Unnamed: 0
int64 0
832k
| id
float64 2.49B
32.1B
| type
stringclasses 1
value | created_at
stringlengths 19
19
| repo
stringlengths 7
112
| repo_url
stringlengths 36
141
| action
stringclasses 3
values | title
stringlengths 1
744
| labels
stringlengths 4
574
| body
stringlengths 9
211k
| index
stringclasses 10
values | text_combine
stringlengths 96
211k
| label
stringclasses 2
values | text
stringlengths 96
188k
| binary_label
int64 0
1
|
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
21,030
| 27,969,937,306
|
IssuesEvent
|
2023-03-25 00:20:06
|
darktable-org/darktable
|
https://api.github.com/repos/darktable-org/darktable
|
closed
|
New blending layers mode
|
feature: new scope: image processing no-issue-activity
|
Is it possible to add a value+saturation and lightness+chroma blend mode?
Basically this copies the hue from the bottom layer
|
1.0
|
New blending layers mode - Is it possible to add a value+saturation and lightness+chroma blend mode?
Basically this copies the hue from the bottom layer
|
process
|
new blending layers mode is it possible to add a value saturation and lightness chroma blend mode basically this copies the hue from the bottom layer
| 1
|
216,619
| 7,310,207,563
|
IssuesEvent
|
2018-02-28 14:23:00
|
AmpersandTarski/Ampersand
|
https://api.github.com/repos/AmpersandTarski/Ampersand
|
opened
|
MYSQL error 1069: Too many keys specified; max 64 keys allowed in query
|
bug component:prototype generator priority:high
|
Consider the following script:
~~~
CONTEXT Issue758
r1 :: C * C1 [UNI] r2 :: C * C2 [UNI] r3 :: C * C3 [UNI] r4 :: C * C4 [UNI] r5 :: C * C5 [UNI]
r6 :: C * C6 [UNI] r7 :: C * C7 [UNI] r8 :: C * C8 [UNI] r9 :: C * C9 [UNI] r10 :: C * C0 [UNI]
r11 :: C * C1 [UNI] r12 :: C * C2 [UNI] r13 :: C * C3 [UNI] r14 :: C * C4 [UNI] r15 :: C * C5 [UNI]
r16 :: C * C6 [UNI] r17 :: C * C7 [UNI] r18 :: C * C8 [UNI] r19 :: C * C9 [UNI] r20 :: C * C0 [UNI]
r21 :: C * C1 [UNI] r22 :: C * C2 [UNI] r23 :: C * C3 [UNI] r24 :: C * C4 [UNI] r25 :: C * C5 [UNI]
r26 :: C * C6 [UNI] r27 :: C * C7 [UNI] r28 :: C * C8 [UNI] r29 :: C * C9 [UNI] r30 :: C * C0 [UNI]
r31 :: C * C1 [UNI] r32 :: C * C2 [UNI] r33 :: C * C3 [UNI] r34 :: C * C4 [UNI] r35 :: C * C5 [UNI]
r36 :: C * C6 [UNI] r37 :: C * C7 [UNI] r38 :: C * C8 [UNI] r39 :: C * C9 [UNI] r40 :: C * C0 [UNI]
r41 :: C * C1 [UNI] r42 :: C * C2 [UNI] r43 :: C * C3 [UNI] r44 :: C * C4 [UNI] r45 :: C * C5 [UNI]
r46 :: C * C6 [UNI] r47 :: C * C7 [UNI] r48 :: C * C8 [UNI] r49 :: C * C9 [UNI] r50 :: C * C0 [UNI]
r51 :: C * C1 [UNI] r52 :: C * C2 [UNI] r53 :: C * C3 [UNI] r54 :: C * C4 [UNI] r55 :: C * C5 [UNI]
r56 :: C * C6 [UNI] r57 :: C * C7 [UNI] r58 :: C * C8 [UNI] r59 :: C * C9 [UNI] r60 :: C * C0 [UNI]
r61 :: C * C1 [UNI] r62 :: C * C2 [UNI] r63 :: C * C3 [UNI] r64 :: C * C4 [UNI] r65 :: C * C0 [UNI]
ENDCONTEXT
~~~
If I compile it with Ampersand-v3.9.1 [development:b051de7], the database is not created properly. In the ERROR log, I see lines such as:
~~~
[2018-02-28 15:06:45] API.ERROR: MYSQL error 1069: Too many keys specified; max 64 keys allowed in query:CREATE INDEX "C_r63" ON "C" ("r63") [] []
~~~
As a consequence, applications that have this many (univalent) relations will not run. This currently happens in projects that we do, where we need to create simple/flat forms, and as a consequence, there are many relations that have SRC=Form and TGT=SomeOtherConcept.
A (cumbersome) workaround for this is to remove `CREATE INDEX` statements from `mysql-installer.json`, such that for every concept, no more than 63 (or 64) keys are left over. After all, these keys seem to only affect performance.
It would be nice if the generator would not generate more than these 63/64 keys, so that such applications would (continue to) run.
|
1.0
|
MYSQL error 1069: Too many keys specified; max 64 keys allowed in query - Consider the following script:
~~~
CONTEXT Issue758
r1 :: C * C1 [UNI] r2 :: C * C2 [UNI] r3 :: C * C3 [UNI] r4 :: C * C4 [UNI] r5 :: C * C5 [UNI]
r6 :: C * C6 [UNI] r7 :: C * C7 [UNI] r8 :: C * C8 [UNI] r9 :: C * C9 [UNI] r10 :: C * C0 [UNI]
r11 :: C * C1 [UNI] r12 :: C * C2 [UNI] r13 :: C * C3 [UNI] r14 :: C * C4 [UNI] r15 :: C * C5 [UNI]
r16 :: C * C6 [UNI] r17 :: C * C7 [UNI] r18 :: C * C8 [UNI] r19 :: C * C9 [UNI] r20 :: C * C0 [UNI]
r21 :: C * C1 [UNI] r22 :: C * C2 [UNI] r23 :: C * C3 [UNI] r24 :: C * C4 [UNI] r25 :: C * C5 [UNI]
r26 :: C * C6 [UNI] r27 :: C * C7 [UNI] r28 :: C * C8 [UNI] r29 :: C * C9 [UNI] r30 :: C * C0 [UNI]
r31 :: C * C1 [UNI] r32 :: C * C2 [UNI] r33 :: C * C3 [UNI] r34 :: C * C4 [UNI] r35 :: C * C5 [UNI]
r36 :: C * C6 [UNI] r37 :: C * C7 [UNI] r38 :: C * C8 [UNI] r39 :: C * C9 [UNI] r40 :: C * C0 [UNI]
r41 :: C * C1 [UNI] r42 :: C * C2 [UNI] r43 :: C * C3 [UNI] r44 :: C * C4 [UNI] r45 :: C * C5 [UNI]
r46 :: C * C6 [UNI] r47 :: C * C7 [UNI] r48 :: C * C8 [UNI] r49 :: C * C9 [UNI] r50 :: C * C0 [UNI]
r51 :: C * C1 [UNI] r52 :: C * C2 [UNI] r53 :: C * C3 [UNI] r54 :: C * C4 [UNI] r55 :: C * C5 [UNI]
r56 :: C * C6 [UNI] r57 :: C * C7 [UNI] r58 :: C * C8 [UNI] r59 :: C * C9 [UNI] r60 :: C * C0 [UNI]
r61 :: C * C1 [UNI] r62 :: C * C2 [UNI] r63 :: C * C3 [UNI] r64 :: C * C4 [UNI] r65 :: C * C0 [UNI]
ENDCONTEXT
~~~
If I compile it with Ampersand-v3.9.1 [development:b051de7], the database is not created properly. In the ERROR log, I see lines such as:
~~~
[2018-02-28 15:06:45] API.ERROR: MYSQL error 1069: Too many keys specified; max 64 keys allowed in query:CREATE INDEX "C_r63" ON "C" ("r63") [] []
~~~
As a consequence, applications that have this many (univalent) relations will not run. This currently happens in projects that we do, where we need to create simple/flat forms, and as a consequence, there are many relations that have SRC=Form and TGT=SomeOtherConcept.
A (cumbersome) workaround for this is to remove `CREATE INDEX` statements from `mysql-installer.json`, such that for every concept, no more than 63 (or 64) keys are left over. After all, these keys seem to only affect performance.
It would be nice if the generator would not generate more than these 63/64 keys, so that such applications would (continue to) run.
|
non_process
|
mysql error too many keys specified max keys allowed in query consider the following script context c c c c c c c c c c c c c c c c c c c c c c c c c c c c c c c c c c c c c c c c c c c c c c c c c c c c c c c c c c c c c c c c c endcontext if i compile it with ampersand the database is not created properly in the error log i see lines such as api error mysql error too many keys specified max keys allowed in query create index c on c as a consequence applications that have this many univalent relations will not run this currently happens in projects that we do where we need to create simple flat forms and as a consequence there are many relations that have src form and tgt someotherconcept a cumbersome workaround for this is to remove create index statements from mysql installer json such that for every concept no more than or keys are left over after all these keys seem to only affect performance it would be nice if the generator would not generate more than these keys so that such applications would continue to run
| 0
|
302,468
| 22,825,308,226
|
IssuesEvent
|
2022-07-12 08:03:36
|
livepeer/livepeer-studio-docs
|
https://api.github.com/repos/livepeer/livepeer-studio-docs
|
closed
|
Fix -- “About Streaming Protocols” links to MistServer
|
documentation
|
“About Streaming Protocols” links to MistServer with no context.
|
1.0
|
Fix -- “About Streaming Protocols” links to MistServer - “About Streaming Protocols” links to MistServer with no context.
|
non_process
|
fix “about streaming protocols” links to mistserver “about streaming protocols” links to mistserver with no context
| 0
|
370,969
| 10,959,472,248
|
IssuesEvent
|
2019-11-27 11:28:52
|
kubernetes-sigs/azuredisk-csi-driver
|
https://api.github.com/repos/kubernetes-sigs/azuredisk-csi-driver
|
opened
|
incremental snapshot support
|
kind/feature priority/important-longterm
|
**Is your feature request related to a problem? Please describe.**
<!-- A clear and concise description of what the problem is. Ex. I'm always frustrated when [...] -->
**Describe the solution you'd like in detail**
<!-- A clear and concise description of what you want to happen. -->
Current snapshot is full snapshot, incremental snapshot is in Preview, we should support that in near future.
https://azure.microsoft.com/en-us/blog/introducing-cost-effective-increment-snapshots-of-azure-managed-disks-in-preview/
**Describe alternatives you've considered**
<!-- A clear and concise description of any alternative solutions or features you've considered. -->
**Additional context**
<!-- Add any other context or screenshots about the feature request here. -->
|
1.0
|
incremental snapshot support - **Is your feature request related to a problem? Please describe.**
<!-- A clear and concise description of what the problem is. Ex. I'm always frustrated when [...] -->
**Describe the solution you'd like in detail**
<!-- A clear and concise description of what you want to happen. -->
Current snapshot is full snapshot, incremental snapshot is in Preview, we should support that in near future.
https://azure.microsoft.com/en-us/blog/introducing-cost-effective-increment-snapshots-of-azure-managed-disks-in-preview/
**Describe alternatives you've considered**
<!-- A clear and concise description of any alternative solutions or features you've considered. -->
**Additional context**
<!-- Add any other context or screenshots about the feature request here. -->
|
non_process
|
incremental snapshot support is your feature request related to a problem please describe describe the solution you d like in detail current snapshot is full snapshot incremental snapshot is in preview we should support that in near future describe alternatives you ve considered additional context
| 0
|
4,514
| 3,870,587,897
|
IssuesEvent
|
2016-04-11 05:02:20
|
lionheart/openradar-mirror
|
https://api.github.com/repos/lionheart/openradar-mirror
|
opened
|
22881933: Siri taxes users with initial delay only when headphones are plugged in
|
classification:ui/usability reproducible:always status:open
|
#### Description
Summary:
I just discovered and celebrated (http://bitsplitting.org/2015/09/28/if-it-aint-fixed-break-it/) the fact that with iPhone 6s, Siri's ability to listen instantly means that there is no longer even a need for an audible or vibration signal that it's ready to process speech. Users can just press the button and start speaking instantly, and it works. And it's awesome.
One gotcha I've run into though, is in the particular case that headphones are plugged in, my phone DOES give a moment's delay before processing Siri instructions, and also plays an audible chime when it's ready. I can't tell if it's the (unnecessary?) chime that is itself delaying Siri's ability to process, or if the fact that headphones are installed somehow defies Siri's ability to be instantly attentive. In any case, this is an unfortunate penalty for using headphones, and destroys the otherwise admirable universal ability to count on Siri to be attentive immediately upon pressing the home button.
Steps to Reproduce:
1. Plug in headphones to an iPhone 6s.
2. Press and hold the home button while IMMEDIATELY asking Siri something e.g. "What time is it?"
Expected Results:
Siri should process and handle the request "What time is it?"
Actual Results:
Siri only gets the tail end of the request, if any, depending on how quickly the chime has been played. In my tests, it often just ends up in "OK, go ahead and ask me something" mode, having totally lost the spoken sentence.
Version:
iOS 9.0.1
Notes:
NOTE: Even if the phone is not silenced, pressing and holding the home button doesn't cause a chime, and doesn't impede Siri's immediate processing of spoken instructions.
Configuration:
iPhone 6s Verizon 128GB.
Attachments:
-
Product Version: 9.0.1
Created: 2015-09-28T18:20:59.147980
Originated: 2015-09-28T14:13:00
Open Radar Link: http://www.openradar.me/22881933
|
True
|
22881933: Siri taxes users with initial delay only when headphones are plugged in - #### Description
Summary:
I just discovered and celebrated (http://bitsplitting.org/2015/09/28/if-it-aint-fixed-break-it/) the fact that with iPhone 6s, Siri's ability to listen instantly means that there is no longer even a need for an audible or vibration signal that it's ready to process speech. Users can just press the button and start speaking instantly, and it works. And it's awesome.
One gotcha I've run into though, is in the particular case that headphones are plugged in, my phone DOES give a moment's delay before processing Siri instructions, and also plays an audible chime when it's ready. I can't tell if it's the (unnecessary?) chime that is itself delaying Siri's ability to process, or if the fact that headphones are installed somehow defies Siri's ability to be instantly attentive. In any case, this is an unfortunate penalty for using headphones, and destroys the otherwise admirable universal ability to count on Siri to be attentive immediately upon pressing the home button.
Steps to Reproduce:
1. Plug in headphones to an iPhone 6s.
2. Press and hold the home button while IMMEDIATELY asking Siri something e.g. "What time is it?"
Expected Results:
Siri should process and handle the request "What time is it?"
Actual Results:
Siri only gets the tail end of the request, if any, depending on how quickly the chime has been played. In my tests, it often just ends up in "OK, go ahead and ask me something" mode, having totally lost the spoken sentence.
Version:
iOS 9.0.1
Notes:
NOTE: Even if the phone is not silenced, pressing and holding the home button doesn't cause a chime, and doesn't impede Siri's immediate processing of spoken instructions.
Configuration:
iPhone 6s Verizon 128GB.
Attachments:
-
Product Version: 9.0.1
Created: 2015-09-28T18:20:59.147980
Originated: 2015-09-28T14:13:00
Open Radar Link: http://www.openradar.me/22881933
|
non_process
|
siri taxes users with initial delay only when headphones are plugged in description summary i just discovered and celebrated the fact that with iphone siri s ability to listen instantly means that there is no longer even a need for an audible or vibration signal that it s ready to process speech users can just press the button and start speaking instantly and it works and it s awesome one gotcha i ve run into though is in the particular case that headphones are plugged in my phone does give a moment s delay before processing siri instructions and also plays an audible chime when it s ready i can t tell if it s the unnecessary chime that is itself delaying siri s ability to process or if the fact that headphones are installed somehow defies siri s ability to be instantly attentive in any case this is an unfortunate penalty for using headphones and destroys the otherwise admirable universal ability to count on siri to be attentive immediately upon pressing the home button steps to reproduce plug in headphones to an iphone press and hold the home button while immediately asking siri something e g what time is it expected results siri should process and handle the request what time is it actual results siri only gets the tail end of the request if any depending on how quickly the chime has been played in my tests it often just ends up in ok go ahead and ask me something mode having totally lost the spoken sentence version ios notes note even if the phone is not silenced pressing and holding the home button doesn t cause a chime and doesn t impede siri s immediate processing of spoken instructions configuration iphone verizon attachments product version created originated open radar link
| 0
|
2,543
| 5,300,988,853
|
IssuesEvent
|
2017-02-10 07:53:28
|
mitchellh/packer
|
https://api.github.com/repos/mitchellh/packer
|
closed
|
Add an "inline" option for passing Vagrantfile template to Vagrant post-processor
|
enhancement post-processor/vagrant
|
This outlines a possible enhancement to the vagrant post-processor.
Just like the shell provisioner/post-processor, it would be really nice to have the option to pass an "inline" vagrantfile_template configuration option to the vagrant post-processor instead of an external file.
The use case for this would be to try to create a more self-contained packer template and try to minimize the number of external files needed to build a box.
|
1.0
|
Add an "inline" option for passing Vagrantfile template to Vagrant post-processor - This outlines a possible enhancement to the vagrant post-processor.
Just like the shell provisioner/post-processor, it would be really nice to have the option to pass an "inline" vagrantfile_template configuration option to the vagrant post-processor instead of an external file.
The use case for this would be to try to create a more self-contained packer template and try to minimize the number of external files needed to build a box.
|
process
|
add an inline option for passing vagrantfile template to vagrant post processor this outlines a possible enhancement to the vagrant post processor just like the shell provisioner post processor it would be really nice to have the option to pass an inline vagrantfile template configuration option to the vagrant post processor instead of an external file the use case for this would be to try to create a more self contained packer template and try to minimize the number of external files needed to build a box
| 1
|
66,595
| 16,658,542,509
|
IssuesEvent
|
2021-06-06 00:25:21
|
spack/spack
|
https://api.github.com/repos/spack/spack
|
closed
|
veloc 1.4, 1.3: build fails: transfer_module.cpp: too many arguments to function 'int AXL_Init()'
|
build-error e4s ecp
|
`veloc@1.4` (and `@1.3`) fails to build using:
* spack@develop (087110bcb013566f6ba392d4c271e891f4b3a2b1 from `Thu Apr 29 16:43:01 2021 +0200`)
* Ubuntu 20.04 - GCC 9.3.0
* Ubuntu 18.04 - GCC 7.5.0
* RHEL 8 - GCC 8.3.1
* RHEL 7 - GCC 9.3.0
Using container: `ecpe4s/ubuntu20.04-runner-x86_64:2021-03-10`
Concrete spec: [veloc-oqsntu.spec.yaml.txt](https://github.com/spack/spack/files/6400144/veloc-oqsntu.spec.yaml.txt)
Build log: [veloc-build-out.txt](https://github.com/spack/spack/files/6400165/veloc-build-out.txt)
```
$> spack mirror add E4S https://cache.e4s.io
$> spack buildcache keys -it
$> spack install --cache-only --only dependencies --include-build-deps -f ./veloc-oqsntu.spec.yaml
... OK
$> spack install --no-cache -f ./veloc-oqsntu.spec.yaml
...
==> Installing veloc-1.4-oqsntu54uhbqae6uw3vlvkdbxzzaet5y
==> Fetching https://spack-llnl-mirror.s3-us-west-2.amazonaws.com/_source-cache/archive/d5/d5d12aedb9e97f079c4428aaa486bfa4e31fe1db547e103c52e76c8ec906d0a8.zip
############################################################################################################################################################################################ 100.0%
==> No patches needed for veloc
==> veloc: Executing phase: 'cmake'
==> veloc: Executing phase: 'build'
==> Error: ProcessError: Command exited with status 2:
'make' '-j16'
4 errors found in build log:
75 [ 47%] Linking C executable heatdis_original
76 cd /tmp/root/spack-stage/spack-stage-veloc-1.4-oqsntu54uhbqae6uw3vlvkdbxzzaet5y/spack-build-oqsntu5/test && /opt/spack/opt/spack/linux-ubuntu20.04-x86_64/gcc-9.3.0/cmake-3.19.7-7zkgd
4xkg62fl5x2upq4mof5dkkkg3u4/bin/cmake -E cmake_link_script CMakeFiles/heatdis_original.dir/link.txt --verbose=1
77 /opt/spack/lib/spack/env/gcc/gcc -O2 -g -DNDEBUG CMakeFiles/heatdis_original.dir/heatdis_original.c.o -o heatdis_original -Wl,-rpath,/opt/spack/opt/spack/linux-ubuntu20.04-x86_64/gc
c-9.3.0/mpich-3.4.1-hm77n22t37spis2wa4wssqtmqnvuhfz6/lib -lm /opt/spack/opt/spack/linux-ubuntu20.04-x86_64/gcc-9.3.0/mpich-3.4.1-hm77n22t37spis2wa4wssqtmqnvuhfz6/lib/libmpi.so
78 make[2]: Leaving directory '/tmp/root/spack-stage/spack-stage-veloc-1.4-oqsntu54uhbqae6uw3vlvkdbxzzaet5y/spack-build-oqsntu5'
79 [ 47%] Built target heatdis_original
80 /tmp/root/spack-stage/spack-stage-veloc-1.4-oqsntu54uhbqae6uw3vlvkdbxzzaet5y/spack-src/src/modules/transfer_module.cpp: In constructor 'transfer_module_t::transfer_module_t(const con
fig_t&)':
>> 81 /tmp/root/spack-stage/spack-stage-veloc-1.4-oqsntu54uhbqae6uw3vlvkdbxzzaet5y/spack-src/src/modules/transfer_module.cpp:54:28: error: too many arguments to function 'int AXL_Init()'
82 54 | int ret = AXL_Init(NULL);
83 | ^
84 In file included from /tmp/root/spack-stage/spack-stage-veloc-1.4-oqsntu54uhbqae6uw3vlvkdbxzzaet5y/spack-src/src/modules/transfer_module.hpp:12,
85 from /tmp/root/spack-stage/spack-stage-veloc-1.4-oqsntu54uhbqae6uw3vlvkdbxzzaet5y/spack-src/src/modules/transfer_module.cpp:1:
86 /opt/spack/opt/spack/linux-ubuntu20.04-x86_64/gcc-9.3.0/axl-0.4.0-kv7mn663t4uj5aw6ssv26zgfzzgt3xev/include/axl.h:58:5: note: declared here
87 58 | int AXL_Init (void);
88 | ^~~~~~~~
89 /tmp/root/spack-stage/spack-stage-veloc-1.4-oqsntu54uhbqae6uw3vlvkdbxzzaet5y/spack-src/src/modules/transfer_module.cpp: In function 'int axl_transfer_file(axl_xfer_t, const string&,
const string&)':
>> 90 /tmp/root/spack-stage/spack-stage-veloc-1.4-oqsntu54uhbqae6uw3vlvkdbxzzaet5y/spack-src/src/modules/transfer_module.cpp:68:45: error: too few arguments to function 'int AXL_Create(axl
_xfer_t, const char*, const char*)'
91 68 | int id = AXL_Create(type, source.c_str());
92 | ^
93 In file included from /tmp/root/spack-stage/spack-stage-veloc-1.4-oqsntu54uhbqae6uw3vlvkdbxzzaet5y/spack-src/src/modules/transfer_module.hpp:12,
94 from /tmp/root/spack-stage/spack-stage-veloc-1.4-oqsntu54uhbqae6uw3vlvkdbxzzaet5y/spack-src/src/modules/transfer_module.cpp:1:
95 /opt/spack/opt/spack/linux-ubuntu20.04-x86_64/gcc-9.3.0/axl-0.4.0-kv7mn663t4uj5aw6ssv26zgfzzgt3xev/include/axl.h:73:5: note: declared here
96 73 | int AXL_Create (axl_xfer_t xtype, const char* name, const char* state_file);
97 | ^~~~~~~~~~
>> 98 make[2]: *** [src/modules/CMakeFiles/veloc-modules.dir/build.make:111: src/modules/CMakeFiles/veloc-modules.dir/transfer_module.cpp.o] Error 1
99 make[2]: *** Waiting for unfinished jobs....
100 make[2]: Leaving directory '/tmp/root/spack-stage/spack-stage-veloc-1.4-oqsntu54uhbqae6uw3vlvkdbxzzaet5y/spack-build-oqsntu5'
>> 101 make[1]: *** [CMakeFiles/Makefile2:281: src/modules/CMakeFiles/veloc-modules.dir/all] Error 2
102 make[1]: Leaving directory '/tmp/root/spack-stage/spack-stage-veloc-1.4-oqsntu54uhbqae6uw3vlvkdbxzzaet5y/spack-build-oqsntu5'
103 make: *** [Makefile:163: all] Error 2
See build log for details:
/tmp/root/spack-stage/spack-stage-veloc-1.4-oqsntu54uhbqae6uw3vlvkdbxzzaet5y/spack-build-out.txt
```
@gonsie
|
1.0
|
veloc 1.4, 1.3: build fails: transfer_module.cpp: too many arguments to function 'int AXL_Init()' - `veloc@1.4` (and `@1.3`) fails to build using:
* spack@develop (087110bcb013566f6ba392d4c271e891f4b3a2b1 from `Thu Apr 29 16:43:01 2021 +0200`)
* Ubuntu 20.04 - GCC 9.3.0
* Ubuntu 18.04 - GCC 7.5.0
* RHEL 8 - GCC 8.3.1
* RHEL 7 - GCC 9.3.0
Using container: `ecpe4s/ubuntu20.04-runner-x86_64:2021-03-10`
Concrete spec: [veloc-oqsntu.spec.yaml.txt](https://github.com/spack/spack/files/6400144/veloc-oqsntu.spec.yaml.txt)
Build log: [veloc-build-out.txt](https://github.com/spack/spack/files/6400165/veloc-build-out.txt)
```
$> spack mirror add E4S https://cache.e4s.io
$> spack buildcache keys -it
$> spack install --cache-only --only dependencies --include-build-deps -f ./veloc-oqsntu.spec.yaml
... OK
$> spack install --no-cache -f ./veloc-oqsntu.spec.yaml
...
==> Installing veloc-1.4-oqsntu54uhbqae6uw3vlvkdbxzzaet5y
==> Fetching https://spack-llnl-mirror.s3-us-west-2.amazonaws.com/_source-cache/archive/d5/d5d12aedb9e97f079c4428aaa486bfa4e31fe1db547e103c52e76c8ec906d0a8.zip
############################################################################################################################################################################################ 100.0%
==> No patches needed for veloc
==> veloc: Executing phase: 'cmake'
==> veloc: Executing phase: 'build'
==> Error: ProcessError: Command exited with status 2:
'make' '-j16'
4 errors found in build log:
75 [ 47%] Linking C executable heatdis_original
76 cd /tmp/root/spack-stage/spack-stage-veloc-1.4-oqsntu54uhbqae6uw3vlvkdbxzzaet5y/spack-build-oqsntu5/test && /opt/spack/opt/spack/linux-ubuntu20.04-x86_64/gcc-9.3.0/cmake-3.19.7-7zkgd
4xkg62fl5x2upq4mof5dkkkg3u4/bin/cmake -E cmake_link_script CMakeFiles/heatdis_original.dir/link.txt --verbose=1
77 /opt/spack/lib/spack/env/gcc/gcc -O2 -g -DNDEBUG CMakeFiles/heatdis_original.dir/heatdis_original.c.o -o heatdis_original -Wl,-rpath,/opt/spack/opt/spack/linux-ubuntu20.04-x86_64/gc
c-9.3.0/mpich-3.4.1-hm77n22t37spis2wa4wssqtmqnvuhfz6/lib -lm /opt/spack/opt/spack/linux-ubuntu20.04-x86_64/gcc-9.3.0/mpich-3.4.1-hm77n22t37spis2wa4wssqtmqnvuhfz6/lib/libmpi.so
78 make[2]: Leaving directory '/tmp/root/spack-stage/spack-stage-veloc-1.4-oqsntu54uhbqae6uw3vlvkdbxzzaet5y/spack-build-oqsntu5'
79 [ 47%] Built target heatdis_original
80 /tmp/root/spack-stage/spack-stage-veloc-1.4-oqsntu54uhbqae6uw3vlvkdbxzzaet5y/spack-src/src/modules/transfer_module.cpp: In constructor 'transfer_module_t::transfer_module_t(const con
fig_t&)':
>> 81 /tmp/root/spack-stage/spack-stage-veloc-1.4-oqsntu54uhbqae6uw3vlvkdbxzzaet5y/spack-src/src/modules/transfer_module.cpp:54:28: error: too many arguments to function 'int AXL_Init()'
82 54 | int ret = AXL_Init(NULL);
83 | ^
84 In file included from /tmp/root/spack-stage/spack-stage-veloc-1.4-oqsntu54uhbqae6uw3vlvkdbxzzaet5y/spack-src/src/modules/transfer_module.hpp:12,
85 from /tmp/root/spack-stage/spack-stage-veloc-1.4-oqsntu54uhbqae6uw3vlvkdbxzzaet5y/spack-src/src/modules/transfer_module.cpp:1:
86 /opt/spack/opt/spack/linux-ubuntu20.04-x86_64/gcc-9.3.0/axl-0.4.0-kv7mn663t4uj5aw6ssv26zgfzzgt3xev/include/axl.h:58:5: note: declared here
87 58 | int AXL_Init (void);
88 | ^~~~~~~~
89 /tmp/root/spack-stage/spack-stage-veloc-1.4-oqsntu54uhbqae6uw3vlvkdbxzzaet5y/spack-src/src/modules/transfer_module.cpp: In function 'int axl_transfer_file(axl_xfer_t, const string&,
const string&)':
>> 90 /tmp/root/spack-stage/spack-stage-veloc-1.4-oqsntu54uhbqae6uw3vlvkdbxzzaet5y/spack-src/src/modules/transfer_module.cpp:68:45: error: too few arguments to function 'int AXL_Create(axl
_xfer_t, const char*, const char*)'
91 68 | int id = AXL_Create(type, source.c_str());
92 | ^
93 In file included from /tmp/root/spack-stage/spack-stage-veloc-1.4-oqsntu54uhbqae6uw3vlvkdbxzzaet5y/spack-src/src/modules/transfer_module.hpp:12,
94 from /tmp/root/spack-stage/spack-stage-veloc-1.4-oqsntu54uhbqae6uw3vlvkdbxzzaet5y/spack-src/src/modules/transfer_module.cpp:1:
95 /opt/spack/opt/spack/linux-ubuntu20.04-x86_64/gcc-9.3.0/axl-0.4.0-kv7mn663t4uj5aw6ssv26zgfzzgt3xev/include/axl.h:73:5: note: declared here
96 73 | int AXL_Create (axl_xfer_t xtype, const char* name, const char* state_file);
97 | ^~~~~~~~~~
>> 98 make[2]: *** [src/modules/CMakeFiles/veloc-modules.dir/build.make:111: src/modules/CMakeFiles/veloc-modules.dir/transfer_module.cpp.o] Error 1
99 make[2]: *** Waiting for unfinished jobs....
100 make[2]: Leaving directory '/tmp/root/spack-stage/spack-stage-veloc-1.4-oqsntu54uhbqae6uw3vlvkdbxzzaet5y/spack-build-oqsntu5'
>> 101 make[1]: *** [CMakeFiles/Makefile2:281: src/modules/CMakeFiles/veloc-modules.dir/all] Error 2
102 make[1]: Leaving directory '/tmp/root/spack-stage/spack-stage-veloc-1.4-oqsntu54uhbqae6uw3vlvkdbxzzaet5y/spack-build-oqsntu5'
103 make: *** [Makefile:163: all] Error 2
See build log for details:
/tmp/root/spack-stage/spack-stage-veloc-1.4-oqsntu54uhbqae6uw3vlvkdbxzzaet5y/spack-build-out.txt
```
@gonsie
|
non_process
|
veloc build fails transfer module cpp too many arguments to function int axl init veloc and fails to build using spack develop from thu apr ubuntu gcc ubuntu gcc rhel gcc rhel gcc using container runner concrete spec build log spack mirror add spack buildcache keys it spack install cache only only dependencies include build deps f veloc oqsntu spec yaml ok spack install no cache f veloc oqsntu spec yaml installing veloc fetching no patches needed for veloc veloc executing phase cmake veloc executing phase build error processerror command exited with status make errors found in build log linking c executable heatdis original cd tmp root spack stage spack stage veloc spack build test opt spack opt spack linux gcc cmake bin cmake e cmake link script cmakefiles heatdis original dir link txt verbose opt spack lib spack env gcc gcc g dndebug cmakefiles heatdis original dir heatdis original c o o heatdis original wl rpath opt spack opt spack linux gc c mpich lib lm opt spack opt spack linux gcc mpich lib libmpi so make leaving directory tmp root spack stage spack stage veloc spack build built target heatdis original tmp root spack stage spack stage veloc spack src src modules transfer module cpp in constructor transfer module t transfer module t const con fig t tmp root spack stage spack stage veloc spack src src modules transfer module cpp error too many arguments to function int axl init int ret axl init null in file included from tmp root spack stage spack stage veloc spack src src modules transfer module hpp from tmp root spack stage spack stage veloc spack src src modules transfer module cpp opt spack opt spack linux gcc axl include axl h note declared here int axl init void tmp root spack stage spack stage veloc spack src src modules transfer module cpp in function int axl transfer file axl xfer t const string const string tmp root spack stage spack stage veloc spack src src modules transfer module cpp error too few arguments to function int axl create axl xfer t const char const char int id axl create type source c str in file included from tmp root spack stage spack stage veloc spack src src modules transfer module hpp from tmp root spack stage spack stage veloc spack src src modules transfer module cpp opt spack opt spack linux gcc axl include axl h note declared here int axl create axl xfer t xtype const char name const char state file make error make waiting for unfinished jobs make leaving directory tmp root spack stage spack stage veloc spack build make error make leaving directory tmp root spack stage spack stage veloc spack build make error see build log for details tmp root spack stage spack stage veloc spack build out txt gonsie
| 0
|
251,365
| 8,014,171,160
|
IssuesEvent
|
2018-07-25 04:56:45
|
wso2/devstudio-tooling-ei
|
https://api.github.com/repos/wso2/devstudio-tooling-ei
|
closed
|
Resources removed through the dev studio did not removed from the remote server
|
Priority/Normal
|
Environment
OS - ubuntu 15.10
Java - JDK jdk1.8.0_66
Dev studio with updates (EI611)
Remote Server - Running in windows server 2012 R2
**Steps to recreate the issue**
1. Create a new Remote Server connection with an artefact to deploy
2. Verify that the artefact deployed successfully in the server
3. Remove the resource from the Dev Studio
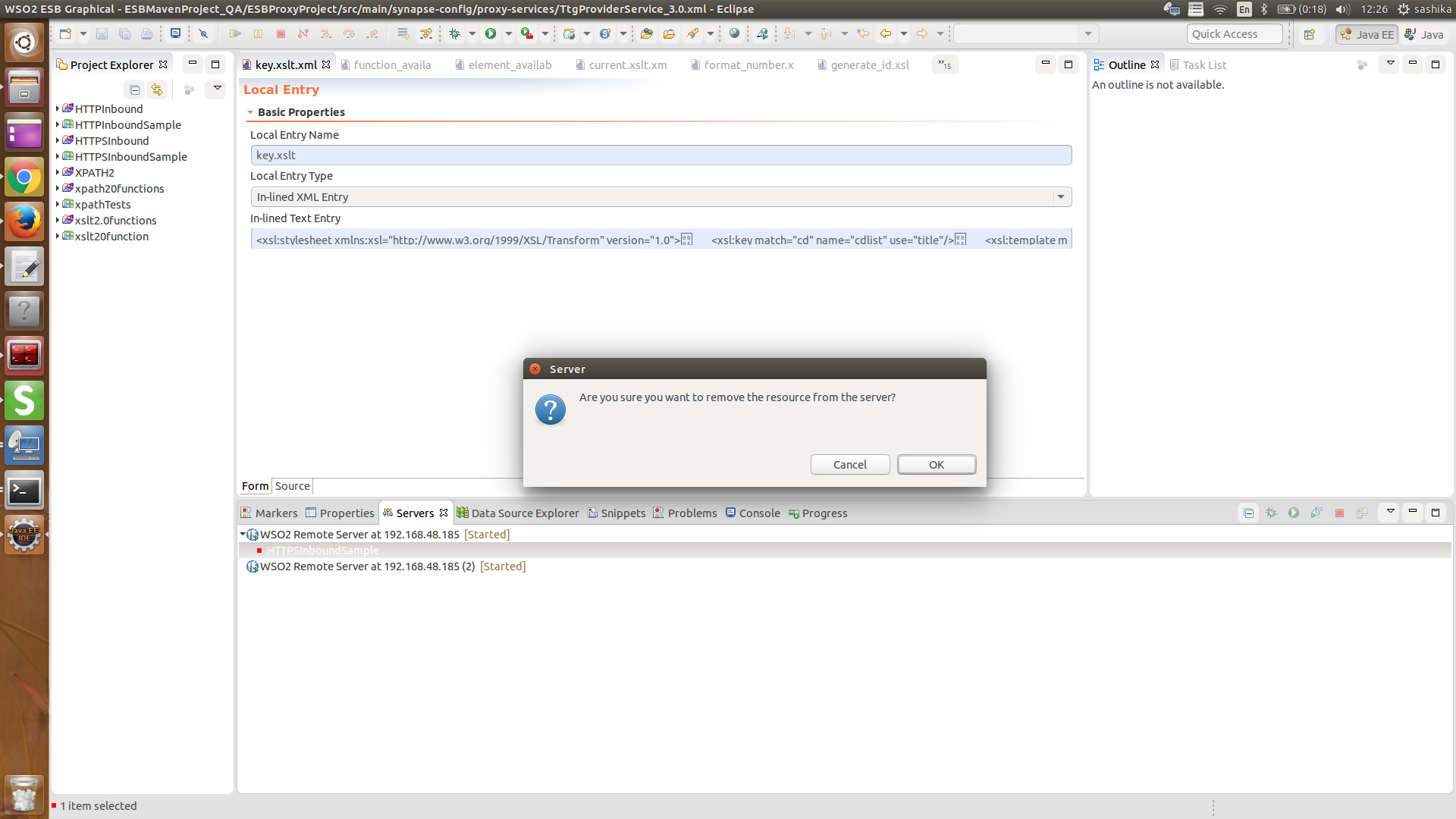
**Observations**
Resource did not remove from the remote server. But removed from the Dev Studio window
|
1.0
|
Resources removed through the dev studio did not removed from the remote server - Environment
OS - ubuntu 15.10
Java - JDK jdk1.8.0_66
Dev studio with updates (EI611)
Remote Server - Running in windows server 2012 R2
**Steps to recreate the issue**
1. Create a new Remote Server connection with an artefact to deploy
2. Verify that the artefact deployed successfully in the server
3. Remove the resource from the Dev Studio
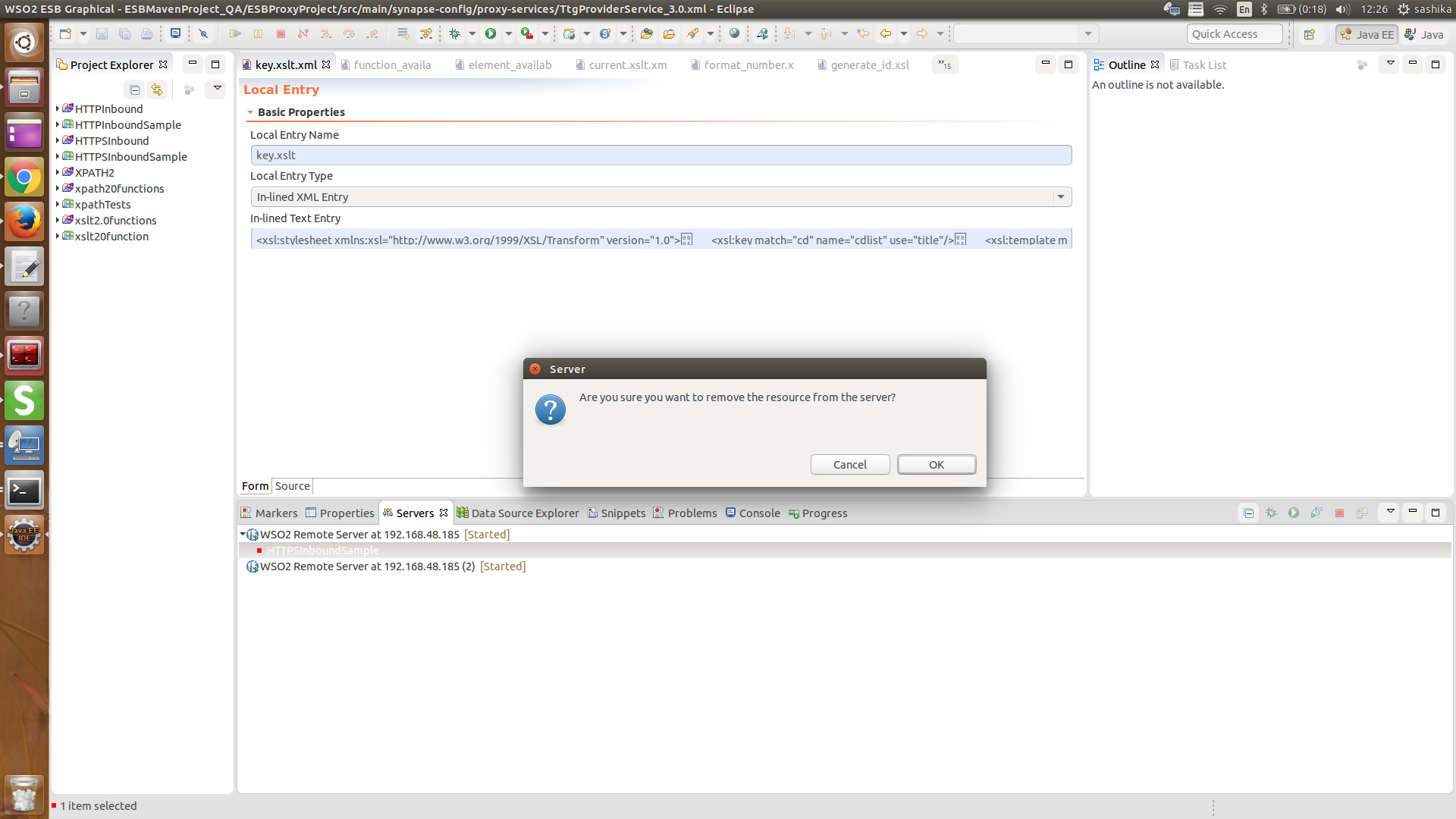
**Observations**
Resource did not remove from the remote server. But removed from the Dev Studio window
|
non_process
|
resources removed through the dev studio did not removed from the remote server environment os ubuntu java jdk dev studio with updates remote server running in windows server steps to recreate the issue create a new remote server connection with an artefact to deploy verify that the artefact deployed successfully in the server remove the resource from the dev studio observations resource did not remove from the remote server but removed from the dev studio window
| 0
|
125,622
| 17,836,454,500
|
IssuesEvent
|
2021-09-03 02:15:43
|
kstring/traefik
|
https://api.github.com/repos/kstring/traefik
|
opened
|
CVE-2021-37713 (High) detected in tar-4.4.8.tgz
|
security vulnerability
|
## CVE-2021-37713 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tar-4.4.8.tgz</b></p></summary>
<p>tar for node</p>
<p>Library home page: <a href="https://registry.npmjs.org/tar/-/tar-4.4.8.tgz">https://registry.npmjs.org/tar/-/tar-4.4.8.tgz</a></p>
<p>
Dependency Hierarchy:
- mocha-webpack-2.0.0-beta.0.tgz (Root Library)
- chokidar-2.1.8.tgz
- fsevents-1.2.9.tgz
- node-pre-gyp-0.12.0.tgz
- :x: **tar-4.4.8.tgz** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The npm package "tar" (aka node-tar) before versions 4.4.18, 5.0.10, and 6.1.9 has an arbitrary file creation/overwrite and arbitrary code execution vulnerability. node-tar aims to guarantee that any file whose location would be outside of the extraction target directory is not extracted. This is, in part, accomplished by sanitizing absolute paths of entries within the archive, skipping archive entries that contain `..` path portions, and resolving the sanitized paths against the extraction target directory. This logic was insufficient on Windows systems when extracting tar files that contained a path that was not an absolute path, but specified a drive letter different from the extraction target, such as `C:some\path`. If the drive letter does not match the extraction target, for example `D:\extraction\dir`, then the result of `path.resolve(extractionDirectory, entryPath)` would resolve against the current working directory on the `C:` drive, rather than the extraction target directory. Additionally, a `..` portion of the path could occur immediately after the drive letter, such as `C:../foo`, and was not properly sanitized by the logic that checked for `..` within the normalized and split portions of the path. This only affects users of `node-tar` on Windows systems. These issues were addressed in releases 4.4.18, 5.0.10 and 6.1.9. The v3 branch of node-tar has been deprecated and did not receive patches for these issues. If you are still using a v3 release we recommend you update to a more recent version of node-tar. There is no reasonable way to work around this issue without performing the same path normalization procedures that node-tar now does. Users are encouraged to upgrade to the latest patched versions of node-tar, rather than attempt to sanitize paths themselves.
<p>Publish Date: 2021-08-31
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-37713>CVE-2021-37713</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.2</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/npm/node-tar/security/advisories/GHSA-5955-9wpr-37jh">https://github.com/npm/node-tar/security/advisories/GHSA-5955-9wpr-37jh</a></p>
<p>Release Date: 2021-08-31</p>
<p>Fix Resolution: tar - 4.4.18, 5.0.10, 6.1.9</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2021-37713 (High) detected in tar-4.4.8.tgz - ## CVE-2021-37713 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tar-4.4.8.tgz</b></p></summary>
<p>tar for node</p>
<p>Library home page: <a href="https://registry.npmjs.org/tar/-/tar-4.4.8.tgz">https://registry.npmjs.org/tar/-/tar-4.4.8.tgz</a></p>
<p>
Dependency Hierarchy:
- mocha-webpack-2.0.0-beta.0.tgz (Root Library)
- chokidar-2.1.8.tgz
- fsevents-1.2.9.tgz
- node-pre-gyp-0.12.0.tgz
- :x: **tar-4.4.8.tgz** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The npm package "tar" (aka node-tar) before versions 4.4.18, 5.0.10, and 6.1.9 has an arbitrary file creation/overwrite and arbitrary code execution vulnerability. node-tar aims to guarantee that any file whose location would be outside of the extraction target directory is not extracted. This is, in part, accomplished by sanitizing absolute paths of entries within the archive, skipping archive entries that contain `..` path portions, and resolving the sanitized paths against the extraction target directory. This logic was insufficient on Windows systems when extracting tar files that contained a path that was not an absolute path, but specified a drive letter different from the extraction target, such as `C:some\path`. If the drive letter does not match the extraction target, for example `D:\extraction\dir`, then the result of `path.resolve(extractionDirectory, entryPath)` would resolve against the current working directory on the `C:` drive, rather than the extraction target directory. Additionally, a `..` portion of the path could occur immediately after the drive letter, such as `C:../foo`, and was not properly sanitized by the logic that checked for `..` within the normalized and split portions of the path. This only affects users of `node-tar` on Windows systems. These issues were addressed in releases 4.4.18, 5.0.10 and 6.1.9. The v3 branch of node-tar has been deprecated and did not receive patches for these issues. If you are still using a v3 release we recommend you update to a more recent version of node-tar. There is no reasonable way to work around this issue without performing the same path normalization procedures that node-tar now does. Users are encouraged to upgrade to the latest patched versions of node-tar, rather than attempt to sanitize paths themselves.
<p>Publish Date: 2021-08-31
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-37713>CVE-2021-37713</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.2</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/npm/node-tar/security/advisories/GHSA-5955-9wpr-37jh">https://github.com/npm/node-tar/security/advisories/GHSA-5955-9wpr-37jh</a></p>
<p>Release Date: 2021-08-31</p>
<p>Fix Resolution: tar - 4.4.18, 5.0.10, 6.1.9</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_process
|
cve high detected in tar tgz cve high severity vulnerability vulnerable library tar tgz tar for node library home page a href dependency hierarchy mocha webpack beta tgz root library chokidar tgz fsevents tgz node pre gyp tgz x tar tgz vulnerable library found in base branch master vulnerability details the npm package tar aka node tar before versions and has an arbitrary file creation overwrite and arbitrary code execution vulnerability node tar aims to guarantee that any file whose location would be outside of the extraction target directory is not extracted this is in part accomplished by sanitizing absolute paths of entries within the archive skipping archive entries that contain path portions and resolving the sanitized paths against the extraction target directory this logic was insufficient on windows systems when extracting tar files that contained a path that was not an absolute path but specified a drive letter different from the extraction target such as c some path if the drive letter does not match the extraction target for example d extraction dir then the result of path resolve extractiondirectory entrypath would resolve against the current working directory on the c drive rather than the extraction target directory additionally a portion of the path could occur immediately after the drive letter such as c foo and was not properly sanitized by the logic that checked for within the normalized and split portions of the path this only affects users of node tar on windows systems these issues were addressed in releases and the branch of node tar has been deprecated and did not receive patches for these issues if you are still using a release we recommend you update to a more recent version of node tar there is no reasonable way to work around this issue without performing the same path normalization procedures that node tar now does users are encouraged to upgrade to the latest patched versions of node tar rather than attempt to sanitize paths themselves publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact high integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution tar step up your open source security game with whitesource
| 0
|
15,286
| 19,286,431,409
|
IssuesEvent
|
2021-12-11 02:51:45
|
allinurl/goaccess
|
https://api.github.com/repos/allinurl/goaccess
|
closed
|
Failed Requests counter not working
|
question log-processing
|
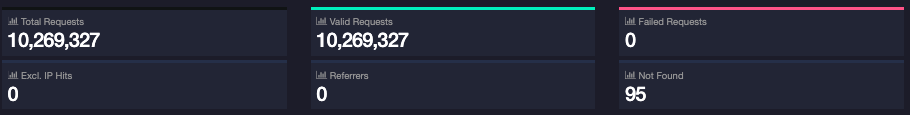
Hi,
I have recently started using GoAccess. Everything is working great, except for one thing.
Failed Requests counter always shows 0, but in status codes, I can see that there are many failed requests by status code.
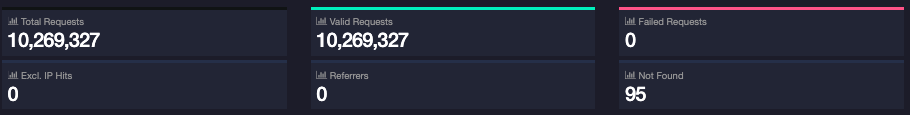

I tried to find some config related to this but with no luck. The version used is 1.5.1. Please advice...
|
1.0
|
Failed Requests counter not working - Hi,
I have recently started using GoAccess. Everything is working great, except for one thing.
Failed Requests counter always shows 0, but in status codes, I can see that there are many failed requests by status code.

I tried to find some config related to this but with no luck. The version used is 1.5.1. Please advice...
|
process
|
failed requests counter not working hi i have recently started using goaccess everything is working great except for one thing failed requests counter always shows but in status codes i can see that there are many failed requests by status code i tried to find some config related to this but with no luck the version used is please advice
| 1
|
9,354
| 12,366,367,301
|
IssuesEvent
|
2020-05-18 10:19:28
|
DiSSCo/user-stories
|
https://api.github.com/repos/DiSSCo/user-stories
|
opened
|
contribution indicators as citizen scientist
|
1. NH museum 4. Data processing ICEDIG-SURVEY Research Specimen level
|
As a Citizen scientist I want to be recognized as contributor so that I can apply for funding to digitize my own collections for this I need contribution indicators as contributor
|
1.0
|
contribution indicators as citizen scientist - As a Citizen scientist I want to be recognized as contributor so that I can apply for funding to digitize my own collections for this I need contribution indicators as contributor
|
process
|
contribution indicators as citizen scientist as a citizen scientist i want to be recognized as contributor so that i can apply for funding to digitize my own collections for this i need contribution indicators as contributor
| 1
|
16,783
| 21,969,940,302
|
IssuesEvent
|
2022-05-25 02:02:23
|
quark-engine/quark-engine
|
https://api.github.com/repos/quark-engine/quark-engine
|
closed
|
Fix README content
|
issue-processing-state-06
|
The README content below needs to update.
The Quark version in the demo image is outdated, and the title doesn't fit the content.
> ## Available In
> <img src="https://i.imgur.com/nz4m8kr.png"/>
>
> [](https://asciinema.org/a/416810)
|
1.0
|
Fix README content - The README content below needs to update.
The Quark version in the demo image is outdated, and the title doesn't fit the content.
> ## Available In
> <img src="https://i.imgur.com/nz4m8kr.png"/>
>
> [](https://asciinema.org/a/416810)
|
process
|
fix readme content the readme content below needs to update the quark version in the demo image is outdated and the title doesn t fit the content available in img src
| 1
|
13,328
| 15,788,808,176
|
IssuesEvent
|
2021-04-01 21:25:26
|
bazelbuild/bazel
|
https://api.github.com/repos/bazelbuild/bazel
|
opened
|
Add capability to serve head docs as https://docs.bazel.build/versions/head/...
|
team-XProduct type: process untriaged
|
This is a would be a convenient first step towards #12200
- versions/master/... and versions/head/... would both serve the same document
- this allows us to change all of the /docs/... tree and bazel-website before renaming the branch itself.
Next steps after all .md files are fixed
- in Bazel CI, push tarball under the new branch name
- eventually, stop serving the old links.
@philwo @floriographygoth
|
1.0
|
Add capability to serve head docs as https://docs.bazel.build/versions/head/... - This is a would be a convenient first step towards #12200
- versions/master/... and versions/head/... would both serve the same document
- this allows us to change all of the /docs/... tree and bazel-website before renaming the branch itself.
Next steps after all .md files are fixed
- in Bazel CI, push tarball under the new branch name
- eventually, stop serving the old links.
@philwo @floriographygoth
|
process
|
add capability to serve head docs as this is a would be a convenient first step towards versions master and versions head would both serve the same document this allows us to change all of the docs tree and bazel website before renaming the branch itself next steps after all md files are fixed in bazel ci push tarball under the new branch name eventually stop serving the old links philwo floriographygoth
| 1
|
380,241
| 26,409,815,372
|
IssuesEvent
|
2023-01-13 11:12:48
|
kula-app/OnLaunch-iOS-Client
|
https://api.github.com/repos/kula-app/OnLaunch-iOS-Client
|
opened
|
Add CONTRIBUTING guide
|
documentation
|
Many Open Source projects on GitHub use a special file called `CONTRIBUTING.md` to describe how the contribution process is defined. This might need to be written according to grants.
Docs:
- https://docs.github.com/en/communities/setting-up-your-project-for-healthy-contributions/setting-guidelines-for-repository-contributors
- https://docs.github.com/en/communities/setting-up-your-project-for-healthy-contributions/creating-a-default-community-health-file
Examples:
- https://github.com/Alamofire/Alamofire/blob/master/CONTRIBUTING.md
- https://github.com/yonaskolb/XcodeGen/blob/master/CONTRIBUTING.md
|
1.0
|
Add CONTRIBUTING guide - Many Open Source projects on GitHub use a special file called `CONTRIBUTING.md` to describe how the contribution process is defined. This might need to be written according to grants.
Docs:
- https://docs.github.com/en/communities/setting-up-your-project-for-healthy-contributions/setting-guidelines-for-repository-contributors
- https://docs.github.com/en/communities/setting-up-your-project-for-healthy-contributions/creating-a-default-community-health-file
Examples:
- https://github.com/Alamofire/Alamofire/blob/master/CONTRIBUTING.md
- https://github.com/yonaskolb/XcodeGen/blob/master/CONTRIBUTING.md
|
non_process
|
add contributing guide many open source projects on github use a special file called contributing md to describe how the contribution process is defined this might need to be written according to grants docs examples
| 0
|
22,721
| 32,040,520,504
|
IssuesEvent
|
2023-09-22 18:54:24
|
metabase/metabase
|
https://api.github.com/repos/metabase/metabase
|
closed
|
Can't aggregate with a custom column that uses coalesce
|
Type:Bug Priority:P2 .Regression Querying/Notebook/Custom Column .Team/QueryProcessor :hammer_and_wrench:
|
### Describe the bug
When you have a custom column that is a number created by a coalesce in the custom column, you can not choose it in the Summarize section for math aggregations.
### To Reproduce
1. Go to Sample Data
2. Click on Orders
3. Join to the People table
4. Create a custom column, "Zero":
<img width="357" alt="image" src="https://github.com/metabase/metabase/assets/22856340/3df8074c-00c1-4e11-9098-e9092f99a57f">
5. Create another custom column, "Total with Zeros":
<img width="305" alt="image" src="https://github.com/metabase/metabase/assets/22856340/5b2a6daf-fc57-4b45-b4db-913f37318768">
6. Go to the Summarize section, choose "Sum of" and attempt to pick "Total with Zeros"
### Expected behavior
It should allow you to pick a custom column that is a number created with a coalesce function
### Logs
_No response_
### Information about your Metabase installation
```JSON
It does not work on master or 47
It does work in 1.45.3.1 and 1.46.6.1-latest patch
```
### Severity
It's pretty annoying. Also not sure what happens if you upgrade - will these reports stop working?
### Additional context
_No response_
|
1.0
|
Can't aggregate with a custom column that uses coalesce - ### Describe the bug
When you have a custom column that is a number created by a coalesce in the custom column, you can not choose it in the Summarize section for math aggregations.
### To Reproduce
1. Go to Sample Data
2. Click on Orders
3. Join to the People table
4. Create a custom column, "Zero":
<img width="357" alt="image" src="https://github.com/metabase/metabase/assets/22856340/3df8074c-00c1-4e11-9098-e9092f99a57f">
5. Create another custom column, "Total with Zeros":
<img width="305" alt="image" src="https://github.com/metabase/metabase/assets/22856340/5b2a6daf-fc57-4b45-b4db-913f37318768">
6. Go to the Summarize section, choose "Sum of" and attempt to pick "Total with Zeros"
### Expected behavior
It should allow you to pick a custom column that is a number created with a coalesce function
### Logs
_No response_
### Information about your Metabase installation
```JSON
It does not work on master or 47
It does work in 1.45.3.1 and 1.46.6.1-latest patch
```
### Severity
It's pretty annoying. Also not sure what happens if you upgrade - will these reports stop working?
### Additional context
_No response_
|
process
|
can t aggregate with a custom column that uses coalesce describe the bug when you have a custom column that is a number created by a coalesce in the custom column you can not choose it in the summarize section for math aggregations to reproduce go to sample data click on orders join to the people table create a custom column zero img width alt image src create another custom column total with zeros img width alt image src go to the summarize section choose sum of and attempt to pick total with zeros expected behavior it should allow you to pick a custom column that is a number created with a coalesce function logs no response information about your metabase installation json it does not work on master or it does work in and latest patch severity it s pretty annoying also not sure what happens if you upgrade will these reports stop working additional context no response
| 1
|
21,314
| 28,508,018,921
|
IssuesEvent
|
2023-04-19 00:02:06
|
metabase/metabase
|
https://api.github.com/repos/metabase/metabase
|
closed
|
[MLv2] Finish implementing temporal bucketing
|
.metabase-lib .Team/QueryProcessor :hammer_and_wrench:
|
- We have `lib.temporal-bucket/temporal-bucket*` right now but we should make sure you can actually use it in real life given the sorts of `:metadata/field` objects the FE lib will actually be using.
- Need a corresponding multimethod to get the temporal bucket associated with a `:metadata/field` or `:field` ref. For `:metadata/field`, it should be saved with a namespaced key.
- Need to be able to remove a temporal bucketing unit
- Need a function to get available units for a given field/field metadata/etc.
- all temporal unit manipulation should happen thru this instead of accessing options or specific keys in the metadata directly.
- If metadata has a temporal unit, then generated `:field-ref`s should include it.
- Temporal unit SHOULD NOT be propagated to the next stage of a query.
- Base type should be updated appropriately based on the unit.
|
1.0
|
[MLv2] Finish implementing temporal bucketing - - We have `lib.temporal-bucket/temporal-bucket*` right now but we should make sure you can actually use it in real life given the sorts of `:metadata/field` objects the FE lib will actually be using.
- Need a corresponding multimethod to get the temporal bucket associated with a `:metadata/field` or `:field` ref. For `:metadata/field`, it should be saved with a namespaced key.
- Need to be able to remove a temporal bucketing unit
- Need a function to get available units for a given field/field metadata/etc.
- all temporal unit manipulation should happen thru this instead of accessing options or specific keys in the metadata directly.
- If metadata has a temporal unit, then generated `:field-ref`s should include it.
- Temporal unit SHOULD NOT be propagated to the next stage of a query.
- Base type should be updated appropriately based on the unit.
|
process
|
finish implementing temporal bucketing we have lib temporal bucket temporal bucket right now but we should make sure you can actually use it in real life given the sorts of metadata field objects the fe lib will actually be using need a corresponding multimethod to get the temporal bucket associated with a metadata field or field ref for metadata field it should be saved with a namespaced key need to be able to remove a temporal bucketing unit need a function to get available units for a given field field metadata etc all temporal unit manipulation should happen thru this instead of accessing options or specific keys in the metadata directly if metadata has a temporal unit then generated field ref s should include it temporal unit should not be propagated to the next stage of a query base type should be updated appropriately based on the unit
| 1
|
40,120
| 20,594,841,731
|
IssuesEvent
|
2022-03-05 10:18:40
|
git-baboo/easy-review
|
https://api.github.com/repos/git-baboo/easy-review
|
closed
|
認証後の画面遷移が遅い問題の解消
|
performance
|
## ✨ 概要
認証後の画面遷移がもっさりしているため、快適に動作するよう改善する。
## 🔥 ゴール
<!-- 例) 〇〇ができる、xxなときに△△する -->
- 認証後の画面遷移が快適に行われる(遅くとも1秒以内に遷移したい)
|
True
|
認証後の画面遷移が遅い問題の解消 - ## ✨ 概要
認証後の画面遷移がもっさりしているため、快適に動作するよう改善する。
## 🔥 ゴール
<!-- 例) 〇〇ができる、xxなときに△△する -->
- 認証後の画面遷移が快適に行われる(遅くとも1秒以内に遷移したい)
|
non_process
|
認証後の画面遷移が遅い問題の解消 ✨ 概要 認証後の画面遷移がもっさりしているため、快適に動作するよう改善する。 🔥 ゴール 認証後の画面遷移が快適に行われる( )
| 0
|
6,276
| 9,247,577,251
|
IssuesEvent
|
2019-03-15 01:29:31
|
googleapis/google-http-java-client
|
https://api.github.com/repos/googleapis/google-http-java-client
|
closed
|
Remove dependency on apache artifact
|
type: process
|
We removed backwards compatibility in `google-http-client` see #606 for more detail. Once we release a new major version, remove the direct dependency between `google-http-client` and `google-http-client-apache`
|
1.0
|
Remove dependency on apache artifact - We removed backwards compatibility in `google-http-client` see #606 for more detail. Once we release a new major version, remove the direct dependency between `google-http-client` and `google-http-client-apache`
|
process
|
remove dependency on apache artifact we removed backwards compatibility in google http client see for more detail once we release a new major version remove the direct dependency between google http client and google http client apache
| 1
|
17,316
| 23,138,168,261
|
IssuesEvent
|
2022-07-28 15:53:12
|
ORNL-AMO/AMO-Tools-Desktop
|
https://api.github.com/repos/ORNL-AMO/AMO-Tools-Desktop
|
closed
|
Process Heating Result units
|
bug Process Heating important
|
When set independent result units (custom results?) switches to MMBTU/hr and will not change


|
1.0
|
Process Heating Result units - When set independent result units (custom results?) switches to MMBTU/hr and will not change


|
process
|
process heating result units when set independent result units custom results switches to mmbtu hr and will not change
| 1
|
14,934
| 18,360,792,789
|
IssuesEvent
|
2021-10-09 06:57:11
|
yandali-damian/LIM015-social-network
|
https://api.github.com/repos/yandali-damian/LIM015-social-network
|
reopened
|
USER HISTORY - 003
|
Good issues Process
|
Como usuario logeado debo poder publicar, visualizar, modificar y eliminar una publicación
- tareas
- [x] estructura HTML de home
> - [x] barra de navegación
> - [x] perfil
> > - [x] mostrar los post personales
> > - [x] Agregar botón para editar foto y nombre
> > - [x] agregar, mostrar ,editar, eliminar
> >> - [x] Imput para realizar publicación
> >> - [x] btn superior en c/u de los post para editar, eliminar
> >> - [x] Alerta modal antes de eliminar un post
> - [x] post home
> > - [x] Crear un botón para mostrar el modal
> >> - [x] Función para mostrar el modal
> > - [x] Crear un modal para publicar un post
> >> - [x] Agregar textarea para el contenido del post
> >> - [x] Agregar botón de publicar
> >> - [x] Agregar botón de cerrar
> >> - [x] Agregar opción de agregar una foto
> >> - [x] Función para publicar post
> >> - [x] Función para cerrar post
> > - [x] agregar, mostrar ,editar, eliminar (personales)
> > - [x] Mostrar post en la vista home
> >> - [x] btn superior en c/u de los post personales para editar, eliminar
> >> - [x] Alerta modal antes de eliminar un post
> >> - [x] ocultar btn superior de los post para editar y eliminar
- [x] home responsive
|
1.0
|
USER HISTORY - 003 - Como usuario logeado debo poder publicar, visualizar, modificar y eliminar una publicación
- tareas
- [x] estructura HTML de home
> - [x] barra de navegación
> - [x] perfil
> > - [x] mostrar los post personales
> > - [x] Agregar botón para editar foto y nombre
> > - [x] agregar, mostrar ,editar, eliminar
> >> - [x] Imput para realizar publicación
> >> - [x] btn superior en c/u de los post para editar, eliminar
> >> - [x] Alerta modal antes de eliminar un post
> - [x] post home
> > - [x] Crear un botón para mostrar el modal
> >> - [x] Función para mostrar el modal
> > - [x] Crear un modal para publicar un post
> >> - [x] Agregar textarea para el contenido del post
> >> - [x] Agregar botón de publicar
> >> - [x] Agregar botón de cerrar
> >> - [x] Agregar opción de agregar una foto
> >> - [x] Función para publicar post
> >> - [x] Función para cerrar post
> > - [x] agregar, mostrar ,editar, eliminar (personales)
> > - [x] Mostrar post en la vista home
> >> - [x] btn superior en c/u de los post personales para editar, eliminar
> >> - [x] Alerta modal antes de eliminar un post
> >> - [x] ocultar btn superior de los post para editar y eliminar
- [x] home responsive
|
process
|
user history como usuario logeado debo poder publicar visualizar modificar y eliminar una publicación tareas estructura html de home barra de navegación perfil mostrar los post personales agregar botón para editar foto y nombre agregar mostrar editar eliminar imput para realizar publicación btn superior en c u de los post para editar eliminar alerta modal antes de eliminar un post post home crear un botón para mostrar el modal función para mostrar el modal crear un modal para publicar un post agregar textarea para el contenido del post agregar botón de publicar agregar botón de cerrar agregar opción de agregar una foto función para publicar post función para cerrar post agregar mostrar editar eliminar personales mostrar post en la vista home btn superior en c u de los post personales para editar eliminar alerta modal antes de eliminar un post ocultar btn superior de los post para editar y eliminar home responsive
| 1
|
18,162
| 24,199,270,830
|
IssuesEvent
|
2022-09-24 10:16:35
|
vladimiry/ElectronMail
|
https://api.github.com/repos/vladimiry/ElectronMail
|
closed
|
Error message on Linux app
|
glitch workaround-exists env-dependent env: linux timeout: webview load timeout: main process
|
Hi,
I have error message with the linux app image, 4.13.2 (but i have too before with 4.13.1).
