id int64 5 1.93M | title stringlengths 0 128 | description stringlengths 0 25.5k | collection_id int64 0 28.1k | published_timestamp timestamp[s] | canonical_url stringlengths 14 581 | tag_list stringlengths 0 120 | body_markdown stringlengths 0 716k | user_username stringlengths 2 30 |
|---|---|---|---|---|---|---|---|---|
1,906,537 | A guide into REACT AND SVELTE | As you journey into frontend development, the first thought that comes to mind is: i want to learn... | 0 | 2024-06-30T11:25:44 | https://dev.to/ejiroosiephri/a-guide-into-react-and-svelte-372p | webdev, hng, hng11, frontendtechnologies | As you journey into frontend development, the first thought that comes to mind is: i want to learn React. Yes about 70% of developers are conversant with react. Why? React is the most popular of frontend UI library.
In this short article, i will be guiding you through other frontend frameworks like react that you prob... | ejiroosiephri |
1,906,533 | Seat Bearings: Providing Stability and Durability in Automotive Seats | Seat Bearings: Keeping Automotive Seats Safe and Comfortable Introduction Are you currently sick and... | 0 | 2024-06-30T11:20:07 | https://dev.to/hdbhf_jjfnf_2d21824853454/seat-bearings-providing-stability-and-durability-in-automotive-seats-36jl | Seat Bearings: Keeping Automotive Seats Safe and Comfortable
Introduction
Are you currently sick and tired with experiencing uncomfortable and unstable if you should be driving or riding in a motor car or automobile? It isn't just you! People encounter vexation once they sit most of the shows genuine in a motor youngs... | hdbhf_jjfnf_2d21824853454 | |
1,906,532 | Embark on a Kubernetes Learning Adventure 🚀 | The article is about a comprehensive collection of 10 Kubernetes-focused challenges provided by LabEx, a leading provider of hands-on programming tutorials. The challenges cover a wide range of Kubernetes topics, including resource monitoring with Prometheus, resource management with LimitRange, container readiness wit... | 27,732 | 2024-06-30T11:19:33 | https://dev.to/labex/embark-on-a-kubernetes-learning-adventure-jkf | kubernetes, coding, programming, tutorial |
Kubernetes, the powerful container orchestration platform, has become a game-changer in the world of modern application deployment and management. LabEx, a leading provider of hands-on programming tutorials, offers a comprehensive collection of Kubernetes-focused challenges that will guide you through the intricacies ... | labby |
1,906,526 | Step-by-step guide to MultiversX smart contract interactions with JavaScript SDK | In the fourth article of the series on MultiversX JavaScript SDK, we will examine how to interact... | 27,816 | 2024-06-30T11:14:07 | https://www.julian.io/articles/multiversx-js-sdk-sc-interactions.html | javascript, multiversx, web3, blockchain | In the fourth article of the series on MultiversX JavaScript SDK, we will examine how to interact with deployed smart contracts. As in the previous article, where we tackled smart contract deployment, we will use the [Piggy Bank](https://github.com/xdevguild/piggy-bank-sc) smart contract as an example.
The script is m... | julian-io |
1,906,531 | Starting my career as a mobile developer: insights and experience. | Mobile dev has become an essential skill in our today's world. As a mobile developer I will share my... | 0 | 2024-06-30T11:10:16 | https://dev.to/jade_carnage_c442d55edf28/starting-my-career-as-a-mobile-developer-insights-and-experience-43n5 | Mobile dev has become an essential skill in our today's world. As a mobile developer I will share my journey and experience in the world of mobile development spaces (platforms)and software architecture pattern. In this I will explain the advantages and disadvantages of cadres and discuss my motivation for joining th... | jade_carnage_c442d55edf28 | |
1,906,529 | H4895 Powder in Stock | The world of reloading is vast and intricate, with enthusiasts constantly on the lookout for the... | 0 | 2024-06-30T11:06:07 | https://dev.to/brassproarmory/h4895-powder-in-stock-p65 |
The world of reloading is vast and intricate, with enthusiasts constantly on the lookout for the best supplies to ensure their ammunition performs at its peak. One such essential reloading component is the [h4895](... | brassproarmory | |
1,906,528 | HNG AND I | I’m so excited to be accepted into the HNG Internship. Still feels like yesterday where I was around... | 0 | 2024-06-30T11:00:05 | https://dev.to/johnpraise/hng-and-i-3bm9 | I’m so excited to be accepted into the HNG Internship. Still feels like yesterday where I was around my desk trying to place my hands around user authentication in Python/Django (backend), I made a lot of research in order to solve that problem which was a fluke in Django 5, it was quite a challenge for someone like me... | johnpraise | |
1,906,527 | DeviceBee is Top Mobile App Development Company Dubai | Leading Mobile App Development Company in Dubai — DeviceBee DeviceBee is leading mobile app... | 0 | 2024-06-30T10:59:35 | https://dev.to/devicebeetechnologies/devicebee-is-top-mobile-app-development-company-dubai-4m9p | devicebee, appdevelopmentdubai, mobileappdeveloperdubai, bestappdevelopmentdubaiuae | **Leading Mobile App Development Company in Dubai — DeviceBee**
DeviceBee is [leading mobile app development company in the UAE](https://www.devicebee.com/mobile-app-development-company-in-the-uae/). Renowned for our expertise in iOS app, android app, hybrid, cross-platform & native , artificial intelligence, on-deman... | devicebeetechnologies |
1,906,448 | React + Vite + Tailwind project | If you want to create a React project without using framework like NextJS or Remix, this article is... | 0 | 2024-06-30T10:48:10 | https://dev.to/thinhkhang97/react-vite-tailwind-project-57pf | webdev, react, vite, tailwindcss | If you want to create a React project without using framework like NextJS or Remix, this article is for you. In this guide I will help you init a `React` project with `Vite` and use `TailwindCss`.
## Prerequisite
* NodeJS version >= 18
Use this command to check your NodeJS version
```bash
node -v
```
## Create reac... | thinhkhang97 |
1,906,523 | Your Weekly Dive into Programming, Web3, and Open-Source Tools | Hello friends, Read directly on website Welcome to this week newsletter. Without wasting much time... | 0 | 2024-06-30T10:41:21 | https://dev.to/shreyvijayvargiya/your-weekly-dive-into-programming-web3-and-open-source-tools-28pb | webdev, javascript, news, programming | Hello friends,
[Read directly on website](ihatereading.in/newsletter)
Welcome to this week newsletter. Without wasting much time let's dive into what's going on this week in programming, tech, and web3.
## ✍️ Blogs
[Trending in React](https://x.com/sebastienlorber/status/1805866982798950684)
Well, what's trendin... | shreyvijayvargiya |
1,906,522 | Backend Development from my view - a little story. | As a front-end developer interested in learning how both ends of an application works, I gave backend... | 0 | 2024-06-30T10:34:14 | https://dev.to/jprof/backend-development-from-my-view-a-little-story-gfn | As a front-end developer interested in learning how both ends of an application works, I gave backend development some of my attention.
It was easier to understand what I was reading as I could understand backend development in my language—Javascript.
There are little differences though:
Browser? No. Node? Yes
CSS? ... | jprof | |
1,906,520 | React vs. Angular: A Comprehensive Comparison | Hi, I am Patricia Nonye, a Frontend Developer with 2+ years experience, on an exciting journey with... | 0 | 2024-06-30T10:29:33 | https://dev.to/tinkerrbelle/react-vs-angular-a-comprehensive-comparison-4cbl | beginners, hng, blog, frontend | Hi, I am Patricia Nonye, a Frontend Developer with 2+ years experience, on an exciting journey with HNG internship. This internship is a unique opportunity to refine my skills, face real-world challenges, contribute with like-minded individuals.
At HNG, we primarily use ReactJS which I enjoy using because of its flexi... | tinkerrbelle |
1,906,519 | Creating and Managing IAM users from Your EC2 instance | Introduction Creating and managing IAM users from an EC2 instance involves a few steps to ensure... | 0 | 2024-06-30T10:27:11 | https://dev.to/rashmitha_v_d0cfc20ba7152/creating-and-managing-iam-users-from-your-ec2-instance-4a6l | **Introduction**
Creating and managing IAM users from an EC2 instance involves a few steps to ensure proper security and access control. Here’s a general guide on how to accomplish this:
**Step 1:**
Create a EC2 instance.
, we built a customizable GUI clock using Python and Tkinter. Let's take it a step further by adding a camera feature that allows users to capture and save images on demand. This p... | scofieldidehen |
1,906,468 | My Programming Journey: Backend | Hello, my name is Jefferson Henry, I’m a software engineer and full stack developer currently... | 0 | 2024-06-30T10:09:59 | https://dev.to/jeff_hen_c38ea40eadf6121b/my-programming-journey-backend-2p2c | webdev, backend, programming, web | Hello, my name is Jefferson Henry, I’m a software engineer and full stack developer currently studying software engineering at Ritman University.
Did you know that about 73.3% of men and 26.6% of women are into tech? Similarly, 7% of the total US workforce works in the tech industry, making tech one of the most dynamic... | jeff_hen_c38ea40eadf6121b |
1,906,467 | Buy Verified Paxful Account | https://dmhelpshop.com/product/buy-verified-paxful-account/ Buy Verified Paxful Account There are... | 0 | 2024-06-30T10:08:01 | https://dev.to/topeciw546/buy-verified-paxful-account-4afo | webdev, javascript, beginners, programming | ERROR: type should be string, got "https://dmhelpshop.com/product/buy-verified-paxful-account/\n\n\nBuy Verified Paxful Account\nThere are several compelling reasons to consider purchasing a verified Paxful account. Firstly, a verified account offers enhanced security, providing peace of mind to all users. Additionally, it opens up a wider range of trading opportunities, allowing individuals to partake in various transactions, ultimately expanding their financial horizons.\n\nMoreover, Buy verified Paxful account ensures faster and more streamlined transactions, minimizing any potential delays or inconveniences. Furthermore, by opting for a verified account, users gain access to a trusted and reputable platform, fostering a sense of reliability and confidence.\n\nLastly, Paxful’s verification process is thorough and meticulous, ensuring that only genuine individuals are granted verified status, thereby creating a safer trading environment for all users. Overall, the decision to Buy Verified Paxful account can greatly enhance one’s overall trading experience, offering increased security, access to more opportunities, and a reliable platform to engage with. Buy Verified Paxful Account.\n\nBuy US verified paxful account from the best place dmhelpshop\nWhy we declared this website as the best place to buy US verified paxful account? Because, our company is established for providing the all account services in the USA (our main target) and even in the whole world. With this in mind we create paxful account and customize our accounts as professional with the real documents. Buy Verified Paxful Account.\n\nIf you want to buy US verified paxful account you should have to contact fast with us. Because our accounts are-\n\nEmail verified\nPhone number verified\nSelfie and KYC verified\nSSN (social security no.) verified\nTax ID and passport verified\nSometimes driving license verified\nMasterCard attached and verified\nUsed only genuine and real documents\n100% access of the account\nAll documents provided for customer security\nWhat is Verified Paxful Account?\nIn today’s expanding landscape of online transactions, ensuring security and reliability has become paramount. Given this context, Paxful has quickly risen as a prominent peer-to-peer Bitcoin marketplace, catering to individuals and businesses seeking trusted platforms for cryptocurrency trading.\n\nIn light of the prevalent digital scams and frauds, it is only natural for people to exercise caution when partaking in online transactions. As a result, the concept of a verified account has gained immense significance, serving as a critical feature for numerous online platforms. Paxful recognizes this need and provides a safe haven for users, streamlining their cryptocurrency buying and selling experience.\n\nFor individuals and businesses alike, Buy verified Paxful account emerges as an appealing choice, offering a secure and reliable environment in the ever-expanding world of digital transactions. Buy Verified Paxful Account.\n\nVerified Paxful Accounts are essential for establishing credibility and trust among users who want to transact securely on the platform. They serve as evidence that a user is a reliable seller or buyer, verifying their legitimacy.\n\nBut what constitutes a verified account, and how can one obtain this status on Paxful? In this exploration of verified Paxful accounts, we will unravel the significance they hold, why they are crucial, and shed light on the process behind their activation, providing a comprehensive understanding of how they function. Buy verified Paxful account.\n\n \n\nWhy should to Buy Verified Paxful Account?\nThere are several compelling reasons to consider purchasing a verified Paxful account. Firstly, a verified account offers enhanced security, providing peace of mind to all users. Additionally, it opens up a wider range of trading opportunities, allowing individuals to partake in various transactions, ultimately expanding their financial horizons.\n\nMoreover, a verified Paxful account ensures faster and more streamlined transactions, minimizing any potential delays or inconveniences. Furthermore, by opting for a verified account, users gain access to a trusted and reputable platform, fostering a sense of reliability and confidence. Buy Verified Paxful Account.\n\nLastly, Paxful’s verification process is thorough and meticulous, ensuring that only genuine individuals are granted verified status, thereby creating a safer trading environment for all users. Overall, the decision to buy a verified Paxful account can greatly enhance one’s overall trading experience, offering increased security, access to more opportunities, and a reliable platform to engage with.\n\n \n\nWhat is a Paxful Account\nPaxful and various other platforms consistently release updates that not only address security vulnerabilities but also enhance usability by introducing new features. Buy Verified Paxful Account.\n\nIn line with this, our old accounts have recently undergone upgrades, ensuring that if you purchase an old buy Verified Paxful account from dmhelpshop.com, you will gain access to an account with an impressive history and advanced features. This ensures a seamless and enhanced experience for all users, making it a worthwhile option for everyone.\n\n \n\nIs it safe to buy Paxful Verified Accounts?\nBuying on Paxful is a secure choice for everyone. However, the level of trust amplifies when purchasing from Paxful verified accounts. These accounts belong to sellers who have undergone rigorous scrutiny by Paxful. Buy verified Paxful account, you are automatically designated as a verified account. Hence, purchasing from a Paxful verified account ensures a high level of credibility and utmost reliability. Buy Verified Paxful Account.\n\nPAXFUL, a widely known peer-to-peer cryptocurrency trading platform, has gained significant popularity as a go-to website for purchasing Bitcoin and other cryptocurrencies. It is important to note, however, that while Paxful may not be the most secure option available, its reputation is considerably less problematic compared to many other marketplaces. Buy Verified Paxful Account.\n\nThis brings us to the question: is it safe to purchase Paxful Verified Accounts? Top Paxful reviews offer mixed opinions, suggesting that caution should be exercised. Therefore, users are advised to conduct thorough research and consider all aspects before proceeding with any transactions on Paxful.\n\n \n\nHow Do I Get 100% Real Verified Paxful Accoun?\nPaxful, a renowned peer-to-peer cryptocurrency marketplace, offers users the opportunity to conveniently buy and sell a wide range of cryptocurrencies. Given its growing popularity, both individuals and businesses are seeking to establish verified accounts on this platform.\n\nHowever, the process of creating a verified Paxful account can be intimidating, particularly considering the escalating prevalence of online scams and fraudulent practices. This verification procedure necessitates users to furnish personal information and vital documents, posing potential risks if not conducted meticulously.\n\nIn this comprehensive guide, we will delve into the necessary steps to create a legitimate and verified Paxful account. Our discussion will revolve around the verification process and provide valuable tips to safely navigate through it.\n\nMoreover, we will emphasize the utmost importance of maintaining the security of personal information when creating a verified account. Furthermore, we will shed light on common pitfalls to steer clear of, such as using counterfeit documents or attempting to bypass the verification process.\n\nWhether you are new to Paxful or an experienced user, this engaging paragraph aims to equip everyone with the knowledge they need to establish a secure and authentic presence on the platform.\n\nBenefits Of Verified Paxful Accounts\nVerified Paxful accounts offer numerous advantages compared to regular Paxful accounts. One notable advantage is that verified accounts contribute to building trust within the community.\n\nVerification, although a rigorous process, is essential for peer-to-peer transactions. This is why all Paxful accounts undergo verification after registration. When customers within the community possess confidence and trust, they can conveniently and securely exchange cash for Bitcoin or Ethereum instantly. Buy Verified Paxful Account.\n\nPaxful accounts, trusted and verified by sellers globally, serve as a testament to their unwavering commitment towards their business or passion, ensuring exceptional customer service at all times. Headquartered in Africa, Paxful holds the distinction of being the world’s pioneering peer-to-peer bitcoin marketplace. Spearheaded by its founder, Ray Youssef, Paxful continues to lead the way in revolutionizing the digital exchange landscape.\n\nPaxful has emerged as a favored platform for digital currency trading, catering to a diverse audience. One of Paxful’s key features is its direct peer-to-peer trading system, eliminating the need for intermediaries or cryptocurrency exchanges. By leveraging Paxful’s escrow system, users can trade securely and confidently.\n\nWhat sets Paxful apart is its commitment to identity verification, ensuring a trustworthy environment for buyers and sellers alike. With these user-centric qualities, Paxful has successfully established itself as a leading platform for hassle-free digital currency transactions, appealing to a wide range of individuals seeking a reliable and convenient trading experience. Buy Verified Paxful Account.\n\n \n\nHow paxful ensure risk-free transaction and trading?\nEngage in safe online financial activities by prioritizing verified accounts to reduce the risk of fraud. Platforms like Paxfu implement stringent identity and address verification measures to protect users from scammers and ensure credibility.\n\nWith verified accounts, users can trade with confidence, knowing they are interacting with legitimate individuals or entities. By fostering trust through verified accounts, Paxful strengthens the integrity of its ecosystem, making it a secure space for financial transactions for all users. Buy Verified Paxful Account.\n\nExperience seamless transactions by obtaining a verified Paxful account. Verification signals a user’s dedication to the platform’s guidelines, leading to the prestigious badge of trust. This trust not only expedites trades but also reduces transaction scrutiny. Additionally, verified users unlock exclusive features enhancing efficiency on Paxful. Elevate your trading experience with Verified Paxful Accounts today.\n\nIn the ever-changing realm of online trading and transactions, selecting a platform with minimal fees is paramount for optimizing returns. This choice not only enhances your financial capabilities but also facilitates more frequent trading while safeguarding gains. Buy Verified Paxful Account.\n\nExamining the details of fee configurations reveals Paxful as a frontrunner in cost-effectiveness. Acquire a verified level-3 USA Paxful account from usasmmonline.com for a secure transaction experience. Invest in verified Paxful accounts to take advantage of a leading platform in the online trading landscape.\n\n \n\nHow Old Paxful ensures a lot of Advantages?\n\nExplore the boundless opportunities that Verified Paxful accounts present for businesses looking to venture into the digital currency realm, as companies globally witness heightened profits and expansion. These success stories underline the myriad advantages of Paxful’s user-friendly interface, minimal fees, and robust trading tools, demonstrating its relevance across various sectors.\n\nBusinesses benefit from efficient transaction processing and cost-effective solutions, making Paxful a significant player in facilitating financial operations. Acquire a USA Paxful account effortlessly at a competitive rate from usasmmonline.com and unlock access to a world of possibilities. Buy Verified Paxful Account.\n\nExperience elevated convenience and accessibility through Paxful, where stories of transformation abound. Whether you are an individual seeking seamless transactions or a business eager to tap into a global market, buying old Paxful accounts unveils opportunities for growth.\n\nPaxful’s verified accounts not only offer reliability within the trading community but also serve as a testament to the platform’s ability to empower economic activities worldwide. Join the journey towards expansive possibilities and enhanced financial empowerment with Paxful today. Buy Verified Paxful Account.\n\n \n\nWhy paxful keep the security measures at the top priority?\nIn today’s digital landscape, security stands as a paramount concern for all individuals engaging in online activities, particularly within marketplaces such as Paxful. It is essential for account holders to remain informed about the comprehensive security protocols that are in place to safeguard their information.\n\nSafeguarding your Paxful account is imperative to guaranteeing the safety and security of your transactions. Two essential security components, Two-Factor Authentication and Routine Security Audits, serve as the pillars fortifying this shield of protection, ensuring a secure and trustworthy user experience for all. Buy Verified Paxful Account.\n\nConclusion\nInvesting in Bitcoin offers various avenues, and among those, utilizing a Paxful account has emerged as a favored option. Paxful, an esteemed online marketplace, enables users to engage in buying and selling Bitcoin. Buy Verified Paxful Account.\n\nThe initial step involves creating an account on Paxful and completing the verification process to ensure identity authentication. Subsequently, users gain access to a diverse range of offers from fellow users on the platform. Once a suitable proposal captures your interest, you can proceed to initiate a trade with the respective user, opening the doors to a seamless Bitcoin investing experience.\n\nIn conclusion, when considering the option of purchasing verified Paxful accounts, exercising caution and conducting thorough due diligence is of utmost importance. It is highly recommended to seek reputable sources and diligently research the seller’s history and reviews before making any transactions.\n\nMoreover, it is crucial to familiarize oneself with the terms and conditions outlined by Paxful regarding account verification, bearing in mind the potential consequences of violating those terms. By adhering to these guidelines, individuals can ensure a secure and reliable experience when engaging in such transactions. Buy Verified Paxful Account.\n\nContact Us / 24 Hours Reply\nTelegram:dmhelpshop\nWhatsApp: +1 (980) 277-2786\nSkype:dmhelpshop\nEmail:dmhelpshop@gmail.com\n\n " | topeciw546 |
1,906,466 | Buy GitHub Accounts | https://dmhelpshop.com/product/buy-github-accounts/ Buy GitHub Accounts GitHub holds a crucial... | 0 | 2024-06-30T10:07:26 | https://dev.to/carika4293/buy-github-accounts-2iem | typescript, machinelearning, discuss, news | https://dmhelpshop.com/product/buy-github-accounts/

Buy GitHub Accounts
GitHub holds a crucial position in the world of coding, making it an indispensable platform for developers. As the largest global code reposi... | carika4293 |
1,906,465 | Exploring the Power of React.js and Next.js in Modern Web Development | Exploring the Power of React.js and Next.js in Modern Web Development In the ever-evolving landscape... | 0 | 2024-06-30T10:04:00 | https://dev.to/biodun_raji/exploring-the-power-of-reactjs-and-nextjs-in-modern-web-development-180e |
Exploring the Power of React.js and Next.js in Modern Web Development
In the ever-evolving landscape of web development, React.js has emerged as a cornerstone technology for building dynamic and responsive user interfaces. As a powerful JavaScript library, React.js enables developers to create interactive web applica... | biodun_raji | |
1,905,343 | 【Kaggle】HMS 2nd Solution explaind | This time, I'll explain the 2nd solution of HMS competition on kaggle. the original solution is... | 0 | 2024-06-29T07:19:57 | https://dev.to/moyuto/kaggle-hms-2nd-solution-explaind-34jj | This time, I'll explain the 2nd solution of HMS competition on kaggle.
