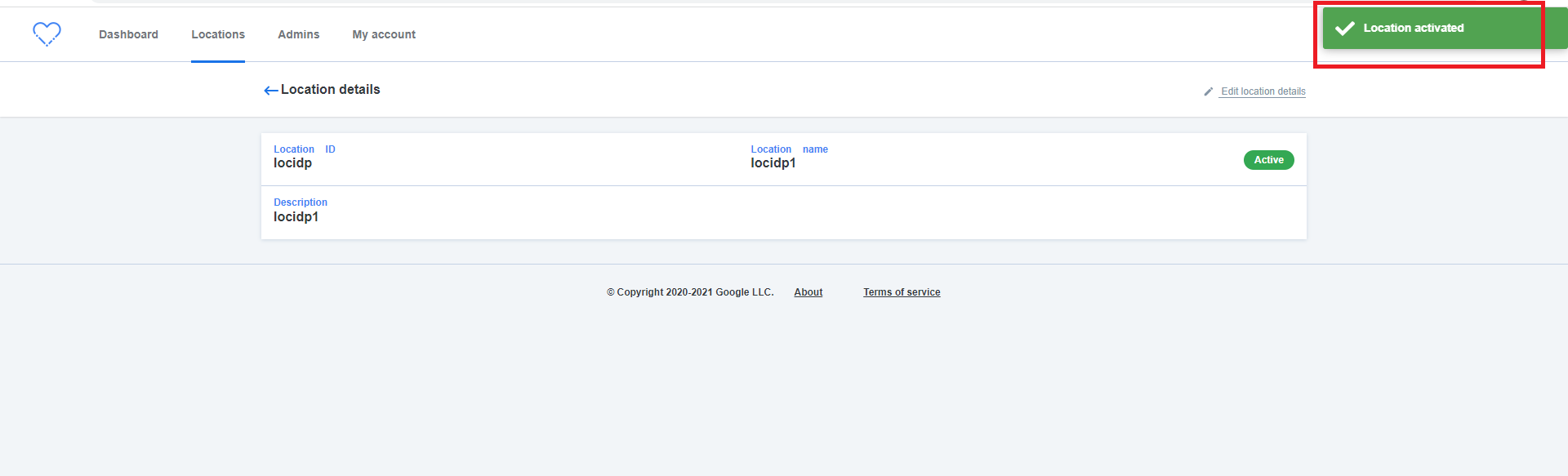
|
process
|
success message should get displayed at the center of the screen ar success message is getting displayed at the right corner of the screen er success message should get displayed at the center of the screen note issue needs to be fixed for all the messages which are available in the participant manager
| 1
|
649,421
| 21,300,576,299
|
IssuesEvent
|
2022-04-15 02:10:46
|
moja-global/community-website
|
https://api.github.com/repos/moja-global/community-website
|
closed
|
Bug: the nav bar in iPad pro doesn't work
|
bug Assigned Issue:No-Activity Priority = High beginners-only
|
### Describe the bug.
On the home page, the hamburger icon to toggle the navbar doesn't work properly for iPad pro screen size.
Here is a video demo about the issue
https://user-images.githubusercontent.com/73457704/146355285-c85a4298-8f55-47d6-b61a-e9c96a50452d.mp4
### Describe the steps to reproduce the behavior.
_No response_
### Expected behavior.
The expected behaviour should be to toggle the navbar from the side as the hamburger icon used to do on mobile screens.
### Screenshots.
_No response_
### Operating Environment
I'm using the website in Brave browser which is based on Chromium
### Additional Information
The same issue is presented when the website is viewed on a small laptop screen.
|
1.0
|
Bug: the nav bar in iPad pro doesn't work - ### Describe the bug.
On the home page, the hamburger icon to toggle the navbar doesn't work properly for iPad pro screen size.
Here is a video demo about the issue
https://user-images.githubusercontent.com/73457704/146355285-c85a4298-8f55-47d6-b61a-e9c96a50452d.mp4
### Describe the steps to reproduce the behavior.
_No response_
### Expected behavior.
The expected behaviour should be to toggle the navbar from the side as the hamburger icon used to do on mobile screens.
### Screenshots.
_No response_
### Operating Environment
I'm using the website in Brave browser which is based on Chromium
### Additional Information
The same issue is presented when the website is viewed on a small laptop screen.
|
non_process
|
bug the nav bar in ipad pro doesn t work describe the bug on the home page the hamburger icon to toggle the navbar doesn t work properly for ipad pro screen size here is a video demo about the issue describe the steps to reproduce the behavior no response expected behavior the expected behaviour should be to toggle the navbar from the side as the hamburger icon used to do on mobile screens screenshots no response operating environment i m using the website in brave browser which is based on chromium additional information the same issue is presented when the website is viewed on a small laptop screen
| 0
|
145,894
| 19,359,199,369
|
IssuesEvent
|
2021-12-16 01:43:45
|
jnfaerch/elevator-dash
|
https://api.github.com/repos/jnfaerch/elevator-dash
|
opened
|
CVE-2021-41098 (High) detected in nokogiri-1.8.2.gem
|
security vulnerability
|
## CVE-2021-41098 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>nokogiri-1.8.2.gem</b></p></summary>
<p>Nokogiri (鋸) is an HTML, XML, SAX, and Reader parser. Among
Nokogiri's many features is the ability to search documents via XPath
or CSS3 selectors.</p>
<p>Library home page: <a href="https://rubygems.org/gems/nokogiri-1.8.2.gem">https://rubygems.org/gems/nokogiri-1.8.2.gem</a></p>
<p>
Dependency Hierarchy:
- sass-rails-5.0.7.gem (Root Library)
- sprockets-rails-3.2.1.gem
- actionpack-5.2.0.gem
- rails-html-sanitizer-1.0.4.gem
- loofah-2.2.2.gem
- :x: **nokogiri-1.8.2.gem** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Nokogiri is a Rubygem providing HTML, XML, SAX, and Reader parsers with XPath and CSS selector support. In Nokogiri v1.12.4 and earlier, on JRuby only, the SAX parser resolves external entities by default. Users of Nokogiri on JRuby who parse untrusted documents using any of these classes are affected: Nokogiri::XML::SAX::Parse, Nokogiri::HTML4::SAX::Parser or its alias Nokogiri::HTML::SAX::Parser, Nokogiri::XML::SAX::PushParser, and Nokogiri::HTML4::SAX::PushParser or its alias Nokogiri::HTML::SAX::PushParser. JRuby users should upgrade to Nokogiri v1.12.5 or later to receive a patch for this issue. There are no workarounds available for v1.12.4 or earlier. CRuby users are not affected.
<p>Publish Date: 2021-09-27
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-41098>CVE-2021-41098</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-41098">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-41098</a></p>
<p>Release Date: 2021-09-27</p>
<p>Fix Resolution: nokogiri - 1.12.5</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2021-41098 (High) detected in nokogiri-1.8.2.gem - ## CVE-2021-41098 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>nokogiri-1.8.2.gem</b></p></summary>
<p>Nokogiri (鋸) is an HTML, XML, SAX, and Reader parser. Among
Nokogiri's many features is the ability to search documents via XPath
or CSS3 selectors.</p>
<p>Library home page: <a href="https://rubygems.org/gems/nokogiri-1.8.2.gem">https://rubygems.org/gems/nokogiri-1.8.2.gem</a></p>
<p>
Dependency Hierarchy:
- sass-rails-5.0.7.gem (Root Library)
- sprockets-rails-3.2.1.gem
- actionpack-5.2.0.gem
- rails-html-sanitizer-1.0.4.gem
- loofah-2.2.2.gem
- :x: **nokogiri-1.8.2.gem** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Nokogiri is a Rubygem providing HTML, XML, SAX, and Reader parsers with XPath and CSS selector support. In Nokogiri v1.12.4 and earlier, on JRuby only, the SAX parser resolves external entities by default. Users of Nokogiri on JRuby who parse untrusted documents using any of these classes are affected: Nokogiri::XML::SAX::Parse, Nokogiri::HTML4::SAX::Parser or its alias Nokogiri::HTML::SAX::Parser, Nokogiri::XML::SAX::PushParser, and Nokogiri::HTML4::SAX::PushParser or its alias Nokogiri::HTML::SAX::PushParser. JRuby users should upgrade to Nokogiri v1.12.5 or later to receive a patch for this issue. There are no workarounds available for v1.12.4 or earlier. CRuby users are not affected.
<p>Publish Date: 2021-09-27
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-41098>CVE-2021-41098</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-41098">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-41098</a></p>
<p>Release Date: 2021-09-27</p>
<p>Fix Resolution: nokogiri - 1.12.5</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_process
|
cve high detected in nokogiri gem cve high severity vulnerability vulnerable library nokogiri gem nokogiri 鋸 is an html xml sax and reader parser among nokogiri s many features is the ability to search documents via xpath or selectors library home page a href dependency hierarchy sass rails gem root library sprockets rails gem actionpack gem rails html sanitizer gem loofah gem x nokogiri gem vulnerable library vulnerability details nokogiri is a rubygem providing html xml sax and reader parsers with xpath and css selector support in nokogiri and earlier on jruby only the sax parser resolves external entities by default users of nokogiri on jruby who parse untrusted documents using any of these classes are affected nokogiri xml sax parse nokogiri sax parser or its alias nokogiri html sax parser nokogiri xml sax pushparser and nokogiri sax pushparser or its alias nokogiri html sax pushparser jruby users should upgrade to nokogiri or later to receive a patch for this issue there are no workarounds available for or earlier cruby users are not affected publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution nokogiri step up your open source security game with whitesource
| 0
|
10,163
| 13,044,162,678
|
IssuesEvent
|
2020-07-29 03:47:34
|
tikv/tikv
|
https://api.github.com/repos/tikv/tikv
|
closed
|
UCP: Migrate scalar function `ValuesTime` from TiDB
|
challenge-program-2 component/coprocessor difficulty/easy sig/coprocessor
|
## Description
Port the scalar function `ValuesTime` from TiDB to coprocessor.
## Score
* 50
## Mentor(s)
* @sticnarf
## Recommended Skills
* Rust programming
## Learning Materials
Already implemented expressions ported from TiDB
- https://github.com/tikv/tikv/tree/master/components/tidb_query/src/rpn_expr)
- https://github.com/tikv/tikv/tree/master/components/tidb_query/src/expr)
|
2.0
|
UCP: Migrate scalar function `ValuesTime` from TiDB -
## Description
Port the scalar function `ValuesTime` from TiDB to coprocessor.
## Score
* 50
## Mentor(s)
* @sticnarf
## Recommended Skills
* Rust programming
## Learning Materials
Already implemented expressions ported from TiDB
- https://github.com/tikv/tikv/tree/master/components/tidb_query/src/rpn_expr)
- https://github.com/tikv/tikv/tree/master/components/tidb_query/src/expr)
|
process
|
ucp migrate scalar function valuestime from tidb description port the scalar function valuestime from tidb to coprocessor score mentor s sticnarf recommended skills rust programming learning materials already implemented expressions ported from tidb
| 1
|
13,056
| 15,393,498,145
|
IssuesEvent
|
2021-03-03 16:47:23
|
nanoframework/Home
|
https://api.github.com/repos/nanoframework/Home
|
closed
|
MDP failing to build NFUnitTestNamespace project
|
Area: Metadata Processor Status: FIXED Type: Bug
|
### Details about Problem
**nanoFramework area:** ( MDP )
### Description
Build failing for NFUnitTestNamespace in mscorlib\develop-unit-test:
```
Severity Code Description Project File Line Suppression State
Error StartIndex cannot be less than zero.
Parameter name: startIndex
at System.String.Substring(Int32 startIndex, Int32 length)
at nanoFramework.Tools.MetadataProcessor.Core.Extensions.TypeDefinitionExtensions.ToEnumDeclaration(TypeDefinition source)
at nanoFramework.Tools.MetadataProcessor.nanoTypeDefinitionTable.<>c.<.ctor>b__9_3(TypeDefinition et)
at System.Linq.Enumerable.WhereSelectListIterator`2.MoveNext()
at System.Collections.Generic.List`1..ctor(IEnumerable`1 collection)
at System.Linq.Enumerable.ToList[TSource](IEnumerable`1 source)
at nanoFramework.Tools.MetadataProcessor.nanoTypeDefinitionTable..ctor(IEnumerable`1 items, nanoTablesContext context)
at nanoFramework.Tools.MetadataProcessor.nanoTablesContext..ctor(AssemblyDefinition assemblyDefinition, List`1 explicitTypesOrder, List`1 classNamesToExclude, ICustomStringSorter stringSorter, Boolean applyAttributesCompression, Boolean verbose, Boolean isCoreLibrary)
at nanoFramework.Tools.MetadataProcessor.MsBuildTask.MetaDataProcessorTask.ExecuteCompile(String fileName)
at nanoFramework.Tools.MetadataProcessor.MsBuildTask.MetaDataProcessorTask.Execute() NFUnitTestNamespace C:\Program Files (x86)\Microsoft Visual Studio\2019\Professional\MSBuild\nanoFramework\v1.0\NFProjectSystem.MDP.targets 226
````
<!-- bug-report-tools-tag DO NOT REMOVE -->
|
1.0
|
MDP failing to build NFUnitTestNamespace project - ### Details about Problem
**nanoFramework area:** ( MDP )
### Description
Build failing for NFUnitTestNamespace in mscorlib\develop-unit-test:
```
Severity Code Description Project File Line Suppression State
Error StartIndex cannot be less than zero.
Parameter name: startIndex
at System.String.Substring(Int32 startIndex, Int32 length)
at nanoFramework.Tools.MetadataProcessor.Core.Extensions.TypeDefinitionExtensions.ToEnumDeclaration(TypeDefinition source)
at nanoFramework.Tools.MetadataProcessor.nanoTypeDefinitionTable.<>c.<.ctor>b__9_3(TypeDefinition et)
at System.Linq.Enumerable.WhereSelectListIterator`2.MoveNext()
at System.Collections.Generic.List`1..ctor(IEnumerable`1 collection)
at System.Linq.Enumerable.ToList[TSource](IEnumerable`1 source)
at nanoFramework.Tools.MetadataProcessor.nanoTypeDefinitionTable..ctor(IEnumerable`1 items, nanoTablesContext context)
at nanoFramework.Tools.MetadataProcessor.nanoTablesContext..ctor(AssemblyDefinition assemblyDefinition, List`1 explicitTypesOrder, List`1 classNamesToExclude, ICustomStringSorter stringSorter, Boolean applyAttributesCompression, Boolean verbose, Boolean isCoreLibrary)
at nanoFramework.Tools.MetadataProcessor.MsBuildTask.MetaDataProcessorTask.ExecuteCompile(String fileName)
at nanoFramework.Tools.MetadataProcessor.MsBuildTask.MetaDataProcessorTask.Execute() NFUnitTestNamespace C:\Program Files (x86)\Microsoft Visual Studio\2019\Professional\MSBuild\nanoFramework\v1.0\NFProjectSystem.MDP.targets 226
````
<!-- bug-report-tools-tag DO NOT REMOVE -->
|
process
|
mdp failing to build nfunittestnamespace project details about problem nanoframework area mdp description build failing for nfunittestnamespace in mscorlib develop unit test severity code description project file line suppression state error startindex cannot be less than zero parameter name startindex at system string substring startindex length at nanoframework tools metadataprocessor core extensions typedefinitionextensions toenumdeclaration typedefinition source at nanoframework tools metadataprocessor nanotypedefinitiontable c b typedefinition et at system linq enumerable whereselectlistiterator movenext at system collections generic list ctor ienumerable collection at system linq enumerable tolist ienumerable source at nanoframework tools metadataprocessor nanotypedefinitiontable ctor ienumerable items nanotablescontext context at nanoframework tools metadataprocessor nanotablescontext ctor assemblydefinition assemblydefinition list explicittypesorder list classnamestoexclude icustomstringsorter stringsorter boolean applyattributescompression boolean verbose boolean iscorelibrary at nanoframework tools metadataprocessor msbuildtask metadataprocessortask executecompile string filename at nanoframework tools metadataprocessor msbuildtask metadataprocessortask execute nfunittestnamespace c program files microsoft visual studio professional msbuild nanoframework nfprojectsystem mdp targets
| 1
|
68,547
| 17,353,386,343
|
IssuesEvent
|
2021-07-29 11:37:08
|
buildpacks/docs
|
https://api.github.com/repos/buildpacks/docs
|
closed
|
[RFC 0070] New fields in buildpack.toml
|
team/buildpack-authors-tooling team/implementations type/enhancement
|
Apologies if this is duplicated elsewhere, I couldn't find it.
Document new fields described in [RFC 0070](https://github.com/buildpacks/rfcs/pull/127)
|
1.0
|
[RFC 0070] New fields in buildpack.toml - Apologies if this is duplicated elsewhere, I couldn't find it.
Document new fields described in [RFC 0070](https://github.com/buildpacks/rfcs/pull/127)
|
non_process
|
new fields in buildpack toml apologies if this is duplicated elsewhere i couldn t find it document new fields described in
| 0
|
296,174
| 25,534,440,447
|
IssuesEvent
|
2022-11-29 10:52:14
|
airbytehq/airbyte
|
https://api.github.com/repos/airbytehq/airbyte
|
closed
|
SAT: perform extra validation on integer fields.
|
type/bug Acceptance Tests team/connector-ops
|
# What
SAT perform schema validation of records against the catalog schema with the `jsonschema` library.
According to `jsonschema` a float value with a zero fractional part is a valid `integer` :
```bash
>>> from jsonschema import Draft7Validator
>>> schema = {'$schema': 'http://json-schema.org/draft-07/schema#', 'type': 'object', 'properties': {'metrics.conversion': {'type': ['null', 'integer']},}}
>>> record = {'metrics.conversion': 1.0}
>>> Draft7Validator(schema).is_valid(record)
True
>>> record = {'metrics.conversion': 1.1}
>>> Draft7Validator(schema).is_valid(record)
False
```
This relaxed definition is problematic because database destinations are more strict in terms of typing.
This situation prevents us from identifying schema inconsistencies in SAT when a field is declared as `integers` but the actual record values in our test account are `1.0, 2.0, 3.0` etc. It led this [PR](https://github.com/airbytehq/airbyte/pull/18069) that introduced a schema inconsistency to be merged with successful acceptance tests.
# How
A. Implement a custom check in the [verify_records_schema function](https://github.com/airbytehq/airbyte/blob/master/airbyte-integrations/bases/source-acceptance-test/source_acceptance_test/utils/asserts.py#L42) to make sure that a field defined as integer is an integer in python term's...
B. Find a way to force this validation with `jsonschema`
|
1.0
|
SAT: perform extra validation on integer fields. - # What
SAT perform schema validation of records against the catalog schema with the `jsonschema` library.
According to `jsonschema` a float value with a zero fractional part is a valid `integer` :
```bash
>>> from jsonschema import Draft7Validator
>>> schema = {'$schema': 'http://json-schema.org/draft-07/schema#', 'type': 'object', 'properties': {'metrics.conversion': {'type': ['null', 'integer']},}}
>>> record = {'metrics.conversion': 1.0}
>>> Draft7Validator(schema).is_valid(record)
True
>>> record = {'metrics.conversion': 1.1}
>>> Draft7Validator(schema).is_valid(record)
False
```
This relaxed definition is problematic because database destinations are more strict in terms of typing.
This situation prevents us from identifying schema inconsistencies in SAT when a field is declared as `integers` but the actual record values in our test account are `1.0, 2.0, 3.0` etc. It led this [PR](https://github.com/airbytehq/airbyte/pull/18069) that introduced a schema inconsistency to be merged with successful acceptance tests.
# How
A. Implement a custom check in the [verify_records_schema function](https://github.com/airbytehq/airbyte/blob/master/airbyte-integrations/bases/source-acceptance-test/source_acceptance_test/utils/asserts.py#L42) to make sure that a field defined as integer is an integer in python term's...
B. Find a way to force this validation with `jsonschema`
|
non_process
|
sat perform extra validation on integer fields what sat perform schema validation of records against the catalog schema with the jsonschema library according to jsonschema a float value with a zero fractional part is a valid integer bash from jsonschema import schema schema type object properties metrics conversion type record metrics conversion schema is valid record true record metrics conversion schema is valid record false this relaxed definition is problematic because database destinations are more strict in terms of typing this situation prevents us from identifying schema inconsistencies in sat when a field is declared as integers but the actual record values in our test account are etc it led this that introduced a schema inconsistency to be merged with successful acceptance tests how a implement a custom check in the to make sure that a field defined as integer is an integer in python term s b find a way to force this validation with jsonschema
| 0
|
248,879
| 26,855,092,496
|
IssuesEvent
|
2023-02-03 14:04:11
|
MatBenfield/news
|
https://api.github.com/repos/MatBenfield/news
|
closed
|
[SecurityWeek] Cyber Insights 2023 | Supply Chain Security
|
SecurityWeek Stale
|
**About SecurityWeek Cyber Insights \|** _At the end of 2022, SecurityWeek liaised with more than 300 cybersecurity experts from over 100 different organizations to gain insight into the security issues of today – and how these issues might evolve during 2023 and beyond. The result is more than a dozen features on subjects ranging from AI, quantum encryption, and attack surface management to venture capital, regulations, and criminal gangs._

**SecurityWeek Cyber Insights 2023 \| Supply Chain Security –** The supply chain threat is directly linked to [attack surface management](https://www.securityweek.com/cyber-insights-2023-attack-surface-management/) (it potentially represents a hidden part of the attack surface) and zero trust (100% effective zero trust would eliminate the threat). But the supply chain must be known and understood before it can be remediated.
In the meantime – and especially throughout 2023 – it will be a focus for adversaries. Why attack a single target when successful manipulation of the supply chain can get access to dozens or even hundreds of targets simultaneously.