I use a debian unstable. The messages not appear at the start, but later.
Invocation timeout of calling "dbGetAccountMetadata" method on "electron-mail:ipcMain-api" channel with 25000ms timeout
And several times this :
Uncaught (in promise): Error: Failed to wait for "webview" service provider initialization (timeout: 15000ms).
Error: Failed to wait for "webview" service provider initialization (timeout: 15000ms).
at file:///tmp/.mount_electrUbjAFi/resources/app.asar/app/web/browser-window/index.mjs:34027:47
at doInnerSub (file:///tmp/.mount_electrUbjAFi/resources/app.asar/app/web/browser-window/index.mjs:27768:68)
at outerNext (file:///tmp/.mount_electrUbjAFi/resources/app.asar/app/web/browser-window/index.mjs:27762:38)
at OperatorSubscriber._this._next (file:///tmp/.mount_electrUbjAFi/resources/app.asar/app/web/browser-window/index.mjs:26507:13)
at OperatorSubscriber.Subscriber.next (file:///tmp/.mount_electrUbjAFi/resources/app.asar/app/web/browser-window/index.mjs:25633:97)
at AsyncAction.<anonymous> (file:///tmp/.mount_electrUbjAFi/resources/app.asar/app/web/browser-window/index.mjs:26434:24)
at AsyncAction._execute (file:///tmp/.mount_electrUbjAFi/resources/app.asar/app/web/browser-window/index.mjs:29637:16)
at AsyncAction.execute (file:///tmp/.mount_electrUbjAFi/resources/app.asar/app/web/browser-window/index.mjs:29630:26)
at AsyncScheduler.flush (file:///tmp/.mount_electrUbjAFi/resources/app.asar/app/web/browser-window/index.mjs:29687:30)
at args.<computed> (file:///tmp/.mount_electrUbjAFi/resources/app.asar/app/web/browser-window/index.mjs:32939:37)
So, if you can sort it out.
I'm not a specialist, so I don't know what's going on.
Good luck, and thank you for your work, this is an application that I really like.
Thouareg
|
1.0
|
Error message on Linux app - Hi,
I have error message with the linux app image, 4.13.2 (but i have too before with 4.13.1).
I use a debian unstable. The messages not appear at the start, but later.
Invocation timeout of calling "dbGetAccountMetadata" method on "electron-mail:ipcMain-api" channel with 25000ms timeout
And several times this :
Uncaught (in promise): Error: Failed to wait for "webview" service provider initialization (timeout: 15000ms).
Error: Failed to wait for "webview" service provider initialization (timeout: 15000ms).
at file:///tmp/.mount_electrUbjAFi/resources/app.asar/app/web/browser-window/index.mjs:34027:47
at doInnerSub (file:///tmp/.mount_electrUbjAFi/resources/app.asar/app/web/browser-window/index.mjs:27768:68)
at outerNext (file:///tmp/.mount_electrUbjAFi/resources/app.asar/app/web/browser-window/index.mjs:27762:38)
at OperatorSubscriber._this._next (file:///tmp/.mount_electrUbjAFi/resources/app.asar/app/web/browser-window/index.mjs:26507:13)
at OperatorSubscriber.Subscriber.next (file:///tmp/.mount_electrUbjAFi/resources/app.asar/app/web/browser-window/index.mjs:25633:97)
at AsyncAction.<anonymous> (file:///tmp/.mount_electrUbjAFi/resources/app.asar/app/web/browser-window/index.mjs:26434:24)
at AsyncAction._execute (file:///tmp/.mount_electrUbjAFi/resources/app.asar/app/web/browser-window/index.mjs:29637:16)
at AsyncAction.execute (file:///tmp/.mount_electrUbjAFi/resources/app.asar/app/web/browser-window/index.mjs:29630:26)
at AsyncScheduler.flush (file:///tmp/.mount_electrUbjAFi/resources/app.asar/app/web/browser-window/index.mjs:29687:30)
at args.<computed> (file:///tmp/.mount_electrUbjAFi/resources/app.asar/app/web/browser-window/index.mjs:32939:37)
So, if you can sort it out.
I'm not a specialist, so I don't know what's going on.
Good luck, and thank you for your work, this is an application that I really like.
Thouareg
|
process
|
error message on linux app hi i have error message with the linux app image but i have too before with i use a debian unstable the messages not appear at the start but later invocation timeout of calling dbgetaccountmetadata method on electron mail ipcmain api channel with timeout and several times this uncaught in promise error failed to wait for webview service provider initialization timeout error failed to wait for webview service provider initialization timeout at file tmp mount electrubjafi resources app asar app web browser window index mjs at doinnersub file tmp mount electrubjafi resources app asar app web browser window index mjs at outernext file tmp mount electrubjafi resources app asar app web browser window index mjs at operatorsubscriber this next file tmp mount electrubjafi resources app asar app web browser window index mjs at operatorsubscriber subscriber next file tmp mount electrubjafi resources app asar app web browser window index mjs at asyncaction file tmp mount electrubjafi resources app asar app web browser window index mjs at asyncaction execute file tmp mount electrubjafi resources app asar app web browser window index mjs at asyncaction execute file tmp mount electrubjafi resources app asar app web browser window index mjs at asyncscheduler flush file tmp mount electrubjafi resources app asar app web browser window index mjs at args file tmp mount electrubjafi resources app asar app web browser window index mjs so if you can sort it out i m not a specialist so i don t know what s going on good luck and thank you for your work this is an application that i really like thouareg
| 1
|
18,043
| 24,053,583,381
|
IssuesEvent
|
2022-09-16 14:48:29
|
hashicorp/terraform-cdk
|
https://api.github.com/repos/hashicorp/terraform-cdk
|
opened
|
Add Github Action to build API docs for PRs
|
enhancement dev-process
|
<!--- Please keep this note for the community --->
### Community Note
- Please vote on this issue by adding a 👍 [reaction](https://blog.github.com/2016-03-10-add-reactions-to-pull-requests-issues-and-comments/) to the original issue to help the community and maintainers prioritize this request
- Please do not leave "+1" or other comments that do not add relevant new information or questions, they generate extra noise for issue followers and do not help prioritize the request
- If you are interested in working on this issue or have submitted a pull request, please leave a comment
<!--- Thank you for keeping this note for the community --->
### Description
Currently we do have a precommit hook that runs `yarn generate-docs:api` (if changes were made to the `cdktf` package). This runs between 3 to 6 minutes and interrupts the workflow.
We should change this to be a Github Workflow that runs on PRs and makes a commit if the docs were outdated (i.e. if running that command produced changes).
<!--- Please leave a helpful description of the feature request here. --->
<!--- Information about code formatting: https://help.github.com/articles/basic-writing-and-formatting-syntax/#quoting-code --->
### References
<!---
Information about referencing Github Issues: https://help.github.com/articles/basic-writing-and-formatting-syntax/#referencing-issues-and-pull-requests
Are there any other GitHub issues (open or closed) or pull requests that should be linked here? Vendor blog posts or documentation?
--->
|
1.0
|
Add Github Action to build API docs for PRs - <!--- Please keep this note for the community --->
### Community Note
- Please vote on this issue by adding a 👍 [reaction](https://blog.github.com/2016-03-10-add-reactions-to-pull-requests-issues-and-comments/) to the original issue to help the community and maintainers prioritize this request
- Please do not leave "+1" or other comments that do not add relevant new information or questions, they generate extra noise for issue followers and do not help prioritize the request
- If you are interested in working on this issue or have submitted a pull request, please leave a comment
<!--- Thank you for keeping this note for the community --->
### Description
Currently we do have a precommit hook that runs `yarn generate-docs:api` (if changes were made to the `cdktf` package). This runs between 3 to 6 minutes and interrupts the workflow.
We should change this to be a Github Workflow that runs on PRs and makes a commit if the docs were outdated (i.e. if running that command produced changes).
<!--- Please leave a helpful description of the feature request here. --->
<!--- Information about code formatting: https://help.github.com/articles/basic-writing-and-formatting-syntax/#quoting-code --->
### References
<!---
Information about referencing Github Issues: https://help.github.com/articles/basic-writing-and-formatting-syntax/#referencing-issues-and-pull-requests
Are there any other GitHub issues (open or closed) or pull requests that should be linked here? Vendor blog posts or documentation?
--->
|
process
|
add github action to build api docs for prs community note please vote on this issue by adding a 👍 to the original issue to help the community and maintainers prioritize this request please do not leave or other comments that do not add relevant new information or questions they generate extra noise for issue followers and do not help prioritize the request if you are interested in working on this issue or have submitted a pull request please leave a comment description currently we do have a precommit hook that runs yarn generate docs api if changes were made to the cdktf package this runs between to minutes and interrupts the workflow we should change this to be a github workflow that runs on prs and makes a commit if the docs were outdated i e if running that command produced changes references information about referencing github issues are there any other github issues open or closed or pull requests that should be linked here vendor blog posts or documentation
| 1
|
15,170
| 18,941,718,299
|
IssuesEvent
|
2021-11-18 04:15:46
|
neuropsychology/NeuroKit
|
https://api.github.com/repos/neuropsychology/NeuroKit
|
opened
|
Generic function for 1/f noise
|
signal processing :chart_with_upwards_trend: Complexity/Chaos :bomb:
|
Would be good to have a generic `signal_1f` function to measure 1/f noise in particular for eeg and ecg signals (many papers have been published on this e.g., see [example](https://www.jneurosci.org/content/jneuro/35/38/13257.full.pdf))
To-do:
- [ ] Dissociate the functionalities for our existing [fractal_psdslope](https://github.com/neuropsychology/NeuroKit/blob/master/neurokit2/complexity/fractal_psdslope.py#L8) - slope itself should be computed in `signal_1f` and this can then be embedded into `fractal_psdslope` which converts to an estimate of fractal dimension
- [ ] Additional parameter considerations for computing 1/f (ref [FOOOF](https://github.com/fooof-tools/fooof) tool)
|
1.0
|
Generic function for 1/f noise - Would be good to have a generic `signal_1f` function to measure 1/f noise in particular for eeg and ecg signals (many papers have been published on this e.g., see [example](https://www.jneurosci.org/content/jneuro/35/38/13257.full.pdf))
To-do:
- [ ] Dissociate the functionalities for our existing [fractal_psdslope](https://github.com/neuropsychology/NeuroKit/blob/master/neurokit2/complexity/fractal_psdslope.py#L8) - slope itself should be computed in `signal_1f` and this can then be embedded into `fractal_psdslope` which converts to an estimate of fractal dimension
- [ ] Additional parameter considerations for computing 1/f (ref [FOOOF](https://github.com/fooof-tools/fooof) tool)
|
process
|
generic function for f noise would be good to have a generic signal function to measure f noise in particular for eeg and ecg signals many papers have been published on this e g see to do dissociate the functionalities for our existing slope itself should be computed in signal and this can then be embedded into fractal psdslope which converts to an estimate of fractal dimension additional parameter considerations for computing f ref tool
| 1
|
4,732
| 7,573,267,797
|
IssuesEvent
|
2018-04-23 17:15:15
|
nodejs/node
|
https://api.github.com/repos/nodejs/node
|
closed
|
child_process.spawn adds flags that might cause non-native shells to fail on windows
|
Windows Subsystem for Linux (WSL) child_process windows
|
<!--
Thank you for reporting an issue.
This issue tracker is for bugs and issues found within Node.js core.
If you require more general support please file an issue on our help
repo. https://github.com/nodejs/help
Please fill in as much of the template below as you're able.
Version: output of `node -v`
Platform: output of `uname -a` (UNIX), or version and 32 or 64-bit (Windows)
Subsystem: if known, please specify affected core module name
If possible, please provide code that demonstrates the problem, keeping it as
simple and free of external dependencies as you are able.
-->
* **Version**: 8.11.1
* **Platform**: Windows 10 64 bit
* **Subsystem**: child_process
<!-- Enter your issue details below this comment. -->
On Windows, when child_process.spawn is given the optional shell parameter (#4598) it makes an assumption that the shell would understand the /c /s flags (cmd.exe or powershell).
This limits the option to use bash (using [WSL](https://github.com/Microsoft/WSL)) on windows.
Can by bypassed by:
```
args = ["\"", cmd].concat(args, "\"");
currentSync = child.spawn("bash -c", args, {stdio: 'pipe', shell: "cmd.exe"});
```
But would be nice to have a better solution.
Thanks,
Idan
|
1.0
|
child_process.spawn adds flags that might cause non-native shells to fail on windows - <!--
Thank you for reporting an issue.
This issue tracker is for bugs and issues found within Node.js core.
If you require more general support please file an issue on our help
repo. https://github.com/nodejs/help
Please fill in as much of the template below as you're able.
Version: output of `node -v`
Platform: output of `uname -a` (UNIX), or version and 32 or 64-bit (Windows)
Subsystem: if known, please specify affected core module name
If possible, please provide code that demonstrates the problem, keeping it as
simple and free of external dependencies as you are able.
-->
* **Version**: 8.11.1
* **Platform**: Windows 10 64 bit
* **Subsystem**: child_process
<!-- Enter your issue details below this comment. -->
On Windows, when child_process.spawn is given the optional shell parameter (#4598) it makes an assumption that the shell would understand the /c /s flags (cmd.exe or powershell).
This limits the option to use bash (using [WSL](https://github.com/Microsoft/WSL)) on windows.
Can by bypassed by:
```
args = ["\"", cmd].concat(args, "\"");
currentSync = child.spawn("bash -c", args, {stdio: 'pipe', shell: "cmd.exe"});
```
But would be nice to have a better solution.
Thanks,
Idan
|
process
|
child process spawn adds flags that might cause non native shells to fail on windows thank you for reporting an issue this issue tracker is for bugs and issues found within node js core if you require more general support please file an issue on our help repo please fill in as much of the template below as you re able version output of node v platform output of uname a unix or version and or bit windows subsystem if known please specify affected core module name if possible please provide code that demonstrates the problem keeping it as simple and free of external dependencies as you are able version platform windows bit subsystem child process on windows when child process spawn is given the optional shell parameter it makes an assumption that the shell would understand the c s flags cmd exe or powershell this limits the option to use bash using on windows can by bypassed by args concat args currentsync child spawn bash c args stdio pipe shell cmd exe but would be nice to have a better solution thanks idan
| 1
|
142
| 2,575,872,000
|
IssuesEvent
|
2015-02-12 03:23:34
|
dominikwilkowski/bronzies
|
https://api.github.com/repos/dominikwilkowski/bronzies
|
closed
|
Create new RESTful API
|
In process
|
I will create a RESTful API for all apps to talk together. This will just handle the questions and high score and won't have a `delete` verb.
|
1.0
|
Create new RESTful API - I will create a RESTful API for all apps to talk together. This will just handle the questions and high score and won't have a `delete` verb.
|
process
|
create new restful api i will create a restful api for all apps to talk together this will just handle the questions and high score and won t have a delete verb
| 1
|
5,984
| 8,805,374,079
|
IssuesEvent
|
2018-12-26 19:13:49
|
dita-ot/dita-ot
|
https://api.github.com/repos/dita-ot/dita-ot
|
closed
|
Related links not processed if map stored in a directory with space character in name
|
bug preprocess priority/medium stale
|
If a map is stored in a directory containing a space character in name the module for the [write] task (class org.dita.dost.writer.DitaLinksWriter) does not process the links in the topics (the links to other topics with role="parent", role="next", role="previous", etc). The fix is very simple: just replace the line 317 which is:
```
file = filename;
```
with something like:
```
file = URLUtil.uncorrect(filename);
```
where the call URLUtil.uncorrect() just replaces each "%20" substring with a space character.
|
1.0
|
Related links not processed if map stored in a directory with space character in name - If a map is stored in a directory containing a space character in name the module for the [write] task (class org.dita.dost.writer.DitaLinksWriter) does not process the links in the topics (the links to other topics with role="parent", role="next", role="previous", etc). The fix is very simple: just replace the line 317 which is:
```
file = filename;
```
with something like:
```
file = URLUtil.uncorrect(filename);
```
where the call URLUtil.uncorrect() just replaces each "%20" substring with a space character.
|
process
|
related links not processed if map stored in a directory with space character in name if a map is stored in a directory containing a space character in name the module for the task class org dita dost writer ditalinkswriter does not process the links in the topics the links to other topics with role parent role next role previous etc the fix is very simple just replace the line which is file filename with something like file urlutil uncorrect filename where the call urlutil uncorrect just replaces each substring with a space character
| 1
|
16,659
| 21,727,157,709
|
IssuesEvent
|
2022-05-11 08:42:56
|
digitalmethodsinitiative/4cat
|
https://api.github.com/repos/digitalmethodsinitiative/4cat
|
opened
|
URL Expansion
|
enhancement processors
|
We have an 'expand URLs' processor, but it only works on top-level datasets. Since expansion takes a long time, it can also be useful to first e.g. extract the x most-used URLs and then expand them; but this is currently not possible. A more generically applicable processor would therefore be useful.
|
1.0
|
URL Expansion - We have an 'expand URLs' processor, but it only works on top-level datasets. Since expansion takes a long time, it can also be useful to first e.g. extract the x most-used URLs and then expand them; but this is currently not possible. A more generically applicable processor would therefore be useful.
|
process
|
url expansion we have an expand urls processor but it only works on top level datasets since expansion takes a long time it can also be useful to first e g extract the x most used urls and then expand them but this is currently not possible a more generically applicable processor would therefore be useful
| 1
|
1,512
| 4,104,102,097
|
IssuesEvent
|
2016-06-05 05:02:34
|
nodejs/node
|
https://api.github.com/repos/nodejs/node
|
closed
|
process.kill can't kill process group on Windows
|
process windows
|
Per [process.kill doc](https://nodejs.org/api/process.html#process_process_kill_pid_signal), it "Send a signal to **a** process". That indicates the API is intended to be used against a single process. However, it then refers to [kill(2) man page][1], which states that the API can also be used against a process group, when `pid < -1`. On Windows, it clearly doesn't support the `pid < -1` case.
Node.js is intended to provide a consistent bahavior as much as possible for cross-platform developing. That means either this support should be added for Windows, or document should be updated and warns developers on the usage.
See Unitech/pm2/issues/1664 for more detail.
```
> var x = child_process.exec('notepad');
undefined
> x.pid
3040
> process.kill(-x.pid)
Error: kill ESRCH
at exports._errnoException (util.js:874:11)
at process.kill (node.js:774:15)
at repl:1:9
at REPLServer.defaultEval (repl.js:164:27)
at bound (domain.js:280:14)
at REPLServer.runBound [as eval] (domain.js:293:12)
at REPLServer.<anonymous> (repl.js:393:12)
at emitOne (events.js:82:20)
at REPLServer.emit (events.js:169:7)
at REPLServer.Interface._onLine (readline.js:210:10)
```
[1]: https://www.google.com/url?sa=t&rct=j&q=&esrc=s&source=web&cd=1&cad=rja&uact=8&ved=0CB4QFjAAahUKEwic7Ovc0-3IAhUQ3GMKHajtABU&url=http%3A%2F%2Flinux.die.net%2Fman%2F2%2Fkill&usg=AFQjCNF7UvxdWGS7UqFYhevXVNkjp8zykw&sig2=N8IE71uYPK42Qf_GPnBqAA
|
1.0
|
process.kill can't kill process group on Windows - Per [process.kill doc](https://nodejs.org/api/process.html#process_process_kill_pid_signal), it "Send a signal to **a** process". That indicates the API is intended to be used against a single process. However, it then refers to [kill(2) man page][1], which states that the API can also be used against a process group, when `pid < -1`. On Windows, it clearly doesn't support the `pid < -1` case.
Node.js is intended to provide a consistent bahavior as much as possible for cross-platform developing. That means either this support should be added for Windows, or document should be updated and warns developers on the usage.
See Unitech/pm2/issues/1664 for more detail.
```
> var x = child_process.exec('notepad');
undefined
> x.pid
3040
> process.kill(-x.pid)
Error: kill ESRCH
at exports._errnoException (util.js:874:11)
at process.kill (node.js:774:15)
at repl:1:9
at REPLServer.defaultEval (repl.js:164:27)
at bound (domain.js:280:14)
at REPLServer.runBound [as eval] (domain.js:293:12)
at REPLServer.<anonymous> (repl.js:393:12)
at emitOne (events.js:82:20)
at REPLServer.emit (events.js:169:7)
at REPLServer.Interface._onLine (readline.js:210:10)
```
[1]: https://www.google.com/url?sa=t&rct=j&q=&esrc=s&source=web&cd=1&cad=rja&uact=8&ved=0CB4QFjAAahUKEwic7Ovc0-3IAhUQ3GMKHajtABU&url=http%3A%2F%2Flinux.die.net%2Fman%2F2%2Fkill&usg=AFQjCNF7UvxdWGS7UqFYhevXVNkjp8zykw&sig2=N8IE71uYPK42Qf_GPnBqAA
|
process
|
process kill can t kill process group on windows per it send a signal to a process that indicates the api is intended to be used against a single process however it then refers to which states that the api can also be used against a process group when pid on windows it clearly doesn t support the pid case node js is intended to provide a consistent bahavior as much as possible for cross platform developing that means either this support should be added for windows or document should be updated and warns developers on the usage see unitech issues for more detail var x child process exec notepad undefined x pid process kill x pid error kill esrch at exports errnoexception util js at process kill node js at repl at replserver defaulteval repl js at bound domain js at replserver runbound domain js at replserver repl js at emitone events js at replserver emit events js at replserver interface online readline js
| 1
|
4,650
| 7,495,214,634
|
IssuesEvent
|
2018-04-07 18:24:36
|
w3c/vc-data-model
|
https://api.github.com/repos/w3c/vc-data-model
|
closed
|
Data Model in Context of Keys, Signatures & Countersignatures
|
Discuss ValidationProcess
|
One of my challenges with the current data model focus of the WG is how it connects to the signatures of that data model. As an implementor, I find that confuses me when I consider claim + one or more signatures.
Lets take a simple verifiable claim (from the [Verifiable Claims Playground](https://w3c-vc.github.io/playground/), which may not be current):
```
{
"@context": "https://schema.org/",
"claim": {
"id": "did:ALICE",
"name": "Alice",
"knows": {
"id": "did:BOB",
"name": "Bob"
}
}
}
```
When signed by one of the signing keys that is available from Alice's set of DID signing keys, it is a claim from an issuer, and has the trust level / authority that you give to that issuer. Is a claim signed any other way invalid?
When both signed by one of the signing keys that is available from Alice's set of DID signing keys AND SEPARATELY by one of the signing keys that is available from Bob's set of DID signing keys, I think this may have greater authority, as if you trust either Bob or Alice it has trust level authority of them individually, but with both signatures it has the trust authority of both.
If signed by Alice, and the entire structure (including signature) is signed by Bob, what does that mean differently than the previous?
When signed ONLY by one of the signing keys that is available from Bob's set of signing keys, but not Alice's, what is it?
When it also signed by a third party (in addition to either Alice's or Bob's keys), that could be a witness claim.
But when it is signed by a third party (w/o Alice's or Bob's keys), what is that? An evidence claim?
When a signed claim above also has a time signature in it (a verifiable time stamp), what does that mean?
I presume if it was signed by an otherwise valid key, but not one that is designated as a signing key, then that claim should be considered invalid?
So in general, as an implementor, how do I know that the signing expresses the intent of the signer about the claim?
|
1.0
|
Data Model in Context of Keys, Signatures & Countersignatures - One of my challenges with the current data model focus of the WG is how it connects to the signatures of that data model. As an implementor, I find that confuses me when I consider claim + one or more signatures.
Lets take a simple verifiable claim (from the [Verifiable Claims Playground](https://w3c-vc.github.io/playground/), which may not be current):
```
{
"@context": "https://schema.org/",
"claim": {
"id": "did:ALICE",
"name": "Alice",
"knows": {
"id": "did:BOB",
"name": "Bob"
}
}
}
```
When signed by one of the signing keys that is available from Alice's set of DID signing keys, it is a claim from an issuer, and has the trust level / authority that you give to that issuer. Is a claim signed any other way invalid?
When both signed by one of the signing keys that is available from Alice's set of DID signing keys AND SEPARATELY by one of the signing keys that is available from Bob's set of DID signing keys, I think this may have greater authority, as if you trust either Bob or Alice it has trust level authority of them individually, but with both signatures it has the trust authority of both.
If signed by Alice, and the entire structure (including signature) is signed by Bob, what does that mean differently than the previous?
When signed ONLY by one of the signing keys that is available from Bob's set of signing keys, but not Alice's, what is it?
When it also signed by a third party (in addition to either Alice's or Bob's keys), that could be a witness claim.
But when it is signed by a third party (w/o Alice's or Bob's keys), what is that? An evidence claim?
When a signed claim above also has a time signature in it (a verifiable time stamp), what does that mean?
I presume if it was signed by an otherwise valid key, but not one that is designated as a signing key, then that claim should be considered invalid?
So in general, as an implementor, how do I know that the signing expresses the intent of the signer about the claim?
|
process
|
data model in context of keys signatures countersignatures one of my challenges with the current data model focus of the wg is how it connects to the signatures of that data model as an implementor i find that confuses me when i consider claim one or more signatures lets take a simple verifiable claim from the which may not be current context claim id did alice name alice knows id did bob name bob when signed by one of the signing keys that is available from alice s set of did signing keys it is a claim from an issuer and has the trust level authority that you give to that issuer is a claim signed any other way invalid when both signed by one of the signing keys that is available from alice s set of did signing keys and separately by one of the signing keys that is available from bob s set of did signing keys i think this may have greater authority as if you trust either bob or alice it has trust level authority of them individually but with both signatures it has the trust authority of both if signed by alice and the entire structure including signature is signed by bob what does that mean differently than the previous when signed only by one of the signing keys that is available from bob s set of signing keys but not alice s what is it when it also signed by a third party in addition to either alice s or bob s keys that could be a witness claim but when it is signed by a third party w o alice s or bob s keys what is that an evidence claim when a signed claim above also has a time signature in it a verifiable time stamp what does that mean i presume if it was signed by an otherwise valid key but not one that is designated as a signing key then that claim should be considered invalid so in general as an implementor how do i know that the signing expresses the intent of the signer about the claim
| 1
|
86,051
| 15,755,321,558
|
IssuesEvent
|
2021-03-31 01:34:13
|
ysmanohar/DashBoard
|
https://api.github.com/repos/ysmanohar/DashBoard
|
opened
|
CVE-2020-7598 (Medium) detected in multiple libraries
|
security vulnerability
|
## CVE-2020-7598 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>minimist-0.0.8.tgz</b>, <b>minimist-0.0.10.tgz</b>, <b>minimist-1.2.0.tgz</b></p></summary>
<p>
<details><summary><b>minimist-0.0.8.tgz</b></p></summary>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-0.0.8.tgz">https://registry.npmjs.org/minimist/-/minimist-0.0.8.tgz</a></p>
<p>Path to dependency file: /DashBoard/bower_components/shadycss/package.json</p>
<p>Path to vulnerable library: DashBoard/bower_components/test-fixture/node_modules/mkdirp/node_modules/minimist/package.json,DashBoard/bower_components/test-fixture/node_modules/mkdirp/node_modules/minimist/package.json,DashBoard/bower_components/test-fixture/node_modules/mkdirp/node_modules/minimist/package.json,DashBoard/bower_components/test-fixture/node_modules/mkdirp/node_modules/minimist/package.json,DashBoard/bower_components/test-fixture/node_modules/mkdirp/node_modules/minimist/package.json,DashBoard/bower_components/test-fixture/node_modules/mkdirp/node_modules/minimist/package.json,DashBoard/bower_components/test-fixture/node_modules/mkdirp/node_modules/minimist/package.json,DashBoard/bower_components/test-fixture/node_modules/mkdirp/node_modules/minimist/package.json,DashBoard/bower_components/test-fixture/node_modules/mkdirp/node_modules/minimist/package.json,DashBoard/bower_components/test-fixture/node_modules/mkdirp/node_modules/minimist/package.json,DashBoard/bower_components/test-fixture/node_modules/mkdirp/node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- istanbul-0.3.22.tgz (Root Library)
- mkdirp-0.5.1.tgz
- :x: **minimist-0.0.8.tgz** (Vulnerable Library)
</details>
<details><summary><b>minimist-0.0.10.tgz</b></p></summary>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-0.0.10.tgz">https://registry.npmjs.org/minimist/-/minimist-0.0.10.tgz</a></p>
<p>Path to dependency file: /DashBoard/bower_components/test-fixture/package.json</p>
<p>Path to vulnerable library: DashBoard/bower_components/test-fixture/node_modules/minimist/package.json,DashBoard/bower_components/test-fixture/node_modules/minimist/package.json,DashBoard/bower_components/test-fixture/node_modules/minimist/package.json,DashBoard/bower_components/test-fixture/node_modules/minimist/package.json,DashBoard/bower_components/test-fixture/node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- karma-0.13.22.tgz (Root Library)
- optimist-0.6.1.tgz
- :x: **minimist-0.0.10.tgz** (Vulnerable Library)
</details>
<details><summary><b>minimist-1.2.0.tgz</b></p></summary>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-1.2.0.tgz">https://registry.npmjs.org/minimist/-/minimist-1.2.0.tgz</a></p>
<p>Path to dependency file: /DashBoard/bower_components/prism/package.json</p>
<p>Path to vulnerable library: DashBoard/bower_components/test-fixture/node_modules/meow/node_modules/minimist/package.json,DashBoard/bower_components/test-fixture/node_modules/meow/node_modules/minimist/package.json,DashBoard/bower_components/test-fixture/node_modules/meow/node_modules/minimist/package.json,DashBoard/bower_components/test-fixture/node_modules/meow/node_modules/minimist/package.json,DashBoard/bower_components/test-fixture/node_modules/meow/node_modules/minimist/package.json,DashBoard/bower_components/test-fixture/node_modules/meow/node_modules/minimist/package.json,DashBoard/bower_components/test-fixture/node_modules/meow/node_modules/minimist/package.json,DashBoard/bower_components/test-fixture/node_modules/meow/node_modules/minimist/package.json,DashBoard/bower_components/test-fixture/node_modules/meow/node_modules/minimist/package.json,DashBoard/bower_components/test-fixture/node_modules/meow/node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- gulp-3.9.1.tgz (Root Library)
- :x: **minimist-1.2.0.tgz** (Vulnerable Library)
</details>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
minimist before 1.2.2 could be tricked into adding or modifying properties of Object.prototype using a "constructor" or "__proto__" payload.
<p>Publish Date: 2020-03-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7598>CVE-2020-7598</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.6</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/substack/minimist/commit/63e7ed05aa4b1889ec2f3b196426db4500cbda94">https://github.com/substack/minimist/commit/63e7ed05aa4b1889ec2f3b196426db4500cbda94</a></p>
<p>Release Date: 2020-03-11</p>
<p>Fix Resolution: minimist - 0.2.1,1.2.3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2020-7598 (Medium) detected in multiple libraries - ## CVE-2020-7598 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>minimist-0.0.8.tgz</b>, <b>minimist-0.0.10.tgz</b>, <b>minimist-1.2.0.tgz</b></p></summary>
<p>
<details><summary><b>minimist-0.0.8.tgz</b></p></summary>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-0.0.8.tgz">https://registry.npmjs.org/minimist/-/minimist-0.0.8.tgz</a></p>
<p>Path to dependency file: /DashBoard/bower_components/shadycss/package.json</p>
<p>Path to vulnerable library: DashBoard/bower_components/test-fixture/node_modules/mkdirp/node_modules/minimist/package.json,DashBoard/bower_components/test-fixture/node_modules/mkdirp/node_modules/minimist/package.json,DashBoard/bower_components/test-fixture/node_modules/mkdirp/node_modules/minimist/package.json,DashBoard/bower_components/test-fixture/node_modules/mkdirp/node_modules/minimist/package.json,DashBoard/bower_components/test-fixture/node_modules/mkdirp/node_modules/minimist/package.json,DashBoard/bower_components/test-fixture/node_modules/mkdirp/node_modules/minimist/package.json,DashBoard/bower_components/test-fixture/node_modules/mkdirp/node_modules/minimist/package.json,DashBoard/bower_components/test-fixture/node_modules/mkdirp/node_modules/minimist/package.json,DashBoard/bower_components/test-fixture/node_modules/mkdirp/node_modules/minimist/package.json,DashBoard/bower_components/test-fixture/node_modules/mkdirp/node_modules/minimist/package.json,DashBoard/bower_components/test-fixture/node_modules/mkdirp/node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- istanbul-0.3.22.tgz (Root Library)
- mkdirp-0.5.1.tgz
- :x: **minimist-0.0.8.tgz** (Vulnerable Library)
</details>
<details><summary><b>minimist-0.0.10.tgz</b></p></summary>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-0.0.10.tgz">https://registry.npmjs.org/minimist/-/minimist-0.0.10.tgz</a></p>
<p>Path to dependency file: /DashBoard/bower_components/test-fixture/package.json</p>
<p>Path to vulnerable library: DashBoard/bower_components/test-fixture/node_modules/minimist/package.json,DashBoard/bower_components/test-fixture/node_modules/minimist/package.json,DashBoard/bower_components/test-fixture/node_modules/minimist/package.json,DashBoard/bower_components/test-fixture/node_modules/minimist/package.json,DashBoard/bower_components/test-fixture/node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- karma-0.13.22.tgz (Root Library)
- optimist-0.6.1.tgz
- :x: **minimist-0.0.10.tgz** (Vulnerable Library)
</details>
<details><summary><b>minimist-1.2.0.tgz</b></p></summary>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-1.2.0.tgz">https://registry.npmjs.org/minimist/-/minimist-1.2.0.tgz</a></p>
<p>Path to dependency file: /DashBoard/bower_components/prism/package.json</p>
<p>Path to vulnerable library: DashBoard/bower_components/test-fixture/node_modules/meow/node_modules/minimist/package.json,DashBoard/bower_components/test-fixture/node_modules/meow/node_modules/minimist/package.json,DashBoard/bower_components/test-fixture/node_modules/meow/node_modules/minimist/package.json,DashBoard/bower_components/test-fixture/node_modules/meow/node_modules/minimist/package.json,DashBoard/bower_components/test-fixture/node_modules/meow/node_modules/minimist/package.json,DashBoard/bower_components/test-fixture/node_modules/meow/node_modules/minimist/package.json,DashBoard/bower_components/test-fixture/node_modules/meow/node_modules/minimist/package.json,DashBoard/bower_components/test-fixture/node_modules/meow/node_modules/minimist/package.json,DashBoard/bower_components/test-fixture/node_modules/meow/node_modules/minimist/package.json,DashBoard/bower_components/test-fixture/node_modules/meow/node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- gulp-3.9.1.tgz (Root Library)
- :x: **minimist-1.2.0.tgz** (Vulnerable Library)
</details>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
minimist before 1.2.2 could be tricked into adding or modifying properties of Object.prototype using a "constructor" or "__proto__" payload.
<p>Publish Date: 2020-03-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7598>CVE-2020-7598</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.6</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/substack/minimist/commit/63e7ed05aa4b1889ec2f3b196426db4500cbda94">https://github.com/substack/minimist/commit/63e7ed05aa4b1889ec2f3b196426db4500cbda94</a></p>
<p>Release Date: 2020-03-11</p>
<p>Fix Resolution: minimist - 0.2.1,1.2.3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_process
|
cve medium detected in multiple libraries cve medium severity vulnerability vulnerable libraries minimist tgz minimist tgz minimist tgz minimist tgz parse argument options library home page a href path to dependency file dashboard bower components shadycss package json path to vulnerable library dashboard bower components test fixture node modules mkdirp node modules minimist package json dashboard bower components test fixture node modules mkdirp node modules minimist package json dashboard bower components test fixture node modules mkdirp node modules minimist package json dashboard bower components test fixture node modules mkdirp node modules minimist package json dashboard bower components test fixture node modules mkdirp node modules minimist package json dashboard bower components test fixture node modules mkdirp node modules minimist package json dashboard bower components test fixture node modules mkdirp node modules minimist package json dashboard bower components test fixture node modules mkdirp node modules minimist package json dashboard bower components test fixture node modules mkdirp node modules minimist package json dashboard bower components test fixture node modules mkdirp node modules minimist package json dashboard bower components test fixture node modules mkdirp node modules minimist package json dependency hierarchy istanbul tgz root library mkdirp tgz x minimist tgz vulnerable library minimist tgz parse argument options library home page a href path to dependency file dashboard bower components test fixture package json path to vulnerable library dashboard bower components test fixture node modules minimist package json dashboard bower components test fixture node modules minimist package json dashboard bower components test fixture node modules minimist package json dashboard bower components test fixture node modules minimist package json dashboard bower components test fixture node modules minimist package json dependency hierarchy karma tgz root library optimist tgz x minimist tgz vulnerable library minimist tgz parse argument options library home page a href path to dependency file dashboard bower components prism package json path to vulnerable library dashboard bower components test fixture node modules meow node modules minimist package json dashboard bower components test fixture node modules meow node modules minimist package json dashboard bower components test fixture node modules meow node modules minimist package json dashboard bower components test fixture node modules meow node modules minimist package json dashboard bower components test fixture node modules meow node modules minimist package json dashboard bower components test fixture node modules meow node modules minimist package json dashboard bower components test fixture node modules meow node modules minimist package json dashboard bower components test fixture node modules meow node modules minimist package json dashboard bower components test fixture node modules meow node modules minimist package json dashboard bower components test fixture node modules meow node modules minimist package json dependency hierarchy gulp tgz root library x minimist tgz vulnerable library vulnerability details minimist before could be tricked into adding or modifying properties of object prototype using a constructor or proto payload publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution minimist step up your open source security game with whitesource
| 0
|
4,347
| 6,550,078,315
|
IssuesEvent
|
2017-09-05 09:35:25
|
GovernIB/portafib
|
https://api.github.com/repos/GovernIB/portafib
|
closed
|
(7) Afegir mètodes o Serveis REST
|
Lloc:WebServices Prioritat:Normal Tipus:Documentacio Versio:1.1.3
|
-- Ve del tiquet #118 Millores per PortaFIB 2.0 --
Afegir els següent mètodes o serveis REST
(1) Mètode REST que retorni les peticions de firma pendents que té un usuari. (Avisos per cada ROL)
(2) Mètode REST que retorni el tipus de document disponibles
(3) Mètode REST echo per proves o per comprovació de credencials
|
1.0
|
(7) Afegir mètodes o Serveis REST - -- Ve del tiquet #118 Millores per PortaFIB 2.0 --
Afegir els següent mètodes o serveis REST
(1) Mètode REST que retorni les peticions de firma pendents que té un usuari. (Avisos per cada ROL)
(2) Mètode REST que retorni el tipus de document disponibles
(3) Mètode REST echo per proves o per comprovació de credencials
|
non_process
|
afegir mètodes o serveis rest ve del tiquet millores per portafib afegir els següent mètodes o serveis rest mètode rest que retorni les peticions de firma pendents que té un usuari avisos per cada rol mètode rest que retorni el tipus de document disponibles mètode rest echo per proves o per comprovació de credencials
| 0
|
54,645
| 13,796,777,381
|
IssuesEvent
|
2020-10-09 20:28:33
|
department-of-veterans-affairs/va.gov-cms
|
https://api.github.com/repos/department-of-veterans-affairs/va.gov-cms
|
closed
|
VA Forms "Owner" field defaults to wrong value
|
Defect VA Forms
|
VA Forms should all be owned by 'Forms' but the default value is 'Public Websites'.
**To Reproduce**
Steps to reproduce the behavior:
1. Go to https://prod.cms.va.gov/node/add/va_form
2. Confirm that 'Owner' field (in Governance section in right rail) is set to 'Public Websites Team'.
**Expected behavior**
The default value for Owner should be 'Forms'
|
1.0
|
VA Forms "Owner" field defaults to wrong value - VA Forms should all be owned by 'Forms' but the default value is 'Public Websites'.
**To Reproduce**
Steps to reproduce the behavior:
1. Go to https://prod.cms.va.gov/node/add/va_form
2. Confirm that 'Owner' field (in Governance section in right rail) is set to 'Public Websites Team'.
**Expected behavior**
The default value for Owner should be 'Forms'
|
non_process
|
va forms owner field defaults to wrong value va forms should all be owned by forms but the default value is public websites to reproduce steps to reproduce the behavior go to confirm that owner field in governance section in right rail is set to public websites team expected behavior the default value for owner should be forms
| 0
|
12,126
| 14,740,806,659
|
IssuesEvent
|
2021-01-07 09:39:30
|
kdjstudios/SABillingGitlab
|
https://api.github.com/repos/kdjstudios/SABillingGitlab
|
closed
|
Speed-E'z Exchange - Merge Accounts
|
anc-process anp-urgent ant-support
|
In GitLab by @kdjstudios on Dec 4, 2018, 08:51
**Submitted by:** <joann@speedez.com>
**Helpdesk:** http://www.servicedesk.answernet.com/profiles/ticket/6203379
**Server:** External
**Client/Site:** Speed Ez
**Account:** Multiple
**Issue:**
I created a new Parent Account on 1002 called Conviva Care Solutions Parent Account. I do not know how to attach the following EXISTING accounts, making them CHILD accounts on 1002. The manager wants one statement with Separate charges for each of the Accounts. I have checked SEPARATE on the Parent Account of 1002. The following accounts need to be Child Accounts: 5387 through 5396, 5191, 5166, 5411, 5412, 5403, 5405.
|
1.0
|
Speed-E'z Exchange - Merge Accounts - In GitLab by @kdjstudios on Dec 4, 2018, 08:51
**Submitted by:** <joann@speedez.com>
**Helpdesk:** http://www.servicedesk.answernet.com/profiles/ticket/6203379
**Server:** External
**Client/Site:** Speed Ez
**Account:** Multiple
**Issue:**
I created a new Parent Account on 1002 called Conviva Care Solutions Parent Account. I do not know how to attach the following EXISTING accounts, making them CHILD accounts on 1002. The manager wants one statement with Separate charges for each of the Accounts. I have checked SEPARATE on the Parent Account of 1002. The following accounts need to be Child Accounts: 5387 through 5396, 5191, 5166, 5411, 5412, 5403, 5405.
|
process
|
speed e z exchange merge accounts in gitlab by kdjstudios on dec submitted by helpdesk server external client site speed ez account multiple issue i created a new parent account on called conviva care solutions parent account i do not know how to attach the following existing accounts making them child accounts on the manager wants one statement with separate charges for each of the accounts i have checked separate on the parent account of the following accounts need to be child accounts through
| 1
|
20,551
| 6,898,056,729
|
IssuesEvent
|
2017-11-24 07:39:00
|
curl/curl
|
https://api.github.com/repos/curl/curl
|
closed
|
"make distclean" fails
|
build
|
### I did this
```
./buildconf
./configure
make distclean
```
### I expected the following
I expected that "make distclean" runs successfully. Instead I got this error message:
```
...
make[1]: Leaving directory '/home/pi/curl/include'
Making distclean in docs
make[1]: Entering directory '/home/pi/curl/docs'
make[1]: *** No rule to make target 'distclean'. Stop.
make[1]: Leaving directory '/home/pi/curl/docs'
Makefile:907: recipe for target 'distclean-recursive' failed
make: *** [distclean-recursive] Error 1
```
### curl/libcurl version
current curl master
### operating system
Linux
|
1.0
|
"make distclean" fails - ### I did this
```
./buildconf
./configure
make distclean
```
### I expected the following
I expected that "make distclean" runs successfully. Instead I got this error message:
```
...
make[1]: Leaving directory '/home/pi/curl/include'
Making distclean in docs
make[1]: Entering directory '/home/pi/curl/docs'
make[1]: *** No rule to make target 'distclean'. Stop.
make[1]: Leaving directory '/home/pi/curl/docs'
Makefile:907: recipe for target 'distclean-recursive' failed
make: *** [distclean-recursive] Error 1
```
### curl/libcurl version
current curl master
### operating system
Linux
|
non_process
|
make distclean fails i did this buildconf configure make distclean i expected the following i expected that make distclean runs successfully instead i got this error message make leaving directory home pi curl include making distclean in docs make entering directory home pi curl docs make no rule to make target distclean stop make leaving directory home pi curl docs makefile recipe for target distclean recursive failed make error curl libcurl version current curl master operating system linux
| 0
|
169,951
| 6,422,037,928
|
IssuesEvent
|
2017-08-09 07:19:10
|
mgoral/subconvert
|
https://api.github.com/repos/mgoral/subconvert
|
opened
|
Add CI job for Python 3.4
|
Internal improvement Low Priority
|
The problem is with pyqt. Qt releases PYPI versions only for Python 3.5+ and travis doesn't want to expose system-side packages to Python's virtualenv.
|
1.0
|
Add CI job for Python 3.4 - The problem is with pyqt. Qt releases PYPI versions only for Python 3.5+ and travis doesn't want to expose system-side packages to Python's virtualenv.
|
non_process
|
add ci job for python the problem is with pyqt qt releases pypi versions only for python and travis doesn t want to expose system side packages to python s virtualenv
| 0
|
3,239
| 6,299,924,044
|
IssuesEvent
|
2017-07-21 01:12:35
|
rubberduck-vba/Rubberduck
|
https://api.github.com/repos/rubberduck-vba/Rubberduck
|
opened
|
Base members of Document-type modules are not resolved
|
bug navigation parse-tree-processing
|
The user-defined members of a document-type class module **are** resolved, but the base members are **not**. This harks back to the dilemma of how to determine the real type of a document-type class. IIRC, we check the VBIDE.properties of the VBComponent to determine the type, but it seems we're not resolving the class as being of the underlying type, and as such, can't identify the base members.
```vb
'Excel
Debug.Print ThisWorkbook.ReadOnly 'ReadOnly NOT recognized
Debug.Print Sheet1.Range("A1").Value 'Value NOT recognized
Debug.Print Chart1.ChartColor 'ChartColor NOT recognized
'Word
Debug.Print ThisDocument.Name 'Name Not recoognized
```
Ref #3153
|
1.0
|
Base members of Document-type modules are not resolved - The user-defined members of a document-type class module **are** resolved, but the base members are **not**. This harks back to the dilemma of how to determine the real type of a document-type class. IIRC, we check the VBIDE.properties of the VBComponent to determine the type, but it seems we're not resolving the class as being of the underlying type, and as such, can't identify the base members.
```vb
'Excel
Debug.Print ThisWorkbook.ReadOnly 'ReadOnly NOT recognized
Debug.Print Sheet1.Range("A1").Value 'Value NOT recognized
Debug.Print Chart1.ChartColor 'ChartColor NOT recognized
'Word
Debug.Print ThisDocument.Name 'Name Not recoognized
```
Ref #3153
|
process
|
base members of document type modules are not resolved the user defined members of a document type class module are resolved but the base members are not this harks back to the dilemma of how to determine the real type of a document type class iirc we check the vbide properties of the vbcomponent to determine the type but it seems we re not resolving the class as being of the underlying type and as such can t identify the base members vb excel debug print thisworkbook readonly readonly not recognized debug print range value value not recognized debug print chartcolor chartcolor not recognized word debug print thisdocument name name not recoognized ref
| 1
|
14,870
| 10,221,252,918
|
IssuesEvent
|
2019-08-16 00:43:50
|
crossplaneio/crossplane
|
https://api.github.com/repos/crossplaneio/crossplane
|
closed
|
Migrate all Crossplane controllers to use kubebuilder 2.0.0 and controller-runtime -0.2.0
|
engineering feature services
|
https://github.com/kubernetes-sigs/kubebuilder/releases/tag/v2.0.0-alpha.2
https://github.com/kubernetes-sigs/controller-runtime/releases/tag/v0.2.0-beta.1
These new releases will likely include some breaking changes. It may be worth assessing how different they are and how soon we would like to upgrade before we invest significantly in standardising our controller patterns.
|
1.0
|
Migrate all Crossplane controllers to use kubebuilder 2.0.0 and controller-runtime -0.2.0 - https://github.com/kubernetes-sigs/kubebuilder/releases/tag/v2.0.0-alpha.2
https://github.com/kubernetes-sigs/controller-runtime/releases/tag/v0.2.0-beta.1
These new releases will likely include some breaking changes. It may be worth assessing how different they are and how soon we would like to upgrade before we invest significantly in standardising our controller patterns.
|
non_process
|
migrate all crossplane controllers to use kubebuilder and controller runtime these new releases will likely include some breaking changes it may be worth assessing how different they are and how soon we would like to upgrade before we invest significantly in standardising our controller patterns
| 0
|
108,405
| 4,344,045,302
|
IssuesEvent
|
2016-07-29 06:22:24
|
openshift/origin
|
https://api.github.com/repos/openshift/origin
|
closed
|
Cannot use bundled oc/kubectl against Kubernetes server
|
component/cli kind/bug priority/P1
|
When running `oc logs <podname>` (same with kubectl as symlink to same binary), returns `Error from server: the server could not find the requested resource`. Subcommands like `get pods` work fine though. Request logs available at https://gist.github.com/jimmidyson/c39576b5a4bad64bab74793d7a8edc9b. Discussed on IRC & looks like it's to do with discovery.
##### Version
oc v1.3.0-alpha.2+47578ec
kubernetes v1.3.0+57fb9ac
features: Basic-Auth
##### Steps To Reproduce
1. Start up kubernetes cluster (minikube's cool for this kinda stuff!)
2. Create a pod
3. Run `oc logs <podname>`
##### Current Result
`Error from server: the server could not find the requested resource`
##### Expected Result
Pod logs
|
1.0
|
Cannot use bundled oc/kubectl against Kubernetes server - When running `oc logs <podname>` (same with kubectl as symlink to same binary), returns `Error from server: the server could not find the requested resource`. Subcommands like `get pods` work fine though. Request logs available at https://gist.github.com/jimmidyson/c39576b5a4bad64bab74793d7a8edc9b. Discussed on IRC & looks like it's to do with discovery.
##### Version
oc v1.3.0-alpha.2+47578ec
kubernetes v1.3.0+57fb9ac
features: Basic-Auth
##### Steps To Reproduce
1. Start up kubernetes cluster (minikube's cool for this kinda stuff!)
2. Create a pod
3. Run `oc logs <podname>`
##### Current Result
`Error from server: the server could not find the requested resource`
##### Expected Result
Pod logs
|
non_process
|
cannot use bundled oc kubectl against kubernetes server when running oc logs same with kubectl as symlink to same binary returns error from server the server could not find the requested resource subcommands like get pods work fine though request logs available at discussed on irc looks like it s to do with discovery version oc alpha kubernetes features basic auth steps to reproduce start up kubernetes cluster minikube s cool for this kinda stuff create a pod run oc logs current result error from server the server could not find the requested resource expected result pod logs
| 0
|
690,879
| 23,675,768,149
|
IssuesEvent
|
2022-08-28 03:36:44
|
angelside/zebra-password-changer-cli-py
|
https://api.github.com/repos/angelside/zebra-password-changer-cli-py
|
closed
|
🔖 print("zebra-zpl-send-cli-py\n")
|
priority: low status: pending type: enhancement
|
It's not ZPL send, it's password reset!
```py
print("zebra-zpl-send-cli-py\n")
```
|
1.0
|
🔖 print("zebra-zpl-send-cli-py\n") - It's not ZPL send, it's password reset!
```py
print("zebra-zpl-send-cli-py\n")
```
|
non_process
|
🔖 print zebra zpl send cli py n it s not zpl send it s password reset py print zebra zpl send cli py n
| 0
|
274,474
| 23,841,671,526
|
IssuesEvent
|
2022-09-06 10:45:49
|
apache/shardingsphere
|
https://api.github.com/repos/apache/shardingsphere
|
closed
|
Add more unit test for ExplainStatementHandler
|
in: test project: OSD2022
|
Hi community,
This issue is for https://github.com/apache/shardingsphere/issues/20305.
## Aim
Add more unit tests for `ExplainStatementHandler` to test its public functions to improve unit test coverage.
Unit test coverage can be viewed at: https://app.codecov.io/gh/apache/shardingsphere/blobs/master/shardingsphere-sql-parser/shardingsphere-sql-parser-statement/src/main/java/org/apache/shardingsphere/sql/parser/sql/dialect/handler/dal/ExplainStatementHandler.java
## Basic Qualifications
- Java
- Maven
- Junit
|
1.0
|
Add more unit test for ExplainStatementHandler - Hi community,
This issue is for https://github.com/apache/shardingsphere/issues/20305.
## Aim
Add more unit tests for `ExplainStatementHandler` to test its public functions to improve unit test coverage.
Unit test coverage can be viewed at: https://app.codecov.io/gh/apache/shardingsphere/blobs/master/shardingsphere-sql-parser/shardingsphere-sql-parser-statement/src/main/java/org/apache/shardingsphere/sql/parser/sql/dialect/handler/dal/ExplainStatementHandler.java
## Basic Qualifications
- Java
- Maven
- Junit
|
non_process
|
add more unit test for explainstatementhandler hi community this issue is for aim add more unit tests for explainstatementhandler to test its public functions to improve unit test coverage unit test coverage can be viewed at basic qualifications java maven junit
| 0
|
43,113
| 11,160,346,368
|
IssuesEvent
|
2019-12-26 09:22:52
|
ChrisCummins/phd
|
https://api.github.com/repos/ChrisCummins/phd
|
opened
|
phd_build Dockerfile and DEPS.txt do redundant work
|
Build System
|
The DEPS.txt files describe the setup commands, which are then copied into the Dockerfile for phd_build. This is fragile and labor-intensive to maintain. Instead, the phd_build Dockerfile could run the bootstrap script.
|
1.0
|
phd_build Dockerfile and DEPS.txt do redundant work - The DEPS.txt files describe the setup commands, which are then copied into the Dockerfile for phd_build. This is fragile and labor-intensive to maintain. Instead, the phd_build Dockerfile could run the bootstrap script.
|
non_process
|
phd build dockerfile and deps txt do redundant work the deps txt files describe the setup commands which are then copied into the dockerfile for phd build this is fragile and labor intensive to maintain instead the phd build dockerfile could run the bootstrap script
| 0
|
37,773
| 5,142,799,367
|
IssuesEvent
|
2017-01-12 14:23:46
|
IDgis/geoportaal-test
|
https://api.github.com/repos/IDgis/geoportaal-test
|
closed
|
Beveiliging inlog en ip-whitelist
|
gebruikerstest wens
|
Aandachtspunt ivm beveiliging: de metadata en gekoppelde bestanden bij gebruikersrestricties hebben staan "intern", die zijn niet via de url te benaderen voor buitenstaanders. Alleen als je bent ingelogged, dan kan je "je eigen geleverde" data en metadata zien.
let op: bij het huidige geoportaal kan je door het aanpassen van de url's ook de gekoppelde bestanden zien, van bestanden die "intern" zouden moeten zijn. Nu zijn deze dus ook extern beschikbaar. Dit moet bij het nieuwe Geoportaal niet meer mogelijk zijn: interne bestanden en metadata die voor "intern" zijn, die kan je alleen benaderen als je werkt op het provinciehuis in Zwolle (met ip-whitelist, mogelijk enkele andere ip-adressen hier ook aan toevoegen)
Vraag is, of dat ook goed gaat met toevoegen van data: hiervoor moet je inloggen. Maar moet je dan ook altijd dat doen via ip van provinciehuis? Nu is dat nog niet zo: ik kan overal inloggen en data en metadata bekijken.
Opmerking nr 29 bij testresultaten 3-2-2016

|
1.0
|
Beveiliging inlog en ip-whitelist - Aandachtspunt ivm beveiliging: de metadata en gekoppelde bestanden bij gebruikersrestricties hebben staan "intern", die zijn niet via de url te benaderen voor buitenstaanders. Alleen als je bent ingelogged, dan kan je "je eigen geleverde" data en metadata zien.
let op: bij het huidige geoportaal kan je door het aanpassen van de url's ook de gekoppelde bestanden zien, van bestanden die "intern" zouden moeten zijn. Nu zijn deze dus ook extern beschikbaar. Dit moet bij het nieuwe Geoportaal niet meer mogelijk zijn: interne bestanden en metadata die voor "intern" zijn, die kan je alleen benaderen als je werkt op het provinciehuis in Zwolle (met ip-whitelist, mogelijk enkele andere ip-adressen hier ook aan toevoegen)
Vraag is, of dat ook goed gaat met toevoegen van data: hiervoor moet je inloggen. Maar moet je dan ook altijd dat doen via ip van provinciehuis? Nu is dat nog niet zo: ik kan overal inloggen en data en metadata bekijken.
Opmerking nr 29 bij testresultaten 3-2-2016

|
non_process
|
beveiliging inlog en ip whitelist aandachtspunt ivm beveiliging de metadata en gekoppelde bestanden bij gebruikersrestricties hebben staan intern die zijn niet via de url te benaderen voor buitenstaanders alleen als je bent ingelogged dan kan je je eigen geleverde data en metadata zien let op bij het huidige geoportaal kan je door het aanpassen van de url s ook de gekoppelde bestanden zien van bestanden die intern zouden moeten zijn nu zijn deze dus ook extern beschikbaar dit moet bij het nieuwe geoportaal niet meer mogelijk zijn interne bestanden en metadata die voor intern zijn die kan je alleen benaderen als je werkt op het provinciehuis in zwolle met ip whitelist mogelijk enkele andere ip adressen hier ook aan toevoegen vraag is of dat ook goed gaat met toevoegen van data hiervoor moet je inloggen maar moet je dan ook altijd dat doen via ip van provinciehuis nu is dat nog niet zo ik kan overal inloggen en data en metadata bekijken opmerking nr bij testresultaten
| 0
|
10,198
| 13,064,786,260
|
IssuesEvent
|
2020-07-30 18:40:35
|
googleapis/google-cloud-cpp
|
https://api.github.com/repos/googleapis/google-cloud-cpp
|
closed
|
Do not allow 'using directives' in header or source files.
|
type: process
|
We need to change the `ci/check-style.sh` script to break the build if a using directive is introduced. See #908 for more details.
cc: @houglum
|
1.0
|
Do not allow 'using directives' in header or source files. - We need to change the `ci/check-style.sh` script to break the build if a using directive is introduced. See #908 for more details.
cc: @houglum
|
process
|
do not allow using directives in header or source files we need to change the ci check style sh script to break the build if a using directive is introduced see for more details cc houglum
| 1
|
177,337
| 21,472,907,758
|
IssuesEvent
|
2022-04-26 11:10:07
|
nanopathi/framework_base_AOSP10_r33_CVE-2021-0315
|
https://api.github.com/repos/nanopathi/framework_base_AOSP10_r33_CVE-2021-0315
|
opened
|
CVE-2021-0442 (High) detected in baseandroid-10.0.0_r34
|
security vulnerability
|
## CVE-2021-0442 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>baseandroid-10.0.0_r34</b></p></summary>
<p>
<p>Android framework classes and services</p>
<p>Library home page: <a href=https://android.googlesource.com/platform/frameworks/base>https://android.googlesource.com/platform/frameworks/base</a></p>
<p>Found in HEAD commit: <a href="https://github.com/nanopathi/framework_base_AOSP10_r33_CVE-2021-0315/commit/3f98702b7da12722be6e7ff9127c63b208782aae">3f98702b7da12722be6e7ff9127c63b208782aae</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/core/jni/android_hardware_input_InputApplicationHandle.cpp</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In updateInfo of android_hardware_input_InputApplicationHandle.cpp, there is a possible control of code flow due to a use after free. This could lead to local escalation of privilege with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-11Android ID: A-174768985
<p>Publish Date: 2021-04-13
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0442>CVE-2021-0442</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://source.android.com/security/bulletin/2021-04-01">https://source.android.com/security/bulletin/2021-04-01</a></p>
<p>Release Date: 2022-02-13</p>
<p>Fix Resolution: android-11.0.0_r34</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2021-0442 (High) detected in baseandroid-10.0.0_r34 - ## CVE-2021-0442 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>baseandroid-10.0.0_r34</b></p></summary>
<p>
<p>Android framework classes and services</p>
<p>Library home page: <a href=https://android.googlesource.com/platform/frameworks/base>https://android.googlesource.com/platform/frameworks/base</a></p>
<p>Found in HEAD commit: <a href="https://github.com/nanopathi/framework_base_AOSP10_r33_CVE-2021-0315/commit/3f98702b7da12722be6e7ff9127c63b208782aae">3f98702b7da12722be6e7ff9127c63b208782aae</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/core/jni/android_hardware_input_InputApplicationHandle.cpp</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In updateInfo of android_hardware_input_InputApplicationHandle.cpp, there is a possible control of code flow due to a use after free. This could lead to local escalation of privilege with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-11Android ID: A-174768985
<p>Publish Date: 2021-04-13
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0442>CVE-2021-0442</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://source.android.com/security/bulletin/2021-04-01">https://source.android.com/security/bulletin/2021-04-01</a></p>
<p>Release Date: 2022-02-13</p>
<p>Fix Resolution: android-11.0.0_r34</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_process
|
cve high detected in baseandroid cve high severity vulnerability vulnerable library baseandroid android framework classes and services library home page a href found in head commit a href found in base branch master vulnerable source files core jni android hardware input inputapplicationhandle cpp vulnerability details in updateinfo of android hardware input inputapplicationhandle cpp there is a possible control of code flow due to a use after free this could lead to local escalation of privilege with no additional execution privileges needed user interaction is not needed for exploitation product androidversions android id a publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution android step up your open source security game with whitesource
| 0
|
3,866
| 6,808,643,813
|
IssuesEvent
|
2017-11-04 06:06:00
|
Great-Hill-Corporation/quickBlocks
|
https://api.github.com/repos/Great-Hill-Corporation/quickBlocks
|
reopened
|
Upper case / lower case confusion in filename storage for caches.
|
apps-ethslurp status-inprocess type-enhancement
|
grabABI for example does not, which makes it confusing if the file exists or not.
From https://github.com/Great-Hill-Corporation/ethslurp/issues/109
|
1.0
|
Upper case / lower case confusion in filename storage for caches. - grabABI for example does not, which makes it confusing if the file exists or not.
