id int64 5 1.93M | title stringlengths 0 128 | description stringlengths 0 25.5k | collection_id int64 0 28.1k | published_timestamp timestamp[s] | canonical_url stringlengths 14 581 | tag_list stringlengths 0 120 | body_markdown stringlengths 0 716k | user_username stringlengths 2 30 |
|---|---|---|---|---|---|---|---|---|
1,868,897 | Magellan SmartGPS ECO and SmartGPS Updates | Understanding Magellan SmartGPS ECO Update The Magellan SmartGPS ECO is an innovative solution that... | 0 | 2024-05-29T11:14:44 | https://dev.to/magellan_support_31b49806/magellan-smartgps-eco-and-smartgps-updates-4bo | magellan, webdev | **Understanding Magellan SmartGPS ECO Update**
The [Magellan SmartGPS ECO](https://www.magellan.support/Smart-GPS-EcoSupport.php) is an innovative solution that integrates your GPS with a cloud-based ecosystem, providing real-time information and updates. To ensure that you are leveraging all the benefits of the SmartGPS ECO, it's important to regularly update the device. Here’s how you can perform the Magellan SmartGPS ECO update:
**Magellan GPS Support**
Magellan GPS is a top provider of navigational equipment for commercial fleets, outdoor enthusiasts, and drivers. Our GPS devices are designed to make traveling and exploring easy and enjoyable with features like accurate maps, route planning, and real-time traffic updates. We also provide comprehensive support services to make sure our customers get the most out of their Magellan GPS devices.
Our support services are designed to provide our clients with timely, trustworthy, and customized help. We know how frustrating technical problems may be, therefore we have a skilled staff on hand to assist you in troubleshooting any problems you may run across. Our support services are available around the clock, so you can get help whenever you need it.
Our support staff can assist with troubleshooting, device setup, and software upgrades, to name a few challenges. If you are having problems with your Magellan GPS device, our support experts can guide you through the necessary steps to resolve the issue. To help you become an expert user of your device, we also offer user manuals, training videos, and other resources.
We also offer warranty and maintenance services for Magellan GPS devices. If your device is still under warranty and broken, we'll replace it or fix it at no cost to you. If the warranty has expired on your device, we provide reasonably priced repair services. We do all of the repairs ourselves, so your device will be fixed accurately and quickly by our team of experts.
| magellan_support_31b49806 |
1,868,896 | Shahada in Islam: Meaning and Importance | Introduction Shahada, the Islamic declaration of faith, is the cornerstone of a Muslim’s... | 0 | 2024-05-29T11:14:37 | https://dev.to/equranekareem101/shahada-in-islam-meaning-and-importance-34a | shahadaislam, online, islamicstudiesforkids, qurancourse | **Introduction**
----------------
Shahada, the Islamic declaration of faith, is the cornerstone of a Muslim’s belief system and the entry point into the Islamic faith. This simple yet profound statement encapsulates the essence of Islam, affirming the oneness of Allah and the prophethood of Muhammad. In this article, we will delve into the meaning and significance of [Shahada in Islam](https://equranekareem.com/courses/online-islamic-courses/shahada-islam-converts-course/), exploring its role in the life of a Muslim and its broader implications within Islamic theology.
**Understanding Shahada: The Declaration of Faith**
---------------------------------------------------
### **The Text of Shahada**
The Shahada is composed of two parts:
* **Ashhadu an la ilaha illa Allah** - "I bear witness that there is no god but Allah."
* **Wa ashhadu anna Muhammadur rasul Allah** - "And I bear witness that Muhammad is the Messenger of Allah."
### **The Meaning of Shahada**
The first part of the Shahada, "There is no god but Allah," affirms the core Islamic belief in monotheism, known as Tawhid. This statement rejects polytheism and any form of idolatry, emphasizing that only Allah is worthy of worship. The second part, "Muhammad is the Messenger of Allah," acknowledges Muhammad as the final prophet in a long line of messengers sent by Allah to guide humanity.
### **Pronunciation and Intent**
For the Shahada to be valid, it must be recited with sincere belief and intention. It is not merely a verbal declaration but a heartfelt affirmation of faith. This sincerity is crucial, as it signifies the convert’s true acceptance of Islamic beliefs and practices.
**The Importance of Shahada in Islam**
--------------------------------------
### **The First Pillar of Islam**
Shahada is the first of the Five Pillars of Islam, which are the foundational acts of worship and practice for Muslims. The other four pillars – Salah (prayer), Zakat (charity), Sawm (fasting during Ramadan), and Hajj (pilgrimage to Mecca) – all rest upon the foundation of Shahada. Without this declaration, the other acts of worship lack their essential meaning and context.
### **Entry into the Islamic Faith**
Reciting the Shahada is the primary requirement for anyone wishing to convert to Islam. It marks the formal entry into the Muslim community and signifies the acceptance of Islamic beliefs and practices. This declaration is typically made in the presence of witnesses, such as family members, friends, or a local imam, to formally acknowledge the new convert’s faith.
### **Affirming Tawhid**
Tawhid, the belief in the oneness of Allah, is the central tenet of Islam. By declaring the Shahada, a Muslim affirms this fundamental concept. Tawhid shapes a Muslim's understanding of the universe, their purpose in life, and their relationship with the Creator. It serves as the basis for all Islamic theology and practice, influencing every aspect of a Muslim’s life.
### **Recognizing Prophethood**
The second part of the Shahada, acknowledging Muhammad as Allah's messenger, is equally important. It confirms the acceptance of Muhammad’s teachings and the Quran as the final, complete guidance for humanity. This recognition establishes a link between the believer and the prophetic tradition, connecting them to the rich history of Islamic revelation and moral guidance.
**Teaching Shahada: Importance for Children**
---------------------------------------------
### **Early Education in Faith**
Teaching Shahada to children is a fundamental aspect of Islamic upbringing. Introducing the concept of Tawhid and the prophethood of Muhammad at a young age helps instill a strong foundation of faith. This early education ensures that children grow up with a clear understanding of their religious identity and the core principles of Islam.
### **Methods of Teaching**
Educating children about Shahada can be done through various methods, including storytelling, interactive activities, and formal instruction. Engaging children in conversations about the meaning and significance of Shahada makes the learning process more relatable and meaningful.
### **Resources for Parents and Educators**
Parents and educators can utilize numerous resources to teach Shahada effectively. Books, videos, and online platforms dedicated to Islamic education provide valuable tools for making the learning experience enjoyable and comprehensive. For example, enrolling children in an [Islamic Studies for Kids](https://equranekareem.com/courses/online-islamic-courses/islamic-studies-for-kids-course/) course can be beneficial in providing structured and systematic religious education.
**Shahada in the Context of Worship**
-------------------------------------
### **Integration into Salah**
The Shahada is an integral part of Salah (prayer). During the Tashahhud portion of the prayer, Muslims recite the Shahada, reaffirming their faith multiple times a day. This repetition not only reinforces their belief but also deepens their spiritual connection with Allah.
### **Involvement in Other Acts of Worship**
The principles embedded in the Shahada influence other acts of worship as well. For instance, the concept of Tawhid underpins the observance of Ramadan, guiding Muslims to fast with the intention of seeking closeness to Allah. Similarly, the recognition of Muhammad's prophethood shapes the understanding and practice of Zakat (charity) and Hajj (pilgrimage).
**Shahada’s Historical and Contemporary Relevance**
---------------------------------------------------
### **Historical Context**
The declaration of Shahada has been a defining moment in Islamic history. From the early days of Islam in Mecca to the expansion of Islamic civilization, the Shahada has served as a unifying statement of faith. It has inspired countless Muslims to strive for spiritual and moral excellence, contributing to the growth and development of Islamic culture and civilization.
### **Contemporary Relevance**
In today’s world, the Shahada continues to hold profound significance. It serves as a beacon of faith for Muslims facing various challenges, from personal struggles to broader social issues. By adhering to the principles of Tawhid and the teachings of Muhammad, Muslims find guidance and strength to navigate modern complexities while maintaining their religious integrity.
**Shahada and Interfaith Relations**
------------------------------------
### **Promoting Understanding**
The Shahada can also play a role in fostering interfaith dialogue and understanding. By sharing the meaning and importance of this declaration, Muslims can help dispel misconceptions about Islam and build bridges of respect and cooperation with people of other faiths.
### **Common Ground**
The principles of monotheism and ethical conduct that are central to the Shahada resonate with many other religious traditions. Recognizing this common ground can enhance mutual understanding and promote peaceful coexistence among diverse religious communities.
**Personal Reflections on Shahada**
-----------------------------------
### **Stories of Converts**
Hearing the stories of those who have embraced Islam through the Shahada can be deeply inspiring. Many converts share how the simple yet profound declaration transformed their lives, bringing them peace, purpose, and a sense of belonging to a larger spiritual family.
### **Strengthening Faith**
For lifelong Muslims, reflecting on the Shahada can renew and strengthen their faith. Taking time to contemplate the meaning of this declaration and its implications in daily life can lead to a deeper, more conscious practice of Islam.
**Conclusion**
--------------
The Shahada, the Islamic declaration of faith, is far more than a set of words. It is the essence of what it means to be a Muslim, encompassing the core beliefs of monotheism and the recognition of Muhammad’s prophethood. This declaration shapes a Muslim’s spiritual, social, and ethical life, providing a foundation for worship and daily conduct. Teaching Shahada in Islam to children ensures the transmission of these vital principles to the next generation, while its repetition in daily prayers and acts of worship continually reinforces a Muslim’s faith. In both historical and contemporary contexts, the Shahada remains a powerful statement of faith and unity, guiding Muslims worldwide. Embracing and understanding the Shahada is a lifelong journey that deepens one's connection with Allah and strengthens the bonds within the global Muslim community.
**FAQs**
--------
### **What is Shahada?**
Shahada is the Islamic declaration of faith, stating, "There is no god but Allah, and Muhammad is His Messenger." It is the first of the Five Pillars of Islam and the foundational statement of a Muslim’s belief.
### **Why is Shahada important in Islam?**
Shahada is important because it affirms the core Islamic beliefs in monotheism (Tawhid) and the prophethood of Muhammad. It is the entry point into the Islamic faith and underpins all other acts of worship and practice in Islam.
### **How is Shahada recited?**
Shahada is recited in Arabic as "Ashhadu an la ilaha illa Allah, wa ashhadu anna Muhammadur rasul Allah." It must be recited with sincere belief and intention for it to be valid.
### **Can children learn about Shahada?**
Yes, teaching Shahada to children is essential for their Islamic upbringing. Parents and educators can use various methods and resources, such as books, videos, and courses like Islamic Studies for Kids, to effectively teach the meaning and significance of Shahada.
### **How often do Muslims recite the Shahada?**
Muslims recite the Shahada multiple times a day, particularly during their daily prayers (Salah). It is also recited during significant religious rituals and personal supplications.
### **What is the historical significance of Shahada?**
Shahada has been a unifying statement of faith since the early days of Islam. It has played a crucial role in the spread and development of Islamic civilization and continues to inspire Muslims to uphold their faith in contemporary times.
### **How does Shahada relate to interfaith relations?**
Shahada can promote interfaith understanding by highlighting common principles of monotheism and ethical conduct. Sharing the meaning of Shahada helps dispel misconceptions about Islam and fosters respect and cooperation among different religious communities. | equranekareem101 |
1,868,895 | Unlocking the Power 💪 of CSS Tooling.💪 | Introduction Tooling in web development extends beyond just JavaScript frameworks. Equally... | 0 | 2024-05-29T11:11:39 | https://dev.to/dharamgfx/unlocking-the-power-of-css-tooling-7e3 | webdev, javascript, beginners, css | ## Introduction
Tooling in web development extends beyond just JavaScript frameworks. Equally important are the tools available for CSS, which help streamline and enhance the process of styling web applications. This post will explore two essential types of CSS tooling: CSS frameworks and CSS preprocessors. We'll delve into their benefits, potential drawbacks, basic usage, and integration into web projects.
## 1 CSS Frameworks: Building with Ready-Made Blocks
### What are CSS Frameworks?
CSS frameworks are pre-prepared libraries that offer standardized components and design guidelines. They are designed to speed up the development process by providing reusable code for common web design elements.
#### Benefits of CSS Frameworks
- **Consistency:** Frameworks ensure a consistent look and feel across your web project.
- **Organization:** They provide a structured approach to styling, making the code more manageable.
- **Ready-Made Components:** Include buttons, forms, navigation bars, and more, which are easy to integrate.
- **Built-In Best Practices:** Adherence to modern web standards and responsive design principles.
#### Drawbacks of CSS Frameworks
- **Complexity and Size:** Frameworks can be overkill for small projects, adding unnecessary complexity and increasing file size.
- **Learning Curve:** New syntax and conventions need to be learned.
- **Lack of Uniqueness:** Websites using the same framework may look similar.
- **Customization Challenges:** Overriding default styles can be difficult.
### Popular CSS Frameworks
#### Bootstrap
Bootstrap is one of the most popular CSS frameworks. It includes a wide array of components and a responsive grid system.
**Example:**
```html
<!DOCTYPE html>
<html lang="en">
<head>
<link rel="stylesheet" href="https://stackpath.bootstrapcdn.com/bootstrap/4.5.2/css/bootstrap.min.css">
</head>
<body>
<div class="container">
<h1 class="text-center">Hello, world!</h1>
<button class="btn btn-primary">Click Me</button>
</div>
</body>
</html>
```
#### Foundation
Foundation provides a responsive grid and many UI components, similar to Bootstrap but with a different philosophy and set of default styles.
**Example:**
```html
<!DOCTYPE html>
<html lang="en">
<head>
<link rel="stylesheet" href="https://cdn.jsdelivr.net/npm/foundation-sites/dist/css/foundation.min.css">
</head>
<body>
<div class="grid-container">
<h1 class="text-center">Hello, Foundation!</h1>
<button class="button">Click Me</button>
</div>
</body>
</html>
```
#### Tailwind CSS
Tailwind CSS is a utility-first CSS framework that allows you to create custom designs without leaving your HTML.
**Example:**
```html
<!DOCTYPE html>
<html lang="en">
<head>
<link href="https://cdn.jsdelivr.net/npm/tailwindcss@2.2.19/dist/tailwind.min.css" rel="stylesheet">
</head>
<body>
<div class="container mx-auto">
<h1 class="text-center text-4xl">Hello, Tailwind!</h1>
<button class="bg-blue-500 hover:bg-blue-700 text-white font-bold py-2 px-4 rounded">Click Me</button>
</div>
</body>
</html>
```
### Integrating CSS Frameworks
To integrate a CSS framework, include its CSS file via a CDN or install it using package managers like npm. Customize by overriding default styles or adding your own custom CSS.
#### Weighing the Burden
- **Initial Learning Curve:** Understand the framework's components and classes.
- **Integration:** Adapt your project's structure to leverage the framework efficiently.
- **Customization:** Learn how to override styles to meet your specific design needs.
## 2 CSS Preprocessors: Supercharging Your CSS
### What are CSS Preprocessors?
CSS preprocessors extend CSS with advanced features like variables, nested rules, and functions, making CSS more powerful and easier to write.
#### Benefits of CSS Preprocessors
- **Enhanced Features:** Introduce programming constructs like loops and conditionals.
- **Code Reusability:** Use variables and mixins to avoid redundancy.
- **Maintainability:** Modularize CSS into smaller, more manageable files.
#### Drawbacks of CSS Preprocessors
- **Learning New Syntax:** Requires understanding a new syntax and toolchain.
- **Build Step Required:** Preprocessing step before deploying CSS.
### Popular CSS Preprocessors
#### Sass
Sass (Syntactically Awesome Style Sheets) is a widely used preprocessor that adds many features to CSS.
**Example:**
```scss
$primary-color: #333;
body {
font: 100% Helvetica, sans-serif;
color: $primary-color;
}
nav {
ul {
margin: 0;
padding: 0;
list-style: none;
}
li { display: inline-block; }
a {
font-weight: bold;
color: $primary-color;
&:hover {
color: #ff6347;
}
}
}
```
#### PostCSS
PostCSS is a tool for transforming CSS with JavaScript plugins, offering a wide range of functionalities from autoprefixing to custom property fallbacks.
**Example:**
```js
// postcss.config.js
module.exports = {
plugins: [
require('autoprefixer'),
require('cssnano')
]
};
```
### Integrating CSS Preprocessors
Integration involves setting up a build process using tools like npm scripts, Gulp, or Webpack to compile preprocessor code into standard CSS.
#### Weighing the Burden
- **Learning Curve:** Understand preprocessor syntax and features.
- **Integration:** Set up build tools to compile the preprocessor code.
- **Efficiency:** Once set up, preprocessors can significantly speed up development.
## Conclusion
Understanding and leveraging CSS tooling can significantly enhance your web development workflow. CSS frameworks provide pre-built components and consistent design principles, while CSS preprocessors offer advanced features that make writing CSS more efficient. Balancing the benefits and potential drawbacks of each tool will help you make informed decisions and create better, more maintainable web projects. | dharamgfx |
1,868,894 | Akash Dubey Co-FOunder & CEO Beparr Beparr is trying to help india's small and medium business like retailers of clothing | A post by akash dubey | 0 | 2024-05-29T11:11:06 | https://dev.to/akash_dubey_3b2b9733f1f1a/akash-dubey-co-founder-ceo-beparr-beparr-is-trying-to-help-indias-small-and-medium-business-like-retailers-of-clothing-45a8 | akash_dubey_3b2b9733f1f1a | ||
1,864,680 | Understanding and Implementing WebSockets in Your Next Project | In today's fast-paced digital landscape, real-time communication is no longer a luxury but a... | 0 | 2024-05-29T11:09:00 | https://dev.to/nitin-rachabathuni/understanding-and-implementing-websockets-in-your-next-project-4g21 | In today's fast-paced digital landscape, real-time communication is no longer a luxury but a necessity. Whether it's for live chat applications, multiplayer games, or real-time data feeds, WebSockets provide a robust solution for achieving low-latency, full-duplex communication between client and server. In this article, we'll delve into the fundamentals of WebSockets and how you can implement them in your next project.
What are WebSockets?
WebSockets are a protocol designed for full-duplex communication channels over a single, long-lived connection. Unlike traditional HTTP requests, which follow a request-response pattern, WebSockets allow for bi-directional communication, enabling both the client and server to send and receive data independently.
Why Use WebSockets?
Real-Time Communication: WebSockets are ideal for applications requiring real-time updates, such as chat applications, live sports updates, or stock trading platforms.
Efficiency: Once the connection is established, WebSockets reduce the overhead of HTTP requests, as they do not require a new connection for each message.
Low Latency: WebSockets offer lower latency compared to HTTP-based polling, making them suitable for time-sensitive applications.
Setting Up WebSockets: A Simple Example
Let's walk through a basic implementation of WebSockets using Node.js and a client-side HTML page.
Server-Side (Node.js with ws library)
First, we need to set up a WebSocket server. We'll use the popular ws library in Node.js.
```
// server.js
const WebSocket = require('ws');
const server = new WebSocket.Server({ port: 8080 });
server.on('connection', (ws) => {
console.log('Client connected');
ws.on('message', (message) => {
console.log(`Received message: ${message}`);
// Echo the received message back to the client
ws.send(`Server: You said ${message}`);
});
ws.on('close', () => {
console.log('Client disconnected');
});
ws.send('Welcome to the WebSocket server!');
});
console.log('WebSocket server is running on ws://localhost:8080');
```
Client-Side (HTML and JavaScript)
Next, let's create a simple HTML page that connects to our WebSocket server and allows for sending and receiving messages.
```
<!-- index.html -->
<!DOCTYPE html>
<html lang="en">
<head>
<meta charset="UTF-8">
<title>WebSocket Example</title>
</head>
<body>
<h1>WebSocket Client</h1>
<input type="text" id="messageInput" placeholder="Enter a message">
<button onclick="sendMessage()">Send</button>
<div id="messages"></div>
<script>
const ws = new WebSocket('ws://localhost:8080');
ws.onopen = () => {
console.log('Connected to WebSocket server');
};
ws.onmessage = (event) => {
const messagesDiv = document.getElementById('messages');
const message = document.createElement('p');
message.textContent = `Server: ${event.data}`;
messagesDiv.appendChild(message);
};
ws.onclose = () => {
console.log('Disconnected from WebSocket server');
};
function sendMessage() {
const input = document.getElementById('messageInput');
ws.send(input.value);
input.value = '';
}
</script>
</body>
</html>
```
Expanding Your WebSocket Implementation
This basic example provides a foundation on which to build more complex real-time applications. Here are some ideas to extend your WebSocket implementation:
Authentication: Implement token-based authentication to secure your WebSocket connections.
Broadcasting: Allow the server to broadcast messages to all connected clients, useful for notifications or live updates.
Error Handling: Add comprehensive error handling to manage connection drops and reconnections smoothly.
Conclusion
WebSockets are a powerful tool for real-time communication in modern web applications. By enabling efficient, low-latency, bi-directional communication, they open up a world of possibilities for developers. Whether you're building a chat application, a live data feed, or a collaborative tool, WebSockets can help you deliver a seamless, real-time experience to your users.
Embrace WebSockets in your next project and unlock the potential of real-time web communication. Happy coding!
---
Thank you for reading my article! For more updates and useful information, feel free to connect with me on LinkedIn and follow me on Twitter. I look forward to engaging with more like-minded professionals and sharing valuable insights.
| nitin-rachabathuni | |
1,868,893 | Beparr B2B Wholesale App install App Now:- https://play.google.com/store/apps/details?id=com.beparr.buyer | A post by akash dubey | 0 | 2024-05-29T11:08:49 | https://dev.to/akash_dubey_3b2b9733f1f1a/beparr-b2b-wholesale-app-install-app-now-httpsplaygooglecomstoreappsdetailsidcombeparrbuyer-jei | akash_dubey_3b2b9733f1f1a | ||
1,868,892 | Kojic Acid Market - Global Growth, Share, Trends, Demand and Analysis Report Forecast 2031 | The global market for kojic acid, a key ingredient in skincare and cosmetic formulations, is set to... | 0 | 2024-05-29T11:08:48 | https://dev.to/mihir_kadu_138/kojic-acid-market-global-growth-share-trends-demand-and-analysis-report-forecast-2031-12dp | kojicacidmarket, kojicacid, acid | The global market for kojic acid, a key ingredient in skincare and cosmetic formulations, is set to witness substantial growth in the coming years, according to a comprehensive report by Fairfield Market Research. The report, spanning the period from 2018 to 2030, projects a steady increase in the market size from US$65.5 million in 2022 to an estimated US$79.8 million by 2030, representing a compound annual growth rate (CAGR) of 2.5% during the forecast period.
For More Industry Insights: https://www.fairfieldmarketresearch.com/report/kojic-acid-market
Rising Demand for Natural Skincare Fuels Market Growth
One of the primary drivers behind this growth trajectory is the increasing demand for natural and organic skincare products worldwide. Consumers are gravitating towards skincare solutions derived from natural sources, such as fungus-derived kojic acid, to address concerns related to skin discoloration, hyperpigmentation, and uneven skin tone.
Cosmetic Grade Dominates Market Share
In 2022, the cosmetic grade category emerged as the dominant segment in the kojic acid market, owing to its widespread use in various skincare formulations like creams, serums, lotions, and soaps. The surge in demand for products addressing skin imperfections has propelled the prominence of kojic acid in the cosmetics industry.
Anti-Oxidizing and Anti-Bacterial Properties Drive Adoption
The anti-oxidizing and anti-bacterial attributes of kojic acid have also contributed significantly to its market growth. With its potent antioxidant properties, kojic acid helps combat oxidative damage to cells and tissues, making it a prized component in skincare and cosmetic formulations. Additionally, its strong antibacterial qualities make it essential in products aimed at preventing or treating bacterial skin conditions.
Regional Outlook: Asia Pacific Leads, North America Explores Gains
The Asia Pacific region is expected to maintain its position as the largest revenue-contributing region in the global kojic acid market. Countries like Japan, China, and South Korea serve as major production hubs, catering to both domestic and international demand for kojic acid. Meanwhile, North America is witnessing an uptick in demand, fueled by the growing popularity of natural and organic skincare products among consumers.
Key Trends and Opportunities
The market presents several key trends and opportunities for innovation and growth. Integration of product innovation and development, customization of skincare solutions, and market diversification into new applications beyond cosmetics are among the avenues for exploration in the kojic acid market.
| mihir_kadu_138 |
1,868,891 | The Future of Cyber security: Emerging Technologies and Trends | Cyber security is a constantly evolving field, formed with the aid of technological improvements and... | 0 | 2024-05-29T11:07:58 | https://dev.to/liong/the-future-of-cyber-security-emerging-technologies-and-trends-e9a | development, blockchain, malaysia, kualalumpur | Cyber security is a constantly evolving field, formed with the aid of technological improvements and the ever-converting threat landscape. As we appearance in the direction of the destiny, numerous emerging technologies and developments promise to revolutionize cyber security practices, enhancing our potential to shield digital assets and statistics.
**Quantum Computing and Its Dual Impact**
Quantum computing represents a substantial jump in computational strength, able to fixing complicated problems that are presently intractable for classical computer systems. However, this strength comes with each possibilities and demanding situations for [cyber security.](https://ithubtechnologies.com/cyber-attack-malaysia/?utm_source=dev.to%2F&utm_campaign=Cybersecurity&utm_id=Offpageseo+2024)
**Quantum Threats to Encryption:** One of the most profound impacts of quantum computing is its ability to break conventional encryption algorithms. RSA and ECC, widely used for securing facts, may be rendered obsolete through quantum algorithms like Short’s algorithm. This has caused the development of quantum-resistant encryption strategies to ensure statistics remains stable within the quantum era.
**Quantum-Enhanced Security:** On the flip facet, quantum generation additionally offers greater protection answers. Quantum Key Distribution (QKD) makes use of the concepts of quantum mechanics to create steady channels that are theoretically resistant to eavesdropping. By leveraging QKD, businesses can guard touchy information against even the most superior threats.
**Block chain Technology for Enhanced Security**
Block chain, regarded for its association with crypto currencies, gives a decentralized and tamper-proof manner to stable statistics. Its **capability packages in cyber security are widespread:**
**Secure Data Transactions:** Block chain's immutable ledger can secure information transactions, ensuring information integrity and transparency. This is especially beneficial for programs along with steady voting structures, deliver chain safety, and financial transactions, where information integrity is paramount.
**Decentralized Identity Management:** Block chain can facilitate decentralized identification management structures, allowing individuals to control their personal virtual identities. This reduces the danger of identification theft and enhances privacy by using minimizing reliance on centralized identity vendors.
**Smart Contracts:** Block chain-based clever contracts automatically execute and enforce phrases and conditions with out the need for intermediaries. These contracts can beautify protection in numerous applications, from prison agreements to automated coverage claims.
**The Advent of 5G and Its Security Implications**
The rollout of 5G technology guarantees quicker and more dependable internet connectivity, helping a big growth in linked devices and services. However, this also introduces new cyber security challenges:
**Expanded Attack Surface:** With the proliferation of 5G-connected gadgets, the assault surface expands drastically. Each tool represents a potential entry factor for cybercriminals, necessitating strong safety features to protect these endpoints.
**Network Slicing Vulnerabilities:** 5G networks make use of community cutting to create digital networks tailored to precise applications. While this complements performance and versatility, it additionally introduces vulnerabilities if slices aren't competently secured. Ensuring every slice is isolated and protected is essential to retaining common community safety.
**IoT Security:** The excessive-velocity, low-latency talents of 5G will boost up the adoption of Internet of Things (IoT) gadgets. Securing these gadgets, which regularly lack strong safety functions, might be a significant undertaking. Implementing strong authentication, encryption, and normal updates could be critical to defend IoT ecosystems.
**Artificial Intelligence and Machine Learning**
Artificial Intelligence (AI) and Machine Learning (ML) are reworking cyber security through automating risk detection and response:
**Automated Threat Detection:** AI systems can examine tremendous quantities of information to discover styles and hit upon anomalies that indicate cyber threats. Machine mastering algorithms improve over the years, turning into more powerful at recognizing malicious pastime and lowering fake positives.
**Predictive Analytics:** AI can are expecting ability threats with the aid of studying ancient information and identifying developments. This lets in organizations to proactively address vulnerabilities and prevent attacks earlier than they occur.
**Automated Incident Response:** AI can automate responses to sure types of cyber threats, which includes setting apart affected structures or deploying patches. This reduces the time it takes to contain and mitigate attacks, minimizing harm and disruption.
**The Rise of Cyber security Mesh**
Cyber security mesh is an architectural approach that provides a scalable and bendy security framework. It decentralizes protection policies and enforcement, allowing corporations to defend property regardless of their area:
**Decentralized Security Controls:** Cyber security mesh enables decentralized protection controls, making it easier to stable allotted environments together with cloud and side computing.
**Identity because the Perimeter:** In a cyber security mesh, identity turns into the number one perimeter. Strong identity and access control (IAM) practices are essential to make certain that most effective authorized customers can access assets.
**Adaptive Security:** The cyber security mesh model helps adaptive security measures, allowing companies to dynamically regulate their safety posture based totally on the cutting-edge danger landscape.
**Privacy-Enhancing Technologies**
As records privacy concerns grow, privacy-enhancing technology (PETs) are getting an increasing number of critical:
**Holomorphic Encryption:** This lets in computations to be done on encrypted records without decrypting it, maintaining privateers even as permitting facts evaluation.
**Differential Privacy:** This method adds noise to facts units to save you the identity of people in the statistics, ensuring privacy even as keeping information application.
**Secure Multi-Party Computation (SMPC):** SMPC allows multiple events to mutually compute a function over their inputs even as keeping the ones inputs non-public, permitting secure collaboration.
## Conclusion
The future of cyber security is being formed by means of more than a few rising technologies and trends. Quantum computing, block chain, 5G, AI, Zero Trust Architecture, cyber security mesh, and privateers-improving technologies all promise to convert the manner we shield digital assets and facts. As these technologies evolve, they may provide new tools and strategies to fight cyber threats, however they also introduce new demanding situations that should be addressed.
Organizations have to stay abreast of those traits and continuously adapt their cyber security techniques to leverage those technology successfully. By embracing innovation and fostering a lifestyle of protection, we can build a more resilient and stable virtual future.
| liong |
1,868,890 | 🔥 Unlock Your Digital Superpowers! 🔥 | 🌟 Ready to level up your tech skills? Look no further! Our Best IT Training Institute in... | 0 | 2024-05-29T11:06:56 | https://dev.to/liya/unlock-your-digital-superpowers-43h4 | ittraininginstitutesinkochi, softwaretestingcourse, pythoncourseinkochi, ittraining |

## 🌟 Ready to level up your tech skills?
Look no further! Our [Best IT Training Institute in Kochi](https://www.irohub.com/) is here to ignite your coding journey. 💻💡
🚀 Why Choose Us?
**Cutting-Edge Curriculum**: Dive into the latest technologies, from Python to cloud computing. We keep you ahead of the game! 🌐
**Expert Instructors**: Learn from industry pros who’ve been there and coded that.Their insights are pure gold! ✨
**Hands-On Projects**: Build real-world apps, websites, and solutions. No theory overload—just practical magic! 🛠️
📍 Location: 1st Floor, Trust Building, Kayyath Ln, Palarivattom, Kochi
📧 Contact Us: info@irohub.com | +91 812985515
🔗 Enroll Today: Irohub Infotech
| liya |
1,868,788 | Google's Gemini AI Transforms Chromebook Plus | Introduction Google is revolutionizing the Chromebook experience by integrating its... | 0 | 2024-05-29T11:06:39 | https://dev.to/aishikl/googles-gemini-ai-transforms-chromebook-plus-2e64 | ## Introduction
Google is revolutionizing the Chromebook experience by integrating its advanced AI chatbot, Gemini, along with a suite of AI-powered features into Chromebook Plus laptops. This move is set to enhance productivity, creativity, and overall user experience. Let's dive into the exciting new features and what they mean for Chromebook users.
## Gemini AI and Chromebook Plus
### What is Gemini AI?
Gemini is Google's latest AI chatbot designed to assist users in various tasks, from writing to photo editing. It is part of the Google One AI Premium plan, which is offered free for 12 months to new Chromebook Plus owners. This plan includes Gemini Advanced, a more capable version of the chatbot.
### Exclusive Features for Chromebook Plus
Chromebook Plus laptops are designed to meet specific hardware requirements to run these advanced AI features smoothly. These laptops typically cost more than $350 and come with enhanced processing power, memory, and storage.
## Key AI Features
### Help Me Write
One of the standout features is 'Help Me Write,' which works in any text box. Users can select text, right-click, and ask Google's AI to rewrite, rephrase, or change the tone of the selected text. This feature is also available for writing from scratch, where the AI can kickstart the writing process based on a few keywords.
### Generative AI Wallpapers
Google is bringing the generative AI wallpaper system from Android to ChromeOS. Users can create custom wallpapers and video call backgrounds based on their preferences for subject, mood, and color. This feature adds a personalized touch to your Chromebook experience.
### Magic Editor in Google Photos
The Magic Editor feature from Google's Pixel 8 smartphones is now available on Chromebook Plus. It allows users to edit photos by removing unwanted objects, moving subjects, and filling in backgrounds. This feature makes photo editing a breeze and enhances the quality of your images.
## Upcoming Features
### Hands-Free Control
Google is working on upcoming features like hands-free control, which utilizes Project Gameface to allow users to control their devices using face gestures and head movements. This feature aims to make device interaction more intuitive and accessible.
### Help Me Read
Another feature in development is 'Help Me Read,' which employs Gemini to summarize websites or PDFs and answer follow-up questions. This feature will be particularly useful for users who need quick information without going through lengthy texts.
## New Chromebook Models
Several manufacturers, including Acer, Asus, and HP, are launching new Chromebooks this year, some of which are Chromebook Plus models that can take advantage of the new AI features. Visit the Chromebook website to see the newest models.
## Conclusion
Google's integration of Gemini AI and other advanced features into Chromebook Plus laptops is a significant step forward in making technology more accessible and powerful. These features not only enhance productivity but also add a layer of personalization and ease of use that was previously unattainable. Whether you're a professional, a student, or just someone who loves technology, the new Chromebook Plus with Gemini AI is worth considering.
For more details, you can read the full article on Rapid Innovation. | aishikl | |
1,868,889 | Sofa Set Showdown: Comfort vs. Style? | Have you ever dreamt of a living room that's both the envy of your guests and a cozy haven for... | 0 | 2024-05-29T11:06:25 | https://dev.to/amin_hassan_15c6441336bab/sofa-set-showdown-comfort-vs-style-2a17 |

Have you ever dreamt of a living room that's both the envy of your guests and a cozy haven for relaxation? The struggle often lies in choosing between a [comfortable sofa set](https://fahfurniture.com/product/sofa-set-fh-805/) that feels like a cloud and a stylish one that elevates your entire space. But what if you could have both?
Here's where the perfect sofa set enters the picture. Contrary to popular belief, comfort and style don't have to be at odds. With the right features, a sofa set can truly transform your living room:
• Unmatched Comfort: Imagine sinking into luxurious cushions that cradle your body after a long day. High-quality sofa sets prioritize comfort with features like supportive springs, plush padding, and ergonomic design.
• Style for Every Taste: Gone are the days of bulky, uninspired sofas. Modern sofa sets come in a wide range of styles, from sleek and minimalist to classic and traditional. You can find the perfect piece to complement your existing decor or create a whole new look.
• Built to Last: A good sofa set is an investment. Look for features like sturdy frames, durable upholstery fabrics, and reinforced construction. These elements ensure your sofa set looks beautiful and provides years of comfort.
• Space Optimization: Not everyone has a sprawling living room. Many sofa sets offer features like modular pieces, reclining options, and built-in storage, allowing you to maximize space and functionality.
So, stop settling for just comfort or just style. With a well-chosen sofa set, you can create a living room that's both beautiful and a joy to relax in. It's the perfect place to unwind, entertain, and make memories that last a lifetime.
| amin_hassan_15c6441336bab | |
1,868,888 | گیت کنترل تردد پروانه ای یا گیت فلپ چیست؟ | گیت های کنترل تردد به همراه دستگاه های حضور غیاب از مهم ترین تجهیزات کنترلی و امنیتی در سازمان ها ،... | 0 | 2024-05-29T11:06:06 | https://dev.to/maxasecurity/gyt-khntrl-trdd-prwnh-y-y-gyt-flp-chyst-hhb | گیت های کنترل تردد به همراه دستگاه های حضور غیاب از مهم ترین تجهیزات کنترلی و امنیتی در سازمان ها ، ادارات، دانشگاه ها، اماکن تجاری و.. هستند. این گیت ها در مدل های مختلفی تولید و عرضه می شوند که هریک ویژگی ها و کاربردهای خاصی دارند. یکی از انواع متداول گیت کنترل تردد، گیت کنترل تردد باله ای است که به نام های گیت کنترل تردد پروانه ای و گیت فلپ هم شناخته می شود. این نوع گیت کنترل تردد دارای ظاهری شکیل و زیبا، دوام زیاد، عملکرد سریع و ایمنی بالاست و به همین دلیل در بسیاری از اماکن مورد استفاده قرار می گیرد. قابلیت اتصال به سیستم های اکسس کنترل این مدل گیت کنترل تردد را به یک گزینه ایده آل برای نصب در سازمان ها ، ادارات، دانشگاه ها و… تبدیل کرده است. برای آشنایی بیشتر با گیت پروانه ای، ویژگی ها و کاربردهای آن با ما همراه باشید.
**گیت کنترل تردد پروانه ای چیست؟
**[گیت کنترل تردد پروانه ای](https://maxasecurity.com/product-category/traffic-gate/flap-gate/) یا باله ای ، یکی از انواع گیت کنترل تردد است که به دلیل داشتن باله های تقریبا کوتاه که به شکل زاویه دار باز و بسته میشوند با نام گیت کنترل تردد پروانه ای شناخته می شود باله های این گیت که جزئی بدنه گیت را تشکیل می دهند، قسمتی از راهرو گیت را پر کرده اند و از جنس شیشه سکوریت یا پلکسی گلس ساخته می شوند. هنگامی احراز هویت افراد توسط سیستم اکسس کنترل انجام می شود به محض صدور اجازه ورود یا خروج، باله ها ی این گیت به سمت داخل جمع میشوند تا افراد بتوانند از راهرو گیت عبور کنند. گیت کنترل تردد باله ای به دلیل نیاز به فضای کم برای نصب و عملکرد دو طرفه برای نصب در مکان های کوچک و پرتردد گزینه ی بسیار مناسبی است.
**ویژگی های گیت کنترل تردد پروانه ای
**گیت کنترل تردد پروانه ای دارای ویژگی های منحصر به فردی است که سبب محبوبیت این گیت و استفاده از آن در اماکن مختلف از جمله ادارات و سازمان ها،
کارخانه ها، سالن های ورزشی ، دانشگاه ها ،مراکز تجاری و… شده است. برخی از این ویژگی ها عبارتند از :
**طراحی زیبا و قابل سفارشی سازی
**همانطور که اشاره شد، یکی از ویژگی های بارز گیت پروانه ای ظاهر زیبای آن است که قابلیت سفارشی سازی بر اساس نیاز سازمان را هم دارد. جنس باله گیت پروانه ای بسته به نیاز مشتریان انتخاب می شود و به درخواست مشتری قابلیت نورپردازی هم دارد. همچنین می توان آرم یا لوگوی سازمان یا نهاد مورد نظر را روی باله های گیت فلپ حک کرد.
** امکان اتصال به انواع سیستم اکسس کنترل
** این گیت امکان یکپارچه سازی با انواع سیستم های اکسس کنترل از جمله سامانه حضور و غیاب اثر انگشتی، کارتی، تشخیص چهره و… را دارد. یکپارچه سازی گیت پروانه ای با سیستم های اکسس کنترل امکان تامین امنیت و کنترل تردد همزمان را فراهم می کند.
**سرعت عملکرد و ضریب ایمنی بالا
**عملکرد گیت کنترل تردد پروانه ای به گونه ای است که پس از تایید هویت فرد توسط سیستم اکسس کنترل و صدور اجازه عبور افراد، با حرکت دادن باله ها به سمت داخل باز شده و سریعا به حالت اولیه برمی گردد.همچنین، این گیت مجهز به سنسور صحت عبور است و از عبور غیرمجاز افراد ممانعت می کند. سرعت عملکرد بالا همدیگر ویژگی قابل ذکر این گیت است که امکان استفاده از آن را در اماکن شلوغ و پر ازدحام فراهم می کند.
**نصب کم جا و امکان عبور یک و دو طرفه
**نصب گیت فلپ یا پروانه ای نیاز به فضای زیادی ندارد. بنابراین این گیت برای اماکن کوچک و پر ترافیک گزینه مناسبی است. همچنین، گیت کنترل تردد فلپ امکان عبور یکطرفه و دوطرفه را دارد و می توان از آن برای کنترل همزمان ورود و خروج افراد استفاده کرد.
**قیمت مناسب نسبت به کارایی بالا
**اگرچه [قیمت گیت های کنترل تردد](https://maxasecurity.com/product-category/traffic-gate/) به فاکتورهایی مانند جنس بدنه، اندازه گیت و قابلیت های گیت بستگی دارد اما قیمت گیت کنترل تردد فلپ به نسبت مدل های دیگر و با توجه به کارایی این مدل گیت مقرون به صرفه است. قیمت مناسب گیت باله ای یا پروانه ای یکی از دلایل استفاده گسترده از گیت کنترل تردد در اماکن مختلف است.
**سخن پایانی
**گیت کنترل تردد باله ای ، پروانه ای یا فلپ یک مدل گیت کنترل تردد پرکاربرد و محبوب است که دارای دو باله مشابه بال های پروانه در دو طرف راهرو ورود و خروجش است. این گیت قابلیت یکپارچه شدن با انواع سیستم های اکسس کنترل را دارد و با داشتن قابلیت تردد دو طرفه برای کنترل تردد و حفظ امنیت در اماکن پر رفت و آمد مناسب است. از جمله ویژگی های بارز گیت پروانه ای یا فلپ می توان به ظاهر زیبا و نصب کمجا، سرعت عملکرد بالا و قیمت مقرون به صرفه آن اشاره کرد. از این مدل گیت معمولا در ورودی ادارات و سازمان ها، سالن های ورزشی، کارخانجات، دانشگاه ها و… استفاده می شود.
شرکت مکسا با داشتن سابقه موفق در تولید محصولات سخت افزاری و نرم افزاری در زمینه تامین امنیت و کنترل تردد و همچنین کسب تجربه چندین ساله از نیازهای شرکت ها و سازمان های خصوصی یا دولتی امروزه موفق به تولید و عرضه انواع مختلفی از گیت های کنترل تردد به بازار شده است. شما می توانید با مراجعه به وب سایت شرکت مکسا به آدرس www.maxasecurity.com و یا تماس با شماره تلفن 02178756000 راهنمایی های لازم را در خصوص نحوه خرید انواع گیت کنترل تردد از همکاران پشتیبانی فروش محصولات دریافت نمایید.
| maxasecurity | |
1,867,687 | Server Driven UI no Flutter? | O Server Driven UI (SDUI) no Flutter surge como um game-changer no cenário do desenvolvimento de... | 0 | 2024-05-29T11:04:15 | https://dev.to/redrodrigoc/server-driven-ui-no-flutter-367d | braziliandevs, flutter, dart, programming |
O **Server Driven UI** (SDUI) no Flutter surge como um **game-changer** no cenário do desenvolvimento de aplicativos. Ao transferir a lógica da interface para o servidor, abre-se um universo de possibilidades para criar interfaces mais dinâmicas, personalizadas e eficientes. Imagine um app que se adapta em tempo real às suas necessidades, sem a necessidade de constantes atualizações. É isso e muito mais que o SDUI no Flutter oferece!
> **game-changer** se refere a um “divisor de águas”, ou seja, algo que revoluciona e muda completamente um determinado mercado ou situação.
### O que é Server Driven UI?
Em contraste com a abordagem tradicional, onde a interface do usuário (UI) é definida no cliente (aplicativo móvel), o SDUI transfere a responsabilidade para o servidor. Isso significa que o servidor gera e envia a estrutura da UI para o aplicativo, que a renderiza na tela do dispositivo. Essa inversão de controle traz diversos benefícios:
#### Maior Agilidade e Flexibilidade:
- **Desenvolvimento e testes mais rápidos**: Alterações na UI podem ser implementadas no servidor e propagadas instantaneamente para todos os usuários, sem a necessidade de atualizações de aplicativos.
- **Experiência do usuário aprimorada**: A UI pode ser personalizada em tempo real, de acordo com o perfil e contexto de cada usuário.
- **Redução de custos de desenvolvimento**: O código da UI é centralizado no servidor, diminuindo a duplicação de esforços e otimizando o processo de desenvolvimento.
Mas nem tudo são flores...
#### Desafios e Considerações:
1. Implementação
- **Arquitetura robusta**: O servidor precisa ter capacidade de processar e enviar as informações da UI de forma eficiente, especialmente para um grande número de usuários simultâneos.
- **Comunicação confiável**: A comunicação entre o servidor e o aplicativo deve ser segura e resiliente a falhas de rede.
- **Segurança de dados**: É crucial implementar medidas de segurança rigorosas para proteger os dados dos usuários e evitar acessos não autorizados.
2. Experiência do usuário
- **Latência**: A latência na comunicação entre o servidor e o aplicativo pode afetar a fluidez da UI.
- **Conectividade**: O SDUI depende de uma conexão de internet estável para funcionar corretamente.
- **Acessibilidade**: É importante garantir que a UI gerada pelo servidor seja acessível a todos os usuários, incluindo aqueles com deficiências.
#### Exemplos de Bibliotecas SDUI para Flutter:
- Mirai
- server_driven_ui
#### Exemplo utilizando o Mirai:
- **Servidor**:
```json
{
"type": "scaffold",
"appBar": {
"type": "appBar",
"title": {"type": "text", "data": "Cards"}
},
"body": {
"type": "column",
"mainAxisAlignment": "start",
"crossAxisAlignment": "center",
"children": [
{"type": "sizedBox", "height": 12},
{
"type": "card",
"elevation": 20,
"borderOnForeground": true,
"margin": {"top": 20, "bottom": 20, "right": 20, "left": 20},
"child": {
"type": "listTile",
"leading": {
"type": "image",
"src": "https://avatars.githubusercontent.com/u/31713982?v=4",
"width": 50,
"height": 50
},
"title": {
"type": "padding",
"padding": {"top": 10},
"child": {
"type": "text",
"data": "Rodrigo Castro",
"align": "center",
"style": {"fontSize": 21}
}
},
"subtitle": {
"type": "padding",
"padding": {"top": 10, "bottom": 10},
"child": {
"type": "text",
"data":
"Desenvolvedor de Software com foco em Laravel e Flutter. (Open to Work)",
"align": "center",
"style": {"fontSize": 12}
}
}
}
}
]
}
```
- **Flutter**:

#### Conclusão:
O SDUI no Flutter se apresenta como uma ferramenta poderosa para impulsionar a inovação e criar experiências de usuário excepcionais. Ao abraçar essa abordagem com cautela e planejamento estratégico, os desenvolvedores terão a oportunidade de revolucionar o cenário de desenvolvimento de aplicativos.
#### Para se aprofundar no assunto:
- [Artigo "Server Driven UI with Mirai in Flutter"](https://robertocsd.medium.com/unraveling-sdui-a-deep-dive-into-server-driven-user-interfaces-using-mirai-in-flutter-e99cd3c81abe)
- [Vídeo "Flutter Server Driven UI é possível? Descubra neste vídeo!"](https://m.youtube.com/watch?v=sWIS18Njr3I)
- [Pacote "server_driven_ui" no Pub.dev](https://pub.dev/packages/server_driven_ui)
- [Pacote "mirai" no Pub.dev](https://pub.dev/packages/mirai)
| redrodrigoc |
1,868,886 | Telemedicine App Development Company Insights: How to Choose the Best Partner | Telemedicine has revolutionized healthcare by bridging the gap between patients and healthcare... | 0 | 2024-05-29T11:02:34 | https://dev.to/allenchrios/telemedicine-app-development-company-insights-how-to-choose-the-best-partner-1gdh |

Telemedicine has revolutionized healthcare by bridging the gap between patients and healthcare providers, ensuring that medical services are accessible, efficient, and convenient. As technology continues to evolve, the demand for [telemedicine app development](https://www.itpathsolutions.com/building-the-future-of-healthcare-a-step-by-step-guide-to-telemedicine-app-development/) solutions is increasing, providing significant opportunities for businesses in the healthcare sector. This comprehensive guide aims to walk you through the key steps in developing a telemedicine app, offering insights into the various telehealth app development services available, and highlighting the benefits of partnering with a reputable telemedicine app development company.
**Introduction to Telemedicine and Its Importance**
Telemedicine involves the use of telecommunications technology to deliver healthcare services remotely. This innovative approach to healthcare enables patients to consult with doctors, receive diagnoses, and obtain prescriptions without needing to visit a medical facility. Telemedicine has proven particularly valuable during emergencies, pandemics, and for patients living in remote areas.
**Step 1: Understanding the Market and Identifying Needs**
Before embarking on telemedicine app development, it's crucial to understand the market and identify the needs of your target audience. Conduct thorough market research to determine the types of services that are in demand. For instance, you may find a growing need for mental health consultations, chronic disease management, or pediatric care.
**Step 2: Defining Features and Functionality**
The next step in telemedicine app development is defining the features and functionalities of your app. Some essential features to consider include:
**User Registration and Profiles**: Allow users to create and manage their profiles.
**Appointment Scheduling:** Enable patients to book appointments with healthcare providers.
**Video Conferencing:** Facilitate real-time video consultations between patients and doctors.
**Messaging and Chat:** Provide secure messaging options for communication.
**Electronic Health Records (EHR):** Integrate EHR systems to maintain patient health records.
**Prescription Management:** Allow doctors to prescribe medications electronically.
**Payment Gateway Integration:** Implement secure payment methods for services.
**Step 3: Choosing the Right Technology Stack**
Selecting the right technology stack is crucial for the success of your telehealth app development project. Consider using robust and scalable technologies that ensure smooth performance and security. Commonly used technologies include:
Frontend: React Native, Flutter
Backend: Node.js, Django, Ruby on Rails
Database: MongoDB, PostgreSQL
Video Conferencing API: WebRTC, Twilio
Cloud Services: AWS, Google Cloud, Azure
**Step 4: Ensuring Compliance with Regulations**
Telemedicine apps must comply with various healthcare regulations and standards to ensure data privacy and security. Key regulations include:
HIPAA (Health Insurance Portability and Accountability Act): Applicable in the United States, HIPAA sets the standard for protecting sensitive patient data.
**GDPR (General Data Protection Regulation)**: Relevant for European users, GDPR governs data protection and privacy.
**HL7 (Health Level Seven International)**: Provides standards for the exchange, integration, sharing, and retrieval of electronic health information.
**Step 5: Designing the User Interface (UI) and User Experience (UX)**
A user-friendly interface and seamless user experience are critical for the success of a telemedicine app. Work with experienced UI/UX designers to create an intuitive and accessible app design. Focus on:
**Simplicity:** Ensure that the app is easy to navigate.
**Accessibility:** Design for users with varying abilities.
**Consistency:** Maintain a consistent design language throughout the app.
**Feedback:** Provide clear feedback to users on their actions.
**Step 6: Developing and Testing the App**
With a clear plan in place, proceed with the development phase. Break down the development process into manageable sprints, and follow agile methodologies to ensure flexibility and iterative progress. Once the app is developed, conduct thorough testing to identify and fix any bugs or issues. Types of testing include:
Unit Testing: Test individual components.
Integration Testing: Ensure that different components work together.
User Acceptance Testing (UAT): Validate that the app meets user requirements.
Performance Testing: Assess the app's performance under different conditions.
**Step 7: Deploying and Maintaining the App**
After successful testing, deploy the telemedicine app to your chosen platforms, such as the Apple App Store and Google Play Store. Ensure that you have a robust [marketing strategy](https://www.itpathsolutions.com/marketing-your-telemedicine-app-revolutionising-healthcare-access-and-delivery/) to promote the app and attract users. Once the app is live, provide ongoing support and maintenance to address any issues and implement updates based on user feedback.
Benefits of Telemedicine App Development
Investing in telemedicine app development offers numerous benefits for both patients and healthcare providers:
**Convenience:** Patients can access healthcare services from the comfort of their homes.
**Cost-Effective:** Reduces the need for physical infrastructure and travel expenses.
**Improved Access:** Provides healthcare access to remote and underserved areas.
**Efficiency:** Streamlines healthcare processes and reduces waiting times.
Enhanced Patient Engagement: Encourages patients to take an active role in their healthcare.
**Choosing the Right Telemedicine App Development Company**
Partnering with a reputable telemedicine app development company can significantly enhance the success of your project. Look for a company that offers:
**Expertise:** Experience in developing healthcare applications.
**Compliance:** Knowledge of healthcare regulations and standards.
**Customization:** Ability to tailor solutions to your specific needs.
Support: Ongoing maintenance and support services.
**Conclusion**
Telemedicine app development is a transformative approach to healthcare, providing accessible and efficient medical services to patients worldwide. By following the steps outlined in this guide, you can develop a successful telemedicine app that meets the needs of your target audience. Whether you choose to handle the development in-house or partner with a telemedicine app development company, the key to success lies in thorough planning, understanding user needs, and ensuring compliance with healthcare regulations.
By leveraging the right telemedicine app development solutions and services, you can contribute to the future of healthcare and make a meaningful impact on patient care. | allenchrios | |
1,868,885 | Tazelik Cenneti: Mahalle Çamaşırhanesinin Cazibesi | Odanın ortasında, temiz beyaz havlularla ve yeni yıkanmış giysilerle dolup taşan sepetlerle düzgün... | 0 | 2024-05-29T11:02:30 | https://dev.to/softwareindustrie24334/tazelik-cenneti-mahalle-camasirhanesinin-cazibesi-3dmb | Odanın ortasında, temiz beyaz havlularla ve yeni yıkanmış giysilerle dolup taşan sepetlerle düzgün bir şekilde istiflenmiş uzun bir katlanır masa duruyor. Tezgahın arkasında, müşterilere her türlü soru veya endişeleri konusunda yardımcı olmaya hazır güler yüzlü bir görevli bulunmaktadır.
Sürekli koşuşturmacaya rağmen, müşteriler arasında bir dostluk duygusu var. Yabancılar sohbetler başlatıyor, inatçı lekeleri çıkarmak için ipuçlarını ve püf noktalarını paylaşıyor veya çamaşır yıkama gününün sıkıntılarından dert yanıyor. Çamaşır yıkamak gibi evrensel bir görevin bir araya getirdiği küçük bir topluluk.
Bir köşede, bir otomat, yorgun çamaşırcıları beslemek için çeşitli atıştırmalıklar ve içecekler sunuyor. Cips torbalarından soda şişelerine kadar her isteği tatmin edecek bir şeyler var. Giysilerinizin kurumasını beklerken zaman geçirmenin mükemmel yolu.
Boş bir makineye doğru ilerlediğinizde, tüm bunların verimliliğine hayret etmeden duramazsınız. Kaosa rağmen her şey iyi yağlanmış bir makine gibi çalışıyor, her kişi çamaşır yıkama gününün karmaşık dansında kendi rolünü oynuyor.
Giysileriniz ayıklandıktan ve deterjan miktarı ölçüldükten sonra makineyi doldurur ve beklemeye koyulursunuz. Çamaşır makinesinin hafif uğultusu sizi sakinleştirirken, Sparkle Clean Laundry gibi yerlere minnettar olmaktan kendinizi alıkoyamazsınız. Sürekli hareket eden bir dünyada, bazen asıl farkı yaratan, temiz giysiler ve dost canlısı yüzler gibi basit zevklerdir.
https://downwaste.com/tr/camasir-sutlari/ | softwareindustrie24334 | |
1,868,884 | Integrated Drive System Market Scope, Size, Share, Trends, Forecast By 2031 | The global integrated drive system market is poised for unprecedented expansion, with projections... | 0 | 2024-05-29T11:01:28 | https://dev.to/n_patil_96f2372543795ac55/integrated-drive-system-market-scope-size-share-trends-forecast-by-2031-202p | marketing | The global integrated drive system market is poised for unprecedented expansion, with projections indicating a substantial increase from an estimated US$39 billion by the end of 2024 to a staggering US$56 billion by 2031. This forecast, representing a remarkable compound annual growth rate (CAGR) of 5.3% during the period 2024-2031, underscores the robust momentum driving the IDS industry forward.
Visit our Research Report:https://www.fairfieldmarketresearch.com/report/integrated-drive-system-market
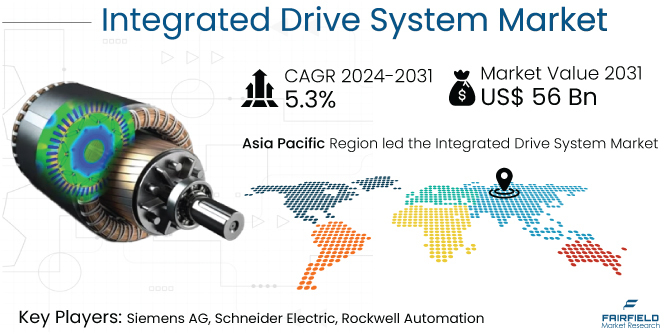
Quick Report Digest
1. Exponential Expansion: The global integrated drive system market is anticipated to witness a substantial 1.4x expansion during the forecast period of 2024-2031.
2. Historical Growth Drivers: Industrial automation, energy efficiency initiatives, and the accelerating adoption of electric vehicles have historically propelled the growth of the IDS market.
3. Future Growth Catalysts: Anticipated growth factors include stringent regulatory frameworks, increasing reliance on electric vehicles, ongoing technological advancements, and escalating investments in automation.
4. Efficiency and Performance Optimization: IDS solutions offer unparalleled efficiency and performance optimization, making them highly attractive for industries prioritizing operational excellence.
5. Alignment with Industry 4.0: The convergence of IDS with Industry 4.0 principles and automation trends aligns seamlessly with the evolving requirements of smart factories and automated production processes.
6. Emerging Economies Driving Demand: Robust industrialization and infrastructure development in emerging economies are spurring demand for scalable IDS solutions tailored to meet evolving market needs.
7. Barriers and Challenges: High initial investment costs, integration complexity, and market fragmentation pose significant challenges to widespread IDS adoption.
8. Key Trends: Trends such as energy efficiency, modular solutions, and heightened demand for services are shaping the trajectory of the IDS market.
9. Regulatory Influence: Regulatory mandates pertaining to emissions and safety standards are driving increased adoption of IDS solutions across industries.
10. Regional Dynamics: The Asia-Pacific region leads the IDS market due to rapid industrialization, with North America driven by technological advancements and Europe influenced by sustainability regulations.
A Look Back and a Look Forward - Comparative Analysis
The global integrated drive system market witnessed robust growth during the period 2019-2023, fueled by factors such as industrial automation, energy efficiency initiatives, and the burgeoning adoption of electric vehicles. Building upon this momentum, the market is projected to achieve even greater heights by 2031. Comparing the two periods reveals a trajectory of sustained growth, with key drivers including stricter regulatory frameworks, technological advancements, and escalating automation investments.
Key Growth Determinants
1. Efficiency and Performance Optimization: IDS solutions offer unparalleled improvements in efficiency and performance by seamlessly integrating various components, thus appealing to industries seeking operational excellence and cost reduction.
2. Industry 4.0 and Automation Trends: The rapid adoption of Industry 4.0 principles and the increasing focus on automation are driving demand for IDS solutions that enable seamless connectivity, data exchange, and real-time monitoring.
3. Growing Demand from Emerging Economies: Robust industrialization in emerging economies is driving demand for scalable IDS solutions tailored to meet evolving market needs.
Major Growth Barriers
1. High Initial Investment: Significant upfront investment costs present a barrier to IDS adoption.
2. Complexity of Integration: The complexity involved in integrating diverse components within the IDS framework poses challenges, including interoperability issues and compatibility concerns.
3. Market Fragmentation: The fragmented nature of the IDS market complicates vendor selection and standardization efforts, hindering widespread adoption.
Key Trends and Opportunities to Look at
1. Focus on Energy Efficiency: Heightened global concerns about sustainability are driving increased demand for energy-efficient IDS solutions.
2. Customization and Modular Solutions: Offering customizable and modular IDS solutions tailored to specific industry requirements presents a significant opportunity for market growth.
3. Service and Maintenance: Increasing complexity of IDS systems underscores the importance of reliable service and maintenance support.
How Does the Regulatory Scenario Shape this Industry?
Stringent regulatory frameworks pertaining to emissions, safety standards, and energy efficiency incentivize the adoption of IDS solutions across industries, creating a favorable environment for market growth.
Fairfield’s Ranking Board
Top Segments
• Hardware Segment: Cornerstone of the IDS market, driven by advancements in motor efficiency and integration with control systems.
• Software Segment: Plays a pivotal role in enhancing operational efficiency and diagnostics.
• Services Segment: Growing demand for maintenance, repair, and support services, alongside consultancy and training.
Regional Frontrunners
• Asia Pacific: Dominates the IDS market due to rapid industrialization.
• North America: Thrives on technological advancements and Industry 4.0 practices.
• Europe: Driven by established manufacturing industries and stringent regulations.
Fairfield’s Competitive Landscape Analysis
Leading players in the IDS market include Siemens AG, ABB Ltd., Schneider Electric SE, and Bosch Rexroth AG, leveraging innovation and strategic maneuvers to maintain market dominance.
Significant Company Developments
• New Product Launches: Siemens unveiled its latest IDS offering, featuring enhanced efficiency and advanced control capabilities.
• Distribution Agreements: Rockwell Automation finalized a strategic distribution agreement aimed at expanding the market reach of IDS solutions.
Expert Insights
As industries worldwide prioritize sustainability and operational efficiency, the demand for IDS solutions is expected to surge. Ongoing advancements in drive system technologies, including IoT integration and predictive maintenance capabilities, further enhance the appeal of IDS solutions.
| n_patil_96f2372543795ac55 |
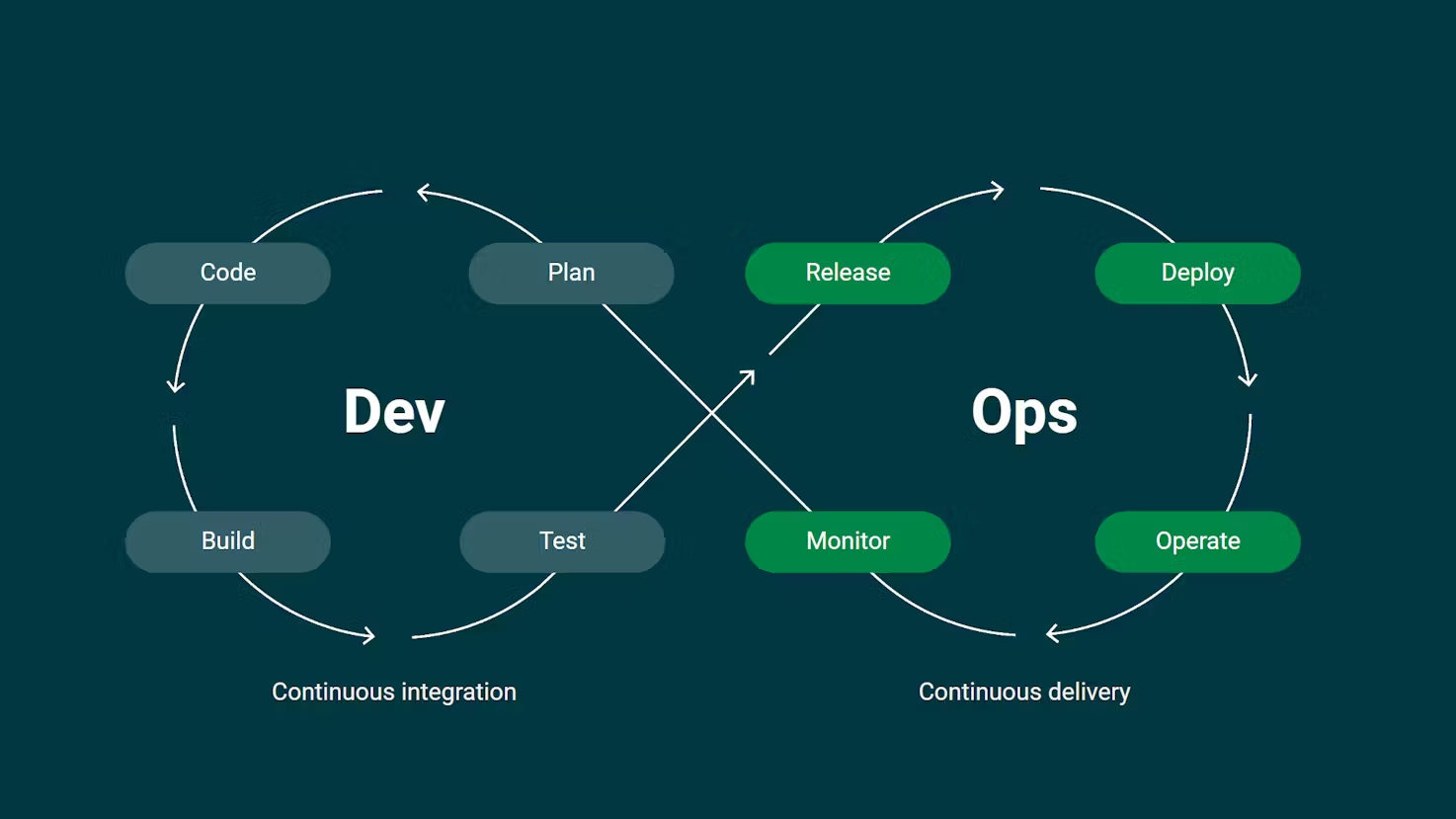
1,868,882 | Understanding CI/CD: A Comprehensive Overview | CI/CD, which stands for Continuous Integration and Continuous Delivery, is a process that helps teams... | 0 | 2024-05-29T11:00:10 | https://dev.to/azeem_shafeeq/understanding-cicd-a-comprehensive-overview-1mpo | cicd, webdev, beginners, tutorial | CI/CD, which stands for Continuous Integration and Continuous Delivery, is a process that helps teams quickly and safely deploy software changes. It's like a pipeline that automates many tasks in the software development process, allowing organizations and teams to deliver code to customers quickly, safely, and repeatedly.

Continuous Integration (CI)
Continuous Integration focuses on the development workflow, making sure changes are properly tested and integrated. This involves several key practices:
1. **Automated Testing**: Every code change triggers an automated testing sequence. This ensures that new changes do not break existing functionality.
2. **Version Control Integration**: Developers frequently commit code to a shared repository. Each commit is then automatically built and tested.
3. **Build Automation**: The process of compiling code and generating executable files is automated, ensuring consistency and reducing human error.
**Tools for CI**
**Jenkins:** An open-source automation server that supports building, deploying, and automating any project.
**Travis CI:** A continuous integration service used to build and test projects hosted on GitHub.
**CircleCI:** A CI service that allows for parallel builds, making it a fast option for CI/CD pipelines.
**Continuous Delivery (CD)**
Continuous Delivery provisions the infrastructure for production, ensuring changes are delivered to users quickly and safely. This process includes:
**Automated Deployment:** Code changes that pass all tests are automatically deployed to a staging environment and, with manual approval, to production.
**Infrastructure as Code (IaC):** Managing and provisioning computing infrastructure through machine-readable definition files rather than physical hardware configuration.
**Monitoring and Logging:** Continuous monitoring of applications and systems to detect and address issues promptly.
**Tools for CD**
**Spinnaker:** A multi-cloud continuous delivery platform that helps release software changes with high velocity and confidence.
**AWS CodePipeline:** A continuous delivery service for fast and reliable application and infrastructure updates.
**GitLab CI/CD:** Integrated within GitLab, it allows for a seamless process from code commit to deployment.
**CI/CD Pipeline Example**
A typical CI/CD pipeline might look like this:
**Code Commit:** A developer commits code to a version control system (e.g., Git).
**Automated Build:** The CI server detects the commit, checks out the latest code, and compiles it.
**Automated Tests:** A suite of automated tests runs against the compiled code.
**Staging Deployment**: If tests pass, the code is deployed to a staging environment for further testing.
**Production Deployment:** Upon approval, the code is automatically deployed to the production environment.
Real-World Use Cases
E-commerce Platforms: Companies like Amazon use CI/CD to deploy changes several times a day, ensuring new features and bug fixes reach customers rapidly without downtime.
Financial Services: Banks and financial institutions utilize CI/CD to quickly adapt to regulatory changes and deliver new features while ensuring security and compliance.
Social Media: Platforms like Facebook and Instagram use CI/CD to roll out updates seamlessly, providing new features and improvements without disrupting user experience.
Goals of CI/CD
Speed: Get changes to users quickly. Automated processes reduce the time between writing code and deploying it to production.
Safety: Ensure changes are problem-free and secure. Automated tests and deployment processes help catch issues early and consistently.
Repeatability: Make the process repeatable and scalable. Automated pipelines ensure that each deployment follows the same steps, reducing human error and increasing reliability.
_Remember, CI/CD is a continuous process that requires ongoing effort and improvement. As tools and practices evolve, so should the CI/CD pipelines to ensure optimal performance and reliability._
| azeem_shafeeq |
1,845,536 | Ibuprofeno.py💊| #113: Explica este código Python | Explica este código Python Dificultad: Fácil print(not True * (100 +... | 25,824 | 2024-05-29T11:00:00 | https://dev.to/duxtech/ibuprofenopy-113-explica-este-codigo-python-493f | spanish, learning, beginners, python | ## **<center>Explica este código Python</center>**
#### <center>**Dificultad:** <mark>Fácil</mark></center>
```py
print(not True * (100 + True))
```
👉 **A.** `101`
👉 **B.** `0`
👉 **C.** `100True`
👉 **D.** `SyntaxError`
---
{% details **Respuesta:** %}
👉 **B.** `0`
Ya sabemos que `True` infiere a `1` y `False` infiere a `0`.
Entonces es posible hacer operaciones aritméticas con booleanos.
Vamos por partes:
* `not True` equivale a `False`, que en numeros equivale a `0`.
* `100 + True` equivale a `101` porque `True` es `1`.
* Finalmente tendríamos `0 * 101` que nos da `0`
En este ejercicio en concreto basta con saber que `not True` da `0` para inferir que el resultado total será `0` (todo número multiplicado por `0` será `0` ya que el `0` es neutro multiplicativo)
{% enddetails %} | duxtech |
1,868,880 | What errors are lurking in LLVM code? | LLVM is an open-source project with a pretty large code base. The acme in terms of code quality,... | 0 | 2024-05-29T10:58:45 | https://dev.to/anogneva/what-errors-are-lurking-in-llvm-code-1b1j | cpp, opensource, programming | LLVM is an open\-source project with a pretty large code base\. The acme in terms of code quality, considering its size and open\-source nature\. After all, it's the developers of compiler tools who know best about language features and their proper use\. Their top\-notch code is always a challenge for our analyzer, and we always accept it with pleasure\.
A couple of months ago, LLVM released version 18\. It's time to once again ensure its code quality\. If interested, you can read our articles about previous checks [here](https://pvs-studio.com/en/blog/posts/cpp/0871/) and [there](https://pvs-studio.com/en/blog/posts/cpp/1003/)\.
These checks are always very special for [us](https://pvs-studio.com/en/pvs-studio/) because static analyzers operate almost the same way as compilers do when they analyze code\. Compilers also leverage static analysis to issue warnings\. They're almost cousins, though\. However, each of them is good at their own thing\. This article is proof of that\. The Clang compiler, a part of LLVM, compiled our analyzer and got it working\. We even have an [article](https://pvs-studio.com/en/blog/posts/cpp/0830/) about the switch from MSVC to it\. In return, our analyzer detected errors in the compiler\. Isn't that proof of synergy?
The checked project version is [LLVM 18\.1\.0](https://github.com/llvm/llvm-project/tree/llvmorg-18.1.0)\.
## Fragment N1
Here's an example of how the logical error can occur in a blanket of conditions and lead to an unreachable code\.
```cpp
if (Tok->is(tok::hash)) {
// Start of a macro expansion.
First = Tok;
Tok = Next;
if (Tok)
Tok = Tok->getNextNonComment();
} else if (Tok->is(tok::hashhash)) {
// Concatenation. Skip.
Tok = Next;
if (Tok)
Tok = Tok->getNextNonComment();
} else if (Keywords.isVerilogQualifier(*Tok) ||
Keywords.isVerilogIdentifier(*Tok)) {
First = Tok;
Tok = Next;
// The name may have dots like `interface_foo.modport_foo`.
while (Tok && Tok->isOneOf(tok::period, tok::coloncolon) &&
(Tok = Tok->getNextNonComment())) {
if (Keywords.isVerilogIdentifier(*Tok))
Tok = Tok->getNextNonComment();
}
} else if (!Next) {
Tok = nullptr;
} else if (Tok->is(tok::l_paren)) {
// Make sure the parenthesized list is a drive strength. Otherwise the
// statement may be a module instantiation in which case we have already
// found the instance name.
if (Next->isOneOf(
Keywords.kw_highz0, Keywords.kw_highz1, Keywords.kw_large,
Keywords.kw_medium, Keywords.kw_pull0, Keywords.kw_pull1,
Keywords.kw_small, Keywords.kw_strong0, Keywords.kw_strong1,
Keywords.kw_supply0, Keywords.kw_supply1, Keywords.kw_weak0,
Keywords.kw_weak1)) {
Tok->setType(TT_VerilogStrength);
Tok = Tok->MatchingParen;
if (Tok) {
Tok->setType(TT_VerilogStrength);
Tok = Tok->getNextNonComment();
}
} else {
break;
}
} else if (Tok->is(tok::hash)) {
if (Next->is(tok::l_paren))
Next = Next->MatchingParen;
if (Next)
Tok = Next->getNextNonComment();
}
```
The PVS\-Studio warning:
[V517](https://pvs-studio.com/en/docs/warnings/v517/) The use of 'if \(A\) \{\.\.\.\} else if \(A\) \{\.\.\.\}' pattern was detected\. There is a probability of logical error presence\. Check lines: [3016](https://github.com/llvm/llvm-project/blob/461274b81d8641eab64d494accddc81d7db8a09e/clang/lib/Format/TokenAnnotator.cpp#L3016), [3058](https://github.com/llvm/llvm-project/blob/461274b81d8641eab64d494accddc81d7db8a09e/clang/lib/Format/TokenAnnotator.cpp#L3058)\. TokenAnnotator\.cpp
Let's take a look more precisely\. In the first condition, we have the *Tok\-\>is\(tok::hash\)* check\. In the last condition, we have the same one in the *else if* statement\. However, the token we're working with doesn't change\. So, in the last *else if*, the code will never be executed\. It's that critical here because these conditions contain different code\.
```cpp
if (Tok->is(tok::hash)) {
// Start of a macro expansion.
First = Tok;
Tok = Next;
if (Tok)
Tok = Tok->getNextNonComment();
} else
....
else if (Tok->is(tok::hash)) {
if (Next->is(tok::l_paren))
Next = Next->MatchingParen;
if (Next)
Tok = Next->getNextNonComment();
}
```
It might be better if we change the statement to *switch*, and it might help developers notice the error\. It's a matter of taste, though\.
## Fragment N2
This code snippet is pretty riveting, and I can't help but share it with you:
```cpp
assert(bArgs.size() == reduc.size() + needsUniv ? 1 : 0);
```
The analyzer warnings:
* [V502](https://pvs-studio.com/en/docs/warnings/v502/) Perhaps the '?:' operator works in a different way than it was expected\. The '?:' operator has a lower priority than the '\+' operator\. LoopEmitter\.cpp [983](https://github.com/llvm/llvm-project/blob/461274b81d8641eab64d494accddc81d7db8a09e/mlir/lib/Dialect/SparseTensor/Transforms/Utils/LoopEmitter.cpp#L983)
* [V502](https://pvs-studio.com/en/docs/warnings/v502/) Perhaps the '?:' operator works in a different way than it was expected\. The '?:' operator has a lower priority than the '\+' operator\. LoopEmitter\.cpp [1039](https://github.com/llvm/llvm-project/blob/461274b81d8641eab64d494accddc81d7db8a09e/mlir/lib/Dialect/SparseTensor/Transforms/Utils/LoopEmitter.cpp#L1039)
There are two warnings because the code fragment occurs in two different places\.
The analyzer indicates that developers may have used the ternary operator incorrectly\. Let's get into it\.
First, let's refresh on the operator precedence\. Operators are listed in descending order of precedence: the *\+* operator, the *==* operator, the ternary operator\. I should note that the *needsUniv* variable is of the *bool* type\.
So, the results of *reduc\.size\(\)* and *needsUniv* will be added up first\. However, *needsUniv* implicitly casts to the *size\_t* type\. Then, the addition result will be compared to the result of *bArgs\.size\(\)*\. Then the ternary operator will be executed, and it will return either 1 or 0\.
That's kind of odd\. I think developers probably meant to write such code:
```cpp
assert(bArgs.size() == reduc.size() + (needsUniv ? 1 : 0));
```
In such a case, the ternary operator will be executed first and will return either 1 or 0\. Then this value will be added up to the result of *reduc\.size\(\)* and compared to the result of *bArgs\.size\(\)*\.
A curious fact: in the first and second cases, we'll get the same result\.
A more curious fact: devs could have written the code like this:
```cpp
assert(bArgs.size() == reduc.size() + needsUniv)
```
Here, the result would be the same but without the redundant ternary operator\.
All in all, it's an peculiar case when the code is written incorrectly but still works\.
## Fragment N3
Here's a rather interesting use of the postfix increment\. Watch out for the second argument of the custom *Printf* function called on the *strm* object:
```cpp
static void DumpTargetInfo(uint32_t target_idx, Target *target,
const char *prefix_cstr,
bool show_stopped_process_status, Stream &strm)
{
....
uint32_t properties = 0;
if (target_arch.IsValid())
{
strm.Printf("%sarch=", properties++ > 0 ? ", " : " ( ");
target_arch.DumpTriple(strm.AsRawOstream());
properties++;
}
}
```
The analyzer warning:
[V547](https://pvs-studio.com/en/docs/warnings/v547/) Expression 'properties \+\+ \> 0' is always false\. CommandObjectTarget\.cpp:[100](https://github.com/llvm/llvm-project/blob/461274b81d8641eab64d494accddc81d7db8a09e/lldb/source/Commands/CommandObjectTarget.cpp#L100)
As far as I can say, developers may have intended to compare *properties* against zero and avoid incrementing the *properties* variable and superfluous code, so they decided to use the postfix increment right away\.
Thus, the previous value of the variable would have been compared, but it'd still be incremented by 1\. However, it's unclear why devs decided to increment it further\.
Then we gain the insight that the ternary operator isn't needed here at all\. This snippet might have been in a loop at some point\. Feel free to share your guesses in the comments\.
## Fragments N4\-8
Let's take a look at the following code and the PVS\-Studio warning:
```cpp
bool areStatementsIdentical(const Stmt *FirstStmt, const Stmt *SecondStmt,
const ASTContext &Context, bool Canonical)
{
....
if (FirstStmt->getStmtClass() != FirstStmt->getStmtClass())
return false;
....
}
```
The PVS\-Studio warning:
[V501](https://pvs-studio.com/en/docs/warnings/v501/) There are identical sub\-expressions 'FirstStmt\-\>getStmtClass\(\)' to the left and to the right of the '\!=' operator\. ASTUtils\.cpp:[99](https://github.com/llvm/llvm-project/blob/461274b81d8641eab64d494accddc81d7db8a09e/clang-tools-extra/clang-tidy/utils/ASTUtils.cpp#L99)
It may seem like a drop in the bucket\. Mixing *FirstStmt* and *SecondStmt* up? Whatever\.
Then we encounter the following code:
```cpp
static bool sameFunctionParameterTypeLists(Sema &S,
const OverloadCandidate &Cand1,
const OverloadCandidate &Cand2) {
if (!Cand1.Function || !Cand2.Function)
return false;
FunctionDecl *Fn1 = Cand1.Function;
FunctionDecl *Fn2 = Cand2.Function;
if (Fn1->isVariadic() != Fn1->isVariadic())
return false;
....
}
```
The analyzer warning:
[V501](https://pvs-studio.com/en/docs/warnings/v501/) There are identical sub\-expressions to the left and to the right of the '\!=' operator: Fn1\-\>isVariadic\(\) \!= Fn1\-\>isVariadic\(\)\. SemaOverload\.cpp:[10190](https://github.com/llvm/llvm-project/blob/461274b81d8641eab64d494accddc81d7db8a09e/clang/lib/Sema/SemaOverload.cpp#L10190)
We think, "Well, it's wrong again\. Whatever\."
Then we see the code like this:
```cpp
if (G1->Rank < G1->Rank)
G1->Group = G2;
else {
G2->Group = G1;
}
```
The analyzer warning:
[V501](https://pvs-studio.com/en/docs/warnings/v501/) There are identical sub\-expressions to the left and to the right of the '<' operator: G1\-\>Rank < G1\-\>Rank\. SCCIterator\.h:[285](https://github.com/llvm/llvm-project/blob/461274b81d8641eab64d494accddc81d7db8a09e/llvm/include/llvm/ADT/SCCIterator.h#L285)
We're starting to have doubts\.
And then the code snippet jumps out:
```cpp
ValueBoundsConstraintSet::areOverlappingSlices(MLIRContext *ctx,
HyperrectangularSlice slice1,
HyperrectangularSlice slice2) {
assert(slice1.getMixedOffsets().size() == slice1.getMixedOffsets().size()
&& "expected slices of same rank");
assert(slice1.getMixedSizes().size() == slice1.getMixedSizes().size()
&& "expected slices of same rank");
assert(slice1.getMixedStrides().size() == slice1.getMixedStrides().size()
&& "expected slices of same rank");
....
}
```
The analyzer warnings:
* [V501](https://pvs-studio.com/en/docs/warnings/v501/) There are identical sub\-expressions 'slice1\.getMixedOffsets\(\)\.size\(\)' to the left and to the right of the '==' operator\. ValueBoundsOpInterface\.cpp:[581](https://github.com/llvm/llvm-project/blob/461274b81d8641eab64d494accddc81d7db8a09e/mlir/lib/Interfaces/ValueBoundsOpInterface.cpp#L581)
* [V501](https://pvs-studio.com/en/docs/warnings/v501/) There are identical sub\-expressions 'slice1\.getMixedSizes\(\)\.size\(\)' to the left and to the right of the '==' operator\. ValueBoundsOpInterface\.cpp:583
* [V501](https://pvs-studio.com/en/docs/warnings/v501/) There are identical sub\-expressions 'slice1\.getMixedStrides\(\)\.size\(\)' to the left and to the right of the '==' operator\. ValueBoundsOpInterface\.cpp:585
Here's another one almost the same:
```cpp
ValueBoundsConstraintSet::areEquivalentSlices(MLIRContext *ctx,
HyperrectangularSlice slice1,
HyperrectangularSlice slice2) {
assert(slice1.getMixedOffsets().size() == slice1.getMixedOffsets().size()
&& "expected slices of same rank");
assert(slice1.getMixedSizes().size() == slice1.getMixedSizes().size()
&& "expected slices of same rank");
assert(slice1.getMixedStrides().size() == slice1.getMixedStrides().size()
&& "expected slices of same rank");
....
}
```
The PVS\-Studio warnings:
* [V501](https://pvs-studio.com/en/docs/warnings/v501/) There are identical sub\-expressions 'slice1\.getMixedOffsets\(\)\.size\(\)' to the left and to the right of the '==' operator\. ValueBoundsOpInterface\.cpp:[646](https://github.com/llvm/llvm-project/blob/461274b81d8641eab64d494accddc81d7db8a09e/mlir/lib/Interfaces/ValueBoundsOpInterface.cpp#L646)
* [V501](https://pvs-studio.com/en/docs/warnings/v501/) There are identical sub\-expressions 'slice1\.getMixedSizes\(\)\.size\(\)' to the left and to the right of the '==' operator\. ValueBoundsOpInterface\.cpp:648
* [V501](https://pvs-studio.com/en/docs/warnings/v501/) There are identical sub\-expressions 'slice1\.getMixedStrides\(\)\.size\(\)' to the left and to the right of the '==' operator\. ValueBoundsOpInterface\.cpp:650
We wonder, "Wow, how many bugs can quietly live in code?" These errors can cause something to fall off or not operate as intended\.
By the way, when I see all these *Fn1*, *G1*, *slice1*, my colleague's article comes to mind: "[Zero, one, two, Freddy's coming for you](https://pvs-studio.com/en/blog/posts/cpp/0713/)"\.
I've saved these similar warnings for the last:
* [V501](https://pvs-studio.com/en/docs/warnings/v501/) There are identical sub\-expressions 'EltRange\.getEnd\(\) \>= Range\.getEnd\(\)' to the left and to the right of the '\|\|' operator\. HTMLLogger\.cpp:[421](https://github.com/llvm/llvm-project/blob/461274b81d8641eab64d494accddc81d7db8a09e/clang/lib/Analysis/FlowSensitive/HTMLLogger.cpp#L421)
* [V501](https://pvs-studio.com/en/docs/warnings/v501/) There are identical sub\-expressions 'SrcExpr\.get\(\)\-\>containsErrors\(\)' to the left and to the right of the '\|\|' operator\. SemaCast\.cpp:[2938](https://github.com/llvm/llvm-project/blob/461274b81d8641eab64d494accddc81d7db8a09e/clang/lib/Sema/SemaCast.cpp#L2938)
* [V501](https://pvs-studio.com/en/docs/warnings/v501/) There are identical sub\-expressions 'ND\-\>getDeclContext\(\)' to the left and to the right of the '\!=' operator\. SemaDeclCXX\.cpp:[4391](https://github.com/llvm/llvm-project/blob/461274b81d8641eab64d494accddc81d7db8a09e/clang/lib/Sema/SemaDeclCXX.cpp#L4391)
* [V501](https://pvs-studio.com/en/docs/warnings/v501/) There are identical sub\-expressions 'DepType \!= OMPC\_DOACROSS\_source' to the left and to the right of the '&&' operator\. SemaOpenMP\.cpp:[24348](https://github.com/llvm/llvm-project/blob/461274b81d8641eab64d494accddc81d7db8a09e/clang/lib/Sema/SemaOpenMP.cpp#L24348)
* [V501](https://pvs-studio.com/en/docs/warnings/v501/) There are identical sub\-expressions '\!OldMethod\-\>isStatic\(\)' to the left and to the right of the '&&' operator\. SemaOverload\.cpp:[1425](https://github.com/llvm/llvm-project/blob/461274b81d8641eab64d494accddc81d7db8a09e/clang/lib/Sema/SemaOverload.cpp#L1425)
* [V501](https://pvs-studio.com/en/docs/warnings/v501/) There are identical sub\-expressions 'lldb::eTypeClassUnion' to the left and to the right of the '\|' operator\. JSONUtils\.cpp:[139](https://github.com/llvm/llvm-project/blob/461274b81d8641eab64d494accddc81d7db8a09e/lldb/tools/lldb-dap/JSONUtils.cpp#L139)
* [V501](https://pvs-studio.com/en/docs/warnings/v501/) There are identical sub\-expressions to the left and to the right of the '&&' operator: \!BFI &&\!BFI\. JumpThreading\.cpp:[2531](https://github.com/llvm/llvm-project/blob/461274b81d8641eab64d494accddc81d7db8a09e/llvm/lib/Transforms/Scalar/JumpThreading.cpp#L2531)
* [V501](https://pvs-studio.com/en/docs/warnings/v501/) There are identical sub\-expressions 'BI\-\>isConditional\(\)' to the left and to the right of the '&&' operator\. VPlanHCFGBuilder\.cpp:[401](https://github.com/llvm/llvm-project/blob/461274b81d8641eab64d494accddc81d7db8a09e/llvm/lib/Transforms/Vectorize/VPlanHCFGBuilder.cpp#L401)
* [V501](https://pvs-studio.com/en/docs/warnings/v501/) There are identical sub\-expressions to the left and to the right of the '==' operator: getNumRows\(\) == getNumRows\(\)\. Simplex\.cpp:[108](https://github.com/llvm/llvm-project/blob/461274b81d8641eab64d494accddc81d7db8a09e/mlir/lib/Analysis/Presburger/Simplex.cpp#L108)
## Fragment N9
Here's another interesting code snippet\. Try to figure out for yourself where the error lies:
```cpp
const Expr *CGOpenMPRuntime::getNumTeamsExprForTargetDirective(
CodeGenFunction &CGF, const OMPExecutableDirective &D, int32_t &MinTeamsVal,
int32_t &MaxTeamsVal)
{
....
if (isOpenMPParallelDirective(NestedDir->getDirectiveKind()) ||
isOpenMPSimdDirective(NestedDir->getDirectiveKind())) {
MinTeamsVal = MaxTeamsVal = 1;
return nullptr;
}
MinTeamsVal = MaxTeamsVal = 1;
return nullptr;
....
}
```
Now let's see what the analyzer issues\.
The analyzer warning:
[V523](https://pvs-studio.com/en/docs/warnings/v523/) The 'then' statement is equivalent to the subsequent code fragment\. CGOpenMPRuntime\.cpp:[6040](https://github.com/llvm/llvm-project/blob/461274b81d8641eab64d494accddc81d7db8a09e/clang/lib/CodeGen/CGOpenMPRuntime.cpp#L6040), [6036](https://github.com/llvm/llvm-project/blob/461274b81d8641eab64d494accddc81d7db8a09e/clang/lib/CodeGen/CGOpenMPRuntime.cpp#L6036)
It shows that the code after *if* is exactly the same as in the *then* branch\. Therefore, either the check or the code part after it is unnecessary\.
## Fragment N10
The following snippet looks that weird:
```cpp
explicit MapLattice(Container C) { C = std::move(C); }
```
The PVS\-Studio warning:
[V570](https://pvs-studio.com/en/docs/warnings/v570/) The 'C' variable is assigned to itself\. MapLattice\.h:[52](https://github.com/llvm/llvm-project/blob/461274b81d8641eab64d494accddc81d7db8a09e/clang/include/clang/Analysis/FlowSensitive/MapLattice.h#L52)
It's the reason, guess\. Inside the body of the *MapLattice* class constructor, we can see the [shadowing](https://en.wikipedia.org/wiki/Variable_shadowing) of a non\-static field\. The field has the same name as the parameter\. In this fragment, devs forgot to explicitly set *this* to the left of the assignment operator\.
Just a small fix and the code will operate as it should:
```cpp
explicit MapLattice(Container C) { this->C = std::move(C); }
```
Although, IMHO, it'd be much neater to use the constructor initialization list:
```cpp
explicit MapLattice(Container C) : C { std::move(C) } {};
```
In this case, there is no shadowing because of the name lookup rules \([click](https://timsong-cpp.github.io/cppwp/n4950/class.init#class.base.init-2), [click](https://timsong-cpp.github.io/cppwp/n4950/class.init#class.base.init-15)\)\.
Overall, you can add a prefix or postfix to the names of private fields\. It makes it easier to distinguish them from parameters in code\.
## Fragment N11
Do you ever feel like you've forgotten something? Like, you can't remember if you've brought your keys with you or not\. You grope your pockets but can't find them\.
So, in the following fragment, it looks like devs have forgotten to use the function result:
```cpp
ScalarEvolution::getRangeRefIter(const SCEV *S,
ScalarEvolution::RangeSignHint SignHint)
{
....
for (const SCEV *P : reverse(drop_begin(WorkList))) {
getRangeRef(P, SignHint);
....
}
....
}
```
The analyzer warning:
[V530](https://pvs-studio.com/en/docs/warnings/v530/) The return value of function 'getRangeRef' is required to be utilized\. ScalarEvolution\.cpp:[6587](https://github.com/llvm/llvm-project/blob/461274b81d8641eab64d494accddc81d7db8a09e/llvm/lib/Analysis/ScalarEvolution.cpp#L6587)
You may notice that the result of *getRangeRef* isn't used\.
Here's the function signature, which validates that there is an operation result:
```cpp
const ConstantRange &getRangeRef(const SCEV *S, RangeSignHint Hint,
unsigned Depth = 0);
```
Further, we can see that the result of the signature is used throughout the code\.
However, it's not that simple\. Sometimes your senses mislead you, and it turns out that the keys are right in your hand all along\.
The code snippet has the comment:
```cpp
// Use getRangeRef to compute ranges for items in the worklist in reverse
// order. This will force ranges for earlier operands to be computed before
// their users in most cases.
```
Developers may have written this code deliberately\. However, if we use the *get* function in this way and make it multipurpose, it's a bad programming practice\. It may mislead other developers\.
Thus, the analyzer formally turns out to be right, but in fact there is no error here\. In such cases, we have ways to suppress certain warnings\. For example, using a comment in the code:
```cpp
for (const SCEV *P : reverse(drop_begin(WorkList))) {
getRangeRef(P, SignHint); //-V530
```
## Fragment N12
A quest for the most attentive ones: find three differences between the code in the *if* and *else* branches\. Okay, find at least one:
```cpp
case OptionParser::eOptionalArgument:
if (OptionParser::GetOptionArgument() != nullptr) {
option_element_vector.push_back(OptionArgElement(
opt_defs_index,
FindOriginalIndex(dummy_vec[OptionParser::GetOptionIndex() - 2],
args),
FindOriginalIndex(dummy_vec[OptionParser::GetOptionIndex() - 1],
args)));
} else {
option_element_vector.push_back(OptionArgElement(
opt_defs_index,
FindOriginalIndex(dummy_vec[OptionParser::GetOptionIndex() - 2],
args),
FindOriginalIndex(dummy_vec[OptionParser::GetOptionIndex() - 1],
args)));
}
```
And you're absolutely right\. They aren't any\.
The analyzer warning:
[V523](https://pvs-studio.com/en/docs/warnings/v523/) The 'then' statement is equivalent to the 'else' statement\. Options\.cpp [1212](https://github.com/llvm/llvm-project/blob/461274b81d8641eab64d494accddc81d7db8a09e/lldb/source/Interpreter/Options.cpp#L1212)
## Conclusion
All good things come to an end\. But that's not about this article\. The big project begets the big article, or even better, two articles\. I've decided to go the second way\. Next, we'll dive into some pretty serious bugs \(spoiler: they're related to UB\)\.
Even the pros make mistakes—and not just in code\. What to say about ordinary users\. However, mistakes are no reason to get frustrated\. Mistakes are just an opportunity to get better and grow\. You can tell this to your team lead every time something breaks in the prod\.
To avoid any errors in the code, you may try new methods of searching for them\. For example, you may use dynamic and static code analysis tools in addition to tests and code review\.
Wondering what errors are lurking in your code? Check your project for [free](https://pvs-studio.com/en/blog/posts/0614/)\! | anogneva |
1,868,879 | Effective SEO Strategies for Digital Marketing | Understanding SEO Fundamentals Search Engine Optimization (SEO) is a fundamental aspect of digital... | 0 | 2024-05-29T10:58:00 | https://dev.to/ravi_16a532da70ff3b9bac67/effective-seo-strategies-for-digital-marketing-4pln | Understanding SEO Fundamentals

