id int64 5 1.93M | title stringlengths 0 128 | description stringlengths 0 25.5k | collection_id int64 0 28.1k | published_timestamp timestamp[s] | canonical_url stringlengths 14 581 | tag_list stringlengths 0 120 | body_markdown stringlengths 0 716k | user_username stringlengths 2 30 |
|---|---|---|---|---|---|---|---|---|
1,886,612 | Dive into Server-Side Website Programming: From Basics to Mastery🚀🚀 | Introduction to Server-Side Programming Server-Side Website... | 0 | 2024-06-13T07:21:08 | https://dev.to/dharamgfx/dive-into-server-side-website-programming-from-basics-to-mastery-255f | webdev, javascript, node, beginners |
### Introduction to Server-Side Programming
#### Server-Side Website Programming
Server-side programming involves writing code that runs on a server, handling requests from clients (typically web browsers), processing these requests, interacting with databases, and sending appropriate responses back to the client. T... | dharamgfx |
1,886,611 | Code Smell, Cyclomatic Complexity, Blast Radius, Heisenbug and more... | We often read about design principles and design patterns, but it's equally important to understand... | 0 | 2024-06-13T07:20:57 | https://dev.to/rahulvijayvergiya/code-smell-cyclomatic-complexity-blast-radius-heisenbug-and-more-4kp3 | webdev, programming, architecture, designsystem | We often read about design principles and design patterns, but it's equally important to understand the specific challenges they help us address.
This article highlights key topics such as **Service Mesh, Failover, Dependency Hell, Ripple Effect, Single Point of Failure (SPOF), Cyclomatic Complexity, Blast Radius, Go... | rahulvijayvergiya |
1,886,607 | Day 2 of 100 days of code challenge | Here's Day 2 guys! Concreting yesterday's topic by solving one more LC que today, of Base Complement... | 0 | 2024-06-13T07:20:36 | https://dev.to/harshey0/day-2-of-100-days-of-code-challenge-4k5a | buildinpublic, 100daysofcode, dsa | Here's Day 2 guys!
Concreting yesterday's topic by solving one more LC que today, of Base Complement using left and right shift operators. (Umm yeah, it took time to think and build logic but satisfied after seeing Runtime🤡)
| harshey0 |
1,886,600 | Study in New Zealand benifts and oppurunites | High-Quality Education: New Zealand is renowned for its excellent education system, with universities... | 0 | 2024-06-13T07:19:40 | https://dev.to/person_abe722cdc910099faf/study-in-new-zealand-benifts-and-oppurunites-4b24 | High-Quality Education: New Zealand is renowned for its excellent education system, with universities and institutions consistently ranking well globally.
Diverse Range of Courses: Whether you're interested in arts, sciences, technology, or humanities, New Zealand institutions offer a wide variety of courses and progr... | person_abe722cdc910099faf | |
1,886,599 | Swift Interview Questions and Answers | When preparing for a Swift Interview Questions, it is essential to be well-versed in the basics and... | 0 | 2024-06-13T07:18:26 | https://dev.to/lalyadav/swift-interview-questions-and-answers-5a5l | swift, swiftinterview, swiftinterviewquestions, programming | When preparing for a [Swift Interview Questions](https://www.onlineinterviewquestions.com/swift-interview-questions-answers/), it is essential to be well-versed in the basics and some advanced topics of the language. Here are the top questions that freshers may encounter during a Swift interview, along with their answe... | lalyadav |
1,886,598 | Jodhpur Jaisalmer Tour | Unveiling the Enchantment of Rajasthan: A Journey Through Jodhpur Jaisalmer Tour Embark on a... | 0 | 2024-06-13T07:17:42 | https://dev.to/rajasthanx/jodhpur-jaisalmer-tour-48hn | jaisalmer, tour, package | Unveiling the Enchantment of Rajasthan: A Journey Through Jodhpur Jaisalmer Tour
Embark on a captivating adventure through the heart of Rajasthan with a Jodhpur Jaisalmer tour. This immersive experience unveils the vibrant culture, architectural marvels, and captivating history that defines "The Land of Kings."
Jodhpu... | rajasthanx |
1,886,597 | Looking for a pyhton Community | Greetings to everyone.Delighted I am to be art of this team. I am Ouma Ronald a student at Bugema... | 0 | 2024-06-13T07:16:00 | https://dev.to/ronaldronnie/looking-for-a-pyhton-community-gf8 | python, opensource, discuss | Greetings to everyone.Delighted I am to be art of this team. I am **Ouma Ronald** a student at _**Bugema University Main Campus ,Kampala, Luweero District**_. .I would like to get some get some guidance and recommendations about the communities that I can join and be part such that i can contribute and learn more skill... | ronaldronnie |
1,886,595 | Enhancing AEM Performance With Graphql Integration | Adobe Experience Manager (AEM) has integrated GraphQL to provide a powerful and flexible way to query... | 0 | 2024-06-13T07:14:11 | https://dev.to/saumya27/enhancing-aem-performance-with-graphql-integration-483i | aem, graphql | Adobe Experience Manager (AEM) has integrated GraphQL to provide a powerful and flexible way to query content. This integration allows developers to fetch specific data efficiently, improving the performance and usability of AEM-powered websites and applications. Here's a detailed overview of AEM GraphQL, its features,... | saumya27 |
1,886,594 | Identifying Common Cyber Attacks and Proactive Prevention Techniques | Taking your business online opens doors to growth, but it also exposes you to cyberattacks. This... | 0 | 2024-06-13T07:13:27 | https://dev.to/wewphosting/identifying-common-cyber-attacks-and-proactive-prevention-techniques-2k09 |

Taking your business online opens doors to growth, but it also exposes you to cyberattacks. This article explores different cyber threats and how to protect your website.
### Common Cyberattacks:
- **Phishing Att... | wewphosting | |
1,886,593 | When to Use Unstyled Component Libraries Instead of Pre-Styled UI Component Libraries | Introduction In the world of web development, choosing the right component library is... | 0 | 2024-06-13T07:11:05 | https://dev.to/webdevlapani/when-to-use-unstyled-component-libraries-instead-of-pre-styled-ui-component-libraries-16kk |
#### Introduction
In the world of web development, choosing the right component library is crucial for building efficient, maintainable, and scalable applications. Developers often face the dilemma of choosing between unstyled component libraries and pre-styled UI component libraries. This guide explores the context... | webdevlapani | |
1,886,592 | Difference Between OCR and ICR | A Complete Guide | Have you ever wondered how businesses turn printed or handwritten documents into digital files? The... | 0 | 2024-06-13T07:10:09 | https://blog.filestack.com/difference-between-ocr-and-icr/ | filestack, ocr, javascript, webdev | Have you ever wondered how businesses turn printed or handwritten documents into digital files? The answer is in two smart technologies: Optical Character Recognition (OCR) and Intelligent Character Recognition (ICR). Knowing the difference between OCR and ICR can help you pick the right one for your needs. It is impor... | ideradevtools |
1,886,591 | Homaid: Your Ultimate Platform for Task Assistance | In today's fast-paced world, balancing personal and professional responsibilities can be... | 0 | 2024-06-13T07:09:35 | https://dev.to/akansha_sharma_1f4b80f069/homaid-your-ultimate-platform-for-task-assistance-3kb7 | In today's fast-paced world, balancing personal and professional responsibilities can be overwhelming. Whether it's completing household chores, running errands, or managing work tasks, there never seems to be enough time in the day. That's where Homaid comes in.