The danger and effectiveness of such attacks is amply illustrated by the [SolarWinds](https://www.securityweek.com/more-cybersecurity-firms-confirm-being-hit-solarwinds-hack), [log4j](https://www.securityweek.com/ics-vendors-respond-log4j-vulnerabilities), [Spring4Shell](https://www.securityweek.com/spring4shell-exploitation-attempts-confirmed-patches-are-released), [Kaseya](https://www.securityweek.com/hackers-demand-70-million-kaseya-ransomware-victim-toll-nears-1500-firms/), and [OpenSSL](https://www.securityweek.com/anxiously-awaited-openssl-vulnerabilitys-severity-downgraded-critical-high) incidents.
## **The missed wake-up calls**
Supply chain attacks are not new. The iconic [Target breach](https://www.securityweek.com/target-hvac-contractor-says-it-was-breached-hackers) of late 2013 was a supply chain breach. The attackers got into Target using credentials stolen from its HVAC provider, Fazio Mechanical Services – that is, via Target’s supply chain.
The 2018 breach of [Ticketmaster](https://www.securityweek.com/ticketmaster-breach-tip-iceberg-major-ongoing-magecart-attacks) was another supply chain breach. A Ticketmaster software supplier, Inbenta, was breached and Inbenta software was modified and weaponized. This was automatically downloaded to Ticketmaster.
Island hopping is another form of supply chain attack. In 2017, [Operation Cloud Hopper](https://www.securityweek.com/operation-cloud-hopper-china-based-hackers-target-managed-service-providers) was revealed. This disclosed that an advanced group, probably APT10, was compromising managed service providers to gain access to the MSP’s customers.
Despite these incidents, it has only been in the last couple of years, fueled by more extensive incidents such as SolarWinds, that industry has become cognizant of the full threat from increasingly sophisticated and wide-ranging supply chain concerns. But we should not forget that the 2017 [NotPetya](https://www.securityweek.com/notpetya-destructive-wiper-disguised-ransomware) incident also started as a supply chain attack. Software from the Ukrainian accounting firm M.E.Doc was weaponized and automatically downloaded by the firm’s customers, before spreading around the globe. Both SolarWinds and NotPetya are believed to be the work of nation state actors.
All forms of supply chain attacks will increase in 2023, and beyond. Chad Skipper, global security technologist at VMware, specifically calls out island hopping. “In 2023, cybercriminals will continue to use island hopping, a technique that aims to hijack an organization’s infrastructure to attack its customers,” he warns. “Remote desktop protocol is regularly used by threat actors during an island-hopping campaign to disguise themselves as system administrators. As we head into the new year, it’s a threat that should be top of mind for all organizations.”
## **Attacks will increase**
That supply chain attacks will increase in 2023 and beyond is the single most extensive prediction for 2023. “Supply chain attacks happen when hackers gain access to a company’s inner workings via a third-party partner, a method that provides them with a much greater amount of privileged information from just one breach,” explains Matt Jackson, senior director security operations at Code42. “This type of attack already rose by more than 300% in 2021, and I anticipate this trend will continue in 2023, with these attacks becoming more complicated and intricate.”
Lucia Milică, Resident CISO, Proofpoint
Lucia Milică, global resident CISO at Proofpoint, worries that despite all the wake-up calls so far, “We are still a long way from having adequate tools to protect against those kinds of digital supply chain vulnerabilities. We predict these concerns will mount in 2023, with our trust in third-party partners and suppliers becoming one of the primary attack channels.”
The result, she added, is, “We expect more tension in supply chain relationships overall, as organizations try to escalate their vendors’ due diligence processes for better understanding the risks, while suppliers scramble to manage the overwhelming focus on their processes.”
Jackson added, “Because many third-party partners are now privy to more sensitive data than ever before, companies can no longer rely on their own cybersecurity prowess to keep information safe,” he said.
“Supply chain attacks purposefully target the smaller organizations first because they’re less likely to have a robust cybersecurity setup, and they can use those companies to get to the bigger fish,” he continued. “In the next year, companies will become even more diligent when deciding on an outside organization to work with, creating an increase in compliance verifications to vet the cyber tools used by these prospective partners.”
[](https://www.securitysummits.com/event/supply-chain-security-summit/) [Supply Chain Security and Third-Party Risk Summit \| Virtual Event March 22, 2023](https://www.securitysummits.com/event/supply-chain-security-summit/)
Anand Raghavan, co-founder and CPO at Armorblox, expands on this theme. “This becomes particularly relevant,” he said, “for the Fortune 500 or Global 2000 companies that have a large ecosystem of suppliers, vendors, and distributors whose security stacks are nowhere as mature as those of large organizations. Large organizations might consider requiring all vendors to follow certain security best practices, including modernizing their email security stack if they want to continue being a vendor in good standing.”
Interestingly, despite all the warnings of an escalating threat, Christopher Budd, senior manager of threat research at Sophos, notes, “Unlike two years ago when the SolarWinds attack put supply chain attacks high on people’s radar, supply chain attacks have faded from prominence.” This may be a misleading premise. The discovery of a vulnerability in a widely used piece of software, such as the log4j vulnerability, will be used by individual cybercriminals and nation state actors alike.
However, targeted attacks such as that against SolarWinds requires resources and skill. These attributes are more usually found only in the more advanced gangs and nation state actors. Such adversaries have another attribute: patience. “Today’s and undoubtedly tomorrow’s threat actors have shown they can play the long game,” warns Pieter Arntz, senior intelligence reporter at Malwarebytes.
Budd also warns that despite their immediate lack of prominence (at the time of writing, but anything could happen tomorrow), “Supply chain may be something that continues to not gather news, similar to 2022. But it will remain a real threat and one that organizations should be prioritizing across the board, in part because effectively countering this threat requires a comprehensive, careful, methodical approach.”
## **The software supply chain**
The primary growth area in supply chain attacks will likely be the software supply chain. “Over the past few years,” explains Eilon Elhadad, senior director of supply chain security at Aqua, “increasing pressure to deliver software faster has widened attack surfaces and introduced severe vulnerabilities.”
**New tools, languages and frameworks that support rapid development at scale are being targeted by malicious actors, who understand the widespread impact that results from attacks to the software supply chain.**
“In 2023,” Elhadad continued, “software supply chain threats will continue to be a significant area of concern. These attacks have a larger potential blast radius to allow hackers to impact entire markets and wreak havoc for organizations.”
Eric Byres, founder and CTO at aDolus, agrees. “Software supply chain attacks will continue to increase exponentially in 2023,” he said; “the ROI on these attacks is just too sweet for professional adversaries to resist.” He notes that supply chain attacks have increased by 742% over the last three years.
Much of the software supply chain threat comes from the growing reliance on open source software libraries as part of the ‘increasing pressure to deliver software faster’. Zack Zornstain, head of supply chain security at Checkmarx, believes the software threat will particularly affect the open source supply.
“We believe that this threat of compromising open source packages will increase as malicious code can endanger the safety of our systems, ranging from ransomware attacks to the exposure of sensitive information, and more. We expect to see this as a general attack vector used both by cyber firms and nation-state actors. SBOM adaptation will help clarify which packages we’re using in applications, but we will need to invest in more controls to ensure the safety of those packages,” he said.
“Organizations should be on high alert for supply chain attacks if they use open-source software,” warns Kevin Kirkwood, deputy CISO at LogRhythm. “Bad actors examine the code and its components to obtain a thorough understanding of its flaws and the most effective ways to exploit them.”
If the source code of an open source software library either has – or can be engineered by bad actors to have – a vulnerability, then every company that downloads and uses that code becomes vulnerable.
“In 2023,” continues Kirkwood, “we’ll see bad actors attack vulnerabilities in low-hanging open-source vendors with the intention of compromising the global supply chain that uses third-party code. Attackers will infect the open-source repositories and chromium stores with malicious code and will wait for developers and other end users to come along and pick up the new sources and plugins.”
Venafi’s Matt Barker, president of cloud native solutions, adds, “We’re seeing many instances of vulnerable code brought inside their firewall by developers trying to go fast using unverified code from GitHub, or copypasta from Stack Overflow.”
He continues, “Thankfully, we’ve reached a collective sense of focus on this area and are seeing tremendous developments in how we tackle it. This is only going to increase through 2023 as we see more start-ups popping up and open source tools like cosign and sigstore designed to help it. Biden’s SBOM initiative has helped bring attention to the requirement, and The OpenSSF is leading in this charge.”
Mark Lambert, VP of products at ArmorCode, expands on this. “As the software supply chain continues to get more complicated, it is vital to know what open source you are indirectly using as part of third-party libraries, services (APIs) or tools. This is where SBOM comes in,” he said. “By requiring a disclosure of all embedded technologies from your vendors, you can perform analysis of those libraries to further assess your risk and react appropriately.”
### **The SBOM**
Biden’s May 2021 Executive Order on Improving the Nation’s Cybersecurity introduced the concept of a software bill of materials (SBOM), effectively if not actually mandating that software bought (or supplied) by government agencies be accompanied with a bill of materials. It described the SBOM as “a formal record containing the details and supply chain relationships of various components used in building software,” and analogous to a list of ingredients on food packaging.
While the advantages of the SBOM may appear obvious in helping software developers understand precisely what is included in the open source libraries they use, it must be said that not everyone is immediately enthusiastic. In December 2022, it emerged that a [lobbying group](https://www.securityweek.com/big-tech-vendors-object-us-gov-sbom-mandate) representing major tech firms such as Amazon, Microsoft, Apple, Intel, AMD, Lenovo, IBM, Cisco, Samsung, TSMC, Qualcomm, Zoom and Palo Alto Networks was urging the OMB to ‘discourage agencies’ from requiring SBOMs. The group argued that the requirement is premature and of limited value — but it didn’t ask for the concept to be abandoned.
It is the complexity and difficulty in both compiling and using an SBOM that is the problem — and it is these concerns that will drive a lot of activity through 2023. The value of the concept outlined in the executive order remains undiminished.
“Incidents such as Log4shell \[log4j\] and the most recent SpookySSL vulnerabilities \[CVE-2022-3602 and CVE-2022-3786\] will push the adoption of a software bill of materials as a core component of achieving effective incident response, while efforts will continue in maturing the SBOM ecosystem (adoption across sectors, tooling, standardization around sharing and exchanging of SBOMs and more),” explains Yotam Perkal, director of vulnerability research at Rezilion.
“One of the big challenges I see in the year ahead is that this is more data for the development teams to manage as they deliver software,” notes Lambert. “In 2023, organizations are going to need ways to automate generating, publishing and ingesting SBOMs – they will need ways to bring the remediation of the associated vulnerabilities into their current application security programs without having to adopt whole new workflows.”
As part of this process, Michael Assraf, CEO and co-founder at Vicarius, said, “We predict that a new market will evolve called binary software composition analysis, which will look for software files that are different from what was pre-packaged and shipped. Automated techniques can utilize machine learning that will find this discrepancy, which will be vital in knowing where your risk lies and how large your attack surface can potentially be.”
Thomas Pace, Co-founder & CEO at NetRise
Thomas Pace, CEO at NetRise, suggests, “SBOM is going to continue to garner mainstream adoption, not just from software/firmware suppliers that are building products they are selling, but also for internal development teams that are building applications and systems for internal use.”
He adds, “The need to be able to rapidly understand the provenance of software components is becoming increasingly critical. Without this visibility, the window for attackers to exploit these vulnerabilities is much too big and puts cyber defenders at a significant disadvantage.” But he also notes, “strong efforts from organizations like Google have moved the ball forward in a positive way. Efforts such as open-source insights provide a lot of visibility for end users and vendors alike to scale out the analysis of these components.”
The problems involved with SBOM generation and use have not yet been solved, but enthusiasm remains. We can expect considerable effort into automating these processes to continue throughout 2023.
Nevertheless, Kurt Baumgartner, principal security researcher at Kaspersky, warns, “Open source projects continue to be polluted with malicious code. Awareness of these issues and challenges increase, but the attacks continue to be effective on a large scale. Despite the best efforts of software bill of materials, complex dependency chains help ensure that malicious code is uncontrolled for a time in some projects.”
## **The physical supply chain**
Despite all companies’ need to be wary of potential software supply chain attacks via the code they develop for their own use, we should not forget that there is a potentially more catastrophic physical supply chain threat. We need only consider the effect the prevention of grain supplies leaving Ukraine (because of the Russia/Ukraine conflict) had on global food supplies to see the potential. Covid-19 also affected many different global supply chains, causing panic buying and popular distress in its early days.
These were not the result of cyberattacks – but many of those physical supply chains could be disrupted by cyberattacks. The [Colonial Pipeline](https://www.securityweek.com/colonial-pipeline-struggles-restart-after-ransomware-attack) incident, although a financially motivated attack, had an immediate effect on the supply of oil to eastern USA. The longer the Ukraine/Russia conflict continues, and the greater that east/west tensions increase, the possibility of physical supply chain cyber disruption will equally increase through 2023, and possibly beyond.
_SecurityWeek_ discussed one such possibility in May 2022: _The Vulnerable Maritime Supply Chain – a Threat to the Global Economy_ [here](https://www.securityweek.com/vulnerable-maritime-supply-chain-threat-global-economy).
Lorri Janssen-Anessi, director of external cyber assessments at BlueVoyant notes that in the utilities and energy sector, “99% of energy companies say they have been negatively impacted by at least one supply chain breach in the past year, representing the highest rate of overall impact in any other industry. Because it remains one of the most frequently attacked verticals, it is especially crucial that it rises to the challenge of supply chain defense in 2023.”
Taylor Gulley, senior application security consultant at nVisium, comments, “The past few years have shown that both the digital supply chain, as well as the physical world supply chain, are very fragile. This fragility is due to a lack of redundancy and resources due to economic constraints or skill gaps. For 2023, this situation will still stand true. Supply chain security is a weak link that needs to be strengthened.”
## **Solutions and the way forward**
Sam Curry, Cybereason
Sam Curry, CSO at Cybereason, believes the SBOM will be an important part of solving the software supply chain problem. “It would be naive in the extreme to think that with thousands of trusted software and service providers to choose from… that the handful of known supply chain compromises were the sum total of them. No. 2023 will show us more, and we will be lucky to learn of them because the attacker can quietly exploit these without tipping their hands.”
He added, “We need to use 2023 to be innovative and vigilant and to find new answers to the supply chain problem, to build on software bills of material, to innovate with the men and women building our software and to find the solutions to deter, to detect and to remove the vulnerabilities and exposures that enable this most insidious and trust eroding of attacks.”
Sharon Chand, Deloitte US’ cyber risk secure supply chain leader, believes that software supply chain security will require continuous realtime monitoring of third-party risks and vulnerabilities in inbound packaged software and firmware components. “For instance,” she said, “this includes implementing leading practice techniques around ingesting SBOMs and correlating the output to emerging vulnerabilities, identifying risk indicators such as geographical origin of the underlying components, and providing visibility to transitive dependencies.”
Christian Borst, EMEA CTO at Vectra AI, suggests collaboration and cooperation across the software industry will be required. “A holistic approach may help turn the tables on the matter: supply chain means partnership – partnership means collaboration and supporting each other. Only as a ‘mesh’ interconnected structure with consistent resiliency can companies thrive in the digital economy. This includes ensuring that they review the security policies of all those in the chain.”
Sounil Yu, CISO at JupiterOne, makes a fitting summary, referencing a paper written by Richard Danzig in July 2014 ( _Surviving on a Diet of Poisoned Fruit: Reducing the National Security Risks of America’s Cyber Dependencies_). “To borrow Richard Danzig’s analogy,” says Yu, “we are on a diet of poisoned fruit with respect to our software supply chain. This poison is not going to go away, so we will need to learn how to survive and thrive under these conditions. Being aware of the risks, through efforts such as SBOM, and managing the risks through compensating controls such as egress filtering, will be a priority in 2023 and the foreseeable future.”
**Related**: [US Gov Issues Software Supply Chain Security Guidance for Customers](https://www.securityweek.com/us-gov-issues-software-supply-chain-security-guidance-customers)
**Related**: [OpenSSF Adopts Microsoft-Built Supply Chain Security Framework](https://www.securityweek.com/openssf-adopts-microsoft-built-supply-chain-security-framework)
**Related**: [Hundreds Infected With ‘Wasp’ Stealer in Ongoing Supply Chain Attack](https://www.securityweek.com/hundreds-infected-wasp-stealer-ongoing-supply-chain-attack)
**Related**: [US Gov Issues Supply Chain Security Guidance for Software Suppliers](https://www.securityweek.com/us-gov-issues-supply-chain-security-guidance-software-suppliers)
The post [Cyber Insights 2023 \| Supply Chain Security](https://www.securityweek.com/cyber-insights-2023-supply-chain-security/) appeared first on [SecurityWeek](https://www.securityweek.com).
<https://www.securityweek.com/cyber-insights-2023-supply-chain-security/>
|
True
|
[SecurityWeek] Cyber Insights 2023 | Supply Chain Security -
**About SecurityWeek Cyber Insights \|** _At the end of 2022, SecurityWeek liaised with more than 300 cybersecurity experts from over 100 different organizations to gain insight into the security issues of today – and how these issues might evolve during 2023 and beyond. The result is more than a dozen features on subjects ranging from AI, quantum encryption, and attack surface management to venture capital, regulations, and criminal gangs._

**SecurityWeek Cyber Insights 2023 \| Supply Chain Security –** The supply chain threat is directly linked to [attack surface management](https://www.securityweek.com/cyber-insights-2023-attack-surface-management/) (it potentially represents a hidden part of the attack surface) and zero trust (100% effective zero trust would eliminate the threat). But the supply chain must be known and understood before it can be remediated.
In the meantime – and especially throughout 2023 – it will be a focus for adversaries. Why attack a single target when successful manipulation of the supply chain can get access to dozens or even hundreds of targets simultaneously.
The danger and effectiveness of such attacks is amply illustrated by the [SolarWinds](https://www.securityweek.com/more-cybersecurity-firms-confirm-being-hit-solarwinds-hack), [log4j](https://www.securityweek.com/ics-vendors-respond-log4j-vulnerabilities), [Spring4Shell](https://www.securityweek.com/spring4shell-exploitation-attempts-confirmed-patches-are-released), [Kaseya](https://www.securityweek.com/hackers-demand-70-million-kaseya-ransomware-victim-toll-nears-1500-firms/), and [OpenSSL](https://www.securityweek.com/anxiously-awaited-openssl-vulnerabilitys-severity-downgraded-critical-high) incidents.
## **The missed wake-up calls**
Supply chain attacks are not new. The iconic [Target breach](https://www.securityweek.com/target-hvac-contractor-says-it-was-breached-hackers) of late 2013 was a supply chain breach. The attackers got into Target using credentials stolen from its HVAC provider, Fazio Mechanical Services – that is, via Target’s supply chain.
The 2018 breach of [Ticketmaster](https://www.securityweek.com/ticketmaster-breach-tip-iceberg-major-ongoing-magecart-attacks) was another supply chain breach. A Ticketmaster software supplier, Inbenta, was breached and Inbenta software was modified and weaponized. This was automatically downloaded to Ticketmaster.
Island hopping is another form of supply chain attack. In 2017, [Operation Cloud Hopper](https://www.securityweek.com/operation-cloud-hopper-china-based-hackers-target-managed-service-providers) was revealed. This disclosed that an advanced group, probably APT10, was compromising managed service providers to gain access to the MSP’s customers.
Despite these incidents, it has only been in the last couple of years, fueled by more extensive incidents such as SolarWinds, that industry has become cognizant of the full threat from increasingly sophisticated and wide-ranging supply chain concerns. But we should not forget that the 2017 [NotPetya](https://www.securityweek.com/notpetya-destructive-wiper-disguised-ransomware) incident also started as a supply chain attack. Software from the Ukrainian accounting firm M.E.Doc was weaponized and automatically downloaded by the firm’s customers, before spreading around the globe. Both SolarWinds and NotPetya are believed to be the work of nation state actors.
All forms of supply chain attacks will increase in 2023, and beyond. Chad Skipper, global security technologist at VMware, specifically calls out island hopping. “In 2023, cybercriminals will continue to use island hopping, a technique that aims to hijack an organization’s infrastructure to attack its customers,” he warns. “Remote desktop protocol is regularly used by threat actors during an island-hopping campaign to disguise themselves as system administrators. As we head into the new year, it’s a threat that should be top of mind for all organizations.”
## **Attacks will increase**
That supply chain attacks will increase in 2023 and beyond is the single most extensive prediction for 2023. “Supply chain attacks happen when hackers gain access to a company’s inner workings via a third-party partner, a method that provides them with a much greater amount of privileged information from just one breach,” explains Matt Jackson, senior director security operations at Code42. “This type of attack already rose by more than 300% in 2021, and I anticipate this trend will continue in 2023, with these attacks becoming more complicated and intricate.”
Lucia Milică, Resident CISO, Proofpoint
Lucia Milică, global resident CISO at Proofpoint, worries that despite all the wake-up calls so far, “We are still a long way from having adequate tools to protect against those kinds of digital supply chain vulnerabilities. We predict these concerns will mount in 2023, with our trust in third-party partners and suppliers becoming one of the primary attack channels.”
The result, she added, is, “We expect more tension in supply chain relationships overall, as organizations try to escalate their vendors’ due diligence processes for better understanding the risks, while suppliers scramble to manage the overwhelming focus on their processes.”
Jackson added, “Because many third-party partners are now privy to more sensitive data than ever before, companies can no longer rely on their own cybersecurity prowess to keep information safe,” he said.
“Supply chain attacks purposefully target the smaller organizations first because they’re less likely to have a robust cybersecurity setup, and they can use those companies to get to the bigger fish,” he continued. “In the next year, companies will become even more diligent when deciding on an outside organization to work with, creating an increase in compliance verifications to vet the cyber tools used by these prospective partners.”
[](https://www.securitysummits.com/event/supply-chain-security-summit/) [Supply Chain Security and Third-Party Risk Summit \| Virtual Event March 22, 2023](https://www.securitysummits.com/event/supply-chain-security-summit/)
Anand Raghavan, co-founder and CPO at Armorblox, expands on this theme. “This becomes particularly relevant,” he said, “for the Fortune 500 or Global 2000 companies that have a large ecosystem of suppliers, vendors, and distributors whose security stacks are nowhere as mature as those of large organizations. Large organizations might consider requiring all vendors to follow certain security best practices, including modernizing their email security stack if they want to continue being a vendor in good standing.”