the [original solution](https://www.kaggle.com/competitions/hms-harmful-brain-activity-classification/discussion/492254) is here:
https://www.kaggle.com/competitions/hms-harmful-brain-activity-classification/discussion/492254
# 0. Competiton explan... | moyuto | |
1,906,461 | Implementing Batch Write Operations in Firestore with Express | Learn how to use Express to implement a Firestore batch write operation for improved performance and reliability in your web applications. | 0 | 2024-06-30T10:00:46 | https://dev.to/itselftools/implementing-batch-write-operations-in-firestore-with-express-5h64 | javascript, node, firebase, firestore |
At [itselftools.com](https://itselftools.com), our experience in developing over 30 applications utilizing technologies like Next.js and Firebase has offered us profound insights into efficient data handling and server management. One of the common scenarios we frequently handle in our cloud applications is performing... | antoineit |
1,906,460 | Front End technologies | Frontend development has witnessed a remarkable evolution in recent years, with the emergence of... | 0 | 2024-06-30T10:00:44 | https://dev.to/0yama/front-end-technologies-1ii |
Frontend development has witnessed a remarkable evolution in recent years, with the emergence of powerful libraries and frameworks that have redefined the way web applications are built. Beforehand when there were no technologies it took more time and mental energy to build a complex website or web-based software , ... | 0yama | |
1,906,459 | Keep listening or do your job and finish | People talk a lot about so-called design patterns (usually referencing those made in the famous book... | 0 | 2024-06-30T09:58:09 | https://dev.to/altavir/keep-listening-or-do-your-job-and-finish-2hej | kotlin, api | People talk a lot about so-called design patterns (usually referencing those made in the [famous book](https://en.wikipedia.org/wiki/Design_Patterns) for C++). Though those patterns themselves are not universal, they change from language to language and their usage strongly depends on the specific task at hand. Howeve... | altavir |
1,906,458 | c program for counting numbers | hello everyone i've been writing this program for counting numbers and i want to print it from... | 0 | 2024-06-30T09:57:46 | https://dev.to/legend01/c-program-for-counting-numbers-4o8p | c | **hello everyone i've been writing this program for counting numbers and i want to print it from certain starting point to certain extent**
```
//counting machine
#include<stdio.h>
int main()
{
int q1,q2,q3,q4,q5,q6,c=0,NOL,st;
printf("enter the number from where to how much combinations you want: ");
sca... | legend01 |
1,906,457 | Buy Verified Paxful Account | https://dmhelpshop.com/product/buy-verified-paxful-account/ Buy Verified Paxful Account There are... | 0 | 2024-06-30T09:56:18 | https://dev.to/carika4293/buy-verified-paxful-account-bl5 | programming, tutorial, react, ai | ERROR: type should be string, got "https://dmhelpshop.com/product/buy-verified-paxful-account/\n\n\n\n\nBuy Verified Paxful Account\nThere are several compelling reasons to consider purchasing a verified Paxful account. Firstly, a verified account offers enhanced security, providing peace of mind to all users. Additionally, it opens up a wider range of trading opportunities, allowing individuals to partake in various transactions, ultimately expanding their financial horizons.\n\nMoreover, Buy verified Paxful account ensures faster and more streamlined transactions, minimizing any potential delays or inconveniences. Furthermore, by opting for a verified account, users gain access to a trusted and reputable platform, fostering a sense of reliability and confidence.\n\nLastly, Paxful’s verification process is thorough and meticulous, ensuring that only genuine individuals are granted verified status, thereby creating a safer trading environment for all users. Overall, the decision to Buy Verified Paxful account can greatly enhance one’s overall trading experience, offering increased security, access to more opportunities, and a reliable platform to engage with. Buy Verified Paxful Account.\n\nBuy US verified paxful account from the best place dmhelpshop\nWhy we declared this website as the best place to buy US verified paxful account? Because, our company is established for providing the all account services in the USA (our main target) and even in the whole world. With this in mind we create paxful account and customize our accounts as professional with the real documents. Buy Verified Paxful Account.\n\nIf you want to buy US verified paxful account you should have to contact fast with us. Because our accounts are-\n\nEmail verified\nPhone number verified\nSelfie and KYC verified\nSSN (social security no.) verified\nTax ID and passport verified\nSometimes driving license verified\nMasterCard attached and verified\nUsed only genuine and real documents\n100% access of the account\nAll documents provided for customer security\nWhat is Verified Paxful Account?\nIn today’s expanding landscape of online transactions, ensuring security and reliability has become paramount. Given this context, Paxful has quickly risen as a prominent peer-to-peer Bitcoin marketplace, catering to individuals and businesses seeking trusted platforms for cryptocurrency trading.\n\nIn light of the prevalent digital scams and frauds, it is only natural for people to exercise caution when partaking in online transactions. As a result, the concept of a verified account has gained immense significance, serving as a critical feature for numerous online platforms. Paxful recognizes this need and provides a safe haven for users, streamlining their cryptocurrency buying and selling experience.\n\nFor individuals and businesses alike, Buy verified Paxful account emerges as an appealing choice, offering a secure and reliable environment in the ever-expanding world of digital transactions. Buy Verified Paxful Account.\n\nVerified Paxful Accounts are essential for establishing credibility and trust among users who want to transact securely on the platform. They serve as evidence that a user is a reliable seller or buyer, verifying their legitimacy.\n\nBut what constitutes a verified account, and how can one obtain this status on Paxful? In this exploration of verified Paxful accounts, we will unravel the significance they hold, why they are crucial, and shed light on the process behind their activation, providing a comprehensive understanding of how they function. Buy verified Paxful account.\n\n \n\nWhy should to Buy Verified Paxful Account?\nThere are several compelling reasons to consider purchasing a verified Paxful account. Firstly, a verified account offers enhanced security, providing peace of mind to all users. Additionally, it opens up a wider range of trading opportunities, allowing individuals to partake in various transactions, ultimately expanding their financial horizons.\n\nMoreover, a verified Paxful account ensures faster and more streamlined transactions, minimizing any potential delays or inconveniences. Furthermore, by opting for a verified account, users gain access to a trusted and reputable platform, fostering a sense of reliability and confidence. Buy Verified Paxful Account.\n\nLastly, Paxful’s verification process is thorough and meticulous, ensuring that only genuine individuals are granted verified status, thereby creating a safer trading environment for all users. Overall, the decision to buy a verified Paxful account can greatly enhance one’s overall trading experience, offering increased security, access to more opportunities, and a reliable platform to engage with.\n\n \n\nWhat is a Paxful Account\nPaxful and various other platforms consistently release updates that not only address security vulnerabilities but also enhance usability by introducing new features. Buy Verified Paxful Account.\n\nIn line with this, our old accounts have recently undergone upgrades, ensuring that if you purchase an old buy Verified Paxful account from dmhelpshop.com, you will gain access to an account with an impressive history and advanced features. This ensures a seamless and enhanced experience for all users, making it a worthwhile option for everyone.\n\n \n\nIs it safe to buy Paxful Verified Accounts?\nBuying on Paxful is a secure choice for everyone. However, the level of trust amplifies when purchasing from Paxful verified accounts. These accounts belong to sellers who have undergone rigorous scrutiny by Paxful. Buy verified Paxful account, you are automatically designated as a verified account. Hence, purchasing from a Paxful verified account ensures a high level of credibility and utmost reliability. Buy Verified Paxful Account.\n\nPAXFUL, a widely known peer-to-peer cryptocurrency trading platform, has gained significant popularity as a go-to website for purchasing Bitcoin and other cryptocurrencies. It is important to note, however, that while Paxful may not be the most secure option available, its reputation is considerably less problematic compared to many other marketplaces. Buy Verified Paxful Account.\n\nThis brings us to the question: is it safe to purchase Paxful Verified Accounts? Top Paxful reviews offer mixed opinions, suggesting that caution should be exercised. Therefore, users are advised to conduct thorough research and consider all aspects before proceeding with any transactions on Paxful.\n\n \n\nHow Do I Get 100% Real Verified Paxful Accoun?\nPaxful, a renowned peer-to-peer cryptocurrency marketplace, offers users the opportunity to conveniently buy and sell a wide range of cryptocurrencies. Given its growing popularity, both individuals and businesses are seeking to establish verified accounts on this platform.\n\nHowever, the process of creating a verified Paxful account can be intimidating, particularly considering the escalating prevalence of online scams and fraudulent practices. This verification procedure necessitates users to furnish personal information and vital documents, posing potential risks if not conducted meticulously.\n\nIn this comprehensive guide, we will delve into the necessary steps to create a legitimate and verified Paxful account. Our discussion will revolve around the verification process and provide valuable tips to safely navigate through it.\n\nMoreover, we will emphasize the utmost importance of maintaining the security of personal information when creating a verified account. Furthermore, we will shed light on common pitfalls to steer clear of, such as using counterfeit documents or attempting to bypass the verification process.\n\nWhether you are new to Paxful or an experienced user, this engaging paragraph aims to equip everyone with the knowledge they need to establish a secure and authentic presence on the platform.\n\nBenefits Of Verified Paxful Accounts\nVerified Paxful accounts offer numerous advantages compared to regular Paxful accounts. One notable advantage is that verified accounts contribute to building trust within the community.\n\nVerification, although a rigorous process, is essential for peer-to-peer transactions. This is why all Paxful accounts undergo verification after registration. When customers within the community possess confidence and trust, they can conveniently and securely exchange cash for Bitcoin or Ethereum instantly. Buy Verified Paxful Account.\n\nPaxful accounts, trusted and verified by sellers globally, serve as a testament to their unwavering commitment towards their business or passion, ensuring exceptional customer service at all times. Headquartered in Africa, Paxful holds the distinction of being the world’s pioneering peer-to-peer bitcoin marketplace. Spearheaded by its founder, Ray Youssef, Paxful continues to lead the way in revolutionizing the digital exchange landscape.\n\nPaxful has emerged as a favored platform for digital currency trading, catering to a diverse audience. One of Paxful’s key features is its direct peer-to-peer trading system, eliminating the need for intermediaries or cryptocurrency exchanges. By leveraging Paxful’s escrow system, users can trade securely and confidently.\n\nWhat sets Paxful apart is its commitment to identity verification, ensuring a trustworthy environment for buyers and sellers alike. With these user-centric qualities, Paxful has successfully established itself as a leading platform for hassle-free digital currency transactions, appealing to a wide range of individuals seeking a reliable and convenient trading experience. Buy Verified Paxful Account.\n\n \n\nHow paxful ensure risk-free transaction and trading?\nEngage in safe online financial activities by prioritizing verified accounts to reduce the risk of fraud. Platforms like Paxfu implement stringent identity and address verification measures to protect users from scammers and ensure credibility.\n\nWith verified accounts, users can trade with confidence, knowing they are interacting with legitimate individuals or entities. By fostering trust through verified accounts, Paxful strengthens the integrity of its ecosystem, making it a secure space for financial transactions for all users. Buy Verified Paxful Account.\n\nExperience seamless transactions by obtaining a verified Paxful account. Verification signals a user’s dedication to the platform’s guidelines, leading to the prestigious badge of trust. This trust not only expedites trades but also reduces transaction scrutiny. Additionally, verified users unlock exclusive features enhancing efficiency on Paxful. Elevate your trading experience with Verified Paxful Accounts today.\n\nIn the ever-changing realm of online trading and transactions, selecting a platform with minimal fees is paramount for optimizing returns. This choice not only enhances your financial capabilities but also facilitates more frequent trading while safeguarding gains. Buy Verified Paxful Account.\n\nExamining the details of fee configurations reveals Paxful as a frontrunner in cost-effectiveness. Acquire a verified level-3 USA Paxful account from usasmmonline.com for a secure transaction experience. Invest in verified Paxful accounts to take advantage of a leading platform in the online trading landscape.\n\n \n\nHow Old Paxful ensures a lot of Advantages?\n\nExplore the boundless opportunities that Verified Paxful accounts present for businesses looking to venture into the digital currency realm, as companies globally witness heightened profits and expansion. These success stories underline the myriad advantages of Paxful’s user-friendly interface, minimal fees, and robust trading tools, demonstrating its relevance across various sectors.\n\nBusinesses benefit from efficient transaction processing and cost-effective solutions, making Paxful a significant player in facilitating financial operations. Acquire a USA Paxful account effortlessly at a competitive rate from usasmmonline.com and unlock access to a world of possibilities. Buy Verified Paxful Account.\n\nExperience elevated convenience and accessibility through Paxful, where stories of transformation abound. Whether you are an individual seeking seamless transactions or a business eager to tap into a global market, buying old Paxful accounts unveils opportunities for growth.\n\nPaxful’s verified accounts not only offer reliability within the trading community but also serve as a testament to the platform’s ability to empower economic activities worldwide. Join the journey towards expansive possibilities and enhanced financial empowerment with Paxful today. Buy Verified Paxful Account.\n\n \n\nWhy paxful keep the security measures at the top priority?\nIn today’s digital landscape, security stands as a paramount concern for all individuals engaging in online activities, particularly within marketplaces such as Paxful. It is essential for account holders to remain informed about the comprehensive security protocols that are in place to safeguard their information.\n\nSafeguarding your Paxful account is imperative to guaranteeing the safety and security of your transactions. Two essential security components, Two-Factor Authentication and Routine Security Audits, serve as the pillars fortifying this shield of protection, ensuring a secure and trustworthy user experience for all. Buy Verified Paxful Account.\n\nConclusion\nInvesting in Bitcoin offers various avenues, and among those, utilizing a Paxful account has emerged as a favored option. Paxful, an esteemed online marketplace, enables users to engage in buying and selling Bitcoin. Buy Verified Paxful Account.\n\nThe initial step involves creating an account on Paxful and completing the verification process to ensure identity authentication. Subsequently, users gain access to a diverse range of offers from fellow users on the platform. Once a suitable proposal captures your interest, you can proceed to initiate a trade with the respective user, opening the doors to a seamless Bitcoin investing experience.\n\nIn conclusion, when considering the option of purchasing verified Paxful accounts, exercising caution and conducting thorough due diligence is of utmost importance. It is highly recommended to seek reputable sources and diligently research the seller’s history and reviews before making any transactions.\n\nMoreover, it is crucial to familiarize oneself with the terms and conditions outlined by Paxful regarding account verification, bearing in mind the potential consequences of violating those terms. By adhering to these guidelines, individuals can ensure a secure and reliable experience when engaging in such transactions. Buy Verified Paxful Account.\n\n \n\nContact Us / 24 Hours Reply\nTelegram:dmhelpshop\nWhatsApp: +1 (980) 277-2786\nSkype:dmhelpshop\nEmail:dmhelpshop@gmail.com" | carika4293 |