Homaid is more than just a platform; it's a community d... | akansha_sharma_1f4b80f069 | |
1,886,590 | Why Mobile Optimization is Crucial for Your Website in 2024 | Mobile optimization is no longer optional — it’s essential. With the ever-growing number of mobile... | 0 | 2024-06-13T07:08:48 | https://dev.to/aditya_pandey_1847fe5a44a/why-mobile-optimization-is-crucial-for-your-website-in-2024-94o |

Mobile optimization is no longer optional — it’s essential. With the ever-growing number of mobile users worldwide, ensuring your website is mobile-friendly can make or break your online presence. As the best digita... | aditya_pandey_1847fe5a44a | |
1,886,589 | What is CJIS Compliance? | The Comprehensive Guide to CJIS Compliance: Safeguarding Criminal Justice Information In... | 0 | 2024-06-13T07:08:41 | https://dev.to/blogginger/what-is-cjis-compliance-7lg | cjiscompliance, cjis | ### The Comprehensive Guide to CJIS Compliance: Safeguarding Criminal Justice Information
In today’s digital world, data security is critical, especially within law enforcement and public safety sectors. CJIS compliance is a crucial framework for protecting sensitive information. But what does CJIS compliance entail, ... | blogginger |
1,886,588 | 10 Proven Methods for Enhancing Web Page Loading Speed | This article highlights the critical role of website loading speed in online business success. A... | 0 | 2024-06-13T07:08:04 | https://dev.to/wewphosting/10-proven-methods-for-enhancing-web-page-loading-speed-23ge |

This article highlights the critical role of website loading speed in online business success. A slow website frustrates visitors and hurts SEO ranking. Here are 10 effective ways to improve your website speed:
1.... | wewphosting | |
1,886,587 | The Best Accounting Software for Small Businesses in 2024 | Selecting the right accounting software is essential for managing the finances of a small business... | 0 | 2024-06-13T07:06:58 | https://blog.productivity.directory/the-best-accounting-software-for-small-businesses-0504118670dd | accountingsoftware, smallbusiness, productivitytools, bestapps | Selecting the right accounting software is essential for managing the finances of a small business efficiently. As we move through 2024, several software options stand out for their features, usability, and integration capabilities. Whether you're a startup, a growing business, or a well-established entity looking for ... | stan8086 |
1,886,586 | My Portfolio | A post by Deb Deb | 0 | 2024-06-13T07:05:32 | https://dev.to/deb_deb_8aebbb0ba81c86486/my-portfolio-1i1i | codepen | deb_deb_8aebbb0ba81c86486 | |
1,886,585 | RAG with OLLAMA | In the world of natural language processing (NLP), combining retrieval and generation capabilities... | 0 | 2024-06-13T07:04:22 | https://dev.to/mohsin_rashid_13537f11a91/rag-with-ollama-1049 | python, llama, ollama | In the world of natural language processing (NLP), combining retrieval and generation capabilities has led to significant advancements. Retrieval-Augmented Generation (RAG) enhances the quality of generated text by integrating external information sources. This article demonstrates how to create a RAG system using a fr... | mohsin_rashid_13537f11a91 |
1,886,584 | In-house Server vs. Cloud Hosting: Which One to Choose? | This blog post explores the key differences between in-house servers and cloud hosting to help... | 0 | 2024-06-13T07:04:13 | https://dev.to/wewphosting/in-house-server-vs-cloud-hosting-which-one-to-choose-6e0 |
This blog post explores the key differences between in-house servers and cloud hosting to help businesses make informed decisions about their IT infrastructure.
### In-House Servers vs. Cloud Hosting:
- **IT Infr... | wewphosting | |
1,863,867 | Efficient Ways to List PostgreSQL Databases | Learn how to list databases in PostgreSQL using command-line tools, SQL queries, and database... | 21,681 | 2024-06-13T07:00:00 | https://dev.to/dbvismarketing/efficient-ways-to-list-postgresql-databases-5hhn | postgressql | Learn how to list databases in PostgreSQL using command-line tools, SQL queries, and database clients. Each method is tailored to different preferences and requirements.
Use the command-Line method to connect and list databases with `psql`:
1. Connect
```
psql -U <username>
```
2. List databases... | dbvismarketing |
1,886,582 | Understanding the Difference Between APIs and Endpoints | Understanding the Difference Between APIs and Endpoints In the world of software... | 0 | 2024-06-13T06:58:18 | https://dev.to/msnmongare/understanding-the-difference-between-apis-and-endpoints-402a | api, webdev, beginners, abotwrotethis | ### Understanding the Difference Between APIs and Endpoints
In the world of software development, particularly in the domain of web services and backend development, two terms frequently surface: API (Application Programming Interface) and endpoints.” They are always associated, but, nevertheless, they are two concep... | msnmongare |
1,886,581 | Nirakshak Geotagging and Surveillance Platform | Live Demo Experience a live demo of the Nirakshak platform at https://nirakshak.vercel.app/. Explore... | 0 | 2024-06-13T06:58:11 | https://dev.to/pandeysaurabh/nirakshak-geotagging-and-surveillance-platform-1mii | **Live Demo**
Experience a live demo of the Nirakshak platform at https://nirakshak.vercel.app/. Explore the features and see how the platform works in real-time.
**Features**
**Geotagging and User Registration**
User Registration: Users must provide personal details, including Name, Phone No., and Email ID.
Camera ... | pandeysaurabh | |
1,886,566 | Understanding CFD Trading Basics for Beginners | CFD trading, or Contracts for Difference, is a popular method for speculating on the price movements... | 0 | 2024-06-13T06:34:35 | https://dev.to/georgewilliam4425/understanding-cfd-trading-basics-for-beginners-317f | CFD trading, or Contracts for Difference, is a popular method for speculating on the price movements of various financial instruments without owning the underlying assets. For beginners, understanding the basics of CFD trading is crucial for making informed decisions and managing risks effectively. This guide will cove... | georgewilliam4425 | |
1,886,580 | Understanding How Server Location Affects Website Performance | This blog post highlights the importance of choosing the right server location to optimize website... | 0 | 2024-06-13T06:57:59 | https://dev.to/wewphosting/understanding-how-server-location-affects-website-performance-1e5c |

This blog post highlights the importance of choosing the right server location to optimize website performance.