From https://github.com/Great-Hill-Corporation/ethslurp/issues/109
|
process
|
upper case lower case confusion in filename storage for caches grababi for example does not which makes it confusing if the file exists or not from
| 1
|
10,193
| 13,050,142,776
|
IssuesEvent
|
2020-07-29 15:04:21
|
DataDog/integrations-core
|
https://api.github.com/repos/DataDog/integrations-core
|
closed
|
Work around to allow `exact_match: false` in Window's process integration
|
integration/process
|
Per this [comment](https://github.com/DataDog/integrations-core/blob/3fbe97799224e5ed6838b43df909fab33e8a2ab8/process/datadog_checks/process/data/conf.yaml.example#L79) and this section of the [docs](https://docs.datadoghq.com/agent/faq/windows-agent-ddagent-user/#process-check) setting the process integrations `exact_match` to `false` no longer works on Windows. Is there any work around to allow regex search of processes on Windows?
|
1.0
|
Work around to allow `exact_match: false` in Window's process integration - Per this [comment](https://github.com/DataDog/integrations-core/blob/3fbe97799224e5ed6838b43df909fab33e8a2ab8/process/datadog_checks/process/data/conf.yaml.example#L79) and this section of the [docs](https://docs.datadoghq.com/agent/faq/windows-agent-ddagent-user/#process-check) setting the process integrations `exact_match` to `false` no longer works on Windows. Is there any work around to allow regex search of processes on Windows?
|
process
|
work around to allow exact match false in window s process integration per this and this section of the setting the process integrations exact match to false no longer works on windows is there any work around to allow regex search of processes on windows
| 1
|
15,386
| 19,571,366,807
|
IssuesEvent
|
2022-01-04 10:19:31
|
prisma/prisma
|
https://api.github.com/repos/prisma/prisma
|
closed
|
Studio CLI: `prisma studio` errors with `ENOENT: no such file or directory, open '/[...]/prisma/schema.prisma'` after opening when using a custom name for the Prisma schema file
|
bug/2-confirmed kind/bug process/candidate topic: prisma-client tech/typescript team/client topic: schema file
|
### Bug description
Related errors https://github.com/prisma/studio/issues/819 and https://github.com/prisma/prisma/issues/10936
errors with in Studio UI after opening via CLI
```
ENOENT: no such file or directory, open '/[...]/repro/prisma/schema.prisma'
```
Even though the file name is `schema1.prisma`
### How to reproduce
- Rename a prisma schema to `schema1.prisma`
- run `npx prisma studio --schema prisma/schema1.prisma`
### Expected behavior
Passing `--schema=prisma/schema1.prisma` or any filename different than "schema.prisma" should work.
### Prisma information
```
datasource db {
provider = "postgres"
url = "[...]"
}
generator client {
provider = "prisma-client-js"
}
model User {
id Int @id
}
```
### Environment & setup
OS: Mac OS
Database: PostgreSQL
Node.js version: 14
### Prisma Version
```
prisma : 3.7.0
@prisma/client : 3.7.0
Current platform : darwin
Query Engine (Node-API) : libquery-engine 8746e055198f517658c08a0c426c7eec87f5a85f (at node_modules/@prisma/engines/libquery_engine-darwin.dylib.node)
Migration Engine : migration-engine-cli 8746e055198f517658c08a0c426c7eec87f5a85f (at node_modules/@prisma/engines/migration-engine-darwin)
Introspection Engine : introspection-core 8746e055198f517658c08a0c426c7eec87f5a85f (at node_modules/@prisma/engines/introspection-engine-darwin)
Format Binary : prisma-fmt 8746e055198f517658c08a0c426c7eec87f5a85f (at node_modules/@prisma/engines/prisma-fmt-darwin)
Default Engines Hash : 8746e055198f517658c08a0c426c7eec87f5a85f
Studio : 0.445.0
```
|
1.0
|
Studio CLI: `prisma studio` errors with `ENOENT: no such file or directory, open '/[...]/prisma/schema.prisma'` after opening when using a custom name for the Prisma schema file - ### Bug description
Related errors https://github.com/prisma/studio/issues/819 and https://github.com/prisma/prisma/issues/10936
errors with in Studio UI after opening via CLI
```
ENOENT: no such file or directory, open '/[...]/repro/prisma/schema.prisma'
```
Even though the file name is `schema1.prisma`
### How to reproduce
- Rename a prisma schema to `schema1.prisma`
- run `npx prisma studio --schema prisma/schema1.prisma`
### Expected behavior
Passing `--schema=prisma/schema1.prisma` or any filename different than "schema.prisma" should work.
### Prisma information
```
datasource db {
provider = "postgres"
url = "[...]"
}
generator client {
provider = "prisma-client-js"
}
model User {
id Int @id
}
```
### Environment & setup
OS: Mac OS
Database: PostgreSQL
Node.js version: 14
### Prisma Version
```
prisma : 3.7.0
@prisma/client : 3.7.0
Current platform : darwin
Query Engine (Node-API) : libquery-engine 8746e055198f517658c08a0c426c7eec87f5a85f (at node_modules/@prisma/engines/libquery_engine-darwin.dylib.node)
Migration Engine : migration-engine-cli 8746e055198f517658c08a0c426c7eec87f5a85f (at node_modules/@prisma/engines/migration-engine-darwin)
Introspection Engine : introspection-core 8746e055198f517658c08a0c426c7eec87f5a85f (at node_modules/@prisma/engines/introspection-engine-darwin)
Format Binary : prisma-fmt 8746e055198f517658c08a0c426c7eec87f5a85f (at node_modules/@prisma/engines/prisma-fmt-darwin)
Default Engines Hash : 8746e055198f517658c08a0c426c7eec87f5a85f
Studio : 0.445.0
```
|
process
|
studio cli prisma studio errors with enoent no such file or directory open prisma schema prisma after opening when using a custom name for the prisma schema file bug description related errors and errors with in studio ui after opening via cli enoent no such file or directory open repro prisma schema prisma even though the file name is prisma how to reproduce rename a prisma schema to prisma run npx prisma studio schema prisma prisma expected behavior passing schema prisma prisma or any filename different than schema prisma should work prisma information datasource db provider postgres url generator client provider prisma client js model user id int id environment setup os mac os database postgresql node js version prisma version prisma prisma client current platform darwin query engine node api libquery engine at node modules prisma engines libquery engine darwin dylib node migration engine migration engine cli at node modules prisma engines migration engine darwin introspection engine introspection core at node modules prisma engines introspection engine darwin format binary prisma fmt at node modules prisma engines prisma fmt darwin default engines hash studio
| 1
|
4,627
| 7,472,783,034
|
IssuesEvent
|
2018-04-03 13:41:06
|
threefoldfoundation/tfchain
|
https://api.github.com/repos/threefoldfoundation/tfchain
|
reopened
|
node indicates it is not synced while it is
|
process_wontfix
|
```
rob$ ./tfchainc
Synced: No
Height: 656
Progress (estimated): 0%
```
<img width="626" alt="screen shot 2018-03-05 at 11 05 03" src="https://user-images.githubusercontent.com/3511318/36969210-2a59a116-2065-11e8-8856-a0ca5b9ba00d.png">
|
1.0
|
node indicates it is not synced while it is - ```
rob$ ./tfchainc
Synced: No
Height: 656
Progress (estimated): 0%
```
<img width="626" alt="screen shot 2018-03-05 at 11 05 03" src="https://user-images.githubusercontent.com/3511318/36969210-2a59a116-2065-11e8-8856-a0ca5b9ba00d.png">
|
process
|
node indicates it is not synced while it is rob tfchainc synced no height progress estimated img width alt screen shot at src
| 1
|
10,761
| 13,549,206,299
|
IssuesEvent
|
2020-09-17 07:51:30
|
timberio/vector
|
https://api.github.com/repos/timberio/vector
|
closed
|
New `now` function
|
domain: mapping domain: processing type: feature
|
The `now` function generates a new timestamp for the current time in UTC.
## Examples
```
.timestamp = now()
```
|
1.0
|
New `now` function - The `now` function generates a new timestamp for the current time in UTC.
## Examples
```
.timestamp = now()
```
|
process
|
new now function the now function generates a new timestamp for the current time in utc examples timestamp now
| 1
|
12,676
| 15,046,103,807
|
IssuesEvent
|
2021-02-03 06:47:51
|
prisma/prisma
|
https://api.github.com/repos/prisma/prisma
|
opened
|
Migrate: Postgres connection string without port prints `undefined`
|
process/candidate team/migrations
|
I have a Postgres connection string of this form:
```
postgres://postgres:pw@lol.hello.eu-west-1.rds.amazonaws.com/my-db
```
When I do `prisma db push`, I get this:
```
Datasource "db": PostgreSQL database "my-db", schema "public" at "lol.hello.eu-west-1.rds.amazonaws.com:undefined"
```
It seems like we should fill in the default value for the port if it's not in the connection string.
|
1.0
|
Migrate: Postgres connection string without port prints `undefined` - I have a Postgres connection string of this form:
```
postgres://postgres:pw@lol.hello.eu-west-1.rds.amazonaws.com/my-db
```
When I do `prisma db push`, I get this:
```
Datasource "db": PostgreSQL database "my-db", schema "public" at "lol.hello.eu-west-1.rds.amazonaws.com:undefined"
```
It seems like we should fill in the default value for the port if it's not in the connection string.
|
process
|
migrate postgres connection string without port prints undefined i have a postgres connection string of this form postgres postgres pw lol hello eu west rds amazonaws com my db when i do prisma db push i get this datasource db postgresql database my db schema public at lol hello eu west rds amazonaws com undefined it seems like we should fill in the default value for the port if it s not in the connection string
| 1
|
5,373
| 8,202,753,625
|
IssuesEvent
|
2018-09-02 13:28:50
|
linnovate/root
|
https://api.github.com/repos/linnovate/root
|
reopened
|
Notification-line: discussion not send a notification
|
Process bug
|
@abrahamos
open new discussion.
fill the fields.
assign yourself as admin.
there is no notification about that.
|
1.0
|
Notification-line: discussion not send a notification - @abrahamos
open new discussion.
fill the fields.
assign yourself as admin.
there is no notification about that.
|
process
|
notification line discussion not send a notification abrahamos open new discussion fill the fields assign yourself as admin there is no notification about that
| 1
|
9,713
| 12,708,904,296
|
IssuesEvent
|
2020-06-23 11:23:40
|
dita-ot/dita-ot
|
https://api.github.com/repos/dita-ot/dita-ot
|
closed
|
embedded svg graphics
|
bug preprocess priority/medium stale
|
I made some experiments and had some issues with it. I'd like to fix it on my own but need some help...
Here's the sample [embedded-svg-test.txt](https://github.com/dita-ot/dita-ot/files/42944/embedded-svg-test.txt)
``` xml
<?xml version="1.0" encoding="UTF-8"?>
<?xml-model href="urn:oasis:names:tc:dita:rng:topic.rng:1.3" schematypens="http://relaxng.org/ns/structure/1.0"?>
<topic id="conref-topic">
<title>Embedded SVG Test</title>
<body>
<fig>
<svg-container>
<svg xmlns="http://www.w3.org/2000/svg" width="600px" height="100px">
<defs>
<linearGradient id="BackgroundGradient" x1="0%" y1="0%" x2="100%" y2="100%">
<stop offset="0%" style="stop-color:rgb(248,252,255);stop-opacity:1"/>
<stop offset="50%" style="stop-color:rgb(228,232,255);stop-opacity:1"/>
<stop offset="100%" style="stop-color:rgb(158,162,185);stop-opacity:1"/>
</linearGradient>
</defs>
<rect x="2.5" y="2.5" width="595" height="95" rx="30" ry="30" fill="url(#BackgroundGradient)" stroke-width="5" stroke="rgb(85,90,100)"/>
<text x="300" y="50" dy="0.3em" style="text-anchor: middle" font-size="50">Embedded SVG Test</text>
</svg>
</svg-container>
</fig>
</body>
</topic>
```
The 1st issue is that some preprocessing step seems to change the namespace of all child elements of svg to the default namespace. I'd appreciate some hints which step might do this - and why. I think it is wrong to change any namespaces within a foreign element!?
here's the result I found in the temp folder [stage1.txt](https://github.com/dita-ot/dita-ot/files/42948/stage1.txt)
``` xml
<?xml version="1.0" encoding="UTF-8" standalone="yes"?><topic xmlns:ditaarch="http://dita.oasis-open.org/architecture/2005/" xmlns:dita-ot="http://dita-ot.sourceforge.net/ns/201007/dita-ot" xmlns:opentopic-index="http://www.idiominc.com/opentopic/index" class="- topic/topic " ditaarch:DITAArchVersion="1.2" domains="(topic abbrev-d) (topic equation-d) (topic hazard-d) (topic hi-d) (topic indexing-d) (topic markup-d xml-d) (topic markup-d) (topic mathml-d) (topic pr-d) (topic relmgmt-d) (topic svg-d) (topic sw-d) (topic ui-d) (topic ut-d) a(props deliveryTarget)" id="conref-topic" xtrc="topic:1;3:26" xtrf="file:/C:/Entwicklung/Experiments/embedded-svg-dita-ot/embedded-svg-test.dita">
<title class="- topic/title " xtrc="title:1;4:9" xtrf="file:/C:/Entwicklung/Experiments/embedded-svg-dita-ot/embedded-svg-test.dita">Embedded SVG Test</title>
<body class="- topic/body " xtrc="body:1;5:8" xtrf="file:/C:/Entwicklung/Experiments/embedded-svg-dita-ot/embedded-svg-test.dita">
<fig class="- topic/fig " xtrc="fig:1;6:8" xtrf="file:/C:/Entwicklung/Experiments/embedded-svg-dita-ot/embedded-svg-test.dita">
<svg-container class="+ topic/foreign svg-d/svg-container " xtrc="svg-container:1;7:19" xtrf="file:/C:/Entwicklung/Experiments/embedded-svg-dita-ot/embedded-svg-test.dita">
<svg xmlns="http://www.w3.org/2000/svg" contentScriptType="text/ecmascript" contentStyleType="text/css" height="100px" preserveAspectRatio="xMidYMid meet" version="1.1" width="600px" zoomAndPan="magnify">
<defs xmlns="">
<linearGradient xmlns:ns1="http://www.w3.org/1999/xlink" id="BackgroundGradient" ns1:actuate="onLoad" ns1:show="other" ns1:type="simple" x1="0%" x2="100%" y1="0%" y2="100%">
<stop offset="0%" style="stop-color:rgb(248,252,255);stop-opacity:1"/>
<stop offset="50%" style="stop-color:rgb(228,232,255);stop-opacity:1"/>
<stop offset="100%" style="stop-color:rgb(158,162,185);stop-opacity:1"/>
</linearGradient>
</defs>
<rect xmlns="" fill="url(#BackgroundGradient)" height="95" rx="30" ry="30" stroke="rgb(85,90,100)" stroke-width="5" width="595" x="2.5" y="2.5"/>
<text xmlns="" class="- topic/text " dy="0.3em" font-size="50" style="text-anchor: middle" x="300" y="50">Embedded SVG Test</text>
</svg>
</svg-container>
</fig>
</body>
<opentopic-index:index.groups/></topic>
```
There's a workaround to add a prefix to all svg elements that leads to the next issue: svg-container is not supported by the pdf plugin. But I could easily add an appropriate template.
|
1.0
|
embedded svg graphics - I made some experiments and had some issues with it. I'd like to fix it on my own but need some help...
Here's the sample [embedded-svg-test.txt](https://github.com/dita-ot/dita-ot/files/42944/embedded-svg-test.txt)
``` xml
<?xml version="1.0" encoding="UTF-8"?>
<?xml-model href="urn:oasis:names:tc:dita:rng:topic.rng:1.3" schematypens="http://relaxng.org/ns/structure/1.0"?>
<topic id="conref-topic">
<title>Embedded SVG Test</title>
<body>
<fig>
<svg-container>
<svg xmlns="http://www.w3.org/2000/svg" width="600px" height="100px">
<defs>
<linearGradient id="BackgroundGradient" x1="0%" y1="0%" x2="100%" y2="100%">
<stop offset="0%" style="stop-color:rgb(248,252,255);stop-opacity:1"/>
<stop offset="50%" style="stop-color:rgb(228,232,255);stop-opacity:1"/>
<stop offset="100%" style="stop-color:rgb(158,162,185);stop-opacity:1"/>
</linearGradient>
</defs>
<rect x="2.5" y="2.5" width="595" height="95" rx="30" ry="30" fill="url(#BackgroundGradient)" stroke-width="5" stroke="rgb(85,90,100)"/>
<text x="300" y="50" dy="0.3em" style="text-anchor: middle" font-size="50">Embedded SVG Test</text>
</svg>
</svg-container>
</fig>
</body>
</topic>
```
The 1st issue is that some preprocessing step seems to change the namespace of all child elements of svg to the default namespace. I'd appreciate some hints which step might do this - and why. I think it is wrong to change any namespaces within a foreign element!?
here's the result I found in the temp folder [stage1.txt](https://github.com/dita-ot/dita-ot/files/42948/stage1.txt)
``` xml
<?xml version="1.0" encoding="UTF-8" standalone="yes"?><topic xmlns:ditaarch="http://dita.oasis-open.org/architecture/2005/" xmlns:dita-ot="http://dita-ot.sourceforge.net/ns/201007/dita-ot" xmlns:opentopic-index="http://www.idiominc.com/opentopic/index" class="- topic/topic " ditaarch:DITAArchVersion="1.2" domains="(topic abbrev-d) (topic equation-d) (topic hazard-d) (topic hi-d) (topic indexing-d) (topic markup-d xml-d) (topic markup-d) (topic mathml-d) (topic pr-d) (topic relmgmt-d) (topic svg-d) (topic sw-d) (topic ui-d) (topic ut-d) a(props deliveryTarget)" id="conref-topic" xtrc="topic:1;3:26" xtrf="file:/C:/Entwicklung/Experiments/embedded-svg-dita-ot/embedded-svg-test.dita">
<title class="- topic/title " xtrc="title:1;4:9" xtrf="file:/C:/Entwicklung/Experiments/embedded-svg-dita-ot/embedded-svg-test.dita">Embedded SVG Test</title>
<body class="- topic/body " xtrc="body:1;5:8" xtrf="file:/C:/Entwicklung/Experiments/embedded-svg-dita-ot/embedded-svg-test.dita">
<fig class="- topic/fig " xtrc="fig:1;6:8" xtrf="file:/C:/Entwicklung/Experiments/embedded-svg-dita-ot/embedded-svg-test.dita">
<svg-container class="+ topic/foreign svg-d/svg-container " xtrc="svg-container:1;7:19" xtrf="file:/C:/Entwicklung/Experiments/embedded-svg-dita-ot/embedded-svg-test.dita">
<svg xmlns="http://www.w3.org/2000/svg" contentScriptType="text/ecmascript" contentStyleType="text/css" height="100px" preserveAspectRatio="xMidYMid meet" version="1.1" width="600px" zoomAndPan="magnify">
<defs xmlns="">
<linearGradient xmlns:ns1="http://www.w3.org/1999/xlink" id="BackgroundGradient" ns1:actuate="onLoad" ns1:show="other" ns1:type="simple" x1="0%" x2="100%" y1="0%" y2="100%">
<stop offset="0%" style="stop-color:rgb(248,252,255);stop-opacity:1"/>
<stop offset="50%" style="stop-color:rgb(228,232,255);stop-opacity:1"/>
<stop offset="100%" style="stop-color:rgb(158,162,185);stop-opacity:1"/>
</linearGradient>
</defs>
<rect xmlns="" fill="url(#BackgroundGradient)" height="95" rx="30" ry="30" stroke="rgb(85,90,100)" stroke-width="5" width="595" x="2.5" y="2.5"/>
<text xmlns="" class="- topic/text " dy="0.3em" font-size="50" style="text-anchor: middle" x="300" y="50">Embedded SVG Test</text>
</svg>
</svg-container>
</fig>
</body>
<opentopic-index:index.groups/></topic>
```
There's a workaround to add a prefix to all svg elements that leads to the next issue: svg-container is not supported by the pdf plugin. But I could easily add an appropriate template.
|
process
|
embedded svg graphics i made some experiments and had some issues with it i d like to fix it on my own but need some help here s the sample xml xml model href urn oasis names tc dita rng topic rng schematypens embedded svg test embedded svg test the issue is that some preprocessing step seems to change the namespace of all child elements of svg to the default namespace i d appreciate some hints which step might do this and why i think it is wrong to change any namespaces within a foreign element here s the result i found in the temp folder xml embedded svg test embedded svg test there s a workaround to add a prefix to all svg elements that leads to the next issue svg container is not supported by the pdf plugin but i could easily add an appropriate template
| 1
|
40,067
| 5,270,318,994
|
IssuesEvent
|
2017-02-06 04:02:50
|
openbmc/openbmc-test-automation
|
https://api.github.com/repos/openbmc/openbmc-test-automation
|
opened
|
[Tools] - Github issues converted into CSV format - Accomadating new python coding guidelines
|
Test
|
Code is already checkin and couple of review also happened. This is associate with
#235
Now I am not able to go back to my branch. Having lot of issues.
So the new requirement on adopting new python coding guidelines will be taken up in this.
|
1.0
|
[Tools] - Github issues converted into CSV format - Accomadating new python coding guidelines - Code is already checkin and couple of review also happened. This is associate with
#235
Now I am not able to go back to my branch. Having lot of issues.
So the new requirement on adopting new python coding guidelines will be taken up in this.
|
non_process
|
github issues converted into csv format accomadating new python coding guidelines code is already checkin and couple of review also happened this is associate with now i am not able to go back to my branch having lot of issues so the new requirement on adopting new python coding guidelines will be taken up in this
| 0
|
55,557
| 8,000,909,486
|
IssuesEvent
|
2018-07-22 21:36:35
|
pangeo-data/pangeo
|
https://api.github.com/repos/pangeo-data/pangeo
|
closed
|
Help with documentation on dask-jobqueue
|
documentation stale
|
Hi All,
The PBSCluster that was incubated in this repository was moved over to [dask-jobqueue](https://github.com/dask/dask-jobqueue/) where it grew friends like SGECluster, SLURMCluster, as well as improved stability, continuous integration, and maintainers. That project could use your help in a few ways:
1. If you're using Dask/XArray on an HPC system, please give it a shot
2. If you're able to provide examples on how to set up dask-jobqueue on your cluster please consider submitting that example to live in [the examples documentation](http://dask-jobqueue.readthedocs.io/en/latest/examples.html). This could either be a PR to that github repository or just a comment to [this issue](https://github.com/dask/dask-jobqueue/issues/40) on improving documentation in that library. It would be nice to see examples that engage keywords like project id, queue id, network interface, resource spec, etc..
3. If these keywords are new to you then please speak up and lets sort things out to make sure that things work cleanly on your system so that others who come later can see these examples and copy-paste to get something reasonable.
Thank you all for your help
|
1.0
|
Help with documentation on dask-jobqueue - Hi All,
The PBSCluster that was incubated in this repository was moved over to [dask-jobqueue](https://github.com/dask/dask-jobqueue/) where it grew friends like SGECluster, SLURMCluster, as well as improved stability, continuous integration, and maintainers. That project could use your help in a few ways:
1. If you're using Dask/XArray on an HPC system, please give it a shot
2. If you're able to provide examples on how to set up dask-jobqueue on your cluster please consider submitting that example to live in [the examples documentation](http://dask-jobqueue.readthedocs.io/en/latest/examples.html). This could either be a PR to that github repository or just a comment to [this issue](https://github.com/dask/dask-jobqueue/issues/40) on improving documentation in that library. It would be nice to see examples that engage keywords like project id, queue id, network interface, resource spec, etc..
3. If these keywords are new to you then please speak up and lets sort things out to make sure that things work cleanly on your system so that others who come later can see these examples and copy-paste to get something reasonable.
Thank you all for your help
|
non_process
|
help with documentation on dask jobqueue hi all the pbscluster that was incubated in this repository was moved over to where it grew friends like sgecluster slurmcluster as well as improved stability continuous integration and maintainers that project could use your help in a few ways if you re using dask xarray on an hpc system please give it a shot if you re able to provide examples on how to set up dask jobqueue on your cluster please consider submitting that example to live in this could either be a pr to that github repository or just a comment to on improving documentation in that library it would be nice to see examples that engage keywords like project id queue id network interface resource spec etc if these keywords are new to you then please speak up and lets sort things out to make sure that things work cleanly on your system so that others who come later can see these examples and copy paste to get something reasonable thank you all for your help
| 0
|
9,813
| 12,824,306,512
|
IssuesEvent
|
2020-07-06 13:17:02
|
symfony/symfony
|
https://api.github.com/repos/symfony/symfony
|
closed
|
[Process] Permission Denied writing to sf_proc_00.out.lock when file is generated by a different AppPoolIdentity User
|
Bug Process Status: Needs Review
|
**Symfony version(s) affected**: 4.4.8|5.1.2
- OS: Windows 10
- Server: IIS version 10
- PHP version 7.3
- Laravel version 6.18
Note: Bug originally encountered on Laravel 6.18 using symfony/process 4.4.8. I have replicated the issue on a fresh symfony/skeleton 5.1.2 base with the process package required through composer.
**Description**
When two or more sites are running IIS / FastCGI as different AppPoolIdentity users with limited group permissions to the sys_temp_dir, the first to write sf_proc_00.* files used by the Process class takes ownership, however any additional sites that attempt to write to this file will receive the following error:
`A temporary file could not be opened to write the process output: fopen(C:\WINDOWS\TEMP\sf_proc_00.out.lock): failed to open stream: Permission denied`
Our permissions are configured to prevent one site from modifying temporary files that are created by another.
**How to reproduce**
1. In IIS: Add two sites using the Symfony\Process component with different Application Pools
2. In IIS Application Pools: For both application pools used, select "Advanced Settings" and confirm the "Identity" field is set to the built-in "ApplicationPoolIdentity" account,
3. In IIS Feature Panel: For both sites, select "Authentication" > "Anonymous Authentication", ensure it is enabled and click "Edit..." then select "Application Pool Identity" and click OK.
4. Set limited permissions for the IIS_IUSRS group on the sys_temp_dir (this is C:\Windows\Temp on my machine). Verify the Users group does not exceed these permissions.
- Permissions used in testing: List folder / read data, Read attributes, Read extended attributes, Create files / write data, Read permissions
5. For both sites, create some code that uses the Process class to run a command. (See Additional Context for the sample code I used to test)
6. In Site A, run the code using the Process class and check the sys_temp_dir to confirm sf_proc_00 files were generated.
7. In Site B, attempt to run the code using the Process class to throw the Permission Denied error.
**Possible Solution**
Perhaps a solution could be incrementing the filename when the lock files exist, but cannot be opened for writing, and removing the sf_proc_## files used in the WindowsPipes destructor.
I have limited experience in using the Process class, I'll post the code that has fixed it in my particular instance, however I do not know if it is ideal for all use cases.
symfony\process\Pipes\WindowsPipes.php, Line 58: (Try next iteration if lock file exists)
```php
if (!$h = fopen($file.'.lock', 'w')) {
if (file_exists($file.'.lock'))
continue 2;
restore_error_handler();
throw new RuntimeException('A temporary file could not be opened to write the process output: '.$lastError);
}
```
symfony\process\Pipes\WindowsPipes.php, Line 88: (Remove files on destruct)
```php
public function __destruct()
{
$this->close();
foreach ($this->files as $file) {
unlink($file);
unlink($file.'.lock');
}
}
```
**Additional context**
During replication, I made a simple controller that dumps output of the `dir` command for testing:
src\Controller\HomeController.php:
```php
<?php
namespace App\Controller;
use Symfony\Component\HttpFoundation\Response;
use Symfony\Component\Process\Exception\ProcessFailedException;
use Symfony\Component\Process\Process;
class HomeController
{
public function index()
{
$process = new Process(['dir']);
$process->run();
if(!$process->isSuccessful())
throw new ProcessFailedException($process);
return new Response($process->getOutput());
}
}
```
And attached it to the base route:
config\routes.yaml:
```yaml
index:
path: /
controller: App\Controller\HomeController::index
```
The same code was used on both Site A and B.
|
1.0
|
[Process] Permission Denied writing to sf_proc_00.out.lock when file is generated by a different AppPoolIdentity User - **Symfony version(s) affected**: 4.4.8|5.1.2
- OS: Windows 10
- Server: IIS version 10
- PHP version 7.3
- Laravel version 6.18
Note: Bug originally encountered on Laravel 6.18 using symfony/process 4.4.8. I have replicated the issue on a fresh symfony/skeleton 5.1.2 base with the process package required through composer.
**Description**
When two or more sites are running IIS / FastCGI as different AppPoolIdentity users with limited group permissions to the sys_temp_dir, the first to write sf_proc_00.* files used by the Process class takes ownership, however any additional sites that attempt to write to this file will receive the following error:
`A temporary file could not be opened to write the process output: fopen(C:\WINDOWS\TEMP\sf_proc_00.out.lock): failed to open stream: Permission denied`
Our permissions are configured to prevent one site from modifying temporary files that are created by another.
**How to reproduce**
1. In IIS: Add two sites using the Symfony\Process component with different Application Pools
2. In IIS Application Pools: For both application pools used, select "Advanced Settings" and confirm the "Identity" field is set to the built-in "ApplicationPoolIdentity" account,
3. In IIS Feature Panel: For both sites, select "Authentication" > "Anonymous Authentication", ensure it is enabled and click "Edit..." then select "Application Pool Identity" and click OK.
4. Set limited permissions for the IIS_IUSRS group on the sys_temp_dir (this is C:\Windows\Temp on my machine). Verify the Users group does not exceed these permissions.
- Permissions used in testing: List folder / read data, Read attributes, Read extended attributes, Create files / write data, Read permissions
5. For both sites, create some code that uses the Process class to run a command. (See Additional Context for the sample code I used to test)
6. In Site A, run the code using the Process class and check the sys_temp_dir to confirm sf_proc_00 files were generated.
7. In Site B, attempt to run the code using the Process class to throw the Permission Denied error.
**Possible Solution**
Perhaps a solution could be incrementing the filename when the lock files exist, but cannot be opened for writing, and removing the sf_proc_## files used in the WindowsPipes destructor.
I have limited experience in using the Process class, I'll post the code that has fixed it in my particular instance, however I do not know if it is ideal for all use cases.
symfony\process\Pipes\WindowsPipes.php, Line 58: (Try next iteration if lock file exists)
```php
if (!$h = fopen($file.'.lock', 'w')) {
if (file_exists($file.'.lock'))
continue 2;
restore_error_handler();
throw new RuntimeException('A temporary file could not be opened to write the process output: '.$lastError);
}
```
symfony\process\Pipes\WindowsPipes.php, Line 88: (Remove files on destruct)
```php
public function __destruct()
{
$this->close();
foreach ($this->files as $file) {
unlink($file);
unlink($file.'.lock');
}
}
```
**Additional context**
During replication, I made a simple controller that dumps output of the `dir` command for testing:
src\Controller\HomeController.php:
```php
<?php
namespace App\Controller;
use Symfony\Component\HttpFoundation\Response;
use Symfony\Component\Process\Exception\ProcessFailedException;
use Symfony\Component\Process\Process;
class HomeController
{
public function index()
{
$process = new Process(['dir']);
$process->run();
if(!$process->isSuccessful())
throw new ProcessFailedException($process);
return new Response($process->getOutput());
}
}
```
And attached it to the base route:
config\routes.yaml:
```yaml
index:
path: /
controller: App\Controller\HomeController::index
```
The same code was used on both Site A and B.
|
process
|
permission denied writing to sf proc out lock when file is generated by a different apppoolidentity user symfony version s affected os windows server iis version php version laravel version note bug originally encountered on laravel using symfony process i have replicated the issue on a fresh symfony skeleton base with the process package required through composer description when two or more sites are running iis fastcgi as different apppoolidentity users with limited group permissions to the sys temp dir the first to write sf proc files used by the process class takes ownership however any additional sites that attempt to write to this file will receive the following error a temporary file could not be opened to write the process output fopen c windows temp sf proc out lock failed to open stream permission denied our permissions are configured to prevent one site from modifying temporary files that are created by another how to reproduce in iis add two sites using the symfony process component with different application pools in iis application pools for both application pools used select advanced settings and confirm the identity field is set to the built in applicationpoolidentity account in iis feature panel for both sites select authentication anonymous authentication ensure it is enabled and click edit then select application pool identity and click ok set limited permissions for the iis iusrs group on the sys temp dir this is c windows temp on my machine verify the users group does not exceed these permissions permissions used in testing list folder read data read attributes read extended attributes create files write data read permissions for both sites create some code that uses the process class to run a command see additional context for the sample code i used to test in site a run the code using the process class and check the sys temp dir to confirm sf proc files were generated in site b attempt to run the code using the process class to throw the permission denied error possible solution perhaps a solution could be incrementing the filename when the lock files exist but cannot be opened for writing and removing the sf proc files used in the windowspipes destructor i have limited experience in using the process class i ll post the code that has fixed it in my particular instance however i do not know if it is ideal for all use cases symfony process pipes windowspipes php line try next iteration if lock file exists php if h fopen file lock w if file exists file lock continue restore error handler throw new runtimeexception a temporary file could not be opened to write the process output lasterror symfony process pipes windowspipes php line remove files on destruct php public function destruct this close foreach this files as file unlink file unlink file lock additional context during replication i made a simple controller that dumps output of the dir command for testing src controller homecontroller php php php namespace app controller use symfony component httpfoundation response use symfony component process exception processfailedexception use symfony component process process class homecontroller public function index process new process process run if process issuccessful throw new processfailedexception process return new response process getoutput and attached it to the base route config routes yaml yaml index path controller app controller homecontroller index the same code was used on both site a and b
| 1
|
16,272
| 20,868,048,072
|
IssuesEvent
|
2022-03-22 09:19:40
|
quark-engine/quark-engine
|
https://api.github.com/repos/quark-engine/quark-engine
|
closed
|
Add description for the restriction of parallel analysis
|
work-in-progress issue-processing-state-06
|
**Is your feature request related to a problem? Please describe.**
In #311 , we added a restriction for the parallel analysis to avoid exhausting the memory. This restriction sometimes overwrites the arguments that users assign. However, it is not well-described in the [document](https://quark-engine.readthedocs.io/en/latest/) and [README](https://github.com/quark-engine/quark-engine#readme).
**Describe the solution you'd like.**
Indicate this restriction clearly in the document and README.
|
1.0
|
Add description for the restriction of parallel analysis - **Is your feature request related to a problem? Please describe.**
In #311 , we added a restriction for the parallel analysis to avoid exhausting the memory. This restriction sometimes overwrites the arguments that users assign. However, it is not well-described in the [document](https://quark-engine.readthedocs.io/en/latest/) and [README](https://github.com/quark-engine/quark-engine#readme).
**Describe the solution you'd like.**
Indicate this restriction clearly in the document and README.
|
process
|
add description for the restriction of parallel analysis is your feature request related to a problem please describe in we added a restriction for the parallel analysis to avoid exhausting the memory this restriction sometimes overwrites the arguments that users assign however it is not well described in the and describe the solution you d like indicate this restriction clearly in the document and readme
| 1
|
46,303
| 5,795,265,192
|
IssuesEvent
|
2017-05-02 16:40:35
|
healthlocker/healthlocker
|
https://api.github.com/repos/healthlocker/healthlocker
|
closed
|
Account - epic
|
2. SLaM SU access epic please-test
|
I suspect this needs to be an epic as it's quite complicated. Not sure how to sort this out though.

These are the different important parts:
- Connect with SLaM
- See/view my profile details
-- SLaM user (+ update phone and address / clinician notified)
-- Non-SLaM user
- Update security details (password and security question) #127
- Research and C4C consent
Can I get people's thoughts on this?
|
1.0
|
Account - epic - I suspect this needs to be an epic as it's quite complicated. Not sure how to sort this out though.

These are the different important parts:
- Connect with SLaM
- See/view my profile details
-- SLaM user (+ update phone and address / clinician notified)
-- Non-SLaM user
- Update security details (password and security question) #127
- Research and C4C consent
Can I get people's thoughts on this?
|
non_process
|
account epic i suspect this needs to be an epic as it s quite complicated not sure how to sort this out though these are the different important parts connect with slam see view my profile details slam user update phone and address clinician notified non slam user update security details password and security question research and consent can i get people s thoughts on this
| 0
|
143,510
| 19,184,615,324
|
IssuesEvent
|
2021-12-05 01:06:36
|
AlexRogalskiy/github-action-user-contribution
|
https://api.github.com/repos/AlexRogalskiy/github-action-user-contribution
|
opened
|
CVE-2021-37712 (High) detected in tar-6.1.0.tgz
|
security vulnerability
|
## CVE-2021-37712 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tar-6.1.0.tgz</b></p></summary>
<p>tar for node</p>
<p>Library home page: <a href="https://registry.npmjs.org/tar/-/tar-6.1.0.tgz">https://registry.npmjs.org/tar/-/tar-6.1.0.tgz</a></p>
<p>Path to dependency file: github-action-user-contribution/package.json</p>
<p>Path to vulnerable library: github-action-user-contribution/node_modules/tar/package.json,github-action-user-contribution/node_modules/npm/node_modules/tar/package.json</p>
<p>
Dependency Hierarchy:
- editorconfig-checker-4.0.2.tgz (Root Library)
- :x: **tar-6.1.0.tgz** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The npm package "tar" (aka node-tar) before versions 4.4.18, 5.0.10, and 6.1.9 has an arbitrary file creation/overwrite and arbitrary code execution vulnerability. node-tar aims to guarantee that any file whose location would be modified by a symbolic link is not extracted. This is, in part, achieved by ensuring that extracted directories are not symlinks. Additionally, in order to prevent unnecessary stat calls to determine whether a given path is a directory, paths are cached when directories are created. This logic was insufficient when extracting tar files that contained both a directory and a symlink with names containing unicode values that normalized to the same value. Additionally, on Windows systems, long path portions would resolve to the same file system entities as their 8.3 "short path" counterparts. A specially crafted tar archive could thus include a directory with one form of the path, followed by a symbolic link with a different string that resolves to the same file system entity, followed by a file using the first form. By first creating a directory, and then replacing that directory with a symlink that had a different apparent name that resolved to the same entry in the filesystem, it was thus possible to bypass node-tar symlink checks on directories, essentially allowing an untrusted tar file to symlink into an arbitrary location and subsequently extracting arbitrary files into that location, thus allowing arbitrary file creation and overwrite. These issues were addressed in releases 4.4.18, 5.0.10 and 6.1.9. The v3 branch of node-tar has been deprecated and did not receive patches for these issues. If you are still using a v3 release we recommend you update to a more recent version of node-tar. If this is not possible, a workaround is available in the referenced GHSA-qq89-hq3f-393p.
<p>Publish Date: 2021-08-31
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-37712>CVE-2021-37712</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.6</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/npm/node-tar/security/advisories/GHSA-qq89-hq3f-393p">https://github.com/npm/node-tar/security/advisories/GHSA-qq89-hq3f-393p</a></p>
<p>Release Date: 2021-08-31</p>
<p>Fix Resolution: tar - 4.4.18, 5.0.10, 6.1.9</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2021-37712 (High) detected in tar-6.1.0.tgz - ## CVE-2021-37712 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tar-6.1.0.tgz</b></p></summary>
<p>tar for node</p>
<p>Library home page: <a href="https://registry.npmjs.org/tar/-/tar-6.1.0.tgz">https://registry.npmjs.org/tar/-/tar-6.1.0.tgz</a></p>
<p>Path to dependency file: github-action-user-contribution/package.json</p>
<p>Path to vulnerable library: github-action-user-contribution/node_modules/tar/package.json,github-action-user-contribution/node_modules/npm/node_modules/tar/package.json</p>
<p>
Dependency Hierarchy:
- editorconfig-checker-4.0.2.tgz (Root Library)
- :x: **tar-6.1.0.tgz** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The npm package "tar" (aka node-tar) before versions 4.4.18, 5.0.10, and 6.1.9 has an arbitrary file creation/overwrite and arbitrary code execution vulnerability. node-tar aims to guarantee that any file whose location would be modified by a symbolic link is not extracted. This is, in part, achieved by ensuring that extracted directories are not symlinks. Additionally, in order to prevent unnecessary stat calls to determine whether a given path is a directory, paths are cached when directories are created. This logic was insufficient when extracting tar files that contained both a directory and a symlink with names containing unicode values that normalized to the same value. Additionally, on Windows systems, long path portions would resolve to the same file system entities as their 8.3 "short path" counterparts. A specially crafted tar archive could thus include a directory with one form of the path, followed by a symbolic link with a different string that resolves to the same file system entity, followed by a file using the first form. By first creating a directory, and then replacing that directory with a symlink that had a different apparent name that resolved to the same entry in the filesystem, it was thus possible to bypass node-tar symlink checks on directories, essentially allowing an untrusted tar file to symlink into an arbitrary location and subsequently extracting arbitrary files into that location, thus allowing arbitrary file creation and overwrite. These issues were addressed in releases 4.4.18, 5.0.10 and 6.1.9. The v3 branch of node-tar has been deprecated and did not receive patches for these issues. If you are still using a v3 release we recommend you update to a more recent version of node-tar. If this is not possible, a workaround is available in the referenced GHSA-qq89-hq3f-393p.
<p>Publish Date: 2021-08-31
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-37712>CVE-2021-37712</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.6</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/npm/node-tar/security/advisories/GHSA-qq89-hq3f-393p">https://github.com/npm/node-tar/security/advisories/GHSA-qq89-hq3f-393p</a></p>
<p>Release Date: 2021-08-31</p>
<p>Fix Resolution: tar - 4.4.18, 5.0.10, 6.1.9</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_process
|
cve high detected in tar tgz cve high severity vulnerability vulnerable library tar tgz tar for node library home page a href path to dependency file github action user contribution package json path to vulnerable library github action user contribution node modules tar package json github action user contribution node modules npm node modules tar package json dependency hierarchy editorconfig checker tgz root library x tar tgz vulnerable library found in base branch master vulnerability details the npm package tar aka node tar before versions and has an arbitrary file creation overwrite and arbitrary code execution vulnerability node tar aims to guarantee that any file whose location would be modified by a symbolic link is not extracted this is in part achieved by ensuring that extracted directories are not symlinks additionally in order to prevent unnecessary stat calls to determine whether a given path is a directory paths are cached when directories are created this logic was insufficient when extracting tar files that contained both a directory and a symlink with names containing unicode values that normalized to the same value additionally on windows systems long path portions would resolve to the same file system entities as their short path counterparts a specially crafted tar archive could thus include a directory with one form of the path followed by a symbolic link with a different string that resolves to the same file system entity followed by a file using the first form by first creating a directory and then replacing that directory with a symlink that had a different apparent name that resolved to the same entry in the filesystem it was thus possible to bypass node tar symlink checks on directories essentially allowing an untrusted tar file to symlink into an arbitrary location and subsequently extracting arbitrary files into that location thus allowing arbitrary file creation and overwrite these issues were addressed in releases and the branch of node tar has been deprecated and did not receive patches for these issues if you are still using a release we recommend you update to a more recent version of node tar if this is not possible a workaround is available in the referenced ghsa publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution tar step up your open source security game with whitesource
| 0
|
3,938
| 2,610,084,420
|
IssuesEvent
|
2015-02-26 18:25:43
|
chrsmith/dsdsdaadf
|
https://api.github.com/repos/chrsmith/dsdsdaadf
|
opened
|
深圳彩光如何祛痘痘
|
auto-migrated Priority-Medium Type-Defect
|
```
深圳彩光如何祛痘痘【深圳韩方科颜全国热线400-869-1818,24小
时QQ4008691818】深圳韩方科颜专业祛痘连锁机构,机构以韩国��
�方——韩方科颜这一国妆准字号治疗型权威,祛痘佳品,韩�
��科颜专业祛痘连锁机构,采用韩国秘方配合专业“不反弹”
健康祛痘技术并结合先进“先进豪华彩光”仪,开创国内专��
�治疗粉刺、痤疮签约包治先河,成功消除了许多顾客脸上的�
��痘。
```
-----
Original issue reported on code.google.com by `szft...@163.com` on 14 May 2014 at 6:57
|
1.0
|
深圳彩光如何祛痘痘 - ```
深圳彩光如何祛痘痘【深圳韩方科颜全国热线400-869-1818,24小
时QQ4008691818】深圳韩方科颜专业祛痘连锁机构,机构以韩国��
�方——韩方科颜这一国妆准字号治疗型权威,祛痘佳品,韩�
��科颜专业祛痘连锁机构,采用韩国秘方配合专业“不反弹”
健康祛痘技术并结合先进“先进豪华彩光”仪,开创国内专��
�治疗粉刺、痤疮签约包治先河,成功消除了许多顾客脸上的�
��痘。
```
-----
Original issue reported on code.google.com by `szft...@163.com` on 14 May 2014 at 6:57
|
non_process
|
深圳彩光如何祛痘痘 深圳彩光如何祛痘痘【 , 】深圳韩方科颜专业祛痘连锁机构,机构以韩国�� �方——韩方科颜这一国妆准字号治疗型权威,祛痘佳品,韩� ��科颜专业祛痘连锁机构,采用韩国秘方配合专业“不反弹” 健康祛痘技术并结合先进“先进豪华彩光”仪,开创国内专�� �治疗粉刺、痤疮签约包治先河,成功消除了许多顾客脸上的� ��痘。 original issue reported on code google com by szft com on may at
| 0
|
157,170
| 5,996,366,501
|
IssuesEvent
|
2017-06-03 13:39:18
|
universAAL/tools.eclipse-plugins
|
https://api.github.com/repos/universAAL/tools.eclipse-plugins
|
closed
|
Integrate ontology plugins into one?
|
feature request imported priority 4
|
_Originally Opened: @erlendstav (2012-01-24 17:16:46_)
_Originally Closed: 2013-02-27 15:49:46_
Input from TSB developers, July 8, 2011:
Integration of the three/four different plug-ins in only one in order to make the installation process easier. Maybe this is not possible since you rely in existing well known plug-ins.
--
From: _this issue has been automatically imported from our old issue tracker_
|
1.0
|
Integrate ontology plugins into one? - _Originally Opened: @erlendstav (2012-01-24 17:16:46_)
_Originally Closed: 2013-02-27 15:49:46_
Input from TSB developers, July 8, 2011:
Integration of the three/four different plug-ins in only one in order to make the installation process easier. Maybe this is not possible since you rely in existing well known plug-ins.
--
From: _this issue has been automatically imported from our old issue tracker_
|
non_process
|
integrate ontology plugins into one originally opened erlendstav originally closed input from tsb developers july integration of the three four different plug ins in only one in order to make the installation process easier maybe this is not possible since you rely in existing well known plug ins from this issue has been automatically imported from our old issue tracker
| 0
|
8,689
| 11,827,008,066
|
IssuesEvent
|
2020-03-21 20:48:02
|
Ultimate-Hosts-Blacklist/whitelist
|
https://api.github.com/repos/Ultimate-Hosts-Blacklist/whitelist
|
closed
|
NTP servers- False Positives
|
whitelisting process
|
*@p1r473 commented on Mar 21, 2020, 3:04 AM UTC:*
Domains:
pool.ntp.org
[www.pool.ntp.org](http://www.pool.ntp.org)
These are servers for Network Time Protocol and are totally benign
*This issue was moved by [funilrys](https://github.com/funilrys) from [mitchellkrogza/Ultimate.Hosts.Blacklist#554](https://github.com/mitchellkrogza/Ultimate.Hosts.Blacklist/issues/554).*
|
1.0
|
NTP servers- False Positives - *@p1r473 commented on Mar 21, 2020, 3:04 AM UTC:*
Domains:
pool.ntp.org
[www.pool.ntp.org](http://www.pool.ntp.org)
These are servers for Network Time Protocol and are totally benign
*This issue was moved by [funilrys](https://github.com/funilrys) from [mitchellkrogza/Ultimate.Hosts.Blacklist#554](https://github.com/mitchellkrogza/Ultimate.Hosts.Blacklist/issues/554).*
|
process
|
ntp servers false positives commented on mar am utc domains pool ntp org these are servers for network time protocol and are totally benign this issue was moved by from
| 1
|
8,018
| 11,206,594,880
|
IssuesEvent
|
2020-01-05 22:32:24
|
qlixed/python-memwiper
|
https://api.github.com/repos/qlixed/python-memwiper
|
closed
|
Error about Interned strings
|
in process
|
On interpreter close we get an error trying to remove the interned string, as the overwrited one is not in the interned dict.
|
1.0
|
Error about Interned strings - On interpreter close we get an error trying to remove the interned string, as the overwrited one is not in the interned dict.
|
process
|
error about interned strings on interpreter close we get an error trying to remove the interned string as the overwrited one is not in the interned dict
| 1
|
452,834
| 13,060,094,054
|
IssuesEvent
|
2020-07-30 11:50:23
|
StargateMC/IssueTracker
|
https://api.github.com/repos/StargateMC/IssueTracker
|
closed
|
Suggestion - Holomap Change
|
1.12.2 Low Priority suggestion
|
## What is your suggestion?
>Change the holomap so you’re able to select a few planets from each other galaxy. This keeps the lag still lowered from what it was when all parts of each galaxy were displayed.
## How will this benefit players?
>Players who prefer to use the holo map when warping rather than the warp controller can do so.
>Why is this important?
>Personally I find the holo map a lot easier to use than the warp controller.
## How will this change for players?
>Players can continue to use the holo map to warp while keeping lag reduced.
## Do you consider this suggestion a:
- [ ] Must (Important to keep players happy)
- [x] Should (Beneficial to players, but can do without)
- [ ]Could (Beneficial to players, there is no important reason to do it
|
1.0
|
Suggestion - Holomap Change -
## What is your suggestion?
>Change the holomap so you’re able to select a few planets from each other galaxy. This keeps the lag still lowered from what it was when all parts of each galaxy were displayed.
## How will this benefit players?
>Players who prefer to use the holo map when warping rather than the warp controller can do so.
>Why is this important?
>Personally I find the holo map a lot easier to use than the warp controller.
## How will this change for players?
>Players can continue to use the holo map to warp while keeping lag reduced.
## Do you consider this suggestion a:
- [ ] Must (Important to keep players happy)
- [x] Should (Beneficial to players, but can do without)
- [ ]Could (Beneficial to players, there is no important reason to do it
|
non_process
|
suggestion holomap change what is your suggestion change the holomap so you’re able to select a few planets from each other galaxy this keeps the lag still lowered from what it was when all parts of each galaxy were displayed how will this benefit players players who prefer to use the holo map when warping rather than the warp controller can do so why is this important personally i find the holo map a lot easier to use than the warp controller how will this change for players players can continue to use the holo map to warp while keeping lag reduced do you consider this suggestion a must important to keep players happy should beneficial to players but can do without could beneficial to players there is no important reason to do it
| 0
|
13,817
| 16,581,039,159
|
IssuesEvent
|
2021-05-31 11:53:05
|
bisq-network/proposals
|
https://api.github.com/repos/bisq-network/proposals
|
closed
|
Integrate with OpenDEX for Bitcoin-to-Crypto Trading
|
an:idea re:processes
|
> _This is a Bisq Network proposal. Please familiarize yourself with the [submission and review process](https://docs.bisq.network/proposals.html)._
<!-- Please do not remove the text above. -->
@initCCG [brought up the idea](https://github.com/opendexnetwork/opendex/issues/23#issuecomment-716966084) to integrate trading on [OpenDEX](https://opendex.network/) within the bisq app. Feasible? Definitely. But admittedly not trivial and not a small feat. I am putting this out here as an early-stage proposal to get early feedback from the bisq community.
How I see it, there are several ways how to go about it:
1. Implement the [OpenDEX protocol](https://opendex.network/read/00-introduction) directly in the bisq java stack, package the minimum necessary swap clients into the bisq app: lnd(light) + connext(light)
2. Use an existing [OpenDEX implementation](https://opendex.network/trade/implementations), packaged within within the bisq app along with necessary lnd(light) + connext(light) swap clients
3. Merely provide bisq users with instructions how to externally set up an OpenDEX environment and allow connecting to & visual control+trading of such environment through the bisq app.
|
1.0
|
Integrate with OpenDEX for Bitcoin-to-Crypto Trading - > _This is a Bisq Network proposal. Please familiarize yourself with the [submission and review process](https://docs.bisq.network/proposals.html)._
<!-- Please do not remove the text above. -->
@initCCG [brought up the idea](https://github.com/opendexnetwork/opendex/issues/23#issuecomment-716966084) to integrate trading on [OpenDEX](https://opendex.network/) within the bisq app. Feasible? Definitely. But admittedly not trivial and not a small feat. I am putting this out here as an early-stage proposal to get early feedback from the bisq community.
How I see it, there are several ways how to go about it:
1. Implement the [OpenDEX protocol](https://opendex.network/read/00-introduction) directly in the bisq java stack, package the minimum necessary swap clients into the bisq app: lnd(light) + connext(light)
2. Use an existing [OpenDEX implementation](https://opendex.network/trade/implementations), packaged within within the bisq app along with necessary lnd(light) + connext(light) swap clients
3. Merely provide bisq users with instructions how to externally set up an OpenDEX environment and allow connecting to & visual control+trading of such environment through the bisq app.
|
process
|
integrate with opendex for bitcoin to crypto trading this is a bisq network proposal please familiarize yourself with the initccg to integrate trading on within the bisq app feasible definitely but admittedly not trivial and not a small feat i am putting this out here as an early stage proposal to get early feedback from the bisq community how i see it there are several ways how to go about it implement the directly in the bisq java stack package the minimum necessary swap clients into the bisq app lnd light connext light use an existing packaged within within the bisq app along with necessary lnd light connext light swap clients merely provide bisq users with instructions how to externally set up an opendex environment and allow connecting to visual control trading of such environment through the bisq app
| 1
|
642
| 3,103,693,503
|
IssuesEvent
|
2015-08-31 11:49:57
|
e-government-ua/i
|
https://api.github.com/repos/e-government-ua/i
|
closed
|
На дашборде реализовать возможность выбора одного из нескольких доступных шаблонов формы печати для таски, вместо одного.
|
bug hi priority In process of testing test
|
- [x] 1. Возле кнопки "Роздрукувати" (справа) разместить комбобокс, в котором перечислять все доступные шаблоны для печати.
- [x] 2. Список шаблонов формировать так:
- [x] 2.1. Смотреть все поля в форме, с id=sPatternPrint_*
- [x] 2.2. Брать название шаблона из атрибута "name" каждого из полей п.п.2.1.
- [x] 2.3. Сортировать пункты комбобокса в порядке id п.п.1.1.
(т.е. sPatternPrint_1, sPatternPrint_2, sPatternPrint_3)
- [x] 3. Поправить работу кнопки "Роздрукувати" так, чтоб использовалось значение (value) выбранного поля (вместо текущего варианта реализации, когда берется значение поля sBody)
|
1.0
|
На дашборде реализовать возможность выбора одного из нескольких доступных шаблонов формы печати для таски, вместо одного. - - [x] 1. Возле кнопки "Роздрукувати" (справа) разместить комбобокс, в котором перечислять все доступные шаблоны для печати.
- [x] 2. Список шаблонов формировать так:
- [x] 2.1. Смотреть все поля в форме, с id=sPatternPrint_*
- [x] 2.2. Брать название шаблона из атрибута "name" каждого из полей п.п.2.1.
- [x] 2.3. Сортировать пункты комбобокса в порядке id п.п.1.1.
(т.е. sPatternPrint_1, sPatternPrint_2, sPatternPrint_3)
- [x] 3. Поправить работу кнопки "Роздрукувати" так, чтоб использовалось значение (value) выбранного поля (вместо текущего варианта реализации, когда берется значение поля sBody)
|
process
|
на дашборде реализовать возможность выбора одного из нескольких доступных шаблонов формы печати для таски вместо одного возле кнопки роздрукувати справа разместить комбобокс в котором перечислять все доступные шаблоны для печати список шаблонов формировать так смотреть все поля в форме с id spatternprint брать название шаблона из атрибута name каждого из полей п п сортировать пункты комбобокса в порядке id п п т е spatternprint spatternprint spatternprint поправить работу кнопки роздрукувати так чтоб использовалось значение value выбранного поля вместо текущего варианта реализации когда берется значение поля sbody
| 1
|
182,987
| 6,676,140,209
|
IssuesEvent
|
2017-10-05 03:15:33
|
classifiedz/classifiedz.github.io
|
https://api.github.com/repos/classifiedz/classifiedz.github.io
|
closed
|
AD CARD: Add another pill of different colour beside the current green price pill to indicate the date the ad was posted.
|
enhancement Low Priority question
|
Format for the date could use is MM/DD so it doesn't take up a lot of room, and will give the user an idea of when the ad was posted.
|
1.0
|
AD CARD: Add another pill of different colour beside the current green price pill to indicate the date the ad was posted. - Format for the date could use is MM/DD so it doesn't take up a lot of room, and will give the user an idea of when the ad was posted.
|
non_process
|
ad card add another pill of different colour beside the current green price pill to indicate the date the ad was posted format for the date could use is mm dd so it doesn t take up a lot of room and will give the user an idea of when the ad was posted
| 0
|
265,484
| 23,172,302,884
|
IssuesEvent
|
2022-07-30 22:47:24
|
foundry-rs/foundry
|
https://api.github.com/repos/foundry-rs/foundry
|
closed
|
feat: enable saving and loading of corpus for deterministic fuzzing
|
A-fuzzing T-feature Cmd-forge-test C-forge P-normal
|
### Component
Forge
### Describe the feature you would like
Add `--save-corpus` and `--load-corpus <path>` options to allow replaying of an entire fuzz campaign. I think proptest has methods to facilitate this but need to double check. It would also be great if saving a corpus saves off all inputs used (as opposed to just rng seeds) so they can be inspected/analyzed
### Additional context
_No response_
|
1.0
|
feat: enable saving and loading of corpus for deterministic fuzzing - ### Component
Forge
### Describe the feature you would like
Add `--save-corpus` and `--load-corpus <path>` options to allow replaying of an entire fuzz campaign. I think proptest has methods to facilitate this but need to double check. It would also be great if saving a corpus saves off all inputs used (as opposed to just rng seeds) so they can be inspected/analyzed
### Additional context
_No response_
|
non_process
|
feat enable saving and loading of corpus for deterministic fuzzing component forge describe the feature you would like add save corpus and load corpus options to allow replaying of an entire fuzz campaign i think proptest has methods to facilitate this but need to double check it would also be great if saving a corpus saves off all inputs used as opposed to just rng seeds so they can be inspected analyzed additional context no response
| 0
|
183,498
| 14,234,344,385
|
IssuesEvent
|
2020-11-18 13:28:28
|
mindsdb/mindsdb_native
|
https://api.github.com/repos/mindsdb/mindsdb_native
|
closed
|
Test with broken datasets
|
current priority test
|
Run tests with datasets that we artificially break. I.e.
1. Null out values (replace with `null`, `None`, `0`)
2. Mess up a few values in a column (shifting values around columns would be an ideal way to do it)
3. Predict with data types that aren't in the training datasets (e.g. pass a string for a numeircal input)
4. Remove the target values from certain rows
5. Append random characters to dates & numbers
... etc
Initially we just need to validate this doesn't break stuff, than we can start looking into the behavior exhibited (i.e. if mindsdb is still able to properly salvage the datasets by ignoring the corrupt values)
|
1.0
|
Test with broken datasets - Run tests with datasets that we artificially break. I.e.
1. Null out values (replace with `null`, `None`, `0`)
2. Mess up a few values in a column (shifting values around columns would be an ideal way to do it)
3. Predict with data types that aren't in the training datasets (e.g. pass a string for a numeircal input)
4. Remove the target values from certain rows
5. Append random characters to dates & numbers
... etc
Initially we just need to validate this doesn't break stuff, than we can start looking into the behavior exhibited (i.e. if mindsdb is still able to properly salvage the datasets by ignoring the corrupt values)
|
non_process
|
test with broken datasets run tests with datasets that we artificially break i e null out values replace with null none mess up a few values in a column shifting values around columns would be an ideal way to do it predict with data types that aren t in the training datasets e g pass a string for a numeircal input remove the target values from certain rows append random characters to dates numbers etc initially we just need to validate this doesn t break stuff than we can start looking into the behavior exhibited i e if mindsdb is still able to properly salvage the datasets by ignoring the corrupt values
| 0
|
142,450
| 13,025,166,178
|
IssuesEvent
|
2020-07-27 13:07:59
|
espressomd/espresso
|
https://api.github.com/repos/espressomd/espresso
|
closed
|
Document openmpi symbol loading code
|
Core Documentation
|
The function `mpi_init` in communication.cpp contains the following code:
```c++
#ifdef OPEN_MPI
openmpi_fix_vader();
void *handle = nullptr;
int mode = RTLD_NOW | RTLD_GLOBAL;
#ifdef RTLD_NOLOAD
mode |= RTLD_NOLOAD;
#endif
void *_openmpi_symbol = dlsym(RTLD_DEFAULT, "MPI_Init");
if (!_openmpi_symbol) {
fprintf(stderr, "%d: Aborting because unable to find OpenMPI symbol.\n",
this_node);
errexit();
}
Dl_info _openmpi_info;
dladdr(_openmpi_symbol, &_openmpi_info);
if (!handle)
handle = dlopen(_openmpi_info.dli_fname, mode);
if (!handle) {
fprintf(stderr,
"%d: Aborting because unable to load libmpi into the "
"global symbol space.\n",
this_node);
errexit();
}
#endif
```
It needs to be documented what this is doing and why it is needed. Also it is not clear to me that
this is safe in all circumstances, e.g. what happens if the shared has already be loaded before.
|
1.0
|
Document openmpi symbol loading code - The function `mpi_init` in communication.cpp contains the following code:
```c++
#ifdef OPEN_MPI
openmpi_fix_vader();
void *handle = nullptr;
int mode = RTLD_NOW | RTLD_GLOBAL;
#ifdef RTLD_NOLOAD
mode |= RTLD_NOLOAD;
#endif
void *_openmpi_symbol = dlsym(RTLD_DEFAULT, "MPI_Init");
if (!_openmpi_symbol) {
fprintf(stderr, "%d: Aborting because unable to find OpenMPI symbol.\n",
this_node);
errexit();
}
Dl_info _openmpi_info;
dladdr(_openmpi_symbol, &_openmpi_info);
if (!handle)
handle = dlopen(_openmpi_info.dli_fname, mode);
if (!handle) {
fprintf(stderr,
"%d: Aborting because unable to load libmpi into the "
"global symbol space.\n",
this_node);
errexit();
}
#endif
```
It needs to be documented what this is doing and why it is needed. Also it is not clear to me that
this is safe in all circumstances, e.g. what happens if the shared has already be loaded before.
|
non_process
|
document openmpi symbol loading code the function mpi init in communication cpp contains the following code c ifdef open mpi openmpi fix vader void handle nullptr int mode rtld now rtld global ifdef rtld noload mode rtld noload endif void openmpi symbol dlsym rtld default mpi init if openmpi symbol fprintf stderr d aborting because unable to find openmpi symbol n this node errexit dl info openmpi info dladdr openmpi symbol openmpi info if handle handle dlopen openmpi info dli fname mode if handle fprintf stderr d aborting because unable to load libmpi into the global symbol space n this node errexit endif it needs to be documented what this is doing and why it is needed also it is not clear to me that this is safe in all circumstances e g what happens if the shared has already be loaded before
| 0
|
18,140
| 24,186,137,711
|
IssuesEvent
|
2022-09-23 13:28:18
|
GIScience/sketch-map-tool
|
https://api.github.com/repos/GIScience/sketch-map-tool
|
opened
|
Use UUIDs for output file locations and status updates
|
component:analyses component:map-generation component:upload-processing priority:high
|
Instead of different combinations of bboxes, paper formats, times, random character sequences etc. use UUIDs for storing output files, their status updates, and retrieving them. As a first step directories whith the UUID as name can be used to achieve that.
|
1.0
|
Use UUIDs for output file locations and status updates - Instead of different combinations of bboxes, paper formats, times, random character sequences etc. use UUIDs for storing output files, their status updates, and retrieving them. As a first step directories whith the UUID as name can be used to achieve that.
|
process
|
use uuids for output file locations and status updates instead of different combinations of bboxes paper formats times random character sequences etc use uuids for storing output files their status updates and retrieving them as a first step directories whith the uuid as name can be used to achieve that
| 1
|
21,235
| 3,691,540,625
|
IssuesEvent
|
2016-02-26 00:35:22
|
OrchardCMS/Orchard2
|
https://api.github.com/repos/OrchardCMS/Orchard2
|
closed
|
Should zones have no tags
|
needsdesign
|
Right now in `ZoneShapes`, as in O1 we render a `div` tag a `zone zone-name` classes for a layout zone.
I think we should render zone bare, and let the layout define how it is done. It's not harder anyway to define the tagging in the layout. but it much harder to remove the tag afterwards.