1,906,456 | Buy verified cash app account | https://dmhelpshop.com/product/buy-verified-cash-app-account/ Buy verified cash app account Cash... | 0 | 2024-06-30T09:48:27 | https://dev.to/carika4293/buy-verified-cash-app-account-1bo1 | webdev, javascript, beginners, programming | ERROR: type should be string, got "https://dmhelpshop.com/product/buy-verified-cash-app-account/\n\n\n\n\nBuy verified cash app account\nCash app has emerged as a dominant force in the realm of mobile banking within the USA, offering unparalleled convenience for digital money transfers, deposits, and trading. As the foremost provider of fully verified cash app accounts, we take pride in our ability to deliver accounts with substantial limits. Bitcoin enablement, and an unmatched level of security.\n\nOur commitment to facilitating seamless transactions and enabling digital currency trades has garnered significant acclaim, as evidenced by the overwhelming response from our satisfied clientele. Those seeking buy verified cash app account with 100% legitimate documentation and unrestricted access need look no further. Get in touch with us promptly to acquire your verified cash app account and take advantage of all the benefits it has to offer.\n\nWhy dmhelpshop is the best place to buy USA cash app accounts?\nIt’s crucial to stay informed about any updates to the platform you’re using. If an update has been released, it’s important to explore alternative options. Contact the platform’s support team to inquire about the status of the cash app service.\n\nClearly communicate your requirements and inquire whether they can meet your needs and provide the buy verified cash app account promptly. If they assure you that they can fulfill your requirements within the specified timeframe, proceed with the verification process using the required documents.\n\nOur account verification process includes the submission of the following documents: [List of specific documents required for verification].\n\nGenuine and activated email verified\nRegistered phone number (USA)\nSelfie verified\nSSN (social security number) verified\nDriving license\nBTC enable or not enable (BTC enable best)\n100% replacement guaranteed\n100% customer satisfaction\nWhen it comes to staying on top of the latest platform updates, it’s crucial to act fast and ensure you’re positioned in the best possible place. If you’re considering a switch, reaching out to the right contacts and inquiring about the status of the buy verified cash app account service update is essential.\n\nClearly communicate your requirements and gauge their commitment to fulfilling them promptly. Once you’ve confirmed their capability, proceed with the verification process using genuine and activated email verification, a registered USA phone number, selfie verification, social security number (SSN) verification, and a valid driving license.\n\nAdditionally, assessing whether BTC enablement is available is advisable, buy verified cash app account, with a preference for this feature. It’s important to note that a 100% replacement guarantee and ensuring 100% customer satisfaction are essential benchmarks in this process.\n\nHow to use the Cash Card to make purchases?\nTo activate your Cash Card, open the Cash App on your compatible device, locate the Cash Card icon at the bottom of the screen, and tap on it. Then select “Activate Cash Card” and proceed to scan the QR code on your card. Alternatively, you can manually enter the CVV and expiration date. How To Buy Verified Cash App Accounts.\n\nAfter submitting your information, including your registered number, expiration date, and CVV code, you can start making payments by conveniently tapping your card on a contactless-enabled payment terminal. Consider obtaining a buy verified Cash App account for seamless transactions, especially for business purposes. Buy verified cash app account.\n\nWhy we suggest to unchanged the Cash App account username?\nTo activate your Cash Card, open the Cash App on your compatible device, locate the Cash Card icon at the bottom of the screen, and tap on it. Then select “Activate Cash Card” and proceed to scan the QR code on your card.\n\nAlternatively, you can manually enter the CVV and expiration date. After submitting your information, including your registered number, expiration date, and CVV code, you can start making payments by conveniently tapping your card on a contactless-enabled payment terminal. Consider obtaining a verified Cash App account for seamless transactions, especially for business purposes. Buy verified cash app account. Purchase Verified Cash App Accounts.\n\nSelecting a username in an app usually comes with the understanding that it cannot be easily changed within the app’s settings or options. This deliberate control is in place to uphold consistency and minimize potential user confusion, especially for those who have added you as a contact using your username. In addition, purchasing a Cash App account with verified genuine documents already linked to the account ensures a reliable and secure transaction experience.\n\n \n\nBuy verified cash app accounts quickly and easily for all your financial needs.\nAs the user base of our platform continues to grow, the significance of verified accounts cannot be overstated for both businesses and individuals seeking to leverage its full range of features. How To Buy Verified Cash App Accounts.\n\nFor entrepreneurs, freelancers, and investors alike, a verified cash app account opens the door to sending, receiving, and withdrawing substantial amounts of money, offering unparalleled convenience and flexibility. Whether you’re conducting business or managing personal finances, the benefits of a verified account are clear, providing a secure and efficient means to transact and manage funds at scale.\n\nWhen it comes to the rising trend of purchasing buy verified cash app account, it’s crucial to tread carefully and opt for reputable providers to steer clear of potential scams and fraudulent activities. How To Buy Verified Cash App Accounts. With numerous providers offering this service at competitive prices, it is paramount to be diligent in selecting a trusted source.\n\nThis article serves as a comprehensive guide, equipping you with the essential knowledge to navigate the process of procuring buy verified cash app account, ensuring that you are well-informed before making any purchasing decisions. Understanding the fundamentals is key, and by following this guide, you’ll be empowered to make informed choices with confidence.\n\n \n\nIs it safe to buy Cash App Verified Accounts?\nCash App, being a prominent peer-to-peer mobile payment application, is widely utilized by numerous individuals for their transactions. However, concerns regarding its safety have arisen, particularly pertaining to the purchase of “verified” accounts through Cash App. This raises questions about the security of Cash App’s verification process.\n\nUnfortunately, the answer is negative, as buying such verified accounts entails risks and is deemed unsafe. Therefore, it is crucial for everyone to exercise caution and be aware of potential vulnerabilities when using Cash App. How To Buy Verified Cash App Accounts.\n\nCash App has emerged as a widely embraced platform for purchasing Instagram Followers using PayPal, catering to a diverse range of users. This convenient application permits individuals possessing a PayPal account to procure authenticated Instagram Followers.\n\nLeveraging the Cash App, users can either opt to procure followers for a predetermined quantity or exercise patience until their account accrues a substantial follower count, subsequently making a bulk purchase. Although the Cash App provides this service, it is crucial to discern between genuine and counterfeit items. If you find yourself in search of counterfeit products such as a Rolex, a Louis Vuitton item, or a Louis Vuitton bag, there are two viable approaches to consider.\n\n \n\nWhy you need to buy verified Cash App accounts personal or business?\nThe Cash App is a versatile digital wallet enabling seamless money transfers among its users. However, it presents a concern as it facilitates transfer to both verified and unverified individuals.\n\nTo address this, the Cash App offers the option to become a verified user, which unlocks a range of advantages. Verified users can enjoy perks such as express payment, immediate issue resolution, and a generous interest-free period of up to two weeks. With its user-friendly interface and enhanced capabilities, the Cash App caters to the needs of a wide audience, ensuring convenient and secure digital transactions for all.\n\nIf you’re a business person seeking additional funds to expand your business, we have a solution for you. Payroll management can often be a challenging task, regardless of whether you’re a small family-run business or a large corporation. How To Buy Verified Cash App Accounts.\n\nImproper payment practices can lead to potential issues with your employees, as they could report you to the government. However, worry not, as we offer a reliable and efficient way to ensure proper payroll management, avoiding any potential complications. Our services provide you with the funds you need without compromising your reputation or legal standing. With our assistance, you can focus on growing your business while maintaining a professional and compliant relationship with your employees. Purchase Verified Cash App Accounts.\n\nA Cash App has emerged as a leading peer-to-peer payment method, catering to a wide range of users. With its seamless functionality, individuals can effortlessly send and receive cash in a matter of seconds, bypassing the need for a traditional bank account or social security number. Buy verified cash app account.\n\nThis accessibility makes it particularly appealing to millennials, addressing a common challenge they face in accessing physical currency. As a result, ACash App has established itself as a preferred choice among diverse audiences, enabling swift and hassle-free transactions for everyone. Purchase Verified Cash App Accounts.\n\n \n\nHow to verify Cash App accounts\nTo ensure the verification of your Cash App account, it is essential to securely store all your required documents in your account. This process includes accurately supplying your date of birth and verifying the US or UK phone number linked to your Cash App account.\n\nAs part of the verification process, you will be asked to submit accurate personal details such as your date of birth, the last four digits of your SSN, and your email address. If additional information is requested by the Cash App community to validate your account, be prepared to provide it promptly. Upon successful verification, you will gain full access to managing your account balance, as well as sending and receiving funds seamlessly. Buy verified cash app account.\n\n \n\nHow cash used for international transaction?\nExperience the seamless convenience of this innovative platform that simplifies money transfers to the level of sending a text message. It effortlessly connects users within the familiar confines of their respective currency regions, primarily in the United States and the United Kingdom.\n\nNo matter if you’re a freelancer seeking to diversify your clientele or a small business eager to enhance market presence, this solution caters to your financial needs efficiently and securely. Embrace a world of unlimited possibilities while staying connected to your currency domain. Buy verified cash app account.\n\nUnderstanding the currency capabilities of your selected payment application is essential in today’s digital landscape, where versatile financial tools are increasingly sought after. In this era of rapid technological advancements, being well-informed about platforms such as Cash App is crucial.\n\nAs we progress into the digital age, the significance of keeping abreast of such services becomes more pronounced, emphasizing the necessity of staying updated with the evolving financial trends and options available. Buy verified cash app account.\n\nOffers and advantage to buy cash app accounts cheap?\nWith Cash App, the possibilities are endless, offering numerous advantages in online marketing, cryptocurrency trading, and mobile banking while ensuring high security. As a top creator of Cash App accounts, our team possesses unparalleled expertise in navigating the platform.\n\nWe deliver accounts with maximum security and unwavering loyalty at competitive prices unmatched by other agencies. Rest assured, you can trust our services without hesitation, as we prioritize your peace of mind and satisfaction above all else.\n\nEnhance your business operations effortlessly by utilizing the Cash App e-wallet for seamless payment processing, money transfers, and various other essential tasks. Amidst a myriad of transaction platforms in existence today, the Cash App e-wallet stands out as a premier choice, offering users a multitude of functions to streamline their financial activities effectively. Buy verified cash app account.\n\nTrustbizs.com stands by the Cash App’s superiority and recommends acquiring your Cash App accounts from this trusted source to optimize your business potential.\n\nHow Customizable are the Payment Options on Cash App for Businesses?\nDiscover the flexible payment options available to businesses on Cash App, enabling a range of customization features to streamline transactions. Business users have the ability to adjust transaction amounts, incorporate tipping options, and leverage robust reporting tools for enhanced financial management.\n\nExplore trustbizs.com to acquire verified Cash App accounts with LD backup at a competitive price, ensuring a secure and efficient payment solution for your business needs. Buy verified cash app account.\n\nDiscover Cash App, an innovative platform ideal for small business owners and entrepreneurs aiming to simplify their financial operations. With its intuitive interface, Cash App empowers businesses to seamlessly receive payments and effectively oversee their finances. Emphasizing customization, this app accommodates a variety of business requirements and preferences, making it a versatile tool for all.\n\nWhere To Buy Verified Cash App Accounts\nWhen considering purchasing a verified Cash App account, it is imperative to carefully scrutinize the seller’s pricing and payment methods. Look for pricing that aligns with the market value, ensuring transparency and legitimacy. Buy verified cash app account.\n\nEqually important is the need to opt for sellers who provide secure payment channels to safeguard your financial data. Trust your intuition; skepticism towards deals that appear overly advantageous or sellers who raise red flags is warranted. It is always wise to prioritize caution and explore alternative avenues if uncertainties arise.\n\nThe Importance Of Verified Cash App Accounts\nIn today’s digital age, the significance of verified Cash App accounts cannot be overstated, as they serve as a cornerstone for secure and trustworthy online transactions.\n\nBy acquiring verified Cash App accounts, users not only establish credibility but also instill the confidence required to participate in financial endeavors with peace of mind, thus solidifying its status as an indispensable asset for individuals navigating the digital marketplace.\n\nWhen considering purchasing a verified Cash App account, it is imperative to carefully scrutinize the seller’s pricing and payment methods. Look for pricing that aligns with the market value, ensuring transparency and legitimacy. Buy verified cash app account.\n\nEqually important is the need to opt for sellers who provide secure payment channels to safeguard your financial data. Trust your intuition; skepticism towards deals that appear overly advantageous or sellers who raise red flags is warranted. It is always wise to prioritize caution and explore alternative avenues if uncertainties arise.\n\nConclusion\nEnhance your online financial transactions with verified Cash App accounts, a secure and convenient option for all individuals. By purchasing these accounts, you can access exclusive features, benefit from higher transaction limits, and enjoy enhanced protection against fraudulent activities. Streamline your financial interactions and experience peace of mind knowing your transactions are secure and efficient with verified Cash App accounts.\n\nChoose a trusted provider when acquiring accounts to guarantee legitimacy and reliability. In an era where Cash App is increasingly favored for financial transactions, possessing a verified account offers users peace of mind and ease in managing their finances. Make informed decisions to safeguard your financial assets and streamline your personal transactions effectively.\n\nContact Us / 24 Hours Reply\nTelegram:dmhelpshop\nWhatsApp: +1 (980) 277-2786\nSkype:dmhelpshop\nEmail:dmhelpshop@gmail.com\n\n\n\n\n\n" | carika4293 |
1,906,450 | What is Associative Arrays in Computer Science | In computer science, an associative array, map, symbol table, or dictionary is an abstract data type... | 0 | 2024-06-30T09:40:57 | https://dev.to/m__mdy__m/what-is-associative-arrays-in-computer-science-1dhe | webdev, beginners, programming, tutorial | In computer science, an associative array, map, symbol table, or dictionary is an abstract data type that stores a collection of (key, value) pairs, such that each possible key appears at most once in the collection. In mathematical terms, an associative array is a function with a finite domain. It supports 'lookup', '... | m__mdy__m |
1,906,454 | AI in Educational Technology: Transforming Learning Experiences | Introduction The integration of Artificial Intelligence (AI) in the educational... | 27,673 | 2024-06-30T09:40:55 | https://dev.to/rapidinnovation/ai-in-educational-technology-transforming-learning-experiences-dpg | ## Introduction
The integration of Artificial Intelligence (AI) in the educational technology
industry marks a transformative era in how educational content is delivered,
personalized, and accessed. AI technologies are increasingly being employed to
enhance the learning experience, making education more engaging, acce... | rapidinnovation | |
1,906,453 | Using Multiple DbContexts in a Single Query Execution | Introduction to DbContexts This article delves into how to manage and use multiple DbContexts in a... | 0 | 2024-06-30T09:34:05 | https://nilebits.com/blog/2024/06/multiple-dbcontexts-in-a-single-query/ | csharp, dotnet, microservices, oop | Introduction to DbContexts
This article delves into how to manage and use multiple DbContexts in a single query execution efficiently. We will explore various techniques, their pros and cons, and provide ample code examples to illustrate the concepts.
One well-liked Object-Relational Mapping (ORM) framework for.NET a... | amr-saafan |
1,906,452 | Bootstrap vs. Tailwind CSS: Which CSS Framework is Best for Your Web Development Project? | Introduction When building websites, choosing the right CSS framework can make a big... | 0 | 2024-06-30T09:33:03 | https://dev.to/hamda_mohamed_8e071c7a84b/bootstrap-vs-tailwind-css-which-css-framework-is-best-for-your-web-development-project-19ej | ### Introduction
When building websites, choosing the right CSS framework can make a big difference. Two popular frameworks are Bootstrap and Tailwind CSS. This article will compare these two to help you decide which one fits your needs best. I'll also share what I expect from the HNG Internship.
### Bootstrap: The C... | hamda_mohamed_8e071c7a84b | |
1,906,375 | How to add Favicons in Django (2024) | What is a favicon? According to W3C: A favicon is a small image displayed next to the page... | 0 | 2024-06-30T09:31:17 | https://dev.to/someab/how-to-add-favicons-in-django-2024-48da | django, favicon, html, tutorial | ## What is a favicon?
According to W3C: A favicon is a small image displayed next to the page title in the browser tab [More Info & Interactive Tool](https://www.w3schools.com/html/html_favicon.asp)
## How having a favicon helps?
 issues. This blog post will explain how I overcame this problem and share my aspirations for the HNG ... | caleb_fadare |
1,906,424 | Avoid the Chaos: How to Properly Manage Python Packages with Virtual Environments | Managing environments In embarking on projects, I've learned the hard way that starting... | 0 | 2024-06-30T09:23:22 | https://matteospanio.github.io/blog/2024/python-environments/ | python, programming, productivity, development | ## Managing environments
In embarking on projects, I've learned the hard way that starting without the right tools can lead to wasted time and frustration. This has been evident in my tendency to recklessly install packages, turning my system's Python environment into a chaotic mess. Despite the availability of better... | matteospanio |
1,906,426 | Cells with Odd Values in a Matrix(LeetCode-easy) | INTRODUCTION We, have given two array one is main array matrix and other is indices[is a... | 26,929 | 2024-06-30T09:18:08 | https://dev.to/rifat87/cells-with-odd-values-in-a-matrix-2ikh | leetcode, problem, dsa, java | #INTRODUCTION

We, have given two array one is main array matrix and other is indices[is a 2D array]. Each indices value consist two things one is row value and another is column value, indices[i] = [ri, ci]. And o... | rifat87 |
1,906,425 | hire a golang developer | Experienced Golang Developer Seeking New Opportunities About Me: Hire A Golang... | 0 | 2024-06-30T09:16:42 | https://dev.to/irishgeoff22/hire-a-golang-developer-25dj | webdev, go, freelance |
**Experienced Golang Developer Seeking New Opportunities**
---
**About Me:**
[Hire A Golang Developer](https://geoffrey.lol)
Proficient Golang developer with 5 years of experience in building, optimizing, and maintaining software applications. Passionate about leveraging Go’s unique features to create robust and s... | irishgeoff22 |
1,906,422 | what is mining process? | The process mining is an umbrella term for a combination of data mining and process management... | 0 | 2024-06-30T09:13:21 | https://dev.to/mobina_shahvar_0b01d8c3e9/mining-process-3jk5 | learning, automation, writing | The [process mining](https://samatoos.ir/articles/what-is-mining-process/) is an umbrella term for a combination of data mining and process management techniques that use advanced algorithms, machine learning, and statistical methods to analyze organizations' data.