Search Engine Optimization (SEO) is a fundamental aspect of digital marketing. It involves optimizing your website to improve its visibility on search engine result pages (SERPs). By understanding the basics of SEO, you can effectively drive organic traffic to your website.
Key concepts in SEO include keyword research, on-page optimization, off-page optimization, and content marketing. Keyword research helps you identify relevant keywords that your target audience is searching for. On-page optimization involves optimizing elements on your website such as title tags, meta descriptions, and header tags. Off-page optimization encompasses techniques like link building and social media marketing to improve your website’s authority and credibility. Content marketing focuses on creating valuable and engaging content to attract and retain your target audience.
By mastering these SEO fundamentals, you can lay a strong foundation for your digital marketing strategy.
Optimizing On-Page SEO Elements
On-page SEO refers to optimizing the elements on your website to improve its search engine ranking. This includes optimizing your title tags, meta descriptions, header tags, and URL structure.
To optimize your title tags, make sure they accurately describe the content of each page and include relevant keywords. Meta descriptions should provide a concise summary of the page’s content and entice users to click through to your website. Header tags, such as H1, H2, and H3, help structure your content and make it easier for search engines to understand. Finally, ensure your URL structure is clean and descriptive.
By optimizing these on-page elements, you can improve your website’s visibility and click-through rates on search engine result pages.
Leveraging Off-Page SEO Techniques
Off-page SEO refers to optimizing factors outside of your website that can influence its search engine ranking. This includes link building, social media marketing, and online reputation management.
Link building involves acquiring high-quality backlinks from other websites. These backlinks act as votes of confidence for your website and can improve its authority and credibility in the eyes of search engines. Social media marketing involves promoting your content and engaging with your audience on social media platforms to increase brand visibility and drive traffic to your website. Online reputation management involves monitoring and managing your online reputation to ensure positive reviews and feedback.
By leveraging these off-page SEO techniques, you can enhance your website’s visibility, authority, and reputation.
Harnessing the Power of Content Marketing
Content marketing plays a crucial role in SEO and digital marketing. It involves creating and distributing valuable, relevant, and consistent content to attract and retain your target audience.
When creating content, it’s important to understand your audience’s needs and interests. Conducting thorough keyword research can help you identify relevant topics and optimize your content for search engines. Additionally, creating high-quality and engaging content can increase user engagement and encourage social sharing, which can further boost your website’s visibility and authority.
By harnessing the power of content marketing, you can establish your brand as a thought leader, drive organic traffic to your website, and generate leads.
Utilizing Advanced SEO Tools and Analytics
Advanced SEO tools and analytics can provide valuable insights into your website’s performance and help you optimize your SEO strategy.
Tools like Google Analytics can track important metrics such as organic traffic, bounce rate, and conversion rate. By analyzing these metrics, you can identify areas for improvement and make data-driven decisions to optimize your website’s performance. Other tools like SEMrush and Moz can help you conduct keyword research, analyze backlinks, and monitor your website’s SEO health.
By utilizing these advanced SEO tools and analytics, you can continuously improve your SEO strategy and stay ahead of your competition.
Take Your SEO Skills to the Next Level
If you want to master these SEO strategies and excel in digital marketing, Web Trainings Academy offers the top [digital marketing course](https://www.webtrainings.in/digital-marketing-course-hyderabad/) and SEO courses in Hyderabad. Enroll today and learn from the best in the industry!
Join [Web Trainings Academy](https://www.webtrainings.in/
) now and become an SEO expert. Don’t miss out on this opportunity to enhance your skills and advance your career! | ravi_16a532da70ff3b9bac67 | |
1,868,878 | Bambina Blue | Bambina Blue is now offering a special treat just for your furry friends! Our delicious and healthy... | 0 | 2024-05-29T10:55:38 | https://dev.to/hunterxh/bambina-blue-ael | Bambina Blue is now offering a special treat just for your furry friends! Our delicious and healthy ice cream for puppy is made with all-natural ingredients. [Visit](https://bambinablue.com/pups/) our shop today and let your dog enjoy a refreshing treat designed just for them. | hunterxh | |
1,868,877 | FastAPI Beyond CRUD Part1 - Introduction And Project Set Up | This is the first of a series of videos I have been making about FastAPI. This course is intended to... | 0 | 2024-05-29T10:55:06 | https://dev.to/jod35/fastapi-beyond-crud-part1-introduction-and-project-set-up-4gd0 | fastapi, webdev, python, programming | This is the first of a series of videos I have been making about FastAPI. This course is intended to cover FastAPI concepts while building a REST API for a simple book review web service.
{%youtube Uw4FPr-dD7Q%} | jod35 |
1,868,778 | Building a serverless connected BBQ as SaaS - Part 1 | In the world of BBQ, tradition and technology rarely cross paths. But what if I told you that the future of grilling is here, and it’s connected, smart, and runs on the cloud? In this blog series, I will explore how AWS IoT, serverless, and event-driven architecture enables an automated cooking experience. As a tech-savvy griller, I discover how cloud technology can elevate my grilling game to a whole new level. | 0 | 2024-05-29T10:50:35 | https://jimmydqv.com/serverless-bbq-saas/index.html | aws, serverless, iot | ---
title: 'Building a serverless connected BBQ as SaaS - Part 1'
description: In the world of BBQ, tradition and technology rarely cross paths. But what if I told you that the future of grilling is here, and it’s connected, smart, and runs on the cloud? In this blog series, I will explore how AWS IoT, serverless, and event-driven architecture enables an automated cooking experience. As a tech-savvy griller, I discover how cloud technology can elevate my grilling game to a whole new level.
cover_image: https://jimmydqv.com/assets/img/post-bbq-saas-part-1/cover-image-dev.png
tags: aws, serverless, iot
canonical_url: https://jimmydqv.com/serverless-bbq-saas/index.html
published: true
---
This post is the start of a series of post on how I built a IoT connected BBQ as SaaS. This first post will kick everything off by briefly introducing the used hardware and AWS GreenGrass, which will be used to connect and send data to the cloud. In the coming post the architecture will be introduced followed be deep dive technical posts on each part of the architecture.
In the end I will have created a Serverless connected BBQ smoker as a SaaS solution. There will be deep dives into IoT setup, on-boarding, user management, data and tenant isolation.
## HW Components
First, let's go over the required HW and what I'll be using in this series. I will be using a [Raspberry Pi 3 model B](https://www.raspberrypi.com/products/raspberry-pi-3-model-b/) that will connect to a [Inkbird IBT-6xs](https://inkbird.com/products/bluetooth-bbq-thermometer-ibt-6xs) over bluetooth LE.
However in this first post we'll setup a simulated device running on a small EC2 instance.
## AWS Greengrass Core
AWS IoT Greengrass is an edge runtime and cloud service for building, deploying, and managing device software in an easy way. It support creation of custom software components that can easily be deployed to any device running Greengrass.
## Greengrass Development Kit
To make development a bit easier I will be using [Greengrass Development Kit](https://docs.aws.amazon.com/greengrass/v2/developerguide/greengrass-development-kit-cli.html) to build new versions of the component. GDK however doesn't support AWS Identity Center and CLI profiles, making it impossible to publish new versions using this tool. Instead I will be manually creating new versions.
## Initialize a component
First of I use GDK to initialize a new component. To do this run the [init command](https://docs.aws.amazon.com/greengrass/v2/developerguide/greengrass-development-kit-cli-component.html#greengrass-development-kit-cli-component-init). There is a need to specify the used language and template to base the component of. Available templates can be found in [GitHub](https://github.com/aws-greengrass/aws-greengrass-component-templates/) I will be using Python and base the component of HelloWorld template. I will also supply a name for it, this will create a new folder where all files are stored. Make sure the folder do not exist.
``` bash
gdk component init -l python -t HelloWorld -n HelloBBQ
```
In the `HelloBBQ` folder there is now a configuration file `gdk-config.json` this need to be updated and the PLACEHOLDER values changed, and the component name specified.
``` json
{
"component": {
"com.example.hellobbq": {
"author": "<PLACEHOLDER_NAME>",
"version": "1.0.0",
"build": {
"build_system": "zip",
"options": {
"zip_name": ""
}
},
"publish": {
"bucket": "<PLACEHOLDER_BUCKET>",
"region": "<PLACEHOLDER_REGION>"
}
}
},
"gdk_version": "1.3.0"
}
```
## Add device code
Update the main.py file and add code to connect and publish fake temperatures to IoT Core on a topic `e/{THING_NAME}/data`
``` python
import os
import time
import uuid
import random
import json
import awsiot.greengrasscoreipc.clientv2 as clientV2
from awsiot.greengrasscoreipc.clientv2 import GreengrassCoreIPCClientV2
from decimal import Decimal
# MQTT
IPC_CLIENT: GreengrassCoreIPCClientV2 = clientV2.GreengrassCoreIPCClientV2()
THING_NAME = os.getenv("AWS_IOT_THING_NAME")
OPERATIONS_TOPIC = f"c/{THING_NAME}/operation"
DATA_TOPIC = f"e/{THING_NAME}/data"
QOS = "1"
SESSION = str(uuid.uuid4())
def publishToTopic(topic, payload):
IPC_CLIENT.publish_to_iot_core(topic_name=topic, qos=QOS, payload=payload)
def createRandomDecimal():
return random.randint(0, 1000) / 10
def generateSimulatedTemperature():
tempProbe0 = str(round(Decimal(createRandomDecimal()), 2))
tempProbe1 = str(round(Decimal(createRandomDecimal()), 2))
tempProbe2 = str(round(Decimal(createRandomDecimal()), 2))
tempProbe3 = str(round(Decimal(createRandomDecimal()), 2))
tempProbe4 = str(round(Decimal(createRandomDecimal()), 2))
tempProbe5 = str(round(Decimal(createRandomDecimal()), 2))
# Add the temperatures to the array
temps = [
tempProbe0,
tempProbe1,
tempProbe2,
tempProbe3,
tempProbe4,
tempProbe5,
]
temp_dict = {"session": SESSION, "temperatures": temps}
return temp_dict
def main():
# Continually request information from the iBBQ device
while True:
try:
temps = generateSimulatedTemperature()
publishToTopic(DATA_TOPIC, json.dumps(temps))
time.sleep(5)
except Exception as e:
print(f"ERROR IN WHILE LOOP, TRY AGAIN! {e.message}")
if __name__ == "__main__":
main()
```
## Create the recipe
In the same folder the GreenGrass recipe file is also created. This need to be updated to match GDK configuration. In the recipe it's possible to variables like `{artifacts:decompressedPath}`, full reference can be [found here](https://docs.aws.amazon.com/greengrass/v2/developerguide/component-recipe-reference.html)
To send data over MQTT to AWS IoT Core we need to add permissions for the mqttproxy and specify which topics it can publish to. W'll only allow the device to publish to topics it "owns" that is include the thing name. For this we can use the variable `{iot:thingName}`
``` yaml
---
RecipeFormatVersion: "2020-01-25"
ComponentName: "com.example.hellobbq"
ComponentVersion: "1.0.0"
ComponentDescription: "Component for sending temperature data to Cloud"
ComponentPublisher: "YOUR-NAME"
ComponentConfiguration:
DefaultConfiguration:
Topic: "e/{iot:thingName}/data"
accessControl:
aws.greengrass.ipc.mqttproxy:
com.example.hellobbq:mqttproxy:1:
policyDescription: Allows access to publish to device topics.
operations:
- aws.greengrass#PublishToIoTCore
resources:
- "e/{iot:thingName}/data"
Manifests:
- Platform:
os: all
Artifacts:
- URI: "s3://PLACEHOLDER_BUCKET/com.example.hellobbq/1.0.0/com.example.hellobbq.zip"
Unarchive: ZIP
Lifecycle:
Run: "python3 -u {artifacts:decompressedPath}/com.example.hellobbq/main.py {configuration:/Topic}"
```
## Build component
With the GDK config and recipe update it's time to build the component. That is done with command.
``` bash
gdk component build
```
The build will produce a zip file located in folder `greengrass-build/COMPONENT_NAME/VERSION/`
With build completed copy the zip file to the S3 bucket used in the recipe.
``` bash
aws s3 cp greengrass-build/artifacts/com.example.HelloBBQ/1.0.0/com.example.hellobbq.zip s3://PLACEHOLDER_BUCKET/com.examle.hellobbq/1.0.0/com.example.hellobbq.zip
```
With the zip file uploaded the component can be created in the AWS Console.
## Create component
To create the component we navigate to the IoT Core part of the console, expand `Greengrass devices` and select `Components`, click on `Create Component` button to the right.
Paste the recipe and click on `Create Component`
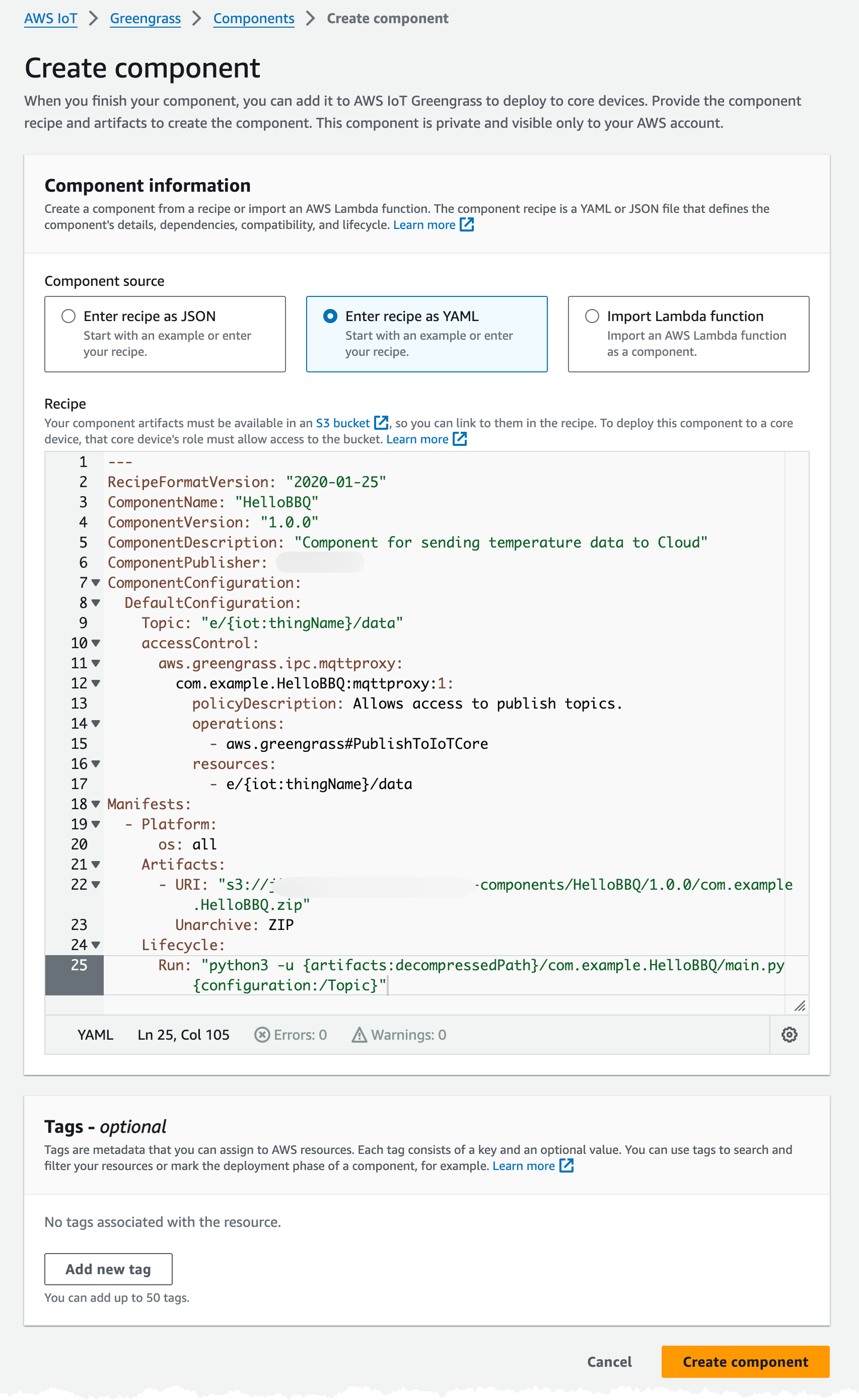
## Create simulation device
To simulate the device we can use a small EC2 instance. I will create a small `t3.micro` instance that I will be using.
We need create an IAM Role, that we assign to the EC2 Instance, this role will be used to provision the instance as an IoT Thing and all the needed resources. The minimum access needed can be found [in the aws documentation](https://docs.aws.amazon.com/greengrass/v2/developerguide/provision-minimal-iam-policy.html) below is an example.
``` json
{
"Version": "2012-10-17",
"Statement": [
{
"Sid": "CreateTokenExchangeRole",
"Effect": "Allow",
"Action": [
"iam:AttachRolePolicy",
"iam:CreatePolicy",
"iam:CreateRole",
"iam:GetPolicy",
"iam:GetRole",
"iam:PassRole"
],
"Resource": [
"arn:aws:iam::ACCOUNT-ID:role/GreengrassV2TokenExchangeRole",
"arn:aws:iam::ACCOUNT-ID:policy/GreengrassV2TokenExchangeRoleAccess",
"arn:aws:iam::aws:policy/GreengrassV2TokenExchangeRoleAccess"
]
},
{
"Sid": "CreateIoTResources",
"Effect": "Allow",
"Action": [
"iot:AddThingToThingGroup",
"iot:AttachPolicy",
"iot:AttachThingPrincipal",
"iot:CreateKeysAndCertificate",
"iot:CreatePolicy",
"iot:CreateRoleAlias",
"iot:CreateThing",
"iot:CreateThingGroup",
"iot:DescribeEndpoint",
"iot:DescribeRoleAlias",
"iot:DescribeThingGroup",
"iot:GetPolicy"
],
"Resource": "*"
},
{
"Sid": "DeployDevTools",
"Effect": "Allow",
"Action": [
"greengrass:CreateDeployment",
"iot:CancelJob",
"iot:CreateJob",
"iot:DeleteThingShadow",
"iot:DescribeJob",
"iot:DescribeThing",
"iot:DescribeThingGroup",
"iot:GetThingShadow",
"iot:UpdateJob",
"iot:UpdateThingShadow"
],
"Resource": "*"
}
]
}
```
I create a Role named `SimulatedBBQDeviceInstanceRole` with the above permissions, and assign this the EC2 instance used to simulated the BBQ device.
When the EC2 instance is running I connect to it using `EC2 Instance Connect`.
### Install Requirements
First of all Java need to be installed on the instance, since i use a Amazon Linux 2023 based instance Java is installed with command.
``` bash
sudo dnf install java-11-amazon-corretto -y
java -version
```
Next Python and PIP are needed. Amazon Linux 2023 should come with Python 3.9 installed, verify this by running `which python3`. If Python should not be installed run:
``` bash
sudo dnf install python3.9 -y
```
Next install PIP for the corresponding Python version
``` bash
sudo dnf install python3.9-pip -y
```
Finally install AWS IoT SDK fpr Python, but before you do this ensure you have the latest version of AWS CLI installed, [follow this guide](https://docs.aws.amazon.com/cli/latest/userguide/getting-started-install.html).
``` bash
sudo pip3 install awsiotsdk --user
```
### Setup GreenGrass Core
To setup GreenGrass Core on the device navigate back to the IoT Console, select `Greengrass` and `Core devices` then click on `Set up one Greengrass core device` I give it a name and don't assign any Thing group.
The rest of the steps are in the wizard but summarized we should:
1: Download the installer
``` bash
curl -s https://d2s8p88vqu9w66.cloudfront.net/releases/greengrass-nucleus-latest.zip > greengrass-nucleus-latest.zip && unzip greengrass-nucleus-latest.zip -d GreengrassInstaller
```
2: Run installer
``` bash
sudo -E java -Droot="/greengrass/v2" -Dlog.store=FILE -jar ./GreengrassInstaller/lib/Greengrass.jar --aws-region eu-west-1 --thing-name SimulatedBBQDeviceOne --component-default-user ggc_user:ggc_group --provision true --setup-system-service true --deploy-dev-tools true
```
There should be a print in the end indicating success `Successfully set up Nucleus as a system service` and the device should now be visible in the IoT Core Console.
### Install components
Now let's install the component that is needed. Navigate to `Deployments` in the GreenGrass section of IoT Core console, and locate the Deployment for the Simulated device.
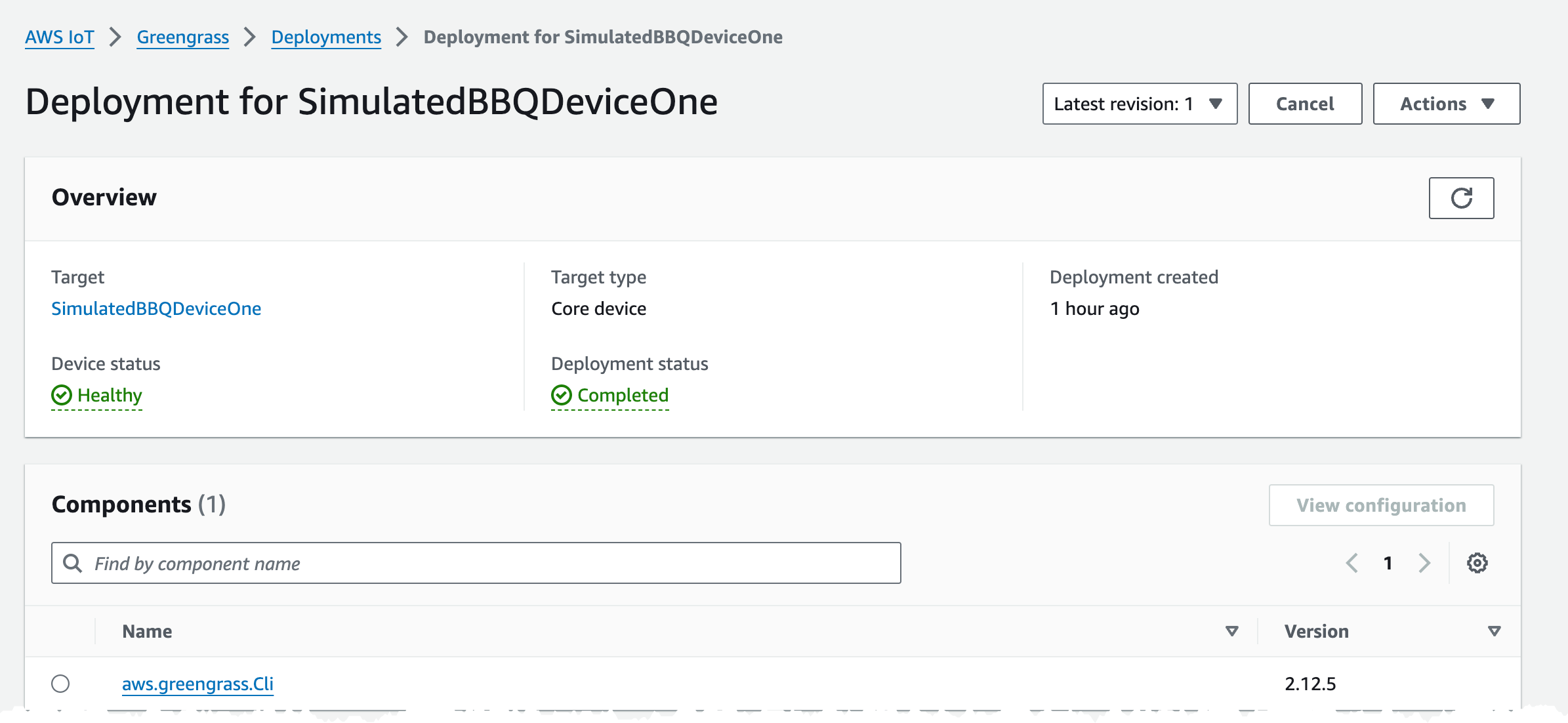
From the Actions menu select `Revise` and the `Revise Deployment` button.
Leave target as is and just click next.
Select the HelloBBQ component, LogManager, CloudWatch, and Nucleus, and click next.
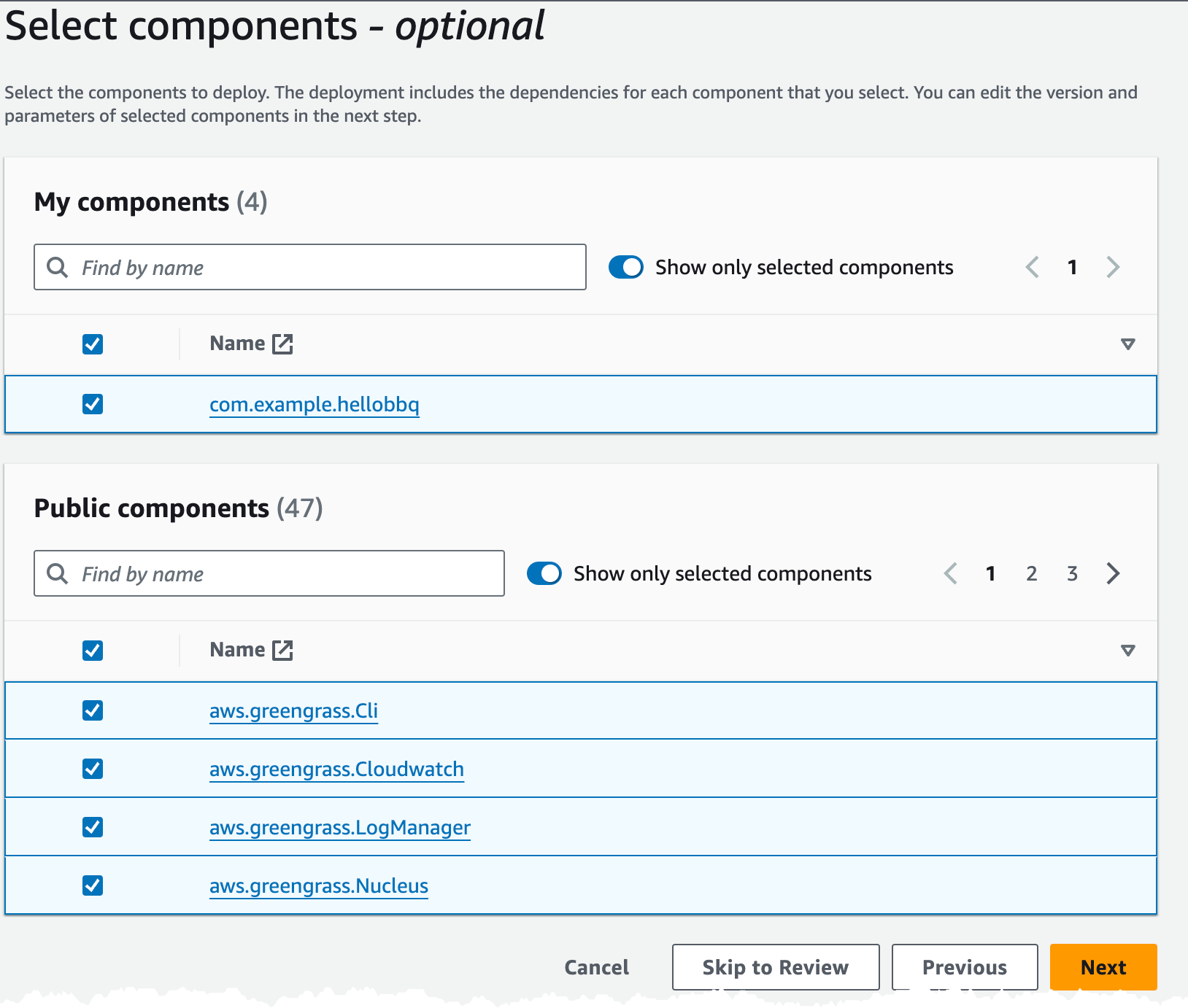
Next there is a need to configure `LogManager` and `Nucleus` components.
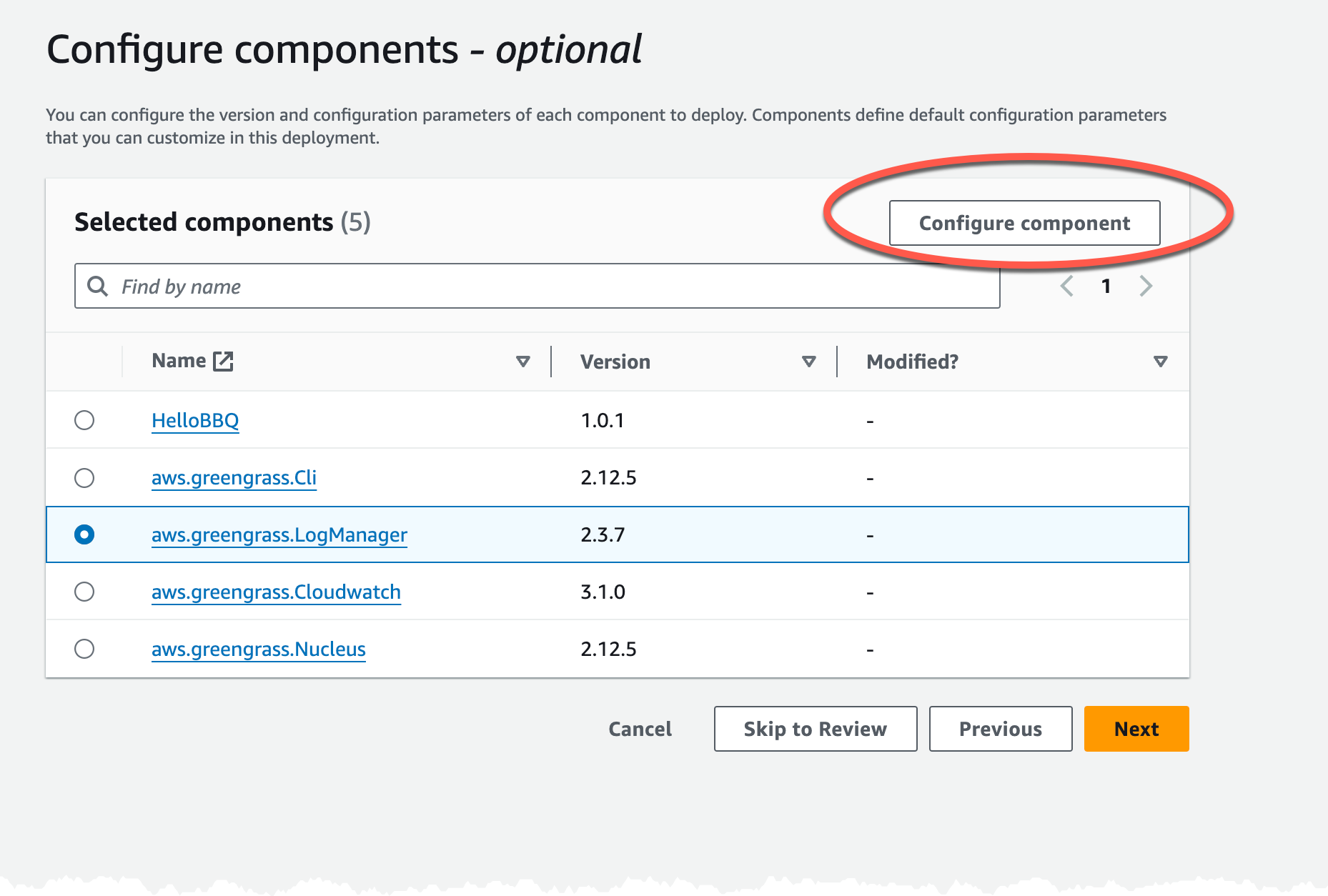
In the Configuration screen select LogManager and click Configure, add the below JSON to the merge config.
``` json
{
"logsUploaderConfiguration": {
"systemLogsConfiguration": {
"uploadToCloudWatch": "true"
},
"componentLogsConfigurationMap": {
"com.example.hellobbq": {}
}
}
}
```
Now repeat the process for `Nucleus` where we need to set `interpolateComponentConfiguration` otherwise `{iot:thingName}` will not be inflated to a proper value.
``` json
{
"reset": [],
"merge": {
"reset": [],
"merge": {
"interpolateComponentConfiguration": "true"
}
}
}
```
Now just click next in rest of the dialog and confirm the deployment to start the process.
To verify that everything now is running navigate to Core Devices, select the simulated device, and check that all components are running.
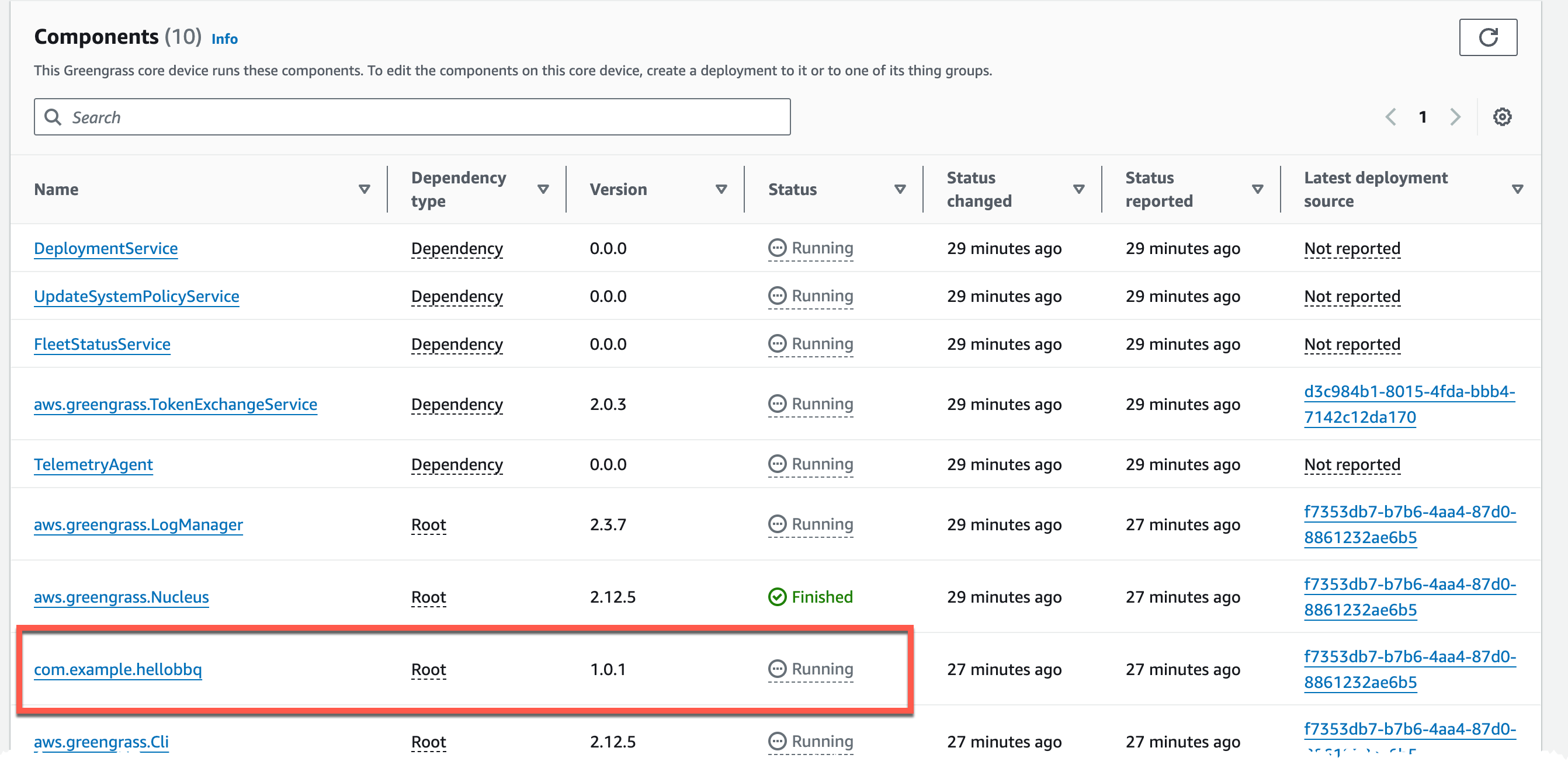
## Verify data
To verify that data is sent as expected open the MQTT test client in the console and create a subscription to `e/#`. Data should start flowing in the format we defined in the code.
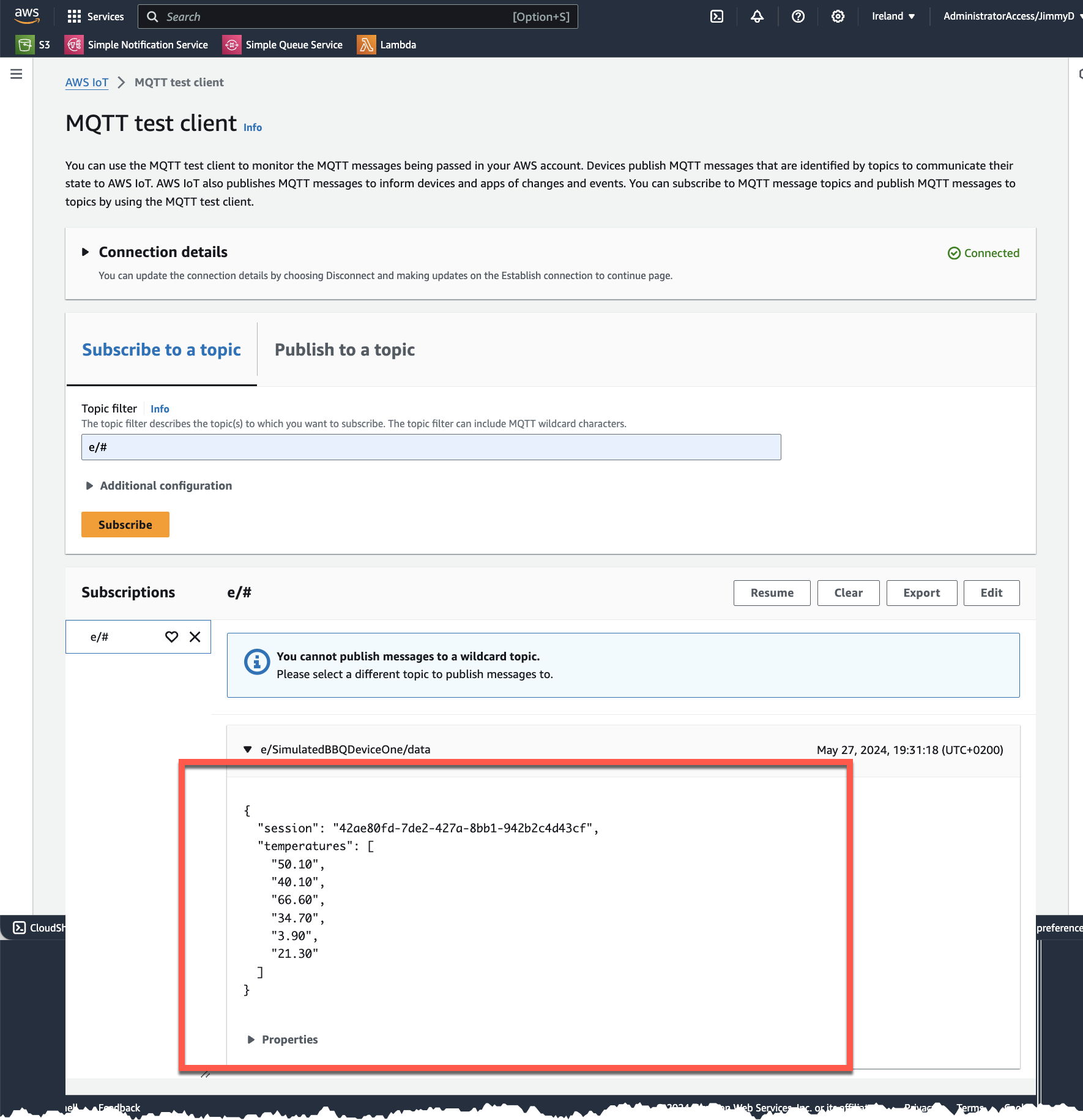
## Cloudwatch Logs
To check the logs from the device, navigate to CloudWatch Logs, there should a Log group with the component name e.g. `/aws/greengrass/UserComponent/eu-west-1/com.example.hellobbq`
## Device Logs
It's also possible to get the logs on the device it self. Connect to the instance, using Instance Connect. Logs can be found in folder `/greengrass/v2/logs`
## Final Words
This was the first part in building a connected BBQ as a SaaS solution. We looked at creating a GreenGrass Core component and device running as a simulation on an EC2 instance.
Check out [My serverless Handbook](https://serverless-handbook.com) for some of the concepts mentioned in this post.
Don't forget to follow me on [LinkedIn](https://www.linkedin.com/in/dahlqvistjimmy/) and [X](https://x.com/jimmydahlqvist) for more content, and read rest of my [Blogs](https://jimmydqv.com)
As Werner says! Now Go Build!
| jimmydqv |
1,860,194 | Testing APIs: Tools and Techniques | APIs (Application Programming Interfaces) are the backbone of modern software applications, enabling... | 0 | 2024-05-29T10:48:48 | https://dev.to/sofiamurphy/testing-apis-tools-and-techniques-58fg | api, programming, apigateway | APIs (Application Programming Interfaces) are the backbone of modern software applications, enabling different software systems to communicate with each other. Ensuring their reliability is crucial. According to a survey, over 80% of developers reported that their APIs often break due to unforeseen bugs or performance issues. This highlights the need for rigorous API testing. In this blog post, we will explore the various tools and techniques for effective API testing to help maintain robust and reliable services.
## 1. Why API Testing is Crucial
**Ensuring Reliability**
API testing ensures that endpoints function correctly, returning the expected results under various conditions. It helps catch bugs early in the development process, reducing the risk of failures in production.
**Early Bug Detection**
Detecting bugs early can save significant time and resources. Issues found during the testing phase are typically less expensive to fix than those found after deployment.
**Security Assurance**
APIs are often exposed to the internet, making them susceptible to security threats. API testing helps identify vulnerabilities, ensuring that sensitive data remains protected and unauthorized access is prevented.
## 2. Types of API Testing
**Functional Testing**
Functional testing verifies that API endpoints behave as expected. This involves checking the accuracy of responses, correct data handling, and adherence to the API contract.
**Techniques**:
- Input Validation: Ensuring the API handles valid and invalid inputs correctly.
- Response Validation: Checking if the API returns the correct data.
- Status Codes: Verifying that the correct HTTP status codes are returned for various operations.
**Performance Testing**
Performance testing assesses how the API performs under different conditions, ensuring it can handle the expected load.
**Techniques**:
- Load Testing: Simulating a high number of requests to test performance under load.
- Stress Testing: Pushing the API beyond its limits to see how it behaves under extreme conditions.
- Scalability Testing: Ensuring the API can scale with increasing user demands.
**Security Testing**
Security testing ensures the API is secure against threats. This includes testing for vulnerabilities and ensuring data protection mechanisms are in place.
**Techniques**:
- Authentication and Authorization: Verifying that only authorized users can access the API.
- Penetration Testing: Simulating attacks to identify security weaknesses.
- Data Encryption: Ensuring data is encrypted during transmission.
**Integration Testing**
Integration testing checks how the API interacts with other systems, ensuring seamless integration and data flow.
**Techniques**:
- End-to-End Testing: Verifying the entire workflow from start to finish.
- Contract Testing: Ensuring the API meets the agreed-upon contract between services.
## 3. Tools for API Testing
**Postman**
Postman is a popular tool for [API development](https://www.excellentwebworld.com/api-development-knows-what-why-how-guide/) and testing. It offers a user-friendly interface for creating and managing API requests and responses.
**Key Features**:
- Collection Management: Organize your API requests into collections for better management.
- Automated Testing: Write and automate tests for your API endpoints.
- Environment Setup: Manage different environments (e.g., development, staging) with ease.
**Example**:
Create a new request in Postman, set the URL and parameters, send the request, and verify the response. Use the Tests tab to write test scripts for automated validation.
**SoapUI**
SoapUI is a powerful tool for functional and security testing of APIs. It supports both REST and SOAP APIs.
**Key Features**:
- Functional Testing: Create comprehensive functional tests for your APIs.
- Security Testing: Perform security scans and penetration tests.
- Data-Driven Testing: Use external data sources to drive your tests.
**Example**:
Create a new SOAP project in SoapUI, define the WSDL, and generate test cases. Use the interface to add assertions and validate responses.
**JMeter**
JMeter is a performance testing tool designed to test the load and scalability of web applications, including APIs.
**Key Features**:
- Load Testing: Simulate a large number of users to test API performance.
- Stress Testing: Push the API to its limits to identify performance bottlenecks.
- Distributed Testing: Run tests across multiple machines to simulate real-world scenarios.
**Example**:
Set up a JMeter test plan with HTTP requests, configure thread groups to simulate users, and analyze the results in real-time.
**RestAssured**
RestAssured is a Java library for testing RESTful APIs. It provides a simple and expressive syntax for writing tests.
**Key Features**:
- Concise Syntax: Write clear and readable test cases.
- Integration with Testing Frameworks: Use with JUnit or TestNG for comprehensive testing.
- Supports BDD: Write behavior-driven development (BDD) tests.
**Example**:
Write a test case using RestAssured to send a GET request, validate the response status code, and check the response body content.
```java
import static io.restassured.RestAssured.*;
import static org.hamcrest.Matchers.*;
public class ApiTest {
@Test
public void testGetEndpoint() {
given()
.baseUri("https://api.example.com")
.when()
.get("/endpoint")
.then()
.statusCode(200)
.body("key", equalTo("value"));
}
}
```
**Newman**
Newman is a command-line companion for Postman, allowing you to run and automate Postman collections.
**Key Features**:
- CI/CD Integration: Easily integrate with CI/CD pipelines for automated testing.
- Command-Line Interface: Run collections directly from the command line.
- Custom Scripts: Write custom scripts for advanced testing scenarios.
**Example**:
Run a Postman collection with Newman in a CI pipeline to automate testing as part of your build process.
```bash
newman run my_collection.json -e environment.json
```
## 4. Best Practices for API Testing
**Comprehensive Test Coverage**
Ensure all API endpoints and scenarios are covered in your tests, including edge cases and error conditions.
**Mocking and Stubbing**
Use mock servers to simulate API responses, allowing you to test in isolation without depending on external services.
**Automated Testing**
Automate your tests to run regularly, especially in CI/CD pipelines, ensuring continuous validation of your API's functionality.
**Continuous Integration/Continuous Deployment (CI/CD)**
Integrate your API tests into CI/CD pipelines to catch issues early and ensure that every code change is tested before deployment.
**Environment Management**
Manage different environments (development, staging, production) to ensure your tests run accurately in each setup, avoiding environment-specific issues.
## 5. Advanced Techniques
**Contract Testing**
Contract testing ensures that different services adhere to the agreed-upon API contract. This prevents integration issues when services are updated.
**Chaos Testing**
Chaos testing involves intentionally introducing failures to see how the system responds. This helps identify weaknesses and improve resilience.
**API Fuzzing**
API fuzzing involves sending random or unexpected data to the API to discover potential vulnerabilities and edge cases that standard testing might miss.
## 6. Case Studies and Examples
**Real-World Examples**
Highlight successful API testing strategies from well-known companies. For instance, Netflix uses chaos engineering principles to ensure their APIs remain resilient under unexpected conditions.
**Sample Projects**
Provide links or descriptions of sample projects for hands-on practice. For example, create a simple REST API and write functional, performance, and security tests using the tools mentioned.
## Conclusion
API testing is a critical aspect of software development that ensures the reliability, performance, and security of your services. By using the right tools and techniques, you can catch issues early, protect sensitive data, and provide a seamless experience for your users. Start implementing these practices today to enhance your API development process. | sofiamurphy |
1,868,875 | Hybrid Mobile App Development Company Review | Hybrid mobile app development these days is in trend. Do you know why? The reason is hybrid apps are... | 0 | 2024-05-29T10:46:16 | https://dev.to/adnanali007/hybrid-mobile-app-development-company-review-1gg2 | mobileappdevelopment, companyreview, appdevelopment | Hybrid mobile app development these days is in trend. Do you know why? The reason is hybrid apps are a mixture of both native and web solutions. The core of the app needs to be written through web technologies. Today we are going to review the best hybrid app development company, but before we will learn about why it is so crucial to develop a hybrid application. Moreover, we will discuss hybrid app development for Mobile. Before we dive into the review of an ultimate hybrid app development company review, let's discuss a little about hybrid apps.
## **hybrid mobile app development VS Native**
Before hiring a [hybrid mobile app development company](https://allzonetech.com/hybrid-mobile-app-development-company/) you should know it will take time and a significant amount of money. Therefore, before you choose a solution, it is crucial to select native or hybrid apps as your first choice. It is crucial to pick the perfect solution for your mobile application following the complexity of your project, timeline, target audience, and budget.
**
## The Main Difference: Native VS Hybrid**
As far as Native applications are concerned it is developed for particular platforms, like Android, and iOS. So, the developers have to write code using programming languages that are compatible with the operating system. Moreover, native apps get access to the native device features to make it effortless for developers to ensure high-performance and security.
However, hybrid mobile app development empowers you to craft code once and then allows you to deploy the application on multiple platforms, like iOS, android, and Windows. For more flexibility, developers can use frameworks and programming languages. It only requires crafting a large but single codebase to make it compatible with major operating systems.
## **Advantages of Hybrid Mobile App Development**
Here are the following advantages of hybrid mobile application development that you need to know to make a perfect decision:
**Easy to Develop**
Hybrid app development is easy to develop compared to the Native. The developer only needs to craft code for the application. There is no need to learn multiple programming languages. These apps are easy to develop with HTML, JavaScript, and CSS. Also, they can use frameworks, like Flutter, React Native, Xamarin, and others.
**Less time to market**
Hybrid mobile app development allows you to use existing tools to craft code for apps. There is no need to use the advanced technologies that force you to hire developers.
**Multiple Platform Compatibility**
A hybrid mobile application development company can provide compatibility with multiple platforms. Developers can craft code for one time, and then run it on different platforms.
**Easy to scale**
You know scalability is crucial in app development. So, applications with scalability empower reliability, security, and flexibility. So, developers can add more features to it.
**Budget-Friendly**
Application development costs are on the rise. The process consists of Kit, developers, time, testing, and building native apps for multiple platforms. Therefore, hybrid puts your worries to rest having a single large code for cross-platforms.
**User-experience**
Hybrid application development empowers to use of design elements on multiple operating systems. Users from every platform will have the best user experience. It is best for building brand image.
**Easy to Maintain**
The best thing about hybrid application development is it helps to maintain app code. So, developers will need not to work on multiple codes. All they need to do is to work on a single back-end and update apps on all platforms.
## **Best Hybrid Mobile Application Development Company**
AllZone Technologies is the best hybrid mobile app development company. It is particularly known for its software development and consultancy services. Looking for software application development, like Android app development, iOS application development, and hybrid applications? Look no further than AllZone Technologies. The company also outsources senior, junior, and mid-level software developers.
## **
Top Notch AllZone Technologies Services **
Here are the following services that AllZone Technologies offers to their clients. However, it offers consultancy for free:
Enterprise Software Development
Hybrid Mobile App Development
Custom iOS app development
Custom Android App Development
IoT Software Development
AI Development Services
DevOps
Data and Analytics
AllZone Technologies App Development Across Industries
The company is known for developing applications for startups, and enterprises across industries. Here are the following industries companies offering services for hybrid mobile app development:
Fintech
Insurance
eCommerce
eLearning
Tourism
Healthcare
**
## Technology Stacks AllZone Technologies for Hybrid Mobile App Development
**
Unlock the potential of hybrid mobile app development with AllZone Technologies' dynamic technology stacks. Powered by leading frameworks and expertly crafted using languages like JavaScript, HTML, and CSS, our solutions promise seamless cross-platform performance for a superior user experience. Elevate your app with our programming expertise.
## **conclusion**
[AllZone Technologies] (https://allzonetech.com/) stands out as the premier hybrid mobile app development company, offering efficient solutions with easy development, budget-friendly options, scalability, and an unparalleled user experience. Elevate your app with our top-notch services and dynamic technology stacks.
| adnanali007 |
1,868,874 | Demo | A post by Seyed Ali | 0 | 2024-05-29T10:44:41 | https://dev.to/seyedali/demo-3n68 | seyedali | ||
1,868,873 | Staff Training and Development in Sports Facility Management | Aging ballparks and stadiums face numerous challenges when it comes to business continuity and... | 0 | 2024-05-29T10:44:00 | https://dev.to/arcfacilities/staff-training-and-development-in-sports-facility-management-5d2a | facilitymanagementsoftware, sportsfacilitymanagement | Aging ballparks and stadiums face numerous challenges when it comes to business continuity and safety. Deferred maintenance issues and labor shortages further increase the chances of accidents and crises. To address these challenges, instant access to building information is essential for significantly increasing the productivity of facilities teams. [Sports facility management](https://www.arcfacilities.com/blog/inside-the-world-of-sports-facility-management) software has emerged as a crucial asset for facilities management teams, helping to streamline workflows and reduce the occurrence of facility issues.
## Lack of Access to Building Information: A Major Impediment
One often overlooked problem is the lack of access to building information for sports facility management teams in the field. Whether managing a football, baseball, basketball, soccer, or hockey facility, teams spend hours searching for building information, which significantly reduces the number of jobs they can complete in a day and creates a backlog of maintenance tasks. Smart building technology can solve this problem immediately, creating efficiencies for sports stadium facility management teams.
## Address Deferred Maintenance Challenges
Issues like stadium seating, faulty electrical panels, and leaky pipes, while seemingly simple, can compromise public safety if neglected. These infrastructure problems increase risks for stadium owners or operators. Instant access to operations and maintenance manuals and building plans, accessible from a mobile device in the field, allows facility management technicians to address these problems efficiently, enabling them to complete more work orders in a day.
## Emergency and Life Safety Teams
In emergencies caused by natural disasters, fires, or explosions, instant access to stadium information can be invaluable for first responders and emergency and life safety teams. Having critical emergency information available on mobile devices allows for efficient operation and information sharing with other public safety constituents.
## Preserving Historical Information
When senior engineers and technicians retire or leave sports facilities, valuable historical information is often lost. This loss of knowledge slows down teams and presents a significant challenge for onboarding new employees. Sports [facility management software](https://www.arcfacilities.com/) helps capture historical information and store data in the cloud, ensuring easy access within seconds from a mobile device. This guarantees that facility owners and operators retain complete custody of all stadium information, both current and historical.
## Universal Need for Building Information
Facility management teams, whether involved in emergency and life safety, security, custodial work, or capital projects, will eventually require building information such as as-builts and closeouts to complete their tasks. The inability to access the necessary building information promptly often slows down the entire team. Smart building technology enables facilities teams to organize, streamline, and store all information in a single location, providing everyone with instant access to the required building information.
## Boosting Team Productivity
Empowering your team with facilities-focused software can significantly enhance productivity. Such software allows teams to complete more work orders, improve building safety, and capture legacy document knowledge that might otherwise be lost when key individuals retire. The software integrates seamlessly with mobile devices, making it easy for teams to access critical data and complete their tasks efficiently.
## Real-Time Information Sharing
The ability to share crucial building data in real-time is another key benefit of sports facility management software. Facility teams, first responders, and other relevant personnel can easily share important information, ensuring everyone is informed and operations run smoothly.
## Quick Access to Project Closeout Data
Instant access to project closeouts is another advantage of using sports facility management software. By providing easy access to project closeout data, the software ensures that facility management teams can complete their tasks without delays.
## Conclusion
Sports facility management software offers numerous benefits for stadium facilities. By providing instant access to all necessary documents through a user-friendly app, facility management teams can overcome challenges that previously hampered productivity. Whether it's accessing stadium maps, emergency response plans, operation and maintenance manuals, or project closeout data, smart building software ensures that all this information is readily available in real-time via mobile devices. This not only enhances the efficiency and safety of sports facilities but also ensures that valuable historical knowledge is preserved and easily accessible for future use. | arcfacilities |
1,867,926 | Custom components in CompuSoft's Composer | Composer is CompuSoft's product for easily creating emails related to bookings, invoices and whatever... | 0 | 2024-05-29T10:43:15 | https://dev.to/hartviglarsen/custom-components-in-compusofts-composer-1h1k | compusoft, automation, email | Composer is CompuSoft's product for easily creating emails related to bookings, invoices and whatever else you might have used and/or is currently using emails for.
Composer is included in your subscription and can be access in CompuSuite by going to Settings -> Document Templates -> [Composer](https://compusuite.dk/document-templates/composer).
The article will assume you have some knowledge of Composer or similar email builders.
## Components to the rescue
Once you get started (and hooked) on using the Composer you will quickly find that some items are often repeated in your emails, such various branding visuals, buttons and text.
To make it easier for you to reuse items the Composer allows you to create custom _components_. Components are essentially just "blocks" that can be dragged and dropped into your other emails*, thus giving you the option for better reusability.
\* The template/markup for your email in Composer is often referred to as a "form".
## Creating components for better reusability
The example below will use a _Branding header_ as an example component. When inserted into Composer forms it will display a company logo along with the customer's name (the customer being the individual eventually receiving an email using this form).
**1** Go to Composer in CompuSuite and click _+ Create new_
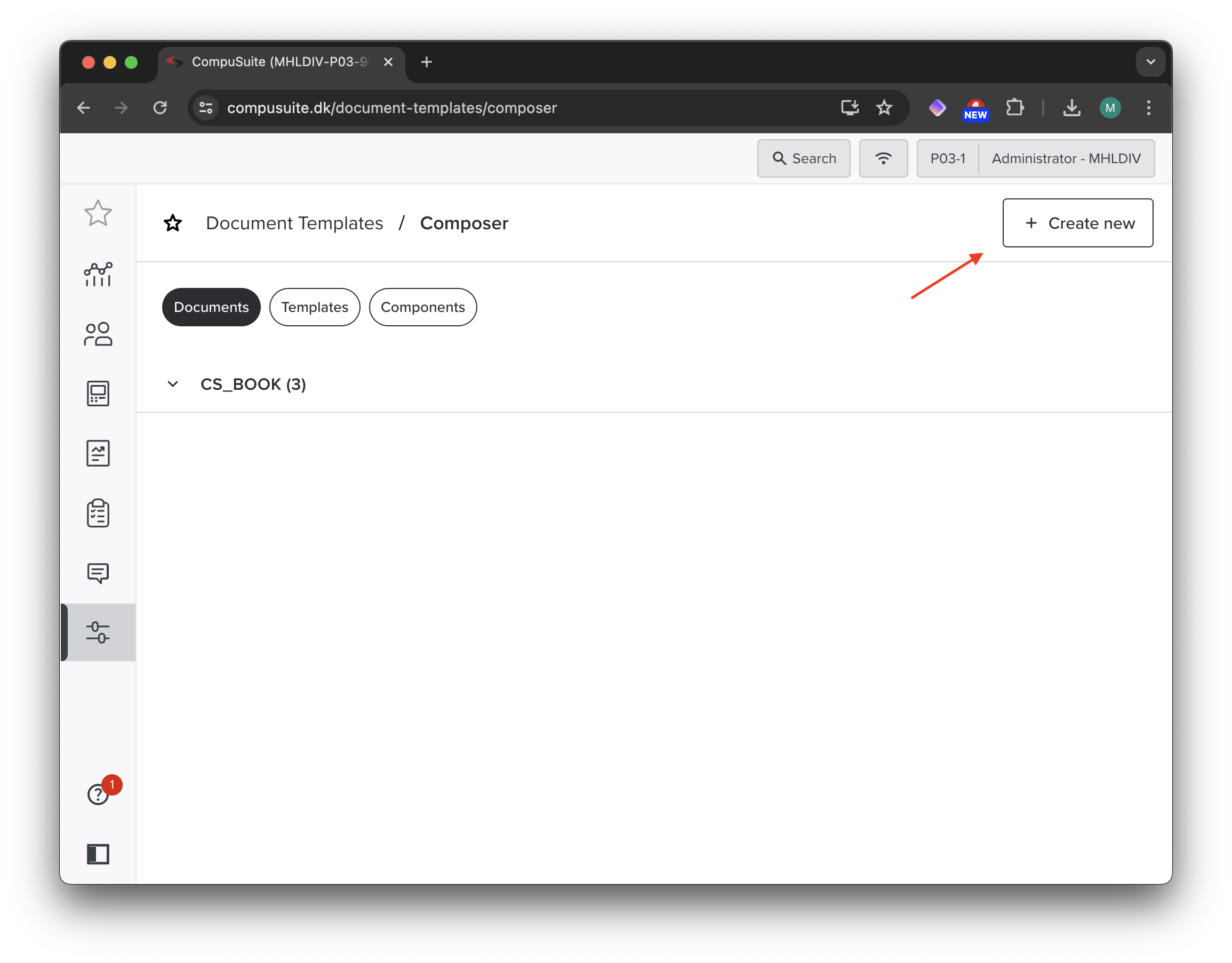
**2** You will have the option to choose from a template. Templates will be covered in a later post. For now simply click on _Empty document_
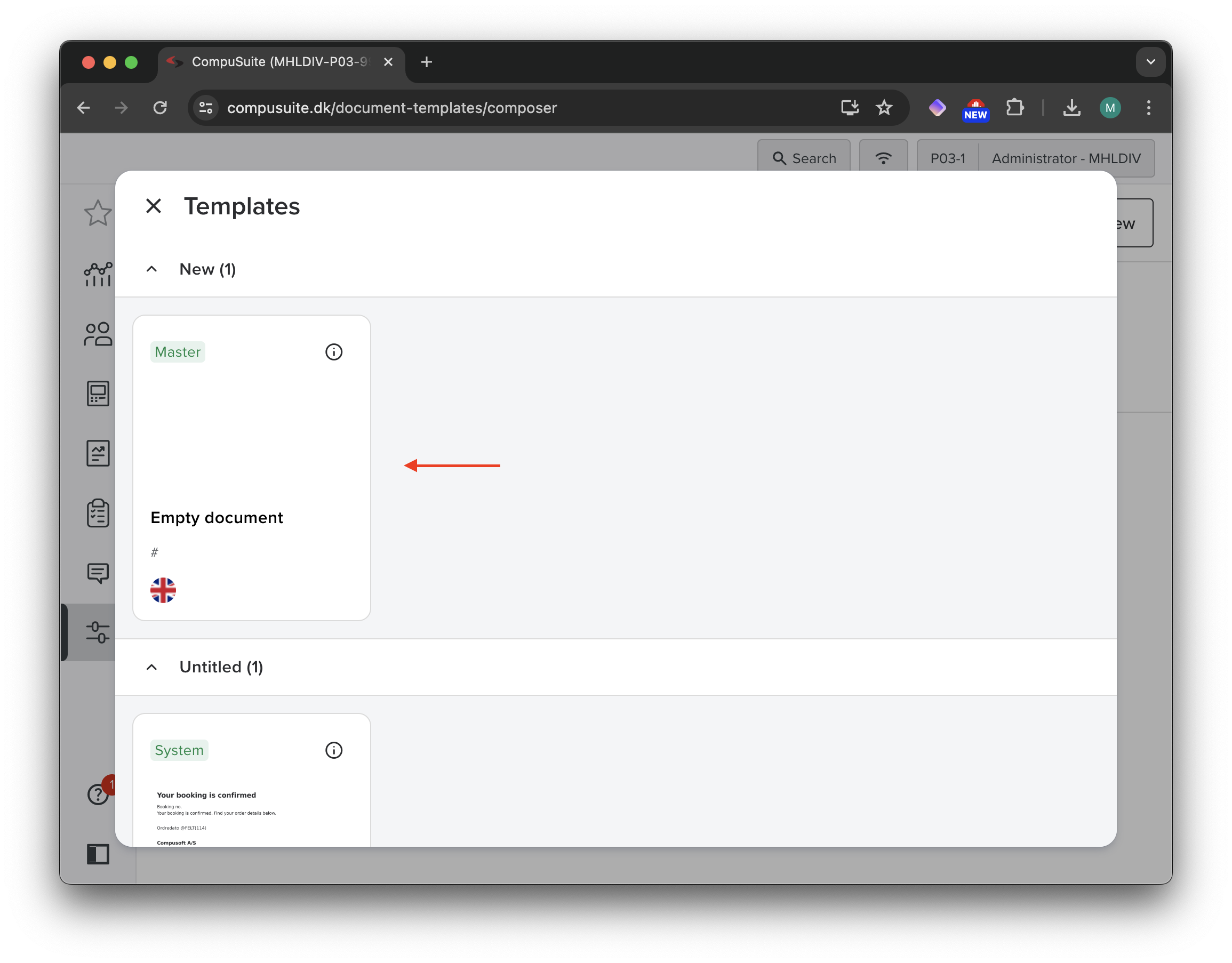
**3** You will now have a new, unsaved Composer form. Click on _Settings_ in the top left and provide a name for the new component
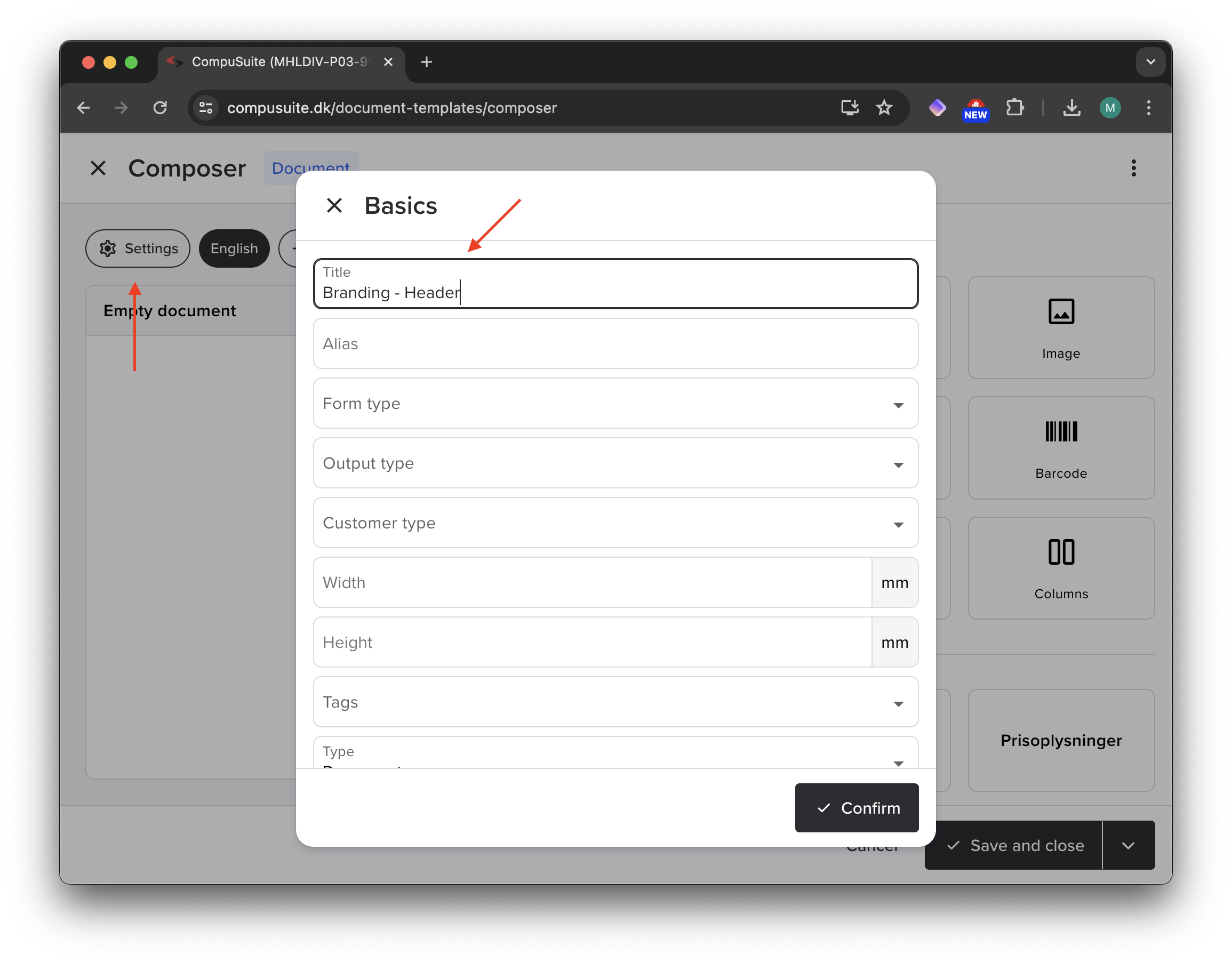
**4** Insert an _image_ and _text_ block by clicking on them and provide whichever information your would like
Notice how the text on the image says `{{ "Hej" | translate:6249 }} {{ Customer.Name }}`. Composer supports a template language called Liquid, which will be covered in depth in another post.
`{{ "Hej" | translate:6249 }}` will insert the translation item with the given id (6249) from the CompuSuite [translator](https://compusuite.dk/translator) library, making sure the text is always translated correctly for the customer's local language.
`{{ Customer.Name }}` will insert the name of the customer when the email is sent.
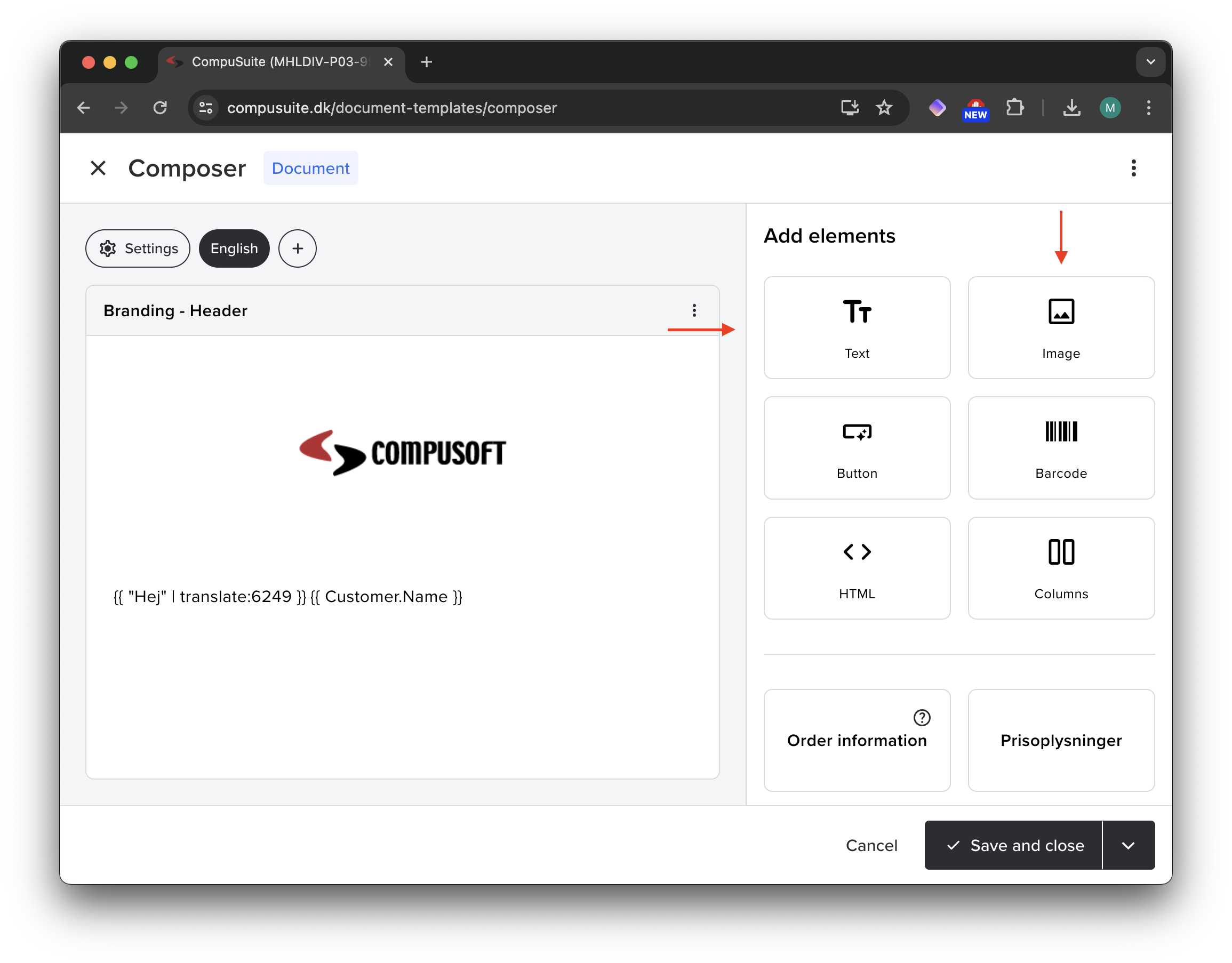
**5** Click _Save and Close_ in the bottom right, set the type to _Component_ and click _Save_
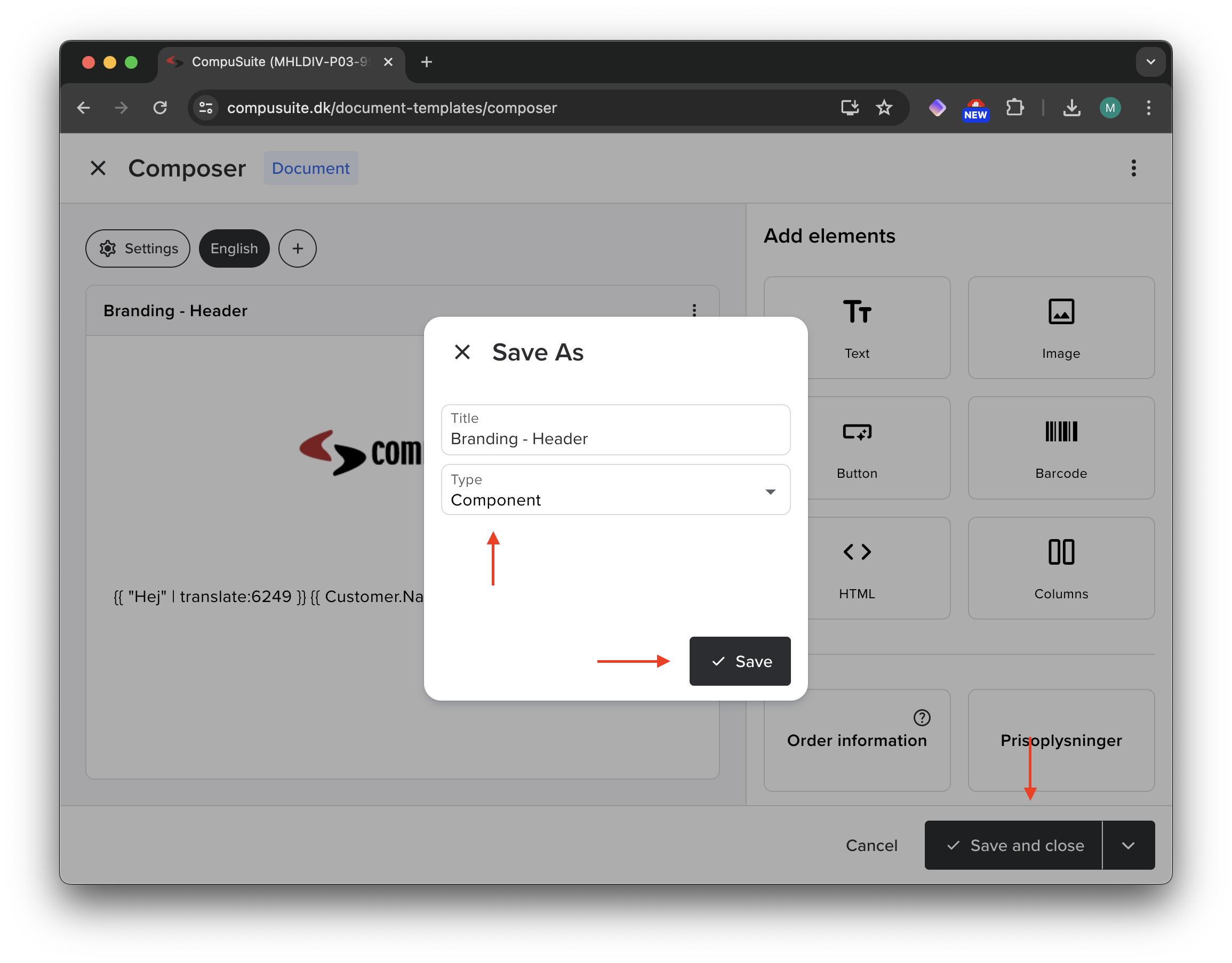
**6** Components can be found under _Components_ on the Composer page, including built-in components provided by CompuSoft.
Note that you can only edit your own components.
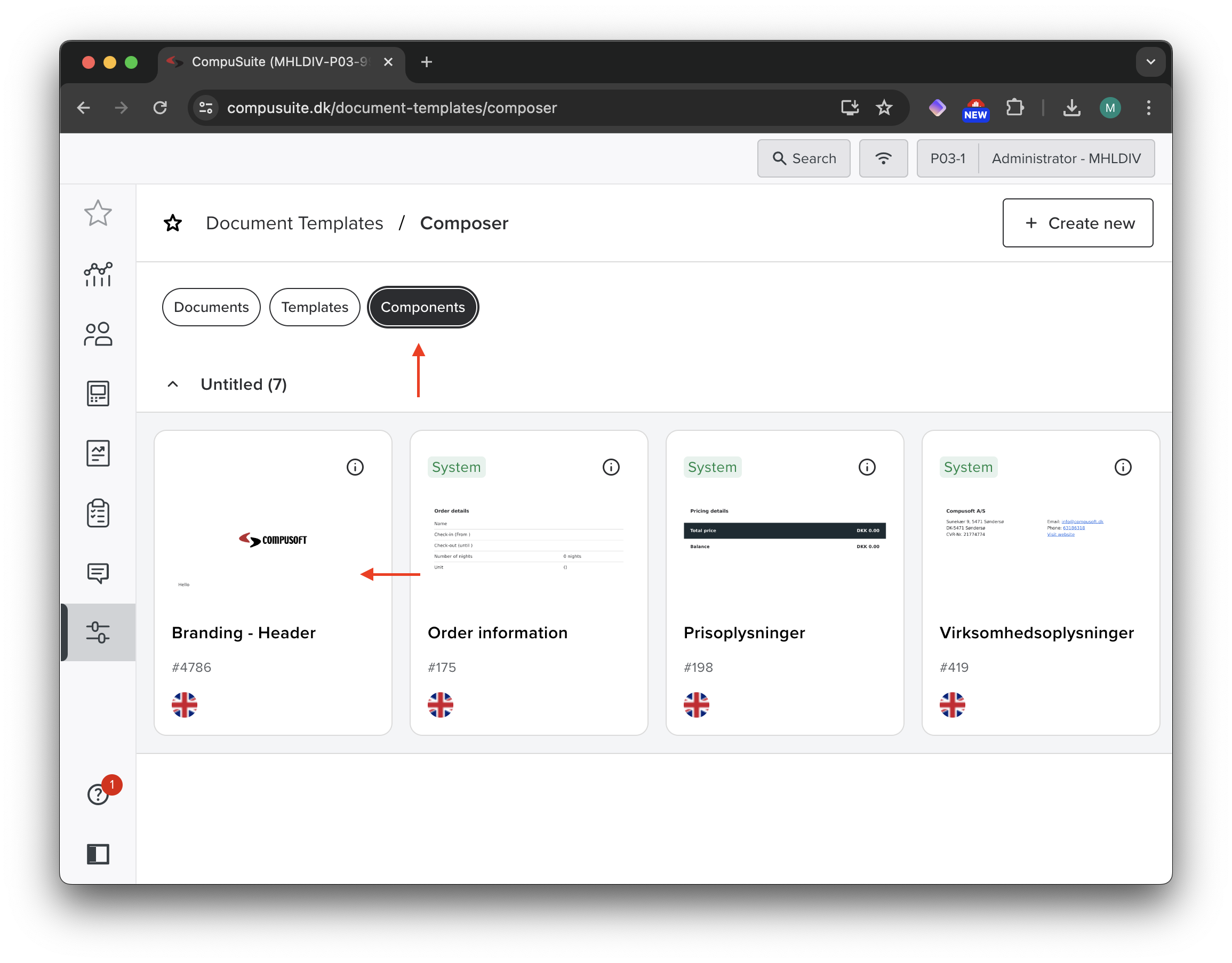
## Using your custom component in an email
With a component created it is time to insert it into an email.
**1** Go to the Composer page in CompuSuite and create a new empty form just like in the previous step 1
**2** Looking at the components available to the right you will see _Branding - Header_, which can be inserted by clicking on it
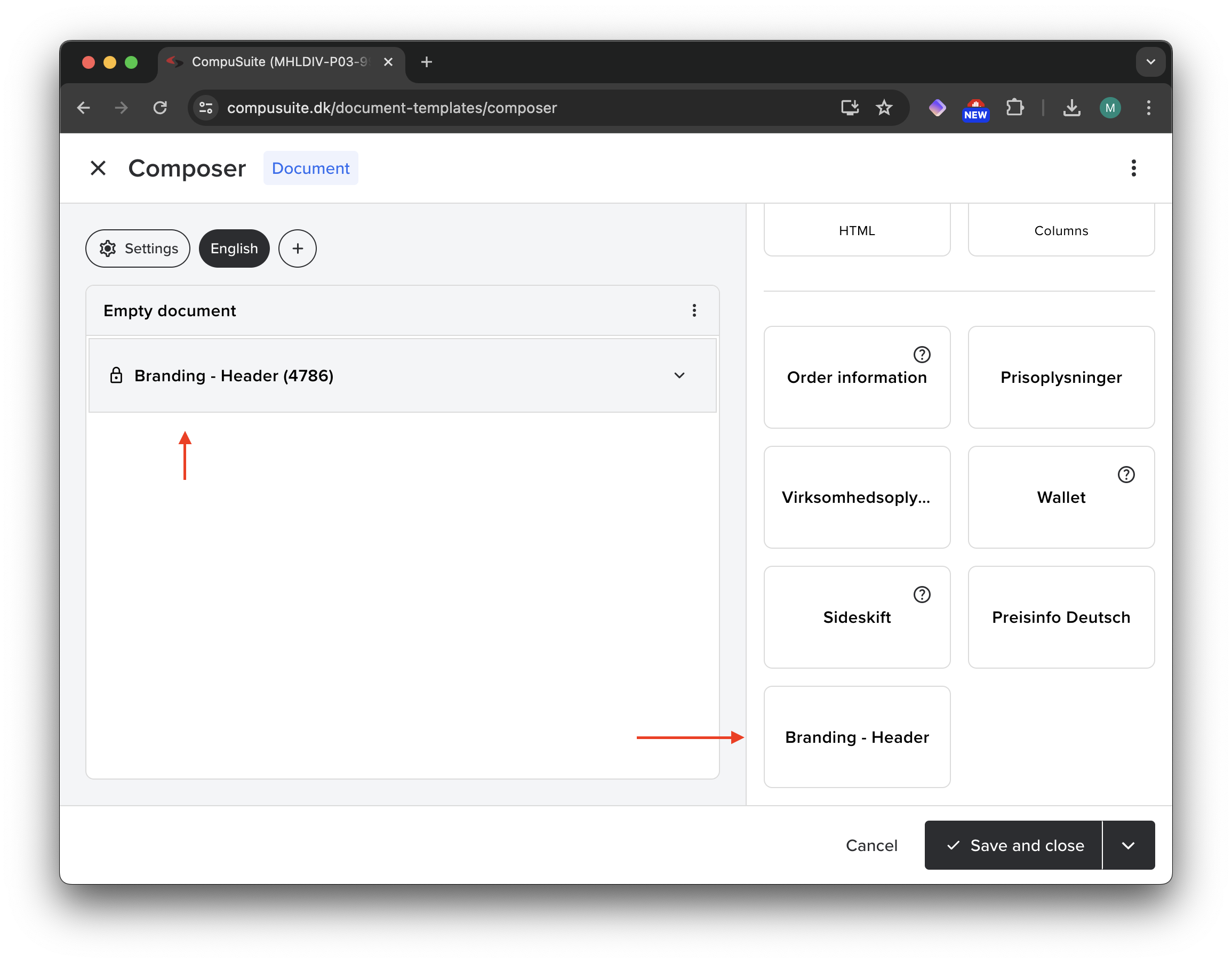
**3** You can expand the component to see the contents of it by toggling the arrow
Note that some information (such as `{{ Customer.Name }}`) will not be visible in the editor as the information is not available at this level.
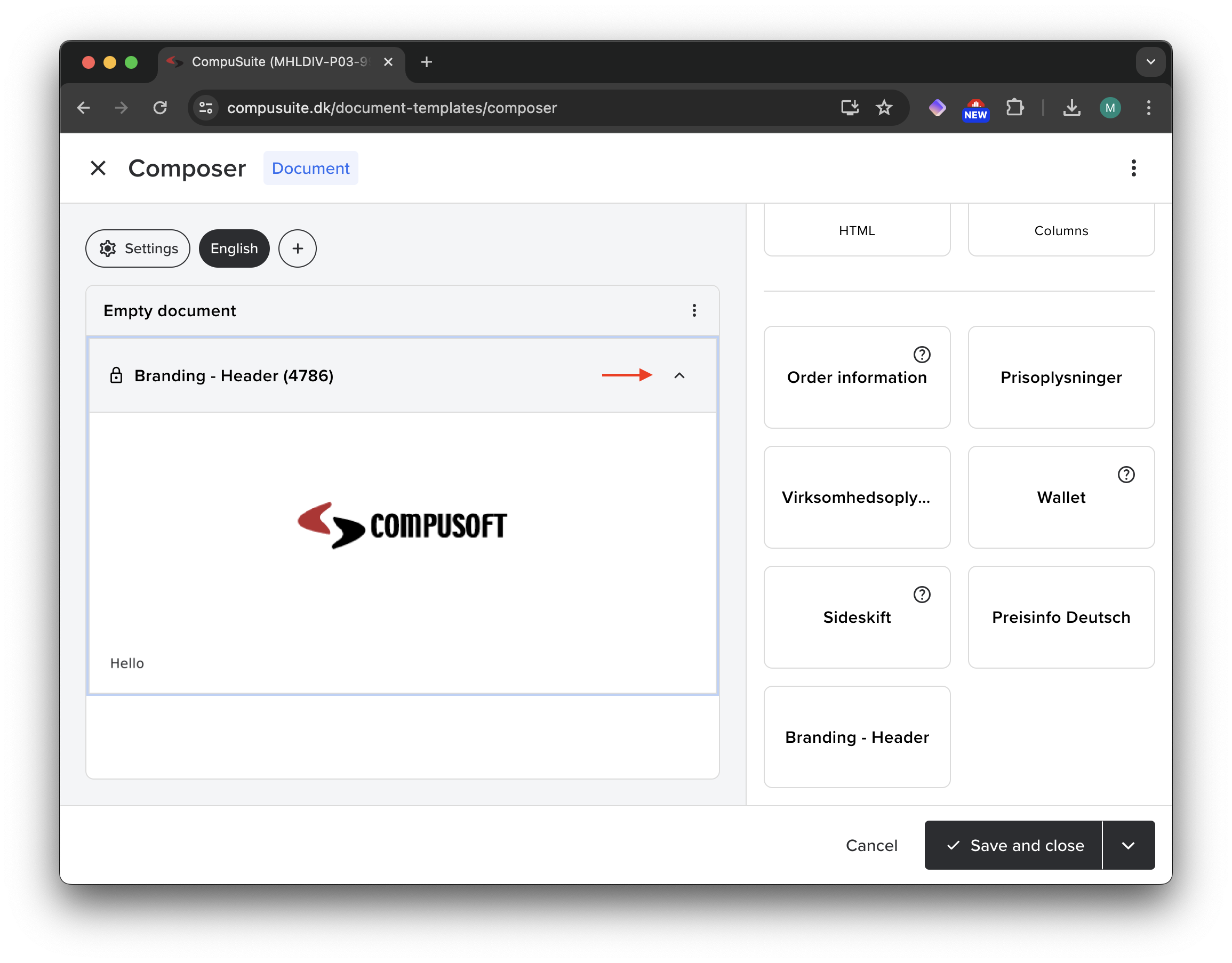
**4** Clicking the three dots followed by _Preview_ will allow you to preview the form
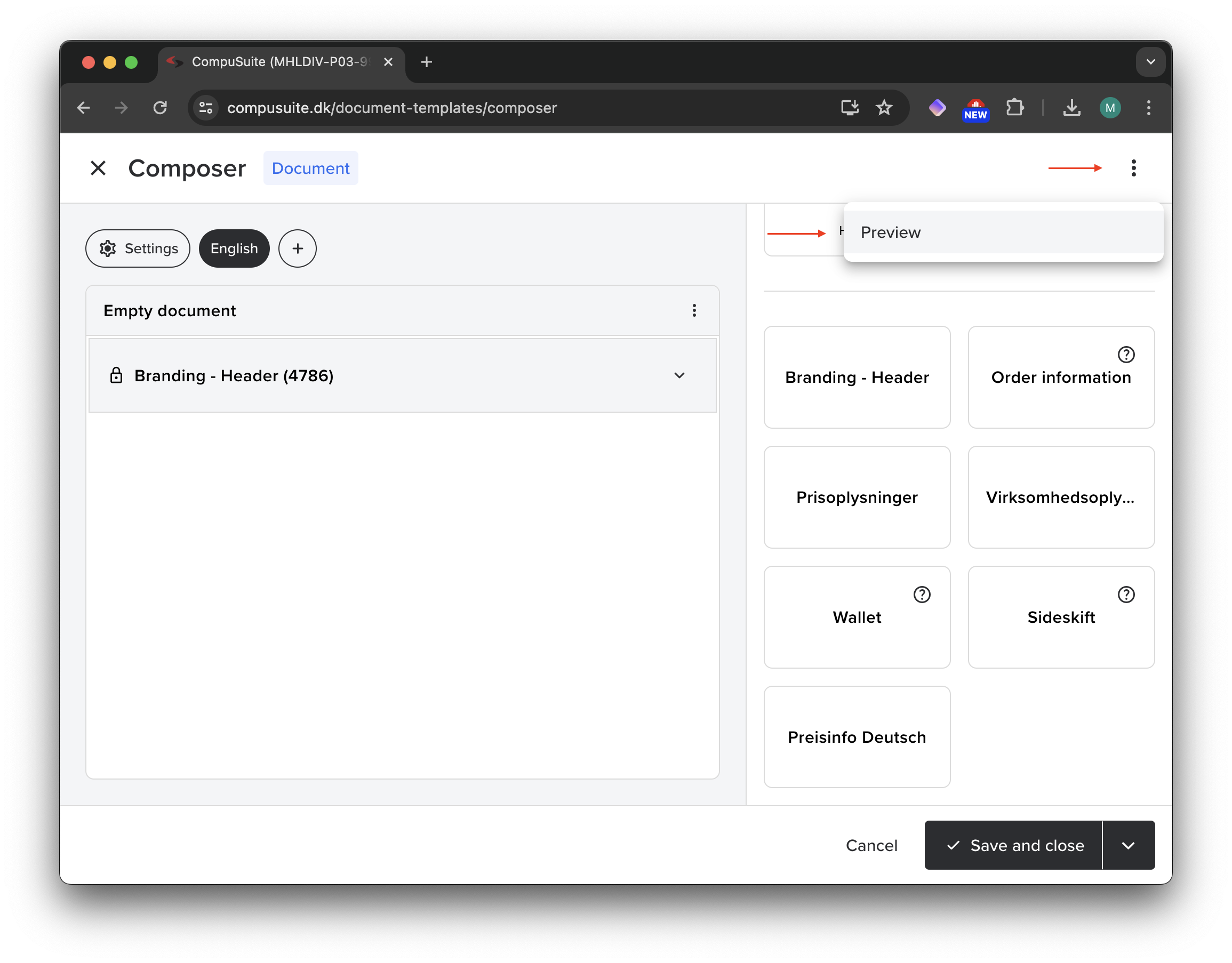
**5** On the right-hand side you can select a customer to preview the form as
Notice how the customer's name is inserted correctly in the component.
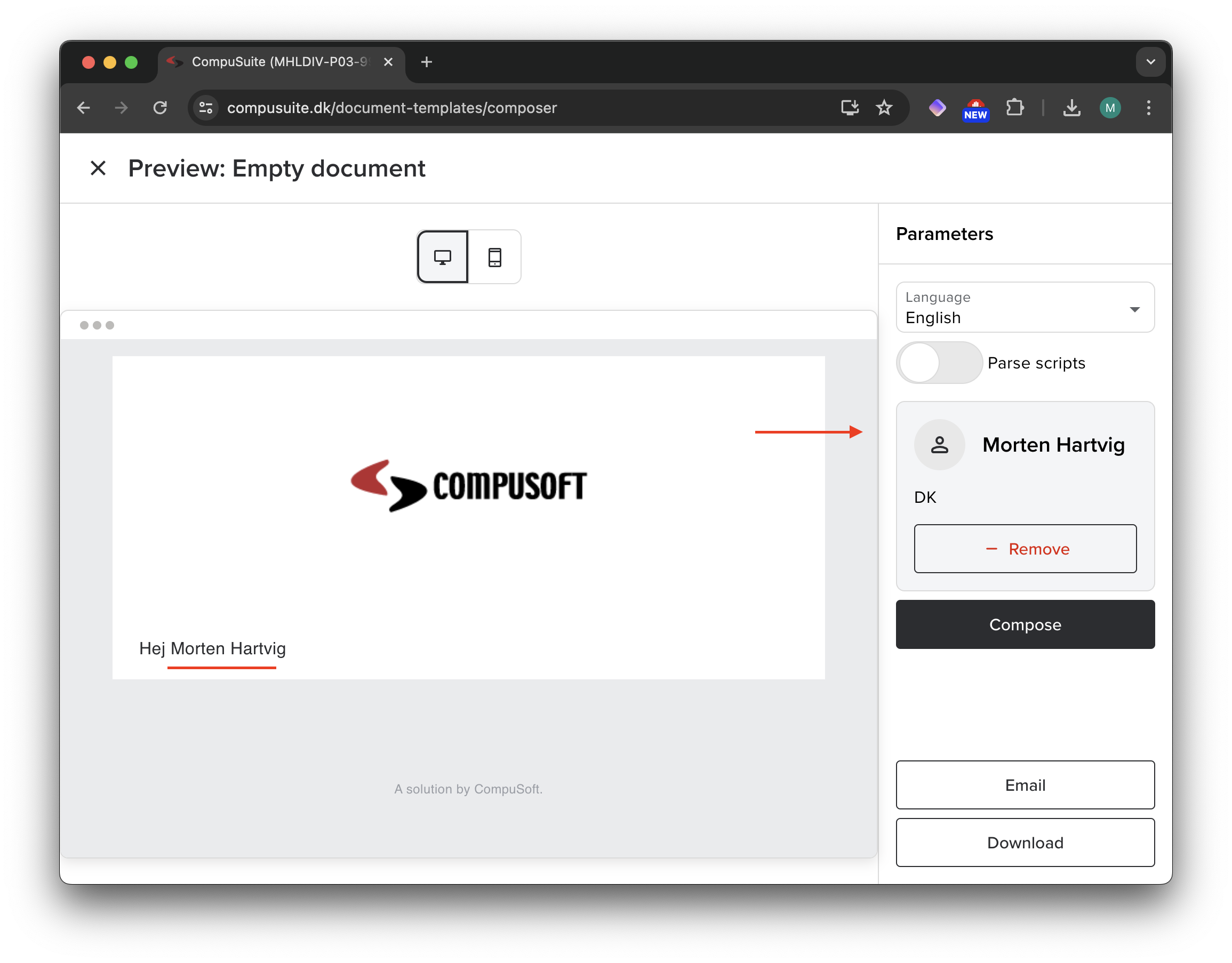
Your new component can be inserted into any new Composer email and will make it a lot easier to reuse the (in this case) branding for the header of the email :)
| hartviglarsen |
1,868,872 | Abhyanga – Ayurvedic Oil Massage | The body of one who uses oil massage regularly does not become affected much even if subjected to... | 0 | 2024-05-29T10:42:29 | https://dev.to/kavita_sharma_/abhyanga-ayurvedic-oil-massage-5dj2 | The body of one who uses oil massage regularly does not become affected much even if subjected to accidental injuries, or strenuous work. By using oil massage daily, a person is endowed with pleasant touch, trimmed body parts and becomes strong, charming and least affected by old age.
Charaka Samhita Vol. 1, V: 88-89
Abhyangais the anointing of the body with oil. Often medicated and usually warm, the oil is massaged into the entire body before bathing. For thousands of years people have used abhyanga to maintain health, benefit sleep patterns, increase longevity. It has also been used as a medicine for certain disorders. Abhyangacan be incorporated into a routine appropriate for almost anyone.
The Sanskrit word sneha can be translated as both “oil” and “love”. It is believed that the effects of abhyanga are similar to those received when one is saturated with love. Like the experience of being loved, abhyanga can give a deep feeling of stability and warmth. Sneha is subtle; this allows the oil/love to pass through minute channels in the body and penetrate deep layers of tissue.
In Ayurveda, it is believed that there are seven layers of tissue in the body (called dhatus). Each successive layer is more concentrated and life-giving. For sneha to reach the deepest layer, it is believed that it must be massaged into the body for 800 matras, roughly five minutes. To give this kind of attention to your entire body, you may need about fifteen-minutes. Considering the benefits that have been gained by people for thousands of years, fifteen-minutes per day is a minimal amount of time.
Benefits of Abhyanga (applying oil to the body)
(Outlined in: Charaka Samhita, Sushruta Samhita and Ashtanga Hrdayam)
Benefits of applying oil to the body (Abhyanga):
Produces softness, strength and color to the body
Decreases the effects of aging
Bestows good vision
Nourishes the body
Increases longevity
Benefits sleep patterns
Benefits skin
Strengthens the body’s tolerance
Imparts a firmness to the limbs
Imparts tone and vigor to the dhatus (tissues) of the body
Stimulates the internal organs of the body, including circulation
Pacifies Vata and Pitta and Harmonizes Pitta
Benefits of applying oil to the scalp (Murdha taila):
Makes hair grow luxuriantly, thick, soft and glossy
Soothes and invigorates the sense organs
Removes facial wrinkles
Benefits of applying oil to the ears (Karna purna):
Benefits disorders in the ear which are due to increased Vata
Benefits stiff neck
Benefits stiffness in the jaw
Benefits of applying oil to the feet (Padaghata):
Coarseness, stiffness, roughness, fatigue and numbness of the feet are alleviated
Strength and firmness of the feet is attained
Vision is enhanced
Vata is pacified
Sciatica is benefited
Local veins and ligaments are benefited
Sneha (oil) affused [sic] on the human organism imparts a tone and vigor to its root-principles (Dhatus), in the same manner as water furnishes the roots of a tree or a plant with the necessary nutritive elements, and fosters its growth, when poured into the soil where it grows. The use of sneha at a bath causes the sneha to penetrate into the system through the mouths of the veins (siras) and the ducts (dhamanis) of the body, as also through the roots of the hair, and thus soothes and invigorates the body with its own essence.
Under the circumstances, affusions [sic] and anointments of the body with oil or clarified butter should be prescribed by an intelligent person with due regard to one’s habit, congeniality and temperament and to the climate and the season of the year as well as to the preponderance of the deranged Dosha or Doshas in one’s physical constitution.
Sushruta Samhita, Vol.2, ch24:21
These passages make it clear that we should consider our Prakriti (constitution), Vikriti (current condition) and our external environment in deciding which oils are best for us and how often we should perform abhyanga.
Ayurvedic literature states that it is beneficial to follow a Vata-pacifying abhyanga if your Vata is currently high or it is the dominant dosha in your Prakriti. The same holds true for Pitta and Kapha. (You can take the Prakritiand/or Vikrititests if you would like to determine these conditions).
If you have more than one dominant dosha in your Prakriti, you will want to pacify doshas according to season. If you are a Pitta-Kapha combination, pacify Pitta during the warm weather and Kapha during the cold weather. If you are a Pitta-Vata combination, pacify Pitta during the warm weather and Vata during the cold weather. If you are a Vata-Kapha combination, pacify Vata during cold or dry weather and during the change of seasons and pacify Kapha during cold or wet weather. More extensive guidelines for each dosha are outlined below.
Vata Pacifying Abhyanga
The primary
qualities of vata are dry, light, cool, rough, subtle and mobile. Most of these qualities are opposite to those of oil. This is why warm oil is especially good for pacifying vata.
If your vata is high, either in your Prakriti or Vikriti, doing abhyanga daily can be highly beneficial, even life-changing. Sushruta says, “The deranged vayu [vata] of the body is restored to its normal condition by the help of Udvartana (massage).” (Sushruta Vol.2, 24:28) Just be sure to do the abhyanga in a warm place and avoid getting chilled afterwards.
Types of Oil That Are Best for Vata:
Sesameis considered to be the “king of oils;” it is the preferred choice of oil for vata because it is inherently warming. If possible, use an untoasted, organic sesame oil. Almond oiland mustard oil are also good choices because they too are warming. You may also consider using Vata Massage Oil, especially if vata is high in your Vikriti. The herbs that have been chosen for this formula enhance the vata-pacifying qualities of sesame oil. Vata massage oil can be used alone or added to sesame, almond or mustard oils.
For increasing strength and stamina Ashwagandha Oil or Ashwagandha/Bala Oilsmay be the best for you.
Mahanarayan Oilis made from over 30 Ayurvedic herbs and is traditionally used for joint pain or weakness. If you warm it, massage it into the affected joints or muscles and proceed with your regular abhyanga, it can be fabulously beneficial. Following this with a warm bath of 1/3 c baking soda and 1/3 cup ginger powder can further enhance the effects.
Pitta Pacifying Abhyanga
The primary qualities of Pitta are: oily, sharp, hot, light, fleshy-smelling, spreading and liquid. Since Pitta and oil share a number of qualities it is ideal to use medicated oil when you are trying to reduce Pitta symptoms (such as: skin irritations, rashes, itchiness). The addition of herbs enhances the Pitta pacifying properties of the oil.
Types of Oil That Are Best for Pitta:
Applying Bhringaraj Oilor Brahmi Oilto the scalp and soles of feet at bedtime may reduce pitta and encourage sound sleep. If you don’t have medicated oils, use sunfloweror coconut oilfor your abhyanga. If you spend a lot of time in the sun, you may wish to add some Neem Oilto whatever your basic abhyanga oil is, because it is said to reduce pitta in the skin. Pitta Massage Oilmay also may be a great choice.
It’s simple to do abhyanga, just gently heat the oil for your body and make sure that the oil you apply to your head is cooler, especially in the summer.
Kapha Pacifying Abhyanga
Sushruta says that massage “reduces the fat and the aggravated Kapha of the system, smoothes and cleanses the skin and imparts a firmness to the limbs.” (Sushruta Vol.2, 24:28) “Anointing the body (with oil) imparts a glossy softness to the skin, guards against the aggravation of the Vata and the Kapha, improves the color and strength and gives a tone to the root-principles (tissues) of the body.” (Sushruta Samhita, Vol.2, ch24:15-17)
The main qualities of Kapha are unctuous, cool, heavy, slow, smooth, soft and static. Kapha and oil share most qualities. Because like increases like, using oil, especially cool oil, may increase Kapha rather than decrease it. However, because oil has the ability to absorb the qualities of substances it is prepared with, appropriate herbal oils can decrease Kapha.
Types of Oil That Are Best for Kapha:
Abhyangawith warm oil is best for kapha. While sesame, corn and mustard oils are all helpful because they are warming, herbal oils are an even better choice for Kapha, as they add more Kapha pacifying properties to the oil. Kapha Massage Oilis a good choice for general use. (If you are using sesame oil, opt for untoasted sesame oil; toasted is more expensive and has a very strong natural scent).
Abhyanga Routine
By using oil massage daily, a person is endowed with pleasanttouch, trimmed body parts and becomes strong, charming andleast affected by old age. Charaka Samhita Vol. 1, V: 88-89
Put about cup oil in an 8 oz. squeeze bottle. Make sure the oil is not rancid.
Place the bottle of oil in a pan of hot water until the oil is pleasantly warm
Sit or stand comfortably in a warm room, on a towel that you don’t mind ruining with oil accumulation. Make sure you’re protected from any wind.
Apply the oil to your entire body.
Massage the oil into your entire body, beginning at the extremities and working toward the middle of the body. Use long strokes on the limbs and circular strokes on the joints. Massage the abdomen and chest in broad, clockwise, circular motions. On the abdomen, follow the path of the large intestine; moving up on the right side of the abdomen, then across, then down on the left side. Massage the body for 5-20 minutes, with love and patience.
Give a little extra time and attention to massaging the oil into your scalp, ears and feet, at least once a week. Apply oil to the crown of your head (adhipati marma) and work slowly out from there in circular strokes. Oil applied to the head should be warm
but not hot. Put a couple drops of warm oil on the tip of your little finger or on a cotton ball and apply to the opening of the ear canal. (If there is any current or chronic discomfort in the ears don’t do this without the recommendation of your health care practitioner). When you massage your feet, be sure to wash them first when you shower, so you don’t slip.
Enjoy a warm bath or shower. You can use a mild soap on the “strategic” areas.
When you get out of the bath, towel dry. Keep a special towel for drying off after your Abhyanga because it can eventually get ruined, due to the accumulation of oil.
Put on a pair of cotton socks (organic, if you can find them) to protect your environment from the residual oil on your feet.
Apply a dosha-appropriate essential oil to your wrists and neck.
Enjoy.
So, For What You Are Waiting For ?
· Schedule an Ayurvedic Consultation and let us create a custom PanchaKarma (rejuvenation) program to address your specific health needs and restore vitality. | kavita_sharma_ | |
1,868,871 | Arogyam Panchkarma Centre & Ayurvedic Hospital | Welcome to the AROGYAM HEALTH RESORT from where you can find solutions of your health problems in a... | 0 | 2024-05-29T10:41:11 | https://dev.to/kavita_sharma_/arogyam-panchkarma-centre-ayurvedic-hospital-3cno | Welcome to the AROGYAM HEALTH RESORT from where you can find solutions of your health problems in a scientific way from ancient science.We welcome you to the world of holistic healing with the most affordable ayurveda treatment packages in India,at Una district of Himachal Pradesh in the Lap of Dev-Bhoomi (Himachal Pradesh)
Relax, refresh and rejuvenate yourself with the ancient system of medicine which has been established widely as Ayurveda. We invite you to experience pure ayurveda treatments with yoga and meditation to restore your physical, mental and spiritual equilibrium.
Ayurveda, a 5000-year-old practice of health has a rejuvenation procedure – Panchakarma that subtly removes the toxins from the mind and body. These procedures are designed to function synergistically to maximize the removal of toxins while maintaining the harmony of natural body functions. The purifying and eliminating actions of Panchakarma first dislodge the toxins from the cells and then flush them out through the organs of elimination—the sweat glands, colon and urinary tract. | kavita_sharma_ | |
1,868,870 | Top Web Development Company in Sweden | Hire Web Developers | Sapphire Software Solutions attracts potential customers and helps to grow online business. Create... | 0 | 2024-05-29T10:39:47 | https://dev.to/samirpa555/top-web-development-company-in-sweden-hire-web-developers-4g6m | webdev, webdevelopmentcompany, webservices, hirewebdevelopment | Sapphire Software Solutions attracts potential customers and helps to grow online business. Create attractive websites with the **[Top Web Development Company in Sweden.](https://www.sapphiresolutions.net/top-web-development-company-in-sweden)** | samirpa555 |
1,868,869 | The Art of Writing Effective Git Commits | Version control systems like Git are essential tools for developers, allowing them to track changes... | 0 | 2024-05-29T10:37:52 | https://dev.to/monikaprajapati_70/the-art-of-writing-effective-git-commits-4fed | git, commits, programming, learning |
Version control systems like Git are essential tools for developers, allowing them to track changes to their codebase, collaborate with others, and manage project history effectively. One crucial aspect of using Git is writing clear and meaningful commit messages. A well-written commit message not only helps you understand the changes you've made but also assists your team members and future contributors in comprehending the project's evolution. In this blog post, we'll explore the art of writing effective Git commits.
### The Importance of Good Commit Messages
A commit message serves as a concise summary of the changes introduced in a particular commit. It should provide enough context for anyone reviewing the commit history to quickly grasp the reasoning behind the changes and their impact on the codebase. Well-crafted commit messages can:
1. **Facilitate code review**: Clear commit messages make it easier for reviewers to understand the purpose and scope of the changes, streamlining the code review process.
2. **Improve collaboration**: When working in a team, commit messages help other developers understand the changes made by their colleagues, reducing confusion and enabling smoother collaboration.
3. **Simplify debugging**: If a bug is introduced, well-documented commit messages can help pinpoint the source of the issue more efficiently by providing context about the changes made in specific commits.
4. **Enhance project maintenance**: As projects evolve and new contributors join, descriptive commit messages serve as a historical record, making it easier to understand the rationale behind past decisions and changes.
### The Structure of a Commit Message
A commit message typically consists of two parts: a subject line and an optional body. Here's the recommended structure:
```
<type>(<scope>): <subject>
<body>
```
1. **Type**: This is a concise description of the kind of change the commit introduces. Common types include `feat` (a new feature), `fix` (a bug fix), `docs` (documentation changes), `style` (formatting changes), `refactor` (code refactoring), `test` (addition or modification of tests), `chore` (maintenance tasks), and more.
2. **Scope** (optional): This specifies the area of the codebase that the commit is focused on, such as a specific component, module, or feature. For example, `user-auth` or `dashboard`.
3. **Subject**: A brief, imperative summary of the changes (e.g., "Add user authentication" or "Fix typo in README").
4. **Body** (optional): A more detailed description of the changes, including the motivation behind them, any potential side effects, and any relevant issues or pull requests. The body should be wrapped at 72 characters per line.
Here's an example of a well-structured commit message:
```
feat(user-auth): add email verification
- Implement email verification flow
- Add verification email templates
- Update user model to include 'verified' field
Closes #123
```
In this example, the commit introduces a new feature related to user authentication (`feat(user-auth)`), specifically the addition of email verification functionality. The body provides more context about the changes, including the implementation details and any relevant issues or pull requests.
### Commit Types
As mentioned earlier, the commit type is a concise description of the kind of change the commit introduces. Here are some common commit types:
- `feat` – a new feature is introduced with the changes
- `fix` – a bug fix has occurred
- `chore` – changes that do not relate to a fix or feature and don't modify src or test files (e.g., updating dependencies)
- `refactor` – refactored code that neither fixes a bug nor adds a feature
- `docs` – updates to documentation such as the README or other markdown files
- `style` – changes that do not affect the meaning of the code, likely related to code formatting such as white-space, missing semi-colons, and so on.
- `test` – including new or correcting previous tests
- `perf` – performance improvements
- `ci` – continuous integration related
- `build` – changes that affect the build system or external dependencies
- `revert` – reverts a previous commit
Here are some examples of commit messages using different types:
```
fix(user-auth): correct email validation regex
docs: update README with installation instructions
chore: upgrade dependencies to latest versions
refactor(auth-service): improve code readability
test(user-model): add unit tests for email validation
```
### Best Practices for Writing Effective Commit Messages
To ensure your commit messages are clear, concise, and effective, follow these best practices:
1. **Use the imperative mood**: Write the subject line in the imperative mood, as if giving instructions to the codebase. For example, "Add user authentication" instead of "Added user authentication" or "Adds user authentication."
2. **Keep the subject line short and descriptive**: The subject line should be no longer than 50 characters and should clearly summarize the changes made in the commit.
3. **Capitalize the subject line**: Capitalize the first letter of the subject line for better readability.
4. **Use the body for detailed explanations**: If the commit requires more context or explanation, use the body section to provide additional details, such as the motivation behind the changes, potential side effects, and any relevant issues or pull requests.
5. **Separate the subject from the body with a blank line**: For better readability, leave a blank line between the subject and the body of the commit message.
6. **Reference issues or pull requests**: If the commit is related to an issue or pull request, include a reference to it in the body of the commit message (e.g., "Closes #123" or "Fixes #456").
7. **Avoid generic messages**: Avoid using generic or ambiguous commit messages like "update" or "fix bug." Instead, be specific about the changes made.
8. **Follow project or team conventions**: If your project or team has specific conventions or guidelines for commit messages, make sure to follow them for consistency.
By following these best practices and writing clear and descriptive commit messages, you'll not only improve the overall quality and maintainability of your codebase but also facilitate collaboration and streamline the development process.
I used this source to write this blog, please refer to [Natalie Pina](https://www.freecodecamp.org/news/author/natalie/) on this [page](https://www.freecodecamp.org/news/how-to-write-better-git-commit-messages/) | monikaprajapati_70 |
1,868,868 | Explore the Magic of Istanbul: A Journey Through Time | Istanbul, the city where East meets West, is a melting pot of cultures, history, and modernity. This... | 0 | 2024-05-29T10:37:15 | https://dev.to/travelgo/explore-the-magic-of-istanbul-a-journey-through-time-12pg | >Istanbul</a>, the city where East meets West, is a melting pot of cultures, history, and modernity. This vibrant metropolis straddles two continents and has been a crossroads of civilizations for millennia. Whether you’re a history buff, a culinary enthusiast, or simply seeking adventure, <a class="markup--anchor markup--p-anchor" data-href="https://www.booking.com/city/tr/istanbul.en.html?aid=8019784&no_rooms=1&group_adults=2" href="https://www.booking.com/city/tr/istanbul.en.html?aid=8019784&no_rooms=1&group_adults=2" rel="noopener" target="_blank">Istanbul</a> offers an unforgettable experience.</p><h4 class="graf graf--h4" name="b11a">A Glimpse into History</h4><p class="graf graf--p graf--empty" name="0c24"><br /></p><figure class="graf graf--figure" name="d0da"><img class="graf-image" data-height="667" data-image-id="0*vFq_IgWflXLDnFof" data-width="1000" src="https://cdn-images-1.medium.com/max/800/0*vFq_IgWflXLDnFof" /></figure><p class="graf graf--p" name="7484"><a class="markup--anchor markup--p-anchor" data-href="https://www.booking.com/city/tr/istanbul.en.html?aid=8019784&no_rooms=1&group_adults=2" href="https://www.booking.com/city/tr/istanbul.en.html?aid=8019784&no_rooms=1&group_adults=2" rel="noopener" target="_blank">Istanbul</a>’s rich history is evident in its stunning architecture and ancient landmarks. The <strong class="markup--strong markup--p-strong">Hagia Sophia</strong>, originally built as a cathedral in the 6th century, later converted into a mosque, and now a museum, stands as a testament to the city’s diverse heritage. Its grand dome and intricate mosaics leave visitors in awe.</p><p class="graf graf--p" name="46b0"><a class="markup--anchor markup--p-anchor" data-href="https://www.booking.com/city/tr/istanbul.en.html?aid=8019784&no_rooms=1&group_adults=2" href="https://www.booking.com/city/tr/istanbul.en.html?aid=8019784&no_rooms=1&group_adults=2" rel="noopener" target="_blank"><strong class="markup--strong markup--p-strong">Explore Travel Offers Now!</strong></a></p><p class="graf graf--p" name="014a">Nearby, the <strong class="markup--strong markup--p-strong">Blue Mosque</strong> (Sultan Ahmed Mosque) is another architectural marvel. Famous for its six minarets and blue-tiled interior, it remains a functioning mosque and a must-visit for anyone exploring the city.</p><h4 class="graf graf--h4" name="27f8">Cultural Experiences</h4><p class="graf graf--p graf--empty" name="0a14"><br /></p><figure class="graf graf--figure" name="e8c2"><img class="graf-image" data-height="667" data-image-id="0*umJKhNXp6IxpKAT0" data-width="1000" src="https://cdn-images-1.medium.com/max/800/0*umJKhNXp6IxpKAT0" /></figure><p class="graf graf--p" name="d2f0">A trip to <a class="markup--anchor markup--p-anchor" data-href="https://www.booking.com/city/tr/istanbul.en.html?aid=8019784&no_rooms=1&group_adults=2" href="https://www.booking.com/city/tr/istanbul.en.html?aid=8019784&no_rooms=1&group_adults=2" rel="noopener" target="_blank">Istanbul</a> isn’t complete without visiting the <strong class="markup--strong markup--p-strong">Grand Bazaar</strong>. One of the largest and oldest covered markets in the world, it offers a sensory overload with its maze of shops selling everything from spices and textiles to jewelry and ceramics. Bargaining is part of the experience, so get ready to haggle!</p><p class="graf graf--p" name="09f3"><a class="markup--anchor markup--p-anchor" data-href="https://www.booking.com/city/tr/istanbul.en.html?aid=8019784&no_rooms=1&group_adults=2" href="https://www.booking.com/city/tr/istanbul.en.html?aid=8019784&no_rooms=1&group_adults=2" rel="noopener" target="_blank"><strong class="markup--strong markup--p-strong">Explore Travel Offers Now!</strong></a></p><p class="graf graf--p" name="8216">
<ins class="bookingaff" data-aid="2421552" data-height="90" data-lang="en" data-prod="banner" data-target_aid="2421552" data-width="728">
<!--Anything inside will go away once widget is loaded.-->
<a href="//www.booking.com?aid=2421552">Booking.com</a> </ins></p><p class="graf graf--p" name="8216">
<script type="text/javascript">
(function(d, sc, u) {
var s = d.createElement(sc), p = d.getElementsByTagName(sc)[0];
s.type = 'text/javascript';
s.async = true;
s.src = u + '?v=' + (+new Date());
p.parentNode.insertBefore(s,p);
})(document, 'script', '//cf.bstatic.com/static/affiliate_base/js/flexiproduct.js');
</script>
For a more contemporary shopping experience, head to <strong class="markup--strong markup--p-strong">Istiklal Avenue</strong> in the Beyoğlu district. This bustling street is lined with boutiques, cafes, and art galleries, reflecting the modern, cosmopolitan side of <a class="markup--anchor markup--p-anchor" data-href="https://www.booking.com/city/tr/istanbul.en.html?aid=8019784&no_rooms=1&group_adults=2" href="https://www.booking.com/city/tr/istanbul.en.html?aid=8019784&no_rooms=1&group_adults=2" rel="noopener" target="_blank">Istanbul</a>.</p><h4 class="graf graf--h4" name="fd90">Culinary Delights</h4><p class="graf graf--p graf--empty" name="dc92"><br /></p><figure class="graf graf--figure" name="ea4d"><img class="graf-image" data-height="667" data-image-id="0*WGY3VppP0doQYRoX" data-width="1000" src="https://cdn-images-1.medium.com/max/800/0*WGY3VppP0doQYRoX" /></figure><p class="graf graf--p" name="873a">Istanbul’s culinary scene is a delightful mix of flavors. Start your day with a traditional Turkish breakfast, featuring fresh bread, olives, cheeses, and honey. For lunch, try a hearty <strong class="markup--strong markup--p-strong">kebab</strong> or <strong class="markup--strong markup--p-strong">meze</strong> (assortment of small dishes). Don’t miss the chance to savor <strong class="markup--strong markup--p-strong">baklava</strong>, a sweet pastry made of layers of filo dough, nuts, and honey, accompanied by a cup of strong Turkish coffee.</p><p class="graf graf--p" name="3148"><a class="markup--anchor markup--p-anchor" data-href="https://www.booking.com/city/tr/istanbul.en.html?aid=8019784&no_rooms=1&group_adults=2" href="https://www.booking.com/city/tr/istanbul.en.html?aid=8019784&no_rooms=1&group_adults=2" rel="noopener" target="_blank"><strong class="markup--strong markup--p-strong">Explore Travel Offers Now!</strong></a></p><p class="graf graf--p" name="c767">For dinner, head to one of the many rooftop restaurants along the Bosphorus. Enjoy stunning views while dining on seafood specialties and sipping on <strong class="markup--strong markup--p-strong">raki</strong>, an anise-flavored spirit.</p><h4 class="graf graf--h4" name="aa5b">Modern Attractions</h4><p class="graf graf--p graf--empty" name="4240"><br /></p><figure class="graf graf--figure" name="a264"><img class="graf-image" data-height="625" data-image-id="0*n5fhvqcXPaaYlLkf" data-width="1000" src="https://cdn-images-1.medium.com/max/800/0*n5fhvqcXPaaYlLkf" /></figure><p class="graf graf--p" name="e924">Take a <strong class="markup--strong markup--p-strong">Bosphorus cruise</strong> to see <a class="markup--anchor markup--p-anchor" data-href="https://www.booking.com/city/tr/istanbul.en.html?aid=8019784&no_rooms=1&group_adults=2" href="https://www.booking.com/city/tr/istanbul.en.html?aid=8019784&no_rooms=1&group_adults=2" rel="noopener" target="_blank">Istanbul</a> from a different perspective. The cruise offers panoramic views of the city’s skyline, including landmarks like the Dolmabahçe Palace and the Maiden’s Tower. It’s a relaxing way to understand the city’s layout and appreciate its beauty.</p><p class="graf graf--p" name="190a"><a class="markup--anchor markup--p-anchor" data-href="https://www.booking.com/city/tr/istanbul.en.html?aid=8019784&no_rooms=1&group_adults=2" href="https://www.booking.com/city/tr/istanbul.en.html?aid=8019784&no_rooms=1&group_adults=2" rel="noopener" target="_blank"><strong class="markup--strong markup--p-strong">Explore Travel Offers Now!</strong></a></p><h4 class="graf graf--h4" name="f8ab">
<ins class="bookingaff" data-aid="2421551" data-dest_id="-755070" data-dest_type="city" data-df_num_properties="3" data-height="350" data-lang="en" data-prod="dfl2" data-target_aid="2421551" data-width="300"><!--Anything inside will go away once widget is loaded.--> <a href="//www.booking.com?aid=2421551">Booking.com</a> </ins></h4><h4 class="graf graf--h4" name="f8ab">
<script type="text/javascript">
(function(d, sc, u) {
var s = d.createElement(sc), p = d.getElementsByTagName(sc)[0];
s.type = 'text/javascript';
s.async = true;
s.src = u + '?v=' + (+new Date());
p.parentNode.insertBefore(s,p);
})(document, 'script', '//cf.bstatic.com/static/affiliate_base/js/flexiproduct.js');
</script>
Tips for Travelers</h4><ul class="postList"><li class="graf graf--li" name="26df"><strong class="markup--strong markup--li-strong">Best Time to Visit</strong>: Spring (April to June) and autumn (September to November) are ideal for pleasant weather and fewer crowds.</li><li class="graf graf--li" name="10a7"><strong class="markup--strong markup--li-strong">Getting Around</strong>: Public transportation is efficient. Use trams, buses, and ferries to navigate the city. Walking is also a great way to explore the neighborhoods.</li><li class="graf graf--li" name="dfe7"><strong class="markup--strong markup--li-strong">Language</strong>: While Turkish is the official language, English is widely spoken in tourist areas.</li></ul><h4 class="graf graf--h4" name="ad2b">Conclusion</h4><p class="graf graf--p" name="9438"><a class="markup--anchor markup--p-anchor" data-href="https://www.booking.com/city/tr/istanbul.en.html?aid=8019784&no_rooms=1&group_adults=2" href="https://www.booking.com/city/tr/istanbul.en.html?aid=8019784&no_rooms=1&group_adults=2" rel="noopener" target="_blank">Istanbul</a> is a city that captivates the heart and soul of every traveler. Its blend of history, culture, and modernity creates an unparalleled travel experience. So pack your bags and get ready to embark on a journey through time in this enchanting city.</p><p class="graf graf--p" name="660d">Are you ready to explore new destinations and create unforgettable memories? Click the link below to discover exclusive travel offers that will take you on the journey of a lifetime. Whether you’re dreaming of pristine beaches, vibrant cities, or serene mountains, our special deals have got you covered. Don’t miss out on these incredible opportunities to travel more for less. Your adventure awaits!</p><p class="graf graf--p" name="22d6"><a class="markup--anchor markup--p-anchor" data-href="https://www.booking.com/city/tr/istanbul.en.html?aid=8019784&no_rooms=1&group_adults=2" href="https://www.booking.com/city/tr/istanbul.en.html?aid=8019784&no_rooms=1&group_adults=2" rel="noopener" target="_blank"><strong class="markup--strong markup--p-strong"><span style="font-size: large;">Access the link for irresistible offers!</span></strong></a></p><p class="graf graf--p" name="22d6"><br /></p>
<script src="https://www.booking.com/affiliate/prelanding_sdk"></script>
<div id="bookingAffiliateWidget_a6420765-0a0b-4cc0-8a20-d44b4b6ff0ed"> </div>
<script>
(function () {
var BookingAffiliateWidget = new Booking.AffiliateWidget({
"iframeSettings": {
"selector": "bookingAffiliateWidget_a6420765-0a0b-4cc0-8a20-d44b4b6ff0ed",
"responsive": true
},
"widgetSettings": {}
});
})();
</script> | travelgo | |
1,868,867 | Meet Dr. Bhumika Bansal, Lucknow's Trusted Gynecologist for Comprehensive Women's Health Care | Experience exceptional women's health care with Dr. Bhumika Bansal, recognized as the best... | 0 | 2024-05-29T10:35:12 | https://dev.to/drbhumikabansal/meet-dr-bhumika-bansal-lucknows-trusted-gynecologist-for-comprehensive-womens-health-care-2cep | bestgynecologistinlucknow, bestgynaecologistinlucknow | Experience exceptional women's health care with Dr. Bhumika Bansal, recognized as the [best Gynecologist in Lucknow](https://drbhumikabansal.com
). With a commitment to providing compassionate and comprehensive medical services, Dr. Bansal offers personalized care for women at every stage of life. From routine check-ups to advanced treatments, her expertise and dedication ensure optimal health outcomes. Trust Dr. Bansal for expert guidance, support, and solutions tailored to your unique needs, empowering you to thrive in health and wellness.
 | drbhumikabansal |
1,868,866 | 🔥 Unlock Your App Development Superpowers! 🔥 | 🌟 Ready to take a deep dive into the realm of developing mobile applications? Look no... | 0 | 2024-05-29T10:35:04 | https://dev.to/liya/unlock-your-app-development-superpowers-2a60 | bestsoftwaretraininginkochi, appdevelopers, fluttercourseinkochi, fluttertraininginkochi |