The ContentZone behavior would not be altered though.
|
1.0
|
Should zones have no tags - Right now in `ZoneShapes`, as in O1 we render a `div` tag a `zone zone-name` classes for a layout zone.
I think we should render zone bare, and let the layout define how it is done. It's not harder anyway to define the tagging in the layout. but it much harder to remove the tag afterwards.
The ContentZone behavior would not be altered though.
|
non_process
|
should zones have no tags right now in zoneshapes as in we render a div tag a zone zone name classes for a layout zone i think we should render zone bare and let the layout define how it is done it s not harder anyway to define the tagging in the layout but it much harder to remove the tag afterwards the contentzone behavior would not be altered though
| 0
|
4,686
| 7,522,666,130
|
IssuesEvent
|
2018-04-12 21:12:44
|
dotnet/corefx
|
https://api.github.com/repos/dotnet/corefx
|
closed
|
Mass spawning of processes slower than with mono
|
area-System.Diagnostics.Process enhancement tenet-performance
|
Continuing discussion from #26291 :
I know it's in the enhancement department, but since I felt a significant difference testing mono and .Net Core I decided to time it.
The following snip takes 15s vs 10s in .Net Core 2.1 preview 2 vs. mono 5.8.1 :
```c#
var stopwatch = Stopwatch.StartNew();
for (int i = 0; i < 10000; i++)
Process.Start("echo", i.ToString());
Console.WriteLine("Took " + stopwatch.Elapsed);
```
33% slower launch times for processes seems significant to me.
(I'm on Darwin. You know best if this concerns all *nix)
[EDIT] Add C# syntax highlighting by @karelz
|
1.0
|
Mass spawning of processes slower than with mono - Continuing discussion from #26291 :
I know it's in the enhancement department, but since I felt a significant difference testing mono and .Net Core I decided to time it.
The following snip takes 15s vs 10s in .Net Core 2.1 preview 2 vs. mono 5.8.1 :
```c#
var stopwatch = Stopwatch.StartNew();
for (int i = 0; i < 10000; i++)
Process.Start("echo", i.ToString());
Console.WriteLine("Took " + stopwatch.Elapsed);
```
33% slower launch times for processes seems significant to me.
(I'm on Darwin. You know best if this concerns all *nix)
[EDIT] Add C# syntax highlighting by @karelz
|
process
|
mass spawning of processes slower than with mono continuing discussion from i know it s in the enhancement department but since i felt a significant difference testing mono and net core i decided to time it the following snip takes vs in net core preview vs mono c var stopwatch stopwatch startnew for int i i i process start echo i tostring console writeline took stopwatch elapsed slower launch times for processes seems significant to me i m on darwin you know best if this concerns all nix add c syntax highlighting by karelz
| 1
|
19,056
| 25,074,367,528
|
IssuesEvent
|
2022-11-07 14:30:17
|
eobermuhlner/big-math
|
https://api.github.com/repos/eobermuhlner/big-math
|
closed
|
Prepare release 2.3.1
|
development process
|
- [x] add release number header to release note
- [x] rename release note
- [x] create empty release note for next release from `template_release_note.md`
- [x] change version in `build.gradle` of `big-math` subproject
- [x] change version in pom.xml
- [ ] upload artifacts to maven central
- [x] run `./gradlew clean`
- [x] run `./gradlew :ch.obermuhlner.math.big:uploadArchives`
- [x] go to https://oss.sonatype.org/
- [x] in tab 'Staging Repositories' locate own Repository (typically at the end of the list)
- [x] verify content of own Repository (version number!)
- [x] `Close` own Repository
- [x] `Refresh` until `Release` becomes enabled
- [x] `Release` own Repository
- [ ] create github release from same artifacts
- [x] Create new draft release
- [x] Copy content of release note into draft release
- [x] Add artefacts from gradle build to draft release
- [x] big-math-*.jar
- [x] big-math-*-javadoc.jar
- [x] big-math-*-sources.jar
- [x] Verify all changes are committed and pushed
- [x] Create a new tag in release
- [x] Publish release
- [x] update readme
- [x] add generated javadoc to `docs/javadoc`
- [x] update `docs/index.md`
- [ ] update dependent projects
- [x] create regression project for new release
- [x] edit new `build.gradle` to use new release library
- [x] edit `settings.gradle` to add new regression project
- [x] run `./run_regression_analysis.sh`
|
1.0
|
Prepare release 2.3.1 - - [x] add release number header to release note
- [x] rename release note
- [x] create empty release note for next release from `template_release_note.md`
- [x] change version in `build.gradle` of `big-math` subproject
- [x] change version in pom.xml
- [ ] upload artifacts to maven central
- [x] run `./gradlew clean`
- [x] run `./gradlew :ch.obermuhlner.math.big:uploadArchives`
- [x] go to https://oss.sonatype.org/
- [x] in tab 'Staging Repositories' locate own Repository (typically at the end of the list)
- [x] verify content of own Repository (version number!)
- [x] `Close` own Repository
- [x] `Refresh` until `Release` becomes enabled
- [x] `Release` own Repository
- [ ] create github release from same artifacts
- [x] Create new draft release
- [x] Copy content of release note into draft release
- [x] Add artefacts from gradle build to draft release
- [x] big-math-*.jar
- [x] big-math-*-javadoc.jar
- [x] big-math-*-sources.jar
- [x] Verify all changes are committed and pushed
- [x] Create a new tag in release
- [x] Publish release
- [x] update readme
- [x] add generated javadoc to `docs/javadoc`
- [x] update `docs/index.md`
- [ ] update dependent projects
- [x] create regression project for new release
- [x] edit new `build.gradle` to use new release library
- [x] edit `settings.gradle` to add new regression project
- [x] run `./run_regression_analysis.sh`
|
process
|
prepare release add release number header to release note rename release note create empty release note for next release from template release note md change version in build gradle of big math subproject change version in pom xml upload artifacts to maven central run gradlew clean run gradlew ch obermuhlner math big uploadarchives go to in tab staging repositories locate own repository typically at the end of the list verify content of own repository version number close own repository refresh until release becomes enabled release own repository create github release from same artifacts create new draft release copy content of release note into draft release add artefacts from gradle build to draft release big math jar big math javadoc jar big math sources jar verify all changes are committed and pushed create a new tag in release publish release update readme add generated javadoc to docs javadoc update docs index md update dependent projects create regression project for new release edit new build gradle to use new release library edit settings gradle to add new regression project run run regression analysis sh
| 1
|
203,797
| 7,077,951,188
|
IssuesEvent
|
2018-01-10 00:39:01
|
google/google-api-java-client
|
https://api.github.com/repos/google/google-api-java-client
|
closed
|
Update appengine samples to maven-gae-plugin
|
1 star Type-Sample imported priority: p2
|
_From [yan...@google.com](https://code.google.com/u/111815493751521097215/) on April 16, 2012 06:57:22_
See: http://codereview.appspot.com/6007055/ We need to make the same changes to the other *-appengine-sample's.
_Original issue: http://code.google.com/p/google-api-java-client/issues/detail?id=458_
|
1.0
|
Update appengine samples to maven-gae-plugin - _From [yan...@google.com](https://code.google.com/u/111815493751521097215/) on April 16, 2012 06:57:22_
See: http://codereview.appspot.com/6007055/ We need to make the same changes to the other *-appengine-sample's.
_Original issue: http://code.google.com/p/google-api-java-client/issues/detail?id=458_
|
non_process
|
update appengine samples to maven gae plugin from on april see we need to make the same changes to the other appengine sample s original issue
| 0
|
21,751
| 30,267,413,147
|
IssuesEvent
|
2023-07-07 12:57:01
|
h4sh5/pypi-auto-scanner
|
https://api.github.com/repos/h4sh5/pypi-auto-scanner
|
opened
|
reprepbuild 0.11.0 has 3 GuardDog issues
|
guarddog silent-process-execution
|
https://pypi.org/project/reprepbuild
https://inspector.pypi.io/project/reprepbuild
```{
"dependency": "reprepbuild",
"version": "0.11.0",
"result": {
"issues": 3,
"errors": {},
"results": {
"silent-process-execution": [
{
"location": "RepRepBuild-0.11.0/src/reprepbuild/bibtex.py:54",
"code": " cp = subprocess.run(\n args,\n cwd=workdir,\n stdin=subprocess.DEVNULL,\n stdout=subprocess.DEVNULL,\n stderr=subprocess.DEVNULL,\n )",
"message": "This package is silently executing an external binary, redirecting stdout, stderr and stdin to /dev/null"
},
{
"location": "RepRepBuild-0.11.0/src/reprepbuild/latex.py:79",
"code": " subprocess.run(\n args,\n cwd=workdir,\n check=True,\n stdin=subprocess.DEVNULL,\n stdout=subprocess.DEVNULL,\n stderr=subprocess.DEVNULL,\n )",
"message": "This package is silently executing an external binary, redirecting stdout, stderr and stdin to /dev/null"
},
{
"location": "RepRepBuild-0.11.0/src/reprepbuild/latexdep.py:83",
"code": " subprocess.run(\n args,\n cwd=workdir,\n check=False,\n stdin=subprocess.DEVNULL,\n stdout=subprocess.DEVNULL,\n stderr=subprocess.DEVNULL,\n )",
"message": "This package is silently executing an external binary, redirecting stdout, stderr and stdin to /dev/null"
}
]
},
"path": "/tmp/tmpg8yd9i0g/reprepbuild"
}
}```
|
1.0
|
reprepbuild 0.11.0 has 3 GuardDog issues - https://pypi.org/project/reprepbuild
https://inspector.pypi.io/project/reprepbuild
```{
"dependency": "reprepbuild",
"version": "0.11.0",
"result": {
"issues": 3,
"errors": {},
"results": {
"silent-process-execution": [
{
"location": "RepRepBuild-0.11.0/src/reprepbuild/bibtex.py:54",
"code": " cp = subprocess.run(\n args,\n cwd=workdir,\n stdin=subprocess.DEVNULL,\n stdout=subprocess.DEVNULL,\n stderr=subprocess.DEVNULL,\n )",
"message": "This package is silently executing an external binary, redirecting stdout, stderr and stdin to /dev/null"
},
{
"location": "RepRepBuild-0.11.0/src/reprepbuild/latex.py:79",
"code": " subprocess.run(\n args,\n cwd=workdir,\n check=True,\n stdin=subprocess.DEVNULL,\n stdout=subprocess.DEVNULL,\n stderr=subprocess.DEVNULL,\n )",
"message": "This package is silently executing an external binary, redirecting stdout, stderr and stdin to /dev/null"
},
{
"location": "RepRepBuild-0.11.0/src/reprepbuild/latexdep.py:83",
"code": " subprocess.run(\n args,\n cwd=workdir,\n check=False,\n stdin=subprocess.DEVNULL,\n stdout=subprocess.DEVNULL,\n stderr=subprocess.DEVNULL,\n )",
"message": "This package is silently executing an external binary, redirecting stdout, stderr and stdin to /dev/null"
}
]
},
"path": "/tmp/tmpg8yd9i0g/reprepbuild"
}
}```
|
process
|
reprepbuild has guarddog issues dependency reprepbuild version result issues errors results silent process execution location reprepbuild src reprepbuild bibtex py code cp subprocess run n args n cwd workdir n stdin subprocess devnull n stdout subprocess devnull n stderr subprocess devnull n message this package is silently executing an external binary redirecting stdout stderr and stdin to dev null location reprepbuild src reprepbuild latex py code subprocess run n args n cwd workdir n check true n stdin subprocess devnull n stdout subprocess devnull n stderr subprocess devnull n message this package is silently executing an external binary redirecting stdout stderr and stdin to dev null location reprepbuild src reprepbuild latexdep py code subprocess run n args n cwd workdir n check false n stdin subprocess devnull n stdout subprocess devnull n stderr subprocess devnull n message this package is silently executing an external binary redirecting stdout stderr and stdin to dev null path tmp reprepbuild
| 1
|
1,471
| 4,049,583,944
|
IssuesEvent
|
2016-05-23 14:39:16
|
dita-ot/dita-ot
|
https://api.github.com/repos/dita-ot/dita-ot
|
opened
|
Disable topicpull for transtypes that don't need it
|
feature P2 preprocess
|
Disable topicpull for transtypes that handle their own link text resolution to remove unneeded processing. This will apply to e.g. PDF that will resolve links inside the FO processing. It should be easy to disable topicpull and topicpull should not contain processing that has other side-effects.
|
1.0
|
Disable topicpull for transtypes that don't need it - Disable topicpull for transtypes that handle their own link text resolution to remove unneeded processing. This will apply to e.g. PDF that will resolve links inside the FO processing. It should be easy to disable topicpull and topicpull should not contain processing that has other side-effects.
|
process
|
disable topicpull for transtypes that don t need it disable topicpull for transtypes that handle their own link text resolution to remove unneeded processing this will apply to e g pdf that will resolve links inside the fo processing it should be easy to disable topicpull and topicpull should not contain processing that has other side effects
| 1
|
278,131
| 30,702,208,215
|
IssuesEvent
|
2023-07-27 01:11:33
|
Nivaskumark/CVE-2020-0114-frameworks_base_afterfix
|
https://api.github.com/repos/Nivaskumark/CVE-2020-0114-frameworks_base_afterfix
|
opened
|
CVE-2023-21081 (High) detected in multiple libraries
|
Mend: dependency security vulnerability
|
## CVE-2023-21081 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>baseandroid-11.0.0_r39</b>, <b>baseandroid-11.0.0_r39</b>, <b>baseandroid-11.0.0_r39</b>, <b>baseandroid-11.0.0_r39</b></p></summary>
<p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
In multiple functions of PackageInstallerService.java and related files, there is a possible way to bypass background activity launch restrictions due to a logic error in the code. This could lead to local escalation of privilege with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-11 Android-12 Android-12L Android-13Android ID: A-230492955
<p>Publish Date: 2023-04-19
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-21081>CVE-2023-21081</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://android.googlesource.com/platform/frameworks/base/+/6aba151873bfae198ef9eceb10f943e18b52d58c">https://android.googlesource.com/platform/frameworks/base/+/6aba151873bfae198ef9eceb10f943e18b52d58c</a></p>
<p>Release Date: 2023-04-19</p>
<p>Fix Resolution: android-13.0.0_r38</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2023-21081 (High) detected in multiple libraries - ## CVE-2023-21081 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>baseandroid-11.0.0_r39</b>, <b>baseandroid-11.0.0_r39</b>, <b>baseandroid-11.0.0_r39</b>, <b>baseandroid-11.0.0_r39</b></p></summary>
<p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
In multiple functions of PackageInstallerService.java and related files, there is a possible way to bypass background activity launch restrictions due to a logic error in the code. This could lead to local escalation of privilege with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-11 Android-12 Android-12L Android-13Android ID: A-230492955
<p>Publish Date: 2023-04-19
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-21081>CVE-2023-21081</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://android.googlesource.com/platform/frameworks/base/+/6aba151873bfae198ef9eceb10f943e18b52d58c">https://android.googlesource.com/platform/frameworks/base/+/6aba151873bfae198ef9eceb10f943e18b52d58c</a></p>
<p>Release Date: 2023-04-19</p>
<p>Fix Resolution: android-13.0.0_r38</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_process
|
cve high detected in multiple libraries cve high severity vulnerability vulnerable libraries baseandroid baseandroid baseandroid baseandroid vulnerability details in multiple functions of packageinstallerservice java and related files there is a possible way to bypass background activity launch restrictions due to a logic error in the code this could lead to local escalation of privilege with no additional execution privileges needed user interaction is not needed for exploitation product androidversions android android android android id a publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution android step up your open source security game with mend
| 0
|
5,246
| 8,039,259,750
|
IssuesEvent
|
2018-07-30 17:49:11
|
GoogleCloudPlatform/google-cloud-python
|
https://api.github.com/repos/GoogleCloudPlatform/google-cloud-python
|
closed
|
Logging systests: 'list_metrics' returning extra entries
|
api: logging flaky testing type: process
|
See the [first error here](https://circleci.com/gh/GoogleCloudPlatform/google-cloud-python/6995):
```python
________________________ TestLogging.test_list_metrics _________________________
self = <test_system.TestLogging testMethod=test_list_metrics>
def test_list_metrics(self):
METRIC_NAME = 'test-list-metrics%s' % (_RESOURCE_ID,)
metric = Config.CLIENT.metric(
METRIC_NAME, DEFAULT_FILTER, DEFAULT_DESCRIPTION)
self.assertFalse(metric.exists())
before_metrics = list(Config.CLIENT.list_metrics())
before_names = set(metric.name for metric in before_metrics)
metric.create()
self.to_delete.append(metric)
self.assertTrue(metric.exists())
after_metrics = list(Config.CLIENT.list_metrics())
after_names = set(metric.name for metric in after_metrics)
self.assertEqual(after_names - before_names,
> set([METRIC_NAME]))
E AssertionError: Items in the first set but not the second:
E u'test-create-metric-6992-1529965066'
tests/system/test_system.py:343: AssertionError
```
My hypothesis is that overlapping CI runs are causing the extra metrics instances to be present.
|
1.0
|
Logging systests: 'list_metrics' returning extra entries - See the [first error here](https://circleci.com/gh/GoogleCloudPlatform/google-cloud-python/6995):
```python
________________________ TestLogging.test_list_metrics _________________________
self = <test_system.TestLogging testMethod=test_list_metrics>
def test_list_metrics(self):
METRIC_NAME = 'test-list-metrics%s' % (_RESOURCE_ID,)
metric = Config.CLIENT.metric(
METRIC_NAME, DEFAULT_FILTER, DEFAULT_DESCRIPTION)
self.assertFalse(metric.exists())
before_metrics = list(Config.CLIENT.list_metrics())
before_names = set(metric.name for metric in before_metrics)
metric.create()
self.to_delete.append(metric)
self.assertTrue(metric.exists())
after_metrics = list(Config.CLIENT.list_metrics())
after_names = set(metric.name for metric in after_metrics)
self.assertEqual(after_names - before_names,
> set([METRIC_NAME]))
E AssertionError: Items in the first set but not the second:
E u'test-create-metric-6992-1529965066'
tests/system/test_system.py:343: AssertionError
```
My hypothesis is that overlapping CI runs are causing the extra metrics instances to be present.
|
process
|
logging systests list metrics returning extra entries see the python testlogging test list metrics self def test list metrics self metric name test list metrics s resource id metric config client metric metric name default filter default description self assertfalse metric exists before metrics list config client list metrics before names set metric name for metric in before metrics metric create self to delete append metric self asserttrue metric exists after metrics list config client list metrics after names set metric name for metric in after metrics self assertequal after names before names set e assertionerror items in the first set but not the second e u test create metric tests system test system py assertionerror my hypothesis is that overlapping ci runs are causing the extra metrics instances to be present
| 1
|
6,192
| 9,104,381,675
|
IssuesEvent
|
2019-02-20 18:01:33
|
EthVM/ethvm
|
https://api.github.com/repos/EthVM/ethvm
|
closed
|
MongoSink issues
|
bug milestone:1 priority:high project:processing
|
I managed to capture a couple of related exceptions on our Mongo Sink:
- [x] Decimal 128 issue
- [x] Timeout randomly appears
- [x] It appears that some entries are missing on the db (see #333)
---
Here I leave a trace to further analyze it and is related to BigDecimal128:
```
ka-connect_1 | [2019-02-04 17:36:57,371] INFO Batch processing completed in 72 ms (io.enkrypt.kafka.connect.sinks.mongo.MongoSinkTask)
kafka-connect_1 | [2019-02-04 17:36:57,372] INFO Processing {} records (io.enkrypt.kafka.connect.sinks.mongo.MongoSinkTask)
kafka-connect_1 | [2019-02-04 17:36:57,374] INFO Processing Balances collection with 3 chunks (io.enkrypt.kafka.connect.sinks.mongo.MongoSinkTask)
kafka-connect_1 | [2019-02-04 17:36:57,400] INFO Chunk write complete. Collection = Balances, inserts = 0, updates = 184, upserts = 16, deletes = 0 (io.enkrypt.kafka.connect.sinks.mongo.MongoSinkTask)
kafka-connect_1 | [2019-02-04 17:36:57,439] INFO Chunk write complete. Collection = Balances, inserts = 0, updates = 174, upserts = 26, deletes = 0 (io.enkrypt.kafka.connect.sinks.mongo.MongoSinkTask)
kafka-connect_1 | [2019-02-04 17:36:57,457] INFO Chunk write complete. Collection = Balances, inserts = 0, updates = 85, upserts = 15, deletes = 0 (io.enkrypt.kafka.connect.sinks.mongo.MongoSinkTask)
kafka-connect_1 | [2019-02-04 17:36:57,457] INFO Batch processing completed in 85 ms (io.enkrypt.kafka.connect.sinks.mongo.MongoSinkTask)
kafka-connect_1 | [2019-02-04 17:36:57,459] INFO Processing {} records (io.enkrypt.kafka.connect.sinks.mongo.MongoSinkTask)
kafka-connect_1 | [2019-02-04 17:36:57,462] INFO Processing Balances collection with 3 chunks (io.enkrypt.kafka.connect.sinks.mongo.MongoSinkTask)
kafka-connect_1 | [2019-02-04 17:36:57,497] INFO Chunk write complete. Collection = Balances, inserts = 0, updates = 190, upserts = 10, deletes = 0 (io.enkrypt.kafka.connect.sinks.mongo.MongoSinkTask)
kafka-connect_1 | [2019-02-04 17:36:57,524] INFO Chunk write complete. Collection = Balances, inserts = 0, updates = 173, upserts = 27, deletes = 0 (io.enkrypt.kafka.connect.sinks.mongo.MongoSinkTask)
kafka-connect_1 | [2019-02-04 17:36:57,543] INFO Chunk write complete. Collection = Balances, inserts = 0, updates = 89, upserts = 11, deletes = 0 (io.enkrypt.kafka.connect.sinks.mongo.MongoSinkTask)
kafka-connect_1 | [2019-02-04 17:36:57,543] INFO Batch processing completed in 84 ms (io.enkrypt.kafka.connect.sinks.mongo.MongoSinkTask)
kafka-connect_1 | [2019-02-04 17:36:57,546] INFO Processing {} records (io.enkrypt.kafka.connect.sinks.mongo.MongoSinkTask)
kafka-connect_1 | [2019-02-04 17:36:57,549] ERROR WorkerSinkTask{id=enkryptio-mongo-ancillary-sink-0} Task threw an uncaught and unrecoverable exception. Task is being killed and will not recover until manually restarted. (org.apache.kafka.connect.runtime.WorkerSinkTask)
kafka-connect_1 | java.lang.NumberFormatException: Conversion to Decimal128 would require inexact rounding of 231584178474632390847141970017375815706539969331281128078915168015826259177872
kafka-connect_1 | at org.bson.types.Decimal128.ensureExactRounding(Decimal128.java:244)
kafka-connect_1 | at org.bson.types.Decimal128.clampAndRound(Decimal128.java:233)
kafka-connect_1 | at org.bson.types.Decimal128.<init>(Decimal128.java:169)
kafka-connect_1 | at org.bson.types.Decimal128.<init>(Decimal128.java:156)
kafka-connect_1 | at io.enkrypt.kafka.connect.sinks.mongo.StructToBsonConverter.convert(StructToBsonConverter.kt:278)
kafka-connect_1 | at io.enkrypt.kafka.connect.sinks.mongo.StructToBsonConverter.convert$default(StructToBsonConverter.kt:242)
kafka-connect_1 | at io.enkrypt.kafka.connect.sinks.mongo.KafkaTopics$8.invoke(MongoSinkTask.kt:368)
kafka-connect_1 | at io.enkrypt.kafka.connect.sinks.mongo.KafkaTopics$8.invoke(MongoSinkTask.kt:348)
kafka-connect_1 | at io.enkrypt.kafka.connect.sinks.mongo.MongoSinkTask.put(MongoSinkTask.kt:91)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerSinkTask.deliverMessages(WorkerSinkTask.java:565)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerSinkTask.poll(WorkerSinkTask.java:323)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerSinkTask.iteration(WorkerSinkTask.java:226)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerSinkTask.execute(WorkerSinkTask.java:194)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerTask.doRun(WorkerTask.java:175)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerTask.run(WorkerTask.java:219)
kafka-connect_1 | at java.util.concurrent.Executors$RunnableAdapter.call(Executors.java:511)
kafka-connect_1 | at java.util.concurrent.FutureTask.run(FutureTask.java:266)
kafka-connect_1 | at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1149)
kafka-connect_1 | at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:624)
kafka-connect_1 | at java.lang.Thread.run(Thread.java:748)
kafka-connect_1 | [2019-02-04 17:36:57,551] INFO WorkerSinkTask{id=enkryptio-mongo-ancillary-sink-0} Committing offsets synchronously using sequence number 3: {pending-transactions-3=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, miner-list-10=OffsetAndMetadata{offset=47961, leaderEpoch=null, metadata=''}, contract-creator-list-10=OffsetAndMetadata{offset=3155, leaderEpoch=null, metadata=''}, block-metrics-by-block-4=OffsetAndMetadata{offset=94786, leaderEpoch=null, metadata=''}, contract-destructions-8=OffsetAndMetadata{offset=140, leaderEpoch=null, metadata=''}, uncles-10=OffsetAndMetadata{offset=8664, leaderEpoch=null, metadata=''}, contract-creations-2=OffsetAndMetadata{offset=2387, leaderEpoch=null, metadata=''}, contract-metadata-0=OffsetAndMetadata{offset=4485, leaderEpoch=null, metadata=''}, pending-transactions-11=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, miner-list-2=OffsetAndMetadata{offset=112834, leaderEpoch=null, metadata=''}, transactions-3=OffsetAndMetadata{offset=7231, leaderEpoch=null, metadata=''}, contract-creator-list-2=OffsetAndMetadata{offset=3173, leaderEpoch=null, metadata=''}, contract-destructions-0=OffsetAndMetadata{offset=142, leaderEpoch=null, metadata=''}, uncles-2=OffsetAndMetadata{offset=8648, leaderEpoch=null, metadata=''}, contract-creations-10=OffsetAndMetadata{offset=2460, leaderEpoch=null, metadata=''}, token-transfers-4=OffsetAndMetadata{offset=45211, leaderEpoch=null, metadata=''}, address-tx-counts-3=OffsetAndMetadata{offset=142606, leaderEpoch=null, metadata=''}, balances-4=OffsetAndMetadata{offset=98076, leaderEpoch=null, metadata=''}, transactions-11=OffsetAndMetadata{offset=7235, leaderEpoch=null, metadata=''}, address-tx-counts-11=OffsetAndMetadata{offset=142764, leaderEpoch=null, metadata=''}, aggregate-block-metrics-by-day-8=OffsetAndMetadata{offset=1386, leaderEpoch=null, metadata=''}, aggregate-block-metrics-by-day-0=OffsetAndMetadata{offset=1353, leaderEpoch=null, metadata=''}, contract-creator-list-9=OffsetAndMetadata{offset=3165, leaderEpoch=null, metadata=''}, block-metrics-by-block-5=OffsetAndMetadata{offset=94724, leaderEpoch=null, metadata=''}, pending-transactions-2=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, contract-creations-1=OffsetAndMetadata{offset=2470, leaderEpoch=null, metadata=''}, contract-destructions-9=OffsetAndMetadata{offset=159, leaderEpoch=null, metadata=''}, miner-list-9=OffsetAndMetadata{offset=49872, leaderEpoch=null, metadata=''}, contract-creator-list-1=OffsetAndMetadata{offset=3118, leaderEpoch=null, metadata=''}, pending-transactions-10=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, uncles-9=OffsetAndMetadata{offset=8650, leaderEpoch=null, metadata=''}, contract-creations-9=OffsetAndMetadata{offset=2420, leaderEpoch=null, metadata=''}, token-transfers-5=OffsetAndMetadata{offset=45206, leaderEpoch=null, metadata=''}, address-tx-counts-2=OffsetAndMetadata{offset=142268, leaderEpoch=null, metadata=''}, contract-destructions-1=OffsetAndMetadata{offset=174, leaderEpoch=null, metadata=''}, transactions-2=OffsetAndMetadata{offset=7341, leaderEpoch=null, metadata=''}, miner-list-1=OffsetAndMetadata{offset=80878, leaderEpoch=null, metadata=''}, uncles-1=OffsetAndMetadata{offset=8637, leaderEpoch=null, metadata=''}, address-tx-counts-10=OffsetAndMetadata{offset=142428, leaderEpoch=null, metadata=''}, transactions-10=OffsetAndMetadata{offset=7415, leaderEpoch=null, metadata=''}, balances-5=OffsetAndMetadata{offset=97620, leaderEpoch=null, metadata=''}, aggregate-block-metrics-by-day-7=OffsetAndMetadata{offset=1345, leaderEpoch=null, metadata=''}, contract-creator-list-8=OffsetAndMetadata{offset=3257, leaderEpoch=null, metadata=''}, pending-transactions-1=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, contract-destructions-10=OffsetAndMetadata{offset=162, leaderEpoch=null, metadata=''}, block-metrics-by-block-10=OffsetAndMetadata{offset=88674, leaderEpoch=null, metadata=''}, contract-creations-0=OffsetAndMetadata{offset=2400, leaderEpoch=null, metadata=''}, contract-creator-list-0=OffsetAndMetadata{offset=3154, leaderEpoch=null, metadata=''}, pending-transactions-9=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, contract-destructions-2=OffsetAndMetadata{offset=156, leaderEpoch=null, metadata=''}, uncles-8=OffsetAndMetadata{offset=8641, leaderEpoch=null, metadata=''}, miner-list-4=OffsetAndMetadata{offset=25571, leaderEpoch=null, metadata=''}, balances-10=OffsetAndMetadata{offset=98137, leaderEpoch=null, metadata=''}, transactions-1=OffsetAndMetadata{offset=6648, leaderEpoch=null, metadata=''}, contract-creations-8=OffsetAndMetadata{offset=2503, leaderEpoch=null, metadata=''}, token-transfers-2=OffsetAndMetadata{offset=39540, leaderEpoch=null, metadata=''}, address-tx-counts-5=OffsetAndMetadata{offset=142644, leaderEpoch=null, metadata=''}, uncles-0=OffsetAndMetadata{offset=8653, leaderEpoch=null, metadata=''}, balances-2=OffsetAndMetadata{offset=61655, leaderEpoch=null, metadata=''}, transactions-9=OffsetAndMetadata{offset=6336, leaderEpoch=null, metadata=''}, aggregate-block-metrics-by-day-10=OffsetAndMetadata{offset=1353, leaderEpoch=null, metadata=''}, token-transfers-10=OffsetAndMetadata{offset=39538, leaderEpoch=null, metadata=''}, block-metrics-by-block-1=OffsetAndMetadata{offset=86541, leaderEpoch=null, metadata=''}, aggregate-block-metrics-by-day-2=OffsetAndMetadata{offset=1303, leaderEpoch=null, metadata=''}, miner-list-11=OffsetAndMetadata{offset=198769, leaderEpoch=null, metadata=''}, block-metrics-by-block-3=OffsetAndMetadata{offset=86472, leaderEpoch=null, metadata=''}, contract-destructions-11=OffsetAndMetadata{offset=135, leaderEpoch=null, metadata=''}, pending-transactions-0=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, contract-creator-list-7=OffsetAndMetadata{offset=3283, leaderEpoch=null, metadata=''}, miner-list-3=OffsetAndMetadata{offset=20093, leaderEpoch=null, metadata=''}, balances-11=OffsetAndMetadata{offset=58696, leaderEpoch=null, metadata=''}, uncles-7=OffsetAndMetadata{offset=8668, leaderEpoch=null, metadata=''}, block-metrics-by-block-11=OffsetAndMetadata{offset=86638, leaderEpoch=null, metadata=''}, contract-destructions-3=OffsetAndMetadata{offset=165, leaderEpoch=null, metadata=''}, pending-transactions-8=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, contract-creations-7=OffsetAndMetadata{offset=2580, leaderEpoch=null, metadata=''}, token-transfers-3=OffsetAndMetadata{offset=39526, leaderEpoch=null, metadata=''}, address-tx-counts-4=OffsetAndMetadata{offset=142115, leaderEpoch=null, metadata=''}, transactions-0=OffsetAndMetadata{offset=5450, leaderEpoch=null, metadata=''}, balances-3=OffsetAndMetadata{offset=59110, leaderEpoch=null, metadata=''}, token-transfers-11=OffsetAndMetadata{offset=39558, leaderEpoch=null, metadata=''}, aggregate-block-metrics-by-day-9=OffsetAndMetadata{offset=1239, leaderEpoch=null, metadata=''}, transactions-8=OffsetAndMetadata{offset=7419, leaderEpoch=null, metadata=''}, block-metrics-by-block-2=OffsetAndMetadata{offset=86594, leaderEpoch=null, metadata=''}, aggregate-block-metrics-by-day-1=OffsetAndMetadata{offset=1500, leaderEpoch=null, metadata=''}, miner-list-6=OffsetAndMetadata{offset=201347, leaderEpoch=null, metadata=''}, contract-creator-list-6=OffsetAndMetadata{offset=3199, leaderEpoch=null, metadata=''}, block-metrics-by-block-8=OffsetAndMetadata{offset=86561, leaderEpoch=null, metadata=''}, contract-destructions-4=OffsetAndMetadata{offset=149, leaderEpoch=null, metadata=''}, uncles-6=OffsetAndMetadata{offset=8648, leaderEpoch=null, metadata=''}, contract-creations-6=OffsetAndMetadata{offset=2483, leaderEpoch=null, metadata=''}, token-transfers-0=OffsetAndMetadata{offset=33859, leaderEpoch=null, metadata=''}, pending-transactions-7=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, token-transfers-8=OffsetAndMetadata{offset=28445, leaderEpoch=null, metadata=''}, address-tx-counts-7=OffsetAndMetadata{offset=142919, leaderEpoch=null, metadata=''}, balances-8=OffsetAndMetadata{offset=59066, leaderEpoch=null, metadata=''}, transactions-7=OffsetAndMetadata{offset=7380, leaderEpoch=null, metadata=''}, aggregate-block-metrics-by-day-4=OffsetAndMetadata{offset=1264, leaderEpoch=null, metadata=''}, token-exchange-rates-0=OffsetAndMetadata{offset=1633, leaderEpoch=null, metadata=''}, balances-0=OffsetAndMetadata{offset=58741, leaderEpoch=null, metadata=''}, contract-creator-list-5=OffsetAndMetadata{offset=3120, leaderEpoch=null, metadata=''}, block-metrics-by-block-9=OffsetAndMetadata{offset=86384, leaderEpoch=null, metadata=''}, contract-creations-5=OffsetAndMetadata{offset=2351, leaderEpoch=null, metadata=''}, token-transfers-1=OffsetAndMetadata{offset=33886, leaderEpoch=null, metadata=''}, contract-destructions-5=OffsetAndMetadata{offset=171, leaderEpoch=null, metadata=''}, transactions-6=OffsetAndMetadata{offset=7410, leaderEpoch=null, metadata=''}, miner-list-5=OffsetAndMetadata{offset=230980, leaderEpoch=null, metadata=''}, balances-9=OffsetAndMetadata{offset=58681, leaderEpoch=null, metadata=''}, pending-transactions-6=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, uncles-5=OffsetAndMetadata{offset=8649, leaderEpoch=null, metadata=''}, token-transfers-9=OffsetAndMetadata{offset=33909, leaderEpoch=null, metadata=''}, address-tx-counts-6=OffsetAndMetadata{offset=142615, leaderEpoch=null, metadata=''}, balances-1=OffsetAndMetadata{offset=49604, leaderEpoch=null, metadata=''}, aggregate-block-metrics-by-day-11=OffsetAndMetadata{offset=1369, leaderEpoch=null, metadata=''}, aggregate-block-metrics-by-day-3=OffsetAndMetadata{offset=1288, leaderEpoch=null, metadata=''}, block-metrics-by-block-0=OffsetAndMetadata{offset=86396, leaderEpoch=null, metadata=''}, block-metrics-by-block-6=OffsetAndMetadata{offset=86649, leaderEpoch=null, metadata=''}, contract-creator-list-4=OffsetAndMetadata{offset=3144, leaderEpoch=null, metadata=''}, contract-destructions-6=OffsetAndMetadata{offset=156, leaderEpoch=null, metadata=''}, miner-list-8=OffsetAndMetadata{offset=15984, leaderEpoch=null, metadata=''}, transactions-5=OffsetAndMetadata{offset=7361, leaderEpoch=null, metadata=''}, contract-creations-4=OffsetAndMetadata{offset=2492, leaderEpoch=null, metadata=''}, address-tx-counts-1=OffsetAndMetadata{offset=125460, leaderEpoch=null, metadata=''}, pending-transactions-5=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, uncles-4=OffsetAndMetadata{offset=9706, leaderEpoch=null, metadata=''}, miner-list-0=OffsetAndMetadata{offset=122118, leaderEpoch=null, metadata=''}, token-transfers-6=OffsetAndMetadata{offset=33839, leaderEpoch=null, metadata=''}, address-tx-counts-9=OffsetAndMetadata{offset=118699, leaderEpoch=null, metadata=''}, balances-6=OffsetAndMetadata{offset=39469, leaderEpoch=null, metadata=''}, aggregate-block-metrics-by-day-6=OffsetAndMetadata{offset=1361, leaderEpoch=null, metadata=''}, pending-transactions-4=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, contract-creator-list-11=OffsetAndMetadata{offset=3151, leaderEpoch=null, metadata=''}, miner-list-7=OffsetAndMetadata{offset=69448, leaderEpoch=null, metadata=''}, uncles-11=OffsetAndMetadata{offset=9661, leaderEpoch=null, metadata=''}, block-metrics-by-block-7=OffsetAndMetadata{offset=86598, leaderEpoch=null, metadata=''}, contract-destructions-7=OffsetAndMetadata{offset=157, leaderEpoch=null, metadata=''}, contract-creator-list-3=OffsetAndMetadata{offset=3078, leaderEpoch=null, metadata=''}, contract-creations-3=OffsetAndMetadata{offset=2418, leaderEpoch=null, metadata=''}, address-tx-counts-0=OffsetAndMetadata{offset=118494, leaderEpoch=null, metadata=''}, transactions-4=OffsetAndMetadata{offset=7511, leaderEpoch=null, metadata=''}, uncles-3=OffsetAndMetadata{offset=9672, leaderEpoch=null, metadata=''}, contract-creations-11=OffsetAndMetadata{offset=2381, leaderEpoch=null, metadata=''}, token-transfers-7=OffsetAndMetadata{offset=33862, leaderEpoch=null, metadata=''}, address-tx-counts-8=OffsetAndMetadata{offset=118679, leaderEpoch=null, metadata=''}, balances-7=OffsetAndMetadata{offset=39373, leaderEpoch=null, metadata=''}, aggregate-block-metrics-by-day-5=OffsetAndMetadata{offset=1265, leaderEpoch=null, metadata=''}} (org.apache.kafka.connect.runtime.WorkerSinkTask)
kafka-connect_1 | [2019-02-04 17:36:57,559] ERROR WorkerSinkTask{id=enkryptio-mongo-ancillary-sink-0} Task threw an uncaught and unrecoverable exception (org.apache.kafka.connect.runtime.WorkerTask)
kafka-connect_1 | org.apache.kafka.connect.errors.ConnectException: Exiting WorkerSinkTask due to unrecoverable exception.
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerSinkTask.deliverMessages(WorkerSinkTask.java:587)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerSinkTask.poll(WorkerSinkTask.java:323)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerSinkTask.iteration(WorkerSinkTask.java:226)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerSinkTask.execute(WorkerSinkTask.java:194)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerTask.doRun(WorkerTask.java:175)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerTask.run(WorkerTask.java:219)
kafka-connect_1 | at java.util.concurrent.Executors$RunnableAdapter.call(Executors.java:511)
kafka-connect_1 | at java.util.concurrent.FutureTask.run(FutureTask.java:266)
kafka-connect_1 | at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1149)
kafka-connect_1 | at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:624)
kafka-connect_1 | at java.lang.Thread.run(Thread.java:748)
kafka-connect_1 | Caused by: java.lang.NumberFormatException: Conversion to Decimal128 would require inexact rounding of 231584178474632390847141970017375815706539969331281128078915168015826259177872
kafka-connect_1 | at org.bson.types.Decimal128.ensureExactRounding(Decimal128.java:244)
kafka-connect_1 | at org.bson.types.Decimal128.clampAndRound(Decimal128.java:233)
kafka-connect_1 | at org.bson.types.Decimal128.<init>(Decimal128.java:169)
kafka-connect_1 | at org.bson.types.Decimal128.<init>(Decimal128.java:156)
kafka-connect_1 | at io.enkrypt.kafka.connect.sinks.mongo.StructToBsonConverter.convert(StructToBsonConverter.kt:278)
kafka-connect_1 | at io.enkrypt.kafka.connect.sinks.mongo.StructToBsonConverter.convert$default(StructToBsonConverter.kt:242)
kafka-connect_1 | at io.enkrypt.kafka.connect.sinks.mongo.KafkaTopics$8.invoke(MongoSinkTask.kt:368)
kafka-connect_1 | at io.enkrypt.kafka.connect.sinks.mongo.KafkaTopics$8.invoke(MongoSinkTask.kt:348)
kafka-connect_1 | at io.enkrypt.kafka.connect.sinks.mongo.MongoSinkTask.put(MongoSinkTask.kt:91)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerSinkTask.deliverMessages(WorkerSinkTask.java:565)
kafka-connect_1 | ... 10 more
kafka-connect_1 | [2019-02-04 17:36:57,559] ERROR WorkerSinkTask{id=enkryptio-mongo-ancillary-sink-0} Task is being killed and will not recover until manually restarted (org.apache.kafka.connect.runtime.WorkerTask)
kafka-connect_1 | [2019-02-04 17:36:57,561] INFO Closed connection [connectionId{localValue:4, serverValue:50}] to mongodb:27017 because the pool has been closed. (org.mongodb.driver.connection)
kafka-connect_1 | [2019-02-04 17:36:57,563] INFO [Consumer clientId=consumer-5, groupId=connect-enkryptio-mongo-ancillary-sink] Sending LeaveGroup request to coordinator kafka-1:9091 (id: 2147483646 rack: null) (org.apache.kafka.clients.consumer.internals.AbstractCoordinator)
```
---
Also, sometimes, while processing we obtain a random disconnection (I think is more related to the fact we are sending big chunks of data, as @brianmcgee and myself discussed). I'll leave here also a trace to have it:
```
kafka-connect_1 | [2019-02-04 15:33:09,585] WARN Got socket exception on connection [connectionId{localValue:20, serverValue:34}] to mongodb:27017. All connections to mongodb:27017 will be closed. (org.mongodb.driver.connection)
kafka-connect_1 | [2019-02-04 15:33:09,586] WARN Got socket exception on connection [connectionId{localValue:19, serverValue:33}] to mongodb:27017. All connections to mongodb:27017 will be closed. (org.mongodb.driver.connection)
kafka-connect_1 | [2019-02-04 15:33:09,586] INFO Closed connection [connectionId{localValue:19, serverValue:33}] to mongodb:27017 because there was a socket exception raised by this connection. (org.mongodb.driver.connection)
kafka-connect_1 | [2019-02-04 15:33:09,587] ERROR WorkerSinkTask{id=enkryptio-mongo-ancillary-sink-0} Task threw an uncaught and unrecoverable exception. Task is being killed and will not recover until manually restarted. (org.apache.kafka.connect.runtime.WorkerSinkTask)
kafka-connect_1 | com.mongodb.MongoSocketReadException: Prematurely reached end of stream
kafka-connect_1 | at com.mongodb.internal.connection.SocketStream.read(SocketStream.java:112)
kafka-connect_1 | at com.mongodb.internal.connection.InternalStreamConnection.receiveResponseBuffers(InternalStreamConnection.java:570)
kafka-connect_1 | at com.mongodb.internal.connection.InternalStreamConnection.receiveMessage(InternalStreamConnection.java:441)
kafka-connect_1 | at com.mongodb.internal.connection.InternalStreamConnection.receiveCommandMessageResponse(InternalStreamConnection.java:295)
kafka-connect_1 | at com.mongodb.internal.connection.InternalStreamConnection.sendAndReceive(InternalStreamConnection.java:255)
kafka-connect_1 | at com.mongodb.internal.connection.UsageTrackingInternalConnection.sendAndReceive(UsageTrackingInternalConnection.java:99)
kafka-connect_1 | at com.mongodb.internal.connection.DefaultConnectionPool$PooledConnection.sendAndReceive(DefaultConnectionPool.java:444)
kafka-connect_1 | at com.mongodb.internal.connection.CommandProtocolImpl.execute(CommandProtocolImpl.java:72)
kafka-connect_1 | at com.mongodb.internal.connection.DefaultServer$DefaultServerProtocolExecutor.execute(DefaultServer.java:200)
kafka-connect_1 | at com.mongodb.internal.connection.DefaultServerConnection.executeProtocol(DefaultServerConnection.java:269)
kafka-connect_1 | at com.mongodb.internal.connection.DefaultServerConnection.command(DefaultServerConnection.java:131)
kafka-connect_1 | at com.mongodb.operation.MixedBulkWriteOperation.executeCommand(MixedBulkWriteOperation.java:419)
kafka-connect_1 | at com.mongodb.operation.MixedBulkWriteOperation.executeBulkWriteBatch(MixedBulkWriteOperation.java:257)
kafka-connect_1 | at com.mongodb.operation.MixedBulkWriteOperation.access$700(MixedBulkWriteOperation.java:68)
kafka-connect_1 | at com.mongodb.operation.MixedBulkWriteOperation$1.call(MixedBulkWriteOperation.java:201)
kafka-connect_1 | at com.mongodb.operation.MixedBulkWriteOperation$1.call(MixedBulkWriteOperation.java:192)
kafka-connect_1 | at com.mongodb.operation.OperationHelper.withReleasableConnection(OperationHelper.java:424)
kafka-connect_1 | at com.mongodb.operation.MixedBulkWriteOperation.execute(MixedBulkWriteOperation.java:192)
kafka-connect_1 | at com.mongodb.operation.MixedBulkWriteOperation.execute(MixedBulkWriteOperation.java:67)
kafka-connect_1 | at com.mongodb.client.internal.MongoClientDelegate$DelegateOperationExecutor.execute(MongoClientDelegate.java:193)
kafka-connect_1 | at com.mongodb.client.internal.MongoCollectionImpl.executeBulkWrite(MongoCollectionImpl.java:467)
kafka-connect_1 | at com.mongodb.client.internal.MongoCollectionImpl.bulkWrite(MongoCollectionImpl.java:447)
kafka-connect_1 | at com.mongodb.client.internal.MongoCollectionImpl.bulkWrite(MongoCollectionImpl.java:442)
kafka-connect_1 | at io.enkrypt.kafka.connect.sinks.mongo.MongoSinkTask.put(MongoSinkTask.kt:102)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerSinkTask.deliverMessages(WorkerSinkTask.java:565)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerSinkTask.poll(WorkerSinkTask.java:323)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerSinkTask.iteration(WorkerSinkTask.java:226)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerSinkTask.execute(WorkerSinkTask.java:194)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerTask.doRun(WorkerTask.java:175)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerTask.run(WorkerTask.java:219)
kafka-connect_1 | at java.util.concurrent.Executors$RunnableAdapter.call(Executors.java:511)
kafka-connect_1 | at java.util.concurrent.FutureTask.run(FutureTask.java:266)
kafka-connect_1 | at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1149)
kafka-connect_1 | at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:624)
kafka-connect_1 | at java.lang.Thread.run(Thread.java:748)
kafka-connect_1 | [2019-02-04 15:33:09,587] INFO Exception in monitor thread while connecting to server mongodb:27017 (org.mongodb.driver.cluster)
kafka-connect_1 | com.mongodb.MongoSocketOpenException: Exception opening socket
kafka-connect_1 | at com.mongodb.internal.connection.SocketStream.open(SocketStream.java:70)
kafka-connect_1 | at com.mongodb.internal.connection.InternalStreamConnection.open(InternalStreamConnection.java:126)
kafka-connect_1 | at com.mongodb.internal.connection.DefaultServerMonitor$ServerMonitorRunnable.run(DefaultServerMonitor.java:131)
kafka-connect_1 | at java.lang.Thread.run(Thread.java:748)
kafka-connect_1 | Caused by: java.net.ConnectException: Connection refused (Connection refused)
kafka-connect_1 | at java.net.PlainSocketImpl.socketConnect(Native Method)
kafka-connect_1 | at java.net.AbstractPlainSocketImpl.doConnect(AbstractPlainSocketImpl.java:350)
kafka-connect_1 | at java.net.AbstractPlainSocketImpl.connectToAddress(AbstractPlainSocketImpl.java:206)
kafka-connect_1 | at java.net.AbstractPlainSocketImpl.connect(AbstractPlainSocketImpl.java:188)
kafka-connect_1 | at java.net.SocksSocketImpl.connect(SocksSocketImpl.java:392)
kafka-connect_1 | at java.net.Socket.connect(Socket.java:589)
kafka-connect_1 | at com.mongodb.internal.connection.SocketStreamHelper.initialize(SocketStreamHelper.java:64)
kafka-connect_1 | at com.mongodb.internal.connection.SocketStream.initializeSocket(SocketStream.java:79)
kafka-connect_1 | at com.mongodb.internal.connection.SocketStream.open(SocketStream.java:65)
kafka-connect_1 | ... 3 more
kafka-connect_1 | [2019-02-04 15:33:09,628] INFO Exception in monitor thread while connecting to server mongodb:27017 (org.mongodb.driver.cluster)
kafka-connect_1 | com.mongodb.MongoSocketOpenException: Exception opening socket
kafka-connect_1 | at com.mongodb.internal.connection.SocketStream.open(SocketStream.java:70)
kafka-connect_1 | at com.mongodb.internal.connection.InternalStreamConnection.open(InternalStreamConnection.java:126)
kafka-connect_1 | at com.mongodb.internal.connection.DefaultServerMonitor$ServerMonitorRunnable.run(DefaultServerMonitor.java:131)
kafka-connect_1 | at java.lang.Thread.run(Thread.java:748)
kafka-connect_1 | Caused by: java.net.ConnectException: Connection refused (Connection refused)
kafka-connect_1 | at java.net.PlainSocketImpl.socketConnect(Native Method)
kafka-connect_1 | at java.net.AbstractPlainSocketImpl.doConnect(AbstractPlainSocketImpl.java:350)
kafka-connect_1 | at java.net.AbstractPlainSocketImpl.connectToAddress(AbstractPlainSocketImpl.java:206)
kafka-connect_1 | at java.net.AbstractPlainSocketImpl.connect(AbstractPlainSocketImpl.java:188)
kafka-connect_1 | at java.net.SocksSocketImpl.connect(SocksSocketImpl.java:392)
kafka-connect_1 | at java.net.Socket.connect(Socket.java:589)
kafka-connect_1 | at com.mongodb.internal.connection.SocketStreamHelper.initialize(SocketStreamHelper.java:64)
kafka-connect_1 | at com.mongodb.internal.connection.SocketStream.initializeSocket(SocketStream.java:79)
kafka-connect_1 | at com.mongodb.internal.connection.SocketStream.open(SocketStream.java:65)
kafka-connect_1 | ... 3 more
kafka-connect_1 | [2019-02-04 15:33:09,628] INFO Closed connection [connectionId{localValue:20, serverValue:34}] to mongodb:27017 because there was a socket exception raised by this connection. (org.mongodb.driver.connection)
kafka-connect_1 | [2019-02-04 15:33:09,629] INFO WorkerSinkTask{id=enkryptio-mongo-ancillary-sink-0} Committing offsets synchronously using sequence number 7: {pending-transactions-3=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, miner-list-10=OffsetAndMetadata{offset=33379, leaderEpoch=null, metadata=''}, contract-creator-list-10=OffsetAndMetadata{offset=3155, leaderEpoch=null, metadata=''}, block-metrics-by-block-4=OffsetAndMetadata{offset=31857, leaderEpoch=null, metadata=''}, contract-destructions-8=OffsetAndMetadata{offset=140, leaderEpoch=null, metadata=''}, uncles-10=OffsetAndMetadata{offset=2853, leaderEpoch=null, metadata=''}, contract-creations-2=OffsetAndMetadata{offset=1808, leaderEpoch=null, metadata=''}, contract-metadata-0=OffsetAndMetadata{offset=4485, leaderEpoch=null, metadata=''}, pending-transactions-11=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, miner-list-2=OffsetAndMetadata{offset=38713, leaderEpoch=null, metadata=''}, transactions-3=OffsetAndMetadata{offset=1346, leaderEpoch=null, metadata=''}, contract-creator-list-2=OffsetAndMetadata{offset=3173, leaderEpoch=null, metadata=''}, contract-destructions-0=OffsetAndMetadata{offset=142, leaderEpoch=null, metadata=''}, uncles-2=OffsetAndMetadata{offset=2850, leaderEpoch=null, metadata=''}, contract-creations-10=OffsetAndMetadata{offset=1871, leaderEpoch=null, metadata=''}, token-transfers-4=OffsetAndMetadata{offset=11199, leaderEpoch=null, metadata=''}, address-tx-counts-3=OffsetAndMetadata{offset=47472, leaderEpoch=null, metadata=''}, balances-4=OffsetAndMetadata{offset=39234, leaderEpoch=null, metadata=''}, transactions-11=OffsetAndMetadata{offset=1314, leaderEpoch=null, metadata=''}, address-tx-counts-11=OffsetAndMetadata{offset=47770, leaderEpoch=null, metadata=''}, aggregate-block-metrics-by-day-8=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, aggregate-block-metrics-by-day-0=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, contract-creator-list-9=OffsetAndMetadata{offset=3165, leaderEpoch=null, metadata=''}, block-metrics-by-block-5=OffsetAndMetadata{offset=31804, leaderEpoch=null, metadata=''}, pending-transactions-2=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, contract-creations-1=OffsetAndMetadata{offset=1869, leaderEpoch=null, metadata=''}, contract-destructions-9=OffsetAndMetadata{offset=159, leaderEpoch=null, metadata=''}, miner-list-9=OffsetAndMetadata{offset=32456, leaderEpoch=null, metadata=''}, contract-creator-list-1=OffsetAndMetadata{offset=3118, leaderEpoch=null, metadata=''}, pending-transactions-10=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, uncles-9=OffsetAndMetadata{offset=2851, leaderEpoch=null, metadata=''}, contract-creations-9=OffsetAndMetadata{offset=801, leaderEpoch=null, metadata=''}, token-transfers-5=OffsetAndMetadata{offset=11197, leaderEpoch=null, metadata=''}, address-tx-counts-2=OffsetAndMetadata{offset=47566, leaderEpoch=null, metadata=''}, contract-destructions-1=OffsetAndMetadata{offset=174, leaderEpoch=null, metadata=''}, transactions-2=OffsetAndMetadata{offset=1405, leaderEpoch=null, metadata=''}, miner-list-1=OffsetAndMetadata{offset=49458, leaderEpoch=null, metadata=''}, uncles-1=OffsetAndMetadata{offset=2852, leaderEpoch=null, metadata=''}, address-tx-counts-10=OffsetAndMetadata{offset=47738, leaderEpoch=null, metadata=''}, transactions-10=OffsetAndMetadata{offset=1449, leaderEpoch=null, metadata=''}, balances-5=OffsetAndMetadata{offset=39170, leaderEpoch=null, metadata=''}, aggregate-block-metrics-by-day-7=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, contract-creator-list-8=OffsetAndMetadata{offset=3257, leaderEpoch=null, metadata=''}, pending-transactions-1=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, contract-destructions-10=OffsetAndMetadata{offset=162, leaderEpoch=null, metadata=''}, block-metrics-by-block-10=OffsetAndMetadata{offset=31842, leaderEpoch=null, metadata=''}, contract-creations-0=OffsetAndMetadata{offset=791, leaderEpoch=null, metadata=''}, contract-creator-list-0=OffsetAndMetadata{offset=3154, leaderEpoch=null, metadata=''}, pending-transactions-9=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, contract-destructions-2=OffsetAndMetadata{offset=156, leaderEpoch=null, metadata=''}, uncles-8=OffsetAndMetadata{offset=2849, leaderEpoch=null, metadata=''}, miner-list-4=OffsetAndMetadata{offset=25571, leaderEpoch=null, metadata=''}, balances-10=OffsetAndMetadata{offset=39317, leaderEpoch=null, metadata=''}, transactions-1=OffsetAndMetadata{offset=1379, leaderEpoch=null, metadata=''}, contract-creations-8=OffsetAndMetadata{offset=793, leaderEpoch=null, metadata=''}, token-transfers-2=OffsetAndMetadata{offset=11192, leaderEpoch=null, metadata=''}, address-tx-counts-5=OffsetAndMetadata{offset=47596, leaderEpoch=null, metadata=''}, uncles-0=OffsetAndMetadata{offset=2851, leaderEpoch=null, metadata=''}, balances-2=OffsetAndMetadata{offset=39226, leaderEpoch=null, metadata=''}, transactions-9=OffsetAndMetadata{offset=1448, leaderEpoch=null, metadata=''}, aggregate-block-metrics-by-day-10=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, token-transfers-10=OffsetAndMetadata{offset=11203, leaderEpoch=null, metadata=''}, block-metrics-by-block-1=OffsetAndMetadata{offset=31776, leaderEpoch=null, metadata=''}, aggregate-block-metrics-by-day-2=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, miner-list-11=OffsetAndMetadata{offset=58099, leaderEpoch=null, metadata=''}, block-metrics-by-block-3=OffsetAndMetadata{offset=31747, leaderEpoch=null, metadata=''}, contract-destructions-11=OffsetAndMetadata{offset=135, leaderEpoch=null, metadata=''}, pending-transactions-0=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, contract-creator-list-7=OffsetAndMetadata{offset=3283, leaderEpoch=null, metadata=''}, miner-list-3=OffsetAndMetadata{offset=20093, leaderEpoch=null, metadata=''}, balances-11=OffsetAndMetadata{offset=39173, leaderEpoch=null, metadata=''}, uncles-7=OffsetAndMetadata{offset=2852, leaderEpoch=null, metadata=''}, block-metrics-by-block-11=OffsetAndMetadata{offset=31742, leaderEpoch=null, metadata=''}, contract-destructions-3=OffsetAndMetadata{offset=165, leaderEpoch=null, metadata=''}, pending-transactions-8=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, contract-creations-7=OffsetAndMetadata{offset=701, leaderEpoch=null, metadata=''}, token-transfers-3=OffsetAndMetadata{offset=11203, leaderEpoch=null, metadata=''}, address-tx-counts-4=OffsetAndMetadata{offset=47610, leaderEpoch=null, metadata=''}, transactions-0=OffsetAndMetadata{offset=1457, leaderEpoch=null, metadata=''}, balances-3=OffsetAndMetadata{offset=39445, leaderEpoch=null, metadata=''}, token-transfers-11=OffsetAndMetadata{offset=11209, leaderEpoch=null, metadata=''}, aggregate-block-metrics-by-day-9=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, transactions-8=OffsetAndMetadata{offset=1455, leaderEpoch=null, metadata=''}, block-metrics-by-block-2=OffsetAndMetadata{offset=31790, leaderEpoch=null, metadata=''}, aggregate-block-metrics-by-day-1=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, miner-list-6=OffsetAndMetadata{offset=56852, leaderEpoch=null, metadata=''}, contract-creator-list-6=OffsetAndMetadata{offset=3199, leaderEpoch=null, metadata=''}, block-metrics-by-block-8=OffsetAndMetadata{offset=31779, leaderEpoch=null, metadata=''}, contract-destructions-4=OffsetAndMetadata{offset=149, leaderEpoch=null, metadata=''}, uncles-6=OffsetAndMetadata{offset=2852, leaderEpoch=null, metadata=''}, contract-creations-6=OffsetAndMetadata{offset=774, leaderEpoch=null, metadata=''}, token-transfers-0=OffsetAndMetadata{offset=11185, leaderEpoch=null, metadata=''}, pending-transactions-7=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, token-transfers-8=OffsetAndMetadata{offset=11215, leaderEpoch=null, metadata=''}, address-tx-counts-7=OffsetAndMetadata{offset=47808, leaderEpoch=null, metadata=''}, balances-8=OffsetAndMetadata{offset=39522, leaderEpoch=null, metadata=''}, transactions-7=OffsetAndMetadata{offset=1449, leaderEpoch=null, metadata=''}, aggregate-block-metrics-by-day-4=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, token-exchange-rates-0=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, balances-0=OffsetAndMetadata{offset=39256, leaderEpoch=null, metadata=''}, contract-creator-list-5=OffsetAndMetadata{offset=3120, leaderEpoch=null, metadata=''}, block-metrics-by-block-9=OffsetAndMetadata{offset=31729, leaderEpoch=null, metadata=''}, contract-creations-5=OffsetAndMetadata{offset=757, leaderEpoch=null, metadata=''}, token-transfers-1=OffsetAndMetadata{offset=11220, leaderEpoch=null, metadata=''}, contract-destructions-5=OffsetAndMetadata{offset=171, leaderEpoch=null, metadata=''}, transactions-6=OffsetAndMetadata{offset=1450, leaderEpoch=null, metadata=''}, miner-list-5=OffsetAndMetadata{offset=69489, leaderEpoch=null, metadata=''}, balances-9=OffsetAndMetadata{offset=39119, leaderEpoch=null, metadata=''}, pending-transactions-6=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, uncles-5=OffsetAndMetadata{offset=2849, leaderEpoch=null, metadata=''}, token-transfers-9=OffsetAndMetadata{offset=11212, leaderEpoch=null, metadata=''}, address-tx-counts-6=OffsetAndMetadata{offset=47804, leaderEpoch=null, metadata=''}, balances-1=OffsetAndMetadata{offset=29991, leaderEpoch=null, metadata=''}, aggregate-block-metrics-by-day-11=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, aggregate-block-metrics-by-day-3=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, block-metrics-by-block-0=OffsetAndMetadata{offset=31747, leaderEpoch=null, metadata=''}, block-metrics-by-block-6=OffsetAndMetadata{offset=31775, leaderEpoch=null, metadata=''}, contract-creator-list-4=OffsetAndMetadata{offset=3144, leaderEpoch=null, metadata=''}, contract-destructions-6=OffsetAndMetadata{offset=156, leaderEpoch=null, metadata=''}, miner-list-8=OffsetAndMetadata{offset=15984, leaderEpoch=null, metadata=''}, transactions-5=OffsetAndMetadata{offset=1403, leaderEpoch=null, metadata=''}, contract-creations-4=OffsetAndMetadata{offset=684, leaderEpoch=null, metadata=''}, address-tx-counts-1=OffsetAndMetadata{offset=47546, leaderEpoch=null, metadata=''}, pending-transactions-5=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, uncles-4=OffsetAndMetadata{offset=2853, leaderEpoch=null, metadata=''}, miner-list-0=OffsetAndMetadata{offset=58095, leaderEpoch=null, metadata=''}, token-transfers-6=OffsetAndMetadata{offset=11196, leaderEpoch=null, metadata=''}, address-tx-counts-9=OffsetAndMetadata{offset=47859, leaderEpoch=null, metadata=''}, balances-6=OffsetAndMetadata{offset=19768, leaderEpoch=null, metadata=''}, aggregate-block-metrics-by-day-6=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, pending-transactions-4=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, contract-creator-list-11=OffsetAndMetadata{offset=3151, leaderEpoch=null, metadata=''}, miner-list-7=OffsetAndMetadata{offset=59356, leaderEpoch=null, metadata=''}, uncles-11=OffsetAndMetadata{offset=2843, leaderEpoch=null, metadata=''}, block-metrics-by-block-7=OffsetAndMetadata{offset=31819, leaderEpoch=null, metadata=''}, contract-destructions-7=OffsetAndMetadata{offset=157, leaderEpoch=null, metadata=''}, contract-creator-list-3=OffsetAndMetadata{offset=3078, leaderEpoch=null, metadata=''}, contract-creations-3=OffsetAndMetadata{offset=514, leaderEpoch=null, metadata=''}, address-tx-counts-0=OffsetAndMetadata{offset=47517, leaderEpoch=null, metadata=''}, transactions-4=OffsetAndMetadata{offset=1544, leaderEpoch=null, metadata=''}, uncles-3=OffsetAndMetadata{offset=2852, leaderEpoch=null, metadata=''}, contract-creations-11=OffsetAndMetadata{offset=1489, leaderEpoch=null, metadata=''}, token-transfers-7=OffsetAndMetadata{offset=11189, leaderEpoch=null, metadata=''}, address-tx-counts-8=OffsetAndMetadata{offset=47772, leaderEpoch=null, metadata=''}, balances-7=OffsetAndMetadata{offset=19677, leaderEpoch=null, metadata=''}, aggregate-block-metrics-by-day-5=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}} (org.apache.kafka.connect.runtime.WorkerSinkTask)
kafka-connect_1 | [2019-02-04 15:33:09,629] ERROR WorkerSinkTask{id=enkryptio-mongo-block-sink-0} Task threw an uncaught and unrecoverable exception. Task is being killed and will not recover until manually restarted. (org.apache.kafka.connect.runtime.WorkerSinkTask)
kafka-connect_1 | com.mongodb.MongoSocketReadException: Prematurely reached end of stream
kafka-connect_1 | at com.mongodb.internal.connection.SocketStream.read(SocketStream.java:112)
kafka-connect_1 | at com.mongodb.internal.connection.InternalStreamConnection.receiveResponseBuffers(InternalStreamConnection.java:570)
kafka-connect_1 | at com.mongodb.internal.connection.InternalStreamConnection.receiveMessage(InternalStreamConnection.java:441)
kafka-connect_1 | at com.mongodb.internal.connection.InternalStreamConnection.receiveCommandMessageResponse(InternalStreamConnection.java:295)
kafka-connect_1 | at com.mongodb.internal.connection.InternalStreamConnection.sendAndReceive(InternalStreamConnection.java:255)
kafka-connect_1 | at com.mongodb.internal.connection.UsageTrackingInternalConnection.sendAndReceive(UsageTrackingInternalConnection.java:99)
kafka-connect_1 | at com.mongodb.internal.connection.DefaultConnectionPool$PooledConnection.sendAndReceive(DefaultConnectionPool.java:444)
kafka-connect_1 | at com.mongodb.internal.connection.CommandProtocolImpl.execute(CommandProtocolImpl.java:72)
kafka-connect_1 | at com.mongodb.internal.connection.DefaultServer$DefaultServerProtocolExecutor.execute(DefaultServer.java:200)
kafka-connect_1 | at com.mongodb.internal.connection.DefaultServerConnection.executeProtocol(DefaultServerConnection.java:269)
kafka-connect_1 | at com.mongodb.internal.connection.DefaultServerConnection.command(DefaultServerConnection.java:131)
kafka-connect_1 | at com.mongodb.operation.MixedBulkWriteOperation.executeCommand(MixedBulkWriteOperation.java:419)
kafka-connect_1 | at com.mongodb.operation.MixedBulkWriteOperation.executeBulkWriteBatch(MixedBulkWriteOperation.java:257)
kafka-connect_1 | at com.mongodb.operation.MixedBulkWriteOperation.access$700(MixedBulkWriteOperation.java:68)
kafka-connect_1 | at com.mongodb.operation.MixedBulkWriteOperation$1.call(MixedBulkWriteOperation.java:201)
kafka-connect_1 | at com.mongodb.operation.MixedBulkWriteOperation$1.call(MixedBulkWriteOperation.java:192)
kafka-connect_1 | at com.mongodb.operation.OperationHelper.withReleasableConnection(OperationHelper.java:424)
kafka-connect_1 | at com.mongodb.operation.MixedBulkWriteOperation.execute(MixedBulkWriteOperation.java:192)
kafka-connect_1 | at com.mongodb.operation.MixedBulkWriteOperation.execute(MixedBulkWriteOperation.java:67)
kafka-connect_1 | at com.mongodb.client.internal.MongoClientDelegate$DelegateOperationExecutor.execute(MongoClientDelegate.java:193)
kafka-connect_1 | at com.mongodb.client.internal.MongoCollectionImpl.executeBulkWrite(MongoCollectionImpl.java:467)
kafka-connect_1 | at com.mongodb.client.internal.MongoCollectionImpl.bulkWrite(MongoCollectionImpl.java:447)
kafka-connect_1 | at com.mongodb.client.internal.MongoCollectionImpl.bulkWrite(MongoCollectionImpl.java:442)
kafka-connect_1 | at io.enkrypt.kafka.connect.sinks.mongo.MongoSinkTask.put(MongoSinkTask.kt:102)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerSinkTask.deliverMessages(WorkerSinkTask.java:565)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerSinkTask.poll(WorkerSinkTask.java:323)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerSinkTask.iteration(WorkerSinkTask.java:226)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerSinkTask.execute(WorkerSinkTask.java:194)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerTask.doRun(WorkerTask.java:175)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerTask.run(WorkerTask.java:219)
kafka-connect_1 | at java.util.concurrent.Executors$RunnableAdapter.call(Executors.java:511)
kafka-connect_1 | at java.util.concurrent.FutureTask.run(FutureTask.java:266)
kafka-connect_1 | at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1149)
kafka-connect_1 | at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:624)
kafka-connect_1 | at java.lang.Thread.run(Thread.java:748)
kafka-connect_1 | [2019-02-04 15:33:09,630] INFO WorkerSinkTask{id=enkryptio-mongo-block-sink-0} Committing offsets synchronously using sequence number 7: {blocks-0=OffsetAndMetadata{offset=1353783, leaderEpoch=null, metadata=''}} (org.apache.kafka.connect.runtime.WorkerSinkTask)
kafka-connect_1 | [2019-02-04 15:33:09,632] ERROR WorkerSinkTask{id=enkryptio-mongo-block-sink-0} Task threw an uncaught and unrecoverable exception (org.apache.kafka.connect.runtime.WorkerTask)
kafka-connect_1 | org.apache.kafka.connect.errors.ConnectException: Exiting WorkerSinkTask due to unrecoverable exception.