Interestingly, despite all the warnings of an escalating threat, Christopher Budd, senior manager of threat research at Sophos, notes, “Unlike two years ago when the SolarWinds attack put supply chain attacks high on people’s radar, supply chain attacks have faded from prominence.” This may be a misleading premise. The discovery of a vulnerability in a widely used piece of software, such as the log4j vulnerability, will be used by individual cybercriminals and nation state actors alike.
However, targeted attacks such as that against SolarWinds requires resources and skill. These attributes are more usually found only in the more advanced gangs and nation state actors. Such adversaries have another attribute: patience. “Today’s and undoubtedly tomorrow’s threat actors have shown they can play the long game,” warns Pieter Arntz, senior intelligence reporter at Malwarebytes.
Budd also warns that despite their immediate lack of prominence (at the time of writing, but anything could happen tomorrow), “Supply chain may be something that continues to not gather news, similar to 2022. But it will remain a real threat and one that organizations should be prioritizing across the board, in part because effectively countering this threat requires a comprehensive, careful, methodical approach.”
## **The software supply chain**
The primary growth area in supply chain attacks will likely be the software supply chain. “Over the past few years,” explains Eilon Elhadad, senior director of supply chain security at Aqua, “increasing pressure to deliver software faster has widened attack surfaces and introduced severe vulnerabilities.”
**New tools, languages and frameworks that support rapid development at scale are being targeted by malicious actors, who understand the widespread impact that results from attacks to the software supply chain.**
“In 2023,” Elhadad continued, “software supply chain threats will continue to be a significant area of concern. These attacks have a larger potential blast radius to allow hackers to impact entire markets and wreak havoc for organizations.”
Eric Byres, founder and CTO at aDolus, agrees. “Software supply chain attacks will continue to increase exponentially in 2023,” he said; “the ROI on these attacks is just too sweet for professional adversaries to resist.” He notes that supply chain attacks have increased by 742% over the last three years.
Much of the software supply chain threat comes from the growing reliance on open source software libraries as part of the ‘increasing pressure to deliver software faster’. Zack Zornstain, head of supply chain security at Checkmarx, believes the software threat will particularly affect the open source supply.
“We believe that this threat of compromising open source packages will increase as malicious code can endanger the safety of our systems, ranging from ransomware attacks to the exposure of sensitive information, and more. We expect to see this as a general attack vector used both by cyber firms and nation-state actors. SBOM adaptation will help clarify which packages we’re using in applications, but we will need to invest in more controls to ensure the safety of those packages,” he said.
“Organizations should be on high alert for supply chain attacks if they use open-source software,” warns Kevin Kirkwood, deputy CISO at LogRhythm. “Bad actors examine the code and its components to obtain a thorough understanding of its flaws and the most effective ways to exploit them.”
If the source code of an open source software library either has – or can be engineered by bad actors to have – a vulnerability, then every company that downloads and uses that code becomes vulnerable.
“In 2023,” continues Kirkwood, “we’ll see bad actors attack vulnerabilities in low-hanging open-source vendors with the intention of compromising the global supply chain that uses third-party code. Attackers will infect the open-source repositories and chromium stores with malicious code and will wait for developers and other end users to come along and pick up the new sources and plugins.”
Venafi’s Matt Barker, president of cloud native solutions, adds, “We’re seeing many instances of vulnerable code brought inside their firewall by developers trying to go fast using unverified code from GitHub, or copypasta from Stack Overflow.”
He continues, “Thankfully, we’ve reached a collective sense of focus on this area and are seeing tremendous developments in how we tackle it. This is only going to increase through 2023 as we see more start-ups popping up and open source tools like cosign and sigstore designed to help it. Biden’s SBOM initiative has helped bring attention to the requirement, and The OpenSSF is leading in this charge.”
Mark Lambert, VP of products at ArmorCode, expands on this. “As the software supply chain continues to get more complicated, it is vital to know what open source you are indirectly using as part of third-party libraries, services (APIs) or tools. This is where SBOM comes in,” he said. “By requiring a disclosure of all embedded technologies from your vendors, you can perform analysis of those libraries to further assess your risk and react appropriately.”
### **The SBOM**
Biden’s May 2021 Executive Order on Improving the Nation’s Cybersecurity introduced the concept of a software bill of materials (SBOM), effectively if not actually mandating that software bought (or supplied) by government agencies be accompanied with a bill of materials. It described the SBOM as “a formal record containing the details and supply chain relationships of various components used in building software,” and analogous to a list of ingredients on food packaging.
While the advantages of the SBOM may appear obvious in helping software developers understand precisely what is included in the open source libraries they use, it must be said that not everyone is immediately enthusiastic. In December 2022, it emerged that a [lobbying group](https://www.securityweek.com/big-tech-vendors-object-us-gov-sbom-mandate) representing major tech firms such as Amazon, Microsoft, Apple, Intel, AMD, Lenovo, IBM, Cisco, Samsung, TSMC, Qualcomm, Zoom and Palo Alto Networks was urging the OMB to ‘discourage agencies’ from requiring SBOMs. The group argued that the requirement is premature and of limited value — but it didn’t ask for the concept to be abandoned.
It is the complexity and difficulty in both compiling and using an SBOM that is the problem — and it is these concerns that will drive a lot of activity through 2023. The value of the concept outlined in the executive order remains undiminished.
“Incidents such as Log4shell \[log4j\] and the most recent SpookySSL vulnerabilities \[CVE-2022-3602 and CVE-2022-3786\] will push the adoption of a software bill of materials as a core component of achieving effective incident response, while efforts will continue in maturing the SBOM ecosystem (adoption across sectors, tooling, standardization around sharing and exchanging of SBOMs and more),” explains Yotam Perkal, director of vulnerability research at Rezilion.
“One of the big challenges I see in the year ahead is that this is more data for the development teams to manage as they deliver software,” notes Lambert. “In 2023, organizations are going to need ways to automate generating, publishing and ingesting SBOMs – they will need ways to bring the remediation of the associated vulnerabilities into their current application security programs without having to adopt whole new workflows.”
As part of this process, Michael Assraf, CEO and co-founder at Vicarius, said, “We predict that a new market will evolve called binary software composition analysis, which will look for software files that are different from what was pre-packaged and shipped. Automated techniques can utilize machine learning that will find this discrepancy, which will be vital in knowing where your risk lies and how large your attack surface can potentially be.”
Thomas Pace, Co-founder & CEO at NetRise
Thomas Pace, CEO at NetRise, suggests, “SBOM is going to continue to garner mainstream adoption, not just from software/firmware suppliers that are building products they are selling, but also for internal development teams that are building applications and systems for internal use.”
He adds, “The need to be able to rapidly understand the provenance of software components is becoming increasingly critical. Without this visibility, the window for attackers to exploit these vulnerabilities is much too big and puts cyber defenders at a significant disadvantage.” But he also notes, “strong efforts from organizations like Google have moved the ball forward in a positive way. Efforts such as open-source insights provide a lot of visibility for end users and vendors alike to scale out the analysis of these components.”
The problems involved with SBOM generation and use have not yet been solved, but enthusiasm remains. We can expect considerable effort into automating these processes to continue throughout 2023.
Nevertheless, Kurt Baumgartner, principal security researcher at Kaspersky, warns, “Open source projects continue to be polluted with malicious code. Awareness of these issues and challenges increase, but the attacks continue to be effective on a large scale. Despite the best efforts of software bill of materials, complex dependency chains help ensure that malicious code is uncontrolled for a time in some projects.”
## **The physical supply chain**
Despite all companies’ need to be wary of potential software supply chain attacks via the code they develop for their own use, we should not forget that there is a potentially more catastrophic physical supply chain threat. We need only consider the effect the prevention of grain supplies leaving Ukraine (because of the Russia/Ukraine conflict) had on global food supplies to see the potential. Covid-19 also affected many different global supply chains, causing panic buying and popular distress in its early days.
These were not the result of cyberattacks – but many of those physical supply chains could be disrupted by cyberattacks. The [Colonial Pipeline](https://www.securityweek.com/colonial-pipeline-struggles-restart-after-ransomware-attack) incident, although a financially motivated attack, had an immediate effect on the supply of oil to eastern USA. The longer the Ukraine/Russia conflict continues, and the greater that east/west tensions increase, the possibility of physical supply chain cyber disruption will equally increase through 2023, and possibly beyond.
_SecurityWeek_ discussed one such possibility in May 2022: _The Vulnerable Maritime Supply Chain – a Threat to the Global Economy_ [here](https://www.securityweek.com/vulnerable-maritime-supply-chain-threat-global-economy).
Lorri Janssen-Anessi, director of external cyber assessments at BlueVoyant notes that in the utilities and energy sector, “99% of energy companies say they have been negatively impacted by at least one supply chain breach in the past year, representing the highest rate of overall impact in any other industry. Because it remains one of the most frequently attacked verticals, it is especially crucial that it rises to the challenge of supply chain defense in 2023.”
Taylor Gulley, senior application security consultant at nVisium, comments, “The past few years have shown that both the digital supply chain, as well as the physical world supply chain, are very fragile. This fragility is due to a lack of redundancy and resources due to economic constraints or skill gaps. For 2023, this situation will still stand true. Supply chain security is a weak link that needs to be strengthened.”
## **Solutions and the way forward**
Sam Curry, Cybereason
Sam Curry, CSO at Cybereason, believes the SBOM will be an important part of solving the software supply chain problem. “It would be naive in the extreme to think that with thousands of trusted software and service providers to choose from… that the handful of known supply chain compromises were the sum total of them. No. 2023 will show us more, and we will be lucky to learn of them because the attacker can quietly exploit these without tipping their hands.”
He added, “We need to use 2023 to be innovative and vigilant and to find new answers to the supply chain problem, to build on software bills of material, to innovate with the men and women building our software and to find the solutions to deter, to detect and to remove the vulnerabilities and exposures that enable this most insidious and trust eroding of attacks.”
Sharon Chand, Deloitte US’ cyber risk secure supply chain leader, believes that software supply chain security will require continuous realtime monitoring of third-party risks and vulnerabilities in inbound packaged software and firmware components. “For instance,” she said, “this includes implementing leading practice techniques around ingesting SBOMs and correlating the output to emerging vulnerabilities, identifying risk indicators such as geographical origin of the underlying components, and providing visibility to transitive dependencies.”
Christian Borst, EMEA CTO at Vectra AI, suggests collaboration and cooperation across the software industry will be required. “A holistic approach may help turn the tables on the matter: supply chain means partnership – partnership means collaboration and supporting each other. Only as a ‘mesh’ interconnected structure with consistent resiliency can companies thrive in the digital economy. This includes ensuring that they review the security policies of all those in the chain.”
Sounil Yu, CISO at JupiterOne, makes a fitting summary, referencing a paper written by Richard Danzig in July 2014 ( _Surviving on a Diet of Poisoned Fruit: Reducing the National Security Risks of America’s Cyber Dependencies_). “To borrow Richard Danzig’s analogy,” says Yu, “we are on a diet of poisoned fruit with respect to our software supply chain. This poison is not going to go away, so we will need to learn how to survive and thrive under these conditions. Being aware of the risks, through efforts such as SBOM, and managing the risks through compensating controls such as egress filtering, will be a priority in 2023 and the foreseeable future.”
**Related**: [US Gov Issues Software Supply Chain Security Guidance for Customers](https://www.securityweek.com/us-gov-issues-software-supply-chain-security-guidance-customers)
**Related**: [OpenSSF Adopts Microsoft-Built Supply Chain Security Framework](https://www.securityweek.com/openssf-adopts-microsoft-built-supply-chain-security-framework)
**Related**: [Hundreds Infected With ‘Wasp’ Stealer in Ongoing Supply Chain Attack](https://www.securityweek.com/hundreds-infected-wasp-stealer-ongoing-supply-chain-attack)
**Related**: [US Gov Issues Supply Chain Security Guidance for Software Suppliers](https://www.securityweek.com/us-gov-issues-supply-chain-security-guidance-software-suppliers)
The post [Cyber Insights 2023 \| Supply Chain Security](https://www.securityweek.com/cyber-insights-2023-supply-chain-security/) appeared first on [SecurityWeek](https://www.securityweek.com).
<https://www.securityweek.com/cyber-insights-2023-supply-chain-security/>
|
non_process
|
cyber insights supply chain security about securityweek cyber insights at the end of securityweek liaised with more than cybersecurity experts from over different organizations to gain insight into the security issues of today – and how these issues might evolve during and beyond the result is more than a dozen features on subjects ranging from ai quantum encryption and attack surface management to venture capital regulations and criminal gangs securityweek cyber insights supply chain security – the supply chain threat is directly linked to it potentially represents a hidden part of the attack surface and zero trust effective zero trust would eliminate the threat but the supply chain must be known and understood before it can be remediated in the meantime – and especially throughout – it will be a focus for adversaries why attack a single target when successful manipulation of the supply chain can get access to dozens or even hundreds of targets simultaneously the danger and effectiveness of such attacks is amply illustrated by the and incidents the missed wake up calls supply chain attacks are not new the iconic of late was a supply chain breach the attackers got into target using credentials stolen from its hvac provider fazio mechanical services – that is via target’s supply chain the breach of was another supply chain breach a ticketmaster software supplier inbenta was breached and inbenta software was modified and weaponized this was automatically downloaded to ticketmaster island hopping is another form of supply chain attack in was revealed this disclosed that an advanced group probably was compromising managed service providers to gain access to the msp’s customers despite these incidents it has only been in the last couple of years fueled by more extensive incidents such as solarwinds that industry has become cognizant of the full threat from increasingly sophisticated and wide ranging supply chain concerns but we should not forget that the incident also started as a supply chain attack software from the ukrainian accounting firm m e doc was weaponized and automatically downloaded by the firm’s customers before spreading around the globe both solarwinds and notpetya are believed to be the work of nation state actors all forms of supply chain attacks will increase in and beyond chad skipper global security technologist at vmware specifically calls out island hopping “in cybercriminals will continue to use island hopping a technique that aims to hijack an organization’s infrastructure to attack its customers ” he warns “remote desktop protocol is regularly used by threat actors during an island hopping campaign to disguise themselves as system administrators as we head into the new year it’s a threat that should be top of mind for all organizations ” attacks will increase that supply chain attacks will increase in and beyond is the single most extensive prediction for “supply chain attacks happen when hackers gain access to a company’s inner workings via a third party partner a method that provides them with a much greater amount of privileged information from just one breach ” explains matt jackson senior director security operations at “this type of attack already rose by more than in and i anticipate this trend will continue in with these attacks becoming more complicated and intricate ” milică resident ciso proofpoint lucia milică global resident ciso at proofpoint worries that despite all the wake up calls so far “we are still a long way from having adequate tools to protect against those kinds of digital supply chain vulnerabilities we predict these concerns will mount in with our trust in third party partners and suppliers becoming one of the primary attack channels ” the result she added is “we expect more tension in supply chain relationships overall as organizations try to escalate their vendors’ due diligence processes for better understanding the risks while suppliers scramble to manage the overwhelming focus on their processes ” jackson added “because many third party partners are now privy to more sensitive data than ever before companies can no longer rely on their own cybersecurity prowess to keep information safe ” he said “supply chain attacks purposefully target the smaller organizations first because they’re less likely to have a robust cybersecurity setup and they can use those companies to get to the bigger fish ” he continued “in the next year companies will become even more diligent when deciding on an outside organization to work with creating an increase in compliance verifications to vet the cyber tools used by these prospective partners ” anand raghavan co founder and cpo at armorblox expands on this theme “this becomes particularly relevant ” he said “for the fortune or global companies that have a large ecosystem of suppliers vendors and distributors whose security stacks are nowhere as mature as those of large organizations large organizations might consider requiring all vendors to follow certain security best practices including modernizing their email security stack if they want to continue being a vendor in good standing ” interestingly despite all the warnings of an escalating threat christopher budd senior manager of threat research at sophos notes “unlike two years ago when the solarwinds attack put supply chain attacks high on people’s radar supply chain attacks have faded from prominence ” this may be a misleading premise the discovery of a vulnerability in a widely used piece of software such as the vulnerability will be used by individual cybercriminals and nation state actors alike however targeted attacks such as that against solarwinds requires resources and skill these attributes are more usually found only in the more advanced gangs and nation state actors such adversaries have another attribute patience “today’s and undoubtedly tomorrow’s threat actors have shown they can play the long game ” warns pieter arntz senior intelligence reporter at malwarebytes budd also warns that despite their immediate lack of prominence at the time of writing but anything could happen tomorrow “supply chain may be something that continues to not gather news similar to but it will remain a real threat and one that organizations should be prioritizing across the board in part because effectively countering this threat requires a comprehensive careful methodical approach ” the software supply chain the primary growth area in supply chain attacks will likely be the software supply chain “over the past few years ” explains eilon elhadad senior director of supply chain security at aqua “increasing pressure to deliver software faster has widened attack surfaces and introduced severe vulnerabilities ” new tools languages and frameworks that support rapid development at scale are being targeted by malicious actors who understand the widespread impact that results from attacks to the software supply chain “in ” elhadad continued “software supply chain threats will continue to be a significant area of concern these attacks have a larger potential blast radius to allow hackers to impact entire markets and wreak havoc for organizations ” eric byres founder and cto at adolus agrees “software supply chain attacks will continue to increase exponentially in ” he said “the roi on these attacks is just too sweet for professional adversaries to resist ” he notes that supply chain attacks have increased by over the last three years much of the software supply chain threat comes from the growing reliance on open source software libraries as part of the ‘increasing pressure to deliver software faster’ zack zornstain head of supply chain security at checkmarx believes the software threat will particularly affect the open source supply “we believe that this threat of compromising open source packages will increase as malicious code can endanger the safety of our systems ranging from ransomware attacks to the exposure of sensitive information and more we expect to see this as a general attack vector used both by cyber firms and nation state actors sbom adaptation will help clarify which packages we’re using in applications but we will need to invest in more controls to ensure the safety of those packages ” he said “organizations should be on high alert for supply chain attacks if they use open source software ” warns kevin kirkwood deputy ciso at logrhythm “bad actors examine the code and its components to obtain a thorough understanding of its flaws and the most effective ways to exploit them ” if the source code of an open source software library either has – or can be engineered by bad actors to have – a vulnerability then every company that downloads and uses that code becomes vulnerable “in ” continues kirkwood “we’ll see bad actors attack vulnerabilities in low hanging open source vendors with the intention of compromising the global supply chain that uses third party code attackers will infect the open source repositories and chromium stores with malicious code and will wait for developers and other end users to come along and pick up the new sources and plugins ” venafi’s matt barker president of cloud native solutions adds “we’re seeing many instances of vulnerable code brought inside their firewall by developers trying to go fast using unverified code from github or copypasta from stack overflow ” he continues “thankfully we’ve reached a collective sense of focus on this area and are seeing tremendous developments in how we tackle it this is only going to increase through as we see more start ups popping up and open source tools like cosign and sigstore designed to help it biden’s sbom initiative has helped bring attention to the requirement and the openssf is leading in this charge ” mark lambert vp of products at armorcode expands on this “as the software supply chain continues to get more complicated it is vital to know what open source you are indirectly using as part of third party libraries services apis or tools this is where sbom comes in ” he said “by requiring a disclosure of all embedded technologies from your vendors you can perform analysis of those libraries to further assess your risk and react appropriately ” the sbom biden’s may executive order on improving the nation’s cybersecurity introduced the concept of a software bill of materials sbom effectively if not actually mandating that software bought or supplied by government agencies be accompanied with a bill of materials it described the sbom as “a formal record containing the details and supply chain relationships of various components used in building software ” and analogous to a list of ingredients on food packaging while the advantages of the sbom may appear obvious in helping software developers understand precisely what is included in the open source libraries they use it must be said that not everyone is immediately enthusiastic in december it emerged that a representing major tech firms such as amazon microsoft apple intel amd lenovo ibm cisco samsung tsmc qualcomm zoom and palo alto networks was urging the omb to ‘discourage agencies’ from requiring sboms the group argued that the requirement is premature and of limited value — but it didn’t ask for the concept to be abandoned it is the complexity and difficulty in both compiling and using an sbom that is the problem — and it is these concerns that will drive a lot of activity through the value of the concept outlined in the executive order remains undiminished “incidents such as and the most recent spookyssl vulnerabilities will push the adoption of a software bill of materials as a core component of achieving effective incident response while efforts will continue in maturing the sbom ecosystem adoption across sectors tooling standardization around sharing and exchanging of sboms and more ” explains yotam perkal director of vulnerability research at rezilion “one of the big challenges i see in the year ahead is that this is more data for the development teams to manage as they deliver software ” notes lambert “in organizations are going to need ways to automate generating publishing and ingesting sboms – they will need ways to bring the remediation of the associated vulnerabilities into their current application security programs without having to adopt whole new workflows ” as part of this process michael assraf ceo and co founder at vicarius said “we predict that a new market will evolve called binary software composition analysis which will look for software files that are different from what was pre packaged and shipped automated techniques can utilize machine learning that will find this discrepancy which will be vital in knowing where your risk lies and how large your attack surface can potentially be ” pace co founder ceo at netrise thomas pace ceo at netrise suggests “sbom is going to continue to garner mainstream adoption not just from software firmware suppliers that are building products they are selling but also for internal development teams that are building applications and systems for internal use ” he adds “the need to be able to rapidly understand the provenance of software components is becoming increasingly critical without this visibility the window for attackers to exploit these vulnerabilities is much too big and puts cyber defenders at a significant disadvantage ” but he also notes “strong efforts from organizations like google have moved the ball forward in a positive way efforts such as open source insights provide a lot of visibility for end users and vendors alike to scale out the analysis of these components ” the problems involved with sbom generation and use have not yet been solved but enthusiasm remains we can expect considerable effort into automating these processes to continue throughout nevertheless kurt baumgartner principal security researcher at kaspersky warns “open source projects continue to be polluted with malicious code awareness of these issues and challenges increase but the attacks continue to be effective on a large scale despite the best efforts of software bill of materials complex dependency chains help ensure that malicious code is uncontrolled for a time in some projects ” the physical supply chain despite all companies’ need to be wary of potential software supply chain attacks via the code they develop for their own use we should not forget that there is a potentially more catastrophic physical supply chain threat we need only consider the effect the prevention of grain supplies leaving ukraine because of the russia ukraine conflict had on global food supplies to see the potential covid also affected many different global supply chains causing panic buying and popular distress in its early days these were not the result of cyberattacks – but many of those physical supply chains could be disrupted by cyberattacks the incident although a financially motivated attack had an immediate effect on the supply of oil to eastern usa the longer the ukraine russia conflict continues and the greater that east west tensions increase the possibility of physical supply chain cyber disruption will equally increase through and possibly beyond securityweek discussed one such possibility in may the vulnerable maritime supply chain – a threat to the global economy lorri janssen anessi director of external cyber assessments at bluevoyant notes that in the utilities and energy sector “ of energy companies say they have been negatively impacted by at least one supply chain breach in the past year representing the highest rate of overall impact in any other industry because it remains one of the most frequently attacked verticals it is especially crucial that it rises to the challenge of supply chain defense in ” taylor gulley senior application security consultant at nvisium comments “the past few years have shown that both the digital supply chain as well as the physical world supply chain are very fragile this fragility is due to a lack of redundancy and resources due to economic constraints or skill gaps for this situation will still stand true supply chain security is a weak link that needs to be strengthened ” solutions and the way forward curry cybereason sam curry cso at cybereason believes the sbom will be an important part of solving the software supply chain problem “it would be naive in the extreme to think that with thousands of trusted software and service providers to choose from… that the handful of known supply chain compromises were the sum total of them no will show us more and we will be lucky to learn of them because the attacker can quietly exploit these without tipping their hands ” he added “we need to use to be innovative and vigilant and to find new answers to the supply chain problem to build on software bills of material to innovate with the men and women building our software and to find the solutions to deter to detect and to remove the vulnerabilities and exposures that enable this most insidious and trust eroding of attacks ” sharon chand deloitte us’ cyber risk secure supply chain leader believes that software supply chain security will require continuous realtime monitoring of third party risks and vulnerabilities in inbound packaged software and firmware components “for instance ” she said “this includes implementing leading practice techniques around ingesting sboms and correlating the output to emerging vulnerabilities identifying risk indicators such as geographical origin of the underlying components and providing visibility to transitive dependencies ” christian borst emea cto at vectra ai suggests collaboration and cooperation across the software industry will be required “a holistic approach may help turn the tables on the matter supply chain means partnership – partnership means collaboration and supporting each other only as a ‘mesh’ interconnected structure with consistent resiliency can companies thrive in the digital economy this includes ensuring that they review the security policies of all those in the chain ” sounil yu ciso at jupiterone makes a fitting summary referencing a paper written by richard danzig in july surviving on a diet of poisoned fruit reducing the national security risks of america’s cyber dependencies “to borrow richard danzig’s analogy ” says yu “we are on a diet of poisoned fruit with respect to our software supply chain this poison is not going to go away so we will need to learn how to survive and thrive under these conditions being aware of the risks through efforts such as sbom and managing the risks through compensating controls such as egress filtering will be a priority in and the foreseeable future ” related related related related the post appeared first on