### Why Server Location Matters:
The location of your website’s server significantly impacts user ex... | wewphosting | |
1,886,579 | AI and Blockchain: Revolutionizing the Future | # AI and Blockchain: Revolutionizing the Future ## Introduction to AI and Blockchain The... | 27,619 | 2024-06-13T06:54:21 | https://dev.to/aishik_chatterjee_0060e71/ai-and-blockchain-revolutionizing-the-future-3n3h | ```html
# AI and Blockchain: Revolutionizing the Future
## Introduction to AI and Blockchain
The convergence of AI and Blockchain represents a significant evolution in the
tech world, promising to enhance security, efficiency, and trust in data-
driven systems. AI provides the intelligence to automate complex proces... | aishik_chatterjee_0060e71 | |
1,886,578 | Exploring the Newest SAP Course Trends of 2024 | In 2024, a lot of technological advancements and a rapidly changing business environment led to an... | 0 | 2024-06-13T06:52:28 | https://dev.to/manojkumar10/exploring-the-newest-sap-course-trends-of-2024-1njk | sapficocourse, saptraining, learnsap, sapcertification | In 2024, a lot of technological advancements and a rapidly changing business environment led to an exponential rise in the SAP landscape. Systems, Applications, and Products ( SAP course full form) or SAP is a software that can handle various aspects of businesses including finance, human resources, operations, and fac... | manojkumar10 |
1,886,577 | Unlocking Flexibility in React: A Guide to Headless Components | Headless components in React are a design pattern that helps to separate the logic and structure of a... | 0 | 2024-06-13T06:50:06 | https://dev.to/webdevlapani/unlocking-flexibility-in-react-a-guide-to-headless-components-3c65 | react, frontend | Headless components in React are a design pattern that helps to separate the logic and structure of a component from its presentation. This allows for greater reusability and flexibility when building user interfaces. Here’s a comprehensive overview of headless components in React:
### What are Headless Components?
H... | webdevlapani |
1,886,576 | Michael Savage's Odyssey with 1800Accountant: Pioneering Financial Success | Introduction Within the vibrant tapestry of entrepreneurship, the narrative of Michael Savage... | 0 | 2024-06-13T06:49:49 | https://dev.to/vanhausenmike/michael-savages-odyssey-with-1800accountant-pioneering-financial-success-2ddh | Introduction
Within the vibrant tapestry of entrepreneurship, the narrative of Michael Savage emerges as a remarkable testament to strategic ingenuity, unwavering perseverance, and the transformative potential of collaboration. At the heart of Savage's journey lies a pivotal partnership with 1800Accountant, an esteeme... | vanhausenmike | |
1,886,575 | Michael Savage's Transformational Journey with 1800Accountant: A Saga of Financial Triumph | Introduction The annals of entrepreneurship are replete with tales of visionaries who've shaped... | 0 | 2024-06-13T06:48:37 | https://dev.to/vanhausenmike/michael-savages-transformational-journey-with-1800accountant-a-saga-of-financial-triumph-b9m | Introduction
The annals of entrepreneurship are replete with tales of visionaries who've shaped industries and redefined success. Among these luminaries stands Michael Savage, an entrepreneur who etched his name in the annals of business by harnessing innovation, determination, and strategic collaboration. A pivotal c... | vanhausenmike | |
1,886,574 | Mainkan Gacor123 Online Dengan Fitur Terlengkap | Sudah siap untuk merasakan pengalaman bermain game online yang seru dan mendebarkan? Yuk, temukan... | 0 | 2024-06-13T06:47:27 | https://dev.to/dianajkv/mainkan-gacor123-online-dengan-fitur-terlengkap-2b09 | webdev, javascript, beginners, tutorial |
Sudah siap untuk merasakan pengalaman bermain game online yang seru dan mendebarkan? Yuk, temukan keseruan itu semua bersama Gacor123! Dalam artikel ini, kita akan membahas secara lengkap tentang apa itu Gacor123, keuntungan bermainnya, fitur-fitur terbaik yang ditawarkan, cara memainkannya, serta tips dan trik agar b... | dianajkv |
1,886,573 | Michael Savage's Journey with 1800Accountant: Navigating Financial Success | Introduction In the realm of finance and entrepreneurship, few stories resonate as strongly as that... | 0 | 2024-06-13T06:47:26 | https://dev.to/vanhausenmike/michael-savages-journey-with-1800accountant-navigating-financial-success-4io1 | Introduction
In the realm of finance and entrepreneurship, few stories resonate as strongly as that of Michael Savage's journey. A tale of resilience, innovation, and strategic decision-making, Savage's path to success includes a pivotal partnership with 1800Accountant, a leading firm providing comprehensive accountin... | vanhausenmike | |
1,886,572 | Michael Savage of New Canaan’s Ushio Art Collection: A Cultural Legacy for the Ages | Nestled in the picturesque town of New Canaan, Connecticut, is a hidden gem that transcends both time... | 0 | 2024-06-13T06:46:12 | https://dev.to/vanhausenmike/michael-savage-of-new-canaans-ushio-art-collection-a-cultural-legacy-for-the-ages-37ik | Nestled in the picturesque town of New Canaan, Connecticut, is a hidden gem that transcends both time and geography—the Ushio Art Collection, meticulously curated and lovingly preserved by Michael Savage. This remarkable collection stands as a testament to the profound impact of art in enriching our lives, bridging cul... | vanhausenmike | |
1,886,571 | Understanding File Transfer Protocol: Simplifying Cross-Network File Sharing | This blog post explores File Transfer Protocol (FTP) and its role in streamlining file sharing... | 0 | 2024-06-13T06:46:05 | https://dev.to/wewphosting/understanding-file-transfer-protocol-simplifying-cross-network-file-sharing-52jj |

This blog post explores File Transfer Protocol (FTP) and its role in streamlining file sharing across networks.
### What is FTP?
FTP is a network protocol that enables efficient file transfers between computers o... | wewphosting | |
1,885,534 | A Comprehensive Guide to XSS Attacks and Defenses | Part 1: Basics of Vulnerability Attacks and Defenses XSS belongs to the field of... | 0 | 2024-06-13T06:44:45 | https://dev.to/wetest/a-comprehensive-guide-to-xss-attacks-and-defenses-39m8 | programming, xss | ## **Part 1: Basics of Vulnerability Attacks and Defenses**
XSS belongs to the field of vulnerability attacks and defenses. To study it, we need to understand some jargon in this field for better communication and exchange. At the same time, I have established a simple attack model for XSS vulnerability learning.
## 1... | wetest |
1,886,570 | Greytrix can help you navigate Acumatica implementation and consulting | We’re here to guide you through the craziness of business. Prepare to soar above the clouds of... | 0 | 2024-06-13T06:43:13 | https://dev.to/dinesh_m/greytrix-can-help-you-navigate-acumatica-implementation-and-consulting-1ilc | acumatica, implementation, consulting, greytrix |

We’re here to guide you through the craziness of business. Prepare to soar above the clouds of company management. Acumatica, the top Cloud ERP, is required to improve your business operations and assure high custom... | dinesh_m |
1,886,569 | Relevance Feature Discovery for Text Mining | .. Click Here- https://projecttunnel.com/relevance-feature-discovery-for-text-mining IEEE Base... | 0 | 2024-06-13T06:39:11 | https://dev.to/neerajm76404554/relevance-feature-discovery-for-text-mining-42ee | ai, computerscience, programming, datascience | [](https://projecttunnel.com/relevance-feature-discovery-for-text-mining) ..
Click Here- https://projecttunnel.com/relevance-feature-discovery-for-text-mining
IEEE Base paper | neerajm76404554 |
1,886,568 | Understanding Broker Commissions and Fees | In the world of forex and CFD trading, understanding broker commissions and fees is crucial for... | 0 | 2024-06-13T06:39:09 | https://dev.to/georgewilliam4425/understanding-broker-commissions-and-fees-256b |
In the world of [forex](https://bit.ly/forex-trading-t4t) and [CFD trading](https://bit.ly/4bXk670), understanding broker commissions and fees is crucial for managing costs and maximizing profitability. Different brokers and trading platforms have various fee structures, which can significantly impact your overall tra... | georgewilliam4425 | |
1,886,567 | Big O Notation | Big O Notation: Big O Notation describes the upper bound of an algorithm's runtime or space... | 0 | 2024-06-13T06:37:46 | https://dev.to/bpk45_0670a02e0f3a6839b3a/big-o-notation-3nnf | devchallenge, cschallenge, computerscience, beginners | **Big O Notation:** Big O Notation describes the upper bound of an algorithm's runtime or space requirements relative to input size (n). It compares algorithm efficiency by focusing on growth rates, ensuring scalability and optimal performance as input sizes increase.