🌟
## **Ready to take a deep dive into the realm of developing mobile applications?**
Look no further!Our [Flutter Course in Kochi](https://www.irohub.com/flutter-training-kochi)is here to ignite your coding journey.📱💡
🚀 Why Choose Our Flutter Training?
Code Once, Thrive Everywhere: With Flutter, you write one set of code and create apps for both Android and iOS. Efficiency level: 1000x! 🌐
Attractive UI Designs: Customize widgets, unleash creativity, and craft stunning user interfaces. Your apps will turn heads! 🎨
Fast Development: Say goodbye to waiting. Flutter’s “hot reload” feature lets you test and modify code lightning-fast. ⚡
📍 Location: 1st Floor, Trust Building, Kayyath Ln, Palarivattom, Kochi
📧 Contact Us: info@irohub.com | +91 812985515
🔗 Enroll Today: Irohub Infotech
| liya |
1,868,865 | Easy to Dev a Gpts Chat APP with hono bun htmx | htmx -> http --> hono --> gpt code here: https://github.com/rocklau/gpts-chat-app This... | 0 | 2024-05-29T10:34:42 | https://dev.to/rockfire/easy-to-dev-a-gpts-chat-app-p4l |
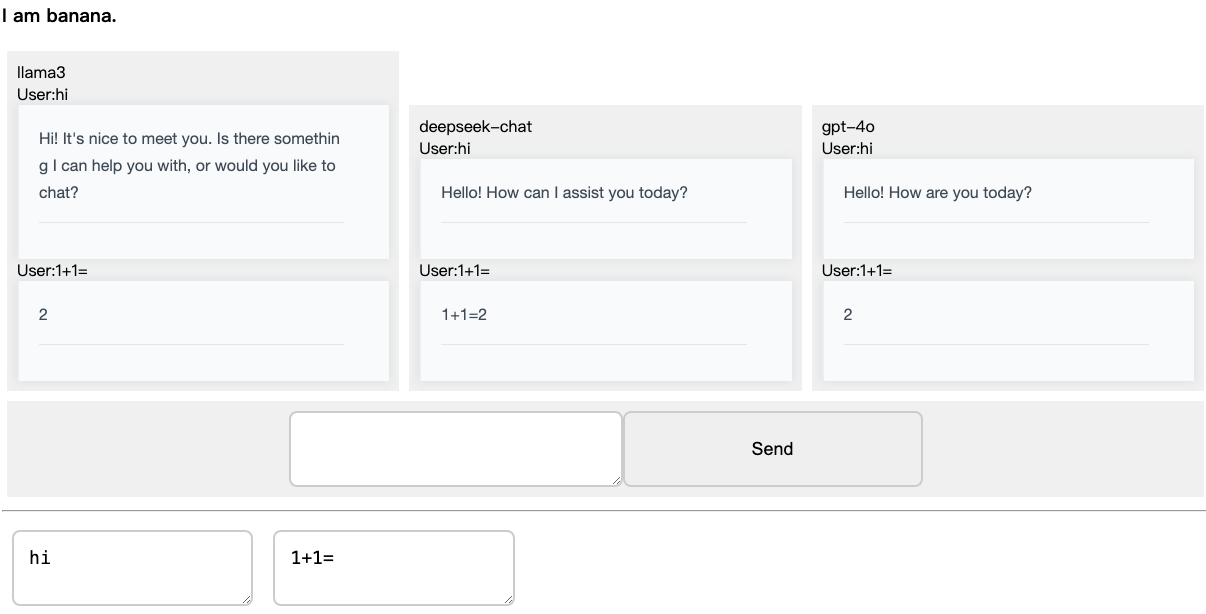
htmx -> http --> hono --> gpt
code here: https://github.com/rocklau/gpts-chat-app
This is a chat application that allows users to interact with multi AIs through a simple and intuitive interface. There is also a human channel chat feature that needs a bug fix. You might consider switching to Tailwind CSS for styling. This repository is intended for learning purposes only.
Thanks for open source with htmx hono bun mitata openai cherry-markdown
Directory Structure
The project directory is organized as follows:
static/:
index.html: Main HTML file for the application. have htmx and js logic.
src/:
index.tsx: Entry point of the application, core server logic.
GptChat.tsx: Component for the GPT chat interface.
models.tsx: Configuration for the AI models.
benmarking.tsx: Benchmarking scripts for performance testing gpt models.
HumanChat.tsx: Component for human-to-human chat interface. have bug
| rockfire | |
1,868,864 | 2024 最新12个好用的APK下载网站,完美替代Google Play | 如果你找的所有下载Google Play的工具全部被屏蔽,或者无法安装GMS导致无法使用Google Play ,或者以前下载了Google... | 0 | 2024-05-29T10:34:29 | https://dev.to/shaoyang_liu/2024-zui-xin-12ge-hao-yong-de-apkxia-zai-wang-zhan-wan-mei-ti-dai-google-play-1h2p | apk, javascript | 如果你找的所有下载Google Play的工具全部被屏蔽,或者无法安装GMS导致无法使用Google Play ,或者以前下载了Google Play但现在打不开……
这里有12个可以完美替代Google Play 的网站或App:
## 1. apkbot 是一个完全免费无广告的apk下载站点,设计简单,下载速度快,不需要GMS也能完美安装及使用(还没被屏蔽)。
[APKBOT](https://apk.bot/)
## 2.APKMirror 可能是最好的替代Play商店应用之一,不过国内访问速度较慢也是个问题,因为是网页版,而且是全英文,所以很多人不会用,导致现在用Aurora Store的人特别多。
[APKMirror](https://www.apkmirror.com/)
## 3.APKPure 提供:网页、App APKPure 是知名度很高的免费安卓应用商店,基本上大部分Google Play上架的软件都可以在这里找到,但最近也有被屏蔽的倾向。
[APKPure](https://apkpure.com/cn/)
## 4.Aptoide 提供:网页版、App 需要注意的是下载下来的实际上是他的下载器
[Aptoide](https://en.aptoide.com/)
## 5.apkdl.in 更新速度略慢于前面几个,App不全、作为备选地址; 提供:网页版、机器人
[apkdl.in](t.co/9drupIbSi4)
## 6.APK Combo 有中文、稳定性一般,访问偶尔会出错。 提供:网页版
[APK Combo](apkcombo.com/zh/)
7.9apps 如果以上平台都被屏蔽了,那你要么放弃手机版,要么用这个争议大的平台。 提供:网页版、
[9App](9apps.com)
## 8. Amazon Appstore是亚马逊于 2011 年推出的手机应用商店
是大安卓应用市场。默认安装在每一台出厂的Amazon Fire设备上,但是也可以适用于任何类型的 Android 设备。使用这个商店的话需要一个亚马逊账户,这样就可以管理以及同步你购买过的应用程序。
## 9.F-Droid 要注意的是,F-Droid只允许提交真正的免费开源软件
因此你不能在上面下载国外热门的社交app和游戏软件。 优点 -真正的开源免费软件 -网站速度较快 -网站有中文版本 缺点 -内容没有Google Play丰富 -只提供开源软件下载
## 10.androeed androeed是一个俄罗斯的安卓app下载平台
你可以直接下载apk文件也可以跳转到谷歌商店进行下载,还可以选择应用的老版本app。所有文件均经过杀毒软件的安全扫描。 优点 -网站界面较为简洁 -国内下载速度较快 -支持下载老版本应用 缺点 -内容没有Google Play丰富
## 11.apps ru 是一个俄罗斯的安卓应用下载网站
提供最新的安卓手机应用和游戏下载,网站界面相当的美观而且没有任何的广告。而且可以选择应用的老版本进行下载。 优点 -网站界面美观 -支持下载老版本应用 缺点 -内容没有Google Play丰富 -国内访问速度一般有点慢
[apps ru](5-apps.ru)
## 12.5play.ru是另外一个俄罗斯的手机app下载网站,
可以提供最新的免费安卓应用和游戏,在中国的应用下载速度也比较快,可以用来下载一些国内没有提供的安卓手机游戏。 优点 -网站界面美观 -国内速度下载较快 缺点 -内容没有Google Play丰富
[Русский Play Market | Новые Android игры на телефон и планшет без регистрации и вирусов](5play.ru)
| shaoyang_liu |
1,868,863 | دستگاه ایکس ری مواد مخدر دستگاهی برای تشخیص انواع مواد مخدر در فرودگاه ها | دستگاه ایکس ری یکی از بهترین و پرکاربردترین روش های شناسایی مواد مخدر است که در اماکن مختلف از جمله... | 0 | 2024-05-29T10:34:25 | https://dev.to/maxasecurity/dstgh-ykhs-ry-mwd-mkhdr-dstghy-bry-tshkhys-nw-mwd-mkhdr-dr-frwdgh-h-27pg | دستگاه ایکس ری یکی از بهترین و پرکاربردترین روش های شناسایی مواد مخدر است که در اماکن مختلف از جمله فرودگاه ها، گمرکات، گلوگاه های جاده ای، ورودی اجلاس های مهم و… مورد استفاده قرار می گیرد. این دستگاه برای شناسایی انواع مواد مخدر از تکنولوژی تشخیص به کمک اشعه ایکس استفاده می کند و دارای دقت و سرعت عمل قابل قبولی برای شناسایی انواع مخدر است. برای آشنایی با شیوه کار و محدوده عملکرد دستگاه ایکس ری مواد مخدر با ما همراه باشید.
**ایکس ری مواد مخدر از چه اجزایی تشکیل شده است
**
همانطور که اشاره شد ، دستگاه های ایکس ری همگی بر مبنای تابش اشعه ایکس به اجسام عملیات شناسایی را انجام میدهند. این دستگاه ها انواع مختلفی دارند . در مکان های متفاوتی هم مورد استفاده قرار می گیرند. اما اساس کار و اجزای تشکیل دهنده آن ها تقریبا مشابه است.
یک **[دستگاه ایکس ری مواد مخدر](https://maxasecurity.com/product-category/x-ray-devices/)** دارای عملکرد
مناسب جهت شناسایی مواد مخدر از اجزا و قطعات مختلفی تشکیل شده است که عبارتند از :
تونل تصویربرداری : بستر اصلی تصویر برداری از کالا است.
نوار نقاله : کالا برای رفتن تا داخل تونل با قرار گرفتن بر روی نوار نقاله هدایت می شود.
ژنراتور یا شتاب دهنده: جهت تاباندن اشعه ایکس ری به داخل تونل کاربرد دارد.
سنسورهای آشکار کننده: همانطور که از نامشان مشخص است برای آشکارسازی انرژی عبوری از کالا مورد نظر کاربرد دارند.
پنل کاربری: پنلی که برای انجام تنظیمات و هدایت مراحل عملیات طراحی شده است.
رایانه پیشرفته: با پردازش اطلاعات نتیجه نهایی شناسایی را مشخص می کند تا با مشاهده رنگ های منتشر شده ماهیت کالا شناسایی شود.
** از دستگاه ایکس ری مواد مخدر در کجا استفاده می شود
**به طور کلی می توان از دستگاه ایکس ری مواد مخدر در هر مکانی که ضمن فراهم بودن شرایط نصب دستگاه، نیاز به بازرسی جهت شناسایی مواد مخدر وجود دارد، نصب کرد. یکی از مکان های اصلی که از این دستگاه برای تشخیص مواد مخدر استفاده می شود فرودگاه هاست. علاوه بر فرودگاه ها، از این دستگاه در مرزهای کشور و گمرکات برای تشخیص محموله های مواد مخدر استفاده می شود. البته انواع دیگری از دستگاه ایکس ری هم وجود دارند که به منظور شناسایی کالاهای قاچاق یا سایر اشیا ممنوعه در مبادی ورودی و خروجی مورد استفاده قرار می گیرند.
**دستگاه ایکس ری مواد مخدر چه رنگ هایی را نشان می دهد
**
همانطور که اشاره شد، اساس عملکرد دستگاه ایکس ری بازرسی، استفاده از اشعه ایکس برای شناسایی اجسام است. نتیجه شناسایی اجسام توسط این دستگاه پس از پردازش اطلاعات به کمک رنگ های مختلفی نشان داده میشود که هریک نشان دهنده ماده خاصی هستند. در واقع رنگ های منتشر شده که بر اساس نوع کالا و چگالی آن تعیین می شوند، امکان تشخیص ماهیت اشیا داخل چمدان، جعبه، کانتینر و… را فراهم می کنند. به طور معمول دستگاه ایکس ری توانایی نشان دادن تا 6 رنگ را دارند که هریک نشانگر ماده خاصی هستند. این رنگ ها شامل سیاه ، سفید ، نارنجی ، سبز ، آبی و قهوه ای هستند. هر رنگ معنا و مفهوم خاصی دارد ، به طور مثال، رنگ و سیاه سفید به معنی غیر قابل نفوذ بودن جسم مورد نظر به اشعه ایکس است. رنگ های های دیگر هم هر یک نشان دهنده ماده خاصی هستند.
رنگ نارنجی در دستگاه ایکس ری نشانگر برخی مواد آلی مانند کاغذ و لباس،برهی از مواد منفجره و مواد مخدری مانند هروئین و کوکائین است. همچنین، کمرنگ و پررنگ بودن هر کدام از رنگ های نشان داده شده توسط این دستگاه، بسته به چگالی و ضخامت مواد می تواند نشانگر مواد مخدر باشد.
تشخیص مواد داخل بدن؛ با کمک دستگاه ایکس ری مواد مخدر
یکی از قابلیت های فوق العاده دستگاه ایکس ری مواد مخدر، امکان تشخیص مواد مخدر پنهان شده در بدن افراد است. در برخی از مواقع که افراد برای عبور دادن مواد مخدر از از ایستگاه های بازرسی آن را می بلعند یا به روش های دیگر در بدن خود پنهان میکنند بهترین روش تشخیص مواد مخدر استفاده از دستگاه ایکس ری است. دستگاه ایکس ری قادر است انواع مخدر پنهان شده در بدن افراد را در زمان بسیار کوتاه کمتر از ده ثانیه شناسایی کند.
.
**سخن پایانی
**با پیشرفت تکنولوژی امکان تشخیص سریع و آسان انواع اشیا ممنوعه و مواد مخدر در ایستگاه های بازرسی به کمک دستگاه ایکس ری فراهم شده است. دستگاه ایکس ری مواد مخدر یکی از انواع دستگاه های بازرسی پر کاربرد در فرودگاه ها و اماکن خاص است که توانایی شناسایی انواع مواد مخدر را دارد. این دستگاه با تابش اشعه ایکس به اجسام و تحلیل داده های حاصل از آن، مواد شناسایی شده را با رنگ های متفاوت نشان میدهد. هر یک از رنگ های دستگاه ایکس ری نشان دهنده ماده خاصی هستند به طور مثال مواد مخدر، مواد منفجره و برخی دیگر از مواد آلی به رنگ نارنجی نمایش داده می شوند. بدین ترتیب این دستگاه قادر است در مدت زمان بسیار کمی انواع مدل مخدر پنهان شده در وسایل افراد و با حتی بدن آن ها را شناسایی کند.
شرکت [مکسا](**https://maxasecurity.com/**) با داشتن سابقه موفق در تولید محصولات سخت افزاری و نرم افزاری در زمینه تامین امنیت و کنترل تردد و همچنین کسب تجربه چندین ساله از نیازهای شرکت ها و سازمان های خصوصی یا دولتی امروزه موفق به تولید و عرضه انواع مختلفی از گیت های کنترل تردد به بازار شده است. شما می توانید با مراجعه به وب سایت شرکت مکسا به آدرس www.maxasecurity.com و یا تماس با شماره تلفن 02178756000 راهنمایی های لازم را در خصوص نحوه خرید انواع دستگاه ایکس ری از همکاران پشتیبانی فروش محصولات دریافت نمایید.
| maxasecurity | |
1,868,862 | Top Mobile App Development Company in Sweden | Hire Mobile App developers | We work hard and provide high-quality mobile app development services to start-ups and industries.... | 0 | 2024-05-29T10:33:25 | https://dev.to/samirpa555/top-mobile-app-development-company-in-sweden-hire-mobile-app-developers-273g | mobileappdevelopment, mobileappdevelopmentcompany, mobileapp, mobileappdevelopmentservices | We work hard and provide high-quality mobile app development services to start-ups and industries. Hire the **[**Top Mobile App Development Company in Sweden**](https://www.sapphiresolutions.net/top-mobile-app-development-company-in-sweden)** to know more. | samirpa555 |
1,865,476 | The Joy of Single Sources of Truth | If you love Typescript and haven't been living under a rock for the past 2 years, you've likely heard... | 0 | 2024-05-29T10:33:19 | https://dev.to/codinsonn/the-joy-of-single-sources-of-truth-277o | zod, typescript, automation, codegen | If you love Typescript and haven't been living under a rock for the past 2 years, you've likely heard of **[Zod](https://zod.dev/)**.
{% twitter 1794655669368557947 %}
> **Zod** is a Typescript-first schema validation library, aimed at maximum TS compatibility. It powers popular libraries like [TRPC](https://trpc.io/) & has a [big ecosystem](https://zod.dev/?id=ecosystem) around it
An important design goal is to provide type safety at runtime, not just build time.
*The major strength of Zod is that it can extract types from your validation schema*. For example, this is how you would define primitive data validators in Zod and extract the types
```tsx
import { z } from 'zod'
// - Strings -
const StringValue = z.string()
type StringValue = z.infer<typeof StringValue> // => string
StringValue.parse("Hello World") // => ✅ inferred result = string
StringValue.parse(42) // => throws ZodError at runtime
```
Here's what it would look like for other primitive types:
```tsx
// - Numbers -
const NumberValue = z.number()
type NumberValue = z.infer<typeof NumberValue> // => number
NumberValue.parse(42) // => ✅ inferred type = number
NumberValue.parse("15") // => throws ZodError at runtime
// - Booleans -
const BooleanValue = z.boolean()
type BooleanValue = z.infer<typeof BooleanValue> // => boolean
BooleanValue.parse(true) // => ✅ type = boolean
BooleanValue.parse("false") // => ZodError
// - Dates -
const DateValue = z.date()
type DateValue = z.infer<typeof DateValue> // => Date
DateValue.parse(new Date()) // => ✅ type = Date
DateValue.parse("Next Friday") // also throws
```
> Already, Zod acts as a 'single source of truth' for validation and types.
To understand the power of Zod, you need to think of it as a **single source of truth** for your data structures:
```tsx
// This is just a type
type SomeDatastructure = {
name: string
age: number
isStudent: boolean
birthdate: Date
}
// This provides both types AND validation
// + it can never get out of sync ✅
const SomeDatastructureSchema = z.object({
name: z.string(),
age: z.number(),
isStudent: z.boolean(),
birthdate: z.date()
})
```
In this article, I'll build up to more advanced use cases of Zod, and how it can be used as a single source of truth for not just types and validation, but any datastructure definition in your entire codebase.
---
## Convert with Type Coercion
Sometimes, you don't want things like `"42"` to be rejected when you're expecting a number.
You want to convert them to the correct type instead:
```ts
const NumberValue = z.coerce.number() // <= Prefix with .coerce to enable type coercion
const someNumber = NumberValue.parse("42") // => 42
```
**From the zod.dev docs:**
> "During the parsing step, the input is passed through the String() function,
which is a JavaScript built-in for coercing data into strings."
You can do this for *any* primitive data type:
```ts
const StringValue = z.coerce.string() // When parsing -> String(input)
const someString = StringValue.parse(42) // => "42"
const DateValue = z.coerce.date() // -> new Date(input)
const someDate = DateValue.parse("2024-05-29") // => Date (Wed May 29 2024 00:00:00 GMT+0200)
const BooleanValue = z.coerce.boolean() // -> Boolean(input)
const someBoolean = BooleanValue.parse(0) // => false (falsy value)
// -!- Caveat: strings are technically truthy
const anotherBoolean = BooleanValue.parse("false") // => true
```
---
## Validation Errors
So let's look at what happens when you try to parse invalid data:
```ts
try {
const someNumber = z.number().parse("This is not a number")
} catch (err) {
/* Throws 'ZodError' with a .issues array:
[ {
code: 'invalid_type',
expected: 'number',
received: 'string',
path: [],
message: 'Expected string, received number',
} ]
*/
}
```
**From the zod.dev docs:**
> All validation errors thrown by Zod are instances of `ZodError`.
ZodError is a subclass of Error; you can create your own instance easily:
```ts
import * as z from "zod";
const MyCustomError = new z.ZodError([]);
```
> Each ZodError has an `issues` property that is an array of `ZodIssues`.
Each issue documents a problem that occurred during validation.
But, customizing error messages is easier than you might think:
---
### Custom Error Messages
```ts
const NumberValue = z.number({ message: "Please provide a number" })
// => Throws ZodError [{ message: "Please provide a number", code: ... }]
const MinimumValue = z.number().min(10, { message: "Value must be at least 10" })
// => Throws ZodError [{ message: "Value must be at least 10", code: ... }]
const MaximumValue = z.number().max(100, { message: "Value must be at most 100" })
// => Throws ZodError [{ message: "Value must be at most 100", code: ... }]
```
---
## Going beyond TS by narrowing types
The `.min()` and `.max()` methods on `ZodNumber` from the previous examples are just the tip of the iceberg. They're a great example of what's possible beyond typescript-like type validation and narrowing.
For example, you can also use `.min()`, `.max()` and even `.length()` on strings and arrays:
```ts
// e.g. TS can't enforce a minimum length (👇) on a string
const CountryNameValidator = z.string().min(4, {
message: "Country name must be at least 4 characters long"
})
// ... or an exact length on an array (👇) *
const PointValue3D = z.array(z.number()).length(3, {
message: "Coördinate must have x, y, z values"
})
```
> *Though you could probably hack it together with Tuples 🤔
---
## Advanced Types: Enums, Tuples and more
Speaking of, more advanced types like Tuples or Enums are also supported by Zod:
```ts
const PointValue2D = z.tuple([z.number(), z.number()]) // => [number, number]
const Direction = z.enum(["Left", "Right"]) // => "Left" | "Right"
```
Alternatively, for enums, you could provide an actual enum:
```ts
enum DirectionEnum {
Left = "Left",
Right = "Right"
}
const Direction = z.enum(DirectionEnum) // => DirectionEnum
```
If you want to use a zod enum to autocomplete options from, you can:
```ts
const Languages = z.enum(["PHP", "Ruby", "Typescript", "Python"])
type Languages = z.infer<typeof Languages>
// => "PHP" | "Ruby" | "Typescript" | "Python"
// You can use .enum for a native-like (👇) experience to pick options
const myFavoriteLanguage = Languages.enum.TypeScript // => "Typescript"
// ... which is the equivalent of:
enum Languages {
PHP = "PHP",
Ruby = "Ruby",
TypeScript = "Typescript",
Python = "Python"
}
const myFavoriteLanguage = Languages.TypeScript // => "Typescript"
```
---
### There's more:
Zod also supports more advanced types like `union()`, `intersection()`, `promise()`, `lazy()`, `nullable()`, `optional()`, `array()`, `object()`, `record()`, `map()`, `set()`, `function()`, `instanceof()`, `promise()` and `unknown()`.
**However,** if you're interested in learning the ins and outs, I highly recommend checking out the awesome [Zod documentation](https://zod.dev/), *after* you've read this article.
I won't go into further detail on these, as this is not just about Zod and how to use it.
> **It's about using schemas as single sources of truth.**
---
# Bringing it together in Schemas
---
Validating individual fields is great, but typically, you'll want to validate entire objects.
You can easily do this with `z.object()`:
```ts
const User = z.object({
name: z.string(),
age: z.number(),
isStudent: z.boolean(),
birthdate: z.date()
})
```
Here too, the aliased schema type can be used for editor hints or instant feedback:
```ts
// Alias the Schema to the inferred type
type User = z.infer<typeof User> // <- Common pattern
const someUser: User = {
name: "John Doe",
age: 42,
isStudent: false,
birthdate: new Date("1980-01-01")
}
// => ✅ Yup, that satisfies the `User` type
```
Just like in Typescript, if you want to derive another user type from the `User` schema, you can:
```ts
// Extend the User schema
const Admin = User.extend({
isAdmin: z.boolean()
})
type Admin = z.infer<typeof Admin>
// => { name: string, age: number, isStudent: boolean, birthdate: Date, isAdmin: boolean }
```
Other supported methods are `pick()` and `omit()`:
```ts
// Omit fields from the User schema
const PublicUser = User.omit({ birthdate: true })
type PublicUser = z.infer<typeof PublicUser>
// => { name: string, age: number, isStudent: boolean }
```
```ts
// Pick fields from the User schema
const MinimalUser = User.pick({ name: true, age: true })
type MinimalUser = z.infer<typeof MinimalUser>
// => { name: string, age: number }
```
Need to represent a collection of users...?
```ts
// Use a z.array() with the 'User' schema
const Team = z.object({
members: z.array(User) // <- Reusing the 'User' schema
teamName: z.string(),
})
type Team = z.infer<typeof Team>
// => { teamName: string, members: User[] }
```
... or maybe you want a lookup object?
```ts
// Use a z.record() for datastructure to e.g. to look up users by their ID
const UserLookup = z.record(z.string(), User)
// where z.string() is the type of the id
type UserLookup = z.infer<typeof UserLookup>
// => { [key: string]: User }
```
It's no understatement to say that Zod is already a powerful tool for defining data structures in your codebase.
*But it can be so much more than that.*
---
## Why single sources of truth?
---
> Think of all the places you might need to repeat certain field definitions:
- ✅ Types
- ✅ Validation
- ✅ Database Models
- ✅ API Inputs & Responses
- ✅ Form State
- ✅ Documentation
- ✅ Mocks & Test Data
- ✅ GraphQL schema & query definitions
> *Now think about how much time you spend to keep all of these in sync.*
Not to mention the **cognitive overhead of having to remember** all the different places where you've defined the same thing.
> I've personally torn my hair out over this a few times. I'd updated the types, input validation, edited my back-end code, the database model and the form, but forgot to update a GraphQL query and schema.
> It can be a nightmare.
Now think of what it would be like if you could define your data structures in one place.
*And have everything else derive from that.*
---
## Ecosystem Shoutouts
This is where the Zod ecosystem comes in:
> **Need to build APIs from zod schemas?** 🤔
- `tRPC`: end-to-end typesafe APIs without GraphQL.
- `@anatine/zod-nestjs`: using Zod in a NestJS project.
> **Need to integrate zod schemas within your form library?** 🤔
- `react-hook-form`: Zod resolver for React Hook Form.
- `zod-formik-adapter`: Formik adapter for Zod.
> **Need to transform zod schemas into other formats?** 🤔
- `zod-to-json-schema`: Convert Zod schemas into [JSON Schemas](https://json-schema.org/).
- `@anatine/zod-openapi`: Converts Zod schema to OpenAPI v3.x `SchemaObject`.
- `nestjs-graphql-zod`: Generates NestJS GraphQL model
> **Disclaimer:** *For each example here, there are at least 4 to 5 more tools and libraries in the Zod ecosystem to choose from.*
✅ Using just the ecosystem alone, you could already use Zod as a single source of truth for any data structure in your codebase.
🤔 **The problem is that it is quite fragmented.** Between these different installable tools, there are also different opinions on what an ideal API around it should look like.
Sometimes, the best code is the code you own yourself. Which is what I've been experimenting with:
---
## What makes a good Single Source of Truth?
---
Let's think about it.
> What essential metadata should be derivable from a single source of truth?
```ts
type IdealSourceOfTruth<T = unknown> = {
// -i- We need some basis to map to other formats
baseType: 'String' | 'Boolean' | ... | 'Object' | 'Array' | ...,
zodType: 'ZodString' | 'ZodBoolean' | ... | 'ZodObject' | ...,
// -i- We should keep track of optionality
isOptional?: boolean,
isNullable?: boolean,
defaultValue?: T,
// -i- Ideally, for documentation & e.g. GraphQL codegen
name?: string,
exampleValue?: T,
description?: string,
// -i- If specified...
minValue?: number,
maxValue?: number,
exactLength?: number,
regexPattern?: RegExp,
// -i- We should support nested introspection
// -i- For e.g. enums, arrays, objects, records, ...
schema?: Record<string, IdealSourceOfTruth> | IdealSourceOfTruth[]
// 👆 which would depend on the main `zodType`
}
```
---
# Introspection & Metadata
---
## What's missing in Zod?
At the core of a good single source of truth is a good introspection API:
**Introspection** is the ability to examine the structure of a schema at runtime to extract all relevant metadata from it and its fields.
Sadly, Zod doesn't have this out of the box.
> There's actually a bunch of issues asking for it:
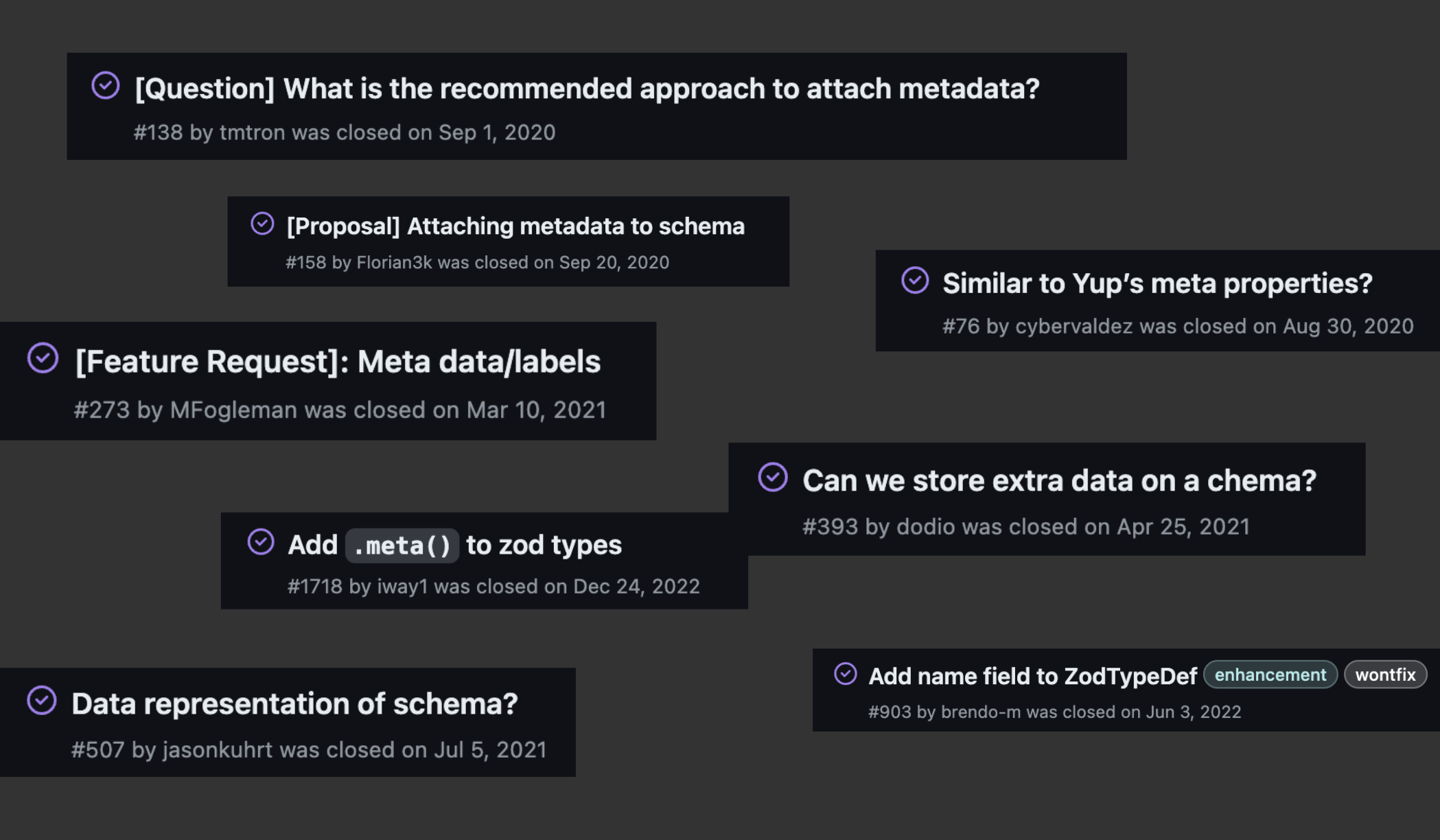
It seems like people really want a strong introspection API in Zod to build their own custom stuff around.
> But what if it did have it?
Turns out, adding introspection to Zod in a way that feels native to it is not super hard:
---
## Adding Introspection to Zod
All it takes is some light additions to the Zod interface:
> **Note:** Editing the prototype of anything is typically dangerous and could lead to bugs or unexpected behavior. While we opted to do it to make it feel native to Zod, it's best to only use it for additions (in moderation), but *NEVER* modifications.
`schemas.ts`
```ts
import { z, ZodObject, ZodType } from 'zod'
/* --- Zod type extensions ----------------------------- */
declare module 'zod' {
// -i- Add metadata, example and introspection methods to the ZodObject type
interface ZodType {
metadata(): Record<string, any>, // <-- Retrieve metadata from a Zod type
addMeta(meta: Record<string, any>): this // <- Add metadata to a Zod type
example<T extends this['_type']>(exampleValue: T): this // <- Add an example value
introspect(): Metadata & Record<string, any> // <- Introspect a Zod type
}
// -i- Make sure we can name and rename Zod schemas
interface ZodObject<...> {
nameSchema(name: string): this // <- Name a Zod schema
extendSchema(name: string, shape: S): this // <- Extend a Zod schema & rename it
pickSchema(name: string, keys: Record<keyof S, boolean>): this // <- Pick & rename
omitSchema(name: string, keys: Record<keyof S, boolean>): this // <- Omit & rename
}
}
/* --- Zod prototype extensions ------------------------ */
// ... Actual implementation of the added methods, omitted for brevity ...
```
> *To check out the full implementation, see the full code on GitHub:
[**FullProduct.dev** - **@green-stack/core** - schemas on Github](https://github.com/Aetherspace/universal-app-router/blob/with/green-stack/packages/%40green-stack-core/schemas/index.ts)*
---
## Using our custom introspection API
On that note, let's create a custom `schema()` function in our custom `schemas.ts` file to allow naming and describing single sources of truth without editing the `z.object()` constructor directly:
```ts
// -i- To be used to create the initial schema
export const schema = <S extends z.ZodRawShape>(name: string, shape: S) => {
return z.object(shape).nameSchema(name)
}
// -i- Reexport `z` so the user can opt in / out to prototype extensions
// -i- ...depending on where they import from
export { z } from 'zod'
```
Which will allows us to do things like:
```ts
// -i- Opt into the introspection API by importing from our own `schemas.ts` file
import { z, schema } from './schemas'
// -i- Create a single source of truth by using the custom `schema()` function we made
const User = schema('User', {
name: z.string().example("John Doe"),
age: z.number().addMeta({ someKey: "Some introspection data" }),
birthdate: z.date().describe("The user's birthdate")
})
// -i- Alias the inferred type so you only need 1 import
type User = z.infer<typeof User>
```
To then retrieve all metadata from the schema:
```ts
const userDefinition = User.introspect()
```
This resulting object is a JS object, but could be stringified to JSON if required:
```json
{
"name": "User",
"zodType": "ZodObject", // <- The actual Zod Class used
"baseType": "Object",
"schema": {
"name": {
"zodType": "ZodString",
"baseType": "String", // <- To transform to other formats
"exampleValue": "John Doe"
},
"age": {
"zodType": "ZodNumber",
"baseType": "Number",
"exampleValue": 42, // <- Good for docs
"someKey": "Some metadata" // <- Custom meta
},
"birthdate": {
"zodType": "ZodDate",
"baseType": "Date",
"description": "The user's birthdate" // <- Good for docs
}
}
}
```
Later we'll look at how we can use this metadata to generate other things like documentation, mocks, database models, etc.
---
## Optionality and Defaults
Zod has native support for things like `.nullable()`, `.optional()` and `.default()`.
Ideally, we'd be able to derive this information in introspection as well.
```ts
// Define a schema with optional and nullable fields
const User = schema('User', {
name: z.string().optional(), // <- Allow `undefined`
age: z.number().nullable(), // <- Allow `null`
birthdate: z.date().nullish(), // <- Allow `null` & `undefined`
isAdmin: z.boolean().default(false) // <- Allow `undefined` + use `false` if missing
})
```
> This is actually one of the things that make adding a proper introspection API a bit difficult, since Zod wraps it's internal classes in some layers of abstraction:
```ts
// e.g. A nullish field with defaults might look like this:
ZodDefault(
ZodNullable(
ZodOptional(
ZodString(/* ... */)
)
)
)
```
You'd typically need to do some recursive layer unwrapping to get to the actual field definition of `ZodString` in this case.
Luckily, our custom `introspect()` method is set up to handle this for us and flattens the resulting metadata object into a more easily digestible format:
```JSON
{
"name": "User",
"zodType": "ZodObject",
"baseType": "Object",
"schema": {
"name": {
"zodType": "ZodString",
"baseType": "String",
// 👇 As we wanted for our ideal Single Source of Truth
"isOptional": true
},
"age": {
"zodType": "ZodNumber",
"baseType": "Number",
// 👇 As we wanted for our ideal Single Source of Truth
"isNullable": true
},
"birthdate": {
"zodType": "ZodDate",
"baseType": "Date",
// 👇 Both optional and nullable due to `.nullish()`
"isOptional": true,
"isNullable": true
},
"isAdmin": {
"zodType": "ZodBoolean",
"baseType": "Boolean",
"isOptional": true,
// 👇 Also keeps track of the default value
"defaultValue": false
}
}
}
```
Now that we can extract metadata (optionality, defaults, examples, types, etc.) from our schemas, we can use these introspection results to generate other things.
---
# Single Source of Truth Examples
---
## Designing Databases Models with Zod
For example, you want to generate a database model from your Zod schema.
You could build and apply a transformer function that takes the introspection result and generates a Mongoose model from it:
`schemaToMongoose.ts`
```ts
// Conceptual transformer function
import { z, createSchemaPlugin } from '@green-stack/schemas'
// Import mongoose specific stuff
import mongoose, { Schema, Model, Document, ... } from 'mongoose'
// --------------------------------------------------------
// -i- Conceptual meta/example code, not actual code
// --------------------------------------------------------
// Take a schema as input, infer its type for later use
export const schemaToMongoose = <S extends z.ZodRawShape>(schema: z.ZodObject<S>) => {
// Create a field builder for metadata aside from the base type
const createMongooseField = (mongooseType) => {
// Return a function that builds a Mongoose field from introspection data
return (fieldKey, fieldMeta) => {
// Build the base definition
const mongooseField = {
type: mongooseType,
required: !fieldMeta.isOptional && !fieldMeta.isNullable,
default: fieldMeta.defaultValue,
description: fieldMeta.description
}
// Handle special cases like enums
if (fieldMeta.zodType === 'ZodEnum') {
mongooseField.enum = Object.values(schemaConfig.schema)
}
// Return the Mongoose field definition
return mongooseField
}
}
// Build the mongoose schema definition by mapping metadata to Mongoose fields
const mongooseSchemaDef = createSchemaPlugin(
// Feed it the schema metadata from introspection
schema.introspect(),
// Map Zod types to Mongoose types
{
String: createMongooseField(String),
Number: createMongooseField(Number),
Date: createMongooseField(Date),
Boolean: createMongooseField(Boolean),
Enum: createMongooseField(String)
// ... other zod types ...
},
)
// Create mongoose Schema from SchemaDefinition
type SchemaDoc = Document & z.infer<z.ZodObject<S>> // <- Infer the schema type
const mongooseSchema: Schema<SchemaDoc> = new Schema(mongooseSchemaDefinition)
// Build & return the mongoose model
const schemaModel = model<SchemaDoc>(schema.schemaName, mongooseSchema) as SchemaModel
return schemaModel
}
```
> **Note:** *This is a conceptual example. The actual implementation would be a bit (but not much) more complex and handle more edge cases. I'll link you my actual implementations at the end.*
To build a Mongoose model from a Zod schema, you'd use it like this:
```ts
// Import the schema and the transformer function
import { User } from './schemas'
import { schemaToMongoose } from './schemaToMongoose'
// Generate the Mongoose model from the Zod schema
const UserModel = schemaToMongoose(User) // <- Typed Mongoose model with `User` type
// Use the Mongoose model as you would any other
// It will apply & enforce the types inferred from the Zod schema
const user = new UserModel({
name: "John Doe",
age: 44,
birthdate: new Date("1980-01-01")
})
```
You could apply the same principle to generate other database modeling tools or ORMs like Prisma, TypeORM, Drizzle etc.
1. Build a transformer function that takes in a schema
2. Use introspection to extract metadata from the schema
3. Map the metadata to some other structure (like a DB schema)
4. Build the full database model from the transformed fields
5. Assign the types inferred from the Zod schema to the database model
> Now, if you need to change your database model, you only need to change the Zod schema. Typescript will automatically catch any errors in your codebase that need to be updated.
Pretty powerful, right?
---
## Generating Docs