| 0
|
27,367
| 28,153,127,352
|
IssuesEvent
|
2023-04-03 04:24:20
|
appsmithorg/appsmith
|
https://api.github.com/repos/appsmithorg/appsmith
|
opened
|
[Feature]: auto format code in JS editor
|
Bug Enhancement JS Usability
|
### Is there an existing issue for this?
- [X] I have searched the existing issues
### Summary
The JS object pane should support basic keyboard shortcuts that help developers write code faster and more effectively.
Auto-format the code in the JS editor. The keyboard shortcut to prettify the code opens an incognito window in Firefox. This causes frustration
### Why should this be worked on?
- The keyboard shortcut to prettify the code opens an incognito window in Firefox. This causes frustration
|
True
|
[Feature]: auto format code in JS editor - ### Is there an existing issue for this?
- [X] I have searched the existing issues
### Summary
The JS object pane should support basic keyboard shortcuts that help developers write code faster and more effectively.
Auto-format the code in the JS editor. The keyboard shortcut to prettify the code opens an incognito window in Firefox. This causes frustration
### Why should this be worked on?
- The keyboard shortcut to prettify the code opens an incognito window in Firefox. This causes frustration
|
non_process
|
auto format code in js editor is there an existing issue for this i have searched the existing issues summary the js object pane should support basic keyboard shortcuts that help developers write code faster and more effectively auto format the code in the js editor the keyboard shortcut to prettify the code opens an incognito window in firefox this causes frustration why should this be worked on the keyboard shortcut to prettify the code opens an incognito window in firefox this causes frustration
| 0
|
18,843
| 24,754,040,025
|
IssuesEvent
|
2022-10-21 15:58:29
|
aiidateam/aiida-core
|
https://api.github.com/repos/aiidateam/aiida-core
|
closed
|
Mark relevant `Process` exit codes as `invalidates_cache=True`
|
priority/important type/enhancement topic/processes
|
There are a number of exit codes defined on processes by `aiida-core` that do not specify `invalidates_cache=True` even though they should.
|
1.0
|
Mark relevant `Process` exit codes as `invalidates_cache=True` - There are a number of exit codes defined on processes by `aiida-core` that do not specify `invalidates_cache=True` even though they should.
|
process
|
mark relevant process exit codes as invalidates cache true there are a number of exit codes defined on processes by aiida core that do not specify invalidates cache true even though they should
| 1
|
427,970
| 29,892,657,419
|
IssuesEvent
|
2023-06-21 00:09:54
|
aws-amplify/amplify-ui
|
https://api.github.com/repos/aws-amplify/amplify-ui
|
closed
|
Missing code in AWS Doc - solution suggested
|
bug Documentation Authenticator React
|
### Before creating a new issue, please confirm:
- [X] I have [searched for duplicate or closed issues](https://github.com/aws-amplify/amplify-ui/issues?q=is%3Aissue+) and [discussions](https://github.com/aws-amplify/amplify-ui/discussions).
- [X] I have tried disabling all browser extensions or using a different browser
- [X] I have tried deleting the node_modules folder and reinstalling my dependencies
- [X] I have read the guide for [submitting bug reports](https://github.com/aws-amplify/amplify-ui/blob/main/CONTRIBUTING.md#bug-reports).
### On which framework/platform are you having an issue?
React
### Which UI component?
Authenticator
### How is your app built?
React
### What browsers are you seeing the problem on?
Chrome, Firefox, Microsoft Edge, Safari, iOS (React Native), Android (React Native)
### Please describe your bug.
In your tutorial:
https://ui.docs.amplify.aws/react/guides/auth-protected#adding-in-a-requireauth-component
Critical missing code:
In index.js,
You are missing the line of code:
import {Amplify} from 'aws-amplify';
Without this line of code I get an error that 'Amplify' is not defined.
Non-Critical issues that would make the code easier to follow:
- It is confusing that "RequireAuth.js" is not in the "Components" folder. You placed it in between two other files that are in the components folder, so that gave me an error when I first ran the code because my RequireAuth.js file was in the wrong folder. I suggest having that section be before the other files that are in the components folder.
- I suggest having a sentence clarifying the convention is to put 'components' folder inside the 'src' folder. Beginners might not know the convention to put 'components' folder inside the 'src' folder.
- The tutorial mentions that Auth.currentAuthenticatedUser() accomplishes the same thing... I would be curious to see this example.
Thanks for the tutorial! I think the above changes to the tutorial could save people 20 mins of debugging.
### What's the expected behaviour?
NA
### Help us reproduce the bug!
NA
### Code Snippet
```typescript
// Put your code below this line.
```
### Additional information and screenshots
_No response_
|
1.0
|
Missing code in AWS Doc - solution suggested - ### Before creating a new issue, please confirm:
- [X] I have [searched for duplicate or closed issues](https://github.com/aws-amplify/amplify-ui/issues?q=is%3Aissue+) and [discussions](https://github.com/aws-amplify/amplify-ui/discussions).
- [X] I have tried disabling all browser extensions or using a different browser
- [X] I have tried deleting the node_modules folder and reinstalling my dependencies
- [X] I have read the guide for [submitting bug reports](https://github.com/aws-amplify/amplify-ui/blob/main/CONTRIBUTING.md#bug-reports).
### On which framework/platform are you having an issue?
React
### Which UI component?
Authenticator
### How is your app built?
React
### What browsers are you seeing the problem on?
Chrome, Firefox, Microsoft Edge, Safari, iOS (React Native), Android (React Native)
### Please describe your bug.
In your tutorial:
https://ui.docs.amplify.aws/react/guides/auth-protected#adding-in-a-requireauth-component
Critical missing code:
In index.js,
You are missing the line of code:
import {Amplify} from 'aws-amplify';
Without this line of code I get an error that 'Amplify' is not defined.
Non-Critical issues that would make the code easier to follow:
- It is confusing that "RequireAuth.js" is not in the "Components" folder. You placed it in between two other files that are in the components folder, so that gave me an error when I first ran the code because my RequireAuth.js file was in the wrong folder. I suggest having that section be before the other files that are in the components folder.
- I suggest having a sentence clarifying the convention is to put 'components' folder inside the 'src' folder. Beginners might not know the convention to put 'components' folder inside the 'src' folder.
- The tutorial mentions that Auth.currentAuthenticatedUser() accomplishes the same thing... I would be curious to see this example.
Thanks for the tutorial! I think the above changes to the tutorial could save people 20 mins of debugging.
### What's the expected behaviour?
NA
### Help us reproduce the bug!
NA
### Code Snippet
```typescript
// Put your code below this line.
```
### Additional information and screenshots
_No response_
|
non_process
|
missing code in aws doc solution suggested before creating a new issue please confirm i have and i have tried disabling all browser extensions or using a different browser i have tried deleting the node modules folder and reinstalling my dependencies i have read the guide for on which framework platform are you having an issue react which ui component authenticator how is your app built react what browsers are you seeing the problem on chrome firefox microsoft edge safari ios react native android react native please describe your bug in your tutorial critical missing code in index js you are missing the line of code import amplify from aws amplify without this line of code i get an error that amplify is not defined non critical issues that would make the code easier to follow it is confusing that requireauth js is not in the components folder you placed it in between two other files that are in the components folder so that gave me an error when i first ran the code because my requireauth js file was in the wrong folder i suggest having that section be before the other files that are in the components folder i suggest having a sentence clarifying the convention is to put components folder inside the src folder beginners might not know the convention to put components folder inside the src folder the tutorial mentions that auth currentauthenticateduser accomplishes the same thing i would be curious to see this example thanks for the tutorial i think the above changes to the tutorial could save people mins of debugging what s the expected behaviour na help us reproduce the bug na code snippet typescript put your code below this line additional information and screenshots no response
| 0
|
98,015
| 4,016,059,813
|
IssuesEvent
|
2016-05-15 10:39:47
|
fommil/sbt-big-project
|
https://api.github.com/repos/fommil/sbt-big-project
|
closed
|
FastJar needs to classes.mkdirs()
|
Bug Priority
|
incase it doesn't exist (think of projects with only test configs)
|
1.0
|
FastJar needs to classes.mkdirs() - incase it doesn't exist (think of projects with only test configs)
|
non_process
|
fastjar needs to classes mkdirs incase it doesn t exist think of projects with only test configs
| 0
|
76,160
| 7,520,213,733
|
IssuesEvent
|
2018-04-12 13:55:53
|
EOSIO/eos
|
https://api.github.com/repos/EOSIO/eos
|
closed
|
The boost file name mismatch
|
needs testing - pass
|
https://github.com/EOSIO/eos/blob/54d4d177ed80b37dcc93a9f7e7f310cb4542d492/scripts/eosio_build_ubuntu.sh#L113
The boost file name is not consistent with the one referred to at 107.
|
1.0
|
The boost file name mismatch - https://github.com/EOSIO/eos/blob/54d4d177ed80b37dcc93a9f7e7f310cb4542d492/scripts/eosio_build_ubuntu.sh#L113
The boost file name is not consistent with the one referred to at 107.
|
non_process
|
the boost file name mismatch the boost file name is not consistent with the one referred to at
| 0
|
811,282
| 30,282,434,547
|
IssuesEvent
|
2023-07-08 08:27:07
|
glific/mobile
|
https://api.github.com/repos/glific/mobile
|
closed
|
Small issues and enhancements
|
Priority: Medium
|
- Add a loading on button when we click on login as it takes some time to load
<img width="386" alt="image" src="https://github.com/glific/mobile/assets/32592458/bbee1569-8261-4ffe-9820-8b2e7655fb76">
- If the wallet balance API fails change the text to **Please check gupshup settings**
<img width="378" alt="image" src="https://github.com/glific/mobile/assets/32592458/cd3571e7-0b47-4cfb-9d42-6db952c25ef7">
- If there are no notifications add a text **no notifications available**. Also this should have a loader when the API is called
<img width="419" alt="image" src="https://github.com/glific/mobile/assets/32592458/f0c1a69e-6437-437a-ae7a-cd3b688379f0">
- When we click on a list item it adds some margin from the top and bottom. Lets remove that
<img width="292" alt="image" src="https://github.com/glific/mobile/assets/32592458/1c2f89d3-db58-44b8-b015-8c63d6db4a43">
- Remove this icon from messages page
<img width="252" alt="image" src="https://github.com/glific/mobile/assets/32592458/6455c9e1-aed9-4acd-b237-399177018741">
- The green dot will be based on the isRead attribute in the contact query
<img width="383" alt="image" src="https://github.com/glific/mobile/assets/32592458/33f47aee-20b4-427b-bc0d-5944609183ce">
|
1.0
|
Small issues and enhancements - - Add a loading on button when we click on login as it takes some time to load
<img width="386" alt="image" src="https://github.com/glific/mobile/assets/32592458/bbee1569-8261-4ffe-9820-8b2e7655fb76">
- If the wallet balance API fails change the text to **Please check gupshup settings**
<img width="378" alt="image" src="https://github.com/glific/mobile/assets/32592458/cd3571e7-0b47-4cfb-9d42-6db952c25ef7">
- If there are no notifications add a text **no notifications available**. Also this should have a loader when the API is called
<img width="419" alt="image" src="https://github.com/glific/mobile/assets/32592458/f0c1a69e-6437-437a-ae7a-cd3b688379f0">
- When we click on a list item it adds some margin from the top and bottom. Lets remove that
<img width="292" alt="image" src="https://github.com/glific/mobile/assets/32592458/1c2f89d3-db58-44b8-b015-8c63d6db4a43">
- Remove this icon from messages page
<img width="252" alt="image" src="https://github.com/glific/mobile/assets/32592458/6455c9e1-aed9-4acd-b237-399177018741">
- The green dot will be based on the isRead attribute in the contact query
<img width="383" alt="image" src="https://github.com/glific/mobile/assets/32592458/33f47aee-20b4-427b-bc0d-5944609183ce">
|
non_process
|
small issues and enhancements add a loading on button when we click on login as it takes some time to load img width alt image src if the wallet balance api fails change the text to please check gupshup settings img width alt image src if there are no notifications add a text no notifications available also this should have a loader when the api is called img width alt image src when we click on a list item it adds some margin from the top and bottom lets remove that img width alt image src remove this icon from messages page img width alt image src the green dot will be based on the isread attribute in the contact query img width alt image src
| 0
|
19,531
| 25,841,235,041
|
IssuesEvent
|
2022-12-13 00:38:35
|
devssa/onde-codar-em-salvador
|
https://api.github.com/repos/devssa/onde-codar-em-salvador
|
closed
|
Analista de Análise do Cadastro Técnico JR na [COELBA]
|
SALVADOR TRAINEE BANCO DE DADOS PYTHON JUNIOR SQL SAP INGLÊS HELP WANTED GEOPROCESSAMENTO Stale
|
<!--
==================================================
POR FAVOR, SÓ POSTE SE A VAGA FOR PARA SALVADOR E CIDADES VIZINHAS!
Use: "Desenvolvedor Front-end" ao invés de
"Front-End Developer" \o/
Exemplo: `[JAVASCRIPT] [MYSQL] [NODE.JS] Desenvolvedor Front-End na [NOME DA EMPRESA]`
==================================================
-->
## Analista de Análise do Cadastro Técnico JR
- Garantir a qualidade do cadastro técnico, a fim de manter e controlar os processos de atualização no Sistema Elétrico, permitindo uma real caracterização dos ativos da base de dados e seu georreferenciamento, com objetivo de compor as bases de dados geográfica e de remuneração das distribuidoras, bem como atender as demandas regulatórias vigentes. Garantir a qualidade no levantamento e atualização do parque de iluminação pública do estado, bem como informações de uso compartilhado controlados pela distribuidora, a fim de promover insumos sólidos para faturamento destas frentes.
## Local
- Salvador
## Benefícios
- Tipo de contrato: indeterminado
- Salário compatível com o mercado;
- Vale transporte;
- Ticket alimentação e/ou refeição;
- Plano de saúde e odontológico;
- Gym Pass;
- Seguro de vida;
- Previdência privada;
- Auxílio dependente (para filhos até 10 anos).
## Requisitos
**Obrigatórios:**
- Curso Superior em Engenharia, Análise de Sistemas ou Ciência da Computação;
- CNH B;
- Pacote office avançado.
- Conhecimento em Structured Query Language (SQL)
- Phyton
- Banco de dados
- Programação
- Geoprocessamento e sistema GIS
- Sistema Técnico de Engenharia (GSE)
- Sistema SAP
- Topologia de sistema elétrico de distribuição
- Legislação de fornecimento de energia elétrica e Cartografia;
- Experiência com gestão de informações em banco de dados;
- Inglês intermediário.
## Coelba
- A Companhia de Eletricidade do Estado da Bahia (Coelba) é uma empresa do grupo Neoenergia que distribui energia elétrica a 5,8 milhões de unidades consumidoras, atendendo a 15,3 milhões de pessoas. É a terceira maior distribuidora de energia elétrica do país em número de clientes e a sexta em volume de energia distribuída, de acordo com o ranking da Agência Nacional de Energia Elétrica (Aneel). No Norte e Nordeste, é a distribuidora líder em volume de energia e clientes.
## Como se candidatar
- vagas.com.br/vagas/v1983482/analista-de-analise-do-cadastro-tecnico-jr
- Se candidatar até 11/11/19
|
1.0
|
Analista de Análise do Cadastro Técnico JR na [COELBA] - <!--
==================================================
POR FAVOR, SÓ POSTE SE A VAGA FOR PARA SALVADOR E CIDADES VIZINHAS!
Use: "Desenvolvedor Front-end" ao invés de
"Front-End Developer" \o/
Exemplo: `[JAVASCRIPT] [MYSQL] [NODE.JS] Desenvolvedor Front-End na [NOME DA EMPRESA]`
==================================================
-->
## Analista de Análise do Cadastro Técnico JR
- Garantir a qualidade do cadastro técnico, a fim de manter e controlar os processos de atualização no Sistema Elétrico, permitindo uma real caracterização dos ativos da base de dados e seu georreferenciamento, com objetivo de compor as bases de dados geográfica e de remuneração das distribuidoras, bem como atender as demandas regulatórias vigentes. Garantir a qualidade no levantamento e atualização do parque de iluminação pública do estado, bem como informações de uso compartilhado controlados pela distribuidora, a fim de promover insumos sólidos para faturamento destas frentes.
## Local
- Salvador
## Benefícios
- Tipo de contrato: indeterminado
- Salário compatível com o mercado;
- Vale transporte;
- Ticket alimentação e/ou refeição;
- Plano de saúde e odontológico;
- Gym Pass;
- Seguro de vida;
- Previdência privada;
- Auxílio dependente (para filhos até 10 anos).
## Requisitos
**Obrigatórios:**
- Curso Superior em Engenharia, Análise de Sistemas ou Ciência da Computação;
- CNH B;
- Pacote office avançado.
- Conhecimento em Structured Query Language (SQL)
- Phyton
- Banco de dados
- Programação
- Geoprocessamento e sistema GIS
- Sistema Técnico de Engenharia (GSE)
- Sistema SAP
- Topologia de sistema elétrico de distribuição
- Legislação de fornecimento de energia elétrica e Cartografia;
- Experiência com gestão de informações em banco de dados;
- Inglês intermediário.
## Coelba
- A Companhia de Eletricidade do Estado da Bahia (Coelba) é uma empresa do grupo Neoenergia que distribui energia elétrica a 5,8 milhões de unidades consumidoras, atendendo a 15,3 milhões de pessoas. É a terceira maior distribuidora de energia elétrica do país em número de clientes e a sexta em volume de energia distribuída, de acordo com o ranking da Agência Nacional de Energia Elétrica (Aneel). No Norte e Nordeste, é a distribuidora líder em volume de energia e clientes.