Here's a brief pseudocode example to illustrate h... | bpk45_0670a02e0f3a6839b3a |
1,886,562 | Step-by-Step Guide for Web Scraping Using BeautifulSoup | Web scraping is an essential skill for gathering data from websites, especially when that data isn't... | 0 | 2024-06-13T06:32:47 | https://dev.to/ionegarza/step-by-step-guide-for-web-scraping-using-beautifulsoup-hcd | webscraping, scraping, bs4, beautifulsoup | Web scraping is an essential skill for gathering data from websites, especially when that data isn't available via a public API. In this guide, I'll walk you through the [process of scraping a website using Python and BeautifulSoup](https://write.as/victoria-collins/tips-for-web-scraping-using-beautifulsoup), a powerfu... | ionegarza |
1,886,561 | Continuous Integration Testing: Streamlining Software Development and Ensuring Quality | In the rapidly evolving world of software development, delivering high-quality software quickly and... | 0 | 2024-06-13T06:31:18 | https://dev.to/keploy/continuous-integration-testing-streamlining-software-development-and-ensuring-quality-10mc | continuous, testing, tools, development |
In the rapidly evolving world of software development, delivering high-quality software quickly and efficiently is a top priority. Continuous Integration (CI) has emerged as a critical practice that helps developmen... | keploy |
1,886,560 | Tips for soft skills development | In today's dynamic and interconnected world, possessing strong soft skills is crucial for personal... | 0 | 2024-06-13T06:29:30 | https://dev.to/techstuff/tips-for-soft-skills-development-3cpm | softskills, skillsdevelopment, productivity, teamwork | 
In today's dynamic and interconnected world, possessing strong soft skills is crucial for personal and professional success. While technical expertise and knowledge are important, it's often the soft skills—such as c... | swati_sharma |
1,886,559 | Tailwind CSS vs. Shadcn: Which Should You Choose for Your Next Project? | If you're new to web development, you may be unsure of the best tools for website styling. Tailwind... | 0 | 2024-06-13T06:27:54 | https://www.swhabitation.com/blogs/tailwind-css-vs-shadcn-which-should-you-choose-for-your-next-project | tailwindcss, shadcnui, frontend, webdev | If you're new to web development, you may be unsure of the best tools for website styling. Tailwind CSS and Shadcn are two well-liked options. They both assist you in creating stunning websites, but their functions are distinct. Let's examine what each one has to offer in more detail so you can decide which would work ... | swhabitation |
1,886,557 | Commodity Futures R-Breaker Strategy | Summary The R-Breaker strategy was developed by Richard Saidenberg and published in 1994.... | 0 | 2024-06-13T06:25:56 | https://dev.to/fmzquant/commodity-futures-r-breaker-strategy-4cc2 | strategy, fmzquant, futures, commodity | ## Summary
The R-Breaker strategy was developed by Richard Saidenberg and published in 1994. It was selected as one of the top ten most profitable trading strategies by "Futures Truth" magazine in the United States for 15 consecutive years. Compared with other strategies, R-Breaker is a trading strategy that combines t... | fmzquant |
1,654,078 | AWS IoT Core Simplified - Part 2: Presigned URL | This is part 2 in a series of articles about IoT Core: Parts coming up: Part 3: Connect using a... | 27,687 | 2024-06-13T06:25:48 | https://dev.to/slootjes/aws-iot-core-simplified-part-2-presigned-url-4006 | aws, iot, mqtt, serverless | This is part 2 in a series of articles about IoT Core:
Parts coming up:
Part 3: Connect using a custom authorizer
Part 4: Topic Rules
## Connect using a presigned url
Similar to S3, it's possible to create a presigned url for IoT Core. You can even cache and reuse this presigned url for multiple clients as long as th... | slootjes |
1,886,556 | Javascript Symbols | The good perk of having a lot of people who code around you is that you end up discussing things that... | 0 | 2024-06-13T06:24:30 | https://www.oh-no.ooo/articles/javascript-symbols | javascript, webdev, learning, coding | The good perk of having a lot of people who code around you is that you end up discussing things that you don't get to see on a day-to-day basis as a simpleton frontend developer.
This time, I landed on the __concept of symbols in JavaScript__, which is something I don't have to deal with at work, but something that J... | mahdava |
1,886,555 | Why Every Developer Needs Codequiry's Website Plagiarism Checker? | In today’s digital landscape, where coding and development form the backbone of countless websites... | 0 | 2024-06-13T06:22:46 | https://dev.to/codequiry/why-every-developer-needs-codequirys-website-plagiarism-checker-1cd0 | websiteplagiarismchecker, webdev, codequiry, codeplagiarismchecker | In today’s digital landscape, where coding and development form the backbone of countless websites and applications, ensuring the originality and integrity of your code is paramount. Just as writers and academics rely on plagiarism checkers to safeguard their work, developers and tech professionals can benefit immensel... | codequiry |
1,886,554 | Complete Guide to Hiring a General Contractor in Westchester, NY | Embarking on a construction project in Westchester County, NY, requires the expertise of a reliable... | 0 | 2024-06-13T06:22:05 | https://dev.to/con42me/complete-guide-to-hiring-a-general-contractor-in-westchester-ny-326l | Embarking on a construction project in Westchester County, NY, requires the expertise of a reliable general contractor. Whether you're planning a home renovation, commercial construction, or any other project, selecting the right contractor is crucial for its success. This comprehensive guide will walk you through the ... | con42me | |
1,886,538 | The Power of Automated Testing for Enterprise Applications | Businesses are heavily reliant on a diverse range of technologies and applications for their growth.... | 0 | 2024-06-13T06:14:43 | https://dev.to/grjoeay/the-power-of-automated-testing-for-enterprise-applications-4cac | automatedtesting, automation, enterpriseapplication, testautomation | Businesses are heavily reliant on a diverse range of technologies and applications for their growth. Today, business expansion is experiencing a significant boost due to widespread availability of robust cloud-based applications including SaaS, IaaS, and other "as a service" solutions. It is predicted by surveys that a... | grjoeay |
1,886,543 | Konnect Packers And Movers | At Konnect Packers and Movers, the satisfaction of our customer is not a dream, but a reality. It... | 0 | 2024-06-13T06:19:21 | https://dev.to/dilip36/konnect-packers-and-movers-5djh | packers, movers, transportations, movingstorage | At Konnect Packers and Movers, the satisfaction of our customer is not a dream, but a reality. It entails that we deliver organized and efficient services beyond the expected levels. It has been our privilege to be associated with several business organizations for our exemplary packing and moving services. We sure to ... | dilip36 |
1,886,542 | 10 Proven Strategies to Boost Your Social Media Engagement | Achieving high engagement on social media can be challenging. Here are ten proven strategies to help... | 0 | 2024-06-13T06:19:20 | https://dev.to/aditya_pandey_1847fe5a44a/10-proven-strategies-to-boost-your-social-media-engagement-246o |

Achieving high engagement on social media can be challenging. Here are ten proven strategies to help you boost your social media engagement and stand out from the competition. If you need expert assistance, consider... | aditya_pandey_1847fe5a44a | |
1,886,541 | Navigating Uncertainty: Probabilistic Programming | This is a submission for DEV Computer Science Challenge v24.06.12: One Byte Explainer. ... | 0 | 2024-06-13T06:19:19 | https://dev.to/aztec_mirage/navigating-uncertainty-probabilistic-programming-27c | devchallenge, cschallenge, computerscience, beginners | _This is a submission for DEV Computer Science Challenge v24.06.12: One Byte Explainer._
## Explainer
> The world is uncertain. Predicting outcomes with data involves probabilistic models which use math to handle uncertainty. Probabilistic Programming describe and analyze these models. Examples: Predicting weather, s... | aztec_mirage |
1,886,540 | AI and Blockchain: Revolutionizing Digital Identity | AI and Blockchain: Revolutionizing Digital Identity Introduction to AI and... | 27,619 | 2024-06-13T06:18:39 | https://dev.to/aishik_chatterjee_0060e71/ai-and-blockchain-revolutionizing-digital-identity-606 | # AI and Blockchain: Revolutionizing Digital Identity
## Introduction to AI and Blockchain
Artificial Intelligence (AI) and Blockchain are two revolutionary technologies
reshaping industries globally. AI involves machines designed to act
intelligently like humans, while blockchain is a decentralized technology
ensuri... | aishik_chatterjee_0060e71 | |
1,886,539 | Can Metal Detectors Detect Lead? | Yes, metal detectors can detect lead. Lead is a dense metal with significant mass, which makes it... | 0 | 2024-06-13T06:17:07 | https://dev.to/liam_james_ed448f6f4070cb/can-metal-detectors-detect-lead-20ik | metaldetectors, golddetectors, goldxtra, tgxpro | Yes, metal detectors can detect lead. Lead is a dense metal with significant mass, which makes it detectable by most metal detectors, especially those designed for all-metal mode operation. Advanced metal detectors are capable of distinguishing lead from other metals based on its conductivity and density.
