Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1
value | created_at stringlengths 19 19 | repo stringlengths 4 112 | repo_url stringlengths 33 141 | action stringclasses 3
values | title stringlengths 1 1.02k | labels stringlengths 4 1.54k | body stringlengths 1 262k | index stringclasses 17
values | text_combine stringlengths 95 262k | label stringclasses 2
values | text stringlengths 96 252k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
85,208 | 3,688,026,741 | IssuesEvent | 2016-02-25 10:59:47 | sklipus/testREST | https://api.github.com/repos/sklipus/testREST | opened | Git Origin: another PB | Priority: High Status: Ready for Package | **Git Origin: another PB**
Three days after the quarrel, Prince Stepan Arkadyevitch
Oblonsky--Stiva, as he was called in the fashionable world--woke
up at his usual hour, that is, at eight o'clock in the morning,
not in his wife's bedroom, but on the leather-covered sofa in his
study. He turned over his stout, w... | 1.0 | Git Origin: another PB - **Git Origin: another PB**
Three days after the quarrel, Prince Stepan Arkadyevitch
Oblonsky--Stiva, as he was called in the fashionable world--woke
up at his usual hour, that is, at eight o'clock in the morning,
not in his wife's bedroom, but on the leather-covered sofa in his
study. He... | non_test | git origin another pb git origin another pb three days after the quarrel prince stepan arkadyevitch oblonsky stiva as he was called in the fashionable world woke up at his usual hour that is at eight o clock in the morning not in his wife s bedroom but on the leather covered sofa in his study he... | 0 |
5,257 | 26,602,528,960 | IssuesEvent | 2023-01-23 16:45:04 | webtorrent/webtorrent | https://api.github.com/repos/webtorrent/webtorrent | closed | Use Browserify builtins feature to specify Chrome App builtins instead of "chromeapp" package.json field | enhancement help wanted accepted discuss at maintainers call | To support a Chrome App build for the Brave Browser WebTorrent extension, I added replacements for the Node Builtins that work in a Chrome App environment. For example, `net` is replaced by `chrome-net`, `dgram` is replaced by `chrome-dgram`, and `dns` is replaced by `chrome-dns`, etc.
In order to pull this off, we ... | True | Use Browserify builtins feature to specify Chrome App builtins instead of "chromeapp" package.json field - To support a Chrome App build for the Brave Browser WebTorrent extension, I added replacements for the Node Builtins that work in a Chrome App environment. For example, `net` is replaced by `chrome-net`, `dgram` i... | non_test | use browserify builtins feature to specify chrome app builtins instead of chromeapp package json field to support a chrome app build for the brave browser webtorrent extension i added replacements for the node builtins that work in a chrome app environment for example net is replaced by chrome net dgram i... | 0 |
175,933 | 13,617,598,770 | IssuesEvent | 2020-09-23 17:14:43 | openshift/odo | https://api.github.com/repos/openshift/odo | closed | Add docker version coverage for docker devfile push | area/testing kind/feature lifecycle/rotten | /kind feature
<!--
Welcome! - We kindly ask you to:
1. Fill out the issue template below
2. Use the Google group if you have a question rather than a bug or feature request.
The group is at: https://groups.google.com/forum/#!forum/odo-users
Thanks for understanding, and for contributing to the pr... | 1.0 | Add docker version coverage for docker devfile push - /kind feature
<!--
Welcome! - We kindly ask you to:
1. Fill out the issue template below
2. Use the Google group if you have a question rather than a bug or feature request.
The group is at: https://groups.google.com/forum/#!forum/odo-users
Th... | test | add docker version coverage for docker devfile push kind feature welcome we kindly ask you to fill out the issue template below use the google group if you have a question rather than a bug or feature request the group is at thanks for understanding and for contributing to ... | 1 |
20,143 | 10,605,103,100 | IssuesEvent | 2019-10-10 19:41:37 | toggl/mobileapp | https://api.github.com/repos/toggl/mobileapp | closed | Deduplicate expensive Rx calls | foundation performance | ## 🚧 Refactor Proposal
We are doing some expensive calls on Rx more than once. this is impacting our startup times.
## Technical aspects
We need to check each expensive call we make using Rx and make sure that we are using Connect/RefCount correctly to avoid multiple subscribers making multiple calls. | True | Deduplicate expensive Rx calls - ## 🚧 Refactor Proposal
We are doing some expensive calls on Rx more than once. this is impacting our startup times.
## Technical aspects
We need to check each expensive call we make using Rx and make sure that we are using Connect/RefCount correctly to avoid multiple subscribers m... | non_test | deduplicate expensive rx calls 🚧 refactor proposal we are doing some expensive calls on rx more than once this is impacting our startup times technical aspects we need to check each expensive call we make using rx and make sure that we are using connect refcount correctly to avoid multiple subscribers m... | 0 |
194,358 | 14,676,357,641 | IssuesEvent | 2020-12-30 19:58:32 | apache/buildstream | https://api.github.com/repos/apache/buildstream | closed | Loader tests are broken | bug important tests | [See original issue on GitLab](https://gitlab.com/BuildStream/buildstream/-/issues/335)
In GitLab by [[Gitlab user @tristanvb]](https://gitlab.com/tristanvb) on Apr 3, 2018, 06:46
Note that these tests are some of the last tests which still need to be ported to use the `Cli` fixture from `testutils`...
When running:
... | 1.0 | Loader tests are broken - [See original issue on GitLab](https://gitlab.com/BuildStream/buildstream/-/issues/335)
In GitLab by [[Gitlab user @tristanvb]](https://gitlab.com/tristanvb) on Apr 3, 2018, 06:46
Note that these tests are some of the last tests which still need to be ported to use the `Cli` fixture from `tes... | test | loader tests are broken in gitlab by on apr note that these tests are some of the last tests which still need to be ported to use the cli fixture from testutils when running sh setup py test addoptps tests loader the tests consistently fail with an assertion because the p... | 1 |
279,068 | 24,196,414,302 | IssuesEvent | 2022-09-24 00:52:28 | ValveSoftware/steam-for-linux | https://api.github.com/repos/ValveSoftware/steam-for-linux | closed | No more sound via Remote Play. | Audio Streaming Need Retest | I also notice that Steam is not in the pulseaudio list anymore.

#### Your system information
* Steam client version (build number or date): Mar 25 2020
* Distribution (e.g. Ubuntu): ... | 1.0 | No more sound via Remote Play. - I also notice that Steam is not in the pulseaudio list anymore.

#### Your system information
* Steam client version (build number or date): Mar 25 202... | test | no more sound via remote play i also notice that steam is not in the pulseaudio list anymore your system information steam client version build number or date mar distribution e g ubuntu manjaro opted into steam client beta yes have you checked for system updates yes ... | 1 |
24,393 | 4,076,855,231 | IssuesEvent | 2016-05-30 03:37:31 | coreos/etcd | https://api.github.com/repos/coreos/etcd | closed | Test: TestIssue3699 times out | area/testing | ```
goroutine 12943 [sleep]:
time.Sleep(0x989680)
/usr/local/golang/1.6.2/go/src/runtime/time.go:59 +0xf9
github.com/coreos/etcd/integration.(*cluster).waitMembersMatch(0xc8231b7200, 0xc82000ea20, 0xc820187e00, 0x4, 0x4)
/home/runner/workspace/src/github.com/coreos/etcd/gopath/src/github.com/coreos/etcd/integrat... | 1.0 | Test: TestIssue3699 times out - ```
goroutine 12943 [sleep]:
time.Sleep(0x989680)
/usr/local/golang/1.6.2/go/src/runtime/time.go:59 +0xf9
github.com/coreos/etcd/integration.(*cluster).waitMembersMatch(0xc8231b7200, 0xc82000ea20, 0xc820187e00, 0x4, 0x4)
/home/runner/workspace/src/github.com/coreos/etcd/gopath/src... | test | test times out goroutine time sleep usr local golang go src runtime time go github com coreos etcd integration cluster waitmembersmatch home runner workspace src github com coreos etcd gopath src github com coreos etcd integration cluster go github com coreos... | 1 |
802 | 2,639,994,552 | IssuesEvent | 2015-03-11 08:44:47 | FRosner/spawncamping-dds | https://api.github.com/repos/FRosner/spawncamping-dds | opened | Upgrade to Spark 1.3 | Build Spark | - [ ] Upgrade dependency
- [ ] API for SchemaRDD / Data frame
This will probably end up in DDS 2.x because it breaks the API when working with Spark 1.2. Does it make sense to backport patches to 1.x branch? | 1.0 | Upgrade to Spark 1.3 - - [ ] Upgrade dependency
- [ ] API for SchemaRDD / Data frame
This will probably end up in DDS 2.x because it breaks the API when working with Spark 1.2. Does it make sense to backport patches to 1.x branch? | non_test | upgrade to spark upgrade dependency api for schemardd data frame this will probably end up in dds x because it breaks the api when working with spark does it make sense to backport patches to x branch | 0 |
301,491 | 9,220,945,413 | IssuesEvent | 2019-03-11 18:43:16 | chocolatey/choco | https://api.github.com/repos/chocolatey/choco | closed | Feature/switch to halt install if dependency requires a reboot | 3 - Done Enhancement Priority_HIGH | As per https://groups.google.com/forum/#!topic/chocolatey/jP4cv8TDUcU, it's probably a good idea to add a switch so that install/upgrade will halt if a dependency requires a reboot. For example, I have a package that has a dependency on PowerShell 3+ - chocolately installed PowerShell v5 but then logged this and then c... | 1.0 | Feature/switch to halt install if dependency requires a reboot - As per https://groups.google.com/forum/#!topic/chocolatey/jP4cv8TDUcU, it's probably a good idea to add a switch so that install/upgrade will halt if a dependency requires a reboot. For example, I have a package that has a dependency on PowerShell 3+ - ch... | non_test | feature switch to halt install if dependency requires a reboot as per it s probably a good idea to add a switch so that install upgrade will halt if a dependency requires a reboot for example i have a package that has a dependency on powershell chocolately installed powershell but then logged this and then... | 0 |
755,641 | 26,434,963,670 | IssuesEvent | 2023-01-15 09:12:13 | projectdiscovery/tlsx | https://api.github.com/repos/projectdiscovery/tlsx | closed | Pre-Handshake doesn't work and completes the handshake | Priority: High Status: Completed Type: Bug | ### tlsx version:
`main|dev`
### Current Behavior:
`-pre-handshake/-ps` completes the whole TLS handshake without early exit at certificate phase
### Expected Behavior:
Early exit at server certificate phase for TLS<1.2
### Steps To Reproduce:
```console
$ tlsx -ps -u scanme.sh -json
```
 - autoclosed | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>threadfix_api-1.1.1-py3-none-any.whl</b></p></summary>
<p></p>
<p>Path to vulnerable library: /Python/Pip/requirements.txt</p>
<p>
<p>Found in HEAD commit: <a href=... | True | threadfix_api-1.1.1-py3-none-any.whl: 2 vulnerabilities (highest severity is: 7.5) - autoclosed - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>threadfix_api-1.1.1-py3-none-any.whl</b></p></summary>
<p></p>
<p>Pa... | non_test | threadfix api none any whl vulnerabilities highest severity is autoclosed vulnerable library threadfix api none any whl path to vulnerable library python pip requirements txt found in head commit a href vulnerabilities cve severity cvss dependency... | 0 |
85,648 | 24,647,595,327 | IssuesEvent | 2022-10-17 15:56:08 | expo/expo | https://api.github.com/repos/expo/expo | closed | TypeError: undefined is not an object (evaluating 'gl.getProgramInfoLog(program).trim') | needs review incomplete issue: missing or invalid repro Development Builds | ### Summary
I am working with `expo-bare-workflow`. My app is using `expo-gl` and `three.js` for rendering animations for my app.
While developing, app works smoothly and reflects the changes smoothly, but once I navigate from one navigation stack to another one application crashes with the following error:
```b... | 1.0 | TypeError: undefined is not an object (evaluating 'gl.getProgramInfoLog(program).trim') - ### Summary
I am working with `expo-bare-workflow`. My app is using `expo-gl` and `three.js` for rendering animations for my app.