## Como se candidatar
- vagas.com.br/vagas/v1983482/analista-de-analise-do-cadastro-tecnico-jr
- Se candidatar até 11/11/19
|
process
|
analista de análise do cadastro técnico jr na por favor só poste se a vaga for para salvador e cidades vizinhas use desenvolvedor front end ao invés de front end developer o exemplo desenvolvedor front end na analista de análise do cadastro técnico jr garantir a qualidade do cadastro técnico a fim de manter e controlar os processos de atualização no sistema elétrico permitindo uma real caracterização dos ativos da base de dados e seu georreferenciamento com objetivo de compor as bases de dados geográfica e de remuneração das distribuidoras bem como atender as demandas regulatórias vigentes garantir a qualidade no levantamento e atualização do parque de iluminação pública do estado bem como informações de uso compartilhado controlados pela distribuidora a fim de promover insumos sólidos para faturamento destas frentes local salvador benefícios tipo de contrato indeterminado salário compatível com o mercado vale transporte ticket alimentação e ou refeição plano de saúde e odontológico gym pass seguro de vida previdência privada auxílio dependente para filhos até anos requisitos obrigatórios curso superior em engenharia análise de sistemas ou ciência da computação cnh b pacote office avançado conhecimento em structured query language sql phyton banco de dados programação geoprocessamento e sistema gis sistema técnico de engenharia gse sistema sap topologia de sistema elétrico de distribuição legislação de fornecimento de energia elétrica e cartografia experiência com gestão de informações em banco de dados inglês intermediário coelba a companhia de eletricidade do estado da bahia coelba é uma empresa do grupo neoenergia que distribui energia elétrica a milhões de unidades consumidoras atendendo a milhões de pessoas é a terceira maior distribuidora de energia elétrica do país em número de clientes e a sexta em volume de energia distribuída de acordo com o ranking da agência nacional de energia elétrica aneel no norte e nordeste é a distribuidora líder em volume de energia e clientes como se candidatar vagas com br vagas analista de analise do cadastro tecnico jr se candidatar até
| 1
|
570,151
| 17,019,822,397
|
IssuesEvent
|
2021-07-02 17:04:09
|
modrinth/knossos
|
https://api.github.com/repos/modrinth/knossos
|
closed
|
If you're in the search and you click on the mods tab, the url updates, but not the page
|
bug priority: minor status: confirmed type: functional
|
**Describe the bug**
When you're on the mods search page, and you click `Mods` in the header, the url displayed in the browser updates, but the contents of the page doesn't
**To Reproduce**
Steps to reproduce the behavior:
1. Go to the mods search page
2. Click on put something in the search bar
3. Click `Mods` in the header
4. See url update, but not the page
**Expected behavior**
The query to be cleared, and the page updated
|
1.0
|
If you're in the search and you click on the mods tab, the url updates, but not the page - **Describe the bug**
When you're on the mods search page, and you click `Mods` in the header, the url displayed in the browser updates, but the contents of the page doesn't
**To Reproduce**
Steps to reproduce the behavior:
1. Go to the mods search page
2. Click on put something in the search bar
3. Click `Mods` in the header
4. See url update, but not the page
**Expected behavior**
The query to be cleared, and the page updated
|
non_process
|
if you re in the search and you click on the mods tab the url updates but not the page describe the bug when you re on the mods search page and you click mods in the header the url displayed in the browser updates but the contents of the page doesn t to reproduce steps to reproduce the behavior go to the mods search page click on put something in the search bar click mods in the header see url update but not the page expected behavior the query to be cleared and the page updated
| 0
|
2,694
| 5,541,014,912
|
IssuesEvent
|
2017-03-22 11:39:59
|
Polymap4/polymap4-core
|
https://api.github.com/repos/Polymap4/polymap4-core
|
closed
|
[Process] Area of interest
|
Process
|
Make a module that slects and processes the area of interest of a GridCoverage.
|
1.0
|
[Process] Area of interest - Make a module that slects and processes the area of interest of a GridCoverage.
|
process
|
area of interest make a module that slects and processes the area of interest of a gridcoverage
| 1
|
7,379
| 10,514,634,652
|
IssuesEvent
|
2019-09-28 02:15:12
|
metabase/metabase
|
https://api.github.com/repos/metabase/metabase
|
closed
|
Filtering against datetimes broken in SQLite
|
.Backend Database/SQLite Priority:P1 Query Processor Type:Bug
|
It doesn't fail entirely, but rather returns a set of mystery results rather than the correct ones. We had previously assumed this was a bug with timezone support in SQLite. It wasn't. We were using the wrong format for datetime literals, which we splice directly into the query for other reasons.
SQLite, like most SQL databases, uses `yyyy-MM-dd HH:mm:ss` formatted strings, rather than ISO-8601 `yyyy-MM-ddTHH:mm:ss` strings. Once I tracked down and fixed this bug I was able to actually remove several incorrect special cases in some of our tests that we had assumed were timezone issues.
|
1.0
|
Filtering against datetimes broken in SQLite - It doesn't fail entirely, but rather returns a set of mystery results rather than the correct ones. We had previously assumed this was a bug with timezone support in SQLite. It wasn't. We were using the wrong format for datetime literals, which we splice directly into the query for other reasons.
SQLite, like most SQL databases, uses `yyyy-MM-dd HH:mm:ss` formatted strings, rather than ISO-8601 `yyyy-MM-ddTHH:mm:ss` strings. Once I tracked down and fixed this bug I was able to actually remove several incorrect special cases in some of our tests that we had assumed were timezone issues.
|
process
|
filtering against datetimes broken in sqlite it doesn t fail entirely but rather returns a set of mystery results rather than the correct ones we had previously assumed this was a bug with timezone support in sqlite it wasn t we were using the wrong format for datetime literals which we splice directly into the query for other reasons sqlite like most sql databases uses yyyy mm dd hh mm ss formatted strings rather than iso yyyy mm ddthh mm ss strings once i tracked down and fixed this bug i was able to actually remove several incorrect special cases in some of our tests that we had assumed were timezone issues
| 1
|
19,718
| 26,073,796,452
|
IssuesEvent
|
2022-12-24 06:59:47
|
pyanodon/pybugreports
|
https://api.github.com/repos/pyanodon/pybugreports
|
closed
|
Postprocessing doesn't factor in recipes with result.amount = 0
|
mod:pypostprocessing postprocess-fail compatibility
|
### Mod source
Github
### Which mod are you having an issue with?
- [ ] pyalienlife
- [ ] pyalternativeenergy
- [ ] pycoalprocessing
- [ ] pyfusionenergy
- [ ] pyhightech
- [ ] pyindustry
- [ ] pypetroleumhandling
- [X] pypostprocessing
- [ ] pyrawores
### Operating system
>=Windows 10
### What kind of issue is this?
- [X] Compatibility
- [ ] Locale (names, descriptions, unknown keys)
- [ ] Graphical
- [ ] Crash
- [ ] Progression
- [ ] Balance
- [X] Pypostprocessing failure
- [ ] Other
### What is the problem?
When a recipe like the following exists, PyPP may still consider this relevant to a dependency loop.
```lua
local target_fluid = data.raw.fluid.water
data:extend(
{
{
type = "recipe",
name = ("pypp-"..target_fluid.name),
icons = target_fluid.icons or {{icon = target_fluid.icon, icon_size = target_fluid.icon_size}},
category = "crafting-with-fluid",
energy_required = 1,
subgroup = "fill-barrel",
order = "b[fill-crude-oil-barrel]",
enabled = true,
ingredients = {},
results=
{
{type="fluid", name=target_fluid.name, amount=0}
}
}
})
```
### Steps to reproduce
1. Activate pycp, pypp and the test mod
2. Observe crash
### Additional context
[pypp_breakmod.zip](https://github.com/pyanodon/pybugreports/files/9793675/pypp_breakmod.zip)
### Log file
[factorio-current.log](https://github.com/pyanodon/pybugreports/files/9793676/factorio-current.log)
|
2.0
|
Postprocessing doesn't factor in recipes with result.amount = 0 - ### Mod source
Github
### Which mod are you having an issue with?
- [ ] pyalienlife
- [ ] pyalternativeenergy
- [ ] pycoalprocessing
- [ ] pyfusionenergy
- [ ] pyhightech
- [ ] pyindustry
- [ ] pypetroleumhandling
- [X] pypostprocessing
- [ ] pyrawores
### Operating system
>=Windows 10
### What kind of issue is this?
- [X] Compatibility
- [ ] Locale (names, descriptions, unknown keys)
- [ ] Graphical
- [ ] Crash
- [ ] Progression
- [ ] Balance
- [X] Pypostprocessing failure
- [ ] Other
### What is the problem?
When a recipe like the following exists, PyPP may still consider this relevant to a dependency loop.
```lua
local target_fluid = data.raw.fluid.water
data:extend(
{
{
type = "recipe",
name = ("pypp-"..target_fluid.name),
icons = target_fluid.icons or {{icon = target_fluid.icon, icon_size = target_fluid.icon_size}},
category = "crafting-with-fluid",
energy_required = 1,
subgroup = "fill-barrel",
order = "b[fill-crude-oil-barrel]",
enabled = true,
ingredients = {},
results=
{
{type="fluid", name=target_fluid.name, amount=0}
}
}
})
```
### Steps to reproduce
1. Activate pycp, pypp and the test mod
2. Observe crash
### Additional context
[pypp_breakmod.zip](https://github.com/pyanodon/pybugreports/files/9793675/pypp_breakmod.zip)
### Log file
[factorio-current.log](https://github.com/pyanodon/pybugreports/files/9793676/factorio-current.log)
|
process
|
postprocessing doesn t factor in recipes with result amount mod source github which mod are you having an issue with pyalienlife pyalternativeenergy pycoalprocessing pyfusionenergy pyhightech pyindustry pypetroleumhandling pypostprocessing pyrawores operating system windows what kind of issue is this compatibility locale names descriptions unknown keys graphical crash progression balance pypostprocessing failure other what is the problem when a recipe like the following exists pypp may still consider this relevant to a dependency loop lua local target fluid data raw fluid water data extend type recipe name pypp target fluid name icons target fluid icons or icon target fluid icon icon size target fluid icon size category crafting with fluid energy required subgroup fill barrel order b enabled true ingredients results type fluid name target fluid name amount steps to reproduce activate pycp pypp and the test mod observe crash additional context log file
| 1
|
17,818
| 6,517,712,333
|
IssuesEvent
|
2017-08-28 02:37:38
|
Tirocupidus/TheExiledRPOverhaul
|
https://api.github.com/repos/Tirocupidus/TheExiledRPOverhaul
|
closed
|
Ice arrow recipe still 10 shards
|
easy fix ready for build
|
This wasn't fixed at least in the tooltip, haven't tried to make.
|
1.0
|
Ice arrow recipe still 10 shards - This wasn't fixed at least in the tooltip, haven't tried to make.
|
non_process
|
ice arrow recipe still shards this wasn t fixed at least in the tooltip haven t tried to make
| 0
|
250,769
| 21,335,179,204
|
IssuesEvent
|
2022-04-18 13:47:14
|
WordPress/gutenberg
|
https://api.github.com/repos/WordPress/gutenberg
|
opened
|
[Flaky Test] Inserts the filtered hello world block even when filter added after block registration
|
[Type] Flaky Test
|
<!-- __META_DATA__:{"failedTimes":1,"totalCommits":1,"baseCommit":"33a5d514892c254760b5fceb17e72a9faefa1218"} -->
**Flaky test detected. This is an auto-generated issue by GitHub Actions. Please do NOT edit this manually.**
## Test title
Inserts the filtered hello world block even when filter added after block registration
## Test path
`/home/runner/work/gutenberg/gutenberg/test/e2e/specs/editor/plugins/block-api.spec.js`
## Flaky rate (_estimated_)
`1 / 2` runs
## Errors
|
1.0
|
[Flaky Test] Inserts the filtered hello world block even when filter added after block registration - <!-- __META_DATA__:{"failedTimes":1,"totalCommits":1,"baseCommit":"33a5d514892c254760b5fceb17e72a9faefa1218"} -->
**Flaky test detected. This is an auto-generated issue by GitHub Actions. Please do NOT edit this manually.**
## Test title
Inserts the filtered hello world block even when filter added after block registration
## Test path
`/home/runner/work/gutenberg/gutenberg/test/e2e/specs/editor/plugins/block-api.spec.js`
## Flaky rate (_estimated_)
`1 / 2` runs
## Errors
|
non_process
|
inserts the filtered hello world block even when filter added after block registration flaky test detected this is an auto generated issue by github actions please do not edit this manually test title inserts the filtered hello world block even when filter added after block registration test path home runner work gutenberg gutenberg test specs editor plugins block api spec js flaky rate estimated runs errors
| 0
|
3,598
| 6,627,561,383
|
IssuesEvent
|
2017-09-23 04:49:57
|
renocollective/member-portal
|
https://api.github.com/repos/renocollective/member-portal
|
opened
|
Add contribution guidelines
|
docs process
|
Document the process required for contributing to this project, both in technical terms and process terms.
- [ ] Add a [`CONTRIBUTING.md` file](https://help.github.com/articles/setting-guidelines-for-repository-contributors/)
- [ ] Add a [Pull Request template](https://help.github.com/articles/creating-a-pull-request-template-for-your-repository/)
|
1.0
|
Add contribution guidelines - Document the process required for contributing to this project, both in technical terms and process terms.
- [ ] Add a [`CONTRIBUTING.md` file](https://help.github.com/articles/setting-guidelines-for-repository-contributors/)
- [ ] Add a [Pull Request template](https://help.github.com/articles/creating-a-pull-request-template-for-your-repository/)
|
process
|
add contribution guidelines document the process required for contributing to this project both in technical terms and process terms add a add a
| 1
|
140,668
| 18,906,120,661
|
IssuesEvent
|
2021-11-16 09:16:42
|
VerdantSparks/vuejs-aspnetcore-ssr
|
https://api.github.com/repos/VerdantSparks/vuejs-aspnetcore-ssr
|
closed
|
CVE-2019-16769 (Medium) detected in serialize-javascript-1.9.1.tgz
|
security vulnerability
|
## CVE-2019-16769 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>serialize-javascript-1.9.1.tgz</b></p></summary>
<p>Serialize JavaScript to a superset of JSON that includes regular expressions and functions.</p>
<p>Library home page: <a href="https://registry.npmjs.org/serialize-javascript/-/serialize-javascript-1.9.1.tgz">https://registry.npmjs.org/serialize-javascript/-/serialize-javascript-1.9.1.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/vuejs-aspnetcore-ssr/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/vuejs-aspnetcore-ssr/node_modules/vue-server-renderer/node_modules/serialize-javascript/package.json</p>
<p>
Dependency Hierarchy:
- vue-server-renderer-2.6.10.tgz (Root Library)
- :x: **serialize-javascript-1.9.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/VerdantSparks/vuejs-aspnetcore-ssr/commit/c217828eede1712e885e8472f9506ea9e766c0d8">c217828eede1712e885e8472f9506ea9e766c0d8</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Affected versions of this package are vulnerable to Cross-site Scripting (XSS). It does not properly mitigate against unsafe characters in serialized regular expressions. This vulnerability is not affected on Node.js environment since Node.js's implementation of RegExp.prototype.toString() backslash-escapes all forward slashes in regular expressions. If serialized data of regular expression objects are used in an environment other than Node.js, it is affected by this vulnerability.
<p>Publish Date: 2019-12-05
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16769>CVE-2019-16769</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>5.0</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16769">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16769</a></p>
<p>Release Date: 2019-12-05</p>
<p>Fix Resolution: v2.1.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2019-16769 (Medium) detected in serialize-javascript-1.9.1.tgz - ## CVE-2019-16769 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>serialize-javascript-1.9.1.tgz</b></p></summary>
<p>Serialize JavaScript to a superset of JSON that includes regular expressions and functions.</p>
<p>Library home page: <a href="https://registry.npmjs.org/serialize-javascript/-/serialize-javascript-1.9.1.tgz">https://registry.npmjs.org/serialize-javascript/-/serialize-javascript-1.9.1.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/vuejs-aspnetcore-ssr/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/vuejs-aspnetcore-ssr/node_modules/vue-server-renderer/node_modules/serialize-javascript/package.json</p>
<p>
Dependency Hierarchy:
- vue-server-renderer-2.6.10.tgz (Root Library)
- :x: **serialize-javascript-1.9.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/VerdantSparks/vuejs-aspnetcore-ssr/commit/c217828eede1712e885e8472f9506ea9e766c0d8">c217828eede1712e885e8472f9506ea9e766c0d8</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Affected versions of this package are vulnerable to Cross-site Scripting (XSS). It does not properly mitigate against unsafe characters in serialized regular expressions. This vulnerability is not affected on Node.js environment since Node.js's implementation of RegExp.prototype.toString() backslash-escapes all forward slashes in regular expressions. If serialized data of regular expression objects are used in an environment other than Node.js, it is affected by this vulnerability.
<p>Publish Date: 2019-12-05
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16769>CVE-2019-16769</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>5.0</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16769">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16769</a></p>
<p>Release Date: 2019-12-05</p>
<p>Fix Resolution: v2.1.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_process
|
cve medium detected in serialize javascript tgz cve medium severity vulnerability vulnerable library serialize javascript tgz serialize javascript to a superset of json that includes regular expressions and functions library home page a href path to dependency file tmp ws scm vuejs aspnetcore ssr package json path to vulnerable library tmp ws scm vuejs aspnetcore ssr node modules vue server renderer node modules serialize javascript package json dependency hierarchy vue server renderer tgz root library x serialize javascript tgz vulnerable library found in head commit a href vulnerability details affected versions of this package are vulnerable to cross site scripting xss it does not properly mitigate against unsafe characters in serialized regular expressions this vulnerability is not affected on node js environment since node js s implementation of regexp prototype tostring backslash escapes all forward slashes in regular expressions if serialized data of regular expression objects are used in an environment other than node js it is affected by this vulnerability publish date url a href cvss score details base score metrics not available suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource
| 0
|
163,234
| 12,708,078,558
|
IssuesEvent
|
2020-06-23 09:55:46
|
WoWManiaUK/Redemption
|
https://api.github.com/repos/WoWManiaUK/Redemption
|
closed
|
[ICC/Gunship] Damage of incinerating blast
|
Fix - Tester Confirmed
|
**What is Happening:**
Our current formula is: 1000 + energyLeft²
with 100 energy, max damage will be: 1000 + 10000 = 11k
Problem is: if you check http://worldoflogs.com/reports/udqni9w8roj989w7/xe/?x=spell+%3D+%22Incinerating+Blast%22
and http://worldoflogs.com/reports/ul76xm556v85ir2v/xe/?x=spell+%3D+%22Incinerating+Blast%22
You will see that this spell can hit more then 11k.
**What Should happen:** I cant determine the exactly formula for this. But looks like we are missing about 20% of damage.
So, i'm adding 20% more damage for this spell.
Has other issue, fixed too.
if incinerating blast hits 5k in boat, it should hit 5k in npcs that spell hit too.
Right now, it always hit 1k in npcs, instead hit same thing that hit in boat.
|
1.0
|
[ICC/Gunship] Damage of incinerating blast - **What is Happening:**
Our current formula is: 1000 + energyLeft²
with 100 energy, max damage will be: 1000 + 10000 = 11k
Problem is: if you check http://worldoflogs.com/reports/udqni9w8roj989w7/xe/?x=spell+%3D+%22Incinerating+Blast%22
and http://worldoflogs.com/reports/ul76xm556v85ir2v/xe/?x=spell+%3D+%22Incinerating+Blast%22
You will see that this spell can hit more then 11k.
**What Should happen:** I cant determine the exactly formula for this. But looks like we are missing about 20% of damage.
So, i'm adding 20% more damage for this spell.
Has other issue, fixed too.
if incinerating blast hits 5k in boat, it should hit 5k in npcs that spell hit too.
Right now, it always hit 1k in npcs, instead hit same thing that hit in boat.
|
non_process
|
damage of incinerating blast what is happening our current formula is energyleft² with energy max damage will be problem is if you check and you will see that this spell can hit more then what should happen i cant determine the exactly formula for this but looks like we are missing about of damage so i m adding more damage for this spell has other issue fixed too if incinerating blast hits in boat it should hit in npcs that spell hit too right now it always hit in npcs instead hit same thing that hit in boat
| 0
|
16,092
| 20,261,157,186
|
IssuesEvent
|
2022-02-15 07:35:49
|
quark-engine/quark-engine
|
https://api.github.com/repos/quark-engine/quark-engine
|
closed
|
Prepare to release version v22.2.1
|
work-in-progress issue-processing-state-04
|
Update the version number in `__init__.py` for the latest release of Quark.
In this release, the following changes will be included.
- #301
- #304
- #300
- #303
|
1.0
|
Prepare to release version v22.2.1 - Update the version number in `__init__.py` for the latest release of Quark.
In this release, the following changes will be included.
- #301
- #304
- #300
- #303
|
process
|
prepare to release version update the version number in init py for the latest release of quark in this release the following changes will be included
| 1
|
198,964
| 15,017,262,009
|
IssuesEvent
|
2021-02-01 10:37:19
|
toru-ver4/sample_code
|
https://api.github.com/repos/toru-ver4/sample_code
|
closed
|
create a test pattern to distinguish between 8-bit and 10-bit
|
test pattern
|
# Overview
* Create a test pattern to distinguish between 8-bit and 10-bit.
* Previously I created an achromatic pattern, but this time I'll create a chromatic pattern.
# Detail
* "The Spears & Munsil UHD HDR Benchmark" uses some color patterns.
* For example, Yellow-Blue and Cyan-Red.
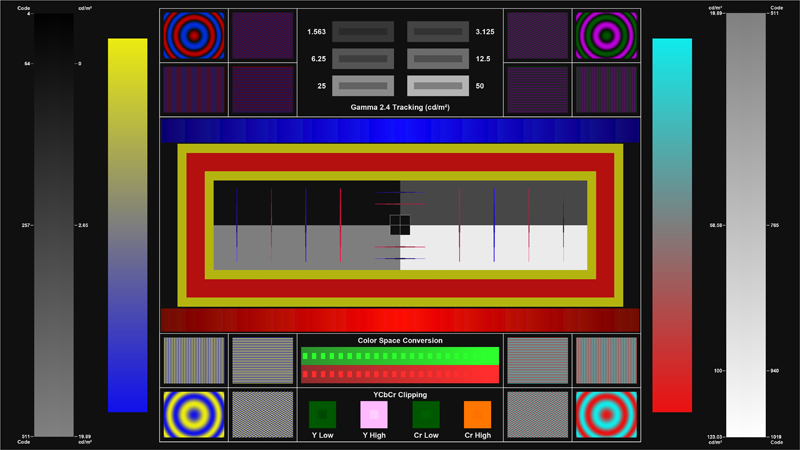
* I'll refer to this.
|
1.0
|
create a test pattern to distinguish between 8-bit and 10-bit - # Overview
* Create a test pattern to distinguish between 8-bit and 10-bit.
* Previously I created an achromatic pattern, but this time I'll create a chromatic pattern.