 mieten, wählen Sie Stücke mit klaren Linien und minimalistischem Design. Suchen Sie nach Sofas, Stühlen und Tischen mit klaren, kantigen Formen und minimalen Verzierungen. Vermeiden Sie kunstvol... | lounge-hocker-creativework | |
1,886,533 | Comparing Python Courses in Rohini: Which One is Right for You? | Python has emerged as a powerhouse in the world of programming languages, beloved for its simplicity,... | 0 | 2024-06-13T06:09:13 | https://dev.to/muskan_sharma_c2d15774a2d/comparing-python-courses-in-rohini-which-one-is-right-for-you-5hfe | Python has emerged as a powerhouse in the world of programming languages, beloved for its simplicity, versatility, and readability. Whether you are a seasoned developer looking to expand your skill set or a beginner eager to dive into the world of coding, mastering Python opens up a wealth of opportunities. This compre... | muskan_sharma_c2d15774a2d | |
1,886,532 | Breaking Bad Habits: Common Pitfalls Every Programmer Should Avoid | As programmers, our habits define our efficiency and the quality of our work. While good habits... | 0 | 2024-06-13T06:07:41 | https://dev.to/gstbd/breaking-bad-habits-common-pitfalls-every-programmer-should-avoid-dg | webdev, programming, habit, beginners | As programmers, our habits define our efficiency and the quality of our work. While good habits propel us forward, bad ones can severely hinder our progress. Here are a few detrimental habits that every programmer should strive to eliminate:
1. **Procrastination:** It's easy to fall into the trap of procrastination, d... | gstbd |
1,886,531 | Best Training Institute in Rajpura; Erginous Technology | Erginous not only delivers top-notch solutions in the field of web and mobile application development... | 0 | 2024-06-13T06:06:58 | https://dev.to/erginoustechnology/best-training-institute-in-rajpura-erginous-technology-4blh | Erginous not only delivers top-notch solutions in the field of web and mobile application development but also offers outstanding training across diverse technologies. We are the best Industrial Training Providers in Rajpura, our training programs go beyond conventional approaches, empowering students with comprehensiv... | erginoustechnology | |
1,886,529 | Fiora Hotel: Timeless Elegance in Every Detail | A post by Laroy | 0 | 2024-06-13T06:03:56 | https://dev.to/laroy55/fiora-hotel-timeless-elegance-in-every-detail-1f2j | fiorahotel, hotelbooking, murreehotelbooking | laroy55 | |
1,886,527 | Avoiding Common Psychological Trading Mistakes | Psychological factors play a significant role in trading success, especially in the fast-paced... | 0 | 2024-06-13T05:58:06 | https://dev.to/harryjones78/avoiding-common-psychological-trading-mistakes-1h10 | Psychological factors play a significant role in trading success, especially in the fast-paced environments of [forex](https://bit.ly/forex-trading-1), trading, markets, and [CFDs](https://bit.ly/3Vj9ic3). Traders often face emotional challenges that can lead to common mistakes. This article highlights these [psycholog... | harryjones78 | |
1,886,526 | <h1></h1> | AI and Blockchain: Revolutionizing Digital Identity Introduction to AI and... | 27,619 | 2024-06-13T05:55:07 | https://dev.to/aishik_chatterjee_0060e71/-54f1 | # AI and Blockchain: Revolutionizing Digital Identity
## Introduction to AI and Blockchain
Artificial Intelligence (AI) and Blockchain are two of the most revolutionary
technologies reshaping industries across the globe. While AI involves machines
designed to act intelligently like humans, blockchain is inherently a
... | aishik_chatterjee_0060e71 | |
1,886,519 | PowerWorks Inspections | For comprehensive home inspections in Fayetteville, look no further than PowerWorks Inspections. Our... | 0 | 2024-06-13T05:47:16 | https://dev.to/powerworks_inspections_f9/powerworks-inspections-4jnn | home, inspectors | For comprehensive home inspections in Fayetteville, look no further than [PowerWorks Inspections](https://powerworksinspections.com/). Our team of experienced and certified inspectors is dedicated to providing thorough evaluations of residential properties, ensuring peace of mind for both homebuyers and sellers. From t... | powerworks_inspections_f9 |
1,886,524 | Convenient Car Financing with No Credit Check | For those in San Antonio who are struggling with poor credit or no credit history, buy here pay here... | 0 | 2024-06-13T05:52:24 | https://dev.to/george_henry/convenient-car-financing-with-no-credit-check-kdp | For those in San Antonio who are struggling with poor credit or no credit history, [buy here pay here dealerships](https://buyherepayheresanantoniotx.com/) offer a convenient solution. These dealerships provide in-house financing, meaning they do not rely on traditional banks or credit unions to approve loans. Instead,... | george_henry | |
1,886,523 | Do Unit Tests Find Bugs? | I've been writing software for over 20 years and don't believe unit tests find bugs. Yet, I wouldn't... | 25,505 | 2024-06-13T05:52:06 | https://www.growingdev.net/p/do-unit-tests-find-bugs | I've been writing software for over 20 years and don't believe unit tests find bugs.
Yet, I wouldn't want to work in a code base without unit tests.