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerSinkTask.deliverMessages(WorkerSinkTask.java:587)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerSinkTask.poll(WorkerSinkTask.java:323)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerSinkTask.iteration(WorkerSinkTask.java:226)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerSinkTask.execute(WorkerSinkTask.java:194)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerTask.doRun(WorkerTask.java:175)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerTask.run(WorkerTask.java:219)
kafka-connect_1 | at java.util.concurrent.Executors$RunnableAdapter.call(Executors.java:511)
kafka-connect_1 | at java.util.concurrent.FutureTask.run(FutureTask.java:266)
kafka-connect_1 | at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1149)
kafka-connect_1 | at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:624)
kafka-connect_1 | at java.lang.Thread.run(Thread.java:748)
kafka-connect_1 | Caused by: com.mongodb.MongoSocketReadException: Prematurely reached end of stream
kafka-connect_1 | at com.mongodb.internal.connection.SocketStream.read(SocketStream.java:112)
kafka-connect_1 | at com.mongodb.internal.connection.InternalStreamConnection.receiveResponseBuffers(InternalStreamConnection.java:570)
kafka-connect_1 | at com.mongodb.internal.connection.InternalStreamConnection.receiveMessage(InternalStreamConnection.java:441)
kafka-connect_1 | at com.mongodb.internal.connection.InternalStreamConnection.receiveCommandMessageResponse(InternalStreamConnection.java:295)
kafka-connect_1 | at com.mongodb.internal.connection.InternalStreamConnection.sendAndReceive(InternalStreamConnection.java:255)
kafka-connect_1 | at com.mongodb.internal.connection.UsageTrackingInternalConnection.sendAndReceive(UsageTrackingInternalConnection.java:99)
kafka-connect_1 | at com.mongodb.internal.connection.DefaultConnectionPool$PooledConnection.sendAndReceive(DefaultConnectionPool.java:444)
kafka-connect_1 | at com.mongodb.internal.connection.CommandProtocolImpl.execute(CommandProtocolImpl.java:72)
kafka-connect_1 | at com.mongodb.internal.connection.DefaultServer$DefaultServerProtocolExecutor.execute(DefaultServer.java:200)
kafka-connect_1 | at com.mongodb.internal.connection.DefaultServerConnection.executeProtocol(DefaultServerConnection.java:269)
kafka-connect_1 | at com.mongodb.internal.connection.DefaultServerConnection.command(DefaultServerConnection.java:131)
kafka-connect_1 | at com.mongodb.operation.MixedBulkWriteOperation.executeCommand(MixedBulkWriteOperation.java:419)
kafka-connect_1 | at com.mongodb.operation.MixedBulkWriteOperation.executeBulkWriteBatch(MixedBulkWriteOperation.java:257)
kafka-connect_1 | at com.mongodb.operation.MixedBulkWriteOperation.access$700(MixedBulkWriteOperation.java:68)
kafka-connect_1 | at com.mongodb.operation.MixedBulkWriteOperation$1.call(MixedBulkWriteOperation.java:201)
kafka-connect_1 | at com.mongodb.operation.MixedBulkWriteOperation$1.call(MixedBulkWriteOperation.java:192)
kafka-connect_1 | at com.mongodb.operation.OperationHelper.withReleasableConnection(OperationHelper.java:424)
kafka-connect_1 | at com.mongodb.operation.MixedBulkWriteOperation.execute(MixedBulkWriteOperation.java:192)
kafka-connect_1 | at com.mongodb.operation.MixedBulkWriteOperation.execute(MixedBulkWriteOperation.java:67)
kafka-connect_1 | at com.mongodb.client.internal.MongoClientDelegate$DelegateOperationExecutor.execute(MongoClientDelegate.java:193)
kafka-connect_1 | at com.mongodb.client.internal.MongoCollectionImpl.executeBulkWrite(MongoCollectionImpl.java:467)
kafka-connect_1 | at com.mongodb.client.internal.MongoCollectionImpl.bulkWrite(MongoCollectionImpl.java:447)
kafka-connect_1 | at com.mongodb.client.internal.MongoCollectionImpl.bulkWrite(MongoCollectionImpl.java:442)
kafka-connect_1 | at io.enkrypt.kafka.connect.sinks.mongo.MongoSinkTask.put(MongoSinkTask.kt:102)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerSinkTask.deliverMessages(WorkerSinkTask.java:565)
kafka-connect_1 | ... 10 more
kafka-connect_1 | [2019-02-04 15:33:09,632] ERROR WorkerSinkTask{id=enkryptio-mongo-block-sink-0} Task is being killed and will not recover until manually restarted (org.apache.kafka.connect.runtime.WorkerTask)
kafka-connect_1 | [2019-02-04 15:33:09,633] INFO [Consumer clientId=consumer-15, groupId=connect-enkryptio-mongo-block-sink] Sending LeaveGroup request to coordinator kafka-1:9091 (id: 2147483646 rack: null) (org.apache.kafka.clients.consumer.internals.AbstractCoordinator)
kafka-connect_1 | [2019-02-04 15:33:09,640] ERROR WorkerSinkTask{id=enkryptio-mongo-ancillary-sink-0} Task threw an uncaught and unrecoverable exception (org.apache.kafka.connect.runtime.WorkerTask)
kafka-connect_1 | org.apache.kafka.connect.errors.ConnectException: Exiting WorkerSinkTask due to unrecoverable exception.
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerSinkTask.deliverMessages(WorkerSinkTask.java:587)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerSinkTask.poll(WorkerSinkTask.java:323)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerSinkTask.iteration(WorkerSinkTask.java:226)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerSinkTask.execute(WorkerSinkTask.java:194)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerTask.doRun(WorkerTask.java:175)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerTask.run(WorkerTask.java:219)
kafka-connect_1 | at java.util.concurrent.Executors$RunnableAdapter.call(Executors.java:511)
kafka-connect_1 | at java.util.concurrent.FutureTask.run(FutureTask.java:266)
kafka-connect_1 | at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1149)
kafka-connect_1 | at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:624)
kafka-connect_1 | at java.lang.Thread.run(Thread.java:748)
kafka-connect_1 | Caused by: com.mongodb.MongoSocketReadException: Prematurely reached end of stream
kafka-connect_1 | at com.mongodb.internal.connection.SocketStream.read(SocketStream.java:112)
kafka-connect_1 | at com.mongodb.internal.connection.InternalStreamConnection.receiveResponseBuffers(InternalStreamConnection.java:570)
kafka-connect_1 | at com.mongodb.internal.connection.InternalStreamConnection.receiveMessage(InternalStreamConnection.java:441)
kafka-connect_1 | at com.mongodb.internal.connection.InternalStreamConnection.receiveCommandMessageResponse(InternalStreamConnection.java:295)
kafka-connect_1 | at com.mongodb.internal.connection.InternalStreamConnection.sendAndReceive(InternalStreamConnection.java:255)
kafka-connect_1 | at com.mongodb.internal.connection.UsageTrackingInternalConnection.sendAndReceive(UsageTrackingInternalConnection.java:99)
kafka-connect_1 | at com.mongodb.internal.connection.DefaultConnectionPool$PooledConnection.sendAndReceive(DefaultConnectionPool.java:444)
kafka-connect_1 | at com.mongodb.internal.connection.CommandProtocolImpl.execute(CommandProtocolImpl.java:72)
kafka-connect_1 | at com.mongodb.internal.connection.DefaultServer$DefaultServerProtocolExecutor.execute(DefaultServer.java:200)
kafka-connect_1 | at com.mongodb.internal.connection.DefaultServerConnection.executeProtocol(DefaultServerConnection.java:269)
kafka-connect_1 | at com.mongodb.internal.connection.DefaultServerConnection.command(DefaultServerConnection.java:131)
kafka-connect_1 | at com.mongodb.operation.MixedBulkWriteOperation.executeCommand(MixedBulkWriteOperation.java:419)
kafka-connect_1 | at com.mongodb.operation.MixedBulkWriteOperation.executeBulkWriteBatch(MixedBulkWriteOperation.java:257)
kafka-connect_1 | at com.mongodb.operation.MixedBulkWriteOperation.access$700(MixedBulkWriteOperation.java:68)
kafka-connect_1 | at com.mongodb.operation.MixedBulkWriteOperation$1.call(MixedBulkWriteOperation.java:201)
kafka-connect_1 | at com.mongodb.operation.MixedBulkWriteOperation$1.call(MixedBulkWriteOperation.java:192)
kafka-connect_1 | at com.mongodb.operation.OperationHelper.withReleasableConnection(OperationHelper.java:424)
kafka-connect_1 | at com.mongodb.operation.MixedBulkWriteOperation.execute(MixedBulkWriteOperation.java:192)
kafka-connect_1 | at com.mongodb.operation.MixedBulkWriteOperation.execute(MixedBulkWriteOperation.java:67)
kafka-connect_1 | at com.mongodb.client.internal.MongoClientDelegate$DelegateOperationExecutor.execute(MongoClientDelegate.java:193)
kafka-connect_1 | at com.mongodb.client.internal.MongoCollectionImpl.executeBulkWrite(MongoCollectionImpl.java:467)
kafka-connect_1 | at com.mongodb.client.internal.MongoCollectionImpl.bulkWrite(MongoCollectionImpl.java:447)
kafka-connect_1 | at com.mongodb.client.internal.MongoCollectionImpl.bulkWrite(MongoCollectionImpl.java:442)
kafka-connect_1 | at io.enkrypt.kafka.connect.sinks.mongo.MongoSinkTask.put(MongoSinkTask.kt:102)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerSinkTask.deliverMessages(WorkerSinkTask.java:565)
kafka-connect_1 | ... 10 more
kafka-connect_1 | [2019-02-04 15:33:09,641] ERROR WorkerSinkTask{id=enkryptio-mongo-ancillary-sink-0} Task is being killed and will not recover until manually restarted (org.apache.kafka.connect.runtime.WorkerTask)
kafka-connect_1 | [2019-02-04 15:33:09,651] INFO [Consumer clientId=consumer-16, groupId=connect-enkryptio-mongo-ancillary-sink] Sending LeaveGroup request to coordinator kafka-1:9091 (id: 2147483646 rack: null) (org.apache.kafka.clients.consumer.internals.AbstractCoordinator)
```
|
1.0
|
MongoSink issues - I managed to capture a couple of related exceptions on our Mongo Sink:
- [x] Decimal 128 issue
- [x] Timeout randomly appears
- [x] It appears that some entries are missing on the db (see #333)
---
Here I leave a trace to further analyze it and is related to BigDecimal128:
```
ka-connect_1 | [2019-02-04 17:36:57,371] INFO Batch processing completed in 72 ms (io.enkrypt.kafka.connect.sinks.mongo.MongoSinkTask)
kafka-connect_1 | [2019-02-04 17:36:57,372] INFO Processing {} records (io.enkrypt.kafka.connect.sinks.mongo.MongoSinkTask)
kafka-connect_1 | [2019-02-04 17:36:57,374] INFO Processing Balances collection with 3 chunks (io.enkrypt.kafka.connect.sinks.mongo.MongoSinkTask)
kafka-connect_1 | [2019-02-04 17:36:57,400] INFO Chunk write complete. Collection = Balances, inserts = 0, updates = 184, upserts = 16, deletes = 0 (io.enkrypt.kafka.connect.sinks.mongo.MongoSinkTask)
kafka-connect_1 | [2019-02-04 17:36:57,439] INFO Chunk write complete. Collection = Balances, inserts = 0, updates = 174, upserts = 26, deletes = 0 (io.enkrypt.kafka.connect.sinks.mongo.MongoSinkTask)
kafka-connect_1 | [2019-02-04 17:36:57,457] INFO Chunk write complete. Collection = Balances, inserts = 0, updates = 85, upserts = 15, deletes = 0 (io.enkrypt.kafka.connect.sinks.mongo.MongoSinkTask)
kafka-connect_1 | [2019-02-04 17:36:57,457] INFO Batch processing completed in 85 ms (io.enkrypt.kafka.connect.sinks.mongo.MongoSinkTask)
kafka-connect_1 | [2019-02-04 17:36:57,459] INFO Processing {} records (io.enkrypt.kafka.connect.sinks.mongo.MongoSinkTask)
kafka-connect_1 | [2019-02-04 17:36:57,462] INFO Processing Balances collection with 3 chunks (io.enkrypt.kafka.connect.sinks.mongo.MongoSinkTask)
kafka-connect_1 | [2019-02-04 17:36:57,497] INFO Chunk write complete. Collection = Balances, inserts = 0, updates = 190, upserts = 10, deletes = 0 (io.enkrypt.kafka.connect.sinks.mongo.MongoSinkTask)
kafka-connect_1 | [2019-02-04 17:36:57,524] INFO Chunk write complete. Collection = Balances, inserts = 0, updates = 173, upserts = 27, deletes = 0 (io.enkrypt.kafka.connect.sinks.mongo.MongoSinkTask)
kafka-connect_1 | [2019-02-04 17:36:57,543] INFO Chunk write complete. Collection = Balances, inserts = 0, updates = 89, upserts = 11, deletes = 0 (io.enkrypt.kafka.connect.sinks.mongo.MongoSinkTask)
kafka-connect_1 | [2019-02-04 17:36:57,543] INFO Batch processing completed in 84 ms (io.enkrypt.kafka.connect.sinks.mongo.MongoSinkTask)
kafka-connect_1 | [2019-02-04 17:36:57,546] INFO Processing {} records (io.enkrypt.kafka.connect.sinks.mongo.MongoSinkTask)
kafka-connect_1 | [2019-02-04 17:36:57,549] ERROR WorkerSinkTask{id=enkryptio-mongo-ancillary-sink-0} Task threw an uncaught and unrecoverable exception. Task is being killed and will not recover until manually restarted. (org.apache.kafka.connect.runtime.WorkerSinkTask)
kafka-connect_1 | java.lang.NumberFormatException: Conversion to Decimal128 would require inexact rounding of 231584178474632390847141970017375815706539969331281128078915168015826259177872
kafka-connect_1 | at org.bson.types.Decimal128.ensureExactRounding(Decimal128.java:244)
kafka-connect_1 | at org.bson.types.Decimal128.clampAndRound(Decimal128.java:233)
kafka-connect_1 | at org.bson.types.Decimal128.<init>(Decimal128.java:169)
kafka-connect_1 | at org.bson.types.Decimal128.<init>(Decimal128.java:156)
kafka-connect_1 | at io.enkrypt.kafka.connect.sinks.mongo.StructToBsonConverter.convert(StructToBsonConverter.kt:278)
kafka-connect_1 | at io.enkrypt.kafka.connect.sinks.mongo.StructToBsonConverter.convert$default(StructToBsonConverter.kt:242)
kafka-connect_1 | at io.enkrypt.kafka.connect.sinks.mongo.KafkaTopics$8.invoke(MongoSinkTask.kt:368)
kafka-connect_1 | at io.enkrypt.kafka.connect.sinks.mongo.KafkaTopics$8.invoke(MongoSinkTask.kt:348)
kafka-connect_1 | at io.enkrypt.kafka.connect.sinks.mongo.MongoSinkTask.put(MongoSinkTask.kt:91)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerSinkTask.deliverMessages(WorkerSinkTask.java:565)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerSinkTask.poll(WorkerSinkTask.java:323)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerSinkTask.iteration(WorkerSinkTask.java:226)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerSinkTask.execute(WorkerSinkTask.java:194)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerTask.doRun(WorkerTask.java:175)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerTask.run(WorkerTask.java:219)
kafka-connect_1 | at java.util.concurrent.Executors$RunnableAdapter.call(Executors.java:511)
kafka-connect_1 | at java.util.concurrent.FutureTask.run(FutureTask.java:266)
kafka-connect_1 | at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1149)
kafka-connect_1 | at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:624)
kafka-connect_1 | at java.lang.Thread.run(Thread.java:748)
kafka-connect_1 | [2019-02-04 17:36:57,551] INFO WorkerSinkTask{id=enkryptio-mongo-ancillary-sink-0} Committing offsets synchronously using sequence number 3: {pending-transactions-3=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, miner-list-10=OffsetAndMetadata{offset=47961, leaderEpoch=null, metadata=''}, contract-creator-list-10=OffsetAndMetadata{offset=3155, leaderEpoch=null, metadata=''}, block-metrics-by-block-4=OffsetAndMetadata{offset=94786, leaderEpoch=null, metadata=''}, contract-destructions-8=OffsetAndMetadata{offset=140, leaderEpoch=null, metadata=''}, uncles-10=OffsetAndMetadata{offset=8664, leaderEpoch=null, metadata=''}, contract-creations-2=OffsetAndMetadata{offset=2387, leaderEpoch=null, metadata=''}, contract-metadata-0=OffsetAndMetadata{offset=4485, leaderEpoch=null, metadata=''}, pending-transactions-11=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, miner-list-2=OffsetAndMetadata{offset=112834, leaderEpoch=null, metadata=''}, transactions-3=OffsetAndMetadata{offset=7231, leaderEpoch=null, metadata=''}, contract-creator-list-2=OffsetAndMetadata{offset=3173, leaderEpoch=null, metadata=''}, contract-destructions-0=OffsetAndMetadata{offset=142, leaderEpoch=null, metadata=''}, uncles-2=OffsetAndMetadata{offset=8648, leaderEpoch=null, metadata=''}, contract-creations-10=OffsetAndMetadata{offset=2460, leaderEpoch=null, metadata=''}, token-transfers-4=OffsetAndMetadata{offset=45211, leaderEpoch=null, metadata=''}, address-tx-counts-3=OffsetAndMetadata{offset=142606, leaderEpoch=null, metadata=''}, balances-4=OffsetAndMetadata{offset=98076, leaderEpoch=null, metadata=''}, transactions-11=OffsetAndMetadata{offset=7235, leaderEpoch=null, metadata=''}, address-tx-counts-11=OffsetAndMetadata{offset=142764, leaderEpoch=null, metadata=''}, aggregate-block-metrics-by-day-8=OffsetAndMetadata{offset=1386, leaderEpoch=null, metadata=''}, aggregate-block-metrics-by-day-0=OffsetAndMetadata{offset=1353, leaderEpoch=null, metadata=''}, contract-creator-list-9=OffsetAndMetadata{offset=3165, leaderEpoch=null, metadata=''}, block-metrics-by-block-5=OffsetAndMetadata{offset=94724, leaderEpoch=null, metadata=''}, pending-transactions-2=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, contract-creations-1=OffsetAndMetadata{offset=2470, leaderEpoch=null, metadata=''}, contract-destructions-9=OffsetAndMetadata{offset=159, leaderEpoch=null, metadata=''}, miner-list-9=OffsetAndMetadata{offset=49872, leaderEpoch=null, metadata=''}, contract-creator-list-1=OffsetAndMetadata{offset=3118, leaderEpoch=null, metadata=''}, pending-transactions-10=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, uncles-9=OffsetAndMetadata{offset=8650, leaderEpoch=null, metadata=''}, contract-creations-9=OffsetAndMetadata{offset=2420, leaderEpoch=null, metadata=''}, token-transfers-5=OffsetAndMetadata{offset=45206, leaderEpoch=null, metadata=''}, address-tx-counts-2=OffsetAndMetadata{offset=142268, leaderEpoch=null, metadata=''}, contract-destructions-1=OffsetAndMetadata{offset=174, leaderEpoch=null, metadata=''}, transactions-2=OffsetAndMetadata{offset=7341, leaderEpoch=null, metadata=''}, miner-list-1=OffsetAndMetadata{offset=80878, leaderEpoch=null, metadata=''}, uncles-1=OffsetAndMetadata{offset=8637, leaderEpoch=null, metadata=''}, address-tx-counts-10=OffsetAndMetadata{offset=142428, leaderEpoch=null, metadata=''}, transactions-10=OffsetAndMetadata{offset=7415, leaderEpoch=null, metadata=''}, balances-5=OffsetAndMetadata{offset=97620, leaderEpoch=null, metadata=''}, aggregate-block-metrics-by-day-7=OffsetAndMetadata{offset=1345, leaderEpoch=null, metadata=''}, contract-creator-list-8=OffsetAndMetadata{offset=3257, leaderEpoch=null, metadata=''}, pending-transactions-1=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, contract-destructions-10=OffsetAndMetadata{offset=162, leaderEpoch=null, metadata=''}, block-metrics-by-block-10=OffsetAndMetadata{offset=88674, leaderEpoch=null, metadata=''}, contract-creations-0=OffsetAndMetadata{offset=2400, leaderEpoch=null, metadata=''}, contract-creator-list-0=OffsetAndMetadata{offset=3154, leaderEpoch=null, metadata=''}, pending-transactions-9=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, contract-destructions-2=OffsetAndMetadata{offset=156, leaderEpoch=null, metadata=''}, uncles-8=OffsetAndMetadata{offset=8641, leaderEpoch=null, metadata=''}, miner-list-4=OffsetAndMetadata{offset=25571, leaderEpoch=null, metadata=''}, balances-10=OffsetAndMetadata{offset=98137, leaderEpoch=null, metadata=''}, transactions-1=OffsetAndMetadata{offset=6648, leaderEpoch=null, metadata=''}, contract-creations-8=OffsetAndMetadata{offset=2503, leaderEpoch=null, metadata=''}, token-transfers-2=OffsetAndMetadata{offset=39540, leaderEpoch=null, metadata=''}, address-tx-counts-5=OffsetAndMetadata{offset=142644, leaderEpoch=null, metadata=''}, uncles-0=OffsetAndMetadata{offset=8653, leaderEpoch=null, metadata=''}, balances-2=OffsetAndMetadata{offset=61655, leaderEpoch=null, metadata=''}, transactions-9=OffsetAndMetadata{offset=6336, leaderEpoch=null, metadata=''}, aggregate-block-metrics-by-day-10=OffsetAndMetadata{offset=1353, leaderEpoch=null, metadata=''}, token-transfers-10=OffsetAndMetadata{offset=39538, leaderEpoch=null, metadata=''}, block-metrics-by-block-1=OffsetAndMetadata{offset=86541, leaderEpoch=null, metadata=''}, aggregate-block-metrics-by-day-2=OffsetAndMetadata{offset=1303, leaderEpoch=null, metadata=''}, miner-list-11=OffsetAndMetadata{offset=198769, leaderEpoch=null, metadata=''}, block-metrics-by-block-3=OffsetAndMetadata{offset=86472, leaderEpoch=null, metadata=''}, contract-destructions-11=OffsetAndMetadata{offset=135, leaderEpoch=null, metadata=''}, pending-transactions-0=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, contract-creator-list-7=OffsetAndMetadata{offset=3283, leaderEpoch=null, metadata=''}, miner-list-3=OffsetAndMetadata{offset=20093, leaderEpoch=null, metadata=''}, balances-11=OffsetAndMetadata{offset=58696, leaderEpoch=null, metadata=''}, uncles-7=OffsetAndMetadata{offset=8668, leaderEpoch=null, metadata=''}, block-metrics-by-block-11=OffsetAndMetadata{offset=86638, leaderEpoch=null, metadata=''}, contract-destructions-3=OffsetAndMetadata{offset=165, leaderEpoch=null, metadata=''}, pending-transactions-8=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, contract-creations-7=OffsetAndMetadata{offset=2580, leaderEpoch=null, metadata=''}, token-transfers-3=OffsetAndMetadata{offset=39526, leaderEpoch=null, metadata=''}, address-tx-counts-4=OffsetAndMetadata{offset=142115, leaderEpoch=null, metadata=''}, transactions-0=OffsetAndMetadata{offset=5450, leaderEpoch=null, metadata=''}, balances-3=OffsetAndMetadata{offset=59110, leaderEpoch=null, metadata=''}, token-transfers-11=OffsetAndMetadata{offset=39558, leaderEpoch=null, metadata=''}, aggregate-block-metrics-by-day-9=OffsetAndMetadata{offset=1239, leaderEpoch=null, metadata=''}, transactions-8=OffsetAndMetadata{offset=7419, leaderEpoch=null, metadata=''}, block-metrics-by-block-2=OffsetAndMetadata{offset=86594, leaderEpoch=null, metadata=''}, aggregate-block-metrics-by-day-1=OffsetAndMetadata{offset=1500, leaderEpoch=null, metadata=''}, miner-list-6=OffsetAndMetadata{offset=201347, leaderEpoch=null, metadata=''}, contract-creator-list-6=OffsetAndMetadata{offset=3199, leaderEpoch=null, metadata=''}, block-metrics-by-block-8=OffsetAndMetadata{offset=86561, leaderEpoch=null, metadata=''}, contract-destructions-4=OffsetAndMetadata{offset=149, leaderEpoch=null, metadata=''}, uncles-6=OffsetAndMetadata{offset=8648, leaderEpoch=null, metadata=''}, contract-creations-6=OffsetAndMetadata{offset=2483, leaderEpoch=null, metadata=''}, token-transfers-0=OffsetAndMetadata{offset=33859, leaderEpoch=null, metadata=''}, pending-transactions-7=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, token-transfers-8=OffsetAndMetadata{offset=28445, leaderEpoch=null, metadata=''}, address-tx-counts-7=OffsetAndMetadata{offset=142919, leaderEpoch=null, metadata=''}, balances-8=OffsetAndMetadata{offset=59066, leaderEpoch=null, metadata=''}, transactions-7=OffsetAndMetadata{offset=7380, leaderEpoch=null, metadata=''}, aggregate-block-metrics-by-day-4=OffsetAndMetadata{offset=1264, leaderEpoch=null, metadata=''}, token-exchange-rates-0=OffsetAndMetadata{offset=1633, leaderEpoch=null, metadata=''}, balances-0=OffsetAndMetadata{offset=58741, leaderEpoch=null, metadata=''}, contract-creator-list-5=OffsetAndMetadata{offset=3120, leaderEpoch=null, metadata=''}, block-metrics-by-block-9=OffsetAndMetadata{offset=86384, leaderEpoch=null, metadata=''}, contract-creations-5=OffsetAndMetadata{offset=2351, leaderEpoch=null, metadata=''}, token-transfers-1=OffsetAndMetadata{offset=33886, leaderEpoch=null, metadata=''}, contract-destructions-5=OffsetAndMetadata{offset=171, leaderEpoch=null, metadata=''}, transactions-6=OffsetAndMetadata{offset=7410, leaderEpoch=null, metadata=''}, miner-list-5=OffsetAndMetadata{offset=230980, leaderEpoch=null, metadata=''}, balances-9=OffsetAndMetadata{offset=58681, leaderEpoch=null, metadata=''}, pending-transactions-6=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, uncles-5=OffsetAndMetadata{offset=8649, leaderEpoch=null, metadata=''}, token-transfers-9=OffsetAndMetadata{offset=33909, leaderEpoch=null, metadata=''}, address-tx-counts-6=OffsetAndMetadata{offset=142615, leaderEpoch=null, metadata=''}, balances-1=OffsetAndMetadata{offset=49604, leaderEpoch=null, metadata=''}, aggregate-block-metrics-by-day-11=OffsetAndMetadata{offset=1369, leaderEpoch=null, metadata=''}, aggregate-block-metrics-by-day-3=OffsetAndMetadata{offset=1288, leaderEpoch=null, metadata=''}, block-metrics-by-block-0=OffsetAndMetadata{offset=86396, leaderEpoch=null, metadata=''}, block-metrics-by-block-6=OffsetAndMetadata{offset=86649, leaderEpoch=null, metadata=''}, contract-creator-list-4=OffsetAndMetadata{offset=3144, leaderEpoch=null, metadata=''}, contract-destructions-6=OffsetAndMetadata{offset=156, leaderEpoch=null, metadata=''}, miner-list-8=OffsetAndMetadata{offset=15984, leaderEpoch=null, metadata=''}, transactions-5=OffsetAndMetadata{offset=7361, leaderEpoch=null, metadata=''}, contract-creations-4=OffsetAndMetadata{offset=2492, leaderEpoch=null, metadata=''}, address-tx-counts-1=OffsetAndMetadata{offset=125460, leaderEpoch=null, metadata=''}, pending-transactions-5=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, uncles-4=OffsetAndMetadata{offset=9706, leaderEpoch=null, metadata=''}, miner-list-0=OffsetAndMetadata{offset=122118, leaderEpoch=null, metadata=''}, token-transfers-6=OffsetAndMetadata{offset=33839, leaderEpoch=null, metadata=''}, address-tx-counts-9=OffsetAndMetadata{offset=118699, leaderEpoch=null, metadata=''}, balances-6=OffsetAndMetadata{offset=39469, leaderEpoch=null, metadata=''}, aggregate-block-metrics-by-day-6=OffsetAndMetadata{offset=1361, leaderEpoch=null, metadata=''}, pending-transactions-4=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, contract-creator-list-11=OffsetAndMetadata{offset=3151, leaderEpoch=null, metadata=''}, miner-list-7=OffsetAndMetadata{offset=69448, leaderEpoch=null, metadata=''}, uncles-11=OffsetAndMetadata{offset=9661, leaderEpoch=null, metadata=''}, block-metrics-by-block-7=OffsetAndMetadata{offset=86598, leaderEpoch=null, metadata=''}, contract-destructions-7=OffsetAndMetadata{offset=157, leaderEpoch=null, metadata=''}, contract-creator-list-3=OffsetAndMetadata{offset=3078, leaderEpoch=null, metadata=''}, contract-creations-3=OffsetAndMetadata{offset=2418, leaderEpoch=null, metadata=''}, address-tx-counts-0=OffsetAndMetadata{offset=118494, leaderEpoch=null, metadata=''}, transactions-4=OffsetAndMetadata{offset=7511, leaderEpoch=null, metadata=''}, uncles-3=OffsetAndMetadata{offset=9672, leaderEpoch=null, metadata=''}, contract-creations-11=OffsetAndMetadata{offset=2381, leaderEpoch=null, metadata=''}, token-transfers-7=OffsetAndMetadata{offset=33862, leaderEpoch=null, metadata=''}, address-tx-counts-8=OffsetAndMetadata{offset=118679, leaderEpoch=null, metadata=''}, balances-7=OffsetAndMetadata{offset=39373, leaderEpoch=null, metadata=''}, aggregate-block-metrics-by-day-5=OffsetAndMetadata{offset=1265, leaderEpoch=null, metadata=''}} (org.apache.kafka.connect.runtime.WorkerSinkTask)
kafka-connect_1 | [2019-02-04 17:36:57,559] ERROR WorkerSinkTask{id=enkryptio-mongo-ancillary-sink-0} Task threw an uncaught and unrecoverable exception (org.apache.kafka.connect.runtime.WorkerTask)
kafka-connect_1 | org.apache.kafka.connect.errors.ConnectException: Exiting WorkerSinkTask due to unrecoverable exception.
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerSinkTask.deliverMessages(WorkerSinkTask.java:587)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerSinkTask.poll(WorkerSinkTask.java:323)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerSinkTask.iteration(WorkerSinkTask.java:226)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerSinkTask.execute(WorkerSinkTask.java:194)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerTask.doRun(WorkerTask.java:175)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerTask.run(WorkerTask.java:219)
kafka-connect_1 | at java.util.concurrent.Executors$RunnableAdapter.call(Executors.java:511)
kafka-connect_1 | at java.util.concurrent.FutureTask.run(FutureTask.java:266)
kafka-connect_1 | at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1149)
kafka-connect_1 | at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:624)
kafka-connect_1 | at java.lang.Thread.run(Thread.java:748)
kafka-connect_1 | Caused by: java.lang.NumberFormatException: Conversion to Decimal128 would require inexact rounding of 231584178474632390847141970017375815706539969331281128078915168015826259177872
kafka-connect_1 | at org.bson.types.Decimal128.ensureExactRounding(Decimal128.java:244)
kafka-connect_1 | at org.bson.types.Decimal128.clampAndRound(Decimal128.java:233)
kafka-connect_1 | at org.bson.types.Decimal128.<init>(Decimal128.java:169)
kafka-connect_1 | at org.bson.types.Decimal128.<init>(Decimal128.java:156)
kafka-connect_1 | at io.enkrypt.kafka.connect.sinks.mongo.StructToBsonConverter.convert(StructToBsonConverter.kt:278)
kafka-connect_1 | at io.enkrypt.kafka.connect.sinks.mongo.StructToBsonConverter.convert$default(StructToBsonConverter.kt:242)
kafka-connect_1 | at io.enkrypt.kafka.connect.sinks.mongo.KafkaTopics$8.invoke(MongoSinkTask.kt:368)
kafka-connect_1 | at io.enkrypt.kafka.connect.sinks.mongo.KafkaTopics$8.invoke(MongoSinkTask.kt:348)
kafka-connect_1 | at io.enkrypt.kafka.connect.sinks.mongo.MongoSinkTask.put(MongoSinkTask.kt:91)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerSinkTask.deliverMessages(WorkerSinkTask.java:565)
kafka-connect_1 | ... 10 more
kafka-connect_1 | [2019-02-04 17:36:57,559] ERROR WorkerSinkTask{id=enkryptio-mongo-ancillary-sink-0} Task is being killed and will not recover until manually restarted (org.apache.kafka.connect.runtime.WorkerTask)
kafka-connect_1 | [2019-02-04 17:36:57,561] INFO Closed connection [connectionId{localValue:4, serverValue:50}] to mongodb:27017 because the pool has been closed. (org.mongodb.driver.connection)
kafka-connect_1 | [2019-02-04 17:36:57,563] INFO [Consumer clientId=consumer-5, groupId=connect-enkryptio-mongo-ancillary-sink] Sending LeaveGroup request to coordinator kafka-1:9091 (id: 2147483646 rack: null) (org.apache.kafka.clients.consumer.internals.AbstractCoordinator)
```
---
Also, sometimes, while processing we obtain a random disconnection (I think is more related to the fact we are sending big chunks of data, as @brianmcgee and myself discussed). I'll leave here also a trace to have it:
```
kafka-connect_1 | [2019-02-04 15:33:09,585] WARN Got socket exception on connection [connectionId{localValue:20, serverValue:34}] to mongodb:27017. All connections to mongodb:27017 will be closed. (org.mongodb.driver.connection)
kafka-connect_1 | [2019-02-04 15:33:09,586] WARN Got socket exception on connection [connectionId{localValue:19, serverValue:33}] to mongodb:27017. All connections to mongodb:27017 will be closed. (org.mongodb.driver.connection)
kafka-connect_1 | [2019-02-04 15:33:09,586] INFO Closed connection [connectionId{localValue:19, serverValue:33}] to mongodb:27017 because there was a socket exception raised by this connection. (org.mongodb.driver.connection)
kafka-connect_1 | [2019-02-04 15:33:09,587] ERROR WorkerSinkTask{id=enkryptio-mongo-ancillary-sink-0} Task threw an uncaught and unrecoverable exception. Task is being killed and will not recover until manually restarted. (org.apache.kafka.connect.runtime.WorkerSinkTask)
kafka-connect_1 | com.mongodb.MongoSocketReadException: Prematurely reached end of stream
kafka-connect_1 | at com.mongodb.internal.connection.SocketStream.read(SocketStream.java:112)
kafka-connect_1 | at com.mongodb.internal.connection.InternalStreamConnection.receiveResponseBuffers(InternalStreamConnection.java:570)
kafka-connect_1 | at com.mongodb.internal.connection.InternalStreamConnection.receiveMessage(InternalStreamConnection.java:441)
kafka-connect_1 | at com.mongodb.internal.connection.InternalStreamConnection.receiveCommandMessageResponse(InternalStreamConnection.java:295)
kafka-connect_1 | at com.mongodb.internal.connection.InternalStreamConnection.sendAndReceive(InternalStreamConnection.java:255)
kafka-connect_1 | at com.mongodb.internal.connection.UsageTrackingInternalConnection.sendAndReceive(UsageTrackingInternalConnection.java:99)
kafka-connect_1 | at com.mongodb.internal.connection.DefaultConnectionPool$PooledConnection.sendAndReceive(DefaultConnectionPool.java:444)
kafka-connect_1 | at com.mongodb.internal.connection.CommandProtocolImpl.execute(CommandProtocolImpl.java:72)
kafka-connect_1 | at com.mongodb.internal.connection.DefaultServer$DefaultServerProtocolExecutor.execute(DefaultServer.java:200)
kafka-connect_1 | at com.mongodb.internal.connection.DefaultServerConnection.executeProtocol(DefaultServerConnection.java:269)
kafka-connect_1 | at com.mongodb.internal.connection.DefaultServerConnection.command(DefaultServerConnection.java:131)
kafka-connect_1 | at com.mongodb.operation.MixedBulkWriteOperation.executeCommand(MixedBulkWriteOperation.java:419)
kafka-connect_1 | at com.mongodb.operation.MixedBulkWriteOperation.executeBulkWriteBatch(MixedBulkWriteOperation.java:257)
kafka-connect_1 | at com.mongodb.operation.MixedBulkWriteOperation.access$700(MixedBulkWriteOperation.java:68)
kafka-connect_1 | at com.mongodb.operation.MixedBulkWriteOperation$1.call(MixedBulkWriteOperation.java:201)
kafka-connect_1 | at com.mongodb.operation.MixedBulkWriteOperation$1.call(MixedBulkWriteOperation.java:192)
kafka-connect_1 | at com.mongodb.operation.OperationHelper.withReleasableConnection(OperationHelper.java:424)
kafka-connect_1 | at com.mongodb.operation.MixedBulkWriteOperation.execute(MixedBulkWriteOperation.java:192)
kafka-connect_1 | at com.mongodb.operation.MixedBulkWriteOperation.execute(MixedBulkWriteOperation.java:67)
kafka-connect_1 | at com.mongodb.client.internal.MongoClientDelegate$DelegateOperationExecutor.execute(MongoClientDelegate.java:193)
kafka-connect_1 | at com.mongodb.client.internal.MongoCollectionImpl.executeBulkWrite(MongoCollectionImpl.java:467)
kafka-connect_1 | at com.mongodb.client.internal.MongoCollectionImpl.bulkWrite(MongoCollectionImpl.java:447)
kafka-connect_1 | at com.mongodb.client.internal.MongoCollectionImpl.bulkWrite(MongoCollectionImpl.java:442)
kafka-connect_1 | at io.enkrypt.kafka.connect.sinks.mongo.MongoSinkTask.put(MongoSinkTask.kt:102)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerSinkTask.deliverMessages(WorkerSinkTask.java:565)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerSinkTask.poll(WorkerSinkTask.java:323)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerSinkTask.iteration(WorkerSinkTask.java:226)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerSinkTask.execute(WorkerSinkTask.java:194)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerTask.doRun(WorkerTask.java:175)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerTask.run(WorkerTask.java:219)
kafka-connect_1 | at java.util.concurrent.Executors$RunnableAdapter.call(Executors.java:511)
kafka-connect_1 | at java.util.concurrent.FutureTask.run(FutureTask.java:266)
kafka-connect_1 | at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1149)
kafka-connect_1 | at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:624)
kafka-connect_1 | at java.lang.Thread.run(Thread.java:748)
kafka-connect_1 | [2019-02-04 15:33:09,587] INFO Exception in monitor thread while connecting to server mongodb:27017 (org.mongodb.driver.cluster)
kafka-connect_1 | com.mongodb.MongoSocketOpenException: Exception opening socket
kafka-connect_1 | at com.mongodb.internal.connection.SocketStream.open(SocketStream.java:70)
kafka-connect_1 | at com.mongodb.internal.connection.InternalStreamConnection.open(InternalStreamConnection.java:126)
kafka-connect_1 | at com.mongodb.internal.connection.DefaultServerMonitor$ServerMonitorRunnable.run(DefaultServerMonitor.java:131)
kafka-connect_1 | at java.lang.Thread.run(Thread.java:748)
kafka-connect_1 | Caused by: java.net.ConnectException: Connection refused (Connection refused)
kafka-connect_1 | at java.net.PlainSocketImpl.socketConnect(Native Method)
kafka-connect_1 | at java.net.AbstractPlainSocketImpl.doConnect(AbstractPlainSocketImpl.java:350)
kafka-connect_1 | at java.net.AbstractPlainSocketImpl.connectToAddress(AbstractPlainSocketImpl.java:206)
kafka-connect_1 | at java.net.AbstractPlainSocketImpl.connect(AbstractPlainSocketImpl.java:188)
kafka-connect_1 | at java.net.SocksSocketImpl.connect(SocksSocketImpl.java:392)
kafka-connect_1 | at java.net.Socket.connect(Socket.java:589)
kafka-connect_1 | at com.mongodb.internal.connection.SocketStreamHelper.initialize(SocketStreamHelper.java:64)
kafka-connect_1 | at com.mongodb.internal.connection.SocketStream.initializeSocket(SocketStream.java:79)
kafka-connect_1 | at com.mongodb.internal.connection.SocketStream.open(SocketStream.java:65)
kafka-connect_1 | ... 3 more
kafka-connect_1 | [2019-02-04 15:33:09,628] INFO Exception in monitor thread while connecting to server mongodb:27017 (org.mongodb.driver.cluster)
kafka-connect_1 | com.mongodb.MongoSocketOpenException: Exception opening socket
kafka-connect_1 | at com.mongodb.internal.connection.SocketStream.open(SocketStream.java:70)
kafka-connect_1 | at com.mongodb.internal.connection.InternalStreamConnection.open(InternalStreamConnection.java:126)
kafka-connect_1 | at com.mongodb.internal.connection.DefaultServerMonitor$ServerMonitorRunnable.run(DefaultServerMonitor.java:131)
kafka-connect_1 | at java.lang.Thread.run(Thread.java:748)
kafka-connect_1 | Caused by: java.net.ConnectException: Connection refused (Connection refused)
kafka-connect_1 | at java.net.PlainSocketImpl.socketConnect(Native Method)
kafka-connect_1 | at java.net.AbstractPlainSocketImpl.doConnect(AbstractPlainSocketImpl.java:350)
kafka-connect_1 | at java.net.AbstractPlainSocketImpl.connectToAddress(AbstractPlainSocketImpl.java:206)
kafka-connect_1 | at java.net.AbstractPlainSocketImpl.connect(AbstractPlainSocketImpl.java:188)
kafka-connect_1 | at java.net.SocksSocketImpl.connect(SocksSocketImpl.java:392)
kafka-connect_1 | at java.net.Socket.connect(Socket.java:589)
kafka-connect_1 | at com.mongodb.internal.connection.SocketStreamHelper.initialize(SocketStreamHelper.java:64)
kafka-connect_1 | at com.mongodb.internal.connection.SocketStream.initializeSocket(SocketStream.java:79)
kafka-connect_1 | at com.mongodb.internal.connection.SocketStream.open(SocketStream.java:65)
kafka-connect_1 | ... 3 more
kafka-connect_1 | [2019-02-04 15:33:09,628] INFO Closed connection [connectionId{localValue:20, serverValue:34}] to mongodb:27017 because there was a socket exception raised by this connection. (org.mongodb.driver.connection)
kafka-connect_1 | [2019-02-04 15:33:09,629] INFO WorkerSinkTask{id=enkryptio-mongo-ancillary-sink-0} Committing offsets synchronously using sequence number 7: {pending-transactions-3=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, miner-list-10=OffsetAndMetadata{offset=33379, leaderEpoch=null, metadata=''}, contract-creator-list-10=OffsetAndMetadata{offset=3155, leaderEpoch=null, metadata=''}, block-metrics-by-block-4=OffsetAndMetadata{offset=31857, leaderEpoch=null, metadata=''}, contract-destructions-8=OffsetAndMetadata{offset=140, leaderEpoch=null, metadata=''}, uncles-10=OffsetAndMetadata{offset=2853, leaderEpoch=null, metadata=''}, contract-creations-2=OffsetAndMetadata{offset=1808, leaderEpoch=null, metadata=''}, contract-metadata-0=OffsetAndMetadata{offset=4485, leaderEpoch=null, metadata=''}, pending-transactions-11=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, miner-list-2=OffsetAndMetadata{offset=38713, leaderEpoch=null, metadata=''}, transactions-3=OffsetAndMetadata{offset=1346, leaderEpoch=null, metadata=''}, contract-creator-list-2=OffsetAndMetadata{offset=3173, leaderEpoch=null, metadata=''}, contract-destructions-0=OffsetAndMetadata{offset=142, leaderEpoch=null, metadata=''}, uncles-2=OffsetAndMetadata{offset=2850, leaderEpoch=null, metadata=''}, contract-creations-10=OffsetAndMetadata{offset=1871, leaderEpoch=null, metadata=''}, token-transfers-4=OffsetAndMetadata{offset=11199, leaderEpoch=null, metadata=''}, address-tx-counts-3=OffsetAndMetadata{offset=47472, leaderEpoch=null, metadata=''}, balances-4=OffsetAndMetadata{offset=39234, leaderEpoch=null, metadata=''}, transactions-11=OffsetAndMetadata{offset=1314, leaderEpoch=null, metadata=''}, address-tx-counts-11=OffsetAndMetadata{offset=47770, leaderEpoch=null, metadata=''}, aggregate-block-metrics-by-day-8=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, aggregate-block-metrics-by-day-0=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, contract-creator-list-9=OffsetAndMetadata{offset=3165, leaderEpoch=null, metadata=''}, block-metrics-by-block-5=OffsetAndMetadata{offset=31804, leaderEpoch=null, metadata=''}, pending-transactions-2=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, contract-creations-1=OffsetAndMetadata{offset=1869, leaderEpoch=null, metadata=''}, contract-destructions-9=OffsetAndMetadata{offset=159, leaderEpoch=null, metadata=''}, miner-list-9=OffsetAndMetadata{offset=32456, leaderEpoch=null, metadata=''}, contract-creator-list-1=OffsetAndMetadata{offset=3118, leaderEpoch=null, metadata=''}, pending-transactions-10=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, uncles-9=OffsetAndMetadata{offset=2851, leaderEpoch=null, metadata=''}, contract-creations-9=OffsetAndMetadata{offset=801, leaderEpoch=null, metadata=''}, token-transfers-5=OffsetAndMetadata{offset=11197, leaderEpoch=null, metadata=''}, address-tx-counts-2=OffsetAndMetadata{offset=47566, leaderEpoch=null, metadata=''}, contract-destructions-1=OffsetAndMetadata{offset=174, leaderEpoch=null, metadata=''}, transactions-2=OffsetAndMetadata{offset=1405, leaderEpoch=null, metadata=''}, miner-list-1=OffsetAndMetadata{offset=49458, leaderEpoch=null, metadata=''}, uncles-1=OffsetAndMetadata{offset=2852, leaderEpoch=null, metadata=''}, address-tx-counts-10=OffsetAndMetadata{offset=47738, leaderEpoch=null, metadata=''}, transactions-10=OffsetAndMetadata{offset=1449, leaderEpoch=null, metadata=''}, balances-5=OffsetAndMetadata{offset=39170, leaderEpoch=null, metadata=''}, aggregate-block-metrics-by-day-7=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, contract-creator-list-8=OffsetAndMetadata{offset=3257, leaderEpoch=null, metadata=''}, pending-transactions-1=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, contract-destructions-10=OffsetAndMetadata{offset=162, leaderEpoch=null, metadata=''}, block-metrics-by-block-10=OffsetAndMetadata{offset=31842, leaderEpoch=null, metadata=''}, contract-creations-0=OffsetAndMetadata{offset=791, leaderEpoch=null, metadata=''}, contract-creator-list-0=OffsetAndMetadata{offset=3154, leaderEpoch=null, metadata=''}, pending-transactions-9=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, contract-destructions-2=OffsetAndMetadata{offset=156, leaderEpoch=null, metadata=''}, uncles-8=OffsetAndMetadata{offset=2849, leaderEpoch=null, metadata=''}, miner-list-4=OffsetAndMetadata{offset=25571, leaderEpoch=null, metadata=''}, balances-10=OffsetAndMetadata{offset=39317, leaderEpoch=null, metadata=''}, transactions-1=OffsetAndMetadata{offset=1379, leaderEpoch=null, metadata=''}, contract-creations-8=OffsetAndMetadata{offset=793, leaderEpoch=null, metadata=''}, token-transfers-2=OffsetAndMetadata{offset=11192, leaderEpoch=null, metadata=''}, address-tx-counts-5=OffsetAndMetadata{offset=47596, leaderEpoch=null, metadata=''}, uncles-0=OffsetAndMetadata{offset=2851, leaderEpoch=null, metadata=''}, balances-2=OffsetAndMetadata{offset=39226, leaderEpoch=null, metadata=''}, transactions-9=OffsetAndMetadata{offset=1448, leaderEpoch=null, metadata=''}, aggregate-block-metrics-by-day-10=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, token-transfers-10=OffsetAndMetadata{offset=11203, leaderEpoch=null, metadata=''}, block-metrics-by-block-1=OffsetAndMetadata{offset=31776, leaderEpoch=null, metadata=''}, aggregate-block-metrics-by-day-2=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, miner-list-11=OffsetAndMetadata{offset=58099, leaderEpoch=null, metadata=''}, block-metrics-by-block-3=OffsetAndMetadata{offset=31747, leaderEpoch=null, metadata=''}, contract-destructions-11=OffsetAndMetadata{offset=135, leaderEpoch=null, metadata=''}, pending-transactions-0=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, contract-creator-list-7=OffsetAndMetadata{offset=3283, leaderEpoch=null, metadata=''}, miner-list-3=OffsetAndMetadata{offset=20093, leaderEpoch=null, metadata=''}, balances-11=OffsetAndMetadata{offset=39173, leaderEpoch=null, metadata=''}, uncles-7=OffsetAndMetadata{offset=2852, leaderEpoch=null, metadata=''}, block-metrics-by-block-11=OffsetAndMetadata{offset=31742, leaderEpoch=null, metadata=''}, contract-destructions-3=OffsetAndMetadata{offset=165, leaderEpoch=null, metadata=''}, pending-transactions-8=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, contract-creations-7=OffsetAndMetadata{offset=701, leaderEpoch=null, metadata=''}, token-transfers-3=OffsetAndMetadata{offset=11203, leaderEpoch=null, metadata=''}, address-tx-counts-4=OffsetAndMetadata{offset=47610, leaderEpoch=null, metadata=''}, transactions-0=OffsetAndMetadata{offset=1457, leaderEpoch=null, metadata=''}, balances-3=OffsetAndMetadata{offset=39445, leaderEpoch=null, metadata=''}, token-transfers-11=OffsetAndMetadata{offset=11209, leaderEpoch=null, metadata=''}, aggregate-block-metrics-by-day-9=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, transactions-8=OffsetAndMetadata{offset=1455, leaderEpoch=null, metadata=''}, block-metrics-by-block-2=OffsetAndMetadata{offset=31790, leaderEpoch=null, metadata=''}, aggregate-block-metrics-by-day-1=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, miner-list-6=OffsetAndMetadata{offset=56852, leaderEpoch=null, metadata=''}, contract-creator-list-6=OffsetAndMetadata{offset=3199, leaderEpoch=null, metadata=''}, block-metrics-by-block-8=OffsetAndMetadata{offset=31779, leaderEpoch=null, metadata=''}, contract-destructions-4=OffsetAndMetadata{offset=149, leaderEpoch=null, metadata=''}, uncles-6=OffsetAndMetadata{offset=2852, leaderEpoch=null, metadata=''}, contract-creations-6=OffsetAndMetadata{offset=774, leaderEpoch=null, metadata=''}, token-transfers-0=OffsetAndMetadata{offset=11185, leaderEpoch=null, metadata=''}, pending-transactions-7=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, token-transfers-8=OffsetAndMetadata{offset=11215, leaderEpoch=null, metadata=''}, address-tx-counts-7=OffsetAndMetadata{offset=47808, leaderEpoch=null, metadata=''}, balances-8=OffsetAndMetadata{offset=39522, leaderEpoch=null, metadata=''}, transactions-7=OffsetAndMetadata{offset=1449, leaderEpoch=null, metadata=''}, aggregate-block-metrics-by-day-4=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, token-exchange-rates-0=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, balances-0=OffsetAndMetadata{offset=39256, leaderEpoch=null, metadata=''}, contract-creator-list-5=OffsetAndMetadata{offset=3120, leaderEpoch=null, metadata=''}, block-metrics-by-block-9=OffsetAndMetadata{offset=31729, leaderEpoch=null, metadata=''}, contract-creations-5=OffsetAndMetadata{offset=757, leaderEpoch=null, metadata=''}, token-transfers-1=OffsetAndMetadata{offset=11220, leaderEpoch=null, metadata=''}, contract-destructions-5=OffsetAndMetadata{offset=171, leaderEpoch=null, metadata=''}, transactions-6=OffsetAndMetadata{offset=1450, leaderEpoch=null, metadata=''}, miner-list-5=OffsetAndMetadata{offset=69489, leaderEpoch=null, metadata=''}, balances-9=OffsetAndMetadata{offset=39119, leaderEpoch=null, metadata=''}, pending-transactions-6=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, uncles-5=OffsetAndMetadata{offset=2849, leaderEpoch=null, metadata=''}, token-transfers-9=OffsetAndMetadata{offset=11212, leaderEpoch=null, metadata=''}, address-tx-counts-6=OffsetAndMetadata{offset=47804, leaderEpoch=null, metadata=''}, balances-1=OffsetAndMetadata{offset=29991, leaderEpoch=null, metadata=''}, aggregate-block-metrics-by-day-11=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, aggregate-block-metrics-by-day-3=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, block-metrics-by-block-0=OffsetAndMetadata{offset=31747, leaderEpoch=null, metadata=''}, block-metrics-by-block-6=OffsetAndMetadata{offset=31775, leaderEpoch=null, metadata=''}, contract-creator-list-4=OffsetAndMetadata{offset=3144, leaderEpoch=null, metadata=''}, contract-destructions-6=OffsetAndMetadata{offset=156, leaderEpoch=null, metadata=''}, miner-list-8=OffsetAndMetadata{offset=15984, leaderEpoch=null, metadata=''}, transactions-5=OffsetAndMetadata{offset=1403, leaderEpoch=null, metadata=''}, contract-creations-4=OffsetAndMetadata{offset=684, leaderEpoch=null, metadata=''}, address-tx-counts-1=OffsetAndMetadata{offset=47546, leaderEpoch=null, metadata=''}, pending-transactions-5=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, uncles-4=OffsetAndMetadata{offset=2853, leaderEpoch=null, metadata=''}, miner-list-0=OffsetAndMetadata{offset=58095, leaderEpoch=null, metadata=''}, token-transfers-6=OffsetAndMetadata{offset=11196, leaderEpoch=null, metadata=''}, address-tx-counts-9=OffsetAndMetadata{offset=47859, leaderEpoch=null, metadata=''}, balances-6=OffsetAndMetadata{offset=19768, leaderEpoch=null, metadata=''}, aggregate-block-metrics-by-day-6=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, pending-transactions-4=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}, contract-creator-list-11=OffsetAndMetadata{offset=3151, leaderEpoch=null, metadata=''}, miner-list-7=OffsetAndMetadata{offset=59356, leaderEpoch=null, metadata=''}, uncles-11=OffsetAndMetadata{offset=2843, leaderEpoch=null, metadata=''}, block-metrics-by-block-7=OffsetAndMetadata{offset=31819, leaderEpoch=null, metadata=''}, contract-destructions-7=OffsetAndMetadata{offset=157, leaderEpoch=null, metadata=''}, contract-creator-list-3=OffsetAndMetadata{offset=3078, leaderEpoch=null, metadata=''}, contract-creations-3=OffsetAndMetadata{offset=514, leaderEpoch=null, metadata=''}, address-tx-counts-0=OffsetAndMetadata{offset=47517, leaderEpoch=null, metadata=''}, transactions-4=OffsetAndMetadata{offset=1544, leaderEpoch=null, metadata=''}, uncles-3=OffsetAndMetadata{offset=2852, leaderEpoch=null, metadata=''}, contract-creations-11=OffsetAndMetadata{offset=1489, leaderEpoch=null, metadata=''}, token-transfers-7=OffsetAndMetadata{offset=11189, leaderEpoch=null, metadata=''}, address-tx-counts-8=OffsetAndMetadata{offset=47772, leaderEpoch=null, metadata=''}, balances-7=OffsetAndMetadata{offset=19677, leaderEpoch=null, metadata=''}, aggregate-block-metrics-by-day-5=OffsetAndMetadata{offset=0, leaderEpoch=null, metadata=''}} (org.apache.kafka.connect.runtime.WorkerSinkTask)
kafka-connect_1 | [2019-02-04 15:33:09,629] ERROR WorkerSinkTask{id=enkryptio-mongo-block-sink-0} Task threw an uncaught and unrecoverable exception. Task is being killed and will not recover until manually restarted. (org.apache.kafka.connect.runtime.WorkerSinkTask)
kafka-connect_1 | com.mongodb.MongoSocketReadException: Prematurely reached end of stream
kafka-connect_1 | at com.mongodb.internal.connection.SocketStream.read(SocketStream.java:112)
kafka-connect_1 | at com.mongodb.internal.connection.InternalStreamConnection.receiveResponseBuffers(InternalStreamConnection.java:570)
kafka-connect_1 | at com.mongodb.internal.connection.InternalStreamConnection.receiveMessage(InternalStreamConnection.java:441)
kafka-connect_1 | at com.mongodb.internal.connection.InternalStreamConnection.receiveCommandMessageResponse(InternalStreamConnection.java:295)
kafka-connect_1 | at com.mongodb.internal.connection.InternalStreamConnection.sendAndReceive(InternalStreamConnection.java:255)
kafka-connect_1 | at com.mongodb.internal.connection.UsageTrackingInternalConnection.sendAndReceive(UsageTrackingInternalConnection.java:99)
kafka-connect_1 | at com.mongodb.internal.connection.DefaultConnectionPool$PooledConnection.sendAndReceive(DefaultConnectionPool.java:444)
kafka-connect_1 | at com.mongodb.internal.connection.CommandProtocolImpl.execute(CommandProtocolImpl.java:72)
kafka-connect_1 | at com.mongodb.internal.connection.DefaultServer$DefaultServerProtocolExecutor.execute(DefaultServer.java:200)
kafka-connect_1 | at com.mongodb.internal.connection.DefaultServerConnection.executeProtocol(DefaultServerConnection.java:269)
kafka-connect_1 | at com.mongodb.internal.connection.DefaultServerConnection.command(DefaultServerConnection.java:131)
kafka-connect_1 | at com.mongodb.operation.MixedBulkWriteOperation.executeCommand(MixedBulkWriteOperation.java:419)
kafka-connect_1 | at com.mongodb.operation.MixedBulkWriteOperation.executeBulkWriteBatch(MixedBulkWriteOperation.java:257)
kafka-connect_1 | at com.mongodb.operation.MixedBulkWriteOperation.access$700(MixedBulkWriteOperation.java:68)
kafka-connect_1 | at com.mongodb.operation.MixedBulkWriteOperation$1.call(MixedBulkWriteOperation.java:201)
kafka-connect_1 | at com.mongodb.operation.MixedBulkWriteOperation$1.call(MixedBulkWriteOperation.java:192)
kafka-connect_1 | at com.mongodb.operation.OperationHelper.withReleasableConnection(OperationHelper.java:424)
kafka-connect_1 | at com.mongodb.operation.MixedBulkWriteOperation.execute(MixedBulkWriteOperation.java:192)
kafka-connect_1 | at com.mongodb.operation.MixedBulkWriteOperation.execute(MixedBulkWriteOperation.java:67)
kafka-connect_1 | at com.mongodb.client.internal.MongoClientDelegate$DelegateOperationExecutor.execute(MongoClientDelegate.java:193)
kafka-connect_1 | at com.mongodb.client.internal.MongoCollectionImpl.executeBulkWrite(MongoCollectionImpl.java:467)
kafka-connect_1 | at com.mongodb.client.internal.MongoCollectionImpl.bulkWrite(MongoCollectionImpl.java:447)
kafka-connect_1 | at com.mongodb.client.internal.MongoCollectionImpl.bulkWrite(MongoCollectionImpl.java:442)
kafka-connect_1 | at io.enkrypt.kafka.connect.sinks.mongo.MongoSinkTask.put(MongoSinkTask.kt:102)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerSinkTask.deliverMessages(WorkerSinkTask.java:565)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerSinkTask.poll(WorkerSinkTask.java:323)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerSinkTask.iteration(WorkerSinkTask.java:226)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerSinkTask.execute(WorkerSinkTask.java:194)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerTask.doRun(WorkerTask.java:175)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerTask.run(WorkerTask.java:219)
kafka-connect_1 | at java.util.concurrent.Executors$RunnableAdapter.call(Executors.java:511)
kafka-connect_1 | at java.util.concurrent.FutureTask.run(FutureTask.java:266)
kafka-connect_1 | at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1149)
kafka-connect_1 | at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:624)
kafka-connect_1 | at java.lang.Thread.run(Thread.java:748)
kafka-connect_1 | [2019-02-04 15:33:09,630] INFO WorkerSinkTask{id=enkryptio-mongo-block-sink-0} Committing offsets synchronously using sequence number 7: {blocks-0=OffsetAndMetadata{offset=1353783, leaderEpoch=null, metadata=''}} (org.apache.kafka.connect.runtime.WorkerSinkTask)
kafka-connect_1 | [2019-02-04 15:33:09,632] ERROR WorkerSinkTask{id=enkryptio-mongo-block-sink-0} Task threw an uncaught and unrecoverable exception (org.apache.kafka.connect.runtime.WorkerTask)
kafka-connect_1 | org.apache.kafka.connect.errors.ConnectException: Exiting WorkerSinkTask due to unrecoverable exception.