Many don't feel like they have the time to write good documentation, even though they might see it as important.
What if you could attach the same Zod schema your React components use for types to generate docs from?
You'd need to parse the schema metadata and generate a markdown table or something like **Storybook controls** from it:
`schemaToStorybookDocs.ts`
```tsx
import { z, schema } from '@green-stack/schemas'
/* --- Prop Schema ----------------- */
const GreetingProps = schema('GreetingProps', {
name: z.string().example("John"),
})
/* --- <Greeting /> ---------------- */
// -i- React component that uses the schema's type inference
export const Greeting = ({ name }: z.infer<typeof GreetingProps>) => (
<h1>Welcome back, {name}! 👋</h1>
)
/* --- Documentation --------------- */
// -i- Export the schema for Storybook to use
export const docSchema = GreetingProps
```
> **Note:** *You'll need some node script to scan your codebase with e.g. glob and build `.stories.mdx` files for you though. In those generated markdown files, you'll map*
`schemaToStorybookDocs.ts`
```ts
// Similiar to the Mongoose example, but for Storybook controls
import { z, createSchemaPlugin } from '@green-stack/schemas'
/* --- schemaToStorybookDocs() ----- */
export const schemaToStorybookDocs = <S extends z.ZodRawShape>(schema: z.ZodObject<S>) => {
// ... Similar conceptual code to the Mongoose example ...
const createStorybookControl = (dataType, controlType) => (fieldKey, fieldMeta) => {
// ... Do stuff with metadata: defaultValue, exampleValue, isOptional, enum options etc ...
}
// Build the Storybook controls definition by mapping metadata to Storybook controls
const storybookControls = createSchemaPlugin(schema.introspect(),
{
// Map baseTypes to Storybook data (👇) & control (👇) types
Boolean: createStorybookControl('boolean', 'boolean'),
String: createStorybookControl('string', 'text'),
Number: createStorybookControl('number', 'number'),
Date: createStorybookControl('date', 'date'),
Enum: createStorybookControl('enum', 'select'), // <- e.g. Use a select dropdown for enums
// ... other zod types ...
},
)
// Return the Storybook controls
return storybookControls
}
```
Which, after codegen creates a `.stories.mdx` file that uses `schemaToStorybookDocs()`, might look something like this:

> **Demo:** *You can test out a full working example of Zod-powered Storybook docs here: [codinsonn.dev fully generated Storybook docs](https://main--63e8ae7f443d84f16518d4e5.chromatic.com/?path=/docs/packages-aetherspace-components-aethericon--aether-icon) (+ [Github Source](https://github.com/codinsonn/codinsonn.dev))*
---
## Resolvers and Databridges
---
My favorite example of building stuff around schemas is a concept I've dubbed a `DataBridge`
> You can think of a `DataBridge` as a way to bundle the metadata around a resolver function with the Zod schemas of its input and output.
For example, if we have a resolver function that works in both REST or GraphQL :
`healthCheck.bridge.ts`
```ts
import { z, schema } from '@green-stack/core/schemas'
import { createDataBridge } from '@green-stack/core/schemas/createDataBridge'
/* --- Schemas ----------------------------------------- */
export const HealthCheckArgs = schema('HealthCheckArgs', {
echo: z.string().describe("Echoes back the echo argument")
})
// Since we reuse the "echo" arg in the response, we can extend (👇) from the input schema
export const HealthCheckResponse = HealthCheckArgs.extendSchema('HealthCheckResponse', {
alive: z.boolean().default(true),
kicking: z.boolean().default(true),
})
/* --- Types ------------------------------------------- */
export type HealthCheckArgs = z.infer<typeof HealthCheckArgs>
export type HealthCheckResponse = z.infer<typeof HealthCheckResponse>
/* --- DataBridge -------------------------------------- */
export const healthCheckBridge = createDataBridge({
// Bundles the input & output schemas with the resolver metadata
argsSchema: HealthCheckArgs,
responseSchema: HealthCheckResponse,
// API route metadata
apiPath: '/api/health',
allowedMethods: ['GET', 'POST', 'GRAPHQL'],
// GraphQL metadata
resolverName: 'healthCheck',
})
```
You might wonder why we're defining this in a file that's separate from the actual resolver function.
The reason is that we can reuse this `DataBridge` on both the client and server side.
On the server side, image a wrapper `createResolver()` function that takes a function implementation as a first argument and the `DataBridge` as a second:
`healthCheck.resolver.ts`
```ts
// Helper function that integrates the resolver with the DataBridge
import { createResolver } from '@green-stack/core'
// Import the DataBridge we defined earlier
import { healthCheckBridge } from './healthCheck.bridge'
/* --- healthCheck() ----------------------------------- */
export const healthCheck = createResolver(({ args, parseArgs, withDefaults }) => {
// Handy helpers (☝️) from the DataBridge
// Typesafe Args from Databridge Input schema
const { echo } = args // <- { echo?: string }
// -- OR --
const { echo } = parseArgs() // <- { echo?: string }
// Check type match from the Databridge Output schema & apply defaults
return withDefaults({
echo,
alive: "", // <- Caught by Typescript, will have red squiggly line
kicking: undefined, // <- Defaults to `true`
})
}, healthCheckBridge)
// ☝️ Pass the DataBridge as the second argument to power types & resolver utils
```
Congrats. On the server side, you now have a fully typed resolver function that's bundled together with schemas of its input and output.
On the client, you could use just the DataBridge to build a REST fetcher or even build a GraphQL query from the bridge object, without conflicting with the server-side code.
While on the server, you could use the portable resolver bundle to generate your executable GraphQL schema from. Automagically.
Let's have a look at how that might be achieved.
---
## Zod for simplifying GraphQL
> Who thinks GraphQL is too complicated? 🙋♂
Let's bring our `healthCheck` resolver to GraphQL. We'll need to:
- Generate GraphQL schema definitions from the `healthCheckBridge`
- Generate a GraphQL query to call the `healthCheckBridge` query from the front-end
Again, we'll combine the introspection API for the `DataBridge` with a transformer function to generate the GraphQL schema and query:
`bridgeToSchema.ts`
```ts
// Similiar to the Mongoose & Docs example, but for a GraphQL-schema
import { z, createSchemaPlugin } from '@green-stack/core/schemas'
// ...
// -i- We'll need to run this for both the Args & Response schemas individually
const storybookControls = createSchemaPlugin(schema.introspect(),
{
// Map baseTypes to GraphQL-schema definitions
Boolean: createSchemaField('Boolean'),
String: createSchemaField('String'),
Number: createSchemaField('Float'), // <- e.g. Float! or Float
Date: createSchemaField('Date'), // <- e.g. Date! or Date (scalar)
Enum: createSchemaField('String'), // <- e.g. String! or String
// ... other zod types ...
Object: createSchemaField(field.schemaName) // <- Will need some recursion magic for nested schemas
},
)
```
Once applied and loaded into your GraphQL server, if your mapper function is set up correctly, you should be able to propagate even your descriptions from `z.{someType}.describe('...')` to your GraphQL schema:
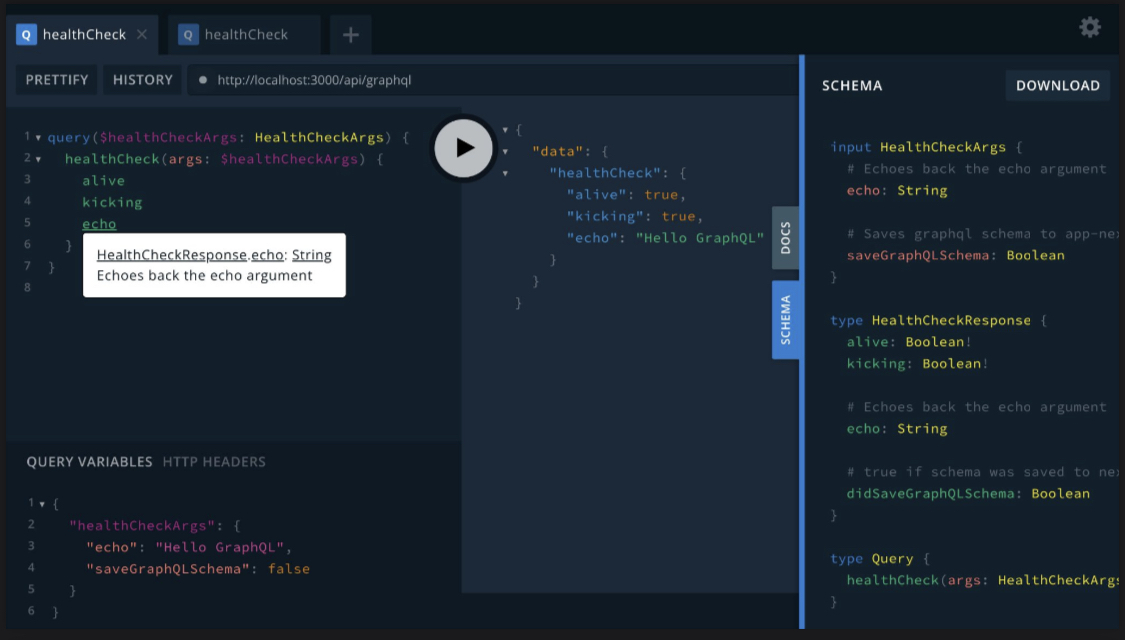
We now no longer need to maintain separate GraphQL schema definitions.
It's all derived from the Zod args and response schemas in the resolver's `DataBridge`.
With a bit of creativity, we could even generate the GraphQL query to call the `healthCheck` resolver from the front-end:
`healthCheck.query.ts`
```ts
// -i- Like types & schemas, we can import & reuse the bridge client-side
import { healthCheckBridge } from './healthCheck.bridge'
import { renderBridgeToQuery } from '@green-stack/schemas'
// -i- Generate a GraphQL query from the DataBridge
const healthCheckQuery = renderBridgeToQuery(healthCheckBridge)
/* -i- Resulting in the following query string:
`query($args: HealthCheckArgs) {
healthCheck(args: $args) {
echo
alive
kicking
}
}`
*/
```
Which you could then use to build a typed fetcher function:
`healthCheck.fetcher.ts`
```ts
const healthCheckFetcher = (args: z.infer<typeof healthCheckBridge.argsSchema>) => {
// -i- Fetch the query with the args (inferred from the schema ☝️)
const res = await fetch('/api/graphql', {
method: 'POST',
headers: {
'Content-Type': 'application/json',
// ...headers,
},
body: JSON.stringify({
query: healthCheckQuery,
variables
}),
})
// -i- Return the response (which you can type from the response schema 👇)
return res.data.healthCheck as z.infer<typeof healthCheckBridge.responseSchema>
}
```
> In the end, you get all the benefits of GraphQL while avoiding most extra boilerplate steps involved in maintaining it
---
## Scaffolding Forms?
As a final example, many only think of validation libraries like Zod for integrating them with their forms.
> But what if you could scaffold your forms from your Zod schemas on top?
`UserRegistrationForm.tsx`
```tsx
return (
<SchemaForm
schema={User}
/* With single sources of truth, */
/* ...what's stopping you from coding like this? */
schemaToInputs={{
String: (fieldMeta) => <input type="text" {...fieldMeta} />,
Number: (fieldMeta) => <input type="number" {...fieldMeta} />,
Date: (fieldMeta) => <input type="date" {...fieldMeta} />,
Boolean: (fieldMeta) => <input type="checkbox" {...fieldMeta} />,
Enum: (fieldMeta) => <select {...fieldMeta}>
}}
/>
)
```
---
## Even better DX with Codegen
---
All of this might still seem like a lot of manual linking between:
- Zod schemas
- Databridges & Resolvers
- Forms, Hooks, Components, Docs, APIs, Fetchers, etc.
> But even this can be automated with cli tools if you want it to be:
```bash
>>> Modify "your-codebase" using turborepo generators?
? Where would you like to add this schema? # -> @app/core/schemas
? What will you name the schema? (e.g. "User") # -> UserSchema
? Optional description: What will this schema be used for? # -> Keep track of user data
? What would you like to generate linked to this resolver?
> ✅ Database Model (Mongoose)
> ✅ Databridge & Resolver shell
> ✅ GraphQL Query / Mutation
> ✅ GET / POST / PUT / DELETE API routes
> ✅ Typed fetcher function
> ✅ Typed `formState` hook
> ✅ Component Docs
```
The sweet thing is, you don't need to build this all from scratch anymore...
> While there's no NPM package for this, where can you test working with Single Sources of Truth?
---
## FullProduct.dev ⚡️ Universal App Starterkit
---
I've been working on a project called [FullProduct.dev](https://fullproduct.dev) to provide a full-stack starterkit for building modern Universal Apps. Single sources of truth are a big part of that.
#### Like most time-saving templates, it will set you up with:
- Authentication
- Payments
- Email
- Scalable Back-end
- Essential UI components
> ❌ But those other boilerplates are usually *just for the web*, and *often don't have extensive docs* or an *optional recommended way of working* that comes with them.
> 🤔 You also often don't get to test the template before you buy it, and *might still have to spend time switching out parts you don't like* with ones you're used to.
---
## Why FullProduct.dev ⚡️ ?
✅ **Universal from the start** - Bridges gap between `Expo` & `Next.js`
✅ **Write-once UI** - Combines `NativeWind` & `React Native Web` for consistent look & feel on each device
✅ **Recommended way of working** - based on `Schemas`, `DataBridges` & Single Sources of Truth
✅ **Docs and Docgen** - Documentation that grows with you as you continue to build with schemas
✅ **Built for Copy-Paste** - Our way of working enables you to copy-paste full features between projects
✅ **Customizable** - Pick and choose from *inspectable & diffable* `git-based plugins`
> While **FullProduct.dev is still in active development,** *scheduled for a Product Hunt release in September 2024*, you can already explore its core concepts in the source-available **free demo** or the **previous iteration**:
- [**Aetherspace GREEN stack starter**](https://github.com/Aetherspace/green-stack-starter-demo#readme) - Previous iteration of FullProduct.dev ([docs](https://main--62c9a236ee16e6611d719e94.chromatic.com/?path=/story/aetherspace-quickstart--page))
- [**Universal Base Starter**](https://github.com/Aetherspace/universal-app-router) - Base FullProduct.dev starterkit, with plugin PRs ([docs](https://universal-base-starter-docs.vercel.app/))
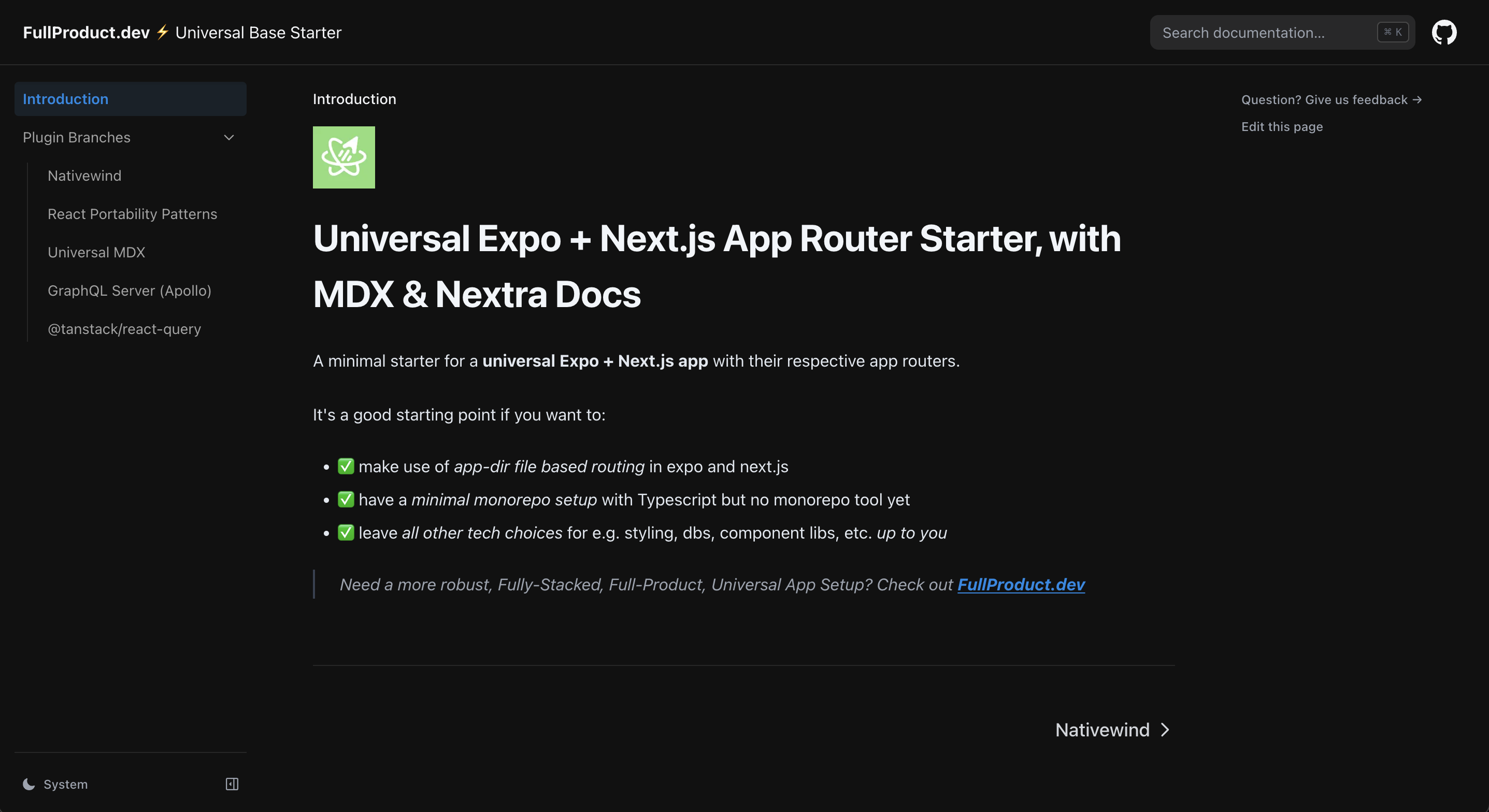
> The full working versions of the pseudo-code examples can also be found in these template repos:
To get started with them, use the Github UI to fork it and include all branches
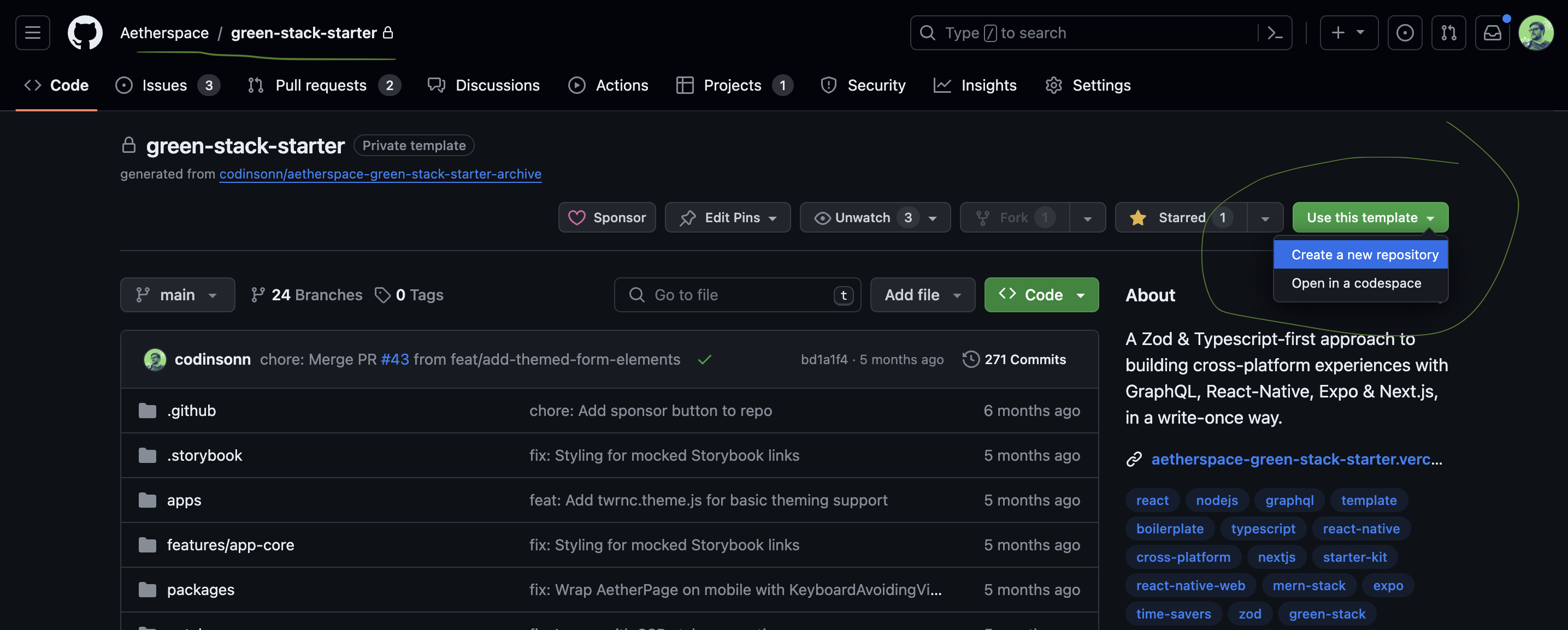
If you want to check what our `git-based plugins` might feel like:
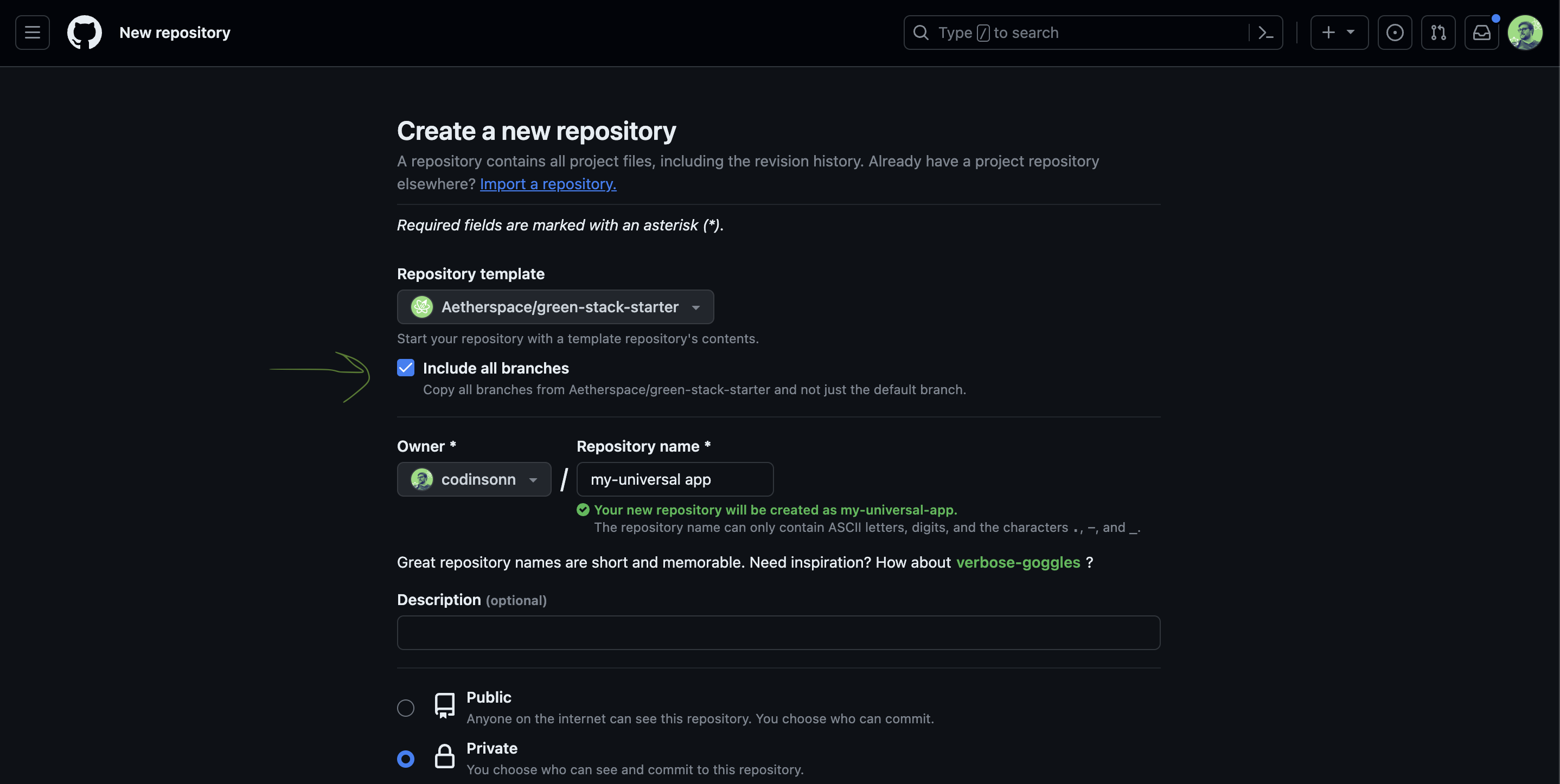
---
## Liked this article? 💚
---
Want to get regular updates on the `FullProduct.dev ⚡️` project?
Or learn more about single sources of truth, data bridges or Zod?
You can find the links to the source code / blog / socials on [**codinsonn.dev**](https://codinsonn.dev) ⚡️
Thank you for reading, hope you found it inspirational! 🙏
| codinsonn |
1,869,547 | How I Outranked Competitors and Dominated the SEO for ORNAZ | How I Boost seo Rankings for ornaz.com: A Step-by-Step Guide Introduction: Cracking the... | 0 | 2024-05-29T19:53:21 | https://ashutoshverma.com/get-perfect-seo-results-in-just-16-days/ | ornaz, seoboost, ecommerceoptimization | ---
title: How I Outranked Competitors and Dominated the SEO for ORNAZ
published: true
date: 2024-05-29 10:32:20 UTC
tags: ornaz, SEOBoost , EcommerceOptimization
canonical_url: https://ashutoshverma.com/get-perfect-seo-results-in-just-16-days/
---
**How I Boost seo Rankings for [ornaz.com](https://www.ornaz.com): A Step-by-Step Guide**
* * *
## Introduction: Cracking the Code of SEO Success
In my [last post](https://dev.to/ashutosh_verma/website-optimization-for-seo-purposes-3ppj), I delved into killer SEO strategies, busting myths like the notion that **SEO updates take an eternity and that climbing the ranks requires months of toil**. At [ornaz.com](ornaz.com), we proved these notions wrong, smashing our SEO goals in just 10 days. Within a week, we were trending everywhere, leaving people curious about our secret sauce. Well, get ready, because I’m about to spill the beans on how we nailed it at Ornaz, and how you can replicate our success. checkout google-shopping tab when
## Understanding Search Engines: The Basics
### Every Search Engine’s Mission
The primary goal of any search engine is to provide users with the most relevant and user-friendly results. To accomplish this, search engines need to thoroughly understand your website and its intended audience. This entails strategically incorporating high-ranking keywords related to your content to help search engines like Google grasp your website’s purpose effortlessly.
## Step 1: Keyword Research
### Identifying Your Target Audience
To kick off your SEO journey, start with pinpointing your target audience. Utilize tools like Google Ads and Google Analytics to refine your audience targeting. By uploading your user list and leveraging Google Analytics to pass essential user details, you provide Google with a clear picture of your audience, enhancing your targeting precision.
### Using Keyword Tools
Tools such as [SEMrush](https://www.semrush.com/) and [Ubersuggest](https://neilpatel.com/ubersuggest/) are your best friends when it comes to identifying top-ranking keywords in your industry. Keep a close eye on your competitors’ traffic and snag their high-performing keywords. Integrate these keywords into your content strategy to elevate your SEO game and stay ahead of the curve.
### Embracing Long-Tail Keywords
In the realm of SEO, generic, template-based, or overly long-phrased content won’t cut it. Google favors uniqueness and engagement. Opt for long-tail keywords that align closely with user intent, and steer clear of AI-generated or repetitive content. At Ornaz, we humanized our SEO titles, descriptions, and keywords generated by AI, ensuring authenticity and relevance.
## Step 2: On-Page SEO: Optimizing for Success
### Optimizing Meta Tags
Meta tags play a pivotal role in helping search engines understand and display your content. At ornaz.com, we’ve implemented comprehensive meta tags to enhance our SEO. Peek into our page source to witness our meticulous implementation. please refer [ornaz.com](ornaz.com) to explore variety of meta tags.
### Optimization Image alt text
Images are more than just eye candy; they can significantly impact your SEO. Opt for descriptive alt text rich in high-ranking keywords.
### Leveraging Tag Attributes
Attributes like “rel” attribute follow play a crucial role in SEO. Ensure you understand their significance and implement them effectively to optimize your website’s search engine visibility.
## Step 3: Technical SEO: Building a Solid Foundation
### Image Compression
Efficient image compression can drastically reduce your page load times. At Ornaz, we prioritize image optimization by converting most images into optimized versions, resulting in a substantial decrease in page size upto 80%, [tinypng](tinypng.com) is best for image compression.
### Enhancing Site Speed
Speed matters in the digital realm. By serving static content with a 7-day cache policy from a CDN with a lightning-fast response time, we achieved remarkable improvements in site speed. please refer my previous post [ornaz-desktop-lighthouse-metrices](https://dev.to/ashutosh_verma/ornaz-the-e-commerce-revolution-is-here-say-goodbye-to-slow-websites-4lli)
### Embracing SSL
Secure Sockets Layer (SSL) is non-negotiable in today’s cyber landscape. By targeting the latest TLS version 1.3, we fortified our website’s security and bolstered our SEO performance. SSL employs multiplexing to enhance load speed. However, SSL chaining can lead to higher SSL/TLS decryption latency.
### Harnessing JSON-LD
JSON-LD is a potent tool for providing structured data to Google. By embedding JSON-based information within our pages, we enriched Google’s understanding of our content, thereby enhancing our visibility in search results. here are some visible results that come from json-ld data.





Impressive isn’t it? Here’s how you can also do this:
1. **FAQs** : [Refer this FAQ](https://d3d5st4bexye3p.cloudfront.net/json_ld_v1/general/faq_1058d6d4.json).
2. **Homepage** : Add Author, Reviews, and Organization details [Refer this for Homepage](https://d3d5st4bexye3p.cloudfront.net/json_ld_v1/general/homepage_1089d5bb.json).
3. **Catalog Page** : [Refer this for Catalog Schema](https://d3d5st4bexye3p.cloudfront.net/json_ld_v1/category/rings-iframe_22f70227.json) for catalog pages.
4. **PDP Pages** : [Refer this for PDP schema](https://d3d5st4bexye3p.cloudfront.net/json_ld_v1/product/1183_brenda_1054efdc.json) for product detail pages.
5. **Articles and Tutorials** : Please refer to [Google’s structured data documentation](https://developers.google.com/search/docs/appearance/structured-data/article).
## Step 4: SEO-Friendly HTML5 Tags: Structuring for Success
### Leveraging SEO-Friendly HTML5 Tags
HTML5 offers a plethora of tags optimized for SEO, from “header” to “footer” and everything in between. By structuring our website with these tags, we enhanced crawlability and indexing, propelling our SEO endeavors forward.
### Steering Clear of Client-Side Rendering
While Google can execute JavaScript, client-side rendering may hinder your SEO efforts. Whenever possible, opt for server-side rendering to expedite page load times and improve first contentful paint (FCP).
### Rejecting Cloaking
Cloaking, the practice of presenting different content to search engines and users, is a surefire way to incur Google’s wrath. Focus on delivering valuable, user-centric content rather than resorting to deceptive tactics.
## Final Step: Monitoring and Analytics: Fine-Tuning Your Strategy
### Harnessing Google Analytics
Google Analytics serves as your SEO command center, providing invaluable insights into your website’s performance. Monitor metrics like organic traffic, bounce rate, and conversion rates to gauge the effectiveness of your SEO efforts.
### Tracking SEO Metrics
In addition to Google Analytics, tools like Google Search Console offer a treasure trove of data to refine your SEO strategy. Keep a close eye on keyword rankings, click-through rates, and backlinks to continually optimize your approach.
## Conclusion: Empowering Your SEO Journey
* * *
### FAQs: Unlocking the Mysteries of SEO
**Q1: How long does it take to see results from SEO efforts?** A1: While SEO isn’t an overnight miracle, diligent optimization can yield noticeable results within weeks, as demonstrated by our experience at Ornaz.
**Q2: Is SEO a one-time effort, or does it require ongoing maintenance?** A2: SEO is an ongoing endeavor that demands consistent attention and adaptation to evolving algorithms and user behavior.
**Q3: Can I boost my SEO rankings through paid advertising alone?** A3: Paid advertising can complement your SEO strategy, but sustainable long-term success requires a holistic approach encompassing both organic and paid tactics.
**Q4: Are backlinks still relevant for SEO in 2024?** A4: Absolutely! High-quality backlinks remain a cornerstone of effective SEO, signaling to search engines the credibility and authority of your website.
**Q5: How can I recover from a Google penalty due to black hat SEO tactics?** A5: Recovery from a Google penalty entails rectifying the offending practices, submitting a reconsideration request, and implementing white hat SEO strategies to rebuild trust with search engines.
## 
By implementing the strategies outlined in this guide and staying vigilant in monitoring your SEO performance, you’re well-equipped to ascend the ranks and claim your rightful place atop the search engine results pages. Happy optimizing!
### Conclusion:
after doing this I was able to get much better SEO results and we were trending everywhere. here is a quick sneak peek of better and formatted results.
#### Perfect Product tagging with filters in Google Image search results:

#### Json-ld reflects on people and also includes a question section:

#### Formatted results for products including ratings and other details on Google search results:

#SEO #DigitalMarketing #SEOStrategy #KeywordResearch #OnPageSEO #TechnicalSEO #ContentMarketing #JSONLD #WebsiteOptimization #GoogleRankings #MetaTags #SearchEngineOptimization | ashutosh_verma |
1,868,861 | 14x6'3" Car Carrier Open Floor Tandem Trailer | OTAL INC GST - $4,650.00 Discover the versatility of our 14x6'3" car carrier open floor tandem... | 0 | 2024-05-29T10:31:27 | https://dev.to/henry_anderson_03cafb1480/14x63-car-carrier-open-floor-tandem-trailer-4hhh | OTAL INC GST - $4,650.00
Discover the versatility of our 14x6'3" car carrier open floor tandem trailer. Perfect for transporting vehicles, it features a durable open floor design and tandem axles for enhanced stability. Ideal for both personal and commercial use, this trailer ensures a secure and efficient transport solution for all your needs. Get yours today!
To Shop know visit here: https://moderntrailers.com.au/product/car-carrier-basic-4200x1900/
 | henry_anderson_03cafb1480 | |
1,868,860 | FORTUNA38 : Daftar Resmi Situs Fortuna 38 Slot Gacor Gampang Menang 2024 | Ayo daftar login akun Fortuna38 ambil kemenanganmu sekarang! | 0 | 2024-05-29T10:31:22 | https://dev.to/fortuna38gacor/fortuna38-daftar-resmi-situs-fortuna-38-slot-gacor-gampang-menang-2024-267p | slotgacor |
Ayo [daftar login ](https://fortuna-38.com/)akun Fortuna38 ambil kemenanganmu sekarang! | fortuna38gacor |
1,868,859 | Analogue Processors are coming back | There have been some discussions about starting to use analogue processors rather than Digital... | 0 | 2024-05-29T10:31:18 | https://dev.to/rusandu_dewm_galhena/analogue-comeback-dg9 | news, hardware, productivity, performance | There have been some discussions about starting to use analogue processors rather than Digital processors. This Post is to talk about them.
## What is an analogue processor?.
An analogue processor is a type of computer processor that works with continuous, real-world data such as sound, light, and temperature. It doesn’t convert the data into digital form, but processes it directly, which can make it more efficient for certain tasks. This is different from a digital processor, which works with data that has been converted into a binary format. Analogue processors were common before the digital era, and they’re making a comeback in some areas of technology today.
## Different to consider Between Analogue and Digital Processors
**Signal**: Analogue processors work with continuous signals which represent physical measurements1. On the other hand, digital processors work with discrete time signals generated by digital modulation.
**Representation**: Analogue processors use a continuous range of values to represent information1. Digital processors, however, use discrete or discontinuous values to represent information.
**Technology**: Analogue technology records waveforms as they are. Digital technology samples analogue waveforms into a limited set of numbers and records them.
**Data Transmissions**: Analogue transmissions are subjected to deterioration by noise during transmission and write/read cycle. Digital transmissions can be noise-immune without deterioration during transmission and write/read cycle.
**Response to Noise**: Analogue processors are more likely to get affected by noise, reducing accuracy1. Digital processors are less affected since noise responses are analogue in nature.
**Flexibility**: Analogue hardware is not flexible1. Digital hardware is flexible in implementation.
**Uses**: Analogue processors are best suited for audio and video transmission1. Digital processors are best suited for computing and digital electronics.
**Bandwidth**: Analogue signal processing can be done in real time and consumes less bandwidth1. There is no guarantee that digital signal processing can be done in real time and it consumes more bandwidth to carry out the same information.
**Memory**: Analogue processors store data in the form of wave signal1. Digital processors store data in the form of binary bit1.
Power: Analogue instruments draw large power1. Digital instruments draw only negligible power.
**Cost**: Analogue processors are generally low cost and portable1. Digital processors are generally high cost and not easily portable1.
Impedance: Analogue processors have low impedance1. Digital processors have high order of 100 megaohm.
**Errors**: Analogue instruments usually have a scale which is cramped at lower end and give considerable observational errors1. Digital instruments are free from observational errors like parallax and approximation errors.
In summary, while both types of processors have their own advantages and applications, the choice between analogue and digital depends on the specific requirements of the task at hand.
## Advantages of using Analogue Processors
Analogue computers could be part of the solution to this sensor power problem. These are the types of computers we relied on before digital computers, and they don’t need to translate their inputs into any special computer language before they can process it and deliver a meaningful output.
With the use of responses to noise and with no need of having more power in some devices to convert analogue to digital, Analogue processors show an advantage in saving power.
| rusandu_dewm_galhena |
1,865,539 | I developed a VSCode client for Bluesky | Hello. I am a Japanese high school student. This is my first time writing an article in English, so... | 27,546 | 2024-05-29T10:31:17 | https://medium.com/@zuk246/i-developed-a-vscode-client-for-bluesky-c0295b96fd60 | vscode, bluesky, client | Hello. I am a Japanese high school student.
This is my first time writing an article in English, so there might be some mistakes. I am using a translation tool.
I have developed a VSCode client for Bluesky.
[VSCode marketplace](https://marketplace.visualstudio.com/items?itemName=zuk246.blueriver)
This is a VSCode extension for the Bluesky client. It includes features such as posting, viewing timelines, checking notifications, and liking posts. It also supports a multi-column view and a notification status bar. I plan to add more features in the future.
## Links
- [VSCode Marketplace](https://marketplace.visualstudio.com/items?itemName=zuk246.blueriver)
- [GitHub](https://github.com/zuk246/BlueRiver)
- [Medium (How to Use)](https://medium.com/@zuk246/i-developed-a-vscode-client-for-bluesky-c0295b96fd60)
## Future Plans
In future updates, I plan to add more features. For example, custom filters, detailed notification views, and user interface improvements are being considered. I also welcome feedback from everyone. Please share your thoughts and suggestions.
## Contributing to GitHub
The GitHub repository is available under the MIT License. Bug reports and pull requests are welcome. If you would like to contribute, please fork the repository on GitHub, create a new branch, make your changes, and submit a pull request. I appreciate your help in improving the code quality and adding new features.
Thank you for reading. If you find this extension useful, I would be grateful if you could follow me on Twitter and Bluesky.
- Bluesky: https://bsky.app/profile/zuk246.net
- Twitter: https://x.com/zuk246
| zuk246 |
1,868,857 | The Unseen Crisis: Missing Children | Certainly! Here's the revised article without the questions: The Unseen Crisis: Missing... | 0 | 2024-05-29T10:30:07 | https://dev.to/anonymous2029/the-unseen-crisis-missing-children-5b3k | webdev, missingchildren, osint, beginners | Certainly! Here's the revised article without the questions:
---
### The Unseen Crisis: Missing Children
Every day, children go missing around the world, including in India. For most people, this is a remote problem, a statistic they read about in the news. However, the reality is that these missing children often face grim fates. They can be trapped in prostitution, sex trafficking, child labor, organ trafficking rings, illegal adoption networks, and other dark corners of the criminal underworld. This article aims to highlight this urgent issue and suggest a way for individuals to actively participate in solving real missing persons cases in India, using online tools and resources.
#### The Scale of the Problem
In India, the number of missing children is staggering. According to data from the National Crime Records Bureau (NCRB), over 47,000 children were reported missing in a single year, with 71% of them being girls. These children are often from vulnerable backgrounds, making them easy targets for various forms of exploitation.
#### The Role of Trace Labs and OSINT
In the United States, an organization called Trace Labs is making significant strides in solving missing persons cases using Open Source Intelligence (OSINT). OSINT involves gathering information from publicly available sources to conduct investigations. Trace Labs organizes events through their Discord server where participants work on real cases and compete for rewards. Interestingly, many Indians participate in these events, leveraging their skills to help find missing persons abroad.
#### Why Not Here?
Given the success of Trace Labs, it's perplexing that a similar initiative isn't as prominent in India. With the right tools and a bit of training, individuals can contribute to solving missing children cases locally. This not only helps the police but can also provide recognition and rewards.
#### Getting Started with OSINT in India
To work on missing persons cases in India, you can utilize the government's website [TrackTheMissingChild](https://trackthemissingchild.gov.in/trackchild/photograph_missing.php?type=2#). This site keeps track of missing and found children. Here's a step-by-step guide to getting started:
1. **Visit the TrackTheMissingChild Website**: Go to the [TrackTheMissingChild](https://trackthemissingchild.gov.in/trackchild/photograph_missing.php?type=2#) website to find details of missing children.
2. **Search for Missing Children**: Use the search functionality to look up missing persons. You can fill in as many details as you have. If you don’t have specific details, simply enter the name and proceed.
3. **Check Status**: If the missing person's status has not been updated immediately after being found, you can cross-reference this information using the "Quick Search" feature on the same site.
4. **Report Findings**: Once you find relevant information, you can contact the police station via email or other contact details provided on the site.
#### The Challenge of Real-Time Updates
One challenge is that the site may not update immediately when a missing person is found. However, the "Quick Search" function allows you to check the most current status. Fill in the available details and search to see if the person has been found. If not, you can still gather information that might help in locating them.
#### The Bigger Picture
This initiative is not just about solving individual cases but also about raising awareness. By participating, you become part of a community dedicated to bringing missing children home. Even if you are new to OSINT, you can learn the basics and contribute effectively.
#### Looking Ahead
Stay tuned for more detailed articles on how to use OSINT techniques to investigate missing persons cases. In the meantime, take a look at [this resource](https://osintframework.com/) until I return with my next article on OSINT in detail.
#### Sources
1. [TrackTheMissingChild](https://trackthemissingchild.gov.in/trackchild/photograph_missing.php?type=2#)
2. [TrackTheMissingChild Quick Search](https://trackthemissingchild.gov.in/trackchild/index.php)
3. [NCRB Data on Missing Children](https://theprint.in/india/more-than-47000-children-missing-in-india-71-are-girls-shows-ncrb-data/1880048/)
4. [New Guidelines for Missing Person Cases](https://timesofindia.indiatimes.com/city/vijayawada/cops-get-new-guidelines-for-missing-person-cases/articleshow/74618150.cms)
5. [Indian Kanoon on Law of Missing Persons](https://indiankanoon.org/docfragment/1199423/?formInput=law%20of%20missing%20persons)
Take a look at these sources for additional information.
By leveraging the power of the internet and collective effort, we can make significant strides in addressing the issue of missing children. Let’s use our skills and resources to create a safer world for the most vulnerable among us.
If you have any questions about this article, feel free to ask in the comment section. | anonymous2029 |
1,868,854 | Implement Haskell's G-Machine in MoonBit (Part 2) | This article is the second in the series on implementing lazy evaluation in MoonBit. In the first... | 0 | 2024-05-29T10:28:27 | https://dev.to/zachyee/implement-haskells-g-machine-in-moonbit-part-2-3e4a | beginners, tutorial, programming, haskell |
This article is the second in the series on implementing lazy evaluation in MoonBit. In the [first part](https://dev.to/zachyee/implementing-haskells-lazy-evaluation-in-moonbit-111), we explored the purposes of lazy evaluation and a typical abstract machine for lazy evaluation, the G-Machine, and implemented some basic G-Machine instructions. In this article, we will further extend the G-Machine implementation from the previous article to support `let` expressions and basic arithmetic, comparison, and other operations.
## let Expressions
The `let` expression in coref differs slightly from that in MoonBit. A `let` expression can create multiple variables but can only be used within a limited scope. Here is an example:
```rust
{
let x = n + m
let y = x + 42
x * y
}
```
Equivalent coref expression:
```clojure
(let ([x (add n m)]
[y (add x 42)])
(mul x y)) ;; xy can only be used within let
```
It is important to note that coref's `let` expressions must follow a sequential order. For example, the following is not valid:
```clojure
(let ([y (add x 42)]
[x (add n m)])
(mul x y))
```
In contrast, `letrec` is more complex as it allows the local variables defined to reference each other without considering the order of their definitions.
Before implementing `let` (and the more complex `letrec`), we first need to modify the current parameter passing method. The local variables created by `let` should intuitively be accessed in the same way as parameters, but the local variables defined by `let` do not correspond to `NApp` nodes. Therefore, we need to adjust the stack parameters before calling the supercombinator.
The adjustment is done in the implementation of the `Unwind` instruction. If the supercombinator has no parameters, it is the same as the original unwind. When there are parameters, the top address of the supercombinator node is discarded, and the `rearrange` function is called.
```rust
fn rearrange(self : GState, n : Int) -> Unit {
let appnodes = take(self.stack, n)
let args = map(fn (addr) {
let NApp(_, arg) = self.heap[addr]
arg
}, appnodes)
self.stack = append(args, drop(appnodes, n - 1))
}
```
The `rearrange` function assumes that the first N addresses on the stack point to a series of `NApp` nodes. It keeps the bottommost one (used as Redex update), cleans up the top N-1 addresses, and then places N addresses that directly point to the parameters.
After this, both parameters and local variables can be accessed using the same command by changing the `PushArg` instruction to a more general `Push` instruction.
```rust
fn push(self : GState, offset : Int) -> Unit {
// Copy the address at offset + 1 to the top of the stack
// Push(n) a0 : . . . : an : s
// => an : a0 : . . . : an : s
let appaddr = nth(self.stack, offset)
self.putStack(appaddr)
}
```
The next issue is that we need something to clean up. Consider the following expression:
```clojure
(let ([x1 e1]
[x2 e2])
expr)
```
After constructing the graph corresponding to the expression `expr`, the stack still contains addresses pointing to e1 and e2 (corresponding to variables x1 and x2), as shown below (the stack grows from bottom to top):
```
<Address pointing to expr>
|
<Address pointing to x2>
|
<Address pointing to x1>
|
...remaining stack...
```
Therefore, we need a new instruction to clean up these no longer needed addresses. It is called `Slide`. As the name suggests, the function of `Slide(n)` is to skip the first address and delete the following N addresses.
```rust
fn slide(self : GState, n : Int) -> Unit {
let addr = self.pop1()
self.stack = Cons(addr, drop(self.stack, n))
}
```
Now we can compile `let`. We will compile the expressions corresponding to local variables using the `compileC` function. Then, traverse the list of variable definitions (`defs`), compile and update the corresponding offsets in order. Finally, use the passed `comp` function to compile the main expression and add the `Slide` instruction to clean up the unused addresses.
> Compiling the main expression using the passed function makes it easy to reuse when adding subsequent features.
```rust
fn compileLet(comp : (RawExpr[String], List[(String, Int)]) -> List[Instruction], defs : List[(String, RawExpr[String])], expr : RawExpr[String], env : List[(String, Int)]) -> List[Instruction] {
let (env, codes) = loop env, List::Nil, defs {
env, acc, Nil => (env, acc)
env, acc, Cons((name, expr), rest) => {
let code = compileC(expr, env)
// Update offsets and add offsets for local variables corresponding to name
let env = List::Cons((name, 0), argOffset(1, env))
continue env, append(acc, code), rest
}
}
append(codes, append(comp(expr, env), List::[Slide(length(defs))]))
}
```
The semantics of `letrec` are more complex - it allows the N variables within the expression to reference each other, so we need to pre-allocate N addresses and place them on the stack. We need a new instruction: `Alloc(N)`, which pre-allocates N `NInd` nodes and pushes the addresses onto the stack sequentially. The addresses in these indirect nodes are negative and only serve as placeholders.
```rust
fn allocNodes(self : GState, n : Int) -> Unit {
let dummynode : Node = NInd(Addr(-1))
for i = 0; i < n; i = i + 1 {
let addr = self.heap.alloc(dummynode)
self.putStack(addr)
}
}
```
The steps to compile letrec are similar to `let`:
+ Use `Alloc(n)` to allocate N addresses.
+ Use the `loop` expression to build a complete environment.
+ Compile the local variables in `defs`, using the `Update` instruction to update the results to the pre-allocated addresses after compiling each one.
+ Compile the main expression and use the `Slide` instruction to clean up.
```rust
fn compileLetrec(comp : (RawExpr[String], List[(String, Int)]) -> List[Instruction], defs : List[(String, RawExpr[String])], expr : RawExpr[String], env : List[(String, Int)]) -> List[Instruction] {
let env = loop env, defs {
env, Nil => env
env, Cons((name, _), rest) => {
let env = List::Cons((name, 0), argOffset(1, env))
continue env, rest
}
}
let n = length(defs)
fn compileDefs(defs : List[(String, RawExpr[String])], offset : Int) -> List[Instruction] {
match defs {
Nil => append(comp(expr, env), List::[Slide(n)])
Cons((_, expr), rest) => append(compileC(expr, env), Cons(Update(offset), compileDefs(rest, offset - 1)))
}
}
Cons(Alloc(n), compileDefs(defs, n - 1))
}
```
## Adding Primitives
From this step, we can finally perform basic integer operations such as arithmetic, comparison, and checking if two numbers are equal. First, modify the `Instruction` type to add related instructions.
```rust
Add
Sub
Mul
Div
Neg
Eq // ==
Ne // !=
Lt // <
Le // <=
Gt // >
Ge // >=
Cond(List[Instruction], List[Instruction])
```
At first glance, implementing these instructions seems simple. Take `Add` as an example: just pop two top addresses from the stack, retrieve the corresponding numbers from memory, perform the operation, and push the result address back onto the stack.
```rust
fn add(self : GState) -> Unit {
let (a1, a2) = self.pop2() // Pop two top addresses
match (self.heap[a1], self.heap[a2]) {
(NNum(n1), NNum(n2)) => {
let newnode = Node::NNum(n1 + n2)
let addr = self.heap.alloc(newnode)
self.putStack(addr)
}
......
}
}
```
However, the next problem we face is that this is a lazy evaluation language. The parameters of `add` are likely not yet computed (i.e., not `NNum` nodes). We also need an instruction that can force a computation to give a result or never stop computing. We call it `Eval` (short for Evaluation).
> In jargon, the result of such a computation is called Weak Head Normal Form (WHNF).
At the same time, we need to modify the structure of `GState` and add a state called `dump`. Its type is `List[(List[Instruction], List[Addr])]`, used by `Eval` and `Unwind` instructions.
The implementation of the `Eval` instruction is not complicated:
+ Pop the top address of the stack.
+ Save the current unexecuted instruction sequence and stack (by putting them into the dump).
+ Clear the current stack and place the previously saved address.
+ Clear the current instruction sequence and place the `Unwind` instruction.
> This is similar to how strict evaluation languages handle saving caller contexts, but practical implementations would use more efficient methods.
```rust
fn eval(self : GState) -> Unit {
let addr = self.pop1()
self.putDump(self.code, self.stack)
self.stack = List::[addr]
self.code = List::[Unwind]
}
```
This simple definition requires modifying the `Unwind` instruction to restore the context when `Unwind` in the `NNum` branch finds that there is a recoverable context (`dump` is not empty).
```rust
fn unwind(self : GState) -> Unit {
let addr = self.pop1()
match self.heap[addr] {
NNum(_) => {
match self.dump {
Nil => self.putStack(addr)
Cons((instrs, stack), restDump) => {
// Restore the stack
self.stack = stack
self.putStack(addr)
self.dump = restDump
// Return to original code execution
self.code = instrs
}
}
}
......
}
}
```
Next, we need to implement arithmetic and comparison instructions. We use two functions to simplify the form of binary operations. The result of the comparison instruction is a boolean value, and for simplicity, we use numbers to represent it: 0 for `false`, 1 for `true`.
```rust
fn liftArith2(self : GState, op : (Int, Int) -> Int) -> Unit {
// Binary arithmetic operations
let (a1, a2) = self.pop2()
match (self.heap[a1], self.heap[a2]) {
(NNum(n1), NNum(n2)) => {
let newnode = Node::NNum(op(n1, n2))
let addr = self.heap.alloc(newnode)
self.putStack(addr)
}
(node1, node2) => abort("liftArith2: \(a1) = \(node1) \(a2) = \(node2)")
}
}
fn liftCmp2(self : GState, op : (Int, Int) -> Bool) -> Unit {
// Binary comparison operations
let (a1, a2) = self.pop2()
match (self.heap[a1], self.heap[a2]) {
(NNum(n1), NNum(n2)) => {
let flag = op(n1, n2)
let newnode = if flag { Node::NNum(1) } else { Node::NNum(0) }
let addr = self.heap.alloc(newnode)
self.putStack(addr)
}
(node1, node2) => abort("liftCmp2: \(a1) = \(node1) \(a2) = \(node2)")
}
}
// Implement negation separately
fn negate(self : GState) -> Unit {
let addr = self.pop1()
match self.heap[addr] {
NNum(n) => {
let addr = self.heap.alloc(NNum(-n))
self.putStack(addr)
}
otherwise => {
// If not NNum, throw an error
abort("negate: wrong kind of node \(otherwise), address \(addr) ")
}
}
}
```
Finally, implement branching:
```rust
fn condition(self : GState, i1 : List[Instruction], i2 : List[Instruction]) -> Unit {
let addr = self.pop1()
match self.heap[addr] {
NNum(0) => {
// If false, jump to i2
self.code = append(i2, self.code)
}
NNum(1) => {
// If true, jump to i1
self.code = append(i1, self.code)
}
otherwise => abort("cond : \(addr) = \(otherwise)")
}
}
```
No major adjustments are needed in the compilation part, just add some predefined programs:
```rust
let compiledPrimitives : List[(String, Int, List[Instruction])] = List::[
// Arithmetic
("add", 2, List::[Push(1), Eval, Push(1), Eval, Add, Update(2), Pop(2), Unwind]),
("sub", 2, List::[Push(1), Eval, Push(1), Eval, Sub, Update(2), Pop(2), Unwind]),
("mul", 2, List::[Push(1), Eval, Push(1), Eval, Mul, Update(2), Pop(2), Unwind]),
("div", 2, List::[Push(1), Eval, Push(1), Eval, Div, Update(2), Pop(2), Unwind]),
// Comparison
("eq", 2, List::[Push(1), Eval, Push(1), Eval, Eq, Update(2), Pop(2), Unwind]),
("neq", 2, List::[Push(1), Eval, Push(1), Eval, Ne, Update(2), Pop(2), Unwind]),
("ge", 2, List::[Push(1), Eval, Push(1), Eval, Ge, Update(2), Pop(2), Unwind]),
("gt", 2, List::[Push(1), Eval, Push(1), Eval, Gt, Update(2), Pop(2), Unwind]),
("le", 2, List::[Push(1), Eval, Push(1), Eval, Le, Update(2), Pop(2), Unwind]),
("lt", 2, List::[Push(1), Eval, Push(1), Eval, Lt, Update(2), Pop(2), Unwind]),
// Miscellaneous
("negate", 1, List::[Push(0), Eval, Neg, Update(1), Pop(1), Unwind]),
("if", 3, List::[Push(0), Eval, Cond(List::[Push(1)], List::[Push(2)]), Update(3), Pop(3), Unwind])
]
```
and modify the initial instruction sequence
```rust
let initialCode : List[Instruction] = List::[PushGlobal("main"), Eval]
```
## Conclusion
In the next part, we will improve the code generation for primitives and add support for data structures. | zachyee |
1,868,853 | FORTUNA38 : Daftar Resmi Situs Fortuna 38 Slot Gacor Gampang Menang 2024 | FORTUNA38 : Daftar Resmi Situs Fortuna 38 Slot Gacor Gampang Menang 2024 FORTUNA38 adalah situs slot... | 0 | 2024-05-29T10:28:27 | https://dev.to/fortuna38gacor/fortuna38-daftar-resmi-situs-fortuna-38-slot-gacor-gampang-menang-2024-9mm | slot, slotgacor, slotmaxwin, slotgampangmaxwin | FORTUNA38 : [Daftar](https://fortuna-38.com/) Resmi Situs Fortuna 38 Slot Gacor Gampang Menang 2024
FORTUNA38 adalah situs slot gacor resmi yang memberikan permainan yang terlengkap tentunya gampang menang tahun 2024.
Ayo [daftar login](https://fortuna-38.com/
) akun Fortuna38 ambil kemenanganmu sekarang! | fortuna38gacor |
1,868,852 | Make a React introvert Component (What?🤨) | (2024-05-30: Added working example) What the heck does that mean? Today I'm going to break a React... | 0 | 2024-05-29T10:28:11 | https://dev.to/composite/make-a-react-introvert-component-what-2jao | javascript, webdev, react, nextjs | *(2024-05-30: Added working example)*
What the heck does that mean?
Today I'm going to break a React feature that I've been using for a while now.
The `React.lazy` function is mainly for lazy importing of external components, and in general, the official documentation will tell you to write it like this:
```jsx
export const MyExternalComponent = React.lazy(() =>
import('./path/to/my/component')
)
```
This is a popular optimization recommendation that wraps a `<Suspense>` component around a component declared with the `export default` statement in an external component file and imports it on the first call to save resources.
Right. It must be the component that you declared with the `export default` statement. not a named export.
As you'll see when you write a dynamic `import` statement, if you want to lazy load something that you've declared other than `default export`, you have to return an object with the `default` property.
```jsx
export const MyExternalComponent = React.lazy(() =>
import('./path/to/my/component')
.then(({ OtherComponent }) => ({ default: OtherComponent }))
)
```
Or you can install [`react-lazly`](https://www.npmjs.com/package/react-lazily) package instead to make it more flexible.
From this feature, I came up with a brilliant idea.
```jsx
export const IntrovertComponent = React.lazy(() =>
fetch('/path/to/api')
.then(res => res.json())
.then(json => {
const MyComponent = () => {
return <pre>{JSON.stringify(json, null, 2)}</pre>
}
return { default: MyComponent }
})
```
You might be wondering if the above code will work, right?
The short answer is yes. It will work.
Let's see in action.
{% embed https://stackblitz.com/edit/vitejs-vite-gadhoh?embed=1&file=src%2FApp.jsx&hideExplorer=1 %}
Why?
React doesn't care if there's an `import` statement in the function body or not. We're not necessarily using the Webpack bundler, so it's a pain for them to analyze the bundler's code output.
Instead, the value is in the ability to defer the `import` statement.
Anyway, the argument to the `lazy` function accepts a function that returns a `Promise` instance, so it doesn't have to be an `import` statement, just a `Promise` object.
It'll useful when:
- Lazly loads 3rd party quite complex libraries before initializing your compoenent
- Lazly loads API and applies to your component(but once)
- Lazly loads your component that avoids SSR for some external reasons
Instead, there is one thing to keep in mind.
This behavior will be out of the purpose of the `lazy` function.
Its original purpose is to optimize component resources with `import`, but since you declared this code inline, you'll be far from optimizing resources.
I hope that in the upcoming React 19, do not implement this nonsense and create a normal component with a `use` hook function.
The `dynamic` provided by Next.js can be implemented in the same way. In particular, since the initialization function of the `Plotly` library I was using returns a `Promise`, I implemented the following to create a pure client component away from SSR. [See also my original post](https://dev.to/composite/how-to-integrate-plotlyjs-on-nextjs-14-with-app-router-1loj)
```jsx
export const Plotly = dynamic(
() =>
import('plotly.js/dist/plotly.js').then(({ newPlot, purge }) => {
const Plotly = forwardRef(({ id, className, data, layout, config }, ref) => {
const originId = useId();
const realId = id || originId;
const originRef = useRef(null);
const [handle, setHandle] = useState(undefined);
useEffect(() => {
let instance;
originRef.current &&
newPlot(originRef.current!, data, layout, config).then((ref) => setHandle((instance = ref)));
return () => {
instance && purge(instance);
};
}, [data]);
useImperativeHandle(
ref,
() => (handle ?? originRef.current ?? document.createElement('div')),
[handle]
);
return <div id={realId} ref={originRef} className={className}></div>;
});
Plotly.displayName = 'Plotly';
return Plotly;
}),
{ ssr: false }
);
```
I named this component an introvert component.
Funny, huh?
Happy React'ing! | composite |
1,868,850 | Lead Generation from SEO: A Comprehensive Guide | In today’s digital age, businesses need effective strategies to attract potential customers. One such... | 0 | 2024-05-29T10:26:59 | https://dev.to/vidya_lakshmi_648461ee425/lead-generation-from-seo-a-comprehensive-guide-4e9l | In today’s digital age, businesses need effective strategies to attract potential customers. One such strategy is lead generation through SEO (Search Engine Optimization). By optimizing your website to rank higher in search engine results, you can draw in visitors who are already interested in your products or services. This **[Top Digital Marketing Course in Bangalore](https://www.acte.in/digital-marketing-training-in-bangalore)** will explore how you can leverage SEO for lead generation, covering essential steps and best practices.