While developing, app works smoothly and reflects the changes smoothly, but once I navigate from... | non_test | typeerror undefined is not an object evaluating gl getprograminfolog program trim summary i am working with expo bare workflow my app is using expo gl and three js for rendering animations for my app while developing app works smoothly and reflects the changes smoothly but once i navigate from... | 0 |
512,066 | 14,887,682,972 | IssuesEvent | 2021-01-20 18:41:50 | neo-one-suite/neo-one | https://api.github.com/repos/neo-one-suite/neo-one | closed | Update blockchain for preview4 changes | area/node priority/important-soon | - [x] (1) investigate this change for calculating verificationCost https://github.com/neo-project/neo/pull/1931
- [x] (2) onPersist / postPersist + trigger changes https://github.com/neo-project/neo/pull/2022
- [x] (3) asynchronous oracle blockchain changes https://github.com/neo-project/neo/pull/1738
- [x] (4) chec... | 1.0 | Update blockchain for preview4 changes - - [x] (1) investigate this change for calculating verificationCost https://github.com/neo-project/neo/pull/1931
- [x] (2) onPersist / postPersist + trigger changes https://github.com/neo-project/neo/pull/2022
- [x] (3) asynchronous oracle blockchain changes https://github.com/... | non_test | update blockchain for changes investigate this change for calculating verificationcost onpersist postpersist trigger changes asynchronous oracle blockchain changes check these changes in blockchain for oracle | 0 |
268,085 | 23,343,672,357 | IssuesEvent | 2022-08-09 15:55:53 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | opened | kvserver: add perf testing for long time until store dead + long node downtime | C-enhancement C-performance A-kv-distribution A-testing | **Describe the problem**
In a support case we saw that foreground app traffic was affected in v21.1 during a rolling restart:
- cluster had "time until store dead" set to 8 hours
- node was down for 20-30mn
- upon restart of node, SQL perf tanked
We're expecting the problem was caused due to KV snapshot hicc... | 1.0 | kvserver: add perf testing for long time until store dead + long node downtime - **Describe the problem**
In a support case we saw that foreground app traffic was affected in v21.1 during a rolling restart:
- cluster had "time until store dead" set to 8 hours
- node was down for 20-30mn
- upon restart of node, ... | test | kvserver add perf testing for long time until store dead long node downtime describe the problem in a support case we saw that foreground app traffic was affected in during a rolling restart cluster had time until store dead set to hours node was down for upon restart of node sql pe... | 1 |
176,584 | 13,646,617,757 | IssuesEvent | 2020-09-25 23:44:13 | Azure/azure-sdk-for-java | https://api.github.com/repos/Azure/azure-sdk-for-java | closed | Keyvault keys Readme issues | Client Docs KeyVault needs-team-triage test-manual-pass | 1.
Section [Link](https://github.com/Azure/azure-sdk-for-java/tree/master/sdk/keyvault/azure-security-keyvault-keys#prerequisites):
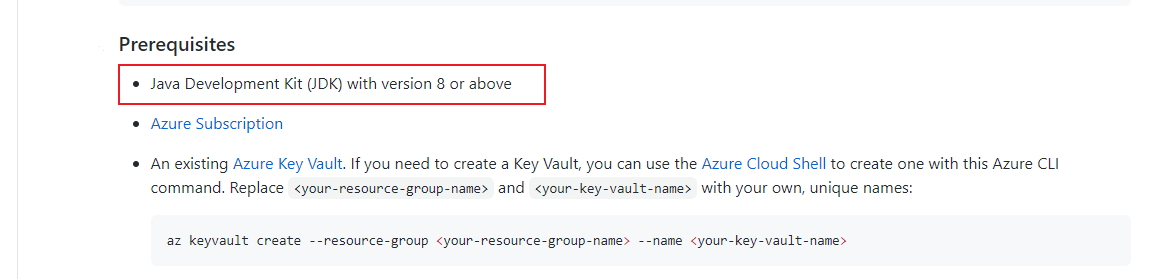
Suggestion:
Add hyperlink for `Java Development Kit(JDK) ` https://docs.... | 1.0 | Keyvault keys Readme issues - 1.
Section [Link](https://github.com/Azure/azure-sdk-for-java/tree/master/sdk/keyvault/azure-security-keyvault-keys#prerequisites):
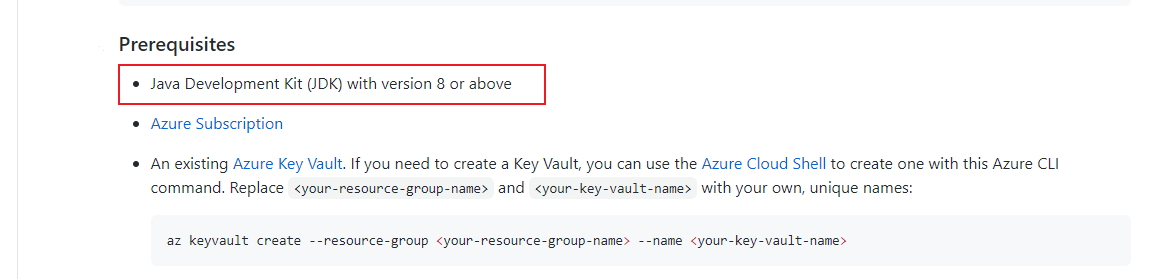
Suggestion:
Add hyperlink for `Java Develo... | test | keyvault keys readme issues section suggestion add hyperlink for java development kit jdk jongio for notification | 1 |
289,225 | 24,968,924,398 | IssuesEvent | 2022-11-01 22:14:14 | gradido/gradido | https://api.github.com/repos/gradido/gradido | closed | 🚀 [Feature] Implement Fullstack Tests as Github Workflow | feature test | <!-- You can find the latest issue templates here https://github.com/ulfgebhardt/issue-templates -->
## 🚀 Feature
<!-- Give a short summary of the Feature. Use Screenshots if you want. -->
Implement Fullstack Tests as Github Workflow
- [x] Have at least one Fullstack-Test automatically running on each PR | 1.0 | 🚀 [Feature] Implement Fullstack Tests as Github Workflow - <!-- You can find the latest issue templates here https://github.com/ulfgebhardt/issue-templates -->
## 🚀 Feature
<!-- Give a short summary of the Feature. Use Screenshots if you want. -->
Implement Fullstack Tests as Github Workflow
- [x] Have at l... | test | 🚀 implement fullstack tests as github workflow 🚀 feature implement fullstack tests as github workflow have at least one fullstack test automatically running on each pr | 1 |
309,896 | 23,310,770,875 | IssuesEvent | 2022-08-08 08:03:50 | cri-o/cri-o | https://api.github.com/repos/cri-o/cri-o | closed | Rootless cri-o documentation | help wanted good first issue lifecycle/stale kind/documentation | I want to run rootless kubernetes, crio, crun. For the beginning, I want to run rootfull kubelet and rootless crio+crun. The information for this is very spare.
https://kubernetes.io/docs/tasks/administer-cluster/kubelet-in-userns/ suggests setting the variable `_CRIO_ROOTLESS=1`, but cri-o does not document this ... | 1.0 | Rootless cri-o documentation - I want to run rootless kubernetes, crio, crun. For the beginning, I want to run rootfull kubelet and rootless crio+crun. The information for this is very spare.
https://kubernetes.io/docs/tasks/administer-cluster/kubelet-in-userns/ suggests setting the variable `_CRIO_ROOTLESS=1`, bu... | non_test | rootless cri o documentation i want to run rootless kubernetes crio crun for the beginning i want to run rootfull kubelet and rootless crio crun the information for this is very spare suggests setting the variable crio rootless but cri o does not document this variable advises for creating a ... | 0 |
236,390 | 7,749,003,553 | IssuesEvent | 2018-05-30 10:00:52 | Gloirin/m2gTest | https://api.github.com/repos/Gloirin/m2gTest | closed | 0003142:
mix of english and german ("denglisch") when sending mail | Felamimail low priority | **Reported by robert.lischke on 20 Oct 2010 09:05**
**Version:** git master
The message "Transferring Nachricht" is a mix of English and German, it should read "Übertrage Nachricht".
**Steps to reproduce:** Start the German version of Tine 2.0
Start Mail
Create a new message
Click on "Sen... | 1.0 | 0003142:
mix of english and german ("denglisch") when sending mail - **Reported by robert.lischke on 20 Oct 2010 09:05**
**Version:** git master
The message "Transferring Nachricht" is a mix of English and German, it should read "Übertrage Nachricht".
**Steps to reproduce:** Start the German vers... | non_test | mix of english and german denglisch when sending mail reported by robert lischke on oct version git master the message quot transferring nachricht quot is a mix of english and german it should read quot übertrage nachricht quot steps to reproduce start the german version of tine ... | 0 |
116,030 | 9,818,798,099 | IssuesEvent | 2019-06-13 20:13:05 | magento-engcom/msi | https://api.github.com/repos/magento-engcom/msi | closed | MFTF Order with Configurable product with drop-down attribute on multy stock mode canceled from Admin | MFTF (Functional Test Coverage) | https://app.hiptest.com/projects/69435/test-plan/folders/432042/scenarios/1446500 | 1.0 | MFTF Order with Configurable product with drop-down attribute on multy stock mode canceled from Admin - https://app.hiptest.com/projects/69435/test-plan/folders/432042/scenarios/1446500 | test | mftf order with configurable product with drop down attribute on multy stock mode canceled from admin | 1 |
302,013 | 26,118,061,098 | IssuesEvent | 2022-12-28 09:07:14 | wazuh/wazuh | https://api.github.com/repos/wazuh/wazuh | closed | Release 4.4.0 - Alpha 2 - E2E UX tests - Wazuh Dashboard | type/release tracking type/release release test/4.4.0 | The following issue aims to run the specified test for the current release candidate, report the results, and open new issues for any encountered errors.
## Modules test information
|||
|----------------------------------|------ |
| **Main release candidate issue** | https://github.com/wazuh/wazuh/issues/15746 ... | 1.0 | Release 4.4.0 - Alpha 2 - E2E UX tests - Wazuh Dashboard - The following issue aims to run the specified test for the current release candidate, report the results, and open new issues for any encountered errors.
## Modules test information
|||
|----------------------------------|------ |
| **Main release candida... | test | release alpha ux tests wazuh dashboard the following issue aims to run the specified test for the current release candidate report the results and open new issues for any encountered errors modules test information main release candidate... | 1 |
205,573 | 15,648,043,989 | IssuesEvent | 2021-03-23 04:48:33 | YCPRadioTelescope/YCP-RT-ControlRoom | https://api.github.com/repos/YCPRadioTelescope/YCP-RT-ControlRoom | closed | Create unit tests for Acceleration in DatabaseOperationsTests | Entities Testing good first issue | We have database operations for Acceleration, but we don't use acceleration data anywhere in the control room, so...how do we know they really work? We don't, so we must test them.
For this, we want to create two test functions:
- `TestAddAndRetrieveAccelerationData`
- `TestAddAndRetrieveMultipleAccelerationData`
... | 1.0 | Create unit tests for Acceleration in DatabaseOperationsTests - We have database operations for Acceleration, but we don't use acceleration data anywhere in the control room, so...how do we know they really work? We don't, so we must test them.
For this, we want to create two test functions:
- `TestAddAndRetrieveAc... | test | create unit tests for acceleration in databaseoperationstests we have database operations for acceleration but we don t use acceleration data anywhere in the control room so how do we know they really work we don t so we must test them for this we want to create two test functions testaddandretrieveac... | 1 |
2,302 | 2,716,362,956 | IssuesEvent | 2015-04-10 18:37:05 | swift-nav/libsbp | https://api.github.com/repos/swift-nav/libsbp | opened | Generate C bitmask #defines for bit fields | enhancement Message/Code Generation | * A single #define for single-bit fields
* Mask and offset #define for multi-bit fields
e.g. for MSG_HEARTBEAT,
```
#define SBP_MSG_HEARTBEAT_FLAGS_EXT_ANT (1<<31)
#define SBP_MSG_HEARTBEAT_FLAGS_NAP_ERR (1<<2)
#define SBP_MSG_HEARTBEAT_FLAGS_IO_ERR (1<<1)
#define SBP_MSG_HEARTBEAT_FLAGS_SYS_ERR (1<<0)
```
N... | 1.0 | Generate C bitmask #defines for bit fields - * A single #define for single-bit fields
* Mask and offset #define for multi-bit fields
e.g. for MSG_HEARTBEAT,
```
#define SBP_MSG_HEARTBEAT_FLAGS_EXT_ANT (1<<31)
#define SBP_MSG_HEARTBEAT_FLAGS_NAP_ERR (1<<2)
#define SBP_MSG_HEARTBEAT_FLAGS_IO_ERR (1<<1)
#define SBP... | non_test | generate c bitmask defines for bit fields a single define for single bit fields mask and offset define for multi bit fields e g for msg heartbeat define sbp msg heartbeat flags ext ant define sbp msg heartbeat flags nap err define sbp msg heartbeat flags io err define sbp ... | 0 |
6,548 | 14,859,905,031 | IssuesEvent | 2021-01-18 19:25:00 | Lens-Platform/Startup | https://api.github.com/repos/Lens-Platform/Startup | opened | Authentication Handler & Authentication Service (Development & Production Deployment) | architecture: documentation documentation: core documentation: service domain: backend have: must | The primary goal of this feature is to serve as the primary means of authentication within the backend system. Authentication will be comprised of 2 services and through interactions between such services provide api-consumers with JWT tokens.