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerSinkTask.deliverMessages(WorkerSinkTask.java:587)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerSinkTask.poll(WorkerSinkTask.java:323)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerSinkTask.iteration(WorkerSinkTask.java:226)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerSinkTask.execute(WorkerSinkTask.java:194)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerTask.doRun(WorkerTask.java:175)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerTask.run(WorkerTask.java:219)
kafka-connect_1 | at java.util.concurrent.Executors$RunnableAdapter.call(Executors.java:511)
kafka-connect_1 | at java.util.concurrent.FutureTask.run(FutureTask.java:266)
kafka-connect_1 | at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1149)
kafka-connect_1 | at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:624)
kafka-connect_1 | at java.lang.Thread.run(Thread.java:748)
kafka-connect_1 | Caused by: com.mongodb.MongoSocketReadException: Prematurely reached end of stream
kafka-connect_1 | at com.mongodb.internal.connection.SocketStream.read(SocketStream.java:112)
kafka-connect_1 | at com.mongodb.internal.connection.InternalStreamConnection.receiveResponseBuffers(InternalStreamConnection.java:570)
kafka-connect_1 | at com.mongodb.internal.connection.InternalStreamConnection.receiveMessage(InternalStreamConnection.java:441)
kafka-connect_1 | at com.mongodb.internal.connection.InternalStreamConnection.receiveCommandMessageResponse(InternalStreamConnection.java:295)
kafka-connect_1 | at com.mongodb.internal.connection.InternalStreamConnection.sendAndReceive(InternalStreamConnection.java:255)
kafka-connect_1 | at com.mongodb.internal.connection.UsageTrackingInternalConnection.sendAndReceive(UsageTrackingInternalConnection.java:99)
kafka-connect_1 | at com.mongodb.internal.connection.DefaultConnectionPool$PooledConnection.sendAndReceive(DefaultConnectionPool.java:444)
kafka-connect_1 | at com.mongodb.internal.connection.CommandProtocolImpl.execute(CommandProtocolImpl.java:72)
kafka-connect_1 | at com.mongodb.internal.connection.DefaultServer$DefaultServerProtocolExecutor.execute(DefaultServer.java:200)
kafka-connect_1 | at com.mongodb.internal.connection.DefaultServerConnection.executeProtocol(DefaultServerConnection.java:269)
kafka-connect_1 | at com.mongodb.internal.connection.DefaultServerConnection.command(DefaultServerConnection.java:131)
kafka-connect_1 | at com.mongodb.operation.MixedBulkWriteOperation.executeCommand(MixedBulkWriteOperation.java:419)
kafka-connect_1 | at com.mongodb.operation.MixedBulkWriteOperation.executeBulkWriteBatch(MixedBulkWriteOperation.java:257)
kafka-connect_1 | at com.mongodb.operation.MixedBulkWriteOperation.access$700(MixedBulkWriteOperation.java:68)
kafka-connect_1 | at com.mongodb.operation.MixedBulkWriteOperation$1.call(MixedBulkWriteOperation.java:201)
kafka-connect_1 | at com.mongodb.operation.MixedBulkWriteOperation$1.call(MixedBulkWriteOperation.java:192)
kafka-connect_1 | at com.mongodb.operation.OperationHelper.withReleasableConnection(OperationHelper.java:424)
kafka-connect_1 | at com.mongodb.operation.MixedBulkWriteOperation.execute(MixedBulkWriteOperation.java:192)
kafka-connect_1 | at com.mongodb.operation.MixedBulkWriteOperation.execute(MixedBulkWriteOperation.java:67)
kafka-connect_1 | at com.mongodb.client.internal.MongoClientDelegate$DelegateOperationExecutor.execute(MongoClientDelegate.java:193)
kafka-connect_1 | at com.mongodb.client.internal.MongoCollectionImpl.executeBulkWrite(MongoCollectionImpl.java:467)
kafka-connect_1 | at com.mongodb.client.internal.MongoCollectionImpl.bulkWrite(MongoCollectionImpl.java:447)
kafka-connect_1 | at com.mongodb.client.internal.MongoCollectionImpl.bulkWrite(MongoCollectionImpl.java:442)
kafka-connect_1 | at io.enkrypt.kafka.connect.sinks.mongo.MongoSinkTask.put(MongoSinkTask.kt:102)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerSinkTask.deliverMessages(WorkerSinkTask.java:565)
kafka-connect_1 | ... 10 more
kafka-connect_1 | [2019-02-04 15:33:09,632] ERROR WorkerSinkTask{id=enkryptio-mongo-block-sink-0} Task is being killed and will not recover until manually restarted (org.apache.kafka.connect.runtime.WorkerTask)
kafka-connect_1 | [2019-02-04 15:33:09,633] INFO [Consumer clientId=consumer-15, groupId=connect-enkryptio-mongo-block-sink] Sending LeaveGroup request to coordinator kafka-1:9091 (id: 2147483646 rack: null) (org.apache.kafka.clients.consumer.internals.AbstractCoordinator)
kafka-connect_1 | [2019-02-04 15:33:09,640] ERROR WorkerSinkTask{id=enkryptio-mongo-ancillary-sink-0} Task threw an uncaught and unrecoverable exception (org.apache.kafka.connect.runtime.WorkerTask)
kafka-connect_1 | org.apache.kafka.connect.errors.ConnectException: Exiting WorkerSinkTask due to unrecoverable exception.
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerSinkTask.deliverMessages(WorkerSinkTask.java:587)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerSinkTask.poll(WorkerSinkTask.java:323)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerSinkTask.iteration(WorkerSinkTask.java:226)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerSinkTask.execute(WorkerSinkTask.java:194)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerTask.doRun(WorkerTask.java:175)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerTask.run(WorkerTask.java:219)
kafka-connect_1 | at java.util.concurrent.Executors$RunnableAdapter.call(Executors.java:511)
kafka-connect_1 | at java.util.concurrent.FutureTask.run(FutureTask.java:266)
kafka-connect_1 | at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1149)
kafka-connect_1 | at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:624)
kafka-connect_1 | at java.lang.Thread.run(Thread.java:748)
kafka-connect_1 | Caused by: com.mongodb.MongoSocketReadException: Prematurely reached end of stream
kafka-connect_1 | at com.mongodb.internal.connection.SocketStream.read(SocketStream.java:112)
kafka-connect_1 | at com.mongodb.internal.connection.InternalStreamConnection.receiveResponseBuffers(InternalStreamConnection.java:570)
kafka-connect_1 | at com.mongodb.internal.connection.InternalStreamConnection.receiveMessage(InternalStreamConnection.java:441)
kafka-connect_1 | at com.mongodb.internal.connection.InternalStreamConnection.receiveCommandMessageResponse(InternalStreamConnection.java:295)
kafka-connect_1 | at com.mongodb.internal.connection.InternalStreamConnection.sendAndReceive(InternalStreamConnection.java:255)
kafka-connect_1 | at com.mongodb.internal.connection.UsageTrackingInternalConnection.sendAndReceive(UsageTrackingInternalConnection.java:99)
kafka-connect_1 | at com.mongodb.internal.connection.DefaultConnectionPool$PooledConnection.sendAndReceive(DefaultConnectionPool.java:444)
kafka-connect_1 | at com.mongodb.internal.connection.CommandProtocolImpl.execute(CommandProtocolImpl.java:72)
kafka-connect_1 | at com.mongodb.internal.connection.DefaultServer$DefaultServerProtocolExecutor.execute(DefaultServer.java:200)
kafka-connect_1 | at com.mongodb.internal.connection.DefaultServerConnection.executeProtocol(DefaultServerConnection.java:269)
kafka-connect_1 | at com.mongodb.internal.connection.DefaultServerConnection.command(DefaultServerConnection.java:131)
kafka-connect_1 | at com.mongodb.operation.MixedBulkWriteOperation.executeCommand(MixedBulkWriteOperation.java:419)
kafka-connect_1 | at com.mongodb.operation.MixedBulkWriteOperation.executeBulkWriteBatch(MixedBulkWriteOperation.java:257)
kafka-connect_1 | at com.mongodb.operation.MixedBulkWriteOperation.access$700(MixedBulkWriteOperation.java:68)
kafka-connect_1 | at com.mongodb.operation.MixedBulkWriteOperation$1.call(MixedBulkWriteOperation.java:201)
kafka-connect_1 | at com.mongodb.operation.MixedBulkWriteOperation$1.call(MixedBulkWriteOperation.java:192)
kafka-connect_1 | at com.mongodb.operation.OperationHelper.withReleasableConnection(OperationHelper.java:424)
kafka-connect_1 | at com.mongodb.operation.MixedBulkWriteOperation.execute(MixedBulkWriteOperation.java:192)
kafka-connect_1 | at com.mongodb.operation.MixedBulkWriteOperation.execute(MixedBulkWriteOperation.java:67)
kafka-connect_1 | at com.mongodb.client.internal.MongoClientDelegate$DelegateOperationExecutor.execute(MongoClientDelegate.java:193)
kafka-connect_1 | at com.mongodb.client.internal.MongoCollectionImpl.executeBulkWrite(MongoCollectionImpl.java:467)
kafka-connect_1 | at com.mongodb.client.internal.MongoCollectionImpl.bulkWrite(MongoCollectionImpl.java:447)
kafka-connect_1 | at com.mongodb.client.internal.MongoCollectionImpl.bulkWrite(MongoCollectionImpl.java:442)
kafka-connect_1 | at io.enkrypt.kafka.connect.sinks.mongo.MongoSinkTask.put(MongoSinkTask.kt:102)
kafka-connect_1 | at org.apache.kafka.connect.runtime.WorkerSinkTask.deliverMessages(WorkerSinkTask.java:565)
kafka-connect_1 | ... 10 more
kafka-connect_1 | [2019-02-04 15:33:09,641] ERROR WorkerSinkTask{id=enkryptio-mongo-ancillary-sink-0} Task is being killed and will not recover until manually restarted (org.apache.kafka.connect.runtime.WorkerTask)
kafka-connect_1 | [2019-02-04 15:33:09,651] INFO [Consumer clientId=consumer-16, groupId=connect-enkryptio-mongo-ancillary-sink] Sending LeaveGroup request to coordinator kafka-1:9091 (id: 2147483646 rack: null) (org.apache.kafka.clients.consumer.internals.AbstractCoordinator)
```
|
process
|
mongosink issues i managed to capture a couple of related exceptions on our mongo sink decimal issue timeout randomly appears it appears that some entries are missing on the db see here i leave a trace to further analyze it and is related to ka connect info batch processing completed in ms io enkrypt kafka connect sinks mongo mongosinktask kafka connect info processing records io enkrypt kafka connect sinks mongo mongosinktask kafka connect info processing balances collection with chunks io enkrypt kafka connect sinks mongo mongosinktask kafka connect info chunk write complete collection balances inserts updates upserts deletes io enkrypt kafka connect sinks mongo mongosinktask kafka connect info chunk write complete collection balances inserts updates upserts deletes io enkrypt kafka connect sinks mongo mongosinktask kafka connect info chunk write complete collection balances inserts updates upserts deletes io enkrypt kafka connect sinks mongo mongosinktask kafka connect info batch processing completed in ms io enkrypt kafka connect sinks mongo mongosinktask kafka connect info processing records io enkrypt kafka connect sinks mongo mongosinktask kafka connect info processing balances collection with chunks io enkrypt kafka connect sinks mongo mongosinktask kafka connect info chunk write complete collection balances inserts updates upserts deletes io enkrypt kafka connect sinks mongo mongosinktask kafka connect info chunk write complete collection balances inserts updates upserts deletes io enkrypt kafka connect sinks mongo mongosinktask kafka connect info chunk write complete collection balances inserts updates upserts deletes io enkrypt kafka connect sinks mongo mongosinktask kafka connect info batch processing completed in ms io enkrypt kafka connect sinks mongo mongosinktask kafka connect info processing records io enkrypt kafka connect sinks mongo mongosinktask kafka connect error workersinktask id enkryptio mongo ancillary sink task threw an uncaught and unrecoverable exception task is being killed and will not recover until manually restarted org apache kafka connect runtime workersinktask kafka connect java lang numberformatexception conversion to would require inexact rounding of kafka connect at org bson types ensureexactrounding java kafka connect at org bson types clampandround java kafka connect at org bson types java kafka connect at org bson types java kafka connect at io enkrypt kafka connect sinks mongo structtobsonconverter convert structtobsonconverter kt kafka connect at io enkrypt kafka connect sinks mongo structtobsonconverter convert default structtobsonconverter kt kafka connect at io enkrypt kafka connect sinks mongo kafkatopics invoke mongosinktask kt kafka connect at io enkrypt kafka connect sinks mongo kafkatopics invoke mongosinktask kt kafka connect at io enkrypt kafka connect sinks mongo mongosinktask put mongosinktask kt kafka connect at org apache kafka connect runtime workersinktask delivermessages workersinktask java kafka connect at org apache kafka connect runtime workersinktask poll workersinktask java kafka connect at org apache kafka connect runtime workersinktask iteration workersinktask java kafka connect at org apache kafka connect runtime workersinktask execute workersinktask java kafka connect at org apache kafka connect runtime workertask dorun workertask java kafka connect at org apache kafka connect runtime workertask run workertask java kafka connect at java util concurrent executors runnableadapter call executors java kafka connect at java util concurrent futuretask run futuretask java kafka connect at java util concurrent threadpoolexecutor runworker threadpoolexecutor java kafka connect at java util concurrent threadpoolexecutor worker run threadpoolexecutor java kafka connect at java lang thread run thread java kafka connect info workersinktask id enkryptio mongo ancillary sink committing offsets synchronously using sequence number pending transactions offsetandmetadata offset leaderepoch null metadata miner list offsetandmetadata offset leaderepoch null metadata contract creator list offsetandmetadata offset leaderepoch null metadata block metrics by block offsetandmetadata offset leaderepoch null metadata contract destructions offsetandmetadata offset leaderepoch null metadata uncles offsetandmetadata offset leaderepoch null metadata contract creations offsetandmetadata offset leaderepoch null metadata contract metadata offsetandmetadata offset leaderepoch null metadata pending transactions offsetandmetadata offset leaderepoch null metadata miner list offsetandmetadata offset leaderepoch null metadata transactions offsetandmetadata offset leaderepoch null metadata contract creator list offsetandmetadata offset leaderepoch null metadata contract destructions offsetandmetadata offset leaderepoch null metadata uncles offsetandmetadata offset leaderepoch null metadata contract creations offsetandmetadata offset leaderepoch null metadata token transfers offsetandmetadata offset leaderepoch null metadata address tx counts offsetandmetadata offset leaderepoch null metadata balances offsetandmetadata offset leaderepoch null metadata transactions offsetandmetadata offset leaderepoch null metadata address tx counts offsetandmetadata offset leaderepoch null metadata aggregate block metrics by day offsetandmetadata offset leaderepoch null metadata aggregate block metrics by day offsetandmetadata offset leaderepoch null metadata contract creator list offsetandmetadata offset leaderepoch null metadata block metrics by block offsetandmetadata offset leaderepoch null metadata pending transactions offsetandmetadata offset leaderepoch null metadata contract creations offsetandmetadata offset leaderepoch null metadata contract destructions offsetandmetadata offset leaderepoch null metadata miner list offsetandmetadata offset leaderepoch null metadata contract creator list offsetandmetadata offset leaderepoch null metadata pending transactions offsetandmetadata offset leaderepoch null metadata uncles offsetandmetadata offset leaderepoch null metadata contract creations offsetandmetadata offset leaderepoch null metadata token transfers offsetandmetadata offset leaderepoch null metadata address tx counts offsetandmetadata offset leaderepoch null metadata contract destructions offsetandmetadata offset leaderepoch null metadata transactions offsetandmetadata offset leaderepoch null metadata miner list offsetandmetadata offset leaderepoch null metadata uncles offsetandmetadata offset leaderepoch null metadata address tx counts offsetandmetadata offset leaderepoch null metadata transactions offsetandmetadata offset leaderepoch null metadata balances offsetandmetadata offset leaderepoch null metadata aggregate block metrics by day offsetandmetadata offset leaderepoch null metadata contract creator list offsetandmetadata offset leaderepoch null metadata pending transactions offsetandmetadata offset leaderepoch null metadata contract destructions offsetandmetadata offset leaderepoch null metadata block metrics by block offsetandmetadata offset leaderepoch null metadata contract creations offsetandmetadata offset leaderepoch null metadata contract creator list offsetandmetadata offset leaderepoch null metadata pending transactions offsetandmetadata offset leaderepoch null metadata contract destructions offsetandmetadata offset leaderepoch null metadata uncles offsetandmetadata offset leaderepoch null metadata miner list offsetandmetadata offset leaderepoch null metadata balances offsetandmetadata offset leaderepoch null metadata transactions offsetandmetadata offset leaderepoch null metadata contract creations offsetandmetadata offset leaderepoch null metadata token transfers offsetandmetadata offset leaderepoch null metadata address tx counts offsetandmetadata offset leaderepoch null metadata uncles offsetandmetadata offset leaderepoch null metadata balances offsetandmetadata offset leaderepoch null metadata transactions offsetandmetadata offset leaderepoch null metadata aggregate block metrics by day offsetandmetadata offset leaderepoch null metadata token transfers offsetandmetadata offset leaderepoch null metadata block metrics by block offsetandmetadata offset leaderepoch null metadata aggregate block metrics by day offsetandmetadata offset leaderepoch null metadata miner list offsetandmetadata offset leaderepoch null metadata block metrics by block offsetandmetadata offset leaderepoch null metadata contract destructions offsetandmetadata offset leaderepoch null metadata pending transactions offsetandmetadata offset leaderepoch null metadata contract creator list offsetandmetadata offset leaderepoch null metadata miner list offsetandmetadata offset leaderepoch null metadata balances offsetandmetadata offset leaderepoch null metadata uncles offsetandmetadata offset leaderepoch null metadata block metrics by block offsetandmetadata offset leaderepoch null metadata contract destructions offsetandmetadata offset leaderepoch null metadata pending transactions offsetandmetadata offset leaderepoch null metadata contract creations offsetandmetadata offset leaderepoch null metadata token transfers offsetandmetadata offset leaderepoch null metadata address tx counts offsetandmetadata offset leaderepoch null metadata transactions offsetandmetadata offset leaderepoch null metadata balances offsetandmetadata offset leaderepoch null metadata token transfers offsetandmetadata offset leaderepoch null metadata aggregate block metrics by day offsetandmetadata offset leaderepoch null metadata transactions offsetandmetadata offset leaderepoch null metadata block metrics by block offsetandmetadata offset leaderepoch null metadata aggregate block metrics by day offsetandmetadata offset leaderepoch null metadata miner list offsetandmetadata offset leaderepoch null metadata contract creator list offsetandmetadata offset leaderepoch null metadata block metrics by block offsetandmetadata offset leaderepoch null metadata contract destructions offsetandmetadata offset leaderepoch null metadata uncles offsetandmetadata offset leaderepoch null metadata contract creations offsetandmetadata offset leaderepoch null metadata token transfers offsetandmetadata offset leaderepoch null metadata pending transactions offsetandmetadata offset leaderepoch null metadata token transfers offsetandmetadata offset leaderepoch null metadata address tx counts offsetandmetadata offset leaderepoch null metadata balances offsetandmetadata offset leaderepoch null metadata transactions offsetandmetadata offset leaderepoch null metadata aggregate block metrics by day offsetandmetadata offset leaderepoch null metadata token exchange rates offsetandmetadata offset leaderepoch null metadata balances offsetandmetadata offset leaderepoch null metadata contract creator list offsetandmetadata offset leaderepoch null metadata block metrics by block offsetandmetadata offset leaderepoch null metadata contract creations offsetandmetadata offset leaderepoch null metadata token transfers offsetandmetadata offset leaderepoch null metadata contract destructions offsetandmetadata offset leaderepoch null metadata transactions offsetandmetadata offset leaderepoch null metadata miner list offsetandmetadata offset leaderepoch null metadata balances offsetandmetadata offset leaderepoch null metadata pending transactions offsetandmetadata offset leaderepoch null metadata uncles offsetandmetadata offset leaderepoch null metadata token transfers offsetandmetadata offset leaderepoch null metadata address tx counts offsetandmetadata offset leaderepoch null metadata balances offsetandmetadata offset leaderepoch null metadata aggregate block metrics by day offsetandmetadata offset leaderepoch null metadata aggregate block metrics by day offsetandmetadata offset leaderepoch null metadata block metrics by block offsetandmetadata offset leaderepoch null metadata block metrics by block offsetandmetadata offset leaderepoch null metadata contract creator list offsetandmetadata offset leaderepoch null metadata contract destructions offsetandmetadata offset leaderepoch null metadata miner list offsetandmetadata offset leaderepoch null metadata transactions offsetandmetadata offset leaderepoch null metadata contract creations offsetandmetadata offset leaderepoch null metadata address tx counts offsetandmetadata offset leaderepoch null metadata pending transactions offsetandmetadata offset leaderepoch null metadata uncles offsetandmetadata offset leaderepoch null metadata miner list offsetandmetadata offset leaderepoch null metadata token transfers offsetandmetadata offset leaderepoch null metadata address tx counts offsetandmetadata offset leaderepoch null metadata balances offsetandmetadata offset leaderepoch null metadata aggregate block metrics by day offsetandmetadata offset leaderepoch null metadata pending transactions offsetandmetadata offset leaderepoch null metadata contract creator list offsetandmetadata offset leaderepoch null metadata miner list offsetandmetadata offset leaderepoch null metadata uncles offsetandmetadata offset leaderepoch null metadata block metrics by block offsetandmetadata offset leaderepoch null metadata contract destructions offsetandmetadata offset leaderepoch null metadata contract creator list offsetandmetadata offset leaderepoch null metadata contract creations offsetandmetadata offset leaderepoch null metadata address tx counts offsetandmetadata offset leaderepoch null metadata transactions offsetandmetadata offset leaderepoch null metadata uncles offsetandmetadata offset leaderepoch null metadata contract creations offsetandmetadata offset leaderepoch null metadata token transfers offsetandmetadata offset leaderepoch null metadata address tx counts offsetandmetadata offset leaderepoch null metadata balances offsetandmetadata offset leaderepoch null metadata aggregate block metrics by day offsetandmetadata offset leaderepoch null metadata org apache kafka connect runtime workersinktask kafka connect error workersinktask id enkryptio mongo ancillary sink task threw an uncaught and unrecoverable exception org apache kafka connect runtime workertask kafka connect org apache kafka connect errors connectexception exiting workersinktask due to unrecoverable exception kafka connect at org apache kafka connect runtime workersinktask delivermessages workersinktask java kafka connect at org apache kafka connect runtime workersinktask poll workersinktask java kafka connect at org apache kafka connect runtime workersinktask iteration workersinktask java kafka connect at org apache kafka connect runtime workersinktask execute workersinktask java kafka connect at org apache kafka connect runtime workertask dorun workertask java kafka connect at org apache kafka connect runtime workertask run workertask java kafka connect at java util concurrent executors runnableadapter call executors java kafka connect at java util concurrent futuretask run futuretask java kafka connect at java util concurrent threadpoolexecutor runworker threadpoolexecutor java kafka connect at java util concurrent threadpoolexecutor worker run threadpoolexecutor java kafka connect at java lang thread run thread java kafka connect caused by java lang numberformatexception conversion to would require inexact rounding of kafka connect at org bson types ensureexactrounding java kafka connect at org bson types clampandround java kafka connect at org bson types java kafka connect at org bson types java kafka connect at io enkrypt kafka connect sinks mongo structtobsonconverter convert structtobsonconverter kt kafka connect at io enkrypt kafka connect sinks mongo structtobsonconverter convert default structtobsonconverter kt kafka connect at io enkrypt kafka connect sinks mongo kafkatopics invoke mongosinktask kt kafka connect at io enkrypt kafka connect sinks mongo kafkatopics invoke mongosinktask kt kafka connect at io enkrypt kafka connect sinks mongo mongosinktask put mongosinktask kt kafka connect at org apache kafka connect runtime workersinktask delivermessages workersinktask java kafka connect more kafka connect error workersinktask id enkryptio mongo ancillary sink task is being killed and will not recover until manually restarted org apache kafka connect runtime workertask kafka connect info closed connection to mongodb because the pool has been closed org mongodb driver connection kafka connect info sending leavegroup request to coordinator kafka id rack null org apache kafka clients consumer internals abstractcoordinator also sometimes while processing we obtain a random disconnection i think is more related to the fact we are sending big chunks of data as brianmcgee and myself discussed i ll leave here also a trace to have it kafka connect warn got socket exception on connection to mongodb all connections to mongodb will be closed org mongodb driver connection kafka connect warn got socket exception on connection to mongodb all connections to mongodb will be closed org mongodb driver connection kafka connect info closed connection to mongodb because there was a socket exception raised by this connection org mongodb driver connection kafka connect error workersinktask id enkryptio mongo ancillary sink task threw an uncaught and unrecoverable exception task is being killed and will not recover until manually restarted org apache kafka connect runtime workersinktask kafka connect com mongodb mongosocketreadexception prematurely reached end of stream kafka connect at com mongodb internal connection socketstream read socketstream java kafka connect at com mongodb internal connection internalstreamconnection receiveresponsebuffers internalstreamconnection java kafka connect at com mongodb internal connection internalstreamconnection receivemessage internalstreamconnection java kafka connect at com mongodb internal connection internalstreamconnection receivecommandmessageresponse internalstreamconnection java kafka connect at com mongodb internal connection internalstreamconnection sendandreceive internalstreamconnection java kafka connect at com mongodb internal connection usagetrackinginternalconnection sendandreceive usagetrackinginternalconnection java kafka connect at com mongodb internal connection defaultconnectionpool pooledconnection sendandreceive defaultconnectionpool java kafka connect at com mongodb internal connection commandprotocolimpl execute commandprotocolimpl java kafka connect at com mongodb internal connection defaultserver defaultserverprotocolexecutor execute defaultserver java kafka connect at com mongodb internal connection defaultserverconnection executeprotocol defaultserverconnection java kafka connect at com mongodb internal connection defaultserverconnection command defaultserverconnection java kafka connect at com mongodb operation mixedbulkwriteoperation executecommand mixedbulkwriteoperation java kafka connect at com mongodb operation mixedbulkwriteoperation executebulkwritebatch mixedbulkwriteoperation java kafka connect at com mongodb operation mixedbulkwriteoperation access mixedbulkwriteoperation java kafka connect at com mongodb operation mixedbulkwriteoperation call mixedbulkwriteoperation java kafka connect at com mongodb operation mixedbulkwriteoperation call mixedbulkwriteoperation java kafka connect at com mongodb operation operationhelper withreleasableconnection operationhelper java kafka connect at com mongodb operation mixedbulkwriteoperation execute mixedbulkwriteoperation java kafka connect at com mongodb operation mixedbulkwriteoperation execute mixedbulkwriteoperation java kafka connect at com mongodb client internal mongoclientdelegate delegateoperationexecutor execute mongoclientdelegate java kafka connect at com mongodb client internal mongocollectionimpl executebulkwrite mongocollectionimpl java kafka connect at com mongodb client internal mongocollectionimpl bulkwrite mongocollectionimpl java kafka connect at com mongodb client internal mongocollectionimpl bulkwrite mongocollectionimpl java kafka connect at io enkrypt kafka connect sinks mongo mongosinktask put mongosinktask kt kafka connect at org apache kafka connect runtime workersinktask delivermessages workersinktask java kafka connect at org apache kafka connect runtime workersinktask poll workersinktask java kafka connect at org apache kafka connect runtime workersinktask iteration workersinktask java kafka connect at org apache kafka connect runtime workersinktask execute workersinktask java kafka connect at org apache kafka connect runtime workertask dorun workertask java kafka connect at org apache kafka connect runtime workertask run workertask java kafka connect at java util concurrent executors runnableadapter call executors java kafka connect at java util concurrent futuretask run futuretask java kafka connect at java util concurrent threadpoolexecutor runworker threadpoolexecutor java kafka connect at java util concurrent threadpoolexecutor worker run threadpoolexecutor java kafka connect at java lang thread run thread java kafka connect info exception in monitor thread while connecting to server mongodb org mongodb driver cluster kafka connect com mongodb mongosocketopenexception exception opening socket kafka connect at com mongodb internal connection socketstream open socketstream java kafka connect at com mongodb internal connection internalstreamconnection open internalstreamconnection java kafka connect at com mongodb internal connection defaultservermonitor servermonitorrunnable run defaultservermonitor java kafka connect at java lang thread run thread java kafka connect caused by java net connectexception connection refused connection refused kafka connect at java net plainsocketimpl socketconnect native method kafka connect at java net abstractplainsocketimpl doconnect abstractplainsocketimpl java kafka connect at java net abstractplainsocketimpl connecttoaddress abstractplainsocketimpl java kafka connect at java net abstractplainsocketimpl connect abstractplainsocketimpl java kafka connect at java net sockssocketimpl connect sockssocketimpl java kafka connect at java net socket connect socket java kafka connect at com mongodb internal connection socketstreamhelper initialize socketstreamhelper java kafka connect at com mongodb internal connection socketstream initializesocket socketstream java kafka connect at com mongodb internal connection socketstream open socketstream java kafka connect more kafka connect info exception in monitor thread while connecting to server mongodb org mongodb driver cluster kafka connect com mongodb mongosocketopenexception exception opening socket kafka connect at com mongodb internal connection socketstream open socketstream java kafka connect at com mongodb internal connection internalstreamconnection open internalstreamconnection java kafka connect at com mongodb internal connection defaultservermonitor servermonitorrunnable run defaultservermonitor java kafka connect at java lang thread run thread java kafka connect caused by java net connectexception connection refused connection refused kafka connect at java net plainsocketimpl socketconnect native method kafka connect at java net abstractplainsocketimpl doconnect abstractplainsocketimpl java kafka connect at java net abstractplainsocketimpl connecttoaddress abstractplainsocketimpl java kafka connect at java net abstractplainsocketimpl connect abstractplainsocketimpl java kafka connect at java net sockssocketimpl connect sockssocketimpl java kafka connect at java net socket connect socket java kafka connect at com mongodb internal connection socketstreamhelper initialize socketstreamhelper java kafka connect at com mongodb internal connection socketstream initializesocket socketstream java kafka connect at com mongodb internal connection socketstream open socketstream java kafka connect more kafka connect info closed connection to mongodb because there was a socket exception raised by this connection org mongodb driver connection kafka connect info workersinktask id enkryptio mongo ancillary sink committing offsets synchronously using sequence number pending transactions offsetandmetadata offset leaderepoch null metadata miner list offsetandmetadata offset leaderepoch null metadata contract creator list offsetandmetadata offset leaderepoch null metadata block metrics by block offsetandmetadata offset leaderepoch null metadata contract destructions offsetandmetadata offset leaderepoch null metadata uncles offsetandmetadata offset leaderepoch null metadata contract creations offsetandmetadata offset leaderepoch null metadata contract metadata offsetandmetadata offset leaderepoch null metadata pending transactions offsetandmetadata offset leaderepoch null metadata miner list offsetandmetadata offset leaderepoch null metadata transactions offsetandmetadata offset leaderepoch null metadata contract creator list offsetandmetadata offset leaderepoch null metadata contract destructions offsetandmetadata offset leaderepoch null metadata uncles offsetandmetadata offset leaderepoch null metadata contract creations offsetandmetadata offset leaderepoch null metadata token transfers offsetandmetadata offset leaderepoch null metadata address tx counts offsetandmetadata offset leaderepoch null metadata balances offsetandmetadata offset leaderepoch null metadata transactions offsetandmetadata offset leaderepoch null metadata address tx counts offsetandmetadata offset leaderepoch null metadata aggregate block metrics by day offsetandmetadata offset leaderepoch null metadata aggregate block metrics by day offsetandmetadata offset leaderepoch null metadata contract creator list offsetandmetadata offset leaderepoch null metadata block metrics by block offsetandmetadata offset leaderepoch null metadata pending transactions offsetandmetadata offset leaderepoch null metadata contract creations offsetandmetadata offset leaderepoch null metadata contract destructions offsetandmetadata offset leaderepoch null metadata miner list offsetandmetadata offset leaderepoch null metadata contract creator list offsetandmetadata offset leaderepoch null metadata pending transactions offsetandmetadata offset leaderepoch null metadata uncles offsetandmetadata offset leaderepoch null metadata contract creations offsetandmetadata offset leaderepoch null metadata token transfers offsetandmetadata offset leaderepoch null metadata address tx counts offsetandmetadata offset leaderepoch null metadata contract destructions offsetandmetadata offset leaderepoch null metadata transactions offsetandmetadata offset leaderepoch null metadata miner list offsetandmetadata offset leaderepoch null metadata uncles offsetandmetadata offset leaderepoch null metadata address tx counts offsetandmetadata offset leaderepoch null metadata transactions offsetandmetadata offset leaderepoch null metadata balances offsetandmetadata offset leaderepoch null metadata aggregate block metrics by day offsetandmetadata offset leaderepoch null metadata contract creator list offsetandmetadata offset leaderepoch null metadata pending transactions offsetandmetadata offset leaderepoch null metadata contract destructions offsetandmetadata offset leaderepoch null metadata block metrics by block offsetandmetadata offset leaderepoch null metadata contract creations offsetandmetadata offset leaderepoch null metadata contract creator list offsetandmetadata offset leaderepoch null metadata pending transactions offsetandmetadata offset leaderepoch null metadata contract destructions offsetandmetadata offset leaderepoch null metadata uncles offsetandmetadata offset leaderepoch null metadata miner list offsetandmetadata offset leaderepoch null metadata balances offsetandmetadata offset leaderepoch null metadata transactions offsetandmetadata offset leaderepoch null metadata contract creations offsetandmetadata offset leaderepoch null metadata token transfers offsetandmetadata offset leaderepoch null metadata address tx counts offsetandmetadata offset leaderepoch null metadata uncles offsetandmetadata offset leaderepoch null metadata balances offsetandmetadata offset leaderepoch null metadata transactions offsetandmetadata offset leaderepoch null metadata aggregate block metrics by day offsetandmetadata offset leaderepoch null metadata token transfers offsetandmetadata offset leaderepoch null metadata block metrics by block offsetandmetadata offset leaderepoch null metadata aggregate block metrics by day offsetandmetadata offset leaderepoch null metadata miner list offsetandmetadata offset leaderepoch null metadata block metrics by block offsetandmetadata offset leaderepoch null metadata contract destructions offsetandmetadata offset leaderepoch null metadata pending transactions offsetandmetadata offset leaderepoch null metadata contract creator list offsetandmetadata offset leaderepoch null metadata miner list offsetandmetadata offset leaderepoch null metadata balances offsetandmetadata offset leaderepoch null metadata uncles offsetandmetadata offset leaderepoch null metadata block metrics by block offsetandmetadata offset leaderepoch null metadata contract destructions offsetandmetadata offset leaderepoch null metadata pending transactions offsetandmetadata offset leaderepoch null metadata contract creations offsetandmetadata offset leaderepoch null metadata token transfers offsetandmetadata offset leaderepoch null metadata address tx counts offsetandmetadata offset leaderepoch null metadata transactions offsetandmetadata offset leaderepoch null metadata balances offsetandmetadata offset leaderepoch null metadata token transfers offsetandmetadata offset leaderepoch null metadata aggregate block metrics by day offsetandmetadata offset leaderepoch null metadata transactions offsetandmetadata offset leaderepoch null metadata block metrics by block offsetandmetadata offset leaderepoch null metadata aggregate block metrics by day offsetandmetadata offset leaderepoch null metadata miner list offsetandmetadata offset leaderepoch null metadata contract creator list offsetandmetadata offset leaderepoch null metadata block metrics by block offsetandmetadata offset leaderepoch null metadata contract destructions offsetandmetadata offset leaderepoch null metadata uncles offsetandmetadata offset leaderepoch null metadata contract creations offsetandmetadata offset leaderepoch null metadata token transfers offsetandmetadata offset leaderepoch null metadata pending transactions offsetandmetadata offset leaderepoch null metadata token transfers offsetandmetadata offset leaderepoch null metadata address tx counts offsetandmetadata offset leaderepoch null metadata balances offsetandmetadata offset leaderepoch null metadata transactions offsetandmetadata offset leaderepoch null metadata aggregate block metrics by day offsetandmetadata offset leaderepoch null metadata token exchange rates offsetandmetadata offset leaderepoch null metadata balances offsetandmetadata offset leaderepoch null metadata contract creator list offsetandmetadata offset leaderepoch null metadata block metrics by block offsetandmetadata offset leaderepoch null metadata contract creations offsetandmetadata offset leaderepoch null metadata token transfers offsetandmetadata offset leaderepoch null metadata contract destructions offsetandmetadata offset leaderepoch null metadata transactions offsetandmetadata offset leaderepoch null metadata miner list offsetandmetadata offset leaderepoch null metadata balances offsetandmetadata offset leaderepoch null metadata pending transactions offsetandmetadata offset leaderepoch null metadata uncles offsetandmetadata offset leaderepoch null metadata token transfers offsetandmetadata offset leaderepoch null metadata address tx counts offsetandmetadata offset leaderepoch null metadata balances offsetandmetadata offset leaderepoch null metadata aggregate block metrics by day offsetandmetadata offset leaderepoch null metadata aggregate block metrics by day offsetandmetadata offset leaderepoch null metadata block metrics by block offsetandmetadata offset leaderepoch null metadata block metrics by block offsetandmetadata offset leaderepoch null metadata contract creator list offsetandmetadata offset leaderepoch null metadata contract destructions offsetandmetadata offset leaderepoch null metadata miner list offsetandmetadata offset leaderepoch null metadata transactions offsetandmetadata offset leaderepoch null metadata contract creations offsetandmetadata offset leaderepoch null metadata address tx counts offsetandmetadata offset leaderepoch null metadata pending transactions offsetandmetadata offset leaderepoch null metadata uncles offsetandmetadata offset leaderepoch null metadata miner list offsetandmetadata offset leaderepoch null metadata token transfers offsetandmetadata offset leaderepoch null metadata address tx counts offsetandmetadata offset leaderepoch null metadata balances offsetandmetadata offset leaderepoch null metadata aggregate block metrics by day offsetandmetadata offset leaderepoch null metadata pending transactions offsetandmetadata offset leaderepoch null metadata contract creator list offsetandmetadata offset leaderepoch null metadata miner list offsetandmetadata offset leaderepoch null metadata uncles offsetandmetadata offset leaderepoch null metadata block metrics by block offsetandmetadata offset leaderepoch null metadata contract destructions offsetandmetadata offset leaderepoch null metadata contract creator list offsetandmetadata offset leaderepoch null metadata contract creations offsetandmetadata offset leaderepoch null metadata address tx counts offsetandmetadata offset leaderepoch null metadata transactions offsetandmetadata offset leaderepoch null metadata uncles offsetandmetadata offset leaderepoch null metadata contract creations offsetandmetadata offset leaderepoch null metadata token transfers offsetandmetadata offset leaderepoch null metadata address tx counts offsetandmetadata offset leaderepoch null metadata balances offsetandmetadata offset leaderepoch null metadata aggregate block metrics by day offsetandmetadata offset leaderepoch null metadata org apache kafka connect runtime workersinktask kafka connect error workersinktask id enkryptio mongo block sink task threw an uncaught and unrecoverable exception task is being killed and will not recover until manually restarted org apache kafka connect runtime workersinktask kafka connect com mongodb mongosocketreadexception prematurely reached end of stream kafka connect at com mongodb internal connection socketstream read socketstream java kafka connect at com mongodb internal connection internalstreamconnection receiveresponsebuffers internalstreamconnection java kafka connect at com mongodb internal connection internalstreamconnection receivemessage internalstreamconnection java kafka connect at com mongodb internal connection internalstreamconnection receivecommandmessageresponse internalstreamconnection java kafka connect at com mongodb internal connection internalstreamconnection sendandreceive internalstreamconnection java kafka connect at com mongodb internal connection usagetrackinginternalconnection sendandreceive usagetrackinginternalconnection java kafka connect at com mongodb internal connection defaultconnectionpool pooledconnection sendandreceive defaultconnectionpool java kafka connect at com mongodb internal connection commandprotocolimpl execute commandprotocolimpl java kafka connect at com mongodb internal connection defaultserver defaultserverprotocolexecutor execute defaultserver java kafka connect at com mongodb internal connection defaultserverconnection executeprotocol defaultserverconnection java kafka connect at com mongodb internal connection defaultserverconnection command defaultserverconnection java kafka connect at com mongodb operation mixedbulkwriteoperation executecommand mixedbulkwriteoperation java kafka connect at com mongodb operation mixedbulkwriteoperation executebulkwritebatch mixedbulkwriteoperation java kafka connect at com mongodb operation mixedbulkwriteoperation access mixedbulkwriteoperation java kafka connect at com mongodb operation mixedbulkwriteoperation call mixedbulkwriteoperation java kafka connect at com mongodb operation mixedbulkwriteoperation call mixedbulkwriteoperation java kafka connect at com mongodb operation operationhelper withreleasableconnection operationhelper java kafka connect at com mongodb operation mixedbulkwriteoperation execute mixedbulkwriteoperation java kafka connect at com mongodb operation mixedbulkwriteoperation execute mixedbulkwriteoperation java kafka connect at com mongodb client internal mongoclientdelegate delegateoperationexecutor execute mongoclientdelegate java kafka connect at com mongodb client internal mongocollectionimpl executebulkwrite mongocollectionimpl java kafka connect at com mongodb client internal mongocollectionimpl bulkwrite mongocollectionimpl java kafka connect at com mongodb client internal mongocollectionimpl bulkwrite mongocollectionimpl java kafka connect at io enkrypt kafka connect sinks mongo mongosinktask put mongosinktask kt kafka connect at org apache kafka connect runtime workersinktask delivermessages workersinktask java kafka connect at org apache kafka connect runtime workersinktask poll workersinktask java kafka connect at org apache kafka connect runtime workersinktask iteration workersinktask java kafka connect at org apache kafka connect runtime workersinktask execute workersinktask java kafka connect at org apache kafka connect runtime workertask dorun workertask java kafka connect at org apache kafka connect runtime workertask run workertask java kafka connect at java util concurrent executors runnableadapter call executors java kafka connect at java util concurrent futuretask run futuretask java kafka connect at java util concurrent threadpoolexecutor runworker threadpoolexecutor java kafka connect at java util concurrent threadpoolexecutor worker run threadpoolexecutor java kafka connect at java lang thread run thread java kafka connect info workersinktask id enkryptio mongo block sink committing offsets synchronously using sequence number blocks offsetandmetadata offset leaderepoch null metadata org apache kafka connect runtime workersinktask kafka connect error workersinktask id enkryptio mongo block sink task threw an uncaught and unrecoverable exception org apache kafka connect runtime workertask kafka connect org apache kafka connect errors connectexception exiting workersinktask due to unrecoverable exception kafka connect at org apache kafka connect runtime workersinktask delivermessages workersinktask java kafka connect at org apache kafka connect runtime workersinktask poll workersinktask java kafka connect at org apache kafka connect runtime workersinktask iteration workersinktask java kafka connect at org apache kafka connect runtime workersinktask execute workersinktask java kafka connect at org apache kafka connect runtime workertask dorun workertask java kafka connect at org apache kafka connect runtime workertask run workertask java kafka connect at java util concurrent executors runnableadapter call executors java kafka connect at java util concurrent futuretask run futuretask java kafka connect at java util concurrent threadpoolexecutor runworker threadpoolexecutor java kafka connect at java util concurrent threadpoolexecutor worker run threadpoolexecutor java kafka connect at java lang thread run thread java kafka connect caused by com mongodb mongosocketreadexception prematurely reached end of stream kafka connect at com mongodb internal connection socketstream read socketstream java kafka connect at com mongodb internal connection internalstreamconnection receiveresponsebuffers internalstreamconnection java kafka connect at com mongodb internal connection internalstreamconnection receivemessage internalstreamconnection java kafka connect at com mongodb internal connection internalstreamconnection receivecommandmessageresponse internalstreamconnection java kafka connect at com mongodb internal connection internalstreamconnection sendandreceive internalstreamconnection java kafka connect at com mongodb internal connection usagetrackinginternalconnection sendandreceive usagetrackinginternalconnection java kafka connect at com mongodb internal connection defaultconnectionpool pooledconnection sendandreceive defaultconnectionpool java kafka connect at com mongodb internal connection commandprotocolimpl execute commandprotocolimpl java kafka connect at com mongodb internal connection defaultserver defaultserverprotocolexecutor execute defaultserver java kafka connect at com mongodb internal connection defaultserverconnection executeprotocol defaultserverconnection java kafka connect at com mongodb internal connection defaultserverconnection command defaultserverconnection java kafka connect at com mongodb operation mixedbulkwriteoperation executecommand mixedbulkwriteoperation java kafka connect at com mongodb operation mixedbulkwriteoperation executebulkwritebatch mixedbulkwriteoperation java kafka connect at com mongodb operation mixedbulkwriteoperation access mixedbulkwriteoperation java kafka connect at com mongodb operation mixedbulkwriteoperation call mixedbulkwriteoperation java kafka connect at com mongodb operation mixedbulkwriteoperation call mixedbulkwriteoperation java kafka connect at com mongodb operation operationhelper withreleasableconnection operationhelper java kafka connect at com mongodb operation mixedbulkwriteoperation execute mixedbulkwriteoperation java kafka connect at com mongodb operation mixedbulkwriteoperation execute mixedbulkwriteoperation java kafka connect at com mongodb client internal mongoclientdelegate delegateoperationexecutor execute mongoclientdelegate java kafka connect at com mongodb client internal mongocollectionimpl executebulkwrite mongocollectionimpl java kafka connect at com mongodb client internal mongocollectionimpl bulkwrite mongocollectionimpl java kafka connect at com mongodb client internal mongocollectionimpl bulkwrite mongocollectionimpl java kafka connect at io enkrypt kafka connect sinks mongo mongosinktask put mongosinktask kt kafka connect at org apache kafka connect runtime workersinktask delivermessages workersinktask java kafka connect more kafka connect error workersinktask id enkryptio mongo block sink task is being killed and will not recover until manually restarted org apache kafka connect runtime workertask kafka connect info sending leavegroup request to coordinator kafka id rack null org apache kafka clients consumer internals abstractcoordinator kafka connect error workersinktask id enkryptio mongo ancillary sink task threw an uncaught and unrecoverable exception org apache kafka connect runtime workertask kafka connect org apache kafka connect errors connectexception exiting workersinktask due to unrecoverable exception kafka connect at org apache kafka connect runtime workersinktask delivermessages workersinktask java kafka connect at org apache kafka connect runtime workersinktask poll workersinktask java kafka connect at org apache kafka connect runtime workersinktask iteration workersinktask java kafka connect at org apache kafka connect runtime workersinktask execute workersinktask java kafka connect at org apache kafka connect runtime workertask dorun workertask java kafka connect at org apache kafka connect runtime workertask run workertask java kafka connect at java util concurrent executors runnableadapter call executors java kafka connect at java util concurrent futuretask run futuretask java kafka connect at java util concurrent threadpoolexecutor runworker threadpoolexecutor java kafka connect at java util concurrent threadpoolexecutor worker run threadpoolexecutor java kafka connect at java lang thread run thread java kafka connect caused by com mongodb mongosocketreadexception prematurely reached end of stream kafka connect at com mongodb internal connection socketstream read socketstream java kafka connect at com mongodb internal connection internalstreamconnection receiveresponsebuffers internalstreamconnection java kafka connect at com mongodb internal connection internalstreamconnection receivemessage internalstreamconnection java kafka connect at com mongodb internal connection internalstreamconnection receivecommandmessageresponse internalstreamconnection java kafka connect at com mongodb internal connection internalstreamconnection sendandreceive internalstreamconnection java kafka connect at com mongodb internal connection usagetrackinginternalconnection sendandreceive usagetrackinginternalconnection java kafka connect at com mongodb internal connection defaultconnectionpool pooledconnection sendandreceive defaultconnectionpool java kafka connect at com mongodb internal connection commandprotocolimpl execute commandprotocolimpl java kafka connect at com mongodb internal connection defaultserver defaultserverprotocolexecutor execute defaultserver java kafka connect at com mongodb internal connection defaultserverconnection executeprotocol defaultserverconnection java kafka connect at com mongodb internal connection defaultserverconnection command defaultserverconnection java kafka connect at com mongodb operation mixedbulkwriteoperation executecommand mixedbulkwriteoperation java kafka connect at com mongodb operation mixedbulkwriteoperation executebulkwritebatch mixedbulkwriteoperation java kafka connect at com mongodb operation mixedbulkwriteoperation access mixedbulkwriteoperation java kafka connect at com mongodb operation mixedbulkwriteoperation call mixedbulkwriteoperation java kafka connect at com mongodb operation mixedbulkwriteoperation call mixedbulkwriteoperation java kafka connect at com mongodb operation operationhelper withreleasableconnection operationhelper java kafka connect at com mongodb operation mixedbulkwriteoperation execute mixedbulkwriteoperation java kafka connect at com mongodb operation mixedbulkwriteoperation execute mixedbulkwriteoperation java kafka connect at com mongodb client internal mongoclientdelegate delegateoperationexecutor execute mongoclientdelegate java kafka connect at com mongodb client internal mongocollectionimpl executebulkwrite mongocollectionimpl java kafka connect at com mongodb client internal mongocollectionimpl bulkwrite mongocollectionimpl java kafka connect at com mongodb client internal mongocollectionimpl bulkwrite mongocollectionimpl java kafka connect at io enkrypt kafka connect sinks mongo mongosinktask put mongosinktask kt kafka connect at org apache kafka connect runtime workersinktask delivermessages workersinktask java kafka connect more kafka connect error workersinktask id enkryptio mongo ancillary sink task is being killed and will not recover until manually restarted org apache kafka connect runtime workertask kafka connect info sending leavegroup request to coordinator kafka id rack null org apache kafka clients consumer internals abstractcoordinator
| 1
|
3,786
| 6,773,106,449
|
IssuesEvent
|
2017-10-27 03:22:46
|
neuropoly/spinalcordtoolbox
|
https://api.github.com/repos/neuropoly/spinalcordtoolbox
|
closed
|
Major refactoring using more object-oriented approach
|
bug card:WORK_IN_PROCESS priority:HIGH sct_get_centerline testing
|
working PR: https://github.com/neuropoly/spinalcordtoolbox/pull/1453
- [ ] Major refactoring using Class Param() defined in `sct_testing` and compatible with `sct_pipeline`. This will prevent all the duplication across test_XX files and facilitate the access to testing-related variables through the passing of a single class `param_test`
- [ ] test_sct_get_centerline: cannot import name ind2sub (see below)
~~~
sct_pipeline -f sct_get_centerline -d ${PATH_TESTING} -p \"-i t2/t2.nii.gz -c t2\"
--
Spinal Cord Toolbox (master/f1d83e1ce3d3b1a597762a535747e0ef643448b2)
Running /home/neuropoly/sct/scripts/sct_pipeline.py -f sct_get_centerline -d /mnt/Public_JCA/sct_testing/large -p "-i"
Check folder existence...
Testing started on: 2017-09-11 07:05:01
SCT version/commit/branch: dev/f1d83e1ce3d3b1a597762a535747e0ef643448b2/master
OS: linux (Linux-3.10.0-514.26.2.el7.x86_64-x86_64-with-centos-7.3.1611-Core)
Hostname: rosenberg.neuro.polymtl.ca
CPU cores: 40
RAM: MemTotal: 528085088 kB
total used free shared buff/cache available
Mem: 515708 30132 408674 811 76900 483134
Swap: 10231 0 10231
Command: "sct_get_centerline -i t2/t2.nii.gz -c t2
Dataset: /mnt/Public_JCA/sct_testing/large/
Number of subjects to process: 1278
Error on line 323
cannot import name ind2sub
local variable 'results' referenced before assignment
~~~
|
1.0
|
Major refactoring using more object-oriented approach - working PR: https://github.com/neuropoly/spinalcordtoolbox/pull/1453
- [ ] Major refactoring using Class Param() defined in `sct_testing` and compatible with `sct_pipeline`. This will prevent all the duplication across test_XX files and facilitate the access to testing-related variables through the passing of a single class `param_test`
- [ ] test_sct_get_centerline: cannot import name ind2sub (see below)
~~~
sct_pipeline -f sct_get_centerline -d ${PATH_TESTING} -p \"-i t2/t2.nii.gz -c t2\"
--
Spinal Cord Toolbox (master/f1d83e1ce3d3b1a597762a535747e0ef643448b2)
Running /home/neuropoly/sct/scripts/sct_pipeline.py -f sct_get_centerline -d /mnt/Public_JCA/sct_testing/large -p "-i"
Check folder existence...
Testing started on: 2017-09-11 07:05:01
SCT version/commit/branch: dev/f1d83e1ce3d3b1a597762a535747e0ef643448b2/master
OS: linux (Linux-3.10.0-514.26.2.el7.x86_64-x86_64-with-centos-7.3.1611-Core)
Hostname: rosenberg.neuro.polymtl.ca
CPU cores: 40
RAM: MemTotal: 528085088 kB
total used free shared buff/cache available
Mem: 515708 30132 408674 811 76900 483134
Swap: 10231 0 10231
Command: "sct_get_centerline -i t2/t2.nii.gz -c t2
Dataset: /mnt/Public_JCA/sct_testing/large/
Number of subjects to process: 1278
Error on line 323
cannot import name ind2sub
local variable 'results' referenced before assignment
~~~
|
process
|
major refactoring using more object oriented approach working pr major refactoring using class param defined in sct testing and compatible with sct pipeline this will prevent all the duplication across test xx files and facilitate the access to testing related variables through the passing of a single class param test test sct get centerline cannot import name see below sct pipeline f sct get centerline d path testing p i nii gz c spinal cord toolbox master running home neuropoly sct scripts sct pipeline py f sct get centerline d mnt public jca sct testing large p i check folder existence testing started on sct version commit branch dev master os linux linux with centos core hostname rosenberg neuro polymtl ca cpu cores ram memtotal kb total used free shared buff cache available mem swap command sct get centerline i nii gz c dataset mnt public jca sct testing large number of subjects to process error on line cannot import name local variable results referenced before assignment
| 1
|
16,059
| 20,201,753,913
|
IssuesEvent
|
2022-02-11 15:54:30
|
cypress-io/cypress
|
https://api.github.com/repos/cypress-io/cypress
|
closed
|
Unification App, Test Runner: Write E2E tests around "Reporter Header"
|
process: tests type: chore stage: needs review
|
### What would you like?
Write end-to-end tests to cover the new Unification work in 10.0-release branch for "[Reporter Header](https://docs.google.com/spreadsheets/d/1iPwi89aW6aYeA0VT1XOhYdAWLuScW0okrlfcL9fzh3s/edit#gid=0)" in the App's Test Runner.
### Why is this needed?
_No response_
### Other
_No response_
|
1.0
|
Unification App, Test Runner: Write E2E tests around "Reporter Header" - ### What would you like?
Write end-to-end tests to cover the new Unification work in 10.0-release branch for "[Reporter Header](https://docs.google.com/spreadsheets/d/1iPwi89aW6aYeA0VT1XOhYdAWLuScW0okrlfcL9fzh3s/edit#gid=0)" in the App's Test Runner.
### Why is this needed?
_No response_
### Other
_No response_
|
process
|
unification app test runner write tests around reporter header what would you like write end to end tests to cover the new unification work in release branch for in the app s test runner why is this needed no response other no response
| 1
|
432
| 2,860,040,927
|
IssuesEvent
|
2015-06-03 14:06:57
|
tomchristie/django-rest-framework
|
https://api.github.com/repos/tomchristie/django-rest-framework
|
closed
|
Standard response to usage questions.
|
Process
|
I think we should probably have a standard response to usage questions.
@jpadilla's wording [here](https://github.com/tomchristie/django-rest-framework/issues/2830#issuecomment-93824132) seems suitably brief and appropriate...
> The [discussion group](https://groups.google.com/forum/#!forum/django-rest-framework) is the best place to take this discussion and other usage questions. Thanks!
/cc @carltongibson @xordoquy @kevin-brown @jpadilla
|
1.0
|
Standard response to usage questions. - I think we should probably have a standard response to usage questions.
@jpadilla's wording [here](https://github.com/tomchristie/django-rest-framework/issues/2830#issuecomment-93824132) seems suitably brief and appropriate...
> The [discussion group](https://groups.google.com/forum/#!forum/django-rest-framework) is the best place to take this discussion and other usage questions. Thanks!
/cc @carltongibson @xordoquy @kevin-brown @jpadilla
|
process
|
standard response to usage questions i think we should probably have a standard response to usage questions jpadilla s wording seems suitably brief and appropriate the is the best place to take this discussion and other usage questions thanks cc carltongibson xordoquy kevin brown jpadilla
| 1
|
6,319
| 9,334,321,241
|
IssuesEvent
|
2019-03-28 16:04:59
|
elastic/beats
|
https://api.github.com/repos/elastic/beats
|
closed
|
[libbeat] add_host_metadata failing on RedHat Linux
|
:Processors bug libbeat
|
On RedHat 7.5 the `host.os.family` is not being populated. The other `host.os` fields are being correctly populated.
The system in question has:
```
$cat /etc/redhat-release
Red Hat Enterprise Linux Server release 7.5 (Maipo)
```
For confirmed bugs, please report:
- Version: Filebeat 6.4.2
- Operating System: RedHat Linux 7.5
|
1.0
|
[libbeat] add_host_metadata failing on RedHat Linux - On RedHat 7.5 the `host.os.family` is not being populated. The other `host.os` fields are being correctly populated.
The system in question has:
```
$cat /etc/redhat-release
Red Hat Enterprise Linux Server release 7.5 (Maipo)
```
For confirmed bugs, please report:
- Version: Filebeat 6.4.2
- Operating System: RedHat Linux 7.5
|
process
|
add host metadata failing on redhat linux on redhat the host os family is not being populated the other host os fields are being correctly populated the system in question has cat etc redhat release red hat enterprise linux server release maipo for confirmed bugs please report version filebeat operating system redhat linux
| 1
|
4,558
| 7,389,368,525
|
IssuesEvent
|
2018-03-16 08:24:30
|
KetchPartners/kmsprint2
|
https://api.github.com/repos/KetchPartners/kmsprint2
|
opened
|
When Opp Actvity Tiggers CPM
|
Axure Prototype Process enhancement
|
# Baseline: Service Task when CPM Triggered
Feedback notification of the selected writer of proposal
<img width="360" alt="base5" src="https://user-images.githubusercontent.com/29525920/37510548-d6803e2c-28d1-11e8-8ac7-1d883300eef0.png">
|
1.0
|
When Opp Actvity Tiggers CPM - # Baseline: Service Task when CPM Triggered
Feedback notification of the selected writer of proposal
<img width="360" alt="base5" src="https://user-images.githubusercontent.com/29525920/37510548-d6803e2c-28d1-11e8-8ac7-1d883300eef0.png">
|
process
|
when opp actvity tiggers cpm baseline service task when cpm triggered feedback notification of the selected writer of proposal img width alt src
| 1
|
10,754
| 13,543,312,404
|
IssuesEvent
|
2020-09-16 18:45:28
|
kubernetes/minikube
|
https://api.github.com/repos/kubernetes/minikube
|
closed
|
add minikube to github virtual environment base images
|
kind/process lifecycle/rotten priority/backlog
|
there are many projects and tools installed by default in the github base image (including other local-kubernetes) tools https://github.com/actions/virtual-environments
minikube is missing there.
|
1.0
|
add minikube to github virtual environment base images - there are many projects and tools installed by default in the github base image (including other local-kubernetes) tools https://github.com/actions/virtual-environments
minikube is missing there.
|
process
|
add minikube to github virtual environment base images there are many projects and tools installed by default in the github base image including other local kubernetes tools minikube is missing there
| 1
|
4,847
| 7,739,896,318
|
IssuesEvent
|
2018-05-28 18:13:49
|
codeforireland2/transparentwater_backend_new
|
https://api.github.com/repos/codeforireland2/transparentwater_backend_new
|
closed
|
Set up eslint and CI
|
development process
|
Set up eslint and CI tools to keep track of changes. Enable passing these as checks when merging pull requests
|
1.0
|
Set up eslint and CI - Set up eslint and CI tools to keep track of changes. Enable passing these as checks when merging pull requests
|
process
|
set up eslint and ci set up eslint and ci tools to keep track of changes enable passing these as checks when merging pull requests
| 1
|
24,969
| 12,463,244,729
|
IssuesEvent
|
2020-05-28 10:15:50
|
usi-verification-and-security/opensmt
|
https://api.github.com/repos/usi-verification-and-security/opensmt
|
closed
|
Assertion violation at src/tsolvers/lasolver/Simplex.cc:227
|
QF_LIA performance
|
Hi, for the following formula,
~~~~
(set-logic QF_LIA)
(declare-fun i2 () Int)
(declare-fun i4 () Int)
(declare-fun i5 () Int)
(assert (distinct i2 858))
(assert (< i5 i4))
(push 1)
(assert (= (* (- i2 i5) 7) 1000))
(push 1)
(assert false)
(check-sat)
(assert true)
(check-sat)
(assert false)
(check-sat)
(pop 1)
(check-sat)
~~~~
opensmt (commit 04c7fa3) throws an assertion violation
~~~~
; this binary is compiled in debug mode (slow)
; git hash: e9e14b4bc1cae5fb95a34ce2108642cc6d6ef068
unsat
unsat
unsat
opensmt: /home/opensmt/src/tsolvers/lasolver/Simplex.cc:227: Simplex::Explanation Simplex::assertBoundOnVar(LVRef, LABoundRef): Assertion `!model->isUnbounded(it)' failed.
Aborted (core dumped)
~~~~
|
True
|
Assertion violation at src/tsolvers/lasolver/Simplex.cc:227 - Hi, for the following formula,
~~~~
(set-logic QF_LIA)
(declare-fun i2 () Int)
(declare-fun i4 () Int)
(declare-fun i5 () Int)
(assert (distinct i2 858))
(assert (< i5 i4))
(push 1)
(assert (= (* (- i2 i5) 7) 1000))
(push 1)
(assert false)
(check-sat)
(assert true)
(check-sat)
(assert false)
(check-sat)
(pop 1)
(check-sat)
~~~~
opensmt (commit 04c7fa3) throws an assertion violation
~~~~
; this binary is compiled in debug mode (slow)
; git hash: e9e14b4bc1cae5fb95a34ce2108642cc6d6ef068
unsat
unsat
unsat
opensmt: /home/opensmt/src/tsolvers/lasolver/Simplex.cc:227: Simplex::Explanation Simplex::assertBoundOnVar(LVRef, LABoundRef): Assertion `!model->isUnbounded(it)' failed.
Aborted (core dumped)
~~~~
|
non_process
|
assertion violation at src tsolvers lasolver simplex cc hi for the following formula set logic qf lia declare fun int declare fun int declare fun int assert distinct assert push assert push assert false check sat assert true check sat assert false check sat pop check sat opensmt commit throws an assertion violation this binary is compiled in debug mode slow git hash unsat unsat unsat opensmt home opensmt src tsolvers lasolver simplex cc simplex explanation simplex assertboundonvar lvref laboundref assertion model isunbounded it failed aborted core dumped
| 0
|
11,472
| 14,333,513,106
|
IssuesEvent
|
2020-11-27 06:02:10
|
timberio/vector
|
https://api.github.com/repos/timberio/vector
|
opened
|
New `merge_multiline` transform (macro)
|
domain: processing domain: transforms have: should meta: idea needs: approval needs: requirements needs: rfc transform: reduce type: feature
|
To simplify the task of merging multi-line logs, we should consider a macro (#3791) that wraps the `reduce` transform with defaults the achieve this. This will likely require a spec or an RFC to agree on the strategies and approach.