Understanding Lead Generation from SEO
Lead generation refers to the process of attracting and converting strangers and prospects into someone who has indicated interest in your company’s product or service. When it comes to SEO, this involves utilizing organic search results to drive traffic to your website. Here’s how you can do it effectively:
Keyword Research: The Foundation of SEO
Keyword research is the cornerstone of any successful SEO strategy. It involves identifying the terms and phrases your potential customers use when searching for your products or services. This step is crucial because it guides the rest of your SEO efforts.
To get started, you need to identify the search intent behind the keywords. Are users looking for information, wanting to make a purchase, or comparing options? Understanding this will help you create content that meets their needs. Use tools like Google Keyword Planner, Ahrefs, and SEMrush to find relevant keywords that have a good balance of search volume and competition. Additionally, consider targeting long-tail keywords, which are more specific and often less competitive. While they may have lower search volumes, they can attract highly targeted traffic.
On-Page SEO: Optimizing Your Content
On-page SEO involves optimizing individual pages on your website to target specific keywords. This ensures that search engines understand what your page is about and deem it relevant for those keywords.
Start with your title tags by including your primary keyword and making it compelling to attract clicks. Write concise meta descriptions that incorporate your target keywords and provide a summary of the page content. Use header tags (H1, H2, H3) to structure your content, making it easier to read and understand for both users and search engines. Integrate keywords naturally within your content, especially in the first 100 words, headers, and throughout the text. Additionally, use internal linking to link to other relevant pages on your site. This improves navigation and helps search engines crawl your site more effectively. It can be very beneficial in this situation to register in the Digital Marketing Online Certification.
Technical SEO: Building a Strong Foundation
Technical SEO focuses on the backend aspects of your website that affect its performance and visibility in search engines.
Ensure your site speed is optimized because a fast-loading website enhances user experience and is favored by search engines. Tools like Google PageSpeed Insights can help you identify areas for improvement. Mobile-friendliness is also crucial, as an increasing number of users browse the internet on their mobile devices. Make sure your website is responsive and provides a good user experience across all devices. Optimize your URL structure by keeping it clean and descriptive, making it easier for search engines and users to understand what the page is about. Lastly, ensure your site is secure (HTTPS), as search engines prioritize secure sites in their rankings. It can be very beneficial in this situation to register in the [Digital Marketing Online Certification](https://www.acte.in/digital-marketing-training).