The below set of tasks are crucial in order to drive this feature to pro... | 1.0 | Authentication Handler & Authentication Service (Development & Production Deployment) - The primary goal of this feature is to serve as the primary means of authentication within the backend system. Authentication will be comprised of 2 services and through interactions between such services provide api-consumers with ... | non_test | authentication handler authentication service development production deployment the primary goal of this feature is to serve as the primary means of authentication within the backend system authentication will be comprised of services and through interactions between such services provide api consumers with ... | 0 |
273,596 | 23,769,203,511 | IssuesEvent | 2022-09-01 14:59:49 | Lightning-AI/lightning | https://api.github.com/repos/Lightning-AI/lightning | opened | Can sharded be resumed with a different number of devices? | priority: 2 tests strategy: sharded | ## 🚀 Feature
Does this work?
```
model = BoringModel()
trainer = Trainer(strategy="ddp_sharded_spawn", fast_dev_run=True, gpus=2)
trainer.fit(model)
checkpoint_path = os.path.join(tmpdir, "model.pt")
trainer.save_checkpoint(checkpoint_path)
model = BoringModel()
trainer = Trainer(strategy="ddp_sharded... | 1.0 | Can sharded be resumed with a different number of devices? - ## 🚀 Feature
Does this work?
```
model = BoringModel()
trainer = Trainer(strategy="ddp_sharded_spawn", fast_dev_run=True, gpus=2)
trainer.fit(model)
checkpoint_path = os.path.join(tmpdir, "model.pt")
trainer.save_checkpoint(checkpoint_path)
m... | test | can sharded be resumed with a different number of devices 🚀 feature does this work model boringmodel trainer trainer strategy ddp sharded spawn fast dev run true gpus trainer fit model checkpoint path os path join tmpdir model pt trainer save checkpoint checkpoint path m... | 1 |
90,093 | 18,059,167,612 | IssuesEvent | 2021-09-20 12:08:30 | cosmos/cosmos-sdk | https://api.github.com/repos/cosmos/cosmos-sdk | reopened | Refactor client & server Configs | C:CLI Type: Code Hygiene pinned | <!-- < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < ☺
v ✰ Thanks for opening an issue! ✰
v Before smashing the submit button please review the template.
v Word of caution: poorly thought-out proposals may be rejected
v without deliberati... | 1.0 | Refactor client & server Configs - <!-- < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < ☺
v ✰ Thanks for opening an issue! ✰
v Before smashing the submit button please review the template.
v Word of caution: poorly thought-out proposals may be rejected
v ... | non_test | refactor client server configs ☺ v ✰ thanks for opening an issue ✰ v before smashing the submit button please review the template v word of caution poorly thought out proposals may be rejected v ... | 0 |
336,024 | 30,114,755,851 | IssuesEvent | 2023-06-30 10:31:46 | w7sst/MorseRunner | https://api.github.com/repos/w7sst/MorseRunner | opened | Add support for A1CLUB Weekly Contest (AWT) | contest | ## Contest information
<!-- Describe the contest you would like to see added.
1. Contest name.
2. Please include the URL to the contest rules.
3. Please include the name of required contest call history file name.
N1MMLoggerPlus provides a searchable database at https://n1mmwp.hamdocs.com/mmfiles/categories/callhi... | 1.0 | Add support for A1CLUB Weekly Contest (AWT) - ## Contest information
<!-- Describe the contest you would like to see added.
1. Contest name.
2. Please include the URL to the contest rules.
3. Please include the name of required contest call history file name.
N1MMLoggerPlus provides a searchable database at https:... | test | add support for weekly contest awt contest information describe the contest you would like to see added contest name please include the url to the contest rules please include the name of required contest call history file name provides a searchable database at of call history files ... | 1 |
192,983 | 14,634,300,949 | IssuesEvent | 2020-12-24 04:59:03 | github-vet/rangeloop-pointer-findings | https://api.github.com/repos/github-vet/rangeloop-pointer-findings | closed | ovh/cds: engine/api/repositories_manager_test.go; 3 LoC | fresh test tiny |
Found a possible issue in [ovh/cds](https://www.github.com/ovh/cds) at [engine/api/repositories_manager_test.go](https://github.com/ovh/cds/blob/56af877c7efa9dabf3a12147d7ae8e1caa6d69db/engine/api/repositories_manager_test.go#L35-L37)
Below is the message reported by the analyzer for this snippet of code. Beware that... | 1.0 | ovh/cds: engine/api/repositories_manager_test.go; 3 LoC -
Found a possible issue in [ovh/cds](https://www.github.com/ovh/cds) at [engine/api/repositories_manager_test.go](https://github.com/ovh/cds/blob/56af877c7efa9dabf3a12147d7ae8e1caa6d69db/engine/api/repositories_manager_test.go#L35-L37)
Below is the message repo... | test | ovh cds engine api repositories manager test go loc found a possible issue in at below is the message reported by the analyzer for this snippet of code beware that the analyzer only reports the first issue it finds so please do not limit your consideration to the contents of the below message func... | 1 |
42,181 | 5,428,258,914 | IssuesEvent | 2017-03-03 15:30:05 | brave/browser-laptop | https://api.github.com/repos/brave/browser-laptop | opened | Linux test run for 0.13.5 RC3 | OS/linux-distros tests | ## Installer
1. [ ] Check that installer is close to the size of last release.
2. [ ] Check signature: If OS Run `spctl --assess --verbose /Applications/Brave.app/` and make sure it returns `accepted`. If Windows right click on the installer exe and go to Properties, go to the Digital Signatures tab and double cli... | 1.0 | Linux test run for 0.13.5 RC3 - ## Installer
1. [ ] Check that installer is close to the size of last release.
2. [ ] Check signature: If OS Run `spctl --assess --verbose /Applications/Brave.app/` and make sure it returns `accepted`. If Windows right click on the installer exe and go to Properties, go to the Digit... | test | linux test run for installer check that installer is close to the size of last release check signature if os run spctl assess verbose applications brave app and make sure it returns accepted if windows right click on the installer exe and go to properties go to the digital sign... | 1 |
314,666 | 27,016,508,640 | IssuesEvent | 2023-02-10 19:56:41 | hashicorp/terraform-provider-google | https://api.github.com/repos/hashicorp/terraform-provider-google | closed | Failing test(s): TestAccDNSManagedZone_dnsManagedZoneQuickstartExample | size/s priority/1 test failure crosslinked | ### Affected Resource(s)
<!--- Please list the affected resources and data sources. --->
* google_dns_managed_zone
<!--- This is a template for reporting test failures on nightly builds. It should only be used by core contributors who have access to our CI/CD results. --->
<!-- i.e. "Consistently since X da... | 1.0 | Failing test(s): TestAccDNSManagedZone_dnsManagedZoneQuickstartExample - ### Affected Resource(s)
<!--- Please list the affected resources and data sources. --->
* google_dns_managed_zone
<!--- This is a template for reporting test failures on nightly builds. It should only be used by core contributors who hav... | test | failing test s testaccdnsmanagedzone dnsmanagedzonequickstartexample affected resource s google dns managed zone failure rate since impacted tests testaccdnsmanagedzone dnsmanagedzonequickstartexample nightly builds message error error creati... | 1 |
45,745 | 5,956,601,552 | IssuesEvent | 2017-05-28 18:20:25 | ZeroK-RTS/Zero-K | https://api.github.com/repos/ZeroK-RTS/Zero-K | closed | Lagmonitor with AI ally: income distributed but units not | design decision | When you are the sole human player and have AI allies, and go AFK, your income gets distributed to the bots but your units are not.
I think income should stay in this case. | 1.0 | Lagmonitor with AI ally: income distributed but units not - When you are the sole human player and have AI allies, and go AFK, your income gets distributed to the bots but your units are not.
I think income should stay in this case. | non_test | lagmonitor with ai ally income distributed but units not when you are the sole human player and have ai allies and go afk your income gets distributed to the bots but your units are not i think income should stay in this case | 0 |
539,831 | 15,795,599,345 | IssuesEvent | 2021-04-02 13:26:50 | wso2/product-apim | https://api.github.com/repos/wso2/product-apim | closed | Issue in DB2 scripts | API-M 4.0.0 Priority/High Type/Bug | ### Description:
Error thrown in following tables when running the DB2 scripts:
- **IDN_USER_FUNCTIONALITY_MAPPING**
```sql
CREATE TABLE IDN_USER_FUNCTIONALITY_MAPPING (
ID VARCHAR(255) NOT NULL,
USER_ID VARCHAR(255) NOT NULL,
TENANT_ID INTEGER NOT NULL,
FUNCTIONALITY_ID VARCHAR(255) NOT NULL,
IS_FUNCTI... | 1.0 | Issue in DB2 scripts - ### Description:
Error thrown in following tables when running the DB2 scripts:
- **IDN_USER_FUNCTIONALITY_MAPPING**
```sql
CREATE TABLE IDN_USER_FUNCTIONALITY_MAPPING (
ID VARCHAR(255) NOT NULL,
USER_ID VARCHAR(255) NOT NULL,
TENANT_ID INTEGER NOT NULL,
FUNCTIONALITY_ID VARCHAR(255... | non_test | issue in scripts description error thrown in following tables when running the scripts idn user functionality mapping sql create table idn user functionality mapping id varchar not null user id varchar not null tenant id integer not null functionality id varchar not null... | 0 |
106,566 | 9,166,848,523 | IssuesEvent | 2019-03-02 07:40:34 | elastic/kibana | https://api.github.com/repos/elastic/kibana | closed | WebDriver is stuck without logs and fails on mocha timeout | failed-test test test_infra | While working on WebDriver migration we noticed strange failures in CI when WebDriver is stuck (no logs provided) and fails within time on reaching mocha timeout for suite/test.
Example:
```
[00:07:48] │ debg Find.findByCssSelector('[data-test-subj~="visualizationLoader"]') with timeout=10000
[00:... | 3.0 | WebDriver is stuck without logs and fails on mocha timeout - While working on WebDriver migration we noticed strange failures in CI when WebDriver is stuck (no logs provided) and fails within time on reaching mocha timeout for suite/test.
Example:
```
[00:07:48] │ debg Find.findByCssSelector('[data... | test | webdriver is stuck without logs and fails on mocha timeout while working on webdriver migration we noticed strange failures in ci when webdriver is stuck no logs provided and fails within time on reaching mocha timeout for suite test example │ debg find findbycssselector with timeo... | 1 |
446,753 | 31,558,400,716 | IssuesEvent | 2023-09-03 00:20:59 | vercel/next.js | https://api.github.com/repos/vercel/next.js | closed | Docs: Does next/link scroll prop false disable scrolling to element? | template: documentation | ### What is the improvement or update you wish to see?
I'm using the scroll prop as `scroll={false}` on some links and it doesn't stop from scrolling to the element. Just checking to see if the docs seen [here](https://nextjs.org/docs/api-reference/next/link#disable-scrolling-to-the-top-of-the-page:~:text=To%20preve... | 1.0 | Docs: Does next/link scroll prop false disable scrolling to element? - ### What is the improvement or update you wish to see?
I'm using the scroll prop as `scroll={false}` on some links and it doesn't stop from scrolling to the element. Just checking to see if the docs seen [here](https://nextjs.org/docs/api-referen... | non_test | docs does next link scroll prop false disable scrolling to element what is the improvement or update you wish to see i m using the scroll prop as scroll false on some links and it doesn t stop from scrolling to the element just checking to see if the docs seen are accurate about this is the... | 0 |
89,471 | 8,204,533,973 | IssuesEvent | 2018-09-03 06:59:43 | humera987/HumTestData | https://api.github.com/repos/humera987/HumTestData | opened | humz_proj_test : ApiV1DataRecords@randomDeleteAllDeleteOtherRbac | humz_proj_test | Project : humz_proj_test
Job : UAT
Env : UAT
Region : FXLabs/US_WEST_1
Result : fail
Status Code : 200
Headers : {X-Content-Type-Options=[nosniff], X-XSS-Protection=[1; mode=block], Cache-Control=[no-cache, no-store, max-age=0, must-revalidate], Pragma=[no-cache], Expires=[0], X-Frame-Options=[DENY]... | 1.0 | humz_proj_test : ApiV1DataRecords@randomDeleteAllDeleteOtherRbac - Project : humz_proj_test
Job : UAT
Env : UAT
Region : FXLabs/US_WEST_1
Result : fail
Status Code : 200
Headers : {X-Content-Type-Options=[nosniff], X-XSS-Protection=[1; mode=block], Cache-Control=[no-cache, no-store, max-age=0, must-... | test | humz proj test randomdeletealldeleteotherrbac project humz proj test job uat env uat region fxlabs us west result fail status code headers x content type options x xss protection cache control pragma expires x frame options content type transfer encoding... | 1 |
233,914 | 19,086,112,867 | IssuesEvent | 2021-11-29 06:18:17 | boostcampwm-2021/iOS06-MateRunner | https://api.github.com/repos/boostcampwm-2021/iOS06-MateRunner | opened | [단위 테스트] AddMateViewModel | test | ## 🗣 설명
- Input에 대해 Output이 정상적으로 반환되는지 테스트합니다.