Process mining is a set of data-driven techniques for... | mobina_shahvar_0b01d8c3e9 |
1,906,421 | Buy Negative Google Reviews | https://dmhelpshop.com/product/buy-negative-google-reviews/ Buy Negative Google Reviews Negative... | 0 | 2024-06-30T09:04:11 | https://dev.to/narofa1781/buy-negative-google-reviews-3b4j | devops, productivity, opensource, node | ERROR: type should be string, got "https://dmhelpshop.com/product/buy-negative-google-reviews/\n\n\n\n\nBuy Negative Google Reviews\nNegative reviews on Google are detrimental critiques that expose customers’ unfavorable experiences with a business. These reviews can significantly damage a company’s reputation, presenting challenges in both attracting new customers and retaining current ones. If you are considering purchasing negative Google reviews from dmhelpshop.com, we encourage you to reconsider and instead focus on providing exceptional products and services to ensure positive feedback and sustainable success.\n\nWhy Buy Negative Google Reviews from dmhelpshop\nWe take pride in our fully qualified, hardworking, and experienced team, who are committed to providing quality and safe services that meet all your needs. Our professional team ensures that you can trust us completely, knowing that your satisfaction is our top priority. With us, you can rest assured that you’re in good hands.\n\nIs Buy Negative Google Reviews safe?\nAt dmhelpshop, we understand the concern many business persons have about the safety of purchasing Buy negative Google reviews. We are here to guide you through a process that sheds light on the importance of these reviews and how we ensure they appear realistic and safe for your business. Our team of qualified and experienced computer experts has successfully handled similar cases before, and we are committed to providing a solution tailored to your specific needs. Contact us today to learn more about how we can help your business thrive.\n\nBuy Google 5 Star Reviews\nReviews represent the opinions of experienced customers who have utilized services or purchased products from various online or offline markets. These reviews convey customer demands and opinions, and ratings are assigned based on the quality of the products or services and the overall user experience. Google serves as an excellent platform for customers to leave reviews since the majority of users engage with it organically. When you purchase Buy Google 5 Star Reviews, you have the potential to influence a large number of people either positively or negatively. Positive reviews can attract customers to purchase your products, while negative reviews can deter potential customers.\n\nIf you choose to Buy Google 5 Star Reviews, people will be more inclined to consider your products. However, it is important to recognize that reviews can have both positive and negative impacts on your business. Therefore, take the time to determine which type of reviews you wish to acquire. Our experience indicates that purchasing Buy Google 5 Star Reviews can engage and connect you with a wide audience. By purchasing positive reviews, you can enhance your business profile and attract online traffic. Additionally, it is advisable to seek reviews from reputable platforms, including social media, to maintain a positive flow. We are an experienced and reliable service provider, highly knowledgeable about the impacts of reviews. Hence, we recommend purchasing verified Google reviews and ensuring their stability and non-gropability.\n\nLet us now briefly examine the direct and indirect benefits of reviews:\nReviews have the power to enhance your business profile, influencing users at an affordable cost.\nTo attract customers, consider purchasing only positive reviews, while negative reviews can be acquired to undermine your competitors. Collect negative reports on your opponents and present them as evidence.\nIf you receive negative reviews, view them as an opportunity to understand user reactions, make improvements to your products and services, and keep up with current trends.\nBy earning the trust and loyalty of customers, you can control the market value of your products. Therefore, it is essential to buy online reviews, including Buy Google 5 Star Reviews.\nReviews serve as the captivating fragrance that entices previous customers to return repeatedly.\nPositive customer opinions expressed through reviews can help you expand your business globally and achieve profitability and credibility.\nWhen you purchase positive Buy Google 5 Star Reviews, they effectively communicate the history of your company or the quality of your individual products.\nReviews act as a collective voice representing potential customers, boosting your business to amazing heights.\nNow, let’s delve into a comprehensive understanding of reviews and how they function:\nGoogle, with its significant organic user base, stands out as the premier platform for customers to leave reviews. When you purchase Buy Google 5 Star Reviews , you have the power to positively influence a vast number of individuals. Reviews are essentially written submissions by users that provide detailed insights into a company, its products, services, and other relevant aspects based on their personal experiences. In today’s business landscape, it is crucial for every business owner to consider buying verified Buy Google 5 Star Reviews, both positive and negative, in order to reap various benefits.\n\nWhy are Google reviews considered the best tool to attract customers?\nGoogle, being the leading search engine and the largest source of potential and organic customers, is highly valued by business owners. Many business owners choose to purchase Google reviews to enhance their business profiles and also sell them to third parties. Without reviews, it is challenging to reach a large customer base globally or locally. Therefore, it is crucial to consider buying positive Buy Google 5 Star Reviews from reliable sources. When you invest in Buy Google 5 Star Reviews for your business, you can expect a significant influx of potential customers, as these reviews act as a pheromone, attracting audiences towards your products and services. Every business owner aims to maximize sales and attract a substantial customer base, and purchasing Buy Google 5 Star Reviews is a strategic move.\n\nAccording to online business analysts and economists, trust and affection are the essential factors that determine whether people will work with you or do business with you. However, there are additional crucial factors to consider, such as establishing effective communication systems, providing 24/7 customer support, and maintaining product quality to engage online audiences. If any of these rules are broken, it can lead to a negative impact on your business. Therefore, obtaining positive reviews is vital for the success of an online business\n\nWhat are the benefits of purchasing reviews online?\nIn today’s fast-paced world, the impact of new technologies and IT sectors is remarkable. Compared to the past, conducting business has become significantly easier, but it is also highly competitive. To reach a global customer base, businesses must increase their presence on social media platforms as they provide the easiest way to generate organic traffic. Numerous surveys have shown that the majority of online buyers carefully read customer opinions and reviews before making purchase decisions. In fact, the percentage of customers who rely on these reviews is close to 97%. Considering these statistics, it becomes evident why we recommend buying reviews online. In an increasingly rule-based world, it is essential to take effective steps to ensure a smooth online business journey.\n\nBuy Google 5 Star Reviews\nMany people purchase reviews online from various sources and witness unique progress. Reviews serve as powerful tools to instill customer trust, influence their decision-making, and bring positive vibes to your business. Making a single mistake in this regard can lead to a significant collapse of your business. Therefore, it is crucial to focus on improving product quality, quantity, communication networks, facilities, and providing the utmost support to your customers.\n\nReviews reflect customer demands, opinions, and ratings based on their experiences with your products or services. If you purchase Buy Google 5-star reviews, it will undoubtedly attract more people to consider your offerings. Google is the ideal platform for customers to leave reviews due to its extensive organic user involvement. Therefore, investing in Buy Google 5 Star Reviews can significantly influence a large number of people in a positive way.\n\nHow to generate google reviews on my business profile?\nFocus on delivering high-quality customer service in every interaction with your customers. By creating positive experiences for them, you increase the likelihood of receiving reviews. These reviews will not only help to build loyalty among your customers but also encourage them to spread the word about your exceptional service. It is crucial to strive to meet customer needs and exceed their expectations in order to elicit positive feedback. If you are interested in purchasing affordable Google reviews, we offer that service.\n\n\n\n\n\nContact Us / 24 Hours Reply\nTelegram:dmhelpshop\nWhatsApp: +1 (980) 277-2786\nSkype:dmhelpshop\nEmail:dmhelpshop@gmail.com" | narofa1781 |
1,906,420 | Buy Negative Google Reviews | https://dmhelpshop.com/product/buy-negative-google-reviews/ Buy Negative Google Reviews Negative... | 0 | 2024-06-30T09:03:15 | https://dev.to/revojop836/buy-negative-google-reviews-4ng2 | webdev, javascript, beginners, programming | ERROR: type should be string, got "https://dmhelpshop.com/product/buy-negative-google-reviews/\n\n\nBuy Negative Google Reviews\nNegative reviews on Google are detrimental critiques that expose customers’ unfavorable experiences with a business. These reviews can significantly damage a company’s reputation, presenting challenges in both attracting new customers and retaining current ones. If you are considering purchasing negative Google reviews from dmhelpshop.com, we encourage you to reconsider and instead focus on providing exceptional products and services to ensure positive feedback and sustainable success.\n\nWhy Buy Negative Google Reviews from dmhelpshop\nWe take pride in our fully qualified, hardworking, and experienced team, who are committed to providing quality and safe services that meet all your needs. Our professional team ensures that you can trust us completely, knowing that your satisfaction is our top priority. With us, you can rest assured that you’re in good hands.\n\nIs Buy Negative Google Reviews safe?\nAt dmhelpshop, we understand the concern many business persons have about the safety of purchasing Buy negative Google reviews. We are here to guide you through a process that sheds light on the importance of these reviews and how we ensure they appear realistic and safe for your business. Our team of qualified and experienced computer experts has successfully handled similar cases before, and we are committed to providing a solution tailored to your specific needs. Contact us today to learn more about how we can help your business thrive.\n\nBuy Google 5 Star Reviews\nReviews represent the opinions of experienced customers who have utilized services or purchased products from various online or offline markets. These reviews convey customer demands and opinions, and ratings are assigned based on the quality of the products or services and the overall user experience. Google serves as an excellent platform for customers to leave reviews since the majority of users engage with it organically. When you purchase Buy Google 5 Star Reviews, you have the potential to influence a large number of people either positively or negatively. Positive reviews can attract customers to purchase your products, while negative reviews can deter potential customers.\n\nIf you choose to Buy Google 5 Star Reviews, people will be more inclined to consider your products. However, it is important to recognize that reviews can have both positive and negative impacts on your business. Therefore, take the time to determine which type of reviews you wish to acquire. Our experience indicates that purchasing Buy Google 5 Star Reviews can engage and connect you with a wide audience. By purchasing positive reviews, you can enhance your business profile and attract online traffic. Additionally, it is advisable to seek reviews from reputable platforms, including social media, to maintain a positive flow. We are an experienced and reliable service provider, highly knowledgeable about the impacts of reviews. Hence, we recommend purchasing verified Google reviews and ensuring their stability and non-gropability.\n\nLet us now briefly examine the direct and indirect benefits of reviews:\nReviews have the power to enhance your business profile, influencing users at an affordable cost.\nTo attract customers, consider purchasing only positive reviews, while negative reviews can be acquired to undermine your competitors. Collect negative reports on your opponents and present them as evidence.\nIf you receive negative reviews, view them as an opportunity to understand user reactions, make improvements to your products and services, and keep up with current trends.\nBy earning the trust and loyalty of customers, you can control the market value of your products. Therefore, it is essential to buy online reviews, including Buy Google 5 Star Reviews.\nReviews serve as the captivating fragrance that entices previous customers to return repeatedly.\nPositive customer opinions expressed through reviews can help you expand your business globally and achieve profitability and credibility.\nWhen you purchase positive Buy Google 5 Star Reviews, they effectively communicate the history of your company or the quality of your individual products.\nReviews act as a collective voice representing potential customers, boosting your business to amazing heights.\nNow, let’s delve into a comprehensive understanding of reviews and how they function:\nGoogle, with its significant organic user base, stands out as the premier platform for customers to leave reviews. When you purchase Buy Google 5 Star Reviews , you have the power to positively influence a vast number of individuals. Reviews are essentially written submissions by users that provide detailed insights into a company, its products, services, and other relevant aspects based on their personal experiences. In today’s business landscape, it is crucial for every business owner to consider buying verified Buy Google 5 Star Reviews, both positive and negative, in order to reap various benefits.\n\nWhy are Google reviews considered the best tool to attract customers?\nGoogle, being the leading search engine and the largest source of potential and organic customers, is highly valued by business owners. Many business owners choose to purchase Google reviews to enhance their business profiles and also sell them to third parties. Without reviews, it is challenging to reach a large customer base globally or locally. Therefore, it is crucial to consider buying positive Buy Google 5 Star Reviews from reliable sources. When you invest in Buy Google 5 Star Reviews for your business, you can expect a significant influx of potential customers, as these reviews act as a pheromone, attracting audiences towards your products and services. Every business owner aims to maximize sales and attract a substantial customer base, and purchasing Buy Google 5 Star Reviews is a strategic move.\n\nAccording to online business analysts and economists, trust and affection are the essential factors that determine whether people will work with you or do business with you. However, there are additional crucial factors to consider, such as establishing effective communication systems, providing 24/7 customer support, and maintaining product quality to engage online audiences. If any of these rules are broken, it can lead to a negative impact on your business. Therefore, obtaining positive reviews is vital for the success of an online business\n\nWhat are the benefits of purchasing reviews online?\nIn today’s fast-paced world, the impact of new technologies and IT sectors is remarkable. Compared to the past, conducting business has become significantly easier, but it is also highly competitive. To reach a global customer base, businesses must increase their presence on social media platforms as they provide the easiest way to generate organic traffic. Numerous surveys have shown that the majority of online buyers carefully read customer opinions and reviews before making purchase decisions. In fact, the percentage of customers who rely on these reviews is close to 97%. Considering these statistics, it becomes evident why we recommend buying reviews online. In an increasingly rule-based world, it is essential to take effective steps to ensure a smooth online business journey.\n\nBuy Google 5 Star Reviews\nMany people purchase reviews online from various sources and witness unique progress. Reviews serve as powerful tools to instill customer trust, influence their decision-making, and bring positive vibes to your business. Making a single mistake in this regard can lead to a significant collapse of your business. Therefore, it is crucial to focus on improving product quality, quantity, communication networks, facilities, and providing the utmost support to your customers.\n\nReviews reflect customer demands, opinions, and ratings based on their experiences with your products or services. If you purchase Buy Google 5-star reviews, it will undoubtedly attract more people to consider your offerings. Google is the ideal platform for customers to leave reviews due to its extensive organic user involvement. Therefore, investing in Buy Google 5 Star Reviews can significantly influence a large number of people in a positive way.\n\nHow to generate google reviews on my business profile?\nFocus on delivering high-quality customer service in every interaction with your customers. By creating positive experiences for them, you increase the likelihood of receiving reviews. These reviews will not only help to build loyalty among your customers but also encourage them to spread the word about your exceptional service. It is crucial to strive to meet customer needs and exceed their expectations in order to elicit positive feedback. If you are interested in purchasing affordable Google reviews, we offer that service.\n\n\n\n\n\nContact Us / 24 Hours Reply\nTelegram:dmhelpshop\nWhatsApp: +1 (980) 277-2786\nSkype:dmhelpshop\nEmail:dmhelpshop@gmail.com" | revojop836 |
1,906,418 | Buy Verified Paxful Account | https://dmhelpshop.com/product/buy-verified-paxful-account/ Buy Verified Paxful Account There are... | 0 | 2024-06-30T08:57:14 | https://dev.to/narofa1781/buy-verified-paxful-account-j4k | tutorial, programming, beginners, javascript | ERROR: type should be string, got "https://dmhelpshop.com/product/buy-verified-paxful-account/\n\n\n\n\nBuy Verified Paxful Account\nThere are several compelling reasons to consider purchasing a verified Paxful account. Firstly, a verified account offers enhanced security, providing peace of mind to all users. Additionally, it opens up a wider range of trading opportunities, allowing individuals to partake in various transactions, ultimately expanding their financial horizons.\n\nMoreover, Buy verified Paxful account ensures faster and more streamlined transactions, minimizing any potential delays or inconveniences. Furthermore, by opting for a verified account, users gain access to a trusted and reputable platform, fostering a sense of reliability and confidence.\n\nLastly, Paxful’s verification process is thorough and meticulous, ensuring that only genuine individuals are granted verified status, thereby creating a safer trading environment for all users. Overall, the decision to Buy Verified Paxful account can greatly enhance one’s overall trading experience, offering increased security, access to more opportunities, and a reliable platform to engage with. Buy Verified Paxful Account.\n\nBuy US verified paxful account from the best place dmhelpshop\nWhy we declared this website as the best place to buy US verified paxful account? Because, our company is established for providing the all account services in the USA (our main target) and even in the whole world. With this in mind we create paxful account and customize our accounts as professional with the real documents. Buy Verified Paxful Account.\n\nIf you want to buy US verified paxful account you should have to contact fast with us. Because our accounts are-\n\nEmail verified\nPhone number verified\nSelfie and KYC verified\nSSN (social security no.) verified\nTax ID and passport verified\nSometimes driving license verified\nMasterCard attached and verified\nUsed only genuine and real documents\n100% access of the account\nAll documents provided for customer security\nWhat is Verified Paxful Account?\nIn today’s expanding landscape of online transactions, ensuring security and reliability has become paramount. Given this context, Paxful has quickly risen as a prominent peer-to-peer Bitcoin marketplace, catering to individuals and businesses seeking trusted platforms for cryptocurrency trading.\n\nIn light of the prevalent digital scams and frauds, it is only natural for people to exercise caution when partaking in online transactions. As a result, the concept of a verified account has gained immense significance, serving as a critical feature for numerous online platforms. Paxful recognizes this need and provides a safe haven for users, streamlining their cryptocurrency buying and selling experience.\n\nFor individuals and businesses alike, Buy verified Paxful account emerges as an appealing choice, offering a secure and reliable environment in the ever-expanding world of digital transactions. Buy Verified Paxful Account.\n\nVerified Paxful Accounts are essential for establishing credibility and trust among users who want to transact securely on the platform. They serve as evidence that a user is a reliable seller or buyer, verifying their legitimacy.\n\nBut what constitutes a verified account, and how can one obtain this status on Paxful? In this exploration of verified Paxful accounts, we will unravel the significance they hold, why they are crucial, and shed light on the process behind their activation, providing a comprehensive understanding of how they function. Buy verified Paxful account.\n\n \n\nWhy should to Buy Verified Paxful Account?\nThere are several compelling reasons to consider purchasing a verified Paxful account. Firstly, a verified account offers enhanced security, providing peace of mind to all users. Additionally, it opens up a wider range of trading opportunities, allowing individuals to partake in various transactions, ultimately expanding their financial horizons.\n\nMoreover, a verified Paxful account ensures faster and more streamlined transactions, minimizing any potential delays or inconveniences. Furthermore, by opting for a verified account, users gain access to a trusted and reputable platform, fostering a sense of reliability and confidence. Buy Verified Paxful Account.\n\nLastly, Paxful’s verification process is thorough and meticulous, ensuring that only genuine individuals are granted verified status, thereby creating a safer trading environment for all users. Overall, the decision to buy a verified Paxful account can greatly enhance one’s overall trading experience, offering increased security, access to more opportunities, and a reliable platform to engage with.\n\n \n\nWhat is a Paxful Account\nPaxful and various other platforms consistently release updates that not only address security vulnerabilities but also enhance usability by introducing new features. Buy Verified Paxful Account.\n\nIn line with this, our old accounts have recently undergone upgrades, ensuring that if you purchase an old buy Verified Paxful account from dmhelpshop.com, you will gain access to an account with an impressive history and advanced features. This ensures a seamless and enhanced experience for all users, making it a worthwhile option for everyone.\n\n \n\nIs it safe to buy Paxful Verified Accounts?\nBuying on Paxful is a secure choice for everyone. However, the level of trust amplifies when purchasing from Paxful verified accounts. These accounts belong to sellers who have undergone rigorous scrutiny by Paxful. Buy verified Paxful account, you are automatically designated as a verified account. Hence, purchasing from a Paxful verified account ensures a high level of credibility and utmost reliability. Buy Verified Paxful Account.\n\nPAXFUL, a widely known peer-to-peer cryptocurrency trading platform, has gained significant popularity as a go-to website for purchasing Bitcoin and other cryptocurrencies. It is important to note, however, that while Paxful may not be the most secure option available, its reputation is considerably less problematic compared to many other marketplaces. Buy Verified Paxful Account.\n\nThis brings us to the question: is it safe to purchase Paxful Verified Accounts? Top Paxful reviews offer mixed opinions, suggesting that caution should be exercised. Therefore, users are advised to conduct thorough research and consider all aspects before proceeding with any transactions on Paxful.