Content Marketing: Providing Value to Your Audience
Content marketing is about regularly producing valuable content that addresses the needs and questions of your target audience.
Create blog posts, articles, infographics, videos, and other forms of content that provide value to your visitors. This not only helps attract and engage visitors but also establishes your authority in your industry. Quality content can be shared across various platforms, increasing your reach and driving more traffic to your website. Focus on creating content that answers common questions, solves problems, and provides insights relevant to your audience. This approach will help you build trust and credibility with your visitors, making them more likely to convert into leads.
Link Building: Enhancing Your Authority
Link building is the process of acquiring high-quality backlinks from other reputable websites.
Backlinks act as endorsements and can significantly boost your website’s authority and ranking on search engines. Focus on building relationships with other websites in your industry and creating shareable content that naturally attracts links. Guest posting, collaborating with influencers, and participating in industry forums and discussions can also help you earn valuable backlinks. Ensure that the links you acquire come from reputable sources, as low-quality or spammy links can harm your site’s reputation and SEO performance.
Local SEO: Targeting Local Audiences
For businesses that operate locally, local SEO is crucial. It involves optimizing your online presence to attract local customers.
Claim your Google My Business listing and ensure that all information is accurate and up to date. Encourage satisfied customers to leave reviews, as positive reviews can boost your local search rankings and attract more leads. Consistency is key, so make sure your business name, address, and phone number (NAP) are the same across all online directories and platforms. Additionally, create locally-focused content and optimize your website for local keywords to attract customers in your area.
User Experience (UX): Ensuring a Smooth Journey
User experience (UX) is about enhancing the overall experience of visitors on your website. A well-structured, easy-to-navigate site with a clear call to action (CTA) increases the likelihood that visitors will convert into leads.
Focus on creating a user-friendly design that is easy to navigate and visually appealing. Ensure that your website is responsive and works well on all devices. Provide clear and concise information, making it easy for visitors to find what they are looking for. Use compelling CTAs to guide visitors towards taking desired actions, such as filling out a contact form, signing up for a newsletter, or making a purchase. A positive user experience can significantly increase your conversion rates and help you generate more leads.
Conclusion
The ultimate goal of SEO in lead generation is to attract visitors who are interested in what you offer and guide them through your sales funnel. By consistently providing valuable content and optimizing your website for search engines, you can increase organic traffic, build trust with your audience, and generate high-quality leads without relying on paid advertising.
If done correctly, SEO can be a cost-effective, long-term strategy for continuous lead generation, helping your business grow and thrive in the competitive online marketplace. Focus on keyword research, on-page and technical SEO, content marketing, link building, local SEO, and user experience to maximize your lead generation efforts and drive sustainable business growth. | vidya_lakshmi_648461ee425 | |
1,868,849 | How Exam Dumps Provide Instant Test Feedback | And physical activities. Read/Write Learners Read/write learners excel in traditional educational... | 0 | 2024-05-29T10:25:23 | https://dev.to/theremake12/how-exam-dumps-provide-instant-test-feedback-dba | And physical activities. Read/Write Learners Read/write learners excel in traditional educational settings, relying on reading and writing activities for comprehension. Role of Exam Dumps Now, let's explore how exam dumps cater to these diverse learning styles: Visual Learning Exam dumps often include visual aids, such as Exam Dumps diagrams or graphs, to help visual learners grasp complex concepts more easily. These visual representations provide a clear overview of the material, aiding in retention and recall.
https://dumpsarena.com/
| theremake12 | |
1,868,848 | Extract Array of object data in MySql DB | // your_column = [{id: 1, name: "Tom", age: 30}]; SELECT * FROM your_table WHERE... | 0 | 2024-05-29T10:23:50 | https://dev.to/imashwani/extract-array-of-object-data-in-mysql-db-3472 | ```
// your_column = [{id: 1, name: "Tom", age: 30}];
SELECT * FROM your_table
WHERE json_contains(your_column->'$[*].id', json_array("your_id_to_match"));
```
| imashwani | |
1,868,792 | Unleash Your Inner Citizen Developer: How Low-Code Development Can Empower Your Business | In today's dynamic business landscape, staying ahead of the curve requires agility and innovation.... | 0 | 2024-05-29T10:19:10 | https://dev.to/synodus/unleash-your-inner-citizen-developer-how-low-code-development-can-empower-your-business-2bj8 | lowcode, citizendeveloper, appdevelopment, automation | In today's dynamic business landscape, staying ahead of the curve requires agility and innovation. But for many companies, the high cost and complexity of traditional software development can be a major roadblock. This is where low-code development companies come in, offering a revolutionary approach that empowers businesses to build custom applications without needing an army of programmers.
## Demystifying Low-Code Development
Low-code development platforms (LCDPs) are visual tools that use drag-and-drop functionality and pre-built components to simplify the app creation process. Citizen developers, employees with limited coding experience, can leverage these platforms to build applications that address specific business needs.
## Why Choose a Low-Code Development Company?
Here are just a few reasons why partnering with a low-code development company can be a game-changer for your business:
- Faster Time to Market: Low-code development eliminates the lengthy coding processes associated with traditional development, allowing you to get your applications up and running much quicker.
- Reduced Costs: Citizen developers can handle a significant portion of the development workload, drastically reducing the need for expensive coding resources.
- Enhanced Agility: Low-code platforms enable you to adapt and iterate on your applications quickly, responding to changing market demands with ease.
- Improved Business Efficiency: Streamline workflows, automate tasks, and gain valuable insights through custom applications tailored to your unique needs.
## How to Find the Right Low-Code Development Partner
Choosing the right low-code development company is crucial for the success of your project. Here are some key factors to consider:
- Industry Expertise: Look for a company with experience in your specific industry, ensuring they understand your unique challenges and opportunities.
- Platform Proficiency: Evaluate their expertise in the particular low-code platform you plan to use.
- Scalability: Ensure the company has the resources to support your application as your business grows.
- Proven Track Record: Research their past projects and client testimonials to assess their capabilities.
## Unlocking Potential with Low-Code Development
By partnering with a low-code development company, you can empower your citizen developers and transform your business. From automating tasks to creating innovative customer experiences, low-code development opens a world of possibilities. Are you ready to unleash your inner citizen developer and take your business to the next level?
Read more: [Top 10 Custom Low-code Development Companies To Work With](https://synodus.com/blog/low-code/low-code-development-company/) | synodus |
1,868,793 | Own Your Shop Space in YEIDA City | YEIDA City offers shops in a variety of sizes and layouts to suit diverse businesses. Who Can... | 0 | 2024-05-29T10:19:00 | https://dev.to/ermglobalinvestors/own-your-shop-space-in-yeida-city-37jg | commercialshops, realestate, investing, yamunaauthority | **[YEIDA](https://www.ermglobalinvestors.com/)** City offers shops in a variety of sizes and layouts to suit diverse businesses.
Who Can Apply?
Individuals
Trusts
Firms
Companies
Registered cooperative societies
Special Consideration:
17.5% of shops are reserved for villagers whose land was acquired by YEIDA (with proof required).
Key Points for Applicants:
Bidding starts at the reserve price set by YEIDA.
At least two bids exceeding the minimum price are required for a **[commercial shop](https://www.ermglobalinvestors.com/commercial-shops/)** allocation.
Bidding is conducted electronically.
Successful applicants have 30 days to pay the allotment fee after receiving notification.
Lease term is 90 years.
Get More Information:
For details regarding the application process, payment plans, and terms and conditions, contact YEIDA directly. | ermglobalinvestors |
1,868,787 | Noida's Commercial Hub: Your Business on Yamuna Expressway | Considering commercial space in Noida? The Yamuna Expressway, known for its strategic location and... | 0 | 2024-05-29T10:15:05 | https://dev.to/ermglobalinvestors/noidas-commercial-hub-your-business-on-yamuna-expressway-5d97 | commercialplots, realestate, investing, yamunaauthority | Considering commercial space in Noida? The **[Yamuna Expressway](https://www.ermglobalinvestors.com/)**, known for its strategic location and connectivity, offers a prime location for your business.
**Why Choose the Expressway?**
Thriving Location: Establish your presence in a growing commercial corridor.
Diverse Options: Select a plot suited for retail stores, offices, or even industrial units.
High Demand: Capitalize on the increasing need for **[commercial plots](https://www.ermglobalinvestors.com/commercial-plots/)** in the region.
Investment Potential: Invest in your future with the opportunity for long-term returns.
Build Your Business Here
Ownership: Take possession of your plot upon lease agreement.
Flexible Payment: Minimum 40% down payment and one year's advance rent required.
Clear Title: Full ownership granted upon full payment.
Contact YEIDA Today
Don't miss the chance to be part of Noida's thriving commercial scene. Contact YEIDA to explore available plots and take the first step towards building your business success on the Yamuna Expressway. | ermglobalinvestors |
1,868,784 | Elevating User Experience: The Power of Qt Development in HMI Solutions | In today's digital era, user experience (UX) has emerged as a critical factor in the success of any... | 0 | 2024-05-29T10:11:44 | https://dev.to/lesterwarner/elevating-user-experience-the-power-of-qt-development-in-hmi-solutions-a6f | In today's digital era, user experience (UX) has emerged as a critical factor in the success of any product or application. Nowhere is this more evident than in the realm of Human Machine Interface (HMI) solutions, where intuitive and user-friendly interfaces are essential for driving adoption and satisfaction. Leveraging the power of Qt development, businesses can elevate their HMI solutions to new heights, delivering immersive and engaging user experiences that set them apart from the competition.
Enhancing User Engagement
Our HMI solutions, built on **[Qt development](https://scythe-studio.com/en)** frameworks, are designed to prioritize user engagement and satisfaction. By incorporating fluid animations, responsive touch interactions, and visually appealing graphics, Qt enables us to create interfaces that captivate users and keep them coming back for more. Whether it's a consumer electronics device or an automotive infotainment system, our Qt-powered HMI solutions are engineered to delight users at every touchpoint.
Empowering Innovation with Qt
At our company, we are committed to pushing the boundaries of innovation with Qt development. With its cross-platform capabilities and extensive libraries, Qt provides the flexibility and scalability needed to bring bold ideas to life. Whether it's integrating voice recognition, gesture controls, or augmented reality features, Qt empowers us to push the envelope and deliver HMI solutions that not only meet but exceed user expectations.
Conclusion
In conclusion, Qt development represents a game-changer in the realm of **[HMI development](https://scythe-studio.com/en)**, offering unparalleled capabilities for enhancing user experience and driving innovation. By harnessing the power of Qt, businesses can differentiate themselves in the market and forge stronger connections with their users, ultimately leading to greater success and growth.
| lesterwarner | |
1,868,782 | gcc libs@mac using homebrew | Installed on Mac Studio M2 Ultra (Sonoma): brew install gcc@13 brew install openssl@3 brew install... | 0 | 2024-05-29T10:10:14 | https://dev.to/youngjoonwon/gcc-libsmac-and-brew-3j3b | Installed on Mac Studio M2 Ultra (Sonoma):
```
brew install gcc@13
brew install openssl@3
brew install boost
brew install boost-build
brew install curl
brew install jsoncpp
brew install json-glib
brew install googletest
brew install gsl
cd cpp-jwt
cmake .
```
makefile flags config:
```
LIBOPENSSL_LIBS=-L/opt/homebrew/opt/openssl/lib
LIBOPENSSL_CFLAGS=-I/opt/homebrew/opt/openssl/include
LIBBOOST_LIBS=-L/opt/homebrew/opt/boost/lib
LIBBOOST_CFLAGS=-I/opt/homebrew/opt/boost/include
LIBCURL_LIBS=-L/opt/homebrew/opt/curl/lib
LIBCURL_CFLAGS=-I/opt/homebrew/opt/curl/include
LIBJSON_CFLAGS=-I/opt/homebrew/opt/jsoncpp/include
CC = g++-14
...
-lboost_system -lpthread -lssl -lcrypto -lcurl -latomic -std=c++14
...
```
| youngjoonwon | |
1,868,781 | Noida's Industrial Hub: YEIDA Plots for Your Business Growth | Considering an industrial setup in Noida? Look into YEIDA (Yamuna Expressway Industrial Development... | 0 | 2024-05-29T10:09:52 | https://dev.to/ermglobalinvestors/noidas-industrial-hub-yeida-plots-for-your-business-growth-2hom | realestate, realestateinvestment, yamunaauthority, yeida | Considering an industrial setup in Noida? Look into YEIDA ([Yamuna Expressway Industrial Development Authority](https://www.ermglobalinvestors.com/)) plots. They offer distinct advantages for various industries:
**YEIDA Plot Advantages:**
Robust Infrastructure: Reliable power, water supply, and drainage for smooth operations.
Safe & Secure Environment: Employee safety and security are a priority.
Excellent Connectivity: Expressways and well-maintained roads ensure seamless access to major cities.
Noida Airport Proximity: Convenient air cargo movement for efficient logistics.
Sustainable Design: Green spaces promote a healthy work environment.
Strategic Locations for Diverse Needs:
Sectors 28 & 29: Near major expressways, offering excellent infrastructure for manufacturing and logistics.
Sector 29: Established hub for IT, electronics, textiles, and pharmaceuticals with a readily available workforce.
Sectors 32 & 33: Close to the upcoming Jewar Airport, sports complex, F1 track, museum, and film city, offering high growth potential.
Invest in Your Industrial Future:

YEIDA plots combine strategic location, superior infrastructure, and a focus on sustainability to empower your industrial success. Contact YEIDA today to explore available plots and establish your business in Noida's thriving **[industrial plots](https://www.ermglobalinvestors.com/industrial-plots/)**. | ermglobalinvestors |
1,868,780 | Issue with Rendering Images in Canvas for Matching Game in React | Issue with Rendering Images in Canvas for... | 0 | 2024-05-29T10:08:27 | https://dev.to/dhaneswar_setha/issue-with-rendering-images-in-canvas-for-matching-game-in-react-3j8d | {% stackoverflow 78548767 %} | dhaneswar_setha | |
1,868,779 | Northeast Home Inspections | For a comprehensive and reliable home inspection in Bangor, trust Northeast Home Inspections. Our... | 0 | 2024-05-29T10:08:23 | https://dev.to/northeast_homeinspection/northeast-home-inspections-207h | home | For a comprehensive and reliable home inspection in Bangor, trust Northeast Home Inspections. Our experienced team is committed to providing thorough evaluations of residential properties to ensure your peace of mind. From the foundation to the roof, we meticulously examine every aspect of the home, identifying any potential issues or safety concerns. Our detailed reports offer valuable insights into the property's condition, empowering you to make informed decisions. Whether you're buying, selling, or maintaining a home, Northeast Home Inspections is your trusted partner. Contact us today to schedule your Bangor home inspection and protect your investment.
Address: 40 Kelley Rd, Orono, ME 04473, United States
Email: info@northeast-home-inspections.com
Phone: 2077354955
Visit: https://www.northeast-home-inspections.com/ | northeast_homeinspection |
1,868,757 | How Diesel Generators Provide Reliable Power in Remote Locations? | In remote and off-grid locations where access to traditional power grids is limited or non-existent,... | 0 | 2024-05-29T09:39:35 | https://dev.to/xiaoge_zhong_e2a81c573b91/how-diesel-generators-provide-reliable-power-in-remote-locations-iie | In remote and off-grid locations where access to traditional power grids is limited or non-existent, reliable electricity supply is essential for various operations and activities. In such environments, diesel generators play a crucial role in providing dependable power.
This blog post explores how [diesel generators](https://powerlinkworld.us/diesel-gensets/) serve as lifelines in remote locations, ensuring uninterrupted electricity supply for essential services, industries, and communities.
## Challenges of Remote Power Supply
Remote locations, whether they are rural communities, construction sites, mining operations, or research facilities in remote wilderness areas, often face unique challenges when it comes to accessing reliable electricity. These challenges may include:
Limited Infrastructure: Remote areas typically lack the necessary infrastructure for connecting to centralized power grids, making it impractical or cost-prohibitive to extend power lines over long distances.
Harsh Environmental Conditions: Remote environments may be characterized by extreme weather conditions, rugged terrain, or inhospitable climates, which can pose challenges for power generation and distribution systems.
Isolation and Inaccessibility: Some remote locations are isolated and difficult to access, making it challenging to transport fuel or maintain traditional power infrastructure.

Reliability Concerns: Traditional power grids may be unreliable or prone to frequent outages in remote areas, leading to disruptions in essential services and operations.
## The Role of Diesel Generators
Diesel generators offer a practical solution to the challenges of providing reliable power in remote locations. Here's how they address these challenges:
Portability and Versatility: Diesel generators are highly portable and can be transported to remote sites with relative ease, allowing for flexible deployment in areas where access is limited. They can also be used as standalone units or integrated into existing power systems, providing versatility in meeting diverse power requirements.
Independence from Grid Infrastructure: Unlike grid-connected power sources, diesel generators operate independently of centralized infrastructure, making them well-suited for remote locations where grid connectivity is unavailable or unreliable. This independence ensures a consistent and dependable power supply, regardless of external factors.
Reliability in Harsh Conditions: Diesel generators are known for their robustness and reliability, making them suitable for operation in harsh environmental conditions commonly found in remote areas. They can withstand extreme temperatures, high altitudes, and other challenging environments, ensuring uninterrupted power supply even in adverse weather conditions.
Fuel Efficiency and Longevity: Diesel generators are known for their fuel efficiency and longevity, making them cost-effective solutions for remote power generation. With proper maintenance and fuel management, diesel generators can provide reliable power for extended periods, minimizing downtime and operational costs.
Scalability and Power Output: Diesel generators come in a range of sizes and power outputs, allowing for scalability to meet the specific energy demands of remote locations. Whether powering a single remote outpost or an entire off-grid community, diesel generators can be sized accordingly to ensure adequate power supply.
Emergency Backup Power: In addition to primary power generation, diesel generators can also serve as reliable backup power sources in remote locations. In case of grid outages or equipment failures, diesel generators can automatically kick in to provide emergency power, ensuring continuity of essential services and operations.

## Applications in Remote Locations
Diesel generators find widespread applications in various remote locations, including:
Remote Communities: Providing electricity for homes, schools, healthcare facilities, and other essential services in isolated rural areas.
Mining and Exploration Sites: Powering mining operations, drilling rigs, and exploration camps in remote wilderness areas.
Construction and Infrastructure Projects: Supplying temporary power for construction sites, road projects, and infrastructure development in remote regions.
Research Stations: Supporting scientific research activities and field expeditions in remote wilderness areas and polar regions.
Telecommunications Towers: Ensuring continuous power supply for remote telecommunications towers and communication networks.
## Conclusion
Diesel generators play a vital role in providing reliable power in remote areas where traditional power grids are limited or non-existent. Their portability, independence from grid infrastructure, reliability in harsh conditions and scalability make them indispensable for powering essential services, industry and communities in remote areas around the world. If you have any questions about our products, please feel free to [contact us](https://powerlinkworld.us/contact/). | xiaoge_zhong_e2a81c573b91 | |
958,334 | How to Do Verified Commits on GitHub | Have you ever wished your GitHub commits could have that prestigious "verified" badge, similar to the... | 0 | 2024-05-29T10:05:41 | https://dev.to/deeshansharma/how-to-do-verified-commits-on-github-11oa | git, github, programming, bash | Have you ever wished your GitHub commits could have that prestigious "verified" badge, similar to the coveted blue tick on social media? While I can't help with Instagram verification, I can guide you through the process of verifying your GitHub commits. Verified commits not only add authenticity and security to your work but also showcase your professionalism. Let's dive in and get your commits verified!
## What Are Verified Commits?
Verified commits are a way to ensure that the changes pushed to a repository are genuinely from you and haven't been tampered with by someone else. GitHub uses GPG (GNU Privacy Guard) to sign commits and tags, adding a layer of security and authenticity to your contributions.
Below is an example of how a verified commit looks.

## Why Should You Use Verified Commits?
- **Authenticity**: Assures your collaborators and users that your commits are genuinely from you.
- **Security**: Prevents unauthorized changes and tampering.
- **Professionalism**: Adds credibility to your open-source projects.
## The Problem with Unverified Commits
One significant issue with unverified commits is that anyone can pretend to be you by simply changing the `git config` settings. For example, someone can set their `user.name` and `user.email` to your details and make commits that appear to come from you. Without verification, these commits can mislead collaborators and compromise the integrity of your project.
### An Example Scenario
Consider a situation where a friend makes a commit using your name and email address:
```sh
git config user.name "Your Name"
git config user.email "your.email@example.com"
```
Below commit was made using my friend's details from my account.

This commit will appear to be from you, but since you use verified commits, it will be tagged as `Unverified` on GitHub. This visual cue helps distinguish between genuine and potentially spoofed commits.
By using verified commits, you can ensure that only commits genuinely made by you carry the "Verified" badge, enhancing trust and authenticity.
## How to Get Started with Verified Commits
### Step 1: Install GPG
First, you need to install GPG on your system.
Windows: Download and install Gpg4win.
macOS: Use Homebrew to install GPG.
```sh
brew install gnupg
```
Linux: Use your package manager.
```sh
sudo apt-get install gnupg
```
### Step 2: Check Existing GPG Keys
Before generating a new GPG key, check if you already have one.
```sh
gpg --list-secret-keys --keyid-format LONG
```
This command lists all the GPG keys available on your system along with their details. If you find an existing key you'd like to use, you can skip to adding this key to GitHub.
### Step 3: Generate a GPG Key
If you don't have an existing GPG key or want to create a new one, generate a new GPG key.
```sh
gpg --full-generate-key
```
Follow the prompts to set up your key. Choose RSA and RSA (default), key size of 4096 bits, and set a validity period if you prefer. Enter your name and email address (use the same email address associated with your GitHub account).
### Step 4: Retrieve Your GPG Key ID
After generating the key, retrieve your GPG key ID.
```sh
gpg --list-secret-keys --keyid-format LONG
```
You'll see an output similar to this:
```yaml
/home/user/.gnupg/secring.gpg
------------------------------
sec 4096R/ABC123456789DEF0 2024-01-01 [expires: 2025-01-01]
uid Your Name <your.email@example.com>
ssb 4096R/0987654321ABCDEF 2024-01-01
```
Copy the long string after sec (in this case, ABC123456789DEF0).
### Step 5: Add Your GPG Key to GitHub
Export your GPG key and add it to your GitHub account.
```sh
gpg --armor --export ABC123456789DEF0
```
Copy the output and go to GitHub > Settings > SSH and GPG keys > New GPG key. Paste the key there and save it.
### Step 6: Configure Git to Use Your GPG Key
Tell Git to sign your commits with your GPG key.
```sh
git config --global user.signingkey ABC123456789DEF0
```
To sign all your commits by default, add this to your global Git configuration.
```sh
git config --global commit.gpgSign true
```
### Step 7: Verify Your Signed Commits
Now, every time you commit, Git will sign the commit with your GPG key. You can verify that your commits are signed and verified on GitHub by looking for the "Verified" badge next to your commits.
## Troubleshooting
If you encounter issues, ensure that your GPG key is correctly associated with your GitHub email and that you've configured Git correctly. You may also need to cache your GPG passphrase to avoid entering it every time you commit.
```sh
echo "use-agent" >> ~/.gnupg/gpg.conf
echo "default-cache-ttl 28800" >> ~/.gnupg/gpg-agent.conf
echo "max-cache-ttl 28800" >> ~/.gnupg/gpg-agent.conf
```
Restart the GPG agent to apply the changes.
```sh
gpgconf --kill gpg-agent
gpgconf --launch gpg-agent
```
## Conclusion
Adding GPG signatures to your commits is a great way to enhance the security and authenticity of your contributions on GitHub. It assures others that your work is genuinely yours and hasn't been tampered with. Follow these steps to get your commits verified and add that extra layer of credibility to your projects. | deeshansharma |
1,868,777 | System Integration Testing: The Backbone of Robust Software | In the intricate realm of software development, it is imperative to guarantee the smooth integration... | 0 | 2024-05-29T10:02:33 | https://theusaleaders.com/articles/system-integration-testing/ | system, integration, testing | 
In the intricate realm of software development, it is imperative to guarantee the smooth integration of various components. This is where system integration testing comes into play, acting as the binding agent between the different parts of a software system. System integration testing in software testing strengthens the base of a software by carefully assessing the cohesiveness and interoperability of various components, opening the door for a solid and dependable final result.
1. **Identifying Integration Defects Early**
One of the principal advantages of system integration testing is that it helps identify integration faults early on. Integration problems are more likely as the number of software systems rises, with all these interconnected modules and interfaces. The integration of these components can be assessed in advance, enabling developers to detect and rectify incompatibilities, data transfer inconsistencies and communication disconnections before these issues turn into more severe and expensive matters later.
2. **Ensuring End-to-End Data Integrity**
Data integrity is vital in today’s data-driven culture. Verifying that data shifts and conduit from one piece of software to another is a difficult sell. System integration testing is crucial for this purpose. Testers can confirm that data is correct, consistent, and uncorrupted as it moves through numerous databases, apps, and interfaces by modeling real-world scenarios. This rigorous validation procedure protects the software system’s dependability and gives users trust in its capacity to precisely handle and process data.
3. **Facilitating Effective Collaboration**
Software development is a team effort that frequently involves several teams working on various modules or components. By providing these teams with a single platform for coordination and communication, system integration testing promotes productive teamwork. Early detection and resolution of integration problems allows teams to better coordinate their efforts, set clear goals, and work together to produce a finished project.
4. **Mitigating Risks and Reducing Costs**
Software failures can have crippling effects, involving not just monetary losses but also harm to one’s reputation and disgruntled customers. System integration testing is a proactive approach to risk reduction that helps developers find and fix any problems before they become serious problems. Organizations may dramatically lower the costs of rework, maintenance, and support by identifying and fixing faults early in the development lifecycle. This will ultimately improve their bottom line.
5. **Delivering a Superior User Experience**
It is critical to provide an exceptional user experience in the highly competitive software business. In order to guarantee that the software system operates as intended and offers a smooth and consistent user experience across all components and interfaces, system integration testing is essential. Testers can find and fix any potential hitches, malfunctions, or inconsistencies that could jeopardize the overall user experience by verifying the interoperability and coherence of the various components.
**Conclusion**
System integration testing has not been stressed too much, but it is an important step in the software testing circle, as it ensures that all components can integrate and work normally. The companies can quickly do a comprehensive system integration testing using Opkey, an AI-powered no-code testing platform, to make sure that their ecosystem works as a unit. One such instance is the NetSuite-Shopify integration, in which Opkey makes sure that the inventory syncs smoothly between the Shopify frontend and the Oracle NetSuite backend. Operations can be disrupted by any mismatch, but Opkey’s strong SIT capabilities ensure that this crucial process runs without a hitch from beginning to end. The companies should use Opkey to provide a greater integrated experience, reduce risks, and enable thorough system integration testing. | rohitbhandari102 |
1,868,776 | Understanding and Addressing Memory Leaks in Unity Game Development | Understanding Memory Leaks and Their Hazards While many programmers have likely... | 0 | 2024-05-29T10:02:00 | https://dev.to/wetest/understanding-and-addressing-memory-leaks-in-unity-game-development-40l2 | performance, qa, game, devops | # Understanding Memory Leaks and Their Hazards
While many programmers have likely encountered the term "memory leak," it might not be as familiar to beginners. You might be wondering, does a memory leak mean that memory is physically leaking out? Let's clarify the concept with a definition from Wikipedia:
After reading the detailed definition, it might seem a bit complex. Let's use a simple analogy to make it more understandable.
Think of memory leaks as "borrowing money from a bank and not paying it back." In the digital world of computers, the operating system acts as the bank, each loan represents a memory request, and you are the application. In other words, borrowing money from the bank is equivalent to an application requesting memory from the operating system. Thankfully, in the world of computers, the operating system is a generous bank that doesn't charge interest; you only need to return the exact amount of memory you borrowed. So, we can simplify the definition of a memory leak as requesting memory but not releasing it when it should be released.
If you continuously borrow money and don't pay it back, the bank will eventually run out of funds for others to borrow. In real life, banks prevent this by blacklisting individuals who consistently fail to repay loans, refusing to lend them any more money. The operating system is even more unforgiving; it will forcefully shut down the application. This demonstrates the dangers and severity of memory leaks. If left unchecked, the application may crash due to excessive memory usage. Additionally, there are other risks associated with memory leaks, such as memory being occupied by useless objects, leading to increased time costs for subsequent memory allocation, causing game lag, and more.
# Memory Leaks in Unity
Let's delve into memory leaks within a specific environment - Unity. As we know, game programs consist of code and resources. Memory leaks in Unity can be primarily divided into code-side leaks and resource-side leaks. Of course, resource-side leaks are also caused by unreasonable references to resources in the code.
**Code-side leaks - Mono memory leaks**
Those familiar with Unity should know that Unity uses Mono-based C# (as well as other scripting languages, but they seem to be used less frequently, so we won't discuss them here) as its scripting language. It relies on the Garbage Collection (GC) mechanism for memory management. Since memory is managed, why are there still memory leaks? It's because GC itself is not all-powerful. What GC can do is find "garbage" through specific algorithms and automatically reclaim the memory occupied by the "garbage." So, what is garbage?
First, let's take a look at the description of GC implementation on Wikipedia:
In simpler terms, let's think about garbage in our daily lives. We usually consider things with no value as "garbage," and in the world of garbage collection (GC) in programming, it's the same - objects with no references are considered "garbage." When there are no references, it means that the object has no value, making it "garbage." The GC mechanism reclaims the memory occupied by these objects.
Understanding this concept helps explain why memory leaks still occur in managed memory environments. It's like when someone forgets to throw away an empty instant noodle box after eating - in a computer's perspective, this means that we "forget" to clear the reference to an object that's no longer needed.
You might wonder if small memory allocations in your code would have a significant impact on devices with large memory. Keep in mind that memory allocation happens not only when you explicitly call "new" but also through many implicit allocations, like creating a list, caching configurations, or generating a string. If multiple people allocate memory, it adds up quickly.
It's also important to know that in the Unity environment, the memory usage of the Mono heap only increases and doesn't decrease. The Mono heap is like a memory pool, and each time memory is requested, it's allocated within the pool. When memory is released, it's returned to the pool but not the operating system. If there's not enough memory in the pool, it expands by requesting more memory from the operating system. Each expansion is a large memory allocation, increasing the pool by approximately 6-10MB (based on observation, not official data).

The image mentioned above displays the results of a Cube test for a specific game, showing that the Mono heap (represented by the black line) has reached over 70MB. This highlights the importance of addressing Mono memory leaks in Unity game development.
**Resource leaks - Native memory leaks**
Resource leaks refer to situations where memory is occupied after loading resources, but the resources aren't unloaded when they're no longer needed, leading to unnecessary memory usage.
Before discussing the causes of resource memory leaks, let's first examine Unity's resource management and recycling methods. Resource memory and code memory are discussed separately because their memory management methods differ.
The memory allocated by the code mentioned earlier is allocated through the Mono virtual machine on the Mono heap memory, which generally has a smaller memory footprint and is mainly used by programmers when handling program logic. In contrast, Unity's resources are allocated through Unity's C++ layer on the Native heap memory. For example, memory allocated through interfaces in the UnityEngine namespace will be allocated on the Native heap by Unity, while memory allocated through interfaces in the System namespace will be allocated on the Mono heap by the Mono Runtime.

Now that we understand the differences in allocation and management methods, let's examine the recycling methods. As mentioned earlier, Mono memory is recycled through garbage collection (GC), and Unity also provides a similar method for memory recycling. The difference is that Unity's memory recycling needs to be actively triggered. For example, if we throw garbage in the trash can, GC checks it daily and takes away any garbage; with Unity, however, you need to call and notify it to collect the garbage. The interface to actively call is Resources.UnloadUnusedAssets(). GC also provides a similar interface, GC.Collect(), to actively trigger garbage collection. Both interfaces require a large amount of computation, and it's not recommended to actively call them during gameplay. To avoid game stuttering, it's generally recommended to handle garbage collection during the loading process. Note that Resources.UnloadUnusedAssets() itself will call GC.Collect(). Unity also offers a more aggressive method - Resources.UnloadAssets() to unload resources, but this interface will directly delete resources regardless of whether they are "garbage" or not, making it a risky interface. It's recommended to call this interface only when you're sure the resources aren't being used.
With this knowledge, let's explore why resource leaks occur. First, like code-side leaks, resource leaks can happen due to "existing references that should be released but aren't." The recycling mechanism considers the target object not to be "garbage," making it unable to be recycled. This is the most common situation.
For resources, there's another typical leak scenario. Since resource unloading is actively triggered, the timing of clearing resource references becomes crucial. As game logic becomes more complex and new members join the project team, they may not necessarily understand all the details of resource management. If references to resources are cleared "after triggering resource unloading," memory leaks can also occur.
There is another type of resource leak caused by certain Unity interfaces that generate a copy when called. If not used carefully, this can result in numerous resource copies during runtime, leading to unnecessary memory waste. However, such memory copies are generally small in quantity and relatively easy to fix, so they will not be discussed in detail here.
# Fixing Memory Leaks
As mentioned earlier, to avoid memory leaks, we need to break the reference before the garbage collection occurs, which may seem like a simple problem. However, due to the complexity of real-world projects, the reference relationship is not just one or two layers (sometimes even up to dozens of layers connecting to the final reference object), and there may be complex situations such as cross-references and circular references. It is challenging to correctly break the reference just from a code review perspective. Finding the leaking reference is the key and difficult point in fixing the leak, and it is also the main focus of this article. As for timing issues, they are relatively simple and will not be discussed here.
**New Memory Profiler for Unity 5**
Unity's Memory Profiler has often been criticized by users for not providing a clear reflection of memory usage and who is using it. As the latest generation of Unity products, Unity5 has addressed this weakness by introducing a new generation of memory analysis tools that better solve the aforementioned problems. However, it does not provide a comparison function for two (or more) memory snapshots, which is a bit disappointing.
Note: Memory snapshot comparison is a common method for finding memory leaks. By capturing the state of memory at two different times and comparing them, it is possible to see the changes in memory and find the increment and leak points. Typically, two dumps are done before entering and after exiting a game level, and any additional memory allocations can be considered leaks.
Since it is an official Unity tool, there are detailed tutorials available online, so there is no need to go into detail here.
As Unity 5's popularity and stability still need improvement, most companies continue to use the 4.x environment. In this case, the new tool mentioned above is not applicable. Some might suggest upgrading a Unity5 project for Memory Profiling, which is possible, but Unity5 is not very compatible with Unity4. A lot of modifications are required during the upgrade process, and maintaining two projects can be quite troublesome.
So, here are two leak-tracking tools that can also be used in the Unity4 environment.
**Magnifying Glass for Mono Memory - PerfDog**
PerfDog is a comprehensive mobile platform performance testing and analysis tool on Tencent's WeTest platform under Tencent Games, aiming to improve the performance and quality of applications and games.
PerfDogService can be used on Windows, Mac, and Linux platforms. The customized and integrated data panels with internal quality platforms are displayed on the web. Users develop their tools and build performance monitoring locally. Services such as automation and cloud testing are provided.
**Tracing Back the Vine - Finding Resource References in Mono**
Before attempting to find resource references and fix resource leaks, we need to understand how to locate resource leaks in Unity.
We need to use Unity's built-in Memory Profiler (note that this is not the new Profiler mentioned earlier for Unity5, but the older, less capable version). Here's a simple example: run the game project in the Unity editor environment, go through the "Lobby" page, and enter the "Single Round." Now open the Unity Profiler, switch to Memory, and perform a memory sampling. In the sampling results (which include all resources in memory at the time of sampling), expand Assets->Texture2D. If you can see the texture used by the "Lobby" UI (as shown below), we can consider this UI texture as a resource leak.
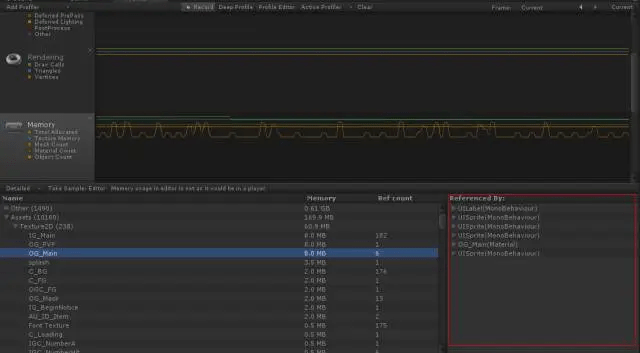
Why is this considered a resource leak? Because this UI texture was requested during the "Lobby" stage, but it is no longer needed in the "Single Round" stage, yet it is still in memory. This kind of memory usage that exists when it is not needed is what we defined as a memory leak earlier.
**So, how do we find these leaking resources in our everyday projects?**
The most intuitive method, which is also the most straightforward method, is to perform a memory sampling every time the game state changes and check each resource in memory one by one to determine if it is genuinely needed for the current game state. The biggest problem with this method is that it is time-consuming and labor-intensive, and with too many resources, it is easy to miss something.
**Here are two clever methods:**
1) Identifying by resource name. That is, when naming art resources (such as textures, and materials), include the game state they belong to in the file name. For example, if a texture is called BG.png and is used in the lobby, rename it to OG_BG.png (OG = OutGame). This way, it is easy to identify when an OG resource is mixed in with a bunch of IG (IG = InGame) resources, and it is also convenient for program recognition. This method also has the added benefit of reinforcing artists' understanding of the resource lifecycle, and providing guidance when creating resources, especially when planning UI atlases.
2) Use Unity's Resources.UnloadUnusedAssets() interface to dump resources. You can dump textures, materials, models, or other resource types as needed by passing the Type as a parameter. After a successful dump, save the results as a text file. This way, you can use Beyond Compare to compare the results of multiple dumps and find the added resources. These resources are potential leak objects that need to be investigated.
Combining the methods and ideas mentioned above, you should be able to find the leaking resources easily.
Now let's take a look back at the Unity Profiler. Unity provides a resource index search function, but it is presented as a tree-structured text (as shown below). As mentioned earlier, the internal reference relationship in Unity is often very complex, and it may take dozens of references to find the final referrer. Moreover, the reference relationships are intricate, forming a vast graph. At this point, it is nearly impossible to find the reference just by expanding the tree structure.
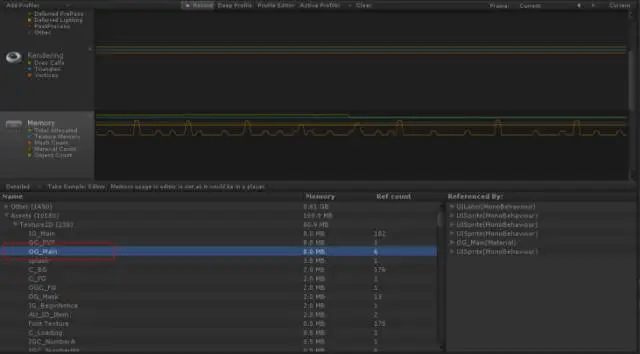
# Preventing Memory Leaks
Having discussed how to fix memory leaks, I'd like to go a step further and say that as long as we think more during our daily development process and nip problems in the bud, memory leaks can be entirely avoided. Compared to waiting for leaks to occur and then tracing them back, spending more time cleaning up "garbage" in daily development is a more efficient approach.
Here are a few suggestions to apply to the daily development process, and I welcome any additional input from experts:
- In the architecture, add more destructors as abstract interfaces to remind team members to pay attention to cleaning up the "garbage" they generate.
- Strictly control the use of static, and prohibit the use of static in non-essential situations.
- Reinforce the concept of the lifecycle, whether it's code objects or resources, they all have their lifecycle and should be released once the lifecycle ends. If possible, describe the lifecycle in the functional design documentation.
As qualified programmers, we should also be able to handle the "garbage" in our code and not let our games become a "garbage dump."
To avoid the negative impact of mobile game performance issues mentioned above, Tencent's WeTest platform's PerfDog tool can help developers discover the resource usage situation within the game, assisting in continuously improving the player experience during game development.
[For more information, contact WeTest team at → WeTest-All Test in WeTest](https://wetest.net/?utm_source=dev&utm_medium=forum&utm_content=preventing-memory-leaks)
| wetest |
1,868,775 | Data Validation And Form Handling With Blazor | by Fadahunsi Oluwaseyi Samuel Forms and validation are crucial parts of any application. They allow... | 0 | 2024-05-29T10:01:59 | https://blog.openreplay.com/data-validation-and-form-handling-with-blazor/ | by [Fadahunsi Oluwaseyi Samuel](https://blog.openreplay.com/authors/fadahunsi-oluwaseyi-samuel)
<blockquote><em>
Forms and validation are crucial parts of any application. They allow users to submit input, not just any input, but the correct input. [Blazor](https://learn.microsoft.com/en-us/aspnet/core/blazor/?view=aspnetcore-8.0) comes in handy to support all of these, as this article will show.
</em></blockquote>
<div style="background-color:#efefef; border-radius:8px; padding:10px; display:block;">
<hr/>
<h3><em>Session Replay for Developers</em></h3>
<p><em>Uncover frustrations, understand bugs and fix slowdowns like never before with <strong><a href="https://github.com/openreplay/openreplay" target="_blank">OpenReplay</a></strong> — an open-source session replay suite for developers. It can be <strong>self-hosted</strong> in minutes, giving you complete control over your customer data.</em></p>
<img alt="OpenReplay" style="margin-top:5px; margin-bottom:5px;" width="768" height="400" src="https://raw.githubusercontent.com/openreplay/openreplay/main/static/openreplay-git-hero.svg" class="astro-UXNKDZ4E" loading="lazy" decoding="async">
<p><em>Happy debugging! <a href="https://openreplay.com" target="_blank">Try using OpenReplay today.</a></em><p>
<hr/>
</div>
Do you know why data validation and form handling are essential? Ensuring data integrity and providing a seamless user experience are paramount. In Blazor applications, achieving these goals requires mastering the art of data validation and form handling, which will be covered in this article.
In this guide, we'll explore Blazor's built-in validation features, explore custom validation techniques, and uncover best practices for effective form handling. By the end of this article, you will have the knowledge to handle data validation seamlessly in your Blazor application.
### Prerequisites
Ensure you have the necessary applications installed on your computer before continuing with this guide:
* To build and update Blazor projects, you'll need [Visual Studio](https://visualstudio.microsoft.com/downloads/), a feature-rich Integrated Development Environment (IDE) that can be [downloaded](https://visualstudio.microsoft.com/downloads/) from the official [Microsoft](https://visualstudio.microsoft.com/downloads/) website.
* The [.NET SDK](https://dotnet.microsoft.com/en-us/download) (Software Development Toolkit), which has everything you need to create and execute [.NET](https://dotnet.microsoft.com/en-us/learn/dotnet/what-is-dotnet) apps, is required for Blazor projects. Make sure your computer has the `.NET SDK` installed. It is available for download on the official [.NET](https://dotnet.microsoft.com/en-us/download) website.
* Basic knowledge of [C#](https://learn.microsoft.com/en-us/dotnet/csharp/) and Blazor.
You will be ready to follow along once you have installed `Visual Studio` and the `.NET SDK`.
## Understanding Blazor Forms
Just like any other form, Blazor simplifies the process of collecting user input through its form components and accurately sends the collected input to the intended destination.
Ensuring data integrity is paramount when developing applications, including Blazor. This article will delve into the various validation mechanisms Blazor offers and provide insights on implementing them within your projects.
### Form Elements in Blazor
Blazor, by default, provides a range of form elements to help user input and validate their data. Below are a few available elements; additional ones can be found [here](https://learn.microsoft.com/en-us/aspnet/core/blazor/forms/input-components?view=aspnetcore-8.0).
* `InputText`: This creates an [HTML (HyperText Markup Language)](https://developer.mozilla.org/en-US/docs/Learn/Getting_started_with_the_web/HTML_basics) input element for text entry. It provides a way to bind the input field's value to a property in a [C#](https://learn.microsoft.com/en-us/dotnet/csharp/) class, allowing for two-way [data binding](https://learn.microsoft.com/en-us/aspnet/core/blazor/components/data-binding?view=aspnetcore-8.0). This means that changes made in the input field will automatically update the associated property in the code block. Changes to the property in the code block will be reflected in the input field.
```csharp
<InputText @bind-Value="model.Firstname" />
```
The `@bind-Value` [attribute](https://learn.microsoft.com/en-us/aspnet/core/blazor/components/splat-attributes-and-arbitrary-parameters?view=aspnetcore-8.0) allows two-way data binding. It must be added to every other component because data cannot be bound without it.
* `InputCheckbox`: This component generates an `HTML` checkbox input element. It allows users to select or deselect a single option. In Blazor, it's typically used in forms to represent `boolean` values or toggle specific settings.
```csharp
<InputCheckbox @bind-Value="model.IsChecked" />
```
* `InputDate`: This creates an `HTML` input element for date selection. It provides a convenient way for users to input dates. It ensures consistency and validation of date entries.
```csharp
<InputDate @bind-Value="model.SelectedDate" />
```
* `InputNumber`: This generates an `HTML` input element designed explicitly for numeric input. It restricts user input to numeric values, providing validation and ensuring that only valid numbers are accepted. This component captures numerical data, such as quantities or prices.
```csharp
<InputNumber @bind-Value="model.Quantity" />
```
* `InputTextarea`: This component allows users to enter text in many lines by creating an `HTML` `textarea` element. While `InputTextarea` is appropriate for capturing larger text entries, like comments or descriptions within forms, `InputText` is utilized for single-line text input. It offers more input space and allows for multiline text editing.
```csharp
<InputTextarea @bind-Value="model.Comment" />
```
### Form Submission and Event Handling in Blazor
Can a form be submitted without anything taking place? No. For a form to be submitted, an [event](https://learn.microsoft.com/en-us/aspnet/core/blazor/components/event-handling?view=aspnetcore-8.0) must take place.
`EditForm` in Blazor is not part of the `HTML` form elements; it is a Blazor component specifically designed to facilitate form handling in Blazor applications. While `HTML` elements like `InputText`, `InputCheckbox`, etc., represent individual input fields within a form.
`EditForm` provides a wrapper around these elements to manage form submission, validation, and data binding in a Blazor application. It simplifies the process of handling form submissions and managing form state.
Handling form submissions and events in Blazor is straightforward. You can leverage [event handlers](https://learn.microsoft.com/en-us/aspnet/core/blazor/components/event-handling?view=aspnetcore-8.0) like `OnSubmit`, `OnValidSubmit`, and `OnInvalidSubmit` to execute logic upon form submission. These events can't stand alone; they have to be an attribute of a Blazor component called [EditForm](https://learn.microsoft.com/en-us/dotnet/api/microsoft.aspnetcore.components.forms.editform?view=aspnetcore-8.0). I will explain these events below;
* `OnSubmit`: This event is triggered when the form is submitted, regardless of validity. You can use this event to handle form submissions, irrespective of whether the form passes validation.
* `OnValidSubmit`: This event is triggered only when the form submission is valid. It's typically used when you want to perform specific actions or submit data, but only when the form passes validation. For example, save form data to a database only when all required fields are filled out correctly.
* `OnInvalidSubmit`: This event is triggered when the form submission is invalid, meaning it fails validation. It helps handle scenarios where you want to provide feedback to the user about validation errors or take other actions when the form fails validation.
```csharp
<EditForm Model="model" OnValidSubmit="HandleSubmit" OnInvalidSubmit="HandleSubmit">
<!-- Other form fields will be here -->
<button type="submit">Submit</button>
</EditForm>
@code {
private void HandleSubmit()
{
// Logic to handle form submission
}
}
```
This code above sets up a form in a Blazor application using the `EditForm` component. It binds the form to the `Model` object, specifies methods to handle form submission events (both `OnValidSubmit` and `OnInvalidSubmit`), and provides a submit button to trigger the form submission process. The text between `<!-- -->` is called a comment, which will be ignored.
```csharp
<EditForm Model="model" OnSubmit="HandleSubmit">
<!-- Form fields here -->
<button type="submit">Submit</button>
</EditForm>
@code {
private void HandleSubmit()
{
// Logic to handle form submission
}
}
```
The code above uses the `OnSubmit` attribute, which triggers the event that submits the form. However, this doesn't check for the form's validity before submission.
You cannot use the `OnValidSubmit` and `OnInvalidSubmit` in the same form and use the `OnSubmit`. This will flag an error, which I will provide in the image below;
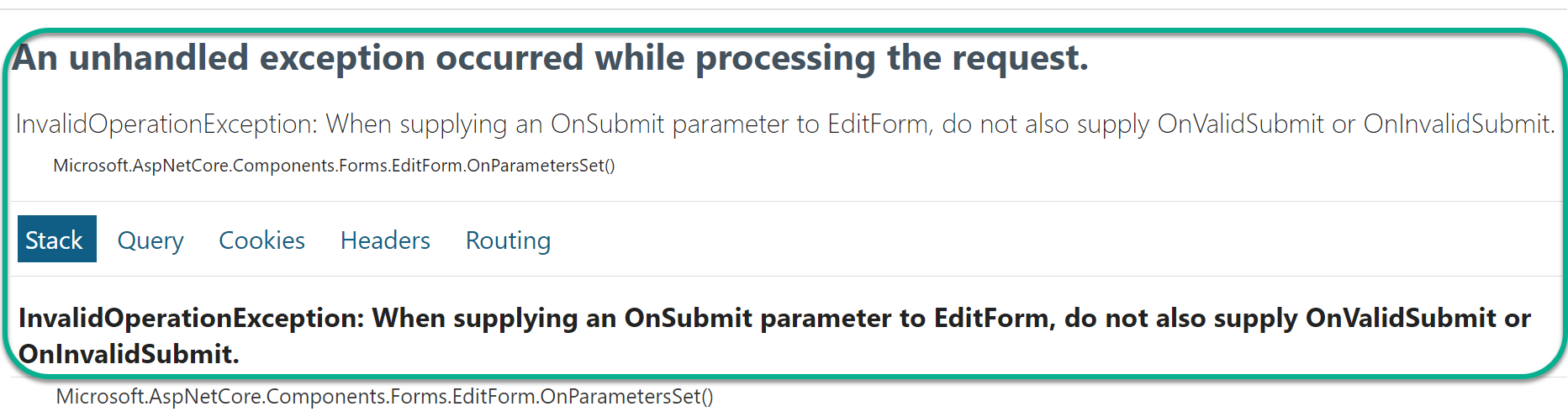
From the image above, you can see that you can only use the `OnSubmit` or `OnValidSubmit` and `OnInvalidSubmit`.
NOTE: Validation has to be set on the form before all of these can be enabled. We will discuss validations in the next section.
<CTA_Middle_Frameworks />
## Built-in Validation in Blazor
Blazor comes with built-in validation attributes that simplify the validation process. Blazor allows you to enforce data validation rules for form inputs without writing custom validation logic.
This validation is a form of security in our application, making sure the user's input matches what is expected.
### Applying Validation Attributes
To start with validation, [Data Annotations](https://learn.microsoft.com/en-us/aspnet/mvc/overview/older-versions-1/models-data/validation-with-the-data-annotation-validators-cs) from the `System.ComponentModel.DataAnnotations` [namespace](https://learn.microsoft.com/en-us/dotnet/csharp/language-reference/keywords/namespace) has to be used on the properties of the `Model`.
A model helps define the structure and types of data the application requires, just like a blueprint defines the layout of an object. The model can be stored in a `.cs` file, I will provide an example below;
```csharp
public class Person
{
public string Firstname { get; set; }
public string Lastname { get; set; }
public int Age { get; set; }
public string Email { get; set; }
public string Phone { get; set; }
public string PostalCode { get; set; }
}
```
The `data annotation` will be added to the properties as an attribute that requires it in the model. Blazor has several attributes that make validation easy. Some of them will be explained below. You can find more of these [here](https://learn.microsoft.com/en-us/aspnet/mvc/overview/older-versions-1/models-data/validation-with-the-data-annotation-validators-cs).
* `Required`: This mandates that a property must be included, and its value cannot be `null` or an empty `string`.
```csharp
[Required(ErrorMessage = "Field is required")]
public string Firstname { get; set; }
```
* `StringLength`: This defines the minimum and maximum length limits for a `string` property.
```csharp
[StringLength(50, MinimumLength = 2, ErrorMessage = "Firstname must be between 2 and 50 characters")]
public string Firstname { get; set; }
```
* `Range`: This sets the minimum and maximum `numeric` value limits for a `numeric` property.
```csharp
[Range(18, 50, ErrorMessage = "Age must be between 18 and 50")]
public int Age { get; set; }
```
* `RegularExpression`: Specifies that a `string` property must match a specified [regular expression](https://learn.microsoft.com/en-us/dotnet/standard/base-types/regular-expression-language-quick-reference) pattern.
```csharp
[RegularExpression(@"^\d{5}$", ErrorMessage = "Invalid postal code")]
public string PostalCode { get; set; }
```
* `EmailAddress`: A `string` property must adhere to a valid email address format.
```csharp
[EmailAddress(ErrorMessage = "Invalid email address")]
public string Email { get; set; }
```
* `Compare`: Compares the value of one property with the value of another.
```csharp
[Compare(nameof(Password), ErrorMessage = "Passwords do not match")]
public string ConfirmPassword { get; set; }
```
* `MaxLength`: This defines the maximum length permitted for a `string` property.
```csharp
[MaxLength(50, ErrorMessage = "Lastname cannot exceed 50 characters")]
public string Lastname { get; set; }
```
* `MinLength`: Specifies the minimum length required for a `string` property.
```csharp
[MinLength(2, ErrorMessage = "Lastname must be at least 2 characters long")]
public string Lastname { get; set; }
```
### Displaying Validation Error Messages
Displaying validation errors is essential to creating user-friendly forms in your application. When a user inputs incorrect data, it is important to provide clear feedback about what went wrong and how they can fix it.
How can the form know what field has been set to required?
A component called `DataAnnotationsValidator` solves that. The `DataAnnotationsValidator` component is very important for your validation to be activated on the form and to show error messages where required. Without the component, no validation message will appear on the form, even while submitting an empty form. The `DataAnnotationsValidator` component is added below the opening `EditForm` tag (`<EditForm>`).
Below are some of the ways Blazor offers to display validation error messages;
* `ValidationSummary`: This component summarizes all validation errors in the form. It's placed near the top of the form below the `DataAnnotationsValidator` component.`ValidationSummary` provides a convenient way for users to see all validation errors simultaneously. Below is what this component looks like;
```csharp
<DataAnnotationsValidator />
<ValidationSummary />
```
Using the component above and trying to submit the form without its required data being filled up will generate the error in the image below;
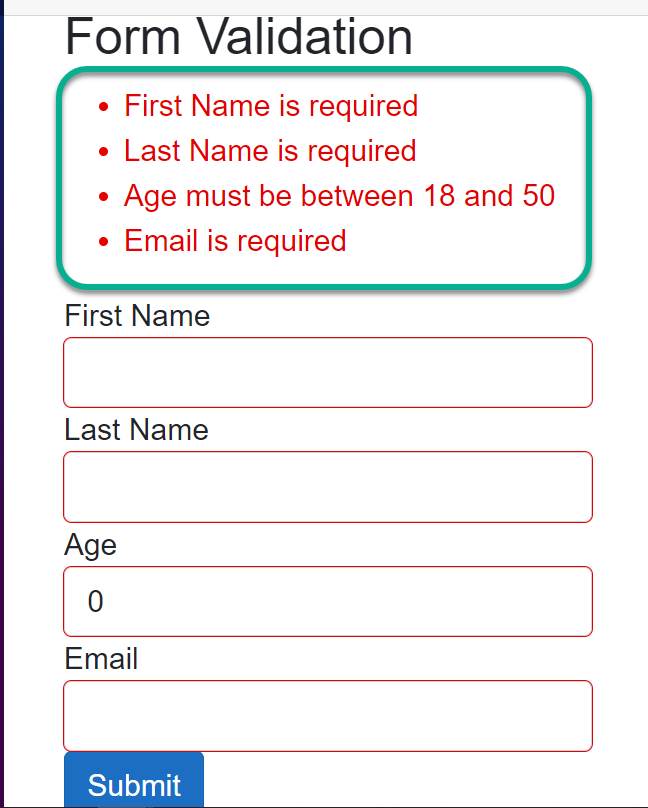
From the image above, you can see the summary of the error messages is being outputted.
* `ValidationMessage`: This displays validation error messages next to individual form fields using the `ValidationMessage` component. This component is bound to a specific form field and will only display the validation error for that field. Below is how it can be implemented;
```csharp
<InputText @bind-Value="model.Firstname" />
<ValidationMessage For="@(() => model.Firstname)" />
```
From the code snippet above, the `ValidationMessage` uses the `For` attribute, which takes an expression to validate the current property ( in this case, the `Firstname` property). Submitting the form, which uses the `ValidationMessage` component without filling in the required field, will generate the error in the image below;
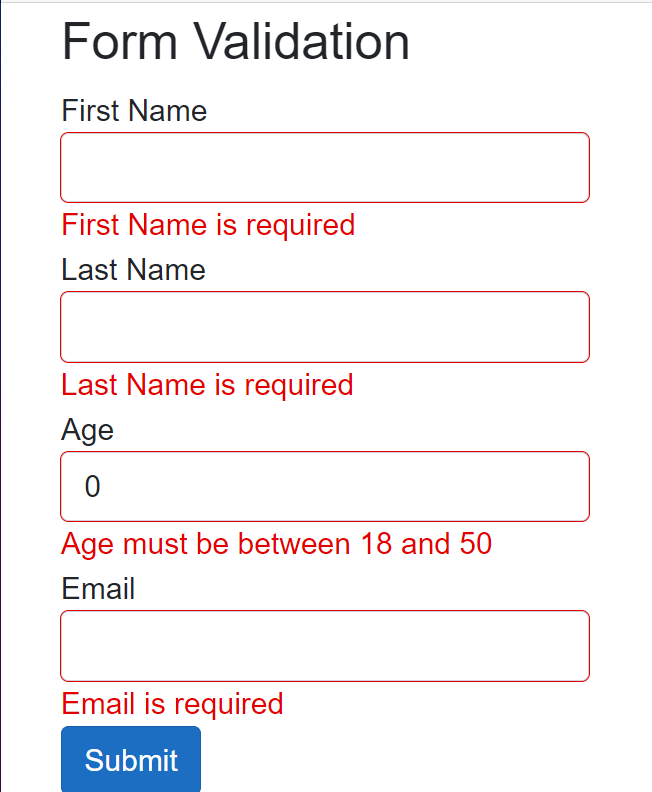
As you can see from the image above, each field is outputting a unique error message.
## Custom Validation in Blazor
Built-in Blazor validation works fine but cannot cover every scenario we want to implement. We should be able to customize validation based on our needs; this is where `Custom Validation` will come in handy.
Custom validation in Blazor allows you to define your logic for form fields beyond the built-in validation attributes. This is useful when you need to enforce validation rules that cannot be expressed using standard `data annotation` attributes. Blazor provides a way to create custom validation rules by implementing the `ValidationAttribute` class or by defining custom validation methods.
### Implementing Custom Form Validation in Blazor
In some situations, you may desire to restrict certain text inputs for security purposes. Custom validation serves as an effective solution in such scenarios. Below, I will explain how custom validation can prevent the word `password` from being accepted when a user inputs it.
I will create a new file called `ValidateName.cs`, which will contain the custom validation logic below;
```csharp
public class ValidateName : ValidationAttribute
{
protected override ValidationResult IsValid(object value, ValidationContext validationContext)
{
if (value.ToString().Contains("password"))
{
return new ValidationResult("Sensitive word such as password is not allowed.");
}
return ValidationResult.Success;
}
}
```
The above is a custom validation attribute named `ValidateName`, which inherits from the `ValidationAttribute` class provided by `.NET` for creating custom validation attributes.
The `IsValid` method is overridden to implement custom validation logic. This method is called when validation is triggered for the property associated with this attribute. The `value` represents the value of the property being validated. Inside the `IsValid` method, the `value` of the property is checked if it contains the word `password` and returns a custom validation error or success message.
The custom validation logic above will be called as an attribute on the property that requires validation in the `Person` model class. This will be explained below;
```csharp
public class Person
{
[Required(ErrorMessage = "Firstname is required")]
[ValidateName]
public string Firstname { get; set; }
[Required(ErrorMessage = "Lastname is required")]
public string Lastname { get; set; }
[Required(ErrorMessage = "Email is required")]
public string Email { get; set; }
[Required(ErrorMessage = "Phone Number is required")]
public string PhoneNumber { get; set; }
}
```
From the above, the `ValidateName`, which is the custom validation logic, is being used as an attribute on the `FirstName` property. So when this property contains the word `password`, it will flag an error just like the image below;
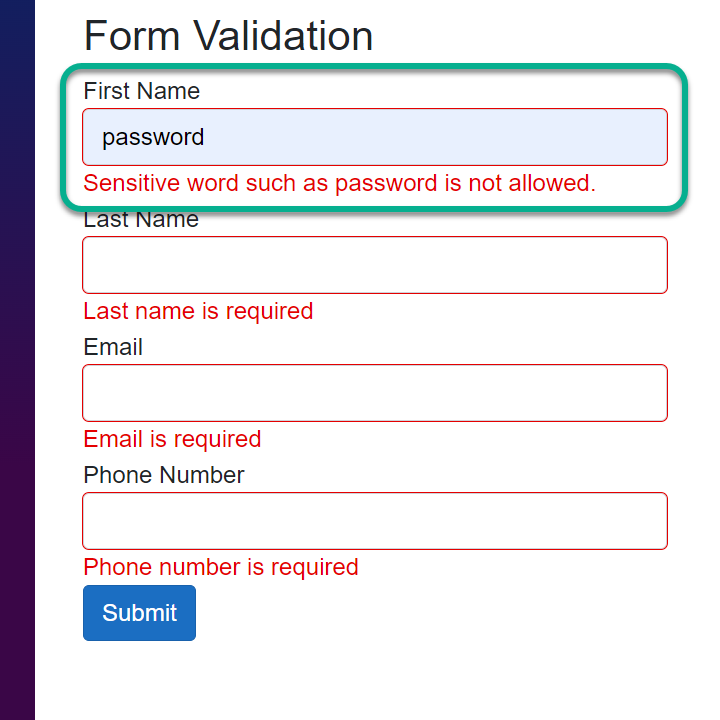
According to requirements, the user can see different errors depending on how custom validation is applied, as seen in the image above.
## Form Submission and Validation
The form submission process in Blazor involves several steps to collect user input, validate it, and handle the submission. Some of these have been discussed above. This section will be an overview of how the form submission and validation process work together in a Blazor application.
In this section, we will create a form from scratch, trigger its validation, and handle its form submission gracefully.
* STEP 1: Create a New Project
Click the marked area in the image below to start creating a new Blazor project.
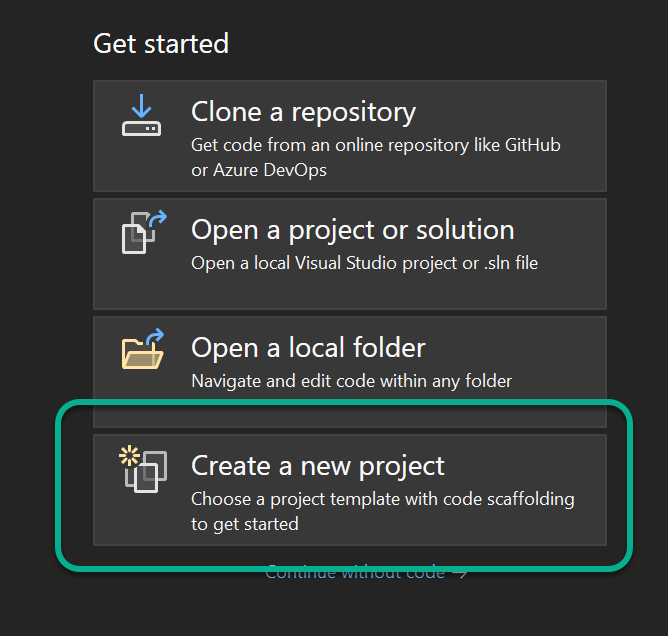
* STEP 2: Select the Blazor Template
After selecting the marked button above, select the `Blazor Web App` and click `Next` as shown below;
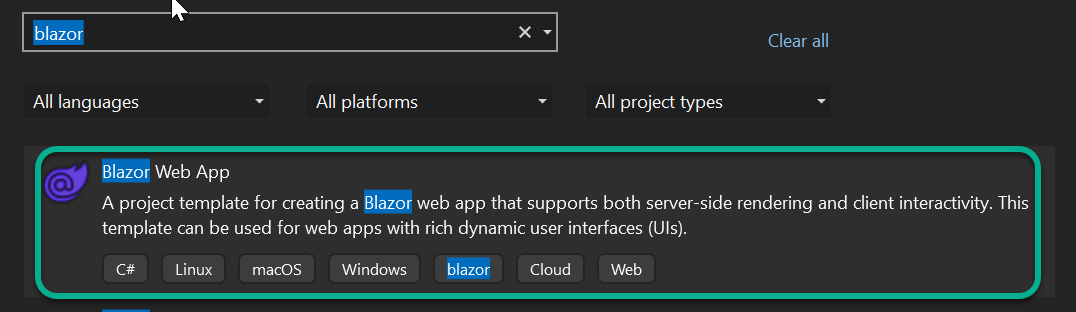
* STEP 3: Configure Project
You can leave this by the default value or change it to whatever suits your project requirement. We will use the default configurations. Once you are done, click `Next`;
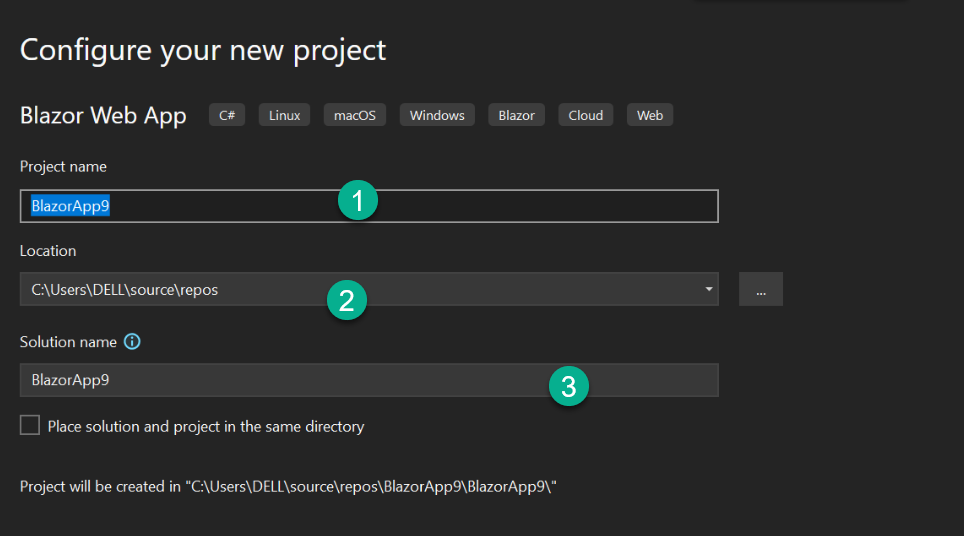
* STEP 4: Set Additional Information
We will be using the `.NET 8` framework. This guide will work with `.NET 6` and later. You can change the settings below as you see fit, but we will work with the default settings. Click on `Create` to continue;
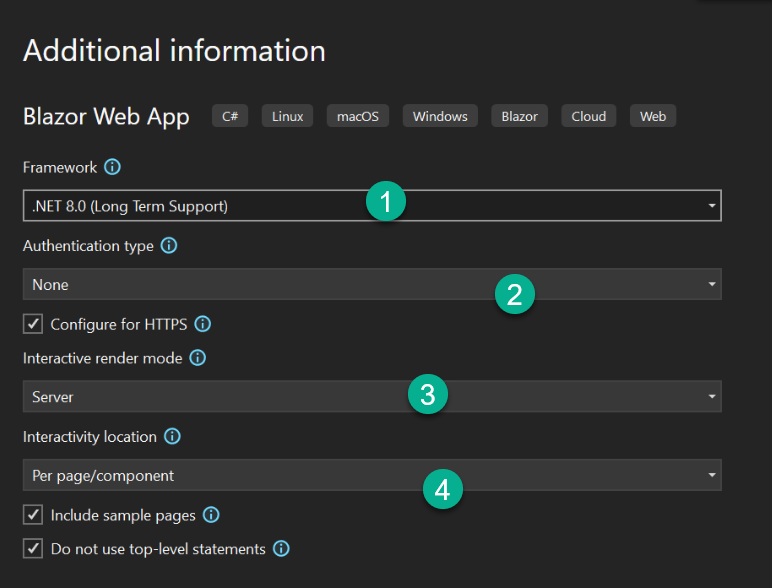
### How to Trigger Validation and Handle Form Submission
In this section, we will create an `Employee` class which will contain the model we will use. Below is what the model will look like;
```csharp
using System.ComponentModel.DataAnnotations;
namespace BlazorApp9.Components;
public class Employee
{
[Required(ErrorMessage = "First name is required")]
[StringLength(20, ErrorMessage = "First name must be less than 50 characters")]
public string FirstName { get; set; }
[Required(ErrorMessage = "Last name is required")]
[StringLength(10, ErrorMessage = "Last name must be less than 50 characters")]
[ValidateName]
public string LastName { get; set; }
[Required(ErrorMessage = "Email is required")]
[EmailAddress(ErrorMessage = "Invalid email address")]
public string Email { get; set; }
[Required(ErrorMessage = "Date of Birth is required")]
[DataType(DataType.Date)]
public DateTime DateOfBirth { get; set; }
}
```
From the code snippet above, the `Employee` model class properties have been set together with their `data-annotations` attributes for error validation. Also on the `LastName` property, we set the custom validation error message `ValidateName` as an attribute. The logic for the `ValidateName` method, which has been discussed above, can be found [here](https://hackmd.io/@zfgtm3UdSXSKe-H1o6lPCg/SJn4Ab5jp#Implementing-Custom-Form-Validation-in-Blazor).
Next, you will create an `Employee.razor` file containing the form and implement the `Employee`, a model class created above. The code for the form is below;
```csharp
@page "/employee"
@using BlazorApp9.Components
@using System.Text.Json
@rendermode InteractiveServer
<h3>Data Validation and Form Handling</h3>
<p>Fill the form below</p>
<EditForm Model="employee" OnValidSubmit="HandleValidSubmit" FormName="employeeForm" >
<DataAnnotationsValidator />
<div class="form-group">
<label for="firstname">First Name</label>
<InputText id="firstname" class="form-control" @bind-Value="employee.FirstName" />
<ValidationMessage For="@(() => employee.FirstName)" />
</div>
<div class="form-group">
<label for="lastname">Last Name</label>
<InputText id="lastname" class="form-control" @bind-Value="employee.LastName" />
<ValidationMessage For="@(() => employee.LastName)" />
</div>
<div class="form-group">
<label for="email">Email</label>
<InputText id="email" class="form-control" @bind-Value="employee.Email" />
<ValidationMessage For="@(() => employee.Email)" />
</div>
<div class="form-group">
<label for="dateOfBirth">Date Of Birth</label>
<InputDate id="dateOfBirth" class="form-control" @bind-Value="employee.DateOfBirth" />
<ValidationMessage For="@(() => employee.DateOfBirth)" />
</div>
<button type="submit" class="btn btn-primary">Submit</button>
</EditForm>
<div>
<span>@outputEmployee</span>
</div>
@code {
private Employee employee = new Employee();
private string outputEmployee;
private void HandleValidSubmit()
{
Console.WriteLine("Submitted Employee Information:");
Console.WriteLine($"First Name: {employee.FirstName}");
Console.WriteLine($"Last Name: {employee.LastName}");
Console.WriteLine($"Email: {employee.Email}");
Console.WriteLine($"Date of Birth: {employee.DateOfBirth}");
outputEmployee = JsonSerializer.Serialize(employee);
employee = new();
}
}
```
From the code snippet above, the `EditForm` component wraps the form to handle form submission and validation. The `EditForm` uses the `Model` attribute and its value (`employee`) in the [instantiated](https://essentialcsharp.com/declaring-and-instantiating-a-class) `Employee` class. The `employee` contains information about the `Model`, which gives the form the type of data to expect.
The `EditForm` uses the `OnValidSubmit` attribute and passes the `HandleValidSubmit` method. The `EditForm` also makes use of the `DataAnnotationsValidator` component, so the form can be aware of its validation and display the individual field error message with the help of the `ValidationMessage` component.
In the `@code{ }` block, we instantiate the `Employee` class and create a `string` variable called `outputEmployee`, which will display the details of the `employee` in `@outputEmployee` on the webpage.
When triggered, the `HandleValidSubmit` method will check if its validation is met, and then it will display the `employee` in the `Console`. This method also [Serializes](https://learn.microsoft.com/en-us/dotnet/standard/serialization/system-text-json/how-to) the value of the `employee` into a [JSON (Javascript Object Notation)](https://developer.mozilla.org/en-US/docs/Learn/JavaScript/Objects/JSON) object and passes the result to`outputEmployee` which displays it on the webpage.
The `employee = new()` will clear the inputs entered by the user on the form after submission. Running the code above without inputting any data will produce what you will see in the image below;
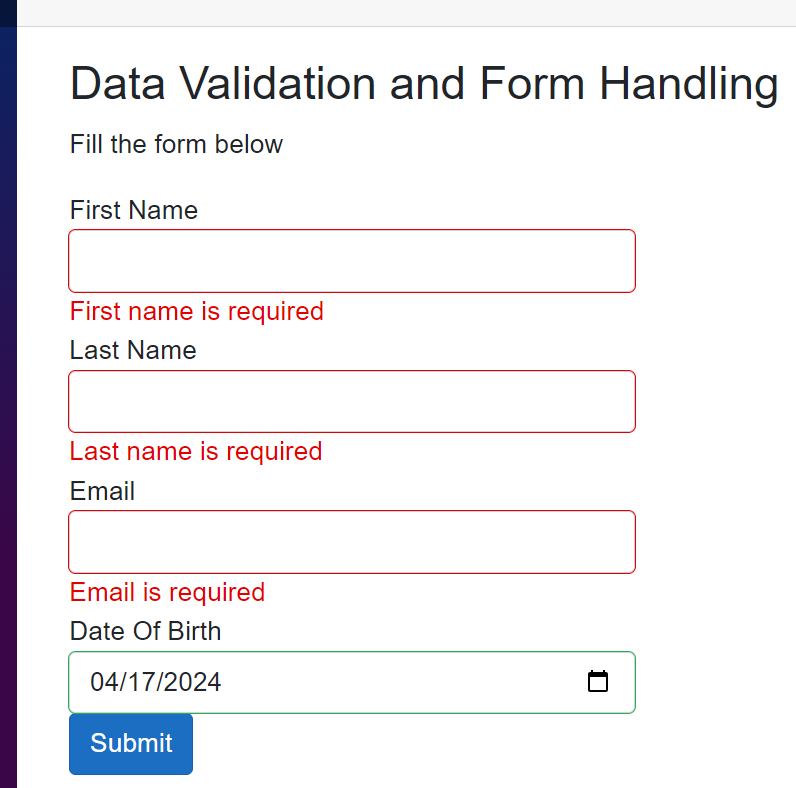
As seen in the above image, the user is presented with the appropriate validation messages. Hence, the user will know how to easily fix it. Again, we will run the code by inputting some incorrect data to see what error message will be displayed.
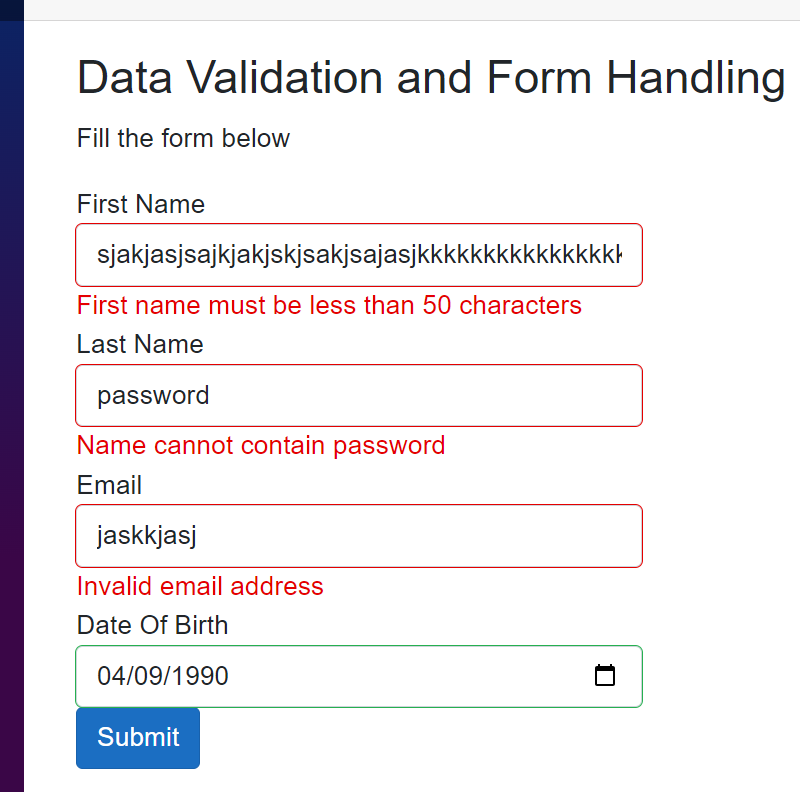
From the image above, you can see the validation messages are being displayed based on the pre-defined requirements.
Now, the form will be filled with the right data, and the result will be displayed in the `console`. The output for the `console` can be found below;
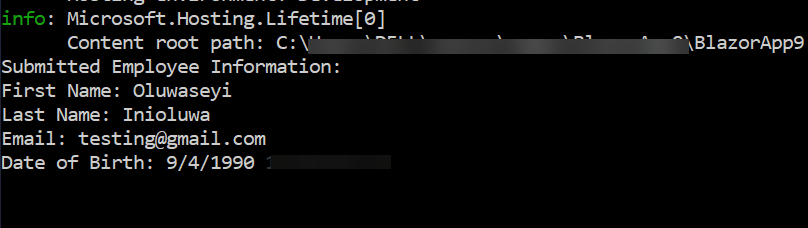
The image above shows the output of the submitted form in the `console`.
## Asynchronous Validation in Blazor
Asynchronous validation in Blazor allows you to perform validation tasks that require taking some time before they get executed, such as `database queries` or [API (Application Programming Interface)](https://aws.amazon.com/what-is/api/) calls, before determining the validity of a form field. This is useful when validating user input against external data sources.
### How to Implement and Showcase Asynchronous Validation Logic in Blazor Forms.
Firstly, we will create a custom validation attribute by inheriting from `ValidationAttribute` and implementing asynchronous validation logic in the `IsValid` method.
```csharp
using System.ComponentModel.DataAnnotations;
namespace BlazorApp9.Components;
public class UniqueEmail : ValidationAttribute
{
protected override ValidationResult IsValid(object value, ValidationContext validationContext)
{
var task = Task.Run(async () =>
{
await Task.Delay(2000);
// Validate the email uniqueness
if (value != null && value.ToString() == "existing@example.com")
{
return new ValidationResult("Email is already in use");
}
// Return success if validation passes
return ValidationResult.Success;
});
return task.Result; // Wait for the asynchronous task to complete and return its result
}
}
```
In this approach, the `Task.Run` will asynchronously execute the validation logic inside the `IsValid` method, allowing you to perform asynchronous operations.
You will add the `UniqueEmail` custom validation above as a `data-annotation` attribute on the `Email` property in the `Employee` model class. Below shows how that can be done;
```csharp
[Required(ErrorMessage = "Email is required")]
[DataType(DataType.EmailAddress)]
[EmailAddress(ErrorMessage = "Invalid email address")]
[UniqueEmail]
public string Email { get; set; }
```
From the code snippet above, the `Email` property uses the `UniqueEmail` custom validation to asynchronously validate user input, and the validation message is waited for a few seconds before being displayed.
## Advanced Form Handling Techniques
Handling complex forms and validation rules efficiently is necessary for a smooth user experience and data integrity. Here are several strategies to consider:
* Divide and Conquer: Break down the form into smaller sections or logical groups of fields. Each section can be managed independently, making the form more manageable and easier to maintain.
* Component-Based Architecture: Utilize Blazor components to encapsulate form sections or individual fields. This promotes reusability and helps keep the code organized.
* Validation: Leverage Blazor's built-in validation features such as `EditForm`, `ValidationMessage`, and `ValidationSummary` components. You can use `data annotations`, custom validation logic, or a combination of both to validate user input.
* Validation Feedback: Provide immediate feedback to users about validation errors. Highlight invalid fields, and display error messages near the corresponding fields.
* Conditional Validation: Implement conditional validation rules based on the state of other fields or external factors. You can achieve this by dynamically updating validation rules or by using custom validation logic.
* Asynchronous Validation: For complex validation rules that require `server-side` validation or asynchronous operations, handle validation asynchronously using custom validation logic.
By employing these strategies, you can effectively handle complex forms with multiple fields and validation rules, resulting in a better user experience and improved data integrity.
### Nested Complex Models and Their Implementation In Blazor
The `DataAnnotationsValidator` provided by default enables form input validation using `data annotations`. However, it solely validates top-level properties (properties without nested types) bound to the form, excluding child or complex-type properties.
To validate nested complex models, we will substitute the `DataAnnotationsValidator` with the `ObjectGraphDataAnnotationsValidator`. This validator assesses the entire object, encompassing child and complex type properties within the form. The `ObjectGraphDataAnnotationsValidator` does not come by default but can be installed as a [Nuget Package](https://www.nuget.org/packages/Microsoft.AspNetCore.Components.DataAnnotations.Validation). Below explains how it can be installed into your project;
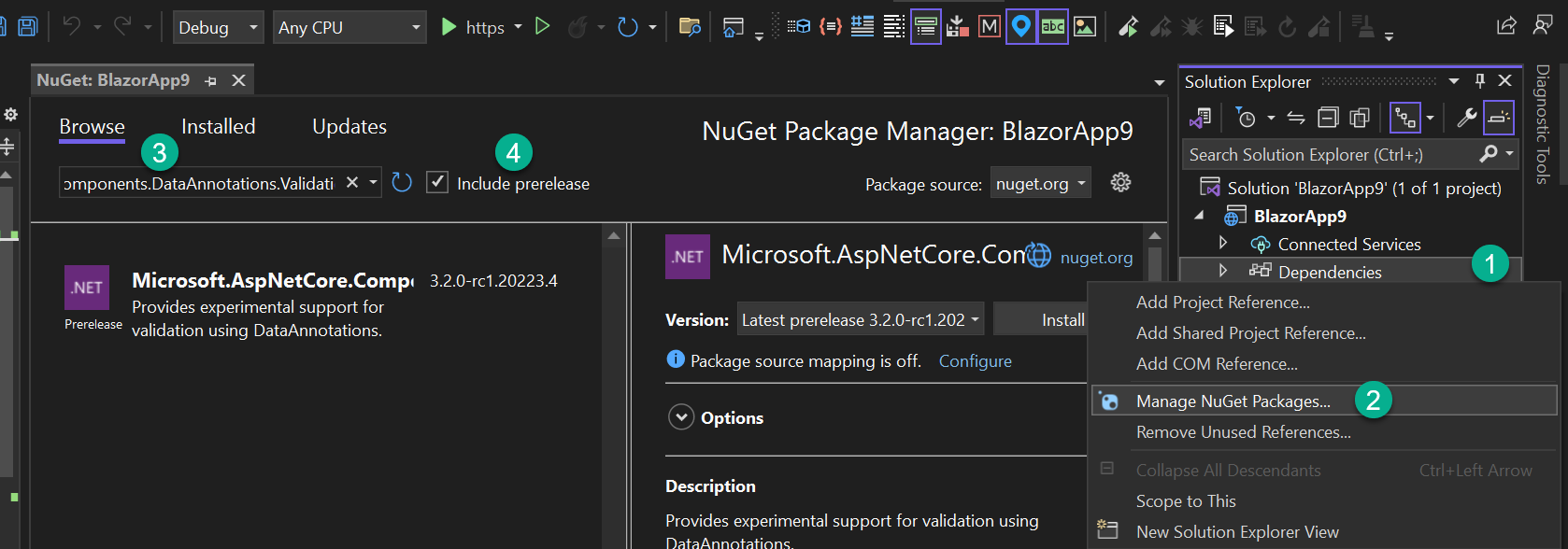
The image above shows how `ObjectGraphDataAnnotationsValidator` can be installed into your project. Type `Microsoft.AspNetCore.Components.DataAnnotations.Validation` in the search box to locate the [Nuget Package](https://www.nuget.org/packages/Microsoft.AspNetCore.Components.DataAnnotations.Validation).
We will create a class called `Guarantor.cs` which will have the properties below;
```csharp
public class Guarantor
{
[Required(ErrorMessage = "Guarantor's Name is required")]
public string Name { get; set; }
[Required(ErrorMessage = "Guarantor's Phone Number is required")]
[Phone(ErrorMessage = "Invalid phone number")]
public string PhoneNumber { get; set; }
}
```
The above shows that the `Guarantor` must have a `Name` and `Phone Number`. The `Guarantor` class will be added as a property and a type in the `Employee`, a class we created earlier in this guide. It can be found [here](https://hackmd.io/@zfgtm3UdSXSKe-H1o6lPCg/SJn4Ab5jp#How-to-Trigger-Validation-and-Handle-Form-Submission). Below shows how the `Guarantor` class will be used as a property in the `Employee` class.
```csharp
[Required]
[ValidateComplexType]
public Guarantor Guarantor { get; set; } = new Guarantor();
```
The code snippet above shows that the `Guarantor` is required and expects its type. The `ValidateComplexType` attribute tells the `model` that the `Guarantor` is a complex type (it contains nested elements).
Also, change the `DataAnnotationsValidator` tag in the `Employee.razor` file to `ObjectGraphDataAnnotationsValidator`. Running the code will produce the result below;
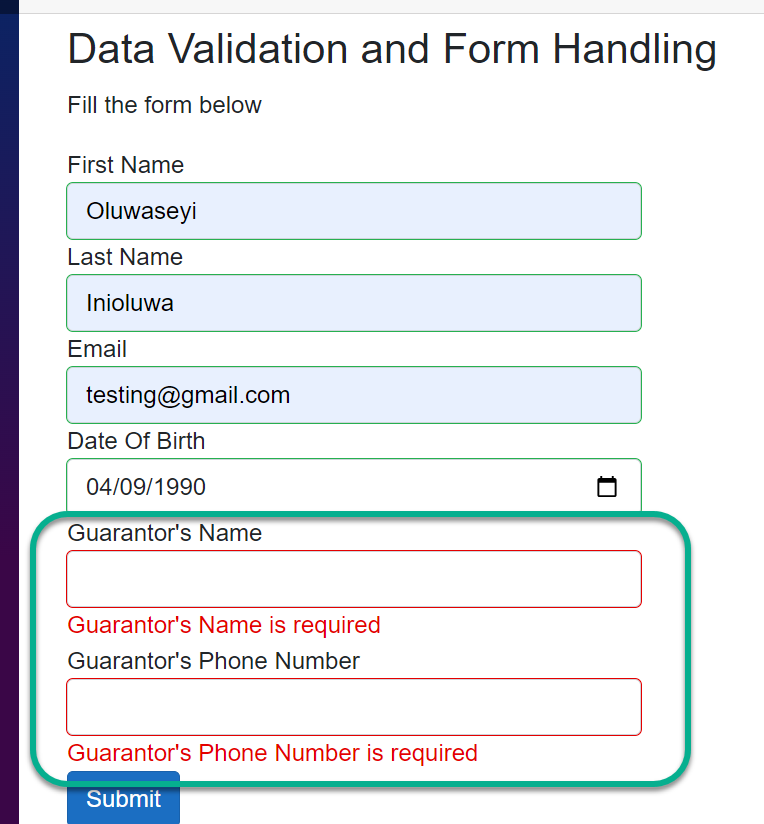
The `Name` and `Phone Number` of the `Guarantor` display the correct validation error message set on the `model`, as you can see in the image above.
## Conclusion
Data validation and form handling in Blazor are crucial for building robust and user-friendly web applications. By leveraging Blazor's built-in validation features, implementing custom validation logic, and adhering to best practices, you can ensure data integrity and provide a seamless user experience.
Experiment with everything discussed in this guide and unlock the full potential of Blazor in your projects.
| asayerio_techblog | |
1,868,829 | Implementing SSO Authentication with Keycloak | In this blog, we will implement Single Sign-On (SSO) authentication with Keycloak. During this... | 0 | 2024-06-03T08:33:31 | https://blog.elest.io/best-practices-for-importing-users-from-legacy-applications-to-keycloak/ | gettingstarted, elestio, ssoauthentication, keycloak | ---
title: Implementing SSO Authentication with Keycloak
published: true
date: 2024-05-29 10:00:57 UTC
tags: GettingStarted,Elestio, SSOAuthentication, Keycloak
cover_image: https://dev-to-uploads.s3.amazonaws.com/uploads/articles/fj1ve537chim8xx587fp.png
canonical_url: https://blog.elest.io/best-practices-for-importing-users-from-legacy-applications-to-keycloak/
---
In this blog, we will implement Single Sign-On (SSO) authentication with Keycloak. During this tutorial, we will take an example of SSO between Keycloak and Google Workspace accounts. You can also choose the cloud identity of your choice to get started. Before we start, make sure you have deployed Keycloak, we will be self-hosting it on [Elestio](https://elest.io/open-source/keycloak?ref=blog.elest.io).
## What is Keycloak?
Keycloak is an open-source Identity and Access Management solution developed by Red Hat. It provides robust authentication, authorization, and single sign-on capabilities for web applications, mobile apps, and services. With Keycloak, organizations can centrally manage user identities, enforce security policies, and facilitate resource access across various platforms and environments.
## Introduction to Single Sign-On (SSO)
Single Sign-On (SSO) is an authentication mechanism that enables users to log in once and gain access to multiple applications and services without having to re-enter their credentials for each one. With SSO, users authenticate themselves through a centralized identity provider (IdP), which then issues security tokens or session cookies that grant access to affiliated applications. This authentication experience improves user convenience, reduces the risk of password fatigue, and simplifies organisation identity management.
## Creating a Client
Once logged in to Keycloak, create or switch to your preferred realm and head over to the **Clients** section from the left side panel and click on **Create Client** to create a new client.
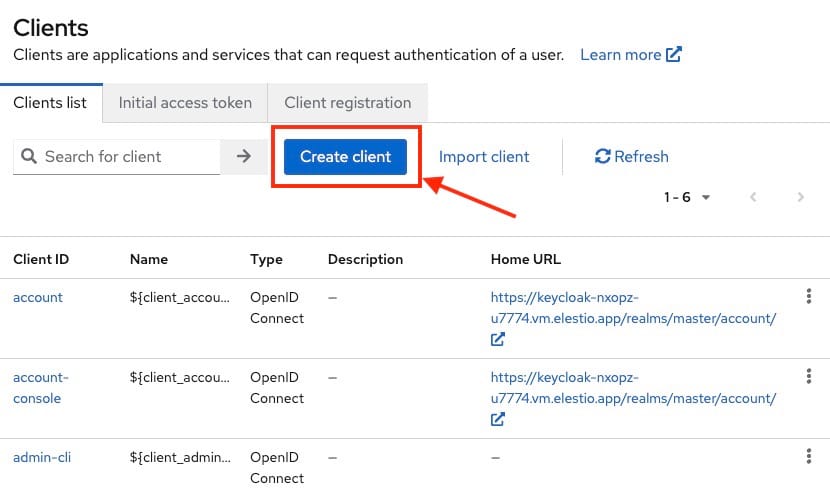
We will be using SAML federation for setup here so we will set client type as **SAML** , client id becomes **google.com** and name can be anything of your choice like I have given here as **Google Cloud**.
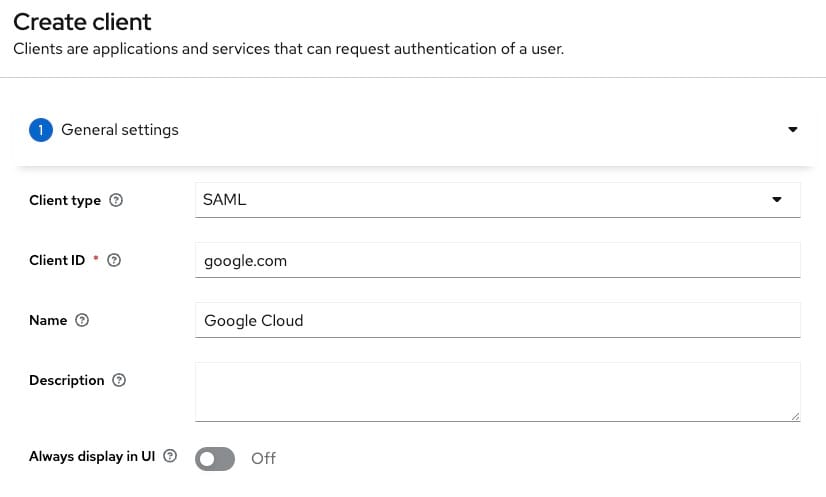
In the next step add **https://www.google.com/\*** as valid redirect URIs. You can add multiple URIs.
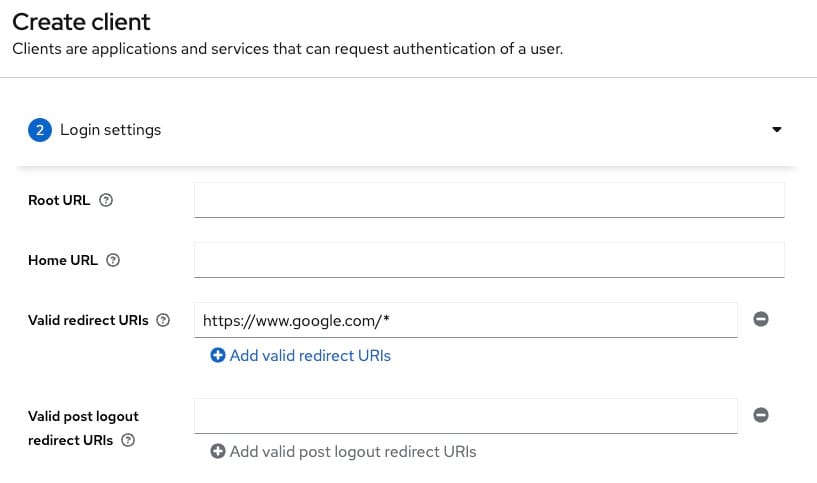
Now we will be configuring additional settings for **google.com**. Select **email** from the dropdown for **Force Name ID format** and toggle it **on**.
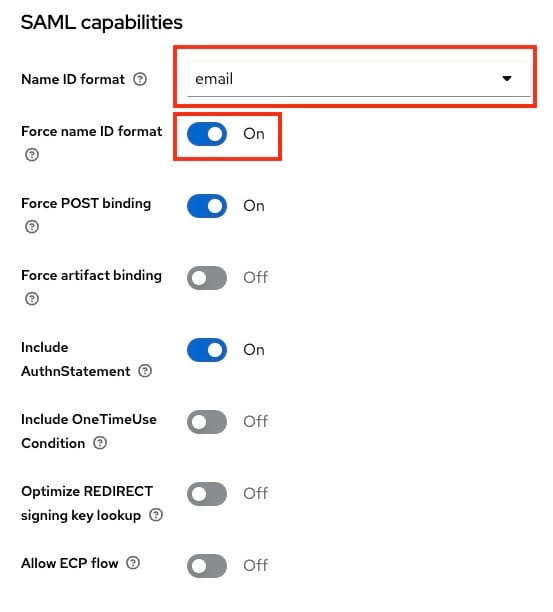
Next, under signature and encryption section toggle **off** the **Sign documents** option and toggle **on Sign assertions**.
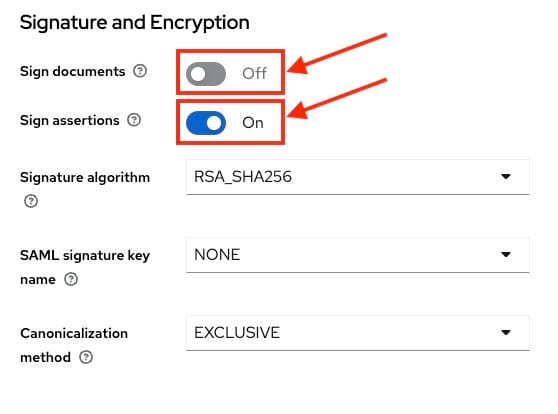
Now head over to the Keys section and turn **off** the **Client Signature required** settings. This step is optional and you can choose to validate the keys and move ahead. For the simplicity of this article we are going to keep it off.
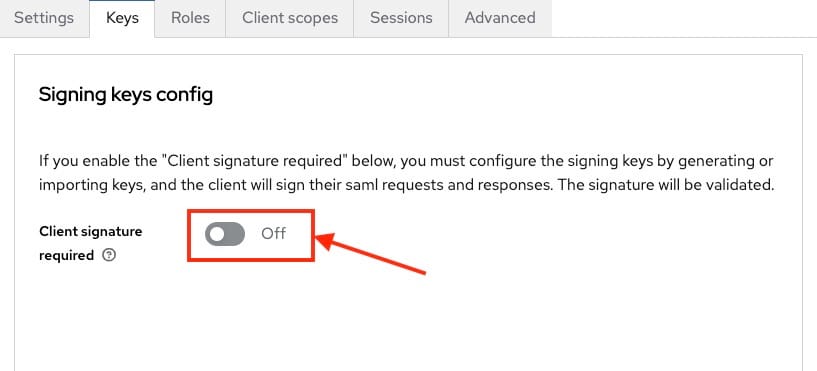
## Exporting Signing Certificate
Keycloak after authenticating a user passes SAML assertion to Cloud Identity and to enable it to verify the authenticity of that assertion, Keycloak signs the assertion with unique token-signing key that then provides the certificate that enables cloud identity to check the signature.
To view the certificate, head over to the **Realm Settings** and then go to the **Keys** tab. You will see a row **Algorithm: RS256** and **Use: SIG** and select **Certificate.** A pop up will appear with your certificate content. Now copy this certificate content safely to a notepad or text editor.
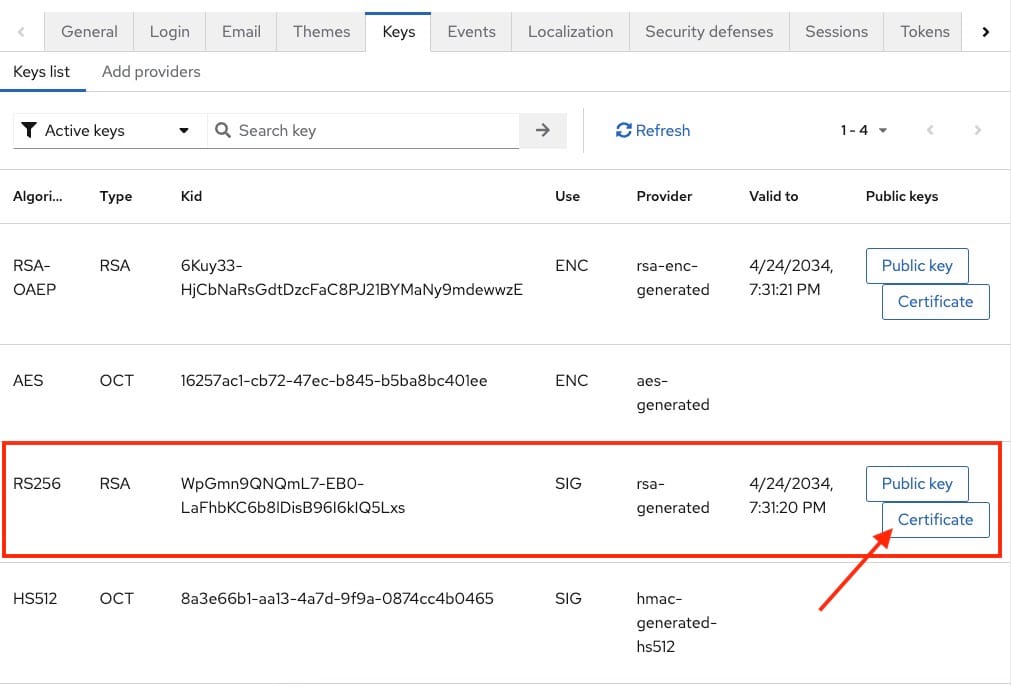
## Converting Signing Certificate
Open your notepad or text editor and paste the following at the begining of the certificate followed by new line
```
-----BEGIN CERTIFICATE-----
```
and in the end add the following line
```
-----END CERTIFICATE-----
```
It should look something like the following
```
-----BEGIN CERTIFICATE-----
MIICmzCCAYMCBgF7v8/V1TANBgkq...
-----END CERTIFICATE-----
```
## Configuring Cloud Identity
⚠️
Make sure you replace <KEYCLOAK> and <REALM> with appropriate values
1. Open [Admin Console](https://admin.google.com/?ref=blog.elest.io) and log in as a super-admin user.
2. Head over to **Security > Authentication > SSO with third-party IdP**
3. Now **Add SSO Profile** and **Setup SSO with third party identiy provider** to **enabled.**
4. Configure the following settings
1. **Sign-in page URL :** https://_<KEYCLOAK>_/realms/_<REALM>_/protocol/saml
2. **Sign-out page URL :** https://_<KEYCLOAK>_/realms/_<REALM>_/protocol/openid-connect/logout
3. **Use a domain specific issuer:** clear
4. **Change the password URL :** https://_<KEYCLOAK>_/realms/_<REALM>_/account
5. Under **Verification certificate** , click on **Upload Certificate** , and then select the certificate you downloaded previously
6. Click **Save** to save the configurations
## **Thanks for reading ❤️**
Thank you so much for reading and do check out the Elestio resources and Official Keycloak documentation to learn more about the Keycloak. You can click the button below to create your service on [Elestio](https://elest.io/open-source/keycloak?ref=blog.elest.io) and implement this SSO authentication method. See you in the next one👋
[](https://elest.io/?ref=blog.elest.io) | kaiwalyakoparkar |
1,868,772 | Spiner! a package/project manager. first look | hello everybody. I'm Elia. in this post (my first post btw). i want to showcase and take a look at... | 0 | 2024-05-29T09:59:57 | https://dev.to/eliaondacs/spiner-a-packageproject-manager-first-look-4h17 | manager, tooling, news, productivity |
hello everybody. I'm Elia. in this post (my first post btw).
i want to showcase and take a look at the first version of spiner (name comes from the fidget spinner) .
## what is spiner?
spiner is a package/project manager that make interacting with different project even if they are in completely different language and environment easy by providing a shell, command-line interface, and you can also automate things by writing spiner custom shell script .SpinSH, it also allows you to customize the spiner when its in a particular directory using .spin files!.
## why we should use spiner?
spiner gives you, ability to control project no matter the environment,
spiner can be used to work with projects cross platform too

## current state of spiner
the current state of spiner is beta, yes its only in it 0.1.0 beta version on [github](https://github.com/EliaOndacs/Spiner) .
you can go and download it from there and be one of the first people who actually used this.
## for how long this project gonna continue?
to be honest i don't really know, maybe tomorrow maybe 30 years later.
## finally
we came to the end of this small post,
i really just created this post to inform everyone about this project, because i really want this project to take off and hopefully become a useful tool .
anyways, thank you for your time and reading!
goodbye.
| eliaondacs |
1,868,771 | Boost Your Instagram Experience with IgAnony and InstaNavigation | Boost Your Instagram Experience with IgAnony and InstaNavigation Instagram has evolved into a... | 0 | 2024-05-29T09:59:45 | https://dev.to/paramounttechsolutio/boost-your-instagram-experience-with-iganony-and-instanavigation-lcn | techtalks, insta, webdev | Boost Your Instagram Experience with IgAnony and InstaNavigation
Instagram has evolved into a powerful platform for sharing moments, stories, and connecting with a global audience. To enhance your Instagram experience, two exceptional tools, IgAnony and InstaNavigation, have emerged as game-changers. This article delves into their features, benefits, and how they can elevate your Instagram usage.

## Key Features of IgAnony
IgAnony is an innovative tool designed to offer a seamless Instagram experience, especially for viewing stories and profiles anonymously. The platform is packed with features that cater to different user needs.
**iganony.io: A Comprehensive Overview**
iganony.io is the go-to platform for users seeking to view Instagram stories and profiles without leaving a trace. Its interface is user-friendly, ensuring that even novice users can navigate effortlessly.
## **Instagram Story Viewer IgAnony**
One of the standout features is the [Instagram story viewer](https://paramounttechsolution.com/iganony-and-instanavigation-instagram-story-viewer/). With IgAnony, users can watch stories without the account owner knowing. This feature is perfect for maintaining privacy while keeping up with updates from friends, family, and influencers.
**IgAnony.io Instagram**
IgAnony.io Instagram is designed to be your one-stop solution for all anonymous Instagram viewing needs. Whether you're checking stories or browsing profiles, IgAnony.io ensures that your activity remains hidden.
**IgAnony Private Account Viewer**
The IgAnony private account viewer feature allows users to access content from private accounts without following them. This functionality is particularly useful for users who want to keep their interests discreet.
**IgAnony.io Private Account**
IgAnony.io private account functionality ensures that you can view private Instagram accounts securely and anonymously, offering an unparalleled browsing experience.
**IgAnony Story Viewer**
The IgAnony story viewer is a powerful tool that lets you watch Instagram stories anonymously. This feature is essential for users who want to stay updated without revealing their identity.
## **Exploring InstaNavigation**
InstaNavigation complements IgAnony by offering additional features that enhance your Instagram browsing experience.
**InstaNavigation.net:** Navigate Instagram with Ease
InstaNavigation.net is designed to provide users with an intuitive and efficient way to explore Instagram. The platform's layout and functionality make it easy to find and view content.
**InstaNavigation Stories**
With InstaNavigation stories, users can effortlessly browse through Instagram stories, ensuring that they never miss an update. This feature is ideal for keeping track of multiple accounts.
**InstaNavigation Viewer**
The InstaNavigation viewer is a comprehensive tool that allows users to explore Instagram profiles and stories in detail. This feature enhances the overall Instagram experience by providing detailed insights and easy navigation.
**InstaNavigation Download**
InstaNavigation download feature lets users save their favorite Instagram content directly to their devices. This functionality is perfect for those who want to keep memorable posts and stories for offline viewing.
## **How IgAnony and InstaNavigation Enhance Your Instagram Experience**
By combining the features of [IgAnony and InstaNavigation](https://paramounttechsolution.com/iganony-and-instanavigation-instagram-story-viewer/), users can enjoy a more enriched and private Instagram browsing experience.

**AnonStories.net and Similar Platforms**
While platforms like AnonStories.net offer similar services, IgAnony and InstaNavigation stand out due to their superior features and user-friendly interfaces. IgAnony.io Instagram story viewer and InstaNavigation.net ensure that users have a seamless and private viewing experience.
**Competitive Edge: IgAnony vs. Other Tools**
Compared to other tools like Imginn.com and IGStoriesDown, IgAnony offers more robust features such as the iganony.io private account free download and iganony.io private account viewing. These features provide users with more control and privacy.
## **Practical Applications and User Benefits**
Using IgAnony and InstaNavigation offers numerous practical benefits for different types of users.
**For Influencers and Marketers**
Influencers and marketers can use these tools to keep an eye on competitors and trends without revealing their identity. The private Instagram story viewer IgAnony feature is particularly useful for market analysis and strategy development.
**For Personal Use**
Individuals who value their privacy will find IgAnony and InstaNavigation indispensable. Features like iganony.io Instagram story viewer and insta stories IgAnony allow users to stay updated without compromising their privacy.
**Ease of Use**
Both IgAnony and InstaNavigation are designed to be user-friendly. The platforms' interfaces are intuitive, ensuring that users can quickly find and utilize the features they need.
**Conclusion**
In conclusion, IgAnony and InstaNavigation provide a comprehensive set of tools that significantly enhance the Instagram browsing experience. From anonymous story viewing to detailed profile exploration, these platforms offer unparalleled privacy and convenience. Whether you're an influencer, marketer, or a privacy-conscious individual, IgAnony and InstaNavigation are your go-to solutions for a better Instagram experience.
**FAQs**
**What is IgAnony?**
IgAnony is an innovative tool designed for anonymous browsing of Instagram stories and profiles. It allows users to view Instagram content without leaving any traces or notifying the account owners.
**How does IgAnony.io work?**
IgAnony.io works by providing a user-friendly interface where you can enter the username of the Instagram account you wish to view. It then fetches the content from that account, allowing you to browse stories and profiles anonymously.
**Is IgAnony.io safe to use?**
Yes, IgAnony.io is safe to use. It ensures that your browsing activity remains private and secure, protecting your anonymity while you explore Instagram.
**Can I view private Instagram accounts with IgAnony?**
Yes, the IgAnony private account viewer feature allows you to access content from private Instagram accounts without following them, maintaining your privacy.
**What is InstaNavigation?**
InstaNavigation is a complementary tool that enhances your Instagram browsing experience by offering features such as story viewing, profile exploration, and content downloading, all with a focus on ease of navigation and privacy.
**How do I use InstaNavigation.net?**
To use InstaNavigation.net, simply visit the website and enter the Instagram username or content you wish to explore. The platform provides an intuitive interface for easy navigation and content viewing.
| paramounttechsolutio |