```swift
struct Input {
let searchButtonDidTap: Observable<Void>
let searchBarTextEvent: Observable<String>
}
struct Output {
let loadData = PublishRelay<Bool>()
}
```
## 📋 체크리스트
> 구현해야하는 이슈 체크리스트
- [ ] ... | 1.0 | [단위 테스트] AddMateViewModel - ## 🗣 설명
- Input에 대해 Output이 정상적으로 반환되는지 테스트합니다.
```swift
struct Input {
let searchButtonDidTap: Observable<Void>
let searchBarTextEvent: Observable<String>
}
struct Output {
let loadData = PublishRelay<Bool>()
}
```
## 📋 체크리스트
... | test | addmateviewmodel 🗣 설명 input에 대해 output이 정상적으로 반환되는지 테스트합니다 swift struct input let searchbuttondidtap observable let searchbartextevent observable struct output let loaddata publishrelay 📋 체크리스트 구현해야하는 이슈 체크리스트 ... | 1 |
69,464 | 7,134,926,964 | IssuesEvent | 2018-01-22 22:36:49 | SlateFoundation/slate-cbl | https://api.github.com/repos/SlateFoundation/slate-cbl | closed | Add course section to collapsed tasks | ready for testing | Instead of the Type of Experience or the examples in the screenshot (MYTHBUSTERS, etc) have that show the task's course section name.

| 1.0 | Add course section to collapsed tasks - Instead of the Type of Experience or the examples in the screenshot (MYTHBUSTERS, etc) have that show the task's course section name.

| test | add course section to collapsed tasks instead of the type of experience or the examples in the screenshot mythbusters etc have that show the task s course section name | 1 |
93,805 | 8,444,889,991 | IssuesEvent | 2018-10-18 19:48:15 | CoastalResilienceNetwork/GeositeFramework | https://api.github.com/repos/CoastalResilienceNetwork/GeositeFramework | closed | Ensure JS loads and works correctly | Task 1 tested/verified | Meant as a follow-up card in case fixes in #1108 does not address all of the issues.
The expectation that, after this card is completed, the site should generally be functional and resemble the existing site in functionality.
Requires #1108 | 1.0 | Ensure JS loads and works correctly - Meant as a follow-up card in case fixes in #1108 does not address all of the issues.
The expectation that, after this card is completed, the site should generally be functional and resemble the existing site in functionality.
Requires #1108 | test | ensure js loads and works correctly meant as a follow up card in case fixes in does not address all of the issues the expectation that after this card is completed the site should generally be functional and resemble the existing site in functionality requires | 1 |
446,710 | 31,553,049,243 | IssuesEvent | 2023-09-02 09:43:15 | nguyenvulong/QA | https://api.github.com/repos/nguyenvulong/QA | opened | [Latex] - cell color and resizebox, adjustbox in table | documentation | Use `adjustbox` instead of `resizebox`, see https://stackoverflow.com/questions/48272281/latex-how-to-fit-a-large-table-in-a-page. `adjustbox` will not screw up your row or cell color like `resizebox`.
Make sure to add this line in the preamble `\usepackage{adjustbox}`
<img width="1333" alt="image" src="https://g... | 1.0 | [Latex] - cell color and resizebox, adjustbox in table - Use `adjustbox` instead of `resizebox`, see https://stackoverflow.com/questions/48272281/latex-how-to-fit-a-large-table-in-a-page. `adjustbox` will not screw up your row or cell color like `resizebox`.
Make sure to add this line in the preamble `\usepackage{ad... | non_test | cell color and resizebox adjustbox in table use adjustbox instead of resizebox see adjustbox will not screw up your row or cell color like resizebox make sure to add this line in the preamble usepackage adjustbox img width alt image src | 0 |
202,993 | 15,864,062,726 | IssuesEvent | 2021-04-08 13:27:42 | SAP/openui5 | https://api.github.com/repos/SAP/openui5 | closed | walkthrough step 16, reference to deprecated method in text | documentation enhancement in progress | OpenUI5 version: 1.81.0 and current nightly
Steps to reproduce the problem:
1. read doc for "step 16", below code for HelloPanel.controller.js
2. notice "sap.ui.xmlfragment", which is not used in code
What is the expected result?
the text should mention the method used in the code sample, that is sap.ui.core.F... | 1.0 | walkthrough step 16, reference to deprecated method in text - OpenUI5 version: 1.81.0 and current nightly
Steps to reproduce the problem:
1. read doc for "step 16", below code for HelloPanel.controller.js
2. notice "sap.ui.xmlfragment", which is not used in code
What is the expected result?
the text should men... | non_test | walkthrough step reference to deprecated method in text version and current nightly steps to reproduce the problem read doc for step below code for hellopanel controller js notice sap ui xmlfragment which is not used in code what is the expected result the text should mention the ... | 0 |
712,485 | 24,497,100,515 | IssuesEvent | 2022-10-10 09:36:49 | AY2223S1-CS2103T-W13-4/tp | https://api.github.com/repos/AY2223S1-CS2103T-W13-4/tp | closed | Improve Testing for `AddTaskCommand` and `ListTasksCommand` | type.Task priority.Medium | To minimize bugs and also so that our test coverage doesn't drop too low.
Things to do:
- [ ] Add tests for `AddTaskCommand`
- [ ] Add tests for `Task`
- [ ] Add tests for `TaskList`
- [ ] Add tests for `ListTasksCommand` | 1.0 | Improve Testing for `AddTaskCommand` and `ListTasksCommand` - To minimize bugs and also so that our test coverage doesn't drop too low.
Things to do:
- [ ] Add tests for `AddTaskCommand`
- [ ] Add tests for `Task`
- [ ] Add tests for `TaskList`
- [ ] Add tests for `ListTasksCommand` | non_test | improve testing for addtaskcommand and listtaskscommand to minimize bugs and also so that our test coverage doesn t drop too low things to do add tests for addtaskcommand add tests for task add tests for tasklist add tests for listtaskscommand | 0 |
389,227 | 11,499,420,667 | IssuesEvent | 2020-02-12 13:55:32 | Longwelwind/swords-and-ravens | https://api.github.com/repos/Longwelwind/swords-and-ravens | closed | Resolving order of tracks is unhandy | priority:low type:qol | 
Cant make it work to place the order I want. Bara, Lanni, Tyrell, GJ
I guess on 6p games this might be even worse. How is this intended to work? Shall I click a house symbol and move it then?
I manage... | 1.0 | Resolving order of tracks is unhandy - 
Cant make it work to place the order I want. Bara, Lanni, Tyrell, GJ
I guess on 6p games this might be even worse. How is this intended to work? Shall I click a hou... | non_test | resolving order of tracks is unhandy cant make it work to place the order i want bara lanni tyrell gj i guess on games this might be even worse how is this intended to work shall i click a house symbol and move it then i managed it finally but i don t know how i finally came to that result | 0 |
202,006 | 15,244,013,352 | IssuesEvent | 2021-02-19 12:08:24 | spring-projects/spring-framework | https://api.github.com/repos/spring-projects/spring-framework | closed | Dependency on Servlet 4.0 in spring-test makes it challenging to have Servlet 3.1 at runtime | in: test in: web type: regression | Spring Framework 5.x is documented as requiring only Servlet 3.1 (EE7). However, a recent change (commit f22e2ac578f6db8f988cbbee0af5f381a86fdd04 by @rstoyanchev, included in 5.3.4) introduces a reference to `javax.servlet.http.HttpServletMapping` into `MockHttpServletRequest`.
The referenced API is part of Servlet ... | 1.0 | Dependency on Servlet 4.0 in spring-test makes it challenging to have Servlet 3.1 at runtime - Spring Framework 5.x is documented as requiring only Servlet 3.1 (EE7). However, a recent change (commit f22e2ac578f6db8f988cbbee0af5f381a86fdd04 by @rstoyanchev, included in 5.3.4) introduces a reference to `javax.servlet.ht... | test | dependency on servlet in spring test makes it challenging to have servlet at runtime spring framework x is documented as requiring only servlet however a recent change commit by rstoyanchev included in introduces a reference to javax servlet http httpservletmapping into mockhttpserv... | 1 |
157,309 | 12,369,703,647 | IssuesEvent | 2020-05-18 15:38:41 | gtDMMB/RNAStructViz | https://api.github.com/repos/gtDMMB/RNAStructViz | closed | Mac OS load files browser bottom widget sometimes does not display correctly | Proposed fix in place >= v2.3.4-testing 🍎 Mac OSX | # Demonstration of the problem (active bug)
This error has been noticed on multiple Mac machine installs, but we have so far yet to be able to reproduce the bug exactly. After using RNAStructViz for a while, sometimes, when clicking on "*Load Files*" to open more structures, the bottom widget fails to display correc... | 1.0 | Mac OS load files browser bottom widget sometimes does not display correctly - # Demonstration of the problem (active bug)
This error has been noticed on multiple Mac machine installs, but we have so far yet to be able to reproduce the bug exactly. After using RNAStructViz for a while, sometimes, when clicking on "*... | test | mac os load files browser bottom widget sometimes does not display correctly demonstration of the problem active bug this error has been noticed on multiple mac machine installs but we have so far yet to be able to reproduce the bug exactly after using rnastructviz for a while sometimes when clicking on ... | 1 |
347,003 | 24,887,432,943 | IssuesEvent | 2022-10-28 08:59:35 | HowSuen/ped | https://api.github.com/repos/HowSuen/ped | opened | Wrong command given in User Guide for undounmark | severity.Medium type.DocumentationBug | 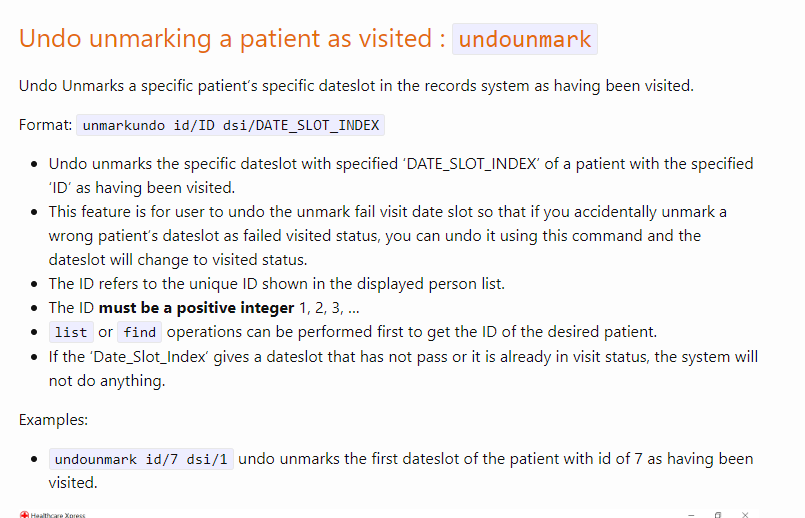
It is unclear whether it is supposed to be "undounmark" or "unmarkundo"
<!--session: 1666943648811-895d188d-8396-44b2-a6d6-5763549694a9-->
<!--Version: Web v3.4.4--> | 1.0 | Wrong command given in User Guide for undounmark - 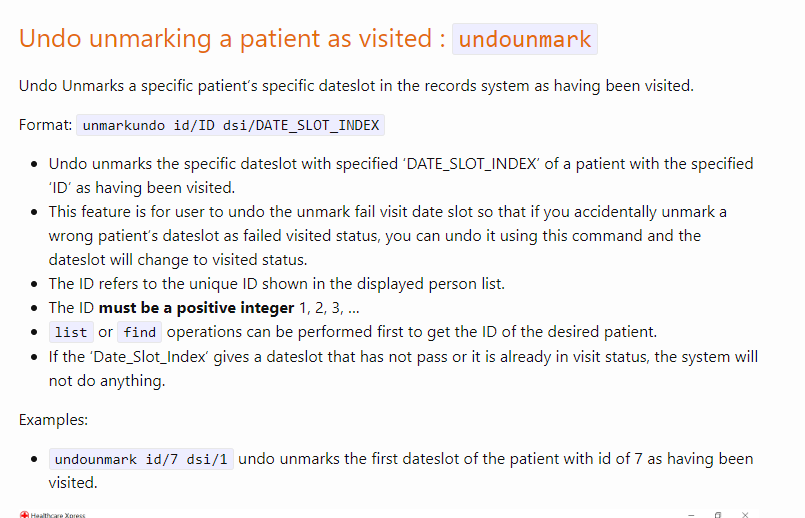
It is unclear whether it is supposed to be "undounmark" or "unmarkundo"
<!--session: 1666943648811-895d188d-8396-44b2-a6d6-5763549694a9-->
<!--Version: We... | non_test | wrong command given in user guide for undounmark it is unclear whether it is supposed to be undounmark or unmarkundo | 0 |
191,275 | 22,215,728,893 | IssuesEvent | 2022-06-08 01:17:36 | dreamboy9/mongo | https://api.github.com/repos/dreamboy9/mongo | opened | CVE-2022-31799 (Medium) detected in bottle-0.12.19-py3-none-any.whl | security vulnerability | ## CVE-2022-31799 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bottle-0.12.19-py3-none-any.whl</b></p></summary>
<p>Fast and simple WSGI-framework for small web-applications.</p>
... | True | CVE-2022-31799 (Medium) detected in bottle-0.12.19-py3-none-any.whl - ## CVE-2022-31799 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bottle-0.12.19-py3-none-any.whl</b></p></summar... | non_test | cve medium detected in bottle none any whl cve medium severity vulnerability vulnerable library bottle none any whl fast and simple wsgi framework for small web applications library home page a href path to dependency file src third party wiredtiger bench workgen ... | 0 |
272,418 | 23,672,518,835 | IssuesEvent | 2022-08-27 15:30:24 | red/red | https://api.github.com/repos/red/red | closed | [CRASH] on-deep-change* locals cannot point to itself & `local` corruption | status.built status.tested type.bug test.written | **Describe the bug**
Snippet 1:
```
?: func ['x] [print [x uppercase form type? x: get x tab mold/flat :x]]
o: make deep-reactor! [
on-deep-change*: func [o w t a n i p /local x] [
y: context? 'o
; local: p: x: :y
p: x: :y
? y
? p
? x
? local
]
x: []
append x 1
]
```
Produces outpu... | 2.0 | [CRASH] on-deep-change* locals cannot point to itself & `local` corruption - **Describe the bug**
Snippet 1:
```
?: func ['x] [print [x uppercase form type? x: get x tab mold/flat :x]]
o: make deep-reactor! [
on-deep-change*: func [o w t a n i p /local x] [
y: context? 'o
; local: p: x: :y
p: x: :y
... | test | on deep change locals cannot point to itself local corruption describe the bug snippet func o make deep reactor on deep change func y context o local p x y p x y y p x local x append x produces output y f... | 1 |
198,811 | 22,674,138,935 | IssuesEvent | 2022-07-04 01:20:51 | JMD60260/llsolidaires | https://api.github.com/repos/JMD60260/llsolidaires | opened | CVE-2022-25758 (Medium) detected in scss-tokenizer-0.2.3.tgz | security vulnerability | ## CVE-2022-25758 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>scss-tokenizer-0.2.3.tgz</b></p></summary>
<p>A tokenzier for Sass' SCSS syntax</p>
<p>Library home page: <a href="h... | True | CVE-2022-25758 (Medium) detected in scss-tokenizer-0.2.3.tgz - ## CVE-2022-25758 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>scss-tokenizer-0.2.3.tgz</b></p></summary>
<p>A token... | non_test | cve medium detected in scss tokenizer tgz cve medium severity vulnerability vulnerable library scss tokenizer tgz a tokenzier for sass scss syntax library home page a href path to dependency file package json path to vulnerable library node modules scss tokenizer ... | 0 |
13,411 | 3,332,091,759 | IssuesEvent | 2015-11-11 18:36:52 | zfsonlinux/zfs | https://api.github.com/repos/zfsonlinux/zfs | closed | Build bots can't handle dependencies | Test Suite | Just looked at #3656 and it occurred to me that the build-bots can't handle dependencies. This happen every now and then, especially to SPL (don't know if we have/need other dependencies than that).