## Example
For example, it's very common for log lines to start with a date, but subsequent lines will not:
```
[2020-08-24 11:49:14,389] foobar.rb:6:in `/': divided by 0 (ZeroDivisionError)
from foobar.rb:6:in `bar'
from foobar.rb:2:in `foo'
from foobar.rb:9:in `<main>'
```
The date can come in a variety of forms and we should think about ways to detect dates easily. Perhaps this will require a new Remap function?
Users could merge this line with a simple, pre-configured transform:
```toml
[transform.merge_lines]
type = "merge_multiline"
group_by = "file"
```
## Requirements
- [ ] Spec or RFC that covers the strategies and approach.
|
1.0
|
New `merge_multiline` transform (macro) - To simplify the task of merging multi-line logs, we should consider a macro (#3791) that wraps the `reduce` transform with defaults the achieve this. This will likely require a spec or an RFC to agree on the strategies and approach.
## Example
For example, it's very common for log lines to start with a date, but subsequent lines will not:
```
[2020-08-24 11:49:14,389] foobar.rb:6:in `/': divided by 0 (ZeroDivisionError)
from foobar.rb:6:in `bar'
from foobar.rb:2:in `foo'
from foobar.rb:9:in `<main>'
```
The date can come in a variety of forms and we should think about ways to detect dates easily. Perhaps this will require a new Remap function?
Users could merge this line with a simple, pre-configured transform:
```toml
[transform.merge_lines]
type = "merge_multiline"
group_by = "file"
```
## Requirements
- [ ] Spec or RFC that covers the strategies and approach.
|
process
|
new merge multiline transform macro to simplify the task of merging multi line logs we should consider a macro that wraps the reduce transform with defaults the achieve this this will likely require a spec or an rfc to agree on the strategies and approach example for example it s very common for log lines to start with a date but subsequent lines will not foobar rb in divided by zerodivisionerror from foobar rb in bar from foobar rb in foo from foobar rb in the date can come in a variety of forms and we should think about ways to detect dates easily perhaps this will require a new remap function users could merge this line with a simple pre configured transform toml type merge multiline group by file requirements spec or rfc that covers the strategies and approach
| 1
|
409,326
| 11,960,426,139
|
IssuesEvent
|
2020-04-05 03:04:42
|
flatlify/flatlify
|
https://api.github.com/repos/flatlify/flatlify
|
opened
|
Content items that have referenced items is throwing an error
|
Priority:High bug
|
Steps to reproduce:
- checkout `demo-content` branch
- open http://localhost:3000/react-admin#/season/0
Actual:
- Pages throws an error presumably on a failed getMany request
Expected:
- The page should display referenced content
|
1.0
|
Content items that have referenced items is throwing an error - Steps to reproduce:
- checkout `demo-content` branch
- open http://localhost:3000/react-admin#/season/0
Actual:
- Pages throws an error presumably on a failed getMany request
Expected:
- The page should display referenced content
|
non_process
|
content items that have referenced items is throwing an error steps to reproduce checkout demo content branch open actual pages throws an error presumably on a failed getmany request expected the page should display referenced content
| 0
|
267
| 2,699,091,182
|
IssuesEvent
|
2015-04-03 14:20:00
|
mkdocs/mkdocs
|
https://api.github.com/repos/mkdocs/mkdocs
|
opened
|
mkdocs.org isn't updating
|
Process
|
I guess this is due to the transition from @tomchristie's account to the MkDocs org. The changes are available at http://mkdocs.github.io/mkdocs/
@tomchristie Can you update DNS settings? I guess that is what we need.
|
1.0
|
mkdocs.org isn't updating - I guess this is due to the transition from @tomchristie's account to the MkDocs org. The changes are available at http://mkdocs.github.io/mkdocs/
@tomchristie Can you update DNS settings? I guess that is what we need.
|
process
|
mkdocs org isn t updating i guess this is due to the transition from tomchristie s account to the mkdocs org the changes are available at tomchristie can you update dns settings i guess that is what we need
| 1
|
4,753
| 7,613,080,075
|
IssuesEvent
|
2018-05-01 19:53:52
|
MicrosoftDocs/azure-docs
|
https://api.github.com/repos/MicrosoftDocs/azure-docs
|
closed
|
Feedback to SPA samples
|
active-directory cxp doc-enhancement in-process triaged
|
This document is very useful, but I have 1 feedback. In general, developers tend to use Angular, React and View to develop SPA, but in this page, only refer Angular sample. If there is React and View sample, I believe many developer will save time and can use Azure AD in the app.
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: eb17b3eb-2e68-4ff1-1478-3b64df354980
* Version Independent ID: 230ddb4b-4340-b7bb-b42b-960904c302e3
* Content: [Azure Active Directory for developers](https://docs.microsoft.com/en-us/azure/active-directory/develop/active-directory-developers-guide)
* Content Source: [articles/active-directory/develop/active-directory-developers-guide.md](https://github.com/Microsoft/azure-docs/blob/master/articles/active-directory/develop/active-directory-developers-guide.md)
* Service: **active-directory**
* GitHub Login: @jmprieur
* Microsoft Alias: **jmprieur**
|
1.0
|
Feedback to SPA samples - This document is very useful, but I have 1 feedback. In general, developers tend to use Angular, React and View to develop SPA, but in this page, only refer Angular sample. If there is React and View sample, I believe many developer will save time and can use Azure AD in the app.
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: eb17b3eb-2e68-4ff1-1478-3b64df354980
* Version Independent ID: 230ddb4b-4340-b7bb-b42b-960904c302e3
* Content: [Azure Active Directory for developers](https://docs.microsoft.com/en-us/azure/active-directory/develop/active-directory-developers-guide)
* Content Source: [articles/active-directory/develop/active-directory-developers-guide.md](https://github.com/Microsoft/azure-docs/blob/master/articles/active-directory/develop/active-directory-developers-guide.md)
* Service: **active-directory**
* GitHub Login: @jmprieur
* Microsoft Alias: **jmprieur**
|
process
|
feedback to spa samples this document is very useful but i have feedback in general developers tend to use angular react and view to develop spa but in this page only refer angular sample if there is react and view sample i believe many developer will save time and can use azure ad in the app document details ⚠ do not edit this section it is required for docs microsoft com ➟ github issue linking id version independent id content content source service active directory github login jmprieur microsoft alias jmprieur
| 1
|
5,343
| 8,170,584,251
|
IssuesEvent
|
2018-08-27 08:15:56
|
DevExpress/testcafe-hammerhead
|
https://api.github.com/repos/DevExpress/testcafe-hammerhead
|
closed
|
A client's url resolving mechanism works wrong
|
AREA: client BROWSER: IE11 COMPLEXITY: easy SYSTEM: URL processing TYPE: bug
|
Server's url resolver works as shown below:
```js
url.resolve('', 'http://localhost/path/'); // 'http://localhost/path/'
url.resolve('', 'http://localhost/path/123'); // 'http://localhost/path/123'
```
Client's url resolver works as shown below:
```js
resolver.updateBase('http://localhost/path/', document);
resolver.resolve('', document);
// 'http://localhost/path' - lost last slash in all browsers
resolver.updateBase('http://localhost/path/123', document);
resolver.resolve('', document);
// 'http://localhost/path' - lost last slash and path after it only in ie11
```
|
1.0
|
A client's url resolving mechanism works wrong - Server's url resolver works as shown below:
```js
url.resolve('', 'http://localhost/path/'); // 'http://localhost/path/'
url.resolve('', 'http://localhost/path/123'); // 'http://localhost/path/123'
```
Client's url resolver works as shown below:
```js
resolver.updateBase('http://localhost/path/', document);
resolver.resolve('', document);
// 'http://localhost/path' - lost last slash in all browsers
resolver.updateBase('http://localhost/path/123', document);
resolver.resolve('', document);
// 'http://localhost/path' - lost last slash and path after it only in ie11
```
|
process
|
a client s url resolving mechanism works wrong server s url resolver works as shown below js url resolve url resolve client s url resolver works as shown below js resolver updatebase document resolver resolve document lost last slash in all browsers resolver updatebase document resolver resolve document lost last slash and path after it only in
| 1
|
20,289
| 26,923,136,350
|
IssuesEvent
|
2023-02-07 11:57:34
|
prisma/prisma
|
https://api.github.com/repos/prisma/prisma
|
opened
|
`npx prisma migrate resolve --applied 0_init` + `The migration 0_init could not be found.` + Windows PowerShell
|
bug/2-confirmed kind/bug process/candidate team/schema
|
Placeholder issue
|
1.0
|
`npx prisma migrate resolve --applied 0_init` + `The migration 0_init could not be found.` + Windows PowerShell - Placeholder issue
|
process
|
npx prisma migrate resolve applied init the migration init could not be found windows powershell placeholder issue
| 1
|
11,532
| 14,405,374,480
|
IssuesEvent
|
2020-12-03 18:36:31
|
dita-ot/dita-ot
|
https://api.github.com/repos/dita-ot/dita-ot
|
closed
|
Unhandled error in image metadata reader breaks entire processing
|
bug preprocess priority/high
|
Attaching the stack trace someone obtains when the image metadata reader attempts to read the metadata for a JPEG image:
\plugins\org.dita.html5\build_dita2html5.xml:108: java.lang.ArrayIndexOutOfBoundsException
at com.sun.imageio.plugins.jpeg.JPEGBuffer.loadBuf(Unknown Source)
at com.sun.imageio.plugins.jpeg.JPEGBuffer.scanForFF(Unknown Source)
at com.sun.imageio.plugins.jpeg.JPEGMetadata.<init>(Unknown Source)
at com.sun.imageio.plugins.jpeg.JPEGImageReader.getImageMetadata(Unknown Source)
at org.dita.dost.writer.ImageMetadataFilter.readBitmapMetadata(ImageMetadataFilter.java:209)
at org.dita.dost.writer.ImageMetadataFilter.readMetadata(ImageMetadataFilter.java:177)
at java.util.HashMap.computeIfAbsent(Unknown Source)
at org.dita.dost.writer.ImageMetadataFilter.startElement(ImageMetadataFilter.java:116)
Because the ImageMetadataFilter throws outside any runtime exception, this error also breaks the publishing process.
|
1.0
|
Unhandled error in image metadata reader breaks entire processing - Attaching the stack trace someone obtains when the image metadata reader attempts to read the metadata for a JPEG image:
\plugins\org.dita.html5\build_dita2html5.xml:108: java.lang.ArrayIndexOutOfBoundsException
at com.sun.imageio.plugins.jpeg.JPEGBuffer.loadBuf(Unknown Source)
at com.sun.imageio.plugins.jpeg.JPEGBuffer.scanForFF(Unknown Source)
at com.sun.imageio.plugins.jpeg.JPEGMetadata.<init>(Unknown Source)
at com.sun.imageio.plugins.jpeg.JPEGImageReader.getImageMetadata(Unknown Source)
at org.dita.dost.writer.ImageMetadataFilter.readBitmapMetadata(ImageMetadataFilter.java:209)
at org.dita.dost.writer.ImageMetadataFilter.readMetadata(ImageMetadataFilter.java:177)
at java.util.HashMap.computeIfAbsent(Unknown Source)
at org.dita.dost.writer.ImageMetadataFilter.startElement(ImageMetadataFilter.java:116)
Because the ImageMetadataFilter throws outside any runtime exception, this error also breaks the publishing process.
|
process
|
unhandled error in image metadata reader breaks entire processing attaching the stack trace someone obtains when the image metadata reader attempts to read the metadata for a jpeg image plugins org dita build xml java lang arrayindexoutofboundsexception at com sun imageio plugins jpeg jpegbuffer loadbuf unknown source at com sun imageio plugins jpeg jpegbuffer scanforff unknown source at com sun imageio plugins jpeg jpegmetadata unknown source at com sun imageio plugins jpeg jpegimagereader getimagemetadata unknown source at org dita dost writer imagemetadatafilter readbitmapmetadata imagemetadatafilter java at org dita dost writer imagemetadatafilter readmetadata imagemetadatafilter java at java util hashmap computeifabsent unknown source at org dita dost writer imagemetadatafilter startelement imagemetadatafilter java because the imagemetadatafilter throws outside any runtime exception this error also breaks the publishing process
| 1
|
2,196
| 5,039,045,978
|
IssuesEvent
|
2016-12-18 16:04:52
|
processing/processing
|
https://api.github.com/repos/processing/processing
|
closed
|
Can't update libraries - JARs are locked
|
preprocessor
|
After downloading, message appears: `Could not move contribution to backup folder.`
Processing locks all the library JAR files after start, so they can't be moved or deleted. As soon as I quit Processing, files are unlocked and I'm able to rename or delete library folders and JARs again.
It's probabaly something with PreprocessingService indexing libraries for import suggestions, when I stop the PreprocessingService I don't have this problem anymore.
|
1.0
|
Can't update libraries - JARs are locked - After downloading, message appears: `Could not move contribution to backup folder.`
Processing locks all the library JAR files after start, so they can't be moved or deleted. As soon as I quit Processing, files are unlocked and I'm able to rename or delete library folders and JARs again.
It's probabaly something with PreprocessingService indexing libraries for import suggestions, when I stop the PreprocessingService I don't have this problem anymore.
|
process
|
can t update libraries jars are locked after downloading message appears could not move contribution to backup folder processing locks all the library jar files after start so they can t be moved or deleted as soon as i quit processing files are unlocked and i m able to rename or delete library folders and jars again it s probabaly something with preprocessingservice indexing libraries for import suggestions when i stop the preprocessingservice i don t have this problem anymore
| 1
|
3,739
| 6,733,147,615
|
IssuesEvent
|
2017-10-18 13:59:32
|
york-region-tpss/stp
|
https://api.github.com/repos/york-region-tpss/stp
|
closed
|
Bulk Create Nursery Taggings
|
form process workflow
|
Be able to create nursery tagging based on given range and comma delimited list.
|
1.0
|
Bulk Create Nursery Taggings - Be able to create nursery tagging based on given range and comma delimited list.
|
process
|
bulk create nursery taggings be able to create nursery tagging based on given range and comma delimited list
| 1
|
22,160
| 30,702,800,690
|
IssuesEvent
|
2023-07-27 02:00:07
|
lizhihao6/get-daily-arxiv-noti
|
https://api.github.com/repos/lizhihao6/get-daily-arxiv-noti
|
opened
|
New submissions for Thu, 27 Jul 23
|
event camera white balance isp compression image signal processing image signal process raw raw image events camera color contrast events AWB
|
## Keyword: events
### Event-based Vision for Early Prediction of Manipulation Actions
- **Authors:** Daniel Deniz, Cornelia Fermuller, Eduardo Ros, Manuel Rodriguez-Alvarez, Francisco Barranco
- **Subjects:** Computer Vision and Pattern Recognition (cs.CV); Artificial Intelligence (cs.AI)
- **Arxiv link:** https://arxiv.org/abs/2307.14332
- **Pdf link:** https://arxiv.org/pdf/2307.14332
- **Abstract**
Neuromorphic visual sensors are artificial retinas that output sequences of asynchronous events when brightness changes occur in the scene. These sensors offer many advantages including very high temporal resolution, no motion blur and smart data compression ideal for real-time processing. In this study, we introduce an event-based dataset on fine-grained manipulation actions and perform an experimental study on the use of transformers for action prediction with events. There is enormous interest in the fields of cognitive robotics and human-robot interaction on understanding and predicting human actions as early as possible. Early prediction allows anticipating complex stages for planning, enabling effective and real-time interaction. Our Transformer network uses events to predict manipulation actions as they occur, using online inference. The model succeeds at predicting actions early on, building up confidence over time and achieving state-of-the-art classification. Moreover, the attention-based transformer architecture allows us to study the role of the spatio-temporal patterns selected by the model. Our experiments show that the Transformer network captures action dynamic features outperforming video-based approaches and succeeding with scenarios where the differences between actions lie in very subtle cues. Finally, we release the new event dataset, which is the first in the literature for manipulation action recognition. Code will be available at https://github.com/DaniDeniz/EventVisionTransformer.
## Keyword: event camera
### Memory-Efficient Graph Convolutional Networks for Object Classification and Detection with Event Cameras
- **Authors:** Kamil Jeziorek, Andrea Pinna, Tomasz Kryjak
- **Subjects:** Computer Vision and Pattern Recognition (cs.CV); Image and Video Processing (eess.IV)
- **Arxiv link:** https://arxiv.org/abs/2307.14124
- **Pdf link:** https://arxiv.org/pdf/2307.14124
- **Abstract**
Recent advances in event camera research emphasize processing data in its original sparse form, which allows the use of its unique features such as high temporal resolution, high dynamic range, low latency, and resistance to image blur. One promising approach for analyzing event data is through graph convolutional networks (GCNs). However, current research in this domain primarily focuses on optimizing computational costs, neglecting the associated memory costs. In this paper, we consider both factors together in order to achieve satisfying results and relatively low model complexity. For this purpose, we performed a comparative analysis of different graph convolution operations, considering factors such as execution time, the number of trainable model parameters, data format requirements, and training outcomes. Our results show a 450-fold reduction in the number of parameters for the feature extraction module and a 4.5-fold reduction in the size of the data representation while maintaining a classification accuracy of 52.3%, which is 6.3% higher compared to the operation used in state-of-the-art approaches. To further evaluate performance, we implemented the object detection architecture and evaluated its performance on the N-Caltech101 dataset. The results showed an accuracy of 53.7 % mAP@0.5 and reached an execution rate of 82 graphs per second.
## Keyword: events camera
There is no result
## Keyword: white balance
There is no result
## Keyword: color contrast
There is no result
## Keyword: AWB
There is no result
## Keyword: ISP
### Heterogeneous Embodied Multi-Agent Collaboration
- **Authors:** Xinzhu Liu, Di Guo, Huaping Liu
- **Subjects:** Computer Vision and Pattern Recognition (cs.CV)
- **Arxiv link:** https://arxiv.org/abs/2307.13957
- **Pdf link:** https://arxiv.org/pdf/2307.13957
- **Abstract**
Multi-agent embodied tasks have recently been studied in complex indoor visual environments. Collaboration among multiple agents can improve work efficiency and has significant practical value. However, most of the existing research focuses on homogeneous multi-agent tasks. Compared with homogeneous agents, heterogeneous agents can leverage their different capabilities to allocate corresponding sub-tasks and cooperate to complete complex tasks. Heterogeneous multi-agent tasks are common in real-world scenarios, and the collaboration strategy among heterogeneous agents is a challenging and important problem to be solved. To study collaboration among heterogeneous agents, we propose the heterogeneous multi-agent tidying-up task, in which multiple heterogeneous agents with different capabilities collaborate with each other to detect misplaced objects and place them in reasonable locations. This is a demanding task since it requires agents to make the best use of their different capabilities to conduct reasonable task planning and complete the whole task. To solve this task, we build a heterogeneous multi-agent tidying-up benchmark dataset in a large number of houses with multiple rooms based on ProcTHOR-10K. We propose the hierarchical decision model based on misplaced object detection, reasonable receptacle prediction, as well as the handshake-based group communication mechanism. Extensive experiments are conducted to demonstrate the effectiveness of the proposed model. The project's website and videos of experiments can be found at https://hetercol.github.io/.
### Analysis of Video Quality Datasets via Design of Minimalistic Video Quality Models
- **Authors:** Wei Sun, Wen Wen, Xiongkuo Min, Long Lan, Guangtao Zhai, Kede Ma
- **Subjects:** Computer Vision and Pattern Recognition (cs.CV); Multimedia (cs.MM); Image and Video Processing (eess.IV)
- **Arxiv link:** https://arxiv.org/abs/2307.13981
- **Pdf link:** https://arxiv.org/pdf/2307.13981
- **Abstract**
Blind video quality assessment (BVQA) plays an indispensable role in monitoring and improving the end-users' viewing experience in various real-world video-enabled media applications. As an experimental field, the improvements of BVQA models have been measured primarily on a few human-rated VQA datasets. Thus, it is crucial to gain a better understanding of existing VQA datasets in order to properly evaluate the current progress in BVQA. Towards this goal, we conduct a first-of-its-kind computational analysis of VQA datasets via designing minimalistic BVQA models. By minimalistic, we restrict our family of BVQA models to build only upon basic blocks: a video preprocessor (for aggressive spatiotemporal downsampling), a spatial quality analyzer, an optional temporal quality analyzer, and a quality regressor, all with the simplest possible instantiations. By comparing the quality prediction performance of different model variants on eight VQA datasets with realistic distortions, we find that nearly all datasets suffer from the easy dataset problem of varying severity, some of which even admit blind image quality assessment (BIQA) solutions. We additionally justify our claims by contrasting our model generalizability on these VQA datasets, and by ablating a dizzying set of BVQA design choices related to the basic building blocks. Our results cast doubt on the current progress in BVQA, and meanwhile shed light on good practices of constructing next-generation VQA datasets and models.
### PNT-Edge: Towards Robust Edge Detection with Noisy Labels by Learning Pixel-level Noise Transitions
- **Authors:** Wenjie Xuan, Shanshan Zhao, Yu Yao, Juhua Liu, Tongliang Liu, Yixin Chen, Bo Du, Dacheng Tao
- **Subjects:** Computer Vision and Pattern Recognition (cs.CV)
- **Arxiv link:** https://arxiv.org/abs/2307.14070
- **Pdf link:** https://arxiv.org/pdf/2307.14070
- **Abstract**
Relying on large-scale training data with pixel-level labels, previous edge detection methods have achieved high performance. However, it is hard to manually label edges accurately, especially for large datasets, and thus the datasets inevitably contain noisy labels. This label-noise issue has been studied extensively for classification, while still remaining under-explored for edge detection. To address the label-noise issue for edge detection, this paper proposes to learn Pixel-level NoiseTransitions to model the label-corruption process. To achieve it, we develop a novel Pixel-wise Shift Learning (PSL) module to estimate the transition from clean to noisy labels as a displacement field. Exploiting the estimated noise transitions, our model, named PNT-Edge, is able to fit the prediction to clean labels. In addition, a local edge density regularization term is devised to exploit local structure information for better transition learning. This term encourages learning large shifts for the edges with complex local structures. Experiments on SBD and Cityscapes demonstrate the effectiveness of our method in relieving the impact of label noise. Codes will be available at github.
### MAMo: Leveraging Memory and Attention for Monocular Video Depth Estimation
- **Authors:** Rajeev Yasarla, Hong Cai, Jisoo Jeong, Yunxiao Shi, Risheek Garrepalli, Fatih Porikli
- **Subjects:** Computer Vision and Pattern Recognition (cs.CV)
- **Arxiv link:** https://arxiv.org/abs/2307.14336
- **Pdf link:** https://arxiv.org/pdf/2307.14336
- **Abstract**
We propose MAMo, a novel memory and attention frame-work for monocular video depth estimation. MAMo can augment and improve any single-image depth estimation networks into video depth estimation models, enabling them to take advantage of the temporal information to predict more accurate depth. In MAMo, we augment model with memory which aids the depth prediction as the model streams through the video. Specifically, the memory stores learned visual and displacement tokens of the previous time instances. This allows the depth network to cross-reference relevant features from the past when predicting depth on the current frame. We introduce a novel scheme to continuously update the memory, optimizing it to keep tokens that correspond with both the past and the present visual information. We adopt attention-based approach to process memory features where we first learn the spatio-temporal relation among the resultant visual and displacement memory tokens using self-attention module. Further, the output features of self-attention are aggregated with the current visual features through cross-attention. The cross-attended features are finally given to a decoder to predict depth on the current frame. Through extensive experiments on several benchmarks, including KITTI, NYU-Depth V2, and DDAD, we show that MAMo consistently improves monocular depth estimation networks and sets new state-of-the-art (SOTA) accuracy. Notably, our MAMo video depth estimation provides higher accuracy with lower latency, when omparing to SOTA cost-volume-based video depth models.
## Keyword: image signal processing
There is no result
## Keyword: image signal process
There is no result
## Keyword: compression
### Sparse Double Descent in Vision Transformers: real or phantom threat?
- **Authors:** Victor Quétu, Marta Milovanovic, Enzo Tartaglione
- **Subjects:** Computer Vision and Pattern Recognition (cs.CV)
- **Arxiv link:** https://arxiv.org/abs/2307.14253
- **Pdf link:** https://arxiv.org/pdf/2307.14253
- **Abstract**
Vision transformers (ViT) have been of broad interest in recent theoretical and empirical works. They are state-of-the-art thanks to their attention-based approach, which boosts the identification of key features and patterns within images thanks to the capability of avoiding inductive bias, resulting in highly accurate image analysis. Meanwhile, neoteric studies have reported a ``sparse double descent'' phenomenon that can occur in modern deep-learning models, where extremely over-parametrized models can generalize well. This raises practical questions about the optimal size of the model and the quest over finding the best trade-off between sparsity and performance is launched: are Vision Transformers also prone to sparse double descent? Can we find a way to avoid such a phenomenon? Our work tackles the occurrence of sparse double descent on ViTs. Despite some works that have shown that traditional architectures, like Resnet, are condemned to the sparse double descent phenomenon, for ViTs we observe that an optimally-tuned $\ell_2$ regularization relieves such a phenomenon. However, everything comes at a cost: optimal lambda will sacrifice the potential compression of the ViT.
### Event-based Vision for Early Prediction of Manipulation Actions
- **Authors:** Daniel Deniz, Cornelia Fermuller, Eduardo Ros, Manuel Rodriguez-Alvarez, Francisco Barranco
- **Subjects:** Computer Vision and Pattern Recognition (cs.CV); Artificial Intelligence (cs.AI)
- **Arxiv link:** https://arxiv.org/abs/2307.14332
- **Pdf link:** https://arxiv.org/pdf/2307.14332
- **Abstract**
Neuromorphic visual sensors are artificial retinas that output sequences of asynchronous events when brightness changes occur in the scene. These sensors offer many advantages including very high temporal resolution, no motion blur and smart data compression ideal for real-time processing. In this study, we introduce an event-based dataset on fine-grained manipulation actions and perform an experimental study on the use of transformers for action prediction with events. There is enormous interest in the fields of cognitive robotics and human-robot interaction on understanding and predicting human actions as early as possible. Early prediction allows anticipating complex stages for planning, enabling effective and real-time interaction. Our Transformer network uses events to predict manipulation actions as they occur, using online inference. The model succeeds at predicting actions early on, building up confidence over time and achieving state-of-the-art classification. Moreover, the attention-based transformer architecture allows us to study the role of the spatio-temporal patterns selected by the model. Our experiments show that the Transformer network captures action dynamic features outperforming video-based approaches and succeeding with scenarios where the differences between actions lie in very subtle cues. Finally, we release the new event dataset, which is the first in the literature for manipulation action recognition. Code will be available at https://github.com/DaniDeniz/EventVisionTransformer.
## Keyword: RAW
There is no result
## Keyword: raw image
There is no result
|
2.0
|
New submissions for Thu, 27 Jul 23 - ## Keyword: events
### Event-based Vision for Early Prediction of Manipulation Actions
- **Authors:** Daniel Deniz, Cornelia Fermuller, Eduardo Ros, Manuel Rodriguez-Alvarez, Francisco Barranco
- **Subjects:** Computer Vision and Pattern Recognition (cs.CV); Artificial Intelligence (cs.AI)
- **Arxiv link:** https://arxiv.org/abs/2307.14332
- **Pdf link:** https://arxiv.org/pdf/2307.14332
- **Abstract**
Neuromorphic visual sensors are artificial retinas that output sequences of asynchronous events when brightness changes occur in the scene. These sensors offer many advantages including very high temporal resolution, no motion blur and smart data compression ideal for real-time processing. In this study, we introduce an event-based dataset on fine-grained manipulation actions and perform an experimental study on the use of transformers for action prediction with events. There is enormous interest in the fields of cognitive robotics and human-robot interaction on understanding and predicting human actions as early as possible. Early prediction allows anticipating complex stages for planning, enabling effective and real-time interaction. Our Transformer network uses events to predict manipulation actions as they occur, using online inference. The model succeeds at predicting actions early on, building up confidence over time and achieving state-of-the-art classification. Moreover, the attention-based transformer architecture allows us to study the role of the spatio-temporal patterns selected by the model. Our experiments show that the Transformer network captures action dynamic features outperforming video-based approaches and succeeding with scenarios where the differences between actions lie in very subtle cues. Finally, we release the new event dataset, which is the first in the literature for manipulation action recognition. Code will be available at https://github.com/DaniDeniz/EventVisionTransformer.
## Keyword: event camera
### Memory-Efficient Graph Convolutional Networks for Object Classification and Detection with Event Cameras
- **Authors:** Kamil Jeziorek, Andrea Pinna, Tomasz Kryjak
- **Subjects:** Computer Vision and Pattern Recognition (cs.CV); Image and Video Processing (eess.IV)
- **Arxiv link:** https://arxiv.org/abs/2307.14124
- **Pdf link:** https://arxiv.org/pdf/2307.14124
- **Abstract**
Recent advances in event camera research emphasize processing data in its original sparse form, which allows the use of its unique features such as high temporal resolution, high dynamic range, low latency, and resistance to image blur. One promising approach for analyzing event data is through graph convolutional networks (GCNs). However, current research in this domain primarily focuses on optimizing computational costs, neglecting the associated memory costs. In this paper, we consider both factors together in order to achieve satisfying results and relatively low model complexity. For this purpose, we performed a comparative analysis of different graph convolution operations, considering factors such as execution time, the number of trainable model parameters, data format requirements, and training outcomes. Our results show a 450-fold reduction in the number of parameters for the feature extraction module and a 4.5-fold reduction in the size of the data representation while maintaining a classification accuracy of 52.3%, which is 6.3% higher compared to the operation used in state-of-the-art approaches. To further evaluate performance, we implemented the object detection architecture and evaluated its performance on the N-Caltech101 dataset. The results showed an accuracy of 53.7 % mAP@0.5 and reached an execution rate of 82 graphs per second.
## Keyword: events camera
There is no result
## Keyword: white balance
There is no result
## Keyword: color contrast
There is no result
## Keyword: AWB
There is no result
## Keyword: ISP
### Heterogeneous Embodied Multi-Agent Collaboration
- **Authors:** Xinzhu Liu, Di Guo, Huaping Liu
- **Subjects:** Computer Vision and Pattern Recognition (cs.CV)
- **Arxiv link:** https://arxiv.org/abs/2307.13957
- **Pdf link:** https://arxiv.org/pdf/2307.13957
- **Abstract**
Multi-agent embodied tasks have recently been studied in complex indoor visual environments. Collaboration among multiple agents can improve work efficiency and has significant practical value. However, most of the existing research focuses on homogeneous multi-agent tasks. Compared with homogeneous agents, heterogeneous agents can leverage their different capabilities to allocate corresponding sub-tasks and cooperate to complete complex tasks. Heterogeneous multi-agent tasks are common in real-world scenarios, and the collaboration strategy among heterogeneous agents is a challenging and important problem to be solved. To study collaboration among heterogeneous agents, we propose the heterogeneous multi-agent tidying-up task, in which multiple heterogeneous agents with different capabilities collaborate with each other to detect misplaced objects and place them in reasonable locations. This is a demanding task since it requires agents to make the best use of their different capabilities to conduct reasonable task planning and complete the whole task. To solve this task, we build a heterogeneous multi-agent tidying-up benchmark dataset in a large number of houses with multiple rooms based on ProcTHOR-10K. We propose the hierarchical decision model based on misplaced object detection, reasonable receptacle prediction, as well as the handshake-based group communication mechanism. Extensive experiments are conducted to demonstrate the effectiveness of the proposed model. The project's website and videos of experiments can be found at https://hetercol.github.io/.
### Analysis of Video Quality Datasets via Design of Minimalistic Video Quality Models
- **Authors:** Wei Sun, Wen Wen, Xiongkuo Min, Long Lan, Guangtao Zhai, Kede Ma
- **Subjects:** Computer Vision and Pattern Recognition (cs.CV); Multimedia (cs.MM); Image and Video Processing (eess.IV)
- **Arxiv link:** https://arxiv.org/abs/2307.13981
- **Pdf link:** https://arxiv.org/pdf/2307.13981
- **Abstract**
Blind video quality assessment (BVQA) plays an indispensable role in monitoring and improving the end-users' viewing experience in various real-world video-enabled media applications. As an experimental field, the improvements of BVQA models have been measured primarily on a few human-rated VQA datasets. Thus, it is crucial to gain a better understanding of existing VQA datasets in order to properly evaluate the current progress in BVQA. Towards this goal, we conduct a first-of-its-kind computational analysis of VQA datasets via designing minimalistic BVQA models. By minimalistic, we restrict our family of BVQA models to build only upon basic blocks: a video preprocessor (for aggressive spatiotemporal downsampling), a spatial quality analyzer, an optional temporal quality analyzer, and a quality regressor, all with the simplest possible instantiations. By comparing the quality prediction performance of different model variants on eight VQA datasets with realistic distortions, we find that nearly all datasets suffer from the easy dataset problem of varying severity, some of which even admit blind image quality assessment (BIQA) solutions. We additionally justify our claims by contrasting our model generalizability on these VQA datasets, and by ablating a dizzying set of BVQA design choices related to the basic building blocks. Our results cast doubt on the current progress in BVQA, and meanwhile shed light on good practices of constructing next-generation VQA datasets and models.
### PNT-Edge: Towards Robust Edge Detection with Noisy Labels by Learning Pixel-level Noise Transitions
- **Authors:** Wenjie Xuan, Shanshan Zhao, Yu Yao, Juhua Liu, Tongliang Liu, Yixin Chen, Bo Du, Dacheng Tao
- **Subjects:** Computer Vision and Pattern Recognition (cs.CV)
- **Arxiv link:** https://arxiv.org/abs/2307.14070
- **Pdf link:** https://arxiv.org/pdf/2307.14070
- **Abstract**
Relying on large-scale training data with pixel-level labels, previous edge detection methods have achieved high performance. However, it is hard to manually label edges accurately, especially for large datasets, and thus the datasets inevitably contain noisy labels. This label-noise issue has been studied extensively for classification, while still remaining under-explored for edge detection. To address the label-noise issue for edge detection, this paper proposes to learn Pixel-level NoiseTransitions to model the label-corruption process. To achieve it, we develop a novel Pixel-wise Shift Learning (PSL) module to estimate the transition from clean to noisy labels as a displacement field. Exploiting the estimated noise transitions, our model, named PNT-Edge, is able to fit the prediction to clean labels. In addition, a local edge density regularization term is devised to exploit local structure information for better transition learning. This term encourages learning large shifts for the edges with complex local structures. Experiments on SBD and Cityscapes demonstrate the effectiveness of our method in relieving the impact of label noise. Codes will be available at github.
### MAMo: Leveraging Memory and Attention for Monocular Video Depth Estimation
- **Authors:** Rajeev Yasarla, Hong Cai, Jisoo Jeong, Yunxiao Shi, Risheek Garrepalli, Fatih Porikli
- **Subjects:** Computer Vision and Pattern Recognition (cs.CV)
- **Arxiv link:** https://arxiv.org/abs/2307.14336
- **Pdf link:** https://arxiv.org/pdf/2307.14336
- **Abstract**
We propose MAMo, a novel memory and attention frame-work for monocular video depth estimation. MAMo can augment and improve any single-image depth estimation networks into video depth estimation models, enabling them to take advantage of the temporal information to predict more accurate depth. In MAMo, we augment model with memory which aids the depth prediction as the model streams through the video. Specifically, the memory stores learned visual and displacement tokens of the previous time instances. This allows the depth network to cross-reference relevant features from the past when predicting depth on the current frame. We introduce a novel scheme to continuously update the memory, optimizing it to keep tokens that correspond with both the past and the present visual information. We adopt attention-based approach to process memory features where we first learn the spatio-temporal relation among the resultant visual and displacement memory tokens using self-attention module. Further, the output features of self-attention are aggregated with the current visual features through cross-attention. The cross-attended features are finally given to a decoder to predict depth on the current frame. Through extensive experiments on several benchmarks, including KITTI, NYU-Depth V2, and DDAD, we show that MAMo consistently improves monocular depth estimation networks and sets new state-of-the-art (SOTA) accuracy. Notably, our MAMo video depth estimation provides higher accuracy with lower latency, when omparing to SOTA cost-volume-based video depth models.
## Keyword: image signal processing
There is no result
## Keyword: image signal process
There is no result
## Keyword: compression
### Sparse Double Descent in Vision Transformers: real or phantom threat?
- **Authors:** Victor Quétu, Marta Milovanovic, Enzo Tartaglione
- **Subjects:** Computer Vision and Pattern Recognition (cs.CV)
- **Arxiv link:** https://arxiv.org/abs/2307.14253
- **Pdf link:** https://arxiv.org/pdf/2307.14253
- **Abstract**
Vision transformers (ViT) have been of broad interest in recent theoretical and empirical works. They are state-of-the-art thanks to their attention-based approach, which boosts the identification of key features and patterns within images thanks to the capability of avoiding inductive bias, resulting in highly accurate image analysis. Meanwhile, neoteric studies have reported a ``sparse double descent'' phenomenon that can occur in modern deep-learning models, where extremely over-parametrized models can generalize well. This raises practical questions about the optimal size of the model and the quest over finding the best trade-off between sparsity and performance is launched: are Vision Transformers also prone to sparse double descent? Can we find a way to avoid such a phenomenon? Our work tackles the occurrence of sparse double descent on ViTs. Despite some works that have shown that traditional architectures, like Resnet, are condemned to the sparse double descent phenomenon, for ViTs we observe that an optimally-tuned $\ell_2$ regularization relieves such a phenomenon. However, everything comes at a cost: optimal lambda will sacrifice the potential compression of the ViT.
### Event-based Vision for Early Prediction of Manipulation Actions
- **Authors:** Daniel Deniz, Cornelia Fermuller, Eduardo Ros, Manuel Rodriguez-Alvarez, Francisco Barranco
- **Subjects:** Computer Vision and Pattern Recognition (cs.CV); Artificial Intelligence (cs.AI)
- **Arxiv link:** https://arxiv.org/abs/2307.14332
- **Pdf link:** https://arxiv.org/pdf/2307.14332
- **Abstract**
Neuromorphic visual sensors are artificial retinas that output sequences of asynchronous events when brightness changes occur in the scene. These sensors offer many advantages including very high temporal resolution, no motion blur and smart data compression ideal for real-time processing. In this study, we introduce an event-based dataset on fine-grained manipulation actions and perform an experimental study on the use of transformers for action prediction with events. There is enormous interest in the fields of cognitive robotics and human-robot interaction on understanding and predicting human actions as early as possible. Early prediction allows anticipating complex stages for planning, enabling effective and real-time interaction. Our Transformer network uses events to predict manipulation actions as they occur, using online inference. The model succeeds at predicting actions early on, building up confidence over time and achieving state-of-the-art classification. Moreover, the attention-based transformer architecture allows us to study the role of the spatio-temporal patterns selected by the model. Our experiments show that the Transformer network captures action dynamic features outperforming video-based approaches and succeeding with scenarios where the differences between actions lie in very subtle cues. Finally, we release the new event dataset, which is the first in the literature for manipulation action recognition. Code will be available at https://github.com/DaniDeniz/EventVisionTransformer.
## Keyword: RAW
There is no result
## Keyword: raw image
There is no result
|
process
|
new submissions for thu jul keyword events event based vision for early prediction of manipulation actions authors daniel deniz cornelia fermuller eduardo ros manuel rodriguez alvarez francisco barranco subjects computer vision and pattern recognition cs cv artificial intelligence cs ai arxiv link pdf link abstract neuromorphic visual sensors are artificial retinas that output sequences of asynchronous events when brightness changes occur in the scene these sensors offer many advantages including very high temporal resolution no motion blur and smart data compression ideal for real time processing in this study we introduce an event based dataset on fine grained manipulation actions and perform an experimental study on the use of transformers for action prediction with events there is enormous interest in the fields of cognitive robotics and human robot interaction on understanding and predicting human actions as early as possible early prediction allows anticipating complex stages for planning enabling effective and real time interaction our transformer network uses events to predict manipulation actions as they occur using online inference the model succeeds at predicting actions early on building up confidence over time and achieving state of the art classification moreover the attention based transformer architecture allows us to study the role of the spatio temporal patterns selected by the model our experiments show that the transformer network captures action dynamic features outperforming video based approaches and succeeding with scenarios where the differences between actions lie in very subtle cues finally we release the new event dataset which is the first in the literature for manipulation action recognition code will be available at keyword event camera memory efficient graph convolutional networks for object classification and detection with event cameras authors kamil jeziorek andrea pinna tomasz kryjak subjects computer vision and pattern recognition cs cv image and video processing eess iv arxiv link pdf link abstract recent advances in event camera research emphasize processing data in its original sparse form which allows the use of its unique features such as high temporal resolution high dynamic range low latency and resistance to image blur one promising approach for analyzing event data is through graph convolutional networks gcns however current research in this domain primarily focuses on optimizing computational costs neglecting the associated memory costs in this paper we consider both factors together in order to achieve satisfying results and relatively low model complexity for this purpose we performed a comparative analysis of different graph convolution operations considering factors such as execution time the number of trainable model parameters data format requirements and training outcomes our results show a fold reduction in the number of parameters for the feature extraction module and a fold reduction in the size of the data representation while maintaining a classification accuracy of which is higher compared to the operation used in state of the art approaches to further evaluate performance we implemented the object detection architecture and evaluated its performance on the n dataset the results showed an accuracy of map and reached an execution rate of graphs per second keyword events camera there is no result keyword white balance there is no result keyword color contrast there is no result keyword awb there is no result keyword isp heterogeneous embodied multi agent collaboration authors xinzhu liu di guo huaping liu subjects computer vision and pattern recognition cs cv arxiv link pdf link abstract multi agent embodied tasks have recently been studied in complex indoor visual environments collaboration among multiple agents can improve work efficiency and has significant practical value however most of the existing research focuses on homogeneous multi agent tasks compared with homogeneous agents heterogeneous agents can leverage their different capabilities to allocate corresponding sub tasks and cooperate to complete complex tasks heterogeneous multi agent tasks are common in real world scenarios and the collaboration strategy among heterogeneous agents is a challenging and important problem to be solved to study collaboration among heterogeneous agents we propose the heterogeneous multi agent tidying up task in which multiple heterogeneous agents with different capabilities collaborate with each other to detect misplaced objects and place them in reasonable locations this is a demanding task since it requires agents to make the best use of their different capabilities to conduct reasonable task planning and complete the whole task to solve this task we build a heterogeneous multi agent tidying up benchmark dataset in a large number of houses with multiple rooms based on procthor we propose the hierarchical decision model based on misplaced object detection reasonable receptacle prediction as well as the handshake based group communication mechanism extensive experiments are conducted to demonstrate the effectiveness of the proposed model the project s website and videos of experiments can be found at analysis of video quality datasets via design of minimalistic video quality models authors wei sun wen wen xiongkuo min long lan guangtao zhai kede ma subjects computer vision and pattern recognition cs cv multimedia cs mm image and video processing eess iv arxiv link pdf link abstract blind video quality assessment bvqa plays an indispensable role in monitoring and improving the end users viewing experience in various real world video enabled media applications as an experimental field the improvements of bvqa models have been measured primarily on a few human rated vqa datasets thus it is crucial to gain a better understanding of existing vqa datasets in order to properly evaluate the current progress in bvqa towards this goal we conduct a first of its kind computational analysis of vqa datasets via designing minimalistic bvqa models by minimalistic we restrict our family of bvqa models to build only upon basic blocks a video preprocessor for aggressive spatiotemporal downsampling a spatial quality analyzer an optional temporal quality analyzer and a quality regressor all with the simplest possible instantiations by comparing the quality prediction performance of different model variants on eight vqa datasets with realistic distortions we find that nearly all datasets suffer from the easy dataset problem of varying severity some of which even admit blind image quality assessment biqa solutions we additionally justify our claims by contrasting our model generalizability on these vqa datasets and by ablating a dizzying set of bvqa design choices related to the basic building blocks our results cast doubt on the current progress in bvqa and meanwhile shed light on good practices of constructing next generation vqa datasets and models pnt edge towards robust edge detection with noisy labels by learning pixel level noise transitions authors wenjie xuan shanshan zhao yu yao juhua liu tongliang liu yixin chen bo du dacheng tao subjects computer vision and pattern recognition cs cv arxiv link pdf link abstract relying on large scale training data with pixel level labels previous edge detection methods have achieved high performance however it is hard to manually label edges accurately especially for large datasets and thus the datasets inevitably contain noisy labels this label noise issue has been studied extensively for classification while still remaining under explored for edge detection to address the label noise issue for edge detection this paper proposes to learn pixel level noisetransitions to model the label corruption process to achieve it we develop a novel pixel wise shift learning psl module to estimate the transition from clean to noisy labels as a displacement field exploiting the estimated noise transitions our model named pnt edge is able to fit the prediction to clean labels in addition a local edge density regularization term is devised to exploit local structure information for better transition learning this term encourages learning large shifts for the edges with complex local structures experiments on sbd and cityscapes demonstrate the effectiveness of our method in relieving the impact of label noise codes will be available at github mamo leveraging memory and attention for monocular video depth estimation authors rajeev yasarla hong cai jisoo jeong yunxiao shi risheek garrepalli fatih porikli subjects computer vision and pattern recognition cs cv arxiv link pdf link abstract we propose mamo a novel memory and attention frame work for monocular video depth estimation mamo can augment and improve any single image depth estimation networks into video depth estimation models enabling them to take advantage of the temporal information to predict more accurate depth in mamo we augment model with memory which aids the depth prediction as the model streams through the video specifically the memory stores learned visual and displacement tokens of the previous time instances this allows the depth network to cross reference relevant features from the past when predicting depth on the current frame we introduce a novel scheme to continuously update the memory optimizing it to keep tokens that correspond with both the past and the present visual information we adopt attention based approach to process memory features where we first learn the spatio temporal relation among the resultant visual and displacement memory tokens using self attention module further the output features of self attention are aggregated with the current visual features through cross attention the cross attended features are finally given to a decoder to predict depth on the current frame through extensive experiments on several benchmarks including kitti nyu depth and ddad we show that mamo consistently improves monocular depth estimation networks and sets new state of the art sota accuracy notably our mamo video depth estimation provides higher accuracy with lower latency when omparing to sota cost volume based video depth models keyword image signal processing there is no result keyword image signal process there is no result keyword compression sparse double descent in vision transformers real or phantom threat authors victor quétu marta milovanovic enzo tartaglione subjects computer vision and pattern recognition cs cv arxiv link pdf link abstract vision transformers vit have been of broad interest in recent theoretical and empirical works they are state of the art thanks to their attention based approach which boosts the identification of key features and patterns within images thanks to the capability of avoiding inductive bias resulting in highly accurate image analysis meanwhile neoteric studies have reported a sparse double descent phenomenon that can occur in modern deep learning models where extremely over parametrized models can generalize well this raises practical questions about the optimal size of the model and the quest over finding the best trade off between sparsity and performance is launched are vision transformers also prone to sparse double descent can we find a way to avoid such a phenomenon our work tackles the occurrence of sparse double descent on vits despite some works that have shown that traditional architectures like resnet are condemned to the sparse double descent phenomenon for vits we observe that an optimally tuned ell regularization relieves such a phenomenon however everything comes at a cost optimal lambda will sacrifice the potential compression of the vit event based vision for early prediction of manipulation actions authors daniel deniz cornelia fermuller eduardo ros manuel rodriguez alvarez francisco barranco subjects computer vision and pattern recognition cs cv artificial intelligence cs ai arxiv link pdf link abstract neuromorphic visual sensors are artificial retinas that output sequences of asynchronous events when brightness changes occur in the scene these sensors offer many advantages including very high temporal resolution no motion blur and smart data compression ideal for real time processing in this study we introduce an event based dataset on fine grained manipulation actions and perform an experimental study on the use of transformers for action prediction with events there is enormous interest in the fields of cognitive robotics and human robot interaction on understanding and predicting human actions as early as possible early prediction allows anticipating complex stages for planning enabling effective and real time interaction our transformer network uses events to predict manipulation actions as they occur using online inference the model succeeds at predicting actions early on building up confidence over time and achieving state of the art classification moreover the attention based transformer architecture allows us to study the role of the spatio temporal patterns selected by the model our experiments show that the transformer network captures action dynamic features outperforming video based approaches and succeeding with scenarios where the differences between actions lie in very subtle cues finally we release the new event dataset which is the first in the literature for manipulation action recognition code will be available at keyword raw there is no result keyword raw image there is no result
| 1
|
262,060
| 27,850,882,256
|
IssuesEvent
|
2023-03-20 18:35:53
|
jgeraigery/chatbot-watson-android
|
https://api.github.com/repos/jgeraigery/chatbot-watson-android
|
opened
|
lint-gradle-26.5.3.jar: 18 vulnerabilities (highest severity is: 7.5)
|
Mend: dependency security vulnerability
|
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>lint-gradle-26.5.3.jar</b></p></summary>
<p></p>
<p>Path to dependency file: /app/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.apache.commons/commons-compress/1.12/84caa68576e345eb5e7ae61a0e5a9229eb100d7b/commons-compress-1.12.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/chatbot-watson-android/commit/59cf4251b46bc8fc950c9283359fabf1d97b885c">59cf4251b46bc8fc950c9283359fabf1d97b885c</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (lint-gradle version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2021-36090](https://www.mend.io/vulnerability-database/CVE-2021-36090) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | commons-compress-1.12.jar | Transitive | N/A* | ❌ |
| [CVE-2019-17359](https://www.mend.io/vulnerability-database/CVE-2019-17359) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | bcprov-jdk15on-1.56.jar | Transitive | N/A* | ❌ |
| [CVE-2022-3509](https://www.mend.io/vulnerability-database/CVE-2022-3509) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | protobuf-java-3.4.0.jar | Transitive | N/A* | ❌ |
| [CVE-2018-1000180](https://www.mend.io/vulnerability-database/CVE-2018-1000180) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | bcprov-jdk15on-1.56.jar | Transitive | N/A* | ❌ |
| [CVE-2021-35517](https://www.mend.io/vulnerability-database/CVE-2021-35517) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | commons-compress-1.12.jar | Transitive | N/A* | ❌ |
| [CVE-2021-35516](https://www.mend.io/vulnerability-database/CVE-2021-35516) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | commons-compress-1.12.jar | Transitive | N/A* | ❌ |
| [CVE-2021-35515](https://www.mend.io/vulnerability-database/CVE-2021-35515) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | commons-compress-1.12.jar | Transitive | N/A* | ❌ |
| [CVE-2022-3171](https://www.mend.io/vulnerability-database/CVE-2022-3171) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | protobuf-java-3.4.0.jar | Transitive | N/A* | ❌ |
| [WS-2019-0379](https://github.com/apache/commons-codec/commit/48b615756d1d770091ea3322eefc08011ee8b113) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | commons-codec-1.10.jar | Transitive | N/A* | ❌ |
| [CVE-2020-15522](https://www.mend.io/vulnerability-database/CVE-2020-15522) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.9 | bcprov-jdk15on-1.56.jar | Transitive | N/A* | ❌ |
| [CVE-2021-22569](https://www.mend.io/vulnerability-database/CVE-2021-22569) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.5 | protobuf-java-3.4.0.jar | Transitive | N/A* | ❌ |
| [CVE-2020-17521](https://www.mend.io/vulnerability-database/CVE-2020-17521) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.5 | groovy-all-2.4.15.jar | Transitive | N/A* | ❌ |
| [CVE-2018-11771](https://www.mend.io/vulnerability-database/CVE-2018-11771) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.5 | commons-compress-1.12.jar | Transitive | N/A* | ❌ |
| [CVE-2018-1324](https://www.mend.io/vulnerability-database/CVE-2018-1324) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.5 | commons-compress-1.12.jar | Transitive | N/A* | ❌ |
| [CVE-2022-24329](https://www.mend.io/vulnerability-database/CVE-2022-24329) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | kotlin-stdlib-1.3.50.jar | Transitive | N/A* | ❌ |
| [CVE-2020-13956](https://www.mend.io/vulnerability-database/CVE-2020-13956) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | httpclient-4.5.6.jar | Transitive | N/A* | ❌ |
| [CVE-2020-26939](https://www.mend.io/vulnerability-database/CVE-2020-26939) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | bcprov-jdk15on-1.56.jar | Transitive | N/A* | ❌ |
| [CVE-2020-8908](https://www.mend.io/vulnerability-database/CVE-2020-8908) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 3.3 | guava-27.0.1-jre.jar | Transitive | N/A* | ❌ |
<p>*For some transitive vulnerabilities, there is no version of direct dependency with a fix. Check the "Details" section below to see if there is a version of transitive dependency where vulnerability is fixed.</p>
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-36090</summary>
### Vulnerable Library - <b>commons-compress-1.12.jar</b></p>
<p>Apache Commons Compress software defines an API for working with
compression and archive formats. These include: bzip2, gzip, pack200,
lzma, xz, Snappy, traditional Unix Compress, DEFLATE and ar, cpio,
jar, tar, zip, dump, 7z, arj.</p>
<p>Path to dependency file: /app/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.apache.commons/commons-compress/1.12/84caa68576e345eb5e7ae61a0e5a9229eb100d7b/commons-compress-1.12.jar</p>
<p>
Dependency Hierarchy:
- lint-gradle-26.5.3.jar (Root Library)
- sdk-common-26.5.3.jar
- sdklib-26.5.3.jar
- :x: **commons-compress-1.12.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/chatbot-watson-android/commit/59cf4251b46bc8fc950c9283359fabf1d97b885c">59cf4251b46bc8fc950c9283359fabf1d97b885c</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
When reading a specially crafted ZIP archive, Compress can be made to allocate large amounts of memory that finally leads to an out of memory error even for very small inputs. This could be used to mount a denial of service attack against services that use Compress' zip package.
<p>Publish Date: 2021-07-13
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-36090>CVE-2021-36090</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://commons.apache.org/proper/commons-compress/security-reports.html">https://commons.apache.org/proper/commons-compress/security-reports.html</a></p>
<p>Release Date: 2021-07-13</p>
<p>Fix Resolution: org.apache.commons:commons-compress:1.21</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-17359</summary>
### Vulnerable Library - <b>bcprov-jdk15on-1.56.jar</b></p>
<p>The Bouncy Castle Crypto package is a Java implementation of cryptographic algorithms. This jar contains JCE provider and lightweight API for the Bouncy Castle Cryptography APIs for JDK 1.5 to JDK 1.8.</p>
<p>Library home page: <a href="http://www.bouncycastle.org/java.html">http://www.bouncycastle.org/java.html</a></p>
<p>Path to dependency file: /app/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.bouncycastle/bcprov-jdk15on/1.56/a153c6f9744a3e9dd6feab5e210e1c9861362ec7/bcprov-jdk15on-1.56.jar</p>
<p>
Dependency Hierarchy:
- lint-gradle-26.5.3.jar (Root Library)
- sdk-common-26.5.3.jar
- :x: **bcprov-jdk15on-1.56.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/chatbot-watson-android/commit/59cf4251b46bc8fc950c9283359fabf1d97b885c">59cf4251b46bc8fc950c9283359fabf1d97b885c</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The ASN.1 parser in Bouncy Castle Crypto (aka BC Java) 1.63 can trigger a large attempted memory allocation, and resultant OutOfMemoryError error, via crafted ASN.1 data. This is fixed in 1.64.
<p>Publish Date: 2019-10-08
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-17359>CVE-2019-17359</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-17359">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-17359</a></p>
<p>Release Date: 2019-10-08</p>
<p>Fix Resolution: org.bouncycastle:bcprov-jdk15on:1.64</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-3509</summary>
### Vulnerable Library - <b>protobuf-java-3.4.0.jar</b></p>
<p>Core Protocol Buffers library. Protocol Buffers are a way of encoding structured data in an
efficient yet extensible format.</p>
<p>Library home page: <a href="https://developers.google.com/protocol-buffers/">https://developers.google.com/protocol-buffers/</a></p>
<p>Path to dependency file: /app/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.google.protobuf/protobuf-java/3.4.0/b32aba0cbe737a4ca953f71688725972e3ee927c/protobuf-java-3.4.0.jar</p>
<p>
Dependency Hierarchy:
- lint-gradle-26.5.3.jar (Root Library)
- sdk-common-26.5.3.jar
- :x: **protobuf-java-3.4.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/chatbot-watson-android/commit/59cf4251b46bc8fc950c9283359fabf1d97b885c">59cf4251b46bc8fc950c9283359fabf1d97b885c</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A parsing issue similar to CVE-2022-3171, but with textformat in protobuf-java core and lite versions prior to 3.21.7, 3.20.3, 3.19.6 and 3.16.3 can lead to a denial of service attack. Inputs containing multiple instances of non-repeated embedded messages with repeated or unknown fields causes objects to be converted back-n-forth between mutable and immutable forms, resulting in potentially long garbage collection pauses. We recommend updating to the versions mentioned above.
<p>Publish Date: 2022-12-12
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-3509>CVE-2022-3509</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-3509">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-3509</a></p>
<p>Release Date: 2022-12-12</p>
<p>Fix Resolution: com.google.protobuf:protobuf-java:3.16.3,3.19.6,3.20.3,3.21.7</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2018-1000180</summary>
### Vulnerable Library - <b>bcprov-jdk15on-1.56.jar</b></p>
<p>The Bouncy Castle Crypto package is a Java implementation of cryptographic algorithms. This jar contains JCE provider and lightweight API for the Bouncy Castle Cryptography APIs for JDK 1.5 to JDK 1.8.</p>
<p>Library home page: <a href="http://www.bouncycastle.org/java.html">http://www.bouncycastle.org/java.html</a></p>
<p>Path to dependency file: /app/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.bouncycastle/bcprov-jdk15on/1.56/a153c6f9744a3e9dd6feab5e210e1c9861362ec7/bcprov-jdk15on-1.56.jar</p>
<p>
Dependency Hierarchy:
- lint-gradle-26.5.3.jar (Root Library)
- sdk-common-26.5.3.jar
- :x: **bcprov-jdk15on-1.56.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/chatbot-watson-android/commit/59cf4251b46bc8fc950c9283359fabf1d97b885c">59cf4251b46bc8fc950c9283359fabf1d97b885c</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Bouncy Castle BC 1.54 - 1.59, BC-FJA 1.0.0, BC-FJA 1.0.1 and earlier have a flaw in the Low-level interface to RSA key pair generator, specifically RSA Key Pairs generated in low-level API with added certainty may have less M-R tests than expected. This appears to be fixed in versions BC 1.60 beta 4 and later, BC-FJA 1.0.2 and later.
<p>Publish Date: 2018-06-05
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-1000180>CVE-2018-1000180</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-1000180">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-1000180</a></p>
<p>Release Date: 2018-06-05</p>
<p>Fix Resolution: org.bouncycastle:bc-fips:1.0.2;org.bouncycastle:bcprov-jdk15on:1.60;org.bouncycastle:bcprov-jdk14:1.60;org.bouncycastle:bcprov-ext-jdk14:1.60;org.bouncycastle:bcprov-ext-jdk15on:1.60;org.bouncycastle:bcprov-debug-jdk14:1.60;org.bouncycastle:bcprov-debug-jdk15on:1.60</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-35517</summary>
### Vulnerable Library - <b>commons-compress-1.12.jar</b></p>
<p>Apache Commons Compress software defines an API for working with
compression and archive formats. These include: bzip2, gzip, pack200,
lzma, xz, Snappy, traditional Unix Compress, DEFLATE and ar, cpio,
jar, tar, zip, dump, 7z, arj.</p>
<p>Path to dependency file: /app/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.apache.commons/commons-compress/1.12/84caa68576e345eb5e7ae61a0e5a9229eb100d7b/commons-compress-1.12.jar</p>
<p>
Dependency Hierarchy:
- lint-gradle-26.5.3.jar (Root Library)
- sdk-common-26.5.3.jar
- sdklib-26.5.3.jar
- :x: **commons-compress-1.12.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/chatbot-watson-android/commit/59cf4251b46bc8fc950c9283359fabf1d97b885c">59cf4251b46bc8fc950c9283359fabf1d97b885c</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
When reading a specially crafted TAR archive, Compress can be made to allocate large amounts of memory that finally leads to an out of memory error even for very small inputs. This could be used to mount a denial of service attack against services that use Compress' tar package.
<p>Publish Date: 2021-07-13
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-35517>CVE-2021-35517</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://commons.apache.org/proper/commons-compress/security-reports.html">https://commons.apache.org/proper/commons-compress/security-reports.html</a></p>
<p>Release Date: 2021-07-13</p>
<p>Fix Resolution: org.apache.commons:commons-compress:1.21</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-35516</summary>
### Vulnerable Library - <b>commons-compress-1.12.jar</b></p>
<p>Apache Commons Compress software defines an API for working with
compression and archive formats. These include: bzip2, gzip, pack200,
lzma, xz, Snappy, traditional Unix Compress, DEFLATE and ar, cpio,
jar, tar, zip, dump, 7z, arj.</p>
<p>Path to dependency file: /app/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.apache.commons/commons-compress/1.12/84caa68576e345eb5e7ae61a0e5a9229eb100d7b/commons-compress-1.12.jar</p>
<p>
Dependency Hierarchy:
- lint-gradle-26.5.3.jar (Root Library)
- sdk-common-26.5.3.jar
- sdklib-26.5.3.jar
- :x: **commons-compress-1.12.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/chatbot-watson-android/commit/59cf4251b46bc8fc950c9283359fabf1d97b885c">59cf4251b46bc8fc950c9283359fabf1d97b885c</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
When reading a specially crafted 7Z archive, Compress can be made to allocate large amounts of memory that finally leads to an out of memory error even for very small inputs. This could be used to mount a denial of service attack against services that use Compress' sevenz package.
<p>Publish Date: 2021-07-13
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-35516>CVE-2021-35516</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://commons.apache.org/proper/commons-compress/security-reports.html">https://commons.apache.org/proper/commons-compress/security-reports.html</a></p>
<p>Release Date: 2021-07-13</p>
<p>Fix Resolution: org.apache.commons:commons-compress:1.21</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-35515</summary>
### Vulnerable Library - <b>commons-compress-1.12.jar</b></p>
<p>Apache Commons Compress software defines an API for working with
compression and archive formats. These include: bzip2, gzip, pack200,
lzma, xz, Snappy, traditional Unix Compress, DEFLATE and ar, cpio,
jar, tar, zip, dump, 7z, arj.</p>
<p>Path to dependency file: /app/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.apache.commons/commons-compress/1.12/84caa68576e345eb5e7ae61a0e5a9229eb100d7b/commons-compress-1.12.jar</p>
<p>
Dependency Hierarchy:
- lint-gradle-26.5.3.jar (Root Library)
- sdk-common-26.5.3.jar
- sdklib-26.5.3.jar
- :x: **commons-compress-1.12.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/chatbot-watson-android/commit/59cf4251b46bc8fc950c9283359fabf1d97b885c">59cf4251b46bc8fc950c9283359fabf1d97b885c</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
When reading a specially crafted 7Z archive, the construction of the list of codecs that decompress an entry can result in an infinite loop. This could be used to mount a denial of service attack against services that use Compress' sevenz package.
<p>Publish Date: 2021-07-13
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-35515>CVE-2021-35515</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://commons.apache.org/proper/commons-compress/security-reports.html">https://commons.apache.org/proper/commons-compress/security-reports.html</a></p>
<p>Release Date: 2021-07-13</p>
<p>Fix Resolution: org.apache.commons:commons-compress:1.21</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-3171</summary>
### Vulnerable Library - <b>protobuf-java-3.4.0.jar</b></p>
<p>Core Protocol Buffers library. Protocol Buffers are a way of encoding structured data in an
efficient yet extensible format.</p>
<p>Library home page: <a href="https://developers.google.com/protocol-buffers/">https://developers.google.com/protocol-buffers/</a></p>
<p>Path to dependency file: /app/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.google.protobuf/protobuf-java/3.4.0/b32aba0cbe737a4ca953f71688725972e3ee927c/protobuf-java-3.4.0.jar</p>
<p>
Dependency Hierarchy:
- lint-gradle-26.5.3.jar (Root Library)
- sdk-common-26.5.3.jar
- :x: **protobuf-java-3.4.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/chatbot-watson-android/commit/59cf4251b46bc8fc950c9283359fabf1d97b885c">59cf4251b46bc8fc950c9283359fabf1d97b885c</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A parsing issue with binary data in protobuf-java core and lite versions prior to 3.21.7, 3.20.3, 3.19.6 and 3.16.3 can lead to a denial of service attack. Inputs containing multiple instances of non-repeated embedded messages with repeated or unknown fields causes objects to be converted back-n-forth between mutable and immutable forms, resulting in potentially long garbage collection pauses. We recommend updating to the versions mentioned above.