\n\n \n\nHow Do I Get 100% Real Verified Paxful Accoun?\nPaxful, a renowned peer-to-peer cryptocurrency marketplace, offers users the opportunity to conveniently buy and sell a wide range of cryptocurrencies. Given its growing popularity, both individuals and businesses are seeking to establish verified accounts on this platform.\n\nHowever, the process of creating a verified Paxful account can be intimidating, particularly considering the escalating prevalence of online scams and fraudulent practices. This verification procedure necessitates users to furnish personal information and vital documents, posing potential risks if not conducted meticulously.\n\nIn this comprehensive guide, we will delve into the necessary steps to create a legitimate and verified Paxful account. Our discussion will revolve around the verification process and provide valuable tips to safely navigate through it.\n\nMoreover, we will emphasize the utmost importance of maintaining the security of personal information when creating a verified account. Furthermore, we will shed light on common pitfalls to steer clear of, such as using counterfeit documents or attempting to bypass the verification process.\n\nWhether you are new to Paxful or an experienced user, this engaging paragraph aims to equip everyone with the knowledge they need to establish a secure and authentic presence on the platform.\n\nBenefits Of Verified Paxful Accounts\nVerified Paxful accounts offer numerous advantages compared to regular Paxful accounts. One notable advantage is that verified accounts contribute to building trust within the community.\n\nVerification, although a rigorous process, is essential for peer-to-peer transactions. This is why all Paxful accounts undergo verification after registration. When customers within the community possess confidence and trust, they can conveniently and securely exchange cash for Bitcoin or Ethereum instantly. Buy Verified Paxful Account.\n\nPaxful accounts, trusted and verified by sellers globally, serve as a testament to their unwavering commitment towards their business or passion, ensuring exceptional customer service at all times. Headquartered in Africa, Paxful holds the distinction of being the world’s pioneering peer-to-peer bitcoin marketplace. Spearheaded by its founder, Ray Youssef, Paxful continues to lead the way in revolutionizing the digital exchange landscape.\n\nPaxful has emerged as a favored platform for digital currency trading, catering to a diverse audience. One of Paxful’s key features is its direct peer-to-peer trading system, eliminating the need for intermediaries or cryptocurrency exchanges. By leveraging Paxful’s escrow system, users can trade securely and confidently.\n\nWhat sets Paxful apart is its commitment to identity verification, ensuring a trustworthy environment for buyers and sellers alike. With these user-centric qualities, Paxful has successfully established itself as a leading platform for hassle-free digital currency transactions, appealing to a wide range of individuals seeking a reliable and convenient trading experience. Buy Verified Paxful Account.\n\n \n\nHow paxful ensure risk-free transaction and trading?\nEngage in safe online financial activities by prioritizing verified accounts to reduce the risk of fraud. Platforms like Paxfu implement stringent identity and address verification measures to protect users from scammers and ensure credibility.\n\nWith verified accounts, users can trade with confidence, knowing they are interacting with legitimate individuals or entities. By fostering trust through verified accounts, Paxful strengthens the integrity of its ecosystem, making it a secure space for financial transactions for all users. Buy Verified Paxful Account.\n\nExperience seamless transactions by obtaining a verified Paxful account. Verification signals a user’s dedication to the platform’s guidelines, leading to the prestigious badge of trust. This trust not only expedites trades but also reduces transaction scrutiny. Additionally, verified users unlock exclusive features enhancing efficiency on Paxful. Elevate your trading experience with Verified Paxful Accounts today.\n\nIn the ever-changing realm of online trading and transactions, selecting a platform with minimal fees is paramount for optimizing returns. This choice not only enhances your financial capabilities but also facilitates more frequent trading while safeguarding gains. Buy Verified Paxful Account.\n\nExamining the details of fee configurations reveals Paxful as a frontrunner in cost-effectiveness. Acquire a verified level-3 USA Paxful account from usasmmonline.com for a secure transaction experience. Invest in verified Paxful accounts to take advantage of a leading platform in the online trading landscape.\n\n \n\nHow Old Paxful ensures a lot of Advantages?\n\nExplore the boundless opportunities that Verified Paxful accounts present for businesses looking to venture into the digital currency realm, as companies globally witness heightened profits and expansion. These success stories underline the myriad advantages of Paxful’s user-friendly interface, minimal fees, and robust trading tools, demonstrating its relevance across various sectors.\n\nBusinesses benefit from efficient transaction processing and cost-effective solutions, making Paxful a significant player in facilitating financial operations. Acquire a USA Paxful account effortlessly at a competitive rate from usasmmonline.com and unlock access to a world of possibilities. Buy Verified Paxful Account.\n\nExperience elevated convenience and accessibility through Paxful, where stories of transformation abound. Whether you are an individual seeking seamless transactions or a business eager to tap into a global market, buying old Paxful accounts unveils opportunities for growth.\n\nPaxful’s verified accounts not only offer reliability within the trading community but also serve as a testament to the platform’s ability to empower economic activities worldwide. Join the journey towards expansive possibilities and enhanced financial empowerment with Paxful today. Buy Verified Paxful Account.\n\n \n\nWhy paxful keep the security measures at the top priority?\nIn today’s digital landscape, security stands as a paramount concern for all individuals engaging in online activities, particularly within marketplaces such as Paxful. It is essential for account holders to remain informed about the comprehensive security protocols that are in place to safeguard their information.\n\nSafeguarding your Paxful account is imperative to guaranteeing the safety and security of your transactions. Two essential security components, Two-Factor Authentication and Routine Security Audits, serve as the pillars fortifying this shield of protection, ensuring a secure and trustworthy user experience for all. Buy Verified Paxful Account.\n\nConclusion\nInvesting in Bitcoin offers various avenues, and among those, utilizing a Paxful account has emerged as a favored option. Paxful, an esteemed online marketplace, enables users to engage in buying and selling Bitcoin. Buy Verified Paxful Account.\n\nThe initial step involves creating an account on Paxful and completing the verification process to ensure identity authentication. Subsequently, users gain access to a diverse range of offers from fellow users on the platform. Once a suitable proposal captures your interest, you can proceed to initiate a trade with the respective user, opening the doors to a seamless Bitcoin investing experience.\n\nIn conclusion, when considering the option of purchasing verified Paxful accounts, exercising caution and conducting thorough due diligence is of utmost importance. It is highly recommended to seek reputable sources and diligently research the seller’s history and reviews before making any transactions.\n\nMoreover, it is crucial to familiarize oneself with the terms and conditions outlined by Paxful regarding account verification, bearing in mind the potential consequences of violating those terms. By adhering to these guidelines, individuals can ensure a secure and reliable experience when engaging in such transactions. Buy Verified Paxful Account.\n\n \n\nContact Us / 24 Hours Reply\nTelegram:dmhelpshop\nWhatsApp: +1 (980) 277-2786\nSkype:dmhelpshop\nEmail:dmhelpshop@gmail.com" | narofa1781 |
1,906,412 | Node.js Asynchronous Architecture | Node.js is single threaded and operates asynchronously using the "Single Threaded Event Loop"... | 0 | 2024-06-30T08:48:05 | https://dev.to/tofail/how-nodejs-handl-multiple-task-being-single-threaded-3lh7 | node, javascript, webdev | Node.js is single threaded and operates asynchronously using the "Single Threaded Event Loop" architecture and handles multiple concurrent clients efficiently without multithreading. Node.js is actually designed to build distributed applications with many nodes and that's the reason why it's called Node. Actually, the ... | tofail |
1,906,417 | Seek a business partner that pays well | If you can create a large number of Google vocie accounts, please contact me. We also need a large... | 0 | 2024-06-30T08:56:16 | https://dev.to/jest_ferreira_d2c4636a915/seek-a-business-partner-that-pays-well-4im | If you can create a large number of Google vocie accounts, please contact me. We also need a large number of other social accounts such as Europe, America, South Korea, Japan, etc., including Facebook, Twitter, LinkedIn, index, etc. We will pay you handsomely, and all accounts will be used for charitable business promo... | jest_ferreira_d2c4636a915 | |
1,906,416 | Buy Verified Paxful Account | https://dmhelpshop.com/product/buy-verified-paxful-account/ Buy Verified Paxful Account There are... | 0 | 2024-06-30T08:56:07 | https://dev.to/revojop836/buy-verified-paxful-account-1p0m | webdev, javascript, beginners, programming | ERROR: type should be string, got "https://dmhelpshop.com/product/buy-verified-paxful-account/\n\n\nBuy Verified Paxful Account\nThere are several compelling reasons to consider purchasing a verified Paxful account. Firstly, a verified account offers enhanced security, providing peace of mind to all users. Additionally, it opens up a wider range of trading opportunities, allowing individuals to partake in various transactions, ultimately expanding their financial horizons.\n\nMoreover, Buy verified Paxful account ensures faster and more streamlined transactions, minimizing any potential delays or inconveniences. Furthermore, by opting for a verified account, users gain access to a trusted and reputable platform, fostering a sense of reliability and confidence.\n\nLastly, Paxful’s verification process is thorough and meticulous, ensuring that only genuine individuals are granted verified status, thereby creating a safer trading environment for all users. Overall, the decision to Buy Verified Paxful account can greatly enhance one’s overall trading experience, offering increased security, access to more opportunities, and a reliable platform to engage with. Buy Verified Paxful Account.\n\nBuy US verified paxful account from the best place dmhelpshop\nWhy we declared this website as the best place to buy US verified paxful account? Because, our company is established for providing the all account services in the USA (our main target) and even in the whole world. With this in mind we create paxful account and customize our accounts as professional with the real documents. Buy Verified Paxful Account.\n\nIf you want to buy US verified paxful account you should have to contact fast with us. Because our accounts are-\n\nEmail verified\nPhone number verified\nSelfie and KYC verified\nSSN (social security no.) verified\nTax ID and passport verified\nSometimes driving license verified\nMasterCard attached and verified\nUsed only genuine and real documents\n100% access of the account\nAll documents provided for customer security\nWhat is Verified Paxful Account?\nIn today’s expanding landscape of online transactions, ensuring security and reliability has become paramount. Given this context, Paxful has quickly risen as a prominent peer-to-peer Bitcoin marketplace, catering to individuals and businesses seeking trusted platforms for cryptocurrency trading.\n\nIn light of the prevalent digital scams and frauds, it is only natural for people to exercise caution when partaking in online transactions. As a result, the concept of a verified account has gained immense significance, serving as a critical feature for numerous online platforms. Paxful recognizes this need and provides a safe haven for users, streamlining their cryptocurrency buying and selling experience.\n\nFor individuals and businesses alike, Buy verified Paxful account emerges as an appealing choice, offering a secure and reliable environment in the ever-expanding world of digital transactions. Buy Verified Paxful Account.\n\nVerified Paxful Accounts are essential for establishing credibility and trust among users who want to transact securely on the platform. They serve as evidence that a user is a reliable seller or buyer, verifying their legitimacy.\n\nBut what constitutes a verified account, and how can one obtain this status on Paxful? In this exploration of verified Paxful accounts, we will unravel the significance they hold, why they are crucial, and shed light on the process behind their activation, providing a comprehensive understanding of how they function. Buy verified Paxful account.\n\n \n\nWhy should to Buy Verified Paxful Account?\nThere are several compelling reasons to consider purchasing a verified Paxful account. Firstly, a verified account offers enhanced security, providing peace of mind to all users. Additionally, it opens up a wider range of trading opportunities, allowing individuals to partake in various transactions, ultimately expanding their financial horizons.\n\nMoreover, a verified Paxful account ensures faster and more streamlined transactions, minimizing any potential delays or inconveniences. Furthermore, by opting for a verified account, users gain access to a trusted and reputable platform, fostering a sense of reliability and confidence. Buy Verified Paxful Account.\n\nLastly, Paxful’s verification process is thorough and meticulous, ensuring that only genuine individuals are granted verified status, thereby creating a safer trading environment for all users. Overall, the decision to buy a verified Paxful account can greatly enhance one’s overall trading experience, offering increased security, access to more opportunities, and a reliable platform to engage with.\n\n \n\nWhat is a Paxful Account\nPaxful and various other platforms consistently release updates that not only address security vulnerabilities but also enhance usability by introducing new features. Buy Verified Paxful Account.\n\nIn line with this, our old accounts have recently undergone upgrades, ensuring that if you purchase an old buy Verified Paxful account from dmhelpshop.com, you will gain access to an account with an impressive history and advanced features. This ensures a seamless and enhanced experience for all users, making it a worthwhile option for everyone.\n\n \n\nIs it safe to buy Paxful Verified Accounts?\nBuying on Paxful is a secure choice for everyone. However, the level of trust amplifies when purchasing from Paxful verified accounts. These accounts belong to sellers who have undergone rigorous scrutiny by Paxful. Buy verified Paxful account, you are automatically designated as a verified account. Hence, purchasing from a Paxful verified account ensures a high level of credibility and utmost reliability. Buy Verified Paxful Account.\n\nPAXFUL, a widely known peer-to-peer cryptocurrency trading platform, has gained significant popularity as a go-to website for purchasing Bitcoin and other cryptocurrencies. It is important to note, however, that while Paxful may not be the most secure option available, its reputation is considerably less problematic compared to many other marketplaces. Buy Verified Paxful Account.\n\nThis brings us to the question: is it safe to purchase Paxful Verified Accounts? Top Paxful reviews offer mixed opinions, suggesting that caution should be exercised. Therefore, users are advised to conduct thorough research and consider all aspects before proceeding with any transactions on Paxful.\n\n \n\nHow Do I Get 100% Real Verified Paxful Accoun?\nPaxful, a renowned peer-to-peer cryptocurrency marketplace, offers users the opportunity to conveniently buy and sell a wide range of cryptocurrencies. Given its growing popularity, both individuals and businesses are seeking to establish verified accounts on this platform.\n\nHowever, the process of creating a verified Paxful account can be intimidating, particularly considering the escalating prevalence of online scams and fraudulent practices. This verification procedure necessitates users to furnish personal information and vital documents, posing potential risks if not conducted meticulously.\n\nIn this comprehensive guide, we will delve into the necessary steps to create a legitimate and verified Paxful account. Our discussion will revolve around the verification process and provide valuable tips to safely navigate through it.\n\nMoreover, we will emphasize the utmost importance of maintaining the security of personal information when creating a verified account. Furthermore, we will shed light on common pitfalls to steer clear of, such as using counterfeit documents or attempting to bypass the verification process.\n\nWhether you are new to Paxful or an experienced user, this engaging paragraph aims to equip everyone with the knowledge they need to establish a secure and authentic presence on the platform.\n\nBenefits Of Verified Paxful Accounts\nVerified Paxful accounts offer numerous advantages compared to regular Paxful accounts. One notable advantage is that verified accounts contribute to building trust within the community.\n\nVerification, although a rigorous process, is essential for peer-to-peer transactions. This is why all Paxful accounts undergo verification after registration. When customers within the community possess confidence and trust, they can conveniently and securely exchange cash for Bitcoin or Ethereum instantly. Buy Verified Paxful Account.\n\nPaxful accounts, trusted and verified by sellers globally, serve as a testament to their unwavering commitment towards their business or passion, ensuring exceptional customer service at all times. Headquartered in Africa, Paxful holds the distinction of being the world’s pioneering peer-to-peer bitcoin marketplace. Spearheaded by its founder, Ray Youssef, Paxful continues to lead the way in revolutionizing the digital exchange landscape.\n\nPaxful has emerged as a favored platform for digital currency trading, catering to a diverse audience. One of Paxful’s key features is its direct peer-to-peer trading system, eliminating the need for intermediaries or cryptocurrency exchanges. By leveraging Paxful’s escrow system, users can trade securely and confidently.\n\nWhat sets Paxful apart is its commitment to identity verification, ensuring a trustworthy environment for buyers and sellers alike. With these user-centric qualities, Paxful has successfully established itself as a leading platform for hassle-free digital currency transactions, appealing to a wide range of individuals seeking a reliable and convenient trading experience. Buy Verified Paxful Account.\n\n \n\nHow paxful ensure risk-free transaction and trading?\nEngage in safe online financial activities by prioritizing verified accounts to reduce the risk of fraud. Platforms like Paxfu implement stringent identity and address verification measures to protect users from scammers and ensure credibility.\n\nWith verified accounts, users can trade with confidence, knowing they are interacting with legitimate individuals or entities. By fostering trust through verified accounts, Paxful strengthens the integrity of its ecosystem, making it a secure space for financial transactions for all users. Buy Verified Paxful Account.\n\nExperience seamless transactions by obtaining a verified Paxful account. Verification signals a user’s dedication to the platform’s guidelines, leading to the prestigious badge of trust. This trust not only expedites trades but also reduces transaction scrutiny. Additionally, verified users unlock exclusive features enhancing efficiency on Paxful. Elevate your trading experience with Verified Paxful Accounts today.\n\nIn the ever-changing realm of online trading and transactions, selecting a platform with minimal fees is paramount for optimizing returns. This choice not only enhances your financial capabilities but also facilitates more frequent trading while safeguarding gains. Buy Verified Paxful Account.\n\nExamining the details of fee configurations reveals Paxful as a frontrunner in cost-effectiveness. Acquire a verified level-3 USA Paxful account from usasmmonline.com for a secure transaction experience. Invest in verified Paxful accounts to take advantage of a leading platform in the online trading landscape.\n\n \n\nHow Old Paxful ensures a lot of Advantages?\n\nExplore the boundless opportunities that Verified Paxful accounts present for businesses looking to venture into the digital currency realm, as companies globally witness heightened profits and expansion. These success stories underline the myriad advantages of Paxful’s user-friendly interface, minimal fees, and robust trading tools, demonstrating its relevance across various sectors.\n\nBusinesses benefit from efficient transaction processing and cost-effective solutions, making Paxful a significant player in facilitating financial operations. Acquire a USA Paxful account effortlessly at a competitive rate from usasmmonline.com and unlock access to a world of possibilities. Buy Verified Paxful Account.\n\nExperience elevated convenience and accessibility through Paxful, where stories of transformation abound. Whether you are an individual seeking seamless transactions or a business eager to tap into a global market, buying old Paxful accounts unveils opportunities for growth.\n\nPaxful’s verified accounts not only offer reliability within the trading community but also serve as a testament to the platform’s ability to empower economic activities worldwide. Join the journey towards expansive possibilities and enhanced financial empowerment with Paxful today. Buy Verified Paxful Account.\n\n \n\nWhy paxful keep the security measures at the top priority?\nIn today’s digital landscape, security stands as a paramount concern for all individuals engaging in online activities, particularly within marketplaces such as Paxful. It is essential for account holders to remain informed about the comprehensive security protocols that are in place to safeguard their information.\n\nSafeguarding your Paxful account is imperative to guaranteeing the safety and security of your transactions. Two essential security components, Two-Factor Authentication and Routine Security Audits, serve as the pillars fortifying this shield of protection, ensuring a secure and trustworthy user experience for all. Buy Verified Paxful Account.\n\nConclusion\nInvesting in Bitcoin offers various avenues, and among those, utilizing a Paxful account has emerged as a favored option. Paxful, an esteemed online marketplace, enables users to engage in buying and selling Bitcoin. Buy Verified Paxful Account.\n\nThe initial step involves creating an account on Paxful and completing the verification process to ensure identity authentication. Subsequently, users gain access to a diverse range of offers from fellow users on the platform. Once a suitable proposal captures your interest, you can proceed to initiate a trade with the respective user, opening the doors to a seamless Bitcoin investing experience.\n\nIn conclusion, when considering the option of purchasing verified Paxful accounts, exercising caution and conducting thorough due diligence is of utmost importance. It is highly recommended to seek reputable sources and diligently research the seller’s history and reviews before making any transactions.\n\nMoreover, it is crucial to familiarize oneself with the terms and conditions outlined by Paxful regarding account verification, bearing in mind the potential consequences of violating those terms. By adhering to these guidelines, individuals can ensure a secure and reliable experience when engaging in such transactions. Buy Verified Paxful Account.\n\nContact Us / 24 Hours Reply\nTelegram:dmhelpshop\nWhatsApp: +1 (980) 277-2786\nSkype:dmhelpshop\nEmail:dmhelpshop@gmail.com\n\n " | revojop836 |
1,906,415 | Web Components vs. Vanilla JavaScript: A Niche Comparison in Frontend Technologies | In the world of frontend development, countless tools help developers create dynamic web... | 0 | 2024-06-30T08:54:00 | https://dev.to/caleb_fadare/web-components-vs-vanilla-javascript-a-niche-comparison-in-frontend-technologies-34mo | webdev, javascript, webcomponents, programming | In the world of frontend development, countless tools help developers create dynamic web applications. While ReactJS is popular—especially here at HNG—it's worth exploring other frontend technologies. Today, we'll compare Web Components and Vanilla JavaScript.