We've talked about adding dependency info in the commit log before (last one I think was 6e9710f7c33a7440904b39fb4e6b6... | 1.0 | Build bots can't handle dependencies - Just looked at #3656 and it occurred to me that the build-bots can't handle dependencies. This happen every now and then, especially to SPL (don't know if we have/need other dependencies than that).
We've talked about adding dependency info in the commit log before (last one I ... | test | build bots can t handle dependencies just looked at and it occurred to me that the build bots can t handle dependencies this happen every now and then especially to spl don t know if we have need other dependencies than that we ve talked about adding dependency info in the commit log before last one i thi... | 1 |
49,475 | 3,002,893,709 | IssuesEvent | 2015-07-24 19:55:37 | jayway/powermock | https://api.github.com/repos/jayway/powermock | closed | maven dependency on powermock-api-easymock doesn't bring in easymock | bug imported Priority-Medium wontfix | _From [onlyn...@gmail.com](https://code.google.com/u/103888227351071805244/) on January 08, 2013 22:42:16_
What steps will reproduce the problem? 1. Added the following to my pom.xml:
\<dependency>
\<groupId>org.powermock</groupId>
\<artifactId>powermock-api-easymock</artifactId>
\<version>... | 1.0 | maven dependency on powermock-api-easymock doesn't bring in easymock - _From [onlyn...@gmail.com](https://code.google.com/u/103888227351071805244/) on January 08, 2013 22:42:16_
What steps will reproduce the problem? 1. Added the following to my pom.xml:
\<dependency>
\<groupId>org.powermock</groupId>
... | non_test | maven dependency on powermock api easymock doesn t bring in easymock from on january what steps will reproduce the problem added the following to my pom xml org powermock powermock api easymock test ran mvn test got the fol... | 0 |
5,157 | 2,776,127,922 | IssuesEvent | 2015-05-04 19:59:47 | SvitlanaShepitsena/svet-newspaper-material | https://api.github.com/repos/SvitlanaShepitsena/svet-newspaper-material | closed | From the Editor/Radio section rendering bug on large screen (should be column starting from medium) | bug Design | d | 1.0 | From the Editor/Radio section rendering bug on large screen (should be column starting from medium) - d | non_test | from the editor radio section rendering bug on large screen should be column starting from medium d | 0 |
100,908 | 21,558,839,920 | IssuesEvent | 2022-04-30 22:04:27 | aws/aws-cli | https://api.github.com/repos/aws/aws-cli | closed | Response from AWS-CLI in Windows encoded ANSI independent of Terminal encoding | unicode guidance closed-for-staleness | ### Describe the bug
I installed AWS-CLIv2 in Windows 10 and Git for Windows. Using Command Prompt or Git Bash I am able to execute queries like "aws s3 ls" and "aws connect xxxx". My query response includes a localized character "é". The query works and using --debug parameter I see the response back from the servi... | 1.0 | Response from AWS-CLI in Windows encoded ANSI independent of Terminal encoding - ### Describe the bug
I installed AWS-CLIv2 in Windows 10 and Git for Windows. Using Command Prompt or Git Bash I am able to execute queries like "aws s3 ls" and "aws connect xxxx". My query response includes a localized character "é". T... | non_test | response from aws cli in windows encoded ansi independent of terminal encoding describe the bug i installed aws in windows and git for windows using command prompt or git bash i am able to execute queries like aws ls and aws connect xxxx my query response includes a localized character é the que... | 0 |
326,390 | 27,988,336,767 | IssuesEvent | 2023-03-26 23:14:10 | unifyai/ivy | https://api.github.com/repos/unifyai/ivy | reopened | Fix jax_numpy_dtype.test_jax_numpy_can_cast | JAX Frontend Sub Task Failing Test | | | |
|---|---|
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/4526951745/jobs/7972435662" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/4526951745/jobs/7972435662" rel="noopener ... | 1.0 | Fix jax_numpy_dtype.test_jax_numpy_can_cast - | | |
|---|---|
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/4526951745/jobs/7972435662" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/r... | test | fix jax numpy dtype test jax numpy can cast tensorflow img src torch img src numpy img src jax img src failed ivy tests test ivy test frontends test jax test jax numpy dtype py test jax numpy can cast e assertionerror the results from backend... | 1 |
4,592 | 3,407,298,739 | IssuesEvent | 2015-12-04 01:47:20 | mitchellh/packer | https://api.github.com/repos/mitchellh/packer | closed | vmware-vmx: HTTPIP and HTTPPort are empty in vmx_data | builder/vmware question | I'm using Packer to customize one of CoreOS's prebuild VMX/VMDKs. CoreOS has the ability to fetch its config by reading `guestinfo.coreos.config.url` from its VMX. The issue is, setting this in `vmx_data` to something like `http://{{.HTTPIP}}:{{.HTTPPort}}/cloud-config.yml` results in `http://<no value>:<no value>/clou... | 1.0 | vmware-vmx: HTTPIP and HTTPPort are empty in vmx_data - I'm using Packer to customize one of CoreOS's prebuild VMX/VMDKs. CoreOS has the ability to fetch its config by reading `guestinfo.coreos.config.url` from its VMX. The issue is, setting this in `vmx_data` to something like `http://{{.HTTPIP}}:{{.HTTPPort}}/cloud-c... | non_test | vmware vmx httpip and httpport are empty in vmx data i m using packer to customize one of coreos s prebuild vmx vmdks coreos has the ability to fetch its config by reading guestinfo coreos config url from its vmx the issue is setting this in vmx data to something like results in value cloud config ym... | 0 |
568,441 | 16,979,802,082 | IssuesEvent | 2021-06-30 07:20:59 | johnvanbreda/naturespot-d8 | https://api.github.com/repos/johnvanbreda/naturespot-d8 | closed | Wild Places / Parish page species links not working | Priority 1 | The links to the species pages on the species list tabs of both Wild Places and Parish pages return the home page.
| 1.0 | Wild Places / Parish page species links not working - The links to the species pages on the species list tabs of both Wild Places and Parish pages return the home page.
| non_test | wild places parish page species links not working the links to the species pages on the species list tabs of both wild places and parish pages return the home page | 0 |
95,298 | 10,869,585,810 | IssuesEvent | 2019-11-15 07:59:17 | pfb1001/GESPRO_GESTION_DE_VERSIONES | https://api.github.com/repos/pfb1001/GESPRO_GESTION_DE_VERSIONES | closed | Pasar memoria doc a latex | documentation | * Revisar imágenes.
* Revisar bibliografía.
* bibentry (http://gking.harvard.edu/files/bibentry2.pdf).
### Documentación
* [x] Resumen
* [x] Introducción
* [x] Objetivos del proyecto
* [x] Conceptos teóricos
* [x] Técnicas y herramientas
* [x] Aspectos relevantes
* [x] Trabajos relacionados
* [x] ... | 1.0 | Pasar memoria doc a latex - * Revisar imágenes.
* Revisar bibliografía.
* bibentry (http://gking.harvard.edu/files/bibentry2.pdf).
### Documentación
* [x] Resumen
* [x] Introducción
* [x] Objetivos del proyecto
* [x] Conceptos teóricos
* [x] Técnicas y herramientas
* [x] Aspectos relevantes
* [x] T... | non_test | pasar memoria doc a latex revisar imágenes revisar bibliografía bibentry documentación resumen introducción objetivos del proyecto conceptos teóricos técnicas y herramientas aspectos relevantes trabajos relacionados conclusiones y líneas de trabajo... | 0 |
276,379 | 23,990,015,035 | IssuesEvent | 2022-09-13 23:32:00 | Azure/azure-sdk-tools | https://api.github.com/repos/Azure/azure-sdk-tools | closed | Shorten internal assets SHA link | Asset-Sync Test-Proxy | Right now, it's
```text
<language repo root>
/.assets
/Azure/azure-sdk-assets
/<SHA generated from relative path of assets.json>
/<cloned recordings>
```
I want to get that down to a single 10 character directory so that the structure is instead.
```text
<language repo roo... | 1.0 | Shorten internal assets SHA link - Right now, it's
```text
<language repo root>
/.assets
/Azure/azure-sdk-assets
/<SHA generated from relative path of assets.json>
/<cloned recordings>
```
I want to get that down to a single 10 character directory so that the structure is inst... | test | shorten internal assets sha link right now it s text assets azure azure sdk assets i want to get that down to a single character directory so that the structure is instead text assets | 1 |
121,588 | 10,180,013,583 | IssuesEvent | 2019-08-09 09:14:31 | sylabs/singularity | https://api.github.com/repos/sylabs/singularity | closed | [E2E] Improve coverage for verify command | Testing e2e | ## Version of Singularity:
All.
### Expected behavior
All commands expected to succeed should be tested.
Part of issue #4078
### Actual behavior
- [ ] singularity verify --groupid
- [ ] singularity verify --id
- [ ] singularity verify --url
### Steps to reproduce behavior
N/A.
| 1.0 | [E2E] Improve coverage for verify command - ## Version of Singularity:
All.
### Expected behavior
All commands expected to succeed should be tested.