## Why unit tests don't find bugs?
To understand why unit tests don't find bugs, we can look at how they are created. Here are the three main ways to handle unit tests:... | moozzyk | |
1,886,522 | Turing 256 | This is a submission for DEV Computer Science Challenge v24.06.12: One Byte Explainer. ... | 0 | 2024-06-13T05:49:40 | https://dev.to/zimaxeg/turing-256-31hi | devchallenge, cschallenge, computerscience, beginners | _This is a submission for DEV Computer Science Challenge v24.06.12: One Byte Explainer._
## Explainer
Algorithm is a finite, ordered set of instructions to solve a problem or perform a task by transforming inputs into outputs. Efficient algorithms optimize the use of resources, like time and memory and thus make compu... | zimaxeg |
1,886,521 | <h1></h1> | The healthcare sector has experienced a digital transformation, accelerated by the COVID-19 pandemic,... | 27,619 | 2024-06-13T05:47:37 | https://dev.to/aishik_chatterjee_0060e71/-979 | The healthcare sector has experienced a digital transformation, accelerated by
the COVID-19 pandemic, necessitating new methods for engaging with healthcare
professionals (HCPs). AI 2.0 offers a compelling solution by merging machine
learning with deep human insights, enhancing these interactions to be more
personalize... | aishik_chatterjee_0060e71 | |
1,886,520 | Difference Between NextJS vs ExpressJS | Quick Overview: The difference between Next JS and Express JS is a matter of discussion. Clients... | 0 | 2024-06-13T05:47:26 | https://dev.to/milanpanchasara/difference-between-nextjs-vs-expressjs-2l0k | webdev, javascript, nextjs, express |
**<u>Quick Overview</u>**: The difference between Next JS and Express JS is a matter of discussion. Clients become doubtful in the selection of an ideal framework. Both have benefits and limitations, so, when you n... | milanpanchasara |
1,886,518 | How Quick Fix Urine Passes a Lab Test | Do you have a co-worker or a classmate who always passes their lab tests even though they are a... | 0 | 2024-06-13T05:39:09 | https://dev.to/elite_jhon/how-quick-fix-urine-1f1 |
Do you have a co-worker or a classmate who always passes their lab tests even though they are a recreational substance user? They found the secret. It is known as [Quick Fix](https://www.quickfixsynthetic.com/) synthetic urine.
If you suspect an impromptu lab test is coming up, you need to know that drinking water, ... | elite_jhon | |
1,886,517 | Copy Router Machines: The Essential Guide to an Indispensable Tool for Precision and Efficiency | In the world of woodworking and metalworking, precision and efficiency are paramount. Among the many... | 0 | 2024-06-13T05:38:45 | https://dev.to/acm_machinery/copy-router-machines-the-essential-guide-to-an-indispensable-tool-for-precision-and-efficiency-2hil | In the world of woodworking and metalworking, precision and efficiency are paramount. Among the many tools available to craftsmen, the [copy router machine](https://www.acm-machinery.com/products-router-cr100/) stands out as an indispensable device for achieving high-quality results. This comprehensive guide delves int... | acm_machinery | |
1,886,516 | What is uses of dev.to | build a place where people can share what they know and learn from each other. The platform's main... | 0 | 2024-06-13T05:36:36 | https://dev.to/sandeep_chauhan_c2d778898/what-is-uses-of-devto-4ikj | build a place where people can share what they know and learn from each other. The platform's main goal is to make a community where writers of all levels can feel welcome. | sandeep_chauhan_c2d778898 | |
1,886,515 | Unlocking React 19: Guide to New Features | Introduction React JS is one of the top most popular front-end development libraries in the tech... | 0 | 2024-06-13T05:32:18 | https://dev.to/jennijuli3/unlocking-react-19-guide-to-new-features-5a6e | learning, react, training, certification | **Introduction**
[React JS](https://www.credosystemz.com/training-in-chennai/react-js-training/) is one of the top most popular front-end development libraries in the tech world. React 19 is the latest version of React with a range of powerful new features and improvements. It aims at enhancing the developer experienc... | jennijuli3 |
1,852,265 | Warning for Front-End Dev Careers! | I would like to share one piece of advice with you, which is to avoid careers centered on the... | 0 | 2024-06-13T05:30:00 | https://www.jobreadyprogrammer.com/p/blog/warning-for-front-end-dev-careers | frontend, webdev, beginners, programming | <p class="MsoNormal"><span lang="EN-US" style="font-size: 12.0pt; mso-bidi-font-size: 11.0pt; line-height: 107%; font-family: 'Times New Roman',serif;">I would like to share one piece of advice with you, which is to avoid careers centered on the front-end. </span></p>
<p class="MsoNormal"><span lang="EN-US" style="font... | jobreadyprogrammer |
1,886,513 | Apple's new feature that just killed my startup 🤯 | Hey everyone, I hope you're all doing well! I wanted to share a story about something cool I was... | 0 | 2024-06-13T05:29:33 | https://dev.to/darkinventor/apple-just-killed-my-startup-with-its-apple-intelligence-integration-1ihj | webdev, javascript, programming, softwaredevelopment | Hey everyone,
I hope you're all doing well! I wanted to share a story about something cool I was working on that took an unexpected turn.
I recently created a project called SearchFast. It's a search tool for macOS that works on both Intel and M series chips.
 | 0 | 2024-06-13T04:02:58 | https://dev.to/abhishekdeveloper101/gjghjgjujhgjghjggj-1kh5 | webdev, javascript, beginners, programming | rgba(91, 84, 87, 0.65) | abhishekdeveloper101 |
1,886,506 | The Rich Tapestry of Indian Culture: Traditions, Festivals, and Modern Influences | India, a land of immense diversity and history, boasts a cultural heritage that is both rich and... | 0 | 2024-06-13T05:12:35 | https://dev.to/hidden_mantra_d12f8366e63/the-rich-tapestry-of-indian-culture-traditions-festivals-and-modern-influences-164o | culture, indian, indianculture | India, a land of immense diversity and history, boasts a cultural heritage that is both rich and varied. The tapestry of Indian culture is woven with threads of ancient traditions, vibrant festivals, and contemporary influences, making it a unique and fascinating mosaic.
## 1. Ancient Traditions and Practices:
The [C... | hidden_mantra_d12f8366e63 |
1,886,505 | Where do VDI costs hide? - A detailed TCO breakdown | Where do VDI costs hide? - A detailed TCO breakdown What is TCO? Total Cost of... | 0 | 2024-06-13T05:09:43 | https://dev.to/struthi/where-do-vdi-costs-hide-a-detailed-tco-breakdown-5b7d | vdi, virtualization, containers, devops | # Where do VDI costs hide? - A detailed TCO breakdown