## Web Components: Building Custom Elements Natively
... | caleb_fadare |
1,906,414 | The Ultimate Guide to Booking a Party Bus in Perth | Are you looking to take your next celebration in Perth to the next level? Look no further than a... | 0 | 2024-06-30T08:51:29 | https://dev.to/sadman_sadik_e2929557d86d/the-ultimate-guide-to-booking-a-party-bus-in-perth-63k | webdev, beginners, javascript, programming | Are you looking to take your next celebration in Perth to the next level? Look no further than a party bus! Party buses have become the ultimate way to elevate any event, whether it's a birthday bash, a hen or stag do, a corporate function, or just a fun night out with friends. In this comprehensive guide, we'll explor... | sadman_sadik_e2929557d86d |
1,906,413 | Buy verified cash app account | https://dmhelpshop.com/product/buy-verified-cash-app-account/ Buy verified cash app account Cash... | 0 | 2024-06-30T08:48:25 | https://dev.to/narofa1781/buy-verified-cash-app-account-58bk | webdev, javascript, beginners, programming | ERROR: type should be string, got "https://dmhelpshop.com/product/buy-verified-cash-app-account/\n\n\n\n\nBuy verified cash app account\nCash app has emerged as a dominant force in the realm of mobile banking within the USA, offering unparalleled convenience for digital money transfers, deposits, and trading. As the foremost provider of fully verified cash app accounts, we take pride in our ability to deliver accounts with substantial limits. Bitcoin enablement, and an unmatched level of security.\n\nOur commitment to facilitating seamless transactions and enabling digital currency trades has garnered significant acclaim, as evidenced by the overwhelming response from our satisfied clientele. Those seeking buy verified cash app account with 100% legitimate documentation and unrestricted access need look no further. Get in touch with us promptly to acquire your verified cash app account and take advantage of all the benefits it has to offer.\n\nWhy dmhelpshop is the best place to buy USA cash app accounts?\nIt’s crucial to stay informed about any updates to the platform you’re using. If an update has been released, it’s important to explore alternative options. Contact the platform’s support team to inquire about the status of the cash app service.\n\nClearly communicate your requirements and inquire whether they can meet your needs and provide the buy verified cash app account promptly. If they assure you that they can fulfill your requirements within the specified timeframe, proceed with the verification process using the required documents.\n\nOur account verification process includes the submission of the following documents: [List of specific documents required for verification].\n\nGenuine and activated email verified\nRegistered phone number (USA)\nSelfie verified\nSSN (social security number) verified\nDriving license\nBTC enable or not enable (BTC enable best)\n100% replacement guaranteed\n100% customer satisfaction\nWhen it comes to staying on top of the latest platform updates, it’s crucial to act fast and ensure you’re positioned in the best possible place. If you’re considering a switch, reaching out to the right contacts and inquiring about the status of the buy verified cash app account service update is essential.\n\nClearly communicate your requirements and gauge their commitment to fulfilling them promptly. Once you’ve confirmed their capability, proceed with the verification process using genuine and activated email verification, a registered USA phone number, selfie verification, social security number (SSN) verification, and a valid driving license.\n\nAdditionally, assessing whether BTC enablement is available is advisable, buy verified cash app account, with a preference for this feature. It’s important to note that a 100% replacement guarantee and ensuring 100% customer satisfaction are essential benchmarks in this process.\n\nHow to use the Cash Card to make purchases?\nTo activate your Cash Card, open the Cash App on your compatible device, locate the Cash Card icon at the bottom of the screen, and tap on it. Then select “Activate Cash Card” and proceed to scan the QR code on your card. Alternatively, you can manually enter the CVV and expiration date. How To Buy Verified Cash App Accounts.\n\nAfter submitting your information, including your registered number, expiration date, and CVV code, you can start making payments by conveniently tapping your card on a contactless-enabled payment terminal. Consider obtaining a buy verified Cash App account for seamless transactions, especially for business purposes. Buy verified cash app account.\n\nWhy we suggest to unchanged the Cash App account username?\nTo activate your Cash Card, open the Cash App on your compatible device, locate the Cash Card icon at the bottom of the screen, and tap on it. Then select “Activate Cash Card” and proceed to scan the QR code on your card.\n\nAlternatively, you can manually enter the CVV and expiration date. After submitting your information, including your registered number, expiration date, and CVV code, you can start making payments by conveniently tapping your card on a contactless-enabled payment terminal. Consider obtaining a verified Cash App account for seamless transactions, especially for business purposes. Buy verified cash app account. Purchase Verified Cash App Accounts.\n\nSelecting a username in an app usually comes with the understanding that it cannot be easily changed within the app’s settings or options. This deliberate control is in place to uphold consistency and minimize potential user confusion, especially for those who have added you as a contact using your username. In addition, purchasing a Cash App account with verified genuine documents already linked to the account ensures a reliable and secure transaction experience.\n\n \n\nBuy verified cash app accounts quickly and easily for all your financial needs.\nAs the user base of our platform continues to grow, the significance of verified accounts cannot be overstated for both businesses and individuals seeking to leverage its full range of features. How To Buy Verified Cash App Accounts.\n\nFor entrepreneurs, freelancers, and investors alike, a verified cash app account opens the door to sending, receiving, and withdrawing substantial amounts of money, offering unparalleled convenience and flexibility. Whether you’re conducting business or managing personal finances, the benefits of a verified account are clear, providing a secure and efficient means to transact and manage funds at scale.\n\nWhen it comes to the rising trend of purchasing buy verified cash app account, it’s crucial to tread carefully and opt for reputable providers to steer clear of potential scams and fraudulent activities. How To Buy Verified Cash App Accounts. With numerous providers offering this service at competitive prices, it is paramount to be diligent in selecting a trusted source.\n\nThis article serves as a comprehensive guide, equipping you with the essential knowledge to navigate the process of procuring buy verified cash app account, ensuring that you are well-informed before making any purchasing decisions. Understanding the fundamentals is key, and by following this guide, you’ll be empowered to make informed choices with confidence.\n\n \n\nIs it safe to buy Cash App Verified Accounts?\nCash App, being a prominent peer-to-peer mobile payment application, is widely utilized by numerous individuals for their transactions. However, concerns regarding its safety have arisen, particularly pertaining to the purchase of “verified” accounts through Cash App. This raises questions about the security of Cash App’s verification process.\n\nUnfortunately, the answer is negative, as buying such verified accounts entails risks and is deemed unsafe. Therefore, it is crucial for everyone to exercise caution and be aware of potential vulnerabilities when using Cash App. How To Buy Verified Cash App Accounts.\n\nCash App has emerged as a widely embraced platform for purchasing Instagram Followers using PayPal, catering to a diverse range of users. This convenient application permits individuals possessing a PayPal account to procure authenticated Instagram Followers.\n\nLeveraging the Cash App, users can either opt to procure followers for a predetermined quantity or exercise patience until their account accrues a substantial follower count, subsequently making a bulk purchase. Although the Cash App provides this service, it is crucial to discern between genuine and counterfeit items. If you find yourself in search of counterfeit products such as a Rolex, a Louis Vuitton item, or a Louis Vuitton bag, there are two viable approaches to consider.\n\n \n\nWhy you need to buy verified Cash App accounts personal or business?\nThe Cash App is a versatile digital wallet enabling seamless money transfers among its users. However, it presents a concern as it facilitates transfer to both verified and unverified individuals.\n\nTo address this, the Cash App offers the option to become a verified user, which unlocks a range of advantages. Verified users can enjoy perks such as express payment, immediate issue resolution, and a generous interest-free period of up to two weeks. With its user-friendly interface and enhanced capabilities, the Cash App caters to the needs of a wide audience, ensuring convenient and secure digital transactions for all.\n\nIf you’re a business person seeking additional funds to expand your business, we have a solution for you. Payroll management can often be a challenging task, regardless of whether you’re a small family-run business or a large corporation. How To Buy Verified Cash App Accounts.\n\nImproper payment practices can lead to potential issues with your employees, as they could report you to the government. However, worry not, as we offer a reliable and efficient way to ensure proper payroll management, avoiding any potential complications. Our services provide you with the funds you need without compromising your reputation or legal standing. With our assistance, you can focus on growing your business while maintaining a professional and compliant relationship with your employees. Purchase Verified Cash App Accounts.\n\nA Cash App has emerged as a leading peer-to-peer payment method, catering to a wide range of users. With its seamless functionality, individuals can effortlessly send and receive cash in a matter of seconds, bypassing the need for a traditional bank account or social security number. Buy verified cash app account.\n\nThis accessibility makes it particularly appealing to millennials, addressing a common challenge they face in accessing physical currency. As a result, ACash App has established itself as a preferred choice among diverse audiences, enabling swift and hassle-free transactions for everyone. Purchase Verified Cash App Accounts.\n\n \n\nHow to verify Cash App accounts\nTo ensure the verification of your Cash App account, it is essential to securely store all your required documents in your account. This process includes accurately supplying your date of birth and verifying the US or UK phone number linked to your Cash App account.\n\nAs part of the verification process, you will be asked to submit accurate personal details such as your date of birth, the last four digits of your SSN, and your email address. If additional information is requested by the Cash App community to validate your account, be prepared to provide it promptly. Upon successful verification, you will gain full access to managing your account balance, as well as sending and receiving funds seamlessly. Buy verified cash app account.\n\n \n\nHow cash used for international transaction?\nExperience the seamless convenience of this innovative platform that simplifies money transfers to the level of sending a text message. It effortlessly connects users within the familiar confines of their respective currency regions, primarily in the United States and the United Kingdom.\n\nNo matter if you’re a freelancer seeking to diversify your clientele or a small business eager to enhance market presence, this solution caters to your financial needs efficiently and securely. Embrace a world of unlimited possibilities while staying connected to your currency domain. Buy verified cash app account.\n\nUnderstanding the currency capabilities of your selected payment application is essential in today’s digital landscape, where versatile financial tools are increasingly sought after. In this era of rapid technological advancements, being well-informed about platforms such as Cash App is crucial.\n\nAs we progress into the digital age, the significance of keeping abreast of such services becomes more pronounced, emphasizing the necessity of staying updated with the evolving financial trends and options available. Buy verified cash app account.\n\nOffers and advantage to buy cash app accounts cheap?\nWith Cash App, the possibilities are endless, offering numerous advantages in online marketing, cryptocurrency trading, and mobile banking while ensuring high security. As a top creator of Cash App accounts, our team possesses unparalleled expertise in navigating the platform.\n\nWe deliver accounts with maximum security and unwavering loyalty at competitive prices unmatched by other agencies. Rest assured, you can trust our services without hesitation, as we prioritize your peace of mind and satisfaction above all else.\n\nEnhance your business operations effortlessly by utilizing the Cash App e-wallet for seamless payment processing, money transfers, and various other essential tasks. Amidst a myriad of transaction platforms in existence today, the Cash App e-wallet stands out as a premier choice, offering users a multitude of functions to streamline their financial activities effectively. Buy verified cash app account.\n\nTrustbizs.com stands by the Cash App’s superiority and recommends acquiring your Cash App accounts from this trusted source to optimize your business potential.\n\nHow Customizable are the Payment Options on Cash App for Businesses?\nDiscover the flexible payment options available to businesses on Cash App, enabling a range of customization features to streamline transactions. Business users have the ability to adjust transaction amounts, incorporate tipping options, and leverage robust reporting tools for enhanced financial management.\n\nExplore trustbizs.com to acquire verified Cash App accounts with LD backup at a competitive price, ensuring a secure and efficient payment solution for your business needs. Buy verified cash app account.\n\nDiscover Cash App, an innovative platform ideal for small business owners and entrepreneurs aiming to simplify their financial operations. With its intuitive interface, Cash App empowers businesses to seamlessly receive payments and effectively oversee their finances. Emphasizing customization, this app accommodates a variety of business requirements and preferences, making it a versatile tool for all.\n\nWhere To Buy Verified Cash App Accounts\nWhen considering purchasing a verified Cash App account, it is imperative to carefully scrutinize the seller’s pricing and payment methods. Look for pricing that aligns with the market value, ensuring transparency and legitimacy. Buy verified cash app account.\n\nEqually important is the need to opt for sellers who provide secure payment channels to safeguard your financial data. Trust your intuition; skepticism towards deals that appear overly advantageous or sellers who raise red flags is warranted. It is always wise to prioritize caution and explore alternative avenues if uncertainties arise.\n\nThe Importance Of Verified Cash App Accounts\nIn today’s digital age, the significance of verified Cash App accounts cannot be overstated, as they serve as a cornerstone for secure and trustworthy online transactions.\n\nBy acquiring verified Cash App accounts, users not only establish credibility but also instill the confidence required to participate in financial endeavors with peace of mind, thus solidifying its status as an indispensable asset for individuals navigating the digital marketplace.\n\nWhen considering purchasing a verified Cash App account, it is imperative to carefully scrutinize the seller’s pricing and payment methods. Look for pricing that aligns with the market value, ensuring transparency and legitimacy. Buy verified cash app account.\n\nEqually important is the need to opt for sellers who provide secure payment channels to safeguard your financial data. Trust your intuition; skepticism towards deals that appear overly advantageous or sellers who raise red flags is warranted. It is always wise to prioritize caution and explore alternative avenues if uncertainties arise.\n\nConclusion\nEnhance your online financial transactions with verified Cash App accounts, a secure and convenient option for all individuals. By purchasing these accounts, you can access exclusive features, benefit from higher transaction limits, and enjoy enhanced protection against fraudulent activities. Streamline your financial interactions and experience peace of mind knowing your transactions are secure and efficient with verified Cash App accounts.\n\nChoose a trusted provider when acquiring accounts to guarantee legitimacy and reliability. In an era where Cash App is increasingly favored for financial transactions, possessing a verified account offers users peace of mind and ease in managing their finances. Make informed decisions to safeguard your financial assets and streamline your personal transactions effectively.\n\nContact Us / 24 Hours Reply\nTelegram:dmhelpshop\nWhatsApp: +1 (980) 277-2786\nSkype:dmhelpshop\nEmail:dmhelpshop@gmail.com\n\n\n\n" | narofa1781 |
1,906,410 | Buy verified cash app account | https://dmhelpshop.com/product/buy-verified-cash-app-account/ Buy verified cash app account Cash... | 0 | 2024-06-30T08:45:55 | https://dev.to/revojop836/buy-verified-cash-app-account-48id | webdev, javascript, beginners, programming | ERROR: type should be string, got "https://dmhelpshop.com/product/buy-verified-cash-app-account/\n\n\nBuy verified cash app account\nCash app has emerged as a dominant force in the realm of mobile banking within the USA, offering unparalleled convenience for digital money transfers, deposits, and trading. As the foremost provider of fully verified cash app accounts, we take pride in our ability to deliver accounts with substantial limits. Bitcoin enablement, and an unmatched level of security.\n\nOur commitment to facilitating seamless transactions and enabling digital currency trades has garnered significant acclaim, as evidenced by the overwhelming response from our satisfied clientele. Those seeking buy verified cash app account with 100% legitimate documentation and unrestricted access need look no further. Get in touch with us promptly to acquire your verified cash app account and take advantage of all the benefits it has to offer.\n\nWhy dmhelpshop is the best place to buy USA cash app accounts?\nIt’s crucial to stay informed about any updates to the platform you’re using. If an update has been released, it’s important to explore alternative options. Contact the platform’s support team to inquire about the status of the cash app service.\n\nClearly communicate your requirements and inquire whether they can meet your needs and provide the buy verified cash app account promptly. If they assure you that they can fulfill your requirements within the specified timeframe, proceed with the verification process using the required documents.\n\nOur account verification process includes the submission of the following documents: [List of specific documents required for verification].\n\nGenuine and activated email verified\nRegistered phone number (USA)\nSelfie verified\nSSN (social security number) verified\nDriving license\nBTC enable or not enable (BTC enable best)\n100% replacement guaranteed\n100% customer satisfaction\nWhen it comes to staying on top of the latest platform updates, it’s crucial to act fast and ensure you’re positioned in the best possible place. If you’re considering a switch, reaching out to the right contacts and inquiring about the status of the buy verified cash app account service update is essential.\n\nClearly communicate your requirements and gauge their commitment to fulfilling them promptly. Once you’ve confirmed their capability, proceed with the verification process using genuine and activated email verification, a registered USA phone number, selfie verification, social security number (SSN) verification, and a valid driving license.\n\nAdditionally, assessing whether BTC enablement is available is advisable, buy verified cash app account, with a preference for this feature. It’s important to note that a 100% replacement guarantee and ensuring 100% customer satisfaction are essential benchmarks in this process.\n\nHow to use the Cash Card to make purchases?\nTo activate your Cash Card, open the Cash App on your compatible device, locate the Cash Card icon at the bottom of the screen, and tap on it. Then select “Activate Cash Card” and proceed to scan the QR code on your card. Alternatively, you can manually enter the CVV and expiration date. How To Buy Verified Cash App Accounts.\n\nAfter submitting your information, including your registered number, expiration date, and CVV code, you can start making payments by conveniently tapping your card on a contactless-enabled payment terminal. Consider obtaining a buy verified Cash App account for seamless transactions, especially for business purposes. Buy verified cash app account.\n\nWhy we suggest to unchanged the Cash App account username?\nTo activate your Cash Card, open the Cash App on your compatible device, locate the Cash Card icon at the bottom of the screen, and tap on it. Then select “Activate Cash Card” and proceed to scan the QR code on your card.\n\nAlternatively, you can manually enter the CVV and expiration date. After submitting your information, including your registered number, expiration date, and CVV code, you can start making payments by conveniently tapping your card on a contactless-enabled payment terminal. Consider obtaining a verified Cash App account for seamless transactions, especially for business purposes. Buy verified cash app account. Purchase Verified Cash App Accounts.\n\nSelecting a username in an app usually comes with the understanding that it cannot be easily changed within the app’s settings or options. This deliberate control is in place to uphold consistency and minimize potential user confusion, especially for those who have added you as a contact using your username. In addition, purchasing a Cash App account with verified genuine documents already linked to the account ensures a reliable and secure transaction experience.\n\n \n\nBuy verified cash app accounts quickly and easily for all your financial needs.\nAs the user base of our platform continues to grow, the significance of verified accounts cannot be overstated for both businesses and individuals seeking to leverage its full range of features. How To Buy Verified Cash App Accounts.\n\nFor entrepreneurs, freelancers, and investors alike, a verified cash app account opens the door to sending, receiving, and withdrawing substantial amounts of money, offering unparalleled convenience and flexibility. Whether you’re conducting business or managing personal finances, the benefits of a verified account are clear, providing a secure and efficient means to transact and manage funds at scale.\n\nWhen it comes to the rising trend of purchasing buy verified cash app account, it’s crucial to tread carefully and opt for reputable providers to steer clear of potential scams and fraudulent activities. How To Buy Verified Cash App Accounts. With numerous providers offering this service at competitive prices, it is paramount to be diligent in selecting a trusted source.\n\nThis article serves as a comprehensive guide, equipping you with the essential knowledge to navigate the process of procuring buy verified cash app account, ensuring that you are well-informed before making any purchasing decisions. Understanding the fundamentals is key, and by following this guide, you’ll be empowered to make informed choices with confidence.\n\n \n\nIs it safe to buy Cash App Verified Accounts?\nCash App, being a prominent peer-to-peer mobile payment application, is widely utilized by numerous individuals for their transactions. However, concerns regarding its safety have arisen, particularly pertaining to the purchase of “verified” accounts through Cash App. This raises questions about the security of Cash App’s verification process.\n\nUnfortunately, the answer is negative, as buying such verified accounts entails risks and is deemed unsafe. Therefore, it is crucial for everyone to exercise caution and be aware of potential vulnerabilities when using Cash App. How To Buy Verified Cash App Accounts.