Part of issue #4078
### Actual behavior
- [ ] singularity verify --groupid
- [ ] singularity verify --id
- [ ] singularity verify --url
### Steps to r... | test | improve coverage for verify command version of singularity all expected behavior all commands expected to succeed should be tested part of issue actual behavior singularity verify groupid singularity verify id singularity verify url steps to reproduce beha... | 1 |
378,876 | 26,342,121,358 | IssuesEvent | 2023-01-10 18:34:50 | Epistimio/orion | https://api.github.com/repos/Epistimio/orion | opened | Add testing to checkpointing tutorial | documentation ci | There is no testing on the checkpointing tutorial: https://orion.readthedocs.io/en/stable/auto_tutorials/code_2_hyperband_checkpoint.html. Once we setup a local github worker to run the SpeechBrain tutorial tests (https://github.com/Epistimio/orion/pull/1007), we should also setup tests for the checkpointing tutorial. | 1.0 | Add testing to checkpointing tutorial - There is no testing on the checkpointing tutorial: https://orion.readthedocs.io/en/stable/auto_tutorials/code_2_hyperband_checkpoint.html. Once we setup a local github worker to run the SpeechBrain tutorial tests (https://github.com/Epistimio/orion/pull/1007), we should also setu... | non_test | add testing to checkpointing tutorial there is no testing on the checkpointing tutorial once we setup a local github worker to run the speechbrain tutorial tests we should also setup tests for the checkpointing tutorial | 0 |
63,202 | 15,500,045,336 | IssuesEvent | 2021-03-11 08:49:02 | SciML/ModelingToolkit.jl | https://api.github.com/repos/SciML/ModelingToolkit.jl | closed | build_function (CTarget) generates wrong code | build_targets | The following model contains the cubic term `Δq^3 = (q - θ)^3`. This term does not appear to be present in the generated c-code, reproduced below
```julia
@parameters t, k, k₃, Jₘ, Jₐ, c, tx
@variables θ(t) q(t) #u(t)
@derivatives D'~t
Δq = q - θ
Δv = (D(q) - D(θ))
eqs = [
D(D(q)) ~ -(k * Δq + k₃ * Δq^3... | 1.0 | build_function (CTarget) generates wrong code - The following model contains the cubic term `Δq^3 = (q - θ)^3`. This term does not appear to be present in the generated c-code, reproduced below
```julia
@parameters t, k, k₃, Jₘ, Jₐ, c, tx
@variables θ(t) q(t) #u(t)
@derivatives D'~t
Δq = q - θ
Δv = (D(q) - D(θ)... | non_test | build function ctarget generates wrong code the following model contains the cubic term δq q θ this term does not appear to be present in the generated c code reproduced below julia parameters t k k₃ jₘ jₐ c tx variables θ t q t u t derivatives d t δq q θ δv d q d θ ... | 0 |
168,778 | 13,102,420,069 | IssuesEvent | 2020-08-04 06:40:14 | elastic/cloud-on-k8s | https://api.github.com/repos/elastic/cloud-on-k8s | closed | TestUpdateKibanaSecureSettings is flaky | >flaky_test v1.2.1 | https://devops-ci.elastic.co/job/cloud-on-k8s-e2e-tests-snapshot-versions/106/testReport/
```
=== RUN TestUpdateKibanaSecureSettings/secure_settings_should_eventually_be_set_in_all_nodes_keystore
Retries (5m0s timeout): ................................................................................
utils.g... | 1.0 | TestUpdateKibanaSecureSettings is flaky - https://devops-ci.elastic.co/job/cloud-on-k8s-e2e-tests-snapshot-versions/106/testReport/
```
=== RUN TestUpdateKibanaSecureSettings/secure_settings_should_eventually_be_set_in_all_nodes_keystore
Retries (5m0s timeout): ...................................................... | test | testupdatekibanasecuresettings is flaky run testupdatekibanasecuresettings secure settings should eventually be set in all nodes keystore retries timeout utils go error trace utils go ... | 1 |
144,413 | 11,615,552,810 | IssuesEvent | 2020-02-26 14:23:51 | ansible/awx | https://api.github.com/repos/ansible/awx | closed | Remove style overrides on Patternfly components and layouts | component:ui_next priority:medium state:needs_test | ##### ISSUE TYPE
- Task
##### SUMMARY
We're moving away from our small style tweaks to stock Patternfly components in favor of using them out of the box. This means that things like [app.scss](https://github.com/ansible/awx/blob/devel/awx/ui_next/src/app.scss) and [Chip.jsx](https://github.com/ansible/awx/blob/d... | 1.0 | Remove style overrides on Patternfly components and layouts - ##### ISSUE TYPE
- Task
##### SUMMARY
We're moving away from our small style tweaks to stock Patternfly components in favor of using them out of the box. This means that things like [app.scss](https://github.com/ansible/awx/blob/devel/awx/ui_next/src/... | test | remove style overrides on patternfly components and layouts issue type task summary we re moving away from our small style tweaks to stock patternfly components in favor of using them out of the box this means that things like and have got to go this issue covers searching for and remo... | 1 |
32,047 | 2,743,371,738 | IssuesEvent | 2015-04-21 21:20:32 | nprapps/graeae | https://api.github.com/repos/nprapps/graeae | closed | Seamus: is scraping by "date=current" going to mean we miss things? | Priority: High | If the story and pub dates diverge by more than a day? How does the dating work? | 1.0 | Seamus: is scraping by "date=current" going to mean we miss things? - If the story and pub dates diverge by more than a day? How does the dating work? | non_test | seamus is scraping by date current going to mean we miss things if the story and pub dates diverge by more than a day how does the dating work | 0 |
7,863 | 2,938,440,772 | IssuesEvent | 2015-07-01 10:47:20 | pfnet/chainer | https://api.github.com/repos/pfnet/chainer | closed | Make tests for examples | test | I want to run examples in CI environment to check their correctness.
| 1.0 | Make tests for examples - I want to run examples in CI environment to check their correctness.
| test | make tests for examples i want to run examples in ci environment to check their correctness | 1 |
235,807 | 19,430,297,906 | IssuesEvent | 2021-12-21 11:07:55 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | roachtest: jepsen/monotonic/start-stop-2 failed | C-test-failure O-robot O-roachtest branch-master release-blocker | roachtest.jepsen/monotonic/start-stop-2 [failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=3948712&tab=buildLog) with [artifacts](https://teamcity.cockroachdb.com/viewLog.html?buildId=3948712&tab=artifacts#/jepsen/monotonic/start-stop-2) on master @ [3f95a4bd83cce2952a12497de82692866b4da659](https://github.... | 2.0 | roachtest: jepsen/monotonic/start-stop-2 failed - roachtest.jepsen/monotonic/start-stop-2 [failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=3948712&tab=buildLog) with [artifacts](https://teamcity.cockroachdb.com/viewLog.html?buildId=3948712&tab=artifacts#/jepsen/monotonic/start-stop-2) on master @ [3f95a4b... | test | roachtest jepsen monotonic start stop failed roachtest jepsen monotonic start stop with on master home agent work go src github com cockroachdb cockroach pkg cmd roachtest cluster go github com cockroachdb cockroach pkg cmd roachtest tests runjepsen home agent work ... | 1 |
158,889 | 20,035,490,399 | IssuesEvent | 2022-02-02 11:25:00 | kapseliboi/coronavirus-dashboard | https://api.github.com/repos/kapseliboi/coronavirus-dashboard | opened | CVE-2018-11694 (High) detected in node-sass-4.14.1.tgz | security vulnerability | ## CVE-2018-11694 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-sass-4.14.1.tgz</b></p></summary>
<p>Wrapper around libsass</p>
<p>Library home page: <a href="https://registry.n... | True | CVE-2018-11694 (High) detected in node-sass-4.14.1.tgz - ## CVE-2018-11694 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-sass-4.14.1.tgz</b></p></summary>
<p>Wrapper around libs... | non_test | cve high detected in node sass tgz cve high severity vulnerability vulnerable library node sass tgz wrapper around libsass library home page a href path to dependency file package json path to vulnerable library node modules node sass package json dependency hi... | 0 |
322,700 | 27,625,919,930 | IssuesEvent | 2023-03-10 06:45:01 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | opened | pkg/ccl/importerccl/importerccl_test: TestImportMultiRegion failed | C-test-failure O-robot branch-master | pkg/ccl/importerccl/importerccl_test.TestImportMultiRegion [failed](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_StressBazel/8997899?buildTab=log) with [artifacts](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_StressBazel/8997899?buildTab=artifacts#/) on master @ [d4... | 1.0 | pkg/ccl/importerccl/importerccl_test: TestImportMultiRegion failed - pkg/ccl/importerccl/importerccl_test.TestImportMultiRegion [failed](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_StressBazel/8997899?buildTab=log) with [artifacts](https://teamcity.cockroachdb.com/buildConfiguration/Cockroac... | test | pkg ccl importerccl importerccl test testimportmultiregion failed pkg ccl importerccl importerccl test testimportmultiregion with on master github com cockroachdb cockroach pkg testutils testcluster testcluster go github com cockroachdb cockroach pkg testutils testcluster newtestclus... | 1 |
292,382 | 25,207,358,825 | IssuesEvent | 2022-11-13 20:58:10 | Test-Automation-Crash-Course-24-10-22/team_05 | https://api.github.com/repos/Test-Automation-Crash-Course-24-10-22/team_05 | opened | Test case 2. Oliinyk Vlad | TestCase | **Descriptions:**
Check if function Installing app for mobile device
**Preconditions:**
1. Open the website https://rozetka.com.ua/ua/
**Test steps**
| Title | Step | Expected result |
| ------------- | ------------- | ------------- |
| Installing app for mobile device | Click the button "Downoload app... | 1.0 | Test case 2. Oliinyk Vlad - **Descriptions:**
Check if function Installing app for mobile device
**Preconditions:**
1. Open the website https://rozetka.com.ua/ua/
**Test steps**
| Title | Step | Expected result |
| ------------- | ------------- | ------------- |
| Installing app for mobile device | Cli... | test | test case oliinyk vlad descriptions check if function installing app for mobile device preconditions open the website test steps title step expected result installing app for mobile device click the button downoload ... | 1 |
160,771 | 20,118,451,084 | IssuesEvent | 2022-02-07 22:19:16 | sureng-ws-ibm/t1 | https://api.github.com/repos/sureng-ws-ibm/t1 | opened | grunt-1.0.3.tgz: 7 vulnerabilities (highest severity is: 9.8) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>grunt-1.0.3.tgz</b></p></summary>
<p>The JavaScript Task Runner</p>
<p>Library home page: <a href="https://registry.npmjs.org/grunt/-/grunt-1.0.3.tgz">https://registr... | True | grunt-1.0.3.tgz: 7 vulnerabilities (highest severity is: 9.8) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>grunt-1.0.3.tgz</b></p></summary>
<p>The JavaScript Task Runner</p>
<p>Library home page: <a href="htt... | non_test | grunt tgz vulnerabilities highest severity is vulnerable library grunt tgz the javascript task runner library home page a href path to dependency file package json path to vulnerable library node modules grunt package json found in head commit a href vuln... | 0 |
86,942 | 17,107,273,796 | IssuesEvent | 2021-07-09 20:01:53 | paulevsGitch/BetterEnd | https://api.github.com/repos/paulevsGitch/BetterEnd | closed | [Suggestion] Allow recipe jsons to have an nbt tag on the output item. | enhancement in dev code suggestion | Allow recipe jsons to have an nbt tag on the output item, like this:
```
"input":
{
"item": "minecraft:book"
},
"output":
{
"item": "minecraft:enchanted_book",
"nbt": "{StoredEnchantments:[{id:\"ffenchants:buoyancy\"}]}"
}, | 1.0 | [Suggestion] Allow recipe jsons to have an nbt tag on the output item. - Allow recipe jsons to have an nbt tag on the output item, like this:
```
"input":
{
"item": "minecraft:book"
},
"output":
{
"item": "minecraft:enchanted_book",
"nbt": "{StoredEnchantments:[{id:\"ffenchants:buoyancy\"... | non_test | allow recipe jsons to have an nbt tag on the output item allow recipe jsons to have an nbt tag on the output item like this input item minecraft book output item minecraft enchanted book nbt storedenchantments | 0 |
240,164 | 20,014,571,584 | IssuesEvent | 2022-02-01 10:42:08 | limanmys/core | https://api.github.com/repos/limanmys/core | closed | Sunucu Bilgileri | testing | Sunucularda anahtar kullanılıyor ise sunucu bilgileri kısmında giriş yapmış kullanıcı gösterilmelidir.
Whoami komutunun çıktısı gösterilebilir. (Windows powershell ve linux bash'de aynı şekilde çalışmakta)

 no longer works on Debian 9 due to issues running the old, [INITIAL_VERSION](https://github.com/certbot/certbot/blob/60e734c9690dc84bcea968d1d2041d17cbdeec27/tests/letstest/scripts/test_leauto... | 1.0 | Update INITIAL_VERSION in test_leauto_updates.sh - [This test](https://github.com/certbot/certbot/blob/master/tests/letstest/scripts/test_letsencrypt_auto_certonly_standalone.sh) no longer works on Debian 9 due to issues running the old, [INITIAL_VERSION](https://github.com/certbot/certbot/blob/60e734c9690dc84bcea968d1... | test | update initial version in test leauto updates sh no longer works on debian due to issues running the old of certbot auto which is set up to then test the upgrade to the latest version we can fix the problem by updating initial version to which also allows us to test on fedora | 1 |
418,977 | 12,216,182,348 | IssuesEvent | 2020-05-01 14:37:18 | buddyboss/buddyboss-platform | https://api.github.com/repos/buddyboss/buddyboss-platform | closed | Server goes away when activate platform plugin with 60000 users | Has-PR bug component: activity priority: high | **Describe the bug**
When we activate the platform plugin with 60000 or more users server goes away.