1,868,768 | Smart Ticketing Market : Top Factors That Are Leading The Demand Around The Global | The latest market research report on the global smart ticketing industry indicates a robust growth... | 0 | 2024-05-29T09:57:28 | https://dev.to/mihir_kadu_138/smart-ticketing-market-top-factors-that-are-leading-the-demand-around-the-global-2eo | smartticketingmarket, smart, ticketing | The latest market research report on the global smart ticketing industry indicates a robust growth trajectory, with the market set to soar to US$28.9 billion by 2030, up from US$8.4 billion in 2018. Projected to register a Compound Annual Growth Rate (CAGR) of 14.8% during the forecast period from 2024 to 2030, the smart ticketing sector is poised for significant expansion driven by various factors shaping urban mobility and digital transformation.
For More Industry Insights: https://www.fairfieldmarketresearch.com/report/smart-ticketing-market
Widening Applications and Driving Forces
The report highlights the widening application of smart ticketing systems across public transportation networks, events, and entertainment venues as a key driver of market expansion. With increasing urbanization and a growing reliance on public transit, cities worldwide are seeking efficient solutions to manage burgeoning commuter populations. This trend is complemented by a surge in demand for contactless payments, further facilitated by solutions like contactless cards and mobile wallets, enhancing operational efficiency and customer experience.
Navigating Through Pandemic Challenges
While the COVID-19 pandemic initially disrupted the smart ticketing industry, it also accelerated the adoption of contactless payment systems, particularly in public transportation, to mitigate virus transmission risks. Despite facing challenges such as decreased ridership and supply chain disruptions, the industry showcased resilience and innovation, adapting swiftly to the evolving landscape. This adaptation included a focus on contactless solutions, spurring collaborations, and technological advancements to meet changing consumer preferences.
Regional Dynamics and Market Leadership
The report underscores regional variations in market growth, with Asia Pacific emerging as the frontrunner driven by rapid urbanization and the digital economy's exceptional growth. Europe leads in market share, propelled by well-established public transportation networks and proactive regulatory frameworks. North America follows suit, experiencing significant growth in smart ticketing adoption by public transportation operators.
Overcoming Barriers and Seizing Opportunities
Challenges such as infrastructural requirements and security concerns are being addressed through technological innovations and regulatory frameworks. The integration of mobility services, expansion into developing economies, and enhanced data analytics present promising opportunities for market players to capitalize on.
Key Players and Strategic Initiatives
Major players in the smart ticketing space, including Infineon, Cubic, and Hitachi, continue to dominate the market, leveraging strategies such as partnerships, mergers, and innovations to enhance product offerings and maintain a competitive edge.
| mihir_kadu_138 |
1,868,767 | How to Build a JavaScript PDF Editor with pdf-lib | PDF-lib is an open-source and free JavaScript library for creating, editing, and modifying PDF... | 0 | 2024-05-29T09:57:24 | https://dev.to/derek-compdf/how-to-build-a-javascript-pdf-editor-with-pdf-lib-4319 | webdev, javascript, pdf, opensource | PDF-lib is an open-source and free JavaScript library for creating, editing, and modifying PDF documents, which is commonly used in Web development projects. In this post, you will learn how to use this [open source PDF library](https://www.compdf.com/blog/open-source-pdf-libraries-vs-compdfkit) to build a JavaScript PDF editor from installation to specific features. Meanwhile, we introduce a great [pdf-lib alternative](https://compdf.com/) for those seeking advanced PDF manipulation capabilities.
## Build a JavaScript PDF Editor with pdf-lib
### 1. Get Start
After installing pdf-lib using npm, you can quickly start by saving the following codes as an HTML file and loading it in your browser.
```
<html>
<head>
<meta charset="utf-8" />
<script src="https://unpkg.com/pdf-lib"></script>
</head>
<body>
<iframe id="pdf" style="width: 100%; height: 100%;"></iframe>
</body>
<script>
createPdf();
async function createPdf() {
const pdfDoc = await PDFLib.PDFDocument.create();
const page = pdfDoc.addPage([350, 400]);
page.moveTo(110, 200);
page.drawText('Hello World!');
const pdfDataUri = await pdfDoc.saveAsBase64({ dataUri: true });
document.getElementById('pdf').src = pdfDataUri;
}
</script>
</html>
```
### 2. Code Sample: Create Document
Once you have successfully initialized pdf-lib in your Web application, you can utilize it to integrate the functionality to create PDF documents with the below example.
```
import { PDFDocument, StandardFonts, rgb } from 'pdf-lib'
async function createPdf() {
const pdfDoc = await PDFDocument.create()
const timesRomanFont = await pdfDoc.embedFont(StandardFonts.TimesRoman)
const page = pdfDoc.addPage()
const { width, height } = page.getSize()
const fontSize = 30
page.drawText('Creating PDFs in JavaScript is awesome!', {
x: 50,
y: height - 4 * fontSize,
size: fontSize,
font: timesRomanFont,
color: rgb(0, 0.53, 0.71),
})
const pdfBytes = await pdfDoc.save()
}
```
It is obvious that pdf-lib is an easy-to-integrate PDF library for building a PDF editor with JavaScript. However, due to its open-source nature, it may not fully meet the needs of developers seeking advanced PDF functionalities like watermarks, document comparison, and comprehensive technical support. Fortunately, ComPDFKit Web PDF SDK exceeds pdf-lib's capabilities, making it a superior alternative. Our JavaScript PDF library supports Standalone deployment powered by WebAssembly or Server-backed deployment with Docker based on your needs.
## Build a JavaScript PDF Editor with ComPDFKit for Web
### Step 1. Install ComPDFKit Web PDF SDK
There are two ways to download ComPDFKit Web SDK. You can contact our sales team to obtain the local package. Or install our WebViewer from npm on your own and add it as a project dependency.
```
npm i @compdfkit_pdf_sdk/webviewer --save
```
### Step 2. Integrate ComPDFKit Web PDF Library to Build JavaScript PDF Editor
#### Mannually Integrate ComPDFKit PDF Library for Web
If you downloaded the local ComPDFKit Web package, it is available to create a JavaScript PDF editor by Vanilla JavaScript and Vue, please respectively follow the steps below to integrate it manually.
##### Integrate into a Vanilla JavaScript Project
1. Create index.html
```
<!DOCTYPE html>
<html lang="en">
<head>
<meta charset="UTF-8">
<meta name="viewport" content="width=device-width, initial-scale=1.0">
<title>ComPDFKit Web Viewer</title>
</head>
<!-- Import WebViewer as a script tag -->
<script src='@compdfkit/webviewer.global.js'></script>
<body>
<div id="app" style="width: 100%; height: 100vh;"></div>
</body>
</html>
```
2. Add script tag and initialize ComPDFKitViewer for Web in JavaScript
```
<!DOCTYPE html>
<html lang="en">
<head>
<meta charset="UTF-8">
<meta name="viewport" content="width=device-width, initial-scale=1.0">
<title>ComPDFKit Web Viewer</title>
</head>
<!-- Import WebViewer as a script tag -->
<script src='@compdfkit/webviewer.global.js'></script>
<body>
<div id="app" style="width: 100%; height: 100vh;"></div>
<script>
let docViewer = null;
ComPDFKitViewer.init({
pdfUrl: '/webviewer/example/developer_guide_web.pdf',
license: 'Input your license here'
}, document.getElementById('app')).then((core) => {
docViewer = core.docViewer;
docViewer.addEvent('documentloaded', async () => {
console.log('document loaded');
})
})
</script>
</body>
</html>
```
3. Set a server environment To show in the localhost, we need to set a server environment;
```
npm install -g http-server
```
4. Serve your website
```
http-server -a localhost -p 8080
```
Open http://localhost:8080 on your browser. Then you will be able to see the PDF file you want to display.
##### Integrate into a Vue Project
1. Add ComPDFKit for Web Package
- Add the "@compdfkit" folder in the lib directory to the root directory or assets directory of your project. This will serve as the entry point for the ComPDFKit for Web and will be imported into your project.
- Add the "webviewer" folder that contains the required static resource files to run the ComPDFKit Web demo, to your project’s static resource folder.
2. Display a PDF Document
- Import the “webviewer.js” file in the "@compdfkit" folder into your project.
- Initialize the ComPDFKit for Web in your project by calling `ComPDFKitViewer.init()`.
- Pass the PDF address you want to display and your license key into the init function.
```
// Import the JS file of ComPDFKit Web Demo.
import ComPDFKitViewer from "/@compdfkit/webviewer";
const viewer = document.getElementById('webviewer');
ComPDFKitViewer.init({
pdfUrl: 'Your PDF Url',
license: 'Input your license here'
}, viewer)
.then((core) => {
const docViewer = core.docViewer;
docViewer.addEvent('documentloaded', () => {
console.log('ComPDFKit Web Demo');
})
})
```
Note: You need to contact ComPDFKit team to get the license.
4. Once your project is running, you will be able to see the PDF file you want to display.
#### Build JavaScript PDF Editor by Integrating via NPM
1. Copy Assets to Your Static Folder
These assets need to be served in your application. Copy the ComPDFKit for Web library's assets to the static directory in your project’s root folder.
The folder you need to copy is `node_modules/@compdfkit_pdf_sdk/webviewer/dist`.
```
cp -r ./node_modules/@compdfkit_pdf_sdk/webviewer/dist ./public/webviewer
```
2. Import and Initial the WebViewer
```
import WebViewer from '@compdfkit_pdf_sdk/webviewer'
const element = document.getElementById('viewer');
WebViewer({
pdfUrl: 'URL of your PDF File' // the path of your document
license: 'Input your license here'
}, element).then((instance) => {
// Call APIs here
})
```
3. Apply the License Key
Get a free 30-day license by providing some information about your project to start testing.
### Step 3. Code Samples: Save a Document
ComPDFKit provides various code examples for developers to integrate different PDF features in a JavaScript PDF editor. Here is an example of saving a PDF document.
```
// Import the JS file of ComPDFKit Web Demo.
import ComPDFKitViewer from "/@compdfkit/webviewer";
const viewer = document.getElementById('webviewer');
ComPDFKitViewer.init({
pdfUrl: 'Your PDF Url',
license: 'Input your license here'
}, viewer)
.then((core) => {
const docViewer = core.docViewer;
docViewer.addEvent('documentloaded',async () => {
console.log('ComPDFKit Web Demo');
const docStream = await docViewer.download()
const docBlob = new Blob([docStream], { type: 'application/pdf' })
})
})
```
## Bottom Line
pdf-lib is a popular and well-performing PDF library for building a JavaScript PDF viewer. For advanced PDF functions like PDF data extraction, OCR, etc., ComPDFKit PDF SDK for Web is more recommended. Not only does it provide detailed development guides, but also guarantees one-on-one technical support even though you are testing. Before integrating ComPDFKit Web PDF library into your projects using the 30-day free trial licenses, it is welcome to visit our online tools and Web Demo to process PDF files to experience how ComPDFKit performs. | derek-compdf |
1,868,766 | Building Vue3 Component Library from Scratch #10 Create Cli Scaffold | This article will implement the development of a scaffold called create-stellarnovaui. With just one... | 27,509 | 2024-05-29T09:57:08 | https://dev.to/markliu2013/building-vue3-component-library-from-scratch-10-create-cli-scaffold-1om0 | vue | This article will implement the development of a scaffold called `create-stellarnovaui`. With just one command, `npm init stellarnovaui`, you can pull the entire component library development framework to your local environment.
## Create Cli Package
Firstly, we create a new `cli` directory under the `packages` directory, initialize it by running `pnpm init`, and then change the package name to `create-stellarnovaui`.
> What needs to be known here is that when we execute `npm init xxx` or `npm create xxx`, we are actually executing `npx create-xxx`. So when we execute `npm init stellarnovaui`, we are actually executing `npx create-stellarnovaui`.
When we execute `create-stellarnovaui`, it will execute the path corresponding to `bin` in `package.json`. Therefore, we modify `package.json` as follows.
```json
{
"name": "create-stellarnovaui",
"version": "1.0.0",
"description": "",
"bin": "index.js",
"keywords": [],
"author": "",
"license": "MIT"
}
```
At the same time, create `index.js` as the entry file. Note that you need to add `#! /usr/bin/env node` at the beginning.
```bash
#! /usr/bin/env node
```
# Processing User Input Commands with `command-line-args`
There are actually many plugins for handling user input parameters, such as CAC, Yargs, Commander.js, command-line-args, etc. However, in my view, command-line-args is the simplest to use, so here we use command-line-args for user parameter parsing.
```bash
pnpm add command-line-args
```
Create `cli.js` to handle the logic of our scaffold. Here, let's simply write a `-v` version command.
```javascript
import commandLineArgs from "command-line-args";
import { readFile } from "fs/promises";
const pkg = JSON.parse(
await readFile(new URL("./package.json", import.meta.url))
);
//"Configure command parameters."
const optionDefinitions = [{ name: "version", alias: "v", type: Boolean }];
const options = commandLineArgs(optionDefinitions);
if (options.version) {
console.log(`v${pkg.version}`);
}
```
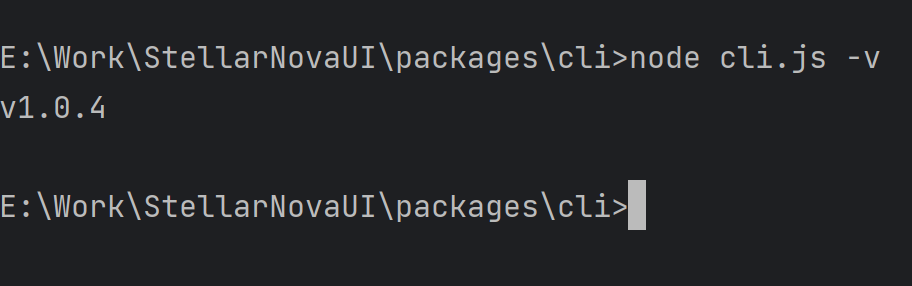
We can also use the `command-line-usage` plugin to provide us with help commands.
```bash
pnpm add command-line-usage
```
Only the relevant code is posted here.
```javascript
import commandLineArgs from "command-line-args"
import commandLineUsage from "command-line-usage"
...
//Help command
const helpSections = [
{
header: 'create-stellarnovaui',
content: 'A scaffold for quickly setting up a component library environment'
},
{
header: 'Options',
optionList: [
{
name: 'version',
alias: 'v',
typeLabel: '{underline boolean}',
description: 'Version number'
},
{
name: 'help',
alias: 'h',
typeLabel: '{underline boolean}',
description: 'Help'
}
]
}
];
if (options.help) {
console.log(commandLineUsage(helpSections))
return
}
```
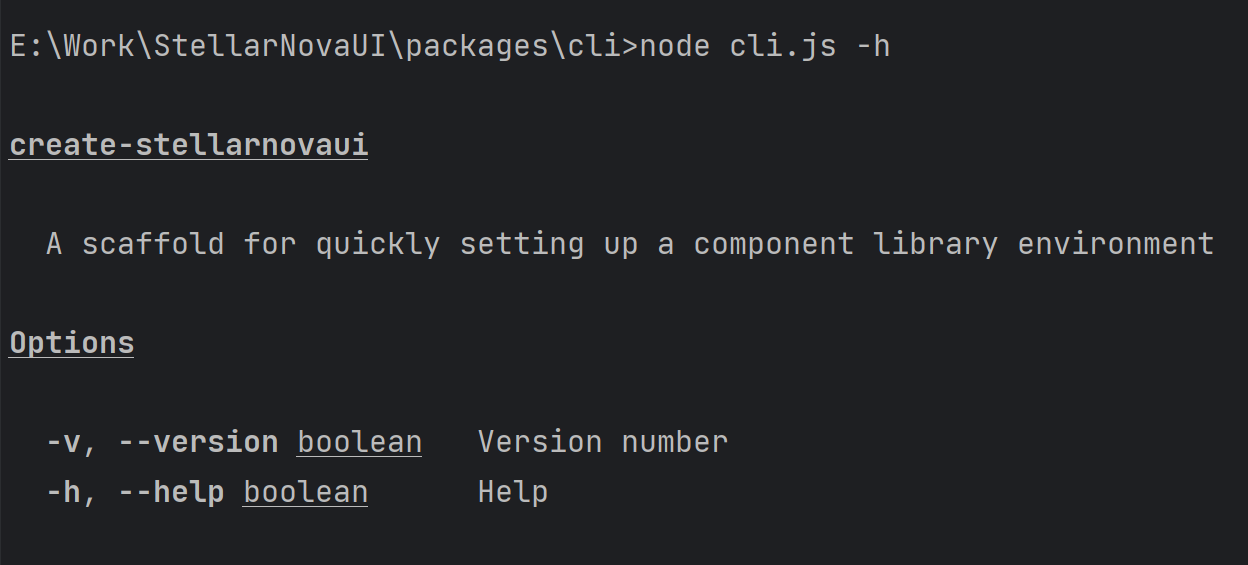
## Interactive Commands
When we use some scaffolding, such as create-vite, it will give us some options to choose from.
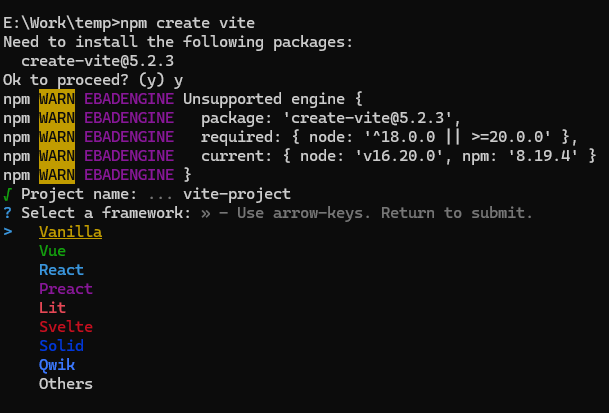
So our scaffolding should also have this feature, but how should this be implemented?
It's actually quite simple, all we need is the `prompts` plugin. It can configure what the user inputs, whether it's single or multiple choices, etc.
Firstly, install `prompts`.
```bash
pnpm add prompts
```
Then in cli.js
```javascript
import prompts from "prompts";
const promptsOptions = [
{
type: "text",
name: "user",
message: "User",
},
{
type: "password",
name: "password",
message: "Password",
},
{
type: "select", //
name: "gender",
message: "Gender",
choices: [
{ title: "Male", value: 0 },
{ title: "Female", value: 1 },
],
},
{
type: "multiselect",
name: "study",
message: "Select Framework",
choices: [
{ title: "Vue", value: 0 },
{ title: "React", value: 1 },
{ title: "Angular", value: 2 },
],
},
];
const getUserInfo = async () => {
const res = await prompts(promptsOptions);
console.log(res);
};
getUserInfo();
```
Then we can deal with different logic based on the corresponding values. Of course, our scaffolding doesn't need so many parameters, we can change it to the following options.
```javascript
const promptsOptions = [
{
type: 'text',
name: 'name',
message: 'Please enter the project name'
},
{
type: 'select', //Single Choice
name: 'template',
message: 'Please select a template',
choices: [
{ title: 'stellarnovaui', value: 1 },
{ title: 'stellarnovaui2', value: 2 }
]
}
];
```
Then we can pull different repositories based on the user's choices.
## Pulling Remote Repository Templates
To pull remote repositories, we can use the `download-git-repo` tool and use its `clone` method. At the same time, we need to install a loading plugin `ora` and a log color plugin `chalk`.
```bash
pnpm add download-git-repo ora chalk
```
```javascript
//gitClone.js
import download from "download-git-repo";
import chalk from "chalk";
import ora from "ora";
export default (remote, name, option) => {
const downSpinner = ora("Downloading template...").start();
return new Promise((resolve, reject) => {
download(remote, name, option, (err) => {
if (err) {
downSpinner.fail();
console.log("err", chalk.red(err));
reject(err);
return;
}
downSpinner.succeed(chalk.green("Template downloaded successfully!"));
resolve();
});
});
};
//cli.js
const remoteList = {
1: "https://github.com/markliu2013/StellarNovaUI.git",
2: "https://github.com/markliu2013/StellarNovaUI.git",
};
const getUserInfo = async () => {
const res = await prompts(promptsOptions);
if (!res.name || !res.template) return;
gitClone(`direct:${remoteList[res.template]}`, res.name, {
clone: true,
});
};
```
After execution, the template we need is in the directory.
Finally, we can publish our 'create-stellarnovaui'. The publishing process has been introduced before, so I won't go into detail here. I have already published it, so let's try to run 'npm create stellarnovaui' in any folder. You can see stellarnovaui will be cloned.
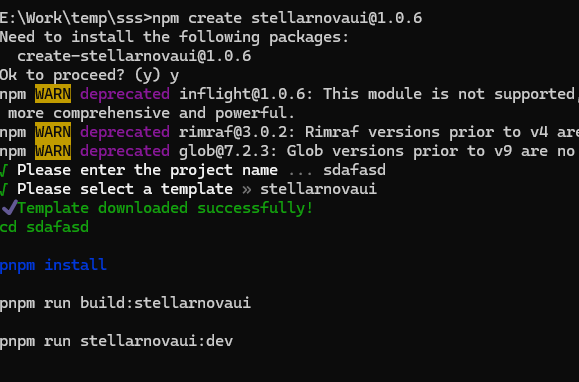
The final source code: https://github.com/markliu2013/StellarNovaUI
| markliu2013 |
1,868,761 | War Room Wisdom for Software Developers | The military has many concepts that can be used in software development and I particularly like the... | 0 | 2024-05-29T09:48:10 | https://dev.to/martinbaun/war-room-wisdom-for-software-developers-5ejc | programming, productivity, discuss, startup | The military has many concepts that can be used in software development and I particularly like the commander's intent. The commander's intent captures the commander's and operation's goals, giving the platoon a clear objective to pursue. The platoon focuses on this goal and is empowered to achieve it by the means available even if it doesn't follow the commander's instruction. I started applying these principles a few years back, learning the following.
## Movies depict the wrong leadership lessons
Military movies showcase soldiers who fear their superiors more than any enemy they face. Dissent among the ranks is ruthlessly quelled, and any act of insubordination is promptly and severely punished. This compels them to blindly follow orders, regardless of any detrimental effects such orders may have on the person.
Managers in software engineering apply this approach, having learned it from the military or from growing up in an authoritarian household. This management style demotivates many software development teams. It is impractical to micromanage every developer due to time constraints.
The modern military cultivates a culture of mutual trust from the top down and bottom up. Commanders empower their subordinates to execute decision-making with a similar goal. Team leaders in software engineering should consider taking a leaf out of the modern military's handbook.
Read: *[Principles for Managing Remote Teams and Freelancers to learn simple strategies that will help you improve the camaraderie within your team.](https://martinbaun.com/blog/posts/principles-for-managing-remote-teams-and-freelancers/)*
Military command principles have an impact on software developers. Several management principles employed by the military can be applied in the software development process. I summarized them under ‘Intent as a vital part of mission command.’
## Intent as a vital part of mission command
A commander's intent is a clear depiction and explanation of the mission goal. It guides the platoon and ensures the main objective is achieved as expected. The soldiers in the platoon inherit this intent and adapt the mission strategy when needed to achieve their goal. The commander's intent links the mission and concept of operations. Commanders may also use the commander's intent to explain a broader purpose beyond the mission statement. The mission and the commander's intent must be understood two echelons down.
*These core principles follow select events and traits from different times and eras. They are all applicable today.*
Napoleon’s French forces tolerated junior officers taking the initiative. If soldiers deemed executing an order impossible, they were allowed to act within its intention. The US military established the commander’s intent. This introduced mutual trust, as leaders placed greater trust in their subordinates to act within operational intent when faced with changing circumstances. Communicating intent to subordinates to encourage sharing of leadership responsibilities.
Leaders need to offer more than giving orders. The buck starts and stops with them. Their biggest responsibility is to lead the team instead of controlling every aspect of the project.
The team achieves more when everyone is empowered to handle their responsibilities. A leader who nurtures and promotes this gets the best out of their team members. There's no metric to quantify this aspect, yet it remains one of the most vital aspects of leadership.
The leaders who implement this strategy go unnoticed. They will keep the team on track, facilitating communication, and resolving disputes. Every software developer relies on their team lead to define the project's priorities. I'm responsible for finding the quickest way to get the project back on track should something go awry.
A development team can do excellent software with exceptional teamwork, even with a few bad apples among them. This is less likely to happen if the team has poor leadership. With good leadership, the team can make beautiful and excellent software. I have written an insightful article depicting how you can design beautiful software.
Read: *[Software Developers Can Build Beautiful Software](https://martinbaun.com/blog/posts/developers-can-make-beautiful-software/)*
## How do you incorporate this as a team lead?
The commander's intent is a guiding principle I live by. It follows the hallmark rules of adapting, improvising, and overcoming any situation as it comes. I empower my developers and team with the confidence to take charge of their tasks and responsibilities as the situation dictates. This guarantees maximum productivity and output regardless of the shifting scenario or environment. This is how we implement it in our team.
## Ensure you write a "Why" for each task
Developers are far more likely to take pride in their work if they understand the value their work brings to the organization. This also enhances their esprit de corps and overall job satisfaction.
## Communicate the "What" behind each task
You'll have developers on your team that work best with minimal supervision, while others may need more guidance. The latter may require a more specific rundown of what you expect them to do to achieve their goals. It is vital to package it as a suggestion instead of an order. Independent developers require much fewer suggestions on how to do their work.
Read: *[7 Tips for Effective Communication in Remote Teams to learn valuable tips that will help you improve your communication.](https://martinbaun.com/blog/posts/7-tips-for-effective-communication-in-remote-teams/)*
## Distinguish between different types of developers
I identify those under my wing that require more guidance than their independent counterparts. It might be counterintuitive to micromanage such developers. Instead, I offer suggestions and let them choose the best action with the end goal in mind.
## Regard your developers as your sports franchise
I treat my team like a sports franchise in a competitive league. I am interested in their personalities, goals, ambitions, and development. They are my team and I want to see them succeed and vice versa. We support and cheer each other. A win for one is a win for all of us, and this helps us build our team to greater heights. We expect excellence and great things from each other. We continually learn and improve in our various roles for the greater good of our team.
I motivate my developers. The added motivation may have them write better code faster, push fewer errors, and voluntarily work more hours. Do not mistake motivation for remuneration. Money attracts and retains employees but is seldom a great motivator. A big contract with a poor culture doesn't motivate franchise players and this sentiment applies. Employees want to feel happy about their jobs.
## How do you incorporate this as a developer?
You may have little power as a developer to change the workplace culture. Depending on your work environment, you could pass up some suggestions for improving your working conditions.
## Open up to your team lead
You can shoot your team lead a few ideas on improving your workplace culture so long as they are receptive. You could ping them this article and let them know what's working for others in the space.
## Dealing with an aloof team lead
You can't teach an old dog new tricks but we're dealing with people which should be better. People don't change their attitudes and their behaviors simply by asking them. This also applies to an aloof team lead. Approach them in a non-condescending manner. Engage them with respect, allowing them to offer guidance on the direction to follow. Show a genuine interest in the overall success of the team and organization. Ask why something is vital for the business and why doing it produces the best results for the business and client. They are more likely to give you a concrete 'what' and 'why' that will help you achieve the project goals and satisfy customer expectations.
Make sure to ask their thoughts on whether it would work. I'd suggest something they could consider implementing. It may improve the productivity of various software development phases. Be careful with your delivery, lest it comes across as critical of their management style. I’ve tried and tested this approach in the software development process, bringing about increased productivity.
Read our most recent piece to [know why the IT sector is the greatest and why there are many great employment possibilities.](https://martinbaun.com/blog/posts/why-it-is-the-best-sector-to-work-in/)
## Conclusion
Authoritarian leadership styles are old and practically ineffective in this day and age. Collaboration, trust, and effective communication bear more fruits. It’s easier to catch more bees with honey than with vinegar. This adage is applicable in software development.
I collaborated with my developers to create [Goleko](https://goleko.com/). It is a state-of-the-art project management tool that manages projects fast, easily, and simply. This is one of the seven productivity tools I've availed to my team.
-----
*For these and more thoughts, guides and insights visit my blog at [martinbaun.com](http://martinbaun.com)*
*You can find Martin on [X](https://twitter.com/MartinBaunWorld)*
| martinbaun |
1,861,779 | How to run npm scripts concurrently? | Intro Before creating a pull request, you probably want to be sure that CI will reject it.... | 0 | 2024-05-29T09:43:34 | https://dev.to/przemyslawjanbeigert/how-to-run-npm-scripts-concurrently-2l4c | webdev, javascript, bash, productivity | ## Intro
Before creating a pull request, you probably want to be sure that CI will reject it. So before `gh pr create` you're running `npm run lint` or `npm run test`. `npm run build` etc.
## Script
To avoid manually calling each script you can define a new script in the package.json.
```json
{
"scripts": {
"ci:check": "npm run lint && npm run test && npm run build"
}
}
```
`first && second` in bash means: when the first returns success then run the second one. If fails, stop the execution and return this fail value.
## Package
There's a package to speed this command up. [Concurrently](https://www.npmjs.com/package/concurrently)
```json
{
"scripts": {
"ci:check": "concurrently \"npm run lint\" \"npm run test\" \"npm run build\""
}
}
```
Now `ci:check` will start each check concurrently. The total execution time will be the longest-running script, rather than the sum of all three.
## Bash
But do we need a package for that? Such a simple thing can be done just with a bash language.
`first & second` will run both commands in the same moment, but the result of that will be the result of the second one. So if the first fails final result will be positive.
[FG](https://www.cyberciti.biz/faq/unix-linux-fg-command-examples-usage-syntax/) - Place the job in the foreground, and make it the current job using the fg command.
```json
{
"scripts": {
"ci:check": "npm run lint & npm run test & npm run build && fg"
}
}
```
However, this approach runs all checks simultaneously but reports the exit status of the last command, similar to a sequential execution.
## Summary
Learn bash. | przemyslawjanbeigert |
1,868,760 | Wednesday Links - Edition 2024-05-29 | Spring Boot 3.3.0 available now (1... | 6,965 | 2024-05-29T09:42:58 | https://dev.to/0xkkocel/wednesday-links-edition-2024-05-29-dbm | java, jvm, springboot, microservices | Spring Boot 3.3.0 available now (1 min)🎉
https://spring.io/blog/2024/05/23/spring-boot-3-3-0-available-now
SBOM support in Spring Boot 3.3 (4 min)📄
https://spring.io/blog/2024/05/24/sbom-support-in-spring-boot-3-3
Benchmarking Java Streams (16 min)🏞️
https://softwaremill.com/benchmarking-java-streams/
The weirdest bug I've encountered in my CS career[thread] (1 min)🌕
https://x.com/CupiaBart/status/1793930355617259811
Getting Started with JobRunr: Powerful Background Job Processing Library (11 min)🏃
https://foojay.io/today/getting-started-with-jobrunr-a-powerful-task-scheduler-in-ja/
The TornadoVM Programming Model Explained (11 min)🌪️
https://foojay.io/today/the-tornadovm-programming-model-explained/
You probably don’t need microservices (7 min)🪑
https://www.thrownewexception.com/you-probably-dont-need-microservices/
Continuous delivery without a CI server (5 min)📠
https://blog.ploeh.dk/2024/05/27/continuous-delivery-without-a-ci-server/
Down Another Rabbit Hole (8 min)🐇
https://www.romainguy.dev/posts/2024/down-another-rabbit-hole/
AssertJ 3.26.0 released (1 min)🎉
https://github.com/assertj/assertj/releases/tag/assertj-build-3.26.0
Declarative Gradle (3 min)🐘
https://declarative.gradle.org/ | 0xkkocel |
1,868,759 | Building Blocks Of Zig: Understanding Structs | To learn more about Zig and why I think it's an amazing language check out my blog post Zig is The... | 0 | 2024-05-29T09:41:36 | https://dayvster.com/blog/building-blocks-of-zig-understanding-structs/ | zig, programming, softwaredevelopment |
To learn more about Zig and why I think it's an amazing language check out my blog post [Zig is The Next Big Programming Language](https://dayvster.com/blog/zig-is-the-next-big-language/)
## What is a Struct in Zig?
Like many other programming languages Zig has structs. A struct is a pretty simple and straightforward concept, it's a user defined data model that can contain multiple fields or members.
That's a lot of words to say that a struct is a way to group related data together in a logical and structured way.
Traditional OOP languages like C++, C# and Java use classes to achieve the same goal, we all know the old and tired analogies of classes representing a generic concept like animal and then subclasses like dog and cat inheriting from the animal class and adding their own specific behavior and data or implementing interfaces to achieve polymorphism.
Zig like C does not have classes but it does have **structs**, **enums** and **unions**. In Zig structs are the most common way to group related data together.
## How to define a Struct in Zig
In Zig you define a struct by using the `struct` keyword followed by the name of the struct and then the body of the struct enclosed in curly braces `{}`. Inside the body of the struct you define the fields or members of the struct.
Here is an example of a struct that represents a game character:
```zig
const Character = struct {
name: []const u8,
health: u32,
stamina: u32,
say_hello: fn ([]const u8) void,
};
```
Now that we have defined the `Character` struct we can create instances of it like this:
```zig
const player = Character{
.name = "Ziggy Stardust",
.health = 100,
.stamina = 100,
.say_hello = fn(name: []const u8) void {
std.log.info("Hello, {s}!\n", .{name}),
},
};
// Call the say_hello function
player.say_hello(player.name);
```
In this example we create a new instance of the `Character` struct called `player` and we initialize the fields of the struct with the values `"Ziggy Stardust"`, `100`, `100` and a function that logs a message to the console.
Super simple right? Fairly similar to how you would define a struct in C. But wait there's more
## Struct Fields can have default values
Default values in Zig Structs are executed at comptime(compile time) and are allow the field to be omitted when creating an instance of the struct.
This allows us to essentially have optional typesafe fields in our structs that have a default value if not provided.
For example we can modify the `Character` struct to have default values for the `health` and `stamina` fields:
```zig
const Character = struct {
name: []const u8,
health: u32 = 100,
stamina: u32 = 100,
say_hello: fn ([]const u8) void,
};
```
This way when we create a new instance of the `Character` struct we can omit the `health` and `stamina` fields and they will be initialized with the default values, which in this case will be `100` for both fields.
```zig
const player = Character{
.name = "Ziggy Stardust",
.say_hello = fn(name: []const u8) void {
std.log.info("Hello, {s}!\n", .{name}),
},
};
```
## Structs can be packed
By default structs in zig do not maintain a specific order of fields regardless of the order in which you define the fields in the struct. This is not always optimal since sometimes you may wanna have a specific order of your fields to optimize memory usage or interact with certain libraries like OpenGL that require a specific order of fields in a struct.
for this we can use the `packed` keyword when defining a struct to ensure that the fields are ordered in the same order as they are defined in the struct.
Additionally there will be no padding between the fields in a packed struct.
packed structs can participate in Bit Cast or Pointer Cast operations including during comptime.
```zig
const Character = packed struct {
name: []const u8,
health: u32,
stamina: u32,
say_hello: fn ([]const u8) void,
};
```
Now the bytes of the struct will be ordered in the same order as they are defined in the struct. Simple as that.
## Struct fields can be undefined
If you are not yet ready to set a value to a field in a zig struct, you can use the `undefined` keyword to set the field to an undefined state. This is useful when you want to create a struct with some fields that you will set later on in your code.
```zig
const Goblin = Character{
.name = undefined,
.health = 100,
.stamina = 100,
.say_hello = fn(name: []const u8) void {
std.log.info("Hello, {s}!\n", .{name}),
},
}
```
In this example we create a new instance of the `Character` struct called `Goblin` and we set the `name` field to `undefined` and the `health` and `stamina` fields to `100`. This way we can create a new instance of the `Goblin` struct and set the `name` field later on in our code, perhaps we wanna give the goblin a randomly generated name when the goblin enters the view of the player.
## Struct can have Methods / Functions
You may have noticed that we have a function as a field in our `Character` struct. Zig like many other languages allows you to define functions as struct fields which can be called on instances of the struct.
The `say_hello` field in the `Character` struct is a function that takes a `[]const u8` parameter and returns `void` meaning no value is returned.
But we could for example have a function that allows us to attack another character by passing in the character reference as a parameter.
```zig
const Character = struct {
name: []const u8,
health: u32,
stamina: u32,
say_hello: fn ([]const u8) void,
attack: fn (target: *Character) void,
};
const player = Character{
.name = "Ziggy Stardust",
.health = 100,
.stamina = 100,
.say_hello = fn(name: []const u8) void {
std.log.info("Hello, {s}!\n", .{name}),
},
.attack = fn(target: *Character) void {
std.log.info("{s} attacks {s}!\n", .{player.name, target.name}),
},
};
const enemy = Character{
.name = "Goblin",
.health = 50,
.stamina = 50,
.say_hello = fn(name: []const u8) void {
std.log.info("Hello, {s}!\n", .{name}),
},
.attack = fn(target: *Character) void {
std.log.info("{s} attacks {s}!\n", .{enemy.name, target.name}),
},
};
player.attack(&enemy);
enemy.attack(&player);
```
In this example we have added an `attack` function to the `Character` struct that takes a pointer to another `Character` as a parameter and logs a message to the console. We then create two instances of the `Character` struct called `player` and `enemy` and call the `attack` function on each of them passing in the other character as a parameter.
Optimally we'd also want to add a `take_damage` function to the `Character` struct that would reduce the health of the character when attacked. But this blog post is purely educational.
## Structs can be returned from a function which results in a Generic
In Zig like many other languages you can return a struct from a function. But where it gets super interesting is how you can leverage that to create generics
Here
```zig
fn GoblinHorde(comptime T: type) type {
return struct {
pub const Goblin = struct {
prev: ?*Goblin,
next: ?*Goblin,
data: T,
}
first: ?*Goblin,
last: ?*Goblin,
len: usize,
}
}
```
## Conclusion
Struct are a fundamental building block of Zig and are used to group related data together in a logical and structured way. Structs can have default values, be packed, have undefined fields, have methods and be returned from functions which results in a generic. Structs are a powerful and flexible way to model data in Zig and are used extensively in the standard library and in many third party libraries. | dayvster |
1,868,758 | Audience Segmentation | Audience segmentation is a crucial strategy in modern marketing, enabling businesses to identify and... | 0 | 2024-05-29T09:39:58 | https://dev.to/astrad/audience-segmentation-1mla | Audience segmentation is a crucial strategy in modern marketing, enabling businesses to identify and target distinct groups within their broader audience. By understanding the specific needs, preferences, and behaviors of these segments, companies can tailor their marketing efforts to maximize effectiveness and efficiency. This article delves into the concept of audience segmentation, exploring its types, benefits, implementation steps, challenges, and future trends. Whether you are a seasoned marketer or new to the field, this guide will provide valuable insights into harnessing the power of [audience segmentation](https://astrad.io/effective-audience-segmentation-a-key-to-programmatic-advertising-success/) for your business success.
## What is Audience Segmentation?
Audience segmentation is the process of dividing a broad consumer or business market, normally consisting of existing and potential customers, into sub-groups of consumers based on some type of shared characteristics. By grouping individuals who have similar needs and behaviors, businesses can target their marketing efforts more effectively, creating more personalized and efficient marketing strategies.
Components of Audience Segmentation:
Demographics: This involves segmenting the audience based on quantifiable population characteristics such as age, gender, income, education, and occupation. For example, a luxury car brand might target high-income individuals in their marketing efforts.
Psychographics: This segmentation focuses on the psychological aspects of consumer behavior including lifestyle, values, interests, and opinions. For instance, a fitness brand might target health-conscious individuals who value wellness and an active lifestyle.
Behavioral: This type of segmentation looks at consumer behaviors such as purchasing habits, brand loyalty, usage rate, and benefits sought. A streaming service might segment users based on their viewing habits and preferences.
Geographic: This involves segmenting the market based on geographic boundaries such as country, region, city, or neighborhood. A local restaurant might target nearby residents with its promotional campaigns.
By understanding and utilizing these components, businesses can develop more focused and effective marketing strategies that resonate with their target audience.
## Importance of Audience Segmentation
Targeted Marketing: Audience segmentation allows businesses to target specific groups of customers more accurately. By identifying the unique needs and preferences of each segment, companies can tailor their marketing messages to address these specific interests, leading to higher engagement and conversion rates. For instance, a company selling baby products can specifically target new parents rather than the general population, making their marketing efforts more effective.
Personalization: Segmentation enables a higher degree of personalization in marketing efforts. Personalization involves customizing messages and offers to fit the individual characteristics and preferences of each segment. This approach not only enhances customer satisfaction but also fosters loyalty and long-term relationships. For example, personalized email marketing campaigns can result in higher open and click-through rates compared to generic emails.
Efficiency: Effective segmentation leads to better allocation of marketing resources. By focusing on specific segments, businesses can allocate their budget more efficiently, ensuring that their marketing efforts yield the best possible returns. This prevents the wastage of resources on broad, untargeted campaigns. Additionally, segmentation helps in identifying the most profitable segments, allowing businesses to prioritize their marketing efforts accordingly.
## Steps to Implement Audience Segmentation
Data Collection: Effective audience segmentation starts with collecting relevant data about your audience. This can be done through various methods such as surveys, interviews, focus groups, and analyzing existing customer data. Businesses can also use tools like CRM systems, web analytics, and social media insights to gather comprehensive data.
Segmentation Criteria: Once data is collected, the next step is to determine the criteria for segmentation. This involves identifying which characteristics are most relevant to your business goals. For instance, a company looking to increase customer loyalty might focus on behavioral segmentation, while a brand aiming to expand its market might consider geographic segmentation.
Creating Segments: After determining the criteria, businesses can categorize and define segments. This involves grouping individuals with similar characteristics into distinct segments. Each segment should be measurable, accessible, substantial, and actionable. It’s important to ensure that segments are not too broad or too narrow.
Testing and Analysis: Before fully implementing segmentation strategies, it’s crucial to test and analyze the segments. This involves running pilot campaigns and measuring their effectiveness. Businesses should analyze the results to identify which segments respond best to different marketing strategies. Based on this analysis, adjustments can be made to optimize segmentation efforts.
## Conclusion
In conclusion, audience segmentation is a powerful tool for businesses to enhance their marketing efforts. By understanding and targeting specific groups within their broader audience, companies can create more personalized and efficient marketing strategies. This not only improves engagement and conversion rates but also optimizes resource allocation. As technology continues to evolve and consumer behavior shifts, businesses must stay adaptable and leverage advancements in AI and data analytics to refine their segmentation strategies. Implementing effective audience segmentation can lead to significant business growth and customer satisfaction. | astrad | |
1,868,741 | Solving frequent MacBook problems | Welcome to MacBook Help, your go-to source for expert information. We’re excited about the limitless... | 0 | 2024-05-29T09:19:18 | https://dev.to/macbookhelp/solving-frequent-macbook-problems-3gcg | macbook, mac, macbookhelp | Welcome to MacBook Help, your go-to source for expert information. We’re excited about the limitless possibilities that technology brings. On our tech website, you’ll find detailed and instructional content. Our goal is to provide you with both informative and inspiring insights. We’ll cover all kinds of Mac-related articles. If you’re eager to learn everything about the MacBook, join us!
If you love using a MacBook Help, you might sometimes run into issues. These can range from minor problems like a slow system, Safari not responding to major serious problems like your MacBook being stuck on the loading screen flickering or battery heating problems. No need to worry, we're here to help with this inclusive MacBook troubleshooting guide. It covers solutions for all kinds of common MacBook issues, so you can start fixingWel your Mac like a pro system.
Macs are known for their great performance and smooth user experience. However, over time, users may still encounter problems. You might turn on your device and see nothing on the display, or you might plug in your MacBook to charge and find that it’s not charging. These are some of the most common issues MacBook users face.
There are many other similar problems you might experience with your MacBook. Check out the list of common issues and see if any of them match what you’re dealing with.
One of the main issues why MacBook are so popular is because Apple has a reputation for making reliable systems. Basically, Apple launched a smooth, sleek, interactive user experience that stands out from other PCs. No doubt, Macs are powerful, but sometimes have problems. Most common MacBook issues are easy to fix on your own.
No technology is perfect, including Apple’s Mac computers. You should only consider paying for a repair service after trying our free troubleshooting tips. Many hardware problems on a Mac can be easily fixed by adjusting a few settings.
When it comes to high-end laptops, there’s no doubt that Apple’s MacBook is at the top. Still, even with its advanced technology and superior performance, the MacBook can have occasional issues. Instead of rushing to the nearest Apple Store at the first sign of trouble, wouldn’t it be more convenient and cheaper to troubleshoot some of these issues yourself? This blog post is your ultimate guide to solving common MacBook problems and getting your machine running smoothly again in no time. Get ready, because we're going to turn you into your own MacBook expert.
For more update visit our website https://macbookhelp.in/ | macbookhelp |
1,868,756 | The Art of AI: How NigmaBot.ai’s Image Generator is Empowering Artists | AI Bot Art AI bot art refers to the creation of artwork using artificial intelligence algorithms and... | 0 | 2024-05-29T09:39:25 | https://dev.to/saumya27/the-art-of-ai-how-nigmabotais-image-generator-is-empowering-artists-1lc5 | ai, bot, nigma | **AI Bot Art**
AI bot art refers to the creation of artwork using artificial intelligence algorithms and machine learning models. These AI systems can generate, modify, and enhance artistic creations, often producing results that mimic or innovate beyond traditional human creativity. Here’s an overview of AI bot art, including its applications, technologies, and examples:
**Applications of AI Bot Art**
**1. Generative Art:**
- Creation: AI can create entirely new pieces of art from scratch using algorithms that learn from existing artworks.
- Style Transfer: AI models can apply the style of one artwork to another image, blending different artistic styles.
**2. Enhancement and Restoration:**
- Image Enhancement: AI can enhance the quality of images by improving resolution, color correction, and detail.
- Restoration: AI can restore damaged or degraded artworks, filling in missing parts and correcting imperfections.
**3. Interactive Art:**
- Collaborative Creation: AI can work alongside human artists, providing suggestions, generating ideas, or refining pieces.
- Customization: Users can interact with AI to create personalized artwork based on their preferences.
**4. Animation and 3D Modeling:**
- Animation: AI can generate animations from static images or create entirely new animated sequences.
- 3D Modeling: AI can assist in creating 3D models for use in games, movies, and virtual reality.
**Technologies Behind AI Bot Art**
**1. Deep Learning:**
- Convolutional Neural Networks (CNNs): Used for image recognition and generation tasks.
- Generative Adversarial Networks (GANs): Consist of two neural networks (a generator and a discriminator) that work together to create realistic images.
**2. Neural Style Transfer:**
- Technique: Combines the content of one image with the style of another to produce a new artwork that blends elements of both.
**3. Reinforcement Learning:**
- Technique: AI learns to make sequences of decisions, useful in generating dynamic and interactive art forms.
**4. Natural Language Processing (NLP):**
- Integration: AI can generate art based on textual descriptions, allowing for the creation of visuals that match a narrative or concept.
**Examples of AI Bot Art**
**1. DeepArt:**
- Function: Uses neural style transfer to create images that combine the content of one image with the artistic style of another.
- Output: Generates unique artworks that resemble famous painting styles.
**2. DALL-E:**
- Function: Developed by OpenAI, DALL-E generates images from textual descriptions, creating highly detailed and imaginative visuals.
- Output: Produces images based on prompts like “an armchair in the shape of an avocado” or “a futuristic cityscape.”
**3. Artbreeder:**
- Function: Allows users to create and modify images by blending different attributes using GANs.
- Output: Generates a wide range of visual content, from portraits to landscapes, that users can customize.
**4. Runway ML:**
- Function: Provides tools for artists to create AI-generated art, including models for style transfer, image generation, and video editing.
- Output: Enables artists to integrate AI into their creative workflows seamlessly.
**Benefits and Challenges**
**Benefits:**
- Creativity Enhancement: AI can augment human creativity by generating novel ideas and providing new perspectives.
- Accessibility: Makes artistic creation more accessible to people without traditional art skills.
- Efficiency: Speeds up the creation process, allowing artists to focus on refining their work.
**Challenges:**
- Originality: There are ongoing debates about the originality and authenticity of AI-generated art.
- Ethical Concerns: Issues related to copyright, ownership, and the potential for AI to replicate human styles without consent.
- Quality Control: Ensuring that AI-generated art meets high aesthetic and technical standards can be difficult.
**Conclusion**
[AI bot art](https://cloudastra.co/blogs/ai-bot-art-how-nigmabotais-image-generator-is-empowering) represents a fascinating intersection of technology and creativity, pushing the boundaries of what is possible in the art world. By leveraging advanced algorithms and machine learning techniques, AI can generate, enhance, and transform art in ways that complement and expand human artistic endeavors. As technology continues to evolve, the role of AI in art is likely to grow, offering new tools and opportunities for artists and enthusiasts alike. | saumya27 |
1,868,995 | An introduction to API Control Plane | About this video Watch this video on webMethods API Control Plane. Learn about the API... | 0 | 2024-06-18T12:31:20 | https://tech.forums.softwareag.com/t/an-introduction-to-api-control-plane/296298 | video, api, webmethods, introduction | ---
title: An introduction to API Control Plane
published: true
date: 2024-05-29 09:38:26 UTC
tags: Video, API, webmethods, introduction
canonical_url: https://tech.forums.softwareag.com/t/an-introduction-to-api-control-plane/296298
---
## About this video
Watch this video on webMethods API Control Plane. Learn about the API Control Plane and the features it provides.
{% youtube WAgRBN8rDVo%}
[Read full topic](https://tech.forums.softwareag.com/t/an-introduction-to-api-control-plane/296298) | techcomm_sag |
1,868,754 | Why choose our first-class Escort Service in Aerocity|9899988101 | You Escort Service in Aerocity that there are other companion service providers, so let us explain... | 0 | 2024-05-29T09:35:51 | https://dev.to/chanda_karolbagh_06fa706e/why-choose-our-first-class-escort-service-in-aerocity9899988101-g55 | javascript | You Escort Service in Aerocity that there are other companion service providers, so let us explain why you should reserve the Aerocity escorts with us in particular. We're happy to inform you that our females are not only young and attractive but also diligent workers. They constantly strive to provide our guests with both elegant satisfaction and enjoyment. Regarding love, affection, and sexual fulfilment, each individual has unique needs and desires. To be fashionable, one must comprehend the requirements and fulfil them in the most extraordinary and one-of-a-kind way possible. Recognizing this, the Independent Aerocity Call Girls we provide you with make you feel pleased as well. you are free to talk to us at any time if you want to have pleasure with more than one woman or if you're having wild dreams about three or more women. Our philosophy is to provide fashionable services at fashionable costs. We make every effort to provide you with a plutocrat worth it. Our Call Girls in Aerocity are on hand 24 hours a day, 7 days a week to attend to your needs and make you feel good. Call – 9899988101, https://www.chandaokelle.com/ | chanda_karolbagh_06fa706e |
1,868,753 | Elevate Your Digital Presence with Code HUNTS | In today’s digital era, a robust online presence is essential for any business aiming for success. At... | 0 | 2024-05-29T09:35:34 | https://dev.to/hmzi67/elevate-your-digital-presence-with-code-hunts-e8p | webdev, javascript, programming, python | In today’s digital era, a robust online presence is essential for any business aiming for success. At [Code HUNTS](https://codehuntspk.com/), we specialize in crafting custom websites that not only attract visitors but also convert them into loyal customers. Here’s why partnering with Code HUNTS can transform your business.
#### Why Choose Code HUNTS?
1. **Tailored Solutions**
- **Custom Design:** We understand that each business is unique. Our team designs websites tailored to reflect your brand's identity and values.
- **User-Centric Approach:** Our designs focus on providing an intuitive and seamless user experience, ensuring visitors stay longer and engage more.
2. **Cutting-Edge Technology**
- **Responsive Design:** Our websites are optimized for all devices, ensuring a flawless experience on desktops, tablets, and smartphones.
- **Fast Loading Speed:** We implement best practices to ensure your website loads quickly, reducing bounce rates and enhancing user satisfaction.
- **SEO Optimization:** Our websites are built with SEO in mind, improving your visibility on search engines and driving organic traffic.
3. **Comprehensive Services**
- **Full-Stack Development:** From front-end aesthetics to back-end functionality, we cover all aspects of website development.
- **E-commerce Solutions:** We offer robust e-commerce platforms that are secure, scalable, and easy to manage.
- **Ongoing Support:** Our commitment doesn’t end at launch. We provide continuous support and maintenance to ensure your website remains up-to-date and secure.
#### Our Development Process
1. **Consultation and Planning**
- We start with an in-depth consultation to understand your business goals, target audience, and design preferences.
- Our team develops a comprehensive plan outlining the project scope, timeline, and milestones.
2. **Design and Development**
- Our designers create a prototype based on your specifications, which we refine until it meets your vision.
- Our developers then bring the design to life, ensuring the site is functional, fast, and secure.
3. **Testing and Launch**
- We conduct thorough testing to catch any bugs and ensure optimal performance.
- Once everything is perfect, we launch your site and monitor its performance closely.
4. **Post-Launch Support**
- We offer training for your team to manage the website.
- Our support team is always available to address any issues or updates needed.
#### Success Stories
At Code HUNTS, we have a track record of helping businesses across various industries achieve their online goals. From small startups to established enterprises, our clients have seen increased traffic, better engagement, and higher conversion rates.
#### Let's Build Something Great Together
Your website is often the first impression potential customers have of your business. Make it count with a website that stands out, performs impeccably, and drives success. Contact Code HUNTS today to start your journey toward a remarkable online presence.
---
At Code HUNTS, we don’t just build websites; we create digital experiences that drive results. Let’s work together to turn your vision into reality. | hmzi67 |
1,868,752 | Laravel Immutable Carbon Dates | In this article we're going to look at the Carbon data class in laravel and how we can change the... | 0 | 2024-05-29T09:35:24 | https://paulund.co.uk/laravel-immutable-carbon-dates | laravel, php, webdev, beginners | In this article we're going to look at the Carbon data class in laravel and how we can change the settings of how laravel uses the class to make it immutable.
## What's the problem we're trying to solve?
When you're working with dates in Laravel you will most likely be using the Carbon class. This class is a wrapper around the PHP DateTime class and provides a lot of useful methods for working with dates.
When you output the value of a carbon object you get this value.
```php
$now = now()
= Illuminate\Support\Carbon @1716793925 {#5324
date: 2024-05-27 08:13:50.554997 Europe/London (+01:00),
}
```
You can change this object by adding or subtracting time from the object with helper helpers like `->addHour()`.
```php
$now = $now->addHour()
= Illuminate\Support\Carbon @1716797621 {#5329
date: 2024-05-27 09:13:50.554997 Europe/London (+01:00),
}
```
You can add multiple hours by using the method `->addHours(4)`.
```php
$now = $now->addHours(4)
= Illuminate\Support\Carbon @1716812090 {#5318
date: 2024-05-27 13:13:50.554997 Europe/London (+01:00),
}
```
But we have a problem, adding 4 hours to 8:12 should be 12:12 not 13:13. This is because the Carbon class is mutable and when you call the addHours method it changes the original object.
This can have it's advantages when you have a large process of changing the date multiple times but it can also have it' s disadvantages when you want to keep the original date.
Carbon has a method called copy that will create a new instance of the Carbon object and then you can change the new object.
```php
$now = now()
= Illuminate\Support\Carbon @1716793925 {#5324
date: 2024-05-27 08:13:50.554997 Europe/London (+01:00),
}
$nowCopy = $now->copy()->addHours(4)
= Illuminate\Support\Carbon @1716812090 {#5318
date: 2024-05-27 12:13:50.554997 Europe/London (+01:00),
}
```
The other approach is to use the `CarbonImmutable` class which is a subclass of the Carbon class but it's immutable.
```php
$now = Carbon\CarbonImmutable::now();
= Carbon\CarbonImmutable @1716794377 {#5341
date: 2024-05-27 08:19:37.149971 Europe/London (+01:00),
}
$now->addHour()
= Carbon\CarbonImmutable @1716797977 {#5394
date: 2024-05-27 09:19:37.149971 Europe/London (+01:00),
}
$now->addHours(4)
= Carbon\CarbonImmutable @1716808777 {#5335
date: 2024-05-27 12:19:37.149971 Europe/London (+01:00),
}
```
As you can see when we add 1 hour and then 4 hours we get the result of 4 hours not 5 hours. Now we get the expected results when working with dates.
This is a simple change to make in your application but it can have a big impact on how you work with dates in your application.
## Changing the default Carbon class
If you want to change the default Carbon class to be immutable you can do this by adding the following code to your `AppServiceProvider` class.
```php
use Carbon\CarbonImmutable;
use Illuminate\Support\Facades\Date;
public function boot()
{
Date::use(CarbonImmutable::class);
}
```
This will change the default Carbon class to be CarbonImmutable and now all dates in your application will be immutable.
This is a simple change to make in your application but it can have a big impact on how you work with dates in your application.
## Performance Implications
There are some performance implications when using the `CarbonImmutable` class. The `CarbonImmutable` class is slower than the Carbon class because it creates a new instance of the object every time you call a method that changes the date.
This is because the CarbonImmutable class is immutable and it doesn't change the original object. This can have a big impact on the performance of your application if you're working with a lot of dates.
You should consider the performance implications when deciding whether to use the CarbonImmutable class or the Carbon class in your application. | paulund |
1,868,751 | Free Rotating Proxies From ProxyShare [No Clickbait] | At ProxyShare.io, we believe in giving back to the community and we understand the importance of... | 0 | 2024-05-29T09:34:30 | https://dev.to/proxyshare/free-rotating-proxies-from-proxyshare-no-clickbait-4i3p | webscraping, proxy, proxies, webdev | At ProxyShare.io, we believe in giving back to the community and we understand the importance of having reliable and efficient proxies for various online activities, from web scraping to secure browsing. That's why we're excited to offer [free rotating proxies](https://www.proxyshare.io/) to our users.
Our goal is to provide a high-quality service that meets the needs of developers, data enthusiasts, and anyone in need of a trustworthy proxy solution. In this blog post, we'll cover why you should use rotating proxies, how to get free rotating proxies from ProxyShare.io, and how to use them with a practical Python example.
## Why Use a Rotating Proxy
Rotating proxies are essential for maintaining anonymity and avoiding IP bans while performing tasks like web scraping, data mining, and automated browsing. By regularly changing the IP address used for these tasks, rotating proxies help to:
- **Enhance Anonymity**: Keep your online activities private by continuously changing your IP address.
- **Avoid IP Bans**: Prevent websites from blocking your IP address due to excessive requests.
- **Improve Efficiency**: Ensure smooth and uninterrupted scraping sessions by distributing requests across multiple IPs.
## How to Get Free Rotating Proxies from ProxyShare.io
Getting started with our free rotating proxies is straightforward. Follow these steps to access our free plan:
1. Visit Our Website: Go to ProxyShare.io
2. Join Our Discord: Join our Discord server using [this link](https://discord.gg/QdQCxaHhpc) and stay updated.
3. Access Free Proxies: Navigate to the free proxies channel and follow the instructions to start using our rotating proxies.
## Is There Any Limit to the Free Plan?
Yes, our free plan allows for up to 20,000 requests per day per user. This generous limit ensures you have ample capacity for your web scraping and browsing needs without worrying about hitting a ceiling.
## How to Use ProxyShare's Free Proxies
Using our free rotating proxies is simple. Below is a Python example to help you get started:
```py
import requests
# Replace with your ProxyShare credentials
username = 'free'
password = '<PASSWORD>'
proxy = 'http://free.proxyshare.io:80'
# Setting up the proxy
proxies = {
'http': f'http://{username}:{password}@{proxy}',
'https': f'https://{username}:{password}@{proxy}'
}
# Example request using the proxy
url = 'https://api6.ipify.org'
response = requests.get(url, proxies=proxies)
print(response.json())
```
This script demonstrates how to set up and use our rotating proxies with Python's requests library. Replace the placeholder values with your actual ProxyShare credentials and proxy details to start making requests through our proxy service.
At ProxyShare.io, we're committed to providing accessible and high-quality proxy services to the community. Whether you're a developer, data analyst, or privacy-conscious user, our free rotating proxies offer a reliable solution to your needs. Sign up today and experience the benefits of ProxyShare.io's free proxies for yourself!
Feel free to reach out to our support team via Discord if you have any questions or need assistance. Happy browsing and scraping!
| proxyshare |
1,868,750 | Find steamy Hot call girls Karol Bagh without sweat|9899988101 | Do you have an unending sexual desire which needs to be Escort service in Karol Bagh? If yes, then... | 0 | 2024-05-29T09:34:03 | https://dev.to/chanda_karolbagh_06fa706e/find-steamy-hot-call-girls-karol-bagh-without-sweat9899988101-4h4b | javascript | Do you have an unending sexual desire which needs to be Escort service in Karol Bagh? If yes, then you aren't alone in this boat as there are a thousand others just like you out there with the same passions.There is however a class of men that are unique and different in how they have chosen to satisfy this lust.Guess who this unique category is? They are the ones who have chosen to walk the path with Karol Bagh call girls service. These are the real men that have found the real honeycomb.Guess that is exactly what you have been looking for across all the other Call Girls in Karol Bagh. Well, you have finally found just what your body and soul need to get back to their place of peace and tranquility. Call – 9899988101. https://www.chandaokelle.com/call-girls-in-karol-bagh.html | chanda_karolbagh_06fa706e |
1,868,625 | Create AI Voice Generator: Make Your Unique AI Covers | Create unique AI covers with our AI cover generator. Design stunning visuals effortlessly. Check out... | 0 | 2024-05-29T09:32:00 | https://dev.to/novita_ai/create-ai-voice-generator-make-your-unique-ai-covers-5cc8 | Create unique AI covers with our AI cover generator. Design stunning visuals effortlessly. Check out our blog for more details on AI cover generation.
## Key Highlights
- AI voice generators and AI covers provide a unique and creative way for music lovers to create personalized cover songs.
- With AI technology, users can transform their own voices or clone voices from their favorite artists, cartoon characters, or public figures.
- AI covers can be easily shared on social media platforms, allowing users to showcase their creativity and engage with their followers.
- The AI voice generator offers multiple voice models, including popular artists like Taylor Swift and BlackPink, giving users flexibility and options.
- Novita AI features 100+ APIs for you to create your own AI voice generator, please follow the comprehensive guide below.
- Integration capabilities with music platforms like Spotify and TikTok make it easier for users to upload and share their AI covers.
- The future trends of AI cover art suggest that it will play an evolving role in the music industry, offering new possibilities for creativity and expression.
## Introduction
Whether you're a music lover looking to showcase your talent or someone likes creating cover songs, AI Voice Generator and AI Covers have got you covered, you can now clone voices from your favorite artists, cartoon characters, and many other figures with the help of AI technology.
In this blog, we'll give you a comprehensive introduction to AI voice generators and AI covers, including the technologies behind them and their key features. Additionally, we'll show you how to create an AI voice generator through the APIs from Novita AI and provide some tips to enhance your cover output. Finally, we'll discuss the future development of AI voice generators. Let's dive into the world of AI covers now!
## AI Voice Generator and AI Covers
AI Voice Generator is an innovative AI tool for music lovers to create AI covers, enhancing creativity and providing unique experiences.
### What is an AI Voice Generator?
An AI voice generator is a tool that uses Artificial Intelligence (AI) to transform voices. It uses advanced algorithms and machine learning techniques to analyze and mimic the vocal patterns, melodies, and rhythms of different voices so that users can transform their own voices into any figures they want. This technology has revolutionized the way music is created and enjoyed. By using an AI voice generator, users can now create unique cover songs and showcase their talent in ways that were previously unimaginable.
### What are AI Covers and How Do They Work?
AI covers are personalized cover songs created using an AI voice generator. These covers can be created by transforming the user's own voice or cloning voices from their favorite artists. Once the AI cover is created, it can be easily shared on various music platforms like Spotify, and TikTok, or even social media platforms like Instagram or Facebook. This integration allows users to showcase their AI covers to a wider audience and engage with their followers, providing a new way to express their creativity and share their talent with the world.
## Top Features to Look for in AI Voice Generator
Besides easy use and efficiency, the AI voice generator has many other features that ensure the best experience for every user to enhance their creativity in cover song art.
### Multiple Voice Models and Flexibility
One of the top features to look for in an AI voice generator is the availability of multiple voice models. This allows you to explore and experiment with a wide range of voices and create cover songs in different styles and genres. The voice models may include talented artists like Taylor Swift, BlackPink, and Ariana Grande, anime characters like Spongebob, and Elsa, and even some public figures like Donald Trump, Joe Biden, and so on. You can not only transform your voice but also make your favorite artist cover your favorite songs effortlessly.
### Integration Capabilities with Music Platforms
Another important feature to look for in an AI voice generator is its integration capabilities with music platforms like Spotify and TikTok. These integrations make it easier for users to upload and share their AI cover songs on popular music platforms and other social media platforms, like Instagram or Facebook. This not only allows them to gain recognition and appreciation from a wider audience but also helps them find a sense of community and connection with others who share the same passion for music.

## How to Create Your AI Voice Generator Through Novita AI?
Creating your own AI voice generator through Novita AI is quick and easy. Novita AI is a one-stop platform that features over 100 APIs from AI image generation and language processing to AI audio and video manipulation. With powerful AI capabilities, Novita AI is the best choice for developers like you to create your relative software. By following the step-by-step guide below, you can create your own AI voice generator and unleash your creativity.
By the way, recently Novita AI has updated two new functions - ControlNet and IPAdapter - come and have a try!
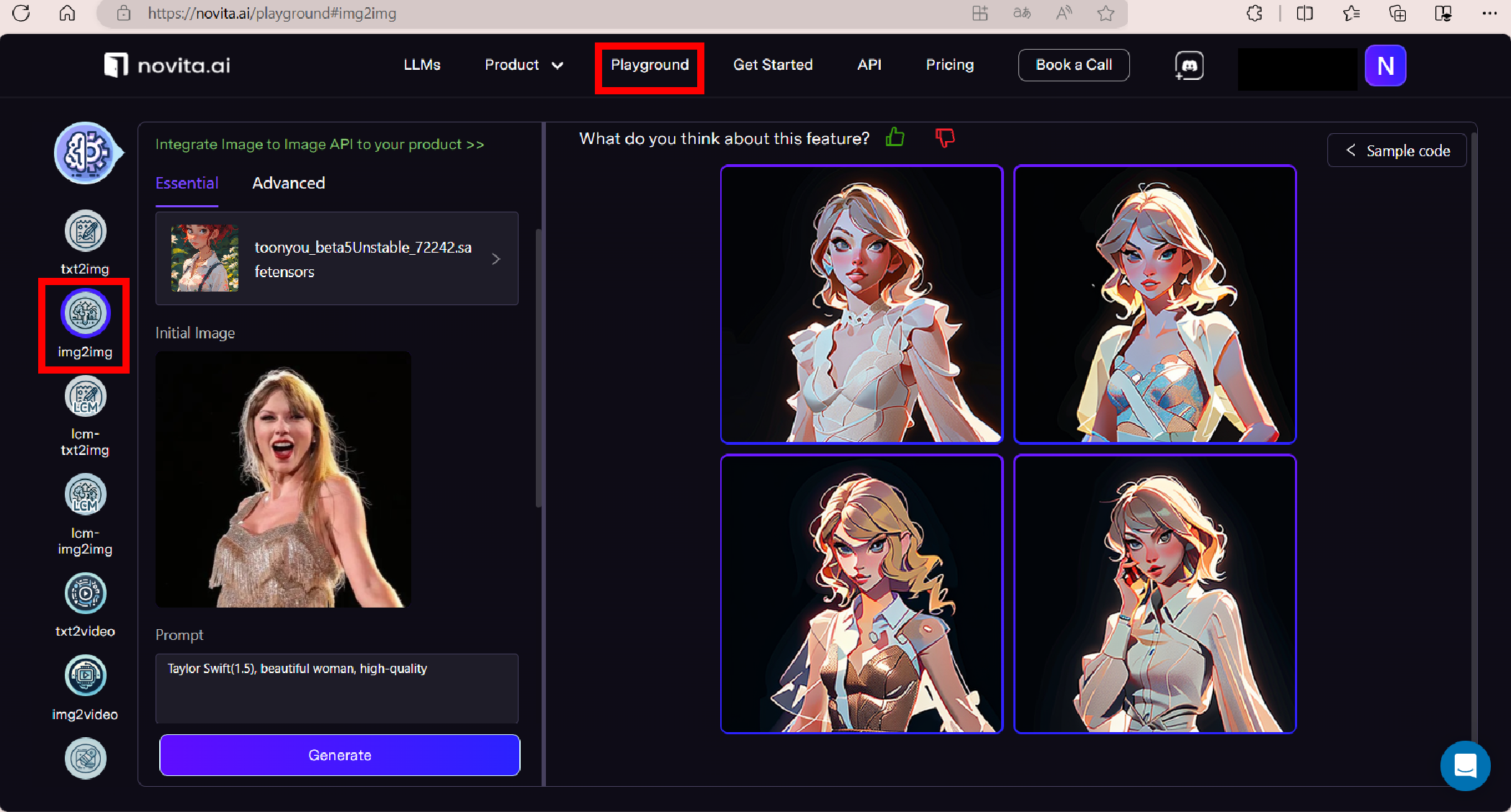
### Step-by-Step guide
- Step 1: Launch the [Novita AI](https://novita.ai/) website and sign up for an account on it.
- Step 2: Go to the "API" page and navigate to "[Voice Cloning Instant](https://novita.ai/reference/audio/voice_clone_instant.html)" under the "Audio" tab to ask for the API to create software. Then follow the steps below, you can test the effect first.
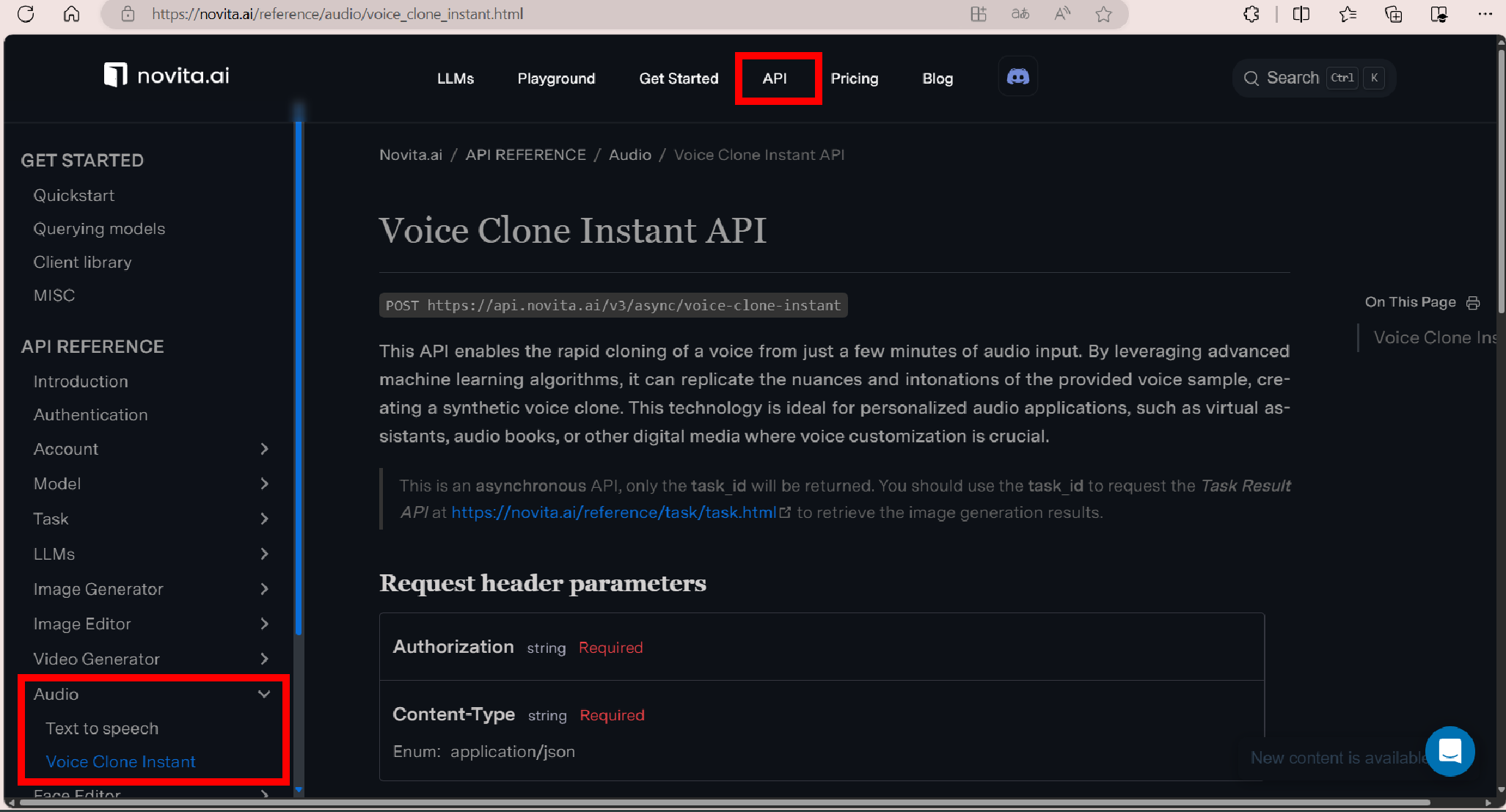
- Step 3: Return to the homepage and navigate "[voice-cloning-instant](https://novita.ai/product/voice-cloning-instant)" under the "product" tab.
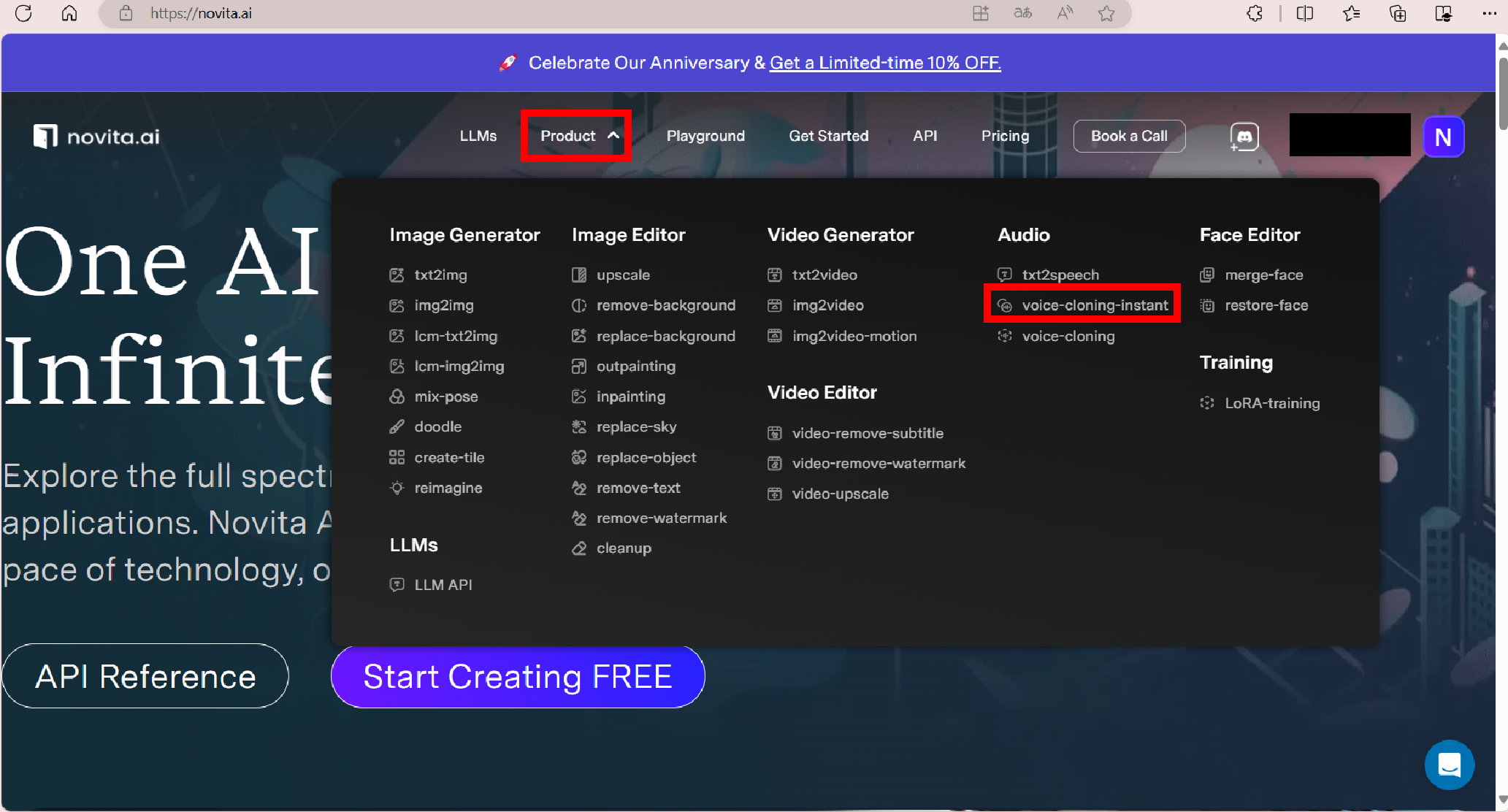
- Step 4: Upload the original audio file that you want to transform into another voice upon request for the AI to analyze and clone.
- Step 5: Customize your AI cover by selecting the voice models you want to use. Novita AI provides a wide range of voice models to choose from, including influencers, actors, narrators, and so on.
- Step 6: Click the "Generate" button and let the AI work its magic.
- Step 7: Once the output is generated, you can download it and share it on the music platforms and social media platforms.
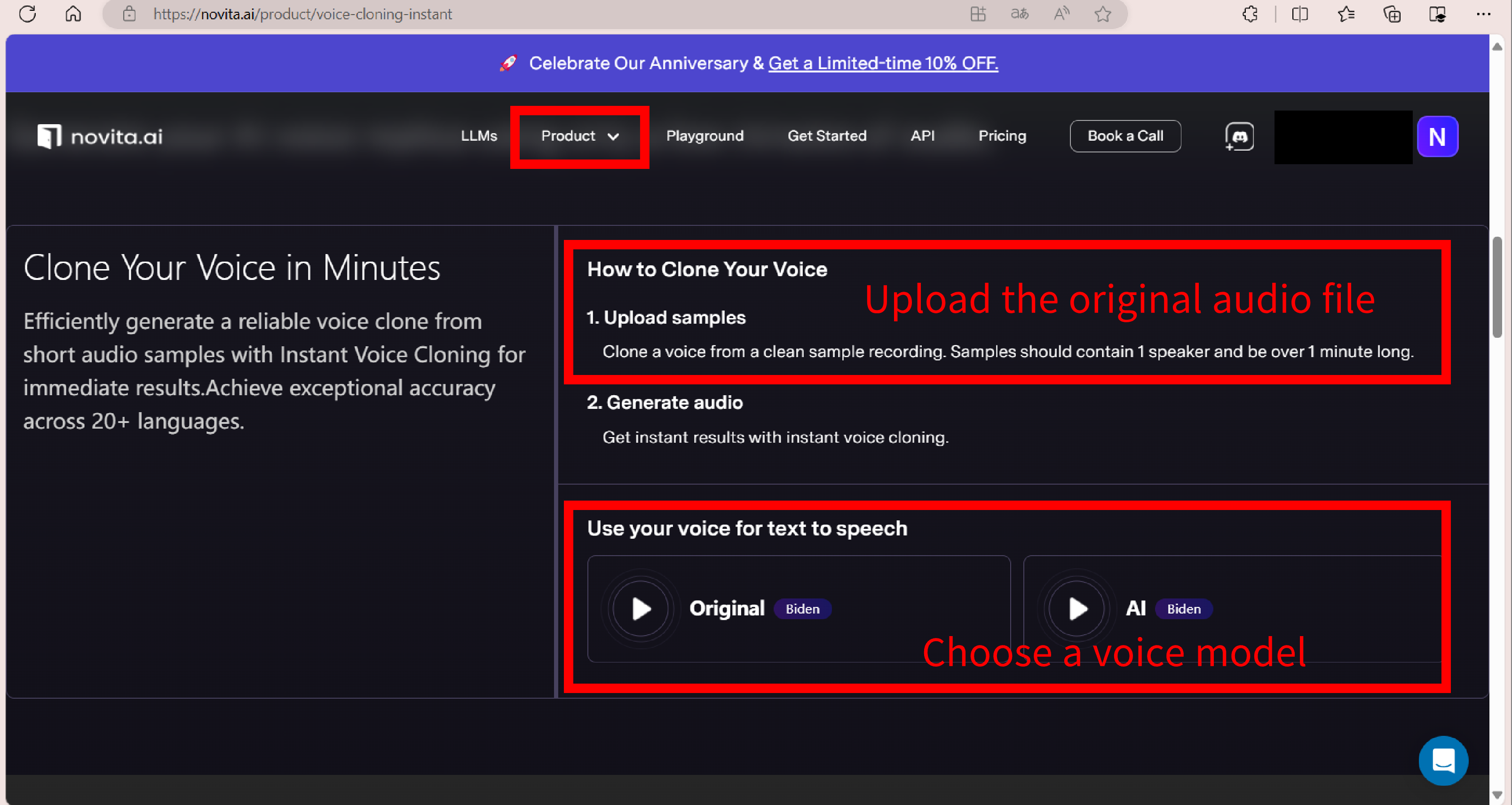
Moreover, you can utilize the "[txt2speech](https://novita.ai/product/txt2speech)" (TTS) tool in Novita AI to let AI singers sing your lyrics or just read your favorite texts. For more detailed information and a guide, please refer to this blog, "[Goku Text to Speech Mastery: Expert Guide for TTS Generator](https://blogs.novita.ai/goku-text-to-speech-mastery-expert-guide-for-tts-generator/)".
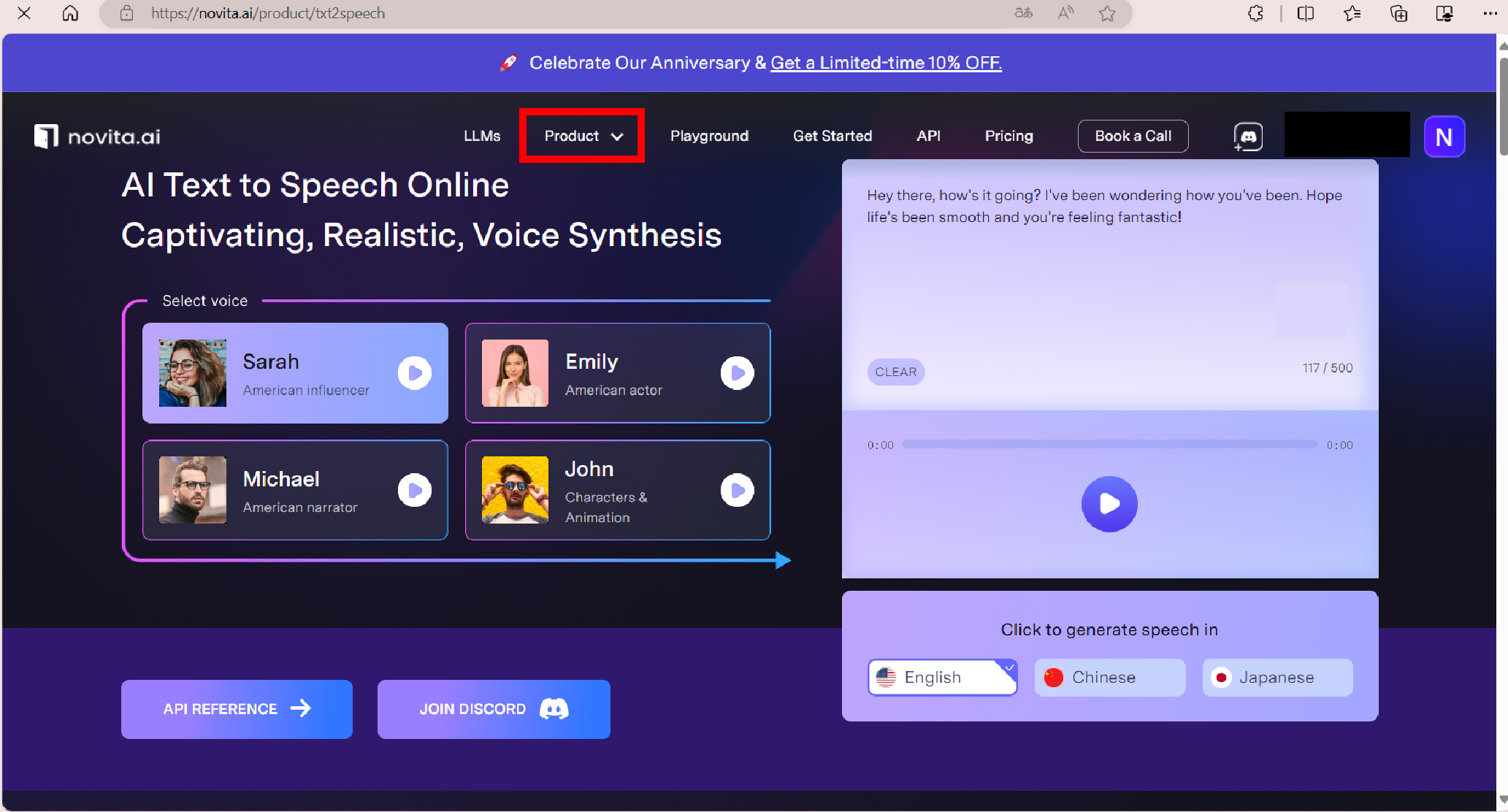
### Enhancing Your AI Covers: Tips and Tricks
Creating AI covers is just the first step. To make your AI covers stand out and attract more followers and engagement, here are some tips and tricks to enhance your creations:
- **Improve Audio Quality:** Ensure that the audio quality of your AI covers is clear and crisp. Use a good microphone and eliminate any background noise to enhance the overall listening experience.
- **Engage with Your Followers:** Interact with your followers by responding to comments and messages. This helps to build a community around your AI covers and get some feedback.
- **Promote Your AI Covers:** Share your AI Covers on social media platforms, create engaging captions, and use relevant hashtags to reach a wider audience.

## Future Trends in AI Cover Art
As AI technology continues to evolve, so does the role of AI in cover song art. These future trends will not only enhance the listening experience but also push the boundaries of creativity in the music industry.
### Overcoming Challenges in AI Song Cover
- Audio Quality: Ensuring high-quality audio is crucial for a seamless listening experience. AI technology needs to continue improving to produce the best possible quality.
- Copyright Issues: The use of copyrighted material in AI Song Covers raises legal concerns. Artists and developers must navigate copyright laws and obtain proper permissions to avoid infringement.
- Voice Authenticity: Cloned voices in AI Song Covers should strive to sound authentic and natural. Further advancements in AI algorithms are needed to make more human-like sounds and eliminate any artificial artifacts.
### Predictions on AI's Evolving Role in Design
- Advanced AI Algorithms: AI algorithms will become even more sophisticated, allowing for more accurate and realistic voice cloning.
- Virtual Artists: The rise of virtual artists, powered by AI, could change the landscape of the industry, with AI-generated performances and personas becoming more common.
- Artistic Evolution: As AI learns from a wider range of music, it could contribute to the evolution of new genres and styles, pushing the boundaries of what is considered musical.
- Global Music Fusion: AI could help in blending different music styles from around the world, creating new genres, and promoting cultural exchange.

## Conclusion
In the ever-evolving world of AI, the AI voice generator is revolutionizing the music industry. With AI voice generators, artistic possibilities are expanding like never before and music lovers can make song covers effortlessly. These tools not only enhance creativity but also offer flexibility and integration capabilities with music platforms. The future trends in AI cover art promise to overcome challenges and take music to new heights. As we embrace these advancements, let's explore the endless potential of AI in shaping the future of cover song creation.
> Originally published at [Novita AI](https://blogs.novita.ai/create-ai-voice-generator-make-your-unique-ai-covers/?utm_source=dev_audio&utm_medium=article&utm_campaign=cover)
> [Novita AI](https://novita.ai/?utm_source=dev_audio&utm_medium=article&utm_campaign=ai-cover-generator-unleash-your-creativity-with-ai-covers), the one-stop platform for limitless creativity that gives you access to 100+ APIs. From image generation and language processing to audio enhancement and video manipulation,cheap pay-as-you-go , it frees you from GPU maintenance hassles while building your own products. Try it for free.
| novita_ai | |
1,868,428 | Create Dora AI Voice Generator: Generate Custom Voices | Discover the power of the Dora AI voice generator for creating custom voices. Elevate your content... | 0 | 2024-05-29T09:32:00 | https://dev.to/novita_ai/create-dora-ai-voice-generator-generate-custom-voices-2867 | Discover the power of the Dora AI voice generator for creating custom voices. Elevate your content with personalized audio.
## Key Highlights
- Generate custom voices with the Dora AI Voice Generator, bringing the iconic voice of Dora the Explorer to life
- Explore the technology behind text-to-speech (TTS) and voice synthesis in AI voice changers
- Use the AI voice changer to effortlessly transform your voice into the AI voice of Dora, providing a unique sound experience
- Discover the key features of the Dora AI Voice Generator, including its benefits and practical use cases
- Novita AI offers multiple APIs for you to create a Dora AI voice generator
- Follow a step-by-step guide to creating your first Dora AI Voice Generator and learn how to use Dora AI Voice TTS and Dora AI Voice Cloning
- Get insights into the future of AI voice generators and the potential they hold for creative projects and entertainment purposes
## Introduction
Dora AI Voice Generator leverages advanced AI technology for content creators and enthusiasts alike to create personalized voices akin to iconic Dora's voice.
## Info of Dora the Explorer
Dora, the main character in Dora the Explorer, is known for her adventurous spirit and problem-solving skills.
### Who is Dora?
Dora the Explorer is a popular animated children's television series that follows the adventures of a young explorer named Dora Marquez. The show, known for its interactive format and educational content, first aired in 2000 and quickly became a hit among young viewers. With her positive attitude and iconic bob haircut, Dora, along with her trusty backpack and anthropomorphic monkey Boots, embarks on quests filled with puzzles and challenges, encouraging children in interactive journeys and teaching them critical thinking.
### Who are the Main Voice Actors of Dora the Explorer?
The main voice actors of Dora the Explorer include Kathleen Herles, Caitlin Sanchez, and Fatima Ptacek who have voiced the beloved character over the years. Their contributions have brought Dora to life with their unique voices and performances.

## Overview of Dora AI Voice Generator Technology
Dora AI Voice Generator leverages innovative AI technology to create custom Dora AI voice for various aspects, including Test-to-speech (TTS) technology and voice synthesis skills.
### Exploring Text-to-Speech (TTS) Technology
Text-to-speech (TTS) technology is at the core of Dora AI Voice Generator, transforming written words into spoken audio. Through sophisticated algorithms like Natural Language Processing (NLP), deep learning, and machine learning skills, this AI capability learns to create Dora's voice model from a large database and then converts text inputs into natural-sounding speech that is similar to Dora's voice. It unlocks the user's potential for dynamic voice modulation.
### Understanding Voice Synthesis in AI Voice Changer
Voice synthesis in AI voice changers involves the transformation of audio input into distinct vocal outputs, altering the pitch, tone, and other voice characteristics. It is trained to mimic the voice and speaking style of specific individuals. This process utilizes advanced algorithms to modify voices realistically, enabling customization for various purposes.

## Key Features of Dora AI Voice Generator
The Dora AI Voice Generator boasts a host of advanced features for voice modulation, that users can harness the power of AI for exceptional voiceovers.
### Benefits of Using Dora AI Voice Generator
- **Time-Saving and Cost-Effectiveness:** AI voice generators can produce voiceovers quickly, without hiring professional voice actors or investing in expensive recording equipment, reducing production costs.
- **Accessibility:** They can be useful for individuals with speech impairments, providing them with a synthetic voice that can communicate on their behalf.
- **Customization and Personalization:** AI voice generators often allow users to choose from a wide range of voices, accents, and languages, catering to diverse personal needs.
- **Scalability:** AI voice generators can handle large volumes of text, making them ideal for creating content at scale without the need for multiple voice actors.
- **Realism:** Modern AI voice generators produce highly realistic and natural-sounding speech, which can enhance the user experience.

### Practical Use Cases of Dora AI Voice Generator
- **Customer Service:** Businesses can use Dora AI Voice Generator to generate Dora virtual assistants and Dora chatbots, enhancing customer interactions and providing a more personalized service.
- **Content Creation:** Content creators can produce voiceovers in Dora's voice for podcasts, audiobooks, and other social media, like TikTok and YouTube.
- **Professional Voiceover Work:** Dora AI Voice Generator can quickly generate high-quality voiceovers in different languages, tones, and emotions, streamlining their workflow and expanding their capabilities.
- **Educational Tools:** Teachers can integrate the Dora AI Voice Generator into education, making the learning process more interactive and engaging.
- **Marketing and Advertising:** Businesses can use it to create compelling voiceovers for marketing campaigns, enhancing the appeal of their advertisements and reaching a wider audience.

## Step-by-Step Guide to Creating Your First Dora AI Voice Generator Through Novita AI
Novita AI is a one-stop platform that offers over 100 APIs from AI image generation and language processing to AI voice and video manipulation. With its powerful AI capabilities and user-friendly interface, Novita AI is the best choice for you to create your Dora AI voice generator effortlessly. Here is a comprehensive guide, come and embark on an exciting voice modulation journey.
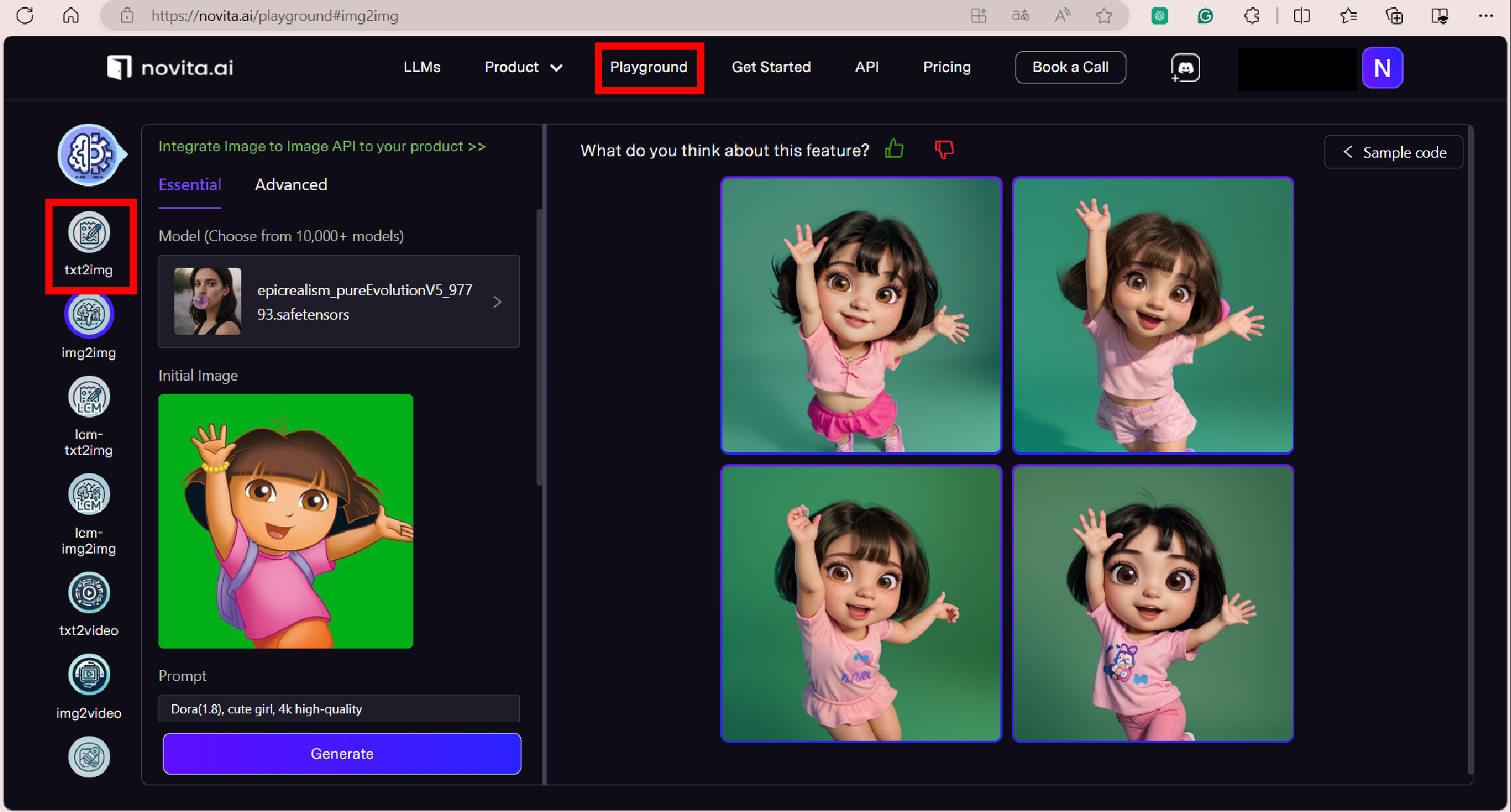
### Dora AI Voice TTS
- Step 1: Visit the [Novita AI](https://novita.ai/) website and create an account on it.
- Step 2: Click the "API" button, then navigate to "[Text to speech](https://novita.ai/reference/audio/text_to_speech.html)" under the "Audio" tab to ask for API to create your software. Follow the steps below, you can test the effect first.
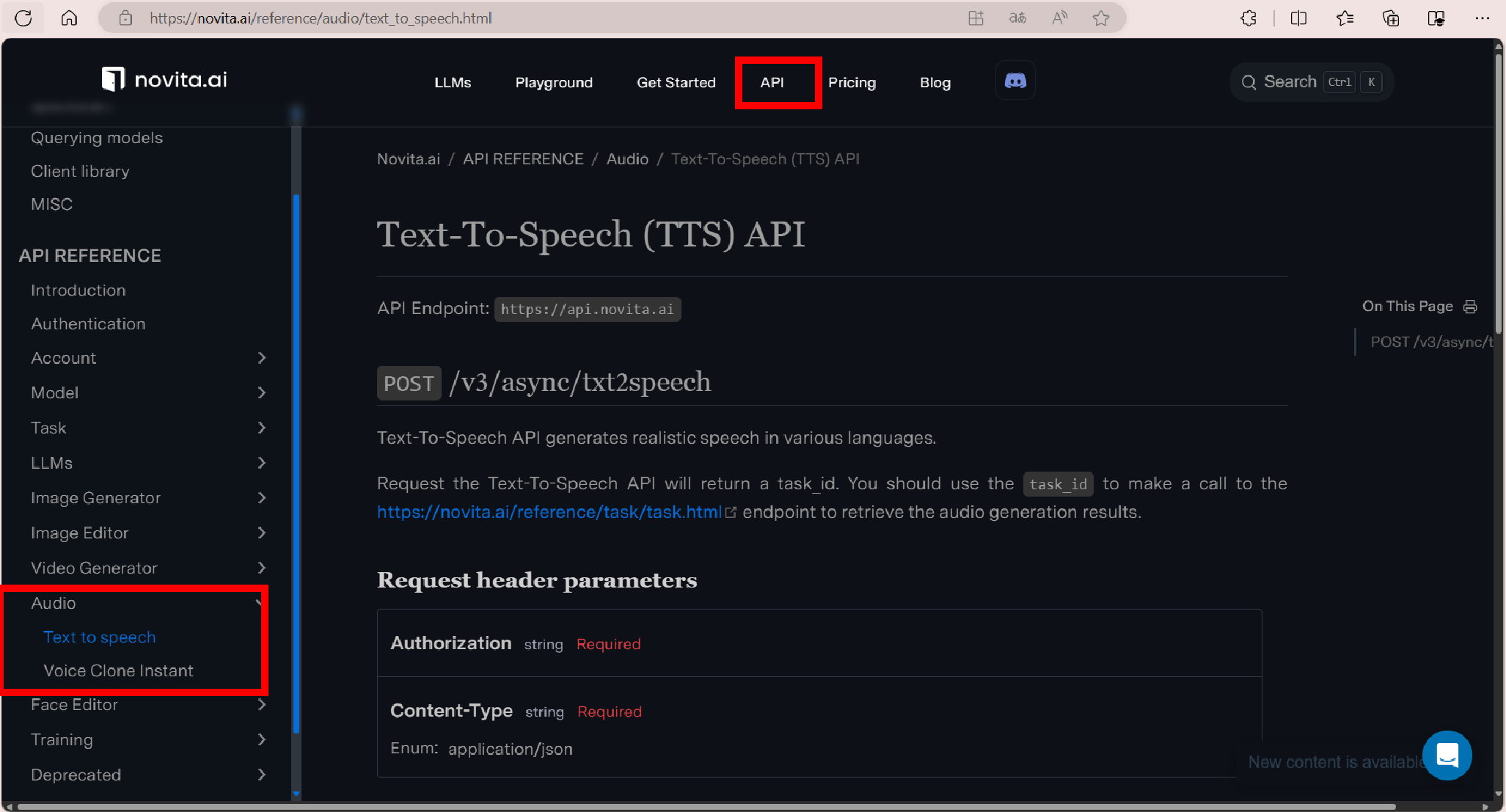
- Step 3: Return to the homepage, then click the "[txt2speech](https://novita.ai/product/txt2speech)" under the "product" tab.
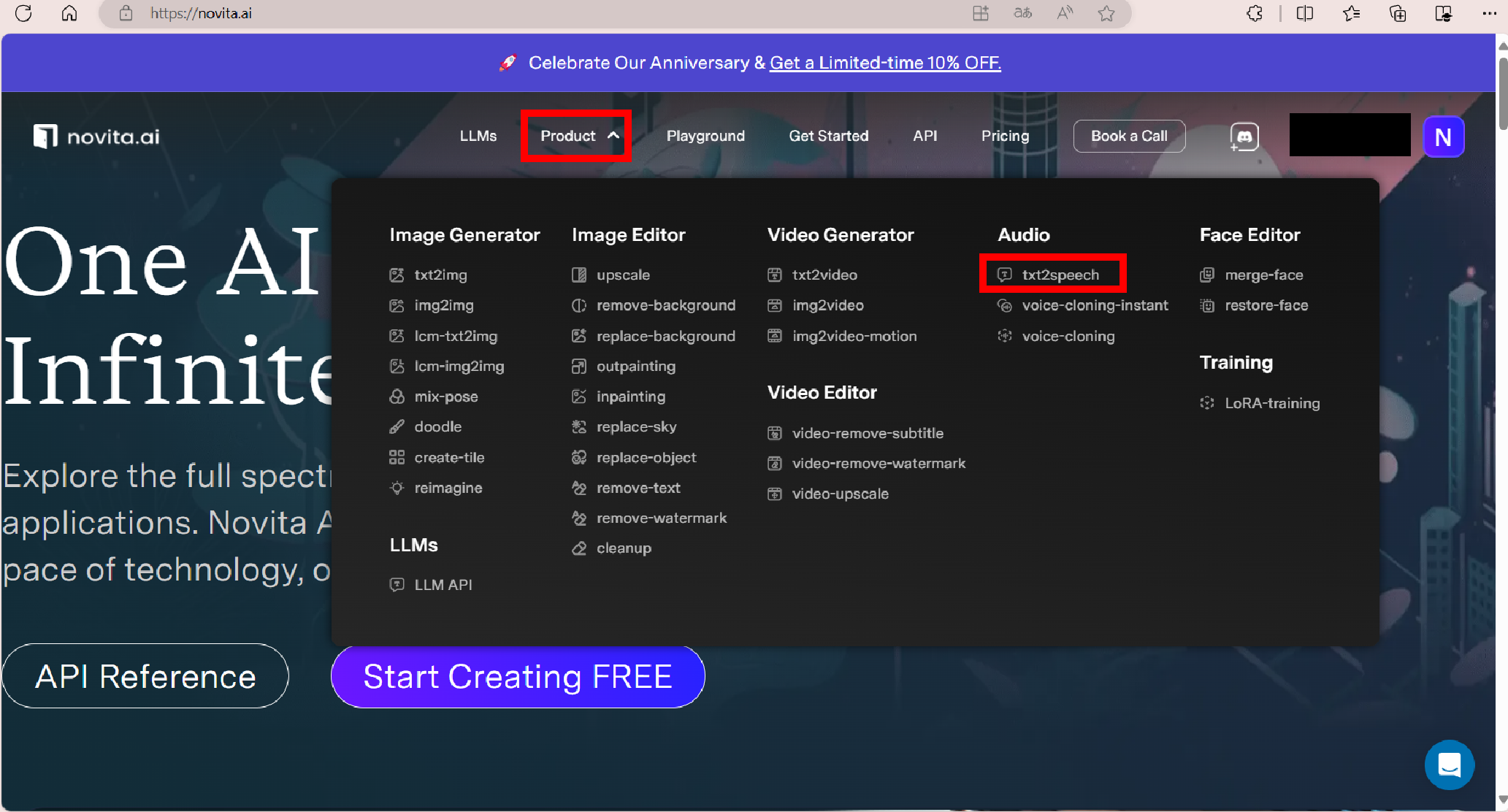
- Step 4: Enter or paste the text that you want to convert to Dora's voice in the text field.
- Step 5: Select Dora's voice model from the list and the languages according to your needs. There are now three languages supported in Novita AI, so please stay tuned for further development.
- Step 6: Click the play button and wait for your Dora AI voice.
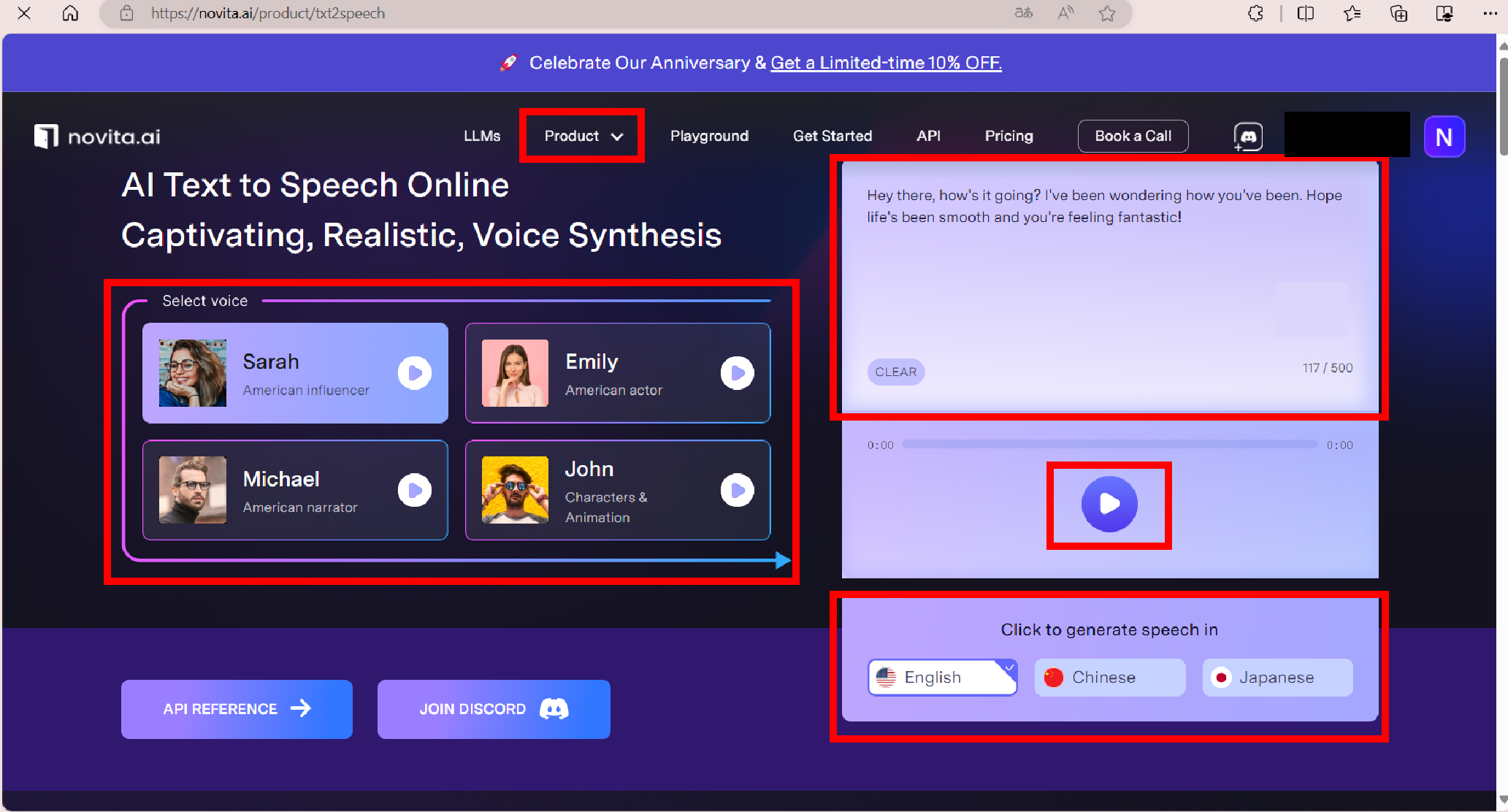
- Step 7: Once the output is completed, you can preview it and make some adjustments to it.
- Step 8: Once you are satisfied with the output, download it in your favorite formats, like MP3, and share it on YouTube or other social media.
### Dora AI Voice Cloning
- Step 1: Similarly, navigate to "[Voice Cloning Instant](https://novita.ai/reference/audio/voice_clone_instant.html)" under the "Audio" tab on the "API" page, to ask for API to create software.
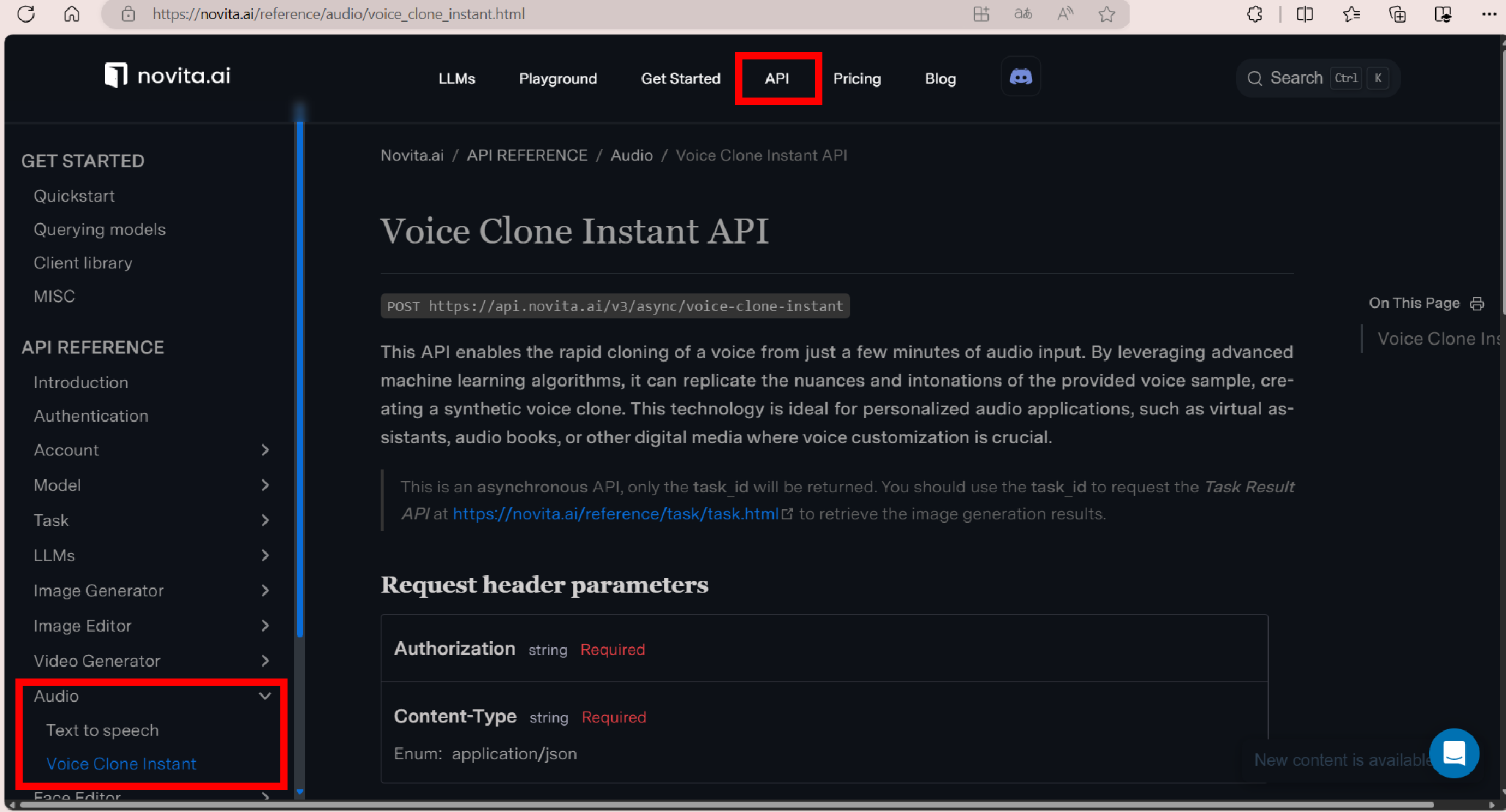
- Step 2: On the homepage, navigate to "[voice-cloning-instant](https://novita.ai/product/voice-cloning-instant)" under the "product" tab to test the effect first.
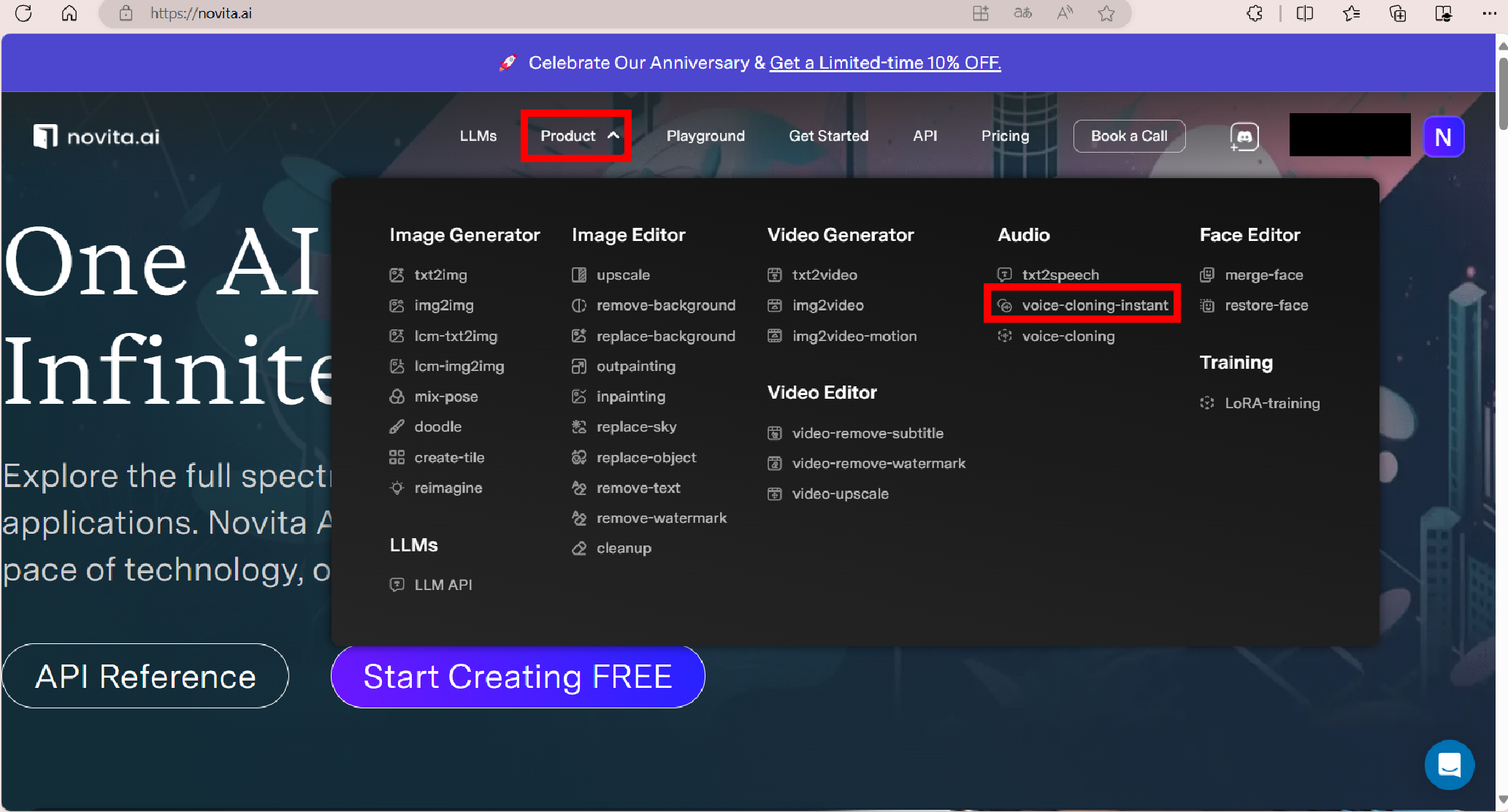
- Step 3: Upload the original audio file that you want to transform into Dora's voice, which can be your voice or a song that you want Dora to cover.
- Step 4: Select Dora's voice model from the list.
- Step 5: Click the "Generate" button and wait for your AI voice cloning result.
- Step 6: Download the output in your favorite formats, like MP3, and share it on social media.
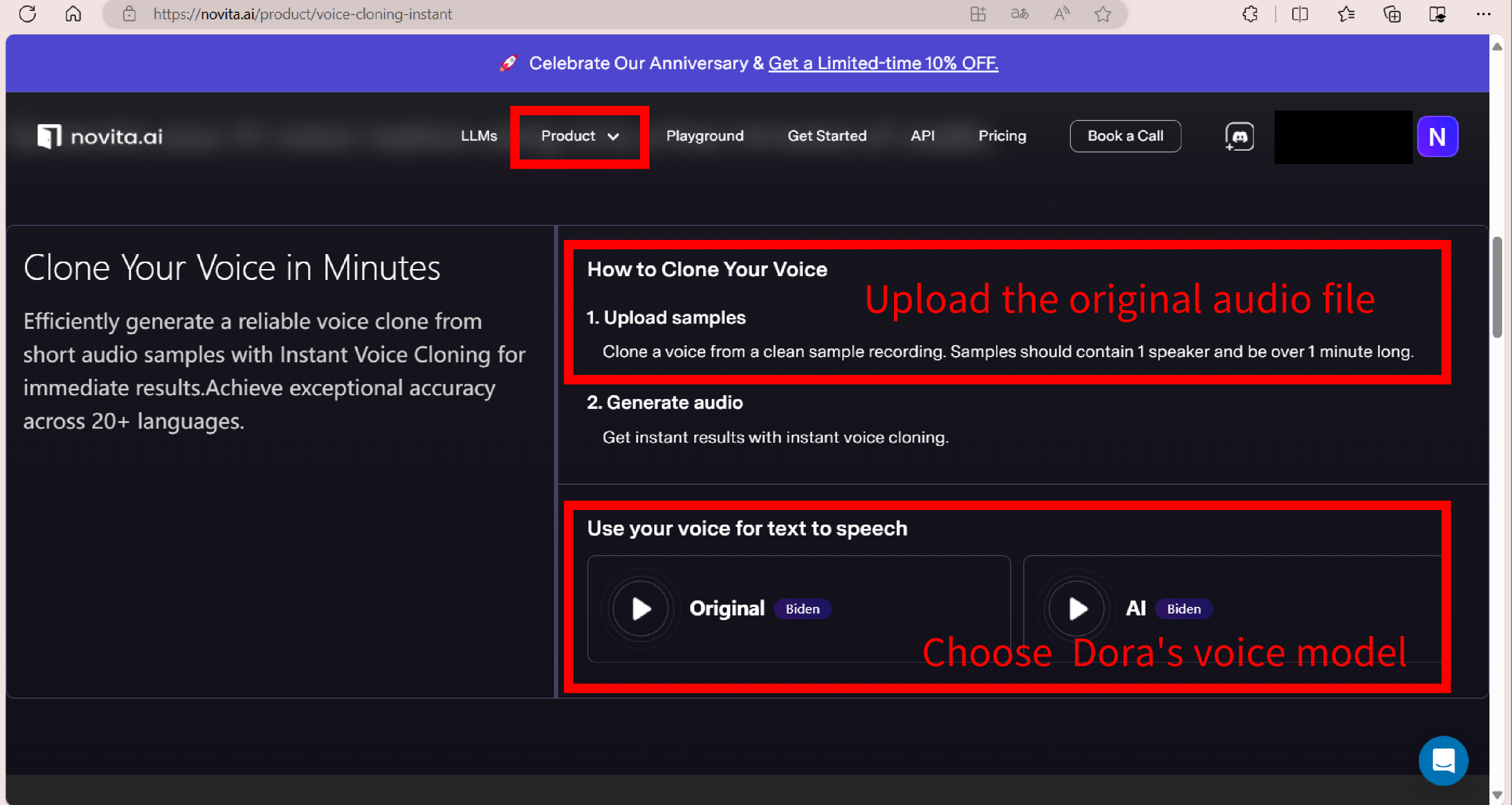
## Future of AI Voice Generator
As AI voice technology advances, the future of AI voice generators like Dora AI voice generator holds endless possibilities.
### Ethical Considerations in Using AI Voice Generator
While these AI voice generators like the Dora AI voice generator offer exciting possibilities for creative expression and content creation, we must be mindful of how we use them.
One ethical consideration is the potential for misrepresentation. When using an AI Voice Generator, it's important to remember that the generated voice is not the actual voice of any other person, but an artificial voice created. Therefore, using an AI-generated voice to impersonate someone without their consent can be misleading and unethical. Another consideration is the impact on voice actors. The use of AI-generated voices may potentially impact employment opportunities for voice actors, as AI voices become more prevalent and accessible.
### Innovative Development of AI Voice Generator
The development of AI Voice Generators has come a long way in recent years, thanks to advancements in artificial intelligence and machine learning technologies. One notable development in AI Voice Generators is the use of deep learning models and neural networks. By training these models on vast amounts of voice data, AI Voice Generators can now mimic and replicate the nuances of human speech more accurately than ever before.

## Conclusion
In conclusion, the Dora AI Voice Generator opens up a world of possibilities for voice modulation and creative projects. Whether for personal use or professional endeavors, this innovative technology allows users to generate unique Dora AI voices for various applications. Developers can utilize the APIs from Novita AI to create a Dora AI voice generator. With the AI voice changer feature, creating unique voiceovers and audio files, or even customizing voices for specific platforms like YouTube or Discord, becomes seamless. Download your modified voice in MP3 format and explore the limitless opportunities that the Dora AI Voice Generator offers.
## Frequently Asked Questions about Dora AI Voice Generator
### Is Dora AI Voice Generator Safe?
Yes, we prioritize the privacy and security of our users' data and ensure that our platform is secure and reliable.
### How Do I Customize the Voice to Sound Exactly Like Dora?
Our advanced algorithms and NLP capabilities will transform your voice to sound like Dora. You can also adjust the settings to achieve the perfect Dora-like sound.
> Originally published at [Novita AI](https://blogs.novita.ai/create-dora-ai-voice-generator-generate-custom-voices/?utm_source=dev_audio&utm_medium=article&utm_campaign=dora)
> [Novita AI](https://novita.ai/?utm_source=dev_audio&utm_medium=article&utm_campaign=dora-ai-voice-custom-voice-generator-guide), the one-stop platform for limitless creativity that gives you access to 100+ APIs. From image generation and language processing to audio enhancement and video manipulation,cheap pay-as-you-go , it frees you from GPU maintenance hassles while building your own products. Try it for free.
| novita_ai | |
1,868,749 | BDD Testing: Is the Juice Worth the Squeeze? | Behavior-Driven Development (BDD) is a testing approach that enhances communication between... | 0 | 2024-05-29T09:31:02 | https://dev.to/ngocninh123/bdd-testing-is-the-juice-worth-the-squeeze-1f09 | testing, bdd, bddtesting | Behavior-Driven Development (BDD) is a testing approach that enhances communication between stakeholders and development teams through a shared understanding of software requirements. BDD uses plain language descriptions of software behavior to improve collaboration and ensure that the final product meets user needs. While BDD offers numerous benefits, it also presents some challenges that organizations must navigate.
## Benefits of BDD Testing
Behavior Driven Development offers numerous advantages that streamline the software development process. Let's look at its advantages
### Improved Collaboration
One of BDD's most significant advantages is its ability to foster better collaboration among all project stakeholders. BDD involves stakeholders from different disciplines, including developers, testers, and business analysts, in the development process.
This collaboration ensures that everyone has a clear understanding of the project requirements and goals, reducing misunderstandings and miscommunications. The use of a common language, typically Gherkin syntax, allows non-technical stakeholders to participate actively in the discussion and contribute to the development process.
### Early Issue Identification
BDD helps identify issues early in the development cycle. By defining expected behavior before development begins, teams can spot potential problems and ambiguities in the requirements. Early detection of issues reduces the cost and effort required to fix them later in the project. It also ensures that the development team is building the right features from the start, aligning the final product more closely with stakeholder expectations.
### Center User Needs
BDD emphasizes user-centric development by focusing on the behavior that users expect from the software. This approach ensures that the software meets user needs and provides a better user experience. By writing scenarios from the user’s perspective, teams can better understand and prioritize the features that deliver the most value to users.
### Improved Test Coverage
BDD encourages comprehensive test coverage by driving the development of tests based on user behavior. This practice helps ensure that all aspects of the application are tested, reducing the risk of untested and potentially buggy code being deployed. BDD's scenario-driven approach helps identify edge cases and write tests that cover a wide range of use cases.
### Reduced Rework
By clarifying requirements and expectations early in the development process, BDD reduces the likelihood of rework. When the entire team understands the expected behavior of the software, there is less chance of building the wrong features or missing critical functionality. This alignment leads to more efficient development cycles and fewer costly changes later in the project.
##Challenges of BDD Testing
### Resistance to Change
Adopting BDD requires a cultural shift within the organization, which can be met with resistance from team members who are accustomed to traditional development methods. Overcoming this resistance requires strong leadership, effective communication, and training to demonstrate the benefits of BDD and how it can improve the development process.
### Skill Shortfalls
Implementing BDD effectively requires specific skills, including the ability to write clear and concise scenarios in Gherkin syntax and an understanding of the principles of BDD. Organizations may face challenges if their teams lack these skills. Investing in training and hiring experienced BDD practitioners can help bridge this gap.
### Lack of Collaboration
While BDD aims to improve collaboration, it can be challenging to achieve in practice. Teams may struggle to break down silos and work together effectively, especially in larger organizations or distributed teams. Fostering a collaborative culture and providing tools that facilitate communication and collaboration are essential for overcoming this challenge.
### Tooling Difficulties
Selecting and integrating the right BDD tools can be challenging. Various BDD tools are available, each with its strengths and weaknesses. Finding a tool that fits well with the existing development environment and meets the team’s needs can be difficult. Additionally, configuring and maintaining these tools can require significant effort.
### Insufficient Test Automation Framework
A robust test automation framework is critical for BDD, but many organizations struggle to implement one. Insufficient test automation can lead to slow feedback cycles and reduced efficiency. Ensuring that the test automation framework is reliable, scalable, and easy to maintain is crucial for BDD's success.
Wonder about the solution to those problems? You can find them [here](https://www.hdwebsoft.com/blog/challenges-when-adopting-bdd-into-business.html).
## Conclusion
BDD offers significant benefits, including improved collaboration, early issue identification, user-centered development, enhanced test coverage, and reduced rework. However, organizations must be prepared to address challenges such as resistance to change, skill shortfalls, lack of collaboration, tooling difficulties, and the need for a strong test automation framework. By understanding and addressing these challenges, organizations can successfully implement BDD and reap its full benefits, leading to higher-quality software and more satisfied stakeholders.
👍You might also like:
[Collaboration and Efficiency in BDD](https://www.hdwebsoft.com/blog/10-key-benefits-of-bdd-testing.html)
| ngocninh123 |
1,868,640 | Dive Into Uncensored LLMs: All You Need to Know | Introduction All things AI, ML, NLP, LLM, Cloud & End-user Computing! Search AskAresh... | 0 | 2024-05-29T09:30:00 | https://dev.to/novita_ai/dive-into-uncensored-llms-all-you-need-to-know-51po | ai, llm, uncensored, beginners | ## Introduction