\n\nCash App has emerged as a widely embraced platform for purchasing Instagram Followers using PayPal, catering to a diverse range of users. This convenient application permits individuals possessing a PayPal account to procure authenticated Instagram Followers.\n\nLeveraging the Cash App, users can either opt to procure followers for a predetermined quantity or exercise patience until their account accrues a substantial follower count, subsequently making a bulk purchase. Although the Cash App provides this service, it is crucial to discern between genuine and counterfeit items. If you find yourself in search of counterfeit products such as a Rolex, a Louis Vuitton item, or a Louis Vuitton bag, there are two viable approaches to consider.\n\n \n\nWhy you need to buy verified Cash App accounts personal or business?\nThe Cash App is a versatile digital wallet enabling seamless money transfers among its users. However, it presents a concern as it facilitates transfer to both verified and unverified individuals.\n\nTo address this, the Cash App offers the option to become a verified user, which unlocks a range of advantages. Verified users can enjoy perks such as express payment, immediate issue resolution, and a generous interest-free period of up to two weeks. With its user-friendly interface and enhanced capabilities, the Cash App caters to the needs of a wide audience, ensuring convenient and secure digital transactions for all.\n\nIf you’re a business person seeking additional funds to expand your business, we have a solution for you. Payroll management can often be a challenging task, regardless of whether you’re a small family-run business or a large corporation. How To Buy Verified Cash App Accounts.\n\nImproper payment practices can lead to potential issues with your employees, as they could report you to the government. However, worry not, as we offer a reliable and efficient way to ensure proper payroll management, avoiding any potential complications. Our services provide you with the funds you need without compromising your reputation or legal standing. With our assistance, you can focus on growing your business while maintaining a professional and compliant relationship with your employees. Purchase Verified Cash App Accounts.\n\nA Cash App has emerged as a leading peer-to-peer payment method, catering to a wide range of users. With its seamless functionality, individuals can effortlessly send and receive cash in a matter of seconds, bypassing the need for a traditional bank account or social security number. Buy verified cash app account.\n\nThis accessibility makes it particularly appealing to millennials, addressing a common challenge they face in accessing physical currency. As a result, ACash App has established itself as a preferred choice among diverse audiences, enabling swift and hassle-free transactions for everyone. Purchase Verified Cash App Accounts.\n\n \n\nHow to verify Cash App accounts\nTo ensure the verification of your Cash App account, it is essential to securely store all your required documents in your account. This process includes accurately supplying your date of birth and verifying the US or UK phone number linked to your Cash App account.\n\nAs part of the verification process, you will be asked to submit accurate personal details such as your date of birth, the last four digits of your SSN, and your email address. If additional information is requested by the Cash App community to validate your account, be prepared to provide it promptly. Upon successful verification, you will gain full access to managing your account balance, as well as sending and receiving funds seamlessly. Buy verified cash app account.\n\n \n\nHow cash used for international transaction?\nExperience the seamless convenience of this innovative platform that simplifies money transfers to the level of sending a text message. It effortlessly connects users within the familiar confines of their respective currency regions, primarily in the United States and the United Kingdom.\n\nNo matter if you’re a freelancer seeking to diversify your clientele or a small business eager to enhance market presence, this solution caters to your financial needs efficiently and securely. Embrace a world of unlimited possibilities while staying connected to your currency domain. Buy verified cash app account.\n\nUnderstanding the currency capabilities of your selected payment application is essential in today’s digital landscape, where versatile financial tools are increasingly sought after. In this era of rapid technological advancements, being well-informed about platforms such as Cash App is crucial.\n\nAs we progress into the digital age, the significance of keeping abreast of such services becomes more pronounced, emphasizing the necessity of staying updated with the evolving financial trends and options available. Buy verified cash app account.\n\nOffers and advantage to buy cash app accounts cheap?\nWith Cash App, the possibilities are endless, offering numerous advantages in online marketing, cryptocurrency trading, and mobile banking while ensuring high security. As a top creator of Cash App accounts, our team possesses unparalleled expertise in navigating the platform.\n\nWe deliver accounts with maximum security and unwavering loyalty at competitive prices unmatched by other agencies. Rest assured, you can trust our services without hesitation, as we prioritize your peace of mind and satisfaction above all else.\n\nEnhance your business operations effortlessly by utilizing the Cash App e-wallet for seamless payment processing, money transfers, and various other essential tasks. Amidst a myriad of transaction platforms in existence today, the Cash App e-wallet stands out as a premier choice, offering users a multitude of functions to streamline their financial activities effectively. Buy verified cash app account.\n\nTrustbizs.com stands by the Cash App’s superiority and recommends acquiring your Cash App accounts from this trusted source to optimize your business potential.\n\nHow Customizable are the Payment Options on Cash App for Businesses?\nDiscover the flexible payment options available to businesses on Cash App, enabling a range of customization features to streamline transactions. Business users have the ability to adjust transaction amounts, incorporate tipping options, and leverage robust reporting tools for enhanced financial management.\n\nExplore trustbizs.com to acquire verified Cash App accounts with LD backup at a competitive price, ensuring a secure and efficient payment solution for your business needs. Buy verified cash app account.\n\nDiscover Cash App, an innovative platform ideal for small business owners and entrepreneurs aiming to simplify their financial operations. With its intuitive interface, Cash App empowers businesses to seamlessly receive payments and effectively oversee their finances. Emphasizing customization, this app accommodates a variety of business requirements and preferences, making it a versatile tool for all.\n\nWhere To Buy Verified Cash App Accounts\nWhen considering purchasing a verified Cash App account, it is imperative to carefully scrutinize the seller’s pricing and payment methods. Look for pricing that aligns with the market value, ensuring transparency and legitimacy. Buy verified cash app account.\n\nEqually important is the need to opt for sellers who provide secure payment channels to safeguard your financial data. Trust your intuition; skepticism towards deals that appear overly advantageous or sellers who raise red flags is warranted. It is always wise to prioritize caution and explore alternative avenues if uncertainties arise.\n\nThe Importance Of Verified Cash App Accounts\nIn today’s digital age, the significance of verified Cash App accounts cannot be overstated, as they serve as a cornerstone for secure and trustworthy online transactions.\n\nBy acquiring verified Cash App accounts, users not only establish credibility but also instill the confidence required to participate in financial endeavors with peace of mind, thus solidifying its status as an indispensable asset for individuals navigating the digital marketplace.\n\nWhen considering purchasing a verified Cash App account, it is imperative to carefully scrutinize the seller’s pricing and payment methods. Look for pricing that aligns with the market value, ensuring transparency and legitimacy. Buy verified cash app account.\n\nEqually important is the need to opt for sellers who provide secure payment channels to safeguard your financial data. Trust your intuition; skepticism towards deals that appear overly advantageous or sellers who raise red flags is warranted. It is always wise to prioritize caution and explore alternative avenues if uncertainties arise.\n\nConclusion\nEnhance your online financial transactions with verified Cash App accounts, a secure and convenient option for all individuals. By purchasing these accounts, you can access exclusive features, benefit from higher transaction limits, and enjoy enhanced protection against fraudulent activities. Streamline your financial interactions and experience peace of mind knowing your transactions are secure and efficient with verified Cash App accounts.\n\nChoose a trusted provider when acquiring accounts to guarantee legitimacy and reliability. In an era where Cash App is increasingly favored for financial transactions, possessing a verified account offers users peace of mind and ease in managing their finances. Make informed decisions to safeguard your financial assets and streamline your personal transactions effectively.\n\nContact Us / 24 Hours Reply\nTelegram:dmhelpshop\nWhatsApp: +1 (980) 277-2786\nSkype:dmhelpshop\nEmail:dmhelpshop@gmail.com" | revojop836 |
1,906,408 | Camtasia Studio 2023.1.1 Crack + Keygen [Latest-2023] Keys | Camtasia Studio 2023.1.1 crack is the latest iteration of TechSmith’s renowned video editing and... | 0 | 2024-06-30T08:41:10 | https://dev.to/mrwood/camtasia-studio-202311-crack-keygen-latest-2023-keys-3ef3 | [Camtasia Studio 2023.1.1 crack](https://owncracks.com/camtasia-studio-2024-1-1-crack-keygen/) is the latest iteration of TechSmith’s renowned video editing and screen recording software. Designed to be user-friendly while packing powerful features, it caters to both novices and professionals. This article delves into ... | mrwood | |
1,906,407 | [DAY 66-68] I built a drum set app using React | Hi everyone! Welcome back to another blog where I document the things I learned in web development. I... | 27,380 | 2024-06-30T08:40:55 | https://dev.to/thomascansino/day-66-68-i-built-a-drum-set-app-using-react-4i19 | buildinpublic, react, webdev, javascript | Hi everyone! Welcome back to another blog where I document the things I learned in web development. I do this because it helps retain the information and concepts as it is some sort of an active recall.
On days 66-68, after completing the first 2 projects in the front end course (the random quote machine and the markd... | thomascansino |
1,906,042 | Use AWS Serverless to sell items in Habitica | I use Habitica daily. It is a very strong motivator to keep me on track with my daily tasks. However,... | 0 | 2024-06-30T08:38:00 | https://pabis.eu/blog/2024-06-30-Habitica-Item-Seller-Lambda-SAM.html | lambda, aws, habitica | I use Habitica daily. It is a very strong motivator to keep me on track with my daily tasks. However, I already collected all the free pets and mounts and so I don't need most of the items I collect. Selling them is a pain as you have to sell one item with each click. But Habitica has a [remarkable API](https://habitic... | ppabis |
1,906,406 | Understanding Declarative Programming in React | React is a popular JavaScript library used for building user interfaces, and one of its core... | 27,828 | 2024-06-30T08:37:26 | https://imabhinav.dev/blog/understanding-declarative-programming-in-react-8-36-51 | webdev, javascript, react, beginners | React is a popular JavaScript library used for building user interfaces, and one of its core principles is **declarative programming**. To understand why React is declarative, we first need to grasp what declarative programming is and how it contrasts with **imperative programming**.
### Declarative vs. Imperative Pro... | imabhinavdev |
1,902,778 | 40 Days Of Kubernetes (7/40) | Day 7/40 Pod In Kubernetes Explained | Imperative VS Declarative Way | YAML... | 0 | 2024-06-29T20:13:24 | https://dev.to/sina14/40-days-of-kubernetes-740-4hg9 | kubernetes, 40daysofkubernetes | ## Day 7/40
# Pod In Kubernetes Explained | Imperative VS Declarative Way | YAML Tutorial
[Video Link](https://www.youtube.com/watch?v=_f9ql2Y5Xcc)
@piyushsachdeva
[Git Repository](https://github.com/piyushsachdeva/CKA-2024/)
[My Git Repo](https://github.com/sina14/40daysofkubernetes)
There are 2 ways of configuratio... | sina14 |
1,906,404 | Top Cloud Providers in 2024 | As we move further into the digital age, cloud computing continues to be a cornerstone of... | 0 | 2024-06-30T08:25:48 | https://dev.to/devops_den/top-cloud-providers-in-2024-fne | devops, beginners, aws, azure | As we move further into the digital age, cloud computing continues to be a cornerstone of technological advancement. The landscape of cloud service providers is evolving rapidly, with new players entering the market and established giants continuously innovating. Here’s a look at the top cloud providers in 2024 and wha... | devops_den |
1,906,403 | Ummy Video Downloader 1.15.0.0 Crack Latest [2023 Download] | Introduction to Ummy Video Downloader In the digital age, video content has become a... | 0 | 2024-06-30T08:25:36 | https://dev.to/mrwood/ummy-video-downloader-11500-crack-latest-2023-download-2ag1 | ##Introduction to Ummy Video Downloader
In the digital age, video content has become a significant part of our daily consumption, be it for entertainment, education, or information. With the increasing demand for offline access to videos, various tools and software have been developed to facilitate video downloading. A... | mrwood | |
1,906,398 | Understanding JavaScript Closures: A Comprehensive Guide | Introduction Consider a situation where you require a function that retains its state... | 0 | 2024-06-30T08:25:00 | https://dev.to/mukeshb/understanding-javascript-closures-a-comprehensive-guide-306p | javascript, webdev, tutorial, beginners | ## **Introduction**
Consider a situation where you require a function that retains its state between calls. This can be achieved using closures. JavaScript closures are a key concept that permits functions to utilize variables from their surrounding scope even after the outer function has finished executing. This guide... | mukeshb |
1,906,402 | Renderización Dinámica de Componentes en Vue 3 y Nuxt 3: Guía Práctica y Caso Real | Componentes dinámicos en Vue y Nuxt: Guía Práctica y Caso Real Nuxt 3 ofrece una forma... | 0 | 2024-06-30T08:22:00 | https://dev.to/nyambe/renderizacion-dinamica-de-componentes-en-vue-3-y-nuxt-3-guia-practica-y-caso-real-4054 | nuxt, espanol, vue, nuxt3 |
## Componentes dinámicos en Vue y Nuxt: Guía Práctica y Caso Real
Nuxt 3 ofrece una forma flexible y muy potente de renderizar diferentes componentes basados en condiciones dinámicas. Esto es especialmente útil cuando el componente exacto a renderizar no se puede determinar hasta el tiempo de ejecución.
## Configura... | nyambe |
1,906,383 | window.ai - running AI LOCALLY from DevTools! 🤯 | On-device AI in the browser is here - kinda. It is currently in Chrome canary which means, it will... | 0 | 2024-06-30T08:17:39 | https://dev.to/grahamthedev/windowai-running-ai-locally-from-devtools-202j | ai, webdev, javascript | On-device AI in the browser is here - kinda.
It is currently in Chrome canary which means, it will be here soon(ish).
In this article I will show you how to get it running on your device, so that you can have a play with it and see what use cases you can think of.
And I will just say this: Running `window.ai` from D... | grahamthedev |
1,906,401 | Latest Newsletter: Liberalism, Free Speech, and Even More Politics (Issue #170) | AR & VR, memecoins, macro, digital media publications, liberalism, national debt, history of elections, free speech, state dysfunction, resolving disputes, UK politics, authoritarianism, sad tech | 0 | 2024-06-30T08:14:09 | https://dev.to/mjgs/latest-newsletter-liberalism-free-speech-and-even-more-politics-issue-170-mln | javascript, tech, webdev, discuss | ---
title: Latest Newsletter: Liberalism, Free Speech, and Even More Politics (Issue #170)
published: true
description: AR & VR, memecoins, macro, digital media publications, liberalism, national debt, history of elections, free speech, state dysfunction, resolving disputes, UK politics, authoritarianism, sad tech
tags... | mjgs |
1,906,400 | TNod User & Password Finder 1.8.0 Final Beta Cracked Free Download | In today's digital age, securing access to premium software often comes at a cost. However, tools... | 0 | 2024-06-30T08:14:06 | https://dev.to/ownsoftware/tnod-user-password-finder-180-final-beta-cracked-free-download-2m3h | In today's digital age, securing access to premium software often comes at a cost. However, tools like TNod User & Password Finder 1.8.0 Final Beta provide a solution by enabling users to find valid license keys for ESET antivirus products. This article explores the features, benefits, and downloading process of [TNod ... | jesonjame | |
1,906,399 | High-Speed Facebook to MP4 Conversion with FBload | Experience the fastest way to convert Facebook videos to MP4 with FBload. Our advanced technology... | 0 | 2024-06-30T08:08:52 | https://dev.to/gloriahewitt/high-speed-facebook-to-mp4-conversion-with-fbload-363l | Experience the fastest way to convert [Facebook videos to MP4](https://fbload.online/fb-to-mp4) with FBload. Our advanced technology guarantees high-speed conversions without compromising video quality, always providing the best results. | gloriahewitt | |
1,906,397 | Luhn's Algorithm: Credit Card Validation | The challenge At some point in my backend journey, I was faced with the challenge to... | 0 | 2024-06-30T07:58:28 | https://dev.to/talk2onyx/luhns-algorithm-credit-card-validation-2plk | programming, laravel, algorithms | ## The challenge
At some point in my backend journey, I was faced with the challenge to validate credit cards numbers, submitted by users on an application that processes subscription-based payment for a service.
Let’s imagine we are creating an e-commerce website. The site is looking good and we are ready to impleme... | talk2onyx |
1,906,366 | 100 Days of Code Week 1 | July 1, 2024 FSE 1 Web Development Foundations Get started with the foundations. By the... | 0 | 2024-06-30T07:49:45 | https://dev.to/jacobsternx/100-days-of-code-week-1-3igb | 100daysofcode, webdev, javascript, beginners | July 1, 2024
### FSE 1 Web Development Foundations
* Get started with the foundations. By the end of this section, you'll be able to build a stylized and responsive website with HTML and CSS
#### Fundamentals of HTML
* FSE 1.1 Web Dev - Fundamentals of HTML
#### Fundamentals of CSS
* FSE 1.2 Web Dev - Fundamentals... | jacobsternx |
1,906,394 | AAct Portable Activator Free Download: Your Ultimate Guide | In today’s digital age, activation of software plays a crucial role in ensuring that you get the most... | 0 | 2024-06-30T07:43:07 | https://dev.to/roseberry/aact-portable-activator-free-download-your-ultimate-guide-4114 | software, productivity | In today’s digital age, activation of software plays a crucial role in ensuring that you get the most out of your applications. One such tool that has gained popularity is the [AAct Portable Activator 4.3.1 Cracked](https://owncracks.com/aact-portable-activator-crack/). This article will provide a comprehensive guide o... | roseberry |
1,906,392 | Scaling databases with AWS RDS and read replicas | Amazon Web Services (AWS) Relational Database Service (RDS) is a managed service that simplifies the... | 0 | 2024-06-30T07:41:42 | https://dev.to/vivekalhat/scaling-databases-with-aws-rds-and-read-replicas-58h9 | aws, cloud, database, tutorial | Amazon Web Services (AWS) Relational Database Service (RDS) is a managed service that simplifies the process of configuring, operating, and scaling a relational database in the cloud. AWS RDS is a versatile choice that supports several database engines including PostgreSQL, MySQL, Oracle, MariaDB, Microsoft SQL Server,... | vivekalhat |
1,906,393 | Exclusive Interview With John Lilic: His Path to Web3, the Evolution of Blockchain, And the Value of Partnerships | In recent decades, technological innovations have changed the way we think about finance, networking,... | 0 | 2024-06-30T07:38:06 | https://36crypto.com/exclusive-interview-with-john-lilic-his-path-to-web3-the-evolution-of-blockchain-and-the-value-of-partnerships/ | cryptocurrency, blockchain, interview | In recent decades, technological innovations have changed the way we think about finance, networking, and personal security. Among the most impressive achievements of this time are the development of blockchain technology and Web3. What started as a cryptocurrency concept quickly grew into a profound transformation of ... | deniz_tutku |
1,904,998 | How to Customize GitHub Profile: Part 4 | Welcome back to the fourth part of my series on customizing your GitHub profile! In this article,... | 0 | 2024-06-30T07:33:48 | https://dev.to/ryoichihomma/how-to-customize-github-profile-part-4-29h | github, githubprofile, githubportfolio, developer | Welcome back to the fourth part of my series on customizing your GitHub profile! In this article, we'll delve into the fun and interactive contribution animation. This animation not only adds a unique flair to your profile but also visually represents your contributions in an engaging way.
[Part 1](https://dev.to/ryoic... | ryoichihomma |
1,906,391 | Running Livebook as a Systemd Service for Your User | Livebook is a powerful tool for creating and sharing interactive notebooks with Elixir. To make it... | 0 | 2024-06-30T07:32:15 | https://dev.to/dkuku/running-livebook-as-a-systemd-service-for-your-user-1b9c | livebook, linux, elixir | Livebook is a powerful tool for creating and sharing interactive notebooks with Elixir. To make it even more convenient, you can set it up to run as a systemd service for your user. This ensures that Livebook starts automatically whenever you log in, and runs in the background without requiring root permissions. Here’s... | dkuku |
1,906,390 | This is not a button | Check out this Pen I made! | 0 | 2024-06-30T07:29:21 | https://dev.to/tim_tom_13d2d04a6b587c4a3/this-is-not-a-button-51p0 | codepen, ai | Check out this Pen I made!
{% codepen https://codepen.io/tim-tom-the-flexboxer/pen/JjqQLYO %} | tim_tom_13d2d04a6b587c4a3 |
1,906,389 | This is not a button | Check out this Pen I made! | 0 | 2024-06-30T07:29:20 | https://dev.to/tim_tom_13d2d04a6b587c4a3/this-is-not-a-button-b70 | codepen, ai | Check out this Pen I made!
{% codepen https://codepen.io/tim-tom-the-flexboxer/pen/JjqQLYO %} | tim_tom_13d2d04a6b587c4a3 |
1,906,388 | Assignment_Two | A post by Mugisha Thomas | 0 | 2024-06-30T07:27:54 | https://dev.to/mugisha_thomas_9b97be8af6/assignmenttwo-2i41 | mugisha_thomas_9b97be8af6 | ||
1,906,387 | Setting Up Android Studio on Linux | Android development on Linux is straightforward and provides a powerful platform for app creation.... | 0 | 2024-06-30T07:24:10 | https://dev.to/sahilverma_dev/setting-up-android-studio-on-linux-4nga | linux, android, appdev | Android development on Linux is straightforward and provides a powerful platform for app creation. This guide will walk you through installing Android Studio, Java Development Kit (JDK), and setting up necessary environment variables.
## 1. Installing Android Studio
Android Studio is the official Integrated Developme... | sahilverma_dev |
1,906,381 | FullStack React Native Bootcamp | This course will not follow any regular way of teaching. Instead, it's like a hop-on-hop-off tourist... | 0 | 2024-06-30T07:12:15 | https://dev.to/subraatakumar/fullstack-react-native-bootcamp-1nb6 | reactnative, typescript, learning, javascript | This course will not follow any regular way of teaching. Instead, it's like a hop-on-hop-off tourist bus, stopping at important places where you should spend some time. I will explain these topics to you like a tourist guide, highlighting the key points and ensuring you get the most out of each stop.
, a chance for all of us to come up with solutions to two weekly tasks. My solutions are written in Python first, and then converted to Perl. It's a great way for us all to practice some coding.
[Chall... | simongreennet | |
1,904,263 | My Wins of Week 🌟 | Hi Awesome People on Internet!👋 I'm JK 🧑💻, & Hers my Wins of the Weeeeeeeeeeeek! ... | 27,912 | 2024-06-30T07:06:54 | https://dev.to/developedbyjk/my-wins-of-week-4him | weeklyretro |
## `Hi Awesome People on Internet!👋`

I'm **JK** 🧑💻, & Hers my Wins of the Weeeeeeeeeeeek!