Its happen due to function `bp_activity_favorites_upgrade_data()`
**To Reproduce**
Steps to reproduce the behavior:
1. Go to Admin
2. Click on Plugins
3. Activate BuddyBoss Platform
4. See error
**Expected ... | 1.0 | Server goes away when activate platform plugin with 60000 users - **Describe the bug**
When we activate the platform plugin with 60000 or more users server goes away.
Its happen due to function `bp_activity_favorites_upgrade_data()`
**To Reproduce**
Steps to reproduce the behavior:
1. Go to Admin
2. Click on Pl... | non_test | server goes away when activate platform plugin with users describe the bug when we activate the platform plugin with or more users server goes away its happen due to function bp activity favorites upgrade data to reproduce steps to reproduce the behavior go to admin click on plugins ... | 0 |
543,235 | 15,879,067,940 | IssuesEvent | 2021-04-09 11:56:59 | wso2/product-is | https://api.github.com/repos/wso2/product-is | closed | Per SP configs for consent receipt attributes | Priority/High Severity/Minor improvement | Following options should be available at the SP config level for user consent collection for SSO
- Jurisdiction
- Policy URL
- Language | 1.0 | Per SP configs for consent receipt attributes - Following options should be available at the SP config level for user consent collection for SSO
- Jurisdiction
- Policy URL
- Language | non_test | per sp configs for consent receipt attributes following options should be available at the sp config level for user consent collection for sso jurisdiction policy url language | 0 |
227,917 | 18,109,773,610 | IssuesEvent | 2021-09-23 01:06:25 | influxdata/ui | https://api.github.com/repos/influxdata/ui | opened | Telegraf Refresh: e2e test for adding a plugin to an existing Telegraf configuration | enhancement team/ui area/testing team/dumplings | Create a Cypress e2e test for Data > Sources > input plugin > Add to an existing configuration to ensure that:
- [ ] happy path of adding to an existing configuration works
- [ ] user can add a duplicate by confirming
- [ ] user can close the overlay during any step, restart from beginning, and then successfully c... | 1.0 | Telegraf Refresh: e2e test for adding a plugin to an existing Telegraf configuration - Create a Cypress e2e test for Data > Sources > input plugin > Add to an existing configuration to ensure that:
- [ ] happy path of adding to an existing configuration works
- [ ] user can add a duplicate by confirming
- [ ] user... | test | telegraf refresh test for adding a plugin to an existing telegraf configuration create a cypress test for data sources input plugin add to an existing configuration to ensure that happy path of adding to an existing configuration works user can add a duplicate by confirming user can close... | 1 |
108,999 | 16,825,828,484 | IssuesEvent | 2021-06-17 18:25:49 | brogers588/spring-boot | https://api.github.com/repos/brogers588/spring-boot | opened | CVE-2018-1000632 (High) detected in dom4j-1.6.1.jar | security vulnerability | ## CVE-2018-1000632 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>dom4j-1.6.1.jar</b></p></summary>
<p>dom4j: the flexible XML framework for Java</p>
<p>Library home page: <a href="h... | True | CVE-2018-1000632 (High) detected in dom4j-1.6.1.jar - ## CVE-2018-1000632 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>dom4j-1.6.1.jar</b></p></summary>
<p>dom4j: the flexible XML f... | non_test | cve high detected in jar cve high severity vulnerability vulnerable library jar the flexible xml framework for java library home page a href path to dependency file spring boot spring boot tests spring boot smoke tests spring boot smoke test build gradle path... | 0 |
183,336 | 14,224,446,386 | IssuesEvent | 2020-11-17 19:41:09 | angular/angular | https://api.github.com/repos/angular/angular | closed | Async in unit tests does not handle unresolved promises | P4 comp: docs comp: testing feature freq2: medium | ## I'm submitting a...
<!-- Check one of the following options with "x" -->
<pre><code>
[ ] Regression (a behavior that used to work and stopped working in a new release)
[x] Bug report <!-- Please search GitHub for a similar issue or PR before submitting -->
[ ] Feature request
[ ] Documentation issue or reques... | 1.0 | Async in unit tests does not handle unresolved promises - ## I'm submitting a...
<!-- Check one of the following options with "x" -->
<pre><code>
[ ] Regression (a behavior that used to work and stopped working in a new release)
[x] Bug report <!-- Please search GitHub for a similar issue or PR before submitting -... | test | async in unit tests does not handle unresolved promises i m submitting a regression a behavior that used to work and stopped working in a new release bug report feature request documentation issue or request support request please do not submit support request here instead see ... | 1 |
39,491 | 9,487,781,364 | IssuesEvent | 2019-04-22 17:50:40 | extnet/Ext.NET | https://api.github.com/repos/extnet/Ext.NET | opened | Mouse wheel in NumberField and SpinnerField inverted between 4.7.x and 4.8.x | 4.x defect review-after-extjs-upgrade sencha | Found: 4.8.1
Ext.NET forum thread: [Mouse wheel in number field has changed behavior](https://forums.ext.net/showthread.php?62640)
The mouse wheel behavior in form fields `Ext.form.field.Number` and "Ext.form.field.Spinner` has been inverted between Ext JS 6.6.0 and 6.7.0. Historically, at least about version 4 (Ex... | 1.0 | Mouse wheel in NumberField and SpinnerField inverted between 4.7.x and 4.8.x - Found: 4.8.1
Ext.NET forum thread: [Mouse wheel in number field has changed behavior](https://forums.ext.net/showthread.php?62640)
The mouse wheel behavior in form fields `Ext.form.field.Number` and "Ext.form.field.Spinner` has been inve... | non_test | mouse wheel in numberfield and spinnerfield inverted between x and x found ext net forum thread the mouse wheel behavior in form fields ext form field number and ext form field spinner has been inverted between ext js and historically at least about version ext net it ... | 0 |
6,643 | 2,855,140,862 | IssuesEvent | 2015-06-02 07:38:07 | glensc/nagios-plugin-check_raid | https://api.github.com/repos/glensc/nagios-plugin-check_raid | closed | uninitialized value when battery is failed | arcconf need test data | When the battery is failed got those error.
/usr/lib/nagios/plugins/check_raid
Use of uninitialized value in string ne at /usr/lib/nagios/plugins/check_raid line 2887.
Use of uninitialized value in concatenation (.) or string at /usr/lib/nagios/plugins/check_raid line 2889.
Use of uninitialized value in concatena... | 1.0 | uninitialized value when battery is failed - When the battery is failed got those error.
/usr/lib/nagios/plugins/check_raid
Use of uninitialized value in string ne at /usr/lib/nagios/plugins/check_raid line 2887.
Use of uninitialized value in concatenation (.) or string at /usr/lib/nagios/plugins/check_raid line 2... | test | uninitialized value when battery is failed when the battery is failed got those error usr lib nagios plugins check raid use of uninitialized value in string ne at usr lib nagios plugins check raid line use of uninitialized value in concatenation or string at usr lib nagios plugins check raid line ... | 1 |
127,272 | 5,027,777,569 | IssuesEvent | 2016-12-15 16:23:37 | savoirfairelinux/sous-chef | https://api.github.com/repos/savoirfairelinux/sous-chef | opened | Too many information for the payment types | high priority member | ### Expected Behaviour
The payment type should be optional in the client's creation form.
The values should be:
- EFT
- Credit
- 3rd Party
### Actual Behaviour
The payment type is mandatory in the client's creation form.
The values are:
- Check
- Cash
- EFT
- Credit
### Steps to reproduce
* Go... | 1.0 | Too many information for the payment types - ### Expected Behaviour
The payment type should be optional in the client's creation form.
The values should be:
- EFT
- Credit
- 3rd Party
### Actual Behaviour
The payment type is mandatory in the client's creation form.
The values are:
- Check
- Cash
- EF... | non_test | too many information for the payment types expected behaviour the payment type should be optional in the client s creation form the values should be eft credit party actual behaviour the payment type is mandatory in the client s creation form the values are check cash eft ... | 0 |
27,774 | 4,328,889,943 | IssuesEvent | 2016-07-26 15:16:25 | mautic/mautic | https://api.github.com/repos/mautic/mautic | closed | Date selection ends in a HTTP 500 error | Bug Ready To Test | ## Description
When I browse email stats for a mailing and try to select a different time range using the widget, Mautic responds with a HTTP 500 error.
[2016-07-07 11:28:20] mautic.CRITICAL: Uncaught PHP Exception Symfony\Component\Debug\Exception\UndefinedMethodException: "Attempted to call an undefined method named... | 1.0 | Date selection ends in a HTTP 500 error - ## Description
When I browse email stats for a mailing and try to select a different time range using the widget, Mautic responds with a HTTP 500 error.
[2016-07-07 11:28:20] mautic.CRITICAL: Uncaught PHP Exception Symfony\Component\Debug\Exception\UndefinedMethodException: "A... | test | date selection ends in a http error description when i browse email stats for a mailing and try to select a different time range using the widget mautic responds with a http error mautic critical uncaught php exception symfony component debug exception undefinedmethodexception attempted to call an unde... | 1 |
73,584 | 7,345,073,822 | IssuesEvent | 2018-03-07 16:23:07 | PressForward/pressforward | https://api.github.com/repos/PressForward/pressforward | closed | Items nominated and then sent to draft from all content do not appear as drafts | Test bug | If an item is nominated and then sent to draft from all content, it does not appear as a drafted post. This issue was likely introduced while fixing the nomination count for the same process. See issue #959 | 1.0 | Items nominated and then sent to draft from all content do not appear as drafts - If an item is nominated and then sent to draft from all content, it does not appear as a drafted post. This issue was likely introduced while fixing the nomination count for the same process. See issue #959 | test | items nominated and then sent to draft from all content do not appear as drafts if an item is nominated and then sent to draft from all content it does not appear as a drafted post this issue was likely introduced while fixing the nomination count for the same process see issue | 1 |
184,063 | 21,784,788,687 | IssuesEvent | 2022-05-14 01:19:21 | rgordon95/ecommerce-react-redux-saga-demo | https://api.github.com/repos/rgordon95/ecommerce-react-redux-saga-demo | opened | CVE-2022-1650 (High) detected in eventsource-0.1.6.tgz | security vulnerability | ## CVE-2022-1650 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>eventsource-0.1.6.tgz</b></p></summary>
<p>W3C compliant EventSource client for Node.js</p>
<p>Library home page: <a hr... | True | CVE-2022-1650 (High) detected in eventsource-0.1.6.tgz - ## CVE-2022-1650 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>eventsource-0.1.6.tgz</b></p></summary>
<p>W3C compliant Event... | non_test | cve high detected in eventsource tgz cve high severity vulnerability vulnerable library eventsource tgz compliant eventsource client for node js library home page a href path to dependency file ecommerce react redux saga demo redux saga cart package json path to vu... | 0 |
342,357 | 10,315,688,519 | IssuesEvent | 2019-08-30 08:12:40 | gilesknap/gphotos-sync | https://api.github.com/repos/gilesknap/gphotos-sync | closed | Null response in mediaItems.batchGet | Bug in Google API? Low Priority | I've just noticed that my own library sync cron job has been getting a large number of these errors during July:-
```
07-31 21:39:28 Null response in mediaItems.batchGet dict_keys(['AIfuE
...
```
This is the same as shown in #98. Nothing new has ended up in my bad_ids file.
This needs to be investigated. | 1.0 | Null response in mediaItems.batchGet - I've just noticed that my own library sync cron job has been getting a large number of these errors during July:-
```
07-31 21:39:28 Null response in mediaItems.batchGet dict_keys(['AIfuE
...