# Detail
* "The Spears & Munsil UHD HDR Benchmark" uses some color patterns.
* For example, Yellow-Blue and Cyan-Red.
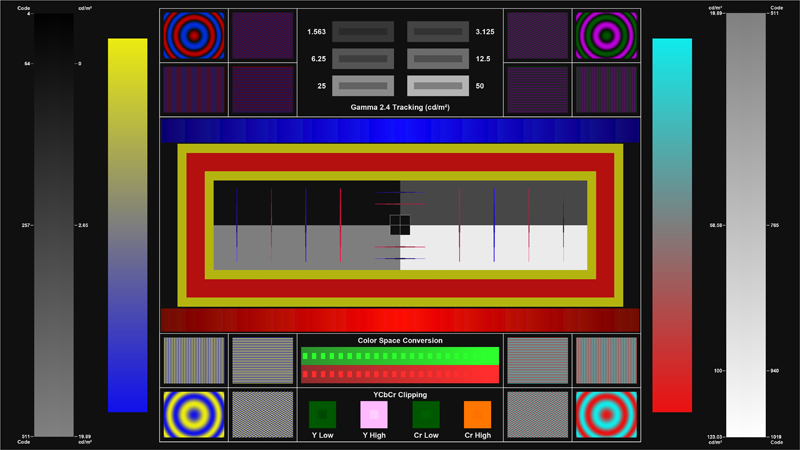
* I'll refer to this.
|
non_process
|
create a test pattern to distinguish between bit and bit overview create a test pattern to distinguish between bit and bit previously i created an achromatic pattern but this time i ll create a chromatic pattern detail the spears munsil uhd hdr benchmark uses some color patterns for example yellow blue and cyan red i ll refer to this
| 0
|
6,478
| 3,023,872,934
|
IssuesEvent
|
2015-08-02 00:17:26
|
librenms/librenms
|
https://api.github.com/repos/librenms/librenms
|
closed
|
docs: install mariadb
|
Documentation
|
It maybe better to install mariadb instead of mysql?
If needed I'll update documentation.
|
1.0
|
docs: install mariadb - It maybe better to install mariadb instead of mysql?
If needed I'll update documentation.
|
non_process
|
docs install mariadb it maybe better to install mariadb instead of mysql if needed i ll update documentation
| 0
|
20,485
| 27,143,587,997
|
IssuesEvent
|
2023-02-16 18:06:12
|
carbon-design-system/ibm-cloud-cognitive
|
https://api.github.com/repos/carbon-design-system/ibm-cloud-cognitive
|
closed
|
Single add select release review
|
type: process improvement component: AddSelect
|
## Review for release
### Readiness
- [x] One or more scenarios for a design pattern have been identified as a
useful unit of functionality to publish.
- [x] A functioning component or components delivering those scenarios have been
delivered and merged to main.
- [ ] Design maintainer has approved the implementation for those scenarios (via
a comment on the relevant issue/epic).
### Engineering review
- [x] Breaking changes have only been introduced with prior approval, discussion
and documented in release notes. Ideally deprecation notices in the prior
major version must have been added in a timely fashion.
- [x] The implementation takes into account, and does not impair, remaining and
anticipated design scenarios.
- [x] Public component features (names, props, etc) are consistent with
Carbon-defined conventions and are consistent internally. Where there
isn't an existing convention to apply, ensure robust precedents are being
established.
- [x] The UI produced is accessible, responsive, translatable, cross-browser,
and responds to the currently set Carbon theme.
- [x] Components are functional components using hooks.
- [x] Public components which produce DOM structures support className.
- [x] Public components support a ref (via React.forwardRef).
- [x] Public component supports a Devtools attribute
- [x] All significant DOM elements have meaningful classes.
- [x] Additional attributes that are not identified as props (such as title,
aria-\*, etc) are passed through to an appropriate DOM node of the
component as HTML attributes.
- [x] No warnings, errors or log messages in the console.
- [x] Each public component JS is exported in /src/components/index.js, each
public component SCSS is included in /src/components/\_index.scss, and
each public component has a flag in package-settings.js.
- [x] Each public component SCSS lists all of the Carbon and C&CS components
imported and used by the JavaScript code and explicitly imports the SCSS
for each of these components.
### Standards
- [x] No linter warnings or errors are produced.
- [x] Carbon tokens (theme, layout, motion) are used unless the design specifies
otherwise.
- [x] All components utilizing motion must include reduced-motion queries for
accessibility purposes - read more here.
- [x] Code is formatted according to prettier rules (no use of
//prettier-ignore).
- [x] Code is clear, maintainable and follows standard React practices and the
code guidelines.
- [x] Copyright header in every source file (js, css, scss etc.) with the
appropriate years.
### Testing
- [x] There is a set of test cases for the components.
- [x] The tests exercise all inputs (props, slots, etc) and verify appropriate
outputs.
- [x] The tests validate the behaviors and interactions defined in the design
where practical.
- [x] The tests achieve 100% coverage. Usage of istanbul ignore is appropriate
and not extensive.
- [x] No warnings, errors or log messages in the test output.
### Documentation
- [x] Source code is satisfactorily commented and provides DocGen comments for
all public components and their props.
- [x] There is a story for each design scenario. The stories expose all relevant
props and actions, and additional usage documentation and code samples are
available on the 'Docs' tab along with the props table.
- [x] There is a sandbox (or multiple sandboxes if appropriate) on CodeSandbox
for the components.
|
1.0
|
Single add select release review - ## Review for release
### Readiness
- [x] One or more scenarios for a design pattern have been identified as a
useful unit of functionality to publish.
- [x] A functioning component or components delivering those scenarios have been
delivered and merged to main.
- [ ] Design maintainer has approved the implementation for those scenarios (via
a comment on the relevant issue/epic).
### Engineering review
- [x] Breaking changes have only been introduced with prior approval, discussion
and documented in release notes. Ideally deprecation notices in the prior
major version must have been added in a timely fashion.
- [x] The implementation takes into account, and does not impair, remaining and
anticipated design scenarios.
- [x] Public component features (names, props, etc) are consistent with
Carbon-defined conventions and are consistent internally. Where there
isn't an existing convention to apply, ensure robust precedents are being
established.
- [x] The UI produced is accessible, responsive, translatable, cross-browser,
and responds to the currently set Carbon theme.
- [x] Components are functional components using hooks.
- [x] Public components which produce DOM structures support className.
- [x] Public components support a ref (via React.forwardRef).
- [x] Public component supports a Devtools attribute
- [x] All significant DOM elements have meaningful classes.
- [x] Additional attributes that are not identified as props (such as title,
aria-\*, etc) are passed through to an appropriate DOM node of the
component as HTML attributes.
- [x] No warnings, errors or log messages in the console.
- [x] Each public component JS is exported in /src/components/index.js, each
public component SCSS is included in /src/components/\_index.scss, and
each public component has a flag in package-settings.js.
- [x] Each public component SCSS lists all of the Carbon and C&CS components
imported and used by the JavaScript code and explicitly imports the SCSS
for each of these components.
### Standards
- [x] No linter warnings or errors are produced.
- [x] Carbon tokens (theme, layout, motion) are used unless the design specifies
otherwise.
- [x] All components utilizing motion must include reduced-motion queries for
accessibility purposes - read more here.
- [x] Code is formatted according to prettier rules (no use of
//prettier-ignore).
- [x] Code is clear, maintainable and follows standard React practices and the
code guidelines.
- [x] Copyright header in every source file (js, css, scss etc.) with the
appropriate years.
### Testing
- [x] There is a set of test cases for the components.
- [x] The tests exercise all inputs (props, slots, etc) and verify appropriate
outputs.
- [x] The tests validate the behaviors and interactions defined in the design
where practical.
- [x] The tests achieve 100% coverage. Usage of istanbul ignore is appropriate
and not extensive.
- [x] No warnings, errors or log messages in the test output.
### Documentation
- [x] Source code is satisfactorily commented and provides DocGen comments for
all public components and their props.
- [x] There is a story for each design scenario. The stories expose all relevant
props and actions, and additional usage documentation and code samples are
available on the 'Docs' tab along with the props table.
- [x] There is a sandbox (or multiple sandboxes if appropriate) on CodeSandbox
for the components.
|
process
|
single add select release review review for release readiness one or more scenarios for a design pattern have been identified as a useful unit of functionality to publish a functioning component or components delivering those scenarios have been delivered and merged to main design maintainer has approved the implementation for those scenarios via a comment on the relevant issue epic engineering review breaking changes have only been introduced with prior approval discussion and documented in release notes ideally deprecation notices in the prior major version must have been added in a timely fashion the implementation takes into account and does not impair remaining and anticipated design scenarios public component features names props etc are consistent with carbon defined conventions and are consistent internally where there isn t an existing convention to apply ensure robust precedents are being established the ui produced is accessible responsive translatable cross browser and responds to the currently set carbon theme components are functional components using hooks public components which produce dom structures support classname public components support a ref via react forwardref public component supports a devtools attribute all significant dom elements have meaningful classes additional attributes that are not identified as props such as title aria etc are passed through to an appropriate dom node of the component as html attributes no warnings errors or log messages in the console each public component js is exported in src components index js each public component scss is included in src components index scss and each public component has a flag in package settings js each public component scss lists all of the carbon and c cs components imported and used by the javascript code and explicitly imports the scss for each of these components standards no linter warnings or errors are produced carbon tokens theme layout motion are used unless the design specifies otherwise all components utilizing motion must include reduced motion queries for accessibility purposes read more here code is formatted according to prettier rules no use of prettier ignore code is clear maintainable and follows standard react practices and the code guidelines copyright header in every source file js css scss etc with the appropriate years testing there is a set of test cases for the components the tests exercise all inputs props slots etc and verify appropriate outputs the tests validate the behaviors and interactions defined in the design where practical the tests achieve coverage usage of istanbul ignore is appropriate and not extensive no warnings errors or log messages in the test output documentation source code is satisfactorily commented and provides docgen comments for all public components and their props there is a story for each design scenario the stories expose all relevant props and actions and additional usage documentation and code samples are available on the docs tab along with the props table there is a sandbox or multiple sandboxes if appropriate on codesandbox for the components
| 1
|
16,682
| 21,784,970,041
|
IssuesEvent
|
2022-05-14 02:00:07
|
ymgw55/MLPapers
|
https://api.github.com/repos/ymgw55/MLPapers
|
closed
|
All-but-the-Top: Simple and Effective Postprocessing for Word Representations
|
Word Embeddings post-process isotropy
|
# Information
### URL
https://openreview.net/forum?id=HkuGJ3kCb
### Authors
[Jiaqi Mu](https://openreview.net/profile?email=jiaqimu2%40illinois.edu), [Pramod Viswanath](https://openreview.net/profile?email=pramodv%40illinois.edu)
### Published at
ICLR 2018
<!---
### Date of issue
### Related Websites
### Package
### Code
--->
# Reading Motivation
#115 で "making static embedding isotropic is beneficial to lexical and sentence-level tasks." として紹介.
# Summary
word2vec, glove などの分散表現は, 言語的な規則を捉える能力があると考えられている. この論文では, シンプルかつ直感に反する postprocess のテクニックを提案. その手法とは, 分散表現から, ボキャブラリーの平均の分散表現と, いくつかの支配的な方向のベクトルを取り除くというものである. この手法は, 気軽に実行できて, 分散表現の性能を上げることができる. 実際にこの postprocess は, 数ある既存の分散表現で, 複数の言語で, 様々な単語レベル・文レベルのタスクで性能が確認できた. つまりそれぞれのタスクで, postprocess をした分散表現の方が生の分散表現より一貫して性能が良かった.
# Background
* 分散表現で PCA を考えると, 比較的小さなある値 D (例えば D = 10) 以降は, variance は大体一定.
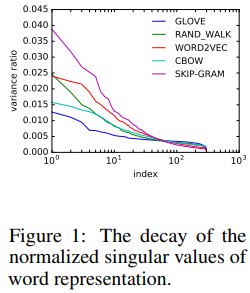
* PCA の1番目, 2番目に分散が大きい成分の方向に射影した時の分散表現の図. 色は ferquency.
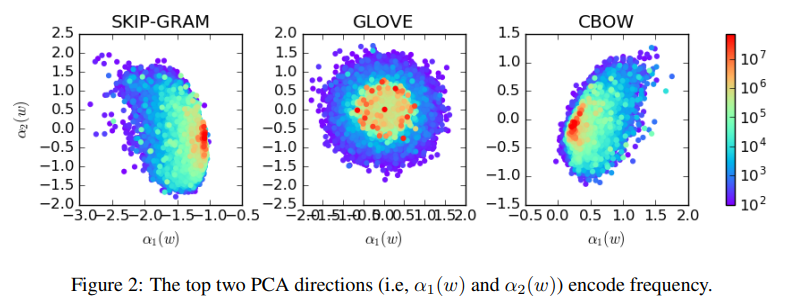
<!--
# Contribution
--->
# Proposed Method
V はボキャブラリーの集合, D は PCA で取り除く dominant な方向の数. d を分散表現の次元として, D = d / 100 が目安.
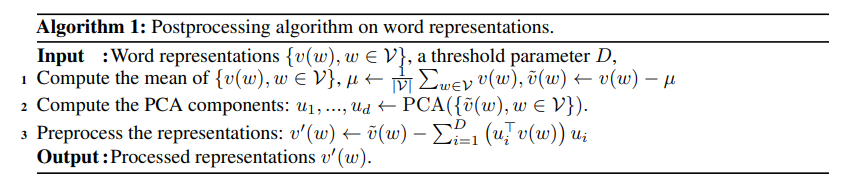
* 導出
#184 で定義された parittion function は以下
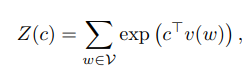
なお partition function の日本語名は分配関数であり, 統計力学で用いられる, "ある系の物理量の統計集団的平均を計算する際に用いられる規格化定数" とのこと.
V が等方的なら, 任意の c について, Z(c) が大体同じになってほしいので, isotropy を測る量を以下で定義
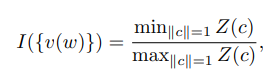
I(V) が 1 に近いほど, V は等方的. exp の定義から Z(c) は以下のように書ける.
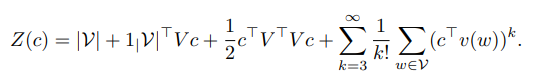
これより, 1次の近似, 2次の近似を考えることで提案手法が導出される.
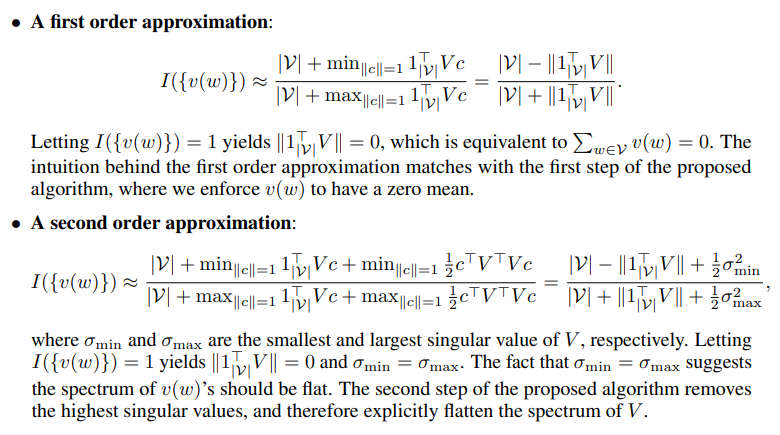
1次の近似では, d 次元ベクトル 1^T V と c の内積を考えればよく, I(V) = 1 となるのは, 平均 = 0 のとき.
2次の近似では, PCA の定義を考えて, I(V) = 1 となるのは, V の最大の特異値と最小の特異値が等しい時で, これはベクトルの集合が全方向に等方的な場合であり, 全ての特異値が flat. Background でみたように D 番目以降は分散は flat になるので, 提案手法では dominant な固有値を除くことで, 残りの固有値は flat になり I(V) が 1 に近づく, すなわち V の分散表現が等方的になる.
なお実用上, max Z(c), min Z(c) は解析的に求まらないので, c を V^T V の固有ベクトルに制限して考える.
# Experiment
* postprocess 後, isotropy は増加する.
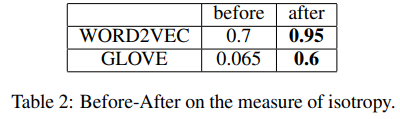
* postprocess 後, Z(c) は, c によらず大体一定になる.
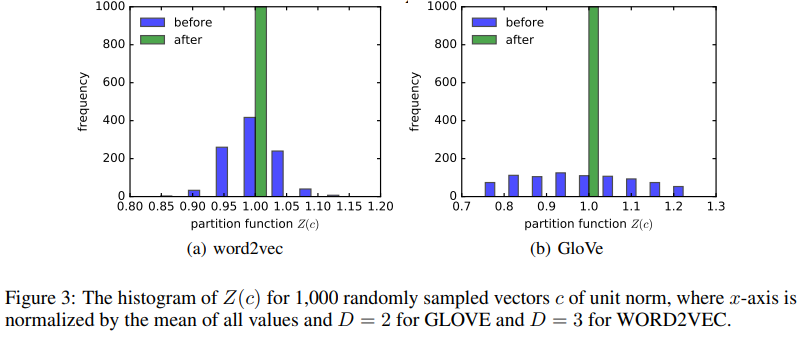
* 単語レベル・文レベルのタスクで性能が上がったが, アナロジータスクでは, わずかな性能上昇しか見られなかった. これは, w1 と w2 の関係と, w3 と w4 の関係を比較する際, w2 - w1 + w3 との cosine similarity が一番大きいものを w4 の候補として採用するが, postprocess をしなくても w2 - w1 で既に, 平均と dominant な方向の情報が落ちているためと考えられる.
<!---
# Consideration
# Question
# Relation
--->
# Before Papers & Books
#184
# Next Papers & Books
#115
<!--
# Memo
--->
|
1.0
|
All-but-the-Top: Simple and Effective Postprocessing for Word Representations - # Information
### URL
https://openreview.net/forum?id=HkuGJ3kCb
### Authors
[Jiaqi Mu](https://openreview.net/profile?email=jiaqimu2%40illinois.edu), [Pramod Viswanath](https://openreview.net/profile?email=pramodv%40illinois.edu)
### Published at
ICLR 2018
<!---
### Date of issue
### Related Websites
### Package
### Code
--->
# Reading Motivation
#115 で "making static embedding isotropic is beneficial to lexical and sentence-level tasks." として紹介.
# Summary
word2vec, glove などの分散表現は, 言語的な規則を捉える能力があると考えられている. この論文では, シンプルかつ直感に反する postprocess のテクニックを提案. その手法とは, 分散表現から, ボキャブラリーの平均の分散表現と, いくつかの支配的な方向のベクトルを取り除くというものである. この手法は, 気軽に実行できて, 分散表現の性能を上げることができる. 実際にこの postprocess は, 数ある既存の分散表現で, 複数の言語で, 様々な単語レベル・文レベルのタスクで性能が確認できた. つまりそれぞれのタスクで, postprocess をした分散表現の方が生の分散表現より一貫して性能が良かった.
# Background
* 分散表現で PCA を考えると, 比較的小さなある値 D (例えば D = 10) 以降は, variance は大体一定.
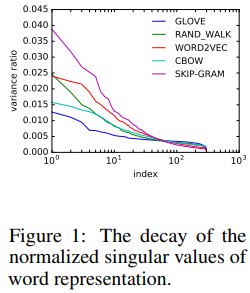
* PCA の1番目, 2番目に分散が大きい成分の方向に射影した時の分散表現の図. 色は ferquency.
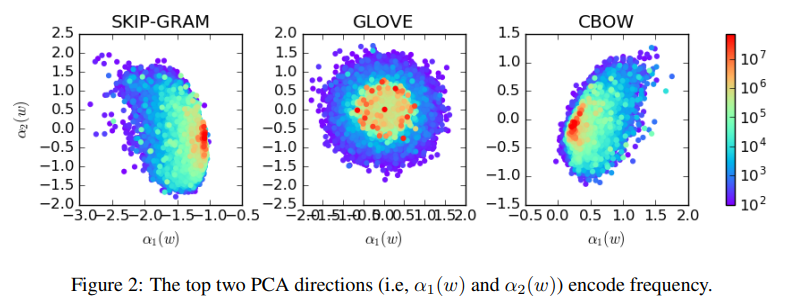
<!--
# Contribution
--->
# Proposed Method
V はボキャブラリーの集合, D は PCA で取り除く dominant な方向の数. d を分散表現の次元として, D = d / 100 が目安.
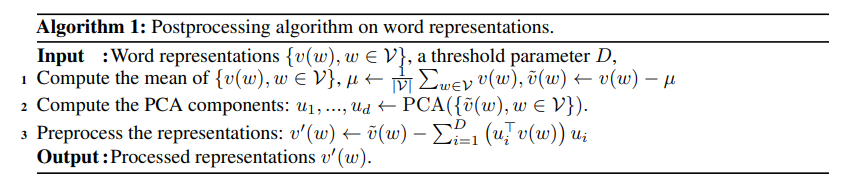
* 導出
#184 で定義された parittion function は以下
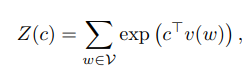
なお partition function の日本語名は分配関数であり, 統計力学で用いられる, "ある系の物理量の統計集団的平均を計算する際に用いられる規格化定数" とのこと.
V が等方的なら, 任意の c について, Z(c) が大体同じになってほしいので, isotropy を測る量を以下で定義
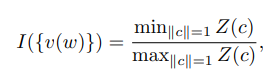
I(V) が 1 に近いほど, V は等方的. exp の定義から Z(c) は以下のように書ける.
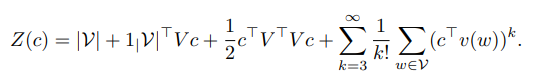
これより, 1次の近似, 2次の近似を考えることで提案手法が導出される.