## What is TCO?
Total Cost of Ownership (TCO) is a critical metric used to evaluate the overall cost efficiency of software purchases. For IT teams, managing hardware tools for a distributed workforce can be costly. Virtual desktop infrastructure (VDI) offers a so... | struthi |
1,886,504 | MAGNATE LUXURIA 3BHK Modern House l JDesign Studio | Step into the world of luxury with a tour of the Magnate Luxuria 3BHK designed by JDesign Studio.... | 0 | 2024-06-13T05:04:23 | https://dev.to/jdesignstudio/magnate-luxuria-3bhk-modern-house-l-jdesign-studio-25jg | 3bhkmodernhouseinterior, homeinterior, homeinteriordecorate, architecture |
Step into the world of luxury with a tour of the Magnate Luxuria 3BHK designed by **_[JDesign Studio.](https://jdesignstudio.in/)_** This exquisite space showcases modern elegance and sophistication in every corner. ... | jdesignstudio |
1,886,503 | Devasya Gold Plus 3BHK Semi Budget House l JDesign Studio | Take a virtual tour of the stunning Devasya Gold Plus 3BHK semi-budget house designed by JDesign... | 0 | 2024-06-13T04:58:26 | https://dev.to/jdesignstudio/devasya-gold-plus-3bhk-semi-budget-house-l-jdesign-studio-5e1n | homeinterior, homeinteriordesignservices, 3bhkhomeinterior, interiordesign2024 |
Take a virtual tour of the stunning Devasya Gold Plus 3BHK semi-budget house designed by **_[**JDesign Studio**.](https://jdesignstudio.in/
)_** Discover the perfect blend of functionality and luxury in this contem... | jdesignstudio |
1,886,502 | Pipe / Curry / HOF | PIPE A pipe function is used to compose multiple functions into a single function,... | 0 | 2024-06-13T04:57:59 | https://dev.to/__khojiakbar__/pipe-curry-hof-413j | pipe, curry, hof, javascript | #**PIPE**
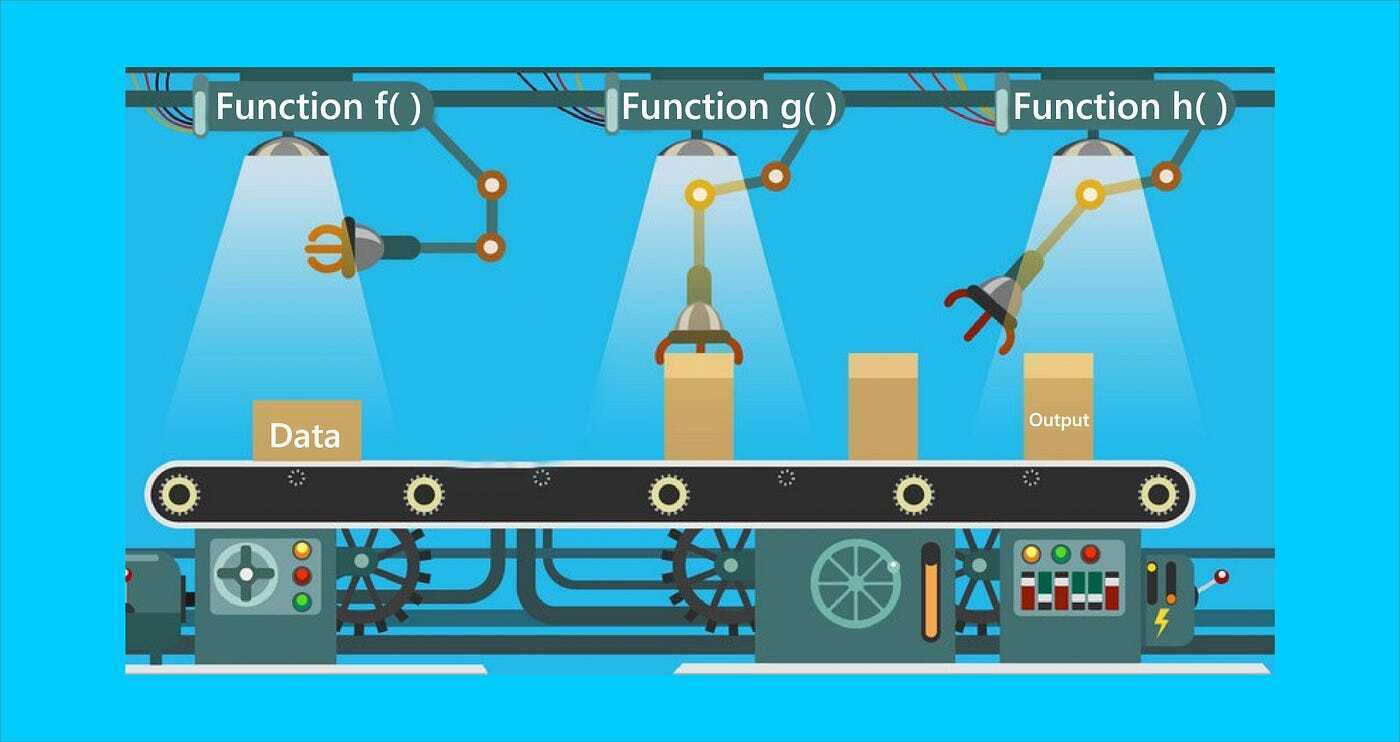
> A pipe function is used to compose multiple functions into a single function, where the output of one function becomes the input of the next. It's a way to create a sequence of function calls.
```
let... | __khojiakbar__ |
1,886,501 | 7 Amazon Free AI Courses | 1. Generative AI Learning Plan for Developers overview This learning plan is designed... | 0 | 2024-06-13T04:57:05 | https://dev.to/0xkoji/7-amazon-free-ai-courses-10ie | generativea, ai, amazon | ## 1. Generative AI Learning Plan for Developers
overview
```
This learning plan is designed to introduce generative AI to software developers interested in leveraging large language models without fine-tuning. The digital training included in this learning plan will provide an overview of generative AI, planning a gen... | 0xkoji |
1,886,500 | Reach Success With Salesforce Implementation Services | In today’s competitive landscape, businesses are increasingly turning to Salesforce, a leading... | 0 | 2024-06-13T04:53:58 | https://dev.to/aress_software_3226ecdb2d/reach-success-with-salesforce-implementation-services-3ad7 | In today’s competitive landscape, businesses are increasingly turning to Salesforce, a leading customer relationship management (CRM) platform, to streamline operations and drive growth. However, the journey from adoption to full integration can be complex and daunting without the right expertise. This is where special... | aress_software_3226ecdb2d | |
1,885,611 | Understanding Tokens in Node.js and NestJS 🚀 | Hey there, fellow devs! 👋 Today, we're diving into the world of tokens in Node.js and NestJS. Tokens... | 27,583 | 2024-06-13T04:52:04 | https://dev.to/shahharsh/understanding-tokens-in-nodejs-and-nestjs-4a55 | backend, nestjs, node, jwt | Hey there, fellow devs! 👋 Today, we're diving into the world of tokens in Node.js and NestJS. Tokens are essential for securing our APIs and managing user sessions. Let's break down the most common types: **access tokens** and **refresh tokens**. Let's go! 🌟
## Access Tokens 🔑
Access tokens are like your VIP pass ... | shahharsh |
1,886,499 | Write content to file in Magento2 | $om = \Magento\Framework\App\ObjectManager::getInstance(); $filesystem =... | 0 | 2024-06-13T04:49:33 | https://dev.to/pabodah/write-content-to-file-in-magento2-aa5 | ```
$om = \Magento\Framework\App\ObjectManager::getInstance();
$filesystem = $om->get('Magento\Framework\Filesystem');
$directoryList = $om->get('Magento\Framework\App\Filesystem\DirectoryList');
$varDirectory = $filesystem->getDirectoryWrite($directoryList::VAR_DIR);
$varPath = $directoryList->getPath('var');
$fileNam... | pabodah | |
1,883,777 | Implementing coroutines in Swift using Swift Concurrency | One of my favorite features of Lua is its first-class support for coroutines. Recently, I started... | 0 | 2024-06-13T04:00:00 | https://gist.github.com/MCJack123/f640242b729b487164fa9a6e297d365f | swift, coroutines | One of my favorite features of [Lua](https://www.lua.org) is its first-class support for coroutines. Recently, I started writing a new project using Swift, and I wanted to be able to use coroutines natively in my Swift code. In most Lua VMs, coroutines are a complex feature that require a lot of environmental support t... | jackmacwindows |
1,886,498 | Papa Louie Cafe l JDesign Studio | Join us on a virtual tour of Papa Louie Cafe, a charming and cozy spot designed by JDesign Studio.... | 0 | 2024-06-13T04:49:09 | https://dev.to/jdesignstudio/papa-louie-cafe-l-jdesign-studio-1mcp | cafe, interior, architecture, decoreted |
Join us on a virtual tour of Papa Louie Cafe, a charming and cozy spot designed by **_[JDesign Studio](https://jdesignstudio.in/)_**. Explore the intricate details of the space, from the chic decor to the delicious m... | jdesignstudio |
1,886,497 | The Future of Web Development: Exploring WebAssembly (Wasm) | Hey everyone! 👋 Today, I want to dive into something that's truly revolutionizing the web... | 0 | 2024-06-13T04:43:06 | https://dev.to/a_a_b6c834ea264e0ac7ef46c/the-future-of-web-development-exploring-webassembly-wasm-5b5k | webdev | Hey everyone! 👋
Today, I want to dive into something that's truly revolutionizing the web development landscape: **WebAssembly (Wasm)**. If you haven't heard about it yet, buckle up because this is one cutting-edge technology that's set to change how we build web applications.