#🎢
This week has been full of exciting developments, and I'm thrilled to share my progress with you.
---
.*
## What I Built
<!-- Share an overview about your project. -->
A Dynamic and Interactive E-Commerce Application.
## Demo
<!-- Share a link to your Wix Studio app and include some screenshots here. -->
Link: https://wilcrat.wixsite... | wilsonjuma254 |
1,906,377 | Difference Between Javascript and TypeSript | ** JavaScript ** Dynamic Typing: JavaScript is a dynamically typed language, meaning that... | 0 | 2024-06-30T06:45:03 | https://dev.to/darshan_kumar_c9883cffc18/difference-between-javascript-and-typesript-4cka | **
## JavaScript
**
Dynamic Typing: JavaScript is a dynamically typed language, meaning that variables can hold any value, and types are checked at runtime.
**Flexibility:** The flexibility of JavaScript allows for rapid development and prototyping.
**Compatibility:** JavaScript is natively supported by all web browse... | darshan_kumar_c9883cffc18 | |
1,906,374 | 8 mistakes that noob product managers make. Tips from a productperson who has been through it all | Product managers have the power to determine whether a project will take off or go broke. Below, one... | 0 | 2024-06-30T06:40:25 | https://dev.to/ispmanager/8-mistakes-that-noob-product-managers-make-tips-from-a-productperson-who-has-been-through-it-all-44no | learning, career, startup, product | Product managers have the power to determine whether a project will take off or go broke. Below, one from ispmanager discusses the most common mistakes that novice product managers tend to make in both startups and well-established projects and how to avoid them.
## Four mistakes product managers make in startups
Star... | ispmanager_com |
1,906,040 | Difference between normal links & tag links in Next.js | Today in this blog we will talk about the effect of using "a" tag & "Link" tag in Next.js. Are... | 0 | 2024-06-30T06:33:20 | https://dev.to/parsafarahani84/difference-between-normal-links-tag-links-in-nextjs-8m7 | webdev, javascript, react, programming | Today in this blog we will talk about the effect of using "a" tag & "Link" tag in Next.js. Are they really different from each other?
Sure they are, let me explain.
## Normal Links
When you use normal links like this:
```
<a href="./users">Click Here</a>
```
every time that you click the link and navigate to other pa... | parsafarahani84 |
1,906,373 | Trying DevOps things | Hello Everyone, As I continue my journey in the realm of DevOps, I've delved deeply into the... | 0 | 2024-06-30T06:32:00 | https://dev.to/dgtak/trying-devops-things-k6n | Hello Everyone,
As I continue my journey in the realm of DevOps, I've delved deeply into the intricacies of Linux administration and the vast potential of cloud computing. Every day brings a new challenge, from optimizing cloud infrastructures to automating deployment pipelines. The principles of continuous integratio... | dgtak | |
1,906,372 | The Ultimate Guide to Laravel: A PHP Framework for Modern Web Applications | Introduction Laravel has revolutionized the PHP development landscape, becoming one of the... | 0 | 2024-06-30T06:27:38 | https://dev.to/arafatweb/the-ultimate-guide-to-laravel-a-php-framework-for-modern-web-applications-2c3g | webdev, laravel, php, beginners |
### Introduction
Laravel has revolutionized the PHP development landscape, becoming one of the most popular frameworks for developing modern web applications. Known for its rich syntax, powerful tools, and extensive community support, Laravel provides developers with a solid foundation for building scalable, maintaina... | arafatweb |
1,906,367 | AWS: Your Ally in Amplifying Reliability with GenAI | Generative AI, or the Large Language Models, is by far one of the most exciting technologies we have... | 0 | 2024-06-30T06:21:23 | https://dev.to/aws-builders/aws-your-ally-in-amplifying-reliability-with-genai-41of | sre, genai, aws, awsbedrock | Generative AI, or the Large Language Models, is by far one of the most exciting technologies we have seen. It has far-reaching consequences, impacting various fields. Site Reliability Engineering is currently experiencing its moment, with GenAI revolutionizing operations. I refer to this as SRE 2.0, a new and improved ... | indika_wimalasuriya |
1,906,370 | How SHELL-GPT Revolutionized My Workflow | Hey everyone, I just had to share my excitement about this incredible tool called SHELL-GPT. As a... | 0 | 2024-06-30T06:13:36 | https://dev.to/karleeov/how-shell-gpt-revolutionized-my-workflow-4o88 | shellgpt, sgpt, ai, terminal | Hey everyone, I just had to share my excitement about this incredible tool called SHELL-GPT. As a casual blogger and tech enthusiast, I'm always on the lookout for ways to streamline my work and make my life easier. Well, let me tell you, SHELL-GPT has been an absolute game-changer!
First off, for those of you who are... | karleeov |
1,906,368 | Exploring the Cool Refreshment of Strawberry Ice – RAZ TN9000 Disposable Vape | With the rapid evolution of vaping technology, enthusiasts are continually seeking new flavors and... | 0 | 2024-06-30T05:59:00 | https://dev.to/john7535/exploring-the-cool-refreshment-of-strawberry-ice-raz-tn9000-disposable-vape-1bjm | raz, vape | With the rapid evolution of vaping technology, enthusiasts are continually seeking new flavors and experiences. Among the latest innovations, the Strawberry Ice flavor in the RAZ TN9000 Disposable Vape has captured the attention of vape aficionados worldwide. Combining the nostalgic sweetness of ripe strawberries with ... | john7535 |
1,906,365 | PHP in the Age of AI: Don't Overlook This Web Powerhouse for Your Next Smart Project | Thereafter, PHP might very well prove to be the unsung hero of the AI revolution. While Python gets... | 0 | 2024-06-30T05:35:16 | https://dev.to/kareem-khaled/php-in-the-age-of-ai-dont-overlook-this-web-powerhouse-for-your-next-smart-project-1hie | ai, php, webdev, softwareengineering | Thereafter, PHP might very well prove to be the unsung hero of the AI revolution. While Python gets huge exposure, PHP's varied strengths make it compelling for many AI-fueled web applications. But let me make something clear: This is not about declaring PHP as "the best" for AI. It's a reminder, especially to software... | kareem-khaled |
1,906,517 | Malicious Software Removal Tool (MRT) in Windows 11? | How to use this tool in Windows 11? MSRT is not a replacement for a full antivirus... | 0 | 2024-07-01T05:33:30 | https://winsides.com/malicious-software-removal-tool-in-windows-11/ | beginners, devops, windows, tips | ---
title: Malicious Software Removal Tool (MRT) in Windows 11?
published: true
date: 2024-06-30 05:28:46 UTC
tags: beginners, devops, windows, tips
canonical_url: https://winsides.com/malicious-software-removal-tool-in-windows-11/
cover_image: https://winsides.com/wp-content/uploads/2024/06/Malicious-Software-Removal-... | vigneshwaran_vijayakumar |
1,906,364 | Introducing Material UI: Exploring 5+ MUI Dashboard Templates | Material UI is a design system based on Google’s Material Design language, introduced in 2014, and... | 0 | 2024-06-30T05:22:55 | https://themewagon.com/blog/material-ui-with-5-mui-templates/ | webdev, opensource, mui, frontend | Material UI is a design system based on Google’s Material Design language, introduced in 2014, and works with various JavaScript frameworks apart from React, such as Angular.js, Next.js, and Vue.js. Material UI, later rebranded as MUI, is a design system that helps ensure consistent visual language throughout your webs... | themewagon |
1,906,330 | function declarations vs function expressions in Javascript 🤔✌️ | When it comes to defining functions in JavaScript, there are two primary ways to do so: function... | 0 | 2024-06-30T05:22:13 | https://dev.to/rajusaha/function-declarations-vs-function-expressions-in-javascript-353l | webdev, javascript, beginners, tutorial | When it comes to defining functions in JavaScript, there are two primary ways to do so: function declarations and function expressions. While they may seem similar, there are key differences between them that can impact the behavior of your code. Let’s explore these differences in detail.
## Function Declaration
A fun... | rajusaha |
1,906,332 | how to Learn Dijkstra's Algorithm? | Learning Dijkstra's algorithm, a fundamental algorithm in computer science for finding the shortest... | 0 | 2024-06-30T05:17:40 | https://dev.to/fridaymeng/how-to-learn-dijkstras-algorithm-17e3 |
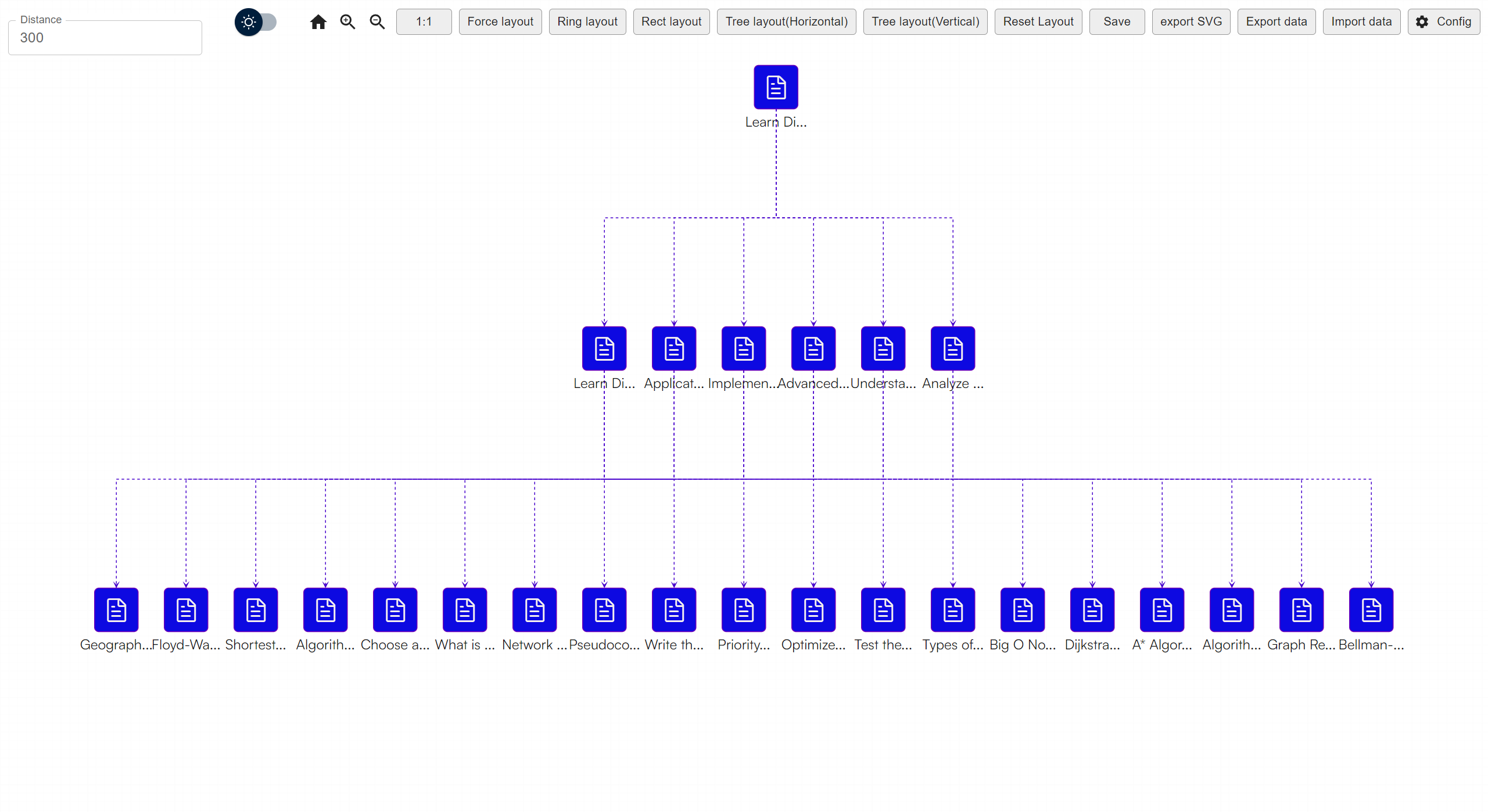
Learning Dijkstra's algorithm, a fundamental algorithm in computer science for finding the shortest paths between nodes in a graph, involves understanding its theory, practical implementation, and applications. Her... | fridaymeng | |
1,906,329 | DAY 6 PROJECT: POLL SYSTEM | Building a Poll System with HTML, CSS, and JavaScript This project is a simple,... | 0 | 2024-06-30T05:08:54 | https://dev.to/shrishti_srivastava_/day-6-project-poll-system-47n0 | webdev, javascript, beginners, programming | ## Building a Poll System with HTML, CSS, and JavaScript
This project is a simple, interactive poll system built using HTML, CSS, and JavaScript. It allows users to vote for their favourite programming language from options like JavaScript, Python, Java, and C++.
The results are dynamically displayed with visual bars... | shrishti_srivastava_ |
1,906,328 | From Zero to Hero: Building Your First Serverless Application with AWS Lambda | Serverless computing has revolutionized the way we develop and deploy applications. By abstracting... | 0 | 2024-06-30T05:00:10 | https://dev.to/raazketan/from-zero-to-hero-building-your-first-serverless-application-with-aws-lambda-5h2i | Serverless computing has revolutionized the way we develop and deploy applications. By abstracting away server management, serverless architectures allow developers to focus on writing code and solving problems without worrying about infrastructure. One of the most popular services for serverless applications is AWS La... | raazketan | |
1,906,325 | My 100 Days of Code Challenge Starts Now! | It all starts now! June 29, 2024 100 days of code #100DaysOfCode #100DOC Codecademy Full Stack... | 0 | 2024-06-30T04:47:37 | https://dev.to/jacobsternx/my-100-days-of-code-challenge-starts-now-4ai3 | 100daysofcode, beginners, webdev, javascript | It all starts now!
June 29, 2024
100 days of code
\#100DaysOfCode \#100DOC
* Codecademy Full Stack Engineer certificate
* FSE certificate is composed of 6 courses
* Each course is composed of ~8 Lessons and Projects
* Each course has 2 assessments
* My coding aim is to hustle and shine at least 4 hours per day
* Daily... | jacobsternx |
1,906,326 | How to Scale an Existing Ruby on Rails Product from x to 10x | Scaling a Ruby on Rails product, especially one with a messy codebase, is a challenging yet rewarding... | 0 | 2024-06-30T04:32:00 | https://dev.to/praveenkumar/how-to-scale-an-existing-ruby-on-rails-product-from-x-to-10x-24j7 | rails, coderefactoring, scalability, webdev | Scaling a Ruby on Rails product, especially one with a messy codebase, is a challenging yet rewarding journey. The key lies in methodically refactoring your codebase, implementing best practices, and optimizing performance. Here’s a roadmap to guide you through this transformation.
### **1. Identify and Address Code S... | praveenkumar |
1,906,295 | 6 Useful Resources for Beginners in Front-End Development | Are you a beginner in front-end development? Then you are in the right place. In this post, I'll... | 27,911 | 2024-06-30T04:30:00 | https://rhythmusbyte.blogspot.com/2024/06/frontend-resources-part1.html | webdev, beginners, learning, frontend | Are you a beginner in front-end development? Then you are in the right place. In this post, I'll share some useful resources for aspiring front-end developers. I hope it will help you.
Before that, if you are not focusing on the front end and are focusing on something else, regardless of the programming language, you... | rhythmusbyte |
1,906,324 | Unleash Your AI Potential with this Go-Powered Neural Network Tutorial! 🤖 | Learn how to build a simple artificial neural network using the Go programming language, covering machine learning principles and practical implementation. | 27,801 | 2024-06-30T04:28:26 | https://getvm.io/tutorials/how-to-build-a-simple-artificial-neural-network-with-go | getvm, programming, freetutorial, technicaltutorials |
Hey there, fellow developers! 👋 Are you curious about the world of machine learning and artificial intelligence, but haven't quite figured out how to dive in? Well, I've got the perfect resource for you – a step-by-step guide on building a simple artificial neural network using the Go programming language!
## Highl... | getvm |
1,906,323 | Live Coding Clerk, into Next.js with James Perkins | Original: https://codingcat.dev/podcast/cwcc-0-9-clerk-with-appwrite Clerk React is a React... | 26,111 | 2024-06-30T04:23:24 | https://codingcat.dev/podcast/cwcc-0-9-clerk-with-appwrite | webdev, javascript, beginners, podcast |
Original: https://codingcat.dev/podcast/cwcc-0-9-clerk-with-appwrite
{% youtube https://youtu.be/4P_ax04-T4c %}
Clerk React is a React Hooks library that makes it easy to build CRUD applications. The library provides a set of high-level hooks that abstract away the details of managing state, fetching data, and handl... | codercatdev |
1,906,306 | The Devrel Digest June 2024: One Whole Year of the DevRel Digest | Happy first birthday to the DevRel Digest! One year ago, I decided to start writing the... | 25,904 | 2024-06-30T04:18:46 | https://dev.to/lizzzzz/the-devrel-digest-june-2024-one-whole-year-of-the-devrel-digest-57ag | devrel | ---
title: "The Devrel Digest June 2024: One Whole Year of the DevRel Digest"
published: true
series: The DevRel Digest
---
## Happy first birthday to the DevRel Digest!
One year ago, I decided to start writing the DevRel Digest. At that point, it had been only three months since I was laid off. It had been recommend... | lizzzzz |
1,906,303 | How to Learn Any New Skill with Ease? | Ever felt that burning desire to create something but were stuck, unsure of where to start? I've been... | 0 | 2024-06-30T04:11:22 | https://dev.to/praveenkumar/how-to-learn-any-new-skill-with-ease-34al | learning, mvp, startup, skilldevelopment | Ever felt that burning desire to create something but were stuck, unsure of where to start? I've been there too, overwhelmed by the vastness of what I didn't know. Today, I'm sharing my journey from a place of curiosity to launching a product with 10,000 users. These lessons, learned over a decade ago, still hold true ... | praveenkumar |
1,906,272 | Remove Duplicate Elements from JavaScript Array | Removing duplicate elements from a JavaScript array is a common task that developers often need to... | 0 | 2024-06-30T02:41:27 | https://dev.to/d8578raj/remove-duplicate-elements-from-javascript-array-3862 | Removing duplicate elements from a JavaScript array is a common task that developers often need to perform. [JavaScript](https://www.school247.org/javascript/) offers several methods to achieve this, each suitable for different scenarios.
## 1. Remove Duplicates Using the `Set` Object
The `Set` object lets you store ... | d8578raj | |
1,906,302 | Twitter Profile Banner Part 1 | Original: https://codingcat.dev/podcast/twitter-profile-banner-part-1 Hanging out with James Q... | 26,111 | 2024-06-30T04:07:41 | https://codingcat.dev/podcast/twitter-profile-banner-part-1 | webdev, javascript, beginners, podcast |
Original: https://codingcat.dev/podcast/twitter-profile-banner-part-1
{% youtube https://youtu.be/9LvknDBbEx4 %}
Hanging out with James Q Quick and trying to build a Twitter Banner updater. | codercatdev |
1,906,300 | From Idea to Launch: My 30-Day MVP Journey | In the fast-paced world of tech startups, turning an idea into a working product is a wild ride,... | 0 | 2024-06-30T04:04:54 | https://dev.to/praveenkumar/from-idea-to-launch-my-30-day-mvp-journey-2635 | hasura, flutter, cto, mvp | In the fast-paced world of tech startups, turning an idea into a working product is a wild ride, filled with hurdles and uncertainties. As the CTO of Storya, I faced the challenge of transforming a simple no-code prototype into a solid MVP in just 30 days. This journey wasn’t just about coding; it was about strategic p... | praveenkumar |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.