```
This is the same as shown in #98. Nothing new has ended up in my bad_ids fil... | non_test | null response in mediaitems batchget i ve just noticed that my own library sync cron job has been getting a large number of these errors during july null response in mediaitems batchget dict keys aifue this is the same as shown in nothing new has ended up in my bad ids file ... | 0 |
212,280 | 16,437,492,395 | IssuesEvent | 2021-05-20 10:54:22 | open-telemetry/opentelemetry-java-instrumentation | https://api.github.com/repos/open-telemetry/opentelemetry-java-instrumentation | opened | Flaky test ArmeriaHttpClientTest trace request with callback and parent | area:tests bug sporadic test failure | https://scans.gradle.com/s/gbcpfr5wicl5e
```
assert traces.size() == expectedSize
| | | |
| 2 | 1
| false
[[TestSpanData{spanContext=ImmutableSpanContext{traceId=0dc4c0c38d4cad64b0fef0231b6017ac, spanId=aa218e3cf3b2b8be, traceFlags=00, traceState=A... | 2.0 | Flaky test ArmeriaHttpClientTest trace request with callback and parent - https://scans.gradle.com/s/gbcpfr5wicl5e
```
assert traces.size() == expectedSize
| | | |
| 2 | 1
| false
[[TestSpanData{spanContext=ImmutableSpanContext{traceId=0dc4c0c38d4c... | test | flaky test armeriahttpclienttest trace request with callback and parent assert traces size expectedsize false remote false valid true parentspancontext immutablespancontext traceid spanid traceflags tr... | 1 |
18,349 | 5,624,816,235 | IssuesEvent | 2017-04-04 17:55:23 | joomla/joomla-cms | https://api.github.com/repos/joomla/joomla-cms | closed | Filters set in com_content stay active in com_menu | No Code Attached Yet | ### Steps to reproduce the issue

### Expected result
In com_menu when creating new article have no filters active
### Actual result
Filters set prior in com_content are active in co... | 1.0 | Filters set in com_content stay active in com_menu - ### Steps to reproduce the issue

### Expected result
In com_menu when creating new article have no filters active
### Actual resu... | non_test | filters set in com content stay active in com menu steps to reproduce the issue expected result in com menu when creating new article have no filters active actual result filters set prior in com content are active in com menu when creating a new article by menu item system in... | 0 |
129,631 | 10,581,120,898 | IssuesEvent | 2019-10-08 08:31:46 | hazelcast/hazelcast | https://api.github.com/repos/hazelcast/hazelcast | opened | CountDownLatchAdvancedTest.testNewRaftGroupMemberSchedulesTimeoutsWithSnapshot | Module: CP Subsystem Source: Internal Team: Core Type: Test-Failure | `master` (commit b90190b38324fbea8b9e5e26a5285ef9d39d0efd)
Failed on CorrettoJDK8 : http://jenkins.hazelcast.com/view/Official%20Builds/job/Hazelcast-3.x-CorrettoJDK8/33/testReport/junit/com.hazelcast.cp.internal.datastructures.countdownlatch/CountDownLatchAdvancedTest/testNewRaftGroupMemberSchedulesTimeoutsWithSnap... | 1.0 | CountDownLatchAdvancedTest.testNewRaftGroupMemberSchedulesTimeoutsWithSnapshot - `master` (commit b90190b38324fbea8b9e5e26a5285ef9d39d0efd)
Failed on CorrettoJDK8 : http://jenkins.hazelcast.com/view/Official%20Builds/job/Hazelcast-3.x-CorrettoJDK8/33/testReport/junit/com.hazelcast.cp.internal.datastructures.countdow... | test | countdownlatchadvancedtest testnewraftgroupmemberschedulestimeoutswithsnapshot master commit failed on stacktrace java lang assertionerror at org junit assert fail assert java at org junit assert asserttrue assert java at org junit assert assertfalse assert java at org jun... | 1 |
393,085 | 11,609,916,992 | IssuesEvent | 2020-02-26 01:26:28 | yidongnan/grpc-spring-boot-starter | https://api.github.com/repos/yidongnan/grpc-spring-boot-starter | closed | Support gRPC Java version 1.26.0+ | enhancement high priority incompatibility | **The problem**
If you upgrade to gRPC Java 1.26.0 the GrpcClient annotated stub is no longer able to construct itself. It throws a NoSuchMethod exception for the constructor.
**The solution**
Revert back to 1.25.x
**Alternatives considered**
An alternative methodology of constructing this class by refle... | 1.0 | Support gRPC Java version 1.26.0+ - **The problem**
If you upgrade to gRPC Java 1.26.0 the GrpcClient annotated stub is no longer able to construct itself. It throws a NoSuchMethod exception for the constructor.
**The solution**
Revert back to 1.25.x
**Alternatives considered**
An alternative methodology... | non_test | support grpc java version the problem if you upgrade to grpc java the grpcclient annotated stub is no longer able to construct itself it throws a nosuchmethod exception for the constructor the solution revert back to x alternatives considered an alternative methodology of... | 0 |
56,062 | 6,499,966,670 | IssuesEvent | 2017-08-23 00:45:18 | EFForg/https-everywhere | https://api.github.com/repos/EFForg/https-everywhere | closed | [Idea] Tor Onion services | Ruleset Testing | Some websites are providing access as a Tor Onion service, like:
- DuckDuckGo - http://3g2upl4pq6kufc4m.onion/
- Facebook - https://facebookcorewwwi.onion/
- Tor Project - http://bt3ehg7prnlm6tyv.onion/
- Wikileaks - http://gjlng65kwikileax.onion/
Roger Dingledine (original developer of Tor along with Nick Mathewson a... | 1.0 | [Idea] Tor Onion services - Some websites are providing access as a Tor Onion service, like:
- DuckDuckGo - http://3g2upl4pq6kufc4m.onion/
- Facebook - https://facebookcorewwwi.onion/
- Tor Project - http://bt3ehg7prnlm6tyv.onion/
- Wikileaks - http://gjlng65kwikileax.onion/
Roger Dingledine (original developer of Tor... | test | tor onion services some websites are providing access as a tor onion service like duckduckgo facebook tor project wikileaks roger dingledine original developer of tor along with nick mathewson and paul syverson says something like tor onion services vs https only websites is like https... | 1 |
370,535 | 10,933,530,142 | IssuesEvent | 2019-11-24 02:57:09 | cuappdev/uplift-ios | https://api.github.com/repos/cuappdev/uplift-ios | closed | Convert MiscellaneousInfoView to a collection view cell | Priority: High | To accommodate for the overall framework for the facilities section, change `MiscellaneousInfoView` to be a subclass of `UICollectionViewCell`. | 1.0 | Convert MiscellaneousInfoView to a collection view cell - To accommodate for the overall framework for the facilities section, change `MiscellaneousInfoView` to be a subclass of `UICollectionViewCell`. | non_test | convert miscellaneousinfoview to a collection view cell to accommodate for the overall framework for the facilities section change miscellaneousinfoview to be a subclass of uicollectionviewcell | 0 |
80,546 | 15,586,294,684 | IssuesEvent | 2021-03-18 01:36:57 | saurockSaurav/weather-information-api | https://api.github.com/repos/saurockSaurav/weather-information-api | opened | CVE-2020-24750 (High) detected in jackson-databind-2.8.11.3.jar | security vulnerability | ## CVE-2020-24750 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.8.11.3.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core strea... | True | CVE-2020-24750 (High) detected in jackson-databind-2.8.11.3.jar - ## CVE-2020-24750 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.8.11.3.jar</b></p></summary>
<p>G... | non_test | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file weather information api we... | 0 |
224,320 | 17,172,514,333 | IssuesEvent | 2021-07-15 07:16:58 | cyberbotics/webots | https://api.github.com/repos/cyberbotics/webots | closed | Robotino: remove NUE restriction | documentation | https://cyberbotics.com/doc/guide/robotino3:
remove this line:
`And in WorldInfo the coordinateSystem must be set to "NUE".`
background:
the robotino uses asymmetric friction between wheels and floor (cylinder/box), coulombFriction [ 0, 2, 0]. there was a bug, robotino needed worlds with NUE coordinate system. no... | 1.0 | Robotino: remove NUE restriction - https://cyberbotics.com/doc/guide/robotino3:
remove this line:
`And in WorldInfo the coordinateSystem must be set to "NUE".`
background:
the robotino uses asymmetric friction between wheels and floor (cylinder/box), coulombFriction [ 0, 2, 0]. there was a bug, robotino needed wo... | non_test | robotino remove nue restriction remove this line and in worldinfo the coordinatesystem must be set to nue background the robotino uses asymmetric friction between wheels and floor cylinder box coulombfriction there was a bug robotino needed worlds with nue coordinate system now it can drive in... | 0 |
193,935 | 14,665,620,388 | IssuesEvent | 2020-12-29 14:37:49 | status-im/status-react | https://api.github.com/repos/status-im/status-react | opened | java.lang.NullPointerException when creating account or recovering it from seed phrase | bug e2e test blocker help to reproduce | # Bug Report
## Problem
Several times in weeks (so ~0.5% cases) e2e are failed on account creation (or recovering from seed phrase) with error.
Several times I faced with this error on real device.
#### Expected behavior
no error
#### Actual behavior
 e2e are failed on account creation (or recovering from seed phrase) with error.
Several times I faced with this error on real device.
#### Expected behavior
n... | test | java lang nullpointerexception when creating account or recovering it from seed phrase bug report problem several times in weeks so cases are failed on account creation or recovering from seed phrase with error several times i faced with this error on real device expected behavior no ... | 1 |
14,629 | 3,412,435,502 | IssuesEvent | 2015-12-05 21:58:27 | galenframework/galen | https://api.github.com/repos/galenframework/galen | closed | For mobile resolutions, scrollbar need to be removed when page opens up while execution | c3 enhancement p3 ready for test | For mobile resolutions, scroll bar on right side of window need to be removed when page opens up while execution. scroll bar consumes almost 17 px of page and so the content of webpage behaves differently when same page is viewed using Ctrl+Shft+M | 1.0 | For mobile resolutions, scrollbar need to be removed when page opens up while execution - For mobile resolutions, scroll bar on right side of window need to be removed when page opens up while execution. scroll bar consumes almost 17 px of page and so the content of webpage behaves differently when same page is viewed ... | test | for mobile resolutions scrollbar need to be removed when page opens up while execution for mobile resolutions scroll bar on right side of window need to be removed when page opens up while execution scroll bar consumes almost px of page and so the content of webpage behaves differently when same page is viewed u... | 1 |
66,221 | 6,993,211,979 | IssuesEvent | 2017-12-15 10:25:24 | edenlabllc/ehealth.api | https://api.github.com/repos/edenlabllc/ehealth.api | closed | no_tax_id additional verifications | epic/no_tax_id kind/task status/test | - [x] In Employee Request and Create legal_entity make field 'no_tax_id' optional (set false by default)
- [x] for Create legal_entity if 'no_tax_id'=true answer with 422 verification error 'no_tax_id must be false'
- [x] for Employee_request if no_tax_id=false check that tax_id has next pattern: ^[0-9]{10}$
- [x] for ... | 1.0 | no_tax_id additional verifications - - [x] In Employee Request and Create legal_entity make field 'no_tax_id' optional (set false by default)
- [x] for Create legal_entity if 'no_tax_id'=true answer with 422 verification error 'no_tax_id must be false'
- [x] for Employee_request if no_tax_id=false check that tax_id has... | test | no tax id additional verifications in employee request and create legal entity make field no tax id optional set false by default for create legal entity if no tax id true answer with verification error no tax id must be false for employee request if no tax id false check that tax id has next pa... | 1 |
26,126 | 2,684,185,139 | IssuesEvent | 2015-03-28 18:49:25 | ConEmu/old-issues | https://api.github.com/repos/ConEmu/old-issues | closed | Infinite tab opening for jumplist item "Powershell -version 2.0" | 1 star bug imported Priority-Medium | _From [zippy1...@gmail.com](https://code.google.com/u/104528604277004292328/) on September 26, 2012 06:45:40_
Required information! OS version: Win7 SP1 x64 ConEmu version: 120925
As of the latest build of ConEmu , I have been have been getting some "infinite tab" issues. It seems to occur whenever I start up Pow... | 1.0 | Infinite tab opening for jumplist item "Powershell -version 2.0" - _From [zippy1...@gmail.com](https://code.google.com/u/104528604277004292328/) on September 26, 2012 06:45:40_
Required information! OS version: Win7 SP1 x64 ConEmu version: 120925
As of the latest build of ConEmu , I have been have been getting so... | non_test | infinite tab opening for jumplist item powershell version from on september required information os version conemu version as of the latest build of conemu i have been have been getting some infinite tab issues it seems to occur whenever i start up powershell exe with par... | 0 |
5,139 | 7,036,009,509 | IssuesEvent | 2017-12-28 05:33:08 | Microsoft/vsts-tasks | https://api.github.com/repos/Microsoft/vsts-tasks | closed | Cannot Run Service Fabric Tasks on Deployment Groups | Area: Release Area: ServiceFabric enhancement Status: Resolved | Hi everyone, so we ran into an issue this week where we need to run the Service Fabric related tasks in a Deployment Group (details below). I found these pull requests (#3412, #3527) that add the `runsOn` property that limits the tasks to only build agents, making it so that we can't use them on Deployment Groups. I ca... | 1.0 | Cannot Run Service Fabric Tasks on Deployment Groups - Hi everyone, so we ran into an issue this week where we need to run the Service Fabric related tasks in a Deployment Group (details below). I found these pull requests (#3412, #3527) that add the `runsOn` property that limits the tasks to only build agents, making ... | non_test | cannot run service fabric tasks on deployment groups hi everyone so we ran into an issue this week where we need to run the service fabric related tasks in a deployment group details below i found these pull requests that add the runson property that limits the tasks to only build agents making it so ... | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.