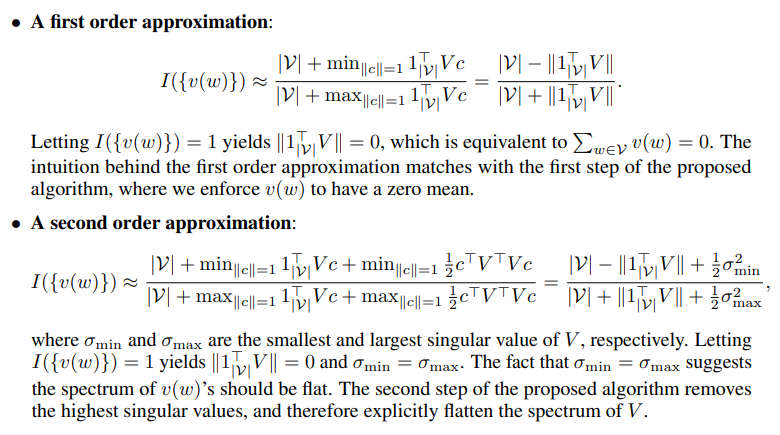
1次の近似では, d 次元ベクトル 1^T V と c の内積を考えればよく, I(V) = 1 となるのは, 平均 = 0 のとき.
2次の近似では, PCA の定義を考えて, I(V) = 1 となるのは, V の最大の特異値と最小の特異値が等しい時で, これはベクトルの集合が全方向に等方的な場合であり, 全ての特異値が flat. Background でみたように D 番目以降は分散は flat になるので, 提案手法では dominant な固有値を除くことで, 残りの固有値は flat になり I(V) が 1 に近づく, すなわち V の分散表現が等方的になる.
なお実用上, max Z(c), min Z(c) は解析的に求まらないので, c を V^T V の固有ベクトルに制限して考える.
# Experiment
* postprocess 後, isotropy は増加する.
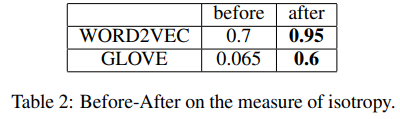
* postprocess 後, Z(c) は, c によらず大体一定になる.
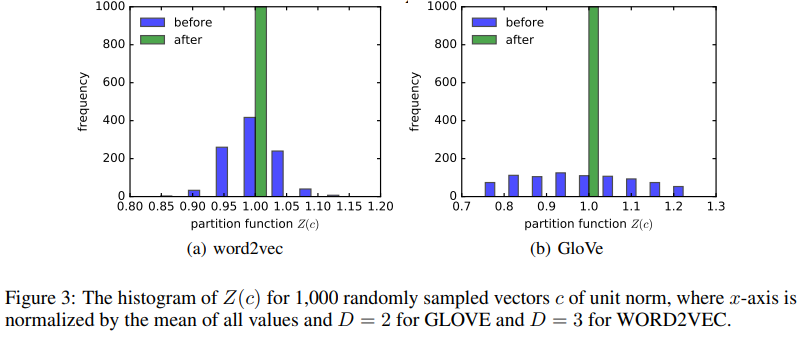
* 単語レベル・文レベルのタスクで性能が上がったが, アナロジータスクでは, わずかな性能上昇しか見られなかった. これは, w1 と w2 の関係と, w3 と w4 の関係を比較する際, w2 - w1 + w3 との cosine similarity が一番大きいものを w4 の候補として採用するが, postprocess をしなくても w2 - w1 で既に, 平均と dominant な方向の情報が落ちているためと考えられる.
<!---
# Consideration
# Question
# Relation
--->
# Before Papers & Books
#184
# Next Papers & Books
#115
<!--
# Memo
--->
|
process
|
all but the top simple and effective postprocessing for word representations information url authors published at iclr date of issue related websites package code reading motivation で making static embedding isotropic is beneficial to lexical and sentence level tasks として紹介 summary glove などの分散表現は 言語的な規則を捉える能力があると考えられている この論文では シンプルかつ直感に反する postprocess のテクニックを提案 その手法とは 分散表現から ボキャブラリーの平均の分散表現と いくつかの支配的な方向のベクトルを取り除くというものである この手法は 気軽に実行できて 分散表現の性能を上げることができる 実際にこの postprocess は 数ある既存の分散表現で 複数の言語で 様々な単語レベル・文レベルのタスクで性能が確認できた つまりそれぞれのタスクで postprocess をした分散表現の方が生の分散表現より一貫して性能が良かった background 分散表現で pca を考えると 比較的小さなある値 d 例えば d 以降は variance は大体一定 pca 色は ferquency contribution proposed method v はボキャブラリーの集合 d は pca で取り除く dominant な方向の数 d を分散表現の次元として d d が目安 導出 で定義された parittion function は以下 なお partition function の日本語名は分配関数であり 統計力学で用いられる ある系の物理量の統計集団的平均を計算する際に用いられる規格化定数 とのこと v が等方的なら 任意の c について z c が大体同じになってほしいので isotropy を測る量を以下で定義 i v が に近いほど v は等方的 exp の定義から z c は以下のように書ける これより d 次元ベクトル t v と c の内積を考えればよく i v となるのは 平均 のとき pca の定義を考えて i v となるのは v の最大の特異値と最小の特異値が等しい時で これはベクトルの集合が全方向に等方的な場合であり 全ての特異値が flat background でみたように d 番目以降は分散は flat になるので 提案手法では dominant な固有値を除くことで 残りの固有値は flat になり i v が に近づく すなわち v の分散表現が等方的になる なお実用上 max z c min z c は解析的に求まらないので c を v t v の固有ベクトルに制限して考える experiment postprocess 後 isotropy は増加する postprocess 後 z c は c によらず大体一定になる 単語レベル・文レベルのタスクで性能が上がったが アナロジータスクでは わずかな性能上昇しか見られなかった これは と の関係と と の関係を比較する際 との cosine similarity が一番大きいものを の候補として採用するが postprocess をしなくても で既に 平均と dominant な方向の情報が落ちているためと考えられる consideration question relation before papers books next papers books memo
| 1
|
19,108
| 25,159,990,405
|
IssuesEvent
|
2022-11-10 16:07:25
|
googleapis/google-cloud-python
|
https://api.github.com/repos/googleapis/google-cloud-python
|
closed
|
Dependency Dashboard
|
type: process
|
This issue lists Renovate updates and detected dependencies. Read the [Dependency Dashboard](https://docs.renovatebot.com/key-concepts/dashboard/) docs to learn more.
## Edited/Blocked
These updates have been manually edited so Renovate will no longer make changes. To discard all commits and start over, click on a checkbox.
- [ ] <!-- rebase-branch=renovate/virtualenv-20.x -->[chore(deps): update dependency virtualenv to v20.16.6](../pull/10728)
- [ ] <!-- rebase-branch=renovate/google-api-core-2.x -->[chore(deps): update dependency google-api-core to v2.10.2](../pull/10734)
- [ ] <!-- rebase-branch=renovate/google-auth-2.x -->[chore(deps): update dependency google-auth to v2.14.1](../pull/10735)
## Open
These updates have all been created already. Click a checkbox below to force a retry/rebase of any.
- [ ] <!-- rebase-branch=renovate/protobuf-3.x -->[chore(deps): update dependency protobuf to v3.20.3](../pull/10727)
- [ ] <!-- rebase-branch=renovate/wheel-0.x -->[chore(deps): update dependency wheel to v0.38.4](../pull/10771)
- [ ] <!-- rebase-branch=renovate/click-8.x -->[chore(deps): update dependency click to v8.1.3](../pull/10732)
- [ ] <!-- rebase-branch=renovate/gcp-releasetool-1.x -->[chore(deps): update dependency gcp-releasetool to v1.9.1](../pull/10733)
- [ ] <!-- rebase-branch=renovate/protobuf-4.x -->[chore(deps): update dependency protobuf to v4](../pull/10753)
- [ ] <!-- rebase-all-open-prs -->**Click on this checkbox to rebase all open PRs at once**
## Detected dependencies
<details><summary>cloudbuild</summary>
<blockquote>
<details><summary>containers/python-bootstrap-container/cloudbuild.yaml</summary>
</details>
</blockquote>
</details>
<details><summary>dockerfile</summary>
<blockquote>
<details><summary>.kokoro/docker/docs/Dockerfile</summary>
- `ubuntu 22.04`
</details>
<details><summary>containers/python-bootstrap-container/Dockerfile</summary>
- `python 3.11.0-buster`
</details>
</blockquote>
</details>
<details><summary>github-actions</summary>
<blockquote>
<details><summary>.github/workflows/docs.yml</summary>
- `actions/checkout v3`
- `actions/setup-python v4`
- `actions/checkout v3`
- `actions/setup-python v4`
</details>
<details><summary>.github/workflows/lint.yml</summary>
- `actions/checkout v3`
- `actions/setup-python v4`
</details>
<details><summary>.github/workflows/main.yml</summary>
- `actions/checkout v3`
- `actions/setup-python v4`
- `googleapis/code-suggester v4`
</details>
<details><summary>.github/workflows/unittest.yml</summary>
- `actions/checkout v3`
- `actions/setup-python v4`
- `actions/upload-artifact v3`
- `actions/checkout v3`
- `actions/setup-python v4`
- `actions/checkout v3`
- `actions/setup-python v4`
- `actions/download-artifact v3`
</details>
</blockquote>
</details>
<details><summary>pip_requirements</summary>
<blockquote>
<details><summary>.kokoro/requirements.txt</summary>
- `argcomplete ==2.0.0`
- `attrs ==22.1.0`
- `bleach ==5.0.1`
- `cachetools ==5.2.0`
- `certifi ==2022.9.24`
- `cffi ==1.15.1`
- `charset-normalizer ==3.0.0`
- `click ==8.0.4`
- `colorlog ==6.7.0`
- `commonmark ==0.9.1`
- `cryptography ==38.0.3`
- `distlib ==0.3.6`
- `docutils ==0.19`
- `filelock ==3.8.0`
- `gcp-docuploader ==0.6.4`
- `gcp-releasetool ==1.8.7`
- `google-api-core ==2.8.2`
- `google-auth ==2.11.0`
- `google-cloud-core ==2.3.2`
- `google-cloud-storage ==2.6.0`
- `google-crc32c ==1.5.0`
- `google-resumable-media ==2.4.0`
- `googleapis-common-protos ==1.56.4`
- `idna ==3.4`
- `importlib-metadata ==5.0.0`
- `jaraco-classes ==3.2.3`
- `jeepney ==0.8.0`
- `jinja2 ==3.1.2`
- `keyring ==23.11.0`
- `markupsafe ==2.1.1`
- `more-itertools ==9.0.0`
- `nox ==2022.8.7`
- `packaging ==21.3`
- `pkginfo ==1.8.3`
- `platformdirs ==2.5.3`
- `protobuf ==3.20.2`
- `py ==1.11.0`
- `pyasn1 ==0.4.8`
- `pyasn1-modules ==0.2.8`
- `pycparser ==2.21`
- `pygments ==2.13.0`
- `PyJWT ==2.6.0`
- `pyparsing ==3.0.9`
- `pyperclip ==1.8.2`
- `python-dateutil ==2.8.2`
- `readme-renderer ==37.3`
- `requests ==2.28.1`
- `requests-toolbelt ==0.10.1`
- `rfc3986 ==2.0.0`
- `rich ==12.6.0`
- `rsa ==4.9`
- `secretstorage ==3.3.3`
- `six ==1.16.0`
- `twine ==4.0.1`
- `typing-extensions ==4.4.0`
- `urllib3 ==1.26.12`
- `virtualenv ==20.16.4`
- `webencodings ==0.5.1`
- `wheel ==0.38.3`
- `zipp ==3.10.0`
- `setuptools ==65.5.1`
</details>
<details><summary>scripts/requirements.txt</summary>
- `requests ==2.28.1`
</details>
</blockquote>
</details>
<details><summary>pip_setup</summary>
<blockquote>
<details><summary>packages/google-cloud-contentwarehouse/setup.py</summary>
- `google-api-core >= 1.33.2, <3.0.0dev,!=2.0.*,!=2.1.*,!=2.2.*,!=2.3.*,!=2.4.*,!=2.5.*,!=2.6.*,!=2.7.*`
- `proto-plus >= 1.22.0, <2.0.0dev`
- `protobuf >=3.19.5,<5.0.0dev,!=3.20.0,!=3.20.1,!=4.21.0,!=4.21.1,!=4.21.2,!=4.21.3,!=4.21.4,!=4.21.5`
- `grpc-google-iam-v1 >= 0.12.4, < 1.0.0dev`
- `google-cloud-documentai >= 1.2.1, < 3.0.0dev`
</details>
<details><summary>packages/google-cloud-discoveryengine/setup.py</summary>
- `google-api-core >= 1.33.2, <3.0.0dev,!=2.0.*,!=2.1.*,!=2.2.*,!=2.3.*,!=2.4.*,!=2.5.*,!=2.6.*,!=2.7.*`
- `proto-plus >= 1.22.0, <2.0.0dev`
- `protobuf >=3.19.5,<5.0.0dev,!=3.20.0,!=3.20.1,!=4.21.0,!=4.21.1,!=4.21.2,!=4.21.3,!=4.21.4,!=4.21.5`
</details>
<details><summary>packages/google-cloud-enterpriseknowledgegraph/setup.py</summary>
- `google-api-core >= 1.33.2, <3.0.0dev,!=2.0.*,!=2.1.*,!=2.2.*,!=2.3.*,!=2.4.*,!=2.5.*,!=2.6.*,!=2.7.*`
- `proto-plus >= 1.22.0, <2.0.0dev`
- `protobuf >=3.19.5,<5.0.0dev,!=3.20.0,!=3.20.1,!=4.21.0,!=4.21.1,!=4.21.2,!=4.21.3,!=4.21.4,!=4.21.5`
</details>
<details><summary>packages/google-geo-type/setup.py</summary>
- `google-api-core >= 1.33.2, <3.0.0dev,!=2.0.*,!=2.1.*,!=2.2.*,!=2.3.*,!=2.4.*,!=2.5.*,!=2.6.*,!=2.7.*`
- `proto-plus >= 1.22.0, <2.0.0dev`
- `protobuf >=3.19.5,<5.0.0dev,!=3.20.0,!=3.20.1,!=4.21.0,!=4.21.1,!=4.21.2,!=4.21.3,!=4.21.4,!=4.21.5`
</details>
<details><summary>packages/google-maps-addressvalidation/setup.py</summary>
- `google-api-core >= 1.33.2, <3.0.0dev,!=2.0.*,!=2.1.*,!=2.2.*,!=2.3.*,!=2.4.*,!=2.5.*,!=2.6.*,!=2.7.*`
- `proto-plus >= 1.22.0, <2.0.0dev`
- `protobuf >=3.19.5,<5.0.0dev,!=3.20.0,!=3.20.1,!=4.21.0,!=4.21.1,!=4.21.2,!=4.21.3,!=4.21.4,!=4.21.5`
- `google-geo-type <1.0.0dev`
</details>
</blockquote>
</details>
---
- [ ] <!-- manual job -->Check this box to trigger a request for Renovate to run again on this repository
|
1.0
|
Dependency Dashboard - This issue lists Renovate updates and detected dependencies. Read the [Dependency Dashboard](https://docs.renovatebot.com/key-concepts/dashboard/) docs to learn more.
## Edited/Blocked
These updates have been manually edited so Renovate will no longer make changes. To discard all commits and start over, click on a checkbox.
- [ ] <!-- rebase-branch=renovate/virtualenv-20.x -->[chore(deps): update dependency virtualenv to v20.16.6](../pull/10728)
- [ ] <!-- rebase-branch=renovate/google-api-core-2.x -->[chore(deps): update dependency google-api-core to v2.10.2](../pull/10734)
- [ ] <!-- rebase-branch=renovate/google-auth-2.x -->[chore(deps): update dependency google-auth to v2.14.1](../pull/10735)
## Open
These updates have all been created already. Click a checkbox below to force a retry/rebase of any.
- [ ] <!-- rebase-branch=renovate/protobuf-3.x -->[chore(deps): update dependency protobuf to v3.20.3](../pull/10727)
- [ ] <!-- rebase-branch=renovate/wheel-0.x -->[chore(deps): update dependency wheel to v0.38.4](../pull/10771)
- [ ] <!-- rebase-branch=renovate/click-8.x -->[chore(deps): update dependency click to v8.1.3](../pull/10732)
- [ ] <!-- rebase-branch=renovate/gcp-releasetool-1.x -->[chore(deps): update dependency gcp-releasetool to v1.9.1](../pull/10733)
- [ ] <!-- rebase-branch=renovate/protobuf-4.x -->[chore(deps): update dependency protobuf to v4](../pull/10753)
- [ ] <!-- rebase-all-open-prs -->**Click on this checkbox to rebase all open PRs at once**
## Detected dependencies
<details><summary>cloudbuild</summary>
<blockquote>
<details><summary>containers/python-bootstrap-container/cloudbuild.yaml</summary>
</details>
</blockquote>
</details>
<details><summary>dockerfile</summary>
<blockquote>
<details><summary>.kokoro/docker/docs/Dockerfile</summary>
- `ubuntu 22.04`
</details>
<details><summary>containers/python-bootstrap-container/Dockerfile</summary>
- `python 3.11.0-buster`
</details>
</blockquote>
</details>
<details><summary>github-actions</summary>
<blockquote>
<details><summary>.github/workflows/docs.yml</summary>
- `actions/checkout v3`
- `actions/setup-python v4`
- `actions/checkout v3`
- `actions/setup-python v4`
</details>
<details><summary>.github/workflows/lint.yml</summary>
- `actions/checkout v3`
- `actions/setup-python v4`
</details>
<details><summary>.github/workflows/main.yml</summary>
- `actions/checkout v3`
- `actions/setup-python v4`
- `googleapis/code-suggester v4`
</details>
<details><summary>.github/workflows/unittest.yml</summary>
- `actions/checkout v3`
- `actions/setup-python v4`
- `actions/upload-artifact v3`
- `actions/checkout v3`
- `actions/setup-python v4`
- `actions/checkout v3`
- `actions/setup-python v4`
- `actions/download-artifact v3`
</details>
</blockquote>
</details>
<details><summary>pip_requirements</summary>
<blockquote>
<details><summary>.kokoro/requirements.txt</summary>
- `argcomplete ==2.0.0`
- `attrs ==22.1.0`
- `bleach ==5.0.1`
- `cachetools ==5.2.0`
- `certifi ==2022.9.24`
- `cffi ==1.15.1`
- `charset-normalizer ==3.0.0`
- `click ==8.0.4`
- `colorlog ==6.7.0`
- `commonmark ==0.9.1`
- `cryptography ==38.0.3`
- `distlib ==0.3.6`
- `docutils ==0.19`
- `filelock ==3.8.0`
- `gcp-docuploader ==0.6.4`
- `gcp-releasetool ==1.8.7`
- `google-api-core ==2.8.2`
- `google-auth ==2.11.0`
- `google-cloud-core ==2.3.2`
- `google-cloud-storage ==2.6.0`
- `google-crc32c ==1.5.0`
- `google-resumable-media ==2.4.0`
- `googleapis-common-protos ==1.56.4`
- `idna ==3.4`
- `importlib-metadata ==5.0.0`
- `jaraco-classes ==3.2.3`
- `jeepney ==0.8.0`
- `jinja2 ==3.1.2`
- `keyring ==23.11.0`
- `markupsafe ==2.1.1`
- `more-itertools ==9.0.0`
- `nox ==2022.8.7`
- `packaging ==21.3`
- `pkginfo ==1.8.3`
- `platformdirs ==2.5.3`
- `protobuf ==3.20.2`
- `py ==1.11.0`
- `pyasn1 ==0.4.8`
- `pyasn1-modules ==0.2.8`
- `pycparser ==2.21`
- `pygments ==2.13.0`
- `PyJWT ==2.6.0`
- `pyparsing ==3.0.9`
- `pyperclip ==1.8.2`
- `python-dateutil ==2.8.2`
- `readme-renderer ==37.3`
- `requests ==2.28.1`
- `requests-toolbelt ==0.10.1`
- `rfc3986 ==2.0.0`
- `rich ==12.6.0`
- `rsa ==4.9`
- `secretstorage ==3.3.3`
- `six ==1.16.0`
- `twine ==4.0.1`
- `typing-extensions ==4.4.0`
- `urllib3 ==1.26.12`
- `virtualenv ==20.16.4`
- `webencodings ==0.5.1`
- `wheel ==0.38.3`
- `zipp ==3.10.0`
- `setuptools ==65.5.1`
</details>
<details><summary>scripts/requirements.txt</summary>
- `requests ==2.28.1`
</details>
</blockquote>
</details>
<details><summary>pip_setup</summary>
<blockquote>
<details><summary>packages/google-cloud-contentwarehouse/setup.py</summary>
- `google-api-core >= 1.33.2, <3.0.0dev,!=2.0.*,!=2.1.*,!=2.2.*,!=2.3.*,!=2.4.*,!=2.5.*,!=2.6.*,!=2.7.*`
- `proto-plus >= 1.22.0, <2.0.0dev`
- `protobuf >=3.19.5,<5.0.0dev,!=3.20.0,!=3.20.1,!=4.21.0,!=4.21.1,!=4.21.2,!=4.21.3,!=4.21.4,!=4.21.5`
- `grpc-google-iam-v1 >= 0.12.4, < 1.0.0dev`
- `google-cloud-documentai >= 1.2.1, < 3.0.0dev`
</details>
<details><summary>packages/google-cloud-discoveryengine/setup.py</summary>
- `google-api-core >= 1.33.2, <3.0.0dev,!=2.0.*,!=2.1.*,!=2.2.*,!=2.3.*,!=2.4.*,!=2.5.*,!=2.6.*,!=2.7.*`
- `proto-plus >= 1.22.0, <2.0.0dev`
- `protobuf >=3.19.5,<5.0.0dev,!=3.20.0,!=3.20.1,!=4.21.0,!=4.21.1,!=4.21.2,!=4.21.3,!=4.21.4,!=4.21.5`
</details>
<details><summary>packages/google-cloud-enterpriseknowledgegraph/setup.py</summary>
- `google-api-core >= 1.33.2, <3.0.0dev,!=2.0.*,!=2.1.*,!=2.2.*,!=2.3.*,!=2.4.*,!=2.5.*,!=2.6.*,!=2.7.*`
- `proto-plus >= 1.22.0, <2.0.0dev`
- `protobuf >=3.19.5,<5.0.0dev,!=3.20.0,!=3.20.1,!=4.21.0,!=4.21.1,!=4.21.2,!=4.21.3,!=4.21.4,!=4.21.5`
</details>
<details><summary>packages/google-geo-type/setup.py</summary>
- `google-api-core >= 1.33.2, <3.0.0dev,!=2.0.*,!=2.1.*,!=2.2.*,!=2.3.*,!=2.4.*,!=2.5.*,!=2.6.*,!=2.7.*`
- `proto-plus >= 1.22.0, <2.0.0dev`
- `protobuf >=3.19.5,<5.0.0dev,!=3.20.0,!=3.20.1,!=4.21.0,!=4.21.1,!=4.21.2,!=4.21.3,!=4.21.4,!=4.21.5`
</details>
<details><summary>packages/google-maps-addressvalidation/setup.py</summary>
- `google-api-core >= 1.33.2, <3.0.0dev,!=2.0.*,!=2.1.*,!=2.2.*,!=2.3.*,!=2.4.*,!=2.5.*,!=2.6.*,!=2.7.*`
- `proto-plus >= 1.22.0, <2.0.0dev`
- `protobuf >=3.19.5,<5.0.0dev,!=3.20.0,!=3.20.1,!=4.21.0,!=4.21.1,!=4.21.2,!=4.21.3,!=4.21.4,!=4.21.5`
- `google-geo-type <1.0.0dev`
</details>
</blockquote>
</details>
---
- [ ] <!-- manual job -->Check this box to trigger a request for Renovate to run again on this repository
|
process
|
dependency dashboard this issue lists renovate updates and detected dependencies read the docs to learn more edited blocked these updates have been manually edited so renovate will no longer make changes to discard all commits and start over click on a checkbox pull pull pull open these updates have all been created already click a checkbox below to force a retry rebase of any pull pull pull pull pull click on this checkbox to rebase all open prs at once detected dependencies cloudbuild containers python bootstrap container cloudbuild yaml dockerfile kokoro docker docs dockerfile ubuntu containers python bootstrap container dockerfile python buster github actions github workflows docs yml actions checkout actions setup python actions checkout actions setup python github workflows lint yml actions checkout actions setup python github workflows main yml actions checkout actions setup python googleapis code suggester github workflows unittest yml actions checkout actions setup python actions upload artifact actions checkout actions setup python actions checkout actions setup python actions download artifact pip requirements kokoro requirements txt argcomplete attrs bleach cachetools certifi cffi charset normalizer click colorlog commonmark cryptography distlib docutils filelock gcp docuploader gcp releasetool google api core google auth google cloud core google cloud storage google google resumable media googleapis common protos idna importlib metadata jaraco classes jeepney keyring markupsafe more itertools nox packaging pkginfo platformdirs protobuf py modules pycparser pygments pyjwt pyparsing pyperclip python dateutil readme renderer requests requests toolbelt rich rsa secretstorage six twine typing extensions virtualenv webencodings wheel zipp setuptools scripts requirements txt requests pip setup packages google cloud contentwarehouse setup py google api core proto plus protobuf grpc google iam google cloud documentai packages google cloud discoveryengine setup py google api core proto plus protobuf packages google cloud enterpriseknowledgegraph setup py google api core proto plus protobuf packages google geo type setup py google api core proto plus protobuf packages google maps addressvalidation setup py google api core proto plus protobuf google geo type check this box to trigger a request for renovate to run again on this repository
| 1
|
8,531
| 5,798,461,482
|
IssuesEvent
|
2017-05-03 01:53:27
|
usnistgov/800-63-3
|
https://api.github.com/repos/usnistgov/800-63-3
|
closed
|
Usability recommendations go against best practices for protecting authentication information and reducing the ability of an attacker to gain intelligence
|
63A decline usability
|
**Organization Name (N/A, if individual)**: CMS
**Organization Type**: 1
**Document (63-3, 63A, 63B, or 63C)**: 800-63A
**Reference (Include section and paragraph number)**: Section 10.1 (Usability Considerations Common to Authenticators),
Para 5,
Bullet 5,
Sub bullet 5
Section 10.2.1 (Memorized Secrets),
Para 1
Section 10.4 (Biometrics Usability Considerations), Typical Usage,
Bullet 5
,
**Comment (Include rationale for comment)**: Usability recommendations go against best practices for protecting authentication information and reducing the ability of an attacker to gain intelligence
Usability recommendations go against best practices for protecting authentication information and reducing the ability of an attacker to gain intelligence:
1) Informing the user when the "throttle" (login-disabled) expires
2) Copy and paste functionality for memorized secrets
All recommendations must be consistent with NIST guidance. Additionally, there may be agency policy that precludes displaying this type of intelligence.