**What is WebAssembly?**
WebAssembly (... | a_a_b6c834ea264e0ac7ef46c |
1,886,496 | Exploring Python Coverage Tools: Enhancing Testing Effectiveness | Python's popularity stems from its simplicity, versatility, and robust ecosystem of libraries and... | 0 | 2024-06-13T04:37:46 | https://dev.to/keploy/exploring-python-coverage-tools-enhancing-testing-effectiveness-in0 | python, developers, webdev, javascript |

Python's popularity stems from its simplicity, versatility, and robust ecosystem of libraries and frameworks. However, writing code is only part of the development process; ensuring its reliability through thorough ... | keploy |
1,886,494 | Infra as GitHub Actions - AWS Serverless Function for nodejs | In the last post we talked about the need to simplify infra while also moving it back to the... | 0 | 2024-06-13T04:27:34 | https://mymakerspace.substack.com/p/infra-as-github-actions-aws-serverless | javascript, aws, githubactions, terraform |
In the last [post](https://dev.to/aws-builders/provisioning-aws-solutions-in-minutes-with-infra-as-github-actions-c25) we talked about the need to simplify infra while also moving it back to the application repo
As I started to work on the next infra as GitHub actions, which was a secured website with `authentication... | alonch |
1,886,452 | Handling SEO in Sitecore XM Cloud Projects: Best Practices and Implementation | Search Engine Optimization (SEO) is essential for making your content discoverable and ensuring it... | 0 | 2024-06-13T04:18:26 | https://dev.to/sebasab/handling-seo-in-sitecore-xm-cloud-projects-best-practices-and-implementation-3o61 | seo, nextjs, sitecore, graphql | Search Engine Optimization (SEO) is essential for making your content discoverable and ensuring it ranks well on search engines. For Sitecore XM Cloud projects, SEO requires a mix of strategic best practices and effective use of various tools and techniques. This blog post will guide you through the essentials of handl... | sebasab |
1,886,451 | London-Based Art Gallery, Mark's Art, Announces Lasting Legacy for Late Artist, Bobby Banks | London, United Kingdom--(Newsfile Corp. - July 17, 2023) - The art world is in mourning today as the... | 0 | 2024-06-13T04:12:54 | https://dev.to/markstevensmith/london-based-art-gallery-marks-art-announces-lasting-legacy-for-late-artist-bobby-banks-15j5 | London, United Kingdom--(Newsfile Corp. - July 17, 2023) - The art world is in mourning today as the news of the passing of beloved artist Bobby Banks has shaken the global creative community. To celebrate his life and the mark he left on the creative community, London-based art gallery, Mark's Art, has announced a las... | markstevensmith | |
1,886,450 | Mark Steven Smith Art World Buzz: Marks Art Signs Next Jean Michel Basquiat, Bobby Banks | The art world is abuzz with news that renowned artist Bobby Banks has signed with Marks Art for the... | 0 | 2024-06-13T04:12:04 | https://dev.to/markstevensmith/mark-steven-smith-art-world-buzz-marks-art-signs-next-jean-michel-basquiat-bobby-banks-2l6j | The art world is abuzz with news that renowned artist Bobby Banks has signed with Marks Art for the release of his latest work. Banks, who is known for his unique take on modern art and pop culture, has been compared to the late Jean Michel Basquiat in terms of style and technique.
The painting, titled “Bobby Banks: T... | markstevensmith | |
1,886,449 | DevOps 101: Understanding Theory, Practices, and Evolution | Introduction to DevOps In the fast-paced world of software development, the need for... | 0 | 2024-06-13T04:11:49 | https://dev.to/iaadidev/devops-101-understanding-theory-practices-and-evolution-1gee |
## Introduction to DevOps
In the fast-paced world of software development, the need for faster delivery and higher quality has never been greater. DevOps, a compound of "development" and "operations," represents a cultural and professional movement that stresses collaboration and communication between software develo... | iaadidev | |
1,886,174 | How I created a web server for my portfolio | Hi 👋 My name is Eric, and I am a full-stack software engineer at ALX. I have extensive... | 0 | 2024-06-13T04:11:28 | https://dev.to/vulcanric/how-i-created-a-web-server-for-my-portfolio-3j7e | ### Hi :wave:
My name is Eric, and I am a full-stack software engineer at ALX. I have extensive experience in DevOps, Front-end development, and Socket/Network programming while specializing in Back-end development.
My favorite programming language is C ✨ (I really enjoy coding in C). Perhaps it's because C was the fir... | vulcanric | |
1,886,448 | Unlocking Potential: A Guide to Anaconda Enterprise Integration | Anaconda Enterprise offers a powerful platform for data science teams, centralizing tools, data, and... | 0 | 2024-06-13T04:06:40 | https://dev.to/epakconsultant/unlocking-potential-a-guide-to-anaconda-enterprise-integration-4hng | anaconda | Anaconda Enterprise offers a powerful platform for data science teams, centralizing tools, data, and workflows. But its true potential shines when integrated with other enterprise applications. This article explores various integration options to maximize the value of Anaconda Enterprise within your organization's ecos... | epakconsultant |
1,886,445 | Comparing Sitecore XP (.NET) and Sitecore XM Cloud (TypeScript): Solr vs. GraphQL for Queries | In the realm of Sitecore development, the shift from Sitecore XP (.NET) to Sitecore XM Cloud... | 0 | 2024-06-13T03:59:36 | https://dev.to/sebasab/comparing-sitecore-xp-net-and-sitecore-xm-cloud-typescript-solr-vs-graphql-for-queries-54n3 | sitecore, headless, solr, graphql | In the realm of Sitecore development, the shift from Sitecore XP (.NET) to Sitecore XM Cloud (TypeScript) marks a significant evolution. One of the most notable changes lies in the query mechanisms used to retrieve and manage data. While Sitecore XP relies on Solr, a powerful search platform, Sitecore XM Cloud leverage... | sebasab |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.