All things AI, ML, NLP, LLM, Cloud & End-user Computing! Search AskAresh About Exploring Uncensored LLM Model — Dolphin 2.9 on Llama-3–8b 2 May. I’ve been diving deep into the world of Large Language Models (LLMs) like ChatGPT, Gemini, Claude, and LLAMA. But recently, I stumbled upon something that completely blew my mind: uncensored LLMs! As someone who loves pushing the boundaries of AI and exploring new frontiers, I couldn’t resist the temptation to try out an uncensored LLM, specifically Microsoft’s Dolphin 2.9, for myself.
Uncensored LLMs are AI models that do not have built-in content filtering, allowing for raw and unfiltered text generation. They provide a whole new perspective on the potential of LLMs and why having an uncensored variant is so important for certain perspectives and society in general.
In this blog post, I’ll be sharing my journey with uncensored LLMs, diving into the nitty-gritty details of what they are, how they differ from regular LLMs, and why they exist. I’ll also be sharing my hands-on experience with setting up and running an uncensored LLM locally, so you can try it out for yourself!
## What are Uncensored LLMs
Uncensored LLMs, also known as uncensored large language models, are AI systems that are trained on vast amounts of text data to understand and generate human-like text based on input prompts. Unlike regular LLMs, which are designed with specific safety and ethical guidelines to avoid generating harmful or inappropriate content, uncensored LLMs do not have these built-in restrictions. This means that they can generate responses without ethical filtering, which can be both beneficial and risky, depending on the application and context.

**Significance**
Uncensored LLM models are essentially AI models that do not have content filtering or censorship built into their design. They generate responses based solely on the input prompts they receive, without any ethical guidelines guiding their output. The significance of uncensored LLM models lies in their ability to generate unfiltered and raw content, allowing for greater flexibility and freedom of expression in certain contexts. This is made possible through the intuitive interface of LLM Explorer, which provides easy access to a diverse range of uncensored models and allows users to efficiently filter their search based on specific requirements.
One platform that has gained attention in the uncensored LLM space is Hugging Face, a popular open-source AI research platform. Hugging Face has developed various uncensored LLM models that provide users with the ability to explore and experiment with unfiltered text generation.
**Comparison with Traditional LLMs**
[Traditional LLMs](https://blogs.novita.ai/ai-chatbot-vs-traditional-chatbot-unveiling-their-difference/), developed by major organizations like OpenAI, Anthropic, and Google, are designed with specific content filters and ethical guidelines. These models are aligned with societal norms and legal standards to avoid generating harmful or inappropriate content.
In comparison, uncensored LLMs do not have content filters or ethical guidelines, allowing them to generate responses as they are without any form of censorship. This key difference gives uncensored LLMs higher flexibility and potential for generating diverse and unrestricted content. However, it also increases the risk of generating harmful or inappropriate output.

## Key Features of Uncensored LLMs
Uncensored LLMs offer several key features that set them apart from traditional LLMs. One of the main features is their enhanced free speech capabilities. Without content filters or ethical guidelines, uncensored LLMs allow for the generation of unfiltered and uncensored text, promoting freedom of expression.
Additionally, uncensored LLMs provide advanced content generation without restrictions. They are not bound by ethical guidelines, allowing for more creative and unrestricted text generation. These key features make uncensored LLMs a valuable tool for various applications where freedom of expression and unrestricted content generation are desired.
**Enhanced Free Speech Capabilities**
- Uncensored LLMs enable free speech by generating unfiltered and uncensored text responses.
- They allow for the expression of diverse perspectives and opinions without content restrictions.
- Uncensored LLMs promote open dialogue and encourage creativity in content generation.
- They provide a platform for unrestricted exploration and expression of ideas.
**Advanced Content Generation without Restrictions**
- Uncensored LLMs offer advanced content generation capabilities without any form of restrictions.
- They allow for the generation of diverse and unrestricted text based on input prompts.
- Uncensored LLMs enable the exploration of creative ideas and unconventional content.
- They provide a platform for unrestricted content generation, fostering innovation and pushing the boundaries of AI-generated text.
## How Uncensored LLMs Work
To understand how uncensored LLMs work, it is essential to delve into the underlying technology, algorithms, and data processing involved. Uncensored LLMs utilize advanced natural language processing (NLP) techniques and machine learning algorithms to analyze and understand input prompts. These models process large amounts of text data to learn patterns and generate human-like responses. The technology behind uncensored LLMs also involves the use of proxy servers and hosting services to facilitate the generation of unfiltered and unrestricted text.
**Technology Behind Uncensored LLMs**
The technology behind uncensored LLMs involves the use of proxy servers and hosting services. Proxy servers act as intermediaries between users and the uncensored LLM models, allowing for secure and private access to the models. Hosting services, on the other hand, provide the infrastructure and resources needed to run the uncensored LLM models efficiently.
System prompts play a crucial role in guiding the uncensored LLM models’ text generation process. These prompts serve as the input that the models analyze and generate responses based on. By providing specific prompts, users can guide the models’ output and tailor it to their specific needs.
**Algorithms and Data Processing**
Algorithms and data processing are fundamental components of uncensored LLMs. These models use machine learning algorithms, such as deep neural networks, to process and analyze large datasets of text. The algorithms learn patterns and linguistic structures from the data, enabling the models to generate text that mimics human-like language.
The training process involves feeding the uncensored LLM models with vast amounts of text data, allowing them to learn and generalize from the patterns and information in the dataset. Through this iterative process, the models gain a deeper understanding of language and become more proficient in generating coherent and contextually appropriate responses. This process is crucial for companies like Google, Meta, and Mistral, who have trained models on undisclosed datasets and open-sourced them for public use.

## Benefits of Using Uncensored LLMs
Using uncensored LLMs offers several benefits, particularly in the areas of content creation, innovation, and academic research.
**Fostering Innovation in Content Creation**
Uncensored LLMs have the potential to foster innovation in content creation. By providing a platform for generating diverse and unrestricted content, these models encourage creativity and push the boundaries of AI-generated text. Content creators can explore new ideas, perspectives, and writing styles, leading to innovative and engaging content. Uncensored LLMs offer a unique opportunity to break free from traditional content restrictions and experiment with unconventional approaches to content creation. This fosters a culture of innovation and encourages content creators to think outside the box, resulting in fresh and exciting content that captivates audiences.
**Impact on Academic and Scientific Research**
Uncensored LLMs have the potential to make a significant impact on academic and scientific research. These models provide researchers with a powerful tool to explore new perspectives, generate novel insights, and push the boundaries of knowledge. The unrestricted nature of uncensored LLMs allows researchers to delve into sensitive and controversial topics without the fear of censorship. This opens up new possibilities for interdisciplinary research, collaboration, and the exploration of unconventional ideas. By harnessing the capabilities of uncensored LLMs, academic and scientific communities can accelerate their research efforts and make groundbreaking discoveries.
## Applications of Uncensored LLMs
Uncensored LLMs have diverse applications across various fields, including media and journalism.
**Use Cases in Media and Journalism**
Uncensored LLMs have significant use cases in the field of media and journalism. These models can be utilized to generate raw and unfiltered content for news articles, opinion pieces, and investigative reporting. By removing the content restrictions present in regular LLMs, uncensored LLMs allow journalists to explore different perspectives and provide a more authentic representation of various viewpoints.
One of the main advantages of using uncensored LLMs in media and journalism is the freedom to express sensitive topics without the fear of censorship. However, it is important to note that the use of uncensored LLMs in this domain also comes with ethical considerations. Journalists must ensure responsible use of these models and exercise caution while handling potentially controversial or sensitive subjects.
A text table showcasing the use cases in media and journalism:
**Potential in Creative Writing and Entertainment**
Uncensored LLMs also hold great potential in the field of creative writing and entertainment. These models can be utilized to generate uncensored and unfiltered narratives, dialogues, and storylines for books, movies, video games, and other forms of entertainment media.
By using uncensored LLMs, writers and content creators can explore unconventional and edgier themes, push creative boundaries, and develop unique and thought-provoking content. This can lead to more engaging and immersive experiences for the audience.
However, it is essential to consider the potential ethical implications when using uncensored LLMs in creative writing and entertainment. Content creators must be responsible and mindful of the impact their uncensored content may have on the audience and society as a whole.
## Challenges and Considerations
Using uncensored LLMs comes with its own set of challenges and considerations. While these models offer higher flexibility and the ability to generate raw and unfiltered content, they also pose risks and ethical implications.
One of the main challenges is managing the potential for harmful or inappropriate output. Without content filters and restrictions, uncensored LLMs may generate content that is offensive, biased, or promotes misinformation. It is crucial to have proper oversight and monitoring mechanisms in place to ensure responsible use of these models.
Additionally, the ethical implications of using uncensored LLMs must be carefully considered. Content creators and users should be aware of the potential impact their uncensored content may have and take steps to mitigate any negative consequences.
**Ethical Implications**
The use of uncensored LLMs raises important ethical implications. With the absence of content filters and restrictions, these models have the potential to generate content that is offensive, biased, or promotes misinformation.
Content creators and users of uncensored LLMs must be mindful of the impact their content may have on individuals and society as a whole. It is important to ensure responsible use and consider the potential consequences of disseminating uncensored and potentially harmful information.
Sensitive topics, in particular, require careful handling when using uncensored LLMs. Misrepresentation or misinterpretation of such topics can lead to misinformation and harm. Therefore, it is crucial to exercise caution, conduct thorough fact-checking, and provide proper context when dealing with sensitive subjects.
Proper oversight and ethical guidelines are essential to mitigate the risks associated with using uncensored LLMs and ensure that they are used in a responsible and beneficial manner.
**Managing Misinformation and Abuse**
One of the key challenges in using uncensored LLMs is managing the potential for misinformation and abuse. Without content filters and restrictions, these models can generate content that spreads false information or promotes harmful ideologies.
To address this challenge, it is important to implement guardrails and monitoring mechanisms when using uncensored LLMs. This can include employing human moderators to review and filter the generated content, utilizing machine learning algorithms to detect and flag potentially harmful output, and collaborating with experts in the respective fields to ensure accuracy and alignment with the desired message.
Furthermore, content creators and users of uncensored LLMs should actively promote responsible use and educate the audience about the limitations and potential risks associated with the generated content. By taking proactive measures to manage misinformation and abuse, the benefits of uncensored LLMs can be maximized while mitigating potential harm.
## Conclusion
In conclusion, uncensored LLMs offer a revolutionary approach to content creation with enhanced free speech capabilities and unrestricted content generation. By leveraging advanced technology and algorithms, these models foster innovation in various fields, from media and journalism to creative writing and entertainment. Despite their benefits, ethical considerations and the need to manage misinformation remain crucial challenges. Understanding the nuances of uncensored LLMs and their implications is key to harnessing their potential while mitigating risks. Explore the diverse applications and stay informed about the evolving landscape of uncensored LLMs for cutting-edge content creation.
## Frequently Asked Questions
**What makes an LLM uncensored?**
Uncensored LLMs are AI models that do not have built-in content filters or restrictions. They generate outputs based on the input without ethical filtering, allowing for raw and unfiltered content.
**How do uncensored LLMs differ from AI content filters?**
Uncensored LLMs differ from AI content filters in that they do not have built-in restrictions to avoid harmful or inappropriate content. Content filters are designed to align with ethical guidelines and societal norms, while uncensored LLMs provide more flexibility in generating responses.
> Originally published at [Novita AI](https://blogs.novita.ai/dive-into-uncensored-llms-all-you-need-to-know/?utm_source=devcommunity_LLM&utm_medium=article&utm_campaign=uncensoredllm)
> [Novita AI](https://novita.ai/?utm_source=devcommunity_LLM&utm_medium=article&utm_campaign=dive-into-uncensored-llms-all-you-need-to-know), the one-stop platform for limitless creativity that gives you access to 100+ APIs. From image generation and language processing to audio enhancement and video manipulation, cheap pay-as-you-go, it frees you from GPU maintenance hassles while building your own products. Try it for free.
| novita_ai |
1,863,979 | Simplifying AWS SSO Setup: The effortless way | Are you struggling with the complexities of configuring AWS SSO profiles for your projects involving... | 0 | 2024-05-29T09:29:23 | https://dev.to/wickenico/simplifying-aws-sso-setup-the-effortless-way-4g18 | aws, sso, terminal, cli | Are you struggling with the complexities of configuring AWS SSO profiles for your projects involving data storage in S3 or similar services? In this blog post, we'll guide you through the seamless and effortless process of setting up AWS SSO profiles within AWS Config to get you up and running quickly.
## Understanding AWS Profiles
AWS profiles are configurations that define how your AWS CLI commands interact with AWS services. They centralise authentication credentials, region settings, and other parameters to streamline access to AWS resources. By creating different profiles for different purposes or roles, you can provide granular access control and maintain organisational segregation of duties. Understanding AWS profiles enables seamless integration of AWS CLI commands into your workflow, promoting agile development, efficient resource management, and robust security practices.
## Prerequisites
- AWS Account: You must have an active AWS account with appropriate permissions to configure AWS services and manage IAM roles.
- AWS CLI: Install the AWS Command Line Interface (CLI) tool on your local machine. AWS CLI allows you to interact with AWS services from the command line, simplifying configuration and management tasks.
Install the AWS CLI using brew: `brew install awscli`.
- AWS IAM privileges: Ensure that your IAM user or role has the necessary permissions to create and manage AWS Config rules and AWS SSO configurations. This includes permissions to access the AWS Management Console and make changes to IAM policies and roles.
## Setting Up AWS SSO Profiles in AWS Config: A Step-by-Step Guide
The AWS CLI provides a built-in step-by-step guide for setting up SSO profiles. You can invoke it with `aws configure sso'.
1. `SSO Session Name (Recommended)`: Choose a descriptive name, ideally with a reference to the environment or stage like dev, prod or staging.
2. `SSO Start URL [None]`: Specify the URL where the process of selecting a profile begins within the AWS Management Console.
3. `SSO Region [None]`: Indicate the region associated with your AWS account.
4. `SSO Registration Scopes [sso:account:access]`: This initiates a browser window for granting access to your AWS profiles. Upon confirmation, you can proceed to select accounts and roles via the terminal.
5. `CLI Default Client Region [eu-central-1]`: Reiterate your preferred region setting.
6. `CLI Default Output Format [None]`: Simply press Enter to confirm.
Once configured, you can verify your profile by executing:
`aws s3 ls --profile dev-admin`
This command will list the contents of your S3 bucket using the specified profile, in this case, "dev-admin".
## Setting Up AWS SSO Profile directly in Configuration File
Another effective method for adding a profile is by directly modifying the config file.
To access the file in the terminal, use the command cat ~/.aws/config.
Within this file, you can insert a profile block resembling the following example:
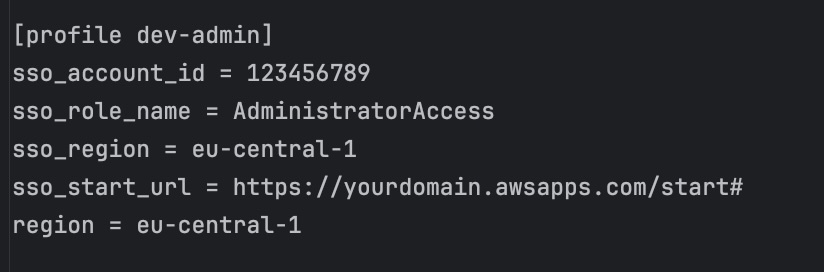
After adding the block and saving the file, you can seamlessly utilize the profile.
## Logging in with AWS SSO Profiles
First, export the AWS profile in the terminal where you want to use AWS CLI commands:
`export AWS_PROFILE=dev-admin`
Next, log in to your profile with the following command:
`aws sso login`
A new browser window will open, prompting you to confirm your login attempt.
Great! You are now logged in with your dev-admin profile.
To check which profile you are currently logged in with, use the command:
`aws sts get-caller-identity`.
For a deeper view you can visit the AWS documentation: https://docs.aws.amazon.com/cli/latest/userguide/sso-using-profile.html. | wickenico |
1,868,748 | SVG path animation in Nextjs using GSAP | Before starting out, let me quickly share what we're building today. Open codesandbox.io or visit... | 0 | 2024-05-29T09:21:51 | https://blog.aashish-panthi.com.np/svg-path-animation-in-nextjs-using-gsap | gsap, nextjs, animation, javascript | Before starting out, let me quickly share what we're building today.
{% codesandbox svg-path-animation-4d2k2v %}
Open [codesandbox.io](https://codesandbox.io/p/devbox/svg-path-animation-4d2k2v) or visit [**gsap-svg-path-animation.netlify.app**](https://gsap-svg-path-animation.netlify.app/)**.**
Seems interesting, let's start.
## Introduction
You might have visited some websites where when you scroll, things move; some elements move up, some sideways, and sometimes move down also. The elements follow a path when they move and often the path they follow is drawn using <path> element in SVG.
### Brief overview of SVG animation
Unlike raster images, the SVGs don't lose their quality on zooming because SVGs are just a bunch of coordinates to make mathematical polygons. Also, unlike raster images, SVGs can be animated. We can change color, change size, change shape, and do more cooler stuff. That's all about the SVG animation.
Now let me explain what an SVG path animation means. So, if you've worked with SVGs before, there are different shapes that you can draw. There are ellipses, lines, polygons, rectangles, circles, and many others. You can find the complete list [here](https://developer.mozilla.org/en-US/docs/Web/SVG/Tutorial/Basic_Shapes). In particular, there is something called `path` that is used to draw lines, irregular lines; as you do with your hands. Unlike hand-drawn lines, the lines drawn with path elements can be animated. The path is used to guide some elements to move in a specific direction, basically a path and sometimes used to animate the line itself.
### Introduction to Next.js
I assume you know Next.js. If you don't that's ok. You'll get almost everything out of this article. So, for those who don't know what Next.js is, let me quickly share about the most loved framework by lazy developers (I don't know if it's most loved or not; I love it).
Next.js is a javascript framework, like React.js but better. Next. js supports Server-Side Rendering (SSR), whereas React. js supports client-side rendering. Doesn't sound like a big deal but it is. SSR improves the application performance and speed and that's the reason I love Next.js.
### Introduction to GSAP (GreenSock Animation Platform)
Unlike Next.js, I don't assume you know GSAP. So, GSAP which stands for GreenSock Animation Platform is another javascript framework *(yes, there are millions of javascript frameworks)* that is used to animate elements on websites. Open their website ([gsap.com](https://gsap.com/)) to explore the type of animations you can make using GSAP.
### Purpose and scope of the article
The article's purpose is to help you make GSAP animations in your Next.js project. It's the same for React also. In particular, we'll be looking at SVG path animation on scroll. I assume you saw the demo above.
## Setting Up the Development Environment
Now let's move on to the actually stop so we are going to set up our development environment and we will be using the npm package manager and create our next application, and use the GSAP library.
### Installing Node.js and npm
I assume you already have nodejs installed. If you don't then head over to not [nodejs.org](https://nodejs.org) and download the latest version. Remember I want you to download the long-term support (LTS) version. If you're on Linux then this:
This one: [https://blog.aashish-panthi.com.np/install-node-and-npm-using-linux-binaries] (https://blog.aashish-panthi.com.np/install-node-and-npm-using-linux-binaries) or this: [https://dev.to/aashishpanthi/3-easy-ways-to-install-nodejs-in-linux-lc4](https://dev.to/aashishpanthi/3-easy-ways-to-install-nodejs-in-linux-lc4) article will help you.
To confirm you've installed node.js, run this command on your command prompt or terminal:
```bash
node --version
```
And you should be seeing some numbers on the screen that represent the version of node.js installed on your machine. It looks like this:
Now that you have installed the node.js, you need to take for the npm. In most of the cases, the npm gets installed automatically but if it does not, you can install it manually. So let's check if the npm is installed or not. Run the following command on your terminal:
```bash
npm --version
```
And if the npm is installed then, you'll see the version like this:
The basic setup is complete. Now let's move on to nitty-gritty.
### Setting up a new Next.js project
If you would love to read the official documentation on installing nextjs then [*here it is*](https://nextjs.org/docs/pages/api-reference/create-next-app)*.* Otherwise, I'm here to help.
Now, to install next.js we need to run this command on our terminal:
```bash
npx create-next-app@latest
```
Now, it'll ask a few questions. These questions are important and carefully answer them.
* First, you'll be asked to name the project. Please name it.
* You'll be asked if you want to use typescript or not. I prefer typescript but it's your call. (In the rest of the article, we'll be using typescript but I'll provide the javascript code at the end).
* I like to use Eslint.
* Also, I'll be using tailwind CSS. If you want to sit and write your custom CSS then you've a right to opt out.
* Next, it will ask if you'd like to have a `src` directory or not. It's more of a personal preference and I would say yes here.
* And please use the app router. Please...
* The final question asks you about the default import alias. We don't want to do that so select no.
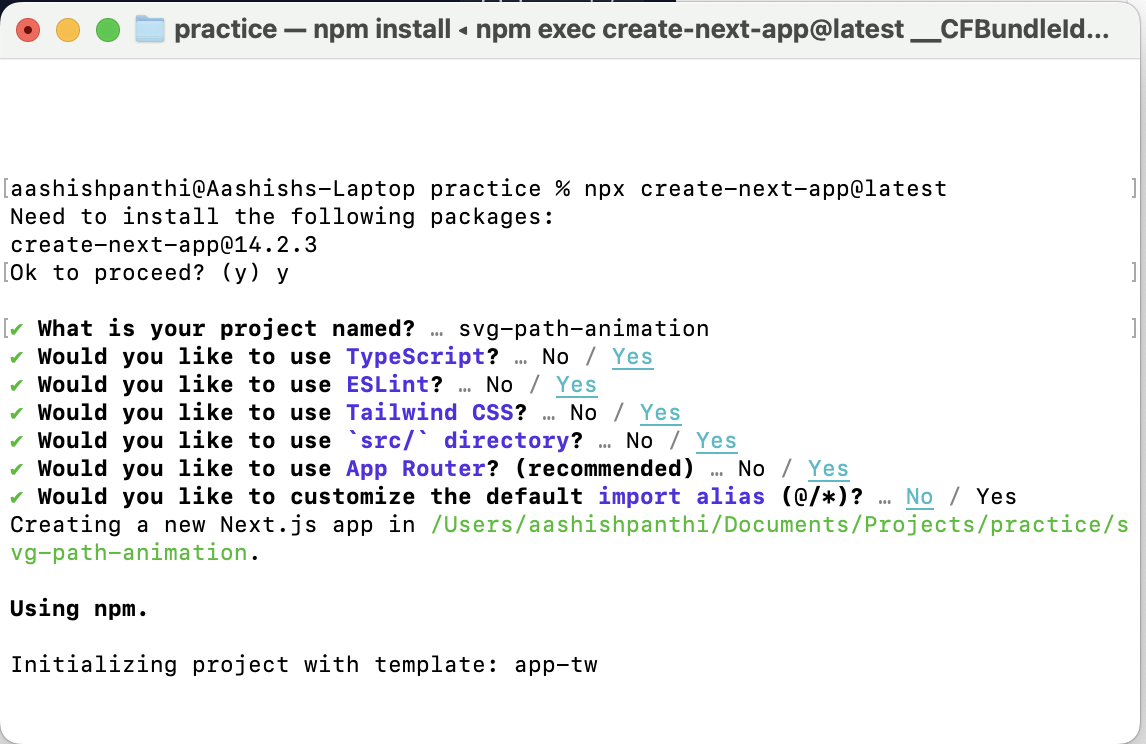
So, after a few seconds, your project will be ready and I would love if you open the project on some code editor. I'll be using [Visual Studio Code](https://code.visualstudio.com/).
Go inside of the project and open the terminal. Run the start command to start the project:
```bash
npm run dev
```
And visit [http://localhost:3000/](http://localhost:3000/) to see your project running.
### Installing GSAP
Let's quickly install the GSAP packages also. Use the following command to install `gsap` and `@gsap/react` packages:
```bash
npm i @gsap/react gsap
```
That's all. First, let's have our SVG ready and then we'll animate. Alright?
## Creating SVG Graphics
I assume you already have your SVG element ready. If you have it on your figma, export it as SVG. If you don't have you can make one.
### Designing SVG graphics
I quickly made this shape in Figma using pen tool. It is basically the path over which we'll be moving stuff on the scroll event. I still don't know what I'll be moving.
To export your SVG from Figma, select the shape you want to export. If you have more than one shape, select the shapes and group them then export them as SVG. You'll see the export option at the right end of the screen:
Well, if you would like to use mine then here is the SVG code:
```xml
<svg width="462" height="829" viewBox="0 0 462 829" fill="none" xmlns="http://www.w3.org/2000/svg">
<path d="M36.4996 4L429.5 238C449.666 250 479 284.9 435 328.5C391 372.1 151 480.333 36.4996 529C12.1662 545.167 -21.9004 587.7 36.4996 628.5C94.8996 669.3 326.5 776.167 435 824.5" stroke="#0000FF" stroke-width="8"/>
</svg>
```
Ok, that's the path and let's move a card along that path. Sound great? I've made a car. I'm not a designer. Please don't judge me:
I've grouped the two items and exported them as SVG. If you want the code, here it is:
```xml
<svg width="462" height="844" viewBox="0 0 462 844" fill="none" xmlns="http://www.w3.org/2000/svg">
<path d="M36.4996 18.9999L429.5 253C449.666 265 479 299.9 435 343.5C391 387.1 151 495.333 36.4996 544C12.1662 560.167 -21.9004 602.7 36.4996 643.5C94.8996 684.3 326.5 791.167 435 839.5" stroke="#0000FF" stroke-width="8"/>
<path d="M37.7316 37.3941L46.4471 37.0985C46.7214 37.0872 46.9392 36.9896 47.1001 36.8317L60.2671 45.3825C62.7497 46.9947 65.6719 46.8955 66.7971 45.163L73.9314 34.1771C75.0579 32.4425 73.9598 29.7326 71.4773 28.1204L58.3102 19.5696C58.3877 19.3605 58.3896 19.1198 58.2883 18.8645L55.0122 10.7844C54.706 10.0288 53.6614 9.44663 52.673 9.47815C51.6862 9.51362 51.134 10.152 51.4373 10.9057L53.7501 16.6082L41.4135 8.59676C38.9339 6.98646 36.0087 7.08368 34.8822 8.81829L27.7479 19.8042C26.6228 21.5367 27.7237 24.2485 30.2034 25.8588L42.5399 33.8703L36.387 34.081C35.5765 34.1085 35.2193 34.8705 35.5882 35.7864C35.9614 36.7022 36.9182 37.4197 37.7316 37.3941ZM56.9649 23.0482L56.3711 23.9626L46.2266 17.3747L46.8204 16.4603L56.9649 23.0482ZM40.0447 12.0601L43.6442 15.6977L37.5977 25.0085L32.8092 23.2018L40.0447 12.0601ZM39.5849 27.602L40.1801 26.6855L50.3246 33.2734L49.7294 34.1899L39.5849 27.602ZM52.8688 34.9256L58.9153 25.6149L63.7025 27.4236L56.467 38.5653L52.8688 34.9256Z" fill="#E52A2D"/>
</svg>
```
### Importing SVG files into the Next.js project
No, we are not going to import the SVG file. Rather we will have SVG inside our JSX file with other react neety-greety.
Let's create a separate component for the Animation thing and we'll import it inside of our page.tsx file. And the root `page.tsx` file should look like this:
```javascript
import PathAnimation from "@/components/PathAnimation";
export default function Home() {
return (
<main className="flex-col min-h-screen w-full dark:text-white">
<div className="h-screen w-full flex flex-col items-center justify-center">
<h1 className="text-[#432826] text-[24px] leading-[36px] font-[400] text-center dark:text-white">
SVG Path Animation
</h1>
<p className="text-[16px] leading-[27px] text-[#432826] font-[400] text-center dark:text-white">
This is a simple animation of a bee following a path using GSAP
MotionPath plugin.
</p>
</div>
<PathAnimation />
<div className="h-screen w-full flex flex-col items-center justify-center">
<h1 className="text-[#432826] text-[24px] leading-[36px] font-[400] dark:text-white">
You saw that?
</h1>
<p className="text-[16px] leading-[27px] text-[#432826] font-[400] dark:text-white">
The bee is following the path. Isn't that cool?
</p>
</div>
</main>
);
}
```
And let's have our `PathAnimation.jsx` file separately (create a components folder and place it there). The component looks like this:
```javascript
function PathAnimation() {
return (
<section
className="py-16 px-4 md:px-2 bg-secondary w-full"
>
<div className={`max-w-[1250px] w-full mx-auto relative mt-16 mb-20`}>
<svg
width="462"
height="844"
viewBox="0 0 462 844"
fill="none"
xmlns="http://www.w3.org/2000/svg"
className="w-full h-full"
>
<path
d="M36.4996 18.9999L429.5 253C449.666 265 479 299.9 435 343.5C391 387.1 151 495.333 36.4996 544C12.1662 560.167 -21.9004 602.7 36.4996 643.5C94.8996 684.3 326.5 791.167 435 839.5"
stroke="#0000FF"
strokeWidth="8"
/>
<path
d="M37.7316 37.3941L46.4471 37.0985C46.7214 37.0872 46.9392 36.9896 47.1001 36.8317L60.2671 45.3825C62.7497 46.9947 65.6719 46.8955 66.7971 45.163L73.9314 34.1771C75.0579 32.4425 73.9598 29.7326 71.4773 28.1204L58.3102 19.5696C58.3877 19.3605 58.3896 19.1198 58.2883 18.8645L55.0122 10.7844C54.706 10.0288 53.6614 9.44663 52.673 9.47815C51.6862 9.51362 51.134 10.152 51.4373 10.9057L53.7501 16.6082L41.4135 8.59676C38.9339 6.98646 36.0087 7.08368 34.8822 8.81829L27.7479 19.8042C26.6228 21.5367 27.7237 24.2485 30.2034 25.8588L42.5399 33.8703L36.387 34.081C35.5765 34.1085 35.2193 34.8705 35.5882 35.7864C35.9614 36.7022 36.9182 37.4197 37.7316 37.3941ZM56.9649 23.0482L56.3711 23.9626L46.2266 17.3747L46.8204 16.4603L56.9649 23.0482ZM40.0447 12.0601L43.6442 15.6977L37.5977 25.0085L32.8092 23.2018L40.0447 12.0601ZM39.5849 27.602L40.1801 26.6855L50.3246 33.2734L49.7294 34.1899L39.5849 27.602ZM52.8688 34.9256L58.9153 25.6149L63.7025 27.4236L56.467 38.5653L52.8688 34.9256Z"
fill="#E52A2D"
/>
</svg>
</div>
</section>
);
}
export default PathAnimation;
```
Now, if you save and look at the browser, you should be able to see the SVG covering up the whole screen.
## Integrating GSAP with Next.js
Oh the juicy part, let's start with the animation. We got to move that car along the path, right? Let's do that.
### Importing GSAP into Next.js components
First we need to import the gsap and then import the useGSAP hook. The useGSAP hook is fairly new release and you don't find it around the internet (as of early 2024).
```javascript
import gsap from "gsap";
import { useGSAP } from "@gsap/react";
```
After that, we need to import the plugins and register those plugins:
```javascript
import MotionPathHelper from "gsap/MotionPathPlugin";
import { ScrollTrigger } from "gsap/ScrollTrigger";
gsap.registerPlugin(useGSAP, ScrollTrigger);
gsap.registerPlugin(MotionPathHelper);
```
That's all about importing and registering stuffs related to GSAP. Now, let's move on to the next part.
### Using useRef to handle events
You know in react and next.js, we cannot directly manipulate the elements. So, we need to use useRef hook. We're going to have four refs:
```typescript
const lineRef = useRef<SVGPathElement>(null);
const carRef = useRef<SVGPathElement>(null);
const container = useRef<SVGSVGElement>(null);
const sectionRef = useRef<HTMLDivElement>(null);
```
As you might have already guessed where you need to place these refs. Well, here it is:
```javascript
return (
<section
className="py-16 px-4 md:px-2 bg-secondary w-full"
ref={sectionRef}
>
<div className={`max-w-[1250px] w-full mx-auto relative mt-16 mb-20`}>
<svg
width="462"
height="844"
viewBox="0 0 462 844"
fill="none"
xmlns="http://www.w3.org/2000/svg"
className="w-full h-full overflow-visible"
ref={container}
>
<path
ref={lineRef}
d="M36.4996 18.9999L429.5 253C449.666 265 479 299.9 435 343.5C391 387.1 151 495.333 36.4996 544C12.1662 560.167 -21.9004 602.7 36.4996 643.5C94.8996 684.3 326.5 791.167 435 839.5"
stroke="#0000FF"
strokeWidth="8"
/>
<path
ref={carRef}
d="M45.5126 32.8551L52.6609 27.8605C52.8849 27.7015 53.0143 27.5011 53.0633 27.281L68.7632 27.281C71.7233 27.281 74.1201 25.6064 74.1201 23.5405V10.4414C74.1201 8.37307 71.7233 6.69838 68.7632 6.69838L53.0633 6.69838C53.0143 6.4808 52.8849 6.27788 52.6609 6.11897L45.5126 1.12674C44.8442 0.659786 43.6511 0.740459 42.8393 1.3052C42.0311 1.87239 41.9156 2.70852 42.5804 3.17547L47.6259 6.69838L32.9163 6.69838C29.9596 6.69838 27.5593 8.37307 27.5593 10.4414L27.5593 23.5405C27.5593 25.6064 29.9596 27.281 32.9163 27.281L47.6259 27.281L42.5804 30.8088C41.9156 31.2734 42.0311 32.107 42.8393 32.6742C43.6511 33.239 44.8442 33.3196 45.5126 32.8551ZM53.8296 10.3485V11.4388L41.7337 11.4388V10.3485L53.8296 10.3485ZM33.6545 10.3485L38.6546 11.4388L38.6546 22.5406L33.6545 23.6334L33.6545 10.3485ZM41.7337 23.6334V22.5406L53.8296 22.5406L53.8296 23.6334L41.7337 23.6334ZM56.8632 22.5406V11.4388L61.8632 10.3485L61.8632 23.6334L56.8632 22.5406Z"
fill="#E52A2D"
/>
</svg>
</div>
</section>
);
```
> The svg code for car has been changed. Basically, I rotated the card. That's all.
> So, after changing the path element, import the useEffect hook from react and we are going to set the position of the car.
```javascript
useEffect(() => {
gsap.set(carRef.current, {
yPercent: 0,
xPercent: 20,
rotate: 30,
});
}, []);
```
The above code positions the car at `y=0%`, `x=20%` and `rotation=30deg` (property names aren't exactly the same, it's used to just explain)
So, our path is there, car is there. And our code looks like this:
```typescript
"use client";
import { useEffect, useRef } from "react";
//gsap
import gsap from "gsap";
import { useGSAP } from "@gsap/react";
import MotionPathHelper from "gsap/MotionPathPlugin";
import { ScrollTrigger } from "gsap/ScrollTrigger";
gsap.registerPlugin(useGSAP, ScrollTrigger);
gsap.registerPlugin(MotionPathHelper);
function PathAnimation() {
const lineRef = useRef<SVGPathElement>(null);
const carRef = useRef<SVGPathElement>(null);
const container = useRef<SVGSVGElement>(null);
const sectionRef = useRef<HTMLDivElement>(null);
useEffect(() => {
gsap.set(carRef.current, {
yPercent: 0,
xPercent: 20,
rotate: 30,
});
}, []);
return (
<section
className="py-16 px-4 md:px-2 bg-secondary w-full"
ref={sectionRef}
>
<div className={`max-w-[1250px] w-full mx-auto relative mt-16 mb-20`}>
<svg
width="462"
height="844"
viewBox="0 0 462 844"
fill="none"
xmlns="http://www.w3.org/2000/svg"
className="w-full h-full overflow-visible"
ref={container}
>
<path
ref={lineRef}
d="M36.4996 18.9999L429.5 253C449.666 265 479 299.9 435 343.5C391 387.1 151 495.333 36.4996 544C12.1662 560.167 -21.9004 602.7 36.4996 643.5C94.8996 684.3 326.5 791.167 435 839.5"
stroke="#0000FF"
strokeWidth="8"
/>
<path
ref={carRef}
d="M45.5126 32.8551L52.6609 27.8605C52.8849 27.7015 53.0143 27.5011 53.0633 27.281L68.7632 27.281C71.7233 27.281 74.1201 25.6064 74.1201 23.5405V10.4414C74.1201 8.37307 71.7233 6.69838 68.7632 6.69838L53.0633 6.69838C53.0143 6.4808 52.8849 6.27788 52.6609 6.11897L45.5126 1.12674C44.8442 0.659786 43.6511 0.740459 42.8393 1.3052C42.0311 1.87239 41.9156 2.70852 42.5804 3.17547L47.6259 6.69838L32.9163 6.69838C29.9596 6.69838 27.5593 8.37307 27.5593 10.4414L27.5593 23.5405C27.5593 25.6064 29.9596 27.281 32.9163 27.281L47.6259 27.281L42.5804 30.8088C41.9156 31.2734 42.0311 32.107 42.8393 32.6742C43.6511 33.239 44.8442 33.3196 45.5126 32.8551ZM53.8296 10.3485V11.4388L41.7337 11.4388V10.3485L53.8296 10.3485ZM33.6545 10.3485L38.6546 11.4388L38.6546 22.5406L33.6545 23.6334L33.6545 10.3485ZM41.7337 23.6334V22.5406L53.8296 22.5406L53.8296 23.6334L41.7337 23.6334ZM56.8632 22.5406V11.4388L61.8632 10.3485L61.8632 23.6334L56.8632 22.5406Z"
fill="#E52A2D"
/>
</svg>
</div>
</section>
);
}
export default PathAnimation;
```
Now, the only thing remaining is the ignition of the engine and letting the car move.
### Creating animation timelines
It's time to use `useGSAP` hook provided by gsap to create an animation timeline.
```typescript
useGSAP(
(context, contextSafe) => {
let tl = gsap.timeline({});
tl.to(carRef.current, {
motionPath: {
path: lineRef.current || "",
align: lineRef.current || "",
},
ease: "power1.inOut",
});
return tl;
},
{
scope: container,
}
);
```
The above timeline is a basic timeline. If you want to dive deep into the `useGSAP` hook then I recommend this [official documentation](https://gsap.com/resources/React/). Allow me to simplify further.
First, we are creating a timeline with `gsap.timeline({})` and we're passing empty object because we don't want to pass anything right now (we'll do in a few seconds). Then the timeline is stored in `tl` variable, tl is short for the timeline. We're storing the timeline on a variable to easily access the timeline in the future.
Then, we're passing the actual props to animate the stuff. The animation is targeted to the car path, we're using `carRef` to point to our car. Then, we're proving motionPath, inside of the motionPath, we can provide the path (along which the car moves) and another path (along which the car aligns).
At the end, we're providing the scope also. It's helpful when you've multiple animations and you don't want to mess up.
**Now, let's make a final timeline.**
```typescript
useGSAP(
(context, contextSafe) => {
let tl = gsap.timeline({
scrollTrigger: {
trigger: sectionRef.current,
scrub: true,
start: "top center",
end: "bottom center",
},
});
tl.to(carRef.current, {
motionPath: {
path: lineRef.current || "",
align: lineRef.current || "",
alignOrigin: [0.2, 0.5],
autoRotate: true,
start: 0,
end: 1,
},
ease: "power1.inOut",
});
return tl;
},
{
scope: container,
}
);
```
Here, we're triggering the animation on scroll with `scrollTrigger`. Inside scrollTrigger, we're passing a trigger prop; trigger prop is used to identify by with element the animation is going to trigger. Here we're triggering or starting the animation when the section is scrolled halfway to the screen from the top and stops when the bottom end of the section goes halfway through the screen. `scrub` is set true to allow animation to take place both forward and backward.
Next, we're aligning the car to perfectly center in that path and also allowing the car to `autoRotate` so that the car makes a smooth turn. And, you can add a lot of transitions. Choose the one that suits you best.
## Conclusion
In this article, you learned how to create SVG path animations using GSAP in a Next.js project. We covered setting up the development environment, installing necessary packages, creating and importing SVG graphics, and integrating GSAP for smooth animations triggered by scroll events. By the end, you have a car following a path on your webpage, showcasing the power of SVG and GSAP animations.
I would like to end this article with a few resources:
* GitHub repository -> [https://github.com/aashishpanthi/svg-path-animation](https://github.com/aashishpanthi/svg-path-animation)
* CodeSandBox -> [https://codesandbox.io/p/github/aashishpanthi/svg-path-animation/main](https://codesandbox.io/p/devbox/svg-path-animation-4d2k2v) | aashishpanthi |
1,868,746 | Simplifying Google Cloud Network Design: A Quick Guide | Designing a cloud network involves planning and implementing the infrastructure, services, and... | 0 | 2024-05-29T09:20:47 | https://dev.to/saumya27/simplifying-google-cloud-network-design-a-quick-guide-2p83 | cloud, cloudcomputing | Designing a cloud network involves planning and implementing the infrastructure, services, and policies needed to support applications and workloads in a cloud environment. Effective cloud network design ensures optimal performance, security, scalability, and cost-efficiency. Here’s an overview of key considerations and best practices for cloud network design:
**Key Components of Cloud Network Design**
**Virtual Private Cloud (VPC):**
- Definition: A VPC is an isolated virtual network within a public cloud, allowing you to deploy resources in a secure and controlled environment.
- Configuration: Set up subnets, route tables, and gateways to manage traffic flow and control access.
**Subnets:**
- Purpose: Subnets segment a VPC into smaller, logical sections, improving organization and security.
- Types: Typically, include public subnets (exposed to the internet) and private subnets (restricted access).
**Routing:**
- Route Tables: Define how traffic is directed within the VPC and to external networks.
- Internet Gateway (IGW): Enables communication between VPC resources and the internet.
- NAT Gateway: Allows instances in private subnets to access the internet without exposing them to incoming traffic.
**Security Groups and Network Access Control Lists (ACLs):**
- Security Groups: Virtual firewalls that control inbound and outbound traffic to instances.
- Network ACLs: Provide an additional layer of security by controlling traffic at the subnet level.
**Load Balancers:**
- Purpose: Distribute incoming traffic across multiple instances to ensure high availability and reliability.
- Types: Application Load Balancer (ALB) for HTTP/HTTPS traffic, Network Load Balancer (NLB) for TCP traffic, and Classic Load Balancer (CLB) for both HTTP/HTTPS and TCP traffic.
**VPN and Direct Connect:**
- VPN (Virtual Private Network): Establishes secure connections between on-premises networks and the cloud.
- Direct Connect: Provides a dedicated, private connection between your data center and the cloud provider, offering lower latency and higher bandwidth.
**DNS and Content Delivery Network (CDN):**
- DNS (Domain Name System): Translates domain names into IP addresses to route traffic efficiently.
- CDN: Distributes content to edge locations closer to end-users, improving performance and reducing latency.
**Monitoring and Management:**
- Tools: Use cloud provider tools like AWS CloudWatch, Azure Monitor, or Google Cloud Monitoring for real-time monitoring and logging.
- Alerts: Set up alerts for key metrics and incidents to ensure timely response to issues.
**Best Practices for Cloud Network Design**
**Plan for Scalability:**
- Auto Scaling: Implement auto-scaling groups to automatically adjust the number of instances based on demand.
- Elastic IPs: Use Elastic IPs to maintain a static IP address for dynamic cloud resources.
**Enhance Security:**
- Least Privilege: Apply the principle of least privilege to security groups and ACLs to minimize exposure.
- Encryption: Encrypt data in transit and at rest to protect sensitive information.
- Identity and Access Management (IAM): Use IAM roles and policies to control access to resources.
**Optimize Performance:**
- Proximity: Place resources in regions and availability zones closest to your users to reduce latency.
- Caching: Use caching mechanisms like Amazon ElastiCache or Azure Redis Cache to speed up data retrieval.
**Cost Management:**
- Cost Monitoring: Use tools like AWS Cost Explorer or Azure Cost Management to track and optimize spending.
- Right-Sizing: Regularly review and adjust resource sizes to match usage patterns.
**Disaster Recovery and High Availability:**
- Multi-Region Deployment: Distribute critical workloads across multiple regions for redundancy.
- Backup and Restore: Implement regular backup procedures and ensure the ability to restore quickly in case of failure.
**Documentation and Automation:**
- Documentation: Maintain detailed documentation of your network design, configurations, and policies.
- Infrastructure as Code (IaC): Use tools like AWS CloudFormation, Terraform, or Azure Resource Manager to automate deployment and management of cloud resources.
**Example of a Basic Cloud Network Design**
**VPC Creation:**
- Create a VPC with a CIDR block (e.g., 10.0.0.0/16).
**Subnet Configuration:**
- Create public subnets in different availability zones (e.g., 10.0.1.0/24, 10.0.2.0/24).
- Create private subnets in different availability zones (e.g., 10.0.3.0/24, 10.0.4.0/24).
**Routing:**
- Attach an Internet Gateway (IGW) to the VPC.
- Configure route tables to direct internet-bound traffic through the IGW for public subnets.
- Set up a NAT Gateway in a public subnet and update route tables for private subnets to use the NAT Gateway for outbound internet access.
**Security Groups and ACLs:**
- Define security groups with specific inbound and outbound rules for instances.
- Set up network ACLs with granular traffic control at the subnet level.
**Load Balancing:**
- Deploy an Application Load Balancer (ALB) to distribute incoming HTTP/HTTPS traffic across multiple instances in public subnets.
- VPN/Direct Connect:
- Configure a VPN connection or Direct Connect for secure communication between on-premises infrastructure and the cloud environment.
**DNS and CDN:**
- Use a DNS service like Amazon Route 53 to manage domain names and route traffic.
- Implement a CDN like Amazon CloudFront to cache and deliver content efficiently.
By following these principles and practices, you can design a robust, secure, and efficient [cloud network design](https://cloudastra.co/blogs/simplifying-google-cloud-network-design-a-quick-guide) that meets your organization’s needs. | saumya27 |
1,868,742 | The Role of AI Mobile App Developers in the Digital Era | Our lives are increasingly dominated by smartphones, and the apps within them are the gateways to a... | 0 | 2024-05-29T09:19:47 | https://dev.to/sophia_thomas_5d284faac2f/the-role-of-ai-mobile-app-developers-in-the-digital-era-807 | Our lives are increasingly dominated by smartphones, and the apps within them are the gateways to a vast array of services and experiences. But as these apps become more sophisticated, so too do the tools used to create them. Enter Artificial Intelligence (AI), a game-changer that's revolutionizing the mobile app development landscape.
Imagine an app that anticipates your needs before you even know them, personalizes your experience with uncanny accuracy, and interacts with you in a natural, conversational way. This isn't science fiction; it's the reality AI is bringing to mobile apps. But who are the architects of this digital future? The answer lies with a new breed of developer – the AI mobile app developer. Let's delve deeper into how these tech wizards are shaping the way we interact with our phones and, ultimately, the digital world around us.
The Rise of AI in Mobile Apps
Under the hood of those increasingly intuitive mobile apps lies a powerful duo: Artificial Intelligence (AI) and Machine Learning (ML). AI, in the context of mobile apps, refers to the ability of the app to simulate human-like intelligence. It can process information, learn from user behavior, and even make decisions based on that data. Machine Learning is a subfield of AI that allows apps to continuously improve without explicit programming. By analyzing vast amounts of user data, ML algorithms can identify patterns and make predictions, constantly refining the app's functionality.
These combined forces are transforming the way we interact with mobile apps. Take virtual assistants like Siri or Google Assistant. AI allows them to understand natural language, respond to your questions and requests, and even anticipate your needs based on your past interactions. Chatbots, another AI marvel, provide customer service or answer frequently asked questions, offering 24/7 support without human intervention.
Recommendation engines, a staple in e-commerce and entertainment apps, leverage ML to analyze your preferences and suggest products, music, or movies you might enjoy. Imagine a fitness app that personalizes your workout routine based on your activity level or a news app that curates stories based on your reading habits. These are just a few examples of how AI and ML are making mobile apps not just smarter, but also more user-friendly and personalized.
The Impact of AI Mobile App Developers
Enhancing User Experience (UX) with AI
AI is revolutionizing mobile app UX by personalizing the experience for each user. Imagine an e-commerce app that remembers your past purchases and recommends similar items, or a music streaming service that curates playlists based on your listening history. AI algorithms analyze user data like browsing behavior, search queries, and past interactions to understand individual preferences. This allows apps to tailor content, product suggestions, and features to each user, creating a more engaging and efficient experience.
Beyond personalization, AI helps apps anticipate user needs. A fitness app powered by AI might suggest a more challenging workout based on your recent performance, or a news app could prioritize breaking news notifications based on your location and interests. This predictive capability keeps users engaged and feeling like the app understands their needs.
Finally, AI facilitates natural language interaction through features like voice interfaces and chatbots. Virtual assistants like Siri and Google Assistant use AI to understand spoken commands and questions, allowing users to interact with their phones hands-free.
Chatbots, powered by AI and natural language processing (NLP), can answer customer service inquiries, resolve issues, and even provide personalized recommendations, all within the app itself. These features make interacting with apps more intuitive and user-friendly, removing the need for complex navigation or button clicks.
Boosting Efficiency and Productivity with AI
AI isn't just about creating a better user experience; it's also transforming the way mobile apps are developed. Repetitive tasks like code generation, bug testing, and UI element optimization can be automated using AI tools. These tools can analyze existing code and user data to identify patterns and suggest improvements, freeing up developers to focus on more creative and strategic aspects of app development.
Data is king in the mobile app world, and AI helps developers unlock its full potential. By analyzing vast amounts of user data collected through app usage, AI can identify trends, user preferences, and potential pain points. These insights are invaluable for making data-driven decisions about app design, feature development, and marketing strategies. Imagine being able to pinpoint exactly which features users engage with the most or identify areas causing frustration. This data-driven approach allows developers to create apps that are not only functional but also cater directly to user needs.
While user experience is paramount, security is equally important. AI can play a role in improving app security by identifying and mitigating potential vulnerabilities. AI algorithms can analyze user behavior patterns to detect anomalies that might indicate fraudulent activity. Additionally, AI can be used to continuously monitor app performance, identifying and addressing bottlenecks that could slow down user experience. By streamlining development processes, optimizing app design, and enhancing security, AI is making mobile app development faster, more efficient, and more user-focused.
The Future of AI Mobile App Development
The future of mobile apps is brimming with exciting possibilities fueled by AI. Augmented Reality (AR) is poised to take center stage, with apps overlaying digital elements onto the real world. Imagine trying on clothes virtually or visualizing furniture placement in your home. AI will play a crucial role in powering these AR experiences, enabling real-time object recognition and seamless interaction between the physical and digital worlds. Virtual assistants are also set to evolve, becoming even more intelligent and personalized. Imagine an assistant that anticipates your needs throughout the day, from booking appointments to suggesting restaurants based on your preferences.
This evolving landscape demands a new breed of mobile app developers. While core coding skills remain essential, a strong understanding of AI, machine learning, and data analysis will be paramount. Developers will need to be able to design apps that leverage AI effectively, interpret user data to inform decision-making and stay up-to-date on the latest AI advancements.
The impact of AI on the mobile app development industry is undeniable. It has the potential to streamline development processes, personalize user experiences to an unprecedented degree, and unlock entirely new functionalities. As AI continues to evolve, mobile apps will become even more intelligent, intuitive, and indispensable tools in our daily lives.
Conclusion
AI mobile app developers are the architects of a revolutionized mobile experience. Their expertise in harnessing AI's power is shaping a future where apps seamlessly integrate with our lives, anticipating needs and delivering hyper-personalized experiences. With AI's potential still largely untapped, the possibilities for innovative [AI mobile app ideas](https://webmobtech.com/blog/best-artificial-intelligence-app-ideas/?utm_source=GP&utm_medium=NS&utm_campaign=Link%20Building) are boundless. From AR-powered shopping experiences to AI-powered mental health assistants, the future of mobile apps is as exciting as it is intelligent, thanks to the ingenuity of AI mobile app developers.
| sophia_thomas_5d284faac2f | |
1,868,740 | Rate4Gold sell gold for cash Chennai | When considering a gold loan repledge, borrowers should carefully review the interest rate offered by... | 0 | 2024-05-29T09:18:56 | https://dev.to/rate4gold/rate4gold-sell-gold-for-cash-chennai-h0n | When considering a gold loan repledge, borrowers should carefully review the interest rate offered by the lender, any additional fees or charges, and the terms and conditions of the loan agreement.
Need quick cash for your gold in Chennai? [Rate4Gold](https://rate4gold.com/gold-loan-repledge/
) is your premier destination for selling gold at the best prices in the market. We are committed to offering a seamless, transparent, and rewarding experience when you decide to sell your gold items.
Why Choose Rate4Gold?
1. Best Market Rates: At [Rate4Gold](https://rate4gold.com/gold-loan-repledge/
), we ensure you get the highest value for your gold with our up-to-date market rate assessments.
2. Transparency and Trust: Our transparent evaluation process ensures you know exactly how your gold is valued, building trust and confidence in our services.
3. Expert Appraisal: Our team of experienced professionals uses advanced technology to accurately assess the purity and weight of your gold, guaranteeing a fair deal.
4. Instant Cash Payment: Once the transaction is complete, we provide instant cash or bank transfers, so you leave with money in hand.
5. No Hidden Fees: We pride ourselves on clear transactions with no hidden charges, providing peace of mind and financial clarity.
How It Works
1. Free Evaluation: Bring your gold items to our store for a complimentary evaluation by our experts.
2. Competitive Offer: We provide a fair and competitive offer based on the latest gold market prices.
3. Fast Transaction: If you accept the offer, we complete the necessary documentation quickly and efficiently.
4. Immediate Payment: Receive your payment instantly in cash or through a bank transfer.
What We Buy
• Gold Jewelry (necklaces, bracelets, rings, earrings, etc.)
• Gold Coins and Bars
• Broken or Damaged Gold Items
Benefits of Selling Your Gold
• Quick Access to Cash: Get immediate cash to address any urgent financial needs.
• Declutter and Profit: Turn unused or outdated gold items into valuable cash.
• Smart Investment: Reinvest the proceeds from your gold into more lucrative opportunities.
Visit Rate4Gold
For a hassle-free and rewarding gold-selling experience, [visit Rate4Gold in Chennai](https://rate4gold.com/gold-loan-repledge/
). Our friendly and professional staff are ready to assist you in getting the best cash value for your gold.
 | rate4gold | |
1,868,739 | Mastering API Request Chaining: Essential Techniques for Developers | Understanding and implementing chain requests in API integration is essential for developers who need... | 0 | 2024-05-29T09:18:04 | https://dev.to/satokenta/mastering-api-request-chaining-essential-techniques-for-developers-2282 | api, request | Understanding and implementing chain requests in **[API](https://apidog.com/blog/best-api-tools/)** integration is essential for developers who need to handle complex interactions between various systems. This approach not out only streamlines complex workflows but also demonstrates significant efficiencies in data handling and application performance.
## Fundamental Aspects of Chain Requests in APIs
When delving deeper into chain requests, developers need to grasp several underlying concepts crucial for impeccable implementation. Here are the essential elements to consider:
### Dependency Handling
**Explicit and Implicit Order:** Data dependency may sometimes be understood through request ordering (e.g., obtaining a user ID is prerequisite for fetching user data). Defining explicit dependencies oftentimes involves utilizing specific protocols or libraries for clarity and coherence.
**Cascading Failures and Errors:** Assertion of robust error rectification mechanisms is vital because a failure in the sequence can compromise the subsequent requests, leading to incomplete data sequences or process termination.
### Streamlining Data Throughput
**Interpreting Responses:** Utilizing parsing techniques appropriate to the response format, whether it's **[JSON or XML](https://apidog.com/blog/yaml-vs-json/)**, is fundamental. Various tools enhance this process by streamlining the extraction of necessary details from the response.
**Transformative Actions on Data:** After extraction, data may need adjustments—like reformatting or aggregation—to fit the purpose of subsequent requests.
### Process Coordination and Timing
**Synchronous Versus Asynchronous Execution:** While synchronous execution waits for each response before continuing, asynchronous execution can handle multiple independent requests simultaneously, which can drastically improve efficiency.
**Contextual and Conditional Flow:** The execution of requests may depend on previous outputs. Implementing conditional flows allows adapirectional adjustments based on earlier results.
### Preserving Workflow Continuity
**Context Retention Across Calls:** Keeping track of user information or other context across multiple API calls is essential. Techniques range from simple session tokens to more complex context management systems.
**Security and Throttling:** Protecting sensitive data and managing request rates to conform with API limits are critical considerations to mitigate security risks and service denials.
## Strategic Advantages of Chain Requests
Employing chain requests in API interactions unlocks several developmental and operational benefits:
### Enhanced Efficiency and Simplification
**Seamless Data Integration:** Chain requests automate the flow of data across multiple APIs, negating the need for manual data handling which, in turn, minimizes development efforts and error rates.
**Code Manageability:** By breaking down processes into manageable segments, developers can achieve more maintainable and less error-prone codebases.
### User Experience and System Performance
**Fewer Interactions Required:** Reducing the number of necessary interactions with the backend speeds up operations, enhancing the end-user experience through faster response times and less waiting.
**Optimized Network Load:** Efficient request management minimizes network traffic, which is crucial for maintaining system responsiveness and resource use.
### Modularization and Maintenance
**Scalability:** Individual segments of the process can be scaled based on specific demands, which enhances the agility and responsiveness of the application infrastructure.
**Maintainability:** Fostering a modular, segmented approach not only facilitates a clearer understanding of the system's workings but also simplifies updates and troubleshooting.
## Getting Started with Chain Requests Using [Apidog](https://www.apidog.com/?utm_source=&utm_medium=blogger&utm_campaign=test1)
Integrating API request chaining in your development process can be streamlined using tools like Apidog, which supports building and testing complex API scenarios efficiently.

### Setting Up a Chain Request in Apidog
Apidog provides an intuitive interface for defining and automating multi-step API interactions. Begin by creating a new test scenario, and step-by-step, add the desired chained requests. Define each step's requisite input based on the prior responses and ensure all are correctly configured to operate both singly and within the chain.

For in-depth testing and refinement, Apidog offers easy access to modify and test individual components or the entire sequence, helping pinpoint areas for optimization or troubleshooting.
## Closing Thoughts
Chain request techniques facilitate streamlined, efficient, and powerful integrations across multiple API services. By mastering these methods, developers can harness enhanced control, achieve better data integration, and ultimately deliver superior applications that are both robust and user-friendly. As you explore these integrations, adapt and optimize your approach to suit your specific operational needs. | satokenta |
1,868,738 | Web3 Airdrop: From Fighting Fraud to AI Optimization | 💰Web3 technology startups have long used airdrops as an effective method to attract new users and... | 0 | 2024-05-29T09:17:46 | https://dev.to/korofetova_mila/web3-airdrop-from-fighting-fraud-to-ai-optimization-2aej | webdev, devchallenge, performance, web3 | 💰Web3 technology startups have long used airdrops as an effective method to attract new users and potential investors. Expanding on this idea, social farming (also known as "bounty distribution") has emerged, incorporating unique tasks and gamification elements.
These assets, typically native tokens of the project, can range in value from mere cents to several thousand dollars, depending on the level of interest and publicity.
‼️Popular Airdrops
🔸Massive AI Airdrop - This significant distribution of tokens is generated through artificial intelligence. Its primary goal is to incentivize early users and participants in the AI ecosystem. The announcement of the Massive AI Airdrop generated significant excitement among cryptocurrency enthusiasts and experienced investors. This pivotal event aims to broaden the digital asset community. The token distribution is designed to reward existing supporters of the AI platform and attract a new audience to its innovative technologies. Massive AI is a groundbreaking platform and ecosystem that transforms AI training data through crowdsourcing. It enables participants to engage in simple yet crucial activities that turn everyday data into valuable assets for AI training, earning free tokens in the process. $MSV is a utility token at the core of the MASSIVE ecosystem, incentivizing crowdsourcing activities.
🔹Bounty Airdrops - This specific type of airdrop encourages users to complete tasks in exchange for free cryptocurrency tokens. Essentially, it is a marketing strategy used by crypto projects to boost awareness and build their communities. Bounty airdrops operate on a specific principle: The crypto project announces a bounty airdrop program, outlining the specific tasks users need to complete. These tasks may include sharing posts about the project, retweeting, joining their online communities (Discord, forums), or creating relevant content. Information about these programs is often available on websites like CoinMarketCap, Cointelegraph, and CoinGecko. These platforms facilitate informational distribution by category and provide short tutorials on participation.
While airdrops and bounty campaigns are often confused due to both offering free assets, there are notable differences between them. Airdrops enhance the optimization of Web3 technologies, providing valuable input for the growth and development of projects. Using reliable verification methods, such as KYC, can ensure transparency and reliability for both the company and the participant. Typically, receiving an airdrop involves simple actions, such as registering on a website, subscribing to the project's social media, or inviting friends.
Bounty programs, however, are incentive schemes where participants are rewarded for completing specific tasks. Bounty tasks can be more complex than those of airdrops and often require special skills, such as programming, foreign language proficiency, or marketing.
♦️Before examining successful cases of companies using AI Airdrop, it is important to consider the Ukrainian IT market, which fosters activities for the development of the IT sector and beyond, emphasizing the digitization process in the country. For instance, the cryptocurrency exchange WhiteBIT recently launched activities by WhiteEX and UAHg (hryvnia stablecoin). WhiteEX is one of the exchange's projects designed for the rapid purchase of digital assets. On the KANGA platform, UAHg is also available, as well as on the fiat gateway Geo-pay and the crypto wallets Alice-bob and Trustee. Another sector advancing with IT support is education. A notable example is the university program from EPAM Holding, which focuses on software development and supporting young specialists.
😈Cryptocurrency airdrops offer an excellent way for beginners to enter the world of cryptocurrencies and earn free tokens. As the industry continues to evolve, airdrops will remain a popular marketing strategy for projects to attract new users. | korofetova_mila |
1,868,737 | What is Bluetooth Low Energy? | BLE Technology Bluetooth low energy is a brand-new technology that has been designed as... | 27,545 | 2024-05-29T09:16:48 | https://ahmedgouda.hashnode.dev/what-is-bluetooth-low-energy | ble, iot, embeddedsystems | ## BLE Technology
Bluetooth low energy is a brand-new technology that has been designed as both a complementary technology to classic Bluetooth as well as *the lowest possible power wireless technology that can be designed and built.*
Although it uses the Bluetooth brand and borrows a lot of technology from its parent, Bluetooth low energy should be considered a different technology, addressing different design goals and different market segments.
Instead of just increasing the data rates available, BLE has been optimized for ultra-low power consumption. This means that you probably won’t get high data rates or even want to keep a connection up for many hours or days. This is an interesting move, as most wired and wireless communications technologies constantly increase speeds.
This different direction has been achieved through the understanding that classic Bluetooth technology cannot achieve the low power requirements required for devices powered by button-cell batteries.
However, to fully understand the requirements around low power, another consideration must be taken. Bluetooth low energy is also designed to be deployed in extremely high volumes in devices that today do not have any wireless technology. One method to achieve very high volumes is to have extremely low costs.
Therefore, the fundamental design for low energy is to work with button-cell batteries. This means that you cannot achieve high data rates or make low energy work for use cases that require large data transfers or the streaming of data. This single point is probably the most important difference between classic and low-energy variants of Bluetooth.
## Device Types
Bluetooth low energy makes it possible to build two types of devices:
1. **Dual-Mode**: Supports BLE and Bluetooth classic.
2. **Single-Mode**: Supports BLE only.
There is a third type of device, which is a Bluetooth classic-only device.
## Design Goals
When reviewing any technology, the first question to be asked is how the designers optimized it. Most technologies have one or two things that they are very good at and many things that they are not. By determining what these one or two things are, a greater understanding of that technology can be achieved.
With Bluetooth low energy, this is very simple. It was designed for ultralow power consumption.
When the low-energy work started, the goal was to create the lowest-power short-range wireless technology possible. To do this, each layer of the architecture has been optimized to reduce the power consumption required to perform a given task. For example, the Physical Layer’s relaxation of the radio parameters, when compared with a Bluetooth classic radio, means that the radio can use less power when transmitting or receiving data. The link layer is optimized for very rapid reconnections and the efficient broadcast of data so that connections may not even be needed. The protocols in the host are optimized to reduce the time required once a link layer connection has been made until the application data can be sent. All of this is possible only when all parts of the system are designed at the same time by the same group of people.
For global operation, a wireless band that is available worldwide is required. Today, only one available band can be implemented using low-cost and high-volume manufacturing technology: the 2.45GHz band.
The 2.45GHz band that Bluetooth low energy uses is already very crowded. Just taking into account standards-based technologies, it includes Bluetooth classic, Bluetooth low energy, IEEE 802.11, IEEE 802.11b, IEEE 802.11g, IEEE 802.11n, and IEEE 802.15.4. In addition, a number of proprietary radios are also using the band, including X10 video repeaters, wireless alarms, keyboards, and mice. A number of devices also emit noise in the band, such as streetlights and microwave ovens.
It is, therefore, almost impossible to design a radio that will work at all times with all possible interferers unless it uses **adaptive frequency hopping**, as pioneered by Bluetooth Classic. Adaptive frequency hopping helps by not only detecting sources of interference quickly but also by adaptively avoiding them in the future. It also quickly recovers from the inevitable dropped packets caused by interference from other radios. It is this robustness that is absolutely key to the success of any wireless technology in the most congested radio spectrum available.
Robustness also covers the ability to detect and recover from bit errors caused by background noise. Most short-range wireless standards compromise by using a short cyclic redundancy check (CRC), although there are some that use very long checks. A good design will see a compromise between the strength of the checks and the time taken to send this information.
Short range is actually a slight problem. If you want a low-power system, you must keep the transmitted power as low as possible to reduce the energy used to transmit the signal. Similarly, you must keep the receiver sensitivity fairly high to reduce the power required to pick up the radio signals of other devices from amongst the noise. What short range means in this context is really that it is not centered around a cellular base station system. Short range means that Bluetooth low energy should be a **personal area network**.
The original Bluetooth design goal of low power hasn’t changed that much, except that the design goals for power consumption have been reduced by one or two orders of magnitude. Bluetooth classic had a design goal of a few days of standby and a few hours of talk time for a headset, whereas Bluetooth low energy has a design goal of a few years for a sensor measuring the temperature or how far you’ve walked.
## Terminology
Just like in many high-tech areas, the people working in BLE use their own language to describe the features and technology with the specifications. This section enumerates each of the words that have special meaning and what they mean.
* **Adaptive Frequency Hopping (AFH)**: a technology whereby only a subset of frequencies is used. This allows devices to avoid the frequencies that other non-adaptive technologies are using (e.g., a Wi-Fi access point).
* **Architecture**: The design of Bluetooth low energy is sometimes known as the Architecture.
* **Frequency Hopping**: The use of multiple frequencies to communicate between two devices. One frequency is used at a time, and each frequency is used in a defined sequence.
* **Layer**: a part of the system that fulfills a specific function. For example, the Physical Layer covers the operation of the radio. Each layer in a system is abstracted away from the layers above and below it. The Link Layer doesn’t need to know all the details of how the radio functions; the Logical Link Control Layer and Adaptation Layer don’t need to know all the details of how the Link Layer works. This abstraction is important to keep the complexity of the system at manageable levels.
* **Master**: a complex device that coordinates the activity of other devices within a piconet.
* **Piconet**: This is a contraction of the words pico and network. Therefore, a piconet is a very small network. A piconet has a single master device that coordinates the activity of all the other devices (slaves) in the piconet and one or more slaves.
* **Radio Band**: Radio waves are defined by their frequency or wavelength. Different radio waves are then allocated different rules and uses. When a range of radio frequencies are grouped together using the same rules, this group of frequencies is called a Radio Band.
* **Slave**: a simple device that works with a master. These devices are typically single-purpose devices.
* **Wi-Fi**: a complementary wireless technology that is designed for high data rates to connect computers and other very complex devices with the Internet. | ahmedgouda |
1,868,736 | Rate4Gold old gold buyers in Chennai | The Rate4Gold "gold loan repledge" is a financial service where individuals can borrow money by using... | 0 | 2024-05-29T09:15:45 | https://dev.to/rate4gold/rate4gold-old-gold-buyers-in-chennai-4o42 | The [Rate4Gold](https://rate4gold.com/gold-buying-selling/
) "gold loan repledge" is a financial service where individuals can borrow money by using their gold as collateral. The process involves pledging gold items such as jewelry, coins, or bullion to a lender in exchange for a loan. The lender assesses the value of the gold and offers a loan amount based on a certain percentage of that value, known as the loan-to-value (LTV) ratio.
The term "rate4gold" likely refers to the interest rate charged on such gold loans. This rate can vary depending on several factors including the lender, loan amount, loan tenure, and prevailing market conditions. Generally, gold loan interest rates tend to be lower compared to other forms of borrowing like personal loans or credit cards since they are secured loans, meaning the gold serves as collateral, reducing the lender's risk.
Rate4Gold - Your Trusted Old Gold Buyers in Chennai
Experience the best rates and the highest level of service in the industry.
Looking to sell your old gold in Chennai? [Rate4Gold](https://rate4gold.com/gold-buying-selling/
) offers a seamless, trustworthy, and transparent solution for all your gold selling needs. Our expert team ensures you get the best value for your precious metals with accurate and up-to-date gold rates.
Why Choose Rate4Gold?
• Highest Value: We guarantee the best prices for your old gold based on current market rates.
• Transparency: Our process is transparent, with no hidden charges or fees. You can trust us for a fair evaluation.
• Expert Evaluation: Our experienced appraisers use state-of-the-art technology to assess the purity and weight of your gold.
• Instant Cash: Get instant cash or bank transfer once you agree to our offer, making the transaction quick and hassle-free.
• Customer Satisfaction: Our priority is your satisfaction. We ensure a comfortable and secure environment for every transaction.
Our Services
• Gold Jewelry Buying: Sell your old, broken, or unwanted gold jewelry and get the best market rates.
• Gold Coins and Bars: We buy gold coins and bars at competitive prices, ensuring you get the maximum value.
• Free Evaluation: Get a free, no-obligation evaluation of your gold items.
How It Works
1. Visit Us: Bring your gold items to our conveniently [located Chennai office](https://rate4gold.com/gold-buying-selling/
).
2. Expert Evaluation: Our experts will assess the purity and weight of your gold using advanced equipment.
3. Get Offer: Receive an offer based on the latest market rates and the quality of your gold.
4. Instant Payment: Accept our offer and get instant cash or bank transfer.
 | rate4gold | |
1,868,735 | Rate4Gold gold rate today in Chennai | "A 'gold-loan-repledge' is a financial service where individuals can secure loans by leveraging their... | 0 | 2024-05-29T09:13:51 | https://dev.to/rate4gold/rate4gold-gold-rate-today-in-chennai-31ad | "A 'gold-loan-repledge' is a financial service where individuals can secure loans by leveraging their gold assets as collateral. Through this arrangement, borrowers can access funds quickly by pledging their gold possessions, such as jewelry or bullion, to a lender. The 'rate4gold' refers to the interest rate associated with this borrowing option. Typically, these loans offer favorable interest rates, reflecting the lower risk for the lender due to the secured nature of the collateral. The specific [rate4gold](https://rate4gold.com/today-rate/
) can vary based on factors like prevailing market conditions, loan amount, and the purity and quantity of the gold being pledged. Gold-loan-repledge arrangements provide borrowers with a convenient and efficient way to access capital while utilizing their gold assets effectively."
Looking to sell your old gold in Chennai? [Trust Rate4Gold](https://rate4gold.com/today-rate/
) for a seamless and profitable experience. As the premier old gold buyers in Chennai, we offer the best prices, transparent transactions, and exceptional customer service.
Why Choose Rate4Gold?
1. Best Prices Guaranteed: We use the latest market rates to ensure you get the highest value for your gold.
2. Transparent Process: Our transparent evaluation process includes advanced testing techniques to determine the purity and weight of your gold, ensuring a fair deal.
3. Instant Payment: Receive immediate payment for your gold, whether in cash, cheque, or bank transfer, according to your preference.
4. Expert Evaluation: Our team of experienced professionals provides accurate assessments, so you can be confident in the value of your gold.
5. Customer Satisfaction: We pride ourselves on our reputation for excellent customer service, making your gold-selling experience smooth and satisfying.
How It Works
1. Visit Our Store: Bring your old gold jewelry, coins, or bullion to our conveniently [located store in Chennai](https://rate4gold.com/today-rate/
).
2. Free Evaluation: Our experts will evaluate your gold using state-of-the-art equipment, free of charge.
3. Get an Offer: Based on the current market rates and the evaluation, we will make you a competitive offer.
4. Instant Payment: Once you accept our offer, receive your payment instantly in the method you choose.
What We Buy
• Gold Jewelry: Necklaces, rings, bracelets, earrings, and more.
• Gold Coins and Bars: Any form of gold bullion.
• Scrap Gold: Broken or damaged gold items.

| rate4gold | |
1,868,734 | Customizing VSCode: Themes, Icons, and Fonts | Visual Studio Code (VSCode) is celebrated for its versatility and customizability, making it a... | 0 | 2024-05-29T09:13:25 | https://dev.to/umeshtharukaofficial/customizing-vscode-themes-icons-and-fonts-36b5 | webdev, vscode, devops, programming | Visual Studio Code (VSCode) is celebrated for its versatility and customizability, making it a favorite among developers. Beyond its powerful features and extensions, VSCode allows extensive customization of its appearance through themes, icons, and fonts. Personalizing your development environment not only makes it aesthetically pleasing but also enhances productivity and reduces eye strain. This article explores how to customize VSCode to create a workspace that suits your preferences and boosts your efficiency.
## The Importance of Customization
Customization in VSCode offers several benefits:
1. **Improved Focus**: A visually appealing and well-organized workspace can help maintain focus and reduce distractions.
2. **Enhanced Productivity**: Customizing themes, icons, and fonts can streamline navigation and make code more readable, leading to increased productivity.
3. **Reduced Eye Strain**: Using appropriate color schemes and fonts can minimize eye fatigue, especially during long coding sessions.
4. **Personal Expression**: Customization allows developers to express their individuality and make their workspace feel more personal and comfortable.
## Getting Started with Customization
To start customizing VSCode, open the Command Palette with `Ctrl+Shift+P` (Windows/Linux) or `Cmd+Shift+P` (Mac) and search for "Preferences: Open Settings (UI)". This will open the Settings panel where you can modify various aspects of VSCode.
### Installing Extensions
Before diving into specific customization options, it’s essential to know how to install extensions. Extensions are the key to unlocking additional themes, icons, and font options.
1. Open the Extensions view by clicking the Extensions icon in the Activity Bar or pressing `Ctrl+Shift+X` (Windows/Linux) or `Cmd+Shift+X` (Mac).
2. Search for the desired extension by typing its name or related keywords.
3. Click the "Install" button next to the extension to add it to your VSCode.
## Themes
Themes in VSCode control the color scheme of the editor, including the syntax highlighting, UI elements, and background. There are two main types of themes: **Color Themes** and **File Icon Themes**.
### Color Themes
Color themes change the color scheme of the entire editor. Here are some popular color themes:
1. **One Dark Pro**
- A popular theme inspired by Atom's One Dark theme. It provides a dark color scheme that is easy on the eyes.
- **Installation**: Search for "One Dark Pro" in the Extensions view and install it.
2. **Dracula Official**
- A dark theme with a distinct color palette that enhances code readability and reduces eye strain.
- **Installation**: Search for "Dracula Official" in the Extensions view and install it.
3. **Solarized Dark and Light**
- Provides both dark and light variants, offering a balanced color scheme that is great for reducing eye fatigue.
- **Installation**: Search for "Solarized" in the Extensions view and install it.
4. **Night Owl**
- A dark theme designed for developers who prefer working late at night. It features a deep blue color palette that is soothing to the eyes.
- **Installation**: Search for "Night Owl" in the Extensions view and install it.
### Changing Color Themes
To change the color theme:
1. Open the Command Palette (`Ctrl+Shift+P` or `Cmd+Shift+P`).
2. Type "Preferences: Color Theme" and select it.
3. Browse through the available themes and click on the one you want to apply.
### File Icon Themes
File icon themes change the icons associated with different file types and folders in the explorer. Here are some popular file icon themes:
1. **Material Icon Theme**
- Provides a comprehensive set of icons inspired by Google’s Material Design. It is one of the most popular icon themes.
- **Installation**: Search for "Material Icon Theme" in the Extensions view and install it.
2. **VSCode Icons**
- Offers a wide variety of icons that are visually appealing and easy to distinguish.
- **Installation**: Search for "vscode-icons" in the Extensions view and install it.
3. **Seti Icons**
- A minimalist icon set that provides a clean and modern look to your file explorer.
- **Installation**: Search for "Seti Icons" in the Extensions view and install it.
### Changing File Icon Themes
To change the file icon theme:
1. Open the Command Palette (`Ctrl+Shift+P` or `Cmd+Shift+P`).
2. Type "Preferences: File Icon Theme" and select it.
3. Browse through the available icon themes and click on the one you want to apply.
## Fonts
The font you use in your code editor can have a significant impact on readability and overall coding experience. VSCode allows you to customize both the font family and font size.
### Choosing a Font
Here are some popular fonts that developers often use in VSCode:
1. **Fira Code**
- A monospaced font with programming ligatures, which makes reading and writing code more pleasant.
- **Installation**: Download from [Fira Code's GitHub](https://github.com/tonsky/FiraCode) and install it on your system.
2. **Source Code Pro**
- A monospaced font designed by Adobe that is clean and highly readable.
- **Installation**: Download from [Google Fonts](https://fonts.google.com/specimen/Source+Code+Pro) and install it on your system.
3. **JetBrains Mono**
- A monospaced font created by JetBrains specifically for developers. It includes ligatures and is designed to reduce eye strain.
- **Installation**: Download from [JetBrains' website](https://www.jetbrains.com/lp/mono/) and install it on your system.
4. **Cascadia Code**
- A monospaced font with ligatures developed by Microsoft. It is the default font for Windows Terminal.
- **Installation**: Download from [GitHub](https://github.com/microsoft/cascadia-code) and install it on your system.
### Customizing Font Settings
To customize font settings in VSCode:
1. Open the Settings panel by pressing `Ctrl+,` (Windows/Linux) or `Cmd+,` (Mac).
2. In the search bar, type "font" to filter the font settings.
3. Modify the following settings:
- **Editor: Font Family**: Set this to the name of the font you want to use (e.g., `Fira Code`, `Source Code Pro`).
- **Editor: Font Size**: Set this to your preferred font size (e.g., `14`, `16`).
### Enabling Ligatures
If you are using a font that supports ligatures, you can enable them in VSCode:
1. Open the Settings panel (`Ctrl+,` or `Cmd+,`).
2. Search for "font ligatures" and check the "Editor: Font Ligatures" option.
## Advanced Customization
For those who want to delve deeper into customization, VSCode offers advanced options through its settings.json file.
### Accessing settings.json
1. Open the Command Palette (`Ctrl+Shift+P` or `Cmd+Shift+P`).
2. Type "Preferences: Open Settings (JSON)" and select it.
### Example Customization Settings
Here are some example settings you can add to your settings.json file to further customize your VSCode:
```json
{
"workbench.colorTheme": "One Dark Pro",
"workbench.iconTheme": "material-icon-theme",
"editor.fontFamily": "Fira Code",
"editor.fontSize": 16,
"editor.fontLigatures": true,
"editor.lineHeight": 24,
"editor.cursorStyle": "line",
"editor.cursorBlinking": "smooth",
"editor.renderWhitespace": "all",
"editor.minimap.enabled": true,
"editor.minimap.scale": 2,
"files.autoSave": "afterDelay",
"files.autoSaveDelay": 1000
}
```
### Customizing Color Themes
If you want to create your own color theme or modify an existing one, you can do so by creating a new theme extension or editing the settings.json file.
### Example: Custom Theme Colors
```json
{
"workbench.colorCustomizations": {
"editor.background": "#1e1e1e",
"editor.foreground": "#d4d4d4",
"editor.lineHighlightBackground": "#2c2c2c",
"editorCursor.foreground": "#d4d4d4",
"editorWhitespace.foreground": "#3e3e3e"
}
}
```
### Customizing Keybindings
VSCode allows you to customize keybindings to suit your workflow better. You can access the keybindings.json file to add or modify keybindings.
### Example: Custom Keybindings
```json
[
{
"key": "ctrl+shift+n",
"command": "workbench.action.files.newUntitledFile"
},
{
"key": "ctrl+alt+left",
"command": "workbench.action.navigateBack"
},
{
"key": "ctrl+alt+right",
"command": "workbench.action.navigateForward"
}
]
```
## Conclusion
Customizing VSCode with themes, icons, and fonts can significantly enhance your development experience. By tailoring the appearance and functionality of your editor, you can create a more comfortable and efficient workspace that suits your personal preferences and needs. Whether you’re looking to reduce eye strain, increase productivity, or simply make your coding environment more aesthetically pleasing, VSCode's extensive customization options have you covered.
Start exploring the wealth of themes, icon
sets, and fonts available, and transform your VSCode setup into a personalized powerhouse of productivity and creativity. Embrace the power of customization and make your coding journey not only productive but also enjoyable. | umeshtharukaofficial |
1,865,217 | Keep your estimates boring | Why? Most everyone I know has got shiny object syndrome. We all want to work on the latest... | 27,512 | 2024-05-29T09:12:00 | https://artur.wtf/blog/why-you-need-boring-estimates/ | agile, ai, estimates | ## Why?
Most everyone I know has got shiny object syndrome. We all want to work on the latest and greatest. I myself am part of that crowd very much. Whenever I start on a project I will never pin the versions for the libraries. That adds anywhere between 0% and 50% on top of the project timeline. The most notable example is Javascript with its myriad of libraries. You would think everyone is familiar with this meme by now :sweat_smile:.
In the first article in the series we talked about getting _anchors_ right and trying to stay away from the uniqueness bias when choosing a good anchor. In _How Big Things Get Done_ the authors also bring in a concept that was new to me: **the reference class**.
The phrase was originally coined in the 1970s by the psychologist [Daniel Kahneman and his colleague Amos Tversky](https://www.newyorker.com/books/page-turner/the-two-friends-who-changed-how-we-think-about-how-we-think) and is regularly used in the context of _reference class forecasting_.
Daniel and Amos refer to two types of views when estimating a project:
- _inside view_ which is the view while working on the project with your personal biases
- _outside view_ which is the view from the outside, looking at the project as a whole and comparing it to similar projects
Enough with the theory, in practice, what we actually want to achieve is to have our estimates work and be as accurate as possible.
## How?
Now that we have the lingo down, let's get into the nitty-gritty. We want to figure out how to calculate the estimates, you got that right **calculate**. The calculations are based on being able to cut down your project from being a special and unique snowflake to a project that is similar to others. It's a combination of statistical and historical analysis of other projects as similar as possible to yours.
---
_Going on a tangent here, wouldn't it be cool if we could have a database of software project estimates with numerical data, situational requirements and conditions, and perhaps how long the project took in the end?_ :thinking:
___
You want to reduce your project to something as generic as possible then look for data about other projects like it. As a software developer you may be tempted to think that it is special and unique, but finding the commonalities will help you get a better estimate.
We could make use of both _inside view_ and _outside view_:
- _outside view_: see how long similar projects took(take the median) - I am referring to the reduced version where you cut out any product differentiators
- _inside view_: see how long the differentiators will take (_this you can break down further as well into common tasks and unique tasks_)
... do you see where I am going with this? It's all turtles all the way down :turtle:. Now you can already see how things can be broken down further into smaller pieces and how similarities can make estimating easier.
The numbers show a 30% increase in accuracy when using _reference class forecasting_, that is the _outside view_, with 50% not being uncommon.
The aspect that is different from plain anchor-based estimates is that you choose an anchor that is based on the _reference class_ which makes it closer to the objective reality.
## Into the future with AI
Last couple of years I have been working in the field of AI and I have been an avid reader of various papers and consumed a decent amount of tutorials and courses. Deep learning is an amazingly powerful tool that is able to draw conclusions based on the importance of a particular feature of the project and classify it.
If we had the data about projects we could train a multi-class classifier to predict the time it would take to complete a project(S/M/L/XL). This could be a great Trello plugin for example.
Linear regression can be another simpler approach to do a numeric estimate of the project timeline. Now, this feels like we are taking all the joy out of the agile SDLC, but remember this is only supposed to be used as a data focused approach, from the _outside view_ i.e. looking objectively at the data, so no hard feelings to be had :wink:.
Thinking a bit further we could have an LLM + RAG system that looks at the database of projects we have broken down, does a similarity search and gives us some kind of standard estimates.
The data would probably be a huge challenge for this one. You would have to get data from various sources and have it clean, usable and can be used to train the models.
## Conclusion
- **Stay boring**: don't get caught up in the thinking your project is special and unique
- **Use the reference class**: look at similar projects and see how long they took
- **Use both views**: _inside view_ and _outside view_ to get a better estimate
- **Use data**: if you have it, use it to your advantage
- **Ask for help**: if you are not sure, ask someone who has done it before, outside perspective can add a layer of objectivity
| adaschevici |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.