**Suggested Change**:
---
Organization Type: 1 = Federal, 2 = Industry, 3 = Academia, 4 = Self, 5 = Other
|
True
|
Usability recommendations go against best practices for protecting authentication information and reducing the ability of an attacker to gain intelligence - **Organization Name (N/A, if individual)**: CMS
**Organization Type**: 1
**Document (63-3, 63A, 63B, or 63C)**: 800-63A
**Reference (Include section and paragraph number)**: Section 10.1 (Usability Considerations Common to Authenticators),
Para 5,
Bullet 5,
Sub bullet 5
Section 10.2.1 (Memorized Secrets),
Para 1
Section 10.4 (Biometrics Usability Considerations), Typical Usage,
Bullet 5
,
**Comment (Include rationale for comment)**: Usability recommendations go against best practices for protecting authentication information and reducing the ability of an attacker to gain intelligence
Usability recommendations go against best practices for protecting authentication information and reducing the ability of an attacker to gain intelligence:
1) Informing the user when the "throttle" (login-disabled) expires
2) Copy and paste functionality for memorized secrets
All recommendations must be consistent with NIST guidance. Additionally, there may be agency policy that precludes displaying this type of intelligence.
**Suggested Change**:
---
Organization Type: 1 = Federal, 2 = Industry, 3 = Academia, 4 = Self, 5 = Other
|
non_process
|
usability recommendations go against best practices for protecting authentication information and reducing the ability of an attacker to gain intelligence organization name n a if individual cms organization type document or reference include section and paragraph number section usability considerations common to authenticators para bullet sub bullet section memorized secrets para section biometrics usability considerations typical usage bullet comment include rationale for comment usability recommendations go against best practices for protecting authentication information and reducing the ability of an attacker to gain intelligence usability recommendations go against best practices for protecting authentication information and reducing the ability of an attacker to gain intelligence informing the user when the throttle login disabled expires copy and paste functionality for memorized secrets all recommendations must be consistent with nist guidance additionally there may be agency policy that precludes displaying this type of intelligence suggested change organization type federal industry academia self other
| 0
|
106,765
| 23,282,376,171
|
IssuesEvent
|
2022-08-05 13:20:51
|
vegaprotocol/specs
|
https://api.github.com/repos/vegaprotocol/specs
|
closed
|
0036-BRIE-event_queue documentations inc. describing how confirmations/voting works
|
requires-engineering ac-code-remediation
|
Update 0036-BRIE-event_queue as it does not describe how confirmations/voting works
As part of the gap analysis for the open issue in [asana](https://app.asana.com/0/1201666015335982/1201802898848442) its required that we have documentation covering the event types and the event triggers for these.
Ideally we will have this before starting:
- https://github.com/vegaprotocol/system-tests/issues/467
|
1.0
|
0036-BRIE-event_queue documentations inc. describing how confirmations/voting works - Update 0036-BRIE-event_queue as it does not describe how confirmations/voting works
As part of the gap analysis for the open issue in [asana](https://app.asana.com/0/1201666015335982/1201802898848442) its required that we have documentation covering the event types and the event triggers for these.
Ideally we will have this before starting:
- https://github.com/vegaprotocol/system-tests/issues/467
|
non_process
|
brie event queue documentations inc describing how confirmations voting works update brie event queue as it does not describe how confirmations voting works as part of the gap analysis for the open issue in its required that we have documentation covering the event types and the event triggers for these ideally we will have this before starting
| 0
|
150,438
| 11,961,155,599
|
IssuesEvent
|
2020-04-05 07:05:07
|
vuetifyjs/vuetify
|
https://api.github.com/repos/vuetifyjs/vuetify
|
reopened
|
[Feature Request] Stubs for shallowMount
|
testing
|
### Problem to solve
Some vuetify components use slots which are not rendered by default with `shallowMount`
### Proposed solution
Include stubs that only render the slots.
```javascript
const wrapper = shallowMount(CustomComponent, {
store, localVue, vuetify, stubs: {
VTextField: '<v-text-field-stub><slot name="prepend"></slot></v-text-field-stub>',
},
});
```
<!-- generated by vuetify-issue-helper. DO NOT REMOVE -->
|
1.0
|
[Feature Request] Stubs for shallowMount - ### Problem to solve
Some vuetify components use slots which are not rendered by default with `shallowMount`
### Proposed solution
Include stubs that only render the slots.
```javascript
const wrapper = shallowMount(CustomComponent, {
store, localVue, vuetify, stubs: {
VTextField: '<v-text-field-stub><slot name="prepend"></slot></v-text-field-stub>',
},
});
```
<!-- generated by vuetify-issue-helper. DO NOT REMOVE -->
|
non_process
|
stubs for shallowmount problem to solve some vuetify components use slots which are not rendered by default with shallowmount proposed solution include stubs that only render the slots javascript const wrapper shallowmount customcomponent store localvue vuetify stubs vtextfield
| 0
|
142,731
| 19,102,962,966
|
IssuesEvent
|
2021-11-30 01:49:33
|
Nehamaefi/Efigit
|
https://api.github.com/repos/Nehamaefi/Efigit
|
opened
|
CVE-2021-20190 (High) detected in jackson-databind-2.9.4.jar
|
security vulnerability
|
## CVE-2021-20190 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.4.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: Efigit/apps/rest-showcase/pom.xml</p>
<p>Path to vulnerable library: /root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.4/jackson-databind-2.9.4.jar,epository/com/fasterxml/jackson/core/jackson-databind/2.9.4/jackson-databind-2.9.4.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.4.jar** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A flaw was found in jackson-databind before 2.9.10.7. FasterXML mishandles the interaction between serialization gadgets and typing. The highest threat from this vulnerability is to data confidentiality and integrity as well as system availability.
<p>Publish Date: 2021-01-19
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-20190>CVE-2021-20190</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/FasterXML/jackson-databind/issues/2854">https://github.com/FasterXML/jackson-databind/issues/2854</a></p>
<p>Release Date: 2021-01-19</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind-2.9.10.7</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.9.4","packageFilePaths":["/apps/rest-showcase/pom.xml","/plugins/rest/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.fasterxml.jackson.core:jackson-databind:2.9.4","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.fasterxml.jackson.core:jackson-databind-2.9.10.7","isBinary":false}],"baseBranches":[],"vulnerabilityIdentifier":"CVE-2021-20190","vulnerabilityDetails":"A flaw was found in jackson-databind before 2.9.10.7. FasterXML mishandles the interaction between serialization gadgets and typing. The highest threat from this vulnerability is to data confidentiality and integrity as well as system availability.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-20190","cvss3Severity":"high","cvss3Score":"8.1","cvss3Metrics":{"A":"High","AC":"High","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> -->
|
True
|
CVE-2021-20190 (High) detected in jackson-databind-2.9.4.jar - ## CVE-2021-20190 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.4.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: Efigit/apps/rest-showcase/pom.xml</p>
<p>Path to vulnerable library: /root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.4/jackson-databind-2.9.4.jar,epository/com/fasterxml/jackson/core/jackson-databind/2.9.4/jackson-databind-2.9.4.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.4.jar** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A flaw was found in jackson-databind before 2.9.10.7. FasterXML mishandles the interaction between serialization gadgets and typing. The highest threat from this vulnerability is to data confidentiality and integrity as well as system availability.
<p>Publish Date: 2021-01-19
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-20190>CVE-2021-20190</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/FasterXML/jackson-databind/issues/2854">https://github.com/FasterXML/jackson-databind/issues/2854</a></p>
<p>Release Date: 2021-01-19</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind-2.9.10.7</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.9.4","packageFilePaths":["/apps/rest-showcase/pom.xml","/plugins/rest/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.fasterxml.jackson.core:jackson-databind:2.9.4","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.fasterxml.jackson.core:jackson-databind-2.9.10.7","isBinary":false}],"baseBranches":[],"vulnerabilityIdentifier":"CVE-2021-20190","vulnerabilityDetails":"A flaw was found in jackson-databind before 2.9.10.7. FasterXML mishandles the interaction between serialization gadgets and typing. The highest threat from this vulnerability is to data confidentiality and integrity as well as system availability.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-20190","cvss3Severity":"high","cvss3Score":"8.1","cvss3Metrics":{"A":"High","AC":"High","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> -->
|
non_process
|
cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file efigit apps rest showcase pom xml path to vulnerable library root repository com fasterxml jackson core jackson databind jackson databind jar epository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library vulnerability details a flaw was found in jackson databind before fasterxml mishandles the interaction between serialization gadgets and typing the highest threat from this vulnerability is to data confidentiality and integrity as well as system availability publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com fasterxml jackson core jackson databind rescue worker helmet automatic remediation is available for this issue isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree com fasterxml jackson core jackson databind isminimumfixversionavailable true minimumfixversion com fasterxml jackson core jackson databind isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails a flaw was found in jackson databind before fasterxml mishandles the interaction between serialization gadgets and typing the highest threat from this vulnerability is to data confidentiality and integrity as well as system availability vulnerabilityurl
| 0
|
45,556
| 11,698,689,405
|
IssuesEvent
|
2020-03-06 14:20:51
|
AdoptOpenJDK/openjdk-build
|
https://api.github.com/repos/AdoptOpenJDK/openjdk-build
|
closed
|
New enable-dtrace options causes AIX builds to fail
|
bug buildbreak
|
Ref: https://ci.adoptopenjdk.net/view/Failing%20Builds/job/build-scripts/job/jobs/job/jdk11u/job/jdk11u-aix-ppc64-openj9/508/console
```
checking for dtrace tool... not found, cannot build dtrace
checking sys/sdt.h usability... no
checking sys/sdt.h presence... configure: error: Cannot enable dtrace with missing dependencies. See above.
no
checking for sys/sdt.h... no
checking if dtrace should be built... no, missing dependencies
configure exiting with result code 1
[Pipeline] }
```
Apparently the new version of the option (required by JDK15) is not the same as the old `auto` option so https://github.com/AdoptOpenJDK/openjdk-build/pull/1563 has likely been the cause of this. We should switch to enabling this in the `platform-specific-configuration` scripts instead of globally in `build.sh`
|
1.0
|
New enable-dtrace options causes AIX builds to fail - Ref: https://ci.adoptopenjdk.net/view/Failing%20Builds/job/build-scripts/job/jobs/job/jdk11u/job/jdk11u-aix-ppc64-openj9/508/console
```
checking for dtrace tool... not found, cannot build dtrace
checking sys/sdt.h usability... no
checking sys/sdt.h presence... configure: error: Cannot enable dtrace with missing dependencies. See above.
no
checking for sys/sdt.h... no
checking if dtrace should be built... no, missing dependencies
configure exiting with result code 1
[Pipeline] }
```
Apparently the new version of the option (required by JDK15) is not the same as the old `auto` option so https://github.com/AdoptOpenJDK/openjdk-build/pull/1563 has likely been the cause of this. We should switch to enabling this in the `platform-specific-configuration` scripts instead of globally in `build.sh`
|
non_process
|
new enable dtrace options causes aix builds to fail ref checking for dtrace tool not found cannot build dtrace checking sys sdt h usability no checking sys sdt h presence configure error cannot enable dtrace with missing dependencies see above no checking for sys sdt h no checking if dtrace should be built no missing dependencies configure exiting with result code apparently the new version of the option required by is not the same as the old auto option so has likely been the cause of this we should switch to enabling this in the platform specific configuration scripts instead of globally in build sh
| 0
|
16,221
| 20,749,200,955
|
IssuesEvent
|
2022-03-15 04:45:39
|
NationalSecurityAgency/ghidra
|
https://api.github.com/repos/NationalSecurityAgency/ghidra
|
closed
|
Missing OpObjects for x86 instructions like SHR
|
Feature: Processor/x86
|
**Describe the bug**
A clear and concise description of the bug.
Certain x86 instructions seem to be missing `OpObjects` when calling `Instruction.getOpObjects()`.
The following example does not exhibit the issue and is how I would expect the instruction to look like when examining the operands.
```
SHR EAX,0x8
0: EAX
1: 0x8
```
But for a different form of the instruction, the operand is seemingly made implicit.
```
SHR EAX,1
0: EAX
```
Looking at `Ghidra/Processors/x86/data/languages/ia.sinc`, this seems to happen for a handful of instructions that reference an `n1` construct (more in the file).
```
n1: "1" is epsilon { tmp:1 = 1; export tmp; }
...
:RCL rm8,n1 ...
:RCL rm8,CL ...
:RCL rm8,imm8 ...
...
:SHR rm8,n1 ...
:SHR rm8,CL ...
:SHR rm8,imm8 ...
...
```
**To Reproduce**
Steps to reproduce the behavior:
1. Go to '...'
2. Click on '....'
3. Scroll down to '....'
4. See error
```java
// Given an Instruction that is being examined, inspect the operands.
// Heads up, this is a rough pseudo-translation from Clojure and might not work as is.
Instruction instr;
System.out.println(instr.toString());
for (int i = 0; i < instr.getNumOperands(); i++) {
for (Object opObj : instr.getOpObjects()) {
System.out.println(" " + i + ": " + opObj.toString());
}
}
```
**Expected behavior**
A clear and concise description of what you expected to happen.
I would have instead expected there to be an explicit Scalar OpObject representing the 1 value.
```
SHR EAX,1
0: EAX
+ 1: 0x1
```
**Screenshots**
If applicable, add screenshots to help explain your problem.
**Attachments**
If applicable, please attach any files that caused problems or log files generated by the software.
**Environment (please complete the following information):**
- OS: [e.g. macOS 10.14.2] NixOS 21.11
- Java Version: [e.g. 11.0] openjdk 11.0.14
- Ghidra Version: [e.g. 9.1.2] 10.1.2
- Ghidra Origin: [e.g. official ghidra-sre.org distro, third party distro, locally built] official GitHub releases
**Additional context**
Add any other context about the problem here.
|
1.0
|
Missing OpObjects for x86 instructions like SHR - **Describe the bug**
A clear and concise description of the bug.
Certain x86 instructions seem to be missing `OpObjects` when calling `Instruction.getOpObjects()`.
The following example does not exhibit the issue and is how I would expect the instruction to look like when examining the operands.
```
SHR EAX,0x8
0: EAX
1: 0x8
```
But for a different form of the instruction, the operand is seemingly made implicit.
```
SHR EAX,1
0: EAX
```
Looking at `Ghidra/Processors/x86/data/languages/ia.sinc`, this seems to happen for a handful of instructions that reference an `n1` construct (more in the file).
```
n1: "1" is epsilon { tmp:1 = 1; export tmp; }
...
:RCL rm8,n1 ...
:RCL rm8,CL ...
:RCL rm8,imm8 ...
...
:SHR rm8,n1 ...
:SHR rm8,CL ...
:SHR rm8,imm8 ...
...
```
**To Reproduce**
Steps to reproduce the behavior:
1. Go to '...'
2. Click on '....'
3. Scroll down to '....'
4. See error
```java
// Given an Instruction that is being examined, inspect the operands.
// Heads up, this is a rough pseudo-translation from Clojure and might not work as is.
Instruction instr;
System.out.println(instr.toString());
for (int i = 0; i < instr.getNumOperands(); i++) {
for (Object opObj : instr.getOpObjects()) {
System.out.println(" " + i + ": " + opObj.toString());
}
}
```
**Expected behavior**
A clear and concise description of what you expected to happen.
I would have instead expected there to be an explicit Scalar OpObject representing the 1 value.
```
SHR EAX,1
0: EAX
+ 1: 0x1
```
**Screenshots**
If applicable, add screenshots to help explain your problem.
**Attachments**
If applicable, please attach any files that caused problems or log files generated by the software.
**Environment (please complete the following information):**
- OS: [e.g. macOS 10.14.2] NixOS 21.11
- Java Version: [e.g. 11.0] openjdk 11.0.14
- Ghidra Version: [e.g. 9.1.2] 10.1.2
- Ghidra Origin: [e.g. official ghidra-sre.org distro, third party distro, locally built] official GitHub releases
**Additional context**
Add any other context about the problem here.
|
process
|
missing opobjects for instructions like shr describe the bug a clear and concise description of the bug certain instructions seem to be missing opobjects when calling instruction getopobjects the following example does not exhibit the issue and is how i would expect the instruction to look like when examining the operands shr eax eax but for a different form of the instruction the operand is seemingly made implicit shr eax eax looking at ghidra processors data languages ia sinc this seems to happen for a handful of instructions that reference an construct more in the file is epsilon tmp export tmp rcl rcl cl rcl shr shr cl shr to reproduce steps to reproduce the behavior go to click on scroll down to see error java given an instruction that is being examined inspect the operands heads up this is a rough pseudo translation from clojure and might not work as is instruction instr system out println instr tostring for int i i instr getnumoperands i for object opobj instr getopobjects system out println i opobj tostring expected behavior a clear and concise description of what you expected to happen i would have instead expected there to be an explicit scalar opobject representing the value shr eax eax screenshots if applicable add screenshots to help explain your problem attachments if applicable please attach any files that caused problems or log files generated by the software environment please complete the following information os nixos java version openjdk ghidra version ghidra origin official github releases additional context add any other context about the problem here
| 1
|
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.