<p>Publish Date: 2022-10-12
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-3171>CVE-2022-3171</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-h4h5-3hr4-j3g2">https://github.com/advisories/GHSA-h4h5-3hr4-j3g2</a></p>
<p>Release Date: 2022-10-12</p>
<p>Fix Resolution: com.google.protobuf:protobuf-java:3.16.3,3.19.6,3.20.3,3.21.7;com.google.protobuf:protobuf-javalite:3.16.3,3.19.6,3.20.3,3.21.7;com.google.protobuf:protobuf-kotlin:3.19.6,3.20.3,3.21.7;com.google.protobuf:protobuf-kotlin-lite:3.19.6,3.20.3,3.21.7;google-protobuf - 3.19.6,3.20.3,3.21.7</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> WS-2019-0379</summary>
### Vulnerable Library - <b>commons-codec-1.10.jar</b></p>
<p>The Apache Commons Codec package contains simple encoder and decoders for
various formats such as Base64 and Hexadecimal. In addition to these
widely used encoders and decoders, the codec package also maintains a
collection of phonetic encoding utilities.</p>
<p>Path to dependency file: /app/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/commons-codec/commons-codec/1.10/4b95f4897fa13f2cd904aee711aeafc0c5295cd8/commons-codec-1.10.jar</p>
<p>
Dependency Hierarchy:
- lint-gradle-26.5.3.jar (Root Library)
- sdk-common-26.5.3.jar
- sdklib-26.5.3.jar
- httpmime-4.5.6.jar
- httpclient-4.5.6.jar
- :x: **commons-codec-1.10.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/chatbot-watson-android/commit/59cf4251b46bc8fc950c9283359fabf1d97b885c">59cf4251b46bc8fc950c9283359fabf1d97b885c</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache commons-codec before version “commons-codec-1.13-RC1” is vulnerable to information disclosure due to Improper Input validation.
<p>Publish Date: 2019-05-20
<p>URL: <a href=https://github.com/apache/commons-codec/commit/48b615756d1d770091ea3322eefc08011ee8b113>WS-2019-0379</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2019-05-20</p>
<p>Fix Resolution: commons-codec:commons-codec:1.13</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2020-15522</summary>
### Vulnerable Library - <b>bcprov-jdk15on-1.56.jar</b></p>
<p>The Bouncy Castle Crypto package is a Java implementation of cryptographic algorithms. This jar contains JCE provider and lightweight API for the Bouncy Castle Cryptography APIs for JDK 1.5 to JDK 1.8.</p>
<p>Library home page: <a href="http://www.bouncycastle.org/java.html">http://www.bouncycastle.org/java.html</a></p>
<p>Path to dependency file: /app/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.bouncycastle/bcprov-jdk15on/1.56/a153c6f9744a3e9dd6feab5e210e1c9861362ec7/bcprov-jdk15on-1.56.jar</p>
<p>
Dependency Hierarchy:
- lint-gradle-26.5.3.jar (Root Library)
- sdk-common-26.5.3.jar
- :x: **bcprov-jdk15on-1.56.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/chatbot-watson-android/commit/59cf4251b46bc8fc950c9283359fabf1d97b885c">59cf4251b46bc8fc950c9283359fabf1d97b885c</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Bouncy Castle BC Java before 1.66, BC C# .NET before 1.8.7, BC-FJA before 1.0.1.2, 1.0.2.1, and BC-FNA before 1.0.1.1 have a timing issue within the EC math library that can expose information about the private key when an attacker is able to observe timing information for the generation of multiple deterministic ECDSA signatures.
<p>Publish Date: 2021-05-20
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-15522>CVE-2020-15522</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.9</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-15522">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-15522</a></p>
<p>Release Date: 2021-05-20</p>
<p>Fix Resolution: C#- release-1.8.7, Java- 1.66</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2021-22569</summary>
### Vulnerable Library - <b>protobuf-java-3.4.0.jar</b></p>
<p>Core Protocol Buffers library. Protocol Buffers are a way of encoding structured data in an
efficient yet extensible format.</p>
<p>Library home page: <a href="https://developers.google.com/protocol-buffers/">https://developers.google.com/protocol-buffers/</a></p>
<p>Path to dependency file: /app/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.google.protobuf/protobuf-java/3.4.0/b32aba0cbe737a4ca953f71688725972e3ee927c/protobuf-java-3.4.0.jar</p>
<p>
Dependency Hierarchy:
- lint-gradle-26.5.3.jar (Root Library)
- sdk-common-26.5.3.jar
- :x: **protobuf-java-3.4.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/chatbot-watson-android/commit/59cf4251b46bc8fc950c9283359fabf1d97b885c">59cf4251b46bc8fc950c9283359fabf1d97b885c</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
An issue in protobuf-java allowed the interleaving of com.google.protobuf.UnknownFieldSet fields in such a way that would be processed out of order. A small malicious payload can occupy the parser for several minutes by creating large numbers of short-lived objects that cause frequent, repeated pauses. We recommend upgrading libraries beyond the vulnerable versions.
<p>Publish Date: 2022-01-10
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-22569>CVE-2021-22569</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-wrvw-hg22-4m67">https://github.com/advisories/GHSA-wrvw-hg22-4m67</a></p>
<p>Release Date: 2022-01-10</p>
<p>Fix Resolution: com.google.protobuf:protobuf-java:3.16.1,3.18.2,3.19.2; com.google.protobuf:protobuf-kotlin:3.18.2,3.19.2; google-protobuf - 3.19.2</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2020-17521</summary>
### Vulnerable Library - <b>groovy-all-2.4.15.jar</b></p>
<p>Groovy: A powerful, dynamic language for the JVM</p>
<p>Library home page: <a href="http://groovy-lang.org">http://groovy-lang.org</a></p>
<p>Path to dependency file: /app/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.codehaus.groovy/groovy-all/2.4.15/423a17aeb2f64bc6f76e8e44265a548bec80fd42/groovy-all-2.4.15.jar</p>
<p>
Dependency Hierarchy:
- lint-gradle-26.5.3.jar (Root Library)
- :x: **groovy-all-2.4.15.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/chatbot-watson-android/commit/59cf4251b46bc8fc950c9283359fabf1d97b885c">59cf4251b46bc8fc950c9283359fabf1d97b885c</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache Groovy provides extension methods to aid with creating temporary directories. Prior to this fix, Groovy's implementation of those extension methods was using a now superseded Java JDK method call that is potentially not secure on some operating systems in some contexts. Users not using the extension methods mentioned in the advisory are not affected, but may wish to read the advisory for further details. Versions Affected: 2.0 to 2.4.20, 2.5.0 to 2.5.13, 3.0.0 to 3.0.6, and 4.0.0-alpha-1. Fixed in versions 2.4.21, 2.5.14, 3.0.7, 4.0.0-alpha-2.
<p>Publish Date: 2020-12-07
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-17521>CVE-2020-17521</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://issues.apache.org/jira/browse/GROOVY-9824">https://issues.apache.org/jira/browse/GROOVY-9824</a></p>
<p>Release Date: 2020-12-07</p>
<p>Fix Resolution: org.codehaus.groovy:groovy-all:2.4.21,2.5.14,3.0.7</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-11771</summary>
### Vulnerable Library - <b>commons-compress-1.12.jar</b></p>
<p>Apache Commons Compress software defines an API for working with
compression and archive formats. These include: bzip2, gzip, pack200,
lzma, xz, Snappy, traditional Unix Compress, DEFLATE and ar, cpio,
jar, tar, zip, dump, 7z, arj.</p>
<p>Path to dependency file: /app/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.apache.commons/commons-compress/1.12/84caa68576e345eb5e7ae61a0e5a9229eb100d7b/commons-compress-1.12.jar</p>
<p>
Dependency Hierarchy:
- lint-gradle-26.5.3.jar (Root Library)
- sdk-common-26.5.3.jar
- sdklib-26.5.3.jar
- :x: **commons-compress-1.12.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/chatbot-watson-android/commit/59cf4251b46bc8fc950c9283359fabf1d97b885c">59cf4251b46bc8fc950c9283359fabf1d97b885c</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
When reading a specially crafted ZIP archive, the read method of Apache Commons Compress 1.7 to 1.17's ZipArchiveInputStream can fail to return the correct EOF indication after the end of the stream has been reached. When combined with a java.io.InputStreamReader this can lead to an infinite stream, which can be used to mount a denial of service attack against services that use Compress' zip package.
<p>Publish Date: 2018-08-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-11771>CVE-2018-11771</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-11771">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-11771</a></p>
<p>Release Date: 2018-08-16</p>
<p>Fix Resolution: 1.18</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-1324</summary>
### Vulnerable Library - <b>commons-compress-1.12.jar</b></p>
<p>Apache Commons Compress software defines an API for working with
compression and archive formats. These include: bzip2, gzip, pack200,
lzma, xz, Snappy, traditional Unix Compress, DEFLATE and ar, cpio,
jar, tar, zip, dump, 7z, arj.</p>
<p>Path to dependency file: /app/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.apache.commons/commons-compress/1.12/84caa68576e345eb5e7ae61a0e5a9229eb100d7b/commons-compress-1.12.jar</p>
<p>
Dependency Hierarchy:
- lint-gradle-26.5.3.jar (Root Library)
- sdk-common-26.5.3.jar
- sdklib-26.5.3.jar
- :x: **commons-compress-1.12.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/chatbot-watson-android/commit/59cf4251b46bc8fc950c9283359fabf1d97b885c">59cf4251b46bc8fc950c9283359fabf1d97b885c</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A specially crafted ZIP archive can be used to cause an infinite loop inside of Apache Commons Compress' extra field parser used by the ZipFile and ZipArchiveInputStream classes in versions 1.11 to 1.15. This can be used to mount a denial of service attack against services that use Compress' zip package.
<p>Publish Date: 2018-03-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-1324>CVE-2018-1324</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-1324">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-1324</a></p>
<p>Release Date: 2018-03-16</p>
<p>Fix Resolution: 1.16</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-24329</summary>
### Vulnerable Library - <b>kotlin-stdlib-1.3.50.jar</b></p>
<p>Kotlin Standard Library for JVM</p>
<p>Library home page: <a href="https://kotlinlang.org/">https://kotlinlang.org/</a></p>
<p>Path to dependency file: /app/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.jetbrains.kotlin/kotlin-stdlib/1.3.50/b529d1738c7e98bbfa36a4134039528f2ce78ebf/kotlin-stdlib-1.3.50.jar</p>
<p>
Dependency Hierarchy:
- lint-gradle-26.5.3.jar (Root Library)
- sdk-common-26.5.3.jar
- kotlin-reflect-1.3.50.jar
- :x: **kotlin-stdlib-1.3.50.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/chatbot-watson-android/commit/59cf4251b46bc8fc950c9283359fabf1d97b885c">59cf4251b46bc8fc950c9283359fabf1d97b885c</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In JetBrains Kotlin before 1.6.0, it was not possible to lock dependencies for Multiplatform Gradle Projects.
<p>Publish Date: 2022-02-25
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-24329>CVE-2022-24329</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-2qp4-g3q3-f92w">https://github.com/advisories/GHSA-2qp4-g3q3-f92w</a></p>
<p>Release Date: 2022-02-25</p>
<p>Fix Resolution: org.jetbrains.kotlin:kotlin-stdlib:1.6.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2020-13956</summary>
### Vulnerable Library - <b>httpclient-4.5.6.jar</b></p>
<p>Apache HttpComponents Client</p>
<p>Path to dependency file: /app/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.apache.httpcomponents/httpclient/4.5.6/1afe5621985efe90a92d0fbc9be86271efbe796f/httpclient-4.5.6.jar</p>
<p>
Dependency Hierarchy:
- lint-gradle-26.5.3.jar (Root Library)
- sdk-common-26.5.3.jar
- sdklib-26.5.3.jar
- httpmime-4.5.6.jar
- :x: **httpclient-4.5.6.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/chatbot-watson-android/commit/59cf4251b46bc8fc950c9283359fabf1d97b885c">59cf4251b46bc8fc950c9283359fabf1d97b885c</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache HttpClient versions prior to version 4.5.13 and 5.0.3 can misinterpret malformed authority component in request URIs passed to the library as java.net.URI object and pick the wrong target host for request execution.
<p>Publish Date: 2020-12-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-13956>CVE-2020-13956</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bugzilla.redhat.com/show_bug.cgi?id=CVE-2020-13956">https://bugzilla.redhat.com/show_bug.cgi?id=CVE-2020-13956</a></p>
<p>Release Date: 2020-12-02</p>
<p>Fix Resolution: org.apache.httpcomponents:httpclient:4.5.13;org.apache.httpcomponents:httpclient-osgi:4.5.13;org.apache.httpcomponents.client5:httpclient5:5.0.3;org.apache.httpcomponents.client5:httpclient5-osgi:5.0.3</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2020-26939</summary>
### Vulnerable Library - <b>bcprov-jdk15on-1.56.jar</b></p>
<p>The Bouncy Castle Crypto package is a Java implementation of cryptographic algorithms. This jar contains JCE provider and lightweight API for the Bouncy Castle Cryptography APIs for JDK 1.5 to JDK 1.8.</p>
<p>Library home page: <a href="http://www.bouncycastle.org/java.html">http://www.bouncycastle.org/java.html</a></p>
<p>Path to dependency file: /app/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.bouncycastle/bcprov-jdk15on/1.56/a153c6f9744a3e9dd6feab5e210e1c9861362ec7/bcprov-jdk15on-1.56.jar</p>
<p>
Dependency Hierarchy:
- lint-gradle-26.5.3.jar (Root Library)
- sdk-common-26.5.3.jar
- :x: **bcprov-jdk15on-1.56.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/chatbot-watson-android/commit/59cf4251b46bc8fc950c9283359fabf1d97b885c">59cf4251b46bc8fc950c9283359fabf1d97b885c</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Legion of the Bouncy Castle BC before 1.61 and BC-FJA before 1.0.1.2, attackers can obtain sensitive information about a private exponent because of Observable Differences in Behavior to Error Inputs. This occurs in org.bouncycastle.crypto.encodings.OAEPEncoding. Sending invalid ciphertext that decrypts to a short payload in the OAEP Decoder could result in the throwing of an early exception, potentially leaking some information about the private exponent of the RSA private key performing the encryption.
<p>Publish Date: 2020-11-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-26939>CVE-2020-26939</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2020-11-02</p>
<p>Fix Resolution: org.bouncycastle:bcprov-jdk14:1.61,org.bouncycastle:bcprov-ext-debug-jdk15on:1.61,org.bouncycastle:bcprov-debug-jdk15on:1.61,org.bouncycastle:bcprov-ext-jdk15on:1.61,org.bouncycastle:bcprov-jdk15on:1.61</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> CVE-2020-8908</summary>
### Vulnerable Library - <b>guava-27.0.1-jre.jar</b></p>
<p>Guava is a suite of core and expanded libraries that include
utility classes, google's collections, io classes, and much
much more.</p>
<p>Library home page: <a href="https://github.com/google/guava">https://github.com/google/guava</a></p>
<p>Path to dependency file: /app/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.google.guava/guava/27.0.1-jre/bd41a290787b5301e63929676d792c507bbc00ae/guava-27.0.1-jre.jar</p>
<p>
Dependency Hierarchy:
- lint-gradle-26.5.3.jar (Root Library)
- lint-26.5.3.jar
- :x: **guava-27.0.1-jre.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/chatbot-watson-android/commit/59cf4251b46bc8fc950c9283359fabf1d97b885c">59cf4251b46bc8fc950c9283359fabf1d97b885c</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A temp directory creation vulnerability exists in all versions of Guava, allowing an attacker with access to the machine to potentially access data in a temporary directory created by the Guava API com.google.common.io.Files.createTempDir(). By default, on unix-like systems, the created directory is world-readable (readable by an attacker with access to the system). The method in question has been marked @Deprecated in versions 30.0 and later and should not be used. For Android developers, we recommend choosing a temporary directory API provided by Android, such as context.getCacheDir(). For other Java developers, we recommend migrating to the Java 7 API java.nio.file.Files.createTempDirectory() which explicitly configures permissions of 700, or configuring the Java runtime's java.io.tmpdir system property to point to a location whose permissions are appropriately configured.
<p>Publish Date: 2020-12-10
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-8908>CVE-2020-8908</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>3.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-8908">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-8908</a></p>
<p>Release Date: 2020-12-10</p>
<p>Fix Resolution: v30.0</p>
</p>
<p></p>
</details>
|
True
|
lint-gradle-26.5.3.jar: 18 vulnerabilities (highest severity is: 7.5) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>lint-gradle-26.5.3.jar</b></p></summary>
<p></p>
<p>Path to dependency file: /app/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.apache.commons/commons-compress/1.12/84caa68576e345eb5e7ae61a0e5a9229eb100d7b/commons-compress-1.12.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/chatbot-watson-android/commit/59cf4251b46bc8fc950c9283359fabf1d97b885c">59cf4251b46bc8fc950c9283359fabf1d97b885c</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (lint-gradle version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2021-36090](https://www.mend.io/vulnerability-database/CVE-2021-36090) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | commons-compress-1.12.jar | Transitive | N/A* | ❌ |
| [CVE-2019-17359](https://www.mend.io/vulnerability-database/CVE-2019-17359) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | bcprov-jdk15on-1.56.jar | Transitive | N/A* | ❌ |
| [CVE-2022-3509](https://www.mend.io/vulnerability-database/CVE-2022-3509) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | protobuf-java-3.4.0.jar | Transitive | N/A* | ❌ |
| [CVE-2018-1000180](https://www.mend.io/vulnerability-database/CVE-2018-1000180) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | bcprov-jdk15on-1.56.jar | Transitive | N/A* | ❌ |
| [CVE-2021-35517](https://www.mend.io/vulnerability-database/CVE-2021-35517) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | commons-compress-1.12.jar | Transitive | N/A* | ❌ |
| [CVE-2021-35516](https://www.mend.io/vulnerability-database/CVE-2021-35516) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | commons-compress-1.12.jar | Transitive | N/A* | ❌ |
| [CVE-2021-35515](https://www.mend.io/vulnerability-database/CVE-2021-35515) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | commons-compress-1.12.jar | Transitive | N/A* | ❌ |
| [CVE-2022-3171](https://www.mend.io/vulnerability-database/CVE-2022-3171) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | protobuf-java-3.4.0.jar | Transitive | N/A* | ❌ |
| [WS-2019-0379](https://github.com/apache/commons-codec/commit/48b615756d1d770091ea3322eefc08011ee8b113) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | commons-codec-1.10.jar | Transitive | N/A* | ❌ |
| [CVE-2020-15522](https://www.mend.io/vulnerability-database/CVE-2020-15522) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.9 | bcprov-jdk15on-1.56.jar | Transitive | N/A* | ❌ |
| [CVE-2021-22569](https://www.mend.io/vulnerability-database/CVE-2021-22569) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.5 | protobuf-java-3.4.0.jar | Transitive | N/A* | ❌ |
| [CVE-2020-17521](https://www.mend.io/vulnerability-database/CVE-2020-17521) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.5 | groovy-all-2.4.15.jar | Transitive | N/A* | ❌ |
| [CVE-2018-11771](https://www.mend.io/vulnerability-database/CVE-2018-11771) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.5 | commons-compress-1.12.jar | Transitive | N/A* | ❌ |
| [CVE-2018-1324](https://www.mend.io/vulnerability-database/CVE-2018-1324) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.5 | commons-compress-1.12.jar | Transitive | N/A* | ❌ |
| [CVE-2022-24329](https://www.mend.io/vulnerability-database/CVE-2022-24329) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | kotlin-stdlib-1.3.50.jar | Transitive | N/A* | ❌ |
| [CVE-2020-13956](https://www.mend.io/vulnerability-database/CVE-2020-13956) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | httpclient-4.5.6.jar | Transitive | N/A* | ❌ |
| [CVE-2020-26939](https://www.mend.io/vulnerability-database/CVE-2020-26939) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | bcprov-jdk15on-1.56.jar | Transitive | N/A* | ❌ |
| [CVE-2020-8908](https://www.mend.io/vulnerability-database/CVE-2020-8908) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 3.3 | guava-27.0.1-jre.jar | Transitive | N/A* | ❌ |
<p>*For some transitive vulnerabilities, there is no version of direct dependency with a fix. Check the "Details" section below to see if there is a version of transitive dependency where vulnerability is fixed.</p>
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-36090</summary>
### Vulnerable Library - <b>commons-compress-1.12.jar</b></p>
<p>Apache Commons Compress software defines an API for working with
compression and archive formats. These include: bzip2, gzip, pack200,
lzma, xz, Snappy, traditional Unix Compress, DEFLATE and ar, cpio,
jar, tar, zip, dump, 7z, arj.</p>
<p>Path to dependency file: /app/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.apache.commons/commons-compress/1.12/84caa68576e345eb5e7ae61a0e5a9229eb100d7b/commons-compress-1.12.jar</p>
<p>
Dependency Hierarchy:
- lint-gradle-26.5.3.jar (Root Library)
- sdk-common-26.5.3.jar
- sdklib-26.5.3.jar
- :x: **commons-compress-1.12.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/chatbot-watson-android/commit/59cf4251b46bc8fc950c9283359fabf1d97b885c">59cf4251b46bc8fc950c9283359fabf1d97b885c</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
When reading a specially crafted ZIP archive, Compress can be made to allocate large amounts of memory that finally leads to an out of memory error even for very small inputs. This could be used to mount a denial of service attack against services that use Compress' zip package.
<p>Publish Date: 2021-07-13
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-36090>CVE-2021-36090</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://commons.apache.org/proper/commons-compress/security-reports.html">https://commons.apache.org/proper/commons-compress/security-reports.html</a></p>
<p>Release Date: 2021-07-13</p>
<p>Fix Resolution: org.apache.commons:commons-compress:1.21</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-17359</summary>
### Vulnerable Library - <b>bcprov-jdk15on-1.56.jar</b></p>
<p>The Bouncy Castle Crypto package is a Java implementation of cryptographic algorithms. This jar contains JCE provider and lightweight API for the Bouncy Castle Cryptography APIs for JDK 1.5 to JDK 1.8.</p>
<p>Library home page: <a href="http://www.bouncycastle.org/java.html">http://www.bouncycastle.org/java.html</a></p>
<p>Path to dependency file: /app/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.bouncycastle/bcprov-jdk15on/1.56/a153c6f9744a3e9dd6feab5e210e1c9861362ec7/bcprov-jdk15on-1.56.jar</p>
<p>
Dependency Hierarchy:
- lint-gradle-26.5.3.jar (Root Library)
- sdk-common-26.5.3.jar
- :x: **bcprov-jdk15on-1.56.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/chatbot-watson-android/commit/59cf4251b46bc8fc950c9283359fabf1d97b885c">59cf4251b46bc8fc950c9283359fabf1d97b885c</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The ASN.1 parser in Bouncy Castle Crypto (aka BC Java) 1.63 can trigger a large attempted memory allocation, and resultant OutOfMemoryError error, via crafted ASN.1 data. This is fixed in 1.64.
<p>Publish Date: 2019-10-08
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-17359>CVE-2019-17359</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-17359">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-17359</a></p>
<p>Release Date: 2019-10-08</p>
<p>Fix Resolution: org.bouncycastle:bcprov-jdk15on:1.64</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-3509</summary>
### Vulnerable Library - <b>protobuf-java-3.4.0.jar</b></p>
<p>Core Protocol Buffers library. Protocol Buffers are a way of encoding structured data in an
efficient yet extensible format.</p>
<p>Library home page: <a href="https://developers.google.com/protocol-buffers/">https://developers.google.com/protocol-buffers/</a></p>
<p>Path to dependency file: /app/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.google.protobuf/protobuf-java/3.4.0/b32aba0cbe737a4ca953f71688725972e3ee927c/protobuf-java-3.4.0.jar</p>
<p>
Dependency Hierarchy:
- lint-gradle-26.5.3.jar (Root Library)
- sdk-common-26.5.3.jar
- :x: **protobuf-java-3.4.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/chatbot-watson-android/commit/59cf4251b46bc8fc950c9283359fabf1d97b885c">59cf4251b46bc8fc950c9283359fabf1d97b885c</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A parsing issue similar to CVE-2022-3171, but with textformat in protobuf-java core and lite versions prior to 3.21.7, 3.20.3, 3.19.6 and 3.16.3 can lead to a denial of service attack. Inputs containing multiple instances of non-repeated embedded messages with repeated or unknown fields causes objects to be converted back-n-forth between mutable and immutable forms, resulting in potentially long garbage collection pauses. We recommend updating to the versions mentioned above.
<p>Publish Date: 2022-12-12
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-3509>CVE-2022-3509</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-3509">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-3509</a></p>
<p>Release Date: 2022-12-12</p>
<p>Fix Resolution: com.google.protobuf:protobuf-java:3.16.3,3.19.6,3.20.3,3.21.7</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2018-1000180</summary>
### Vulnerable Library - <b>bcprov-jdk15on-1.56.jar</b></p>
<p>The Bouncy Castle Crypto package is a Java implementation of cryptographic algorithms. This jar contains JCE provider and lightweight API for the Bouncy Castle Cryptography APIs for JDK 1.5 to JDK 1.8.</p>
<p>Library home page: <a href="http://www.bouncycastle.org/java.html">http://www.bouncycastle.org/java.html</a></p>
<p>Path to dependency file: /app/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.bouncycastle/bcprov-jdk15on/1.56/a153c6f9744a3e9dd6feab5e210e1c9861362ec7/bcprov-jdk15on-1.56.jar</p>
<p>
Dependency Hierarchy:
- lint-gradle-26.5.3.jar (Root Library)
- sdk-common-26.5.3.jar
- :x: **bcprov-jdk15on-1.56.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/chatbot-watson-android/commit/59cf4251b46bc8fc950c9283359fabf1d97b885c">59cf4251b46bc8fc950c9283359fabf1d97b885c</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Bouncy Castle BC 1.54 - 1.59, BC-FJA 1.0.0, BC-FJA 1.0.1 and earlier have a flaw in the Low-level interface to RSA key pair generator, specifically RSA Key Pairs generated in low-level API with added certainty may have less M-R tests than expected. This appears to be fixed in versions BC 1.60 beta 4 and later, BC-FJA 1.0.2 and later.
<p>Publish Date: 2018-06-05
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-1000180>CVE-2018-1000180</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-1000180">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-1000180</a></p>
<p>Release Date: 2018-06-05</p>
<p>Fix Resolution: org.bouncycastle:bc-fips:1.0.2;org.bouncycastle:bcprov-jdk15on:1.60;org.bouncycastle:bcprov-jdk14:1.60;org.bouncycastle:bcprov-ext-jdk14:1.60;org.bouncycastle:bcprov-ext-jdk15on:1.60;org.bouncycastle:bcprov-debug-jdk14:1.60;org.bouncycastle:bcprov-debug-jdk15on:1.60</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-35517</summary>
### Vulnerable Library - <b>commons-compress-1.12.jar</b></p>
<p>Apache Commons Compress software defines an API for working with
compression and archive formats. These include: bzip2, gzip, pack200,
lzma, xz, Snappy, traditional Unix Compress, DEFLATE and ar, cpio,
jar, tar, zip, dump, 7z, arj.</p>
<p>Path to dependency file: /app/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.apache.commons/commons-compress/1.12/84caa68576e345eb5e7ae61a0e5a9229eb100d7b/commons-compress-1.12.jar</p>
<p>
Dependency Hierarchy:
- lint-gradle-26.5.3.jar (Root Library)
- sdk-common-26.5.3.jar
- sdklib-26.5.3.jar
- :x: **commons-compress-1.12.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/chatbot-watson-android/commit/59cf4251b46bc8fc950c9283359fabf1d97b885c">59cf4251b46bc8fc950c9283359fabf1d97b885c</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
When reading a specially crafted TAR archive, Compress can be made to allocate large amounts of memory that finally leads to an out of memory error even for very small inputs. This could be used to mount a denial of service attack against services that use Compress' tar package.
<p>Publish Date: 2021-07-13
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-35517>CVE-2021-35517</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://commons.apache.org/proper/commons-compress/security-reports.html">https://commons.apache.org/proper/commons-compress/security-reports.html</a></p>
<p>Release Date: 2021-07-13</p>
<p>Fix Resolution: org.apache.commons:commons-compress:1.21</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-35516</summary>
### Vulnerable Library - <b>commons-compress-1.12.jar</b></p>
<p>Apache Commons Compress software defines an API for working with
compression and archive formats. These include: bzip2, gzip, pack200,
lzma, xz, Snappy, traditional Unix Compress, DEFLATE and ar, cpio,
jar, tar, zip, dump, 7z, arj.</p>
<p>Path to dependency file: /app/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.apache.commons/commons-compress/1.12/84caa68576e345eb5e7ae61a0e5a9229eb100d7b/commons-compress-1.12.jar</p>
<p>
Dependency Hierarchy:
- lint-gradle-26.5.3.jar (Root Library)
- sdk-common-26.5.3.jar
- sdklib-26.5.3.jar
- :x: **commons-compress-1.12.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/chatbot-watson-android/commit/59cf4251b46bc8fc950c9283359fabf1d97b885c">59cf4251b46bc8fc950c9283359fabf1d97b885c</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
When reading a specially crafted 7Z archive, Compress can be made to allocate large amounts of memory that finally leads to an out of memory error even for very small inputs. This could be used to mount a denial of service attack against services that use Compress' sevenz package.
<p>Publish Date: 2021-07-13
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-35516>CVE-2021-35516</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://commons.apache.org/proper/commons-compress/security-reports.html">https://commons.apache.org/proper/commons-compress/security-reports.html</a></p>
<p>Release Date: 2021-07-13</p>
<p>Fix Resolution: org.apache.commons:commons-compress:1.21</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-35515</summary>
### Vulnerable Library - <b>commons-compress-1.12.jar</b></p>
<p>Apache Commons Compress software defines an API for working with
compression and archive formats. These include: bzip2, gzip, pack200,
lzma, xz, Snappy, traditional Unix Compress, DEFLATE and ar, cpio,
jar, tar, zip, dump, 7z, arj.</p>
<p>Path to dependency file: /app/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.apache.commons/commons-compress/1.12/84caa68576e345eb5e7ae61a0e5a9229eb100d7b/commons-compress-1.12.jar</p>
<p>
Dependency Hierarchy:
- lint-gradle-26.5.3.jar (Root Library)
- sdk-common-26.5.3.jar
- sdklib-26.5.3.jar
- :x: **commons-compress-1.12.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/chatbot-watson-android/commit/59cf4251b46bc8fc950c9283359fabf1d97b885c">59cf4251b46bc8fc950c9283359fabf1d97b885c</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
When reading a specially crafted 7Z archive, the construction of the list of codecs that decompress an entry can result in an infinite loop. This could be used to mount a denial of service attack against services that use Compress' sevenz package.
<p>Publish Date: 2021-07-13
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-35515>CVE-2021-35515</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://commons.apache.org/proper/commons-compress/security-reports.html">https://commons.apache.org/proper/commons-compress/security-reports.html</a></p>
<p>Release Date: 2021-07-13</p>
<p>Fix Resolution: org.apache.commons:commons-compress:1.21</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-3171</summary>
### Vulnerable Library - <b>protobuf-java-3.4.0.jar</b></p>
<p>Core Protocol Buffers library. Protocol Buffers are a way of encoding structured data in an
efficient yet extensible format.</p>
<p>Library home page: <a href="https://developers.google.com/protocol-buffers/">https://developers.google.com/protocol-buffers/</a></p>
<p>Path to dependency file: /app/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.google.protobuf/protobuf-java/3.4.0/b32aba0cbe737a4ca953f71688725972e3ee927c/protobuf-java-3.4.0.jar</p>
<p>
Dependency Hierarchy:
- lint-gradle-26.5.3.jar (Root Library)
- sdk-common-26.5.3.jar
- :x: **protobuf-java-3.4.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/chatbot-watson-android/commit/59cf4251b46bc8fc950c9283359fabf1d97b885c">59cf4251b46bc8fc950c9283359fabf1d97b885c</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A parsing issue with binary data in protobuf-java core and lite versions prior to 3.21.7, 3.20.3, 3.19.6 and 3.16.3 can lead to a denial of service attack. Inputs containing multiple instances of non-repeated embedded messages with repeated or unknown fields causes objects to be converted back-n-forth between mutable and immutable forms, resulting in potentially long garbage collection pauses. We recommend updating to the versions mentioned above.
<p>Publish Date: 2022-10-12
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-3171>CVE-2022-3171</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-h4h5-3hr4-j3g2">https://github.com/advisories/GHSA-h4h5-3hr4-j3g2</a></p>
<p>Release Date: 2022-10-12</p>
<p>Fix Resolution: com.google.protobuf:protobuf-java:3.16.3,3.19.6,3.20.3,3.21.7;com.google.protobuf:protobuf-javalite:3.16.3,3.19.6,3.20.3,3.21.7;com.google.protobuf:protobuf-kotlin:3.19.6,3.20.3,3.21.7;com.google.protobuf:protobuf-kotlin-lite:3.19.6,3.20.3,3.21.7;google-protobuf - 3.19.6,3.20.3,3.21.7</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> WS-2019-0379</summary>
### Vulnerable Library - <b>commons-codec-1.10.jar</b></p>
<p>The Apache Commons Codec package contains simple encoder and decoders for
various formats such as Base64 and Hexadecimal. In addition to these
widely used encoders and decoders, the codec package also maintains a
collection of phonetic encoding utilities.</p>
<p>Path to dependency file: /app/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/commons-codec/commons-codec/1.10/4b95f4897fa13f2cd904aee711aeafc0c5295cd8/commons-codec-1.10.jar</p>
<p>
Dependency Hierarchy:
- lint-gradle-26.5.3.jar (Root Library)
- sdk-common-26.5.3.jar
- sdklib-26.5.3.jar
- httpmime-4.5.6.jar
- httpclient-4.5.6.jar
- :x: **commons-codec-1.10.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/chatbot-watson-android/commit/59cf4251b46bc8fc950c9283359fabf1d97b885c">59cf4251b46bc8fc950c9283359fabf1d97b885c</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache commons-codec before version “commons-codec-1.13-RC1” is vulnerable to information disclosure due to Improper Input validation.
<p>Publish Date: 2019-05-20
<p>URL: <a href=https://github.com/apache/commons-codec/commit/48b615756d1d770091ea3322eefc08011ee8b113>WS-2019-0379</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2019-05-20</p>
<p>Fix Resolution: commons-codec:commons-codec:1.13</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2020-15522</summary>
### Vulnerable Library - <b>bcprov-jdk15on-1.56.jar</b></p>
<p>The Bouncy Castle Crypto package is a Java implementation of cryptographic algorithms. This jar contains JCE provider and lightweight API for the Bouncy Castle Cryptography APIs for JDK 1.5 to JDK 1.8.</p>
<p>Library home page: <a href="http://www.bouncycastle.org/java.html">http://www.bouncycastle.org/java.html</a></p>
<p>Path to dependency file: /app/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.bouncycastle/bcprov-jdk15on/1.56/a153c6f9744a3e9dd6feab5e210e1c9861362ec7/bcprov-jdk15on-1.56.jar</p>
<p>
Dependency Hierarchy:
- lint-gradle-26.5.3.jar (Root Library)
- sdk-common-26.5.3.jar
- :x: **bcprov-jdk15on-1.56.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/chatbot-watson-android/commit/59cf4251b46bc8fc950c9283359fabf1d97b885c">59cf4251b46bc8fc950c9283359fabf1d97b885c</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Bouncy Castle BC Java before 1.66, BC C# .NET before 1.8.7, BC-FJA before 1.0.1.2, 1.0.2.1, and BC-FNA before 1.0.1.1 have a timing issue within the EC math library that can expose information about the private key when an attacker is able to observe timing information for the generation of multiple deterministic ECDSA signatures.
<p>Publish Date: 2021-05-20
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-15522>CVE-2020-15522</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.9</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-15522">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-15522</a></p>
<p>Release Date: 2021-05-20</p>
<p>Fix Resolution: C#- release-1.8.7, Java- 1.66</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2021-22569</summary>
### Vulnerable Library - <b>protobuf-java-3.4.0.jar</b></p>
<p>Core Protocol Buffers library. Protocol Buffers are a way of encoding structured data in an
efficient yet extensible format.</p>
<p>Library home page: <a href="https://developers.google.com/protocol-buffers/">https://developers.google.com/protocol-buffers/</a></p>
<p>Path to dependency file: /app/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.google.protobuf/protobuf-java/3.4.0/b32aba0cbe737a4ca953f71688725972e3ee927c/protobuf-java-3.4.0.jar</p>
<p>
Dependency Hierarchy:
- lint-gradle-26.5.3.jar (Root Library)
- sdk-common-26.5.3.jar
- :x: **protobuf-java-3.4.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/chatbot-watson-android/commit/59cf4251b46bc8fc950c9283359fabf1d97b885c">59cf4251b46bc8fc950c9283359fabf1d97b885c</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
An issue in protobuf-java allowed the interleaving of com.google.protobuf.UnknownFieldSet fields in such a way that would be processed out of order. A small malicious payload can occupy the parser for several minutes by creating large numbers of short-lived objects that cause frequent, repeated pauses. We recommend upgrading libraries beyond the vulnerable versions.
<p>Publish Date: 2022-01-10
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-22569>CVE-2021-22569</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-wrvw-hg22-4m67">https://github.com/advisories/GHSA-wrvw-hg22-4m67</a></p>
<p>Release Date: 2022-01-10</p>
<p>Fix Resolution: com.google.protobuf:protobuf-java:3.16.1,3.18.2,3.19.2; com.google.protobuf:protobuf-kotlin:3.18.2,3.19.2; google-protobuf - 3.19.2</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2020-17521</summary>
### Vulnerable Library - <b>groovy-all-2.4.15.jar</b></p>
<p>Groovy: A powerful, dynamic language for the JVM</p>
<p>Library home page: <a href="http://groovy-lang.org">http://groovy-lang.org</a></p>
<p>Path to dependency file: /app/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.codehaus.groovy/groovy-all/2.4.15/423a17aeb2f64bc6f76e8e44265a548bec80fd42/groovy-all-2.4.15.jar</p>
<p>
Dependency Hierarchy:
- lint-gradle-26.5.3.jar (Root Library)
- :x: **groovy-all-2.4.15.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/chatbot-watson-android/commit/59cf4251b46bc8fc950c9283359fabf1d97b885c">59cf4251b46bc8fc950c9283359fabf1d97b885c</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache Groovy provides extension methods to aid with creating temporary directories. Prior to this fix, Groovy's implementation of those extension methods was using a now superseded Java JDK method call that is potentially not secure on some operating systems in some contexts. Users not using the extension methods mentioned in the advisory are not affected, but may wish to read the advisory for further details. Versions Affected: 2.0 to 2.4.20, 2.5.0 to 2.5.13, 3.0.0 to 3.0.6, and 4.0.0-alpha-1. Fixed in versions 2.4.21, 2.5.14, 3.0.7, 4.0.0-alpha-2.
<p>Publish Date: 2020-12-07
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-17521>CVE-2020-17521</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://issues.apache.org/jira/browse/GROOVY-9824">https://issues.apache.org/jira/browse/GROOVY-9824</a></p>
<p>Release Date: 2020-12-07</p>
<p>Fix Resolution: org.codehaus.groovy:groovy-all:2.4.21,2.5.14,3.0.7</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-11771</summary>
### Vulnerable Library - <b>commons-compress-1.12.jar</b></p>
<p>Apache Commons Compress software defines an API for working with
compression and archive formats. These include: bzip2, gzip, pack200,
lzma, xz, Snappy, traditional Unix Compress, DEFLATE and ar, cpio,
jar, tar, zip, dump, 7z, arj.</p>
<p>Path to dependency file: /app/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.apache.commons/commons-compress/1.12/84caa68576e345eb5e7ae61a0e5a9229eb100d7b/commons-compress-1.12.jar</p>
<p>
Dependency Hierarchy:
- lint-gradle-26.5.3.jar (Root Library)
- sdk-common-26.5.3.jar
- sdklib-26.5.3.jar
- :x: **commons-compress-1.12.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/chatbot-watson-android/commit/59cf4251b46bc8fc950c9283359fabf1d97b885c">59cf4251b46bc8fc950c9283359fabf1d97b885c</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
When reading a specially crafted ZIP archive, the read method of Apache Commons Compress 1.7 to 1.17's ZipArchiveInputStream can fail to return the correct EOF indication after the end of the stream has been reached. When combined with a java.io.InputStreamReader this can lead to an infinite stream, which can be used to mount a denial of service attack against services that use Compress' zip package.
<p>Publish Date: 2018-08-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-11771>CVE-2018-11771</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-11771">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-11771</a></p>
<p>Release Date: 2018-08-16</p>
<p>Fix Resolution: 1.18</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-1324</summary>
### Vulnerable Library - <b>commons-compress-1.12.jar</b></p>
<p>Apache Commons Compress software defines an API for working with
compression and archive formats. These include: bzip2, gzip, pack200,
lzma, xz, Snappy, traditional Unix Compress, DEFLATE and ar, cpio,
jar, tar, zip, dump, 7z, arj.</p>
<p>Path to dependency file: /app/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.apache.commons/commons-compress/1.12/84caa68576e345eb5e7ae61a0e5a9229eb100d7b/commons-compress-1.12.jar</p>
<p>
Dependency Hierarchy:
- lint-gradle-26.5.3.jar (Root Library)
- sdk-common-26.5.3.jar
- sdklib-26.5.3.jar
- :x: **commons-compress-1.12.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/chatbot-watson-android/commit/59cf4251b46bc8fc950c9283359fabf1d97b885c">59cf4251b46bc8fc950c9283359fabf1d97b885c</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A specially crafted ZIP archive can be used to cause an infinite loop inside of Apache Commons Compress' extra field parser used by the ZipFile and ZipArchiveInputStream classes in versions 1.11 to 1.15. This can be used to mount a denial of service attack against services that use Compress' zip package.
<p>Publish Date: 2018-03-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-1324>CVE-2018-1324</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-1324">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-1324</a></p>
<p>Release Date: 2018-03-16</p>
<p>Fix Resolution: 1.16</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-24329</summary>
### Vulnerable Library - <b>kotlin-stdlib-1.3.50.jar</b></p>
<p>Kotlin Standard Library for JVM</p>
<p>Library home page: <a href="https://kotlinlang.org/">https://kotlinlang.org/</a></p>
<p>Path to dependency file: /app/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.jetbrains.kotlin/kotlin-stdlib/1.3.50/b529d1738c7e98bbfa36a4134039528f2ce78ebf/kotlin-stdlib-1.3.50.jar</p>
<p>
Dependency Hierarchy:
- lint-gradle-26.5.3.jar (Root Library)
- sdk-common-26.5.3.jar
- kotlin-reflect-1.3.50.jar
- :x: **kotlin-stdlib-1.3.50.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/chatbot-watson-android/commit/59cf4251b46bc8fc950c9283359fabf1d97b885c">59cf4251b46bc8fc950c9283359fabf1d97b885c</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In JetBrains Kotlin before 1.6.0, it was not possible to lock dependencies for Multiplatform Gradle Projects.
<p>Publish Date: 2022-02-25
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-24329>CVE-2022-24329</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-2qp4-g3q3-f92w">https://github.com/advisories/GHSA-2qp4-g3q3-f92w</a></p>
<p>Release Date: 2022-02-25</p>
<p>Fix Resolution: org.jetbrains.kotlin:kotlin-stdlib:1.6.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2020-13956</summary>
### Vulnerable Library - <b>httpclient-4.5.6.jar</b></p>
<p>Apache HttpComponents Client</p>
<p>Path to dependency file: /app/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.apache.httpcomponents/httpclient/4.5.6/1afe5621985efe90a92d0fbc9be86271efbe796f/httpclient-4.5.6.jar</p>
<p>
Dependency Hierarchy:
- lint-gradle-26.5.3.jar (Root Library)
- sdk-common-26.5.3.jar
- sdklib-26.5.3.jar
- httpmime-4.5.6.jar
- :x: **httpclient-4.5.6.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/chatbot-watson-android/commit/59cf4251b46bc8fc950c9283359fabf1d97b885c">59cf4251b46bc8fc950c9283359fabf1d97b885c</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache HttpClient versions prior to version 4.5.13 and 5.0.3 can misinterpret malformed authority component in request URIs passed to the library as java.net.URI object and pick the wrong target host for request execution.
<p>Publish Date: 2020-12-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-13956>CVE-2020-13956</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bugzilla.redhat.com/show_bug.cgi?id=CVE-2020-13956">https://bugzilla.redhat.com/show_bug.cgi?id=CVE-2020-13956</a></p>
<p>Release Date: 2020-12-02</p>
<p>Fix Resolution: org.apache.httpcomponents:httpclient:4.5.13;org.apache.httpcomponents:httpclient-osgi:4.5.13;org.apache.httpcomponents.client5:httpclient5:5.0.3;org.apache.httpcomponents.client5:httpclient5-osgi:5.0.3</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2020-26939</summary>
### Vulnerable Library - <b>bcprov-jdk15on-1.56.jar</b></p>
<p>The Bouncy Castle Crypto package is a Java implementation of cryptographic algorithms. This jar contains JCE provider and lightweight API for the Bouncy Castle Cryptography APIs for JDK 1.5 to JDK 1.8.</p>
<p>Library home page: <a href="http://www.bouncycastle.org/java.html">http://www.bouncycastle.org/java.html</a></p>
<p>Path to dependency file: /app/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.bouncycastle/bcprov-jdk15on/1.56/a153c6f9744a3e9dd6feab5e210e1c9861362ec7/bcprov-jdk15on-1.56.jar</p>
<p>
Dependency Hierarchy:
- lint-gradle-26.5.3.jar (Root Library)
- sdk-common-26.5.3.jar
- :x: **bcprov-jdk15on-1.56.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/chatbot-watson-android/commit/59cf4251b46bc8fc950c9283359fabf1d97b885c">59cf4251b46bc8fc950c9283359fabf1d97b885c</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Legion of the Bouncy Castle BC before 1.61 and BC-FJA before 1.0.1.2, attackers can obtain sensitive information about a private exponent because of Observable Differences in Behavior to Error Inputs. This occurs in org.bouncycastle.crypto.encodings.OAEPEncoding. Sending invalid ciphertext that decrypts to a short payload in the OAEP Decoder could result in the throwing of an early exception, potentially leaking some information about the private exponent of the RSA private key performing the encryption.
<p>Publish Date: 2020-11-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-26939>CVE-2020-26939</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2020-11-02</p>
<p>Fix Resolution: org.bouncycastle:bcprov-jdk14:1.61,org.bouncycastle:bcprov-ext-debug-jdk15on:1.61,org.bouncycastle:bcprov-debug-jdk15on:1.61,org.bouncycastle:bcprov-ext-jdk15on:1.61,org.bouncycastle:bcprov-jdk15on:1.61</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> CVE-2020-8908</summary>
### Vulnerable Library - <b>guava-27.0.1-jre.jar</b></p>
<p>Guava is a suite of core and expanded libraries that include
utility classes, google's collections, io classes, and much
much more.</p>
<p>Library home page: <a href="https://github.com/google/guava">https://github.com/google/guava</a></p>
<p>Path to dependency file: /app/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.google.guava/guava/27.0.1-jre/bd41a290787b5301e63929676d792c507bbc00ae/guava-27.0.1-jre.jar</p>
<p>
Dependency Hierarchy:
- lint-gradle-26.5.3.jar (Root Library)
- lint-26.5.3.jar
- :x: **guava-27.0.1-jre.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/chatbot-watson-android/commit/59cf4251b46bc8fc950c9283359fabf1d97b885c">59cf4251b46bc8fc950c9283359fabf1d97b885c</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A temp directory creation vulnerability exists in all versions of Guava, allowing an attacker with access to the machine to potentially access data in a temporary directory created by the Guava API com.google.common.io.Files.createTempDir(). By default, on unix-like systems, the created directory is world-readable (readable by an attacker with access to the system). The method in question has been marked @Deprecated in versions 30.0 and later and should not be used. For Android developers, we recommend choosing a temporary directory API provided by Android, such as context.getCacheDir(). For other Java developers, we recommend migrating to the Java 7 API java.nio.file.Files.createTempDirectory() which explicitly configures permissions of 700, or configuring the Java runtime's java.io.tmpdir system property to point to a location whose permissions are appropriately configured.
<p>Publish Date: 2020-12-10
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-8908>CVE-2020-8908</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>3.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-8908">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-8908</a></p>
<p>Release Date: 2020-12-10</p>
<p>Fix Resolution: v30.0</p>
</p>
<p></p>
</details>
|
non_process
|
lint gradle jar vulnerabilities highest severity is vulnerable library lint gradle jar path to dependency file app build gradle path to vulnerable library home wss scanner gradle caches modules files org apache commons commons compress commons compress jar found in head commit a href vulnerabilities cve severity cvss dependency type fixed in lint gradle version remediation available high commons compress jar transitive n a high bcprov jar transitive n a high protobuf java jar transitive n a high bcprov jar transitive n a high commons compress jar transitive n a high commons compress jar transitive n a high commons compress jar transitive n a high protobuf java jar transitive n a medium commons codec jar transitive n a medium bcprov jar transitive n a medium protobuf java jar transitive n a medium groovy all jar transitive n a medium commons compress jar transitive n a medium commons compress jar transitive n a medium kotlin stdlib jar transitive n a medium httpclient jar transitive n a medium bcprov jar transitive n a low guava jre jar transitive n a for some transitive vulnerabilities there is no version of direct dependency with a fix check the details section below to see if there is a version of transitive dependency where vulnerability is fixed details cve vulnerable library commons compress jar apache commons compress software defines an api for working with compression and archive formats these include gzip lzma xz snappy traditional unix compress deflate and ar cpio jar tar zip dump arj path to dependency file app build gradle path to vulnerable library home wss scanner gradle caches modules files org apache commons commons compress commons compress jar dependency hierarchy lint gradle jar root library sdk common jar sdklib jar x commons compress jar vulnerable library found in head commit a href found in base branch master vulnerability details when reading a specially crafted zip archive compress can be made to allocate large amounts of memory that finally leads to an out of memory error even for very small inputs this could be used to mount a denial of service attack against services that use compress zip package publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org apache commons commons compress cve vulnerable library bcprov jar the bouncy castle crypto package is a java implementation of cryptographic algorithms this jar contains jce provider and lightweight api for the bouncy castle cryptography apis for jdk to jdk library home page a href path to dependency file app build gradle path to vulnerable library home wss scanner gradle caches modules files org bouncycastle bcprov bcprov jar dependency hierarchy lint gradle jar root library sdk common jar x bcprov jar vulnerable library found in head commit a href found in base branch master vulnerability details the asn parser in bouncy castle crypto aka bc java can trigger a large attempted memory allocation and resultant outofmemoryerror error via crafted asn data this is fixed in publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org bouncycastle bcprov cve vulnerable library protobuf java jar core protocol buffers library protocol buffers are a way of encoding structured data in an efficient yet extensible format library home page a href path to dependency file app build gradle path to vulnerable library home wss scanner gradle caches modules files com google protobuf protobuf java protobuf java jar dependency hierarchy lint gradle jar root library sdk common jar x protobuf java jar vulnerable library found in head commit a href found in base branch master vulnerability details a parsing issue similar to cve but with textformat in protobuf java core and lite versions prior to and can lead to a denial of service attack inputs containing multiple instances of non repeated embedded messages with repeated or unknown fields causes objects to be converted back n forth between mutable and immutable forms resulting in potentially long garbage collection pauses we recommend updating to the versions mentioned above publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com google protobuf protobuf java cve vulnerable library bcprov jar the bouncy castle crypto package is a java implementation of cryptographic algorithms this jar contains jce provider and lightweight api for the bouncy castle cryptography apis for jdk to jdk library home page a href path to dependency file app build gradle path to vulnerable library home wss scanner gradle caches modules files org bouncycastle bcprov bcprov jar dependency hierarchy lint gradle jar root library sdk common jar x bcprov jar vulnerable library found in head commit a href found in base branch master vulnerability details bouncy castle bc bc fja bc fja and earlier have a flaw in the low level interface to rsa key pair generator specifically rsa key pairs generated in low level api with added certainty may have less m r tests than expected this appears to be fixed in versions bc beta and later bc fja and later publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org bouncycastle bc fips org bouncycastle bcprov org bouncycastle bcprov org bouncycastle bcprov ext org bouncycastle bcprov ext org bouncycastle bcprov debug org bouncycastle bcprov debug cve vulnerable library commons compress jar apache commons compress software defines an api for working with compression and archive formats these include gzip lzma xz snappy traditional unix compress deflate and ar cpio jar tar zip dump arj path to dependency file app build gradle path to vulnerable library home wss scanner gradle caches modules files org apache commons commons compress commons compress jar dependency hierarchy lint gradle jar root library sdk common jar sdklib jar x commons compress jar vulnerable library found in head commit a href found in base branch master vulnerability details when reading a specially crafted tar archive compress can be made to allocate large amounts of memory that finally leads to an out of memory error even for very small inputs this could be used to mount a denial of service attack against services that use compress tar package publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org apache commons commons compress cve vulnerable library commons compress jar apache commons compress software defines an api for working with compression and archive formats these include gzip lzma xz snappy traditional unix compress deflate and ar cpio jar tar zip dump arj path to dependency file app build gradle path to vulnerable library home wss scanner gradle caches modules files org apache commons commons compress commons compress jar dependency hierarchy lint gradle jar root library sdk common jar sdklib jar x commons compress jar vulnerable library found in head commit a href found in base branch master vulnerability details when reading a specially crafted archive compress can be made to allocate large amounts of memory that finally leads to an out of memory error even for very small inputs this could be used to mount a denial of service attack against services that use compress sevenz package publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org apache commons commons compress cve vulnerable library commons compress jar apache commons compress software defines an api for working with compression and archive formats these include gzip lzma xz snappy traditional unix compress deflate and ar cpio jar tar zip dump arj path to dependency file app build gradle path to vulnerable library home wss scanner gradle caches modules files org apache commons commons compress commons compress jar dependency hierarchy lint gradle jar root library sdk common jar sdklib jar x commons compress jar vulnerable library found in head commit a href found in base branch master vulnerability details when reading a specially crafted archive the construction of the list of codecs that decompress an entry can result in an infinite loop this could be used to mount a denial of service attack against services that use compress sevenz package publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org apache commons commons compress cve vulnerable library protobuf java jar core protocol buffers library protocol buffers are a way of encoding structured data in an efficient yet extensible format library home page a href path to dependency file app build gradle path to vulnerable library home wss scanner gradle caches modules files com google protobuf protobuf java protobuf java jar dependency hierarchy lint gradle jar root library sdk common jar x protobuf java jar vulnerable library found in head commit a href found in base branch master vulnerability details a parsing issue with binary data in protobuf java core and lite versions prior to and can lead to a denial of service attack inputs containing multiple instances of non repeated embedded messages with repeated or unknown fields causes objects to be converted back n forth between mutable and immutable forms resulting in potentially long garbage collection pauses we recommend updating to the versions mentioned above publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com google protobuf protobuf java com google protobuf protobuf javalite com google protobuf protobuf kotlin com google protobuf protobuf kotlin lite google protobuf ws vulnerable library commons codec jar the apache commons codec package contains simple encoder and decoders for various formats such as and hexadecimal in addition to these widely used encoders and decoders the codec package also maintains a collection of phonetic encoding utilities path to dependency file app build gradle path to vulnerable library home wss scanner gradle caches modules files commons codec commons codec commons codec jar dependency hierarchy lint gradle jar root library sdk common jar sdklib jar httpmime jar httpclient jar x commons codec jar vulnerable library found in head commit a href found in base branch master vulnerability details apache commons codec before version “commons codec ” is vulnerable to information disclosure due to improper input validation publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version release date fix resolution commons codec commons codec cve vulnerable library bcprov jar the bouncy castle crypto package is a java implementation of cryptographic algorithms this jar contains jce provider and lightweight api for the bouncy castle cryptography apis for jdk to jdk library home page a href path to dependency file app build gradle path to vulnerable library home wss scanner gradle caches modules files org bouncycastle bcprov bcprov jar dependency hierarchy lint gradle jar root library sdk common jar x bcprov jar vulnerable library found in head commit a href found in base branch master vulnerability details bouncy castle bc java before bc c net before bc fja before and bc fna before have a timing issue within the ec math library that can expose information about the private key when an attacker is able to observe timing information for the generation of multiple deterministic ecdsa signatures publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution c release java cve vulnerable library protobuf java jar core protocol buffers library protocol buffers are a way of encoding structured data in an efficient yet extensible format library home page a href path to dependency file app build gradle path to vulnerable library home wss scanner gradle caches modules files com google protobuf protobuf java protobuf java jar dependency hierarchy lint gradle jar root library sdk common jar x protobuf java jar vulnerable library found in head commit a href found in base branch master vulnerability details an issue in protobuf java allowed the interleaving of com google protobuf unknownfieldset fields in such a way that would be processed out of order a small malicious payload can occupy the parser for several minutes by creating large numbers of short lived objects that cause frequent repeated pauses we recommend upgrading libraries beyond the vulnerable versions publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com google protobuf protobuf java com google protobuf protobuf kotlin google protobuf cve vulnerable library groovy all jar groovy a powerful dynamic language for the jvm library home page a href path to dependency file app build gradle path to vulnerable library home wss scanner gradle caches modules files org codehaus groovy groovy all groovy all jar dependency hierarchy lint gradle jar root library x groovy all jar vulnerable library found in head commit a href found in base branch master vulnerability details apache groovy provides extension methods to aid with creating temporary directories prior to this fix groovy s implementation of those extension methods was using a now superseded java jdk method call that is potentially not secure on some operating systems in some contexts users not using the extension methods mentioned in the advisory are not affected but may wish to read the advisory for further details versions affected to to to and alpha fixed in versions alpha publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org codehaus groovy groovy all cve vulnerable library commons compress jar apache commons compress software defines an api for working with compression and archive formats these include gzip lzma xz snappy traditional unix compress deflate and ar cpio jar tar zip dump arj path to dependency file app build gradle path to vulnerable library home wss scanner gradle caches modules files org apache commons commons compress commons compress jar dependency hierarchy lint gradle jar root library sdk common jar sdklib jar x commons compress jar vulnerable library found in head commit a href found in base branch master vulnerability details when reading a specially crafted zip archive the read method of apache commons compress to s ziparchiveinputstream can fail to return the correct eof indication after the end of the stream has been reached when combined with a java io inputstreamreader this can lead to an infinite stream which can be used to mount a denial of service attack against services that use compress zip package publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution cve vulnerable library commons compress jar apache commons compress software defines an api for working with compression and archive formats these include gzip lzma xz snappy traditional unix compress deflate and ar cpio jar tar zip dump arj path to dependency file app build gradle path to vulnerable library home wss scanner gradle caches modules files org apache commons commons compress commons compress jar dependency hierarchy lint gradle jar root library sdk common jar sdklib jar x commons compress jar vulnerable library found in head commit a href found in base branch master vulnerability details a specially crafted zip archive can be used to cause an infinite loop inside of apache commons compress extra field parser used by the zipfile and ziparchiveinputstream classes in versions to this can be used to mount a denial of service attack against services that use compress zip package publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution cve vulnerable library kotlin stdlib jar kotlin standard library for jvm library home page a href path to dependency file app build gradle path to vulnerable library home wss scanner gradle caches modules files org jetbrains kotlin kotlin stdlib kotlin stdlib jar dependency hierarchy lint gradle jar root library sdk common jar kotlin reflect jar x kotlin stdlib jar vulnerable library found in head commit a href found in base branch master vulnerability details in jetbrains kotlin before it was not possible to lock dependencies for multiplatform gradle projects publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org jetbrains kotlin kotlin stdlib cve vulnerable library httpclient jar apache httpcomponents client path to dependency file app build gradle path to vulnerable library home wss scanner gradle caches modules files org apache httpcomponents httpclient httpclient jar dependency hierarchy lint gradle jar root library sdk common jar sdklib jar httpmime jar x httpclient jar vulnerable library found in head commit a href found in base branch master vulnerability details apache httpclient versions prior to version and can misinterpret malformed authority component in request uris passed to the library as java net uri object and pick the wrong target host for request execution publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org apache httpcomponents httpclient org apache httpcomponents httpclient osgi org apache httpcomponents org apache httpcomponents osgi cve vulnerable library bcprov jar the bouncy castle crypto package is a java implementation of cryptographic algorithms this jar contains jce provider and lightweight api for the bouncy castle cryptography apis for jdk to jdk library home page a href path to dependency file app build gradle path to vulnerable library home wss scanner gradle caches modules files org bouncycastle bcprov bcprov jar dependency hierarchy lint gradle jar root library sdk common jar x bcprov jar vulnerable library found in head commit a href found in base branch master vulnerability details in legion of the bouncy castle bc before and bc fja before attackers can obtain sensitive information about a private exponent because of observable differences in behavior to error inputs this occurs in org bouncycastle crypto encodings oaepencoding sending invalid ciphertext that decrypts to a short payload in the oaep decoder could result in the throwing of an early exception potentially leaking some information about the private exponent of the rsa private key performing the encryption publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version release date fix resolution org bouncycastle bcprov org bouncycastle bcprov ext debug org bouncycastle bcprov debug org bouncycastle bcprov ext org bouncycastle bcprov cve vulnerable library guava jre jar guava is a suite of core and expanded libraries that include utility classes google s collections io classes and much much more library home page a href path to dependency file app build gradle path to vulnerable library home wss scanner gradle caches modules files com google guava guava jre guava jre jar dependency hierarchy lint gradle jar root library lint jar x guava jre jar vulnerable library found in head commit a href found in base branch master vulnerability details a temp directory creation vulnerability exists in all versions of guava allowing an attacker with access to the machine to potentially access data in a temporary directory created by the guava api com google common io files createtempdir by default on unix like systems the created directory is world readable readable by an attacker with access to the system the method in question has been marked deprecated in versions and later and should not be used for android developers we recommend choosing a temporary directory api provided by android such as context getcachedir for other java developers we recommend migrating to the java api java nio file files createtempdirectory which explicitly configures permissions of or configuring the java runtime s java io tmpdir system property to point to a location whose permissions are appropriately configured publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact low integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution
| 0
|
101,486
| 12,688,779,036
|
IssuesEvent
|
2020-06-21 00:54:08
|
zulip/zulip
|
https://api.github.com/repos/zulip/zulip
|
closed
|
Improve the styling of /accounts/go/ page
|
area: portico design enhancement good first issue in progress
|
This is a followup up issue of #10565
There are a lot of improvements that can be made to the styling of `/accounts/go/` page. Some suggestions that were already made
> I'm not altogether happy with the "Next" button styling/text and I think that could use another round of work, - Tim Abbott
> For follow-up I would also left-justify the "Don't know your .." and "Need to get your group .." text.
(At least the "Don't know your .." text; could be convinced otherwise for "Need to get your ..") - Rishi
Feel free to make any other styling changes that you will think would improve the page as well :)
|
1.0
|
Improve the styling of /accounts/go/ page - This is a followup up issue of #10565
There are a lot of improvements that can be made to the styling of `/accounts/go/` page. Some suggestions that were already made
> I'm not altogether happy with the "Next" button styling/text and I think that could use another round of work, - Tim Abbott
> For follow-up I would also left-justify the "Don't know your .." and "Need to get your group .." text.
(At least the "Don't know your .." text; could be convinced otherwise for "Need to get your ..") - Rishi
Feel free to make any other styling changes that you will think would improve the page as well :)
|
non_process
|
improve the styling of accounts go page this is a followup up issue of there are a lot of improvements that can be made to the styling of accounts go page some suggestions that were already made i m not altogether happy with the next button styling text and i think that could use another round of work tim abbott for follow up i would also left justify the don t know your and need to get your group text at least the don t know your text could be convinced otherwise for need to get your rishi feel free to make any other styling changes that you will think would improve the page as well
| 0
|
1,932
| 4,761,812,166
|
IssuesEvent
|
2016-10-25 09:26:01
|
nodejs/node
|
https://api.github.com/repos/nodejs/node
|
closed
|
Mention case-insensitivity in process.env docs
|
doc good first contribution process test
|
On Windows OS, environment variables are case-insensitive.
```
14:46 $ node
> process.env.foo = "lol"
'lol'
> process.env.fOo
'lol'
```
I think it could be beneficial to make a note about this in the docs.
|
1.0
|
Mention case-insensitivity in process.env docs - On Windows OS, environment variables are case-insensitive.
```
14:46 $ node
> process.env.foo = "lol"
'lol'
> process.env.fOo
'lol'
```
I think it could be beneficial to make a note about this in the docs.
|
process
|
mention case insensitivity in process env docs on windows os environment variables are case insensitive node process env foo lol lol process env foo lol i think it could be beneficial to make a note about this in the docs
| 1
|
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.